This is the multi-page printable view of this section. Click here to print.
User Guide
- 1: Samsung Cloud Platform
- 1.1: New Features
- 1.2: Overview
- 1.3: Getting Started with Console
- 1.3.1: Log In
- 1.3.2: Console
- 1.3.3: Integrated Management
- 1.4: Copilot
- 2: Compute
- 2.1: Virtual Server
- 2.1.1: Overview
- 2.1.1.1: Server Type
- 2.1.1.2: Monitoring Metrics
- 2.1.1.3: ServiceWatch Metrics
- 2.1.2: How-to guides
- 2.1.2.1: Image
- 2.1.2.2: Keypair
- 2.1.2.3: Server Group
- 2.1.2.4: Change IP
- 2.1.2.5: Configure Linux NTP
- 2.1.2.6: Configure RHEL Repo and WKMS
- 2.1.2.7: Install ServiceWatch Agent
- 2.1.3: API Reference
- 2.1.4: CLI Reference
- 2.1.5: Release Note
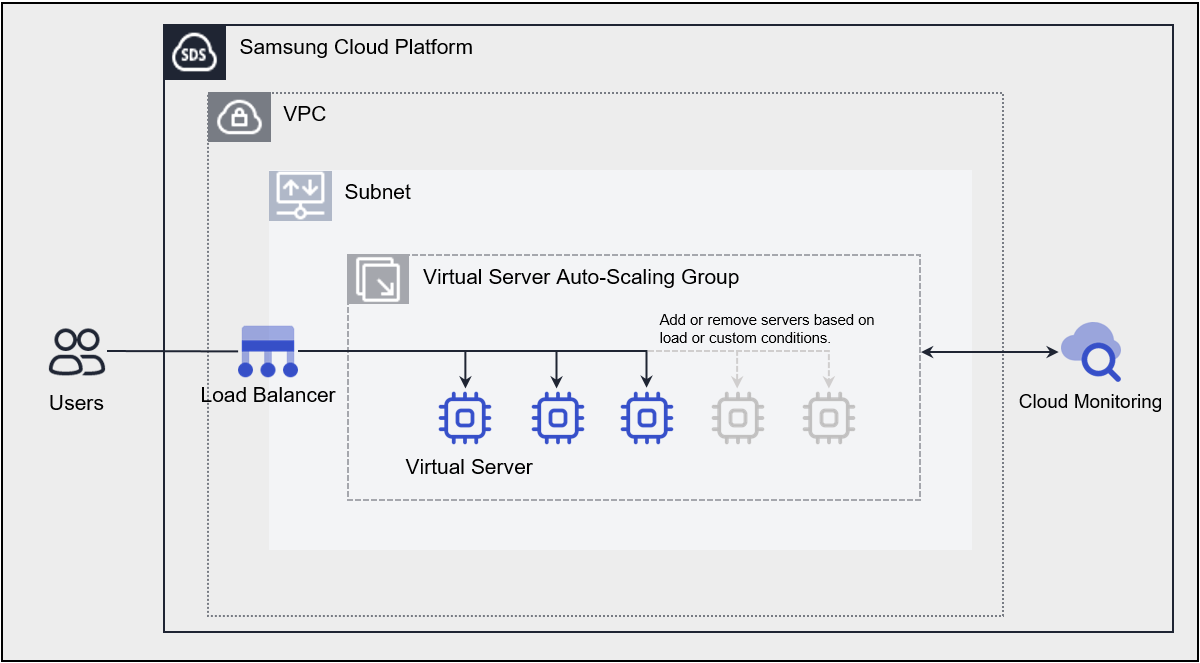
- 2.2: Virtual Server Auto-Scaling
- 2.2.1: Overview
- 2.2.1.1: Monitoring Metrics
- 2.2.1.2: ServiceWatch Metrics
- 2.2.2: How-to guides
- 2.2.2.1: Launch Configuration
- 2.2.2.2: Manage Policy
- 2.2.2.3: Manage Schedule
- 2.2.2.4: Manage Notification
- 2.2.3: API Reference
- 2.2.4: CLI Reference
- 2.2.5: Release Note
- 2.3: GPU Server
- 2.3.1: Overview
- 2.3.1.1: Server type
- 2.3.1.2: Monitoring Metrics
- 2.3.1.3: ServiceWatch Metrics
- 2.3.2: How-to guides
- 2.3.2.1: Manage Image
- 2.3.2.2: Manage Keypair
- 2.3.2.3: Use Multi-instance GPU on GPU Server
- 2.3.2.4: Use NVSwitch on GPU Server
- 2.3.2.5: Install ServiceWatch Agent
- 2.3.3: API Reference
- 2.3.4: CLI Reference
- 2.3.5: Release Note
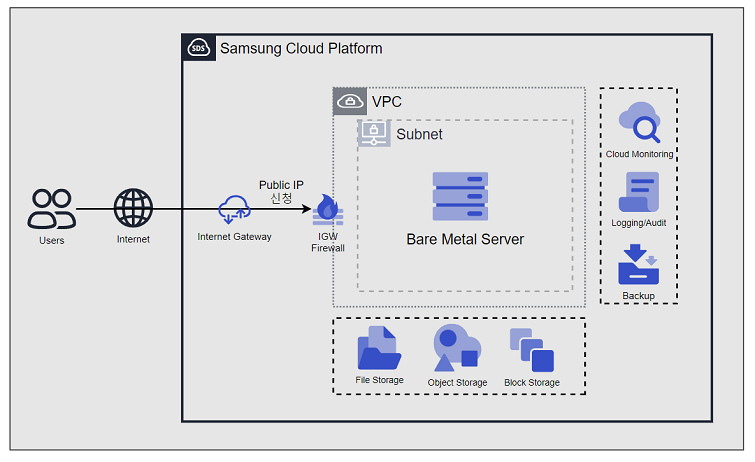
- 2.4: Bare Metal Server
- 2.4.1: Overview
- 2.4.1.1: Server Type
- 2.4.1.2: Monitoring Metrics
- 2.4.2: How-to guides
- 2.4.2.1: Install ServiceWatch Agent
- 2.4.2.2: Setting up RHEL Repo and WKMS
- 2.4.3: API Reference
- 2.4.4: CLI Reference
- 2.4.5: Release Note
- 2.5: Multi-node GPU Cluster
- 2.5.1: Overview
- 2.5.1.1: Server type
- 2.5.1.2: Monitoring Metrics
- 2.5.2: How-to guides
- 2.5.2.1: Manage Cluster Fabric
- 2.5.2.2: Install ServiceWatch Agent
- 2.5.2.3: Multi-node GPU Cluster Service Scope and Inspection Guide
- 2.5.3: Release Note
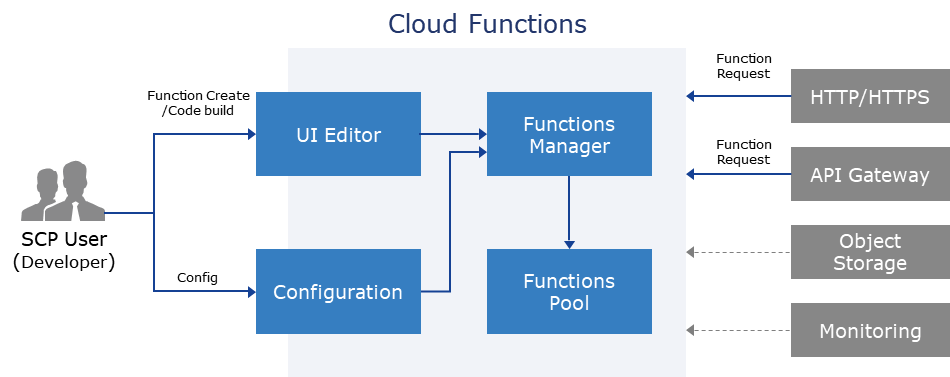
- 2.6: Cloud Functions
- 2.6.1: Overview
- 2.6.1.1: ServiceWatch Metrics
- 2.6.2: How-to guides
- 2.6.2.1: Configure Trigger
- 2.6.2.2: Blueprint Detailed Guide
- 2.6.2.3: Integrate PrivateLink Service
- 2.6.2.4: Resource-based Policy Guide
- 2.6.3: API Reference
- 2.6.4: CLI Reference
- 2.6.5: Release Note
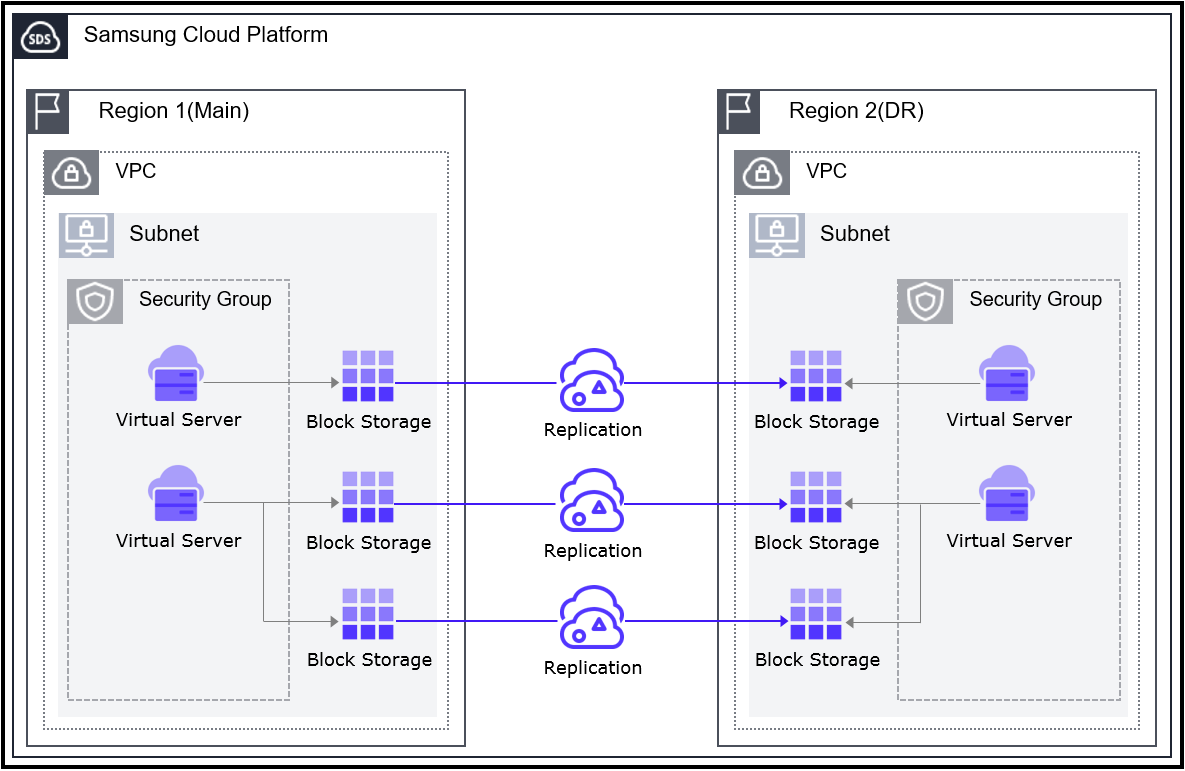
- 2.7: Virtual Server DR
- 2.7.1: Overview
- 2.7.2: Release Note
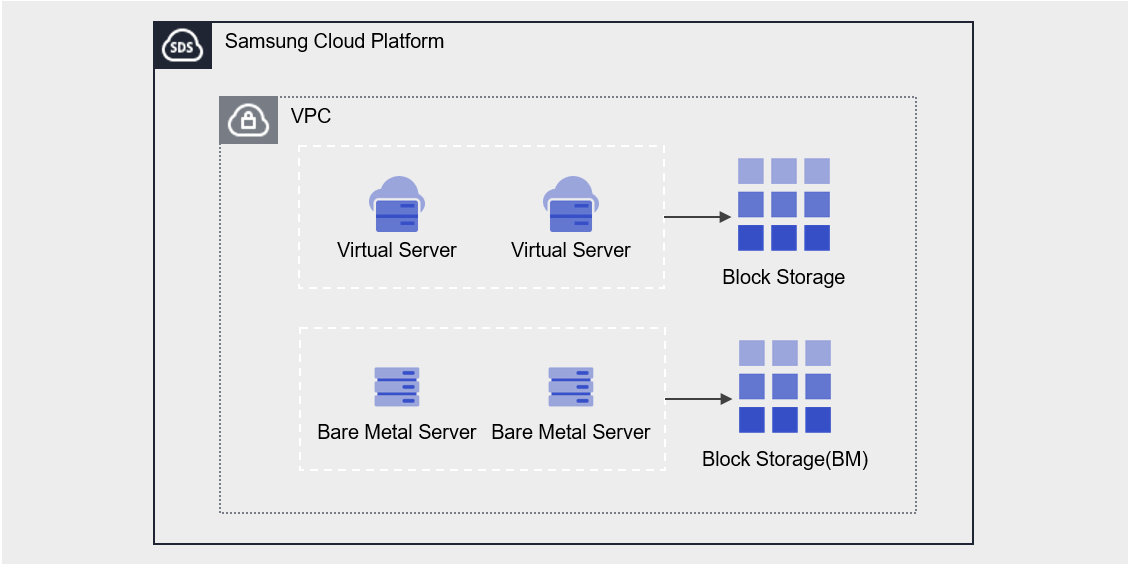
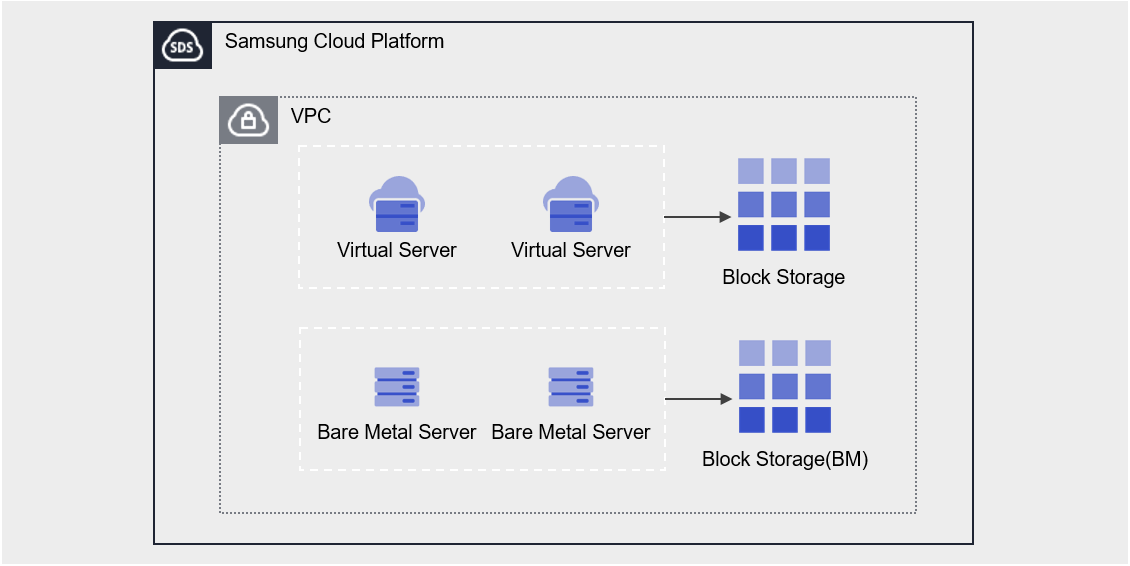
- 2.8: Block Storage
- 2.8.1: Overview
- 2.8.1.1: Monitoring Metrics
- 2.8.2: How-to guides
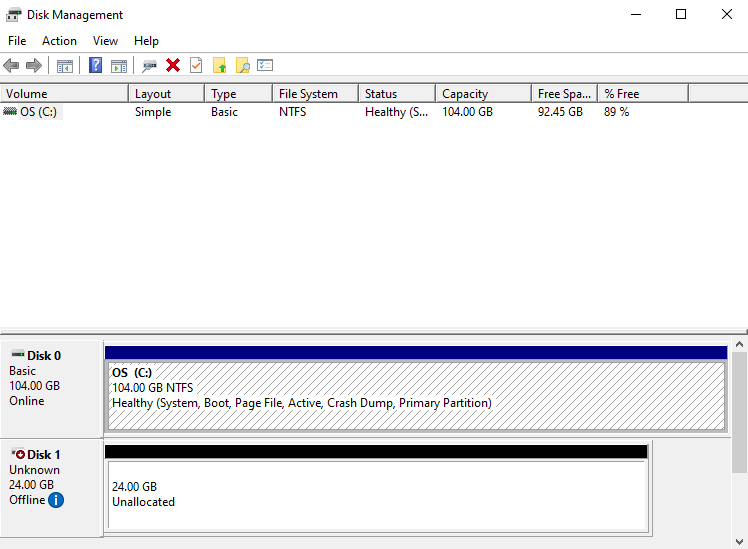
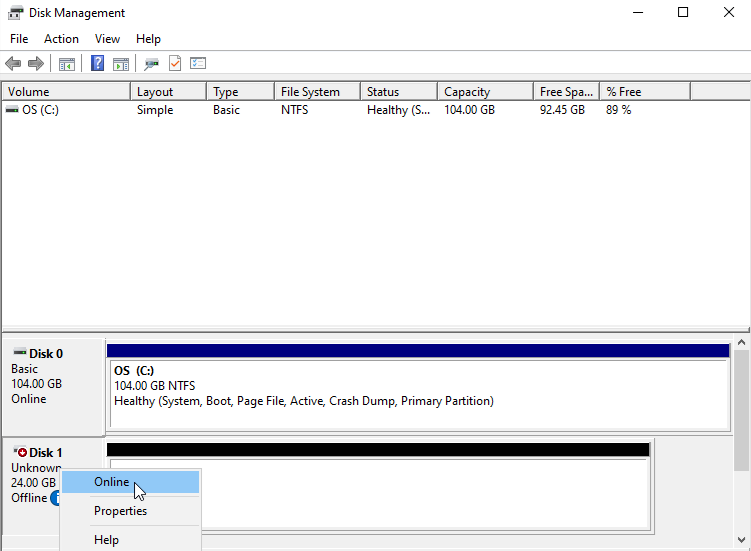
- 2.8.2.1: Connect to Server
- 2.8.2.2: Use Snapshot
- 2.8.2.3: Move Volume
- 2.8.3: API Reference
- 2.8.4: CLI Reference
- 2.8.5: Release Note
- 3: Storage
- 3.1: Block Storage(BM)
- 3.1.1: Overview
- 3.1.1.1: Monitoring Metrics
- 3.1.2: How-to Guides
- 3.1.2.1: Connect to Server
- 3.1.2.2: Use Snapshot
- 3.1.2.3: Use Replication
- 3.1.2.4: Use Volume Group
- 3.1.3: API Reference
- 3.1.4: CLI Reference
- 3.1.5: Release Note
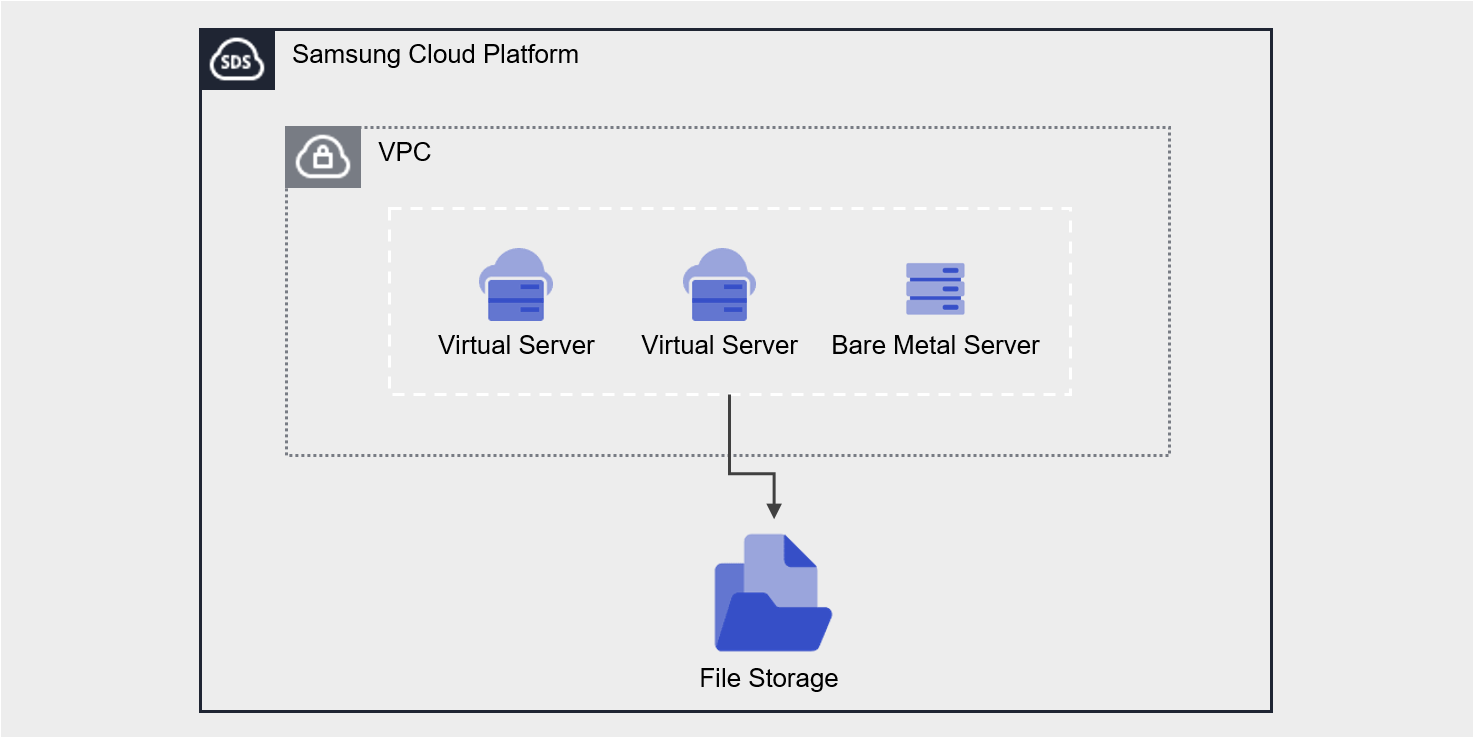
- 3.2: File Storage
- 3.2.1: Overview
- 3.2.1.1: Monitoring Metrics
- 3.2.1.2: ServiceWatch Metrics
- 3.2.2: How-to guides
- 3.2.2.1: Connect to Server
- 3.2.2.2: Use Snapshot
- 3.2.2.3: File-level Recovery
- 3.2.2.4: Use Disk Backup
- 3.2.2.5: Use Replication
- 3.2.3: API Reference
- 3.2.4: CLI Reference
- 3.2.5: Release Note
- 3.3: Object Storage
- 3.3.1: Overview
- 3.3.1.1: Amazon S3 Usage Guide
- 3.3.1.2: Monitoring Metrics
- 3.3.1.3: ServiceWatch Metrics
- 3.3.2: How-to guides
- 3.3.2.1: Access Control
- 3.3.2.2: File and Folder Management
- 3.3.2.3: Version Management
- 3.3.2.4: Permission Management
- 3.3.2.5: Replication Policy Management
- 3.3.3: Release Note
- 3.4: Archive Storage
- 3.4.1: Overview
- 3.4.1.1: ServiceWatch Metrics
- 3.4.2: How-to guides
- 3.4.2.1: Manage Archiving Policy
- 3.4.2.2: Use Version Management
- 3.4.2.3: Archive Recovery
- 3.4.3: API Reference
- 3.4.4: CLI Reference
- 3.4.5: Release Note
- 3.5: Backup
- 3.5.1: Overview
- 3.5.2: How-to guides
- 3.5.2.1: Instant Backup
- 3.5.2.2: Recovery
- 3.5.2.3: Use Backup Agent
- 3.5.2.4: Install Backup Agent
- 3.5.2.5: Use Replication
- 3.5.3: API Reference
- 3.5.4: CLI Reference
- 3.5.5: Release Note
- 3.6: Parallel File Storage
- 3.6.1: Overview
- 3.6.2: How-to guides
- 3.6.2.1: Use Snapshot
- 3.6.2.2: Install Agent
- 3.6.2.3: File-level Recovery
- 3.6.3: API Reference
- 3.6.4: CLI Reference
- 3.6.5: Release Note
- 4: Container
- 4.1: Kubernetes Engine
- 4.1.1: Overview
- 4.1.1.1: Monitoring Metrics
- 4.1.1.2: ServiceWatch Metrics
- 4.1.2: How-to guides
- 4.1.2.1: Managing Nodes
- 4.1.2.2: Managing Namespaces
- 4.1.2.3: Manage Workloads
- 4.1.2.4: Manage services and ingresses
- 4.1.2.5: Managing Storage
- 4.1.2.6: Configuration(Configuration) Management
- 4.1.2.7: Manage Permissions
- 4.1.3: Kubernetes Engine Usage Guide
- 4.1.3.1: Access Cluster
- 4.1.3.2: Authentication and Authorization
- 4.1.3.3: Using type LoadBalancer service
- 4.1.3.4: Usage Considerations
- 4.1.3.5: Version information
- 4.1.4: API Reference
- 4.1.5: CLI Reference
- 4.1.6: Release Note
- 4.2: Container Registry
- 4.2.1: Overview
- 4.2.1.1: Monitoring Metrics
- 4.2.1.2: ServiceWatch Metrics
- 4.2.2: How-to guides
- 4.2.2.1: Manage Repository
- 4.2.2.2: Manage Images and Tags
- 4.2.2.3: Manage Image Security Vulnerabilities
- 4.2.2.4: Manage Image Tag Deletion Policy
- 4.2.2.5: Use Container Registry with CLI
- 4.2.2.6: Example of Registry and Repository Policies
- 4.2.3: API Reference
- 4.2.4: CLI Reference
- 4.2.5: Release Note
- 5: Networking
- 5.1: VPC
- 5.1.1: Overview
- 5.1.1.1: ServiceWatch Metrics
- 5.1.2: How-to guides
- 5.1.2.1: Subnet
- 5.1.2.2: Port
- 5.1.2.3: Internet Gateway
- 5.1.2.4: NAT Gateway
- 5.1.2.5: Public IP
- 5.1.2.6: Private NAT
- 5.1.2.7: VPC Endpoint
- 5.1.2.8: VPC Peering
- 5.1.2.9: Transit Gateway
- 5.1.2.10: PrivateLink Service
- 5.1.2.11: PrivateLink Endpoint
- 5.1.2.12: NAT Logging
- 5.1.3: API Reference
- 5.1.4: CLI Reference
- 5.1.5: Release Note
- 5.2: Security Group
- 5.2.1: Overview
- 5.2.2: How-to guides
- 5.2.2.1: Security Group Logging
- 5.2.2.2: Migration Rules
- 5.2.3: API Reference
- 5.2.4: CLI Reference
- 5.2.5: Release Note
- 5.3: Load Balancer
- 5.3.1: Overview
- 5.3.1.1: ServiceWatch metric
- 5.3.2: How-to guides
- 5.3.2.1: LB Server Groups
- 5.3.2.2: LB Health Check
- 5.3.3: API Reference
- 5.3.4: CLI Reference
- 5.3.5: Release Note
- 5.4: DNS
- 5.4.1: Overview
- 5.4.1.1: TLD List
- 5.4.1.2: ServiceWatch Metrics
- 5.4.2: How-to guides
- 5.4.2.1: Private DNS
- 5.4.2.2: Hosted Zone
- 5.4.2.3: Public Domain Name
- 5.4.3: Release Note
- 5.5: VPN
- 5.5.1: Overview
- 5.5.1.1: ServiceWatch Metrics
- 5.5.2: How-to guides
- 5.5.2.1: VPN Tunnel
- 5.5.3: API Reference
- 5.5.4: CLI Reference
- 5.5.5: Release Note
- 5.6: Firewall
- 5.6.1: Overview
- 5.6.2: How-to guides
- 5.6.2.1: Firewall Logging
- 5.6.2.2: Migration Rules
- 5.6.3: API Reference
- 5.6.4: CLI Reference
- 5.6.5: Release Note
- 5.7: Direct Connect
- 5.7.1: Overview
- 5.7.1.1: ServiceWatch Metrics
- 5.7.2: How-to guides
- 5.7.3: API Reference
- 5.7.4: CLI Reference
- 5.7.5: Release Note
- 5.8: Cloud LAN-Campus
- 5.8.1: Overview
- 5.8.2: How-to guides
- 5.8.2.1: Campus Firewall Request Service
- 5.8.3: Release Note
- 5.9: Cloud LAN-Campus
- 5.9.1: Overview
- 5.9.2: How-to guides
- 5.9.3: Release Note
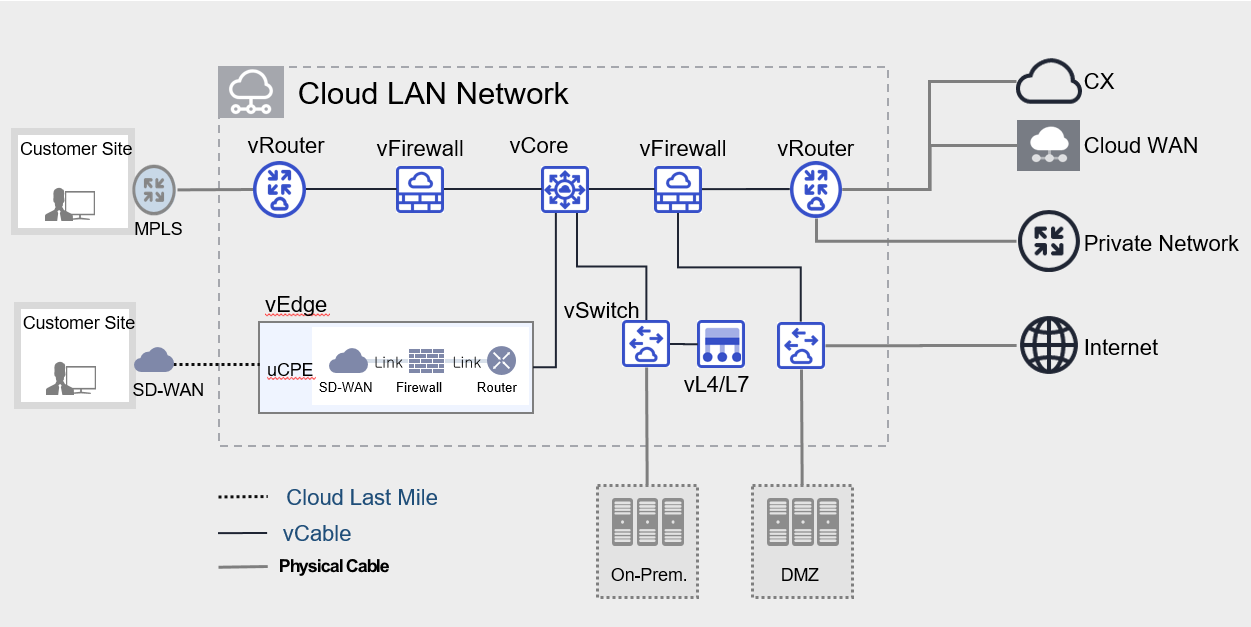
- 5.10: Cloud LAN-Data Center
- 5.10.1: Overview
- 5.10.2: How-to guides
- 5.10.3: Release Note
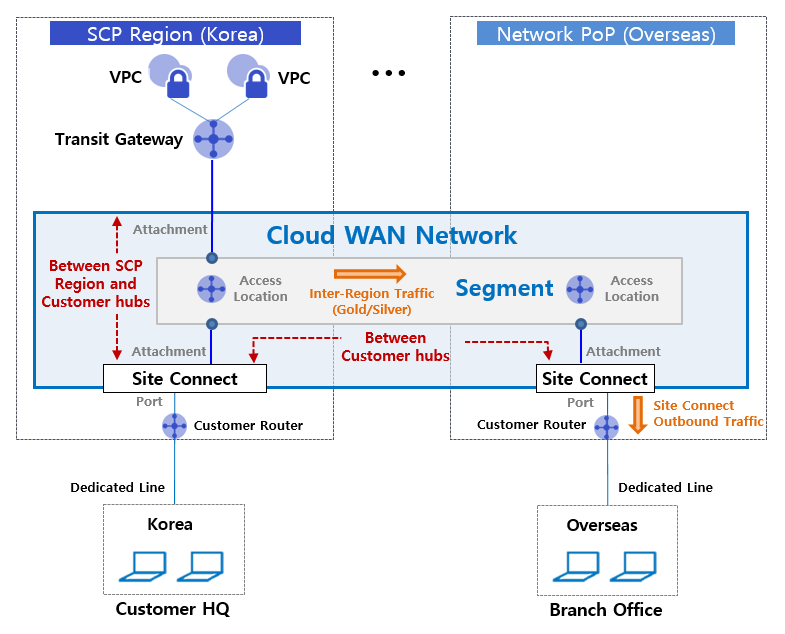
- 5.11: Cloud WAN
- 5.11.1: Overview
- 5.11.1.1: Monitoring Metrics
- 5.11.2: How-to guides
- 5.11.3: Release Note
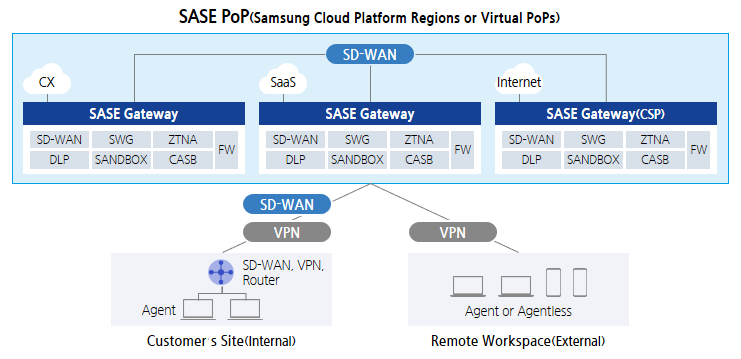
- 5.12: SASE
- 5.12.1: Overview
- 5.12.2: How-to guides
- 5.12.2.1: SASE Lastmile
- 5.12.3: Release Note
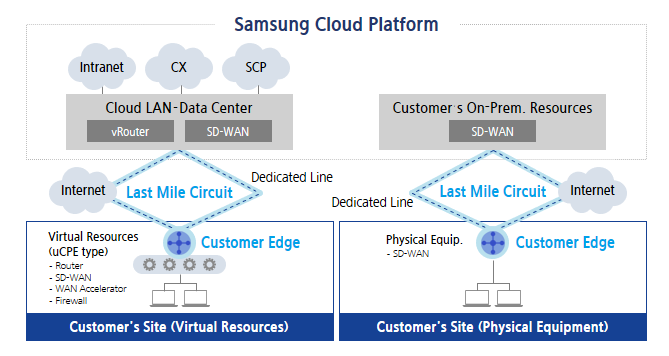
- 5.13: Cloud Last Mile
- 5.13.1: Overview
- 5.13.2: How-to guides
- 5.13.2.1: Circuit and Edge
- 5.13.3: Release Note
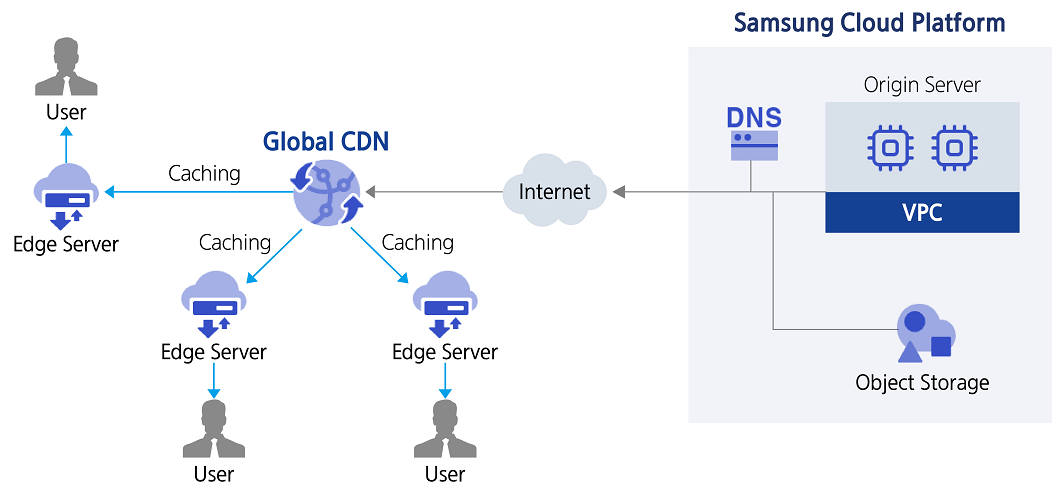
- 5.14: Global CDN
- 5.14.1: Overview
- 5.14.1.1: ServiceWatch Metrics
- 5.14.2: How-to guides
- 5.14.3: API Reference
- 5.14.4: CLI Reference
- 5.14.5: Release Note
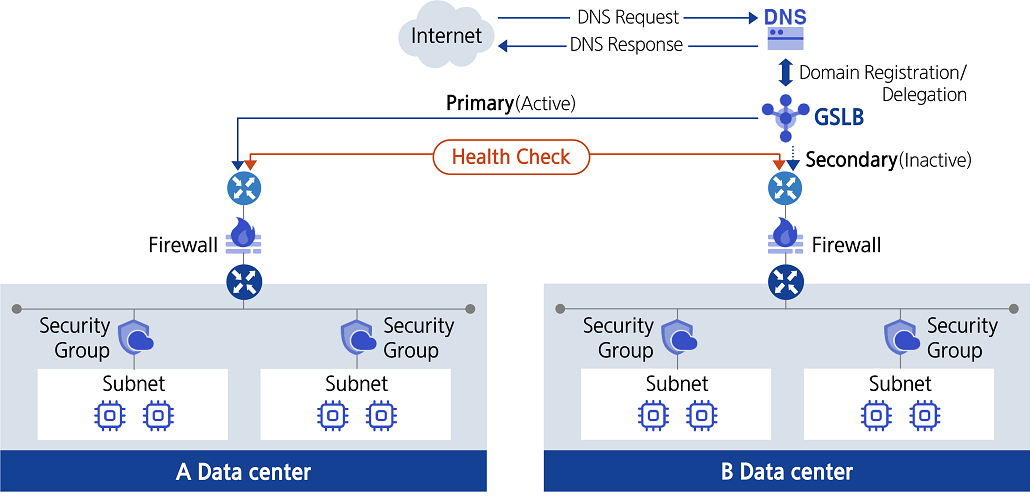
- 5.15: GSLB
- 5.15.1: Overview
- 5.15.2: How-to guides
- 5.15.3: API Reference
- 5.15.4: CLI Reference
- 5.15.5: Release Note
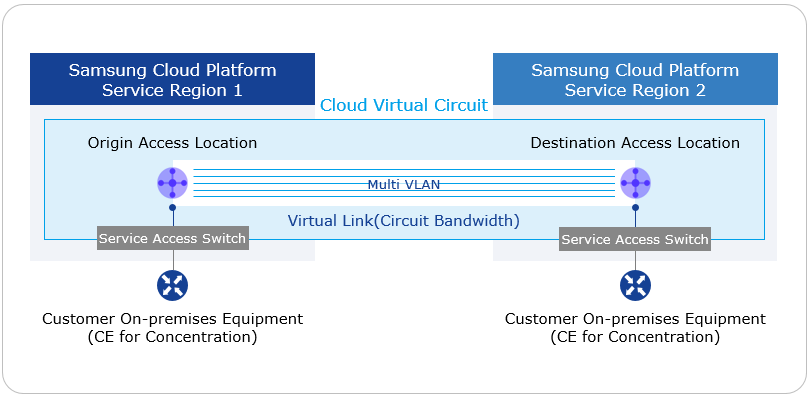
- 5.16: Cloud Virtual Circuit
- 5.16.1: Overview
- 5.16.2: How-to guides
- 5.16.3: Release Note
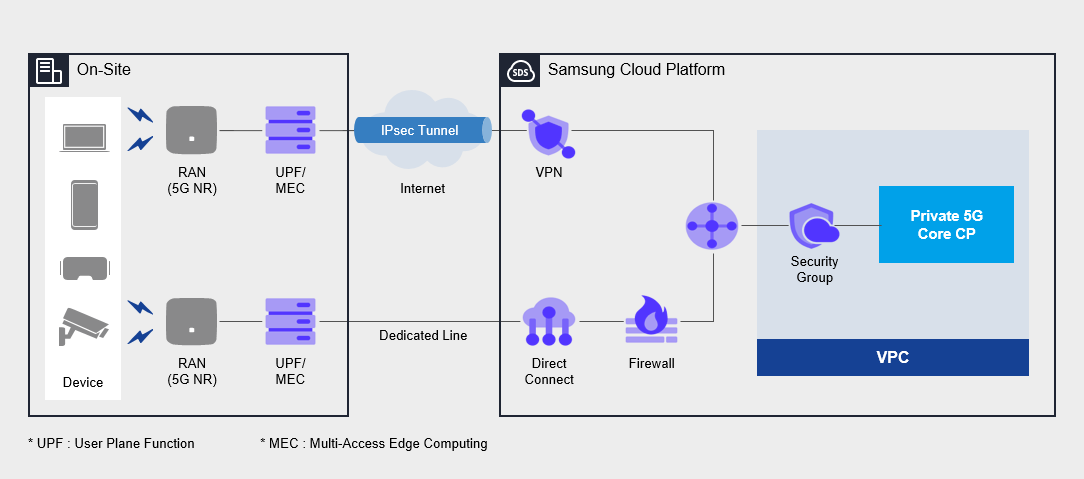
- 5.17: Private 5G Cloud
- 5.17.1: Overview
- 5.17.2: How-to guides
- 5.17.3: Release Note
- 6: Database
- 6.1: EPAS(DBaaS)
- 6.1.1: Overview
- 6.1.1.1: Server Types
- 6.1.1.2: Monitoring metrics
- 6.1.2: How-to guides
- 6.1.2.1: DB Service Manage
- 6.1.2.2: Backing up and restoring the database
- 6.1.2.3: Configure Read Replica
- 6.1.2.4: EPAS(DBaaS) Server Connection
- 6.1.2.5: Extension Usage
- 6.1.3: API Reference
- 6.1.4: CLI Reference
- 6.1.5: Release Note
- 6.2: PostgreSQL(DBaaS)
- 6.2.1: Overview
- 6.2.1.1: Server Types
- 6.2.1.2: Monitoring metrics
- 6.2.2: How-to guides
- 6.2.2.1: DB Service Manage
- 6.2.2.2: Backing up and restoring the DB
- 6.2.2.3: Configure Read Replica
- 6.2.2.4: DB Server Connection
- 6.2.2.5: Extension Use
- 6.2.3: API Reference
- 6.2.4: CLI Reference
- 6.2.5: Release Note
- 6.3: MariaDB(DBaaS)
- 6.3.1: Overview
- 6.3.1.1: Server Types
- 6.3.1.2: Monitoring Metrics
- 6.3.1.3: ServiceWatch Metrics
- 6.3.2: How-to guides
- 6.3.2.1: DB Service Manage
- 6.3.2.2: Backing up and restoring the database
- 6.3.2.3: Configure Read Replica
- 6.3.2.4: MariaDB(DBaaS) Server Connection
- 6.3.3: API Reference
- 6.3.4: CLI Reference
- 6.3.5: Release Note
- 6.4: MySQL(DBaaS)
- 6.4.1: Overview
- 6.4.1.1: Server Types
- 6.4.1.2: Monitoring metrics
- 6.4.1.3: ServiceWatch Metrics
- 6.4.2: How-to guides
- 6.4.2.1: DB Service Manage
- 6.4.2.2: Backing up and restoring the database
- 6.4.2.3: Configure Read Replica
- 6.4.2.4: MySQL(DBaaS) Server Connection
- 6.4.3: API Reference
- 6.4.4: CLI Reference
- 6.4.5: Release Note
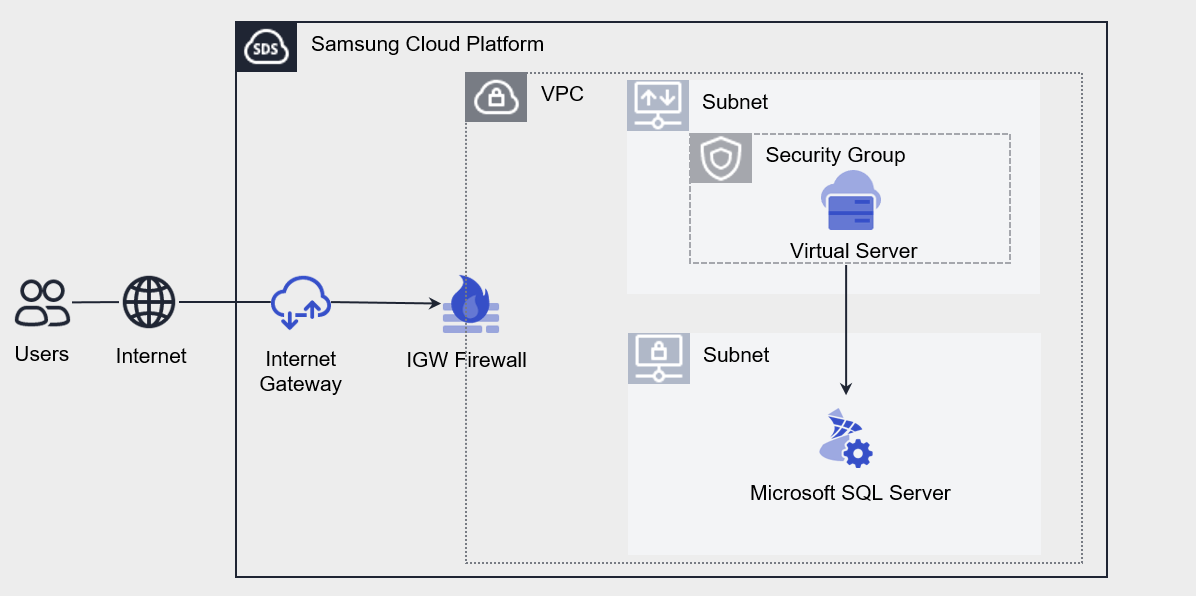
- 6.5: Microsoft SQL Server(DBaaS)
- 6.5.1: Overview
- 6.5.1.1: Server Types
- 6.5.1.2: Monitoring metrics
- 6.5.2: How-to guides
- 6.5.2.1: DB Service Manage
- 6.5.2.2: Backing up and restoring the DB
- 6.5.2.3: Secondary Add
- 6.5.2.4: Microsoft SQL Server(DBaaS) Server Connection
- 6.5.3: API Reference
- 6.5.4: CLI Reference
- 6.5.5: Release Note
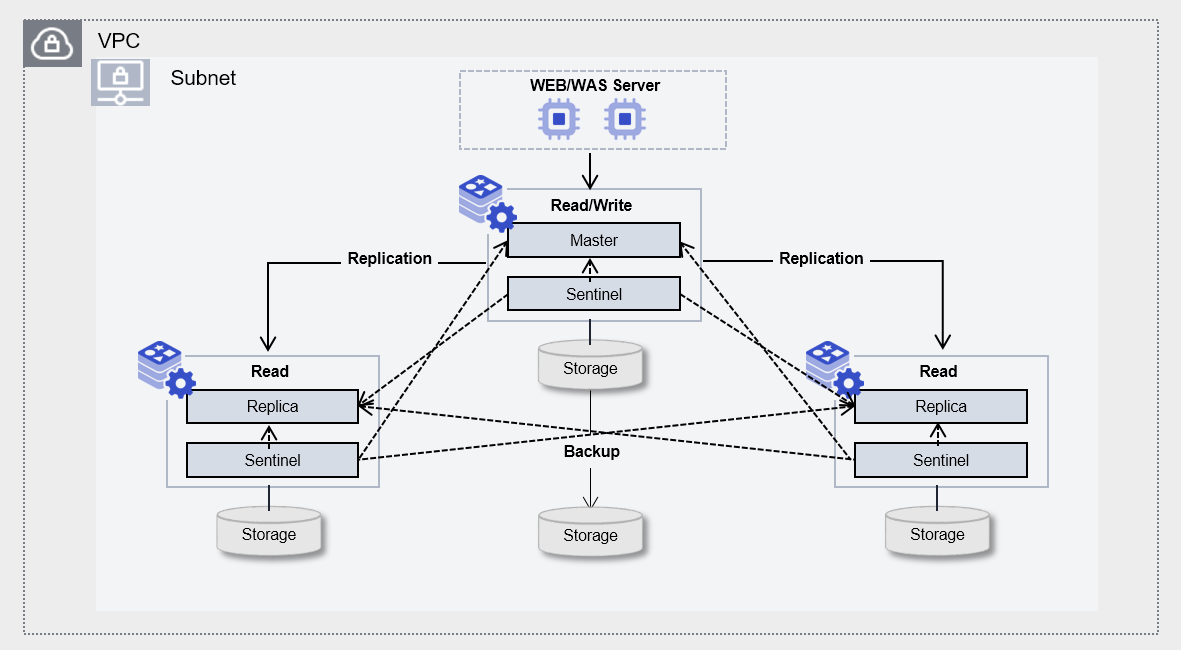
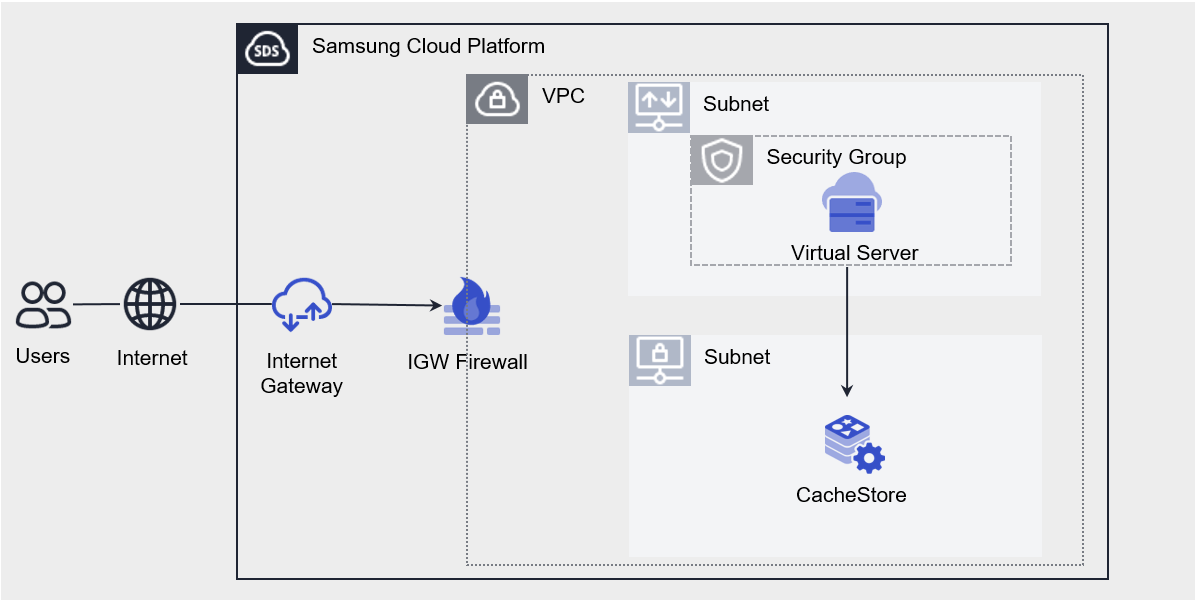
- 6.6: CacheStore(DBaaS)
- 6.6.1: Overview
- 6.6.1.1: Server Types
- 6.6.1.2: Monitoring metrics
- 6.6.2: How-to guides
- 6.6.2.1: CacheStore Service Manage
- 6.6.2.2: CacheStore Backup and Restore
- 6.6.2.3: CacheStore(DBaaS) Server Connection
- 6.6.3: API Reference
- 6.6.4: CLI Reference
- 6.6.5: Release Note
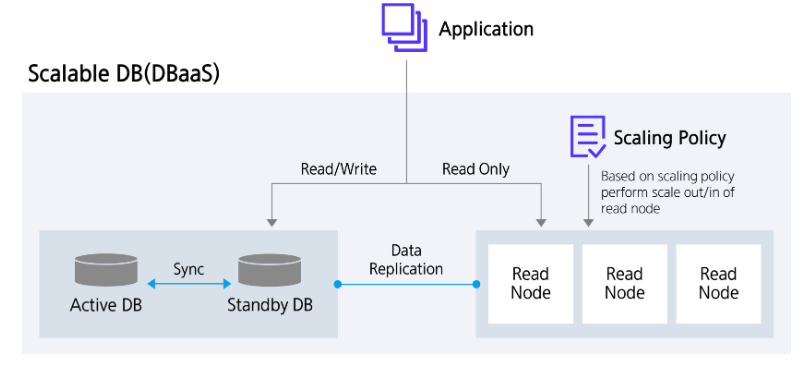
- 6.7: Scalable DB(DBaaS)
- 6.7.1: Overview
- 6.7.1.1: Server Types
- 6.7.1.2: ServiceWatch Metrics
- 6.7.2: How-to guides
- 6.7.2.1: Read Node Manage
- 6.7.2.2: Backup DB
- 6.7.3: Release Note
- 7: Data Analytics
- 7.1: Event Streams
- 7.1.1: Overview
- 7.1.1.1: Server Type
- 7.1.1.2: Monitoring Metrics
- 7.1.1.3: ServiceWatch Metrics
- 7.1.2: How-to guides
- 7.1.3: API Reference
- 7.1.4: CLI Reference
- 7.1.5: Release Note
- 7.2: Search Engine
- 7.2.1: Overview
- 7.2.1.1: Server Type
- 7.2.1.2: Monitoring metrics
- 7.2.2: How-to guides
- 7.2.3: API Reference
- 7.2.4: CLI Reference
- 7.2.5: Release Note
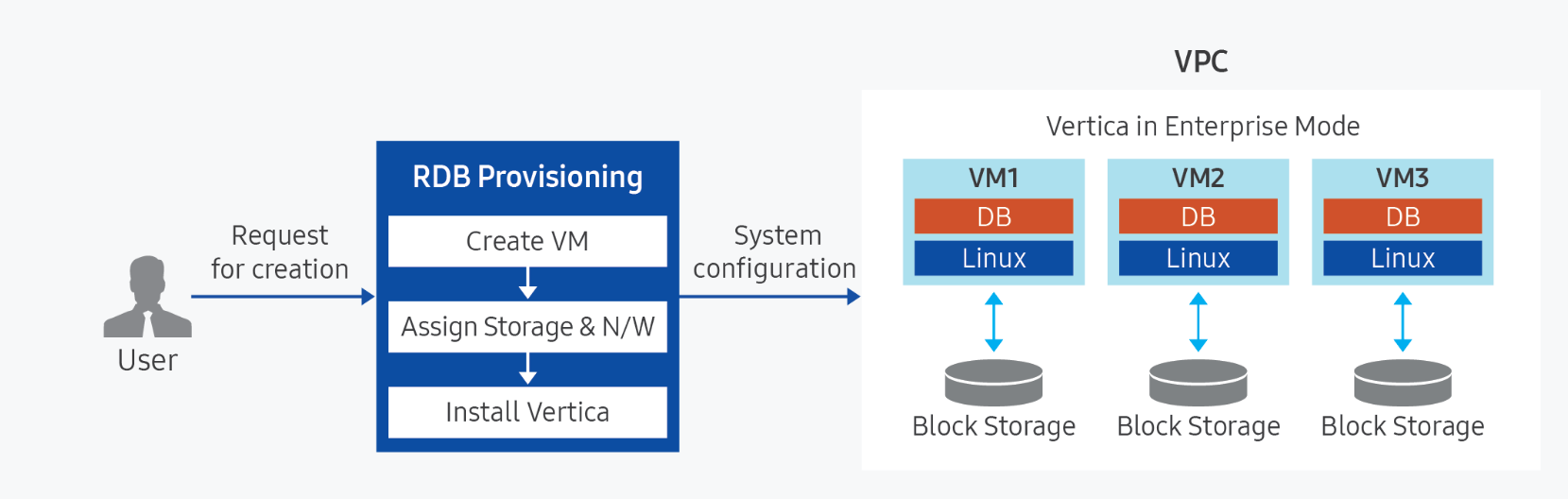
- 7.3: Vertica(DBaaS)
- 7.3.1: Overview
- 7.3.1.1: Server Type
- 7.3.1.2: Monitoring metrics
- 7.3.2: How-to guides
- 7.3.2.1: Backing up and restoring Vertica
- 7.3.3: API Reference
- 7.3.4: CLI Reference
- 7.3.5: Release Note
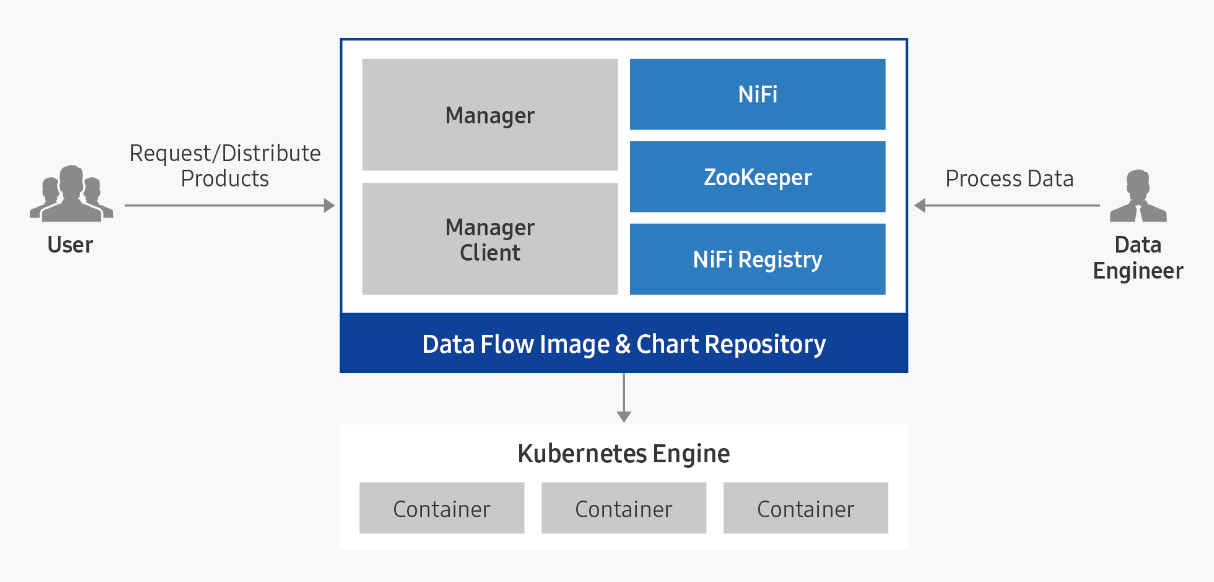
- 7.4: Data Flow
- 7.4.1: Overview
- 7.4.1.1: ServiceWatch metric
- 7.4.2: How-to guides
- 7.4.2.1: Data Flow Services
- 7.4.2.2: Install Ingress Controller
- 7.4.3: API Reference
- 7.4.4: CLI Reference
- 7.4.5: Release Note
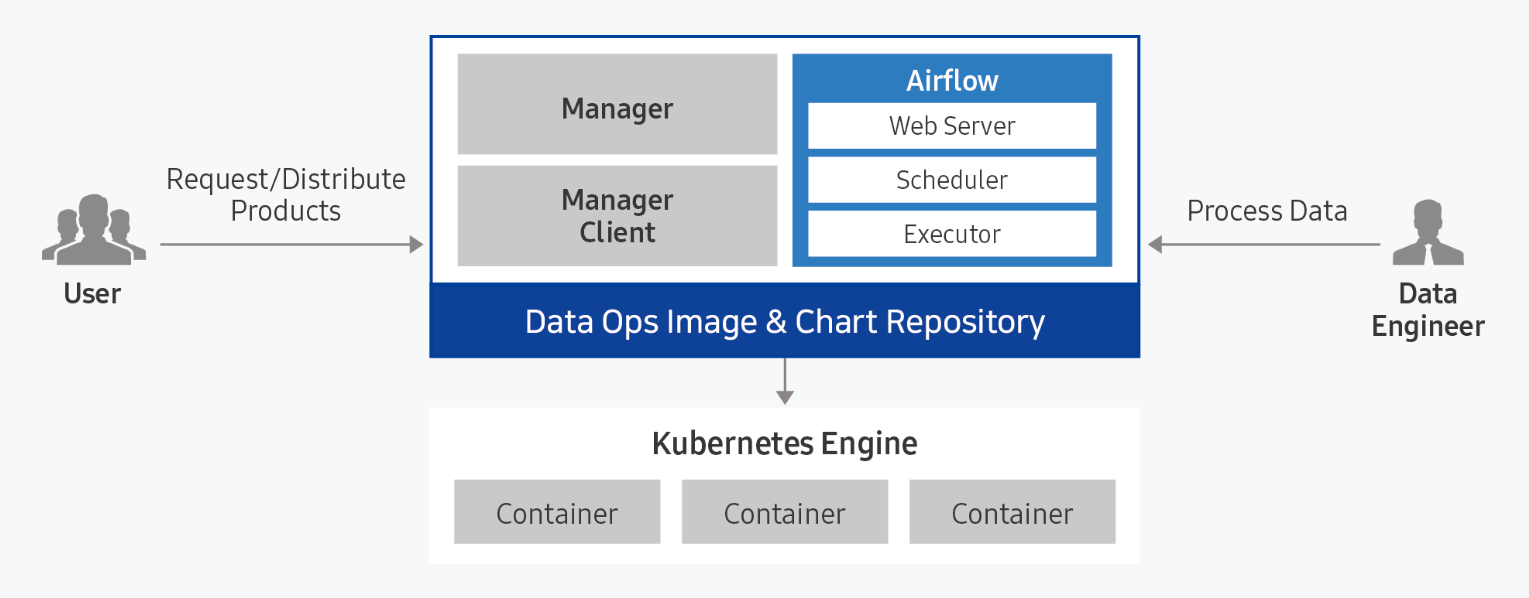
- 7.5: Data Ops
- 7.5.1: Overview
- 7.5.1.1: ServiceWatch metric
- 7.5.2: How-to guides
- 7.5.2.1: Data Ops Services
- 7.5.2.2: Installing Ingress Controller
- 7.5.3: API Reference
- 7.5.4: CLI Reference
- 7.5.5: Release Note
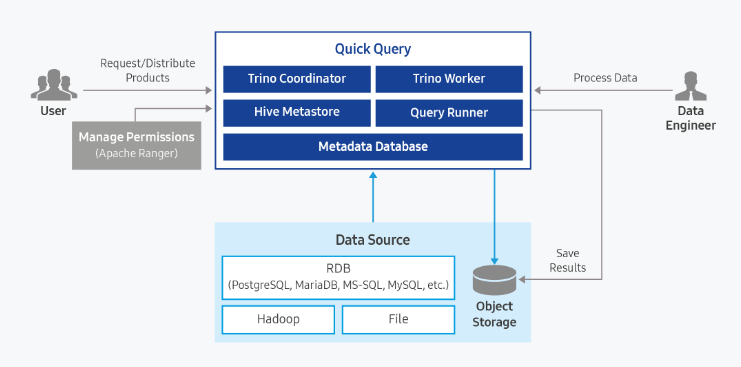
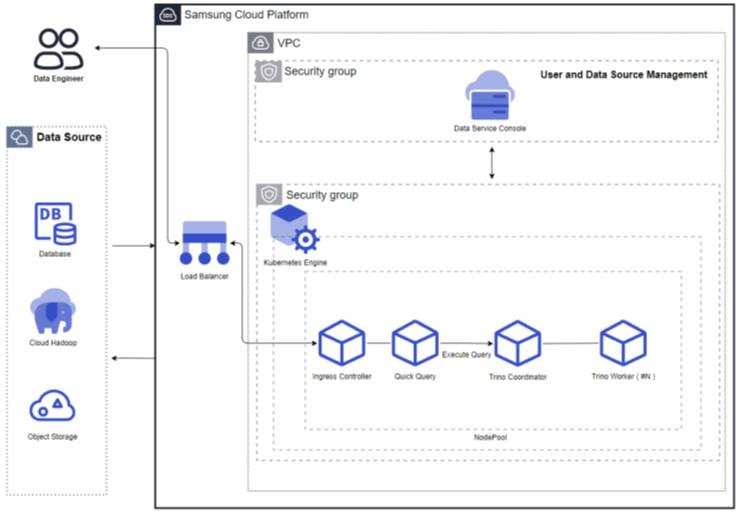
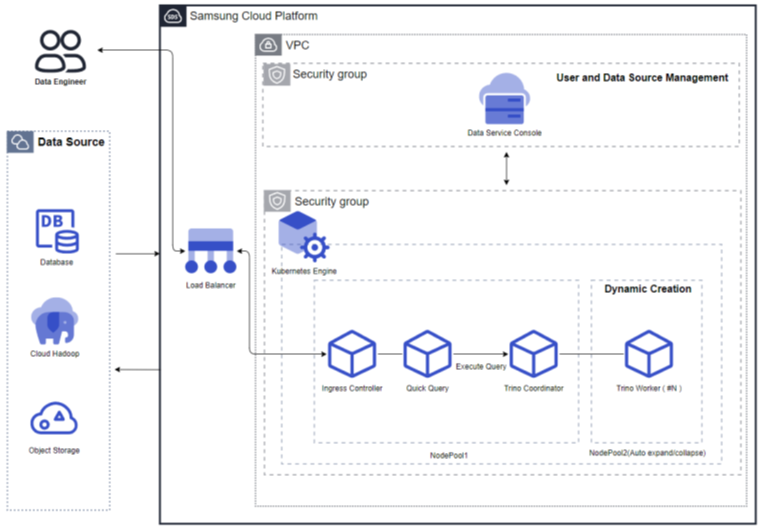
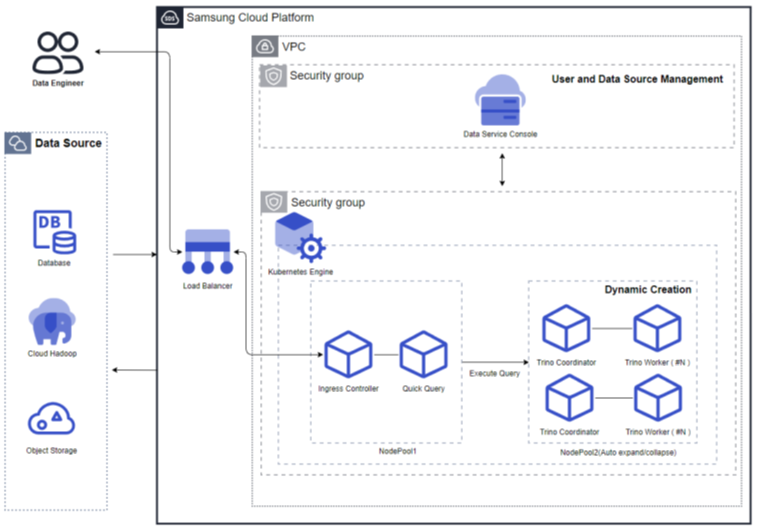
- 7.6: Quick Query
- 7.6.1: Overview
- 7.6.1.1: ServiceWatch metric
- 7.6.2: How-to guides
- 7.6.3: API Reference
- 7.6.4: CLI Reference
- 7.6.5: Release Note
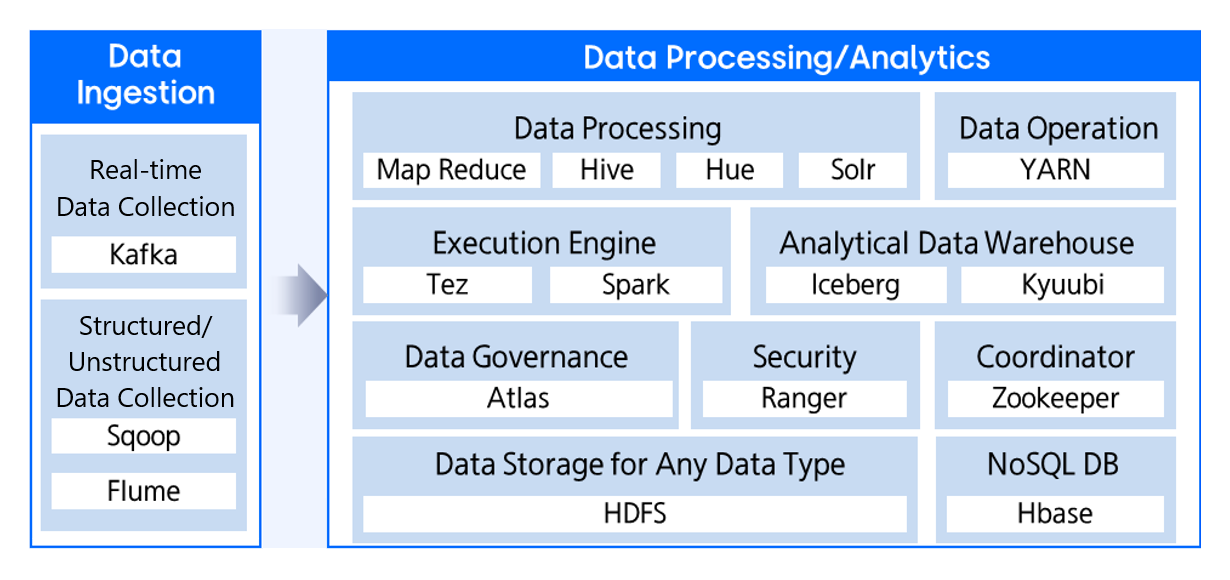
- 7.7: Cloud Hadoop
- 7.7.1: Overview
- 7.7.1.1: ServiceWatch metric
- 7.7.2: How-to guides
- 7.7.3: API Reference
- 7.7.4: Release Note
- 8: Application Service
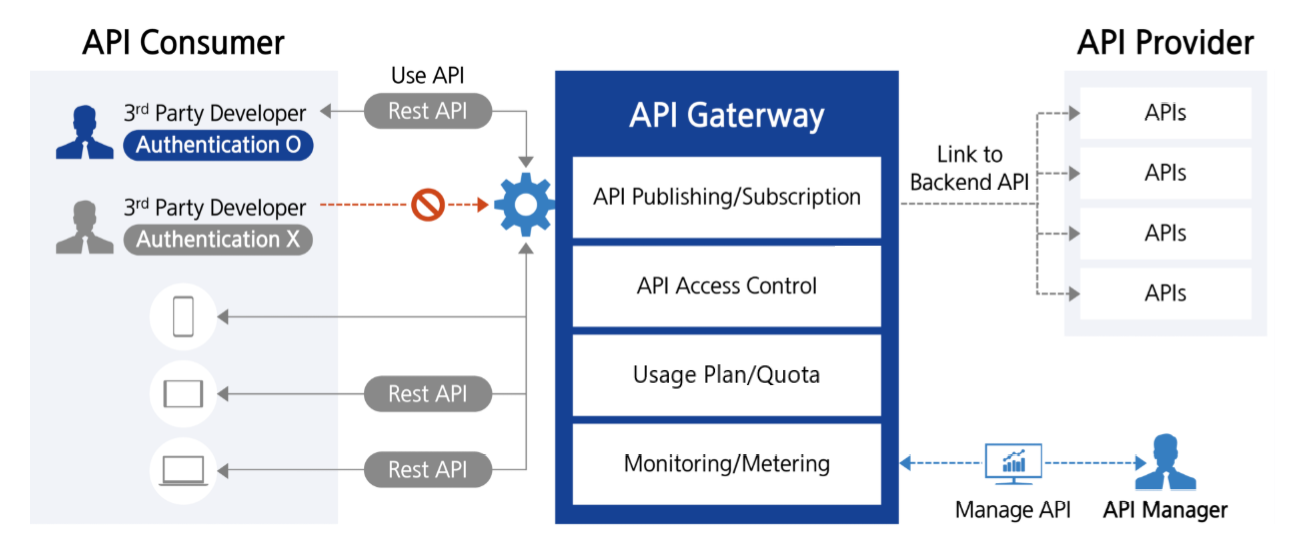
- 8.1: API Gateway
- 8.1.1: Overview
- 8.1.1.1: ServiceWatch metric
- 8.1.2: How-to guides
- 8.1.2.1: Resource-Based Policy Guide
- 8.1.3: API Reference
- 8.1.4: CLI Reference
- 8.1.5: Release Note
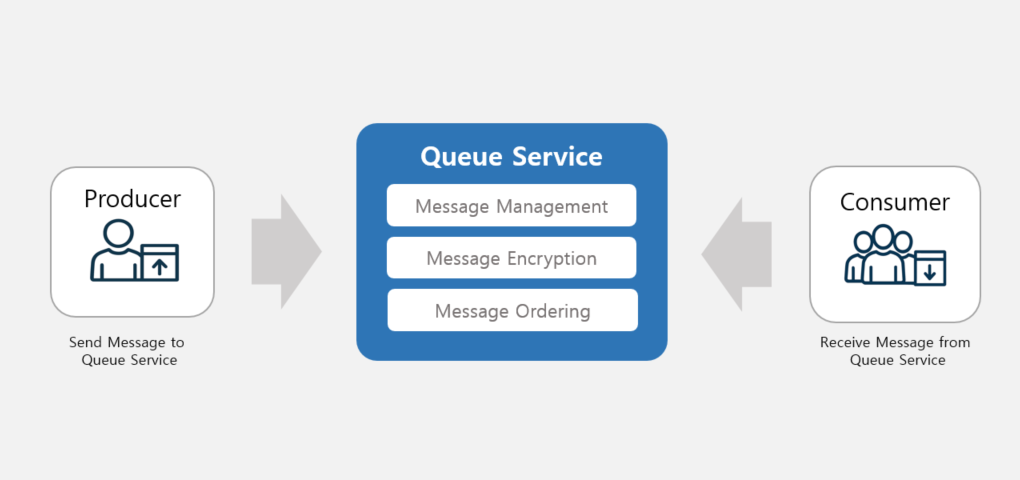
- 8.2: Queue Service
- 8.2.1: Message API reference
- 8.2.2: How to guides
- 8.2.3: Overview
- 8.2.3.1: ServiceWatch Metrics
- 8.2.4: CLI Reference
- 8.2.5: API Reference
- 8.2.6: Release Note
- 9: Security
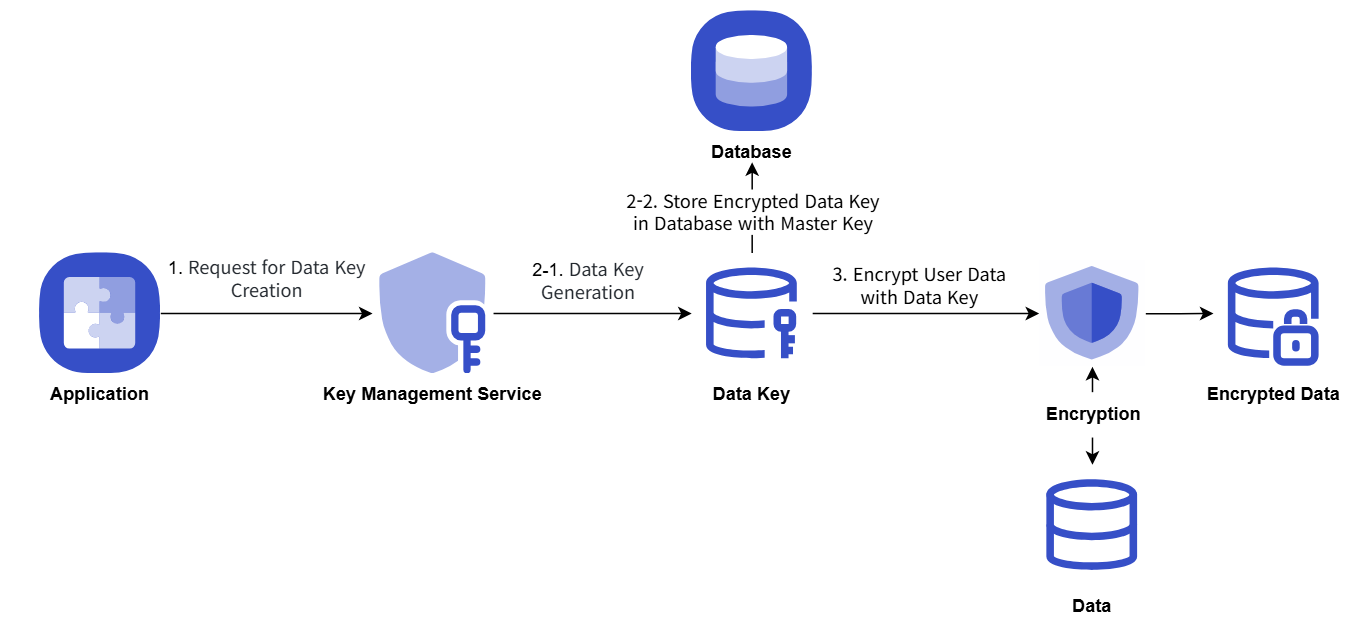
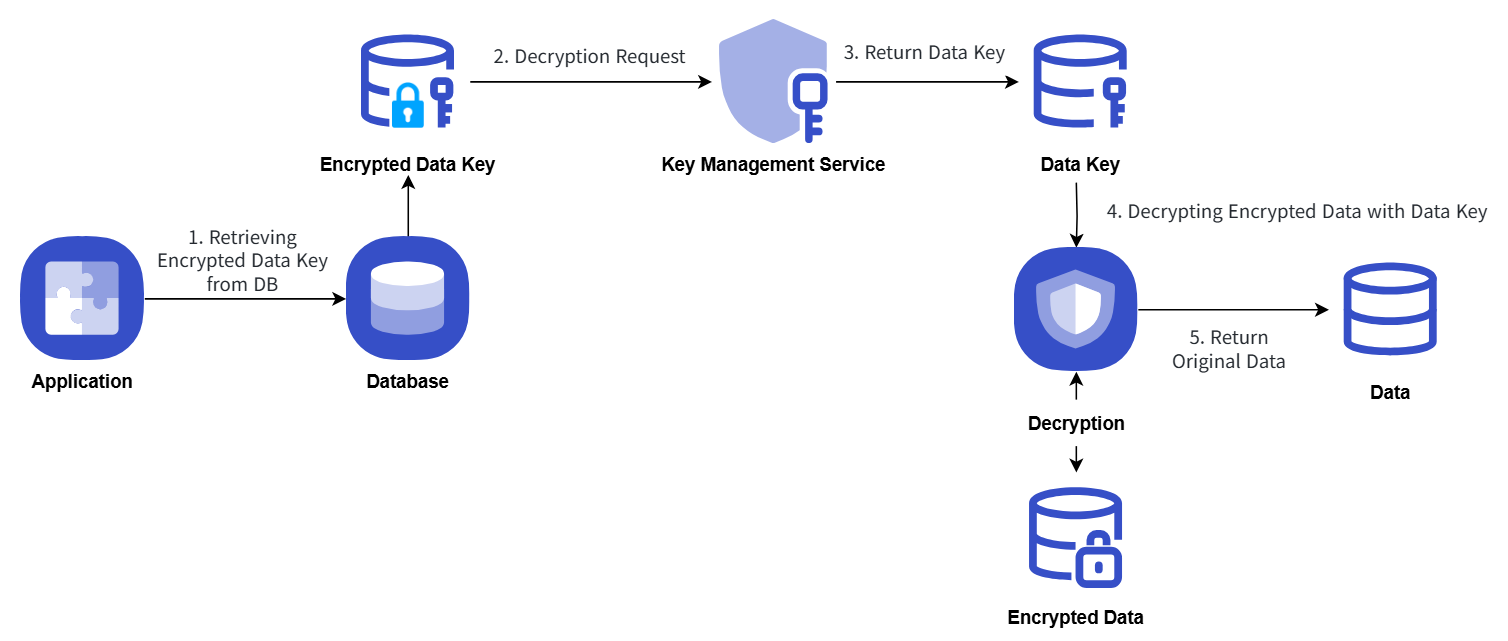
- 9.1: Key Management Service
- 9.1.1: Overview
- 9.1.2: How-to guides
- 9.1.2.1: Encryption Example Using Key Management Service Keys
- 9.1.2.2: Platform-managed Key
- 9.1.3: API Reference
- 9.1.4: CLI Reference
- 9.1.5: Release Note
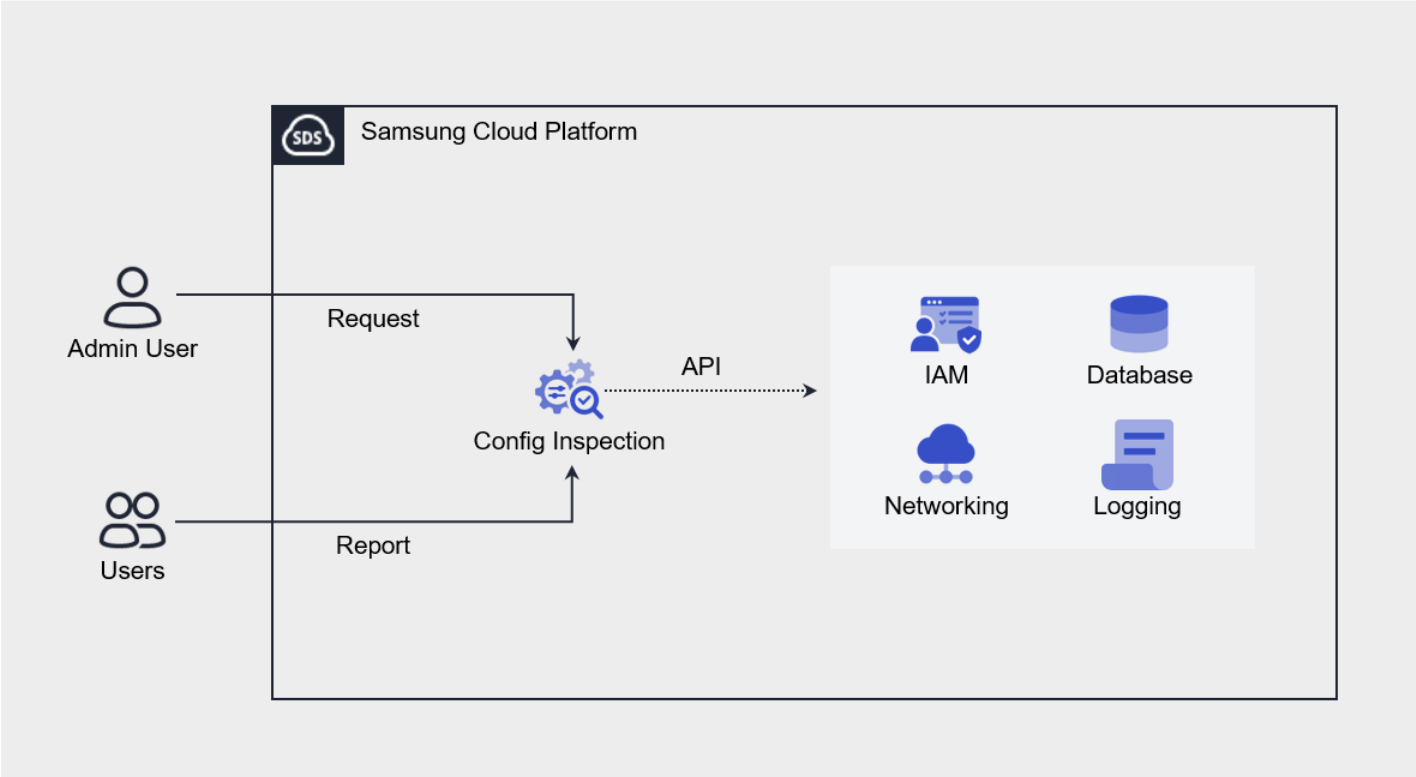
- 9.2: Config Inspection
- 9.2.1: Overview
- 9.2.1.1: Checklist
- 9.2.2: How-to guides
- 9.2.2.1: Check Dashboard
- 9.2.2.2: Manage Diagnosis Results
- 9.2.2.3: Pre-configuration
- 9.2.3: Release Note
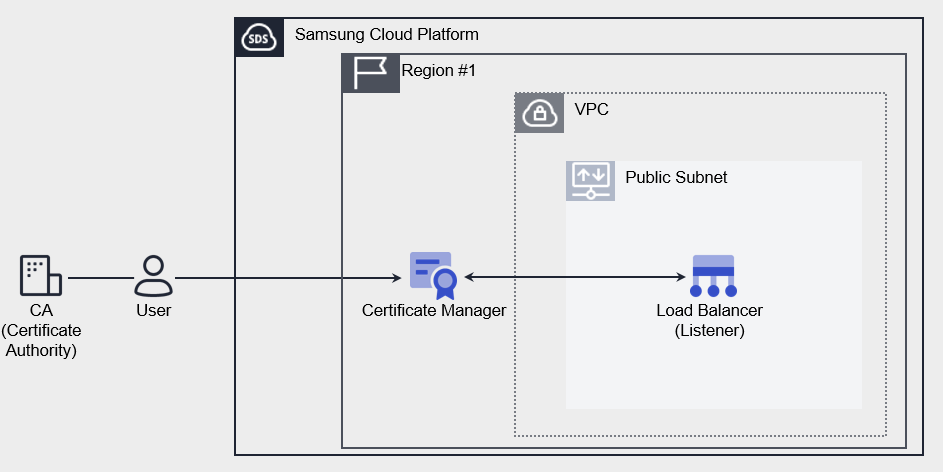
- 9.3: Certificate Manager
- 9.3.1: Overview
- 9.3.2: How-to guides
- 9.3.2.1: Extract Certificate Chain
- 9.3.3: API Reference
- 9.3.4: CLI Reference
- 9.3.5: Release Note
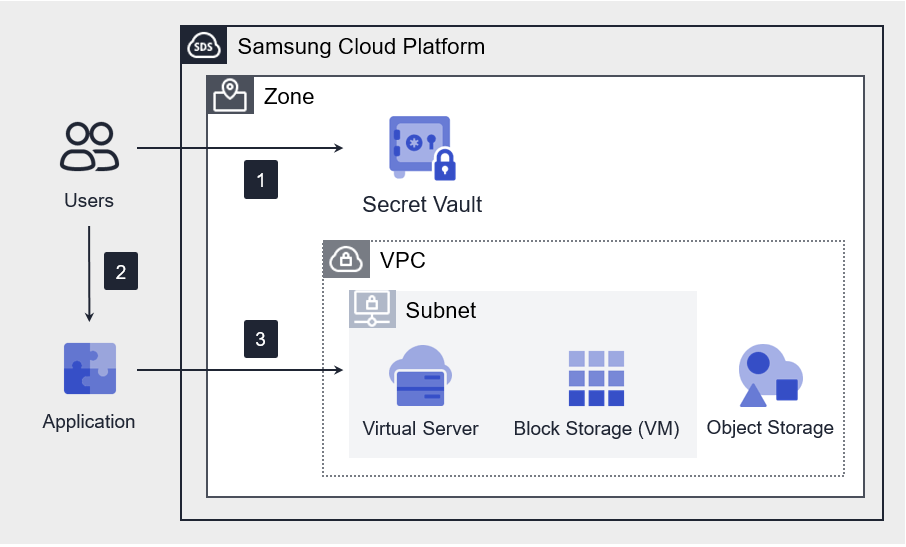
- 9.4: Secret Vault
- 9.4.1: Overview
- 9.4.2: How-to guides
- 9.4.3: API Reference
- 9.4.4: CLI Reference
- 9.4.5: Release Note
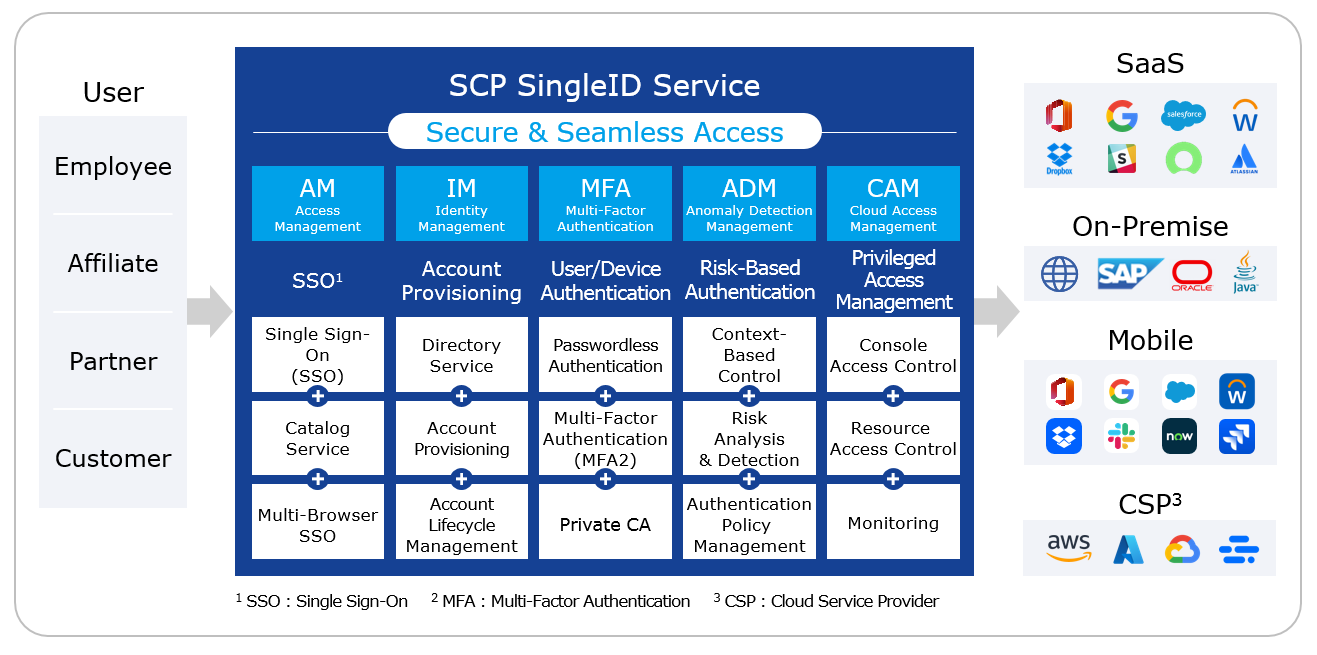
- 9.5: SingleID
- 9.5.1: Overview
- 9.5.2: How-to guides
- 9.5.2.1: SingleID Manuals
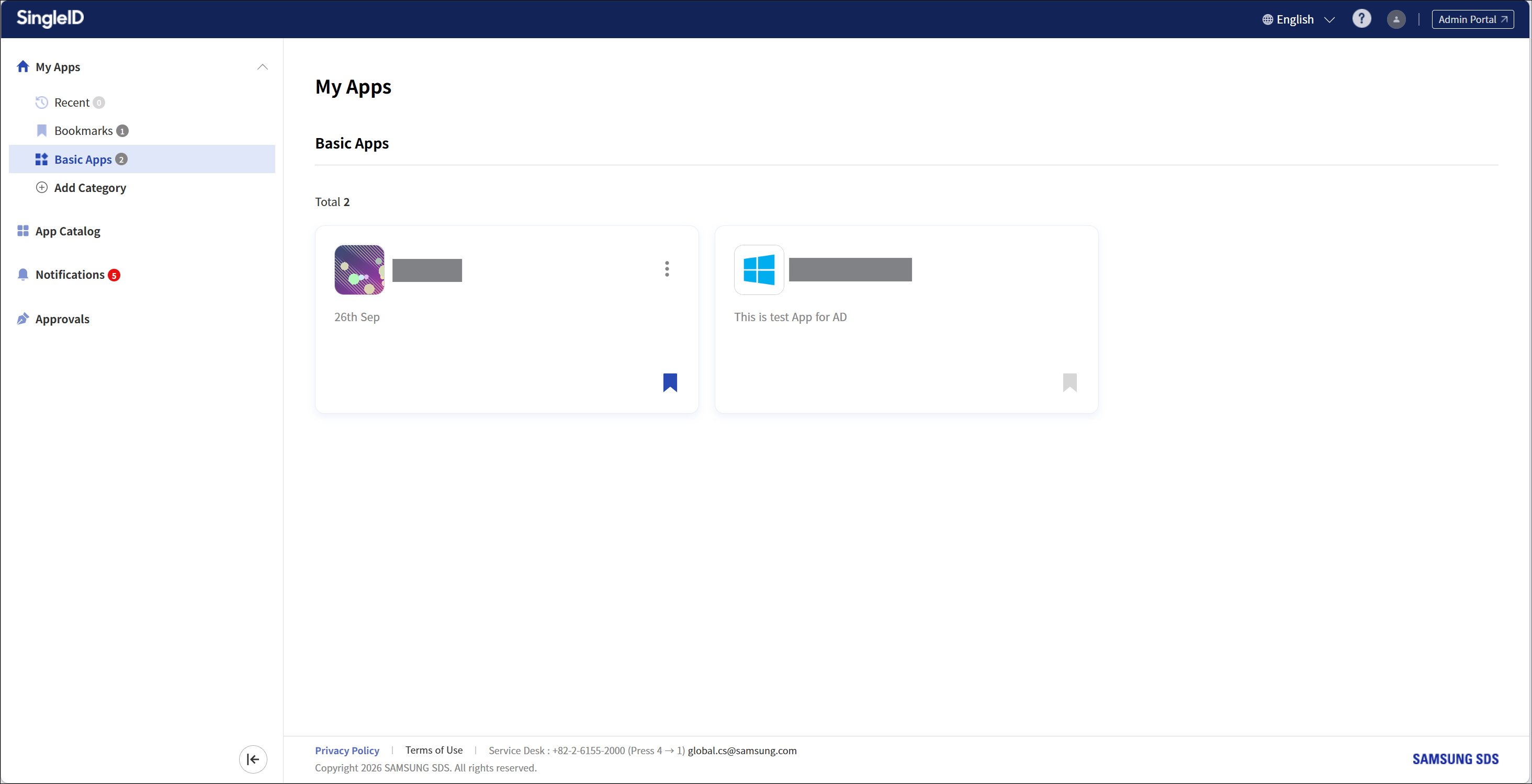
- 9.5.2.1.1: User Portal
- 9.5.2.1.1.1: Announcements and Language Settings
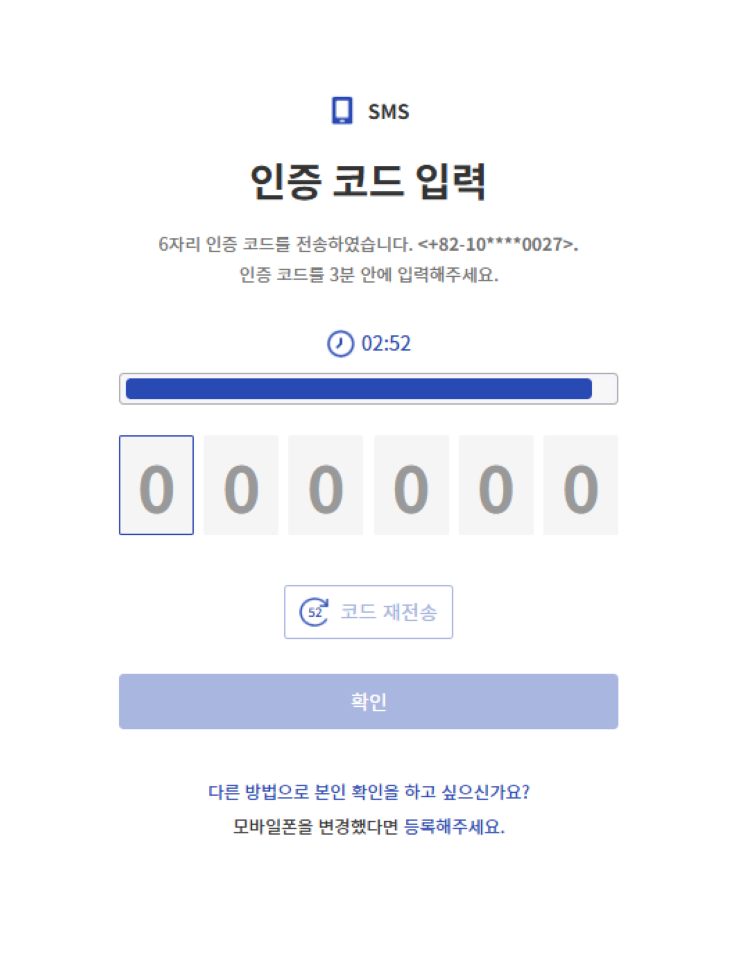
- 9.5.2.1.1.2: Log in using an authentication method
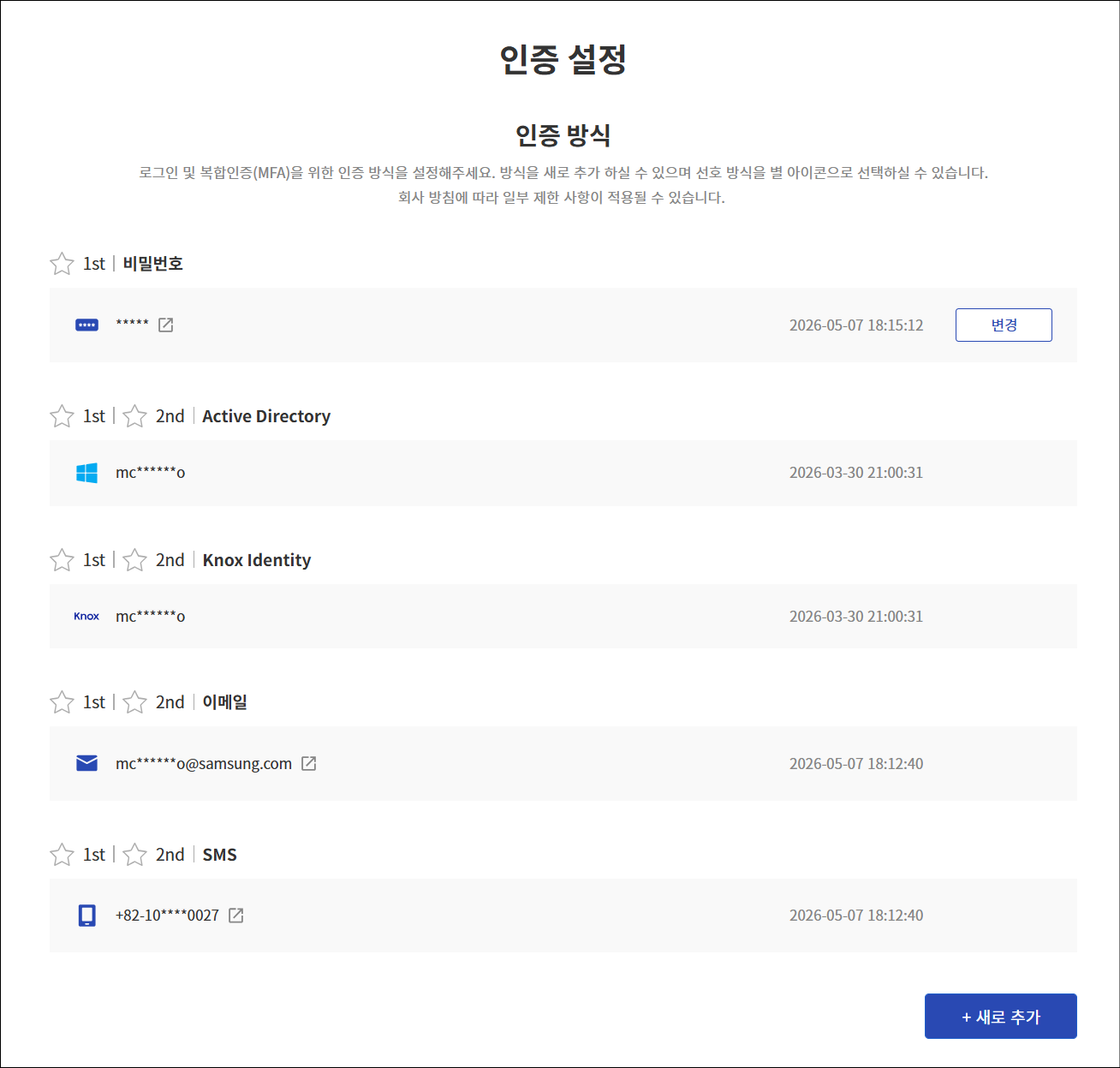
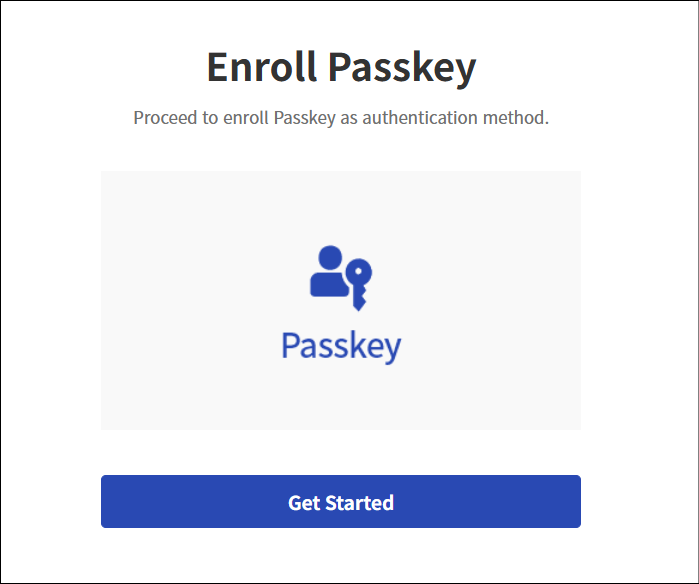
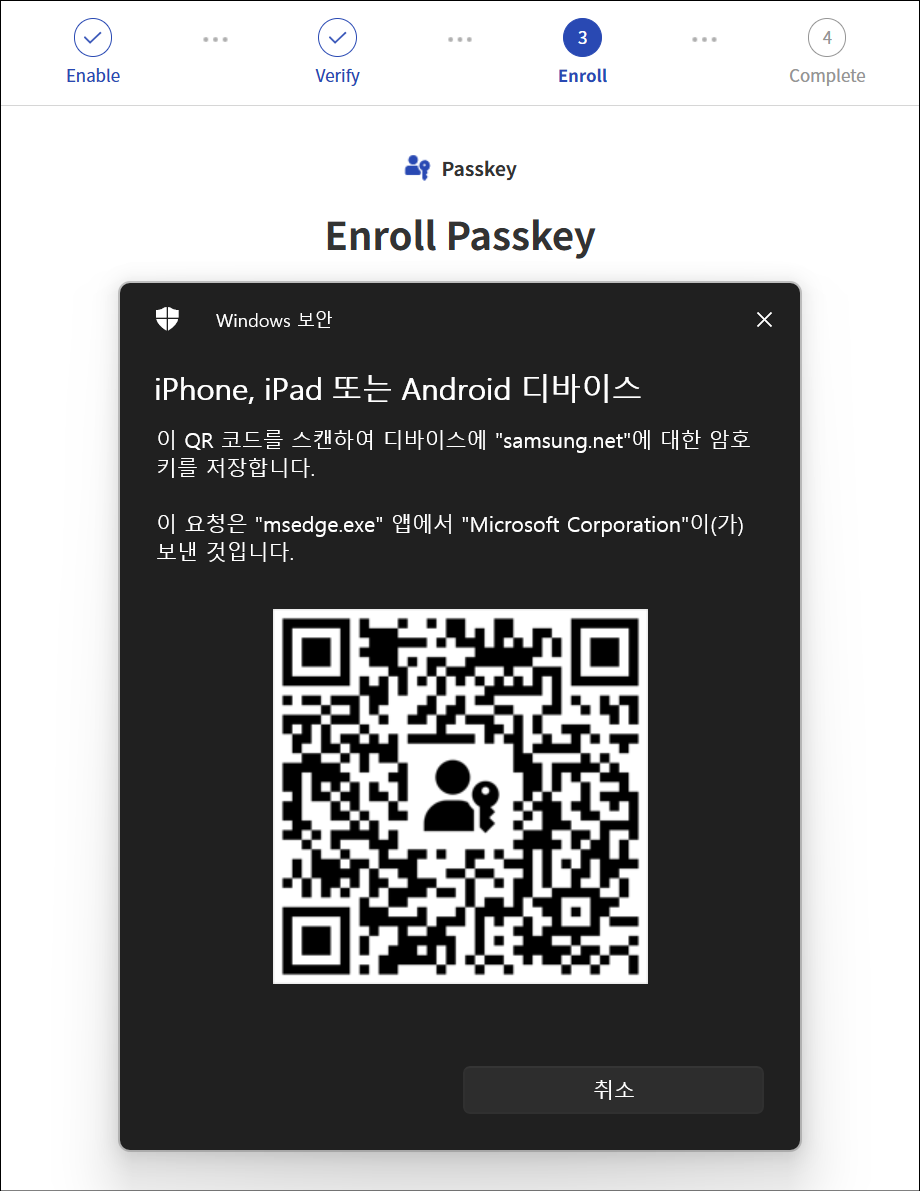
- 9.5.2.1.1.3: Register authentication tool
- 9.5.2.1.1.4: Sign Up
- 9.5.2.1.1.5: Find ID and Reset Password
- 9.5.2.1.1.6: Privacy Policy, Terms of Service, Service Desk
- 9.5.2.1.1.7: PC SSO Agent
- 9.5.2.1.1.8: My App
- 9.5.2.1.1.9: App Catalog
- 9.5.2.1.1.10: Notification
- 9.5.2.1.1.11: Approval Request
- 9.5.2.1.1.12: Personal Profile
- 9.5.2.1.2: Admin Portal
- 9.5.2.1.2.1: Dashboard
- 9.5.2.1.2.2: Integration
- 9.5.2.1.2.3: Identity Store
- 9.5.2.1.2.4: Policy
- 9.5.2.1.2.5: Terms and Conditions
- 9.5.2.1.2.6: Settings
- 9.5.2.1.2.7: Monitoring
- 9.5.2.1.2.8: Open Source licence
- 9.5.2.1.3: MFA Portal
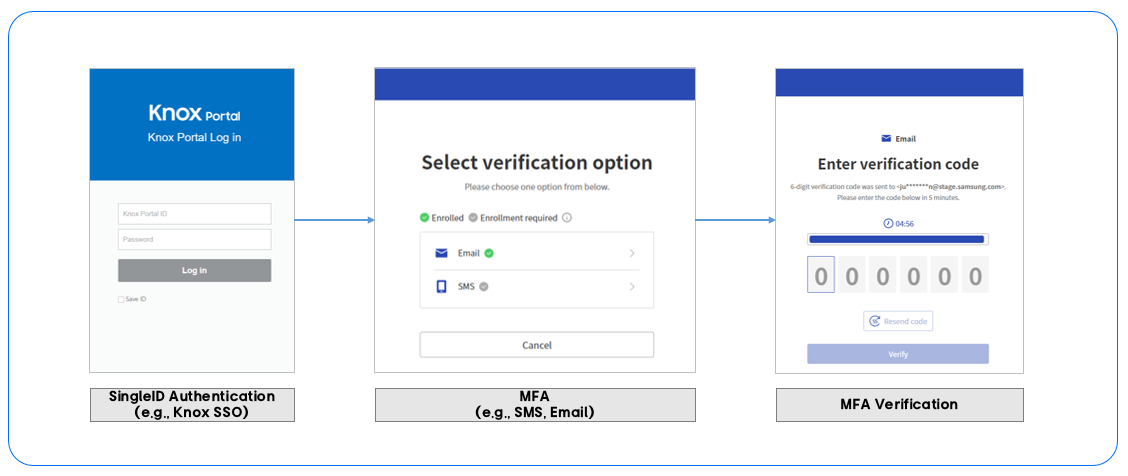
- 9.5.2.1.3.1: Log in using an authentication method
- 9.5.2.1.3.2: Register authentication tool
- 9.5.2.1.3.3: policy
- 9.5.2.1.3.4: Configure Privacy Settings
- 9.5.2.1.3.5: Settings
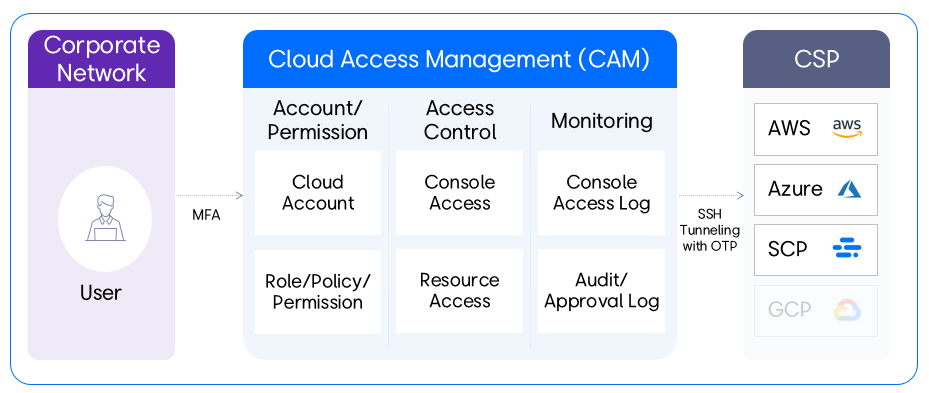
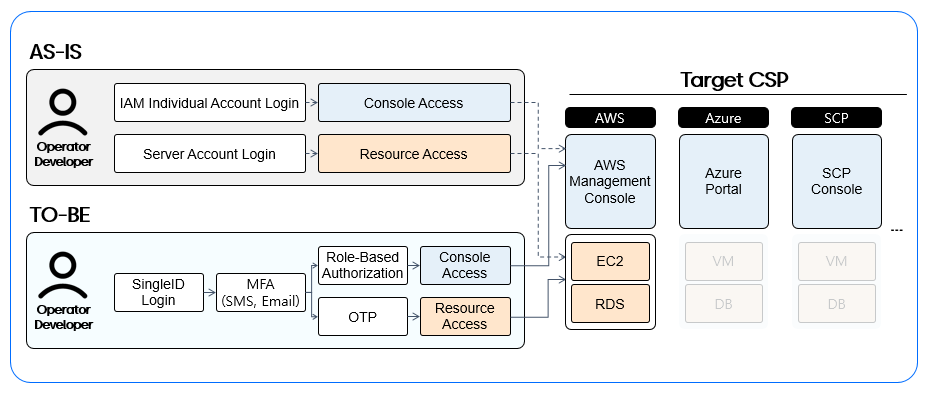
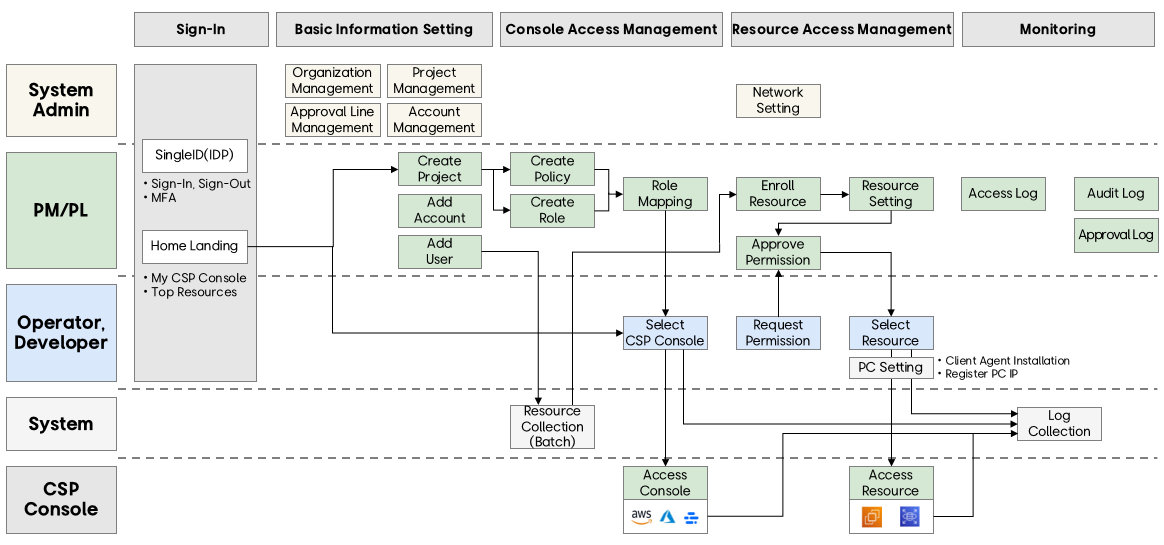
- 9.5.2.1.4: CAM Portal
- 9.5.2.1.4.1: Getting Started
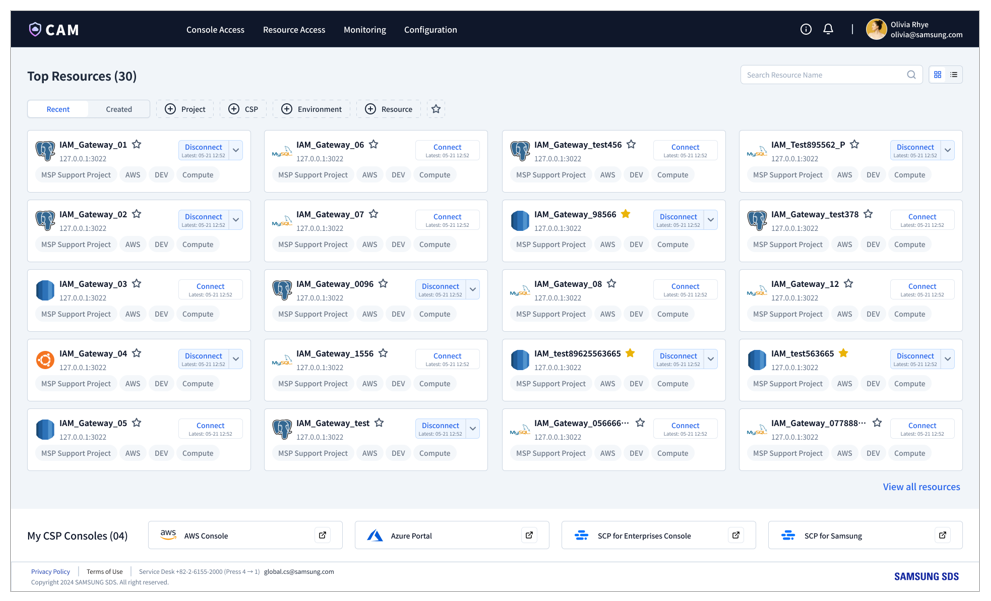
- 9.5.2.1.4.2: Home
- 9.5.2.1.4.3: Console Access
- 9.5.2.1.4.4: Resource Access
- 9.5.2.1.4.5: Monitoring
- 9.5.2.1.4.6: Configuration
- 9.5.2.1.5: SingleID Authenticator Manual Overview
- 9.5.2.1.5.1: Install App
- 9.5.2.1.5.2: User Authentication
- 9.5.2.1.5.3: Manage Authentication Method
- 9.5.2.1.5.4: Manage Service List
- 9.5.2.1.5.5: Open Source Licence(Android)
- 9.5.2.1.5.6: Open Source Licence(ISO)
- 9.5.2.1.6: Open API guides
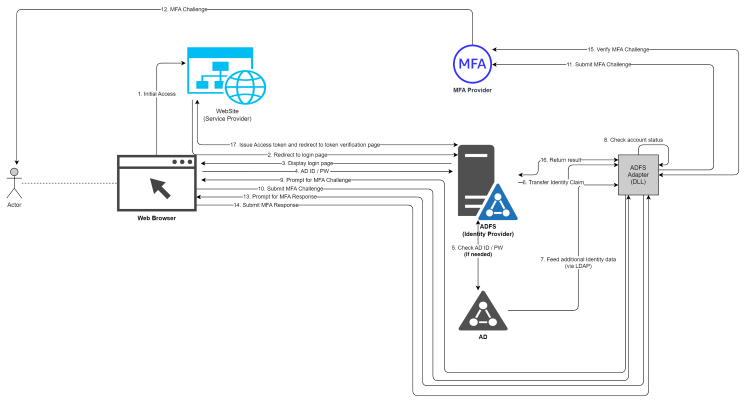
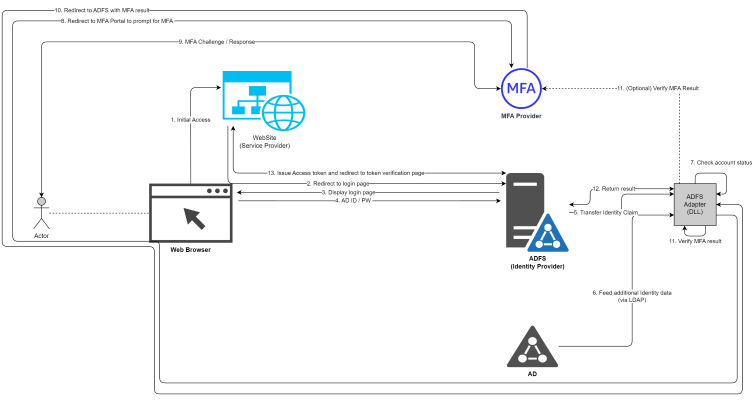
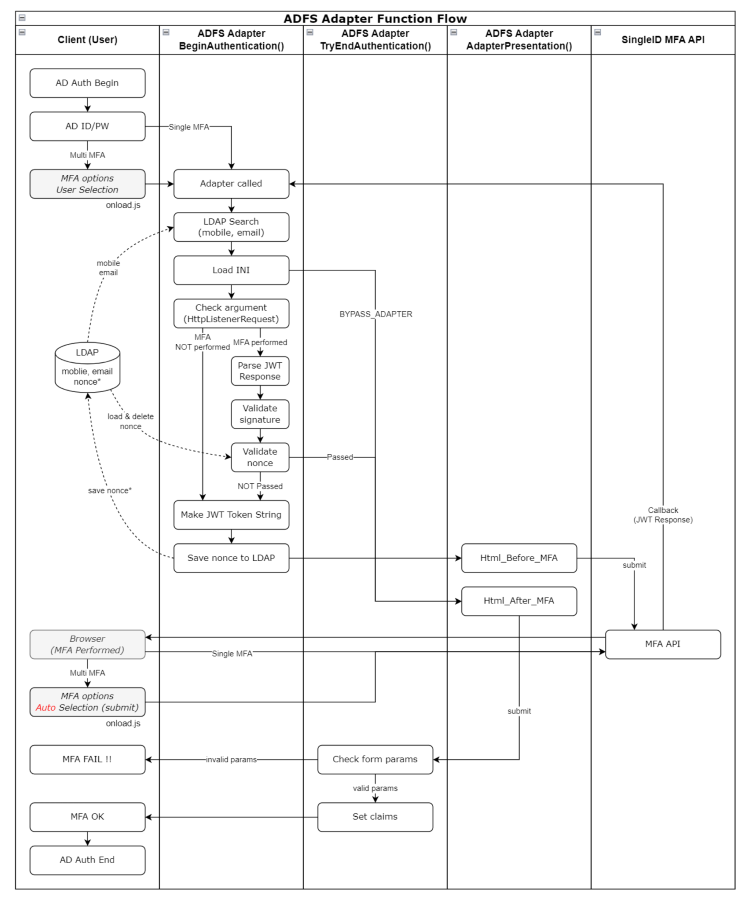
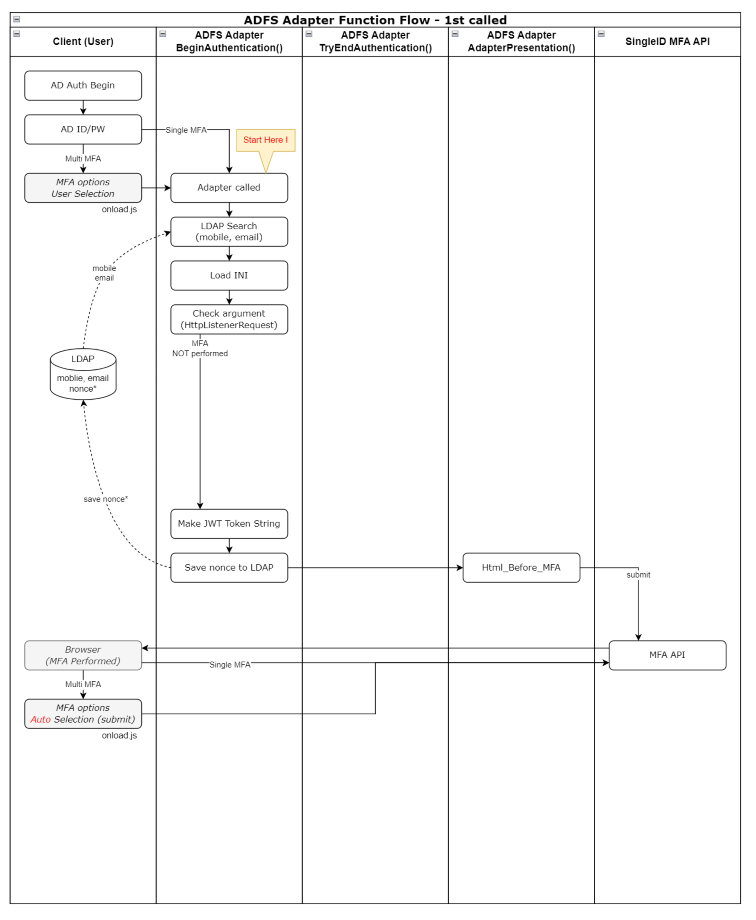
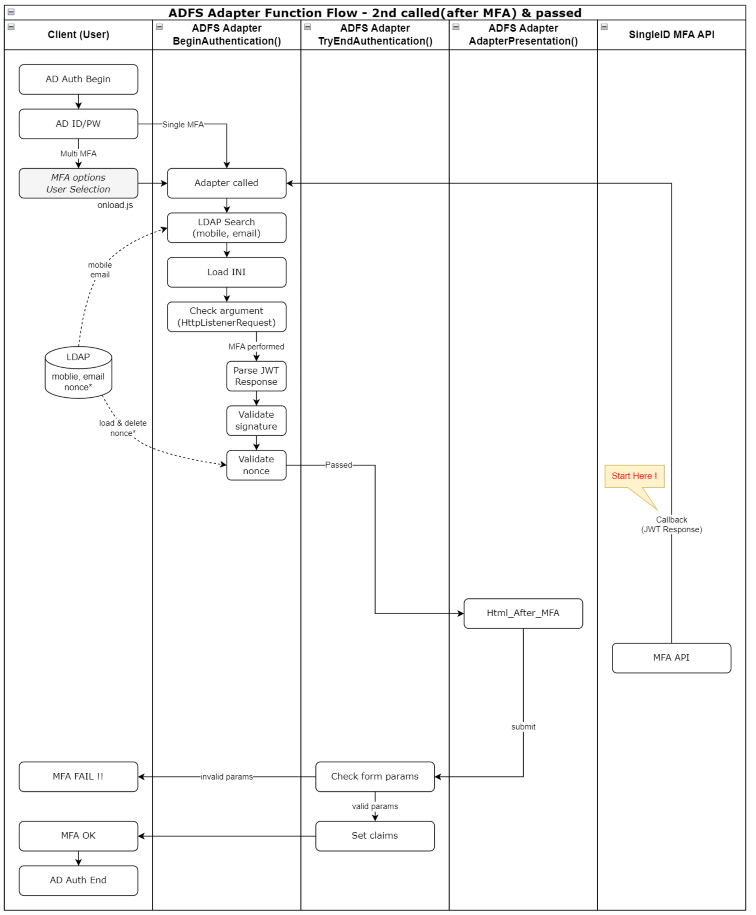
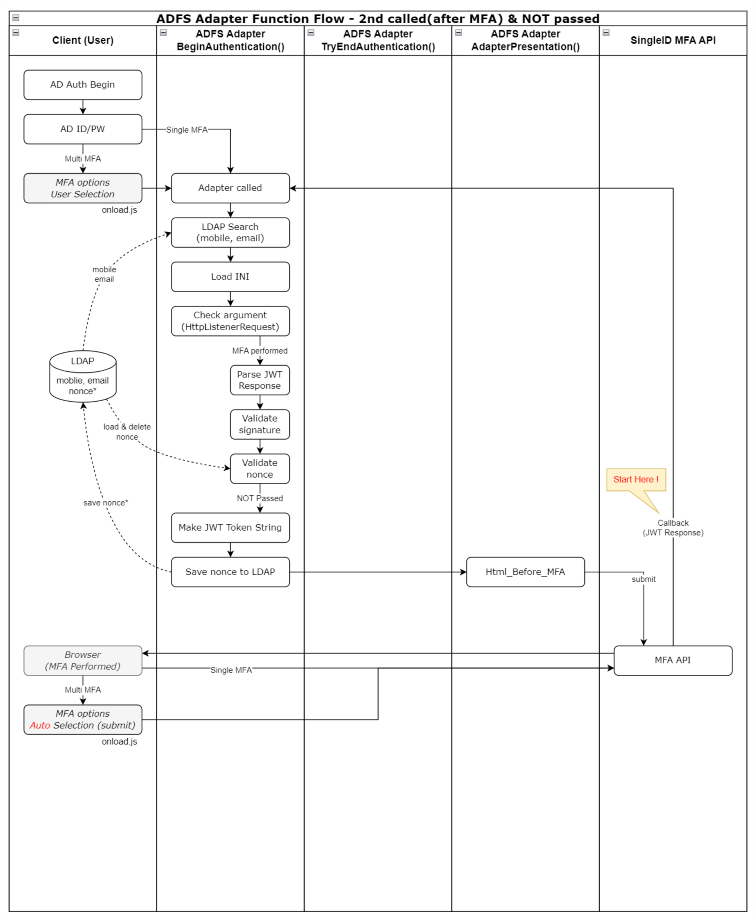
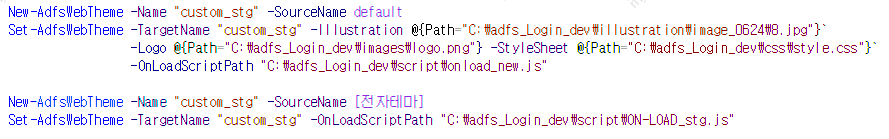
- 9.5.2.1.6.1: ADFS Adapter Guide
- 9.5.2.1.6.2: Adapter Configuration Guide
- 9.5.3: Release Note
- 9.6: WAF
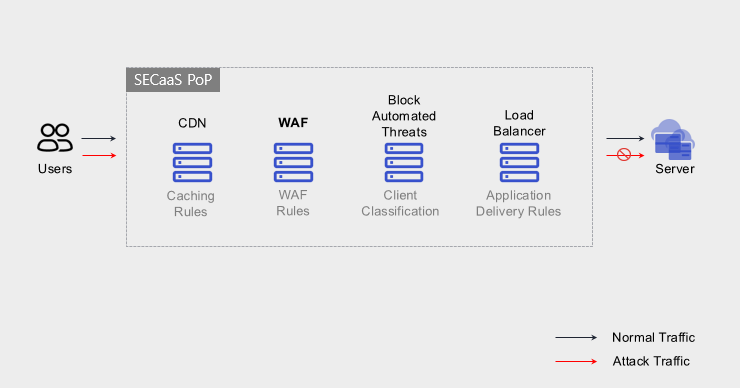
- 9.6.1: Overview
- 9.6.2: How-to guides
- 9.6.2.1: WAF Preparation
- 9.6.2.2: WAF Service Application
- 9.6.2.3: WAF Service Outage Response
- 9.6.3: Release Note
- 9.7: WAF
- 9.7.1: Overview
- 9.7.2: How-to guides
- 9.7.3: Release Note
- 9.8: WAF
- 9.8.1: Overview
- 9.8.2: How-to guides
- 9.8.2.1: WAF Build Process Guide
- 9.8.3: Release Note
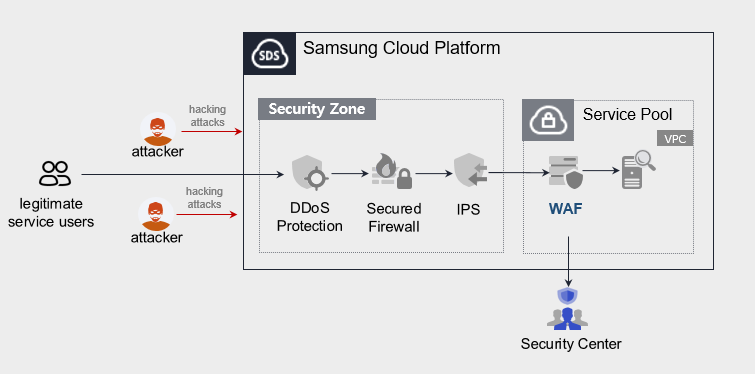
- 9.9: DDoS Protection
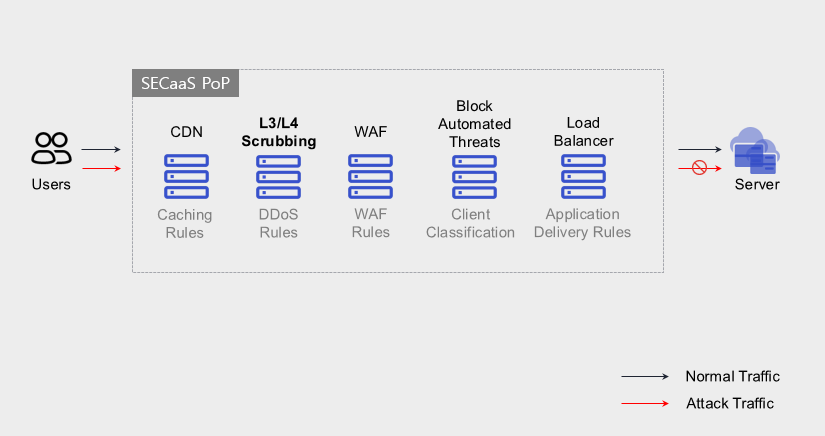
- 9.9.1: Overview
- 9.9.2: How-to guides
- 9.9.3: Release Note
- 9.10: DDoS Protection
- 9.10.1: Overview
- 9.10.2: How-to guides
- 9.10.3: Release Note
- 9.11: IPS
- 9.11.1: Overview
- 9.11.2: How-to guides
- 9.11.3: Release Note
- 9.12: Secured Firewall
- 9.12.1: Overview
- 9.12.2: How-to guides
- 9.12.3: Release Note
- 9.13: Secured VPN
- 9.13.1: Overview
- 9.13.2: How-to guides
- 9.13.2.1: Secured VPN Build Process Guide
- 9.13.3: Release Note
- 9.14: FPMS
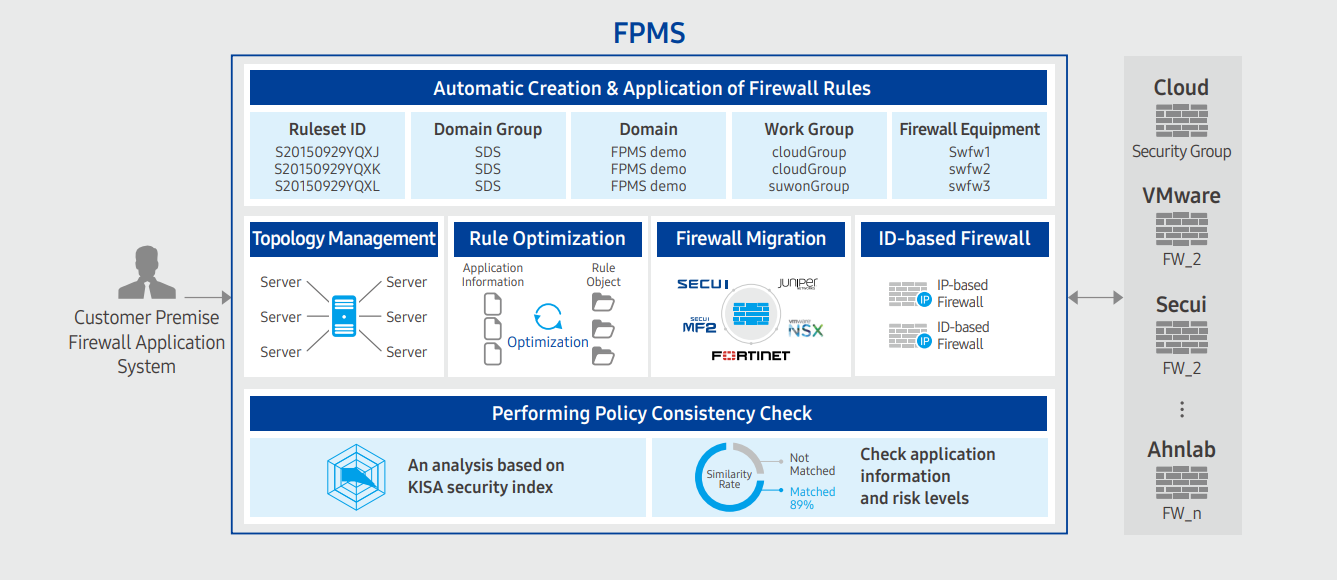
- 9.14.1: Overview
- 9.14.2: How-to guides
- 9.14.3: Release Note
- 9.15: Secrets Manager
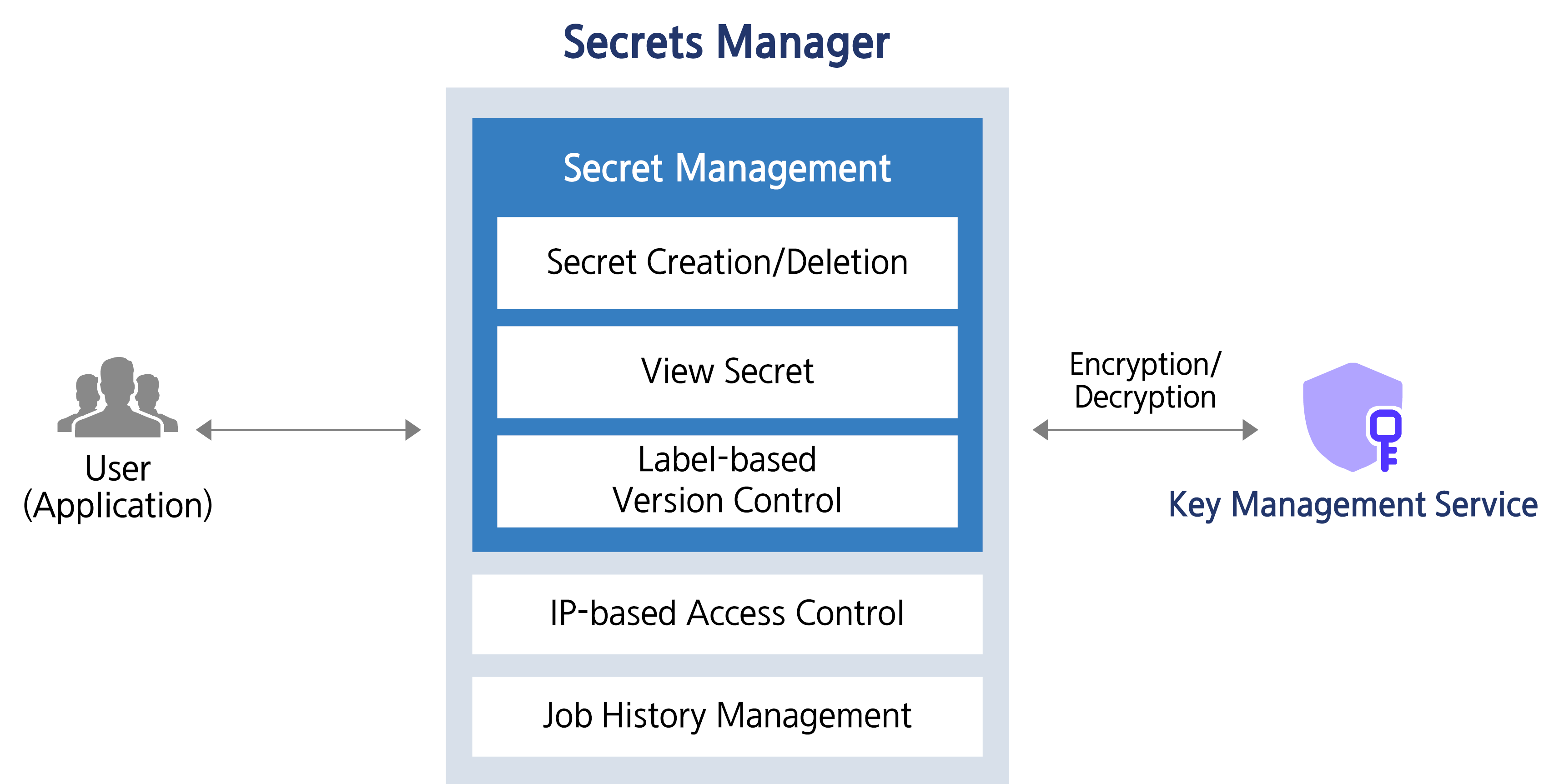
- 9.15.1: Overview
- 9.15.2: How-to guides
- 9.15.2.1: Secret Retrieval API Reference
- 9.15.3: Release Note
- 9.16: DDoS Protection
- 9.16.1: Overview
- 9.16.2: How-to guides
- 9.16.2.1: DDoS Protection Preparation
- 9.16.2.2: DDoS Protection Service Application
- 9.16.2.3: DDoS Protection Service Outage Response
- 9.16.3: Release Note
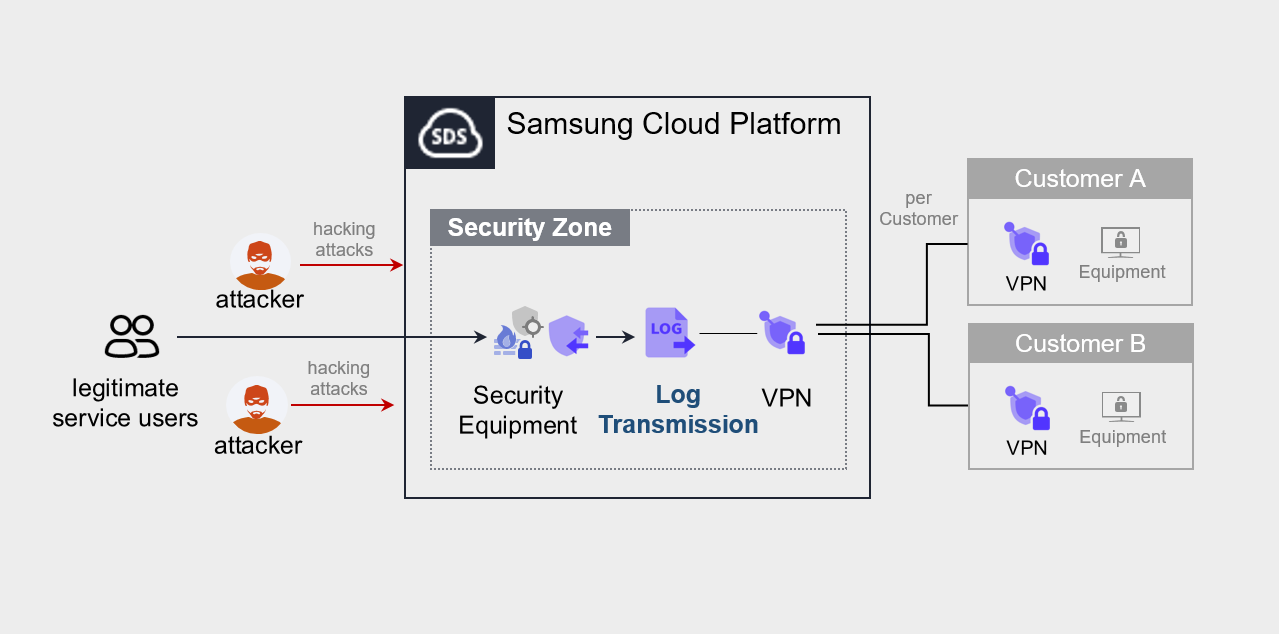
- 9.17: Log Transmission
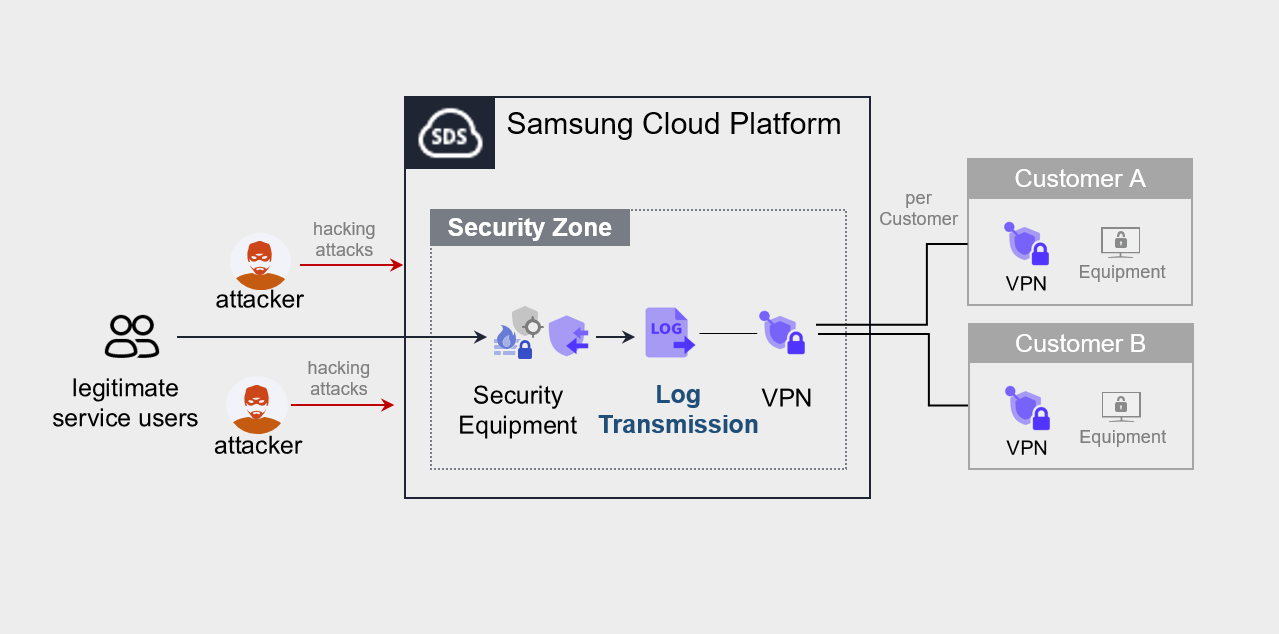
- 9.17.1: Overview
- 9.17.2: How-to guides
- 9.17.3: Release Note
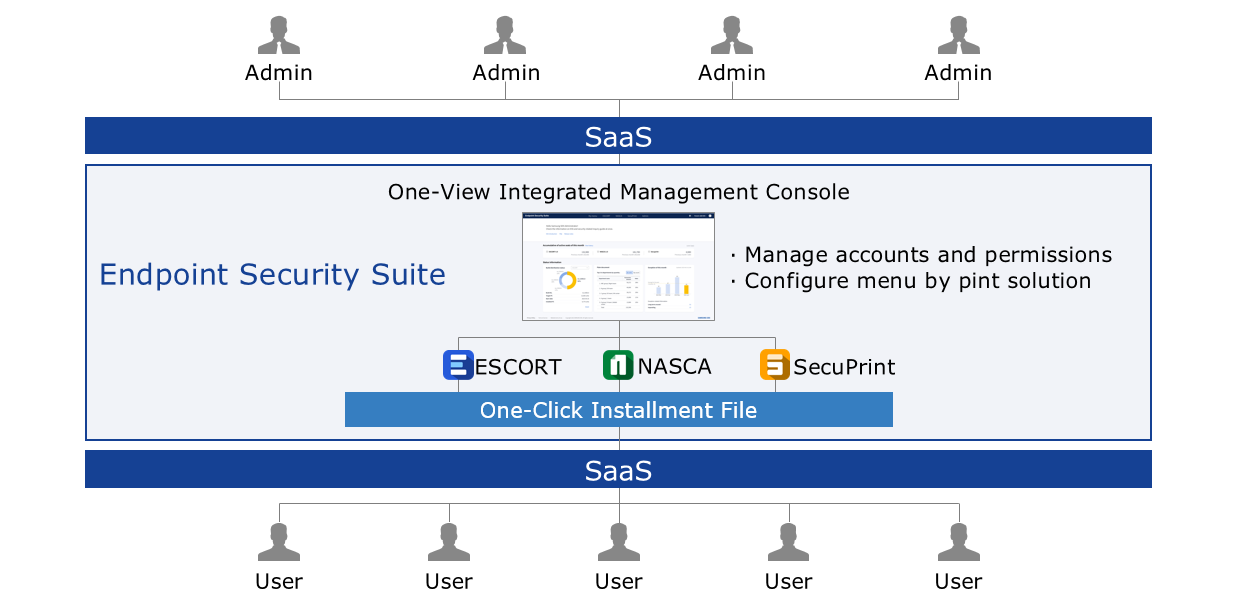
- 9.18: ESS(Endpoint Security Suite)
- 9.18.1: Overview
- 9.18.2: How-to guides
- 9.18.3: Release Note
- 9.19: Log Transmission
- 9.19.1: Overview
- 9.19.2: How-to guides
- 9.19.3: Release Note
- 10: Management
- 10.1: Architecture Diagram
- 10.1.1: Overview
- 10.1.2: How-to Guides
- 10.1.3: Release Note
- 10.2: Cloud Control
- 10.2.1: Overview
- 10.2.2: How-to guides
- 10.2.2.1: Managing Guardrails
- 10.2.2.2: Managing Organizations
- 10.2.2.3: Managing Accounts
- 10.2.3: API Reference
- 10.2.4: CLI Reference
- 10.2.5: Release Note
- 10.3: Cloud Monitoring
- 10.3.1: Overview
- 10.3.2: How-to guides
- 10.3.2.1: Using Monitoring Dashboards
- 10.3.2.2: Performance Analysis
- 10.3.2.3: Log Analysis
- 10.3.2.4: Managing Events
- 10.3.2.5: Using Custom Dashboards
- 10.3.2.6: Managing Agents
- 10.3.2.7: Appendix A. Service-specific Monitoring Targets
- 10.3.2.8: Appendix B. Service-specific Performance Metrics
- 10.3.2.9: Appendix C. Service-specific Status Checks
- 10.3.3: API Reference
- 10.3.4: Release Note
- 10.4: IAM
- 10.4.1: Overview
- 10.4.2: How-to Guides
- 10.4.2.1: User Group
- 10.4.2.2: Users
- 10.4.2.3: Policy
- 10.4.2.4: Role
- 10.4.2.5: Credential Providers
- 10.4.2.6: My Info.
- 10.4.2.7: JSON Writing Guide
- 10.4.3: API Reference
- 10.4.4: CLI Reference
- 10.4.5: Release Note
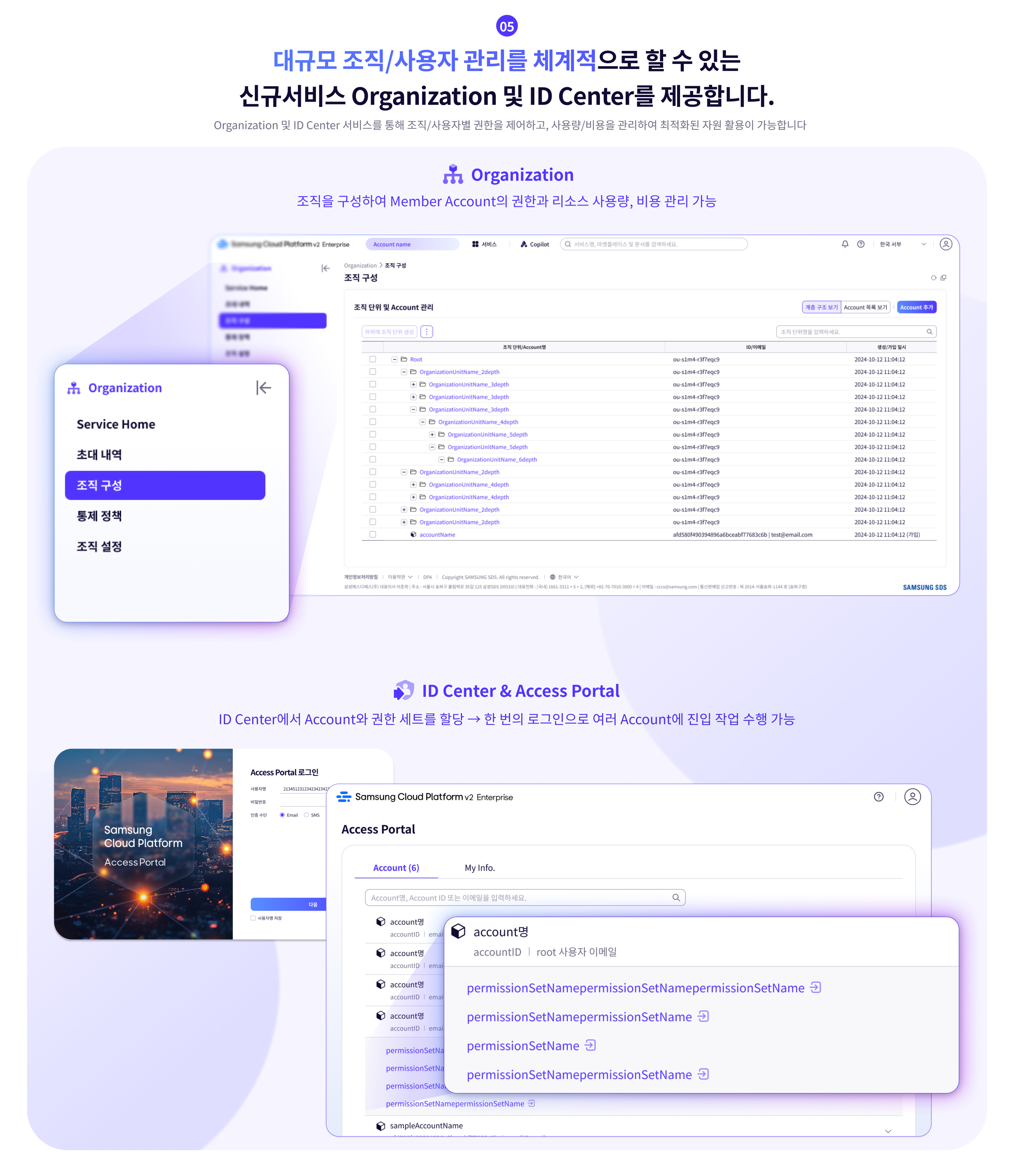
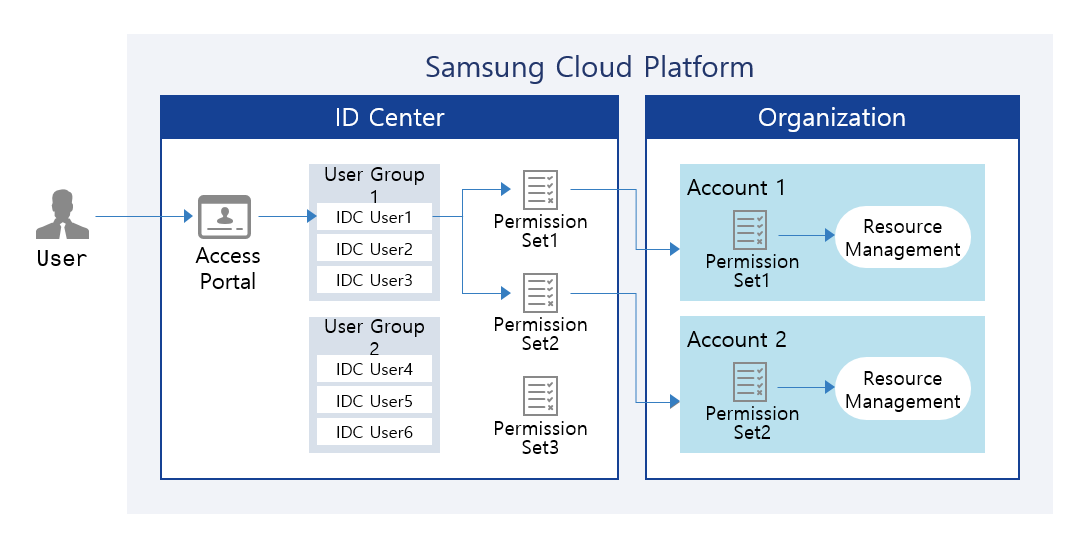
- 10.5: ID Center
- 10.5.1: Overview
- 10.5.2: How-to guides
- 10.5.2.1: Managing ID Center Users
- 10.5.2.2: Managing ID Center User Groups
- 10.5.2.3: Assigning ID Center Account
- 10.5.2.4: Managing ID Center Permission Sets
- 10.5.2.5: Using ID Center Access Portal
- 10.5.3: Release Note
- 10.6: Logging&Audit
- 10.6.1: Overview
- 10.6.2: How-to guides
- 10.6.2.1: Managing Trails
- 10.6.3: API Reference
- 10.6.4: CLI Reference
- 10.6.5: Release Note
- 10.7: Notification Manager
- 10.7.1: Overview
- 10.7.2: How-to Guides
- 10.7.2.1: Notification Policy
- 10.7.3: Release Note
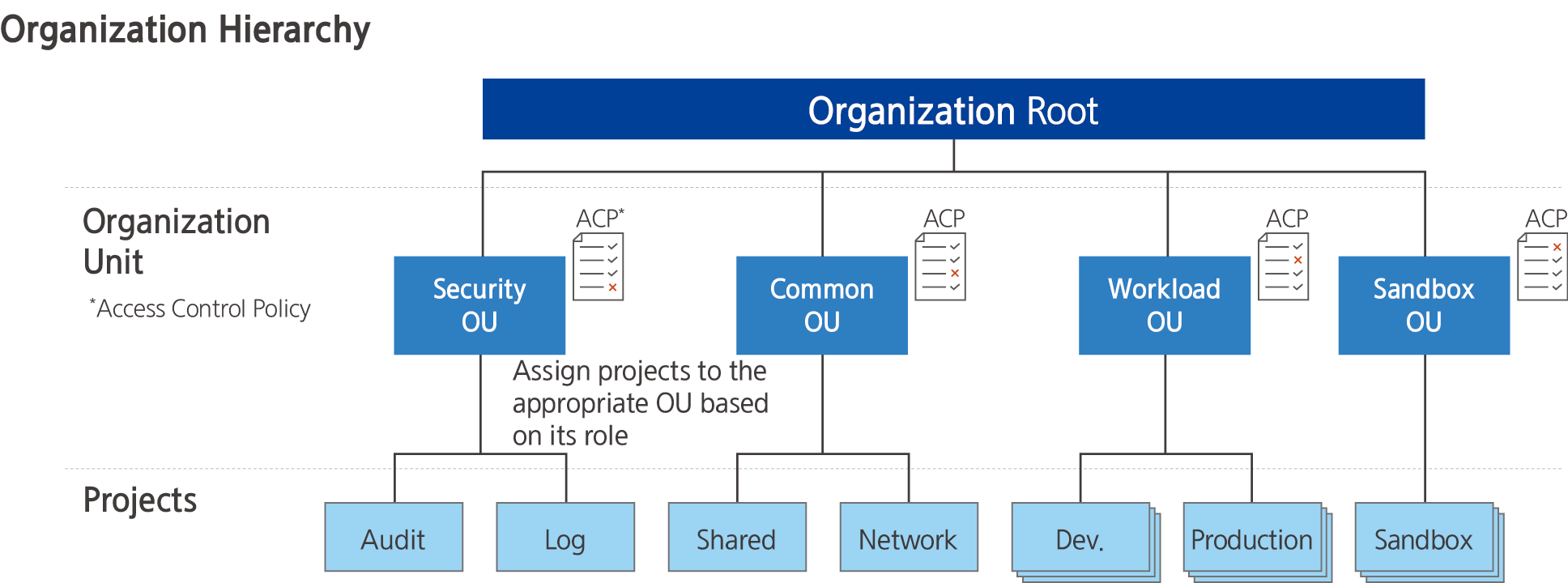
- 10.8: Organization
- 10.8.1: Overview
- 10.8.2: How-to guides
- 10.8.2.1: Organization Configuration Information
- 10.8.2.2: Organization Control Policy
- 10.8.3: API Reference
- 10.8.4: CLI Reference
- 10.8.5: Release Note
- 10.9: Resource Explorer
- 10.9.1: Overview
- 10.9.2: How-to Guides
- 10.9.3: Release Note
- 10.10: Resource Groups
- 10.10.1: Overview
- 10.10.2: How-to Guides
- 10.10.3: Release Note
- 10.11: ServiceWatch
- 10.11.1: Overview
- 10.11.1.1: Metric
- 10.11.1.2: Alert
- 10.11.1.3: Log
- 10.11.1.4: Event
- 10.11.1.5: ServiceWatch integration service
- 10.11.1.6: Custom Metrics and Logs
- 10.11.2: How-to guides
- 10.11.2.1: Managing Dashboards and Widgets
- 10.11.2.2: Alert
- 10.11.2.3: indicator
- 10.11.2.4: Log
- 10.11.2.5: Event
- 10.11.2.6: Using ServiceWatch Agent
- 10.11.3: API Reference
- 10.11.4: CLI Reference
- 10.11.5: ServiceWatch Event Reference
- 10.11.5.1: ServiceWatch Event
- 10.11.5.1.1: Multi-node GPU Cluster
- 10.11.5.1.2: MySQL(DBaaS)
- 10.11.5.1.3: Global CDN
- 10.11.5.1.4: Data Flow
- 10.11.5.1.5: GSLB
- 10.11.5.1.6: Cloud Control
- 10.11.5.1.7: Cloud WAN
- 10.11.5.1.8: Object Storage
- 10.11.5.1.9: VPC
- 10.11.5.1.10: GPU Server
- 10.11.5.1.11: Virtual Server
- 10.11.5.1.12: Firewall
- 10.11.5.1.13: ID Center
- 10.11.5.1.14: Microsoft SQL Server(DBaaS)
- 10.11.5.1.15: Block Storage(BM)
- 10.11.5.1.16: Resource Groups
- 10.11.5.1.17: Cloud Functions
- 10.11.5.1.18: AI&MLOps Platform
- 10.11.5.1.19: Event Streams
- 10.11.5.1.20: Security Group
- 10.11.5.1.21: Archive Storage
- 10.11.5.1.22: API Gateway
- 10.11.5.1.23: Load Balancer
- 10.11.5.1.24: Data Ops
- 10.11.5.1.25: Scalable DB(DBaaS)
- 10.11.5.1.26: Cloud LAN-Campus
- 10.11.5.1.27: EPAS(DBaaS)
- 10.11.5.1.28: PostreSQL(DBaaS)
- 10.11.5.1.29: Logging&Audit
- 10.11.5.1.30: Search Engine
- 10.11.5.1.31: DNS
- 10.11.5.1.32: VPN
- 10.11.5.1.33: Secrets Manager
- 10.11.5.1.34: Quick Query
- 10.11.5.1.35: File Storage
- 10.11.5.1.36: CacheStore(DBaaS)
- 10.11.5.1.37: Secret Vault
- 10.11.5.1.38: Queue Service
- 10.11.5.1.39: Kubernetes Engine
- 10.11.5.1.40: Config Inspection
- 10.11.5.1.41: Cloud LAN-Datacenter
- 10.11.5.1.42: Identity Access Management
- 10.11.5.1.43: Bare Metal Server
- 10.11.5.1.44: ServiceWatch
- 10.11.5.1.45: MariaDB(DBaaS)
- 10.11.5.1.46: Container Registry
- 10.11.5.1.47: Vertica(DBaaS)
- 10.11.5.1.48: Backup
- 10.11.5.1.49: Organization
- 10.11.5.1.50: Cloud ML
- 10.11.5.1.51: Certificate Manager
- 10.11.5.1.52: Key Management Service
- 10.11.5.1.53: Direct Connect
- 10.11.5.1.54: Support Center
- 10.11.6: Release Note
- 10.12: Support Center
- 10.12.1: Overview
- 10.12.2: How-to Guides
- 10.12.2.1: Contact Us
- 10.12.2.2: Support Plan
- 10.12.2.3: Knowledge Center
- 10.12.3: Release Note
- 10.13: Quota Service
- 10.13.1: Overview
- 10.13.2: How-to guides
- 10.13.2.1: Organization Quota Template
- 10.13.3: Release Note
- 11: Financial Management
- 11.1: Cost Management
- 11.1.1: Overview
- 11.1.2: How-to Guides
- 11.1.2.1: Usage and Billing Details
- 11.1.2.2: Payment History
- 11.1.2.3: Cost Analysis
- 11.1.2.4: Credit Management
- 11.1.2.5: Budget Management
- 11.1.2.6: Cost Savings
- 11.1.2.7: Account
- 11.1.2.8: Payment Management
- 11.1.2.9: carbon emissions
- 11.1.2.10: EDP Report
- 11.1.3: Release Note
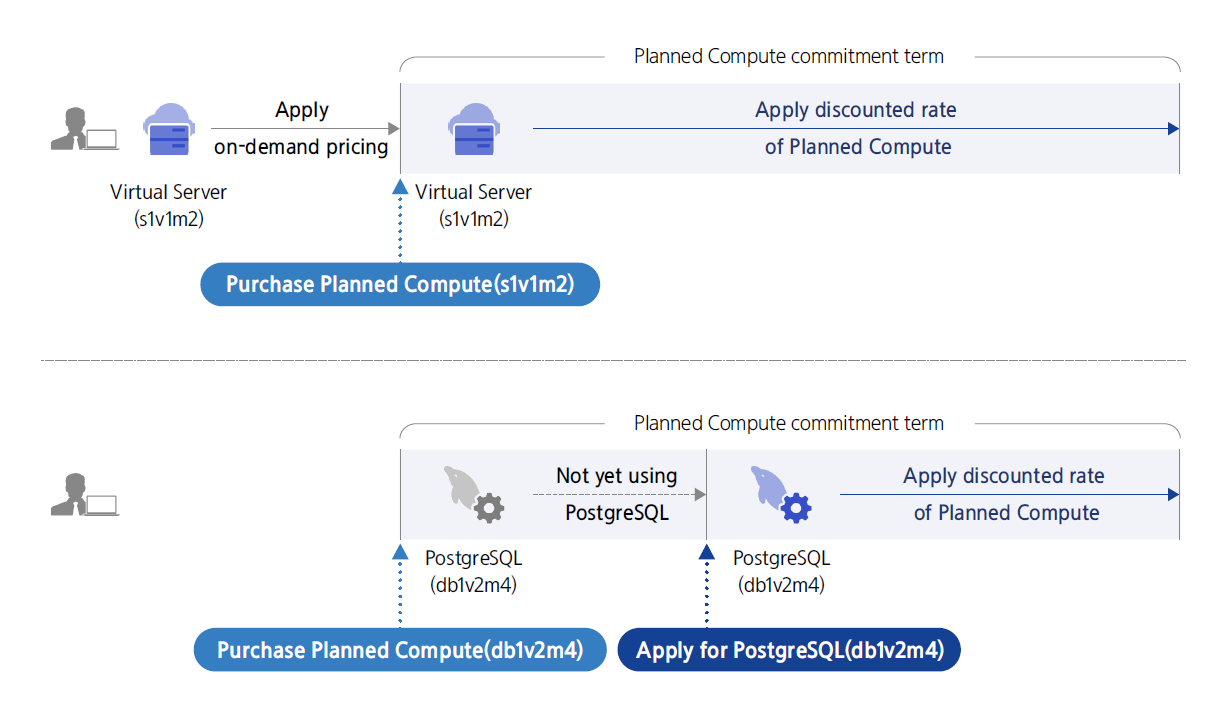
- 11.2: Planned Compute
- 11.2.1: Overview
- 11.2.2: How-to Guides
- 11.2.3: Release Note
- 11.3: Marketplace
- 11.3.1: Overview
- 11.3.2: How-to Guides
- 11.3.3: Release Note
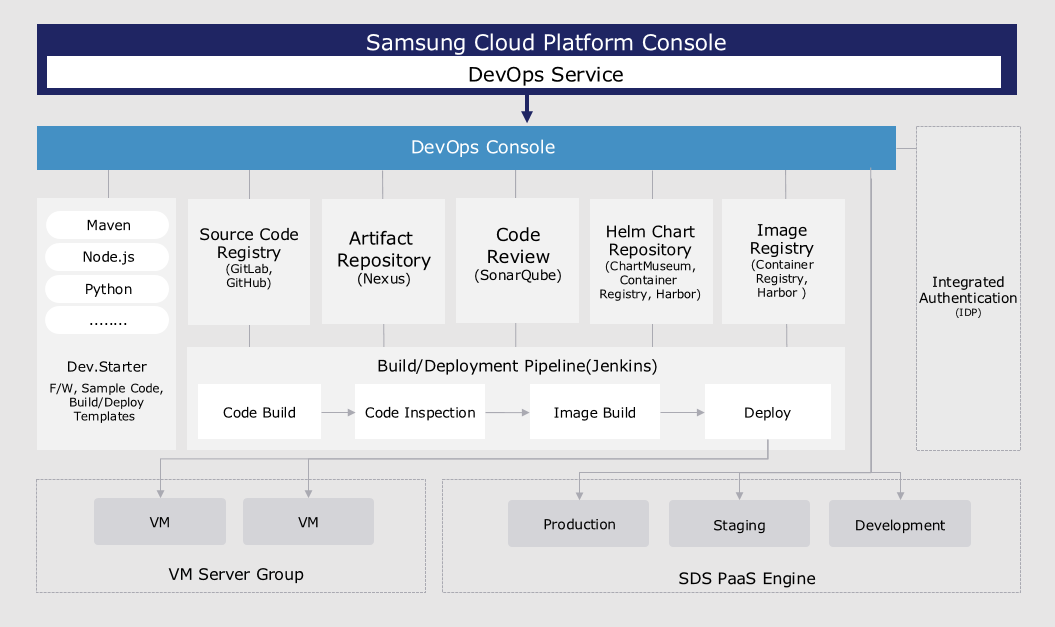
- 12: DevOps Tools
- 12.1: DevOps Service
- 12.1.1: Overview
- 12.1.2: How-to guides
- 12.1.3: API Reference
- 12.1.4: CLI Reference
- 12.1.5: Release Note
- 12.2: DevOps Console
- 12.2.1: Overview
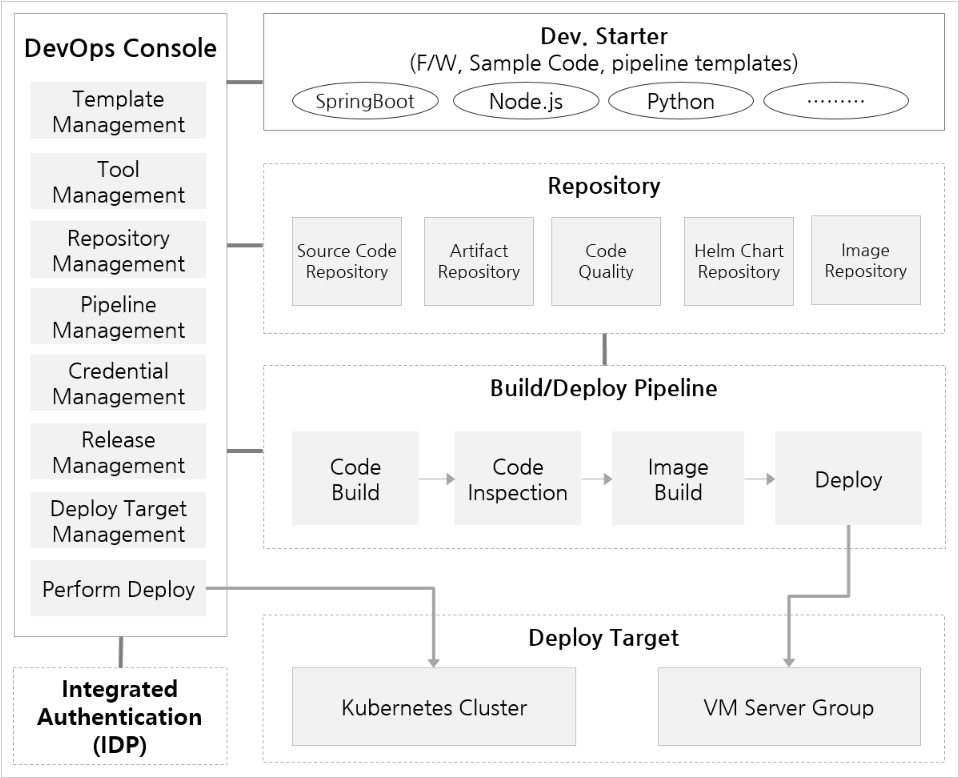
- 12.2.1.1: DevOps Console Introduction
- 12.2.1.2: Roles
- 12.2.1.3: Screen Configuration
- 12.2.2: Getting Started
- 12.2.2.1: Getting Started with DevOps Console
- 12.2.2.1.1: Registration Information
- 12.2.2.2: Tutorial (From Project Creation to Build/Deploy)
- 12.2.2.2.1: Add Build/Deploy (Helm Chart Deployment)
- 12.2.2.2.2: Add Build/Deploy (Workload Deployment)
- 12.2.2.2.3: Add Build/Deploy (VM Deployment)
- 12.2.2.2.4: Check Deployment Target Namespace Permissions (Before Project Creation)
- 12.2.3: Project
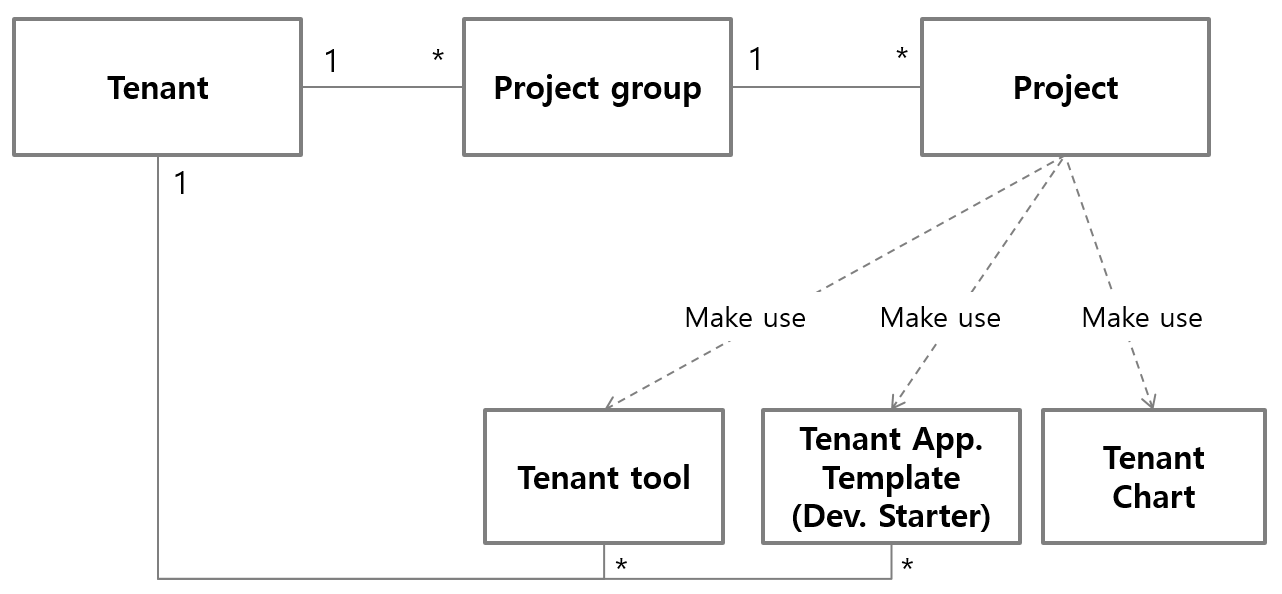
- 12.2.3.1: Project Overview
- 12.2.3.2: Create Project
- 12.2.3.2.1: Create Project (Helm Chart Deployment)
- 12.2.3.2.2: Create Project (Workload Deployment)
- 12.2.3.2.3: Create Project (ArgoCD Deployment)
- 12.2.3.2.4: Create Project (VM Deployment)
- 12.2.3.2.5: Create Project (Empty)
- 12.2.3.3: Start Project
- 12.2.3.4: Project Dashboard
- 12.2.3.5: Project Members
- 12.2.4: Build/Deploy
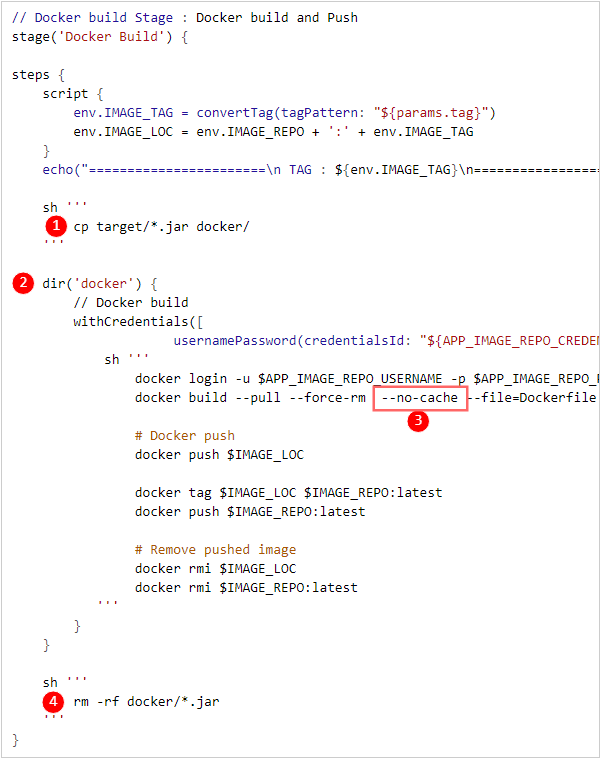
- 12.2.4.1: Build Pipeline
- 12.2.4.1.1: Stage
- 12.2.4.1.2: Multibranch Pipeline
- 12.2.4.2: Kubernetes Deployment
- 12.2.4.2.1: Helm Release
- 12.2.4.2.2: Workload
- 12.2.4.2.3: Blue/Green Deployment
- 12.2.4.2.4: Canary Deployment
- 12.2.4.2.5: Istio
- 12.2.4.2.6: ArgoCD
- 12.2.4.3: VM Deployment
- 12.2.4.4: Helm Install
- 12.2.4.5: Ingress/Service Management
- 12.2.4.6: Kubernetes Secret Management
- 12.2.4.7: Environment Variable Management
- 12.2.5: Project Group
- 12.2.5.1: Project Group Overview
- 12.2.5.2: Create Project Group
- 12.2.5.3: Project Group Dashboard
- 12.2.6: Tenant
- 12.2.6.1: Tenant Management
- 12.2.6.2: Tenant Dashboard
- 12.2.6.3: Tenant Notice
- 12.2.7: Repository
- 12.2.7.1: Code Repository
- 12.2.7.2: Artifact Repository
- 12.2.7.3: Image Repository
- 12.2.7.4: Chart Repository
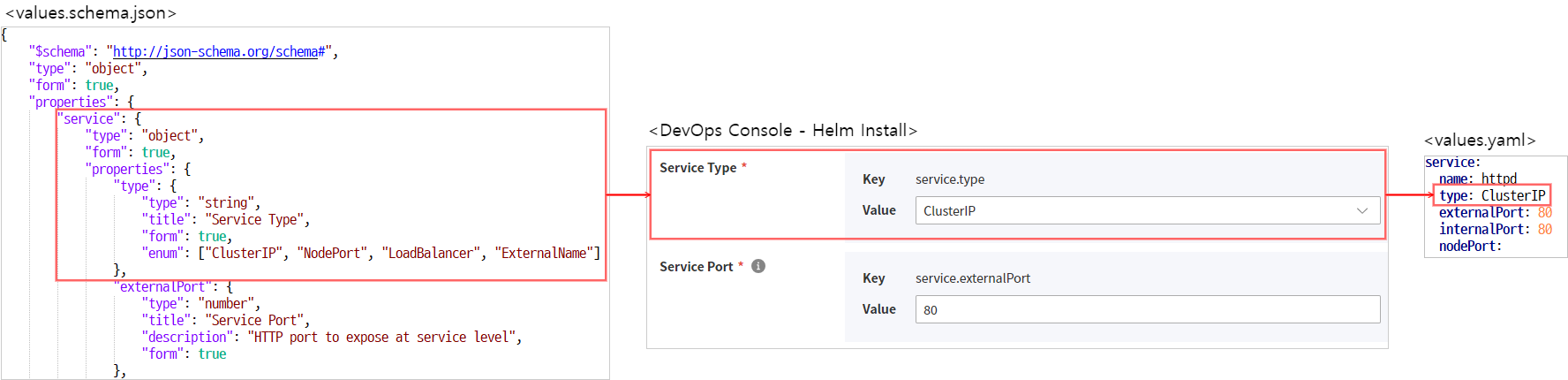
- 12.2.7.5: Helm Chart
- 12.2.7.5.1: Creating Helm Charts with Form Input Support
- 12.2.8: Quality
- 12.2.8.1: Code Quality
- 12.2.9: Tools & Templates
- 12.2.9.1: Tool Management
- 12.2.9.2: App Template
- 12.2.9.3: Register User-installed Jenkins Tool
- 12.2.10: Deployment Target
- 12.2.10.1: K8S Cluster
- 12.2.10.1.1: Verify Cluster Admin Token
- 12.2.10.2: VM Server Group
- 12.2.10.3: Request Permission
- 12.2.11: Release Management
- 12.2.11.1: Release Management
- 12.2.11.2: Workflow Management
- 12.2.11.3: Approval Template Settings
- 12.2.11.4: Task
- 12.2.11.5: JIRA Project
- 12.2.12: Release Note
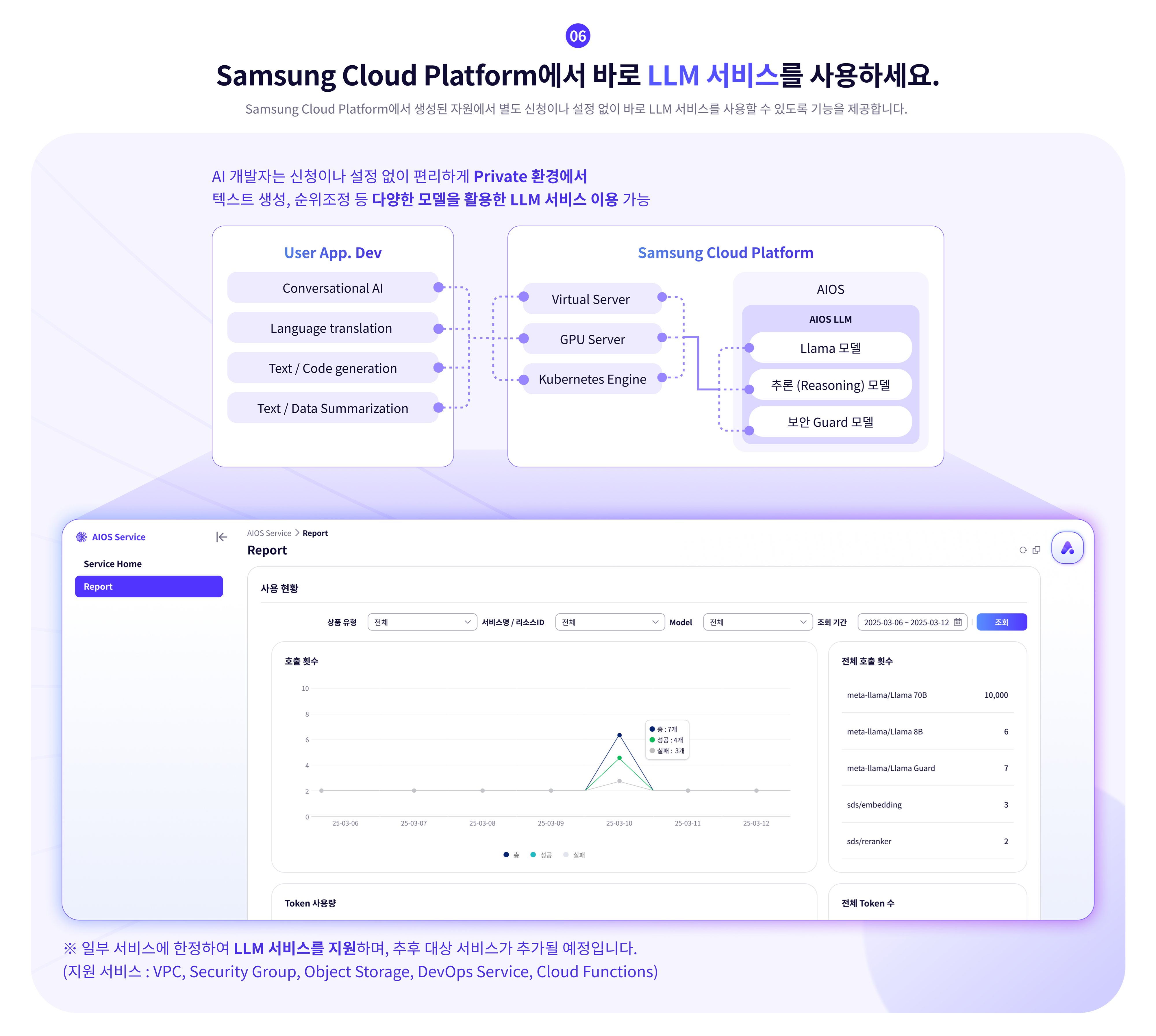
- 13: AI-ML
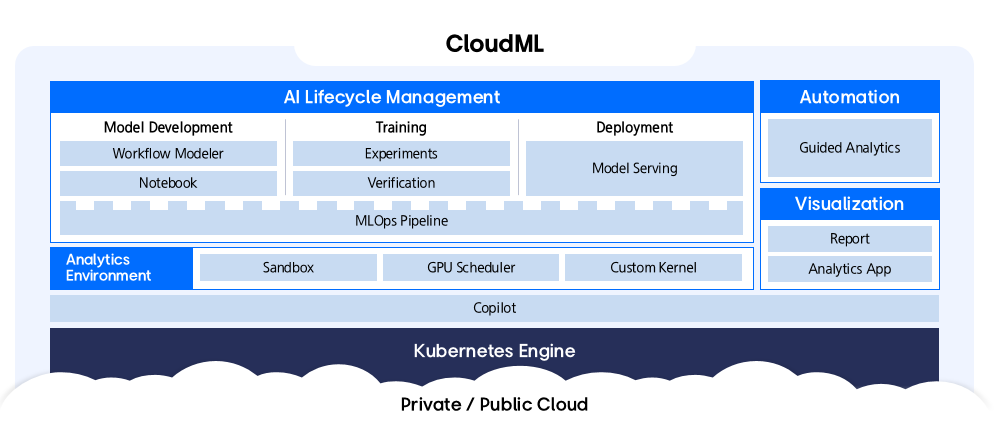
- 13.1: CloudML
- 13.1.1: Overview
- 13.1.2: How-to guides
- 13.1.2.1: Kubernetes Cluster Configuration
- 13.1.3: API Reference
- 13.1.4: CLI Reference
- 13.1.5: Release Note
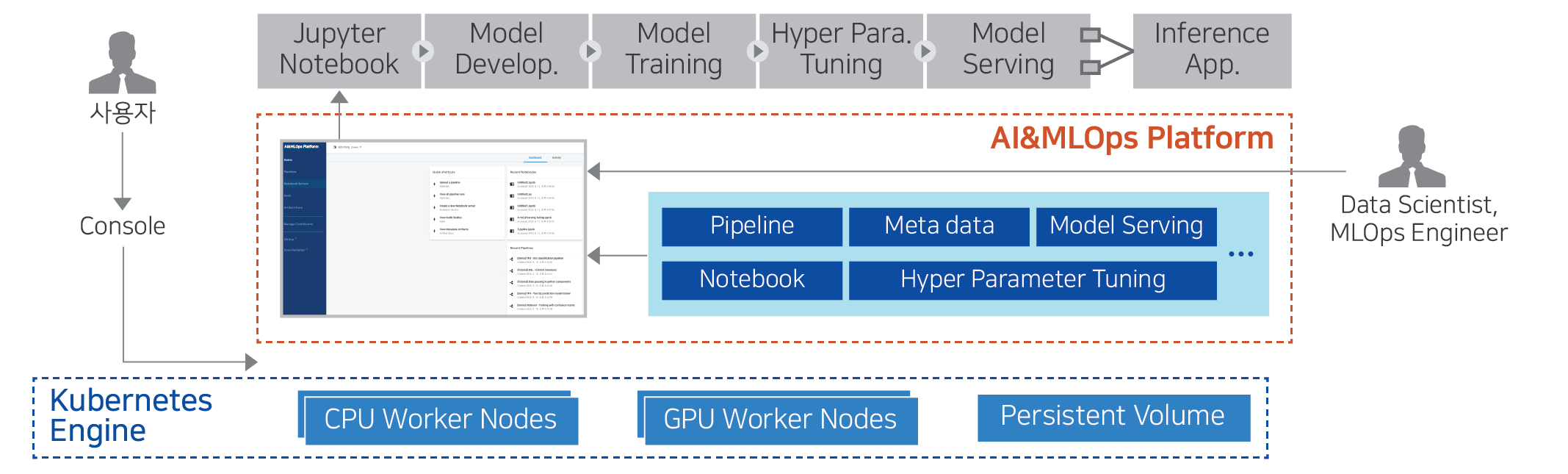
- 13.2: AI&MLOps Platform
- 13.2.1: Overview
- 13.2.2: How-to guides
- 13.2.2.1: Cluster Deployment
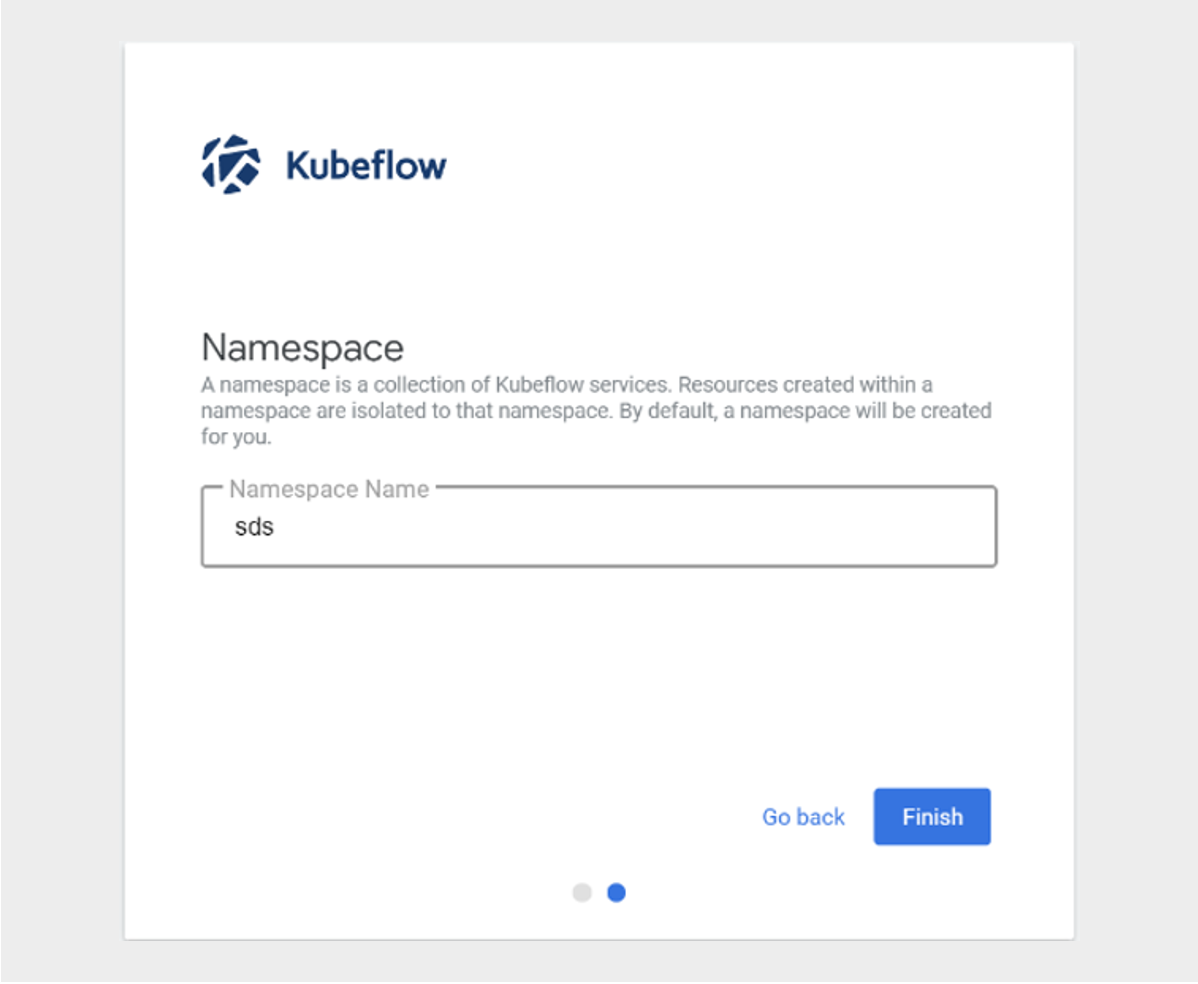
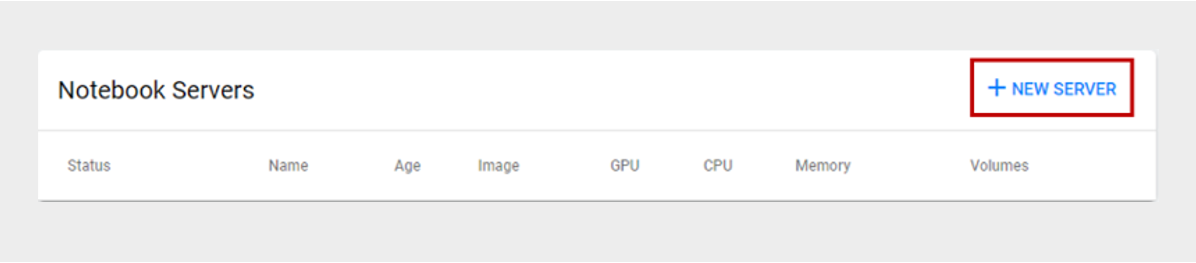
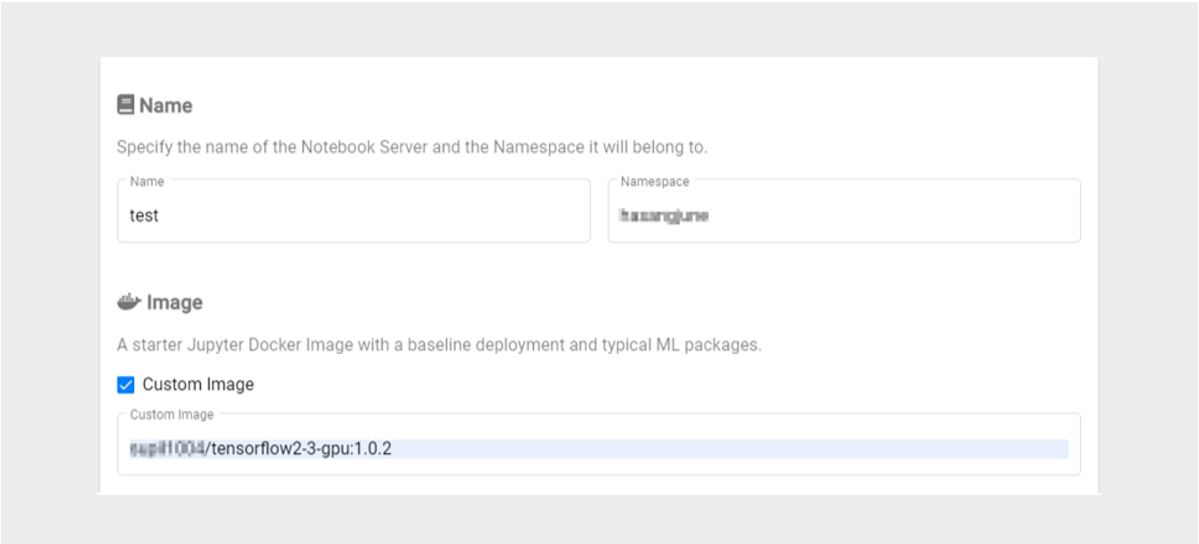
- 13.2.2.2: Kubeflow Usage Guide
- 13.2.3: API Reference
- 13.2.4: CLI Reference
- 13.2.5: Release Note
- 14: Hybrid Cloud
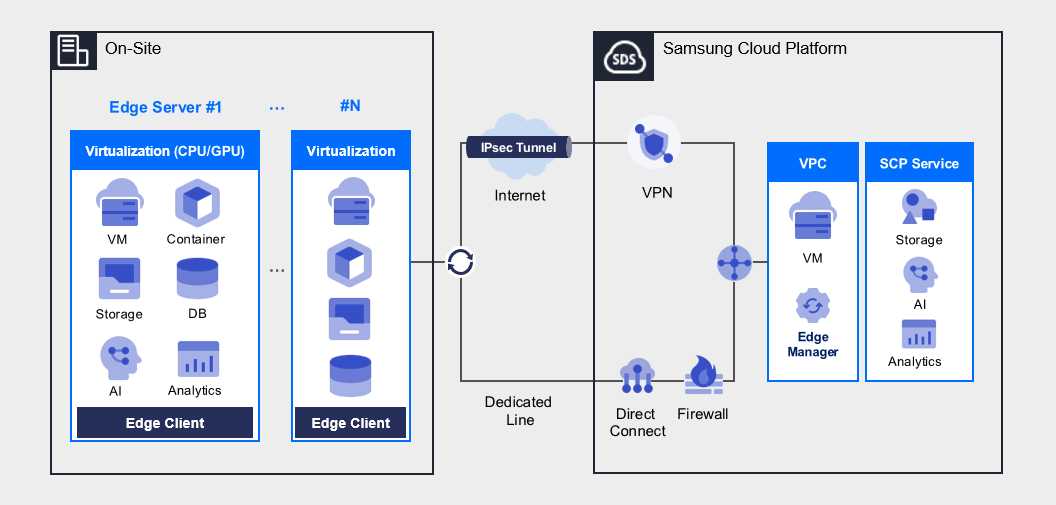
- 14.1: Edge Server
- 14.1.1: Overview
- 14.1.2: How-to guides
- 14.1.3: Release Note
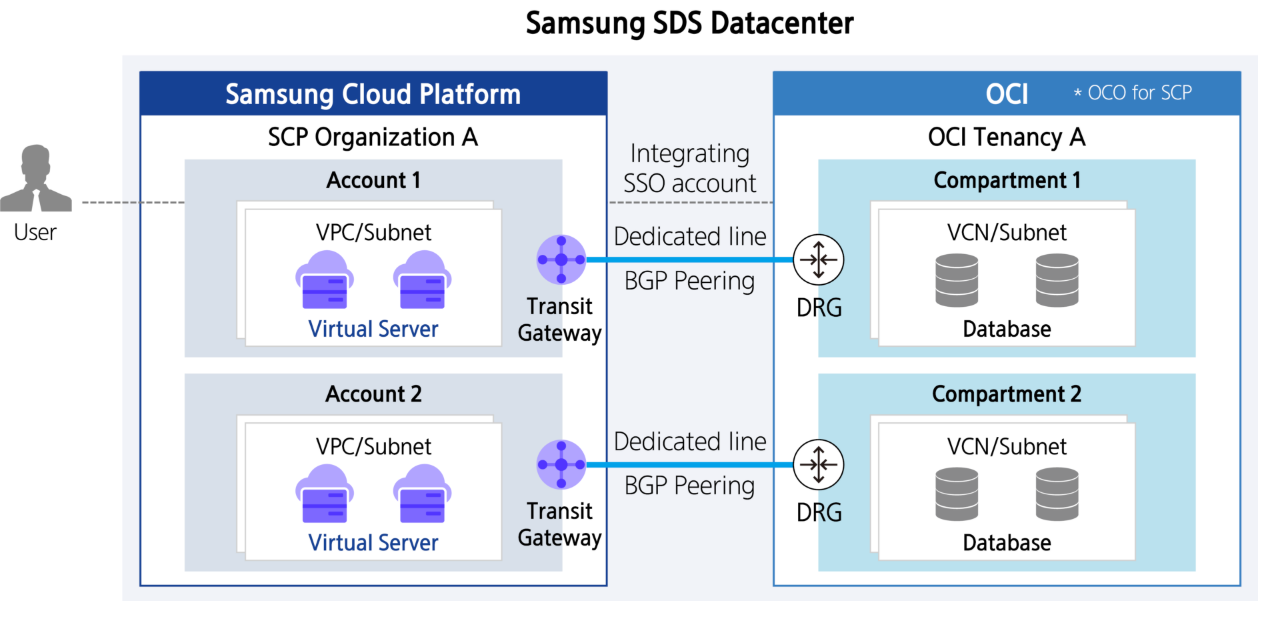
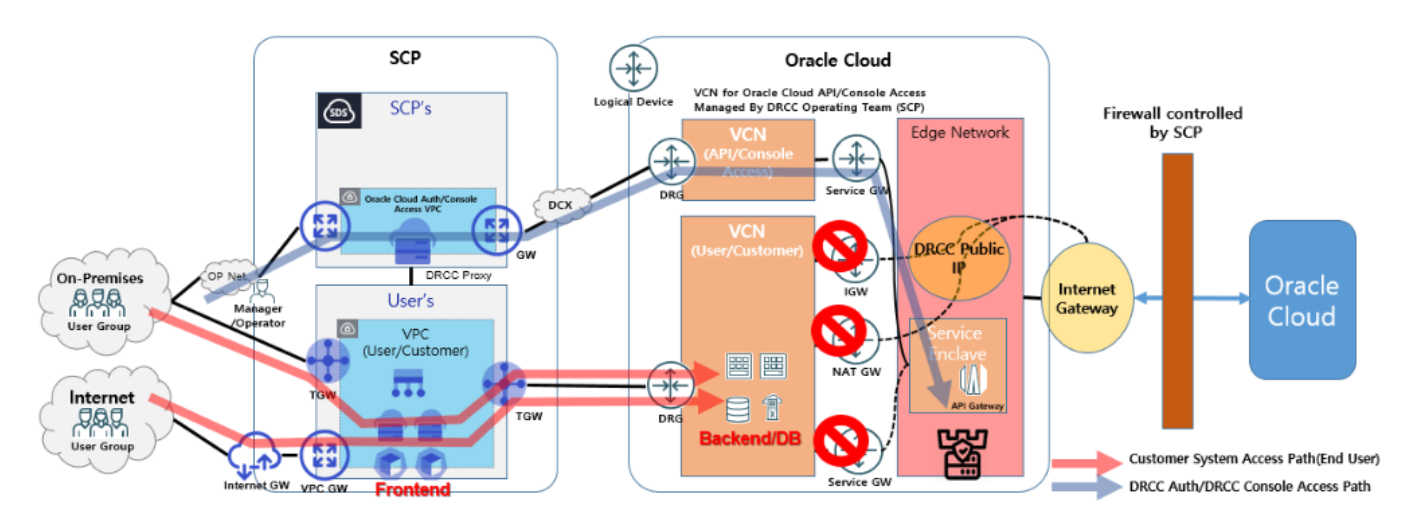
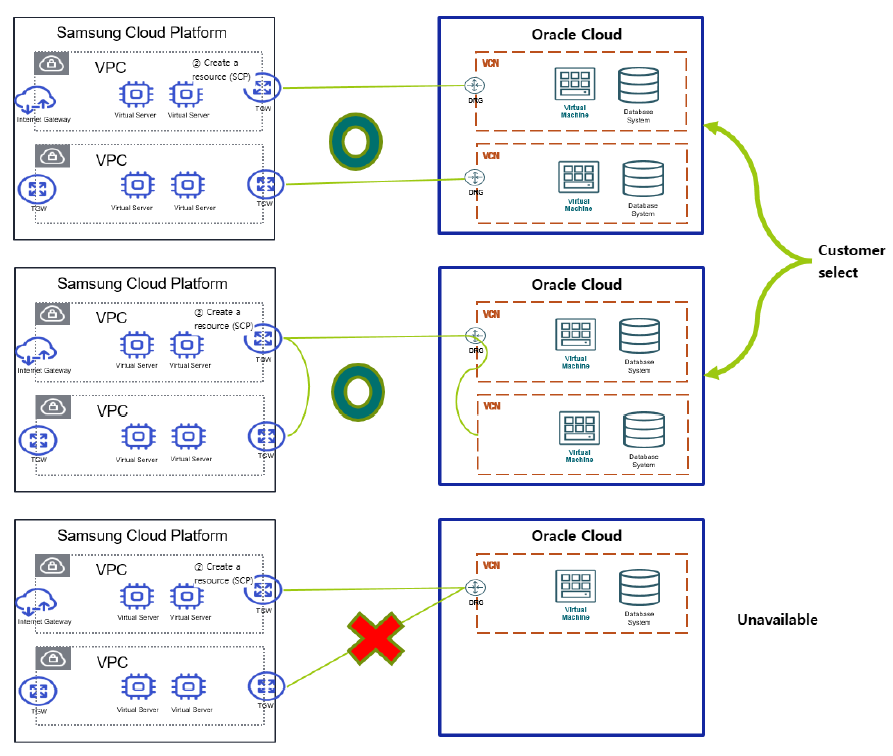
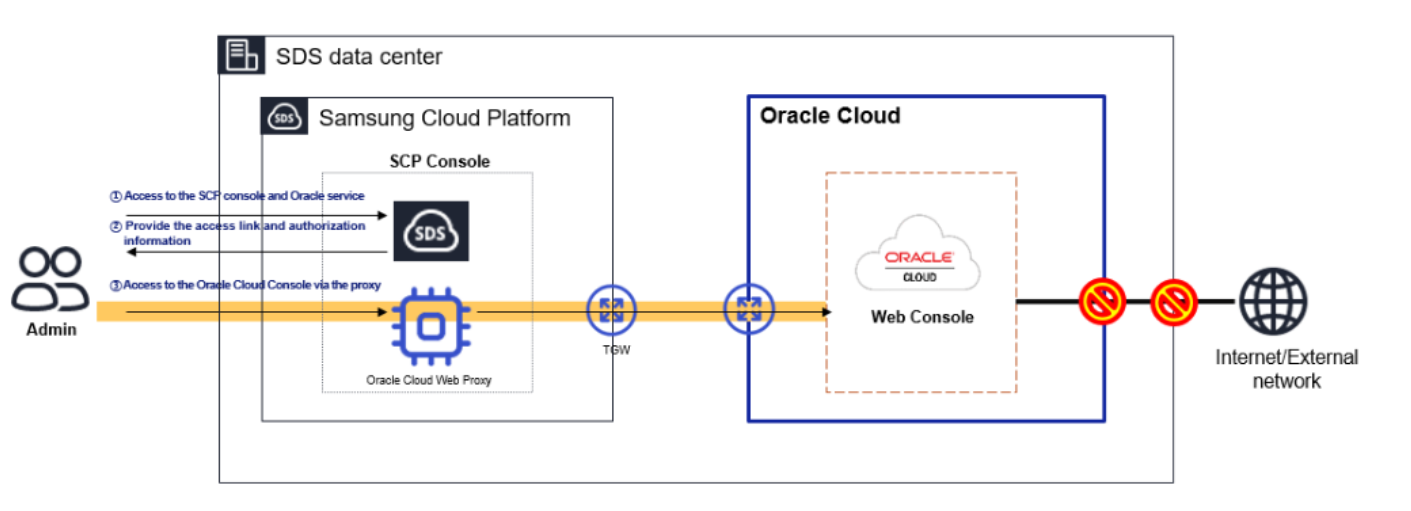
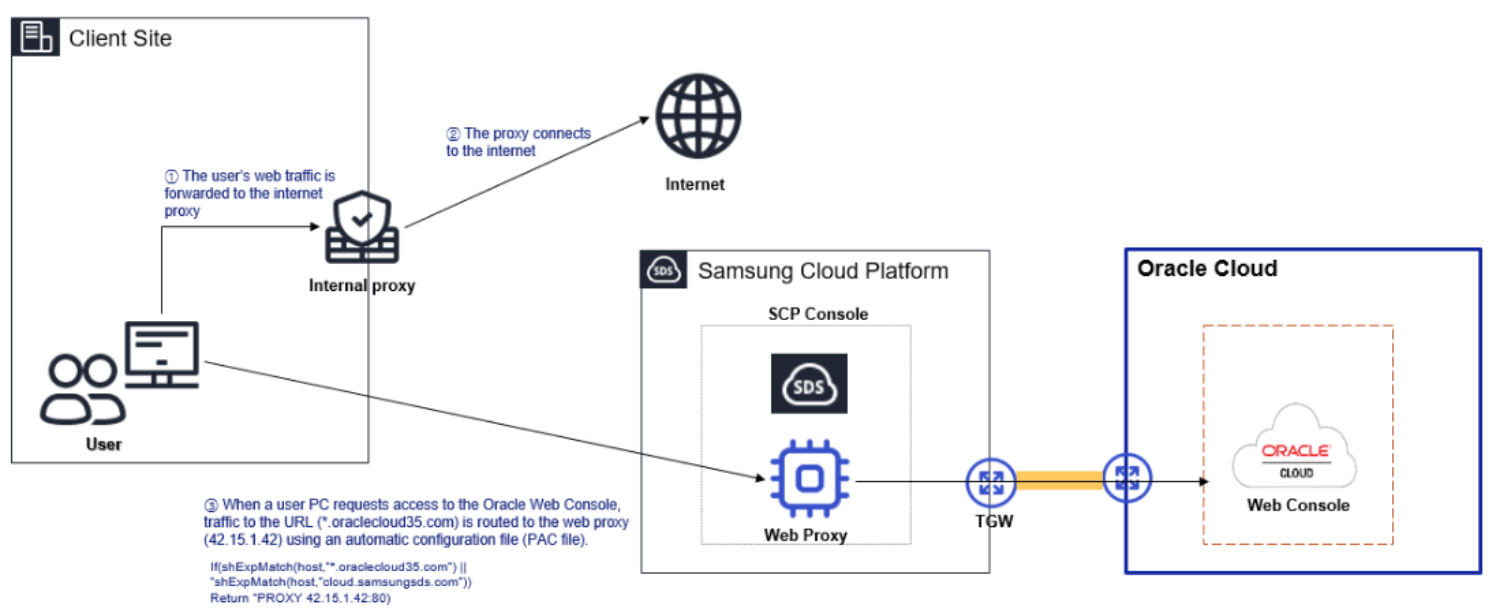
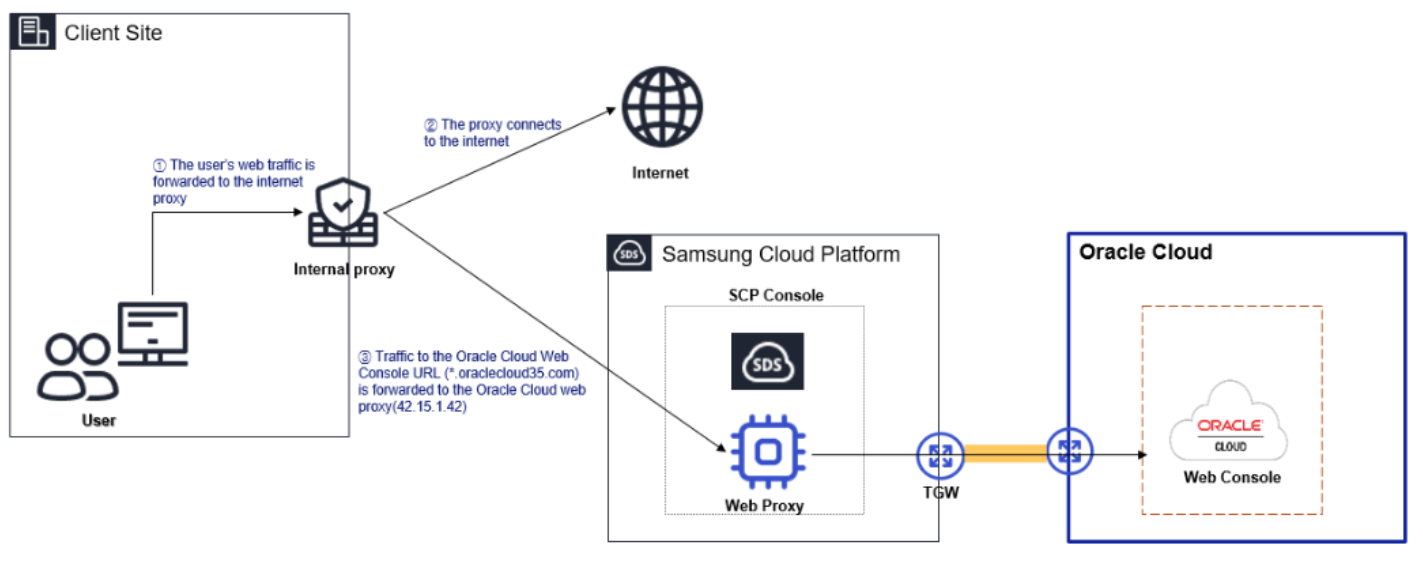
- 14.2: Oracle Services
- 14.2.1: Overview
- 14.2.2: How-to guides
- 14.2.3: Release Note
- 15: Developer Tools
- 15.1: MCP Server
- 15.1.1: Overview
- 15.1.2: How-to guides
- 15.1.2.1: Docs mcp server
- 15.1.3: Release Note
- 16: Release note
- 17: Glossary
- 18:
1 - Samsung Cloud Platform
1.1 - New Features
New feature
Explore the new features of the Samsung Cloud Platform Console~
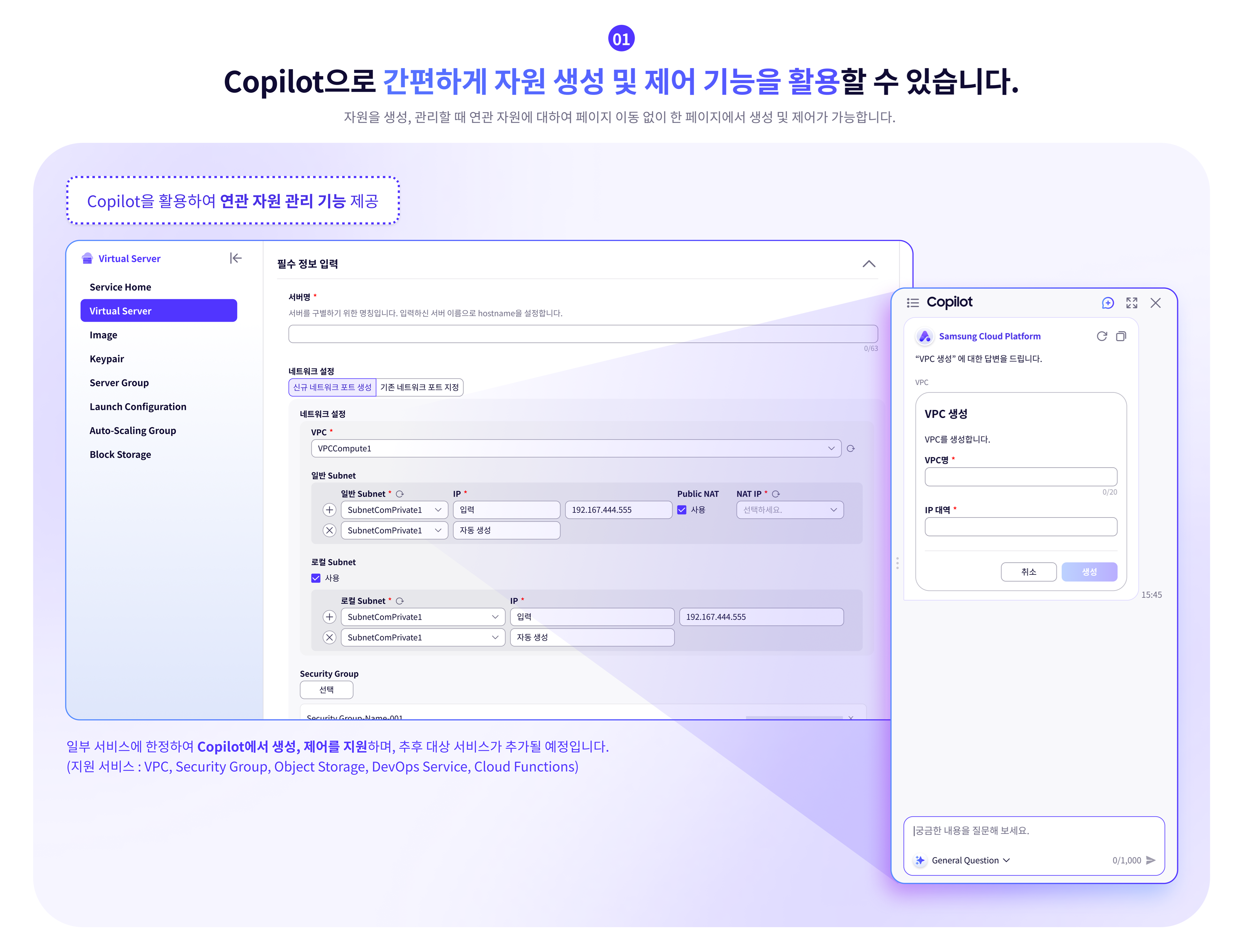
Resource Management Using Copilot
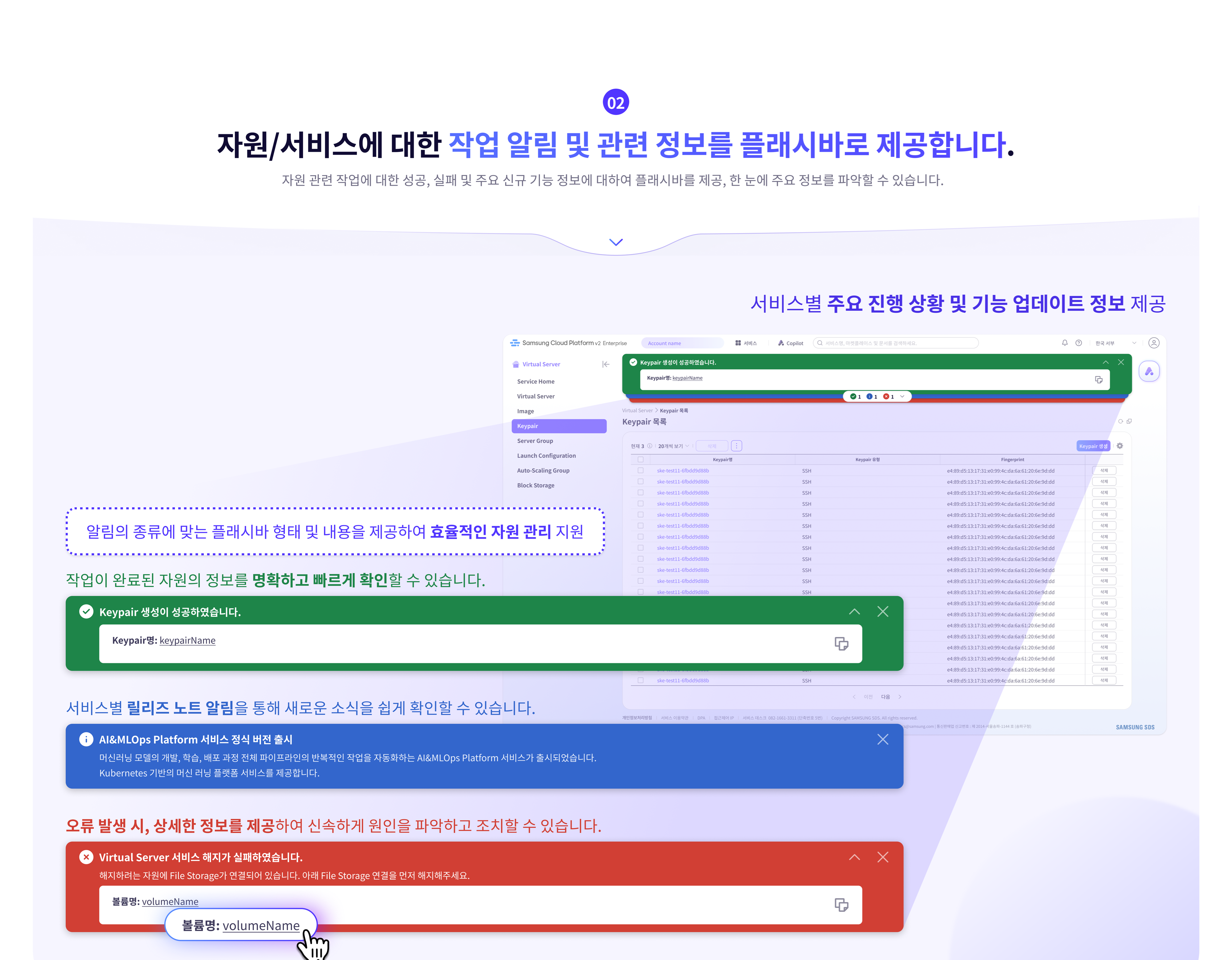
Information about resources/services
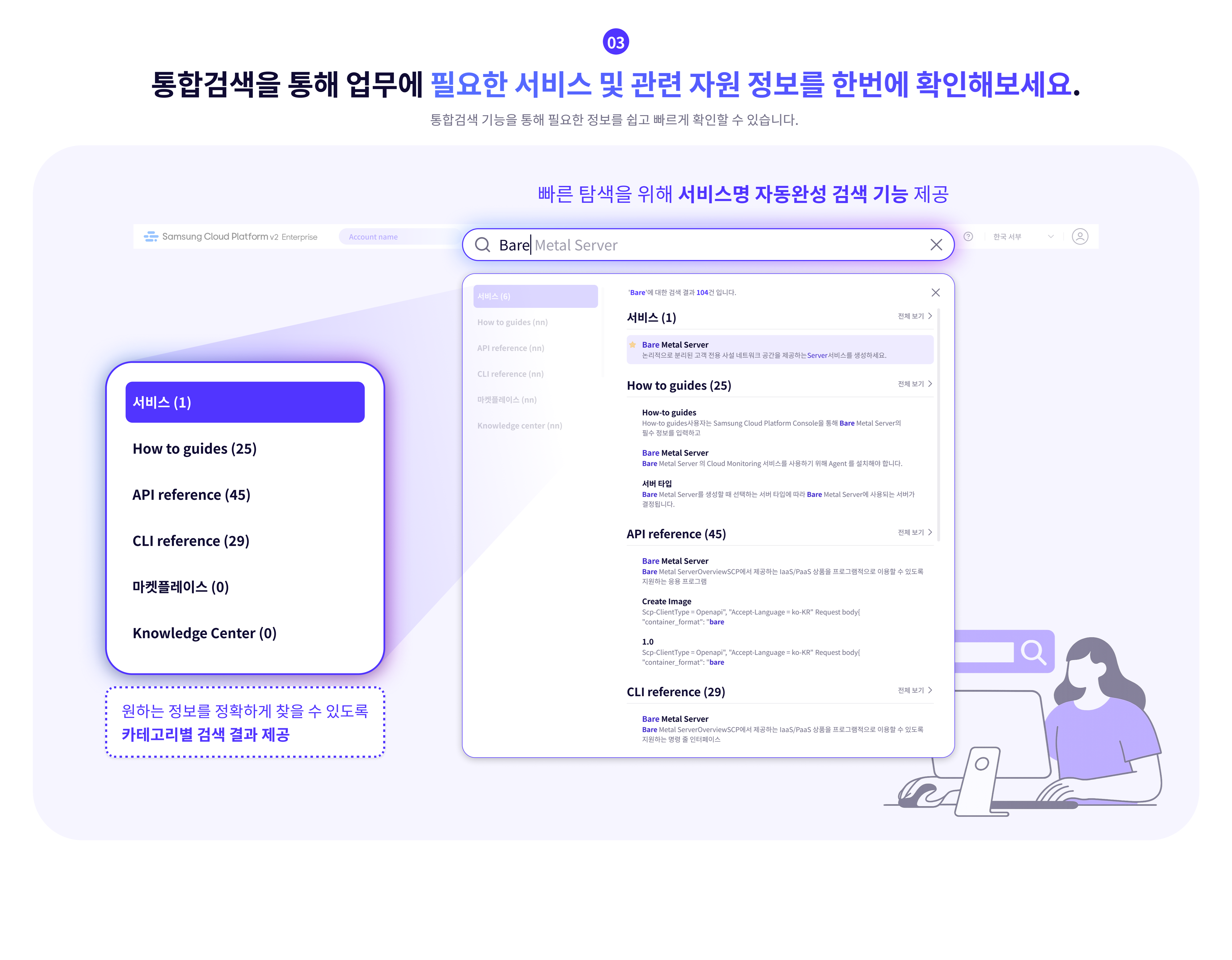
Easy and fast integrated search
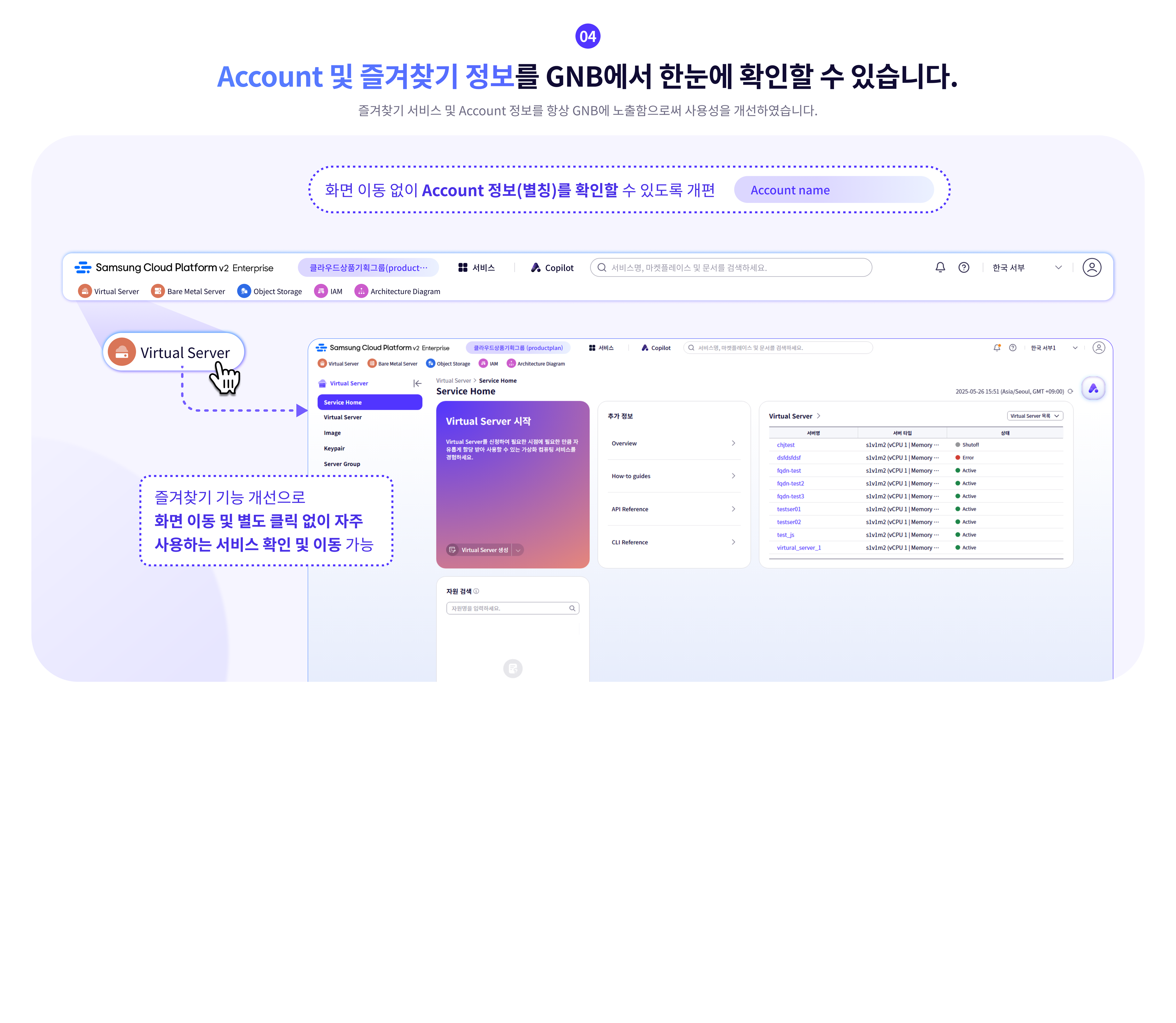
Improving accessibility of Account and Favorites
Providing services for large-scale organizations and systematic user management
LLM service that can be used without a separate application
1.2 - Overview
Samsung Cloud Platform
Samsung Cloud Platform is a cloud environment that virtualizes and provides various resource pools such as computing, storage, networking, and databases needed by enterprises.
Through the Samsung Cloud Platform, you can use the required resources in a cloud environment without needing to provide hardware or physical space. Since charges are billed based on actual usage, efficient budget management is possible, and companies can reduce costs associated with building and managing their own server environments.
The main terms used in Samsung Cloud Platform are as follows.
term | Detailed description |
|---|---|
| Region | Consists of one or more data centers to ensure availability as geographically separated cloud service delivery units. |
| Account | The basic unit and billing unit required to use the Samsung Cloud Platform service |
| Root user | User who created the Account and holds top-level privileges |
| IAM user | A user with restricted permissions created by the root user within the account |
| Service | Various types of IT services and infrastructure (Compute, Storage, Network, etc.) provided by Samsung Cloud Platform |
| Resource (resource) | An individual unit entity (Entity) that is created and managed as the user uses the service. |
Component
Samsung Cloud Platform provides a Service Portal, Console, and Documentation.
Category | Detailed description |
|---|---|
| Service Portal | Service and pricing overview for Samsung Cloud Platform, as well as information such as customer support |
| Console | Self-service interface that provides functions such as creating accounts and resources, and checking costs on the Samsung Cloud Platform. |
| Documetation | As a documentation service for Samsung Cloud Platform, it provides user guides, API/CLI references, and more. |
region
Regions are geographically distinct units of cloud service provision, composed of one or more data centers to ensure availability. Services offered on the Samsung Cloud Platform are managed by region, so the services provided may vary slightly. Refer to the user guide for each service.
| Region name | Region |
|---|---|
| Western Korea | Korea West (kr-west1) |
| Eastern Korea | Korea East (kr-east1) |
| South Korea (administrative) | South Korea South 1 (kr-south1) |
| South Korea (public) | South Korea 2 (kr-south2) |
| South Korea (Internet) | South Korea South 3(kr-south3) |
Account
To use the Samsung Cloud Platform, you need to create an Account, which can be done through sign‑up. A user who signs up and creates an Account becomes the Account’s root user and is responsible for payment. Once you sign up and register a payment method, you can create resources.
The root user can create users in IAM and add them to user groups. Users created in this way are IAM users.
The typical flow from a user creating an account to setting up a cloud environment and performing tasks is as follows.
- When a user signs up, an Account is created and they become a Root user.
- If a root user registers a payment method, they can create resources on the Samsung Cloud Platform.
- The root user creates IAM users and adds them to user groups so they can perform tasks according to their respective permissions.
- IAM users request the required services as needed to carry out their tasks.
The detailed responsibilities for each role are as follows.
| role | Job responsibilities |
|---|---|
| Root user | User with the highest privileges of the Account
|
| IAM user | User with limited permissions within the Account
|
1.3 - Getting Started with Console
1.3.1 - Log In
To use the Samsung Cloud Platform Console, you need to create an Account, and you can create an Account through sign‑up. A user who signs up and creates an Account becomes the Account’s root user and is responsible for the Account’s payment. After signing up and registering a payment method, you can create resources. For details, see Register a payment method.
Sign Up
To use the Samsung Cloud Platform Console, you need to create an Account, which can be done through sign‑up. To create an Account in the Samsung Cloud Platform Console, follow these steps.
On the login page, select the user type Root User and then click the Sign Up button. You will be taken to the Sign Up page.
On the Sign Up page, complete Identity Verification.
- When identity verification is complete, click the Next button.
Item Required statusExplanation Prevent automatic input Required Enter the characters displayed in the image into the input field. email Required Email to be used as subscriber ID - Enter the email address and click the Duplicate Check and Verify button
Table. Personal authentication information - In Enter registration information, select the region information and agree to the terms.
Item RequiredExplanation region Required Select subscriber region Agree to the Terms of Service Required Check if the service terms are agreed. Consent to collection and use of personal information Required Check consent for collection and use of personal information Consent for overseas transfer of personal data Required Check consent for overseas transfer of personal data Are you at least 14 years old? Required Check if the user is 14 years or older. Consent to the collection and use of personal information Select Check consent for collection and use of personal information Table. Sign-up information input - Enter the required fields in Member Information Input.
Item RequiredExplanation ID(email) Required Email to be used as subscriber ID - Display email information used for identity verification
username Required Subscriber name - Can be entered using Korean, English, numbers, and spaces, up to 60 characters
Account name Required Account for the subscriber - Can be entered using Korean, English, numbers, and spaces, up to 60 characters
Password Required The subscriber can enter a password of 9 to 20 characters - Include at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%&*^)
- The ID cannot be used as the password
- Cannot use the same character three or more times consecutively
- Passwords that are easy to guess are not allowed
- Sequences of four or more consecutive letters or numbers are not allowed
- Password change interval: 90 days
Confirm Password Required Confirm the password the subscriber will use mobile phone number Required Enter mobile phone number - Enter the mobile phone number and click the Verify button to issue a verification code
- Enter the verification code received on the mobile phone and click the Confirm button
- If the verification code is valid, identity verification is completed
Notification language Required Set the language for notifications such as email and SMS provided by Samsung Cloud Platform - After logging in, change it in Notification Popover > Notification Settings
Table. Member information input information
- When identity verification is complete, click the Next button.
