This is the multi-page printable view of this section. Click here to print.
API Gateway
1 - Overview
Service Overview
API Gateway is a service that makes it easy to create, manage, and monitor APIs. It allows you to define API-related resources and methods in a consistent format and apply built-in security access. Additionally, you can easily and conveniently monitor API usage and performance metrics.
Features
- Convenient API Management: You can conveniently register and manage APIs through the console, and it provides JWT (Json Web Token) for access permission management. It is also integrated with SCP Cloud Functions, allowing Cloud Functions to be invoked via the API Gateway.
- Stable Traffic Handling: API Gateway can manage backend system traffic through usage plans. Usage plans allow you to set the maximum number of calls per hour (hourly/daily/monthly), and by doing so, they prevent excessive traffic from entering, enabling stable service usage.
- Easy and convenient monitoring: Provides a dashboard with various management features, including API version management that links different deployment versions per stage, and allows you to monitor API usage. Through this, you can quickly and easily understand performance metrics such as API calls, response times, and error counts.
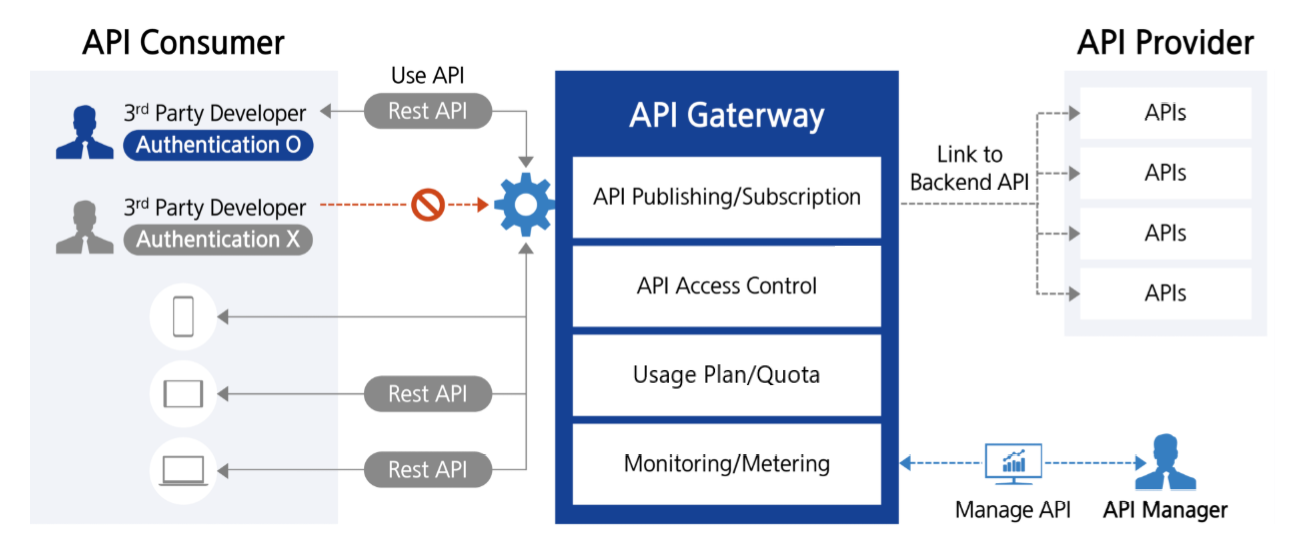
Service Diagram
- A developer (3rd party Developer) can access various backend services via a single endpoint (API Gateway) using Rest API.
- API Gateway can route the request to the appropriate backend service or Cloud Function.
- When authentication and authorization are required, the user is verified with JWT.
- Request data is transformed as needed, and responses from multiple services are aggregated into a single result through the API Gateway.
- When traffic is high, you can improve service reliability by applying load balancing and rate limiting (rate limiting).
- Supports web clients calling APIs from other domains via CORS configuration.
- All requests and responses are logged and monitored by the API Gateway service, enabling rapid detection of failures and anomalies.
- You can separate stages by environment—development, testing, production—to manage API versions and utilize the required version. API management, security policy enforcement, and related tasks can be handled consistently from a central point through the API Gateway service.
