This is the multi-page printable view of this section. Click here to print.
Firewall
- 1: Overview
- 2: How-to guides
- 2.1: Firewall Logging
- 2.2: Migration Rules
- 3: API Reference
- 4: CLI Reference
- 5: Release Note
1 - Overview
Service Overview
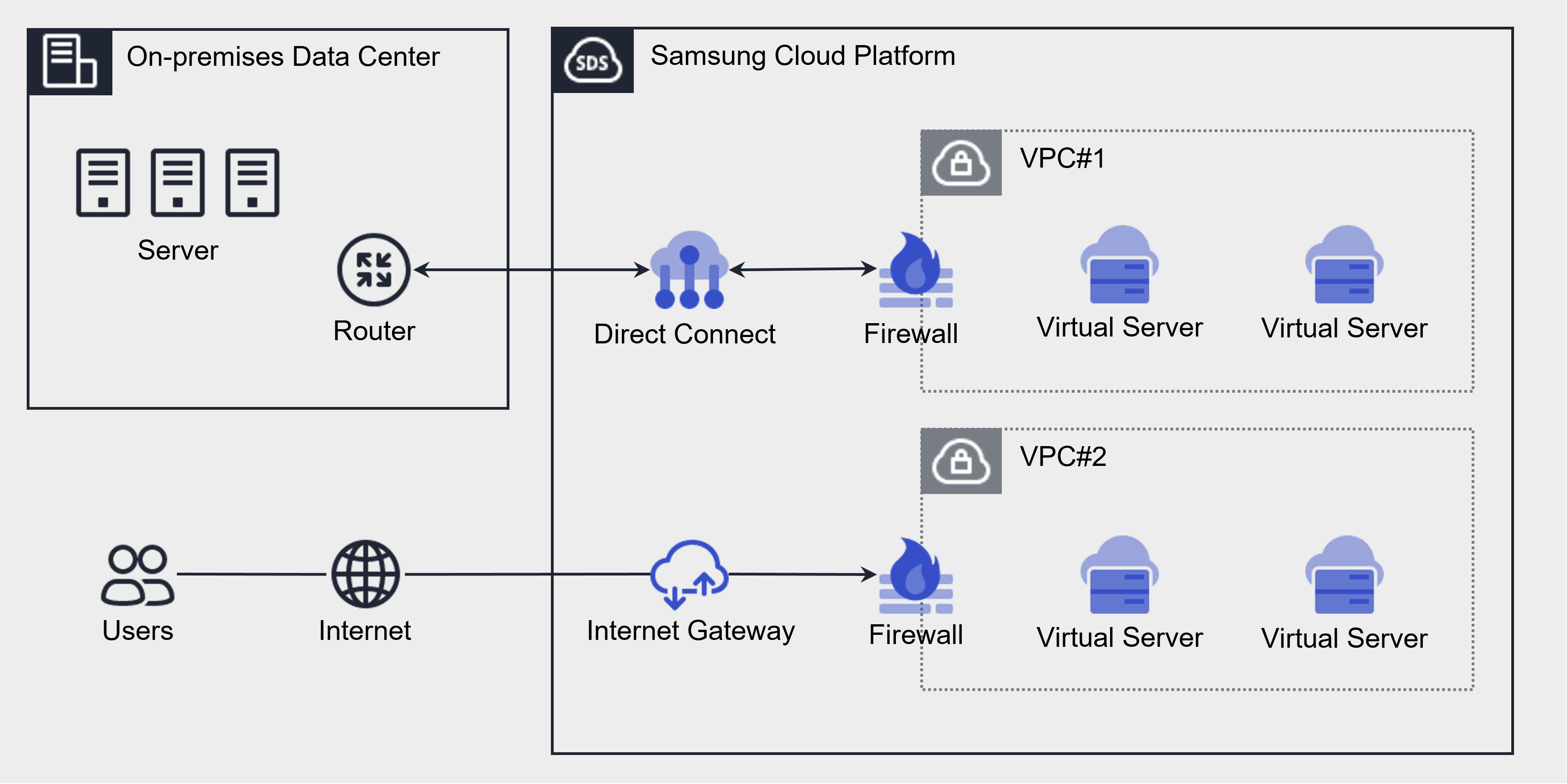
A firewall is a virtual logical firewall service that controls traffic occurring in the VPC and Load Balancer of Samsung Cloud Platform.