After entering all the information, click the Complete button, and a verification email will be sent to the entered email address.
- Click the Verify button in the received email to complete registration.
Log in
In the Samsung Cloud Platform Console, there are two types of users: Root users and IAM users. A Root user is the account creator who performs tasks that require unlimited access permissions. An IAM user is a user within an account who performs daily tasks, and a Root user can create IAM users. For detailed information about user creation, see IAM.
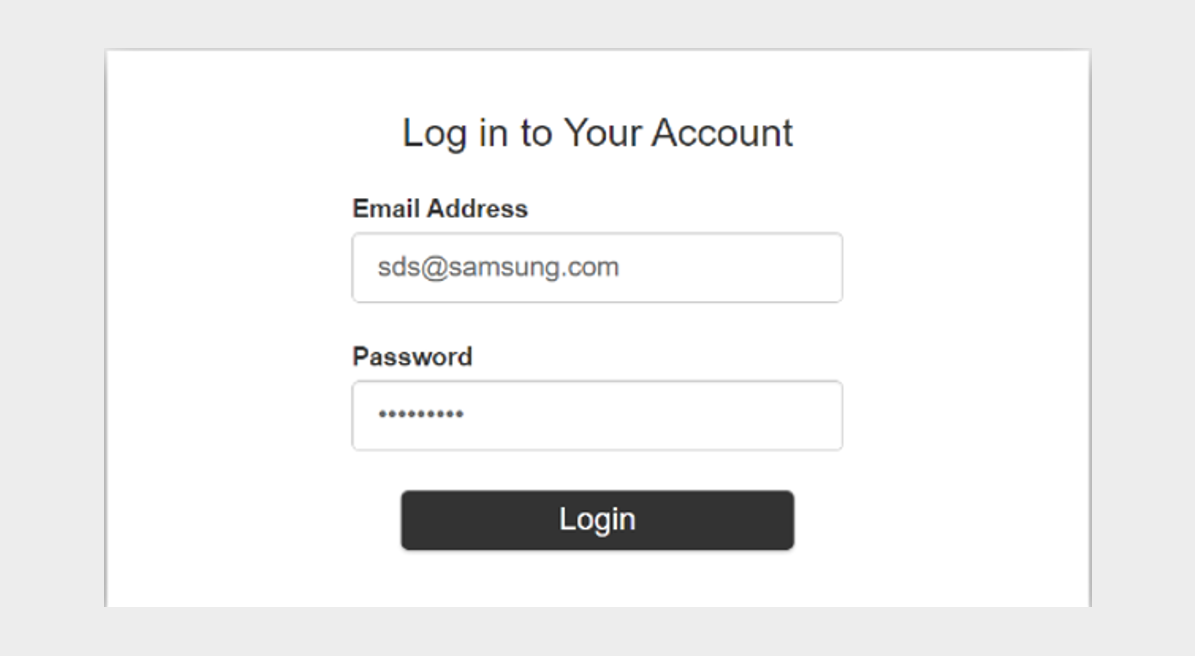
Log in as root user
To log in to the Samsung Cloud Platform Console as the Root user, follow these steps.
- On the login page, select the user type Root User, enter the ID (email), and click the Next button.
- Navigate to the Root user login page. Enter the password.
- Select the method to send the verification code, and click the Send Verification Code button.
- Enter the received verification code and click the Login button.
- If login succeeds, you will be redirected to the Console Home page.
- Please enter the password and verification code correctly. If you enter the password or verification code incorrectly five or more times, your account will be locked for security.
- If the account is locked, provide the locked account information to the user.
- If an allowed IP is configured, login from an unauthorized IP is not possible. Click the Access Allowed IP Not Set item to lift the IP restriction.
- If you have removed the allowed IP setting and logged in, for security go to the Management > IAM > My info. page and reset it. For more details, see Manage Access IP.
IAM user login
To log in to the Samsung Cloud Platform Console as an IAM user, follow these steps.
- On the login page, select the user type as IAM user, enter the Account information, and then click the Next button.
- Go to the IAM User Login page. Enter the IAM Username and Password.
- Select the authentication method and click the Next button.
- Enter the received verification code and click the Next button.
- If login succeeds, you will be redirected to the Console Home page.
- If an IAM user loses their password, they can click the Find Password button to reset the password.
- In the Password Recovery popup window, use your login information (Account information, IAM username) and the pre‑registered email account to reset your password, then log in again.
- Please enter the password and verification code correctly. If you enter the password or verification code incorrectly five or more times, your account will be locked for security.
- If the account is locked, provide the locked account information to the user or administrator.
- If an allowed IP is configured, login from an unauthorized IP is not possible. Click the Access Allowed IP Not Set item to lift the IP restriction.
- If you have removed the allowed IP setting and logged in, go to the Management > IAM > My info. page and reset it for security. For more details, refer to Managing Access IP.
Switch User
After logging into the Samsung Cloud Platform Console, you can switch to a Root user or an IAM user.
To switch users, follow the steps below.
- On the Console Home page, click the User Switch button to the right of the Account name. The User Switch popup opens.
- Click the user name you want to change among the usernames for each Account. A popup indicating user switching will open.
- After verifying the user name, click the Confirm button. The user switch completes and you are redirected to the Console Home page.
Changing the console language
You can set the language to be used in the Samsung Cloud Platform Console.
Change on the login page
- To change the language displayed in the Samsung Cloud Platform Console, click the user language in the upper right of the login page, select the desired language, and then log in.
Change on the Console page
- If you are logged into the Samsung Cloud Platform Console, you can change the language by clicking the language selector at the bottom of the page.
Edit User Information
You can change user information such as username, password, and mobile phone number.
To edit user information, click My menu > My Info. at the top right of the Console.
1.3.2 - Console
When you first log in to the Samsung Cloud Platform Console, you are taken to the Console page.
Console
On the Console page, you can view the Console Home page and configure its widgets. You can also view the list of all services in the Samsung Cloud Platform. The Console left menu’s Console Home and All Services provide the following functions.
| Provided features | description |
|---|---|
| Console Home | In the Console Home of the Console, important information about the Samsung Cloud Platform is provided, and shortcut widgets for services are offered
|
| All services | View all Samsung Cloud Platform service categories and service listings in the Console, and navigate to the respective service
|
Console Home
When you first log in to the Samsung Cloud Platform Console, you are taken to the Console page, and on the Console page, the Console Home page is displayed by default.
Console Home consists of widgets, and can be changed by clicking the Dashboard Settings button in the upper right corner.
| Provided features | Explanation |
|---|---|
| Welcome | Greeting and Samsung Cloud Platform phrase introduction
|
| Recent Visit Service | List of recently visited services
|
| Copilot | Introduction to Copilot or list of conversations with Copilot
|
| Architecture Diagram | Provide resource information in diagram form to easily grasp relationships between resources at a glance
|
| Notice | Samsung Cloud Platform Console Announcements |
| Register payment method | Register a payment method to use all resources of the Samsung Cloud Platform Console
|
| Support Center | A service that provides the technical support, standard architecture, incident response, and service inquiries/answers needed when using the Samsung Cloud Platform Console
|
| This month’s usage and estimated amount | Predict this month’s estimated amount and check the billed amount
|
| User access trend | Daily user access count for the past week, including duplicates. |
| Service Status | Service status by service category
|
| This month’s carbon emissions | Carbon emission data generated when using services on the Samsung Cloud Platform Console
|
Configure the Dashboard
- On the Console page, click Console Home in the left menu. You will be taken to the Console Home page.
- When you first log in, the default page is the Console > Console Home screen.
- On the Console Home page, click the Dashboard Settings button at the top right. The Dashboard Settings popup opens.
- Dashboard Settings popup’s Widget Settings: modify the widget items and their order displayed on Console Home.
- Welcome All widgets except the Welcome widget can be configured by the user.
- If you select the widget’s checkbox, you can add it to the dashboard; if you deselect the checkbox, you can remove it from the dashboard.
- You can change the order by clicking and holding the hamburger button next to the widget name and moving it up or down.
- Dashboard Settings popup’s Widget Settings: selecting Select All selects all widgets. Deselecting Select All deselects all widgets except Welcome.
- After reviewing widget changes in the Preview of the Dashboard Settings popup, click the Save button.
- You can preview the configured widget in the preview displayed on the right.
- Check the changed settings on the Console Home page.
All services
You can view the service categories and list of services offered by Samsung Cloud Platform at a glance, and navigate to the respective service.
1.3.3 - Integrated Management
Integrated management refers to the set of functions located at the top of the Samsung Cloud Platform Console.
Integrated Management Feature
In integrated management, you can view the service list and also see the list of services you recently visited. You can converse with Copilot, and you can view notifications received in the Samsung Cloud Platform Console. You can view the Samsung Cloud Platform region and see the list of regions that can be changed. In the My menu, you can view the user’s information and Account information.
| Category | Detailed description |
|---|---|
| service | Search for Samsung Cloud Platform services, etc., and go to the service
|
| Copilot | Copilot provided by Samsung Cloud Platform
|
| Unified Search | Search Samsung Cloud Platform services, internal Console documents, Marketplace, etc.
|
| Notification | Check notifications received from the Samsung Cloud Platform Console
|
| Support | Support Center, Documentation, can navigate to Announcements
|
| Region | You can view the region of Samsung Cloud Platform and check the list of regions that can be changed
|
| My menu | Check user and Account information
|
Service
You can search for services provided by the Samsung Cloud Platform by keyword, service category, recent visits, favorites, etc., and navigate to the service.
| Category | Detailed description |
|---|---|
| Search term lookup | Search within the service using a keyword
|
| Recent visit | List of recently visited services
|
| Bookmark | List of bookmarked services
|
| All services | A list of all services sorted in ascending order |
Add to Favorites
You can add the service to your favorites.
- Click the Service button at the top of the Console. 1. service Navigate to the popup window.
- In the Service popup, search for the service you want to add to favorites from All Services or Recent Visits. 2. Click the star icon to the left of the service name to add it to your favorites.
- Check that the star shape has been changed to yellow.
- In Service > Favorites, you can view the services you added to favorites.
- You can also view the services you bookmarked at the top of the console.
Check Favorites
You can view the services added to your favorites and navigate to the corresponding service.
- Click the Service button at the top of the Console. 1. Navigate to the Service popup window.
- Click Bookmark in the Service popup window. 2. You can view the services added to your favorites.
- In Service > Favorites, click the name of the service you want to navigate to. 3. Go to the service.
Remove from favorites
You can remove services added to your favorites.
- Click the Service button at the top of the Console. 1. Go to the Service page.
- In the Service popup, click Bookmark. 2. You can view the services added to your favorites.
- Deselect the star icon to the left of the service name you added to favorites.
- All services, etc., you can deselect the star icon to the left of the service name anywhere within service.
- In Service > Favorites, you can see that the service you unfavorited has been removed.
- The service that was unfavorited is also removed from the top of the Console.
Copilot
Copilot is a generative AI-based conversational assistant that can help understand, build, scale, and operate the Samsung Cloud Platform. In the Samsung Cloud Platform Console, you can click the Copilot icon to start a conversation with Copilot.
For more details, refer to Copilot. Below are a few example questions you can ask Copilot.
Example question
- How can I check the estimated charges?
- How do I create a Virtual Server?
- Please show the list of Virtual Server resources in my Account.
- Find the 192.168.21.1 IP among the Virtual Servers.
- How do I add a user to a user group?
- Download cost details
- What is the estimated bill amount for this month?
Unified Search
You can easily find services and documents provided by Samsung Cloud Platform using the unified search.
To find the desired service or document using the unified search, follow these steps.
Enter the keyword you want to search for in the integrated search box. 1. The search results popup opens.
- When you enter a keyword in the unified search box, the keyword is auto‑completed and a popup with the search results for the completed keyword opens.
- When you click the View All button in the search results category, the full results from that category are displayed.
Category Detailed description Service, documents within Condole, Marketplace Enter a keyword with at least two characters Resource name, Resource ID Enter the resource name or resource ID you are looking for in the form /+ resource name (or resource ID)- The resource name (or resource ID) must be at least two characters
Table. How to enter keywords for each search itemReference- After entering a keyword, click Ask Copilot to verify the keyword through Copilot.
- For detailed information about Copilot, see Copilot 개요.
Click the information you want to view in the search results popup. 2. Go to the page.
The range that can be found using the integrated search is as follows.
- Service and resource names, and resource IDs in Samsung Cloud Platform
- User guide documents: How-to guides, API reference, CLI reference
- Knowledge Center
- Marketplace
Notification
You can view notifications received in the Samsung Cloud Platform Console and navigate to the notification settings.
| Category | Detailed description |
|---|---|
| Notification List | The latest 10 notifications received in the Samsung Cloud Platform Console
|
| Notification Settings | When you click the Notification Settings button, you will be taken to the Notification popup’s Notification Settings
|
Check notification details
- Click the Notification button at the top right of the Console to view the latest 10 notifications received by the Console.
- When you select a specific notification item from the list of the latest 10 notifications, you are taken to the notification detail popup window.
Category Detailed description Resource name Name of the resource that triggered the alert Notification type Notification occurrence type - Notice: Alerts received regarding notices
- Service: Alerts received per service
- Cost Management: Alerts received regarding Cost Management
- IAM: Alerts received regarding IAM
- Notification Manager: Alerts received regarding Notification Manager
- Support: Alerts received regarding Support such as inquiries and service requests
Constructor Notification creator Notification creation date and time Notification creation timestamp Table. Notification detail information items
Check notification settings
- If you click the Notification button at the top right of the Console, you can view the latest 10 notifications received by the Console.
- Click the Notification Settings button next to Notification. 2. Notifications > Notification Settings navigates to the popup window.
- Notifications > Notification Settings You can view the notification settings status in the popup window.
Category Detailed description Notification language Language for receiving notifications Notification Target > Notification Type Notification types by recipient - Announcements: Notifications received about announcements
- Service: Notifications received per service
- Cost Management: Notifications received about Cost Management
- IAM: Notifications received about IAM
- Notification Manager: Notifications received about Notification Manager
- Support: Notifications received about Support, such as inquiries and service requests
Table. Notification Settings Items
Modify Notification Settings
- If you click the Notification button at the top right of the Console, you can view the latest 10 notifications received by the Console.
- Click the Notification Settings button next to Notification. 2. Notifications > Notification Settings navigates to the popup window.
- Notification > Notification Settings You can view the notification settings status in the popup window.
- Notification > Notification Settings In the popup window, you can edit the notification settings by clicking the Edit button.
Category Detailed description Notification language Language for receiving notifications Notification Target > Notification Type You can select the notification type (email, SMS) to receive for each notification target. The default setting is email - Announcements: notifications received about announcements
- Service: notifications received per service
- Cost Management: notifications received about Cost Management
- IAM: notifications received about IAM
- Notification Manager:notifications received about Notification Manager
- Support: notifications received about Support, such as inquiries and service requests
Table. Notification Settings Edit Items
Support
In Support, we provide Support Center, Documentation, Announcements.
- Support Center provides technical support, standard architecture, incident response, and service inquiries/answers needed when using Samsung Cloud Platform. * Please refer to Support Center.
- Documentation is a user guide that clearly and simply provides concepts of various services, how to use the Console, and ways to utilize them. * Please refer to the User Guide.
- Notice is a notice provided to users in the Samsung Cloud Platform Console.
Region
You can view the region of the Samsung Cloud Platform and check the list of regions that can be changed.
The services offered by Samsung Cloud Platform are managed on a per‑region basis, so the services provided may vary slightly. A region is a geographically distinct unit for delivering cloud services, composed of one or more data centers to ensure availability. For some services such as the Samsung Cloud Platform Console or IAM, you do not need to select a region because they are global services.
| Region name | Region |
|---|---|
| Global | - |
| Western Korea | Korea West (kr-west1) |
| East Korea | Korea East (kr-east1) |
| South Korea (administrative) | South Korea 1 (kr-south1) |
| South Korea (public) | South Korea 2 (kr-south2) |
| South Korea (Internet) | South Korea South 3 (kr-south3) |
My menu
If you click the profile-shaped button at the top right of the Console, you can see the features provided in the My menu. You can view the Account ID, IAM username, or Root username, and you can navigate to Account, My Info., Cost Management.
| Provided features | Explanation |
|---|---|
| Account ID | Account ID logged in to Samsung Cloud Platform Console |
| IAM username or Root username | IAM user name or Root user name logged in to the Samsung Cloud Platform Console |
| time zone | User-configured time zone
|
| Account | Account information
|
| My Info. | Provides user basic information and authentication key management functions. |
| Cost Management | You can view usage and billing details, payment history, and cost analysis, and manage Credit, budget, Account, and payment methods
|
| role switching | Can switch to another role
|
| Logout | Log out of the Samsung Cloud Platform Console |
1.4 - Copilot
Copilot Overview
You can use the Samsung Cloud Platform more conveniently through the generative AI‑based assistant service Copilot. Users can easily leverage Copilot using familiar interfaces and natural language, enabling them to conduct work accurately and efficiently.
You can start a conversation with Copilot by clicking the Copilot button in the Samsung Cloud Platform Console.
- Clearly state the reason for requesting the work and the final objective to ensure an accurate response.
- To solve complex problems, start by requesting small and simple requirements step by step.
- We use the terminology used in the Samsung Cloud Platform.
- Please be careful not to enter any sensitive information related to work, as it cannot be used.
- Answers generated based on generative AI may contain inaccurate information, so be sure to review them before use.
- For general questions regarding the Samsung Cloud Platform, please select General Inquiry, and for questions about the resources you are using, please select Resource Lookup.
Using Copilot
You can use Copilot via the Copilot button at the top of the Samsung Cloud Platform Console and the Copilot button at the bottom right.
You can also use Copilot via the Copilot widget on the dashboard of the Console Home page, which is the first login screen of the Samsung Cloud Platform Console.
- Click the Copilot button at the top of the console. 1. Copilot popup window opens.
- Copilot Please check the popup window. 2. The features provided by Copilot are as follows.
Category Detailed description Ask a question > General query General questions about using Samsung Cloud Platform - Example questions
- How do I create a Virtual Server?
- How can I check the estimated charges?
- What is the estimated bill for this month?
- General inquiry see
Ask a question > View Resource Question about resources used in Samsung Cloud Platform - Example question
- Show the list of Virtual Server resources in my Account.
- Find the 192.168.21.1 IP among the Virtual Servers
- Resource Query see
Start a new conversation Start a new conversation - Start a new chat Reference
Open in new window Display Copilot popup in a new tab - View in a new window Reference
Conversation List Check the list of previous conversations - 대화 목록 확인하기 Reference
Recommended Prompt Copilot’s recommended question list - Use recommended prompt Reference
Add tag information Add tag information to a specific resource or project - Add tag information Reference
Table. Copilot-provided featuresReference Tip- When you drag text in the Samsung Cloud Platform Console, the Copilot button appears. * Click the Copilot button to search the text with Copilot.
- On the creation page of each service, clicking the info button displayed next to an item provides a detailed guide via Copilot.
- You can enable or disable the Copilot Recommendation feature in My info under the My menu.
- Example questions
General query
Through Copilot, you can ask general questions about the features and usage of the Samsung Cloud Platform.
To make a general query to Copilot, follow the steps below.
- Click the Copilot button at the top of the console. 1. Copilot popup window opens.
- In the bottom prompt of the Copilot popup, select General Query and ask a comprehensive question about Samsung Cloud Platform.
- example question
- Service that must be created in advance before creating a Virtual Server
- What network settings are required to create a Virtual Server?
- Clearly state the reason for requesting the work and the final objective to ensure an accurate response.
- To solve complex problems, start by requesting small and simple requirements step by step.
- We use the terminology used in Samsung Cloud Platform.
- Please be careful not to enter any sensitive information related to work, as it cannot be used.
- Answers generated based on generative AI may contain inaccurate information, so be sure to review them before use.
- For overall questions related to the Samsung Cloud Platform, please select General Inquiry, and for questions about the resources you are using, select Resource Lookup.
Query Resource
You can ask questions about resources created in Samsung Cloud Platform through Copilot.
To ask Copilot questions about resources, follow these steps.
- Click the Copilot button at the top of the console. 1. Copilot popup window opens.
- Copilot In the bottom prompt of the popup window, select View Resource and ask Samsung Cloud Platform about the resource.
- example question
- Please show the list of Virtual Servers.
- Active state Load Balancer
- Clearly state the reason for requesting the work and the final objective to ensure an accurate response.
- To solve complex problems, begin by requesting small, simple requirements in stages.
- We use the terminology employed in Samsung Cloud Platform.
- Please ensure you do not enter any sensitive information related to work, as it cannot be used.
- Answers generated based on generative AI may contain inaccurate information, so be sure to review them before use.
- For overall questions related to the Samsung Cloud Platform, please select General Inquiry, and for questions about the resources you are using, select Resource Lookup.
Start a new conversation
You can start a new conversation with Copilot.
To start a new conversation with Copilot, follow these steps.
- Click the Copilot button at the top of the console. 1. Copilot popup window opens.
- Copilot Click the Start new conversation button in the top right corner of the popup window. 2. A new conversation is starting.
Check conversation list
You can view the list of conversations you had with Copilot.
To view the list of conversations with Copilot, follow these steps.
- Click the Copilot button at the top of the console. 1. Copilot popup window opens.
- Copilot click the Conversation List button in the top‑left corner of the popup window. 2. Conversation List expands.
- In the Conversation list, click the conversation you want to view to go to that conversation.
Check recommended prompts
You can view the recommended prompt questions provided by Copilot.
To view the Copilot recommended prompt questions, follow these steps.
- Click the Copilot button at the top of the console. 1. Navigate to the Copilot popup window.
- Click the Recommended Prompt button on the left side of the bottom prompt in the Copilot popup window. 2. Recommended Prompt The popup window opens.
- Recommended Prompt You can view the questions needed for your work in the popup window.
Category Detailed description Product - Are there any prerequisite services that must be set up before creating a Virtual Server?
- What are the constraints that differ between Virtual Server and Bare Metal Server?
- Are there any precautions to take when using a Bare Metal Server?
Fee - What is the contract rate policy?
- What time period is used as the basis for charge calculation?
- How can I check the estimated charges?
member - How do I register for an IAM account?
- How can I recover my password if I forget it?
- How do I change user information and password?
etc. - How should the network configuration and firewall settings be set up to access a Samsung Cloud Platform Virtual Machine from an overseas local internal network?
- If there are errors or improvement suggestions while using the service, how should I contact support?
Table. Recommended Prompt Question Items
Add tag information
You can add tag information to a specific resource or project.
To add tag information, follow these steps.
Click the Copilot button at the top of the console. 1. Copilot popup window opens.
Enter the tag addition command along with the name of the resource or project for which you want to add tag information in the bottom prompt of the Copilot popup window.
- Example: Add a tag value to Virtual Server Project1
Copilot After entering the tag save information displayed in the popup window, click the Save button.
Category required statusDetailed description Service name Required Home region of Cloud Control - Cloud Control sets the default region as the home region and cannot be changed
- All regions except the default region are managed by Cloud Control
Resource name Required Enter the primary organizational unit within the landing zone - Case-sensitive English letters, up to 128 characters
- The primary organizational unit includes shared Accounts (Log Account, Audit Account)
- Security: Name of the primary organizational unit for the shared Account
- Can be modified after the landing zone is created
tag value Required Add Tag - Add Tag after clicking the Add Tag button, enter or select Key, Value values
- Key value required
- Up to 10 can be added
Table. Tag storage itemsWhen the popup notifying tag saving opens, click the Confirm button.
View in a new window
You can view and use Copilot in a new browser tab.
To use Copilot in a new tab, follow these steps.
- Click the Copilot button at the top of the console. 1. Copilot popup window opens.
- Click the View new window button at the upper right of Copilot. 2. It opens in a new tab of Copilot’s browser.
- Click the Copilot tab opened in the browser. 3. Go to the Copilot page.
- Use the desired features on the Copilot page.
| Category | Detailed description |
|---|---|
| Ask a question > General query | General questions about using Samsung Cloud Platform
|
| Ask a question > View Resource | Question about resources used in Samsung Cloud Platform
|
| Start a new conversation | Start a new conversation
|
| Conversation List | Check the list of previous conversations
|
| Recommended Prompt List | Display list of recommended questions from Copilot
|
2 - Compute
Leveraging the country’s top reliability, we conveniently and elastically provide optimal computing resources tailored to each use case.
2.1 - Virtual Server
2.1.1 - Overview
Service Overview
Virtual Server is a cloud computing-optimized virtual server that lets you freely allocate the amount you need at the required time without having to purchase infrastructure resources such as CPU and memory individually. In a cloud environment, you can use resources with optimized performance according to your computing purpose, such as development, testing, and application execution.
Features
Easy and convenient computing environment setup: Through a web-based Console, users can easily perform self-service provisioning of Virtual Servers, as well as resource and cost management. If you need to change the capacity of major resources such as CPU or Memory while using a Virtual Server, you can easily scale up or down without operator intervention.
Providing various types of services: Provides virtualized vCore/Memory resources according to predefined server types (1~128 vCore).
- General Virtual Server: Provides commonly used computing specs (up to 16 vCore, 256 GB)
- High-capacity Virtual Server: Provided when resources larger than the standard Virtual Server spec are needed.
Strong Security Implementation: By using the Security Group service, you can control inbound/outbound traffic communicating with the external Internet or other VPCs (Virtual Private Cloud) to securely protect the server. Additionally, real-time monitoring enables stable operation of computing resources.
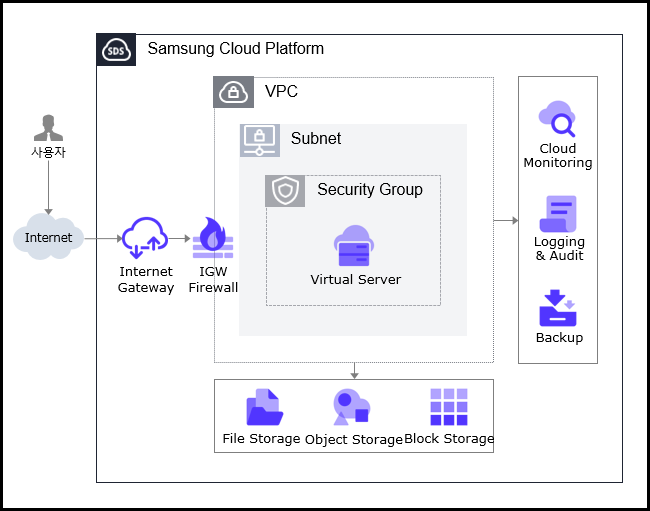
Service Architecture Diagram
Provided features
Virtual Server provides the following features.
- Auto Provisioning and Management: Provides Virtual Server provisioning, resource management, and cost management functions through a web-based Console. If you need to change the capacity of major resources such as CPU or Memory while using Virtual Server, you can modify the server type immediately using the server type modification feature.
- Standard Server Types and Image Provision: Provides virtualized vCore/Memory resources according to standard server types, and offers standard OS images.
- Storage Connection: Provides additional attached storage beyond the OS disk. Block Storage, File Storage, and Object Storage can be attached and used.
- Network Connection: You can connect the standard subnet/IP settings of the Virtual Server and the Public NAT IP. Provides a local subnet connection for inter-server communication. This can be modified on the detail page.
- Security Group Application: Use the Security Group service to control inbound and outbound traffic communicating with external internet or other VPCs, thereby securely protecting the server.
- Monitoring: You can view monitoring information for computing resources such as CPU, Memory, and Disk through the Cloud Monitoring service.
- Backup and Recovery: You can back up and restore the Virtual Server Image using the Backup service.
- Cost Management: You can create, stop, or terminate servers as needed, and since billing is based on actual usage time, you can monitor costs according to consumption.
- ServiceWatch Service Integration: You can monitor data using the ServiceWatch service.
Component
Virtual Server provides standard server types and standard OS images. Users can select and use them according to the desired service scale.
Image
You can create and manage images. The main features are as follows.
- Image creation: You can create an Image from the configuration of a Virtual Server you are using, and you can also create an Image by uploading your Image file to Object Storage.
- Create Shared Image: You can create an Image with Visibility set to Private as a Shared Image that can be shared.
- Share with another Account: You can share the Image with another Account.
- Refer to the How-to guides > Image document for how to create and use images.
Keypair
To ensure a more secure OS login, we strengthen security by providing a Key Pair instead of the ID/Password entry method. The main features are as follows.
- Keypair creation: Generate a user credential to connect to the Virtual Server.
- Retrieve Public Key: You can load a file or manually enter the public key to retrieve it.
- Refer to the How-to guides > Keypair document for creating and using keypairs.
Server Group
Through Server Group settings, you can position the Block Storage added when creating a Virtual Server close to or distributed across racks and hosts. The main features are as follows.
- Server Group Creation: You can set Virtual Servers belonging to the same Server Group as Anti-Affinity(Distributed placement), Affinity(Proximate placement), or Partition(Virtual Server and Block Storage distributed placement).
- Refer to the How-to guides > Server Group document for how to create and use Server Groups.
OS Image provided version
The OS images provided by Virtual Server are as follows
| OS Image version | EoS Date |
|---|---|
| Alma Linux 8.10 | 2029-05-31 |
| Alma Linux 9.6 | 2025-11-17 |
| Oracle Linux 8.10 | 2029-07-31 |
| Oracle Linux 9.6 | 2025-11-25 |
| RHEL 8.10 | 2029-05-31 |
| RHEL 9.4 | 2026-04-30 |
| RHEL 9.6 | 2027-05-31 |
| Rocky Linux 8.10 | 2029-05-31 |
| Rocky Linux 9.6 | 2025-11-30 |
| Ubuntu 22.04 | 2027-06-30 |
| Ubuntu 24.04 | 2029-06-30 |
| Windows 2019 | 2029-01-09 |
| Windows 2022 | 2031-10-14 |
| Windows 2016 | 2027-01-12 |
- Linux operating systems such as Alma Linux and Rocky Linux provide only even Minor versions, except for the final release of a Major version. This policy ensures the stability and consistency of the SCP system. We recommend checking the EOS (End of Support) and EOL (End of Life) dates for the operating system, and, if necessary, applying new or additional individual packages to maintain a stable environment.
Server type
The server types supported by Virtual Server are as follows. For detailed information about server types, see Virtual Server Server Types.
Standard s1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | s1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Constraints
- When creating a Virtual Server with Rocky Linux or Oracle Linux, additional configuration is required for time synchronization (NTP: Network Time Protocol). For other images, it is set automatically and no separate configuration is needed.
For more details, refer to Linux NTP Setup. - If you created RHEL and Windows Server before August 2025, you need to modify the RHEL Repository and WKMS (Windows Key Management Service) settings.
For more details, see RHEL Repo and WKMS Configuration.
Preliminary Service
This is a list of services that need to be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
2.1.1.1 - Server Type
Virtual Server server type
Virtual Server provides server types that match the intended use. Server types consist of various combinations such as CPU, Memory, and Network Bandwidth. The host server used for a Virtual Server is determined by the server type selected when creating the Virtual Server. Please choose a server type based on the specifications of the application you plan to run on the Virtual Server.
The server types supported by Virtual Server are as follows.
Standard s1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | s1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
s1 server type
The s1 server type of Virtual Server is offered with standard specifications (vCPU, Memory) and is suitable for various applications.
- First generation of Samsung Cloud Platform v2: Intel 3rd generation (Ice Lake) Xeon Gold 6342 Processor with up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | s1v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | s1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | s1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | s1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | s1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | s1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | s1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | s1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | s1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | s1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | s1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | s1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | s1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | s1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | s1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | s1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | s1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | s1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | s1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | s1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | s1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | s1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | s1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | s1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | s1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | s1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | s1v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | s1v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | s1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | s1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | s1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | s1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | s1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | s1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | s1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | s1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | s1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | s1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | s1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | s1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | s1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
s2 server type
The Virtual Server s2 server type is offered with standard specifications (vCPU, Memory) and is suitable for various applications.
- Samsung Cloud Platform v2, 2nd generation: Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | CPU vCore | Memory | Network Bandwidth(Gbps) |
|---|---|---|---|---|
| Standard | s2v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | s2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | s2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | s2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | s2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | s2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | s2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | s2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | s2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | s2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | s2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | s2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | s2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | s2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | s2v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | s2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | s2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | s2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | s2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | s2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | s2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | s2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | s2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | s2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | s2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | s2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | s2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | s2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | s2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | s2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | s2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | s2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | s2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | s2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | s2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | s2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | s2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | s2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | s2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | s2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | s2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
h2 Server Type
The h2 server type of Virtual Server is offered with high-capacity specifications and is suitable for applications that require large-scale data processing.
- Second generation of Samsung Cloud Platform v2: Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | h2v24m48 | 24 vCore | 48 GB | Up to 25 Gbps |
| High Capacity | h2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | h2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | h2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | h2v32m64 | 32 vCore | 64 GB | Maximum 25 Gbps |
| High Capacity | h2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | h2v32m256 | 32 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | h2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | h2v48m96 | 48 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | h2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | h2v48m384 | 48 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | h2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | h2v64m128 | 64 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | h2v64m256 | 64 vCore | 256 GB | Up to 25 Gbps |
| High Capacity | h2v64m512 | 64 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | h2v64m768 | 64 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | h2v72m144 | 72 vCore | 144 GB | Up to 25 Gbps |
| High Capacity | h2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | h2v72m576 | 72 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | h2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | h2v96m192 | 96 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | h2v96m384 | 96 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | h2v96m768 | 96 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | h2v96m1152 | 96 vCore | 1152 GB | Maximum 25 Gbps |
| High Capacity | h2v128m256 | 128 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | h2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | h2v128m1024 | 128 vCore | 1024 GB | Up to 25 Gbps |
| High Capacity | h2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
2.1.1.2 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Starting after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by leveraging ServiceWatch released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a seamless monitoring environment.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
Virtual Server Monitoring Metrics
The table below shows the monitoring metrics of Virtual Server that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
Provides basic monitoring metrics even without installing an agent, as shown below table. Please check the Virtual Server monitoring metrics (default). Additionally, the metrics that can be viewed by installing the Agent are in the table below. Virtual Server additional monitoring metrics (Agent installation required)** Please refer to it.
For Windows OS, memory-related metrics can only be viewed after installing the Agent.
| Performance items | Detailed description | unit |
|---|---|---|
| Memory Total [Basic] | bytes of usable memory | bytes |
| Memory Used [Basic] | Current memory usage in bytes | bytes |
| Memory Swap In [Basic] | bytes of the replaced memory | bytes |
| Memory Swap Out [Basic] | bytes of the replaced memory | bytes |
| Memory Free [Basic] | bytes of unused memory | bytes |
| Disk Read Bytes [Basic] | Read bytes | bytes |
| Disk Read Requests [Basic] | Number of read requests | cnt |
| Disk Write Bytes [Basic] | write bytes | bytes |
| Disk Write Requests [Basic] | Number of write requests | cnt |
| CPU Usage [Basic] | Average system CPU usage over 1 minute | % |
| Instance State [Basic] | Instance status | state |
| Network In Bytes [Basic] | Received bytes | bytes |
| Network In Dropped [Basic] | Incoming packet drop | cnt |
| Network In Packets [Basic] | Number of received packets | cnt |
| Network Out Bytes [Basic] | sent bytes | bytes |
| Network Out Dropped [Basic] | Transmit packet drop | cnt |
| Network Out Packets [Basic] | Number of transmitted packets | cnt |
| Performance items | Detailed description | unit |
|---|---|---|
| Core Usage [IO Wait] | Ratio of CPU time spent in wait state (disk wait) | % |
| Core Usage [System] | Proportion of CPU time spent in kernel space | % |
| Core Usage [User] | Proportion of CPU time spent in user space | % |
| CPU Cores | Number of CPU cores on the host | cnt |
| CPU Usage [Active] | Percentage of CPU time used other than Idle and IOWait states | % |
| CPU Usage [Idle] | It is the proportion of CPU time spent in idle state. | % |
| CPU Usage [IO Wait] | This is the proportion of CPU time spent in a waiting state (disk wait). | % |
| CPU Usage [System] | Percentage of CPU time used by the kernel | % |
| CPU Usage [User] | Percentage of CPU time used in user space | % |
| CPU Usage/Core [Active] | Percentage of CPU time used other than Idle and IOWait states | % |
| CPU Usage/Core [Idle] | It is the proportion of CPU time spent in idle state. | % |
| CPU Usage/Core [IO Wait] | This is the proportion of CPU time spent in a waiting state (disk wait). | % |
| CPU Usage/Core [System] | Percentage of CPU time used by the kernel | % |
| CPU Usage/Core [User] | Percentage of CPU time used in user space | % |
| DiskCPU Usage [IO Request] | Proportion of CPU time during which I/O requests to the device were executed | % |
| Disk Queue Size [Avg] | The average queue length of requests executed for the device. | num |
| Disk Read Bytes | The number of bytes read per second from the device. | bytes |
| Disk Read Bytes [Delta Avg] | Average of system.diskio.read.bytes_delta for individual disks | bytes |
| Disk Read Bytes [Delta Max] | Maximum system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta Min] | Minimum of system.diskio.read.bytes_delta for individual disks | bytes |
| Disk Read Bytes [Delta Sum] | Sum of system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta] | Delta of the system.diskio.read.bytes value for each Disk | bytes |
| Disk Read Bytes [Success] | Total bytes successfully read | bytes |
| Disk Read Requests | Number of read requests to the disk device per second | cnt |
| Disk Read Requests [Delta Avg] | Average of system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Max] | Maximum system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Min] | Minimum of system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Sum] | Sum of the system.diskio.read.count_delta of individual disks | cnt |
| Disk Read Requests [Success Delta] | Delta of system.diskio.read.count for each Disk | cnt |
| Disk Read Requests [Success] | Total number of successful reads | cnt |
| Disk Request Size [Avg] | It is the average size of requests executed on the device (unit: sectors). | num |
| Disk Service Time [Avg] | Average service time (milliseconds) of input requests executed on the device. | ms |
| Disk Wait Time [Avg] | Average time taken for requests executed on the supported device. | ms |
| Disk Wait Time [Read] | Average disk wait time | ms |
| Disk Wait Time [Write] | Average disk wait time | ms |
| Disk Write Bytes [Delta Avg] | Average of system.diskio.write.bytes_delta for each disk | bytes |
| Disk Write Bytes [Delta Max] | Maximum system.diskio.write.bytes_delta of individual disks | bytes |
| Disk Write Bytes [Delta Min] | Minimum of system.diskio.write.bytes_delta for individual disks | bytes |
| Disk Write Bytes [Delta Sum] | Sum of system.diskio.write.bytes_delta for individual disks | bytes |
| Disk Write Bytes [Delta] | Delta of the system.diskio.write.bytes value for each Disk | bytes |
| Disk Write Bytes [Success] | Total number of bytes successfully written | bytes |
| Disk Write Requests | Number of write requests to the disk device per second | cnt |
| Disk Write Requests [Delta Avg] | Average of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Max] | Maximum system.diskio.write.count_delta of individual disks | cnt |
| Disk Write Requests [Delta Min] | Minimum of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Sum] | Sum of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Success Delta] | Delta of system.diskio.write.count for each Disk | cnt |
| Disk Write Requests [Success] | Total number of successful writes | cnt |
| Disk Writes Bytes | Bytes per second written to the device | bytes |
| Filesystem Hang Check | filesystem(local/NFS) hang check(normal:1, abnormal:0) | status |
| Filesystem Nodes | Total number of file nodes in the file system. | cnt |
| Filesystem Nodes [Free] | It is the total number of available file nodes in the file system. | cnt |
| Filesystem Size [Available] | Disk space (bytes) available to unauthorized users | bytes |
| Filesystem Size [Free] | Available disk space (bytes) | bytes |
| Filesystem Size [Total] | Total disk space (bytes) | bytes |
| Filesystem Usage | Used disk space percentage | % |
| Filesystem Usage [Avg] | Average of individual filesystem.used.pct | % |
| Filesystem Usage [Inode] | iNode usage rate | % |
| Filesystem Usage [Max] | Maximum among individual filesystem.used.pct | % |
| Filesystem Usage [Min] | Min among individual filesystem.used.pct | % |
| Filesystem Usage [Total] | - | % |
| Filesystem Used | Used disk space (bytes) | bytes |
| Filesystem Used [Inode] | iNode usage | bytes |
| Memory Free | Total available memory (bytes) | bytes |
| Memory Free [Actual] | Actual usable Memory (bytes) | bytes |
| Memory Free [Swap] | Available Swap memory | bytes |
| Memory Total | Total Memory | bytes |
| Memory Total [Swap] | Total Swap memory. | bytes |
| Memory Usage | Percentage of used memory | % |
| Memory Usage [Actual] | Percentage of memory actually used | % |
| Memory Usage [Cache Swap] | cached swap usage | % |
| Memory Usage [Swap] | Percentage of used Swap memory | % |
| Memory Used | Used Memory | bytes |
| Memory Used [Actual] | Actual memory used (bytes) | bytes |
| Memory Used [Swap] | Used Swap memory | bytes |
| Collisions | Network collision | cnt |
| Network In Bytes | Number of received bytes | bytes |
| Network In Bytes [Delta Avg] | Average of system.network.in.bytes_delta for individual networks | bytes |
| Network In Bytes [Delta Max] | Maximum system.network.in.bytes_delta for each Network | bytes |
| Network In Bytes [Delta Min] | Minimum of system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Sum] | Sum of system.network.in.bytes_delta for individual networks | bytes |
| Network In Bytes [Delta] | Delta of received byte count | bytes |
| Network In Dropped | Number of deleted packets among incoming packets | cnt |
| Network In Errors | Number of errors during reception | cnt |
| Network In Packets | Number of received packets | cnt |
| Network In Packets [Delta Avg] | Average of system.network.in.packets_delta for individual Networks | cnt |
| Network In Packets [Delta Max] | Maximum of system.network.in.packets_delta for each Network | cnt |
| Network In Packets [Delta Min] | Minimum of system.network.in.packets_delta for each Network | cnt |
| Network In Packets [Delta Sum] | Sum of system.network.in.packets_delta for individual Networks | cnt |
| Network In Packets [Delta] | Delta of received packet count | cnt |
| Network Out Bytes | Number of transmitted bytes | bytes |
| Network Out Bytes [Delta Avg] | Average of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta Max] | Maximum system.network.out.bytes_delta for each Network | bytes |
| Network Out Bytes [Delta Min] | Minimum of system.network.out.bytes_delta for individual Networks | bytes |
| Network Out Bytes [Delta Sum] | Sum of system.network.out.bytes_delta for individual Networks | bytes |
| Network Out Bytes [Delta] | Delta of transmitted byte count | bytes |
| Network Out Dropped | Number of deleted packets among outgoing packets | cnt |
| Network Out Errors | Number of errors during transmission | cnt |
| Network Out Packets | Number of transmitted packets | cnt |
| Network Out Packets [Delta Avg] | Average of system.network.out.packets_delta for each Network | cnt |
| Network Out Packets [Delta Max] | Maximum system.network.out.packets_delta for each Network | cnt |
| Network Out Packets [Delta Min] | Minimum of system.network.out.packets_delta for each Network | cnt |
| Network Out Packets [Delta Sum] | Sum of system.network.out.packets_delta for individual networks | cnt |
| Network Out Packets [Delta] | Delta of transmitted packet count | cnt |
| Open Connections [TCP] | All open TCP connections | cnt |
| Open Connections [UDP] | All open UDP connections | cnt |
| Port Usage | Connectable port utilization | % |
| SYN Sent Sockets | Number of sockets in SYN_SENT state (when connecting from local to remote) | cnt |
| Kernel PID Max | kernel.pid_max value | cnt |
| Kernel Thread Max | kernel.threads-max value | cnt |
| Process CPU Usage | Percentage of CPU time consumed by the process since the last update | % |
| Process CPU Usage/Core | Percentage of CPU time used by the process since the last event | % |
| Process Memory Usage | Proportion of main memory (RAM) occupied by a process | % |
| Process Memory Used | Resident Set size. The amount of memory a process occupies in RAM. | bytes |
| Process PID | process pid | pid |
| Process PPID | Parent process PID | pid |
| Processes [Dead] | Number of deadProcesses | cnt |
| Processes [Idle] | idle Processes count | cnt |
| Processes [Running] | running Processes count | cnt |
| Processes [Sleeping] | sleeping processes count | cnt |
| Processes [Stopped] | stopped processes count | cnt |
| Processes [Total] | Total number of processes | cnt |
| Processes [Unknown] | Number of processes whose status cannot be retrieved or is unknown | cnt |
| Processes [Zombie] | Number of zombie processes | cnt |
| Running Process Usage | process usage | % |
| Running Processes | Number of running processes | cnt |
| Running Thread Usage | Thread usage rate | % |
| Running Threads | Total number of threads running in running processes | cnt |
| Context Switches | context switch count (per second) | cnt |
| Load/Core [1 min] | The load over the last 1 minute divided by the number of cores | cnt |
| Load/Core [15 min] | The load over the last 15 minutes divided by the number of cores | cnt |
| Load/Core [5 min] | The load over the last 5 minutes divided by the number of cores | cnt |
| Multipaths [Active] | External storage connection path status = active count | cnt |
| Multipaths [Failed] | External storage connection path status = failed count | cnt |
| Multipaths [Faulty] | External storage connection path status = faulty count | cnt |
| NTP Offset last | sample’s measured offset (time difference between NTP server and local environment) | num |
| Run Queue Length | Execution queue length | num |
| Uptime | OS uptime (milliseconds) | ms |
| Context Switchies CPU | context switch count (per second) | cnt |
| Disk Read Bytes [Sec] | Number of bytes read in one second from a Windows logical disk
| cnt |
| Disk Read Time [Avg] | Data read average time (seconds)
| sec |
| Disk Transfer Time [Avg] | Disk average wait time (seconds)
| sec |
| Disk Write Bytes [Sec] | Number of bytes written in one second on a Windows logical disk
| cnt |
| Disk Write Time [Avg] | Average data write time (seconds)
| sec |
| Pagingfile Usage | paging file usage
| % |
| Pool Used [Non Paged] | Nonpaged Pool usage in kernel memory
| bytes |
| Pool Used [Paged] | Paged Pool usage in kernel memory
| bytes |
| Process [Running] | Number of currently running processes
| cnt |
| Threads [Running] | Number of currently running threads
| cnt |
| Threads [Waiting] | Number of threads waiting for processor time
| cnt |
2.1.1.3 - ServiceWatch Metrics
Virtual Server sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals. If detailed monitoring is enabled, you can view data collected at 1‑minute intervals.
See How-to guides > ServiceWatch Enable Detailed Monitoring for instructions on enabling detailed monitoring of Virtual Server.
Basic Metrics
The following are the basic metrics for the Virtual Server namespace.
The indicators whose names are displayed in bold below are the indicators selected as key metrics among the default metrics provided by Virtual Server. The key metrics are used to build service dashboards that are automatically generated for each service in ServiceWatch. They can also be viewed on the Monitoring tab of the Virtual Server detail page.
Each metric provides guidance in the user guide on which statistical value is meaningful to query, and among the meaningful statistics, the values shown in bold text are the primary statistics. In the service dashboard or monitoring tab, you can view primary metrics using these primary statistics.
| Performance item (indicator name) | Detailed description | unit | meaningful statistics | |
|---|---|---|---|---|
| Instance State | Instance status display
| None |
| |
| CPU Usage | CPU usage | Percent |
| |
| Disk Read Bytes | Bytes read from block device (bytes) | Bytes |
| |
| Disk Read Requests | Number of read requests on a block device | Count |
| |
| Disk Write Bytes | Write capacity (bytes) on block device | Bytes |
| |
| Disk Write Requests | Number of write requests on block device | Count |
| |
| Network In Bytes | Received bytes on the network interface | Bytes |
| |
| Network In Dropped | Number of packet drops received on the network interface | Count |
| |
| Network In Packets | Number of packets received on the network interface | Count |
| |
| Network Out Bytes | Data transmitted on the network interface (bytes) | Bytes |
| |
| Network Out Dropped | Number of packet drops transmitted from the network interface | Count |
| |
| Network Out Packets | Number of packets transmitted on the network interface | Count |
|
2.1.2 - How-to guides
Users can create the service by entering the required information for a Virtual Server and selecting detailed options through the Samsung Cloud Platform Console.
Create Virtual Server
You can create and use a Virtual Server service in the Samsung Cloud Platform Console.
To create a Virtual Server, follow these steps.
Click the All Services > Compute > Virtual Server menu. 1. Navigate to the Service Home page of the Virtual Server.
On the Service Home page, click the Create Virtual Server button. 2. Navigate to the Create Virtual Server page.
On the Virtual Server Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image Required Select the provided Image type - Standard: Samsung Cloud Platform standard provided Image
- Alma Linux, Oracle Linux, RHEL, Rocky Linux, Ubuntu, Windows
- Custom: User-created Image
- Kubernetes: Image for Kubernetes
- RHEL, Ubuntu
- Marketplace: Image subscribed from Marketplace
Image version Required Select version of the selected Image - Provide version list of the server Image
Table. Virtual Server Image and version selection input items - Standard: Samsung Cloud Platform standard provided Image
- In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Number of servers Required Number of servers to create concurrently - Only numeric input is allowed, and enter a value between 1~100
Service Type > Server Type Required Virtual Server server type - Standard: standard specifications commonly used
- High Capacity: large‑capacity server specifications beyond Standard
- For detailed information about the server types provided by Virtual Server, see Virtual Server 서버 타입
Service Type > Planned Compute Required Planned Compute-configured resource status - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service creation page
- For more details, refer to Planned Compute Apply
Block Storage Essential Block Storage settings used by the server according to purpose - Basic OS: Area where the OS is installed and used
- Capacity is entered in Units, and the minimum size varies by OS Image type
- Alma Linux: Enter a value between 2~1,536
- Oracle Linux: Enter a value between 7~1,536
- RHEL: Enter a value between 2~1,536
- Rocky Linux: Enter a value between 2~1,536
- Ubuntu: Enter a value between 2~1,536
- Windows: Enter a value between 4~1,536
- SSD: High‑performance general volume
- HDD: General volume
- SSD/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management Service) encryption keys
- Encryption can be applied only at initial creation and cannot be changed afterward
- Using the SSD_KMS disk type may cause performance degradation
- SSD_Provisioned: SSD volume with configurable IOPS and Throughput
- Capacity is entered in Units, and the minimum size varies by OS Image type
- Additional: Used when extra user space beyond the OS area is needed
- After selecting Use, enter the storage type and capacity
- To add storage, click the + button; to delete, click the x button (up to 25 can be added)
- Capacity is entered in Units, with a value between 1~1,536
- 1 Unit equals 8 GB, so 8~12,288 GB are created
- SSD: High‑performance general volume
- HDD: General volume
- SSD/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management Service) encryption keys
- Encryption can be applied only at initial creation and cannot be changed afterward
- Using the SSD_KMS disk type may cause performance degradation
- SSD/HDD_MultiAttach: Volume that can be attached to two or more servers
- SSD_Provisioned: SSD volume with configurable IOPS and Throughput
- For details on each Block Storage type, see Block Storage 생성하기
- Delete on termination: When Delete on Termination is selected, the volume is terminated together with the server
- A volume with an existing snapshot is not deleted even when Delete on termination is enabled
- A multi‑attach volume can be deleted only when the server being removed is the last remaining server attached to the volume
- Max IOPS: Enter a maximum IOPS value between 5,000~20,000
- Not configurable for disk types HDD, HDD_KMS, HDD_MultiAttach
- Max Throughput: Enter a maximum Throughput value between 250~1,000
- Not configurable for disk types HDD, HDD_KMS, HDD_MultiAttach
Server Group Select After selecting Use for setting Anti-Affinity (distributed placement), Affinity (proximate placement), Partition (distributed placement of Virtual Server and Block Storage) for servers belonging to the same Server Group - , select the Server Group
- , choose Create New to create the Server Group
Servers belonging to the same Server Group are placed in a Best Effort manner according to the selected policy The policy can be selected among Anti-Affinity (distributed placement), Affinity (proximate placement), Partition (distributed placement of Virtual Server and Block Storage) Table. Virtual Server service information input itemsCautionWhen using the Partition (distributed placement of Virtual Server and Block Storage) policy among Server Group policies, you cannot allocate additional Block Storage Volumes after creating a Virtual Server, so create all required Block Storage during the Virtual Server creation step. - Required Information Input area, please enter or select the required information.
Category required statusDetailed description Server name Essential Enter a name to distinguish the server when the selected number of servers is 1 - Set the hostname to the entered server name
- Enter using English letters, numbers, spaces, and special characters (
-,_) within 63 characters
Network Settings > Create New Network Port Required Set the network where the Virtual Server will be installed - VPC Name: Select a pre‑created VPC
- General Subnet: Select a pre‑created general Subnet
- IP can be set to auto‑generate or user‑provided; if input is selected, the user can manually enter the IP
- NAT: Available only when there is a single server and the VPC is attached to an Internet Gateway. Checking Use allows selection of a NAT IP
- NAT IP: Select a NAT IP
- If no NAT IP is available, click the Create New button to generate a Public IP
- Refresh button to view and select the created Public IP
- Creating a Public IP incurs charges according to the Public IP pricing policy
- Local Subnet (optional): Select Use for a local Subnet
- It is not a required element for creating the service
- A pre‑created local Subnet must be selected
- IP can be set to auto‑generate or user‑provided; if input is selected, the user can manually enter the IP
- Security Group: Settings required to access the server
- Select: Choose a pre‑created Security Group
- Create New: If no applicable Security Group exists, it can be created separately in the Security Group service
- Up to 5 can be selected
- If no Security Group is set, all connections are blocked by default
- A Security Group must be configured to allow required connections
Network Settings > Specify Existing Network Port Required Set the network where the Virtual Server will be installed - VPC: Select a pre‑created VPC
- General Subnet: Select a pre‑created general Subnet and port
- NAT: Available only when there is a single server and the VPC is attached to an Internet Gateway. When enabled, you can select a NAT IP
- NAT IP: Select a NAT IP
- If no NAT IP is available to select, click the Create New button to generate a Public IP
- Refresh button to view and select the created Public IP
- Local Subnet (Optional): Choose Use for the local Subnet
- Select a pre‑created local Subnet and port
Keypair Required User authentication method to use when connecting to the server - Create new: Create a new one if a new keypair is required
- Refer to Keypair 생성하기
- Default login account list by OS
- Alma Linux: almalinux
- Oracle Linux: cloud-user
- RHEL: cloud-user
- Rocky Linux: rocky
- Ubuntu: ubuntu
- Windows: sysadmin
Table: Required input fields for Virtual Server - Additional Information Input area, please enter or select the required information.
Category required statusDetailed description Lock Select Lock usage setting - Using the lock prevents actions such as server termination, start, stop, etc., from being executed, preventing misoperations due to mistakes
Init script Select the script that runs when the server starts - The init script must be written as a Batch script for Windows, a Shell script or cloud‑init for Linux, depending on the Image type.
- Up to 45,000 bytes can be entered
tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Virtual Server additional information input fields
- Select the required information in the Image and version selection area.
Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the Virtual Server List page.
- When entering the server name, if spaces and special characters (
_) are used, the OS hostname will have spaces and special characters (_) changed to the special character (-) and be set. * Refer to this when setting the OS hostname.- Example: If the server name is ‘server name_01’, the OS hostname is set to ‘server-name-01’.
- If you need to manage server names uniquely, specify a different server name (Prefix) when creating them.
- When creating a server, because the numbering does not automatically increment based on the server name (Prefix), a Virtual Server with the same name can be created.
- Example: If you first create two Virtual Servers using the server name (Prefix) ’test’, ’test-1’ and ’test-2’ will be created. * After that, even if you create two Virtual Servers again using the prefix ’test’, ’test-1’ and ’test-2’ will be created.
- If you create a Virtual Server with Rocky Linux or Oracle Linux, additional configuration is required for time synchronization (NTP: Network Time Protocol). * For more details, please refer to Linux NTP 설정하기.
- If RHEL and Windows Server were created before July 2025, you need to modify the RHEL Repository and WKMS (Windows Key Management Service) settings. For detailed information, refer to RHEL Repo 및 WKMS 설정하기.
Check Virtual Server detailed information
The Virtual Server service allows you to view and edit the entire resource list and detailed information. The Virtual Server Details page includes the Details, Monitoring, Tags, Activity Log tabs.
To view detailed information about the Virtual Server service, follow these steps.
- All Services > Compute > Virtual Server menu, click it. 1. Navigate to the Service Home page of the Virtual Server.
- On the Service Home page, click the Virtual Server menu. 2. Go to the Virtual Server List page.
- On the Virtual Server List page, click the resource to view detailed information. 3. Navigate to the Virtual Server Details page.
- Virtual Server Details page displays status information and additional feature information, and consists of Details, Monitoring, Tags, Activity Log tabs.
- For detailed information about Virtual Server Add-on Features, please refer to Virtual Server Management Add-on Features.
Category Detailed description Virtual Server status Status of a user-created Virtual Server - Build: State where a Build command has been received
- Building: Build in progress
- Networking: Server creation networking process
- Scheduling: Server creation scheduling process
- Block_Device_Mapping: Attaching Block Storage during server creation
- Spawning: Server creation process is ongoing
- Active: Available state
- Powering_off: State when a shutdown request is made
- Deleting: Server deletion in progress
- Reboot_Started: Reboot in progress
- Error: Error state
- Migrating: Server is being migrated to another host
- Reboot: Reboot command has been received
- Rebooting: Restart in progress
- Rebuild: Rebuild command has been received
- Rebuilding: State when a Rebuild request is made
- Rebuild_Spawning: Rebuild process is ongoing
- Resize: Resize command has been received
- Resizing: Resize in progress
- Resize_Prep: State when a server type change is requested
- Resize_Migrating: Server is being moved to another host while resizing
- Resize_Migrated: Server has completed moving to another host during resize
- Resize_Finish: Resize completed
- Revert_Resize: Resize or migration of the server failed for some reason. The target server is cleaned up and the original server is restarted
- Shutoff: State when powering off is completed
- Verity_ Resize: After a server type change request and Resize_Prep, the server type is confirmed or can be reverted
- Resize_Reverting: State when a server type revert is requested
- Resize_Confirming: State while confirming the server’s Resize request
Server control Buttons to change server status - Start: Start a stopped server
- Stop: Stop a running server
- Restart: Restart a running server
Image generation Create a user Image from the current server’s Image - For detailed Image creation instructions, see Create Image
Console log View console logs of the current server - You can check the console logs output by the current server. For more details, see 콘솔 로그 확인하기
Create dump Create a dump of the current server - Dump file is created inside the Virtual Server
- Refer to Dump 생성하기 for detailed dump creation instructions
Rebuild The OS area data and settings of the existing Virtual Server are deleted, and it is rebuilt on a new server - For details, see Rebuild 수행하기
Service termination Button to cancel the service Table. Virtual Server status information and additional functions
Detailed Information
Virtual Server List page lets you view detailed information of the selected resource and, if needed, modify the information.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Modifier | User who edited the service information |
| Modification timestamp | Date and time the service information was modified |
| Server name | Server name
|
| Server type | vCPU, memory information display
|
| Image name | Server OS Image and version
|
| Lock | Show lock usage status
|
| Server group | Server group name to which the server belongs
|
| Keypair name | Server authentication information set by the user
|
| Planned Compute | Resource status with Planned Compute configured
|
| ServiceWatch detailed monitoring | ServiceWatch detailed monitoring activation status display
|
| Network | Network information of the Virtual Server
|
| Local Subnet | Local Subnet information of the Virtual Server
|
| Block Storage | Server-connected Block Storage information
|
Monitoring
You can monitor the ServiceWatch metrics of the resources selected on the Virtual Server List page. In the Monitoring tab, you can view monitoring charts for the Virtual Server, and each chart is based on the available Service Watch metrics.
| Category | Detailed description |
|---|---|
| Period setting area | Select the period applied to the chart
|
| Time Zone Settings Section | Select time zone for the chart |
| Reset button | Reset all manipulations and settings made on the chart |
| Refresh Settings Area | Select chart refresh interval
|
| Go to the service dashboard | Navigate to the ServiceWatch dashboard list screen |
| More | Display additional tasks for managing charts
|
| graph area | Data graph collected over the chart’s applied period
|
- The metrics provided by basic monitoring are data collected at 5‑minute intervals.
- For detailed information about the ServiceWatch metrics of Virtual Server, refer to Virtual Server ServiceWatch metrics.
Tag
Virtual Server List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Virtual Server List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Control Virtual Server Operation
If you need to control the operation of a created Virtual Server resource, you can perform the task from the Virtual Server List or Virtual Server Details page. You can start, stop, and restart a running server.
Getting Started with Virtual Server
You can start a Virtual Server that is Shutoff. To start the Virtual Server, follow these steps.
- Click the All Services > Compute > Virtual Server menu. 1. Navigate to the Service Home page of the Virtual Server.
- On the Service Home page, click the Virtual Server menu. 2. Go to the Virtual Server List page.
- Virtual Server List page, click the resource to start among the shutoff servers, and navigate to the Virtual Server Details page.
- On the Virtual Server List page, you can Start each resource via the right More button.
- After selecting multiple servers with checkboxes, you can control multiple servers simultaneously using the Start button at the top.
- Virtual Server Details page, click the Start button at the top to start the server. 4. Check the status of the modified server in the Status Indicator item.
- When the Virtual Server start is complete, the server status changes from Shutoff to Active.
- For detailed information about the Virtual Server status, please refer to Virtual Server Detailed Information.
Stop Virtual Server
You can stop a Virtual Server that is running (Active). To stop the Virtual Server, follow the steps below.
- Click the All Services > Compute > Virtual Server menu. 1. Navigate to the Service Home page of the Virtual Server.
- On the Service Home page, click the Virtual Server menu. 2. Go to the Virtual Server List page.
- On the Virtual Server List page, click the resource to stop among the active servers, and proceed to the Virtual Server Details page.
- On the Virtual Server List page, you can stop each resource via the right More button.
- After selecting multiple servers with checkboxes, you can control multiple servers simultaneously using the Stop button at the top.
- On the Virtual Server Details page, click the Stop button at the top to start the server. 4. Check the status of the modified server in the Status Indicator item.
- When the Virtual Server shutdown is complete, the server status changes from Active to Shutoff.
- For detailed information about the Virtual Server status, please refer to Virtual Server Detailed Information.
Restart Virtual Server
You can restart the created Virtual Server. To restart the Virtual Server, follow these steps.
- Click the All Services > Compute > Virtual Server menu. 1. Navigate to the Service Home page of the Virtual Server.
- On the Service Home page, click the Virtual Server menu. 2. Go to the Virtual Server List page.
- On the Virtual Server List page, click the resource to restart, and go to the Virtual Server Details page.
- On the Virtual Server list page, you can restart each resource via the right More button.
- After selecting multiple servers with checkboxes, you can control multiple servers simultaneously using the Restart button at the top.
- On the Virtual Server Details page, click the Restart button at the top to start the server. 4. Check the status of the changed server in the Status Display section.
- During a Virtual Server restart, the server status goes through Rebooting and finally changes to Active.
- For detailed information about the Virtual Server status, please refer to Virtual Server Detailed Information.
Managing Virtual Server Resources
If you need server control and management functions for the created Virtual Server resources, you can perform tasks on the Virtual Server List or Virtual Server Details page.
Create Image
You can create an image of a running Virtual Server.
This content explains how to create a user image on a running Virtual Server.
- On the Virtual Server list or Virtual Server details page, click the Create Image button to create a user Image.
- Refer to Image Detailed Guide: Creating an Image for the method of creating an Image by uploading an Image file owned by the user.
To create an Image of a Virtual Server, follow these steps.
Click the All Services > Compute > Virtual Server menu. 1. Navigate to the Service Home page of Virtual Server.
On the Service Home page, click the Virtual Server menu. 2. Navigate to the Virtual Server List page.
On the Virtual Server List page, click the resource to create an Image. 3. Navigate to the Virtual Server Details page.
On the Virtual Server Details page, click the Create Image button. 4. Go to the Image creation page.
- Enter the required information in the Service Information Input area.
Category required statusDetailed description Image name Required the name of the Image to be created - English letters, numbers, spaces, and special characters (
-,_) within 200 characters
Table. Image service information input fields - English letters, numbers, spaces, and special characters (
- Enter the required information in the Service Information Input area.
Check the input information and click the Complete button.
- When creation is complete, check the created resources on the All Services > Compute > Virtual Server > Image List page.
- When an Image is created, the generated Image is stored in the Object Storage used as internal storage. * Therefore, a usage fee will be charged for image storage.
- Since the file system of an Image created from an Active Virtual Server cannot be guaranteed to be intact, it is recommended to stop the server before creating the Image.
Edit Server Type
You can modify the server type of a Virtual Server.
To modify the server type of a Virtual Server, follow these steps.
- Click the All Services > Compute > Virtual Server menu. 1. Navigate to the Service Home page of the Virtual Server.
- On the Service Home page, click the Virtual Server menu. 2. Go to the Virtual Server List page.
- On the Virtual Server List page, click the resource you want to control. 3. Go to the Virtual Server Details page.
- On the Virtual Server Details page, check the server status and click the Edit button for the server type. 4. Edit Server Type popup window opens.
- Edit Server Type In the popup window, after changing the server type, click the Confirm button.
- If you modify the Virtual Server’s server type, the Virtual Server status changes to a state related to performing a resize.
- For detailed information about the Virtual Server status, please refer to Virtual Server Detailed Information.
Service Architecture Diagram
Provided features
Virtual Server Auto-Scaling provides the following features.
- Launch Configuration: It is a configuration template used to create a Virtual Server in an Auto-Scaling Group. When creating a Launch Configuration, you set information about the Virtual Server such as the image, server type, Key Pair, Block Storage, etc.
- Server Count Adjustment: Provides several ways to adjust the number of servers. By using policies, you can add a Virtual Server when load exceeds a threshold and release the Virtual Server when demand is low, maintaining application availability while reducing costs. You can also add and release Virtual Servers according to a predefined schedule, and manually adjust the number of servers in an Auto-Scaling Group as needed.
- Load Balancer Integration: You can use a Load Balancer to evenly distribute application traffic across Virtual Servers. Whenever a Virtual Server is added or removed, it is automatically registered with or deregistered from the Load Balancer.
- Network Connection: You can connect the Auto-Scaling Group’s standard subnet, automatic IP allocation, and Public NAT IP. Provides a local subnet connection for inter-server communication.
- Security Group Application: Security Group is a virtual logical firewall that controls inbound/outbound traffic generated on a Virtual Server. Inbound rules control incoming traffic to the Virtual Server, and outbound rules control outgoing traffic from the Virtual Server.
- Monitoring: You can view monitoring data such as CPU, Memory, and Disk of Virtual Servers created in an Auto-Scaling Group via the ServiceWatch service. Based on the monitoring data, you can set load thresholds using Auto-Scaling policies, and when thresholds are exceeded, you can add or remove servers.
Component
Virtual Server Auto-Scaling creates an Auto-Scaling Group through a Launch Configuration and monitors and manages the servers.
Launch Configuration
This is a Configuration template used to create a Virtual Server in an Auto-Scaling Group. The main features are as follows.
- Image: Provides OS standard images and Custom images created by the user. Users can select and use them according to the service they wish to configure.
- Keypair: Provides the Keypair method for secure OS access.
- Init script: Users can define a script to be executed when the Virtual Server starts.
- For more details, refer to Launch Configuration Create.
Auto-Scaling Group
Launch Configuration is used as a pre-configuration template for creating servers. By creating an Auto-Scaling Group, you can adjust and manage the number of servers. The main features are as follows.
- Launch Configuration: A Configuration template used to create a Virtual Server in an Auto-Scaling Group.
- Server Count Setting: Virtual Server Auto-Scaling provides several ways to adjust the number of servers in an Auto-Scaling Group.
- Fixed Server Count Method: When creating an Auto-Scaling Group, this method keeps the default settings using the configured number of servers without any additional schedules or policies. Refer to Create Auto-Scaling Group to set the Min, Desired, and Max server counts.
- Server Count Manual Adjustment Method: In an Auto-Scaling Group, you can increase or decrease the number of servers by modifying the server count to the desired amount. You can choose whether to manually set the desired server count. Please refer to 서버 수 수정하기.
- Schedule reservation method: You can schedule daily, weekly, monthly, or one-time, and set the desired number of servers at the specified time. This is useful when you can predict when to scale the number of servers up or down. If you use the schedule method, please refer to Manage Schedules to add and manage schedules.
- Policy Mode: You can use a policy to dynamically adjust servers. When a monitoring metric exceeds a configured threshold, the number of servers is adjusted. At this time, you can choose one of three methods to adjust the server count: increase or decrease by a specified number, increase or decrease by a specified percentage, or fix the server count to a given value. When servers are started or terminated due to a policy, the monitoring metric (CPU utilization) may temporarily exceed the threshold registered in the policy. However, because this is a brief moment, a cooldown period is set to avoid treating it as an abnormal situation. If you want to use the policy mode, see Managing Policies.
- Load Balancer: Automatically connects and disconnects to the Load Balancer registered in the Auto-Scaling Group whenever a Virtual Server is added or terminated.
- Refer to Auto-Scaling Group Detailed Information for detailed information about the Load Balancer of an Auto-Scaling Group.
Constraints
The constraints of Virtual Server Auto-Scaling are as follows.
| Category | Explanation |
|---|---|
| Number of Virtual Servers per Auto-Scaling Group | 50 or fewer |
| Number of policies per Auto-Scaling Group | 12 or fewer |
| Number of schedules per Auto-Scaling Group | 20 or fewer |
| Number of LB server groups and ports per Auto-Scaling Group | 3 or fewer |
- If the Image you are using is a discontinued standard Image, Scale-out will not work.
If the Image you are using is Custom Image, Scale out will continue to operate correctly even after that version is discontinued. - We recommend replacing the Launch Configuration with the latest version of the Image or a Custom Image before the current Image reaches end of support.
- For detailed information about the OS Image provided by Virtual Server, see OS Image Provided Versions.
Prior Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
2.2.1.1 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by using ServiceWatch, released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a smooth monitoring environment.
Detailed information about ServiceWatch is available in the ServiceWatch Overview.
Virtual Server Auto-Scaling is a service provided for Virtual Servers that offers individual Virtual Server monitoring metrics and monitoring metrics provided by policies based on Cloud Monitoring.
Virtual Server Monitoring Metrics
The table below shows the monitoring metrics of Virtual Server that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
Memory-related metrics are not provided for Windows OS.
| Performance items | Detailed description | unit |
|---|---|---|
| Memory Total [Basic] | bytes of usable memory | bytes |
| Memory Used [Basic] | bytes of currently used memory | bytes |
| Memory Swap In [Basic] | bytes of the replaced memory | bytes |
| Memory Swap Out [Basic] | bytes of the replaced memory | bytes |
| Memory Free [Basic] | bytes of unused memory | bytes |
| Disk Read Bytes [Basic] | Read bytes | bytes |
| Disk Read Requests [Basic] | Number of read requests | cnt |
| Disk Write Bytes [Basic] | write bytes | bytes |
| Disk Write Requests [Basic] | Number of write requests | cnt |
| CPU Usage [Basic] | Average system CPU usage over 1 minute | % |
| Instance State [Basic] | Instance status | state |
| Network In Bytes [Basic] | Received bytes | bytes |
| Network In Dropped [Basic] | Incoming packet drop | cnt |
| Network In Packets [Basic] | Number of received packets | cnt |
| Network Out Bytes [Basic] | sent bytes | bytes |
| Network Out Dropped [Basic] | Transmit packet drop | cnt |
| Network Out Packets [Basic] | Number of transmitted packets | cnt |
Monitoring metrics provided by Cloud Monitoring-based policies
The table below shows the monitoring metrics provided by the policy of a Cloud Monitoring‑based Auto‑Scaling Group. For detailed information on policy settings based on Cloud Monitoring, see 정책 관리하기.
| Performance items | Detailed description | unit |
|---|---|---|
| CPU Usage [Basic] | Average system CPU usage over 1 minute | % |
| Memory Used [Basic] | bytes of currently used memory | bytes |
| Network In Bytes [Basic] | Received bytes | bytes |
| Network In Packets [Basic] | Number of received packets | cnt |
| Network Out Bytes [Basic] | sent bytes | bytes |
| Network Out Packets [Basic] | Number of transmitted packets | cnt |
2.2.1.2 - ServiceWatch Metrics
Virtual Server Auto-Scaling is a service provided for Virtual Servers that offers individual Virtual Server monitoring metrics and monitoring metrics supplied by ServiceWatch-based policies.
Virtual Server Monitoring Metrics
The basic metrics provided by Virtual Server can be found in ServiceWatch > Virtual Server Basic Metrics.
ServiceWatch monitoring metrics provided by the Auto-Scaling Group policy
The table below shows the ServiceWatch monitoring metrics provided by the Auto-Scaling Group policy. For detailed information on configuring Auto-Scaling Group policies, see Managing Policies.
| Performance items | Detailed description | unit |
|---|---|---|
| CPU Usage | CPU usage | Percent |
| Network In Bytes | Received bytes on the network interface | Bytes |
| Network In Packets | Number of packets received on the network interface | Count |
| Network Out Bytes | Data transmitted on the network interface (bytes) | Bytes |
| Network Out Packets | Number of packets transmitted on the network interface | Count |
2.2.2 - How-to guides
Users can create the service by entering the required information for an Auto-Scaling Group and selecting detailed options through the Samsung Cloud Platform Console.
Create Auto-Scaling Group
You can create and use the Auto-Scaling Group service from the Samsung Cloud Platform Console.
To create an Auto-Scaling Group, follow these steps.
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
On the Auto-Scaling Group List page, click the Create Auto-Scaling Group button. You will be taken to the Create Auto-Scaling Group page.
On the Auto-Scaling Group Creation page, enter the information required to create the service.
- In the Launch Configuration area, select the Launch Configuration.
- Launch Configuration creation button can be clicked to create a new Launch Configuration.
- Enter or select the required information in the Service Information Input area.
Category Whether requiredDetailed description Auto-Scaling Group name Required Auto-Scaling Group name - Manage servers of the same type and purpose as a group
Server name Required Server name to be created within the Auto-Scaling Group - The server name is automatically assigned as a combination of the entered server name and a sequence, serving as an identifier to distinguish servers created within the Auto-Scaling Group.
Number of servers Required Number of servers to create in the Auto-Scaling Group - Enter a value between 0 and 20 (Min≤Desired≤Max)
- Min: Set the minimum number of servers the Auto-Scaling Group should maintain
- Desired: Set the target number of servers within the Auto-Scaling Group; also indicates the number of servers initially created when the Auto-Scaling Group is created
- Max: Set the maximum number of servers the Auto-Scaling Group can maintain
- After creating the Auto-Scaling Group, you can adjust the settings using the Edit button. For details, see Modify Server Count
Desired server count manual setting Selection Select whether to manually change the Desired number of servers - Even after creating the Auto-Scaling Group, configure it via the Edit button. For details, refer to Manually edit Desired server count
Network Settings > Network Settings Required Network settings for Auto-Scaling Group - Select the desired VPC and standard Subnet
- IP can only be auto-generated.
- When you select local Subnet, you can choose the desired local Subnet, and IP can only be auto-generated
Network Settings > Security Group Selection To allow required connections, you need to configure a Security Group - If you do not configure a Security Group, all inbound and outbound traffic will be blocked according to the default rule (Any/Deny)
- For Linux servers, allow SSH traffic
- For Windows servers, allow RDP traffic
- Even after creating an Auto-Scaling Group, configure it using the modify button. For details, refer to Configure Security Group
Load Balancer Selection Connect the Auto-Scaling Group to a Load Balancer - Register the Auto-Scaling Group’s servers as members of the LB server group
- LB server group: Select a LB server group that exists in the chosen VPC
- Port: Enter a value between 1 and 65,534
- Press the + button to add an LB server group (up to a total of three LB server groups and ports are allowed)
- LB server groups that use Weighted Round Robin or Weighted Least Connection load balancing cannot be selected
- Draining Timeout value: After checking Draining Timeout as Enabled, you can set the Draining Timeout value
- Draining Timeout: The waiting period before removing a server from the Load Balancer
- Since sessions may remain connected to the server, setting a Draining Timeout and waiting allows safe session termination
- If the Load Balancer is unused, Draining Timeout cannot be set
- The default is 300 seconds; you can enter a value from 1 second up to 3,600 seconds.
- Draining Timeout: The waiting period before removing a server from the Load Balancer
- Changes can be made after creating the Auto-Scaling Group; for details, see Using Auto-Scaling Group Load Balancer
Table. Auto-Scaling Group service information input items - In the Scaling policy setting area, set the scaling policy.
- For detailed information on policy settings, refer to Add Policy.
Category RequiredDetailed description Current setting Selection Set scaling policy now - Add Policy button click shows policy information input fields
Set later Selection After creating an Auto-Scaling Group, set policies on the detail information page Table. Auto-Scaling Group scaling policy configuration items
- For detailed information on policy settings, refer to Add Policy.
- In the Notification Settings area, configure the notification recipients and notification method.
- For detailed information on notification settings, see Add Notification.
Category Required?Detailed description Current setting Selection Set the notification recipients and notification method now - Click the Add Notification button to open the Add Notification popup
- For detailed information about notification settings, see the details
- In the notification recipients list, click the Edit button to modify the notification information
Set later Selection After creating an Auto-Scaling Group, set the notification recipients and notification method on the details page. Table. Auto-Scaling Group notification configuration items
- For detailed information on notification settings, see Add Notification.
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Status check Selection Check the status of Virtual Server and Load Balancer and replace servers that are Unhealthy - Virtual Server status check: Enabled is the default and cannot be changed
- Load Balancer status check: Enabled only when a Load Balancer is connected in the service information input area
- Grace period: Set the time to defer status checks until the newly added server operates normally
- Enter 0 to disable the status check grace period
tag Selection Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Auto-Scaling Group additional information input fieldsCautionA server that the user changes to Stop is not considered Unhealthy, so even when using the health check feature, the server will not be replaced.
- In the Launch Configuration area, select the Launch Configuration.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- When creation is complete, check the created Auto-Scaling Group on the Auto-Scaling Group list page.
Check detailed information of Auto-Scaling Group
Auto-Scaling Group service allows you to view and edit the full resource list and detailed information. The Auto-Scaling Group Details page is composed of Details, Policies, Schedule, Virtual Server, Load Balancer, Tags, Operation History tabs.
To view detailed information about the Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to view detailed information. You will be taken to the Auto-Scaling Group Details page.
- Auto-Scaling Group Details page displays status information and additional feature information, and consists of Details, Policies, Schedule, Virtual Server, Load Balancer, Tags, Activity History tabs.
Category Detailed description Auto-Scaling Group status Status of the Auto-Scaling Group created by the user - Creating: Creating Auto-Scaling Group
- In Service: Serviceable state
- Scale In: Scale In in progress
- Scale Out: Scale Out in progress
- Cool Down: Cooling down
- Terminating: Terminating Auto-Scaling Group
- Attach to LB: Attaching to Load Balancer
- Detach from LB: Detaching from Load Balancer
Delete Auto-Scaling Group Button to delete Auto-Scaling Group Table. Auto-Scaling Group status information and additional features
- Auto-Scaling Group Details page displays status information and additional feature information, and consists of Details, Policies, Schedule, Virtual Server, Load Balancer, Tags, Activity History tabs.
Detailed Information
Auto-Scaling Group List page lets you view detailed information of the selected resource and modify it if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Auto-Scaling Group name | Auto-Scaling Group name |
| Launch Configuration name | When creating an Auto-Scaling Group, the selected Launch Configuration name
|
| Number of servers | Current number of instances in the Auto-Scaling Group and the configured Min, Desired, Max instance counts
|
| Manually set the desired number of servers | Desired server count manual setting enable/disable
|
| VPC | VPC information of the Auto-Scaling Group |
| General Subnet | General Subnet and NAT IP usage information for the Auto-Scaling Group |
| Local Subnet | Local Subnet of Auto-Scaling Group |
| Security Group | Auto-Scaling Group’s Security Group
|
| Status check | Whether to use the replacement function for Virtual Server and Load Balancer in Unhealthy state
|
Policy
On the Auto-Scaling Group List page, you can view the policy list of the selected resource and, if needed, add or manage policies.
| Category | Detailed description |
|---|---|
| Category | Policy Type
|
| Policy Name | Name for policy-specific categorization |
| Execution conditions | Conditions to trigger the policy
|
| execution unit | Method of executing the policy
|
| Cool down | The waiting time (seconds) when a server is started or terminated due to a policy
|
| More > Edit | Modify the policy information
|
| More > Enable | Enable this policy
|
| More > Disable | Disable the policy
|
Schedule
On the Auto-Scaling Group List page, you can view the schedule list of the selected resource and, if necessary, add or manage schedules.
| Category | Detailed description |
|---|---|
| Name | Schedule name |
| Min | Minimum number of servers set in the schedule |
| Desired | Number of target servers set in the schedule |
| Max | Maximum number of servers set in the schedule |
| period | Schedule execution frequency
|
| Date/Day of Week | Schedule execution date or day of week
|
| Execution time | Schedule execution time |
| time zone | Schedule execution time window |
| status | Schedule status |
| More > Edit | Edit the schedule information |
| More > Activate | Activate this schedule
|
| More > Disable | Deactivate this schedule
|
| Add schedule | Add a new schedule |
| Delete | Delete the selected schedule from the list |
Virtual Server
Auto-Scaling Group List You can view the Virtual Server list of the selected resource on the page.
| Category | Detailed description |
|---|---|
| Server name | If you click the Server Name of the server created in the Auto-Scaling Group
|
| IP | IP assigned to the server |
| Creation date and time | The date and time the server was created |
| status | Result of status check for Virtual Server and Load Balancer
|
Load Balancer
On the Auto-Scaling Group List page, you can view the Load Balancer list of the selected resource, and, if needed, add or manage Load Balancers.
| Category | Detailed description |
|---|---|
| Draining Timeout | Draining Timeout usage
|
| Load Balancer | Load Balancer usage
|
| Load Balancer > Load Balancer name | Load Balancer name to attach to the Auto-Scaling Group |
| Load Balancer > LB server group | LB server group of the Load Balancer
|
| Load Balancer > Port | Port registered as a member in the LB server group |
- The LB server group member information configured in the Auto-Scaling Group can also be viewed in LB Server Group Connected Resources.
- Also, if manual connection/disconnection between the server and the Load Balancer is required, see Add LB Server Group Member.
Notification
Auto-Scaling Group List page allows you to view the notification recipients and notification methods for the selected resource.
| Category | Detailed description |
|---|---|
| Notification recipient | Name of the notification recipient |
| Notification recipient’s email | |
| Create server | Whether to send notifications when a server creation-related alert occurs
|
| Server termination | Whether to send a notification when a server termination-related alert occurs
|
| When the policy execution condition is satisfied | Whether to generate a notification when the policy execution condition is satisfied |
| status | Notification activation status
|
| More > Edit | Edit the notification information |
| Show more > Enable | Enable this notification information
|
| More > Disable | Disable this notification information
|
| Add notification | Add a new notification |
| Delete | Delete the selected notification from the list |
tag
Auto-Scaling Group List page lets you view the tag information of selected resources, and add, modify, or delete them.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
You can view the operation history of the selected resource on the Auto-Scaling Group List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Auto-Scaling Group Managing Resources
If you need to manage a created Auto-Scaling Group, you can perform actions on the Auto-Scaling Group Details page.
Edit Launch Configuration
You can modify the Launch Configuration of an Auto-Scaling Group.
To modify the Launch Configuration of an Auto-Scaling Group, follow these steps.
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group list page.
On the Auto-Scaling Group List page, click the resource you want to edit the Launch Configuration for. You will be taken to the Auto-Scaling Group Details page.
Launch Configuration name. Click the Edit button. The Launch Configuration Edit popup opens. You can view the list of selectable Launch Configurations.
CategoryDetailed description Launch Configuration name Launch Configuration name image Launch Configuration OS Image Server type Launch Configuration server type Block Storage Launch Configuration Block Storage Settings Number of Auto-Scaling Groups Number of Auto-Scailg Groups with Launch Configuration applied View Details Button to view Launch Configuration details Table. Launch Configuration list itemsIn the Launch Configuration Edit popup, select the Launch Configuration to modify, then click the Confirm button. The Launch Configuration Edit Notification popup opens. Check the message in the Launch Configuration Edit Notification popup and click the Confirm button.
Edit server count
You can modify the number of servers in the Auto-Scaling Group.
To modify the number of servers in an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group list page.
- On the Auto-Scaling Group List page, click the resource to edit the server count. You will be taken to the Auto-Scaling Group Details page.
- Click the Edit button for server count. The Edit Server Count popup opens.
- Modify Server Count In the popup window, after entering the required fields, click the Confirm button.
Category RequiredDetailed description Number of servers > Min Required Minimum number of servers to modify - Set the number of servers that the Auto-Scaling Group should maintain at a minimum
Number of servers > Desired Required Target server count to modify - Set the target server count within the Auto-Scaling Group
- Desired server count manual setting is disabled; you cannot modify the Desired server count. To modify the Desired server count, see Desired server count manual setting modification
Number of servers > Max Required Target number of servers to modify - Set the maximum number of servers the Auto-Scailg Group can maintain
Table. Auto-Scailg Group server count modification items
Terminate Virtual Server Created by Auto-Scaling Group
Virtual Servers created in an Auto-Scaling Group can be terminated by clicking the terminate button on the Virtual Server’s detail page or by modifying the server count.
- Be careful, as data cannot be recovered after terminating the service.
- To cancel the service, first disconnect the File Storage and disable the Lock. If the File Storage is connected or a Lock is set, you cannot cancel the Virtual Server.
- If you terminate a Virtual Server created in an Auto-Scaling Group, the associated Load Balancer is automatically detached.
- When a Virtual Server is terminated, the status of the attached Storage is as follows.
- If Delete on termination is not set: the volume will not be deleted even if the Virtual Server is terminated.
- When Delete on termination is set: terminating the Virtual Server deletes the volume. However, if a Snapshot exists, the volume is not deleted even when Delete on termination is set.
- Multi attach volume: It can be deleted only when the server you are deleting is the last remaining server attached to the volume.
Cancel on the Virtual Server detail page
To cancel a Virtual Server on the Virtual Server detail page, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server menu. You will be taken to the Virtual Server List page.
- On the Virtual Server List page, select the Virtual Server created by the Auto-Scaling Group. Navigate to the Virtual Server Details page.
- Click the Cancel Service button on the Virtual Server Details page. A popup confirming the server termination will appear.
- Click the Confirm button. Server termination is complete.
Cancel by adjusting the server count
To cancel a Virtual Server by modifying the server count, follow the steps below.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to terminate the Virtual Server. You will be taken to the Auto-Scaling Group Details page.
- Click the Edit button of the Server Count item. The Server Count Edit popup opens.
- Server Count Edit In the popup window, after reducing the Desired number, click the Confirm button. As the Desired server count is adjusted, the Virtual Server will be terminated.
- If Desired server count manual setting is set to unused, you cannot modify the Desired server count. To modify the Desired server count, see Desired server count manual setting modification.
- When a Virtual Server is terminated, the Desired server count remains unchanged, and scale‑out proceeds according to the Desired check batch.
Modify manual setting of desired server count
You can manually change the Desired server count of the Auto-Scaling Group.
To modify the manual setting of the Desired server count for an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to manually change the Desired server count. You will be taken to the Auto-Scaling Group Details page.
- Click the Edit button for the server count. The Desired server count manual setting popup opens.
- Desired server count manual setting After selecting whether to use it in the popup window, click the Confirm button.
Configure Security Group
You can configure the Security Group of an Auto-Scaling Group.
Follow these steps to configure the Security Group of an Auto-Scaling Group.
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
On the Auto-Scaling Group List page, click the resource to configure the Security Group. You will be taken to the Auto-Scaling Group Details page.
Click the Edit button for Security Group. Security Group Edit popup opens. You can view the list of selectable Security Groups.
Category Detailed description Security Group name Security Group name Table. Security Group list itemsSecurity Group edit In the popup window, after selecting the Security Group, click the Confirm button. Security Group edit notification popup opens. Check the message of the Security Group edit notification popup and click the Confirm button.
Change status check
You can configure it to check the status of Virtual Server and Load Balancer and automatically replace servers that are in an Unhealthy state.
- The Load Balancer status check feature can only be used when a Load Balancer is in use.
- A server that the user changes to Stop is not considered Unhealthy, so even if you use the health check feature, the server will not be replaced.
- Click the All Services > Compute > Virtual Server menu. Go to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Go to the Auto-Scaling Group list page.
- On the Auto-Scaling Group List page, click the resource for which you want to change the Load Balancer health check function. You will be taken to the Auto-Scaling Group Details page.
- Click the Edit button of Status Check. Status Check Edit popup window opens.
- Status Check Edit In the popup, choose whether to enable Load Balancer Status Check.
- After entering the Grace period, click the Confirm button.
- If you do not want to use the grace period, set the grace period to 0.
Manage Additional Information for Auto-Scaling Group
You can set the Load Balancer of an Auto-Scaling Group to enabled and select the LB server group. For an Auto-Scaling Group that is using a Load Balancer, you can change it to disabled.
Modify Load Balancer Draining Timeout
You can set the Load Balancer Draining Timeout of an Auto-Scaling Group.
The Draining Timeout is the time to wait before detaching a server from the Load Balancer.
- Because sessions may remain connected to the server, setting a Draining Timeout and waiting allows you to clean up sessions more safely.
- If the Load Balancer is unused, Draining Timeout cannot be set.
- The default is 300 seconds, and it can be set from a minimum of 1 second up to a maximum of 3,600 seconds.
To set the Load Balancer Draining Timeout of an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
- Auto-Scaling Group List page, click the resource to set the Load Balancer Draining Timeout. You will be taken to the Auto-Scaling Group Details page.
- Click the Load Balancer tab. You will be taken to the Load Balancer list page.
- Click the Edit button for Draining Timeout. The Draining Timeout Edit popup opens.
- Draining Timeout Edit In the popup window, select whether to use Draining Timeout, and enter the Draining Timeout duration (seconds).
- Draining Timeout Edit After verifying the input values in the popup window, click the Confirm button. Draining Timeout Edit Notification popup window opens. Check the message in the notification popup and click the Confirm button.
Using Load Balancer
You can modify the Load Balancer of an Auto-Scaling Group. To configure the Load Balancer of an Auto-Scaling Group, follow these steps.
- When a server in the Auto-Scaling Group is created, it is automatically added as a member of the selected Load Balancer’s LB server group, and when the server is terminated, it is removed from the LB server group’s members.
- If Draining Timeout is used, after waiting for the Draining Timeout (seconds), the server is removed from the LB server group’s members.
- When a Member is separated due to Load Balancer modification, it waits in the Detach from LB state; when a Member is separated due to Scale In, it waits in the Scale In state.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource that will use the Load Balancer. Navigate to the Auto-Scaling Group Details page.
- Click the Load Balancer tab. You will be taken to the Load Balancer list page.
- Click the Edit button of the Load Balancer. The Load Balancer Edit popup opens.
- Load Balancer Edit Please select whether to use it in the popup. Selecting Use allows you to choose a Load Balancer.
Category Detailed description LB server group LB server group name - Select the LB server group that is created in the selected VPC
- LB server groups that use Weighted Round Robin or Weighted Least Connection load balancing cannot be selected
Port Port information of the LB server group - When registering as a member of the LB server group, enter the required port information in the registration details.
- Enter a value between 1 and 65,534
Table. Load Balancer list items- Click the + button to add an LB server group. Up to three are allowed. Click the X button to remove the added Load Balancer.
- Check the Load Balancer list and click the Confirm button. Load Balancer Modification Notification popup opens. Verify the message in the notification popup and click the Confirm button.
- Please be careful, as separating or connecting servers from the Load Balancer may affect the service.
- If Draining Timeout is in use, setting the Load Balancer to unused or removing some of the attached Load Balancers with the X button will not detach immediately. After waiting for the Draining Timeout (seconds), the server is detached from the Load Balancer. At that time, the Auto-Scaling Group remains in the Detach from LB state.
- The LB server group member information configured in the Auto-Scaling Group can also be viewed in LB Server Group Connected Resources.
- Also, if manual connection/disconnection between the server and Load Balancer is required, please refer to Register LB Server Group Member.
Not Using Load Balancer
You can modify the Auto-Scaling Group’s Load Balancer to be unused. To set the Auto-Scaling Group’s Load Balancer to unused, follow these steps.
- Please be careful as there may be service impact when separating or connecting servers from the Load Balancer.
- If Draining Timeout is in use, setting the Load Balancer to unused or removing some of the attached Load Balancers with the X button will not detach immediately. After waiting for the Draining Timeout (seconds), the server is detached from the Load Balancer. At that time, the Auto-Scaling Group remains in the Detach from LB state.
- Click the All Services > Compute > Virtual Server menu. Go to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to change the Load Balancer to unused. You will be taken to the Auto-Scaling Group Details page.
- Click the Load Balancer tab. You will be taken to the Load Balancer list page.
- Click the Edit button of the Load Balancer. The Load Balancer Edit popup opens.
- Load Balancer edit Choose whether to use it in the popup window. If you deselect Use, Load Balancer will no longer be used.
- Use deselection, and click the Confirm button. Load Balancer Modification Notification popup opens. Verify the message in the notification popup and click the Confirm button.
Delete Auto-Scaling Group
Deleting an unused Auto-Scaling Group can reduce operational costs. However, terminating an Auto-Scaling Group may cause the running service to stop immediately, so you should thoroughly consider the impact of service interruption before proceeding with the termination.
To terminate an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to terminate. Navigate to the Auto-Scaling Group Details page.
- Click the Auto-Scaling Group Delete button.
- After the deletion is complete, verify that the resource has been removed on the Auto-Scaling Group List page.
2.2.2.1 - Launch Configuration
To create an Auto-Scaling Group, a Launch Configuration must be created in advance.
Create Launch Configuration
You can create and use the Launch Configuration service in the Samsung Cloud Platform Console.
To create a Launch Configuration, follow these steps.
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Launch Configuration menu. Navigate to the Launch Configuration List page.
On the Launch Configuration list page, click the Create Launch Configuration button. You will be taken to the Create Launch Configuration page.
On the Launch Configurationp Creation page, in the Image and Version Selection area, select the required information and click the Next button.
ReferencePlease refer to the server type in Virtual Server OS Image Provisioning Versions for images selectable in Launch Configuration.Enter the required information in the Service Information Input area of the Launch Configurationp Creation page.
Category Required statusDetailed description Launch Configuration name Required Launch Configuration name - Name used to distinguish the Launch Configuration
Service Type > Server Type Required Launch Configuration server type - Standard: Standard specifications commonly used
- High Capacity: Large-scale server specifications beyond Standard
- Refer to Virtual Server Server Type for selectable server types
Block Storage Required Configure Block Storage according to the purpose of the Launch Configuration - Basic OS: The area where the OS is installed and used
- Enter the size in Units, and the minimum size varies depending on the OS image type
- Alma Linux: Enter a value between 2 and 1,536
- Oracle Linux: Enter a value between 5 and 1,536
- RHEL: Enter a value between 2 and 1,536
- Rocky Linux: Enter a value between 2 and 1,536
- Ubuntu: Enter a value between 1 and 1,536
- Windows: Enter a value between 4 and 1,536
- SSD: High‑performance general volume
- HDD: General volume
- SSD/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management System) encryption keys
- Encryption can be applied only at initial creation and cannot be changed afterward
- Performance degradation occurs when using the SSD_KMS disk type
- Enter the size in Units, and the minimum size varies depending on the OS image type
- Additional: Use when extra space beyond the OS area is needed
- After selecting Use, enter the storage type and size
- Click the + button to add storage, or the x button to delete (up to 25 can be added)
- Enter the size in Units, with a value between 1 and 1,536
- Since 1 Unit equals 8 GB, this creates 8 GB to 12,288 GB
- SSD: High‑performance general volume
- HDD: General volume
- SSD/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management System) encryption keys
- Encryption can be applied only at initial creation and cannot be changed afterward
- Performance degradation occurs when using the SSD_KMS disk type
- SSD_MultiAttach: Volume that can be attached to more than one server
- For details on each Block Storage type, see Create Block Storage
Keypair Required Select the user authentication method for the Launch Configuration - Server authentication information for accessing the servers created by generating an Auto-Scaling Group with a Launch Configuration
- New creation: Create a new one if a new Keypair is required
- Refer to Create Keypair for how to create a new Keypair
- Default login account list by OS
- Alma Linux: almalinux
- RHEL: cloud-user
- Rocky Linux: rocky
- Ubuntu: ubuntu
- Windows: sysadmin
File Storage Settings Selection Scale-out/Scale-in can be set to automatically connect File Storage - Volume: After clicking the Select button, choose the Volume to use in the Select File Storage popup
- Up to 5 can be selected
- The selected Volume can be deleted by clicking the X button
Table. Launch Configuration service information input itemsOn the Launch Configuration Creation page, after entering information in the Additional Information Input area, click the Next button.
Category RequiredDetailed description Init Script Selection Script that runs when the server of an Auto Scaling Group using a Launch Configuration starts - Enter within 45,000 bytes
- The init script must be a batch script for Windows, a shell script for Linux, or cloud‑init, depending on the selected image.
tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Launch Configuration additional information input fieldsVerify creation information Check the information you entered on the page and the estimated amount, and click the Create button.
- When creation is complete, verify the created Launch Configuration on the Launch Configuration List page.
View Launch Configuration Details
The Launch Configuration service allows you to view and edit the full list of resources and detailed information. Launch Configuration Details page consists of Details, Tags, Activity Log tabs.
To view detailed information of the Launch Configuration, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Launch Configuration menu. Navigate to the Launch Configuration List page.
- On the Launch Configuration List page, click the resource you want to view detailed information for. You will be taken to the Launch Configuration Details page.
- Launch Configuration Details At the top of the page, status information and additional feature information are displayed, and it consists of Details, Tags, Activity History tabs.
Category Detailed description Launch Configuration status User-created Launch Configuration status - Active: Available
Delete Launch Configuration Delete Launch Configuration button Table. Launch Configuration status information and additional features
- Launch Configuration Details At the top of the page, status information and additional feature information are displayed, and it consists of Details, Tags, Activity History tabs.
Detailed information
Launch Configuration list page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Launch Configuration name | Launch Configuration name |
| image | When creating a Launch Configuration, the selected image name
|
| Number of Auto-Scaling Groups | Number of Auto Scaling Groups using a Launch Configuration |
| Server type | Server type set in Launch Configuration |
| Block Storage | Block Storage information per server configured in the Launch Configuration
|
| Keypair | Server authentication information set in the Launch Configuration
|
| Init Script | The Init Script set in the Launch Configuration
|
| File Storage Settings | File Storage Volume name set in the Launch Configuration
|
tag
Launch Configuration List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
You can view the operation history of the selected resource on the Launch Configuration List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Delete Launch Configuration
Deleting unused Launch Configurations can reduce operational costs. However, terminating a Launch Configuration may cause running services to stop immediately, so you should carefully consider the impact of service interruption before proceeding with the termination.
To delete a Launch Configuration, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Launch Configuration menu. Go to the Launch Configuration List page.
- On the Launch Configuration List page, click the resource to be terminated. Navigate to the Launch Configuration Details page.
- Launch Configuration Delete Click the button.
- After deletion is complete, verify on the Launch Configuration List page that the resource has been removed.
2.2.2.2 - Manage Policy
You can dynamically adjust the number of servers in an Auto-Scaling Group based on monitoring metrics. When the metric exceeds the threshold you set, the server count is adjusted. At that time, you can choose one of three methods to adjust the server count: increase or decrease by a specified number, increase or decrease by a specified percentage, or fix the server count to a given value. When servers are launched or terminated due to a policy, the monitoring metric, such as CPU utilization, may temporarily exceed the threshold registered in the policy. However, because this is a brief moment, a cooldown period is set to avoid treating it as an abnormal condition. You can add and manage policies for an Auto-Scaling Group created in the Samsung Cloud Platform Console.
Add Policy
You can add policies to an Auto-Scaling Group. To add a policy to an Auto-Scaling Group, follow these steps.
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
Auto-Scaling Group List page, click the resource you want to view detailed information for. You will be taken to the Auto-Scaling Group Details page.
Click the Policy Tab. You will be taken to the Policy Tab page.
Click the Add Policy button. The Add Policy popup window opens.
Category RequiredDetailed description Category Required Policy Category - Scale In: return server count
- Scale Out: increase server count
Policy Name Required Name for policy-specific categorization Execution conditions Required Conditions to execute the policy - Statistic: How to calculate the Metric Type
- Average: Average of servers in the Auto-Scaling Group
- Min: Minimum value among servers in the Auto-Scaling Group
- Max: Maximum value among servers in the Auto-Scaling Group
- Metric Type: CPU Usage, Network In(bytes), Network Out(bytes), Network In(Packets), Network Out(Packets)
- Operator:
>=><=<
- Threshold: Threshold corresponding to the Metric Type
- Period: Continuous duration required to trigger the condition (the condition must be continuously satisfied for N minutes for the policy to execute)
execution unit Required Policy execution method - Policy Type: Select the type of policy to execute.
- Increase or decrease the number of servers by a specified count: Increase or decrease the server count to the Target Value
- Increase or decrease the number of servers by a specified ratio: Increase or decrease by the Target Value ratio
- Fix the number of servers to the entered value: Fix the server count according to the Target Value
- Target Value: The number or ratio to apply for the selected Policy Type
cooldown Required The waiting time (seconds) when a server is started or terminated due to a policy - The default is 300 seconds, and it can be set between a minimum of 60 seconds and a maximum of 3,600 seconds.
Table. Add Policy Popup ItemsReferencePolicy > Cooldown Settings
- When a server is started or terminated due to a policy, it waits for the configured cooldown period. Temporarily, the monitoring metric CPU utilization may exceed the threshold defined in the policy. However, because this is a transient moment rather than a condition for adjusting the number of servers, it is not considered an abnormal situation, and the system waits by applying the cooldown time.
guidePolicy execution operates within the configured Min/Max server count range.
- Even if you input values outside the Min/Max server count range—such as increasing, returning, or fixing the number of servers—it operates within the configured Min/Max server count.
- Example: When the minimum number of servers is 3, even if you set the server count fixed to 1, the server count does not drop to 1 and remains at the minimum of 3.
Add Policy After entering the required values in the popup window, click the Confirm button. The added policy can be viewed in the Policy List.
Policy creation example
The following is an explanation of the policy example. Please refer to it when creating a policy.
| Category | Execution Conditions | execution unit | cooldown |
|---|---|---|---|
| Scale Out | Average CPU Usage >= 60% occurs for 1 minute | Increase the server count by the specified number, incrementing by one unit. | 300 seconds |
- If the average CPU usage of the servers in the Auto-Scaling Group exceeds 60% for one minute, a server is added one at a time.
- When a server is added, the cooldown period is 300 seconds, and during this time, no server addition or removal due to policy occurs.
- After the cooldown period ends, the policy execution conditions are checked again.
| Category | Execution Conditions | execution unit | cooldown |
|---|---|---|---|
| Scale In | Min CPU Usage <= 5% occurs for 1 minute | Scale the number of servers up or down by the specified ratio, returning 50%. | 300 seconds |
- If the minimum CPU usage of servers in the Auto-Scaling Group remains below 5% for 1 minute, 50% of the current servers will be terminated.
- When a server is terminated, the cooldown period is 300 seconds, and during this time, no server additions or removals occur due to policy.
- After the cooldown period ends, the policy execution conditions are checked again.
| Category | Execution Conditions | Execution Unit | cooldown |
|---|---|---|---|
| Scale Out | Max CPU Usage >= 90% occurs for 1 minute | Fix the number of servers to 5 based on the entered value | 300 seconds |
- If the maximum CPU usage among the servers in the Auto-Scaling Group exceeds 90% for 1 minute and the current number of servers is less than 5, servers will be created up to a total of 5.
- During server creation, the cooldown period is 300 seconds, and no server additions or removals due to policy occur during the cooldown period.
- After the cooldown period ends, the policy execution conditions are checked again.
Edit Policy
You can modify the policies of an Auto-Scaling Group. To modify the policies of an Auto-Scaling Group, follow these steps.
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
Auto-Scaling Group List page, click the resource to view detailed information. You will be taken to the Auto-Scaling Group Details page.
Click the Policy Tab. You will be taken to the Policy Tab page.
Click the More > Edit button for the policy you want to modify. The Policy Edit Popup opens.
Category RequiredDetailed description Category Required Policy Classification - Scale In: Return server count
- Scale Out: Increase server count
Policy Name Required Name for policy-specific categorization Execution conditions Required Conditions to execute the policy - Statistic: Method to calculate the Metric Type
- Average: Average of servers in the Auto-Scaling Group
- Min: Minimum value among servers in the Auto-Scaling Group
- Max: Maximum value among servers in the Auto-Scaling Group
- Metric Type: CPU Usage, Network In(bytes), Network Out(bytes), Network In(Packets), Network Out(Packets)
- Operator:
>=><=<
- Threshold: Threshold corresponding to the Metric Type
- Period: Continuous duration (in minutes) that triggers the execution condition
execution unit Required Policy execution method - Policy Type: Select the type of policy to execute.
- Increase or decrease the number of servers by a specified count: Increase or reduce the server count to the Target Value
- Increase or decrease the number of servers by a specified ratio: Increase or reduce by the Target Value ratio
- Fix the number of servers to the entered value: Fix the server count according to the Target Value
- Target Value: The number or ratio to execute the selected Policy Type
Cool down Required The waiting time (seconds) when a server is started or terminated due to a policy - The default is 300 seconds, and it can be set from a minimum of 1 second up to a maximum of 3,600 seconds
Table. Policy edit popup itemsEdit Policy In the popup window, after entering the required values, click the Confirm button.
Policy addition and modification constraints
When adding or modifying a policy, constraints exist based on the policy classification, execution conditions, and the scope of those conditions. Below is an example of constraints for the policy. Refer to the constraint examples to add or modify the policy.
Example 1 - Need to check for duplicate registration of policy classification/execution conditions
Policy classification (Scale Out or Scale In) and execution condition (Metric type) cannot be registered redundantly with the same values.
| Policy classification | Policy Name | Execution Condition(Statistic) | Execution condition(Metric type) | Execution condition range |
|---|---|---|---|---|
Scale Out | ScaleOutPolicy | Average | CPU Usage | >= 60% |
If a policy is registered as above, you cannot add a policy with the category (Scale Out) execution condition (Metric type=CPU Usage) or modify it to that condition.
Example 2 - Need to verify the execution condition range for execution conditions (Metric type) and execution conditions (Statistic) according to policy classification
When the policy type (Scale Out or Scale In) differs, duplicate registration of the execution condition range (Comparison operator + Threshold) is not allowed for the same execution condition (Metric type) and execution condition (Statistic).
| Policy classification | Policy Name | Execution condition(Statistic) | Execution condition(Metric type) | Execution condition range |
|---|---|---|---|---|
Scale Out | ScaleOutPolicy | Average | CPU Usage | >= 60% |
If a policy is registered as shown above, you cannot add a policy as below or modify it under the following conditions.
If the average CPU Usage is 60% or higher, a Scale Out policy is already registered; therefore, registering a Scale In policy when the average CPU Usage is 60% or lower would duplicate the 60% execution condition and cannot be added.
| Policy Classification | Policy Name | Execution Condition(Statistic) | Execution condition(Metric type) | Execution condition range |
|---|---|---|---|---|
Scale In | AddUpdatePolicy | Average | CPU Usage | <= 60% |
Example 3 - Need to verify the execution condition range for execution conditions (Metric type) and execution conditions (Statistic) according to policy classification
When the policy classification (Scale Out or Scale In) differs, duplicate registration of the execution condition range (Comparison operator + Threshold) is not allowed for the same execution condition (Metric type) and execution condition (Statistic).
| Policy classification | Policy Name | Execution condition(Statistic) | Execution condition (Metric type) | Execution condition range |
|---|---|---|---|---|
Scale In | ScaleInPolicy | Average | CPU Usage | <= 10% |
If a policy is registered as shown above, you cannot add a policy as below or modify it under the following conditions.
When the average CPU Usage is 10% or less, a Scale In policy is already registered; therefore, if the average CPU Usage is less than 60% / 60% or less / 10% or more / exceeds 9%, you cannot register a Scale Out policy because the execution condition ranges would overlap.
| Policy classification | Policy Name | Execution Condition(Statistic) | Execution condition(Metric type) | Execution condition range |
|---|---|---|---|---|
Scale Out | AddUpdatePolicy1 | Average | CPU Usage | < 60% |
Scale Out | AddUpdatePolicy2 | Average | CPU Usage | <= 60% |
Scale Out | AddUpdatePolicy3 | Average | CPU Usage | >= 10% |
Scale Out | AddUpdatePolicy4 | Average | CPU Usage | > 9% |
Example 4 - Execution conditions (Metric type) and execution conditions (Statistic) can be registered according to the execution condition range based on policy classification
If the policy type (Scale Out or Scale In) differs, you can register when the execution condition (Metric type) is the same but the execution condition (Statistic) is different, or when the execution condition range (Comparison operator + Threshold) does not overlap.
| Policy classification | Policy Name | Execution Condition(Statistic) | Execution condition (Metric type) | Execution Condition Range |
|---|---|---|---|---|
Scale Out | ScaleOutPolicy | Average | CPU Usage | >= 60% |
If a policy is already registered as shown above, you can add a policy as below or modify it with the following conditions. Registration is possible when the execution condition ranges do not overlap, or when the execution condition (Statistic) differs.
| Policy classification | Policy Name | Execution Condition(Statistic) | Execution condition (Metric type) | Execution condition range |
|---|---|---|---|---|
Scale In | AddUpdatePolicy1 | Average | CPU Usage | <= 10% |
Scale In | AddUpdatePolicy2 | Min | CPU Usage | <= 60% |
Delete Policy
You can delete a policy of an Auto-Scaling Group. To delete a policy of an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
- Auto-Scaling Group List page: click the resource you want to view details for. You will be taken to the Auto-Scaling Group Details page.
- Click the Policy Tab. You will be taken to the Policy Tab page.
- Select the policy to delete and click the Delete button. The Policy Deletion Confirmation popup opens.
- Policy Deletion Confirmation Check the popup window and click the Confirm button.
2.2.2.3 - Manage Schedule
You can schedule reservations daily, weekly, monthly, or one-time, and set the desired number of servers at the specified time. This is useful when you can predict when you need to decrease or increase the number of servers.
Add schedule
You can add a schedule to an Auto-Scaling Group. To add a schedule to an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
- Auto-Scaling Group List page, click the resource you want to view detailed information for. You will be taken to the Auto-Scaling Group Details page.
- Click the Schedule Tab. You will be taken to the Schedule Tab page.
- Click the Add Schedule button. The Add Schedule popup window opens.
Category requiredDetailed description Schedule name Required Name to distinguish by schedule Select server count Required Select the number of servers to adjust when executing the schedule - Min: The minimum number of servers the Auto-Scailg Group should maintain
- Desired: The target number of servers within the Auto-Scailg Group
- Max: The maximum number of servers the Auto-Scailg Group can maintain
Enter the number of servers Required Enter the value for the selected number of servers - Min value: Enter a value between 0 and 50. (Min≤Desired≤Max)
- Desired value: Enter a value between 0 and 50. (Min≤Desired≤Max)
- Max value: Enter a value between 0 and 50. (Min≤Desired≤Max)
Period Required Schedule execution frequency - Daily: You can set the Start date, End date, and Permanent options for a daily schedule. You can also set the Time and Time zone
- Weekly: You can set the Start date, End date, Permanent options, and the Time and Time zone. You can also select the Day of week on which the weekly schedule will run.
- Monthly: You can set the Start date, End date, Permanent options, and the Time and Time zone. You can also enter the Date on which the monthly schedule will run
- One-time: You can set the Time and Time zone. You can also set the Date on which the one-time schedule will run
Start date Selection Set schedule start date - Cannot set a date earlier than the current date. The default is the current date.
End date Selection Set schedule end date - Cannot set a date earlier than the current date. The default is the current date plus 7 days.
permanent Selection When configuring permanently, set the schedule end date to 9999-12-31 time Required Schedule execution time setting - Can be set in 30‑minute increments. Times earlier than the current date or current time cannot be set
time zone Required Schedule execution time zone (example: Asia/Seoul (GMT +09:00)) day of the week Required When Period is set to Weekly, select the Day of the week to execute the schedule Date Required - When Period is set to Monthly, enter the Date on which the schedule will run
- Enter one or more values from -31 to 31, excluding 0. (Example: 3,4,5)
- When Period is set to Once, set the Date on which the schedule will run
- Setting a date earlier than the current date is not allowed. The default is the current date.
Table. Schedule addition popup items - Add Schedule After entering the required values in the popup window, click the Confirm button.
- Add Schedule Confirmation After checking the message in the popup window, click the Confirm button.
If you select the schedule frequency as monthly, you must enter the schedule execution date, Date. Refer to the information below to register the schedule.
- If you input a number greater than 0, it represents the day of the month.
- Example: If you enter 1, you get August 1, September 1, …, December 1
- If you enter a number less than 0, the calculation starts from the end of each month.
- Entering -1 means the last day of each month.
- Example: August 31, September 30, …, December 31
- If you enter -2, it means the day before the last day of each month.
- Example: August 30, September 29, …, December 30
- Since the last day of each month varies—31, 30, 29, or 28 days—we allow calculation from the end of the month using negative numbers, as shown above, to handle schedules that need to run on the month’s final day.
- Entering -1 means the last day of each month.
- When the schedule runs, if the Min server count set in the schedule is greater than the Desired server count, or if the Max server count is less than the Desired server count, the Desired server count is also adjusted.
- If there are schedules with overlapping execution times, they may not run correctly. Please try to avoid overlapping execution times as much as possible.
Modify schedule
You can modify the schedule of an Auto-Scaling Group. To modify the schedule of an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource for which you want to view detailed information. You will be taken to the Auto-Scaling Group Details page.
- Click the Schedule Tab. You will be taken to the Schedule Tab page.
- Click the More > Edit button of the schedule you want to modify. The Edit Schedule popup window will open.
Category requiredDetailed description Schedule name Required Name to distinguish by schedule Select number of servers Required Select the number of servers to adjust when executing the schedule - Min: The minimum number of servers the Auto-Scailg Group should maintain
- Desired: The target number of servers within the Auto-Scailg Group
- Max: The maximum number of servers the Auto-Scailg Group can maintain
Enter number of servers Required Enter the value for the selected number of servers - Min value: Enter a value between 0 and 50. (Min≤Desired≤Max)
- Desired value: Enter a value between 0 and 50. (Min≤Desired≤Max)
- Max value: Enter a value between 0 and 50. (Min≤Desired≤Max)
period Required Schedule execution frequency - Daily: You can set the Start Date and End Date, and Permanent setting for the daily schedule. You can also set the Time and Time Zone
- Weekly: You can set the Start Date and End Date, Permanent setting, and the Time and Time Zone. You can also select the Day of Week for the Weekly schedule to run.
- Monthly: You can set the Start Date and End Date, Permanent setting, and the Time and Time Zone. You can also enter the Date for the Monthly schedule to run.
- Once: You can set the Time and Time Zone. You can also set the Date for the Once schedule to run
Start date Selection Set schedule start date - Cannot set a date earlier than the current date. The default is the current date.
End date Selection Set schedule end date - Cannot set a date earlier than the current date. The default is the current date plus 7 days.
Permanent Selection When configuring permanently, set the schedule end date to 9999-12-31. time Required Schedule execution time setting - Can be set in 30‑minute increments. Times earlier than the current date or current time cannot be set
time zone Required Schedule execution time zone (example: Asia/Seoul (GMT +09:00)) day of the week Required When Period is weekly, select the day of the week to run the schedule. Date Required - When Period is set to Monthly, enter the Date on which the schedule will run
- Enter one or more values from -31 to 31, excluding 0. (Example: 3,4,5)
- When Period is set to Once, set the Date on which the schedule will run
- Cannot set a date earlier than the current date. The default is the current date.
Table. Schedule edit popup items - Schedule Edit After entering the required values in the popup window, click the Confirm button.
- Schedule Modification Confirmation After checking the message in the popup window, click the Confirm button.
Delete schedule
You can delete the schedule of an Auto-Scaling Group. To delete the schedule of an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource for which you want to view detailed information. You will be taken to the Auto-Scaling Group Details page.
- Click the Schedule Tab. You will be taken to the Schedule Tab page.
- Select the schedule to delete and click the Delete button. Schedule Deletion Confirmation popup will open.
- Schedule Deletion Confirmation Check the popup window and click the Confirm button.
2.2.2.4 - Manage Notification
You can designate a notification recipient and send alert messages via E‑mail or SMS for specific situations.
- The notification method (E-mail or SMS) can be set on the Notification Settings page by selecting Notification Target as Service > Virtual Server Auto-Scaling.
- For details on editing notification settings, refer to Edit Notification Settings.
Add notification
You can add notifications to an Auto-Scaling Group. To add notifications to an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to which you want to add notification information. You will be taken to the Auto-Scaling Group Details page.
- Click the Notification Tab. You will be taken to the Notification Tab page.
- Click the Add Notification button. The Add Notification popup opens.
- Add Notification After entering the required values in the popup window, click the Confirm button.
Category Detailed description Notification timing Notification timing when an Auto-Scaling Group alert occurs - Server creation, Server termination, Server creation failure, Server termination failure, When policy execution conditions are met
- Multiple selection allowed
Notification recipient User who will receive the notification when an alert occurs - Click the Add Notification Recipient button to select a user
- Only Samsung Cloud Platform users can be selected as recipients
Table. Notification items
- Add Notification Confirmation After checking the message in the popup window, click the Confirm button.
Edit Notification
You can modify the notification settings of an Auto-Scaling Group. To modify the notification settings of an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. Navigate to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to edit the notification information. You will be taken to the Auto-Scaling Group Details page.
- Click the Notification Tab. You will be taken to the Notification Tab page.
- In the notification list, click the More > Edit button for the notification you want to modify. The Edit Notification popup window will open.
- Edit Notification After editing the notification information in the popup window, click the Confirm button.
Category Detailed description Notification timing Notification timing when an Auto-Scaling Group alert occurs - Server creation, Server termination, Server creation failure, Server termination failure, When policy execution conditions are met
- Multiple selection allowed
Table. Notification edit items - Edit Notification Confirmation After checking the message in the popup window, click the Confirm button.
Delete Notification
You can delete notifications for an Auto-Scaling Group. To delete notifications for an Auto-Scaling Group, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Auto-Scaling Group menu. You will be taken to the Auto-Scaling Group List page.
- On the Auto-Scaling Group List page, click the resource to edit the notification information. You will be taken to the Auto-Scaling Group Details page.
- Click the Notification Tab. You will be taken to the Notification Tab page.
- In the notification list, select the notification you want to delete, then click the Delete button. The Delete Notification Confirmation popup will open.
- Delete Notification Confirmation Review the popup window and click the Confirm button.
2.2.3 - API Reference
2.2.4 - CLI Reference
2.2.5 - Release Note
Virtual Server Auto-Scaling
- The Virtual Server and Load Balancer status check feature has been added.
- Check the status of Virtual Server and Load Balancer and automatically replace servers that are in an Unhealthy state.
- You can attach File Storage to a Launch Configuration.
- When creating a Launch Configuration, you can attach up to five File Storage Volumes.
- You can monitor data by integrating with the ServiceWatch service.
- The termination feature for Virtual Servers created in an Auto-Scaling Group has been improved.
- When a Virtual Server is terminated, the Load Balancer is automatically detached.
- The Desired server count remains unchanged, and scale-out is performed according to the Desired check batch.
- Added a notification feature to Virtual Server Auto-Scaling.
- You can add notification settings in the creation or detail screen of an Auto-Scaling Group.
- You can set scaling policies when creating an Auto-Scaling Group.
- Added a Metric Type to the Auto-Scaling Group policy.
- Add: Memory Usage, Network In(bytes), Network Out(bytes), Network In(Packets), Network Out(Packets)
- You can set the Draining Timeout when connecting to a Load Balancer.
- In an Auto-Scaling Group, up to 50 Virtual Servers can be connected, and up to 3 LB server groups and ports can be attached.
- Virtual Server Auto-Scaling feature change
- It will be released in conjunction with the Load Balancer service launching in February 2025.
- The NAT configuration feature has been added to the Auto-Scaling Group.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Virtual Server Auto-Scaling creates an Auto-Scaling Group through a Launch Configuration and monitors and manages the servers.
- Provides a scheduling method that allows setting the desired number of servers at a specified time, and a policy method that adjusts the number of servers based on CPU utilization.
2.3 - GPU Server
2.3.1 - Overview
Service Overview
GPU Server is a virtualized computing service that lets you freely allocate and use infrastructure resources such as CPU, GPU, and memory provided by the server, without having to purchase them individually, and allocate as much as needed at the required time. It is suitable for tasks that require fast computation speed, such as AI model experimentation, prediction, and inference in a cloud environment, and you can flexibly select and use resources with optimized performance based on the type and scale of the work. The GPU Server provides the following features.
Provided Features
- GPU Server Management: Through a web-based console, users can directly Self Service create, delete, and modify GPU Server provisioning, monitoring, and billing.
- Product offerings by GPU quantity: Depending on the project’s purpose and scale, you can freely select the number of H100/A100 GPUs to configure a virtual server.
- High‑Performance GPU Provision: We provide a high‑performance GPU server at physical‑server level using a pass‑through method.
- Storage Connection: Provides additional attached storage besides the OS disk. * You can connect and use Block Storage, File Storage, and Object Storage.
- Strong Security Application: Use the Security Group service to control inbound/outbound traffic exchanged with the external internet or other VPC(Virtual Private Cloud), securely protecting the server.
- Monitoring: You can view monitoring information such as the status of computing resources—including CPU, Memory, Disk, and GPU—through the Cloud Monitoring service.
- Network Configuration Management: The server’s subnet/IP can be easily changed from the values set at initial creation. * NAT IP provides a management feature that lets you enable or disable it as needed.
- Key Pair method: To ensure a secure OS access method, we provide a Key Pair method instead of ID/PW login.
- Image Management: You can create and manage Custom Images, and it provides sharing functionality between projects.
- ServiceWatch Service Integration Offering: You can monitor data through the ServiceWatch service.
Component
GPU Server provides GPUs, NVSwitch, and NVLink on top of virtualized computing resources.
- NVSwitch can only be enabled and used for instance types that allocate eight GPUs on a single GPU server.
Specifications by GPU Type
GPU (Graphic Processing Unit) performs the calculations needed to create images that compose the computer screen, and because it is specialized for parallel processing, it can handle large amounts of data quickly, processing large-scale parallel operations such as artificial intelligence (AI) and data analysis.
The following are the specifications of the GPU Types offered by the GPU Server service.
| Category | A100 Type | H100 Type | B300 Type |
|---|---|---|---|
| GPU Architecture | NVIDIA Ampere | NVIDIA Hopper | NVIDIA Blackwell Ultra |
| GPU Memory | 80 GiB | 80 GiB | 268 GiB |
| GPU Transistors | 54 billion 7N TSMC | 80 billion 4N TSMC | 208 billion 4NP TSMC |
| FP16 Tensor Core (Dense) | 312 TFLOPs | 989 TFLOPs | 2.25 PFLOPs |
| FP8 Tensor Core (Dense) | Not supported | 1,979 TFLOPs | 4.5 PFLOPs |
| FP4 Tensor Core (Dense) | Unsupported | Not supported | 13.5 PFLOPs |
| GPU Memory Bandwidth | 2,039 GB/s HBM2e | 3,352 GB/s HBM3 | 8 TB/s HBM3e |
| NVLink performance | NVLink 3 | NVLink 4 | NVLink 5 |
| NVLink Signaling Rate | 25 GB/s (x12) | 25 GB/s (x18) | 50 GB/s (x18) |
| NVSwitch GPU-to-GPU bandwidth | 600 GB/s | 900 GB/s | 1.8 TB/s |
| Total NVSwitch aggregate bandwidth | 4.8 TB/s | 7.2 TB/s | 14.4 TB/s |
Server type
The server types offered by the GPU Server are as follows. For detailed information about the server types provided by GPU Server, refer to GPU Server 서버 타입.
| Category | Server type | CPU vCore | Memory(GB) | Number of GPUs |
|---|---|---|---|---|
| GPU-A100-1 | g1v16a1 | 16 | 234 | 1 |
| GPU-A100-1 | g1v32a2 | 32 | 468 | 2 |
| GPU-A100-1 | g1v64a4 | 64 | 936 | 4 |
| GPU-A100-1 | g1v128a8 | 128 | 1,872 | 8 |
| GPU-H100-2 | g2v12h1 | 12 | 234 | 1 |
| GPU-H100-2 | g2v24h2 | 24 | 468 | 2 |
| GPU-H100-2 | g2v48h4 | 48 | 936 | 4 |
| GPU-H100-2 | g2v96h8 | 96 | 1,872 | 8 |
| GPU-B300-3 | g3v16b1 | 16 | 480 | 1 |
| GPU-B300-3 | g3v32b2 | 32 | 960 | 2 |
| GPU-B300-3 | g3v64b4 | 64 | 1,920 | 4 |
| GPU-B300-3 | g3v128b8 | 128 | 3,840 | 8 |
OS and GPU driver version
The operating systems (OS) supported by the GPU Server are as follows. Note that GPUs of type B300 are supported only from a specific GPU version onward, so please be careful when selecting images.
| OS | OS version | GPU driver version | Server type classification |
|---|---|---|---|
| Ubuntu | 24.04 | 580.126.20 | GPU-B300-3, GPU-H100-2, GPU-A100-1 |
| Ubuntu | 24.04 | 570.195.03 | GPU-H100-2, GPU-A100-1 |
| Ubuntu | 22.04 | 535.183.06 | GPU-H100-2, GPU-A100-1 |
| RHEL | 9.6 | 580.126.20 | GPU-B300-3, GPU-H100-2, GPU-A100-1 |
| RHEL | 8.10 | 580.126.20 | GPU-B300-3, GPU-H100-2, GPU-A100-1 |
| RHEL | 8.10 | 535.183.06 | GPU-H100-2, GPU-A100-1 |
Preceding Service
This is a service that must be installed in advance before creating this service. Please prepare by referring to the user guide provided in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
2.3.1.1 - Server type
GPU Server server type
GPU servers are categorized by the GPU type they provide, and the GPU used in a GPU server is determined by the server type selected when creating the GPU server. Please select the server type based on the specifications of the application you want to run on the GPU server.
The server types supported by the GPU Server are as follows.
GPU-H100-2 g2v12h1
Category | example | Detailed description |
|---|---|---|
| Server type | GPU-H100-2 | Provided server type classification
|
| Server specifications | g2 | Provided server type classification and generation
|
| Server specifications | v12 | Number of vCores
|
| Server specifications | h1 | GPU type and quantity
|
g1 server type
The g1 server type is a GPU Server that uses the NVIDIA A100 Tensor Core GPU, suitable for high-performance applications.
- Up to 8 NVIDIA A100 Tensor Core GPUs provided
- Equipped with 6,912 CUDA cores and 432 Tensor cores per GPU
- Supports up to 128 vCPUs and 1,920 GB of memory
- Networking speed up to 40 Gbps
- 600 GB/s GPU and NVIDIA NVSwitch P2P communication
| Category | Server type | GPU | CPU | Memory | GPU Memory | Network Bandwidth |
|---|---|---|---|---|---|---|
| GPU-A100-1 | g1v16a1 | 1 | 16 vCore | 234 GB | 80 GiB | Maximum 20 Gbps |
| GPU-A100-1 | g1v32a2 | 2 | 32 vCore | 468 GB | 160 GiB | Up to 20 Gbps |
| GPU-A100-1 | g1v64a4 | 4 | 64 vCore | 936 GB | 320 GiB | Maximum 40 Gbps |
| GPU-A100-1 | g1v128a8 | 8 | 128 vCore | 1,872 GB | 640 GiB | Maximum 40 Gbps |
g2 server type
The g2 server type is a GPU Server that uses the NVIDIA H100 Tensor Core GPU, making it suitable for high-performance applications.
- Up to 8 NVIDIA H100 Tensor Core GPUs provided
- Equipped with 16,896 CUDA cores and 528 Tensor cores per GPU
- Supports up to 96 vCPUs and 1,920 GB of memory
- Networking speed up to 40 Gbps
- 900 GB/s GPU and NVIDIA NVSwitch P2P communication
| Category | Server type | GPU | CPU | Memory | GPU Memory | Network Bandwidth |
|---|---|---|---|---|---|---|
| GPU-H100-2 | g2v12h1 | 1 | 12 vCore | 234 GB | 80 GiB | Up to 20 Gbps |
| GPU-H100-2 | g2v24h2 | 2 | 24 vCore | 468 GB | 160 GiB | Up to 20 Gbps |
| GPU-H100-2 | g2v48h4 | 4 | 48 vCore | 936 GB | 320 GiB | Maximum 40 Gbps |
| GPU-H100-2 | g2v96h8 | 8 | 96 vCore | 1,872 GB | 640 GiB | Maximum 40 Gbps |
g3 server type
The g3 server type is a GPU Server that uses the NVIDIA B300 Tensor Core GPU, making it suitable for high-performance applications.
- Up to 8 NVIDIA B300 Tensor Core GPUs provided
- Equipped with 20,480 CUDA cores and 640 Tensor cores per GPU
- Supports up to 128 vCPUs and 3,840 GB of memory.
- Maximum 40 Gbps networking speed
- 1.8 TB/s GPU and NVIDIA NVSwitch P2P communication
| Category | Server type | GPU | CPU | Memory | GPU Memory | Network Bandwidth |
|---|---|---|---|---|---|---|
| GPU-B300-3 | g3v16b1 | 1 | 16 vCore | 480 GB | 268 GiB | Up to 20 Gbps |
| GPU-B300-3 | g3v32b2 | 2 | 32 vCore | 960 GB | 536 GiB | Up to 20 Gbps |
| GPU-B300-3 | g3v64b4 | 4 | 64 vCore | 1,920 GB | 1,072 GiB | Up to 40 Gbps |
| GPU-B300-3 | g3v128b8 | 8 | 128 vCore | 3,840 GB | 2,144 GiB | Maximum 40 Gbps |
2.3.1.2 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by leveraging ServiceWatch released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a seamless monitoring environment.
If you are collecting metrics and logs through the Cloud Monitoring Agent, you need to switch to the ServiceWatch Agent.
For detailed information about ServiceWatch, please refer to ServiceWatch Overview.
Detailed information about ServiceWatch Agent can be found in the ServiceWatch Agent.
GPU Server Monitoring Metrics
The table below shows the monitoring metrics of the GPU server that can be viewed through Cloud Monitoring.
Even without installing the Agent, it provides basic monitoring metrics and the table below. Please check the GPU Server monitoring metrics (provided by default). Additionally, the metrics that can be viewed by installing the Agent are in the table. Please refer to the additional monitoring metrics for GPU Server (Agent installation required).
For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
| Performance Item Name | Explanation | unit |
|---|---|---|
| Memory Total [Basic] | bytes of usable memory | bytes |
| Memory Used [Basic] | bytes of currently used memory | bytes |
| Memory Swap In [Basic] | bytes of the replaced memory | bytes |
| Memory Swap Out [Basic] | bytes of the replaced memory | bytes |
| Memory Free [Basic] | bytes of unused memory | bytes |
| Disk Read Bytes [Basic] | Read bytes | bytes |
| Disk Read Requests [Basic] | Number of read requests | cnt |
| Disk Write Bytes [Basic] | write bytes | bytes |
| Disk Write Requests [Basic] | Number of write requests | cnt |
| CPU Usage [Basic] | Average system CPU usage over 1 minute | % |
| Instance State [Basic] | Instance status | state |
| Network In Bytes [Basic] | Received bytes | bytes |
| Network In Dropped [Basic] | Incoming packet drop | cnt |
| Network In Packets [Basic] | Number of received packets | cnt |
| Network Out Bytes [Basic] | sent bytes | bytes |
| Network Out Dropped [Basic] | Transmit packet drop | cnt |
| Network Out Packets [Basic] | Number of transmitted packets | cnt |
| Performance Item Name | Explanation | unit |
|---|---|---|
| GPU Count | Number of GPUs | cnt |
| GPU Memory Usage | Memory usage rate | % |
| GPU Memory Used | Memory usage | MB |
| GPU Temperature | GPU temperature | ℃ |
| GPU Usage | utilization | % |
| GPU Usage [Avg] | Overall average GPU utilization (%) | % |
| GPU Power Cap | Maximum power capacity of the GPU | W |
| GPU Power Usage | Current GPU power usage | W |
| GPU Memory Usage [Avg] | GPU Memory Uti. AVG | % |
| GPU Count in use | Number of GPUs in use by jobs on the node | cnt |
| Execution Status for nvidia-smi | Result of running the nvidia-smi command | status |
| Core Usage [IO Wait] | Ratio of CPU time spent in wait state (disk wait) | % |
| Core Usage [System] | Proportion of CPU time spent in kernel space | % |
| Core Usage [User] | Proportion of CPU time spent in user space | % |
| CPU Cores | Number of CPU cores on the host | cnt |
| CPU Usage [Active] | Percentage of CPU time used, excluding Idle and IOWait states | % |
| CPU Usage [Idle] | It is the proportion of CPU time spent in idle state. | % |
| CPU Usage [IO Wait] | The proportion of CPU time spent in a waiting state (disk wait). | % |
| CPU Usage [System] | Percentage of CPU time used by the kernel | % |
| CPU Usage [User] | Percentage of CPU time used in user space. | % |
| CPU Usage/Core [Active] | Percentage of CPU time used other than Idle and IOWait states | % |
| CPU Usage/Core [Idle] | It is the proportion of CPU time spent in idle state. | % |
| CPU Usage/Core [IO Wait] | This is the proportion of CPU time spent in a waiting state (disk wait). | % |
| CPU Usage/Core [System] | Percentage of CPU time used by the kernel | % |
| CPU Usage/Core [User] | Percentage of CPU time used in user space. | % |
| Disk CPU Usage [IO Request] | Proportion of CPU time during which I/O requests to the device were executed | % |
| Disk Queue Size [Avg] | The average queue length of requests executed for the device. | num |
| Disk Read Bytes | The number of bytes read per second from the device. | bytes |
| Disk Read Bytes [Delta Avg] | Average of system.diskio.read.bytes_delta for individual disks | bytes |
| Disk Read Bytes [Delta Max] | Maximum system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta Min] | Minimum system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta Sum] | Sum of the system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta] | Delta of the system.diskio.read.bytes value for each disk | bytes |
| Disk Read Bytes [Success] | Total number of bytes successfully read. | bytes |
| Disk Read Requests | Number of read requests to the disk device per second | cnt |
| Disk Read Requests [Delta Avg] | Average of the system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Max] | Maximum system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Min] | Minimum of system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Sum] | Sum of system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Success Delta] | Delta of system.diskio.read.count for each disk | cnt |
| Disk Read Requests [Success] | Total number of successful reads | cnt |
| Disk Request Size [Avg] | The average size of requests executed on the device (unit: sectors). | num |
| Disk Service Time [Avg] | Average service time (milliseconds) of input requests executed on the device. | ms |
| Disk Wait Time [Avg] | Average time taken for requests executed on the supported device. | ms |
| Disk Wait Time [Read] | Average disk wait time | ms |
| Disk Wait Time [Write] | Average disk wait time | ms |
| Disk Write Bytes [Delta Avg] | Average of system.diskio.write.bytes_delta for each disk | bytes |
| Disk Write Bytes [Delta Max] | Maximum system.diskio.write.bytes_delta of individual disks | bytes |
| Disk Write Bytes [Delta Min] | Minimum of system.diskio.write.bytes_delta for individual disks | bytes |
| Disk Write Bytes [Delta Sum] | Sum of system.diskio.write.bytes_delta for individual disks | bytes |
| Disk Write Bytes [Delta] | Delta of the system.diskio.write.bytes value for each disk | bytes |
| Disk Write Bytes [Success] | Total number of bytes successfully written. | bytes |
| Disk Write Requests | Number of write requests to the disk device per second | cnt |
| Disk Write Requests [Delta Avg] | Average of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Max] | Maximum system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Min] | Minimum of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Sum] | Sum of the system.diskio.write.count_delta of individual disks | cnt |
| Disk Write Requests [Success Delta] | Delta of system.diskio.write.count for each disk | cnt |
| Disk Write Requests [Success] | Total number of successful writes | cnt |
| Disk Writes Bytes | It is the number of bytes per second written to the device. | bytes |
| Filesystem Hang Check | filesystem (local/NFS) hang check (normal:1, abnormal:0) | status |
| Filesystem Nodes | It is the total number of file nodes in the file system. | cnt |
| Filesystem Nodes [Free] | It is the total number of available file nodes in the file system. | cnt |
| Filesystem Size [Available] | Disk space (bytes) available to unauthorized users | bytes |
| Filesystem Size [Free] | Available disk space (bytes) | bytes |
| Filesystem Size [Total] | Total disk space (bytes) | bytes |
| Filesystem Usage | Used disk space percentage | % |
| Filesystem Usage [Avg] | Average of individual filesystem.used.pct values | % |
| Filesystem Usage [Inode] | inode usage | % |
| Filesystem Usage [Max] | Maximum among individual filesystem.used.pct | % |
| Filesystem Usage [Min] | minimum among individual filesystem.used.pct | % |
| Filesystem Usage [Total] | - | % |
| Filesystem Used | Used disk space (bytes) | bytes |
| Filesystem Used [Inode] | inode usage | bytes |
| Memory Free | Total amount of available memory (bytes). | bytes |
| Memory Free [Actual] | Actual usable memory (bytes). | bytes |
| Memory Free [Swap] | Available swap memory. | bytes |
| Memory Total | total memory | bytes |
| Memory Total [Swap] | Total swap memory. | bytes |
| Memory Usage | Percentage of used memory | % |
| Memory Usage [Actual] | Percentage of memory actually used | % |
| Memory Usage [Cache Swap] | cached swap usage rate | % |
| Memory Usage [Swap] | Percentage of used swap memory | % |
| Memory Used | used memory | bytes |
| Memory Used [Actual] | Actual memory used (bytes). | bytes |
| Memory Used [Swap] | Swap memory used. | bytes |
| Collisions | Network collision | cnt |
| Network In Bytes | Number of received bytes | bytes |
| Network In Bytes [Delta Avg] | Average of system.network.in.bytes_delta for individual networks | bytes |
| Network In Bytes [Delta Max] | Maximum of system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Min] | Minimum system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Sum] | Sum of system.network.in.bytes_delta for individual networks | bytes |
| Network In Bytes [Delta] | Delta of received byte count | bytes |
| Network In Dropped | Number of deleted packets among incoming packets | cnt |
| Network In Errors | Number of errors during reception | cnt |
| Network In Packets | Number of received packets | cnt |
| Network In Packets [Delta Avg] | Average of system.network.in.packets_delta for each network | cnt |
| Network In Packets [Delta Max] | Maximum of system.network.in.packets_delta for each network | cnt |
| Network In Packets [Delta Min] | Minimum of system.network.in.packets_delta for individual networks | cnt |
| Network In Packets [Delta Sum] | Sum of system.network.in.packets_delta for individual networks | cnt |
| Network In Packets [Delta] | Delta of received packet count | cnt |
| Network Out Bytes | Number of transmitted bytes | bytes |
| Network Out Bytes [Delta Avg] | Average of system.network.out.bytes_delta for each network | bytes |
| Network Out Bytes [Delta Max] | Maximum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta Min] | Minimum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta Sum] | Sum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta] | Delta of transmitted byte count | bytes |
| Network Out Dropped | Number of deleted packets among outgoing packets. | cnt |
| Network Out Errors | Number of errors during transmission | cnt |
| Network Out Packets | Number of transmitted packets | cnt |
| Network Out Packets [Delta Avg] | Average of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Max] | Maximum of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Min] | Minimum of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Sum] | Sum of system.network.out.packets_delta for individual networks | cnt |
| Network Out Packets [Delta] | Delta of transmitted packet count | cnt |
| Open Connections [TCP] | All open TCP connections | cnt |
| Open Connections [UDP] | All open UDP connections | cnt |
| Port Usage | Available port usage rate | % |
| SYN Sent Sockets | Number of sockets in SYN_SENT state (when connecting from local to remote) | cnt |
| Kernel PID Max | kernel.pid_max value | cnt |
| Kernel Thread Max | kernel.threads-max value | cnt |
| Process CPU Usage | Percentage of CPU time consumed by the process since the last update. | % |
| Process CPU Usage/Core | Percentage of CPU time used by the process since the last event. | % |
| Process Memory Usage | Proportion of main memory (RAM) occupied by a process | % |
| Process Memory Used | Resident Set size. The amount of memory a process occupies in RAM. | bytes |
| Process PID | process pid | PID |
| Process PPID | parent process PID | PID |
| Processes [Dead] | Number of dead processes | cnt |
| Processes [Idle] | Number of idle processes | cnt |
| Processes [Running] | Number of running processes | cnt |
| Processes [Sleeping] | Number of sleeping processes | cnt |
| Processes [Stopped] | stopped processes count | cnt |
| Processes [Total] | Total number of processes | cnt |
| Processes [Unknown] | Number of processes with an unsearchable or unknown status | cnt |
| Processes [Zombie] | Zombie processes count | cnt |
| Running Process Usage | process usage rate | % |
| Running Processes | Number of running processes | cnt |
| Running Thread Usage | Thread usage rate | % |
| Running Threads | Total number of threads running in running processes | cnt |
| Context Switches | context switch count (per second) | cnt |
| Load/Core [1 min] | The load over the last 1 minute divided by the number of cores | cnt |
| Load/Core [15 min] | The load over the last 15 minutes divided by the number of cores | cnt |
| Load/Core [5 min] | The load over the last 5 minutes divided by the number of cores | cnt |
| Multipaths [Active] | External storage connection path status = active count | cnt |
| Multipaths [Failed] | External storage connection path status = failed count | cnt |
| Multipaths [Faulty] | External storage connection path status = faulty count | cnt |
| NTP Offset | measured offset of the last sample (the time difference between the NTP server and the local environment) | num |
| Run Queue Length | Execution queue length | num |
| Uptime | OS uptime (milliseconds). | ms |
| Context Switchies | CPU context switch count (per second) | cnt |
| Disk Read Bytes [Sec] | Number of bytes read from a Windows logical disk in 1 second | cnt |
| Disk Read Time [Avg] | Average data read time (seconds) | sec |
| Disk Transfer Time [Avg] | Disk average wait time | sec |
| Disk Usage | Disk usage | % |
| Disk Write Bytes [Sec] | Number of bytes written in one second on a Windows logical disk | cnt |
| Disk Write Time [Avg] | Average data write time (seconds) | sec |
| Pagingfile Usage | Paging file usage | % |
| Pool Used [Non Paged] | Nonpaged Pool usage in kernel memory | bytes |
| Pool Used [Paged] | Paged Pool usage in kernel memory | bytes |
| Process [Running] | Number of currently running processes | cnt |
| Threads [Running] | Number of currently running threads | cnt |
| Threads [Waiting] | Number of threads waiting for processor time | cnt |
2.3.1.3 - ServiceWatch Metrics
The GPU Server sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals. If detailed monitoring is enabled, you can view data collected at 1‑minute intervals.
- The basic and detailed monitoring of the GPU Server are provided with the same metrics as the Virtual Server, and the namespace is also provided as Virtual Server.
- GPU-related metrics are provided through ServiceWatch Agent, and for instructions on collecting metrics using ServiceWatch Agent, refer to the ServiceWatch Agent guide.
Refer to How-to guides > ServiceWatch Detailed Monitoring Activation for how to enable detailed monitoring of the GPU Server.
Basic Metrics
The following are the basic metrics for the Virtual Server namespace.
The indicators whose names are displayed in bold below are the key indicators selected among the basic indicators provided by Virtual Server. The key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric indicates through the user guide which statistical value is meaningful to view for that metric, and among the meaningful statistics, the statistical values shown in bold text are the primary statistics. In the service dashboard, you can view primary metrics using the primary statistical values.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| Instance State | Instance status display
| None |
|
| CPU Usage | CPU usage | Percent |
|
| Disk Read Bytes | Bytes read from block device (bytes) | Bytes |
|
| Disk Read Requests | Number of read requests on a block device | Count |
|
| Disk Write Bytes | Write capacity (bytes) on block device | Bytes |
|
| Disk Write Requests | Number of write requests on block device | Count |
|
| Network In Bytes | Received bytes (capacity) on the network interface | Bytes |
|
| Network In Dropped | Number of packet drops received on the network interface | Count |
|
| Network In Packets | Number of packets received on the network interface | Count |
|
| Network Out Bytes | Data transmitted on the network interface (bytes) | Bytes |
|
| Network Out Dropped | Number of packet drops transmitted from the network interface | Count |
|
| Network Out Packets | Number of packets transmitted on the network interface | Count |
|
2.3.2 - How-to guides
Users can create the service by entering the required GPU Server information and selecting detailed options through the Samsung Cloud Platform Console.
Creating a GPU Server
You can create and use a GPU Server service from the Samsung Cloud Platform Console.
To create a GPU server, follow the steps below.
Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
On the Service Home page, click the GPU Server Creation button. You will be taken to the GPU Server Creation page.
On the GPU Server Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and Version Selection area.
Category Required statusDetailed description Image Required Select the type of Image provided - Standard: Samsung Cloud Platform standard provided Image
- RHEL, Ubuntu
- Custom: User-created Image
- Kubernetes: Image for Kubernetes
- Ubuntu
Image version Required Select the version of the chosen Image - Provides a list of versions for the offered server Image
- For detailed information about the provided server image, see OS and GPU driver versions
Table. GPU Server image and version selection input fields - Standard: Samsung Cloud Platform standard provided Image
- Service Information Input area, enter or select the required information.
Category Required statusDetailed description Number of servers Required Number of GPU Server servers to create concurrently - Only numeric input is allowed, enter a value between 1 and 100
Service Type > Server Type Required GPU Server server type - Indicates the specifications of a GPU-type server, allowing selection of servers with 1, 2, 4, or 8 GPUs
- For detailed information about the server types provided by GPU Server, refer to GPU Server Server Types
Service Type > Planned Compute Selection Resource status with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, refer to Apply for Planned Compute
Block Storage Required Configure the Block Storage used by the GPU Server according to its purpose - Basic: The area where the OS is installed and used
- Capacity can be entered in units (the minimum capacity varies depending on the OS image type)
- RHEL: Values between 3 and 1,536 can be entered
- Ubuntu: Values between 3 and 1,536 can be entered
- SSD: High‑performance general volume
- HDD: General volume
- SSD/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management System) encryption keys
- Encryption can be applied only at initial creation (cannot be changed after creation)
- Performance degradation occurs when using the SSD_KMS disk type
- SSD_Provisioned: SSD volume with configurable IOPS and throughput
- Capacity can be entered in units (the minimum capacity varies depending on the OS image type)
- Additional: Used when the user needs extra space beyond the OS area
- After selecting Use, enter the storage type and capacity
- To add storage, click the + button (up to 25 can be added); to delete, click the x button
- Capacity can be entered in units, with values between 1 and 1,536
- Since 1 Unit equals 8 GB, this creates 8 GB to 12,288 GB
- SSD: High‑performance general volume
- HDD: General volume
- SSD/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management System) encryption keys
- Encryption can be applied only at initial creation (cannot be changed after creation)
- Performance degradation may occur when using the SSD_KMS disk type
- HDD/SSD_MultiAttach: Volume that can be attached to two or more servers
- SSD_Provisioned: SSD volume with configurable IOPS and throughput
- For details on each Block Storage type, refer to Create Block Storage
- Delete on termination: If Delete on Termination is set to Enabled, the volume is terminated together with the server
- Volumes with existing snapshots are not deleted even if Delete on termination is set to Enabled
- A multi‑attach volume can be deleted only when the server being removed is the last remaining server attached to the volume
Max IOPS Required Enter a maximum IOPS value between 5,000~20,000 - Can be set only when disk type is SSD_Provisioned
Max Throughput Required Enter the maximum Throughput value between 250~1,000 - Disk type can be set only when it is SSD_Provisioned
Table. GPU Server Service Configuration Items - In the Required Information Input area, enter or select the necessary information.
Category required or notDetailed description Server name Required Enter a name to distinguish the server when the selected number of servers is 1 - Set the hostname using the entered server name
- Enter within 63 characters using letters, numbers, spaces, and special characters (
-_)
Server name Prefix Required Enter a Prefix to distinguish each server generated when the selected number of servers is 2 or more - Automatically generated in the form of user input value (prefix) + ‘
-#’
- Enter within 59 characters using letters, numbers, spaces, and special characters (
-,_)
Network Settings > Create New Network Port Required Configure the network where the GPU Server will be installed - Select a pre‑created VPC.
- General Subnet: Select a pre‑created general Subnet
- IP can be set to auto‑generate or manual entry; if manual is chosen, the user can directly input the IP
- NAT: Available only when there is a single server and the VPC is attached to an Internet Gateway. Checking Use enables selection of a NAT IP
- NAT IP: Select a NAT IP
- If no NAT IP is available, click the Create New button to generate a Public IP
- Click the Refresh button to view and select the created Public IP
- Creating a Public IP incurs charges according to the Public IP pricing policy
- Local Subnet (optional): Choose Use for a local Subnet
- It is not a required element for creating the service
- A pre‑created local Subnet must be selected
- IP can be set to auto‑generate or manual entry; selecting Manual allows the user to input the IP directly
- Security Group: Settings required to access the server
- Select: Choose a pre‑created Security Group
- Create New: If no applicable Security Group exists, you can create one separately in the Security Group service
- Up to 5 can be selected
- If no Security Group is set, all connections are blocked by default
- You must configure a Security Group to allow required connections
Network Settings > Existing Network Port Assignment Required Set the network where the GPU server will be installed - Select a pre-created VPC
- General Subnet: Select a pre-created general Subnet and Port
- NAT: Available only when there is a single server and the VPC is connected to an Internet Gateway. When you check to use it, you can select a NAT IP.
- NAT IP: Select a NAT IP
- If there is no NAT IP to select, click the Create New button to generate a Public IP
- Click the Refresh button to view and select the created Public IP
- Local Subnet (optional): Select Use for the local Subnet
- Select a pre-created local Subnet and Port
Keypair Required User authentication methods to use when connecting to the server - New creation: Create a new keypair if one is needed
- Refer to Keypair 생성하기 for how to create a new keypair
- Default login accounts by OS
- RHEL: cloud-user
- Ubuntu: ubuntu
Table. Required input fields for GPU Server - Enter or select the required information in the Additional Information Input area.
Category RequiredDetailed description Lock Selection Lock usage setting - When Lock is enabled, it prevents actions such as server termination, start, and stop from being executed, thereby avoiding malfunctions caused by mistakes
Init script Selection Script executed when the server starts - The init script must be written as a Batch script for Windows, a Shell script for Linux, or cloud‑init, depending on the image type.
- Up to 45,000 bytes can be entered
tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. GPU Server additional information input fields
- Select the required information in the Image and Version Selection area.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the GPU Server List page.
Check GPU Server detailed information
GPU Server service allows you to view and edit the full resource list and detailed information. GPU Server Details page consists of Details, Tags, Job History tabs.
To view detailed information about the GPU Server service, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- On the GPU Server List page, click the resource you want to view details for. You will be taken to the GPU Server Details page.
- GPU Server Details page displays status information and additional feature information, and is composed of Details, Tags, Activity History tabs.
- GPU Server Additional Features for detailed information, please refer to GPU Server Management Additional Features.
Category Detailed description GPU Server status Status of user-created GPU Server - Build: State where the Build command has been received
- Building: Build in progress
- Networking: Server creation networking process
- Scheduling: Server creation scheduling process
- Block_Device_Mapping: Connecting Block Storage during server creation
- Spawning: Server creation process is ongoing
- Active: Available state
- Powering_off: State when a stop request is made
- Deleting: Server deletion in progress
- Reboot_Started: Reboot in progress
- Error: Error state
- Migrating: Server migrating to another host
- Reboot: State where the Reboot command has been received
- Rebooting: Rebooting
- Rebuild: State where the Rebuild command has been received
- Rebuilding: State during Rebuild request
- Rebuild_Spawning: Rebuild process is ongoing
- Resize: State where the Resize command has been received
- Resizing: Resizing in progress
- Resize_Prep: State when a server type change is requested
- Resize_Migrating: Server is migrating to another host while resizing
- Resize_Migrated: Server has completed migration to another host during resizing
- Resize_Finish: Resize completed
- Revert_Resize: Resize or migration of the server failed for some reason. The target server is cleaned up and the original server is restarted
- Shutoff: State when powering off is completed
- Verity_Resize: After Resize_Prep following a server type change request, the server type is confirmed or can be reverted
- Resize_Reverting: State when a server type revert is requested
- Resize_Confirming: State confirming the server’s Resize request
Server control Buttons to change server status - Start: start a stopped server
- Stop: stop a running server
- Restart: restart a running server
Image generation Create a custom user image from the current server image Console log View console logs of the current server - You can view the console logs output by the current server. For more details, see Check console logs.
Create dump Generate a dump of the current server - The dump file is created inside the GPU Server
- For detailed dump creation instructions, refer to Create Dump
Rebuild All data and settings of the existing server are deleted, and a new server is configured - For detailed information, see Execute Rebuild.
Service termination Cancel service button Table. GPU Server status information and additional features
Detailed Information
GPU Server List page lets you view detailed information of the selected resource and edit it if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Server name | Server name |
| Server type | vCPU, memory, GPU information display
|
| image name | Service OS image and version |
| Lock | Indicates whether Lock is used or not
|
| Keypair name | Server authentication information set by the user |
| Planned Compute | Resource status with Planned Compute configured
|
| LLM Endpoint | URL for using LLM
|
| ServiceWatch Detailed Monitoring | When enabled, data monitoring is possible in the ServiceWatch service
|
| Network | Network information of the GPU Server
|
| Local Subnet | Local Subnet information of the GPU Server
|
| Block Storage | Information of Block Storage attached to the server
|
tag
GPU Server List page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the job history of the selected resource on the GPU Server List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Control GPU Server Operation
If you need to control the operation of a created GPU Server resource, you can perform the task on the GPU Server List or GPU Server Details page. You can start, stop, and restart a running server.
Getting Started with GPU Server
You can start a shutoff GPU Server. To start a GPU Server, follow the steps below.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of the GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- On the GPU Server List page, click the resource you want to start among the shutoff servers, and navigate to the GPU Server Details page.
- GPU Server List page allows you to Start each resource via the right More button.
- After selecting multiple servers with checkboxes, you can control multiple servers simultaneously using the Start button at the top.
- GPU Server Details page, click the Start button at the top to start the server. In the Status Display section, verify the updated server status.
- When the GPU Server startup is complete, the server status changes from Shutoff to Active.
- For detailed information about the GPU Server status, refer to GPU Server detailed information.
Stopping the GPU Server
You can stop a running (Active) GPU Server. To stop the GPU Server, follow the steps below.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- On the GPU Server List page, click the resource to stop among the servers that are running (Active), and navigate to the GPU Server Details page.
- On the GPU Server List page, you can Stop each resource via the right More button.
- After selecting multiple servers with checkboxes, you can control multiple servers simultaneously using the Stop button at the top.
- GPU Server Details page, click the Stop button at the top to start the server. Check the changed server status in the Status Display item.
- When the GPU server shutdown is complete, the server status changes from Active to Shutoff.
- For detailed information about the GPU Server status, please refer to GPU Server Detailed Information.
Restart GPU Server
You can restart the created GPU Server. To restart the GPU Server, follow the steps below.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- On the GPU Server List page, click the resource to restart and go to the GPU Server Details page.
- On the GPU Server list page, you can restart each resource using the right More button.
- After selecting multiple servers with checkboxes, you can control multiple servers simultaneously using the Restart button at the top.
- GPU Server Details on the page, click the Restart button at the top to start the server. Check the updated server status in the Status Display field.
- During a GPU Server restart, the server status goes through Rebooting and finally changes to Active.
- For detailed information about the GPU Server status, refer to GPU Server detailed information.
GPU Server resource management
If you need server control and management functions for the created GPU Server resources, you can perform the tasks on the GPU Server Resource List or GPU Server Details page.
Create Image
You can create an image of a running GPU server.
This guide explains how to create a custom user image from the image of a running GPU server.
- On the GPU Server List or GPU Server Details page, click the Create Image button to create a user Custom Image.
To create an image of the GPU Server, follow these steps.
Click the All Services > Compute > GPU Server menu. Navigate to the Service Home page of the GPU Server.
On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
On the GPU Server List page, click the resource to create an Image. You will be taken to the GPU Server Details page.
Click the Create Image button on the GPU Server Details page. You will be taken to the Image Creation page.
- Enter the required information in the Service Information Input area.
Category Required statusDetailed description image name Required Enter the name of the image to be created - using English letters, numbers, spaces, and special characters (
-_) within 200 characters
Table. Image service information input fields - using English letters, numbers, spaces, and special characters (
- Enter the required information in the Service Information Input area.
Check the input information and click the Create button.
- When creation is complete, check the created resources on the All Services > Compute > GPU Server > Image List page.
- When you create an Image, the generated Image is stored in the Object Storage used as internal storage. Therefore, Object Storage usage fees are applied.
- Since the file system of an image created from an active GPU server cannot be guaranteed to be intact, it is recommended to stop the server before creating the image.
Enabling detailed monitoring for ServiceWatch
By default, the GPU Server is linked to the basic monitoring of the ServiceWatch and Virtual Server namespaces. You can enable detailed monitoring as needed to identify operational issues more quickly and take action. For detailed information about ServiceWatch, see ServiceWatch Overview.
To enable detailed ServiceWatch monitoring on the GPU Server, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- On the GPU Server List page, click the resource to enable ServiceWatch detailed monitoring. You will be taken to the GPU Server Details page.
- On the GPU Server Details page, click the ServiceWatch detailed monitoring Edit button. You will be taken to the ServiceWatch Detailed Monitoring Edit popup.
- ServiceWatch Detailed Monitoring Edit In the popup window, select Enable, review the instructions, and click the Confirm button.
- On the GPU Server Details page, check the ServiceWatch detailed monitoring items.
Disable detailed monitoring of ServiceWatch
To disable detailed monitoring of ServiceWatch on the GPU Server, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- GPU Server List page, click the resource to disable ServiceWatch detailed monitoring. Navigate to the GPU Server Details page.
- GPU Server Details page, click the ServiceWatch detailed monitoring Edit button. You will be taken to the ServiceWatch detailed monitoring Edit popup.
- ServiceWatch Detailed Monitoring Edit In the popup window, after deselecting Enabled, review the guidance message and click the Confirm button.
- On the GPU Server Details page, view the ServiceWatch detailed monitoring items.
GPU Server Management Additional Features
GPU Server can view Console logs, generate Dumps, and perform Rebuilds for server management. To view Console logs, generate Dumps, or Rebuild a GPU Server, follow the steps below.
Check console log
You can view the current console log of the GPU Server.
To view the console logs of the GPU server, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the GPU Server’s Service Home page.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- On the GPU Server List page, click the resource to view the console log. You will be taken to the GPU Server Details page.
- On the GPU Server Details page, click the Console Log button. You will be taken to the Console Log popup.
- Console Log Verify the console log displayed in the popup window.
Create Dump
To create a dump file on the GPU Server, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- GPU Server List page, click the resource to view detailed information. You will be taken to the GPU Server Details page.
- On the GPU Server Details page, click the Create Dump button.
- The dump file is created inside the GPU server.
Perform Rebuild
You can delete all data and settings of the existing GPU Server and rebuild it on a new server.
Follow these steps to perform a Rebuild of the GPU Server.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- GPU Server List page, click the resource to perform Rebuild. GPU Server Details page will be displayed.
- On the GPU Server Details page, click the Rebuild button.
- During a GPU Server Rebuild, the server status changes to Rebuilding, and when the Rebuild is complete, it returns to its state before the Rebuild.
- For detailed information about the GPU Server status, refer to Check GPU Server details.
Terminate GPU Server
If you terminate an unused GPU Server, you can reduce operating costs. However, terminating a GPU Server may cause the running service to stop immediately, so you should carefully consider the impact of service interruption before proceeding with the termination.
To cancel the GPU Server, follow the steps below.
- Click the All Services > Compute > GPU Server menu. Go to the GPU Server’s Service Home page.
- On the Service Home page, click the GPU Server menu. You will be taken to the GPU Server List page.
- On the GPU Server List page, select the resource to cancel and click the Cancel Service button.
- The termination of attached storage depends on the Delete on termination setting, so refer to Termination constraints.
- After termination is complete, check on the GPU Server List page whether the resources have been terminated.
Cancellation constraints
When a GPU Server termination request cannot be processed, a popup will provide guidance. Please refer to the cases below.
- If File Storage is connected please disconnect the File Storage connection first.
- When the LB Pool is connected, please disconnect the LB Pool connection first.
- If Lock is set please change the Lock setting to disabled and try again.
Termination of attached storage depends on the Delete on termination setting.
- Whether the volume is deleted also depends on the Delete on termination setting.
- Delete on termination If not set: Even if you terminate the GPU Server, the volume will not be deleted.
- When Delete on termination is set: If you terminate the GPU Server, the associated volume will be deleted.
- Volumes that have snapshots will not be deleted even if Delete on termination is set.
- A Multi‑attach volume can be deleted only when the server being deleted is the last remaining server attached to the volume.
2.3.2.1 - Manage Image
Users can create the service by entering the required information for the Image service within the GPU Server service and selecting detailed options through the Samsung Cloud Platform Console.
Create Image
You can create an image of a running GPU Server. To create an image of a GPU Server, please refer to Image Creation.
Check Image detailed information
Image service allows you to view and edit the full resource list and detailed information. The Image Details page consists of Detailed Information, Tags, Operation History tabs.
To view detailed information of the Image service, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the Image menu. You will be taken to the Image list page.
- On the Image List page, click the resource to view detailed information. You will be taken to the Image Detail page.
- Image Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description Image status Status of user-created Image - Active: Available state
- Queued: Image has been uploaded and is waiting for processing after creation
- Importing: Image has been uploaded and is currently being processed after creation
Share with another account Image can be shared with another Account - The Image’s Visibility must be set to Shared in order to be shared with another Account
Delete image Button to delete the Image - Once the Image is deleted, it cannot be restored
Table. GPU Server Image status information and additional features
- Image Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
Image list page lets you view detailed information of the selected resource and modify it if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Image name |
| Resource ID | Image ID |
| constructor | User who created the Image |
| Creation date and time | Image creation timestamp |
| editor | User who edited the Image |
| Modification date | Image modification timestamp |
| image name | Image name |
| Minimum disk | Minimum disk capacity (GB) of the Image
|
| Minimum RAM | Minimum RAM size (GB) of the Image |
| OS type | OS type of the image |
| OS hash algorithm | OS hash algorithm method |
| Visibility | Display access permissions for the image
|
| Protected | Select whether image deletion is prohibited
|
| image file URL | Image file URL uploaded when generating an image
|
| Sharing status | Current status of sharing images with another Account
|
tag
On the Image List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Image List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Image Resource Management
Describes the control and management functions of the generated Image.
Share to another Account
To share an Image with another Account, follow the steps below.
- Log in to the account to be shared and click the All Services > Compute > GPU Server menu. Go to the GPU Server’s Service Home page.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- On the Image List page, click the Image you want to control. You will be taken to the Image Details page.
- Click the Share to another Account button. Navigate to the Share image to another Account page.
- Share with another Account feature allows you to share an Image with another Account. To share an Image with another Account, the Image’s Visibility must be Shared.
- Share image to another Account page, enter the required information, and click the Done button.
Category RequiredDetailed description image name - Name of the image to share - Input not allowed
Image ID - Shareable image ID - Input not allowed
Shared Account ID Required Enter another Account ID to share - English letters, numbers, special characters
-within 64 characters
Table. Required input fields for sharing images to another Account - You can view the information in the sharing status of the Image Details page.
- When the request is first made, the status is Pending, and it changes to Accepted once approval is completed by the account receiving the share.
Receive sharing from another Account
To receive an Image shared from another Account, follow these steps.
- Log in to the account to be shared and click the All Services > Compute > GPU Server menu. Navigate to the GPU Server’s Service Home page.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- On the Image List page, click the Receive Image Share button. You will be taken to the Receive Image Share popup.
- Receive Image Sharing In the popup window, enter the Image’s resource ID you want to receive, and click the Confirm button.
- When image sharing is complete, you can view the shared Image in the Image list.
Delete Image
You can delete unused Images. However, since an Image cannot be recovered after deletion, you should carefully consider the impact before performing the deletion.
To delete the Image, follow these steps.
- Click the All Services > Compute > GPU Server menu. Go to the GPU Server’s Service Home page.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Image list page, select the resource to delete, and click the Delete button.
- On the Image List page, select multiple Image check boxes and click the Delete button at the top of the resource list.
- After deletion is complete, verify on the Image list page that the resource has been removed.
2.3.2.2 - Manage Keypair
Users can create the service by entering the required Keypair information within the GPU Server service and selecting detailed options through the Samsung Cloud Platform Console.
Create a Keypair
You can create and use the Keypair service while using the GPU Server service in the Samsung Cloud Platform Console.
To create a keypair, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- On the Keypair List page, click the Keypair Create button. You will be taken to the Keypair Create page.
- Enter the required information in the Service Information Input area.
Category RequiredDetailed description Keypair name Required Enter the name of the Keypair to create - using English letters, numbers, spaces, and special characters (
-,_) within 255 characters
Keypair type Required ssh Table. Keypair service information input fields - using English letters, numbers, spaces, and special characters (
- Additional Information Input area, please enter or select the required information.
Category Required statusDetailed description tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Keypair additional information input fieldsCaution- After creation is complete, you can download the Key only once. Since reissuance is not possible, make sure it has been downloaded.
- Store the downloaded Private Key in a safe place.
- Enter the required information in the Service Information Input area.
- Check the input information and click the Create button.
- After creation is complete, check the created resources on the Keypair List page.
View detailed information of the Keypair
The Keypair service allows you to view and edit the full resource list and detailed information. Keypair Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about a keypair, follow these steps.
- Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- On the Keypair List page, click the resource to view its details. You will be taken to the Keypair Details page.
- Keypair Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
Keypair List page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Keypair name |
| Resource ID | Keypair’s unique resource ID |
| constructor | User who created the keypair |
| Creation date and time | Keypair creation timestamp |
| editor | User who modified the keypair information |
| Modification date | Date and time the keypair information was modified |
| Keypair name | Keypair name |
| Fingerprint | A unique value for identifying the key |
| User ID | User ID of the keypair creator |
| public key | Public key information |
tag
On the Keypair List page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Keypair List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Keypair Resource Management
Describes the control and management functions of a keypair.
Get public key
To retrieve the public key, follow these steps.
Click the All Services > Compute > GPU Server menu. You will be taken to the Service Home page of GPU Server.
On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
On the Keypair List page, click the More button at the top and then click the Import Public Key button. You will be taken to the Import Public Key page.
- Enter or select the required information in the Required Information Input area.
Category RequiredDetailed description Keypair name Required Name of the Keypair to create Keypair type Required ssh public key Required Enter public key - Load file: Select the Attach file button to attach the public key file
- Only files with the following extension (.pem) can be attached
- Enter public key: Paste the copied public key value
- The public key value can be copied from the Keypair Details page
Table. Required input fields for retrieving the public key - Load file: Select the Attach file button to attach the public key file
- Enter or select the required information in the Required Information Input area.
Review the entered information and click the Complete button.
- Once creation is complete, check the created resources on the Keypair List page.
Delete Keypair
You can delete unused Keypairs. However, once a Keypair is deleted it cannot be recovered, so please review the impact thoroughly beforehand before proceeding with deletion.
To delete a keypair, follow these steps.
- Click the All Services > Compute > GPU Server menu. Go to the Service Home page of GPU Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- On the Keypair List page, select the resource to delete, and click the Delete button.
- On the Keypair List page, select multiple Keypair check boxes and click the Delete button at the top of the resource list.
- After deletion is complete, check the Keypair List page to confirm that the resource has been removed.
2.3.2.3 - Use Multi-instance GPU on GPU Server
After creating a GPU Server, you can enable the MIG (Multi-instance GPU) feature on the GPU Server’s VM (Guest OS) and create an instance for use.
NVIDIA Multi-instance GPU Introduction
NVIDIA Multi-instance GPU (hereafter referred to as MIG) supports safely partitioning a GPU into GPU instances and running CUDA applications starting with the NVIDIA Ampere architecture. Through this, multiple users can each utilize different GPU resources to achieve optimal GPU utilization. This feature is especially useful for workloads that do not fully utilize the GPU’s computing capacity, and users can run multiple workloads in parallel to maximize utilization.
Using Multi-instance GPU feature
To use the MIG feature, create an NVIDIA GPU Server on the Samsung Cloud Platform, then enable and disable MIG. The order of applying and removing MIG is as follows.
- MIG can be used on Samsung Cloud Platform’s next-generation GPU Server or MNGC (Multi-node GPU Cluster).
- For system requirements to use MIG, refer to the NVIDIA Multi-Instance GPU User Guide.
Applying and Using MIG
After activating the MIG and creating an Instance to assign tasks, the tasks proceed in the following order.
Activate MIG
Check the GPU status on the VM Instance (GuestOS) before applying MIG.
- Check whether MIG mode is Disabled.Color mode
$ nvidia-smi Mon Sep 27 08:37:08 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | 0 | | N/A 32C P0 59W / 400W | 0MiB / 81251MiB | 0% Default | | | | Disabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+$ nvidia-smi Mon Sep 27 08:37:08 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | 0 | | N/A 32C P0 59W / 400W | 0MiB / 81251MiB | 0% Default | | | | Disabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+Code block. nvidia-smi command - Check GPU disabled status (1) Color mode$ nvidia-smi –L GPU 0: NVIDIA A100-SXM-80GB (UUID: GPU-c956838f-494a-92b2-6818-56eb28fe25e0)$ nvidia-smi –L GPU 0: NVIDIA A100-SXM-80GB (UUID: GPU-c956838f-494a-92b2-6818-56eb28fe25e0)Code block. nvidia-smi command - Check GPU disabled status (2)
- Check whether MIG mode is Disabled.
Enable MIG (Enable) for each GPU on the VM Instance (GuestOS) and reboot the VM Instance.
Color mode$ nvidia-smi –I 0 –mig 1 Enabled MIG mode for GPU 00000000:05:00.0 All done. # reboot$ nvidia-smi –I 0 –mig 1 Enabled MIG mode for GPU 00000000:05:00.0 All done. # rebootCode block. nvidia-smi command - enable MIG
When using a GPU and configuring MIG, you may encounter the following warning message. If the warning appears, check whether any programs are running on the GPU.
Warning: MIG mode is in pending enable state for GPU 00000000:05:00.0: In use by another client. 00000000:05:00.0 is currently being used by one or more other processes (e.g. CUDA application or a monitoring application such as another instance of nvidia-smi).
- Check the GPU status after applying MIG on the VM Instance(GuestOS).
- Check whether MIG mode is Enabled.Color mode
$ nvidia-smi Mon Sep 27 09:44:33 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | On | | N/A 32C P0 59W / 400W | 0MiB / 81251MiB | 0% Default | | | | Enabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | No MIG devices found | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+$ nvidia-smi Mon Sep 27 09:44:33 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | On | | N/A 32C P0 59W / 400W | 0MiB / 81251MiB | 0% Default | | | | Enabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | No MIG devices found | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+Code block. nvidia-smi command - Check GPU activation status (1) Color mode$ nvidia-smi –L GPU 0: NVIDIA A100-SXM-80GB (UUID: GPU-c956838f-494a-92b2-6818-56eb28fe25e0)$ nvidia-smi –L GPU 0: NVIDIA A100-SXM-80GB (UUID: GPU-c956838f-494a-92b2-6818-56eb28fe25e0)Code block. nvidia-smi command - Check GPU activation status (2)
- Check whether MIG mode is Enabled.
GPU Instance creation
If you have enabled MIG and verified its status, you can create a GPU Instance.
- Check the list of MIG GPU Instance profiles that can be created.Color mode
$ nvidia-smi mig -i [GPU ID] -lgip$ nvidia-smi mig -i [GPU ID] -lgipCode block. nvidia-smi command - view MIG GPU Instance profile list
$ nvidia-smi mig -i 0 -lgip
+-----------------------------------------------------------------------------+
| GPU instance profiles: |
| GPU Name ID Instances Memory P2P SM DEC ENC |
| Free/Total GiB CE JPEG OFA |
| ============================================================================= |
| 0 MIG 1g.10gb 19 7/7 9.50 No 14 0 0 |
| 1 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 1g.10gb+me 20 1/1 9.50 No 14 0 0 |
| 1 1 1 |
+-----------------------------------------------------------------------------+
| 0 MIG 2g.20gb 14 3/3 19.50 No 28 1 0 |
| 2 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 3g.40gb 9 2/2 39.50 No 42 2 0 |
| 3 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 4g.40gb 5 1/1 39.50 No 56 2 0 |
| 4 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 7g.80gb 0 1/1 79.25 No 98 0 0 |
| 7 1 1 |
+-----------------------------------------------------------------------------+$ nvidia-smi mig -i 0 -lgip
+-----------------------------------------------------------------------------+
| GPU instance profiles: |
| GPU Name ID Instances Memory P2P SM DEC ENC |
| Free/Total GiB CE JPEG OFA |
| ============================================================================= |
| 0 MIG 1g.10gb 19 7/7 9.50 No 14 0 0 |
| 1 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 1g.10gb+me 20 1/1 9.50 No 14 0 0 |
| 1 1 1 |
+-----------------------------------------------------------------------------+
| 0 MIG 2g.20gb 14 3/3 19.50 No 28 1 0 |
| 2 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 3g.40gb 9 2/2 39.50 No 42 2 0 |
| 3 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 4g.40gb 5 1/1 39.50 No 56 2 0 |
| 4 0 0 |
+-----------------------------------------------------------------------------+
| 0 MIG 7g.80gb 0 1/1 79.25 No 98 0 0 |
| 7 1 1 |
+-----------------------------------------------------------------------------+- After creating a MIG GPU Instance, check it.
Create GPU Instance
Color mode$ nvidia-smi mig -i [GPU ID] -cgi [Profile ID]$ nvidia-smi mig -i [GPU ID] -cgi [Profile ID]code block. nvidia-smi command - GPU Instance creation Color mode$ nvidia-smi mig -i 0 -cgi 0 Successfully created GPU instance ID 0 on GPU 0 using profile MIG 7g.80gb (ID 0)$ nvidia-smi mig -i 0 -cgi 0 Successfully created GPU instance ID 0 on GPU 0 using profile MIG 7g.80gb (ID 0)Code block. nvidia-smi command - Example of creating a GPU Instance Check GPU Instance
Color mode$ nvidia-smi mig -i [GPU ID] -lgi$ nvidia-smi mig -i [GPU ID] -lgicode block. nvidia-smi command - check GPU Instance Color mode$ nvidia-smi mig -i 0 -lgi +--------------------------------------------------------+ | GPU instances: | | GPU Name Profile Instance Placement | | ID ID Start:Size | | ======================================================== | | 0 MIG 7g.80gb 0 0 0:8 | +--------------------------------------------------------+$ nvidia-smi mig -i 0 -lgi +--------------------------------------------------------+ | GPU instances: | | GPU Name Profile Instance Placement | | ID ID Start:Size | | ======================================================== | | 0 MIG 7g.80gb 0 0 0:8 | +--------------------------------------------------------+Code block. nvidia-smi command - example of checking GPU Instance
Compute Instance creation
If you have created a GPU Instance, you can create a Compute Instance.
Check the MIG Compute Instance profiles you can create.
Color mode$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -lcip$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -lcipCode block. nvidia-smi command - Check MIG Compute Instance profile Color mode$ nvidia-smi mig -i 0 -gi 0 -lcip +---------------------------------------------------------------------------------+ | Compute instance profiles: | | GPU GPU Name Profile Instances Exclusive Shared | | GPU Instance ID Free/Total SM DEC ENC OFA | | ID CE JPEG | | ================================================================================= | | 0 0 MIG 1c.7g.80gb 0 7/5 14 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 2c.7g.80gb 1 3/3 28 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 3c.7g.80gb 2 2/2 42 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 4c.7g.80gb 3 1/1 56 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 7g.80gb 4* 1/1 98 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+$ nvidia-smi mig -i 0 -gi 0 -lcip +---------------------------------------------------------------------------------+ | Compute instance profiles: | | GPU GPU Name Profile Instances Exclusive Shared | | GPU Instance ID Free/Total SM DEC ENC OFA | | ID CE JPEG | | ================================================================================= | | 0 0 MIG 1c.7g.80gb 0 7/5 14 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 2c.7g.80gb 1 3/3 28 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 3c.7g.80gb 2 2/2 42 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 4c.7g.80gb 3 1/1 56 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+ | 0 0 MIG 7g.80gb 4* 1/1 98 5 0 1 | | 7 1 | +---------------------------------------------------------------------------------+Code block. Example of MIG Compute Instance profile list Create and verify a MIG Compute Instance.
- MIG Compute Instance creationColor mode
$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -cci [Compute Profile ID]$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -cci [Compute Profile ID]code block. nvidia-smi command - Create MIG Compute Instance Color mode$ nvidia-smi mig -i 0 -gi 0 -cci 4 Successfully created compute instance ID 0 on GPU instance ID 0 using profile MIG 7g.80gb(ID 4)$ nvidia-smi mig -i 0 -gi 0 -cci 4 Successfully created compute instance ID 0 on GPU instance ID 0 using profile MIG 7g.80gb(ID 4)Code block. nvidia-smi command - Example of creating a MIG Compute Instance - Check MIG Compute InstanceColor mode
$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] –lci$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] –lcicode block. nvidia-smi command - check MIG Compute Instance Color mode$ nvidia-smi mig -i 0 -gi 0 –lci +-----------------------------------------------------------------+ | Compute instance profiles: | | GPU GPU Name Profile Instances Placement | | GPU Instance ID ID Start:Size | | ID | | ================================================================= | | 0 0 MIG 7g.80gb 4 0 0:7 | +-----------------------------------------------------------------+$ nvidia-smi mig -i 0 -gi 0 –lci +-----------------------------------------------------------------+ | Compute instance profiles: | | GPU GPU Name Profile Instances Placement | | GPU Instance ID ID Start:Size | | ID | | ================================================================= | | 0 0 MIG 7g.80gb 4 0 0:7 | +-----------------------------------------------------------------+Code block. Example of checking MIG Compute Instance Color mode$ nvidia-smi –L GPU 0: NVIDIA A100-SXM-80GB (UUID: GPU-c956838f-494a-92b2-6818-56eb28fe25e0) MIG 7g.80gb Device 0: (UUID: MIG-53e20040-758b-5ecb-948e-c626d03a9a32)$ nvidia-smi –L GPU 0: NVIDIA A100-SXM-80GB (UUID: GPU-c956838f-494a-92b2-6818-56eb28fe25e0) MIG 7g.80gb Device 0: (UUID: MIG-53e20040-758b-5ecb-948e-c626d03a9a32)Code block. nvidia-smi command - Check GPU status (1) Color mode$ nvidia-smi Mon Sep 27 09:52:17 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | On | | N/A 32C P0 49W / 400W | 0MiB / 81251MiB | N/A Default | | | | Enabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | 0 0 0 0 | 0MiB / 81251MiB | 98 0 | 7 0 5 1 1 | | | 1MiB / 13107... | | | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+$ nvidia-smi Mon Sep 27 09:52:17 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | On | | N/A 32C P0 49W / 400W | 0MiB / 81251MiB | N/A Default | | | | Enabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | 0 0 0 0 | 0MiB / 81251MiB | 98 0 | 7 0 5 1 1 | | | 1MiB / 13107... | | | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+Code block. nvidia-smi command - Check GPU status (2)
- MIG Compute Instance creation
Using MIG
- Use the MIG Instance to perform the Job.
- Example of task executionColor mode
$ docker run --gpus '"device=[GPU ID]:[MIG ID]"' -rm nvcr.io/nvidia/cuda nvidia-smi$ docker run --gpus '"device=[GPU ID]:[MIG ID]"' -rm nvcr.io/nvidia/cuda nvidia-smiCode block. Task execution example - You can see an example of the work performed as follows.Color mode
$ docker run --gpus '"device=0:0"' -rm -it --network=host --shm-size=1g --ipc=host -v /root/.ssh/:/root/.ssh ================ == TensorFlow == ================ NVIDIA Release 21.08-tf1 (build 26012104) TensorFlow Version 1.15.5 Container image Copyright (c) 2021, NVIDIA CORPORATION. All right reserved. ... # Run Python process root@d622a93c9281:/workspace# python /workspace/nvidia-examples/cnn/resnet.py --num_iter 100 ... PY 3.8.10 (default, Jun 2 2021, 10:49:15) [GCC 9.4.0] TF 1.15.5 ...$ docker run --gpus '"device=0:0"' -rm -it --network=host --shm-size=1g --ipc=host -v /root/.ssh/:/root/.ssh ================ == TensorFlow == ================ NVIDIA Release 21.08-tf1 (build 26012104) TensorFlow Version 1.15.5 Container image Copyright (c) 2021, NVIDIA CORPORATION. All right reserved. ... # Run Python process root@d622a93c9281:/workspace# python /workspace/nvidia-examples/cnn/resnet.py --num_iter 100 ... PY 3.8.10 (default, Jun 2 2021, 10:49:15) [GCC 9.4.0] TF 1.15.5 ...Code block. Operation result
- Example of task execution
- Check the GPU usage. (Create JOB process)
- When the job runs, you can see that a process is allocated to the MIG device and its utilization increases.Color mode
$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -lcip$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -lcipcode block. nvidia-smi command - check GPU utilization - You can check the GPU usage as shown below.Color mode
+-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | 0 0 0 0 | 66562MiB / 81251MiB | 98 0 | 7 0 5 1 1 | | | 5MiB / 13107... | | | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | 0 0 0 17483 C python 66559MiB | +-----------------------------------------------------------------------------++-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | 0 0 0 0 | 66562MiB / 81251MiB | 98 0 | 7 0 5 1 1 | | | 5MiB / 13107... | | | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | 0 0 0 17483 C python 66559MiB | +-----------------------------------------------------------------------------+Code block. Example of checking GPU utilization.
- When the job runs, you can see that a process is allocated to the MIG device and its utilization increases.
Delete and release MIG Instance
Follow these steps to delete the MIG instance and detach the MIG.
Compute Instance Delete
- Delete the Compute Instance.Color mode
$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] –dci $ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -ci [Compute Instance] –dci$ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] –dci $ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] -ci [Compute Instance] –dciCode block. nvidia-smi command - Delete Compute Instance Color mode$ nvidia-smi mig -i 0 -gi 0 –lci +-----------------------------------------------------------------+ | Compute instance profiles: | | GPU GPU Name Profile Instances Placement | | GPU Instance ID ID Start:Size | | ID | | ================================================================= | | 0 0 MIG 7g.80gb 4 0 0:7 | +-----------------------------------------------------------------+$ nvidia-smi mig -i 0 -gi 0 –lci +-----------------------------------------------------------------+ | Compute instance profiles: | | GPU GPU Name Profile Instances Placement | | GPU Instance ID ID Start:Size | | ID | | ================================================================= | | 0 0 MIG 7g.80gb 4 0 0:7 | +-----------------------------------------------------------------+code block. Example of checking MIG Compute Instance Color mode$ nvidia-smi mig -i 0 -gi 0 –dci Successfully destroyed compute instance ID 0 from GPU instance ID 0$ nvidia-smi mig -i 0 -gi 0 –dci Successfully destroyed compute instance ID 0 from GPU instance ID 0Code block. Compute Instance deletion example Color mode$ nvidia-smi mig -i 0 -gi 0 –lci No compute instances found: Not found$ nvidia-smi mig -i 0 -gi 0 –lci No compute instances found: Not foundCode block. Confirm Compute Instance deletion
Delete GPU Instance
- Delete the GPU Instance.Color mode
$ nvidia-smi mig -i [GPU ID] –dgi $ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] –dgi$ nvidia-smi mig -i [GPU ID] –dgi $ nvidia-smi mig -i [GPU ID] -gi [GPU Instance ID] –dgiCode block. nvidia-smi command - Delete GPU Instance Color mode$ nvidia-smi mig -i 0 -lgi +--------------------------------------------------------+ | GPU instances: | | GPU Name Profile Instance Placement | | ID ID Start:Size | | ======================================================== | | 0 MIG 7g.80gb 0 0 0:8 | +--------------------------------------------------------+$ nvidia-smi mig -i 0 -lgi +--------------------------------------------------------+ | GPU instances: | | GPU Name Profile Instance Placement | | ID ID Start:Size | | ======================================================== | | 0 MIG 7g.80gb 0 0 0:8 | +--------------------------------------------------------+Code block. nvidia-smi command - Example of checking GPU Instance Color mode$ nvidia-smi mig -i 0 -dgi Successfully destroyed GPU instance ID 0 from GPU 0$ nvidia-smi mig -i 0 -dgi Successfully destroyed GPU instance ID 0 from GPU 0Code block. nvidia-smi command - GPU Instance deletion example Color mode$ nvidia-smi mig -i 0 -lgi No GPU instances found: Not found$ nvidia-smi mig -i 0 -lgi No GPU instances found: Not foundcode block. nvidia-smi command - example of deleting a GPU Instance
Disable MIG feature (deactivation)
- After disabling MIG (Disable), reboot.Color mode
$ nvidia-smi -mig 0 Disabled MIG Mode for GPU 00000000:05:00.0 All done.$ nvidia-smi -mig 0 Disabled MIG Mode for GPU 00000000:05:00.0 All done.Code block. nvidia-smi command - disable MIG Color mode$ nvidia-smi Mon Sep 30 05:18:28 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | 0 | | N/A 33C P0 60W / 400W | 0MiB / 81251MiB | 0% Default | | | | Disabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | No MIG devices found | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+$ nvidia-smi Mon Sep 30 05:18:28 2021 +-----------------------------------------------------------------------------+ | NVIDIA-SMI 470.57.02 Driver Version: 470.57.02 CUDA Version: 11.4 | | -------------------------------+----------------------+---------------------- | | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | ===============================+======================+====================== | | 0 NVDIA A100-SXM... Off | 00000000:05:00.0 Off | 0 | | N/A 33C P0 60W / 400W | 0MiB / 81251MiB | 0% Default | | | | Disabled | +-------------------------------+----------------------+----------------------+ +-----------------------------------------------------------------------------+ | MIG devices: | +-----------------------------------------------------------------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ============================================================================= | | No MIG devices found | +-----------------------------------------------------------------------------+ +-----------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ============================================================================= | | No running processes found | +-----------------------------------------------------------------------------+Code block. nvidia-smi command - check GPU status
2.3.2.4 - Use NVSwitch on GPU Server
After creating a GPU Server, you can enable the NVSwitch feature on the GPU Server’s VM (Guest OS) and use fast GPU-to-GPU P2P communication.
Exploring NVIDIA NVSwitch for Multi GPU
NVLink expands I/O by directly connecting multiple GPUs within a server both bidirectionally and GPU-to-GPU. Using NVSwitch, you can connect all GPUs in a server with full NVLink bandwidth.
Checking NVSwitch operation
Check the NVIDIA Fabric Manager, NVIDIA NVLink topology, and NVIDIA NVLink Status on the GPU server.
NVIDIA Fabric Manager operating status
Verify that active (running) is displayed when operating normally.
~$ systemctl status nvidia-fabricmanager
nvidia-fabricmanager.service - NVIDIA fabric manager service
Loaded: loaded (/lib/systemd/system/nvidia-fabricmanager.service; enabled; vendor preset: enabled)
Active: active (running) since Mon 2026-02-02 16:23:27 KST; 32min ago
Main PID: 2191 (nv-fabricmanage)
Tasks: 18 (limit: 629145)
Memory: 18.0M
CPU: 33.461s
CGroup: /system.slice/nvidia-fabricmanager.service
└─2191 /usr/bin/nv-fabricmanager -c /usr/share/nvidia/nvswitch/fabricmanager.cfgnvidia-fabricmanager.service - NVIDIA fabric manager service
Loaded: loaded (/lib/systemd/system/nvidia-fabricmanager.service; enabled; vendor preset: enabled)
Active: active (running) since Mon 2026-02-02 16:23:27 KST; 32min ago
Main PID: 2191 (nv-fabricmanage)
Tasks: 18 (limit: 629145)
Memory: 18.0M
CPU: 33.461s
CGroup: /system.slice/nvidia-fabricmanager.service
└─2191 /usr/bin/nv-fabricmanager -c /usr/share/nvidia/nvswitch/fabricmanager.cfgCheck NVIDIA NVLink topology
Check the NVIDIA NVLink topology.
~$ nvidia-smi topo -m
nvidia-smi topo -m
GPU0 GPU1 GPU2 GPU3 GPU4 GPU5 GPU6 GPU7 CPU Affinity NUMA Affinity GPU NUMA ID
GPU0 X NV12 NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU1 NV12 X NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU2 NV12 NV12 X NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU3 NV12 NV12 NV12 X NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU4 NV12 NV12 NV12 NV12 X NV12 NV12 NV12 0-127 0-7 N/A
GPU5 NV12 NV12 NV12 NV12 NV12 X NV12 NV12 0-127 0-7 N/A
GPU6 NV12 NV12 NV12 NV12 NV12 NV12 X NV12 0-127 0-7 N/A
GPU7 NV12 NV12 NV12 NV12 NV12 NV12 NV12 X 0-127 0-7 N/A
Legend:
X = Self
SYS = Connection traversing PCIe as well as the SMP interconnect between NUMA nodes (e.g., QPI/UPI)
NODE = Connection traversing PCIe as well as the interconnect between PCIe Host Bridges within a NUMA node
PHB = Connection traversing PCIe as well as a PCIe Host Bridge (typically the CPU)
PXB = Connection traversing multiple PCIe bridges (without traversing the PCIe Host Bridge)
PIX = Connection traversing at most a single PCIe bridge
NV# = Connection traversing a bonded set of # NVLinksnvidia-smi topo -m
GPU0 GPU1 GPU2 GPU3 GPU4 GPU5 GPU6 GPU7 CPU Affinity NUMA Affinity GPU NUMA ID
GPU0 X NV12 NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU1 NV12 X NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU2 NV12 NV12 X NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU3 NV12 NV12 NV12 X NV12 NV12 NV12 NV12 0-127 0-7 N/A
GPU4 NV12 NV12 NV12 NV12 X NV12 NV12 NV12 0-127 0-7 N/A
GPU5 NV12 NV12 NV12 NV12 NV12 X NV12 NV12 0-127 0-7 N/A
GPU6 NV12 NV12 NV12 NV12 NV12 NV12 X NV12 0-127 0-7 N/A
GPU7 NV12 NV12 NV12 NV12 NV12 NV12 NV12 X 0-127 0-7 N/A
Legend:
X = Self
SYS = Connection traversing PCIe as well as the SMP interconnect between NUMA nodes (e.g., QPI/UPI)
NODE = Connection traversing PCIe as well as the interconnect between PCIe Host Bridges within a NUMA node
PHB = Connection traversing PCIe as well as a PCIe Host Bridge (typically the CPU)
PXB = Connection traversing multiple PCIe bridges (without traversing the PCIe Host Bridge)
PIX = Connection traversing at most a single PCIe bridge
NV# = Connection traversing a bonded set of # NVLinksCheck NVIDIA NVLink Status
Check the NVIDIA NVLink Status.
~$ nvidia-smi topo -m
GPU 1: NVIDIA A100-SXM4-80GB (UUID: GPU-64a2f685-bb12-c4af-105c-0726ece9c8d7)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 2: NVIDIA A100-SXM4-80GB (UUID: GPU-2269851b-71cd-f6c7-50c5-ba1525cf3ce8)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 3: NVIDIA A100-SXM4-80GB (UUID: GPU-4c397bbf-95fc-5c29-918a-a429cbe45a7a)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 4: NVIDIA A100-SXM4-80GB (UUID: GPU-0e350204-9fb6-2cbe-538e-8f7849658eb8)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 5: NVIDIA A100-SXM4-80GB (UUID: GPU-45f0c453-4760-edd4-3af9-25c5ea7473a5)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 6: NVIDIA A100-SXM4-80GB (UUID: GPU-38409794-bb34-430e-3c50-90b42cb2bb72)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 7: NVIDIA A100-SXM4-80GB (UUID: GPU-3fb478aa-801b-eb64-55c2-0ffc3f2ce404)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/sGPU 1: NVIDIA A100-SXM4-80GB (UUID: GPU-64a2f685-bb12-c4af-105c-0726ece9c8d7)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 2: NVIDIA A100-SXM4-80GB (UUID: GPU-2269851b-71cd-f6c7-50c5-ba1525cf3ce8)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 3: NVIDIA A100-SXM4-80GB (UUID: GPU-4c397bbf-95fc-5c29-918a-a429cbe45a7a)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 4: NVIDIA A100-SXM4-80GB (UUID: GPU-0e350204-9fb6-2cbe-538e-8f7849658eb8)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 5: NVIDIA A100-SXM4-80GB (UUID: GPU-45f0c453-4760-edd4-3af9-25c5ea7473a5)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 6: NVIDIA A100-SXM4-80GB (UUID: GPU-38409794-bb34-430e-3c50-90b42cb2bb72)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s
GPU 7: NVIDIA A100-SXM4-80GB (UUID: GPU-3fb478aa-801b-eb64-55c2-0ffc3f2ce404)
Link 0: 25 GB/s
Link 1: 25 GB/s
Link 2: 25 GB/s
Link 3: 25 GB/s
Link 4: 25 GB/s
Link 5: 25 GB/s
Link 6: 25 GB/s
Link 7: 25 GB/s
Link 8: 25 GB/s
Link 9: 25 GB/s
Link 10: 25 GB/s
Link 11: 25 GB/s2.3.2.5 - Install ServiceWatch Agent
Users can install the ServiceWatch Agent on a GPU server to collect custom metrics and logs.
ServiceWatch Agent
There are two main types of agents that need to be installed on a GPU server to collect custom metrics and logs for ServiceWatch. It is a Prometheus Exporter and Open Telemetry Collector.
| Category | Detailed description | |
|---|---|---|
| Prometheus Exporter | Provide metrics of a specific application or service in a format that Prometheus can scrape
| |
| Open Telemetry Collector | Acts as a centralized collector that gathers telemetry data such as metrics and logs from distributed systems, processes (filtering, sampling, etc.) it, and exports it to multiple backends (e.g., Prometheus, Jaeger, Elasticsearch, etc.)
|
If you have configured a Kubernetes Engine on a GPU server, please check GPU metrics using the metrics provided by the Kubernetes Engine.
- If you install the DCGM Exporter on a GPU server configured with Kubernetes Engine, it may not operate correctly.
Pre-configuration for Using ServiceWatch Agent
To utilize the ServiceWatch Agent, please refer to Prerequisite Settings for ServiceWatch Agent and prepare the prerequisite settings.
Install Prometheus Exporter for GPU metrics (for Ubuntu)
Install the Prometheus Exporter for collecting metrics from the GPU server according to the steps below.
Verify NVDIA Driver Installation
- Check the installed NVDIA Driver.Color mode
nvidia-smi --query-gpu driver_version --format csvnvidia-smi --query-gpu driver_version --format csvCode block. NVDIA Driver version check command Color modedriver_version 535.183.06 ... 535.183.06driver_version 535.183.06 ... 535.183.06Code block. NVDIA Driver version check example
NVSwitch Configuration and Query (NSCQ) Library Installation
Install cuda-keyring.
Color modewget https://developer.download.nvidia.com/compute/cuda/repos/<distro>/<arch>/cuda-keyring_1.1-1_all.debwget https://developer.download.nvidia.com/compute/cuda/repos/<distro>/<arch>/cuda-keyring_1.1-1_all.debcode block. NSCQ library download command Color modesudo dpkg -i cuda-keyring_1.1-1_all.deb apt updatesudo dpkg -i cuda-keyring_1.1-1_all.deb apt updateCode block. NSCQ library installation command Color modenvidia-smi --query-gpu driver_version --format csvnvidia-smi --query-gpu driver_version --format csvCode block. NVDIA Driver version check command Color modedriver_version 535.183.06 ... 535.183.06driver_version 535.183.06 ... 535.183.06code block. Example of checking NVDIA driver version Install libnvidia-nscq.
Color modeapt-cache policy libnvidia-nscq-535apt-cache policy libnvidia-nscq-535Code block. NSCQ library apt-cache command Color modelibnvidia-nscq-535: Installed: (none) Candidate: 535.247.01-1 Version table: 535.247.01-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages ... 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.216.01-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.183.06-1 600 # Install the version that matches the driver 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.183.01-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.54.03-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packageslibnvidia-nscq-535: Installed: (none) Candidate: 535.247.01-1 Version table: 535.247.01-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages ... 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.216.01-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.183.06-1 600 # Install the version that matches the driver 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.183.01-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 535.54.03-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 PackagesCode block. NSCQ library apt-cache command result Color modeapt install libnvidia-nscq-535=535.183.06-1apt install libnvidia-nscq-535=535.183.06-1Code block. NSCQ library installation command
It must be installed with the same version as the NVDIA Driver.
- Example) driver version: 535.183.06, libnvdia-nscq version: 535.183.06-1
NVSwitch Device Monitoring API(NVSDM) Library Installation
- Install the NVSDM library.Color mode
apt-cache policy libnvsdmapt-cache policy libnvsdmCode block. NVSDM library apt-cache command Color modelibnvsdm: Installed: (none) Candidate: 580.105.08-1 Version table: 580.105.08-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.95.05-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.82.07-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.65.06-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packageslibnvsdm: Installed: (none) Candidate: 580.105.08-1 Version table: 580.105.08-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.95.05-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.82.07-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.65.06-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 PackagesCode block. NVSDM library apt-cache command result Color modeapt install libnvsdm=580.105.08-1apt install libnvsdm=580.105.08-1Code block. Install NVSDM library
Install NVIDIA DCGM (for Ubuntu)
Install the DCGM Exporter according to the steps below.
- DCGM(datacenter-gpu-manager) Installation
- datacenter-gpu-manager-exporter installation
- DCGM Service Activation and Start
DCGM(datacenter-gpu-manager) Installation
refers to a specific version of NVIDIA’s Data Center GPU Manager (DCGM) tool, which is a package for managing and monitoring NVIDIA data center GPUs. In particular, cuda12 indicates that this management tool is installed for the CUDA 12 version, and datacenter-gpu-manager-4 refers to the 4.x version of DCGM. This tool provides a variety of features, including GPU status monitoring, diagnostics, alert system, and power/clock management.
- Check the CUDA version.Color mode
nvidia-smi | grep CUDAnvidia-smi | grep CUDACode block. Check CUDA version Color mode| NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 || NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 |Code block. Example of CUDA version check result Color modeCUDA_VERSION=12CUDA_VERSION=12Code block. CUDA version setting command - Install datacenter-gpu-manager-cuda.Color mode
apt install datacenter-gpu-manager-4-cuda${CUDA_VERSION}apt install datacenter-gpu-manager-4-cuda${CUDA_VERSION}Code block. datacenter-gpu-manager-cuda installation command
Install datacenter-gpu-manager-exporter
It is a tool that, based on NVIDIA Data Center GPU Manager (DCGM), collects various GPU metrics such as GPU usage, memory usage, temperature, and power consumption, and exposes them for use in monitoring systems like Prometheus.
- Install datacenter-gpu-manager-exporter.Color mode
apt install datacenter-gpu-manager-exporterapt install datacenter-gpu-manager-exporterCode block. datacenter-gpu-manager-exporter installation command - Check the DCGM Exporter configuration file.Color mode
cat /usr/lib/systemd/system/nvidia-dcgm-exporter.service | grep ExecStartcat /usr/lib/systemd/system/nvidia-dcgm-exporter.service | grep ExecStartCode block. Command to check the datacenter-gpu-manager-exporter configuration file Color modeExecStart=/usr/bin/dcgm-exporter -f /etc/dcgm-exporter/default-counters.csvExecStart=/usr/bin/dcgm-exporter -f /etc/dcgm-exporter/default-counters.csvcode block. Example of verification result for the datacenter-gpu-manager-exporter configuration file - When installing the DCGM Exporter, review the provided configuration and remove
#for the required metrics, and add#for the unnecessary metrics.Color modevi /etc/dcgm-exporter/default-counters.csv ## Example ## ... DCGM_FI_PROF_PIPE_TENSOR_ACTIVE, gauge, Ratio of cycles the tensor (HMMA) pipe is active. DCGM_FI_PROF_DRAM_ACTIVE, gauge, Ratio of cycles the device memory interface is active sending or receiving data. # DCGM_FI_PROF_PIPE_FP64_ACTIVE, gauge, Ratio of cycles the fp64 pipes are active. # DCGM_FI_PROF_PIPE_FP32_ACTIVE, gauge, Ratio of cycles the fp32 pipes are active. ...vi /etc/dcgm-exporter/default-counters.csv ## Example ## ... DCGM_FI_PROF_PIPE_TENSOR_ACTIVE, gauge, Ratio of cycles the tensor (HMMA) pipe is active. DCGM_FI_PROF_DRAM_ACTIVE, gauge, Ratio of cycles the device memory interface is active sending or receiving data. # DCGM_FI_PROF_PIPE_FP64_ACTIVE, gauge, Ratio of cycles the fp64 pipes are active. # DCGM_FI_PROF_PIPE_FP32_ACTIVE, gauge, Ratio of cycles the fp32 pipes are active. ...Code block. Example of datacenter-gpu-manager-exporter metric configuration
Enable and start DCGM service
Enable and start the nvdia-dcgm service.
Color modesystemctl enable --now nvidia-dcgmsystemctl enable --now nvidia-dcgmCode block. nvdia-dcgm service activation and start command Enable and start the nvdia-dcgm-exporter service.
Color modesystemctl enable --now nvidia-dcgm-exportersystemctl enable --now nvidia-dcgm-exporterCode block. nvdia-dcgm-exporter service activation and start command
For more details, refer to ServiceWatch > ServiceWatch Agent 사용하기.
Install Prometheus Exporter for GPU metrics (for RHEL)
Install the ServiceWatch Agent to collect metrics from the GPU server according to the steps below.
NVDIA Driver installation verification (for RHEL)
- Check the installed NVDIA Driver.Color mode
nvidia-smi --query-gpu driver_version --format csvnvidia-smi --query-gpu driver_version --format csvCode block. NVDIA Driver version check command Color modedriver_version 535.183.06 ... 535.183.06driver_version 535.183.06 ... 535.183.06Code block. Example of checking NVDIA Driver version
NVSwitch Configuration and Query (NSCQ) Library installation (for RHEL)
The NVSwitch Configuration and Query (NSCQ) Library is required for Hopper or earlier generation GPUs.
- For RHEL, verify that libnvdia-nscq is installed and install it if necessary.
Checking the libnvdia-nscq package.
Color moderpm -qa | grep libnvidia-nscq libnvidia-nscq-535-535.183.06-1.x86_64rpm -qa | grep libnvidia-nscq libnvidia-nscq-535-535.183.06-1.x86_64Code block. Check NSCQ library package Add the CUDA Repository to DNF.
Color modednf config-manager --add-repo https://developer.download.nvidia.com/compute/cuda/repos/rhel8/x86_64/cuda-rhel8.repodnf config-manager --add-repo https://developer.download.nvidia.com/compute/cuda/repos/rhel8/x86_64/cuda-rhel8.repoCode block. Add DNF Repository NVDIA Driver status reset
Color modednf module reset nvidia-driverdnf module reset nvidia-driverCode block. Initialize the state of the NVIDIA Driver DNF module Color modeUpdating Subscription Management repositories. Last metadata expiration check: 0:03:15 ago on Wed 19 Nov 2025 01:23:48 AM EST. Dependencies resolved. ============================================= Package Architecture Version Repository Size ============================================= Disabling module profiles: nvidia-driver/default nvidia-driver/fm Resetting modules: nvidia-driver Transaction Summary ============================================= Is this ok [y/N]: yUpdating Subscription Management repositories. Last metadata expiration check: 0:03:15 ago on Wed 19 Nov 2025 01:23:48 AM EST. Dependencies resolved. ============================================= Package Architecture Version Repository Size ============================================= Disabling module profiles: nvidia-driver/default nvidia-driver/fm Resetting modules: nvidia-driver Transaction Summary ============================================= Is this ok [y/N]: yCode block. Example of the status initialization result of the NVIDIA Driver DNF module. Enable the NVDIA Driver module.
Color modednf module enable nvidia-driver:535-opendnf module enable nvidia-driver:535-opencode block. NVDIA Driver module activation Color modeUpdating Subscription Management repositories. Last metadata expiration check: 0:04:22 ago on Wed 19 Nov 2025 01:23:48 AM EST. Dependencies resolved. ============================================= Package Architecture Version Repository Size ============================================= Enabling module streams: nvidia-driver 535-open Transaction Summary ============================================= Is this ok [y/N]: yUpdating Subscription Management repositories. Last metadata expiration check: 0:04:22 ago on Wed 19 Nov 2025 01:23:48 AM EST. Dependencies resolved. ============================================= Package Architecture Version Repository Size ============================================= Enabling module streams: nvidia-driver 535-open Transaction Summary ============================================= Is this ok [y/N]: yCode block. Example of NVDIA Driver module activation result Check the libnvdia-nscq module list.
Color modednf list libnvidia-nscq-535 --showduplicatesdnf list libnvidia-nscq-535 --showduplicatesCode block. Check libnvdia-nscq module list Install libnvdia-nscq.
Color modednf install libnvidia-nscq-535-535.183.06-1dnf install libnvidia-nscq-535-535.183.06-1code block. libnvdia-nscq installation command
NVSwitch Device Monitoring API(NVSDM) Library Installation (for RHEL)
Check the NVSDM library module list.
Color modednf list libnvsdm --showduplicatesdnf list libnvsdm --showduplicatesCode block. Check NVSDM library module list Color modelibnvsdm: Installed: (none) Candidate: 580.105.08-1 Version table: 580.105.08-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.95.05-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.82.07-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.65.06-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packageslibnvsdm: Installed: (none) Candidate: 580.105.08-1 Version table: 580.105.08-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.95.05-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.82.07-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 Packages 580.65.06-1 600 600 https://developer.download.nvidia.com/compute/cuda/repos/ubuntu2204/x86_64 PackagesCode block. Example of NVSDM library module list verification results. Install libnvsdm.
Color modednf install libnvsdm-580.105.08-1dnf install libnvsdm-580.105.08-1Code block. Install NVSDM library Color modeUpdating Subscription Management repositories. Last metadata expiration check: 0:08:18 ago on Wed 19 Nov 2025 01:05:28 AM EST. Dependencies resolved. ========================================================================= Package Architecture Version Repository Size ========================================================================= Installing: libnvsdm x86_64 580.105.08-1 cuda-rhel8-x86_64 675 k Installing dependencies: infiniband-diags x86_64 48.0-1.el8 rhel-8-for-x86_64-baseos-rpms 323 k libibumad x86_64 48.0-1.el8 rhel-8-for-x86_64-baseos-rpms 34 k Transaction Summary ========================================================================= Install 3 Packages Total download size: 1.0 M Installed size: 3.2 M Is this ok [y/N]: yUpdating Subscription Management repositories. Last metadata expiration check: 0:08:18 ago on Wed 19 Nov 2025 01:05:28 AM EST. Dependencies resolved. ========================================================================= Package Architecture Version Repository Size ========================================================================= Installing: libnvsdm x86_64 580.105.08-1 cuda-rhel8-x86_64 675 k Installing dependencies: infiniband-diags x86_64 48.0-1.el8 rhel-8-for-x86_64-baseos-rpms 323 k libibumad x86_64 48.0-1.el8 rhel-8-for-x86_64-baseos-rpms 34 k Transaction Summary ========================================================================= Install 3 Packages Total download size: 1.0 M Installed size: 3.2 M Is this ok [y/N]: yCode block. Example of the NVSDM library installation command result
Install NVIDIA DCGM (for RHEL)
Install Node Exporter according to the steps below.
- DCGM(datacenter-gpu-manager) Installation
- datacenter-gpu-manager-exporter installation
- DCGM Service Activation and Start
DCGM(datacenter-gpu-manager) Installation (for RHEL)
refers to a specific version of NVIDIA’s Data Center GPU Manager (DCGM) tool, which is a package for managing and monitoring NVIDIA data center GPUs. In particular, cuda12 indicates that this management tool is installed for the CUDA 12 version, and datacenter-gpu-manager-4 refers to the 4.x version of DCGM. This tool provides various features, including GPU status monitoring, diagnostics, alert system, and power/clock management.
- Add the CUDA repository to DNF.Color mode
dnf config-manager --add-repo https://developer.download.nvidia.com/compute/cuda/repos/rhel8/x86_64/cuda-rhel8.repodnf config-manager --add-repo https://developer.download.nvidia.com/compute/cuda/repos/rhel8/x86_64/cuda-rhel8.repocode block. Add DNF Repository - Check the CUDA version.Color mode
nvidia-smi | grep CUDAnvidia-smi | grep CUDACode block. Check CUDA version Color mode| NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 || NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 |Code block. Example of CUDA version check result Color modeCUDA_VERSION=12CUDA_VERSION=12Code block. CUDA version setting command - Check the list of datacenter-gpu-manager-cuda modules.Color mode
dnf list datacenter-gpu-manager-4-cuda${CUDA_VERSION} --showduplicatesdnf list datacenter-gpu-manager-4-cuda${CUDA_VERSION} --showduplicatesCode block. Check the datacenter-gpu-manager-cuda module list Color modeUpdating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:00:34 ago on Wed 19 Nov 2025 12:26:56 AM EST. Available Packages datacenter-gpu-manager-4-cuda12.x86_64 1:4.0.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.1.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.1.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.2-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.3-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.3-2 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.3.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.3.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.4.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.4.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.4.2-1 cuda-rhel8-x86_64Updating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:00:34 ago on Wed 19 Nov 2025 12:26:56 AM EST. Available Packages datacenter-gpu-manager-4-cuda12.x86_64 1:4.0.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.1.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.1.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.2-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.3-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.2.3-2 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.3.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.3.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.4.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.4.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-4-cuda12.x86_64 1:4.4.2-1 cuda-rhel8-x86_64Code block. Example of checking the list of datacenter-gpu-manager-cuda modules. - Install datacenter-gpu-manager-cuda.Color mode
dnf install datacenter-gpu-manager-4-cuda${CUDA_VERSION}dnf install datacenter-gpu-manager-4-cuda${CUDA_VERSION}Code block. Install datacenter-gpu-manager-cuda Color modeUpdating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:07:12 ago on Wed 19 Nov 2025 12:26:56 AM EST. Dependencies resolved. =================================================================================================== Package Architecture Version Repository Size =================================================================================================== Installing: datacenter-gpu-manager-4-cuda12 x86_64 1:4.4.2-1 cuda-rhel8-x86_64 554 M Installing dependencies: datacenter-gpu-manager-4-core x86_64 1:4.4.2-1 cuda-rhel8-x86_64 9.9 M Installing weak dependencies: datacenter-gpu-manager-4-proprietary x86_64 1:4.4.2-1 cuda-rhel8-x86_64 5.3 M datacenter-gpu-manager-4-proprietary-cuda12 x86_64 1:4.4.2-1 cuda-rhel8-x86_64 289 M Transaction Summary ==================================================================================================== Install 4 Packages ... Is this ok [y/N]: yUpdating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:07:12 ago on Wed 19 Nov 2025 12:26:56 AM EST. Dependencies resolved. =================================================================================================== Package Architecture Version Repository Size =================================================================================================== Installing: datacenter-gpu-manager-4-cuda12 x86_64 1:4.4.2-1 cuda-rhel8-x86_64 554 M Installing dependencies: datacenter-gpu-manager-4-core x86_64 1:4.4.2-1 cuda-rhel8-x86_64 9.9 M Installing weak dependencies: datacenter-gpu-manager-4-proprietary x86_64 1:4.4.2-1 cuda-rhel8-x86_64 5.3 M datacenter-gpu-manager-4-proprietary-cuda12 x86_64 1:4.4.2-1 cuda-rhel8-x86_64 289 M Transaction Summary ==================================================================================================== Install 4 Packages ... Is this ok [y/N]: yCode block. Example of datacenter-gpu-manager-cuda installation result
datacenter-gpu-manager-exporter installation (for RHEL)
It is a tool that, based on NVIDIA Data Center GPU Manager (DCGM), collects various GPU metrics such as GPU usage, memory usage, temperature, and power consumption, and exposes them for use in monitoring systems like Prometheus.
Add the CUDA Repository to DNF. 1. (If you have already performed this command, proceed to the next step.)
Color modednf config-manager --add-repo https://developer.download.nvidia.com/compute/cuda/repos/rhel8/x86_64/cuda-rhel8.repodnf config-manager --add-repo https://developer.download.nvidia.com/compute/cuda/repos/rhel8/x86_64/cuda-rhel8.repoCode block. Add DNF Repository Check the CUDA version. 2. (If you have already performed this command, proceed to the next step.)
Color modenvidia-smi | grep CUDAnvidia-smi | grep CUDACode block. Check CUDA version Color mode| NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 || NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 |Code block. Example of CUDA version check result Color modeCUDA_VERSION=12CUDA_VERSION=12Code block. CUDA version setting command Check the datacenter-gpu-manager-exporter module list.
Color modednf list datacenter-gpu-manager-exporter --showduplicatesdnf list datacenter-gpu-manager-exporter --showduplicatesCode block. Check the list of datacenter-gpu-manager-exporter modules Color modeUpdating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:02:11 ago on Wed 19 Nov 2025 12:26:56 AM EST. Available Packages datacenter-gpu-manager-exporter.x86_64 4.0.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.1.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.1.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.1.3-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.5.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.5.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.5.2-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.6.0-1 cuda-rhel8-x86_64Updating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:02:11 ago on Wed 19 Nov 2025 12:26:56 AM EST. Available Packages datacenter-gpu-manager-exporter.x86_64 4.0.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.1.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.1.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.1.3-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.5.0-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.5.1-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.5.2-1 cuda-rhel8-x86_64 datacenter-gpu-manager-exporter.x86_64 4.6.0-1 cuda-rhel8-x86_64code block. Example of checking the module list of datacenter-gpu-manager-exporter Install datacenter-gpu-manager-cuda. dcgm-exporter 4.5.X requires glibc 2.34 or newer, but because RHEL 9 provides glibc 2.34, we install it by specifying version 4.1.3-1.
Color modednf install datacenter-gpu-manager-exporter-4.1.3-1dnf install datacenter-gpu-manager-exporter-4.1.3-1Code block. Install datacenter-gpu-manager-cuda Color modeUpdating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:07:12 ago on Wed 19 Nov 2025 12:26:56 AM EST. Dependencies resolved. ==================================================================================================== Package Architecture Version Repository Size ==================================================================================================== Installing: datacenter-gpu-manager-exporter x86_64 4.1.3-1 cuda-rhel8-x86_64 26 M Is this ok [y/N]: yUpdating Subscription Management repositories. Unable to read consumer identity This system is not registered with an entitlement server. You can use subscription-manager to register. Last metadata expiration check: 0:07:12 ago on Wed 19 Nov 2025 12:26:56 AM EST. Dependencies resolved. ==================================================================================================== Package Architecture Version Repository Size ==================================================================================================== Installing: datacenter-gpu-manager-exporter x86_64 4.1.3-1 cuda-rhel8-x86_64 26 M Is this ok [y/N]: yCode block. Example of datacenter-gpu-manager-cuda installation result Color modecat /usr/lib/systemd/system/nvidia-dcgm-exporter.service | grep ExecStartcat /usr/lib/systemd/system/nvidia-dcgm-exporter.service | grep ExecStartCode block. datacenter-gpu-manager-exporter configuration file Color modeExecStart=/usr/bin/dcgm-exporter -f /etc/dcgm-exporter/default-counters.csvExecStart=/usr/bin/dcgm-exporter -f /etc/dcgm-exporter/default-counters.csvCode block. Example of the result of checking the datacenter-gpu-manager-exporter configuration file. When installing the DCGM Exporter, review the provided configuration and remove
#for required metrics, and add#for unnecessary metrics.Color modevi /etc/dcgm-exporter/default-counters.csv ## Example ## ... DCGM_FI_PROF_PIPE_TENSOR_ACTIVE, gauge, Ratio of cycles the tensor (HMMA) pipe is active. DCGM_FI_PROF_DRAM_ACTIVE, gauge, Ratio of cycles the device memory interface is active sending or receiving data. # DCGM_FI_PROF_PIPE_FP64_ACTIVE, gauge, Ratio of cycles the fp64 pipes are active. # DCGM_FI_PROF_PIPE_FP32_ACTIVE, gauge, Ratio of cycles the fp32 pipes are active. ...vi /etc/dcgm-exporter/default-counters.csv ## Example ## ... DCGM_FI_PROF_PIPE_TENSOR_ACTIVE, gauge, Ratio of cycles the tensor (HMMA) pipe is active. DCGM_FI_PROF_DRAM_ACTIVE, gauge, Ratio of cycles the device memory interface is active sending or receiving data. # DCGM_FI_PROF_PIPE_FP64_ACTIVE, gauge, Ratio of cycles the fp64 pipes are active. # DCGM_FI_PROF_PIPE_FP32_ACTIVE, gauge, Ratio of cycles the fp32 pipes are active. ...Code block. Example of datacenter-gpu-manager-exporter metric configuration
Enable and start DCGM service (for RHEL)
Activating and starting the nvdia-dcgm service.
Color modesystemctl enable --now nvidia-dcgmsystemctl enable --now nvidia-dcgmCode block. nvdia-dcgm service activation and start command Enable and start the nvdia-dcgm-exporter service.
Color modesystemctl enable --now nvidia-dcgm-exportersystemctl enable --now nvidia-dcgm-exporterCode block. nvdia-dcgm-exporter service activation and start command
For more details, refer to ServiceWatch > Using ServiceWatch Agent.
DCGM Exporter metric
DCGM Exporter Key Metrics
Among the metrics provided by the DCGM Exporter, the main GPU metrics are as follows.
| Category | DCGM Field | Prometheus Metric Type | Summary | |
|---|---|---|---|---|
| Clocks | DCGM_FI_DEV_SM_CLOCK | gauge | SM clock frequency (in MHz) | |
| Clocks | DCGM_FI_DEV_MEM_CLOCK | gauge | Memory clock frequency (in MHz) | |
| Temperature | DCGM_FI_DEV_GPU_TEMP | gauge | GPU temperature (in C) | |
| Power | DCGM_FI_DEV_POWER_USAGE | gauge | Power draw (in W) | |
| Utilization | DCGM_FI_DEV_GPU_UTIL | gauge | GPU utilization (in %) | |
| Utilization | DCGM_FI_DEV_MEM_COPY_UTIL | gauge | Memory utilization (in %) | |
| Memory Usage | DCGM_FI_DEV_FB_FREE | gauge | Frame buffer memory free (in MiB) | |
| Memory Usage | DCGM_FI_DEV_FB_USED | gauge | Frame buffer memory used (in MiB) | |
| Nvlink | DCGM_FI_DEV_NVLINK_BANDWIDTH_TOTAL(8 GPU only) | counter | Total number of NVLink bandwidth counters for all lanes |
DCGM Exporter metric collection configuration
Please refer to the default metrics of DCGM Exporter at DCGM Exporter > 기본 지표.
- Besides the default configuration, remove
#from default-counters.csv for any additional metrics you want to set. - For default metrics you do not wish to collect, add
#or delete the corresponding entry.
# Format
# If line starts with a '#' it is considered a comment
# DCGM FIELD, Prometheus metric type, help message
# Clocks
DCGM_FI_DEV_SM_CLOCK, gauge, SM clock frequency (in MHz).
DCGM_FI_DEV_MEM_CLOCK, gauge, Memory clock frequency (in MHz).
# Temperature
DCGM_FI_DEV_MEMORY_TEMP, gauge, Memory temperature (in C).
DCGM_FI_DEV_GPU_TEMP, gauge, GPU temperature (in C).
# Power
DCGM_FI_DEV_POWER_USAGE, gauge, Power draw (in W).
DCGM_FI_DEV_TOTAL_ENERGY_CONSUMPTION, counter, Total energy consumption since boot (in mJ).
# PCIE
# DCGM_FI_PROF_PCIE_TX_BYTES, counter, Total number of bytes transmitted through PCIe TX via NVML.
# DCGM_FI_PROF_PCIE_RX_BYTES, counter, Total number of bytes received through PCIe RX via NVML.
...# Format
# If line starts with a '#' it is considered a comment
# DCGM FIELD, Prometheus metric type, help message
# Clocks
DCGM_FI_DEV_SM_CLOCK, gauge, SM clock frequency (in MHz).
DCGM_FI_DEV_MEM_CLOCK, gauge, Memory clock frequency (in MHz).
# Temperature
DCGM_FI_DEV_MEMORY_TEMP, gauge, Memory temperature (in C).
DCGM_FI_DEV_GPU_TEMP, gauge, GPU temperature (in C).
# Power
DCGM_FI_DEV_POWER_USAGE, gauge, Power draw (in W).
DCGM_FI_DEV_TOTAL_ENERGY_CONSUMPTION, counter, Total energy consumption since boot (in mJ).
# PCIE
# DCGM_FI_PROF_PCIE_TX_BYTES, counter, Total number of bytes transmitted through PCIe TX via NVML.
# DCGM_FI_PROF_PCIE_RX_BYTES, counter, Total number of bytes received through PCIe RX via NVML.
...2.3.3 - API Reference
2.3.4 - CLI Reference
2.3.5 - Release Note
GPU Server
- Add Kubernetes image
- When creating a GPU Server, you can select the Kubernetes image (Ubuntu).
- An SSD volume with configurable IOPS and throughput has been added.
- When creating Block Storage, you can select the SSD_Provisioned disk type.
- You can set the maximum IOPS and Throughput values.
- Provision of ServiceWatch service integration
- You can monitor data through the ServiceWatch service.
- When creating a GPU server, you can select a RHEL image.
- Keypair management feature has been added.
- You can generate a keypair for use, or retrieve a public key and apply it.
- Add GPU Server feature
- The IP, Public NAT IP, and Private NAT IP configuration features have been added.
- An LLM Endpoint is provided for LLM usage.
- The method for sharing images between accounts has changed.
- You can create a new Image for sharing and share it.
- Add GPU Server usage guide
- Added the guides Using Multi-instance GPU on GPU Server and Using NVSwitch on GPU Server.
- GPU Server RHEL OS and GPU driver versions have been added.
- Add GPU Server feature
- NAT configuration feature has been added to the GPU Server.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have officially launched the GPU Server service.
- We have launched a virtualization computing service that lets you allocate and use infrastructure resources such as CPU, GPU, and memory provided by the server as needed, without having to purchase them individually.
2.4 - Bare Metal Server
2.4.1 - Overview
Service Overview
Bare Metal Server does not use virtualization technology and is a high-performance cloud computing service that can allocate and use physically separated computing resources such as CPU and memory exclusively. It is not affected by other cloud users, allowing you to reliably operate performance-sensitive services.
Features
Easy and convenient computing environment setup: Through the web-based Console, you can easily handle everything from Bare Metal Server provisioning to resource management and cost management. You can receive a server with standard specs (CPU, Memory, Disk) allocated exclusively and use it immediately.
Providing High-Performance Computing Environment: We provide servers suitable for workloads that require large capacity and high performance—such as real-time (Real-Time) systems, HPC (High Performance Computing), and servers that demand excessive I/O usage—in a physically isolated environment.
Efficient Service Delivery: Ensure performance and stability through optimal server selection and in-house testing. Customers can choose the optimal resources that fit their service environment from the various specifications of Bare Metal Servers offered by Samsung Cloud Platform.
Service Architecture Diagram
Provided features
Bare Metal Server provides the following features.
- Auto Provisioning (Auto Provisioning) and Management: Through the web-based Console, you can easily provision Bare Metal Servers, manage resources, and control costs.
- Providing various types of server types and OS images: Provides CPU, Memory, and Disk resources of standard server types, and offers a variety of standard OS images.
- Storage Connection: Provides additional attached storage beyond the OS disk. You can connect and use Block Storage, File Storage, and Object Storage.
- Network Connection: You can connect the standard subnet/IP settings of a Bare Metal Server and a Public NAT IP. Provides a local subnet connection for inter-server communication. This can be modified on the detail page.
- Monitoring: You can view monitoring information such as CPU, Memory, and Disk, which are computing resources, through Cloud Monitoring. To use the Cloud Monitoring service for Bare Metal Server, you must install the Agent. Please be sure to install the Agent for stable Bare Metal Server service usage. For more details, see Bare Metal Server Monitoring Metrics.
- Backup and Recovery: You can back up and restore the Bare Metal Server’s filesystem using the Backup service.
- Efficient Cost Management: You can easily create or terminate servers as needed, and because billing is based on actual usage time, you can use it cost‑effectively in various unpredictable situations.
- Local disk partition creation You can create and use up to 10 local disk partitions.
- Terraform Provisioning: Provides an IaC environment using Terraform.
Components
Bare Metal Server provides various standard OS images and standard server types. Users can select and use them according to the scale of the service they want to configure.
OS Image provided version
The OS images supported by Bare Metal Server are as follows
| OS Image version | EoS Date |
|---|---|
| Oracle Linux 9.6 | 2032-06-30 |
| RHEL 8.10 | 2029-05-31 |
| RHEL 9.4 | 2026-04-30 |
| RHEL 9.6 | 2027-05-31 |
| Rocky Linux 8.10 | 2029-05-31 |
| Rocky Linux 9.6 | 2025-11-30 |
| Ubuntu 22.04 | 2027-06-30 |
| Ubuntu 24.04 | 2029-06-30 |
| Windows 2019 | 2029-01-09 |
| Windows 2022 | 2031-10-14 |
- Oracle Linux, RHEL, and Rocky Linux only provide even-numbered minor versions. Check the OS Image’s EOS (End of Support)/EOL (End of Life) Date.
- To ensure stable OS operation, apply new or additional individual packages yourself.
Server type
The server types supported by Bare Metal Server are as follows. For detailed information about the server types supported by Bare Metal Server, see Bare Metal Server Server Types.
s3v16m64_metal
| Category | example | Detailed description |
|---|---|---|
| Server generation | s3 | Provided server categories and generations
|
| CPU vCore | v16 | Number of vCores
|
| Memory | m64 | Memory capacity
|
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
2.4.1.1 - Server Type
Bare Metal Server server type
Bare Metal Server provides server types that suit the intended use. Server types are composed of various combinations such as CPU and Memory. The server used for a Bare Metal Server is determined by the server type selected when creating the Bare Metal Server. Please select a server type based on the specifications of the application you intend to run on the Bare Metal Server.
The server types supported by Bare Metal Server are as follows.
s3v16m64_metal
Category | example | Detailed description |
|---|---|---|
| Server generation | s3 | Provided server categories and generations
|
| CPU vCore | v16 | Number of vCores
|
| Memory | m64 | Memory Capacity
|
s4/h4 server type
The Bare Metal Server s4 server type is offered with standard specifications (vCPU, Memory) and, because it receives physically isolated resources, it is suitable for high-performance applications. Additionally, the Bare Metal Server h4 server type is offered with high-capacity specifications and is suitable for high-performance applications that require large-scale data processing.
- Supports a total of five vCPU options (16, 32, 64, 96, 128 vCore)
- Intel 6th Generation (Granite Rapids) Processor
- Supports up to 64 physical cores, 128 vCPUs, and 2,048 GB of memory
- Provides two internal disks up to 1.92 TB each (for OS use)
| Server type | Physical CPU | vCPU | Memory | CPU Type | Internal Disk(OS) | ||
|---|---|---|---|---|---|---|---|
| s4v16m64_metal | 8 Core | 16 vCore | 64 GB | Intel Xeon 6507P up to 4.3 GHz | 480GB * 2EA | ||
| s4v16m128_metal | 8 Core | 16 vCore | 128 GB | Intel Xeon 6507P up to 4.3 GHz | 480GB * 2EA | ||
| s4v16m256_metal | 8 Core | 16 vCore | 256 GB | Intel Xeon 6507P with a maximum frequency of 4.3 GHz | 480GB * 2EA | ||
| h4v32m128_metal | 16 Core | 32 vCore | 128 GB | Intel Xeon 6517P up to 4.0 GHz | 960GB * 2EA | ||
| h4v32m256_metal | 16 Core | 32 vCore | 256 GB | Intel Xeon 6517P up to 4.0 GHz | 960GB * 2EA | ||
| h4v32m512_metal | 16 Core | 32 vCore | 512 GB | Intel Xeon 6517P up to 4.0 GHz | 960GB * 2EA | ||
| h4v64m256_metal | 32 Core | 64 vCore | 256 GB | Intel Xeon 6737P up to 4.0 GHz | 1.92TB * 2EA | ||
| h4v64m512_metal | 32 Core | 64 vCore | 512 GB | Intel Xeon 6737P up to 4.0 GHz | 1.92TB * 2EA | ||
| h4v64m1024_metal | 32 Core | 64 vCore | 1024 GB | Intel Xeon 6737P up to 4.0 GHz | 1.92TB * 2EA | ||
| h4v96m512_metal | 48 Core | 96 vCore | 512 GB | Intel Xeon 6520P up to 3.4 GHz | 1.92TB * 2EA | ||
| h4v96m768_metal | 48 Core | 96 vCore | 768 GB | Intel Xeon 6520P with a maximum frequency of 3.4 GHz | 1.92TB * 2EA | ||
| h4v96m2048_metal | 48 Core | 96 vCore | 2048 GB | Intel Xeon 6520P up to 3.4 GHz | 1.92TB * 2EA | ||
| h4v128m512_metal | 64 Core | 128 vCore | 512 GB | Intel Xeon 6737P up to 4.0 GHz | 1.92TB * 2EA | ||
| h4v128m1024_metal | 64 Core | 128 vCore | 1024 GB | Intel Xeon 6737P up to 4.0 GHz | 1.92TB * 2EA | ||
| h4v128m2048_metal | 64 Core | 128 vCore | 2048 GB | Intel Xeon 6737P up to 4.0 GHz | 1.92TB * 2EA |
s3/h3 server type
The Bare Metal Server s3 server type is offered with standard specifications (vCPU, Memory) and is suitable for high‑performance applications because it receives physically isolated resources. Additionally, the Bare Metal Server h3 server type is offered with high-capacity specifications and is suitable for high-performance applications that require large-scale data processing.
