CAM Portal
Overview
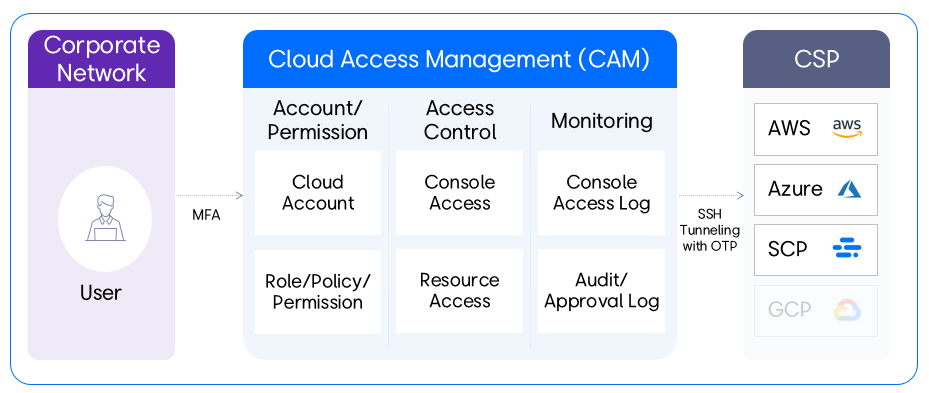
CAM (Cloud Access Management) is a service for managing cloud console and resource access, providing users with easy and convenient access to cloud consoles and resources.
Users can access the portal from a PC located on the company network through multi-factor authentication. Instead of using a password, a one-time token is issued to access the cloud consoles and resources, and all console access history, activity history, and approval history can be monitored.
Service Scenario
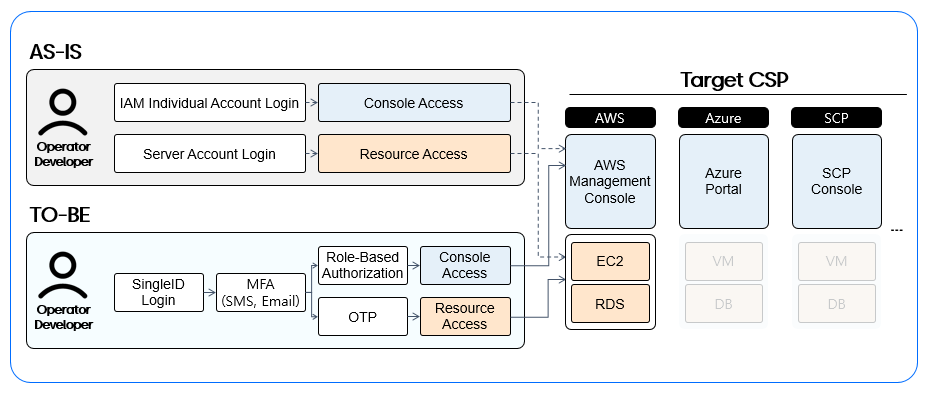
In the past, users accessed the console and resources directly with their IAM personal accounts, but now CAM provides a unified access channel.
- Step 1: During the transition period, the TO-BE access channel is newly configured and operated in parallel with the AS-IS access channel.
- Step 2: After the Cut-Over, the AS-IS access channel is blocked, and the TO-BE channel is switched.
Key Features
User Scenario
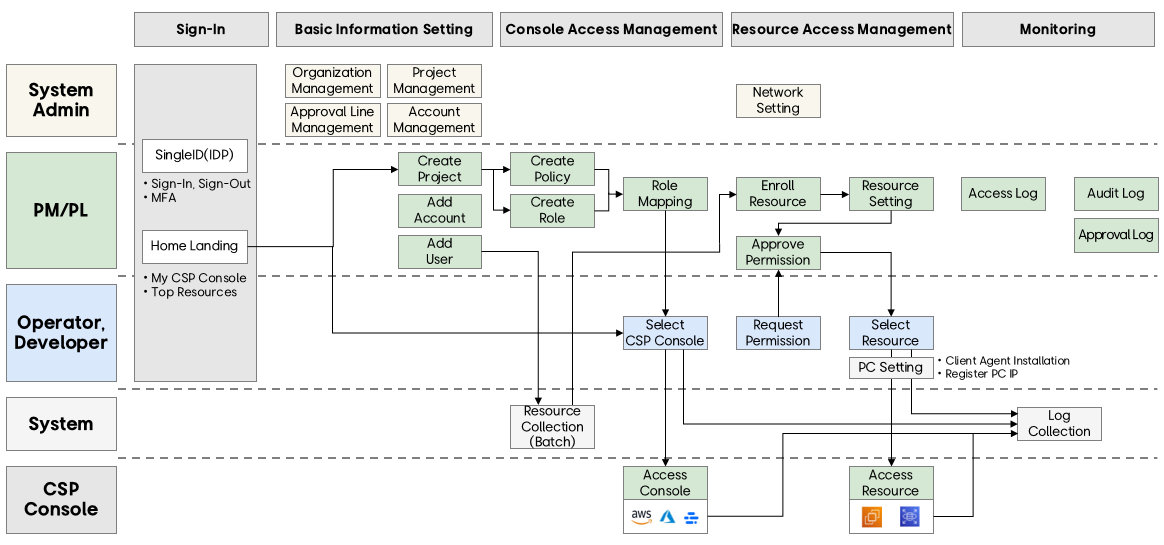
The user scenario proceeds in the following order:
- Sign-In → Basic Information Setting → Console Access Control → Resource Access Control → Monitoring
Login & Home
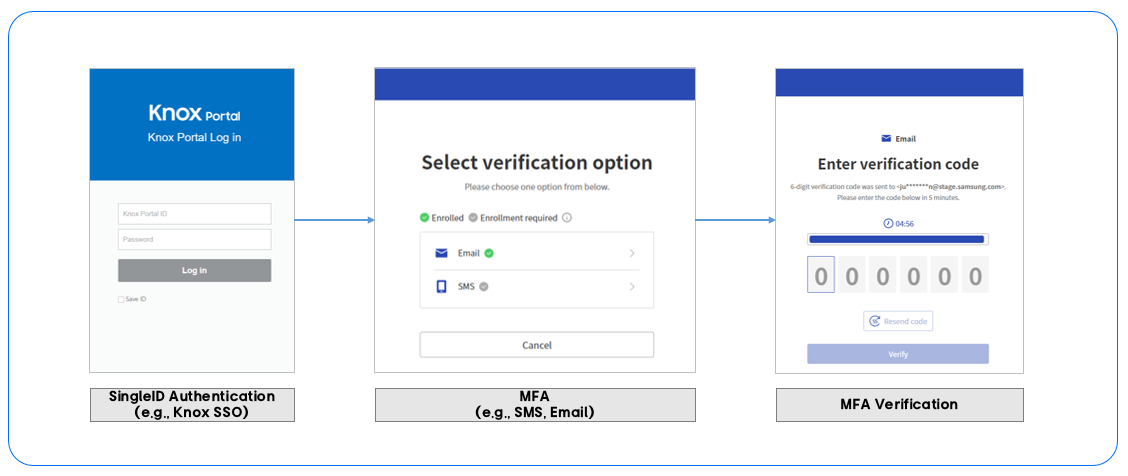
Users log in with their SingleID or SSO account (e.g., Knox Portal) and proceed with multi-factor authentication. After entering the authentication code received via SMS or email, the login process is completed and access to CAM is granted.