Provided features
API Gateway provides the following features.
API Management and Operations
- Custom Domain Name: Connect a custom domain to the API to provide a unique URL for the user
- REST API Creation and Management: Define resources and methods (GET, POST, etc.) and configure authentication methods
- API version and stage management: Operate the same API in multiple versions simultaneously and manage changes.
- Routing: Route requests to various backend services based on the URI path or request headers.
- Monitoring and Logging: API performance monitoring and log recording possible(‘available in December 2025)
API security
- IP ACL configuration: Control access so that only specific IPs can connect, enhancing security.
- Cloud Functions Integration: Integrate with serverless computing to execute business logic in response to external requests
- CORS Support: Set Cross-Origin Resource Sharing(CORS) to allow resource access from other domains
Component
API
An API is a collection of resources and methods integrated with backend HTTP endpoints, Cloud Functions, or other SCP services. An API provides the logical interface of the actual service and can be deployed to multiple stages for use in various environments (development, production, etc.).
resource
Resources are logical units that represent specific endpoints (URI paths) within an API. Each resource can be organized in a tree structure and can have multiple HTTP methods. For example,
/users
,
/orders
become individual resources.
Method
Methods define the HTTP actions (e.g., GET, POST, PUT, DELETE, etc.) that can be performed on each resource. Each method is integrated with a specific backend to process actual data or execute functionality.
Stage
The stage is a named reference to a specific point in time (snapshot) of an API deployment, distinguishing environments in the API lifecycle such as development (dev), testing (test), and production (prod). Each stage has its own unique URL, and separate settings can be configured per environment, including caching, logging, throttling, stage variables, and so on. Stages support various operational scenarios such as environment-specific configurations and traffic segregation.
endpoint
An endpoint is a unique URL address that a client uses to access the API. A separate endpoint is created for each stage.
Integration
Integration defines how API methods connect to the actual backend (HTTP endpoint, Function). By transforming request and response data, handling authentication, and using mapping templates, you can finely control the integration with the backend.
JWT (Json Web Token)
It is a token-based web standard (RFC 7519) used for authentication and authorization. JWT encodes a JSON object composed of three parts (Header, Payload, Signature) using Base64 URL‑safe encoding, and applies an electronic signature with a secret key or public key to prevent tampering. When securely exchanging authentication information and permissions between a server and client, or between services, it is placed in the HTTP header, enabling stateless (Stateless) authentication without session storage.
CORS (Cross-Origin Resource Sharing)
It is a mechanism that bypasses the Same-Origin Policy applied in web browsers for security reasons, allowing resource sharing between servers of different origins (when the protocol, domain, or port differs). The server specifies which origins are allowed via HTTP response headers (e.g., Access-Control-Allow-Origin, etc.), enabling the client (browser) to safely perform cross-origin requests. If CORS is not properly configured, the browser blocks requests for resources from other origins, which is a web-standard security policy that must be considered when using various resources such as external API calls, fonts, images, and videos.
Provision status by region
API Gateway is available in the environments below.
| region | Provision status |
|---|---|
| Korea West 1 (kr-west1) | Provide |
| Korea East 1 (kr-east1) | Provide |
| South Korea 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that can be optionally configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Compute | Cloud Functions | A service that runs application code in a serverless computing environment
|
1.1 - ServiceWatch metric
API Gateway sends metrics to ServiceWatch. The metrics provided by basic monitoring are data collected at 1‑minute intervals.
Basic Metrics
The following are the default metrics for the API Gateway namespace.
The metrics whose names are displayed in bold below are the key metrics selected from the default metrics provided by API Gateway. Key metrics are used to configure service dashboards that are automatically built for each service in ServiceWatch.
Each metric guides users via the user guide on which statistical value is meaningful when querying that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using primary statistical values.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| API Total Requests | Total number of calls for this API | Count |
|
| 4XX Error | Number of calls that received a 4XX error response from the API | Count |
|
| 5XX Error | Number of calls that received a 5XX error response from the API | Count |
|
| Latency | Total latency of the API (ms) | Milliseconds |
|
| Integration Latency | Latency (ms) from the API to the backend | Milliseconds |
|
2 - How-to guides
Through the Samsung Cloud Platform Console, users can enter the required information for the API Gateway service and select detailed options to create the service.