- Supports a total of five vCPU options (16, 32, 64, 96, 128 vCore)
- Intel 4th Generation (Sapphire Rapids) Processor
- Supports up to 64 physical cores, 128 vCPUs, and 2,048 GB of memory.
- Provides two internal disks up to 1.92 TB (for OS use)
| Server type | Physical CPU | vCPU | Memory | CPU Type | Internal Disk(OS) | ||
|---|---|---|---|---|---|---|---|
| s3v16m64_metal | 8 Core | 16 vCore | 64 GB | Intel Xeon Gold 6434 up to 4.1 GHz | 480 GB * 2EA | ||
| s3v16m128_metal | 8 Core | 16 vCore | 128 GB | Intel Xeon Gold 6434 up to 4.1 GHz | 480 GB * 2EA | ||
| s3v16m256_metal | 8 Core | 16 vCore | 256 GB | Intel Xeon Gold 6434 up to 4.1 GHz | 480 GB * 2EA | ||
| h3v32m128_metal | 16 Core | 32 vCore | 128 GB | Intel Xeon Gold 6444Y up to 4.0 GHz | 960 GB * 2EA | ||
| h3v32m256_metal | 16 Core | 32 vCore | 256 GB | Intel Xeon Gold 6444Y up to 4.0 GHz | 960 GB * 2EA | ||
| h3v32m512_metal | 16 Core | 32 vCore | 512 GB | Intel Xeon Gold 6444Y up to 4.0 GHz | 960 GB * 2EA | ||
| h3v64m256_metal | 32 Core | 64 vCore | 256 GB | Intel Xeon Gold 6448H up to 3.2 GHz | 1.92 TB * 2EA | ||
| h3v64m512_metal | 32 Core | 64 vCore | 512 GB | Intel Xeon Gold 6448H up to 3.2 GHz | 1.92 TB * 2EA | ||
| h3v64m1024_metal | 32 Core | 64 vCore | 1024 GB | Intel Xeon Gold 6448H up to 3.2 GHz | 1.92 TB * 2EA | ||
| h3v96m384_metal | 48 Core | 96 vCore | 384 GB | Intel Xeon Gold 6442Y, up to 3.3 GHz | 1.92 TB * 2EA | ||
| h3v96m768_metal | 48 Core | 96 vCore | 768 GB | Intel Xeon Gold 6442Y up to 3.3 GHz | 1.92 TB * 2EA | ||
| h3v96m1536_metal | 48 Core | 96 vCore | 1536 GB | Intel Xeon Gold 6442Y, up to 3.3 GHz | 1.92 TB * 2EA | ||
| h3v128m512_metal | 64 Core | 128 vCore | 512 GB | Intel Xeon Gold 6448H up to 3.2 GHz | 1.92 TB * 2EA | ||
| h3v128m1024_metal | 64 Core | 128 vCore | 1024 GB | Intel Xeon Gold 6448H up to 3.2 GHz | 1.92 TB * 2EA | ||
| h3v128m2048_metal | 64 Core | 128 vCore | 2048 GB | Intel Xeon Gold 6448H up to 3.2 GHz | 1.92 TB * 2EA |
s2/h2 server type
The Bare Metal Server s2 server type is offered with standard specifications (vCPU, Memory) and, because it receives physically isolated resources, it is suitable for high-performance applications.
Additionally, the Bare Metal Server h2 server type is offered with high-capacity specifications and is suitable for high-performance applications that require large-scale data processing.
- Supports five vCPU options (16, 24, 32, 72, 96 vCore)
- Intel 3rd‑Generation (Ice Lake) Processor
- Supports up to 48 physical cores, 96 vCPUs, and 1,024 GB of memory.
- Provides two internal disks up to 1.92 TB for OS use
| Server type | Physical CPU | vCPU | Memory | CPU Type | Internal Disk(OS) | |
|---|---|---|---|---|---|---|
| s2v16m64_metal | 8 Core | 16 vCore | 64 GB | Intel Xeon Gold 6334 with a maximum frequency of 3.6 GHz | 480 GB * 2EA | |
| s2v16m128_metal | 8 Core | 16 vCore | 128 GB | Intel Xeon Gold 6334 with a maximum frequency of 3.6 GHz | 480 GB * 2EA | |
| s2v16m256_metal | 8 Core | 16 vCore | 256 GB | Intel Xeon Gold 6334 with a maximum frequency of 3.6 GHz | 480 GB * 2EA | |
| h2v24m96_metal | 12 Core | 24 vCore | 96 GB | Intel Xeon Gold 5317 up to 3.4 GHz | 960 GB * 2EA | |
| h2v24m192_metal | 12 Core | 24 vCore | 192 GB | Intel Xeon Gold 5317 up to 3.4 GHz | 960 GB * 2EA | |
| h2v24m384_metal | 12 Core | 24 vCore | 384 GB | Intel Xeon Gold 5317 up to 3.4 GHz | 960 GB * 2EA | |
| h2v32m128_metal | 16 Core | 32 vCore | 128 GB | Intel Xeon Gold 6346 with a maximum frequency of 3.6 GHz | 960 GB * 2EA | |
| h2v32m256_metal | 16 Core | 32 vCore | 256 GB | Intel Xeon Gold 6346 up to 3.6 GHz | 960 GB * 2EA | |
| h2v32m512_metal | 16 Core | 32 vCore | 512 GB | Intel Xeon Gold 6346 up to 3.6 GHz | 960 GB * 2EA | |
| h2v72m256_metal | 36 Core | 72 vCore | 256 GB | Intel Xeon Gold 6354, up to 3.6 GHz | 1.92 TB * 2EA | |
| h2v72m512_metal | 36 Core | 72 vCore | 512 GB | Intel Xeon Gold 6354 with a maximum frequency of 3.6 GHz | 1.92 TB * 2EA | |
| h2v72m1024_metal | 36 Core | 72 vCore | 1024 GB | Intel Xeon Gold 6354 with a maximum frequency of 3.6 GHz | 1.92 TB * 2EA | |
| h2v96m384_metal | 48 Core | 96 vCore | 384 GB | Intel Xeon Gold 6342 up to 3.3 GHz | 1.92 TB * 2EA | |
| h2v96m768_metal | 48 Core | 96 vCore | 768 GB | Intel Xeon Gold 6342 up to 3.3 GHz | 1.92 TB * 2EA |
2.4.1.2 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by leveraging ServiceWatch released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a seamless monitoring environment.
If you are collecting metrics and logs through the Cloud Monitoring Agent, you need to switch to the ServiceWatch Agent.
For detailed information about ServiceWatch, please refer to ServiceWatch Overview.
Detailed information about ServiceWatch Agent can be found in the ServiceWatch Agent.
Bare Metal Server Monitoring Metrics
The table below shows the monitoring metrics of Bare Metal Server that can be viewed through Cloud Monitoring.
| Performance items | Detailed description | unit |
|---|---|---|
| Core Usage [IO Wait] | Ratio of CPU time spent in wait state (disk wait) | % |
| Core Usage [System] | Proportion of CPU time spent in kernel space | % |
| Core Usage [User] | Proportion of CPU time spent in user space | % |
| CPU Cores | Number of CPU cores on the host | cnt |
| CPU Usage [Active] | Percentage of CPU time used, excluding Idle and IOWait states | % |
| CPU Usage [Idle] | It is the proportion of CPU time spent in idle state. | % |
| CPU Usage [IO Wait] | Ratio of CPU time spent in wait state (disk wait) | % |
| CPU Usage [System] | Percentage of CPU time used by the kernel | % |
| CPU Usage [User] | Percentage of CPU time used in user space | % |
| CPU Usage/Core [Active] | Percentage of CPU time used other than Idle and IOWait states | % |
| CPU Usage/Core [Idle] | Ratio of CPU time spent in idle state | % |
| CPU Usage/Core [IO Wait] | Ratio of CPU time spent in wait state (disk wait) | % |
| CPU Usage/Core [System] | Percentage of CPU time used by the kernel | % |
| CPU Usage/Core [User] | Percentage of CPU time used in user space | % |
| Disk CPU Usage [IO Request] | Proportion of CPU time during which I/O requests to the device were executed | % |
| Disk Queue Size [Avg] | Average queue length of requests executed for the device | num |
| Disk Read Bytes | Bytes per second read from the device | bytes |
| Disk Read Bytes [Delta Avg] | Average of system.diskio.read.bytes_delta for individual disks | bytes |
| Disk Read Bytes [Delta Max] | Maximum system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta Min] | minimum system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta Sum] | Sum of system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta] | Delta of the system.diskio.read.bytes value for each Disk | bytes |
| Disk Read Bytes [Success] | Total bytes successfully read | bytes |
| Disk Read Requests | Number of read requests to the disk device per second | cnt |
| Disk Read Requests [Delta Avg] | Average of system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Max] | Maximum system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Min] | Minimum of individual Disks’ system.diskio.read.count_delta | cnt |
| Disk Read Requests [Delta Sum] | Sum of system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Success Delta] | Delta of system.diskio.read.count for each Disk | cnt |
| Disk Read Requests [Success] | Total number of successful reads | cnt |
| Disk Request Size [Avg] | Average size of requests executed on the device (unit: sectors) | num |
| Disk Service Time [Avg] | Average service time (ms) of input requests executed on the device | ms |
| Disk Wait Time [Avg] | Average time taken for requests executed on the device to be supported | ms |
| Disk Wait Time [Read] | Average disk wait time | ms |
| Disk Wait Time [Write] | Disk average wait time | ms |
| Disk Write Bytes [Delta Avg] | Average of system.diskio.write.bytes_delta for individual disks | bytes |
| Disk Write Bytes [Delta Max] | Maximum system.diskio.write.bytes_delta of individual disks | bytes |
| Disk Write Bytes [Delta Min] | Minimum of system.diskio.write.bytes_delta for individual disks | bytes |
| Disk Write Bytes [Delta Sum] | Sum of system.diskio.write.bytes_delta of individual disks | bytes |
| Disk Write Bytes [Delta] | individual Disk’s system.diskio.write.bytes value delta | bytes |
| Disk Write Bytes [Success] | Total bytes successfully written | bytes |
| Disk Write Requests | Number of write requests to the disk device per second | cnt |
| Disk Write Requests [Delta Avg] | Average of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Max] | Maximum system.diskio.write.count_delta of individual disks | cnt |
| Disk Write Requests [Delta Min] | Minimum of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Sum] | Sum of system.diskio.write.count_delta of individual disks | cnt |
| Disk Write Requests [Success Delta] | Delta of system.diskio.write.count for each Disk | cnt |
| Disk Write Requests [Success] | Total number of successful writes | cnt |
| Disk Writes Bytes | Bytes per second written to the device | bytes |
| Filesystem Hang Check | filesystem(local/NFS) hang check (normal:1, abnormal:0) | status |
| Filesystem Nodes | Total number of file nodes in the file system | cnt |
| Filesystem Nodes [Free] | Total number of available file nodes in the file system | cnt |
| Filesystem Size [Available] | Disk space (bytes) available to unauthorized users | bytes |
| Filesystem Size [Free] | Available disk space (bytes) | bytes |
| Filesystem Size [Total] | Total disk space (bytes) | bytes |
| Filesystem Usage | Used disk space percentage | % |
| Filesystem Usage [Avg] | Average of individual filesystem.used.pct | % |
| Filesystem Usage [Inode] | inode usage | % |
| Filesystem Usage [Max] | Maximum among individual filesystem.used.pct | % |
| Filesystem Usage [Min] | minimum among individual filesystem.used.pct | % |
| Filesystem Usage [Total] | Total filesystem usage | % |
| Filesystem Used | Used disk space (bytes) | bytes |
| Filesystem Used [Inode] | inode usage | bytes |
| Memory Free | Total amount of available memory (bytes). Memory used by system cache and buffers is not included. | bytes |
| Memory Free [Actual] | Actual usable memory (bytes). | bytes |
| Memory Free [Swap] | Available swap memory. | bytes |
| Memory Total | total memory | bytes |
| Memory Total [Swap] | Total swap memory. | bytes |
| Memory Usage | Percentage of used memory | % |
| Memory Usage [Actual] | Percentage of memory actually used | % |
| Memory Usage [Cache Swap] | cached swap usage | % |
| Memory Usage [Swap] | Percentage of used swap memory | % |
| Memory Used | used memory | bytes |
| Memory Used [Actual] | Actual used memory (bytes). The value obtained by subtracting used memory from total memory. | bytes |
| Memory Used [Swap] | Used swap memory | bytes |
| Collisions | Network collision | cnt |
| Network In Bytes | Number of received bytes | bytes |
| Network In Bytes [Delta Avg] | Average of system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Max] | Maximum of system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Min] | Minimum of system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Sum] | Sum of system.network.in.bytes_delta for individual networks | bytes |
| Network In Bytes [Delta] | Delta of received byte count | bytes |
| Network In Dropped | Number of deleted packets among incoming packets | cnt |
| Network In Errors | Number of errors during reception | cnt |
| Network In Packets | Number of received packets | cnt |
| Network In Packets [Delta Avg] | Average of system.network.in.packets_delta for each network | cnt |
| Network In Packets [Delta Max] | Maximum of system.network.in.packets_delta for each network | cnt |
| Network In Packets [Delta Min] | Minimum of system.network.in.packets_delta for each network | cnt |
| Network In Packets [Delta Sum] | Sum of system.network.in.packets_delta for individual networks | cnt |
| Network In Packets [Delta] | Delta of received packet count | cnt |
| Network Out Bytes | Number of transmitted bytes | bytes |
| Network Out Bytes [Delta Avg] | Average of system.network.out.bytes_delta for each network | bytes |
| Network Out Bytes [Delta Max] | Maximum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta Min] | Minimum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta Sum] | Sum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta] | Delta of transmitted byte count | bytes |
| Network Out Dropped | Number of deleted packets among outgoing packets | cnt |
| Network Out Errors | Number of errors during transmission | cnt |
| Network Out Packets | Number of transmitted packets | cnt |
| Network Out Packets [Delta Avg] | Average of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Max] | Maximum of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Min] | Minimum of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Sum] | Sum of system.network.out.packets_delta for individual networks | cnt |
| Network Out Packets [Delta] | Delta of transmitted packet count | cnt |
| Open Connections [TCP] | All open TCP connections | cnt |
| Open Connections [UDP] | All open UDP connections | cnt |
| Port Usage | Available port usage rate | % |
| SYN Sent Sockets | Number of sockets in SYN_SENT state (when connecting from local to remote) | cnt |
| Kernel PID Max | kernel.pid_max value | cnt |
| Kernel Thread Max | kernel.threads-max value | cnt |
| Process CPU Usage | Percentage of CPU time consumed by the process since the last update | % |
| Process CPU Usage/Core | Percentage of CPU time used by the process since the last event | % |
| Process Memory Usage | The proportion of main memory (RAM) occupied by a process | % |
| Process Memory Used | Resident Set size. The amount of memory a process occupies in RAM. | bytes |
| Process PID | process pid | pid |
| Process PPID | Parent process PID | pid |
| Processes [Dead] | Number of dead processes | cnt |
| Processes [Idle] | Number of idle processes | cnt |
| Processes [Running] | Number of running processes | cnt |
| Processes [Sleeping] | sleeping processes count | cnt |
| Processes [Stopped] | number of stopped processes | cnt |
| Processes [Total] | Total number of processes | cnt |
| Processes [Unknown] | Number of processes with an unknown or unsearchable status | cnt |
| Processes [Zombie] | zombie processes count | cnt |
| Running Process Usage | process usage | % |
| Running Processes | Number of running processes | cnt |
| Running Thread Usage | Thread usage | % |
| Running Threads | Total number of threads running in running processes | cnt |
| Context Switches | context switch count (per second) | cnt |
| Load/Core [1 min] | The load over the last 1 minute divided by the number of cores | cnt |
| Load/Core [15 min] | The load over the last 15 minutes divided by the number of cores | cnt |
| Load/Core [5 min] | The load over the last 5 minutes divided by the number of cores | cnt |
| Multipaths [Active] | External storage connection path status = active count | cnt |
| Multipaths [Failed] | External storage connection path status = failed count | cnt |
| Multipaths [Faulty] | External storage connection path status = faulty count | cnt |
| NTP Offset | measured offset of the last sample (the time difference between the NTP server and the local environment) | num |
| Run Queue Length | Execution queue length | num |
| Uptime | OS uptime (uptime). (milliseconds) | ms |
| Context Switchies | CPU context switch count (per second) | cnt |
| Disk Read Bytes [Sec] | Bytes read per second from the Windows logical disk | cnt |
| Disk Read Time [Avg] | Average data read time (seconds) | sec |
| Disk Transfer Time [Avg] | Disk average wait time | sec |
| Disk Usage | Disk usage | % |
| Disk Write Bytes [Sec] | Number of bytes written in one second on a Windows logical disk | cnt |
| Disk Write Time [Avg] | Average data write time (seconds) | sec |
| Pagingfile Usage | Paging file usage | % |
| Pool Used [Non Paged] | Nonpaged Pool usage in kernel memory | bytes |
| Pool Used [Paged] | Paged Pool usage in kernel memory | bytes |
| Process [Running] | Number of currently running processes | cnt |
| Threads [Running] | Current number of running threads | cnt |
| Threads [Waiting] | Number of threads waiting for processor time | cnt |
2.4.2 - How-to guides
Users can create the service by entering the required information for a Bare Metal Server and selecting detailed options through the Samsung Cloud Platform Console.
Create Bare Metal Server
You can create and use the Bare Metal Server service from the Samsung Cloud Platform Console.
To create a Bare Metal Server, follow these steps.
- Click the All Services > Compute > Bare Metal Server menu. Navigate to the Service Home page of the Bare Metal Server.
- On the Service Home page, click the Create Bare Metal Server button. You will be taken to the Create Bare Metal Server page.
- On the Bare Metal Server Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and Version Selection area.
Category Required statusDetailed description image Required Select the type of image provided - RHEL
- Rocky Linux
- Ubuntu
- Windows
Image version Required Select version of the chosen image - Provide a list of versions for the supplied server image
Table. Bare Metal Server image and version input fields - Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Number of servers Required Number of Bare Metal Server instances to create simultaneously - Only numeric input is allowed, and it must be between 1 and 5
Service Type > Server Type Required Bare Metal Server server type - Select the desired vCPU, Memory, Disk specifications
- For detailed information about the server types provided by Bare Metal Server, refer to Bare Metal Server Server Type
Service Type > Planned Compute Required Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Go to the Planned Compute application page
- For more details, refer to Planned Compute Apply
Automation account Required Automatically create an account to provide automation features after creating a Bare Metal Server - This account is used only for inter-system interfaces
- The password is encrypted and cannot be accessed from outside the system
- If the account is deleted, network changes and some automation functions may be restricted
Table. Bare Metal Server Service Information Input Items - In the Required Information Input area, enter or select the necessary information.
Category RequiredDetailed description Administrator account Required Set the administrator account and password to be used when connecting to the server - RHEL and Ubuntu OS are provided with a fixed root account
- For Windows OS, enter 5 to 20 characters using lowercase letters and numbers
AdministratorNot allowed
Server name Required When the selected number of servers is 1, enter a name to distinguish the Bare Metal Server - Set the hostname to the entered server name
- Start with a lowercase English letter, and use lowercase letters, numbers, and special characters (
-) to enter between 3 and 15 characters
- Must not end with a special character (
-)
Server name Prefix Required Enter a prefix to distinguish each Bare Metal Server generated when the selected number of servers is 2 or more - Automatically generated in the form of user input value (prefix) + ‘
-###’
- Must start with a lowercase English letter and be 3 to 15 characters long, using lowercase letters, numbers, and special characters (
-)
- Must not end with a special character (
-)
Network Settings Required Set the network where the Bare Metal Server will be installed - Select a pre‑created VPC
- General Subnet: Select a pre‑created general Subnet
- IP can be set to auto‑generate or user input, and if input is selected, the user enters the IP manually
- NAT: Available only when there is a single server and the VPC is attached to an Internet Gateway
- Checking the option allows selection of a NAT IP
- NAT IP: Select a NAT IP
- If no NAT IP is available, click the Create New button to generate a Public IP
- Refresh button to view and select the created Public IP
- Creating a Public IP incurs charges according to the Public IP pricing policy
- Local Subnet (optional): Choose to use a local Subnet
- It is not a required element for creating the service
- Select a pre‑created local Subnet
- IP can be set to auto‑generate or user input, and if input is selected, the user enters the IP manually
Table. Required information input fields for Bare Metal Server
- Select the required information in the Image and Version Selection area.
Please use a firewall, etc., to control traffic access for the Bare Metal Server. Security Groups are not provided.
Bare Metal Server’s firewall can only be used to control traffic between the Bare Metal Server and Virtual Server. To use the Bare Metal Server’s firewall, follow the steps below.
- Separate the VPC of Bare Metal Server: Separate them so that Bare Metal Server and Virtual Server do not use the same VPC.
- Create Transit Gateway: Create a Transit Gateway.
- Integration between the Virtual Server’s VPC and the Bare Metal Server’s VPC uses a Transit Gateway.
- When creating a Transit Gateway integration in the VPC of a Bare Metal Server, you must also create the Bare Metal Server’s firewall.
- Firewall Rule registration: Add a rule to the Bare Metal Server’s firewall.
- On the Bare Metal Server Creation page, in the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description Local disk partition Selection Set usage of local disk partitions - Up to 10 partitions can be created, including the root partition
- Up to 90% of total capacity can be used
- After checking Use, partition information can be set
- Set root partition information
- Partition type: flat or lvm selectable
- Partition name: enter partition name
- Partition type can be entered only when it is lvm
- Enter up to 15 characters starting with a letter and containing letters, numbers, and special characters (
-_)
- Partition size: enter at least 50 GB
- Filesystem type: select according to the image used
- For RHEL, Rocky Linux: xfs, ext4
- For Ubuntu: ext4, xfs, btrfs
- For SLES: btrfs, xfs, ext4
- Mount point: start with special character
/and include letters, numbers, and special characters (-_) up to 15 characters- Filesystem type cannot be entered when it is swap
- Available capacity: 90% of the default disk capacity provided when selecting a server
- When setting Partition size, the remaining capacity is automatically calculated and displayed
- The total size of partition disks cannot exceed the available capacity
- Set additional partition information
- Partition type: flat or lvm selectable
- Partition name: enter partition name
- Partition type can be entered only when it is lvm
- Enter up to 15 characters starting with a letter and containing letters, numbers, and special characters (
-_)
- Partition size: enter at least 1 GB
- Filesystem type: select according to the image used>
- For RHEL, Rocky Linux: xfs, ext4, swap
- For Ubuntu: ext4, xfs, btrfs, swap
- For SLES: btrfs, xfs, ext4, swap
- Mount point: start with special character
/and include letters, numbers, and special characters (-_) up to 15 characters- Filesystem type cannot be entered when it is swap
- Available capacity: 90% of the default disk capacity provided when selecting a server
- When setting Partition size, the remaining capacity is automatically calculated and displayed
- The total size of partition disks cannot exceed the available capacity
Placement Group Selection Servers belonging to the same Placement group are distributed across different racks - Provides distributed placement for up to two servers belonging to the same Placement group
- For distributed placement of three or more servers, add additional Placement groups
- Applicable only at initial creation and cannot be modified afterward
- If you terminate the last server in a Placement group, that Placement group is automatically deleted
Lock Selection Using a lock prevents accidental actions that could terminate, start, or stop the server. Hyper Threading Selection Set the logical core count to operate at twice the number of physical cores - To turn off Hyper-Threading, clear the checkbox
- Cannot be changed after server creation
Init Script Selection Script to run when the server starts - The Init Script must be selected differently depending on the image type
- For Windows: select Batch Script
- For Linux: Shell Script
Table. Bare Metal Server additional information entry fields - Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the Bare Metal Server List page.
Bare Metal Server Check detailed information
Bare Metal Server service allows you to view and edit the full resource list and detailed information. The Bare Metal Server Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the Bare Metal Server, follow these steps.
- All Services > Compute > Bare Metal Server Click the menu. Navigate to the Service Home page of Bare Metal Server.
- On the Service Home page, click the Bare Metal Server menu. You will be taken to the Bare Metal Server List page.
- Bare Metal Server List page, click the resource to view detailed information. You will be taken to the Bare Metal Server Details page.
- The Bare Metal Server Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description Bare Metal Server status Status of user-created Bare Metal Server - Creating: state while the server is being created
- Running:: state after creation, ready for use
- Editing:: state while IP is being changed
- Unknown: error state
- Starting: state while the server is starting
- Stopping: state while the server is stopping
- Stopped: state after the server has stopped
- Terminating: state while termination is in progress
- Terminated: state after termination is complete
Server control Button to change server status - Start: Start a stopped server
- Stop: Stop a running server
Service termination Cancel service button Table. Bare Metal Server status information and additional features
- The Bare Metal Server Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
Bare Metal Server List page lets you view detailed information of the selected resource and modify it if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Server name | Server name |
| Image/Version | Server OS image and version |
| Server type | Display vCPU and memory information |
| Planned Compute | Resource status with Planned Compute configured
|
| Lock | Display whether Lock is enabled or disabled
|
| Hyper Threading | Indicates whether Hyper Threading is enabled/disabled
|
| Network | Network information of the Bare Metal Server
|
| Local Subnet | Local Subnet information of the Bare Metal Server
|
| Block Storage | Block Storage information connected to the server
|
| Init Script | View the Init Script content entered when creating the server |
tag
On the Bare Metal Server List page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Bare Metal Server List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Bare Metal Server Resource Management
If you need server control and management functions for the created Bare Metal Server resources, you can perform the tasks on the Bare Metal Server List or Bare Metal Server Details page.
Bare Metal Server Operation Control
You can start, stop, and restart a running Bare Metal Server.
To control the operation of a Bare Metal Server, follow these steps.
- Click the All Services > Compute > Bare Metal Server menu. You will be taken to the Service Home page of the Bare Metal Server.
- On the Service Home page, click the Bare Metal Server menu. You will be taken to the Bare Metal Server List page.
- Bare Metal Server List page allows you to select multiple servers and control them simultaneously using the Start and Stop buttons at the top of the table.
- Bare Metal Server Details page also allows you to start and stop the server.
- On the Bare Metal Server List page, click the resource to control its operation and navigate to the Bare Metal Server Details page.
- Check the server status and complete the changes using each Server Management button.
- Start: Starts a stopped server.
- Stop: Stops the running server.
When a Bare Metal Server is stopped, the server’s power is turned off.
- Since it may affect running applications or storage, we recommend shutting down the OS before stopping.
- After shutting down the OS, be sure to also stop it in the Console.
- If a Bare Metal Server cannot be started when a start request is made, see the following.
- When lock is set: Change the lock setting to disabled, then try again.
- If the Bare Metal Server’s status is not Stopped: Change the Bare Metal Server’s status to Stopped, then try again.
- If a stop request for a Bare Metal Server cannot be fulfilled, see the following.
- When Lock is set: Change the Lock setting to disabled, then try again.
- If the Bare Metal Server’s status is not Running: Change the Bare Metal Server’s status to Running, then try again.
Add Block Storage
You can add Block Storage to a Bare Metal Server.
To add Block Storage, follow the steps below.
- Click the All Services > Compute > Bare Metal Server menu. Navigate to the Service Home page of the Bare Metal Server.
- Click the Bare Metal Server menu on the Service Home page. You will be taken to the Bare Metal Server List page.
- On the Bare Metal Server List page, click the server to which you want to add Block Storage. You will be taken to the Bare Metal Server Details page.
- On the Bare Metal Server Details page, click the Add button in the Block Storage section.
- When the popup confirming the addition of Block Storage opens, click the Confirm button. You will be taken to the Block Storage (BM) Creation page.
- On the Block Storage(BM) Creation page, enter the information required to create the service and create a Block Storage.
- For detailed information on creating Block Storage (BM), please refer to Create Block Storage(BM).
- Go to the Bare Metal Server Details page where Block Storage was added and verify that Block Storage has been added.
Terminate Bare Metal Server
Terminating an unused Bare Metal Server can reduce operating costs. However, terminating a Bare Metal Server may cause the running service to stop immediately, so you should proceed with termination only after fully considering the impact of service interruption.
To terminate a Bare Metal Server, follow the steps below.
- Click the All Services > Compute > Bare Metal Server menu. Navigate to the Service Home page of the Bare Metal Server.
- Click the Bare Metal Server menu on the Service Home page. You will be taken to the Bare Metal Server List page.
- Bare Metal Server List page, select the resource to terminate, and click the Terminate Service button.
- You can select multiple resources and delete them simultaneously.
- You can also delete it by clicking the Service Termination button on the Bare metal Server Details page of the resource to be terminated.
- When termination is complete, verify on the Bare Metal Server list page that the resource has been terminated.
Cancellation constraints
If termination is not possible when requesting cancellation of a Bare Metal Server, a popup will inform you. Please refer to the cases below.
When Block Storage(BM) is attached (simultaneous termination of two or more servers): Please detach the Block Storage(BM) first.
- For detailed information on how to cancel, see Block Storage(BM) Cancellation.
When File Storage is connected: First disconnect the File Storage connection.
- For detailed information on how to cancel, refer to File Storage Cancellation.
When Lock is set: Change the Lock setting to disabled, then try again.
If there are resources connected to Backup Agent or Load Balancer: First disconnect the connections of those resources.
If resource management tasks for the Bare Metal Server are in progress on the same account: After the Bare Metal Server resource management task is completed, please try again.
If the Bare Metal Server’s status is not Running or Stopped: Change the Bare Metal Server’s status to Running or Stopped, then try again.
If the selection includes a server that cannot be terminated simultaneously: Select only resources that can be terminated and try again.
Configure local Subnet
After completing the creation of a Bare Metal Server, when adding a local Subnet on the Bare Metal Server Details page, the user must directly configure the network settings of the local Subnet.
first connection(kr-west)
There is no local Subnet currently connected to the Bare Metal Server, and if you are adding the first connection, follow the guide below.
This guide applies to kr-west (Korea West) when adding the first local Subnet connection to the server.
- kr-south(South Korea) guide can be found in the First Connection (kr-south) chapter.
Linux - Configuring Subnet on Ubuntu
To add a local Subnet and configure the network on an Ubuntu operating system, follow these steps.
On the Bare Metal Server Details page, check the Interface Name.
Retrieve the network configuration information.
Color mode[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1Code block. View network configuration file After adding a new VLAN, set the IP for the bonding configuration.
- Replace the ID and IP in the example code with the assigned ID and IP.Color mode
[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: bond-mgt: interfaces: - ens2f1 // **Bare Metal Server Details** page: enter the Interface Name you verified. - ens4f1 // **Bare Metal Server Details** page: enter the Interface Name you verified. mtu: 1500 parameters: mii-monitor-interval: 100 mode: active-backup transmit-hash-policy: layer2 ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1 vlans: bond-mgt.20: // Enter the Vlan ID you verified in the SCP Console instead of 20. addresses: - 192.168.0.10/24 // Set it to the local Subnet IP confirmed in the SCP Console. id: 20 // Set it to the VLAN ID verified in the SCP Console. link: bond-mgt mtu: 1500[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: bond-mgt: interfaces: - ens2f1 // **Bare Metal Server Details** page: enter the Interface Name you verified. - ens4f1 // **Bare Metal Server Details** page: enter the Interface Name you verified. mtu: 1500 parameters: mii-monitor-interval: 100 mode: active-backup transmit-hash-policy: layer2 ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1 vlans: bond-mgt.20: // Enter the Vlan ID you verified in the SCP Console instead of 20. addresses: - 192.168.0.10/24 // Set it to the local Subnet IP confirmed in the SCP Console. id: 20 // Set it to the VLAN ID verified in the SCP Console. link: bond-mgt mtu: 1500Code block. IP configuration
- Replace the ID and IP in the example code with the assigned ID and IP.
Apply the changes to the system.
Color mode# netplan apply# netplan applyCode block. Apply changes Check the interface status.
Color mode# ip a or # bash /usr/local/bin/ip.sh# ip a or # bash /usr/local/bin/ip.shCode block. Interface lookup
Linux – Configuring Subnet on CentOS/Red Hat
After adding a local Subnet on a CentOS/Red Hat operating system, follow these steps to configure the network.
On the Bare Metal Server Details page, check the Interface Name.
Modify the following command and execute it.
Color mode#!/usr/bin/bash IP_ADDR="10.1.1.3/24" // Set the local Subnet IP as verified in the Console. VLAN_ID="7" // Set the Vlan ID you verified in the console. BOND_NAME="bond-mgt" BOND_IF_name1="ens2f1" // **Bare Metal Server Details** Enter the Interface Name as shown on the page. BOND_IF_name2="ens4f0" // **Bare Metal Server Details** page, enter the Interface Name you verified. # Delete Connection nmcli con down "Bond ${BOND_NAME}" nmcli con del "Bond ${BOND_NAME}" nmcli con down "System ${BOND_IF_name1}" nmcli con down "System ${BOND_IF_name2}" nmcli con del "System ${BOND_IF_name1}" nmcli con del "System ${BOND_IF_name2}" # Create Bonding nmcli con add con-name ${BOND_NAME} type bond ifname ${BOND_NAME} nmcli conn mod ${BOND_NAME} con-name "Bond ${BOND_NAME}" nmcli conn mod "Bond ${BOND_NAME}" ipv4.method disabled nmcli conn mod "Bond ${BOND_NAME}" ipv6.method ignore nmcli conn mod "Bond ${BOND_NAME}" connect.autoconnect yes nmcli conn mod "Bond ${BOND_NAME}" +bond.options mode=active-backup \ +bond.options xmit_hash_policy=layer2 +bond.options miimon=100 +bond.options num_grat_arp=1 \ +bond.options downdelay=0 +bond.options updelay=0 # Assign bond-slave nmcli conn add type bond-slave ifname ${BOND_IF_name1} con-name "${BOND_IF_name1}" master ${BOND_NAME} nmcli conn mod ${BOND_IF_name1} con-name "System ${BOND_IF_name1}" nmcli conn add type bond-slave ifname ${BOND_IF_name2} con-name "${BOND_IF_name2}" master ${BOND_NAME} nmcli conn mod ${BOND_IF_name2} con-name "System ${BOND_IF_name2}" # Connection UP nmcli conn up "Bond ${BOND_NAME}" # add vlan nmcli conn add type vlan ifname "${BOND_NAME}.${VLAN_ID}" con-name "${BOND_NAME}.${VLAN_ID}" id ${VLAN_ID} dev ${BOND_NAME} nmcli con mod ${BOND_NAME}.${VLAN_ID} con-name "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.addresses ${IP_ADDR} nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.method manual nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv6.method "ignore" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" connect.autoconnect yes nmcli con up "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli device reapply ${BOND_NAME}.${VLAN_ID}#!/usr/bin/bash IP_ADDR="10.1.1.3/24" // Set the local Subnet IP as verified in the Console. VLAN_ID="7" // Set the Vlan ID you verified in the console. BOND_NAME="bond-mgt" BOND_IF_name1="ens2f1" // **Bare Metal Server Details** Enter the Interface Name as shown on the page. BOND_IF_name2="ens4f0" // **Bare Metal Server Details** page, enter the Interface Name you verified. # Delete Connection nmcli con down "Bond ${BOND_NAME}" nmcli con del "Bond ${BOND_NAME}" nmcli con down "System ${BOND_IF_name1}" nmcli con down "System ${BOND_IF_name2}" nmcli con del "System ${BOND_IF_name1}" nmcli con del "System ${BOND_IF_name2}" # Create Bonding nmcli con add con-name ${BOND_NAME} type bond ifname ${BOND_NAME} nmcli conn mod ${BOND_NAME} con-name "Bond ${BOND_NAME}" nmcli conn mod "Bond ${BOND_NAME}" ipv4.method disabled nmcli conn mod "Bond ${BOND_NAME}" ipv6.method ignore nmcli conn mod "Bond ${BOND_NAME}" connect.autoconnect yes nmcli conn mod "Bond ${BOND_NAME}" +bond.options mode=active-backup \ +bond.options xmit_hash_policy=layer2 +bond.options miimon=100 +bond.options num_grat_arp=1 \ +bond.options downdelay=0 +bond.options updelay=0 # Assign bond-slave nmcli conn add type bond-slave ifname ${BOND_IF_name1} con-name "${BOND_IF_name1}" master ${BOND_NAME} nmcli conn mod ${BOND_IF_name1} con-name "System ${BOND_IF_name1}" nmcli conn add type bond-slave ifname ${BOND_IF_name2} con-name "${BOND_IF_name2}" master ${BOND_NAME} nmcli conn mod ${BOND_IF_name2} con-name "System ${BOND_IF_name2}" # Connection UP nmcli conn up "Bond ${BOND_NAME}" # add vlan nmcli conn add type vlan ifname "${BOND_NAME}.${VLAN_ID}" con-name "${BOND_NAME}.${VLAN_ID}" id ${VLAN_ID} dev ${BOND_NAME} nmcli con mod ${BOND_NAME}.${VLAN_ID} con-name "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.addresses ${IP_ADDR} nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.method manual nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv6.method "ignore" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" connect.autoconnect yes nmcli con up "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli device reapply ${BOND_NAME}.${VLAN_ID}Code block. IP configuration script Check the interface status.
Color mode# ip a or # bash /usr/local/bin/ip.sh# ip a or # bash /usr/local/bin/ip.shCode block. Interface lookup
Configuring Subnet on Windows
After adding a local Subnet on the Windows operating system, follow these steps to configure the network.
Windows Start icon, right-click it, then run the Windows PowerShell(Administrator) program.
On the Bare Metal Server Details page, check the Interface Name.
Run ncpa.cpl from the Windows Run menu.
Check whether the interface is enabled, and enable it if necessary.
- Activate the Interface Name confirmed on the Bare Metal Server Details page.
- Activate the Interface Name confirmed on the Bare Metal Server Details page.
Create a teaming.
Color modePS C:\> New-NetLbfoTeam –Name “bond-mgt” –TeamMembers ens2f1,ens4f1 PS C:\> Set-NetLbfoTeam –Name “bond-mgt” –LoadBalancingAlgorithm DynamicPS C:\> New-NetLbfoTeam –Name “bond-mgt” –TeamMembers ens2f1,ens4f1 PS C:\> Set-NetLbfoTeam –Name “bond-mgt” –LoadBalancingAlgorithm DynamicCode block. Create Teaming After adding a new VLAN, configure the IP.
- Enter the VLAN ID and local Subnet IP verified on the Bare Metal Server Details page.Color mode
PS C:\> Add-NetLbfoTeamNIC -Team bond_bond-mgt -VlanID 20 -Name bond-mgt.20 PS C:\> Get-NetAdapter PS C:\> netsh interface ip set address bond-mgt.20 static “192.168.0.10/24”PS C:\> Add-NetLbfoTeamNIC -Team bond_bond-mgt -VlanID 20 -Name bond-mgt.20 PS C:\> Get-NetAdapter PS C:\> netsh interface ip set address bond-mgt.20 static “192.168.0.10/24”Code block. Windows IP configuration
- Enter the VLAN ID and local Subnet IP verified on the Bare Metal Server Details page.
In the Windows Run menu, execute ncpa.cpl to check the interface status.
First connection(kr-south)
If there is no local Subnet already connected to the Bare Metal Server and you are adding the first connection, follow the guide below.
This guide is for kr-south(Korea region) when adding the first local Subnet connection to the server.
- The guide for kr-west(Korea West) is in the First link (kr-west) chapter.
Linux - Configuring Subnet on Ubuntu
To add a local Subnet and configure the network on an Ubuntu operating system, follow these steps.
After adding a new VLAN, set the IP.
- Change the ID and IP in the example code to the assigned ID and IP.Color mode
[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: bond-mgt: interfaces: - ens2f1 - ens4f1 mtu: 1500 parameters: mii-monitor-interval: 100 mode: active-backup transmit-hash-policy: layer2 ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1 vlans: bond-mgt.20: addresses: - 192.168.0.10/24 id: 20 link: bond-mgt mtu: 1500 vlans: bond-mgt.21: // Enter the VLAN ID you verified in the console instead of 21. addresses: - 192.168.0.20/24 // Set it to the local Subnet IP you verified in the Console. id: 21 // Set to the VLAN ID verified in the console. link: bond-mgt mtu: 1500[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: bond-mgt: interfaces: - ens2f1 - ens4f1 mtu: 1500 parameters: mii-monitor-interval: 100 mode: active-backup transmit-hash-policy: layer2 ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1 vlans: bond-mgt.20: addresses: - 192.168.0.10/24 id: 20 link: bond-mgt mtu: 1500 vlans: bond-mgt.21: // Enter the VLAN ID you verified in the console instead of 21. addresses: - 192.168.0.20/24 // Set it to the local Subnet IP you verified in the Console. id: 21 // Set to the VLAN ID verified in the console. link: bond-mgt mtu: 1500Code block. Add VLAN and configure IP
- Change the ID and IP in the example code to the assigned ID and IP.
Apply the changes to the system.
Color mode# netplan apply# netplan applyCode block. Reflect changes. Check the interface status.
Color mode# ip a or # bash /usr/local/bin/ip.sh# ip a or # bash /usr/local/bin/ip.shCode block. Interface lookup
Linux – Configuring Subnet on CentOS/Red Hat
After adding a local Subnet on a CentOS/Red Hat operating system, follow these steps to configure the network.
- Check the Bond Name for the local Subnet.Color mode
# sh /usr/local/bin/ip.sh# sh /usr/local/bin/ip.shCode block. Verify bonding - Modify the following command and execute it.Color mode
#!/usr/bin/bash IP_ADDR="10.1.1.3/24" // Set the local Subnet IP as observed in the console. VLAN_ID="7" // Set the Vlan ID you verified in the console. BOND_NAME="bond-mgt" // Set the Bond Name identified in step 1. # add vlan nmcli conn add type vlan ifname "${BOND_NAME}.${VLAN_ID}" con-name "${BOND_NAME}.${VLAN_ID}" id ${VLAN_ID} dev ${BOND_NAME} nmcli con mod ${BOND_NAME}.${VLAN_ID} con-name "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.addresses ${IP_ADDR} nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.method manual nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv6.method "ignore" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" connect.autoconnect yes nmcli con up "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli device reapply ${BOND_NAME}.${VLAN_ID}#!/usr/bin/bash IP_ADDR="10.1.1.3/24" // Set the local Subnet IP as observed in the console. VLAN_ID="7" // Set the Vlan ID you verified in the console. BOND_NAME="bond-mgt" // Set the Bond Name identified in step 1. # add vlan nmcli conn add type vlan ifname "${BOND_NAME}.${VLAN_ID}" con-name "${BOND_NAME}.${VLAN_ID}" id ${VLAN_ID} dev ${BOND_NAME} nmcli con mod ${BOND_NAME}.${VLAN_ID} con-name "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.addresses ${IP_ADDR} nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.method manual nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv6.method "ignore" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" connect.autoconnect yes nmcli con up "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli device reapply ${BOND_NAME}.${VLAN_ID}Code block. IP configuration script - Check the interface status.Color mode
# ip a or # bash /usr/local/bin/ip.sh# ip a or # bash /usr/local/bin/ip.shCode block. Interface lookup
Configuring Subnet on Windows
After adding a local Subnet on the Windows operating system, follow these steps to configure the network.
Windows Start icon, right-click it, then run the Windows PowerShell(Administrator) program.
Check the Teaming name for the local Subnet.
Color modePS C:\> Get-NetAdapterPS C:\> Get-NetAdapterCode block. Check Windows interface After adding a new VLAN, configure the IP.
- Enter the Teaming name verified in step 2, and the Vlan ID and local Subnet IP verified in the Console.Color mode
PS C:\> Add-NetLbfoTeamNIC -Team bond_bond-mgt -VlanID 20 -Name bond-mgt.20 PS C:\> Get-NetAdapter PS C:\> netsh interface ip set address bond-mgt.20 static “192.168.0.10/24”PS C:\> Add-NetLbfoTeamNIC -Team bond_bond-mgt -VlanID 20 -Name bond-mgt.20 PS C:\> Get-NetAdapter PS C:\> netsh interface ip set address bond-mgt.20 static “192.168.0.10/24”code block. Create Teaming
- Enter the Teaming name verified in step 2, and the Vlan ID and local Subnet IP verified in the Console.
Run ncpa.cpl from the Windows Run menu to check the interface status.
Add second connection (kr-west, kr-south)
If there is a local subnet connected to the Bare Metal Server, the guide for the second additional connection is below.
Since a Bonding was already created when connecting the first local Subnet, there is no need to create a Bonding when connecting the second local Subnet.
Please refer to the details below.
Linux - Setting up Subnet on Ubuntu
To add a local Subnet and configure the network on an Ubuntu operating system, follow these steps.
After adding a new VLAN, configure the IP.
- Change the ID and IP in the example code to the assigned ID and IP.Color mode
[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: bond-mgt: interfaces: - ens2f1 - ens4f1 mtu: 1500 parameters: mii-monitor-interval: 100 mode: active-backup transmit-hash-policy: layer2 ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1 vlans: bond-mgt.20: addresses: - 192.168.0.10/24 id: 20 link: bond-mgt mtu: 1500 vlans: bond-mgt.21: // Enter the VLAN ID you verified on the console instead of 21. addresses: - 192.168.0.20/24 // Set it to the local Subnet IP verified in the console. id: 21 // Set it to the VLAN ID verified in the console. link: bond-mgt mtu: 1500[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: bond-mgt: interfaces: - ens2f1 - ens4f1 mtu: 1500 parameters: mii-monitor-interval: 100 mode: active-backup transmit-hash-policy: layer2 ethernets: ens2f1: match: macaddress: 68:05:ca:d4:09:91 mtu: 1500 set-name: ens2f1 ens4f1: match: macaddress: 68:05:ca:d4:09:01 mtu: 1500 set-name: ens4f1 vlans: bond-mgt.20: addresses: - 192.168.0.10/24 id: 20 link: bond-mgt mtu: 1500 vlans: bond-mgt.21: // Enter the VLAN ID you verified on the console instead of 21. addresses: - 192.168.0.20/24 // Set it to the local Subnet IP verified in the console. id: 21 // Set it to the VLAN ID verified in the console. link: bond-mgt mtu: 1500Code block. Add VLAN and configure IP
- Change the ID and IP in the example code to the assigned ID and IP.
Apply the changes to the system.
Color mode# netplan apply# netplan applyCode block. Reflect changes Check the interface status.
Color mode# ip a or # bash /usr/local/bin/ip.sh# ip a or # bash /usr/local/bin/ip.shCode block. Interface lookup
Linux – Setting Subnet on CentOS/Red Hat
After adding a local Subnet on a CentOS/Red Hat operating system, follow these steps to configure the network.
- Verify the Bond Name for the local Subnet.Color mode
# sh /usr/local/bin/ip.sh# sh /usr/local/bin/ip.shCode block. Verify bonding - Modify the following command and execute it.Color mode
#!/usr/bin/bash IP_ADDR="10.1.1.3/24" // Set the local Subnet IP as observed in the console. VLAN_ID="7" // Set the Vlan ID as observed in the console. BOND_NAME="bond-mgt" // Set the Bond Name confirmed in step 1. # add vlan nmcli conn add type vlan ifname "${BOND_NAME}.${VLAN_ID}" con-name "${BOND_NAME}.${VLAN_ID}" id ${VLAN_ID} dev ${BOND_NAME} nmcli con mod ${BOND_NAME}.${VLAN_ID} con-name "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.addresses ${IP_ADDR} nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.method manual nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv6.method "ignore" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" connect.autoconnect yes nmcli con up "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli device reapply ${BOND_NAME}.${VLAN_ID}#!/usr/bin/bash IP_ADDR="10.1.1.3/24" // Set the local Subnet IP as observed in the console. VLAN_ID="7" // Set the Vlan ID as observed in the console. BOND_NAME="bond-mgt" // Set the Bond Name confirmed in step 1. # add vlan nmcli conn add type vlan ifname "${BOND_NAME}.${VLAN_ID}" con-name "${BOND_NAME}.${VLAN_ID}" id ${VLAN_ID} dev ${BOND_NAME} nmcli con mod ${BOND_NAME}.${VLAN_ID} con-name "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.addresses ${IP_ADDR} nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv4.method manual nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" ipv6.method "ignore" nmcli con mod "Vlan ${BOND_NAME}.${VLAN_ID}" connect.autoconnect yes nmcli con up "Vlan ${BOND_NAME}.${VLAN_ID}" nmcli device reapply ${BOND_NAME}.${VLAN_ID}Code block. IP configuration script - Check the interface status.Color mode
# ip a or # bash /usr/local/bin/ip.sh# ip a or # bash /usr/local/bin/ip.shCode block. Interface lookup
Configuring Subnet on Windows
After adding a local Subnet on the Windows operating system, follow these steps to configure the network.
Windows Start icon, right‑click it, then launch the Windows PowerShell(Administrator) program.
Check the Teaming name for the local Subnet.
Color modePS C:\> Get-NetAdapterPS C:\> Get-NetAdapterCode block. Check Windows interface After adding a new Vlan, configure the IP.
- Enter the Teaming name confirmed in step 2, the Vlan ID, and the local Subnet IP confirmed in the Console.Color mode
PS C:\> Add-NetLbfoTeamNIC -Team bond_bond-mgt -VlanID 20 -Name bond-mgt.20 PS C:\> Get-NetAdapter PS C:\> netsh interface ip set address bond-mgt.20 static “192.168.0.10/24”PS C:\> Add-NetLbfoTeamNIC -Team bond_bond-mgt -VlanID 20 -Name bond-mgt.20 PS C:\> Get-NetAdapter PS C:\> netsh interface ip set address bond-mgt.20 static “192.168.0.10/24”Code block. Create Teaming
- Enter the Teaming name confirmed in step 2, the Vlan ID, and the local Subnet IP confirmed in the Console.
Run ncpa.cpl from the Windows Run menu to check the interface status.
Change IP
The IP address may be changed to carry out migration, server replacement, and similar operations.
- If you proceed with changing the IP, you will no longer be able to communicate using that IP, and you cannot cancel the IP change while it is in progress.
- If the server is running the Load Balancer service, you must delete the old IP from the LB server group and directly add the new IP as a member of the LB server group.
- Servers using Public NAT and Privat NAT must disable and then reconfigure Public NAT and Privat NAT after an IP change.
- If you are using Public NAT and Privat NAT, first disable Public NAT and Privat NAT, complete the IP change, and then reconfigure.
- Whether to use Public NAT and Privat NAT can be changed by clicking the Edit button for Public NAT IP and Privat NAT on the Bare Metal Server Details page.
To change the IP, follow the steps below.
Click the All Services > Compute > Bare Metal Server menu. Navigate to the Service Home page of the Bare Metal Server.
Click the Bare Metal Server menu on the Service Home page. You will be taken to the Bare Metal Server List page.
Bare Metal Server List page, click the server whose IP you want to change. You will be taken to the Bare Metal Server Details page.
On the Bare Metal Server Details page, click the Edit button next to the IP item.
When the popup notifying IP modification opens, click the Confirm button. The IP Change popup opens.
In the IP Change popup, complete Step 1, Step 2, and Step 3 in order.
information- When changing an IP, the detailed configuration method for the IP change step varies depending on the subnet of the IP to be changed. Be sure to refer to the following examples and perform the work for each step.
- When changing to an IP that uses the same subnet: Change to an IP in the same Subnet See
- When changing to an IP that uses a different subnet: see Changing to an IP in a different Subnet
- When each step is completed successfully, the task status in the upper right corner is shown as Completed, and you can proceed to the next step.
- When performing the final check of Step 3, it is recommended to restart the server before proceeding with the inspection.
- When changing an IP, the detailed configuration method for the IP change step varies depending on the subnet of the IP to be changed. Be sure to refer to the following examples and perform the work for each step.
After confirming that all tasks have completed successfully, click the Confirm button.
Change to an IP in the same Subnet
This document explains how to configure IP settings per operating system when the IP to be changed uses the same subnet.
Linux – centos/redhat operating system
Step 1
Follow the procedure below to carry out Step 1.
- Select the Subnet to modify.
- Enter the IP address to change.
- Click the IP Allocation Request button.
- If a popup window notifying you of an IP change opens, click the Confirm button.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.CautionIf you proceed with the IP allocation request for Step 1, you cannot cancel or revert the IP change.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 2
Follow the procedure below to carry out Step 2.
For the IP change operation, connect to the target server using the NAT IP.
guideTo prevent situations where communication becomes impossible during operation, we recommend connecting via another Virtual Server or Bare Metal Server created in the same subnet.Enter the IP assigned in Step 1 and configure the new IP on the server.
- In the following example, replace
172.17.34.150with the assigned IP address. - After checking the information of the Interface you want to change on the server, replace it with
bond-srv.9in the following example.Color mode# nmcli con mod "Vlan bond-srv.9" ipv4.addresses 172.17.34.150/24 # nmcli con mod "Vlan bond-srv.9" ipv4.method manual # nmcli device reapply bond-srv.9# nmcli con mod "Vlan bond-srv.9" ipv4.addresses 172.17.34.150/24 # nmcli con mod "Vlan bond-srv.9" ipv4.method manual # nmcli device reapply bond-srv.9Code block. IP settings to change information- Setting the IP disconnects the terminal session.
- Step 2 After completing the task, if the task status changes to Completed, you can reconnect to the terminal.
- In the following example, replace
When all tasks are completed, select the Step 2 completion checkbox in the IP Change popup window.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.information
- If the task status of Step 2 has changed to Completed but you still have issues with terminal access, go to the All Services > Management > Support Center Contact Us menu and submit an inquiry.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 3
Follow the procedure below to carry out Step 3 work.
Connect to the server subject to IP change using the NAT IP and check the communication status.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.Color mode
# bash /usr/local/bin/ip.sh# bash /usr/local/bin/ip.shCode block. Communication status check ReferenceThe NAT IP does not change.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.
After all tasks are completed, restart the server and perform a final check.
ReferenceIt is recommended to perform the final check after restarting the server.If there are no issues in the final inspection results, select the work completion checkbox for Step 3 in the IP Change popup window.
Linux – Ubuntu operating system
Step 1
Follow the procedure below to carry out Step 1.
- Select the Subnet to modify.
- Enter the IP address to change.
- IP Allocation Request Click the button.
- When a popup indicating IP change verification opens, click the Confirm button.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.CautionIf you proceed with the IP allocation request of Step 1, you cannot cancel or revert the IP change.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 2
Follow the procedure below to perform Step 2.
To perform the IP change, connect to the target server using its NAT IP.
InformationTo prevent situations where communication becomes impossible during operation, we recommend connecting via another Virtual Server or Bare Metal Server created in the same subnet.Enter the IP assigned in Step 1 and configure the new IP on the server.
- In the following example, replace
172.17.34.150/24with the assigned IP address. - After checking the information of the Interface you want to change on the server, replace it with the following example
bond-srv.9.Color mode[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: addresses: - 172.17.34.150/24 # Enter the IP assigned in Step1. gateway4: 172.17.34.2 id: 9 link: bond-srv mtu: 1500 bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srv[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: addresses: - 172.17.34.150/24 # Enter the IP assigned in Step1. gateway4: 172.17.34.2 id: 9 link: bond-srv mtu: 1500 bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srvCode block. Change IP setting
- In the following example, replace
Use the Netplan apply command to apply the changes to the system.
Color mode[root@localhost ~]# netplan apply[root@localhost ~]# netplan applyCode block. Run Netplan apply information- Setting the IP disconnects the terminal session.
- Step 2 After completing the task, if the task status changes to Completed, you can reconnect to the terminal.
When all tasks are completed, select the task completion checkbox for Step 2 in the IP change popup window.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.information
- If the task status of Step 2 has changed to Completed but you still experience issues with terminal access, go to the All Services > Management > Support Center Contact Us menu and submit an inquiry.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 3
Follow the procedure below to carry out Step 3.
Connect to the server subject to IP change using the NAT IP and check the communication status.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.Color mode
# bash /usr/local/bin/ip.sh# bash /usr/local/bin/ip.shCode block. Communication status check referenceThe NAT IP does not change.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.
After all tasks are completed, restart the server and then perform a final check.
ReferenceIt is recommended to perform the final check after restarting the server.If the final inspection results show no issues, select the work completion checkbox for Step 3 in the IP Change popup window.
Windows operating system
Step 1
Follow the procedure below to perform Step 1 work.
- Select the Subnet to modify.
- Enter the IP address to change.
- Click the IP Allocation Request button.
- When the pop-up that notifies you of an IP change appears, click the Confirm button.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.CautionIf you proceed with the IP allocation request of Step 1, you cannot cancel or revert the IP change.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 2
Follow the procedure below to perform Step 2.
To perform the IP change, connect to the target server using its NAT IP.
InformationTo prevent communication failures during operation, we recommend connecting through another Virtual Server or Bare Metal Server created in the same subnet.Right-click the Windows Start icon, then run Windows PowerShell(Administrator).
Enter the assigned IP from Step 1 and set the IP to be changed on the server.
- In the following example, replace
172.17.34.150with the assigned IP address.Color modePS C:\> netsh interface ip set address "bond-srv.20" static 172.17.34.150 255.255.255.0PS C:\> netsh interface ip set address "bond-srv.20" static 172.17.34.150 255.255.255.0code block. Change IP setting information- Setting the IP disconnects the terminal session.
- Step 2 After completing the task, if the task status changes to Completed, you can reconnect to the terminal.
- In the following example, replace
When all tasks are completed, select the task completion checkbox for Step 2 in the IP change popup window.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.Information
- If the task status of Step 2 has changed to Completed but you still have issues with terminal access, go to the All Services > Management > Support Center Contact Us menu and submit an inquiry.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 3
Follow the procedure below to carry out Step 3.
Connect to the server targeted for IP change using its NAT IP and verify the communication status.
- Use the following command to verify whether any pre‑change configuration remains and to confirm that the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.Color mode
PS C:\> Get-NetIPAddress | Format-TablePS C:\> Get-NetIPAddress | Format-TableCode block. Communication status check ReferenceThe NAT IP does not change.
- Use the following command to verify whether any pre‑change configuration remains and to confirm that the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.
After all tasks are completed, restart the server and then perform a final check.
ReferenceIt is recommended to perform the final check after restarting the server.If there are no issues in the final inspection results, select the work completion checkbox for Step 3 in the IP Change popup window.
Change to an IP of a different Subnet
This explains how to configure IP settings for each operating system when the IP to be changed uses a different subnet.
Linux – centos/redhat operating system
Step 1
Follow the procedure below to carry out Step 1.
- Select the Subnet to modify.
- Enter the IP address to change.
- Click the IP Allocation Request button.
- If a popup window notifying you of an IP change opens, click the Confirm button.
- When the operation completes successfully, Vlan ID verification, Default Gateway verification information is displayed, and the task status in the upper right corner shows Completed.CautionIf you proceed with the IP allocation request for Step 1, you cannot cancel or revert the IP change.
- When the operation completes successfully, Vlan ID verification, Default Gateway verification information is displayed, and the task status in the upper right corner shows Completed.
Step 2
Follow the steps below to carry out Step 2.
For the IP change operation, connect to the target server using the NAT IP.
informationTo prevent situations where communication becomes impossible during operation, we recommend connecting via another Virtual Server or Bare Metal Server created in the same subnet.To add the IP to the server, add a new VLAN and configure the IP.
- Add VLAN: Create the interface for the Vlan ID identified in Step 1. In the following example, replace
20with the assigned ID. - IP configuration: Enter the IP assigned in Step 1. In the following example, replace
192.168.0.10/24with the assigned IP.Color mode# nmcli conn add type vlan ifname "bond-srv.20" con-name "bond-srv.20" id 20 dev bond-srv # nmcli con mod bond-srv.20 con-name "Vlan bond-srv.20" # nmcli con mod "Vlan bond-srv.20" ipv4.addresses 192.168.0.10/24 # nmcli con mod "Vlan bond-srv.20" ipv4.method manual # nmcli con mod "Vlan bond-srv.20" ipv6.method "ignore" # nmcli con up "Vlan bond-srv.20"# nmcli conn add type vlan ifname "bond-srv.20" con-name "bond-srv.20" id 20 dev bond-srv # nmcli con mod bond-srv.20 con-name "Vlan bond-srv.20" # nmcli con mod "Vlan bond-srv.20" ipv4.addresses 192.168.0.10/24 # nmcli con mod "Vlan bond-srv.20" ipv4.method manual # nmcli con mod "Vlan bond-srv.20" ipv6.method "ignore" # nmcli con up "Vlan bond-srv.20"Code block. IP settings to change
- Add VLAN: Create the interface for the Vlan ID identified in Step 1. In the following example, replace
Configure the default gateway for the new VLAN.
- Default gateway setting: Enter the Default gateway IP assigned in Step 1. In the following example, replace
192.168.0.1with the assigned Default gateway IP.Color mode# nmcli con mod "Vlan bond-srv.20" ipv4.gateway 192.168.0.1 # nmcli device reapply bond-srv.20# nmcli con mod "Vlan bond-srv.20" ipv4.gateway 192.168.0.1 # nmcli device reapply bond-srv.20Code block. Change IP settings Info- Setting a Default Gateway on a new VLAN disconnects the terminal session.
- Step 2 After completing the task, if the task status changes to Completed, you can reconnect to the terminal.
- Default gateway setting: Enter the Default gateway IP assigned in Step 1. In the following example, replace
When all tasks are completed, select the task completion checkbox of Step 2 in the IP change popup window.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.information
- If the task status of Step 2 has changed to Completed but you still experience issues with terminal access, go to the All Services > Management > Support Center’s Contact Us menu and make an inquiry.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 3
Follow the procedure below to proceed with Step 3.
Connect to the server to be changed using the NAT IP.
After verifying the Default Gateway IP of the existing (pre-change) interface, delete it.
- In the example below, replace
192.168.10.1with the IP you have verified.Color mode# ip route del default via 192.168.10.1# ip route del default via 192.168.10.1Code block. Delete the Default Gateway IP of the existing interface.
- In the example below, replace
Connect to the server subject to IP change using the NAT IP and check the communication status.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.Color mode
# netstat –nr # bash /usr/local/bin/ip.sh# netstat –nr # bash /usr/local/bin/ip.shCode block. Communication status check ReferenceThe NAT IP does not change.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.
Verify the VLAN information of the existing IP and delete it from the server.
- Enter the verified ID in place of
30in the following example.Color mode# nmcli con delete "Vlan bond-srv.30"# nmcli con delete "Vlan bond-srv.30"Code block. Delete the VLAN information of the existing IP.
- Enter the verified ID in place of
After all tasks are completed, restart the server and then perform a final check.
ReferenceIt is recommended to perform the final check after restarting the server.If the final inspection results show no issues, select the work completion checkbox for Step 3 in the IP Change popup window.
Linux – Ubuntu operating system
Step 1
Follow the procedure below to perform Step 1.
- Select the Subnet to modify.
- Enter the IP address to change.
- Click the IP Allocation Request button.
- When a popup notifying you of an IP change opens, click the Confirm button.
- When the operation completes successfully, Vlan ID verification, Default Gateway verification information is displayed, and the operation status in the upper right corner shows Completed.CautionIf you proceed with the IP allocation request of Step 1, you cannot cancel or revert the IP change.
- When the operation completes successfully, Vlan ID verification, Default Gateway verification information is displayed, and the operation status in the upper right corner shows Completed.
Step 2
Follow the procedure below to perform Step 2.
To perform the IP change, connect to the target server using its NAT IP.
InformationTo prevent situations where communication becomes impossible during operation, we recommend connecting via another Virtual Server or Bare Metal Server created in the same subnet.To add the IP to the server, add a new VLAN and configure the IP and Default Gateway.
- In the following example, this is the part where content is added at the bottom of the Step 1 task description.
- In the following example, enter the assigned ID and IP instead of ID and IP.Color mode
[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: addresses: - 172.17.34.150/24 gateway4: 172.17.34.2 id: 9 link: bond-srv mtu: 1500 bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srv # Create the interface for the Vlan ID identified in Step1. # Enter the IP assigned in Step1. # Enter the Default gateway IP assigned in Step1. bond-srv.20: addresses: - 192.168.0.10/24 gateway4: 192.168.0.1 id: 20 link: bond-srv mtu: 1500[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: addresses: - 172.17.34.150/24 gateway4: 172.17.34.2 id: 9 link: bond-srv mtu: 1500 bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srv # Create the interface for the Vlan ID identified in Step1. # Enter the IP assigned in Step1. # Enter the Default gateway IP assigned in Step1. bond-srv.20: addresses: - 192.168.0.10/24 gateway4: 192.168.0.1 id: 20 link: bond-srv mtu: 1500Code block. Change IP settings
Use the Netplan apply command to apply the changes to the system.
Color mode[root@localhost ~]# netplan apply[root@localhost ~]# netplan applyCode block. Run Netplan apply Info- Setting a new Default Gateway disconnects the terminal session.
- Step 2 After completing the task, if the task status changes to Completed, you can reconnect to the terminal.
When all tasks are completed, select the task completion checkbox of Step 2 in the IP change popup window.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.information
- If the task status of Step 2 has changed to Completed but you still experience issues with terminal access, go to the All Services > Management > Support Center’s Contact Us menu and make an inquiry.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 3
Follow the procedure below to proceed with Step 3.
Connect to the server to be changed using the NAT IP.
Check the Default Gateway IP of the existing (pre‑change) interface, then delete it.
- In the following example, the Delete this line row is the part that gets deleted.Color mode
[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: addresses: - 172.17.34.150/24 gateway4: 172.17.34.2 #Delete this line id: 9 link: bond-srv mtu: 1500 bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srv bond-srv.20: addresses: - 192.168.0.10/24 gateway4: 192.168.0.1 id: 20 link: bond-srv mtu: 1500[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: addresses: - 172.17.34.150/24 gateway4: 172.17.34.2 #Delete this line id: 9 link: bond-srv mtu: 1500 bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srv bond-srv.20: addresses: - 192.168.0.10/24 gateway4: 192.168.0.1 id: 20 link: bond-srv mtu: 1500Code block. Delete the Default Gateway IP of the existing interface.
- In the following example, the Delete this line row is the part that gets deleted.
Connect to the IP change target server using the NAT IP and check the communication status.
- Use the following command to verify whether any pre‑change configuration remains and that the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.Color mode
# netstat –nr # bash /usr/local/bin/ip.sh# netstat –nr # bash /usr/local/bin/ip.shCode block. Communication status check ReferenceThe NAT IP does not change.
- Use the following command to verify whether any pre‑change configuration remains and that the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.
Delete the existing IP.
- In the following example, the Delete this line row is the part that gets deleted.Color mode
[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: #Delete this line addresses: #Delete this line - 172.17.34.150/24 # Delete this line gateway4: 172.17.34.2 #Delete this line id: 9 # Delete this line link: bond-srv #Delete this line mtu: 1500 #Delete this line bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srv bond-srv.20: addresses: - 192.168.0.10/24 gateway4: 192.168.0.1 id: 20 link: bond-srv mtu: 1[root@localhost ~]# vi /etc/netplan/50-cloud-init.yaml network: bonds: ...................... omitted ethernets: ...................... omitted vlans: bond-srv.9: #Delete this line addresses: #Delete this line - 172.17.34.150/24 # Delete this line gateway4: 172.17.34.2 #Delete this line id: 9 # Delete this line link: bond-srv #Delete this line mtu: 1500 #Delete this line bond-srv.350: addresses: - 172.16.87.150/24 routes: - to: 172.17.87.0/24 via: 172.16.87.1 - to: 172.17.87.0/24 via: 172.16.87.1 id: 350 link: bond-srv bond-srv.20: addresses: - 192.168.0.10/24 gateway4: 192.168.0.1 id: 20 link: bond-srv mtu: 1Code block. Delete existing IP
- In the following example, the Delete this line row is the part that gets deleted.
Apply the changes to the system.
Color mode[root@localhost ~]# netplan apply [root@localhost ~]# ip link delete bond-srv.9 # Additional steps when deleting VLAN[root@localhost ~]# netplan apply [root@localhost ~]# ip link delete bond-srv.9 # Additional steps when deleting VLANCode block. Apply changes After all tasks are completed, restart the server and then perform a final check.
- If there are no issues in the final inspection results, select the work completion checkbox for Step 3 in the IP change popup window.
Windows operating system
Step 1
Follow the procedure below to carry out Step 1.
- Select the Subnet to modify.
- Enter the IP address to change.
- Click the IP Allocation Request button.
- If a popup notifying IP change verification opens, click the Confirm button.
- When the operation completes successfully, Vlan ID verification, Default Gateway verification information is displayed, and the operation status in the upper right corner shows Completed.CautionIf you proceed with the IP allocation request for Step 1, you cannot cancel or revert the IP change.
- When the operation completes successfully, Vlan ID verification, Default Gateway verification information is displayed, and the operation status in the upper right corner shows Completed.
Step 2
Follow the procedure below to carry out Step 2.
To perform the IP change, connect to the target server using its NAT IP.
informationTo prevent situations where communication becomes impossible during operation, we recommend connecting via another Virtual Server or Bare Metal Server created in the same subnet.Windows Start icon, right-click it, then run Windows PowerShell(Administrator).
Add a VLAN and configure the IP and default gateway.
- Add VLAN: Create the interface for the Vlan ID identified in Step 1. In the following example, replace
20with the assigned ID. - IP configuration: Enter the IP assigned in Step 1. In the following example, replace
46with the ifindex obtained via Get-NetAdapter, and replace 192.168.0.10 with the assigned IP. - Default gateway setting: Enter the Default gateway IP assigned in Step 1. In the following example, replace
192.168.0.1with the assigned Default gateway IP.Color modePS C:\> Add-NetLbfoTeamNIC -Team bond_bond-srv -VlanID 20 -Name bond-srv.20 -Confirm:$false PS C:\> Get-NetAdapter PS C:\> New-NetIPAddress -InterfaceIndex 46 -IPAddress 192.168.0.10 -PrefixLength 24 –defaultgateway 192.168.0.1PS C:\> Add-NetLbfoTeamNIC -Team bond_bond-srv -VlanID 20 -Name bond-srv.20 -Confirm:$false PS C:\> Get-NetAdapter PS C:\> New-NetIPAddress -InterfaceIndex 46 -IPAddress 192.168.0.10 -PrefixLength 24 –defaultgateway 192.168.0.1code block. Change IP settings information- Setting a new Default Gateway disconnects the terminal session.
- Step 2 After completing the task, if the task status changes to Completed, you can reconnect to the terminal.
- Add VLAN: Create the interface for the Vlan ID identified in Step 1. In the following example, replace
When all tasks are completed, select the task completion checkbox of Step 2 in the IP change popup window.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.information
- If the task status of Step 2 has changed to Completed but you still experience issues with terminal access, go to the All Services > Management > Support Center Contact Us menu and submit an inquiry.
- When the task completes successfully, the task status in the upper right corner is displayed as Completed.
Step 3
Follow the procedure below to carry out Step 3.
Connect to the IP-change target server using the NAT IP.
Run the interface index (ifindex) to check the existing Default Gateway IP.
Color modePS C:\> Get-NetAdapter Name InterfaceDescription ifIndex Status MacAddress LinkSpeed ---- -------------------- ------- ------ ---------- --------- bond-srv.9 Microsoft Network Adapter Multiple...#4 30 Up 40-A6-B7-27-96-D5 50 Gbps bond-srv Microsoft Network Adapter Multiple...#3 19 Up 40-A6-B7-27-96-D5 50 Gbps bond-iscsi Microsoft Network Adapter Multiple...#2 18 Up 40-A6-B7-27-96-D4 50 Gbps bond-backup Microsoft Network Adapter Multiplexo... 22 Up 68-05-CA-C9-EB-88 20 Gbps eno2 Intel(R) Ethernet Connection X722 fo... 12 Disabled 38-68-DD-36-A0-59 1 Gbps ens3f0 Intel(R) Ethernet Network Adapter XX... 11 Up 40-A6-B7-27-96-D4 25 Gbps ………………………………………….. omittedPS C:\> Get-NetAdapter Name InterfaceDescription ifIndex Status MacAddress LinkSpeed ---- -------------------- ------- ------ ---------- --------- bond-srv.9 Microsoft Network Adapter Multiple...#4 30 Up 40-A6-B7-27-96-D5 50 Gbps bond-srv Microsoft Network Adapter Multiple...#3 19 Up 40-A6-B7-27-96-D5 50 Gbps bond-iscsi Microsoft Network Adapter Multiple...#2 18 Up 40-A6-B7-27-96-D4 50 Gbps bond-backup Microsoft Network Adapter Multiplexo... 22 Up 68-05-CA-C9-EB-88 20 Gbps eno2 Intel(R) Ethernet Connection X722 fo... 12 Disabled 38-68-DD-36-A0-59 1 Gbps ens3f0 Intel(R) Ethernet Network Adapter XX... 11 Up 40-A6-B7-27-96-D4 25 Gbps ………………………………………….. omittedcode block. Run Get-NetAdapter Color modePS C:\> get-netroute -ifindex 30 ifIndex DestinationPrefix NextHop RouteMetric PolicyStore ------- ----------------- ------- ----------- ----------- 30 255.255.255.255/32 0.0.0.0 256 ActiveStore 30 224.0.0.0/4 0.0.0.0 256 ActiveStore 30 172.17.35.0/24 172.17.35.1 256 ActiveStore 30 172.17.34.255/32 0.0.0.0 256 ActiveStore 30 172.17.34.14/32 0.0.0.0 256 ActiveStore 30 172.17.34.0/24 0.0.0.0 256 ActiveStore 30 0.0.0.0/0 172.17.34.1 1 ActiveStorePS C:\> get-netroute -ifindex 30 ifIndex DestinationPrefix NextHop RouteMetric PolicyStore ------- ----------------- ------- ----------- ----------- 30 255.255.255.255/32 0.0.0.0 256 ActiveStore 30 224.0.0.0/4 0.0.0.0 256 ActiveStore 30 172.17.35.0/24 172.17.35.1 256 ActiveStore 30 172.17.34.255/32 0.0.0.0 256 ActiveStore 30 172.17.34.14/32 0.0.0.0 256 ActiveStore 30 172.17.34.0/24 0.0.0.0 256 ActiveStore 30 0.0.0.0/0 172.17.34.1 1 ActiveStorecode block. Execute -ifindex Delete the existing Default Gateway IP.
- In the following example, replace
30with the ifindex obtained using Get-NetAdapter, and replace172.17.34.1with the IP you verified.Color modePS C:\> Remove-NetRoute -ifIndex 30 -DestinationPrefix 0.0.0.0/0 -NextHop 172.17.34.1 -Confirm:$falsePS C:\> Remove-NetRoute -ifIndex 30 -DestinationPrefix 0.0.0.0/0 -NextHop 172.17.34.1 -Confirm:$falseCode block. Delete Default Gateway IP Color modePS C:\> get-netroute -ifindex 30 ifIndex DestinationPrefix NextHop RouteMetric PolicyStore ------- ----------------- ------- ----------- ----------- 30 255.255.255.255/32 0.0.0.0 256 ActiveStore 30 224.0.0.0/4 0.0.0.0 256 ActiveStore 30 172.17.34.255/32 0.0.0.0 256 ActiveStore 30 172.17.34.14/32 0.0.0.0 256 ActiveStore 30 172.17.34.0/24 0.0.0.0 256 ActiveStorePS C:\> get-netroute -ifindex 30 ifIndex DestinationPrefix NextHop RouteMetric PolicyStore ------- ----------------- ------- ----------- ----------- 30 255.255.255.255/32 0.0.0.0 256 ActiveStore 30 224.0.0.0/4 0.0.0.0 256 ActiveStore 30 172.17.34.255/32 0.0.0.0 256 ActiveStore 30 172.17.34.14/32 0.0.0.0 256 ActiveStore 30 172.17.34.0/24 0.0.0.0 256 ActiveStorecode block. -ifindex execution Information- If you delete the existing Default Gateway, the terminal session will be disconnected.
- Step 2 After completing the task, if the task status changes to Completed, you can reconnect to the terminal.
- In the following example, replace
Connect to the server targeted for IP change using its NAT IP and verify the communication status.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.Color mode
PS C:\> netstat –nr | findstr Default PS C:\> Get-NetIPAddress | Format-TablePS C:\> netstat –nr | findstr Default PS C:\> Get-NetIPAddress | Format-TableCode block. Communication status check ReferenceThe NAT IP does not change.
- Use the following command to verify whether any pre‑change configuration remains and whether the change was applied correctly. If you can connect successfully to the target server whose IP was changed, the new IP is communicating properly.
Check the VLAN information of the existing IP in the Team information.
Color modePS C:\> Get-NetLbfoTeam Name : bond_bond-srv Members : {ens6f1, ens3f1} TeamNics : {bond-srv, bond-srv.9} TeamingMode : SwitchIndependent LoadBalancingAlgorithm : Dynamic Status : Up Name : bond_bond-iscsi Members : {ens6f0, ens3f0} TeamNics : bond-iscsi TeamingMode : SwitchIndependent LoadBalancingAlgorithm : Dynamic Status : Up Name : bond_bond-backup Members : {ens2f0, ens4f1} TeamNics : bond-backup TeamingMode : SwitchIndependent LoadBalancingAlgorithm : Dynamic Status : Up PS C:\> Get-NetAdapter Name InterfaceDescription ifIndex Status MacAddress LinkSpeed ---- -------------------- ------- ------ ---------- --------- bond-srv.9 Microsoft Network Adapter Multiple...#4 30 Up 40-A6-B7-27-96-D5 50 Gbps bond-srv Microsoft Network Adapter Multiple...#3 19 Up 40-A6-B7-27-96-D5 50 Gbps bond-iscsi Microsoft Network Adapter Multiple...#2 18 Up 40-A6-B7-27-96-D4 50 Gbps bond-backup Microsoft Network Adapter Multiplexo... 22 Up 68-05-CA-C9-EB-88 20 Gbps eno2 Intel(R) Ethernet Connection X722 fo... 12 Disabled 38-68-DD-36-A0-59 1 Gbps ens3f0 Intel(R) Ethernet Network Adapter XX... 11 Up 40-A6-B7-27-96-D4 25 Gbps ………………………………………….. omittedPS C:\> Get-NetLbfoTeam Name : bond_bond-srv Members : {ens6f1, ens3f1} TeamNics : {bond-srv, bond-srv.9} TeamingMode : SwitchIndependent LoadBalancingAlgorithm : Dynamic Status : Up Name : bond_bond-iscsi Members : {ens6f0, ens3f0} TeamNics : bond-iscsi TeamingMode : SwitchIndependent LoadBalancingAlgorithm : Dynamic Status : Up Name : bond_bond-backup Members : {ens2f0, ens4f1} TeamNics : bond-backup TeamingMode : SwitchIndependent LoadBalancingAlgorithm : Dynamic Status : Up PS C:\> Get-NetAdapter Name InterfaceDescription ifIndex Status MacAddress LinkSpeed ---- -------------------- ------- ------ ---------- --------- bond-srv.9 Microsoft Network Adapter Multiple...#4 30 Up 40-A6-B7-27-96-D5 50 Gbps bond-srv Microsoft Network Adapter Multiple...#3 19 Up 40-A6-B7-27-96-D5 50 Gbps bond-iscsi Microsoft Network Adapter Multiple...#2 18 Up 40-A6-B7-27-96-D4 50 Gbps bond-backup Microsoft Network Adapter Multiplexo... 22 Up 68-05-CA-C9-EB-88 20 Gbps eno2 Intel(R) Ethernet Connection X722 fo... 12 Disabled 38-68-DD-36-A0-59 1 Gbps ens3f0 Intel(R) Ethernet Network Adapter XX... 11 Up 40-A6-B7-27-96-D4 25 Gbps ………………………………………….. omittedcode block. Run Get-NetLbfoTeam Delete the Vlan information of the existing IP from the server.
- In the following example, replace
30with the ID you verified.Color modePS C:\> Remove-NetLbfoTeamNic -Team bond_bond-srv -VlanID 30 -Confirm:$false PS C:\> Get-NetAdapter Name InterfaceDescription ifIndex Status MacAddress LinkSpeed ---- -------------------- ------- ------ ---------- --------- bond-srv Microsoft Network Adapter Multiple...#3 19 Up 40-A6-B7-27-96-D5 50 Gbps bond-iscsi Microsoft Network Adapter Multiple...#2 18 Up 40-A6-B7-27-96-D4 50 Gbps bond-backup Microsoft Network Adapter Multiplexo... 22 Up 68-05-CA-C9-EB-88 20 Gbps eno2 Intel(R) Ethernet Connection X722 fo... 12 Disabled 38-68-DD-36-A0-59 1 Gbps ens3f0 Intel(R) Ethernet Network Adapter XX... 11 Up 40-A6-B7-27-96-D4 25 Gbps ………………………………………….. omittedPS C:\> Remove-NetLbfoTeamNic -Team bond_bond-srv -VlanID 30 -Confirm:$false PS C:\> Get-NetAdapter Name InterfaceDescription ifIndex Status MacAddress LinkSpeed ---- -------------------- ------- ------ ---------- --------- bond-srv Microsoft Network Adapter Multiple...#3 19 Up 40-A6-B7-27-96-D5 50 Gbps bond-iscsi Microsoft Network Adapter Multiple...#2 18 Up 40-A6-B7-27-96-D4 50 Gbps bond-backup Microsoft Network Adapter Multiplexo... 22 Up 68-05-CA-C9-EB-88 20 Gbps eno2 Intel(R) Ethernet Connection X722 fo... 12 Disabled 38-68-DD-36-A0-59 1 Gbps ens3f0 Intel(R) Ethernet Network Adapter XX... 11 Up 40-A6-B7-27-96-D4 25 Gbps ………………………………………….. omittedcode block. Run Get-NetLbfoTeam
- In the following example, replace
After all tasks are completed, restart the server and then perform a final check.
ReferenceIt is recommended to perform the final check after restarting the server.If there are no issues in the final inspection results, select the Step 3 work completion checkbox in the IP Change popup window.
Configuring RHEL Repository
The Samsung Cloud Platform Console provides the SCP RHEL Repository to support user environments where external access is restricted, such as VPC Private Subnets.
You can use the RHEL Repository to install and download the same packages as the official RHEL Repository.
To configure the RHEL Repository, please refer to RHEL Repository Configuration Guide.
- If a user created RHEL before August 2025 through the Samsung Cloud Platform Console, they must modify the RHEL Repository settings.
- Since the SCP RHEL Repository synchronizes with each region’s local repository according to an internal schedule, it is recommended to switch to an external public mirror site to apply the latest patches quickly.
- Samsung Cloud Platform provides the latest repository for the specified major version.
2.4.2.1 - Install ServiceWatch Agent
Users can install the ServiceWatch Agent on a Bare Metal Server to collect custom metrics and logs.
ServiceWatch Agent
On a Bare Metal Server, the agents that need to be installed to collect ServiceWatch’s custom metrics and logs can be divided into two main types. It is a Prometheus Exporter and Open Telemetry Collector.
| Category | Detailed description | |
|---|---|---|
| Prometheus Exporter | Provide metrics of a specific application or service in a format that Prometheus can scrape
| |
| Open Telemetry Collector | Acts as a centralized collector that gathers telemetry data such as metrics and logs from distributed systems, processes (filtering, sampling, etc.) it, and exports it to multiple backends (e.g., Prometheus, Jaeger, Elasticsearch, etc.)
|
Pre-configuration for Using ServiceWatch Agent
To use the ServiceWatch Agent, please refer to Prerequisite Settings for ServiceWatch Agent and prepare the prerequisite settings.
2.4.2.2 - Setting up RHEL Repo and WKMS
The Samsung Cloud Platform Console provides the SCP RHEL Repository to support user environments where external access is restricted, such as VPC Private Subnet. You can use the SCP RHEL Repository to install and download the same packages as the official RHEL Repository.
- If a user created RHEL before August 2025 through the Samsung Cloud Platform Console, they must modify the RHEL Repository settings.
- Since the SCP RHEL Repository synchronizes with each Region Local Repository according to an internal schedule, it is recommended to switch to an external public mirror site to apply the latest patches quickly.
- Samsung Cloud Platform provides the latest repository for the specified major version.
RHEL Repository Configuration Guide
When using RHEL, you can configure the SCP RHEL Repository to install and download the same packages as the official RHEL Repository. To set up the RHEL Repository, follow these steps.
On the Virtual Server, as the OS root user, use the cat command to check the
/etc/yum.repos.d/scp.rhel8.repoor/etc/yum.repos.d/scp.rhel9.repoconfiguration.Color modecat /etc/yum.repos.d/scp.rhel8.repocat /etc/yum.repos.d/scp.rhel8.repoCode block. Verify repo configuration (RHEL8) Color modecat /etc/yum.repos.d/scp.rhel9.repocat /etc/yum.repos.d/scp.rhel9.repoCode block. Verify repo configuration (RHEL9) - When checking the configuration file, the following result is displayed.Color mode
[rhel-8-baseos] name=rhel-8-baseos gpgcheck=0 enabled=1 baseurl=http://scp-rhel8-ip/rhel/8/baseos [rhel-8-baseos-debug] name=rhel-8-baseos-debug gpgcheck=0 enabled=1 baseurl=http://scp-rhel8-ip/rhel/8/baseos-debug [rhel-8-appstream] name=rhel-8-appstream gpgcheck=0 enabled=1 baseurl=http://scp-rhel8-ip/rhel/8/appstream[rhel-8-baseos] name=rhel-8-baseos gpgcheck=0 enabled=1 baseurl=http://scp-rhel8-ip/rhel/8/baseos [rhel-8-baseos-debug] name=rhel-8-baseos-debug gpgcheck=0 enabled=1 baseurl=http://scp-rhel8-ip/rhel/8/baseos-debug [rhel-8-appstream] name=rhel-8-appstream gpgcheck=0 enabled=1 baseurl=http://scp-rhel8-ip/rhel/8/appstreamCode block. Check repo configuration (RHEL8) Color mode[rhel-9-for-x86_64-baseos-rpms] name=rhel-9-for-x86_64-baseos-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/baseos gpgcheck=0 enabled=1 [rhel-9-for-x86_64-appstream-rpms] name=rhel-9-for-x86_64-appstream-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/appstream gpgcheck=0 enabled=1 [codeready-builder-for-rhel-9-x86_64-rpms] name=codeready-builder-for-rhel-9-x86_64-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/codeready-builder gpgcheck=0 enabled=1 [rhel-9-for-x86_64-highavailability-rpms] name=rhel-9-for-x86_64-highavailability-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/ha gpgcheck=0 enabled=1 [rhel-9-for-x86_64-supplementary-rpms] name=rhel-9-for-x86_64-supplementary-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/supplementary gpgcheck=0 enabled=1[rhel-9-for-x86_64-baseos-rpms] name=rhel-9-for-x86_64-baseos-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/baseos gpgcheck=0 enabled=1 [rhel-9-for-x86_64-appstream-rpms] name=rhel-9-for-x86_64-appstream-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/appstream gpgcheck=0 enabled=1 [codeready-builder-for-rhel-9-x86_64-rpms] name=codeready-builder-for-rhel-9-x86_64-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/codeready-builder gpgcheck=0 enabled=1 [rhel-9-for-x86_64-highavailability-rpms] name=rhel-9-for-x86_64-highavailability-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/ha gpgcheck=0 enabled=1 [rhel-9-for-x86_64-supplementary-rpms] name=rhel-9-for-x86_64-supplementary-rpms baseurl=http://scp-rhel9-ip/rhel/$releasever/x86_64/supplementary gpgcheck=0 enabled=1Code block. Verify repo configuration (RHEL9)
- When checking the configuration file, the following result is displayed.
Use a text editor (e.g., vim) to open the
/etc/hostsfile.Modify the
/etc/hostsfile with the following content and save it.Color mode198.19.2.13 scp-rhel8-ip scp-rhel9-ip scp-rhel-ip198.19.2.13 scp-rhel8-ip scp-rhel9-ip scp-rhel-ipcode block. Change /etc/hosts file settings Use the yum command to verify the RHEL Repository connection configured on the server.
Color modeyum repolist –vyum repolist –vCode block. Verify repository connection settings - If the RHEL repository is successfully connected, you can view the repository list.Color mode
Repo-id : rhel-8-appstream Repo-name : rhel-8-appstream Repo-revision : 1718903734 Repo-updated : Fri 21 Jun 2024 02:15:34 AM KST Repo-pkgs : 38,260 Repo-available-pkgs: 25,799 Repo-size : 122 G Repo-baseurl : http://scp-rhel8-ip/rhel/8/appstream Repo-expire : 172,800 second(s) (last: Thu 08 Aug 2024 07:27:57 AM KST) Repo-filename : /etc/yum.repos.d/scp.rhel8.repo Repo-id : rhel-8-baseos Repo-name : rhel-8-baseos Repo-revision : 1718029433 Repo-updated : Mon 10 Jun 2024 11:23:52 PM KST Repo-pkgs : 17,487 Repo-available-pkgs: 17,487 Repo-size : 32 G Repo-baseurl : http://scp-rhel8-ip/rhel/8/baseos Repo-expire : 172,800 second(s) (last: Thu 08 Aug 2024 07:27:57 AM KST) Repo-filename : /etc/yum.repos.d/scp.rhel8.repo Repo-id : rhel-8-baseos-debug Repo-name : rhel-8-baseos-debug Repo-revision : 1717662461 Repo-updated : Thu 06 Jun 2024 05:27:41 PM KST Repo-pkgs : 17,078 Repo-available-pkgs: 17,078 Repo-size : 100 G Repo-baseurl : http://scp-rhel8-ip/rhel/8/baseos-debug Repo-expire : 172,800 second(s) (last: Thu 08 Aug 2024 07:27:57 AM KST) Repo-filename : /etc/yum.repos.d/scp.rhel8.repoRepo-id : rhel-8-appstream Repo-name : rhel-8-appstream Repo-revision : 1718903734 Repo-updated : Fri 21 Jun 2024 02:15:34 AM KST Repo-pkgs : 38,260 Repo-available-pkgs: 25,799 Repo-size : 122 G Repo-baseurl : http://scp-rhel8-ip/rhel/8/appstream Repo-expire : 172,800 second(s) (last: Thu 08 Aug 2024 07:27:57 AM KST) Repo-filename : /etc/yum.repos.d/scp.rhel8.repo Repo-id : rhel-8-baseos Repo-name : rhel-8-baseos Repo-revision : 1718029433 Repo-updated : Mon 10 Jun 2024 11:23:52 PM KST Repo-pkgs : 17,487 Repo-available-pkgs: 17,487 Repo-size : 32 G Repo-baseurl : http://scp-rhel8-ip/rhel/8/baseos Repo-expire : 172,800 second(s) (last: Thu 08 Aug 2024 07:27:57 AM KST) Repo-filename : /etc/yum.repos.d/scp.rhel8.repo Repo-id : rhel-8-baseos-debug Repo-name : rhel-8-baseos-debug Repo-revision : 1717662461 Repo-updated : Thu 06 Jun 2024 05:27:41 PM KST Repo-pkgs : 17,078 Repo-available-pkgs: 17,078 Repo-size : 100 G Repo-baseurl : http://scp-rhel8-ip/rhel/8/baseos-debug Repo-expire : 172,800 second(s) (last: Thu 08 Aug 2024 07:27:57 AM KST) Repo-filename : /etc/yum.repos.d/scp.rhel8.repoCode block. Check repository list
- If the RHEL repository is successfully connected, you can view the repository list.
Windows Key Management Service Configuration Guide
When using Windows Server on Samsung Cloud Platform, you can authenticate genuine licenses by utilizing the Key Management Service provided by Samsung Cloud Platform. To authenticate genuine copies using the Key Management Service, follow these steps.
Right-click the Windows Start icon, then run cmd from Windows PowerShell (Administrator) or the Windows Run menu.
Run the following command in Windows PowerShell(Administrator) or cmd to register the KMS Server.
Color modeslmgr /skms 198.19.2.23:1688slmgr /skms 198.19.2.23:1688code block. WKMS configuration Run the KMS Server registration command, verify the notification popup indicating successful registration, and then click the OK button.
Run the following command in Windows PowerShell(Administrator) or cmd to activate Windows.
Color modeslmgr /atoslmgr /atoCode block. Windows Server activation settings After confirming the notification popup indicating that activation was successful, click the OK button.
In Windows PowerShell(Administrator) or cmd, run the following command to verify that the product is properly activated.
Color modeslmgr /dlvslmgr /dlvCode block. Verify Windows Server activation After confirming the notification popup indicating that product activation was successful, click the OK button.
2.4.3 - API Reference
2.4.4 - CLI Reference
2.4.5 - Release Note
Bare Metal Server
- The 4th‑generation BM based on the Intel 6th‑generation (Granite Rapids) Processor has been released.
- Bare Metal Server s4 and h4 server types have been added.
- Detailed information about the s4/h4 server type can be found in s3/h3 server type.
- Provides local disk partition functionality
- Now you can create and use up to 10 Local disk partitions.
- You can terminate multiple resources simultaneously from the Bare Metal Server list.
- You can change the IP of a regular Subnet.
- OS Image has been added.
- RHEL 8.10, Ubuntu 24.04
- Add Bare Metal Server feature
- Distribute servers belonging to the same Placement group across different racks.
- Additional OS images provided (RHEL 9.4, Rocky Linux 8.6, Rocky Linux 9.4)
- Add a 3rd‑generation (s3/h3) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For more information, refer to Bare Metal Server 서버 타입.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have officially launched the Bare Metal Server service.
- We have launched a Bare Metal Server service that lets customers use a physical server without virtualization, exclusively for their own use.
2.5 - Multi-node GPU Cluster
2.5.1 - Overview
Service Overview
Multi-node GPU Cluster is a service that provides physical GPU servers without virtualization for large-scale high-performance AI computation. You can use two or more Bare Metal Servers equipped with GPUs to cluster multiple GPUs, and conveniently operate GPU servers in conjunction with Samsung Cloud Platform’s high‑performance storage and networking services.
Provided Features
The Multi-node GPU Cluster provides the following features.
- Auto Provisioning and Management: Through the web-based Console, you can easily provision servers of the standard GPU Bare Metal model equipped with 8 GPUs and manage resources and costs.
- Network Connection: You can cluster multiple GPUs on two or more Bare Metal Servers via high‑speed interconnects, and by configuring a GPU Direct RDMA (Remote Direct Memory Access) environment, you can directly process data I/O between GPU memories, enabling high‑speed AI/Machine Learning computation.
- Storage Connection: Provides various additional attached storage besides the OS disk. * High-performance SSD NAS File Storage, Block Storage, and Object Storage directly integrated with a high-speed network can also be used together.
- Network Configuration Management: The server’s subnet/IP can be easily changed from the values set at initial creation. * NAT IP provides a management feature that allows you to enable or disable it as needed.
- Monitoring: You can view monitoring information for computing resources such as CPU, GPU, Memory, and Disk through Cloud Monitoring. * To use the Cloud Monitoring service of a Multi-node GPU Cluster, you need to install the Agent. * Please install the Agent to ensure stable service. * For more details, please refer to Multi-node GPU Cluster Monitoring Metrics.
- Terraform Provision: Provides an IaC environment via Terraform.
Component
Multi-node GPU Cluster provides GPUs as a Bare Metal Sever type with standard images and server types. NVSwitch and NVLink are provided.
Specifications by GPU Type
GPU (Graphic Processing Unit) is specialized for parallel operations that process large amounts of data quickly, enabling large-scale parallel computation in fields such as artificial intelligence (AI) and data analysis.
The following are the specifications of GPU types offered by the Multi-node GPU Cluster service.
| Category | H100 Type | B300 Type |
|---|---|---|
| GPU Architecture | NVIDIA Hopper | NVIDIA Blackwell Ultra |
| GPU Memory | 80 GiB | 268 GiB |
| GPU Transistors | 80 billion 4N TSMC | 208 billion 4NP TSMC |
| FP16 Tensor Core (Dense) | 989 TFLOPs | 2.25 PFLOPs |
| FP8 Tensor Core (Dense) | 1979 TFLOPs | 4.5 PFLOPs |
| FP4 Tensor Core (Dense) | Not supported | 13.5 PFLOPs |
| GPU Memory Bandwidth | 3,352 GB/s HBM3 | 8 TB/s HBM3e |
| NVLink performance | NVLink 4 | NVLink 5 |
| NVLink Signaling Rate | 25 GB/s (x18) | 50 GB/s (x18) |
| NVSwitch GPU-to-GPU bandwidth | 900 GB/s | 1.8 TB/s |
| Total NVSwitch aggregate bandwidth | 7.2 TB/s | 14.4 TB/s |
OS and GPU driver version
The operating systems (OS) supported by the Multi-node GPU Cluster are as follows.
| OS | OS version | GPU driver version |
|---|---|---|
| Ubuntu | 22.04 | 535.86.10, 535.183.06 |
| Ubuntu | 24.04 | 580.105.08 |
Server type
The format of server types provided by the Multi-node GPU Cluster is as follows.
- Example: when the server type is g2c96h8_metal
| Category | example | Detailed description |
|---|---|---|
| Server generation | g2 | Provided server generation
|
| CPU | c96 | Number of cores
|
| GPU | h8 | GPU type and quantity
|
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
2.5.1.1 - Server type
Multi-node GPU Cluster server type
Multi-node GPU Cluster is categorized based on the GPU Type it provides, and the GPU used in a Multi-node GPU Cluster is determined by the server type selected when creating a GPU Node. Select the server type based on the specifications of the application you want to run on a multi-node GPU cluster.
The server types supported by the Multi-node GPU Cluster are as follows.
- Example: when the server type is g2c96h8_metal.
Category example Detailed description Server generation g2 Provided server generation - g2
- g means GPU server specification
- 2 means generation
CPU c96 Number of cores - c96: Allocated cores are physical cores
GPU h8 GPU type and quantity - h8: h means GPU type, and 8 means GPU quantity
Table. Multi-node GPU Cluster server type format - g2
g2 server type
The g2 server type is a GPU Bare Metal Server that uses NVIDIA H100 SXM GPUs, suitable for large-scale high-performance AI computation.
- 8 NVIDIA Hopper Architecture-based H100 GPUs provided
- Provides 1,979 TFLOPS FP8 Tensor Core performance per GPU, 989 TFLOPS FP16 Tensor Core performance.
- Supports up to 96 vCPUs and 2,048 GB of memory
- Supports up to 1,600 Gb/s NVIDIA InfiniBand RDMA network.
- Service network up to 100 Gbps
- 900 GB/s GPU P2P communication via NVSwitch within a node
| Server type | GPU | GPU Memory | CPU(Core) | Memory | Disk | GPU P2P |
|---|---|---|---|---|---|---|
| g2c96h8_metal | H100 | 640 GiB | 96 vCore | 2 TB | SSD (OS) 960 GB * 2, NVMeSSD 3.84 TB * 4 | 900 GB/s NVSwitch |
g3 server type
The g3 server type is a GPU Bare Metal Server that uses NVIDIA B300 SXM GPUs, suitable not only for large-scale high-performance AI computation but also for LLM inference and AI deployment for generative AI.
- 8 NVIDIA Blackwell Ultra Architecture-based B300 GPUs provided
- Provides 13.5 PFLOPS FP4 Tensor Core and 4.5 PFLOPS FP8 Tensor Core performance per GPU.
- Supports up to 128 vCPUs and 4,096 GB of memory
- Supports up to 6,400 Gb/s NVIDIA InfiniBand RDMA network
- Service network up to 100 Gbps
- 1.8 TB/s GPU P2P communication via NVSwitch within a node
| Server type | GPU | GPU Memory | CPU(Core) | Memory | Disk | GPU P2P |
|---|---|---|---|---|---|---|
| g3c128b8_metal | B300 | 2.1 TiB | 128 vCore | 4 TB | SSD (OS) 960 GB * 2, NVMeSSD 3.84 TB * 4 | 1.8 TB/s NVSwitch |
2.5.1.2 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, from after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With a new alternative service, you can continuously perform resource monitoring by leveraging ServiceWatch released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a seamless monitoring environment.
If you are collecting metrics and logs through the Cloud Monitoring Agent, you need to switch to the ServiceWatch Agent.
For more details about ServiceWatch, please refer to ServiceWatch Overview.
Detailed information about ServiceWatch Agent: please refer to the ServiceWatch Agent
Multi-node GPU Cluster Monitoring Metrics
The table below shows the monitoring metrics of a Multi-node GPU Cluster that can be viewed through Cloud Monitoring.
Multi-node GPU Cluster [Cluster]
| Performance items | Detailed description | unit |
|---|---|---|
| Memory Total [Basic] | bytes of usable memory | bytes |
| Memory Used [Basic] | Current memory usage in bytes | bytes |
| Memory Swap In [Basic] | bytes of the replaced memory | bytes |
| Memory Swap Out [Basic] | bytes of the replaced memory | bytes |
| Memory Free [Basic] | bytes of unused memory | bytes |
| Disk Read Bytes [Basic] | Read bytes | bytes |
| Disk Read Requests [Basic] | Number of read requests | cnt |
| Disk Write Bytes [Basic] | write bytes | bytes |
| Disk Write Requests [Basic] | Number of write requests | cnt |
| CPU Usage [Basic] | Average system CPU usage over 1 minute | % |
| Instance State [Basic] | Instance status | state |
| Network In Bytes [Basic] | Received bytes | bytes |
| Network In Dropped [Basic] | Incoming packet drop | cnt |
| Network In Packets [Basic] | Number of received packets | cnt |
| Network Out Bytes [Basic] | sent bytes | bytes |
| Network Out Dropped [Basic] | Transmit packet drop | cnt |
| Network Out Packets [Basic] | Number of transmitted packets | cnt |
| Performance items | Detailed description | unit |
|---|---|---|
| Cluster GPU Count | GPU Count SUM in Cluster
| cnt |
| Cluster GPU Count In Use | Number of GPUs being used by jobs within the cluster
| cnt |
| Cluster GPU Usage | GPU Utilization AVG within the cluster
| % |
| Cluster GPU Memory Usage [Avg] | Cluster GPU Memory Utilization AVG
| % |
Multi-node GPU Cluster [Node]
| Performance items | Detailed description | unit |
|---|---|---|
| Memory Total [Basic] | bytes of usable memory | bytes |
| Memory Used [Basic] | Current memory usage in bytes | bytes |
| Memory Swap In [Basic] | bytes of the replaced memory | bytes |
| Memory Swap Out [Basic] | bytes of the replaced memory | bytes |
| Memory Free [Basic] | bytes of unused memory | bytes |
| Disk Read Bytes [Basic] | Read bytes | bytes |
| Disk Read Requests [Basic] | Number of read requests | cnt |
| Disk Write Bytes [Basic] | write bytes | bytes |
| Disk Write Requests [Basic] | Number of write requests | cnt |
| CPU Usage [Basic] | Average system CPU usage over 1 minute | % |
| Instance State [Basic] | Instance status | state |
| Network In Bytes [Basic] | Received bytes | bytes |
| Network In Dropped [Basic] | Incoming packet drop | cnt |
| Network In Packets [Basic] | Number of received packets | cnt |
| Network Out Bytes [Basic] | sent bytes | bytes |
| Network Out Dropped [Basic] | Transmit packet drop | cnt |
| Network Out Packets [Basic] | Number of transmitted packets | cnt |
| Performance items | Detailed description | unit |
|---|---|---|
| GPU Count | Number of GPUs | cnt |
| GPU Temperature | GPU temperature | ℃ |
| GPU Usage | utilization | % |
| GPU Usage [Avg] | Overall average GPU utilization (%) | % |
| GPU Power Cap | Maximum power capacity of the GPU | W |
| GPU Power Usage | Current GPU power usage | W |
| GPU Memory Usage [Avg] | GPU Memory Uti. AVG | % |
| GPU Count in use | Number of GPUs in use by jobs on the node | cnt |
| Execution Status for nvidia-smi | Result of running the nvidia-smi command | status |
| Core Usage [IO Wait] | Ratio of CPU time spent in wait state (disk wait) | % |
| Core Usage [System] | Proportion of CPU time spent in kernel space | % |
| Core Usage [User] | Proportion of CPU time spent in user space | % |
| CPU Cores | The number of CPU cores on the host. The maximum value of the unnormalized ratio is 100%* of a core. The unnormalized ratio already incorporates this value, and its maximum is 100%* of a core. | cnt |
| CPU Usage [Active] | Percentage of CPU time used excluding Idle and IOWait states (when all 4 cores are used at 100%: 400%) | % |
| CPU Usage [Idle] | It is the proportion of CPU time spent in idle state. | % |
| CPU Usage [IO Wait] | This is the proportion of CPU time spent in a waiting state (disk wait). | % |
| CPU Usage [System] | Percentage of CPU time used by the kernel (when all 4 cores are used at 100%: 400%) | % |
| CPU Usage [User] | Percentage of CPU time used in user space. (If all 4 cores are used at 100%, it is 400%) | % |
| CPU Usage/Core [Active] | Percentage of CPU time used excluding Idle and IOWait states (value normalized by the number of cores; 100% when all four cores are fully utilized) | % |
| CPU Usage/Core [Idle] | It is the proportion of CPU time spent in idle state. | % |
| CPU Usage/Core [IO Wait] | This is the proportion of CPU time spent in a waiting state (disk wait). | % |
| CPU Usage/Core [System] | Percentage of CPU time used by the kernel (value normalized by the number of cores; 100% when all 4 cores are fully utilized) | % |
| CPU Usage/Core [User] | Percentage of CPU time used in user space. (Value normalized by the number of cores; 100% when all 4 cores are fully utilized) | % |
| Disk CPU Usage [IO Request] | It is the proportion of CPU time during which I/O requests for the device were executed (device bandwidth utilization). If this value approaches 100%, the device becomes saturated. | % |
| Disk Queue Size [Avg] | The average queue length of requests executed for the device. | num |
| Disk Read Bytes | The number of bytes read per second from the device. | bytes |
| Disk Read Bytes [Delta Avg] | Average of system.diskio.read.bytes_delta for individual disks | bytes |
| Disk Read Bytes [Delta Max] | Maximum system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta Min] | Minimum system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta Sum] | Sum of the system.diskio.read.bytes_delta of individual disks | bytes |
| Disk Read Bytes [Delta] | Delta of the system.diskio.read.bytes value for each disk | bytes |
| Disk Read Bytes [Success] | Total number of bytes successfully read. On Linux, assuming a sector size of 512, it is the number of sectors read multiplied by 512. | bytes |
| Disk Read Requests | Number of read requests to the disk device per second | cnt |
| Disk Read Requests [Delta Avg] | Average of the system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Max] | Maximum system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Min] | Minimum of system.diskio.read.count_delta for individual disks | cnt |
| Disk Read Requests [Delta Sum] | Sum of system.diskio.read.count_delta of individual disks | cnt |
| Disk Read Requests [Success Delta] | Delta of system.diskio.read.count for each disk | cnt |
| Disk Read Requests [Success] | Total number of successful reads | cnt |
| Disk Request Size [Avg] | Average size of requests executed on the device (unit: sectors). | num |
| Disk Service Time [Avg] | Average service time (ms) of input requests executed on the device. | ms |
| Disk Wait Time [Avg] | Average time taken for requests executed on the supported device. | ms |
| Disk Wait Time [Read] | Average disk wait time | ms |
| Disk Wait Time [Write] | Average disk wait time | ms |
| Disk Write Bytes [Delta Avg] | Average of system.diskio.write.bytes_delta for each disk | bytes |
| Disk Write Bytes [Delta Max] | Maximum system.diskio.write.bytes_delta of individual disks | bytes |
| Disk Write Bytes [Delta Min] | Minimum of system.diskio.write.bytes_delta for individual disks | bytes |
| Disk Write Bytes [Delta Sum] | Sum of the system.diskio.write.bytes_delta of individual disks | bytes |
| Disk Write Bytes [Delta] | Delta of the system.diskio.write.bytes value for each disk | bytes |
| Disk Write Bytes [Success] | Total number of bytes successfully written. On Linux, assuming a sector size of 512, it is the number of sectors written multiplied by 512. | bytes |
| Disk Write Requests | Number of write requests to the disk device per second | cnt |
| Disk Write Requests [Delta Avg] | Average of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Max] | Maximum system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Min] | Minimum of system.diskio.write.count_delta for individual disks | cnt |
| Disk Write Requests [Delta Sum] | Sum of the system.diskio.write.count_delta of individual disks | cnt |
| Disk Write Requests [Success Delta] | Delta of system.diskio.write.count for each disk | cnt |
| Disk Write Requests [Success] | Total number of successful writes | cnt |
| Disk Writes Bytes | It is the number of bytes per second written to the device. | bytes |
| Filesystem Hang Check | filesystem (local/NFS) hang check (normal:1, abnormal:0) | status |
| Filesystem Nodes | It is the total number of file nodes in the file system. | cnt |
| Filesystem Nodes [Free] | It is the total number of available file nodes in the file system. | cnt |
| Filesystem Size [Available] | Disk space (bytes) that unauthorized users can use. | bytes |
| Filesystem Size [Free] | Available disk space (bytes) | bytes |
| Filesystem Size [Total] | Total disk space (bytes) | bytes |
| Filesystem Usage | Used disk space percentage | % |
| Filesystem Usage [Avg] | Average of individual filesystem.used.pct | % |
| Filesystem Usage [Inode] | inode usage | % |
| Filesystem Usage [Max] | Maximum among individual filesystem.used.pct | % |
| Filesystem Usage [Min] | minimum of individual filesystem.used.pct | % |
| Filesystem Usage [Total] | - | % |
| Filesystem Used | Used disk space (bytes) | bytes |
| Filesystem Used [Inode] | inode usage | bytes |
| Memory Free | Total amount of available memory (bytes). Memory used by system cache and buffers is not included (see system.memory.actual.free). | bytes |
| Memory Free [Actual] | Actual usable memory (bytes). The calculation method varies by OS: on Linux, it is MemAvailable from /proc/meminfo, or if meminfo cannot be used, it is calculated from available memory plus cache and buffers. On OSX, it is the sum of usable memory and inactive memory. On Windows, it corresponds to a value such as system.memory.free. | bytes |
| Memory Free [Swap] | Available swap memory. | bytes |
| Memory Total | total memory | bytes |
| Memory Total [Swap] | Total swap memory. | bytes |
| Memory Usage | Percentage of used memory
| % |
| Memory Usage [Actual] | Percentage of memory actually used
| % |
| Memory Usage [Cache Swap] | Cached swap usage rate | % |
| Memory Usage [Swap] | Percentage of used swap memory | % |
| Memory Used | used memory | bytes |
| Memory Used [Actual] | Actual used memory (bytes). The value obtained by subtracting used memory from total memory. Available memory is calculated differently for each OS (see system.actual.free). | bytes |
| Memory Used [Swap] | Used swap memory. | bytes |
| Collisions | Network collision | cnt |
| Network In Bytes | Number of received bytes | bytes |
| Network In Bytes [Delta Avg] | Average of system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Max] | Maximum of system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Min] | Minimum system.network.in.bytes_delta for each network | bytes |
| Network In Bytes [Delta Sum] | Sum of system.network.in.bytes_delta for individual networks | bytes |
| Network In Bytes [Delta] | Delta of received byte count | bytes |
| Network In Dropped | Number of deleted packets among incoming packets | cnt |
| Network In Errors | Number of errors during reception | cnt |
| Network In Packets | Number of received packets | cnt |
| Network In Packets [Delta Avg] | Average of system.network.in.packets_delta for individual networks | cnt |
| Network In Packets [Delta Max] | Maximum of system.network.in.packets_delta for each network | cnt |
| Network In Packets [Delta Min] | Minimum of system.network.in.packets_delta for each network | cnt |
| Network In Packets [Delta Sum] | Sum of system.network.in.packets_delta for individual networks | cnt |
| Network In Packets [Delta] | Delta of received packet count | cnt |
| Network Out Bytes | Number of transmitted bytes | bytes |
| Network Out Bytes [Delta Avg] | Average of system.network.out.bytes_delta for each network | bytes |
| Network Out Bytes [Delta Max] | Maximum system.network.out.bytes_delta of individual networks | bytes |
| Network Out Bytes [Delta Min] | Minimum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta Sum] | Sum of system.network.out.bytes_delta for individual networks | bytes |
| Network Out Bytes [Delta] | Delta of transmitted byte count | bytes |
| Network Out Dropped | Number of deleted packets among outgoing packets. This value is not reported by the operating system, so it is always 0 on Darwin and BSD. | cnt |
| Network Out Errors | Number of errors during transmission | cnt |
| Network Out Packets | Number of transmitted packets | cnt |
| Network Out Packets [Delta Avg] | Average of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Max] | Maximum of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Min] | Minimum of system.network.out.packets_delta for each network | cnt |
| Network Out Packets [Delta Sum] | Sum of system.network.out.packets_delta for individual networks | cnt |
| Network Out Packets [Delta] | Delta of transmitted packet count | cnt |
| Open Connections [TCP] | All open TCP connections | cnt |
| Open Connections [UDP] | All open UDP connections | cnt |
| Port Usage | Available port usage rate | % |
| SYN Sent Sockets | Number of sockets in SYN_SENT state (when connecting from local to remote) | cnt |
| Kernel PID Max | kernel.pid_max value | cnt |
| Kernel Thread Max | kernel.threads-max value | cnt |
| Process CPU Usage | Percentage of CPU time consumed by the process since the last update. This value is similar to the %CPU value shown for the process by the top command on Unix systems. | % |
| Process CPU Usage/Core | The percentage of CPU time used by the process since the last event. Normalized by the number of cores, with values ranging from 0 to 100%. | % |
| Process Memory Usage | Proportion of main memory (RAM) occupied by a process | % |
| Process Memory Used | Resident Set size. The amount of memory a process occupies in RAM. In Windows, the current working set size. | bytes |
| Process PID | process pid | PID |
| Process PPID | parent process PID | PID |
| Processes [Dead] | Number of dead processes | cnt |
| Processes [Idle] | Number of idle processes | cnt |
| Processes [Running] | Number of running processes | cnt |
| Processes [Sleeping] | Number of sleeping processes | cnt |
| Processes [Stopped] | stopped processes count | cnt |
| Processes [Total] | Total number of processes | cnt |
| Processes [Unknown] | Number of processes with an unknown or unsearchable status | cnt |
| Processes [Zombie] | Number of zombie processes | cnt |
| Running Process Usage | process usage | % |
| Running Processes | Number of running processes | cnt |
| Running Thread Usage | Thread usage rate | % |
| Running Threads | Total number of threads running in running processes | cnt |
| Instance Status | Instance status | state |
| Context Switches | context switch count (per second) | cnt |
| Load/Core [1 min] | The load over the last 1 minute divided by the number of cores | cnt |
| Load/Core [15 min] | The load over the last 15 minutes divided by the number of cores | cnt |
| Load/Core [5 min] | The load over the last 5 minutes divided by the number of cores | cnt |
| Multipaths [Active] | External storage connection path status = active count | cnt |
| Multipaths [Failed] | External storage connection path status = failed count | cnt |
| Multipaths [Faulty] | External storage connection path status = faulty count | cnt |
| NTP Offset | measured offset of the last sample (the time difference between the NTP server and the local environment) | num |
| Run Queue Length | Execution queue length | num |
| Uptime | OS uptime(uptime). (milliseconds) | ms |
| Context Switchies | CPU context switch count (per second) | cnt |
| Disk Read Bytes [Sec] | Number of bytes read from a Windows logical disk in 1 second | cnt |
| Disk Read Time [Avg] | Average data read time (seconds) | sec |
| Disk Transfer Time [Avg] | Disk average wait time | sec |
| Disk Usage | Disk usage | % |
| Disk Write Bytes [Sec] | Number of bytes written in one second on a Windows logical disk | cnt |
| Disk Write Time [Avg] | Average data write time (seconds) | sec |
| Pagingfile Usage | Paging file usage | % |
| Pool Used [Non Paged] | Nonpaged Pool usage in kernel memory | bytes |
| Pool Used [Paged] | Paged Pool usage in kernel memory | bytes |
| Process [Running] | Number of currently running processes | cnt |
| Threads [Running] | Number of currently running threads | cnt |
| Threads [Waiting] | Number of threads waiting for processor time | cnt |
2.5.2 - How-to guides
Users can create the service by entering the required information for the Multi-node GPU Cluster service and selecting detailed options through the Samsung Cloud Platform Console.
Multi-node GPU Cluster Getting Started
You can create and use a Multi-node GPU Cluster service in the Samsung Cloud Platform Console.
This service consists of a GPU Node and a Cluster Fabric service.
Create GPU Node
Multi-node GPU Cluster To create a Multi-node GPU Cluster, follow the steps below.
- All Services > Compute > Multi-node GPU Cluster menu, click it. Navigate to the Service Home page of Multi-node GPU Cluster.
- On the Service Home page, click the Create GPU Node button. You will be taken to the Create GPU Node page.
- On the GPU Node Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and Version Selection area.
Category required or notDetailed description image Required Select the type of image provided - Ubuntu
Image version Required Select version of the chosen image - Provide a list of versions for the supplied server image
Table. GPU Node image and version selection options - In the Service Information Input area, enter or select the required information.
Category RequiredDetailed description Number of servers Required Number of GPU Node servers to create simultaneously - Only numeric input is allowed, and the minimum number of servers to create is 2.
- Only during the initial setup can you create 2 or more, and subsequent expansions can be done one at a time.
Service Type > Server Type Required GPU Node server type - Select the desired CPU, Memory, GPU, and Disk specifications
- For detailed information about the server types provided by GPU Node, refer to Multi-node GPU Cluster Server Type
Service Type > Planned Compute Required Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, refer to Apply for Planned Compute
Table. GPU Node Service Information Input Items - In the Required Information Input area, enter or select the necessary information.
Category RequiredDetailed description Administrator account Required Set the administrator account and password to be used when connecting to the server - Ubuntu OS is provided with root fixed
Server name Prefix Required Enter a Prefix to distinguish each GPU Node generated when the selected number of servers is 2 or more - Automatically generated in the form of user input value (prefix) + ‘
-###’
- Must start with a lowercase English letter and be entered using lowercase letters, numbers, and special characters (
-) within 3 to 11 characters
- Must not end with a special character (
-)
Network Settings Required Set the network where the GPU Node will be installed - VPC name: select a pre‑created VPC
- General Subnet name: select a pre‑created general Subnet
- IP can be auto‑generated or manually entered; if manual input is chosen, the user enters the IP directly
- NAT: usable only when there is a single server and the VPC is attached to an Internet Gateway. Check to use, and you can select a NAT IP (initially it can be created only with two or more servers, so modify it on the resource detail page)
- NAT IP: select a NAT IP
- If no NAT IP is available, click the Create new button to generate a Public IP
- Click the Refresh button to view and select the created Public IP
- Creating a Public IP incurs charges according to the Public IP pricing
Table. Required input fields for GPU Node - In the Cluster Selection area, create or select a Cluster Fabric.
Category Required statusDetailed description Cluster Fabric Required Configure a group of GPU Node servers that can apply GPU Direct RDMA together - Optimal GPU performance and speed can be achieved only within the same Cluster Fabric
- When creating a new Cluster Fabric, *New Input > select Node pool, then enter the name of the Cluster Fabric to create
- To add to an existing Cluster Fabric, Existing Input > select Node pool, then select the previously created Cluster Fabric
Table. GPU Node Cluster Fabric selection items - Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Lock Selection Using a lock prevents accidental actions that could terminate, start, or stop the server. Init Script Selection Script to run when the server starts - The Init Script must be selected differently depending on the image type
- For Linux: Choose Shell Script or cloud-init
tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. GPU Node additional information input fields - The Init Script must be selected differently depending on the image type
- Select the required information in the Image and Version Selection area.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- When creation is complete, check the created resources on the GPU Node List page.
- When creating a service, the GPU MIG/ECC settings are reset. However, to ensure the correct settings are applied, perform an initial reboot, verify that the settings have taken effect, and then proceed.
- For detailed information on resetting GPU MIG/ECC settings, refer to the GPU MIG/ECC Reset Settings Checklist Guide.
Check GPU Node details
The Multi-node GPU Cluster service allows you to view and edit the full resource list and detailed information of GPU nodes.
GPU Node Details page consists of Details, Tags, Job History tabs.
To view detailed information about the GPU Node, follow these steps.
All Services > Compute > Multi-node GPU Cluster > GPU Node menu, click it. Navigate to the Service Home page of Multi-node GPU Cluster.
On the Service Home page, click the GPU Node menu. You will be taken to the GPU Node List page.
- Resource items beyond the required columns can be added via the Settings button.
Category Required statusDetailed description Resource ID Selection User-created GPU Node ID Cluster Fabric name Required User-created Cluster Fabric name Server name Required User-created GPU Node name Server type Required Server type of the GPU Node - Users can view the number of cores, memory capacity, and GPU type and quantity of the resources they created
image Required User-created GPU Node image version IP Required IP of the GPU node created by the user status Required Status of the user-created GPU node Creation date and time Selection GPU Node creation timestamp Table. GPU Node resource list items
- Resource items beyond the required columns can be added via the Settings button.
On the GPU Node List page, click the resource for which you want to view detailed information. You will be taken to the GPU Node Details page.
- GPU Server Details At the top of the page, status information and descriptions of additional features are displayed.
Category Detailed description GPU Node status Status of user-created GPU Node - Creating: server is being created
- Running:: creation completed and available
- Editing:: IP is being changed
- Unknown: error state
- Starting: server is starting
- Stopping: server is stopping
- Stopped: server stopped
- Terminating: terminating
- Terminated: termination completed
Server control Button to change server status - Start: Start a stopped server
- Stop: Stop a running server
Service termination Cancel service button Table. GPU Node status information and additional features
- GPU Server Details At the top of the page, status information and descriptions of additional features are displayed.
Detailed Information
On the GPU Node List page’s Details Tab, you can view the detailed information of the selected resource and edit the information if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Server name | Server name |
| Node pool | A collection of nodes that can be grouped into the same Cluster Fabric |
| Cluster Fabric name | User-created Cluster Fabric name |
| Image/Version | Server OS image and version |
| Server type | CPU, memory, GPU, information display |
| Planned Compute | Resource status with Planned Compute configured
|
| Lock | Display whether Lock is enabled or disabled
|
| Network | GPU Node network information
|
| Block Storage | Block Storage information attached to the server
|
| Init Script | View the Init Script content entered when creating the server |
tag
On the GPU Node List page’s Tag Tab, you can view the selected resource’s tag information, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the GPU Node List page’s Job History Tab, you can view the job history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Control GPU Node Operation
If you need server control and management functions for the created GPU Node resources, you can perform tasks on the GPU Node List or GPU Node Details page. You can start and stop the resources of a running GPU node.
Getting Started with GPU Node
You can start a GPU Node that is stopped (Stopped). To start a GPU Node, follow the steps below.
- Click the All Services > Compute > Multi-node GPU Cluster menu. Go to the Service Home page of Multi-node GPU Cluster.
- On the Service Home page, click the GPU Node menu. You will be taken to the GPU Node List page.
- On the GPU Node List page, after selecting individual or multiple servers with the checkboxes, you can Start using the More button at the top.
- On the GPU Node List page, click the resource. Navigate to the GPU Node Detail page.
- On the GPU Node Details page, click the Start button at the top to start the server.
- Check the server status and complete the status change.
Stopping GPU Node
You can stop a GPU Node that is running (Active). To stop a GPU Node, follow the steps below.
- Click the All Services > Compute > Multi-node GPU Cluster menu. Go to the Service Home page of Multi-node GPU Cluster.
- On the Service Home page, click the GPU Node menu. You will be taken to the GPU Node List page.
- GPU Node List page allows you to control individual or multiple servers by selecting the checkboxes and using the Stop button at the top.
- On the GPU Node List page, click the resource. You will be taken to the GPU Node Details page.
- On the GPU Node Details page, click the Stop button at the top to stop the server.
- Check the server status and complete the status change.
Terminate GPU Node
You can terminate unused GPU Nodes to reduce operating costs. However, terminating a service may cause the running service to stop immediately, so you should carefully consider the impact of service interruption before proceeding with termination.
To cancel a GPU Node, follow the steps below.
- Click the All Services > Compute > Multi-node GPU Server menu. Navigate to the Service Home page of the Multi-node GPU Cluster.
- On the Service Home page, click the Cluster Fabric menu. You will be taken to the Cluster Fabric list page.
- Cluster Fabric List page, select the resources to terminate, and click the Service Termination button.
- Resources that use the same Cluster Fabric can be terminated simultaneously.
- When termination is complete, check on the GPU Node List page whether the resources have been terminated.
The cases where a GPU Node cannot be terminated are as follows.
- When Block Storage(BM) is connected: Please disconnect the Block Storage(BM) connection first.
- If File Storage is connected: Please disconnect the File Storage first.
- When Lock is set: Please change the Lock setting to disabled and try again.
- If the selection includes a server that cannot be terminated simultaneously: Please re-select only resources that can be terminated.
- If the server you want to terminate has a different Cluster Fabric: Select only resources that use the same Cluster Fabric.
2.5.2.1 - Manage Cluster Fabric
Cluster Fabric is a service that helps manage the servers (GPU Node) included in a GPU Cluster. By using Cluster Fabric, you can move servers between GPU Clusters in the same Node pool and optimize GPU performance and speed within the same GPU Cluster.
Creating Cluster Fabric
Cluster Fabric can be created together with a GPU Node, and it cannot be created or deleted separately. If all GPU Nodes within a Cluster Fabric are terminated, the Cluster Fabric is automatically deleted.
If you have not created a GPU Node, please create a GPU Node first. For more information, see GPU Node 생성하기.
Check Cluster Fabric details
- Cluster Fabric can be created together when a GPU node is created, and it cannot be created or deleted independently.
- If all GPU nodes in the Cluster Fabric are terminated, the Cluster Fabric is automatically deleted.
- If you have not created a GPU Node, please create a GPU Node first. For more details, refer to GPU Node 생성하기.
On the Cluster Fabric List page and the Cluster Fabric Details page, you can view the generated Cluster Fabric list and details and move the server.
Click the All Services > Compute > Multi-node GPU Server menu. Go to the Service Home page of the Multi-node GPU Cluster.
On the Service Home page, click the Cluster Fabric menu. You will be taken to the Cluster Fabric List page.
- On the Cluster Fabric List page, you can view the resource list of GPU clusters created by the user.
- Resource items beyond the required columns can be added via the Settings button.
Category RequiredDetailed description Resource ID Selection User-created Cluster Fabric ID Cluster Fabric name Required User-created Cluster Fabric name Node pool Selection A collection of nodes that can be grouped into the same Cluster Fabric Number of servers Selection Number of GPU Nodes Server type Selection Server type of GPU Node - Users can view the number of cores, memory capacity, and GPU type and count of the resources they created
status Selection Status of the user-created Cluster Fabric Creation date and time Select Cluster Fabric creation timestamp Table. Cluster Fabric resource list items
On the Cluster Fabric List page, click the resource to view detailed information. You will be taken to the Cluster Fabric Details page.
- Cluster Fabric Details At the top of the page, status information and descriptions of additional features are displayed.
Category Detailed description Cluster Fabric status Status of the user-created Cluster Fabric - Creating: State while the cluster is being created
- Active: State when creation is complete and the cluster is usable
- Editing: State while the IP is being changed
- Deleting: State while being terminated
- Deleted: State after termination is complete
Add target server A feature that allows moving a server from another cluster to the target cluster. Table. Cluster Fabric status information and additional features
- Cluster Fabric Details At the top of the page, status information and descriptions of additional features are displayed.
Detailed Information
On the Cluster Fabric List page’s Details Tab, you can view detailed information of the selected resource and retrieve servers from another cluster.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Cluster Fabric name | User-created Cluster Fabric name |
| Node pool | A set of nodes that can be grouped into the same Cluster Fabric |
| target server | GPU Node list bound to Cluster Fabric
|
Import Cluster Fabric Server
Cluster Fabric Details page’s add target server feature allows you to import servers from another cluster and add them to the selected cluster.
- Click the All Services > Compute > Multi-node GPU Server menu. Navigate to the Service Home page of the Multi-node GPU Cluster.
- On the Service Home page, click the Cluster Fabric menu. You will be taken to the Cluster Fabric list page.
- On the Cluster Fabric List page, click the resource to view detailed information. You will be taken to the Cluster Fabric Details page.
- In the target server of the Details tab, click the Add button on the right.
- The add target server popup window opens.
- Select a cluster from Cluster Fabric.
- GPU nodes associated with the selected cluster are listed; select the GPU node you want to retrieve.
- The selected GPU Node’s name is displayed at the bottom.
- Press the Confirm button to complete.
- Pressing the Cancel button cancels the operation.
- Verify that the GPU node added on the target server is displayed.
- The add target server popup window opens.
Terminate Cluster Fabric
If all GPU Nodes in the Cluster Fabric are terminated, the Cluster Fabric is automatically deleted. For more information, see Terminate GPU Node.
2.5.2.2 - Install ServiceWatch Agent
Users can install the ServiceWatch Agent on GPU nodes of a Multi-node GPU Cluster to collect custom metrics and logs.
ServiceWatch Agent
In a Multi-node GPU Cluster, the agents that need to be installed on GPU nodes to collect ServiceWatch custom metrics and logs can be divided into two main types. It is a Prometheus Exporter and Open Telemetry Collector.
| Category | Detailed description | |
|---|---|---|
| Prometheus Exporter | Provide metrics of a specific application or service in a format that Prometheus can scrape
| |
| Open Telemetry Collector | Acts as a centralized collector that gathers telemetry data such as metrics and logs from distributed systems, processes (filtering, sampling, etc.) it, and exports it to multiple backends (e.g., Prometheus, Jaeger, Elasticsearch, etc.)
|
If you have configured a Kubernetes Engine on a GPU node, please view the GPU metrics using the metrics provided by the Kubernetes Engine.
- If you install the DCGM Exporter on a GPU node where Kubernetes Engine is configured, it may not operate correctly.
Pre-configuration for Using ServiceWatch Agent
To use the ServiceWatch Agent, please refer to Prerequisite Settings for ServiceWatch Agent and prepare the prerequisite settings.
2.5.2.3 - Multi-node GPU Cluster Service Scope and Inspection Guide
Multi-node GPU Cluster Service Scope
If an IaaS hardware-level issue occurs with the Multi-node GPU Cluster service, you can receive technical support through Contact Us in the Support Center. However, the risks associated with changes such as OS kernel updates or application installations are the user’s responsibility, so technical support is limited; please be mindful when performing tasks such as system updates.
IaaS hardware level issue
- HW fault event messages generated within the server by the IPMI hardware monitoring console.
- GPU HW operation error observed in the nvdia-smi command
- HW error messages that occur during inspection of InfiniBand HCA cards or InfiniBand Switches
IaaS HW Inspection Guide
After applying for the Multi-node GPU Cluster service, it is recommended to check the IaaS HW level according to the inspection guide.
Intel E810 driver update
Check the version of the Intel E810 driver and, if necessary, refer to the following procedure to perform an update.
- Server manufacturer Intel E810 driver minimum recommended version: 1.15.4 or later
- Driver download: Intel Network Adapter Driver for 800 Series Devices under Linux
You can use the lspci command to verify whether an E810 NIC device is present.
If the E810 NIC is valid, the PCIe device is identified as follows using the E810-C information (if there is no E810 NIC device, this operation is not performed).
<div class="code-block-buttons">
<button class="code-block-download">
<div class="code-block-download-icon">
<svg width="14" height="16" viewBox="0 0 14 16" fill="none" xmlns="http://www.w3.org/2000/svg"><path d="M13.999 14.4353v-2.998C13.999 11.0232 13.6602 10.6853 13.2461 10.6853S12.5 11.0232 12.5 11.4373v2.2519H1.5V11.4373C1.5 11.0232 1.16211 10.6853.748047 10.6853.333984 10.6853 976563e-9 11.0232 976562e-9 11.4373v2.998C976562e-9 14.8494.333984 15.1892.748047 15.1892H13.2461c.414099999999999.0.7529-.3398.7529-.7539z" fill="#5135ff"/><path d="M1.41169 6.21654c.25876-.32345.73073-.37589 1.05417-.11713l3.78463 3.0277V1.56104c0-.41422.33578-.750005.75-.750005.41421.0.75.335785.75.750005V9.12208L11.5288 6.09941C11.8523 5.84065 12.3242 5.89309 12.583 6.21654 12.8418 6.53999 12.7893 7.01196 12.4659 7.27071L6.99734 11.6455 1.52882 7.27071c-.32345-.25875-.37589-.73072-.11713-1.05417z" fill="#5135ff"/></svg></div>
Sample Code Download
</button>
<button class="code-block-copy">
<div class="code-block-copy-icon">
<svg width="14" height="14" viewBox="0 0 14 14" fill="none" xmlns="http://www.w3.org/2000/svg"><path fill-rule="evenodd" clip-rule="evenodd" d="M10 4.00012V1c0-.552285-.44772-1-1-1H1C.447715.0.0.447715.0 1V9c0 .55228.447715 1 1 1H3.99988v3.0001C3.99988 13.5515 4.44849 14 4.99988 14H10.0002l3.9997-3.9995V5c0-.55139-.448600000000001-.99988-1-.99988H10zM1.4 1.4V8.6H3.99988V5c0-.55139.44861-.99988 1-.99988H8.6V1.4H1.4zM5.3999 12.6H9.08295V9.78301C9.08295 9.39641 9.39635 9.08301 9.78295 9.08301H12.5999V5.40015h-7.2V12.6zm6.1375-2.117-1.0545 1.0544V10.483h1.0545z" fill="currentcolor"/></svg></div>
Copy Code
</button>
</div>
lspci | grep E810
0000:6a:00.0 Ethernet controller: Intel Corporation Ethernet Controller E810-C for QSFP (rev 02) 0000:6a:00.1 Ethernet controller: Intel Corporation Ethernet Controller E810-C for QSFP (rev 02)lspci | grep E810
0000:6a:00.0 Ethernet controller: Intel Corporation Ethernet Controller E810-C for QSFP (rev 02) 0000:6a:00.1 Ethernet controller: Intel Corporation Ethernet Controller E810-C for QSFP (rev 02)</div>
To update the driver, follow the steps below.
Move the base driver tar file to the desired directory.
Color mode/usr/local/src/usr/local/srcDirectory navigation example Untar / unzip the Archiver file.
- x.x.x is the version number of the driver tar file.Color mode
tar zxf ice-x.x.x.tar.gztar zxf ice-x.x.x.tar.gzuntar example
- x.x.x is the version number of the driver tar file.
Change the driver to the src directory.
- x.x.x is the version number of the driver tar file.Color mode
cd ice-x.x.x/src/cd ice-x.x.x/src/Example of changing to the src directory
- x.x.x is the version number of the driver tar file.
Compile the driver module.
Color modemake installmake installDriver module compilation example After the update is complete, check the version.
Color modelsmod | grep ice modinfo ice | grep versionlsmod | grep ice modinfo ice | grep versionVersion check example
Check NVIDIA driver
To check the NVIDIA driver (nvidia-smi topo, IB nv_peer_mem status) and inspect the IaaS hardware level, follow these steps.
Check the GPU driver status.
Color mode~$ nvidia-smi~$ nvidia-smiExample code for checking GPU driver status Color modeThu Jan 29 14:48:31 2026 +---------------------------------------------------------------------------------------+ | NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 | |-----------------------------------------+----------------------+----------------------+ | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | =========================================+======================+====================== | | 0 NVIDIA A100-SXM4-80GB On | 00000000:00:05.0 Off | On | | N/A 36C P0 52W / 400W | 0MiB / 81920MiB | N/A Default | | | | Enabled | +-----------------------------------------+----------------------+----------------------+ | 1 NVIDIA A100-SXM4-80GB On | 00000000:00:06.0 Off | 0 | | N/A 36C P0 61W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 2 NVIDIA A100-SXM4-80GB On | 00000000:00:07.0 Off | 0 | | N/A 36C P0 64W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 3 NVIDIA A100-SXM4-80GB On | 00000000:00:08.0 Off | 0 | | N/A 40C P0 64W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 4 NVIDIA A100-SXM4-80GB On | 00000000:00:09.0 Off | 0 | | N/A 36C P0 63W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 5 NVIDIA A100-SXM4-80GB On | 00000000:00:0A.0 Off | 0 | | N/A 40C P0 64W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 6 NVIDIA A100-SXM4-80GB On | 00000000:00:0B.0 Off | 0 | | N/A 39C P0 65W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 7 NVIDIA A100-SXM4-80GB On | 00000000:00:0C.0 Off | 0 | | N/A 39C P0 60W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ +---------------------------------------------------------------------------------------+ | MIG devices: | +------------------+--------------------------------+-----------+-----------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ==================+================================+===========+======================= | | No MIG devices found | +---------------------------------------------------------------------------------------+ +---------------------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ======================================================================================= | | No running processes found | +---------------------------------------------------------------------------------------+Thu Jan 29 14:48:31 2026 +---------------------------------------------------------------------------------------+ | NVIDIA-SMI 535.183.06 Driver Version: 535.183.06 CUDA Version: 12.2 | |-----------------------------------------+----------------------+----------------------+ | GPU Name Persistence-M | Bus-Id Disp.A | Volatile Uncorr. ECC | | Fan Temp Perf Pwr:Usage/Cap | Memory-Usage | GPU-Util Compute M. | | | | MIG M. | | =========================================+======================+====================== | | 0 NVIDIA A100-SXM4-80GB On | 00000000:00:05.0 Off | On | | N/A 36C P0 52W / 400W | 0MiB / 81920MiB | N/A Default | | | | Enabled | +-----------------------------------------+----------------------+----------------------+ | 1 NVIDIA A100-SXM4-80GB On | 00000000:00:06.0 Off | 0 | | N/A 36C P0 61W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 2 NVIDIA A100-SXM4-80GB On | 00000000:00:07.0 Off | 0 | | N/A 36C P0 64W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 3 NVIDIA A100-SXM4-80GB On | 00000000:00:08.0 Off | 0 | | N/A 40C P0 64W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 4 NVIDIA A100-SXM4-80GB On | 00000000:00:09.0 Off | 0 | | N/A 36C P0 63W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 5 NVIDIA A100-SXM4-80GB On | 00000000:00:0A.0 Off | 0 | | N/A 40C P0 64W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 6 NVIDIA A100-SXM4-80GB On | 00000000:00:0B.0 Off | 0 | | N/A 39C P0 65W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ | 7 NVIDIA A100-SXM4-80GB On | 00000000:00:0C.0 Off | 0 | | N/A 39C P0 60W / 400W | 0MiB / 81920MiB | 0% Default | | | | Disabled | +-----------------------------------------+----------------------+----------------------+ +---------------------------------------------------------------------------------------+ | MIG devices: | +------------------+--------------------------------+-----------+-----------------------+ | GPU GI CI MIG | Memory-Usage | Vol | Shared | | ID ID Dev | BAR1-Usage | SM Unc | CE ENC DEC OFA JPG | | | | ECC | | | ==================+================================+===========+======================= | | No MIG devices found | +---------------------------------------------------------------------------------------+ +---------------------------------------------------------------------------------------+ | Processes: | | GPU GI CI PID Type Process name GPU Memory | | ID ID Usage | | ======================================================================================= | | No running processes found | +---------------------------------------------------------------------------------------+GPU driver status example Check the NVSwitch and NVLink hardware status.
Check NVSwitch status
Color mode~$ nvidia-smi nvlink --status~$ nvidia-smi nvlink --statusNVSwitch status check example Color modeGPU 1: NVIDIA A100-SXM4-80GB (UUID: GPU-64a2f685-bb12-c4af-105c-0726ece9c8d7) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 2: NVIDIA A100-SXM4-80GB (UUID: GPU-2269851b-71cd-f6c7-50c5-ba1525cf3ce8) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 3: NVIDIA A100-SXM4-80GB (UUID: GPU-4c397bbf-95fc-5c29-918a-a429cbe45a7a) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 4: NVIDIA A100-SXM4-80GB (UUID: GPU-0e350204-9fb6-2cbe-538e-8f7849658eb8) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 5: NVIDIA A100-SXM4-80GB (UUID: GPU-45f0c453-4760-edd4-3af9-25c5ea7473a5) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 6: NVIDIA A100-SXM4-80GB (UUID: GPU-38409794-bb34-430e-3c50-90b42cb2bb72) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 7: NVIDIA A100-SXM4-80GB (UUID: GPU-3fb478aa-801b-eb64-55c2-0ffc3f2ce404) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/sGPU 1: NVIDIA A100-SXM4-80GB (UUID: GPU-64a2f685-bb12-c4af-105c-0726ece9c8d7) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 2: NVIDIA A100-SXM4-80GB (UUID: GPU-2269851b-71cd-f6c7-50c5-ba1525cf3ce8) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 3: NVIDIA A100-SXM4-80GB (UUID: GPU-4c397bbf-95fc-5c29-918a-a429cbe45a7a) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 4: NVIDIA A100-SXM4-80GB (UUID: GPU-0e350204-9fb6-2cbe-538e-8f7849658eb8) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 5: NVIDIA A100-SXM4-80GB (UUID: GPU-45f0c453-4760-edd4-3af9-25c5ea7473a5) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 6: NVIDIA A100-SXM4-80GB (UUID: GPU-38409794-bb34-430e-3c50-90b42cb2bb72) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/s GPU 7: NVIDIA A100-SXM4-80GB (UUID: GPU-3fb478aa-801b-eb64-55c2-0ffc3f2ce404) Link 0: 25 GB/s Link 1: 25 GB/s Link 2: 25 GB/s Link 3: 25 GB/s Link 4: 25 GB/s Link 5: 25 GB/s Link 6: 25 GB/s Link 7: 25 GB/s Link 8: 25 GB/s Link 9: 25 GB/s Link 10: 25 GB/s Link 11: 25 GB/sNVSwitch status example Check NVLinks hardware status
Color mode~$ nvidia-smi topo -m~$ nvidia-smi topo -mExample code for checking NVLink hardware status Color modeGPU0 GPU1 GPU2 GPU3 GPU4 GPU5 GPU6 GPU7 CPU Affinity NUMA Affinity GPU NUMA ID GPU0 X NV12 NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU1 NV12 X NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU2 NV12 NV12 X NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU3 NV12 NV12 NV12 X NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU4 NV12 NV12 NV12 NV12 X NV12 NV12 NV12 0-127 0-7 N/A GPU5 NV12 NV12 NV12 NV12 NV12 X NV12 NV12 0-127 0-7 N/A GPU6 NV12 NV12 NV12 NV12 NV12 NV12 X NV12 0-127 0-7 N/A GPU7 NV12 NV12 NV12 NV12 NV12 NV12 NV12 X 0-127 0-7 N/A Legend: X = Self SYS = Connection traversing PCIe as well as the SMP interconnect between NUMA nodes (e.g., QPI/UPI) NODE = Connection traversing PCIe as well as the interconnect between PCIe Host Bridges within a NUMA node PHB = Connection traversing PCIe as well as a PCIe Host Bridge (typically the CPU) PXB = Connection traversing multiple PCIe bridges (without traversing the PCIe Host Bridge) PIX = Connection traversing at most a single PCIe bridge NV# = Connection traversing a bonded set of # NVLinksGPU0 GPU1 GPU2 GPU3 GPU4 GPU5 GPU6 GPU7 CPU Affinity NUMA Affinity GPU NUMA ID GPU0 X NV12 NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU1 NV12 X NV12 NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU2 NV12 NV12 X NV12 NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU3 NV12 NV12 NV12 X NV12 NV12 NV12 NV12 0-127 0-7 N/A GPU4 NV12 NV12 NV12 NV12 X NV12 NV12 NV12 0-127 0-7 N/A GPU5 NV12 NV12 NV12 NV12 NV12 X NV12 NV12 0-127 0-7 N/A GPU6 NV12 NV12 NV12 NV12 NV12 NV12 X NV12 0-127 0-7 N/A GPU7 NV12 NV12 NV12 NV12 NV12 NV12 NV12 X 0-127 0-7 N/A Legend: X = Self SYS = Connection traversing PCIe as well as the SMP interconnect between NUMA nodes (e.g., QPI/UPI) NODE = Connection traversing PCIe as well as the interconnect between PCIe Host Bridges within a NUMA node PHB = Connection traversing PCIe as well as a PCIe Host Bridge (typically the CPU) PXB = Connection traversing multiple PCIe bridges (without traversing the PCIe Host Bridge) PIX = Connection traversing at most a single PCIe bridge NV# = Connection traversing a bonded set of # NVLinksNVLink HW status check code example
Check the InfiniBand (IB) HCA card hardware status and link.
Color modeuser@bm-dev-001:~$ ibdev2netdev -vuser@bm-dev-001:~$ ibdev2netdev -vHW status check command example Color modecat: /sys/class/infiniband/mlx5_0/device/vpd: Permission denied 0000:45:00.0 mlx5_0 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs18 (Down) cat: /sys/class/infiniband/mlx5_1/device/vpd: Permission denied 0000:0e:00.0 mlx5_1 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs17 (Down) cat: /sys/class/infiniband/mlx5_2/device/vpd: Permission denied 0000:c5:00.0 mlx5_2 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs20 (Down) cat: /sys/class/infiniband/mlx5_3/device/vpd: Permission denied 0000:85:00.0 mlx5_3 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs19 (Down) user@bm-dev-001:~$cat: /sys/class/infiniband/mlx5_0/device/vpd: Permission denied 0000:45:00.0 mlx5_0 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs18 (Down) cat: /sys/class/infiniband/mlx5_1/device/vpd: Permission denied 0000:0e:00.0 mlx5_1 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs17 (Down) cat: /sys/class/infiniband/mlx5_2/device/vpd: Permission denied 0000:c5:00.0 mlx5_2 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs20 (Down) cat: /sys/class/infiniband/mlx5_3/device/vpd: Permission denied 0000:85:00.0 mlx5_3 (MT4123 - ) fw 20.29.1016 port 1 (ACTIVE) ==> ibs19 (Down) user@bm-dev-001:~$Example of HW status check result Color moderoot@bm-dev-001:~# ibstatroot@bm-dev-001:~# ibstatExample of link verification command Color modeCA 'mlx5_0' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff5060ac System image GUID: 0x88e9a4ffff5060ac Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 8 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff5060ac Link layer: InfiniBand CA 'mlx5_1' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff504080 System image GUID: 0x88e9a4ffff504080 Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 5 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff504080 Link layer: InfiniBand CA 'mlx5_2' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff505038 System image GUID: 0x88e9a4ffff505038 Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 2 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff505038 Link layer: InfiniBand CA 'mlx5_3' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff504094 System image GUID: 0x88e9a4ffff504094 Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 7 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff504094 Link layer: InfiniBandCA 'mlx5_0' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff5060ac System image GUID: 0x88e9a4ffff5060ac Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 8 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff5060ac Link layer: InfiniBand CA 'mlx5_1' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff504080 System image GUID: 0x88e9a4ffff504080 Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 5 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff504080 Link layer: InfiniBand CA 'mlx5_2' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff505038 System image GUID: 0x88e9a4ffff505038 Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 2 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff505038 Link layer: InfiniBand CA 'mlx5_3' CA type: MT4123 Number of ports: 1 Firmware version: 20.29.1016 Hardware version: 0 Node GUID: 0x88e9a4ffff504094 System image GUID: 0x88e9a4ffff504094 Port 1: State: Active Physical state: LinkUp Rate: 200 Base lid: 7 LMC: 0 SM lid: 1 Capability mask: 0x2651e848 Port GUID: 0x88e9a4ffff504094 Link layer: InfiniBandLink verification result example
Check IB bandwidth communication
Check the IB bandwidth communication status (ib_send_bw) and follow the steps below to inspect the IaaS hardware level.
Check the name of the IB HCA interface.
- In the following example, IB ports:
mlx5_0,mlx5_4,mlx_5_5,mlx5_8Color mode~$ ibdev2netdev -v~$ ibdev2netdev -vExample of checking IB HCA interface name Color mode0000:1a:00.0 mlx5_0 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp26s0 (Down) 0000:1b:00.0 mlx5_1 (MT4123 - 1028SN ) Mellanox ConnectX-6 Single Port VPI HDR QSFP Adapter fw 20.38.1002 port 1 (ACTIVE) ==> bond-nas (Up) 0000:3c:00.0 mlx5_2 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp60s0 (Down) 0000:4d:00.0 mlx5_3 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp77s0 (Down) 0000:5e:00.0 mlx5_4 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp94s0 (Down) 0000:9c:00.0 mlx5_5 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp156s0 (Down) 0000:9d:00.0 mlx5_6 (MT4123 - 1028SN ) Mellanox ConnectX-6 Single Port VPI HDR QSFP Adapter fw 20.38.1002 port 1 (ACTIVE) ==> bond-nas (Up) 0000:bc:00.0 mlx5_7 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp188s0 (Down) 0000:cc:00.0 mlx5_8 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp204s0 (Down) 0000:dc:00.0 mlx5_9 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp220s0 (Down)0000:1a:00.0 mlx5_0 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp26s0 (Down) 0000:1b:00.0 mlx5_1 (MT4123 - 1028SN ) Mellanox ConnectX-6 Single Port VPI HDR QSFP Adapter fw 20.38.1002 port 1 (ACTIVE) ==> bond-nas (Up) 0000:3c:00.0 mlx5_2 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp60s0 (Down) 0000:4d:00.0 mlx5_3 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp77s0 (Down) 0000:5e:00.0 mlx5_4 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp94s0 (Down) 0000:9c:00.0 mlx5_5 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp156s0 (Down) 0000:9d:00.0 mlx5_6 (MT4123 - 1028SN ) Mellanox ConnectX-6 Single Port VPI HDR QSFP Adapter fw 20.38.1002 port 1 (ACTIVE) ==> bond-nas (Up) 0000:bc:00.0 mlx5_7 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp188s0 (Down) 0000:cc:00.0 mlx5_8 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (ACTIVE) ==> ibp204s0 (Down) 0000:dc:00.0 mlx5_9 (MT4129 - 1028SN ) Nvidia ConnectX-7 Single Port Infiniband NDR OSFP Adapter fw 28.38.1002 port 1 (DOWN ) ==> ibp220s0 (Down)Example of IB HCA interface name verification result
- In the following example, IB ports:
Use the SERVER Side command to check the communication status.
Color mode~$ ib_send_bw -d mlx5_0 -i 1 –F~$ ib_send_bw -d mlx5_0 -i 1 –FSERVER Side command example Color mode************************************ * Waiting for client to connect... * * ************************************ --------------------------------------------------------------------------------------- Send BW Test Dual-port : OFF Device : mlx5_0 Number of qps : 1 Transport type : IB Connection type : RC Using SRQ : OFF PCIe relax order: ON ibv_wr* API : ON TX depth : 128 CQ Moderation : 100 Mtu : 4096[B] Link type : IB Max inline data : 0[B] rdma_cm QPs : OFF Data ex. method : Ethernet --------------------------------------------------------------------------------------- local address: LID 0x0f QPN 0x6d95 PSN 0xb974a remote address: LID 0x01 QPN 0x6dd2 PSN 0xc8a18c --------------------------------------------------------------------------------------- #bytes #iterations BW peak[MB/sec] BW average[MB/sec] MsgRate[Mpps] 65536 1000 0.00 19827.40 0.317238 ---------------------------------------------------------------------------------------************************************ * Waiting for client to connect... * * ************************************ --------------------------------------------------------------------------------------- Send BW Test Dual-port : OFF Device : mlx5_0 Number of qps : 1 Transport type : IB Connection type : RC Using SRQ : OFF PCIe relax order: ON ibv_wr* API : ON TX depth : 128 CQ Moderation : 100 Mtu : 4096[B] Link type : IB Max inline data : 0[B] rdma_cm QPs : OFF Data ex. method : Ethernet --------------------------------------------------------------------------------------- local address: LID 0x0f QPN 0x6d95 PSN 0xb974a remote address: LID 0x01 QPN 0x6dd2 PSN 0xc8a18c --------------------------------------------------------------------------------------- #bytes #iterations BW peak[MB/sec] BW average[MB/sec] MsgRate[Mpps] 65536 1000 0.00 19827.40 0.317238 ---------------------------------------------------------------------------------------Example of mutual communication status check result Use the CLIENT Side command to check the communication status.
Color mode~$ ib_send_bw -d mlx5_0 -i 1 -F <SERVER Side IP>~$ ib_send_bw -d mlx5_0 -i 1 -F <SERVER Side IP>CLIENT Side command example Color mode--------------------------------------------------------------------------------------- Send BW Test Dual-port : OFF Device : mlx5_0 Number of qps : 1 Transport type : IB Connection type : RC Using SRQ : OFF PCIe relax order: ON ibv_wr* API : ON RX depth : 512 CQ Moderation : 100 Mtu : 4096[B] Link type : IB Max inline data : 0[B] rdma_cm QPs : OFF Data ex. method : Ethernet --------------------------------------------------------------------------------------- local address: LID 0x01 QPN 0x6dd2 PSN 0xc8a18c remote address: LID 0x0f QPN 0x6d95 PSN 0xb974a --------------------------------------------------------------------------------------- #bytes #iterations BW peak[MB/sec] BW average[MB/sec] MsgRate[Mpps] 65536 1000 19008.49 19006.37 0.304102 ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ Send BW Test Dual-port : OFF Device : mlx5_0 Number of qps : 1 Transport type : IB Connection type : RC Using SRQ : OFF PCIe relax order: ON ibv_wr* API : ON RX depth : 512 CQ Moderation : 100 Mtu : 4096[B] Link type : IB Max inline data : 0[B] rdma_cm QPs : OFF Data ex. method : Ethernet --------------------------------------------------------------------------------------- local address: LID 0x01 QPN 0x6dd2 PSN 0xc8a18c remote address: LID 0x0f QPN 0x6d95 PSN 0xb974a --------------------------------------------------------------------------------------- #bytes #iterations BW peak[MB/sec] BW average[MB/sec] MsgRate[Mpps] 65536 1000 19008.49 19006.37 0.304102 ---------------------------------------------------------------------------------------Example of mutual communication status check result
Check IB service related kernel modules
Check the relevant kernel modules for the IB service (lsmod) to inspect the IaaS hardware level.
Check IB service-related kernel module - nvidia_peermem
Color mode~$ lsmod | grep nvidia_peermem~$ lsmod | grep nvidia_peermemExample command to check nvidia_peermem Color modenvidia_peermem 16384 0 ib_core 425984 9 rdma_cm,ib_ipoib,nvidia_peermem,iw_cm,ib_umad,rdma_ucm,ib_uverbs,mlx5_ib,ib_cm nvidia 56524800 451 nvidia_uvm,nvidia_peermem,nvidia_modesetnvidia_peermem 16384 0 ib_core 425984 9 rdma_cm,ib_ipoib,nvidia_peermem,iw_cm,ib_umad,rdma_ucm,ib_uverbs,mlx5_ib,ib_cm nvidia 56524800 451 nvidia_uvm,nvidia_peermem,nvidia_modesetExample of nvidia_peermem check result Check IB service related kernel modules - IB Card (HCA) driver
Color mode~$ lsmod|egrep 'ib_|_ib|mlx'~$ lsmod|egrep 'ib_|_ib|mlx'Example command to check the IB Card (HCA) driver Color modemlx5_ib 393216 0 ib_uverbs 163840 2 irdma,mlx5_ib ib_core 393216 3 irdma,ib_uverbs,mlx5_ib mlx5_core 1593344 1 mlx5_ib mlxfw 32768 1 mlx5_core psample 20480 1 mlx5_core tls 114688 1 mlx5_core pci_hyperv_intf 16384 1 mlx5_core ib_ipoib 139264 0 ib_cm 131072 2 rdma_cm,ib_ipoib ib_umad 40960 0 mlx5_ib 454656 0 ib_uverbs 135168 2 rdma_ucm,mlx5_ib ib_core 434176 9 rdma_cm,ib_ipoib,nvidia_peermem,iw_cm,ib_umad,rdma_ucm,ib_uverbs,mlx5_ib,ib_cm libcrc32c 16384 5 nf_conntrack,nf_nat,btrfs,nf_tables,raid456 mlx5_core 2064384 1 mlx5_ib mlx_compat 69632 11 rdma_cm,ib_ipoib,mlxdevm,iw_cm,ib_umad,ib_core,rdma_ucm,ib_uverbs,mlx5_ib,ib_cm,mlx5_coremlx5_ib 393216 0 ib_uverbs 163840 2 irdma,mlx5_ib ib_core 393216 3 irdma,ib_uverbs,mlx5_ib mlx5_core 1593344 1 mlx5_ib mlxfw 32768 1 mlx5_core psample 20480 1 mlx5_core tls 114688 1 mlx5_core pci_hyperv_intf 16384 1 mlx5_core ib_ipoib 139264 0 ib_cm 131072 2 rdma_cm,ib_ipoib ib_umad 40960 0 mlx5_ib 454656 0 ib_uverbs 135168 2 rdma_ucm,mlx5_ib ib_core 434176 9 rdma_cm,ib_ipoib,nvidia_peermem,iw_cm,ib_umad,rdma_ucm,ib_uverbs,mlx5_ib,ib_cm libcrc32c 16384 5 nf_conntrack,nf_nat,btrfs,nf_tables,raid456 mlx5_core 2064384 1 mlx5_ib mlx_compat 69632 11 rdma_cm,ib_ipoib,mlxdevm,iw_cm,ib_umad,ib_core,rdma_ucm,ib_uverbs,mlx5_ib,ib_cm,mlx5_coreExample of IB Card (HCA) driver verification result
Check storage physical disk resources and Multi-Path
Verify the storage physical disk resources and Multi-Path to assess the IaaS hardware level.
Storage Physical Disk Resource Check Results
Color moderoot@bm-dev-002:/tmp# fdisk –lroot@bm-dev-002:/tmp# fdisk –lExample of storage physical disk resource check result Multi-Path verification result
Color moderoot@bm-dev-002:/tmp# multipath –llroot@bm-dev-002:/tmp# multipath –llExample of Multi-Path verification result
Check Service Network after new deployment of Multi-node GPU Cluster
Use the following command to verify that the MII Status of Bonding and Slave Interface is up.
Service Network check command
Color mode~$ cat /proc/net/bonding/bond-srv~$ cat /proc/net/bonding/bond-srvExample command to check Service Network Service Network check result
Color modeEthernet Channel Bonding Driver: v5.15.0-25-generic Bonding Mode: fault-tolerance (active-backup) Primary Slave: None Currently Active Slave: ens9f0 MII Status: up MII Polling Interval (ms): 100 Up Delay (ms): 0 Down Delay (ms): 0 Peer Notification Delay (ms): 0 Slave Interface: ens9f0 MII Status: up Speed: 100000 Mbps Duplex: full Link Failure Count: 0 Permanent HW addr: 30:3e:a7:02:35:70 Slave queue ID: 0 Slave Interface: ens11f0 MII Status: up Speed: 100000 Mbps Duplex: full Link Failure Count: 0 Permanent HW addr: 30:3e:a7:02:2f:e8 Slave queue ID: 0Ethernet Channel Bonding Driver: v5.15.0-25-generic Bonding Mode: fault-tolerance (active-backup) Primary Slave: None Currently Active Slave: ens9f0 MII Status: up MII Polling Interval (ms): 100 Up Delay (ms): 0 Down Delay (ms): 0 Peer Notification Delay (ms): 0 Slave Interface: ens9f0 MII Status: up Speed: 100000 Mbps Duplex: full Link Failure Count: 0 Permanent HW addr: 30:3e:a7:02:35:70 Slave queue ID: 0 Slave Interface: ens11f0 MII Status: up Speed: 100000 Mbps Duplex: full Link Failure Count: 0 Permanent HW addr: 30:3e:a7:02:2f:e8 Slave queue ID: 0Example of Service Network verification result
Multi-node GPU Cluster: Verify time synchronization with the Time Server after new deployment
The OS image includes the installation of the chrony daemon and configuration for SCP NTP server synchronization. Use the following command to verify whether a line marked with ^* exists in the MS Name column.
Command to check the chrony daemon source and synchronization status
Color mode~$ chronyc sources -V~$ chronyc sources -VExample of status check command Result of checking chrony daemon status
Color modeMS Name/IP address Stratum Poll Reach LastRx Last sample =============================================================================== ^* 198.19.0.54 4 10 377 1040 -16us[ -37us] +/- 9982usMS Name/IP address Stratum Poll Reach LastRx Last sample =============================================================================== ^* 198.19.0.54 4 10 377 1040 -16us[ -37us] +/- 9982usExample of checking the chrony daemon status
2.5.3 - Release Note
Multi-node GPU Cluster
- The Ubuntu image version 24.04 has been added.
- The B300 GPU server type has been added.
- Provides an IaC environment using Terraform.
- You can terminate multiple resources simultaneously from the GPU Node list.
- It must be a node that uses the same DataSet and Cluster Fabric.
- Integrated with Cloud Monitoring.
- You can view key performance metrics in real time with Cloud Monitoring.
- We have launched the Multi-node GPU Cluster service.
- We provide a service that offers physical GPU servers without virtualization for large-scale, high-performance AI computing.
2.6 - Cloud Functions
2.6.1 - Overview
Service Overview
Cloud Functions is a serverless computing-based FaaS (Function as a Service) that lets you easily run function‑based applications without provisioning servers. Users don’t have to hassle with managing servers or containers for scaling, and can focus on writing code and deploying applications.
Features
- Easy and Convenient Development Environment: Developers can easily create Function resources that connect to events across multiple environments using a Code Editor suitable for the selected runtime, and can write and invoke code with ease.
- Serverless Computing: You can use a serverless code execution service for development in the Samsung Cloud Platform environment. * The resources required to invoke and run function-based applications are allocated and managed by the Samsung Cloud Platform according to the scale of execution.
- Efficient Cost Management: The invoked Function aggregates usage (total number of calls, total execution time) and is billed for the time actually used to run the application. * Functions with low usage can have the Cloud Functions scaler adjusted to a scale-to-zero state, so they do not consume resources, enabling efficient cost management.
Service diagram
Provided Features
Cloud Functions provides the following features.
- Code Development Environment: Create Runtime-optimized functions, write and edit code
- Refer to 구성 요소 > Runtime for supported runtimes.
- Function execution, environment management, monitoring: endpoint definition, Token management, access control configuration, trigger configuration, etc., runtime environment/variable definition and modification, artifact invocation/testing for Deploy/Test, service deployment, progress status monitoring/logging
- Serverless Computing: All elements required for code writing and deployment are managed by Samsung Cloud Platform, with automatic scaling adjustments based on deployment.
- Sample Code Provided: By providing various sample codes through Blueprint, you can start easily and quickly
Component
Runtime
Cloud Functions currently supports the following runtimes. Additional continuously supported runtimes will also be added.
| Runtime | Version | Deprecation date |
|---|---|---|
| GO | 1.21 | 2026.7.30 |
| GO | 1.23 | 2026.7.30 |
| GO | 1.25 | - |
| java | 17 | - |
| Node.js | 18 | 2026.7.30 |
| Node.js | 20 | 2026.7.30 |
| Node.js | 22 | - |
| Node.js | 24 | - |
| PHP | 8.1 | 2026.7.30 |
| PHP | 8.4 | - |
| PHP | 8.5 | - |
| Python | 3.9 | 2026.7.30 |
| Python | 3.10 | - |
| Python | 3.11 | - |
| Python | 3.14 | - |
Runtime scheduled for deprecation
- For Runtime versions slated for deprecation, technical support is expected to end within 60 days (End of Technical Support) (detailed schedule will be announced on the console).
- When technical support for a Runtime version ends, security patches and updates will no longer be applied to that Runtime version.
- Already created functions can be used continuously without a call time limit, but they cannot be modified.
- We do not guarantee bugs, errors, defects, or vulnerabilities that arise in Runtime versions for which technical support has ended.
- We recommend migrating to and using an alternative version of a function that is scheduled for deprecation to ensure safe usage.
Provision status by region
The Cloud Functions service is available in the environments below.
| Region | Whether provided |
|---|---|
| Korea West 1 (kr-west1) | Provide |
| Korea East 1 (kr-east1) | Provided |
| South Korea 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preceding Service
This is a list of services that can be configured as optional before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Application Service | API Gateway | A service that easily manages and monitors APIs |
2.6.1.1 - ServiceWatch Metrics
Cloud Functions sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the Cloud Functions namespace.
The metrics whose names are displayed in bold below are the metrics selected as key metrics among the default metrics provided by Cloud Functions. The key metrics are used to build service dashboards that are automatically created per service in ServiceWatch. You can also view the key metrics on the Monitoring tab of the Cloud Functions detail page.
Each metric guides users, through the user guide, on which statistical values are meaningful when querying that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard or monitoring tab, you can view key metrics using these primary statistics.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| Invocations | Average number of times the function is called per unit time | Count |
|
| Success Calls | Average number of times the runtime code operates correctly and returns a response code per unit time during a function call. | Count |
|
| Error Calls | Average number of calls per unit time that encounter errors during function invocation, including runtime errors due to response timeouts and logic errors. | Count |
|
| Memory Usage | Average memory usage per unit time while the function is executing | Kilobytes |
|
| Active Operations | When a function is called multiple times simultaneously, the average number of tasks generated per unit time for concurrent processing. | Count |
|
2.6.2 - How-to guides
Users can create the service by entering the required information for Cloud Functions and selecting detailed options through the Samsung Cloud Platform Console.
Creating Cloud Functions
All Services > Compute > Cloud Functions Click the menu. 1. Go to the Service Home page of Cloud Functions.
On the Service Home page, click the Create Cloud Functions button. 2. Go to the Create Cloud Functions page.
On the Create Cloud Functions page, enter the information required to create the service.
Category RequiredDetailed description Function name Required Enter the name of the Funtion to create - Start with a lowercase English letter and use lowercase English letters, numbers, and special characters (
-) to enter between 3 and 64 characters
Runtime Required Select Runtime creation method - New: Create a new Runtime
- Start with Blueprint: Write using the Runtime source code provided by the service
Runtime & Vesion Essential Select Runtime and Version - When Create New is selected
- Refer to the Runtime & Version list in Components > Runtime
- For the Java runtime, UI code editing is not supported, but you can import a JAR file from Object Storage and execute it
- When Start with Blueprint is selected
- You can view a source code example by clicking the View Source Code button for that Runtime & Version
- Refer to the Blueprint Detailed Guide for more information on Blueprint settings
- If the Runtime version has reached End of Technical Support (EoTS), it cannot be modified after creation
Table. Cloud Functions service information input fields- Start with a lowercase English letter and use lowercase English letters, numbers, and special characters (
Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- When creation is complete, check the created resources on the Cloud Functions list page.
View Cloud Functions details
Cloud Functions Details page consists of Details, Monitoring, Logs, Code, Configuration, Triggers, Tags, Job History tabs.
To view detailed information about the Cloud Functions service, follow these steps.
- All Services > Compute > Cloud Functions Click the menu. 1. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. 2. Function list Go to the page.
- On the Function list page, click the resource to view detailed information. 3. Navigate to the Function Details page.
- Function Details page displays status information and additional feature information, and consists of Details, Monitoring, Logs, Code, Configuration, Triggers, Tags, Job History tabs.
Category Detailed description Cloud Functions status Cloud Functions status information - Ready: green icon, a state where normal function invocations are possible
- Not Ready: gray icon, a state where normal function invocations are not possible
- Deploying: yellow icon, a state where the function is being created or updated, which triggers the next action
- Function creation and modification
- Code tab: edit code in the editor
- Code tab: inspect jar file
- Trigger tab: add and modify
- Configuration tab: modify
- Running: blue icon, a state where normal function invocations are possible and a cold‑start prevention policy is applied
Service cancellation Cancel service button Table. Cloud Functions status information and additional features
- Function Details page displays status information and additional feature information, and consists of Details, Monitoring, Logs, Code, Configuration, Triggers, Tags, Job History tabs.
Detailed Information
Function list page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name
|
| Resource ID | Service’s unique resource ID |
| Constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Modifier | User who modified the service |
| Modification date | Date and time of service modification |
| Function name | Name of the Cloud Function |
| Runtime | Runtime types and versions
|
- Even after technical support for the Runtime version ends, functions that have already been created can continue to be used without any call time limit. * However, security patches and updates for that Runtime version will not be applied.
- Bugs, errors, defects, or vulnerabilities that occur in Runtime versions that are no longer supported are not covered.
- If support for a Runtime has ended, the user must create a replacement Runtime version and then manually delete the function of the previous version.
- To use this function safely, create a new instance using the Lastest or Stable version.
Monitoring
Function List page lets you view the Cloud Functions usage information for the selected resource.
| Category | Detailed description |
|---|---|
| Number of calls | Average number of times the function is called per unit time (instances) |
| execution time | Average execution time (seconds) of the function per unit time |
| Memory usage | Average memory usage (KB) during the function execution per unit time |
| Current number of tasks | When the function is called multiple times simultaneously, the average number of tasks (count) generated per unit time for concurrent processing. |
| Successful call count | Average number of times (cases) the runtime code operated correctly and returned a response code per unit time during a function call. |
| Failed call count | Average number of calls with errors per unit time during function invocation
|
log
Function list page allows you to view the Cloud Functions logs of the selected resource.
| Category | Detailed description |
|---|---|
| unit period | Select the period to view Cloud Functions log information
|
| log message | Functions are displayed in order, starting with the most recent occurrence. |
code
Function List page lets you view and edit the Cloud Functions code of the selected resource.
The way to view and edit source code varies depending on the runtime used.
- Inline Editor: Node.js, Python, PHP, Go
- Compressed file (.jar/.zip) execution: Java
| Category | Detailed description |
|---|---|
| source code | Inline editor method |
| code information | Display code information |
| Edit | After clicking the Edit button, you can modify the code in the inline editor. |
| Category | Detailed description |
|---|---|
| source code | Execution method for compressed files (.jar/.zip) |
| code information | Display compressed file information
|
| Edit | Jar file can be modified
|
- If technical support for the runtime version has ended, you cannot modify the code. * Also, because security patches and updates are not applied, create and use the function anew with the Latest or Stable version to ensure safe usage.
- In the case of Java Runtime, it does not provide a UI code editing feature, and you must select a compressed file (.jar/.zip) from a bucket in the Object Storage service.
- If a user does not have an authentication key generated for the Object Storage service, they cannot execute Import from Object Storage, so they must create an authentication key in advance.
- For detailed information on creating an authentication key, see Creating an Authentication Key.
- The Object Storage bucket for the Cloud Functions service must have its access control set to allow.
- For detailed information on Object Storage access control, see Allowing Cloud Functions Service Access.
Configuration
On the Function list page, you can view the Cloud Functions configuration of the selected resource.
| Category | Detailed description |
|---|---|
| General configuration | Memory and timeout settings of Cloud Function
|
| function URL | Issue an HTTPS URL address that can access the function
|
| environment variable | Set runtime environment variables
|
| Private connection configuration | Can be used in conjunction with PrivateLink Service
|
| Permission | Add and manage resource policies for IAM-based functions
|
- If technical support for the Runtime version has been discontinued, configuration items cannot be modified. * Also, because security patches and updates are not applied, create and use the function anew with the Latest or Stable version to ensure safe usage.
- If access control is disabled, the registered access information is deleted, making function access control impossible, which can expose the system to security attacks such as external scanning, hacking, etc.
- CPU cores proportional to the memory allocation of General configuration are automatically assigned.
- If the minimum number of executions of General configuration is 1 or more, Cold Start is prevented, but continuous costs are incurred.
Trigger
On the Function List page, you can view and configure the trigger information of the selected resource. By setting a trigger, you can automatically execute the Function when an event occurs.
| Category | Detailed description |
|---|---|
| Cronjob | Use Cronjob as a trigger
|
| API Gateway | Use API Gateway as a trigger
|
- If technical support for the Runtime version has ended, you cannot modify the trigger item. * Also, because security patches and updates are not applied, create and use the function anew with the Latest or Stable version to ensure safe usage.
- If the Cronjob trigger is called before the function’s timeout, the function will execute concurrently, increasing both the execution count and the total time. * Therefore, be cautious because continuous additional costs can lead to high expenses.
- If the status is Deploying, it cannot be modified.
- Refer to Setting up triggers for trigger configuration.
Tag
In the Tag tab, you can view the resource’s tag information, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Job History page allows you to view the resource’s job history.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Changing Java Runtime code
If you are using Java Runtime, you cannot modify the code directly, so you must select and replace the archive file (.jar/.zip) in the bucket of the Object Storage service.
To modify a compressed file, follow these steps.
All Services > Compute > Cloud Functions menu, click. 1. Navigate to the Service Home page of Cloud Functions.
On the Service Home page, click the Function menu. 2. Go to the Function list page.
On the Function List page, click the resource to change the compressed file in the code. 3. Go to the Function Details page.
Click the Edit button on the Code tab of the Function Details page. 4. Edit Function code Navigate to the page.
Click the Import from Object Storage button. 5. Import from Object Storage The popup window opens.
Category Detailed description Java Runtime Java Runtime Information Handler information Handler information - Execution Class: Automatically entered when setting the archive file (.jar/.zip)
- Execution Method: Automatically entered when setting the archive file (.jar/.zip)
Compressed file (.jar/.zip) Set the archive file to modify - Archive file name (.jar/.zip): Displays the name of the archive file. Import from Object Storage after configuration, it is entered automatically
- Import from Object Storage: Configure the Object Storage to retrieve the archive file (.jar/.zip)
Table. Cloud Functions Details - Function Code Modification ItemsEnter the URL information of the Object Storage to retrieve the compressed file in Object Storage URL, then click the Confirm button. 6. The notification popup opens.
- URL information can be found in the Folder List tab of the detailed page of the Object Storage to retrieve, under the File Information > Private URL item.
Click the Confirm button. 7. On the Function code edit page, the name of the imported compressed file is displayed in the Compressed file name (.jar/.zip).
Click the Save button.
- Users without a generated authentication key cannot execute Import from Object Storage.
- If the URL does not exist or the archive file matches any of the following, it cannot be changed.
- When using an unsupported file extension
- If there are harmful files inside the compressed file.
- If the size exceeds the supported limit
Terminate Cloud Functions
To cancel the Cloud Functions service, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. 1. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. 2. Navigate to the Function list page.
- On the Function List page, click the resource you want to terminate and then click the Terminate Service button.
- When the termination is complete, check on the Function list page whether the resource has been terminated.
2.6.2.1 - Configure Trigger
Configure Trigger
- By default, all triggers can be added in Cloud Functions.
- If it is triggered for a specific product, it should be passed to Cloud Functions.
Setting up Cronjob trigger
To set up a Cronjob trigger, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function list page.
- Function List page, click the resource for which you want to set a trigger. You will be taken to the Function Details page.
- After clicking the Trigger tab, click the Add Trigger button. Set it. The Add Trigger popup window opens.
- Add Trigger In the popup, select Cronjob from Trigger Type. A required information input area appears at the bottom.
Category Detailed description Cronjob configuration Set the trigger’s repeat frequency - Can be set in minutes, hours, days, months, weekdays
Timezone setting Set the trigger’s reference time zone Table. Cronjob Trigger Required Information Items - After entering the required information, click the Confirm button.
- When the popup notifying an addition opens, click the Confirm button.
Configure API Gateway Trigger
To set up an API Gateway trigger, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- Click the resource to set the trigger on the Function List page. Go to the Function Details page.
- Click the Trigger tab, then click the Add Trigger button. Set it. The Add Trigger popup opens.
- In the Add Trigger popup, select API Gateway under Trigger Type. A required information input area appears at the bottom.
Category Detailed description API name Select API - You can select an existing API or create a new one
Stage Select deployment target - You can select an existing stage or create a new one
Table. API Gateway Trigger Required Information Items - After entering the required information, click the Confirm button.
- When the popup notifying the addition opens, click the Confirm button.
Configure Multi-Trigger
You can attach multiple triggers to a single function.
Modify Trigger
To modify the added trigger, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function list page.
- On the Function List page, click the resource to edit the trigger. You will be taken to the Function Details page.
- Click the Trigger tab, then in the trigger list, click the Edit button of the trigger whose settings you want to modify. The Edit Trigger popup window opens.
- Edit Trigger After modifying the settings in the popup window, click the Confirm button.
- The configuration values differ depending on the trigger type (refer to Cronjob Trigger, API Gateway Trigger).
- When the edit notification popup appears, click Confirm.
Delete Trigger
To delete a trigger, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- Function List page, click the resource for which you want to set a trigger. You will be taken to the Function Details page.
- In the Trigger tab’s trigger list, select the trigger you want to delete, then click the Delete button.
- When the popup notifying you of trigger deletion opens, click the Confirm button.
2.6.2.2 - Blueprint Detailed Guide
Blueprint Overview
When creating Cloud Functions, you can set a Blueprint to utilize the Runtime source code provided by Cloud Functions. Refer to the following for the Blueprint items provided by Cloud Functions.
| Category | Detailed description | Remarks |
|---|---|---|
| Hello World | When the function is invoked, it responds with Hello Serverless World! | |
| Execution after timeout | It outputs code that should run after the function call timeout but does not execute. | PHP, Python not supported |
| HTTP request body | Parse the request body. | PHP not supported |
| Send HTTP requests | The Cloud function sends an HTTP request. | PHP not supported |
| Print logs | Logs the user’s Samsung Cloud Platform Console request. | PHP not supported |
| Throw a custom error | Enter the error logic directly to handle the error. | |
| Using Environment Variable | Configure environment variables within the Cloud function and execute it. |
Hello World
Hello World Explains the response-receiving configuration and a function call example (using the function URL).
Hello World Setup
To set up Hello World, follow these steps.
Click the All Services > Compute > Cloud Functions menu. Go to the Service Home page of Cloud Functions.
On the Service Home page, click the Function menu. You will be taken to the Function List page.
Function List page, click the resource to be called via URL. You will be taken to the Function Detail page.
After clicking the Configuration tab, click the Edit button for the Function URL item. The Edit Function URL popup window opens.
In the Function URL Edit popup, set Activation status to Enabled, then click the Confirm button.
Category Detailed description Enable status Configure the use of the function URL Authentication type Select whether to use IAM authentication for requests to the function URL Access control Add accessible IPs to enable management - Set to Use, then you can input and add a public access IP
Table. Required input fields when adding a triggerAfter navigating to the Code tab, click the Edit button. You will be taken to the Function Code Edit page.
After adding the handling logic for success and failure cases, click the Save button.
- Node.js source codeColor mode
exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ const response = { statusCode: 200, body: JSON.stringify('Hello Serverless World!'), }; return response; };exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ const response = { statusCode: 200, body: JSON.stringify('Hello Serverless World!'), }; return response; };Hello World - Node.js source code - Python source codeColor mode
import json def handle_request(params): # User writing area (Function details) return { 'statusCode': 200, 'body': json.dumps('Hello Serverless World!') }import json def handle_request(params): # User writing area (Function details) return { 'statusCode': 200, 'body': json.dumps('Hello Serverless World!') }Hello World - Python source code - PHP source codeColor mode
<?php function handle_request() { # User writing area (Function details) $res = array( 'statusCode' => 200, 'body' => 'Hello Serverless World!', ); return $res; } ?><?php function handle_request() { # User writing area (Function details) $res = array( 'statusCode' => 200, 'body' => 'Hello Serverless World!', ); return $res; } ?>Hello World - PHP source code
- Node.js source code
Check function call
On the Function Details page, in the Configuration tab, invoke the function URL and then verify the response.
Hello Serverless World!
Execution after timeout
Describes configuring execution after timeout (Execution after timeout) and provides an example of invoking the function (using the function URL).
Configure execution after timeout
To set Execution after timeout, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- On the Function List page, click the resource for which you want to set a trigger. You will be taken to the Function Details page.
- After clicking the Trigger tab, click the Add Trigger button. The Add Trigger popup window opens.
- Add Trigger In the popup window, after selecting the Trigger Type item, enter the required information displayed at the bottom and click the OK button.
- Required information varies depending on the trigger type.
Trigger Types Input field API Gateway - API name: Select an existing API or create a new one
- Stage: Select an existing stage or create a new one
Cronjob - Refer to the example and enter the trigger’s repeat frequency(minute, hour, day, month, day of week)
- Timezone setting: select the reference time zone to apply
Table. Required input fields when adding a trigger
- Required information varies depending on the trigger type.
- After moving to the Code tab, click the Edit button. You will be taken to the Function Code Edit page.
- After adding the handling logic for success and failure cases, click the Save button.
- Node.js source codeColor mode
exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ console.log("Hello world 3"); await delay(3000); const response = { statusCode: 200, body: JSON.stringify('Hello Serverless World!'), }; return response; }; const delay = (ms) => { return new Promise(resolve=>{ setTimeout(resolve,ms) }) }exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ console.log("Hello world 3"); await delay(3000); const response = { statusCode: 200, body: JSON.stringify('Hello Serverless World!'), }; return response; }; const delay = (ms) => { return new Promise(resolve=>{ setTimeout(resolve,ms) }) }Execution after timeout - Node.js source code
- Node.js source code
Check function call
On the Function Detail page’s Configuration tab, invoke the function URL and, after a brief period, check the response.
Hello Serverless World!
HTTP request body
Explains the configuration for parsing the Request Body and an example of calling the function (using the function URL).
Setting HTTP request body
To set the HTTP request body, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- Function List page, click the resource to set the trigger. You will be taken to the Function Details page.
- After clicking the Trigger tab, click the Add Trigger button. The Add Trigger popup window opens.
- Add Trigger In the popup window, select the Trigger Type option, then fill in the required information shown at the bottom and click the OK button.
- Required information varies depending on the trigger type.
Trigger Types Input field API Gateway - API name: Select an existing API or create a new one
- Stage: Select an existing stage or create a new one
Cronjob - Refer to the example and enter the trigger’s repeat frequency (minutes, hours, day, month, day of week)
- Timezone setting: select the reference time zone to apply
Table. Required input fields when adding a trigger
- Required information varies depending on the trigger type.
- After moving to the Code tab, click the Edit button. You will be taken to the Function Code Edit page.
- After adding the handling logic for success and failure cases, click the Save button.
- Node.js source codeColor mode
exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ const response = { statusCode: 200, body: JSON.stringify(params.body), }; return response; };exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ const response = { statusCode: 200, body: JSON.stringify(params.body), }; return response; };Execution after timeout - Node.js source code - Python source codeColor mode
import json def handle_request(params): # User writing area (Function details) return { 'statusCode': 200, 'body': json.dumps(params.json) }import json def handle_request(params): # User writing area (Function details) return { 'statusCode': 200, 'body': json.dumps(params.json) }Execution after timeout - Python source code
- Node.js source code
Check function call
In the Configuration tab of the Function Details page, after calling the Function URL, check the Body data, request Body value, and response Body value.
Request Body value
Color mode{ "testKey" :"cloud-001", "testNames": [ { "name": "Son" }, { "name": "Kim" } ], "testCode":"test" }{ "testKey" :"cloud-001", "testNames": [ { "name": "Son" }, { "name": "Kim" } ], "testCode":"test" }Request Body value Response Body value
Color mode{ "testKey" :"cloud-001", "testNames": [ { "name": "Son" }, { "name": "Kim" } ], "testCode":"test" }{ "testKey" :"cloud-001", "testNames": [ { "name": "Son" }, { "name": "Kim" } ], "testCode":"test" }Response Body value
Send HTTP requests
Explains the HTTP request configuration and an example of calling a function (using the function URL).
Send HTTP requests Configure
To configure Send HTTP requests, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- Click the resource to set the trigger on the Function List page. Go to the Function Details page.
- After clicking the Trigger tab, click the Add Trigger button. The Add Trigger popup window opens.
- Add Trigger In the popup window, after selecting the Trigger Type item, enter the required information displayed at the bottom and click the OK button.
- Required information varies depending on the trigger type.
Trigger Types Input field API Gateway - API name: Select an existing API or create a new one
- Stage: Select an existing stage or create a new one
Cronjob - Refer to the example and enter the trigger’s repeat frequency (minutes, hours, day, month, day of week)
- Timezone setting: select the reference time zone to apply
Table. Required input items when adding a trigger
- Required information varies depending on the trigger type.
- After moving to the Code tab, click the Edit button. You will be taken to the Function Code Edit page.
- After adding the handling logic for success and failure cases, click the Save button.
- Node.js source codeColor mode
const request = require('request'); /** * @description User writing area (Function details) */ exports.handleRequest = async function (params) { return await sendRequest(params); }; async function sendRequest(req) { return new Promise((resolve, reject) => { // Port 80 and Port 443 are available url = "https://example.com"; // Destination URL const options = { uri: url, method:'GET', json: true, strictSSL: false, rejectUnauthorized: false } request(options, (error, response, body) => { if (error) { reject(error); } else { resolve({ statusCode: response.statusCode, body: JSON.stringify(body) }); } }); }); }const request = require('request'); /** * @description User writing area (Function details) */ exports.handleRequest = async function (params) { return await sendRequest(params); }; async function sendRequest(req) { return new Promise((resolve, reject) => { // Port 80 and Port 443 are available url = "https://example.com"; // Destination URL const options = { uri: url, method:'GET', json: true, strictSSL: false, rejectUnauthorized: false } request(options, (error, response, body) => { if (error) { reject(error); } else { resolve({ statusCode: response.statusCode, body: JSON.stringify(body) }); } }); }); }Send HTTP requests - Node.js source code - Python source codeColor mode
import json import requests def handle_request(params): # User writing area (Function details) # Port 80 and Port 443 are available url = "https://example.com" # Destination URL try: response = requests.get(url, verify=True) return { 'statusCode': response.status_code, 'body': json.dumps(response.text) } except requests.exceptions.RequestException as e: return str(e)import json import requests def handle_request(params): # User writing area (Function details) # Port 80 and Port 443 are available url = "https://example.com" # Destination URL try: response = requests.get(url, verify=True) return { 'statusCode': response.status_code, 'body': json.dumps(response.text) } except requests.exceptions.RequestException as e: return str(e)Send HTTP requests - Python source code
- Node.js source code
Check Function Call
On the Function Details page, after invoking the function URL in the Configuration tab, verify the response.
<!doctype html>
<html>
<head>
<title>Example Domain</title>
<meta charset="utf-8" />
<meta http-equiv="Content-type" content="text/html; charset=utf-8" />
<meta name="viewport" content="width=device-width, initial-scale=1" />
<style type="text/css">
body {
background-color: #f0f0f2;
margin: 0;
padding: 0;
font-family: -apple-system, system-ui, BlinkMacSystemFont, "Segoe UI", "Open Sans", "Helvetica Neue", Helvetica, Arial, sans-serif;
}
div {
width: 600px;
margin: 5em auto;
padding: 2em;
background-color: #fdfdff;
border-radius: 0.5em;
box-shadow: 2px 3px 7px 2px rgba(0,0,0,0.02);
}
a:link, a:visited {
color: #38488f;
text-decoration: none;
}
@media (max-width: 700px) {
div {
margin: 0 auto;
width: auto;
}
}
</style>
</head>
<body>
<div>
<h1>Example Domain</h1>
<p>This domain is for use in illustrative examples in documents. You may use this
domain in literature without prior coordination or asking for permission.</p>
<p><a href="https://www.iana.org/domains/example">More information...</a></p>
</div>
</body>
</html><!doctype html>
<html>
<head>
<title>Example Domain</title>
<meta charset="utf-8" />
<meta http-equiv="Content-type" content="text/html; charset=utf-8" />
<meta name="viewport" content="width=device-width, initial-scale=1" />
<style type="text/css">
body {
background-color: #f0f0f2;
margin: 0;
padding: 0;
font-family: -apple-system, system-ui, BlinkMacSystemFont, "Segoe UI", "Open Sans", "Helvetica Neue", Helvetica, Arial, sans-serif;
}
div {
width: 600px;
margin: 5em auto;
padding: 2em;
background-color: #fdfdff;
border-radius: 0.5em;
box-shadow: 2px 3px 7px 2px rgba(0,0,0,0.02);
}
a:link, a:visited {
color: #38488f;
text-decoration: none;
}
@media (max-width: 700px) {
div {
margin: 0 auto;
width: auto;
}
}
</style>
</head>
<body>
<div>
<h1>Example Domain</h1>
<p>This domain is for use in illustrative examples in documents. You may use this
domain in literature without prior coordination or asking for permission.</p>
<p><a href="https://www.iana.org/domains/example">More information...</a></p>
</div>
</body>
</html>Print logs
This explains how to configure log output and an example of calling a function (using the function URL).
Configure Print logs
Print logs To set up response receiving, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- Function List page, click the resource to set the trigger. Function Details page will be displayed.
- After clicking the Trigger tab, click the Add Trigger button. The Add Trigger popup window opens.
- In the Add Trigger popup, select the Trigger Type item, then enter the required information displayed at the bottom and click the OK button.
- Required information varies depending on the trigger type.
Trigger Types Input field API Gateway - API name: Select an existing API or create a new one
- Stage: Select an existing stage or create a new one
Cronjob - Refer to the example and enter the trigger’s repeat frequency(minutes, hours, day, month, day of week)
- Timezone setting: select the reference time zone to apply
Table. Required input fields when adding a trigger
- Required information varies depending on the trigger type.
- After moving to the Code tab, click the Edit button. You will be taken to the Function Code Edit page.
- After adding the handling logic for success and failure cases, click the Save button.
- Node.js source codeColor mode
const winston = require('winston'); // Log module setting const logger = winston.createLogger({ format: winston.format.combine( winston.format.timestamp(), winston.format.printf(info => info.timestamp + ' ' + info.level + ': ' + info.message) ), transports: [ new winston.transports.Console() ] }); exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ const response = { statusCode: 200, body: JSON.stringify(params.body), }; logger.info(JSON.stringify(response, null, 2)); return response; };const winston = require('winston'); // Log module setting const logger = winston.createLogger({ format: winston.format.combine( winston.format.timestamp(), winston.format.printf(info => info.timestamp + ' ' + info.level + ': ' + info.message) ), transports: [ new winston.transports.Console() ] }); exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ const response = { statusCode: 200, body: JSON.stringify(params.body), }; logger.info(JSON.stringify(response, null, 2)); return response; };Print logs - Node.js source code - Python source codeColor mode
import json import logging # Log module setting logging.basicConfig(level=logging.INFO) def handle_request(params): # User writing area (Function details) response = { 'statusCode': 200, 'body': json.dumps(params.json) } logging.info(response) return responseimport json import logging # Log module setting logging.basicConfig(level=logging.INFO) def handle_request(params): # User writing area (Function details) response = { 'statusCode': 200, 'body': json.dumps(params.json) } logging.info(response) return responsePrint logs - Python source code
- Node.js source code
Check Function Call
After calling the function URL in the Configuration tab of the Function Details page, check the log in the Log tab.
[2023-09-07] 12:06:23] "host": "scf-xxxxxxxxxxxxxxxxxxxxx",
[2023-09-07] 12:06:23] "ce-id": "xxxxxxxxxxxxxxxxxxxxx",
[2023-09-07] 12:06:23] "ce-source": "xxxxxxxxxxxxxxxxxxxxx",[2023-09-07] 12:06:23] "host": "scf-xxxxxxxxxxxxxxxxxxxxx",
[2023-09-07] 12:06:23] "ce-id": "xxxxxxxxxxxxxxxxxxxxx",
[2023-09-07] 12:06:23] "ce-source": "xxxxxxxxxxxxxxxxxxxxx",Throw a custom error
Explains setting up a custom error (Throw a custom error) and an example of calling a function (using a function URL).
Configure Throw a custom error
To configure Throw a custom error, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- Click the resource to set the trigger on the Function List page. Go to the Function Details page.
- After clicking the Trigger tab, click the Add Trigger button. The Add Trigger popup window opens.
- Add Trigger In the popup window, after selecting the Trigger Type item, enter the required information displayed at the bottom and click the OK button.
- Required information varies depending on the trigger type.
Trigger Types Input field API Gateway - API name: Select an existing API or create a new one
- Stage: Select an existing stage or create a new one
Cronjob - Refer to the example and enter the trigger’s repeat frequency (minutes, hours, day, month, day of week)
- Timezone setting: select the reference time zone to apply
Table. Required input fields when adding a trigger
- Required information varies depending on the trigger type.
- After moving to the Code tab, click the Edit button. You will be taken to the Function Code Edit page.
- After adding the handling logic for success and failure cases, click the Save button.
- Node.js source codeColor mode
class CustomError extends Error { constructor(message) { super(message); this.name = 'CustomError'; } } exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ throw new CustomError('This is a custom error!'); };class CustomError extends Error { constructor(message) { super(message); this.name = 'CustomError'; } } exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ throw new CustomError('This is a custom error!'); };Throw a custom error - Node.js source code - Python source codeColor mode
class CustomError(Exception): def __init__(self, message): self.message = message def handle_request(parmas): raise CustomError('This is a custom error!')class CustomError(Exception): def __init__(self, message): self.message = message def handle_request(parmas): raise CustomError('This is a custom error!')Throw a custom error - Python source code - PHP source codeColor mode
<?php class CustomError extends Exception { public function __construct($message) { parent::__construct($message); $this->message = $message; } } function handle_request() { throw new CustomError('This is a custom error!'); } ?><?php class CustomError extends Exception { public function __construct($message) { parent::__construct($message); $this->message = $message; } } function handle_request() { throw new CustomError('This is a custom error!'); } ?>Throw a custom error - PHP source code
- Node.js source code
Check Function Call
On the Function Details page, after calling the Function URL in the Configuration tab, verify whether an error occurred in the Log tab.
Using Environment Variable
Explains the use of environment variables (Using Environment Variable) settings and a function call example (using function URL).
Using Environment Variable Configure
To configure Using Environment Variable, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function List page.
- Click the resource to set the trigger on the Function List page. Go to the Function Details page.
- After clicking the Trigger tab, click the Add Trigger button. The Add Trigger popup window opens.
- In the Add Trigger popup, select the Trigger Type item, then enter the required information displayed at the bottom and click the OK button.
- Required information varies depending on the trigger type.
Trigger Types Input field API Gateway - API name: Select an existing API or create a new one
- Stage: Select an existing stage or create a new one
Cronjob - Refer to the example and enter the trigger’s repeat frequency(minutes, hours, days, months, day of week)
- Timezone setting: select the reference time zone to apply
Table. Required input fields when adding a trigger
- Required information varies depending on the trigger type.
- After moving to the Code tab, click the Edit button. You will be taken to the Function Code Edit page.
- After adding the handling logic for success and failure cases, click the Save button.
- Node.js source codeColor mode
exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ return process.env.test; };exports.handleRequest = async function (params) { /** * @description User writing area (Function details) */ return process.env.test; };Using Environment Variable - Node.js source code - Python source codeColor mode
import json import os def handle_request(params): # User writing area (Function details) return os.environ.get("test")import json import os def handle_request(params): # User writing area (Function details) return os.environ.get("test")Using Environment Variable - Python source code - PHP source codeColor mode
import json def handle_request(params): # User writing area (Function details) return os.environ.get("test")import json def handle_request(params): # User writing area (Function details) return os.environ.get("test")Using Environment Variable - PHP source code
- Node.js source code
- After moving to the Configuration tab, click the Edit button in the Environment Variables area. The Edit Environment Variables popup will open.
- After entering the environment variable information, click the Confirm button.
Category Detailed description Name Enter the key value value Enter the value Table. Environment Variable Input Items
Check function call
On the Function Details page, after calling the function URL in the Configuration tab, check the environment variable value in the Log tab.
2.6.2.3 - Integrate PrivateLink Service
By integrating Cloud Functions with the PrivateLink service, you can connect VPCs within the Samsung Cloud Platform to other VPCs, and VPCs to services, without using the external internet.
The data uses only the internal network, providing high security, and does not require public IP, NAT, VPN, or an internet gateway.
Enable PrivateLink Service
To connect the PrivateLink Service, you must first enable the service.
To enable the PrivateLink service, follow these steps.
- All Services > Compute > Cloud Functions Click the menu. 1. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. 2. Go to the Function list page.
- On the Function List page, click the resource to associate with PrivateLink. 3. Function Details page.
- On the Function Details page, click the Configuration tab.
- In Private connection configuration, click the Edit button of PrivateLink Service. 5. PrivateLink Service Edit The popup window opens.
- PrivateLink Service Edit In the popup window, after checking the Use item of Activation Status, click the Confirm button. 6. Configuration tab’s Private connection configuration displays PrivateLink Service information.
| Category | Detailed description |
|---|---|
| Private URL | PrivateLink Service URL information |
| PrivateLink Service ID | PrivateLink Service ID information |
| Request Endpoint Management | List of PrivateLink Endpoints that requested a PrivateLink Service connection
|
Integrating PrivateLink Service
You can expose the function for private access from another VPC by integrating with PrivateLink Service.
To integrate the PrivateLink service, review the following tasks.
- Register the domain for the PrivateLink Endpoint IP address and the Private URL address to invoke the issued Private URL.
192.168.0.13 abc123.scf.private.kr-west1.qa2.samsungsdscloud.com - When invoking the PrivateLink Service, verify IAM authentication based on the credentials of the Endpoint creator required for the Endpoint.
Create PrivateLink Endpoint
Create an entry point to access the PrivateLink Service of the user VPC.
To create a PrivateLink Endpoint, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. 1. Go to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. 2. Go to the Function list page.
- On the Function list page, click the resource to associate with PrivateLink. 3. Function Details Go to the page.
- On the Function Details page, click the Configuration tab.
- Click the Add button in Private connection configuration of PrivateLink Endpoint. 5. Add PrivateLink Endpoint The popup window opens.
- Add PrivateLink Service in the popup window, after entering the PrivateLink Service ID and Alias information, click the Confirm button.
- When the popup indicating creation opens, click the Confirm button. 7. Configuration tab’s Private connection configuration displays PrivateLink Endpoint information.
| Category | Detailed description |
|---|---|
| PrivateLink Endpoint ID | PrivateLink Endpoint ID information |
| PrivateLink Service ID | PrivateLink Service ID information |
| Alias | hostalias information that can be used instead of an IP address for accessing a PrivateLink Endpoint |
| status | Approval status of PrivateLink Endpoint
|
Integrating APIGW Private EPS
To connect the SCF Endpoint and the APIGW Private Endpoint, you must specify the Private URL in the SCF Endpoint Alias instead of the APIGW EPS resource path.
- Private URL example:
181b6126ef6d4e4b81370df5.apigw.private.kr-west1.s.samsungsdscloud.com/get/resourcepath
To integrate APIGW Private EPS, refer to the following code.
const request = require('request');
/**
* @description User writing area (Function details)
*/
exports.handleRequest = async function (params) {
return await sendRequest(params);
};
async function sendRequest(req) {
return new Promise((resolve, reject) => {
// Port 80 and Port 443 are available
url = "https://{alias}/{resource_path}"; // Destination URL
/**
{alias} is the alias name entered when creating an Endpoint within the function
{resoure_path} is the resource path (/get/resourcepath) specified in the Private URL of APIGW EPS
*/
const options = {
uri: url,
method:'GET',
json: true,
strictSSL: false,
rejectUnauthorized: false
}
request(options, (error, response, body) => {
if (error) {
reject(error);
} else {
resolve({
statusCode: response.statusCode,
body: JSON.stringify(body)
});
}
});
});
}const request = require('request');
/**
* @description User writing area (Function details)
*/
exports.handleRequest = async function (params) {
return await sendRequest(params);
};
async function sendRequest(req) {
return new Promise((resolve, reject) => {
// Port 80 and Port 443 are available
url = "https://{alias}/{resource_path}"; // Destination URL
/**
{alias} is the alias name entered when creating an Endpoint within the function
{resoure_path} is the resource path (/get/resourcepath) specified in the Private URL of APIGW EPS
*/
const options = {
uri: url,
method:'GET',
json: true,
strictSSL: false,
rejectUnauthorized: false
}
request(options, (error, response, body) => {
if (error) {
reject(error);
} else {
resolve({
statusCode: response.statusCode,
body: JSON.stringify(body)
});
}
});
});
}2.6.2.4 - Resource-based Policy Guide
Resource-based policy overview
The resource-based policy (Resource-based Policy) of Cloud Functions is a policy granted to a resource that can decide to allow or deny (Effect) an action (Action) on a specific resource for a principal (Principal). You can directly define the principal that can invoke a function by using resource-based policies.
You can allow function calls by defining the following in a resource-based policy.
- User of the specified Samsung Cloud Platform account
- Specified source IP address range or CIDR block
A source policy is defined as a JSON policy document attached to the API, which controls whether the specified security principal (typically an IAM role or group) can call the API.
| Category | description | example |
|---|---|---|
| Principal | Specify the caller of the function | Specific object storage bucket, API Gateway, other Samsung Cloud Platform accounts, etc. |
| Task(Action) | Define the allowed functions | Mostly scf:InvokeFunction |
| Condition(Condition) | Restrict to allow only in specific situations | Allow only requests originating from a bucket with a specific SRN. |
- Cloud Functions’ resource-based policies leverage the rules of IAM’s resource-based policies.
- For instructions on creating or modifying policies using JSON, refer to the JSON Mode Utilization Guide.
Resource-based policy usage scenario
The primary use cases for resource-based policies are as follows.
Resource-based policy scenario
The resource-based policy scenarios used when a Cloud Functions function runs are as follows.
| Category | description | Reference example |
|---|---|---|
| Function URL - Authentication Type None | It is required when generating a function URL for invocation.
| Function URL (Auth Type None) Example |
| Function URL - Authentication Type IAM |
| Function URL (authentication type IAM) example |
| API Gateway trigger | It is required when API Gateway calls Lambda to handle external API requests.
| API Gateway Trigger Example |
| PrivateLink connection | You can connect a PrivateLink Service to define the function for private access from another VPC.
| PrivateLink connection example |
User addition usage scenario
Although it is not automatically registered as a resource-based policy for Cloud Functions, users can add and use it as needed. The scenarios that users can add and utilize are as follows.
- Cross-Account Access
- If an IAM user in account A wants to invoke a Lambda in account B, register account A in the function policy of account B.
- Hybrid Access Control
- It can be configured so that access is allowed only when both conditions are met—a specific user and a specific IP range—rather than merely restricting by account or IP alone.
Resource-based policy management for Cloud Functions
To view and configure resource-based policies for Cloud Functions, follow these steps.
- Click the All Services > Compute > Cloud Functions menu. Navigate to the Service Home page of Cloud Functions.
- On the Service Home page, click the Function menu. You will be taken to the Function list page.
- On the Function List page, click the resource for which you want to set a policy. You will be taken to the Function Details page.
- Click the Configuration tab on the Function Details page.
- Click the Edit button of the Resource-based policy permission item. The Resource policy edit popup window opens.
- In the Resource Policy edit popup, after selecting the Policy Template, write the policy.
- For policy examples by policy template, refer to Resource-based policy examples.
- When the writing is complete, click the Confirm button.
- Click the Delete button to delete the registered policy.
Example of resource-based policy
Users can define additional resource-based policies as needed or modify existing policies for use.
- For some features, a resource‑based policy (or credential) must be registered to use them in Cloud Functions.
- In the resource-based policy examples described in this guide, Cloud Functions automatically registers the example resource-based policies when each feature is enabled or linked.
Function URL - Authentication Type None
Principal is /* a policy that allows public calls.
Policy Template
{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["NONE"]
}
},
"Effect": "Allow"
"Principal": "*"
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "InvokeFunctionURLAllowPublicAccess"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["NONE"]
}
},
"Effect": "Allow"
"Principal": "*"
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "InvokeFunctionURLAllowPublicAccess"
}
],
"Version": "2024-07-01"
}Policy example
{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["NONE"]
}
},
"Effect": "Allow"
"Principal": "*"
"Resource": ["srn:e::accountID:kr-west1::scf:cloud-function/functionsID"],
"Sid": "InvokeFunctionURLAllowPublicAccess"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["NONE"]
}
},
"Effect": "Allow"
"Principal": "*"
"Resource": ["srn:e::accountID:kr-west1::scf:cloud-function/functionsID"],
"Sid": "InvokeFunctionURLAllowPublicAccess"
}
],
"Version": "2024-07-01"
}Function URL - Authentication Type IAM
This policy permits a specific user to invoke a public URL.
Policy Template
{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["SCP_IAM"]
}
},
"Effect": "Allow"
"Principal": {
"scp": ["srn:{{Environment}}::{{AccountID}}:::iam:user/{{UserId}}"]
},
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "Statement1"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["SCP_IAM"]
}
},
"Effect": "Allow"
"Principal": {
"scp": ["srn:{{Environment}}::{{AccountID}}:::iam:user/{{UserId}}"]
},
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "Statement1"
}
],
"Version": "2024-07-01"
}Policy Example
{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["SCP_IAM"]
}
},
"Effect": "Allow"
"Principal": "*",
"Resource": ["srn:e::accountID:kr-west1::scf:cloud-function/functionsID"],
"Sid": "accountID-iam-invokefunctionurl"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": ["scf:InvokeFunctionUrl"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": ["SCP_IAM"]
}
},
"Effect": "Allow"
"Principal": "*",
"Resource": ["srn:e::accountID:kr-west1::scf:cloud-function/functionsID"],
"Sid": "accountID-iam-invokefunctionurl"
}
],
"Version": "2024-07-01"
}API Gateway trigger
Principal is a policy that permits public calls with a * principal.
Policy Template
{
"Statement": [
{
"Action": ["scf:InvokeFunction"],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['x-scf-request-obj-srn']": ["{{ApiGatewayMethodSrn}}"]
}
},
"Effect": "Allow",
"Principal": {
"Service": ["apigateway.samsungsdscloud.com"]
},
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "Statement1"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": ["scf:InvokeFunction"],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['x-scf-request-obj-srn']": ["{{ApiGatewayMethodSrn}}"]
}
},
"Effect": "Allow",
"Principal": {
"Service": ["apigateway.samsungsdscloud.com"]
},
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "Statement1"
}
],
"Version": "2024-07-01"
}Policy Example
{
"Statement": [
{
"Action": [
scf:InvokeFunction
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['x-scf-request-obj-srn']": [
srn:e::accountID:kr-west1::apigateway:method/MethodID/*/GET/test
]
}
},
"Effect": "Allow"
"Principal": {
"Service": [
"apigateway.samsungsdscloud.com"
]
},
"Resource": [
srn:e::accountID:kr-west1::scf:cloud-function/functionID
],
"Sid": "999e9a9999de4d4683c9e10c74ee999z"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
scf:InvokeFunction
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['x-scf-request-obj-srn']": [
srn:e::accountID:kr-west1::apigateway:method/MethodID/*/GET/test
]
}
},
"Effect": "Allow"
"Principal": {
"Service": [
"apigateway.samsungsdscloud.com"
]
},
"Resource": [
srn:e::accountID:kr-west1::scf:cloud-function/functionID
],
"Sid": "999e9a9999de4d4683c9e10c74ee999z"
}
],
"Version": "2024-07-01"
}PrivateLink connection
This is a policy that allows function calls through a Privatelink Endpoint for specific users.
Policy Template
{
"Statement": [
{
"Action": ["scf:InvokeFunction"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionPrivatelinkServiceAuthType": ["SCP_IAM"]
}
},
"Effect": "Allow"
"Principal": {
"scp": ["srn:{{Environment}}::{{AccountID}}:::iam:user/{{UserId}}"]
},
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "Statement1"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": ["scf:InvokeFunction"],
"Condition": {
"StringEquals": {
"scf:CloudFunctionPrivatelinkServiceAuthType": ["SCP_IAM"]
}
},
"Effect": "Allow"
"Principal": {
"scp": ["srn:{{Environment}}::{{AccountID}}:::iam:user/{{UserId}}"]
},
"Resource": ["{{CloudFunctionSrn}}"],
"Sid": "Statement1"
}
],
"Version": "2024-07-01"
}Policy Example
{
"Statement": [
{
"Action": [
scf:InvokeFunction
],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": [
SCP_IAM
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountID:::iam:user/userID
]
},
"Resource": [
srn:e::accountID:kr-west1::scf:cloud-function/functionID
],
"Sid": "rrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrr-privatelink-invokefunction"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
scf:InvokeFunction
],
"Condition": {
"StringEquals": {
"scf:CloudFunctionAuthType": [
SCP_IAM
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountID:::iam:user/userID
]
},
"Resource": [
srn:e::accountID:kr-west1::scf:cloud-function/functionID
],
"Sid": "rrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrrr-privatelink-invokefunction"
}
],
"Version": "2024-07-01"
}2.6.3 - API Reference
2.6.4 - CLI Reference
2.6.5 - Release Note
Cloud Functions
- Technical support end-of-life information (EoTS) for the Runtime version is provided.
- When technical support ends, security patches and updates for that Runtime version will no longer be applied.
- Already created functions can be used continuously without any call time limit. * However, we do not guarantee bugs, errors, defects, or vulnerabilities that occur in Runtime versions for which technical support has ended.
- Technical support will be discontinued. The Runtime versions are as follows (see the full supported Runtime versions at Rutime version).
- GO: 1.21, 1.23
- Node.js: 18, 20
- PHP 8.1
- Python: 3.9
- Including runtime of additionally excluded functions
- The AIOS service integration has been stopped.
- Since the AIOS service has been discontinued, the AIOS integration service has been removed from Cloud Functions.
- You can set a resource-based policy on a function.
- Resource-based policies are policies applied to the function itself that allow external access.
- You can use resource-based policies to allow or deny actions on specific resources to a specific principal (Principal).
- You can use functions in conjunction with the AIOS service.
- You can integrate Cloud Functions with AIOS to leverage LLMs.
- You can use functions in conjunction with the PrivateLink service.
- Through a Private connection (PrivateLink), you can establish internal connections between VPCs and between a VPC and services on the Samsung Cloud Platform without traversing the Internet.
- The feature to upload Java Runtime executable files has been added.
- You can import and configure a Java Runtime executable archive file (.jar/.zip) in Object Storage.
- We have officially launched the Cloud Functions service.
- It is a serverless computing‑based FaaS (Function as a Service) that lets you easily run function‑style applications without server provisioning.
2.7 - Virtual Server DR
When the system is disrupted due to various disaster situations and risk factors, you can replicate the Block Storage attached to a Virtual Server in another region to restore normal operation quickly.
2.7.1 - Overview
Service Overview
Virtual Server DR is a service that quickly restores the system by replicating the Virtual Server and its attached Block Storage to a region different from the one currently in use. Even if the system is disrupted due to various disaster situations or unexpected events, you can quickly restore normal operation by using Virtual Server DR.
- The Virtual Server DR service can be configured using partner solutions sold on the Samsung Cloud Platform Marketplace.
- For detailed information on using the Marketplace, please refer to Marketplace.
- When you purchase and use a service sold on the Marketplace, a delegated tax invoice is issued in accordance with a separate agreement with the Marketplace software supplier.
- If you request a partner solution product for Virtual Server DR from the Marketplace, the request information will be emailed to the responsible person. Coordinate product details and schedule with the person in charge. Software installation and charges will be billed based on the confirmed date.
- The services sold in the Marketplace of Samsung Cloud Platform are offered by individual sellers, and Samsung SDS serves as an e‑commerce intermediary, not a party to the sales. Accordingly, Samsung SDS does not guarantee or assume responsibility for the service information or transactions conducted by individual sellers.
Features
- Easy DR Environment Setup: You can easily configure a Virtual Server for DR setup through partner solutions in the Marketplace of Samsung Cloud Platform.
- Various Environment Configurations: Using partner solutions, you can configure various environments such as physical to virtual (P2V) and virtual to virtual (V2V) environments, and it supports multiple operating systems (Windows, Linux).
Service Architecture Diagram
Provided features
For the main features, please refer to the Product Catalog Details page of the partner solution sold on the Samsung Cloud Platform Marketplace.
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare accordingly.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
| Compute | Virtual Server | Virtual server optimized for cloud computing |
2.7.2 - Release Note
Virtual Server DR
- We have officially launched the Virtual Server DR service.
- When the system is interrupted by various disaster scenarios and risk factors, it can be restored to normal operation in a short time.
2.8 - Block Storage
2.8.1 - Overview
Service Overview
Block Storage is a high-performance storage that stores data in block units arranged in a fixed size and layout.
Suitable for large-scale, high-performance requirements such as databases and mail servers, and users can directly allocate volumes on the server for use.
Features
- Large Volume Provisioning: OS configuration volumes are created with at least the minimum size per image and can be expanded up to 12 TB, and data storage volumes outside the OS can be created and expanded from a minimum of 8 GB to a maximum of 12 TB. Capacity expansion is performed reliably while online.
- High-Performance Full SSD Offering: It provides high durability and availability based on redundant controllers and Disk Array RAID. Since a Full SSD disk is provided by default, it is suitable for high-speed data processing tasks such as database workloads.
- Snapshot Backup: Data that has been modified or deleted can be recovered using the image snapshot feature. The user selects a snapshot created at the desired point in time from the list and performs the recovery.
Service Architecture Diagram
Provided features
Block Storage provides the following features.
- Volume Name: Users can set or modify the name for each volume.
- Capacity: Volumes can be created with sizes from a minimum of 8 GB up to a maximum of 12 TB, and can be expanded while in use. The OS default volume can be created with at least the minimum size for each image.
- Connection Server: You can select a Virtual Server to connect or disconnect.
- Multi-Server Connection (Multi Attach): Connect to two or more servers, with no limit on the number of servers per volume, and a Virtual Server can connect up to 26 volumes.
- Encryption: All volumes of Block Storage have AES-256 algorithm encryption applied by default, and when a volume is of HDD/SSD_KMS disk type, additional in‑transit encryption is provided for the segment between the instance and the Block Storage attached to the instance.
- Snapshot: The image snapshot feature allows recovery of modified or deleted data. Users select a snapshot created at the desired point in time from the list to restore it.
- Volume Transfer: You can transfer a volume to another Account using the volume transfer feature.
- Monitoring: IOPS, Latency, Throughput, etc. monitoring information can be viewed through the Cloud Monitoring service.
Component
You can create a volume by entering the capacity and selecting the disk type according to the user’s service scale and performance requirements. When using the snapshot feature, you can restore data to the desired point in time.
Volume
A volume (Volume) is the basic creation unit of the Block Storage service and is used as data storage space. Users select a name, capacity, and disk type to create a volume, then attach it to a Virtual Server for use.
The volume name generation rules are as follows.
-, _) within 255 characters.snapshot
A snapshot (Snapshot) is an image backup of a volume at a specific point in time. Users can view the snapshot name and creation timestamp in the snapshot list to select the snapshot they want to restore, and through that snapshot they can recover data that was changed or deleted.
The following considerations apply when using snapshots.
- The snapshot creation time is based on Asia/Seoul (GMT +09:00).
- Select the snapshot recovery button to restore the Block Storage volume to the latest snapshot.
- If you select a specific snapshot from the snapshot list, you can recover by creating a new volume based on the snapshot.
- Snapshots are billed based on the size of the original Block Storage, so please delete any unnecessary snapshots.
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
2.8.1.1 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by leveraging ServiceWatch released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a seamless monitoring environment.
Block Storage planned to be integrated with ServiceWatch from the July 2026 release onward is.
Detailed information about ServiceWatch is available in the ServiceWatch Overview.
Block Storage Monitoring Metrics
The table below shows the monitoring metrics for Block Storage that can be viewed in Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
| Performance Item Name | Explanation | unit |
|---|---|---|
| Volume Total | Total byte count | bytes |
| IOPS [Read] | iops(read) | iops |
| IOPS [Write] | iops(write) | iops |
| Latency Time [Read] | Read latency | usec |
| Latency Time [write] | Latency (write) | usec |
| Throughput [Read] | Throughput (read) | bytes/s |
| Throughput [Write] | Throughput (write) | bytes/s |
2.8.2 - How-to guides
Users can create the service by entering the required information for Block Storage and selecting detailed options through the Samsung Cloud Platform Console.
Create Block Storage
You can create and use the Block Storage service in the Samsung Cloud Platform Console.
To create a Block Storage, follow these steps.
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Block Storage menu. Go to the Block Storage List page.
On the Block Storage page, click the Create Service button. You will be taken to the Block Storage Creation page.
On the Block Storage Creation page, enter the information required to create the service and select detailed options.
Category Required or notDetailed description Volume name Required Volume name - English letters, numbers, spaces, and special characters(
-,_) using to input up to 255 characters
snapshot Selection Select the snapshot to use when creating a volume from a snapshot - After checking the Use option, snapshot selection is possible
- When creating a service via snapshot recovery volume creation, provide the recovery snapshot name
- If not selected, an empty volume is created
Disk type Required Select Disk Type - SSD_Provisioned: SSD volume with configurable IOPS and throughput
- SSD/HDD: Standard SSD/HDD volume
- SSD/HDD_KMS: Additional encrypted volume
- SSD/HDD_MultiAttach: Volume that can be attached to more than one server
- Cannot be modified after service creation
- When creating a service via snapshot recovery volume creation, it is set identical to the original and cannot be modified
capacity Selection Capacity setting - Can be created within 8~12,228GB
- Enter the number of units provided in 8GB increments
- Enter a capacity that is equal to or larger than the original when creating the service via snapshot recovery volume creation
Max IOPS Required Enter the maximum IOPS value between 5,000 and 20,000 - Can be set only when disk type is SSD_Provisioned
Max Throughput Required Enter the maximum Throughput value between 250 and 1,000 - Can be set only when the disk type is SSD_Provisioned
Table. Block Storage Service Information Input Items- English letters, numbers, spaces, and special characters(
Check the detailed information and estimated billing amount generated in the Summary panel, and click the Create button.
- When creation is complete, check the created resource on the Block Storage List page.
- All volumes of Block Storage are encrypted by default with the AES-256 algorithm.
- Windows-based Virtual Servers cannot use MultiAttach disks. Use a separate replication method or solution.
- If the volume is of HDD/SSD_KMS disk type, we additionally provide in‑transit encryption for the block storage segment connected to the instance.
View Block Storage Details
The Block Storage service allows you to view and edit the full resource list and detailed information. Block Storage Detail page consists of Detail Information, Snapshot List, Tags, Operation History tabs.
Follow these steps to view detailed information about the Block Storage service.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Navigate to the Block Storage List page.
- On the Block Storage List page, click the resource for which you want to view detailed information. You will be taken to the Block Storage Details page.
- Block Storage Details page displays status information and additional feature information, and consists of Details, Snapshot List, Tags, Activity History tabs.
Category Detailed description Volume status Volume status - Creating: In progress
- Downloading: In progress (applying OS image)
- Available: Created, server connection available
- Reserved: Waiting for server connection
- Attaching: Connecting to server
- Detaching: Server connection detached
- In Use: Server connection established
- Deleting: Terminating service
- Awaiting Transfer: Waiting for volume transfer
- Extending: Expanding capacity
- Error Extending: Abnormal state during capacity expansion
- Backing Up: Backing up volume
- Restoring Backup: Restoring volume backup
- Error Backing Up: Abnormal state during volume backup
- Error Restoring: Abnormal state during volume backup restoration
- Error Deleting: Abnormal state during deletion
- Error Managing: Abnormal state
- Error: Abnormal state
- Maintenance: Temporary maintenance state
- Reverting: Restoring snapshot
Previous volume Move the volume to another Account - For detailed information about moving volumes, see 볼륨 이전
Create snapshot Immediately create a snapshot at the time of creation - For detailed information on snapshot creation, see Creating a Snapshot
Snapshot recovery Recover the volume using the latest snapshot in Available state - For detailed information on snapshot recovery, see 스냅샷 복구하기
Service termination Cancel service button Table. Status Information and Additional Features
- Block Storage Details page displays status information and additional feature information, and consists of Details, Snapshot List, Tags, Activity History tabs.
Detailed information
Block Storage List page lets you view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | service group |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who modified the service |
| Modification date | Date and time the service was modified |
| Volume name | Volume name
|
| Volume ID | Volume unique ID |
| Disk type | Disk type |
| type | Classification by volume creation method and usage |
| capacity | Volume capacity
|
| Max IOPS | Required |
| Max Throughput | Required |
| Connection server | Connected Virtual Server
|
Snapshot List
Block Storage List page allows you to view the snapshot of the selected resource.
| Category | Detailed description |
|---|---|
| Snapshot name | Snapshot name |
| Explanation | Snapshot description |
| Volume capacity | Snapshot target Block Storage original volume capacity
|
| Creation timestamp | Snapshot creation time |
| status | Snapshot status
|
| Additional features > More | Snapshot management button
|
| Delete | Select the snapshots to delete from the snapshot list and delete them all at once. |
Snapshots can affect volume capacity management. Delete unnecessary snapshots after use.
- Snapshot recovery can be performed while the server is not connected.
- The snapshot creation time is based on Asia/Seoul (GMT +09:00).
- When the snapshot recovery button is clicked, the volume is restored to the latest snapshot in the Available state.
- When you select Create recovery volume on the snapshot list page, a new volume based on the snapshot is created without modifying the existing volume.
- Snapshots that contain vProtect are temporary snapshots created when using the Backup service and are not charged.
tag
Block Storage List page lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
On the Block Storage List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Block Storage Resources
If you need to modify the settings of a created Block Storage or add or remove connected servers, you can perform the tasks on the Block Storage Details page.
Edit volume name
You can rename a volume. To rename a volume, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Navigate to the Block Storage list page.
- On the Block Storage List page, click the resource whose volume name you want to edit. You will be taken to the Block Storage Details page.
- Click the Edit button of the Volume name. The Edit Volume Name popup window opens.
- Enter the volume name and click the Confirm button.
-, _)Increase capacity
You can expand the volume capacity. To expand the capacity, follow the steps below.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- Block Storage List page, click the resource to expand capacity. You will be taken to the Block Storage Details page.
- Click the Capacity Edit button. The Capacity Edit popup window opens.
- Enter the capacity and click the Confirm button.
- Size reduction is not provided.
- After expanding the capacity, you cannot restore from snapshots taken before the expansion.
- Snapshots created before the capacity expansion can only be used to recover by creating a new volume.
- Expansion to a larger capacity than the current one is possible within the range of 8 to 12,228 GB.
- Enter the number of Units provided in 8GB increments.
Modify connection server
You can connect to or disconnect from the server. To modify the connected server, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- Block Storage List page, click the resource to edit the attached server. You will be taken to the Block Storage Details page.
- When adding a Virtual Server connection, click the Add button in the Connection Server field. The Add Connection Server popup window will open.
- After selecting the Virtual Server you want to connect to, click the Confirm button.
- If you are disconnecting the Virtual Server, click the Connection Server item’s Disconnect button.
- Be sure to perform the disconnect operation (Umount, Disk Offline) on the server before proceeding with the release.
- You can connect a Virtual Server created in the same location as the Block Storage.
- A Virtual Server that uses a Partition with a Server Group policy cannot be connected.
- HDD/SSD_MultiAttach disk type can be attached to two or more Virtual Servers, and there is no limit on the number of connections.
- A Windows-based Virtual Server cannot use MultiAttach disks and must use a separate replication method or solution.
- A Virtual Server can attach up to 26 volumes, including the OS by default.
- The OS default volume cannot be modified on the connected server, and the service cannot be terminated.
- When adding a connected server, it can be used after performing the connection tasks (Mount, Disk Online) on the server. For detailed information about server connections, refer to Connecting to Server.
Cancel Block Storage
You can reduce operating costs by terminating unused Block Storage. However, terminating the service may cause the running service to stop immediately, so you should carefully consider the impact of service interruption before proceeding with the termination.
- Please note that data cannot be recovered after termination.
- In the following cases, you cannot delete a Block Storage volume.
- Connecting to server
- OS default volume
- Connect Custom image to Virtual Server
- When the volume status is not Available, Error, Error Extending, Error Restoring, or Error Managing
- If you select two or more volumes to cancel, only the volumes that can be canceled will be canceled.
To cancel Block Storage, follow the steps below.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- On the Block Storage List page, select the resource to terminate, and click the Terminate Service button.
- After termination is complete, verify on the Block Storage List page that the resource has been terminated.
2.8.2.1 - Connect to Server
When using a volume on the server, a connect or disconnect operation is required.
On the Block Storage Details page, add a connected server, then access the server to perform connection operations (Mount, Disk Online). After use, perform disconnection operations (Umount, Disk Offline) and then remove the connected server.
Connect to Server (Mount, Disk Online)
To use the volume added to the connected server, you must log into the server and perform the connection tasks (Mount, Disk Online). Follow the steps below.
Linux operating system
- Server OS: LINUX
- Mount location: /data
- Volume size: 24 GB
- File system: ext3, ext4, xfs etc
- Additional allocated disk: /dev/vdb
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- On the Block Storage List page, click the resource to be used on the connected server. Navigate to the Block Storage Details page.
- After verifying the server in the Connection Server item, connect.
- Refer to the steps below to mount the volume (Mount).
Switch to root privileges
$ sudo -iCheck Disk
# lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 diskCreate partition
# fdisk /dev/vdb Command (m for help): n Partition type: p primary (0 primary, 0 extended, 4 free) e extended Select (default p): p Partition number (1-4, default 1): 1 First sector (2048-50331646, default 2048): Last sector, +/-sectors or +/-size{K,M,G,T,P} (2048-50331646, default 50331646): Created a new partition 1 of type 'Linux' and of size 24 GiB. Command (m for help): w The partition table has been altered! Calling ioctl() to re-read partition table. Syncing disks.Partition format setting (example: ext4)
# lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part # mkfs.ext4 /dev/vdb1 mke2fs 1.46.5 (30-Dec-2021) ... Writing superblocks and filesystem accounting information: doneVolume Mount
# mkdir /data # mount /dev/vdb1 /data # lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part /data # vi /etc/fstab (추가) /dev/vdb1 /data ext4 defaults 0 0
| Item | Explanation |
|---|---|
| cat /etc/fstab | File system information file
|
| df -h | Check the total disk usage of mounted disks |
| fdisk -l | Check partition information
|
| command | Explanation |
|---|---|
| m | Check the usage of the fdisk command |
| n | Create a new partition |
| p | Verify the updated partition information |
| t | Change the system ID of the partition |
| w | Save partition information and exit fdisk. |
Windows operating system
- Click the All Services > Compute > Virtual Server menu. Navigate to the Virtual Server Service Home page.
- Click the Block Storage menu. You will be taken to the Block Storage List page.
- On the Block Storage List page, click the resource to be used on the connected server. You will be taken to the Block Storage Details page.
- Connection Server item, verify the server and then connect.
- Refer to the steps below to connect the volume (Disk Online).
After right-clicking the Windows Start icon, run
Computer Management.In the Computer Management tree structure, select
Storage > Disk ManagementCheck Disk
Disk Online
Disk initialization
Partition format
Check volume
Disconnect server (Umount, Disk Offline)
Access the server, perform the disconnect operations (Umount, Disk Offline), and then disconnect the server from the Console.
Follow the next procedure.
- If you disconnect the server from the console without performing the disconnect operations (Umount, Disk Offlline) on the server, a server state error (Hang) may occur.
- Be sure to perform the OS tasks first.
- For the OS default volume, you cannot modify the connected server or cancel the service.
Linux operating system
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Navigate to the Block Storage List page.
- On the Block Storage List page, click the resource to detach the attached server. You will be taken to the Block Storage Details page.
- After verifying the server in the Connection Server item, connect.
- Refer to the steps below to unmount the volume(Umount).
- Volume Umount
# umount /dev/vdb1 /data
# lsblk
NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT
vda 252:0 0 24G 0 disk
├─vda1 252:1 0 23.9G 0 part [SWAP]
└─vda14 252:14 0 4M 0 part /
└─vda15 252:15 0 106M 0 part /boot/efi
vdb 252:16 0 24G 0 disk
└─vdb1 252:17 0 24G 0 part
# vi /etc/fstab
(삭제) /dev/vdb1 /data ext4 defaults 0 0
Windows operating system
Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
Click the Block Storage menu. Go to the Block Storage List page.
Block Storage List page, click the resource to detach the connected server. Navigate to the Block Storage Details page.
In the Connection Server field, verify the server before connecting.
Unmount the mounted file system.
Please follow the procedure below to detach the volume (Disk Offline).
Right-click the Windows Start icon, then run
Computer Management.In the Computer Management tree structure, select
Storage > Disk ManagementRight-click the disk to be removed, then run
OfflineCheck disk status
2.8.2.2 - Use Snapshot
You can create, delete, or restore snapshots of a created Block Storage using snapshots. You can perform these actions on the Block Storage Details page and the Snapshot List page.
Creating a Snapshot
You can create a snapshot of the current point in time. To create a snapshot, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- On the Block Storage List page, click the resource for which you want to create a snapshot. You will be taken to the Block Storage Details page.
- Click the Create Snapshot button. The Create Snapshot popup window opens.
- Enter the Snapshot name and description, then click the Confirm button. This creates a snapshot of the current point in time.
- Click the Snapshot List button. You will be taken to the Block Storage Snapshot List page.
- Check the generated snapshot.
Edit Snapshot
You can edit snapshot information. To modify the snapshot name or description, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Go to the Service Home page of Virtual Server.
- Click the Block Storage menu. Navigate to the Block Storage List page.
- Block Storage List page, click the resource to edit the snapshot information. You will be taken to the Block Storage Details page.
- Click the Snapshot List button. You will be taken to the Block Storage Snapshot List page.
- After confirming the snapshot to edit, click the More button.
- Click the Edit button. The Snapshot Edit popup window opens.
- Enter the Snapshot name or Description, and click the Confirm button.
Recover snapshot
Block Storage volumes can be restored to the latest snapshot while in the Available state. To restore a snapshot, follow the steps below.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- On the Block Storage List page, click the resource to restore from a snapshot. You will be taken to the Block Storage Details page.
- If there are servers added in the Connected Server item, connect to the server and perform the disconnect operations (Umount, Disk Offline).
- For detailed information about disconnecting the server, see Disconnecting the Server.