The home screen provides a personalized screen that allows users to access cloud consoles and resources with one click, making it easy for users to access consoles and resources.
Configuration
After creating a project, users can easily register their CSP (Cloud Service Provider) account. Additionally, users can be added to the project to provide project-specific permissions.
Console Access
Roles and policies can be created to set and control access permissions to the cloud console. Roles can be mapped to specific accounts and users, defining which users can access the CSP console and their permission levels.
Resource Access
Cloud resource access permissions are managed. To manage cloud resource access, users first request permissions, download and install the PC client agent, and register their access IP address. Once set up, users can access their desired resources from their personalized resource list.
1 - Getting Started
This manual aims to help users quickly understand the essential features and processes required to effectively use CAM.
Network Environment
Access is only possible in a network environment allowed by each tenant.
- CAM Portal, Console Access: Access is possible from a network environment allowed by each tenant.
- DEV, STG, ETC Resource Access: Access is possible from a network environment allowed by each tenant.
- PRD Resource Access: Access is only possible from a network environment with internet blocked, so access is only possible from a specific IP range for each tenant.
- Additional individual PC environment settings are required.
Pre-work
To use the CAM portal, some pre-work is necessary.
If you are a PM (Project Manager) or PL (Project Leader) group user, please check the cloud account and resource preparation below and prepare the environment in advance.
Cloud Account Preparation
To register and manage accounts in CAM, you need to create a role in the CSPs (AWS, Azure, SCP) and configure it with the policies required by CAM, and then assume the role in CAM.
Guide
If it’s not in the document Configuration > Add Account for reference.
Resource Preparation
Resource Configuration
To register and access resources in CAM, some setup work is required during resource configuration.
First, you must allow password-based connections. This configuration is necessary to access resources through CAM because a one-time password is issued for SSH connections when accessing resources in CAM.
Additionally, if the resource type is Compute, the following configuration must be added.
- Add the following content to a file named /etc/sudoers.
- Ubuntu: %sudo ALL=(ALL) NOPASSWD:ALL
- Amazon Linux: %wheel ALL=(ALL) NOPASSWD: ALL
- Restart the server with systemctl restart sshd.service.
Network Settings
To access resources through CAM, you need to configure the firewall and security group registration in the tenant’s network environment so that CAM can access the resources. Please check the necessary information with the tenant administrator and proceed with the network settings.
Service Scope
CAM currently supports AWS, Azure, SCP CSPs and plans to expand to more CSPs sequentially.
| Item | Description |
|---|
| AWS | Amazon Web Services |
| IAM (Console) | AWS Identity and Access Management |
| SCP | Samsung Cloud Platform (KR EAST1 region, KR WEST1 region) |
| EC2 | Elastic Compute Cloud |
| RDS | Relational Database Service |
Table. CSP Abbreviations
| OS | Version |
|---|
| Ubuntu | Ubuntu Server 24.04 LTS |
| Ubuntu | Ubuntu Server 22.04 LTS |
| Amazon Linux | Amazon Linux 2023 AMI |
| Redhat | Red Hat Enterprise Linux 9.4 |
Table. OS
| DB Engine | Version |
|---|
| PostgreSQL | 16.x |
| MySQL | 8.0.x |
| Aurora PostgreSQL | 15.x |
| Aurora MySQL | 3.05.x |
| Aurora MySQL | 3.04.x |
| Aurora MySQL | 3.03.x |
| MariaDB | 10.11.10x |
Table. DB
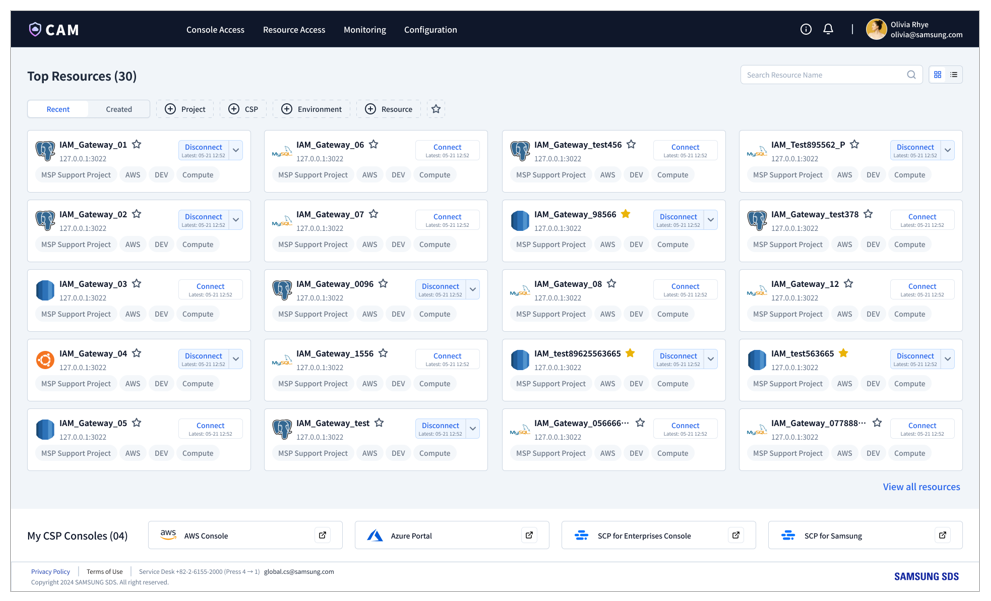
2 - Home
After logging in, you can access your CSP console and personally assigned resources with one click from your personalized homepage. Operators and developers can access approved consoles and resources quickly and easily from one place, streamlining their work.
The CAM (Cloud Access Management) home screen is divided into two sections:
- Top Resources
- My CSP Consoles
Both sections provide access to assigned resources and CSP consoles.
Top Resources
This section displays a list of the top 30 accessible resources.
Card View and List View
Resources are provided in card view by default, and you can switch to list view according to your preference.