The resources that can be applied in the firewall are Internet Gateway, Direct Connect, and Load Balancer, and you can set rules for communication between the VPC and the Internet, and between the VPC and the customer network, enabling secure network management.
When a firewall is first created, it blocks all inbound and outbound traffic according to the default rule (Any Deny).
Users can specify an IP address, port, and protocol to create inbound/outbound rules, and only traffic permitted by the created rules can communicate.
Component
The components that make up a firewall are as follows.
| Component | Detailed description |
|---|---|
| Applicable target | Resources to which the firewall will be applied
|
| Firewall size | Firewall is offered in five sizes according to rule quota
|
| Firewall rule |
|
Constraints
The Firewall of Samsung Cloud Platform has a rule quota (limit) that can be created per size. When creating a Firewall, it is created by default as Extra Small, and you can change the Firewall size on the Firewall Details page of the Samsung Cloud Platform Console.
| Size | Rule quota | Detailed description |
|---|---|---|
| Extra Small | 5 | Maximum number of rules that can be created: 5 |
| Small | 100 items | Maximum number of rules that can be generated: 100 |
| Medium | 200 | Maximum number of rules that can be generated: 200 |
| Large | 500 | Maximum number of rules that can be generated: 500 |
| Extra Large | 1,000 items | Maximum number of rules that can be generated: 1,000 |
Preceding Service
This is a list of services that must be pre-configured before creating a Firewall service. Please refer to the user guide (reference link) provided below for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Direct Connect | A service that quickly and securely connects the customer’s network with the Samsung Cloud Platform network. |
| Networking | Load Balancer | A service that distributes traffic across multiple servers to maintain stable service. |
2 - How-to guides
Users can create the Firewall service by entering the required information and selecting detailed options through the Samsung Cloud Platform Console.
Create Firewall
You can create and use a Firewall service in the Samsung Cloud Platform Console.
The Firewall service must be enabled in the prerequisite service of Networking to be created. The enabled Firewall can be viewed in the Firewall list.
- Firewalls cannot be created independently, unlike other services in the Samsung Cloud Platform Console.
To enable the firewall, follow these steps.
Click the All Services > Networking > Firewall menu. Navigate to the Firewall’s Service Home page.
On the Service Home page, click the service you want to create. You will be redirected to the service creation page.
- VPC Creation: Configure the VPC service’s Internet Gateway and Transit Gateway firewall.
- When creating a VPC’s Internet Gateway service, set the Use Firewall option to Enabled. For detailed instructions, refer to Create Internet Gateway.
- Create a Transit Gateway service for the VPC and apply for the associated service of the Uplink Firewall. For detailed instructions, refer to Create Transit Gateway.
- Direct Connet Creation: When creating a Direct Connect service, set the Firewall Use option to Enabled. For detailed instructions, refer to Direct Connect 생성하기.
- Load Balancer Creation: When creating a Load Balancer service, set the Firewall Use option to Enabled. For detailed instructions, see Load Balancer Creation.
- VPC Creation: Configure the VPC service’s Internet Gateway and Transit Gateway firewall.
After the prerequisite service creation is complete, verify that the corresponding Firewall resource appears in the Firewall list.
Check firewall detailed information
The Firewall service can view and edit the full resource list and detailed information in the resource management menu.
To view detailed information about the firewall, follow these steps.
- Click the All Services > Networking > Firewall menu. Go to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- The Firewall List page shows the information below.
Category Detailed description Firewall name Automatically generated in the Firewall pre-service type_Firewall format Firewall classification Firewall pre-service type (Internet Gateway, Direct Connect, Load Balancer) Size User-selected Firewall size VPC name VPC name connected to the firewall Connection name Automatically generate in the format preceding service name_Firewall for services using Firewall. Number of rules Number of rules used on this firewall Whether to use Whether the firewall is used (enabled) or not used (disabled) - If not used, the Any Allow rule is applied and no charges are incurred for the firewall
status Firewall status display - More button can be clicked to set On/Off
Table. Firewall resource list items
- The Firewall List page shows the information below.
- On the Firewall List page, click the resource to view detailed information. It navigates to the Firewall Details page.
- Firewall Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity Log tabs.
Category Detailed description Service status Firewall status display - Creating: In progress
- Active: Operational
- Editing: In progress
- Deploying: Completed
- Deleting: In progress
- Error: Occurred
Table. Firewall status information
- Firewall Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity Log tabs.