- On the Block Storage Details page, click the Disconnect button in the Connected Server item to remove the server. The connected server will be removed.
- For detailed information on disconnecting the connection server, refer to Modify Connection Server.
- Click the Snapshot List button. You will be taken to the Block Storage Snapshot List page.
- Check the latest snapshot in the Available state. The volume will be restored from that snapshot.
- Click the Snapshot Recovery button. The Snapshot Recovery popup window opens.
- After verifying the Snapshot name and Creation timestamp, click the Confirm button.
- When recovery starts, the status becomes Reverting, and when it completes, it becomes Available.
- Detailed Information page button, click it. It navigates to the Block Storage Detailed Page.
- Click the Add button of the Connection Server. Reconnect the Virtual Server.
- For detailed information about adding a connection server, refer to Edit Connection Server.
- After connecting to the added server, perform the connection tasks (Mount, Disk Online) according to the operating system.
- For detailed information about server connection, please refer to Connect to Server.
- Snapshot recovery can be performed while the server is not connected.
- If you want to restore from a snapshot that is not the latest, you can recover by creating a recovery volume.
- Recovery is not possible in the following situations.
- When a Block Storage volume is not in the Available state.
- If a server is attached to a Block Storage volume
- If there are no recoverable snapshots.
- If the latest snapshot changes while creating a recovery.
- If the latest snapshot is not in the Available state.
- When the snapshot’s volume size differs from the Block Storage volume size (in case the volume was expanded)
Create a snapshot recovery volume
You can create a volume using a snapshot. To create a snapshot recovery volume, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Go to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- On the Block Storage List page, click the resource to create a snapshot recovery volume. You will be taken to the Block Storage Details page.
- Click the Snapshot List button. You will be taken to the Block Storage Snapshot List page.
- After checking the Snapshot Name, Description and Creation Time, click the More button of the snapshot you want to restore.
- Click Create recovery volume. The Create snapshot recovery volume popup opens.
- Click the Confirm button. Go to the Create Block Storage page.
- On the Block Storage Creation page, enter the information required to create the service and select detailed options.
- Enter the volume name and size. You can specify a size that is greater than or equal to the original volume.
- The disk type is set to match the original and cannot be modified.
Category RequiredDetailed description Volume name Required Volume name - Enter up to 255 characters using English letters, numbers, spaces, and special characters (
-,_)
Disk type Required Select Disk Type - SSD_Provisioned: SSD volume with configurable IOPS and Throughput
- SSD/HDD: Standard SSD/HDD volume
- SSD/HDD_KMS: Additional encrypted volume
- SSD/HDD_MultiAttach: Volume that can be attached to more than one server
- Cannot be modified after service creation
- SSD_Provisioned: SSD volume with configurable IOPS and Throughput
- When creating the service via snapshot recovery volume creation, it is set identical to the original and cannot be modified
capacity Selection Capacity setting - Can be created within 8~12,228 GB
- Enter the number of units provided in 8 GB increments
- Enter a capacity equal to or larger than the original when creating the service via snapshot recovery volume creation
Max IOPS Required Enter the maximum IOPS value between 5,000 and 20,000 - Can be configured only when Disk type is SSD_Provisioned
Max Throughput Required Enter the maximum Throughput value between 250 and 1,000 - Disk type can be set only when it is SSD_Provisioned
Recovery snapshot name Selection Name of the recovery snapshot used when creating the volume - Provide the recovery snapshot name when creating a service via snapshot recovery volume creation
Table. Block Storage Service Information Input Items - Enter up to 255 characters using English letters, numbers, spaces, and special characters (
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- When creation is complete, check the created resource on the Block Storage List page.
Delete Snapshot
You can select a snapshot to delete. To delete a snapshot, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. You will be taken to the Block Storage list page.
- On the Block Storage List page, click the resource to delete the snapshot. You will be taken to the Block Storage Details page.
- Click the Snapshot List button. You will be taken to the Block Storage Snapshot List page.
- After checking Snapshot Name, Description and Creation Time, click the More button of the snapshot you want to delete.
- Click the Delete button. The snapshot will be removed from the Snapshot List page.
2.8.2.3 - Move Volume
You can transfer a volume to another account, and when you do, the volume is removed from its original location. You can perform volume transfer on the Block Storage List or Block Storage Details page.
Previous volume
You can transfer a volume to another Account within the same region. To transfer a volume, follow the steps below.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- On the Block Storage List page, after selecting the resource to migrate, click the More > Migrate Volume button at the top left of the list.
- Or click the Volume Migration button at the top of the Block Storage Details page of the resource to be migrated.
- When the popup indicating volume transfer opens, verify the volume name you want to transfer, then click the Confirm button.
- When the pop‑up for previous completion opens, click the Confirm button. The Volume Transfer ID and Approval Key information will be downloaded as a text file.
- The volume changes to Awaiting Transfer state.
- Volume migration is possible within the same region.
- Volume migration is possible only when the volume is in Available state. If it is in In Use state, disconnect all attached servers.
Cancel previous volume
You can cancel after creating a volume migration. To cancel a volume migration, follow the steps below.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Go to the Block Storage List page.
- Block Storage List page, click the resource to cancel the volume migration. You will be taken to the Block Storage Details page.
- If the volume is in Awaiting Transfer status, it can be canceled.
- Click the Cancel previous volume button. The Cancel previous volume popup will open.
- After confirming the volume name for which you want to cancel the volume transfer, click the Confirm button.
- The volume changes to Available state.
Get previous volume
You can receive a volume from another Account within the same region. To receive a volume, follow these steps.
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Block Storage menu. Navigate to the Block Storage List page.
- On the Block Storage List page, click the More > Receive Volume Transfer button at the top left of the list. The Receive Volume Transfer popup opens.
- Volume Migration: Enter the Volume Migration ID and Approval Key provided when creating it.
- A volume is created on the Block Storage list page.
- It takes time for the changes to be applied.
- The transferred volume is removed from the account that initiated the volume transfer.
2.8.3 - API Reference
2.8.4 - CLI Reference
2.8.5 - Release Note
Block Storage
- An SSD volume with configurable IOPS and throughput has been added.
- When creating Block Storage, you can select the SSD_Provisioned disk type.
- You can set the IOPS and Throughput range.
- IOPS: 5,000 ~ 20,000
- Throughput: 250 ~ 1,000
- During the preview period, there is no additional charge; charges will be applied later.
- Snapshots are billed based on the size of the original Block Storage.
- Integrated with Cloud Monitoring.
- You can view IOPS, Latency, and Throughput information in Cloud Monitoring.
- Block Storage feature change
- HDD disk types have been added, and you can select the added type (HDD, HDD_MultiAttach, HDD_KMS) according to your purpose.
- Samsung Cloud Platform common feature changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Added the SSD_KMS disk type.
- When SSD_KMS is selected, encryption using a KMS (Key Management Service) encryption key is added.
- We have launched a high‑performance storage service suitable for handling large‑scale data and database workloads.
- We have launched a high-performance storage service suitable for handling large-scale data and database workloads.
3 - Storage
We provide data storage services that enhance reliability and efficiency through various storage configurations.
3.1 - Block Storage(BM)
3.1.1 - Overview
Service Overview
Block Storage is a high-performance storage that stores data in block units arranged in a fixed size and order.
Suitable for large-scale, high-performance requirements such as databases and mail servers, and users can directly allocate volumes on the server for use.
Features
- Large volume provision: You can create volumes up to 16 TB in size.
- Full SSD-based high performance: Provides high durability and availability based on redundant controllers and Disk Array RAID. Since a Full SSD disk is provided by default, it is suitable for high-speed data processing tasks such as database workloads.
- Snapshot Backup: Data that has been modified or deleted can be recovered using the image snapshot feature. The user selects a snapshot created at the desired point in time from the list and performs the recovery.
- Replication: Creates an identical replica volume at a different location, and users can set the data replication schedule. If the original volume becomes unavailable due to failures or disasters, services can be provided through the replica volume.
Configuration diagram
Provided features
Block Storage provides the following features.
- Volume Name: Users can set or edit the name for each volume.
- Capacity: Volumes can be created with capacities ranging from a minimum of 1 GB up to a maximum of 16 TB.
- Connection Server : You can select Bare Metal Server or Multi Node GPU Cluster to connect or disconnect.
- Multi-Server Connection (Multi Attach): Supports up to 5 server connections, with no limit on the number of volumes that can be attached to a Bare Metal Server.
- Encryption: All volumes are encrypted with the AES-256 algorithm by default, regardless of disk type.
- Snapshot: Using the image snapshot feature, you can create a snapshot at a specific point in time or generate snapshots at regular intervals.
- Capacity: the capacity of the snapshot storage space
- Schedule: Snapshot auto-creation interval
- Recovery: Recover the original volume to the latest snapshot, or select a snapshot at a specific point in time to create a recovery volume
- Recovery copy a separate volume created with the same capacity as the original (additional cost incurred)
- Replication: It replicates the volume to another location, and the user can set the replication schedule.
- A replicated volume can also serve as the primary using the snapshot feature in the event of a disaster.
- Volume Group: Set up to 16 Block Storage volumes as a group. Snapshots and replication can be configured at the group level.
- Monitoring: You can view monitoring information such as IOPS, latency, and throughput through the Cloud Monitoring service.
Component
You can create a volume by entering the size and selecting the disk type according to the user’s service scale and performance requirements.
When using the snapshot feature, you can restore data to the desired point in time.
Volume
A volume (Volume) is the basic creation unit of the Block Storage service and is used as data storage space. Users create a volume by setting the name, capacity, disk type, snapshot, etc., and then connect it to a Bare Metal Server for use.
The volume name generation rules are as follows.
- It must start with an English letter and can be set using English letters, numbers, and special characters (
-) within 3 to 28 characters.
Snapshot
Snapshot is an image backup of a volume at a specific point in time. Users can view the snapshot name and creation time in the snapshot list to select the snapshot they want to restore, and can recover data that was modified or deleted using that snapshot.
The following are considerations when using snapshots.
- The snapshot creation time is based on Asia/Seoul (GMT +09:00).
- Snapshots can be created up to a maximum of 1,023. (Automatic creation via schedule is limited to a maximum of 128.)
- Automatic creation is possible through snapshot schedule configuration.
- Because snapshot capacity is added to Block Storage (BM) charges, adjust the size of your snapshot storage.
Volume Group
A Volume Group is a group-level management feature that allows users who configure databases and applications across two or more volumes to create consistent-point snapshots and replications. Users can create a Volume Group by selecting a name and a target Block Storage.
Preceding Service
This is a list of services that must be pre-configured before creating the service. For details, refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Bare Metal Server | High-performance physical server used without virtualization |
3.1.1.1 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, Starting after the September 2026 release, monitoring of Samsung Cloud Platform resources via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by using ServiceWatch, released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a smooth monitoring environment.
Block Storage is planned to be integrated with ServiceWatch from after the July 2026 release.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
Block Storage BM Monitoring Metrics
The table below shows the monitoring metrics for Block Storage BM that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
| Performance Item Name | Explanation | unit |
|---|---|---|
| Instance Status | Block Storage volume status | status |
| Volume Total | Total byte count | bytes |
| IOPS [Total] | iops(total) | iops |
| IOPS [Read] | iops(read) | iops |
| IOPS [Write] | iops(write) | iops |
| IOPS [Other] | iops(other) | iops |
| Latency Time [Total] | Total latency | usec |
| Latency Time [Read] | Read latency | usec |
| Latency Time [write] | Latency (write) | usec |
| Latency Time [Other] | Latency (Other) | usec |
| Throughput [Total] | Throughput (total) | bytes/s |
| Throughput [Read] | Throughput (read) | bytes/s |
| Throughput [Write] | Throughput (write) | bytes/s |
| Throughput [Other] | Throughput (Other) | bytes/s |
3.1.2 - How-to Guides
Users can create the service by entering the required information for Block Storage (BM) and selecting detailed options through the Samsung Cloud Platform Console.
Block Storage(BM) Create
You can create and use the Block Storage (BM) service in the Samsung Cloud Platform Console.
To create Block Storage (BM), follow the steps below.
Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
Click the Block Storage(BM) Create button on the Service Home page. You will be taken to the Block Storage(BM) Create page.
Block Storage(BM) Creation page, input the information needed to create the service, and choose detailed options.
Category Required statusDetailed description Volume name Required Volume name - must start with an English letter and be 3~28 characters using English letters, numbers, and special characters (
-)
- cannot be modified after service creation
Disk type Required Select Disk Type - SSD: High-performance general volume
- HDD: General volume
- Cannot be modified after service creation
capacity Required Capacity setting - Enter a number between 1~16,384 GB
- Cannot be modified after service creation
Max IOPS Required Enter IOPS value - Enter a number between 5,000~20,000
- HDD type does not provide performance metric setting function
Max Throughput Required Enter the throughput speed (MB/s) - Enter a number between 250~1,000
- HDD type does not provide performance metric configuration functionality
Connection server Required Connect Bare Metal Server selection - Provides up to 8 Bare Metal Server connections
- No limit on the number of volumes that can be attached to a Bare Metal Server
Table. Block Storage (BM) Service Information Input Items- must start with an English letter and be 3~28 characters using English letters, numbers, and special characters (
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the Block Storage(BM) List page.
- Regardless of disk type, all volumes have server-side encryption based on the AES-256 algorithm applied by default.
- The snapshot schedule can be set on the detail page.
- The performance metrics (IOPS, Throughput) of the configured storage are based on maximum values and do not guarantee consistent values.
Configure iSCSI
Volumes created by the user in addition to the OS’s default volume must be configured with iSCSI.
After checking the IP provided in the iSCSI Information on the Block Storage(BM) Details page, follow the iSCSI configuration steps for each OS.
Linux operating system
The iSCSI information (Storage Target IP) was written assuming 10.40.40.41, 10.40.40.42.
- Check the iSCSI information on the Block Storage (BM) detail page.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to be used on the connected server. You will be taken to the Block Storage(BM) Details page.
- Connection Server item, verify the server and then connect.
- Proceed with iSCSI configuration by referring to the steps below.
- Discover the connection information for the Storage (target IP).Color mode
[root@localhost ~]# iscsiadm -m discovery -t st -p 10.40.40.41 10.40.40.41:3260,1024 iqn.2000-05.com.3pardata:20210002ac026169 [root@localhost ~]# iscsiadm -m discovery -t st -p 10.40.40.42 10.40.40.42:3260,1025 iqn.2000-05.com.3pardata:20220002ac026169[root@localhost ~]# iscsiadm -m discovery -t st -p 10.40.40.41 10.40.40.41:3260,1024 iqn.2000-05.com.3pardata:20210002ac026169 [root@localhost ~]# iscsiadm -m discovery -t st -p 10.40.40.42 10.40.40.42:3260,1025 iqn.2000-05.com.3pardata:20220002ac026169code block. Storage (target IP) connection information Discovery - Connect to the storage (target IP). If it is already connected, proceed to the next step.Color mode
[root@localhost ~]# iscsiadm -m node -p 10.40.40.41:3260 --login Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] (multiple) Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] (multiple) Login to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] successful. Login to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] successful [root@localhost ~]# iscsiadm -m node -p 10.40.40.42:3260 --login Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] (multiple) Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] (multiple) Login to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] successful. Login to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] successful.[root@localhost ~]# iscsiadm -m node -p 10.40.40.41:3260 --login Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] (multiple) Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] (multiple) Login to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] successful. Login to [iface: default, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] successful [root@localhost ~]# iscsiadm -m node -p 10.40.40.42:3260 --login Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] (multiple) Logging in to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] (multiple) Login to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] successful. Login to [iface: default, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] successful.Code block. Storage (target IP) connection - To minimize search time, delete all unused Storage (target IP).Color mode
[root@localhost ~]# iscsiadm -m node show 100.100.100.10:3260,1026 iqn.1992-08.com.netapp:sn.c9adbd09cf301d039ea2bc878:vs.3 10.40.40.41:3260,1024 iqn.2000-05.com.3pardata:20210002ac026169 10.40.40.42:3260,1025 iqn.2000-05.com.3pardata:20220002ac026169 [root@localhost ~]# iscsiadm -m node -o delete -p 100.100.100.10:3260[root@localhost ~]# iscsiadm -m node show 100.100.100.10:3260,1026 iqn.1992-08.com.netapp:sn.c9adbd09cf301d039ea2bc878:vs.3 10.40.40.41:3260,1024 iqn.2000-05.com.3pardata:20210002ac026169 10.40.40.42:3260,1025 iqn.2000-05.com.3pardata:20220002ac026169 [root@localhost ~]# iscsiadm -m node -o delete -p 100.100.100.10:3260Code block. Delete unused Storage (target IP) - Please rescan to verify the additional disk.Color mode
[root@localhost ~]# iscsiadm -m session --rescan Rescanning session [sid: 65, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] Rescanning session [sid: 66, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] Rescanning session [sid: 67, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] Rescanning session [sid: 68, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260][root@localhost ~]# iscsiadm -m session --rescan Rescanning session [sid: 65, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] Rescanning session [sid: 66, target: iqn.2000-05.com.3pardata:20210002ac026169, portal: 10.40.40.41,3260] Rescanning session [sid: 67, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260] Rescanning session [sid: 68, target: iqn.2000-05.com.3pardata:20220002ac026169, portal: 10.40.40.42,3260]code block. Rescan - Configure Auto Login to log in automatically even after a reboot.Color mode
[root@localhost ~]# iscsiadm -m node --op=update -n node.conn[0].startup -v automatic [root@localhost ~]# iscsiadm -m node --op=update -n node.startup -v automatic[root@localhost ~]# iscsiadm -m node --op=update -n node.conn[0].startup -v automatic [root@localhost ~]# iscsiadm -m node --op=update -n node.startup -v automaticCode block. Auto Login setting - Verify the configuration using the following command.Color mode
[root@localhost ~]# lsblk[root@localhost ~]# lsblkCode block. Verify configuration.
- Discover the connection information for the Storage (target IP).
Windows operating system
The iSCSI information (Storage Target IP) was assumed to be 10.40.40.41, 10.40.40.42.
- Check the iSCSI information on the Block Storage (BM) detail page.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to be used on the connected server. You will be taken to the Block Storage(BM) Details page.
- After checking the server in the Connection Server item, connect.
- Proceed with iSCSI configuration by referring to the steps below.
- Open Command Prompt (Admin) and run powershell.Color mode
Windows PowerShell Copyright (C) Microsoft Corporation. All rights reserved. PS C:\Users> cd .. PS C:\>Windows PowerShell Copyright (C) Microsoft Corporation. All rights reserved. PS C:\Users> cd .. PS C:\>Code block. powershell execution - Start the volume service.Color mode
PS C:\> Set-Service -Name MSiSCSI -StartupType Automatic PS C:\> Start-Service -Name MSiSCSI PS C:\> get-service -Name MSiSCSI | select -Property Name, DisplayName, Status, StartType Name DisplayName Status StartType ------- -------------- ------- ----------- MSiSCSI Microsoft iSCSI Initiator Service Running AutomaticPS C:\> Set-Service -Name MSiSCSI -StartupType Automatic PS C:\> Start-Service -Name MSiSCSI PS C:\> get-service -Name MSiSCSI | select -Property Name, DisplayName, Status, StartType Name DisplayName Status StartType ------- -------------- ------- ----------- MSiSCSI Microsoft iSCSI Initiator Service Running AutomaticCode block. Start volume service - Install Multipath I/O. If the Restart Needed item is displayed as Yes, a restart is required.Color mode
PS C:\> Install-WindowsFeature -name Multipath-IO Success Restart Needed Exit Code Feature Result ------- -------------- --------- ----------------- True No Success {Multipath I/O}PS C:\> Install-WindowsFeature -name Multipath-IO Success Restart Needed Exit Code Feature Result ------- -------------- --------- ----------------- True No Success {Multipath I/O}code block. Multipath I/O installation - Modify the Initiator Port Address.
If you are not an Active Directory member, skip this procedure. The Initiator Port Address only needs to be modified when you are an Active Directory member.- iqn is generated based on the hostname, but when joined to Active Directory, it is changed to DNS format.
Since it is registered in Storage based on the default hostname, for iqn.1991-05.com.microsoft:iqn01.scp.com, iqn01 is the hostname. Remove the DNS information and change it to the name registered when creating the OS in the user Console, such as iqn.1991-05.com.microsoft:iqn01. - If you are not an AD member, no changes are required.Color mode
PS C:\> $address = (Get-InitiatorPort | select NodeAddress) PS C:\> echo $address NodeAddress ----------- iqn.1991-05.com.microsoft:iqn01.scp.com PS C:\> Set-InitiatorPort -NodeAddress $address.NodeAddress -NewNodeAddress "iqn.1991-05.com.microsoft:iqn01" PS C:\> Get-InitiatorPort | select NodeAddress NodeAddress ----------- iqn.1991-05.com.microsoft:iqn01PS C:\> $address = (Get-InitiatorPort | select NodeAddress) PS C:\> echo $address NodeAddress ----------- iqn.1991-05.com.microsoft:iqn01.scp.com PS C:\> Set-InitiatorPort -NodeAddress $address.NodeAddress -NewNodeAddress "iqn.1991-05.com.microsoft:iqn01" PS C:\> Get-InitiatorPort | select NodeAddress NodeAddress ----------- iqn.1991-05.com.microsoft:iqn01Code block. Modify Initiator Port Address
- iqn is generated based on the hostname, but when joined to Active Directory, it is changed to DNS format.
- Set the Storage (target Portal) address as a variable.Color mode
PS C:\> $TargetPortalAddresses = @("10.40.40.41", "10.40.40.42")PS C:\> $TargetPortalAddresses = @("10.40.40.41", "10.40.40.42")Code block. Set the Storage (target Portal) address as a variable. - Discover Storage (target Portal).Color mode
PS C:\> Foreach ($TargetPortalAddress in $TargetPortalAddresses){ New-IscsiTargetPortal -TargetPortalAddress $TargetPortalAddress } InitiatorInstanceName : InitiatorPortalAddress : IsDataDigest : False IsHeaderDigest : False TargetPortalAddress : 10.40.40.41 TargetPortalPortNumber : 3260 PSComputerName : InitiatorInstanceName : InitiatorPortalAddress : IsDataDigest : False IsHeaderDigest : False TargetPortalAddress : 10.40.40.42 TargetPortalPortNumber : 3260 PSComputerName :PS C:\> Foreach ($TargetPortalAddress in $TargetPortalAddresses){ New-IscsiTargetPortal -TargetPortalAddress $TargetPortalAddress } InitiatorInstanceName : InitiatorPortalAddress : IsDataDigest : False IsHeaderDigest : False TargetPortalAddress : 10.40.40.41 TargetPortalPortNumber : 3260 PSComputerName : InitiatorInstanceName : InitiatorPortalAddress : IsDataDigest : False IsHeaderDigest : False TargetPortalAddress : 10.40.40.42 TargetPortalPortNumber : 3260 PSComputerName :code block. Storage (target Portal) Discovery - Connect the disk (target).Color mode
PS C:\> Foreach ($TargetPortalAddress in $TargetPortalAddresses){ Get-IscsiTarget | Connect-IscsiTarget -IsMultipathEnabled $true -IsPersistent $true -TargetPortalAddress $TargetPortalAddress } AuthenticationType : NONE InitiatorInstanceName : ROOT\ISCSIPRT\0000_0 InitiatorNodeAddress : iqn.1991-05.com.microsoft:iqn01 InitiatorPortalAddress : 0.0.0.0 InitiatorSideIdentifier : 400001370000 IsConnected : True IsDataDigest : False IsDiscovered : True IsHeaderDigest : False IsPersistent : True NumberOfConnections : 1 SessionIdentifier : ffffcd0b7ba58010-4000013700000006 TargetNodeAddress : iqn.1992-08.com.netapp:sn.f807925eeae311ec9270d039ea38b250:vs.3 TargetSideIdentifier : 1100 PSComputerName : AuthenticationType : NONE InitiatorInstanceName : ROOT\ISCSIPRT\0000_0 InitiatorNodeAddress : iqn.1991-05.com.microsoft:iqn01 InitiatorPortalAddress : 0.0.0.0 InitiatorSideIdentifier : 400001370002 IsConnected : True IsDataDigest : False IsDiscovered : True IsHeaderDigest : False IsPersistent : True NumberOfConnections : 1 SessionIdentifier : ffffcd0b7ba58010-4000013700000007 TargetNodeAddress : iqn.1992-08.com.netapp:sn.f807925eeae311ec9270d039ea38b250:vs.3 TargetSideIdentifier : 1000 PSComputerName :IsHeaderDigest : False TargetPortalAddress : 10.40.40.42 TargetPortalPortNumber : 3260 PSComputerName :PS C:\> Foreach ($TargetPortalAddress in $TargetPortalAddresses){ Get-IscsiTarget | Connect-IscsiTarget -IsMultipathEnabled $true -IsPersistent $true -TargetPortalAddress $TargetPortalAddress } AuthenticationType : NONE InitiatorInstanceName : ROOT\ISCSIPRT\0000_0 InitiatorNodeAddress : iqn.1991-05.com.microsoft:iqn01 InitiatorPortalAddress : 0.0.0.0 InitiatorSideIdentifier : 400001370000 IsConnected : True IsDataDigest : False IsDiscovered : True IsHeaderDigest : False IsPersistent : True NumberOfConnections : 1 SessionIdentifier : ffffcd0b7ba58010-4000013700000006 TargetNodeAddress : iqn.1992-08.com.netapp:sn.f807925eeae311ec9270d039ea38b250:vs.3 TargetSideIdentifier : 1100 PSComputerName : AuthenticationType : NONE InitiatorInstanceName : ROOT\ISCSIPRT\0000_0 InitiatorNodeAddress : iqn.1991-05.com.microsoft:iqn01 InitiatorPortalAddress : 0.0.0.0 InitiatorSideIdentifier : 400001370002 IsConnected : True IsDataDigest : False IsDiscovered : True IsHeaderDigest : False IsPersistent : True NumberOfConnections : 1 SessionIdentifier : ffffcd0b7ba58010-4000013700000007 TargetNodeAddress : iqn.1992-08.com.netapp:sn.f807925eeae311ec9270d039ea38b250:vs.3 TargetSideIdentifier : 1000 PSComputerName :IsHeaderDigest : False TargetPortalAddress : 10.40.40.42 TargetPortalPortNumber : 3260 PSComputerName :code block. Disk (target) connection - Refresh the storage (target) information.Color mode
PS C:\> Update-IscsiTargetPS C:\> Update-IscsiTargetCode block. Storage (target) information Refresh - Register the Multipath I/O DSM and create an MPIO Disk.
When creating an MPIO disk, a prompt appears if a reboot is required. Press Y or the Enter key to reboot.Color modePS C:\> New-MSDSMSupportedHW -VendorId MSFT2005 -ProductId iSCSIBusType_0x9 PS C:\> Update-MPIOClaimedHW Confirm Are you sure you want to perform this action? The operation may require a system restart. [Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "Y"): FalsePS C:\> New-MSDSMSupportedHW -VendorId MSFT2005 -ProductId iSCSIBusType_0x9 PS C:\> Update-MPIOClaimedHW Confirm Are you sure you want to perform this action? The operation may require a system restart. [Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "Y"): Falsecode block. Multipath I/O DSM registration, MPIO Disk creation - Check the list and path of Multipath I/O disks.
You can check MPIO disk information using the mpclaim.exe command. Enter the generated MPIO disk number to view the disk path and status.Color modePS C:\> mpclaim.exe -s -d For more information about a particular disk, use 'mpclaim -s -d #' where # is the MPIO disk number. MPIO Disk System Disk LB Policy DSM Name ------------------------------------------------------------------------------- MPIO Disk3 Disk 1 RR Microsoft DSM PS C:\> mpclaim.exe -s -d 3 MPIO Disk3: 02 Paths, Round Robin, Symmetric Access Controlling DSM: Microsoft DSM SN: 600A098038314853475D543544614131 Supported Load Balance Policies: FOO RR RRWS LQD WP LB Path ID State SCSI Address Weight --------------------------------------------------------------------------- 0000000077040001 Active/Optimized 004|000|001|000 0 TPG_State : Active/Optimized , TPG_Id: 1000, : 25 0000000077040000 Active/Optimized 004|000|000|000 0 TPG_State : Active/Optimized , TPG_Id: 1001, : 26PS C:\> mpclaim.exe -s -d For more information about a particular disk, use 'mpclaim -s -d #' where # is the MPIO disk number. MPIO Disk System Disk LB Policy DSM Name ------------------------------------------------------------------------------- MPIO Disk3 Disk 1 RR Microsoft DSM PS C:\> mpclaim.exe -s -d 3 MPIO Disk3: 02 Paths, Round Robin, Symmetric Access Controlling DSM: Microsoft DSM SN: 600A098038314853475D543544614131 Supported Load Balance Policies: FOO RR RRWS LQD WP LB Path ID State SCSI Address Weight --------------------------------------------------------------------------- 0000000077040001 Active/Optimized 004|000|001|000 0 TPG_State : Active/Optimized , TPG_Id: 1000, : 25 0000000077040000 Active/Optimized 004|000|000|000 0 TPG_State : Active/Optimized , TPG_Id: 1001, : 26Code block. Check Multipath I/O Disk list and path - Check in Disk Management.
- Open Command Prompt (Admin) and run powershell.
View detailed information of Block Storage (BM)
Block Storage(BM) service allows you to view and edit the full resource list and detailed information. Block Storage(BM) Details page consists of Details, Snapshot List, Replication, Operation History tabs.
To view detailed information about the Block Storage(BM) service, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to view detailed information. You will be taken to the Block Storage(BM) Details page.
- Block Storage(BM) Details page displays status information and additional feature information, and consists of Details, Snapshot List, Replication, Tags, Operation History tabs.
Category Detailed description Volume status Volume status - Creating: In progress
- Available: Creation completed, server connection possible
- Attaching: Connecting to server
- Detaching: Disconnecting from server
- In Use: Server connection established
- Deleting: Service termination in progress
- Editing: Changing settings
- Error Deleting: Abnormal state while deleting
- Error: Abnormal state while creating
Clone creation Create a replica in a different location - For more information on creating a replica, see Creating a Replica
Create snapshot Create a snapshot at a specific point in time - For detailed information on creating snapshots, refer to Creating a Snapshot
Service termination Cancel service button Table. Status information and additional features
- Block Storage(BM) Details page displays status information and additional feature information, and consists of Details, Snapshot List, Replication, Tags, Operation History tabs.
Detailed information
Block Storage(BM) List page lets you view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation Date/Time | Service creation timestamp |
| Editor | User who modified the service |
| Modification date | Date and time the service was modified |
| Volume name | Volume Name
|
| Category | Distinguish original status regarding duplication |
| Storage volume name | Volume name within the storage device
|
| capacity | Volume size
|
| Max IOPS | The IOPS value set when creating the service
|
| Max Throughput | Throughput speed (MB/s) set when creating the service
|
| Disk type | Disk type |
| Encryption | Encryption status
|
| Volume Group | Name of the Volume Group the volume belongs to |
| iSCSI information | Storage Target IP information for server connection |
| Snapshot capacity | Snapshot storage capacity
|
| Snapshot schedule | Snapshot auto-creation interval
|
| Recovery copy | Snapshot name
|
| Connection server | Connected Bare Metal Server
|
Snapshot list
Block Storage(BM) List page lets you view the snapshot of the selected resource.
| Category | Detailed description |
|---|---|
| Snapshot usage | Total size of stored snapshots |
| Snapshot name | Snapshot name |
| capacity | Snapshot capacity |
| Creation Date/Time | Snapshot creation time |
| Additional features > More | Snapshot management button
|
| Delete | Select the snapshots to delete from the snapshot list and delete them all at once. |
- If the maximum number of snapshots or the snapshot space threshold (around 90%) is exceeded, older snapshots are deleted first.
- If the snapshot capacity usage is high (around 90%), replication may be stopped.
- Snapshots can be created up to a maximum of 1,023 (with up to 128 automatically created via schedule), and if the maximum number is exceeded, no further snapshots can be created.
- Snapshot recovery must be performed while all connected servers are disconnected (Umount, Disk Offline), and the restored volume can be used after it is reconnected (Mount, Disk Online).
- A recovery copy can only be created once, and it is a separate volume that incurs charges identical to the original.
- The snapshot creation date and time is based on Asia/Seoul (GMT +09:00).
- When using replication, snapmirror files cannot be deleted.
- When using a Volume Group, set the snapshot schedule on the Volume Group (BM) detail information screen. The created snapshots can be viewed in the Block Storage (BM) snapshot list.
Clone
Block Storage(BM) List page lets you view the replication information of the selected resource.
| Category | Detailed description |
|---|---|
| Replication Policy | User-configured replication policy
|
| Replication cycle | Replication interval of the source set by the user
|
| Replication status | Replication progress status according to policy settings |
| Lag Time | Time elapsed since the last successful replication
|
| Volume information | Volume information for original and replica
|
- When a replica is created, a copy with the same disk type is generated.
- Replication can be created after configuring the snapshot size.
- If you are using a Volume Group, check the replication information on the Volume Group(BM) list page.
- A replica can modify the connected server when the replication policy is stopped or deleted.
- A replica can use the snapshot feature after the replication policy is deleted.
- If the replication policy is stopped or the replication status is completed, you can modify the policy and schedule in the replica.
tag
On the Block Storage(BM) List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
Block Storage(BM) List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Block Storage(BM) Managing Resources
If you need to modify the settings of a created Block Storage (BM) or add or remove connected servers, you can perform the tasks on the Block Storage(BM) Details page.
Edit volume name
You can modify the name of a volume. To rename a volume, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource whose volume name you want to edit. You will be taken to the Block Storage(BM) Details page.
- Click the Edit button for Volume name. The Edit Volume Name popup opens.
- Enter the volume name and click the Confirm button.
-) within 3 to 28 characters.Increase capacity
You can increase the volume size. To increase the size, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to expand its capacity. You will be taken to the Block Storage(BM) Details page.
- Click the capacity edit button. The Capacity Edit popup opens.
- After adding the capacity you want to expand (1/~16,384 GB) to the current capacity and entering the total, click the Confirm button.
- Capacity can be expanded only for the original volume that does not use the snapshot feature.
- Size reduction is not provided.
Modify Snapshot Size
You can modify the capacity of the snapshot storage. To modify the snapshot capacity, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- Block Storage(BM) List page: click the resource to modify the snapshot capacity. You will be taken to the Block Storage(BM) Details page.
- Click the Edit button of the Snapshot Capacity item. The Snapshot Capacity Edit popup window opens.
- Set the Use status and generation capacity (%), then click the Confirm button.
- Generation Capacity(%) can be selected in increments of 50 between 100 and ~500.
- Charges vary depending on snapshot usage and size. (Example: with a volume size of 10 GB and snapshot creation size of 100%, a total of 20 GB is billed.)
- If the maximum number of snapshots or the snapshot space threshold (around 90%) is exceeded, older snapshots are deleted first.
- If the size after modification is smaller than the original, older snapshots will be deleted first.
- When changed to unused, all snapshots will be deleted.
- Replication can be created after setting the snapshot capacity.
- After configuring the snapshot size, it can be added to the Volume Group.
- If the snapshot capacity usage is high (around 90%), replication may be stopped.
- Replicas can use the snapshot feature after the replication policy has been deleted.
Edit Snapshot Schedule
You can modify the automatic snapshot creation interval. To modify the snapshot schedule, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to edit the snapshot schedule. You will be taken to the Block Storage(BM) Details page.
- Click the Edit button for the Snapshot Schedule item. The Snapshot Schedule Edit popup opens.
- Set the snapshot auto creation status and creation interval, then click the Confirm button.
- If you want to automatically create snapshots based on the creation cycle, select automatic creation as enabled.
- Select the generation cycle as daily, hourly, or as weekly, day of week, hourly.
- The snapshot schedule is based on Asia/Seoul (GMT +09:00).
- You can register a schedule after configuring the snapshot capacity.
- You cannot add it to a Volume Group when configuring a snapshot schedule.
Edit Max IOPS
You can modify the Max IOPS value. To modify the Max IOPS value, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- Block Storage(BM) List page, click the resource whose IOPS value you want to modify. You will be taken to the Block Storage(BM) Details page.
- Click the Edit button of Max IOPS. The Max IOPS Edit popup opens.
- After entering the Max IOPS value to change, click the Confirm button.
- The Max IOPS value can be set to a value between 5,000 and 20,000.
- The Max IOPS value can be modified after the server is initially attached.
- For a recovery copy, the Max IOPS value cannot be modified.
Edit Max Throughput
You can modify the Max Throughput speed. To modify the Max Throughput speed, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- From the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- Block Storage(BM) List on the page, click the resource to modify the Throughput speed. You will be taken to the Block Storage(BM) Details page.
- Click the Edit button of Max Throughput. The Max Throughput Edit popup opens.
- After entering the Max Throughput speed to change, click the Confirm button.
- The Max Throughput speed can be set to a value between 250 and 1,000.
- The Max Throughput speed can be modified after the initial server attach.
- For recovery copies, the Max Throughput speed cannot be adjusted.
Edit Connection Server
You can connect or disconnect the Bare Metal Server, Multi Node GPU Cluster. To modify the connected server, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to edit the connected server. You will be taken to the Block Storage(BM) Details page.
- When adding a connection server, click the Add button in the Connection Server item. The Add Connection Server popup opens.
- After selecting the server you want to connect to, click the Confirm button.
- If you need to disconnect the server, click the Disconnect button in the Connection Server field.
- Be sure to log into the server, perform the disconnect operations (Umount, Disk Offline), and then disconnect.
- Connect to the server and be sure to perform the disconnect operations (Umount, Disk Offline) before detaching the connected server. Detaching without OS operations may cause a status error (Hang) on the connected server. For detailed information on detaching the server, refer to Detaching the Server.
- You can connect up to eight Bare Metal Servers created in the same location as the Block Storage.
- There is no limit on the number of volume connections for a Bare Metal Server.
- When adding a connected server, you can use it after performing the connection tasks (Mount, Disk Online) on the server. For detailed information about server connections, refer to Server Connection Guide.
- Connect to the server and be sure to perform the disconnect operations (Umount, Disk Offline) before detaching the connected server. Detaching without OS operations may cause a status error (Hang) on the connected server. For detailed information on detaching the server, refer to Detach Server.
- A replica can modify the connected server when the replication policy is stopped or deleted.
Cancel Block Storage(BM)
You can reduce operating costs by terminating unused Block Storage(BM). However, terminating the service may cause the running service to stop immediately, so you should carefully consider the impact of service interruption before proceeding with the termination.
- Please note that data cannot be recovered after termination.
- If a connected server exists, you can terminate it after removing all associated resources.
- You can only delete the volume when it is in the Available or Error state.
- If a replication policy is in use, you can cancel it after removing the policy from the associated replica.
- If a Volume Group is being used, you can cancel after disconnecting the associated Volume Group.
- If a recovery copy of the original exists, you can delete the recovery copy before terminating.
To cancel Block Storage, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. Navigate to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, select the resource to terminate and click the Terminate Service button.
- After termination is complete, verify on the Block Storage(BM) List page that the resource has been terminated.
3.1.2.1 - Connect to Server
When using a volume on the server, a connect or disconnect operation is required.
On the Block Storage(BM) Details page, after adding a connected server, log in to the server to configure Multi Path and perform connection tasks (Mount, Disk Online). After use, perform disconnection tasks (Umount, Disk Offline) and remove the connected server.
Configure Multi Path
Before using the volume on the connected server, Multi Path configuration is required. Follow the steps below.
Linux operating system
Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
On the Block Storage(BM) List page, click the resource to configure Multi Path. You will be taken to the Block Storage(BM) Details page.
In the Connection Server item, verify the server and then connect. Configure Multi Path according to the guide below.
Device Check
- The created volume can be verified with the
fdisk -lcommand.
- The created volume can be verified with the
Verify DM-Multipath configuration
- In the volume detection process, the Linux system automatically applies Multi Path, which can be verified with the
multipath –llcommand. - Volumes with Multi Path applied use Multipath device names such as
/dev/mapper/#####instead of the/dev/sd#format, and can be verified with thefdisk –lcommand.
- In the volume detection process, the Linux system automatically applies Multi Path, which can be verified with the
iSCSI replacement timeout value setting
- When connecting iSCSI, set the
replacement timeout.
# vi /etc/iscsi/iscsid.conf node.session.timeo.replacement_timeout = 5 (default 120 값을 5 로 변경)- After modifying the above, restart the iscsi service.
# systemctl restart iscsid- When connecting iSCSI, set the
Windows operating system
Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
On the Block Storage(BM) List page, click the resource to set Multi Path. You will be taken to the Block Storage(BM) Details page.
In the Connection Server item, verify the server and then connect. Configure Multi Path according to the guide below.
Device Check
- Click the Start > Server Manager menu to launch Server Manager.
- When you click the Server Manager > File and Storage Services > Volumes > Disks menu, you can view the iscsi device.
- Since Multi-Path is not yet configured, a single device appears as multiple devices for each path.
Install MPIO (Reboot required)
Click Server Manager > DashBoard > Add roles and features.
Add Roles and Features Wizard When the popup window opens, click the Next button.
On the Select installation type page, select Role-based or feature-based installation, and click the Next button.
Select destination server(Server selection) On the page, the current server is automatically detected. Verify the information and click the Next button.
Select features(Feature selection) page, select Features from the left menu, check Multipath I/O, then click the Next button.
Confirm installation selections(Confirm installation selections) on the page, after checking Restart the destination server automatically if required, when the popup appears, click Yes and click the Install button.
The installation starts and automatically reboots.
When reconnecting to the server, the installation is already complete. Click the close button to close the wizard popup window.
Click Server Manager > DashBoard > tools > MPIO.
In the Discover Multi-Paths tab, check Add support for iSCSI devices and click the Add button.
- If the message appears, reboot the server.
After the reboot, you can check NETAPP Devices in MPIO devices.
In the Windows Run dialog (Command Prompt), run diskmgmt.msc to open the Disk management popup window.
- You can confirm that MPIO is applied by checking the properties of the volume created in the Block Storage (BM) service.
- You can confirm that MPIO is applied by checking the properties of the volume created in the Block Storage (BM) service.
Connect to Server (Mount, Disk Online)
To use the volume added to the connected server, you must log into the server and perform the connection tasks (Mount, Disk Online). Follow the steps below.
Linux operating system
- Server OS: LINUX
- Mount location: /data
- Volume size: 24 GB
- File system: ext3, ext4, xfs etc
- Additional allocated disk: /dev/vdb
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to which you want to connect the server. You will be taken to the Block Storage(BM) Details page.
- Connected Server item, check the server and then connect. Mount the volume according to the guide below.
- Switch to root privilegesColor mode
$ sudo -i$ sudo -iCode block. Switch to root privileges - Check DiskColor mode
# lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk# lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 diskCode block. Check disk - Create partitionColor mode
# fdisk /dev/vdb Command (m for help): n Partition type: p primary (0 primary, 0 extended, 4 free) e extended Select (default p): p Partition number (1-4, default 1): 1 First sector (2048-50331646, default 2048): Last sector, +/-sectors or +/-size{K,M,G,T,P} (2048-50331646, default 50331646): Created a new partition 1 of type 'Linux' and of size 24 GiB. Command (m for help): w The partition table has been altered! Calling ioctl() to re-read partition table. Syncing disks.# fdisk /dev/vdb Command (m for help): n Partition type: p primary (0 primary, 0 extended, 4 free) e extended Select (default p): p Partition number (1-4, default 1): 1 First sector (2048-50331646, default 2048): Last sector, +/-sectors or +/-size{K,M,G,T,P} (2048-50331646, default 50331646): Created a new partition 1 of type 'Linux' and of size 24 GiB. Command (m for help): w The partition table has been altered! Calling ioctl() to re-read partition table. Syncing disks.Code block. Create partition - Partition format setting (example: ext4)Color mode
# lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part # mkfs.ext4 /dev/vdb1 mke2fs 1.46.5 (30-Dec-2021) Writing superblocks and filesystem accounting information: done# lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part # mkfs.ext4 /dev/vdb1 mke2fs 1.46.5 (30-Dec-2021) Writing superblocks and filesystem accounting information: doneCode block. Partition format setting - Volume MountColor mode
# mkdir /data # mount /dev/vdb1 /data # lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part /data # vi /etc/fstab (add) /dev/vdb1 /data ext4 defaults 0 0# mkdir /data # mount /dev/vdb1 /data # lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part /data # vi /etc/fstab (add) /dev/vdb1 /data ext4 defaults 0 0Code block. Volume mount Item Explanation cat /etc/fstab This is the filesystem information file for the Linux system. It is used when the server starts. df -h Check the total disk usage mounted on a Linux system. fdisk -l Check partition information. - Physical disks are displayed as
/dev/sda,/dev/sdb,/dev/sdcwith letters such asa,b,c
- Disk partitions are displayed as
/dev/sda1,/dev/sda2,/dev/sda3with numbers such as1,2,3
Table. Refer to the Mount commandcommand Explanation m Check the usage of the fdisk command. n Create a new partition. p Verify the updated partition information. t Change the system ID of the partition. w Save the partition information and exit the fdisk configuration. Table. Refer to the partition creation command (fdisk). - Physical disks are displayed as
- Switch to root privileges
Windows operating system
Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
On the Block Storage(BM) List page, click the resource to connect the server. You will be taken to the Block Storage(BM) Details page.
From the Connected Server item, verify the server and then connect. Follow the guide below to attach the volume (Disk Online).
- Right-click the Windows Start icon and run Computer Management.
- In the Computer Management tree structure, select Storage > Disk Management.
- Check Disk
- Disk Online
- Disk initialization
- Partition format
- Check volume
Disconnect Server (Umount, Disk Offline)
Connect to the server and perform the disconnect operations (Umount, Disk Offline), then you must disconnect the server from the Console. Follow the steps below.
Linux operating system
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to detach the server connection. You will be taken to the Block Storage(BM) Details page.
- After checking the server in the Connected Server item, connect. Follow the guide below to unmount the volume (Umount).
- Volume UmountColor mode
# umount /dev/vdb1 /data # lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part # vi /etc/fstab (delete) /dev/vdb1 /data ext4 defaults 0 0# umount /dev/vdb1 /data # lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT vda 252:0 0 24G 0 disk ├─vda1 252:1 0 23.9G 0 part [SWAP] └─vda14 252:14 0 4M 0 part / └─vda15 252:15 0 106M 0 part /boot/efi vdb 252:16 0 24G 0 disk └─vdb1 252:17 0 24G 0 part # vi /etc/fstab (delete) /dev/vdb1 /data ext4 defaults 0 0code block. volume Umount
- Volume Umount
Windows operating system
Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
On the Service Home page, click the Block Storage(BM) menu. Navigate to the Block Storage(BM) List page.
On the Block Storage(BM) List page, click the resource to detach the server connection. You will be taken to the Block Storage(BM) Details page.
In the Connected Server item, verify the server before connecting. Follow the guide below to detach the volume (Disk Offline).
- Windows Start icon right-click, then run Computer Management
- In the Computer Management tree structure, select Storage > Disk Management
- Right-click the disk to be removed, then run Offline.
- Check disk status
3.1.2.2 - Use Snapshot
You can create, delete, or recover a snapshot of a created Block Storage (BM). You can perform these actions on the Block Storage (BM) Details page and the Snapshot List page.
Create Snapshot
Users can create a snapshot at the desired point in time.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- Click the resource to create a snapshot on the Block Storage(BM) List page. Navigate to the Block Storage(BM) Details page.
- Check the setting status of the Snapshot Capacity item.
- Snapshots can be created only when storage space has been secured by configuring snapshot capacity.
- For detailed information, refer to Modify Snapshot Capacity.
- Click the Create Snapshot button. The Create Snapshot popup opens.
- Click the Create button. It creates a snapshot of the current point in time.
- Click the Snapshot List page. You will be taken to the Block Storage(BM) Snapshot list page.
- Check the generated snapshot.
- If the maximum number of snapshots or the snapshot space threshold (around 90%) is exceeded, older snapshots are deleted first.
- If the usage rate within the snapshot capacity is high (around 90%), replication may be stopped.
- If there is a volume in the Volume Group with snapshot capacity not set, you cannot create a snapshot. Set the snapshot capacity for all volumes first.
- Snapshots can be created up to a maximum of 1,023 (with up to 128 automatically generated via schedule), and if the maximum number is exceeded, no further snapshots can be created.
- The snapshot creation time is based on Asia/Seoul (GMT +09:00).
- If you want to automatically create snapshots using a schedule, set the snapshot schedule on the Block Storage(BM) Details page.
- For detailed information about the snapshot schedule, refer to Modify Snapshot Schedule.
- Capacity can be expanded only for the original volume that does not use the snapshot feature.
Recover Snapshot
Block Storage(BM) volumes can be restored from a snapshot. To restore a snapshot, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- Block Storage(BM) List Click the resource to restore from a snapshot. Block Storage(BM) Details page will be opened.
- If a server has been added in the Connected Server item, connect to the server and then perform the disconnect tasks (Umount, Disk Offline).
- For more details, refer to Disconnect Server.
- Click the Snapshot List page. Navigate to the Block Storage(BM) Snapshot List page.
- After checking the Snapshot name and Creation timestamp, click the More button of the snapshot you want to restore.
- Recover button, click it. The snapshot recovery popup opens.
- After verifying the snapshot name and creation time, click the Confirm button. Recover the Block Storage volume from the snapshot.
- Click the Details button. Navigate to the Block Storage(BM) Details page.
- Connection Server If a server has been added to this item, connect to the server and perform the connection tasks (Mount, Disk Online).
- For detailed information, refer to Connect to Server.
- Snapshot recovery must be performed while all connected servers are disconnected (Umount, Disk Offline), and the restored volume can be used after it is reconnected (Mount, Disk Online).
- After the snapshot recovery is completed, all snapshots created after the snapshot used for recovery are deleted.
- When restoring a snapshot, the volume is restored to that point in time.
- If you are using Volume Group(BM), you can perform snapshot recovery from the detail page of Volume Group(BM).
Create a recovery copy
You can create a recovery copy from a snapshot of a Block Storage (BM) volume. To create a snapshot recovery copy, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to restore from a snapshot. You will be taken to the Block Storage(BM) Details page.
- If a server has been added in the Connected Server item, connect to the server and then perform the disconnect tasks (Umount, Disk Offline).
- For more details, refer to Disconnect Server.
- Click the Snapshot List page. Go to the Block Storage(BM) Snapshot List page.
- After confirming the Snapshot name and Creation timestamp, click the More button of the snapshot you want to create a recovery copy for.
- Click the Create Recovery button. The snapshot recovery creation popup opens.
- After entering the Recovery volume name, click the Create button. A popup notifying the creation of the recovery image will appear.
- Click the Confirm button. The recovery copy creation request is complete.
- Only one recovery copy can be created per original.
- A recovery copy is a separate volume created with the same capacity as the original, and it incurs additional costs.
- If you are using Volume Group(BM), you can create a recovery copy on the detail page of Volume Group(BM).
Delete Snapshot
You can select a snapshot to delete. To delete a snapshot, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to delete the snapshot. You will be taken to the Block Storage(BM) Details page.
- Click Snapshot List. It navigates to the Block Storage(BM) Snapshot List page.
- After confirming the Snapshot name and creation time, click the More button of the snapshot you want to delete.
- Click the Delete button. The snapshot will be removed from the Snapshot List page.
- After selecting the snapshots to delete from the snapshot list, you can click the Delete button at the top of the list to delete them all at once.Reference
- Snapshots that contain snapmirror in the snapshot name cannot be deleted. snapmirror is included in the snapshot name when a replication is created.
- If you are using Volume Group(BM), you can delete snapshots from the detail page of Volume Group(BM).
- After selecting the snapshots to delete from the snapshot list, you can click the Delete button at the top of the list to delete them all at once.
3.1.2.3 - Use Replication
After creating a replica of the generated Block Storage(BM) in another location, you can synchronize it periodically. You can perform the tasks on the Block Storage(BM) Details page and the Replication page.
- The kr-south region does not provide Block Storage (BM) replication functionality.
Create Clone
You can create a replica volume in a different location.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource for which you want to create a replica. You will be taken to the Block Storage(BM) Details page.
- Check the setting status of the Snapshot Capacity item.
- Replication can be created only when storage space is available through snapshot capacity configuration.
- For detailed information, refer to Modify Snapshot Capacity.
- Click the Create Clone button. The Create Clone popup opens.
- Enter the Replication location, Replication volume name, and Replication schedule, then click the Create button. It creates a replica with the same disk type.
- Replication Location: Select a location different from the original Block Storage(BM) volume.
- Replication Volume Name: Start with an English letter and use English letters, numbers, and special characters (
-) to enter 3 to 28 characters. - Replication interval: Select from 5 minutes, 1 hour, daily, weekly, monthly. Replication will be performed using the interval below.
- Daily: every day 23:59:00
- Weekly: Every Sunday 23:59:00
- Monthly: 1st day of each month 23:59:00
- Click the Clone page.
You will be taken to the Clone page. - Check the replication information.
- When selecting the volume name of the source or replica, you are taken to the volume’s Block Storage(BM) Details page.
- When a replica is created, a copy with the same disk type is generated.
- After setting the snapshot size, you can create a replica, and the disk type of the created replica is the same as the original.
- If the snapshot capacity utilization is high (around 90%), replication may be stopped.
- After setting the snapshot capacity, volumes added to the Volume Group can be replicated at the group level on the Volume Group page.
- You can create one replica per volume, and data transfer charges apply for cross‑region replication.
- A volume created by cloning cannot be added to a Volume Group.
- If you are using a Volume Group, you can view replication information in the Volume Group (BM).
Edit replication policy
You can change the replication status by modifying the replication policy.
To modify the replication policy, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- On the Block Storage(BM) List page, click the resource to edit the replication policy. You will be taken to the Block Storage(BM) Details page.
- Click the Replication page. Go to the Block Storage(BM) Replication page.
- Click the Edit button of the Replication Policy. The Edit Replication Policy popup opens.
- Use: performs replication. If it is Paused, you can change it to Use.
- Pause: Temporarily stops replication. If use, you can modify to Pause.
- Delete: Delete the replica. If Paused, it can be changed to Delete, and after deletion, replication cannot be used again.
- Check the updated Replication Policy on the Block Storage(BM) Replication page.
- When deleting a policy, please note the following.
- After the policy is deleted, the replica will not be reverted to the original, and you cannot create a replica.
- After deleting the policy, you cannot connect to existing replicas, and you can only create new replicas.
- Data stored only in the replica after a pause will be deleted when replication is used again.
- When using a replication policy, replicas are in Read only state and cannot be modified. Unmount from all connected resources before using replication.
- You can mount on the connected server only when the replication policy is deleted or paused.
Edit replication cycle
You can change the synchronization interval between the original and the replica by modifying the replication interval.
To modify the replication interval, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Block Storage(BM) menu. You will be taken to the Block Storage(BM) List page.
- Click the resource to modify the replication interval on the Block Storage(BM) List page. You will be taken to the Block Storage(BM) Details page.
- Click the Replication page. Go to the Block Storage(BM) Replication page.
- Click the Edit button of Replication Cycle. Replication Cycle Edit popup opens.
- Replication interval: Select from 5 minutes, 1 hour, daily, weekly, monthly. Replication will be performed using the interval below.
- Daily: 23:59:00
- Weekly: Every Sunday 23:59:00
- Monthly: 1st day of each month 23:59:00
- Replication interval: Select from 5 minutes, 1 hour, daily, weekly, monthly. Replication will be performed using the interval below.
- Check the modified Replication Interval on the Block Storage(BM) Replication page.
3.1.2.4 - Use Volume Group
The Volume Group(BM) service allows you to configure up to 16 Block Storage(BM) volumes as a group, enabling the creation of consistent point-in-time snapshots and replications.
Users can create the service by entering the required information for the Volume Group (BM) and selecting detailed options through the Samsung Cloud Platform Console.
Create Volume Group (BM)
You can create and use a Volume Group (BM) service in the Samsung Cloud Platform Console.
To create a Block Storage, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- Click the Volume Group(BM) menu. Navigate to the Volume Group(BM) List page.
- On the Volume Group(BM) page, click the Volume Group(BM) Create button. You will be taken to the Volume Group(BM) Create page.
Category RequiredDetailed description Volume Group name Required Volume Group name - must start with an English letter and be 3 to 28 characters using English letters, numbers, and special characters (
-)
- cannot be modified after service creation
target volume Required Add target volume to Volume Group - After clicking the Add button, select the target volume in the add target popup
- Target volume criteria
- Snapshot size: Set
- Snapshot auto-creation, creation interval: Not used
- Replication: Not used
- Up to 16 can be added
Table. Volume Group (BM) Service Information Input Items - must start with an English letter and be 3 to 28 characters using English letters, numbers, and special characters (
- Click the Create button.
- When creation is complete, check the created resources on the Volume Group(BM) List page.
- When adding a target volume, you can add the corresponding volume to the Volume Group (BM).
- Snapshot capacity: Set
- Automatic snapshot creation, creation interval: unused
- Clone: Unused
- You can add up to 16 target volumes.
Check detailed information of Volume Group (BM)
Volume Group(BM) service allows you to view and edit the full resource list and detailed information. Volume Group(BM) Details page consists of Details, Snapshot List, Replication, Operation History tabs.
To view detailed information about the Volume Group(BM) service, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource to view detailed information. It navigates to the Volume Group(BM) Detail page.
- Volume Group(BM) Details page displays status information and additional feature information, and consists of Details, Snapshot List, Replication, Tags, Operation History tabs.
Category Detailed description Volume Group status Volume Group status - Creating: In progress
- Available: Creation complete, server connection possible
- Deleting: Service termination in progress
- Editing: Changing settings
- Error Deleting: Abnormal state during deletion
- Error: Abnormal state during creation
Clone creation Create a replica at another location - For details on creating a replica, see Create a replica
- Replication is not possible if the snapshot size is not set or a replication policy already exists
Create snapshot Create a snapshot at a specific point in time - For detailed information on snapshot creation, see Creating a Snapshot
Service termination Cancel service button Table. Status information and additional features
- Volume Group(BM) Details page displays status information and additional feature information, and consists of Details, Snapshot List, Replication, Tags, Operation History tabs.
Detailed information
Volume Group(BM) List page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource Name
|
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who modified the service |
| Modification date | Date and time the service was modified |
| Volume Group name | Volume Group name |
| Category | Distinguish original status related to duplication |
| Storage Volume Group name | Volume Group name within the storage device
|
| Snapshot schedule | Snapshot auto-creation interval
|
| Recovery copy | Snapshot name of the Volume Group
|
| target volume | Block Storage (BM) added to the Volume Group
|
Snapshot list
Volume Group(BM) resource list page allows you to view the snapshot of the selected resource.
| Category | Detailed description |
|---|---|
| Snapshot name | Snapshot name |
| Creation Date/Time | Snapshot creation time |
| Additional features > More | Snapshot management button
|
- When a snapshot is created in a Volume Group, the snapshot is created in Block Storage (BM).
- When using Volume Group snapshots, manage the snapshot capacity and count of the target volume.
- If the maximum number of snapshots or the snapshot space threshold (around 90%) is exceeded, older snapshots are deleted first.
- If the snapshot capacity usage is high (around 90%), replication may be stopped.
- Snapshots can be created up to a maximum of 1,023 (with up to 128 automatically generated through scheduling), and if the maximum number is exceeded, no additional snapshots can be created.
- Snapshot recovery must be performed while all connected servers are disconnected (Umount, Disk Offline), and the restored volume can be used after it is reconnected (Mount, Disk Online).
- The snapshot creation time is based on Asia/Seoul (GMT +09:00).
- When using replication, snapmirror files cannot be deleted.
- When using a Volume Group, set the snapshot schedule on the Volume Group (BM) detail information screen. The created snapshots can be viewed in the Block Storage (BM) snapshot list.
Clone
Volume Group(BM) Resource List page allows you to view the replication information of the selected resource.
| Category | Detailed description |
|---|---|
| Replication Policy | User-configured replication policy
|
| Replication cycle | Replication interval of the source set by the user
|
| Replication status | Replication progress status according to policy settings |
| Lag Time | Time elapsed since the last successful replication
|
| Volume information | Volume information for the source and replica
|
- If the snapshot capacity usage is high (around 90%), replication may be stopped.
- When a clone is created, a replica with the same disk type is generated.
- Replication can be created after setting the snapshot capacity.
- If you are using a Volume Group, view the replication information on the Volume Group (BM) resource list page.
- Replica Block Storage can modify the attached server when the replication policy is paused or deleted.
- Replica Block Storage can use the snapshot feature after the replication policy is deleted.
- If the replication policy is stopped or the replication status is completed, you can modify the policy and schedule on the replica.
Tag
Volume Group(BM) List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
Volume Group(BM) Resource List You can view the operation history of the selected resource on this page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Volume Group(BM) Managing Resources
If you need to modify the settings of a created Volume Group (BM) or add or remove target volumes, you can perform the operation on the Volume Group(BM) Details page.
Edit Snapshot Schedule
You can modify the automatic snapshot creation interval. To modify the snapshot schedule, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. Navigate to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource to modify the snapshot schedule. You will be taken to the Volume Group(BM) Details page.
- Click the Edit button for the Snapshot Schedule item. The Snapshot Schedule Edit popup opens.
- Set the snapshot auto creation status and creation interval, then click the Confirm button.
- If you want to automatically create snapshots based on the Creation Cycle, select Automatic Creation as Enabled.
- Generation cycle can be selected daily, hourly, or weekly, day of week, hourly. Please select.
When using Volume Group snapshots, manage the snapshot capacity and count of the target volume.
- Snapshots can be created up to a maximum of 1,023 (with up to 128 automatically generated through scheduling), and if the maximum number is exceeded, no additional snapshots can be created.
Edit target volume
You can add or detach the target volume. To modify the target volume, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource to edit the target volume. You will be taken to the Volume Group(BM) Details page.
- If you are adding a target volume, click the Add button of the Target Volume item. The Add Volume popup window opens.
- When disconnecting a volume, click the Disconnect button in the Target Volume item.
- After selecting the volume you want to add, click the Confirm button.
- When adding a target volume, you can add the corresponding volume to the Volume Group (BM).
- Snapshot capacity: setting
- Automatic snapshot creation, creation interval: unused
- Clone: Unused
- You can add up to 16 target volumes.
Using Volume Group (BM) Snapshots
You can create, delete, or recover using snapshots for the created Volume Group (BM). You can perform these actions on the Volume Group (BM) Details page and the Snapshot List page.
Creating a Snapshot
Users can create a snapshot at the desired point in time.
- A replica can delete the replication policy, set the snapshot size for all block storage within the volume group, and then create a snapshot.
- Recovery images cannot create snapshots.
To create a snapshot, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- From the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource to create a snapshot. You will be taken to the Volume Group(BM) Details page.
- Click the Create Snapshot button. The Create Snapshot popup window opens.
- Click the Confirm button. Generates a snapshot of the current point in time.
- Click the Snapshot List page. Navigate to the Volume Group(BM) Snapshot list page.
- Check the generated snapshot.
- When creating a snapshot in a Volume Group, a snapshot is also created on the connected target volume.
- Manage the snapshot capacity and number of snapshots for the target volume to use Volume Group snapshots.
- If the maximum number of snapshots or the snapshot space threshold (around 90%) is exceeded, older snapshots are deleted first.
- If the snapshot capacity usage is high (around 90%), replication may be stopped.
- Snapshots can be created up to a maximum of 1,023 (with up to 128 automatically generated via schedule), and if the maximum number is exceeded, no further snapshots can be created.
- The snapshot creation time is based on Asia/Seoul (GMT +09:00).
- The snapshot storage space is applied based on the settings you configured on the target volume’s Block Storage(BM) Details page.
- If you want to automatically create snapshots using a schedule, set the snapshot schedule on the Volume Group(BM) Details page.
- For detailed information about snapshot schedules, see Update Snapshot Schedule.
Recover Snapshot
You can restore all target volumes of the Volume Group(BM) from a snapshot. To restore from a snapshot, follow the steps below.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. Navigate to the Volume Group(BM) List page.
- Volume Group(BM) List On the page, click the resource to restore from a snapshot. Volume Group(BM) Details You will be taken to the page.
- Click the volume name of the volume added to the Target volume to go to the Block Storage(BM) Details page.
- If a server has been added in the Connected Server item, connect to the server and then perform the disconnect operations (Umount, Disk Offline).
- For more details, see Disconnect Server.
- On the Volume Group(BM) Details page, click the Snapshot List page. You will be taken to the Volume Group(BM) Snapshot List page.
- After checking the Snapshot name and Creation time, click the More button of the snapshot you want to restore.
- Click the Recover button. The snapshot recovery popup will open.
- After verifying the Snapshot name and Creation time, click the Confirm button. The target volumes will be restored from the snapshot.
- Click the Detailed Information button. It navigates to the Volume Group(BM) Detailed page.
- Click the volume name of the volume added to the Target volume. It will navigate to the Block Storage (BM) Details page.
- If there is a server added in the Connection Server item, after connecting to the server, perform the connection tasks (Mount, Disk Online).
- For detailed information, refer to Connect to Server.
- Snapshot recovery must be performed when all target volumes on the connected server are unmounted (Umount, Disk Offline), and the recovered volume can be used after being remounted (Mount, Disk Online).
- After the snapshot recovery is completed, all snapshots created after the snapshot used for recovery will be deleted.
Create a backup
You can create a recovery copy from a snapshot of the target volume. To create a snapshot recovery copy, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource for which you want to create a recovery copy. You will be taken to the Volume Group(BM) Details page.
- From the Volume Group(BM) Details page, click the Snapshot List page. You will be taken to the Volume Group(BM) Snapshot List page.
- After checking the snapshot name and creation timestamp, click the More button of the snapshot for which you want to create a recovery copy.
- Click the Create Recovery button. The snapshot recovery creation popup opens.
- After entering Prefix, click the Confirm button. A popup indicating that a backup is being created will open.
- The recovery copy’s name is created as the entered Prefix value + original Block Storage name.
- Click the Create button. The backup creation request has been completed.
- Only one recovery copy can be created per original.
- A recovery copy is a separate volume created with the same capacity as the original, and it incurs additional costs.
Delete snapshot
You can select a snapshot to delete. To delete a snapshot, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource to delete the snapshot. You will be taken to the Volume Group(BM) Details page.
- Click Snapshot List. Navigate to the Volume Group (BM) Snapshot List page.
- After confirming the Snapshot name and creation time, click the More button of the snapshot you want to delete.
- Click the Delete button. The snapshot will be removed from the Snapshot List page.
Using replication for Volume Group (BM)
The created Volume Group (BM) can be synchronized at regular, consistent points after creating a replica at another location. You can perform tasks on the Volume Group(BM) Details page and the Replication page.
Create a Clone
You can create a replicated Volume Group and volume at a different location.
To create a copy, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource for which you want to create a replica. You will be taken to the Volume Group(BM) Details page.
- Click the Create Clone button. The Create Clone popup opens.
- Enter Replication Location, Replication Volume Group, Replication Block Storage Name Prefix, and Replication Interval, then click the Create button. It creates a replica Block Storage volume with the same Volume Group and disk type as the source.
- Replication Location: Select a location different from the original Volume Group (BM).
- Clone Volume Group name: Start with an English letter and use English letters, numbers, and special characters (
-) to enter 3~28 characters. - Replication Block Storage Name Prefix: Start with an English letter and use English letters, numbers, and special characters (
-) to enter 3 to 28 characters.- A replica Block Storage (BM) is created with a volume name of ‘Replica Block Storage name Prefix + original Block Storage volume name’.
- Replication interval: Select from 5 minutes, 1 hour, daily, weekly, or monthly. Replication will be performed at the selected interval.
- Daily: daily 23:59:00
- Weekly: Every Sunday 23:59:00
- Monthly: 1st of each month 23:59:00
- Click the Clone page. You will be taken to the Clone page.
- Check the replication information.
- When selecting the Volume Group name of the original or replica, you will be taken to the Volume Group(BM) Details page.
- When creating a replica in a Volume Group, a replica Volume Group and Block Storage (BM) are created.
- The replica Block Storage has the same disk type as the original.
- You can create one replica per Volume Group, and data transfer charges apply for cross‑region replication.
Edit replication policy
You can change the replication status by modifying the replication policy.
To modify the replication policy, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Go to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource you want to modify the replication policy for. You will be taken to the Volume Group(BM) Details page.
- Click the Clone page. Navigate to the Volume Group(BM) Clone page.
- Click the Edit button of the Replication Policy. The Edit Replication Policy popup opens.
- Enabled: performs replication. If Paused, you can modify it to Enabled.
- Pause: Temporarily stops replication. If Use, it can be changed to Pause.
- Delete: Delete the replica. Paused can be changed to Delete, and after deletion you cannot use replication again.
- Check the modified Replication Policy on the Volume Group(BM) Replication page.
- When deleting a policy, please note the following.
- After the policy is deleted, the replica does not revert to the original, and you cannot create a replica.
- After deleting the policy, you cannot connect to existing replicas, and you can only create new replicas.
- After a pause, data stored only in the replica will be deleted when replication is used again.
- When using a replication policy, replicas are in Read only state and cannot be modified. Unmount from all connected resources before using replication.
Edit replication interval
You can change the synchronization interval between the original and the replica by modifying the replication interval.
To modify the replication interval, follow these steps.
- Click the All Services > Storage > Block Storage(BM) menu. Navigate to the Service Home page of Block Storage(BM).
- On the Service Home page, click the Volume Group(BM) menu. You will be taken to the Volume Group(BM) List page.
- On the Volume Group(BM) List page, click the resource whose replication schedule you want to modify. You will be taken to the Volume Group(BM) Details page.
- Click the Clone page. Navigate to the Volume Group (BM) Clone page.
- Click the Edit button of Replication Cycle. The Edit Replication Cycle popup opens.
- Replication interval: Select from 5 minutes, 1 hour, daily, weekly, or monthly. Replication will be performed at the selected interval.
- Daily: 23:59:00
- Weekly: Every Sunday 23:59:00
- Monthly: 1st day of each month 23:59:00
- Replication interval: Select from 5 minutes, 1 hour, daily, weekly, or monthly. Replication will be performed at the selected interval.
- Check the modified replication interval on the Volume Group(BM) Replication page.
Cancel Volume Group (BM)
You can delete an unused Volume Group (BM).
Volume Group(BM) has no separate termination procedure, and it is automatically deleted when you disconnect all volumes in the target volume item.
3.1.3 - API Reference
3.1.4 - CLI Reference
3.1.5 - Release Note
Block Storage(BM)
- The configuration range for the volume performance metrics (IOPS, Throughput) has been changed.
- Max IOPS: 5,000 ~ 20,000
- Max Throughput: 250 ~ 1,000
- Provides volume expansion feature
- Volume expansion is possible only for the original volume that does not use snapshots.
- You can set the volume’s performance metrics (IOPS, Throughput) and edit them on the details page.
- IOPS: 3,000 ~ 16,000
- Throughput: 125 ~ 1,000
- There is no separate charge during the preview period (billing is scheduled for the first half of 2026).
- A feature to create a recovery using snapshots has been added.
- A recovery copy is a separate volume created with the same capacity as the original, and it incurs additional costs.
- HDD disk type has been added. When creating Block Storage (BM), you can select the HDD disk.
- Provides an IaC environment through Terraform.
- You can use the snapshot feature on a cloned volume.
- Integrated with Cloud Monitoring.
- You can view IOPS, Latency, and Throughput information in Cloud Monitoring.
- Block Storage(BM) feature change
- The replication feature that allows Block Storage(BM) volumes to be replicated to another location has been added.
- A Volume Group feature has been added that allows you to set up to 16 Block Storage (BM) volumes as a group to create consistent point-in-time snapshots and replication.
- For detailed information, refer to Block Storage(BM) Overview.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have launched a high-performance storage service suitable for handling large-scale data and database workloads.
3.2 - File Storage
3.2.1 - Overview
Service Overview
File Storage enables servers connected via a network to easily store and share data, making it a storage solution suitable for application environments that use multiple servers.
You can choose the disk type according to the required performance level, and it will automatically expand or shrink based on the user’s data volume without any capacity limits.
Features
- Free volume usage: The volume capacity automatically expands or contracts based on data creation and deletion without any user configuration. There is no cost for creating the volume; only usage fees for the stored data capacity are incurred.
- Various Disk Types Available: Users can select a disk type based on their usage purpose. They can use HDDs that store large amounts of data cost‑effectively, SSDs that provide reduced response times and high IOPS performance, and high‑performance SSDs.
- Snapshot Backup: The image snapshot feature enables recovery of modified or deleted data, and when performing disk backup, snapshots can be stored in a location different from the original. Users select a snapshot created at the desired point in time from the list to perform the recovery.
- Replication: Creates an identical replica volume at a different location, and users can set the data replication interval. If the original volume becomes unavailable due to failures or disasters, service can be provided through the replica volume.
Configuration diagram
Provided features
File Storage provides the following features.
- Volume Name: Users can set a name for each volume.
- Disk type: You can select a disk type based on the user’s performance requirements.
- HDD: Standard volume
- SSD: high‑performance general volume
- High‑Performance SSD: Performance‑optimized volume that can be attached to a Multi-node GPU Cluster
- Protocol: You can select the protocol based on the user’s OS image.
- NFS: Primarily used on Linux operating systems
- CIFS: Primarily used on Windows operating systems
- Flexible Volume Usage: Provides flexible volume sizing based on the amount of stored data without requiring user capacity settings.
- Connected Resources: can be connected and used from Virtual Server, Bare Metal Server, and Multi-node GPU Cluster.
- Encryption: Regardless of disk type, all volumes are encrypted with the XTS-AES-256 algorithm.
- Snapshot: The image snapshot feature allows immediate or scheduled snapshot creation.
- Retention Count: The number of snapshots retained that are automatically created by the schedule
- Schedule: Snapshot auto-creation interval
- Recovery: restore the original volume to the latest snapshot, or select a snapshot at a specific point in time to create a recovery volume
- Replication: It replicates the volume to another location, and the user can set the replication schedule.
- Disk Backup: You can store snapshots on a backup-dedicated HDD storage and select the backup location.
- VPC Endpoint connection: File Storage can be used via a Private Network connection from an external network.
- Monitoring: usage, IOPS, Throughput, and other monitoring data can be viewed through the Cloud Monitoring service.
- ServiceWatch Service Integration: You can monitor data using the ServiceWatch service.
Component
You can create a volume by selecting the disk type and protocol according to the user’s service environment and performance requirements.
When using the snapshot feature, you can restore data to the desired point in time.
Volume
Volume(Volume) is the basic creation unit of the File Storage service and is used as data storage space. Users select a name, disk type, and protocol (CIFS/NFS) to create a volume, then connect it to one or more Server for use.
The volume name generation rules are as follows.
- It must start with a lowercase English letter and can be set to 3~21 characters using lowercase letters, numbers, and special characters (
_).
Snapshot
Snapshot is an image backup taken at a specific point in time. Using the image snapshot feature, you can recover changed or deleted data or store snapshots in a location different from the original when performing disk backups. Users select the snapshot created at the desired point in time from the snapshot list to perform a recovery.
The following are considerations when using snapshots.
- The snapshot creation time is based on Asia/Seoul (GMT +09:00). Snapshots can be created up to a maximum of 800, excluding those generated by schedule. (Automatic creation via schedule is limited to a maximum of 128)
- Select the snapshot recovery button to restore the File Storage volume to the latest snapshot.
- If you select a specific snapshot from the snapshot list, you can recover by creating a new volume based on that snapshot.
- Automatic creation is possible through snapshot schedule configuration.
- Since snapshot storage is included in File Storage usage and incurs charges, adjust the storage capacity by setting the snapshot retention period.
Preceding Service
This is a list of services that must be pre-configured before creating the service. Refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
| Compute | Bare Metal Server | High-performance physical server used without virtualization |
3.2.1.1 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by using ServiceWatch, released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a smooth monitoring environment.
Detailed information about ServiceWatch: see the ServiceWatch Overview.
File Storage Monitoring Metrics
The table below shows the monitoring metrics for File Storage that can be viewed in Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
| Performance Item Name | Explanation | unit |
|---|---|---|
| Instance Status | File Storage Volume Status | status |
| Volume Used | Usage | bytes |
| Volume Usage | Utilization | % |
| Volume Total | Total byte count | bytes |
| IOPS [Total] | iops(total) | iops |
| IOPS [Read] | iops(read) | iops |
| IOPS [Write] | iops(write) | iops |
| IOPS [Other] | iops(other) | iops |
| Latency Time [Total] | Latency (total) | usec |
| Latency Time [Read] | Read latency | usec |
| Latency Time [write] | Latency (write) | usec |
| Latency Time [Other] | Latency (Other) | usec |
| Throughput [Total] | Throughput (total) | bytes/s |
| Throughput [Read] | Throughput (read) | bytes/s |
| Throughput [Write] | Throughput (write) | bytes/s |
| Throughput [Other] | Throughput (Other) | bytes/s |
3.2.1.2 - ServiceWatch Metrics
File Storage sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 1‑minute intervals.
Basic Metrics
The following are the basic metrics for the File Storage namespace.
The indicators whose names are displayed in bold below are the indicators selected as major metrics among the basic metrics provided by File Storage. Key metrics are used to configure service dashboards that are automatically generated for each service in ServiceWatch.
Each metric indicates, via the user guide, which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
| Indicator Name | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| status | File storage volume status | None | - |
| total_byte | Total bytes of file storage | Bytes |
|
| iops_read | IOPS (read) | - |
|
| iops_write | IOPS (write) | - |
|
| latency_read | Read latency | Microseconds |
|
| latency_write | Latency (write) | Microseconds |
|
| throughput_read | Throughput (read) | Bytes/Second |
|
| throughput_write | Throughput (write) | Bytes/Second |
|
3.2.2 - How-to guides
Users can create a service by entering the required information for File Storage and selecting detailed options through the Samsung Cloud Platform Console.
- Service fees are charged based on usage without capacity limits.
- Volumes are allocated 100 TB by default. If you need to use more than 100 TB, please inquire via Support Center’s Contact Us.
- Cost Management’s Payment Management, when you add or modify company information, the Mount name (IP information) of File Storage is automatically changed.
- Before modifying company information, be sure to check the service impact caused by changing the mount name (IP information).
Create File Storage
You can create and use the File Storage service from the Samsung Cloud Platform Console.
To create a File Storage, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the Create File Storage button. You will be taken to the Create File Storage page.
- File Storage Creation page, enter the information required to create the service, and select detailed options.
Category Whether requiredDetailed description Volume name Required Volume name - must start with a lowercase English letter and be 3 to 21 characters using lowercase letters, numbers, and special characters (
_)
- is generated as ‘user input value + {6-character UUID composed of lowercase English letters and numbers}’
- cannot be modified after the service is created
Disk types Required Select Disk Type - Disk Type
- HDD: Standard Volume
- SSD: High‑Performance Standard Volume
- High‑Performance SSD: Performance‑Optimized Volume that can be attached to a Multi‑node GPU Cluster
- Cannot be modified after service creation
- When creating a snapshot recovery volume, it is set identical to the original and cannot be modified
Protocol Required Protocols for sharing volumes over the network from a server - NFS: primarily used on Linux operating systems
- CIFS: primarily used on Windows operating systems
- When creating a service, the snapshot recovery volume is set identical to the original and cannot be modified
Protocol > Password Required Set the account password for volume access when using the CIFS protocol - Enter 6 to 20 characters, including English letters, numbers, and special characters(
$%{}[]"\excluded)
Protocol > Password Confirmation Required Confirm account password - Re-enter the same password
Recovery snapshot name Select Name of the recovery snapshot used when creating the volume - Provide the recovery snapshot name when creating a service through snapshot recovery volume creation
Table. File Storage Service Information Input Items - must start with a lowercase English letter and be 3 to 21 characters using lowercase letters, numbers, and special characters (
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the File Storage List page.
- Regardless of disk type, all volumes have server-side encryption based on the XTS-AES-256 algorithm applied by default.
- The snapshot schedule can be set on the detail page.
View File Storage Details
The File Storage service allows you to view and edit the full resource list and detailed information. The File Storage Details page consists of the Detailed Information, Snapshot List, Replication, Disk Backup, Tags, Operation History tabs.
To view detailed information about the File Storage service, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. Go to the File Storage list page.
- On the File Storage List page, click the resource to view detailed information. You will be taken to the File Storage Details page.
- File Storage Details page displays status information and additional feature information, and consists of Details, Snapshot List, Replication, Disk Backup, Tags, Job History tabs.
Category Detailed description Volume status Volume status representation - Creating: Creating
- Creating From Snapshot: Creating a new volume from snapshot
- Available: Created, server connection available
- Deleting: Deleting
- Error Deleting: Abnormal state during deletion
- Inactive: Abnormal state
- Error: Abnormal state during creation
- Migrating: Temporary maintenance state
- Migrating To: Temporary maintenance state
- Reverting: Reverting snapshot
- Reverting Error: Snapshot revert error
Clone creation Create a replica at another location - Backups and replicas are unavailable
- For detailed information on creating replicas, see Creating a replica reference
Create disk backup Create a backup copy to store snapshots on backup-dedicated HDD storage - Available for HDD, SSD disk types
- Up to 2 backup copies can be created
- Backup copies and replicas are not available
- For details on creating a disk backup, see 디스크 백업 생성하기 reference
Create snapshot Immediately create a snapshot at the time of creation - For detailed information on snapshot creation, refer to Snapshot Creation
More > Snapshot Recovery Recover the volume using the latest snapshot in Available state - For details on snapshot recovery, refer to Recover Snapshot
More > File-level recovery Enable file-level recovery within snapshots - For detailed information on file-level recovery, see Using file-level recovery.
More > Disable file-level recovery Disable file-level recovery within snapshotsDisable file-level recovery see Service termination Button to cancel the service Table. Status information and additional features
- File Storage Details page displays status information and additional feature information, and consists of Details, Snapshot List, Replication, Disk Backup, Tags, Job History tabs.
Detailed information
On the File Storage List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Volume name | Volume name |
| Category | Distinguishing original status for duplication and disk backup |
| Disk type | Disk type |
| Usage | Volume usage |
| Protocol | NFS and CIFS protocols for sharing volumes over the network from a server |
| Mount name | Mount name per volume for server connection
|
| Encryption | Encryption status
|
| Snapshot > Schedule | Snapshot automatic creation schedule
|
| Snapshot > Retention Count | Snapshot retention count
|
| Connection resource | Connected resources (Bare Metal Server, Virtual Server, GPU Server)
|
| VPC Endpoint | Connected VPC Endpoint service
|
Snapshot list
You can view the snapshot of the selected resource on the File Storage List page.
| Category | Detailed description |
|---|---|
| Snapshot usage | Total size of stored snapshots |
| Snapshot name | Snapshot name |
| capacity | Snapshot capacity |
| Creation date and time | Snapshot creation time |
| status | Snapshot status
|
| Additional features > More | Snapshot Management Button
|
- The snapshot creation time is based on Asia/Seoul (GMT +09:00). Snapshots can be created up to a maximum of 800, excluding those generated by schedule. (Automatic creation via schedule is limited to a maximum of 128)
- If replication or disk backup is in use, you cannot delete the snapmirror snapshot.
- When you click the snapshot recovery button, the volume is restored to the latest snapshot in the Available state.
- When selecting to create a recovery volume on the snapshot list page, a new volume based on the snapshot is created without modifying the existing volume.
- The snapshot list can be viewed in both the original and the backup. Replicas can be viewed after the policy is deleted.
- Snapshot creation, recovery, and recovery volume creation are available on the source.
- When using replication or disk backup, you cannot recover with a snapshot; you can only create a recovery volume.
Clone
On the File Storage List page, you can view the replication information of the selected resource.
| Category | Detailed description |
|---|---|
| Replication Policy | User-configured replication policy
|
| Replication cycle | The replication interval of the source set by the user
|
| Replication status | Replication progress status according to policy settings |
| Volume information | Volume information of original and replica
|
- When a clone is created, a replica with the same disk type is generated.
- Replication policy, Replication schedule can be modified in a replica when the replication status is Completed or Stopped.
- The replica’s file-level recovery can be used when the replication status is completed or stopped.
- The replica’s connection server and VPC Endpoint can be modified only when the replication status is stopped.
- Snapshot-related functions for replicas become available after the replication policy is deleted.
Disk backup
File Storage List page allows you to view the disk backup information of the selected resource.
- Disk type must be HDD or SSD; only the original can perform disk backup. It cannot be used on clones or high‑performance SSD.
- You can create up to two backup copies.
| Category | Detailed description |
|---|---|
| Backup Policy | Backup policy set by the user
|
| Backup frequency | User-configured backup interval of the original
|
| Backup status | Backup progress status based on policy settings |
| Number of backup copies | Number of snapshots retained in the backup |
| Volume information | Volume information for original and backup
|
- When creating a backup, it is created as an HDD disk type regardless of the original’s disk type.
- Backup policy, Backup schedule can be modified only when the backup status in the backup set is completed or stopped.
- File-level recovery of a backup can be used when the backup status is Completed or Stopped.
- The backup’s connected server and VPC Endpoint can be modified only when the backup status is stopped.
- Snapshots of the backup can only be deleted.
tag
File Storage List page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
File Storage List page lets you view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing File Storage Resources
If you need to modify the settings of a created File Storage or add or remove connected servers, you can perform the operation on the File Storage Details page.
Edit Snapshot
You can modify the snapshot schedule and retention count. To edit a snapshot, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- Click the File Storage menu on the Service Home page. You will be taken to the File Storage List page.
- On the File Storage List page, click the resource to edit the snapshot settings. You will be taken to the File Storage Details page.
- Click the Edit button of the Snapshot item. Snapshot Edit popup window opens.
- Set the Usage status, Schedule, and Storage Count, then click the Confirm button.
- If you want to automatically create snapshots based on Schedule, select Use.
- Schedule is selected daily, hour-wise, or weekly, day of week, hour-wise.
- Retention count: Enter a number between 1 and 128. If not entered, it defaults to 10.
- If the retention count after modification is lower than the original, older snapshots will be deleted first.
- When set to unused, previously created snapshots are retained.
- Since snapshot storage is included in File Storage usage and incurs charges, adjust the storage capacity by configuring the number of snapshots to retain.
- The snapshot schedule is based on Asia/Seoul (GMT +09:00).
Edit linked resources
You can connect or disconnect resources. To modify a connected resource, follow these steps.
- All Services > Storage > File Storage menu, click it. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
- On the File Storage List page, click the resource you want to edit. You will be taken to the File Storage Details page.
- Click the Edit button of the Linked Resource item. The Select Linked Resource popup opens.
- After selecting or deselecting the resource, click the Confirm button.
- You can select multiple resources simultaneously.
- You can connect up to 300 resources at the same location. If you need to connect more than 300, use the API.
- When adding a connected server, you can use it after performing the connection tasks (Mount, network drive connection) on the server. For detailed information about server connections, see Connect to Server.
- The replica’s connected server can be modified when the replication status is stopped.
- The backup’s linked server can be modified when the backup status is stopped.
Edit VPC Endpoint
You can connect or disconnect a VPC Endpoint.
To modify the connection resource, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage list page.
- On the File Storage List page, click the resource to modify the VPC Endpoint connection. Then go to the File Storage Details page.
- Click the Edit button of the VPC Endpoint item. The Select VPC Endpoint popup window opens.
- After selecting or deselecting the resource, click the Confirm button.
- You can select multiple resources simultaneously.
- Connect to the server and be sure to perform the disconnect operation (Umount, disconnect network drive) before releasing the VPC Endpoint. If you release it without OS operations, a status error (Hang) may occur on the connected server. For detailed information on disconnecting the server, see 서버 연결 해제하기.
- High‑performance SSD disks can also share data by connecting a VPC Endpoint, but be aware that they do not guarantee sufficient performance for connecting internal VPC resources.
- High‑performance SSD disk type: after checking the connection IP in the VPC Endpoint section, apply for the VPC Endpoint service. You can add a VPC Endpoint created based on the connection IP.
- The VPC Endpoint of a replica can be modified only when the replication status is stopped.
- The VPC Endpoint of the backup can be modified only when the backup status is stopped.
Cancel File Storage
You can reduce operating costs by terminating unused File Storage. However, terminating the service may cause the running service to stop immediately, so you should thoroughly consider the impact of service interruption before proceeding with the termination.
- Please note that data cannot be recovered after termination.
- You can cancel the service of a File Storage volume that has no attached resources. Remove all connected servers before canceling the service.
- You can terminate the service for a File Storage volume that does not have a VPC Endpoint connection. Remove all VPC Endpoints before terminating the service.
- If the volume is in the Available, Error, or Inactive state, it can be deleted.
- The original that is using replication or disk backup can be terminated after deleting the corresponding policy.
- Replication policy: pause > delete
- Backup policy: pause > service termination
- A replica can be terminated after the replication policy is deleted.
- Backup copies can be terminated after the backup policy is stopped.
To cancel File Storage, follow the steps below.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
- On the File Storage list page, select the resource to cancel and click the Cancel Service button.
- When termination is complete, verify on the File Storage List page whether the resource has been terminated.
3.2.2.1 - Connect to Server
When using a volume on the server, a connect or disconnect operation is required.
File Storage Details on the page, after adding a connected server, access the server and perform the connection tasks (Mount, network drive connection). After use, perform the disconnection tasks (Umount, disconnect network drive) and then remove the connected server.
Connect to server (Mount, network drive connection)
To use the volume added to the connected server, you must log into the server and perform the connection tasks (Mount, network drive connection). Follow the steps below.
Linux operating system (NFS)
- Mount information: 10.10.10.10:/filestorage
- Mount location: /data
Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
On the File Storage List page, click the resource to be used on the connected server. You will be taken to the File Storage Details page.
Check the server in the Connection Server item and then connect.
Refer to the procedure below to mount the volume.
Switch to root privileges
$ sudo -iPackage installation (Redhat family)
# yum install nfs-utilsPackage installation (Debian-based)
# apt-get install nfs-commonEnable and start NFS-related daemon
# systemctl enable rpcbind.service # systemctl start rpcbind.serviceVolume Mount
# mkdir /data # mount -t nfs -o vers=3,noresvport 10.10.10.10:/filestorage /data # vi /etc/fstab (추가) 10.10.10.10:/filestorage /data nfs defaults,vers=3,_netdev,noresvport 0 0
- Supports NFS Version 3.
Windows operating system (CIFS)
Click the All Services > Storage > File Storage menu. Go to the Service Home page of File Storage.
On the Service Home page, click the File Storage menu. You will be taken to the File Storage list page.
On the File Storage List page, click the resource to be used on the connected server. You will be taken to the File Storage Details page.
In the Connection Server item, verify the server and then connect.
Refer to the steps below to connect the volume (network drive).
- In File Explorer, right-click This PC and click Connect network drive.
- Refer to the detailed information of the File Storage volume to be connected, enter the drive and folder, and then click Finish.
- To set it to reconnect automatically when the server restarts, select Reconnect when logging in.
In the network credential input popup, enter the account name (ID) and password, then click Confirm.
- Check the account name (ID) on the File Storage Details page.
- The password is the password set during File Storage creation.
- If you connect two or more volumes with the CIFS protocol enabled, add the storage IP and storage name to the hosts file before connecting.
* Mount명 \\10.10.10.10\filestorage1 \\10.10.10.10\filestorage2 * hosts 파일 내용 추가 10.10.10.10 filestoragename1 #설명 10.10.10.10 filestoragename2 #설명 * hosts 파일에 작성된 이름 사용 filestorage1 연결 시: \\ filestoragename1\filestorage1 filestorage2 연결 시: \\ filestoragename2\filestorage2
Disconnect server (Umount, disconnect network drive)
After connecting to the server and performing the disconnect tasks (Umount, disconnecting the network drive), you must detach the server in the Console. Follow the steps below.
Linux operating system (NFS)
Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
On the File Storage List page, click the resource to detach the connected server. Go to the File Storage Details page.
In the Connection Server field, verify the server information and then connect to the server.
Refer to the commands listed in the table below to carry out the unmount (Umount) operation.
- Volume Umount
# umount /data # vi /etc/fstab (삭제) 10.10.10.10:/filestorage /data nfs defaults,vers=3,_netdev,noresvport 0 0
- Volume Umount
Windows operating system (CIFS)
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage list page.
- On the File Storage List page, click the resource to disconnect the server. Navigate to the File Storage Details page.
- In the Connection Server field, verify the server information and then connect to the server.
- Refer to the steps below to disconnect the volume (disconnect the network drive).
In
File Explorer, right-click thenetwork drivethat is already connected.Please select
Disconnect network drive
3.2.2.2 - Use Snapshot
You can create, delete, or restore snapshots of a created File Storage. You can perform these actions on the File Storage Details page and the Snapshot List page.
Create Snapshot
You can create a snapshot of the current point in time immediately. To create a snapshot, follow the steps below.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
- File Storage List page, click the resource to create a snapshot. You will be taken to the File Storage Details page.
- Click the Snapshot Creation button. A popup indicating snapshot creation will open.
- Click the Confirm button. Creating a snapshot.
- Click the Snapshot List button. You will be taken to the File Storage Snapshot List page.
- Check the generated snapshot.
- Snapshot charges are included in the File Storage usage fees.
- When using replication or disk backup, you cannot recover with a snapshot; you can only create a recovery volume.
- The snapshot creation time is based on Asia/Seoul (GMT +09:00). Snapshots can be created up to 800, excluding those generated by schedule. (Automatic creation via schedule is limited to 128)
- If you want to automatically generate snapshots using a schedule, configure snapshots on the File Storage Details page.
- For detailed information about the snapshot schedule, see Update Snapshot.
Recover Snapshot
You can restore a File Storage volume to the latest snapshot in the Available state. To restore a snapshot, follow the steps below.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
- On the File Storage List page, click the resource to restore from a snapshot. You will be taken to the File Storage Details page.
- Click the Snapshot List button. You will be taken to the File Storage Snapshot List page.
- Check the latest snapshot in the Available state. The volume will be restored using that snapshot.
- Click the snapshot recovery button. A popup indicating snapshot recovery will open.
- After checking the snapshot name and creation timestamp, click the Confirm button.
- When recovery starts, it becomes Reverting, and when completed, it becomes Available.
- If you want to restore from a snapshot that is not the latest, you can recover by creating a recovery volume.
- During recovery, it restores from the latest snapshot in the Available state, and recovery is not possible in the following situations.
- When the File Storage volume is not in the Available state.
- If there are no recoverable snapshots.
- If the latest snapshot changes while creating a recovery.
- If the latest snapshot is not in the Available state.
Create a snapshot recovery volume
You can create a volume using a snapshot. To create a snapshot recovery volume, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
- On the File Storage List page, click the resource to restore from a snapshot. You will be taken to the File Storage Details page.
- Click the Snapshot List button. You will be taken to the File Storage Snapshot List page.
- After checking the Snapshot Name and Creation Time, click the More button of the snapshot you want to restore.
- Click Create Recovery Volume. A popup window indicating the creation of a snapshot recovery volume opens.
- Click the Confirm button. Go to the File Storage creation page.
- On the File Storage creation page, enter the information required to create the service, and select detailed options.
- Please enter the volume name and password.
- The disk type and protocol are set to match the original and cannot be modified.
Category Required or notDetailed description Volume name Required Volume name - must start with a lowercase English letter and be 3 to 21 characters using lowercase letters, numbers, and special characters (
_)
- is generated as ‘user input value + {6-character UUID composed of lowercase English letters and numbers}’
- cannot be modified after the service is created
Disk type Required Select disk type - HDD: Standard volume
- SSD: High‑performance standard volume
- Cannot be modified after service creation
- When creating a service via snapshot recovery volume, it is set identical to the original and cannot be modified
Protocol Required Protocols for sharing volumes over the network from a server - NFS: primarily used on Linux operating systems
- CIFS: primarily used on Windows operating systems
- When creating a service, the snapshot recovery volume is set identical to the original and cannot be modified
Protocol > Password Required Set the account password for volume access when using the CIFS protocol - Enter 6~20 characters, including English letters, numbers, and special characters(
$%{}[]"\excluded)
Protocol > Password Confirmation Required Confirm account password - Re-enter the same password
Recovery snapshot name Select Name of the recovery snapshot used when creating the volume - Provide the recovery snapshot name when creating a service via snapshot recovery volume creation
Table. File Storage Service Information Input Items - must start with a lowercase English letter and be 3 to 21 characters using lowercase letters, numbers, and special characters (
- Check the detailed information and estimated billing amount generated in the Summary panel, and click the Create button.
- When creation is complete, check the created resource on the File Storage List page.
Delete snapshot
You can select a snapshot to delete. To delete a snapshot, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage list page.
- On the File Storage List page, click the resource to delete the snapshot. Go to the File Storage Details page.
- Click the Snapshot List button. You will be taken to the File Storage Snapshot List page.
- After checking the snapshot name and creation timestamp, click the More button of the snapshot you want to delete.
- Click the Delete button. The snapshot will be removed from the Snapshot List page.
- When using replication, snapmirror files cannot be deleted.
3.2.2.3 - File-level Recovery
You can restore data file by file using the generated snapshot. You can perform the operation on the File Storage Details page.
Using file-level recovery
You can enable the file-level recovery feature for use. After enabling the feature, connect to the server to select and recover data. To perform file-level recovery, follow these steps.
Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
On the Service Home page, click the File Storage menu. You will be taken to the File Storage list page.
On the File Storage List page, click the resource to restore the file. You will be taken to the File Storage Details page.
Click the More button at the top right, then click the File-level Recovery button. The Enable File-level Recovery popup window opens.
Click the Confirm button. Activates the file-level recovery feature.
- When File-level recovery is enabled, the File-level recovery button is displayed as Disable file-level recovery.
In the Connection Server field, verify the server information and then connect to the server.
Refer to the procedure below to recover the data.
Connect to the server and verify the mount name of the File Storage.
Move to the snapshot location under the mount name.
# cd /Mount명/.snapshot/snapshot명- Check the files to be restored at the snapshot location and restore them to the required path.
Disable file-level recovery
You can disable the file-level recovery feature after using it. To disable file-level recovery, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage list page.
- On the File Storage List page, click the resource to disable file-level recovery. You will be taken to the File Storage Details page.
- Click the More button at the top right, then click the Disable File-Level Recovery button. The Disable File-Level Recovery popup will open.
- Click the Confirm button. Disable the file-level recovery function.
3.2.2.4 - Use Disk Backup
After creating a backup of File Storage on a backup-dedicated HDD Storage, you can periodically store snapshots. You can perform the tasks on the File Storage Details page and the Disk Backup page.
- Disk type must be HDD or SSD for disk backup to be possible from the original. It cannot be used with clones or high‑performance SSD.
- You can create up to two backup copies.
Create Disk Backup
You can create a backup volume on a backup-dedicated HDD storage at the original location or elsewhere.
To create a backup volume, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. Go to the File Storage list page.
- On the File Storage List page, click the resource to create a backup. Go to the File Storage Details page.
- Click the Create Disk Backup button. The Create Disk Backup popup window opens.
- After entering the backup information, click the Create button. It creates a backup of the HDD disk type.
- Backup Location: Select the location where the backup will be created.
- Backup Frequency: Choose from 1 hour, daily, weekly, or monthly. Replication will be performed at the selected interval.
- Daily: every day 23:59:00
- Weekly: Every Sunday 23:59:00
- Monthly: 1st day of each month 23:59:00
- Click the Disk Backup page. Navigate to the Disk Backup page.
- disk backup information, please check.
- When selecting the volume name of the original or backup, you are taken to the File Storage Details page of that volume.
- A backup in HDD format is created regardless of the original disk type.
- You can create up to two backups per volume, and inter‑region backups incur additional data transfer charges.
Modify Disk Backup Policy
You can change the backup status by modifying the backup policy. To modify the backup policy, follow the steps below.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. Go to the File Storage list page.
- On the File Storage List page, click the resource to edit the backup policy. You will be taken to the File Storage Details page.
- Click the Disk Backup tab.
- Click the Edit button of the Backup Policy. The Disk Backup Policy Edit popup window opens.
- Enabled: Performs backup. If Paused, you can change it to Enabled.
- Pause: Temporarily stops the backup. If Enabled, you can modify to Pause.
- Delete: Deletes the backup. If it is Paused, it can be changed to Delete, and after deletion the backup cannot be used again.
- Check the updated backup policy on the Disk Backup page of File Storage.
Modify Disk Backup Schedule
You can change the synchronization interval between the original and the backup by modifying the backup schedule. To modify the backup schedule, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. Navigate to the File Storage list page.
- File Storage List page, click the resource whose backup schedule you want to edit. You will be taken to the File Storage Details page.
- Click the Disk Backup page.
- Click the Edit button of Backup schedule. Backup schedule edit popup window opens.
- Select Backup frequency from 1 hour, daily, weekly, or monthly. Snapshots will be created at the selected interval. * Daily: 23:59:00 * Weekly: Every Sunday 23:59:00 * Monthly: 1st day of each month 23:59:00
- Check the updated backup schedule on the Disk Backup page of File Storage.
Modify the number of retained disk backups
You can set the number of snapshots retained in the backup. To modify the backup retention count, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. You will be taken to the File Storage List page.
- On the File Storage List page, click the resource to modify the backup schedule. You will be taken to the File Storage Details page.
- Click the Disk Backup page.
- Click the Edit button of Backup retention count. The Edit disk backup retention count popup opens.
- Backup retention count Please enter. * The retention count can be set from 1 to 128.
- Check the modified backup schedule on the Disk Backup tab of the File Storage Details page.
3.2.2.5 - Use Replication
You can create a replica of the File Storage at another location and synchronize it periodically. You can perform the tasks on the File Storage Details page and the Replication page.
- The kr-south region does not provide File Storage replication functionality.
Create Clone
You can create a replica volume at a different location. To create a replica volume, follow the steps below.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. Go to the File Storage List page.
- On the File Storage List page, click the resource for which you want to create a replica. You will be taken to the File Storage Details page.
- Click the Create Clone button. The Create Clone popup window opens.
- Enter the replication location, replication volume name, password, and replication interval, then click the Create button. It creates a replica with the same disk type.
- Replication location: Choose a location different from the original File Storage volume.
- Replication Volume Name: Begin with a lowercase English letter and use lowercase letters, numbers, and special characters (
_) to enter 3–21 characters. - Password: This is the account password for accessing a CIFS volume. Enter 6 to 20 characters, including letters, numbers, and special characters (
$%{}[]"\excluded). - Replication interval: Select from 5 minutes, 1 hour, daily, weekly, monthly. Replication will be performed using the interval below.
- Daily: every day 23:59:00
- Weekly: Every Sunday 23:59:00
- Monthly: 1st day of each month 23:59:00
- Click the Clone page. You will be taken to the Clone page.
- Check the replication information.
- When selecting the volume name of the original or replica, you are taken to the volume’s File Storage Details page.
- When creating a replica, a replica with the same disk type and protocol is created.
- You can create one replica per volume, and data transfer charges apply for cross‑region replication.
Edit replication policy
You can change the replication status by modifying the replication policy. To modify the replication policy, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. Navigate to the File Storage list page.
- On the File Storage List page, click the resource to edit the replication policy. You will be taken to the File Storage Details page.
- Click the Replication page. Navigate to the File Storage Replication page.
- Click the Edit button of the Replication Policy. The Edit Replication Policy popup window opens.
- Use: performs replication. If it is Paused, you can change it to Use.
- Pause: Temporarily pauses replication. If enabled, you can modify it to Pause.
- Delete: Delete the replica. If it is Paused, you can modify it to Delete, and after deletion you cannot use replication again.
- Check the updated Replication Policy on the File Storage Replication page.
- After deletion, the replica becomes the original, so you cannot replicate back to the previous configuration by modifying the replication policy.
- Data stored only in the replica after a pause will be deleted when replication is used again.
- When using the replication policy, replicas are in read‑only state and data cannot be modified. Unmount from all connected resources before using replication.
- If the replication policy is stopped or the replication status is completed, you can modify the policy and schedule on the replica.
Edit replication cycle
You can change the synchronization interval between the original and the replica by modifying the replication interval. To modify the replication interval, follow these steps.
- Click the All Services > Storage > File Storage menu. Navigate to the Service Home page of File Storage.
- On the Service Home page, click the File Storage menu. Navigate to the File Storage list page.
- On the File Storage List page, click the resource to edit the replication schedule. You will be taken to the File Storage Details page.
- Click the Replication page. Go to the File Storage Replication page.
- Click the Edit button of Replication Cycle. The Edit Replication Cycle popup opens.
- Replication interval: Select from 5 minutes, 1 hour, daily, weekly, or monthly. Replication will be performed at the selected interval.
- Daily: every day 23:59:00
- Weekly: Every Sunday 23:59:00
- Monthly: 1st day of each month 23:59:00
- Replication interval: Select from 5 minutes, 1 hour, daily, weekly, or monthly. Replication will be performed at the selected interval.
- On the File Storage Replication page, check the modified replication schedule.
- If the replication policy is stopped or the replication status is completed, you can modify the policy and interval on the replica.
3.2.3 - API Reference
3.2.4 - CLI Reference
3.2.5 - Release Note
File Storage
- The SSD SAP_E volume dedicated to SAP Account and the SSD SAP_E disk type have been added.
- When using a volume dedicated to the SAP Account, the LIF (storage Mount IP) is automatically transferred when a failover occurs due to a fault.
- It can be used only with a SAP account.
- ServiceWatch service integration provision
- You can monitor data through the ServiceWatch service.
- High‑performance SSD disk type has been added and can be used by connecting to a Multi-node GPU Cluster.
- Disk Backup allows you to store snapshots on a backup-dedicated HDD storage. You can select a location other than the original.
- File Storage feature change
- SSD disk types have been added, enabling you to choose a disk type according to your needs.
- You can create an identical replica volume at a different location and set the data replication interval.
- File Storage can be accessed from external networks via a VPC Endpoint connection.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Since it automatically scales up or down based on usage, users can use the volume without capacity limits.
- You can select the connection target using the access control feature.
- We have launched the File Storage service, a network‑connected storage that enables multiple client servers to share files.
3.3 - Object Storage
3.3.1 - Overview
Service Overview
Object Storage is object storage that allows users to easily store and use the data they want and can be accessed via URL, making data management very convenient. It enables searching and retrieving large-scale data, and you can leverage features such as encryption and version control. Provides both public and private URLs, and public URLs are accessible over the internet.
Features
- S3 API utilization: Through a Restful API, applications can access it easily and quickly, and since it is compatible with Amazon S3, it can be used effortlessly in applications that integrate with Amazon S3.
- Safe Use: Encryption (SSE‑S3), access control, and Public/Private access features are provided, making it suitable for securely storing user data or backup data for service recovery.
- Cost Efficiency: Users do not predefine the bucket’s capacity and are provided storage space with an efficient pricing model that charges only for the amount used.
- Replication: You can perform replication to a bucket in a different location or the same location. * You can configure multiple replication policies, and if the source bucket becomes unavailable due to a failure or disaster, you can provide service through the replica bucket.
Configuration diagram
Provided Features
Object Storage provides the following features.
- Storage Management: Provides Object Storage creation, folder creation, folder deletion, file upload, file download, and file deletion functions.
- Version control: When you use version control, all versions of the uploaded files are managed. * You can easily download previous files by viewing the version list.
- Encryption: If you enable encryption, encryption is provided via the SSE‑S3 method.
- Access Control: Using access control, you can directly enter the Public IP allowed to access Object Storage or select resources (Virtual Server, Bare Metal Server, VPC Endpoint, etc.) within the same Account that are permitted to access.
- Replication: You can perform replication to a bucket in a different location or the same location.
- Multiple replication policies can be configured
- Permission Management: It is provided with Private permission by default, and offers Public permission and permission management features.
- Private permission: Allow file access and download only to users who know the authentication key.
- Public permission: Accessing the file via its URL makes the file publicly available and downloadable to anyone worldwide
- Monitoring: You can view monitoring information such as total file count, data size (Bytes), and HTTP method request counts through the Cloud Monitoring service.
- ServiceWatch Service Integration Offering: You can monitor data through the ServiceWatch service.
Component
Authentication key
The authentication key is a required element that must be created in advance to use Object Storage.
The purpose of using the authentication key is as follows.
- In the Samsung Cloud Platform Console, you need an authentication key to create and access the Object Storage service.
- The API provided by Object Storage is compatible with Amazon S3, and you can use the same tools that leverage Amazon S3. * At this point, entering an authentication key is required, and it is used as a tool to identify whether the user has the appropriate permissions. For detailed instructions on creating and verifying authentication keys, see How-to guides > 인증키 생성하기.
Bucket
A bucket is the top-level folder, and all folders and files exist under the bucket. When you create an Object Storage service in the Samsung Cloud Platform Console, a bucket is created, and you can subsequently upload folders or files.
The bucket name creation rules are as follows.
- Bucket names must be at least 3 characters and at most 63 characters.
- Bucket names can consist only of lowercase English letters, numbers, periods
.and hyphens-. - Bucket names must start with a lowercase letter or a digit.
- Bucket names must not contain two consecutive periods.
- Bucket names cannot end with a period or hyphen.
- Bucket names cannot have a period and hyphen adjacent to each other.
- Bucket names do not use the IP address format (e.g., 192.168.x.x).
- The bucket name cannot be admin.
- Bucket names must be unique within an Account/Region.
- The bucket name you used previously will be available in 1 hour.
| Example of a valid bucket name | Example of an invalid bucket name |
|---|---|
The following bucket names can be used
| The following bucket names cannot be used
|
Folder
A folder (Folder) is used to logically group files.
The folder name generation rules are as follows.
- Folder names can consist of Korean characters, English letters, numbers, and special characters.
- The special characters that cannot be entered are as follows.
| Special characters that cannot be used in folder names |
|---|
|
File
A file (File) refers to data stored in Object Storage and is the same as a regular file.
The filename generation rules are as follows.
- Filenames can consist of Korean characters, English letters, numbers, and special characters.
- The special characters that cannot be entered are as follows.
| Special characters that cannot be used in file names |
|---|
|
Folder names and file names are separated by a slash/. The following are examples of valid folder and file names.
| Example of mixed use of folder and file names |
|---|
|
/), is limited to within 1,024 bytes (based on UTF-8 encoding).URL
You can access the Object Storage bucket via URL. By providing public and private URLs, access is possible not only within the same Samsung Cloud Platform environment but also from external internet environments.
The URL structure is composed as follows.
| URL without using Account ID | URL that uses the Account ID |
|---|---|
| https://[대표URL]/[bucket명]/[폴더명]/[파일명] | https://[대표URL]/[accountId]:[bucket명]/[폴더명]/[파일명] |
| Category | Explanation | example |
|---|---|---|
| Main URL | Representative URL is available at the Object Storage 상세 정보 확인하기 URL
| - |
| accountId | account ID
| c2ef8be0481d4094af3c6d046e536d25 |
| bucket name | User-created bucket name | bucketname |
| Folder name | Folder name where the file is located | folder/folder01/folder02/ |
| Filename | File name | Filename02 |
The full URL information for the file can be viewed at View File Information.
Constraints
The limitations of Object Storage are as follows.
| Category | Explanation |
|---|---|
| Number of creatable Object Storage services | No more than 1,000 per region |
| File name length (including path) | up to 1,024 Bytes |
| File upload size |
|
| Number of files in the bucket | 200 million or fewer |
- It is recommended to store no more than 200 million files per bucket. * If the number of files exceeds 200 million, you may experience a sharp performance degradation, so manage the file count.
- S3 Backend Filesystem solution (ex. * When using s3fs, objectivefs, etc., we recommend not employing version control. * Performance degradation may occur when using version control.
- After changing IAM permissions, performing an Amazon S3 API call may take up to 30 seconds.
- Object Storage cannot be used for file upload and download when the IAM policy uses a temporary authentication type.
- South Korea (kr-south3) region constraints
- File upload and download functions via the Samsung Cloud Platform Console are restricted.
- Use of the S3 API/CLI via a public URL is restricted.
- However, private URL access is possible through resources (such as Virtual Server) created in the Samsung Cloud Platform Console.
- Region constraints for South Korea South 1 (kr-south1) and South Korea South 2 (kr-south2)
- A separate firewall rule must be allowed to enable access to the public URL.
- The public URL can be viewed on the Object Storage detail page. * Object Storage Detailed Information Check please refer to it.
Preceding Service
Object Storage has no prerequisite services.
3.3.1.1 - Amazon S3 Usage Guide
Object Storage provides functions such as creating services, viewing lists, retrieving folder lists, creating folders, uploading files, and downloading files through the Samsung Cloud Platform Console. These functions are also available via an API compatible with Amazon S3. Therefore, tools that use Amazon S3 can be used in the same way.
To use Amazon S3’s utility tools, you need to generate and verify an authentication key. For detailed information, see Create Authentication Key.
Amazon S3 API
The list of Amazon S3 APIs supported by the Samsung Cloud Platform Object Storage service is as follows.
| Category | Detailed description |
|---|---|
| head-bucket | Retrieve bucket information |
| list-buckets | List buckets |
| get-bucket-versioning | Bucket version management query |
| put-bucket-versioning | Bucket version control modification |
| get-bucket-encryption | Retrieve bucket encryption settings |
| put-bucket-encryption | Apply bucket encryption settings |
| delete-bucket-encryption | Delete bucket encryption configuration |
| copy-object | Copy, move, rename objects |
| put-object | Object creation |
| get-object | Object download |
| list-objects | Retrieve object list |
| head-object | Object detail view |
| get-object-acl | Retrieve Object ACL |
| delete-object | Object deletion
|
| list-object-versions | View object version list |
| delete-object | Delete object version |
| presign | Issue a Presigned URL for PUT object |
| get-bucket-acl | Check bucket public permissions |
| create-bucket | Create bucket |
| delete-bucket | Delete bucket |
| get-bucket-cors | Check bucket CORS (Cross OriginResources) configuration |
| put-bucket-cors | Create bucket CORS (PUT) |
| delete-bucket-cors | Delete bucket CORS |
| put-bucket-tagging | Create bucket tagging |
| get-bucket-tagging | Bucket tagging query |
| delete-bucket-tagging | Delete bucket tagging |
| put-bucket-website | Create bucket website |
| get-bucket-website | View bucket website |
| delete-bucket-website | Delete bucket website |
| get-bucket-policy-status | Check bucket policy status |
| put-bucket-acl | Create bucket ACL |
| create-multipart-upload | Create multipart upload |
| upload-part | Perform multipart upload |
| complete-multipart-upload | Multipart upload completed |
| list-multipart-uploads | Multipart upload list |
| abort-multipart-upload | Delete incomplete Multipart upload |
| put-object-tagging | Object tagging creation |
| get-object-tagging | Object tagging query |
| delete-object-tagging | Delete object tagging |
| list-objects-V2 | Object Lookup (v2) |
| put-object-acl | Create object ACL |
| list-parts | Parts lookup |
| put-public-access-block | Create public access block |
| get-public-access-block | public access block lookup |
| delete-public-access-block | Delete public access block |
| put-bucket-lifecycle | Create bucket Lifecycle (only Expiration rule can be used) |
| get-bucket-lifecycle | View Bucket Lifecycle |
| delete-bucket-lifecycle | Delete bucket lifecycle |
| put-bucket-policy | Create bucket policy(* reference) |
| get-bucket-policy | View bucket policy |
| delete-bucket-policy | Delete bucket policy |
| put-bucket-replication | Edit bucket replication policy
|
| get-bucket-replication | Retrieve bucket replication policy |
| delete-bucket-replication | Delete bucket replication policy |
put-bucket-policy when used, refer to the following example.
{
"Statement": [
{
"Action": "s3:*",
"Condition": {
"IpAddress": {
"scp:SourceIp": []
},
"Resource": {
"scp:SourceDBaaSId": [],
"scp:SourceResourceId": [],
"scp:SourceVpcEndpointId": []
},
&#34;Service&#34;: {
&#34;scp:ServiceScf&#34;: &#34;false&#34;
}
},
"Effect": "Allow",
"Principal": "*",
"Resource": [
"Object Storage SRN",
"Object Storage SRN/*"
]
}
],
"Version": "2012-10-17"
}
Action,Effect,Principal,Resourcecannot be modified.- Enter the Object Storage SRN and Object Storage SRN/* in
Resource.
- Enter the Object Storage SRN and Object Storage SRN/* in
ConditioninIpAddress,Resource,Servicecan be modified as follows.IpAddress: Enter a single IP or CIDR format.Resource: Enter each resource ID.Service:falseortrue- For detailed information about permissible targets, refer to Setting Access Control.
Amazon S3 CLI
To use Amazon S3 with the AWS CLI, refer to the Amazon S3 CLI Guide.
Amazon S3 SDK for Java
To use the Amazon S3 SDK for Java, please refer to Amazon S3 SDK Guide.
- Refer to the following for the region parameter required to use the Amazon S3 SDK.
- For Korea West (kr-west1): kr-west
- When South Korea 1,2,3 (kr-south1,2,3): kr-south
- The region parameter is for reference only, and the actual region is determined based on the URL.
- South Korea Region 3 (kr-south3) constraints
- File upload and download capabilities are limited through the Samsung Cloud Platform Console.
- Use of the S3 API/CLI via a public URL is restricted.
- However, private URL access is possible through resources (such as Virtual Server) created in the Samsung Cloud Platform Console.
- South Korea South 1 (kr-south1), South Korea South 2 (kr-south2) region restrictions
- To access the public URL, you must allow a separate firewall configuration.
- You can view the public URL address on the Object Storage details page. Refer to Check Object Storage Details.
3.3.1.2 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by using ServiceWatch, released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a smooth monitoring environment.
Detailed information about ServiceWatch is available in the ServiceWatch Overview.
Object Storage Monitoring Metrics
The table below shows the monitoring metrics for Object Storage that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
| Performance Item Name | Explanation | unit |
|---|---|---|
| Objects | Number of objects stored in the bucket | cnt |
| Bucket Used | Amount of data stored in the bucket (bytes) | bytes |
| Requests [Upload Avg] | Upload usage per bucket | bytes |
| Requests [Download Avg] | Download usage per bucket | bytes |
| Requests [Total] | Total number of HTTP requests executed in the bucket | cnt |
| Requests [Get] | Number of HTTP GET requests executed on objects in the bucket | cnt |
| Requests [Head] | Number of HTTP HEAD requests executed for objects in the bucket | cnt |
| Requests [List] | Number of LIST requests executed for objects in the bucket | cnt |
| Requests [Post] | Number of HTTP POST requests executed on objects in the bucket | cnt |
| Requests [Put] | Number of HTTP PUT requests executed on objects in the bucket | cnt |
| Requests [Delete] | Number of HTTP DELETE requests executed on objects within the bucket | cnt |
3.3.1.3 - ServiceWatch Metrics
Object Storage sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals. In Object Storage, you can view replication metrics by policy in ServiceWatch by enabling ServiceWatch replication metrics per bucket.
Refer to How-to guides > Object Storage Activating Replication Metrics for how to enable ServiceWatch replication metrics.
Basic Metrics
The following are the basic metrics for the Object Storage namespace.
The indicators whose names are displayed in bold below are the key indicators selected from the basic metrics provided by Object Storage. Key metrics are used to configure service dashboards that are automatically generated for each service in ServiceWatch.
Each metric indicates through the user guide which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the statistical values shown in bold text are the primary statistics. In the service dashboard, primary metrics can be viewed using the primary statistical values.
| Performance items | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| object_count | Number of objects stored in the bucket | Count |
|
| object_byte | Amount of data stored in the bucket | Bytes |
|
Replication Metric
The following are replication metrics. Replication metrics are collected per replication policy. Replication metrics are collected only when ServiceWatch replication metrics are enabled for each bucket. The replication metrics are as follows.
| Performance items | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| replication_total_count | Total number of objects to be transferred | Count |
|
| replication_transferred_count | Number of transmitted objects | Count |
|
| replication_progress_count | Number of objects being transferred | Count |
|
| replication_queued_count | Number of objects pending transmission | Count |
|
| replication_pending_count | Number of objects with transmission delay | Count |
|
| replication_failure_count | Number of failed transmission objects | Count |
|
| replication_total_bytes | Total transfer target size | Bytes |
|
| replication_transferred_bytes | Data transferred | Bytes |
|
| replication_max_processing_time | Maximum processing time | Seconds |
|
| replication_avg_processing_time | Average processing time | Seconds |
|
3.3.2 - How-to guides
Users can create the service by entering the required Object Storage information and selecting detailed options through the Samsung Cloud Platform Console.
Create authentication key
To create and use the Object Storage service in the Samsung Cloud Platform Console, you must first generate an authentication key.
You can generate an authentication key at My menu > My Info. > Authentication Key Management > Generate Authentication Key. For more details, refer to IAM > Create Authentication Key.
- Authentication keys (Access Key, Secret Key) are used when authenticating Amazon S3 utilities.
- The authentication key is used not only for Object Storage but also for authentication with OpenAPI and the CLI.
- You can generate up to two authentication keys.
- If the authentication key expires, access to the Object Storage service will be restricted. To ensure smooth service usage, check the authentication key’s expiration period in advance.
- If you disable the authentication key, access permissions to the Object Storage service will be restricted.
Create Object Storage
You can create and use the Object Storage service from the Samsung Cloud Platform Console.
To create an Object Storage, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page of Object Storage.
- Click the Create Object Storage button on the Service Home page. You will be taken to the Create Object Storage page.
- On the Object Storage Creation page, enter the information required to create the service.
Category RequiredDetailed description Bucket name Required Bucket name created by the user - must start with a lowercase letter or digit and be composed of lowercase letters, digits, hyphen
-, and period.using 3 to 63 characters
- period
.cannot appear consecutively two or more times.
- period
.and hyphen-cannot be adjacent.
- period
.or hyphen-cannot be at the end.
- IP address format is not allowed
- admin name is not allowed
- For detailed information about bucket names, see Bucket Naming Rules.
Table. Object Storage required information input fields - must start with a lowercase letter or digit and be composed of lowercase letters, digits, hyphen
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the Object Storage list page.
Check detailed information of Object Storage
Object Storage service allows you to view and edit the full resource list and detailed information.
The Object Storage Details page consists of Details, Folder List, Tags tabs.
To view detailed information about the Object Storage service, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource whose detailed information you want to view. You will be taken to the Object Storage Details page.
- Object Storage Details page displays status information and additional feature information, and consists of Details, Folder List, Replication, Tags tabs.
Category Detailed description Bucket status Bucket status - Active: Available
Service termination Cancel Service button Table. Status information and additional features
- Object Storage Details page displays status information and additional feature information, and consists of Details, Folder List, Replication, Tags tabs.
If needed, please check via the Logging&Audit service. For more details, see Logging & Auddit > How-to Guides.
Detailed Information
Object Storage List page lets you view detailed information of the selected resource and edit it if necessary.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Unique resource ID in the service |
| Bucket name | User-created bucket name |
| Category | Field that distinguishes between original and replica
|
| Usage | Total data usage of the bucket |
| Encryption | Encryption usage information
|
| Version control | Version Management Usage Information
|
| URL | Object Storage provides Public and Private URLs for access
|
| Access Control | When access control is enabled, you can restrict access to the bucket so that only authorized resources can access it
|
Folder list
You can view the list of folders and files stored in the bucket via the Folder List tab.
| Category | Detailed description |
|---|---|
| Name | File name or folder name |
| size | File size |
| Modification date and time | The date and time the file was last modified |
| Additional features > More | File and folder management buttons
|
| New folder | Add new folder
|
| File upload | Upload a new file or a file you are working on
|
| Delete | Delete file or folder
|
| Download | File download
|
- South Korea Region 3 (kr-south3) constraints
- File upload and download capabilities are limited through the Samsung Cloud Platform Console.
- Use of the S3 API/CLI via a public URL is restricted.
- However, private URL access is possible through resources (such as Virtual Server) created in the Samsung Cloud Platform Console.
- South Korea South 1 (kr-south1), South Korea South 2 (kr-south2) region restrictions
- To access the public URL, you must allow a separate firewall configuration.
- You can view the public URL address on the Object Storage details page. Refer to Object Storage Check Detailed Information.
- If the delete marker is the latest version, it cannot be seen in the folder list.
- The delete marker version cannot be viewed in the version list.
Replication
Object Storage List page lets you view and manage the replication information of the selected resource.
| Category | Detailed description |
|---|---|
| Policy Name | Enter the replication policy name
|
| Replication target | Replication target bucket name |
| Clone location | Replication location (region) |
| target file | List of files to be replicated |
| status | Replication policy status
|
| Add | Add a new replication policy
|
| More | Policy management available
|
| Service Watch replication metrics | Enable replication metrics to view monitoring data for Object Storage replication in Service Watch
|
tag
Object Storage List page lets you view, add, modify, or delete the tag information of the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
If needed, please check via the Logging&Audit service. For more details, see Logging&Auddit > How-to Guides.
Object Storage Encryption Configuration
You can configure the bucket to encrypt the data stored in it. After enabling bucket encryption, the encryption settings are applied to uploaded data. When encryption is used, the SSE‑S3 encryption key method and the AES256 encryption algorithm are applied.
In this service, we have launched server‑side encryption (SSE‑S3) using Amazon S3 managed keys as the default method, and server‑side encryption (SSE‑KMS) using Key Management Service (KMS) keys will be offered later according to the service roadmap.
If there is data that was stored before the bucket encryption was configured, the encryption setting will not be applied.
- If you re‑upload the file, the encryption will be applied.
- To enable encryption for existing data, you need to re‑upload it.
Object Storage Follow the steps below to enable bucket encryption.
- Click the All Services > Storage > Object Storage menu. You will be taken to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage list page, click the resource (bucket) to use for encryption. You will be taken to the Object Storage details page.
- On the Object Storage Details page, verify whether encryption is not used.
- If Encryption is unused, click the Edit button.Encryption Edit Popup opens.
- After checking Use for encryption, click the Confirm button.
Terminate Object Storage
You can cancel unused Object Storage to reduce operating costs. However, if you cancel the service, the running service may be stopped immediately, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
- Service termination is possible for buckets that have no stored data.
- If a file is being uploaded, the upload will be canceled.
- Please be careful, as data cannot be recovered after deletion.
To cancel Object Storage, follow the steps below.
- Click the All Services > Storage > Object Storage menu. You will be taken to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage list page, select the resource (bucket) to cancel, and click the Cancel Service button.
- Enter bucket name to confirm cancellation.
- If you have entered the Bucket name correctly, the Confirm button will be activated. Click the Confirm button.
- When termination is complete, verify on the Object Storage list page that the resource has been terminated.
3.3.2.1 - Access Control
If you set bucket access control to enabled, only resources that are permitted can access the bucket. You can enter a public IP or configure settings to allow access to resources created in the Samsung Cloud Platform Console.
Setting up Access Control
You can set the bucket’s access control to enabled.
Object Storage Follow the steps below to configure access control settings.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource (bucket) to set access control. You will be taken to the Object Storage Details page.
- Verify on the Object Storage Details page whether access control is unused.
- Access control is disabled, click the Edit button. Access control edit popup opens.
- After checking Use for access control, click the Confirm button. In the Object Storage Details page, access control will be set to Use.
- Register service resources to grant access using a Public IP, or configure whether to enable access control for the Cloud Functions service.
| Category | Detailed description |
|---|---|
| Allow public IP | Add registered Public IP or CIDR
|
| Allow service resources | Select service resources created in the same Account/Region
|
| Allow Cloud Functions service | Setting whether to allow Object Storage access to modify Java Runtime code in the Cloud Functions service
|
South Korea (kr-south) region constraints
- The South Korea (kr-south) region does not provide Cloud Funtions service, so the Allow Cloud Functions Service feature cannot be used.
Allow public IP access
If the bucket’s access control is set to enabled, you can add a public IP allowance.
To add Public IP access permission in Object Storage, follow the steps below.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource (bucket) for which you want to set access control. You will be taken to the Object Storage Details page.
- On the Object Storage Details page, verify that access control is enabled.
- If Access Control is Disabled, click the Edit button, then change Access Control to Enabled in the Access Control popup.
- When access control is enabled, only the Allow IP Access, Allow Service Resources, Allow Cloud Functions Service lists are displayed.
- Click the Edit button in Allow Public IP. The Edit Allow Public IP popup window opens.
- Enter the Public IP to allow access, and click the Add button.
column Required Detailed description Allow public IP Required Enter a single IP or CIDR format (up to 150 entries) - 192.168.x.x (IP format)
- 192.168.x.x/24 (CIDR format)
Table. Public IP Allowance Edit Popup Input Fields - Verify the items added to the list and click the Confirm button.
- Check the added Public IP in the Object Storage Details page’s Access Control > Allow Public IP list.
- If you modify the public IP allowance, it may take up to 30 seconds for the changes to be applied.
- A maximum of 150 public IPs are allowed.
Allow access to service resources
If access control is set to enabled on the bucket, you can add service resources in the service resource allowance.
To permit access to service resources in Object Storage, follow the steps below.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource (bucket) for which you want to set access control. You will be taken to the Object Storage Details page.
- Verify that Access Control is enabled on the Object Storage Details page.
- If Access Control is Disabled, click the Edit button, then change Access Control to Enabled in the Access Control popup.
- When access control is enabled, only the Allow IP Access, Allow Service Resources, Allow Cloud Functions Service lists are displayed.
- Click the Edit button in Service Resource Allowance. The Service Resource Selection popup opens.
The permissible criteria for each service are as follows.
- Virtual Server/GPU Server/Bare Metal Server/Multi-node GPU Cluster: Allowed per server
- VPC Endpoint: Allow per VPC Endpoint
- PostgreSQL, MariaDB, MySQL, EPAS, Microsoft SQL Server: Allowed per cluster
The following steps are required to access Object Storage from the server.
- Check the Object Storage IP on the server using the nslookup command
- Register a rule through the Security Group or Firewall service and apply it to the server.
- Target address: Object Storage IP confirmed in ①
- Direction : Outbound
- Service: TCP 80, 443 (80 when using http / 443 when using https)
If each service’s status is as follows, granting and revoking access to service resources is possible. If the status is not as listed, previously granted service resources may also be affected.
- Virtual Server/GPU Server: Build, Building, Networking, Scheduling, Block_Device_Mapping, Spawning, Deleting, Error and other states
- Bare Metal Server/Multi-node GPU Cluster: Running, Starting, Stopping, Stopped
- VPC Endpoint: Active
- PostgreSQL/MariaDB/MySQL/EPAS/Microsoft SQL Server: Running
- Select the server to allow access, and click the Confirm button.
- Check the added server in the Object Storage Details page’s Access Control > Allow Service Resources list.
- If you modify the service resource allowance, it may take up to 30 seconds for the changes to be applied.
- Service resources are allowed up to a maximum of 150.
Allow access to Cloud Functions service
If access control on the bucket is set to enabled, you can allow the Cloud Functions service to access Object Storage.
To allow access to the Cloud Functions service from Object Storage, follow these steps.
- Click the All Services > Storage > Object Storage menu. You will be taken to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource (bucket) for which you want to set access control. You will be taken to the Object Storage Details page.
- On the Object Storage Details page, verify that access control is enabled.
- Access Control is Disabled, click the Edit button, then in the Access Control popup, change Access Control to Enabled.
- When access control is enabled, only the Allow IP Access, Allow Service Resources, Allow Cloud Functions Service lists are displayed.
- In the Enable Cloud Functions service, click the Edit button. The Edit Cloud Functions service popup opens.
- After checking Allow, click the Confirm button.
- Once the access permission settings for the Cloud Functions service are completed, the Cloud Fuctions service can retrieve the Java Runtime executable stored in Object Storage.
- In the Cloud Functions service, see Java Runtime 코드 변경하기 for how to load the Java Runtime executable.
South Korea (kr-south) region constraints
- The South Korea (kr-south) region does not provide the Cloud Functions service, so the Allow Cloud Functions Service feature cannot be used.
3.3.2.2 - File and Folder Management
If you need to manage tasks such as storing files in the created Object Storage or downloading stored files, you can perform the operations on the Object Storage Details and Folder List pages.
Create new folder
A new folder may need to be created to store new data in the bucket.
To create a new folder in Object Storage, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource (bucket) where you want to create a new folder. You will be taken to the Object Storage Details page.
- Click the Folder List tab. Navigate to the Folder List page.
- Click the New Folder button. The New Folder popup window opens.
- Enter the folder name to use, and click the Confirm button. A popup indicating that a new folder has been created will appear.
- Folder names must not contain prohibited special characters. For more details, see Folder Name Creation Rules.
- The total path length, including the folder name, file name, and delimiter (
/), must be limited to within 1,024 bytes (based on UTF-8 encoding).
- After clicking the Confirm button, check the created folder in the Folder List.
Upload File
- South Korea Region 3 (kr-south3) constraints
- File upload and download capabilities are limited through the Samsung Cloud Platform Console.
- Use of the S3 API/CLI via a public URL is restricted.
- However, private URL access is possible through resources (such as Virtual Server) created in the Samsung Cloud Platform Console.
- South Korea South 1 (kr-south1), South Korea South 2 (kr-south2) region constraints
- To access the public URL, you must allow a separate firewall configuration.
- You can view the public URL address on the Object Storage details page. Refer to Check Object Storage details.
You can upload a new file or a file you are working on to the bucket. Object Storage Follow the steps below to upload files.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource (bucket) to upload files. You will be taken to the Object Storage Details page.
- Click the Folder List tab. Navigate to the Folder List page.
- Click the File Upload button. The File Upload popup opens.
- After clicking the Attach File button, select the file to upload or drag the file to attach into the popup window.
- You can upload up to three attachment files, each not exceeding 3 GB.
- The attached file name must not contain prohibited special characters. For more information, refer to File Name Creation Rules.
- The total path length, including the folder name, file name, and separator (
/), must be within 1,024 Bytes (based on UTF-8 encoding). - If a duplicate file exists, you cannot upload.
- If you have selected all files, click the Upload button.
- If the upload was successful, check the file in the folder list.
Download File
- South Korea Region 3 (kr-south3) constraints
- File upload and download capabilities are limited through the Samsung Cloud Platform Console.
- Use of the S3 API/CLI via a public URL is restricted.
- However, private URL access is possible through resources (such as Virtual Server) created in the Samsung Cloud Platform Console.
- South Korea South 1 (kr-south1), South Korea South 2 (kr-south2) region restrictions
- To access the public URL, you must allow a separate firewall configuration.
- You can view the public URL address on the Object Storage details page. Refer to Check Object Storage details.
You can download files stored in the bucket. Object Storage Follow these steps to download the file.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource (bucket) you want to download. You will be taken to the Object Storage Details page.
- Click the Folder List tab. Navigate to the Folder List page.
- Click the More > Download button located at the far right of the file. The file download will begin.
- Verify that the file download has completed in the browser.
View file information
You can retrieve information about files stored in the bucket. Object Storage Follow the steps below to retrieve file information.
- All Services > Storage > Object Storage Click the menu. Navigate to the Service Home page.
- Click the Object Storage menu on the Service Home page. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource (bucket) that contains the file you want to view information for. You will be taken to the Object Storage Details page.
- Click the Folder List tab. You will be taken to the Folder List page.
- Click the More > File Info button located at the far right of the file you want to view information for. The File Info popup window will open.
- File Information Check detailed file information in the popup window.
Category Detailed description filename File name Content type Object type Total size File size Modification date and time The most recent modification date and time of the file Permission Whether to allow Public Access URL Provide Public and Private addresses to enable access to file paths via URL - Public: Provided to allow access from external internet networks
- Private: Provides an address accessible from resources created in the same account and region of the Samsung Cloud Platform Console
Table. File information items
Copy file
You can copy a file stored in a bucket to the same location. To copy a file, follow these steps.
- Click the Storage > Object Storage menu. Navigate to the Object Storage List page.
- Object Storage List page, click the resource (bucket) to copy the file. You will be taken to the Object Storage Details page.
- Click the Folder List tab. You will be taken to the Folder List page.
- Click the More > Copy File button at the far right of the file to be copied. The Copy File popup window will open.
- Enter the filename, then click the OK button. A popup indicating file copying will appear.
- Only files whose full path—including bucket name, folder name, file name, and delimiter (
/)—is 1,024 Bytes (based on URL encoding) or less can be copied. - In the Samsung Cloud Platform Console, you can only copy files when the file size is 5 GB or less. If the file size exceeds 5 GB, you can copy it using the S3 API.
- You can copy within the same bucket and folder.
- If the bucket does not use versioning, a file with the same name in the folder will be overwritten.
- After clicking the Confirm button, check the copied file in the Folder List.
Delete files and folders
You can delete files and folders stored in the bucket. Object Storage Follow the steps below to delete files and folders.
- When a folder is deleted, all subfolders and files inside it are also deleted.
- When a file is deleted, all versions are deleted at once.
- Files with object lock (WORM) enabled cannot be deleted.
- Click the All Services > Storage > Object Storage menu. You will be taken to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource (bucket) that contains the file or folder you want to delete. You will be taken to the Object Storage Details page.
- Click the Folder List tab. Navigate to the Folder List page.
- Click the More > Delete button located at the far right of the file or folder you want to delete. The Delete popup window will open.
- After selecting multiple files or folders using the checkboxes on the left, you can delete them all at once by clicking the Delete button at the top.
- Click the Confirm button in the delete popup to complete deletion.
- Check that files or folders have been deleted from the Folder List.
3.3.2.3 - Version Management
By enabling versioning on a bucket, you can track the history of file modifications when uploading files with the same name. You can also view the file’s version list and download previous versions of the file from the list.
Setting up version control
You can enable versioning on the bucket.
Object Storage To set up versioning, follow the steps below.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource (bucket) for which you want to configure versioning. You will be taken to the Object Storage Details page.
- On the Object Storage Details page, verify whether Versioning is unused.
- If Version control is unused, click the Edit button. The Edit version control popup window opens.
- After checking version management as Enabled, click the Confirm button. On the Object Storage Details page, Version Management will be changed to Enabled.
- When you configure version control for the first time, it may take some time for changes to be applied.
- The time required may vary depending on the size of the bucket. Work performed before the configuration is completed may not have the version applied.
Check version list
From the moment version control is configured, you can view and manage versions of file uploads and modifications.
- Version control for file uploads and edits is available from the moment version control is configured.
- All files have a version ID. However, before version control is configured, the version ID is null(-), and files uploaded after version control is set up are assigned a generated version ID.
- For example, if you upload a file with the same name to the same location, the file name remains the same, but a new version file with a different version ID appears in the version list.
Object Storage To check the version list of a file, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource (bucket) that contains the file whose version list you want to view. You will be taken to the Object Storage Details page.
- Click the Folder List tab. The folder and file list will be displayed.
- In the folder and file list, click the More > Version List button located at the far right of the file whose version list you want to view. The Version List popup will open.
Category Detailed description filename File name Modification date File modification date and time Version ID Version ID assigned to each individual file - Before version control is enabled, the version ID of saved files is displayed as null(-)
- Files saved after version control is enabled are assigned a unique version ID
- If a file with the same name is uploaded to the same location, a version ID is generated, a versioned file is added, and it can be viewed in the version list
Etag Object that identifies files, specific version Size Version file size More Provides version file download and delete functions as additional features - File Download: Download the file of the selected version
- To restore a file to a previous version, download the previous version and re‑upload it
- Delete: Delete the file of the selected version
- If all version files are deleted, the original file will also be deleted
- To retain the original file, at least one version must be kept
Delete Delete file - Enable the button when selecting the checkbox of the version file to delete from the list
Table. Version list popup items
Download version file
- South Korea Region 3 (kr-south3) constraints
- File upload and download capabilities are limited through the Samsung Cloud Platform Console.
- Use of the S3 API/CLI via a public URL is restricted.
- However, private URL access is possible through resources (such as Virtual Server) created in the Samsung Cloud Platform Console.
- South Korea South 1 (kr-south1), South Korea South 2 (kr-south2) region restrictions
- To access the public URL, you must allow a separate firewall configuration.
- You can view the public URL address on the Object Storage details page. Refer to Check Object Storage Details.
You can download the version file. To download the version file of a Object Storage file, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource (bucket) that contains the version file to download. You will be taken to the Object Storage Details page.
- Click the Folder List tab. The folder and file list will be displayed.
- In the folder and file list, click the More > Version List button located at the far right of the file for which you want to download the version file. The Version List popup window will open.
- Click the More > File Download button located at the far right of the version file. File download will start.
- Verify that the file download has completed in the browser.
Delete version file
You can delete a file’s version list.
- If you delete all version files, the original file will also be deleted. To avoid deleting the original file, you must keep at least one version.
- Version files with object lock (WORM) enabled cannot be deleted.
Object Storage To delete a file’s version list, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List: Click the resource (bucket) that contains the versioned file you want to delete. You will be taken to the Object Storage Details page.
- Click the Folder List tab. The folder and file list will be displayed.
- In the folder and file list, click the More > Version List button located at the far right of the file whose version list you want to delete. The Version List popup window will open.
- Click the More > Delete button at the far right of the version file you want to download. Deletion will be completed.
3.3.2.4 - Permission Management
Each file is provided with Private permission by default, and each file can be changed to Public permission through permission settings. Private permission allows file access and download only to users who know the Access Key and Secret Key, whereas Public permission allows anyone worldwide to access and download the file via its Public URL, so caution is required.
Check permission management
You can check the file’s permission settings.
Object Storage Follow the steps below to verify file permissions.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource (bucket) that contains the file whose permissions you want to check. You will be taken to the Object Storage Details page.
- Click the Folder List tab. Navigate to the Folder List page.
- Click the More > File Info button located at the far right of the file you want to view file information for. The File Info popup window will open.
- Check the Permissions in the File Information popup window.
Category Detailed description Permission Public Access allowed or Public Access not allowed Table. Permission information description
Allow Public Access
You can set the file’s Public Access permission to Allow. To set the file permissions of Object Storage to allow Public Access, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page: click the resource (bucket) that contains files to allow Public Access. You will be taken to the Object Storage Details page.
- Click the Folder List tab. Navigate to the Folder List page.
- Click the More > File Info button located at the far right of the file you want to view information for. The File Info popup window will open.
- Check that Permission is in Public Access not allowed state, then click the Confirm button.
- Click the More > Permission Management button located at the right end of the file. The Edit Permission Management popup window opens.
- Edit Permission Management popup window, check Permission Management’s Allow Public Access, and click the Confirm button. You will be taken to the Folder List page.
- Click the More > File Info button at the far right of the file. The File Info popup opens.
- Check that Permission is Public Access allowed.
Please enable file sharing only when it is absolutely necessary.
3.3.2.5 - Replication Policy Management
Replication can be performed on a bucket in a different location or the same location.
You can configure multiple replication policies, and if the source bucket becomes unavailable due to a failure or disaster, you can provide the service through the replica bucket.
- The replication feature operates in a 1:N structure, allowing replication within a region or between regions. When performing cross‑region replication, data transfer fees are added.
- The replication feature applies only to files uploaded after the replication policy is set.
- Deleting the versioned file in the source does not delete the files in the replica bucket.
- Example: When configured from Bucket A → Bucket B, even if the version files in Bucket A are deleted, they remain in Bucket B.
- Bidirectional replication can be configured.
- Example: When configured as Bucket A ↔ Bucket B, files uploaded to Bucket A are replicated to Bucket B, and files uploaded to Bucket B are replicated to Bucket A.
- The duplicated file is not duplicated.
- Example: When configured as Bucket A → Bucket B → Bucket C, files replicated from Bucket A → Bucket B are not replicated from Bucket B → Bucket C.
Add replication policy
- You can configure replication on the created bucket.
- To add a replication policy, you must set the version control feature to enabled.
- Refer to Configure Version Management for how to configure the version management feature.
To add a replication policy, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource to which you want to add a replication policy. Then navigate to the Object Storage Details page.
- Click the Clone tab.
- Click the Add button. The Add Replication Policy popup opens.
- After entering the policy information, click the Confirm button. A popup notifying the creation of a replication policy will appear.
| Category | Required or not | Detailed description |
|---|---|---|
| Policy Name | Required | Enter the name of the replication policy
|
| Clone location | Required | Select replication location (region)
|
| Replication bucket name | Required | Select the name of the replica bucket
|
| target file | Required | Select files to duplicate
|
| Delete marker duplication | Select | Whether to use delete marker replication |
- Click the Confirm button. The replication policy will be added.
If there is an invalid policy, you cannot add a replication policy.
- Example: If a replication bucket has been deleted but its policy remains, you cannot add a replication policy.
Modify Replication Policy
You can modify the replication location, replication bucket name, and target file of the replication policy.
- To modify the replication policy, you must set the versioning feature to enabled.
- Refer to Configure Version Management for instructions on configuring the versioning feature.
To modify the replication policy, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource to edit the replication policy. You will be taken to the Object Storage Details page.
- Click the Clone tab.
- In the replication policy list, click the More > Edit button of the policy you want to modify. The Edit Replication Policy popup window will open.
- After modifying the replication policy information, click the Confirm button. A popup notifying the replication policy modification will appear.
| Category | Required? | Detailed description |
|---|---|---|
| Clone location | Required | Select the replication location (region)
|
| Replication bucket name | Required | Enter the name of the replicated bucket
|
| target file | Required | Select files to replicate
|
| Delete marker duplication | Selection | Whether to use delete marker replication |
- Click the Confirm button. The replication policy update is complete.
If there is an invalid policy, you cannot add a replication policy.
- Example: If a replication bucket has been deleted but its policy remains, you cannot add a replication policy.
Changing Replication Policy Status
You can enable or disable the replication policy to change whether it is executed.
To change the replication policy status, follow the steps below.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource whose replication policy status you want to change. You will be taken to the Object Storage Details page.
- Click the Clone tab.
- From the replication policy list, click the More > Enable or More > Disable button for the policy whose status you want to change. A popup will appear notifying you of the replication policy status change.
- Enabled: Performs replication according to the replication policy.
- Disabled: Stops replication.
- Click the Confirm button. The status of the replication policy will change.
Delete replication policy
You can delete unused replication policies.
To modify the replication policy, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- Object Storage List page, click the resource to delete the replication policy. Go to the Object Storage Details page.
- Click the Clone tab.
- In the replication policy list, click the More > Delete button for the policy you want to modify. A popup notifying you of the replication policy deletion will appear.
- Click the Confirm button. The replication policy will be deleted.
- If you change the versioning setting of the source and replica buckets, replication will not function properly.
- If versioning on the source bucket is set to disabled, replication is not performed. Setting it to enabled will replicate files uploaded after the setting.
- If you set versioning of the replica bucket to disabled, replication will be performed but versioning is not possible. If you set it back to enabled, versioning will apply from the point of configuration onward.
- If you delete the source bucket, the configured replication policy will also be deleted.
- If you delete the replica bucket, the replication policy configured on the source bucket is retained.
- If you recreate a replication bucket with the same bucket name as a deleted replication bucket, replication will be performed to that bucket.
Activating ServiceWatch Replication Metrics
By default, Object Storage is integrated with ServiceWatch and basic monitoring. To link Object Storage replication metrics to ServiceWatch, you must enable ServiceWatch replication metric. For more information about ServiceWatch, see ServiceWatch Overview.
- Basic monitoring is provided at no cost, but enabling replication metrics as a detailed monitoring item incurs additional fees.
- The ServiceWatch replication metric, when configured once per bucket, applies to all replication policies of that bucket.
To enable the ServiceWatch replication metric for Object Storage, follow these steps.
- Click the All Services > Storage > Object Storage menu. You will be taken to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage List page.
- On the Object Storage List page, click the resource to enable ServiceWatch replication metrics. Then go to the Object Storage Details page.
- Click the Replication tab on the Object Storage Details page. Proceed to the Replication tab.
- Click the Edit button for the ServiceWatch replication metric. You will be taken to the Edit ServiceWatch replication metric popup.
- ServiceWatch Replication Metric Edit In the popup window, after selecting Enable, review the instructions and click the Confirm button.
- In the Replication tab, view the ServiceWatch replication metric items.
Disabling ServiceWatch Replication Metrics
To disable the ServiceWatch replication metric for Object Storage, follow these steps.
- Click the All Services > Storage > Object Storage menu. Navigate to the Service Home page of Object Storage.
- On the Service Home page, click the Object Storage menu. You will be taken to the Object Storage list page.
- On the Object Storage List page, click the resource to disable ServiceWatch detailed monitoring. Navigate to the Object Storage Details page.
- On the Object Storage Details page, click the Replication tab. Navigate to the Replication tab.
- Click the Edit button for the ServiceWatch replication metric. You will be taken to the Edit ServiceWatch replication metric popup.
- ServiceWatch Replication Metric Edit In the popup window, after deselecting Enable, review the guidance text and click the Confirm button.
- In the Replication tab, check the ServiceWatch replication metric items.
3.3.3 - Release Note
Object Storage
- ServiceWatch service integration provision
- You can monitor data through the ServiceWatch service.
- The replication feature of Object Storage has been added.
- You can perform replication to buckets in a different location or the same location, and you can configure multiple replication policies.
- File copy feature has been added.
- You can copy the desired file within the same bucket and folder.
- The Cloud Functions service has been added to access control.
- You can upload a Java Runtime executable to Cloud Functions.
- The replication feature of Object Storage has been added.
- You can perform replication to buckets in a different location or the same location, and you can configure multiple replication policies.
- File copy feature has been added.
- You can copy the desired file within the same bucket and folder.
- The Cloud Functions service has been added to access control.
- You can upload a Java Runtime executable to Cloud Functions.
- A server resource target product has been added to Object Storage access control.
- Multi-node GPU Cluster, PostgreSQL, MariaDB, MySQL, EPAS, Microsoft SQL Server
- Presigned URL functionality has been added.
- You can download the file using a Presigned URL for the configured duration.
- You can perform Copyobject on encrypted files.
- Additional versions of the Amazon S3 SDK and Amazon S3 CLI are now available.
- Object Storage feature change
- You can use Object Storage from external networks via a VPC Endpoint connection.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have launched an object storage service that simplifies data storage and retrieval.
- We have launched Object Storage, a service that provides space (buckets) for economically storing large volumes of data.
3.4 - Archive Storage
Data stored in Object Storage is automatically transferred to Archive Storage for retention and can be easily restored when needed.
3.4.1 - Overview
Service Overview
Archive Storage is a storage service suitable for long-term retention of large amounts of data. The user can set a schedule to automatically move infrequently accessed data stored in Object Storage to Archive Storage, enabling efficient storage configuration and cost management. Additionally, upon user request, data stored in Archive Storage can be restored to Object Storage for use.
Features
Free Capacity Usage: When you create a bucket in Archive Storage, the bucket automatically expands or contracts based on the user’s data archiving and deletion. There is no cost for creating a storage bucket; you are only charged for storage usage.
Stable Data Recovery: Data that has been stored long-term can be searched and reliably recovered within three hours. During data recovery, select the target file and the Object Storage bucket where you want to store the data to recover it.
Cost Efficiency: By configuring Object Storage and Archive Storage efficiently according to the purpose and frequency of data usage, you can store and manage data at a reasonable cost.
Convenient Use: You can conveniently use features such as creating buckets, setting archiving schedules, and data recovery in the Samsung Cloud Platform Console. After migrating data for all files in Object Storage, you can apply a source deletion policy.
Configuration diagram
Provided features
Archive Storage provides the following features.
- Archiving Plan Configuration: Set a schedule to perform Archiving on all files in the Object Storage bucket.
- Data Recovery: You can recover to the target Object Storage bucket and folder using folders or files stored in Archive Storage.
- Archiving status monitoring: You can check the Archiving status (success, cancelled, failed, in progress, pending, skipped).
- Recovery status monitoring: You can view the recovery status (success, canceled, failed, in progress, pending).
- Encryption: When encryption is set to enabled, encryption is provided via the SSE‑S3 method.
- Version Management: You can manage archived files by version and restore a selected version.
- ServiceWatch Service Integration: You can monitor data using the ServiceWatch service.
Component
Authentication key
To create and access the Archive Storage service in the Samsung Cloud Platform Console, an authentication key is required. Therefore, to use Archive Storage, you must create an authentication key.
Bucket
A bucket is the top-level folder, and all folders and files reside under the bucket. When you create an Archive Storage service in the Samsung Cloud Platform Console, a bucket is created, and you can then upload folders or files.
The bucket name creation rules are as follows.
- Bucket names must be at least 3 characters and at most 63 characters.
- Bucket names can only be composed of lowercase English letters, numbers, periods
., and hyphens-. - Bucket names must start with a lowercase letter or a digit.
- Bucket names must not contain two consecutive periods.
- Bucket names cannot end with a period or hyphen.
- Bucket names cannot have a period and a hyphen adjacent to each other.
- Bucket names do not use the IP address format (e.g., 192.168.x.x).
- The bucket name cannot be admin.
- Bucket names must be unique within an Account/Region.
- The bucket name you previously used will be available after 1 hour.
| Example of a valid bucket name | Example of an invalid bucket name |
|---|---|
The following bucket names can be used
| The following bucket names cannot be used
|
folder
A folder (Folder) is used to logically group files.
The folder naming rules are as follows.
- Folder names can consist of Korean characters, English letters, numbers, and special characters.
- The special characters that cannot be entered are listed below.
| Special characters that cannot be used in folder names |
|---|
|
File
File (File) refers to data stored in Archive Storage and is the same as a regular file.
The filename generation rules are as follows.
- Filenames can consist of Korean characters, English letters, numbers, and special characters.
- The special characters that cannot be entered are listed below.
| Special characters that cannot be used in file names |
|---|
|
Folder names and file names are separated by slash /. The following are examples of valid folder and file names.
| Example of mixed use of folder names and file names |
|---|
|
/), must be within 1,024 bytes (based on UTF-8 encoding).Constraints
The limitations of Archive Storage are as follows.
| Category | description |
|---|---|
| Number of creatable Archive Storage services | 1000 or fewer |
| File name length (including path) | up to 1,024 Bytes |
Preceding Service
This is a list of services that must be pre‑configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Storage | Object Storage | Object storage that simplifies data storage and retrieval |
3.4.1.1 - ServiceWatch Metrics
Archive Storage sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals.
Basic Metrics
The following are the basic metrics for the Archive Storage namespace.
The indicators whose names are shown in bold below are the key indicators selected from the basic metrics provided by Archive Storage. Key metrics are used to configure service dashboards that are automatically generated for each service in ServiceWatch.
Each metric indicates, via the user guide, which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
| Performance items | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| object_count | Number of objects stored in the bucket | Count |
|
| object_byte | Amount of data stored in the bucket | Bytes |
|
3.4.2 - How-to guides
Users can create a service by entering the required information for Archive Storage and selecting detailed options through the Samsung Cloud Platform Console.
Create authentication key
To create and use the Archive Storage service in the Samsung Cloud Platform Console, you need to generate an authentication key in advance.
You can generate an authentication key at My menu > My Info. > Authentication Key Management > Create Authentication Key. For more information, refer to IAM > Create Authentication Key.
- The authentication key is used not only for Archive Storage but also for authentication in OpenAPI and CLI.
- You can generate up to two authentication keys.
- If the authentication key expires, access to the Archive Storage service will be restricted. To ensure smooth service usage, check the key’s expiration period in advance.
- If you disable the authentication key, access to the Archive Storage service will be restricted.
Create Archive Storage
You can create and use the Archive Storage service in the Samsung Cloud Platform Console.
To create Archive Storage, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Create Archive Storage button. You will be taken to the Create Archive Storage page.
- Archive Storage creation page, enter the information required to create the service, and select detailed options.
Category Required statusDetailed description Bucket name Required Bucket name for performing archiving - must start with a lowercase letter or digit and use lowercase letters, digits, dash
-, period.to enter 3~63 characters
- period
.cannot appear consecutively two or more times
- period
.and dash-cannot be adjacent
- period
.or dash-cannot be used to terminate
- IP address format not allowed
- admin name not allowed
- cannot use a bucket name already in use in the same region within the Samsung Cloud Platform Console
- For more details about buckets, see Bucket Naming Rules for reference
Table. Archive Storage service information input fields - must start with a lowercase letter or digit and use lowercase letters, digits, dash
- Summary Check the detailed information and estimated billing amount created in the panel, and click the Create button.
- Once creation is complete, check the created resources on the Archive Storage List page.
- After creating the bucket, configure encryption and versioning for secure data management.
- Encryption and versioning can be configured on the Archive Storage Details page. For more information, see Archive Storage Encryption Settings and Version Management Settings.
View Archive Storage details
Archive Storage Details page consists of Detail Information, Folder List, Archiving History, Recovery History, and Tag tabs.
Follow these steps to view detailed information about the Archive Storage service.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- Archive Storage List page, click the resource to view detailed information. You will be taken to the Archive Storage Details page.
- Archive Storage Details page displays status information and additional feature information, and consists of Details, Folder List, Archiving History, Recovery History, and Tags tabs.
Category Detailed description Archive Storage status Archive Storage status information - Active: available
- Error: abnormal state while being terminated
- Deleting: service termination in progress
Service termination Button to cancel the service Table. Archive Storage status information and additional features
- Archive Storage Details page displays status information and additional feature information, and consists of Details, Folder List, Archiving History, Recovery History, and Tags tabs.
Detailed information
Detailed Information tab allows you to view the resource’s detailed information and edit it if needed.
| Category | Detailed description |
|---|---|
| Service | Service group |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name
|
| Resource ID | Service’s unique resource ID |
| Bucket name | User-created bucket name |
| Usage | Total data usage of the bucket |
| Encryption | Encryption usage information
|
| Version control | Version management usage information
|
| Archiving Policy | Check the configured archiving target and policy actions
|
| Archiving target | Object Storage bucket for archiving |
| Policy work | Archiving policy list
|
- Archiving target can be set only once initially. After setting, it cannot be modified.
- The policy operation performs archiving on all versioned files in Object Storage.
- The archiving policy can only be modified and cannot be deleted.
- The archiving policy is executed once daily, based on the time of addition.
Folder list
Folder List tab allows you to view the list and size of folders that have been archived.
| Category | Detailed description |
|---|---|
| Name | Name of the file or folder that was archived
|
| size | Size of archived files or folders |
| Modification date and time | Last modified date and time of a file or folder |
| More button | Manage selected files or folders
|
Archiving History
Archiving History tab allows you to view the list of archiving performed over a specific period.
| Category | Detailed description |
|---|---|
| Query period | Select the period to view the archiving history
|
| status | Select Archiving status
|
| Policy ID | Archiving policy ID
|
| Execution time | Archiving start time |
| Completion date and time | Archiving completion time |
| status | Archiving status information |
| Cancel | Cancel Archiving Task
|
| Search area |
- Query Period: Select the period to view the Archiving history
- You can query up to a maximum of 90 days
- Status: Select the Archiving status
- All, In Progress, Success, Failure, Canceled, Pending, Skipped can be selected
Recovery History
In the Recovery History tab, you can view the list of Archives that performed recovery operations over a specific period.
| Category | Detailed description |
|---|---|
| Query period | Select the period to view the recovery history
|
| status | Select recovery status
|
| Recovery target | Recovery target Object Storage name
|
| Recovery date and time | Recovery start time |
| Completion Time | Recovery Completion Time |
| status | Recovery status information |
| Cancel recovery operation | Cancel recovery operation
|
Tag
In the Tag tab, you can view the resource’s tag information, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Archive Storage Encryption Configuration
You can configure the bucket to encrypt the data stored in it. After enabling bucket encryption, the encryption settings are applied to uploaded data. When encryption is used, the SSE‑S3 encryption key method and the AES256 encryption algorithm are applied.
Archive Storage’s bucket encryption can provide two options (SSE-S3/SSE-KMS).
- SSE-S3 is server-side encryption (SSE-S3) that uses Amazon S3 managed keys.
- SSE-KMS is server-side encryption (SSE-KMS) that uses Key Management Service (KMS) keys.
- In this service, server-side encryption using Amazon S3 managed keys (SSE‑S3) is released as the default method, and server-side encryption using Key Management Service (KMS) keys (SSE‑KMS) will be offered later according to the service roadmap.
If there is data that was stored before the bucket encryption was configured, the encryption setting will not be applied.
- If you re‑upload the file, the encryption will be applied.
- To enable encryption for existing data, you need to re‑upload it.
To set up encryption, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- On the Archive Storage List page, click the resource (bucket) to use for encryption. You will be taken to the Archive Storage Details page.
- On the Archive Storage Details page, verify that Encryption is Not Used, then click the Edit button. The Edit Encryption popup opens.
- After checking the use of encryption, click the Confirm button.
Archive Storage Terminate
To cancel Archive Storage, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- On the Archive Storage list page, select the resource to cancel, and click the Cancel Service button.
- After termination is complete, verify on the Archive Storage List page that the resource has been terminated.
3.4.2.1 - Manage Archiving Policy
You can add, modify, or delete archiving policies.
Add Archiving Policy
To add an Archiving policy, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- On the Archive Storage List page, click the resource to view detailed information. You will be taken to the Archive Storage Details page.
- Click the Add button of Policy Task. The Archiving Policy Add popup opens.
- After entering the Archiving policy information, click the Confirm button.
Category Detailed description Archiving target Select the Object Storage bucket for archiving - Cannot be modified after initial configuration
- Only buckets within the same region can be added
- Buckets used in policies of other Arcvhie Storage cannot be selected
target file Select files for archiving - Only All can be selected
Policy work When selected, archiving is performed on all versioned objects in Object Storage - When Archive Storage version management is enabled: each version is managed separately
- When Archive Storage version management is disabled: managed by overwriting the current version
execution time Enter the archiving execution point - Enter a number between 1 and 3,650
Table. Archiving policy addition popup items
- Archiving target can be set only once initially. After setting, it cannot be modified.
- The policy operation performs archiving on all versioned files in Object Storage.
- The archiving policy can only be modified and cannot be deleted.
- The archiving policy is executed once daily, based on the time of addition.
- Cannot set an additional policy when the target files for the Archiving policy are set to All.
Modify Archiving Policy
To modify the Archiving policy, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- On the Archive Storage List page, click the resource to view its details. You will be taken to the Archive Storage Details page.
- Policy Actions In the list, select the policy you want to edit, then click the More > Add button on the right. The Edit Archiving Policy popup opens.
- After editing the Archiving policy information, click the Confirm button.
Delete Archiving Policy
To delete the Archiving policy, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. Go to the Archive Storage List page.
- Archive Storage List page: Click the resource to view detailed information. You will be taken to the Archive Storage Details page.
- From the Policy actions list, select the policy you want to delete, then click the More > Delete button on the right. The Delete Archiving Policy popup opens.
- After reviewing the Archiving policy information, click the Confirm button.
–>
Change Archiving Policy Status
You can enable or disable the Archiving policy to control whether it is executed.
To change the Archiving policy status, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- On the Archive Storage List page, click the resource whose Archiving policy status you want to change. You will be taken to the Archive Storage Details page.
- From the Policy Actions list, click the More > Activate or More > Deactivate button for the policy whose status you want to change. A popup notifying the change of the Archiving policy status will open.
- Activation: Perform archiving according to the archiving policy.
- Disable: Stops performing archiving.
- Click the Confirm button. The status of the Archiving policy will be changed.
Cancel archiving operation
To cancel archiving, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage list page.
- On the Archive Storage List page, click the resource to cancel the Archiving operation. Then go to the Archive Storage Details page.
- Click the Archive History tab.
- Check whether the status of the Archiving policy to cancel the job in the Archiving history list is Pending or In Progress.
- Click the Cancel button. A cancel confirmation popup will open.
- Click the Confirm button. The Archiving operation will be canceled.
Understanding how Archiving works
The archiving behavior varies by archiving target as follows.
| Archiving target | Detailed description |
|---|---|
| previous version/current version file | Depends on whether versioning is enabled for Archive Storage
|
| File containing Delete Marker version | Delete Marker versions cannot be archived
|
| Empty folder | Folder cannot be created in Archive Storage |
| Folder containing files | Whether the folder is an Object determines whether the folder is deleted from Object Storage after archiving
|
| When there is no target file | Archiving schedule as is
|
| If the target Object Storage bucket is terminated |
|
- Archiving is performed based on the Etag value of the Object Storage file.
- After archiving, Version ID and Modification Timestamp are changed. However, the Etag value remains the same.
3.4.2.2 - Use Version Management
By enabling versioning on a bucket, you can manage all Object Storage versions in Archive Storage.
Using version control, you can view a file’s version list and select a previous version from the list to restore it.
Setting up version control
To configure the version control feature, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage list page.
- On the Archive Storage List page, click the resource to use the version control feature. You will be taken to the Archive Storage Details page.
- On the Archive Storage Details page, verify that Version Management is Not Used, then click the Edit button.Version Management Edit popup opens.
- After checking Enabled for version management, click the Confirm button. The Version Management on the Archive Storage Details page will be changed to Enabled.
- When you configure version control for the first time, it may take some time for changes to be applied.
- The time required varies depending on the size of the bucket, and versioning may not be applied until the configuration is completed.
Check version list
You can view and manage the list of file versions.
To view and manage the file’s version list, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage list page.
- Archive Storage List page, click the resource to view the version list. Archive Storage Details page will be opened.
- On the Archive Storage Details page, click the Folder List tab.
- Click the More > Version Management button of the file whose version list you want to view. The version list popup will open.
| Category | Detailed description |
|---|---|
| filename | File name under version control |
| Modification date | File modification date and time |
| Version ID | Version ID assigned to each individual file
|
| Etag | Object that can identify a file, specific version |
| Size | Version file size |
| More | Delete or restore the version
|
From the moment version control is configured, you can view and manage the version IDs of archived files.
- Before configuring version control, archived files: the version ID is shown as null(-).
- After configuring version control, the archived file: a version file is added, and a unique version ID is generated and assigned.
Delete version file
To delete unused version files, follow the steps below.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage list page.
- Archive Storage List page, click the resource to view the version list. You will be taken to the Archive Storage Details page.
- On the Archive Storage Details page, click the Folder List tab.
- Click the More > Version Control button of the file whose version file you want to delete. The version list popup will open.
- Click the More > Delete button for the version file you want to delete. The version file will be removed from the version list.
- After selecting all version files to delete, click the Delete button at the top of the list to delete them all at once.
3.4.2.3 - Archive Recovery
Archive Recovery
- Recovery can be performed on a per-file basis, and the data stored in Archive Storage is not deleted after recovery.
- When restoring an archive file, select the bucket and folder in Object Storage and restore to that location. Before starting the restoration, first verify the Object Storage you intend to restore.
Recover from folder list
If you are not using the version control feature, you can recover by selecting the Archive file from the folder list.
To check and recover the archive file, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- On the Archive Storage List page, click the resource to view detailed information. You will be taken to the Archive Storage Details page.
- Click the Folder List tab.
- Select the folder or file name to restore from the folder list. The Delete button and Restore button appear at the top of the list.
- Click the Restore button. The Archive Restore popup opens.
- After selecting the recovery information, click the Confirm button.
Category Detailed description Bucket name Object Storage bucket name Original location Original file or folder location Recovery target Select the bucket to recover Overwrite Select whether to use the overwrite function - When selecting a bucket in Object Storage with versioning enabled as the recovery target, using the overwrite function stores the existing file with the same name as a previous version
Table. Archive recovery popup items
- Recovery may fail due to character length restrictions on files and folders. For the character length restrictions on files and folders, see the File name creation rules and Folder name creation rules.
- After a recovery failure, if you perform the recovery again using the overwrite function, you may be charged duplicate fees.
Recover from version list
When using the version control feature, you can check a file’s version and restore it to the desired version.
- To view and restore a file’s version, set the version control feature to enabled..
- Refer to Configure Version Management for how to configure the versioning feature.
To restore an Archive file using a version file, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage List page.
- Archive Storage List page, click the resource to view detailed information. You will be taken to the Archive Storage Details page.
- Click the Folder List tab.
- In the folder list, click the More > Version Management button for the file whose version list you want to view. The version list popup will open.
- In the version list, click the More > Restore button for the version file you want to recover. The Archive Restore popup window will open.
- After selecting the recovery information, click the Confirm button.
Category Detailed description Bucket name Object Storage bucket name Original location Original file or folder location Version list Modification timestamp, version ID, Etag, and size information of the version to be restored Recovery target Select the bucket to recover Overwrite Select whether to use the overwrite function - When selecting a bucket in Object Storage with versioning enabled as the recovery target, using the overwrite function stores the existing file with the same name as a previous version
Table. Archive recovery popup items
- Recovery may fail due to character length limits on files and folders. For the character length limits on files and folders, see File Name Creation Rules and Folder Name Creation Rules.
- After a recovery failure, if you perform the recovery again using the overwrite function, you may be charged duplicate fees.
Cancel recovery operation
To cancel the recovery operation, follow these steps.
- Click the All Services > Storage > Archive Storage menu. Navigate to the Service Home page of Archive Storage.
- On the Service Home page, click the Archive Storage menu. You will be taken to the Archive Storage list page.
- On the Archive Storage List page, click the resource for which you want to cancel the recovery operation. You will be taken to the Archive Storage Details page.
- Click the Recovery History tab.
- Verify that the status of the recovery target to be canceled in the recovery history list is Pending or In Progress.
- Click the Cancel button. A confirmation popup for canceling the operation will open.
- Click the Confirm button. The recovery operation will be canceled.
Understanding archive recovery methods
The recovery methods according to the type of recovery are as follows.
| Recovery type | Status description |
|---|---|
| General recovery |
|
| If there are no files to recover (overwrite option not used) | Not shown in the status check list |
3.4.3 - API Reference
3.4.4 - CLI Reference
3.4.5 - Release Note
Archive Storage
- ServiceWatch service integration provision
- You can monitor data through the ServiceWatch service.
- You can manage archived folders or files by version.
- Users can view archived folders or files by version and select a desired version to delete or restore.
- We have launched the Archive Storage service.
- Data stored in Object Storage is automatically transferred to Archive Storage for retention and can be easily restored when needed.
3.5 - Backup
3.5.1 - Overview
Service Overview
Backup is a service that backs up and recovers in case of an emergency the user’s data in a safe manner.
Since a backup policy includes the backup target, frequency, retention period, etc., users set a backup plan according to their business environment and requirements.
Features
- Backup Scope: Providing optimal backup and recovery services tailored to various business purposes, ensuring customers’ important data is safely preserved.
- Flexible Policy Configuration: You can set backup policies based on the usage environment and data importance. Users select backup targets and types, and specify retention periods and schedules.
- Backup Network: We minimized potential service impact during backup by using a backup network connection. The backup system and network block unauthorized access through permission management.
- Remote backup: Agentless backup can store backup copies at a different location. If a failure or disaster occurs at the backup site, you can recover using the backup copies stored at the other location.
- Replication: Agent backup can replicate the same backup to another location for storage. The schedule and retention period are set the same as the original, and in case of a failure or disaster at the backup location, recovery can be performed using the backup copy stored at the other location.
Configuration diagram
Provided features
Backup provides the following features.
- Backup target: The user can select the target server for which they want to obtain a backup.
- Backup Save: You can select the storage location for the backup.
- Encryption: AES-256 algorithm encryption is applied.
- Retention Period: You can set the retention period for backups. Backups whose retention period has elapsed are automatically deleted.
- Schedule: This is the automatic backup generation interval.
- Recovery: You can select a backup created at the desired point in time to restore resources.
Component
Backup provides a scheduling feature that automatically creates backup copies at predefined intervals and times. Users set retention periods and other parameters to ensure they can obtain backups from the desired point in time, and depending on the backup target and type, agent configuration may be required.
Backup type
Provides Agentless Backup and Agent Backup, and you can select based on the backup target.
- Agentless Backup: You can back up by creating a Backup service without configuring a separate agent. VM image backups of Virtual Server and GPU Server are considered Agentless Backup.
- Agent Backup: Before creating a Backup service, you need to create a Backup Agent and configure the Agent on the server you want to back up. This applies to filesystem backups.
Backup Category
- Full Backup: Backs up all data.
- Incremental Backup: Backs up data that has changed since the previous backup.
Schedule
Backups are automatically created according to the generation interval set by the user. You can schedule up to 1 Full Backup and up to 6 Incremental Backups.
When using the Immediate Backup feature, you can create a backup at a specific point in time desired by the user, in addition to the scheduled backups.
The backup intervals that can be configured in the schedule are as follows.
Daily: Start Time Select
Every week: day, start time select
Monthly: Week, Day of week, Start time selection
- Start Time: hour (1~23), minute (00, 30) select
- Day: Monday, Tuesday, Wednesday, Thursday, Friday, Saturday, Sunday Select
- Week: 1, 2, 3, 4, select the final week
Retention period
You can set the retention period for backups created through the Backup service.
The retention period can be selected and applied from 2 weeks (14 days), 1 month (31 days), 3 months (93 days), 6 months (186 days), or 1 year (365 days).
Preceding Service
This is a list of services that must be pre‑configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
| Compute | Bare Metal Server | High-performance physical server used without virtualization |
3.5.2 - How-to guides
Users can create a service by entering the required backup information and selecting detailed options through the Samsung Cloud Platform Console.
Create Backup
You can create and use a Backup service in the Samsung Cloud Platform Console.
- If you back up the OS of a Virtual Server or GPU Server using Agent Backup, you can utilize the necessary data after restoring additional storage.
- You can obtain an OS backup by using the image creation feature of Virtual Server and GPU Server.
To create a backup, follow the steps below.
Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
On the Service Home page, click the Create Backup button. You will be taken to the Create Backup page.
On the Backup Creation page, enter the information required to create the service and select detailed options.
Category RequiredDetailed description Backup name Required Backup name - Enter 3 to 30 characters using letters and numbers
- Cannot be edited after service creation
Backup type Required Select Backup Type - (Agentless) VM Image: Perform backup by creating a Backup service without configuring an Agent
- (Agent) Filesystem: Create a Backup Agent service, configure the Agent on the target server, then perform backup by creating a Backup service
- Cannot modify after service creation
Backup Save Required Select storage location for Agentless Backup - One Backup service can be created per storage location
- Servers in the Korea South (kr-south) region can only select the same location
- Cannot modify after service creation
Backup replication Select Select replication option and location for Agent Backup - Replication can only be set when creating the Backup service
- A Backup identical to the original (Backup name, schedule, retention period) is created at the replication location
- The South Korea (kr-south) region is unavailable
- Cannot be modified after service creation
Backup target Required Backup target server - Agentless: Select one pre‑created server from the Virtual Server or GPU Server service
- For GPU Server, the target server location and the backup storage location must be the same
- Agent: Select one pre‑created server from the Virtual Server, GPU Server, or Bare Metal Server service
- Cannot be modified after service creation
Filesystem Required Backup target Filesystem - Enter all or specific Filesystem
- Backup not possible in the following situations
- When the Filesystem used by the operating system is not entered correctly
- When the Filesystem is already registered in another Backup policy
- When it is a File Storage volume
/dev/zero,/dev/null
- When it contains the following special characters per operating system
- Linux:
*<>\
- Linux:
Encryption Required/Optional Encryption status - Agentless: Apply default encryption
- Agent: Choose encryption
- Cannot modify after service creation
Retention period Select Retention period of the recovery target (backup) - Select from 2 weeks (14 days), 1 month (31 days), 3 months (93 days), 6 months (186 days), or 1 year (365 days)
Schedule Select Backup auto-creation schedule - Set 1 Full Backup and up to 6 Incremental Backups
- Select Daily, Weekly, or Monthly
- Daily: Set the start time
- Weekly: Set the day of week and start time
- Monthly: Set the week number, day of week, and start time
- Week number: Choose from 1, 2, 3, 4, or the last week
- Day of week: Choose from Monday, Tuesday, Wednesday, Thursday, Friday, Saturday, Sunday
- Start time: Select in 30‑minute increments (00–23 hours, 00/30 minutes)
Table. Backup service information input fieldsIn the Summary panel, review the detailed information and estimated billing amount, then click the Create button.
- After creation is complete, check the created resources on the Backup List page.
- When creating or terminating a Virtual or GPU Server, it may take about 180 minutes for the backup target list to be updated.
- Virtual Server’s (Agentless) VM Image backup can be performed to a remote location by selecting a storage location (excluding GPU Server).
- To create a remote backup, create a Backup service at the location where the target server for the backup was created. Select the remote location in the Backup Save item.
- Backup target can have one Backup service per region. Creating Backup services in two or more regions ensures reliability against failures and disasters.
- To optimize backup and recovery speed, set the backup storage location to be the same as the target server’s location.
- File Storage volumes cannot be backed up. Therefore, added File Storage is excluded from backup.
- Agentless Backup is encrypted by default and cannot be modified.
- Agent Backup applies server‑side encryption based on the AES‑256 algorithm when encryption is selected, which may cause a performance degradation of approximately 20 ~ 30%.
- The initial backup is created as a Full Backup regardless of the request details.
- If you select a different region for Backup storage or Backup replication, data transfer fees will be added.
View backup details
The Backup service allows you to view and edit the full resource list and detailed information. Backup Details page consists of Details, Schedule, Backup History, Recovery Targets, Recovery History, Replication, Tags, Operation History tabs.
To view detailed information about the Backup service, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, click the resource for which you want to view detailed information. You will be taken to the Backup Details page.
- Backup Details page displays status information and additional feature information, and consists of the Details, Schedule, Backup History, Recovery Target, Recovery History, Replication, Tags, Job History tabs.
Category Detailed description Backup status Backup status information - Creating: In progress
- Available: Creation completed
- Deleting: Service termination in progress
- Editing: Changing settings
- Error: Abnormal state
- Error Deleting: Abnormal state while deleting
- Restoring: In progress
Immediate Backup Create a backup of the current state immediately - For details about immediate backup, see Instant Backup
Service termination Cancel service button Table. Status information and additional features
- Backup Details page displays status information and additional feature information, and consists of the Details, Schedule, Backup History, Recovery Target, Recovery History, Replication, Tags, Job History tabs.
Detailed information
On the Backup List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Service | Service group |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource name
|
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation Date/Time | Service creation timestamp |
| Editor | User who modified the service |
| Modification date | Date and time the service was modified |
| Backup name | Backup name
|
| Category | Distinguish original status regarding duplication |
| Backup type | Backup types related to Agent configuration |
| Encryption | Encryption status |
| Backup target | Backup target server |
| Filesystem | Backup target FileSystem
|
| Retention period | Retention period of the recovery target (backup)
|
Schedule
On the Backup list page, you can view the automatic backup schedule of the selected resources.
| Category | Detailed description |
|---|---|
| Edit schedule | Schedule edit button
|
| Schedule name | Schedule Name
|
| Backup Type | Full, Incremental Backup distinction |
| Backup frequency | User-configured automatic backup generation interval |
- The schedule is based on Asia/Seoul (GMT +09:00).
- The schedule can be set to one Full Backup and up to six Incremental Backups.
- If the status is Available, the schedule can be modified.
- The replica’s schedule is identical to the original and can be viewed in the original.
- If the original is deleted, the replica’s schedule will be removed.
Backup History
On the Backup List page, you can view the immediate Backup and scheduled backup execution history for the selected resources.
| Category | Detailed description |
|---|---|
| Schedule name | Schedule Name
|
| Backup Timestamp | Backup start time |
| Completion date/time | Backup completion time |
| status | Backup status information (success/failure/in progress) |
| Cancel backup | Cancel button during backup
|
- The backup and completion times are based on Asia/Seoul (GMT +09:00).
- Queries can be performed based on the backup timestamp within a maximum of 30 days.
- You can receive a notification when a backup fails and view it in Management > Logging&Audit.
- In clones, the Cancel Backup button is not displayed.
- The backup history for both the primary and replica is provided by the primary.
- Click the Excel Download button at the top of the list to download the retrieved backup history list as an Excel file.
Recovery target
On the Backup list page, you can view the recovery target (backup) of the selected resource.
| Category | Detailed description |
|---|---|
| Schedule | Schedule Name
|
| Backup Timestamp | Backup start time |
| Retention period | Retention period of the recovery target
|
| capacity | Recovery target size |
| Additional features > More | Management buttons for recovery target
|
- Backup time is based on Asia/Seoul (GMT +09:00).
- Queries can be performed based on the backup timestamp within a maximum of 30 days.
- Click the Excel Download button at the top of the list to download the retrieved recovery target list as an Excel file.
Recovery History
On the Backup List page, you can view the recovery execution history of the selected resources.
| Category | Detailed description |
|---|---|
| Schedule | Schedule Name
|
| Recovery server name | Name of the server created through recovery |
| Backup Timestamp | Backup start time of the recovery target used for recovery |
| Recovery date and time | Recovery start time |
| Recovery completion time | Recovery completion time |
| status | Recovery status information (success/failure/in progress) |
- Backup and recovery times are based on Asia/Seoul (GMT +09:00).
- You can query based on the recovery timestamp within a maximum of 30 days.
- You can click the Excel Download button at the top of the list to download the retrieved recovery history list as an Excel file.
Clone
You can view the replication information of the selected resources on the Backup list page.
- Replication tab information is provided only when you set Agent Backup and Backup replication to enabled when applying for the Backup service.
- In the case of Agentless Backup, the replication feature (Replication tab) is not provided, and when applying for the service, you can select a backup storage location to store the backup copy in a different location.
| Category | Detailed description |
|---|---|
| Replication Policy | User-configured replication policy
|
| Replication information | Volume information for original and replica
|
Tag
On the Backup List page, you can view the tag information of the selected resources, and you can add, modify, or delete them.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
On the Backup List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Backup Resources
If you need to modify the schedule or retention period of a created backup, cancel the backup, or delete a recovery target, you can perform these actions on the Backup Details, Schedule, and Recovery Target pages.
Edit Retention Period
You can modify the retention period of a backup. To modify the retention period, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup list page.
- On the Backup List page, click the resource whose retention period you want to modify. You will be taken to the Backup Details page.
- Click the Edit button of Retention Period. The Edit Retention Period popup opens.
- Select the retention period and click the Confirm button.
- Please select from 2 weeks (14 days), 1 month (31 days), 3 months (93 days), 6 months (186 days), or 1 year (365 days).
- On the Backup Details page, check the modified retention period.
- Click the Recovery Target page. Check the modified retention period of the recovery targets.
- Agentless Backup: When the retention period is modified, the retention period of all already created backup copies will be changed uniformly.
- Agent Backup: After modifying the retention period, the changed retention period is applied to the generated backup.
Modify Filesystem
You can modify a registered Filesystem. To modify the Filesystem, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- Click the resource whose retention period you want to modify on the Backup List page. You will be taken to the Backup Details page.
- Click the Filesystem Edit button. The Filesystem Edit popup window opens.
- Modify the Filesystem and click the Confirm button.
- After entering the Filesystem to add, click the Add Target button. The Filesystem will be added to the list.
- Click the X button of the Filesystem you want to delete from the Filesystem list. The Filesystem will be removed from the list.
- A filesystem with the same name or a filesystem registered in another backup cannot be added.
- /dev/zero, /dev/null cannot be added to the filesystem.
- If the following special characters are included, recovery is impossible on each operating system.
- Linux:
:*<>|not allowed - Windows:
/?*<>|not allowed
- Linux:
Edit Schedule
You can modify the backup schedule.
To modify the schedule, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, click the resource whose schedule you want to edit. You will be taken to the Backup Details page.
- Click the Schedule page. Go to the Backup Schedule page.
- Click the Edit Schedule button. The Edit Schedule popup opens.
- Select a schedule and click the Confirm button.
- Daily, Weekly, Monthly please select one.
- Daily: Set the Start time.
- Every week: Set the day of the week and start time.
- Monthly: Week, Day of the week, Start time. Please set them.
- Week: 1, 2, 3, 4, or the final week.
- Day: You can select from Monday, Tuesday, Wednesday, Thursday, Friday, Saturday, Sunday.
- Start Time: can be selected in 30‑minute intervals (00–23 hours, 00/30 minutes).
- The schedule is based on Asia/Seoul (GMT +09:00).
- The schedule can be set to 1 Full Backup and up to 6 Incremental Backups, and at least one Full Backup schedule must be registered.
- If the status is Available, the schedule can be modified.
- After modifying the schedule, the initial backup is created as a Full Backup regardless of the request details.
- When the original is modified, the same changes are applied to the copy.
Cancel backup
You can cancel an ongoing backup. To cancel the backup, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, click the resource to cancel the backup. You will be taken to the Backup Details page.
- Click the Backup History page. You will be taken to the Backup History page.
- Check the backup you want to cancel. If the backup’s status is in progress, you can cancel the backup.
- Click the Backup Cancel button. The Backup Cancel popup window opens.
- Backup name, Backup date and time and other information, then click the Confirm button. The backup will be canceled.
Delete recovery target
You can delete the generated recovery target (backup). To delete a recovery target, follow the steps below.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, click the resource to delete the recovery target. Navigate to the Backup Details page.
- Click the Recovery target page. Go to the Backup recovery target page.
- After selecting all items you want to delete, click the Delete button. The Delete popup window opens.
- After confirming Backup schedule name and Backup date/time, authenticate via the logged-in user’s mobile phone.
- When deleting two or more items, only the count of items to be deleted can be viewed in the popup window.
- When authentication is complete, click the Confirm button. The recovery target will be deleted.
- When deletion is complete, check on the Backup recovery target page whether the target has been deleted.
- You can delete two or more recovery targets using multiple selection.
- Even if you delete the original’s recovery target, the replica will not be deleted.
Cancel backup
You can cancel unused backups to reduce operating costs. However, if you cancel the service, the running service may be stopped immediately, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
- All saved backup data and history will be deleted. Please note that data cannot be recovered after termination.
- If the status is Available, Error, or Error Deleting, cancellation is possible.
- If you cancel the original Backup service, the replica’s schedule will be deleted, but the stored backup data will not be deleted.
- Agent Backup that uses replication cannot be terminated. Change the replication policy to unused in the source, then terminate.
To cancel the backup, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, select the resource to cancel and click the Cancel Service button.
- Authenticate using the logged-in user’s mobile phone. Once authentication is complete, the service will be terminated.
- When termination is complete, check on the Backup list page whether the resource has been terminated.
3.5.2.1 - Instant Backup
You can perform an immediate backup at the current time on a generated backup regardless of any schedule settings. You can perform the operation on the Backup Details page.
Instant Backup
You can create a backup of the current point in time immediately. To perform an immediate backup, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- Backup List page, click the resource to perform the backup. You will be taken to the Backup Details page.
- Click the Instant Backup button. The Instant Backup popup opens.
- Click the Confirm button. It will perform a backup immediately.
- Click the Backup History page. Navigate to the Backup History page.
- Check the ongoing backup.
- If the status is Available, backup can be performed immediately.
- Immediate backup is performed as a full backup.
3.5.2.2 - Recovery
You can perform a restore using the generated backup’s restore target (backup copy). You can perform the operation on the Backup Restore Target page.
Recover VM Image
You can restore using the backup copy designated for recovery.
To recover, follow the steps below.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, click the resource to restore. You will be taken to the Backup Details page.
- Click the Recovery Target page. Go to the Backup Recovery Target page.
- After checking the Schedule and Backup date and time, click the More button of the target you want to restore.
- Click the Restore button. The Backup Restore popup window opens.
- After confirming Backup target and Backup time, enter the recovery location, recovery server name, etc.
- Recovery Location: For remote backups, select the recovery location (target server or backup location).
- Recovery Server Name: Enter using English letters, numbers, spaces, and special characters (
-_) within 63 characters. - Server Type: Set the server type.
- Network Settings: If you are restoring to a location different from the backup target server, configure the network on the recovery server.
- Security Group: Configure the Security Group for the recovery server.
- After reviewing the entered information, click Confirm.
- Click the Recovery History page. Go to the Backup Recovery History page.
- Check the ongoing recovery tasks.
- Recovery is possible when the status is Available.
- The original Security Group, NAT IP, and Delete on termination settings are not restored, so configure them after recovery.
- The original server’s Server Group is not applied to the recovery server.
- The restored server cannot use the Rebuild feature.
- During recovery, a new server is created, and the Block Storage type and Keypair are set the same as the original.
Filesystem Recovery
You can restore using the backup copy designated for recovery. To restore, follow the steps below.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, click the resource to restore. You will be taken to the Backup Details page.
- Click the Recovery Target page. Go to the Backup Recovery Target page.
- After checking the Schedule and Backup date and time, click the More button of the target you want to restore.
- Click the Restore button. The Backup Restore popup window opens.
- Please check Backup target, Backup time, etc.
- Click the Server Selection button for the recovery target item. The Server Selection popup window will open.
- After selecting a server, click Confirm.
- Only servers with a configured Backup Agent can be selected among the servers created in the backup storage location.
- Only servers that use the same Backup Master and OS as the backup target server can be selected.
- From the list below the Filesystem item, select the Filesystem to recover, then enter the Recovery location.
- If you enter the same ‘Backup target server name’ in the top-level restore location, the entire Filesystem will be restored (e.g., source location: servername, restore location: servername)
- Enter the exact name of the filesystem in use on the OS.
- /dev/zero, /dev/null cannot be recovered when entered.
- Recovery is impossible on any operating system if the following special characters are included.
- Linux:
:*<>| - Windows:
/?*<>|
- Linux:
- Overwrite when selected, files with the same type and name are overwritten. If not selected, those files are excluded from recovery.
- After reviewing the entered information, click Confirm.
- Recovery History click the page. Backup Recovery History navigate to the page.
- Check the ongoing recovery tasks.
3.5.2.3 - Use Backup Agent
Users can create and manage the Agent required to use Filesystem backup in the Backup service.
Create Backup Agent
You can create and use the Backup Agent service in the Samsung Cloud Platform Console.
To create a Backup Agent, follow the steps below.
Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
From the Service Home page, click the Backup Agent menu. You will be taken to the Backup Agent list page.
On the Backup Agent List page, click the Create Service button. You will be taken to the Create Backup Agent page.
On the Backup Agent Creation page, enter the information required to create the service.
Category RequiredDetailed description target server Required Select the target server to create a Backup Agent - Click the Select button to choose the server for creating the Backup Agent
- Virtual Server: 1 unit, GPU Server: 1 unit, Bare Metal Server: up to 100 units
Subnet Required Backup network (backup IP and port) Subnet - Select one of the General Subnets created in the VPC connected to the target server
- Select when the target server is a Virtual Server or GPU Server
Table. Backup Agent Service Information Input ItemsSummary Check the detailed information generated in the panel, and click the Done button.
- Once creation is complete, check the created resources on the Backup Agent List page.
- After creating the Backup Agent, connect to the target server and install the Agent.
- If the connection status on the Agent installation and Backup Agent details screen is confirmed as successful, you can create a Backup service to back up the filesystem.
- For performance optimization, use the Subnet and Port selected in the Backup Agent exclusively for backup.
- After creating the Backup Agent service, connect to the target server and install the Backup Agent.
- For detailed information about the Backup Agent installation, please refer to Backup Agent Installation.
- After installation is complete, check the connection status on the Backup Agent Details page.
Check detailed information of Backup Agent
Backup Agent service allows you to view and edit the full resource list and detailed information. Backup Agent Details page consists of Detailed Information, Tags, Job History tabs.
To view detailed information about the Backup Agent service, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- From the Service Home page, click the Backup Agent menu. You will be taken to the Backup Agent list page.
- On the Backup Agent List page, click the resource to view detailed information. You will be taken to the Backup Agent Details page.
- Backup Agent Details page displays status information and additional feature information, and consists of the Detailed Information, Tags, Job History tabs.
Category Detailed description Backup Agent status Backup Agent status information - Creating: In progress
- Available: Creation completed
- Deleting: Service termination in progress
- Error: Abnormal state
Service termination Cancel service button Table. Status information and additional functions
- Backup Agent Details page displays status information and additional feature information, and consists of the Detailed Information, Tags, Job History tabs.
Detailed Information
On the Backup Agent List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name
|
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who modified the service |
| Modification date | Date and time the service was modified |
| Backup Agent name | Backup Agent name |
| Installation file URL | Agent installation file download location |
| Number of backup policies | Number of Backup services connected to the backup target server |
| Backup Master | Management server (Backup Master) name and connection IP |
| Backup Media | Management server (Backup Media) name and connection IP |
| target server | Backup Agent Target Server Information
|
- After creating the Bacup Agent service, connect to the backup target server and install the Backup Agent.
- For detailed information about the Backup Agent installation, please refer to Backup Agent Installation.
- After installation is complete, check the connection status on the Backup Agent Details page.
tag
On the Backup Agent List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Backup Agent list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Backup Agent
You can cancel a Backup Agent you are not using.
- Available, can only be terminated when in an Error state.
- If a Backup service is connected to the Backup Agent, it cannot be terminated.
- Backup policy count is the number of Backup services connected to the Backup Agent. After terminating all connected Backups, terminate the Backup Agent.
To cancel the Backup Agent, follow the steps below.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- From the Service Home page, click the Backup Agent menu. You will be taken to the Backup Agent list page.
- On the Backup Agent List page, select the resource to cancel and click the Cancel Service button.
- After termination is complete, check on the Backup Agent List page whether the resource has been terminated.
3.5.2.4 - Install Backup Agent
To install the Backup Agent, you must first request the Backup Agent service. Refer to Create Backup Agent.
- Backup Agent Apply
- Install Backup Agent
- Register backup in the Backup service
To use an Agent-based backup, you must connect to the target server and install the Backup Agent. After installing the Backup Agent, register the backup through the Backup service.
Pre‑setup work
To install the Backup Agent, verify the installation space, download the Backup Agent files, check the Backup Master/Agent information, and perform other preparatory tasks.
Check backup agent installation space
The required storage for installing the Backup Agent is as follows.
| OS type | Path | Required capacity | Remarks |
|---|---|---|---|
| Linux | /tmp (temporarily used during installation) | 3 GB | When /usr space is insufficient, a separate space can be linked #ln -s separate space /usr/openv |
| Linux | /opt | 3 GB | /usr space is insufficient, a separate space can be linked #ln -s separate space /usr/openv |
| Linux | openv installation path (usually /usr) | 3~5 GB | /usr When /usr space is insufficient, you can link a separate space #ln -s separate space /usr/openv |
| Windows | Veritas installation path (usually C:\) | 3~5 GB | If space on C:\ is insufficient, you can install on another drive. |
| - | installation file | 10 GB |
Download Backup Agent installation file
To download the Backup Agent installation file, follow these steps.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- From the Service Home page, click the Backup Agent menu. You will be taken to the Backup Agent list page.
- On the Backup Agent List page, click the resource for which you want to view detailed information. You will be taken to the Backup Agent Details page.
- After checking the installation file URL, navigate to that URL. You can download the Backup Agent installation file.
Linux OS
If you are using Linux OS, refer to the following example and enter the command.
# cd [다운로드할 위치]
# curl -O 설치파일 → 설치 파일에 복사한 설치 파일 다운로드 URL을 넣어주세요.
Windows OS
If you are using Windows OS, you can download using a web browser or Windows PowerShell.
When using an internet browser
After launching an internet browser, enter the copied installation file download URL into the address bar. Once you navigate to the download page, the download will begin.
- It may take some time to navigate to the download screen.
- If you do not navigate to the download page, use Windows PowerShell to download.
When using Windows PowerShell
- Right-click the Windows Start icon, then run Command Prompt (Admin).
- Run Windows PowerShell in administrator mode.
- Enter the command by referring to the following example.
# wget "다운로드 URL" -OutFile "저장할 파일명"
Check Backup Master and Agent Information
To install the Backup Agent, you need routing settings and Backup Master and Agent information for host file registration. On the Backup Agent Details page, check the Backup Master IP, Backup IP, and Gateway information. Please refer to Check detailed information of Backup Agent.
Configure routing for communication with Backup Master
To communicate with the Backup Master, you must configure routing in the operating system.
Linux OS - CentOS/RHEL
Linux OS - To configure routing on CentOS/RHEL, follow these steps.
- The IP, Gateway, and Vlan ID information for the Backup Master and Agent used in the routing configuration example are as follows.
- Backup Master IP: 10.242.8.4
- Backup IP (Agent IP): 10.252.25.4
- Gateway (Agent Gateway): 10.252.25.1
- vlan: 100
- vlan can be configured in the Config file of a Bare Metal Server. For more details, refer to Configure Local Subnet.
- Use the following command to check the backup network Interface information.
- ip a
- bash /usr/local/bin/ip.sh
- Configure routing using the nmcli command.
# nmcli con mod "Vlan bond-srv.100" +ipv4.routes "10.252.8.0/24 10.252.25.1" # nmcli device reapply bond-srv.100 - Check that the routing configuration has been applied correctly.
# telnet [Backup Master명] 1556
Linux OS - ubuntu
Linux OS - To set up routing on Ubuntu, follow the steps below.
- The IP, Gateway, and Vlan ID information for the Backup Master and Agent used in the routing configuration example are as follows.
- Backup Master IP: 10.242.8.4
- Backup IP (Agent IP): 10.252.25.4
- Gateway (Agent Gateway): 10.252.25.1
- vlan: 100
- vlan can be configured in the Config file of a Bare Metal Server. For more details, see Local Subnet Configuration.
- Use the following command to check the backup network Interface information.
- ip a
- bash /usr/local/bin/ip.sh
Open the 50-cloud-init.yaml file and configure routing.
# vi /etc/netplan/50-cloud-init.yaml (기존 내용에 routes 내용 추가) network: bonds: ...................... 생략 ethernets: ...................... 생략 vlans: bond.srv.100: addresses: ...................... 생략 routes: - to:10.252.8.0/24 via:10.252.25.1 # netplan applyCheck that the routing configuration has been applied correctly.
# telnet [Backup Master명] 1556
Windows OS
To set up routing on Windows OS, follow these steps.
- The IP, Gateway, and Vlan ID information for the Backup Master and Agent used in the routing configuration example are as follows.
- Backup Master IP: 10.242.8.4
- Backup IP (Agent IP): 10.252.25.4
- Gateway (Agent Gateway): 10.252.25.1
- ifindex: 100
- ifindex can be set in the Config file of a Bare Metal Server. For more details, refer to Setting Local Subnet.
- Right-click the Windows Start icon and then launch Command Prompt (Admin).
- Run Windows PowerShell in administrator mode.
- Use the ipconfig and Get‑NetAdapter commands to check the backup network interface index (ifindex) settings.
# ipconfig /all → Agent IP에 할당된 interface name을 확인하세요. # Get-NetAdapter → 위에서 확인한 interface name 참고해 interface index를 확인하세요.
Set up routing using the NetRoute command.
# Get-NetRoute -ifindex 100 # New-NetRoute -ifIndex 100 -DestinationPrefix 10.252.8.0/24 -NextHop 10.252.25.1Check that the routing configuration has been applied correctly.
# telnet [Backup Master명] 1556
Register Backup Master information in the hosts file
To register Backup Master information in the hosts file, follow these steps.
- Open the host file using a file editing tool.
- Linux operating system: /etc/hosts
- Windows operating system: C:\Windows\System32\drivers\etc\hosts
- Open the hosts file and register the Backup Master and Backup Agent information (IP, name).
- You must add .scpbackup after the Backup Agent name as shown in the following example.
10.252.8.4 takre1p1bkm1 10.252.25.4 agent_tgdrhw.scpbackup
Adding ports for Backup Agent (when using Windows Firewall)
If you are using the Windows firewall, you must add the Backup Agent port for communicating with the Backup Master to the Windows firewall.
The ports and settings to add to the Windows firewall are as follows.
- Inbound Rule: (TCP) 1556, 13724 port
- Action: allow the connection
- Profile: select domain, private, and public
Check if the package is installed (when using RHEL 8)
If you are using RHEL 8, the libnsl package must be installed to install the Backup Agent.
- Use the following command to verify that the libnsl package is installed.
# rpm -qa | grep libnsl - If the libnsl package is not installed, use the following command to install the package.
# yum install libnsl
Installing Backup Agent
Install the Backup Agent appropriate for the operating system.
Linux OS
To install the Backup Agent on Linux OS, follow these steps.
- Backup Agent 10.1.1 After moving to the path where the installation file was extracted, change the permissions of the installation-related files.
# chmod 755 installs # chmod –R 755 NBClients - Run ./install.
- [root@bkclientlin ~]# ./install
- After the install description, when confirming whether to proceed with the installation, enter y and press the Enter key.
Do you wish to continue? [y,n] (y) y - When checking the installation status of Software on the client, enter y and press the Enter key.
Do you want to install the ~~~~~~~~~~~~ software for this client? [y,n] (y) y - When checking the Backup master server name, enter Backup Master name and press the Enter key.
Enter the name of the ~~~~~~ master server : bkmaster - When checking the client server configuration name, enter n and then input the Agent information.
- Agent information required: Backup Agent name.scpbackup (e.g., agent_tgdrhw.scpbackup)
Would you like to use "bkclientlin" as the configured name of the ~~~~~~~ client? [y,n] (y) n agent_tgdrhw.scpbackup - Check the Master Server information, and if there are no issues, enter y.
Master server [bkmaster] reports the following CA Certificate fingerprints: SHA-256 Fingerprint: [BB:38:~~~~~~~~] SHA-1 Fingerpritn: [0D:E6:~~~~~~~] Is this correct [y,n] y - When selecting the Java GUI and JRE option, enter 2. The installation of the Java GUI and JRE packages will be omitted.
Choose an option from the list below. 1) Include the Java GUI and JRE 2) Exclude the Java GUI and JRE Java GUI and JRE option: [1,2] (2) :2 Excluding the installation of Java GUI and JRE packages - Check that the installation completed successfully.
Windows OS
To install the Backup Agent on Windows OS, follow these steps.
- After moving to the folder where the Backup Agent 10.1.1 installation file has been extracted, run the Setup.exe file with administrator privileges.
- If the installation archive contains an EEB directory in the format
NB_10.4.0.1_ETXXXXXX_1, you must perform the patch procedure after installing the Backup Agent, following the steps below.- When the Backup Agent installation is complete, go to the
NB_10.4.0.1_ETXXXXXX_1folder. eebinstaller_XXXXXXX_1_AMD64.exeRun the file with administrator privileges.- If there are multiple files, install all of them.
- When the Backup Agent installation is complete, go to the
- In the popup window for selecting the Client to install, select the Client to install, then click the OK button.
- In the Vertias NetBackup popup, select Yes. The installation popup opens, and the installation steps are displayed on the left side of the popup.
- Welcome When the step description is displayed, click the Next button.
- License Agreement When the step description is displayed, select the Agree with the veritas Software License Agreement item, then click the Next button.
- When the Install Type step description is displayed, make sure the Install to the computer only option is checked, then select the Custom installation option. After completing the selection, click the Next button.
- When the Option step description is displayed, verify the installation path and click the Next button. Client option information is displayed.
- Click the Change… button to change the installation path.
- After checking the Client Options information, click the Next button. The Log on information will be displayed.
- After checking the Log on information, click the Next button.
- Safe Abort Option: This option aborts the installation when a system restart is required (optional).
- When the System Name step description is displayed, enter the server environment information and click the Next button. The Master Server information will be displayed.
- Client Name: Enter the Agent information. Backup Agent Name.scpbackup (e.g.: agent_tgdrhw.scpbackup)
- Master Server Name: Enter the Backup Master name.
- After checking the Master Server information, select the I recognize the fingerprint for this host. Proceed with the certificate deployment. item. When you have finished selecting, click the Next button.
- When the Security step description is displayed, verify that the certificate deployment succeeded, then click the Next button.
- When the Install step description is displayed, review the Installation Summary and then click the Install button.
- When the installation is complete, click the Finish button.
Configure Security Group (Linux/Window)
If backing up a Virtual Server or GPU Server, you must configure a Security Group to communicate with the Backup Master. To configure the Security Group, check the backup information on the Backup Agent Details page and register it with the Security Group attached to the Server.
- IP: Backup Master IP
- Inbound / Outboud / (TCP) 1556, 13724 port
- Action: allow the connection
Check Backup Agent status
After the Backup Agent installation is complete, perform a communication test with the Backup Master and check the status.
Linux OS
Follow these steps to perform a communication test with the Backup Master on Linux OS.
- After entering the following command, perform a communication test with Backup Master and check the results.
- Command: # /usr/openv/netbackup/bin/bpclntcmd -pn
- An example of the communication test inspection results is as follows.
# /usr/openv/netbackup/bin/bpclntcmd -pn expecting response from server takre1p1bkm1 agent_tgdrhw.scpbackup agent_tgdrhw.scpbackup 10.252.25.4 52096
- Click the All Services > Storage > Backup menu in the Samsung Cloud Platform Console. Go to the Service Home page of Backup.
- On the Service Home page, click the Backup Agent menu. You will be taken to the Backup Agent List page.
- On the Backup Agent List page, click the resource to verify the communication test. You will be taken to the Backup Agent Details page.
- In the Connection Status item, click the Check Connection Status button. If communication with Backup Master is successful, Success will be displayed.
- Verify that the result values of the Backup Master communication test performed on the OS and the Samsumg Cloud Platform Console are identical.
Windows OS
Follow these steps to perform a communication test with Backup Master on Windows OS.
- After entering the following command, perform a communication test with Backup Master and check the results.
- Command: # [installation path]\Vertitas\NetBackup\bin\bpclntcmd.exe -pn
- An example of the communication test inspection results is as follows.
# C:\Vertitas\NetBackup\bin\bpclntcmd.exe -pn expecting response from server takre1p1bkm1 agent_tgdrhw.scpbackup agent_tgdrhw.scpbackup 10.252.25.4 52096
- In the Samsung Cloud Platform Console, click the All Services > Storage > Backup menu. Navigate to the Service Home page of Backup.
- From the Service Home page, click the Backup Agent menu. You will be taken to the Backup Agent list page.
- On the Backup Agent List page, click the resource to verify the communication test. You will be taken to the Backup Agent Details page.
- In the Connection Status item, click the Check Connection Status button. If communication with Backup Master is successful, Success will be displayed.
- Verify that the result values of the Backup Master communication test performed on the OS and Samsumg Cloud Platform Console are identical.
Delete Backup Agent
If you are not using the Backup Agent, you must remove the Backup Agent installed on each operating system.
Linux OS
To uninstall the Backup Agent on Linux OS, follow the steps below.
- Stop the Backup Agent service.
# /usr/openv/netbackup/bp.kill_all # /opt/VRTSpbx/bin/vxpbx_exchanged stop # /usr/openv/netbackup/bin/vxlogcfg -r -p 51216 - Delete the Backup Agent installation file.
# rpm –qa | grep –i VRTS → Backup Agent package 확인 # rpm –e VRTSnbcfg # /opt/pdde/pddeuninstall.sh –forceclean # rpm -e VRTSnbjava # rpm -e VRTSnbjre # rpm -e VRTSnbclt # rpm -e VRTSpbx # rpm -e VRTSnbpck # rpm -qa | grep -i VRTS → Backup Agent package 확인 후 남은 package 삭제 # rm -rf /usr/openv
Windows OS
To uninstall the Backup Agent on Windows OS, follow these steps.
- Stop the Backup Agent service.
# [설치경로]\Vertitas\NetBackup\bin\bpdown.exe -f -v # [설치경로]\Vertitas\NetBackup\bin\bpps.exe → 남은 Process 확인 후 kill 수행 - From Control Panel > Programs and Features, uninstall the Backup Agent program.
- Delete the Backup Agent installation folder.
3.5.2.5 - Use Replication
You can create a replica of the Agent Backup in a different location.
- The kr-south region does not provide replication functionality.
- Agentless Backup does not provide a replication feature.
- With Agentless Backup, you can select a backup storage location when applying for the service and store the backup copy in a different location.
Create a clone
When creating a Backup service, you can set up replication for use.
To create a backup, follow the steps below.
- Click the All Services > Storage > Backup menu. Go to the Service Home page of Backup.
- On the Service Home page, click the Create Backup button. You will be taken to the Create Backup page.
- On the Backup Creation page, enter the information required to create the service and select detailed options.
Category RequiredDetailed description Backup name Required Backup name - Enter 3 to 30 characters using letters and numbers
- Cannot be edited after service creation
Backup type Required Agent > Filesystem selection Backup replication Select Use after checking, select the clone location (region) - South Korea (kr-south) region is unavailable
Backup target Required After clicking the Select Server button, select one pre‑created server from the Bare Metal Server service. Filesystem Required Enter the target FileSystem for backup - The exact Filesystem used by the operating system must be entered. Incorrect input will prevent backup
- Backup is not possible when /dev/zero, /dev/null is entered
- Backup is not possible if the following special characters are included, depending on the operating system
- Linux:
:*<>\
- Linux:
Encryption Select Select whether to apply encryption Retention period Selection Retention period of the recovery target (backup) - Select from 2 weeks (14 days), 1 month (31 days), 3 months (93 days), 6 months (186 days), 1 year (365 days)
Schedule Select Backup auto-creation schedule - Set 1 Full Backup and up to 6 Incremental Backups
- Select Daily, Weekly, or Monthly
- Daily: Set the start time
- Weekly: Set the day of week and start time
- Monthly: Set the week number, day of week, and start time
- Week number: Choose from 1, 2, 3, 4, or the last week
- Day of week: Choose from Monday, Tuesday, Wednesday, Thursday, Friday, Saturday, Sunday
- Start time: Select in 30‑minute increments (00–23 hours, 00/30 minutes)
Table. Backup service information input fields - Summary Verify the detailed information and estimated billing amount generated in the panel, then click the Complete button.
- Once creation is complete, check the created resources on the Backup List page.
- Agent Backup applies server‑side encryption based on the AES‑256 algorithm when encryption is selected, which may cause a performance degradation of approximately 20 ~ 30%.
- The initial backup is created as a Full Backup regardless of the request details.
- Backup replication If you select a location in a different region, data transfer fees will be added.
Edit replication policy
You can change the replication status by modifying the replication policy.
To modify the replication policy, follow these steps.
- Click the All Services > Storage > Backup menu. You will be taken to the Service Home page of Backup.
- On the Service Home page, click the Backup menu. You will be taken to the Backup List page.
- On the Backup List page, click the resource to edit the replication policy. You will be taken to the Backup Details page.
- On the Backup Details page, click the Clone tab.
- Click the Edit button of the Replication Policy. The Edit Replication Policy popup opens.
- Use: Performs replication. If it is not used, you can modify it to be used.
- Unused: Stop backup replication. If unused, the Backup service can be terminated.
- Check the modified replication policy in the Replication tab of the Backup Details page.
3.5.3 - API Reference
3.5.4 - CLI Reference
3.5.5 - Release Note
Backup
- When performing Agent Backup, Virtual Server and GPU Server have been added as target servers.
- Now you can select one of Virtual Server, GPU Server, or Bare Metal Server.
- Add Backup Replication Tab
- In the Backup detail page, you can view the original and replica information on the Replication tab.
- Add download feature for backup-related information
- In the Backup detail page, you can download the Backup history, recovery targets, and recovery history list as an Excel file.
- Expand recovery scope
- When restoring from an agentless remote backup, you can select the restore location (target server or backup location).
- Expand backup location and target
- Agentless-based remote backup: You can back up and restore to a location different from the backup target server.
- Backup Agent feature added: You can back up the filesystem of a Bare Metal Server by configuring the Agent.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We launched the Backup service to provide a secure data backup and recovery solution.
- Since a backup policy includes the target, frequency, retention period, and other elements, users can configure a backup plan to match their business environment and requirements.
3.6 - Parallel File Storage
3.6.1 - Overview
Service Overview
Parallel File Storage is a high-performance parallel file storage based on All NVMe that can process large amounts of data quickly and efficiently.
Features
- Data Processing Speed Improvement: Distribute file data across multiple storage nodes to improve data processing speed and reduce analysis time.
- Various Field Utilization: Through fast data processing speed and analysis time, it can be used in various areas such as AI/ML analysis, big data analysis, and more.
Configuration diagram
Provided features
Parallel File Storage provides the following features.
- Volume Name: Users can set a name for each volume.
- Snapshot: Create a snapshot to restore to a specific point in time.
- Connected Resource: Can be connected and used in a Multi-node GPU Cluster.
Component
You can create a volume by selecting the disk type and protocol based on the user’s service environment and performance requirements. When using the snapshot feature, you can restore data to the desired point in time.
Volume
A volume (Volume) is the basic creation unit of the Parallel File Storage service and is used as data storage space. Users select a name and capacity to create a volume, then connect and use it in a Multi-node GPU Cluster.
The volume name generation rules are as follows.
- It must start with a lowercase English letter and can be set to 3 to 21 characters using lowercase letters, numbers, and special characters (
_).
Snapshot
Snapshot(Snapshot) is an image backup at a specific point in time. Using the image snapshot feature, you can recover data that has been changed or deleted. The user selects the snapshot created at the desired point in time from the snapshot list and performs the recovery.
You can create up to 50 snapshots.
- You can recover by selecting a specific snapshot from the snapshot list and creating a new volume based on that snapshot.
Preliminary Service
This is a list of services that must be pre-configured before creating the service. For details, refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Multi-node GPU Cluster | Physical GPU server for large‑scale high‑performance AI computation |
3.6.2 - How-to guides
Users can create a service by entering the required information for Parallel File Storage and selecting detailed options through the Samsung Cloud Platform Console.
Creating Parallel File Storage
You can create and use the Parallel File Storage service from the Samsung Cloud Platform Console.
To create a Parallel File Storage, follow these steps.
Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
On the Service Home page, click the Create Parallel File Storage button. You will be taken to the Create Parallel File Storage page.
Parallel File Storage Creation page, enter the information required to create the service.
Category RequiredDetailed description Volume name Required Enter the volume name - must start with a lowercase English letter
- Enter 3 to 21 characters using lowercase letters, numbers, and special characters (
_)
- Generate in the format ‘user input+{6-character UUID composed of lowercase English letters and numbers}’
- Cannot be modified after the service is created
capacity Required Enter the desired capacity - 1 ~ 1000 TB available
- Only expansion is possible after the service is created
Tag Select Add Tag - You can add up to 50 per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Parallel File Storage service creation information input itemsIn the summary panel, review the detailed information you created and the estimated charge amount, then click the Create button.
When the popup indicating creation opens, click the Confirm button.
- When creation is complete, check the created resources on the Parallel File Storage list page.
View Parallel File Storage details
Parallel File Storage service allows you to view and edit the full resource list and detailed information.
Follow these steps to view detailed information about the Parallel File Storage service.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- From the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- On the Parallel File Storage List page, click the resource to view detailed information. You will be taken to the Parallel File Storage Details page.
- Parallel File Storage Details page displays status information and additional feature information, and is composed of Details, Snapshot List, Tags, and Job History tabs.
Category Detailed description Volume status Volume status representation - Creating: Creating
- Available: Created, server connection available
- Extending: Extending capacity
- Deleting: Deleting service
- Error Deleting: Abnormal state while deleting
- Error: Abnormal state while creating
- Error Extending: Abnormal state while extending
Create snapshot Immediately create a snapshot at the time of creation - Up to 50 can be created
- For detailed information on snapshot creation, refer to 스냅샷 생성하기
Service termination Cancel service button Table. Parallel File Storage status information and additional features
- Parallel File Storage Details page displays status information and additional feature information, and is composed of Details, Snapshot List, Tags, and Job History tabs.
Detailed information
On the Parallel File Storage List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date | Service creation timestamp |
| Volume name | Volume name |
| Capacity | Volume capacity
|
| Mount information | Mount information
|
| connected resource | List of Connected Resources (Multi-node GPU Server)
|
Snapshot list
Parallel File Storage List page allows you to view the snapshot of the selected resource.
- To create and manage snapshots, see Using Snapshots.
- You can restore data on a per-file basis using snapshots. For more details, see File-level restoration.
| Category | Detailed description |
|---|---|
| Use snapshot | Total size of stored snapshots |
| Snapshot name | Snapshot name |
| Capacity | Snapshot size |
| Creation date and time | Snapshot creation timestamp |
| status | Snapshot status
|
| Delete | Delete the selected snapshot from the snapshot list |
tag
Parallel File Storage List page allows you to view the tag information of the selected resource and to add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
On the Parallel File Storage list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Parallel File Storage Resource Management
If you need to modify settings for Parallel File Storage or add or remove connected servers, you can perform the tasks on the Parallel File Storage Details page.
Modify capacity
You can expand the capacity of Parallel File Storage.
To modify the capacity, follow the steps below.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- On the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- On the Parallel File Storage List page, click the resource to modify its capacity. You will be taken to the Parallel File Storage Details page.
- Click the Edit button of the Capacity item. The Capacity Edit popup window opens.
- After entering the capacity to be expanded, click the Confirm button.
- You can expand up to a maximum of 1000 TB, including the existing capacity.
- When a popup notifying of capacity expansion opens, click the Confirm button.
Edit linked resources
You can connect resources to Parallel File Storage or disconnect resources that are already connected.
- Additional modifications are not possible while a connection resource is being edited, and you can only modify the connection resource when the volume is in the Available state.
- If communication with the target resource is interrupted or the connection is unavailable, the connection resource cannot be modified.
- When connecting resources, you can link up to 300 resources at the same location. If you exceed 300, use the API.
To modify the connection resource, follow these steps.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- Click the Parallel File Storage menu on the Service Home page. You will be taken to the Parallel File Storage list page.
- Parallel File Storage List page, click the resource you want to edit the connection for. You will be taken to the Parallel File Storage Details page.
- Click the Edit button of the Linked Resource item. The Linked Resource Selection popup opens.
- Select the resource to connect or uncheck the resource to disconnect, then click the Confirm button.
- You can select multiple resources simultaneously.
- The Multi-node GPU Cluster server is connected to the Parallel File Storage via two N/W interfaces. To optimize storage performance, ensure that both N/W connections are properly established.
- Parallel File Storage Details page, if the resource’s connection status is Partial Success, follow the steps below to verify.
- Check whether the two N/W interfaces for connecting Parallel File Storage in the Multi-node GPU Cluster are functioning properly.
- After disconnecting from Parallel File Storage, reconnect.
- On the Parallel File Storage Details page, check the resource’s connection status.
- When disconnecting, you must first access the server and perform the disconnection tasks (Umount, disconnect network drive).
- If the connection is terminated without OS intervention, a status error (Hang) may occur on the connection server.
- Refer to Unmount Server for detailed information on the server unmount operation.
- When adding a connected server, you must first perform the connection tasks (Mount, network drive connection) on the server.
- For detailed information about server connection, see Connecting to Server.
Cancel Parallel File Storage
You can reduce operating costs by terminating unused Parallel File Storage.
However, if you terminate the service, the running service may be stopped immediately, so you should fully consider the impact of the interruption before proceeding with the termination.
- Please note that data cannot be recovered after termination.
- If there are resources connected to Parallel File Storage, you cannot cancel it. Remove all connected resources before canceling the service.
- You can only delete a volume when its status is Available or Error.
To cancel Parallel File Storage, follow the steps below.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- From the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- On the Parallel File Storage list page, select the resource to cancel and click the Cancel Service button.
- You can go to the Parallel File Storage Details page of the resource to be terminated and delete it individually.
- When the pop-up notifying termination opens, click the Confirm button.
- When termination is complete, check on the Parallel File Storage List page whether the resource has been terminated.
3.6.2.1 - Use Snapshot
You can create, delete, or recover using snapshots of Parallel File Storage.
Create Snapshot
You can create snapshots of Parallel File Storage.
To create a snapshot, follow these steps.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- From the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- Parallel File Storage List page, click the resource to create a snapshot. You will be taken to the Parallel File Storage Details page.
- On the Parallel File Storage Details page, click the Create Snapshot button.
- When the popup notifying snapshot creation opens, click the Confirm button.
- Click the Snapshot List button. It takes you to the File Storage snapshot list page.
- Check the generated snapshot.
- You can only restore from the most recent snapshot. To restore from an earlier snapshot, delete the latest snapshot.
- Snapshot charges are included in the File Storage usage fees.
Recover Snapshot
You can restore using the snapshot you created.
To restore from a snapshot, follow these steps.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- From the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- On the Parallel File Storage List page, click the resource to restore the snapshot. You will be taken to the Parallel File Storage Details page.
- On the Parallel File Storage Details page, click the Snapshot List tab.
- Check the latest snapshot with Available status in the snapshot list.
- When restoring, the volume is recovered from the selected snapshot.
- Click the Snapshot Recovery button. The Snapshot Recovery popup opens.
- After checking the snapshot name and creation timestamp, click the Confirm button.
- The snapshot status changes to Reverting when recovery starts and to Available upon completion.
- You can only restore from the most recent snapshot. To restore from an earlier snapshot, delete the latest snapshot.
- During recovery, it restores from the latest snapshot in the Available state, and the situations where recovery is not possible are as follows.
- When the Parallel File Storage volume is not in the Available state
- If there are no recoverable snapshots.
- If the latest snapshot changes while creating a recovery.
- If the latest snapshot is not in Available state.
Delete snapshot
You can delete snapshots of Parallel File Storage.
To delete a snapshot, follow these steps.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- From the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- Parallel File Storage List page, click the resource to delete the snapshot. You will be taken to the Parallel File Storage Detail page.
- On the Parallel File Storage Details page, click the Snapshot List tab.
- In the snapshot list, click the More > Delete button at the far right of the snapshot to be restored.
- When the popup notifying you of snapshot deletion opens, click the Confirm button.
3.6.2.2 - Install Agent
To use the Parallel File Storage service, you must connect to the target server and install the Agent. After installing the Agent, mount on the server to use Parallel File Storage.
Install Agent and Connect to Server (Mount)
The Agent installation and server connection consist of six steps. Follow the procedure below.
- Agent installation
- Account login
- Create Mount Point
- Filesystem Mount
- Check mount
- fstab registration
Install Agent
Install the Agent using the Mount IP.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- On the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- On the Parallel File Storage List page, click the resource to be used on the connected server. You will be taken to the Parallel File Storage Details page.
- After checking the server in the Connection Server item, connect.
- Follow the example below to install the Volume Agent and connect the server (Mount).
curl <Mount IP>:14000/dist/v1/install | sh
root@RESD-s4sr3h:/# curl http://10.102.160.254:14000/dist/v1/install | sh
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 1424 100 1424 0 0 1978k 0 --:--:-- --:--:-- --:--:-- 1390k
Downloading WekaIO CLI 4.2.4.29-hcsf
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 58.7M 100 58.7M 0 0 1079M 0 --:--:-- --:--:-- --:--:-- 1088M
Installing...
Installing agent of version 4.2.4.29-hcsf
The agent is configured to detect cgroups - cgroups v1 not found, cgroups are disabled
Waiting for agent service to be ready
Installation finished successfully
WekaIO CLI 4.2.4.29-hcsf is now installed
Account login
Log in using the mount information for the server mount.
#weka user login -H <Mount IP>
root@RESD-s4sr3h:/# weka user login -H 10.102.160.254
Organization (enter name or ID, default: 0) admin_org
Username: admin_reg
Password: ###########
+------------------------------+
| Login completed successfully |
+------------------------------+
Create Mount Point
Create a mount point on the server to mount the filesystem.
#mkdir /mnt/weka
Filesystem Mount
Mount the filesystem according to the following procedure.
- Use the #ip a command to check the IP and Interface Name information for Mount.
root@RESD-s4sr3h:/# ip a |grep 10.102
inet 10.102.160.248/23 brd 10.102.161.255 scope global ibs4f0.8010
inet 10.102.160.249/23 brd 10.102.161.255 scope global ibP1s8f0.8010
The IP information and Interface Name that can be identified in the above example are as follows.
- IP: 10.102.160.10, 10.102.160.11
- Interface Name: ibs4f0.8010, ibP1s8f0.8010
- Use the verified IP and Interface Name to execute the Mount command.
mount -t wekafs <backend-server-IP-address>/<filesystem-name> -o net=<VF interface>/<synthetic network interface IP address>/mask -o mgmt_ip=<Management-IP> /mnt/weka
root@RESD-s4sr3h:/# mount -t wekafs -o num_cores=8 -o net:ha=ibs4f0.8010,net:ha=ibP1s8f0.8010,mgmt_ip='10.102.160.10+10.102.160.11' 10.102.160.254/wekafs /mnt/weka
Mounting 10.102.161.254/bmtfs on /weka_fs
Basing mount on container client
Downloading [1/21] http://10.102.160.254:14000/dist/v1/image/envoy-fe-e6b882a6bce3c0de8cd9c7833df1a567.squashfs
Downloading [2/21] http://10.102.160.254:14000/dist/v1/image/weka-driver-1.0.0-d10ca9cff59b98778b4314014569e00f.squashfs
Downloading [3/21] http://10.102.160.254:14000/dist/v1/image/weka-driver-igb-uio-4.0.0-7eee7dc5b7f1d85a1be0e448d5e97312.squashfs
Downloading [4/21] http://10.102.160.254:14000/dist/v1/image/container-s3-tmp-1.57f-9cb61c7e0ae3ca9e2b476c191e4e84ab.squashfs
Downloading [5/21] http://10.102.160.254:14000/dist/v1/image/container-smbw-weka-4.7.12.3-9b67132a85a950260f048955dc33c7a9.squashfs
Downloading [6/21] http://10.102.160.254:14000/dist/v1/image/weka-drain-tools-2d01044c641816d9002ca594a6ae9d90.squashfs
Downloading [7/21] http://10.102.160.254:14000/dist/v1/image/container-ganesha-dev-weka-5-11becf16b21c9635daa23a247340a7bd.squashfs
Downloading [8/21] http://10.102.160.254:14000/dist/v1/image/dependencies-1.0.0-9b64fdba87a4d6e6efa9ab5250169ec8.squashfs
Downloading [9/21] http://10.102.160.254:14000/dist/v1/image/weka-container-2.3.0-be66bcc7c9739b15cacd910d7cac031e.squashfs
Downloading [10/21] http://10.102.160.254:14000/dist/v1/image/weka-hostside-faf9aa30ec9ac7521ffbc9589ac23deb.squashfs
Downloading [11/21] http://10.102.160.254:14000/dist/v1/image/api-6f501306831ff9a223a7f706c5a661e1.squashfs
Downloading [12/21] http://10.102.160.254:14000/dist/v1/image/weka-s3-3508f2f1afb4900ab11c4772e327b1ac.squashfs
Downloading [13/21] http://10.102.160.254:14000/dist/v1/image/weka-ganesha-5c6ef6d08e31f80580f50bab7d1b8134.squashfs
Downloading [14/21] http://10.102.160.254:14000/dist/v1/image/dashboard-dfb78995154ab40fb274037ac9fe8a45.squashfs
Downloading [15/21] http://10.102.160.254:14000/dist/v1/image/container-samba-weka-4.7.12.3-69835f740573b7ded6faed1dfe737bed.squashfs
Downloading [16/21] http://10.102.160.254:14000/dist/v1/image/weka-smbw-8a1430e5f0f2cca6d2a4af603d630882.squashfs
Downloading [17/21] http://10.102.160.254:14000/dist/v1/image/ui-1.0.0-5bc747765d326e6e1c3488285822f459.squashfs
Downloading [18/21] http://10.102.160.254:14000/dist/v1/image/weka-samba-8102bcf3d3a81f02755cb2e75b1b8d16.squashfs
Downloading [19/21] http://10.102.160.254:14000/dist/v1/image/weka-node-fbd17baa570969b6da7e5561f1eb652f.squashfs
Downloading [20/21] http://10.102.160.254:14000/dist/v1/image/ofed-b643ca3e4fa06d84416d463afe74a66a.squashfs
Downloading [21/21] http://10.102.160.254:14000/dist/v1/image/driver-uio-pci-generic-1.0.0-322a3daa84c41eeb6f0cafd0802fbf50.squashfs
Finished getting version 4.2.4.29-hcsf
Creating Weka container 'client' in version 4.2.4.29-hcsf
Preparing version 4.2.4.29-hcsf of container client
Base port was not explicitly provided, the container will use 14000
Applying resources
Starting container 'client'
Waiting for container 'client' to join cluster
Container "client" is ready (pid = 392216)
Calling the mount command
Cgroups v1 not found, running without cgroups
Mount completed successfully
Check mount
#df -h Run the command to check whether the filesystem is mounted.
root@RESD-s4sr3h:/# df -h
Filesystem Size Used Avail Use% Mounted on
tmpfs 202G 3.8M 202G 1% /run
/dev/nvme2n1p2 3.5T 37G 3.3T 2% /
tmpfs 1008G 0 1008G 0% /dev/shm
tmpfs 5.0M 0 5.0M 0% /run/lock
/dev/nvme2n1p1 511M 6.1M 505M 2% /boot/efi
tmpfs 202G 4.0K 202G 1% /run/user/0
/dev/loop0 2.0G 47M 2.0G 3% /opt/weka/logs
tmpfs 1008G 12K 1008G 1% /opt/weka/data/agent/tmpfss/cleanup
tmpfs 1008G 2.0G 1006G 1% /opt/weka/data/agent/tmpfss/client-persistent-tmpfs
tmpfs 1008G 0 1008G 0% /opt/weka/data/agent/tmpfss/cross-container-rpc-the-tmpfs
tmpfs 1008G 4.0K 1008G 1% /opt/weka/data/agent/tmpfss/cleanup_before_stop_and_delete
bmtfs 1.9T 537G 1.3T 29% /weka_fs
fstab registration
Register fstab so that it automatically mounts on server Reboot.
To register fstab, run the #vi /etc/fstab command, then add the following command.
root@RESD-s4sr3h:/# cat /etc/fstab
# /etc/fstab: static file system information.
#
# Use 'blkid' to print the universally unique identifier for a
# device; this may be used with UUID= as a more robust way to name devices
# that works even if disks are added and removed. See fstab(5).
#
# <file system> <mount point> <type> <options> <dump> <pass>
# / was on /dev/nvme2n1p2 during curtin installation
/dev/disk/by-uuid/8683a4fb-ee21-47c2-938e-2be0beea2089 / ext4 defaults 0 1
# /boot/efi was on /dev/nvme2n1p1 during curtin installation
/dev/disk/by-uuid/92ED-55CC /boot/efi vfat defaults 0 1
/swap.imgnoneswapsw00
10.102.160.254/wekafs /mnt/weka wekafs num_cores=8,net:ha=ibs4f0.8010,net:ha=ibP1s8f0.8010,mgmt_ip=10.102.160.10+10.102.160.11,x-systemd.requires=wekaagent.service,x-systemd.mount-timeout=infinity,_net
dev 0 0
Disconnect server (Umount)
To disconnect the server, first log into the server and perform the disconnect operation (Umount), then disconnect the server from the Console.
To disconnect from the server, follow these steps.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- On the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- On the Parallel File Storage List page, click the resource to disconnect the server. Navigate to the Parallel File Storage Details page.