Search and Filter
You can use the search function to quickly find a specific resource, and filter resources based on the following items:
- Project
- CSP (Cloud Service Provider)
- Environment (e.g., DEV, STG, PRD, ETC)
- Resource Type (e.g., Compute, DB)
Favorites
You can set favorites using the Favorites (★) icon, and set a favorites filter to filter only resources that have been set as favorites.
Sorting
The resource list can be sorted by two criteria:
- Recent (default sorting)
- Creation Date
You can check the detailed information of resources in both card and list views.
- Resource Name
- Project
- CSP (e.g., AWS, Azure, SCP)
- Environment (e.g., DEV, STG, PRD, ETC)
- Resource Type (e.g., Compute, DB)
Resource Connection/Disconnection
Each resource has the Connect button to connect or disconnect.
If you are already connected to a resource, the following details are displayed:
- Last Connection Date/Time
- Connection Status
Resource Connection
When you click the Connect button on a card or list, a connection popup opens.
To connect to a resource, enter the following details:
- Local Port: Enter a port number between 1024 and 65535 that is not currently in use on your PC.
- Remote Port: Enter the port number of the resource.
- Launch Putty: Select ‘ON’ to automatically run putty during the connection process.
Note
Before attempting to connect, ensure that the client agent is installed and the IP address is registered.
Refer to Resource Access > PC Settings for settings.
Connection Details
When connected to a resource, you can click the dropdown to view detailed connection information, such as user ID, password, and local IP. This information is provided through a popup as details for the user to connect to the resource via SSH.
- User ID: Click the Copy icon on the right to copy the user ID.
- Password: Click the Copy icon on the right to copy the password.
- Local IP: Click the Copy icon on the right to copy the local IP address.
- Client Server IP: Refer to the connected client server IP displayed on the screen.
Resource Disconnection
When connected to a resource, the Disconnect button appears. Click this button to start the disconnection process. A popup will be displayed for final confirmation before the connection is terminated.
My CSP Consoles
The page provides a CSP access link in a sticky footer at the bottom. It offers CSP console access via SAML SSO, allowing you to access it directly without a separate authentication process.
3 - Console Access
The console access feature allows PM and PL group users to manage access to the CSP console by assigning roles and policies to cloud accounts and users. Here, users can access the console with the appropriate permissions based on the settings.
The console access section consists of four main management areas.
- Role Management: Defines and manages the level at which users can access the CSP console.
- Policy Management: Defines new policies and manages the roles mapped to each policy.
- Account Management: Manages cloud accounts and ensures each account is mapped to the correct role permissions.
- User Management: Controls user console access by mapping users to the correct roles, giving them the necessary permissions to access the cloud console.
Role Management
In the role management menu, you can view and manage all roles registered to a project, and filter roles by CSP or project.
Create Role
To create a role, click the Create Role button.
To create a new role, you must fill in the required information in the popup window:
- Project: Select a project from the user’s project list.
- CSP: Select a CSP.
- Role Name: Enter a unique role name and click the Validate button to check for consistency.
- Description: Add a brief description of the role.
View Role
To access detailed information about a role, go to the role management menu and click on the desired role. All project users can view role details, including policies, cloud accounts, and users mapped to the role.
The role view screen displays the following key details:
- Role Information: Basic details related to the role.
- Delete Role: Click the Delete button to remove this role.
- Policies: Displays a list of policies currently mapped to the role.
- Accounts: Displays a list of accounts related to the role.
- Users: Displays a list of users connected to the role.
Note
To set up policy, account, and user mappings, you must first create policies in the policy management menu and ensure that cloud accounts and users are pre-registered to the project.
Note
- The process in CSPs starts after the user addition approval is completed. Therefore, it may take some time for the status to change to Approved and be confirmed in the user’s CSP Role list. (Up to 10 minutes)
- Maximum 10 policies can be mapped to an AWS role.
- Each account has a role limit based on its CSP with up to 800 roles in AWS and up to 5000 in Azure.
- Each user has a role limit based on the CSP with up to 10 roles of AWS and 4000 roles of Azure can be mapped.
Delete Role
To delete a role and remove its mapping, select the role from the list and click the Delete button. Or alternatively, click the Delete button on the View Role page. Confirm the action to delete the role permanently. Removing a policy mapping eliminates the relationship between the role and the related policy.
Policy Management
PM and PL group users can add or delete policies mapped to a role by selecting or deselecting policies from the policy list.
Create Policy
To create a new policy, click Create Policy and fill in the required information:
- Project: Select a project from your list of registered projects.
- CSP: Choose the cloud service provider.
- Policy Name: Enter a name for the policy and validate it.
- JSON Code: Provide the JSON code that defines the policy.
- Description: Include a brief description of the policy.
To map a policy to a role, click the Add button above the policy list to open a popup. In the popup, you can view and select policies defined within the same project. Click the Save button to complete the mapping process. You can map multiple policies at once.
Make sure to check if the desired policy is created in the policy management menu before mapping.
View Policy
To access detailed information about a policy, navigate to the Policy Management section and click on the desired policy. All project users can view policy details, including the roles mapped to the policy.
Delete Policy
To remove a policy mapping from a role, select the policy from the list and click the Delete button. The deleted policy will reappear in the Add Policy popup list, allowing you to add it back if needed. Removing a policy mapping eliminates the relationship between the role and the related policy.
Account Management
PM and PL group users can map cloud accounts to a role or remove them.
View Account
To view account details:
- Navigate to Account Management and click on the desired account.
- All project users can access the account’s details, including a list of roles mapped to that account.
- Project managers or PL group users can also edit or delete roles associated with the account.
Add Role to Account
- To map roles to an account, click the “Add” button above the roles list to open the “Add Roles” pop-up.
- In the pop-up, select roles from the list that belong to the same project as the account, and click the Save button to complete the mapping process.
Note
- Maximum 800 roles can be mapped to an AWS account and 5000 roles to an Azure account.
Delete Role from Account
To remove a role from an account, select the role from the list and click the Delete button. The deleted role will reappear in the Add Role popup, allowing you to add it back if needed. You can delete multiple roles at once.
User Management
Through the user management menu, users can view and manage all users registered to a project. Users can be searched by name.
View User
To view user details:
- Go to the user management menu and click on the user.
- All project users can view user details, including roles mapped to the user.
- PM or PL group users can add or delete roles from the user.
Add Role to User
To map a role to a user, click the Add button above the role list to open the Add Role popup. In the popup, you can view all roles in the user’s project, select the role to add, and click the Create Approval button to proceed with the approval process.
Note
- Each user has a role limit based on the CSP with up to 10 roles of AWS and 4000 roles of Azure can be mapped.
Create Approval
Assigning a role to a user requires an approval process, which is done through the Create Approval popup and sent via Knox approval system or CAM’s own approval system.