Create API
An API is a collection of resources and methods integrated with backend HTTP endpoints, Cloud Functions, or other SCP services. An API provides the logical interface of the actual service and can be deployed across multiple stages for use in various environments (development, production, etc.).
You can create an API in the Samsung Cloud Platform Console and use it.
To create an API, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the Create API button. Navigate to the Create API page.
- On the API creation page, enter the information required to create a service and select detailed options.
- Select the required information in the Service Information Input area.
Category RequiredDetailed description API name Required Enter API name - must start with a lowercase English letter and must not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to enter 3 ~ 50 characters
How to create an API Required Select API creation method - Select Create new or Clone existing API
API to clone Required If you select Existing API Replication as the API creation method, choose from the APIs that have already been created. Explanation Selection Enter additional information or description about the API within 50 characters. API endpoint type Required Path to access the API - Region: Process requests within the region where the API is deployed
- Private: Expose the API so it can only be requested privately from other VPCs
- Selecting Private enables JWT activation
Table. API Service Information Input Items - must start with a lowercase English letter and must not end with a special character (
- Select the required information in the Service Information Input area.
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description tag Selection Add Tag - Click the Add Tag button to create and add a new tag, or to add an existing tag.
- You can add up to 50 tags.
- The newly added tags are applied after the service creation is completed.
Table. API additional information input fields
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resource on the API List page.
Check API detailed information
You can view and edit the complete list of resources and detailed information for the API service. The API Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the API service, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API menu. You will be taken to the API List page.
- On the API List page, click the resource you want to view detailed information for. You will be taken to the API Details page.
- API Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Category Detailed description Status display Status of the API created by the user - Creating: API creation in progress
- Active: API operating normally
- Deleting: API deletion in progress
- Error: API is in an unavailable state due to an internal error
Service termination Cancel service button Table. API status information and additional features
- API Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
On the API Details page, you can view the detailed information of the selected resource and, if needed, edit the information.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| API name | API name |
| API endpoint type | API endpoint type |
| DNS status | DNS status
|
| description | Additional information or description about the API |
Connection Management
Connection Management page lets you manage connection requests for the PrivateLink Service for API Gateway.
| Category | Detailed description |
|---|---|
| Request Endpoint ID | Requested endpoint ID |
| Creation date and time | Service creation date and time |
| status | Resource status value |
| Reject | PrivateLink Service connection request denied |
| Approval | Approve PrivateLink Service connection request |
| Block | Block connected PrivateLink Endpoint |
| Reconnect | Reconnect the blocked PrivateLink Endpoint |
- When the connection status is Rejected or Error, requests such as approval or denial are not possible.
tag
API Details page lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the API Details page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Integrating PrivateLink Service
By integrating the API Gateway service with the PrivateLink service, you can connect ‘API Gateway and VPC’ or ‘API Gateway and other SCP services’ without using the external internet. Data uses only the internal network, enhancing security, and no public IP, NAT, VPN, or internet gateway is required.
Create a PrivateLink service for API Gateway
When creating an API, select the endpoint type as Private. This allows you to expose the API for private access from other VPCs or services.
- Private Endpoint can be designated as a target to use the internal network. For instructions on creating a PrivateLink Endpoint in a user VPC, refer to Create PrivateLink Endpoint.
- For managing connections to the PrivateLink Service for API Gateway, refer to API 상세 정보 확인하기 > 연결 관리.
Create PrivateLink Endpoint
You can create it to use the Entry Point for accessing other PrivateLinks in the API Gateway service.
To create a PrivateLink Endpoint, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
Click the PrivateLink Endpoint menu on the Service Home page. You will be taken to the PrivateLink Endpoint List page.
On the PrivateLink Endpoint List page, click the PrivateLink Endpoint Create button. You will be taken to the PrivateLink Endpoint Create page.
- Enter or select the required information.