- After checking the server information in the Connection Server item, connect to the server.
- Refer to the commands shown in the following example to perform the unmount (Umount) operation.
# umount /mnt/weka
# vi /etc/fstab
3.6.2.3 - File-level Recovery
You can restore data on a per‑file basis using the generated snapshot.
Using file-level recovery
You can connect to the server to select and recover data.
To perform file-level recovery, follow these steps.
- Click the All Services > Storage > Parallel File Storage menu. You will be taken to the Service Home page of Parallel File Storage.
- From the Service Home page, click the Parallel File Storage menu. You will be taken to the Parallel File Storage List page.
- On the Parallel File Storage List page, click the resource to recover the file. You will be taken to the Parallel File Storage Details page.
- In the Connected Resources item, verify the linked server and then connect to that server.
- Check the mount name of the File Storage on the server.
- The mount name is the same as the mount point configured on the server for mounting the filesystem.
- Navigate to the snapshot location under the mount name.
# cd /Mount명/.snapshots/snapshot명 - After checking the files to be restored at the snapshot location, restore them to the required path.
# cp -arp /Mount명/.snapshots/snapshot명/파일/{복구 디렉토리}/
3.6.3 - API Reference
3.6.4 - CLI Reference
3.6.5 - Release Note
Parallel File Storage
- The feature to restore from snapshots has been added.
- You can restore from the most recently created snapshot.
- The Parallel File Storage service has been officially launched.
- It can store file data across multiple storage nodes, enabling fast and efficient processing of large-scale data.
- By achieving fast data processing speed and reducing analysis time, it can be utilized in various fields such as AI/ML analysis and big data analysis.
4 - Container
We provide execution and monitoring environments, as well as open-source software, to ensure containerized applications can operate reliably with Kubernetes.
4.1 - Kubernetes Engine
4.1.1 - Overview
Service Overview
Kubernetes Engine is a service that provides lightweight virtual computing, containers, and a Kubernetes cluster to manage them. Users can leverage a Kubernetes environment without complex preparation by installing, operating, and maintaining the Kubernetes Control Plane.
Features
Standard Kubernetes Environment Setup: You can use a standard Kubernetes environment without additional configuration through the built-in Kubernetes Control Plane. It is compatible with applications in other standard Kubernetes environments, allowing you to use standard Kubernetes applications without modifying code.
Easy Kubernetes Deployment: provides secure communication between the worker node (Worker Node) and the managed control plane, and quickly provisions worker nodes so users can focus on building applications on the provided container environment.
Convenient Kubernetes Management: For enterprise environments, we provide various management features to conveniently use the created Kubernetes clusters, including cluster information lookup and management via a dashboard, namespace management, and workload management functions.
Service Diagram
Provided features
Kubernetes Engine provides the following features.
- Cluster Management: You can create and manage clusters to use the Kubernetes Engine service. After creating a cluster, you can add services needed for operation such as nodes, namespaces, and workloads.
- Node Management: A node is a set of machines that run containerized applications. Every cluster must have at least one worker node to deploy applications. Nodes can be used by defining node pools. Nodes belonging to a node pool must have the same server type, size, and OS image, and creating multiple node pools enables flexible deployment strategies.
- Namespace Management: A namespace is a logical partition within a Kubernetes cluster and is used to specify access permissions or resource usage limits per namespace.
- Workload Management: A workload is an application running on Kubernetes Engine. After creating a namespace, you can add or delete workloads. Workloads are created and managed per item such as Deployment, Pod, StatefulSet, DaemonSet, Job, and CronJob.
- Service and Ingress Management: A service is an abstraction that exposes applications running in a set of pods as a network service, and an ingress is used to expose HTTP and HTTPS paths from outside the cluster to inside the cluster. After creating a namespace, you can create or delete services, endpoints, ingresses, and ingress classes.
- Storage Management: You can create and manage the storage to be used when using Kubernetes Engine. Storage is created and managed per PVC, PV, and StorageClass items.
- Configuration Management: When you need to manage values that change inside containers across multiple environments such as Dev/Prod, creating separate images to handle them via environment variables is inconvenient and wasteful. In Kubernetes, you can manage environment variables or configuration settings as variables that can be changed externally and injected when a Pod is created; at that point you can use ConfigMaps and Secrets.
- Permission Management: When multiple users access a Kubernetes cluster, you can assign permissions per specific API or namespace to define the access scope. By applying Kubernetes’ role-based access control (RBAC) feature, you can set permissions for clusters or namespaces. You can create and manage ClusterRoles, ClusterRoleBindings, Roles, and RoleBindings.
Component
control plane
Control Plane is the component that serves as the master node in the Kubernetes Engine service. The master node is the cluster’s management node, responsible for managing the other nodes in the cluster. A cluster is the basic creation unit of the Kubernetes Engine service and is used for managing node pools, objects, controllers, etc., that belong to it. Users configure the cluster name (cluster name), control plane, network, File Storage, and then create node pools within the cluster for use. The master node assigns work to the cluster, monitors node status, and handles data communication between nodes.
The cluster name creation rules are as follows.
- It must start with a letter and can be set using letters, numbers, and special characters (
-) within 3 to 30 characters. - It must not duplicate an already existing cluster name.
worker node
The worker node (Worker Node) is a compute node in the cluster that performs tasks. It receives task assignments from the cluster’s master node, executes them, and reports the results back to the master node. All nodes created within a node pool and namespace serve as worker nodes.
The rules for creating a node pool, which is a collection of worker nodes, are as follows.
- A node pool must contain at least one node for the application deployment to be possible.
- A maximum of 100 nodes can be created within a node pool.
- Since the maximum number of nodes is 100, you can freely create up to 100 nodes—for example, with 100 node pools you get 1 node per pool, and with 50 node pools you get 2 nodes per pool.
- It is possible to configure block storage attached to a node pool.
- You can configure the server type, size, and OS image for nodes in a node pool, and they must all be identical.
- Through the Auto-Scaling service, you can configure automatic scaling and shrinking of node pools according to the requirements of the deployed application.
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
| Storage | File Storage | A storage that allows multiple clients to share files over the network
|
4.1.1.1 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by using ServiceWatch, released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a seamless monitoring environment.
Detailed information about ServiceWatch is available in the ServiceWatch Overview.
Kubernetes Engine monitoring metrics
The table below shows the monitoring metrics of Kubernetes Engine that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Cluster Namespaces [Active] | Number of namespaces in active state | cnt |
| Cluster Namespaces [Total] | Total number of namespaces in the cluster | cnt |
| Cluster Nodes [Ready] | Number of nodes in READY state | cnt |
| Cluster Nodes [Total] | Total number of nodes in the cluster | cnt |
| Cluster Pods [Failed] | Number of failed-state pods in the cluster | cnt |
| Cluster Pods [Pending] | Number of pending pods in the cluster | cnt |
| Cluster Pods [Running] | Number of pods in running state within the cluster | cnt |
| Cluster Pods [Succeeded] | Number of succeeded pods in the cluster | cnt |
| Cluster Pods [Unknown] | Number of pods in unknown state within the cluster | cnt |
| Instance Status | cluster status | status |
| Namespace Pods [Failed] | Number of failed-state pods in a namespace | cnt |
| Namespace Pods [Pending] | Number of pending pods in a namespace | cnt |
| Namespace Pods [Running] | Number of running pods in a namespace | cnt |
| Namespace Pods [Succeeded] | Number of succeeded-state pods in a namespace | cnt |
| Namespace Pods [Unknown] | Number of pods in unknown state within a namespace | cnt |
| Namespace GPU Clock Frequency | SM clock frequency in the Namespace | MHz |
| Namespace GPU Memory Usage | Memory utilization in the Namespace | % |
| Namespace GPU Usage | GPU utilization in the Namespace | % |
| Node CPU Size [Allocatable] | Node CPU allocatable | cnt |
| Node CPU Size [Capacity] | CPU capacity in the node | cnt |
| Node CPU Usage | CPU usage per node | % |
| Node CPU Usage [Request] | CPU request_ratio within node | % |
| Node CPU Used | CPU utilization within the node | status |
| Node Filesystem Usage | Node FS utilization | % |
| Node Memory Size [Allocatable] | memory allocatable within the node | bytes |
| Node Memory Size [Capacity] | Node memory utilization | bytes |
| Node Memory Usage | Node memory utilization | % |
| Node Memory Usage [Request] | memory request_ratio within node | % |
| Node Memory Workingset | memory working set within the node | bytes |
| Node Network In Bytes | Node network rx bytes | bytes |
| Node Network Out Bytes | Node network tx bytes | bytes |
| Node Network Total Bytes | Node network total bytes | bytes |
| Node Pods [Failed] | Number of pods in failed state within the node | cnt |
| Node Pods [Pending] | Number of pending pods in the node | cnt |
| Node Pods [Running] | Number of running pods per node | cnt |
| Node Pods [Succeeded] | Number of succeeded pods in the node | cnt |
| Node Pods [Unknown] | Number of unknown‑state pods in the node | cnt |
| Pod CPU Usage [Limit] | CPU usage_limit_ratio in the pod | % |
| Pod CPU Usage [Request] | CPU request_ratio in the pod | % |
| Pod CPU Usage | CPU usage within the pod | % |
| Pod GPU Clock Frequency | SM clock frequency in the Pod | MHz |
| Pod GPU Memory Usage | Memory utilization within the Pod | % |
| Pod GPU Usage | GPU utilization within the Pod | % |
| Pod Memory Usage [Limit] | memory usage_limit_ratio in pod | % |
| Pod Memory Usage [Request] | memory request_ratio in pod | % |
| Pod Memory Usage | Memory usage within pod | bytes |
| Pod Network In Bytes | network rx bytes in pod | bytes |
| Pod Network Out Bytes | network tx bytes in pod | bytes |
| Pod Network Total Bytes | Network total bytes in pod | bytes |
| Pod Restart Containers | container restart count in pod | cnt |
| Workload Pods [Running] | - | cnt |
4.1.1.2 - ServiceWatch Metrics
Kubernetes Engine sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the Kubernetes Engine namespace.
The metrics whose names are displayed in bold below are the metrics selected as key metrics among the default metrics provided by Kubernetes Engine. Key metrics are used to configure service dashboards that are automatically generated for each service in ServiceWatch.
Each metric indicates through the user guide which statistical values are meaningful when viewing that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
| Indicator name | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| cluster_up | Cluster up | Count |
|
| cluster_node_count | Cluster node count | Count |
|
| cluster_failed_node_count | Number of failed nodes in the cluster | Count |
|
| cluster_namespace_phase_count | Number of cluster namespace phases | Count |
|
| cluster_pod_phase_count | Number of cluster pod phases | Count |
|
| node_cpu_allocatable | Node CPU allocatable amount | - |
|
| node_cpu_capacity | Node CPU capacity | - |
|
| node_cpu_usage | Node CPU usage | - |
|
| node_cpu_utilization | Node CPU utilization | - |
|
| node_memory_allocatable | Node memory allocatable amount | Bytes |
|
| node_memory_capacity | Node memory capacity | Bytes |
|
| node_memory_usage | Node memory usage | Bytes |
|
| node_memory_utilization | Node memory usage rate | - |
|
| node_network_rx_bytes | Node network received bytes | Bytes/Second |
|
| node_network_tx_bytes | Node network transmitted bytes | Bytes/Second |
|
| node_network_total_bytes | Total bytes of the node network | Bytes/Second |
|
| node_number_of_running_pods | Number of pods running on a node | Count |
|
| namespace_number_of_running_pods | Number of running pods in a namespace | Count |
|
| namespace_deployment_pod_count | Namespace deployment pod count | Count |
|
| namespace_statefulset_pod_count | Namespace StatefulSet pod count | Count |
|
| namespace_daemonset_pod_count | Namespace DaemonSet Pod Count | Count |
|
| namespace_job_active_count | Active namespace job count | Count |
|
| namespace_cronjob_active_count | Number of active namespace cron jobs | Count |
|
| pod_cpu_usage | Pod CPU usage | - |
|
| pod_memory_usage | Pod memory usage | Bytes |
|
| pod_network_rx_bytes | Pod network received bytes | Bytes/Second |
|
| pod_network_tx_bytes | Pod network transmit bytes | Bytes/Second |
|
| pod_network_total_bytes | Pod network total bytes | Count |
|
| container_cpu_usage | Container CPU usage | - |
|
| container_cpu_limit | Container CPU limit | - |
|
| container_cpu_utilization | Container CPU usage | - |
|
| container_memory_usage | Container memory usage | Bytes |
|
| container_memory_limit | Container memory limit | Bytes |
|
| container_memory_utilization | Container memory usage | - |
|
| node_gpu_count | Number of node GPUs | Count |
|
| gpu_temp | GPU temperature | - |
|
| gpu_power_usage | GPU power consumption | - |
|
| gpu_util | GPU utilization | Percent |
|
| gpu_sm_clock | GPU SM clock | - |
|
| gpu_fb_used | GPU FB usage | Megabytes |
|
| gpu_tensor_active | GPU Tensor Utilization | - |
|
| pod_gpu_util | Pod GPU utilization | Percent |
|
| pod_gpu_tensor_active | Pod GPU Tensor Utilization | - |
|
4.1.2 - How-to guides
Users can create a service by entering the required information for the Kubernetes Engine and selecting detailed options through the Samsung Cloud Platform Console.
Create Kubernetes Engine
You can create and use the Kubernetes Engine service in the Samsung Cloud Platform Console.
You can create and manage clusters to use the Kubernetes Engine service. After creating the cluster, you can add services needed for operation such as nodes, namespaces, and workloads.
In the network settings of Kubernetes Engine, you can select up to 4 Security Groups.
- If you manually add a Security Group to a node created by Kubernetes Engine on the Virtual Server service page, it may be automatically removed because it is not managed by Kubernetes Engine.
- For nodes, be sure to add and manage the Security Group in the network settings of the Kubernetes Engine service.
Managed Security Group is automatically managed in Kubernetes Engine.
- Do not use it for any user-defined purpose because if you delete a Managed Security Group or add/delete rules, it will automatically be restored.
Create a cluster
You can create and use a Kubernetes Engine cluster service in the Samsung Cloud Platform Console.
To create a Kubernetes Engine cluster, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Create Cluster button. 2. Navigate to the Create Cluster page.
- Create Cluster page, enter the information needed to create the service, and select detailed options.
- In the Service Information Input area, enter or select the required information.
Category RequiredDetailed description Cluster name Required Cluster name - must start with an English letter and be entered using English letters, numbers, and special characters (
-) within 3 - 30 characters
Control plane settings > Kubernetes version Required Select Kubernetes version Control plane settings > Private endpoint allowed resources Select After selecting Enable, click Add to select the resource to allow access to the private endpoint - Only resources in the same account and the same region can be registered
- Regardless of whether Enable is enabled, the nodes of the cluster can access the private endpoint
Control Plane Settings > Public Endpoint Select After selecting Use, enter the public endpoint Allowed IP range for access as 192.168.99.0/24 - Set the access control IP range to allow external access to the Kubernetes API server endpoint
- If external access is not required, you can disable it to reduce security threats
ServiceWatch log collection Select Set whether to enable log collection so that cluster logs can be viewed in ServiceWatch - Enable selection provides 5 GB of log storage free for all services within the Account, and charges apply based on storage volume when exceeding 5 GB
- If you need to view cluster logs, it is recommended to enable the ServiceWatch log collection feature
Cloud Monitoring log collection Select Set whether to enable log collection so that logs for the cluster can be viewed in Cloud Monitoring - If you select Use, 1 GB of log storage is provided for free across all services in the Account, and any data exceeding 1 GB will be deleted sequentially
Network Settings Essential Network connection settings for the node pool - VPC name: Select a pre‑created VPC
- Subnet name: Select a standard Subnet to use from the subnets of the selected VPC
- Security Group: Click the Select button and then choose a Security Group in the Select Security Group popup
- Up to 4 Security Group can be selected
StorageClass setting Required Select the storage volume to use in the cluster - NFS Volume: After clicking the Search button, select the file storage in the File Storage Selection popup. The default file storage supports only the NFS format
Table. Kubernetes Engine service information input items - must start with an English letter and be entered using English letters, numbers, and special characters (
- Additional Information Input area, please enter or select the required information.
Category required statusDetailed description tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, input or select Key, Value values
Table. Kubernetes Engine additional information input fields
- In the Service Information Input area, enter or select the required information.
- Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- Once creation is complete, verify the created resources on the Cluster List page.
View cluster details
The Kubernetes Engine service allows you to view and edit the full list of resources and detailed information. Cluster Details page consists of Details, Node Pools, Tags, Job History tabs.
To view detailed cluster information, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- Click the Cluster menu on the Service Home page. 2. Navigate to the Cluster List page.
- Cluster List page, click the resource (cluster) whose detailed information you want to view. 3. Navigate to the Cluster Details page.
- Cluster Details page displays the cluster’s status information and detailed information, and it consists of Details, Node Pools, Tags, Job History tabs.
Category Detailed description Cluster status Kubernetes Engine cluster status - Creating: in progress
- Running: creation complete / operational
- Updating: version upgrade in progress
- Deleting: in progress
- Error: error occurred
Service cancellation Button to delete a Kubernetes Engine cluster - To delete a Kubernetes Engine service, you must delete all node pools added to the cluster
- If the service is deleted, the running service may be terminated immediately, so deletion is required after considering the impact of service interruption
Table. Cluster status information and additional features
- Cluster Details page displays the cluster’s status information and detailed information, and it consists of Details, Node Pools, Tags, Job History tabs.
Detailed Information
On the Cluster List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification timestamp | Date and time the service information was modified |
| Cluster name | Cluster name |
| LLM Endpoint | LLM Endpoint information |
| Control area configuration | Check the assigned Kubernetes control plane (Control Plane) version and allowed access scope
|
| Network Settings | View the VPC, Subnet, and Security Group information configured when creating a Kubernetes Engine cluster
|
| StorageClass configuration | If you click the NFS volume name, you can view detailed information on the storage details page |
- The version of Kubernetes Engine is expressed as
[major].[minor].[patch], and you can upgrade only one minor version at a time.- Example: version
1.11.x > 1.13.x(Not allowed) / version1.11.x > 1.12.x(Allowed)
- Example: version
- If you are using a Kubernetes version that has reached end of support or a version that is scheduled to reach end of support, a red exclamation mark will appear to the right of the version. * If this icon is displayed, we recommend upgrading the Kubernetes version.
Node Pool
You can view, add, modify, or delete cluster node pool information. For detailed information on using node pools, refer to 노드 관리하기.
| Category | Detailed description |
|---|---|
| Add node pool | Add a node pool to the current cluster
|
| Node pool list | Check the list of node pools created in the current cluster
|
| More menu | Provides node pool management functionality
|
If a red exclamation‑mark icon appears on the node pool version, the node pool’s server OS is not supported in newer Kubernetes versions. The node pool server OS must be upgraded to ensure stable service.
- To upgrade the node pool version, delete the existing node pool and then create a new node pool with a higher server OS version.
Tag
On the Cluster List page, you can view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Cluster List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Cluster Resources
To manage cluster resources, we provide cluster version upgrades, kubeconfig downloads, and control‑plane logging modification features.
Even without create/delete permissions, Security Group and Virtual Server are created/deleted by Kubernetes Engine for lifecycle management purposes, and the creator/modifier is recorded as System.
Cluster version upgrade
If there is a version available for upgrade from the cluster’s Kubernetes version, you can perform the upgrade on the Cluster Details page.
- Check the following items before upgrading the cluster.
- Check if the cluster’s status is Running
- Check that the status of all node pools in the cluster is Running or Deleting.
- Verify that all node pool versions in the cluster match the cluster version.
- Check whether automatic scaling (up/down) of all node pools in the cluster and the node auto-recovery feature are disabled.
- After upgrading the cluster, proceed with the node pool upgrade. * The control plane and node pool upgrades of a Kubernetes cluster are performed separately.
- You can upgrade only one minor version at a time.
- Example: version 1.12.x > 1.13.x (possible) / version 1.11.x > 1.13.x (not possible)
- After an upgrade, you cannot perform a downgrade or rollback, so to use a previous version again you must create a new cluster.
- User systems that are using an end‑of‑life Kubernetes version may become vulnerable, so upgrade the control plane and node pool versions directly from the Samsung Cloud Platform Console.
- There are no additional costs associated with the upgrade.
- Please conduct compatibility testing of the upgrade version in advance to ensure stable system operation for users.
Pre-upgrade preparation for cluster version
When upgrading the cluster version, there is no need to delete and recreate API objects. For the migrated API, all existing API objects can be read and updated using the new API version. However, due to the deprecated API in older versions of Kubernetes, you may be unable to read or modify existing objects, or create new objects. Therefore, for system stability, we recommend migrating the client and manifest before upgrading.
Migrate the client and manifest using the following method.
- Download the latest version of the client (e.g., kubectl) and install it on the cluster, then modify the YAML to reference the new API.
- Or use a separate plugin (kubectl convert) to convert automatically. For detailed instructions, refer to the Kubernetes official documentation > Install and configure kubectl on Linux.
Upgrading Cluster and Node Pool Versions
To update the cluster and node pool, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engines.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, click the resource (cluster) to upgrade the version. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, click the Edit icon of the Kubernetes version. 4. Cluster version upgrade A popup window opens.
- Select the Kubernetes version to upgrade, and click the Confirm button.
- It may take a few minutes for the cluster upgrade to complete.
- During the upgrade, the cluster status is shown as Updating, and when the upgrade is complete, it is shown as Running.
- When the upgrade is complete, select the Node Pool tab. 6. Navigate to the Node Pool page.
- Click the More button of the node pool item, then click Node Pool Upgrade. 7. Node Pool Version Upgrade A popup window opens.
- Node Pool Version Upgrade After reviewing the message in the popup window, click the Confirm button.
- It may take a few minutes for the node pool upgrade to complete.
- While the upgrade is in progress, the node pool status is shown as Updating, and when the upgrade is complete, it is shown as Running.
Download kubeconfig
You can download the administrator/user kubeconfig settings for the cluster’s public and private endpoints as a yaml document.
To download the cluster’s kubeconfig configuration, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engines.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, click the resource (cluster) to download the kubeconfig. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, click the Download admin kubeconfig/Download user kubeconfig button of the desired endpoint.
- You can download the kubeconfig file in YAML format for each permission.
Modify resources that allow private endpoint access
You can modify the resource settings that allow private endpoint access to the cluster.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engines.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- Cluster List page, click the resource (cluster) whose private endpoint access control you want to modify. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, click the Edit icon for Private Endpoint Access Allowed Resources. 4. Private endpoint access allowed resource edit The popup window opens.
- Private Endpoint Access Allowed Resource Modification In the popup, set the Private Endpoint Access Allowed Resource’s Usage and add the allowed access resource, then click the Confirm button.
Modify public endpoint
You can change the public endpoint settings of the cluster.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engines.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, click the resource (cluster) whose public endpoint access control you want to modify. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, click the Edit icon of the Public Endpoint. 4. Public Endpoint Edit The popup window opens.
- Public Endpoint Edit In the Public Endpoint popup, configure the usage setting and add the allowed IP address range, then click the Confirm button.
Modify control plane log collection settings
You can change the log collection settings of the cluster’s control plane. Detailed logs of the cluster can be viewed in the ServiceWatch service or the Cloud Monitoring service.
Even if you configure log collection in Cloud Monitoring, you can view the cluster logs.
- However, since the Cloud Moniotring log collection feature is scheduled for discontinuation, we recommend using ServiceWatch log collection.
To change the cluster’s control plane log collection settings, follow the steps below.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engines.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- Cluster List page, click the resource (cluster) whose control plane logging you want to modify. 3. Go to the Cluster Details page.
- On the Cluster Details page, click the Edit icon of ServiceWatch log collection. 4. ServiceWatch log collection The popup window opens.
- The Cloud Monitoring log collection feature can also be configured in the same way.
- In the ServiceWatch Log Collection popup, after setting the Use option for ServiceWatch Log Modification, click the Confirm button.
When log collection is enabled, you can view the cluster control plane’s Audit/Event logs in each service. Detailed logs can be viewed on the next page.
Modify Security Group
You can modify the cluster’s Security Group.
In the network settings of Kubernetes Engine, you can select up to 4 Security Groups.
- If you manually add a Security Group to a node created by Kubernetes Engine on the Virtual Server service page, it may be automatically removed because it is not managed by Kubernetes Engine.
- For nodes, be sure to add and manage the Security Group in the network settings of the Kubernetes Engine service.
Managed Security Group is automatically managed in Kubernetes Engine.
- Do not use it for any user-defined purpose because deleting a Managed Security Group or adding/deleting rules will automatically be restored.
To modify the cluster’s Security Group, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engines.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, click the resource (cluster) whose Security Group you want to modify. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, click the Edit icon of the Security Group. 4. Security Group Edit The popup window opens.
- After selecting or deselecting the Security Group to modify, click the Confirm button.
Terminate Cluster
To terminate the cluster, follow the steps below.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engines.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- Cluster List page, click the resource (cluster) whose detailed information you want to view. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, click Cancel Service.
- Service Termination After reviewing the content in the popup window, click the Confirm button.
4.1.2.1 - Managing Nodes
A node is a set of machines that run containerized applications. A cluster must have at least one node to deploy an application. Nodes can be defined in a node pool for use. Nodes belonging to a node pool must have the same server type, size, and OS image, and flexible deployment strategies can be established by creating multiple node pools.
After creating a Kubernetes Engine cluster, add a node pool and modify or delete it as needed.
- It is recommended not to use the OS firewall on Kubernetes Engine nodes that use Calico.
- The firewall settings of Samsung Cloud Platform are set to Inactive by default.
- As shown in the reference link below, it is recommended to set the firewall to a disabled state in environments that use Calico.
- When a node is designated as a Backup service target, it cannot be deleted, so the functions below are unavailable.
- Node pool reduction (including automatic scaling)
- Node pool upgrade
- Automatic node pool recovery
- Delete node pool
Add node pool
A node refers to a machine that runs containerized applications, and at least one node is required to deploy applications in a Kubernetes cluster. After the Kubernetes Engine cluster has been created, add a node pool from the details page.
- In Kubernetes Engine, you can define and use a node pool, which is a set of nodes. * Since the nodes in a node pool use the same server type, size, and OS image, users can devise flexible deployment strategies by using multiple node pools.
In the Virtual Server menu, you can create a node pool using the user’s Custom Image. To create a node pool using a Custom Image, follow these steps.
- Create a Virtual Server that includes a Samsung Cloud Platform Kubernetes Engine image.
- Use the Virtual Server’s Create Image feature to proceed with image creation.
- Select the registered Custom Image and create a node pool.
- For more details, see Virtual Server > Create Image.
To add a node pool, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, select the cluster to which you want to add a node pool. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, select the Node Pool tab, then click the Add Node Pool button. 4. Navigate to the Add Cluster Node Pool page.
- On the Add Cluster Node Pool page, enter the information required to create a node pool and select detailed options.
- In the Service Information Input area, enter or select the required information.
Category Required statusDetailed description Node pool name Required Node pool name - must start with a lowercase English letter and be entered using lowercase English letters, numbers, and special characters (
-) within 3 - 20 characters- cannot end with a special character (
-)
- cannot end with a special character (
Node Pool > Server Type Required Virtual Server server types for the node - Standard: Standard specifications commonly used
- High Capacity: Large-scale server specifications beyond Standard
- GPU: GPU specifications available when securing resources for special requirements such as AI/ML
- For detailed information about the server types offered by Virtual Server, refer to Virtual Server 서버 타입
Node Pool > Server OS Essential Node’s Virtual Sever OS image - Standard: RHEL 8.10, Ubuntu 22.04
- Custom: Custom image for Kubernetes created from the Virtual Server product (RHEL, Ubuntu)
Node Pool > Block Storage Essential Block storage settings used by the node’s Virtual Server - SSD: High‑performance general volume
- HDD: General volume
- SSD/HDD_KMS: Additional encrypted volume that uses encryption keys from Samsung Cloud Platform KMS(Key Management System)
- Encryption can be applied only at initial creation and cannot be changed after the service is created
- Performance degradation occurs when using the SSD_KMS disk type
- SSD_Provisioned: Enter detailed settings for the selected storage type
- Enter a value between 5,000 and 20,000 for the Max IOPS field, and between 250 and 1,000 for the Max Throughput field
- For a Custom Image with SSD_Provisioned, the predetermined values are auto‑filled and the fields are disabled
- Capacity is entered in Units, with a value between 13 and 125
- Since 1 Unit equals 8 GB, this creates 104 ~ 1,000 GB
Node Pool > Server Group Select Apply a pre‑created Server Group in the Virtual Server service on the node - Click Use to set the Server Group usage
- When usage is enabled, select a Server Group
- Supports Affinity or Anti‑Affinity policies
- Partition policy is not supported
- Cannot modify after creating a node pool
- GPU server type cannot be selected
Node pool auto scaling Essential Automatically adjust the number of nodes in a node pool - For configuration, refer to 노드 풀 자동 확장/축소하기
Number of nodes Required Number of nodes to create within a node pool - Enter a value in the range 1 - 100
Automatic node recovery Required When an abnormal node is detected in the node pool, automatically delete and create a new one - For configuration, refer to 노드 풀 자동 복구하기
Keypair Essential User authentication method used to connect to a node’s Virtual Server - New: Create a new one if a new Keypair is required
- Refer to Keypair 생성하기 for how to create a new Keypair
- Default login account list by OS
- Alma Linux: almalinux
- RHEL: cloud-user
- Rocky Linux: rocky
- Ubuntu: ubuntu
- Windows: sysadmin
Label Selection Optionally schedule the workload on a node - Click the Add button to enter the label key and value
- Refer to 노드 풀 레이블 설정하기 for configuration
Tint Select Prevent workloads from being scheduled onto nodes - Add button to click for taint effect, enter key and value
- Refer to 노드 풀 테인트 설정하기 for configuration method
Advanced Settings Selection Settings for detailed areas such as pods and logs for the node - Click Use to choose whether to apply the advanced settings for the node pool you will create
- Refer to Configure advanced node pool settings for the configuration method
Connection resource Select Configure File Storage and Object Storage resources for nodes at the node pool level - Click the Add button to select the File Storage and Object Storage resources to attach to the node pool you will create
- Refer to Configure Linked Resources for Node Pools for the configuration method
Table. Input fields for Kubernetes Engine node pool service information - must start with a lowercase English letter and be entered using lowercase English letters, numbers, and special characters (
- In the Service Information Input area, enter or select the required information.
- Summary Verify the detailed information and estimated charges generated in the panel, then click the Create button.
- When creation is complete, check the created resources on the Cluster Details > Node Pool tab > Node Pool list page.
- When the notification popup opens, click the Confirm button.
Update Node Pool
If needed, modify the number of nodes in the node pool on the Kubernetes Engine details page.
To modify the number of nodes, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- Click the Cluster menu on the Service Home page. 2. Navigate to the Cluster List page.
- Select the cluster whose node count you want to modify on the Cluster List page. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, select the Node Pool tab, then click the Node Pool Name you want to edit. 4. Navigate to the Node Pool Details page.
- On the Node Pool Details page, click the Edit icon to the right of Node Pool Information. 5. Node Pool Edit The popup window opens.
- Edit Node Pool In the popup window, edit the node pool information, then click the Confirm button.
Upgrade Node Pool
If the Kubernetes version of the control plane and the version of the node pool differ, you can upgrade the node pool to synchronize the versions.
After upgrading the cluster, proceed with the node pool upgrade. The control plane and node pool upgrades of a Kubernetes cluster are performed separately.
- When you perform a node pool upgrade, a rolling update is carried out on the nodes belonging to the node pool. During this process, a brief service interruption may occur, which is normal for a rolling update and will automatically recover after a short period.
- The server OS version may vary depending on the Kubernetes version of the node pool.
To upgrade the node pool, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, select the cluster for which you want to perform a node pool version upgrade. 3. Navigate to the Cluster Details page.
- Cluster Details page, select the Node Pool tab, then click More > Node Pool Upgrade at the far right end of the node pool row. 4. Node Pool Version Upgrade A popup window opens.
- You can upgrade the node pool only when the node’s status is Running.
- Node Pool Version Upgrade After reviewing the information in the popup window, click the Confirm button.
Auto-scaling node pools
Node pool auto-scaling is a feature that automatically adjusts the number of node pools by adding new nodes to a specified node pool or removing existing nodes based on workload demands. This feature operates based on the node pool.
- When automatically scaling a node pool up or down, it is adjusted based on the resource requests of the pods running on the node pool’s nodes rather than the actual resource utilization, and it periodically checks the status of pods and nodes and executes automatic scaling operations.
To set up automatic scaling for a node pool, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, select the cluster for which you want to use the node auto-scaling feature. 3. Navigate to the Cluster Details page.
- Cluster Details page, after selecting the Node Pool tab, click the Node Pool name you wish to modify. 4. Navigate to the Node Pool Details page.
- Node Pool Details page, click the Edit icon on the right of Node Pool Information. 5. Edit Node Pool The popup window opens.
- Edit Node Pool in the popup window, select Node Pool Auto Scaling as Enable.
- After entering the minimum and maximum node counts, click the Confirm button.Reference
Node pool auto-scaling settings can also be configured on the cluster node pool creation page.
- Node pool scaling conditions
- When a pod fails to start in the cluster due to insufficient resources (Pending pod occurs)
- Node pool reduction criteria (when all are met)
- If the sum of resource requests (CPU/Memory) of all pods running on a node is less than 50 % of the node’s allocatable resources.
- When all pods running on a node can be scheduled on another node (there must be no pods subject to PDB restrictions, etc.)
- When using automatic node pool scaling, to prevent deletion caused by node reduction, add the following annotation to the node.
cluster-autoscaler.kubernetes.io/scale-down-disabled: “true”
- Node pool scaling conditions
- Node pool auto scaling/downsizing operates only when NotReady nodes constitute 45% or less of the total nodes in the cluster and there are three or fewer such nodes.
- If there are nodes directly attached instead of node pools created by the Kubernetes Engine service, using this feature may cause malfunction.
Automatically Restore Node Pool
Node auto-recovery is a feature that automatically deletes an abnormal node detected in the cluster and creates a new node to restore the node count in the node pool to a normal state. This feature operates based on the node pool.
Node auto-recovery deletes the existing node and creates a new node when communication between K8S Control Planes fails due to node (Virtual Server) problems, a stopped state, network issues, etc., according to the node auto-recovery conditions, so caution is required when using it.
- When creating a node pool, it is restored according to the initially set conditions, and any custom settings made after node creation are not restored.
If there are nodes that were directly connected instead of node pools created by the Kubernetes Engine service, using this feature may cause malfunction.
To configure the node auto-recovery feature, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Go to the Cluster List page.
- On the Cluster List page, select the cluster for which you want to use the node auto-recovery feature. 3. Go to the Cluster Details page.
- On the Cluster Details page, after selecting the Node Pool tab, click the Node Pool name you wish to edit. 4. Navigate to the Node Pool Details page.
- On the Node Pool Details page, click the Edit icon on the right of Node Pool Information. 5. Edit Node Pool A popup window opens.
- Node Pool Edit in the popup window, after selecting Node Auto Recovery as Enable, click the Confirm button.
Node auto-recovery settings can also be configured on the cluster node pool creation page.
- When the node is an auto-recovery target
- If a node reports a NotReady status in consecutive checks for a certain time threshold (approximately 10 minutes)
- When a node does not report its status at all for a certain time threshold (approximately 10 minutes)
- If the node is not a target for automatic recovery
- When a node is first created, it remains in the Creating state instead of reaching the Running state.
- When more than five abnormal nodes occur simultaneously in the same node pool.
Setting node pool labels
Node pool labels are a feature for optionally scheduling workloads onto nodes.
- When applying a node pool label, it is not applied to existing nodes; the label is applied only to nodes created thereafter.
- If you need to apply a label to an existing node, the user must set it directly with kubectl.
To set the node pool label, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- Click the Cluster menu on the Service Home page. 2. Navigate to the Cluster List page.
- On the Cluster List page, select the cluster for which you want to set the node pool label. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, select the Node Pool tab, then click the Node Pool Name you want to edit. 4. Navigate to the Node Pool Details page.
- On the Node Pool Details page, when you click the Edit icon of a label, the Edit Label popup opens.
- In the Label Edit popup, click the Add button to add as many labels as needed.
- Enter the label information and click the Confirm button.
Configure Node Pool Taint
Node pool taint is a feature that prevents workloads from being scheduled onto nodes.
- If you set taints on all node pools, pods required for normal cluster operation may not be scheduled.
- When applying a node pool taint, it does not affect existing nodes; the taint is applied only to nodes created thereafter.
- If you need to apply a taint to an existing node, the user must configure it directly with kubectl.
To configure the node pool taint, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- Select the cluster for which you want to set a node pool taint on the Cluster List page. 3. Navigate to the Cluster Details page.
- Cluster Details page, after selecting the Node Pool tab, click the Node Pool name you wish to modify. 4. Navigate to the Node Pool Details page.
- On the Node Pool Details page, clicking the Edit icon of a taint opens the Edit Taint popup window.
- Tint Edit In the popup window, click the Add button to add the required number of tints.
- Enter the tint information and click the Confirm button.
Configure advanced node pool settings
Node pool advanced settings are a feature for applying detailed configurations such as the number of pods per node, PID, logs, and image garbage collection.
Each setting corresponds to the kubelet configuration as follows.
- Maximum pods per node: maxPods
- Image GC upper limit percent: imageGCHighThresholdPercent
- Image GC low threshold percent: imageGCLowThresholdPercent
- Container log maximum size MB: containerLogMaxSize
- Container log maximum file count: containerLogMaxFiles
- Pod PID limit: podPidsLimit
- Allow unsafe Sysctl: allowedUnsafeSysctls
To configure advanced settings for the node pool, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, select the cluster for which you want to configure advanced node pool settings. 3. Navigate to the Cluster Details page.
- Cluster Details page, after selecting the Node Pool tab, click Create Node Pool. 4. Go to the Create Node Pool page.
- On the Node Pool Creation page, select Advanced Settings to Enable.
- After selecting Use, enter the required information for the displayed items.
- After confirming that the required information has been entered correctly in the Summary tab, click the Create button.
Configure linked resources for node pool
Node pool connection resources are a feature for connecting or disconnecting File Storage and Object Storage on a per‑node‑pool basis.
- Node pool connection resources have a quantity limit.
- You can add up to three File Storage and three Object Storage, for a total of six connection resources.
- StorageClass and Provisioner for the connected resource are not provided.
- Do not arbitrarily modify the connection resources automatically added in the node pool for the File Storage and Object Storage services. * Changes may be reverted or cause unexpected behavior.
To configure node pool connection resources, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, select the cluster for which you want to configure node pool connection resources. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, select the Node Pool tab, then click the Node Pool Name you want to edit. 4. Navigate to the Node Pool Details page.
- When you click the Edit icon of a connection resource on the Node Pool Details page, the Edit Connection Resource popup opens.
- In the Edit Connected Resource popup, clicking the Add button opens the Add Connected Resource popup.
- Add Connected Resource In the popup window, select File Storage and Object Storage.
- After verifying the resources to connect to the node pool, click the Confirm button.
Delete Node Pool
If needed, delete the node pool from the Kubernetes Engine details page.
To delete a node pool, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Cluster menu. 2. Navigate to the Cluster List page.
- On the Cluster List page, select the cluster whose node count you want to modify. 3. Navigate to the Cluster Details page.
- On the Cluster Details page, select the Node Pool tab, then click the More button at the far right of the node pool row. 4. Click Delete Node Pool in the More button.
- Node Pool Deletion In the popup window, select the checkbox, enter the name of the node pool to delete, and click the Confirm button.
- You must select the checkbox in the node deletion confirmation message for the confirm button to become active.
View node details
After creating the cluster, you can view metadata, object information, and other details of the added nodes, and edit resource files using a YAML editor.
To view detailed information about the node pool, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Node menu. 2. Go to the Node List page.
- On the Node List page, select the cluster whose detailed information you want to view from the gear button at the top left, then click the Confirm button.
- Select the node whose detailed information you want to view and click. 4. Navigate to the Node Details page.
Category Detailed descriptionStatus Indicator Display the current status of the node Detailed Information Check the node’s Account information, metadata, and object information YAML Node resources can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Save button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred on the node Pod Check node pod information - A Pod (pod) is the smallest compute unit that can be created, managed, and deployed in Kubernetes Engine
Account Information Check basic information about the Account, such as the Account name, location, and creation time. Metadata Information Check metadata information such as node labels, annotations, and taints. Object Information Internal IP and machine ID, capacity, resources, etc., the object information of the created node is displayed - If GPU resources exist, check the GPU count in the Capacity > Nvidia.com/GPU column
Table. Node detailed information items
4.1.2.2 - Managing Namespaces
A namespace is a logical separation unit within a Kubernetes cluster, used to specify access permissions or resource usage limits per namespace.
Create a namespace
To create a namespace, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Namespace menu. 2. Navigate to the Namespace List page.
- On the Namespace List page, select the cluster where you want to create a namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check detailed namespace information
On the namespace detail page, you can view the namespace status and detailed information.
To view detailed namespace information, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Namespace menu. 2. Navigate to the Namespace List page.
- On the Namespace List page, select the cluster that the namespace requiring detailed information belongs to from the gear button at the top left, then click Confirm.
- On the Namespace List page, select the item you want to view details for and click it. 4. Go to the Namespace Details page.
Category Detailed description Status indicator Display the current state of the namespace Delete Namespace Delete namespace - A namespace containing workloads cannot be deleted. To delete a namespace, you must delete all associated workloads
Detailed Information Check the Account information and metadata of the namespace YAML Namespaces can be edited in the YAML editor - Click the Edit button, modify the namespace, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred within the namespace Pod Check the pod information in the namespace Account information Check basic information about the Account, such as name, location, and creation timestamp. Metadata Information Check the metadata information of the namespace Table. Namespace detailed information items
Delete namespace
To delete a namespace, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Namespace menu. 2. Navigate to the Namespace List page.
- On the Namespace List page, select the cluster that the namespace you want to delete belongs to from the gear button at the top left, then click the Confirm button.
- On the Namespace List page, select the item you want to view details for and click it. 4. Navigate to the Namespace Details page.
- On the Namespace Details page, click Delete Namespace.
- When the notification confirmation window appears, click the Confirm button.
4.1.2.3 - Manage Workloads
The workload is an application running on Kubernetes Engine. You can create a namespace and then add or delete workloads. Workloads are created and then managed for each item: Deployment, Pod, StatefulSet, DaemonSet, Job, and CronJob.
Deployments, Pods, StatefulSets, DaemonSets, Jobs, and CronJobs are defaulted to the cluster (namespace) selected when creating the service. Even if you select a different item in the list, the default cluster (namespace) setting is retained.
- To select a different cluster (namespace), click the gear button on the right side of the list. * Cluster/Namespace Settings In the popup window, select the cluster and namespace to change, and click the Confirm button. * You can view the services created in the selected cluster/namespace.
Managing Deployments
A Deployment refers to a resource that provides updates for Pods and ReplicaSets (ReplicaSet). You can create a deployment in the workload, view its details, or delete it.
Create Deployment
To create a deployment, follow the steps below.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Deployment under the Workload menu. 2. Go to the Deployment List page.
- On the Deployment List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
- The following is an example
.yamlfile that shows the required fields and object spec for creating a Deployment. * (application/deployment.yaml)Color modeapiVersion: apps/v1 kind: Deployment metadata: name: nginx-deployment spec: selector: matchLabels: app: nginx replicas: 2 # tells deployment to run 2 pods matching the template template: metadata: labels: app: nginx spec: containers: - name: nginx image: nginx:1.14.2 ports: - containerPort: 80apiVersion: apps/v1 kind: Deployment metadata: name: nginx-deployment spec: selector: matchLabels: app: nginx replicas: 2 # tells deployment to run 2 pods matching the template template: metadata: labels: app: nginx spec: containers: - name: nginx image: nginx:1.14.2 ports: - containerPort: 80Code block. Required fields and object Spec for deployment creation.
- The following is an example
View deployment details
To view deployment details, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Deployment under the Workload menu. 2. Go to the Deployment List page.
- On the Deployment List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the Deployment List page. 4. Deployment Details page will be opened.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete Deployment Delete the deployment Detailed Information Detailed deployment information can be viewed YAML The deployment’s resource file can be edited in the YAML editor - Edit button, click and modify the resource, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred within the deployment Pod Check the pod information of the deployment - A Pod (pod) is the smallest compute unit that can be created, managed, and deployed in Kubernetes Engine
Account information Check basic information about the Account, such as the Account name, location, and creation time. Metadata Information Check the deployment’s metadata information Object Information Check the deployment’s object information Table. Deployment detailed information items
Delete Deployment
To delete the deployment, follow the steps below.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Deployment under the Workload menu. 2. Navigate to the Deployment List page.
- On the Deployment list page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to delete on the Deployment List page. 4. Navigate to the Deployment Details page.
- On the Deployment Details page, click Delete Deployment.
- When the notification confirmation window appears, click the Confirm button.
Managing Pods
A pod (Pod) is the smallest compute unit in Kubernetes that can be created, managed, and deployed, representing a group of one or more containers. You can create pods in the workload, view their details, or delete them.
Create Pod
To create a pod, follow the steps below.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Pod under the Workload menu. 2. Navigate to the Pod List page.
- On the Pod List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check pod detailed information
To view detailed pod information, follow these steps.
- All Services > Container > Kubernetes Engine menu, click it. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Pod under the Workload menu. 2. Navigate to the Pod List page.
- On the Pod List page, select the cluster and namespace using the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the Pod List page. 4. Navigate to the Pod Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionStatus indicator Display the current status of the pod Delete pod Delete the pod Detailed Information Can view detailed pod information YAML The pod’s resource file can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changes
event Check events that occurred within the pod log Select a container to view the pod’s container information. Account Information Check basic information about the Account, such as name, location, and creation timestamp. Metadata Information Check the pod’s metadata information Object Information Check the pod’s object information Initialization Container Information Check the pod’s init container information Container Information Check the pod’s container information Table. Pod detailed information items
Delete Pod
To delete a pod, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Pod under the Workload menu. 2. Go to the Pod List page.
- On the Pod List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the items you want to delete on the Pod List page. 4. Navigate to the Pod Details page.
- On the Pod Details page, click Delete Pod.
- When the notification dialog appears, click the Confirm button.
Managing StatefulSets
A StatefulSet is a workload API object used to manage an application’s stateful components. You can create a StatefulSet in the workload, view its details, or delete it.
Creating a StatefulSet
To create a StatefulSet, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click StatefulSet under the Workload menu. 2. StatefulSet list page is opened.
- On the StatefulSet list page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check detailed information of StatefulSet
To view detailed information about a StatefulSet, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click StatefulSet under the Workload menu. 2. StatefulSet list page is opened.
- On the StatefulSet List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item whose detailed information you want to view on the StatefulSet List page. 4. Navigate to the StatefulSet Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete StatefulSet Delete the StatefulSet Detailed Information Can view detailed information of a StatefulSet YAML The resource file of a StatefulSet can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred within the StatefulSet Pod Check the pod information of the StatefulSet Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the metadata information of the StatefulSet Object Information Check the object information of the StatefulSet Table. StatefulSet detailed information items
Delete StatefulSet
To delete a StatefulSet, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click StatefulSet under the Workload menu. 2. Navigate to the StatefulSet list page.
- On the StatefulSet List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- StatefulSet list page, select the items you want to delete. 4. Navigate to the StatefulSet Details page.
- On the StatefulSet Details page, click Delete StatefulSet.
- When the notification confirmation window appears, click the Confirm button.
Managing DaemonSets
A DaemonSet is a resource that ensures a copy of a pod runs on every node or on a subset of nodes. You can create a DaemonSet in the workload, view its details, or delete it.
Creating a DaemonSet
To create a DaemonSet, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click DaemonSet under the Workload menu. 2. Go to the DaemonSet list page.
- On the DaemonSet list page, select the cluster and namespace from the gear button at the top left, then click Create object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check DaemonSet detailed information
To view detailed information about a DaemonSet, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click DaemonSet under the Workload menu. 2. Go to the DaemonSet List page.
- On the DaemonSet list page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view details for on the DaemonSet List page. 4. Navigate to the DaemonSet Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries are displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete DaemonSet Delete the DaemonSet Detailed Information Can view detailed DaemonSet information YAML The DaemonSet’s resource file can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changed content
event Check events that occurred within the DaemonSet Pod Check DaemonSet pod information Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the DaemonSet’s metadata information Object Information Check the DaemonSet object information Table. DaemonSet detailed information items
Delete DaemonSet
To delete a DaemonSet, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click DaemonSet under the Workload menu. 2. Navigate to the DaemonSet list page.
- On the DaemonSet list page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the items you want to delete on the DaemonSet List page. 4. DaemonSet Details Navigate to the page.
- On the DaemonSet Details page, click Delete DaemonSet.
- When the notification confirmation window appears, click the Confirm button.
Job Management
A Job is a resource that creates one or more Pods and continues to run Pods until the specified number of Pods have completed successfully. You can create a job in the workload, view its details, or delete it.
Create Job
To create a job, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Job under the Workload menu. 2. Go to the Job List page.
- On the Job List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check job details
To view the job details, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Job under the Workload menu. 2. Navigate to the Job List page.
- On the Job List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the Job List page. 4. Go to the Job Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete Job Delete the job Detailed Information Detailed job information can be viewed YAML You can edit the job’s resource file in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred within the job Pod Check the pod information of the job Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the job’s metadata information Object Information Check job object information Table. Job detail information items
Delete job
To delete a job, follow the steps below.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Job under the Workload menu. 2. Go to the Job List page.
- Job List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the items you want to delete on the Job List page. 4. Navigate to the Job Details page.
- On the Job Details page, click Delete Job.
- When the notification dialog appears, click the Confirm button.
Managing Cron Jobs
A cron job is a resource that runs a job periodically according to a schedule written in cron format. It can be used when executing repetitive tasks at regular intervals, such as backups and report generation. In the workload, you can create a cron job and view or delete its details.
Create a cron job
To create a cron job, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click CronJob under the Workload menu. 2. Navigate to the Cron Job List page.
- On the CronJob List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check detailed cron job information
To view detailed information about the cron job, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click CronJob under the Workload menu. 2. Navigate to the Cron Job List page.
- On the CronJob List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the Cron Job List page. 4. Navigate to the Cron Job Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete cron job Delete the cron job Detailed Information View detailed information of cron jobs YAML The resource file of the cron job can be edited in the YAML editor - Edit button, click and modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changed content
event Check events that occurred within the cron job job View the cron job’s information. Selecting a job item navigates to the job detail page. Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the metadata information of the cron job Object Information Check the object information of the cron job Table. Cron job detailed information items
Delete cron job
To delete a cron job, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click CronJob under the Workload menu. 2. Go to the Cron Job List page.
- On the CronJob List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the items you want to delete on the Cron Job List page. 4. Go to the Cron Job Details page.
- On the Cron Job Details page, click Delete Cron Job.
- When the notification confirmation window appears, click the Confirm button.
4.1.2.4 - Manage services and ingresses
A Service is an abstraction that exposes applications running in a set of Pods as a network service, and an Ingress is used to expose HTTP and HTTPS routes from outside the cluster to inside the cluster. After creating a namespace, you can create or delete services, endpoints, ingresses, and ingress classes.
Services, endpoints, ingresses, and ingress classes are set by default to the cluster (namespace) selected when creating the service. Even if you select a different item in the list, the default cluster (namespace) setting is retained.
- To select a different cluster (namespace), click the gear button on the right side of the list. * Cluster/Namespace Settings In the popup window, select the cluster and namespace you want to change, and click the Confirm button. * You can view the services created in the selected cluster/namespace.
Manage Services
You can create a service and view or delete its details.
Create Service
To create a service, follow these steps.
- All Services > Container > Kubernetes Engine click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Service under the Service and Ingress menu. 2. Go to the Service List page.
- On the Service List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check service detailed information
To view the service details, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Service under the Service and Ingress menu. 2. Go to the Service List page.
- Service List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- On the Service List page, select the item for which you want to view detailed information. 4. Go to the Service Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete Service Delete the service Detailed Information View detailed service information. YAML You can edit the service’s resource file in the YAML editor - Click the Edit button, modify the resource, and then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changes
event Check events that occurred within the service Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the service metadata information Object Information Check the service’s object information Table. Service detailed information items
Delete Service
To delete the service, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Service under the Service and Ingress menu. 2. Navigate to the Service List page.
- Service List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Service List page, select the item you want to delete. 4. Go to the Service Details page.
- On the Service Details page, click Delete Service.
- When the notification dialog appears, click the Confirm button.
Managing Endpoints
You can create an endpoint and view or delete its details.
Create Endpoint
To create an endpoint, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Endpoint under the Service and Ingress menu. 2. Go to the Endpoint List page.
- On the Endpoint List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
View endpoint details
To view detailed endpoint information, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Endpoint under the Service and Ingress menu. 2. Go to the Endpoint List page.
- On the Endpoint List page, select the cluster and namespace using the gear button at the top left, then click Confirm.
- On the Endpoint List page, select the item for which you want to view detailed information. 4. Navigate to the Endpoint Details page.
- When you select Show system objects at the top of the list, the remaining items, excluding the Kubernetes object entries, are displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete Endpoint Delete the endpoint Detailed Information Can view detailed endpoint information YAML The endpoint’s resource file can be edited in the YAML editor - Edit button, click and modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changed content
event Check events that occurred within the endpoint Account information Check basic information about the Account, such as the Account name, location, and creation date/time. Metadata Information Check the endpoint’s metadata information Object Information Check the endpoint’s object information Table. Endpoint detailed information items
Delete endpoint
To delete the endpoint, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Endpoint under the Service and Ingress menu. 2. Go to the Endpoint List page.
- On the Endpoint List page, select the cluster and namespace from the gear button in the top-left, then click Confirm.
- Select the item you want to delete on the Endpoint List page. 4. Navigate to the Endpoint Details page.
- On the Endpoint Details page, click Delete Endpoint.
- When the notification dialog appears, click the Confirm button.
Managing Ingress
Ingress is an API object that manages external access (HTTP, HTTPS) to services within Kubernetes Engine, used to expose workloads externally, and provides L7 load balancing functionality.
Create Ingress
To create an Ingress, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Ingress under the Service and Ingress menu. 2. Navigate to the Ingress List page.
- On the Ingress List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check Ingress detailed information
To view the ingress details, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Ingress under the Service and Ingress menu. 2. Navigate to the Ingress List page.
- On the Ingress List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item whose detailed information you want to view on the Ingress List page. 4. Navigate to the Ingress Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete Ingress Delete ingress Detailed Information Ingress detailed information can be viewed YAML The Ingress resource file can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changes
event Check events that occurred within the ingress Account information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the metadata information of the Ingress Object Information Check the Ingress object’s information Table. Ingress detailed information items
Delete Ingress
To delete the ingress, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Ingress under the Service and Ingress menu. 2. Navigate to the Ingress List page.
- Ingress List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to delete on the Ingress List page. 4. Navigate to the Ingress Details page.
- On the Ingress Details page, click Delete Ingress.
- When the notification confirmation dialog appears, click the Confirm button.
Manage Ingress Class
IngressClass refers to an API resource that enables the use of multiple ingress controllers within a single cluster. Each Ingress must specify a reference class for the IngressClass resource that includes a configuration, including a controller that must implement the class.
Create Ingress Class
To create an Ingress class, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click IngressClass under the Service and Ingress menu. 2. Navigate to the IngressClass List page.
- On the IngressClass List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check detailed information of Ingress class
To view detailed information about the Ingress class, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Ingress Class under the Service and Ingress menu. 2. Navigate to the IngressClass List page.
- IngressClass list page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the IngressClass List page. 4. Navigate to the IngressClass Details page.
- When you select Show system objects at the top of the list, the remaining items, excluding the Kubernetes object entries, are displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete IngressClass Delete Ingress class Detailed Information Detailed information of the Ingress class can be viewed. YAML The resource file of the IngressClass can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changed content
event Check events that occurred within the Ingress class Account information Check basic information about the Account, such as name, location, and creation date/time. Metadata Information Check the metadata information of the Ingress class Object Information Check the object information of the Ingress class Table. Ingress class detailed information items
Delete Ingress Class
To delete an Ingress class, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Ingress Class under the Service and Ingress menu. 2. Navigate to the IngressClass List page.
- IngressClass list page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- On the IngressClass List page, select the items you want to delete. 4. Navigate to the IngressClass Details page.
- On the IngressClass Details page, click Delete IngressClass.
- When the notification dialog appears, click the Confirm button.
4.1.2.5 - Managing Storage
You can create and manage storage for use with Kubernetes Engine. Storage is created and managed for each PVC, PV, and StorageClass.
PVC, PV, and storage class services are set by default to the cluster (namespace) selected when creating the service. Even if you select a different item in the list, the default cluster (namespace) setting is retained.
- To select a different cluster (namespace), click the gear button on the right side of the list. * Cluster/Namespace Settings In the popup window, select the cluster and namespace to change, and click the Confirm button. * You can view the services created in the selected cluster/namespace.
The items associated with each storage type are as follows.
| type | Detailed description |
|---|---|
| Block storage | Supports a storage class that uses the volume of the Block storage product within Virtual Server. |
| Object Storage | Can be integrated with Samsung Cloud Platform products or external Object Storage
|
| File storage | Supports storage classes for NFS and CIFS protocol volumes in conjunction with the File Storage product
|
Managing PVC
Persistent Volume Claim(PVC) is an object defined to allocate the required storage capacity. PVC provides high usability through abstraction and can prevent the problem of data being deleted when the container lifecycle (Container Lifecycle) expires (maintaining Data Persistence).
Create PVC
To create a PVC, follow the steps below.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click PVC under the Storage menu. 2. Go to the PVC List page.
- PVC List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check PVC detailed information
To view detailed PVC information, follow the steps below.
- Click the All Services > Container > Kubernetes Engine menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click PVC under the Storage menu. 2. PVC List Navigate to the page.
- On the PVC List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the PVC List page. 4. PVC Details Go to the page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionStatus display Displays the current status of the PVC. - Bound: Normal connection
Delete PVC Delete PVC Detailed Information Detailed PVC information can be viewed YAML The PVC resource file can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changed content
event Check events that occurred within the PVC Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the PVC metadata information Object Information Check the PVC object information Table. PVC detailed information items
Delete PVC
To delete a PVC, follow the steps below.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click PVC under the Storage menu. 2. PVC List go to the page.
- On the PVC List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- PVC List page, select the items you want to delete. 4. Go to the PVC Details page.
- On the PVC Details page, click Delete PVC.
- When the notification confirmation window appears, click the Confirm button.
On the PVC list page, after selecting the item you want to delete, click Delete to delete the selected PVC.
- Before deleting the PVC, verify that the PV and volume to be deleted are backed up.
Manage PV
Persistent Volume (PV) refers to the physical disk that a system administrator creates in Kubernetes Engine.
Create PV
To create a PV, follow the steps below.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click PV under the Storage menu. 2. Go to the PV List page.
- On the PV List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check PV detailed information
To view detailed PV information, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click PV under the Storage menu. 2. Navigate to the PV list page.
- PV List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- On the PV List page, select the item for which you want to view detailed information. 4. Navigate to the PV Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed description Status display Displays the current status of the PV. - Bound: Normal connection
Delete PV Delete PV Detailed Information Detailed information of the PV can be viewed YAML The PV’s resource file can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changes
event Check events that occurred within the PV Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the PV metadata information Object Information Check PV object information Table. PV detailed information items
Delete PV
To delete a PV, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click PV under the Storage menu. 2. Go to the PV List page.
- On the PV List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to delete on the PV list page. 4. Go to the PV Details page.
- Click Delete PV on the PV Details page.
- When the notification dialog appears, click the Confirm button.
Managing StorageClass
Storage Class (Storage Class) is a Kubernetes resource that defines the type, performance, and other levels of storage.
Kubernetes Engine provides the nfs-subdir-external-sc and bs-sc storage classes by default, and has the following characteristics.
- The nfs-subdir-external-sc storage class shares and uses the file storage attached to the cluster.
- Access mode: RWX - ReadWriteMany Reclaim policy: Delete(deletes the PV and stored data when the PVC is deleted), Retain(keeps the PV and stored data when the PVC is deleted) Capacity expansion: individual PVC expansion not allowed / entire file storage expansion allowed
- The bs-sc storage class supports using SSD-type volumes in conjunction with block storage products.
- Access mode: RWO - ReadWriteOnce Reclaim policy: Delete (deletes PV and stored data when PVC is deleted), Retain (keeps PV and stored data when PVC is deleted)
- Capacity expansion support: individual PVC expansion support (automatic volume expansion in 8 Gi increments)
Predefined storage class
| Storage class | Reclaim Policy* | Allow volume expansion** | Mount options | Remarks |
|---|---|---|---|---|
| nfs-subdir-external-sc (default) | Delete | Not supported | nfsvers=3, noresvport | Basic Volume (NFS) configuration and integration |
| nfs-subdir-external-sc-retain | Retain | Not supported | nfsvers=3, noresvport | Basic Volume (NFS) configuration and integration |
| bs-sc | Delete | Support | - | VirtualServer > Integration with BlockStorage product |
| bs-sc-retain | Retain | Support | - | VirtualServer > Integration with BlockStorage product |
- (*) To use a storage class other than the default, you need to specify the storage class name in PVC’s spec.storageClassName.
- (**) Users can directly change the default storage class (adjust the storageclass.kubernetes.io/is-default-class: “true” annotation)
The characteristics of the reclamation policy are as follows.
- Delete: Deleting the PVC also deletes the associated PV and physical data.
- Retain: Even if the PVC is deleted, the associated PV and physical data are not deleted and are retained. * Physical data not used by the workload may remain in storage, so careful capacity management is required.
When using volume expansion, consider the following.
- nfs-subdir-external-sc storage class
- Cannot resize the PVC. * (Volume expansion not supported)
- All PVs share the total capacity of the File Storage volume, so individual PVC volume expansion is not required.
- bs-sc storage class
- You can expand the PVC capacity. * (Zoom function not supported)
- The requested capacity of a PVC does not guarantee that the corresponding PV will have that amount of capacity. * (support expansion in 8 Gi increments)
Creating a StorageClass
To create a storage class, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Storage Class under the Storage menu. 2. Navigate to the StorageClass List page.
- StorageClass list on the page, select the cluster and namespace from the top‑left gear button, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.ReferenceFor detailed information on the concept of storage classes and object creation, please refer to 쿠버네티스 공식 문서 > 스토리지 클래스.
View detailed storage class information
To view detailed information about the storage class, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click StorageClass under the Storage menu. 2. Navigate to the StorageClass List page.
- On the StorageClass List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the StorageClass List page. 4. Navigate to the StorageClass Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete StorageClass Delete the StorageClass Detailed Information Detailed information of the storage class can be viewed YAML The resource file of the StorageClass can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred within the storage class Account information Check basic information about the Account, such as name, location, and creation time. Metadata Information Check the metadata information of the StorageClass Object Information Check the object information of the storage class Table. StorageClass detailed information items
Delete StorageClass
To delete a storage class, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click StorageClass under the Storage menu. 2. Navigate to the StorageClass List page.
- StorageClass list page, select the cluster and namespace from the top-left gear button, then click Confirm.
- On the StorageClass List page, select the items you want to delete. 4. Navigate to the StorageClass Details page.
- On the StorageClass Details page, click Delete StorageClass.
- When the notification dialog appears, click the Confirm button.CautionOn the storage class list page, after selecting the item you want to delete, click Delete to delete the selected storage class.
4.1.2.6 - Configuration(Configuration) Management
When you need to manage values that change inside a container across various environments such as development and production, creating separate images to handle them via environment variables is inconvenient and costly. In Kubernetes, you can manage environment variables or configuration values as variables so they can be changed externally and injected when a Pod is created; at this point, you can use ConfigMap and Secret.
ConfigMaps and Secrets are defaulted to the cluster (namespace) selected when creating the service. Even if you select a different item in the list, the default cluster (namespace) setting is retained.
- To select a different cluster (namespace), click the gear button on the right side of the list. * Cluster/Namespace Settings In the popup window, select the cluster and namespace to change, and click the Confirm button. * You can view the ConfigMaps and Secret services created in the selected cluster/namespace.
Managing ConfigMaps
Config information used in a namespace can be defined in a ConfigMap and managed.
Create ConfigMap
To create a ConfigMap, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click ConfigMap under the Configuration menu. 2. Navigate to the ConfigMap List page.
- On the ConfigMap List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
View ConfigMap detailed information
To view detailed ConfigMap information, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click ConfigMap under the Configuration menu. 2. Navigate to the ConfigMap list page.
- On the ConfigMap List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the ConfigMap List page. 4. Go to the ConfigMap Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete ConfigMap Delete ConfigMap Detailed Information Detailed ConfigMap information can be viewed YAML The resource file of a ConfigMap can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changed content
event Check events that occurred in the ConfigMap Account Information Check basic information about the Account, such as name, location, and creation time. Metadata Information Check the metadata information of the ConfigMap Object Information Check the object information of the ConfigMap - Data separates rows with
- - -, and value is displayed in a textarea format - Binary data’s value outputs the length value
Table. ConfigMap detailed information items
Delete ConfigMap
To delete a ConfigMap, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click ConfigMap under the Configuration menu. 2. Go to the ConfigMap list page.
- On the ConfigMap List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- On the ConfigMap List page, select the item you want to delete. 4. Navigate to the ConfigMap Details page.
- On the ConfigMap Details page, click Delete ConfigMap.
- When the notification confirmation window appears, click the Confirm button.
Managing Secrets
Using secrets allows you to securely store and manage sensitive information such as passwords, OAuth tokens, and SSH keys.
Create Secret
To create a secret, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Secret under the Configuration menu. 2. Go to the Secret List page.
- On the Secret List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- In the Object Creation Popup, enter the object information and click the Confirm button.
Check secret detailed information
To view the secret details, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Secret under the Configuration menu. 2. Go to the Secret List page.
- On the Secret List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the Secret List page. 4. Go to the Secret Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete secret Delete the secret Detailed Information Detailed information of the secret can be viewed YAML The secret’s resource file can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changed content
event View events that occurred within the secret Account information Check basic information about the Account, such as name, location, and creation timestamp. Metadata Information Check the secret’s metadata information Object Information Check the secret object’s information Table. Secret detailed information items
Delete secret
To delete the secret, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Secret under the Configuration menu. 2. Go to the Secret List page.
- On the Secret List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the items you want to delete on the Secret List page. 4. Navigate to the Secret Details page.
- On the Secret Details page, click Delete Secret.
- When the notification confirmation window appears, click the Confirm button.
4.1.2.7 - Manage Permissions
When multiple users access a Kubernetes cluster, you can assign permissions for specific APIs or namespaces to define access scopes. You can apply Kubernetes’ role-based access control (RBAC) feature to set permissions for each cluster or namespace. You can create and manage ClusterRoles, ClusterRoleBindings, Roles, and RoleBindings.
ClusterRole, ClusterRoleBinding, Role, and RoleBinding services are set by default to the cluster (namespace) selected when creating the service. Even if you select a different item in the list, the default cluster (namespace) setting is retained.
- To select a different cluster (namespace), click the gear button on the right side of the list. * Cluster/Namespace Settings In the popup window, select the cluster and namespace you want to change, and click the Confirm button. * You can view the services created in the selected cluster/namespace.
- The RBAC API declares the following four types of Kubernetes objects.
- Role
- ClusterRole RoleBinding ClusterRoleBinding
- For detailed explanations of RBAC description and modification, refer to the Kubernetes authentication and authorization section.(https://kubernetes.io/docs/reference/access-authn-authz/authentication/)
Managing Cluster Roles
You can set and manage access permissions at the cluster level. You can also set permissions for APIs or resources that are not limited to a namespace.
Create ClusterRole
To create a cluster role, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Cluster Role under the Permissions menu. 2. Go to the Cluster role list page.
- On the Cluster Role List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check detailed information of the cluster role
To view detailed information about the cluster role, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Cluster Role under the Permissions menu. 2. Go to the Cluster role list page.
- Cluster role list page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- ClusterRole list page, select the item you want to view detailed information for. 4. Navigate to the Cluster role details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete ClusterRole Delete the ClusterRole Detailed Information View detailed information of the cluster role YAML The resource file of the ClusterRole can be edited in the YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred within the cluster role Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the metadata information of the ClusterRole Policy Rule Information View the policy rule information of a ClusterRole - Resources: List of resources to which the rule applies
- Non-Resource URLs: Non-Resource URLs are the set of partial URLs that a user needs to access
*is allowed, but only as the final segment of the entire path
- Non-resource URLs are not namespaced, so this field can only be used in a ClusterRole referenced by a ClusterRoleBinding
- A rule can apply to an API resource (e.g., “pods” or “secrets”) or a non-resource URL path (e.g., “/api”), but not to both
- ResourceNames: ResourceNames is an optional whitelist of names that the rule applies to. An empty set means everything is allowed
- Verbs: Verbs are the API actions used in resource requests such as get, list, create, update, patch, watch, delete, deletecollection
- For more information, see the Kubernetes official documentation > API Verbs
Table. Cluster role detailed information items
Delete cluster role
To delete the cluster role, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Cluster Role under the Permissions menu. 2. Navigate to the Cluster Role List page.
- On the Cluster role list page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the items you want to delete on the Cluster role list page. 4. Navigate to the Cluster role details page.
- On the Cluster role details page, click Delete cluster role.
- When the notification confirmation window appears, click the Confirm button.
Managing ClusterRoleBinding
You can create and manage a cluster role binding by linking a cluster role with a specific target.
Create ClusterRoleBinding
To create a ClusterRoleBinding, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click ClusterRoleBinding under the Permissions menu. 2. Navigate to the ClusterRoleBinding List page.
- ClusterRoleBinding List on the page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
View detailed information of ClusterRoleBinding
To view detailed information about the cluster role binding, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click ClusterRoleBinding under the Permissions menu. 2. Navigate to the Cluster Role Binding List page.
- On the ClusterRoleBinding List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view details for on the Cluster Role Binding List page. 4. Navigate to the Cluster Role Binding Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete ClusterRoleBinding Delete the cluster role binding Detailed Information View detailed information of the ClusterRoleBinding YAML The resource file of the cluster role binding can be edited in the YAML editor - Edit button to click and after modifying the resource, click the Done button to apply the changes
- When editing content, click the Diff button to view the changed content
event Check the events that occurred within the ClusterRoleBinding Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the metadata information of the ClusterRoleBinding Role/Target Information Check the role and target information of the ClusterRole Table. Cluster Role Binding detailed information items
Delete ClusterRoleBinding
To delete a ClusterRoleBinding, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click ClusterRoleBinding under the Permissions menu. 2. Go to the Cluster Role Binding List page.
- ClusterRoleBinding List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to delete on the Cluster Role Binding List page. 4. Navigate to the Cluster Role Binding Details page.
- On the Cluster Role Binding Details page, click Delete Cluster Role Binding.
- When the notification confirmation window appears, click the Confirm button.
Manage roles
A role is a rule that specifies permissions for a specific API or resource. You can create and manage permissions that allow access only to the namespace to which the role belongs.
Create role
To create a role, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Role under the Permissions menu. 2. Go to the Roll List page.
- Roles page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
Check roll detailed information
To view detailed roll information, follow the steps below.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Role under the Permissions menu. 2. Go to the Role List page.
- On the Roles List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to view detailed information for on the Roll List page. 4. Roll Details navigate to the page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries will be displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete Role Delete the role Detailed Information View detailed information of the roll YAML The resource files of Roll can be edited in a YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, click the Diff button to view the changes
event Check events that occurred within the roll Account information Check basic information about the Account, such as name, location, and creation date and time. Metadata Information Check the roll’s metadata information Policy Rule Information View Role policy rule information - Resources: List of resources to which the rule applies
- Non-Resource URLs: Non-Resource URLs are the set of partial URLs that a user may access
*is allowed, but only as the final segment of the path
- Non-resource URLs are not namespaced, so this field can only be used in a ClusterRole referenced by a ClusterRoleBinding
- A rule can apply to an API resource (e.g., “pods” or “secrets”) or a non-resource URL path (e.g., “/api”), but not both
- Resource Names: Resource names are an optional whitelist of names the rule applies to; an empty set means all are allowed
- Verbs: Verbs are the API actions used in resource requests such as get, list, create, update, patch, watch, delete, deletecollection
- For more details, see the Kubernetes official documentation > API Verbs
Table. Role detailed information items
Delete role
To delete the role, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Role under the Permissions menu. 2. Navigate to the Role List page.
- Role List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- On the Roll List page, select the item you want to delete. 4. Roll Details page will be opened.
- On the Roll Details page, click Delete Roll.
- When the notification confirmation window appears, click the Confirm button.
Managing Role Bindings
You can create and manage role bindings by linking a role to a specific subject.
Create RoleBinding
To create a role binding, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Role Binding under the Permissions menu. 2. Navigate to the Roll Binding List page.
- On the Roll Binding List page, select the cluster and namespace from the gear button at the top left, then click Create Object.
- Enter the object information in the Object Creation Popup and click the Confirm button.
View detailed role binding information
To view detailed roll binding information, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Role Binding under the Permissions menu. 2. Go to the Roll Binding List page.
- Roll Binding List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Roll Binding List page, select the item you want to view detailed information for. 4. Navigate to the Roll Binding Details page.
- If you select Show system objects at the top of the list, all items except the Kubernetes object entries are displayed.
- Click each tab to view the service information.
Category Detailed descriptionDelete roll binding Delete roll binding Detailed Information View detailed information of roll binding YAML The resource file of RollBinding can be edited in a YAML editor - Click the Edit button, modify the resource, then click the Done button to apply the changes
- When editing content, you can click the Diff button to view the changes
event Check events that occurred within roll binding Account Information Check basic information about the Account, such as name, location, creation time, etc. Metadata Information Check the metadata information of roll binding Role/Target Information Check the role’s responsibilities and target information Table. Role binding detailed information items
Delete Role Binding
To delete the roll binding, follow these steps.
- All Services > Container > Kubernetes Engine Click the menu. 1. Go to the Service Home page of Kubernetes Engine.
- On the Service Home page, click Role Binding under the Permissions menu. 2. Go to the Roll Binding List page.
- Roll Binding List page, select the cluster and namespace from the gear button at the top left, then click Confirm.
- Select the item you want to delete on the Roll Binding List page. 4. Navigate to the Roll Binding Details page.
- On the Roll Binding Details page, click Delete Roll Binding.
- When the notification dialog appears, click the Confirm button.
4.1.3 - Kubernetes Engine Usage Guide
Provides a guide for using Kubernetes Engine.
Kubernetes Engine Utilization Guide
In the Kubernetes Engine usage, the following features are described. For more details, refer to the guide.
| Provision Guide | Explanation |
|---|---|
| Access the cluster | kubectl installation and usage guide, kubeconfig download, login method using kubectl plugin
|
| Authentication and Authorization | Explain the authentication and authorization features and how to integrate them with Kubernetes Engine and IAM
|
| Configure a LoadBalancer type service | Guide to configuring a Service of type LoadBalancer using a Service manifest file
|
| Considerations when using | Explanation of constraints when using SKE
|
| Version information | Kubernetes version and support period description
|
4.1.3.1 - Access Cluster
kubectl Installation and Usage
After creating a Kubernetes Engine service, you can use the Kubernetes command-line tool kubectl to execute commands against your Kubernetes cluster. With kubectl, you can deploy applications, inspect and manage cluster resources, and view logs. You can find how to install and use kubectl in the official Kubernetes documentation.
| Category | Reference URL |
|---|---|
| kubectl installation (Linux) | https://kubernetes.io/docs/tasks/tools/install-kubectl-linux/ |
| kubectl installation (Windows) | https://kubernetes.io/docs/tasks/tools/install-kubectl-windows/ |
| kubectl Introduction | https://kubernetes.io/docs/reference/kubectl/ |
| kubectl Quick Reference | https://kubernetes.io/docs/reference/kubectl/quick-reference/ |
| kubectl command reference | https://kubernetes.io/docs/reference/kubectl/kubectl/ |
You must use a kubectl version that is within the cluster’s minor version difference. For example, if the cluster version is 1.30, you can use kubectl versions 1.29, 1.30, or 1.31.
- Please refer to the following document for the version skew policy of kubectl. https://kubernetes.io/releases/version-skew-policy/#kubectl
To access a Kubernetes cluster with kubectl, you need a kubeconfig file that contains the Kubernetes server address and authentication information.
Kubernetes Engine supports authentication via admin certificate kubeconfig and user authentication key kubeconfig.
Admin certificate kubeconfig
This kubeconfig uses the admin certificate as the authentication method when accessing the Kubernetes API.
Download admin kubeconfig
Kubernetes Engine > Cluster List > Cluster Details > Admin kubeconfig download Click the button to download the kubeconfig file.
- Downloading the admin kubeconfig is allowed only for Admin.
- There are separate private endpoint and public endpoint versions, and each can be downloaded only once.
Use admin kubeconfig
- By default, kubectl looks for a file named config in the $HOME/.kube directory. You can also set the KUBECONFIG environment variable or specify the
kubeconfigflag to use a different kubeconfig file. - Private endpoints are, by default, only accessible from the nodes of the respective cluster. For resources in the same account and the same region, you can allow access by adding them to the private endpoint access control settings.
- If you need to access the cluster from the external internet, setting public endpoint access to enabled allows you to access it using the public endpoint kubeconfig.
User authentication key kubeconfig
This kubeconfig uses the user’s Open API authentication key as the credential when accessing the Kubernetes API.
User kubeconfig download
Kubernetes Engine > Cluster List > Cluster Details > User kubeconfig Download Click the button to download the kubeconfig file.
- Downloading a user’s kubeconfig is allowed only for users with cluster read permissions.
- There are separate ones for private endpoints and public endpoints.
- Since the downloaded kubeconfig file does not contain the authentication key token, you must add the authentication key token information before using it. (See the next paragraph)
Add authentication key token to the user kubeconfig file
Below is an example of a user kubeconfig file. To use the kubeconfig file, you must add the authentication key token (AUTHKEY_TOKEN) information to the token field inside the file.
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0t...
server: https://my-cluster-a1c3e.ske.xxx.samsungsdscloud.com:6443
name: my-cluster-a1c3e
contexts:
- context:
cluster: my-cluster-a1c3e
user: jane.doe
name: jane.doe@my-cluster-a1c3e
current-context: jane.doe@my-cluster-a1c3e
kind: Config
preferences: {}
users:
- name: jane.doe
user:
token: <AUTHKEY_TOKEN> #### Writing requiredapiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0t...
server: https://my-cluster-a1c3e.ske.xxx.samsungsdscloud.com:6443
name: my-cluster-a1c3e
contexts:
- context:
cluster: my-cluster-a1c3e
user: jane.doe
name: jane.doe@my-cluster-a1c3e
current-context: jane.doe@my-cluster-a1c3e
kind: Config
preferences: {}
users:
- name: jane.doe
user:
token: <AUTHKEY_TOKEN> #### Writing requiredAUTHKEY_TOKEN can be generated by concatenating the ACCESS_KEY and SECRET_KEY of the authentication key with a colon (:) and then Base64 encoding it. The following is an example of creating an AUTHKEY_TOKEN in a Linux environment.
$ ACCESS_KEY=5df418813aed051548a72f4a814cf09e
$ SECRET_KEY=6ba7b810-9dad-11d1-80b4-00c04fd430c8
$ AUTHKEY_TOKEN=$(echo -n "$ACCESS_KEY:$SECRET_KEY" | base64 -w0)
$ echo $AUTHKEY_TOKEN
NWRmNDE4ODEzYWVkMDUxNTQ4YTcyZjRhODE0Y2YwOWU6NmJhN2I4MTAtOWRhZC0xMWQxLTgwYjQtMDBjMDRmZDQzMGM4r$ ACCESS_KEY=5df418813aed051548a72f4a814cf09e
$ SECRET_KEY=6ba7b810-9dad-11d1-80b4-00c04fd430c8
$ AUTHKEY_TOKEN=$(echo -n "$ACCESS_KEY:$SECRET_KEY" | base64 -w0)
$ echo $AUTHKEY_TOKEN
NWRmNDE4ODEzYWVkMDUxNTQ4YTcyZjRhODE0Y2YwOWU6NmJhN2I4MTAtOWRhZC0xMWQxLTgwYjQtMDBjMDRmZDQzMGM4r- For detailed information on generating authentication keys, refer to API Reference > Common > Samsung Cloud Platform Open API Call Procedure.
User kubeconfig execution example
You can view an example of executing the user kubeconfig.
When access is blocked by access control or a firewall
$ kubectl --kubeconfig=user-kubeconfig.yaml get namespaces
Unable to connect to the server: dial tcp 123.123.123.123:6443: i/o timeout$ kubectl --kubeconfig=user-kubeconfig.yaml get namespaces
Unable to connect to the server: dial tcp 123.123.123.123:6443: i/o timeoutWhen authentication fails because the AUTHKEY_TOKEN does not match
$ kubectl --kubeconfig=user-kubeconfig.yaml get namespaces
error: You must be logged in to the server (Unauthorized)$ kubectl --kubeconfig=user-kubeconfig.yaml get namespaces
error: You must be logged in to the server (Unauthorized)AUTHKEY_TOKEN when authentication succeeds
$ kubectl --kubeconfig=user-kubeconfig.yaml get namespaces
...
kube-node-lease Active 10d
kube-public Active 10d
kube-system Active 10d$ kubectl --kubeconfig=user-kubeconfig.yaml get namespaces
...
kube-node-lease Active 10d
kube-public Active 10d
kube-system Active 10dAUTHKEY_TOKEN Authentication succeeded but lacks permission
$ kubectl --kubeconfig=user-kubeconfig.yaml get nodes
Error from server (Forbidden): nodes is forbidden: User "jane.doe" cannot list resource "nodes" in API group "" at the cluster scope$ kubectl --kubeconfig=user-kubeconfig.yaml get nodes
Error from server (Forbidden): nodes is forbidden: User "jane.doe" cannot list resource "nodes" in API group "" at the cluster scope4.1.3.2 - Authentication and Authorization
Kubernetes Engine applies Kubernetes authentication and RBAC authorization features. It explains how Kubernetes authentication and authorization functions integrate with Kubernetes Engine and IAM.
Kubernetes authentication and authorization
Describes Kubernetes authentication and RBAC authorization features.
Authentication
The Kubernetes API server obtains the information required for authenticating a user (User) or a service account (ServiceAccount) from certificates or authentication tokens, and then carries out the authentication process.
Authorization
The Kubernetes API server uses the user information obtained through the authentication process to verify, via RBAC-related objects, whether the user has permission for the requested operation. RBAC-related objects come in four types as follows.
| object | Scope | Explanation |
|---|---|---|
| Cluster Role (ClusteRole) | cluster-wide | Definition of permissions across all namespaces in the cluster |
| ClusterRoleBinding(ClusteRoleBinding) | cluster-wide | Definition of the connection between ClusterRole and user |
| Roll (Role) | namespace (namespace) | Permission definition for a specific namespace |
| RoleBinding(RoleBinding) | namespace (namespace) | Definition of the binding between a ClusterRole or Role and a user |
Roll
Kubernetes defines several cluster roles by default. Some of those cluster roles do not include the prefix (system:). These are cluster roles intended for user use. This includes a superuser role (cluster-admin) applied to the entire cluster using a ClusterRoleBinding, and roles (admin, edit, view) applied to a specific namespace using a RoleBinding.
| Default cluster role | Default ClusterRoleBinding | Explanation |
|---|---|---|
| cluster-admin | system:masters group | Allows superuser access that can perform any operation on all resources.
|
| admin | None | Allows administrator access applied within a namespace using role binding. When used in role binding, it grants read/write access to most resources within the namespace, including the ability to create roles and role bindings inside the namespace. This role does not permit write access to resource quotas or the namespace itself. |
| edit | None | Allows read/write access to most objects within the namespace.
|
| view | None | Allows read‑only access to view most objects within a namespace. Roles or role bindings cannot be viewed.
|
If necessary, you can define additional roles (or cluster roles) beyond the default cluster role, as shown below.
# A role that grants permission to view pods in the "default" namespace.
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
namespace: default
name: pod-reader
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list", "watch"]# A role that grants permission to view pods in the "default" namespace.
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
namespace: default
name: pod-reader
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list", "watch"]# Cluster role that grants permission to view nodes
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: node-reader
rules:
- apiGroups: [""]
resources: ["nodes"]
verbs: ["get", "list", "watch"]# Cluster role that grants permission to view nodes
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: node-reader
rules:
- apiGroups: [""]
resources: ["nodes"]
verbs: ["get", "list", "watch"]Role Binding
To manage access to the Kubernetes Engine using Samsung Cloud Platform IAM, you need to understand the relationship between Kubernetes role bindings and IAM. The subjects of a role binding (or cluster role binding) may include individual users (User) or groups (Group).
- User corresponds to the Samsung Cloud Platform username, and Group corresponds to the IAM user group name, respectively.
For RoleBinding/ClusterRoleBinding, subjects.kind can be set to one of the following.
- User: Samsung Cloud Platform is connected to individual users.
- Group: Connected to the Samsung Cloud Platform IAM user group.
The subjects.name of a role binding/cluster role binding can be specified as follows. If the user is a User: individual Samsung Cloud Platform username (e.g., jane.doe) For a group: Samsung Cloud Platform IAM user group name (e.g., ReadPodsGroup)
In this way, the IAM user group is linked to the group defined in the RoleBinding (or ClusterRoleBinding) of the Kubernetes Engine cluster. It is also granted permission to perform the API actions included in the Role (or ClusterRole) associated with the group.
Example) role binding read-pods #1
The example of writing User (individual Samsung Cloud Platform user) in a role binding is as follows.
# This role binding allows the user "jane.doe" to view pods in the "default" namespace.
# The namespace must have a role named "pod-reader".
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: read-pods
namespace: default
roleRef:
# The "roleRef" specifies the link to a Role or ClusterRole.
kind: Role # Must be Role or ClusterRole.
name: pod-reader # Must match the name of the Role or ClusterRole you want to bind to.
apiGroup: rbac.authorization.k8s.io
subjects:
# You can specify one or more "target (subject)".
- kind: User
name: jane.doe
apiGroup: rbac.authorization.k8s.io# This role binding allows the user "jane.doe" to view pods in the "default" namespace.
# The namespace must have a role named "pod-reader".
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: read-pods
namespace: default
roleRef:
# The "roleRef" specifies the link to a Role or ClusterRole.
kind: Role # Must be Role or ClusterRole.
name: pod-reader # Must match the name of the Role or ClusterRole you want to bind to.
apiGroup: rbac.authorization.k8s.io
subjects:
# You can specify one or more "target (subject)".
- kind: User
name: jane.doe
apiGroup: rbac.authorization.k8s.ioWhen a role binding like the above is created in the cluster, a user whose username is jane.doe is granted permission to perform the API actions defined in the pod-reader role.
Example) role binding read-pods #2
The example of creating a group (IAM user group) in role binding is as follows.
# This role binding allows users in the "ReadPodsGroup" group to view pods in the "default" namespace.
# The namespace must have a role called "pod-reader".
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: read-pods
namespace: default
roleRef:
kind: Role
name: pod-reader
apiGroup: rbac.authorization.k8s.io
subjects:
# You can specify one or more "target (subject)".
- kind: Group
name: ReadPodsGroup
apiGroup: rbac.authorization.k8s.io# This role binding allows users in the "ReadPodsGroup" group to view pods in the "default" namespace.
# The namespace must have a role called "pod-reader".
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: read-pods
namespace: default
roleRef:
kind: Role
name: pod-reader
apiGroup: rbac.authorization.k8s.io
subjects:
# You can specify one or more "target (subject)".
- kind: Group
name: ReadPodsGroup
apiGroup: rbac.authorization.k8s.ioIf a role binding like the above is created in the cluster, users in the IAM user group ReadPodsGroup are granted permission to perform the API actions defined in the role pod-reader.
Example) ClusterRoleBinding read-nodes
# This cluster role binding allows users in the "ReadNodesGroup" group to view nodes.
# A cluster role named "node-reader" must exist.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: read-nodes
roleRef:
kind: ClusterRole
name: node-reader
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: Group
name: ReadNodesGroup
apiGroup: rbac.authorization.k8s.io# This cluster role binding allows users in the "ReadNodesGroup" group to view nodes.
# A cluster role named "node-reader" must exist.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: read-nodes
roleRef:
kind: ClusterRole
name: node-reader
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: Group
name: ReadNodesGroup
apiGroup: rbac.authorization.k8s.ioWhen a cluster role binding like the above is created in the cluster, users belonging to the IAM user group ReadNodesGroup are granted permission to perform the API actions defined in the cluster role node-reader.
Predefined roles and role bindings for Samsung Cloud Platform
In the Kubernetes Engine of Samsung Cloud Platform, the cluster role bindings scp-cluster-admin, scp-view, scp-namespace-view, and the cluster role scp-namespace-view are predefined. The table below shows the predefined roles and role bindings for Samsung Cloud Platform and the relationships of Samsung Cloud Platform users. Here, the cluster roles cluster-admin and view are predefined within the Kubernetes cluster. For more details, see role.
| ClusterRoleBinding | ClusterRole | subjects (user) |
|---|---|---|
| scp-cluster-admin | cluster-admin | Cluster creator username (e.g., jane.doe) |
| scp-view | view | - |
| scp-namespace-view | scp-namespace-view | All users authenticated to this cluster |
- According to the cluster role binding scp-cluster-admin, the Kubernetes Engine service creator is granted cluster admin privileges.
- Users or groups registered in the cluster role binding scp-view are granted cluster viewer permissions. It is bound to the predefined Kubernetes cluster role view, and does not grant access to cluster‑scoped resources (e.g., namespaces, nodes, ingress classes, etc.) or to secrets within a namespace. For more details, see role.
- According to the cluster role binding scp-namespace-view, all users authenticated to the cluster are granted permission to view namespaces.
- Predefined roles and role bindings for Samsung Cloud Platform are created once during cluster service creation.
- Users can modify or delete the predefined cluster role bindings and cluster roles for Samsung Cloud Platform as needed.
The details of the predefined roles and role bindings for Samsung Cloud Platform are as follows.
ClusterRoleBinding scp-cluster-admin
Cluster role binding scp-cluster-admin is linked to the cluster role cluster-admin, and is bound to the Samsung Cloud Platform user (Kubernetes Engine cluster creator) according to the subjects field.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
name: scp-cluster-admin
roleRef:
kind: ClusterRole
name: cluster-admin
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: User
name: jane.doe # cluster creator username
apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
name: scp-cluster-admin
roleRef:
kind: ClusterRole
name: cluster-admin
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: User
name: jane.doe # cluster creator username
apiGroup: rbac.authorization.k8s.ioClusterRoleBinding scp-view
ClusterRoleBinding scp-view is bound to the ClusterRole view, and you can add Samsung Cloud Platform users or IAM user groups to the subjects field.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: scp-view
roleRef:
kind: ClusterRole
name: view
apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: scp-view
roleRef:
kind: ClusterRole
name: view
apiGroup: rbac.authorization.k8s.ioClusterRole and ClusterRoleBinding scp-namespace-view
The cluster role scp-namespace-view defines view permissions for namespaces. The cluster role binding scp-namespace-view is bound to the cluster role scp-namespace-view, granting namespace read permissions to all authenticated users in the cluster.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: scp-namespace-view
rules:
- apiGroups: [""]
resources: ["namespaces"]
verbs: ["get", "list", "watch"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: scp-namespace-view
roleRef:
kind: ClusterRole
name: scp-namespace-view
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: Group
name: system:authenticated
apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: scp-namespace-view
rules:
- apiGroups: [""]
resources: ["namespaces"]
verbs: ["get", "list", "watch"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: scp-namespace-view
roleRef:
kind: ClusterRole
name: scp-namespace-view
apiGroup: rbac.authorization.k8s.io
subjects:
- kind: Group
name: system:authenticated
apiGroup: rbac.authorization.k8s.ioIAM user group RBAC use case
This chapter explains examples of granting permissions for each major user scenario. The IAM user groups, ClusterRoleBinding/RoleBinding, and ClusterRole names presented here are just examples to aid understanding. Administrators should define and apply appropriate names and permissions as needed.
| Scope | use case | IAM user group | ClusterRoleBinding/RoleBinding | ClusterRole | Remarks |
|---|---|---|---|---|---|
| cluster | Cluster Administrator | ClusterAdminGroup | ClusterRoleBinding cluster-admin-group | cluster-admin | Administrator for a specific cluster |
| cluster | Cluster Editor | ClusterEditGroup | ClusterRoleBinding cluster-edit-group | edit | Editor for a specific cluster |
| cluster | Cluster Viewer | ClusterViewGroup | ClusterRoleBinding cluster-view-group | view | Viewer for a specific cluster |
| namespace | Namespace Manager | NamespaceAdminGroup | Role binding namespace-admin-group | admin | Administrator for a specific namespace |
| namespace | Namespace editor | NamespaceEditGroup | Role binding namespace-edit-group | edit | Editor for a specific namespace |
| namespace | Namespace viewer | NamespaceViewGroup | Role binding namespace-view-group | view | Viewer for a specific namespace |
Cluster Administrator
To create a cluster administrator, follow these steps.
- Create an IAM user group named ClusterAdminGroup.
- Create a cluster role binding with the following contents in the target cluster.Color mode
apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: cluster-admin-group roleRef: kind: ClusterRole name: cluster-admin apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: ClusterAdminGroup apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: cluster-admin-group roleRef: kind: ClusterRole name: cluster-admin apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: ClusterAdminGroup apiGroup: rbac.authorization.k8s.ioCode block. Create cluster administrator
- It is linked with cluster-admin of the base cluster, granting administrator privileges for that cluster.
Cluster Editor
To create a cluster editor, follow these steps.
- Create an IAM user group named ClusterEditGroup.
- Create a ClusterRoleBinding with the following specifications in the target cluster.Color mode
apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: cluster-edit-group roleRef: kind: ClusterRole name: edit apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: ClusterEditGroup apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: cluster-edit-group roleRef: kind: ClusterRole name: edit apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: ClusterEditGroup apiGroup: rbac.authorization.k8s.ioCode block. Create cluster editor
- It is linked with the edit role of the base cluster, granting editor permissions for that cluster.
Cluster Viewer
To create a cluster viewer, follow these steps.
- Create an IAM user group named ClusterViewGroup.
- Create a ClusterRoleBinding with the following specifications in the target cluster.Color mode
apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: cluster-view-group roleRef: kind: ClusterRole name: view apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: ClusterViewGroup apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: cluster-view-group roleRef: kind: ClusterRole name: view apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: ClusterViewGroup apiGroup: rbac.authorization.k8s.ioCode block. Create cluster viewer
- It is associated with the view role of the default cluster, granting viewer permissions for that cluster.
Namespace Administrator
To create a namespace manager, follow these steps.
- Create an IAM user group named NamespaceAdminGroup.
- Create a RoleBinding with the following contents in the target cluster.Color mode
apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: namespace-admin-group namespace: <namespace_name> roleRef: kind: ClusterRole name: admin apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: NamespaceAdminGroup apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: namespace-admin-group namespace: <namespace_name> roleRef: kind: ClusterRole name: admin apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: NamespaceAdminGroup apiGroup: rbac.authorization.k8s.ioCode block. Create a namespace manager
- It is linked with the admin role of the default cluster, granting administrator privileges for the namespace.
Namespace Editor
To create a namespace editor, follow these steps.
- Create an IAM user group named NamespaceEditGroup.
- Create a RoleBinding with the following specifications in the target cluster.Color mode
apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: namespace-edit-group namespace: <namespace_name> roleRef: kind: ClusterRole name: edit apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: NamespaceEditGroup apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: namespace-edit-group namespace: <namespace_name> roleRef: kind: ClusterRole name: edit apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: NamespaceEditGroup apiGroup: rbac.authorization.k8s.ioCode block. Create namespace editor
- It is linked with the default cluster role edit, granting editor permissions for the namespace.
Namespace Viewer
To create a namespace viewer, follow these steps.
- Create an IAM user group named NamespaceViewGroup.
- Create a RoleBinding with the following contents in the target cluster.Color mode
apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: namespace-view-group namespace: <namespace_name> roleRef: kind: ClusterRole name: view apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: NamespaceViewGroup apiGroup: rbac.authorization.k8s.ioapiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: namespace-view-group namespace: <namespace_name> roleRef: kind: ClusterRole name: view apiGroup: rbac.authorization.k8s.io subjects: - kind: Group name: NamespaceViewGroup apiGroup: rbac.authorization.k8s.ioCode block. Create namespace viewer
- It is associated with the default cluster role view, granting viewer permissions for the namespace.
4.1.3.3 - Using type LoadBalancer service
Service Configuration Method
By creating and applying a Service manifest file (example:
my-lb-svc.yaml
), you can set up a Service of type LoadBalancer.
- The LoadBalancer is created in the cluster subnet by default.
- To create a LoadBalancer in a different Subnet, use the annotation service.beta.kubernetes.io/scp-load-balancer-subnet-id. * For more details, see Annotation detailed settings
To create and apply a type LoadBalancer Service, follow the steps below.
Create the Service manifest file
my-lb-svc.yaml.Color modeapiVersion: v1 kind: Service metadata: name: my-service spec: selector: app.kubernetes.io/name: MyApp ports: - protocol: TCP port: 80 targetPort: 9376 appProtocol: tcp # Refer to the LB service protocol type setting section type: LoadBalancerapiVersion: v1 kind: Service metadata: name: my-service spec: selector: app.kubernetes.io/name: MyApp ports: - protocol: TCP port: 80 targetPort: 9376 appProtocol: tcp # Refer to the LB service protocol type setting section type: LoadBalancerCode block. Service manifest file my-lb-svc.yaml example Deploy the Service manifest using the
kubectl applycommand.Color modekubectl apply -f my-lb-svc.yamlkubectl apply -f my-lb-svc.yamlCode block. Deploy the Service manifest using the kubectl apply command.
- When a type LoadBalancer Service is created, the corresponding Load Balancer service is automatically created. * It may take a few minutes for the configuration to complete.
- Do not arbitrarily modify the automatically generated Load Balancer service and LB server group. * Changes may be reverted or cause unexpected behavior.
- For configurable detailed features, please refer to Annotation detailed settings.
kubectl get servicecommand is used to verify the Load Balancer configuration.Color mode# kubectl get service my-lb-svc NAMESPACE NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE default my-lb-svc LoadBalancer 172.20.49.206 123.123.123.123 80:32068/TCP 3m# kubectl get service my-lb-svc NAMESPACE NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE default my-lb-svc LoadBalancer 172.20.49.206 123.123.123.123 80:32068/TCP 3mCode block. Verify Load Balancer configuration using the `kubectl get service` command
Protocol type
You can create a Service manifest and use it. The following is a simple example.
apiVersion: v1
kind: Service
metadata:
name: my-service
spec:
selector:
...
ports:
- port: 80
targetPort: 9376
protocol: TCP # required (choose one of TCP, UDP)
appProtocol: tcp # optional (leave blank or select one of tcp, http, https)
type: LoadBalancer # type LoadBalancerapiVersion: v1
kind: Service
metadata:
name: my-service
spec:
selector:
...
ports:
- port: 80
targetPort: 9376
protocol: TCP # required (choose one of TCP, UDP)
appProtocol: tcp # optional (leave blank or select one of tcp, http, https)
type: LoadBalancer # type LoadBalancerThe list of protocols (protocol and appProtocol) supported by the Load Balancer Service type in Kubernetes Engine, along with the corresponding settings applied to the Load Balancer service, is as follows.
| Category | (k8s) protocol | (k8s) appProtocol | (LB) Service classification | (LB) LB Listener | (LB) LB server group | (LB) health check |
|---|---|---|---|---|---|---|
| L4 TCP | TCP | (tcp) | L4 | TCP {port} | TCP {nodePort} | TCP {nodePort} |
| L4 UDP | UDP | - | L4 | UDP {port} | UDP {nodePort} | TCP {nodePort} |
| L7 HTTP | TCP | http | L7 | HTTP {port} | TCP {nodePort} | TCP/HTTP {nodePort} |
| L7 HTTPS | TCP | https | L7 | HTTPS {port} | TCP {nodePort} | TCP/HTTP {nodePort} |
- According to the k8s Service manifest spec, you can specify multiple ports for a single service.
Depending on the Load Balancer service type (L4, L7), you cannot mix protocol layers within a single Service.
- In other words, L4 (TCP, UDP) and L7 (HTTP, HTTPS) cannot be used together in a single Service.
L4 Service Manifest Writing Example
apiVersion: v1
kind: Service
metadata:
name: my-service
spec:
selector:
app.kubernetes.io/name: MyApp
ports:
- protocol: TCP
port: 80
targetPort: 9376
type: LoadBalancerapiVersion: v1
kind: Service
metadata:
name: my-service
spec:
selector:
app.kubernetes.io/name: MyApp
ports:
- protocol: TCP
port: 80
targetPort: 9376
type: LoadBalancerL7 Service Manifest Example
apiVersion: v1
kind: Service
metadata:
annotations:
service.beta.kubernetes.io/scp-load-balancer-layer-type: "L7" # required
service.beta.kubernetes.io/scp-load-balancer-client-cert-id: "24da35de187b450eb0cf09fb6fa146de" # required
name: my-service
spec:
selector:
app.kubernetes.io/name: MyApp
ports:
- appProtocol: http # required
protocol: TCP
port: 80
targetPort: 9376
- appProtocol: https # required
protocol: TCP
port: 443
targetPort: 9898
type: LoadBalancer
apiVersion: v1
kind: Service
metadata:
annotations:
service.beta.kubernetes.io/scp-load-balancer-layer-type: "L7" # required
service.beta.kubernetes.io/scp-load-balancer-client-cert-id: "24da35de187b450eb0cf09fb6fa146de" # required
name: my-service
spec:
selector:
app.kubernetes.io/name: MyApp
ports:
- appProtocol: http # required
protocol: TCP
port: 80
targetPort: 9376
- appProtocol: https # required
protocol: TCP
port: 443
targetPort: 9898
type: LoadBalancer
Annotation detailed settings
You can add annotations to the service manifest to configure detailed features.
apiVersion: v1
kind: Service
metatdata:
name: my-lb-svc
annotations:
service.beta.kubernetes.io/scp-load-balancer-public-ip-enabled: "true"
service.beta.kubernetes.io/scp-load-balancer-health-check-interval: "5"
service.beta.kubernetes.io/scp-load-balancer-health-check-timeout: "5"
service.beta.kubernetes.io/scp-load-balancer-health-check-count: "3"
service.beta.kubernetes.io/scp-load-balancer-session-duration-time: "300"
spec:
type: LoadBalancer
...
apiVersion: v1
kind: Service
metatdata:
name: my-lb-svc
annotations:
service.beta.kubernetes.io/scp-load-balancer-public-ip-enabled: "true"
service.beta.kubernetes.io/scp-load-balancer-health-check-interval: "5"
service.beta.kubernetes.io/scp-load-balancer-health-check-timeout: "5"
service.beta.kubernetes.io/scp-load-balancer-health-check-count: "3"
service.beta.kubernetes.io/scp-load-balancer-session-duration-time: "300"
spec:
type: LoadBalancer
...
- If you do not add any annotation to the service, the annotation’s default values are applied.
- Even if the annotation added to the service does not meet the allowed values, the annotation’s default value is applied.
Below is a description of all annotations available for a type LoadBalancer service.
| annotation | Protocol | default | allowed value | example | Explanation |
|---|---|---|---|---|---|
| service.beta.kubernetes.io/scp-load-balancer-source-ranges-firewall-rules | All | false | true, false | false | Automatically add firewall rule (LB source ranges → LB service IP) |
| service.beta.kubernetes.io/scp-load-balancer-snat-healthcheck-firewall-rules | All | false | true,false | false | Automatically add firewall rules (LB Source NAT IP, HealthCheck IP → member IP:Port)
|
| annotation | Protocol | default | allowed value | example | Explanation |
|---|---|---|---|---|---|
| service.beta.kubernetes.io/scp-load-balancer-security-group-id | All | - | UUID | 92d84b44-ee71-493d-9782-3a90481ce5f3 | Automatically add rules to the Security Group corresponding to the specified ID
|
| service.beta.kubernetes.io/scp-load-balancer-security-group-name | All | - | string | security-group-1 | Automatically add rules to the Security Group corresponding to the specified Name
|
| annotation | Protocol | default | allowed value | example | Explanation |
|---|---|---|---|---|---|
| service.beta.kubernetes.io/scp-load-balancer-layer-type | All | L4 | L4, L7 | L4 | Specify the service type of the Load Balancer
|
| service.beta.kubernetes.io/scp-load-balancer-subnet-id | All | - | ID | 7f05eda5e1cf4a45971227c57a6d60fa | Specify the Service Subnet of the Load Balancer
|
| service.beta.kubernetes.io/scp-load-balancer-service-ip | All | - | IP address | 192.168.10.7 | Specify the Service IP of the Load Balancer
|
| service.beta.kubernetes.io/scp-load-balancer-public-ip-enabled | All | false | true, false | false | Specify whether to use the Load Balancer’s Public NAT IP
|
| service.beta.kubernetes.io/scp-load-balancer-public-ip-id | All | - | ID | 4119894bd9614cef83db6f8dda667a20 | Specify the ID of the Public IP to be used as the Load Balancer’s Public NAT IP
|
| annotation | Protocol | default | allowed value | example | Explanation |
|---|---|---|---|---|---|
| service.beta.kubernetes.io/scp-load-balancer-idle-timeout | HTTP, HTTPS | - | 60 - 3600(60-second unit) | 600 | Specify the LB Listener’s idle-timeout (seconds)
|
| service.beta.kubernetes.io/scp-load-balancer-session-duration-time | All | L4: 120L7: - | L4 TCP: 60 - 3600(60-second unit)L4 UDP: 60 - 180(60-second unit)L7: 0 - 120 | 120 | Specify the LB Listener’s session-duration-time (seconds)
|
| service.beta.kubernetes.io/scp-load-balancer-response-timeout | HTTP, HTTPS | - | 0 - 120 | 60 | Specify the LB Listener response-timeout (seconds)
|
| service.beta.kubernetes.io/scp-load-balancer-insert-client-ip | TCP | false | true, false | false | Specify Insert Client IP for LB Listener |
| service.beta.kubernetes.io/scp-load-balancer-x-forwarded-proto | HTTP, HTTPS | false | true, false | false | Specify whether to use the X-Forwarded-Proto header for the LB Listener. |
| service.beta.kubernetes.io/scp-load-balancer-x-forwarded-port | HTTP, HTTPS | false | true, | false | Specify whether to use the X-Forwarded-Port header of the LB Listener |
| service.beta.kubernetes.io/scp-load-balancer-x-forwarded-for | HTTP, HTTPS | false | true, false | false | Specify whether to use the X-Forwarded-For header for the LB Listener. |
| service.beta.kubernetes.io/scp-load-balancer-support-http2 | HTTP, HTTPS | false | true, false | false | Specify whether the LB Listener supports HTTP 2.0. |
| service.beta.kubernetes.io/scp-load-balancer-persistence | TCP, HTTP, HTTPS | "" | "", source-ip, cookie | source-ip | Specify the persistence of the LB Listener (none, source IP, or cookie)
|
| service.beta.kubernetes.io/scp-load-balancer-client-cert-id | HTTPS | - | UUID | 78b9105e00324715b63700933125fa83 | Specify the client SSL certificate ID of the LB Listener
|
| service.beta.kubernetes.io/scp-load-balancer-client-cert-level | HTTPS | HIGH | HIGH, NORMAL, LOW | HIGH | Specify the security level of the client SSL certificate for the LB Listener. |
| service.beta.kubernetes.io/scp-load-balancer-server-cert-level | HTTPS | - | HIGH, NORMAL, LOW | HIGH | Specify the security level of the server SSL certificate for the LB Listener. |
| annotation | Protocol | default | allowed value | example | Explanation |
|---|---|---|---|---|---|
| service.beta.kubernetes.io/scp-load-balancer-lb-method | All | ROUND_ROBIN | ROUND_ROBIN, LEAST_CONNECTION, IP_HASH | ROUND_ROBIN | Specify the load balancing policy for the LB server group |
| annotation | Protocol | default | allowed value | example | Explanation |
|---|---|---|---|---|---|
| service.beta.kubernetes.io/scp-load-balancer-health-check-enabled | All | true | true, false | true | Specify whether to use LB health check |
| service.beta.kubernetes.io/scp-load-balancer-health-check-protocol | All | TCP | TCP, HTTP, HTTPS | TCP | Specify the protocol for the LB health check |
| service.beta.kubernetes.io/scp-load-balancer-health-check-port | All | {nodeport} | 1 - 65534 | 30000 | Specify the health check port of the LB health check
|
| service.beta.kubernetes.io/scp-load-balancer-health-check-count | All | 3 | 1 - 10 | 3 | Specify the number of detection attempts for LB health check |
| service.beta.kubernetes.io/scp-load-balancer-health-check-interval | All | 5 | 1 - 180 | 5 | Specify the LB health check interval |
| service.beta.kubernetes.io/scp-load-balancer-health-check-timeout | All | 5 | 1 - 180 | 5 | Specify the wait time for LB health check |
| service.beta.kubernetes.io/scp-load-balancer-health-check-http-method | HTTP | GET | GET, POST | GET | Specify the HTTP method for the LB health check |
| service.beta.kubernetes.io/scp-load-balancer-health-check-url | HTTP | / | string | /healthz | Specify the URL for the LB health check |
| service.beta.kubernetes.io/scp-load-balancer-health-check-response-code | HTTP | 200 | 200 - 500 | 200 | Specify the response code for the LB health check |
| service.beta.kubernetes.io/scp-load-balancer-health-check-request-data | HTTP | - | string | username=admin&password=1234 | Specify the request string for LB health check
|
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-enabled | All | true | true, false | true | Specify whether to use LB health check for the Service’s {port} port number |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-protocol | All | TCP | TCP, HTTP, HTTPS | TCP | Specify the LB health check protocol for the Service’s {port} port number. |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-port | All | - | 1 - 65534 | 30000 | Specify the LB health check port for the Service’s {port} port number |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-count | All | 3 | 1 - 10 | 3 | Specify the LB health check detection count for the Service’s {port} port number |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-interval | All | 5 | 1 - 180 | 5 | Specify the LB health check interval for the Service’s {port} port number |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-timeout | All | 5 | 1 - 180 | 5 | Specify the LB health check wait time for the Service’s {port} port number. |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-http-method | HTTP | GET | GET, POST | GET | Specify the LB health check HTTP method for the Service’s {port} port number. |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-url | HTTP | / | string | /healthz | Specify the LB health check URL for the Service’s {port} port number. |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-response-code | HTTP | 200 | 200 - 500 | 200 | Specify the LB health check response code for the Service’s {port} port number. |
| service.beta.kubernetes.io/scp-load-balancer-port-{port}-health-check-request-data | HTTP | - | string | username=admin&password=1234 | Specify the LB health check request string for the Service’s {port} port number
|
Constraints
The constraints to consider when using Kubernetes annotations are as follows.
| Constraints | Related annotations |
|---|---|
| When changing the Security Group, rules created in the existing Security Group are not automatically deleted. | service.beta.kubernetes.io/scp-load-balancer-security-group-id service.beta.kubernetes.io/scp-load-balancer-security-group-name |
| Cannot change the service classification (L4/L7) of the Load Balancer. | service.beta.kubernetes.io/scp-load-balancer-layer-type |
| L4 and L7 cannot be used together within the same k8s Service. | service.beta.kubernetes.io/scp-load-balancer-layer-type |
| Cannot change Load Balancer subnet | service.beta.kubernetes.io/scp-load-balancer-subnet-id |
| Cannot change the Load Balancer’s Service IP | service.beta.kubernetes.io/scp-load-balancer-service-ip |
| The LB Listener idle-timeout cannot be changed from enabled to disabled after it has been used. | service.beta.kubernetes.io/scp-load-balancer-idle-timeout |
| The LB Listener session-duration-time cannot be changed from used to unused after it has been used. | service.beta.kubernetes.io/scp-load-balancer-session-duration-time |
| The LB Listener response-timeout cannot be changed from enabled to disabled after it has been used. | service.beta.kubernetes.io/scp-load-balancer-response-timeout |
| LB Listener idle-timeout cannot be set simultaneously with session-duration-time or response-timeout. | service.beta.kubernetes.io/scp-load-balancer-idle-timeout service.beta.kubernetes.io/scp-load-balancer-session-duration-time service.beta.kubernetes.io/scp-load-balancer-response-timeout |
| Cannot use TCP and UDP together on the same port number within the same k8s Service. | - |
L7 Listener’s routing rules only support the default URL path of the LB server group delivery method
| - |
4.1.3.4 - Usage Considerations
Managed Port Constraints
The following ports are used for SKE management and cannot be used for service access. Additionally, if they are blocked by the OS firewall or similar, node functions or some features may not operate correctly.
| Port | Explanation |
|---|---|
| UDP 4789 | calico-vxlan |
| TCP 5473 | calico-typha |
| TCP 10250 | kubelet |
| TCP 19100 | node-exporter |
| TCP 19400 | dcgm-exporter |
kube-reserved resource constraints
kube-reserved is a feature that reserves resources for system daemons that do not run as pods on a node.
- System daemons that do not run as pods include kubelet, container runtime, etc.
For detailed information about kube-reserved, refer to the following document.
Kubernetes Engine reserves CPU and memory based on the following criteria.
| CPU specifications | Memory specifications |
|---|---|
|
|
Example: For a Virtual Server with 16 vCPU cores and 32 GB memory, kube-reserved is calculated as follows.
- CPU: (1 core × 0.06) + (1 core × 0.01) + (2 core × 0.005) + (12 core × 0.0025) = 0.11 core
- Memory: (4 GB × 0.25) + (4 GB × 0.2) + (8 GB × 0.1) + (16 GB × 0.06) = 3.56 GB
Example: The resources reserved based on CPU size are as follows.
| CPU specifications | Resource Specification 1 | Resource Specification 2 | Resource Specification 3 | Resource Specification 4 |
|---|---|---|---|---|
| kube-reserved CPU | 70 m | 80 m | 90 m | 110 m |
- Example: The resources reserved based on memory size are as follows.
| Memory specifications | Resource Specification 1 | Resource Specification 2 | Resource Specification 3 | Resource Specification 4 | Resource Specification 4 | Resource Specification 4 | Resource Specification 4 |
|---|---|---|---|---|---|---|---|
| kube-reserved memory | 1 GB | 1.8 GB | 2.6 GB | 3.56 GB | 5.48 GB | 9.32 GB | 11.88 GB |
4.1.3.5 - Version information
Kubernetes version and support period
Kubernetes version lifecycle
The Kubernetes open-source software (OSS) community releases minor versions three times a year, with a release cycle of approximately 15 weeks. A released minor version goes through a support period of about 14 months (12 months for standard patches, 2 months for maintenance) before reaching EOL (End of Life).
For information on Kubernetes release and EOL dates and support periods, refer to the following link.
Samsung Cloud Platform Kubernetes Engine (SKE) version release plan
SKE validates and supplies the stable patch versions among released OSS minor versions. Therefore, the release timing of the version provided by SKE differs from that of the corresponding OSS version.
Also, for previously released versions, considering factors such as the open‑source EOL timing, technical support will be terminated sequentially from the older versions (End of Tech support, EoTS).
The release schedule and end-of-life schedule for OSS and SKE are as follows.
| version | OSS release | OSS EOL | SKE release | SKE EoTS |
|---|---|---|---|---|
| v1.29 | 2023-12-13 | 2025-02-28 | 2024-10 | 2026-03-31 |
| v1.30 | 2024-04-17 | 2025-06-28 | 2025-02 | 2026-06-30 |
| v1.31 | 2024-08-13 | 2025-10-28 | 2025-07 | 2026-10-28 |
| v1.32 | 2024-12-11 | 2026-02-28 | 2025-10 | 2027-02-28 |
| v1.33 | 2025-04-23 | 2026-06-28 | 2025-12 | 2027-06-28 |
| v1.34 | 2025-08-27 | 2026-10-27 | 2026-03 | 2027-10-27 |
Feature restrictions when technical support ends (EoTS)
If the Kubernetes version provided by SKE reaches end-of-technical-support (EoTS) status, the features supported in that version may be limited.
- Create new cluster → Creation not allowed
- Existing cluster upgrade → upgrade possible (upgrade is possible even if the newer version is EoTS)
- Create node pool from existing cluster → possible
- Since EOL versions may have vulnerabilities, we recommend upgrading to a newer version.
- You can upgrade the control plane and node pools from the Samsung Cloud Platform Console, and no additional costs are incurred for the upgrade.
- For stable operation, perform compatibility testing of the upgrade version before proceeding with the upgrade.
OS and GPU drivers
The OS and GPU driver version information available for each K8s server type is as follows.
- The OS versions provided may vary by K8s version.
- When using GPU nodes, the related K8s components (nvidia-device-plugin, dcgm-exporter) are provisioned by default in the cluster.
- When deploying the gpu-operator, conflicts may occur due to duplicate component configurations. We recommend deployment and use, excluding the default-provided components.
- For end-of-life OSes, creating a node pool is possible, but we recommend using the latest OS version.
| k8s version | Standard and High Capacity | GPU |
|---|---|---|
| v1.29 |
|
|
| v1.30 |
|
|
| v1.31 |
|
|
| v1.32 |
|
|
| v1.33 |
|
|
| v1.34 |
|
|
The OS versions and supported GPU server models for each GPU driver version are as follows.
- When creating a GPU node with the GPU-B300-3 server type, you must use an image with GPU driver version 580.126.20.
| GPU driver version | OS version | Supported model (server type) |
|---|---|---|
| ND 535.183.06 | Ubuntu 22.04 |
|
| ND 570.195.03 | Ubuntu 24.04 |
|
| ND 580.126.20 | Ubuntu 24.04 |
|
4.1.4 - API Reference
4.1.5 - CLI Reference
4.1.6 - Release Note
Kubernetes Engine
- Kubernetes Engine feature changes and bug fixes
- We also provide Block Storage performance metric configuration for node pools.
- We also provide the B300 GPU type among GPU node types.
- When upgrading the node pool, we improved the selection dropdown functionality to consider the GPU driver version.
- type: LB health check protocol has been improved by adding HTTPS.
- Improved the event log timestamp error and the nuri-auth-webhook authentication key expiration and activation status check functionality.
- Kubernetes Engine feature changes
- Supports Kubernetes v1.34.
- Provides a custom image for the node pool’s GPU VM.
- Provides management logic and display functionality for EoTS of cluster and node pool Kubernetes versions and node pool OS versions.
- Provides an OS selection dropdown feature when upgrading a node pool.
- type: LB L7 listener idle-timeout addition and default session-duration-time change are improved.
- Terraform does not provide a kubeconfig feature.
- Kubernetes Engine feature change
- Supports Kubernetes v1.33.
- Provides GPU driver version information on GPU nodes in the node pool.
- Provides the MNGC node in SR request configuration format.
- The maximum Block Storage capacity of the node pool OS is increased from 1 TB to 12 TB to match the VM offering.
- When creating or updating a node pool, we add enhanced label key validation and also provide validation that GPU node pools are not supported in server groups.
- Kubernetes Engine feature changes
- Supports Kubernetes v1.32.
- Provides advanced node pool configuration features.
- Provides node pool server group (Affinity or Anti-affinity) configuration functionality.
- Provides a user Kubeconfig download feature following the admin Kubeconfig download button.
- When upgrading a node pool, we additionally provide upgrade logic that considers the OS version.
- Provides log collection functionality based on ServiceWatch integration.
- Kubernetes Engine feature changes
- Supports Kubernetes version v1.31.
- Provides the cluster’s public endpoint.
- The MNGC (Baremetal) product and the DevOps Service product are added to the cluster’s private endpoint access control targets.
- Provides node pool label and taint configuration functionality.
- Provides Block Storage CSI and kubectl login plugin functionality.
- The kubeconfig vulnerability has been addressed.
- Kubernetes Engine feature changes
- Provides private endpoint and access control features.
- type: LoadBalancer provides functionality.
- Kubernetes Engine feature changes
- Supports Kubernetes v1.30.
- Provides Kubernetes version upgrade functionality for clusters and node pools.
- Provides Multi-Security Group functionality.
- Provides the ability to create Custom Image nodes and GPU nodes.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have launched the Kuberntes Engine product, which provides lightweight virtual computing containers and the Kubernetes clusters that manage them.
- You can create container nodes and centrally manage them through a cluster, enabling deployment of various container applications.
- We have released the beta version of the Kuberntes Engine product.
4.2 - Container Registry
4.2.1 - Overview
Service Overview
Container Registry is a service that provides a registry for storing and managing container images and OCI (Open Container Initiative) standard artifacts. Users can easily store, manage, and share images using the Docker CLI.
Features
- Simple registry management and image distribution: You can easily create a container registry for your project on Samsung Cloud Platform. By using the standard Docker CLI, you can easily pull images for deployment from the Container Registry, streamlining development and service deployment workflows.
- Efficient Container Image Storage: You can easily store container images anytime, anywhere. By integrating with Object Storage, you can store and retrieve images, enabling efficient image management. It also supports the Docker Registry V2 API specification for convenient use.
- Enhanced Security Registry Management: You can securely store and use images using Container Registry. Container Registry encrypts images stored in Object Storage and transfers images via HTTPS. Use resource-based IAM policies of Samsung Cloud Platform to set repository-specific access permissions, and you can use images according to the configured permissions.
- Container Image Vulnerability Analysis: Container Registry provides a feature that analyzes security vulnerabilities in stored container images. Users can view vulnerability results through a simple process of selecting and scanning an image, and can identify and remediate vulnerabilities based on the analysis results.
Service Architecture Diagram
Provided features
Container Registry provides the following features.
- Registry Management: Provides Container Registry creation, deletion, registry access control management (private), and visibility features.
- Repository Management: It is created under the Container Registry and provides functions to create, view, delete repositories, and set security policies.
- Image Management: Container images stored in the repository, providing image Push, image Pull, view, delete, applied tag management, and security policy configuration functions.
- Image Vulnerability Assessment: You can manually or automatically scan OS packages and language packages for security vulnerabilities, as well as secrets embedded in images stored in the Container Registry. Based on the scan results, users can identify and remove known vulnerabilities (CVE) and secrets to prevent the use of insecure images.
Component
Registry
The registry is a repository or collection of repositories used to store, access, and manage container images. Container registries can often support container‑based application development as part of the development and operations process. They can connect directly to container orchestration platforms such as Docker and Kubernetes. A registry acts as an intermediary that shares container images between systems, saving developers time in creating and delivering cloud‑native applications. In the case of Samsung Cloud Platform, it is provided in conjunction with Object Storage and transfers images over HTTPS.
repository
A repository is a logical management unit for image tags. Using a repository allows efficient management of image tags. A repository is a centralized virtual storage that developers use to modify and manage application source code. When developing applications, if there is a need to store and share various types of documents and source code, it enables developers to easily collaborate within the same account, edit simultaneously, and track/manage changes.
image
An image refers to something that includes all files and configuration values required to run a container. An image acts like a class that creates containers, and a container can be seen as the program or process that runs the image. For example, an Ubuntu image contains all files needed to run Ubuntu, and a MySQL image contains all files, IDs, passwords, port information, etc., required to run MySQL.
Preliminary Service
Container Registry has no prerequisite services.
4.2.1.1 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by leveraging ServiceWatch released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a smooth monitoring environment.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
Container Registry monitoring metrics
The table below shows the monitoring metrics for Container Registry that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, see the Cloud Monitoring guide.
| Performance items | Detailed description | unit |
|---|---|---|
| container.registry.status.alive | Registry status | status |
| containerregistry.statics.image.pull.count | Allowed Image Tag (digest) Pull Count | cnt |
| containerregistry.statics.image.denied_pull.count | Number of rejected Image Tag (digest) Pulls | cnt |
| containerregistry.statics.image.push.count | Allowed Image Tag (digest) Push count | cnt |
| containerregistry.statics.image.denied_push.count | Number of rejected Image Tag (digest) pushes | cnt |
| containerregistry.statics.image.scan.count | Allowed Image Tag (digest) Scan count | cnt |
| containerregistry.statics.image.denied_scan.count | Number of rejected Image Tag (digest) scans | cnt |
| containerregistry.statics.tag.deleted.count | Number of deleted Image Tags (digest) | cnt |
| containerregistry.statics.image.created.count | Number of generated images | cnt |
| containerregistry.statics.image.deleted.count | Number of deleted images | cnt |
| containerregistry.statics.login.count | Allowed Registry Login count | cnt |
| containerregistry.statics.denied_login.count | Number of denied registry logins | cnt |
| containerregistry.statics.repository.created.count | Number of generated repositories | cnt |
| containerregistry.statics.repository.deleted.count | Number of deleted repositories | cnt |
4.2.1.2 - ServiceWatch Metrics
Container Registry sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the Container Registry namespace.
The indicators whose names are shown in bold below are the indicators selected as key metrics among the default metrics provided by Container Registry. Key metrics are used to compose the service dashboards that ServiceWatch automatically builds for each service.
Each metric guides users via the user guide on which statistical values are meaningful when viewing that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using the primary statistical values.
| Indicator Name | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| Image Pull Count [Allowed] | Allowed Image Tag (digest) Pull Count | Count/Minute |
|
| Image Push Count [Denied] | Number of rejected Image Tag (digest) pushes | Count/Minute |
|
| Repository Count [Deleted] | Number of Deleted Repositories | Count/Minute |
|
| Repository Count [Created] | Number of created repositories | Count/Minute |
|
| Registry Login Count [Allowed] | Number of allowed Registry Logins | Count/Minute |
|
| Image Scan Count [Denied] | Number of rejected Image Tag (digest) scans | Count/Minute |
|
| Image Pull Count [Denied] | Number of rejected Image Tag (digest) Pulls | Count/Minute |
|
| Registry Login Count [Denied] | Number of denied Registry Logins | Count/Minute |
|
| Image Push Count [Allowed] | Allowed Image Tag (digest) Push count | Count/Minute |
|
| Image Scan Count [Allowed] | Allowed Image Tag (digest) Scan count | Count/Minute |
|
| Image Count [Deleted] | Number of deleted images | Count/Minute |
|
| Image Count [Created] | Number of generated images | Count/Minute |
|
| Image Tag Count [Deleted] | Number of deleted Image Tag (digest) | Count/Minute |
|
4.2.2 - How-to guides
Users can create a service by entering the required information for the Container Registry service and selecting detailed options through the Samsung Cloud Platform Console.
Create Container Registry
You can create and use the Container Registry service in the Samsung Cloud Platform Console.
Follow these steps to create a Container Registry service.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- Click the Create Registry button on the Service Home page. You will be taken to the Create Registry page.
- Registry creation page: enter the information required to create a service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description registry name Required The registry name created by the user - must start with a lowercase English letter and be entered using lowercase English letters and numbers, with a length of 3 to 25 characters
endpoint Required Set access type for registry endpoint - Private: Only private endpoint access control items can be set
- Private&Public: Both private endpoint access control items and public endpoint access control can be set
Private endpoint access control Select Private endpoint access control settings - If you select Use, you can configure it so that only specific resources within the same region’s account, such as the registry, can be accessed
- Click Add for private access allowed resources to add resources that can access the registry using the private endpoint
- If Use is not selected, access is allowed from resources in all subnets within the same region
Public endpoint access control Selection Public endpoint access control settings - If you select Use, you can configure it so that only specific IPs in the same region as the registry can access it.
- Click Add for the allowed public access IP to add the IPs and resources that can access the registry using the public endpoint.
- If Use is not selected, access is allowed from resources in all subnets within the same region.
Visibility Selection Anonymous access setting for registry read (Pull) operations - Selecting Public allows unauthenticated anonymous users to perform read operations (Anonymous Pull) on all registry content.
- This setting can be enabled as Public only when creating the service.
Table. Container Registry Service Information Input ItemsCaution- If you do not select the use of private endpoint access control, the customer’s registry may be exposed to other resources within the Samsung Cloud Platform.
- If you do not select the use of public endpoint access control, external IP access is possible in an internet environment, so the user’s bucket may be exposed externally via the internet. If external access is not required, uncheck the usage checkbox to minimize security threats.
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Container Registry Additional Information Input Fields
- Enter or select the required information in the Service Information Input area.
- Check the detailed information and estimated billing amount generated in the Summary panel, and click the Create button.
- When creation is complete, check the created resource on the Registry list page.
View detailed information of Container Registry
The Container Registry service allows you to view and edit the full list of resources and detailed information. Container Registry Details page consists of Details, Tags, Activity Log tabs.
To view the Container Registry details, follow these steps.
- Click the All Services > Container > Container Registry menu. You will be taken to the Service Home page of Container Registry.
- On the Service Home page, click the Registry menu. You will be taken to the Registry List page.
- On the Registry List page, click the resource (Registry) to view its details. You will be taken to the Registry Details page.
- Registry Details page displays the Registry’s status information and detailed information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description Registry status Registry status - Creating: in progress
- Running: creation complete/operating normally
- Editing: configuration being changed
- Terminating: being deleted
- Error: error occurred
- Unknown: unknown
User Guide Guide to Using a CLI-Based Registry Service termination Button to cancel the service Table. Container Registry status information and additional features
- Registry Details page displays the Registry’s status information and detailed information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
On the Registry list page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| registry name | Registry name |
| Bucket name | The name of the Samsung Cloud Platform Object Storage bucket where the registry data is stored |
| Usage | Data usage of the Object Storage bucket for the registry |
| endpoint | Access type for the registry endpoint
|
| Private endpoint | Private endpoint URL available within the Samsung Cloud Platform network
|
| Public endpoint | Public endpoint URL available within the Samsung Cloud Platform network |
| Private endpoint access control | Private endpoint access control settings
|
| Public endpoint access control | Public endpoint access control settings
|
| Visibility | Anonymous access setting for registry read (Pull) operations
|
tag
Registry list page lets you view, add, modify, or delete tag information for the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Registry list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Container Registry
You can cancel unused Container Registries to reduce operating costs. However, if you cancel the service, any running services may be stopped immediately, so consider the impact of service interruption carefully before proceeding with the cancellation.
- You cannot delete a Registry when resources are linked to it. After terminating the linked services shown in the “Service termination not allowed” popup, delete the Registry.
- When the service is terminated, all data, including the bucket linked to the Registry, will be deleted. Please note that data cannot be recovered after deletion.
To cancel the Container Registry, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Registry menu. You will be taken to the Registry List page.
- Registry List On the page, click the resource (Registry) to view detailed information. You will be taken to the Registry Details page.
- On the Registry Details page, click Service Cancellation.
- Click the checkbox to confirm cancellation and enter the Registry name to delete.
- When you enter the Registry name correctly, the Confirm button becomes active. Click the Confirm button.
- When termination is complete, check on the Registry list page whether the resource has been terminated.
4.2.2.1 - Manage Repository
A repository is a logical management unit for images within a registry. Using a repository, you can set the default security policy for images created underneath.
Creating a Repository
To create a repository, follow these steps.
- Click the All Services > Container > Container Registry menu. Go to the Service Home page of Container Registry.
- On the Service Home page, click the Repository menu. You will be taken to the Repository List page.
- On the Repository list page, click the Create Repository button. You will be taken to the Create Repository page.
- Repository list At the top of the page, click the Settings icon to select an existing registry, or click Create new to create a registry.
- On the Repository creation page, enter the required information and select the detailed options.
- Enter or select the required information in the Service Information Input area.
Category RequiredDetailed description registry name Required Select the registry name for creating the repository - If no registry has been created, you can create a new one using the Create New button
Repository name Required Repository name to create - Enter using lowercase English letters, numbers, and special characters (
-) with a length of 3 to 30 characters (the start and end must be lowercase English letters or numbers only)
Table. Repository Service Information Input Items - In the Repository Basic Policy Input area, enter or select the required information.
Category RequiredDetailed description Image scan option Automatic scanning of image vulnerabilities generated in the repository and setting scan exclusion policies - You can set the default scan policy applied when an image is created in the repository
- If you set automatic scanning to enabled, the image’s vulnerabilities are automatically checked when the image is pushed. In this case, the vulnerability scanning cost is billed.
- If you set the scan exclusion policy to enabled, you can specify which inspection targets and vulnerabilities to exclude during image scanning.
- You can choose to exclude Language Package checks, Secret checks, and vulnerabilities without a Fix Version.
- Excludable vulnerabilities: you can select one of the following levels
- (None / Unknown / Negligible / Low / Medium / High / Critical) Exclude vulnerabilities at or below this level
Image Pull limit Option Policy settings for enabling the image Pull restriction feature and its limit values for images generated in the repository - You can set the default Pull restriction policy applied when an image is created in the repository
- If you set the Pull restriction for unscanned images to Enabled, pulling images that have not been vulnerability‑checked is not allowed
- If you set the Pull restriction policy for vulnerable images to Enabled, pulling an image is prohibited when Critical or High‑level vulnerabilities exceeding the specified values are found. The allowable input and selectable values for this policy are as follows
- Critical: 1 (default) ~ 9,999,999
- High: 1 (default) ~ 9,999,999
- Exclude vulnerabilities without a Fix Version
- When Enabled is selected, vulnerabilities lacking a Fix Version (i.e., when a vulnerable package/library has no patch version) are excluded from the Pull restriction policy
Image lock status option You can set a lock to prevent deletion or updating of all images within the repository - When the repository’s image lock status is Lock, the Lock/Unlock functions for individual images in the repository are disabled.
- Changing the image lock status of a repository that is in Lock state to Unlock enables the Lock/Unlock functions for individual images.
- Pushing new images is allowed.
Delete image tags option You can set an automatic image deletion policy for images stored in the repository - If you select Enabled for deletion policy activation, the image deletion policy is applied.
- If you set Untagged Image automatic deletion, Old Image automatic deletion items to Enabled, the corresponding image deletion policies are applied.
- Enter an automatic deletion period in the deletion policy; the image will be automatically deleted after the specified period has elapsed since its initial push.
- For detailed information on image tag deletion, see Image Tag Deletion Policy Management.
Table. Repository Default Policy Input Items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Explanation Selection Repository description - Enter repository description
tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Repository Additional Information Input Items
- Enter or select the required information in the Service Information Input area.
- The Repository default policy input fields are used to set the default (initial) policy for Images created in the Repository. (They serve as a policy configuration template applied when an Image is created.)
- This setting can be changed on the detail view screen after creating a Repository, and images created after modifying the Repository’s default policy entries will be configured with the updated policy. Images created before the change will retain their original policy.
- The default policy set for the Image can be modified on the Image detail screen.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the Repository List page.
View repository details
Repository service allows you to view and edit the full list of resources and detailed information. The Repository Details page consists of Details, Tags, Activity History tabs.
To view the repository details, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Repository menu. You will be taken to the Repository List page.
- On the Repository List page, click the resource (Repository) to view detailed information. You will be taken to the Repository Details page.
- Repository Details page displays the repository’s status information and detailed information, and consists of Details, Tags, Activity History tabs.
Category Detailed description Repository status Repository status display - Active: available state
- Deleting: deleting state
- Inactive: state where deletion failed, making it unavailable (only deletion request is possible)
- Editing: state where settings are being modified or sub-resources (images, tags) within the image are being deleted
User Guide Repository usage guide - You can check the commands for using images within the repository via CLI
Delete repository Button to delete the repository Table. Status Information and Additional Functions
- Repository Details page displays the repository’s status information and detailed information, and consists of Details, Tags, Activity History tabs.
Detailed Information
Repository list page lets you view detailed information of the selected resource and edit the information if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the repository |
| Creation date and time | Repository creation date and time |
| Editor | User who modified the repository |
| Modification date | Repository modification timestamp |
| Repository name | User-created repository name |
| registry name | Registry name linked to the repository
|
| description | The description entered by the user for the generated repository
|
| image | Link to view the list of stored images in the repository |
| Image scan | Automatic image vulnerability scanning and scan exclusion policy settings for images generated in the repository
|
| Image Pull limit | Policy settings for enabling the image Pull restriction feature and its limit values for images generated in the repository
|
| Image lock status | You can set a lock to prevent deleting or updating any images inside the repository
|
| Delete image tag | Set the automatic image deletion policy for images stored in the repository
|
tag
Repository list page allows you to view the tag information of the selected resource, and to add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Repository list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Delete Repository
To delete a repository, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- Click the Repository menu on the Service Home page. You will be taken to the Repository List page.
- Repository List page, click the resource (Repository) to view its details. You will be taken to the Repository Details page.
- On the Repository Details page, click Delete Repository.
- Delete Repository in the popup window, please enter the Repository name.
- If you enter the Repository name correctly, the Confirm button becomes active. Click the Confirm button.
- When the termination is complete, verify on the Repository list page that the resource has been terminated.
4.2.2.2 - Manage Images and Tags
An image is a logical management unit of a tag. Users can efficiently manage image versions using tags.
Create Image
To generate an image, the repository must be created first. For detailed information on creating a repository, see Repository Management.
- Images are created by pushing an image or OCI-standard artifact via the CLI using the registry endpoint.
- For instructions on pushing an image with the CLI, refer to the official documentation provided by the client tool you are using or see CLI 사용하기.
View image details
Image can view and edit the entire resource list and detailed information. The Image detail page consists of Details, Tags, Delete Policy Test tabs.
To view the image details, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Image List Click the Settings icon at the top of the page and select the Registry name and Repository name where the Image to view detailed information is stored.
- If the desired item is not available, click Create New to register a Registry and Repository, then you can select it.
- On the Image List page, click the resource (Image) to view detailed information. You will be taken to the Image Detail page.
- Image Details page displays the Image’s status information and detailed information, and consists of Details, Tags, Deletion Policy Test tabs.
Category Detailed description Image status Image status representation - Active: available state
- Deleting: deleting state
- Inactive: state where deletion failed and is not usable (only deletion request is possible)
- Editing: state where settings are being modified or image sub-resources (tags) are being deleted
User Guide CLI-based Image Usage Guide Delete Image Delete image button Table. Image status information and additional functions
- Image Details page displays the Image’s status information and detailed information, and consists of Details, Tags, Deletion Policy Test tabs.
Detailed Information
Image list page lets you view detailed information of the selected resource and modify it if necessary.
| Category | Detailed description |
|---|---|
| constructor | User who generated the image |
| Creation date and time | Image creation timestamp |
| editor | User who edited the image |
| Modification date | Image modification timestamp |
| image name | User-generated image name |
| registry name | Registry name and view link of the repository storing the image |
| Pulls | Number of times this image has been pulled |
| Repository name | Repository name and view link for the stored image |
| Explanation | The description entered by the user for the image
|
| Image scan | Image vulnerability automatic scanning and scan exclusion policy settings
|
| Image Pull limit | Setting the usage and limit values of the Image Pull restriction feature
|
| Image lock status | You can set a lock to prevent the selected image from being deleted or updated
|
| Delete image tag | Set the automatic image deletion policy for images stored in the repository
|
Delete Image
To delete the Image, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- Click the Image menu on the Service Home page. You will be taken to the Image List page.
- Image List Click the Settings icon at the top of the page and select the Registry name and Repository name where the Image to be deleted is stored, respectively.
- Image List page, click the resource (Image) you want to delete. You will be taken to the Image Details page.
- On the Image Details page, click the Delete Image button.
- Image Delete When the popup appears, click the Confirm button.
- After the deletion is complete, verify on the Image List page that the resource has been deleted.
Check detailed information of image tag
To view detailed information about the image tag, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Image List Click the Settings icon at the top of the page and select the Registry name and Repository name where the Image to view detailed information is stored.
- Image List page: click the resource (Image) to view detailed information. You will be taken to the Image Details page.
- Image Details Click the Tags tab to the right of the Details tab at the top of the page. You will be taken to the Tags List page.
column Detailed description Tags Tag name of the image Digest - A single image Digest can have multiple tag names
Digest Image Digest value size Image digest size Modification date Image Digest (Tags) Modification Time Inspection date and time Image Digest (Tags) Vulnerability Check Date and Time Vulnerability Assessment Results Image Digest (Tags) Vulnerability Scan Results - Summary of vulnerability count and a button to view scan results are displayed
- View Results button can be clicked to view detailed vulnerability analysis results for image tags
status Status of image Digest (Tags) - Active: normal, usable state
- Deleting: being deleted
- Inactive: deletion failed, not usable (deletion request only)
Copy URL Copy endpoint URL for using image Digest - You can copy the private/public endpoint URL to use in commands for image Digest
More button Menu for selecting deletion, modification, vulnerability assessment, and detailed usage guide for image Digest (Tags) - Delete: Delete the specified image Digest (Tags)
- Edit Tags: In the tag edit window, you can modify the tag name of the image Digest
- Vulnerability Scan: Perform vulnerability assessment on image Digest (Tags)
- Detailed Usage Guide: View a guide for using image Digest (Tags) via CLI
- Tags Lock: Lock selected image Tags to prevent deletion or updates
- Tags Unlock: Unlock the lock to allow deletion or updates of selected image Tags
Table. Tags list items
- Image Details Click the Tags tab to the right of the Details tab at the top of the page. You will be taken to the Tags List page.
Detailed Information
Click the Tags of the image Digest whose details you want to view in the Tags list of the Image details. The detail window for the image Digest (Tags) will appear.
| column | Detailed description | |
|---|---|---|
| Tag information | Display tag name, digest, creation time, and modification time
| |
| Manifest information | Display the manifest type and details
|
- In the tag details window, after reviewing the information and clicking Confirm, the window closes.
Delete image tag
To delete an image tag, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Image List Click the Settings icon at the top of the page and select the Registry name and Repository name where the Image to view detailed information is stored.
- Image List On the page, click the resource (Image) to view detailed information. Image Details page will be opened.
- Image Detail page, click the Tags tab to the right of the Details tab at the top of the page. You will be taken to the Tags List page.
- From the Tags list, select the checkbox located to the left of the tag you want to delete, then click Delete.
- By selecting the checkboxes of multiple items, you can delete multiple tags at once, and you can select and delete up to 50 tags at a time.
- You can delete tags one by one by clicking the Delete button inside the More button located at the far right of the tag to be deleted.
- Delete Tags When the popup window opens, click Confirm.
- After deletion is complete, check on the Tags list page whether the resource has been removed.
Testing image tag deletion policy
To test the configured image tag deletion policy, follow these steps.
- All Services > Container > Container Registry menu, click it. Go to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image list page.
- Image List Click the Settings icon at the top of the page and select the Registry name and Repository name where the Image to view detailed information is stored.
- Image List page: click the resource (Image) to view detailed information. You will be taken to the Image Details page.
- Image Details On the top of the page, click the Delete Policy Test tab to the right of the Details tab. You will be taken to the Delete Policy Test tab page.
- Delete Policy Test tab page, click the Policy Test button for the Tags item to be deleted. The delete policy test will run.
- When the delete policy test execution notification popup opens, click the Confirm button.
- When the test execution request is completed, the phrase Deletion policy test execution request has been completed is displayed.
- When the deletion policy test is complete, check the test results.
- Tags to be deleted field displays the image tags (digests) that are subject to the deletion policy.
4.2.2.3 - Manage Image Security Vulnerabilities
By using the image security vulnerability scanning feature, you can manually or automatically scan OS package security vulnerabilities in images stored in Container Registry and the Secrets contained within the images. Based on the scan results, users can identify and remove known vulnerabilities (CVE) and Secrets, preventing the use of insecure images.
Vulnerability assessment support information
Supported OS
- The vulnerability scanning feature supports checking libraries installed via the package manager on the following operating systems.
| Supported OS |
|---|
| Ubuntu |
| Cent OS |
| Oracle |
| Debian |
| Alpine |
| AlmaLinux |
| AWS Linux |
| Rocky Linux |
| RHEL |
| Suse |
| VMWare Photon |
Supported Language
- The vulnerability assessment feature supports checks for the following Language.
| Supported Language |
|---|
| Python |
| PHP |
| Node.js |
| .NET |
| Go |
| Supported Language |
|---|
| Java |
Support Secret
- The vulnerability scanning feature supports the following types of Secrets contained in the image.
| Support Secret |
|---|
| AWS access key |
| GitHub personal access token |
| GitLab personal access token |
| Asymmetric Private Key |
Checking image security vulnerabilities (manual)
To check image security vulnerabilities, follow the steps below.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Image List Click the Settings icon at the top of the page and select the Registry name and Repository name where the Image for detailed information is stored.
- On the Image List page, click the resource (Image) to check for security vulnerabilities. You will be taken to the Image Details page.
- Image Details Click the Tags tab to the right of the detailed information tab at the top of the page. You will be taken to the Tags tab page.
- On the Tags tab page, click the More button located at the far right of the tag you want to check for security vulnerabilities, then click Vulnerability Check.
- When the vulnerability check notification popup opens, click the Confirm button.
- When the inspection starts, the phrase Vulnerability assessment will be performed. is displayed.
- When the inspection is finished, the Vulnerability Inspection Results item displays a summary of the inspection results and a View Results button. Clicking the View Results button opens a popup that shows detailed analysis of Vulnerabilities by Image Digest (Tags).Reference
- Click the View Results button to see the detailed vulnerability analysis results for the image tag.
- After a vulnerability scan, if a red exclamation mark icon (!) appears in the scan date/time field, it means the vulnerability scan list for the Container Registry service has been updated. Click Vulnerability Scan to re‑scan, as new vulnerability items need to be checked for the image Digest (Tags).
- Click the View Results button to see the detailed vulnerability analysis results for the image tag.
View Image Security Vulnerability Scan Results
To view the vulnerability assessment results, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Click the Settings icon at the top of the Image List page and select the Registry name and Repository name where the Image to be inspected is stored.
- Image List page, click the resource (Image) to check for security vulnerabilities. You will be taken to the Image Details page.
- Image Details Click the Tags tab on the right side of the detailed information tab at the top of the page. You will be taken to the Tags tab page.
- On the Tags tab page, click the View Results button of the Vulnerability Check Result item for the tag whose vulnerability check results you want to view.
- Image Tags Vulnerabilities Check the results in the popup window that displays the detailed analysis results.
View inspection results by vulnerability
Image Tag Vulnerabilities On the detailed page’s Vulnerabilities tab, you can view the image security vulnerability assessment results for each vulnerability.
| Item | Detailed description |
|---|---|
| Vulnerability Assessment | Vulnerability check button
|
| Inspection date and time | Vulnerability assessment date and time |
| Distribution | OS name and version of the image Digest (Tags) under inspection
|
| Total number of vulnerabilities | Summary of vulnerability assessment results
|
In the Vulnerability tab, you can view the list of all discovered vulnerabilities.
| Item | Detailed description |
|---|---|
| CVE | External links to verify the detected vulnerability ID (CVE ID) and detailed information about the vulnerability
|
| Severity | Severity of detected vulnerabilities |
| CVSS | CVSS (Common Vulnerability Scoring System) based vulnerability score |
| Category | Inspection target type of detected vulnerabilities
|
| OS/Language | OS or Language package type of the detected vulnerability
|
| package | Package name with the discovered vulnerability |
| Current version | Current version of the package with the vulnerability (vulnerable version) |
| Revised version | Version of the package with the vulnerability fixed |
| Whether to edit | Whether a version with the vulnerability fixed exists for the package with the discovered vulnerability (whether a vulnerability patch version exists) |
| Expand button | View vulnerability detailed information
|
View inspection results by package
Image Tag Vulnerabilities On the detail page, clicking the Package tab navigates to the package-specific vulnerability page. In the Package tab, you can view the image security vulnerability assessment results by package.
| Item | Detailed description |
|---|---|
| Vulnerability Assessment | Vulnerability assessment button
|
| Inspection date and time | Vulnerability assessment date and time |
| Distribution | OS name and version of the image Digest (Tags) to be inspected
|
| Total number of packages | Overall package information summary
|
In the Package tab, you can view the full list of packages and the lists of packages with detected vulnerabilities and without detected vulnerabilities.
| Item | Detailed description |
|---|---|
| Category | Type of discovered package
|
| OS/Language | Detailed OS or Language type of the discovered package
|
| Package | Detected package name |
| Version | Current version of the package |
| Vulnerability assessment results | Summary of the number of vulnerabilities contained in the package |
| type | OS or language type and details of the discovered package |
Check inspection results by secret unit
Image Tag Vulnerabilities On the detail page, clicking the Secret tab takes you to the vulnerability page for each secret. You can view the image security vulnerability assessment results by secret.
| Item | Detailed description |
|---|---|
| Vulnerability Assessment | Vulnerability check button
|
| Inspection date and time | Vulnerability assessment date and time |
| Distribution | OS name and version of the image Digest (Tags)
|
| Total number of vulnerabilities | Vulnerability Result Summary
|
In the Secrets tab, you can view the complete list of secret files, as well as the lists of files with detected vulnerabilities and files without detected vulnerabilities.
| Item | Detailed description |
|---|---|
| File | File name of detected secret |
| Category | Detected secret type
|
| Severity | Detected secret severity |
| Match | Secret match information in the detected file |
4.2.2.4 - Manage Image Tag Deletion Policy
Users can register and manage image tag deletion policies.
Manage image tag deletion policy
The image tag deletion policy refers to a policy that automatically deletes an image after a specified period has elapsed since the image was first pushed to the repository. Enabling the image tag deletion policy causes image tags (digests) stored in the Container Registry to be automatically deleted according to the configured deletion policy.
- After setting the deletion policy activation to use, the image tag (digest) that first receives the deletion policy will be deleted within a maximum of 3 days (72 hours). Subsequent image tags (digests) to which the deletion policy applies will be deleted within a maximum of 1 day (24 hours).
- Image tags (digests) subject to the deletion policy are permanently deleted and cannot be recovered.
Support Deletion Policy Information
Describes policy information that supports the removal of image tags.
Support Policy
Supports policies that enable automatic deletion and retention period settings for image tags (digests).
| Support Policy |
|---|
| Untagged Image |
| Old Image |
Setting the image tag (digest) deletion policy
To set the image tag (digest) deletion policy, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Click the gear button at the top of the Image List page. The Registry/Repository Settings popup will open.
- Registry/Repository Settings In the popup window, select the Registry name and Repository name where the image to set the deletion policy is stored, and click the Confirm button.
- On the Image List page, click the resource (Image) for which you want to set the deletion policy. You will be taken to the Image Details page.
- On the Image Detail page, in the Detail Information tab, click the Edit icon of the Delete Image Tag item. The Edit Delete Image Tag popup opens.
- Image Tag Delete Edit In the popup window, enter and select the activation status and required information, then click the Confirm button.
- If you select Enable for Deletion policy activation, image tags (digests) will be automatically deleted according to the configured deletion policy.
- Select the deletion policy to apply and enter the period from when the image is first pushed to the repository until it is automatically deleted.
- When the edit notification popup opens, click the Confirm button.
- When the modification is complete, the message Image tag removal edit was successful will be displayed.
Testing image tag (digest) deletion policy
To test the image tag (digest) deletion policy, follow these steps.
- Click the All Services > Container > Container Registry menu. Navigate to the Service Home page of Container Registry.
- On the Service Home page, click the Image menu. You will be taken to the Image List page.
- Image list Click the gear button at the top of the page. Registry/Repository settings A popup window will open.
- Registry/Repository Settings In the popup window, select the Registry name and Repository name where the image to set the deletion policy is stored, and click the Confirm button.
- Image List page, click the resource (Image) to test the deletion policy. You will be taken to the Image Details page.
- On the Image Detail page, click the Delete Policy Test tab. You will be taken to the Delete Policy Test tab page.
- On the Delete Policy Test tab page, to test the configured delete policy, click the Policy Test button below the target Tags.
- When the delete policy test execution notification popup opens, click the Confirm button.
- When the test execution request is completed, the message Deletion policy test execution request has been completed is displayed.
- When the test is completed, the Deletion Target Tags item will display the image tags (digests) that are subject to the deletion policy.
4.2.2.5 - Use Container Registry with CLI
This explains how to log in to the Container Registry using CLI commands and manage container images and Helm charts.
Managing container images with CLI
You can log in to the Container Registry using CLI commands and push or pull container images.
Log in to the Container Registry
The user can log in to the Container Registry using an authentication key.
For detailed information on policies and permission settings, see Management > IAM > Policies.
Log in with an authentication key
Log in using the authentication key’s AccessKey, SecretKey, and the registry endpoint.
- Registry endpoint: can be found on the Container Registry Details page.
- Private endpoint: [registryname-registryid].scr.private.[region].[offering].samsungsdscloud.com
1 docker login <registry_endpoint>
2 Username: <accessKey>
3 Password: <secretKey>
- To log in with an authentication key, create an authentication key on the IAM > Authentication Key Management page, and set the authentication method to Authentication Key Authentication in Security Settings.
- Before modifying Security Settings, be sure to check the guidance text about the authentication key authentication method at the top of the Edit Authentication Key Security Settings popup.
- For detailed information on how to create an authentication key and set up authentication key verification, see Management > IAM > Manage Authentication Keys.
Push image
To push an image to the registry, refer to the following command.
1 docker push [registryname]-[registryid].scr.private.[region].[offering].samsungsdscloud.com/[repository]/[image:tag]
- To push an image to a registry, you need the LoginContainerRegistry permission for the registry you will use and the PushRepositoryImages permission for the repository.
- For detailed information on policy and permission settings, refer to Management > IAM > 정책.
Pull image
To pull an image from the registry, refer to the following command.
1 docker pull [registryname]-[registryid].scr.private.[region].[offering].samsungsdscloud.com/[repository]/[image:tag]
- To pull an image from a registry, you need the LoginContainerRegistry permission for the registry you will use and the PullRepositoryImages permission for the repository.
- For detailed information on policies and permission settings, see Management > IAM > 정책.
Managing Helm charts with CLI
You can log in to the Container Registry using CLI commands and push or pull Helm charts.
Log in to Container Registry
The user can log in to the Container Registry using an authentication key.
For detailed information on policies and permission settings, see Management > IAM > Policy.
Log in with authentication key
Log in using the authentication key’s AccessKey, SecretKey, and the registry endpoint.
- Registry endpoint: Container Registry Details can be found on the page.
- Private endpoint : [registryname-registryid].scr.private.[region].[offering].samsungsdscloud.com
1 helm registry login <registry_endpoint>
2 Username: <accessKey>
3 Password: <secretKey>
- To log in with an authentication key, create an authentication key on the IAM > Authentication Key Management page, and set the authentication method to Authentication Key Authentication in Security Settings.
- Before modifying Security Settings, be sure to review the guidance text about the authentication key method at the top of the Edit Authentication Key Security Settings popup.
- For detailed information on how to create an authentication key and set up authentication key verification, see Management > IAM > Manage Authentication Keys.
Push chart
To push a chart to the registry, refer to the following command.
1 helm push [hello-world-0.1.0].tgz oci://[registryname]-[registryid].scr.private.[region].[offering].samsungsdscloud.com/[mychart]
If you write and execute the command as shown in the example, it saves (uploads) the chart by applying the 0.1.0 tag to the hello-world image in the mychart repository.
- To push a chart to a registry, you need the LoginContainerRegistry permission for the registry you will use and the PushRepositoryImages permission for the repository.
- For detailed information on policies and permission settings, see Management > IAM > Policies.
Pull chart
To pull a chart from the registry, refer to the following command.
1 helm pull oci://[registryname]-[registryid].scr.private.[region].[offering].samsungsdscloud.com/[mychart/hello-world] -version [0.1.0]
By writing and executing the command as shown in the example, you download the chart stored with tag 0.1.0 in the hello-world image of the mychart repository.
- To pull a chart from a registry, you need the LoginContainerRegistry permission for the registry you will use and the PullRepositoryImages permission for the repository.
- For detailed information on policies and permission settings, see Management > IAM > Policy.
4.2.2.6 - Example of Registry and Repository Policies
After creating the Samsung Cloud Platform Container Registry (hereinafter SCR) service, an endpoint is provided. This endpoint provides an example policy that grants specific permissions when using SCR.
- IAM > Policy > Policy List page lets you create permission policies for registries and repositories, and view or edit existing policies.
- For detailed information on policy management, please refer to the Samsung Cloud Platform User Guide’s Management > IAM > 정책.
- Please refer to the required permissions for using Container Registry with the CLI in Using Container Registry with the CLI.
Allow pulling all repository images created in all registries
If you apply the ScrPullOnlyAccess policy provided as an IAM default policy, you can grant IAM users and user groups permission to pull all repository images created in all registries within the account.
To allow pulling all repository images created in all registries, follow these steps.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. 2. Go to the Policy List page.
- On the Policy List page, select ScrPullOnlyAccess. 3. Policy Details navigate to the page.
- On the Policy Details page, select the Connected Targets tab.
- On the Connection Target tab page, connect the target to which you will grant permissions.
- User: Click User Connection above the list to go to the User Connection page. * Select the user to connect and click Done to complete the user connection.
- User Group: Click User Group Link above the list to go to the User Group Link page. * Select the user group to connect and click Done, and the user group connection will be completed.
- Role: Click Role Link above the list to go to the role link page. * Select the role to connect and click Done to complete the role linking.
The ScrPullOnlyAccess policy consists of the following permissions.
- Permission to allow the LoginContainerRegistry Action required for Registry authentication
- Permission to allow the PullRepositoryImages action required for repository image pull
IP access control for SCR endpoints is provided via Private Endpoint Access Control and Public Endpoint Access Control on the Registry detail page.
- Please note that when IP access control is used in the IAM policy for the SCR endpoint, you cannot use Registy and Repository Image via the SCR endpoint.
- Set the IP access control entries to Applied IP: All IPs, Excluded IP: Not used.
Allow pulling and pushing all repository images created in all registries
If you apply the ScrPullPushOnlyAccess policy provided as an IAM default policy, you can grant IAM users and user groups permission to allow Pull and Push for all repository images created in all registries within the account.
To allow Pull and Push for all Repository Images created in all Registries, follow these steps.
- Click the All Services > Management > IAM menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. 2. Go to the Policy List page.
- On the Policy List page, select ScrPullPushOnlyAccess. 3. Navigate to the Policy Details page.
- On the Policy Details page, select the Connection Targets tab.
- On the Connection Target tab page, connect the target to which you will grant permissions.
- User: Click User Connection above the list to go to the User Connection page. * Select the user to connect and click Done to complete the user connection.
- User Group: Clicking User Group Link above the list navigates to the User Group Link page. * Select the user group to connect and click Done, and the user group connection will be completed.
- Role: Click Role Link above the list to go to the role link page. * Select the role to connect and click Complete, then the role connection will be completed.
The ScrPullPushOnlyAccess policy consists of the following permissions.
- Permission to allow the LoginContainerRegistry Action required for Registry authentication
- Permission to allow the PullRepositoryImages Action required for Repository Image Pull
- Permission to allow the PushRepositoryImages Action required for Push
IP access control for SCR endpoints is provided via Private Endpoint Access Control and Public Endpoint Access Control on the Registry detail page.
- Please note that when IP access control is used in the IAM policy for the SCR endpoint, you cannot use Registy and Repository Image via the SCR endpoint.
- Set the IP access control entries to Applied IP: All IPs, Excluded IP: Not used.
Allow pulling all repository images created in a specific registry
By applying the ScrPullOnlyAccess policy provided as an IAM default policy, you can create a policy that allows only Pull for all repository images created in a specific Registry.
To create a pull permission policy for all repository images created in a specific registry, follow these steps.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. 2. Go to the Policy List page.
- On the Policy List page, click Create Policy.
- On the Policy Creation page, enter the Basic Information Input fields and click Next.
- On the Permission Settings page, click Load Policy.
- Load Policy in the window’s list, select ScrPullOnlyAccess and click OK.
- On the Permission Settings page, select the Individual Resource of the Applied Resources item.
- Click Add Resource in the applied resource list.
- In the Add Resource window, select container-registy from the resource type list. 9. In the resource detail list, check the registy resource you want to add, then click Confirm.
- Check the individual resources you added in the applied resources list and click Next.
- Check the input information and click Create. 11. Policy creation is complete.
The ScrPullOnlyAccess policy consists of the following permissions.
- LoginContainerRegistry Action permission
- Permission to allow the PullRepositoryImages action required for repository image pull
IP access control for SCR endpoints is provided via Private Endpoint Access Control and Public Endpoint Access Control on the Registry detail page.
- When creating an IAM policy for using the SCR endpoint, if you use IP access control, please note that you cannot use Registy and Repository Image through the SCR endpoint.
- Set the IP access control entries to Applied IP: All IPs, Excluded IP: Not used.
Allow Image Pull and Push for a Specific Repository Created in a Specific Registry
If you apply the ScrPullPushOnlyAccess policy provided as a default IAM policy, you can create a policy that allows Pull and Push for a specific repository image created in a particular registry.
To create a policy that allows Pull and Push for a specific Repository Image created in a specific Registry, follow these steps.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. 2. Go to the Policy List page.
- On the Policy List page, click Create Policy.
- On the Policy List page, enter the items of Basic Information Input and click Next.
- On the Permission Settings page, click Load Policy.
- In the Load Policy window’s list, select ScrPullPushOnlyAccess and click OK.
- On the Permission Settings page, select the Individual Resource of the Applied Resources item.
- Click Add Resource in the applied resource list.
- In the Add Resource dialog, select the following items.
- Select container-registy from the resource type list. * In the resource detail list, check the registry resource to add, then click Confirm.
- Select the repository from the resource type list. * In the resource detail list, check the repository resource to add, then click Confirm.
- Verify the individual resources you added in the applied resource list and click Next.
- Check the input information and click Create. 12. Policy creation is complete.
The ScrPullPushOnlyAccess policy consists of the following permissions.
- Permission to allow the LoginContainerRegistry Action required for Registry authentication
- Permission to allow the PullRepositoryImages action required for repository image pull
- PushRepositoryImages Action required for Push
IP access control for SCR endpoints is provided via Private Endpoint Access Control and Public Endpoint Access Control on the Registry detail page.
- When creating an IAM policy for using the SCR endpoint, if you use IP access control, please note that you will not be able to use Registy and Repository Image through the SCR endpoint.
- Set the IP access control entries to Applied IP: All IPs, Excluded IP: Not used.
4.2.3 - API Reference
4.2.4 - CLI Reference
4.2.5 - Release Note
Container Registry
- Container Registry feature change
- General-purpose Container Registry OCI (Open Container Initiative) Distribution Spec. * Ensured v1.1.1 compatibility and improved the user Registry.
- Improved internal processes related to the creation/deletion logic of the Container Registry to enhance convenience.
- We added a refresh button where needed, just like with other products, to improve usability.
- Container Registry feature change
- OCI (Open Container Initiative) Distribution Spec for Registry. * Ensured compatibility with v1.1.1 and improved the user Registry.
- We expand the coverage by adding OS and language types to the container image vulnerability assessment targets.
- Container Registry feature changes and improvements
- We additionally offer the image tag deletion policy feature based on count.
- Based on the IP range constraints of the Firewall product, we improve the validation of Public Endpoint access control IP input values.
- Container Registry feature change
- Provides a feature to enable the deletion policy setting for image tag deletion items.
- Provides log collection functionality based on ServiceWatch integration.
- Container Registry feature change
- We provide a Container Registry service based on Object Storage with self‑encryption and S3 API compatibility patches applied.
- Provides public endpoints and access control functionality for the Registry.
- We additionally offer the Multi-Node GPU Cluster product among the Registry’s private endpoint access control targets.
- Provides a function to configure automatic deletion policies for repositories, stored images, and their individual tags (digests).
- Container Registry feature change
- Provides a lock function for images stored in the Registry.
- Provides monitoring capabilities for the Registry in conjunction with the Cloud Monitoring product.
- Provides integration with VPC Endpoint.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- Container Registry is a service that provides a registry and repository where you can easily store, manage, and share container images and OCI (Open Container Initiative) standard artifacts.
- It was released as a temporary version and will be migrated to the official version once the encryption solution is updated.
5 - Networking
We provide a stable and user‑friendly network operating environment optimized for customers’ diverse cloud environments.
5.1 - VPC
5.1.1 - Overview
Service Overview
Samsung Cloud Platform provides VPC services to support the use of a logically isolated, customer-dedicated private network space in the cloud environment.
VPC (Virtual Private Cloud) is a service that provides a logically isolated, customer-dedicated private network space in a cloud environment. Depending on the use case, you can create a General Subnet and a Local Subnet for communication between servers, and freely select NAT Gateway and Internet Gateway to configure various networks. You can create multiple VPCs and operate them independently. VPC Peering enables connectivity configuration between VPCs.
Service Architecture Diagram
Component
Subnet
A Subnet refers to the IP address range of a VPC. Depending on the purpose, use a General Subnet to create Subnets for Public or Private use. It is a service that lets users segment the network within a VPC to match their purpose and scale. Subnet provides a regular Subnet and a Local Subnet for communication between servers.
General Subnet Creation/Query/Deletion: When creating a VPC, a Subnet is created by default and can be used according to its purpose. For example, you can separate and use a Public Subnet that can access the Internet and a Private Subnet that cannot.
VPC Endpoint Subnet Create/Read/Delete: Access to the Samsung Cloud Platform is possible via a private connection from an external network linked to the VPC, enabling entry into the VPC.
Local Subnet Creation/Query/Deletion: It does not allow connections to other subnets or external access, and only permits direct connections between Virtual Server-Virtual Server or Bare Metal Server-Bare Metal Server, so it can be configured only for Virtual Server-Virtual Server communication within the VPC.
Subnet types
It denotes a Sub_network, an IP address space subdivided into smaller units for use in an IP network. Subnet types are divided based on how routing for the Subnet is configured.
| type | Detailed description |
|---|---|
| Public Subnet | A Subnet that can access the internet can be configured using a General Subnet. |
| Private Subnet | A Subnet that cannot access the internet can be configured using a General Subnet. |
| VPC Endpoint Subnet | Subnet configuration that can be used for a VPC Endpoint |
| Local Subnet | Configure a subnet that cannot connect to other subnets or external networks. |
Internet Gateway
Create an Internet Gateway to connect it to a VPC, view its details, or delete an unused Internet Gateway. You can use an Internet Gateway to connect VPC resources to the Internet.
You can assign a Public IP to instances and load balancers that are connected to the internet, allowing external access.
NAT Gateway
You can create a NAT Gateway, connect it to a subnet, view its details, or delete an unused NAT Gateway.
To create a NAT Gateway for a subnet, you must first create an Internet Gateway and attach it to the VPC. When you create a NAT Gateway, internet access is allowed for all resources in the subnet. To restrict internet access, apply firewall rules.
A NAT Gateway can be created for the General type, and it is a service that maps a single representative public IP to a Virtual Server without a public IP NAT for outbound internet usage.
Public IP
If you want to use the same IP address each time you stop and start an instance, reserve a Public IP and use it.
This is a service that creates a desired public IP within the available Public IP Pool of Samsung Cloud Platform and assigns it to compute resources for use.
Compute resources assigned with the designated public IP will not have their IP changed even after reboot.
Port
Provides a connection point to attach a single device, such as a server’s NIC, to the network. This enables adding additional NICs beyond the default provision.
VPC Endpoint
Provides an entry point for the VPC that enables access to the Samsung Cloud Platform via a private connection from an external network connected to the VPC.
VPC Peering
You can communicate via IP through a 1:1 private route between VPCs. By default, peering is provided between VPCs in the same account, and only one connection is allowed between different accounts.
Private NAT
From compute resources within the VPC, you can use Direct Connect to map the customer’s IP and establish a connection.
Transit Gateway
Transit Gateway is a gateway service that easily connects the customer’s network with the Samsung Cloud Platform network and serves as a connection hub for multiple VPCs within the cloud environment.
Through the Transit Gateway, you can configure a variety of network topologies that meet customer requirements. Additionally, it provides independent firewall configurations and routing capabilities for each connected network segment, enabling thorough security management.
PrivateLink
It is a service that connects internal Samsung Cloud Platform data to a private path between the VPC and the SCP service without exposing it to the internet.
- PrivateLink Service is for service providers, and PrivateLink Endpoint is for service users.
Constraints
Samsung Cloud Platform’s VPC limits the number of VPCs and subnets that can be created as follows.
| Category | Default quota | Detailed description |
|---|---|---|
| VPC | 5 | Default VPC creation limit per account |
| VPC IP range | 6 | Number of IP range creation limits per VPC (default 1 + additional 5) |
| VPC Peering | 5 | VPC Peering creation limit per account |
| Subnet | 3 | Maximum number of default subnets per VPC |
| Private NAT | 3 | Default Private NAT creation limit per VPC |
| Transit Gateway | 3 | Maximum number of Transit Gateways per account |
| Transit Gateway connection from VPC | 5 | Maximum number of VPC connections per Transit Gateway (only the same account can be connected) |
Prior Service
VPC has no prerequisite services.
5.1.1.1 - ServiceWatch Metrics
VPC - Internet Gateway sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals.
Basic Metrics
Internet Gateway
The following are the basic metrics for the Internet Gateway namespace.
The indicators whose names are shown in bold below are the indicators selected as major indicators among the basic indicators provided by Internet Gateway. Key metrics are used to configure service dashboards that are automatically built for each service in ServiceWatch.
Each metric provides guidance in the user guide on which statistical value is meaningful to query, and among the meaningful statistics, the values displayed in bold text are the primary statistics. In the service dashboard, primary metrics can be viewed using the primary statistical values.
| Performance items | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| Network In Total Bytes_Internet | Cumulative traffic volume from Internet Gateway → VPC | Bytes |
|
| Network Out Total Bytes _Internet | Cumulative traffic volume heading from VPC → Internet Gateway | Bytes |
|
| Network In Total Bytes _Internet_Delta | Cumulative traffic volume over 5 minutes from Internet Gateway → VPC (Internet) | Bytes |
|
| Network Out Total Bytes _Internet_Delta | Cumulative traffic volume over 5 minutes from VPC → Internet Gateway (Internet) | Bytes |
|
5.1.2 - How-to guides
Users can create the service by entering the required information for the VPC service and selecting detailed options through the Samsung Cloud Platform Console.
Create VPC
You can create and use a VPC service in the Samsung Cloud Platform Console.
To create a VPC, follow these steps.
Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
On the Service Home page, click the Create VPC button. You will be taken to the Create VPC page.
- In the Service Information Input area, enter or select the required information.
Category RequiredDetailed description VPC name Required Name of the VPC to create - Enter using English letters and numbers, 3 to 20 characters
IP range Required IP range to use - in IP range format
/16 ~ /28enter within the range- Example:
192.168.0.0/24
- Example:
Explanation Select Enter description for VPC Table. VPC Service Information Input Items - Enter or select the required information in the Additional Information Input area.
Category Required statusDetailed description tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. VPC additional information input fields
- In the Service Information Input area, enter or select the required information.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the VPC List page.
Check VPC detailed information
The VPC service allows you to view and edit the full list of resources and detailed information. The VPC Details page consists of the Details, IP Range Management, Tags, Activity Log tabs.
To view detailed VPC information, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the VPC menu. You will be taken to the VPC List page.
- VPC List page, click the resource to view its details. You will be taken to the VPC Detail page.
- VPC Details page displays status information and additional feature information, and consists of the Details, IP Range Management, Tags, Activity History tabs.
Category Detailed description status VPC status - Active: operating normally
- Deleting: deletion in progress
- Creating: creation in progress
- Error: unable to determine current status
- If it persists, contact the registered administrator
Service termination Cancel service button - If you cancel the service, the running service may be terminated immediately, so consider the impact of service interruption thoroughly before proceeding with the cancellation
Table. VPC status information and additional features
- VPC Details page displays status information and additional feature information, and consists of the Details, IP Range Management, Tags, Activity History tabs.
Detailed Information
VPC List page lets you view detailed information of the selected resource and edit it if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | VPC name |
| Resource ID | VPC’s unique resource ID |
| constructor | User who created the VPC |
| Creation date | VPC creation timestamp |
| Editor | User who modified the VPC information |
| Modification date and time | Timestamp of VPC information modification |
| VPC name | VPC resource name |
| VPC ID | VPC unique ID |
| External connection | External resource information |
| IP range | VPC IP range |
| description | VPC description
|
IP range management
On the VPC List page, you can view and add the IP range information associated with the selected resource.
| Category | Detailed description |
|---|---|
| IP range | Added IP range information |
| Creation date and time | IP range addition timestamp |
| Add IP range | Add IP range
|
When adding an IP range to a VPC, you cannot add it in the following cases.
- IP range currently used in the VPC
- In the VPC peering rule associated with the current VPC, the destination is the address range added to the peer VPC.
- The address range added as a remote destination in the Direct Connect rule linked to the current VPC.
- The address range whose destination was added as remote in the Transit Gateway rule attached to the current VPC.
- The NAT IP range currently used by the Private NAT attached to the VPC
tag
On the VPC List page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the VPC List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate VPC
You can terminate unused VPCs to reduce operating costs.
- A VPC cannot be deleted if it has associated Subnet, Internet Gateway, or Direct Connect resources.
- You can only terminate when the VPC service status is Acrive or Error.
- If you cancel the service, the currently operating service may be stopped immediately. Proceed with the cancellation only after fully considering the impact of the service interruption.
To terminate the VPC, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the VPC menu. You will be taken to the VPC List page.
- On the VPC List page, select the resource to terminate, and click the Terminate Service button.
- After termination is complete, verify on the VPC List page that the resource has been terminated.
5.1.2.1 - Subnet
Create Subnet
You can create and use the VPC Subnet service in the Samsung Cloud Platform Console.
To create a Subnet, follow these steps.
All Services > Networking > VPC Click the menu. Go to the VPC’s Service Home page.
On the Service Home page, click the Create Subnet button. You will be taken to the Create Subnet page.
- In the Service Information Input area, enter or select the required information.
Category RequiredDetailed description Subnet type Required Select Subnet type - General: Can configure as Public or Private
- Local: Can be assigned by selecting either Virtual Server or Bare Metal Server
- A Local Subnet is a Subnet for communication only between servers and cannot communicate with the outside
- VPC Endpoint: VPC Endpoint can be configured
VPC name Required Select the VPC to which the subnet will be attached from the list of existing VPCs - Click + Create New to create a VPC and then select it
VPC IP range Select Automatically input the CIDR range of the selected VPC Subnet name Required Subnet name to create - Enter using English letters and numbers, within 3 to 20 characters
IP range Required IP range to use - in IP range format
/16 ~ /28Enter within the range- Example:
192.168.0.0/24
- Example:
- IP ranges cannot overlap with IP ranges (other subnets) already in use within the VPC
Gateway IP Required Display the Gateway IP address of the Subnet - The first IP of the entered IP range is automatically filled in
- Cannot be modified after service creation
Table. Subnet service information input fields - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description description Selection Enter description for Subnet IP allocation range Selection You can set the range within the IP range to be used - Select either the entire IP range or an individual specification
- Subnet sub-resources receive IP assignments from the entered entire IP range or from the individually specified range set by the user
- When selecting individual specification, enter the starting IP address and the ending IP address
DNS Name Server Selection After selecting Use, enter DNS Name Server IP. Host path Select Use after selection, enter the host path - Enter the destination IP range and Next Hop IP address
- Destination IP ranges must not overlap each other
tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Subnet additional information input fields
- In the Service Information Input area, enter or select the required information.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- After creation is complete, check the created resources on the Subnet List page.
Check Subnet detailed information
The Subnet service allows you to view and edit the full resource list and detailed information. Subnet Details page consists of Details, Virtual IP Management, Tags, Activity Log tabs.
To view detailed Subnet information, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the Subnet button on the Service Home page. You will be taken to the Subnet List page.
- On the Subnet List page, click the resource for which you want to view detailed information. You will be taken to the Subnet Details page.
- Subnet Details page displays status information and additional feature information, and consists of Details, Virtual IP Management, Tags, Operation History tabs.
Category Detailed description status Subnet status - Creating: Creation in progress
- Active: Operating normally
- Editing: Modification in progress
- Deleting: Deletion in progress
- Failed: State where creation failed
- Error: Current status unknown
- If it occurs continuously, contact the registered administrator
Delete Subnet Subnet Delete Button Table. Subnet status information and additional features
- Subnet Details page displays status information and additional feature information, and consists of Details, Virtual IP Management, Tags, Operation History tabs.
Detailed Information
On the Subnet List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Subnet resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the Subnet |
| Creation date | Subnet creation time |
| Editor | User who modified the Subnet information |
| Modification date and time | Subnet information modification timestamp |
| Subnet type | Subnet type |
| VPC name | The VPC to which the subnet belongs |
| Subnet name | Subnet name |
| Subnet ID | Subnet unique ID |
| IP range | Used IP range |
| Gateway IP | Gateway IP address of the Subnet |
| DHCP IP | the second IP address among the used IP ranges
|
| description | Subnet additional description
|
| IP allocation range | IP allocation range |
| DNS Name Server | Use DNS Name Server |
| Host path | Host route (destination IP range, Next Hop IP address) information |
Virtual IP Management
Subnet List page lets you view the virtual IP information of the selected resource, and you can reserve or delete it.
| Category | Detailed description |
|---|---|
| Virtual IP reservation | Virtual IP usage reservation |
| Virtual IP | Virtual IP information
|
| Public Nat IP | Public NAT IP information |
| Number of connected ports | Number of ports connected to the IP |
| Reservation date and time | Virtual IP reservation date and time |
| Return | Virtual IP Return button
|
- If a Port or NAT IP is attached to a Virtual IP, it cannot be returned. Delete the attached resources first.
- You can return the Virtual IP only when the Subnet status is Active or Error.
tag
On the Subnet List page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Sunnet List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Virtual IP
You can reserve or manage Virtual IPs for use in a Subnet.
Reserve Virtual IP
You can reserve a Virtual IP for use in the Subnet.
To reserve a Virtual IP, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the Subnet button on the Service Home page. You will be taken to the Subnet List page.
- On the Subnet list page, click the resource to reserve a Virtual IP. You will be taken to the Subnet details page.
- On the Subnet Details page, click the Virtual IP Management tab. You will be taken to the Virtual IP Management tab page.
- On the Virtual IP Management tab page, click the Virtual IP Reservation button. The Virtual IP reservation window opens.
- In the Virtual IP Reservation window, set the detailed items and click OK.
- Virtual IP: If you select Auto-Generated, an automatically generated IP will be reserved, and if you select Input, you can reserve an IP that you manually entered.
- Description: Enter additional description for Virtual IP.
- When the reservation confirmation window appears, click Confirm.
Check Virtual IP detailed information
You can view detailed information about the Virtual IP.
To view detailed information about the Virtual IP, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Subnet button. You will be taken to the Subnet List page.
- Subnet list page, click the resource to reserve a Virtual IP. Subnet details page will be displayed.
- On the Subnet Details page, click the Virtual IP Management tab. You will be taken to the Virtual IP Management tab page.
- Click the resource to view on the Virtual IP Management tab page. You will be taken to the Virtual IP Details page.
- *Virtual IP Details The page displays the connected ports and detailed information.
Category Detailed description Virtual IP Virtual IP address Public NAT IP Public NAT IP address and status - Edit icon can be clicked to edit
- Enable after setting, you can select an existing IP or create one to add
- Public NAT IP cannot be modified after configuration; changes require reconfiguration
Connection Port Port information connected to the Virtual IP - Add button to click to add a connected port, you can add by connecting an existing port or creating a new one
- Delete button to click to remove the connected port
Explanation Virtual IP description - Click the Edit icon to modify
constructor User who reserved a Virtual IP Creation date Virtual IP reservation date and time Editor User who modified the Virtual IP information Modification date Date and time the Virtual IP information was modified Table. Virtual IP detailed information items
- *Virtual IP Details The page displays the connected ports and detailed information.
Terminate Subnet
You can delete an unused Subnet.
- You cannot cancel the service if there are connected resources. Delete the connected resources first.
- You can delete a service only when its status is Active or Error.
- Because data cannot be recovered after a service is deleted, be sure to fully consider the impact before proceeding with a Subnet deletion.
To delete a Subnet, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Subnet menu. You will be taken to the Subnet List page.
- On the Subnet List page, click the resource to delete. Navigate to the Subnet Details page.
- On the Subnet Details page, click the Delete button.
- After deletion is complete, check the Subnet list to confirm that the resource has been removed.
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
5.1.2.2 - Port
Create Port
You can create and use a Port service in the Samsung Cloud Platform Console.
To create a port, follow these steps.
Click the All Services > Networking > VPC menu. Navigate to the VPC Service Home page.
On the Service Home page, click the Create Port button. You will be taken to the Create Port page.
- In the Service Information Input area, enter or select the required information.
Category RequiredDetailed description VPC name Required Select the VPC to create the Port - Click + Create New to create the VPC and then select it
Subnet name Required Select the Subnet to create the Port - Click + Create New to create a Subnet and then select it
Port name Required Port name that is easy to identify - Enter using English letters, numbers,
-within 3 to 20 characters
IP allocation method Required Select IP allocation method - Automatic allocation: IP is automatically assigned within the IP allocation range of the Subnet
- Manual entry: The entered IP is assigned within the Subnet’s range
- When Manual entry is selected, enter the IP address to use for the Port in Fixed IP address
Explanation Selection Enter description for Port Security Group Select When Use is selected, you can select up to 5 Security Groups. Table. Port service information input fields - Enter or select the required information in the Additional Information Input area.
Category Required statusDetailed description tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. Port additional information input fields
- In the Service Information Input area, enter or select the required information.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- After creation is complete, check the created resources on the Port List page.
Check detailed information of Port
The Port service allows you to view and edit the full resource list and detailed information. Port Details page consists of Details, Tags, Activity Log tabs.
To view detailed port information, follow these steps.
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the Port menu. You will be taken to the Port List page.
- Port List page, click the resource (Port name) to view detailed information. You will be taken to the Port Details page.
- Port Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description status Port status - Active: Operating normally
- Down: Not connected to the resource, or connected but not functioning
- Error: Current status cannot be determined
- If it occurs continuously, contact the registered administrator
Delete Port Button to delete the port Table. Port status information and additional functions
- Port Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
On the Port list page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Port resource name |
| Resource ID | Unique resource ID in the service |
| Resource ID | Port’s unique resource ID |
| constructor | User who created the Port |
| Creation date and time | Port creation timestamp |
| Editor | User who modified the port information |
| Modification date and time | Date and time the port information was modified |
| Port name | Port resource name |
| Port ID | Port resource ID |
| Subnet name | Click the connected Subnet name or Subnet entry to go to the detail page. |
| Connected resources | Connected device information |
| Static IP | Static IP information |
| MAC address | MAC address information |
| Explanation | Description of the Port
|
| Security Group | Connected Security Group information
|
| Virtual IP | Connected Virtual IP information |
tag
Port list page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Port list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Delete Port
You can release unused ports to reduce operating costs.
- If there are connected resources such as Virtual Server or PrivateLink, you cannot delete the service. Delete the connected resources first.
- After deleting a service, the running service may be stopped immediately. Consider the impact of deleting the service thoroughly before proceeding with the deletion.
To delete a Port, follow these steps.
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the Port menu. You will be taken to the Port List page.
- On the Port List page, click the resource (Port name) you want to delete. You will be taken to the Port Detail page.
- On the Port Details page, click the Delete Port button.
- After the deletion is complete, check whether the resource has been removed from the Port list.
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
5.1.2.3 - Internet Gateway
Create Internet Gateway
You can create and use the Internet Gateway service in the Samsung Cloud Platform Console.
To create an Internet Gateway, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway Creation button. You will be taken to the Internet Gateway Creation page.
- Enter or select the required information in the Service Information Input area.
Category RequiredDetailed description VPC name Required Select the VPC that connects to the Internet Gateway - Click + New to create a VPC and then select it
Category Required Select Internet Gateway type - Choose from Dedicated Internet Gateway, Secured Internet Gateway, Group Gateway
Internet Gateway name Selection Automatically create IGW_{VPC name} Explanation Select Enter a description of the Internet Gateway Use firewall Select Select whether to use the firewall Whether to save firewall logs Select Select whether to save Firewall logs - When using the Firewall, save connection logs
- For more details, see Using Firewall Log Saving
Table. Internet Gateway Service Information Input Items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Internet Gateway additional information input fields
- Enter or select the required information in the Service Information Input area.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the Internet Gateway List page.
Internet Gateway Check detailed information
The Internet Gateway service allows you to view and edit the full resource list and detailed information. Internet Gateway Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the Internet Gateway, follow these steps.
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- On the Service Home page, click the Internet Gateway menu. Navigate to the Internet Gateway list page.
- On the Internet Gateway List page, click the resource to view detailed information. You will be taken to the Internet Gateway Details page.
- Internet Gateway Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Category Detailed description status Internet Gateway status - Creating: Creating resource
- Ative: Normal connection status
- Deleting: Deletion in progress
- Error: Unable to determine current status
- If it persists, contact the registered administrator
Delete Internet Gateway Internet Gateway Delete Button Table. Internet Gateway status information and additional features
- Internet Gateway Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
On the Internet Gateway List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Internet Gateway resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the Internet Gateway |
| Creation date and time | Internet Gateway creation timestamp |
| Editor | User who modified the Internet Gateway information |
| Modification date and time | Date and time the Internet Gateway information was modified |
| Internet Gateway name | Internet Gateway name |
| Internet Gateway ID | Internet Gateway resource ID |
| VPC name | VPC name |
| VPC name | VPC ID |
| Category | Internet Gateway type |
| description | Description of Internet Gateway
|
| Firewall name | Clicking the Firewall takes you to the detail page. |
| Use Fireawall | Use firewall |
| NAT Gateway | Clicking NAT Gateway navigates to the detail page |
| Whether to save NAT logs | NAT log storage
|
tag
Internet Gateway list page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Internet Gateway List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Internet Gateway Resources
You can manage resources, such as enabling Internet Gateway log storage.
Using NAT Log Storage
To store NAT logs, first create a bucket in Object Storage for log storage and configure that bucket in the NAT Logging log repository. Then, when you enable log storage in the NAT detail view, NAT logs will begin to be saved to the Object Storage bucket. The log repository settings can be verified in NAT Logging. For more information, see NAT Logging.
- If you configure a log repository, Object Storage charges for log storage will be applied.
To use NAT log storage, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. Navigate to the Internet Gateway List page.
- On the Internet Gateway List page, click the resource to view detailed information. You will be taken to the Internet Gateway Details page.
- Click the Modify NAT log storage setting button. You will be taken to the Modify NAT log storage setting popup.
- Modify NAT Log Storage Setting In the popup window, select Use for the log repository, and click the Confirm button.
Do not use NAT log storage
To use NAT log storage, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- Internet Gateway List page, click the resource to view detailed information. You will be taken to the Internet Gateway Details page.
- Click the Modify NAT log storage setting button. You will be taken to the Modify NAT log storage setting popup.
- Modify NAT log storage setting In the popup window, deselect Use for the log storage, and click the Confirm button.
- Notification Check the message in the popup window and click the Confirm button.
Delete Internet Gateway
- NAT Gateway, Firewall rules, VPN, etc. If there are connected resources, you cannot terminate the service. Delete the connected resources first.
- After deleting the service, internet communication for resources under the VPC will be interrupted. Proceed with the deletion only after fully considering the impact of deleting the Internet Gateway.
To delete an Internet Gateway, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- On the Internet Gateway List page, click the resource you want to delete. Navigate to the Internet Gateway Details page.
- On the Internet Gateway Details page, click the Delete button.
- After the deletion is complete, verify that the resource has been removed from the Internet Gateway list.
Pre-service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
5.1.2.4 - NAT Gateway
Creating NAT Gateway
You can create and use the NAT Gateway service in the Samsung Cloud Platform Console.
To create a NAT Gateway, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Create NAT Gateway button. You will be taken to the Create NAT Gateway page.
- In the Service Information Input area, enter or select the required information.
Category RequiredDetailed description VPC name Required Select the VPC to connect - + Create new to create a VPC and then select it
Subnet name Required Select the connected Subnet - Click + Create New to create a Subnet and then select it
NAT Gateway name Select Create NAT_GW_{subnet name} IP for NAT Gateway Required Select a Public IP for NAT Gateway - + New Click to create an IP and then select it
description Select Enter a description for the NAT Gateway Table. NAT Gateway Service Information Input Items - Enter or select the required information in the Additional Information Input area.
Category Whether requiredDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. NAT Gateway additional information input fields
- In the Service Information Input area, enter or select the required information.
- In the Summary panel, review the detailed information and estimated billing amount, then click the Create button.
- When creation is complete, verify the created resource on the NAT Gateway list page.
Check NAT Gateway detailed information
The NAT Gateway service allows you to view and edit the full resource list and detailed information. NAT Gateway Details page consists of Details, Tags, Activity Log tabs.
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the NAT Gateway menu. You will be taken to the NAT Gateway List page.
- On the NAT Gateway List page, click the resource whose details you want to view. You will be taken to the NAT Gateway Details page.
- NAT Gateway Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Category Detailed description status NAT Gateway status - Creating: Creation in progress
- Active: Operating normally
- Deleting: Deletion in progress
Delete NAT Gateway Button to terminate the service - Terminate the NAT Gateway when there are no connected services
- Since terminating the service may cause the running service to stop immediately, proceed with the termination only after fully considering the impact of service interruption
Table. NAT Gateway status information and additional features
- NAT Gateway Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
NAT Gateway List page lets you view detailed information of the selected resource and modify it if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | NAT Gateway resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the NAT Gateway |
| Creation Timestamp | NAT Gateway creation timestamp |
| Editor | User who modified NAT Gateway information |
| Modification date and time | Date and time the NAT Gateway information was modified |
| NAT Gateway name | NAT Gateway name |
| NAT Gateway ID | NAT Gateway resource ID |
| VPC name | VPC name connected to NAT Gateway
|
| VPC ID | VPC resource ID connected to the NAT Gateway |
| Subnet name | Subnet name connected to NAT Gateway
|
| Subnet ID | Subnet resource ID connected to the NAT Gateway |
| Subnet IP range | Subnet IP range information |
| IP for NAT Gateway | NAT Gateway IP information |
| description | Description of NAT Gateway
|
tag
NAT Gateway List page lets you view, add, modify, or delete the tag information of the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the NAT Gateway List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Delete NAT Gateway
To delete a NAT Gateway, follow these steps.
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the NAT Gateway menu. Navigate to the NAT Gateway List page.
- Click the resource to view detailed information on the NAT Gateway List page. You will be taken to the NAT Gateway Details page.
- On the NAT Gateway Details page, click the Delete button.
- After deletion is complete, verify that the resource has been removed from the NAT Gateway list.
Pre-service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
5.1.2.5 - Public IP
Create Public IP
You can create and use a Public IP service in the Samsung Cloud Platform Console.
To create a Public IP, follow these steps.
Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
On the Service Home page, click the Public IP reservation button. You will be taken to the Public IP reservation page.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Category Required Select the gateway to reserve the Public IP - Default: Internet Gateway
description Select Enter description for Public IP Table. Public IP Service Information Input Items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. Public IP additional information input fields
- Enter or select the required information in the Service Information Input area.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the Public IP List page.
View detailed information of Public IP
The Public IP service allows you to view and edit the full resource list and detailed information. Public IP Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the public IP, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Public IP menu. You will be taken to the Public IP List page.
- On the Public IP List page, click the resource to view detailed information. You will be taken to the Public IP Detail page.
- Public IP Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description status Public IP status - Attached: attached state
- Reserved: reserved state
- Error: cannot determine current state
- If it occurs continuously, contact the registered administrator
Return Public IP Public IP Return Button Table. Public IP status information and additional features
- Public IP Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
Public IP List page lets you view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Public IP resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the Public IP |
| Creation date | Public IP creation timestamp |
| Editor | User who modified the Public IP information |
| Modification date and time | Date and time the public IP information was modified |
| IP address | Designated (reserved) IP address |
| Category | Gateway information with reserved Public IP |
| Public IP ID | Public IP resource ID |
| description | Description of Public IP
|
| Connection resource type | Resource information associated with the designated (reserved) IP address |
| Connection resource name | Resource name associated with the designated (reserved) IP address |
tag
On the Public IP List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Public IP List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Return Public IP
To delete a Public IP, follow these steps.
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the Public IP button. You will be taken to the Public IP List page.
- On the Public IP List page, click the resource to view detailed information. You will be taken to the Public IP Details page.
- On the Public IP Details page, click the Public IP Release button.
- After the return is completed, check whether the resource has been deleted from the Public IP list.
Pre-service
This is a service that must be installed in advance before creating this service. Please refer to the provided user guide and prepare accordingly.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | It is a service that provides an isolated virtual network in a cloud environment. |
5.1.2.6 - Private NAT
Users can create the Private NAT service by entering the required information and selecting detailed options through the Samsung Cloud Platform Console.
Creating Private NAT
You can create a Private NAT service in the Samsung Cloud Platform Console and use it.
To create a Private NAT, follow these steps.
All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
On the Service Home page, click the Create Private NAT button. 2. Navigate to the Create Private NAT page.
In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Private NAT name Required Enter the Private NAT name - Enter using letters and numbers, 3 to 20 characters
Connection resource type Required Select the connection resource to connect the Private NAT - You can choose between Direct Connect and Transit Gateway
- Transit Gateway can be selected after connecting the uplink line
Connection resource name Essential Display entries of the selected connection resource - Click + New Creation in the list to create a connection resource
NAT IP range Essential Enter the NAT IP range to use - Enter in CIDR format, e.g., 192.168.2.0/23
- Cannot overlap with the connected VPC IP or other Private NAT IP ranges
Explanation Selection Enter description for Private NAT Table. Private NAT Service Information Input ItemsReference- It must not overlap with the IP range of the VPC connected to the selected Direct Connect or Transit Gateway.
- It must not overlap with other Private NAT ranges that are connected to the selected Direct Connect or Transit Gateway.
- It must not overlap with the IP range of the on‑premise network connected to the selected Direct Connect or Transit Gateway.
- Some IP ranges are reserved for management and cannot be used.
Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Tag Selection Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Private NAT additional information input fields
Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- When creation is complete, verify the created resources on the Private NAT List page.
Check Private NAT detailed information
The Private NAT service allows you to view and edit the complete resource list and detailed information. On the Private NAT Details page, it consists of Detail Information, IP Management, Tags, Operation History tabs.
To view detailed information about Private NAT, follow these steps.
- All Services > Networking > VPC menu, click it. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Private NAT menu. 2. Go to the Private NAT List page.
- Private NAT List page, click the resource to view detailed information. 3. Navigate to the Private NAT Details page.
- Private NAT Details page displays status information and additional feature information, and consists of Details, IP Management, Tags, Activity Log tabs.
Category Detailed description status Private NAT status - Active: Running
- Creating: In progress
- Deleting: In progress
- Error: An error occurred
Delete Private NAT Button to delete Private NAT Table. Private NAT status information and additional features
- Private NAT Details page displays status information and additional feature information, and consists of Details, IP Management, Tags, Activity Log tabs.
Detailed Information
Private NAT List page allows you to view detailed information of the selected resource and edit the information if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Private NAT resource name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created a Private NAT |
| Creation date and time | Date and time the Private NAT was created |
| Modifier | User who modified the Private NAT information |
| Modification date | Date and time the Private NAT information was modified |
| Private NAT name | Private NAT resource name |
| Connection resource type | Information about resources connected to Private NAT |
| NAT IP range | NAT IP range information in use |
| Connection resource name | Clicking the resource information or resource name linked to the Private NAT navigates to the detailed information page. |
| Explanation | Description of Private NAT
|
IP Management
Private NAT List page allows you to view the Private NAT IP, and you can reserve or release it.
| Category | Detailed description |
|---|---|
| Private NAT IP List | Active Private NAT list
|
Tag
On the Private NAT List page, you can view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Private NAT List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Private NAT IP
You can reserve or release a Private NAT IP.
Reserve Private NAT IP
To reserve a Private NAT IP, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Private NAT menu. 2. Private NAT List Go to the page.
- Private NAT List page, click the resource to reserve an IP. 3. Go to the Private NAT Details page.
- On the Private NAT Details page, click the IP Management tab. 4. Navigate to the IP Management tab page.
- Click the IP Management tab page’s Private NAT IP Reservation button. 5. The Private NAT IP reservation window appears.
- Enter the Private NAT IP to be used in the Private NAT IP reservation window and click the Confirm button. 6. A notification confirmation dialog appears.
- In the alert dialog, click the Confirm button. 7. Check whether a resource entry has been added to the IP list.
Return Private NAT IP
To return the Private NAT IP, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Private NAT menu. 2. Navigate to the Private NAT List page.
- On the Private NAT List page, click the resource to reserve an IP. 3. Go to the Private NAT Details page.
- On the Private NAT Details page, click the IP Management tab. 4. Navigate to the IP Management tab page.
- On the IP Management tab page, click the Return button for the IP item you want to return. 5. A notification confirmation dialog appears.
- Verify that the selected resource has been deleted from the IP list.
Delete Private NAT
You can cancel unused Private NAT to reduce operating costs.
To cancel Private NAT, follow the steps below.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Private NAT menu. 2. Go to the Private NAT List page.
- On the Private NAT List page, click the resource to delete. 3. Go to the Private NAT Details page.
- On the Private NAT Details page, click the Delete Private NAT button.
- After termination is complete, check whether the resource has been deleted from the Private NAT list.
Preliminary service
This service must be installed in advance before creating this service. Please prepare by referring to the user guide provided in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Direct Connect | A service that securely and quickly connects the customer’s network with the Samsung Cloud Platform environment. |
5.1.2.7 - VPC Endpoint
Create VPC Endpoint
You can create and use a VPC Endpoint service in the Samsung Cloud Platform Console.
To create a VPC Endpoint, follow these steps.
Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
On the Service Home page, click the Create VPC Endpoint button. You will be taken to the Create VPC Endpoint page.
- In the Service Information Input area, enter or select the required information.
Category Required statusDetailed description VPC name Required Select the VPC to create the Endpoint - Click + Create new to create a VPC and then select it
Usage > Target Service Required Select the target service for which to create the VPC Endpoint Purpose > Connected Resources Required Select the resource to create a VPC Endpoint VPC Endpoint name Required Enter the VPC Endpoint name - Enter using letters and numbers, 3 ~ 20 characters
VPC Endpoint IP > Subnet name Required Select VPC Endpoint Subnet - + Create New Click to create a Subnet and then select it
VPC Endpoint IP > IP Required Enter the IP to be used for the VPC Endpoint - Example:
192.168.x.x
description Select Enter a description for the VPC Endpoint Table. VPC Endpoint Service Information Input Items - Enter or select the required information in the Additional Information Input area.
Category Whether requiredDetailed description tag Select Add Tag - Up to 50 can be added per resource
- Add Tag button after clicking, input or select Key, Value values
Table. VPC Endpoint additional information input fieldsReferenceAfter registering the VPC Endpoint, you need to configure the Direct Connect firewall to integrate internal services of the Samsung Cloud Platform. Refer to the port information for each service and register the firewall rules.
Service Port information DNS TCP 53, UDP 53 Object Storage TCP 8080, 8443, 80, 443, 4430 File Storage (NFS) TCP/UDP common 111, 300, 302, 304, 2049, 635, 4045, 4046, 4049
(CIFS) UDP 135, 137, 138, 389 / TCP 135, 139, 445, 40001Container Registry (authentication server, Registry) TCP 443 Table: Allowed ports per target service
- In the Service Information Input area, enter or select the required information.
Summary Verify the detailed information and estimated billing amount generated in the panel, then click the Create button.
- When creation is complete, check the created resources on the VPC Endpoint List page.
Check VPC Endpoint details
The VPC Endpoint service allows you to view and edit the full list of resources and detailed information. VPC Endpoint Details page consists of Details, Tags, Activity Log tabs.
Endpoint To view detailed information, follow these steps.
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- Click the VPC Endpoint menu on the Service Home page. You will be taken to the VPC Endpoint List page.
- On the VPC Endpoint List page, click the resource for which you want to view detailed information. You will be taken to the VPC Endpoint Details page.
- VPC Endpoint Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Category Detailed description status VPC Endpoint status - Active: operating normally
- Creating: creation in progress
- Deleting: deleting resource connection
- Deleted: resource connection deleted
Delete VPC Endpoint Button to delete the VPC Endpoint connection resource Table. VPC Endpoint status information and additional features
- VPC Endpoint Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
VPC Endpoint List page lets you view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | VPC Endpoint resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the VPC Endpoint |
| Creation date and time | VPC Endpoint creation timestamp |
| Editor | User who modified the VPC Endpoint information |
| Modification date | Date and time the VPC Endpoint information was modified |
| VPC Endpoint name | VPC Endpoint name |
| VPC name | Click the connected VPC name or VPC item to go to the detail page. |
| VPC ID | Connected VPC ID |
| Target Service | Connected target information |
| Connection resource information | Connected resource information |
| Subnet name | Endpoint subnet information; click the subnet item to navigate to the detail page. |
| VPC Endpoint IP | VPC Endpoint IP information |
| description | Description of VPC Endpoint
|
tag
On the VPC Endpoint List page, you can view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
VPC Endpoint List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Delete VPC Endpoint
You can cancel unused Endpoints to reduce operating costs.
- If there are connected resources such as Object Storage, Container Registry, you cannot cancel the service. Delete the connected resources first.
- Deleting a VPC Endpoint can cause the running service to stop immediately. Carefully consider the impact of deleting the service before proceeding with the deletion.
To terminate a VPC Endpoint, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the VPC Endpoint menu on the Service Home page. You will be taken to the VPC Endpoint List page.
- On the VPC Endpoint List page, click the resource you want to delete. You will be taken to the VPC Endpoint Details page.
- On the VPC Endpoint Details page, click the Delete Endpoint button.
- When the termination is complete, check whether the resource has been deleted from the VPC Endpoint list.
Pre-service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Direct Connect | A service that securely and quickly connects the customer’s network to the Samsung Cloud Platform |
5.1.2.8 - VPC Peering
Users can create the service by entering the required information for the VPC Peering service and selecting detailed options through the Samsung Cloud Platform Console.
Create VPC Peering
You can create and use the VPC Peering service in the Samsung Cloud Platform Console.
To create a VPC Peering, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Create VPC Peering button. You will be taken to the Create VPC Peering page.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description VPC Peering name Required Enter VPC Peering name - Enter using letters and numbers, 3~20 characters
Requested VPC name Required Select the VPC to request VPC Peering - Click + New in the list to create a VPC
Approved Account Required Select the account of the VPC to approve VPC peering, then select that VPC or enter its information - Same account: select the approved VPC name
- Click + New creation in the list to create a VPC
- Different account: enter the approved Account ID and approved VPC ID
description Select Enter a description of VPC Peering Table. VPC Peering service information input items - In the Additional Information Input area, enter or select the required information.
Category Whether requiredDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. VPC Peering additional information input fields
- Enter or select the required information in the Service Information Input area.
- Check the detailed information and estimated billing amount generated in the Summary panel, and click the Create button.
- When connecting a VPC from another Account, the peering proceeds after an approval process, so the connection may take some time.
- When creation is complete, check the created resource on the VPC Peering List page.
Check VPC Peering details
The VPC Peering service allows you to view and edit the full list of resources and detailed information. VPC Peering Details page consists of Details, Rules, Tags, Activity Log tabs.
To view detailed VPC Peering information, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the VPC Peering menu. You will be taken to the VPC Peering List page.
- VPC Peering List Click the resource to view detailed information on the page. You will be taken to the VPC Peering Details page.
- VPC Peering Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity History tabs.
Category Detailed description status VPC Peering status - Active: operational
- Requesting: connection or deletion request in progress
- Creating: connecting
- Creating Requesting: connection request in progress
- Deleting Requesting: deletion request in progress
- Editing: editing
- Rejected: rejected
- Canceled: canceled
- Error: error occurred
- If it persists, contact the registered administrator
VPC Peering deletion/VPC Peering deletion request Button to request deletion of VPC Peering resources - Cancel Connection Request: Can cancel if a VPC Peering connection was requested
- Approve Connection: Can approve when a VPC Peering connection request is received
- Reject Connection: Click to reject the connection
- Cancel Deletion Request: Can cancel if a VPC Peering deletion was requested
- Approve Deletion: Can approve when a VPC Peering deletion request is received
- Reject Deletion: Click to reject the deletion
- Reapproval Request: Request reapproval when VPC approval was denied
Table. VPC Peering status information and additional features
- VPC Peering Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity History tabs.
Detailed Information
VPC Peering List page lets you view detailed information of the selected resource and edit it if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | VPC Peering resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the VPC Peering |
| Creation date | Timestamp of VPC Peering creation |
| Editor | User who modified the VPC Peering information |
| Modification date and time | Timestamp of VPC Peering information modification |
| VPC Peering name | VPC Peering name |
| Request information | The VPC name and VPC ID information of the VPC that requested VPC Peering, clicking the VPC name navigates to the detail information page
|
| Approval information | The VPC name and VPC ID of the VPC that approved the VPC peering; clicking the VPC name takes you to the detail page
|
| Explanation | Description of VPC Peering
|
rule
VPC Peering List page lets you view the rules associated with the selected resource, and add or remove them.
| Category | Detailed description |
|---|---|
| List of rules | Connected Rules List
|
tag
VPC Peering List page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the VPC Peering List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing VPC Peering Rules
You can add or delete rules for VPC Peering.
Add Rule
- You can add rules only when the VPC peering status is Active.
- If you enter the destination IP incorrectly in the routing configuration, communication failures may occur. Verify the destination IP information once more before creating the rule.
To add a rule to VPC Peering, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the VPC Peering menu on the Service Home page. You will be taken to the VPC Peering List page.
- On the VPC Peering List page, click the resource to delete. Navigate to the VPC Peering Details page.
- On the VPC Peering Details page, click the Rules tab. You will be taken to the Rules tab page.
- On the Rule tab page, click the Add Rule button. The Add Rule dialog appears.
- Enter the origin and destination in the rule addition window and click the Confirm button. A notification confirmation window will appear.
- It must not duplicate an already entered rule.
- You can enter within the IP address range of the destination VPC.
- It should be entered the same as the subnet range.
- The destination IP range 0.0.0.0/0 cannot be used.
- Click the Confirm button in the notification dialog. Verify that the resource entry has been added to the rule list.
Delete Rule
- You can delete the connected rules only when the VPC Peering service status is ACtive or Error.
- If the status of the linked rule is Creating or Deleting, it cannot be deleted.
To delete a VPC Peering rule, follow these steps.
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the VPC Peering menu. You will be taken to the VPC Peering List page.
- On the VPC Peering List page, click the resource you want to delete. Navigate to the VPC Peering Details page.
- VPC Peering Details page, click the Rules tab. You will be taken to the Rules tab page.
- Rule tab page, click the Delete button of the item to delete. A notification confirmation dialog appears.
- Click the Confirm button in the alert dialog. Verify that the selected resource in the rule list has been deleted.
Terminate VPC Peering
You can terminate unused VPC Peering to reduce operating costs.
- If a rule is attached to the VPC Peering, you cannot terminate the service. Delete all attached rules before terminating the service.
- You can only terminate the VPC Peering service when its status is Active, Rejected, Canceled, or Error.
Terminate VPC Peering of the same Account
To terminate a VPC peering within the same account, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the VPC Peering menu on the Service Home page. You will be taken to the VPC Peering List page.
- On the VPC Peering List page, click the resource to delete. Navigate to the VPC Peering Details page.
- On the VPC Peering Details page, click the VPC Peering Delete button.
- After termination is complete, verify that the resource has been deleted from the VPC Peering list.
Terminate VPC Peering connected to another account
To terminate a VPC peering connected to another account, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the VPC Peering menu on the Service Home page. You will be taken to the VPC Peering List page.
- On the VPC Peering List page, click the resource you want to delete. You will be taken to the VPC Peering Details page.
- On the VPC Peering Details page, click the VPC Peering Delete Request button.
- Once the cancellation is complete, verify that the resource has been removed from the VPC Peering list.
- The deletion request must be approved by the counterpart account for the termination to be processed correctly.
Pre-service
This is a service that must be installed in advance before creating this service. Please refer to the provided user guide and prepare accordingly.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
5.1.2.9 - Transit Gateway
Users can create the service by entering the required information for the Transit Gateway service and selecting detailed options through the Samsung Cloud Platform Console.
Create Transit Gateway
You can create and use the Transit Gateway service in the Samsung Cloud Platform Console.
To create a Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Create Transit Gateway button. 2. Go to the Transit Gateway creation page.
- In the Service Information Input area, enter or select the required information.
Category Required statusDetailed description Transit Gateway name Required Enter the Transit Gateway name - Enter using letters and numbers, 3 to 20 characters
Explanation Selection Enter description for Transit Gateway Table: Transit Gateway service information input fields - Additional Information Input area, please enter or select the required information.
Category required statusDetailed description tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Transit Gateway additional information input fields
- In the Service Information Input area, enter or select the required information.
- Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- Once creation is complete, check the created resources on the Transit Gateway List page.
Check Transit Gateway Details
The Transit Gateway service lets you view and modify the complete resource list and detailed information. In the Transit Gateway Details page, it is composed of Details, Connected VPC Management, Rules, Tags, Activity History tabs.
To view the detailed information of the Transit Gateway, follow these steps.
- Click the All Services > Networking > VPC menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- On the Transit Gateway List page, click the resource to view its detailed information. 3. Go to the Transit Gateway Details page.
- Transit Gateway Details page displays status information and additional feature information, and consists of the Details, Connected VPC Management, Rules, Tags, Activity History tabs.
Category Detailed description status Transit Gateway status - Active: Running
- Creating: In progress
- Editing: In progress
- Deleting: In progress
- Error: An error occurred
Delete Transit Gateway Button to delete Transit Gateway resources Table. Transit Gateway status information and additional features
- Transit Gateway Details page displays status information and additional feature information, and consists of the Details, Connected VPC Management, Rules, Tags, Activity History tabs.
Detailed Information
On the Transit Gateway list page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Transit Gateway resource name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the Transit Gateway |
| Creation date and time | Transit Gateway creation time |
| Modifier | User who modified the Transit Gateway information |
| Modification date | Date and time the Transit Gateway information was modified |
| Transit Gateway name | Transit Gateway resource name |
| Use Uplink | Uplink information connected to the Transit Gateway
|
| Explanation | Description of the Transit Gateway
|
| Firewall connection status | Firewall connection management and status display
|
Connected VPC Management
Transit Gateway list page allows you to view the VPCs connected to the selected resource, and to add or delete them.
| Category | Detailed description |
|---|---|
| VPC list | Connected VPC list
|
Rule
On the Transit Gateway list page, you can view the rules attached to the selected resource, and add or delete them.
| Category | Detailed description |
|---|---|
| Rule List | Connected Rules List
|
Tag
On the Transit Gateway list page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Transit Gateway list page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Manage Transit Gateway integration services
You can request, modify, and cancel the Uplink and Firewall connection services required to use the Transit Gateway service.
To request the Transit Gateway integration service, follow the steps below.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- On the Transit Gateway List page, click the resource you want to delete. 3. Go to the Transit Gateway Details page.
- On the Transit Gateway Details page, click Linked Services (IGW, BM VPC), Quick Access to Line Request/Modification/Termination. 4. Navigate to the service request page.
- On the Service Request page, enter or select the required information in the mandatory input fields.
Input field Detailed description Title Enter the title of the service request - Example: TGW Uplink circuit request
Region Select the location of Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
service Select service category and service - Service Category: Networking
- Service: Transit Gateway
Task classification Select the type you want to request - TGW Uplink line request/modification/termination: After selecting the work type, enter detailed information in the service request category field
content Fill in the detailed items of the service request form - Service request type: manually enter one of Apply / Modify / Terminate
- Account name/ID: Enter the account name and ID
- Transit Gateway name/ID: Enter the created Transit Gateway name and ID
- Applicant information: Enter applicant’s email, phone number, etc.
- Service request task type: Choose and enter either Uplink line connection or BM VPC Firewall connection
- Firewall usage: Enter whether the firewall is used
Attachment If you have additional files you want to share, proceed with the upload - Attached files can be up to 5 files, each within 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files can be attached
Table. Linked Service Creation Request Items - On the service request page, click the Request button.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
- When the service request operation is completed, you can view the requested resources on the Transit Gateway Details page.
VPC connection for BareMetal
- VPC Peering does not support firewalls.
- When you cannot use a Security Group, such as with BareMetal, you can configure VPC Peering using a Transit Gateway firewall.
- However, in a peered BM VPC, communication via UpLink (external) is not possible, and it cannot be connected to a Transit Gateway together with other VM VPCs.
Managing VPC connections of the Transit Gateway
You can add or remove VPCs on a Transit Gateway.
Add VPC connection
To add a VPC attachment to a Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- Transit Gateway List page, click the resource you want to delete. 3. Navigate to the Transit Gateway Details page.
- On the Transit Gateway Details page, click the Connected VPC Management tab. 4. Navigate to the Connected VPC Management tab page.
- On the Connected VPC Management tab page, click the Add VPC Connection button. 5. The VPC connection addition window appears.
- In the Add VPC Connection window, select the VPC and click the Confirm button. 6. A notification confirmation window appears.
- Click +New in the list to create a VPC and select it.
- In the alert confirmation dialog, click the Confirm button. 7. Check whether a resource entry has been added in the VPC connection list.
Delete VPC connection
To delete a Transit Gateway’s VPC attachment, follow these steps.
- Click the All Services > Networking > VPC menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- On the Transit Gateway List page, click the resource you want to delete. 3. Go to the Transit Gateway Details page.
- On the Transit Gateway Details page, click the Connected VPC Management tab. 4. Navigate to the Connected VPC Management tab page.
- On the Connected VPC Management tab page, click the Delete button for the item you want to delete. 5. A notification confirmation window appears.
- In the alert dialog, click the Confirm button. 6. Verify whether the selected resource has been deleted from the VPC connection list.
Managing Transit Gateway rules
You can add or delete rules in the Transit Gateway.
Add rule
- You can add rules only when the Transit Gateway service status is Active.
- If the destination IP is entered incorrectly in the routing configuration, communication failures may occur. * Please double-check the destination IP information before creating the rule.
Transit Gateway must complete both routing rule registration and firewall rule registration to operate correctly.
- Register routing rule
- Rule 1: Register VPC - Transit Gateway rule
- Rule 2: VPC - Uplink rule registration (when connecting Uplink line)
- Register firewall rule
- Add a Transit Gateway firewall and add the firewall purpose (e.g., TGW Uplink, TGW BM VPC, etc.).
Next, select the firewall from the firewall product list and register the rule. (When adding a firewall purpose, default set to All/deny)
- Add a Transit Gateway firewall and add the firewall purpose (e.g., TGW Uplink, TGW BM VPC, etc.).
To add a rule to the Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- Transit Gateway List page, click the resource you want to delete. 3. Transit Gateway Details Navigate to the page.
- On the Transit Gateway Details page, click the Rules tab. 4. Go to the Rules tab page.
- On the Rule tab page, click the Add Rule button. 5. The rule addition window appears.
- In the rule addition window, enter the origin and destination, and click the Confirm button. 6. A notification confirmation dialog appears.
Category Detailed description Rule type Select type for adding Transit Gateway rule - Select from VPC-TGW rule, TGW-Uplink rule
Connected VPC name Select the connected VPC when choosing a VPC‑TGW rule origin When selecting a VPC‑TGW rule, the destination is automatically selected when configured. Destination Select rule destination - When selecting a VPC‑TGW rule, set to either VPC or TGW
- When selecting a TGW‑Uplink rule, set to either TGW or remote
- Cannot register if it duplicates an existing rule; can input up to the x.x.x.x/28 range
Destination IP range Enter the destination IP range to use Table. Rule addition input itemsCaution- VPC-TGW rule When entering, check the following items.
- When the destination is a VPC.
- It can be entered within the VPC IP range.
- It should be entered the same as the subnet range.
- 0.0.0.0/0 cannot be used as the destination IP range.
- When the destination is a Transit Gateway.
- Some IP ranges are reserved for management and cannot be used.
- The VPC IP address range cannot be entered.
- The destination IP range 0.0.0.0/0 can be entered only when the VPC’s Internet Gateway is not attached.
- When the destination is a VPC.
- TGW-Uplink Rule When entering, check the following items.
- When the destination is a Transit Gateway.
- You can enter values within the VPC IP address range connected to the Transit Gateway.
- 0.0.0.0/0 cannot be used as the destination IP range.
- When the destination is remote
- You cannot enter the VPC IP address range connected to the Transit Gateway.
- The destination IP range 0.0.0.0/0 can be entered only when the Transit Gateway does not have an Internet Gateway attached.
- D, E class IP ranges cannot be entered.
- When the destination is a Transit Gateway.
- In the alert dialog, click the Confirm button. 7. Check whether a resource entry has been added in the rule list.
Delete rule
- You can delete the rule only when the Transit Gateway service status is Active.
- If the rule status is Creating or Deleting, the rule cannot be deleted.
To delete a Transit Gateway rule, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Navigate to the Transit Gateway List page.
- On the Transit Gateway List page, click the resource you want to delete. 3. Go to the Transit Gateway Details page.
- On the Transit Gateway Details page, click the Rules tab. 4. Navigate to the Rules tab page.
- On the Rules tab page, click the Delete button of the item you want to delete. 5. A notification confirmation window appears.
- In the alert dialog, click the Confirm button. 6. Verify that the selected resource has been deleted from the rule list.
Managing Firewall Connections
You can attach or detach a firewall for use with the Transit Gateway.
Connect to Firewall
To add a Firewall connection to the Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- Transit Gateway List page, click the resource to which you will connect the Firewall. 3. Go to the Transit Gateway Details page.
- On the Transit Gateway Details page, click the Details tab. 4. Go to the Detailed Information tab page.
- On the Detailed Information tab page, click the Connect Firewall button. 5. A firewall connection confirmation window appears.
- In the Firewall connection confirmation window, click the Confirm button. 6. Check the connection status in the Firewall connection status item.
Add Firewall
After the Firwall connection is completed, you can add a Firewall.
To add a Firewall to a Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- Transit Gateway List page, click the resource where you want to add a Firewall. 3. Navigate to the Transit Gateway Details page.
- On the Transit Gateway Details page, click the Detailed Information tab. 4. Go to the Detailed Information tab page.
- On the Detailed Information tab page, click the Add button in the Firewall list. 5. The Firewall addition window appears.
- In the Firewall add dialog, select the purpose and click the Confirm button. 6. Check whether a resource item has been added to the Firewall list.
Delete Firewall
You can delete the firewall after the firewall connection is completed.
To delete a firewall from a Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- On the Transit Gateway List page, click the resource to delete the firewall. 3. Go to the Transit Gateway Details page.
- On the Transit Gateway Details page, click the Details tab. 4. Go to the Detailed Information tab page.
- Click the Delete button on the Detailed Information tab page of the Firewall list. 5. A notification confirmation window appears.
- In the alert dialog, click the Confirm button. 6. Check whether the resource entry has been removed from the Firewall list.
Disconnect Firewall
You can disconnect unused Firewall connections.
To detach the firewall from the Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- Transit Gateway list page, click the resource to detach the Firewall connection. 3. Navigate to the Transit Gateway Details page.
- On the Transit Gateway Details page, click the Details tab. 4. Navigate to the Detailed Information tab page.
- On the Detailed Information tab page, click the Disconnect Firewall button. 5. A notification confirmation window appears.
- In the alert dialog, click the Confirm button. 6. Check the disconnected status in the Firewall connection status item.
Terminate Transit Gateway
You can terminate unused Transit Gateways to reduce operating costs.
- You cannot terminate the service if the uplink connected to the Transit Gateway is in use or if a firewall is connected. * After completing the termination request for the connected resource, cancel the service.
- If VPC resources or rules are attached to the Transit Gateway, the service cannot be terminated. * Delete all linked resources and rules, then terminate the service.
- If the Transit Gateway service status is Creating or Deleting, the service cannot be terminated.
To terminate the Transit Gateway, follow these steps.
- All Services > Networking > VPC Click the menu. 1. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Transit Gateway menu. 2. Go to the Transit Gateway List page.
- On the Transit Gateway List page, click the resource you want to delete. 3. Go to the Transit Gateway Details page.
- On the Transit Gateway Detail page, click the Transit Gateway Delete button.
- After termination is complete, check whether the resource has been deleted from the Transit Gateway list.
Preliminary service
This is a service that must be installed in advance before creating this service. Please prepare by referring to the user guide provided in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | It is a service that provides an isolated virtual network in a cloud environment. |
5.1.2.10 - PrivateLink Service
Users can create the service by entering the required information for the PrivateLink Service and selecting detailed options through the Samsung Cloud Platform Console.
Creating a PrivateLink Service
You can create and use a PrivateLink Service in the Samsung Cloud Platform Console.
To create a PrivateLink Service, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the PrivateLink Service Create button. You will be taken to the PrivateLink Service Create page.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description PrivateLink Service name Required Enter the PrivateLink service name Approval method Required Select approval method for PrivateLink Service input - Automatic: Automatically approve when a PrivateLink Service connection request is received
- Manual: Manually approve after verification when a PrivateLink Service connection request is received
- The approval method cannot be changed after creation
High-speed data transfer Selection The default setting is disabled and not displayed in the Samsung Cloud Platform Console - To use high-speed data transfer, submit a service usage request via Support Center > Contact, and once processing is complete, it can be selected on the screen
VPC name Required Select the VPC to connect - Click + New to create a VPC and then select it
Subnet name Required Select the Subnet of the VPC to connect - Click + New to create a Subnet and then select it
PrivateLink Service IP Required Select the Subnet to connect and enter the PrivateLink Service IP - IP addresses already in use within the Subnet cannot be entered; the first and last IPs of the Subnet IP range cannot be used
Connection resource Required Select resources to connect to the chosen VPC - Load Balancer: Select the Load Balancer to connect (cannot select LB when using a Local subnet)
- IP: Enter the Compute resource IP of the selected VPC
Security Group Select Click the Select button to choose the Security Group to connect - Select up to 5
- If you do not select a Security Group, all connections will be blocked
explanation Select Enter description for PrivateLink Service Table. PrivateLink Service service information input items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description tag Select Add Tag - Up to 50 per resource can be added
- Add Tag button after clicking, input or select Key, Value values
Table. PrivateLink Service additional information input fields
- Enter or select the required information in the Service Information Input area.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- When creation is complete, check the created resource on the PrivateLink Service list page.
PrivateLink product is a service that provides an unidirectional private path (a type of tunnel). The PrivateLink product is used by creating a PrivateLink Service (exit) in the service provider account, creating a PrivateLink Endpoint (entry) in the user account, and then connecting to the PrivateLink Service.
The connection requirements for the PrivateLink product are as follows.
- When creating a PrivateLink Endpoint, you can connect only to the single specified PrivateLink Service per endpoint. (Only one pair of ingress and egress exists)
- Cannot attempt to establish a session to the PrivateLink Endpoint via the PrivateLink Service. (unidirectional)
- In the provider account, when creating a PrivateLink Service, a connection to a single IP is provided by selecting a single LB or by manual entry.
- In a user account, any client that the user account has permitted to access the PrivateLink Endpoint can use the PrivateLink Endpoint.
- It can be used in both General and Local Subnet.
View PrivateLink Service details
The PrivateLink Service allows you to view and edit the full list of resources and detailed information. PrivateLink Service Details page consists of Details, Connection Management, Tags, Activity Log tabs.
To view detailed information about the PrivateLink Service, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- From the Service Home page, click the PrivateLink Service menu. You will be taken to the PrivateLink Service list page.
- On the PrivateLink Service List page, click the resource for which you want to view details. You will be taken to the PrivateLink Service Details page.
- PrivateLink Service Details page displays status information and additional feature information, and consists of Details, Connection Management, Tags, Activity Log tabs.
Category Detailed description status PrivateLink Service status - Active: Running
- Creating: In progress
- Deleting: In progress
- Error: Error occurred
Delete PrivateLink Service Button to delete PrivateLink Service resources Table. PrivateLink Service status information and additional features
- PrivateLink Service Details page displays status information and additional feature information, and consists of Details, Connection Management, Tags, Activity Log tabs.
Detailed Information
On the PrivateLink Service List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | PrivateLink Service resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the PrivateLink Service |
| Creation date and time | PrivateLink Service creation timestamp |
| Editor | User who modified the PrivateLink Service information |
| Modification date and time | Date and time the PrivateLink Service information was modified |
| PrivateLink Service name | PrivateLink Service resource name |
| PrivateLink Service ID | PrivateLink Service ID information |
| connected resource | Connected resources of PrivateLink Service
|
| PrivateLink Service IP | PrivateLink Service IP address |
| VPC name | Connected VPC Information
|
| Subnet name | Connected Subnet information
|
| Port name | Port information of PrivateLink Service
|
| Security Group | Configured Security Group information
|
| Approval method | Approval method for the configured PrivateLink Service |
| High-speed data transmission | Whether to use high-speed data transfer for the configured PrivateLink Service |
| Explanation | Description of the PrivateLink Service
|
Connection Management
On the PrivateLink Service List page, you can view the connection information of the selected resource. You can review connection requests and approve or reject them.
| Category | Detailed description |
|---|---|
| PrivateLink Service List | PrivateLink Service connection list
|
tag
PrivateLink Service List page lets you view, add, modify, or delete tag information for the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
PrivateLink Service List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate PrivateLink Service
You can cancel unused PrivateLink Service to reduce operating costs.
After configuring the Private Endpoint to block or reject connections, delete the PrivateLink Service.
To cancel the PrivateLink Service, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- From the Service Home page, click the PrivateLink Service menu. You will be taken to the PrivateLink Service List page.
- On the PrivateLink Service List page, click the resource to delete. Go to the PrivateLink Service Details page.
- On the PrivateLink Service Details page, click the Delete PrivateLink Service button.
- When the termination is complete, check that the resource has been deleted from the PrivateLink Service list.
Preliminary Service
This is a service that must be installed in advance before creating this service. Please refer to the provided user guide and prepare accordingly.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | It is a service that provides an isolated virtual network in a cloud environment. |
| Networking | Load Balancer | It is a service that distributes server traffic load in a cloud environment. |
5.1.2.11 - PrivateLink Endpoint
Users can create the service by entering the required information for the PrivateLink Endpoint service and selecting detailed options through the Samsung Cloud Platform Console.
Creating a PrivateLink Endpoint
You can create and use a PrivateLink Endpoint service from the Samsung Cloud Platform Console.
To create a PrivateLink Endpoint, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Create PrivateLink Endpoint button. You will be taken to the Create PrivateLink Endpoint page.
- Enter or select the required information in the Service Information Input area.
Category RequiredDetailed description PrivateLink Endpoint name Required Enter the PrivateLink Endpoint name VPC name Required Select VPC to connect - Click + Create new to create a VPC and then select it
Subnet name Required Select the Subnet of the VPC to connect - Click + New to create a Subnet and then select it
PrivateLink Endpoint IP Required Select the Subnet to connect, then enter the PrivateLink Endpoint IP - IP addresses currently in use within the Subnet cannot be entered, and the first and last IPs of the Subnet IP range cannot be used
PrivateLink Endpoint ID Required Enter the PrivateLink Service ID to connect - Enter using letters and numbers, within 3 to 60 characters
- Before applying for the service, you need to verify the Service ID of the PrivateLink Service to connect; after creating the Endpoint, you must provide the Endpoint ID to the service provider
Security Group Select Click the Select button to choose the Security Group to connect - Select up to 5
- If no Security Group is selected, all connections are blocked
description Select Enter description for PrivateLink Endpoint Table. PrivateLink Endpoint service information input fields - Enter or select the required information in the Additional Information Input area.
Category RequiredDetailed description tag Selection Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key and Value values
Table. PrivateLink Endpoint additional information input fields
- Enter or select the required information in the Service Information Input area.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the PrivateLink Endpoint List page.
- To request a connection to a service provider via PrivateLink, you must go through an approval process.
- When applying for a service connection, you must verify the PrivateLink Service ID of the target in advance.
- Before applying for the service, an agreement on usage with the service provider must be completed.
- After the user creates a PrivateLink Endpoint, they must provide the Endpoint ID to the service provider. The service provider can verify the user’s Endpoint ID and promptly approve its use.
Check PrivateLink Endpoint details
PrivateLink Endpoint service allows you to view and edit the full list of resources and detailed information. PrivateLink Endpoint Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the PrivateLink Endpoint, follow these steps.
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the PrivateLink Endpoint menu on the Service Home page. You will be taken to the PrivateLink Endpoint List page.
- On the PrivateLink Endpoint List page, click the resource to view detailed information. You will be taken to the PrivateLink Endpoint Details page.
- PrivateLink Endpoint Details page displays status information and additional feature information, and consists of Details, Connection Management, Tags, Activity Log tabs.
Category Detailed description status PrivateLink Endpoint status - Requesting: connection request/awaiting approval, Cancel request button displayed
- Active: creation completed, operating
- Creating: in progress
- Deleting: in progress
- Disconnected: connection blocked
- Rejected: connection denied, Request approval again button displayed
- Error: error occurred
- Canceled: connection request canceled, Request approval again button displayed
Delete PrivateLink Endpoint Button to delete PrivateLink Endpoint resource Table. PrivateLink Endpoint status information and additional features
- PrivateLink Endpoint Details page displays status information and additional feature information, and consists of Details, Connection Management, Tags, Activity Log tabs.
Detailed Information
On the PrivateLink Endpoint List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | PrivateLink Endpoint resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the PrivateLink Endpoint |
| Creation date and time | PrivateLink Endpoint creation timestamp |
| Editor | User who modified the PrivateLink Endpoint information |
| Modification date and time | Date and time the PrivateLink Endpoint information was modified |
| PrivateLink Endpoint name | PrivateLink Endpoint resource name |
| PrivateLink Endpoint ID | PrivateLink Endpoint ID information |
| PrivateLink Service ID | Connected PrivateLink Service ID information |
| PrivateLink Endpoint IP | PrivateLink Endpoint IP address |
| VPC name | Information about the connected VPC |
| Subnet name | Connected Subnet information |
| Port name | Port information of the PrivateLink Endpoint
|
| Security Group | Configured Security Group information
|
| Explanation | Description of PrivateLink Endpoint
|
tag
PrivateLink Endpoint List page allows you to view, add, modify, or delete the tag information of the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the PrivateLink Endpoint List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate PrivateLink Endpoint
You can terminate unused PrivateLink Endpoints to reduce operating costs.