- Title: Automatically input by the system and cannot be modified.
- Approver: Automatically added by the system, with the option to add approvers and consensus following the approval guide.
- Content: Project and role information is automatically input by the system and cannot be modified.
Delete Role from User
To remove a role from a user, click the Delete button. After a final deletion confirmation, the user’s role mapping will be removed. The removed role will reappear in the Add Role popup, allowing you to add it back if needed. Role removal does not require approval, but re-adding a role does.
4 - Resource Access
You can check all resources with individual permissions and access them. To access resources, a PM or PL group user must register the resources of the cloud account registered in the project and go through the user’s permission request and approval process.
Resources
It shows all resources that have been approved for the user. The user can check the resource list and access the resources directly.
Access
You can access resources by clicking the Connect button, and after connection, it provides connection details.
- Local Port: Enter a port number that is not used for other purposes on your PC.
- Remote Port: Enter the port number of the resource.
- Putty Execution: To automatically run Putty, you need to set it to ON.
Note
Before accessing resources, please make sure to install the client agent and register the IP address.
For more information, refer to Resource Access > PC Settings.
It provides detailed connection information to access resources through SSH.
- User ID: You can copy and use the user ID by clicking the copy icon.
- Password: You can copy and use the password by clicking the copy icon.
- Local IP: You can copy and use the local IP by clicking the copy icon.
- Cloud Server IP: You can copy and use the cloud server IP by clicking the copy icon.
Disconnection
When connected to a resource, the Connect button changes to Disconnect. To disconnect from the resource, click the Disconnect button.
Resource Registration
This menu allows you to register resource information necessary for resource access and shows a list of registered resources.
Registration
To register a resource, cloud account registration must be done in advance in the project menu. PM and PL group users can register resources created in the cloud account. Click the Enrollbutton to move to the resource registration screen and set the resource connection information.
- Project: Select a project registered as a PM or PL group user.
- Account: Select a cloud account registered in the selected project.
- Region: Select the region information of the selected account.
- Resource Type: Select one of Compute or DB.
- Resource: Select a resource that matches the selected criteria.
- Connection Type: Select one of Direct (connect directly to the server) or Bastion (connect through a proxy server).
- Address: Enter the address information of the resource.
- Root User: Provide the IP and password of the root user of the resource.
Note
Before registering a resource, please make sure that cloud account registration and resource creation are completed.
Cloud account registration can be done in Configuration > Project.
Guide
Supported OS/DB
Currently, the OS and DB that can be registered for ‘Resource Registration’ are limited as follows, and supported OS and DB will be continuously added.
| OS | Version |
|---|
| Ubuntu | Ubuntu Server 24.04 LTS |
| Ubuntu | Ubuntu Server 22.04 LTS |
| Amazon Linux | Amazon Linux 2023 AMI |
| Redhat | Red Hat Enterprise Linux 9.4 |
Table. Supported OS
| DB Engine | Version |
|---|
| PostgreSQL | 16.x |
| MySQL | 8.0.x |
| Aurora PostgreSQL | 15.x |
| Aurora MySQL | 3.05.x |
| Aurora MySQL | 3.04.x |
| Aurora MySQL | 3.03.x |
| MariaDB | 10.11.10x |
Table. Supported DB
Network Settings
To register resources in CAM and access resources through CAM, network settings must be done in advance.
Please follow the guide from the tenant administrator and proceed with network settings suitable for each tenant environment, such as firewall registration and security group registration, before registering resources.
Withdrawal
Resources that are no longer used must be deleted from the registered resource list. Select the resource from the resource view or resource registration list and click the “Withdraw” button to prevent further access.
Request Permission
The permission request menu allows you to inquire about the resource permissions of project members and request user-specific CSP resource type permissions.
Request
Users can request resource permissions by type of CSP resource by selecting the period and permission type. All permissions require approval, but when ‘Emergency’ is selected, the permission is granted simultaneously with the approval request, and a related email is sent to the approver.
Resource Information
- Project: Select a project that the user belongs to.
- Account: Select an account registered in the selected project.
- Resource Type: Select one of Compute or DB.
Permission
- Period: Select a period (e.g., 4h, 8h, 24h, 10d, 30d, 12m).
- Emergency: If checked, the permission is granted simultaneously with the approval request, and a related email is sent to the approver.
- Permission Level: Select one of USER, ADMIN, or DBA.
- Comment: Add a comment for approval.
Create Approval
To obtain resource access permissions, an approval process is required. To proceed with the approval process, go through the “Create Approval” popup and send it to Knox Approval, which will proceed through Knox Approval.
- Title: Automatically entered by the system and cannot be modified.
- Approver: Add approvers and consensus according to the guide.
- Content: Project and permission information are automatically entered by the system and cannot be modified.
Withdrawal
To remove permissions that are no longer needed, select the corresponding permission from the permission request list and click the Withdraw button.
PC Settings
To access cloud resources, you must install the client agent and register the IP address of the access environment.
Client Agent Download
Click Download Client Agent to start the download and install the client agent.
User Guide
To access resources, client download and installation are required. Also, if the installation is not completed or the version is not supported, you cannot connect to resources even if other preparations, such as permission and IP registration, are completed.
Installation Guide
To start the installation process, click the Download Client Agent button to download the installation file. After the download is complete, refer to the following information to proceed with the installation.
- Download Location: Specify a folder in the local drive.
- Execution: Select the downloaded file and click Run as Administrator by right-clicking to run it.
IP Registration
Cloud resource access is only possible for registered IPs, and up to 5 IPs can be registered.
Refer to the following information to register an IP.
- To add a new IP, click the Add button.
- To remove an existing IP, select the corresponding IP from the list and click the Delete button.
5 - Monitoring
CAM’s monitoring menu provides essential features for tracking console access history, user activities, and approval history. This feature ensures transparency, security, and compliance by providing insights through detailed information.
Access Log
The Access Log section provides a record of user activities within the CAM console, allowing administrators to track and review access-related actions across projects and cloud environments. It helps ensure security compliance and offers visibility into how and when users interact with cloud resources through the CAM interface.
Console Access Log
The Console Access Log records all events related to console access performed through CAM. This log enables tenant administrators to monitor console connection attempts, view event results, and identify access patterns for AWS, Azure, and SCP accounts.
The Console Access Log page is available under Monitoring > Access Log > Console Access Log.
Console Access Log Features
Log Scope
- Tenant (Company) Administrator: Can view logs for console access within the tenant.
- User: Can only view logs for their own projects.
Log Details
- The Console Access Log captures event data for all console-related activities initiated through CAM.
- Logs are available for all configured tenants and cover access events across AWS, Azure, and SCP.