Category RequiredDetailed description PrivateLink Endpoint name Required Enter PrivateLink Endpoint name - Enter using English letters and numbers, 3 to 20 characters
description Selection Enter additional information or description within 50 characters. PrivateLink Service ID Required Enter the ID of the PrivateLink Service to connect - Check the Service ID with the PrivateLink Service provider in advance, and after creating the Endpoint, provide the Endpoint ID to the provider
- Enter using letters and numbers, 3 to 60 characters
Table. PrivateLink Endpoint creation information input items
- Enter or select the required information.
When data entry or selection is complete, click the Confirm button.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, verify the created resource in the PrivateLink Endpoint list.
- To delete a PrivateLink Endpoint list, select the resource to delete from the list and click the Delete button.
- To request a connection to the service provider via PrivateLink, you must go through an approval process.
- When applying for a service connection, you must verify the PrivateLink Service ID of the target in advance.
- Before applying for the service, an agreement on usage with the service provider must be completed.
- After the user creates a PrivateLink Endpoint, they must provide the Endpoint ID to the service provider. The service provider can verify the user’s Endpoint ID and promptly approve its use.
Check detailed information of PrivateLink Endpoint
You can view and edit the full list of resources and detailed information for a PrivateLink Endpoint. The PrivateLink Endpoint Details page consists of Detailed Information and Operation History tabs.
To view detailed information about the API service, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- Click the PrivateLink Endpoint menu on the Service Home page. You will be taken to the PrivateLink Endpoint List page.
- On the PrivateLink Endpoint List page, click the resource to view detailed information. You will be taken to the PrivateLink Endpoint Details page.
- PrivateLink Endpoint Details page displays status information and additional feature information, and consists of Details and Activity Log tabs.
Category Detailed description Status display PrivateLink Endpoint status - Requesting: connection request pending approval, Cancel request button displayed
- Active: creation completed, operating
- Creating: in progress
- Deleting: deletion in progress
- Disconnected: connection blocked
- Rejected: connection denied, Request re-approval button displayed
- Error: error occurred
- Canceled: connection request canceled, Request re-approval button displayed
Cancel request Cancel connection request Re-request approval Re-requesting a connection after the original request was canceled Table. PrivateLink Endpoint status information and additional features
- PrivateLink Endpoint Details page displays status information and additional feature information, and consists of Details and Activity Log tabs.
Detailed Information
PrivateLink Endpoint Details page lets you view detailed information of the selected resource.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| PrivateLink Endpoint name | PrivateLink Endpoint name |
| PrivateLink Endpoint ID | PrivateLink Endpoint ID |
| PrivateLink Service ID | Connected PrivateLink Service ID |
| API endpoint type | API endpoint type |
| description | Additional information or description about the PrivateLink Endpoint |
Job History
On the PrivateLink Endpoint Details page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Create Resource
A resource is a logical unit that represents a specific endpoint (URI path) within an API. Each resource can be organized in a tree structure and can have multiple HTTP methods.
To create a resource, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Resources menu. Navigate to the Resources page.
Click the Create Resource button on the Resource page. You will be taken to the Create Resource popup.
- Enter or select the required information.
Category RequiredDetailed description resource name Required Enter the resource name - It must start with a lowercase English letter and be 3 to 50 characters using lowercase letters, numbers, and special characters (
-{})
- When using braces, only the format
{character}is allowed and it cannot be left empty
resource path Required Select the path chosen in the resource menu tree Table. Resource creation information input fields - It must start with a lowercase English letter and be 3 to 50 characters using lowercase letters, numbers, and special characters (
- Enter or select the required information.
Click the Confirm button after completing data entry and selection.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, verify the created resource in the resource list.
- To delete a resource, select the resource to delete from the list and click the Delete button.
- A maximum of 300 resources can be created.
- The depth of a resource can be up to 30, including the Root.
Create Method
Methods define the HTTP actions (e.g., GET, POST, PUT, DELETE, etc.) that can be performed on each resource. Each method is integrated with a specific backend to process actual data or execute functionality.
To create a method, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Resources menu. You will be taken to the Resources page.
Click the Create Method button on the Resource page. It navigates to the Create Method popup.
- Enter or select the required information.
Category RequiredDetailed description Method type Required Select method type - The generated value is not displayed in the list.
- Selecting ANY creates methods of all types.