Detailed Information
On the Firewall List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Firewall name | Automatically generated as the connection name for the resource name_Firewall |
| Firewall ID | Service’s unique resource ID |
| Firewall classification | Firewall prerequisite service types (Internet Gateway, Direct Connect, Load Balancer) |
| Size | The Firewall size selected by the user
|
| Firewall rule count/quota | The firewall’s rule quota and the number of rules currently in use |
| VPC name | VPC name connected to the Firewall
|
| VPC ID | VPC ID connected to the firewall |
| Connection name | {Firewall Prerequisite Service Name_Firewall} automatically generated
|
| Log saving option | Firewall log storage option
|
Rule
On the Firewall List page, you can view the rule list of the selected resource and add, modify, or delete rules.
| Category | Detailed description |
|---|---|
| Excel download | Download the currently entered rule list as an Excel (*.xlsx) file |
| Advanced Search | Search for rules that match the conditions set by the user
|
| Rule modification | Rules displayed in the rule list can be edited and deleted
|
| Add rule | Add new Firewall rule
|
| Order | Display rule order, apply top-down according to the rule order |
| Rule ID | Unique ID value for the rule
|
| Rule Index | Unique index value for the rule, used in log analysis |
| Source address | Origin address added to the rule |
| Destination address | Destination address added to the rule, displayed as the IP address according to the entered rule. |
| Service | Protocol and Destination Port |
| Operation | Traffic Allow/Deny distinction due to rules
|
| direction | Firewall traffic direction criteria
|
| Active status | Indicates whether the rule is active; if it is inactive, the rule does not operate. |
| status | Rule status display |
tag
Firewall List page lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Firewall List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Firewall Rule Management
You can add, modify, or delete firewall rules.
- You can add or modify rules only when the firewall status is Active.
- If you do not have permission to view the status in the preceding service, you cannot add a rule.
- The firewall periodically caches the domain rules registered by the user and retains the IP information for a certain period.
- If the cached result of the registered domain rule does not match the user’s IP, communication may be restricted.
Create Rule
In the Rules tab, you can directly input firewall rule information to add it.
To add a firewall rule, follow the steps below.
- Click the All Services > Networking > Firewall menu. Navigate to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- On the Firewall List page, click the resource to which you want to add a rule. You will be taken to the Firewall Details page.
- On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
- Click the Add Rule button on the Rules tab. You will be taken to the Add Rule page.
- Enter the required information on the Manual Input tab page.
- After checking the added rules, click the Complete button.
| Category | Required? | Detailed description |
|---|---|---|
| Rule location | Required | Specify the location of the rule to create |
| Rule ID to copy | Selection | Enter the Firewall rule ID to copy and click the Search button to select. |
| Source address | Required | Source addresses to add to the rule
|
| Destination address | Required | Select the type of destination address to add to the rule
|
| type | Required | Select protocol type to apply the rule
|
| Type > Protocol | Required | Select detailed protocol for the type
|
| Operation | Required | Traffic allow/deny classification based on rules
|
| Direction | Required | Firewall-based traffic direction
|
| Explanation | Selection | Additional description provided by the user |
| Added rule | - | Entered rules verification list
|
| Destination | Required | Destination address type to add to the rule
- Select IP or FQDN
- You can input multiple addresses at once, up to a maximum of 128, using CIDR (IP/Subnet Mask) format with commas (,) and ranges (-)
- Domain names can be entered in bulk using Comma(,) for up to 128 addresses at once
Batch create rules
To add multiple Firewall rules at once, follow these steps.
- Click the All Services > Networking > Firewall menu. Navigate to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- On the Firewall List page, click the resource to which you want to add a rule. You will be taken to the Firewall Details page.
- On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
- Click the Add Rule button on the Rule tab. You will be taken to the Add Rule page.
- Add Rule on the Batch Rule Input tab, click it.
- Please select the rule location. If you do not select a location, it will be added at the very last order of the rule.
- From File Selection, click the Download Form button. The bulk rule entry Excel file will be downloaded.
- Enter the rule information into the batch rule input Excel file, then save it.
- From File Selection, click Attach File to attach the Excel file you created, and click Add.
- You cannot upload if the attached Excel file format differs from the registration form or if the file is encrypted.
- You can upload up to 100 batch registration rules at a time. Uploads are not allowed if you exceed the maximum number of registration rules.
- If the number of rules set for the firewall size is exceeded, you cannot upload the file.
- Added rule Check that the rule you entered appears in the list and adjust its order.
- After checking the added rules, click the Complete button.
Modify Rules
You can select a firewall rule to view and edit its information.