- Log details display information such as event type, date/time, project, account ID, etc.
- Click the Expand icon to view detailed information about all actions. This detailed view provides a deeper understanding of each access attempt. The detailed event information includes:
- Event ID
- Event Source
- Event Result
- Request Type
- User Agent
- Region
- Source IP Address
- User Information
- Use filters such as project, CSP, environment, etc. to narrow down the results.
- Select a period to filter logs. The default period is 30 days.
- Logs are sorted in reverse chronological order, with the most recent actions at the top.
- Each log entry serves as an audit trail to trace console access patterns and user activity across CAM.
- Download all log data for the selected period as an Excel file for offline analysis or record-keeping.
Audit Log
Guide
- Navigate to Monitoring > Audit Log from the menu.
- Select the desired log type: audit log or approval log.
- Use search and filter options to find logs based on criteria such as user, resource type, or period.
- Check the details, including the timestamp of access, user information, and resource details.
The Audit Log section of the monitoring module provides a comprehensive history of user and system actions performed within the CAM portal, divided into two detailed items.
- Audit Log
- Approval Log
Audit Log
The Audit Log section displays the history of operations related to the creation, update, and deletion of data within the CAM portal.
Audit Log Features
Log Scope
- Tenant (Company) Administrator: Can view logs for all projects within the tenant.
- User: Can only view logs for their own projects.
Log Details
- Log details display information such as event type, date/time, user, IP, etc.
- Click the Expand icon to view detailed information about all actions.
- Use filters such as project, event type, user, etc. to narrow down the results.
- Select a period to filter logs. The default period is 30 days.
- Logs are sorted in reverse chronological order, with the most recent actions at the top.
- Download all log data for the selected period as an Excel file for offline analysis or record-keeping.
Approval Log
The Approval Log section provides a history of all approval requests and approval statuses within the CAM.
Approval Log Features
Log Scope
- Tenant (Company) Administrator: Can view approval logs for all projects within the tenant.
- User: Can view approval logs for their own projects.
Log Details
- Log details display approval type, approval status, details, and approval history.
- Check the approval status, such as pending, approved, or rejected.
- Open a specific approval item to view its details.
- Use filters such as project, approval type, approval status, user, etc. to narrow down the results.
- Select a period to filter logs. The default period is 30 days.
- Logs are sorted in reverse chronological order, with the most recent approvals at the top.
- Download all log data for the selected period as an Excel file for offline analysis or record-keeping.
6 - Configuration
The configuration feature enables PM and PL group users to manage essential project settings, account configurations and tenant administrators to set up approval lines and organizational charts.
Project
The project menu allows users to view all projects they belong to. Project details are initially registered by the PM, and can be modified by the PM or PL group users as needed.
Create Project
To create a project, click the Create Project button and enter the project information.
- Project Name: Give a name to the project.
- PM: Designate a project manager who can manage project-related information and permissions. Note that if you designate someone other than yourself, you will no longer be able to manage the project after creation.
- Organization: Select the organization that will carry out the project.
- Description: Enter a description of the project.
View Project
In the View Project screen, PM or PL group users can manage project information and add CSP accounts and users to the project.
- General Information: Displays the project information registered in the Create Project screen.
- Edit: Click the Edit button to modify the project’s general information.
- Delete: Click the Delete button to delete the project.
- Users: Displays a list of users registered to the project.
- Accounts: Displays a list of cloud accounts registered to the project.
Cloud Account Management
PM and PL group users can add new accounts to the project or delete accounts that are no longer in use.
Adding AWS Account
CAM supports a keyless method to enhance security when connecting cloud accounts.
To register an account, you need to create a new role in the AWS IAM service with the policy required by CAM. Follow these steps to create a role in AWS:
- Access the AWS IAM service
- Go to the Roles menu and click Create Role
- Click the Create button in the Access management > Roles section to go to the Create Role screen.
- Create Role > Step 1: Select a trusted entity.
This step is where you enter CAM account information.
- Select AWS account and Another AWS account in order, and enter the CAM account ID 022499039571 in the account ID field.
- Create Role > Step 2: Add permissions
- Assign the CAM policy to the newly created role.
Guide
Search for and select the relevant policy, and proceed to the next step.
- IAMFullAccess
- AmazonEC2FullAccess
- AmazonRDSFullAccess
- AWSCloudTrail_FullAccess
- AmazonS3FullAccess
- AmazonEventBridgeFullAccess
- Create Role > Step 3: Name, review, and create
Enter a role name and click the Create Role button to complete the role creation.
※ The role name created here will be used as the Role Name when registering the account in CAM.
Guide
After creating a role in IAM, go back to the Project View screen in CAM and register the account. Click the Add button above the account list and enter the account information to register the account to the project. To complete the account registration, an approval process is required. Click the Create Approval button to proceed with the approval, which will be sent to an approval system such as Knox for processing. Once the approval is complete, you can view the newly registered account in the account list.
- CSP: Select the CSP.
- Environment: Select the service environment.
- Account Name: Give a name to the account.
- Account ID: Enter the account ID registered in AWS and click the ‘Verify’ button to confirm.
- AWS Type: Set to ON if the account is a Chinese account.
- Role Name: Enter the role name created in the AWS IAM.
Note
Account registration policies may vary depending on the tenant. According to the tenant’s policy, accounts may be restricted to registration in only one project.
- Title: Automatically entered by the system and cannot be modified.
- Approver: The approval line is automatically added by the system, and approvers and agreeers can be added according to the approval guide.
- Content: Account information is automatically entered by the system and cannot be modified.
Adding SCP Account
PM and PL group users can add new SCP account to a CAM project through the Add Account button in the View Project page. CAM supports a keyless connection method for enhanced security, so no credentials are exchanged directly during account registration. Before you begin, make sure that the required setup is completed in the SCP Console.
Note
SCP includes both SCP for Samsung and SCP for Enterprises environments. Depending on your CSP authority or selection, the pre-requisites and steps for adding an account are identical for both.
Step 1. Pre-requisite Setup (One-time Trust Configuration for CAM Account)
Before adding your SCP account in CAM, ensure the following configuration is completed on the SCP side.
This setup allows CAM to securely access the target project and verify account information.
First you will need to setup policy, if it is not already created based on the described steps in the manual below. Then authorize the CAM account via Permission Groups and then add members.
- Create a Policy for CAM Access
Go to SCP Console.
Login and navigate to the IAM > Policies section in SCP Console.