Integration type Required Select endpoint type - Select from HTTP, Cloud Function, PrivateLink
Endpoint URL Required Enter the endpoint URL when HTTP type is selected - The endpoint is a unique URL that the client uses to access the API. Create a separate endpoint for each stage. Various types such as Regional, Edge-Optimized, Private, etc.
- It must be a valid URL starting with http:// or https://, and you must enter it within 500 characters using English letters and special characters (
$-_.+!*’:(){}/)
endpoint Required When Cloud Function type is selected, choose the endpoint - The region is provided as the current region and cannot be changed
URL query string parameter Selection After checking use, enter name - using English letters, numbers, and special characters(
_)
HTTP request header Selection After checking use, enter name - using English letters, numbers, and special characters (
-) to input
Whether to use API Key Selection To limit usage through the usage policy, check Use Table. Method creation information input fields
- Enter or select the required information.
When the information entry and selection are complete, click the Save button.
After checking the message in the notification popup, click the Confirm button.
- After creation is complete, check the created resource in the method list.
- To delete a method, select the resource to delete from the list and click the Delete button.
Methods can be created up to a maximum of 7, with one per type. When created as Any, all types of methods are generated.
| Category | Detailed description |
|---|---|
| service | Service name |
| GET | Resource retrieval (read) |
| POST | Resource creation (registration) |
| PUT | Full resource update (refresh) |
| PATCH | Modify only part of the resource. |
| DELETE | Delete resource |
| OPTIONS | Retrieve the list of HTTP methods supported by this endpoint |
| HEAD | Retrieve only headers without a body (return only metadata, no response body) |
Deploy API
To apply a developing API to the live service environment, API deployment is required.
To deploy the generated API, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Resources menu. You will be taken to the Resources page.
Click the API Deployment button on the Resources page. It opens the API Deployment popup.
- Enter or select the required information.
Category RequiredDetailed description Stage Required Select the stage to deploy the API - New Stage: Create a new stage and deploy
- None Stage: Deploy without selecting a stage
Stage name Required When New Stage is selected, enter a new stage name - that starts with a lowercase English letter and does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) for 3 to 30 characters
Deployment description Selection Enter up to 50 characters describing API deployment. Table. API deployment information input fields
- Enter or select the required information.
Click the Deploy button once information entry and selection are complete.
After checking the message in the notification popup, click the Confirm button.
Create Stage
The stage is a named reference to a specific point in time (snapshot) of an API deployment, distinguishing environments in the API lifecycle such as development (dev), testing (test), and production (prod). Each stage has its own unique URL, and separate settings can be configured per environment for caching, logging, throttling, stage variables, and so on. Stages support various operational scenarios, including Canary releases, environment-specific configurations, and traffic segregation.
To create a stage for deploying the API, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Stage menu. You will be taken to the Stage page.
On the Stage page, click the Create Stage button. You will be taken to the Create Stage popup.
- Enter or select the required information.
Category RequiredDetailed description Stage name Required When New Stage is selected, enter a new stage name - that starts with a lowercase English letter and does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) with a length of 3 ~ 50 characters
Stage description Selection Enter additional information or description about the stage within 100 characters. API deployment version Required Select the API version to deploy - Must start with a lowercase English letter and must not end with a special character (
-), using lowercase letters, numbers, and special characters (-) enter 3 to 50 characters
Table. Stage creation information input fields - that starts with a lowercase English letter and does not end with a special character (
- Enter or select the required information.
Click the Confirm button after completing data entry and selection.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, check the created resources in the stage list.
Check stage detailed information
You can view and edit the stage list and detailed information. The detail page consists of the Stage Details information and the API Deployment Version Management, CORS, Usage Policy tabs.
To view the detailed information of the stage, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- From the Service Home page, click the API Gateway > Stage menu. You will be taken to the Stage page.
- Click the resource to view detailed information in the stage list.
- Stage Details displays status information and additional feature information, and consists of API Deployment Version Management, CORS, Usage Policy tabs.
- To delete a stage, select the resource to delete from the list and click the Delete button.
- To edit a stage, select the resource to modify from the list and click the Edit button.