To modify firewall rules, follow the steps below.
Click the All Services > Networking > Firewall menu. Go to the Service Home page of Firewall.
On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
Firewall List page, click the resource to edit the rule. You will be taken to the Firewall Details page.
On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
Click the Edit Rule button on the Rules tab. You will be taken to the Edit Rule page.
- On the rule edit page, you can configure the items below.
- Enable: Enables the selected rule.
- Disabled: Disables the selected rule. Disabled rules are not applied to preceding services.
- Delete: Delete the selected rule. Clicking Delete will mark the change as Pending Deletion.
- Cancel Deletion: If it is in a pending deletion state, you can cancel the rule deletion.
- On the rule edit page, you can configure the items below.
On the Edit Rule page, click the Edit button for the item you want to modify. The Edit Rule popup will open.
Rule Edit Enter the item you want to modify in the popup window and click the Confirm button.
Category Required? Detailed description Order - The order of rules can be changed by clicking Move Up/Move Down in the added rule list. Rule ID - Cannot be changed to a unique ID value for the rule Rule Index - Unique index value for the rule, usable in log analysis Source address Required Source addresses registered in the rule - in CIDR (IP/Subnet Mask) format, using commas (,) and ranges (-), can be entered and modified up to a maximum of 128 at once
Destination address Required Destination address to add to the rule - in CIDR (IP/Subnet Mask) format, using commas (,) and ranges (-) to input multiple addresses at once, up to a maximum of 128, for modification
type Required Set the protocol type according to the selected destination address entry Operation Required Traffic Allow/Deny classification can be changed by rules - Allow: Allow traffic when it matches the rule
- Deny: Block traffic when it matches the rule
direction Required The access direction of traffic defined by the firewall rule can be changed - Inbound: external → internal
- Outbound: internal → external
Rule location Required Rule position can be changed Active status Required Whether the rule is active; if it is disabled, the rule does not operate. status - State value for the rule description Select User-provided additional description Table. Detailed items for firewall rule modificationAfter reviewing the updated rules, click the Complete button.
Delete rule
To delete a firewall rule, follow the steps below.
- Click the All Services > Networking > Firewall menu. Go to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- Click the resource to edit the rule on the Firewall List page. Navigate to the Firewall Details page.
- On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
- In the Rule tab, click the Edit Rule button. You will be taken to the Edit Rule page.
- On the Edit Rule page, select the rule to delete and click the Delete button.
- When the deletion request is completed, the change item will be marked as Scheduled for deletion.
- Click Cancel Deletion to cancel the rule deletion.
- On the Edit Rule page, click the Complete button.
Managing Firewall Resources
You can modify the firewall size and change the log usage settings.
Modify Firewall Size
To modify the size of the firewall, follow these steps.
- Click the All Services > Networking > Firewall menu. Go to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- Click the resource to edit on the Firewall List page. Navigate to the Firewall Details page.
- On the Firewall Details page, click the Size Edit icon. You will be taken to the Size Edit popup.
- Resize In the popup window, select the size to adjust, and click the Confirm button.
The firewall size is provided as the default Extra Small (rule quota 5), and you can change the firewall size to add firewall rules for use. For more details, refer to Firewall Constraints.
- Firewall fees are charged based on the size of the Firewall service and traffic throughput.
Using Log Storage
To store firewall logs, first create a bucket in Object Storage for the logs and configure that bucket in the log repository of Firewall Logging. Then, by setting log storage in the firewall detail view, firewall logs will be saved to the Object Storage bucket.
- The log storage settings can be checked in Firewall Logging. For more information, see Firewall Logging.
- If you configure a log repository, Object Storage charges for log storage will be applied.
To use firewall log storage, follow these steps.
- Click the All Services > Networking > Firewall menu. Go to the Service Home page.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- Firewall List page, click the resource (Firewall) for which you want to enable log storage. You will be taken to the Firewall Details page.
- On the Firewall Details page, click the Edit icon of Log Save Setting. You will be taken to the Edit Log Save Setting popup.
- Modify Log Saving Option In the popup window, select Use for the log repository, and click the Confirm button.
Disable log storage
To set firewall log storage to disabled, follow these steps.
- Click the All Services > Networking > Firewall menu. You will be taken to the Service Home page.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- Firewall List page, click the resource (Firewall) that does not use log storage. You will be taken to the Firewall Details page.
- Click the Modify Log Save Setting button. You will be taken to the Modify Log Save Setting popup.