Create a Policy with the name ‘CAM_Linked_Policy’
Create a new policy that includes the necessary permissions required for CAM operation based on the following table:
| ID | Action | Reason |
|---|
| [Platform] Permission Management | List, Read, Create, Delete, Update Permission | Create/Delete Policy, Assign Policy to Role |
| [Platform] Resource Management | List, Read | View List and Details of SCP |
| [Platform] Tag Management | List, Read | View Tag List/Information, etc. |
| [Platform] Project Management | List, Read | Assigned Project List/Information |
Table. Policy for CAM Access list
Alternatively, you can also add policy requirements to JSON Mode.
You can connect Permission Group and role later, so Complete Policy creation without checking anything
- Authorize the CAM Account via Permission Groups
- Once the policy is created, link it to the CAM system account using a permission group.
- Step-by-step:
- Navigate to IAM > Permission Groups
- Create a new permission group (e.g., CAM-Access-Group)
- Create a Permission Group with the name ‘CAM_Linked_Group’.
- Attach the CAM policy created above to this group
- When you add User to your project, you will connect User to Permission Group, so now you can Complete Permission Group generation without checking any User.
- Assign CAM Service Account to the Permission Group
- Navigate to the Project Members section in your SCP Console.
- Add the required account as a member of your target project.
- This account represents CAM and will be used for integration.
- To Add it, select the target project > Identity Access Management > Add User > Add Project Member > Add SCP User to Target Project
- Proceed to Add Project Member
- Search CAM users with ‘cam.app@samsung.com’ e-mail address.
- Click the ADD button to select the cam.app user.
- Add the User available from the list. Alternatively, you can search the user by using the search functionality.
- Search user to add as a Project Member.
- Select the Permission Group with the name ‘CAM_Linked_Group’ that you created above and complete the Add Project member operation.
- Connect Permission Groups to complete Adding Project Member
- After completing the above steps, return to the Project View screen in CAM to add your SCP account.
Step 2. Add Account in CAM console
- In CAM, go to View Project > Manage Accounts.
- Click the Add Account button.
- In the pop-up that opens, fill in the following details:
- Select CSP and Environment
- CSP: Choose SCP for Enterprises or SCP for Samsung.
- Environment: Select the environment this account will belong to (e.g., DEV, STG, PRD, or ETC).
- Enter Account Information
- Account Name:
- Enter a name to identify this account within CAM.
- This can be up to 50 characters long.
- Only English letters and numbers are allowed.
- Project ID (from SCP Console):
- Enter the Project ID of the SCP project you prepared earlier.
- Allowed: English letters, numbers, and hyphens only
- Max: 30 characters
- Click Verify after entering the Project ID. CAM checks the following:
- The project exists in SCP.
- The required roles (cam-Administrator, cam-Operator, cam-Developer) are present.
- The project isn’t already registered in another CAM project or awaiting approval elsewhere.
- If any of these conditions are not met, you’ll see a validation message.
Step 3. Create Approval
Once the Project ID is verified and other details are complete, the Create Approval button will become active.
Click it to send the account addition request for approval. Depending on your CAM setup, you can either select the approvers manually or let the system route it to the default approvers.
After approval, the SCP account will appear in the Project Accounts table in CAM.
Adding Azure Account
Before adding an Azure account in CAM, complete the following setup steps in the Microsoft Entra ID and Azure Portal. These steps must be performed by a Tenant Admin.
Step 1: Pre-requisite Setup (One-time Trust and Domain Configuration for CAM Account)
This step ensures that CAM is trusted within the target Azure tenant and has the required access permissions. This step needs to be completed before adding an Azure account in CAM by the Tenant Admin.
These pre-requisites are divided into two sections:
- Trust Configuration
- Domain Configuration
Trust Configuration for CAM Account
This step ensures that CAM is trusted within the target Azure tenant and has the required access permissions. It must be performed by a Tenant Administrator in the target Azure tenant. The purpose is to grant the CAM application the necessary permissions to access resources within Microsoft Entra ID.
To allow CAM to integrate with Azure, the Tenant Administrator must open the CAM Admin Consent URL. This URL triggers a Microsoft Entra Admin Center consent dialog, where the admin can approve the requested permissions for the CAM application.
Obtain the Tenant ID
The CAM Admin Consent URL includes an App Client ID linked to a specific tenant. Before using it, the Tenant ID of the target Azure tenant must be confirmed.
To find your Tenant ID:
- Sign in to the Azure Portal.
- In the left navigation menu, go to Microsoft Entra ID.
- In the Overview tab (first screen), locate the Tenant ID field.
- Copy the Tenant ID for use in the Admin Consent URL.
Access the CAM Admin Consent URL
Open the CAM Admin Consent URL in a web browser.
(https://login.microsoftonline.com/{Your_Tenant_ID}/adminconsent?client_id=39613ae7-2fd4-4f3c-9471-aba2391da0b5)
Replace the placeholder {Your_Tenant_ID} in the URL with the actual Tenant ID you copied earlier.
When prompted, select the Global Administrator account of the target tenant.
This account must have the highest administrative privileges in the tenant.
Review the Consent Agreement displayed. This agreement outlines the exact permissions CAM will be granted.
If you agree, click Accept to approve the integration.
By completing this step, CAM gains access to the tenant-level resources in Microsoft Entra ID.
No Subscription Access Yet: This step does not grant CAM access to Azure subscriptions. Subscription-level access will be configured separately in later steps (Management Group Role creation and Subscription Role assignment).
Verify CAM application registration after granting consent
- In Azure Portal, navigate to Microsoft Entra ID → Enterprise Applications.
- Search for the CAM application.
- Confirm the CAM app appears in the list and is properly registered.
Note
When you grant Admin Consent, you are giving CAM tenant-level recognition.
Domain Configuration for CAM Account
In Azure, domain linkage is required so that you as a user can authenticate through email and integrate with CAM’s Keycloak authentication.
The process of Domain Configuration has two main phases:
| Phase | Who Performs It | Frequency |
|---|
| Create a Domain | Tenant Admin or PM/PL | Once per tenant (maybe repeated for new domains if required) |
| Register your domain in the Azure Tenant | Tenant Admin | Once per tenant (unless additional domains are added later) |
Table. Domain Configuration for CAM Account list
Create a Domain
You can create a public domain using any DNS service that can generate TXT records (e.g., AWS Route 53, SCP DNS).
For this guide, we use SCP DNS as an example.
- Pre-Domain Creation Operations
- Log into SCP DNS.
- Access the SCP console and navigate to the DNS menu.
- Initiate Public Domain Purchase.
- Click Product Request.
- This opens the Purchase Form.
- Fill in the details of Domain Purchase Form.
- Usage Type: Select Public
- Domain Name: Enter desired public domain name.
- Registrant Details: Enter name, email, address, phone number.
- Description and Designation fields.
- Billing Information will be displayed before purchase confirmation.
- Confirm Purchase
- Review the final billed amount.
- Click Next to confirm.