To terminate a PrivateLink Endpoint, follow these steps.
- All Services > Networking > VPC Click the menu. Go to the VPC’s Service Home page.
- Click the PrivateLink Endpoint menu on the Service Home page. You will be taken to the PrivateLink Endpoint List page.
- On the PrivateLink Endpoint List page, click the resource you want to delete. Go to the PrivateLink Endpoint Details page.
- On the PrivateLink Endpoint Details page, click the PrivateLink Endpoint Delete button.
- After termination is complete, check whether the resource has been deleted from the PrivateLink Endpoint list.
Pre-service
This service must be installed in advance before creating it. Please refer to the provided user guide and prepare accordingly.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | It is a service that provides an isolated virtual network in a cloud environment. |
5.1.2.12 - NAT Logging
To store NAT logs, first create a bucket in Object Storage for the logs and configure that bucket in the NAT Logging repository. Then, when you enable log storage in the NAT detail view, NAT logs will begin to be saved to the Object Storage bucket.
To store NAT logs, you need to configure the following steps in order.
- To store NAT logs, you can create a bucket in Object Storage or use an existing bucket. To create a bucket, refer to Object Storage 생성하기.
- To set the bucket for NAT Logging’s log repository, refer to NAT Logging 로그 저장소 사용하기.
- To set the log storage option to Enabled in the NAT detailed view, refer to Using NAT Log Storage.
Using NAT Logging Log Repository
To set NAT log storage to enabled, you must first configure the log repository in NAT Logging.
- Click the All Services > Management > Network Logging > NAT Logging menu. You will be taken to the NAT Logging List page.
- NAT Logging List page, click the top Log Storage Settings button. You will be taken to the Log Storage Settings popup.
- Log storage settings In the popup window, select the log storage bucket. When you select a bucket, the log storage path is displayed.
- Log storage settings In the popup window, after checking Log storage bucket and Log storage path, click the Confirm button.
- Notification After reviewing the message in the popup window, click the Confirm button.
NAT Logging list
If you configure the NAT Logging log storage bucket, the NAT Logging list will be displayed.
- Click the All Services > Management > Network Logging > NAT Logging menu. You will be taken to the NAT Logging List page.
Category requiredDetailed description Resource ID Required NAT resource ID Save target Required NAT resource name Save registration date and time Required NAT log repository registration timestamp Table. NAT Logging list items
Check NAT Logging content
Refer to the information below to check the saved Log.
Stored log example: 2024-10-11T11:19:03,accept,259,17,192.168.2.173,46937,192.168.0.53,53,100.100.14.52,26937
| Category | Explanation |
|---|---|
| 2024-10-11T11:19:03 | Log date and time (2024-10-11, 11:19:03) |
| accept | Action (deny / accept) |
| 259 | Firewall Rule ID (Policy ID) that generated the log |
| 17 | IP Protocol ID
|
| 192.168.2.173 | Source IP |
| 46937 | Departure Port |
| 192.168.0.53 | Destination IP |
| 53 | Destination Port |
| 100.100.14.52 | NAT-translated IP |
| 26937 | NAT-translated Port |
NAT Logging Do not use log storage
In NAT Logging, you can set the log repository to be unused.
- All Services > Management > Network Logging > NAT Logging Click the menu. You will be taken to the NAT Logging List page.
- On the NAT Logging List page, click the top Log Storage Settings button. It will open the Log Storage Settings popup.
- In the Log storage settings popup, select Log storage bucket as Not used, and click the Confirm button.
5.1.3 - API Reference
5.1.4 - CLI Reference
5.1.5 - Release Note
VPC
- Provide VPC IP range addition feature
- You can add a new IP range to the VPC for use.
- Provides Virtual IP functionality
- You can reserve a Virtual IP in a Subnet for use.
- Private NAT feature improvement
- You can also use Private NAT with Transit Gateway.
- You can connect internal Samsung Cloud Platform data to the SCP service via a private path between the VPC and the SCP service without exposing it to the internet.
- Add Transit Gateway feature
- Easily connect the customer’s network with the Samsung Cloud Platform network and serve as a connection hub for multiple VPCs within the cloud environment.
- Add VPC Peering feature
- You can perform IP communication over a 1:1 private route between VPCs.
- Add Private NAT feature
- You can use Direct Connect from compute resources within the VPC to map the customer’s IP and establish a connection.
- Add VPC functionality
- Provides an Endpoint (entry point) that allows access to the Samsung Cloud Platform via a private connection from external networks connected to the VPC.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- A feature to save NAT logs has been added.
- You can determine whether to retain NAT logs and store them in Object Storage.
- The VPC service that provides an isolated virtual network space has been launched.
- The VPC service that provides an isolated virtual network space has been launched.
5.2 - Security Group
5.2.1 - Overview
Service Overview
A Security Group is a virtual logical firewall that controls inbound/outbound traffic generated on virtual servers in Samsung Cloud Platform. The resources that can have a Security Group applied include Virtual Server, Database, Kubernetes Engine, etc. A Security Group is applied to the ports of the target resource, and multiple Security Groups can be applied depending on each resource’s characteristics.
When you first create a Security Group, it blocks all inbound and outbound traffic according to the default rule (Any/Deny).
Users can specify an IP address, port, and protocol to create inbound/outbound rules, and only traffic allowed by the created rules can access the target resources.
Component
The components that make up a Security Group are as follows.
| Component | Detailed description |
|---|---|
| Applicable target | Resources to which the Security Group is applied
|
| Security Group Rules | When a Security Group is first created, it blocks all inbound and outbound traffic according to the default rule (Any/Deny)
|
Constraints
The Security Groups of Samsung Cloud Platform have default quotas (limits) set. There is a maximum number of Security Groups that can be created and a maximum number of Security Group rules. The Samsung Cloud Platform Console is a place where you can view and manage quotas for Samsung Cloud Platform services and request quota increases for many resources.
| Category | Default quota | Detailed description |
|---|---|---|
| Security Group | 100 items | Number of default Security Groups that can be created per account |
| Number of Security Group rules | 100 items | Maximum number of default rules that can be created per Security Group |
| Security Group rule count > project | 1,000 items | Maximum number of default Security Group rules that can be created per account |
Preceding Service
Security Group has no preceding service.
5.2.2 - How-to guides
Users can create the service by entering the required information for the Security Group service and selecting detailed options through the Samsung Cloud Platform Console.
Create Security Group
You can create and use the Security Group service in the Samsung Cloud Platform Console.
To create a Security Group, follow these steps.
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- Click the Create Security Group button on the Service Home page. You will be taken to the Create Security Group page.
- Enter the required information in the Service Information Input area.
Category Required statusDetailed description Security Group name Required Security Group name to create - English letters, numbers, and special characters (
-) can be used, and up to 255 characters can be entered
- Duplicate Security Group names are allowed within the project
Whether to save logs Select Select whether to store Security Group logs - Enabled: Store logs
- Disabled: Do not store logs
- Click Security Group Logging List Shortcut to go to the Security Group Logging list page
Table. Security Group service information input items - English letters, numbers, and special characters (
- Enter the required information in the Service Information Input area.
To store Security Group logs, first create a bucket in Object Storage for the logs, and configure that bucket as the log repository in Security Group Logging.
- The log storage settings can be verified in Security Group Logging, and for more details, refer to Security Group Logging.
- If you configure a log repository, Object Storage charges for log storage will be applied.
* In the **Additional Information Input** area, enter or select the required information.
Category
Required
Detailed description
tag
Select
Add Tag- Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Explanation
Select
User additional description- Up to 255 characters allowed
Table. Security Group additional information input fields
- Check the input information and click the Create button.
- When creation is complete, check the created resources on the Security Group List page.
Check Security Group detailed information
On the Security Group menu’s Security Group List page, you can view and edit the full resource list and detailed information.
To view detailed information about a Security Group, follow these steps.
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- On the Service Home page, click the Security Group menu. You will be taken to the Security Group list page.
- On the Security Group List page, click the resource for which you want to view detailed information. You will be taken to the Security Group Details page.
- Security Group Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity History tabs.
| Category | Detailed description |
|---|---|
| Service status | Security Group status
|
| Service termination | Cancel service button |
Detailed Information
Security Group List lets you view detailed information of the selected resource and edit the information when needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation Date/Time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Security Group name | Resource Name |
| Security Group ID | Unique resource ID in the service |
| Number of Security Group rules | The rule quota and the number of rules currently in use for this Security Group |
| Security Group rule count/Account | Security Group rule quota for the account and the total number of rules in use across all Security Groups in the account |
| description | Additional description written by the user
|
| Whether to save logs | Security Group log storage option
|
| Applicable Service | The service type, service name, and status of the service to which this Security Group is applied |
Rule
Security Group list page lets you view the rule list of the selected resource and add or delete rules.
| Category | Detailed description |
|---|---|
| Excel download | Bulk rule entry Excel file download button |
| More | Additional Function Button
|
| Advanced Search | Rule Detail Search Button |
| Add rule | Add Rule button |
| direction | Traffic direction for servers with Security Group applied
|
| Rule ID | Unique ID value for the rule |
| Target address | Target address for communicating with a server that has a Security Group applied |
| Remote Security Group name | The Security Group resource name displayed when the target is set to a Security Group |
| Remote Security Group ID | Security Group ID displayed when the target is set to a Security Group |
| Service | Protocol and Port |
| Explanation | Additional description written by the user |
| Delete | Delete rule |
tag
Security Group List page lets you view, add, modify, or delete tag information for the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Security Group List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Security Group Resources
You can manage resources such as log storage settings and rule additions for a Security Group.
Using Log Storage
To store Security Group logs, first create a bucket in Object Storage for the logs, and then configure that bucket in the log repository of Security Group Logging.
- The log storage settings can be verified in Security Group Logging, and for more details, refer to Security Group Logging.
- If you configure a log repository, Object Storage charges will be applied for log storage.
To save Security Group logs, follow the steps below.
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- On the Service Home page, click the Security Group menu. You will be taken to the Security Group list page.
- On the Security Group List page, click the resource (Security Group name) for which you want to store logs. You will be taken to the Security Group Details page.
- Click the Edit icon of Log Save Status. You will be taken to the Log Save Status Edit popup window.
- Modify Log Saving Option In the popup window, select Use for the log repository, and click the Confirm button.
Disable log storage
To stop storing Security Group logs, follow these steps.
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- On the Service Home page, click the Security Group menu. You will be taken to the Security Group list page.
- On the Security Group List page, click the resource (Security Group name) that you do not want to log. You will be taken to the Security Group Details page.
- Click the Edit icon of Log Save Option. It navigates to the Log Save Option Edit popup.
- Modify Log Saving Option In the popup window, deselect Use for the log repository, and click the Confirm button.
- Notification Check the message in the popup window and click the OK button.
Add rule
To add a Security Group rule, follow the steps below.
Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
On the Service Home page, click the Security Group menu. You will be taken to the Security Group list page.
Security Group List page, click the resource (Security Group name) to which you want to add a rule. Navigate to the Security Group Details page.
On the Security Group Details page, click the Rules tab. You will be taken to the Rules tab page.
on the Rules tab, click the Add Rule button. You will be taken to the Add Rule popup.
Category RequiredDetailed description Target input method Required Configure rule remote type - CIDR: Set target address by directly entering IP
- Security Group: Set to target the created Security Group
Remote > Target address Required If CIDR is selected, you must enter the target IP address - Enter in CIDR (IP address/subnet mask) format
- using
,and-, you can input multiple addresses at once, up to 100.
- Enter ‘0.0.0.0/0’ to use the entire IP range (ANY).
- using
Remote > Security Group Required When Security Group is selected, a Security Group selection is required. type Required Select protocol type to apply the rule - Select destination port/Type: Select protocol type
- Internet Protocol: Enter protocol numbers, up to 100 can be entered
- All: Select the entire range for destination port/Type and protocol, meaning all ports for all protocols
Type > Protocol Required Select detailed protocol for the type - Select the desired protocol among TCP, UDP, and ICMP; input fields vary depending on the selected protocol
- When ICMP is selected in the protocol, you can set the ICMP Type
- Select a commonly used Type, such as Echo, from the values defined for ICMP Type
- Click the Add button to add an input value
- When TCP/UDP is selected in the protocol, you can choose allowed ports such as SSH, HTTP, etc.
- When entering manually, you can input values from 1 to 65,535, and you can enter up to 100 entries at once using commas (,) or ranges (-)
- Click the Add button to add an input value
- When Internet Protocol is selected in the type
1 ~ 254Enter a protocol number within 1 to 254
direction Required Target application criteria, traffic direction configuration - Inbound rule: External → Server
- Outbound rule: Server → External
Explanation Select Additional description provided by the user Table. Detailed items for adding Security Group rulesAfter reviewing the rules to be added, click the Confirm button.
Batch Create Rules
To add multiple Security Group rules at once, follow these steps.
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- From the Service Home page, click the Security Group menu. You will be taken to the Security Group list page.
- Security Group List page, click the resource (Security Group name) to which you want to add a rule. Security Group Details page will be displayed.
- On the Security Group Details page, click the Rules tab. You will be taken to the Rules tab page.
- Click the Excel Download button on the Rules tab. The bulk rule entry Excel file will be downloaded.
- Enter the rule information into the batch rule entry Excel file, then save it.
- More > Bulk Rule Input Click the button. Bulk Rule Input popup window opens.
- Batch Rule Input In the popup window, click Attach File, attach the Excel file you prepared, and click Upload File.
- You cannot upload the attached Excel file if its format differs from the registration form or if the file is encrypted.
- You can upload up to 100 batch registration rules at a time. If you exceed the maximum number of registration rules, the upload will not be allowed.
- If you exceed the maximum number of rules that can be registered in the Account, you cannot upload the file.
- Rule Confirmation Check the details in the popup window and click the Confirm button.
Delete rule
To delete a Security Group rule, follow these steps.
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- On the Service Home page, click the Security Group menu. You will be taken to the Security Group list page.
- Security Group List page, click the resource (Security Group name) for which you want to add a rule. Security Group Details page will be displayed.
- On the Security Group Details page, click the Rules tab. You will be taken to the Rules tab page.
- In the Rules tab, click the Delete button for the rule you want to delete.
Terminate Security Group
You can delete unused Security Groups.
To delete a Security Group, follow these steps.
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- Click the Security Group menu on the Service Home page. You will be taken to the Security Group List page.
- On the Security Group List page, select the resource (Security Group name) to terminate, and click the Terminate Service button.
- After termination is complete, check on the Security Group list page whether the resource has been deleted.
5.2.2.1 - Security Group Logging
To store Security Group logs, first create a bucket in Object Storage for log storage and configure that bucket in the Security Group Logging repository. Then, on the Security Group Details page, set up log storage, and the Security Group logs will be saved to the Object Storage bucket.
To save Security Group logs, follow these steps.
- To store Security Group logs, you can create a bucket in Object Storage or use an existing bucket. To create a bucket, refer to Object Storage 생성하기.
- To configure the bucket for the log repository of Security Group Logging, refer to Security Group Logging Log Repository Setup.
- In the Security Group detail view, to set log storage to Enabled, please refer to Security Group Enable Log Storage.
Security Group Logging Configure log storage usage
To set the log storage option of a Security Group to Enabled, you must first configure a log repository in Security Group Logging.
To enable the log repository for Security Group Logging, follow these steps.
- All Services > Management > Network Logging > Security Group Logging Click the menu. You will be taken to the Security Group Logging List page.
- On the Security Group Logging List page, click the Log Storage Settings button at the top. You will be taken to the Log Storage Settings popup.
- Log storage settings In the popup window, select the log storage bucket. When you select a bucket, the log storage path is displayed.
- Log storage settings In the popup window, after checking Log storage bucket and Log storage path, click the Confirm button.
- Notification After reviewing the message in the popup window, click the Confirm button.
Query Security Group Logging List
If you configure the log storage bucket for Security Group Logging, you can view the Security Group Logging list.
To view the Security Group Logging list, follow these steps.
- Click the All Services > Management > Network Logging > Security Group Logging menu. Navigate to the Security Group Logging List page.
- Security Group Logging List page, verify the resources in use and the log storage targets.
Category Detailed description Resource ID Security Group ID Save target Security Group name Save registration date and time Security Group log storage registration timestamp Table. Security Group Logging list itemsReferenceAfter configuring the log repository for Security Group Logging, you must set the log storage option to Enabled in the Security Group detail view for logging to begin. For more details, see Security Group Log Storage Usage.
Security Group Logging Check detailed information
The stored logs have different detailed information depending on the protocol. Refer to the information below to view the details.
TCP / UDP
Example of stored log: 2024-10-11T02:18:39,drop,to-lport: tcp,198.19.65.2,6443,192.168.22.131,20427
| Category | Explanation |
|---|---|
| 2024-10-11T02:18:39 | Log date and time (2024-10-11, 02:18:39) |
| drop | Action (drop / allow) |
| to-lport | Direction
|
| tcp | Protocol (tcp / udp / icmp / ip) |
| 192.168.65.2 | Source IP |
| 6443 | Departure Port |
| 192.168.22.131 | Destination IP |
| 20427 | Destination Port |
ICMP
Saved log example: 2024-10-11T02:18:39,allow,to-lport: icmp,192.168.65.2,192.168.22.131,8
| Category | description |
|---|---|
| 2024-10-11T02:18:39 | Log date and time (2024-10-11, 02:18:39) |
| to-lport | Direction
|
| allow | Action (drop / allow) |
| tcp | Protocol (tcp / udp / icmp / ip) |
| 192.168.65.2 | Source IP |
| 192.168.22.131 | Destination IP |
| 8 | ICMP type ID |
IP
Stored log example: 2024-10-11T02:18:39,deny,ip,192.168.65.2,192.168.22.131,103
| Category | Explanation |
|---|---|
| 2024-10-11T02:18:39 | Log date and time (2024-10-11, 02:18:39) |
| deny | Action (drop / allow) |
| ip | Protocol |
| 192.168.65.2 | Source IP |
| 192.168.22.131 | Destination IP |
| 103 | IP Protocol ID
|
Security Group Logging Disable Log Storage Configuration
In Security Group Logging, you can set the log storage to unused.
To disable the log repository for Security Group Logging, follow these steps.
- Click the All Services > Management > Network Logging > Security Group Logging menu. You will be taken to the Security Group Logging List page.
- Security Group Logging List page, click the top Log Storage Settings icon. You will be taken to the Log Storage Settings popup window.
- Log storage configuration in the popup window, select log storage bucket as Not used, and click the Confirm button.
- Log storage settings can be changed when no log storage target is configured.
- To change the log storage bucket, first set it to disabled. Then you can modify it by re-enabling it.
5.2.2.2 - Migration Rules
Users can retrieve rules created in the V1 environment of the Samsung Cloud Platform Console and apply them to the V2 service.
Getting Security Group Rules
You can import rules created in the V1 environment of the Samsung Cloud Platform Console and migrate them to the V2 service for use.
- When a Security Group rule is migrated to the V2 environment using the Migration feature, the Migration label appears before its name.
- If a Security Group rule description exceeds 255 characters, part of the description will be omitted.
- Each Security Group can have up to 200 rules, and any rule that exceeds the maximum allowable quantity will not be registered.
To retrieve the Security Group rules of V1, follow these steps.
All Services > Networking > Security Group menu, click it. 1. Navigate to the Service Home page of the Security Group.
On the Service Home page, click the Migration Rules menu. 2. Go to the Migration Rules page.
Select the rule information to retrieve from the Migration Rules page and click Done.
Category Detailed description Original rule environment SCP v1 (Vmware) Auto-select Applicable target Select the Security Group list in the account to apply the transferred rule Get rules Click the Attach File button to upload the decrypted Security Group rule file - After decrypting and saving the rule file extracted from the original environment, upload it
Rule List View uploaded Security Group rule file details - Delete: Delete selected rule
- Edit: Modify selected rule information, see [Edit transferred Security Group rule](#이관할-Security Group-규칙-수정하기) for details
Table. Migration Rules detailed itemsAfter the Security Group rule transfer request is completed, verify that the transfer item has been added to the Security Group list.
Modify the Security Group rules to be transferred
You can edit each item when retrieving rules created in the V1 environment of the Samsung Cloud Platform Console.
To modify the Security Group rules to be imported from V1, follow these steps.
All Services > Networking > Security Group Click the menu. 1. Navigate to the Service Home page of the Security Group.
On the Service Home page, click the Migration Rules menu. 2. Go to the Migration Rules page.
In the rule import section, click Attach File to upload the Security Group rule file.
In the rule list, click Edit for the rule item you want to modify.
Category Required or notDetailed description Target Input Method Required Remote rule type setting - CIDR: Set the target address by entering the IP directly
- Security Group: Set to the created Security Group
Remote > Target address Essential If CIDR is selected, you need to enter the target IP address - Enter in CIDR (IP address/subnet mask) format
, usingand-you can input multiple addresses up to 100 at once.
- To use the entire IP range (ANY), enter ‘0.0.0.0/0’
Remote > Security Group Essential When Security Group is selected, a Security Group must be chosen. type Required Select protocol type to which the rule will be applied - Select destination port/Type: Select protocol type
- Internet Protocol: Enter protocol numbers, up to 100 entries allowed
- All: Select destination port/Type and protocol for the entire range, meaning all ports for all protocols
Type > Protocol Required Select detailed protocol for the type - Select the desired protocol among TCP, UDP, and ICMP; input fields vary depending on the selected protocol
- When ICMP is selected in the protocol, you can set the ICMP Type
- Select a commonly used Type, such as Echo, from the values defined for ICMP Type
- Click the Add button to add an input value
- When TCP/UDP is selected in the protocol, you can choose allowed ports such as SSH, HTTP, etc.
- When entering manually, you can input values from 1 to 65,535, and you can enter up to 100 entries at once using commas (,) or ranges (-)
- Click the Add button to add an input value
- When Internet Protocol is selected in the type
1 ~ 254Enter a protocol number within the range
direction Essential Set the traffic direction for the applicable target - Inbound rule: external → server
- Outbound rule: server → external
Explanation Selection Additional description written by the user Table. Detailed items of the Security Group rule edit windowWhen the rule information edit is complete, click Confirm in the edit window.
Review the edited rule information and click Done.
5.2.3 - API Reference
5.2.4 - CLI Reference
5.2.5 - Release Note
Security Group
- For user convenience, a Migration Rules page has been added that allows you to import Security Group rules created in the V1 environment and apply them to the V2 service.
- When adding a Security Group rule, multiple service ports can be selected
- Improved the console to allow selecting multiple service ports when adding a rule.
- Add Security Group rule input method
- A feature allowing IP protocol input has been added.
- A feature to select Well-known protocols has been added.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- Improved to allow entering multiple IPs when adding Security Group rules.
- A feature to store Security Group logs has been added.
- You can decide whether to store Security Group logs and store the logs in Object Storage.
- The Security Group service, which provides virtual firewall functionality for instance resources, has been launched.
- You can control inbound and outbound traffic generated from instance resources through the Security Group service.
- The Security Group service, which provides virtual firewall functionality for instance resources, has been launched.
- You can control inbound and outbound traffic generated from instance resources through the Security Group service.
5.3 - Load Balancer
5.3.1 - Overview
Service Overview
The Load Balancer (LB) service of Samsung Cloud Platform automatically distributes traffic to available servers when there is an unpredictable traffic surge or server failure, ensuring the stability and continuity of customer services.
A Load Balancer serves as the service endpoint provided to clients, is deployed in a VPC subnet according to the service type (L4 / L7), and you can configure multiple services by adding listeners to the created Load Balancer.
The Listener receives client requests through the service port and processes traffic according to routing rules. L4 supports TCP / UDP / TLS protocols, and L7 supports HTTP / HTTPS protocols; in L7, you can specify an LB server group for each routing condition or set a redirect response for the request URL.
The LB server group forwards requests received by the Listener to specific servers based on load balancing and health checks. The servers receive client requests from the Load Balancer’s Source NAT IP through the ports configured for the members, and the server status is periodically monitored by the Load Balancer’s health check IP.
LB health check defines the member health check method registered in the LB server group. You can select a default LB health check resource provided for the LB server group, or create a new one to configure monitoring suitable for the application.
Features
- Various load balancing methods: Round Robin, Least Connection, IP Hash, etc., are provided.
- SSL Authentication Encryption and Offloading: Supports SSL offloading and allows selection of encryption level.
- Enhanced Security: Use a firewall to manage Load Balancer communication and view connection logs by storing logs.
Service Architecture Diagram
Provided features
- Load Balancer: Select the service type and configure the IP to be used by the Load Balancer.
- Listener: Set the protocol, port, and routing rules. You can add multiple Listeners to a single Load Balancer.
- LB server group: Sets the load balancing method. LB server group can be attached to a single Load Balancer.
- Member: Select the server to add to the LB server group. You can choose Virtual Server or Bare Metal Server resources created in the same VPC as the Load Balancer, or enter an IP address directly.
- LB health check: Sets the member health check method. LB health checks can be registered and used across multiple LB server groups.
Component
A Load Balancer consists of a Load Balancer (Listener), LB server group (member), and LB health check.
Load Balancer
The components that make up a Load Balancer are as follows. By configuring each component, you can set up load balancing suitable for the customer’s workload.
| Component | Detailed description |
|---|---|
| Service Category | Load Balancer service type
|
| Service Sunbet | Assign the Service IP, Source NAT IP, and Health Check IP required for the Load Balancer in the Subnet range of the VPC Subnet
|
| Service IP | Service IP that the client accesses |
| Source NAT IP | IP used to forward server traffic in the Load Balancer |
| Health check IP | IP used for health checks in the Load Balancer |
| Listener | Resources connected to the Load Balancer
|
LB server group
The elements that make up an LB server group are as follows. Traffic is delivered to members of the LB server group according to the settings of each component.
| Component | Detailed description |
|---|---|
| Protocol | LB server group forwarding protocol |
| Load balancing | Traffic distribution method
|
| LB health check | Member health check method
|
| Member | Server that processes client requests
|
LB health check
The elements that make up the LB health check are as follows. Member health checks are performed according to the settings of each component.
| Component | Detailed description |
|---|---|
| Protocol | Health check protocol |
| Health check port | Port used for health check |
| Period | Health check execution interval |
| Waiting time | Server response latency for health check |
| Detection count | Criteria for determining member health check status (Healthy / Unhealthy) |
Constraints
The Load Balancer of Samsung Cloud Platform has a default quota, which limits the number of Load Balancers, Listeners, LB server groups, and members that can be created. You can manage current usage through the Console and request additional quota for items that can be expanded.
| Item | Default quota | Detailed description |
|---|---|---|
| LOAD_BALANCER.SERVICE_SUBNET.DEFAULT.COUNT | 3 | Number of Service Subnets per VPC that can create a Load Balancer |
| LOAD_BALANCER.DEFAULT.COUNT | 50 | Number of Load Balancers created per Region |
| LOAD_BALANCER.LISTENER.DEFAULT.COUNT | 1000 | Number of Listeners created per Region |
| LOAD_BALANCER.SERVER_GROUP.DEFAULT.COUNT | 1000 | Number of LB server groups created per region |
| LOAD_BALANCER.MEMBER.DEFAULT.COUNT | 1000 | Number of members that can be registered to the entire LB server group per region |
| LOAD_BALANCER.HEALTH_CHECK.DEFAULT.COUNT | 500 | Number of LB health checks created per region |
Preliminary Service
This is a list of services that must be pre-configured before creating a Load Balancer service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
5.3.1.1 - ServiceWatch metric
The Load Balancer sends metrics to ServiceWatch. The metrics provided by basic monitoring are data collected at 5‑minute intervals.
Basic Metrics
The following are the default metrics for the Load Balancer namespace.
The indicators whose names are displayed in bold text below are the key metrics selected from the basic metrics provided by Load Balancer. Key metrics are used to build the service dashboards that are automatically created for each service in ServiceWatch.
Each metric provides guidance in the user guide on which statistical values are meaningful when querying that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using primary statistical values.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| LB Status | Load Balancer status | - | - |
| LB Total Connections | LB cumulative connection count | Count |
|
| LB Total L4 Connections | Cumulative L4 connection count | Count |
|
| LB Total L7 Connections | Cumulative L7 connection count | Count |
|
| LB Total SSL Connections | Cumulative SSL connection count | Count |
|
| LB Total TCP Connections | Cumulative TCP connection count | Count |
|
| LB Current Connections | Current number of active connections | Count |
|
| LB Current SSL Connections | Current SSL connection count | Count |
|
| LB Peak Connections | LB maximum connections | Count |
|
| LB Total Requests | LB cumulative request count | Count |
|
| LB Current Requests | LB current request count | Count |
|
| LB Connection Rate (CPS) | Number of new inbound connections | Count |
|
| LB Forward Bytes | Cumulative bytes transferred from the LB to the server | Bytes |
|
| LB Forward Bytes (Delta) | Cumulative bytes (Delta) delivered from LB to server | Bytes |
|
| LB Forward Packets | Cumulative packets delivered from the LB to the server | Count |
|
| LB Forward Packets (Delta) | Cumulative packets (Delta) delivered from the LB to the server | Count |
|
| LB Reverse Bytes | Cumulative packets delivered from LB to the server | Bytes |
|
| LB Reverse Bytes (Delta) | Cumulative bytes (Delta) received from the server | Bytes |
|
| LB Reverse Packets | Cumulative packets received from the server | Count |
|
| LB Reverse Packets (Delta) | Cumulative packets (Delta) received from the server | Count |
|
| LB Current Responses | LB current response count | Count |
|
| LB Total Success Responses | Cumulative successful response count | Count |
|
| LB Last Response Time | LB last response time | Milliseconds |
|
| LB Fastest Response Time | LB shortest response time | Milliseconds |
|
| LB Slowest Response Time | LB maximum response time | Milliseconds |
|
| LB Total Failure Actions | Number of failures handled in LB | Count |
|
| Listener Status | Listener status | Count |
|
| Listener Total Connections | Listener cumulative connection count | Count |
|
| Listener Total L4 Connections | Cumulative L4 connection count | Count |
|
| Listener Total L7 Connections | Cumulative L7 connection count | Count |
|
| Listener Total SSL Connections | Cumulative SSL connection count | Count |
|
| Listener Total TCP Connections | Cumulative TCP connection count | Count |
|
| Listener Current Connections | Current number of active connections | Count |
|
| Listener Current SSL Connections | Current SSL connection count | Count |
|
| Listener Peak Connections | Maximum number of connections for the listener | Count |
|
| Listener Current Requests | Listener current request count | Count |
|
| Listener Total Requests | Listener cumulative request count | Count |
|
| Listener Connection Rate (CPS) | Number of new inbound connections | Count |
|
| Listener Forward Bytes | Cumulative bytes transferred from the Listener to the server | Bytes |
|
| Listener Forward Bytes (Delta) | Cumulative bytes (Delta) transmitted from the Listener to the server | Bytes |
|
| Listener Forward Packets | Cumulative packets transmitted from the Listener to the server | Count |
|
| Listener Forward Packets (Delta) | Cumulative packets (Delta) transmitted from the Listener to the server | Count |
|
| Listener Reverse Bytes | Cumulative bytes received from the server | Bytes |
|
| Listener Reverse Bytes (Delta) | Cumulative bytes (Delta) received from the server | Bytes |
|
| Listener Reverse Packets | Cumulative packets received from the server | Count |
|
| Listener Reverse Packets (Delta) | Cumulative packets (Delta) received from the server | Count |
|
| Listener Current Responses | Listener current response count | Count |
|
| Listener Total Success Responses | Cumulative successful response count | Count |
|
| Listener Last Response Time | Listener last response time | Milliseconds |
|
| Listener Fastest Response Time | Listener minimum response time | Milliseconds |
|
| Listener Slowest Response Time | Listener maximum response time | Milliseconds |
|
| Listener Total Failure Actions | Number of failures processed in the Listener | Count |
|
| ServerGroup Status | LB server group status | Count |
|
| ServerGroup Request Count | Cumulative request count for LB server group | Count |
|
| ServerGroup Response Count | LB server group cumulative response count | Count |
|
| ServerGroup 2xx Response Count | Number of HTTP 2xx responses | Count |
|
| ServerGroup 3xx Response Count | Number of HTTP 3xx responses | Count |
|
| ServerGroup 4xx Response Count | Number of HTTP 4xx responses | Count |
|
| ServerGroup 5xx Response Count | Number of HTTP 5xx responses | Count |
|
| ServerGroup Healthy Member Count | Number of healthy members | Count |
|
| ServerGroup Unhealthy Member Count | Health check abnormal member count | Count |
|
| ServerGroup Peak Connections | Maximum connections for LB server group | Count |
|
5.3.2 - How-to guides
Users can create a service by entering the required Load Balancer information and selecting detailed options through the Samsung Cloud Platform Console.
Create Load Balancer
You can create and use a Load Balancer service from the Samsung Cloud Platform Console.
To create a Load Balancer, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the Create Load Balancer button. You will be taken to the Create Load Balancer page.
- On the Load Balancer Creation page, enter the information required to create the service and select detailed options.
- In the Service Information Input area, enter or select the required information.
| Category | Required status | Detailed description |
|---|---|---|
| Load Balancer name | Required | Load Balancer resource name
|
| Service Category | Required | Load Balancer service type
|
| VPC name | Required | VPC where the Load Balancer will be created
|
| Service Subnet name | Required | VPC Subnet where the Load Balancer will be created
|
| Service IP | Select | Load Balancer’s service IP
|
| Public NAT IP | Select | Select the Public NAT IP to use in the Load Balancer when allowing service access from external (Internet) sources
|
| Source NAT IP | Selection | IP used for member communication in the Load Balancer
|
| Health check IP | Selection | IP to be used for health checks in the Load Balancer
|
| Use firewall | Select | Set whether to use the firewall
|
| Firewall log storage | Select | Select whether to store Firewall logs
|
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description description Select Enter resource description tag Select Add tags - Up to 50 tags can be added per resource
Table. Load Balancer additional information input fields
- Check the created service information and the estimated billing amount, then click the Create button.
- After creation is complete, check the created resources on the Load Balancer List page.guide
- Load Balancer service does not provide access control for Service IP and service ports.
- When creating a Load Balancer, select Use Firewall to manage communication between the client and the Load Balancer, and between the Load Balancer and members with Firewall rules, and we recommend using Save Firewall Logs to store access logs.
- When creating a service and enabling the Firewall log storage feature, you must configure the log storage first. If the log storage is not configured, you cannot create a Load Balancer service.
CautionWhen using a firewall, you must add rules required for Load Balancer communication. Register the rules, paying attention to the direction for each purpose.
- If you do not add a rule, the Load Balancer service will not operate correctly.
Purpose Source IP Destination IP Protocol Destination Port/Type direction Client → LB connection Client IP LB Service IP Listener protocol Listener service port Outbound LB → Member connection LB Source NAT IP LB server group member IP LB server group protocol Member port Inbound LB → Member health check LB health check IP LB server group member IP Health check protocol Health check port - When the health check port and member port differ, register the member port
Inbound Figures and tables. Add Load Balancer firewall rule - Load Balancer service does not provide access control for Service IP and service ports.
- After creation is complete, check the created resources on the Load Balancer List page.
Check Load Balancer detailed information
The Load Balancer service can be viewed and edited for the resource list and detailed information in the Load Balancer menu. The Load Balancer Details page consists of Details, Connected Resources, Tags, Activity Log tabs.
Follow these steps to view detailed information about the Load Balancer service.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- From the Service Home page, click the Load Balancer menu. You will be taken to the Load Balancer list page.
- Load Balancer List page, click the resource to view its details. You will be taken to the Load Balancer Details page.
- Load Balancer Details page displays status information and additional feature information, and consists of Details, Connected Resources, Tags, Activity History tabs.
Category Detailed description status Load Balancer resource status - Active: Service is operating normally
- Deleting: Service termination request is being processed
- Creating: Service creation request is being processed
- Error: Unable to determine current status due to internal error
- Editing: Service modification request is being processed
Service termination Delete Load Balancer resource Table. Load Balancer status information and additional feature items
- Load Balancer Details page displays status information and additional feature information, and consists of Details, Connected Resources, Tags, Activity History tabs.
Detailed Information
In the Detailed Information tab, you can view the detailed information of the resource selected from the Load Balancer list and edit the necessary information.
| Category | Detailed description |
|---|---|
| Service | service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Creation date | Service creation date and time |
| Modification date and time | Service modification date and time |
| constructor | Service creation request user |
| Editor | User requesting service modification |
| Load Balancer name | Load Balancer name |
| Service IP | Load Balancer’s Service IP (used for communication between client and Load Balancer)
|
| Service Category | Load Balancer service type |
| Source NAT IP | Load Balancer’s Source NAT IP (used for communication between Load Balancer and servers)
|
| VPC name | VPC resource name where the Load Balancer is created
|
| Service Subnet name | Subnet resource name where the Load Balancer was created
|
| Public NAT IP | Load Balancer’s Public NAT IP (used when configuring internet service)
|
| Private NAT IP | Load Balancer’s Private NAT IP
|
| Health check IP | Load Balancer Health Check IP (used when performing health checks on LB server group members)
|
| Explanation | Additional information or description about Load Balancer
|
| Firewall name | Firewall resource name connected to Load Balancer
|
Connected resources
Connected Resources tab lets you view the list of Listeners attached to the Load Balancer, and you can create or delete Listeners.
- In the Connected Resources tab, selecting the Listener item takes you to the Listener Details page where you can view, edit, and delete the detailed information.
- On the Listener Details page, clicking the Edit icon lets you modify the information.
| Category | Detailed description | |
|---|---|---|
| Create Listener | Create Listener button | |
| Listener name | Listener resource name | |
| Routing rules | Routing rules attached to the Listener
| |
| Protocol | Protocol that the Listener receives | |
| Port | Port that the Listener receives | |
| Creation Date/Time | Listener creation time | |
| Delete | Delete Listener button |
tag
Load Balancer List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Work History tab allows you to view the work history of the selected resource.
| Category | Detailed description |
|---|---|
| Work log | Task execution details |
| Work Date/Time | Task execution date and time |
| Resource Type | Resource Type |
| Resource name | Load Balancer name |
| Operation result | Task execution result (success/failure) |
| Operator Information | User information of the performed operation |
Load Balancer Resource Management
You can manage resources such as creating and deleting Load Balancer listeners.
Create Listener
Create a Listener on the Load Balancer to receive client requests and handle traffic according to the Listener configuration.
The protocol that receives client requests varies depending on the Load Balancer service type.
- L4 Load Balancer case: TLS, TCP, UDP protocols
- When using an L7 Load Balancer: HTTP, HTTPS protocols
Creating a Listener in L4 Load Balancer
To create a Listener in the L4 Load Balancer, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the Load Balancer menu. You will be taken to the Load Balancer list page.
- Load Balancer List page, click the Load Balancer resource to create a Listener. You will be taken to the Load Balancer Details page.
- On the Load Balancer Details page, click the Connected Resources tab. You will be taken to the Connected Resources tab page.
- On the Connected Resources tab page, click the Create Listener button in the upper right.
- Enter or select the required information in the Service Information Input area.
- The information that can be entered varies depending on the protocol.
| Category | Required | Detailed description |
|---|---|---|
| Load Balancer | Required | Name of the Load Balancer resource where the Listener will be created |
| Listener name | Required | Listener resource name |
| Protocol | Required | Select Listener receive protocol
|
| service port | Required | Enter Listener receiving port
|
| Routing rules | Required | Routing rule configuration
|
| Session retention time | Required | Client session keep-alive time setting
|
| Proxy Protocol | Select | Set whether to add client IP information to the proxy protocol header (when using TCP protocol)
|
| Persistence | Required | Select Sticky Session method (set when using TCP, TLS protocols)
|
| SSL certificate | Select | Select default encryption certificate and security level (when using the TLS protocol)
|
| Server SSL security level | Required | Select security level when configuring End-to-End SSL (TLS protocol settings)
|
- In the Additional Information Input area, enter or select the required information.
| Category | Required | Detailed description |
|---|---|---|
| Explanation | Select | Enter resource description |
| tag | Select | Add tags
|
- Verify the created service information and click the Create button.
- When creation is complete, verify the created resource on the Load Balancer Details page’s Connected Resources tab.
Creating a Listener in L7 Load Balancer
Follow these steps to create a Listener in an L7 Load Balancer.
- Click the All Services > Networking > Load Balancer menu. Go to the Load Balancer’s Service Home page.
- On the Service Home page, click the Load Balancer menu. You will be taken to the Load Balancer list page.
- On the Load Balancer List page, click the Load Balancer resource for which you want to create a Listener. You will be taken to the Load Balancer Details page.
- Click the Connected Resources tab on the Load Balancer Details page. You will be taken to the Connected Resources tab page.
- On the Connected Resources tab page, click the Create Listener button in the upper right.
- In the Service Information Input area, enter or select the required information.
- The information that can be entered varies depending on the protocol.
| Category | Required status | Detailed description |
|---|---|---|
| Load Balancer | Required | Load Balancer resource name where the Listener is created |
| Listener name | Required | Listener resource name |
| Protocol | Required | Select Listener reception protocol
|
| service port | Required | Listener receive port input
|
| Routing Rules > Routing Action | Required | Select routing processing method
|
| Routing Rules > Routing Conditions | Required | When the routing action is LB server group forwarding, set the LB server group per routing condition
|
| Persistence | Selection | Select Sticky Session mode (set when the routing action is LB server group forwarding)
|
| Listener timeout setting > Session keep-alive time | Select | HTTP connection keep-alive time setting
|
| Listener timeout setting > HTTP connection timeout | Select | Set HTTP response timeout
|
| X-Forwarded-For | Select | Set whether to insert client IP information
|
| X-Forwarded-Proto | Select | Set whether to insert client request protocol information
|
| X-Forwarded-Port | Select | Set whether to insert client request port information
|
| HTTP 2.0 | Select | Set whether to use HTTP/2 for client‑server connections |
| SSL certificate | Select | Select encryption certificate and security level (HTTPS protocol usage)
|
| Server SSL security level | Required | Select security level when configuring End-to-End SSL (HTTPSS protocol setting)
|
The routing rule’s URL path matching method is Starts with(prefix match).
- It checks whether the entered URL path starts with a specific string, and if the beginning matches, the routing rule is applied.
- Example: when the entered URL is
/api/- Matching URL:
/api/users, /api/v1/login, /api/images/logo.png - Unmatched URL:
/auth/api/, /API/users
- Matching URL:
- In the Additional Information Input area, enter or select the required information.
| Category | Required status | Detailed description |
|---|---|---|
| Explanation | Select | Enter resource description |
| tag | Select | Add tags
|
- Verify the created service information and click the Create button.
- When creation is complete, verify the created resource on the Load Balancer Details page’s Connected Resources tab.
SSL security level support items
The list of TLS versions and Cipher Suites supported by the Listener for each SSL security level is as follows.
| Security level | TLS version | Cipher Suite (encryption algorithm) |
|---|---|---|
| High | TLS 1.3 | TLS13_AES_128_GCM_SHA256 TLS13_AES_256_GCM_SHA384 TLS13_CHACHA20_POLY1305_SHA256 |
| Normal/Low | Normal: TLS 1.3, 1.2 Low: TLS 1.3, 1.2, 1.1 | TLS13_AES_128_GCM_SHA256 TLS13_AES_256_GCM_SHA384 TLS13_CHACHA20_POLY1305_SHA256 RC4-MD5 RC4-SHA DES-CBC3-SHA DHE-RSA-AES128-GCM-SHA256 DHE-RSA-AES256-GCM-SHA384 DHE-RSA-CHACHA20-PLY1305 ECDHE-RSA-AES128-SHA ECDHE-RSA-AES256-SHA ECDHE-RSA-AES128-SHA256 ECDHE-RSA-AES256-SHA384 ECDHE-RSA-CHACHA20-POLY135 ECDHE-ECDSA-AES128-SHA ECDHE-ECDSA-AES256-SHA ECDHE-ECDSA-AES128-SHA256 ECDHE-ECDSA-AES256-SHA384 ECDHE-ECDSA-AES128-GCM-SHA256 ECDHE-ECDSA-AES256-GCM-SHA384 ECDHE-ECDSA-CHACHA20-POLY1305 |
Check Listener detailed information
On the Connected Resources tab of the Load Balancer Details page, you can select a Listener to view and edit its detailed information.
To view the Listener’s detailed information, follow these steps.
- Click the All Services > Networking > Load Balancer menu. Navigate to the Load Balancer’s Service Home page.
- On the Service Home page, click the Load Balancer menu. You will be taken to the Load Balancer List page.
- On the Load Balancer List page, click the resource whose details you want to view. You will be taken to the Load Balancer Details page.
- On the Load Balancer Details page, click the Connected Resources tab.
- Click the Listener to view detailed information from the list of connected resources. It navigates to the Listener Details page.
- Listener Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
| Category | Detailed description |
|---|---|
| status | Listener status
|
| Delete Listener | Delete Listener |
Detailed Information
Detailed Information tab allows you to view the Listener’s detailed information and edit the necessary details. Detailed information varies depending on the Load Balancer in use.
L4 Load Balancer Detailed Information
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User requesting listener creation |
| Creation Date/Time | Listener creation time |
| Editor | User requesting listener modification |
| Modification date | Listener modification timestamp |
| Listener name | Listener name |
| Protocol | Listener usage protocol |
| Port | Listener port |
| Session retention time | Client session retention time
|
| Proxy Protocol | Whether to insert client IP information
|
| Persistence | Use of sticky session
|
| Routing rules | Routing action and LB server group information
|
| SSL certificate | Default certificate and SSL security level, expiration date and time information
|
| SNI certificate | SNI Certificate Details
|
| Server SSL security level | Whether server connection is encrypted
|
| Explanation | Additional information about the Listener
|
L7 Load Balancer Detailed Information
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User requesting listener creation |
| Creation Date/Time | Listener creation time |
| Editor | User requesting listener modification |
| Modification date | Listener modification timestamp |
| Listener name | Listener name |
| Protocol | Listener usage protocol |
| Port | Listener port |
| Session retention time | HTTP connection keep-alive time
|
| Client connection keep-alive time | HTTP client connection keep-alive timeout
|
| Server response latency | HTTP server response wait timeout
|
| X-Forwarded-For | Whether to insert client IP information
|
| X-Forwarded-Proto | Whether to insert client request protocol information
|
| X-Forwarded-Port | Whether to insert client request port information
|
| Persistence | Use of sticky session
|
| HTTP 2.0 | Whether to use HTTP/2 for client-server connections
|
| Routing rules | Routing action and routing condition/redirect target information
|
| SSL certificate | Default certificate and SSL security level, expiration date and time information
|
| SNI certificate | SNI Certificate Details
|
| Server SSL security level | Whether server connection is encrypted
|
| Explanation | Additional information about the Listener
|
tag
You can view, add, modify, or delete a Listener’s tag information.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the Listener’s operation history.
| Category | Detailed description |
|---|---|
| Work log | Task execution details |
| Operation Date/Time | Task execution date and time |
| Resource Type | Resource Type |
| Resource Name | Listener name |
| Operation result | Task execution result (success/failure) |
| Operator Information | Information about the user who performed the task |
Modify routing rules
On the Connected Resources tab of the Load Balancer Details page, you can modify the Listener’s routing rules.
To modify the Listener’s routing rules, follow these steps.
- Click the All Services > Networking > Load Balancer menu. Navigate to the Load Balancer’s Service Home page.
- From the Service Home page, click the Load Balancer menu. You will be taken to the Load Balancer list page.
- On the Load Balancer List page, click the resource you want to view details for. You will be taken to the Load Balancer Details page.
- On the Load Balancer Details page, click the Connected Resources tab.
- Click the Listener to add a lighting condition from the list of connected resources. You will be taken to the Listener Details page.
- On the Listener Details page, click the Edit icon of the Routing Rules item. The Edit Routing Rules popup window opens.
- After modifying the routing rule according to the routing action, click the Confirm button.
Category Required statusDetailed description Routing Action - Current routing method (cannot be modified) Routing condition Required If the routing action is LB server group forwarding, routing conditions can be modified - URL path: Modify request URL path and LB server group (up to 20 additions possible)
- Host header: Modify request host and LB server group (up to 20 additions possible)
Redirect target Required When the routing action is URL redirection, the redirect target can be modified - Path: the URL path can be changed
- Host: the host can be changed
- Protocol/Port: cannot be modified (only HTTP → HTTPS redirection is allowed)
Table. Listener routing rule modification items
Delete Listener
To delete an unused Listener, follow these steps.
- Click the All Services > Networking > Load Balancer menu to go to the Load Balancer’s Service Home page.
- Click the Load Balancer menu on the Service Home page. You will be taken to the Load Balancer List page.
- Load Balancer List page, click the Load Balancer resource whose Listener you want to delete. You will be taken to the Load Balancer Details page.
- On the Load Balancer Details page, click the Connected Resources tab. You will be taken to the Connected Resources tab page.
- On the Connected Resources tab page, click the Listener you want to delete. Navigate to the Listener Details page.
- On the Listener Details page, click the Delete Listener button.
Terminate Load Balancer
You can reduce costs by terminating unused Load Balancers. However, since this may affect application services, request termination only after thorough prior review.
In the following cases, the Load Balancer cannot be terminated.
- If there is a Listener attached to the Load Balancer: Delete the attached Listener on the Load Balancer Details page’s Connected Resources tab.
- If you are using a Public NAT IP on the Load Balancer: Load Balancer Details page’s Details tab, deselect the Public NAT IP that is in use.
- If you are using a Private NAT IP on the Load Balancer: Load Balancer Details page’s Details tab, deselect the Private NAT IP in use.
- If there are rules registered in the Firewall: delete the Firewall rules in use from the Load Balancer Details page’s Detailed Information tab.
- If connected to a PrivateLink Service: Check the connected Load Balancer on the PrivateLink Service Details page.
To cancel the Load Balancer, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the Load Balancer menu. You will be taken to the Load Balancer List page.
- Load Balancer List page, click the resource to terminate. You will be taken to the Load Balancer Details page.
- On the Load Balancer Details page, click the Terminate Service button.
- After termination is complete, check the resource termination status in the Load Balancer list.
5.3.2.1 - LB Server Groups
Users can create an LB server group through the Samsung Cloud Platform Console and connect it to a Load Balancer’s listener.
Create LB server group
To create an LB server group, follow these steps.
- Click the All Services > Networking > Load Balancer menu to go to the Load Balancer’s Service Home page.
- On the Service Home page, click the LB Server Group menu. You will be taken to the LB Server Group List page.
- On the LB Server Group List page, click the Create LB Server Group button. You will be taken to the Create LB Server Group page.
- On the Create LB Server Group page, enter the information required to create a service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description LB server group name Required LB server group resource name - Enter using English letters, numbers, and special characters (
-_) with a length of 3 to 63 characters
- LB server group name must be unique within the Account
VPC name Required Select the VPC to create the LB server group - Select the VPC where the Load Balancer that will connect to the LB server group is created
Service Subnet name Required Select the VPC Subnet to create the LB server group - Select the Subnet where the Load Balancer that will connect to the LB server group is created
Load balancing Required Load Balancing Algorithm Selection - Round Robin: Distribute sequentially among registered members
- Weighted round robin: Distribute sequentially in proportion to the weight assigned to each member
- Least Connection: Distribute to the member with the fewest connections
- Weighted least connection: Distribute to the higher‑priority member considering each member’s weight and connection count
- IP Hash: Distribute to a specific member based on the hash value of the client IP address
Protocol Required Select the receiving protocol for the LB server group - Select the protocol to forward to members of the LB server group
LB health check Required Select LB health check - Select an LB health check that was created in the same Service Subnet as the LB server group
Table. LB server group service information input fields - Enter using English letters, numbers, and special characters (
- Enter or select the required information in the Additional Information Input area.
Category Required statusDetailed description Explanation Select Enter resource description tag Select Add tags - Up to 50 tags can be added per resource
Table. LB server group additional information input fields
- Enter or select the required information in the Service Information Input area.
- Check the created service information and the estimated billing amount, and click the Create button.
- When creation is complete, verify the created resources on the LB server group list page.
Check detailed information of LB server group
In the LB Server Group menu, you can view and edit the resource list and detailed information. The LB Server Group Details page consists of Details, Connected Resources, Tags, Operation History tabs.
To view detailed information about the LB server group, follow these steps.
Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
On the Service Home page, click the LB server group menu. You will be taken to the LB server group list page.
- You can modify column visibility by clicking the Settings button at the top right of the table.
Category Display optionDetailed description LB server group name Basic LB server group resource name Protocol Basic LB server group protocol Load Balancer name Basic Load Balancer resource name linked to the LB server group LB Health Check ID Basic LB server group’s LB health check resource name Number of members Basic Number of members registered in the LB server group Creation date and time Basic LB server group creation time status Basic LB server group resource status Table. LB server group list items
- You can modify column visibility by clicking the Settings button at the top right of the table.
On the LB server group list page, click the resource to view detailed information. It navigates to the LB server group details page.
- LB Server Group Details At the top of the page, status information and descriptions of additional features are displayed.
Category Detailed description status LB server group resource status - Active: The service is active and functioning normally
- Deleting: Processing service termination request
- Creating: Processing service creation request
- Error: Cannot determine current status due to an internal error
- If this status persists, please contact through the Support Center
- Editing: Processing service modification request
Delete LB server group Delete LB server group resource Table. LB server group status information and additional feature items
- LB Server Group Details At the top of the page, status information and descriptions of additional features are displayed.
Detailed Information
In the Detailed Information tab, you can view the detailed information of a resource from the LB server group list, and edit it if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| Constructor | User requesting service creation |
| Creation date | Service creation date and time |
| Editor | User requesting service modification |
| Modification date and time | Service modification date and time |
| Load Balancer name | Load Balancer resource name connected to the LB server group
|
| LB server group name | LB server group name |
| VPC name | VPC resource name where the LB server group was created
|
| Service Subnet name | Subnet resource name where the LB server group is created
|
| Port | LB server group forwarding port |
| Protocol | LB server group forwarding protocol |
| Load balancing | LB server group traffic distribution method
|
| LB health check | LB health check resource name
|
| description | LB server group addition description
|
Connected resources
Connected Resources tab allows you to view the list of members connected to the LB server group, and you can add or delete members.
| Category | Detailed description |
|---|---|
| Add member | Add LB Server Group Member button |
| Member name | Member name (server name) added to the LB server group |
| IP address | Member IP address |
| Port | Member receive port |
| weight | Load balancing weight
|
| Activation | Member activation status
|
| Creation date and time | Member addition date/time |
| Health check status | Health check status information
|
| status | Member resource status |
tag
On the LB server group list page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Work History tab allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Work history | Task execution details |
| Operation date and time | Task execution date and time |
| Resource Type | Resource Type |
| Resource Name | LB server group name |
| Operation result | Task execution result (success/failure) |
| Operator Information | User information of the performed operation |
Managing LB Server Group Resources
You can view the member list of an LB server group and add or remove members.
Add member
You can add members to the LB server group to register server resources that will handle client requests.
To add a member to the LB server group, follow these steps.
Click the All Services > Networking > Load Balancer menu to go to the Load Balancer’s Service Home page.
On the Service Home page, click the LB Server Group menu. You will be taken to the LB Server Group List page.
On the LB Server Group List page, click the resource you want to edit detailed information for. You will be taken to the LB Server Group Detail page.
On the LB Server Group Details page, click the Connected Resources tab. You will be taken to the Connected Resources tab page.
On the Connected Resources tab page, click the Add Member button in the upper right.
Add Member After entering the required information in the popup window, click the Confirm button.
Category Required statusDetailed description LB server group name basic LB server group name for adding a member target server Required Server information to add as a member - Virtual Server/Bare Metal Server: Select from the list of servers created in the same VPC as the LB server group
- Enter IP Directly: Enter server IP directly
- Click the Add button to add the target server
Member information Required Member Port and Weight Settings - Member Name: Display the server name and IP to be added as a member
- Port: The port the member will receive
- Weight: The weight applied to load balancing
- When using Weighted Round Robin or Weighted Least Connection load balancing, a value between 1 ~ 1000 is required
Table. LB server group member addition itemClick the OK button in the alert dialog.
Check if members have been added in the Connected Resources tab.
Add the following rule to the Security Group of the server added as a member to allow communication between the Load Balancer and the LB server group members.
- (Direction) Inbound rule, (Target address) Load Balancer’s Source NAT IP, (Protocol) LB server group protocol, (Allowed port) member port
- If the LB server group is in Creating, Editing, Deleting, Error state, you cannot add members.
- If the number of members that can be created in the Account to which the LB server group belongs is exceeded, you cannot add members. The maximum number of members that can be created in a single Account is 1,000.
- Through VPC Peering, you can add a server created in another VPC as a member. After adding the target server by Enter IP Directly, check the Health Check Status of the added member in the Connected Resources tab.
For detailed information, refer to VPC > VPC Peering.
Member Edit
When you click a member name in the member list, you are taken to the Member Details page. You can view the member details, and you can click the Edit icon to change the information.
To edit member details, follow these steps.
- Click the All Services > Networking > Load Balancer menu to go to the Load Balancer’s Service Home page.
- On the Service Home page, click the LB Server Group menu. You will be taken to the LB Server Group List page.
- On the LB Server Group List page, click the resource you want to edit details for. You will be taken to the LB Server Group Details page.
- On the LB Server Group Details page, click the Connected Resources tab. You will be taken to the Connected Resources tab page.
- Linked Resources tab page, click the member you want to edit. You will be taken to the Member Details page.
- Edit the desired member information on the Member Details page.
Weight modification
It can be modified when using weighted load balancing (Weighted Round Robin, Weighted Least Connection).
- Click the Edit icon of the Weight item. In the edit window, enter the weight to edit and click the Confirm button.
Port modification
To edit a member port, click the Edit icon in the Port field. In the edit window, enter the port to edit and click the Confirm button.
Activate edit
To modify member activation, click the Edit icon of the Activation item. In the edit window, set the activation status and click the Confirm button.
Delete member
To delete unused members, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the LB Server Group menu. You will be taken to the LB Server Group List page.
- On the LB Server Group List page, click the resource whose details you want to edit. You will be taken to the LB Server Group Details page.
- On the LB Server Group Details page, click the Connected Resources tab. You will be taken to the Connected Resources tab page.
- Linked Resources tab page, click the member you want to delete. You will be taken to the Member Details page.
- On the Member Details page, click the Delete Member button.
- Check whether the member has been deleted in the Connected Resources tab.
Terminate LB server group
You can terminate an unused LB server group. However, because it may affect the application service, please request termination only after thorough prior review.
The LB server group cannot be terminated in the following cases.
- If the LB server group is being used in a Listener: modify the Listener’s LB server group before deleting the LB server group.
- If there are members registered in the LB server group: Delete all resources attached to the LB server group before terminating the LB server group.
- When using an LB server group in an Auto Scaling Group: configure the load balancer so it is not used by the Auto Scaling Group, or adjust it so that the LB server group is not utilized. For more details, see Auto-Scaling Group > Load Balancer Usage.
To terminate the LB server group, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the LB Server Group menu. You will be taken to the LB Server Group List page.
- From the LB server group list, click the resource to be terminated. You will be taken to the LB server group detail page.
- On the LB server group detail page, click the LB server group delete button.
- Once the termination is complete, check the resource termination status in the LB server group list.
5.3.2.2 - LB Health Check
Users can create LB health checks through the Samsung Cloud Platform Console and use them for LB server groups.
Create LB health check
To create an LB health check, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the LB Health Check menu. You will be taken to the LB Health Check List page.
- On the LB Health Check List page, click the Create LB Health Check button. You will be directed to the Create LB Health Check page.
- On the LB Health Check Creation page, enter the information required to create the service and select detailed options.
- In the Service Information Input area, enter or select the required information.
Category RequiredDetailed description LB health check name Required LB health check resource name - Enter using English uppercase and lowercase letters, numbers, and special characters (
-_) with a length of 3 to 63 characters
- LB health check name must be unique within the Account
VPC name Required Select the VPC to create the LB health check - Select the VPC where the LB server group that will use the LB health check is created
Service Subnet name Required Select the VPC Subnet to create the LB health check - Select the Subnet where the LB server group that will use the LB health check is created
Health check method > Protocol Required Health Check Protocol - Select the protocol to use for member health checks among TCP, HTTP
Health check method > Health check port Required Health check port - Enter a value between 1 and 65,534 to use as the member health check port
Health check method > interval Required Health check interval - Default is 5 seconds, input allowed between 1 and 180 seconds
Health check method > waiting time Required Health check response wait time - Default 5 seconds, can be set between 1 and 180 seconds
- Cannot be set to a value larger than the interval
Health check method > detection count Required Number of times to evaluate health check status - Default value 3 times, input allowed between 1 and 10
Health check method > HTTP method Required Set HTTP request method (HTTP protocol usage setting) - Select GET or POST
Health check method > URL monitor Required Enter health check URL path (set when using HTTP protocol) - Enter using English letters, numbers, and special characters (
/.-_?&=) within 50 characters
Health check method > Response code Required Enter the HTTP response codes to receive from the server (HTTP protocol when used) - Enter response codes in the 200 ~ 500 range
Health check method > request string Required Health check request string input (HTTP protocol POST method setting) - Enter the content to include in the Request Body using English letters, numbers, and special characters (
/.-_?&=) within 255 bytes
Table. LB health check service information input items - Enter using English uppercase and lowercase letters, numbers, and special characters (
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description description Select Enter resource description tag Select Add tags - Up to 50 tags can be added per resource
Table. LB server group additional information input fields
- In the Service Information Input area, enter or select the required information.
- Summary Check the service information and estimated charges created in the panel, and click the Create button.
- When creation is complete, check the created resources on the LB Health Check List page.
Add the following rule to the Security Group of the server added as a member for member health checks in the Load Balancer.
- (Direction) Inbound rule, (Target address) Load Balancer’s health check IP, (Protocol) health check protocol, (Allowed port) health check port
- It is recommended to set the health check port the same as the member port.
- If the health check port and the member port differ, the health check is performed using the member port.
Configure the LB health check to a value that members added to the LB server group can respond to.
- Since the Load Balancer determines member status based on health check responses, the LB health check results may differ from the actual service status.
View detailed LB health check information
In the LB Health Check menu, you can view and edit the resource list and detailed information. The LB Health Check Details page consists of Details, Connected Resources, Tags, Activity Log tabs.
To view detailed LB health check information, follow these steps.
Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
On the Service Home page, click the LB Health Check menu. You will be taken to the LB Health Check List page.
- You can modify the column visibility by clicking the Settings button at the top right of the table.
Category Display optionDetailed description LB health check name Basic LB health check resource name Service Subnet ID Basic VPC Subnet name where the LB health check was created Number of LB server groups Basic Number of LB server groups using LB health check type Basic LB Health Check Type Protocol Basic LB health check protocol Creation date and time Basic LB health check creation timestamp status Basic LB health check resource status Table. LB health check list items
- You can modify the column visibility by clicking the Settings button at the top right of the table.
On the LB Health Check List page, click the resource to view detailed information. You will be taken to the LB Health Check Details page.
- LB Health Check Details At the top of the page, status information and descriptions of additional features are displayed.
Category Detailed description status LB health check resource status - Active: The service is active and functioning normally
- Deleting: Processing service termination request
- Creating: Processing service creation request
- Error: Unable to determine current status due to an internal error
- If this status persists, please contact the Support Center
- Editing: Processing service modification request
Delete LB health check Delete LB health check resource Table. LB health check status information and additional feature items
- LB Health Check Details At the top of the page, status information and descriptions of additional features are displayed.
Detailed Information
Details tab allows you to view the resource’s detailed information from the LB health check list, and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User requesting service creation |
| Creation date and time | Service creation date and time |
| Editor | Service modification request user |
| Modification date and time | Service modification date and time |
| LB health check name | LB health check name |
| type | LB health check type |
| VPC name | VPC to use for LB health check
|
| Service Subnet name | VPC Subnet for LB health checks
|
| Health check method | LB health check method configuration information
|
| description | Additional information about LB health check
|
Connected resource
In the Connected Resources tab, you can view detailed information about the LB server groups associated with the LB Health Check.
| Category | Detailed description |
|---|---|
| LB server group name | LB server group resource name
|
| Protocol | LB health check protocol |
| Load Balancer name | Load Balancer resource name linked to the LB server group |
| Number of members | Number of members added to the LB server group |
| Creation date and time | LB server group creation timestamp |
| status | LB server group resource status
|
tag
LB health check list page lets you view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Work History tab allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Work history | Task execution details |
| Operation Date/Time | Execution date and time |
| Resource Type | Resource Type |
| Resource Name | LB health check name |
| Work result | Task execution result (success/failure) |
| Operator Information | User information of the performed operation |
Modify LB health check method
LB Health Check Details page allows you to modify the health check method.
To modify the LB health check method, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the LB Health Check menu. You will be taken to the LB Health Check List page.
- LB Health Check List page, click the resource you want to edit details for. You will be taken to the LB Health Check Details page.
- On the LB Health Check Details page, click the Edit icon of the Health Check Method. You will be taken to the Edit Health Check Method popup.
- Modify health check method After editing the required information in the popup window, click the Confirm button.
Cancel LB health check
You can cancel the LB health check service you are not using.
- default type LB health check resource cannot be deleted.
- LB health check resources used by the LB server group cannot be deleted.
To disable the LB health check, follow these steps.
- Click the All Services > Networking > Load Balancer menu. You will be taken to the Load Balancer’s Service Home page.
- On the Service Home page, click the LB Health Check menu. You will be taken to the LB Health Check List page.
- Click the resource to terminate from the LB health check list. You will be taken to the LB health check details page.
- On the LB Health Check Details page, click the Delete LB Health Check button.
- Once the termination is complete, check the resource termination status in the LB health check list.
5.3.3 - API Reference
5.3.4 - CLI Reference
5.3.5 - Release Note
Load Balancer
- A feature has been added to enable setting a Private NAT IP on the Service IP.
- The ‘TCP_Proxy’ protocol has been added to the L4 Listener.
- The conditions for creating L4 Listener service ports have been changed.
- It has been changed to allow creating a Listener on the same service port for both TCP and UDP protocols.
- The method for entering L7 Listener routing rules has been changed.
- LB server group forwarding > Modified to allow users to add a ‘/’ path in the URL path.
- LB server group forwarding > The matching method for the entered path in the URL path has been changed from ‘Contains(Include match)’ to ‘Starts with(Start part match)’.
- LB server group forwarding > The ‘Default’ condition for the request host in the host header has been added.
- The method for configuring the LB health check port has been changed.
- You can select either a member port or manual entry, and when using manual entry, specify the port to use.
- Existing LB health checks are changed to the member port. (Same as the current health check method)
- The HTTPS option has been added to the LB health check protocol.
- You can monitor the server’s TLS connection status.
- When using URL redirection in an HTTP Listener, you can specify the target port for the redirection.
- You can add Multi-node GPU Cluster resources to the LB server group members.
- When creating a Load Balancer, you can set the Source NAT IP and health check IP.
- TLS protocol has been added to the L4 Listener.
- You can set up a TLS service over TCP.
- A routing rule option has been added to the L7 Listener.
- Routing conditions allow you to set up branching by URL path or by host.
- Supports multiple SSL certificates.
- By supporting SNI, you can register multiple certificates on a single Listener.
- Add LB health check management feature
- You can create an LB health check, define the required health check method, and connect it to an LB server group for use.
- Support for weighted load balancing of LB server groups
- Weighted Round Robin and Weighted Least Connection have been added to the load balancing options.
- You can set per-member weights to distribute server load.
- Add LB server group member activation feature
- You can choose to activate members of the LB server group by disabling or enabling them.
- A Load Balancer service that provides more stable and enhanced features has been launched.
- Provides an L7 Load Balancer that supports HTTP and HTTPS protocols.
- Provides an L4 Load Balancer that supports TCP and UDP protocols.
5.4 - DNS
5.4.1 - Overview
Service Overview
The DNS service converts domain names, which are convenient for humans to recognize, into numeric IP addresses that the system can identify, allowing access to services.
With the DNS service, users can easily register the desired domain and manage its DNS records themselves.
Features
- Easy Domain Registration: You can register and modify new domains via a web-based console. Without building separate DNS infrastructure or installing DNS solutions, you can easily create and manage domains through the web.
- Support for Various Records: You can configure various resource record types such as A, AAAA, CNAME, TXT, MX, SPF, and it automatically scales to handle large query volumes without user intervention.
- Convenient Hosting Environment Management: You can select and use a Public domain name, which is exposed to the Internet to provide web services, or a Private domain name, which is accessible only to designated internal users without an Internet connection, according to your usage environment and purpose.
Configuration diagram
Provided features
The DNS service provides the following functions.
- Hosting Zone Creation/Management: You can create and manage Public Hosted Zones that are accessible from anywhere via the Internet, and Private Hosted Zones that are not exposed to the Internet and are only accessible within a designated network environment.
- Public Domain Name Application: You can apply for a Public Domain Name that can be accessed from anywhere via the Internet.
- Support for various resource records: You can select and use record types that suit your environment and purpose.
| Record type | Detailed description |
|---|---|
| A | Specify the IPv4 address corresponding to the domain name so that the IP address can be resolved from the domain name. |
| AAAA | Specify the IPv6 address corresponding to the domain name so that the IP address can be resolved from the domain name. |
| TXT | Set text information for the domain |
| CNAME | Assign an alias for the domain name |
| MX | Specify the mail server for the user’s domain and subdomains |
| SPF | To prevent spam mail, verify the sending mail server’s IP address or domain name, etc. (Sender Policy Framework) |
| NS | Name server responsible for this domain (auto-generated) |
| SOA | Define the domain’s initial information (the starting point of authority) (auto-generated) |
Component
Private DNS
To manage private domain names for use only within a designated network environment without exposing them to the internet, you must first create a Private DNS. The Private DNS name is used uniformly across all regions within the account. It can be initially created in any region of the account, and later it can be activated in other regions using the same Private DNS name from the Private DNS list. You can select the VPC to connect to Private DNS for each region. By using a common Private DNS name, you can share and manage the Private Hosted Zone information across all regions.
Hosted Zone
Private Hosted Zone allows you to create and manage domain names that can be used only in the network environment designated for VPCs connected to Private DNS. A Public Hosted Zone can manage the public domain name created through the Samsung Cloud Platform. Through a Hosted Zone, you can create and edit records that match your intended use.
Public Domain Name
You can apply for a Public Domain Name in partnership with Whois, the public domain name management provider. Public Domain Name can be purchased in one-year increments, and you can set or change the automatic renewal (in one-year increments) up to 7 days before the expiration date.
Constraints
The constraints of the DNS service are as follows.
| Category | description |
|---|---|
| Number of Private DNS that can be created per account | 1 |
| Number of Hosted Zones that can be created in an Account | 20 |
| Number of records that can be registered per Hosted Zone | 100 |
- Requests to use Public Domain Name and Public Hosted Zone in the Korea South (kr-south) region are restricted.
Preceding Service
The DNS service has no prerequisite services.
5.4.1.1 - TLD List
TLD (Top-Level Domain) list
The following TLDs are available. When applying for a Public Domain Name, an annual fee is incurred that varies by TLD type.
| TLD type | Public Domain Name registration fee (KRW/year, VAT excluded) |
|---|---|
| .COM | 20,000 |
| .NET | 20,000 |
| .ORG | 20,000 |
| .KR | 24,000 |
| .PE.KR | 16,000 |
| .BIZ | 20,000 |
| .INFO | 20,000 |
| .CN | 65,000 |
| .TV | 90,000 |
| .IN | 65,000 |
| .EU | 80,000 |
| .AC | 286,000 |
| .TW | 100,000 |
| .MOBI | 44,000 |
| .NAME | 30,000 |
| .CC | 90,000 |
| .JP | 198,000 |
| .ASIA | 55,000 |
| .ME | 44,000 |
| .TEL | 44,000 |
| .PRO | 44,000 |
| .SO | 103,000 |
| .SX | 90,000 |
| .CO | 100,000 |
| .XXX | 200,000 |
| .PW | 44,000 |
| .PH | 100,000 |
| .io | 91,000 |
| .app | 42,500 |
| .co.kr | 24,000 |
5.4.1.2 - ServiceWatch Metrics
DNS sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals.
Basic Metrics
The following are the basic metrics for the Private DNS namespace.
The indicators whose names are displayed in bold below are the key indicators selected from the basic indicators provided by Private DNS. Key metrics are used to configure service dashboards that are automatically built for each service in ServiceWatch.
Each metric indicates, via the user guide, which statistical values are meaningful when viewing that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
| Performance items | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| privatedns.operation.per_sec | Number of UDP-based data requests processed per second on user request | Count/Second |
|
| privatedns.query.outbound.per_sec | Number of requests per second sent to external DNS servers for user queries | Count/Second |
|
| privatedns.query.answers_slow | Number of requests sent to external DNS servers for user queries with slow responses (within 1 second) | Count/Second |
|
| privatedns.response.nxdomain.per_sec | Number of NXDOMAIN responses received per second from external DNS servers for user queries | Count/Second |
|
| privatedns.response.servfail.per_sec | Number of SERVFAIL responses received per second from external DNS servers for user queries | Count/Second |
|
5.4.2 - How-to guides
The user explains the items to verify before creating a DNS service through the Samsung Cloud Platform Console.
Preface before Using Private Domain Name Management
Before using Private Domain Name management, first verify the following items.
- To manage private domain names for use only within a designated network environment without exposing them to the internet, you must first create a Private DNS.
- The defined Private DNS name is used uniformly across all regions within the account. It can be initially created in any region within the account, and thereafter, in other regions, it is activated and used from the Private DNS list with the same Private DNS name.
- You can optionally configure the VPCs you want to connect to Private DNS for each region. When first created or activated, no VPC is connected.
- The Private DNS name may already be in use within the Samsung Cloud Platform, and you can verify its availability by performing a duplicate check when entering the domain name.
- Hosted Zone information is shared across all regions. However, some detailed information (SRN, creator, modifier information) can only be viewed in the region where it was originally created.
General usage examples are shown below. For detailed usage instructions, refer to the How-to guides of the respective subservice.
| Order | Subservice | Key procedures |
|---|---|---|
| STEP 1 | Private DNS | Create Private DNS (Region A) → Connect VPC in Region A → Activate Private DNS (Region B) → Connect VPC in Region B |
| STEP 2 | Hosted Zone | Create Private Hosted Zone → Register record |
| STEP 3 | - | View detailed information, edit, and cancel |
Public Domain Name Management: Foreword Before Use
Before using Public Domain Name management, please check the following items first.
- Public Domain Names intended for use on the internet can be managed through a Hosted Zone only for domain names that have been registered via the Samsung Cloud Platform.
- The list of available top-level domains may change.
An example of the typical usage procedure is shown below. For detailed usage instructions, refer to the How-to guides of the respective subservice.
| Category | Subservice | Main Procedure |
|---|---|---|
| STEP 1 | Public Domain Name | Verify availability and apply for the Public Domain Name you wish to use |
| STEP 2 | Hosted Zone | Create a Hosted Zone for the requested Public Domain Name → Register records |
| STEP 3 | - | View detailed information, edit, cancel |
5.4.2.1 - Private DNS
Users can create the service by entering the required information for the Private DNS service and selecting detailed options through the Samsung Cloud Platform Console.
Create Private DNS
You can create and use a Private DNS service in the Samsung Cloud Platform Console.
To request the creation of a Private DNS service, follow the steps below.
- All Services > Networking > DNS Click the menu. Proceed to the Service Home page.
- Click the Private DNS Create button in the dropdown of the Service Home page. You will be taken to the Private DNS Create page.
- On the Private DNS Creation page, enter the information required to create the service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category RequiredDetailed description Private DNS name Required Enter the Private DNS name to use - Enter using 3 - 20 characters, including lowercase letters, numbers, and the special character (-)
- Cannot be the same as an existing name in use
VPC connection Select Register VPC to connect with Private DNS - Click the Select button to choose a VPC
- Up to 5 VPCs can be registered
Table. Private DNS service information input items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description description Selection Enter additional information and description for Private DNS tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Private DNS additional information input fields
- Enter or select the required information in the Service Information Input area.
- Check the creation history and click the Create button.
- When creation is complete, check the created resources on the Private DNS List page.
Check Private DNS detailed information
Private DNS service allows you to view and edit the full resource list and detailed information. Private DNS Details page consists of Details, Tags, Activity Log tabs.
To view the detailed information of Private DNS, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Private DNS menu. You will be taken to the Private DNS List page.
- On the Private DNS List page, click the resource you want to view detailed information for. You will be taken to the Private DNS Details page.
- Private DNS Details page displays the status and detailed information of Private DNS, and consists of Details, Tags, Activity History tabs.
Category Detailed description Service status Private DNS status - Creating: creating
- Activing: activating
- Active: active
- Inactive: inactive
- Editing: editing settings
- Deleting: deleting
- Error: error occurred
Service termination Button to disable Private DNS Table. Private DNS status information and additional features
- Private DNS Details page displays the status and detailed information of Private DNS, and consists of Details, Tags, Activity History tabs.
Detailed Information
Private DNS List page allows you to view detailed information of the selected resource and edit the information if necessary.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Initial creation location | Initial creation location of Private DNS |
| VPC connection | VPC information connected to Private DNS
|
| Explanation | Private DNS description
|
tag
Private DNS List page allows you to view the tag information of the selected resource, and to add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Private DNS List page lets you view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Activating Private DNS from a location other than its initial creation location
You can enable and use Private DNS in regions other than the region where it was originally created.
To enable the Private DNS service, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Private DNS menu. You will be taken to the Private DNS List page.
- Click the More > Activate button of the resource you want to enable from the Private DNS list. A notification dialog will appear.
- The activation button is displayed only for Private DNS entries with Inactive status.
- Click OK in the alert dialog.
Configure VPC connection for Private DNS
You can configure the VPC information connected to the Private DNS service.
To configure the VPC connection for Private DNS, follow these steps.
- Click the All Services > Networking > DNS menu. Go to the DNS Service Home page.
- On the Service Home page, click the Private DNS menu. You will be taken to the Private DNS List page.
- On the Private DNS List page, click the resource you want to view detailed information for. You will be taken to the Private DNS Details page.
- On the Private DNS Details page, click the Edit icon of the VPC connection item. The VPC connection selection popup window opens.
- In the VPC connection selection popup window, select the VPC to connect and click OK.
- Check that the selected VPC is displayed in the VPC connection item.
Terminate Private DNS
You can request termination of the Private DNS service from the Samsung Cloud Platform Console.
To request cancellation of the Private DNS service, follow the steps below.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Private DNS menu. You will be taken to the Private DNS List page.
- On the Private DNS List page, click the resource to view detailed information. You will be taken to the Private DNS Details page.
- On the Private DNS Details page, click the Cancel Service button.
- Once the termination is complete, check the service termination status in the Private DNS list.
5.4.2.2 - Hosted Zone
Users can create the service by entering the required information for the Hosted Zone service and selecting detailed options through the Samsung Cloud Platform Console.
Create Hosted Zone
You can create and use the Hosted Zone service in the Samsung Cloud Platform Console.
To request the creation of a Hosted Zone service, follow the steps below.
All Services > Networking > DNS menu, click it. You will be taken to the Service Home page.
Click the Create Hosted Zone button in the dropdown of the Service Home page. Proceed to the Create Hosted Zone page.
Create Hosted Zone page, enter the information needed to create the service, and choose detailed options.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Usage classification Required Select a domain appropriate for the purpose of the Hosted Zone - Private: Domain that can be used only within the Samsung Cloud Platform
- Public: Domain that can be accessed from outside (the Internet)
Private DNS name to register Required Select from the pre-created Private DNS - Selectable only when Private is chosen in the usage classification
Hosted Zone name to register Required Enter the Hosted Zone name to use - Enter using lowercase letters, numbers, and hyphens (-), within 2 to 63 characters
- When applying for a new domain, click the Check Availability button to verify duplication
Table. Hosted Zone service information input items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Explanation Select Enter additional information and description for the Hosted Zone tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. Hosted Zone additional information input fields
- Enter or select the required information in the Service Information Input area.
Check the generation history and click the Generate button.
- After creation is complete, check the created resources on the Hosted Zone list page.
Check Hosted Zone details
The Hosted Zone service allows you to view and edit the full list of resources and detailed information. Hosted Zone Details page consists of Details, Records, Tags, Activity Log tabs.
To view detailed information about the Hosted Zone, follow these steps.
- All Services > Networking > DNS menu, click it. Then go to the Service Home page.
- On the Service Home page, click the Hosted Zone menu. You will be taken to the Hosted Zone List page.
- On the Hosted Zone List page, click the resource you want to view details for. You will be taken to the Hosted Zone Details page.
- Hosted Zone Details page displays the Hosted Zone’s status information and details, and consists of Details, Records, Tags, Activity History tabs.
Category Detailed description Service status Hosted Zone status - Creating: In progress
- Active: Running
- Editing: Changing settings
- Deleting: Terminating
- Error: An error occurred
Delete Hosted Zone Button to delete the Hosted Zone Table. Hosted Zone status information and additional features
- Hosted Zone Details page displays the Hosted Zone’s status information and details, and consists of Details, Records, Tags, Activity History tabs.
Detailed Information
On the Hosted Zone List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Hosted Zone name | Hosted Zone domain name |
| Usage classification | Display selected usage |
| Private DNS name | Selected Private DNS name |
| description | Hosted Zone description
|
record
On the Hosted Zone List page, you can view the registered record information and add, modify, or delete records. A record is an item that configures communication with the DNS server, informing the server of the IP address associated with the domain and how to handle requests sent to the domain.
| Category | Detailed description |
|---|---|
| Advanced Search | Record detailed search settings button |
| Add record | Add Record button |
| Name | Registered record name |
| type | Record Types
|
| value | IP address of the record |
| TTL | Time for DNS response servers to temporarily store records |
| Auto-generated | Indicate whether automatically generated |
| status | Service status display |
| More menu | Record editing and deletion are possible |
tag
Hosted Zone List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Hosted Zone List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing records of a Hosted Zone
You can add or delete records in the Hosted Zone service.
Add Record
To add a record to a Hosted Zone, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Hosted Zone menu. You will be taken to the Hosted Zone List page.
- On the Hosted Zone List page, click the resource you want to view details for. You will be taken to the Hosted Zone Details page.
- On the Hosted Zone Details page, click the Record tab. You will be taken to the Record tab page.
- Record tab page, click the Add Record button. The Add Record window opens.
- In the Add Record window, select the Type, Name, Value, and TTL fields, then click Confirm. A notification dialog will appear.
Category Detailed description A Enter an IP address in IPv4 format - Click the Add button to add an IP address, up to 8 can be registered
AAAA Enter an IPv6-formatted IP address - Click the Add button to add an IP address, up to 8 can be registered
SPF Enter the IP of the server that sent the spam email - If registering multiple servers, enter in the format v=spf1 ip4:211.214.160.28 ip4:211.214.16.29 ~all
CNAME Enter a record alias in domain name format - Registration is not possible if entered the same as a value of a different record type
MX Enter the priority and mail server address - Click the Add button to add a server address, up to 8 can be registered
- When entering priority, input a value within the range 0 - 65,535; the smaller the value, the higher the priority
TXT Enter text - Enter within 250 characters
Table. Detailed items by record type - Click Confirm in the notification dialog.
- Check that the added item appears in the record list.
Modify Record
To modify a Hosted Zone’s records, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Hosted Zone menu. You will be taken to the Hosted Zone List page.
- On the Hosted Zone List page, click the resource you want to view details for. You will be taken to the Hosted Zone Details page.
- On the Hosted Zone Details page, click the Record tab. You will be taken to the Record tab page.
- On the Record tab page, click the list’s More menu and select Edit. The Record Edit window opens.
- In the record edit window, modify the desired fields and click OK.
- Click OK in the notification dialog.
Delete Record
To delete a record in a Hosted Zone, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Hosted Zone menu. You will be taken to the Hosted Zone List page.
- On the Hosted Zone List page, click the resource to view its details. You will be taken to the Hosted Zone Details page.
- On the Hosted Zone Details page, click the Record tab. You will be taken to the Record tab page.
- Record tab page, click the More menu of the list and click Delete. A confirmation alert opens.
- Click Confirm in the alert dialog.
Terminate Hosted Zone
You can request cancellation of the Hosted Zone service from the Samsung Cloud Platform Console.
To request termination of the Hosted Zone service, follow the steps below.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Hosted Zone menu. You will be taken to the Hosted Zone List page.
- On the Hosted Zone List page, click the resource you want to view details for. You will be taken to the Hosted Zone Details page.
- On the Hosted Zone Details page, click the Hosted Zone Delete button.
- After the termination is complete, check the service termination status in the Hosted Zone list.
5.4.2.3 - Public Domain Name
Users can create the service by entering the required information for the Public Domain Name service and selecting detailed options through the Samsung Cloud Platform Console.
Create Public Domain Name
You can create and use the Public Domain Name service in the Samsung Cloud Platform Console.
To request the creation of a Public Domain Name service, follow these steps.
- All Services > Networking > DNS Click the menu. You will be taken to the Service Home page.
- Click the Public Domain Name Create button in the dropdown of the Service Home page. You will be taken to the Public Domain Name Create page.
- On the Public Domain Name creation page, enter the information required to create the service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category Whether requiredDetailed description Domain name to register Required Enter the Public Domain Name to use - Enter using lowercase letters, numbers, and hyphens (-), within 2 to 63 characters
- When applying for a new domain, click the Check Availability button to verify duplication
Purchase period Required Automatically selected as 1 year Automatic extension Required Set whether to automatically renew when the domain usage period expires - Use selected, enter detailed information
- Registrant Name (Business Name): Enter the registrant name or business name within 30 characters
- Registrant Email: Enter the registrant’s email address
- Registrant Address: Enter the registrant’s company address, click the Find Postal Code button to search and then enter the address
- Phone Number: Enter the registrant’s phone number
Table. Public Domain Name Service Information Input Items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Explanation Select Enter additional information and description for the Public Domain Name tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Public Domain Name additional information input fields
- Enter or select the required information in the Service Information Input area.
- Check the creation history and click the Create button.
- When creation is complete, check the created resource on the Public Domain Name list page.
Check detailed information of Public Domain Name
The Public Domain Name service allows you to view and edit the full resource list and detailed information. The Public Domain Name Details page consists of Details, Registration Info, Tags, Activity Log tabs.
To view detailed information about the Public Domain Name, follow these steps.
- All Services > Networking > DNS menu, click it. You will be taken to the Service Home page.
- On the Service Home page, click the Public Domain Name menu. You will be taken to the Public Domain Name List page.
- Click the resource on the Public Domain Name List page to view detailed information. You will be taken to the Public Domain Name Details page.
- Public Domain Name Details page displays the status information and detailed information of the Public Domain Name, and consists of the Details, Registration Information, Tags, Activity History tabs.
Category Detailed description Service status Public Domain Name status - Creating: In progress
- Active: Running
- Editing: Settings being changed
- Registered: Renewal registration
- Transfer Requested: Domain transfer request completed
- Expired: Usage period expired
Domain transfer between accounts Domain transfer request button between accounts - Cancel Transfer Request: Allows canceling a domain transfer request after the request is completed
- Approve Transfer Request: Allows approving a transfer request when a domain transfer request is received
- Reject Transfer Request: Allows rejecting a transfer request when a domain transfer request is received
Table. Public Domain Name status information and additional features
- Public Domain Name Details page displays the status information and detailed information of the Public Domain Name, and consists of the Details, Registration Information, Tags, Activity History tabs.
Detailed Information
On the Public Domain Name List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| domain name | Public Domain Name domain name |
| Registration date | Public Domain Name domain registration date |
| Purpose classification | Display selected usage |
| Expiration date | Public Domain Name Domain Usage Expiration Date |
| Automatic extension | Display whether the auto-renewal feature is enabled
|
| description | Public Domain Name description
|
Registration Information
On the Public Domain Name List page, you can view and edit domain registration information.
| Category | Detailed description |
|---|---|
| Registrant name (business name) | The registrant’s name or business name entered when applying for the service |
| Registrant email | The email address of the registrant entered when applying for the service |
| Registrant address | The registered company’s address entered when applying for the service |
| phone number | Registrant’s phone number entered during service application |
tag
On the Public Domain Name List page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Public Domain Name List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Public Domain Request Transfer Between Accounts
You can transfer a registered Public Domain to a user of another account.
- If the domain you want to migrate is being used as a Hosted Zone, you cannot request migration. Delete the existing Hosted Zone first, then request migration.
- The domain you want to transfer must have auto-renewal set to unused to make a transfer request. After the domain transfer, you can enable auto-renewal in the account that received the transfer.
- Domain transfer requests can be made only up to one month before the domain’s registration expiration date.
To transfer Public Domain information to another account user, follow the steps below.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Public Domain Name menu. You will be taken to the Public Domain Name list page.
- On the Public Domain Name List page, click the resource to view detailed information. You will be taken to the Public Domain Name Details page.
- Public Domain Name Details on the page, click the Domain Transfer Between Accounts button. The Domain Transfer Between Accounts popup will open.
- Domain transfer between accounts In the popup window, enter the account ID to transfer to and click the Confirm button.
- When the domain transfer request is completed, it changes to the Transfer requested status, and the applicant can click the Cancel transfer request button to cancel the transfer request.
- After a domain transfer request, if a user from another account approves the transfer, the domain information is deleted from the requesting account.
- If the user who received the prior request does not approve within 7 days of the approval request, the prior request will be automatically canceled.
Managing Public Domain Data Transfer Requests
If a user from another account transfers a Public Domain, you can approve or reject the request.
Approve Public Domain information transfer request
To approve a request to move to the Public Domain, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Public Domain Name menu. You will be taken to the Public Domain Name List page.
- Public Domain Name List page, click the resource to view detailed information. You will be taken to the Public Domain Name Details page.
- Public Domain Name Details on the page, click the Approve Previous Request button. In the alert dialog, click the Confirm button.
Public Domain Reject request to transfer information
To reject a request before the Public Domain, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Public Domain Name menu. You will be taken to the Public Domain Name List page.
- Public Domain Name List page: click the resource to view detailed information. You will be taken to the Public Domain Name Details page.
- On the Public Domain Name Details page, click the Reject Previous Request button. In the alert dialog, click the Confirm button.
Modify registration information of Public Domain Name
You can modify the registration information of a Public Domain Name.
To edit the registration information of a Public Domain Name, follow these steps.
- Click the All Services > Networking > DNS menu. Navigate to the DNS Service Home page.
- On the Service Home page, click the Public Domain Name menu. You will be taken to the Public Domain Name List page.
- On the Public Domain Name List page, click the resource to view detailed information. You will be taken to the Public Domain Name Details page.
- On the Public Domain Name Details page, click the Registration Information tab. You will be taken to the Registration Information tab page.
- Registration Information tab page, click the Edit button. You will be taken to the Edit Registration Information page.
- Go to the Edit Registration Information page. Modify the desired items and click the Done button.
5.4.3 - Release Note
DNS
- You can view measurement values for the following five items in conjunction with Service Watch.
- Number of server error responses (unit: seconds)
- NXDOMAIN response count (unit: seconds)
- Number of queries not responding within 1 second (unit: seconds)
- Number of outgoing UDP queries (unit: seconds)
- Number of UDP-based data request processing (unit: seconds)
- Through the Samsung Cloud Platform, a registered Public Domain Name can be transferred to another user account within the allowed period.
- We have officially launched a DNS service that can be used in private networks and internet environments. You can manage Private DNS and Private Hosted Zones for restricted networks, and apply for Public Domain Name registration and manage Public Hosted Zones for internet environments.
- We have launched a beta DNS service that offers domain registration request and management capabilities based on user requests.
5.5 - VPN
5.5.1 - Overview
Service Overview
VPN (Virtual Private Network) is a service that connects the customer’s network to the Samsung Cloud Platform via an encrypted virtual private network.
Features
Prompt Service Delivery You can configure automated services through a web-based console, and after creating a service, you can use the VPN service immediately without any waiting time.
Thorough Secure Connection You can securely connect from a customer’s external network to the customer’s internal network built on the Samsung Cloud Platform via encrypted virtual tunneling using a performance‑ and reliability‑validated IPsec VPN.
Simple operating environment You can easily and quickly manage web-based deployment, capacity provisioning, and service updates without the need for a complex network environment setup.
Efficient Service Use You can manage costs efficiently because you only pay for the amount of service used, without any separate installation fees.
Provided features
VPN provides the following features.
- Provide virtual tunneling encrypted with IPsec
- Compatible VPN: Secui – Bluemax (TG360),Paloalto,Axgate,Cisco-router/ASA/Meraki, Checkpoint,AWS,Azure,Vmware NSX-T
- Create Virtual Private Gateway
- Create a gateway to connect the customer’s network to a private network that cannot be accessed from outside.
- Create VPN Tunnel
- Select IPsec VPN Gateway (maximum of 5 VPN tunnels per VPN Gateway)
- In an IPsec VPN Gateway high-availability configuration, the Standby device automatically operates when a failure occurs on the Active device.
Constraints
| Category | Default quota | Detailed description |
|---|---|---|
| VPN Gateway | 3 | Up to three can be created per account |
| VPN Tunnel | 5 | Up to 5 can be created per VPN Gateway |
Provision status by region
VPN is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3(kr-south3) | Provide |
Preliminary Service
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
5.5.1.1 - ServiceWatch Metrics
VPN sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the VPN namespace.
The indicators whose names are displayed in bold below are the key indicators selected from the basic indicators provided by VPN. Key metrics are used to configure service dashboards that are automatically built for each service in ServiceWatch.
Each metric indicates, via the user guide, which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| Network In Total Bytes _vpn_tunnel | Cumulative traffic volume heading from VPN → VPC | Bytes |
|
| Network Out Total Bytes _vpn_tunnel | Cumulative traffic volume from VPC → VPN | Bytes |
|
| Network In Total Bytes _vpn_tunnel_Delta | Cumulative traffic volume over 5 minutes from VPN → VPC | Bytes |
|
| Network Out Total Bytes _vpn_tunnel_Delta | Cumulative traffic volume over 5 minutes from VPC → VPN | Bytes |
|
5.5.2 - How-to guides
Create VPN
You can create and use a VPN service from the Samsung Cloud Platform Console.
To create a VPN, follow these steps.
Click the All Services > Networking > VPN menu. You will be taken to the VPN Service Home page.
On the Service Home page, click the Create VPN button. You will be taken to the Create VPN page.
On the VPN creation page, enter the information required to create the service and select detailed options.
Enter the required information in the Service Information Input area.
Category Required statusDetailed description VPN Gateway name Required Enter VPN Gateway name - Enter using English letters and numbers, within 3 to 20 characters
Connected VPC name Required Select the VPC connected to the VPN Gateway - Click + New to create a VPC and then select it
Public IP Required Select the IP for communicating with the remote site from the VPN Gateway. Table. VPN Service Information Input ItemsEnter or select the required information in the Additional Information Input area.
Category Required statusDetailed description Explanation Selection User additional description tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values.
Table. VPN service additional information input fields
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- After creation is complete, check the created resources on the VPN List page.
Check VPN detailed information
The VPN service allows you to view and edit the full resource list and detailed information. VPN Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the VPN service, follow these steps.
- Click the All Services > Networking > VPN menu. You will be taken to the VPN’s Service Home page.
- On the Service Home page, click the VPN menu. You will be taken to the VPN List page.
- On the VPN List page, click the resource to view detailed information. You will be taken to the VPN Details page.
- VPC Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
On the VPN List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Service status | Current status
|
| Service termination | Cancel VPN service |
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | VPN resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation timestamp | Service creation timestamp |
| Editor | User who modified the service |
| Modification date and time | Date and time the service information was modified |
| VPN Gateway name | VPN Gateway name |
| Connected VPC name | VPC name connected to VPN |
| Public IP | IP information for communicating with remote sites from the VPN Gateway |
| Explanation | Additional description written by the user
|
tag
On the VPN List page, you can view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the VPN Details page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate VPN
You can terminate unused VPCs to reduce operating costs. However, terminating a service may cause the running service to stop immediately, so you should thoroughly consider the impact of service interruption before proceeding with the termination.
- If there are resources connected to a VPN, such as a VPN Tunnel, they cannot be terminated.
- The VPN service cannot be canceled when its status is Creating or Editing.
To cancel the VPN, follow these steps.
- Click the All Services > Networking > VPN menu. Go to the VPN Service Home page.
- From the Service Home page, click the VPN menu. You will be taken to the VPN List page.
- On the VPN List page, select the resource to cancel. Navigate to the VPN Details page.
- On the VPN Details page, click the Cancel Service button.
- Once the termination is complete, check on the VPN List page whether the resource has been terminated.
5.5.2.1 - VPN Tunnel
Create VPN Tunnel
In the Samsung Cloud Platform Console, you can configure IPSec Tunning with remote sites in the VPN service.
To create a VPN tunnel, follow these steps.
Click the All Services > Networking > VPN menu. Navigate to the VPN Service Home page.
On the Service Home page, click the Create VPN Tunnel button. You will be taken to the Create VPN Tunnel page.
On the VPN Tunnel creation page, enter the information required to create the service, and select detailed options.
Enter the required information in the Service Information Input area.
Category Required statusDetailed description VPN Tunnel name Required Enter VPN Tunnel name - Enter using English letters and numbers, within 3 - 20 characters
VPC Gateway name Required Select the VPN Gateway to connect VPC name Basic Automatically input VPC information connected to the VPN Gateway Public IP Basic Automatic entry of IP information for communicating with remote sites from the VPN Gateway Peer VPN GW IP Required Enter the IP information of the remote VPN - Example: 192.168.10.0
Romote Subnet(CIDR) Required Enter the subnet address of the remote site to connect - After entering the IP address, click the Add button; you can add up to 10 entries
- Example: 20.0.0.0/24
Pre-shared Key Required Enter the shared key (PSK) to be used for IKE mutual authentication between VPN gateways - Enter between 8 and 64 characters
- It is recommended to use a 32-character alphanumeric string
Explanation Select User additional description Table. VPN Tunnel Service Information Input ItemsEnter or select the required information in the Tunnel Settings area.
Category RequiredDetailed description IKE Settings > IKE Version Required Select IKE version IKE Settings > Algorithm Settings Required Select Encryption Algorithm and Digest Algorithm, then click the Add button. IKE configuration > Diffie-Hellman Required Diffie-Hellman Group Selection IKE configuration > SA Lifetime Required Enter the VPN session (Security Association) lifetime IPSec Settings > Algorithm Settings Required Select Encryption Algorithm and Digest Algorithm, then click the Add button. IPSec Settings > Perfect Forward Secrecy (PFS) Required Select whether to use the PFS group IPSec Settings > Diffie-Hellman Required Diffie-Hellman group selection IPSec Settings > SA Lifetime Required Enter the VPN session (Security Association) lifetime Table. VPN Tunnel configuration itemsEnter the required information in the DPD additional settings area.
Category RequiredDetailed description DPD additional settings > DPD probe interval Required Enter DPD test interval - Enter a value between 1 and 3,600 seconds
Table. VPN Tunnel DPD Additional Settings Input ItemsIn the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. VPN Tunnel additional information input fields
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- When creation is complete, check the created resource on the VPN Tunnel List page.
Check VPN Tunnel detailed information
VPN Tunnel service allows you to view and edit the full resource list and detailed information. VPN Tunnel Details page consists of Details, Tags, Activity Log tabs.
To view detailed VPN information, follow these steps.
- Click the All Services > Networking > VPN menu. Navigate to the VPN Service Home page.
- On the Service Home page, click the Create VPN Tunnel button. You will be taken to the VPN Tunnel List page.
- On the VPN Tunnel List page, click the resource to view detailed information. You will be taken to the VPN Tunnel Details page.
- VPN Tunnel Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
| Category | Detailed description |
|---|---|
| Status | Current status
|
| Delete VPN Tunnel | VPN Tunnel delete button |
Detailed Information
On the VPN Tunnel List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | VPN resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| VPN Tunnel name | VPN Tunnel name |
| VPN Gateway name | VPN Gateway name |
| Public IP | Public IP information |
| Peer VPN GW IP | Peer VPN GW Information
|
| Remote Subnet (CIDR) | Remote Sunet information
|
| Pre-shared Key | Pre-shared Key information
|
| status | Current service connection status |
| description | VPN Tunnel additional description
|
| IKE | Click the Edit button to bulk edit configuration information. |
| IKE Version | IKE Version information |
| Encryption Algorithm/Digest Algorithm | Algorithm information |
| Diffie-Hellman | Diffie-Hellman information |
| SA LifeTime | SA LifeTime information |
| IPSec | Click the Edit button to bulk edit the configuration information. |
| Encryption Algorithm/Digest Algorithm | Algorithm information |
| Diffie-Hellman | Diffie-Hellman information |
| SA LifeTime | SA LifeTime information |
| Perfect Forward Secrecy(PFS) | PFS configuration information |
| DPD | DPD probe interval information
|
tag
On the VPN Tunnel List page, you can view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
VPN Tunnel List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Delete VPN Tunnel
You can reduce operational costs by deleting unused VPC tunnels. However, deleting a tunnel may cause the running service to stop immediately, so you should carefully consider the impact of service interruption before proceeding with the deletion.
To cancel the VPN, follow these steps.
- Click the All Services > Networking > VPN menu. You will be taken to the VPN Service Home page.
- On the Service Home page, click the Create VPN Tunnel button. You will be taken to the VPN Tunnel List page.
- On the VPN Tunnel List page, click the resource to view detailed information. You will be taken to the VPN Tunnel Details page.
- VPN Tunnel Delete Click the button.
- After termination is complete, check the VPN Tunnel List page to see if the resource has been deleted.
5.5.3 - API Reference
5.5.4 - CLI Reference
5.5.5 - Release Note
VPN
- You can input up to 10 Romote Subnet (CIDR).
- A VPN service that connects the customer network to the Samsung Cloud Platform via an encrypted (IPSec) virtual private network has been launched.
5.6 - Firewall
5.6.1 - Overview
Service Overview
A firewall is a virtual logical firewall service that controls traffic occurring in the VPC and Load Balancer of Samsung Cloud Platform.
The resources that can be applied in the firewall are Internet Gateway, Direct Connect, and Load Balancer, and you can set rules for communication between the VPC and the Internet, and between the VPC and the customer network, enabling secure network management.
When a firewall is first created, it blocks all inbound and outbound traffic according to the default rule (Any Deny).
Users can specify an IP address, port, and protocol to create inbound/outbound rules, and only traffic permitted by the created rules can communicate.
Component
The components that make up a firewall are as follows.
| Component | Detailed description |
|---|---|
| Applicable target | Resources to which the firewall will be applied
|
| Firewall size | Firewall is offered in five sizes according to rule quota
|
| Firewall rule |
|
Constraints
The Firewall of Samsung Cloud Platform has a rule quota (limit) that can be created per size. When creating a Firewall, it is created by default as Extra Small, and you can change the Firewall size on the Firewall Details page of the Samsung Cloud Platform Console.
| Size | Rule quota | Detailed description |
|---|---|---|
| Extra Small | 5 | Maximum number of rules that can be created: 5 |
| Small | 100 items | Maximum number of rules that can be generated: 100 |
| Medium | 200 | Maximum number of rules that can be generated: 200 |
| Large | 500 | Maximum number of rules that can be generated: 500 |
| Extra Large | 1,000 items | Maximum number of rules that can be generated: 1,000 |
Preceding Service
This is a list of services that must be pre-configured before creating a Firewall service. Please refer to the user guide (reference link) provided below for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Direct Connect | A service that quickly and securely connects the customer’s network with the Samsung Cloud Platform network. |
| Networking | Load Balancer | A service that distributes traffic across multiple servers to maintain stable service. |
5.6.2 - How-to guides
Users can create the Firewall service by entering the required information and selecting detailed options through the Samsung Cloud Platform Console.
Create Firewall
You can create and use a Firewall service in the Samsung Cloud Platform Console.
The Firewall service must be enabled in the prerequisite service of Networking to be created. The enabled Firewall can be viewed in the Firewall list.
- Firewalls cannot be created independently, unlike other services in the Samsung Cloud Platform Console.
To enable the firewall, follow these steps.
Click the All Services > Networking > Firewall menu. Navigate to the Firewall’s Service Home page.
On the Service Home page, click the service you want to create. You will be redirected to the service creation page.
- VPC Creation: Configure the VPC service’s Internet Gateway and Transit Gateway firewall.
- When creating a VPC’s Internet Gateway service, set the Use Firewall option to Enabled. For detailed instructions, refer to Create Internet Gateway.
- Create a Transit Gateway service for the VPC and apply for the associated service of the Uplink Firewall. For detailed instructions, refer to Create Transit Gateway.
- Direct Connet Creation: When creating a Direct Connect service, set the Firewall Use option to Enabled. For detailed instructions, refer to Direct Connect 생성하기.
- Load Balancer Creation: When creating a Load Balancer service, set the Firewall Use option to Enabled. For detailed instructions, see Load Balancer Creation.
- VPC Creation: Configure the VPC service’s Internet Gateway and Transit Gateway firewall.
After the prerequisite service creation is complete, verify that the corresponding Firewall resource appears in the Firewall list.
Check firewall detailed information
The Firewall service can view and edit the full resource list and detailed information in the resource management menu.
To view detailed information about the firewall, follow these steps.
- Click the All Services > Networking > Firewall menu. Go to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- The Firewall List page shows the information below.
Category Detailed description Firewall name Automatically generated in the Firewall pre-service type_Firewall format Firewall classification Firewall pre-service type (Internet Gateway, Direct Connect, Load Balancer) Size User-selected Firewall size VPC name VPC name connected to the firewall Connection name Automatically generate in the format preceding service name_Firewall for services using Firewall. Number of rules Number of rules used on this firewall Whether to use Whether the firewall is used (enabled) or not used (disabled) - If not used, the Any Allow rule is applied and no charges are incurred for the firewall
status Firewall status display - More button can be clicked to set On/Off
Table. Firewall resource list items
- The Firewall List page shows the information below.
- On the Firewall List page, click the resource to view detailed information. It navigates to the Firewall Details page.
- Firewall Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity Log tabs.
Category Detailed description Service status Firewall status display - Creating: In progress
- Active: Operational
- Editing: In progress
- Deploying: Completed
- Deleting: In progress
- Error: Occurred
Table. Firewall status information
- Firewall Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity Log tabs.
Detailed Information
On the Firewall List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Firewall name | Automatically generated as the connection name for the resource name_Firewall |
| Firewall ID | Service’s unique resource ID |
| Firewall classification | Firewall prerequisite service types (Internet Gateway, Direct Connect, Load Balancer) |
| Size | The Firewall size selected by the user
|
| Firewall rule count/quota | The firewall’s rule quota and the number of rules currently in use |
| VPC name | VPC name connected to the Firewall
|
| VPC ID | VPC ID connected to the firewall |
| Connection name | {Firewall Prerequisite Service Name_Firewall} automatically generated
|
| Log saving option | Firewall log storage option
|
Rule
On the Firewall List page, you can view the rule list of the selected resource and add, modify, or delete rules.
| Category | Detailed description |
|---|---|
| Excel download | Download the currently entered rule list as an Excel (*.xlsx) file |
| Advanced Search | Search for rules that match the conditions set by the user
|
| Rule modification | Rules displayed in the rule list can be edited and deleted
|
| Add rule | Add new Firewall rule
|
| Order | Display rule order, apply top-down according to the rule order |
| Rule ID | Unique ID value for the rule
|
| Rule Index | Unique index value for the rule, used in log analysis |
| Source address | Origin address added to the rule |
| Destination address | Destination address added to the rule, displayed as the IP address according to the entered rule. |
| Service | Protocol and Destination Port |
| Operation | Traffic Allow/Deny distinction due to rules
|
| direction | Firewall traffic direction criteria
|
| Active status | Indicates whether the rule is active; if it is inactive, the rule does not operate. |
| status | Rule status display |
tag
Firewall List page lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Firewall List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Firewall Rule Management
You can add, modify, or delete firewall rules.
- You can add or modify rules only when the firewall status is Active.
- If you do not have permission to view the status in the preceding service, you cannot add a rule.
- The firewall periodically caches the domain rules registered by the user and retains the IP information for a certain period.
- If the cached result of the registered domain rule does not match the user’s IP, communication may be restricted.
Create Rule
In the Rules tab, you can directly input firewall rule information to add it.
To add a firewall rule, follow the steps below.
- Click the All Services > Networking > Firewall menu. Navigate to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- On the Firewall List page, click the resource to which you want to add a rule. You will be taken to the Firewall Details page.
- On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
- Click the Add Rule button on the Rules tab. You will be taken to the Add Rule page.
- Enter the required information on the Manual Input tab page.
- After checking the added rules, click the Complete button.
| Category | Required? | Detailed description |
|---|---|---|
| Rule location | Required | Specify the location of the rule to create |
| Rule ID to copy | Selection | Enter the Firewall rule ID to copy and click the Search button to select. |
| Source address | Required | Source addresses to add to the rule
|
| Destination address | Required | Select the type of destination address to add to the rule
|
| type | Required | Select protocol type to apply the rule
|
| Type > Protocol | Required | Select detailed protocol for the type
|
| Operation | Required | Traffic allow/deny classification based on rules
|
| Direction | Required | Firewall-based traffic direction
|
| Explanation | Selection | Additional description provided by the user |
| Added rule | - | Entered rules verification list
|
| Destination | Required | Destination address type to add to the rule
- Select IP or FQDN
- You can input multiple addresses at once, up to a maximum of 128, using CIDR (IP/Subnet Mask) format with commas (,) and ranges (-)
- Domain names can be entered in bulk using Comma(,) for up to 128 addresses at once
Batch create rules
To add multiple Firewall rules at once, follow these steps.
- Click the All Services > Networking > Firewall menu. Navigate to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- On the Firewall List page, click the resource to which you want to add a rule. You will be taken to the Firewall Details page.
- On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
- Click the Add Rule button on the Rule tab. You will be taken to the Add Rule page.
- Add Rule on the Batch Rule Input tab, click it.
- Please select the rule location. If you do not select a location, it will be added at the very last order of the rule.
- From File Selection, click the Download Form button. The bulk rule entry Excel file will be downloaded.
- Enter the rule information into the batch rule input Excel file, then save it.
- From File Selection, click Attach File to attach the Excel file you created, and click Add.
- You cannot upload if the attached Excel file format differs from the registration form or if the file is encrypted.
- You can upload up to 100 batch registration rules at a time. Uploads are not allowed if you exceed the maximum number of registration rules.
- If the number of rules set for the firewall size is exceeded, you cannot upload the file.
- Added rule Check that the rule you entered appears in the list and adjust its order.
- After checking the added rules, click the Complete button.
Modify Rules
You can select a firewall rule to view and edit its information.
To modify firewall rules, follow the steps below.
Click the All Services > Networking > Firewall menu. Go to the Service Home page of Firewall.
On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
Firewall List page, click the resource to edit the rule. You will be taken to the Firewall Details page.
On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
Click the Edit Rule button on the Rules tab. You will be taken to the Edit Rule page.
- On the rule edit page, you can configure the items below.
- Enable: Enables the selected rule.
- Disabled: Disables the selected rule. Disabled rules are not applied to preceding services.
- Delete: Delete the selected rule. Clicking Delete will mark the change as Pending Deletion.
- Cancel Deletion: If it is in a pending deletion state, you can cancel the rule deletion.
- On the rule edit page, you can configure the items below.
On the Edit Rule page, click the Edit button for the item you want to modify. The Edit Rule popup will open.
Rule Edit Enter the item you want to modify in the popup window and click the Confirm button.
Category Required? Detailed description Order - The order of rules can be changed by clicking Move Up/Move Down in the added rule list. Rule ID - Cannot be changed to a unique ID value for the rule Rule Index - Unique index value for the rule, usable in log analysis Source address Required Source addresses registered in the rule - in CIDR (IP/Subnet Mask) format, using commas (,) and ranges (-), can be entered and modified up to a maximum of 128 at once
Destination address Required Destination address to add to the rule - in CIDR (IP/Subnet Mask) format, using commas (,) and ranges (-) to input multiple addresses at once, up to a maximum of 128, for modification
type Required Set the protocol type according to the selected destination address entry Operation Required Traffic Allow/Deny classification can be changed by rules - Allow: Allow traffic when it matches the rule
- Deny: Block traffic when it matches the rule
direction Required The access direction of traffic defined by the firewall rule can be changed - Inbound: external → internal
- Outbound: internal → external
Rule location Required Rule position can be changed Active status Required Whether the rule is active; if it is disabled, the rule does not operate. status - State value for the rule description Select User-provided additional description Table. Detailed items for firewall rule modificationAfter reviewing the updated rules, click the Complete button.
Delete rule
To delete a firewall rule, follow the steps below.
- Click the All Services > Networking > Firewall menu. Go to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- Click the resource to edit the rule on the Firewall List page. Navigate to the Firewall Details page.
- On the Firewall Details page, click the Rules tab. You will be taken to the Rules tab page.
- In the Rule tab, click the Edit Rule button. You will be taken to the Edit Rule page.
- On the Edit Rule page, select the rule to delete and click the Delete button.
- When the deletion request is completed, the change item will be marked as Scheduled for deletion.
- Click Cancel Deletion to cancel the rule deletion.
- On the Edit Rule page, click the Complete button.
Managing Firewall Resources
You can modify the firewall size and change the log usage settings.
Modify Firewall Size
To modify the size of the firewall, follow these steps.
- Click the All Services > Networking > Firewall menu. Go to the Firewall’s Service Home page.
- On the Service Home page, click Firewall List. You will be taken to the Firewall List page.
- Click the resource to edit on the Firewall List page. Navigate to the Firewall Details page.
- On the Firewall Details page, click the Size Edit icon. You will be taken to the Size Edit popup.
- Resize In the popup window, select the size to adjust, and click the Confirm button.
The firewall size is provided as the default Extra Small (rule quota 5), and you can change the firewall size to add firewall rules for use. For more details, refer to Firewall Constraints.
- Firewall fees are charged based on the size of the Firewall service and traffic throughput.
Using Log Storage
To store firewall logs, first create a bucket in Object Storage for the logs and configure that bucket in the log repository of Firewall Logging. Then, by setting log storage in the firewall detail view, firewall logs will be saved to the Object Storage bucket.
- The log storage settings can be checked in Firewall Logging. For more information, see Firewall Logging.
- If you configure a log repository, Object Storage charges for log storage will be applied.
To use firewall log storage, follow these steps.
- Click the All Services > Networking > Firewall menu. Go to the Service Home page.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- Firewall List page, click the resource (Firewall) for which you want to enable log storage. You will be taken to the Firewall Details page.
- On the Firewall Details page, click the Edit icon of Log Save Setting. You will be taken to the Edit Log Save Setting popup.
- Modify Log Saving Option In the popup window, select Use for the log repository, and click the Confirm button.
Disable log storage
To set firewall log storage to disabled, follow these steps.
- Click the All Services > Networking > Firewall menu. You will be taken to the Service Home page.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- Firewall List page, click the resource (Firewall) that does not use log storage. You will be taken to the Firewall Details page.
- Click the Modify Log Save Setting button. You will be taken to the Modify Log Save Setting popup.
- Modify Log Saving Option In the popup window, deselect Use for the log repository, and click the Confirm button.
- Notification Check the message in the popup window and click the Confirm button.
Disable Firewall
The Firewall service cannot be deleted on its own. Deleting the preceding service will also delete the associated Firewall. When you choose not to use the firewall while retaining the preceding service, you can set the firewall to an unused state on the firewall list page.
- If you change the firewall to an unused state, all previously registered rules will be deleted.
- You cannot delete a preceding service if there are firewall rules associated with it. Delete the firewall rules before deleting the preceding service.
To disable the firewall, follow these steps.
- Click the All Services > Networking > Firewall menu. You will be taken to the Service Home page.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, click More > Unused for the resources you want to mark as unused.
- After the usage change is completed, verify on the Firewall List page that the resource’s usage status has been changed to unused.
5.6.2.1 - Firewall Logging
To store firewall logs, first create a bucket in Object Storage for the logs and configure that bucket in the log repository of Firewall Logging. Then, on the Firewall Details page, set up log storage, and the firewall logs will be saved to the Object Storage bucket.
To save firewall logs, configure it according to the following steps.
- To store firewall logs, you can create a bucket in Object Storage or use an existing bucket. To create a bucket, refer to Create Object Storage.
- To set the bucket for the Firewall Logging log repository, refer to Firewall Logging 로그 저장소 사용하기.
- To set the log storage option to Enabled in the detailed view of the Firewall, refer to Using Firewall Log Storage.
Firewall Logging Configure log storage usage
To set the firewall’s log storage to enabled, you must first configure the log repository in Firewall Logging.
To enable the Firewall Logging log repository, follow these steps.
- Click the All Services > Management > Network Logging > Firewall Logging menu. Go to the Firewall Logging List page.
- On the Firewall Logging List page, click the top Log Storage Settings button. You will be taken to the Log Storage Settings popup.
- Log storage settings In the popup window, select the log storage bucket. When you select a bucket, the log storage path is displayed.
- Log storage settings In the popup window, after verifying Log storage bucket and Log storage path, click the Confirm button.
- Notification After reviewing the popup message, click the Confirm button.
View Firewall Logging List
If you configure the Firewall Logging log storage bucket, you can view the Firewall Logging list.
To view the Firewall Logging list, follow these steps.
- Click the All Services > Management > Network Logging > Firewall Logging menu. You will be taken to the Firewall Logging List page.
- On the Firewall Logging List page, verify the resources in use and the log storage targets.
Category Detailed description Resource ID Firewall ID Save target Firewall name Save registration date and time Firewall log repository registration timestamp Table. Firewall Logging list items
Check detailed information of Firewall Logging
Refer to the information below to view the detailed contents of the stored log.
Stored log example: 2024-10-11T11:23:43,deny,0,17,4.1.1.100,45499,192.168.10.10,53
| Category | description |
|---|---|
| 2024-10-11T11:23:43 | Date and time of the log occurrence (2024-10-11, 11:23:43) |
| deny | Action (deny / accept) |
| 0 | Firewall Rule ID (Policy ID) that generated the log |
| 17 | IP Protocol ID
|
| 4.1.1.100 | Source IP |
| 45499 | Departure Port |
| 192.168.10.10 | Destination IP |
| 53 | Destination Port |
Firewall Logging Configure to not use log storage
In Firewall Logging, you can set the log repository to unused.
Firewall Logging To disable the log repository, follow the steps below.
- Click the All Services > Management > Network Logging > Firewall Logging menu. You will be taken to the Firewall Logging List page.
- Firewall Logging List page, click the top Log Storage Settings button. You will be taken to the Log Storage Settings popup.
- Log storage settings In the popup window, select Log storage bucket as Not used, and click the Confirm button.
- Log storage settings can be changed when no log storage target is configured.
- To change the log storage bucket, first set it to disabled. Then you can modify it by re-enabling it.
5.6.2.2 - Migration Rules
Users can retrieve rules created in the V1 environment of the Samsung Cloud Platform Console and apply them to the V2 service.
Get firewall rules
You can import rules created in the V1 environment of the Samsung Cloud Platform Console and migrate them to the V2 service for use.
- When a firewall rule is transferred using the Migration feature, the Migration label appears before its name.
- If a firewall rule description exceeds 100 characters, part of the description will be truncated and appended.
- Rules that exceed the maximum quantity are not registered due to rule quantity limits based on firewall size.
To retrieve the V1 firewall rules, follow these steps.
All Services > Networking > Firewall Click the menu. 1. Navigate to the Service Home page of the Firewall.
On the Service Home page, click the Migration Rules menu. 2. Go to the Migration Rules page.
Select the rule information to retrieve from the Migration Rules page and click Done.
Category Detailed description Original rule environment SCP v1 (Vmware) Auto-select Applicable target Select the Firewall list in the account to which the transferred rule will be applied Get rules Click the File Attachment button to upload the decrypted Firewall rule file - After decrypting and saving the rule file extracted from the original environment, upload
Rule List View uploaded Firewall rule file details - Move Up: Move the selected rule up in the list
- Move Down: Move the selected rule down in the list
- Delete: Delete the selected rule
- Edit: Modify the selected rule information; see Edit Transferable Firewall Rule for details
Rule location Set the position of the selected firewall rule - After the last rule: Move the selected rule after the last rule
- Set before the specified rule / Set after the specified rule: Enter the rule ID to move the selected rule before or after the specified rule
Table. Migration Rules detailed itemsAfter the firewall rule transfer request is completed, verify that the transferred item has been added to the firewall list.
Modify the Firewall rule to be transferred
You can edit each item when retrieving rules created in the V1 environment of the Samsung Cloud Platform Console.
To edit the Firewall rules to be imported from V1, follow these steps.
Click the All Services > Networking > Firewall menu. 1. Navigate to the Service Home page of the Firewall.
On the Service Home page, click the Migration Rules menu. 2. Go to the Migration Rules page.
Click Attach file in the rule import item to upload the Firewall rule file.
In the rule list, click Edit for the rule item you want to modify.
Category Required or not Detailed description origin address Essential Source addresses to add to the rule - in CIDR (IP/Subnet Mask) format, using commas (,), ranges (-) to input multiple addresses, up to a maximum of 128 at once
Destination address Essential Select the type of destination address to add to the rule - IP: In CIDR (IP/Subnet Mask) format, you can enter multiple addresses at once using commas (,) and ranges (-), up to a maximum of 128.
- Domain: In FQDN format, you can enter up to 128 full domain names at once using commas (,).
- The type items vary depending on the selected destination address format.
type Required Select protocol type to which the rule will be applied - Select destination port/Type: Select protocol type
- Internet Protocol: Enter protocol numbers, up to 128 entries allowed
- All: Select destination port/Type and protocol for the entire range, meaning all ports for all protocols
Type > Protocol Required Select detailed protocol for the type - Select the desired protocol among TCP, UDP, and ICMP; input fields vary depending on the selected protocol
- When ICMP is selected in the protocol, you can set the ICMP Type
- Select a commonly used Type, such as Echo, from the values defined for ICMP Type
- Click the Add button to add an input value
- When TCP/UDP is selected in the protocol, you can select allowed ports such as SSH, HTTP, TELNET, etc.
- When entering manually, you can input values from 1 to 65535, and you can enter up to 128 entries at once using commas (,) or ranges (-)
- Click the Add button to add an input value
- When Internet Protocol is selected in the type
1 - 254Enter the protocol number within the range
Operation Required Traffic allow/block classification by rule - Allow: Allow traffic when it matches the rule
- Deny: Block traffic when it matches the rule
Direction Essential Firewall standard traffic direction - Inbound: external → internal
- Outbound: internal → external
Active status Required Set rule activation status - If disabled, the rule does not execute
Explanation Selection Additional description written by the user Table. Detailed items of the Firewall rule edit windowWhen the rule information edit is complete, click Confirm in the edit window.
Review the modified rule information and click Done.
5.6.3 - API Reference
5.6.4 - CLI Reference
5.6.5 - Release Note
Firewall
- For user convenience, a Migration Rules page has been added that allows you to import firewall rules created in the V1 environment and apply them to the V2 service.
- The method for entering and modifying/deleting firewall rules has been changed for user convenience. * When managing firewall rules, you can navigate to a separate page to perform the desired actions.
- Add firewall rule input method
- In the KR WEST and KR EAST regions, you can enter the destination address in FQDN (Fully Qualified Domain Name) format.
- Add firewall rule input method
- A feature to input IP protocols has been added.
- Add firewall functionality
- You can use Firewall in the Load Balancer service.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- A feature to save firewall logs has been added.
- You can decide whether to store firewall logs and store the logs in Object Storage.
- Through the Firewall service, you can control inbound and outbound traffic in a VPC.
- The Firewall service has been released.
5.7 - Direct Connect
5.7.1 - Overview
Service Overview
Samsung Cloud Platform provides a Direct Connect service that supports safe and fast connections between the customer’s network and the Samsung Cloud Platform environment.
Through Direct Connect, you can allocate the internal private network range of an existing system to Samsung Cloud Platform resources for use. You can deploy backend systems such as application servers in a private network range without internet access, and enhance security by applying Samsung Cloud Platform network services such as Security Groups.
Through Direct Connect, customers can seamlessly migrate their existing systems to Samsung Cloud Platform even if they hard-code IP addresses on devices or have architecture dependencies on IP.
Direct Connect Connection Creation
Supports connecting by selecting a single VPC to connect to the customer network.
Access can be blocked through the Direct Connect Firewall, and a Route configuration feature is provided to ensure a secure connection path.
Constraints
| Category | Default quota | Detailed description |
|---|---|---|
| Direct Connect | 5 | Based on the account, you can create one VPC per service zone (1:1). |
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
5.7.1.1 - ServiceWatch Metrics
Direct Connect sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals.
Basic Metrics
The following are the basic metrics for the Direct Connect namespace.
The indicators whose names are displayed in bold below are the key indicators selected from the basic indicators provided by Direct Connect. Key metrics are used to configure service dashboards that are automatically generated for each service in ServiceWatch.
Each metric indicates through the user guide which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the statistical values shown in bold text are the primary statistics. In the service dashboard, primary metrics can be viewed using the primary statistical values.
| Indicator Name | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| DirectConnect Network In Bytes | Cumulative traffic volume toward VPC from Direct Connect | Bytes |
|
| DirectConnect Network Out Bytes | Cumulative traffic volume from VPC to Direct Connect | Bytes |
|
| DirectConnect Network In Bytes_Delta | Cumulative traffic volume over 5 minutes from Direct Connect → VPC | Bytes |
|
| DirectConnect Network Out Bytes_Delta | Cumulative traffic volume over 5 minutes from VPC → Direct Connect | Bytes |
|
5.7.2 - How-to guides
Users can create the service by entering the required information for the Direct Connect service and selecting detailed options through the Samsung Cloud Platform Console.
Create Direct Connect
You can create and use the Direct Connect service in the Samsung Cloud Platform Console.
To create Direct Connect, follow these steps.
Click the All Services > Networking > Direct Connect menu. Navigate to the Service Home page of Direct Connect.
On the Service Home page, click the Create Direct Connect button. You will be taken to the Create Direct Connect page.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Direct Connect name Required A name for Direct Connect that is easy to identify - Enter using English letters (uppercase and lowercase) and numbers, within 3 to 20 characters
Use Uplink Required Bandwidth of the communication port for remote communication - Select port capacity of 1G or 10G
VPC Required Select a VPC for communicating with remote locations Explanation Selection Enter a description of Direct Connect Use firewall Select Select whether to use Direcrt Connect Firewall. Whether to save firewall logs Select Firewall log saving option - Select whether to save firewall logs
- When using the firewall, connection logs are saved
- For more details, refer to Using Firewall Log Saving.
Table. Direct Connect service information input items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Direct Connect additional information input fields
- Enter or select the required information in the Service Information Input area.
Summary Check the detailed information and estimated charges generated in the panel, and click the Complete button.
- Once creation is complete, check the created resources on the Direct Connect List page.
Direct Connect View detailed information
The Direct Connect service allows you to view and edit the full resource list and detailed information from the Resource Management menu. The Direct Connect Details page consists of Details, Rules, Tags, Activity Log tabs.
To view the detailed information of Direct Connect, follow these steps.
- Click the All Services > Networking > Direct Connect menu. You will be taken to Direct Connect’s Service Home page.
- On the Service Home page, click the Direct Connect menu. You will be taken to the Direct Connect List page.
- On the Direct Connect List page, click the resource for which you want to view detailed information. You will be taken to the Direct Connect Details page.
- The Direct Connect Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity History tabs.
Category Detailed description Status Current status - Active: Operating normally
- Deleting: Deletion in progress
- Creating: Creation in progress
- Failed: Failed
- Error: Unable to determine current status
- If it occurs continuously, contact the registered administrator
Service termination Button to terminate the service - Terminate Direct Connect when there are no linked services
- When terminating a service, the running service may be stopped immediately; therefore, proceed with the termination only after fully considering the impact of service interruption
Table. Direct Connect status information and additional features
- The Direct Connect Details page displays status information and additional feature information, and consists of Details, Rules, Tags, Activity History tabs.
Detailed Information
Direct Connect List page lets you view detailed information of the selected resource and, if needed, modify the information.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Direct Connect resource type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Direct Connect resource name |
| Resource ID | Unique resource ID in Direct Connect |
| Constructor | User who created Direct Connect |
| Creation timestamp | Direct Connect creation date and time information |
| Editor | User who modified Direct Connect information |
| Modification date and time | Date and time the Direct Connect information was modified |
| Direct Connect name | Direct Connect VPC resource name |
| Using UPlink | Port range allocated for line connection |
| Line request/cancellation SR shortcut | Service for connecting the line in the Samsung Cloud Platform local segment that connects to the customer’s line
|
| Connected VPC name | Name of the VPC connected to Direct Connect |
| Firewall name | Firewall name |
| Use firewall | Firewall usage |
Rule
You can register or modify communication rules between remote sites and the VPC.
| Category | Detailed description |
|---|---|
| Destination IP | Destination IP information |
| Destination | Routing direction |
| Creation timestamp | Creation timestamp information |
| status | Connection status
|
| Delete | You can delete the rule. |
tag
Direct Connect list page allows you to view, add, modify, or delete the tag information of the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Direct Connect List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Direct Connect Add Rule
- Click the All Services > Networking > Direct Connect menu. You will be taken to the Service Home page of Direct Connect.
- On the Service Home page, click the Direct Connect menu. You will be taken to the Direct Connect List page.
- On the Direct Connect List page, click the resource to which you want to add a rule. You will be taken to that resource’s Direct Connect Details page.
- On the Direct Connect Details page, click the Rules tab.
- Click the Add Rule button in the Rules tab. You will be taken to the Add Rule popup.
- Add Rule Enter the required information in the popup window, and click the Confirm button.
Category Detailed description Destination IP Enter destination IP range - Example:
192.168.25.0/24
Destination Choose between the VPC and the remote location according to the routing direction. Table. Direct Connect rule additional input fields - Example:
Terminate Direct Connect
You can terminate unused VPCs to reduce operating costs. However, terminating a service may cause the running service to stop immediately, so you should thoroughly consider the impact of service interruption before proceeding with the termination.
To cancel Direct Connect, follow the steps below.
- Click the All Services > Networking > Direct Connect menu. You will be taken to Direct Connect’s Service Home page.
- On the Service Home page, click the Direct Connect menu. You will be taken to the Direct Connect List page.
- On the Direct Connect List page, click the resource to terminate. You will be taken to that resource’s Direct Connect Details page.
- On the Direct Connect Details page, click the Cancel Service button.
- When termination is complete, check on the Direct Connect List page whether the resource has been terminated.
5.7.3 - API Reference
5.7.4 - CLI Reference
5.7.5 - Release Note
Direct Connect
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- We are launching the Direct Connect service that quickly and securely connects the customer’s network with the Samsung Cloud Platform network.
5.8 - Cloud LAN-Campus
5.8.1 - Overview
Service Overview
Cloud LAN-Campus is a service that provides a user‑authentication‑based wired and wireless integrated network environment within the customer’s premises. By offering simple user/device authentication, it delivers a wired and wireless integrated network access environment for various purposes that can be freely used regardless of location within the premises, based on SDN (Software Defined Network). It minimizes the need for physical network equipment and uses the cloud to easily connect multiple geographically distributed locations. This allows enterprises to reduce the complexity of infrastructure deployment and operation, and to build a flexible and scalable network environment. Additionally, with network and firewall design/configuration optimized for the customer’s environment, professional operating systems, and enhanced security management, the site network can be operated more reliably and efficiently.
Provided features
Cloud LAN-Campus provides the following features.
- Campus Network: Providing wired and wireless network usage environment and integrated authentication services for the site
- NW Access: Infrastructure (AP, NW Switch, etc.) and SDN system services for site network usage
- NW Authentication: User/device authentication-based network segmentation, integrated management of authentication and security policies across multiple sites, support for various authentication methods (AD, certificates, etc.) and policy operation/management through the service portal (user/administrator)
- Campus Firewall: Enterprise firewall design and integrated configuration, operation, and management service provision
Features
- Rapid Business Site Network Work Environment: Provides a unified wired/wireless network usage environment through a user authentication-based SDN (Software Defined Network) solution. IP Mobility and separated networks based on device purpose are applied instantly, and users can easily perform network topology changes via the service portal.
- Network Security Enhancement: By applying logical network segmentation and an authentication-based unified wired/wireless security management system, consistent security policies can be enforced for users and devices. Even when users access the headquarters and multiple sites, the same network access environment and security policies can be applied, and authentication information is securely managed under the Samsung Cloud Platform security framework.
- Multi-Vendor Acceptance and Total Network Service Provision: Performing multi-vendor network integration certification makes the site’s SDN equipment configuration flexible. Additionally, by providing an integrated service framework instead of the customer designing/building/operating/managing the network infrastructure themselves, operational and management efficiency improves. We provide optimized network designs per site and fast, reliable network services through a dedicated team.
- Service-Type Integrated Billing System: The billing system can reduce initial investment costs, and when needed, network infrastructure can be expanded and capacity increased. It provides usage-based authentication services, and no separate operational staff or maintenance contracts are required.
- Various authentication methods and scalability: We provide the optimal authentication solution for customers using various authentication methods. Additionally, we enable functional expansion through integration with client systems (groupware, security systems, etc.) and allow differentiated policy management based on security levels per site.
Component
Cloud LAN-Campus provides services across the entire on‑premises network. The components are listed below, and related services can be created.
| Category | Detailed description |
|---|---|
| Network authentication |
|
| Service portal | Provision of unified wired/wireless authentication service portal
|
| wired/wireless network | Design and integrated configuration/operation/management of SDN-based wired/wireless networks |
| WIPS | Wireless Intrusion Prevention System Configuration/Operation/Management |
| Network solution | Configuration, operation, and management of network solutions such as DHCP and NMS |
| Firewall | Enterprise firewall design and integrated configuration/operation/management |
Constraints
When using the Cloud LAN-Campus service, there are the following limitations.
- To use CLAN authentication, network communication/connection between the customer’s premises and the Samsung Cloud Platform region is required.
- Use Cloud Last Mile, dedicated lines, VPN, etc.
- If the use of a specific vendor’s network or firewall equipment is required, prior consultation is necessary.
- After creating the service to configure equipment within the site, the service’s start and end times are finalized after consulting with the responsible AM.
- When using AD integration for authentication, the authentication-related policy rules must be properly deployed to the user’s PC in advance.
- AD functional issues require oversight by the client’s AD administrator.
- The network segmentation certificate method is supported for the designated OS type (currently limited to Windows), and additional costs apply beyond the certification fee.
Provision status by region
Cloud LAN-Campus can be provided in the environments below.
| Region | Availability |
|---|---|
| Korea West (kr-west1) | Provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preceding Service
Cloud LAN-Campus has no prerequisite services.
5.8.2 - How-to guides
Users can create the service by entering the required information for the Cloud LAN-Campus service and selecting detailed options through the Samsung Cloud Platform Console.
Create Campus Network
You can create and use the Campus Network service in the Samsung Cloud Platform Console.
- Click the All Services > Networking > Cloud LAN-Campus menu. Navigate to the Cloud LAN-Campus Dashboard page.
- Cloud LAN-Campus Dashboard page, click the Create Campus Network button. You will be taken to the Create Campus Network page.
- On the Campus Network Creation page, after entering the relevant information in the service information input area, click the Complete button.
- Select the service type from NW Access or NW Authentication, and enter the detailed information accordingly.
- NW Access: Select items that require network services, and after creation, the equipment configuration size and monthly service fee are determined through design/consulting.
- NW Authentication: Create an authentication tenant using the generated resource name. Billing is monthly based on usage per tenant, and tenant-specific policy management is available in the CLAN admin portal.
Category Required statusDetailed description Campus Network name Required Enter the Campus Network name to create - Automatic duplicate check is performed, and resources are created with the entered name
- Use English letters, numbers, and special characters (
-_) to input 3-30 characters
Service Category Required Select the type of service to create - Select between NW Access and NW Authentication
Service Category > NW Access Required NW Access Service Creation Item Input - Contract period: Select from 4 to 7 years
- [Wired] NW Access: Select whether to use wired NW
- [Wireless] NW Access: Select whether to use wireless NW
- [Wireless] WIPS usage: Select whether to use wireless WIPS
- Network solution: Select whether to use network solutions such as DHCP
Service Category > NW Authentication Required Select NW network segmentation method - Account/Device: AD integration, network segmentation via account/MAC information, etc.
- Certificate: Network segmentation through certificate binding
Table. Edge Server list items
- Select the service type from NW Access or NW Authentication, and enter the detailed information accordingly.
- After creation is complete, check the created resources on the Campus Network List page.
- When a service is created, the resource status is Request, and the service proceeds under the confirmation of the responsible Samsung SDS AM.
- After creating the service, you can contact the Samsung SDS account manager for progress updates and related inquiries.guide
- When the Cloud LAN-Campus service creation is complete, a customer representative will contact you separately for site consulting and architecture optimization design.
- After completing the consultation with the customer’s representative, network equipment installation work for actual service use within the site proceeds, and service provision begins according to the agreed schedule.
Campus Network Check detailed information
The Cloud LAN-Campus service allows you to view and edit the full resource list and detailed information. Cloud LAN-Campus Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about Cloud LAN-Campus, follow these steps.
- Click the All Services > Networking > Cloud LAN-Campus menu. Navigate to the Service Home page.
- On the Service Home page, click the Campus Network menu. You will be taken to the Campus Network List page.
- On the Campus Network List page, click the resource to view detailed information. You will be taken to the Campus Network Details page.
- Campus Network Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description Service status Service status: Billing is monthly, starting at the Active month and ending at the Deleted month - Request: Service creation status
- Creating: Workplace equipment installation and authentication system setup in progress
- Active: Service in progress
- Deleting: Service termination request status
- Deleted: Service termination completed (removed from resource list)
Service termination Cancel Service button Table. Cloud LAN-Campus status information and additional functions
- Campus Network Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
Campus Network List page lets you view detailed information of the selected resource and edit the information when necessary.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Service’s unique resource ID |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Contract period | Service contract period
|
| Service start date | Service start date |
| Contract expiration date | Service contract expiration date |
| Explanation | Additional description written by the user |
| Service Category | Created service classification information (NW Access / NW Authentication) |
| NW Access | Managed Service Managed Service Information |
| NW Access > [Wired] NW Access | Use wired network service |
| NW Access > [Wired] L2 Quantity | Number of wired Access switches in service |
| NW Access > [Wireless] NW Access | Wireless network service usage |
| NW Access > [Wireless] WIPS | Use of wireless WIPS service |
| NW Access > [Wireless] AP/Sensor quantity | Number of wireless AP/Sensor in service |
| NW Access > Network Solution | Network solution usage |
| NW Access > Network Solution Details | Details of the NW solution in service |
| NW Authentication | CLAN authentication tenant name CLAN authentication CLAN authentication tenant name
|
| NW Authentication >Network Segmentation Status | Number of logically separated network domains, network domain types |
| NW Authentication > Current Month Usage Status | Current month’s CLAN authentication and other authentication usage status |
tag
On the Campus Network List page, you can view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Campus Network List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Campus Network
You can reduce operating costs by terminating the unused service.
To cancel the Campus Network, follow the steps below. To cancel the Cloud Network service, follow these steps.
- Click the All Services > Networking > Cloud LAN-Campus menu. You will be taken to the Cloud LAN-Campus Dashboard page.
- On the Cloud LAN-Campus List page, click the resource to terminate. You will be taken to the Cloud LAN-Campus Details page.
- Cancel Service button, click it.
- After the termination is created, you can contact the Samsung SDS account manager for status updates and related inquiries.
- After the termination is complete, check on the Cloud LAN-Campus list page whether the resource has been terminated.
- If you request termination of the Cloud LAN-Campus service, a customer representative will contact you separately in advance to verify and process the termination.
- The service will be terminated according to the schedule agreed upon with the customer representative.
5.8.2.1 - Campus Firewall Request Service
In the Samsung Cloud Platform Console, you can request the creation or termination of a Campus Firewall service for a Campus Network.
Request to Create Campus Firewall Service
You can create and use the Campus Firewall service in the Samsung Cloud Platform Console.
To request the creation of a Campus Firewall service, follow these steps.
- Click the All Services > Networking > Cloud LAN-Campus menu. Navigate to the Service Home page.
- On the Service Home page, click the Campus Firewall Service Request button. You will be taken to the Support Center > Service Request page.
- On the Service Request page, enter or select the required information in the mandatory input fields.guideSelect Campus Firewall Service Creation for the task type.
Input field Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform - Automatically filled with the account’s region
Service Select the service category and service for the target service (auto-select) - Service Category: Networking
- Service: Cloud LAN-Campus
Task classification Select the Activity you want to perform - Campus Firewall Service Creation: select if you are requesting this service
- Campus Firewall Service Termination: select if you are terminating this service
content Enter detailed information required to create a Campus Firewall service - Company/Corporation Name: Required
- Customer Information (Name / E‑Mail / Phone Number): Enter user information
- Content: Required
Attachment If you have additional files you want to share, proceed with the upload - Attachments can be up to 5 files, each within 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files are allowed
Table. Detailed contents of Campus Firewall service request items - Check the required information entered on the Service Request page, and click the Request button.
- The requested work is expected to take about 5–7 business days.
- Once the service request is completed, a customer representative will contact you separately for site consulting and architecture optimization design.
- After consulting with the customer’s representative is completed, the firewall equipment installation for actual service use within the site proceeds, and service provision begins according to the agreed schedule.
- You can contact the responsible AM at Samsung SDS for progress updates and related inquiries.
Request to cancel Campus Firewall service
You can cancel the Campus Firewall service from the Samsung Cloud Platform Console.
Follow these steps to request termination of the Campus Firewall service.
- Click the All Services > Networking > Cloud LAN-Campus menu. You will be taken to the Service Home page.
- On the Service Home page, click the Campus Firewall Service Request button. You will be taken to the Support Center > Service Request page.
- On the Service Request page, enter or select the required information in the mandatory input fields.InformationSelect Campus Firewall Service Termination as the task type.
Input field Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform - Automatically filled with the region of the Account
Service Select the service category and service for the given service (auto-select) - Service Category: Networking
- Service: Cloud LAN-Campus
Task classification Select the Activity you want to perform - Create Campus Firewall service: select if you are requesting this service
- Terminate Campus Firewall service: select if you are terminating this service
content Enter detailed information required to cancel the Campus Firewall service - Company/Corporation Name: Required
- Customer Information (Name/ E-Mail/ Phone Number): Enter user information
- Content: Required
Attachment If you have additional files you want to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files can be attached
Table. Detailed contents of Campus Firewall service request items - Verify the required information entered on the Service Request page, then click the Request button.
- The requested work is expected to take about 5–7 business days.
- When the service request is completed, a customer representative will contact you separately to cancel the service.
- You can contact the responsible AM at Samsung SDS for progress updates and related inquiries.
5.8.3 - Release Note
Cloud LAN Campus
- We have launched the Cloud LAN Campus service, which provides an authentication‑based integrated wired/wireless network service within the customer’s premises.
5.9 - Cloud LAN-Campus
5.9.1 - Overview
Service Overview
Cloud LAN-Campus is a service that provides a user authentication‑based integrated wired and wireless network environment within the customer’s premises. It offers a versatile integrated network access environment, based on SDN (Software Defined Network), that can be freely used regardless of location within the site through simple user/device authentication. By minimizing physical network equipment and leveraging the cloud, multiple geographically distributed locations can be easily connected. This allows enterprises to reduce the complexity of infrastructure deployment and operation, and to build a flexible, scalable network environment. Additionally, with network design/configuration optimized for the customer’s environment, professional operational systems, and enhanced security management, the site network can be operated more reliably and efficiently.
Provided features
Cloud LAN-Campus provides the following features.
- Campus Network: Providing wired and wireless network usage environment and integrated authentication services for the site
- NW Access: Infrastructure (AP, NW Switch, etc.) and SDN system services for site network usage
- NW Authentication: User/device authentication-based network segmentation, integrated management of authentication/security policies across multiple sites, support for various authentication methods (AD, certificates, etc.) and policy operation/management through the service portal (user/administrator)
Features
- Rapid Business Site Network Work Environment: Provides a unified wired/wireless network usage environment through a user-authentication-based SDN (Software Defined Network) solution. IP Mobility and device-purpose-based separated networks are applied instantly, and users can easily perform network topology changes via the service portal.
- Network Security Enhancement: By applying logical network segmentation and an authentication-based unified wired/wireless security management system, consistent security policies can be enforced for users and devices. Even when users access the headquarters and multiple sites, the same network access environment and security policies can be applied, and authentication information is securely managed under the Samsung Cloud Platform security framework.
- Multi-Vendor Acceptance and Total Network Service Provision: Performing multi-vendor network integration certification makes the SDN equipment configuration at each site flexible. Additionally, by providing an integrated service framework instead of customers designing/building/operating/managing the network infrastructure themselves, operational and management efficiency improves. We deliver fast and reliable network services with site-optimized network designs and dedicated teams.
- Service-based Integrated Billing System: The billing system can reduce initial investment costs, and when needed, network infrastructure can be expanded and capacity increased. It provides usage-based authentication services, and no separate operational staff or maintenance contracts are required.
- Various authentication methods and scalability: We provide the optimal authentication solution for customers using various authentication methods. Additionally, we enable functional expansion through integration with client systems (groupware, security systems, etc.) and allow differentiated policy management based on security levels per site.
Component
Cloud LAN-Campus provides services across the entire network within the site. The components are as follows, and related services can be created.
| Category | Detailed description |
|---|---|
| Network authentication |
|
| Service portal | Provision of unified wired/wireless authentication service portal
|
| wired/wireless network | Design and integrated configuration, operation, and management of SDN-based wired and wireless networks |
| WIPS | Wireless Intrusion Prevention System Configuration/Operation/Management |
| Network solution | Configuration/operation/management of network solutions such as DHCP, NMS |
Constraints
When using the Cloud LAN-Campus service, there are the following limitations.
- Network communication/connection between the customer’s site and the Samsung Cloud Platform region is required to use CLAN authentication.
- Use Cloud Last Mile, dedicated lines, VPN, etc.
- If you need to use network equipment from a specific vendor, prior consultation is required.
- After creating the service to configure equipment within the site, the start and end times of the service are finalized after consultation with the responsible AM.
- When using AD integration for authentication, the authentication-related policy rules must be properly deployed to the user’s PC in advance.
- Issues with AD functionality require management by the client’s AD administrator.
- The network segmentation certificate method is supported for the designated OS type (currently limited to Windows), and additional costs apply beyond the certification fee.
Provision status by region
Cloud LAN-Campus can be provided in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preceding Service
Cloud LAN-Campus has no prerequisite services.
5.9.2 - How-to guides
Users can create the service by entering the required information for the Cloud LAN-Campus service and selecting detailed options through the Samsung Cloud Platform Console.
Campus Network Service Creation Request
You can create and use the Campus Network service in the Samsung Cloud Platform Console.
To request the creation of a Campus Network service, follow these steps.
- Click the All Services > Networking > Cloud LAN-Campus menu. You will be taken to the Service Home page.
- On the Service Home page, click the Cloud LAN-Campus Service Request button. You will be taken to the Support Center > Service Request page.
- On the Service Request page, enter or select the required information in the mandatory input fields.
- In the task type, select Campus Network Service Request.
Input field Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform - Automatically filled with the account’s region
Service Select the service category and service for the given service (auto-select) - Service Category: Networking
- Service: Cloud LAN-Campus
Task classification Select the type you want to perform - Campus Network service request: select if you are requesting a new service
content Enter detailed information required to create a Campus Network service - SCP account name: Enter the account name of Samsung Cloud Platform
- SCP project name: Enter the project name of Samsung Cloud Platform
- Company/Corporation name: Enter the company/corporation name
- Customer information (Name/E-mail/Phone number): Enter user information
- Desired service start date: Enter the service start date
- Network segmentation: Yes / No
- Wired network usage: Yes / No
- Wireless network usage: Yes / No
- Wireless WIPS usage: Yes / No
- Network solution usage (NMS, WAN accelerator, DHCP, etc.): Yes / No
- Estimated contract period: Enter 4 years, 5 years, or 6 years
- Operational service: Yes / No
Attachment If you have additional files you want to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files can be attached
Table. Detailed description of Campus Network service request items
- In the task type, select Campus Network Service Request.
- Verify the required information entered on the Service Request page, then click the Request button.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
- The requested work takes approximately 5 to 7 business days.
- Once the service request is completed, a customer representative will contact you separately for site consulting and architecture optimization design.
- Ask the Samsung SDS account manager about the progress and service-related matters.
Campus Network Service Cancellation Request
You can cancel the Campus Network service in the Samsung Cloud Platform Console.
To request termination of the Campus Network service, follow the steps below.
Click the All Services > Networking > Cloud LAN-Campus menu. Navigate to the Service Home page.
On the Service Home page, click the Cloud LAN-Campus Service Request button. You will be taken to the Support Center > Service Request page.
On the Service Request page, enter or select the required information in the mandatory input fields.
- In the task category, select Campus Network Service Termination.
Input field Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform - Automatically filled with the account’s region
service Select the service category and service for the given service (auto-select) - Service Category: Networking
- Service: Cloud LAN-Campus
Task classification Select the type you want to perform - Campus Network service termination: select if you are requesting to terminate the service
content Enter detailed information required for Campus Network service termination - SCP Account Name: Enter the account name of Samsung Cloud Platform
- SCP Project Name: Enter the project name of Samsung Cloud Platform
- Customer Information (Name/Company/Department/E-mail/Phone Number): Enter user information
- Service Termination Request Date: Enter the service termination date
- Details: Enter additional information
Attachment If you have additional files you want to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files can be attached
Table. Detailed description of Campus Network service request items
- In the task category, select Campus Network Service Termination.
Check the required information entered on the Service Request page, and click the Request button.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
- The requested work takes approximately 5 to 7 business days.
- When the service request is completed, a customer representative will contact you separately to cancel the service.
- Contact the Samsung SDS account manager to inquire about the progress and service-related matters.
5.9.3 - Release Note
Cloud LAN Campus
- We have launched the Cloud LAN Campus service, which provides an authentication‑based integrated wired/wireless network service within the customer’s premises.
5.10 - Cloud LAN-Data Center
5.10.1 - Overview
Service Overview
The Cloud LAN-Data Center can connect various networks such as servers, WAN Edge, and CX (Cloud eXchange) through a shared network infrastructure based on SDDC (Software-Defined Data Center) within a Samsung Cloud Platform region data center or a customer’s on-premises data center.
Features
Cloud LAN-Data Center provides the following features.
- Rapid Network Access: When building a network environment in a Samsung Cloud Platform region or a customer’s on‑premises data center, a fast and secure, enterprise‑customized data center network can be configured using SDDC‑based infrastructure.
- Cost Efficiency: By using logical configurations of virtualized infrastructure and optimized designs by experts, a customer-dedicated network with the same effect as a costly standalone physical network infrastructure can be built. The virtualized network environment reduces costs required for building physical infrastructure such as network equipment, data center floor space, and cabling.
- Operational Continuity Maintenance: We provide a customized operational environment for each company, configured to preserve existing settings such as network security policies, IP schemes, and network protocols required in various on-premises environments.
- Flexible network environment provision: Within an SDDC-based infrastructure, separating edge nodes (external network connection), service nodes (built-in equipment connection), and computing nodes (server connection) enables support for both hardware-type security and network solution appliances that require physical installation in the data center and virtualized equipment.
Provided features
Cloud LAN - Data Center provides the following features.
- Diverse Network Integration Virtualization: Provides virtualized resources for flexible N/W configurations and enables the creation of customer-dedicated networks using various Types of vDevice.
- Network/Security Solution Integration: Provides virtualization solutions in NFV form, and can configure networks by integrating various types of appliances.
Components
Cloud LAN-Data Center is a service that provides connections between various networks through virtual network configurations within a data center. The components are as follows, and related services can be created.
| Category | Detailed description |
|---|---|
| Cloud LAN Network | Virtual space for logically separated network configuration within the Cloud LAN‑Data Center infrastructure |
| vRouter | Virtual resources for connecting external lines (L2, L3) |
| vSwitch | Virtual resources for dedicated customer H/W connections and VLAN provisioning |
| vFirewall | Virtual firewall to protect infrastructure created within the Cloud LAN-Data Center |
| vL4/L7 | Virtual L4/L7 switch for traffic load balancing within the Cloud LAN-Data Center |
| vCore | Virtual resources for Full Mesh routing connections |
| vCable | Virtual Cable for routing connections between virtual resources |
| Interface | Provides a physical interface on the vDevice that can connect hardware equipment and circuits. |
Constraints
When using the Cloud LAN-Data Center service, there are the following limitations.
- Please inquire 1:1 about the available creation capacity per region.
Provision status by region
Cloud LAN-Data Center can be provided in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Pre-service
Cloud LAN-Data Center has no prerequisite services.
5.10.2 - How-to guides
Users can create the service by entering the required information for the Cloud LAN Network service and selecting detailed options through the Samsung Cloud Platform Console.
Create Cloud LAN Network
You can create and use the Cloud LAN Network service in the Samsung Cloud Platform Console.
To request the creation of a Cloud LAN Network service, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the Cloud LAN Network Create button. You will be taken to the Cloud LAN Network Create page.
- On the Cloud LAN Network Creation page, enter the required information in the service information input area, and click the Complete button.
- Enter or select the required information in the service information input area.
Category Required statusDetailed description Cloud LAN Network name Required Enter the name of the Cloud LAN Network to create - Enter 3‑21 characters using English letters, numbers, and special characters
Cloud LAN Network location Required Select Cloud LAN Network location description Select Enter additional information or description about the Cloud LAN Network service. Table. Cloud LAN Network service information input items
- Enter or select the required information in the service information input area.
- In the Additional Information Input area, enter or select the required information.
Category Required?Detailed description tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key and Value values
Table. Cloud LAN Network additional information input fields
- Once creation is complete, check the created resources on the Cloud LAN Network List page.
Check detailed information of Cloud LAN Network
The Cloud LAN Network service allows you to view and edit the list of connected resources and detailed information. Cloud LAN Network Details page consists of Details, Connected Resources, Tags, Activity History tabs.
To view detailed information about the Cloud LAN Network, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. Navigate to the Cloud LAN-Data Center Service Home page.
- Cloud LAN-Data Center Service Home page, click the Cloud LAN Network menu. You will be taken to the Cloud LAN Network list page.
- On the Cloud LAN Network List page, click the resource you want to view detailed information for. You will be taken to the Cloud LAN Network Details page.
- Cloud LAN Network Details page displays status information and additional feature information, and is composed of Details, Connected Resources, Tags, Activity History tabs.
Category Detailed description Service status Service status display - Creating: Creating
- Active: Running
- Deleting: Deleting
- Failed: Creation/Deletion failed
Service termination Cancel Service button Table. Cloud LAN Network status information and additional functions
- Cloud LAN Network Details page displays status information and additional feature information, and is composed of Details, Connected Resources, Tags, Activity History tabs.
Detailed Information
Cloud LAN Network List page lets you view detailed information of the selected resource and modify it if necessary.
| Category | Detailed description |
|---|---|
| Service | service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who modified the service |
| Modification date and time | Date and time the service was modified |
| Service Information | Created service details
|
Connected resource
On the Cloud LAN Network List page, you can view the vDevice information assigned to the selected resources.
| Category | Detailed description |
|---|---|
| vDevice List | Display vDevice information and status assigned to the created service |
tag
Cloud LAN Network List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Cloud LAN Network List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Cloud LAN Network
To cancel the Cloud LAN Network, follow these steps.
- If other resources are connected to the Cloud LAN Network, you cannot cancel the service. Delete all connected resources before canceling the service.
- If the Cloud LAN Network service status is Creating or Deleting, the service cannot be terminated.
- If you cancel the Cloud LAN Network service, it will be deleted immediately and cannot be recovered. Since canceling the service may cause the running service to stop immediately, please carefully consider the impact of service interruption before proceeding with the cancellation.
- Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
- Cloud LAN-Data Center Service Home page, click the Cloud LAN Network menu. You will be taken to the Cloud LAN Network list page.
- On the Cloud LAN Network List page, click the resource you want to view detailed information for. You will be taken to the Cloud LAN Network Detail page.
- On the Cloud LAN Network Details page, click the Service Termination button.
- When the termination is complete, check whether the resource has been deleted in the Cloud LAN Network list.
5.10.2.1 - vDevice
Users can create the service by entering the required information for the vDevice service and selecting detailed options through the Samsung Cloud Platform Console.
Create vDevice
You can create and use the vDevice service in the Samsung Cloud Platform Console.
- To request a vDevice, a Cloud LAN Network must be created. * Check the Cloud LAN Network information before applying for a vDevice.
- The detailed configuration of the generated vDevice uses a separate operating platform (NiO). * For NiO-related inquiries, please submit your request through Support Center > Contact and we will provide guidance.
To request the creation of a vDevice service, follow these steps.
- All Services > Networking > Cloud LAN-Data Center menu, click it. 1. Navigate to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the Create vDevice button. 2. Navigate to the vDevice Creation page.
- On the vDevice Creation page, enter the relevant information in the service information input area.
- Enter or select the required information in the service information input area.
Category required statusDetailed description Cloud LAN Network name Required Select the Cloud LAN Network to assign the vDevice vDevice Type Required Select the type of vDevice to create - vRouter: virtual resource for connecting external lines (L2, L3)
- vSwitch: virtual resource for connecting customer-dedicated hardware and providing VLANs
- vFirewall: virtual firewall for protecting infrastructure created within the Data Center
- vCore: inter-resource connection service for Full-Mesh communication between virtual resources
- vL4/L7: virtual L4/L7 switch for traffic load balancing within Cloud LAN-Data Center
- vTAP : virtual resource for replicating traffic within Cloud LAN-Data Center and sending it to other devices
vDevice Type > vRouter Required Enter the name to create when selecting vRouter - Enter using letters, numbers, and special characters, 3-21 characters long
vDevice Type > vSwitch Required Enter the name to create when selecting a vSwitch - Use English letters, numbers, and special characters, 3-21 characters
vDevice Type > vFirewall Required Select creation information when choosing vFirewall - vFirewall: Enter the name to create
- Vendor: Select vendor
- Type: Choose the plan of the selected vendor
- Redundancy: Choose whether to use redundancy, when Enabled is selected the cost for two firewalls is charged, and when not selected a single configuration is applied
- Log storage option: Choose whether to use log storage, logs are stored on a single server and even if redundancy is selected only one server’s fee is charged
- Contract period: Select contract period
vDevice Type > vCore Required Enter the name to create when selecting vCore - Enter using letters, numbers, and special characters, 3 to 21 characters
vDevice Type > vL4/L7 Required Select creation information when choosing vL4/L7 - vL4/L7 name: Enter the name to create
- Unit: Enter the number of units to use (1-20)
- Redundancy: Choose whether to use firewall redundancy
- Contract period: Select the contract period
vDevice Type > vTAP Required Select creation information when choosing vTAP - vTAP name: Enter the name to create
- Redundancy: Choose whether to use vTAP redundancy
- Contract period: Select contract period
Table. vDevice service information input itemsReferenceWhen applying for a vFirewall, a Firewall Interface is created automatically. Detailed firewall information by vendor is as follows.
vendor Firewall type Interface count Generated vFirewall Interface SECUI 6 Gbs, 5,000 Rules 3 int / ext / dmz.1 SECUI 12 Gbs, 15,000 Rules 3 int / ext / dmz.1 SECUI 30 Gbs, 30,000 Rules 4 int / ext / dmz.1 / dmz.2 SECUI 60 Gbs, 100,000 Rules 5 int / ext / dmz.1 / dmz.2 / dmz.3 Fortinet 1 Gbs, 1,000 Rules 3 int / ext / dmz.1 Table. Detailed Firewall information by vendor - In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. vDevice additional information entry fields
- Enter or select the required information in the service information input area.
- Summary Check the detailed information and estimated charges generated in the panel, and click the Complete button.
- When creation is complete, check the created resources on the vDevice List page.
Check vDevice detailed information
The vDevice service allows you to view and edit the list of connected resources and their detailed information. The vDevice Details page consists of Details, Connected Resources, Tags, Activity History tabs.
To view detailed information about the vDevice, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. 1. Navigate to the Cloud LAN-Data Center Service Home page.
- From the Cloud LAN-Data Center Service Home page, click the vDevice menu. 2. Navigate to the vDevice List page.
- vDevice List page, click the resource to view detailed information. 4. Go to the vDevice Details page.
- vDevice Details page displays status information and additional feature information, and consists of Details, Connected Resources, Tags, Activity History tabs.
Category Detailed description Service status Service status display - Creating: Creating
- Active: Running
- Deleting: Deleting
- Failed: Creation/Deletion failed
Delete vDevice Delete Service button Table. vDevice status information and additional functions
- vDevice Details page displays status information and additional feature information, and consists of Details, Connected Resources, Tags, Activity History tabs.
Detailed Information
On the vDevice List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Service’s unique resource ID |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who modified the service |
| Modification date | Date and time of service modification |
| Service Information | Created service details
|
Connected resource
On the vDevice List page, you can view the resources allocated to the selected resource.
| Category | Detailed description |
|---|---|
| List of connected resources | Display detailed information and status of resources allocated to the created service
|
Tag
On the vDevice list page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the vDevice list page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate vDevice
To terminate the vDevice, follow the steps below.
- Click the All Services > Networking > Cloud LAN-Data Center menu. 1. Navigate to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the vDevice menu. 2. Navigate to the vDevice List page.
- On the vDevice List page, click the resource to view its detailed information. 4. Navigate to the vDevice Details page.
- On the vDevice Detail page, click the vDevice Delete button.
- After termination is complete, check whether the resource has been deleted from the vDevice list.
5.10.2.2 - Interface
Users can create the Interface service by entering its required information and selecting detailed options through the Samsung Cloud Platform Console.
Create Interface
You can create and use an Interface service in the Samsung Cloud Platform Console.
- To request an Interface, a Cloud LAN Network and vDevice must be created. Before requesting an Interface, verify the Cloud LAN Network and vDevice information.
- Interface is a function that assigns a physical port to a pre‑created vDevice. Interface can only be requested for vRouter and vSwitch.
- When a vFirewall is created, interfaces are automatically generated to match the quantity specified for each spec.
To request the creation of an Interface service, follow these steps.
Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
From the Cloud LAN-Data Center Service Home page, click the Create Interface button. You will be taken to the Create Interface page.
On the Interface creation page, enter the relevant information in the service information input area.
- Enter or select the required information in the service information input area.
Category Required statusDetailed description Cloud LAN Network name Required Select the Cloud LAN Network to assign to the Interface vDevice Type Required Select the type of vDevice to use - vRouter: virtual resource for connecting external lines (L2, L3)
- vSwitch: virtual resource for connecting customer-dedicated hardware and providing VLANs
vDevice Type Details Required Select detailed information for vDevice type - vDevice Name: Select a vDevice
- Interface Type: Select the type of Interface to use
- Interface Name: Enter the Interface name
- You can add up to 5 Interface entries; press the (+) button to add an entry, and the (x) button to delete an entry
- Interface Redundancy: Set whether Interface redundancy is enabled; selecting redundancy incurs charges for two ports
- Contract Period: Select the desired contract period
Table. Interface service information input fields - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- Add Tag button after clicking, input or select Key, Value values
Table. Interface additional information input fields
- Enter or select the required information in the service information input area.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resources on the Interface List page.
Check interface detailed information
The Interface service allows you to view and edit the list of connected resources and detailed information. Interface Details page consists of Detailed Information, Tags, Activity Log tabs.
To view detailed information about the Interface, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. Go to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the Interface menu. You will be taken to the Interface List page.
- Click the resource to view detailed information on the Interface List page. You will be taken to the Interface Details page.
- Interface Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description Service status Service status display - Creating: In progress
- Active: Running
- Deleting: In progress
- Failed: Creation/Deletion failed
Delete Interface Delete Service button Table. Interface status information and additional functions
- Interface Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
Interface list page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation Timestamp | Service creation timestamp |
| Editor | User who modified the service |
| Modification date and time | Date and time the service was modified |
| vDevice Type | vDevice Type information |
| vDevice name | vDevice name |
| Interface Type | Interface Type information |
| Port redundancy | Whether to use port redundancy |
| Contract period | Selected contract term |
tag
On the Interface list page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Interface list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Interface
To cancel the Interface, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the Interface menu. You will be taken to the Interface List page.
- On the Interface List page, click the resource for which you want to view detailed information. You will be taken to the Interface Details page.
- On the Interface Details page, click the Delete Interface button.
- When the termination is complete, check whether the resource has been deleted in the Interface list.
5.10.2.3 - vCable
Users can create the service by entering the required information for the vCable service and selecting detailed options through the Samsung Cloud Platform Console.
Create vCable
You can create and use the vCable service in the Samsung Cloud Platform Console.
- To request a vCable, a Cloud LAN Network and a vDevice must be created. Before requesting a vCable, verify the Cloud LAN Network and vDevice information.
- Only vCable configurations between vDevices created in the same Cloud LAN Network are possible.
To request the creation of a vCable service, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the Create vCable button. You will be taken to the Create vCable page.
- On the vCable Creation page, enter the relevant information in the service information input area.
- Enter or select the required information in the service information input area.
Category Required statusDetailed description Cloud LAN Network name Required Select the Cloud LAN Network to assign the vCable. vCable Type Required Select the type of vCable to create - Static: Provides a 1:1 connection between vDevices; when configuring vDevice A and vDevice B, select different virtual resources
- vCore: Provides Multi Peering between vDevices, connecting multiple vDevices to enable connections between vDevices
vCable Type > Details Required Enter detailed information according to vCable Type - vCable Name: Enter the name of the vCable to create
- vDevice A: Select vDevice A
- vDevice B: Select vDevice B
- Select vDevice A and B sequentially; if a vFirewall Interface is selected from the A list, it will not appear in the B list
- When the vCable Type is Static, vCore cannot be selected on vDevice A or vDevice B
- When the vCable Type is vCore, vCore can be selected only on vDevice A
- A vDevice can be connected to only one vCable
- A vFirewall can connect a vCable using a vFirewall Interface
Table. vCable Service Information Input Items - In the Additional Information Input area, enter or select the required information.
Category required or notDetailed description tag Select Add Tag - Up to 50 can be added per resource
- Add Tag After clicking the Add Tag button, enter or select Key, Value values
Table. vCable additional information input fields
- Enter or select the required information in the service information input area.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resources on the vCable List page.
Check vCable detailed information
The vCable service allows you to view and edit the list of connected resources and detailed information. vCable Details page consists of Details, Tags, Activity Log tabs.
To view detailed vCable information, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the vCable menu. You will be taken to the vCable List page.
- Click the resource to view detailed information on the vCable List page. You will be taken to the vCable Detail page.
- vCable Details page displays status information and additional feature information, and consists of Details, Tags, Work History tabs.
Category Detailed description Service status Service status display - Creating: Creating
- Active: Running
- Deleting: Deleting
- Failed: Creation/Deletion failed
Delete vCable Delete Service button Table. vCable status information and additional functions
- vCable Details page displays status information and additional feature information, and consists of Details, Tags, Work History tabs.
Detailed Information
On the vCable List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who modified the service |
| Modification date and time | Date and time the service was modified |
| vDevice Type | vDevice Type categories |
| vDevice A name | vDevice A name |
| vDevice B name | vDevice B name |
tag
On the vCable List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the vCable List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate vCable
To cancel vCable, follow the steps below.
- Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
- On the Cloud LAN-Data Center Service Home page, click the vCable menu. You will be taken to the vCable List page.
- On the vCable List page, click the resource to view its details. You will be taken to the vCable Details page.
- On the vCable Details page, click the Delete vCable button.
- After termination is complete, verify that the resource has been deleted from the vCable list.
5.10.2.4 - vEdge
Users can apply for the service by entering the required information for using the vEdge service through the Samsung Cloud Platform Console.
Create vEdge
You can request and use the vEdge service from the Samsung Cloud Platform Console.
To request the creation of a vEdge service, follow these steps.
- Click the All Services > Networking > Cloud LAN-Data Center menu. You will be taken to the Cloud LAN-Data Center Service Home page.
- On the Service Home page, click the vEdge Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
- On the Service Request page, enter or select the required information in the mandatory input fields.
- In the task category, select vEdge creation.
Input field Detailed description Title Enter the title of the service request - Example: vEdge Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
service Select the service category and service. If you click the vEdge service request button, it is entered automatically - Service Category: Networking
- Service: vEdge
Task classification Select the type you want to request - Create vEdge: select when requesting a new service
content Guidance on the service application process and reference information Attachment If you have a file you want to share via the repository, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only files with the following extensions are allowed: doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif
Table. vEdge Service Creation Request Items
- In the task category, select vEdge creation.
- Check the required information entered on the Service Request page, and click the Request button.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
Check vEdge application details
You can view the vEdge service subscription and cancellation history in the Samsung Cloud Platform Console.
To check the vEdge service application details, follow these steps.
- Click the All Services > Management > Support Center menu. Go to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request menu. You will be taken to the Service Request List page.
- On the Service Request List page, click the Title of the service request you submitted. You will be taken to the Service Request Details page.
- On the Service Request Details page, view the request status and information.
Terminate vEdge
To request cancellation of the vEdge service, follow the steps below.
Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
Service Request page: enter or select the required information in the mandatory input fields.
- Select vEdge termination in the task category.
Input field Detailed description Title Enter the title of the service request - Example: vEdge Service Termination Request
Region Select the location of Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select service category and service - Service Category: Networking
- Service: vEdge
Task classification Select the type of request you want to make - vEdge termination: select if you are terminating the service
content Guide to the service application process and reference information Attachment If you have additional files you want to share, proceed with the upload - You can attach up to 5 files, each within 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files can be attached
Table. vEdge Service Termination Request Items
- Select vEdge termination in the task category.
Check the required information entered on the Service Request page, and click the Request button.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
- Service termination takes 5–7 business days, including the cancellation request date.
5.10.3 - Release Note
Cloud LAN-Data Center
- The services provided in specific Samsung offering regions (kr-west1/kr-east1) have changed.
- The vTAP option has been added to the Cloud LAN - Data Center service in Samsung’s offering.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- We have launched the Cloud LAN-Data Center service, which provides connections between various networks through virtual network configurations within the data center.
5.11 - Cloud WAN
5.11.1 - Overview
Service Overview
Cloud WAN is a service that provides network connectivity between Samsung Cloud Platform global regions and customer locations. This offering is based on network traffic usage and provides differentiated operational management services according to the selected service level.
The Cloud WAN service consists of the customer virtual backbone Cloud WAN Network, the Segment that provides logical network segmentation by purpose, and the Attachment that connects Samsung Cloud Platform Compute resources or receives a dedicated line from the customer’s site and connects it to a Segment.
For example, to configure a backbone network connection from a system in a Samsung Cloud Platform region to a customer’s overseas location, the following settings are required in the user console. First, create the customer’s virtual backbone Cloud WAN Network. Next, select the access location, service level, contract period, and other options to create a segment that fits the intended use. Then, by attaching the segment at the region or the customer’s location, the backbone network between the SCP region and the customer locations is connected, enabling communication between them.
Service Architecture Diagram
Provided features
Cloud WAN provides the following features.
- Rapid Backbone Network Configuration: Customers using Samsung Cloud Platform can select desired site locations, create a virtual global backbone network, and configure a fast and secure cloud network between Samsung Cloud Platform regions and customer sites, as well as among customer sites.
- Providing Various Network Edge Connection Types: By offering various Edge types that can connect to Cloud WAN, Samsung Cloud Platform Compute resources can be conveniently connected via Transit Gateway, and customers’ on‑premise local lines can be connected via Site Connect.
- Cost Optimization Through Multi-Path Selection Feature: Unlike traditional backbone network line services based on line bandwidth, we charge only for the actual usage in the desired segment, and provide a transmission path option (Gold/Silver) selection feature based on traffic characteristics, enabling line cost optimization.
- Service Level-Based Operations Management: Customers can choose the utilization mode of the Cloud WAN backbone transport network, the provided features, monitoring, fault management, and technical support level, and receive differentiated network operations management services according to the selected service level.
Component
The Cloud WAN service provides a global customer virtual backbone network. The components are as follows, and users can create resources directly through the user Console.
| Category | Detailed description |
|---|---|
| Cloud WAN Network | Customer-specific virtual backbone network |
| Segment | Logical virtual routing domains in Cloud WAN Network, categorized by usage
|
| Access Location | Physical base location for constructing a Segment |
| Attachment | Connect Samsung Cloud Platform or the customer’s dedicated line Edge resources |
| Transit Gateway | Edge connection type for connecting Samsung Cloud Platform Compute resources |
| Site Connect | Edge connection type for connecting customer site dedicated line resources (CE equipment) |
| CE equipment | Network equipment that receives the dedicated line at the customer’s site (Customer Edge) |
| Segment Sharing | Provides routing exchange settings to enable mutual communication among resources connected to different segments. |
Constraints
The Cloud WAN service has the following limitations.
- You can create one Cloud WAN Network per account.
- You can create up to five Segments in a single Cloud WAN Network.
- You can create up to 50 Attachments in a single Segment.
- You can create up to 10 Segment Sharings for a single Segment.
- Connections between Segment and Attachment are allowed only within the same project, through request and approval.
- However, Segment Sharing can be linked across different projects through request and approval.
Provision status by region
The Cloud WAN service is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West 1 (kr-west1) | Provided |
| Korea East 1 (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| Korea South 3(kr-south3) | Not provided |
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | Transit Gateway | A service that securely and quickly connects Compute resources within the Samsung Cloud Platform to a Cloud WAN Segment. |
5.11.1.1 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued in September 2026.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously conduct resource monitoring by using ServiceWatch, released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a smooth monitoring environment.
Block Storage is planned to be integrated with ServiceWatch starting after the September 2026 release.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
Cloud WAN monitoring metrics
The table below shows the monitoring metrics for Cloud WAN that can be viewed in Cloud Monitoring. For detailed usage of Cloud Monitoring, see the Cloud Monitoring guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Instance Status | Attachment connection status | status |
| Network in bytes | In bytes (inbound traffic usage per interval) | bytes |
| Network In Error Packets | In Error Packet count (number of received error packets per cycle) | Cnt |
| Network In Packets [Broadcast] | In Broadcast Packet count (number of Broadcast packets per cycle) | Cnt |
| Network In Packets [Dropped] | In Dropped Packet count (number of dropped packets per cycle) | Cnt |
| Network In Packets [Multicast] | In Multicast Packet count (number of Multicast packets per cycle) | Cnt |
| Network In Packets [Unicast] | In Unicast Packet count (number of Unicast packets per cycle) | Cnt |
| Network out bytes | Out bytes(Outbound traffic usage per interval) | bytes |
| Network Out Error Packets | Out Error Packet count (number of transmission error packets per cycle) | Cnt |
| Network Out Packets [Broadcast] | Out Broadcast Packet count (number of Broadcast packets per cycle) | Cnt |
| Network Out Packets [Dropped] | Out Dropped Packet count (number of dropped packets per cycle) | Cnt |
| Network Out Packets [Multicast] | Out Multicast Packet count (number of Multicast packets per cycle) | Cnt |
| Network Out Packets [Unicast] | Out Unicast Packet count (Unicast packet count per cycle) | Cnt |
5.11.2 - How-to guides
Users can enter the required Cloud WAN information and select detailed options to create a service through the Samsung Cloud Platform Console.
Create Cloud WAN Network
You can create and use a Cloud WAN Network in the Samsung Cloud Platform Console.
To create a Cloud WAN Network, follow these steps.
- All Services > Networking > Cloud WAN Click the menu. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Create Cloud WAN Network button. 2. Go to the Create Cloud WAN Network page.
- On the Create Cloud WAN Network page, enter the information required to create the service and select detailed options.
- In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Cloud WAN Network name Required Enter the name of the Cloud WAN Network to create - Enter using English letters (uppercase and lowercase) and numbers, 3 to 20 characters
Table. Cloud WAN Network Service Information Input Items - Additional Information Input area, enter or select the required information.
Category required statusDetailed description Explanation Select Enter resource description tag Select Add tag - Up to 50 tags can be added per resource
Table. Cloud WAN Network additional information entry items
- In the Service Information Input area, enter or select the required information.
- In the summary panel, review the service information and estimated charges, then click the Create button.
- Once creation is complete, check the created resources on the Cloud WAN Network List page.
Check detailed information of Cloud WAN Network
The Cloud WAN Network service can view and edit the full resource list and detailed information from the Cloud WAN Network menu. Cloud WAN Network Details page is composed of the Detail Information, Connected Resources, Tags, and Operation History tabs.
To view detailed information about the Cloud WAN Network, follow these steps.
- Click the All Services > Networking > Cloud WAN menu. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Cloud WAN Network menu. 2. Go to the Cloud WAN Network List page.
- Cloud WAN Network List page, click the resource for which you want to view detailed information. 3. Cloud WAN Network Details Navigate to the page.
- Cloud WAN Network Details page displays status information and additional feature information, and consists of Details, Connected Resources, Tags, Activity History tabs.
Category Detailed description status Current service status - Creating: Service creation in progress
- Active: Service operating normally
- Deleting: Service deletion in progress
- Failed: Service failed
- Error: Service status cannot be determined
Service termination Service termination button - If there are no connected services, the Cloud WAN Network can be terminated
Table. Cloud WAN Network status information and additional feature items
- Cloud WAN Network Details page displays status information and additional feature information, and consists of Details, Connected Resources, Tags, Activity History tabs.
Detailed Information
Detailed Information tab allows you to view the detailed information of the selected Cloud WAN Network.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type (Cloud WAN Network) |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | Service creation request user |
| Creation date and time | Service creation date and time |
| Modifier | Service modification request user |
| Modification timestamp | Service modification date and time |
| Cloud WAN Network name | Cloud WAN Network name |
| Segment count | Number of used segments |
| Explanation | Description of the service
|
Connected resource
In the Connected Resources tab, you can view Segment connection status information.
| Category | Detailed description |
|---|---|
| Segment name | Segment resource name |
| Segment ID | Segment ID information |
| status | Service resource status information |
Tag
In the Tag tab, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
In the Work History tab, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Cloud WAN Network
Terminating an unused Cloud WAN Network can reduce operating costs.
- If there are resources connected to the Cloud WAN Network, the service cannot be terminated. * Delete the connected resources first, then terminate the service.
- If the service status of Cloud WAN Network is Creating or Deleting, the service cannot be terminated.
To cancel the Cloud WAN Network, follow the steps below.
- Click the All Services > Networking > Cloud WAN menu. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Cloud WAN Network menu. 2. Cloud WAN Network List Navigate to the page.
- On the Cloud WAN Network List page, click the resource to terminate. 3. Cloud WAN Network Details Navigate to the page.
- Cloud WAN Network Details on the page, click the Cancel Service button.
- After termination is complete, check the resource termination status in the Cloud WAN Network list.
Create Segment
You can create a Segment in the Samsung Cloud Platform Console and use it.
To create a Segment, follow these steps.
All Services > Networking > Cloud WAN Click the menu. 1. Navigate to the Service Home page of Cloud WAN.
From the Service Home page’s drop-down, click the Create Segment button. 2. Navigate to the Create Segment page.
Segment creation page, enter the information required to create the service and select detailed options.
- In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Cloud WAN Network name Required Select Cloud WAN Network - Click +Create New to create a Cloud WAN Network and then select it
Segment name Selection After entering the Segment name, click the Duplicate Check button Access Location Required Select the location to connect the Segment - Only one Access Location can be selected
- Detailed Information > Connected Resources tab allows adding Access Locations one at a time
- Access Locations can be added up to the number of Cloud WAN service deployment locations
Service type Required Select Segment service type - Select usage region (global)
- * Global is for connecting domestic and overseas regions
- Select service level (PremiumPlusG)
- * Dedicated TAM assignment, advanced technical support service provided
- Select contract term (none, 3 years, 5 years, 7 years)
- * Contract discount rate automatically applied based on term
Multiple paths Selection Multi-path transmission selection (available after July 2026) - Default path: Gold (3-way architecture, critical tasks)
- Optional path : Silver (2-way architecture, standard)
Table. Segment service information entry fields - In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description Explanation Selection Enter description for Segment tag Selection Add tags - Up to 50 tags can be added per resource
Table. Segment additional information input fields
- In the Service Information Input area, enter or select the required information.
In the summary panel, check the service information and estimated charges, and click the Create button.
- When creation is complete, check the created resources on the Segment list page.
After creating the Segment, set the following in the Details > Connected Resources tab.
- Link the attachment created in the same account to the segment.
- To connect between different accounts, configure Segment Sharing.
Check segment detailed information
You can view and edit Segment in the Segment menu, where you can see the full resource list and detailed information. The Segment Details page consists of the Details, Connected Resources, Multi-Path, Tags, Activity History tabs.
To view the detailed information of the Segment, follow these steps.
- All Services > Networking > Cloud WAN Click the menu. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Segment menu. 2. Navigate to the Segment list page.
- On the Segment List page, click the resource to view detailed information. 3. Go to the Segment Details page.
- Segment Details page displays status information and additional feature information, and consists of Details, Connected Resources, Multi-Path, Tags, Activity History tabs.
Category Detailed description status Current service status - Creating: Service is being created
- Active: Service is operating normally
- Deleting: Service deletion requested
- Failed: Service creation failed
- Error: An unknown error occurred in the service
Delete Segment Segment delete button - If there is no connected service, the Segment can be deleted
Table. Segment status information and additional feature items
- Segment Details page displays status information and additional feature information, and consists of Details, Connected Resources, Multi-Path, Tags, Activity History tabs.
Detailed Information
Detailed Information tab allows you to view detailed information of the selected Segment.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type (Segment) |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| Constructor | Service creation request user |
| Creation date and time | Service creation date and time |
| Modifier | Service modification request user |
| Modification date | Service modification date and time |
| Segment name | Segment name |
| Access Location count | Number of access locations (Access Location) connected to the segment |
| Regional classification | Select usage region (global, domestic)
|
| Service level | Select provided service level (PremiumPlusG, LIteG)
|
| Contract period | Service usage commitment period
|
| Attachment count | Number of Attachments linked to Segment |
| Multiple paths | Select the transmission path option (Gold/Silver) used by Segment
|
| Explanation | Description of the Segment
|
Connected resource
In the Connected Resources tab, you can check the connection status information for Access Location, Segment Sharing, and Attachment.
| Category | Detailed description |
|---|---|
| Access Location | Check the location information linked to the Segment
|
| Segment Sharing | To connect between different projects, you can request a Segment Sharing connection
|
| Attachment connection | In Segment, you can request to connect an Attachment created in the same project
|
Multiple Paths
In the Multi-Path tab, you can add or remove optional path rules for multi-path.
Add Multi-Path Rule
To add a multi-path rule, follow these steps.
- All Services > Networking > Cloud WAN menu, click. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Segment menu. 2. Segment list Go to the page.
- Segment List page, click the resource to view detailed information. 3. Go to the Segment Details page.
- On the Segment Details page, click the Multiple Paths tab.
- Click the Add Rule button on the Multi-Path tab page. 5. The add rule popup appears.
- Enter the detailed information in the popup window and click Confirm.
Category required statusDetailed description Departure Access Location Essential Select the source location information of the multipath rule Source IP range Essential Enter the source IP range - When entering an IP address, register the IP range in CIDR format (e.g., 192.168.10.0/24)
Destination IP range Essential Enter destination IP range - When entering an IP address, register the IP range in CIDR format (e.g., 192.168.10.0/24)
- Cannot set both source IP range and destination IP range to 0.0.0.0/0
protocol Selection Select protocol Port direction Selection Select the port direction for the chosen protocol Port number Select If TCP or UDP protocol is selected, enter the port number - Allowed range: 1 - 65,535
- Port numbers can be entered up to a maximum of 5, separated by commas (e.g., 80, 443)
Explanation Selection Enter multiple path rule description Table. Multiple path rule addition input items
- If you enter information identical to an already registered rule, you cannot register it as a new multi‑path rule.
- You can apply for up to 20 multi-path rules.
Checking Multiple Path Rules
To verify the multi-path rule, follow the steps below.
- Click the All Services > Networking > Cloud WAN menu. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Segment menu. 2. Go to the Segment list page.
- Segment List page, click the resource to view detailed information. 3. Go to the Segment Details page.
- Segment Details on the page, click the Multiple Paths tab.
- Multi-Path tab page, view detailed information.
Category Detailed description Departure Access Location Source location information of the multi‑path rule Source IP range Source IP range Destination IP range Destination IP range protocol Protocol information Port direction Protocol port direction Port number Port numbers of TCP and UDP protocols Explanation Explanation of multi-path rule Table. Multi-path rule detailed information items
If you click the Detailed Search button on the right side of the rule list, you can set search filters and perform a search.
- You can quickly view multiple rules by searching with the desired filter among Source Access Location, Source IP, Destination IP, and Description.
Delete Multi-Path Rule
To delete a multi-path rule, follow these steps.
- All Services > Networking > Cloud WAN menu, click. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Segment menu. 2. Segment list Go to the page.
- Segment List page, click the resource to view detailed information. 3. Go to the Segment Details page.
- On the Segment Details page, click the Multiple Paths tab.
- On the Multi-path tab page, click the Delete button. 5. The rule will be deleted.
Tag
In the Tag tab, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Job History tab allows you to view the job history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource change history
|
Delete Segment
Deleting unused Segments can reduce operating costs.
- You cannot delete it if there is an attachment connected to the segment, or if segment sharing or multiple path rules exist. * Delete the connected resources first, then terminate the service.
- If the service status of a Segment is Creating, Deleting, Inactive, or Failed, the service cannot be deleted.
To delete a Segment, follow these steps.
- All Services > Networking > Cloud WAN menu, click it. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Segment menu. 2. Go to the Segment list page.
- Segment list page, click the resource you want to delete. 3. Go to the Segment Details page.
- On the Segment Details page, click the Delete Segment button.
- After deletion is complete, check the resource deletion status in the Segment list.
Create Attachment
You can create and use the Attachment service in the Samsung Cloud Platform Console.
To create an Attachment, follow these steps.
- Click the All Services > Networking > Cloud WAN menu. 1. Navigate to the Service Home page of Cloud WAN.
- From the Service Home page dropdown, click the Create Attachment button. 2. Navigate to the Create Attachment page.
- On the Attachment creation page, enter the information required to create the service and select detailed options.
- In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Cloud WAN Network name Required Select the Cloud WAN Network to request the Attachment - Click +New creation to create a Cloud WAN Network and then select it
Segment name Select Select the Segment to attach the Attachment - +Create New when clicked, a Segment is created and selected
Access Location Required Select the location connected to the Segment Connection type Required Site Connect Detailed connection information settings - Attachment name: Enter attachment name
- ASN information: Enter ASN information within the range 1-65,534. Note that 65,001 cannot be used
- Port capacity: Select port capacity
- BGP Password: Enter the password to be used for BGP (Border Gateway Protocol) when configuring BGP routing with the customer’s Customer Edge equipment
- When establishing a Site Connect connection, additional CE router and SR tasks are performed, taking several days until final connection
Connection type Required Select a connectable Transit Gateway (available after March 2027) - When selecting an Access Location with Multi-AZ enabled, only Transit Gateway can be set in the connection type
- Only Transit Gateway items within the same project are displayed
- TGW items that already have a TGW Peering connection or an Attachment connection are not shown in the list
- When a TGW item is selected, the Attachment name is generated automatically
Table. Attachment service information input fields - Additional Information Input area, enter or select the required information.
Category required statusDetailed description Explanation Select Enter description for Attachment tag Select Add tags - Up to 50 tags can be added per resource
Table. Attachment additional information input fields
- In the Service Information Input area, enter or select the required information.
- In the summary panel, verify the service information and estimated charges, then click the Create button.
- After creation is complete, check the created resources on the Attachment List page.
Check attachment details
Attachment can be viewed and edited in the Attachment menu, where you can see the full resource list and detailed information. The Attachment Details page consists of the Details, Tags, and Work History tabs.
To view the detailed information of the Attachment, follow the steps below.
- Click the All Services > Networking > Cloud WAN menu. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Attachment menu. 2. Go to the Attachment List page.
- On the Attachment list page, click the resource to view detailed information. 3. Navigate to the Attachment Details page.
- Attachment Details page displays status information and additional feature information, and is composed of Details, Tags, Activity History tabs.
Category Detailed description status Current service status - Creating: Creating service
- Active: Service operating normally
- Requesting: Service request in progress, Attachment request can be canceled
- Deleting: Service deletion request in progress
- Failed: Service creation failed
- Error: An unknown error occurred in the service
Delete Attachment Attachment Delete Button Table. Attachment status information and additional feature items
- Attachment Details page displays status information and additional feature information, and is composed of Details, Tags, Activity History tabs.
Detailed Information
Detailed Information tab allows you to view the detailed information of the selected Attachment.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource type (Attachment) |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | Service creation request user |
| Creation date and time | Service creation date and time |
| Modifier | Service modification request user |
| Modification date | Service modification date and time |
| Attachment name | Attachment name |
| Segment name | Name of the Segment linked to the Attachment |
| Access Location | Attachment connection point (Access Location) |
| Connection type | Attachment connection type (Site Connect or Transit Gateway) |
| ASN information | When selecting Site Connect, the AS Number entered directly by the user
|
| Port capacity | Port capacity configured when selecting Site Connect |
| BGP Password | The BGP password entered when selecting Site Connect
|
| Explanation | Description of the attachment
|
tag
In the Tag tab, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Job History tab allows you to view the job history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource change history
|
Delete Attachment
Deleting unused Attachment can reduce operating costs.
To delete the attachment, follow these steps.
- All Services > Networking > Cloud WAN Click the menu. 1. Navigate to the Service Home page of Cloud WAN.
- On the Service Home page, click the Attachment menu. 2. Go to the Attachment list page.
- Attachment List page, click the resource you want to delete. 3. Navigate to the Attachment Details page.
- On the Attachment Details page, click the Attachment Delete button.
- After deletion is complete, check the resource deletion status in the Attachment list.
5.11.3 - Release Note
Cloud WAN
- Cloud WAN > Attachment > Site Connect When you select this type, the BGP Password configuration feature is added when setting up BGP routing with the customer’s Customer Edge equipment.
- Samsung Cloud Platform has launched the Cloud WAN service that provides network connectivity between global regions and customer sites.
5.12 - SASE
5.12.1 - Overview
Service Overview
SASE is a service that integrates network and security functions on a cloud basis, allowing users to securely access corporate assets and applications from anywhere. It routes traffic via optimal paths and provides consistent security services for both internal and external environments through SASE points of presence located in Samsung Cloud Platform global regions.
Features
- Global SASE Fabric: We continuously expand service coverage upon customer demand by linking SASE hubs that utilize the systematic Samsung SDS Global network infrastructure with vPOPs prepared across all regions.
- All in One Security: It covers a security layer that includes advanced SSL/TLS analysis, sophisticated application awareness/policy, and AI/ML‑based real‑time behavior analysis within a single solution, optimizing operational complexity and performance.
- Network/Security Unification: By delivering network and security integrated on a single operating system based on a unified architecture, traffic is processed swiftly.
- End to End Full Managed: Provide the required infrastructure for connecting customer sites as a packaged solution under a single contract, and deliver comprehensive operational services ranging from monitoring to incident notification and reporting.
Service Architecture Diagram
- SASE hub: Configure a gateway and control unit in Samsung SDS Global POP and CSP vPOP to provide network connectivity and security functions
- SASE circuit: Physical circuit connecting the customer site and the SASE hub, configured as an SD‑WAN or VPN over internet/MPLS/dedicated line
- SASE Edge: Customer edge device for connecting to the SASE circuit, using a router/SD‑WAN device/VPN device on‑premises and a PC/mobile or similar customer‑owned endpoint device off‑premises.
Provided features
The SASE service provides the following features.
- WAN Edge Network
- Provide intra- and inter-region communication between various edge devices (SD-WAN devices, routers, VPN devices, PC, Mobile, etc.)
- Providing optimal application-specific routes using SD-WAN
- Provides traffic control (QoS) and TCP acceleration capabilities for high-quality networks.
- SSE(Secure Service Edge) security
- ZTNA: Provide least privilege, security, and private connections for internal applications
- SWG: Provides gateway security to protect internal users from insecure traffic such as that on the Internet.
- CASB: Provides the ability to apply corporate security policies between users and cloud applications.
- FWaaS : Provides inspection and control of all service traffic through a cloud-based firewall
- RBI, DLP, SANDBOX, etc. provide additional advanced security features
- Unified Orchestrator and DEM(Digital Experience Monitoring)
- Integrated network and security management for cloud, on-premises, and edge devices
- Monitoring of user experience (identifying issues such as network performance degradation, app interruptions, and determining their causes)
Constraints
The constraints of the SASE service are as follows.
- Service is unavailable in the China region, but will be offered in the future.
Provision status by region
SASE is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Not provided |
| South Korea 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Prior Service
SASE has no preceding service.
5.12.2 - How-to guides
Users can create the SASE service by entering the required information and selecting detailed options through the Samsung Cloud Platform Console.
Create SASE
You can create and use SASE services in the Samsung Cloud Platform Console.
To request the creation of a SASE service, follow these steps.
- Click the All Services > Networking > SASE menu. Navigate to the Service Home page of SASE.
- On the Service Home page, click the Create SASE button. You will be taken to the Create SASE page.
- On the SASE creation page, enter the information required to create the service.
- Enter the required information in the Service Information Input area.
Category Required statusDetailed description SASE name Required SASE name to be used by the user - Enter using letters and numbers, 3-20 characters
Service level Required Select SASE service level Service Type Required Select SASE service type - Agent type: Enter the number of agents to use in increments of 10, within 1-10,000
- Edge type: Choose whether to enable inter‑region connections, and select the upstream country and connection bandwidth for the site
- Click ‘+’ to add up to 10 items, click ‘X’ to delete an item
Contract period Required Select SASE contract period Other requests option Enter request details when applying for SASE service Table. SASE Service Information Input Items
- Enter the required information in the Service Information Input area.
- Check the detailed information and estimated charges generated in the summary panel, and click the Create button.
- When creation is complete, check the created resource on the Resource List page.
Check SASE detailed information
The SASE service can view and edit the full resource list and detailed information from the SASE menu. The SASE Details page consists of Details, Activity Log tabs.
To view detailed information about SASE, follow these steps.
- Click the All Services > Networking > SASE menu. Navigate to SASE’s Service Home page.
- On the Service Home page, click the SASE menu. You will be taken to the SASE List page.
- On the SASE List page, click the resource to view detailed information. You will be taken to the SASE Details page.
- SASE Details page displays status information and additional feature information, and consists of Detailed Information, Work History tabs.
Category Detailed description status Current service status - Request: Service request in progress
- Creating: Service registration completed
- Active: Service approved and successfully created
- Deleting: Service termination request in progress
Previous state change Previous state change button - In Creating, Active, Deleting states, it is possible to change to the previous state
Service termination Cancel Service button Table. SASE status information and additional feature items
- SASE Details page displays status information and additional feature information, and consists of Detailed Information, Work History tabs.
Detailed Information
Detailed Information tab lets you view the detailed information of the selected SASE.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type (SASE) |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| Constructor | User requesting service creation |
| Creation date and time | Service creation date and time |
| Editor | User requesting service modification |
| Modification date | Service modification date/time |
| Service Details | SASE service selection items
|
| Service level | SASE service level
|
| Contract period | SASE Service Commitment Period |
| Other requests | SASE service request
|
Job History
Work History tab allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate SASE
If you cancel unused SASE, you can reduce operating costs.
To cancel SASE, follow the steps below.
- Click the All Services > Networking > SASE menu. Navigate to the Service Home page of SASE.
- On the Service Home page, click the SASE menu. You will be taken to the SASE List page.
- SASE List page, click the resource to cancel. You will be taken to the SASE Details page.
- On the SASE Details page, click the Service Termination button.
- When the termination is complete, check the resource termination status in the SASE list.
5.12.2.1 - SASE Lastmile
Users can create the service by entering the required information for the SASE Lastmile service and selecting detailed options through the Samsung Cloud Platform Console.
Create SASE Lastmile
You can create and use the SASE Lastmile service in the Samsung Cloud Platform Console.
To request the creation of a SASE Lastmile service, follow these steps.
Click the All Services > Networking > SASE menu. Navigate to the Service Home page of SASE.
On the Service Home page, click the SASE Lastmile Create button. It navigates to the SASE Lastmile Create page.
On the SASE Lastmile Creation page, enter the information required to create the service.
- Enter the required information in the Service Information Input area.
Category Required statusDetailed description SASE name Required Select the SASE service to use - Click + New Creation to create a SASE service and then select it
Site Required Select detailed items for the SASE site to use - Site name: Select the site to use
- Connection bandwidth, Parent country: Automatically fill in selected SASE information
- Circuit: Apply then select circuit1, circuit2
- Customer Edge: Apply then select Customer Edge1, Customer Edge2
Table. SASE Lastmile Service Information Input Items
- Enter the required information in the Service Information Input area.
Verify the detailed information and estimated charges generated in the summary panel, and click the Create button.
- After creation is complete, check the created resource on the Resource List page.
Check detailed information of SASE Lastmile
The SASE Lastmile service can view and edit the full resource list and detailed information from the SASE Lastmile menu. The SASE Lastmile Details page consists of Detail Information, Task History tabs.
To view detailed information about SASE Lastmile, follow these steps.
- Click the All Services > Networking > SASE menu. Navigate to the Service Home page of SASE.
- On the Service Home page, click the SASE Lastmile menu. You will be taken to the SASE Lastmile List page.
- SASE Lastmile List page, click the resource to view detailed information. You will be taken to the SASE Lastmile Details page.
- SASE Lastmile Details page displays status information and additional feature information, and consists of Details, Work History tabs.
Category Detailed description status Current service status - Request: Service request in progress
- Creating: Service request completed
- Active: Service approved and successfully created
- Deleting: Service termination request in progress
Previous state change Previous state change button - In Creating, Active, Deleting states, it is possible to revert to the previous state
Delete SASE Lastmile Cancel Service button Table. SASE Lastmile status information and additional feature items
- SASE Lastmile Details page displays status information and additional feature information, and consists of Details, Work History tabs.
Detailed Information
Detailed Information tab allows you to view detailed information of the selected SASE Lastmile.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type (SASE Lastmile) |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | Service creation request user |
| Creation date and time | Service creation date and time |
| Editor | Service modification request user |
| Modification date | Service modification date and time |
| Site | Site configuration information
|
Job History
Work History tab allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate SASE Lastmile
If you cancel the unused SASE Lastmile, you can reduce operating costs.
To cancel SASE Lastmile, follow the steps below.
- Click the All Services > Networking > SASE menu. Navigate to the Service Home page of SASE.
- On the Service Home page, click the SASE Lastmile menu. You will be taken to the SASE Lastmile List page.
- SASE Lastmile List page, click the resource to cancel. You will be taken to the SASE Lastmile Details page.
- On the SASE Lastmile Details page, click the SASE Lastmile Delete button.
- When the termination is complete, check the resource termination status in the SASE Lastmile list.
5.12.3 - Release Note
SASE
- The automatic ledger creation feature via the Samsung Cloud Platform user console has been added.
- We have launched a SASE service that combines networking and security functions into a single cloud-based platform.
5.13 - Cloud Last Mile
5.13.1 - Overview
Service Overview
Cloud Last Mile is a service that provides Last Mile circuits for network connectivity from the customer’s site to the Samsung Cloud Platform region, as well as Customer Edge resources within the customer’s site. Resources installed and operated at the customer’s site can be easily requested through a service request in the Samsung Cloud Platform user console.
Features
- Provision of Circuits and Edge Packages: We provide Last Mile circuits and Edge resources for connecting the customer’s site to external networks as a package, combining optimal equipment that matches the application types the customer primarily uses.
- Various Edge Connection Types Provided: You can select virtual resources or physical equipment types, and choose from various functions needed for network connections such as routers, SD-WAN, WAN accelerators, firewalls, etc.
- Provision of Last Mile line monitoring service: Samsung Cloud Platform region’s network equipment-connected Last Mile line connection status and traffic usage information can be conveniently checked using the monitoring service. The monitoring service is provided using NiO, Samsung SDS’s proprietary platform.
Service Architecture Diagram
Provided features
The Cloud Last Mile service provides the following features.
- Last Mile line
- Line provision type: dedicated line or internet
- Upstream connection type: Cloud LAN - Data Center, On-Premise equipment in Samsung SDS data center
- Customer Edge Resource Provisioning Type
- uCPE(VNF: Virtual Network Function): router, SD-WAN, WAN accelerator, firewall
- Physical equipment: SD-WAN
- Last Mile line monitoring service
- Monitoring Last Mile line up/down status and traffic usage
Constraints
The constraints of the Cloud Last Mile service are as follows.
- Since it is offered only as a package of the line and Edge equipment, the line or equipment cannot be provided separately.
- Depending on the upstream country’s connection method, it may be necessary to set up customer-dedicated equipment within the Samsung Cloud Platform region.
- When connecting to shared equipment in a higher-tier country, port fees may be charged depending on the associated product.
Provision status by region
Cloud Last Mile is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Prior Service
Cloud Last Mile has no prior service.
5.13.2 - How-to guides
Users can create the Cloud Last Mile service by entering the required information and selecting detailed options through the Samsung Cloud Platform Console.
Create Cloud Last Mile
You can create and use the Cloud Last Mile service in the Samsung Cloud Platform Console.
To request the creation of a Cloud Last Mile service, follow these steps.
Click the All Services > Networking > Cloud Last Mile menu. You will be taken to the Service Home page of Cloud Last Mile.
Click the Create Cloud Last Mile button on the Service Home page. You will be taken to the Create Cloud Last Mile page.
Enter the information required to create the service on the Cloud Last Mile Creation page.
- Enter the required information in the Service Information Input area.
Category Required statusDetailed description Cloud Last Mile name Required Enter the Cloud Last Mile name the user will use - using English letters and numbers, 3-20 characters
Installation area Required Select installation region for Cloud Last Mile Installation address Required Enter Cloud Last Mile installation address Contract period Required Select contract period for Cloud Last Mile service Installation request date Required Select Cloud Last Mile installation request date - Select a date at least two months after today in the calendar
Other requests Option Enter request details when applying for Cloud Last Mile service Table. Cloud Last Mile service information entry items
- Enter the required information in the Service Information Input area.
Check the detailed information created in the summary panel and click the Create button.
- When creation is complete, check the created resource on the Resource List page.
Check detailed information of Cloud Last Mile
The Cloud Last Mile service allows you to view and edit the full resource list and detailed information from the Cloud Last Mile menu. The Cloud Last Mile Details page consists of Details, Connected Resources, and Task History tabs.
To view detailed information about Cloud Last Mile, follow these steps.
- Click the All Services > Networking > Cloud Last Mile menu. You will be taken to the Service Home page of Cloud Last Mile.
- From the Service Home page, click the Cloud Last Mile menu. You will be taken to the Cloud Last Mile List page.
- Cloud Last Mile List page, click the resource to view detailed information. You will be taken to the Cloud Last Mile Detail page.
- Cloud Last Mile Details page displays status information and additional feature information, and consists of Details, Connected Resources, Operation History tabs.
Category Detailed description status Current service status - Request: Service request in progress
- Creating: Service registration completed
- Active: Service approved and successfully created
Service termination Cancel Service button Table. Cloud Last Mile status information and additional feature items
- Cloud Last Mile Details page displays status information and additional feature information, and consists of Details, Connected Resources, Operation History tabs.
Detailed Information
In the Detailed Information tab, you can view the detailed information of the selected Cloud Last Mile.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type (Cloud Last Mile) |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User requesting service creation |
| Creation date and time | Service creation date and time |
| Editor | Service modification request user |
| Modification date and time | Service modification date and time |
| Service Details | Service detailed configuration information
|
Connected resources
In the Connected Resources tab, you can view the Circuit and Edge information linked to the selected Cloud Last Mile.
| Category | Detailed description |
|---|---|
| Circuit and Edge ID | Circuit and Edge ID Information
|
| Resource type | Circuit and Edge resource type |
| Connection type | Circuit and Edge connection type |
| Resource Details | Circuit and Edge resource detailed configuration information |
Job History
In the Work History tab, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Cloud Last Mile
If you cancel the unused Cloud Last Mile, you can reduce operating costs.
To cancel Cloud Last Mile, follow these steps.
- Click the All Services > Networking > Cloud Last Mile menu. You will be taken to the Service Home page of Cloud Last Mile.
- On the Service Home page, click the Cloud Last Mile menu. You will be taken to the Cloud Last Mile list page.
- On the Cloud Last Mile List page, click the resource to be terminated. Proceed to the Cloud Last Mile Details page.
- Click the Cancel Service button on the Cloud Last Mile Details page.
- After termination is complete, check the resource termination status in the Cloud Last Mile list.
5.13.2.1 - Circuit and Edge
Users can create the service by entering the required information for the Circuit and Edge service through the Samsung Cloud Platform Console.
Create Circuit and Edge
You can create and use the Circuit and Edge service in the Samsung Cloud Platform Console.
To request the creation of a Circuit and Edge service, follow the steps below.
Click the All Services > Networking > Cloud Last Mile menu. Navigate to the Service Home page of Cloud Last Mile.
On the Service Home page, click the Create Circuit and Edge button. You will be taken to the Create Circuit and Edge page.
On the Circuit and Edge Creation page, enter the information required to create a service.
- Enter the required information in the Service Information Input area.
Category RequiredDetailed description Cloud Last Mile name Required Select the Cloud Last Mile service to use - + New click to create a Cloud Last Mile service and then select it
Resource type Required Select resource type to use Resource Type > Circuit Required Select the connection type of the circuit - SD-WAN: Select the license to use
- VPN: Choose the line type and enter the line bandwidth
- Enter the line bandwidth within 1-1,000
Resource Type > Customer Edge Required Select usage type for Customer Edge - Physical equipment: Select the manufacturer and performance of the physical equipment to use
- Virtual resources: Enter the Customer Edge name and select the type
- Select cCPE specifications
- Select use with up to three VNF functions, and choose the manufacturer and performance for each item
Table. Input fields for Circuit and Edge service information
- Enter the required information in the Service Information Input area.
Check the detailed information generated in the summary panel, and click the Create button.
- After creation is complete, check the created resource on the Resource List page.
Check detailed information for Circuit and Edge
The Circuit and Edge service allows you to view and edit the full resource list and detailed information from the Circuit and Edge menu. The Circuit and Edge Details page consists of Details, Activity Log tabs.
To view detailed information of Circuit and Edge, follow the steps below.
- Click the All Services > Networking > Cloud Last Mile menu. You will be taken to the Service Home page of Cloud Last Mile.
- On the Service Home page, click the Circuit and Edge menu. You will be taken to the Circuit and Edge list page.
- Circuit and Edge List Click the resource to view detailed information on the page. Circuit and Edge Details page will be opened.
- Circuit and Edge Details page displays status information and additional feature information, and consists of Details, Activity Log tabs.
Category Detailed description status Current service status - Request: Service request in progress
- Creating: Service registration completed
- Active: Service approved and successfully created
- Deleting: Service termination request in progress
Previous state change Previous state change button - In Creating, Active, Deleting states, you can revert to the previous state
Delete Circuit and Edge Cancel Service button Table. Circuit and Edge status information and additional feature items
- Circuit and Edge Details page displays status information and additional feature information, and consists of Details, Activity Log tabs.
Detailed Information
Detailed Information tab allows you to view the detailed information of the selected Circuit and Edge.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type (Circuit and Edge) |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User requesting service creation |
| Creation date and time | Service creation date and time |
| Editor | User requesting service modification |
| Modification date and time | Service modification date and time |
| Service Details | Service detailed configuration information
|
Job History
In the Work History tab, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Circuit and Edge
If you cancel unused Circuit and Edge, you can reduce operating costs.
To cancel Circuit and Edge, follow the steps below.
- Click the All Services > Networking > Cloud Last Mile menu. You will be taken to the Service Home page of Cloud Last Mile.
- On the Service Home page, click the Circuit and Edge menu. You will be taken to the Circuit and Edge list page.
- On the Circuit and Edge List page, click the resource to cancel. You will be taken to the Circuit and Edge Details page.
- Circuit and Edge Details page, click the Circuit and Edge Delete button.
- When termination is complete, check the resource termination status in the Circuit and Edge list.
5.13.3 - Release Note
Cloud Last Mile
- The automatic ledger creation feature via the Samsung Cloud Platform user console has been added.
- We have launched the Cloud Last Mile service, which provides a Last Mile line for network connectivity from the customer’s site to the Samsung Cloud Platform region and Customer Edge resources within the customer’s site.
5.14 - Global CDN
5.14.1 - Overview
Service Overview
Global CDN is a service that delivers static content stored on web servers or object storage to users more quickly and securely through numerous edge servers distributed across a global network. It distributes the load of the origin server during traffic spikes to protect the origin server, and by downloading content from nearby edge servers, it can provide users with fast and reliable web services.
Features
- Easy CDN Service Use: Through the web-based console of Samsung Cloud Platform, you can conveniently request Global CDN services. You can easily configure Samsung Cloud Platform’s origin server settings and the caching policy of Global CDN edge servers, enabling rapid content delivery service usage.
- Service Availability Improvement: Even when many users request content simultaneously, generating excessive traffic, users can access content quickly without any degradation in usability thanks to edge servers distributed across multiple locations. Therefore, when used for tasks that require reliable global services, it ensures service availability.
- Secure Content Usage: Supports HTTP, HTTPS, and HTTP/2 protocols, enabling content integration with various origin servers. When the cached content’s validity period expires or a validation check confirms changes to the origin content, the edge server’s existing cache is removed. Subsequently, when a user requests content, the new content from the origin server is cached, ensuring the user always receives valid, up-to-date content.
- Efficient Cost Management: Even in work environments that require large-scale traffic, such as downloading massive files, stable service is possible without extensive resource usage. Additionally, Global CDN usage fees are charged only based on content consumption, enabling efficient cost management.
Service Architecture Diagram
Provided features
The Global CDN service provides the following features.
- Original Settings: Set the location and path of the origin server, and by providing built‑in compression for origin content, reduce traffic and improve response speed.
- Caching Settings: Set the cached content delivery policy and cache expiration time, and when the content’s validity period expires (TTL expiration), you can delete (Purge) the expired cached content on the edge server.
- Content Protection: By communicating with the origin server via the HTTPS protocol, the security of the content delivery path is strengthened, and the powerful security features of the Global CDN network can protect content and users from DDoS attacks and web‑based attacks.
Component
Connection between the origin and the global CDN network
| Category | Explanation |
|---|---|
| Original location and path configuration | Based on the main name or IP address, set the origin server’s location, protocol, port number, and file path to connect the origin to the Global CDN network |
| Forward host header | Configure the Host header value that the Global CDN forwards to the user when requesting the origin server. |
| Cache key hostname | Configure cache key information to identify content on the Global CDN Edge server |
| Custom header(request) | Set whether to use custom header |
Caching in a Global CDN Network
| Category | description |
|---|---|
| Caching options | Configuring caching options on a global CDN network using the origin server’s Cache-Control and expiration times |
| Content Delivery Policy | Setting a transmission policy based on validity after TTL expiration |
| Cache expiration time | Set expiration time for cached content |
| Detailed policy | Configure usage of Ignore query string, Range request, Custom header |
Constraints
The constraints of the Global CDN service are as follows.
| Category | description |
|---|---|
| Maximum number of domains that can be created per account | 20 |
Provision status by region
Global CDN is available in the environments listed below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Prior Service
The Global CDN service has no prerequisite services.
5.14.1.1 - ServiceWatch Metrics
Global CDN sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 5‑minute intervals.
Basic Metrics
The following are the basic metrics for the Global CDN namespace.
The indicators whose names are displayed in bold below are the key indicators selected from the basic metrics provided by Global CDN. Key metrics are used to configure service dashboards that are automatically built for each service in ServiceWatch.
Each metric provides guidance in the user guide on which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the values displayed in bold text are the primary statistics. In the service dashboard, primary metrics can be viewed using the primary statistical values.
| Performance items | Detailed description | unit | Meaningful statistics |
|---|---|---|---|
| cdn.data.transmitted.bytes.total | Data transferred via the CDN service | Bytes |
|
| cdn.requests.hits.total | Number of service requests received through the CDN service | Count |
|
5.14.2 - How-to guides
Users can create the service by entering the required information for the Global CDN service and selecting detailed options through the Samsung Cloud Platform Console.
Create Global CDN
You can create and use the Global CDN service in the Samsung Cloud Platform Console.
To request the creation of a Global CDN service, follow these steps.
- Click the All Services > Networking > Global CDN menu. Go to the Service Home page.
- On the Service Home page, click the Global CDN Create button. You will be taken to the Global CDN Create page.
- On the Global CDN Creation page, enter the information required to create the service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description CDN name Required Enter the Global CDN name to use - Cannot use the same name as an existing one
CDN domain Required Enter the domain name of the Global CDN to use Table. Global CDN Service Information Input Items - Enter or select the required information in the Original Settings area.
Category RequiredDetailed description Original location > domain or IP Required Enter the origin server location - Enter the domain name (recommended) or the origin server’s public IP directly
Source location > Protocol Required Select protocol to use - The service protocol and the source protocol must be set identically
Original location > Port number Required Enter one source port to use - Allowed source ports: 72, 80-89, 443, 488, 591, 777, 1080, 1088, 1111, 1443, 2080, 7001, 7070, 7612, 7777, 8000-9001, 9090, 9901-9908, 11080-11110, 12900-12949, 45002
Original path Select Enter the directory path of the original file - Example: /aaa/bbb/ccc/
Forward host header Required Set the Host header value delivered to the user when requesting the origin server from the Global CDN - Incoming host header: service domain name
- Origin host name: origin domain name
- Custom Value: Enter the domain name directly in the standard domain format, such as www.abc.com
Cache key hostname Required Configure cache key information to identify content on the Global CDN Edge server - Incoming host header: Use the domain the user accesses as the cache key
- Origin hostname: Use the configured origin domain as the cache key
Custom header (request) Selection When the Global CDN Edge server requests the origin server, change a specific Header - Select Use to enter Header name and Header value
- Add items with the (+) button and delete with the (X) button
- Up to 10 entries can be entered
Table. Global CDN origin configuration input fieldsReference- You can request multiple Global CDN services from a single Account.
- In the Global CDN service, only one origin location can be set.
- Enter or select the required information in the Caching Settings area. Decide how to handle the Cache header delivered to the Global CDN Edge server.
Category RequiredDetailed description Caching options Required Set the caching policy applied to all content delivered to the Global CDN Edge server (recommended: Honor origin cache-control and expires) - Honor origin cache-control and expires: Follows both the origin’s cache-control and expiration policies
- Cache: Follows the Global CDN provider’s policy
- Honor origin expires: Follows the origin’s expiration time policy
- Honor origin cache-control: Follows the origin server’s cache control policy
Content Delivery Policy Required Validate content authenticity with the origin server from the Global CDN Edge server - Provide only valid content: Configure not to send when TTL expires (recommended)
- Provide all cached content: Provide all cached content regardless of TTL expiration
Cache expiration time Required Enter the expiration time for cached content on the Global CDN Edge - Enter a value between 3,600 – 2,592,000 seconds
Ignore query string Selection Set whether to use the query string when applying the caching policy - Use setting ignores the query sting
Allow range request Selection Provides large file optimization for objects larger than 100 MB - Use when enabled, supports optimization up to 1.8 GB
Custom header (response) Select Change a specific Header when requesting the origin server from the Global CDN Edge server - using setting, enter Header name and Header value
- (+) button to add items, and (X) button to delete
- Up to 10 entries can be entered
Table. Global CDN caching configuration input fields - In the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Global CDN additional information input fields
- Enter or select the required information in the Service Information Input area.
- Check the application details and click the Create button.
- When creation is complete, check the created resource on the Global CDN List page.
Check Global CDN detailed information
The Global CDN service allows you to view and edit the full resource list and detailed information. Global CDN Detail page consists of Detailed Information, Tags, Activity Log tabs.
To view detailed information about the Global CDN, follow these steps.
- Click the All Services > Networking > Global CDN menu. Navigate to the Service Home page of Global CDN.
- On the Service Home page, click the Global CDN menu. You will be taken to the Global CDN List page.
- On the Global CDN List page, click the resource to view detailed information. You will be taken to the Global CDN Details page.
- Global CDN Details page displays the status and detailed information of Global CDN, and consists of Details, Tags, Activity History tabs.
Category Detailed description Service status Status of Global CDN - Creating: Creating / when Global CDN starts
- Active: Creation complete / operating, information can be modified
- Inactive/Pending: Operation stopped
- Aborted: Failed to activate after Property creation
- Stopped/stopping: Operation halted / halting
- Editing: Changing settings
- Starting: Starting
- Deleting: Terminating
- Mismatching: When the version of the Console and the Global CDN partner differ
- Error: Error occurred
Start Start Service button Stop Stop Service button Apply Purge Apply Purger feature button Service termination Button to cancel Global CDN Table. Global CDN status information and additional features
- Global CDN Details page displays the status and detailed information of Global CDN, and consists of Details, Tags, Activity History tabs.
Detailed Information
Global CDN List page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| CDN name | CDN name |
| CDN domain | CDN domain information |
| CDN configuration version | Configuration (Property) information applied to the Global CDN service
|
| description | Additional description entered by the user
|
| Original settings | Entered CDN origin information
|
| Caching Settings | Entered CDN description
|
tag
Global CDN List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Global CDN List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Change Global CDN Settings
You can change and apply the Global CDN service settings.
To change the Global CDN settings, follow the steps below.
- Click the All Services > Networking > Global CDN menu. Navigate to the Service Home page of Global CDN.
- On the Service Home page, click the Global CDN menu. You will be taken to the Global CDN List page.
- On the Global CDN List page, click the resource to view detailed information. You will be taken to the Global CDN Details page.
- On the Global CDN Details page, click the Edit button. You will be taken to the Global CDN Edit page.
- Global CDN Edit page, modify the desired information and click Done. An edit notification window will appear.
- Click Confirm in the alert dialog. The service information update is complete.
Control Global CDN Operation
You can stop or restart the Global CDN service.
To control the operation of the Global CDN, follow these steps.
- Click the All Services > Networking > Global CDN menu. Navigate to the Service Home page of Global CDN.
- On the Service Home page, click the Global CDN menu. You will be taken to the Global CDN List page.
- On the Global CDN List page, click the resource to view detailed information. You will be taken to the Global CDN Details page.
- On the Global CDN Details page, click the control button. It controls the service operation.
- Start: Run the Global CDN service.
- Stop: Stops the operation of the Global CDN service.
- Starting or stopping the service takes more than an hour to propagate worldwide.
- If you stop the service, the provision of the service domain will be discontinued. Be careful when using the service stop function.
Applying Global CDN Purge
Purge is a feature that forcibly deletes content cached on CDN Edge servers. If the content is modified before the object expires, you can use Purge to delete the existing content on the CDN Edge and then configure it to be refreshed with the new content.
- When a purge is applied, all content stored on the CDN edge is deleted, which may cause simultaneous content requests from the CDN edge to the origin.
- Executing a purge can increase requests to the origin server, potentially causing load. Exercise caution when applying a purge.
To apply a purge to the Global CDN, follow the steps below.
- Click the All Services > Networking > Global CDN menu. Navigate to the Service Home page of Global CDN.
- On the Service Home page, click the Global CDN menu. You will be taken to the Global CDN List page.
- On the Global CDN List page, click the resource to view detailed information. You will be taken to the Global CDN Details page.
- On the Global CDN Details page, click the Apply Purge button. The Apply Purge window opens.
- In the Purge settings window, configure the detailed items and click OK. An edit notification window will open.
- Content Selection: Select the type of content to which Purge will be applied.
- Path Information Input: When Full Domain is selected, the configured domain information is displayed, and when Path Input is selected, you can directly enter the path excluding the domain.
- Click OK in the alert dialog. The purge will be applied.
Terminate Global CDN
You can request termination of the Global CDN service in the Samsung Cloud Platform Console.
To request termination of the Global CDN service, follow the steps below.
- Click the All Services > Networking > Global CDN menu. Navigate to the Service Home page of Global CDN.
- On the Service Home page, click the Global CDN menu. You will be taken to the Global CDN List page.
- On the Global CDN List page, click the resource to view detailed information. You will be taken to the Global CDN Details page.
- On the Global CDN Details page, click the Cancel Service button.
- After the termination is complete, check the service termination status in the Global CDN list.
5.14.3 - API Reference
5.14.4 - CLI Reference
5.14.5 - Release Note
Global CDN
- By integrating with Service Watch, you can view measurement values for the following two items.
- Check Global CDN status
- Check Global CDN processed data volume
- Data from 30 minutes ago is displayed due to the processing time of external CDN network traffic.
- We have launched a Global CDN service that delivers static content stored on web servers or object storage to users more quickly and securely via edge servers distributed across the global network.
5.15 - GSLB
5.15.1 - Overview
Service Overview
GSLB (Global Server Load Balancing) automatically distributes network traffic to an available adjacent region based on DNS when traffic increases in a specific global area. When a specific server fails, we load‑balance network traffic to an available new resource to ensure the service continues reliably.
Features
- Stable Service Provision: By using the health check function (Health Check) that verifies the normal operation of connected resources, if a failure occurs on a specific server, the resource is immediately Fail over and removed from domain responses, redirecting traffic to other resources to provide stable service.
- Easy Service Port Configuration: Through the web-based console, you can conveniently create GSLB and set/manage service ports. For L4-level load balancing, multiple ports can be configured (e.g., 80, 443, 8080-8090), and you can apply and manage several load balancing rules simultaneously.
- Efficient Cost Management: Because the billing method is granularly applied so that fees are determined based on the number of configured domains, the number of added Health Check resources, and the number of queries, costs can be managed efficiently.
Service Architecture Diagram
Provided features
The GSLB service provides the following features.
- GSLB Creation/Management: You can register multiple resources to a single GSLB.
- Load Balancing Algorithm Selection: Provides the Ratio method, which distributes traffic proportionally to the weight (Weight) of each connection target, and the Round Robin method, which cycles traffic and distributes it evenly.
- Health Check Settings: check interval (Interval), service down detection time (Timeout), response wait time (Probe Timeout), protocols (ICMP, TCP, HTTP, HTTPS), and service ports can be configured.
Constraints
The limitations of the GSLB service are as follows.
| Category | Explanation |
|---|---|
| Maximum number of domains that can be created per account | 20 |
| Maximum number of connectable resources per domain | 8 |
- For GSLB to monitor the target, an allow rule must be added to the target resource’s firewall and security group.
Provision status by region
The GSLB service is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Preliminary Service
The GSLB service has no prerequisite services.
5.15.2 - How-to guides
Users can create the service by entering the required information for the GSLB service and selecting detailed options through the Samsung Cloud Platform Console.
Create GSLB
You can create and use a GSLB service in the Samsung Cloud Platform Console.
To request the creation of a GSLB service, follow these steps.
- All Services > Networking > GSLB Click the menu. You will be taken to the Service Home page.
- On the Service Home page, click the Create GSLB button. You will be taken to the Create GSLB page.
- On the GSLB Creation page, enter the information required to create a service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Purpose Required Automatically input PUBLIC when creating GSLB domain name Required Enter the GSLB domain name to use - Enter using lowercase English letters and numbers, between 4 and 40 characters
- Cannot use the same name as an existing one
Add connection target > IP Required Enter the target IP address Add connection target > Location Required Select the location to perform monitoring for the connection target - It is recommended to specify a location close to the IP server
Add connection target > Description Select Enter additional information or description about the connection target Add connection target > Connection target list Required Display added target IP, location, and description entries - Enter target IP, location, and description, then click the Add button to add the entry
- Up to 8 target connections can be added to a single GSLB service
- Click x to remove an entry from the list, click the Delete All button to remove all entries from the list
Table. GSLB Service Information Input Items - Enter or select the required information in the Connection Target Monitoring Settings area.
Category RequiredDetailed description Health Check Required Select the protocol type for health check - ICMP, TCP, HTTP, HTTPS can be selected (recommended to use HTTPS for security)
Interval Required Enter the time interval (seconds) for performing health checks. Timeout Required Enter the waiting time (seconds) to determine the server’s status (UP or DOWN) during a health check. Probe Timeout Required Enter the response timeout (seconds) - Enter the domain name (recommended) or the origin server’s public IP directly
Service Port Required When using TCP/HTTP/HTTPS protocols, enter the port to be used for health checks - Enter the domain name (recommended) or directly input the origin server’s public IP
User Name Select Enter the username to use when authentication is required for health check communication when using the HTTP/HTTPS protocol. Password Select Enter the password to use when authentication is required for health check communication while using the HTTP/HTTPS protocol - Include English letters, numbers, and special characters (@$!%*#?&) and enter it within 8 - 20 characters
Send String Selection When using the HTTP/HTTPS protocol, enter the string to be sent when checking a specific web page - Example) GET /www/example/index.html
- For HTTP 1.0/1.1, use /r/n for line breaks, and special characters (<, >, #) cannot be used in the string
Receive String Required When using the HTTP/HTTPS protocol, enter the string to be received as a health‑check response - The string must contain only English letters (uppercase and lowercase) and numbers
Table. GSLB connection target monitoring configuration input items - Enter or select the required information in the Load Balancing Policy Settings area.
Category Required statusDetailed description Algorithm Required Select load balancing method - Ratio: Distribute traffic proportionally to the weight (Weight) of each connection target
- Round robin: Distribute traffic evenly based on a round-robin method
Connection target Required Enter Weight for each target when selecting Ratio - Weight is the weighting applied to each target when distributing service requests; enter a value between 0 and 100.
- Click the detail view icon of the description item to view target information
Table. GSLB load balancing policy input items - In the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description Explanation Selection Enter additional information or description about the GSLB service. tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. GSLB additional information input fields
- Enter or select the required information in the Service Information Input area.
- Check the creation history and click the Create button.
- When creation is complete, check the created resource on the GSLB List page.
Check GSLB detailed information
The GSLB service allows you to view and edit the full resource list and detailed information. GSLB Details page consists of Details, Targets, Tags, Activity Log tabs.
To view detailed GSLB information, follow these steps.
- Click the All Services > Networking > GSLB menu. Navigate to the Service Home page of GSLB.
- On the Service Home page, click the GSLB menu. You will be taken to the GSLB List page.
- On the GSLB List page, click the resource to view detailed information. You will be taken to the GSLB Details page.
- The GSLB Details page displays the GSLB’s status and detailed information, and consists of the Details, Targets, Tags, Activity Log tabs.
Category Detailed description Service status GSLB status - Creating: In progress
- Active: Running
- Editing: In progress
- Deleting: In progress
- Error: An error occurred
Service termination Button to cancel GSLB Table. GSLB status information and additional features
- The GSLB Details page displays the GSLB’s status and detailed information, and consists of the Details, Targets, Tags, Activity Log tabs.
Detailed Information
On the GSLB List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Domain name | GSLB domain information |
| Purpose | GSLB usage |
| Algorithm | Configured GSLB algorithm information
|
| Health Check | Configured GSLB health check information
|
| Explanation | Entered GSLB description
|
Connection target
On the GSLB List page, you can view the connection target information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| IP | Destination IP address |
| Resource ID | GSLB Resource ID |
| Location | Location to perform monitoring of the connection target |
| description | Enter additional information or description for the connection target
|
| Whether to use | Indicate whether the connection target is used |
| Weight | Display the weight of the connection target |
| Connection status | Connection status display
|
| Edit connection target | Add or modify connection target
|
tag
On the GSLB List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the GSLB List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Modify connection target information
You can add, modify, or delete GSLB connection target information.
To change the GSLB connection target information, follow these steps.
- Click the All Services > Networking > GSLB menu. Navigate to the Service Home page of GSLB.
- On the Service Home page, click the GSLB menu. Navigate to the GSLB List page.
- On the GSLB List page, click the resource to view its details. You will be taken to the GSLB Details page.
- On the GSLB Details page, click the Connection Targets tab. You will be taken to the Connection Targets tab page.
- Connection Target tab page, click the Edit Connection Target button. You will be taken to the Edit Connection Target page.
- On the Edit Connection Target page, modify the information you want.
- Add: Enter the target IP, select the location, and enter a description, then click the Add button to add the item.
- Delete: To delete the linked target item, click the Delete button.
- You can modify the Weight for each item in the connection target list.
- When the edit is complete, click Done. An edit notification window will open.
- Click OK in the alert dialog. The service information update is complete.
- You can add up to 8 targets to a single GSLB service.
- When adding a connection target, it is recommended to set the location field to a position close to the target server.
Configuring the Regional Routing Controller
You can query the Regional Routing Controller and change its usage status.
To change the usage status of the Regional Routing Controller, follow these steps.
All Services > Networking > GSLB Click the menu. Navigate to the Service Home page of GSLB.
On the Service Home page, click the Regional Routing Controller menu. You will be taken to the Regional Routing Controller List page.
Retrieve the resource to view detailed information on the Regional Routing Controller List page.
- Advanced Search button can be clicked to select domain, connection location, and usage status for the search.
On the Regional Routing Controller List page, view the resource information and change its usage status.
Category Detailed description domain name Registered domain name - When you click the domain name, you will be taken to the GSLB Details > Connection Targets tab page
Purpose Domain purpose Connection location Location to perform monitoring of the connection target Connection target by location Number of connection targets by location Whether to use Display the connection target usage status, and you can change the usage status by clicking the More button - Use: Enable the connection target
- Stop: Disable the connection target
- You can also set usage by selecting a domain from the list and choosing Use or Stop at the top
Table. Regional Routing Controller ListClick Confirm in the alert dialog. The domain usage status change is complete.
Terminate GSLB
You can request termination of the GSLB service in the Samsung Cloud Platform Console.
To request cancellation of the GSLB service, follow the steps below.
- Click the All Services > Networking > GSLB menu. Navigate to the Service Home page of GSLB.
- On the Service Home page, click the GSLB menu. You will be taken to the GSLB List page.
- On the GSLB List page, click the resource you want to view detailed information for. You will be taken to the GSLB Details page.
- On the GSLB Details page, click the Cancel Service button.
- After the termination is complete, check the service termination status in the GSLB list.