- Modify Log Saving Option In the popup window, deselect Use for the log repository, and click the Confirm button.
- Notification Check the message in the popup window and click the Confirm button.
Disable Firewall
The Firewall service cannot be deleted on its own. Deleting the preceding service will also delete the associated Firewall. When you choose not to use the firewall while retaining the preceding service, you can set the firewall to an unused state on the firewall list page.
- If you change the firewall to an unused state, all previously registered rules will be deleted.
- You cannot delete a preceding service if there are firewall rules associated with it. Delete the firewall rules before deleting the preceding service.
To disable the firewall, follow these steps.
- Click the All Services > Networking > Firewall menu. You will be taken to the Service Home page.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, click More > Unused for the resources you want to mark as unused.
- After the usage change is completed, verify on the Firewall List page that the resource’s usage status has been changed to unused.
2.1 - Firewall Logging
To store firewall logs, first create a bucket in Object Storage for the logs and configure that bucket in the log repository of Firewall Logging. Then, on the Firewall Details page, set up log storage, and the firewall logs will be saved to the Object Storage bucket.
To save firewall logs, configure it according to the following steps.
- To store firewall logs, you can create a bucket in Object Storage or use an existing bucket. To create a bucket, refer to Create Object Storage.
- To set the bucket for the Firewall Logging log repository, refer to Firewall Logging 로그 저장소 사용하기.
- To set the log storage option to Enabled in the detailed view of the Firewall, refer to Using Firewall Log Storage.
Firewall Logging Configure log storage usage
To set the firewall’s log storage to enabled, you must first configure the log repository in Firewall Logging.
To enable the Firewall Logging log repository, follow these steps.
- Click the All Services > Management > Network Logging > Firewall Logging menu. Go to the Firewall Logging List page.
- On the Firewall Logging List page, click the top Log Storage Settings button. You will be taken to the Log Storage Settings popup.
- Log storage settings In the popup window, select the log storage bucket. When you select a bucket, the log storage path is displayed.
- Log storage settings In the popup window, after verifying Log storage bucket and Log storage path, click the Confirm button.
- Notification After reviewing the popup message, click the Confirm button.
View Firewall Logging List
If you configure the Firewall Logging log storage bucket, you can view the Firewall Logging list.
To view the Firewall Logging list, follow these steps.
- Click the All Services > Management > Network Logging > Firewall Logging menu. You will be taken to the Firewall Logging List page.
- On the Firewall Logging List page, verify the resources in use and the log storage targets.
Category Detailed description Resource ID Firewall ID Save target Firewall name Save registration date and time Firewall log repository registration timestamp Table. Firewall Logging list items
Check detailed information of Firewall Logging
Refer to the information below to view the detailed contents of the stored log.
Stored log example: 2024-10-11T11:23:43,deny,0,17,4.1.1.100,45499,192.168.10.10,53
| Category | description |
|---|---|
| 2024-10-11T11:23:43 | Date and time of the log occurrence (2024-10-11, 11:23:43) |
| deny | Action (deny / accept) |
| 0 | Firewall Rule ID (Policy ID) that generated the log |
| 17 | IP Protocol ID
|
| 4.1.1.100 | Source IP |
| 45499 | Departure Port |
| 192.168.10.10 | Destination IP |
| 53 | Destination Port |
Firewall Logging Configure to not use log storage
In Firewall Logging, you can set the log repository to unused.
Firewall Logging To disable the log repository, follow the steps below.
- Click the All Services > Management > Network Logging > Firewall Logging menu. You will be taken to the Firewall Logging List page.
- Firewall Logging List page, click the top Log Storage Settings button. You will be taken to the Log Storage Settings popup.
- Log storage settings In the popup window, select Log storage bucket as Not used, and click the Confirm button.
- Log storage settings can be changed when no log storage target is configured.
- To change the log storage bucket, first set it to disabled. Then you can modify it by re-enabling it.
2.2 - Migration Rules
Users can retrieve rules created in the V1 environment of the Samsung Cloud Platform Console and apply them to the V2 service.
Get firewall rules
You can import rules created in the V1 environment of the Samsung Cloud Platform Console and migrate them to the V2 service for use.
- When a firewall rule is transferred using the Migration feature, the Migration label appears before its name.
- If a firewall rule description exceeds 100 characters, part of the description will be truncated and appended.
- Rules that exceed the maximum quantity are not registered due to rule quantity limits based on firewall size.