Stage Details
You can view detailed information of the selected resource on the Stage Details page.
| Category | Detailed description |
|---|---|
| Stage name | Stage name |
| CORS | CORS operation status |
| Stage description | Stage information |
| JWT | JSON Web Token usage status |
| API Key | Whether to use API Key |
| Invoke URL | URL for API call |
| Activation date and time | Stage activation date and time |
| Deployment ID | API deployment ID |
API deployment version management
API deployment version management tab allows you to view the API deployment history.
| Category | Detailed description |
|---|---|
| API Deployment Version Management List | API deployment history
|
| Deployment change | After selecting the resource to change the deployment from the list, click the Change Deployment button. When you click the Confirm button in the notification popup, the active deployment ID is updated immediately. |
CORS (Cross-Origin Resource Sharing)
You can view the CORS list in the CORS tab.
| Category | Detailed description |
|---|---|
| Name | CORS name |
| Mapping Value | Mapping value applied to CORS |
Usage Policy
On the Usage Policy tab, you can view the usage policy attached to the stage.
| Category | Detailed description |
|---|---|
| Usage Policy Name | Usage policy name |
| Usage Policy ID | Usage Policy ID |
| Quota | Quota set in the usage policy |
| Linked API Key Name | API Key name linked to the usage policy |
- When calling the API, you must use the key value of the API Key associated with the stage in the ‘x-scp-apikey’ header.
- Usage policies are linked at the stage level, while quotas are calculated per method that is checked for API Key usage.
Create authentication
JWT (JSON Web Token) is an open standard (RFC 7519) used for user authentication. JWT is a claim-based web token that stores user information as an encrypted token using JSON format.
To generate a JWT, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Authentication menu. You will be taken to the Authentication List page.
On the Authentication List page, click the Create JSON Web Token button. You will be taken to the Create JSON Web Token popup.
- Enter or select the required information.
Category RequiredDetailed description JWT name Required Enter token name - that starts with a lowercase English letter and does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to input 3 to 50 characters
Stage to connect Selection After checking Use, select the stage Table. Authentication creation information input items - that starts with a lowercase English letter and does not end with a special character (
- Enter or select the required information.
After entering information and making selections, click the Confirm button.
After reviewing the message in the notification popup, click the Confirm button. Navigate to the Access Token notification popup.
- Tokens can be viewed only in the Access Token notification popup. If needed, download the Access Token file.
Access Token After checking the message in the notification popup, click the Confirm button.
- After creation is complete, check the created resource in the authentication list.
- To delete a token, select the resource to delete from the list and click the Delete button.
- To edit a token, select Edit from the context menu of the resource you want to modify.
Create Access Control
You can add an allowed IP to restrict API calls to a specific IP address.
- The stage is linked to a single access control. When a stage is first created, the Default access control is applied by default, blocking access from all IPs (All deny). By creating a new access control and attaching it to the stage, you can configure it to be callable only from specific IPs.
- In the following case, access control cannot be created.
- If you exceed the available service quota limit: Check the current allocated value and the additional possible value in the Quota Service.
- If there is no available API, create the API first.
- When the API endpoint type is Private: access control is not supported, but JWT activation is required on that API’s stage.
To create an access control, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
From the Service Home page, click the API Gateway > Access Control menu. Navigate to the Access Control List page.
Access Control List page, click the Create Access Control button. You will be taken to the Create Access Control popup.
- Enter or select the required information.
Category RequiredDetailed description Access control name Required Enter the access control name - that starts with a lowercase English letter, does not end with a special character (
-), and uses lowercase letters, numbers, and special characters (-) within 3 to 50 characters
Public access allowed IP Required Enter IP addresses to allow access - ’,’ you can input up to 100 using ‘,’
Stage to connect Selection After checking Use, select the stage description Selection Enter additional information or description about access control within 50 characters. Table. Access control creation information input fields - that starts with a lowercase English letter, does not end with a special character (
- Enter or select the required information.
After entering information and making selections, click the Confirm button.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, verify the created resource in the access control list.
- To delete an access control list, select the resource to remove from the list and click the Delete button. The default access control cannot be deleted.
- To modify access control, select Edit from the context menu of the resource you want to modify.
Terminate API
You can cancel the unused service to reduce operating costs. However, canceling the service may cause the running service to stop immediately, so you should consider the impact of service interruption thoroughly before proceeding with the cancellation.