- Verify DNS Status
- Once created, the domain will appear in the SCP DNS list.
- Wait until the status shows Active; which suggests it is now publicly usable.
- You now have an active public domain that can be linked to your Azure tenant for user authentication.
Register your Domain in the Azure tenant
Now that the public domain exists, it must be linked to Microsoft Entra ID for authentication.
Pre-Domain Setup Operations (Azure Tenant)
- Sign in to the Azure Portal with a Tenant Administrator account.
- Navigate to Microsoft Entra ID → Custom Domain Names.
- Click +Add Custom Domain.
- Enter your public domain name (the one you created in SCP).
- Click Add Domain.
Generate a TXT Record of the Domain (Azure → SCP DNS)
- Once you add the domain in Azure:
- Azure will display a TXT record value that must be added to your domain’s DNS settings. This is required to verify domain ownership.
- Copy the TX record value from Azure.
Add TXT Record (To SCP / Domain Host)
- Go to SCP DNS then select the Active public domain you created.
- Click Add Record.
- Record Type: Select TXT.
- Value: Paste the TXT record value copied from Azure.
- TTL (Time to Live): Choose according to preference.
- Click Confirm.
- Ensure the record appears in the domain’s DNS list.
Validate Domain in Azure
- Return to the Azure Portal; select Microsoft Entra ID; then select Custom Domain Names.
- Initially, the domain status will be unverified.
- Click the domain and click Verify button.
- Once Azure detects the TXT record (propagation may take several minutes); Status changes to Verified.
- Your public domain is now officially linked to the Azure tenant.
Step 2. Add Account in CAM console
- In CAM, go to View Project > Manage Accounts.
- Click the Add Account button.
- In the pop-up that opens, fill in the following details:
- Select CSP and Environment
- CSP: Choose Azure
- Environment: Select the environment this account will
- Enter Account Information
- Account Name:
- Enter a name to identify this account within CAM.
- This can be up to 50 characters long.
- Only English letters and numbers are allowed.
- Tenant ID (from Azure Portal):
- Enter the Tenant ID.
- Only English letters, numbers, and hyphens are allowed.
- Maximum 36 characters can be entered.
- Click Verify and CAM will check the following:
- Confirm if the Tenant ID format is correct.
- Validate it against Azure to ensure it exists.
- Only after Tenant ID is verified will the Subscription ID field be enabled.
- Subscription ID (from Azure Portal):
- Enter the Subscription ID.
- Only English letters, numbers, and hyphens are allowed.
- Maximum 36 characters can be entered.
- Click Verify and CAM will check the following:
- Confirm if the Subscription ID format is correct.
- Check if the Subscription ID is already linked to another CAM project.
- Check if it is already registered or has a pending approval request.
- Only after Subscription ID is verified will the Federation Domain field be enabled.
- Federation Domain (from Azure Portal):
- Enter the Federation Domain.
- Only English letters, numbers, hyphens, and dots are allowed.
- Maximum 48 characters can be entered.
- Click Verify and CAM will check the following:
- Confirm that the Federation Domain format is correct.
- Ensure it matches an existing verified domain from Azure Domain Configuration.
Step 3. Create Approval
Once all the fields are verified and details are complete, the Create Approval button will become active.
Click it to send the account addition request for approval. Depending on your CAM setup, you can either select the approvers manually or let the system route it to the default approvers.
After approval, the Azure account will appear in the Project Accounts table in CAM.
Delete Account
Click the Delete button in the View Account section to delete an account that is no longer in use.
User Management
PM and PL group users can add or remove users from the project. Only users registered to the project can be granted console and resource access within the project, so users who need console or resource access must be registered as project users.
Add User
Click the Add button above the user list to add a user to the project.
- Name: Search for the user name registered in CAM.
- Group: Select the user’s group.
- PL: Can manage project-related information and has the same permissions as the project manager.
- Operator, Developer: Can view project-related information and request permissions for resources. These users are categorized for project role management but have the same permissions in the CAM portal.
Delete User
Select the user to delete from the user list and click the Delete button.
After deleting a user, the deleted user can no longer view project-related information.
Notice
The Notice section allows Tenant Admins to create and manage notices that are displayed in the GNB Notices panel for users within the tenant. Multiple notices can be active simultaneously. Each notice can include a title, detailed description, optional attachment(s), and a defined display period.
Create Notice
To Create a Notice, click on the Create button on List page. In the Create Notice page, enter the following details:
- Title: Enter a title for the notice.
- Description: Provide the content or message to be displayed.
- Attachment (Optional): Upload supporting files (up to 5 files, with a combined maximum size of 50 MB). Empty files cannot be uploaded and supported file formats include images, documents, .mp4, and .zip.
- Display: Toggle ON to enable the notice for display in the GNB. Once the toggle is turned ON, you can select the Display Period or the date range during which the notice should be visible to users.
Select Save to create the notice. The newly created notice will appear in the Notice list.
View Notice Details
Select any notice title from the list to open the Notice Details page.
All notice information (Title, Description, Attachments, Display Period, Created By, and Created Date) is displayed in read-only mode.
From this view:
- Use Edit to modify the notice.
- Use Delete to permanently remove the notice.
.
Edit Notice
- From the Notice List, select a notice to open its Detail View.
- Select Edit.
- Modify the required fields (Title, Description, Attachment, Display settings, or Date Range).
- Select Save to update the notice.
Note
Changes made to an active notice take effect immediately.
Delete Notice
- From the Notice Detail view page, select Delete.
- Confirm the deletion when prompted.
The selected notice will be removed from the list and will no longer appear in GNB Notices.
Approval Line
Tenant administrators can predefine approval lines that users must specify when creating an approval.
Create Approval Line
To create an approval line, click the Create button and specify the approval case and organization to create.
- Name: Enter a name for the approval line that will not be exposed to users.
- Target: Select when and which organization to apply.
- Approver Guide: Enter the approver information that cannot be automatically designated by the system but must be included in the approval line. If entered, it will be exposed to users as follows.
- Approver: Search for and add the approver’s name to be automatically designated and exposed by the system.
View Approval Line
To view detailed information about an approval line, go to the Approval Line menu and click on the desired approval line. You can view information about all approval lines and modify or delete them.
Modify Approval Line
Click the Edit button in the View Approval Line screen to modify the information.
Delete Approval Line
Click the Delete button to delete an approval line that is no longer in use.
Organization
The organization menu allows tenant administrators to manually manage the tenant’s organization.
Tenant administrators can create organizations, which can be used to manage projects and approval lines by organization unit.
Add Organization
To add an organization, click the Add button and enter the following details in the Add Organization popup.
- Parent (Upper Organization): Select the name of the upper organization. The default value is the tenant name.