To retrieve the V1 firewall rules, follow these steps.
All Services > Networking > Firewall Click the menu. 1. Navigate to the Service Home page of the Firewall.
On the Service Home page, click the Migration Rules menu. 2. Go to the Migration Rules page.
Select the rule information to retrieve from the Migration Rules page and click Done.
Category Detailed description Original rule environment SCP v1 (Vmware) Auto-select Applicable target Select the Firewall list in the account to which the transferred rule will be applied Get rules Click the File Attachment button to upload the decrypted Firewall rule file - After decrypting and saving the rule file extracted from the original environment, upload
Rule List View uploaded Firewall rule file details - Move Up: Move the selected rule up in the list
- Move Down: Move the selected rule down in the list
- Delete: Delete the selected rule
- Edit: Modify the selected rule information; see Edit Transferable Firewall Rule for details
Rule location Set the position of the selected firewall rule - After the last rule: Move the selected rule after the last rule
- Set before the specified rule / Set after the specified rule: Enter the rule ID to move the selected rule before or after the specified rule
Table. Migration Rules detailed itemsAfter the firewall rule transfer request is completed, verify that the transferred item has been added to the firewall list.
Modify the Firewall rule to be transferred
You can edit each item when retrieving rules created in the V1 environment of the Samsung Cloud Platform Console.
To edit the Firewall rules to be imported from V1, follow these steps.
Click the All Services > Networking > Firewall menu. 1. Navigate to the Service Home page of the Firewall.
On the Service Home page, click the Migration Rules menu. 2. Go to the Migration Rules page.
Click Attach file in the rule import item to upload the Firewall rule file.
In the rule list, click Edit for the rule item you want to modify.
Category Required or not Detailed description origin address Essential Source addresses to add to the rule - in CIDR (IP/Subnet Mask) format, using commas (,), ranges (-) to input multiple addresses, up to a maximum of 128 at once
Destination address Essential Select the type of destination address to add to the rule - IP: In CIDR (IP/Subnet Mask) format, you can enter multiple addresses at once using commas (,) and ranges (-), up to a maximum of 128.
- Domain: In FQDN format, you can enter up to 128 full domain names at once using commas (,).
- The type items vary depending on the selected destination address format.
type Required Select protocol type to which the rule will be applied - Select destination port/Type: Select protocol type
- Internet Protocol: Enter protocol numbers, up to 128 entries allowed
- All: Select destination port/Type and protocol for the entire range, meaning all ports for all protocols
Type > Protocol Required Select detailed protocol for the type - Select the desired protocol among TCP, UDP, and ICMP; input fields vary depending on the selected protocol
- When ICMP is selected in the protocol, you can set the ICMP Type
- Select a commonly used Type, such as Echo, from the values defined for ICMP Type
- Click the Add button to add an input value
- When TCP/UDP is selected in the protocol, you can select allowed ports such as SSH, HTTP, TELNET, etc.
- When entering manually, you can input values from 1 to 65535, and you can enter up to 128 entries at once using commas (,) or ranges (-)
- Click the Add button to add an input value
- When Internet Protocol is selected in the type
1 - 254Enter the protocol number within the range
Operation Required Traffic allow/block classification by rule - Allow: Allow traffic when it matches the rule
- Deny: Block traffic when it matches the rule
Direction Essential Firewall standard traffic direction - Inbound: external → internal
- Outbound: internal → external
Active status Required Set rule activation status - If disabled, the rule does not execute
Explanation Selection Additional description written by the user Table. Detailed items of the Firewall rule edit windowWhen the rule information edit is complete, click Confirm in the edit window.
Review the modified rule information and click Done.
3 - API Reference
4 - CLI Reference
5 - Release Note
Firewall
- For user convenience, a Migration Rules page has been added that allows you to import firewall rules created in the V1 environment and apply them to the V2 service.
- The method for entering and modifying/deleting firewall rules has been changed for user convenience. * When managing firewall rules, you can navigate to a separate page to perform the desired actions.
- Add firewall rule input method
- In the KR WEST and KR EAST regions, you can enter the destination address in FQDN (Fully Qualified Domain Name) format.
- Add firewall rule input method
- A feature to input IP protocols has been added.
- Add firewall functionality
- You can use Firewall in the Load Balancer service.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- A feature to save firewall logs has been added.
- You can decide whether to store firewall logs and store the logs in Object Storage.
- Through the Firewall service, you can control inbound and outbound traffic in a VPC.
- The Firewall service has been released.