5.15.3 - API Reference
5.15.4 - CLI Reference
5.15.5 - Release Note
GSLB
- You can control the usage of traffic you want to connect via GSLB on a per-region basis.
- We have launched a GSLB service that can automatically distribute network traffic to adjacent regions based on DNS when traffic increases in a specific global region, providing stable service.
5.16 - Cloud Virtual Circuit
A service that provides 1:1 virtual circuits based on line bandwidth between Global Samsung Cloud Platform regions or customer locations.
5.16.1 - Overview
Service Overview
The Cloud Virtual Circuit service provides a 1:1 virtual circuit based on line bandwidth between global Samsung Cloud Platform regions or customer locations.
Features
Cloud Virtual Circuit offers the following features and benefits.
- Mesh-shaped point-to-point connection: The Samsung Cloud Platform infrastructure is connected across all global regions, allowing point-to-point virtual circuit services to be used anywhere from source to destination.
- No-Contract Short-Term Line Service: Unlike traditional network line services, it offers a no-contract pricing plan, allowing cost-effective use when short-term line service is needed.
- Special Feature Provision: Provides a special function that can split a single virtual circuit into multiple logical circuits for different purposes.
Service Architecture Diagram
Provided features
The Cloud Virtual Circuit service provides the following features.
- Korean and global service provision
- South Korea: Suwon, Sangam, Chuncheon, Gumi, Nonhyeon
- Global: New Jersey, San Jose, São Paulo, London, Frankfurt, Hong Kong, Singapore, Delhi, Dubai, Tokyo
- Provision of point-to-point virtual circuit service between global regions (L2VPN-based)
- You can select the origin and destination access locations in all service regions.
- A single cloud virtual circuit configures up to two virtual links for redundancy.
- Provided circuit bandwidth:
- 10, 20, 50, 100, 200, 300, 400, 500, 600, 700, 800, 900 Mbps
- 1, 2, 3, 4, 5, 6, 7, 8, 9, 10 Gbps
- Provides logical circuit separation (Multi VLAN): Up to five separate VLANs can be used on a single cloud virtual circuit.
Component
Cloud Virtual Circuit provides a 1:1 virtual backbone connection between global locations. The components are as follows, and resources can be created via the related self‑service in the user console.
| Category | content |
|---|---|
| Cloud Virtual Circuit | Virtual resources that accommodate up to two Virtual Links for the same 1:1 endpoint |
| Origin Access Location | 1:1 Virtual circuit’s source Access Location information |
| Destination Access Location | 1:1 virtual circuit destination Access Location information |
| Multi VLAN | A feature that splits a single Virtual Link into multiple logical circuits for provisioning. |
| Virtual Link | Within a Cloud Virtual Circuit, a virtual circuit based on dedicated line bandwidth (line bandwidth, contract term, transmission path level option selection) |
| CE equipment | Network equipment that receives the dedicated line for the customer site (Customer Edge) |
Constraints
Cloud Virtual Circuit has the following limitations.
- For each Cloud Virtual Circuit, you can create up to two Virtual Links.
- The Multi VLAN feature can create up to five per Cloud Virtual Circuit.
Provision status by region
The Cloud Virtual Circuit service can be provided in the following environments.
| Region | Provision status |
|---|---|
| Korea West 1 (kr-west1) | Provided |
| Korea East 1 (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Prior Service
There are no services that need to be pre‑configured before creating this service.
5.16.2 - How-to guides
Users can apply for the Cloud Virtual Circuit service through Service Request in the Samsung Cloud Platform Console.
Apply for Cloud Virtual Circuit
You can request a Cloud Virtual Circuit through the Support Center of the Samsung Cloud Platform Console.
To apply for a Cloud Virtual Circuit, follow the steps below.
Click the All Services > Networking > Cloud Virtual Circuit menu. Navigate to the Service Home page of Cloud Virtual Circuit.
On the Service Home page, click the Cloud Virtual Circuit Service Request button. You will be taken to the Service Request page in the Support Center.
Select and enter the information required to apply for a Cloud Virtual Circuit.
Category Required statusDetailed description Title Required Enter the title of the service request - using Korean, English, numbers, and special characters (
+=,.@-_) within 64 characters
Region Required Select the region to request the service Service Required Networking service group Cloud Virtual Circuit service selection Task classification Required Cloud Virtual Circuit New Application Select content Required Enter information for Cloud Virtual Circuit application Table. Cloud Virtual Circuit Service Request Items- using Korean, English, numbers, and special characters (
Check the input information and click the Request button.
- After submitting a service request, you cannot modify or delete the content you have entered.
- After submitting a service request, you can view the request details on the Support Center’s Service Request List page. Refer to View Service Request Details.
Cloud Virtual Circuit Terminate
You can request the termination of a Cloud Virtual Circuit from the Support Center in the Samsung Cloud Platform Console.
To apply for a Cloud Virtual Circuit, follow the steps below.
Click the All Services > Management > Support Center menu. You will be taken to the Service Home page.
On the Service Home page, click the Cloud Virtual Circuit Service Request menu. You will be taken to the Service Request page.
Select and enter the information required to cancel the Cloud Virtual Circuit.
Category Required statusDetailed description Title Required Enter a title for the service request - using Korean, English, numbers, and special characters(
+=,.@-_) within 64 characters
Region Required Select the region for which you want to request service termination. Service Required Networking service group Cloud Virtual Circuit service selection Task classification Required Cloud Virtual Circuit Cancellation Request Select content Required Enter information for Cloud Virtual Circuit termination request Table. Cloud Virtual Circuit Service Termination Request Items- using Korean, English, numbers, and special characters(
Check the input information and click the Request button.
- After submitting a service request, you cannot modify or delete the content you entered.
- After submitting a service request, you can view the request details on the Support Center’s Service Request List page. Refer to 서비스 요청 상세 정보 확인하기.
5.16.3 - Release Note
Cloud Virtual Circuit
- We have officially launched the Cloud Virtual Circuit service.
- Users can request a 1:1 virtual circuit based on the line bandwidth between Global Samsung Cloud Platform regions or customer sites.
5.17 - Private 5G Cloud
5.17.1 - Overview
Service Overview
Private 5G Cloud is a service based on the Samsung Cloud Platform that provides Private 5G Core and Edge solutions to enterprise customers. By leveraging the cloud, it minimizes the deployment of physical 5G network equipment, enabling the construction of a flexible and scalable network environment optimized for the customer’s private environment, and allowing easy connection of multiple geographically distributed locations.
Provides a dedicated enterprise 5G Core in a cloud environment, ensures service availability through stable operation, and enables real-time processing of large internal data and secure protection of critical data via Edge solutions.
Features
- Stable Operation: Private 5G Cloud combines a 5G Core that has been validated for quality and reliability with cloud security policies. It also provides 24‑hour monitoring services by specialized 5G operations personnel. This enables regular system diagnostics and rapid response in case of failures, allowing the service to be operated stably. Efficient Cost Management: By deploying a Private 5G network on the Samsung Cloud Platform, you can reduce initial investment costs for building a 5G system and minimize operational expenses. It enables a fast and secure cloud‑based Private 5G network, as well as flexible operation and capacity scaling.
- Private Edge Solution Offering: We provide application management and Edge Computing services based on Kubernetes that apply the 3GPP MEC standard. By configuring an Edge Computing service environment within the client’s premises, ultra‑low‑latency data transmission is possible, and because all data and services reside within the client’s premises, the company’s valuable information can be securely protected.. Various Integration Features: You can access a variety of solutions and software validated in the Private 5G Open Lab through the marketplace. Customers can leverage the pre-configured development environment and related ecosystem to adopt emerging technologies such as AI, machine learning, and big data, and can use customized solutions.
Service Architecture Diagram
Provided features
Private 5G Cloud provides the following features. Private 5G Cloud Core: Provision of cloud-based 5G wireless network and authentication services Private 5G Core CP: Processing customer-specific 5G signal control in the cloud domain UPF: Data processing of each customer’s unique service in the customer’s site area 5G network: handling dedicated network services (VPN/dedicated line) between the cloud and the customer’s premises
Component
Private 5G Cloud provides services across the entire 5G network within the customer’s site, and its components are as follows.
5G Core network
- User authentication, session management, data processing
- Customer device registration/deletion/modification/management
Service Portal
- Provision of a 5G integrated service portal
- User portal: Create/modify/manage user policies
- Admin Portal: Authentication Policy Management and Monitoring
Network Solution
Configure cloud network solutions such as VPN and dedicated lines
Provision status by region
Private 5G Cloud can be provided in the environments below.
| Region | Provision status |
|---|---|
| Korea West 1 (kr-west1) | Provided |
| Korea East 1 (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Provide |
| South Korea South 2 (kr-south2) | Provided |
| South Korea 3 (kr-south3) | Provided |
Prior Service
This is a list of services that must be pre‑configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
| Networking | Direct Connect | A service that securely and quickly connects the customer’s network with the Samsung Cloud Platform |
| Networking | Firewall | A service that provides a firewall for traffic between the VPC, the Internet, and the customer’s network. |
| Networking | VPN | A service that connects the customer’s network and Samsung Cloud Platform via an encrypted virtual private network
|
5.17.2 - How-to guides
Users can enter the required information for the Private 5G Cloud service, select detailed options, and create the service through the Samsung Cloud Platform Console.
Create Private 5G Cloud
You can create and use a Private 5G Cloud service from the Samsung Cloud Platform Console.
To create a Private 5G Cloud, follow these steps.
- Click the All Services > Networking > Private 5G Cloud menu. You will be taken to the Private 5G Cloud Service Home page.
- On the Service Home page, click the Private 5G Cloud Service Request button. You will be taken to the Service Request page.
- On the Service Request page, select or enter the required information for Private 5G Cloud.informationIn the task category, select Private 5G Cloud Service Creation and create it.
| Input field | Detailed description |
|---|---|
| Title | Title of the service you want to request |
| Region | Select location of Samsung Cloud Platform
|
| service | Select the service group and service for the given service
|
| Task classification | Select the task to perform
|
| content | Enter detailed information required to create a Private 5G Cloud [Basic Information]
[Application Information]
|
| Attachment | Proceed with upload only if there are additional files you want to share
|
- Review the entered generation information and click the Request button.
- Once creation is complete, check the Service Request List page to see if the resource was created.
- This provisioning process involves steps such as purchasing physical servers, delivery, configuration, and site setup, and requires a minimum of eight weeks of business days.
Check Private 5G Cloud application details
You can view the application and cancellation history of the Private 5G Cloud service in the Samsung Cloud Platform Console.
To view the service application and termination request history of Private 5G Cloud, follow the steps below.
To check your Private 5G Cloud service application details, follow the steps below.
- Click the All Services > Management > Support Center menu. Navigate to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request menu. You will be taken to the Service Request List page.
- On the Service Request List page, click the Title of the service request you submitted. You will be taken to the Service Request Details page.
- Service Request Details page, check the request status and information.
Terminate Private 5G Cloud
You can reduce operating costs by terminating the Private 5G Cloud service whose contract period has expired.
- If you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact of the service interruption.
- To request service termination before the contract period expires, you must first complete the termination of the Private 5G Cloud contract through prior consultation between the user’s contract manager and Samsung SDS contract manager, and then proceed with termination according to the steps below.
To cancel Private 5G Cloud, follow the steps below.
- Click the All Services > Networking > Private 5G Cloud menu. You will be taken to the Private 5G Cloud Service Home page.
- On the Service Home page, click the Private 5G Cloud Service Request button. You will be taken to the Service Request page.
- On the Service Request page, select or enter the required information for Private 5G Cloud.InformationIn the task category, select Private 5G Cloud Service Termination and cancel it.
| Input field | Detailed description |
|---|---|
| Title | Title of the service you want to request |
| Region | Select location of Samsung Cloud Platform
|
| service | Select the service group and service for this service
|
| Task classification | Select the task you want to perform
|
| Content | Private 5G Cloud Enter detailed information required for termination [Basic Information]
|
| Attachment | Only proceed with upload if there are additional files you want to share
|
- Review the entered generation information and click the Request button.
- After the termination is complete, check on the Service Request List page whether the resource has been terminated.
- The termination process is completed after the physical server is returned, and it takes at least 3–4 weeks of business days.
5.17.3 - Release Note
Private 5G Cloud
- A Private 5G Cloud product that provides 5G services to customers based on the Samsung Cloud Platform has been launched.
6 - Database
We provide a service that easily creates and manages relational, unstructured, and analytical databases in a web environment.
6.1 - EPAS(DBaaS)
6.1.1 - Overview
Service Overview
EPAS(DBaaS) is a relational database management system (RDBMS) with high compatibility with Oracle databases. Samsung Cloud Platform provides an environment that automates EPAS installation and performs management functions for operation through a web-based console.
EPAS(DBaaS) is designed as a high‑availability architecture that performs storage‑based data replication and minimizes failover time. To prevent data loss, when the contents of the Active server change, they are synchronously replicated to the Standby server, and up to five read‑only Replica servers for read load balancing and disaster recovery (DR) are provided. Additionally, to prepare for potential issues with the DB server or data, we provide a feature that automatically backs up at a user-specified time, enabling data recovery at the desired point.
Provided Features
EPAS(DBaaS) provides the following features.
- Auto Provisioning: UI allows installation and configuration of Database (DB), and provides an Active‑standby redundancy configuration built on storage replication. * When the active server fails, it automatically fails over to standby.
- Operation Control Management: Provides a function to control the status of running servers. * In addition to start and stop, you can restart if there is a DB issue or to apply configuration changes. * When high availability (HA) is configured, the user can manually perform node switching between Active and Standby via a switch‑over.
- Backup and Recovery: Provides data backup functionality based on its own backup commands. * The backup schedule and retention policy can be set by the user, and additional fees apply based on the backup size. * It also provides a recovery function for backed‑up data, so when the user performs a recovery, a separate database is created and the recovery proceeds to the point in time selected by the user (the backup save point or a user‑specified point). * When restoring to a user-specified point in time, the restore point can be set up to 5 minutes, 10 minutes, 30 minutes, or 1 hour earlier, based on the stored backup and archive files.
- Version Management: Provides a version upgrade (Minor) feature based on certain feature enhancements and security patches. * Whether to perform a backup for a version upgrade can be selected by the user, and if a backup is performed, the data is backed up before applying the patch, after which the DB engine is updated.
- Replica configuration: Up to five Read Replicas can be configured in the same or different regions for read load balancing and disaster recovery (DR).
- Audit configuration: Provides an Audit configuration feature that can monitor users’ DB access and the results of DDL (Data Definition Language)/DML (Data Manipulation Language) operations.
- Parameter management: You can modify DB configuration parameters related to performance improvement and security.
- Service Status Query: Retrieves the final status of the current DB service.
- Monitoring: CPU, memory, DB performance monitoring information can be viewed through the Cloud Monitoring service.
- DB User Management: Query and manage the DB account (user) information registered in the DB.
- DB Access Control Management: Based on DB accounts registered in the DB, you can register and revoke allowed IPs for access.
- Archive Management: You can set the Archive file retention period (1~35 days) on the DB server and configure the Archive mode (On/Off).
- Export DB Log: You can export stored logs to the user’s Object Storage through Audit settings.
- Migration: Synchronize data in real time with the operational database and support migration using replication without service interruption.
- OS Kernel Upgrade: You can upgrade the OS Kernel to apply some feature improvements and security patches.
Component
EPAS (DBaaS) provides pre‑validated engine versions and a variety of server types. Users can select and use it based on the scale of the service they wish to configure.
Engine version
The engine versions supported by EPAS (DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is stopped is set to six months before the EoTS date.
Since the EOS and EoTS dates may change according to the supplier’s policy, please refer to the supplier’s license management policy page for details.
| Provided version | EOS Date (Samsung Cloud Platform new creation stop date) | EoTS Date (Community technical support end date) |
|---|---|---|
| 14.17 | 2026-05-20 | 2026-12-01 |
| 14.18 | 2026-05-20 | 2026-12-01 |
| 14.19 | 2026-05-20 | 2026-12-01 |
| 15.12 | 2027-09 (planned) | 2028-02-13 |
| 15.13 | 2027-09 (planned) | 2028-02-13 |
| 15.14 | 2027-09 (planned) | 2028-02-13 |
| 16.8 | 2028-06 (planned) | 2028-11-09 |
| 16.9 | 2028-06 (planned) | 2028-11-09 |
| 16.10 | 2028-06 (planned) | 2028-11-09 |
| 17.6 | 2029-06 (planned) | 2029-11-08 |
The next version of EPAS is expected to be offered after July 2026. The actual service delivery schedule is subject to change.
- EPAS 15.15
- EPAS 16.11
- EPAS 17.17
Server type
The server types supported by EPAS (DBaaS) are as follows.
For detailed information about the server types provided by EPAS (DBaaS), see EPAS(DBaaS) Server Types.
Standard db1v2m4
| Category | Example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | db1 | Provided server specifications
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
6.1.1.1 - Server Types
EPAS(DBaaS) server type
EPAS (DBaaS) offers server types configured with various combinations of CPU, memory, and network bandwidth. When creating an EPAS (DBaaS), the Database Engine is installed based on the server type selected for the intended purpose.
The server types supported by EPAS (DBaaS) are as follows.
Standard db1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | db1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
db1 server type
The db1 server type of EPAS (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db1v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db1v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
db2 server type
The db2 server type of PostgreSQL (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor, up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
dbh2 server type
The dbh2 server type of EPAS(DBaaS) is provided with high‑capacity server specifications and is suitable for database workloads that require large‑scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | dbh2v24m48 | 24 vCore | 48 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m64 | 32 vCore | 64 GB | Up to 25 Gbps |
| High Capacity | dbh2v32m128 | 32 vCore | 128 GB | Up to 25 Gbps |
| High Capacity | dbh2v32m256 | 32 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m256 | 64 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m768 | 64 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m384 | 96 vCore | 384 GB | Up to 25 Gbps |
| High Capacity | dbh2v96m1152 | 96 vCore | 1152 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
6.1.1.2 - Monitoring metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service, which was released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services by Resource
- New Resources: Resources created after the service improvement work in July 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide monitoring concurrently via Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings linked with existing Cloud Monitoring (e.g. You need to review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Notice of the phased termination schedule for the Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, Cloud Monitoring data cannot be accessed. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
EPAS(DBaaS) Monitoring Metrics
The table below shows the performance monitoring metrics of EPAS (DBaaS) that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
For EPAS (DBaaS) server monitoring metrics, refer to the Virtual Server Monitoring Metrics guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Active Locks [Access Exclusive] | Number of Access Exclusive Locks | cnt |
| Active Locks [Access Share] | Number of Access Share Locks | cnt |
| Active Locks | Number of Active Locks | cnt |
| Active Locks [Total] | Total number of active locks | cnt |
| Active Sessions | Number of Sessions in Active state | cnt |
| Active Sessions [Total] | Total number of Sessions in Active state | cnt |
| Apply Lag Time | Apply lag time | min |
| Check No Replication | Check No Replication value | cnt |
| Check Replication | Check Replication Status value | status |
| Connection Usage | DB connection usage rate (%) | % |
| Connection Usage [Total] | DB connection usage rate (%) | % |
| DB Age Max | Database age (frozen XID) value | age |
| Exclusive Locks | Number of Exclusive Locks | cnt |
| Idle In Transaction Sessions | Number of sessions in Idle in transaction state | cnt |
| Idle In Transaction Sessions [Total] | Total number of sessions in idle in transaction state | cnt |
| Idle Sessions | Number of idle sessions | cnt |
| Idle Sessions [Total] | Total number of idle sessions | cnt |
| Row Exclusive Locks | Number of Row Exclusive Locks | cnt |
| Row Share Locks | Row Share Locks count | cnt |
| Share Locks | Number of Share Locks | cnt |
| Share Row Exclusive Locks | Number of Share Row Exclusive Locks | cnt |
| Share Update Exclusive Locks | Number of Share Update Exclusive Locks | cnt |
| Slowqueries | Number of SQL queries running for a long time (over 5 minutes) | cnt |
| Tablespace Used | Table space size | bytes |
| Tablespace Used [Total] | Table space size | bytes |
| Tablespace Used Bytes [MB] | File system directory usage (MB) | MB |
| Tablespaces [Total] | File system directory usage (MB) | MB |
| Transaction Time Max [Long] | Long-running Transaction time (minutes) | min |
| Transaction Time Max Total [Long] | Long-running Transaction time (minutes) | min |
| Wait Locks | Number of lock-waiting sessions (by DB) | cnt |
| Wait Locks [Long Total] | Number of lock-waiting sessions (300 seconds) | cnt |
| Wait Locks [Long] | Number of sessions waiting due to a lock | cnt |
| Wait Locks [Total] | Total number of sessions waiting due to lock occurrence | cnt |
| Waiting Sessions | Number of Sessions in Waiting state | cnt |
| Waiting Sessions [Total] | Total number of Sessions in Waiting state | cnt |
6.1.2 - How-to guides
Users can create the service by entering the required information for EPAS (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Service per Resource
- New Resources: Resources created after the July 2026 service improvement work are provided with default monitoring using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings linked with existing Cloud Monitoring (ex. You must check the event policies, etc., and perform tasks such as resetting the ServiceWatch service, then complete them.
Notice of the phased termination schedule for Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch is available in the ServiceWatch 개요.
Create EPAS (DBaaS)
You can create and use the EPAS (DBaaS) service in the Samsung Cloud Platform Console.
- Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the creation of the corresponding Database service is not possible.
- When loading more than 2 TB of large data, backups may take a long time or the database’s performance may degrade. * To prevent this, it is necessary to consider operational aspects such as cleaning up unnecessary data or migrating old data to the statistical collection environment.
To create EPAS (DBaaS), follow these steps.
All Services > Database > EPAS(DBaaS) Click the menu. 1. Navigate to the Service Home page of EPAS (DBaaS).
On the Service Home page, click the Create EPAS (DBaaS) button. 2. Go to the EPAS(DBaaS) Create page.
On the Create EPAS (DBaaS) page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version Required Provide EPAS (DBaaS) version list Table. EPAS (DBaaS) Image and version selection items - In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Server name Prefix Required Server name where the DB will be installed - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
-) with a length of 3 to 13 characters
- A postfix such as 001, 002 is appended to the base server name to generate the actual server name
Cluster name required Cluster name composed of DB servers - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for DB installation - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more
- For detailed information about the server types provided by EPAS (DBaaS), refer to EPAS(DBaaS) 서버 타입
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, refer to Planned Compute Application
Service Type > Block Storage Required Block Storage settings used by the DB according to purpose - Base OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select a storage type and then enter the capacity.(For details on each Block Storage type, refer to Block Storage 생성하기)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volume that uses Samsung Cloud Platform KMS(Key Management System) encryption keys
- The configured storage type is applied identically to additional storage
- Capacity must be entered as a multiple of 8 within the range 16 to 5,120
- Because executing SQL or monthly batch jobs can cause service interruption due to large sorts, a separate TEMP storage must be allocated and used
- Add: DATA, Archive, TEMP, Backup data storage areas
- Use after selecting, enter the storage’s purpose and capacity
- The storage type is applied the same as the type set for DATA, and capacity can be entered as a multiple of 8 within the range 16 to 5,120
- To add storage, click the Add button; to delete, click the x button. Up to 9 can be added
- Before transmitting backup data, temporarily store the backup data in the BACKUP storage
- If the data to be backed up exceeds 100 GB and undergoes frequent changes, it is recommended to add a separate BACKUP storage for reliable backup; the backup capacity is advised to be set at about 60 % of the DATA capacity
- If a BACKUP storage is not added, the
/tmparea is used, and backup fails if capacity is insufficient
- For each service, Archive, TEMP, and BACKUP storages are allocated only one Block Storage each
- Select a storage type and then enter the capacity.(For details on each Block Storage type, refer to Block Storage 생성하기)
Redundancy configuration Selection Redundancy configuration status - When redundancy configuration is used, the DB instance is set up as an Active DB and a Standby DB
Network > Common Settings Essential Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- IP can only be generated automatically
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. Use it by checking the box, allowing selection from reserved IPs in the VPC product’s Public IP. For more details, see Public IP 생성하기
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select when you want to apply different settings for each installed server
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- Enter the IP for each server
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. Checking Use makes it possible to select a reserved IP from the VPC product’s Public IP pool. For more details, see Public IP 생성하기.
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, a separate Security Group policy configuration is not required
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of the week, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. EPAS (DBaaS) Service Information Input Items - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
- Enter required database configuration information Enter or select the required information in this area.
Category required statusDetailed description Database name Required Server name applied during DB installation - must start with an English letter and be entered using English letters and numbers, 3 to 20 characters
Database username Required Database user name - An account with the same name is also created on the OS
- Enter using lowercase English letters, 2 to 20 characters
- Restricted database user names can be viewed in the Console
Database password Required Password to use when accessing the DB - Enter 8 to 30 characters, including letters, numbers, and special characters (excluding
“‘)
Database password verification Essential Re-enter the same password to use for DB access Database Port number Required Port number required for DB connection - Enter DB port within the range 1200 ~ 65535
Backup > Use Select Backup usage - Select Use to set backup file retention period, backup start time, and Archive backup interval
Backup > Retention Period Select Backup retention period - Select the backup retention period. Set the file retention period from 7 days to 35 days
- Backup files incur additional charges based on size
Backup > Backup Start Period Selection Backup start time - Select backup start time
- The minute(s) at which the backup runs is set randomly, and the backup end time cannot be set
Backup > Archive backup cycle Select Archive backup interval - Select the archive backup interval
- The archive backup interval is recommended to be 1 hour. Selecting 5 minutes, 10 minutes, or 30 minutes may affect DB performance.
Audit Log Settings Select Whether to store Audit Log - Select Use to configure the Audit Log feature
- DDL, DML, SELECT, and user connection information records are stored
- The user can specify the types of SQL statements to audit via the
edb_audit_statementparameter, and can modify it through the Parameter screen
- Refer to the EDB documentation for detailed information about this parameter
- The user can specify the types of SQL statements to audit via the
- Enabling Audit may degrade database performance
Parameter Essential DB configuration parameters - Click the Query button to view detailed information of the parameters
- Parameters can be modified after the service creation is complete, and the DB must be restarted after modification
Database Encoding Required Character encoding method to be used for the DB - Character set used when storing text data
- The DB is created with the selected encoding as the default setting
DB Locale Required Locale to be used for the DB - settings related to string handling, number/currency/date/time display formats, etc.
- The DB is created with the selected Locale as the default setting
time zone Required Standard time zone for the database License Required EPAS License verification status - Verification item for license usage; if you do not click Confirm, you cannot proceed to the next step
Table. EPAS (DBaaS) Database configuration items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description Tag Select Add Tag - Up to 50 per resource can be added
- Add Tag button, then input or select Key, Value values
Table. EPAS (DBaaS) Additional Information Input Items
- Select the required information in the Image and version selection area.
Check the detailed information and estimated billing amount generated in the Summary panel, and click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
View detailed information of EPAS (DBaaS)
The EPAS (DBaaS) service allows you to view and edit the full list of resources and detailed information. EPAS(DBaaS) Details page consists of Details, Tags, Activity History tabs, and when the DB has a Replica configured, a Replica Information tab is added.
To view detailed information about the EPAS (DBaaS) service, follow the steps below.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource to view detailed information. 3. EPAS(DBaaS) Details Go to the page.
- EPAS(DBaaS) Details The top of the page displays status information and additional feature details.
Category Detailed description Cluster status Cluster status with DB installed - Creating: Creating cluster
- Editing: Cluster is changing to a state of performing an operation
- Error: Cluster encountered an error while performing tasks
- If it occurs continuously, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Restarting the cluster
- Running: Cluster is operating normally
- Starting: Starting the cluster
- Stopped: Cluster is stopped
- Stopping: Cluster is in the process of stopping
- Synchronizing: Synchronizing the cluster
- Terminating: Terminating the cluster
- Unknown: Cluster status is unknown
- If it occurs continuously, contact the administrator
- Upgrading: Cluster is changing to a state of performing an upgrade
Cluster control Button to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
- Switch-Over: Switch a standby cluster to active
More features Cluster Management Buttons - Service Status Synchronization: Real-time DB service status lookup
- Backup History: When backup is configured, verify successful execution and view history
- Database Recovery: Recover the DB based on a specific point in time
- Parameter Management: View and modify DB configuration parameters
- Replica Configuration: Set up a read-only Replica cluster
- Replica Configuration (Other-Region): Set up a disaster recovery Replica in another region; the button is disabled if the account has no region to configure
- DB User Management: View and manage DB account (user) information registered in the DB
- DB Access Control Management: Register and revoke allowed IPs based on DB accounts registered in the DB
- Archive Settings Management: Configure archive file retention period and enable archive mode
- Export DB Log: Export stored logs to the user’s Object Storage via Audit settings
- Migration Configuration: Provides migration functionality using replication
- OS (Kernel) Upgrade: Upgrade the OS kernel version
Service termination Cancel service button Table. EPAS (DBaaS) status information and additional features
- EPAS(DBaaS) Details The top of the page displays status information and additional feature details.
Detailed information
On the EPAS (DBaaS) List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed DB image and version information
|
| Cluster type | Cluster types (Master Cluster, Replica Cluster, Migration Cluster) |
| Cluster name | Cluster name of the DB servers |
| Master cluster name | Replica’s Master cluster name
|
| Database name | Server name applied during DB installation |
| Database username | DB user name |
| Planned Compute | Resource status with Planned Compute configured
|
| maintenance period | DB Maintenance Period Status
|
| Backup | Backup configuration status
|
| Audit Log Settings | Audit Log configuration status
|
| time zone | Standard time zone for the database |
| DB Locale | Locale to use in the DB |
| Database Encoding | Character encoding to use for the DB |
| VIP | Virtual IP information
|
| Network | Network information of the DB installation (VPC, Subnet, VIP, NAT IP(VIP)) |
| IP access control | Service access policy configuration
|
| Active & Standby | Active/Standby server type, base OS, additional Disk information
|
Replica information
The Replica Information tab is enabled only when a Replica is configured in the cluster. Through the Replica Information tab, you can check the Master cluster name, number of replicas, and Replica status.
| Category | Detailed description |
|---|---|
| Master information | Name of the Master cluster |
| Replica count | Number of Replicas created in the Master cluster |
| Replica status | Replica server status created in the Master cluster
|
tag
EPAS (DBaaS) List page lets you view, add, modify, or delete tag information for the selected resource.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
EPAS (DBaaS) List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing EPAS (DBaaS) Resources
If you need to change or restore the existing configuration options of a created EPAS (DBaaS) resource, or require a Replica configuration, you can perform the task on the EPAS(DBaaS) Details page.
Control operation
If changes occur to a running EPAS (DBaaS) resource, you can start, stop, or restart it. Additionally, when HA is configured, you can switch the Active‑Standby servers using a switch‑over.
To control the operation of EPAS (DBaaS), follow the steps below.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Navigate to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource you want to control. 3. EPAS(DBaaS) Details Navigate to the page.
- Check the EPAS (DBaaS) status and complete the change using the control button below.
- Start: DB service is installed on the server and the DB service is running (Running).
- Stop: The server where the DB service is installed and the DB service are stopped (Stopped).
- Restart: Only the DB service will be restarted.
- Switch Over: You can switch the DB’s Active server and Standby server.
Synchronize service status
You can synchronize the real-time service status of EPAS (DBaaS).
To check the service status of EPAS (DBaaS), follow the steps below.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource for which you want to view the service status. 3. EPAS(DBaaS) Details Go to the page.
- Service Status Synchronization Click the button. 4. While it is being queried, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Navigate to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page, click the resource whose server type you want to change. 3. Go to the EPAS(DBaaS) Details page.
- Click the Edit icon of the server type you want to change at the bottom of the detailed information. 4. Edit Server Type The popup window opens.
- Edit Server Type After selecting the server type in the popup window, click the Confirm button.
Add storage
If you need more than 5 TB of data storage, you can add additional storage. For a redundant DB configuration, all redundant servers are added simultaneously.
To add storage, follow these steps.
- It is applied in the same way as the Storage type selected when creating the service.
- For a DB configured with redundancy, adding storage is applied simultaneously to the storage of both the Active DB and the Standby DB.
- If a Replica exists, the storage of the Master cluster cannot be larger than the storage of the Replica. * First expand the Replica storage, then expand the Master cluster storage.
- When adding Archive/Temp storage, the DB restarts and is temporarily unavailable.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Navigate to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to EPAS(DBaaS) List page.
- On the EPAS (DBaaS) List page, click the resource to add storage. 3. EPAS(DBaaS) Details Navigate to the page.
- Click the Disk Add button at the bottom of the detailed information. 4. Additional Storage Request The popup window opens.
- Additional Storage Request In the popup window, after entering the purpose and size, click the Confirm button.
Expand storage
Storage added to the data area can be expanded up to a maximum of 5 TB based on the initially allocated capacity. In the case of a redundant DB configuration, all redundant servers are expanded simultaneously.
To expand storage capacity, follow the steps below.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page, click the resource for which you want to change the server type. 3. EPAS(DBaaS) Details Navigate to the page.
- Click the Edit icon of the additional Disk you want to add at the bottom of the detailed information. 4. Edit Additional Storage The popup window opens.
- Edit Additional Storage In the popup window, after entering the expanded capacity, click the Confirm button.
Cancel EPAS (DBaaS)
You can cancel unused EPAS(DBaaS) to reduce operating costs. However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may occur when the service is discontinued.
- For a DB with a Replica configured, terminating the Master DB does not delete the Replica. * If you also delete the replica, cancel it separately from the resource list.
- If you terminate the DB, all stored data and any configured backup data will be deleted.
To cancel EPAS (DBaaS), follow the steps below.
- All Services > Database > EPAS(DBaaS) menu, click it. 1. Navigate to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page, select the resource to cancel, and click the Cancel Service button.
- After termination is complete, check on the EPAS(DBaaS) list page whether the resource has been terminated.
6.1.2.1 - DB Service Manage
Users can manage EPAS (DBaaS) through the Samsung Cloud Platform Console.
Managing Parameters
Provides a feature that enables easy viewing and modification of database configuration parameters.
Viewing Parameters
To view configuration parameters, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the EPAS(DBaaS) Service Home page.
- On the Service Home page, click the EPAS(DBaaS) menu. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource whose parameters you want to view or modify. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button and then click the Parameter Management button. The Parameter Management popup opens.
- In the Parameter Management popup, click the Search button. The Search Notification popup opens.
- Lookup Notification when the popup window opens, click the Confirm button. Retrieving may take a short amount of time.
Parameter Modify
To modify the configuration parameters, follow the steps below.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the Service Home page of EPAS(DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource whose parameters you want to view or modify. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button and then click the Parameter Management button. The Parameter Management popup opens.
- In the Parameter Management popup, click the Search button. The Search Notification popup opens.
- Lookup Notification When the popup window opens, click the Confirm button. Retrieving may take a short amount of time.
- If editing is required, click the Edit button and enter the changes in the custom value area of the Parameter to be edited.
- When the input is complete, click the Complete button.
DB User Management
Provides management features that allow viewing DB user information and changing status information.
Query DB users
To retrieve DB users, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Go to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource whose DB users you want to view. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button, then click the DB User Management button. You will be directed to the DB User Management page.
- Click the Search button on the DB User Management page. Retrieving may take a short while.
Changing DB User Status
To change the status of the retrieved DB user, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Go to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page, click the resource whose DB user you want to modify. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button, then click the DB User Management button. You will be directed to the DB User Management page.
- On the DB User Management page, click the Search button. Retrieving may take a short time.
- If modification is needed, click the Edit button, and change the status field value or enter remarks.
- When the input is complete, click the Complete button.
Managing DB Access Control
Provides IP-based DB user access control management functionality. Users can directly specify the IPs that can access the database, configuring it so that only authorized IPs are allowed access.
View DB Access Control
Follow these steps to query DB users with IP access control enabled.
- Click the All Services > Database > EPAS(DBaaS) menu. Proceed to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- Click the resource you want to manage access control for on the EPAS(DBaaS) List page. You will be taken to the EPAS(DBaaS) Detail page.
- Click the More button, then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. Retrieving the data may take a moment.
Add DB access control
To add IP access control, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the Service Home page of EPAS(DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource for which you want to add IP access control. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button, then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. The query may take a moment.
- After the query completes, click the Add button. The Add DB Access Control popup window opens.
- Add DB Access Control In the popup window, select the DB username and enter the IP address.
- When the input is complete, click the Save button.
Delete DB access control
To delete IP access control, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Go to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. Navigate to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource for which you want to delete IP access control. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button and then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. Retrieving the data may take a moment.
- When the query is complete, click the Delete button. The Delete popup window opens.
- In the Delete popup, click the Confirm button.
Managing Archive
Provides the ability to configure Archive mode and set the retention period for Archive logs, allowing users to flexibly configure Archive log management policies to suit their operational environment. Additionally, it provides a feature to manually delete archive logs, allowing you to clean up unnecessary log data and manage system resources effectively.
Configure Archive mode
To set the Archive mode, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Go to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. Navigate to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource for which you want to set Archive mode. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button and then click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- On the Archive Settings Management page, click the Search button. The query may take a short time.
- Click the Edit button and select the usage status and retention period.
- When the edit is complete, click the Complete button.
Delete Archive file
To delete the Archive file, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the Service Home page of EPAS(DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource you want to set to Archive mode. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button, then click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- Archive Settings Management page, if you want to delete all Archive files, click the Delete All Archives button; if you only want to delete the backed‑up Archive files, click the Delete Backed‑up Archives button.
Modify Audit Settings
You can modify the Audit log storage settings for EPAS (DBaaS).
To change the Audit log storage settings of EPAS (DBaaS), follow the steps below.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the EPAS(DBaaS) Service Home page.
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page, click the resource whose service status you want to view. You will be taken to the EPAS(DBaaS) Details page.
- Click the Edit icon of Audit Settings at the bottom of the detailed information. The Edit Audit Settings popup window opens.
- Modify Audit Settings After changing the usage in the popup window, click the Confirm button.
- When Enable is selected, the Audit log feature is configured. Enabling the Audit log may degrade DB performance.
- If you disable use, the Audit log storage file will be deleted. Before disabling use, back up the Audit log file separately.
DB Log Export
Supports exporting log data that requires long-term retention among audit logs to Object Storage. Users can directly configure the log types to be stored, the target bucket for export, and the export interval. Based on the configured criteria, logs are copied to the specified Object Storage for retention. Additionally, to efficiently manage disk space, we also provide an option that exports logs to Object Storage while automatically deleting the original log files. By using this option, you can effectively free up storage capacity while safely retaining the necessary log data for long-term storage.
- To use the DB Log export feature, you must create an Object Storage. For creating an Object Storage, please refer to the Object Storage User Guide.
- Please be sure to check the expiration date and time of the authentication key. If the authentication key expires, logs will not be stored in the bucket.
- Please take care to prevent the authentication key information from being exposed externally.
Setting DB Log Export Mode
To set the DB Log export mode, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource for which you want to export the DB Log. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button, then click the DB Log Export button. You will be taken to the DB Log Export page.
- On the DB Log Export page, click the Register button. You will be taken to the DB Log Export Register page.
- After entering the required information on the DB Log Export Registration page, click the Complete button.
Category Required Detailed descriptionLog type Required Log type to be saved Save bucket name Required Object Storage bucket name to be saved Authentication key > Access key Required Access key for accessing the Object Storage you want to store Authentication key > Secret key Required Secret key for accessing the Object Storage you want to store File creation cycle Required File creation frequency in Object Storage Whether to delete the original log Selection Whether to delete the original logs when exporting to Object Storage Table. EPAS (DBaaS) DB Log Export Configuration Items
Managing DB Log Export
To modify, cancel, or immediately export the DB Log export settings, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. Navigate to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. Navigate to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource you want to manage DB Log export for. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button and then click the DB Log Export button. You will be taken to the DB Log Export page.
- DB Log Export On the page, depending on the log type you want to manage, click the More button and then click the Export Now, Edit, Terminate buttons.
- Export Immediately: The selected logs are exported to the bucket of the previously configured Object Storage.
- Edit: Modify the DB Log export mode setting.
- Cancel: Cancel the DB Log export mode setting.
Minor Version Upgrade
We provide version upgrade functionality for some feature improvements and security patches. Only Minor version upgrades within the same Major version are supported.
- First retrieve the service status by synchronizing it, then perform the version upgrade.
- Please perform the version upgrade after configuring a backup. If you do not set up a backup, you may be unable to recover some data if a problem occurs during the upgrade.
- In a DB with a Replica configured, the Master DB version cannot be higher than the Replica version. Please check the Replica’s version first and, if necessary, perform a version upgrade.
- The backed-up data will be automatically deleted after the version upgrade is completed.
To upgrade the Minor Version, follow the steps below.
- Click the All Services > Database > EPAS(DBaaS) menu. Go to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource you want to upgrade the version for. You will be taken to the EPAS(DBaaS) Detail page.
- Click the Edit button in the Image version item. The Version Upgrade popup window opens.
- Version Upgrade In the popup window, select the updated version and backup setting, then click the Confirm button.
- Version Upgrade Notification Click the Confirm button in the popup window.
Configuring Migration
Provides a Migration feature that synchronizes in real time with the live database and replicates using a Replication method without service interruption.
To configure Migration, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. Navigate to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page: click the resource you want to migrate. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button, then click the Migration configuration button. Migration configuration popup window opens.
- Migration configuration In the popup window, review the instructions and click the Confirm button. You will be taken to the Migration configuration page.
- On the Migration configuration page, enter the required information, then click the Check connection button.
- When the connection is complete, click the Complete button.
Category Required Detailed descriptionSource DB Database name Required Database name of the source DB to be migrated Source DB IP Required IP of the Source DB that is the migration target Source DB Port Required Port of the Source DB to be migrated Source DB username Required Username of the source DB that is the migration target Source DB password Required Password of the source DB for migration Table. EPAS(DBaaS) migration configuration items
Promote Migration Cluster to Master Cluster
You can promote a configured Migration Cluster to a Master Cluster.
To promote the Migration Cluster to Master, follow these steps.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) menu on the Service Home page. Navigate to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource to promote to Master. You will be taken to the EPAS(DBaaS) Details page.
- Click the More button, then click the Master Promotion button. The Master Promotion Notification popup window opens.
- Master Promotion Notification in the popup window, click the Confirm button.
Upgrade OS Kernel
The OS Kernel can be upgraded to improve the functionality of the running database and apply security patches.
- The service will be unavailable while the OS upgrade is in progress.
- The upgrade duration may vary depending on the version, and if the upgrade fails, it will be rolled back to the previous configuration.
- After the upgrade is complete, you cannot revert to the previous OS.
To upgrade the OS Kernel, follow the steps below.
- Click the All Services > Database > EPAS(DBaaS) menu. Navigate to the EPAS(DBaaS) Service Home page.
- Click the EPAS(DBaaS) menu on the Service Home page. You will be taken to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource to upgrade the OS Kernel. You will be taken to the EPAS(DBaaS) Detail page.
- Click the More button, then click the OS(Kernel) Upgrade button. The OS(Kernel) Upgrade Notification popup opens.
- OS(Kernel) Upgrade Notification In the popup window, review the instructions and click the Confirm button.
6.1.2.2 - Backing up and restoring the database
Users can configure backups of EPAS (DBaaS) through the Samsung Cloud Platform Console and restore from the backed‑up files.
EPAS(DBaaS) Backup
To ensure that users’ data can be stored safely, EPAS (DBaaS) provides a data backup feature based on its own backup commands. Additionally, you can verify whether the backup was successful using the backup history feature, and you can also delete backed‑up files.
Configure Backup
For instructions on configuring backups for EPAS (DBaaS), see Create EPAS (DBaaS).
To modify the backup settings of the created resource, follow the steps below.
- For reliable backups, we recommend adding a separate BACKUP storage or sufficiently expanding the storage capacity. * Especially when the backup data exceeds 100 GB and undergoes frequent changes, please provision additional storage amounting to approximately 60 % of the data size. * For storage addition and expansion methods, refer to the EPAS(DBaaS) Add Storage and EPAS(DBaaS) Expand Storage guides.
- If a backup is configured, it will be performed at the designated time after the set time, and additional fees will be incurred based on the backup size.
- If you change the backup setting to Unset, backup execution will stop immediately, and the stored backup data will be deleted and can no longer be used.
To set up a backup, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page: click the resource for which you want to configure a backup. 3. EPAS(DBaaS) Details page is accessed.
- Click the Edit button of the backup item. 4. Backup Settings popup window opens.
- When configuring a backup, click Enable in the Backup Settings popup, select the retention period, backup start time, and Archive backup interval, then click the Confirm button.
- If you stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Once user authentication is completed, the backup configuration is disabled and backup execution stops.
- If you stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Check backup history
To view the backup history, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- EPAS(DBaaS) List page, click the resource to view the backup history. 3. Go to the EPAS(DBaaS) Details page.
- Click the Backup History button. 4. The Backup History popup opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup file
To delete the backup history, follow these steps.
- All Services > Database > EPAS(DBaaS) menu, click it. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource to view its backup history. 3. Go to the EPAS(DBaaS) Details page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, check the files you want to delete, then authenticate using the logged-in user’s mobile phone.
- When user authentication is completed, the backup file is deleted.
EPAS(DBaaS) Recover
If recovery is needed from a backup file due to a failure or data loss, the restore function can recover based on a specific point in time. When you perform an EPAS (DBaaS) recovery, a new server is created with the OS image from the initial provisioning point, the database is installed with the version from the backup point, and the recovery proceeds with the database’s configuration information and data.
To restore EPAS (DBaaS), follow the steps below.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- EPAS(DBaaS) resources On the list page, click the resource you want to restore. 3. Navigate to the EPAS(DBaaS) Details page.
- Click the Database Recovery button. 4. Database Recovery Navigate to the page.
- After entering the relevant information in the Database Recovery Configuration area, click the Complete button.
Category required statusDetailed description Recovery Type Required Set the point in time the user wants to recover - Backup point (recommended): Recover based on the backup file. Select from the list of backup points displayed in the list
- Custom point: Recover to a user‑desired point within the range of recoverable backup points. The recoverable period depends on the Archive backup interval setting, allowing recovery to any point from the start of the first backup up to 1 hour/30 minutes/10 minutes/5 minutes before the current time. Select the date and time to recover
Server name prefix Required Recovery DB server name - Start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to enter 3 to 16 characters
- Based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Required Recovery DB cluster name - Enter using English letters, 3 to 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Essential Recovery DB server type - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, refer to Planned Compute 신청하기
Service Type > Block Storage Required Block Storage settings used by the recovery DB - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Applied identically with the storage type set in the original cluster
- Enter capacity as a multiple of 8 within the range 16 to 5,120
- Additional: Storage area for DATA, Archive, TEMP, Backup data
- Applied identically with the storage type set in the original cluster
- In the recovery DB, only DATA, TEMP, and Archive purposes can be added
- After selecting Use, enter the storage purpose and capacity
- To add storage, click the Add button, and to delete, click the x button
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Database username Required Database username - Apply the same username set in the original cluster
Database Port number Required Database Port number - Apply the same Port number configured in the original cluster
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruptions
- If set to not use, Samsung SDS is not responsible for issues arising from unapplied patches.
tag Select Add Tag - Add Tag after clicking the Add Tag button Enter or select Key, Value values
Table. EPAS (DBaaS) recovery configuration items
6.1.2.3 - Configure Read Replica
Users can enter the required information for a Read Replica through the Samsung Cloud Platform Console and create the service using the detailed options.
Configure Replica
You can create replica servers for read‑only or disaster‑recovery purposes through replica configuration. You can create up to 5 replicas per database.
To configure a Replica, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource to configure the Replica. 3. Navigate to the EPAS(DBaaS) Details page.
- Click the Replica configuration button. 4. Go to the Replica configuration page.
- After entering information in the Replica configuration area, click the Complete button.
Category required statusDetailed description Region Required Region to configure the Replica - Replica configuration (Other Region)exposed only when selected
Replica count Required Number of Replicas to configure - Up to 5 can be configured per cluster
- If you select more than one value, additionally enter the Replica name and service type information
Replica name Required Replica server name - Start with a lowercase English letter, and use lowercase letters, numbers, and special characters (
-) to enter 3 to 19 characters
- The entered Replica name is displayed as the cluster name in the list
Service Type > Server Type Required Replica server type - Standard: standard specification commonly used
- High Capacity: large-capacity server with 24 vCore or more
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute Apply
IP access control Selection Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Selection Database maintenance window - If you select Use, set the day, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, we are not responsible for any issues arising from patches not being applied.
Tag Select Add Tag - Add Tag after clicking the button Enter or select Key, Value values
Table. EPAS (DBaaS) Replica configuration items
Reconfigure Replica
If a network outage or replication delay with the Master Cluster occurs, you can use the Replica reconstruction function to replicate the Master Cluster’s data again.
To reconfigure the Replica, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. Go to the EPAS(DBaaS) List page.
- On the EPAS(DBaaS) List page, click the resource to reconfigure the Replica. 3. EPAS(DBaaS) Details Navigate to the page.
- Click the Reconstruct Replica button. 4. Replica Reconfiguration Notification A popup window opens.
- Replica Reconfiguration Notification popup window, click the Confirm button.
Promoting a Replica Cluster to a Master Cluster
You can promote a configured Replica Cluster to a Master Cluster.
To promote a Replica Cluster to Master, follow these steps.
- All Services > Database > EPAS(DBaaS) Click the menu. 1. Go to the Service Home page of EPAS (DBaaS).
- On the Service Home page, click the EPAS(DBaaS) menu. 2. EPAS(DBaaS) List go to the page.
- On the EPAS(DBaaS) List page, click the resource to promote to Master. 3. Go to the EPAS(DBaaS) Details page.
- Click the More button, then click the Promote to Master button. 4. Master Promotion Notification The popup window opens.
- In the Master Promotion Notification popup, click the Confirm button.
6.1.2.4 - EPAS(DBaaS) Server Connection
Scenario Overview
EPAS(DBaaS) Server Connection scenario involves creating a Bastion host (Virtual Server) and a Database service, and accessing the DB service through the Bastion host. To reliably connect to EPAS (DBaaS) in the Samsung Cloud Platform environment, you need to create a Bastion host and establish a network connection using it. To maintain stability and a high level of security, it is recommended to configure the Database service in a Private Subnet environment and set up the Bastion host in a restricted Public Subnet environment.
This scenario primarily describes creating a Bastion host and a Database service, configuring the network environment for Bastion host and Database access, and connecting through a DB client.
Scenario components
You can build the scenario using the following services.
| service group | service | Detailed description | |
|---|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment | |
| Networking | VPC > Subnet | A service that lets users segment the network within a VPC to match their purpose and scale. | |
| Networking | VPC > Public IP | Service that reserves a public IP and allocates and releases it to Compute resources | |
| Networking | VPC > Internet Gateway | A service that connects VPC resources to the Internet | |
| Networking | Security Group | Virtual firewall that controls server traffic | |
| Database | EPAS(DBaaS) | A service that easily creates and manages EPAS in a web environment | |
| Compute | Virtual Server | Virtual server optimized for cloud computing | |
| Compute | Virtual Server > Keypair | Encryption file used to connect to the Virtual Server |
- Since the default policy of a Security Group is Deny All, you must register only the IPs that are allowed.
- The All Open (Any IP, Any Port) policy for In/Outbound can expose cloud resources directly to external threats.
- By specifying the required IP and port and setting a policy, you can strengthen security.
Scenario setup method
Create the services needed to build the scenario by following the steps below.
Configure the network
Describes the process of configuring the network environment for accessing the Bastion Host and Database services.
1-1. Create VPC
- Click the All Services > Networking > VPC menu. You will be taken to the VPC’s Service Home page.
- Click the Create VPC button on the Service Home page. You will be taken to the Create VPC page.
- On the VPC Creation page, enter the information required to create the service.
- Enter the IP range as
192.168.x.0/16
- Enter the IP range as
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resources on the VPC List page.
1-2. Create Subnet
- Click the All Services > Networking > VPC menu. Navigate to the VPC Service Home page.
- On the Service Home page, click the Subnet menu. You will be taken to the Subnet List page.
- Click the Subnet Create button. You will be taken to the Subnet Create page.
- On the Subnet Creation page, enter the information required to create the service.
- Select the Subnet type as General.
- Select a pre‑created VPC.
- Enter the IP range as
192.168.x.0/24.
- In the Summary panel, verify the detailed information and estimated billing amount, then click the Complete button.
- When creation is complete, check the created resources on the Subnet list page.
1-3. Create Internet Gateway
- Click the All Services > Networking > VPC menu. You will be taken to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- Click the Create Internet Gateway button. You will be taken to the Create Internet Gateway page.
- On the Internet Gateway Creation page, enter the required information needed to create the service.
- Select a pre‑created VPC.
- In the Firewall usage item, select Use.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, verify the created resource on the Internet Gateway list page.
1-4. Create Public IP
- Click the All Services > Networking > VPC menu. Navigate to the VPC Service Home page.
- On the Service Home page, click the Public IP menu. You will be taken to the Public IP List page.
- Click the Public IP Reservation button. You will be taken to the Public IP Reservation page.
- On the Public IP reservation page, enter the required information needed to reserve the service.
- In the Summary panel, verify the detailed information and estimated billing amount, then click the Complete button.
- Once creation is complete, check the created resources on the Public IP List page.
1-5. Create Security Group
- Click the All Services > Networking > Security Group menu. Go to the Service Home page of Security Group.
- Click the Create Security Group button on the Service Home page. Navigate to the Create Security Group page.
- On the Security Group creation page, enter the required information needed to create the service.
- Check the input information and click the Complete button.
- Once creation is complete, check the created resources on the Security Group List page.
Create bastion host
Describes the process of configuring a Bastion Host that requires the Database access client to be installed.
2-1. Create Server Keypair
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- Click the Keypair creation button. You will be taken to the Keypair creation page.
- Enter the required information needed to create a service on the Keypair creation page.
- Check the creation information and click the Complete button.
- The key can be downloaded only once, and reissuance is not available.
- Please store the downloaded key in a secure location.
2-2. Create Bastion host
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server Create button. It navigates to the Virtual Server Create page.
- Virtual Server Creation page, enter the required information to create the service.
- Select Windows for the image.
- Select the pre-created VPC and Subnet.
- Click Use NAT, then in 1-4. Create Public IP select the reserved Public IP.
- Connect the Keypair you created in 2-1. Create Server Keypair.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, verify the created resources on the Virtual Server list page.
2-3. Bastion host Check login ID and PW
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Virtual Server menu on the Service Home page. You will be taken to the Virtual Server List page.
- On the Virtual Serve List page, click the resource you created in 2-2. Create Bastion host. You will be taken to the detailed information page of that resource.
- On the detail information page, click the RDP password View button in the Keypair name field. The RDP password View popup window will open.
- In the RDP password lookup popup window, attach the keypair file downloaded from 2-1. 서버 Keypair 생성하기.
- After attaching, click the Password Check button. The ID and Password for accessing the resource are displayed.
- The ID and Password are used later as credentials to access the Bastion host in 5-1. Bastion host 접속하기.
Create Database
Describes the process of creating a Database service.
3-1. EPAS(DBaaS) Service Creation
- Click the All Services > Database > EPAS(DBaaS) menu. Go to the Service Home page of EPAS(DBaaS).
- Click the EPAS(DBaaS) Create button on the Service Home page. You will be taken to the EPAS(DBaaS) Create page.
- Create EPAS (DBaaS) Enter the required information needed to create the service on this page.
- Select the pre‑created VPC and Subnet and connect them.
- Enter the database-related creation details on the required information input screen.
- Add the Bastion host IP in the IP access control settings.
- The Database Port defaults to 2866, but the user can also specify it.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, verify the created resource on the EPAS(DBaaS) list page.
Configuring Rules
It explains the process of configuring rules for a user to connect to the Bastion host and rules for connecting to the Database from the Bastion host.
4-1. Add Security Group Rules
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of the Security Group.
- From the Service Home page, click the Security Group menu. You will be taken to the Security Group List page.
- Select the Security Group resource created in 1-5. Create Security Group. Navigate to the detailed information page of that resource.
- On the detail information page, click the Rules tab. You will be taken to the Rules tab.
- On the Rules tab, click the Add Rule button. You will be taken to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
direction Remote target address Protocol port Explanation Inbound CIDR User PC IP TCP 3389 (RDP) Bastion client PC → Bastion host Outbound CIDR DB IP TCP Database Port (manual entry) Bastion host → Database Table. Security Group rules that need to be added
4-2. Add IGW Firewall Rule
- All Services > Networking > Firewall Click the menu. Go to the Service Home page of the Firewall.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, select the Internet Gateway Resource Name created in 1-3. Internet Gateway 생성하기. You will be taken to the detailed information page for that resource.
- Click the Rules tab on the detail information page. You will be taken to the Rules tab.
- On the Rules tab, click the Add Rule button. You will be taken to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
origin address Destination address Protocol Port Operation direction Explanation Bastion connection PC IP Bastion host IP TCP 3389(RDP) Allow Inbound User PC → Bastion host Table. Internet Gateway Firewall rules that need to be added
Connect to Database
Describes the process of a user accessing the database via a DB client program.
This guide explains how to connect using pgAdmin. Since there are various database client programs and CLI utilities, you may install and use the tool that best fits your needs.
5-1. Connecting to Bastion host
- In the Windows environment of the PC that will connect to the Bastion host, run Remote Desktop Connection, then enter the NAT IP of the Bastion Host and click the Connect button.
- When the remote desktop connection succeeds, the user credential input window opens. Enter the ID and Password verified in 2-3. Bastion host Access ID and PW Check and click the Confirm button.
5-2. Install DB client program (pgAdmin) on the Bastion host
- Go to the official pgAdmin page and download the pgAdmin program.
- pgAdmin program download URL: https://www.pgadmin.org/download/
- Connect the user’s PC hard drive to upload the file to the Bastion host.
- In the Remote Desktop Connection Local Resources tab, click the Details button for the Local Devices and Resources entry.
- Select the local disk of the location where the file was downloaded on the drive, and click the OK button.
- Copy the downloaded file, upload it to the Bastion Host, and click the pgAdmin installer to install.
5-3. Connect to the database using the DB client program (pgAdmin)
- Run pgAdmin and click the Add New Server button.
- Register - Server popup window, enter the Database server information created in 3-1. EPAS(DBaaS) Create Service into the General and Connection tabs, and click the Save button.
Screen (tab) Required input field input value General Name Custom (ex. service name) Connection Host name/address Database server IP Connection Port Database Port Connection Maintenance database Database name Connection Password Database password Table: DB connection client program input fields - Click the name of the database created in pgAdmin to connect.
- After connecting, you can perform simple queries, among other tasks.
6.1.2.5 - Extension Usage
Using EPAS(DBaaS) Extension
You can view the list of extensions that can be installed in the current database with the SQL statement below.
SQL> select * from pg_available_extensions;
In EPAS(DBaaS), the items installed in addition to the default extensions included per version are as follows.
| Extension name | Explanation |
|---|---|
| pg_cron | A scheduler that can schedule jobs using cron syntax within the database. |
| pgvector | Provides AI vector operation features such as vector data types and similarity search. |
| postgis | Provides GIS (Geographic Information System) spatial object storage and spatial query functionality |
If you need to install additional extensions beyond the items above, refer to Support Center > Inquiry and contact us.
- After a request is received, we will review it and proceed with installation. Please note that some extensions may not function properly during replica configuration and recovery.
6.1.3 - API Reference
6.1.4 - CLI Reference
6.1.5 - Release Note
EPAS(DBaaS)
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Strengthen the latest security patches and stability through the OS (Kernel) upgrade feature.
- EPAS(DBaaS) feature addition
- Add Second-Generation Server Type
- Add a 2nd‑generation (db2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see EPAS(DBaaS) 서버 타입.
- DB user and access control management and Archive configuration feature added
- For more details, refer to DB User Management, DB Access Control Management, Archive Management.
- DB Audit Log Export feature added
- For more details, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, refer to Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Migration Configuration.
- Add HDD, HDD_KMS types to Block Storage type
- Add Second-Generation Server Type
- A web-based EPAS (DBaaS) service that allows easy creation and management of EPAS has been launched.
6.2 - PostgreSQL(DBaaS)
6.2.1 - Overview
Service Overview
PostgreSQL (DBaaS) is an open-source relational database management system (RDBMS). Samsung Cloud Platform provides an environment that automates PostgreSQL installation through a web-based console and performs management functions for operation.
PostgreSQL (DBaaS) is designed as a high‑availability architecture that performs storage‑based data replication and minimizes failover time. To prevent data loss, when the contents of the Active server change, they are synchronously replicated to the Standby server, and up to five read‑only Replica servers for read load balancing and disaster recovery (DR) are provided. Additionally, to prepare for potential issues with the DB server or data, we provide a feature that automatically backs up at a user-specified time, enabling recovery of data at the desired point.
Provided Features
PostgreSQL (DBaaS) provides the following features.
- Auto Provisioning: UI allows installation and configuration of Database (DB), and provides an Active‑standby redundancy configuration built on storage replication. * When the active server fails, it automatically fails over to standby.
- Operation Control Management: Provides a function to control the status of running servers. * In addition to start and stop, you can restart if there is a DB issue or to apply configuration changes. * When high availability (HA) is configured, the user can manually perform node switching between Active and Standby via a switch‑over.
- Backup and Recovery: Provides data backup functionality based on its own backup commands. * The backup schedule and retention policy can be set by the user, and additional fees apply based on the backup size. * It also provides a recovery function for backed‑up data, so when the user performs a recovery, a separate database is created and the recovery proceeds to the point in time selected by the user (the backup save point or a user‑specified point). * When restoring to a user-specified point in time, the restore point can be set up to 5 minutes, 10 minutes, 30 minutes, or 1 hour earlier, based on the stored backup files and archive files.
- Version Management: Provides version upgrade (Minor) functionality due to certain feature improvements and security patches. * Whether to perform a backup for a version upgrade can be selected by the user, and if a backup is performed, the data is backed up before applying the patch, after which the DB engine is updated.
- Replica configuration: For load balancing reads and disaster recovery (DR), up to five Read Replicas can be configured in the same or different regions.
- Audit Settings: Supports audit (Audit) functionality for key activities within the database.
- Parameter management: You can modify DB configuration parameters related to performance improvement and security.
- Service Status Query: Retrieves the final status of the current DB service.
- Monitoring: CPU, memory, and DB performance monitoring information can be accessed through the Cloud Monitoring service.
- DB User Management: Query and manage the DB account (user) information registered in the DB.
- DB Access Control Management: Based on DB accounts registered in the DB, you can register and revoke allowed IPs for access.
- Archive Management: You can set the retention period (1 to 35 days) for Archive files on the DB server and configure the Archive mode (On/Off).
- Export DB Log: You can export stored logs to the user’s Object Storage through Audit settings.
- Migration: Synchronize data in real time with the operational database and support migration using replication without service interruption.
- OS kernel upgrade: The OS Kernel can be upgraded to apply certain feature improvements and security patches.
Component
PostgreSQL(DBaaS) provides pre‑validated engine versions and various server types in accordance with the open‑source support policy. Users can select and use it according to the scale of the service they wish to configure.
Engine version
The engine versions supported by PostgreSQL (DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is stopped is set to six months before the EoTS date.
Since the EOS and EoTS dates may change according to the supplier’s policy, please refer to the supplier’s license management policy page for details.
- PostgreSQL: https://www.postgresql.org/support/versioning/
| Provided version | EOS Date (Samsung Cloud Platform new creation stop date) | EoTS Date (Community Technical Support End Date) |
|---|---|---|
| 14.17 | 2026-05-20 | 2026-11-12 |
| 14.18 | 2026-05-20 | 2026-11-12 |
| 14.19 | 2026-05-20 | 2026-11-12 |
| 15.12 | 2027-06 (planned) | 2027-11-11 |
| 15.13 | 2027-06 (planned) | 2027-11-11 |
| 15.14 | 2027-06 (planned) | 2027-11-11 |
| 16.8 | 2028-06 (planned) | 2028-11-09 |
| 16.9 | 2028-06 (planned) | 2028-11-09 |
| 16.10 | 2028-06 (planned) | 2028-11-09 |
| 17.6 | 2029-06 (planned) | 2029-11-08 |
The next version of PostgreSQL is scheduled to be available after July 2026. The actual service delivery schedule is subject to change.
- PostgreSQL 15.15
- PostgreSQL 16.11
- PostgreSQL 17.17
Server type
The server types supported by PostgreSQL (DBaaS) are as follows.
For detailed information about the server types offered by PostgreSQL(DBaaS), see PostgreSQL(DBaaS) Server Types.
Standard db1v2m4
| Category | Example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | db1 | Provided server specifications
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
6.2.1.1 - Server Types
PostgreSQL(DBaaS) server type
PostgreSQL (DBaaS) offers server types composed of various combinations of CPU, Memory, and Network Bandwidth. When creating PostgreSQL(DBaaS), the Database Engine is installed based on the server type chosen for the intended use.
The server types supported by PostgreSQL (DBaaS) are as follows.
Standard db1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | db1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
db1 server type
The db1 server type of PostgreSQL (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db1v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db1v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
db2 server type
The db2 server type of PostgreSQL (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
dbh2 server type
The dbh2 server type of PostgreSQL (DBaaS) is provided with high-capacity server specifications and is suitable for database workloads that require large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | dbh2v24m48 | 24 vCore | 48 GB | Up to 25 Gbps |
| High Capacity | dbh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m64 | 32 vCore | 64 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m256 | 32 vCore | 256 GB | Up to 25 Gbps |
| High Capacity | dbh2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m192 | 48 vCore | 192 GB | Up to 25 Gbps |
| High Capacity | dbh2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m256 | 64 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m768 | 64 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m384 | 96 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m1152 | 96 vCore | 1152 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
6.2.1.2 - Monitoring metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Service per Resource
- New Resources: Resources created after the service improvement work in July 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring via Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings linked with existing Cloud Monitoring (e.g. You must verify items such as event policies and perform tasks such as resetting the ServiceWatch service, then complete them.
Cloud Monitoring Service Phased Termination Schedule Notice
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration within the parallel operation period.**
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
PostgreSQL(DBaaS) Monitoring Metrics
The table below shows performance monitoring metrics for PostgreSQL (DBaaS) that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
For PostgreSQL (DBaaS), refer to the Virtual Server Monitoring Metrics guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Active Locks | Number of Active Locks | cnt |
| Active Locks [Access Exclusive] | Number of Access Exclusive Locks | cnt |
| Active Locks [Access Share] | Number of Access Share Locks | cnt |
| Active Locks [Total] | Total number of active locks | cnt |
| Active Sessions | Number of Sessions in Active state | cnt |
| Active Sessions [Total] | Total number of Sessions in Active state | cnt |
| Apply Lag Time | Apply lag time | min |
| Check No Replication | Check No Replication value | cnt |
| Check Replication | Check Replication Status value | status |
| Connection Usage | DB connection usage rate (%) | % |
| Connection Usage [Total] | DB connection usage rate (%) | % |
| DB Age Max | Database age (frozen XID) value | age |
| Exclusive Locks | Number of Exclusive Locks | cnt |
| Idle In Transaction Sessions | Number of sessions in idle-in-transaction state | cnt |
| Idle In Transaction Sessions [Total] | Total number of sessions in Idle in transaction state | cnt |
| Idle Sessions | Number of idle sessions | cnt |
| Idle Sessions [Total] | Total number of sessions in Idle state | cnt |
| Row Exclusive Locks | Number of Row Exclusive Locks | cnt |
| Row Share Locks | Row Share Locks count | cnt |
| Share Locks | Number of Share Locks | cnt |
| Share Row Exclusive Locks | Number of Share Row Exclusive Locks | cnt |
| Share Update Exclusive Locks | Number of Share Update Exclusive Locks | cnt |
| Slowqueries | Number of SQL queries running for a long time (over 5 minutes) | cnt |
| Tablespace Used | Table space size | bytes |
| Tablespace Used [Total] | Table space size | bytes |
| Tablespace Used Bytes [MB] | File system directory usage (MB) | MB |
| Tablespaces [Total] | File system directory usage (MB) | MB |
| Transaction Time Max [Long] | Long-running Transaction time (minutes) | min |
| Transaction Time Max Total [Long] | Long-running Transaction time (minutes) | min |
| Wait Locks | Number of lock-waiting sessions (by DB) | cnt |
| Wait Locks [Long Total] | Number of lock‑waiting sessions lasting 300 seconds | cnt |
| Wait Locks [Long] | Number of sessions waiting due to lock occurrence | cnt |
| Wait Locks [Total] | Total number of sessions waiting due to lock occurrence | cnt |
| Waiting Sessions | Number of Sessions in Waiting state | cnt |
| Waiting Sessions [Total] | Total number of Sessions in Waiting state | cnt |
6.2.2 - How-to guides
Users can create the service by entering the required information for PostgreSQL (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services by Resource
- New Resources: Resources created after the service improvement work in July 2026 are provided with monitoring using the ServiceWatch service by default.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring via Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings integrated with existing Cloud Monitoring (e.g. You need to review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Notice of the phased termination schedule for Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration work within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
Create PostgreSQL (DBaaS)
You can create and use a PostgreSQL (DBaaS) service from the Samsung Cloud Platform Console.
- Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the creation of the corresponding Database service is not possible.
- When loading more than 2 TB of large data, backups may take a long time or the database’s performance may degrade. * To prevent this, it is necessary to consider operational aspects such as cleaning up unnecessary data or migrating old data to a statistical collection environment.
To create PostgreSQL(DBaaS), follow the steps below.
Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Navigate to the Service Home page of PostgreSQL (DBaaS).
On the Service Home page, click the PostgreSQL(DBaaS) Create button. 2. Navigate to the Create PostgreSQL (DBaaS) page.
Create PostgreSQL (DBaaS) page, enter the information required to create the service and select advanced options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version required Provide a list of PostgreSQL (DBaaS) versions Table. PostgreSQL (DBaaS) Image and version selection options - In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Server name Prefix Required Server name where the DB will be installed - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
-) with a length of 3 to 13 characters
- A postfix such as 001, 002 is appended to the base server name to generate the actual server name
Cluster name Required Cluster name of DB servers - Enter using English letters, 3 to 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for DB installation - Standard: Standard specifications commonly used
- High Capacity: Large-capacity server with 24 vCores or more
- For detailed information about the server types provided by PostgreSQL (DBaaS), refer to PostgreSQL(DBaaS) Server Type
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute Apply
Service Type > Block Storage Required Block Storage configuration used by the DB according to its purpose - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select a storage type and then enter the capacity (refer to Create Block Storage for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volumes that use Samsung Cloud Platform KMS (Key Management System) encryption keys
- The configured storage type is applied identically to additional storage
- Enter capacity as a multiple of 8 within the range 16–5,120
- Because executing SQL or monthly batch jobs can cause large sorts that may interrupt service, a separate TEMP storage must be allocated and used
- Add: DATA, Archive, TEMP, Backup data storage areas
- After selecting Use, enter the storage’s purpose and capacity
- The storage type is applied the same as the type set for DATA, and capacity can be entered as a multiple of 8 within the range 16–5,120
- To add storage, click the Add button; to delete, click the x button. Up to 9 can be added
- Backup data is temporarily stored in the BACKUP storage before transmission
- If the data to be backed up exceeds 100 GB and changes frequently, it is recommended to add a separate BACKUP storage for reliable backup; set the backup capacity to about 60 % of the DATA capacity
- If a BACKUP storage is not added, the
/tmparea is used, and backup will fail if capacity is insufficient
- For each service, Archive, TEMP, and BACKUP storages are allocated only one Block Storage each
- Select a storage type and then enter the capacity (refer to Create Block Storage for details on each Block Storage type)
Redundant configuration Select Redundancy configuration status - When redundancy configuration is used, the DB instance is set up as an Active DB and a Standby DB
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- IP can only be generated automatically
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway; when Use is checked, you can select a reserved IP from the VPC product’s Public IP pool. For more information, see Public IP 생성하기
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select when you want to apply different settings for each installed server
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- Enter the IP for each server
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. If you check Use, you can select a reserved IP from the VPC product’s Public IP. For more details, refer to Public IP 생성하기
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, a separate Security Group policy configuration is not required
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day, start time, and duration
- It is recommended to set a maintenance window for stable management of the database. Patch operations will be performed at the scheduled time, causing service interruption
- If set to not use, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. PostgreSQL (DBaaS) Service Information Input Items - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
- Enter or select the required information in the Database Configuration Required Information Input area.
Category required statusDetailed description Database name Required Server name applied during DB installation - must start with an English letter and be entered using English letters and numbers, 3 to 20 characters
Database username Required DB user name - An account with the same name is also created on the OS
- Enter using lowercase English letters, 2 to 20 characters
- Restricted database user names can be viewed in the Console
Database password Required Password to use when accessing the DB - Enter 8 to 30 characters, including letters, numbers, and special characters (excluding
“‘)
Database password verification Required Re-enter the same password to be used for DB access Database Port number Required Port number required for DB connection - Enter the DB port within the range 1200 ~ 65535
Backup > Use Select Backup usage - Select Use to set the backup file retention period, backup start time, and Archive backup interval
Backup > Retention period Select Backup retention period - Select the backup retention period, set the file retention period from 7 days to 35 days
- Backup files incur additional charges based on size
Backup > Backup Start Period Selection Backup start time - Select backup start time
- The minutes (minutes) during which the backup runs are set randomly, and the backup end time cannot be set
Backup > Archive backup cycle Select Archive backup frequency - Select the archive backup frequency
- The archive backup frequency is recommended to be 1 hour. Selecting 5 minutes, 10 minutes, or 30 minutes may affect DB performance.
Audit Log Settings Select Whether to store Audit Log - Select Enable to configure the Audit Log feature
- DDL, DML, and user connection information records are stored
- Users can specify the type of SQL statements to audit via the
log_statementparameter, and can modify it through the Parameter screen
- For detailed information about this parameter, refer to the PostgreSQL documentation
- Users can specify the type of SQL statements to audit via the
- Enabling Audit may degrade database performance
- DDL, DML, and user connection information records are stored
Parameter Required Parameters to be used in the DB - Lookup button can be clicked to view detailed information of the parameter
- Parameters can be modified after the DB creation is complete, and the DB must be restarted after any modifications
Database Encoding Essential Character encoding method to be used for the DB - Character set used when storing text data
- The DB is created with the selected encoding as the default setting
DB Locale Required Locale to be used for the DB - settings related to string handling, number/currency/date/time formatting, etc.
- The DB is created with default settings using the selected Locale
time zone Required Standard time zone for the database Table. PostgreSQL (DBaaS) Database configuration items - In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description Tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. PostgreSQL (DBaaS) Additional Information Input Fields
- Select the required information in the Image and version selection area.
Summary Review the detailed information and estimated charges generated in the panel, then click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
View PostgreSQL (DBaaS) details
The PostgreSQL (DBaaS) service allows you to view and edit the full list of resources and detailed information. PostgreSQL(DBaaS) Details page consists of Details, Tags, Activity History tabs, and when the DB has a Replica configured, a Replica Information tab is added.
To view detailed information about the PostgreSQL (DBaaS) service, follow the steps below.
- All Services > Database > PostgreSQL(DBaaS) Click the menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- PostgreSQL(DBaaS) List Click the resource on the page to view detailed information. 3. PostgreSQL(DBaaS) Details Go to the page.
- PostgreSQL(DBaaS) Details The top of the page displays status information and additional feature details.
Category Detailed description Cluster status Cluster status with DB installed - Creating: Creating cluster
- Editing: Cluster is transitioning to an operational state
- Error: Cluster encountered an error during operation
- If it occurs continuously, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Restarting cluster
- Running: Cluster is running normally
- Starting: Starting cluster
- Stopped: Cluster is stopped
- Stopping: Cluster is stopping
- Synchronizing: Synchronizing cluster
- Terminating: Terminating cluster
- Unknown: Unknown cluster status
- If it occurs continuously, contact the administrator
- Upgrading: Cluster is transitioning to an upgrading state
Cluster control Button to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
- Switch-Over: Switch a standby cluster to active
View more features Cluster-related management buttons - Service status synchronization: Retrieve real-time DB service status
- Backup history: When backup is configured, verify successful execution and view the history
- Database recovery: Recover the DB based on a specific point in time
- Parameter management: View and modify DB configuration parameters
- Replica configuration: Set up a read‑only Replica cluster
- Replica configuration (Other Region): Set up a disaster‑recovery Replica in another region; if the account has no region to configure, the button is disabled
- DB user management: View and manage DB account (user) information registered in the DB
- DB access control management: Register and revoke allowed IPs based on DB accounts registered in the DB
- Archive settings management: Set archive file retention period and enable archive mode
- Export DB logs: Export logs stored via audit settings to the user’s Object Storage
- Migration configuration: Provide migration functionality using replication method
- OS (Kernel) upgrade: Upgrade the OS kernel version
Service termination Button to cancel the service Table. PostgreSQL (DBaaS) status information and additional features
- PostgreSQL(DBaaS) Details The top of the page displays status information and additional feature details.
Detailed information
PostgreSQL (DBaaS) List page allows you to view detailed information of the selected resource and, if needed, edit the information.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed DB image and version information
|
| Cluster type | Cluster types (Master Cluster, Replica Cluster, Migration Cluster) |
| Cluster name | Cluster name of the DB servers |
| Master cluster name | Replica’s Master cluster name
|
| Database name | Server name applied during DB installation |
| Database username | DB user name |
| Planned Compute | Resources with Planned Compute configured
|
| maintenance period | DB patch work period setting status
|
| Backup | Backup Configuration Status
|
| Audit Log Settings | Audit Log configuration status
|
| time zone | Standard time zone for the database |
| DB Locale | Locale to use for the DB |
| Database Encoding | Character encoding to use for the DB |
| VIP | Virtual IP information
|
| Network | Network information where the DB is installed (VPC, Subnet, VIP, NAT IP(VIP)) |
| IP access control | Service access policy configuration
|
| Active & Standby | Active/Standby server type, default OS, additional Disk information
|
Replica information
Replica information tab is enabled only when a Replica is configured in the cluster. Through the Replica information tab, you can view the Master cluster name, the number of replicas, and the replication status of the Replica.
| Category | Detailed description |
|---|---|
| Master information | Name of the Master cluster |
| Replica count | Number of Replicas created in the Master cluster |
| Replica status | Replica server status in the Master cluster
|
tag
On the PostgreSQL (DBaaS) List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
On the PostgreSQL (DBaaS) List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing PostgreSQL (DBaaS) Resources
If you need to change or restore the existing configuration options of a created PostgreSQL (DBaaS) resource, or require a Replica configuration, you can perform the operation on the PostgreSQL(DBaaS) Details page.
Control operation
If changes occur to a running PostgreSQL (DBaaS) resource, you can start, stop, or restart it. Also, when HA is configured, you can switch the Active‑Standby servers via a switch‑over.
To control the operation of PostgreSQL(DBaaS), follow the steps below.
- All Services > Database > PostgreSQL(DBaaS) Click the menu. 1. Navigate to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- PostgreSQL (DBaaS) List On the page, click the resource you want to control. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Check the PostgreSQL (DBaaS) status and complete the change using the control button below.
- Start: DB service is installed on the server and the DB service is running (Running).
- Stop: The server hosting the DB service and the DB service itself are stopped.
- Restart: Only the DB service will be restarted.
- Switch Over: You can switch the DB’s Active server and Standby server.
Synchronize service status
You can synchronize the real-time service status of PostgreSQL (DBaaS).
To check the service status of PostgreSQL (DBaaS), follow the steps below.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- PostgreSQL(DBaaS) List Click the resource on the page to view the service status. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Click the Service Status Synchronization button. 4. While it is being queried, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- All Services > Database > PostgreSQL(DBaaS) Click the menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- On the PostgreSQL (DBaaS) List page, click the resource whose server type you want to change. 3. PostgreSQL(DBaaS) Details Go to the page.
- Click the Edit icon of the server type you want to change at the bottom of the detailed information. 4. Edit Server Type The popup window opens.
- Edit Server Type After selecting the server type in the popup window, click the Confirm button.
Add storage
If you need more than 5 TB of data storage, you can add additional storage. For a DB configured with redundancy, all redundant servers are added simultaneously.
- It is applied in the same way as the Storage type selected when creating the service.
- In a redundant DB setup, adding storage is applied simultaneously to the storage of both the Active and Standby DBs.
- If a Replica exists, the storage of the Master cluster cannot be larger than the storage of the Replica. * First expand the Replica storage, then expand the Master cluster storage.
- When adding Archive/Temp storage, the DB restarts and is temporarily unavailable.
To add storage, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Go to the page.
- On the PostgreSQL (DBaaS) List page, click the resource to add storage. 3. PostgreSQL(DBaaS) Details Go to the page.
- Click the Add Disk button at the bottom of the details. 4. Additional Storage Request The popup window opens.
- Additional Storage Request In the popup window, after entering the purpose and size, click the Confirm button.
Expand storage
Storage added to the data area can be expanded up to a maximum of 5 TB based on the initially allocated capacity. In a redundant DB configuration, all redundant servers are expanded simultaneously.
To increase storage capacity, follow the steps below.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- On the PostgreSQL(DBaaS) List page, click the resource you want to change the server type for. 3. PostgreSQL(DBaaS) Details Go to the page.
- Click the Edit icon of the additional Disk you want to add at the bottom of the detailed information. 4. Edit Additional Storage The popup window opens.
- Edit Additional Storage In the popup window, after entering the expansion capacity, click the Confirm button.
Cancel PostgreSQL (DBaaS)
You can cancel unused PostgreSQL (DBaaS) to reduce operating costs. However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may occur when the service is discontinued.
- For a DB with a Replica configured, terminating the Master DB does not delete the Replica. * If you also delete the replica, cancel it separately from the resource list.
- If you terminate the DB, all stored data and any configured backup data will be deleted.
To cancel PostgreSQL (DBaaS), follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- On the PostgreSQL (DBaaS) List page, select the resource to cancel and click the Cancel Service button.
- After termination is complete, check on the PostgreSQL(DBaaS) list page whether the resource has been terminated.
6.2.2.1 - DB Service Manage
Users can manage PostgreSQL (DBaaS) through the Samsung Cloud Platform Console.
Managing Parameters
Provides a feature that allows you to easily view and modify database configuration parameters.
Query Parameters
To retrieve configuration parameters, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. You will be taken to the PostgreSQL(DBaaS) List page.
- On the PostgreSQL(DBaaS) List page, click the resource whose parameters you want to view or modify. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button and then click the Parameter Management button. The Parameter Management popup opens.
- Parameter Management in the popup window, click the Search button. The Search Notification popup window opens.
- Lookup Notification when the popup window opens, click the Confirm button. The lookup may take a short amount of time.
Modify Parameter
To modify the configuration parameters, follow the steps below.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. You will be taken to the PostgreSQL(DBaaS) List page.
- On the PostgreSQL(DBaaS) List page, click the resource whose parameters you want to view or modify. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button and then click the Parameter Management button. The Parameter Management popup opens.
- Parameter Management popup window, click the Search button. Search Notification popup window opens.
- Lookup Notification When the popup window opens, click the Confirm button. Retrieving may take a short amount of time.
- If a modification is needed, click the Edit button and enter the changes in the custom value field of the Parameter to be edited.
- When the input is complete, click the Complete button.
DB User Management
Provides management functions to retrieve DB user information and modify status information.
Query DB Users
To retrieve DB users, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. Navigate to the Service Home page of PostgreSQL(DBaaS).
- Click the Service Home page’s PostgreSQL(DBaaS) menu. You will be taken to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List page, click the resource you want to view DB users for. PostgreSQL(DBaaS) Details page will be opened.
- Click the More button and then click the DB User Management button. You will be taken to the DB User Management page.
- DB User Management page, click the Search button. Retrieving the data may take a short time.
Changing DB User Status
Follow these steps to change the status of the retrieved DB user.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. Navigate to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List On the page, click the resource whose DB user you want to modify. PostgreSQL(DBaaS) Details You will be taken to the page.
- Click the More button, then click the DB User Management button. You will be taken to the DB User Management page.
- On the DB User Management page, click the Search button. The query may take a short time.
- If modification is needed, click the Edit button, and change the status field value or enter remarks.
- When the input is complete, click the Complete button.
Managing DB Access Control
Provides IP-based DB user access control management functionality. Users can directly specify the IPs that can access the database, configuring it so that only authorized IPs are allowed access.
Query DB Access Control
Follow these steps to query DB users with IP access control enabled.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. You will be taken to the PostgreSQL(DBaaS) List page.
- On the PostgreSQL(DBaaS) List page, click the resource you want to manage access control for. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button and then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. Retrieving the data may take a short time.
Add DB access control
To add IP access control, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. You will be taken to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List page, click the resource for which you want to add IP access control. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button and then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. Retrieving the data may take a short time.
- When the query is complete, click the Add button. The Add DB Access Control popup window opens.
- Add DB Access Control In the popup window, select the DB username and enter the IP address.
- When the input is complete, click the Complete button.
Delete DB access control
To delete IP access control, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. Go to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List page, click the resource for which you want to delete IP access control. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button, then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. Retrieving the data may take a short time.
- When the query is complete, click the Delete button. The Delete popup window will open.
- Click the Confirm button on the Delete popup.
Manage Archive
Provides the ability to configure Archive mode and set the retention period for Archive logs, allowing users to flexibly configure Archive log management policies to suit their operational environment. Additionally, it provides a feature to manually delete Archive logs, allowing you to clean up unnecessary log data and manage system resources effectively.
Configure Archive mode
To set the Archive mode, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. Navigate to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List page: click the resource for which you want to set Archive mode. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button and then click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- On the Archive Settings Management page, click the Search button. Retrieval may take a short time.
- Click the Edit button and select the usage status and retention period.
- When the edit is complete, click the Done button.
Delete Archive file
To delete the Archive file, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. Navigate to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. Navigate to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List page, click the resource for which you want to set Archive mode. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button and then click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- Archive Settings Management page, if you want to delete all Archive files, click the Delete All Archives button; if you only want to delete backed-up Archive files, click the Delete Backed-up Archives button.
Modify Audit Settings
You can change the Audit log storage settings for PostgreSQL (DBaaS).
Follow these steps to change the Audit log storage settings for PostgreSQL (DBaaS).
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. You will be taken to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List page: click the resource to view the service status. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the Edit icon of Audit Settings at the bottom of the detailed information. The Edit Audit Settings popup window opens.
- Edit Audit Settings After modifying the usage in the popup window, click the Confirm button.
- When Enable is selected, the Audit log feature is configured. Enabling the Audit log may degrade DB performance.
- If you turn off Use, the Audit log storage file will be deleted. Before turning it off, back up the Audit log file separately.
DB Log Export
Supports exporting log data that requires long-term retention among audit logs to Object Storage. Users can directly configure the log types to be stored, the target bucket for export, and the export interval. Based on the configured criteria, logs are copied to the specified Object Storage for retention. Additionally, to efficiently manage disk space, we provide an option that exports logs to Object Storage while automatically deleting the original log files. By using this option, you can effectively free up storage capacity while safely retaining the necessary log data for long-term archiving.
- To use the DB Log export feature, you must create an Object Storage. For creating an Object Storage, please refer to the Object Storage User Guide.
- Please be sure to check the expiration date and time of the authentication key. If the authentication key expires, logs will not be stored in the bucket.
- Please ensure that authentication key information is not exposed externally.
Setting DB Log Export Mode
To set the DB Log export mode, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. Navigate to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. Navigate to the PostgreSQL(DBaaS) List page.
- PostgreSQL(DBaaS) List page, click the resource you want to export the DB Log from. PostgreSQL(DBaaS) Details page will open.
- Click the More button, then click the DB Log Export button. You will be taken to the DB Log Export page.
- On the DB Log Export page, click the Register button. You will be taken to the DB Log Export Register page.
- On the DB Log Export Registration page, after entering the required information, click the Complete button.
Category Required Detailed descriptionLog type Required Log type to be saved Save bucket name Required Object Storage bucket name to be saved Authentication key > Access key Required Access key for accessing the Object Storage you want to store Authentication key > Secret key Required Secret key for accessing the Object Storage you want to store File creation cycle Required File creation frequency in Object Storage Whether to delete original logs Selection Whether to delete the original logs when exporting to Object Storage Table. PostgreSQL (DBaaS) DB Log Export Configuration Items
Managing DB Log Export
To modify, cancel, or immediately export the DB Log export settings, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the Service Home page’s PostgreSQL(DBaaS) menu. You will be taken to the PostgreSQL(DBaaS) List page.
- Click the resource you want to manage DB Log export for on the PostgreSQL(DBaaS) List page. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button, then click the DB Log Export button. You will be taken to the DB Log Export page.
- On the DB Log Export page, click the More button for the log type you want to manage, then click Export Now, Edit, or Cancel.
- Export Immediately: The selected logs are exported to the bucket of the previously configured Object Storage.
- Edit: Modify the DB Log export mode setting.
- Cancel: Cancel the DB Log export mode setting.
Minor Version Upgrade
We provide version upgrade functionality for some feature improvements and security patches. Only Minor version upgrades within the same Major version are supported.
- First retrieve the service status by synchronizing it, then perform the version upgrade.
- Please perform the version upgrade after configuring a backup. If you do not set up a backup, you may be unable to recover some data if a problem occurs during the update.
- In a DB with a Replica configured, the Master DB version cannot be higher than the Replica version. Please check the Replica version first and, if necessary, perform a version upgrade.
- The backed-up data will be automatically deleted after the version upgrade is completed.
To upgrade the Minor Version, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) menu on the Service Home page. You will be taken to the PostgreSQL(DBaaS) List page.
- On the PostgreSQL(DBaaS) List page, click the resource to upgrade the version. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the Edit button in the Image version item. The Version Upgrade popup window opens.
- Version Upgrade In the popup, select the updated version and backup setting, then click the Confirm button.
- Version Upgrade Notification Click the Confirm button in the popup window.
Configure Migration
Provides a Migration feature that synchronizes in real time with the live database and replicates using a Replication method without service interruption.
To configure Migration, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- From the Service Home page, click the PostgreSQL(DBaaS) menu. You will be taken to the PostgreSQL(DBaaS) List page.
- On the PostgreSQL(DBaaS) List page, click the resource to migrate. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button, then click the Migration configuration button. The Migration configuration popup opens.
- In the popup window, review the instructions and click the Confirm button. You will be taken to the Migration configuration page.
- Migration Configuration page, after entering the required information, click the Check Connection button.
- When the connection is complete, click the Complete button.
Category Required Detailed descriptionSource DB Database name Required Database name of the source DB to be migrated Source DB IP Required IP of the Source DB that is the migration target Source DB Port Required Port of the Source DB to be migrated Source DB username Required Username of the source DB that is the migration target Source DB password Required Password of the source DB that is the migration target Table. PostgreSQL (DBaaS) migration configuration items
Promote Migration Cluster to Master Cluster
You can promote a configured Migration Cluster to a Master Cluster.
To promote the Migration Cluster to Master, follow the steps below.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- From the Service Home page, click the PostgreSQL(DBaaS) menu. You will be taken to the PostgreSQL(DBaaS) List page.
- On the PostgreSQL(DBaaS) List page, click the resource to promote to Master. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button and then click the Master Promotion button. The Master Promotion Notification popup window opens.
- In the Master Promotion Notification popup, click the Confirm button.
Upgrade OS Kernel
The OS kernel can be upgraded to improve the functionality of the running database and apply security patches.
- The service will be unavailable while the OS upgrade is in progress.
- The upgrade duration may vary depending on the version, and if the upgrade fails, it will be rolled back to the previous configuration.
- After the upgrade is complete, you cannot revert to the previous OS.
To upgrade the OS kernel, follow the steps below.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. You will be taken to the Service Home page of PostgreSQL(DBaaS).
- From the Service Home page, click the PostgreSQL(DBaaS) menu. You will be taken to the PostgreSQL(DBaaS) list page.
- PostgreSQL(DBaaS) List page, click the resource to upgrade the OS Kernel. You will be taken to the PostgreSQL(DBaaS) Details page.
- Click the More button, then click the OS(Kernel) Upgrade button. The OS(Kernel) Upgrade Notification popup window opens.
- OS(Kernel) Upgrade Notification In the popup window, review the instructions and click the Confirm button.
6.2.2.2 - Backing up and restoring the DB
Users can configure backups of PostgreSQL (DBaaS) through the Samsung Cloud Platform Console and restore from the backed‑up files.
Backing up PostgreSQL(DBaaS)
PostgreSQL (DBaaS) provides a data backup feature based on its own backup commands. Additionally, it provides an optimized backup environment for data protection and management through backup history verification and backup file deletion features.
Configure backup
For backup configuration of PostgreSQL(DBaaS), refer to PostgreSQL(DBaaS) 생성하기.
To modify the backup settings of the created resource, follow the steps below.
For reliable backups, we recommend adding a separate BACKUP storage or sufficiently expanding the storage capacity.
Especially when the backup data exceeds 100 GB and undergoes frequent changes, please provision additional storage amounting to about 60 % of the data size.
For instructions on adding and expanding storage, refer to the PostgreSQL(DBaaS) Add Storage and PostgreSQL(DBaaS) Expand Storage guides.
If a backup is configured, it will run at the designated time after the set schedule, and additional fees will be incurred based on the backup size.
If you change the backup setting to Unset, backup execution will stop immediately, and the stored backup data will be deleted and can no longer be used.
To set up a backup, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Navigate to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- PostgreSQL(DBaaS) List page, click the resource you want to configure backup for. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Click the Edit button of the backup item. 4. Backup Settings popup window opens.
- When setting up a backup, click Enable in the Backup Settings popup, select the retention period, backup start time, and Archive backup interval, and then click the Confirm button.
- If you stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Once user authentication is complete, the backup configuration is disabled and backup execution stops.
- If you stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Check Backup History
To view the backup history, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- PostgreSQL(DBaaS) List page, click the resource to view the backup history. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup file
To delete the backup history, follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. Navigate to the PostgreSQL (DBaaS) List page.
- PostgreSQL(DBaaS) List page, click the resource to view the backup history. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, check the files you want to delete, then authenticate using the logged-in user’s mobile phone.
- When user authentication is completed, the backup file is deleted.
PostgreSQL(DBaaS) Recover
If a failure or data loss requires restoration from a backup file, you can recover using the recovery feature based on a specific point in time. When performing a PostgreSQL (DBaaS) recovery, a new server is created with the OS image from the initial provisioning point, the database is installed with the version from the backup point, and the recovery proceeds with the database’s configuration information and data.
To recover PostgreSQL (DBaaS), follow these steps.
- Click the All Services > Database > PostgreSQL(DBaaS) menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- PostgreSQL(DBaaS) resource Click the resource you want to restore on the list page. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Click the Database Recovery button. 4. Go to the Database Recovery page.
- After entering the relevant information in the Database Recovery Configuration area, click the Complete button.
Category required statusDetailed description Recovery Type Required Set the point in time the user wants to recover - Backup point (recommended): Recover based on the backup file. Select from the list of backup points displayed in the list
- Custom point: Recover to a user-specified point within the range of recoverable backup times. The recoverable period depends on the Archive backup cycle setting, allowing recovery from the start of the first backup up to 1 hour/30 minutes/10 minutes/5 minutes before the current time. Select the desired date and time for the backup
server name prefix Essential Recovery DB server name - must start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to input 3 to 16 characters
- A postfix such as 001, 002 is appended to the base server name, generating the actual server name
Cluster name Required Cluster name of the recovery DB - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for the recovery DB installation - Standard: standard specifications commonly used
- High Capacity: large-capacity server with 24 vCores or more
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service request page
- For more details, see Planned Compute 신청하기
Service Type > Block Storage Required Block Storage settings used by the recovery DB - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Same as the storage type set in the original cluster
- Enter capacity as a multiple of 8 within the range 16 to 5,120
- Additional: Storage area for DATA, Archive, TEMP, Backup data
- Same as the storage type set in the original cluster
- In the recovery DB, only DATA, TEMP, and Archive purposes can be added.
- After selecting Use, enter the storage purpose and capacity
- To add storage, click the Add button; to delete, click the x button
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Database username Required Database username configured in the source DB Database Port number Required Database port number configured in the source DB IP access control Select IP address for accessing the recovery DB - Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.1/32,192.168.10.1/32), then click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable DB management. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
Tag Select Add Tag - Add Tag after clicking the button Enter or select Key, Value values
Table. PostgreSQL (DBaaS) recovery configuration items
6.2.2.3 - Configure Read Replica
Users can enter the required information for a Read Replica through the Samsung Cloud Platform Console and create the service using detailed options.
Configure Replica
Through replica configuration, you can create replica servers for read-only or disaster recovery purposes. You can create up to 5 replicas per database.
To configure a Replica, follow these steps.
- All Services > Database > PostgreSQL(DBaaS) Click the menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- On the PostgreSQL(DBaaS) List page, click the resource to configure a Replica. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Click the Replica configuration button. 4. Go to the Replica configuration page.
- After entering the information in the Replica configuration area, click the Complete button.
Category required statusDetailed description Region Required Region to configure the Replica - Replica configuration (Other Region)is displayed only when selected
Replica count Required Number of Replicas to configure - Up to 5 can be configured per cluster
- If you select more than one value, additionally enter the Replica name and service type information
Replica name Required Replica server name - must start with a lowercase English letter, and using lowercase letters, numbers, and special characters(
-) enter 3 to 19 characters
- The entered Replica name is displayed as the cluster name in the list
Service Type > Server Type Essential Replica server type - Standard: standard specification commonly used
- High Capacity: large-capacity server with 24 vCores or more
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Service Type > Block Storage Required Block Storage configuration for using a replica DB - Basic OS: Area used on the server where the DB is installed
- Applied identically according to the storage type set in the source DB
- Capacity cannot be set
- DATA: Storage area for table data, archive files, etc.
- Applied identically according to the storage type set in the source DB
- Capacity cannot be set
- Additional: Storage area for DATA, Archive, TEMP, Backup data
- Applied identically according to the storage type set in the source DB
- In a replica, only DATA and TEMP purposes can be added
- After selecting Use, enter the storage purpose and capacity. Capacity must be a multiple of 8 within the range 16 to 5,120
- To add storage, click the Add button; to delete, click the x button. Up to 9 can be added.
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, a separate Security Group policy configuration is not required
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - Select Use to set the day, start time, and duration
- It is recommended to configure a maintenance window for stable database management. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, we are not responsible for issues arising from patches not being applied.
tag Selection Add Tag - Add Tag After clicking the Add Tag button, enter or select Key and Value
Table. PostgreSQL (DBaaS) Replica configuration items
Reconfigure Replica
If a network failure or replication delay with the Master Cluster occurs, you can re-replicate the Master Cluster’s data using the Replica reconstruction feature.
To reconfigure the Replica, follow these steps.
- All Services > Database > PostgreSQL(DBaaS) Click the menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- On the PostgreSQL(DBaaS) List page, click the resource to reconfigure the replica. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Replica Reconstruction Click the button. 4. Replica Reconfiguration Notification A popup window opens.
- Replica Reconfiguration Notification popup window, click the Confirm button.
Promoting a Replica Cluster to a Master Cluster
You can promote a fully configured Replica Cluster to a Master Cluster.
To promote a Replica Cluster to Master, follow these steps.
- All Services > Database > PostgreSQL(DBaaS) Click the menu. 1. Go to the Service Home page of PostgreSQL (DBaaS).
- On the Service Home page, click the PostgreSQL(DBaaS) menu. 2. PostgreSQL (DBaaS) List Navigate to the page.
- PostgreSQL(DBaaS) List page, click the resource to promote to Master. 3. PostgreSQL(DBaaS) Details Navigate to the page.
- Click the More button, then click the Master Promotion button. 4. Master Promotion Notification The popup window opens.
- Master Promotion Notification In the popup window, click the Confirm button.
6.2.2.4 - DB Server Connection
Scenario Overview
PostgreSQL(DBaaS) Server Connection The scenario involves creating a Bastion host (Virtual Server) and a Database service, and accessing the DB service through the Bastion host. To reliably connect to PostgreSQL (DBaaS) in the Samsung Cloud Platform environment, you need to create a Bastion host and establish network connectivity using it. It is recommended to configure the Database service in a Private Subnet environment and the Bastion host in a restricted Public Subnet environment to maintain stability and a high level of security.
This scenario primarily describes creating a Bastion host and a Database service, configuring the network environment for Bastion host and Database access, and connecting through a DB client.
Scenario components
You can build the scenario using the following services.
| Service group | service | Detailed description | |
|---|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment | |
| Networking | VPC > Subnet | A service that lets users subdivide the network within a VPC to match their purpose and scale. | |
| Networking | VPC > Public IP | A service that reserves a public IP and allocates and releases it to Compute resources. | |
| Networking | VPC > Internet Gateway | A service that connects VPC resources to the Internet | |
| Networking | Security Group | Virtual firewall that controls server traffic | |
| Database | PostgreSQL(DBaaS) | A service that easily creates and manages EPAS in a web environment | |
| Compute | Virtual Server | Virtual server optimized for cloud computing | |
| Compute | Virtual Server > Keypair | Encryption file used to connect to the Virtual Server |
- Since the default policy of a Security Group is Deny All, you must register only the allowed IPs.
- The All Open (Any IP, Any Port) policy for In/Outbound can expose cloud resources directly to external threats.
- By specifying the required IP and port and setting a policy, you can strengthen security.
Scenario setup method
Create the services needed to build the scenario by following the steps below.
Set up the network
This explains the process of configuring the network environment for accessing the Bastion Host and Database services.
1-1. Create VPC
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- Click the VPC Creation button on the Service Home page. You will be taken to the VPC Creation page.
- On the VPC Creation page, enter the information required to create the service.
- Enter the IP range as
192.168.x.0/16.
- Enter the IP range as
- Summary panel, verify the detailed information and estimated billing amount generated there, and click the Complete button.
- After creation is complete, check the created resources on the VPC List page.
1-2. Create Subnet
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- On the Service Home page, click the Subnet menu. You will be taken to the Subnet List page.
- Click the Create Subnet button. You will be taken to the Create Subnet page.
- On the Subnet Creation page, enter the information required to create the service.
- Select the Subnet type as General.
- Select a pre‑created VPC.
- Enter the IP range as
192.168.x.0/24.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resources on the Subnet List page.
1-3. Create Internet Gateway
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- Click the Create Internet Gateway button. You will be taken to the Create Internet Gateway page.
- On the Internet Gateway Creation page, enter the required information to create the service.
- Select a pre‑created VPC.
- In the Firewall usage option, select Use.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resource on the Internet Gateway list page.
1-4. Create Public IP
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Public IP menu. You will be taken to the Public IP List page.
- Click the Public IP Reservation button. You will be taken to the Public IP Reservation page.
- On the Public IP reservation page, enter the required information needed to reserve the service.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resources on the Public IP List page.
1-5. Create Security Group
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of Security Group.
- Click the Create Security Group button on the Service Home page. You will be taken to the Create Security Group page.
- Security Group creation Enter the required information needed to create the service on the page.
- Check the input information and click the Complete button.
- When creation is complete, check the created resources on the Security Group List page.
Create bastion host
Describes the process of configuring a Bastion Host that requires the database client to be installed.
2-1. Create Server Keypair
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- Click the Create Keypair button. You will be taken to the Create Keypair page.
- On the Keypair Creation page, enter the required information needed to create the service.
- Verify the creation information and click the Complete button.
- The key can be downloaded only on the first attempt, and reissuance is not available.
- Please store the downloaded key in a secure location.
2-2. Create Bastion host
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server Creation button. You will be taken to the Virtual Server Creation page.
- On the Virtual Server Creation page, enter the required information to create the service.
- Select Windows for the image.
- Select the pre‑created VPC and Subnet.
- Click Use NAT, and select the reserved Public IP from 1-4. Create Public IP.
- 2-1. Create Server Keypair Connect the Keypair created there.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resources on the Virtual Server List page.
2-3. Verify Bastion host login ID and password
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- Click the Virtual Server menu on the Service Home page. You will be taken to the Virtual Server List page.
- On the Virtual Serve List page, click the resource you created in 2-2. Bastion host Create. You will be taken to that resource’s detailed information page.
- On the detail page, click the RDP password view button in the Keypair name field. The RDP password view popup window will open.
- In the RDP password lookup popup window, attach the keypair file downloaded from 2-1. 서버 Keypair 생성하기.
- After attaching, click the Password Check button. The ID and Password required to access the resource are displayed.
- The ID and password will later be used as credentials to access the Bastion host in 5-1. Bastion host Connecting.
Create Database
Describes the process of creating a Database service.
3-1. Create PostgreSQL (DBaaS) Service
- Click the All Services > Database > PostgreSQL(DBaaS) menu. Navigate to the Service Home page of PostgreSQL(DBaaS).
- Click the PostgreSQL(DBaaS) Create button on the Service Home page. You will be taken to the PostgreSQL(DBaaS) Create page.
- PostgreSQL(DBaaS) Creation On the page, enter the required information to create the service.
- Select the pre‑created VPC and Subnet and connect them.
- Enter the database-related creation information on the required information input screen.
- Add the Bastion host IP in the IP access control section.
- The Database Port defaults to 2866, but the user can also specify it.
- In the Summary panel, verify the detailed information and estimated billing amount, then click the Complete button.
- After creation is complete, verify the created resource on the PostgreSQL(DBaaS) list page.
Configuring Rules
It explains the process of configuring rules for a user to connect to the Bastion host and rules for connecting to the Database from the Bastion host.
4-1. Security Group Add Security Rules
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of Security Group.
- From the Service Home page, click the Security Group menu. You will be taken to the Security Group List page.
- Select the Security Group resource created in 1-5. Create Security Group. Navigate to the detailed information page of that resource.
- Click the Rules tab on the detail page. You will be taken to the Rules tab.
- On the Rules tab, click the Add Rule button. You will be taken to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
direction remote Target address Protocol Port Explanation Inbound CIDR User PC IP TCP 3389 (RDP) Bastion client PC → Bastion host Outbound CIDR DB IP TCP Database Port (manual entry) Bastion host → Database Table: Security Group rules that need to be added
4-2. Add IGW Firewall Rule
- All Services > Networking > Firewall Click the menu. Go to the Service Home page of the Firewall.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, select the Internet Gateway resource name created in 1-3. Internet Gateway Creation. You will be taken to the detailed information page of that resource.
- Click the Rules tab on the detail information page. You will be taken to the Rules tab.
- Click the Add Rule button on the Rules tab. You will be taken to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
origin address Destination address Protocol Port Operation direction Explanation Bastion connection PC IP Bastion host IP TCP 3389(RDP) Allow Inbound User PC → Bastion host Table. Internet Gateway Firewall rules that need to be added
Connect to Database
Describes the process of a user accessing the database via a DB client program.
This guide explains how to connect using pgAdmin. Since there are various database client programs and CLI utilities, you may install and use the tool that best fits your needs.
5-1. Connecting to Bastion host
- In the Windows environment of the PC that will connect to the Bastion host, run Remote Desktop Connection, then enter the NAT IP of the Bastion Host and click the Connect button.
- When the remote desktop connection succeeds, the user credential input window opens. Enter the ID and Password you verified in 2-3. Bastion host access ID and PW verification and click the Confirm button.
5-2. Install DB connection client program (pgAdmin) on the Bastion host
- Go to the official pgAdmin page and download the pgAdmin program.
- pgAdmin program download URL: https://www.pgadmin.org/download/
- Connect the user’s PC hard drive to upload the file to the Bastion host.
- In the Local Resources tab of the Remote Desktop Connection, click the Details button for the Local Devices and Resources item.
- Select the local disk of the location where the file was downloaded on the drive, and click the OK button.
- Copy the downloaded file, upload it to the Bastion Host, and click the pgAdmin installer to install.
5-3. Connect to the database using the DB client program (pgAdmin)
- Run pgAdmin and click the Add New Server button.
- In the Register - Server popup window, enter the Database server information created in 3-1. PostgreSQL(DBaaS) 서비스 생성하기 into the General and Connection tabs, and click the Save button.
Screen (tab) Required input field input value General Name Custom (ex. service name) Connection Host name/address Database server IP Connection Port Database Port Connection Maintenance database Database name Connection Password Database password Table.DB connection client program input fields - Click the name of the database created in pgAdmin to connect.
- After connecting, you can perform simple queries, among other tasks.
6.2.2.5 - Extension Use
PostgreSQL(DBaaS) Extension usage
You can view the list of extensions that can be installed in the current database with the SQL statement below.
SQL> select * from pg_available_extensions;
PostgreSQL (DBaaS) includes the following items in addition to the default extensions for each version.
| Extension name | Explanation |
|---|---|
| pgaudit | Provides detailed audit logging at the session and object level |
| pg_cron | A scheduler that can schedule jobs using cron syntax within the database. |
| pg_hint_plan | Provides a feature to apply hint clauses to SQL execution plans. |
| pgvector | Provides vector data types and AI vector operation features such as similarity search. |
| postgis | GIS (Geographic Information System) provides spatial object storage and spatial query functionality |
If you need to install additional extensions beyond the items above, refer to Support Center > Inquiry and contact us.
- After a request is received, we will review it and proceed with installation. Please note that some extensions may not function properly during replica configuration and recovery.
6.2.3 - API Reference
6.2.4 - CLI Reference
6.2.5 - Release Note
PostgreSQL(DBaaS)
- The OS (Kernel) upgrade feature enhances the latest security patches and stability.
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Add PostgreSQL (DBaaS) feature
- Add Second-Generation Server Type
- Add a second‑generation (db2) server type based on the Intel 4th‑generation (Sapphire Rapids) processor. For more details, see PostgreSQL(DBaaS) 서버 타입.
- DB user and access control management and Archive configuration feature added
- For more details, see DB User Management, DB Access Control Management, Archive Management.
- DB Audit Log Export feature added
- For more details, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For detailed information, refer to Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Configuring Migration.
- Add HDD, HDD_KMS types to Block Storage type
- Add Second-Generation Server Type
- PostgreSQL(DBaaS) feature change
- Add new PostgreSQL versions: 13.16, 14.13, 15.8
- Add second-generation server type
- Add a 2nd‑generation (dbh2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see PostgreSQL(DBaaS) server type.
- After creating the service, Block Storage capacity expansion is possible.
- Server-specific network IP configuration feature has been added allowing either a common configuration or a server-specific configuration depending on the intended use.
- Samsung Cloud Platform common feature changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- A volume-encrypted storage selection option has been added to the Block Storage type.
- A Role Switch (Active ↔ Standby) feature has been added for the Active DB and Standby DB configured with redundancy.
- It is linked with the cloud monitoring service, enabling performance and log monitoring of DB instances.
- Based on the server type selected by the customer, Planned Compute policy can be set.
- A PostgreSQL (DBaaS) service that enables easy creation and management of PostgreSQL in a web environment has been launched.
6.3 - MariaDB(DBaaS)
6.3.1 - Overview
Service Overview
MariaDB (DBaaS) is an open-source relational database (RDBMS) with high compatibility with MySQL. Samsung Cloud Platform provides an environment that can automate MariaDB installation and perform management functions for operation through a web-based Console.
MariaDB (DBaaS) is designed as a high‑availability architecture that performs storage‑based data replication and minimizes failover time. To prevent data loss, when the contents of the Active server change, they are synchronously replicated to the Standby server, and up to five read‑only Replica servers for read load balancing and disaster recovery (DR) are provided. Additionally, it provides an automatic backup feature at user-specified times to prepare for issues with the DB server or data, enabling recovery of data at the desired point in time.
Provided Features
MariaDB (DBaaS) provides the following features.
- Auto Provisioning (Auto Provisioning): Allows installation and configuration of Database(DB) via UI, and provides an Active-standby redundancy configuration based on storage replication. * When the active server fails, it automatically fails over to standby.
- Operation Control Management: Provides a function to control the status of running servers. * In addition to start and stop, you can restart if there is a DB issue or to apply configuration changes. * When high availability (HA) is configured, the user can manually perform node switching between Active and Standby via a switch‑over.
- Backup and Recovery: Provides data backup functionality based on its own backup commands. * Backup time windows and storage locations can be set by the user, and additional fees are incurred based on the backup size. * It also provides a recovery function for backed‑up data, so when the user performs a recovery, a separate database is created and the recovery proceeds to the point in time selected by the user (the backup save point or a user‑specified point). * When restoring to a user-specified point in time, the restore point can be set up to 5 minutes, 10 minutes, 30 minutes, or 1 hour earlier, based on the stored backup and archive files.
- Version Management: Provides a version upgrade (Minor) feature based on some functionality improvements and security patches. * Whether to perform a backup for a version upgrade can be selected by the user, and if a backup is performed, the data is backed up before applying the patch, after which the DB engine is updated.
- Replica configuration: Up to five Read Replicas can be configured in the same or different regions for read load balancing and disaster recovery (DR).
- Audit configuration: Provides an Audit configuration feature that can monitor users’ DB access and the results of DDL (Data Definition Language)/DML (Data Manipulation Language) operations.
- Parameter management: Performance improvements and security-related DB configuration parameters can be modified.
- Service Status Query: Retrieves the final status of the current DB service.
- Monitoring: CPU, memory, performance monitoring information can be viewed through Cloud Monitoring and Servicewatch.
- DB User Management: Query and manage the DB account (user) information registered in the DB.
- DB Access Control Management: Based on DB accounts registered in the DB, you can register and revoke allowed IPs for access.
- Archive Management: You can set the Archive file retention period (1 to 35 days) on the DB server and configure the Archive mode (On/Off).
- DB Log Export: Through Audit settings, you can export stored logs to the user’s Object Storage.
- Migration: Synchronize data in real time with the operational database and support migration using replication without service interruption.
- OS Kernel Upgrade: You can upgrade the OS Kernel to apply some feature improvements and security patches.
Component
MariaDB(DBaaS) provides pre‑validated engine versions and various server types in accordance with its open‑source support policy. Users can select and use it based on the scale of the service they wish to configure.
Engine version
The engine versions supported by MariaDB (DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is stopped is set to six months before the EoTS date.
Since the EOS and EoTS dates may change according to the supplier’s policy, please refer to the supplier’s license management policy page for details.
- MariaDB (Community): https://mariadb.org/about/#maintenance-policy
| service | Provided version | EOS Date (Samsung Cloud Platform new creation stop date) | EoTS Date (Community technical support end date) |
|---|---|---|---|
| MariaDB (Community) | 10.6.5 | 2026-03-19 | 2026-07-06 |
| 10.6.9 | 2026-03-19 | 2026-07-06 | |
| 10.6.10 | 2026-03-19 | 2026-07-06 | |
| 10.6.12 | 2026-03-19 | 2026-07-06 | |
| 10.6.14 | 2026-03-19 | 2026-07-06 | |
| 10.6.15 | 2026-03-19 | 2026-07-06 | |
| 10.6.16 | 2026-03-19 | 2026-07-06 | |
| 10.6.17 | 2026-03-19 | 2026-07-06 | |
| 10.6.19 | 2026-03-19 | 2026-07-06 | |
| 10.6.22 | 2026-03-19 | 2026-07-06 | |
| 10.11.8 | 2027-09 (planned) | 2028-02-16 | |
| 10.11.9 | 2027-09 (planned) | 2028-02-16 | |
| 10.11.13 | 2027-09 (planned) | 2028-02-16 | |
| 11.4.7 | 2028-12 (planned) | 2029-05-29 |
The next version of MariaDB is scheduled to be available after July 2026. The actual service delivery schedule is subject to change.
- MariaDB 10.11.15
- MariaDB 11.4.10
Server type
The server types supported by MariaDB (DBaaS) are as follows.
For detailed information about the server types offered by MariaDB (DBaaS), refer to MariaDB(DBaaS) Server Types.
Standard db1v2m4
| Category | Example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | db1 | Provided server specifications
|
| Server specifications | v2 | vCore count
|
| Server specifications | m4 | Memory capacity
|
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
6.3.1.1 - Server Types
MariaDB(DBaaS) server type
MariaDB(DBaaS) provides server types composed of various combinations of CPU, memory, and network bandwidth. When creating a MariaDB(DBaaS), the Database Engine is installed according to the server type selected for the intended use.
The server types supported by MariaDB (DBaaS) are as follows.
Standard db1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | db1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
db1 server type
The db1 server type of MariaDB(DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db1v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | db1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db1v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db1v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
db2 server type
The db2 server type of MariaDB (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db2v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | db2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
dbh2 server type
The dbh2 server type of MariaDB (DBaaS) is offered with high-capacity server specifications and is suitable for database workloads that require large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | dbh2v24m48 | 24 vCore | 48 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m64 | 32 vCore | 64 GB | Up to 25 Gbps |
| High Capacity | dbh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m256 | 32 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m256 | 64 vCore | 256 GB | Up to 25 Gbps |
| High Capacity | dbh2v64m768 | 64 vCore | 768 GB | Up to 25 Gbps |
| High Capacity | dbh2v72m288 | 72 vCore | 288 GB | Up to 25 Gbps |
| High Capacity | dbh2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m384 | 96 vCore | 384 GB | Up to 25 Gbps |
| High Capacity | dbh2v96m1152 | 96 vCore | 1152 GB | Up to 25 Gbps |
| High Capacity | dbh2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
6.3.1.2 - Monitoring Metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Service by Resource
- New Resources: Resources created after the service improvement work in March 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, settings configured by users linked with existing Cloud Monitoring (ex. You need to review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Notice of the phased termination schedule for the Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
* Service termination (November 2026 service improvement work)
* All services of Cloud Monitoring, including the API, will be permanently discontinued.
* **After the service ends in November, Cloud Monitoring data cannot be accessed.** * Be sure to complete the ServiceWatch migration within the parallel operation period**.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
MariaDB(DBaaS) Monitoring Metrics
The table below shows the performance monitoring metrics for MariaDB (DBaaS) that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
The server monitoring metrics for MariaDB (DBaaS) can be found in the Virtual Server Monitoring Metrics guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Active Locks | Number of Active Locks | cnt |
| Active Sessions | Number of Active Sessions | cnt |
| Connection Usage [Total] | DB connection session usage rate | % |
| Connections | Number of connections | cnt |
| Connections [MAX] | max connected threads count | cnt |
| Binary Log Used [MB] | binary log usage | MB |
| Data Directory Used [MB] | data directory usage | MB |
| Open Files | Number of open DB files | cnt |
| Open Files [MAX] | Number of DB files that can be opened | cnt |
| Open Files Usage | DB file maximum count usage rate | % |
| Relay Log Used [MB] | relay log usage | MB |
| Instance Status [PID] | mariadbd process | pid |
| Safe PID | mariadbd_safe process | pid |
| Slave Behind Master seconds | Data time difference between Master and Slave (run only on slave) | sec |
| Tablespace Used | Tablespace usage | MB |
| Tablespace Used [Total] | Total tablespace usage | MB |
| Running Threads | running thread count | cnt |
| Slowqueries | Number of SQL queries running for a long time (over 5 minutes) (by DB) | cnt |
| Slowqueries [Total] | Number of long-running (5 minutes or more) SQL queries (total) | cnt |
| Transaction Time [Long] | Maximum transaction execution time | sec |
| Wait Locks | Number of sessions blocked for more than 60 seconds by lock | cnt |
6.3.1.3 - ServiceWatch Metrics
MariaDB sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the namespace MariaDB(DBaaS).
The indicators whose names are shown in bold below are the key indicators selected among the basic metrics provided by MariaDB(DBaaS). The key metrics are used to configure the service dashboards that are automatically built for each service in ServiceWatch.
Each metric guides users, through the user guide, on which statistical values are meaningful when querying that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
OS Basic Metrics
Category | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| CPU | CPU Usage | Percent | CPU usage |
|
| Disk | Disk Usage | Percent | Disk usage |
|
| Disk | Disk Write Bytes | Bytes/Second | Write bandwidth (bytes/second) on block device |
|
| Disk | Disk Read Bytes | Bytes/Second | Read throughput from block device (bytes/second) |
|
| Disk | Disk Write Requests | Count/Second | Number of write requests on block device (requests per second) |
|
| Disk | Disk Read Requests | Count/Second | Number of read requests on block device (requests per second) |
|
| Disk | Average Disk I/O Queue Size | None | Average queue length of requests issued to the block device |
|
| Disk | Disk I/O Utilization | Percent | The proportion of time the block device actually spent handling I/O operations |
|
| Memory | Memory Usage | Percent | Memory usage |
|
| Network | Network In Bytes | Bytes/Second | Received data rate (bytes/second) on the network interface |
|
| Network | Network Out Bytes | Bytes/Second | Transmitted capacity (bytes/second) on the network interface |
|
| Network | TCP Connections | Count/Second | Current total number of successfully established TCP connections |
|
| Network | Network In Packets | Count | Number of packets received on the network interface |
|
| Network | Network Out Packets | Count | Number of packets transmitted on the network interface |
|
| Network | Network In Dropped | Count | Number of packet drops received on the network interface |
|
| Network | Network Out Dropped | Count | Number of packet drops transmitted from the network interface |
|
| Network | Network In Errors | Count | Number of packet errors received on the network interface |
|
| Network | Network Out Errors | Count | Number of packet errors transmitted on the network interface |
|
MariaDB basic metrics
Category | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| Activelock | Active locks | Count | Number of transactions in the InnoDB storage engine that have been in lock wait state for 1 minute (60 seconds) or longer. |
|
| Activesession | Active sessions | Count | Number of active sessions |
|
| Activesession | Connection usage | Percent | DB connection session usage rate |
|
| Activesession | Connections | Count | DB connection session |
|
| Activesession | Aborted Connections | Count/Minute | Number of abnormal terminated connections |
|
| Datafile | Current open files | Count | Number of file descriptors opened by the DB |
|
| Datafile | Max open files | Count | Maximum number of file descriptors the DB can open |
|
| Datafile | Open files usage | Percent | DB file maximum count utilization |
|
| InnoDB | InnoDB buffer pool hit ratio | Percent | The ratio of data read directly from memory without accessing the disk |
|
| InnoDB | Innodb row lock wait transactions | Count | Current number of InnoDB transactions waiting for a row lock |
|
| InnoDB | InnoDB row lock time | Milliseconds | Total time waited due to InnoDB row locks (in milliseconds) |
|
| InnoDB | InnoDB deadlocks | Count/Minute | Number of transactions rolled back due to deadlock |
|
| InnoDB | Table lock waits | Count/Minute | Number of waits that occurred to acquire a table lock |
|
| InnoDB | Temp disk tables | Count/Minute | Number of Temp Tables created on disk |
|
| InnoDB | Innodb log waits | Count | Number of times waited to write the redo log to disk |
|
| State | Instance state | None | Check Scalable DB up/down status
| - |
| State | Slave behind master seconds | Seconds | Replica latency (unit: seconds) |
|
| State | Slave io thread running (Replica Only) | None | I/O Thread status
| - |
| State | Slave SQL thread running (Replica Only) | None | SQL Thread status
| - |
| Tablespace | Tablespace used | Megabytes | Tablespace usage |
|
| Tablespace | Tablespace used(TOTAL) | Megabytes | Tablespace usage (total) |
|
| Transactions | Slow queries | Count | Number of queries running longer than 10 seconds |
|
| Transactions | Long transaction time | Seconds | Long Transaction time |
|
| Transactions | Wait locks | Count | Number of sessions waiting for lock |
|
| Transactions | SQL Queries/Minute | Count/Minute | Queries executed per minute |
|
6.3.2 - How-to guides
Users can create the service by entering the required information for MariaDB (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
According to the policy of Samsung Cloud Platform, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Service per Resource
- New Resources: Resources created after the March 2026 service improvement work are provided with default monitoring using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, settings configured by users linked with existing Cloud Monitoring (e. You must review the event policies, etc., and perform tasks such as resetting the ServiceWatch service, then complete them.
Notice of the phased termination schedule for the Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
Create MariaDB (DBaaS)
You can create and use a MariaDB (DBaaS) service from the Samsung Cloud Platform Console.
- Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the corresponding Database service cannot be created.
- When loading more than 2 TB of large data, backups may take a long time or the database’s performance may degrade. * To prevent this, it is necessary to consider operational aspects such as cleaning up unnecessary data or migrating old data to the statistical collection environment.
To create a MariaDB (DBaaS), follow the steps below.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the Create MariaDB (DBaaS) button. 2. Go to the Create MariaDB (DBaaS) page.
- Create MariaDB (DBaaS) on the page, enter the information required to create the service, and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version Required Provide a list of MariaDB (DBaaS) versions Table. MariaDB (DBaaS) Image and version selection options - In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Server name Prefix Required The server name where the DB will be installed - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
-) with a length of 3 to 13 characters
- a postfix such as 001, 002 is appended to the base server name to generate the actual server name
Cluster name required Cluster name composed of DB servers - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for DB installation - Standard: Standard specifications commonly used
- High Capacity: Large-capacity server with 24 vCores or more
- For detailed information about the server types provided by MariaDB (DBaaS), refer to MariaDB(DBaaS) 서버 타입.
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, refer to Planned Compute Apply
Service Type > Block Storage required Block Storage settings used by the DB according to purpose - Base OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select a storage type and then enter the capacity. (For details on each Block Storage type, refer to Block Storage 생성하기)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volumes that use Samsung Cloud Platform KMS (Key Management System) encryption keys
- The configured storage type is applied identically to additional storage
- Capacity must be entered as a multiple of 8 within the range 16 to 5,120
- Since executing SQL or monthly batch jobs can cause service interruptions due to large sorts, a separate TEMP storage must be allocated and used
- Select a storage type and then enter the capacity. (For details on each Block Storage type, refer to Block Storage 생성하기)
- Add: Storage areas for DATA, Archive, TEMP, Backup data
- After selecting Use, enter the storage’s purpose and capacity
- The storage type is applied the same as the type set for DATA, and capacity can be entered as a multiple of 8 within the range 16 to 5,120
- To add storage, click the Add button; to delete, click the x button. Up to 9 can be added.
- Temporarily store backup data in the BACKUP storage before transmitting it
- If the data to be backed up exceeds 100 GB and undergoes frequent changes, it is recommended to add a separate BACKUP storage for reliable backup. Set the backup capacity to about 60 % of the DATA capacity.
- If a BACKUP storage is not added, the
/tmparea is used, and backup fails if capacity is insufficient
- For each service, only one Block Storage is allocated for Archive, TEMP, and BACKUP
Redundancy configuration Select Redundancy configuration - When redundancy is enabled, the DB instance is configured as an Active DB and a Standby DB
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- IP can only be generated automatically
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. If you check Use, you can select from reserved IPs in the VPC product’s Public IP. For more details, see Public IP 생성하기
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select when you want to apply different settings for each installed server
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- Enter the IP for each server
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. Use when checked, you can select a reserved IP from the VPC product’s Public IP. For more information, see Public IP 생성하기
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruptions
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. MariaDB (DBaaS) Service Information Input Items - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
- Enter required database configuration information Enter or select the required information in this area.
Category required statusDetailed description Database name Required Server name applied during DB installation - must start with an English letter and be entered using English letters and numbers, 3 to 20 characters
Database username Required DB user name - An account with the same name is also created on the OS
- Enter using lowercase English letters, 2 to 20 characters
- Database user names that are restricted can be viewed in the Console
Database password Required Password to use when accessing the DB - Include English letters, numbers, and special characters (
“‘excluded) and enter 8~30 characters
Database password verification Required Re-enter the same password to use for DB access Database Port number Required Port number required for DB connection - Enter the DB port within the range 1200 ~ 65535
Backup > Use Select Backup usage - Select Use to set the backup file retention period, backup start time, and Archive backup interval
Backup > Retention period Select Backup retention period - Select the backup retention period. Set the file retention period from 7 days to 35 days
- Backup files incur additional charges based on size
Backup > Backup Start Period Selection Backup start time - Select backup start time
- The minutes (minutes) at which the backup runs are set randomly, and the backup end time cannot be set
Backup > Archive backup cycle Select Archive backup interval - Select the archive backup interval
- The archive backup interval is recommended to be 1 hour. Selecting 5 minutes, 10 minutes, or 30 minutes may affect DB performance
Audit Log Settings Selection Whether to store Audit Log - Select Use to configure the Audit Log feature
- User connection information records are stored
- Users can specify the types of events to audit via the
server_audit_eventsparameter, and can modify it through the Parameter screen
- For detailed information about this parameter, refer to the MariaDB documentation
- Users can specify the types of events to audit via the
- Enabling Audit may degrade database performance
- User connection information records are stored
ServiceWatch log collection Selection Whether to collect ServiceWatch logs - Select Use to configure the ServiceWatch log collection feature
- For details about the collected logs, see ServiceWatch 지표
- Up to 5 GB per account is provided free of charge for all services, and charges apply based on storage usage for amounts exceeding 5 GB
- When collecting, log groups and log streams are created automatically and cannot be deleted until the resources are removed
- To prevent exceeding 5 GB, it is recommended to delete log data directly or shorten the retention period
Parameter Required Parameters to be used in the DB - Query button can be clicked to view detailed information of the parameters
- Parameters can be modified after the DB creation is complete, and the DB must be restarted after any modifications
DB character set Required Character encoding method to be used for the DB - The character set used when storing text data, set as the default with the selected encoding when the DB is created
time zone Required Standard time zone for the database Table. MariaDB (DBaaS) Database configuration items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description tag Selection Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, input or select Key, Value values
Table. MariaDB (DBaaS) additional information input fields
- Select the required information in the Image and version selection area.
- Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
View detailed information for MariaDB (DBaaS)
The MariaDB (DBaaS) service allows you to view and edit the full list of resources and detailed information. MariaDB(DBaaS) Details page consists of Details, Tags, Activity History tabs, and when the DB has a Replica configured, a Replica Information tab is added.
To view detailed information about the MariaDB (DBaaS) service, follow these steps.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. MariaDB(DBaaS) List page is accessed.
- On the MariaDB(DBaaS) List page, click the resource to view detailed information. 3. MariaDB(DBaaS) Details Go to the page.
- MariaDB(DBaaS) Details The top of the page displays status information and additional feature details.
Category Detailed description Cluster status Cluster status with DB installed - Creating: Cluster is being created
- Editing: Cluster is transitioning to an operation execution state
- Error: Cluster encountered a failure while performing a task
- If this persists, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Cluster is being restarted
- Running: Cluster is operating normally
- Starting: Cluster is starting
- Stopped: Cluster is stopped
- Stopping: Cluster is being stopped
- Synchronizing: Cluster is synchronizing
- Terminating: Cluster is being terminated
- Unknown: Cluster status is unknown
- If this persists, contact the administrator
- Upgrading: Cluster is transitioning to an upgrade execution state
Cluster control Buttons to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
- Switch-Over: Switch a standby cluster to Active
More features Cluster management button - Service status synchronization: Real-time DB service status lookup
- Backup history: When backup is configured, verify successful execution and view history
- Database recovery: Recover the DB based on a specific point in time
- Parameter management: View and modify DB configuration parameters
- Replica configuration: Set up a read‑only Replica cluster
- Replica configuration (Other-Region): Set up a disaster‑recovery Replica in another region; if the target account has no region to configure, the button is disabled
- DB user management: View and manage DB account (user) information registered in the DB
- DB access control management: Register and revoke allowed IPs based on DB accounts registered in the DB
- Archive settings management: Set archive file retention period and enable archive mode
- DB Log export: Export logs stored via Audit settings to the user’s Object Storage
- Migration configuration: Provide migration functionality using replication
- OS (Kernel) upgrade: Upgrade OS kernel version
Service cancellation Cancel service button Table. MariaDB (DBaaS) status information and additional features
- MariaDB(DBaaS) Details The top of the page displays status information and additional feature details.
Detailed information
On the MariaDB (DBaaS) List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed DB image and version information
|
| Cluster type | Cluster types (Master Cluster, Replica Cluster, Migration Cluster) |
| Cluster name | Cluster name of the DB servers |
| Master cluster name | Replica’s Master cluster name
|
| Database name | Server name applied during DB installation |
| Database username | DB user name |
| Planned Compute | Resource status with Planned Compute configured
|
| maintenance period | DB Maintenance Period Status
|
| Backup | Backup Configuration Status
|
| Audit Log Settings | Audit Log configuration status
|
| ServiceWatch log collection | ServiceWatch Log Collection Configuration Status
|
| DB character set | Character encoding to use for the DB |
| time zone | Standard time zone for the database |
| VIP | Virtual IP information
|
| Network | Network information where the DB is installed(VPC, Subnet, VIP, NAT IP(VIP)) |
| IP access control | Service access policy configuration
|
| Active & Standby | Active/Standby server type, base OS, additional Disk information
|
Replica information
Replica information tab is enabled only when a Replica is configured in the cluster. Replica information tab allows you to view the Master cluster name, replica count, and Replica status.
| Category | Detailed description |
|---|---|
| Master information | Name of the Master cluster |
| Replica count | Number of Replicas created in the Master cluster |
| Replica status | Replica server status in the Master cluster
|
tag
MariaDB(DBaaS) List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
MariaDB(DBaaS) List page lets you view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing MariaDB (DBaaS) Resources
If you need to change or restore the existing configuration options of a created MariaDB (DBaaS) resource, or require a Replica configuration, you can perform the operation on the MariaDB(DBaaS) Details page.
Control operation
If changes occur to a running MariaDB (DBaaS) resource, you can start, stop, or restart it. Additionally, when HA is configured, you can switch the Active‑Standby servers using a switch‑over.
To control the operation of MariaDB (DBaaS), follow the steps below.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Go to the MariaDB(DBaaS) List page.
- MariaDB (DBaaS) List page, click the resource to control its operation. 3. MariaDB(DBaaS) Details Go to the page.
- Check the MariaDB (DBaaS) status and complete the change using the control button below.
- Start: The DB service is installed on the server and the DB service is running (Running).
- Stop: The server where the DB service is installed and the DB service are stopped (Stopped).
- Restart: Only the DB service will be restarted.
- Switch Over: You can switch the DB’s Active server and Standby server.
Synchronize Service Status
You can synchronize the real-time service status of MariaDB (DBaaS).
To check the service status of MariaDB (DBaaS), follow the steps below.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource to view the service status. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Service Status Synchronization button. 4. While it is being queried, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Go to the MariaDB(DBaaS) List page.
- On the MariaDB (DBaaS) List page, click the resource to change the server type. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Edit icon for the server type you want to change at the bottom of the detailed information. 4. Edit Server Type popup window opens.
- Server Type Edit In the popup window, select the server type, then click the Confirm button.
Add storage
If you need more than 5 TB of data storage space, you can add additional storage. For a DB configured with redundancy, all redundant servers are added simultaneously.
- It is applied in the same way as the Storage type selected when creating the service.
- For a DB configured with redundancy, adding storage is applied simultaneously to the storage of both the Active DB and the Standby DB.
- If a Replica exists, the storage of the Master cluster cannot be larger than the storage of the Replica. * First expand the Replica storage, then expand the Master cluster storage.
- When adding Archive/Temp storage, the DB restarts and is temporarily unavailable.
To add storage, follow these steps.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB (DBaaS) List page, click the resource to add storage. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Add Disk button at the bottom of the details. 4. Additional Storage Request The popup window opens.
- Additional Storage Request In the popup window, after entering the purpose and size, click the Confirm button.
Expand storage
Storage added to the data area can be expanded up to a maximum of 5 TB based on the initially allocated capacity. In the case of a redundant DB configuration, all redundant servers are expanded simultaneously.
To expand storage capacity, follow the steps below.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- Click the resource to change the server type on the MariaDB (DBaaS) List page. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Edit icon of the additional Disk you want to add at the bottom of the detailed information. 4. Edit Additional Storage The popup window opens.
- Edit Additional Storage In the popup window, after entering the expansion capacity, click the Confirm button.
Cancel MariaDB(DBaaS)
You can cancel unused MariaDB (DBaaS) to reduce operating costs. Note that terminating the service may cause the currently operating service to stop immediately, so you should proceed with the termination only after fully considering the impact of a service interruption.
- For a DB with a Replica configured, terminating the Master DB does not delete the Replica. * If you also delete the replica, please cancel it separately from the resource list.
- If you terminate the DB, all stored data and any backup data that has been configured will be deleted.
To cancel MariaDB (DBaaS), follow the steps below.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, select the resource to cancel, and click the Terminate Service button.
- After termination is complete, check on the MariaDB(DBaaS) list page whether the resource has been terminated.
6.3.2.1 - DB Service Manage
Users can manage MariaDB (DBaaS) through the Samsung Cloud Platform Console.
Managing Parameters
Provides a feature that enables easy viewing and modification of database configuration parameters.
Query Parameter
To view configuration parameters, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- Click the resource whose parameters you want to view or modify on the MariaDB(DBaaS) List page. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the Parameter Management button. The Parameter Management popup opens.
- In the Parameter Management popup, click the Search button. The Search Notification popup opens.
- Lookup Notification When the popup window opens, click the Confirm button. Retrieval may take a short amount of time.
Modify Parameter
To modify the configuration parameters, follow the steps below.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- Click the resource whose parameters you want to view or modify on the MariaDB(DBaaS) List page. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the Parameter Management button. The Parameter Management popup window opens.
- Parameter Management in the popup window, click the Search button. The Search Notification popup window opens.
- Lookup Notification When the popup window opens, click the Confirm button. Retrieving the data may take a short time.
- If a modification is needed, click the Edit button and enter the changes in the custom value field of the Parameter to be edited.
- When the input is complete, click the Complete button.
If you change the character_set_server value, first verify the collation that matches the character set using the command below.
SQL> SHOW COLLATION WHERE Charset = 'character set name';
Set the parameter values for character-set-server, collation-server, and init_connect using the verified collation.
| Item | Detailed description | Restart option |
|---|---|---|
character-set-server | Specify the default character set | Restart required |
collation-server | Specify default collation | Restart required |
init_connect | SQL statements executed when the client connects to the database | No restart required |
Managing DB Users
Provides management functions to retrieve DB user information and modify status information.
Query DB users
To view DB users, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource for which you want to view the DB user. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the DB User Management button. You will be taken to the DB User Management page.
- DB User Management page, click the Search button. It may take a short time to retrieve the data.
Changing DB User Status
To change the status of the retrieved DB user, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- Click the MariaDB(DBaaS) menu on the Service Home page. You will be taken to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource whose DB user you want to modify. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button and then click the DB User Management button. You will be taken to the DB User Management page.
- DB User Management page, click the Search button. Retrieving the data may take a short while.
- If a correction is needed, click the Edit button, then change the status field value or enter remarks.
- When the input is complete, click the Complete button.
Managing DB Access Control
Provides IP-based DB user access control management functionality. Users can directly specify the IPs that may access the database, configuring it so that only authorized IPs are allowed.
Query DB Access Control
Follow these steps to query DB users with IP access control enabled.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- Click the resource you want to manage access control for on the MariaDB(DBaaS) List page. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button and then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. The query may take a moment.
Add DB access control
To add IP access control, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource for which you want to add IP access control. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button and then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. Retrieving the data may take a moment.
- After the query completes, click the Add button. The Add DB Access Control popup opens.
- Add DB Access Control In the popup window, select the DB username and enter the IP address.
- When the input is complete, click the Complete button.
Delete DB access control
To delete IP access control, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. You will be taken to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- MariaDB(DBaaS) List page, click the resource for which you want to delete IP access control. MariaDB(DBaaS) Details page will be opened.
- Click the More button and then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- DB Access Control Management page, click the Search button. Retrieving the data may take a short time.
- When the query is complete, click the Delete button. The Delete popup window opens.
- Delete Click the Confirm button in the popup window.
Managing Archives
Provides the ability to configure Archive mode and set the retention period for Archive logs, allowing users to flexibly configure Archive log management policies to suit their operational environment. Additionally, we provide a feature that allows manual deletion of Archive logs, enabling you to clean up unnecessary log data and manage system resources effectively.
Configure Archive mode
To set the Archive mode, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- MariaDB(DBaaS) List page, click the resource you want to set Archive mode for. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button and then click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- On the Archive Settings Management page, click the Search button. The query may take a short time.
- Click the Edit button and select the usage status and retention period.
- When the edit is complete, click the Done button.
Delete Archive file
To delete the Archive file, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- MariaDB(DBaaS) List page, click the resource you want to set Archive mode for. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- On the Archive Settings Management page, if you want to delete all Archive files, click the Delete All Archives button; if you only want to delete the backed‑up Archive files, click the Delete Backed-up Archive button.
Modify Audit Settings
You can change the Audit log storage settings of MariaDB (DBaaS).
To change the Audit log storage settings of MariaDB(DBaaS), follow the steps below.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Go to the MariaDB(DBaaS) List page.
- MariaDB(DBaaS) List page, click the resource to view the service status. You will be taken to the MariaDB(DBaaS) Details page.
- Click the Edit icon of Audit Settings at the bottom of the detailed information. The Edit Audit Settings popup window opens.
- Modify Audit Settings After changing the usage in the popup window, click the Confirm button.
- When Use is selected, the Audit log feature is enabled. Enabling the Audit log may degrade DB performance.
- If you disable it, the Audit log storage file will be deleted. Back up the Audit log file separately before disabling.
Export DB Log
Supports exporting log data that requires long-term retention among audit logs to Object Storage. Users can directly configure the log types to be stored, the target bucket for export, and the export interval. Based on the configured criteria, logs are copied to the specified Object Storage for retention. Additionally, to efficiently manage disk space, we also provide an option that exports logs to Object Storage while automatically deleting the original log files. By using this option, you can effectively free up storage capacity while safely retaining the necessary log data for long-term storage.
- To use the DB Log export function, you need to create an Object Storage. For creating Object Storage, please refer to the Object Storage User Guide.
- Please be sure to check the expiration date and time of the authentication key. If the authentication key expires, logs will not be stored in the bucket.
- Please ensure that authentication key information is not exposed externally.
Setting DB Log Export Mode
To set the DB Log export mode, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource you want to export the DB Log from. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the DB Log Export button. You will be taken to the DB Log Export page.
- On the DB Log Export page, click the Register button. You will be taken to the DB Log Export Register page.
- After entering the required information on the DB Log Export Registration page, click the Complete button.
Category Required Detailed descriptionLog type Required Log type to be saved Save bucket name Required Object Storage bucket name to be saved Authentication key > Access key Required Access key for accessing the Object Storage you want to store Authentication key > Secret key Required Secret key for accessing the Object Storage you want to store File creation cycle Required File creation interval in Object Storage Whether to delete the original log Selection Whether to delete the original logs when exporting to Object Storage Table. MariaDB (DBaaS) DB Log Export Configuration Items
Managing DB Log Export
To modify, cancel, or immediately export the DB Log export settings, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Go to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource you want to manage DB Log export for. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the DB Log Export button. You will be taken to the DB Log Export page.
- On the DB Log Export page, depending on the log type you want to manage, click the More button and then click the Export Now, Edit, or Cancel button.
- Export Immediately: The selected logs are exported to the bucket of the previously configured Object Storage.
- Edit: Modify the DB Log export mode setting.
- Cancel: Disables the DB Log export mode setting.
Minor Version Upgrade
We provide version upgrade functionality for some feature improvements and security patches. Only Minor version upgrades within the same Major version are supported.
- First retrieve the service status by synchronizing it, then perform the version upgrade.
- Please perform the version upgrade after configuring a backup. If you do not set up a backup, you may be unable to recover some data if a problem occurs during the upgrade.
- In a DB with a Replica configured, the Master DB version cannot be higher than the Replica version. Please check the Replica version first and, if necessary, perform a version upgrade.
- The backed-up data will be automatically deleted after the version upgrade is completed.
To upgrade the Minor Version, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. You will be taken to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource to upgrade the version. Navigate to the MariaDB(DBaaS) Details page.
- Click the Edit icon of the Image version item. The Version Upgrade popup window opens.
- Version Upgrade In the popup, select the updated version and whether to enable backup, then click the Confirm button.
- Version Upgrade Notification Click the Confirm button in the popup window.
Configure Migration
Provides a Migration feature that synchronizes in real time with the live database and replicates using a Replication method without service interruption.
To configure Migration, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. You will be taken to the MariaDB(DBaaS) List page.
- MariaDB(DBaaS) List page, click the resource to migrate. MariaDB(DBaaS) Details page will be opened.
- Click the More button, then click the Migration configuration button. The Migration configuration popup opens.
- Migration configuration In the popup window, check the instructions and click the Confirm button. You will be taken to the Migration configuration page.
- On the Migration configuration page, after entering the required information, click the Check connection button.
- When the connection is complete, click the Complete button.
Category Required Detailed descriptionSource DB Database name Required Database name of the source DB to be migrated Source DB IP Required IP of the Source DB that is the migration target Source DB Port Required Port of the Source DB to be migrated Source DB username Required User name of the source DB for migration Source DB password Required Password of the source DB that is the migration target Table. MariaDB (DBaaS) migration configuration items
Promote Migration Cluster to Master Cluster
You can promote a fully configured Migration Cluster to a Master Cluster.
To promote the Migration Cluster to Master, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource to promote to Master. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the Master Promotion button. The Master Promotion Notification popup opens.
- In the Master Promotion Notification popup, click the Confirm button.
Upgrade OS Kernel
The OS Kernel can be upgraded to improve the functionality of the running database and apply security patches.
- The service will be unavailable while the OS upgrade is in progress.
- The upgrade duration may vary depending on the version, and if the upgrade fails, it will be rolled back to the previous configuration.
- After the upgrade is complete, you cannot revert to the previous OS.
To upgrade the OS Kernel, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource to upgrade the OS Kernel. You will be taken to the MariaDB(DBaaS) Details page.
- Click the More button, then click the OS(Kernel) Upgrade button. The OS(Kernel) Upgrade Notification popup window opens.
- OS(Kernel) Upgrade Notification In the popup window, review the instructions and click the Confirm button.
6.3.2.2 - Backing up and restoring the database
Users can set up backups for MariaDB (DBaaS) through the Samsung Cloud Platform Console and restore from the backed‑up files.
Backing up MariaDB (DBaaS)
PostgreSQL (DBaaS) provides data backup functionality based on its own backup commands. Additionally, it provides an optimized backup environment for data protection and management through backup history verification and backup file deletion features.
Configure backup
Refer to MariaDB(DBaaS) Creating for how to configure backups for MariaDB (DBaaS).
To modify the backup settings of the created resource, follow the steps below.
For reliable backups, we recommend adding separate BACKUP storage or sufficiently expanding storage capacity.
Especially when the backup data exceeds 100 GB and undergoes frequent changes, please secure additional storage amounting to about 60 % of the data size.
For instructions on adding and expanding storage, refer to the MariaDB(DBaaS) Add Storage and MariaDB(DBaaS) Expand Storage guides.
If a backup is configured, it will be performed at the designated time after the set time, and additional fees will be incurred based on the backup size.
If you change the backup setting to unset, backup execution stops immediately, and the stored backup data is deleted and can no longer be used.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- MariaDB(DBaaS) List page: click the resource you want to configure a backup for. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Edit button of the backup item. 4. Backup Settings The popup window opens.
- When setting up a backup, click Use in the Backup Settings popup, select retention period, backup start time, and Archive backup interval, then click the Confirm button.
- If you want to stop the backup configuration, deselect Use in the Backup Settings popup and authenticate via the logged-in user’s mobile phone.
Once user authentication is completed, the backup configuration is disabled and backup execution stops.
- If you want to stop the backup configuration, deselect Use in the Backup Settings popup and authenticate via the logged-in user’s mobile phone.
Check backup history
To check the backup history, follow these steps.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- MariaDB (DBaaS) List page: click the resource to view the backup history. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Backup History button. 4. Backup History the popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup files
To delete the backup file, follow these steps.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- MariaDB (DBaaS) List page: click the resource to view the backup history. 3. MariaDB(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History popup opens.
- Backup History In the popup window, check the files you want to delete, then authenticate via the logged-in user’s mobile phone.
- When user authentication is completed, the backup file is deleted.
Recover MariaDB(DBaaS)
If a backup file must be restored due to a failure or data loss, you can recover to a specific point in time using the recovery feature. When performing a MariaDB(DBaaS) recovery, a new server is created with the OS image from the initial provisioning point, the DB is installed with the version from the backup point, and the recovery proceeds with the DB’s configuration information and data.
To recover MariaDB (DBaaS), follow these steps.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. MariaDB (DBaaS) List Go to the page.
- On the MariaDB (DBaaS) List page, click the resource you want to recover. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Database Recovery button. 4. Go to the Database Recovery page.
- After entering information in the Database recovery configuration area, click the Complete button.
Category required statusDetailed description Recovery Type Required Set the point in time the user wants to recover - Backup point (recommended): Recover based on the backup file. Select from the list of backup points displayed in the list
- Custom point: Recover to a user‑desired point within the range where backup is possible. The recoverable period depends on the Archive backup cycle setting, allowing recovery from the start of the first backup up to 1 hour/30 minutes/10 minutes/5 minutes before the current time. Select the date and time to back up
Server name prefix Required Server name of the recovery DB - Start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to input 3 to 16 characters
- Based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Required Cluster name of the recovery DB - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Essential Server type for the recovery DB installation - Standard: commonly used standard specification
- High Capacity: large-capacity server with 24vCore or more (to be provided later)
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Service Type > Block Storage Required Block Storage settings used by the recovery DB - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Applied identically with the storage type set in the source cluster
- Enter capacity as a multiple of 8 within the range 16 to 5,120
- Additional: Storage area for DATA, Archive, TEMP, Backup data
- Applied identically with the storage type set in the source cluster
- In the recovery DB, only DATA, TEMP, and Archive purposes can be added
- After selecting Use, enter the storage purpose and capacity
- To add storage, click the Add button; to delete, click the x button
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Database username Required Database username configured in the source DB Database Port number Required Database port number set in the source DB IP access control Selection IP address for accessing the recovery DB - IP format (e.g.,
192.168.10.1) or CIDR format (e.g.,192.168.10.1/32,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable DB management. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
tag Select Add Tag - After clicking the Add Tag button, enter or select Key, Value values
Table. MariaDB (DBaaS) recovery configuration items
6.3.2.3 - Configure Read Replica
Users can enter the required information for a Read Replica through the Samsung Cloud Platform Console and create the service using detailed options.
Configure Replica
Through replica configuration, you can create replica servers for read-only or disaster recovery purposes. You can create up to 5 replicas per database.
To configure a Replica, follow these steps.
- All Services > Database > MariaDB (DBaaS) Click the menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. MariaDB (DBaaS) List page is accessed.
- On the MariaDB (DBaaS) List page, click the resource to configure a Replica. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Replica configuration button. 4. Replica configuration Navigate to the page.
- After entering information in the Replica configuration area, click the Complete button.
Category required statusDetailed description Region Required Region to configure the Replica - Replica configuration (Other Region) is displayed only when selected
Replica count Required Number of Replicas to configure - Up to 5 can be configured per cluster
- If you select more than one value, additionally enter the Replica name and service type information
Replica name Required Replica server name - must start with a lowercase English letter, and use lowercase letters, numbers, and special characters (
-) to enter 3 to 19 characters
- The entered Replica name is displayed as the cluster name in the list
Service Type > Server Type Essential Replica server type - Standard: standard specification commonly used
- High Capacity: large-capacity server with 24vCore or more (to be provided later)
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Service Type > Block Storage Required Block Storage configuration using Replica DB - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Applied identically with the storage type set in the source cluster
- Capacity cannot be set
- Additional: DATA, Archive, TEMP, Backup data storage area
- Applied identically with the storage type set in the source cluster
- In a Replica, only DATA and TEMP can be added
- After selecting Use, input the storage purpose and capacity
- To add storage, click the Add button, and to delete, click the x button
- Capacity can be entered in multiples of 8 within the range 16–5,120, and up to a maximum of 9 can be created, including the number set in the source cluster
IP access control Selection Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, a separate Security Group policy configuration is not required
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruptions
- If set to unused, we are not responsible for issues arising from patches not being applied.
tag Select Add Tag - after clicking the Add Tag button, Key, Value enter or select
Table. MariaDB (DBaaS) Replica configuration items
Reconfigure Replica
If a network outage or replication delay with the Master Cluster occurs, you can use the Replica reconstruction function to replicate the Master Cluster’s data again.
To reconfigure the Replica, follow these steps.
- Click the All Services > Database > MariaDB(DBaaS) menu. 1. Go to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource to reconfigure the Replica. 3. MariaDB(DBaaS) Details Go to the page.
- Click the Replica Reconstruction button. 4. Replica Reconfiguration Notice A popup window opens.
- Replica Reconfiguration Notification In the popup window, click the OK button.
Promote Replica Cluster to Master Cluster
You can promote a fully configured Replica Cluster to a Master Cluster.
To promote a Replica Cluster to Master, follow these steps.
- All Services > Database > MariaDB(DBaaS) Click the menu. 1. Navigate to the Service Home page of MariaDB (DBaaS).
- On the Service Home page, click the MariaDB(DBaaS) menu. 2. Navigate to the MariaDB(DBaaS) List page.
- On the MariaDB(DBaaS) List page, click the resource to promote to Master. 3. MariaDB(DBaaS) Details Go to the page.
- Click the More button and then click the Master Promotion button. 4. Master Promotion Notification The popup window opens.
- Master Promotion Notification in the popup window, click the Confirm button.
6.3.2.4 - MariaDB(DBaaS) Server Connection
Scenario Overview
MariaDB(DBaaS) Server Connection scenario involves creating a Bastion host(Virtual Server) and a Database service, and accessing the DB service through the Bastion host. To reliably connect to MariaDB(DBaaS) in the Samsung Cloud Platform environment, you need to create a Bastion host and establish network connectivity using it. To maintain stability and a high level of security, it is recommended to configure the Database service in a Private Subnet environment and set up the Bastion host in a restricted Public Subnet environment.
This scenario primarily describes creating a Bastion host and a Database service, configuring the network environment for Bastion host and Database access, and connecting through a DB client.
Scenario components
You can build the scenario using the following services.
| service group | service | Detailed description | |
|---|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment | |
| Networking | VPC > Subnet | A service that lets users segment the network within a VPC to match their purpose and scale. | |
| Networking | VPC > Public IP | A service that reserves a public IP and allocates and deallocates it to Compute resources. | |
| Networking | VPC > Internet Gateway | A service that connects VPC resources to the Internet | |
| Networking | Security Group | Virtual firewall that controls server traffic | |
| Database | MariaDB(DBaaS) | A service that easily creates and manages MariaDB in a web environment | |
| Compute | Virtual Server | Virtual server optimized for cloud computing | |
| Compute | Virtual Server > Keypair | Encryption file used to connect to the Virtual Server |
- Since the default policy of a Security Group is Deny All, you must register only the IPs that are allowed.
- In/Outbound’s All Open(Any IP, Any Port) policy can expose cloud resources directly to external threats.
- By specifying the required IP and port and setting a policy, you can strengthen security.
Scenario setup method
Create the services needed to build the scenario by following the steps below.
Configure Network
Describes the process of configuring the network environment for accessing the Bastion Host and Database services.
1-1. Create VPC
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- Click the Create VPC button on the Service Home page. You will be taken to the Create VPC page.
- On the VPC creation page, enter the information required to create the service.
- Enter the IP range as
192.168.x.0/16.
- Enter the IP range as
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resources on the VPC List page.
1-2. Create Subnet
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Subnet menu. You will be taken to the Subnet List page.
- Click the Create Subnet button. You will be taken to the Create Subnet page.
- On the Subnet Creation page, enter the information required to create the service.
- Select the Subnet type as General.
- Select a pre‑created VPC.
- Enter the IP range as
192.168.x.0/24.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resources on the Subnet list page.
1-3. Create Internet Gateway
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- Click the Create Internet Gateway button. Navigate to the Create Internet Gateway page.
- On the Internet Gateway Creation page, enter the required information needed to create the service.
- Select a pre‑created VPC.
- In the Firewall usage item, select Use.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, verify the created resource on the Internet Gateway List page.
1-4. Create Public IP
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the Public IP menu on the Service Home page. You will be taken to the Public IP List page.
- Click the Public IP reservation button. You will be taken to the Public IP reservation page.
- Public IP reservation page, enter the required information needed to reserve the service.
- In the Summary panel, verify the detailed information and estimated billing amount, and click the Complete button.
- After creation is complete, check the created resources on the Public IP List page.
1-5. Create Security Group
- Click the All Services > Networking > Security Group menu. Go to the Service Home page of Security Group.
- Click the Create Security Group button on the Service Home page. You will be taken to the Create Security Group page.
- On the Security Group creation page, enter the required information needed to create the service.
- Check the input information and click the Complete button.
- Once creation is complete, check the created resources on the Security Group List page.
Create bastion host
Describes the process of configuring a Bastion Host where the Database access client must be installed.
2-1. Create Server Keypair
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- Click the Create Keypair button. You will be taken to the Create Keypair page.
- Enter the required information needed to create a service on the Keypair creation page.
- Check the creation information and click the Complete button.
- The key can be downloaded only once, and reissuance is not available.
- Please store the downloaded key in a secure location.
2-2. Create Bastion host
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server Creation button. You will be taken to the Virtual Server Creation page.
- On the Virtual Server Creation page, enter the required information to create the service.
- Select Windows for the image.
- Select the pre‑created VPC and Subnet.
- Click Use NAT, and select the Public IP you reserved from 1-4. Create Public IP.
- Connect the Keypair created in 2-1. 서버 Keypair 생성하기.
- In the Summary panel, verify the detailed information and estimated billing amount, then click the Complete button.
- When creation is complete, check the created resources on the Virtual Server List page.
2-3. Verify Bastion host login ID and password
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server menu. You will be taken to the Virtual Server List page.
- On the Virtual Serve List page, click the resource you created in [2-2. Bastion host Creation]. You will be taken to the detailed information page for that resource.
- On the detail information page, click the RDP password view button in the Keypair name field. The RDP password view popup window will open.
- In the RDP password lookup popup window, attach the keypair file downloaded from 2-1. 서버 Keypair 생성하기.
- After attaching, click the Password Check button. The ID and Password required to access the resource are displayed.
- The ID and password will be used later as credentials to connect to the Bastion host in 5-1. Bastion host Connecting.
Create Database
Describes the process of creating a Database service.
3-1. MariaDB(DBaaS) Create Service
- Click the All Services > Database > MariaDB(DBaaS) menu. Navigate to the Service Home page of MariaDB(DBaaS).
- On the Service Home page, click the Create MariaDB (DBaaS) button. You will be taken to the Create MariaDB (DBaaS) page.
- MariaDB(DBaaS) Creation page: enter the required information for service creation.
- Connect by selecting the pre‑created VPC and Subnet.
- Enter the database-related creation details on the required information input screen.
- Add the Bastion host IP in the IP access control settings.
- The Database Port defaults to 2866, but the user can also specify it.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resource on the MariaDB(DBaaS) list page.
Configuring Rules
It describes the process of configuring rules for users to access the Bastion host and rules for accessing the Database from the Bastion host.
4-1. Add security rules to Security Group
- Click the All Services > Networking > Security Group menu. Go to the Service Home page of Security Group.
- Click the Security Group menu on the Service Home page. You will be taken to the Security Group List page.
- Select the Security Group resource created in 1-5. Creating a Security Group. Navigate to the detailed information page for that resource.
- Click the Rules tab on the detail information page. You will be taken to the Rules tab.
- Click the Add Rule button on the Rules tab. It navigates to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
direction Remote Target address Protocol Port Explanation Inbound CIDR User PC IP TCP 3389 (RDP) Bastion access PC → Bastion host Outbound CIDR DB IP TCP Database Port (manual entry) Bastion host → Database Table: Security Group rules that need to be added
4-2. Adding IGW Firewall Rules
- Click the All Services > Networking > Firewall menu. Navigate to the Service Home page of Firewall.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, select the Internet Gateway Resource Name created in 1-3. Internet Gateway 생성하기. You will be taken to the detailed information page for that resource.
- Click the Rules tab on the detail information page. You will be taken to the Rules tab.
- Click the Add Rule button on the Rules tab. You will be taken to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
origin address Destination address Protocol Port Operation direction Explanation Bastion connection PC IP Bastion host IP TCP 3389(RDP) Allow Inbound User PC → Bastion host Table. Internet Gateway Firewall rules that need to be added
Connect to Database
Describes the process of a user accessing the database via a DB client program.
This guide explains how to connect using MySQL Workbench. Since there are various database client programs and CLI utilities, you may install and use the tool that best fits your needs.
5-1. Connecting to Bastion host
- In the Windows environment of the PC that will connect to the Bastion host, run Remote Desktop Connection, then enter the NAT IP of the Bastion Host and click the Connect button.
- When the remote desktop connection succeeds, the user credential input window opens. Enter the ID and Password verified in 2-3. Bastion host Access ID and PW Verification and click the Confirm button.
5-2. Install DB connection client program (MySQL Workbench) on the Bastion host
- Visit the official MySQL page and download the MySQL Workbench program.
- MySQL Workbench program download path: https://dev.mysql.com/downloads/workbench
- Connect the user’s PC hard drive to upload the file to the Bastion host.
- In the Local Resources tab of the Remote Desktop Connection, click the Details button of the Local Devices and Resources item.
- Select the local disk of the location where the file was downloaded on the drive, and click the OK button.
- Copy the downloaded file, upload it to the Bastion Host, and click the MySQL Workbench installer to install.
5-3. Connect to the Database using the DB client program (MySQL Workbench)
- Launch MySQL Workbench and click Database > Manage connections. The Manage Server Connection popup appears.
- In the Manage Server Connection popup, click the New button at the lower left, enter the Database server information created in 3-1. MariaDB(DBaaS) 서비스 생성하기, and click the Test Connection button. A Password popup will appear.
Required input field input value Connection Name Custom (e.g., service name) Host name Database server IP Port Database Port Username Database username Table. DB connection client program input fields - In the Password popup window, enter the password you set in 3-1. MariaDB(DBaaS) Service Creation and click the OK button. When the operation succeeds, click the OK button in the Manage Server Connection popup window.
- Click Database > Connect to Database. The Connect to Database popup window appears.
- Select the Connection Name registered in Stored Connection to connect to the Database. After connecting, you can try simple queries, etc.
6.3.3 - API Reference
6.3.4 - CLI Reference
6.3.5 - Release Note
MariaDB(DBaaS)
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Strengthen the latest security patches and stability through the OS(Kernel) upgrade feature.
- You can monitor metrics and logs by integrating with Servicewatch.
- Add MariaDB (DBaaS) feature
- Add Second-Generation Server Type
- Add a second‑generation (db2) server type based on the Intel 4th‑generation (Sapphire Rapids) processor. For more details, see MariaDB(DBaaS) Server Type.
- DB user and access control management and Archive configuration feature added
- For detailed information, refer to DB User Management, DB Access Control Management, Archive Management.
- DB Audit Log Export feature added
- For detailed information, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Migration Configuration.
- Add HDD, HDD_KMS types to Block Storage
- Add Second-Generation Server Type
- MariaDB (DBaaS) feature change
- Add second-generation server type
- Added a 2nd‑generation (dbh2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see MariaDB(DBaaS) Server Type.
- After the service is created, you can expand the configured Block Storage capacity.
- Server-specific network IP configuration feature added allows either common or server-specific configuration depending on the usage purpose.
- Add second-generation server type
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- A volume-encrypted storage selection option has been added to the Block Storage type.
- A function to switch the Role (Active ↔ Standby) for the Active DB and Standby DB configured with redundancy has been added.
- It is linked with the cloud monitoring service, enabling performance and log monitoring of DB instances.
- Depending on the server type selected by the customer, Planned Compute policy can be set.
- A MariaDB (DBaaS) service that enables easy creation and management of MariaDB in a web environment has been launched.
6.4 - MySQL(DBaaS)
6.4.1 - Overview
Service Overview
MySQL(DBaaS) is an open-source relational database management system (RDBMS). Samsung Cloud Platform provides an environment that can automate MySQL installation and perform management functions for operation through a web-based Console.
MySQL (DBaaS) is designed as a high‑availability architecture that performs storage‑based data replication and minimizes failover time. To prevent data loss, when the contents of the Active server change, they are synchronously replicated to the Standby server, and the read‑only server called Replica, used for read load balancing and disaster recovery (DR), is provided up to five instances. Additionally, it provides an automatic backup feature at user-specified times to prepare for issues with the DB server or data, enabling recovery of data at the desired point in time.
Provided Features
MySQL(DBaaS) provides the following features.
- Auto Provisioning (Auto Provisioning): Allows installation and configuration of Database(DB) via UI, and provides an Active-standby redundancy configuration based on storage replication. * When the active server fails, it automatically fails over to standby.
- Operation Control Management: Provides a function to control the status of running servers. * In addition to start and stop, you can restart if there is a DB issue or to apply configuration changes. * When high availability (HA) is configured, the user can manually perform node switching between Active and Standby via a switch‑over.
- Backup and Recovery: Provides data backup functionality based on its own backup commands. * The backup schedule and retention policy can be set by the user, and additional fees apply based on the backup size. * It also provides a recovery function for backed‑up data, so when the user performs a recovery, a separate database is created and the recovery proceeds to the point in time selected by the user (the backup save point or a user‑specified point). * When restoring to a user-specified point in time, the restore point can be set up to 5 minutes, 10 minutes, 30 minutes, or 1 hour earlier, based on the stored backup and archive files.
- Version Management: Provides a version upgrade (Minor) feature based on certain feature enhancements and security patches. * Whether to perform a backup for a version upgrade can be selected by the user, and if a backup is performed, the data is backed up before applying the patch, after which the DB engine is updated.
- Replica configuration: Up to five Read Replicas can be configured in the same or different regions for read load balancing and disaster recovery (DR).
- Parameter management: Performance improvements and security-related DB configuration parameters can be modified.
- Service Status Query: Retrieves the current DB service’s final status.
- Monitoring: CPU, memory, performance monitoring information can be viewed through Cloud Monitoring and Servicewatch.
- DB User Management: Query and manage the DB account (user) information registered in the DB.
- DB Access Control Management: Based on DB accounts registered in the DB, you can register and revoke allowed IPs for access.
- Archive Management: You can set the retention period (1~35 days) for Archive files on the DB server and configure the Archive mode (On/Off).
- Export DB Log: You can export stored logs to the user’s Object Storage through Audit settings.
- Migration: Synchronize data in real time with the live database and support migration using replication without service interruption.
- OS Kernel Upgrade: The OS kernel can be upgraded to apply certain feature improvements and security patches.
Component
MySQL(DBaaS) provides pre‑validated engine versions and a variety of server types in accordance with the open‑source support policy. Users can select and use it based on the scale of the service they wish to configure.
Engine version
The engine versions supported by MySQL (DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is stopped is set to six months before the EoTS date.
Since the EOS and EoTS dates may change according to the supplier’s policy, please refer to the supplier’s license management policy page for details.
- MySQL (Community): https://www.mysql.com/support/eol-notice.html
| service | Provided version | EOS Date (Samsung Cloud Platform new creation stop date) | EoTS Date (Community Technical Support End Date) |
|---|---|---|---|
| MySQL (Community) | 8.0.28 | 2026-03-19 | 2026-04-30 |
| 8.0.30 | 2026-03-19 | 2026-04-30 | |
| 8.0.32 | 2026-03-19 | 2026-04-30 | |
| 8.0.33 | 2026-03-19 | 2026-04-30 | |
| 8.0.34 | 2026-03-19 | 2026-04-30 | |
| 8.0.35 | 2026-03-19 | 2026-04-30 | |
| 8.0.36 | 2026-03-19 | 2026-04-30 | |
| 8.0.37 | 2026-03-19 | 2026-04-30 | |
| 8.0.41 | 2026-03-19 | 2026-04-30 | |
| 8.0.42 | 2026-03-19 | 2026-04-30 | |
| 8.4.5 | 2031-12 (planned) | 2032-04-30 |
The next version of MySQL is scheduled to be released after July 2026. The actual service delivery schedule is subject to change.
- MySQL 8.4.7
Server type
The server types supported by MySQL (DBaaS) are as follows.
For detailed information about the server types provided by MySQL(DBaaS), see MySQL(DBaaS) 서버 타입.
Standard db1v2m4
| Category | Example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | db1 | Provided server specifications
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
6.4.1.1 - Server Types
MySQL (DBaaS) server type
MySQL(DBaaS) offers server types composed of various combinations of CPU, Memory, and Network Bandwidth. When creating a MySQL(DBaaS), the Database Engine is installed based on the server type selected for the intended use.
The server types supported by MySQL (DBaaS) are as follows.
Standard db1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | db1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
db1 server type
The db1 server type of MySQL (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db1v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db1v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
db2 server type
The db2 server type of MySQL (DBaaS) is provided with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
dbh2 server type
The dbh2 server type of MySQL (DBaaS) is offered with high-capacity server specifications and is suitable for database workloads that require large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | dbh2v24m48 | 24 vCore | 48 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m64 | 32 vCore | 64 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m256 | 32 vCore | 256 GB | Up to 25 Gbps |
| High Capacity | dbh2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m256 | 64 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m768 | 64 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m384 | 96 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m1152 | 96 vCore | 1152 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
6.4.1.2 - Monitoring metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service, which was released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services by Resource
- New Resources: Resources created after the service improvement work in March 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide monitoring in parallel using the Cloud Monitoring service and the ServiceWatch service.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings integrated with existing Cloud Monitoring (e. You need to verify the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete the process.
Cloud Monitoring Service Phased Termination Schedule Notice
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch: see the ServiceWatch 개요.
MySQL(DBaaS) Monitoring Metrics
The table below shows the performance monitoring metrics for MySQL (DBaaS) that can be viewed through Cloud Monitoring. For detailed Cloud Monitoring usage, refer to the Cloud Monitoring guide.
For MySQL (DBaaS) server monitoring metrics, please refer to the Virtual Server Monitoring Metrics guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Active Locks | Number of Active Locks | cnt |
| Active Sessions | Number of Active Sessions | cnt |
| Binary Log Used [MB] | binary log usage | MB |
| Connection Usage [Total] | DB connection session usage | % |
| Connections | Number of connections | cnt |
| Connections [MAX] | Connection count | cnt |
| Connections | max connected threads count | cnt |
| Data Directory Used [MB] | data directory usage | MB |
| Instance Status [PID] | mysqld process pid | pid |
| Open Files | Number of open DB files | cnt |
| Open Files [MAX] | Number of DB files that can be opened | cnt |
| Open Files Usage | DB file maximum count usage rate | % |
| Relay Log Used [MB] | relay log usage (MB) | MB |
| Running Threads | running thread count | cnt |
| Safe PID | safe program pid | pid |
| Slave Behind Master seconds | Time difference with the master node | sec |
| Slowqueries | Number of SQL queries running for a long time (over 5 minutes) (by DB) | cnt |
| Slowqueries [Total] | Number of long-running (over 5 minutes) SQL queries (total) | cnt |
| Tablespace Used | Tablespace usage | MB |
| Tablespace Used [Total] | Total tablespace usage | MB |
| Transaction Time [Long] | Maximum transaction execution time | sec |
| Wait Locks | Number of sessions blocked for more than 60 seconds by lock | cnt |
6.4.1.3 - ServiceWatch Metrics
MySQL sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the namespace MySQL(DBaaS).
The indicators whose names are displayed in bold below are the key indicators selected from the basic metrics provided by MySQL(DBaaS). Key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric guides users via the user guide on which statistical values are meaningful when viewing that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using the primary statistical values.
OS Basic Metrics
Category | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| CPU | CPU Usage | Percent | CPU usage |
|
| Disk | Disk Usage | Percent | Disk usage |
|
| Disk | Disk Write Bytes | Bytes/Second | Write throughput (bytes/second) on block device |
|
| Disk | Disk Read Bytes | Bytes/Second | Read capacity (bytes/second) from block device |
|
| Disk | Disk Write Requests | Count/Second | Number of write requests on block device (requests per second) |
|
| Disk | Disk Read Requests | Count/Second | Number of read requests on block device (requests per second) |
|
| Disk | Average Disk I/O Queue Size | None | Average queue length of requests issued to the block device |
|
| Disk | Disk I/O Utilization | Percent | The proportion of time the block device actually spent handling I/O operations |
|
| Memory | Memory Usage | Percent | Memory usage |
|
| Network | Network In Bytes | Bytes/Second | Received data rate (bytes/second) on the network interface |
|
| Network | Network Out Bytes | Bytes/Second | Transmitted capacity (bytes/second) on the network interface |
|
| Network | TCP Connections | Count/Second | Current total number of successfully established TCP connections |
|
| Network | Network In Packets | Count | Number of packets received on the network interface |
|
| Network | Network Out Packets | Count | Number of packets transmitted on the network interface |
|
| Network | Network In Dropped | Count | Number of packet drops received on the network interface |
|
| Network | Network Out Dropped | Count | Number of packet drops transmitted from the network interface |
|
| Network | Network In Errors | Count | Number of packet errors received on the network interface |
|
| Network | Network Out Errors | Count | Number of packet errors transmitted on the network interface |
|
MySQL Basic Metrics
Classification | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| Activelock | Active locks | Count | Number of transactions in lock wait (Lock Wait) state for 1 minute (60 seconds) or longer in the InnoDB storage engine |
|
| Activesession | Active sessions | Count | Number of active sessions |
|
| Activesession | Connection usage | Percent | Database connection session utilization |
|
| Activesession | Connections | Count | DB connection session |
|
| Datafile | Current open files | Count | Number of file descriptors opened by the DB |
|
| Datafile | Max open files | Count | Maximum number of file descriptors the DB can open |
|
| Datafile | Open files usage | Percent | DB file maximum count utilization |
|
| InnoDB | InnoDB buffer pool hit ratio | Percent | The proportion of data read directly from memory without accessing the disk |
|
| InnoDB | Innodb row lock wait transactions | Count | Current number of InnoDB transactions waiting for a row lock |
|
| InnoDB | InnoDB row lock time | Milliseconds | Total time waited due to InnoDB row locks (in milliseconds) |
|
| InnoDB | InnoDB deadlocks | Count/Minute | Number of deadlock occurrences |
|
| InnoDB | Table lock waits | Count/Minute | Number of waits that occurred to acquire a table lock |
|
| InnoDB | Temp disk tables | Count | Number of Temp Tables created on disk |
|
| InnoDB | Innodb log waits | Count | Number of times waited to write the redo log to disk |
|
| State | Instance state | None | Check MySQL DB Process status up/down
| - |
| State | Slave behind master seconds(8.0) (Replica Only) | Seconds | Replica latency (unit: seconds) |
|
| State | Slave io thread running(8.0) (Replica Only) | None | I/O Thread status
| - |
| State | Slave SQL thread running(8.0) (Replica Only) | None | SQL Thread status
| - |
| State | Replica behind master seconds(8.4+) (Replica Only) | Seconds | Replica latency (unit: seconds) |
|
| State | Replica io thread running(8.4+) (Replica Only) | None | I/O Thread status
| - |
| State | Replica SQL thread running(8.4+) (Replica Only) | None | SQL Thread status
| - |
| Tablespace | Tablespace used | Megabytes | Tablespace usage |
|
| Tablespace | Tablespace used(TOTAL) | Megabytes | Tablespace usage (total) |
|
| Transactions | Slow queries | Count | Number of queries that run for more than 10 seconds |
|
| Transactions | Long transaction time | Seconds | Long Transaction time |
|
| Transactions | Wait locks | Count | Number of sessions waiting for lock |
|
| Transactions | SQL Queries/Minute | Count/Minute | Queries executed per minute |
|
6.4.2 - How-to guides
Users can create the service by entering the required information for MySQL (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Service per Resource
- New Resources: Resources created after the service improvement work in March 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, you must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings integrated with existing Cloud Monitoring (e.g. You must review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Notice of the phased termination schedule for Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
Create MySQL (DBaaS)
You can create and use a MySQL (DBaaS) service from the Samsung Cloud Platform Console.
- Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the corresponding Database service cannot be created.
- When loading more than 2 TB of large data, backups may take a long time or the database’s performance may degrade. * To prevent this, it is necessary to consider operational aspects such as cleaning up unnecessary data or migrating old data to a statistical collection environment.
To create a MySQL (DBaaS), follow the steps below.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Navigate to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the Create MySQL(DBaaS) button. 2. Go to the MySQL(DBaaS) Creation page.
- MySQL (DBaaS) Creation page: enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version Essential Provide a list of MySQL (DBaaS) versions Table. MySQL (DBaaS) Image and version selection options - In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Server name Prefix Required The server name where the DB will be installed - starts with a lowercase English letter and uses lowercase letters, numbers, and the special character (
-) to enter 3 to 13 characters
- A postfix such as 001, 002 is appended based on the server name, creating the actual server name
Cluster name Essential Cluster name of DB servers - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for DB installation - Standard: standard specifications commonly used
- High Capacity: large‑capacity server with 24 vCores or more
- For detailed information about the server types provided by MySQL (DBaaS), refer to MySQL(DBaaS) 서버 타입
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service request page
- For more details, see Planned Compute Apply
Service Type > Block Storage Required Block Storage configuration used by the DB according to its purpose - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volumes that use Samsung Cloud Platform KMS (Key Management System) encryption keys
- The configured storage type is applied identically to additional storage
- Capacity must be entered as a multiple of 8 within the range 16 to 5,120
- Since executing SQL or monthly batch jobs can cause large sorts that may interrupt service, a separate TEMP storage must be allocated and used
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- Add: Storage areas for DATA, Archive, TEMP, Backup data
- After selecting Use, enter the storage’s purpose and capacity
- The storage type is applied the same as the type set for DATA, and capacity can be entered as a multiple of 8 within the range 16 to 5,120
- To add storage, click the Add button; to delete, click the x button. Up to 9 can be added.
- Temporarily store backup data in BACKUP storage before transmitting it
- If the data to be backed up exceeds 100 GB and undergoes frequent changes, it is recommended to add a separate BACKUP storage for reliable backup. Set the backup capacity to about 60 % of the DATA capacity.
- If a BACKUP storage is not added, the
/tmparea is used, and backup will fail if capacity is insufficient
- For each service, only one Block Storage is allocated for Archive, TEMP, and BACKUP
Redundant configuration Select Redundancy configuration - When redundancy is used, the DB instance is configured as separate Active DB and Standby DB
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- IP can only be auto‑generated
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. Use is checked, you can select from reserved IPs in the VPC product’s Public IP. For more details, see Public IP 생성하기
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select when you want to apply different settings for each installed server
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- Enter the IP for each server
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. Use when checked, you can select from reserved IPs in the VPC product’s Public IP. For more information, see Public IP 생성하기
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy.
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. MySQL (DBaaS) Service Configuration Items - starts with a lowercase English letter and uses lowercase letters, numbers, and the special character (
- Enter required database configuration information In this section, enter or select the required information.
Category Required statusDetailed description Database name Required Server name applied during DB installation - must start with an English letter and be entered using English letters and numbers, 3 to 20 characters
Database username Required Database user name - An account with the same name is also created on the OS
- Enter using lowercase English letters, 2 to 20 characters
- Restricted database user names can be viewed in the Console
Database password required Password to use when accessing the DB - Enter 8 to 30 characters, including letters, numbers, and special characters (excluding
“‘)
Database password verification Required Re-enter the same password to use for DB access Database Port number Essential Port number required for DB connection - Enter DB port within the range 1200 ~ 65535
Backup > Use Select Backup usage - Use to select and set backup file retention period, backup start time, and Archive backup interval
Backup > Retention period Select Backup retention period - Select the backup retention period. Set the file retention period from 7 days to 35 days
- Backup files incur additional charges based on size
Backup > Backup Start Period Select Backup start time - Select backup start time
- The minutes during which the backup runs (minutes) are set randomly, and the backup end time cannot be set
Backup > Archive backup cycle Selection Archive backup frequency - Select the archive backup frequency
- The archive backup frequency is recommended at 1 hour. Selecting 5 minutes, 10 minutes, or 30 minutes may affect DB performance
Parameter Required Parameters to be used in the DB - Click the View button to view the parameter’s detailed information
- Parameters can be modified after the DB creation is complete, and after modification the DB must be restarted
DB character set Required Character encoding to use for the database Table case sensitivity Select DB Table case sensitivity time zone Required Standard time zone for the database ServiceWatch log collection Selection Whether to collect ServiceWatch logs - Select Use to enable the ServiceWatch log collection feature
- For details about the collected logs, see ServiceWatch metrics
- Up to 5 GB is provided free of charge for all services within the account, and charges apply based on storage size for usage exceeding 5 GB
- When collecting, log groups and log streams are created automatically, and they cannot be deleted until the resource is removed
- To prevent exceeding 5 GB, it is recommended to delete log data directly or shorten the retention period
Table. MySQL (DBaaS) Database configuration items - Additional Information Input area, please enter or select the required information.
Category required statusDetailed description Tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. MySQL (DBaaS) additional information input fields
- Select the required information in the Image and version selection area.
- Check the detailed information and estimated billing amount generated in the Summary panel, and click the Create button.
- When creation is complete, check the created resources on the Resource List page.
View MySQL (DBaaS) detailed information
The MySQL (DBaaS) service allows you to view and edit the full list of resources and detailed information. MySQL(DBaaS) Details page consists of Details, Tags, Operation History tabs, and when the DB has a Replica configured, a Replica Information tab is added.
To view detailed information about the MySQL (DBaaS) service, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Go to the page.
- On the MySQL(DBaaS) List page, click the resource to view detailed information. 3. MySQL(DBaaS) Details Go to the page.
- MySQL(DBaaS) Details At the top of the page, status information and additional feature details are displayed.
Category Detailed description Cluster status Cluster status with DB installed - Creating: Cluster is being created
- Editing: Cluster is transitioning to an operational state
- Error: Cluster encountered a failure while performing a task
- If this persists, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Cluster is being restarted
- Running: Cluster is operating normally
- Starting: Cluster is starting
- Stopped: Cluster is stopped
- Stopping: Cluster is being stopped
- Synchronizing: Cluster is synchronizing
- Terminating: Cluster is being terminated
- Unknown: Cluster status is unknown
- If this persists, contact the administrator
- Upgrading: Cluster is being upgraded
Cluster control Buttons to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
- Switch-Over: Switch a standby cluster to active
More features Cluster management buttons - Service status synchronization: Real-time DB service status lookup
- Backup history: When backup is configured, verify whether backups run correctly and view the history
- Database recovery: Recover the DB based on a specific point in time
- Parameter management: View and modify DB configuration parameters
- Replica configuration: Set up a read‑only Replica cluster
- Replica configuration (Other-Region): Set up a disaster‑recovery Replica in another region; the button is disabled if the account has no region to configure
- DB user management: View and manage DB account (user) information registered in the DB
- DB access control management: Register and revoke allowed IPs based on DB accounts registered in the DB
- Archive management: Set archive file retention periods and configure archive mode
- DB Log export: Export stored logs to the user’s Object Storage via audit settings
- Migration configuration: Provides migration functionality using replication
- OS (Kernel) upgrade: Upgrade the OS kernel version
Service termination Cancel service button Table. MySQL (DBaaS) status information and additional features
- MySQL(DBaaS) Details At the top of the page, status information and additional feature details are displayed.
Detailed information
MySQL (DBaaS) List page lets you view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed DB image and version information
|
| Cluster type | Cluster types (Master Cluster, Replica Cluster, Migration Cluster) |
| Cluster name | Cluster name of the DB servers |
| Master cluster name | Replica’s Master cluster name
|
| Database name | Server name applied during DB installation |
| Database username | DB user name |
| Planned Compute | Resources with Planned Compute configured
|
| maintenance period | DB Maintenance Period Status
|
| Backup | Backup configuration status
|
| ServiceWatch log collection | ServiceWatch Log Collection Configuration Status
|
| DB character set | Encoding method to be used for the DB |
| Table case sensitivity | DB Table case sensitivity |
| time zone | Standard time zone for the database |
| VIP | Virtual IP information
|
| Network | Network information where the DB is installed (VPC, Subnet, VIP, NAT IP(VIP)) |
| IP access control | Service access policy configuration
|
| Active & Standby | Active/Standby server type, base OS, additional Disk information
|
Replica information
Replica Information tab is enabled only when a Replica is configured in the cluster. Replica information tab allows you to view the Master cluster name, replica count, and Replica status.
| Category | Detailed description |
|---|---|
| Master information | Name of the Master cluster |
| Replica count | Number of Replicas created in the Master cluster |
| Replica status | Replica server status in the Master cluster
|
tag
MySQL(DBaaS) List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
MySQL(DBaaS) List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing MySQL(DBaaS) Resources
If you need to change or restore the existing configuration options of a provisioned MySQL (DBaaS) resource, or set up a replica, you can perform the tasks on the MySQL(DBaaS) Detailed Information page.
Control operation
If changes occur to a running MySQL (DBaaS) resource, you can start, stop, or restart it. Additionally, when HA is configured, you can switch the Active‑Standby servers using a switch‑over.
To control the operation of MySQL (DBaaS), follow the steps below.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. Navigate to the MySQL(DBaaS) List page.
- MySQL(DBaaS) List page, click the resource to control its operation. 3. MySQL(DBaaS) Details Go to the page.
- Check the MySQL (DBaaS) status and complete the change using the control button below.
- Start: DB service is installed on the server and the DB service is running (Running).
- Stop: The server where the DB service is installed and the DB service are stopped (Stopped).
- Restart: Only the DB service will be restarted.
- Switch Over: You can switch the DB’s Active server and Standby server.
Synchronize Service Status
You can synchronize the real-time service status of MySQL (DBaaS).
To check the service status of MySQL (DBaaS), follow the steps below.
- Click the All Services > Database > MySQL (DBaaS) menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Navigate to the page.
- MySQL (DBaaS) List page, click the resource to view its service status. 3. MySQL(DBaaS) Details Navigate to the page.
- Click the Service Status Sync button. 4. While it is being queried, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- If you modify the server type, a server restart is required. * Please separately verify any software license modifications or software settings and their implementation due to specification changes.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. Navigate to the MySQL(DBaaS) List page.
- MySQL(DBaaS) List page: click the resource for which you want to change the server type. 3. Navigate to the MySQL (DBaaS) Details page.
- Click the Edit icon of the server type you want to change at the bottom of the detailed information. 4. Edit Server Type The popup window opens.
- Server Type Edit After selecting the server type in the popup window, click the Confirm button.
Add storage
If you need more than 5 TB of data storage, you can add additional storage. For a redundant DB configuration, all redundant servers are added simultaneously.
- It is applied in the same way as the Storage type selected when creating the service.
- In a high‑availability configured database, adding storage is applied simultaneously to the storage of both the active and standby databases.
- If a Replica exists, the storage of the Master cluster cannot be larger than the storage of the Replica. * Please expand the Replica storage first, then expand the Master cluster storage.
- When adding Archive/Temp storage, the DB restarts and is temporarily unavailable.
To add storage, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. Navigate to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource to add storage. 3. MySQL(DBaaS) Details Navigate to the page.
- Click the Add Disk button at the bottom of the detailed information. 4. Additional Storage Request The popup window opens.
- Additional Storage Request In the popup window, after entering the purpose and size, click the Confirm button.
Expanding storage
Storage added to the data area can be expanded up to a maximum of 5 TB based on the initially allocated capacity. In the case of a redundant DB configuration, all redundant servers are expanded simultaneously.
To expand storage capacity, follow the steps below.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Navigate to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Navigate to the page.
- MySQL(DBaaS) List page, click the resource whose server type you want to change. 3. MySQL(DBaaS) Details Go to the page.
- Click the Edit icon of the additional Disk you want to add at the bottom of the detailed information. 4. Edit Additional Storage The popup window opens.
- Edit Additional Storage In the popup window, after entering the expansion capacity, click the Confirm button.
Cancel MySQL (DBaaS)
You can cancel unused MySQL (DBaaS) to reduce operating costs. However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may occur when the service is discontinued.
- For a DB with a Replica configured, terminating the Master DB does not delete the Replica. * If you also delete the replica, please cancel it separately from the resource list.
- If you terminate the DB, all stored data and any configured backup data will be deleted.
To cancel MySQL (DBaaS), follow the steps below.
- Click the All Services > Database > MySQL(DBaaS) menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Navigate to the page.
- On the MySQL(DBaaS) List page, select the resource to cancel and click the Cancel Service button.
- After termination is complete, check on the MySQL(DBaaS) list page whether the resource has been terminated.
6.4.2.1 - DB Service Manage
Users can manage MySQL (DBaaS) through the Samsung Cloud Platform Console.
Parameter Management
Provides a feature that allows easy viewing and modification of database configuration parameters.
View Parameter
To view configuration parameters, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- Click the resource you want to view or modify parameters for on the MySQL(DBaaS) List page. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button and then click the Parameter Management button. The Parameter Management popup opens.
- Parameter Management popup window, click the Search button. The Search Notification popup window opens.
- Lookup Notification when the popup window opens, click the Confirm button. Retrieving may take a short amount of time.
Modify Parameter
To modify the configuration parameters, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- Click the resource you want to view or modify parameters for on the MySQL(DBaaS) List page. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button, then click the Parameter Management button. The Parameter Management popup opens.
- Parameter Management in the popup window, click the Search button. The Search Notification popup opens.
- Lookup Notification when the popup window opens, click the Confirm button. Retrieving may take a short amount of time.
- If a modification is needed, click the Edit button and enter the changes in the custom value field of the Parameter to be edited.
- When the input is complete, click the Complete button.
If you change the character_set_server value, first verify the collation that matches the character set using the command below.
SQL> SHOW COLLATION WHERE Charset = 'character set name';
Set the parameter values for character-set-server, collation-server, and init_connect with the confirmed collation.
| Item | Detailed description | Whether to restart |
|---|---|---|
character-set-server | Specify the default character set | Restart required |
collation-server | Specify default collation (Collation) | Restart required |
init_connect | SQL statements executed when the client connects to the database | No restart required |
Managing DB Users
Provides management functions to retrieve DB user information and modify status information.
Query DB users
To retrieve DB users, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource for which you want to view DB users. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button and then click the DB User Management button. You will be taken to the DB User Management page.
- On the DB User Management page, click the Search button. Retrieving the data may take a moment.
Changing DB User Status
Follow these steps to change the status of the retrieved DB user.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the MySQL(DBaaS) Service Home page.
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) list page.
- On the MySQL(DBaaS) List page, click the resource for which you want to modify the DB user. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button, then click the DB User Management button. You will be directed to the DB User Management page.
- On the DB User Management page, click the Search button. The query may take a short time.
- If modification is needed, click the Edit button, and change the status field value or enter remarks.
- When the input is complete, click the Complete button.
Managing DB Access Control
Provides IP-based DB user access control management functionality. Users can directly specify the IPs that can access the database, configuring it so that only authorized IPs are allowed access.
Query DB Access Control
Follow these steps to query DB users with IP access control enabled.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- MySQL(DBaaS) List page, click the resource you want to manage access control for. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button and then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the Search button. Retrieving the data may take a moment.
Add DB access control
To add IP access control, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- Click the MySQL(DBaaS) menu on the Service Home page. Navigate to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource for which you want to add IP access control. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button, then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- DB Access Control Management page, click the Search button. Retrieving the data may take a moment.
- After the query completes, click the Add button. The Add DB Access Control popup window opens.
- Add DB Access Control In the popup window, select the DB username and enter the IP address.
- When the input is complete, click the Complete button.
Delete DB access control
To delete IP access control, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource for which you want to delete IP access control. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button, then click the DB Access Control Management button. You will be taken to the DB Access Control Management page.
- On the DB Access Control Management page, click the View button. Retrieving the data may take a short while.
- When the query is complete, click the Delete button. The Delete popup window opens.
- In the Delete popup window, click the Confirm button.
Manage Archive
Provides the ability to configure Archive mode and set the retention period for Archive logs, allowing users to flexibly configure Archive log management policies to suit their operational environment. Additionally, it provides a feature to manually delete Archive logs, allowing you to clean up unnecessary log data and manage system resources effectively.
Configure Archive mode
To set Archive mode, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- Click the resource you want to set Archive mode for on the MySQL(DBaaS) List page. You will be taken to the MySQL(DBaaS) Detail page.
- Click the More button and click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- On the Archive Settings Management page, click the Search button. Retrieval may take a short time.
- Click the Edit button and select the usage status and retention period.
- When the edit is complete, click the Done button.
Delete Archive file
To delete the Archive file, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource for which you want to set Archive mode. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button and then click the Archive Settings Management button. You will be taken to the Archive Settings Management page.
- On the Archive Settings Management page, if you want to delete all Archive files, click Delete All Archives; if you only want to delete the backed‑up Archive files, click the Delete Backed‑up Archive button.
DB Log Export
Supports exporting log data that requires long-term retention among audit logs to Object Storage. Users can directly configure the log types to be stored, the target bucket for export, and the export interval. Based on the configured criteria, logs are copied to the specified Object Storage for retention. Additionally, to efficiently manage disk space, we also provide an option that exports logs to Object Storage while automatically deleting the original log files. By using this option, you can effectively free up storage capacity while safely retaining the necessary log data for long-term storage.
- To use the DB Log export function, you need to create an Object Storage. For creating Object Storage, please refer to the Object Storage User Guide.
- Please be sure to check the expiration date and time of the authentication key. If the authentication key expires, logs will not be stored in the bucket.
- Please ensure that authentication key information is not exposed externally.
Setting DB Log Export Mode
To set the DB Log export mode, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the MySQL(DBaaS) Service Home page.
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- MySQL(DBaaS) List page, click the resource you want to export the DB Log from. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button, then click the Export DB Log button. You will be taken to the Export DB Log page.
- On the DB Log Export page, click the Register button. You will be taken to the DB Log Export Register page.
- After entering the required information on the DB Log Export Registration page, click the Complete button.
Category Required Detailed descriptionLog type Required Log type to be saved Save bucket name Required Object Storage bucket name to be saved Authentication key > Access key Required Access key to access the Object Storage you want to store Authentication key > Secret key Required Secret key to access the Object Storage you want to store File creation cycle Required File creation interval in Object Storage Whether to delete the original log Selection Whether to delete the original logs when exporting to Object Storage Table. MySQL (DBaaS) DB Log Export Configuration Items
Managing DB Log Export
To modify, cancel, or immediately export the DB Log export settings, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource you want to manage DB Log export for. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button and then click the Export DB Log button. You will be taken to the Export DB Log page.
- On the DB Log Export page, depending on the log type you want to manage, click the More button and then click the Export Now, Edit, Cancel buttons.
- Export Immediately: The selected logs are exported to the bucket of the previously configured Object Storage.
- Edit: Modify the DB Log export mode setting.
- Cancel: Disables the DB Log export mode setting.
Minor Version Upgrade
We provide version upgrade functionality for some feature improvements and security patches. Only Minor version upgrades within the same Major version are supported.
- First retrieve the service status by synchronizing it, then perform the version upgrade.
- Please perform the version upgrade after configuring a backup. If you do not set up a backup, you may be unable to recover some data if a problem occurs during the update.
- In a DB with a Replica configured, the Master DB version cannot be higher than the Replica version. Please check the Replica version first and, if necessary, perform a version upgrade.
- The backed-up data will be automatically deleted after the version upgrade is completed.
To upgrade the version, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- Click the resource to upgrade the version on the MySQL(DBaaS) List page. It navigates to the MySQL(DBaaS) Details page.
- Click the Edit button of the Image version item. The Version Upgrade popup window opens.
- Version Upgrade In the popup, select the updated version and backup setting, then click the Confirm button.
- Click the Confirm button in the Version Upgrade Notification popup.
Configure Migration
Provides a Migration feature that synchronizes in real time with the live database and replicates using a Replication method without service interruption.
To configure Migration, follow these steps.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource to migrate. You will be taken to the MySQL(DBaaS) Detail page.
- Click the More button and then click the Migration Configuration button. The Migration Configuration popup window opens.
- In the popup window, review the instructions and click the Confirm button. You will be taken to the Migration configuration page.
- On the Migration configuration page, after entering the required information, click the Check connection button.
- When the connection is complete, click the Complete button.
Category Required Detailed descriptionSource DB Database name Required Database name of the source DB to be migrated Source DB IP Required IP of the Source DB that is the migration target Source DB Port Required Port of the Source DB to be migrated Source DB username Required User name of the Source DB to be migrated Source DB password Required Password of the source DB that is the migration target Table. MySQL (DBaaS) migration configuration items
Promote Migration Cluster to Master Cluster
You can promote a configured Migration Cluster to a Master Cluster.
To promote the Migration Cluster to Master, follow the steps below.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource to promote to Master. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button, then click the Master promotion button. The Master promotion notification popup opens.
- In the Master Promotion Notification popup, click the Confirm button.
Upgrade OS Kernel
The OS kernel can be upgraded to improve the functionality of the running database and apply security patches.
- The service will be unavailable while the OS upgrade is in progress.
- The upgrade duration may vary depending on the version, and if the upgrade fails, it will be rolled back to the previous configuration.
- After the upgrade is complete, you cannot revert to the previous OS.
To upgrade the OS Kernel, follow the steps below.
- Click the All Services > Database > MySQL(DBaaS) menu. Navigate to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. You will be taken to the MySQL(DBaaS) List page.
- On the MySQL(DBaaS) List page, click the resource to upgrade the OS Kernel. You will be taken to the MySQL(DBaaS) Details page.
- Click the More button, then click the OS(Kernel) Upgrade button. The OS(Kernel) Upgrade Notification popup opens.
- OS(Kernel) Upgrade Notification In the popup window, review the instructions and click the Confirm button.
6.4.2.2 - Backing up and restoring the database
Users can configure backups for MySQL (DBaaS) through the Samsung Cloud Platform Console and restore from the backed‑up files.
Backing up MySQL (DBaaS)
PostgreSQL (DBaaS) provides data backup functionality based on its own backup commands. Additionally, it provides an optimized backup environment for data protection and management through backup history verification and backup file deletion features.
Configure Backup
For instructions on configuring backups for MySQL(DBaaS), see MySQL(DBaaS) Creating.
To modify the backup settings of the created resource, follow the steps below.
- For reliable backups, we recommend adding a separate BACKUP storage or sufficiently expanding the storage capacity. * Especially when the backup data exceeds 100 GB and undergoes frequent changes, please secure additional storage amounting to about 60 % of the data size. * For instructions on adding and expanding storage, please refer to the MySQL(DBaaS) Add Storage, MySQL(DBaaS) Expand Storage guides.
- If a backup is configured, it will run at the designated time after the set time, and additional fees will be incurred based on the backup size.
- If you change the backup setting to unset, backup execution stops immediately, and the stored backup data is deleted and can no longer be used.
To set up a backup, follow these steps.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Navigate to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. Navigate to the MySQL(DBaaS) List page.
- MySQL(DBaaS) List page, click the resource for which you want to configure backup. 3. MySQL(DBaaS) Details Go to the page.
- Click the Edit button of the backup item. 4. Backup Settings popup window opens.
- When configuring a backup, click Enable in the Backup Settings popup, select the retention period, backup start time, and Archive backup interval, then click the Confirm button.
- If you wish to stop the backup configuration, deselect Backup Settings in the Use popup and authenticate via the logged-in user’s mobile phone.
When user authentication is complete, the backup configuration is disabled and backup execution stops.
- If you wish to stop the backup configuration, deselect Backup Settings in the Use popup and authenticate via the logged-in user’s mobile phone.
Check backup history
To view the backup history, follow these steps.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL (DBaaS) List Navigate to the page.
- MySQL(DBaaS) List On the page, click the resource for which you want to view the backup history. 3. MySQL(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup files
To delete the backup history, follow these steps.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. Go to the MySQL(DBaaS) List page.
- MySQL(DBaaS) List On the page, click the resource to view the backup history. 3. MySQL(DBaaS) Details Go to the page.
- Click the Backup History button. 4. Backup History popup window opens.
- Backup History In the popup window, check the files you want to delete, then authenticate using the logged-in user’s mobile phone.
- When user authentication is completed, the backup file is deleted.
MySQL(DBaaS) Recover
When a failure or data loss requires restoration from a backup file, the recovery feature enables point‑in‑time restoration. When performing a MySQL (DBaaS) recovery, a new server is created with the OS image from the initial provisioning point, the DB is installed with the version from the backup point, and the recovery proceeds with the DB’s configuration information and data.
To recover MySQL (DBaaS), follow these steps.
- Click the All Services > Database > MySQL (DBaaS) menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Go to the page.
- MySQL(DBaaS) resource On the list page, click the resource you want to restore. 3. MySQL(DBaaS) Details Navigate to the page.
- Click the Database Recovery button. 4. Go to the Database Recovery page.
- Database Recovery Configuration after entering the relevant information in the area, click the Complete button.
Category required statusDetailed description Recovery Type Required Set the point in time the user wants to recover - Backup point (recommended): Recover based on the backup file. Select from the list of backup points displayed in the list
- Custom point: Recover to a user-specified point within the range of recoverable backup times. The recoverable period depends on the Archive backup cycle setting, allowing recovery from the start of the first backup up to 1 hour/30 minutes/10 minutes/5 minutes before the current time. Select the desired date and time for the backup
Server name prefix Required Server name of the recovery DB - Start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to enter 3 to 16 characters
- Based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Required Cluster name of the recovery DB - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for the recovery DB installation - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more (to be provided later)
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute Apply
Service Type > Block Storage Required Block Storage settings used by the recovery DB - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Applied identically with the storage type set in the source cluster
- Enter capacity as a multiple of 8 within the range 16 to 5,120
- Additional: Storage area for DATA, Archive, TEMP, Backup data
- Applied identically with the storage type set in the source cluster
- In the recovery DB, only DATA, TEMP, and Archive purposes can be added
- After selecting Use, enter the storage purpose and capacity
- To add storage, click the Add button; to delete, click the x button
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created ___HTML_MARKER***
Database username Required Database username configured in the source DB Database Port number Required Database port number configured in the source DB IP access control Select IP address for accessing the recovery DB - Enter in IP format (e.g.,
192.168.10.1) or CIDR format (e.g.,192.168.10.1/32,192.168.10.1/32), then click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruption
- If set to not use, Samsung SDS is not responsible for issues arising from unapplied patches.
tag Select Add Tag - Add Tag button after clicking, enter or select Key, Value values
Table. MySQL (DBaaS) recovery configuration items
6.4.2.3 - Configure Read Replica
Users can enter the required information for a Read Replica through the Samsung Cloud Platform Console and create the service using detailed options.
Configure Replica
You can create replica servers for read‑only or disaster‑recovery purposes through replica configuration. You can create up to 5 replicas per database.
To configure a Replica, follow these steps.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Navigate to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Navigate to the page.
- On the MySQL(DBaaS) List page, click the resource to configure a Replica. 3. MySQL(DBaaS) Details Navigate to the page.
- Click the Replica configuration button. 4. Go to the Replica configuration page.
- After entering information in the Replica configuration area, click the Done button.
Category required statusDetailed description Region required Region to configure the Replica - Replica configuration (Other Region) is displayed only when selected
Replica count Required Number of Replicas to configure - Up to 5 can be configured per cluster
- If you select more than one value, additionally enter the Replica name and service type information
Replica name Required Replica server name - Start with a lowercase English letter, and use lowercase letters, numbers, and special characters (
-) to enter 3 to 19 characters
- The entered Replica name is displayed as the cluster name in the list
Service Type > Server Type Required Replica server type - Standard: standard specification commonly used
- High Capacity: large-capacity server with 24 vCores or more
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Apply for Planned Compute
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, a separate Security Group policy configuration is not required
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruptions
- If set to unused, we are not responsible for issues arising from patches not being applied.
Tag Select Add Tag - Add Tag after clicking the button, enter or select Key, Value values
Table. MySQL (DBaaS) Replica configuration items
Reconfigure Replica
If a network outage or replication delay with the Master Cluster occurs, you can use the Replica reconstruction function to replicate the Master Cluster’s data again.
To reconfigure the Replica, follow the steps below.
- All Services > Database > MySQL(DBaaS) Click the menu. 1. Navigate to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Navigate to the page.
- On the MySQL(DBaaS) List page, click the resource to reconfigure the Replica. 3. MySQL(DBaaS) Details Navigate to the page.
- Click the Replica reconstruction button. 4. Replica Reconfiguration Notification A popup window opens.
- Replica Reconfiguration Notification In the popup window, click the Confirm button.
Promoting a Replica Cluster to a Master Cluster
You can promote a configured Replica Cluster to a Master Cluster.
To promote a Replica Cluster to Master, follow these steps.
- Click the All Services > Database > MySQL (DBaaS) menu. 1. Go to the Service Home page of MySQL (DBaaS).
- On the Service Home page, click the MySQL(DBaaS) menu. 2. MySQL(DBaaS) List Go to the page.
- MySQL(DBaaS) List On the page, click the resource to promote to Master. 3. MySQL(DBaaS) Details Go to the page.
- Click the More button and then click the Promote to Master button. 4. Master Promotion Notification The popup window opens.
- In the Master Promotion Notification popup, click the Confirm button.
6.4.2.4 - MySQL(DBaaS) Server Connection
Scenario Overview
MySQL(DBaaS) Server Connection scenario involves creating a Bastion host (Virtual Server) and a Database service, and accessing the DB service through the Bastion host. To reliably connect to MySQL (DBaaS) in the Samsung Cloud Platform environment, you need to create a Bastion host and establish a network connection using it. To maintain stability and a high level of security, it is recommended to configure the Database service in a Private Subnet environment and place the Bastion host in a restricted Public Subnet environment.
This scenario primarily describes creating a Bastion host and a Database service, configuring the network environment for Bastion host and Database access, and connecting through a DB client.
Scenario components
You can build the scenario using the following services.
| Service group | service | Detailed description | |
|---|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment | |
| Networking | VPC > Subnet | A service that lets users subdivide the network within a VPC to match their purpose and scale. | |
| Networking | VPC > Public IP | A service that reserves a public IP and allocates and releases it to Compute resources | |
| Networking | VPC > Internet Gateway | A service that connects VPC resources to the Internet | |
| Networking | Security Group | Virtual firewall that controls server traffic | |
| Database | MySQL(DBaaS) | A service that easily creates and manages MySQL in a web environment | |
| Compute | Virtual Server | Virtual server optimized for cloud computing | |
| Compute | Virtual Server > Keypair | Encryption file used to connect to the Virtual Server |
- Since the default policy of a Security Group is Deny All, you must register only the allowed IPs.
- The All Open (Any IP, Any Port) policy for In/Outbound can expose cloud resources directly to external threats.
- By specifying the required IP and port and setting a policy, you can strengthen security.
Scenario configuration method
Create the services needed to build the scenario by following the steps below.
Set up the network
Describes the process of configuring the network environment for accessing the Bastion Host and Database services.
1-1. Create VPC
- Click the All Services > Networking > VPC menu. You will be taken to the VPC’s Service Home page.
- Click the VPC Creation button on the Service Home page. You will be taken to the VPC Creation page.
- On the VPC Creation page, enter the information required to create the service.
- Enter the IP range as
192.168.x.0/16.
- Enter the IP range as
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resources on the VPC List page.
1-2. Create Subnet
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- On the Service Home page, click the Subnet menu. You will be taken to the Subnet List page.
- Click the Create Subnet button. You will be taken to the Create Subnet page.
- On the Subnet Creation page, enter the information required to create the service.
- Select the Subnet type as General.
- Select a pre‑created VPC.
- Enter the IP range as
192.168.x.0/24.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, verify the created resources on the Subnet list page.
1-3. Create Internet Gateway
- Click the All Services > Networking > VPC menu. Go to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- Click the Create Internet Gateway button. You will be taken to the Create Internet Gateway page.
- On the Internet Gateway Creation page, enter the required information to create the service.
- Select a pre‑created VPC.
- In the Firewall usage option, select Use.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resource on the Internet Gateway List page.
1-4. Create Public IP
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Public IP menu. You will be taken to the Public IP List page.
- Click the Public IP Reservation button. You will be taken to the Public IP Reservation page.
- On the Public IP reservation page, enter the required information to reserve the service.
- In the Summary panel, verify the detailed information and estimated billing amount you generated, and click the Complete button.
- When creation is complete, check the created resources on the Public IP List page.
1-5. Create Security Group
- Click the All Services > Networking > Security Group menu. You will be taken to the Service Home page of the Security Group.
- Click the Create Security Group button on the Service Home page. You will be taken to the Create Security Group page.
- On the Security Group creation page, enter the required information for creating the service.
- Check the input information and click the Complete button.
- When creation is complete, verify the created resource on the Security Group List page.
Create Bastion host
This explains the process of configuring a Bastion Host where the Database access client must be installed.
2-1. Create Server Keypair
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- Click the Create Keypair button. You will be taken to the Create Keypair page.
- Enter the required information needed to create a service on the Keypair creation page.
- Check the creation information and click the Complete button.
- The key can be downloaded only on the first attempt, and reissuance is not available.
- Please store the downloaded key in a secure location.
2-2. Create Bastion host
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Create Virtual Server button. You will be taken to the Create Virtual Server page.
- On the Virtual Server Creation page, enter the required information to create the service.
- Select Windows for the image.
- Select the pre-created VPC and Subnet.
- Click Use NAT, then select the reserved Public IP from 1-4. Create Public IP.
- Connect the Keypair created in 2-1. 서버 Keypair 생성하기.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resources on the Virtual Server List page.
2-3. Bastion host Check login ID and PW
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server menu. You will be taken to the Virtual Server List page.
- On the Virtual Serve List page, click the resource you created in [2-2. Bastion host creation]. You will be taken to the detailed information page of that resource.
- On the detail page, click the RDP password view button in the Keypair name field. The RDP password view popup will open.
- In the RDP password lookup popup window, attach the keypair file downloaded from 2-1. 서버 Keypair 생성하기.
- After attaching, click the Password Check button. The ID and Password for accessing the resource are displayed.
- The ID and password will later be used as credentials to access the Bastion host in 5-1. Bastion host Connecting.
Create Database
Explains the process of creating a Database service.
3-1. Create MySQL(DBaaS) Service
- Click the All Services > Database > MySQL(DBaaS) menu. Go to the Service Home page of MySQL(DBaaS).
- On the Service Home page, click the MySQL(DBaaS) Create button. You will be taken to the MySQL(DBaaS) Create page.
- On the MySQL(DBaaS) Creation page, enter the required information needed to create the service.
- Select the pre‑created VPC and Subnet and connect them.
- Enter the database-related creation details on the required information input screen.
- Add the Bastion host IP in the IP access control settings.
- The Database Port defaults to 2866, but the user can also specify it.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resource on the MySQL(DBaaS) list page.
Configure Rules
It explains the process of configuring rules for a user to connect to the Bastion host and rules for connecting to the Database from the Bastion host.
4-1. Adding security rules to Security Group
- Click the All Services > Networking > Security Group menu. Go to the Service Home page of Security Group.
- Click the Security Group menu on the Service Home page. You will be taken to the Security Group List page.
- Select the Security Group resource created in 1-5. Create Security Group. Navigate to the detailed information page for that resource.
- Click the Rules tab on the detail page. You will be taken to the Rules tab.
- On the Rules tab, click the Add Rule button. The Add Rule popup will appear.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
direction remote Target address Protocol Port Explanation Inbound CIDR User PC IP TCP 3389 (RDP) Bastion client PC → Bastion host Outbound CIDR DB IP TCP Database Port (manual entry) Bastion host → Database Table. Security Group rules that need to be added
4-2. Adding IGW Firewall Rule
- All Services > Networking > Firewall Click the menu. Go to the Service Home page of the Firewall.
- On the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, select the Internet Gateway resource name created in 1-3. Create Internet Gateway. You will be taken to the detailed information page of that resource.
- Click the Rules tab on the detail page. You will be taken to the Rules tab.
- Click the Add Rule button on the Rules tab. You will be taken to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
origin address Destination address Protocol Port operation direction Explanation Bastion connection PC IP Bastion host IP TCP 3389(RDP) Allow Inbound User PC → Bastion host Table. Internet Gateway Firewall rules that should be added
Connect to Database
Describes the process of a user accessing the database via a DB client program.
This guide explains how to connect using MySQL Workbench. Since there are various database client programs and CLI utilities, you may install and use the tool that best fits your needs.
5-1. Connecting to Bastion host
- In the Windows environment of the PC that will connect to the Bastion host, run Remote Desktop Connection, then enter the NAT IP of the Bastion Host and click the Connect button.
- When the remote desktop connection succeeds, the user credential input window opens. Enter the ID and Password verified in 2-3. Check the Bastion host access ID and PW and click the Confirm button.
5-2. Install DB access client program (MySQL Workbench) on the Bastion host
- Visit the official MySQL page and download the MySQL Workbench program.
- MySQL Workbench program download URL: https://dev.mysql.com/downloads/workbench
- Connect the user’s PC hard drive to upload the file to the Bastion host.
- In the Local Resources tab of the Remote Desktop Connection, click the Details button of the Local Devices and Resources item.
- Select the local disk where the file was downloaded on the drive, and click the OK button.
- Copy the downloaded file, upload it to the Bastion Host, and click the MySQL Workbench installer to install.
5-3. Connect to the Database using the DB client program (MySQL Workbench)
- Launch MySQL Workbench and click Database > Manage connections. The Manage Server Connection popup appears.
- Manage Server Connection In the popup window, click the New button at the lower left, enter the Database server information created in 3-1. MySQL(DBaaS) 서비스 생성하기, and click the Test Connection button. A Password popup will appear.
Required input field input value Connection Name Custom (ex. service name) Host name Database server IP Port Database Port Username Database username Table.DB connection client program input fields - In the Password popup, enter the password you set in 3-1. MySQL(DBaaS) Create Service and click the OK button. When the operation completes successfully, click the OK button in the Manage Server Connection popup.
- Click Database > Connect to Database. The Connect to Database popup appears.
- Select the Connection Name registered in Stored Connection to perform a Database connection. After connecting, you can try simple Query, etc.
6.4.3 - API Reference
6.4.4 - CLI Reference
6.4.5 - Release Note
MySQL(DBaaS)
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Strengthen the latest security patches and stability through the OS (Kernel) upgrade feature.
- You can monitor metrics and logs by integrating with Servicewatch.
- Add MySQL (DBaaS) feature
- Add Second-Generation Server Type
- Add a 2nd‑generation (db2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, refer to MySQL(DBaaS) 서버 타입.
- DB user and access control management and Archive configuration feature added
- For detailed information, see DB User Management, DB Access Control Management, Archive Management
- DB Audit Log Export feature added
- For more details, refer to DB Log 내보내기
- Backup notification feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Configuring Migration.
- Block Storage type HDD, HDD_KMS type addition
- Add Second-Generation Server Type
- MySQL (DBaaS) feature change
- Add second-generation server type
- Add a 2nd‑generation (dbh2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see mysql(DBaaS) 서버 타입.
- After the service is created, you can expand the configured Block Storage capacity.
- Server-specific network IP configuration feature added allows common or server-specific settings depending on the usage purpose.
- Add second-generation server type
- Samsung Cloud Platform common feature changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- A MySQL (DBaaS) service that enables easy creation and management of MariaDB in a web environment has been released.
6.5 - Microsoft SQL Server(DBaaS)
6.5.1 - Overview
Service Overview
Microsoft SQL Server (DBaaS) is a representative relational database management system (RDBMS) used in various applications. Samsung Cloud Platform provides an environment that automates Microsoft SQL Server installation and offers management functions for operation through a web-based console.
Microsoft SQL Server (DBaaS) is designed with an Always On-based availability architecture, so when the Primary server’s content changes, it is synchronously replicated to the Secondary server. Additionally, it provides an automatic backup feature at user‑specified times to prepare for issues with the DB server or data, enabling recovery of data at a desired point in time.
Provided features
Microsoft SQL Server (DBaaS) provides the following features.
- Auto Provisioning: UI allows installation and configuration of Database(DB), and provides a Primary-Secondary redundancy configuration based on Always On. When the Primary server fails, it automatically fails over to the Secondary.
- Operation Control Management: Provides functionality to control the state of running servers. In addition to start and stop, restart is possible when there is a DB issue or to apply configuration changes. When configured for high availability (HA), users can manually perform node switching between Primary and Secondary via a switch‑over.
- Backup and Recovery: Provides data backup functionality based on its own backup commands. Users can set the backup time window, retention organization, and Full backup day, and additional fees apply based on backup volume. It also offers a recovery function for backed‑up data, creating a separate DB when the user performs a recovery and restoring to the point in time selected by the user (backup save point, custom point). When restoring to a user‑specified point, the restore time can be set to 5 minutes/10 minutes/30 minutes/1 hour before the stored backup file and archive file.
- Version Management: Provides version upgrade (Minor) functionality for certain feature improvements and security patches. Users can choose whether to perform a backup for the version upgrade, and if a backup is performed, data is backed up before applying the patch, then the DB engine is updated.
- Secondary configuration: You can add a read‑only Read Replica (Secondary Replica), which expands read performance and distributes load.
- Audit Settings: Provides an audit configuration feature that can monitor users’ DB access and the results of DDL (Data Definition Language)/DML (Data Manipulation Language) operations.
- Parameter management: Modification of DB configuration parameters related to performance improvement and security is possible.
- Service Status Query: Retrieves the latest status of the current DB service.
- Monitoring: CPU, memory, DB performance monitoring information can be viewed through the Cloud Monitoring service.
- DB User Management: View and manage DB account (user) information registered in the DB.
- Export DB Log: You can export stored logs to the user’s Object Storage through Audit settings.
Component
Microsoft SQL Server(DBaaS) provides pre-validated engine versions and various server types. Users can select and use them according to the scale of the service they wish to configure.
Engine version
The engine versions supported by Microsoft SQL Server(DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is halted is set to six months before the EoTS date.
Because the supplier’s policy may cause the EOS and EoTS dates to change, please refer to the supplier’s license management policy page for details.
- Microsoft SQL Server: https://learn.microsoft.com/ko-kr/lifecycle/products/?terms=sql%20server
| Provided version | EOS Date (Samsung Cloud Platform new creation stop date) | EoTS Date (Community technical support end date) |
|---|---|---|
| Microsoft SQL Server 2019 Enterprise | 2029-06 (planned) | 2030-01-08(Extended Support) 2025-02-28(Standard Support) |
| Microsoft SQL Server 2019 Standard | 2029-06 (planned) | 2030-01-08(Extended Support) 2025-02-28(Standard Support) |
| Microsoft SQL Server 2022 Enterprise | 2032-06 (planned) | 2033-01-11(Extended Support) 2028-01-11(Standard Support) |
| Microsoft SQL Server 2022 Standard | 2032-06 (planned) | 2033-01-11(Extended Support) 2028-01-11(Standard Support) |
Server type
The server types supported by Microsoft SQL Server (DBaaS) are as follows.
For detailed information about the server types offered by Microsoft SQL Server (DBaaS), refer to Microsoft SQL Server(DBaaS) Server Types.
Standard db1v2m4
| Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | db1 | Provided server specifications
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
6.5.1.1 - Server Types
Microsoft SQL Server(DBaaS) server type
Microsoft SQL Server(DBaaS) provides server types composed of various combinations of CPU, memory, and network bandwidth. When creating a Microsoft SQL Server (DBaaS), the Database Engine is installed according to the server type selected for the intended use.
The server types supported by Microsoft SQL Server (DBaaS) are as follows.
Standard db1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | db1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
db1 server type
The db1 server type of Microsoft SQL Server(DBaaS) is provided with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db1v12m24 | 12 vCore | 24 GB | Maximum 12.5 Gbps |
| Standard | db1v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
db2 server type
The db2 server type of Microsoft SQL Server (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db2v8m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
dbh2 server type
The dbh2 server type of Microsoft SQL Server (DBaaS) is offered with high-capacity server specifications and is suitable for database workloads that require large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | dbh2v24m48 | 24 vCore | 48 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m64 | 32 vCore | 64 GB | Up to 25 Gbps |
| High Capacity | dbh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m256 | 32 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m256 | 64 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m768 | 64 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m384 | 96 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m1152 | 96 vCore | 1152 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
6.5.1.2 - Monitoring metrics
According to the policy of Samsung Cloud Platform, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services by Resource
- New Resources: Resources created after the service improvement work in July 2026 are provided with monitoring using the ServiceWatch service by default.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, the settings configured by users linked with existing Cloud Monitoring (e. You must verify items such as event policies and perform tasks such as resetting the ServiceWatch service, then complete them.
Notice of the phased termination schedule for the Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch is available in the ServiceWatch Overview.
Microsoft SQL Server(DBaaS) Monitoring Metrics
The table below shows the performance monitoring metrics for Microsoft SQL Server (DBaaS) that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
Please refer to the Virtual Server Monitoring Metrics guide for Microsoft SQL Server(DBaaS) server monitoring metrics.
| Performance items | Detailed description | unit |
|---|---|---|
| Active Locks | Number of Active Locks | cnt |
| Active Sessions | Number of Sessions in Active state | cnt |
| Active Transactions [Total] | Number of active transactions | cnt |
| Blocking Session ID | Long-running query (slow query) | ID |
| Connected Users | Number of users connected to the system | cnt |
| Datavolume Size [Free] | Available space | bytes |
| DBFiles [Not Online] | Run a query to verify that all data files are ONLINE. | cnt |
| Instance State [Cluster] | Status during MSSQL cluster configuration | state |
| Instance State [PID] | sqlservr.exe process pid | PID |
| Lock Processes [Blocked] | Number of SQL processes blocked by other processes | cnt |
| Lock Waits [Per Second] | Lock wait count per second | cnt |
| Page IO Latch Wait Time | Page IO latch waits average wait time | ms |
| Slowqueries | Number of SQL queries running for a long time (over 5 minutes) | cnt |
| Slowquery CPU Time | CPU time spent executing SQL that runs for a long time (over 5 minutes) | ms |
| Slowquery Execute Context ID | Context ID linked to the execution task of a SQL that has been running for a long time (over 5 minutes) | ID |
| Slowquery Memory Usage | Memory usage incurred by the execution of SQL that runs for a long time (over 5 minutes) | bytes |
| Slowquery Session ID | Session ID of SQL queries running for a long time (over 5 minutes) | ID |
| Slowquery Wait Duration Time | Total wait time for wait type | ms |
| Tablespace Used | Data volume size | bytes |
| Transaction Time [MAX] | Long-running transaction | cnt |
6.5.2 - How-to guides
Users can create the service by entering the required information for Microsoft SQL Server (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Service per Resource
- New Resources: Resources created after the service improvement work in July 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, you must prepare for the Servicewatch transition *
Performance and log data backup, settings configured by users linked with existing Cloud Monitoring (e.g. You must review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Notice of the phased termination schedule for Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (November 2026 service improvement work)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, Cloud Monitoring data cannot be accessed. * Be sure to complete the ServiceWatch transition work within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
Create Microsoft SQL Server (DBaaS)
You can create and use the Microsoft SQL Server (DBaaS) service from the Samsung Cloud Platform Console.
Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the corresponding Database service cannot be created.
To create a Microsoft SQL Server (DBaaS), follow the steps below.
- Click the All Services > Database > Microsoft SQL Server (DBaaS) menu. 1. Navigate to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) Create button. 2. Go to the Microsoft SQL Server(DBaaS) Create page.
- On the Microsoft SQL Server(DBaaS) Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version Required Provide a list of Microsoft SQL Server (DBaaS) versions Table. Microsoft SQL Server (DBaaS) Image and version selection options - In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Server name Prefix Required Server name where the DB will be installed - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
-) with a length of 3 to 13 characters
- A postfix such as 001, 002 is appended based on the server name to generate the actual server name
Cluster name Required Cluster name of DB servers - Enter in English using 3 to 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for DB installation - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more
- For detailed information about the server types provided by Microsoft SQL Server (DBaaS), refer to Microsoft SQL Server(DBaaS) 서버 타입
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, refer to Planned Compute Apply
Service Type > Block Storage required Block Storage settings used by the DB according to purpose - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volumes that use Samsung Cloud Platform KMS (Key Management System) encryption keys
- The configured storage type is also applied to additional storage
- Capacity must be entered as a multiple of 8 within the range 16 to 5,120
- After selecting Use, enter the storage’s purpose and capacity
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Redundant configuration Select Redundancy configuration status - When redundancy configuration is used, the DB instance is set up as an Active DB and a Standby DB
Network > Common Settings Required Network settings where servers generated by the service are installed - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- IP can only be generated automatically
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. If you check Use, you can select from reserved IPs in the VPC product’s Public IP. For more details, see Public IP 생성하기
Network > Server-specific Settings Required Network settings for servers created by the service - Select when you want to apply different settings for each installed server
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- Enter the IP for each server
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. Use when checked, you can select a reserved IP from the VPC product’s Public IP. For more details, see Public IP 생성하기
IP access control Selection Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. Microsoft SQL Server(DBaaS) Service Configuration Items - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
- Please enter or select the required information in the Enter required database configuration information area.
Category required statusDetailed description Database service name Required Database management unit name - Starts with an uppercase English letter and uses English characters, input 1 ~ 15
Database name > default Required Server name applied during DB installation - must start with an English letter and consist of English letters, numbers, and special characters (
.,_) with a length of 3 to 20 characters
Database name > Add Required Server name applied during DB installation - After selecting use, enter the Database name to install. It must start with an English letter, and using English letters, numbers, and special characters (
.,_), enter 3 - 20 characters
- For each Database, the drive where data is stored can be selected from the drives added in Service Type > Block Storage
- Adding Databases is only possible in the Enterprise edition, and up to 100 can be added
Database username Required DB user name - An account with the same name is also created on the OS
- Enter using lowercase English letters, 2 to 20 characters
- The following names cannot be used as Database user names
- root, user, sdscmpif, hacluster, adm, games, nobody, sshd, system, mail, postfix, sa, maxigent_cl
Database password Required Database connection password - English letters, numbers, and special characters (
“‘excluding) including, enter 8-30 characters
Database password verification Required Check DB connection password - Re-enter the DB connection password identically
Database Port number Required DB connection port number - Enter DB port within the range 1200 - 65535
License Required SQL Server License Key - Enter the issued license key
- If the entered license key is not valid, the service may not be created
Backup > Use Select Backup usage - Select Use to set the backup file retention period, backup start time, Full backup schedule (day of week), and Archive backup interval
Backup > Retention Period Selection Backup retention period - Select the backup retention period. Set the file retention period to 7 days ~ 35 days
- Backup files incur additional charges based on size
Backup > Backup Start Period Selection Backup start time - Select backup start time
- The minutes during which the backup runs (minutes) are set randomly, and the backup end time cannot be set
Backup > Full backup schedule (day of week) Select Full backup schedule - Select the day of the week for full backup execution
- Full backup is performed on a weekly basis
Backup > Archive backup cycle Selection Archive backup frequency - Select the archive backup frequency
- The archive backup frequency is recommended at 1 hour. Selecting 5 minutes, 10 minutes, or 30 minutes may affect DB performance
Audit Log Settings Selection Audit Log storage option - Use to enable the Audit Log feature
- DDL and user connection information records are stored
- Enabling Audit may degrade DB performance
Parameter Required DB configuration parameters - Click the View button to view detailed parameter information
- Parameters can be modified after the service creation is completed, and a DB restart is required after modification
DB Collation Selection Data sorting method - A command that specifies the data sorting and comparison method, which can produce different results depending on the settings.
time zone Required Standard time zone for the database Table. Microsoft SQL Server (DBaaS) Database configuration items - Additional Information Input area, please enter or select the required information.
Category required statusDetailed description tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Microsoft SQL Server (DBaaS) additional information input fields
- Select the required information in the Image and version selection area.
- Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
View detailed information of Microsoft SQL Server (DBaaS)
The Microsoft SQL Server (DBaaS) service allows you to view and edit the full resource list and detailed information. Microsoft SQL Server (DBaaS) Details page consists of Details, Tags, Activity History tabs, and when the DB has a Replica configured, a Replica Information tab is added.
To view detailed information about the Microsoft SQL Server (DBaaS) service, follow these steps.
- Click the All Services > Database > Microsoft SQL Server (DBaaS) menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- From the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Go to the page.
- Microsoft SQL Server(DBaaS) List Click the resource to view detailed information on the page. 3. Microsoft SQL Server(DBaaS) Details Navigate to the page.
- Microsoft SQL Server(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Cluster status Cluster status with DB installed - Creating: Cluster is being created
- Editing: Cluster is transitioning to an operational state
- Error: Cluster encountered a failure while performing a task
- If this persists, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Cluster is being restarted
- Running: Cluster is operating normally
- Starting: Cluster is starting
- Stopped: Cluster is stopped
- Stopping: Cluster is being stopped
- Synchronizing: Cluster is synchronizing
- Terminating: Cluster is being terminated
- Unknown: Cluster status is unknown
- If this persists, contact the administrator
- Upgrading: Cluster is being upgraded
Cluster control Buttons that can change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
- Switch-Over: Switch a standby cluster to Active
More features Cluster management buttons - Service Status Synchronization: Query real-time DB service status
- Backup History: Verify successful backup execution and view backup history when backup is configured
- Database Recovery: Recover the DB based on a specific point in time
- Parameter Management: View and modify DB configuration parameters
- Add Secondary: Configure a read‑only replica cluster
- DB User Management: View and manage DB accounts (users) registered in the DB
- Export DB Log: Export logs stored through audit settings to the user’s Object Storage
Service cancellation Service cancellation button Table. Microsoft SQL Server(DBaaS) status information and additional features
- Microsoft SQL Server(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Detailed information
You can view the detailed information of the selected resource on the Microsoft SQL Server (DBaaS) List page and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed DB image and version information
|
| Cluster name | Cluster name of the configured servers |
| Databse service name | Database Management Unit Name |
| Database username | DB user name |
| Database name > Default Database | Server name applied during DB installation |
| Database name > Add Database | Server name applied during DB installation
|
| Planned Compute | Resource status with Planned Compute configured
|
| maintenance period | DB Maintenance Period Status
|
| Backup | Backup configuration status
|
| Audit Log Settings | Audit Log configuration status
|
| time zone | Standard time zone for the database |
| DB Collation | Data sorting method |
| VIP | Virtual IP information
|
| Network | Network information (VPC, Subnet) where the DB is installed |
| IP access control | Service access policy configuration
|
| Primary & Secondary | Primary/Secondary server type, default OS, additional Disk information
|
tag
Microsoft SQL Server (DBaaS) List You can view the tag information of the selected resource on the page, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
Microsoft SQL Server(DBaaS) List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Microsoft SQL Server (DBaaS) Resources
If you need to change the existing configuration options of a provisioned Microsoft SQL Server (DBaaS) resource, or perform recovery, parameter management, etc., you can perform the tasks on the Microsoft SQL Server(DBaaS) Details page.