To cancel the API, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API menu. You will be taken to the API List page.
- On the API List page, select the resource to cancel and click the Cancel Service button.
- When the termination is complete, verify on the API List page that the resource has been terminated.
Using Report
You can check API traffic, performance, and error status.
To use the Report, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Report menu. You will be taken to the Report page.
- Enter or select the required information.
| Category | Detailed description |
|---|---|
| Search period | Select date to view (default 1 week from today, up to 1 month) |
| Stage name | Stage name under API |
- After entering the information and making selections, you can view the Report information.
| Category | Detailed description |
|---|---|
| TOP Resources 5 | Among the resources invoked by the user, the top five most frequently called with an API status code of 2XX (ties are not shown as duplicate ranks). |
| API call count | Number of calls with API status code 2XX |
| Latency | The time elapsed from when the user sends a request to the API Gateway until a response is received. |
| Integration Latency | The time elapsed from when the API Gateway sends a request to the backend server until it receives a response from the backend. |
| 4XX Error | Number of calls with API status code 4XX |
| 5XX Error | Number of calls with API status code 5XX |
- If a stage is deleted, it cannot be accessed in the Report.
- The report displays data from one hour ago relative to the current time.
Create Usage Policy
The usage policy is established to ensure efficient allocation of server resources, maintain service stability, prevent unnecessary traffic, and avoid misuse.
To create a usage policy, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Usage Policy menu. You will be taken to the Usage Policy page.
- On the Usage Policy page, click the Create Usage Policy button. You will be taken to the Create Usage Policy page.
- Enter or select the required information.
| Category | Required | Detailed description |
|---|---|---|
| API name to connect | Required | Select from the generated AIPs |
| Usage Policy Name | Required | Start with a lowercase English letter and ensure it does not end with a hyphen; use lowercase letters, numbers, and hyphens, and enter 3 to 50 characters. |
| Quota | Required | Enter a value between 1 and 2,000,000,000 per month/day/hour. |
| description | Selection | Enter usage policy description (max 50 chars). |
- When the information entry and selection are complete, click the Complete button.
- After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, check the created resource in the usage policy list.
Create API Key
An API key is used to identify which user or app is calling the API. It is primarily used to limit usage according to usage policies.
To create an API Key, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Usage Policy menu. You will be taken to the Usage Policy page.
- In the list, click the usage policy. It navigates to the Usage Policy Details page.
- On the Usage Policy Details page, click the Create API Key button. You will be taken to the Add API Key popup.
- Enter or select the required information.
| Category | Required | Detailed description |
|---|---|---|
| API Key name | Required | Start with a lowercase English letter and ensure it does not end with a hyphen; use lowercase letters, numbers, and hyphens, and enter 3 to 50 characters. |
| description | Selection | Enter a description of the API Key within 50 characters. |
- Click the Confirm button after completing data entry and selection.
- After checking the message in the notification popup, click the Confirm button.
- When creation is complete, check the created resources on the Usage Policy Details page.
- You can create up to 10 usage policies and 5 API keys.
- Quota is calculated per API Key.
Create Resource Policy
You can fundamentally block unauthorized access with resource-based policies and increase the service’s security level.
To create a resource policy, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Resource Policy menu. You will be taken to the Resource Policy page.
- On the Resource Policy page, click the Create Resource Policy button. You will be taken to the Create Resource Policy page.
- Enter or select the required information in the Service Information Input area.
| Category | Required | Detailed description |
|---|---|---|
| Policy template | Required | Select Policy Template
|
- Click the Complete button after entering information and making selections.
- After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, you can view, modify, or delete the resource policy.
2.1 - Resource-Based Policy Guide
Resource-based policy overview
API Gateway’s resource-based policy (Resource-based Policy) is a policy attached to a resource that can decide to allow or deny (Effect) an action (Action) on a specific resource only for a principal (Principal). You can directly define the principal that can call the API by using resource-based policies.
Through resource-based policies, you can define the following to allow secure API calls.