- Name: Enter the name of the organization to create.
- Display: Set the toggle to ON to expose the organization in the Organization list to users.
View Organization
The View Organization page displays a list of all created organizations. Click on the organization name to view detailed organization information on the right.
You can expand the entire organization list to view all organizations at once, or collapse it to view only the top-level organizations.
Modify Organization
The data entered when creating the organization is displayed, and all data can be modified. Click the Save button after modifying.
Delete Organization
Click the Delete button in the View Organization screen to delete an organization that is no longer in use.
Note
Parent organizations and organizations with registered projects cannot be deleted.
Tenant Administrator
The tenant administrator menu allows you to add, specify, or delete administrators who manage the tenant.
Initially, the user who applied for the service is designated as the tenant administrator, and subsequent administrators can be directly added, deleted, and managed by tenant administrators with administrative privileges.
Tenant administrators can manage tenant-based information through dedicated menus (e.g., Approval Line, Organization, etc.) and view all content within the tenant.
Add Tenant Administrator
To add a tenant administrator, click the Add button and search for and register a user among those registered to the tenant.
Delete Tenant Administrator
Select the user to delete from the tenant administrator list and click the Delete button.
7 - FAQ
Common
I am unable to access the CAM site.
- The CAM site can only be accessed from the allowed internal network of the tenant.
- Please check if the network you are accessing is an accessible environment.
- Refer to Getting Started > Network Environment.
Do I need to process the firewall in advance?
- To access resources through the CAM site, firewall registration must be done in advance from CAM to the accessing resources (Jumphost).
- For the contents required for firewall registration, please inquire with the tenant administrator.
I am unable to log in.
- Membership registration and login follow the SingleID system, so you must go through SingleID’s sign-in process or your company’s SSO process (e.g., Knox SSO), followed by MFA (e.g., SMS, Email, etc.) to access the CAM portal.
- When accessing for the first time, select the MFA method (SMS, Email, etc.), and the OTP will be sent to the phone number or email stored in Knox personal information, if SSO is configured for Knox, and you can log in by entering the OTP. If your phone number has changed, it may take some time for the Knox personal information to be updated and reflected in SingleID, so please try again.
Project
Is there anything I need to prepare in advance to register a cloud account?
- To register an account in CAM, you need to create a new role in CSP IAM and have the CAM service account assume that role.
- Add the policies required by CAM to create a new role and add the CAM service account as a trusted entity.
- For a detailed guide on registering a new role in CSP IAM, please refer to add account section of Configuration manual.
I am unable to register an account.
- When registering an account, the consistency of the account ID and role name is checked.
- Please enter the CSP account ID information in the account ID and the role name information created in CSP IAM according to the guide.
- Also, check if the role was created correctly according to the guide.
- The account information will be exposed on the project screen’s account list only after the approval for account registration is completed.
- If Knox approval system is used as an approval system, please check the approval status in Knox approval.
Console Access
An error message appears on the CSP console login screen.
- The CAM site provides CSP login based on console roles, and if there is no role that the user can log in to, CSP recognizes it as an invalid request and displays an error message.
- If you see the message “Your request included an invalid SAML response,” please request an CSP role from the PM or PL.
- After the PM or PL registers the user to the role and the approval is completed, you can log in by selecting the corresponding role on the CSP console screen.
I am unable to access the CSP console login screen.
- The CAM site has restrictions on accessing some services depending on the access environment.
- While the CAM site can be accessed from the internal network environment, resource access may be allowed only for specific IP ranges for each tenant. Please check your access environment and inquire with the tenant administrator.
I created a role and policy, but the role is not visible on the CSP console login screen.
- It may take a few minutes for the role and policy to be actually created and applied in CSP.
- Or, the user registration and approval for the role must be completed for the registered user to select the role on the CSP console login screen, so please check the user registration and approval status.
I get an ‘Invalid CSP policy JSON.’ error message and policy creation fails.
- This is a CSP error that occurs when the input JSON template is not supported by CSP.
- Please check the input JSON and rewrite it in a valid format.
I get an ‘Unable to complete due to a CSP error response.’ error message and role mapping fails.
- This is a CSP error that occurs when the JSON of the policy being mapped or the policy to be mapped is invalid.
- Please delete the corresponding policy and create a new policy in a JSON format supported by CSP.
Resource Access
Is there anything I need to prepare in advance to access resources?
- To access resources through the CAM site, you need to apply for access permissions by account and resource type and get approval.
- Please apply and get approval through the authority request menu.
- After approval, you need to install the client agent on the PC you want to access and register the IP of the access environment.
- You can install the client agent by clicking the Download Client Agent button in the PC settings menu, and you can register up to 5 IPs.
- Refer to Resource Access > PC Settings.
I get an ‘Access to PRD server resources is restricted to ‘VDI for server connect’ environments where the Internet is blocked.’ error message and resource access fails.
- Access to PRD resources is restricted in general internal network environments.
- PRD resources can only be accessed from specific IP ranges where the Internet is blocked. For tenant-specific restricted environments, please inquire with the tenant administrator.
I get a ‘Resource connect is restricted due to unauthorized IP.’ error message and resource access fails.
- This error occurs because the current access IP is not registered in the CAM site.
- To access resources through the CAM site, you need to register the IP of the access environment in advance.
- Please register the IP of the access environment in the PC settings menu and use it.
- Refer to Resource Access > IP Registration.
I get an ‘Unable to connect to the resource since the local port you entered is already in use.’ error message and resource access fails.
- This message appears when the local port you entered is already in use by another application on your PC.
- Please enter an unused port between 1024 and 65,535 and try again.
What are the supported OS, DB vendors, and versions for enrolling resources?
- Currently, OS supports Ubuntu and Amazon Linux, and DB supports some versions of PostgreSQL, MySQL, Aurora PostgreSQL, and Aurora MySQL.
- For detailed version information of each OS/DB, please refer to Getting Started > Service Scope.
- This message appears when the address information of the resource to be registered is invalid.
- Please check the IP and port information of the address and try again.
I get an ‘Invalid authentication credentials. Please check your credentials, then try again.’ error message and resource registration fails.
- This message appears when the root user information of the resource to be registered is invalid.
- Please check the ID and password information of the root account and try again.
I get an ‘Unable to connect to the resource because the PC agent is not connected.’ error message and resource access fails.
- This occurs when the Client Agent is not automatically executed when the PC is running.
- We recommend restarting the PC to automatically execute the Client Agent, or reinstalling and executing the Client Agent.
I get an ‘Unable to connect to the resource. Please try again after checking the resource status.’ error message and resource access fails.
- This occurs when the resource to be accessed is not in an accessible state.
- Please check if the resource can be accessed through the network and try again after taking necessary actions.