- User of the specified Samsung Cloud Platform account
- Specified source IP address range or CIDR block
A source policy is defined as a JSON policy document attached to the API, which controls whether a specified security principal (typically an IAM role or group) can call the API.
| Category | description | example |
|---|---|---|
| Principal(Principal) | Specify the entity that will call the API | - |
| Task(Action) | Define the allowed features | - |
| Condition(Condition) | Restrict to allow only in specific situations | Allow only requests originating from a specific SRN. |
- API Gateway’s resource-based policies leverage the rules of IAM’s resource-based policies.
- Please refer to the JSON Writing Guide for how to create or modify policies using JSON.
Resource-based policy usage scenario
The primary use cases for resource-based policies are as follows.
Resource-based policy scenario
The resource-based policy scenario used when a specific function of API Gateway operates is as follows.
| Category | description | Reference example |
|---|---|---|
| Default policy | This is the DEFAULT resource policy that is created by default when an API is created.
| Basic Policy Example |
| Allowed Account List | You can define account(s) that can call the API. | Account Allowlist Example |
| IP range blocklist | You can define IP ranges that are not allowed to call the API. | IP range blocklist example |
User addition usage scenario
It is not automatically registered as a resource‑based policy of API Gateway, but users can add and use it as needed. The scenarios that users can add and utilize are as follows.
- Cross-Account Access
- If an IAM user in account A wants to invoke the API of account B, register account A in the function policy of account B.
- Hybrid Access Control
- It can be configured so that access is allowed only when both conditions are met—a specific user and a specific IP range—rather than simply restricting by account or IP alone.
Resource-based policy management for API Gateway
To view and set resource-based policies for API Gateway, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Go to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Resource Policy menu. You will be taken to the Resource Policy page.
- Click the Edit button of the Policy Details item. The Edit Resource Policy popup opens.
- Click the Delete button to delete the registered policy.
- Edit Resource Policy In the popup window, select Policy Template, then write the policy.
- For policy examples by policy template, refer to Resource-based policy example.
- When the writing is complete, click the Done button.
Example of resource-based policy
Users can define additional resource-based policies as needed or modify existing policies for use.
- For some features, a resource-based policy (or credentials) must be registered to use them in API Gateway.
- In the resource-based policy examples described in this guide, API Gateway automatically registers the example resource-based policies when each feature is enabled or linked.
Default Policy
This is a policy that is automatically registered when creating an API.
Policy Template
{
"Statement": [
{
"Action": [
"apigateway:InvokeApigatewayRegion"
],
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
"apigateway:InvokeApigatewayRegion"
],
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}Policy Example
{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow"
"Principal": "*",
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow"
"Principal": "*",
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}Account allowlist
This is a policy that allows only users of a specific SCP account (Root user or IAM Role) to call the API.
Policy Template
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:{{Offering}}::{{AccountID}}:::iam:user/{{UserSrn}}
]
},
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:{{Offering}}::{{AccountID}}:::iam:user/{{UserSrn}}
]
},
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}Policy Example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
"srn:s::accountId1:::iam:user/userId1"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
"srn:s::accountId1:::iam:user/userId1"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}IP range blocklist
It is a policy that allows or blocks only specific IP addresses or CIDR ranges.
Policy Template
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
},
"NotIpAddress": {
"scp:SourceIp": [
{{sourceIpOrCIDRBlock}}
{{sourceIpOrCIDRBlock}}
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
},
"NotIpAddress": {
"scp:SourceIp": [
{{sourceIpOrCIDRBlock}}
{{sourceIpOrCIDRBlock}}
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}Policy example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
"srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1"
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
"srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1"
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}Cross-Account Access
This is a resource policy that allows a user of account B to call a specific API resource of account A.
Policy Example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow"
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow"
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}Hybrid Access Control
It is a resource policy that can define access control policies by combining user credentials (Account) and connection source (IP).
Policy Example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:s::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:s::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}3 - API Reference
4 - CLI Reference
5 - Release Note
API Gateway
- You can set resource-based policies on the API.
- Resource-based policies are policies applied directly to the API to allow external access.
- You can use resource-based policies to allow or deny actions on specific resources to specific principals.
- The API Gateway service, which enables easy management and monitoring of APIs, has been launched.
- You can easily define resources and methods related to the API, and conveniently monitor API usage and performance metrics.