Control operation
If changes occur to a running Microsoft SQL Server (DBaaS) resource, you can start, stop, or restart it. Also, when HA is configured, you can switch the Primary-Secondary servers via a switch-over.
To control the operation of Microsoft SQL Server (DBaaS), follow the steps below.
- Click the All Services > Database > Microsoft SQL Server (DBaaS) menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Navigate to the Microsoft SQL Server(DBaaS) List page.
- Microsoft SQL Server(DBaaS) List On the page, click the resource to control its operation. 3. Microsoft SQL Server(DBaaS) Details Go to the page.
- Check the Microsoft SQL Server(DBaaS) status and complete the change using the control button below.
- Start: the server where the DB service is installed and the DB service is running (Running).
- Stop: The server hosting the DB service and the DB service itself are stopped.
- Restart: Only the DB service will be restarted.
- Switch Over: You can switch the Primary and Secondary servers of the DB.
Synchronize service status
You can synchronize the real-time service status of Microsoft SQL Server (DBaaS).
To check the service status of Microsoft SQL Server (DBaaS), follow the steps below.
- All Services > Database > Microsoft SQL Server(DBaaS) menu, please click. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Navigate to the page.
- Microsoft SQL Server(DBaaS) List Click the resource on the page to view the service status. 3. Microsoft SQL Server(DBaaS) Details Go to the page.
- Click the Service Status Synchronization button. 4. During the query, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- If you modify the server type, a server restart is required. * Please separately verify any software license modifications or software settings and their implementation resulting from server specification changes.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Navigate to the Microsoft SQL Server(DBaaS) List page.
- Microsoft SQL Server(DBaaS) List Click the resource on the page for which you want to change the server type. 3. Microsoft SQL Server(DBaaS) Details Navigate to the page.
- Click the Edit icon of the server type you want to change at the bottom of the detailed information. 4. Edit Server Type The popup window opens.
- Edit Server Type After selecting the server type in the popup window, click the Confirm button.
Add storage
If you need more than 5 TB of data storage, you can add additional storage. For a redundant DB configuration, all redundant servers are added simultaneously.
To add storage capacity, follow the steps below.
- It is applied in the same way as the Storage type selected when creating the service.
- For a high‑availability configured DB, adding storage is applied simultaneously to the storage of the Primary DB and the Secondary DB.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Navigate to the Microsoft SQL Server(DBaaS) List page.
- Microsoft SQL Server(DBaaS) List page, click the resource to add storage. 3. Microsoft SQL Server(DBaaS) Details Navigate to the page.
- Click the Add Disk button at the bottom of the details. 4. Additional Storage Request The popup window opens.
- Additional Storage Request In the popup window, after entering the purpose and size, click the Confirm button.
Expand storage
Storage added to the data area can be expanded up to a maximum of 5 TB based on the initially allocated capacity. In a redundant DB configuration, all redundant servers are expanded simultaneously.
To increase storage capacity, follow the steps below.
- All Services > Database > Microsoft SQL Server(DBaaS) Click the menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Go to the page.
- Microsoft SQL Server(DBaaS) List On the page, click the resource to change the server type. 3. Microsoft SQL Server(DBaaS) Details Navigate to the page.
- Click the Edit icon of the additional Disk you want to add at the bottom of the detailed information. 4. Edit Additional Storage The popup window opens.
- Edit Additional Storage In the popup window, after entering the expansion capacity, click the Confirm button.
Cancel Microsoft SQL Server (DBaaS)
You can reduce operating costs by terminating the unused Microsoft SQL Server (DBaaS). However, if you terminate the service, the running service may be stopped immediately, so you should thoroughly consider the impact of service interruption before proceeding with the termination.
To cancel Microsoft SQL Server(DBaaS), follow the steps below.
- Click the All Services > Database > Microsoft SQL Server (DBaaS) menu. 1. Navigate to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Go to the page.
- Microsoft SQL Server(DBaaS) List on the page, select the resource to cancel, and click the Cancel Service button.
- After termination is complete, check on the Microsoft SQL Server(DBaaS) list page whether the resource has been terminated.
6.5.2.1 - DB Service Manage
Users can manage Microsoft SQL Server (DBaaS) through the Samsung Cloud Platform Console.
Managing the Database
For the Microsoft SQL Server Enterprise edition, you can add a new database. Up to 100 can be added per cluster.
Add Database
To add a Database, follow these steps.
- Click the All Services > Database > Microsoft SQL Server (DBaaS) menu. Navigate to the Service Home page of Microsoft SQL Server (DBaaS).
- Click the Microsoft SQL Server(DBaaS) menu on the Service Home page. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource to add storage. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the Add button in the Database name field. The Add Database popup window opens.
- In the Add Database popup window, click the + button to enter the Database name and select a drive, then click the Confirm button.
Delete Database
To delete the database, follow these steps.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. Navigate to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. Navigate to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource to add storage. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the Edit button for the Database name field. The Add Database Delete popup window opens.
- Additional Database Deletion In the request popup, check the Database you want to delete and click the Delete button. The Database Deletion popup opens.
- Delete Database In the popup window, enter the name of the Database you want to delete, then click the Confirm button.
Managing Parameters
Provides a feature that enables easy viewing and modification of database configuration parameters.
Query Parameter
To view configuration parameters, follow these steps.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. You will be taken to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. Navigate to the Microsoft SQL Server(DBaaS) List page.
- Microsoft SQL Server(DBaaS) List page, click the resource whose parameters you want to view or modify. Microsoft SQL Server(DBaaS) Details page will open.
- Click the More button, then click the Parameter Management button. The Parameter Management popup window opens.
- Parameter Management popup window, click the Search button. Search Notification popup window opens.
- Lookup Notification When the popup window opens, click the Confirm button. The lookup may take a short amount of time.
Modify Parameter
To modify the configuration parameters, follow these steps.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. Go to the Service Home page of Microsoft SQL Server(DBaaS).
- Click the Microsoft SQL Server(DBaaS) menu on the Service Home page. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource whose parameters you want to view or modify. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the More button, then click the Parameter Management button. The Parameter Management popup opens.
- Parameter Management popup window, click the Search button. Search Notification popup window opens.
- Lookup Notification When the popup window opens, click the Confirm button. Retrieving the data may take a short time.
- If modification is needed, click the Edit button and enter the changes in the custom value area of the Parameter to be edited.
- When the input is complete, click the Complete button.
Managing DB Users
Provides functionality to query and manage DB user information.
Query DB Users
To retrieve DB users, follow the steps below.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. Navigate to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource for which you want to view DB users. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the More button, then click the DB User Management button. You will be taken to the DB User Management page.
- DB User Management page, click the Search button. The search may take a short amount of time.
Change DB User Status
Follow these steps to change the status of the retrieved DB user.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. You will be taken to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource whose DB user you want to modify. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the More button, then click the DB User Management button. You will be taken to the DB User Management page.
- On the DB User Management page, click the Search button. Retrieving may take a short time.
- If a correction is needed, click the Edit button, then change the status field value or enter remarks.
- When the input is complete, click the Complete button.
Modify Audit Settings
You can modify the Audit log storage settings for Microsoft SQL Server (DBaaS).
To change the Audit log storage settings of Microsoft SQL Server(DBaaS), follow the steps below.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. Go to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource to view the service status. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the Edit icon of Audit Settings at the bottom of the detailed information. The Edit Audit Settings popup window opens.
- Edit Audit Settings After changing the usage in the popup window, click the Confirm button.
- Use selected, the Audit log feature is enabled. Enabling the Audit log may degrade DB performance.
- Disabling use will delete the Audit log storage file. Back up the Audit log file separately before disabling.
DB Log Export
Supports exporting log data that requires long-term retention among audit logs to Object Storage. Users can directly set the log types to be stored, the target Bucket for export, and the export interval. Based on the configured criteria, logs are copied to the specified Object Storage for retention. Additionally, to efficiently manage disk space, we also provide an option that exports logs to Object Storage while automatically deleting the original log files. By using this option, you can effectively free up storage capacity while safely retaining the necessary log data for long-term storage.
- To use the DB Log export feature, you must create an Object Storage. For creating an Object Storage, please refer to the Object Storage User Guide.
- Please be sure to check the expiration date and time of the authentication key. If the authentication key expires, logs will not be stored in the bucket.
- Please ensure that authentication key information is not exposed externally.
Setting DB Log Export Mode
To set the DB Log export mode, follow these steps.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. You will be taken to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource whose DB Log you want to export. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the More button, then click the DB Log Export button. You will be taken to the DB Log Export page.
- On the DB Log Export page, click the Register button. You will be taken to the DB Log Export Register page.
- On the DB Log Export Registration page, after entering the required information, click the Complete button.
Category Required Detailed descriptionLog type Required Log type to be saved Save bucket name Required Object Storage bucket name to be saved Authentication key > Access key Required Access key to access the Object Storage you want to store Authentication key > Secret key Required Secret key for accessing the Object Storage you want to store File creation interval Required File creation frequency in Object Storage Whether to delete the original log Selection Whether to delete the original logs when exporting to Object Storage Table. Microsoft SQL Server (DBaaS) DB Log Export Configuration Items
Managing DB Log Export
To modify, cancel, or immediately export the DB Log export settings, follow the steps below.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. Navigate to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource you want to manage DB Log export for. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the More button, then click the DB Log Export button. You will be taken to the DB Log Export page.
- On the DB Log Export page, depending on the log type you want to manage, click the More button and then click the Export Now, Edit, or Cancel buttons.
- Export Immediately: The selected logs are exported to the bucket of the previously configured Object Storage.
- Edit: Modify the DB Log export mode settings.
- Cancel: Cancel the DB Log export mode setting.
Minor Version Upgrade
We provide version upgrade functionality for some feature improvements and security patches. Only Minor version upgrades within the same Major version are supported.
- First retrieve the service status by synchronizing it, then perform the version upgrade.
- Please perform the version upgrade after setting up a backup. If you do not set up a backup, you may be unable to recover some data if a problem occurs during the upgrade.
- The backed-up data will be automatically deleted after the version upgrade is completed.
To upgrade the Minor Version, follow the steps below.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. Navigate to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- Microsoft SQL Server(DBaaS) List page, click the resource to upgrade the version. Navigate to the Microsoft SQL Server(DBaaS) Details page.
- Click the Edit button of the Image version item. The Version Upgrade popup window opens.
- Version Upgrade In the popup, select the updated version and backup setting, then click the Confirm button.
- Version Upgrade Notification Click the Confirm button in the popup window.
6.5.2.2 - Backing up and restoring the DB
Users can configure backups of Microsoft SQL Server (DBaaS) through the Samsung Cloud Platform Console and restore from the backed‑up files.
Microsoft SQL Server(DBaaS) Backup
Microsoft SQL Server (DBaaS) provides a data backup feature based on its own backup commands. Additionally, it provides an optimized backup environment for data protection and management through backup history verification and backup file deletion features.
Configure backup
For backup configuration of Microsoft SQL Server (DBaaS), see the Microsoft SQL Server(DBaaS) Creating guide.
To modify the backup settings of the created resource, follow the steps below.
If a backup is configured, it will run at the designated time after the set schedule, and additional fees will be incurred based on the backup size.
- If you change the backup setting to Unset, backup execution will stop immediately, and the stored backup data will be deleted and can no longer be used.
- All Services > Database > Microsoft SQL Server(DBaaS) Click the menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Navigate to the page.
- Microsoft SQL Server(DBaaS) List Click the resource on the page to configure backup. 3. Microsoft SQL Server(DBaaS) Details Navigate to the page.
- Click the Edit button for the backup item. 4. Backup Settings popup opens.
- When setting up a backup, click Use in the Backup Settings popup, select retention period, backup start time, and Archive backup interval, then click the Confirm button.
- If you stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Once user authentication is complete, the backup configuration is disabled and backup execution stops.
- If you stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Check backup history
To view the backup history, follow these steps.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Go to the page.
- Microsoft SQL Server(DBaaS) List page, click the resource to view the backup history. 3. Microsoft SQL Server(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup file
To delete the backup history, follow these steps.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. 1. Go to the Service Home page of Microsoft SQL Server (DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Navigate to the page.
- Microsoft SQL Server(DBaaS) List Click the resource on the page to view the backup history. 3. Microsoft SQL Server(DBaaS) Details Go to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup, check the files you want to delete, then authenticate via the logged-in user’s mobile phone.
- When user authentication is completed, the backup file is deleted.
Microsoft SQL Server(DBaaS) Recovery
If a backup file needs to be restored due to a failure or data loss, the recovery feature allows restoration based on a specific point in time. When you perform a Microsoft SQL Server(DBaaS) recovery, a new server is created with the OS image from the initial provisioning point, the database is installed with the version from the backup point, and the recovery proceeds using the database’s configuration information and data.
To recover Microsoft SQL Server (DBaaS), follow the steps below.
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. 1. Go to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. 2. Microsoft SQL Server(DBaaS) List Navigate to the page.
- Microsoft SQL Server (DBaaS) resource On the list page, click the resource you want to recover. 3. Microsoft SQL Server(DBaaS) Details Go to the page.
- Click the Database Recovery button. 4. Go to the Database Recovery page.
- After entering the relevant information in the Database Recovery Configuration area, click the Complete button.
Category required statusDetailed description Recovery Type required Set the point in time the user wants to recover - Backup point (recommended): Recover based on the backup file. Select from the list of backup points displayed in the list
- Custom point: Recover to a user‑desired point within the range of recoverable backup times. The recoverable period depends on the Archive backup cycle setting, allowing recovery from the initial backup start time up to 1 hour/30 minutes/10 minutes/5 minutes before the current time. Select the date and time to back up
Server name prefix Required Recovery DB server name - Start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to enter 3 to 16 characters
- Based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Essential Recovery DB cluster name - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Recovery DB Server Type - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute Apply
Service Type > Block Storage Required Block Storage settings used by the recovery DB - Base OS: Area where the DB engine is installed
- DATA: Data storage area
- Applied identically with the storage type set in the source cluster
- Enter capacity as a multiple of 8 within the range 16 to 5,120
- Additional: Data storage area
- Applied identically with the storage type set in the source cluster
- In the recovery DB, only DATA and TEMP purposes can be added
- After selecting Use, enter the storage purpose and capacity
- To add storage, click the Add button, and to delete, click the x button
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Database username Required Database username - Apply the same username set in the original cluster
Database Port number Essential Database Port number - Apply the same Port number as set in the original cluster
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruption
- If set to not use, Samsung SDS is not responsible for issues arising from unapplied patches.
tag Selection Add Tag - After clicking the Add Tag button, enter or select Key, Value
Table. Microsoft SQL Server (DBaaS) recovery configuration items
6.5.2.3 - Secondary Add
The user can enter the required information for Secondary through the Samsung Cloud Platform Console and create the service using detailed options.
Add Secondary
You can create a read‑only replica server by configuring a Secondary. To add additional Secondaries, they must be created with a high‑availability (HA) configuration and Enterprise Edition, and the backup feature must be enabled.
To configure Secondary, follow the steps below.
- All Services > Database > Microsoft SQL Server(DBaaS) Click the menu. Navigate to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Microsoft SQL Server(DBaaS) menu. You will be taken to the Microsoft SQL Server(DBaaS) List page.
- On the Microsoft SQL Server(DBaaS) List page, click the resource to configure Secondary. You will be taken to the Microsoft SQL Server(DBaaS) Details page.
- Click the Secondary Add button. Navigate to the Secondary Add page.
- After entering information in the Secondary configuration area, click the Create button.
Category Required statusDetailed description Secondary number Required Number of Secondary to configure - Only one can be configured per cluster
Secondary name Required Secondary server name - must start with a lowercase English letter, and use lowercase letters, numbers, and special characters(
-) to enter 3 to 15 characters
- The entered Secondary name is displayed as the cluster name in the list
Service Type > Server Type Required Secondary server type - Apply the same as the server type set in the source DB
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Go to the Planned Compute service request page
- For more details, refer to Apply for Planned Compute
Network > Common Settings Required Network settings where servers generated by the service are installed - Applied identically to the network settings configured in the original DB
Network > Server-specific Settings Required Network settings for servers deployed by the service - Select when you want to apply different settings per installed server
- Apply the same network settings as configured in the source DB
- When configuring per server
10.10.10.0/24Enter an IP address within the range
License Required SQL Server License Key - Enter the issued license key
- If the entered license key is not valid, the service may not be created
Table. Microsoft SQL Server (DBaaS) Secondary configuration items
6.5.2.4 - Microsoft SQL Server(DBaaS) Server Connection
Scenario Overview
Microsoft SQL Server(DBaaS) server connection scenario involves creating a Bastion host (Virtual Server) and a Database service, and accessing the DB service through the Bastion host. To reliably connect to Microsoft SQL Server(DBaaS) in the Samsung Cloud Platform environment, you need to create a Bastion host and establish network connectivity through it. To maintain stability and a high level of security, it is recommended to configure the Database service in a Private Subnet environment and place the Bastion host in a restricted Public Subnet environment.
This scenario primarily describes creating a Bastion host and a Database service, configuring the network environment for Bastion host and Database access, and connecting through a DB client.
Scenario components
You can build the scenario using the following services.
| Service group | service | Detailed description | |
|---|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment | |
| Networking | VPC > Subnet | A service that lets users subdivide the network within a VPC to match their purpose and scale. | |
| Networking | VPC > Public IP | Service that reserves a public IP and allocates and releases it to Compute resources | |
| Networking | VPC > Internet Gateway | A service that connects VPC resources to the Internet | |
| Networking | Security Group | Virtual firewall that controls server traffic | |
| Database | Microsoft SQL Server(DBaaS) | A service that easily creates and manages Microsoft SQL Server in a web environment | |
| Compute | Virtual Server | Virtual server optimized for cloud computing | |
| Compute | Virtual Server > Keypair | Encryption file used to connect to the Virtual Server |
- Since the default policy of a Security Group is Deny All, you must register only the IPs that are allowed.
- In/Outbound’s All Open(Any IP, Any Port) policy can expose cloud resources directly to external threats.
- By specifying the required IP and port and setting a policy, you can strengthen security.
Scenario setup method
Create the services required to compose the scenario by following the steps below.
Set up the network
Describes the process of configuring the network environment for accessing the Bastion Host and Database services.
1-1. Create VPC
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- Click the VPC Creation button on the Service Home page. You will be taken to the VPC Creation page.
- On the VPC Creation page, enter the information required to create the service.
- Enter the IP range as
192.168.x.0/16.
- Enter the IP range as
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resources on the VPC List page.
1-2. Create Subnet
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- On the Service Home page, click the Subnet menu. You will be taken to the Subnet List page.
- Click the Create Subnet button. You will be taken to the Create Subnet page.
- On the Subnet Creation page, enter the information required to create the service.
- Select the Subnet type as General.
- Select a pre‑created VPC.
- Enter the IP range as
192.168.x.0/24.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resources on the Subnet list page.
1-3. Create Internet Gateway
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- Click the Create Internet Gateway button. Navigate to the Create Internet Gateway page.
- Internet Gateway Creation page, enter the required information for creating the service.
- Select a pre‑created VPC.
- In the Firewall usage option, select Use.
- In the Summary panel, verify the detailed information and estimated billing amount, and click the Complete button.
- Once creation is complete, verify the created resource on the Internet Gateway List page.
1-4. Create Public IP
- Click the All Services > Networking > VPC menu. Navigate to the VPC Service Home page.
- Click the Public IP menu on the Service Home page. You will be taken to the Public IP List page.
- Click the Public IP Reservation button. You will be taken to the Public IP Reservation page.
- On the Public IP reservation page, enter the required information needed to reserve the service.
- In the Summary panel, verify the detailed information and estimated billing amount, then click the Complete button.
- When creation is complete, check the created resources on the Public IP list page.
1-5. Create Security Group
- Click the All Services > Networking > Security Group menu. Navigate to the Service Home page of Security Group.
- Click the Create Security Group button on the Service Home page. You will be taken to the Create Security Group page.
- On the Security Group creation page, enter the required information needed to create the service.
- Check the input information and click the Complete button.
- When creation is complete, check the created resources on the Security Group list page.
Create Bastion host
Describes the process of configuring a Bastion Host that requires the database client to be installed.
2-1. Create Server Keypair
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- Click the Create Keypair button. You will be taken to the Create Keypair page.
- Enter the required information for creating a service on the Keypair creation page.
- Verify the creation information and click the Complete button.
- The key can be downloaded only on the first attempt, and reissuance is not available.
- Please store the downloaded key in a secure location.
2-2. Create Bastion host
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Create Virtual Server button. You will be taken to the Create Virtual Server page.
- On the Virtual Server Creation page, enter the required information to create the service.
- Select Windows for the image.
- Select the pre-created VPC and Subnet.
- Click Use NAT, then select the reserved Public IP from 1-4. Create Public IP.
- Connect the Keypair created in 2-1. 서버 Keypair 생성하기.
- In the Summary panel, verify the detailed information and estimated billing amount, then click the Complete button.
- When creation is complete, check the created resources on the Virtual Server List page.
2-3. Verify Bastion host login ID and PW
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server menu. You will be taken to the Virtual Server List page.
- On the Virtual Serve List page, click the resource you created in 2-2. Bastion host Create. You will be taken to the detailed information page for that resource.
- On the detail information page, click the RDP password view button in the Keypair name field. The RDP password view popup window opens.
- In the popup window, perform RDP password lookup, and attach the keypair file downloaded from 2-1. Create Server Keypair.
- After attaching, click the Password Check button. The ID and Password for accessing the resource are displayed.
- The ID and password will later be used as credentials to connect to the Bastion host in 5-1. Bastion host Connecting.
Create Database
Describes the process of creating a Database service.
3-1. Microsoft SQL Server(DBaaS) Create Service
- Click the All Services > Database > Microsoft SQL Server(DBaaS) menu. Go to the Service Home page of Microsoft SQL Server(DBaaS).
- On the Service Home page, click the Create Microsoft SQL Server (DBaaS) button. Navigate to the Create Microsoft SQL Server (DBaaS) page.
- On the Microsoft SQL Server(DBaaS) Creation page, enter the required information to create the service.
- Select the pre‑created VPC and Subnet and connect them.
- Enter database-related creation details on the required information input screen.
- Add the Bastion host IP in the IP access control settings.
- The database port defaults to 2866, but users can also specify it.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resource on the Microsoft SQL Server(DBaaS) list page.
Configuring Rules
It explains the process of configuring rules for a user to connect to the Bastion host and rules for connecting to the Database from the Bastion host.
4-1. Adding security rules to Security Group
- Click the All Services > Networking > Security Group menu. Go to the Service Home page of Security Group.
- Click the Security Group menu on the Service Home page. You will be taken to the Security Group List page.
- 1-5. Creating a Security Group Select the Security Group resource you created. Navigate to the detailed information page for that resource.
- Click the Rules tab on the detail page. You will be taken to the Rules tab.
- On the Rules tab, click the Add Rule button. It takes you to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
direction remote target address Protocol Port Explanation Inbound CIDR User PC IP TCP 3389 (RDP) Bastion client PC → Bastion host Outbound CIDR DB IP TCP Database Port (manual entry) Bastion host → Database Table. Security Group rules that need to be added
4-2. Add IGW Firewall rule
- All Services > Networking > Firewall Click the menu. Then navigate to the Service Home page of Firewall.
- From the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, select the Internet Gateway resource name created in 1-3. Create Internet Gateway. You will be taken to the detailed information page of that resource.
- Click the Rules tab on the detail information page. You will be taken to the Rules tab.
- Click the Add Rule button on the Rules tab. It navigates to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
origin address Destination address Protocol Port operation direction Explanation Bastion connection PC IP Bastion host IP TCP 3389(RDP) Allow Inbound User PC → Bastion host Table. Internet Gateway Firewall rules that need to be added
Connect to Database
Describes the process of a user accessing the database via a DB client program.
This guide explains how to connect using SSMS(Microsoft SQL Server Management Studio). Since there are various database client programs and CLI utilities, you may install and use the tool that best fits your needs.
5-1. Connect to Bastion host
- In the Windows environment of the PC that will connect to the Bastion host, run Remote Desktop Connection, then enter the NAT IP of the Bastion Host and click the Connect button.
- When the remote desktop connection succeeds, the user credential input window opens. Enter the ID and Password verified in 2-3. Check Bastion host login ID and PW and click the Confirm button.
5-2. Install the DB client program (SSMS) on the Bastion host
- Go to the official Microsoft SQL Server page and download the SSMS program.
- SSMS program download URL: https://learn.microsoft.com/en-us/ssms/download-sql-server-management-studio-ssms
- Connect the user’s PC hard drive to upload the file to the Bastion host.
- In the Remote Desktop Connection’s Local Resources tab, click the Details button for the Local Devices and Resources item.
- Select the local disk of the location where the file was downloaded on the drive, and click the OK button.
- Copy the downloaded file, upload it to the Bastion Host, and click the SSMS (Microsoft SQL Server Management Studio) installation file to install.
5-3. Connect to the Database using the DB client program (SSMS)
- Run SSMS (Microsoft SQL Server Management Studio). A Connect to Server popup will appear.
- Connect to Server In the popup window, enter the Database server information created in 3-1. Microsoft SQL Server(DBaaS) 서비스 생성하기 and click the Connect button.
Required input field input value Server type Database Engine Server name Database server IP, Database Port (ex. 192.168.10.1,2866) Authentication SQL Server Authentication Login Database username Password Database password Encryption Optional Table.DB connection client program input fields - Once the connection is established, the database will be accessed. After connecting, you can execute simple queries, among other tasks.
6.5.3 - API Reference
6.5.4 - CLI Reference
6.5.5 - Release Note
Microsoft SQL Server(DBaaS)
- Add Microsoft SQL Server (DBaaS) feature
- Add 2nd‑generation server type
- Add a 2nd‑generation (db2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see Microsoft SQL Server(DBaaS) 서버 타입.
- DB User and Access Control Management Add
- For more details, refer to DB User Management, DB Access Control Management
- Add DB Audit Log Export feature
- For detailed information, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add HDD, HDD_KMS types to Block Storage type
- Add 2nd‑generation server type
- A Microsoft SQL Server(DBaaS) service that enables easy creation and management of Microsoft SQL Server in a web environment has been launched.
6.6 - CacheStore(DBaaS)
6.6.1 - Overview
Service Overview
CacheStore(DBaaS) is a service that provides the in-memory data stores Redis OSS and Valkey. Samsung Cloud Platform provides an environment that automates the installation of Redis OSS and valkey through a web-based console and performs management functions for operation.
CacheStore (DBaaS) provides a Sentinel architecture consisting of a Master server that performs read/write operations and read‑only Replica servers that replicate the Master data. Sentinel checks the status of DB servers with the engine installed, and when a failure occurs on the Master server, it automatically fails over the Replica servers to the Master server. Additionally, to prepare for potential issues with the DB server or data, we provide a feature that automatically backs up at a user-specified time, enabling data recovery based on the backup point.
Provided Features
CacheStore(DBaaS) provides the following features.
- Auto Provisioning(Auto Provisioning): It is possible to install and configure the Database (DB) via the UI, and a redundant configuration can be set up with a Sentinel-based Single Master server and Replica servers (1 or 2).
- Operation Control Feature: Provides a function to control the status of running servers. * In addition to start and stop, you can restart if there is a DB issue or to apply configuration changes. * When configured for high availability (HA), you can switch the Active-Standby servers via a switch-over.
- Backup and Recovery: Provides data backup functionality based on its own backup commands. * Backup time windows and storage locations can be set by the user, and additional fees apply based on backup size. * It also provides a recovery function for backed‑up data, so when the user performs a recovery, a separate database is created and the recovery proceeds to the point in time selected by the user.
- Parameter Management: Performance improvement and security-related DB configuration parameters can be modified.
- Service Status Query: Retrieves the final status of the current DB service.
- Monitoring: CPU, memory, and DB performance monitoring information can be viewed through the Cloud Monitoring service.
- Minor version upgrade: To apply some feature improvements and security patches, you can perform a Minor version upgrade within the same Major version.
Component
CacheStore (DBaaS) provides pre‑validated engine versions and various server types in accordance with its open‑source support policy. Users can select and use it according to the scale of the service they wish to configure.
Engine version
The engine versions supported by CacheStore (DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is stopped is set to six months before the EoTS date.
Since the EOS and EoTS dates may change according to the supplier’s policy, please refer to the supplier’s license management policy page for details.
- Redis: https://redis.io/docs/latest/operate/oss_and_stack/install/version-mgmt/
- Valkey: https://valkey.io/topics/releases/
| image | Provided version | EoS Date | EoTS Date |
|---|---|---|---|
| Redis OSS Sentinel | 7.2.11 | 2029-06 (planned) | 2029-12-01 |
| valkey Sentinel | 8.1.4 | TBD | TBD |
The next version of CacehStore is scheduled to be offered after July 2026. The actual service delivery schedule is subject to change.
- Redis OSS Sentienl 7.2.14
- Valkey Sentienl 8.1.7
Server type
The server types supported by CacheStore (DBaaS) are as follows.
For detailed information about the server types provided by CacheStore(DBaaS), see CacheStore(DBaaS) Server Types.
Standard redis1v2m4
| Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type
|
| Server specifications | redis1 | Provided server specifications
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
6.6.1.1 - Server Types
CacheStore(DBaaS) server type
CacheStore(DBaaS) offers server types composed of various combinations such as CPU, Memory, and Network Bandwidth. When creating a CacheStore (DBaaS), Redis is installed according to the server type selected for the intended use.
The server types supported by CacheStore(DBaaS) are as follows.
Standard redis1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classification
|
| Server specifications | redis1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
redis1 server type
The redis1 server type of CacheStore (DBaaS) is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | redis1v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | redis1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | redis1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | redis1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | redis1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | redis1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | redis1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | redis1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | redis1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | redis1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | redis1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | redis1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | redis1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | redis1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | redis1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | redis1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | redis1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
css1 server type
The css1 server type of CacheStore (DBaaS) is provided with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | css1v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | css1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | css1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | css1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | css1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | css1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | css1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | css1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | css1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | css1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | css1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | css1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | css1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | css1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | css1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | css1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | css1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
6.6.1.2 - Monitoring metrics
According to the policy of Samsung Cloud Platform, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services by Resource
- New Resources: Resources created after the service improvement work in July 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings integrated with existing Cloud Monitoring (e. You need to review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Cloud Monitoring Service Phased Termination Schedule Notice
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, Cloud Monitoring data cannot be accessed. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
CacheStore(DBaaS) Monitoring Metrics
The table below shows the performance monitoring metrics for CacheStore (DBaaS) that can be viewed through Cloud Monitoring. For detailed usage of Cloud Monitoring, refer to the Cloud Monitoring guide.
For CacheStore (DBaaS) server monitoring metrics, refer to the Virtual Server Monitoring Metrics guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Active Defragmentation Keys [Hits] | Number of keys after defragmentation | cnt |
| Active Defragmentation Keys [Miss] | Number of keys skipped in the active defragmentation removal process | cnt |
| Active Defragmentationd [Hits] | Number of value reallocations performed by the active defragmentation removal process | cnt |
| Active Defragmentations [Miss] | Count of value reallocations interrupted by the active defragmentation removal process | cnt |
| Allocated Bytes [OS] | Number of bytes allocated by CacheStore (DBaaS) and recognized by the operating system (resident set size) | bytes |
| Allocated Bytes [Redis] | Total bytes allocated by CacheStore (DBaaS) | bytes |
| AOF Buffer Size | AOF buffer size | bytes |
| AOF File Size [Current] | AOF current file size | bytes |
| AOF File Size [Lastest Startup] | AOF file size on recent start or rewrite | bytes |
| AOF Rewrite Buffer Size | AOF rewrite buffer size | bytes |
| AOF Rewrite Current Time | If applicable, the time of the ongoing AOF rewrite operation | sec |
| AOF Rewrite Last Time | Final AOF rewrite time | sec |
| Calls | Number of calls that reached command execution (not rejected) | cnt |
| Changes [Last Saved] | Number of changes after the final dump | cnt |
| Client Output Buffer [MAX] | Longest output list among current client connections | cnt |
| Clients [Sentinel] | Number of client connections (Sentinel) | cnt |
| Connected Slaves | Number of connected slaves | cnt |
| Connections [Blocked] | Number of clients pending on blocking calls (BLPOP, BRPOP, BRPOPLPUSH) | cnt |
| Connections [Current] | Number of client connections (excluding slave connections) | cnt |
| Copy On Write Allocated Size [AOF] | COW allocation size during final RBD save operation | bytes |
| Copy On Write Allocated Size [RDB] | COW allocation size during the final RBD save operation | bytes |
| CPU Time [Average] | Average CPU time used per command execution | cnt |
| CPU Time [Total] | Total CPU time used by these commands | usec |
| CPU Usage [System Process] | System CPU usage by background processes | % |
| CPU Usage [System] | System CPU usage on the CacheStore (DBaaS) server | % |
| CPU Usage [User Process] | User CPU usage used by background processes | % |
| CPU Usage [User] | System CPU usage by background processes | % |
| Dataset Used | Dataset size | bytes |
| Disk Used | datadir usage | MB |
| Evicted Keys | Number of evicted keys caused by the maxmemory limit | cnt |
| Fsyncs [Delayed] | Delayed fsync counter | cnt |
| Fsyncs [Pending] | Number of pending fsync operations in the background I/O queue | cnt |
| Full Resyncs | Number of full resynchronizations with the slave | cnt |
| Keys [Expired] | Total number of key expiration events | cnt |
| Keys [Keyspace] | Number of keys in the key space | cnt |
| Lastest Fork Duration Time | Recent fork (fork) operation time | usec |
| Lookup Keys [Hit] | Number of successful key lookups in the dictionary | cnt |
| Lookup Keys [Miss] | Number of failed key lookups in the main dictionary | cnt |
| Lua Engine Memory Used | Memory used by the Lua engine | bytes |
| Master Last Interaction Time Ago | Time elapsed since the final interaction with the master | sec |
| Master Last Interaction Time Ago [Sync] | Time elapsed since the final interaction with the master | sec |
| Master Offset | Current replication offset of the server | pid |
| Master Second Offset | Offset until the replication ID is accepted | pid |
| Master Sync Left Bytes | Remaining bytes before synchronization completes | bytes |
| Memory Fragmentation Rate | Ratio of used_memory_rss to used_memory | % |
| Memory Fragmentation Rate [Allocator] | Fragmentation ratio | % |
| Memory Fragmentation Used | Bytes between used_memory_rss and used_memory | bytes |
| Memory Fragmentation Used [Allocator] | resident byte | bytes |
| Memory Max Value | Memory limit | bytes |
| Memory Resident [Allocator] | resident memory | bytes |
| Memory RSS Rate [Allocator] | Resident ratio | % |
| Memory Used [Active] | Active memory | bytes |
| Memory Used [Allocated] | Allocated memory | bytes |
| Memory Used [Resident] | Resident byte | bytes |
| Network In Bytes [Total] | Total network input (bytes) | bytes |
| Network Out Bytes [Total] | Total network output (bytes) | bytes |
| Network Read Rate | Network read speed (KB/sec) | cnt |
| Network Write Rate | Network write speed (KB/sec) | cnt |
| Partial Resync Requests [Accepted] | Number of accepted partial resynchronization requests | cnt |
| Partial Resync Requests [Denied] | Number of rejected partial resynchronization requests | cnt |
| Peak Memory Consumed | Maximum memory used by CacheStore (DBaaS) | bytes |
| Processed Commands | Number of commands processed per second | cnt |
| Processed Commands [Total] | Total number of processed commands | cnt |
| Pub/Sub Channels | Global count of pub/sub channels with client subscriptions | cnt |
| Pub/Sub Patterns | Global count of publish/subscribe patterns with client subscriptions | cnt |
| RDB Saved Duration Time [Current] | If applicable, the time of the ongoing RDB save operation | sec |
| RDB Saved Duration Time [Last] | Final RDB save operation time | sec |
| Received Connections [Total] | Total number of received connections | cnt |
| Rejected Connections [Total] | Total number of rejected connections | cnt |
| Replication Backlog Actove Count | Replication backlog activation flag | cnt |
| Replication Backlog Master Offset | Master offset of the replication backlog buffer | cnt |
| Replication Backlog Size | Data size of the replication backlog buffer | bytes |
| Replication Backlog Size [Total] | Total size of the replication backlog buffer | bytes |
| Slave Priority | Server priority as a fault remediation target | cnt |
| Slave Replication Offset | Replication offset of the slave server | pid |
| Slow Operations | Number of slow tasks | cnt |
| Sockets [MIGRATE] | Number of sockets opened for migration | cnt |
| Tracked Keys [Expiry] | Number of keys tracked for expiration (applicable only to writable slaves) | cnt |
| Instance Status [PID] | redis-server process PID | pid |
| Sentinel Status [PID] | sentinel process PID | pid |
6.6.2 - How-to guides
Users can create the service by entering the required information for CacheStore (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Service per Resource
- New Resources: Resources created after the July 2026 service improvement work are provided with default monitoring using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings linked with existing Cloud Monitoring (ex. You must review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Notice of the phased termination schedule for Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, you will not be able to view Cloud Monitoring data. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
Create CacheStore (DBaaS)
You can create and use the CacheStore (DBaaS) service from the Samsung Cloud Platform Console.
Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the corresponding Database service cannot be created.
To create a CacheStore (DBaaS), follow the steps below.
- All Services > Database > CacheStore(DBaaS) Click the menu. 1. Go to the Service Home page of CacheStore (DBaaS).
- On the Service Home page, click the Create CacheStore (DBaaS) button. 2. Create CacheStore (DBaaS) Go to the page.
- On the Create CacheStore (DBaaS) page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version Essential Provide version list for CacheStore (DBaaS) Table. CacheStore (DBaaS) Image and version selection items - Enter or select the required information in the Service Information Input area.
Category required statusDetailed description Server name Prefix Required Server name where Redis/Valkey will be installed - must start with a lowercase English letter, and using lowercase letters, numbers, and the special character (
-) input 3 to 13 characters
- Based on the server name, a postfix such as 001, 002 is appended to create the actual server name
Cluster name Required Cluster name where Redis/Valkey is installed - Enter using English letters, 3 to 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for installing Redis/Valkey - Standard: Standard specification commonly used
- For detailed information about the server types provided by CacheStore (DBaaS), refer to CacheStore(DBaaS) 서버 타입.
Service Type > Planned Compute Required Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage preview: Amount applied per resource by Planned Compute
- Create Planned Compute service: Navigate to the Planned Compute service request page
- For more details, see Apply for Planned Compute
Service Type > Block Storage Required Block Storage settings used by the DB according to purpose - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select the storage type and then enter the capacity (refer to Block Storage 생성하기 for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volumes that use Samsung Cloud Platform KMS (Key Management System) encryption keys
- The configured storage type is also applied to additional storage
- Enter the capacity as a multiple of 8 within the range 16 to 5,120
- Select the storage type and then enter the capacity (refer to Block Storage 생성하기 for details on each Block Storage type)
high availability Select High Availability (HA) configuration option - When High Availability (HA) is enabled, it is provided as a Master-Replica setup, and the Replica can be configured with 1 or 2 instances
- Sentinel Port number: The port used for connecting to Sentinel
- Enter a port for Master-Replica communication within the range 1200 to 65535
- Replica count: Number of Replicas to configure
- If 1 is selected, it is configured as Master-Replica-Sentinel
- If 2 is selected, it is configured as Master-Replica-Replica, and Sentinel is automatically installed on the server where Redis is installed
- Set the server type for Sentinel to the minimum specification
Network Required The network where CacheStore (DBaaS) is installed - Select a pre‑created VPC and Subnet to connect
- IP can only be auto‑generated
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC and Subnet
- IP can only be auto‑generated
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select when you want to apply different settings per installed server
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- Enter the IP for each server
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway. Use when checked, you can select from reserved IPs in the VPC product’s Public IP. For more details, see Public IP 생성하기
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy.
- Enter in IP format (e.g.,
192.168.10.1) or CIDR format (e.g.,192.168.10.0/24,192.168.10.1/32) and click the Add button.
- To delete an entered IP, click the x button next to the entered IP.
maintenance period Select CacheStore(DBaaS) maintenance period - If you select Use, set the day, start time, and duration
- It is recommended to set a maintenance period for stable DB management. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. CacheStore (DBaaS) Service Configuration Items - must start with a lowercase English letter, and using lowercase letters, numbers, and the special character (
- Enter or select the required information in the Database Configuration Required Information Input area.
Category required statusDetailed description Backup Select Backup usage - If you select Use, you can set the backup file retention period and backup start time
- Backup files incur additional charges based on their size
- The file retention period can be set from 7 to 35 days
- The minute at which the backup runs (minutes) is set randomly, and the backup end time cannot be configured
Redis/Valkey Port number Required Port number required for Redis/Valkey connection - Enter a port within the range 1200 ~ 65535
Redis/Valkey password Essential Password required when connecting to Redis/Valkey - include letters, numbers, and special characters (excluding
$“‘) and enter 8 to 30 characters
Check Redis/Valkey password Required Re-enter the same password Parameter Required Parameters to use with Redis/Valkey - View button can be clicked to view detailed parameter information
- Parameters can be modified after creation is complete, and a DB restart is required after modification
time zone Required The time zone where the database will be used Table. CacheStore (DBaaS) Database configuration items - Additional Information Input area, enter or select the required information.
Category required statusDetailed description Tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. CacheStore (DBaaS) additional information input fields
- Select the required information in the Image and version selection area.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
View CacheStore (DBaaS) detailed information
The CacheStore (DBaaS) service allows you to view and edit the full list of resources and detailed information. CacheStore(DBaaS) Details page consists of Details, Tags, Activity History tabs.
To view detailed information about the CacheStore (DBaaS) service, follow these steps.
- All Services > Database > CacheStore(DBaaS) Click the menu. 1. Navigate to the Service Home page of CacheStore (DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. 2. Go to the CacheStore(DBaaS) List page.
- CacheStore(DBaaS) List page, click the resource to view its detailed information. 3. CacheStore(DBaaS) Details Go to the page.
- CacheStore(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Cluster status Cluster status with Redis installed - Creating: Cluster is being created
- Editing: Cluster is changing to an operational state
- Error: Cluster encountered an error while performing tasks
- If this persists, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Cluster is being restarted
- Running: Cluster is operating normally
- Starting: Cluster is starting
- Stopped: Cluster is stopped
- Stopping: Cluster is being stopped
- Synchronizing: Cluster is synchronizing
- Terminating: Cluster is being terminated
- Unknown: Cluster status is unknown
- If this persists, contact the administrator
Cluster control Buttons to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
- Switch-Over: Promote a replica cluster to Master
View more add-ons Cluster-related management buttons - Service status synchronization: Real-time Redis/Valkey service status lookup
- Backup history: When backup is configured, verify successful execution and view history
- Database recovery: Recover the DB based on a specific point in time
- Parameter management: View and modify Redis/Valkey configuration parameters
- Rename-Command: Change the name of a Redis/Valkey command
Service termination Button to cancel the service Table. CacheStore(DBaaS) status information and additional features
- CacheStore(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Detailed Information
CacheStore(DBaaS) List page allows you to view detailed information of the selected resource and, if needed, modify the information.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed Redis/Valkey image and version information
|
| Cluster name | Cluster name of the configured Redis/Valkey servers |
| Planned Compute | Resource status with Planned Compute configured
|
| maintenance period | DB patch work period setting status
|
| Backup | Backup Configuration Status
|
| Redis/Valkey Port number | Port number required for connecting to Redis/Valkey |
| time zone | Redis/Valkey time zone |
| Sentinel Port number | Port number for communication between Master and Replica |
| VIP | Virtual IP information
|
| Network | Network information (VPC, Subnet) where CacheStore (DBaaS) is installed |
| IP access control | Service access policy configuration
|
| Master & Replica | Master, Replica server type, base OS, additional Disk information
|
| Sentinel | Sentinel server type, basic OS information
|
Tag
CacheStore(DBaaS) List page lets you view the tag information of the selected resource, and you can add, change, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
On the CacheStore(DBaaS) List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource change history
|
Managing CacheStore (DBaaS) Resources
If you need to change or restore the existing configuration options of a created CacheStore (DBaaS) resource, or modify commands, you can perform the tasks on the CacheStore(DBaaS) Details page.
Control operation
If changes occur to a running CacheStore (DBaaS) resource, you can start, stop, or restart it. Also, when HA is configured, you can switch the Master-Replica servers via a switch‑over.
To control the operation of CacheStore (DBaaS), follow these steps.
- Click the All Services > Database > CacheStore(DBaaS) menu. 1. Navigate to the Service Home page of CacheStore (DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. 2. CacheStore(DBaaS) List Navigate to the page.
- CacheStore(DBaaS) List page, click the resource you want to control. 3. CacheStore(DBaaS) Details Go to the page.
- Check the CacheStore status and complete the change using the control button below.
- Start: the server where the CacheStore service is installed and the CacheStore service is running (Running).
- Stop: The server where the CacheStore service is installed and the CacheStore service can be stopped (Stopped).
- Restart: Only the CacheStore service can be restarted.
- Switch Over: You can switch the Master server and the Replica server.
Synchronize service status
You can synchronize the real-time service status of CacheStore (DBaaS).
To check the service status of CacheStore (DBaaS), follow the steps below.
- Click the All Services > Database > CacheStore(DBaaS) menu. 1. Go to the Service Home page of CacheStore (DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. 2. Navigate to the CacheStore(DBaaS) List page.
- CacheStore(DBaaS) List page, click the resource to view the service status. 3. CacheStore(DBaaS) Details Go to the page.
- Click the Service Status Sync button. 4. While it is being queried, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- All Services > Database > CacheStore(DBaaS) Click the menu. 1. Go to the Service Home page of CacheStore (DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. 2. Go to the CacheStore(DBaaS) List page.
- On the CacheStore(DBaaS) List page, click the resource to change the server type. 3. Go to the CacheStore(DBaaS) Details page.
- Click the Edit icon of the server type you want to change at the bottom of the detailed information. 4. Edit Server Type The popup window opens.
- Edit Server Type After selecting the server type in the popup window, click the Confirm button.
Cancel CacheStore (DBaaS)
You can reduce operating costs by terminating unused CacheStore (DBaaS). However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may occur when the service is discontinued.
To cancel CacheStore(DBaaS), follow the steps below.
- All Services > Database > CacheStore(DBaaS) Click the menu. 1. Navigate to the Service Home page of CacheStore (DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. 2. CacheStore(DBaaS) List Go to the page.
- On the CacheStore(DBaaS) List page, select the resource to cancel, and click the Cancel Service button.
- After termination is complete, check whether the resource has been terminated on the CacheStore(DBaaS) list page.
6.6.2.1 - CacheStore Service Manage
Users can manage CacheStore (DBaaS) through the Samsung Cloud Platform Console.
Parameter Management
Provides a feature that allows you to easily view and edit database configuration parameters.
View Parameters
To view configuration parameters, follow these steps.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. You will be taken to the CacheStore(DBaaS) List page.
- On the CacheStore(DBaaS) List page, click the resource whose parameters you want to view or edit. You will be taken to the CacheStore(DBaaS) Details page.
- Click the More button, then click the Parameter Management button. The Parameter Management popup opens.
- Parameter Management in the popup window, click the Search button. The Search Notification popup window opens.
- View Notification when the popup window opens, click the Confirm button. Retrieving may take a short amount of time.
Modify Parameter
To modify the configuration parameters, follow the steps below.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. You will be taken to the CacheStore(DBaaS) List page.
- On the CacheStore(DBaaS) List page, click the resource whose parameters you want to view or edit. You will be taken to the CacheStore(DBaaS) Details page.
- Click the More button, then click the Parameter Management button. The Parameter Management popup opens.
- In the Parameter Management popup, click the Query button. The Query Notification popup opens.
- Lookup Notification When the popup window opens, click the Confirm button. The lookup may take a short amount of time.
- If a modification is needed, click the Edit button and enter the changes in the custom value field of the Parameter to be edited.
- When the input is complete, click the Complete button.
Rename Command
Provides Redis OSS/Valkey command lookup and command name editing functionality. To look up commands and edit command names, follow these steps.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. You will be taken to the CacheStore(DBaaS) List page.
- On the CacheStore(DBaaS) List page, click the resource whose Command name you want to edit. You will be taken to the CacheStore(DBaaS) Detail page.
- Click the More button, then click the Rename-Command button. You will be taken to the Rename-Command page.
- On the Rename-Command page, click the Lookup button. The Lookup notification popup opens.
- View Notification when the popup window opens, click the Confirm button. Retrieving may take a short amount of time.
- If a modification is needed, click the Edit button and enter the changes in the custom value field of the Command you want to modify.
- When the input is complete, click the Complete button.
Minor Version Upgrade
We provide version upgrade functionality for some feature improvements and security patches. Only Minor version upgrades are supported within the same Major version.
To upgrade the Minor Version, follow the steps below.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. You will be taken to the CacheStore(DBaaS) List page.
- CacheStore(DBaaS) List page, click the resource to upgrade the version. You will be taken to the CacheStore(DBaaS) Details page.
- Click the Edit icon of the Image version item. The Version Upgrade popup window opens.
- Version Upgrade In the popup window, select the revised version, then click the Confirm button.
- Version Upgrade Notification Click the Confirm button in the popup window.
6.6.2.2 - CacheStore Backup and Restore
Users can configure backups of CacheStore (DBaaS) through the Samsung Cloud Platform Console and restore from the backed-up files.
CacheStore(DBaaS) Backup
CacheStore (DBaaS) provides data backup functionality based on its own backup commands. Additionally, it offers a backup environment optimized for data protection and management through backup history verification and backup file deletion features.
Configure backup
For instructions on configuring backups for CacheStore(DBaaS), see CacheStore(DBaaS) Create.
To modify the backup settings of the created resource, follow the steps below.
If a backup is configured, it runs at the specified time after the set schedule, and additional fees apply based on the backup size.
- If you change the backup setting to unset, backup execution stops immediately, and any stored backup data is deleted and can no longer be used.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- Click the CacheStore(DBaaS) menu on the Service Home page. You will be taken to the CacheStore(DBaaS) List page.
- On the CacheStore(DBaaS) List page, click the resource for which you want to set up a backup. You will be taken to the CacheStore(DBaaS) Details page.
- Click the Edit icon of the backup item. The Backup Settings popup window opens.
- When configuring a backup, click Use in the Backup Settings popup, select the retention period, backup start time, and Archive backup interval, then click the Confirm button.
- If you stop the backup configuration, deselect Use in the Backup Settings popup window and click the Confirm button.
Check backup history
To check the backup history, follow these steps.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- Click the CacheStore(DBaaS) menu on the Service Home page. You will be taken to the CacheStore(DBaaS) List page.
- CacheStore(DBaaS) List page, click the resource for which you want to view the backup history. You will be taken to the CacheStore(DBaaS) Details page.
- Click the Backup History button. The Backup History popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup file
To delete the backup history, follow these steps.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- Click the CacheStore(DBaaS) menu on the Service Home page. You will be taken to the CacheStore(DBaaS) List page.
- CacheStore(DBaaS) List Click the resource whose backup history you want to view. You will be taken to the CacheStore(DBaaS) Details page.
- Click the Backup History button. The Backup History popup window opens.
- Backup History popup window, check the files you want to delete, then click the Delete button.
CachStore(DBaaS) Recover
If a failure or data loss requires restoration from a backup file, recovery can be performed based on a specific point in time using the recovery feature.
To restore CacheStore(DBaaS), follow the steps below.
- Click the All Services > Database > CacheStore(DBaaS) menu. Navigate to the Service Home page of CacheStore(DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) menu. You will be taken to the CacheStore(DBaaS) List page.
- On the CacheStore(DBaaS) List page, click the resource you want to recover. You will be taken to the CacheStore(DBaaS) Details page.
- Click the Database Recovery button. You will be taken to the Database Recovery page.
- After entering information in the Database recovery configuration area, click the Complete button.
Category RequiredDetailed description Recovery type Required User sets the desired recovery point - Recover based on the backup file, selecting a point in time from the list displayed for backup files
Server name prefix Required Server name of the recovery DB - Start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to enter 3 to 16 characters
- A postfix such as 001, 002 is appended to the base server name to create the actual server name
Cluster name Required Cluster name of the recovery DB - Enter using English letters, 3 to 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type for the recovery DB - Standard: Standard specifications commonly used
- High Capacity: Large-capacity server with 24 vCores or more (to be provided later)
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied by Planned Compute per resource
- Create Planned Compute Service: Go to the Planned Compute service request page
Service Type > Block Storage Required Block Storage settings used by the recovery DB - Base OS: Area where the DB engine is installed
- DATA: Area where AOF (Append Only File) and RDB (Redis Database) files, etc., are stored
- Apply the same Storage type as configured in the original cluster
- Capacity can be entered as a multiple of 8 within the range 56 to 5,120
Redis/Valkey Port number Required Redis/Valkey port number configured in the source DB IP access control Selection Service Access Policy Settings - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy.
- Enter the IP in jIP format (e.g.,
192.168.10.1) or CIDR format (e.g.,192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the IP
maintenance period Selection CacheStore(DBaaS) DB maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable DB management. Patch operations will be performed at the scheduled time, causing service interruption
- If set to not use, Samsung SDS is not responsible for any issues arising from unapplied patches.
tag Selection Add Tag - Add Tag After clicking the Add Tag button, enter or select Key, Value values
Table. CacheStore (DBaaS) recovery configuration items
6.6.2.3 - CacheStore(DBaaS) Server Connection
Scenario Overview
Connecting to CacheStore (DBaaS) The scenario involves creating a Bastion host (Virtual Server) and a Database service, and accessing the DB service through the Bastion host. To reliably connect to CacheStore (DBaaS) in the Samsung Cloud Platform environment, you need to create a Bastion host and establish a network connection using it. To maintain stability and a high level of security, it is recommended to configure the Database service in a Private Subnet environment and set up the Bastion host in a restricted Public Subnet environment.
This scenario primarily describes creating a Bastion host and a Database service, configuring the network environment for Bastion host and Database access, and connecting through a DB client.
Scenario components
You can build the scenario using the following services.
| Service group | service | Detailed description | |
|---|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment | |
| Networking | VPC > Subnet | A service that lets users subdivide the network within a VPC to match their purpose and scale. | |
| Networking | VPC > Public IP | A service that reserves a public IP and allocates and releases it to Compute resources | |
| Networking | VPC > Internet Gateway | A service that connects VPC resources to the Internet | |
| Networking | Security Group | Virtual firewall that controls server traffic | |
| Database | CacheStore(DBaaS) | A service that easily creates and manages CacheStore in a web environment | |
| Compute | Virtual Server | Virtual server optimized for cloud computing | |
| Compute | Virtual Server > Keypair | Encryption file used to connect to the Virtual Server |
- Since the default policy of a Security Group is Deny All, you must register only the IPs that are allowed.
- The All Open(Any IP, Any Port) policy of In/Outbound can expose cloud resources directly to external threats.
- By specifying the required IP and port and setting a policy, you can strengthen security.
Scenario setup method
Create the services needed to construct the scenario by following the steps below.
Set up the network
Describes the process of configuring the network environment for accessing the Bastion Host and Database services.
1-1. Create VPC
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the Create VPC button on the Service Home page. Navigate to the Create VPC page.
- On the VPC Creation page, enter the information required to create the service.
- Enter the IP range as
192.168.x.0/16
- Enter the IP range as
- Summary panel, verify the detailed information and estimated billing amount generated, and click the Complete button.
- After creation is complete, check the created resources on the VPC List page.
1-2. Create Subnet
- Click the All Services > Networking > VPC menu. You will be taken to the VPC Service Home page.
- On the Service Home page, click the Subnet menu. You will be taken to the Subnet List page.
- Click the Subnet Create button. You will be taken to the Subnet Create page.
- On the Subnet Creation page, enter the information required to create the service.
- Select the Subnet type as General.
- Select a pre‑created VPC.
- Enter the IP range as
192.168.x.0/24.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resources on the Subnet List page.
1-3. Create Internet Gateway
- Click the All Services > Networking > VPC menu. You will be taken to the VPC’s Service Home page.
- On the Service Home page, click the Internet Gateway menu. You will be taken to the Internet Gateway List page.
- Click the Create Internet Gateway button. Navigate to the Create Internet Gateway page.
- Internet Gateway Creation page, enter the required information needed to create the service.
- Select a pre‑created VPC.
- In the Firewall usage item, select Use.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, verify the created resource on the Internet Gateway list page.
1-4. Create Public IP
- Click the All Services > Networking > VPC menu. Navigate to the VPC’s Service Home page.
- Click the Public IP menu on the Service Home page. You will be taken to the Public IP List page.
- Click the Public IP reservation button. You will be taken to the Public IP reservation page.
- On the Public IP reservation page, enter the required information needed to reserve the service.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resources on the Public IP List page.
1-5. Create Security Group
- Click the All Services > Networking > Security Group menu. Go to the Service Home page of Security Group.
- Click the Create Security Group button on the Service Home page. You will be taken to the Create Security Group page.
- On the Security Group creation page, enter the required information needed to create the service.
- Check the input information and click the Complete button.
- Once creation is complete, check the created resources on the Security Group List page.
Create bastion host
Describes the process of configuring a Bastion Host that requires the database client to be installed.
2-1. Create Server Keypair
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Keypair menu. You will be taken to the Keypair List page.
- Click the Create Keypair button. You will be taken to the Create Keypair page.
- On the Keypair creation page, enter the required information for creating the service.
- Check the creation information and click the Complete button.
- The key can be downloaded only once, and reissuance is not available.
- Please store the downloaded key in a secure location.
2-2. Create Bastion host
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Create Virtual Server button. It navigates to the Create Virtual Server page.
- On the Virtual Server Creation page, enter the required information needed to create the service.
- Select Windows for the image.
- Select the pre‑created VPC and Subnet.
- Click Use NAT, and select the reserved Public IP from 1-4. Create Public IP.
- Connect the Keypair created in 2-1. 서버 Keypair 생성하기.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resources on the Virtual Server List page.
2-3. Check Bastion host login ID and PW
- Click the All Services > Compute > Virtual Server menu. Navigate to the Service Home page of Virtual Server.
- On the Service Home page, click the Virtual Server menu. You will be taken to the Virtual Server List page.
- On the Virtual Serve List page, click the resource you created in 2-2. Bastion host Create. You will be taken to the detailed information page for that resource.
- On the detail page, click the RDP password view button in the Keypair name field. The RDP password view popup window will open.
- In the RDP password lookup popup window, attach the keypair file downloaded from 2-1. 서버 Keypair 생성하기.
- After attaching, click the Password verification button. The ID and Password for accessing the resource are displayed.
- This ID and password will be used later as credentials to access the Bastion host in 5-1. Bastion host Connecting.
Create Database
Describes the process of creating a Database service.
3-1. Create CacheStore(DBaaS) Service
- Click the All Services > Database > CacheStore(DBaaS) menu. Go to the Service Home page of CacheStore(DBaaS).
- On the Service Home page, click the CacheStore(DBaaS) Create button. You will be taken to the CacheStore(DBaaS) Create page.
- Enter the required information for creating the service on the CacheStore(DBaaS) Creation page.
- Select the pre‑created VPC and Subnet and connect them.
- Enter the database-related creation details on the required information input screen.
- Add the Bastion host IP in the IP access control section.
- The Database Port defaults to 2866, but the user can also specify it.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, verify the created resource on the CacheStore(DBaaS) list page.
Configuring Rules
It explains the process of configuring rules for a user to connect to the Bastion host and rules for connecting to the Database from the Bastion host.
4-1. Security Group Add Security Rules
- Click the All Services > Networking > Security Group menu. Go to the Service Home page of Security Group.
- On the Service Home page, click the Security Group menu. You will be taken to the Security Group List page.
- Select the Security Group resource created in 1-5. Create Security Group. Go to the detailed information page of that resource.
- Click the Rules tab on the detail information page. You will be taken to the Rules tab.
- Click the Add Rule button in the Rules tab. It navigates to the Add Rule popup.
- Add Rule In the popup window, enter the rule below, and click the Confirm button.
direction Remote Target address Protocol Port Explanation Inbound CIDR User PC IP TCP 3389 (RDP) Bastion client PC → Bastion host Outbound CIDR DB IP TCP Database Port (manual entry) Bastion host → Database Table. Security Group rules that need to be added
4-2. Add IGW Firewall rule
- All Services > Networking > Firewall Click the menu. Go to the Service Home page of Firewall.
- From the Service Home page, click the Firewall menu. You will be taken to the Firewall List page.
- On the Firewall List page, select the Internet Gateway resource name created in 1-3. Internet Gateway 생성하기. You will be taken to the detailed information page for that resource.
- Click the Rules tab on the detail page. You will be taken to the Rules tab.
- Click the Add Rule button on the Rules tab. You will be taken to the Add Rule popup.
- Add Rule In the popup window, enter the rule below and click the Confirm button.
origin address Destination address Protocol Port Operation direction Explanation Bastion connection PC IP Bastion host IP TCP 3389(RDP) Allow Inbound User PC → Bastion host Table. Internet Gateway Firewall rules that need to be added
Connect to Database
Describes the process of a user connecting to a database via a DB client program.
This guide explains how to connect using Another Redis Desktop Manager. Since there are various database client programs and CLI utilities, you may install and use the tool that best fits your needs.
5-1. Connecting to Bastion host
- In the Windows environment of the PC that will connect to the Bastion host, run Remote Desktop Connection, then enter the NAT IP of the Bastion Host and click the Connect button.
- When the remote desktop connection succeeds, the user credential input window opens. Enter the ID and Password you verified in 2-3. Bastion host 접속 ID 및 PW 확인하기 and click the Confirm button.
5-2. Install DB connection client program(Another Redis Desktop Manager) on the Bastion host
- Please download the Another Redis Desktop Manager program.
- Another Redis Desktop Manager program download URL: https://github.com/qishibo/AnotherRedisDesktopManager/releases
- Connect the user’s PC hard drive to upload the file to the Bastion host.
- In the Local Resources tab of the Remote Desktop Connection, click the Details button for the Local Devices and Resources item.
- Select the local disk where the file was downloaded on the drive, and click the OK button.
- Copy the downloaded file, upload it to the Bastion Host, and click the pgAdmin installer to install.
5-3. Connect to the database using the DB client program (Another Redis Desktop Manager)
- Run Another Redis Desktop Manager and click New Connection. The New Connection popup will appear.
- New Connection in the popup window, enter the Database server information created from 3-1. CacheStore(DBaaS) 서비스 생성하기 and click the OK button.
Required input field input value Host Database server IP Port Database Port Password Database password Connection Name Custom (ex. service name) Table.DB connection client program input fields - After connecting, you can check basic Redis information, manage data, and perform CRUD operations on keys.
6.6.3 - API Reference
6.6.4 - CLI Reference
6.6.5 - Release Note
CacheStore(DBaaS)
- We ensure stable service continuity through the Minor version upgrade feature.
- Add CacheStore (DBaaS) feature
- CacheStore(DBaaS) Add new image
- Support for the open-source Valkey image, developed by forking Redis OSS
- 2nd Generation Server Type Add
- Add a second-generation (db2) server type based on the Intel 4th‑generation (Sapphire Rapids) processor. For details, see CacheStore(DBaaS) Server Type.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add HDD, HDD_KMS types to Block Storage type
- CacheStore(DBaaS) Add new image
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Change the service name to CacheStore(DBaaS).
- A volume-encrypted storage selection option has been added to the Block Storage type.
- A Role Switch (Active ↔ Standby) feature for the Active DB and Standby DB configured with redundancy has been added.
- It is linked with the cloud monitoring service, enabling performance and log monitoring of DB instances.
- The Planned Compute policy can be configured according to the server type selected by the customer.
- A Redis (DBaaS) service that enables easy creation and management of Redis OSS in a web environment has been launched.
6.7 - Scalable DB(DBaaS)
6.7.1 - Overview
Service Overview
Scalable DB(DBaaS) is a database service designed to efficiently manage rapidly increasing data processing demands and user load.
Scalable DB (DBaaS) automatically scales resources up or down in response to traffic changes, maintaining optimal performance and availability. This maximizes resource efficiency and provides cost savings.
Additionally, the Proxy Endpoint configuration feature not only distributes database load by separating read/write and read‑only roles, but also enables more efficient independent connection management per application.
By combining these features, users can reduce the complexity of service operations and build a cost‑effective, scalable database environment.
Service Diagram
Provided features
Scalable DB(DBaaS) provides the following features.
- Auto Provisioning: Allows installation and configuration of the Database (DB) via UI, and provides an Active‑standby redundancy configuration built on storage replication. In case of an Active server failure, it automatically fails over to the Standby.
- Operation Control Management: Provides functionality to control the status of running servers. Offers start and stop functions for the entire cluster and restart buttons for each node, supporting a flexible cluster and node management environment for users.
- Scaling feature: Through the automatic scaling feature, read nodes are automatically expanded and contracted according to the policy set by the user. Additionally, users can manually adjust the number of nodes as needed.
- Proxy Endpoint configuration: By using the Proxy Endpoint feature that separates read/write and read‑only connections, it supports database connection optimization and traffic distribution.
- Backup: Provides data backup functionality based on its own backup command. Users can set the backup time window and storage repository, and additional fees are incurred based on backup size.
- Read Node status view: Provides real-time Read Node status view functionality, allowing monitoring of replication lag time (Replication Lag Time) to accurately determine data synchronization status.
- Service Status Query: Retrieves the final status of the current DB service.
- Monitoring: CPU, memory, performance monitoring information can be viewed through Servicewatch.
Component
Scalable DB (DBaaS) provides pre‑validated engine versions and various server types in accordance with its open‑source support policy. Users can select and use them based on the scale of the service they wish to configure.
Engine version
The engine versions supported by Scalable DB (DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is stopped is set to six months before the EoTS date.
The EOS and EoTS dates may change according to the supplier’s policy, so please refer to the supplier’s license management policy page for details.
- MariaDB(Commuity): https://mariadb.org/about/#maintenance-policy
| Provided version | EOS Date (Samsung Cloud Platform new creation stop date) | EoTS Date (Community technical support end date) |
|---|---|---|
| 10.11.13 | 2027-06 (planned) | 2028-02-16 |
Server Type
The server types supported by Scalable DB(DBaaS) are as follows.
For detailed information about the server types provided by Scalable DB (DBaaS), refer to Scalable DB(DBaaS) Server Types.
High Capacity sdbh2v24m48
Category | example | Detailed description |
|---|---|---|
| Server type | High Capacity | Provided server type classification |
| Server specifications | sdbh2 | Provided server type classification and generation
|
| Server specifications | v24 | Number of vCores
|
| Server specifications | m48 | Memory Capacity
|
Provision status by region
Scalable DB(DBaaS) is available in the following environments.
| region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Not provided |
| South Korea 1 (kr-south1) | Provide |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
6.7.1.1 - Server Types
Scalable DB(DBaaS) server type
Scalable DB (DBaaS) offers server types configured with various combinations of CPU, memory, and network bandwidth. When creating a Scalable DB(DBaaS), the Database Engine is installed according to the server type selected for the intended use.
The server types supported by Scalable DB (DBaaS) are as follows.
High Capacity sdbh2v24m48
Category | example | Detailed description |
|---|---|---|
| Server type | High Capacity | Provided server type classification |
| Server specifications | sdbh2 | Provided server type classification and generation
|
| Server specifications | v24 | Number of vCores
|
| Server specifications | m48 | Memory Capacity
|
sdbh2 server type
The dbh2 server type of Scalable DB (DBaaS) is offered with high-capacity server specifications and is suitable for database workloads that require large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | sdbh2v24m48 | 24 vCore | 48 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v32m64 | 32 vCore | 64 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v32m256 | 32 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v64m256 | 64 vCore | 256 GB | Up to 25 Gbps |
| High Capacity | sdbh2v64m768 | 64 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v96m384 | 96 vCore | 384 GB | Up to 25 Gbps |
| High Capacity | sdbh2v96m1152 | 96 vCore | 1152 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | sdbh2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
6.7.1.2 - ServiceWatch Metrics
Scalable DB sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the namespace Scalable DB(DBaaS).
The indicators whose names are shown in bold below are the indicators selected as major indicators among the basic indicators provided by Scalable DB(DBaaS). Key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric indicates through the user guide which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
OS Basic Metrics
Category | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| CPU | CPU Usage | Percent | CPU usage |
|
| Disk | Disk Usage | Percent | Disk usage |
|
| Disk | Disk Write Bytes | Bytes/Second | Write bandwidth (bytes/second) on block device |
|
| Disk | Disk Read Bytes | Bytes/Second | Read capacity (bytes/second) from block device |
|
| Disk | Disk Write Requests | Count/Second | Number of write requests on block device (requests per second) |
|
| Disk | Disk Read Requests | Count/Second | Number of read requests on block device (requests per second) |
|
| Disk | Average Disk I/O Queue Size | None | Average queue length of requests issued to the block device |
|
| Disk | Disk I/O Utilization | Percent | Proportion of time the block device actually handled I/O operations |
|
| Memory | Memory Usage | Percent | Memory usage |
|
| Network | Network In Bytes | Bytes/Second | Received capacity (bytes/second) on the network interface |
|
| Network | Network Out Bytes | Bytes/Second | Transmitted capacity (bytes/second) on the network interface |
|
| Network | TCP Connections | Count/Second | Current total number of successfully established TCP connections |
|
| Network | Network In Packets | Count | Number of packets received on the network interface |
|
| Network | Network Out Packets | Count | Number of packets transmitted on the network interface |
|
| Network | Network In Dropped | Count | Number of packet drops received on the network interface |
|
| Network | Network Out Dropped | Count | Number of packet drops transmitted on the network interface |
|
| Network | Network In Errors | Count | Number of packet errors received on the network interface |
|
| Network | Network Out Errors | Count | Number of packet errors transmitted on the network interface |
|
Scalable DB Basic Metrics
Category | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| Activelock | Active locks | Count | Number of transactions in lock wait (Lock Wait) state for 1 minute (60 seconds) or longer in the InnoDB storage engine |
|
| Activesession | Active sessions | Count | Number of active sessions |
|
| Activesession | Connection usage | Percent | DB connection session usage rate |
|
| Activesession | Connections | Count | DB connection session |
|
| Activesession | Aborted Connections | Count/Minute | Number of abnormal terminated connections |
|
| Datafile | Current open files | Count | Number of file descriptors opened by the DB |
|
| Datafile | Max open files | Count | Maximum number of file descriptors the DB can open |
|
| Datafile | Open files usage | Percent | DB file maximum count utilization |
|
| InnoDB | InnoDB buffer pool hit ratio | Percent | The proportion of data read directly from memory without accessing the disk |
|
| InnoDB | Innodb row lock wait transactions | Count | Current number of InnoDB transactions waiting for a row lock |
|
| InnoDB | InnoDB row lock time | Milliseconds | Total time waited due to InnoDB row locks (in milliseconds) |
|
| InnoDB | InnoDB deadlocks | Count/Minute | Number of transactions rolled back due to deadlock |
|
| InnoDB | Table lock waits | Count/Minute | Number of waits that occurred to acquire a table lock |
|
| InnoDB | Temp disk tables | Count/Minute | Number of Temp Tables created on disk |
|
| InnoDB | Innodb log waits | Count | Number of times waited to write the redo log to disk |
|
| ProxySQL | Proxy Uptime | Seconds | Express the proxy’s uptime in seconds |
|
| ProxySQL | Backend connections(CONNECTED) | Count | Number of sessions connected to the Proxy server |
|
| ProxySQL | Client connections connected | Count | Number of client sessions currently connected to the proxy |
|
| ProxySQL | Queries routed | Count | Number of queries routed to the backend server |
|
| ProxySQL | Backend connections(ACTIVE, IDLE) | Count | Active / idle connection count per endpoint |
|
| ProxySQL | Backend server status | None | Backend server status
|
|
| ProxySQL | Backend conneciton check | Count | Backend server connection success/failure count | - |
| State | Instance state | None | Check Scalable DB status up/down
| - |
| State | Slave behind master seconds | Seconds | Replica latency (unit: seconds) |
|
| State | Slave io thread running (Replica Only) | None | I/O Thread status
| - |
| State | Slave SQL thread running (Replica Only) | None | SQL Thread status
| - |
| Tablespace | Tablespace used | Megabytes | Tablespace usage |
|
| Tablespace | Tablespace used(TOTAL) | Megabytes | Tablespace usage (total) |
|
| Transactions | Slow queries | Count | Number of queries running longer than 10 seconds |
|
| Transactions | Long transaction time | Seconds | Long Transaction time |
|
| Transactions | Wait locks | Count | Number of sessions waiting for lock |
|
| Transactions | SQL Queries/Minute | Count/Minute | Queries executed per minute |
|
6.7.2 - How-to guides
Users can create the service by entering the required information for Scalable DB (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
Create Scalable DB(DBaaS)
You can create and use the Scalable DB (DBaaS) service in the Samsung Cloud Platform Console.
Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the corresponding Database service cannot be created.
To create a Scalable DB (DBaaS), follow the steps below.
All Services > Database > Scalable DB(DBaaS) Click the menu. 1. Go to the Service Home page of Scalable DB (DBaaS).
On the Service Home page, click the Create Scalable DB (DBaaS) button. 2. Create Scalable DB (DBaaS) Navigate to the page.
On the Scalable DB(DBaaS) Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version Required Provide version list of Scalable DB (DBaaS) Table. Scalable DB (DBaaS) Image and version selection items - Service Information Input (Primary Node) Enter or select the required information.
Category required statusDetailed description Server name Prefix Required Server name where the DB will be installed - must start with a lowercase English letter, and using lowercase letters, numbers, and special characters (
-) enter 3 - 13 characters
- Based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Required Cluster name of DB servers - Enter using English letters, 3 - 20 characters
- A cluster is a unit that groups multiple servers
Service Type > Server Type Required Server type on which the DB will be installed - High Capacity: Large-capacity server with 24 vCores or more
- For detailed information about the server types provided by Scalable DB (DBaaS), refer to Scalable DB(DBaaS) 서버 타입.
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute Request
Service Type > Block Storage Required Block Storage settings used by the DB according to purpose - Base OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volumes that use Samsung Cloud Platform KMS (Key Management System) encryption keys
- The configured storage type is applied identically to additional storage
- Capacity must be entered as a multiple of 8 within the range 16–5,120
- Because large sorts during SQL execution or monthly batch jobs can cause service interruptions, a separate TEMP storage must be allocated and used
- Add: Storage areas for DATA, Archive, TEMP, Backup data
- After selecting Use, enter the storage’s purpose and capacity
- The storage type is applied the same as the type set for DATA, and capacity can be entered as a multiple of 8 within the range 16–5,120
- To add storage, click the Add button; to delete, click the x button. Up to 9 can be added
- Before transmitting backup data, temporarily store it in the BACKUP storage
- If the data to be backed up exceeds 100 GB and undergoes frequent changes, it is recommended to add a separate BACKUP storage for reliable backup; the backup capacity is advised to be set at about 60 % of the DATA capacity
- If BACKUP storage is not added, using the
/tmparea is recommended
- For each service, Archive, TEMP, and BACKUP storages are allocated only one Block Storage each
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- IP can only be generated automatically
- The Public NAT feature is available only when the VPC is connected to an Internet Gateway; checking use allows you to select from reserved IPs in the VPC product’s Public IP. For more details, see Public IP 생성하기
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select when you want to apply different settings for each installed server
- Select a pre‑created VPC, Subnet, IP, and Public NAT
- Enter the IP for each server
- When Use is checked, you can select a reserved IP from the VPC product’s Public IP. For more information, refer to Public IP 생성하기
IP access control Selection Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy.
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button.
- To delete an entered IP, click the x button next to the entered IP.
maintenance period Select Database maintenance window - If you select Use, set the day, start time, and duration
- It is recommended to set a maintenance window for stable management of the DB. Patch operations will be performed at the scheduled time, causing service interruption
- If set to not use, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. Scalable DB(DBaaS) Primary Node Service Information Input Items - must start with a lowercase English letter, and using lowercase letters, numbers, and special characters (
- Service Information Input (Read Node) Enter or select the required information in this area.
Category required statusDetailed description Read Node count Required Select the number of Read Nodes to create within the range 1 - 5 - The Host name is automatically assigned as a combination of the server name prefix + r + a three‑digit number (001 - 999) for each Node
Service Type > Server Type Required Server type on which the DB will be installed - High Capacity: large-capacity server with 24 vCores or more
- For detailed information about the server types provided by Scalable DB (DBaaS), refer to Scalable DB(DBaaS) 서버 타입.
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Create Planned Compute Service: Navigate to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Service Type > Block Storage Required Block Storage settings used by the DB according to purpose - Base OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS, HDD_KMS: Additional encrypted volumes that use Samsung Cloud Platform KMS (Key Management System) encryption keys
- The configured storage type is applied identically to additional storage
- Capacity must be entered as a multiple of 8 within the range 16–5,120
- Because large sorts during SQL execution or monthly batch jobs can cause service interruptions, a separate TEMP storage must be allocated and used
- Add: Storage areas for DATA, Archive, TEMP, Backup data
- After selecting Use, enter the storage’s purpose and capacity
- The storage type is applied the same as the type set for DATA, and the capacity can be entered as a multiple of 8 within the range 16–5,120
- To add storage, click the Add button; to delete, click the x button. Up to 9 can be added
- Before transmitting backup data, temporarily store it in the BACKUP storage
- If the data to be backed up exceeds 100 GB and undergoes frequent changes, it is recommended to add a separate BACKUP storage for reliable backup; the backup capacity is advised to be set at about 60 % of the DATA capacity.
- If a BACKUP storage is not added, using the
/tmparea is recommended
- For each service, Archive, TEMP, and BACKUP storages are allocated only one Block Storage each
- Select a storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same configuration to all installed servers
- Automatically apply the same as the Primary Node configuration items
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select when you want to apply different settings for each installed server
- Automatically applied same as the Primary Node configuration items, IP information can be entered manually
Scaling Policy Settings > Node Count Required Enter the number of Read Nodes referenced commonly by both Auto Scaling and Manual Scaling - Min: Enter the minimum number of nodes to maintain based on the scaling policy, within the range 1 - 5
- Max: Enter the maximum number of nodes to maintain based on the scaling policy, within the range 1 - 5
Scaling policy configuration > Auto Scale-out policy option Auto Scale-out policy detailed settings - Use after selecting, set the detailed items of the execution condition of the Auto Scale-out policy
- Enter the wait time for the Cooldown item, after the scaling operation by the policy is completed, before restarting the scaling operation, enter the wait time within the range 60 – 3,600
Scaling Policy Settings > Auto Scale-in Policy option Auto Scale-in policy detailed settings - After selecting Use, configure the detailed items of the execution condition of the Auto Scale-out policy
- Enter the wait time for the Cooldown item; after the scaling operation by the policy is completed, input the wait time within the range of 60 – 3,600 before restarting the scaling operation
Table. Scalable DB (DBaaS) Read Node Service Information Input Items - Enter or select the required information in the Proxy Service Information Input area.
Category required statusDetailed description Proxy Endpoint Settings > Read Endpoint Port Required Set the port to connect to the Read Node that handles read requests - The port cannot be the same as the Database Port and must be entered within the range 1200 - 65535
Proxy Endpoint Settings > Write Endpoint Port Required Set the Port to connect to the Primary Node that will handle write requests - The port cannot be the same as the Database Port and must be entered within the range 1200 - 65535
Proxy Endpoint Settings > Connection Idle Time Required Enter the idle time in milliseconds (ms) before automatically terminating a client connection with no request - Enter a value within the range 0 - 1,728,000,000
Proxy Endpoint Settings > Read Connection Count Required Set the maximum number of connections that a Proxy can create simultaneously with a Read Node - Enter within the range 10 - 100,000
Proxy Endpoint Settings > Write Connection Count Required Set the maximum number of connections that a Proxy can create simultaneously with the Primary Node - Enter within the range 10 - 100,000
Proxy Endpoint Settings > Lagging Time Required Set the Replication delay time allowed for the Read Node - Enter a value in the range 0 - 126,144,000
Table. Scalable DB (DBaaS) Proxy Service Information Input Items - In the Enter required database configuration information area, enter or select the necessary information.
Category required statusDetailed description Database name Required Server name applied during DB installation - must start with an English letter and be entered using English letters and numbers, 3 - 20 characters long
Database username Required DB user name - An account with the same name is also created on the OS
- Enter using lowercase English letters, 2 to 20 characters
- Restricted database user names can be viewed in the Console
Database password Required Password to use when accessing the DB - Enter 8 - 30 characters including letters, numbers, and special characters (excluding
“‘)
Database password verification Required Re-enter the same password to use for DB access Database Port number Required Port number required for DB connection - Enter the DB port within the range 1200 ~ 65535
Backup > Use Selection Backup usage - Select Use to set backup file retention period, backup start time, and Archive backup interval
Backup > Retention Period Selection Backup retention period - Select the backup retention period, set the file retention period from 7 days to 35 days
- Backup files incur additional charges based on size
Backup > Backup Start Time Selection Backup start time - Select backup start time
- The minutes during which the backup runs (minutes) are set randomly, and the backup end time cannot be set
Backup > Archive backup cycle Selection Archive backup interval - Select the archive backup interval
- The archive backup interval is recommended to be 1 hour. Selecting 5 minutes, 10 minutes, or 30 minutes may affect DB performance.
Parameter Required Parameters to be used in the DB - Query button can be clicked to view detailed information of the parameters
DB character set Required Set the DB character set appropriate for the characters (language) to be used in the DB - The DB is created with the selected character set as the default
time zone Required Standard time zone for the database ServiceWatch log collection Selection ServiceWatch log collection status - use to enable the ServiceWatch log collection feature
- For detailed information about the collected logs, see ServiceWatch 지표
- Up to 5 GB is provided free of charge for all services within the account, and charges apply based on storage size for usage exceeding 5 GB
- When collecting, log groups and log streams are created automatically and cannot be deleted until the resources are removed
- To prevent exceeding 5 GB, it is recommended to delete log data directly or shorten the retention period
Table. Essential items for configuring a Scalable DB (DBaaS) database - In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description tag Selection Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Scalable DB (DBaaS) additional information input fields
- Select the required information in the Image and version selection area.
Summary panel, check the detailed information and estimated charges generated, and click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
Scalable DB(DBaaS) View detailed information
The Scalable DB (DBaaS) service allows you to view and edit the full list of resources and detailed information. Scalable DB (DBaaS) Details page consists of Details, Read Node Status View, Auto Scaling Policy, Tags, Operation History tabs.
To view detailed information about the Scalable DB (DBaaS) service, follow these steps.
- All Services > Database > Scalable DB(DBaaS) Click the menu. 1. Go to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Navigate to the Scalable DB(DBaaS) List page.
- On the Scalable DB(DBaaS) List page, click the resource to view detailed information. 3. Scalable DB(DBaaS) Details Navigate to the page.
- Scalable DB(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Cluster status Cluster status with DB installed - Creating: Creating cluster
- Editing: Cluster is transitioning to an operational state
- Error: Cluster encountered an error during operation
- If it occurs continuously, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Restarting cluster
- Running: Cluster is running normally
- Starting: Starting cluster
- Stopped: Cluster is stopped
- Stopping: Cluster is stopping
- Synchronizing: Synchronizing cluster
- Terminating: Terminating cluster
- Unknown: Unknown cluster status
- If it occurs continuously, contact the administrator
- Upgrading: Cluster is upgrading
Cluster control Button to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
View more features Cluster-related management buttons - Service status synchronization: Retrieve real-time DB service status
- Backup history: When backup is configured, verify successful execution and view the history
- Add node: Add a Read Node to the DB; for detailed instructions on adding nodes, see 노드 추가하기
- Delete node: Delete a Read Node from the DB; for detailed instructions on deleting nodes, see 노드 삭제하기
- Proxy Endpoint configuration management: View and modify Proxy Endpoint settings; for detailed instructions on node deletion, see Proxy Endpoint 설정 관리하기
Service termination Button to cancel the service Table. Scalable DB (DBaaS) status information and additional features
- Scalable DB(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Detailed Information
Scalable DB (DBaaS) List page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed DB image and version information
|
| Cluster name | Cluster name of the DB servers |
| Read Endpoint Port | Port connected to the Read Node that handles read requests |
| Write Endpoint Port | Port connected to the Primary Node that handles write requests |
| Database name | Server name applied during DB installation |
| Database username | DB user name |
| Planned Compute | Resources with Planned Compute configured
|
| maintenance period | DB patch work period setting status
|
| Backup | Backup configuration status
|
| DB character set | Character set to use for the DB |
| ServiceWatch log collection | ServiceWatch Log Collection Configuration Status
|
| Scailing policy node count | Scailing policy node count configuration status
|
| time zone | Standard time zone for the database |
| Network | Network information where the DB is installed (VPC, Subnet, VIP, NAT IP(VIP)) |
| IP access control | Service access policy configuration
|
| Resource Management (Primary) | Primary Node configuration information for the DB server |
| Resource Management (Read Node) | Read Node configuration information for the DB server |
Read Node status query
Read Node Status View tab allows the user to view the server status and replication status of the configured Read Node. For detailed information, please refer to Read Node Status Query.
Auto Scaling policy
The Auto Scaling policy tab lets you add, modify, and delete Auto Scaling policies to manage the automatic scaling and shrinking of Read Nodes. For more details, please refer to Auto Scaling 정책 설정하기.
Tag
Scalable DB (DBaaS) List page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Scalable DB(DBaaS) List page lets you view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Scalable DB (DBaaS) Resources
If you need to manage the created Scalable DB (DBaaS) resources, you can perform the tasks on the Scalable DB(DBaaS) Details page.
Control Operation
If a change occurs to a running Scalable DB (DBaaS) resource, you can start or stop it.
To control the operation of Scalable DB(DBaaS), follow the steps below.
- Click the All Services > Database > Scalable DB(DBaaS) menu. 1. Go to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Scalable DB(DBaaS) List Go to the page.
- Scalable DB(DBaaS) List Click the resource you want to control on the page. 3. Scalable DB(DBaaS) Details Navigate to the page.
- Check the status of Scalable DB (DBaaS) and complete the change using the control button below.
- Start: DB service is installed on the server and the DB service is running (Running).
- Stop: The server where the DB service is installed and the DB service are stopped.
Synchronize Service Status
You can synchronize the real-time service status of Scalable DB (DBaaS).
To view and synchronize the service status of Scalable DB (DBaaS), follow the steps below.
- All Services > Database > Scalable DB (DBaaS) Click the menu. 1. Navigate to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Scalable DB(DBaaS) List Navigate to the page.
- Scalable DB(DBaaS) List Click the resource on the page to view the service status. 3. Scalable DB(DBaaS) Details Navigate to the page.
- Service Status Sync Click the button. 4. While it is being queried, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Managing Proxy Endpoint Settings
You can modify the Proxy Endpoint settings of Scalable DB (DBaaS).
To modify the Proxy Endpoint settings of Scalable DB (DBaaS), follow the steps below.
- All Services > Database > Scalable DB(DBaaS) Click the menu. 1. Navigate to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Go to the Scalable DB (DBaaS) List page.
- Scalable DB(DBaaS) List Click the resource on the page to view the service status. 3. Scalable DB(DBaaS) Details Navigate to the page.
- In the add-on menu, click the Proxy Endpoint Settings Management button. 4. Proxy Endpoint Settings Management Navigate to the page.
- On the Proxy Endpoint Settings Management page, click the Search button. 5. Next, when the query alert appears, click the Confirm button.
- On the Proxy Endpoint Settings Management page, click the Edit button. 6. Go to the Proxy Endpoint Settings Edit page.
- On the Edit Proxy Endpoint Settings page, after modifying the desired items, click the Done button.
Scalable DB(DBaaS) Terminate
You can reduce operating costs by terminating unused Scalable DB (DBaaS). Note that terminating the service may cause the currently operating service to stop immediately, so you should proceed with the termination only after fully considering the impact of a service interruption.
- For a DB with a Replica configured, terminating the Master DB does not delete the Replica. * If you delete the replica as well, cancel it separately from the resource list.
- If you terminate the DB, all stored data and any configured backup data will be deleted.
To cancel Scalable DB(DBaaS), follow the steps below.
- Click the All Services > Database > Scalable DB(DBaaS) menu. 1. Go to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Scalable DB(DBaaS) List Navigate to the page.
- On the Scalable DB(DBaaS) List page, select the resource to cancel and click the Cancel Service button.
- After termination is complete, check whether the resource has been terminated on the Scalable DB(DBaaS) list page.
6.7.2.1 - Read Node Manage
Users can manage Read Node through the Samsung Cloud Platform Console.
Read Node status query
Users can view the server status and replication status of the Read Node via the Read Node Status View tab.
To view the Read Node status of the Scalable DB (DBaaS) service, follow these steps.
- Click the All Services > Database > Scalable DB(DBaaS) menu. Navigate to the Service Home page of Scalable DB(DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. You will be taken to the Scalable DB(DBaaS) List page.
- Click the resource to view detailed information on the Scalable DB(DBaaS) List page. You will be taken to the Scalable DB(DBaaS) Details page.
- On the Scalable DB(DBaaS) Details page, click the Read Node Status tab.
- On the Read Node status query page, click the Status Query button.
- When the alert window appears, click the Confirm button. The query results will be displayed in the Read Node status list.
| Category | Detailed description |
|---|---|
| Read Node status | Read Node server status
|
Configure Auto Scaling Policy
Users can add, modify, and delete Auto Scaling policies through the Auto Scalinng policy tab to manage the automatic scaling and shrinking of Read Nodes. Based on CPU utilization metrics, you can set the minimum and maximum number of Read Nodes, allowing flexible adjustment according to workload changes.
Add Auto Scaling policy
The Scailing policy allows only one policy each for Scale In and Scale Out.
- If a pre‑created policy already exists, it cannot be added.
To add an Auto Scaling policy to the Scalable DB (DBaaS) service, follow these steps.
- Click the All Services > Database > Scalable DB(DBaaS) menu. Navigate to the Service Home page of Scalable DB(DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. You will be taken to the Scalable DB(DBaaS) List page.
- Scalable DB(DBaaS) List Click the resource on the page to view detailed information. Scalable DB(DBaaS) Details You will be taken to the page.
- On the Scalable DB(DBaaS) Detail page, click the Auto Scaling Policy tab.
- On the Auto Scaling policy page, click the Add Policy button.
- When the policy addition window appears, click the Scale policy tab to create it.
- If a pre‑created Scale policy exists, that tab is disabled and cannot be selected.
- Set the detailed items of the selected Scale policy and click the Confirm button.
- The added Scale policy is displayed in the list.
Modify Auto Scaling policy
Follow these steps to modify the Auto Scaling policy of the Scalable DB(DBaaS) service.
- Click the All Services > Database > Scalable DB(DBaaS) menu. Navigate to the Service Home page of Scalable DB(DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. You will be taken to the Scalable DB(DBaaS) List page.
- Click the resource to view detailed information on the Scalable DB(DBaaS) List page. You will be taken to the Scalable DB(DBaaS) Details page.
- On the Scalable DB(DBaaS) Details page, click the Auto Scaling Policy tab.
- On the Auto Scaling policy page, click the Edit button for the policy you want to modify.
- When the policy edit window appears, modify the desired information and click the Confirm button.
Delete Auto Scaling policy
To delete the Auto Scaling policy of the Scalable DB (DBaaS) service, follow the steps below.
- Click the All Services > Database > Scalable DB(DBaaS) menu. Navigate to the Service Home page of Scalable DB(DBaaS).
- Click the Scalable DB(DBaaS) menu on the Service Home page. You will be taken to the Scalable DB(DBaaS) List page.
- Click the resource to view detailed information on the Scalable DB(DBaaS) List page. You will be taken to the Scalable DB(DBaaS) Details page.
- On the Scalable DB(DBaaS) Details page, click the Auto Scaling Policy tab.
- On the Auto Scaling policy page, select the policy to delete and click the Delete button.
- When the policy deletion is complete, it disappears from the list.
Add Read Node
When creating a Scalable DB(DBaaS) service, you can add a Read Node under the same conditions as the Primary Node settings you configured.
- You can add nodes only when the cluster status is Running.
- When creating a Scalable DB (DBaaS) service, you cannot add nodes if the configured maximum number of nodes has been reached.
- If there is a Failed Node among the existing Read Nodes, you cannot add a node. Delete the Failed Node and then add the node again.
To add a Read Node to the Scalable DB (DBaaS) service, follow the steps below.
- Click the All Services > Database > Scalable DB(DBaaS) menu. Navigate to the Service Home page of Scalable DB(DBaaS).
- Click the Scalable DB(DBaaS) menu on the Service Home page. You will be taken to the Scalable DB(DBaaS) List page.
- Click the resource to view detailed information on the Scalable DB(DBaaS) List page. You will be taken to the Scalable DB(DBaaS) Details page.
- On the Scalable DB(DBaaS) Details page, click Additional Functions > Add Node. You will be taken to the Add Read Node page.
- Add Read Node Check the specifications on the page and click the Complete button.
- If you need to assign an IP for the Read Node, please enter the IP in the Network > Server-specific Settings > IP field.
Delete Read Node
You can delete the Read Node of the Scalable DB (DBaaS) service.
- Nodes can be deleted only when the cluster status is Running.
- If you delete a node and the remaining number of nodes is less than the configured minimum, you cannot delete the node.
To delete the Read Node of the Scalable DB (DBaaS) service, follow the steps below.
- Click the All Services > Database > Scalable DB(DBaaS) menu. Navigate to the Service Home page of Scalable DB(DBaaS).
- Click the Scalable DB(DBaaS) menu on the Service Home page. Navigate to the Scalable DB(DBaaS) List page.
- Scalable DB(DBaaS) List Click the resource to view detailed information. Scalable DB(DBaaS) Details You will be taken to the page.
- Scalable DB(DBaaS) Details on the page, click Additional Functions > Delete Node.
- When the Delete dialog for Read Node appears, select the items to delete and click the Delete button.
- When the alert window appears, enter the name of the node to delete and click the Confirm button.
- Read Node In the delete dialog, verify that the selected node has been removed from the node list, and click the Confirm button.
6.7.2.2 - Backup DB
Users can configure backups of Scalable DB (DBaaS) through the Samsung Cloud Platform Console.
Scalable DB(DBaaS) Backup
Scalable DB (DBaaS) provides data backup functionality based on its own backup commands. Additionally, it provides a backup environment optimized for data protection and management through backup history verification and backup file deletion functions.
Configure backup
Refer to Scalable DB(DBaaS) 생성하기 for backup configuration of Scalable DB (DBaaS).
To modify the backup settings of the created resource, follow the steps below.
- For reliable backups, we recommend adding a separate BACKUP storage or sufficiently expanding the storage capacity.
- Especially when the backup data exceeds 100 GB and undergoes frequent changes, please provision additional storage amounting to approximately 60 % of the data size.
- If a backup is configured, it will run at the designated time after the set time, and additional fees will apply based on the backup size.
- If you change the backup setting to Unset, backup execution will stop immediately, and the stored backup data will be deleted and can no longer be used.
To set up a backup, follow these steps.
- All Services > Database > Scalable DB(DBaaS) Click the menu. 1. Go to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Scalable DB(DBaaS) List Navigate to the page.
- Scalable DB(DBaaS) List On the page, click the resource to configure backup. 3. Scalable DB(DBaaS) Details Navigate to the page.
- Click the Edit button for the backup item. 4. Backup Settings popup window opens.
- When configuring a backup, click Use in the Backup Settings popup, select the retention period, backup start time, and Archive backup cycle, then click the Confirm button.
- If you wish to stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Once user authentication is complete, the backup configuration is disabled and backup execution stops.
- If you wish to stop the backup configuration, deselect Use in the Backup Settings popup and authenticate using the logged-in user’s mobile phone.
Check backup history
To view the backup history, follow these steps.
- Click the All Services > Database > Scalable DB(DBaaS) menu. 1. Navigate to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Scalable DB(DBaaS) List Go to the page.
- Scalable DB(DBaaS) List page: click the resource to view the backup history. 3. Scalable DB(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup file
To delete the backup history, follow these steps.
- Click the All Services > Database > Scalable DB (DBaaS) menu. 1. Navigate to the Service Home page of Scalable DB (DBaaS).
- On the Service Home page, click the Scalable DB(DBaaS) menu. 2. Scalable DB (DBaaS) List Go to the page.
- Scalable DB(DBaaS) List On the page, click the resource to view the backup history. 3. Scalable DB(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, check the files you want to delete, then authenticate via the logged-in user’s mobile phone.
- When user authentication is completed, the backup file is deleted.
6.7.3 - Release Note
Scalable DB(DBaaS)
- You can monitor logs by integrating with Servicewatch.
- The fully managed Database service, Scalable DB (DBaaS), which flexibly adjusts resources according to traffic changes, has been launched.
7 - Data Analytics
We provide an analytics service that can process big data easily and quickly.
7.1 - Event Streams
7.1.1 - Overview
Service Overview
Event Streams provides fully managed creation and configuration of the open-source Apache Kafka for large-scale, high-volume message data processing. Samsung Cloud Platform automates the creation and configuration of Apache Kafka through a web-based console, allowing users to configure the main components of Apache Kafka—Broker, Zookeeper, and AKHQ—in either a single or clustered setup.
The Event Streams cluster consists of multiple Broker nodes; you can install between 1 and 10 Brokers, typically deploying three or more. Zookeeper can be installed separately to manage the distributed Brokers, but if not installed separately, it is installed on the Broker nodes. Additionally, we provide AKHQ (Apache Kafka HQ), a tool for managing Kafka, allowing users to perform cluster operation and management through it.
Provided features
Event Streams provides the following features.
- Auto Provisioning: You can configure and set up an Apache Kafka cluster via the UI.
- Operation Control Management: Provides functionality to control the status of running servers. In addition to starting and stopping the cluster, restarting is possible to apply configuration changes.
- AKHQ provision: We provide AKHQ, a tool for managing Kafka, enabling users to manage and monitor clusters.
- Add Broker node: If expansion is required to improve cluster performance and stability, you can add a node with the same specifications as the existing Broker nodes.
- Parameter management: You can configure and modify parameters related to performance improvement and security.
- Monitoring: CPU, memory, performance monitoring information can be accessed via Cloud Monitoring and Servicewatch.
Component
Event Streams provides pre‑validated engine versions and various server types in accordance with its open‑source support policy. Users can select and use them based on the scale of the service they wish to configure.
Engine version
The engine versions supported by Event Streams are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is stopped is set to six months before the EoTS date.
The EOS and EoTS dates may change according to the supplier’s policy, so please refer to the supplier’s license management policy page for details.
- Apache Kafka: https://docs.confluent.io/platform/current/installation/versions-interoperability.html
| Provided version | EoS Date | EoTS Date |
|---|---|---|
| 3.8.0 | 2026-07 (planned) | 2026-12-02 |
| 3.9.1 | 2026-09 (planned) | 2027-02-19 |
Server Type
The server types supported by Event Streams are as follows.
For detailed information about the server types provided by Event Streams, refer to Event Streams Server Types.
Standard ess1v2m4
| Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | ess1 | Provided server specifications
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
7.1.1.1 - Server Type
Event Streams server type
Event Streams provides server types composed of various combinations such as CPU, Memory, and Network Bandwidth. When creating Event Streams, Apache kafka is installed according to the server type selected for the intended purpose.
The server types supported by Event Streams are as follows.
Standard ess1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | ess1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Check the node’s minimum specifications as shown below and select the server type.
| Category | vCPU | Memory |
|---|---|---|
| Broker | 2 vCore | 4 GB |
| Zookeeper | 1 vCore | 2 GB |
ess1 server type
The ess1 server type of Event Streams is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 64 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | ess1v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | ess1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | ess1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | ess1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | ess1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | ess1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | ess1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | ess1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | ess1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
ess2 server type
The ess2 server type of Event Streams is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 64 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | CPU vCore | Memory | Network Bandwidth(Gbps) |
|---|---|---|---|---|
| Standard | ess2v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | ess2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | ess2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | ess2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | ess2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | ess2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | ess2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | ess2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | ess2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
esh2 server type
The esh2 server type of Event Streams is offered with high-capacity server specifications and is suitable for database workloads that require large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 32 vCPUs and 128 GB of memory
- Up to 25 Gbps networking speed
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | esh2v32m64 | 32 vCore | 64 GB | Up to 25 Gbps |
| High Capacity | esh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
7.1.1.2 - Monitoring Metrics
According to the policy of Samsung Cloud Platform, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, Event Streams will no longer be able to monitor resources via Cloud Monitoring after the service improvement work in July 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service, which was released in October 2025.
- Resources created after the service improvement work in March 2026 are provided with monitoring based on the ServiceWatch service by default.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
Event Streams monitoring metrics
The table below shows the performance monitoring metrics for Event Streams that can be viewed through Cloud Monitoring. For detailed Cloud Monitoring usage, see the Cloud Monitoring guide.
For Event Streams server monitoring metrics, refer to the Virtual Server Monitoring Metrics guide.
| Performance items | Detailed description | unit |
|---|---|---|
| AKHQ State [PID] | AHKQ process PID | PID |
| Connections [Zookeeper Client] | Number of ZooKeeper connections | cnt |
| Disk Used | datadir usage | bytes |
| Failed [Client Fetch Request] | Client fetch request processing failure count | cnt |
| Failed [Produce Request] | Procucer request processing failure count | cnt |
| Incomming Messages | Number of messages received by the broker | cnt |
| Instance State [PID] | kafka process PID | PID |
| Kibana state [PID] | Kibana process PID | PID |
| Leader Elections | Number of Leader Election occurrences | cnt |
| Leader Elections [Unclean] | Number of Unclean Leader Election occurrences | cnt |
| Log Flushes | Number of log flush occurrences | cnt |
| Network In Bytes | Total bytes received by the entire Topic | bytes |
| Network Out Bytes | Total bytes transmitted by the Topic | bytes |
| Rejected Bytes | Total bytes rejected by the Topic | bytes |
| Request Queue Length | Request queue size | cnt |
| Shards | Cluster shard count | cnt |
| Zookeeper Sessions [Closed] | ZooKeeper closed sessions per second | cnt |
| Zookeeper Sessions [Expired] | ZooKeeper expired sessions per second | cnt |
| Zookeeper State [PID] | zookeeper process PID | PID |
7.1.1.3 - ServiceWatch Metrics
Event Streams sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at 1‑minute intervals.
Basic Metrics
The following are the basic metrics for the Event Streams namespace.
Indicators whose names are shown in bold below are the indicators selected as key metrics among the default metrics provided by Event Streams. Key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric provides guidance in the user guide about which statistical value is meaningful when querying that metric, and among the meaningful statistics, the statistical values displayed in bold text are the primary statistics. In the service dashboard, primary metrics can be viewed using the primary statistical values.
OS Basic Metrics
Category | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| CPU | CPU Usage | Percent | CPU usage |
|
| Disk | Disk Usage | Percent | Disk usage |
|
| Disk | Disk Write Bytes | Bytes/Second | Write throughput (bytes/second) on block device |
|
| Disk | Disk Read Bytes | Bytes/Second | Read capacity (bytes/second) from block device |
|
| Disk | Disk Write Requests | Count/Second | Number of write requests on block device (requests per second) |
|
| Disk | Disk Read Requests | Count/Second | Number of read requests on block device (requests per second) |
|
| Disk | Average Disk I/O Queue Size | None | Average queue length of requests issued to the block device |
|
| Disk | Disk I/O Utilization | Percent | The proportion of time the block device actually spent handling I/O operations |
|
| Memory | Memory Usage | Percent | Memory usage |
|
| Network | Network In Bytes | Bytes/Second | Received data rate (bytes/second) on the network interface |
|
| Network | Network Out Bytes | Bytes/Second | Transmitted capacity (bytes/second) on the network interface |
|
| Network | TCP Connections | Count/Second | Current total number of successfully established TCP connections |
|
| Network | Network In Packets | Count | Number of packets received on the network interface |
|
| Network | Network Out Packets | Count | Number of packets transmitted on the network interface |
|
| Network | Network In Dropped | Count | Number of packet drops received on the network interface |
|
| Network | Network Out Dropped | Count | Number of packet drops transmitted from the network interface |
|
| Network | Network In Errors | Count | Number of packet errors received on the network interface |
|
| Network | Network Out Errors | Count | Number of packet errors transmitted on the network interface |
|
Event Streams basic metrics
Category | Performance items | unit | Detailed description | meaningful statistics |
|---|---|---|---|---|
| JVM | JVM Threads Current | Count | Number of currently active threads |
|
| JVM | JVM Memory Usage | Bytes | Current amount of memory used by the JVM |
|
| JVM | Time spent in GC | None | JVM time spent on garbage collection (GC seconds per minute) |
|
| JVM | Count in GC | Count/Minute | Number of times the JVM executed the garbage collection method |
|
| kafka_controller | Offline Partitions | Count | Number of partitions that cannot be written to or read from because there is no active leader |
|
| kafka_controller | Active Controller | Count | Number of active controllers in the cluster |
|
| kafka_controller | Total of Topics | Count | Number of global topics observed in the active controller |
|
| kafka_controller | Leader Elections | Count/Minute | Leader election when a broker fails |
|
| kafka_controller | Unclean Leader Elections | Count/Minute | Elect a broker with OSR (out-of sync replica) as the leader |
|
| kafka_network | Request Queue | Count | Request queue size |
|
| kafka_server | Zookeeper Expired Sessions | Count/Minute | Zookeeper expired session |
|
| kafka_server | Incoming Messages | Count/Second | Message received by the Broker |
|
| kafka_server | Producer requests | Count/Second | Request (Produce) received by the Broker |
|
| kafka_server | Consumer requests | Count/Second | Request (Fetch) received by the Broker |
|
| kafka_server | Failed Fetch Requests | Count/Minute | Number of failed fetches by the Consumer |
|
| kafka_server | Failed Produce Requests | Count/Minute | Number of failed requests by the Producer |
|
| kafka_server | Incoming Byte Rate | Bytes/Seconds | Byte transmission rate received from client (per broker) |
|
| kafka_server | Outgoing Byte Rate | Bytes/Seconds | Byte transmission rate to the client (by broker) |
|
| kafka_server | Rejected Byte Rate | Bytes/Seconds | Bytes rejected per broker because the record batch size exceeds the max.message.bytes setting |
|
| kafka_server | Online Partitions | Count | Total number of partitions |
|
| kafka_server | Leader Partitions | Count | leader partition count |
|
| kafka_server | Under Replicated Partitions | Count | Number of partitions with insufficient replica count |
|
| kafka_server | Under Minisr Partitions | Count | Number of partitions whose in-sync replica count is less than minIsr |
|
| Systemd | Active Systemd Unit | None | Service Status
| - |
7.1.2 - How-to guides
Users can create the service by entering the required information for Event Streams and selecting detailed options through the Samsung Cloud Platform Console.
According to the policy of Samsung Cloud Platform, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, Event Streams will no longer be able to monitor resources via Cloud Monitoring after the service improvement work in July 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
- Resources created after the service improvement work in March 2026 are provided with monitoring based on the ServiceWatch service by default.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
Create Event Streams
You can create and use the Event Streams service in the Samsung Cloud Platform Console.
Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the creation of the corresponding Database service is not possible.
To create Event Streams, follow these steps.
All Services > Data Analytics > Event Streams click the menu. 1. Navigate to the Service Home page of Event Streams.
On the Service Home page, click the Create Event Streams button. 2. Go to the Create Event Streams page.
Event Streams creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category required statusDetailed description Image version Required Provide a list of Event Streams versions Table. Event Streams service information input items - In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Server name Prefix Required The server name where Apache Kafka will be installed - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
-) with a length of 3 to 13 characters
- A postfix such as 001, 002 is appended to the base server name to generate the actual server name
Cluster name Required Cluster name of the servers - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Broker > Number of Broker Nodes Required Number of Broker Nodes Broker > server type Required Server type for installing the Broker - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more
- For detailed information about the server types provided by Event Streams, see Event Streams server types.
Broker > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Broker > Block Storage Required Block Storage type to be used for the Broker node - Base OS: The area where the engine is installed
- DATA: Data file storage area
- Select the storage type and then enter the capacity (for details on each Block Storage type, see Block Storage 생성하기)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management System) encryption keys
- Enter the capacity as a multiple of 8 within the range 16 to 5,120
- Select the storage type and then enter the capacity (for details on each Block Storage type, see Block Storage 생성하기)
Zookeeper separate installation > use Select Whether to install Zookeeper nodes separately - If you select Use, install Zookeeper nodes separately
- If Zookeeper nodes are not installed separately, the Broker node also performs the Zookeeper role
Zookeeper separate installation > server type Select Server type on which Zookeeper will be installed - Zookeeper nodes provide vCPU 1, Memory 2G or vCPU 2, Memory 4G
Zookeeper separate installation > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute Apply
Separate Zookeeper installation > Block Storage Required Block Storage type to be used for Zookeeper nodes - Default OS: Area where the engine is installed
- DATA: Data file storage area
- After selecting the storage type, enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS/HDD_KMS: Additional encrypted volume using Samsung Cloud Platform KMS (Key Management System) encryption keys
- Enter the capacity as a multiple of 8 within the range 16 to 5,120
- After selecting the storage type, enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
AKHQ > Use Required Whether to install AKHQ - If you select Use, AKHQ will be installed
AKHQ > Server Type Required Server type on which AKHQ will be installed - AKHQ only provides the vCPU 2, Memory 4G type
AKHQ > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
AKHQ > Block Storage Required Block Storage type to be used on the server where AKHQ is installed - Base OS: area where the engine is installed
AKHQ > AKHQ account Required AKHQ account - Enter using lowercase English letters, 2 ~ 20 characters
AKHQ > AKHQ password Required AKHQ account password - English letters, numbers, and special characters (
“‘excluded) including 8 ~ 30 characters
AKHQ > Verify AKHQ password Required Confirm AKHQ account password - Re-enter the AKHQ account password identically
AKHQ > AKHQ Port number Required AKHQ connection port number - The port number is automatically set to 8080 and cannot be modified
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC and Subnet
- IP: only automatic generation is possible
- For Public NAT settings, it is only possible in per‑server configuration
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select if you want to apply different settings per installed server
- Select a pre‑created VPC and Subnet
- IP: Enter the IP for each server
- Public NAT feature is available only when the VPC is connected to an Internet Gateway; checking Use allows selection from the reserved IPs in the VPC product’s Public IP pool. For details, see Public IP 생성하기
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy
- Enter the IP in IP format (e.g.,
192.168.10.1) or CIDR format (e.g.,192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the IP
maintenance period Select Event Streams maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable service management. Patch operations will be performed at the scheduled time, and service interruption may occur
- We are not responsible for issues arising from patches not being applied (set as not used)
Table. Event Streams service configuration items - must start with a lowercase English letter and be entered using lowercase letters, numbers, and the special character (
- Enter required database configuration information In this area, enter or select the required information.
Category required statusDetailed description Zookeeper SASL account Required Zookeeper account - Enter using lowercase English letters, 2 to 20 characters
Zookeeper SASL password Required Zookeeper account password - including English letters, numbers, and special characters (
“‘excluded) and enter 8 to 30 characters
Check Zookeeper SASL password Required Verify Zookeeper account password - Re-enter the Zookeeper SASL account password identically
Zookeeper Port number Required Zookeeper port number 1200 ~ 65535must be entered as one of them, and the Broker port or2888,3888cannot be used
Broker SASL account Required Kafka login account - Enter using lowercase English letters, 2 ~ 20 characters
Broker SASL password Required Kafka login account password - Enter 8 to 30 characters, including English letters, numbers, and special characters (excluding
“‘)
Verify Broker SASL password Required Verify Kafka connection account password - Re-enter the Broker SASL account password identically
Broker Port number Required Kafka port number 1200 ~ 65535can be entered as one of, and the Broker port or2888,3888 cannot be used
Parameter Required Event Streams configuration parameters - View button can be clicked to view detailed information of the parameters
- Parameters can be modified after the service creation is complete, and a restart is required when modified
time zone Select Standard time zone for the service ServiceWatch log collection Select ServiceWatch log collection status - Use to configure the ServiceWatch log collection feature
- For details about the collected logs, refer to ServiceWatch 지표
- It is provided free of charge up to 5 GB for all services within the account, and charges apply based on storage usage for amounts exceeding 5 GB
- When collecting, log groups and log streams are created automatically, and they cannot be deleted until the resources are removed
- To prevent exceeding 5 GB, it is recommended to delete log data directly or shorten the retention period
Table. Required input items for configuring Event Streams Database - In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description tag Select Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag
- You can add up to 50 tags
- The newly added tags are applied after the service creation is completed
Table. Event Streams service additional information input fields
- Select the required information in the Image and version selection area.
Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
View Event Streams details
The Event Streams service lets you view and modify the complete list of resources and their detailed information. The Event Streams Details page consists of the Details, Tags, Activity Log tabs.
To view detailed information about the Event Streams service, follow these steps.
- All Services > Data Analytics > Event Streams Click the menu. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Go to the Event Streams list page.
- On the Event Streams List page, click the resource to view detailed information. 3. Go to the Event Streams Details page.
- Event Streams Details At the top of the page, status information and additional feature details are displayed.
Category Detailed description Cluster status Cluster status - Creating: The cluster is being created
- Editing: The cluster is being changed to an operational state
- Error: The cluster encountered a failure while performing a task
- If this persists, contact the administrator
- Failed: The cluster failed during creation
- Restarting: The cluster is restarting
- Running: The cluster is operating normally
- Starting: The cluster is starting
- Stopped: The cluster is stopped
- Stopping: The cluster is stopping
- Synchronizing: The cluster is synchronizing
- Terminating: The cluster is being terminated
- Unknown: The cluster status is unknown
- If this persists, contact the administrator
- Upgrading: The cluster is being upgraded
Cluster control Button to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
See more features Cluster management buttons - Service status synchronization: Retrieve the current server status and synchronize it to the Console
- Parameter management: View and modify service configuration parameters
- Add Broker Node: Add a Broker Node
- When configured as a cluster, the Add Broker Node button is displayed
Service cancellation Cancel service button Table. Event Streams status information and additional features
- Event Streams Details At the top of the page, status information and additional feature details are displayed.
Detailed information
Event Streams List page allows you to view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | Installed service image and version information
|
| Cluster name | Cluster name of the configured servers |
| Planned Compute | Resource status with Planned Compute configured
|
| maintenance period | Patch work period configuration status
|
| time zone | Standard time zone for the service |
| Zookeeper Port number | Zookeeper port number |
| Broker Port number | Kafka port number |
| AKHQ connection information | AKHQ connection information |
| ServiceWatch log collection | ServiceWatch Log Collection Configuration Status
|
| Network | Installed network information (VPC, Subnet) |
| IP access control | Service access policy settings
|
| Zookeeper | Server type, base OS, and additional Disk information
|
| Broker | Server type, base OS, and additional Disk information for the Broker node
|
| AKHQ | Server type and basic OS information for the AKHQ node
|
tag
Event Streams List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
On the Event Streams List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Event Streams Resources
If you need to change the existing configuration options of a created Event Streams resource, manage parameters, or add a Broker Node configuration, you can perform the tasks on the Event Streams Details page.
Control operation
If changes occur to a running Event Streams resource, you can start, stop, or restart it.
To control the operation of Event Streams, follow these steps.
- All Services > Data Analytics > Event Streams Click the menu. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Go to the Event Streams list page.
- On the Event Streams list page, click the resource you want to control. 3. Go to the Event Streams Details page.
- Check the Event Streams status and complete the change using the control button below.
- Start: Event Streams service is installed on the server and the Event Streams service is running (Running).
- Stop: The server where the Event Streams service is installed and the Event Streams service will be stopped (Stopped).
- Restart: Only the Event Streams service will be restarted.
Synchronize service status
You can query the current server status and synchronize it to the Console.
To synchronize the service status of Event Streams, follow these steps.
- All Services > Data Analytics > Event Streams Click the menu. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Go to the Event Streams list page.
- On the Event Streams List page, click the resource to view the service status. 3. Go to the Event Streams Details page.
- Service Status Sync Click the button. 4. The query takes a short amount of time, and while it is being performed, the cluster changes to the Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Manage Parameters
Provides parameter lookup and edit functionality.
To view and modify configuration parameters, follow the steps below.
- Click the All Services > Data Analytics > Event Streams menu. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Navigate to the Event Streams list page.
- On the Event Streams List page, click the resource whose parameters you want to view and edit. 3. Go to the Event Streams Details page.
- Click the Parameter Management button. 4. Go to the Parameter Management page.
- On the Parameter Management page, click the Search button. 5. Database query The popup window opens.
- To view the Parameter information, click the Confirm button. 6. Retrieving may take a short amount of time.
- You can modify the Parameter information after performing a query.
- To edit the Parameter information, click the Edit button and then enter the changes in the Custom Value field of the Parameter you want to modify.
- When the Application Type is Dynamic, it takes effect immediately, and when it is Static, a service restart is required, causing service interruption.
- When the input is complete, click the Save button.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- If the server type is configured as Standard, it cannot be changed to High Capacity. * If you want to change to High Capacity, create a new service.
- If you modify the server type, a server restart is required. * Please separately verify any SW license modifications or SW settings and their implementation due to specification changes.
- All Services > Data Analytics > Event Streams Click the menu. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Event Streams List navigate to the page.
- On the Event Streams list page, click the resource whose server type you want to change. 3. Go to the Event Streams Details page.
- Click the Edit button for the server type you want to change at the bottom of the detailed information. 4. Edit Server Type popup window opens.
- Server Type Edit After selecting the server type in the popup window, click the Confirm button.
Expand storage
Storage added to the data area can be expanded up to a maximum of 5 TB based on the initially allocated capacity. You can expand storage without stopping Event Streams, and when configured as a cluster, all nodes are expanded simultaneously.
- If encryption is configured on the existing Block Storage, encryption will also be applied to the additional Disk.
- Disk size modification is only possible by increasing it by at least 16 GB over the current disk size.
To increase storage capacity, follow the steps below.
- All Services > Data Analytics > Event Streams click the menu. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Go to the Event Streams list page.
- On the Event Streams list page, click the resource for which you want to change the server type. 3. Go to the Event Streams Details page.
- Click the Edit button for the added Disk you want to expand at the bottom of the detailed information. 4. Disk Edit The popup window opens.
- Disk Edit After entering the expanded capacity in the popup window, click the Confirm button.
Add Broker Node
If you need to expand the Event Streams cluster, you can add nodes with the same specifications as the Broker Node you are using. The added nodes are incorporated into the existing cluster without server downtime, and the existing data is automatically redistributed.
- You can use up to 10 nodes within the cluster. * Please note that additional charges apply to the created nodes.
- During node addition, the cluster’s performance may degrade.
To add a Broker node, follow these steps.
- All Services > Data Analytics > Event Streams menu, please click. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Go to the Event Streams list page.
- On the Event Streams resource list page, click the resource you want to recover. 3. Navigate to the Event Streams Details page.
- Click the Add Broker Node button. 4. Go to the Add Broker Node page.
- After entering the relevant information in the Enter required information area, click the Complete button.
Category required statusDetailed description Server name Required The server name where the Broker is installed - It is set to the server name configured in the original cluster.
Cluster name Required Cluster name - It is set to the cluster name configured in the original cluster.
Additional Node Count Required Number of Nodes to add - Use up to 10 nodes per cluster
Service Type > Server Type Required The server type on which the Broker will be installed - is set to be the same as the server type configured in the original cluster.
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Service Type > Block Storage Required Block Storage settings for the Broker node - The storage type and capacity configured in the original cluster are applied identically
Network Required The network on which the servers are installed - is applied identically to the network configured in the original cluster
Table. Additional items for Event Streams Broker Node
Cancel Event Streams
You can cancel unused Event Streams to reduce operating costs. However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may arise from service interruption.
To cancel Event Streams, follow these steps.
- All Services > Data Analytics > Event Streams Click the menu. 1. Navigate to the Service Home page of Event Streams.
- On the Service Home page, click the Event Streams menu. 2. Go to the Event Streams list page.
- On the Event Streams List page, select the resource to cancel and click the Cancel Service button.
- After the termination is complete, check on the Event Streams list page whether the resource has been terminated.
7.1.3 - API Reference
7.1.4 - CLI Reference
7.1.5 - Release Note
Event Streams
- Provides Terraform.
- Provides additional HDD, HDD_KMS disk types.
- The Event Streams service, which easily creates and manages Apache Kafka clusters in a web environment, has been launched.
7.2 - Search Engine
7.2.1 - Overview
Service Overview
Search Engine provides automated creation and configuration of the distributed search and analytics engines Elasticsearch and OpenSearch through a web-based console. Users can select a server type that matches the system configuration to set up a cluster, and it supports the data analysis and visualization tools Kibana and the OpenSearch dashboard.
- Search Engine provides the Elasticsearch Enterprise version and the OpenSearch version.
- Elasticsearch Enterprise’s software license uses a user-owned license (BYOL, Bring Your Own License), and software licensing policies in cloud environments must follow the vendor’s policies.
The Search Engine Cluster consists of multiple master nodes and data nodes. Data nodes can be installed from a minimum of one up to a maximum of ten, and are typically deployed with three or more. If a master node is not installed separately, the data nodes also perform the master node role, and up to ten can be installed. When master nodes are installed separately, up to 50 data nodes are possible.
Provided features
Search Engine provides the following features.
- Auto Provisioning (Auto Provisioning): You can configure and set up Elasticsearch and OpenSearch clusters via the UI.
- Operation Control Management: Provides functionality to control the status of running servers. In addition to starting and stopping the cluster, it can be restarted to apply configuration values.
- Backup and Recovery: You can back up using the built-in backup feature, and you can restore to the point in time of the backup file.
- Add Data Node: If cluster expansion is required, you can add nodes with the same specifications as the existing data nodes. Up to 10 nodes can be added within the cluster.
- Visualization Tool Support: Provides data analysis and visualization tools, and supports Elasticsearch Kibana or OpenSearch dashboards.
- Monitoring: CPU, memory, and cluster performance monitoring information can be accessed through the Cloud Monitoring service.
Component
Search Engine provides pre‑validated engine versions and various server types in accordance with its open‑source support policy. Users can select and use them based on the scale of the service they wish to configure.
Engine version
The engine versions supported by Search Engine are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is halted is set to six months before the EoTS date.
The EOS and EoTS dates may change according to the supplier’s policy, so please refer to the supplier’s license management policy page for details.
- Elasticsearch: https://www.elastic.co/kr/support/eol
The next version of Search Engine is scheduled to be offered after March 2026. The actual service schedule may change.
- OpenSearch version 3.4.0
| Provided version | EoS Date | EoTS Date |
|---|---|---|
| 8.15.0 | 2027-01 (planned) | 2027-07-15 |
| 8.19.7 | 2027-01 (planned) | 2027-07-15 |
- OpenSearch: https://opensearch.org/releases/
| Provided version | EoS Date | EoTS Date |
|---|---|---|
| 2.19.3 | 2027-01 (planned) | 2027-07-15 |
| 3.4.0 | TBD | TBD |
Server Type
The server types supported by Search Engine are as follows.
For detailed information about the server types provided by Search Engine, see Search Engine Server Types.
Standard se1v2m4
| Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | se1 | Provided server specifications
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
7.2.1.1 - Server Type
Search Engine server type
Search Engine provides server types composed of various combinations such as CPU, Memory, and Network Bandwidth. When creating a Search Engine, Elastic Search is installed according to the server type selected for the intended use.
The server types supported by Search Engine are as follows.
Standard ses1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | db1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
ses1 server type
The ses1 server type of Search Engine is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | ses1v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | ses1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | ses1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | ses1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | ses1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | ses1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | ses1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | ses1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | ses1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | ses1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | ses1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | ses1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | ses1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | ses1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | ses1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | ses1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | ses1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | ses1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | ses1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | ses1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | ses1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | ses1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | ses1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | ses1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | ses1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | ses1v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | ses1v12m48 | 12 vCore | 48 GB | Maximum 12.5 Gbps |
| Standard | ses1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | ses1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | ses1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | ses1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | ses1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | ses1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | ses1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | ses1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | ses1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | ses1v16m64 | 16 vCore | 64 GB | Maximum 12.5 Gbps |
| Standard | ses1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | ses1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | ses1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
ses2 server type
The ses1 server type of Search Engine is offered with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | CPU vCore | Memory | Network Bandwidth(Gbps) |
|---|---|---|---|---|
| Standard | ses2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | ses2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | ses2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | ses2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | ses2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | ses2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | ses2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | ses2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | ses2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | ses2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | ses2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | ses2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | ses2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | ses2v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | ses2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | ses2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | ses2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | ses2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | ses2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | ses2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | ses2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | ses2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | ses2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | ses2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | ses2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | ses2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | ses2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | ses2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | ses2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | ses2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | ses2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | ses2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | ses2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | ses2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | ses2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | ses2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | ses2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | ses2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | ses2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | ses2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
seh2 server type
The seh2 server type of Search Engine is offered with high-capacity server specifications and is suitable for database workloads for large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 72 vCPUs and 288 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | seh2v24m48 | 24 vCore | 48 GB | Maximum 25 Gbps |
| High Capacity | seh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | seh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | seh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | seh2v32m64 | 32 vCore | 64 GB | Maximum 25 Gbps |
| High Capacity | seh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | seh2v32m256 | 32 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | seh2v48m96 | 48 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | seh2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | seh2v64m128 | 64 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | seh2v64m256 | 64 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | seh2v72m144 | 72 vCore | 144 GB | Maximum 25 Gbps |
| High Capacity | seh2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
7.2.1.2 - Monitoring metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Notice on Applying Monitoring Service by Resource
- New Resources: Resources created after the service improvement work in July 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide monitoring concurrently through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings linked with existing Cloud Monitoring (e.g. You need to review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Cloud Monitoring Service Phased Termination Schedule Notice
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, Cloud Monitoring data cannot be accessed. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch is available in the ServiceWatch Overview.
Search Engine Monitoring Metrics
The table below shows the performance monitoring metrics for Event Streams that can be viewed through Cloud Monitoring. For detailed Cloud Monitoring usage, refer to the Cloud Monitoring guide.
Refer to the Virtual Server Monitoring Metrics guide for the Search Engine server monitoring metrics.
| Performance items | Detailed description | unit |
|---|---|---|
| Disk Usage | datadir usage | MB |
| Documents [Deleted] | Total number of deleted documents | cnt |
| Documents [Existing] | Total number of existing documents | cnt |
| Filesystem Bytes [Available] | Available file systems | bytes |
| Filesystem Bytes [Free] | Available file system | bytes |
| Filesystem Bytes [Total] | Total file system | bytes |
| Instance Status [PID] | Elasticsearch process PID | PID |
| JVM Heap Used [Init] | Heap init used by JVM (bytes) | bytes |
| JVM Heap Used [MAX] | Heap max used by JVM (bytes) | bytes |
| JVM Non Heap Used [Init] | init (bytes) outside the heap used by the JVM | bytes |
| JVM Non Heap Used [MAX] | max (bytes) other than the heap used by the JVM | bytes |
| Kibana Connections | Kibana connection | cnt |
| Kibana Memory Heap Allocated [Limit] | Maximum heap size allocated to a Node.js process (bytes) | bytes |
| Kibana Memory Heap Allocated [Total] | Maximum heap size allocated to a Node.js process (bytes) | bytes |
| Kibana Memory Heap Used | Maximum heap size allocated to a Node.js process (bytes) | bytes |
| Kibana Process Uptime | Kibana process | ms |
| Kibana Requests [Disconnected] | Request count metric | cnt |
| Kibana Requests [Total] | Request count metric | cnt |
| Kibana Response Time [Avg] | Response time metric | ms |
| Kibana Response Time [MAX] | Response time metric | ms |
| Kibana Status [PID] | Kibana process PID | PID |
| License Expiry Date [ms] | License expiration date [milisecond] | ms |
| License Status | License status | status |
| License Type | License type | type |
| Queue Time | Queue time | ms |
| Segments | Total number of segments | cnt |
| Segments Bytes | Total segment size (bytes) | bytes |
| Shards | Cluster shard count | cnt |
| Store Bytes | Total storage size (bytes) | bytes |
7.2.2 - How-to guides
Users can create the service by entering the required information for the Search Engine and selecting detailed options through the Samsung Cloud Platform Console.
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services per Resource
- New Resources: Resources created after the service improvement work in July 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, you must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings linked with existing Cloud Monitoring (e. You must verify the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Cloud Monitoring Service Phased Termination Schedule Notice
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, Cloud Monitoring data cannot be accessed. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
Create Search Engine
You can create and use the Search Engine service in the Samsung Cloud Platform Console.
Before creating the service, configure the VPC’s subnet type as General.
- If the subnet type is Local, the creation of the corresponding Database service is not possible.
To create a Search Engine, follow the steps below.
All Services > Database > Search Engine Click the menu. 1. Navigate to the Search Engine’s Service Home page.
On the Service Home page, click the Create Search Engine button. 2. Go to the Create Search Engine page.
Search Engine creation page: enter the information required to create the service and select detailed options.
- Select the required information in the Image and Version Selection area.
Category required statusDetailed description image Required Select the type of image provided - Elasticsearch Enterprise, OpenSearch
Image version Required Select version of the selected image - Provide a version list of the offered server image
Table. Search Engine image and version selection options - In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Server name Prefix Required The server name where Elasticsearch will be installed - must start with a lowercase English letter, and using lowercase letters, numbers, and special characters (
-) be entered with 3 to 13 characters
- based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Required Cluster name of the servers - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Separate MasterNode installation > Use Required Whether to install the Master node separately - If you select Use, install the Master node separately
- If the Master node is not installed separately, the data node also performs the master role
Separate MasterNode installation > Number of MasterNodes Required Number of Master nodes - Master nodes are fixed at three units for recovery (Fail-over)
Separate installation of MasterNode > Server type Required Master node server type - Standard: standard specification commonly used
- High Capacity: large-capacity server with 24 vCores or more
- For detailed information about the server types provided by Search Engine, refer to Search Engine Server Types
Separate MasterNode installation > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute Apply
Separate MasterNode installation > Block Storage Required Block Storage type to be used for the Master node - Basic OS: Area where the engine is installed
- DATA: Data file storage area
- After selecting the storage type, enter the capacity. (For details on each Block Storage type, refer to Create Block Storage)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS/HDD_KMS: Additional encrypted volume using KMS (Key Management System) encryption keys
- Capacity must be entered as a multiple of 8 within the range 16 to 5,120
- After selecting the storage type, enter the capacity. (For details on each Block Storage type, refer to Create Block Storage)
- Add Disk: Data storage area
- After selecting Use, enter the storage capacity
- Click the + button to add storage, or the x button to delete. Up to 9 can be added.
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Number of nodes Required Number of data nodes - When installing the Master node separately, you must select at least 2; otherwise, you must select at least 1.
Service Type > Server Type Required Data node server type - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute Apply
Service Type > Block Storage Required Block Storage types to be used for data nodes - Basic OS: Area where the engine is installed
- DATA: Data file storage area
- After selecting the storage type, enter the capacity. (For details on each Block Storage type, refer to Block Storage 생성하기)
- SSD: High‑performance general volume
- HDD: General volume
- SSD_KMS/HDD_KMS: Additional encrypted volume using KMS (Key Management System) encryption keys
- Enter the capacity as a multiple of 8 within the range 16 to 5,120
- After selecting the storage type, enter the capacity. (For details on each Block Storage type, refer to Block Storage 생성하기)
- Add Disk: Additional storage area for data and backup
- After selecting Use, enter the storage purpose, capacity
- Click the + button to add storage, and the x button to delete. Up to 9 can be added.
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created.
Kibana > Server Type Required Server type for Kibana installation - Standard: standard specification commonly used
Kibana > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute Apply
Kibana > Block Storage Required Block storage type to be used on the server where Kibana is installed - Base OS: Area where the engine is installed
Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC and Subnet
- IP: Only automatic generation is possible
- Public NAT settings are only available in per‑server configuration.
Network > Server-specific Settings Required Network settings where servers generated by the service are installed - Select if you want to apply different settings per installed server
- Select a pre‑created VPC and Subnet
- IP: Enter the IP for each server
- Public NAT feature is available only when the VPC is connected to an Internet Gateway; checking Use allows you to select from reserved IPs in the VPC product’s Public IP. For more information, see Public IP 생성하기
IP access control Select Service Access Policy Settings - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy.
- Enter the IP in IP format (e.g.,
192.168.10.1) or CIDR format (e.g.,192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the IP
maintenance period Select Search Engine maintenance period - If you select Use, set the day of week, start time, and duration
- We recommend setting a maintenance period for the stable management of the service. Patch operations will be performed at the scheduled time, which may cause service interruptions
- If set to not use, we are not responsible for any issues arising from patches not being applied.
Table. Search Engine Service Information Input Items - must start with a lowercase English letter, and using lowercase letters, numbers, and special characters (
- In the Database Configuration Required Information Input area, enter or select the required information.
Category required statusDetailed description Backup > Use Select Whether to use node backup - When selecting node backup usage, choose the retention period and backup start time
Backup > Retention Period Select Backup retention period - Select the backup retention period. Set the file retention period to 7 days ~ 35 days
- Backup files incur additional charges based on size.
Backup > Backup Start Time Select Backup start time - Select backup start time
- The minutes during which the backup runs (minutes) are set randomly, and the backup end time cannot be set
Cluster Port number Required Elasticsearch connection port number 1200 ~ 65535can be entered as one of them, and the internal Elasticsearch port 9300 and Kibana port 5301 cannot be used
Elastic username Required Elasticsearch username - Enter using lowercase English letters, 2 to 20 characters
- The following usernames cannot be used.
- apm_system, beats_system, elastic, kibana, kibana_system, logstash_system, remote_monitoring_user, scp_kibana_system, scp_manager, maxigent_cl
Elastic password Required Elasticsearch login password - Enter 8 to 30 characters, including letters, numbers, and special characters (excluding
“,‘,\)
Check Elastic password Required Check Elasticsearch connection password - Re-enter the Elasticsearch connection password identically
License Key Required Elasticsearch License Key - Enter the entire contents of the issued license file (.json)
- If the entered license key is invalid, the service may not be created.
- OpenSearch does not require a License Key.
time zone Select Standard time zone for the service Table. Required input fields for Search Engine Database configuration - Enter or select the required information in the Additional Information Input area.
Category required statusDetailed description Tag Select Add tag - Add tag Click the button to create and add a tag, or add an existing tag
- You can add up to 50 tags
- The newly added tags are applied after the service creation is completed
Table. Search Engine service additional information input fields
- Select the required information in the Image and Version Selection area.
Summary Check the detailed information and estimated charges generated in the panel, and click the Complete button.
- When creation is complete, check the created resources on the Resource List page.
Check Search Engine Details
The Search Engine service allows you to view and edit the complete resource list and detailed information. Search Engine Details page includes Detail Information, Tags, Activity Log tabs.
To view detailed information about the Search Engine service, follow these steps.
- All Services > Data Analytics > Search Engine menu, click it. 1. Navigate to the Search Engine’s Service Home page.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- Search Engine list page: click the resource to view detailed information. 3. Search Engine Details Navigate to the page.
- Search Engine Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Cluster status Cluster status - Creating: Cluster is being created
- Editing: Cluster is being changed to an operational state
- Error: Cluster encountered a failure while performing a task
- If this persists, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Cluster is restarting
- Running: Cluster is operating normally
- Starting: Cluster is starting
- Stopped: Cluster is stopped
- Stopping: Cluster is stopping
- Synchronizing: Cluster is synchronizing
- Terminating: Cluster is being terminated
- Unknown: Cluster status is unknown
- If this persists, contact the administrator
- Upgrading: Cluster is being upgraded
Cluster control Button to change the cluster state - Start: Starts a stopped cluster.
- Stop: Stops a running cluster.
- Restart: Restarts a running cluster
View more add-ons Cluster management buttons - Service status synchronization: Retrieve the current server status and synchronize it to the Console
- Backup history: When backup is configured, check whether the backup executed successfully and view its history
- Cluster recovery: Recover the cluster based on a specific point in time.
- Add Node: Add a data node.
Service cancellation Cancel service button Table. Search Engine status information and additional features
- Search Engine Details At the top of the page, status information and additional feature information are displayed.
Detailed Information
Search Engine list page lets you view detailed information of the selected resource and, if needed, modify the information.
| Category | Detailed description |
|---|---|
| Server Information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image/Version | Installed service image and version information |
| Cluster name | Cluster name of the configured servers |
| Planned Compute | Resource status with Planned Compute configured
|
| maintenance period | Maintenance Period Status
|
| Backup | Backup configuration status
|
| time zone | Standard time zone for the service |
| License | Elasticsearch license information
|
| Elastic username | Elasticsearch username |
| Kibana access information | Kibana access information |
| Network | Installed network information (VPC, Subnet) |
| IP access control | Set service access policy
|
| Master | Server type, base OS, and additional Disk information for the Master node
|
| Data | Server type, base OS, and additional Disk information
|
| Kibana | Server type and basic OS information for the Kibana node
|
Tag
Search Engine List page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Search Engine List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Search Engine Resource Management
If you need to change the existing configuration options of a created Search Engine resource, manage parameters, or add node configurations, you can perform the tasks on the Search Engine Detailed Information page.
Control Operation
If changes occur to a running Search Engine resource, you can start, stop, or restart it.
To control the operation of the Search Engine, follow these steps.
- Click the All Services > Data Analytics > Search Engine menu. 1. Navigate to the Search Engine’s Service Home page.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- Search Engine list page, click the resource to control its operation. 3. Go to the Search Engine Details page.
- Check the Search Engine status and complete the change using the control button below.
- Start: Search Engine service is installed on the server and Search Engine service is running (Running).
- Stop: The server on which the Search Engine service is installed and the Search Engine service will be stopped (Stopped).
- Restart: Only the Search Engine service will be restarted.
Synchronize Service Status
You can query the current server status and synchronize it to the Console.
To synchronize the service status of the Search Engine, follow these steps.
- All Services > Data Analytics > Search Engine menu, click. 1. Navigate to the Search Engine’s Service Home page.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- On the Search Engine List page, click the resource to view the service status. 3. Navigate to the Search Engine Details page.
- Click the Service Status Synchronization button. 4. The query takes a short amount of time, and while it is being performed, the cluster changes to the Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
To change the server type, follow these steps.
- If the server type is configured as Standard, it cannot be changed to High Capacity. * If you want to change to High Capacity, create a new service.
- If you modify the server type, a server restart is required. * Please separately verify any software license modifications or software settings and their implementation due to specification changes.
- All Services > Data Analytics > Search Engine Click the menu. 1. Navigate to the Service Home page of Search Engine.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- On the Search Engine list page, click the resource to change the server type. 3. Navigate to the Search Engine Details page.
- Click the edit button for the server type you want to change at the bottom of the detailed information. 4. Edit Server Type popup window opens.
- Edit Server Type After selecting the server type in the popup window, click the Confirm button.
Expanding Storage
Storage added to the data area can be expanded up to a maximum of 5 TB, based on the initially allocated capacity. You can expand storage without stopping the Search Engine, and if configured as a cluster, all nodes are expanded simultaneously.
- If encryption is configured on the existing Block Storage, encryption will also be applied to the additional Disk.
- Disk size modification is only possible by increasing it by at least 16 GB over the current disk size.
To increase storage capacity, follow the steps below.
- Click the All Services > Data Analytics > Search Engine menu. 1. Navigate to the Service Home page of Search Engine.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- On the Search Engine list page, click the resource to change the server type. 3. Search Engine Details Navigate to the page.
- Click the Edit button for the added Disk you want to expand at the bottom of the detailed information. 4. Disk Edit The popup window opens.
- Disk Edit after entering the additional capacity in the popup window, click the Confirm button.
Add storage
If you need more than 5 TB of data storage space, you can add additional storage.
- If encryption is configured on the existing Block Storage, encryption will also be applied to the additional Disk.
To add storage capacity, follow the steps below.
- All Services > Data Analytics > Search Engine menu, click. 1. Navigate to the Service Home page of Search Engine.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- On the Search Engine List page, click the resource to add storage. 3. Navigate to the Search Engine Details page.
- Click the Add Disk button at the bottom of the detailed information. 4. Add Disk The popup window opens.
- Add Disk In the popup window, after entering the purpose and size, click the Confirm button.
Search Engine Backup
Through the backup configuration feature, users can set the data retention period and start interval, and through the backup history feature, they can view and delete backup records.
Configure Backup
When creating a Search Engine and setting up backup, refer to the Creating a Search Engine guide, and to modify the backup configuration of the created resource, follow the steps below.
- If a backup is configured, it will run at the designated time after the set time, and additional fees will apply based on the backup size.
- If you change the backup setting to Unset, backup execution stops immediately, and the stored backup data is deleted and can no longer be used.
- Click the All Services > Data Analytics > Search Engine menu. 1. Navigate to the Service Home page of Search Engine.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- On the Search Engine list page, click the resource to set up backup. 3. Navigate to the Search Engine Details page.
- Click the Edit button of the backup item. 4. Backup Edit The popup window opens.
- When setting up a backup, click Use in the Backup Edit popup, select retention period, backup start time, and Archive backup interval, then click the Confirm button.
- If you stop the backup setting, uncheck Use in the Edit Backup popup window, and authenticate via the logged-in user’s mobile phone.
Check backup history
To view the backup history, follow these steps.
- All Services > Data Analytics > Search Engine Click the menu. 1. Navigate to the Search Engine’s Service Home page.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- On the Search Engine List page, click the resource to view the backup history. 3. Go to the Search Engine Details page.
- Click the Backup History button. 4. Backup History popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup file
To delete the backup history, follow these steps.
- All Services > Data Analytics > Search Engine Click the menu. 1. Navigate to the Search Engine’s Service Home page.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- Search Engine List page, click the resource to view the backup history. 3. Navigate to the Search Engine Details page.
- Click the Backup History button. 4. The Backup History popup window opens.
- Backup History In the popup window, check the files you want to delete, then authenticate using the logged-in user’s mobile phone.
Restore Search Engine
If a failure or data loss requires restoration from a backup file, you can recover to a specific point in time using the cluster recovery feature.
To restore the Search Engine, follow these steps.
- Click the All Services > Data Analytics > Search Engine menu. 1. Navigate to the Search Engine’s Service Home page.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- Search Engine Resource On the list page, click the resource you wish to recover. 3. Navigate to the Search Engine Details page.
- Click the Cluster Recovery button. 4. Go to the Cluster Recovery page.
- After entering the relevant information in the Cluster Recovery Configuration area, click the Complete button.
Category required statusDetailed description Recovery point Required Set the point in time the user wants to recover - Select from the list of backup file timestamps displayed
Server name Prefix Required Recovery server name - Start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to enter 3 to 16 characters
- Based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Required Recovery server cluster name - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Number of nodes Required Number of data nodes - Set to be the same as the number of nodes configured in the original cluster.
Service Type > Server Type Required Data node server type - It is set to the same number of nodes as configured in the original cluster.
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute Apply
Service Type > Block Storage Required Block Storage to be used for data nodes - Basic OS: area where the engine is installed
- DATA: data file storage area
- Applied identically as the storage type set in the original cluster
- Enter capacity as a multiple of 8 within the range 16 to 5,120
- Add Disk: additional storage area for data and backup
- After selecting Use, enter the storage purpose and capacity
- Click the + button to add storage, and the x button to delete
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Separate MasterNode installation > Use Required Whether to install the Master node separately - Apply the same based on the installation status of the original cluster
Separate MasterNode installation > Number of MasterNodes Required Number of Master nodes Separate installation of MasterNode > Server type Required Master node server type - It is set to be the same as the number of nodes configured in the original cluster.
Separate MasterNode installation > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Separate MasterNode installation > Block Storage Required Block Storage to be used on the Master node - Basic OS: Area where the engine is installed
- DATA: Data file storage area
- Applied identically with the storage type set in the original cluster
- Enter capacity as a multiple of 8 within the range 16 to 5,120
- Add Disk: Additional data storage area
- After selecting Use, enter the storage capacity
- Click the + button to add storage, or the x button to delete
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Kibana > Server Type Required Kibana node server type - It is set to be the same as the number of nodes configured in the original cluster.
Kibana > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Kibana > Block Storage Required Block Storage to be used on the Kibana node - Base OS: the area where the engine is installed
Cluster Port number Required Elasticsearch connection port number - It is set to the same port number configured in the original cluster.
Licnese Key Required Elasticsearch License Key - Enter the entire contents of the issued license file (.json)
- If the entered license key is invalid, the service may not be created.
- OpenSearch does not require a License Key.
IP access control Select Service Access Policy Settings - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy.
- Enter the IP in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the IP
maintenance period Select maintenance window - If you select Use, you can set the day of week, start time, and duration
- We recommend setting a maintenance window for stable service management. Patch operations will be performed at the scheduled time, causing service interruption
- If set to not use, we are not responsible for issues arising from unapplied patches.
Table. Search Engine Recovery Configuration Items
Add Node
If you need to expand the Search Engine cluster, you can add nodes with the same specifications as the data nodes in use.
- You can use up to 10 nodes within the cluster. * Please note that created nodes will incur additional charges.
- Adding nodes may degrade the cluster’s performance.
To add a node, follow the steps below.
- All Services > Data Analytics > Search Engine Click the menu. 1. Navigate to the Service Home page of Search Engine.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine list page.
- Search Engines Resources Click the resource you want to restore on the list page. 3. Search Engine Details Navigate to the page.
- Click the Add Broker Node button. 4. Go to the Add Broker Node page.
- After entering the relevant information in the Required Information Input area, click the Complete button.
Category required statusDetailed description Server name Prefix Required Data node server name - It is set to the server name configured in the original cluster.
Cluster name Required Cluster name - It is set to the cluster name configured in the original cluster.
Additional Node Count Required Number of Nodes to add - Use up to 10 nodes per cluster
Service Type > Server Type Required Data node server type - It is set the same as the server type configured in the original cluster.
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute 신청하기
Service Type > Block Storage Required Block Storage configuration to be used for data nodes - The storage type and capacity set in the source cluster are applied identically
Network Required the network where the servers are installed - applied identically to the network configured in the original cluster
Table. Search Engine Node additional items
Terminate Search Engine
You can cancel unused Search Engines to reduce operating costs. However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may occur when the service is discontinued.
To cancel the Search Engine, follow these steps.
- All Services > Data Analytics > Search Engine Click the menu. 1. Navigate to the Search Engine’s Service Home page.
- On the Service Home page, click the Search Engine menu. 2. Go to the Search Engine List page.
- On the Search Engine List page, select the resource to cancel, and click the Cancel Service button.
- When the termination is complete, verify on the Search Engine list page whether the resource has been terminated.
7.2.3 - API Reference
7.2.4 - CLI Reference
7.2.5 - Release Note
Search Engine
- OpenSearch 2.17.1 is now offered as a new release.
- Provides Terraform.
- Provides additional HDD, HDD_KMS disk types.
- A Search Engine service that enables easy creation and management of ElasticSearch Enterprise in a web environment has been launched.
7.3 - Vertica(DBaaS)
7.3.1 - Overview
Service Overview
Vertica(DBaaS) is a high-availability enterprise database built on a Data Warehouse for large-scale data analysis and processing. Through a single engine, it serves as a data analytics platform that can perform basic analyses such as querying data from various sources without moving them, as well as AI analyses like machine learning. In the Samsung Cloud Platform, DB management functions such as high‑availability configuration, backup/recovery, patching, parameter management, and monitoring are added to ensure stable management of single instances or critical data, enabling automation of tasks throughout the database lifecycle. Additionally, it provides an automatic backup feature at user‑specified times to support data recovery at the desired point in case of DB server or data issues.
Service Architecture Diagram
Provided features
Vertica(DBaaS) provides the following features.
- Auto Provisioning (Auto Provisioning): Automatically installs the standard version of the Samsung Cloud Platform database based on Virtual Servers of various specifications.
- Cluster Configuration: Provides a self-high-availability architecture in a masterless form.
- Operation Control Management: Provides functionality to control the status of running servers. You can start or stop a server, and it can be restarted if there is a database issue or to apply configuration changes.
- Backup and Recovery: Provides data backup functionality based on proprietary backup commands. Users can set the backup retention period and start time, and additional fees apply based on backup size. It also offers a recovery feature for backed‑up data; when a user initiates recovery, a separate database is created and restored to the point selected by the user (backup creation time or a custom point). For database recovery, you can choose to install the Management Console for use.
- Service Status Query: You can view the final status of the current DB service.
- Monitoring: CPU, memory, DB performance monitoring information can be accessed through the Cloud Monitoring service.
- High-Performance Processing of Large-Scale Data: It guarantees stable performance in a Mixed Workload environment of massive parallel processing (MPP, Massively Parallel Processing) and SQL queries. Vertica processes queries through distributed processing and is designed so that queries can be initiated from any node, eliminating a Single Point of Failure where queries would not execute if a specific node fails.
Component
Vertica(DBaaS) provides pre‑validated engine versions and various server types. Users can select and use them according to the scale of the service they wish to configure.
Engine version
The engine versions supported by Vertica (DBaaS) are as follows.
Technical support can be used until the supplier’s EoTS (End of Technical Service) date, and the EOS date when new creation is halted is set to six months before the EoTS date.
The EOS and EoTS dates may change according to the supplier’s policy, so please refer to the supplier’s license management policy page for details.
| Provided version | EOS date (Samsung Cloud Platform new creation stop date) | EoTS date (supplier technical support end date) |
|---|---|---|
| 24.2.0-2 | 2026-09 (planned) | 2027-04-30 |
Server type
The server types supported by Vertica (DBaaS) are as follows.
For detailed information about the server types provided by Vertica (DBaaS), see Vertica Server Types.
| Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server specifications | Db1 | Provided server specifications
|
| Server specifications | V2 | Number of vCores
|
| Server specifications | M4 | Memory capacity
|
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
7.3.1.1 - Server Type
Vertica(DBaaS) server type
Vertica (DBaaS) offers server types configured with various combinations of CPU, memory, and network bandwidth. When creating Vertica(DBaaS), the Database Engine is installed according to the server type selected for the intended use.
The server types supported by Vertica (DBaaS) are as follows.
Standard db1v2m4
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server type classifications
|
| Server specifications | db1 | Provided server type classification and generation
|
| Server specifications | v2 | Number of vCores
|
| Server specifications | m4 | Memory capacity
|
db1 server type
The db1 server type of Vertica(DBaaS) is provided with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 3rd‑generation (Ice Lake) Xeon Gold 6342 Processor up to 3.3 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db1v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | db1v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db1v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db1v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db1v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db1v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db1v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db1v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db1v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db1v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db1v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db1v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db1v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db1v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db1v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db1v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db1v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db1v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db1v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db1v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db1v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db1v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db1v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db1v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db1v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db1v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db1v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db1v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db1v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db1v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db1v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
db2 server type
The db2 server type of Vertica(DBaaS) is provided with standard specifications (vCPU, Memory) and is suitable for various database workloads.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 16 vCPUs and 256 GB of memory
- Maximum networking speed of 12.5 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| Standard | db2v1m2 | 1 vCore | 2 GB | Up to 10 Gbps |
| Standard | db2v2m4 | 2 vCore | 4 GB | Up to 10 Gbps |
| Standard | db2v2m8 | 2 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v2m16 | 2 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v2m24 | 2 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v2m32 | 2 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m8 | 4 vCore | 8 GB | Up to 10 Gbps |
| Standard | db2v4m16 | 4 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v4m32 | 4 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v4m48 | 4 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v4m64 | 4 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v6m12 | 6 vCore | 12 GB | Up to 10 Gbps |
| Standard | db2v6m24 | 6 vCore | 24 GB | Up to 10 Gbps |
| Standard | db2v6m48 | 6 vCore | 48 GB | Up to 10 Gbps |
| Standard | db2v6m72 | 6 vCore | 72 GB | Up to 10 Gbps |
| Standard | db2v6m96 | 6 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m16 | 8 vCore | 16 GB | Up to 10 Gbps |
| Standard | db2v8m32 | 8 vCore | 32 GB | Up to 10 Gbps |
| Standard | db2v8m64 | 8 vCore | 64 GB | Up to 10 Gbps |
| Standard | db2v8m96 | 8 vCore | 96 GB | Up to 10 Gbps |
| Standard | db2v8m128 | 8 vCore | 128 GB | Up to 10 Gbps |
| Standard | db2v10m20 | 10 vCore | 20 GB | Up to 10 Gbps |
| Standard | db2v10m40 | 10 vCore | 40 GB | Up to 10 Gbps |
| Standard | db2v10m80 | 10 vCore | 80 GB | Up to 10 Gbps |
| Standard | db2v10m120 | 10 vCore | 120 GB | Up to 10 Gbps |
| Standard | db2v10m160 | 10 vCore | 160 GB | Up to 10 Gbps |
| Standard | db2v12m24 | 12 vCore | 24 GB | Up to 12.5 Gbps |
| Standard | db2v12m48 | 12 vCore | 48 GB | Up to 12.5 Gbps |
| Standard | db2v12m96 | 12 vCore | 96 GB | Up to 12.5 Gbps |
| Standard | db2v12m144 | 12 vCore | 144 GB | Up to 12.5 Gbps |
| Standard | db2v12m192 | 12 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v14m28 | 14 vCore | 28 GB | Up to 12.5 Gbps |
| Standard | db2v14m56 | 14 vCore | 56 GB | Up to 12.5 Gbps |
| Standard | db2v14m112 | 14 vCore | 112 GB | Up to 12.5 Gbps |
| Standard | db2v14m168 | 14 vCore | 168 GB | Up to 12.5 Gbps |
| Standard | db2v14m224 | 14 vCore | 224 GB | Up to 12.5 Gbps |
| Standard | db2v16m32 | 16 vCore | 32 GB | Up to 12.5 Gbps |
| Standard | db2v16m64 | 16 vCore | 64 GB | Up to 12.5 Gbps |
| Standard | db2v16m128 | 16 vCore | 128 GB | Up to 12.5 Gbps |
| Standard | db2v16m192 | 16 vCore | 192 GB | Up to 12.5 Gbps |
| Standard | db2v16m256 | 16 vCore | 256 GB | Up to 12.5 Gbps |
dbh2 server type
The dbh2 server type of Vertica (DBaaS) is offered with high-capacity server specifications and is suitable for database workloads that require large-scale data processing.
- Intel 4th‑generation (Sapphire Rapids) Xeon Gold 6448H Processor up to 3.2 GHz
- Supports up to 128 vCPUs and 1,536 GB of memory
- Networking speed up to 25 Gbps
| Category | Server type | vCPU | Memory | Network Bandwidth |
|---|---|---|---|---|
| High Capacity | dbh2v24m48 | 24 vCore | 48 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m96 | 24 vCore | 96 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m192 | 24 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v24m288 | 24 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m64 | 32 vCore | 64 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m128 | 32 vCore | 128 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m256 | 32 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v32m384 | 32 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m192 | 48 vCore | 192 GB | Maximum 25 Gbps |
| High Capacity | dbh2v48m576 | 48 vCore | 576 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m256 | 64 vCore | 256 GB | Maximum 25 Gbps |
| High Capacity | dbh2v64m768 | 64 vCore | 768 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m288 | 72 vCore | 288 GB | Maximum 25 Gbps |
| High Capacity | dbh2v72m864 | 72 vCore | 864 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m384 | 96 vCore | 384 GB | Maximum 25 Gbps |
| High Capacity | dbh2v96m1152 | 96 vCore | 1152 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m512 | 128 vCore | 512 GB | Maximum 25 Gbps |
| High Capacity | dbh2v128m1536 | 128 vCore | 1536 GB | Maximum 25 Gbps |
7.3.1.2 - Monitoring metrics
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be terminated.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services by Resource
- New Resources: Resources created after the service improvement work in July 2026 are monitored by default using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings integrated with existing Cloud Monitoring (e. You must verify items such as event policies and perform tasks such as resetting the ServiceWatch service, then complete them.
Notice of the phased termination schedule for the Cloud Monitoring service
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, Cloud Monitoring data cannot be accessed. * Be sure to complete the ServiceWatch migration work within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch can be found in the ServiceWatch 개요.
Vertica(DBaaS) Monitoring Metrics
The table below shows the performance monitoring metrics for Vertica (DBaaS) that can be viewed through Cloud Monitoring. For detailed Cloud Monitoring usage, see the Cloud Monitoring guide.
The server monitoring metrics for Vertica (DBaaS) are described in the Virtual Server Monitoring Metrics guide.
| Performance items | Detailed description | unit |
|---|---|---|
| Active Locks | Number of Active Locks | cnt |
| Active Sessions | Total number of Sessions in Active state | cnt |
| Instance Status | Node alive status | status |
| Tablespace Used | Tablespace usage | bytes |
7.3.2 - How-to guides
Users can create the service by entering the required information for Vertica (DBaaS) and selecting detailed options through the Samsung Cloud Platform Console.
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, services whose monitoring metrics are linked in Cloud Monitoring will no longer be able to monitor resources through Cloud Monitoring after the service improvement work in November 2026.
After that, resource monitoring can be continuously performed through the ServiceWatch service released in October 2025.
To ensure smooth service usage, proceed with the migration work according to the service termination schedule below.
Guide to Applying Monitoring Services by Resource
- New Resources: Resources created after the July 2026 service improvement work are provided with default monitoring using the ServiceWatch service.
- Existing resources: After the service improvement work in September 2026 We provide concurrent monitoring through Cloud Monitoring and ServiceWatch services.
- During the parallel operation period, we must prepare for the Servicewatch transition. *
Performance and log data backup, user-configured settings integrated with existing Cloud Monitoring (e.g. You must review the event policies, etc., perform tasks such as resetting the ServiceWatch service, and complete them.
Cloud Monitoring Service Phased Termination Schedule Notice
- Console menu termination (September 2026 service improvement work)
- You cannot access the Cloud Monitoring Console through the Console menu; you can only connect via the separate URLs for each region listed below.
- Console menu termination (September 2026 service improvement work)
| Offering | Region | Cloud Monitoring console URL |
|---|---|---|
| Enterprise | kr-west1 | https://console.kr-west1.e.samsungsdscloud.com/console/monitoring |
| Enterprise | kr-east1 | https://console.kr-east1.e.samsungsdscloud.com/console/monitoring |
| Samsung | kr-west1 | https://console.kr-west1.s.samsungsdscloud.com/console/monitoring |
| Samsung | kr-east1 | https://console.kr-east1.s.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south1 | https://console.kr-south1.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south2 | https://console.kr-south2.g.samsungsdscloud.com/console/monitoring |
| Sovereign | kr-south3 | https://console.kr-south3.g.samsungsdscloud.com/console/monitoring |
- Service termination (service improvement work in November 2026)
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
- After the service ends in November, Cloud Monitoring data cannot be accessed. * Be sure to complete the ServiceWatch migration within the parallel operation period**.
- All services of Cloud Monitoring, including the API, will be permanently discontinued.
Detailed information about ServiceWatch: please refer to the ServiceWatch Overview.
Create Vertica (DBaaS)
You can create and use the Vertica (DBaaS) service in the Samsung Cloud Platform Console.
To create Vertica(DBaaS), follow these steps.
All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
On the Service Home page, click the Vertica(DBaaS) Create button. 2. Create navigate to the page.
Vertica(DBaaS) Creation page: enter the information required to create the service and select detailed options.
- Select the required information in the Image and Version Selection area.
Category required statusDetailed description Image version Required Provide a list of Vertica (DBaaS) versions Table. Vertica (DBaaS) image and version input items - Enter or select the required information in the Service Information Input area.
Category required statusDetailed description Server name Prefix Required The server name where Vertica will be installed - must start with a lowercase English letter, and using lowercase letters, numbers, and special characters(
-) input 3 to 13 characters
- Based on the server name, a postfix such as 001, 002 is appended to create the actual server name
Cluster name required Cluster name composed of servers - Enter using English letters, 3 ~ 20 characters
- A cluster is a unit that groups multiple servers
Number of nodes required Number of data nodes - Enter the number of nodes in the range of 1-10
- If you configure the cluster by entering the number of nodes as 2 or more, you achieve high availability (High Availability)
Service Type > Server Type Required Data node server type - Standard: Standard specification commonly used
- High Capacity: Large-capacity server with 24 vCores or more
- For detailed information about the server types provided by Vertica (DBaaS), refer to Vertica(DBaaS) Server Type
Service Type > Planned Compute Select Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute configured that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage Preview: Amount applied per resource by Planned Compute
- Apply for Planned Compute Service: Go to the Planned Compute service application page
- For more details, see Planned Compute Apply
Service Type > Block Storage Essential Block Storage type to be used for data nodes - Base OS: Area where the engine is installed
- DATA: Data file storage area
- After selecting the storage type, enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- SSD: Standard Block Storage
- SSD_KMS: Additional encrypted volume using KMS (Key Management System) encryption keys
- The configured storage type is also applied to additional storage
- Capacity must be entered as a multiple of 8 within the range 16 to 5,120
- After selecting the storage type, enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- Add: DATA, Backup data storage area
- After selecting Use, enter the storage’s purpose, capacity
- To add storage, click the Add button; to delete, click the x button, up to 9 can be added
- Capacity can be entered as a multiple of 8 within the range 16 to 5,120, and up to 9 can be created
Management Console Selection If you select Use, you can configure the Node’s server type and Block Storage settings for cluster management and monitoring. Management Console > Server Type Required Selecting a data node server type for cluster management and monitoring Management Console > Block Storage Required Select the Block Storage type to be used for data nodes for cluster management and monitoring Network > Common Settings Required Network settings for servers created by the service - Select when you want to apply the same settings to all installed servers
- Select a pre‑created VPC and Subnet
- IP: Enter each server’s IP
- Public NAT setting is only available in per‑server settings
Network > Server-specific Settings Required Network settings for the servers created by the service - Select when you want to apply different settings per installed server
- Choose a pre‑created VPC and Subnet
- IP: Enter the IP for each server
- Public NAT requires the VPC to be connected to an Internet Gateway; when use is checked, you can select a reserved IP from the VPC product’s Public IP pool. For details, see Public IP 생성하기.
IP access control Selection Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, a separate Security Group policy configuration is not required.
- Enter in IP format (example:
192.168.10.1) or CIDR format (example:192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Selection Database maintenance window - If you select Use, set the day, start time, and duration
- It is recommended to set a maintenance window for stable DB management. Patch operations will be performed at the scheduled time, causing service interruption
- If set to unused, Samsung SDS is not responsible for issues arising from unapplied patches.
Table. Vertica (DBaaS) service configuration items - must start with a lowercase English letter, and using lowercase letters, numbers, and special characters(
- Enter required database configuration information Enter or select the required information in this area.
Category required statusDetailed description Database name Essential Server name applied during DB installation - must start with an English letter and be entered using English letters and numbers, 3 to 20 characters
Database username Required DB user name - An account with the same name is also created on the OS
- Enter using lowercase English letters, 2 to 20 characters
- Restricted database user names can be checked in the Console
Database password Essential Password to use when accessing the DB - English letters, numbers, and special characters (
“‘excluded) and enter 8~30 characters
Database password verification Required Re-enter the same password to use for DB access Database Port number Required Port number required for DB connection - Enter the DB port within the range 1200 ~ 65535
Backup > Use Select Node backup usage - Select Use to choose the node backup retention period and backup start time
Backup > Retention Period Select Backup retention period - Select the backup retention period. Set the file retention period to 7 days ~ 35 days
- Backup files incur additional charges based on size
Backup > Backup Start Time Select Backup start time - Select backup start time
- The minute(s) at which the backup runs is set randomly, and the backup end time cannot be set
License Key Required Enter the Vertica License Key held by the customer - If the entered license key is invalid, the service cannot be created
DB Locale Required Settings related to string handling, numeric/currency/date/time display formats, etc., to be used with Vertica (DBaaS) - The database is created with default settings based on the selected locale
time zone Required Standard time zone to use with Vertica (DBaaS) Table. Vertica (DBaaS) required configuration items - In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key, Value values
Table. Vertica (DBaaS) additional information input fields
- Select the required information in the Image and Version Selection area.
Summary Review the detailed information and estimated charges generated in the panel, then click the Create button.
- Once creation is complete, verify the created resource on the Resource List page.
View Vertica (DBaaS) detailed information
The Vertica(DBaaS) service allows you to view and edit the full list of resources and detailed information. The Vertica(DBaaS) Details page is composed of Details, Tags, Job History tabs.
To view detailed information about the Vertica (DBaaS) service, follow these steps.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Navigate to the Vertica(DBaaS) List page.
- On the Vertica(DBaaS) List page, click the resource to view detailed information. 3. Vertica(DBaaS) Details Navigate to the page.
- Vertica(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Cluster status Cluster status - Creating: Creating cluster
- Editing: Cluster is changing to an Operation execution state
- Error: Cluster encountered a failure while performing tasks
- If it occurs continuously, contact the administrator
- Failed: Cluster failed during creation
- Restarting: Cluster is restarting
- Running: Cluster is running normally
- Starting: Cluster is starting
- Stopped: Cluster is stopped
- Stopping: Cluster is stopping
- Synchronizing: Cluster is synchronizing
- Terminating: Cluster is terminating
- Unknown: Cluster status is unknown
- If it occurs continuously, contact the administrator
- Upgrading: Cluster is upgrading
Cluster control Button to change the cluster state - Start: Start a stopped cluster
- Stop: Stop a running cluster
- Restart: Restart a running cluster
View more features Cluster-related management buttons - Service status synchronization: Real-time DB service status lookup
- Backup history: When backup is configured, check whether the backup runs correctly and view its history
- Database recovery: Recover the DB based on a specific point in time
Service termination Button to cancel the service Table. Vertica (DBaaS) status information and additional features
- Vertica(DBaaS) Details At the top of the page, status information and additional feature information are displayed.
Detailed information
Vertica(DBaaS) List page lets you view detailed information of the selected resource and, if needed, modify the information.
| Category | Detailed description |
|---|---|
| Server information | Server information configured in this cluster
|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image/Version | Installed DB image and version information |
| Cluster name | Cluster name of the configured servers |
| Database name | Server name applied during DB installation |
| Database username | DB user name |
| Planned Compute | Resources with Planned Compute configured
|
| maintenance period | DB Maintenance Period Status
|
| Backup | Backup Configuration Status
|
| Managed Console | Managed Console resource status configured during DB installation |
| Network | Installed network information (VPC, Subnet) |
| IP access control | Service access policy configuration
|
| time zone | Standard time zone for the Vertica (DBaaS) DB |
| License | Vertica (DBaaS) license information |
| Server Information | Data/Console server type, base OS, additional Disk information
|
tag
Vertica(DBaaS) List page lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
You can view the operation history of the selected resource on the Vertica(DBaaS) List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Vertica (DBaaS) Resources
If you need to change the existing configuration options of a created Vertica(DBaaS) resource or add storage, you can perform the operation on the Vertica(DBaaS) Details page.
Control operation
If changes occur to a running Vertica (DBaaS) resource, you can start, stop, or restart it.
To control the operation of Vertica (DBaaS), follow these steps.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- Click the Vertica(DBaaS) menu on the Service Home page. 2. Navigate to the Vertica(DBaaS) List page.
- Vertica(DBaaS) List page, click the resource to control its operation. 3. Vertica(DBaaS) Details Navigate to the page.
- Check the Vertica (DBaaS) status and complete the change using the control button below.
- Start: The server where the Vertica(DBaaS) service is installed and the Vertica(DBaaS) service is running.
- Stop: The server on which the Vertica (DBaaS) service is installed and the Vertica (DBaaS) service will be stopped (Stopped).
- Restart: Only the Vertica(DBaaS) service will be restarted.
Synchronize service status
You can synchronize the real-time service status of Vertica (DBaaS).
To view the service status of Vertica (DBaaS), follow these steps.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Go to the Vertica(DBaaS) List page.
- On the Vertica(DBaaS) List page, click the resource to view the service status. 3. Vertica(DBaaS) Details Go to the page.
- Click the Service Status Sync button. 4. While it is being queried, the cluster changes to Synchronizing state.
- When the query completes, the status in the server information field is updated, and the cluster changes to the Running state.
Change server type
You can change the configured server type.
- If the server type is configured as Standard, it cannot be changed to High Capacity. * If you want to change to High Capacity, create a new service.
- If you modify the server type, a server restart is required. * Please separately verify any software license modifications or software settings and their implementation due to server specification changes.
To change the server type, follow these steps.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Go to the Vertica(DBaaS) List page.
- Vertica(DBaaS) List On the page, click the resource to change the server type. 3. Vertica(DBaaS) Details Navigate to the page.
- Click the Edit icon of the server type you want to change at the bottom of the detailed information. 4. Edit Server Type popup window opens.
- Edit Server Type After selecting the server type in the popup window, click the Confirm button.
Add storage
If you need more than 5 TB of data storage, you can add additional storage. In a high‑availability configuration (HA cluster), expanding or adding storage capacity is applied simultaneously to all databases.
To add storage, follow these steps.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Navigate to the Vertica(DBaaS) List page.
- On the Vertica(DBaaS) List page, click the resource to add storage. 3. Vertica(DBaaS) Details Navigate to the page.
- Click the Add Disk button at the bottom of the detailed view. 4. Additional Storage Request The popup window opens.
- Additional Storage Request In the popup window, after entering the purpose and size, click the Confirm button.
Expand storage
Storage added to the data area can be expanded up to a maximum of 5 TB, based on the initially allocated capacity. You can expand storage without stopping Vertica (DBaaS), and if it is configured as a cluster, all nodes are expanded simultaneously.
To expand storage capacity, follow the steps below.
- Click the All Services > Data Analytics > Vertica(DBaaS) menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Vertica(DBaaS) List Go to the page.
- On the Vertica(DBaaS) List page, click the resource to change the server type. 3. Go to the Vertica(DBaaS) Details page.
- Click the Edit button for the additional Disk you want to add at the bottom of the detailed information. 4. Edit Additional Storage A popup window opens.
- Edit Additional Storage In the popup window, after entering the expansion capacity, click the Confirm button.
Changing the Recovery DB instance type
After the DB recovery is complete, you can change the instance type on the Recovery details screen.
To change the Recovery DB instance type, follow these steps.
- Click the All Services > Data Analytics > Vertica(DBaaS) menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Navigate to the Vertica(DBaaS) List page.
- On the Vertica(DBaaS) List page, click the resource to change the Recovery DB instance type. 3. Vertica(DBaaS) Details Go to the page.
- Click the Change Instance Type button. 4. Change Instance Type A confirmation dialog will appear.
- The DB instance type is changed from Recovery to Active to provide the same functionality as a single DB.
Cancel Vertica (DBaaS)
You can cancel the unused Vertica (DBaaS) to reduce operating costs. However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may occur when the service is discontinued.
To cancel Vertica(DBaaS), follow the steps below.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Navigate to the Vertica(DBaaS) List page.
- On the Vertica(DBaaS) List page, select the resource to cancel and click the Cancel Service button.
- After termination is complete, check on the Vertica(DBaaS) list page whether the resource has been terminated.
7.3.2.1 - Backing up and restoring Vertica
Users can set up backups for Vertica (DBaaS) via the Samsung Cloud Platform Console and restore from the backed‑up files.
Backing up Vertica (DBaaS)
You can configure the backup feature to ensure that user data is stored securely. Additionally, you can verify whether a backup completed successfully using the backup history feature, and you can also delete backed‑up files.
Configure Backup
For backup configuration of Vertica(DBaaS), please refer to Create Vertica(DBaaS).
To modify the backup settings of Vertica (DBaaS), follow the steps below.
- If a backup is configured, it will run at the designated time after the set time, and additional fees will be incurred based on the backup volume.
- If you change the backup setting to unused, backup execution will stop immediately, and the stored backup data will be deleted and can no longer be used.
- Click the All Services > Data Analytics > Vertica(DBaaS) menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Go to the Vertica(DBaaS) List page.
- Vertica(DBaaS) List page, click the resource to configure a backup. 3. Vertica(DBaaS) Details Navigate to the page.
- Click the Edit button of the backup item. 4. Backup Settings The popup window opens.
- When setting up a backup, click Backup Settings in the popup window, click Enable, select the retention period and backup start time, and click the Confirm button.
- If you want to stop the backup configuration, deselect Use in the Backup Settings popup and authenticate via the logged‑in user’s mobile phone.
Once user authentication is completed, the backup configuration will be disabled and backup execution will stop.
- If you want to stop the backup configuration, deselect Use in the Backup Settings popup and authenticate via the logged‑in user’s mobile phone.
Check backup history
To view the backup history, follow these steps.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Navigate to the Vertica(DBaaS) List page.
- On the Vertica(DBaaS) List page, click the resource to view the backup history. 3. Vertica (DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. The Backup History popup window opens.
- Backup History In the popup window, you can view the backup status, version, backup start time, backup completion time, and size.
Delete backup files
To delete the backup history, follow these steps.
- All Services > Data Analytics > Vertica(DBaaS) Click the menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Go to the Vertica(DBaaS) List page.
- Vertica(DBaaS) List page, click the resource to view the backup history. 3. Vertica(DBaaS) Details Navigate to the page.
- Click the Backup History button. 4. Backup History The popup window opens.
- Backup History In the popup window, check the files you want to delete, then authenticate using the logged-in user’s mobile phone.
- When user authentication is completed, the backup file is deleted.
Recover Vertica(DBaaS)
If a failure or data loss requires restoration from backup files, you can use the cluster recovery feature to recover based on a specific point in time.
To restore Vertica(DBaaS), follow these steps.
- Click the All Services > Data Analytics > Vertica(DBaaS) menu. 1. Go to the Service Home page of Vertica (DBaaS).
- On the Service Home page, click the Vertica(DBaaS) menu. 2. Go to the Vertica(DBaaS) List page.
- On the Vertica(DBaaS) resource list page, click the resource you want to recover. 3. Vertica(DBaaS) Details Go to the page.
- Database Recovery button, click it. 4. Database(DBaaS) Recovery Navigate to the page.
- After entering the relevant information in the Database Recovery area, click the Complete button.
Category required statusDetailed description Recovery Type Required Set the point in time the user wants to recover - Backup point (recommended): Recover based on the backup file. Select from the list of backup file timestamps displayed
- Recovery point: Choose the date and time to recover. Can be selected from the start time of the backup history
Server name Prefix Essential Recovery DB server name - Start with a lowercase English letter and use lowercase letters, numbers, and special characters (
-) to enter 3 to 16 characters
- Based on the server name, a postfix such as 001, 002 is appended to generate the actual server name
Cluster name Required Recovery DB cluster name - Enter using English letters, 3 to 20 characters
- A cluster is a unit that groups multiple servers
Number of nodes Selection Data node count - Set to be the same as the number of nodes configured in the original cluster
Service Type > Server Type Required Recovery DB server type - Standard: standard specification commonly used
- High Capacity: large-capacity server with 24 vCores or more
Service Type > Planned Compute Selection Status of resources with Planned Compute configured - In Use: Number of resources with Planned Compute that are currently in use
- Configured: Number of resources with Planned Compute configured
- Coverage preview: Amount applied per resource by Planned Compute
- Planned Compute Service Application: Go to the Planned Compute service application page
- For more details, refer to Planned Compute Apply
Service Type > Block Storage Required Block Storage settings used by the recovery DB - Basic OS: Area where the DB engine is installed
- DATA: Storage area for table data, archive files, etc.
- Applied identically with the storage type set in the original cluster
- After selecting Use, enter the storage purpose and capacity
- To add storage, click the Add button; to delete, click the x button
- Capacity can be entered in multiples of 8 within the range 16 to 5,120, and up to 9 can be created
Management Console > Server Type Essential Management Console server type - After selecting Use, select the storage purpose and capacity
- Standard: standard specification commonly used
- High Capacity: large-capacity server with 24vCore or more
Management Console > Block Storage Required Block Storage settings used by the Management Console - Select Use, then select Default OS
Database username Required Database username - Apply the same username set in the original cluster
Database password Essential Database password - Apply the same password set in the original cluster
Database Port number Required Database Port number - Apply the same Port number as set in the original cluster
IP access control Select Service Access Policy Configuration - Since the access policy is set for the IP entered on the page, you do not need to configure a separate Security Group policy.
- Enter in IP format (e.g.,
192.168.10.1) or CIDR format (e.g.,192.168.10.0/24,192.168.10.1/32) and click the Add button
- To delete an entered IP, click the x button next to the entered IP
maintenance period Select Database maintenance window - If you select Use, set the day of week, start time, and duration
- It is recommended to set a maintenance window for stable management of the database. Patch operations will be performed at the scheduled time, causing service interruption
- If set to not use, Samsung SDS is not responsible for issues arising from patches not being applied.
License Key Required Enter the Vertica License Key to recover - If the entered license key is invalid, the service cannot be created
tag Selection Add Tag - After clicking the Add Tag button, enter or select Key, Value values
Table. Vertica (DBaaS) recovery configuration items
7.3.3 - API Reference
7.3.4 - CLI Reference
7.3.5 - Release Note
Vertica(DBaaS)
- We have launched the Vertica(DBaaS) service, which can efficiently store data and improve query execution speed with compression and encoding capabilities based on columnar storage.
7.4 - Data Flow
7.4.1 - Overview
Service Overview
Data Flow is a data processing workflow tool that visually creates processing flows for extracting large volumes of data from various data sources and for transforming and transmitting stream/batch data, and it provides the open-source Apache NiFi. Data Flow can be used independently in the Kubernetes Engine cluster environment of Samsung Cloud Platform, or together with other application software.
Provided features
Data Flow provides the following functions.
- Convenient Installation and Management: Data Flow can be easily installed in a standard Kubernetes cluster environment via the web-based Samsung Cloud Platform Console. It automatically configures the architecture required for scalable clustering based on the open-source Apache NiFi, automatically installing ZooKeeper, Registry, and management modules. With Data Flow, you can configure and deploy configuration files, NiFi templates, and other assets needed for service integration.
- Easy Data Flow Management: You can easily create processing flows for stream/batch data in a GUI that matches the user environment, and by authoring data processing flows in a GUI, you can efficiently extract, transmit, and process data between systems.
- NiFi Template Gallery: You can share/distribute reference NiFi templates. Data Flow provides work files for data processing flows commonly used in the field as a gallery, and users can share the data processing flow work they have created.
Component
Data Flow consists of Manager and Service modules, and is provided packaged with Apache NiFi.
Data Flow Manager
Data Flow Manager provides various management functions to enable more efficient use of NiFi.
- You can upload the Nar file created by the customer through the Data Flow Manager for use in the Processor, and upload configuration files to share them.
- Frequently used NiFi templates are packaged as assets and offered in the Gallery, ready for use with a single click.
- Provides real-time monitoring of multiple services configured for the native NiFi service, as well as resource status monitoring.
- You can easily provision configuration information for NiFi components within the cluster.
Data Flow Service
- We provide a data flow management service based on Apache NiFi.
- Automatically configures the architecture required for scalable clustering based on Apache NiFi, and automatically installs the Nifi, ZooKeeper, and Nifi Registry modules.
- When providing Nifi, you can set the Description, required resource size, connection ID/PW, and Host Alias.
- After creating the service, you can modify the Description, required resource size, connection password, Host Alias, and other settings, and apply the changes to the service.
Server spec type
When creating a Data Flow service, check the following.
- Recommended Service Installation Specifications: CPU 21 core, Memory 57 GB, Storage at least 100 GB
- Before creating the Data Flow service, you need to install the Ingress Controller.
- Only one Ingress Controller can be installed in a Kubernetes cluster.
- For more details, refer to Ingress Controller Installation.
Provision status by region
Data Flow is available in the environments below.
| region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Provide |
| South Korea 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that must be pre‑configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Storage | File Storage | Storage that enables multiple client servers to share files over a network connection. |
| Container | Kubernetes Engine | Kubernetes container orchestration service |
7.4.1.1 - ServiceWatch metric
In ServiceWatch, you can view Kubernetes Engine metrics for the Kubernetes Engine created by Data Flow. As with Kubernetes Engine, the metrics provided by default monitoring are data collected at one‑minute intervals.
Basic Metrics
The following are the default metrics for the Kubernetes Engine namespace.
The metrics whose names are displayed in bold below are the key metrics selected from the default metrics provided by Kubernetes Engine. Key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric provides guidance in the user guide on which statistical values are meaningful when querying that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using primary statistical values.
| Indicator name | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| cluster_up | Cluster up | Count |
|
| cluster_node_count | Number of cluster nodes | Count |
|
| cluster_failed_node_count | Number of failed nodes in the cluster | Count |
|
| cluster_namespace_phase_count | Number of cluster namespace phases | Count |
|
| cluster_pod_phase_count | Cluster pod phase count | Count |
|
| node_cpu_allocatable | Node CPU allocatable | - |
|
| node_cpu_capacity | Node CPU capacity | - |
|
| node_cpu_usage | Node CPU usage | - |
|
| node_cpu_utilization | Node CPU usage | - |
|
| node_memory_allocatable | Node memory allocatable amount | Bytes |
|
| node_memory_capacity | Node memory capacity | Bytes |
|
| node_memory_usage | Node memory usage | Bytes |
|
| node_memory_utilization | Node memory usage rate | - |
|
| node_network_rx_bytes | Node network received bytes | Bytes/Second |
|
| node_network_tx_bytes | Node network transmitted bytes | Bytes/Second |
|
| node_network_total_bytes | Total bytes of the node network | Bytes/Second |
|
| node_number_of_running_pods | Number of pods running on a node | Count |
|
| namespace_number_of_running_pods | Number of running pods in the namespace | Count |
|
| namespace_deployment_pod_count | Namespace deployment pod count | Count |
|
| namespace_statefulset_pod_count | Namespace StatefulSet pod count | Count |
|
| namespace_daemonset_pod_count | Namespace daemonset pod count | Count |
|
| namespace_job_active_count | Active namespace job count | Count |
|
| namespace_cronjob_active_count | Number of active namespace cronjobs | Count |
|
| pod_cpu_usage | Pod CPU usage | - |
|
| pod_memory_usage | Pod memory usage | Bytes |
|
| pod_network_rx_bytes | Pod network received bytes | Bytes/Second |
|
| pod_network_tx_bytes | Pod network transmitted bytes | Bytes/Second |
|
| pod_network_total_bytes | Pod network total bytes | Count |
|
| container_cpu_usage | Container CPU usage | - |
|
| container_cpu_limit | Container CPU limit | - |
|
| container_cpu_utilization | Container CPU usage | - |
|
| container_memory_usage | Container memory usage | Bytes |
|
| container_memory_limit | Container memory limit | Bytes |
|
| container_memory_utilization | Container memory usage | - |
|
| node_gpu_count | Node GPU count | Count |
|
| gpu_temp | GPU temperature | - |
|
| gpu_power_usage | GPU power usage | - |
|
| gpu_util | GPU utilization | Percent |
|
| gpu_sm_clock | GPU SM clock | - |
|
| gpu_fb_used | GPU FB usage | Megabytes |
|
| gpu_tensor_active | GPU tensor utilization | - |
|
| pod_gpu_util | Pod GPU utilization | Percent |
|
| pod_gpu_tensor_active | Pod GPU Tensor Utilization Rate | - |
|
7.4.2 - How-to guides
Users can create the service by entering the required Data Flow information and selecting detailed options through the Samsung Cloud Platform Console.
Create Data Flow
You can create and use the Data Flow service in the Samsung Cloud Platform Console.
To create a Data Flow, follow these steps.
Click the All Services > Data Analytics > Data Flow menu. Navigate to the Service Home page of Data Flow.
On the Service Home page, click the Create Data Flow button. You will be taken to the Create Data Flow page.
On the Data Flow creation page, enter the information required to create the service and select detailed options.
- Version selection area, select the required information.
Category Required or optionalDetailed description Data Flow version Required Select version of the selected image - Provide a list of versions for the provided server image
Table. Data Flow version selection item - Enter or select the required information in the Cluster Selection area. To install Data Flow, you must first create nodes for the Kubernetes cluster and the working environment.
Category Required statusDetailed description Cluster name Required Select the cluster to use Ingress Controller Required Select the Ingress Controller installed in the cluster - In the Details tab of the installed Ingress Controller, add the following information to the ConfigMap entry.
- Key: allow-snippet-annotations
- Value: true
Table. Data Flow cluster selection options - In the Details tab of the installed Ingress Controller, add the following information to the ConfigMap entry.
- Enter or select the required information in the Service Information Input area.
Category RequiredDetailed description Data Flow name Required Enter Data Flow name - starting with a lowercase English letter and not ending with a special character (
-), using lowercase English letters, numbers, and special characters (-) to input 3 ~ 30 characters
Storage Class Required Select the storage class used by the selected cluster description Select Enter additional information or description about Data Flow within 150 characters. Domain Settings Required Enter Data Flow domain - Start with a lowercase English letter and ensure it does not end with special characters (
-), using lowercase letters, numbers, and special characters (-) to enter 3 ~ 50 characters
- {Data Flow name}.{configured domain} becomes the Data Flow access URL.
Node Selector Required To install on a specific node, enter a distinguishable label among the node’s labels - If you enter an incorrect node label, installation errors may occur, so verify the node label in advance
- Node labels can be found in the node’s yaml file
account Required Enter Data Flow Manager account - ID: Enter a value between 6 and 30 characters, starting with a lowercase English letter and using lowercase letters and numbers
- Password: Enter 8 to 50 characters, including uppercase letters, lowercase letters, numbers, and special characters (! @ # $ % ^ & *)
- Confirm Password: Re-enter the password exactly the same
Host Alias Selection Add host information to be linked with Data Flow (up to 20 total, including defaults) - Select Use, then click the + button
- Hostname: Enter a hostname or domain format using lowercase letters, numbers, and special characters (
-) with a length of 3 to 63 characters
- IP: Enter in IP format
- Click the X button to delete
- The added host information can be used only if the firewall between the cluster and the server is open
Table. Data Flow service information entry items - starting with a lowercase English letter and not ending with a special character (
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description tag Selection Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag.
- You can add up to 50 tags.
- The newly added tags will be applied after the service creation is completed.
Table. Data Flow additional information input fields
- Version selection area, select the required information.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resource on the Data Flow List page.
Check detailed information of Data Flow
You can view and edit the full list of resources and detailed information of a Data Flow. The Data Flow Details page consists of Details, Tags, Activity Log tabs.
To view detailed information of the Data Flow, follow these steps.
- Click the All Services > Data Analytics > Data Flow menu. Navigate to the Service Home page of Data Flow.
- On the Service Home page, click the Data Flow menu. You will be taken to the Data Flow List page.
- On the Data Flow List page, click the resource to view detailed information. You will be taken to the Data Flow Detail page.
- Data Flow Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Status indicator Data Flow status - Creating: Creating
- Running: Running, Data Flow Services can be created
- Updating: Updating settings
- Terminating: Terminating
- Error: error occurred during creation or service abnormal state
Hosts file configuration information Button to view and copy the host file information for accessing Data Flow Service termination Cancel Service button Table. Data Flow status information and additional functions
- Data Flow Details At the top of the page, status information and additional feature information are displayed.
Detailed Information
On the Data Flow list page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Cluster name | Cluster name of the configured servers |
| Storage Class | Storage class used by the selected cluster |
| Explanation | Additional information or explanation about Data Flow |
| Domain Settings | Data Flow domain name |
| Node Selector | Node Label |
| Web Url | Data Flow URL |
| account | Data Flow Manager account |
| Host Alias | Host information to be connected with Data Flow |
tag
Data Flow List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Data Flow List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Data Flow
You can cancel unused Data Flow to reduce operating costs. However, if you cancel a service, the running service may be terminated immediately, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
To cancel the Data Flow, follow the steps below.
- Click the All Services > Data Analytics > Data Flow menu. Navigate to the Service Home page of Data Flow.
- On the Service Home page, click the Data Flow menu. You will be taken to the Data Flow List page.
- On the Data Flow List page, select the resource to cancel, and click the Cancel Service button.
- When termination is complete, check on the Data Flow List page whether the resource has been terminated.
- Data Flow can be cancelled only after first deleting the associated Data Flow Services.
- If you cancel Data Flow, the created namespace will also be deleted.
7.4.2.1 - Data Flow Services
Users can create the service by entering the required information for Data Flow Services within the Data Flow service through the Samsung Cloud Platform Console and selecting detailed options.
Creating Data Flow Services
Users can add a service by selecting detailed options for Data Flow or by entering configuration values.
To create Data Flow Services, follow these steps.
Click the All Services > Data Analytics > Data Flow menu. You will be taken to the Data Flow Service Home page.
From the Service Home page, click Data Flow Servies. Navigate to the Data Flow Services list page.
On the Data Flow Services List page, click the Data Flow Services Create button. You will be taken to the Data Flow Services Create page.
Data Flow Services Creation page: enter the information required to create the service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category RequiredDetailed description Data Flow name Required Select Data Flow Flow Service name Required Enter Data Flow Services name - Start with a lowercase English letter and ensure it does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to enter 3 to 30 characters
Storage Class Required Select the storage class used by the selected cluster description Selection Enter additional information or description about Data Flow Services within 150 characters. Domain Settings Required Data Flow Services domain input - Start with a lowercase English letter and ensure it does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to enter 3 to 50 characters
- {Data Flow Services name}.{configured domain} becomes the Data Flow Services access URL.
Node Selector Required To install on a specific node, enter a distinguishable label among the node’s Labels - If you enter an incorrect node label, installation errors may occur, so verify the node label in advance
- The node label can be found in the node’s yaml file
Service Workload Required - Nifi: Module that provides Apache Nifi’s services and UI
- Nifi Registry: Module that configures and deploys Nifi templates
- Zookeeper: Module that supports proper distributed processing of Nifi across multiple nodes
account Required Enter Nifi account - ID: Enter a value between 6 and 30 characters, starting with a lowercase English letter and using lowercase letters and numbers
- Password: Enter 8 to 50 characters, including uppercase letters, lowercase letters, numbers, and special characters(
!@#$%^&*)
- Confirm Password: Re-enter the password exactly the same
Table. Data Flow Services service information input items - Start with a lowercase English letter and ensure it does not end with a special character (
- In the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description Host Alias Selection Add host information to be linked with Data Flow (up to 20 total, including defaults) - Select Use, then click the + button
- Hostname: Enter a hostname or domain format using lowercase letters, numbers, and special characters (
-) with a length of 3 to 63 characters
- IP: Enter in IP format
- To delete, click the X button
- The added host information can be used only if the firewall between the cluster and the server is open
tag Selection Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag.
- You can add up to 50 tags.
- The newly added tags will be applied after the service creation is completed.
Table. Data Flow additional information input fields
- Enter or select the required information in the Service Information Input area.
Summary Verify the detailed information and estimated billing amount generated in the panel, then click the Complete button.
- Once creation is complete, check the created resources on the Data Flow Services List page.
Data Flow Services Check detailed information
You can view and edit the complete list of resources and detailed information for Data Flow Services. Data Flow Services Details page consists of Details, Tags, Operation History tabs.
To view detailed information about Data Flow Services, follow these steps.
- Click the All Services > Data Analytics > Data Flow menu. Navigate to the Service Home page of Data Flow.
- On the Service Home page, click the Data Flow Services menu. You will be taken to the Data Flow Services list page.
- On the Data Flow Services List page, click the resource to view detailed information. You will be taken to the Data Flow Services Details page.
- Data Flow Services Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Status display Data Flow Services status - Creating: Creating
- Running: Running
- Updating: Updating configuration
- Terminating: Terminating service
- Error: Creation failed or service unavailable
Hosts file configuration information Button to view and copy the host file information needed to access Data Flow Services Delete Data Flow Services Cancel Service button Table. Data Flow Services status information and additional functions
- Data Flow Services Details At the top of the page, status information and additional feature information are displayed.
Detailed Information
Data Flow Services List page lets you view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Data Flow name | Data Flow name |
| Storage Class | Storage class used by the selected cluster |
| description | Additional information or explanation about Data Flow Services |
| Domain Settings | Data Flow Services domain name |
| Node Selector | Node Label |
| Web Url | Data Flow Services URL |
| account | Airflow account |
| Host Alias | Host information to be connected to Data Flow Services |
tag
Data Flow Services List page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Data Flow Services List page lets you view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Data Flow Services
You can cancel unused Data Flow Services to reduce operating costs. However, if you cancel the service, the running service may be stopped immediately, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
To cancel Data Flow or Data Flow Services, follow the steps below.
- Click the All Services > Data Analytics > Data Flow menu. You will be taken to the Service Home page of Data Flow.
- On the Service Home page, click the Data Flow Services menu. You will be taken to the Data Flow Services list page.
- On the Data Flow Services List page, select the resource to cancel, and click the Data Flow Services Delete button.
- When termination is complete, check on the Data Flow Services list page whether the resource has been terminated.
- If you cancel Data Flow Services, the created namespace will also be deleted.
7.4.2.2 - Install Ingress Controller
The user must install an Ingress Controller before creating a Data Flow service. Only one Ingress Controller should be installed in the Kubernetes cluster.
Installing Ingress Controller using Container Registry
Follow these steps to install the Ingress Controller using the Container Registry.
- After checking the service domain, download the corresponding Ingress Controller image file.Table. Yaml file by domain
- Click the All Services > Container > Kubernetes Engine > Workloads > Pods menu. You will be taken to the Pod List page.
- Click the Create Object button. The Create Object popup window opens.
- After selecting the cluster where you will install Data Flow, copy and paste the contents of the Yaml file.
- Click the Confirm button to complete the installation. The installed Ingress Controller can be viewed in the list.
IngressController For Enterprise (KR-WEST1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerIngressController For Enterprise (KR-EAST1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerIngressController For Samsung (KR-WESTT1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerIngressController For Samsung (KR-EAST1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controller7.4.3 - API Reference
7.4.4 - CLI Reference
7.4.5 - Release Note
Data Flow
- The Data Flow service, which extracts, transforms, and transfers data from various sources and automates data processing workflows, has been launched.
- Provides the open-source Apache NiFi.
7.5 - Data Ops
7.5.1 - Overview
Service Overview
Data Ops is a managed workflow orchestration service based on Apache Airflow that creates workflows for data processing tasks that occur periodically or repeatedly and automates task scheduling. Users can automate the process of delivering useful data to the right place at the required time and monitor the configuration and progress of data pipelines.
Provided features
Data Ops provides the following features.
- Convenient Installation and Management: Data Ops can be easily installed via a web-based Console in a standard Kubernetes cluster environment. Apache Airflow and management modules are installed automatically, and the integrated dashboard provides unified monitoring of the web server and scheduler execution status.
- Dynamic Pipeline Configuration: You can configure pipelines for data tasks based on Python code. Because it integrates with data task scheduling and creates tasks dynamically, you can freely design the desired workflow shape and scheduling.
- Convenient workflow management: DAG (Direct Acyclic Graph: directed acyclic graph) configuration is visualized and managed through a web-based UI, allowing you to easily understand the sequence and parallel relationships of data flow. Additionally, you can easily manage each task’s timeout, retry count, and priority definitions.
Component
Data Ops consists of Manager and Service modules and provides a packaged Apache Airflow.
Data Ops Manager
Data Ops Manager provides various managing features to enable more efficient use of Airflow.
- Through Ops Manager, you can upload Plugin File, Shared File, and Python Library File for use in Ops Service.
- You can easily provision configuration information for Airflow components within the cluster.
- You can manage configuration information for other services within the Airflow cluster and provision it easily.
Data Ops Service
- We provide a managed workflow orchestration service based on Apache Airflow.
- When providing Airflow, you can set the Description, required resource size, DAGs GitSync, and Host Alias.
- After creating the service, you can modify the Description, resource size, DAGs GitSync, and Host Alias to apply changes to the service.
Server spec type
When creating a Data Ops service, check the following.
- Recommended Service Installation Specifications: CPU KubernetesExecutor 43 core, CPU CeleryExecutor 25 core, Memory 50 GB, Storage 100 GB or more
- Before creating the Data Ops service, you need to install the Ingress Controller.
- Only one Ingress Controller can be installed in a Kubernetes cluster.
- For more details, refer to Ingress Controller Installation.
Provision status by region
Data Ops is available in the environments below.
| region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| Korea South 3 (kr-south3) | Not provided |
Pre-service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare them in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Storage | File Storage | Storage that enables multiple client servers to share files over a network connection. |
| Container | Kubernetes Engine | Kubernetes container orchestration service |
7.5.1.1 - ServiceWatch metric
In ServiceWatch, you can view Kubernetes Engine metrics for the Kubernetes Engine created by Data Ops. As with Kubernetes Engine, the metrics provided by default monitoring are data collected at one‑minute intervals.
Basic Metrics
The following are the default metrics for the Kubernetes Engine namespace.
The metrics whose names are displayed in bold below are the key metrics selected from the default metrics provided by Kubernetes Engine. Key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric provides guidance in the user guide on which statistical values are meaningful when querying that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using primary statistical values.
| Indicator name | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| cluster_up | Cluster up | Count |
|
| cluster_node_count | Number of cluster nodes | Count |
|
| cluster_failed_node_count | Number of failed nodes in the cluster | Count |
|
| cluster_namespace_phase_count | Number of cluster namespace phases | Count |
|
| cluster_pod_phase_count | Cluster pod phase count | Count |
|
| node_cpu_allocatable | Node CPU allocatable amount | - |
|
| node_cpu_capacity | Node CPU capacity | - |
|
| node_cpu_usage | Node CPU usage | - |
|
| node_cpu_utilization | Node CPU usage | - |
|
| node_memory_allocatable | Node memory allocatable amount | Bytes |
|
| node_memory_capacity | Node memory capacity | Bytes |
|
| node_memory_usage | Node memory usage | Bytes |
|
| node_memory_utilization | Node memory utilization | - |
|
| node_network_rx_bytes | Node network received bytes | Bytes/Second |
|
| node_network_tx_bytes | Node network transmitted bytes | Bytes/Second |
|
| node_network_total_bytes | Total bytes of the node network | Bytes/Second |
|
| node_number_of_running_pods | Number of pods running on the node | Count |
|
| namespace_number_of_running_pods | Number of running pods in the namespace | Count |
|
| namespace_deployment_pod_count | Namespace deployment pod count | Count |
|
| namespace_statefulset_pod_count | Namespace StatefulSet pod count | Count |
|
| namespace_daemonset_pod_count | Namespace daemonset pod count | Count |
|
| namespace_job_active_count | Active namespace job count | Count |
|
| namespace_cronjob_active_count | Number of active namespace cronjobs | Count |
|
| pod_cpu_usage | Pod CPU usage | - |
|
| pod_memory_usage | Pod memory usage | Bytes |
|
| pod_network_rx_bytes | Pod network received bytes | Bytes/Second |
|
| pod_network_tx_bytes | Pod network transmitted bytes | Bytes/Second |
|
| pod_network_total_bytes | Pod network total bytes | Count |
|
| container_cpu_usage | Container CPU usage | - |
|
| container_cpu_limit | Container CPU limit | - |
|
| container_cpu_utilization | Container CPU usage | - |
|
| container_memory_usage | Container memory usage | Bytes |
|
| container_memory_limit | Container memory limit | Bytes |
|
| container_memory_utilization | Container memory usage | - |
|
| node_gpu_count | Node GPU count | Count |
|
| gpu_temp | GPU temperature | - |
|
| gpu_power_usage | GPU power usage | - |
|
| gpu_util | GPU utilization | Percent |
|
| gpu_sm_clock | GPU SM clock | - |
|
| gpu_fb_used | GPU FB usage | Megabytes |
|
| gpu_tensor_active | GPU Tensor Utilization | - |
|
| pod_gpu_util | Pod GPU utilization | Percent |
|
| pod_gpu_tensor_active | Pod GPU Tensor Utilization Rate | - |
|
7.5.2 - How-to guides
Users can create the service by entering the required Data Ops information and selecting detailed options through the Samsung Cloud Platform Console.
Create Data Ops
You can create and use the Data Ops service in the Samsung Cloud Platform Console.
To create a Data Ops, follow the steps below.
Click the All Services > Data Analytics > Data Ops menu. Navigate to the Service Home page of Data Ops.
On the Service Home page, click the Create Data Ops button. You will be taken to the Create Data Ops page.
On the Data Ops Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Version selection area.
Category RequiredDetailed description Data Ops version Required Select version of the selected image - Provide a list of versions for the provided server image
Table. Data Ops version selection item - Enter or select the required information in the Cluster Selection area. To install Data Ops, you must first create nodes for the Kubernetes cluster and the work environment.
Category RequiredDetailed description Cluster name Required Select the cluster to use Ingress Controller Required Select the Ingress Controller installed in the cluster Table. Data Ops cluster selection options - Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Data Ops name Required Enter Data Ops name - Start with a lowercase English letter and ensure it does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to enter 3 to 30 characters
Storage Class Required Select the storage class used by the selected cluster description Select Enter additional information or description about Data Ops within 150 characters. Domain Settings Required Enter Data Ops domain - Enter 3 to 50 characters, starting with a lowercase English letter and not ending with a special character (
-), using lowercase letters, numbers, and special characters (-)
- {Data Ops name}.{configured domain} becomes the Data Ops access URL.
Node Selector Required To install on a specific node, enter a distinguishable label among the node’s labels - If you enter an incorrect node label, installation errors may occur, so verify the node label in advance
- Node labels can be found in the node’s yaml file
account Required Enter Data Ops Manager account - ID: Start with a lowercase English letter and use lowercase letters and numbers, entering a value between 6 and 30 characters
- Password: Include uppercase (English), lowercase (English), numbers, and special characters (
!@#$%^&*) and enter 8 to 50 characters
- Password Confirmation: Enter the same password again
Host Alias Selection Add host information to be linked with Data Ops (up to 20 total, including defaults) - Select Use, then click the + button
- Hostname: Enter the host name or domain format using lowercase letters, numbers, and special characters (
-) with a length of 3 to 63 characters
- IP: Enter in IP format
- Click the X button to delete
- The firewall between the cluster and the server must be open for the added host information to be usable
Table. Data Ops Service Information Input Items - Start with a lowercase English letter and ensure it does not end with a special character (
- In the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description tag Selection Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag.
- You can add up to 50 tags.
- The newly added tags will be applied after the service creation is completed.
Table. Data Ops additional information input fields
- Select the required information in the Version selection area.
In the Summary panel, verify the detailed information and estimated billing amount, then click the Complete button.
- Once creation is complete, check the created resources on the Data Ops List page.
Check detailed information for Data Ops
You can view and edit the full list of Data Ops resources and detailed information. The Data Ops Details page consists of Details, Tags, Activity History tabs.
To view detailed information about Data Ops, follow these steps.
- Click the All Services > Data Analytics > Data Ops menu. Navigate to the Service Home page of Data Ops.
- On the Service Home page, click the Data Ops menu. You will be taken to the Data Ops List page.
- On the Data Ops List page, click the resource to view detailed information. You will be taken to the Data Ops Detail page.
- Data Ops Details At the top of the page, status information and details about additional features are displayed.
Category Detailed description Status indicator Data Ops status - Creating: Creating
- Running: Running, Data Ops Services are in a creatable state
- Updating: Updating settings
- Terminating: Terminating service
- Error: Error: error occurred during creation or service abnormal state
Hosts file configuration information Button to view and copy the host file information for accessing Data Ops Service termination Button to cancel the service Table. Data Ops status information and additional features
- Data Ops Details At the top of the page, status information and details about additional features are displayed.
Detailed Information
On the Data Ops List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Cluster name | Cluster name of the configured servers |
| Storage Class | Storage class used by the selected cluster |
| description | Additional information or explanation about Data Ops |
| Domain Settings | Data Ops domain name |
| Node Selector | Node Label |
| Web Url | Data Ops URL |
| account | Data Ops Manager account |
| Host Alias | Host information to be connected to Data Ops |
tag
Data Ops list page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Data Ops List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Data Ops
You can cancel unused Data Ops to reduce operating costs. However, if you cancel the service, the running service may be terminated immediately, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
To terminate Data Ops, follow the steps below.
- Click the All Services > Data Analytics > Data Ops menu. Go to the Service Home page of Data Ops.
- On the Service Home page, click the Data Ops menu. You will be taken to the Data Ops List page.
- On the Data Ops List page, select the resource to cancel, and click the Cancel Service button.
- When termination is complete, verify on the Data Ops List page whether the resource has been terminated.
7.5.2.1 - Data Ops Services
Users can create the service by entering the required information for Data Ops Services within the Data Ops service through the Samsung Cloud Platform Console and selecting detailed options.
Create Data Ops Services
Users can add a service by selecting detailed options of Data Ops or by entering configuration values.
To create Data Ops Services, follow these steps.
Click the All Services > Data Analytics > Data Ops menu. Navigate to the Service Home page of Data Ops.
On the Service Home page, click Data Ops Servies. You will be taken to the Data Ops Services list page.
On the Data Ops Services List page, click the Create Data Ops Services button. You will be taken to the Create Data Ops Services page.
On the Data Ops Services Creation page, enter the information required to create the service and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Data Ops name Required Select Data Ops Ops Service name Required Enter the Data Ops Services name - starting with a lowercase English letter and not ending with a special character (
-), using lowercase letters, numbers, and special characters (-) for 3 to 30 characters
Storage Class Required Select the storage class used by the selected cluster Explanation Selection Enter additional information or description about Data Ops Services within 150 characters. Domain Settings Required Data Ops Services domain entry - Enter 3 to 50 characters, starting with a lowercase English letter, not ending with special characters (
-), using lowercase letters, numbers, and special characters (-)
- {Data Ops Services name}.{configured domain} becomes the Data Ops Services access address.
Node Selector Required To install on a specific node, enter a distinguishable label among the node’s Labels - If you enter an incorrect node label, installation errors may occur, so verify the node label in advance
- The node label can be checked in the node’s yaml file
Service Workload Required - Web Server: Provides visualization of DAG components and status, and serves as the Airflow configuration management module
- Scheculer: Manages DAG scheduling and execution to orchestrate various DAGs and their tasks
- Worker: Executes actual orchestration and data processing tasks
- Worker(Kubernetes): When the Worker operates, pods are dynamically created, allowing efficient resource usage. When Kubernetes is selected, the Replica text box is disabled.
- Worker(Celery): When the Worker operates, a static pod is created and maintained, enabling faster handling of a large number of requests. When Celery is selected, the Replica text box is enabled and user input is allowed.
- The selected executor type cannot be changed once chosen
account Required Airflow account input - ID: Start with a lowercase English letter and use lowercase letters and numbers, entering a value between 6 and 30 characters
- Password: Include uppercase (English), lowercase (English), numbers, and special characters (
!@#$%^&*) and enter 8 to 50 characters
- Confirm Password: Re-enter the password identically
Table. Data Ops Services service information input items - starting with a lowercase English letter and not ending with a special character (
- Additional Information Input area, enter or select the required information.
Category required or notDetailed description Host Alias Select Add host information to be linked with Data Ops (up to 20 total, including defaults) - Select Use, then click the + button
- Hostname: Enter the host name or domain format using lowercase letters, numbers, and special characters (
-) with a length of 3 to 63 characters
- IP: Enter in IP format
- Click the X button to delete
- The firewall between the cluster and the server must be open to use the added host information
tag Selection Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag.
- You can add up to 50 tags.
- The newly added tags will be applied after the service creation is completed.
Table. Data Ops additional information input fields
- Enter or select the required information in the Service Information Input area.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resources on the Data Ops Services List page.
Data Ops Services View detailed information
You can view and edit the full list of resources and detailed information for Data Ops Services. The Data Ops Services Details page consists of Details, Tags, Activity History tabs.
Follow these steps to view detailed information about Data Ops Services.
- Click the All Services > Data Analytics > Data Ops menu. You will be taken to the Service Home page of Data Ops.
- On the Service Home page, click the Data Ops Services menu. You will be taken to the Data Ops Services list page.
- On the Data Ops Services List page, click the resource to view detailed information. You will be taken to the Data Ops Services Details page.
- Data Ops Services Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Status display Data Ops Services status - Creating: Creating
- Running: Running
- Updating: Updating configuration
- Terminating: Terminating service
- Error: Creation failed or service unavailable
Hosts file configuration information Button to view and copy host file information for accessing Data Ops Services Delete Data Ops Services Cancel service button Table. Data Ops Services status information and additional features
- Data Ops Services Details At the top of the page, status information and additional feature information are displayed.
Detailed Information
Data Ops Services List page lets you view detailed information of the selected resource and modify the information if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Data Ops name | Data Ops name |
| Storage Class | Storage class used by the selected cluster |
| description | Additional information or explanation about Data Ops Services |
| Domain Settings | Data Ops Services domain name |
| Node Selector | Node Lable |
| Web Url | Data Ops Services URL |
| account | Airflow account |
| Host Alias | Host information to be connected to Data Ops Services |
tag
Data Ops Services List page allows you to view the tag information of the selected resource, and to add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Data Ops Services List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Data Ops Services Terminate
You can cancel unused Data Ops Services to reduce operating costs. However, canceling a service may cause the running service to stop immediately, so you should fully consider the impact of any service interruption before proceeding with the cancellation.
To cancel Data Ops Services, follow the steps below.
- Click the All Services > Data Analytics > Data Ops menu. Go to the Service Home page of Data Ops.
- From the Service Home page, click the Data Ops Services menu. You will be taken to the Data Ops Services list page.
- On the Data Ops Services List page, select the resource to cancel and click the Data Ops Services Delete button.
- When termination is complete, verify on the Data Ops Services List page whether the resource has been terminated.
7.5.2.2 - Installing Ingress Controller
The user must install an Ingress Controller before creating a Data Ops service. Only one Ingress Controller should be installed in the Kubernetes cluster.
Installing Ingress Controller using Container Registry
Follow these steps to install the Ingress Controller using the Container Registry.
- After checking the service domain, you can locate the corresponding Ingress Controller image file and copy or download it.Table. Yaml file by domain
- Click the All Services > Container > Kubernetes Engine > Workloads > Pods menu. You will be taken to the Pod List page.
- Click the Create Object button. The Create Object popup opens.
- After selecting the cluster where you will install Data Ops, copy and paste the contents of the Yaml file.
- Click the Confirm button to complete the installation. The installed Ingress Controller can be viewed in the list.
IngressController For Enterprise (KR-WEST1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerIngressController For Enterprise (KR-EAST1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.e.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerIngressController For Samsung (KR-WEST1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
-
resources:
- namespaces
verbs:
- get
- apiGroups:
-
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-west1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerIngressController For Samsung (KR-EAST1)
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controllerapiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
name: dss-ingress
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- dss-ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
rules:
- apiGroups:
-
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
-
resources:
- nodes
verbs:
- get
- apiGroups:
-
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
-
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
namespace: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: dss-ingress
subjects:
- kind: ServiceAccount
name: dss-ingress
namespace: dss-ingress
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
annotations-risk-level: Critical
kind: ConfigMap
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
---
apiVersion: v1
kind: Service
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
externalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
nodePort: 30708
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
nodePort: 31416
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
type: NodePort
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-ingress-controller
namespace: dss-ingress
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
strategy:
rollingUpdate:
maxUnavailable: 1
type: RollingUpdate
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/dss-ingress-controller
- --election-id=dss-ingress-nginx-leader
- --controller-class=k8s.io/dss-ingress-controller
- --ingress-class=dss-nginx
- --configmap=$(POD_NAMESPACE)/dss-ingress-controller
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: brightixscr.scr.private.kr-east1.s.samsungsdscloud.com/brightics-df/nginx-ingress-controller:v1.12.3
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: false
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
readOnlyRootFilesystem: false
runAsGroup: 82
runAsNonRoot: true
runAsUser: 101
seccompProfile:
type: RuntimeDefault
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: dss-ingress
terminationGracePeriodSeconds: 300
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
annotations:
ingressclass.kubernetes.io/is-default-class: "true"
labels:
app: ingress-controller
app.kubernetes.io/component: controller
app.kubernetes.io/instance: dss-ingress
app.kubernetes.io/name: dss-ingress
app.kubernetes.io/part-of: dss-ingress
app.kubernetes.io/version: 1.12.3
name: dss-nginx
spec:
controller: k8s.io/dss-ingress-controller7.5.3 - API Reference
7.5.4 - CLI Reference
7.5.5 - Release Note
Data Ops
- A Data Ops service that creates workflows for data processing tasks that occur periodically or repeatedly and automates job scheduling has been launched.
- It is a managed workflow orchestration service based on Apache Airflow.
7.6 - Quick Query
7.6.1 - Overview
Service Overview
Quick Query is an interactive query service that allows you to easily and quickly analyze large-scale data using standard SQL. It is automatically installed on a standard Kubernetes cluster, and you can easily and quickly access various data sources such as Cloud Hadoop, Object Storage, and RDB for data retrieval and processing.
Features
- Easy and Fast Data Retrieval: After defining a schema for data stored in Object Storage and executing queries using standard SQL, you can retrieve data easily and quickly. Any user who can work with SQL can easily analyze large data sets, even without being a professional analyst.
- Fast Parallel Distributed Processing: Using the Trino engine capable of parallel distributed processing, queries are automatically split and processed in parallel across multiple nodes simultaneously, allowing rapid query results even for large-scale data.
- Various Service Architectures: We provide a public fixed-resource mode, a public resource-scaling mode, and a personal resource-scaling mode. The public fixed-resource mode supports stable response times for large-scale data queries, while the public resource-scaling mode can be used at a lower cost when usage frequency is irregular. Additionally, the personal resource-scaling mode enables each user to perform analysis tasks in an independent environment, allowing the use of Quick Query with a structure that meets user requirements.
Service Architecture Diagram
Provided features
Quick Query provides the following features.
- Support single access to various data sources (support for 11 types of data sources)
- Automatic saving of result data in Object Storage
- Result reuse feature for identical queries
- Access control feature through Ranger integration
- Data Usage Control Feature
| Category | type | Remarks |
|---|---|---|
| Cloud Hadoop | hive_on_cloud_hadoop iceberg_on_cloud_hadoop | Using Hive Metastore in Cloud Hadoop |
| Object Storage | hive_on_object_storage iceberg_on_object_storag | Deploy and use Hive Metastore in Quick Query |
| RDB | postgresql mariadb sqlserver oracle mysql | JDBC Driver Upload needed (license) |
| TPCDS | tpcds | Built-in Data Source provided by Quick Query |
| TPCH | tpch | Built-in Data Source provided by Quick Query |
| type | select | insert | uptate | delete | create | drop | alter | analyze | call |
|---|---|---|---|---|---|---|---|---|---|
| hive_on_cloud_hadoop | O | O | O | O | O | O | O | O | O |
| iceberg_on_cloud_hadoop | O | O | O | O | O | O | O | O | O |
| hive_on_object_storage | O | O | O | O | O | O | O | O | O |
| iceberg_on_object_storage | O | O | O | O | O | O | O | O | O |
| postgresql | O | O | O | O | O | O | |||
| mariadb | O | O | O | O | O | O | |||
| sqlserver | O | O | O | O | O | O | |||
| greenplum | O | O | O | O | O | O | |||
| oracle | O | O | O | O | O | O | |||
| mysql | O | O | O | O | O | O | |||
| tpcds | O | ||||||||
| tpch | O |
Component
Query Engine Type: Shared
The query engine is structured so that a single instance, once started, can be shared by multiple users.
Fixed Resource Mode (Auto Scaling Disabled): When Auto Scaling is not used, the query engine for the fixed resources is launched according to the resources selected by the user. Because the query engine always runs on the same resources, it can guarantee consistent query performance.
Figure. Fixed resource mode (Auto Scaling not used) Resource Expansion Mode (Auto Scaling enabled): When Auto Scaling is used, the query engine’s Worker nodes automatically scale in/out based on throughput. If the throughput is low, the number of Worker nodes can be reduced to as few as one, and when the throughput increases, the Worker nodes expand. Additionally, resources can be adjusted according to the cluster size.
Figure. Resource expansion mode (using Auto Scaling)
Query Engine Type: Private
Resource Expansion Mode (Auto Scaling Enabled): The personal query engine type runs a separate query engine for each user. Each query engine supports Auto Scale in/out, and if unused for an extended period, the engine automatically stops. When reconnecting for reuse, the query engine automatically restarts. When the throughput is low, the number of Worker nodes can decrease to as few as one, and when the throughput increases, the number of Worker nodes grows. Additionally, resources can be adjusted according to the cluster size.
Figure. Resource Expansion Mode (using Auto Scaling)
Server type
The server types supported by Quick Query are as follows.
| Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server size | s1v2m4 | Provided server specifications
|
The minimum specifications required to use Quick Query are as follows.
| Category | Details | Cluster size (user input value) | Fixed node pool | Auto-scaling node pool |
|---|---|---|---|---|
| Common | Fixed resource mode (Auto Scaling not used) | Replica: 1 CPU: 4 Core Memory: 8GB | 8 Core, 16GB * 4 | N/A |
| Common | Resource expansion mode (Auto Scaling enabled) | Small(1 Core, 4GB) | 8 Core, 16GB * 3 | 8 Core, 16GB * 1 |
| Personal | Resource expansion mode (Auto Scaling enabled) | Small(1 Core, 4GB) | 8 Core, 16GB * 3 | 8 Core, 32GB * 2 |
Provision status by region
Quick Query is available in the following environments.
| region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
| Storage | File Storage | A storage system that enables multiple client servers to share files over a network connection. |
7.6.1.1 - ServiceWatch metric
You can view Kubernetes Engine metrics in ServiceWatch for the Kubernetes Engine created from Quick Query. As with Kubernetes Engine, the metrics provided by default monitoring are data collected at one‑minute intervals.
Basic Metrics
The following are basic metrics for the Kubernetes Engine namespace.
The metrics whose names are shown in bold below are the key metrics selected from the default metrics provided by Kubernetes Engine. Key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric provides guidance in the user guide on which statistical values are meaningful when querying that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using primary statistical values.
| Indicator Name | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| cluster_up | Cluster up | Count |
|
| cluster_node_count | Number of cluster nodes | Count |
|
| cluster_failed_node_count | Number of failed nodes in the cluster | Count |
|
| cluster_namespace_phase_count | Number of cluster namespace phases | Count |
|
| cluster_pod_phase_count | Number of cluster pod phases | Count |
|
| node_cpu_allocatable | Node CPU allocatable amount | - |
|
| node_cpu_capacity | Node CPU capacity | - |
|
| node_cpu_usage | Node CPU usage | - |
|
| node_cpu_utilization | Node CPU usage | - |
|
| node_memory_allocatable | Node memory allocatable amount | Bytes |
|
| node_memory_capacity | Node memory capacity | Bytes |
|
| node_memory_usage | Node memory usage | Bytes |
|
| node_memory_utilization | Node memory usage rate | - |
|
| node_network_rx_bytes | Node network received bytes | Bytes/Second |
|
| node_network_tx_bytes | Node network transmitted bytes | Bytes/Second |
|
| node_network_total_bytes | Total bytes of the node network | Bytes/Second |
|
| node_number_of_running_pods | Number of pods running on the node | Count |
|
| namespace_number_of_running_pods | Number of running pods in the namespace | Count |
|
| namespace_deployment_pod_count | Namespace deployment pod count | Count |
|
| namespace_statefulset_pod_count | Namespace StatefulSet pod count | Count |
|
| namespace_daemonset_pod_count | Number of DaemonSet Pods per Namespace | Count |
|
| namespace_job_active_count | Active namespace job count | Count |
|
| namespace_cronjob_active_count | Number of active namespace cronjobs | Count |
|
| pod_cpu_usage | Pod CPU usage | - |
|
| pod_memory_usage | Pod memory usage | Bytes |
|
| pod_network_rx_bytes | Pod network received bytes | Bytes/Second |
|
| pod_network_tx_bytes | Pod network transmitted bytes | Bytes/Second |
|
| pod_network_total_bytes | Total pod network bytes | Count |
|
| container_cpu_usage | Container CPU usage | - |
|
| container_cpu_limit | Container CPU limit | - |
|
| container_cpu_utilization | Container CPU usage | - |
|
| container_memory_usage | Container memory usage | Bytes |
|
| container_memory_limit | Container memory limit | Bytes |
|
| container_memory_utilization | Container memory usage rate | - |
|
| node_gpu_count | Node GPU count | Count |
|
| gpu_temp | GPU temperature | - |
|
| gpu_power_usage | GPU power consumption | - |
|
| gpu_util | GPU utilization | Percent |
|
| gpu_sm_clock | GPU SM clock | - |
|
| gpu_fb_used | GPU FB usage | Megabytes |
|
| gpu_tensor_active | GPU tensor utilization | - |
|
| pod_gpu_util | Pod GPU utilization | Percent |
|
| pod_gpu_tensor_active | Pod GPU Tensor Utilization Rate | - |
|
7.6.2 - How-to guides
Users can create the service by entering the required Quick Query information and selecting detailed options through the Samsung Cloud Platform Console.
Create Quick Query
You can create and use the Quick Query service in the Samsung Cloud Platform Console.
To create a Quick Query, follow these steps.
Click the All Services > Data Analytics > Quick Query menu. Go to the Service Home page of Quick Query.
On the Service Home page, click the Quick Query Create button. You will be taken to the Quick Query Create page.
On the Quick Query creation page, enter the information required to create the service and select detailed options.
- In the Version selection area, select the required information.
Category Required statusDetailed description Quick Query Required Select Quick Query Service Version - Provide a list of available versions
Table. Quick Query Service Version Selection - In the Service Information Input area, enter or select the required information.
Category Required statusDetailed description Quick Query name Required Enter Quick Query name - Start with a lowercase English letter and ensure it does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to enter 3 ~ 30 characters
description Selection Enter additional information or description about Quick Query within 150 characters. Domain Settings Required Enter Quick Query domain - must start with a lowercase English letter and must not end with a special character (
-,.), using lowercase letters, numbers, and special characters (-,.) to enter 3 to 50 characters
- {Quick Query name}.{configured domain} becomes the Quick Query access URL.
Query engine type Required Select query engine type - Shared: A single query engine is shared among multiple users
- Personal: Each user uses a separate engine
Cluster size Required Select resource capacity for cluster configuration - When the engine type is selected as Public
- If Auto Scaling is set to Enabled, you can choose the cluster capacity from Small, Medium, Large, or Extra Large.
- If Auto Scaling is not set to Enabled, you can configure the cluster capacity by specifying Replica, CPU, and Memory.
- When the engine type is selected as Private
- You can select the cluster capacity from Small, Medium, Large, or Extra Large.
- Engine capacity (when Auto Scaling is enabled)
- Small: 1Core, 4GB
- Medium: 4Core, 16GB
- Large: 8Core, 64GB
- Extra Large: 16Core, 128GB
- Engine capacity (when Auto Scaling is disabled)
- Replica: can be set from 1 to 9, default: 1
- CPU: can be set from 4 to 24 (allowed values: 4, 6, 8, 10, 12, 14, 16, 18, 20, 22, 24), default: 4
- Memory: can be set from 8 to 256 (allowed values: 8, 16, 32, 64, 128, 192, 256), default: 8
Maximum number of concurrent queries Required Select the maximum number of queries to run simultaneously in Quick Query - Selectable values: 32, 64, 96, 128
Data Service Console connection Required Enter Data Service Console domain - that starts with a lowercase English letter and does not end with a special character (
-,.)using lowercase letters, numbers, and special characters (-,.)to enter 3 to 50 characters
Host Alias Selection Add host information to be linked with Quick Query (up to 20 total, including defaults) - After selecting Use, click the + button
- Hostname: Enter 3–63 characters using lowercase letters, numbers, and special characters (
-,.) in host name or domain format
- IP: Enter in IP format
- To delete, click the X button
- The added host information can be used only if the firewall between the cluster and the server is open
Table. Quick Query Service Information Input - Start with a lowercase English letter and ensure it does not end with a special character (
- In the Cluster Information Input area, enter or select the required information.
Category RequiredDetailed description Cluster name Required Enter cluster name - must start with a lowercase English letter and must not end with a special character (
-), using lowercase letters, numbers, and special characters (-) enter 3 to 30 characters
Control area setting Required/Optional - Kubernetes version: Display Kubernetes version
- You can upgrade the Kubernetes version after provisioning.
- Public endpoint access: To enable access to the Kubernetes API server endpoint from outside, select Use and then enter the Access control IP range (cannot be changed after service request).
- Control plane logging: Select whether to enable control plane logging
- If you select Use, you can view the cluster control plane’s Audit/Event logs in Management > Cloud Monitoring > Log Analytics.
- Log storage up to 1GB for all services in the project is provided for free, and logs exceeding 1GB are deleted sequentially.
Network Settings Required Network Connection Settings - VPC: Use the same VPC as the Data Service Console
- Subnet: Select the subnet to use from the chosen VPC’s subnets
- Security Group: After clicking Search, select a security group in the Select Security Group popup
File Storage configuration Required Select file storage volume to use in the cluster - Default Volume (NFS): After clicking Search, select file storage in the File Storage Selection popup
Table. Quick Query Service Cluster Information Input - must start with a lowercase English letter and must not end with a special character (
- Node Pool Information Input Enter or select the required information in this area.
Category Required statusDetailed description Node pool configuration Required/Optional Enter detailed information for the node pool to add - * Items marked with an asterisk are required fields
- If the Query Engine Type is Public and Auto Scaling is set to Disabled, only the Node Pool Configuration (Fixed) option can be configured.
- Keypair: Select the authentication method used when connecting to the Virtual Server
Table. Quick Query Service Node Pool Information Input - * Items marked with an asterisk are required fields
- In the Additional Information Input area, enter or select the required information.
Category Whether requiredDetailed description tag Selection Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag.
- You can add up to 50 tags.
- The newly added tags will be applied after the service creation is completed.
Table. Quick Query Service Additional Information Input
- In the Version selection area, select the required information.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resource on the Quick Query List page.
Quick Query Check detailed information
You can view and edit the complete list of resources and detailed information of the Quick Query service. The Quick Query Details page consists of Detailed Information, Tags, Activity Log tabs.
Follow these steps to view the detailed information of the Quick Query service.
- Click the All Services > Data Analytics > Quick Query menu. Navigate to the Service Home page of Quick Query.
- On the Service Home page, click the Quick Query menu. Navigate to the Quick Query list page.
- Quick Query List page: click the resource to view detailed information. You will be taken to the Quick Query Detail page.
- Quick Query Details At the top of the page, status information and additional feature information are displayed.
Category Detailed description Status display Status of user-created Quick Query - Creating: In progress
- Running: Creation complete, service available
- Updating: Updating settings
- Terminating: Service termination in progress
- Error: Error occurred during creation or service abnormal state
Hosts file configuration information Button to view and copy host file information for accessing Quick Query and Data Service Console Service termination Cancel service button Table. Quick Query Status Information and Additional Features
- Quick Query Details At the top of the page, status information and additional feature information are displayed.
Detailed Information
Quick Query List page allows you to view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Quick Query name | Quick Query name |
| description | Additional information or explanation about Quick Query |
| Version | Quick Query version |
| Service type | Quick Query Service Type |
| Query engine type | Quick Query engine type |
| Engine Spec |
|
| Maximum number of concurrent queries | Maximum number of queries to run simultaneously in Quick Query |
| Domain Settings | Quick Query domain |
| Data Service Console | Data Service Console domain |
| Host Alias | Host information for Quick Query connection |
| Web URL | Web URLs of Data Service Console and Quick Query |
| Cluster name | Cluster name of the configured servers |
| Installation node information | Detailed information of the installed node pool |
tag
Quick Query List page lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Quick Query List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Quick Query Connect
Follow these steps to access Quick Query.
- Check the IP of the Windows system(PC) that will connect to Quick Query.
- Since external access is required, you need to check the system’s public IP.
- Check that the IGW connection in the VPC where Quick Query is installed is enabled.
- An Internet Gateway that can be connected must be configured for external access.
- Add the following to the Windows system’s hosts file. You can view it by clicking Hosts file setting information on the Quick Query detail screen.
- Domain address of Data Service Console
- Domain address of Data Service Console IAM
- Domain address of Quick Query
- Add the following rule to the VPC IGW firewall you selected when applying for the Quick Query service.
Category Protocol Source Target IP Port Inbound TCP User IP Load Balancer service IP 80,443 Table. VPC IGW Firewall Rules - Add the following rule to the Load Balancer Firewall you selected when applying for the Quick Query service.
Category Protocol Source Target IP Port Outbound TCP User IP Load Balancer service IP 80,443 Inbound TCP Load Balancer’s Source NAT IP Subnet range of the Kubernetes Node Pool 30000-32767 TCP Load Balancer’s Health Check IP Subnet range of the Kubernetes Node Pool 30000-32767 Table. Load Balancer Firewall Rules - Add the following rule to the Security Group you selected when applying for the Quick Query service.
Category Protocol Target IP Port Inbound TCP Load Balancer’s Source NAT IP 30000-32767 TCP Load Balancer’s Health Check IP 30000-32767 Table. Security Group Rules - On the Windows system (PC) you want to connect to, launch the Chrome browser and then access the Quick Query URL.
Terminate Quick Query
You can cancel the unused service to reduce operating costs. However, canceling the service may immediately stop the running service, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
To cancel Quick Query, follow the steps below.
- Click the All Services > Data Analytics > Quick Query menu. Go to the Service Home page of Quick Query.
- On the Service Home page, click the Quick Query menu. You will be taken to the Quick Query List page.
- On the Quick Query List page, select the resource to cancel, and click the Cancel Service button.
- After the termination is complete, check on the Quick Query list page whether the resource has been terminated.
7.6.3 - API Reference
7.6.4 - CLI Reference
7.6.5 - Release Note
Quick Query
- The Quick Query service, which allows you to easily analyze large-scale data using standard SQL, has been launched.
7.7 - Cloud Hadoop
7.7.1 - Overview
Service Overview
Cloud Hadoop is a service for easily and quickly analyzing large-scale data, providing a Hadoop cluster (computing resources, management tools, and applications) used for big data processing and analysis in the SCP environment.
Features
Cloud Hadoop provides an automated cluster creation service through the Hadoop Manager and the Hadoop Ecosystem(ecosystem) composed of Spark, HDFS(Hadoop distributed file system), Hive, etc., enabling anyone to easily build, optimize, or flexibly scale infrastructure for big data analysis.
Service Diagram
Provided features
Cloud Hadoop provides the following features.
Provide Hadoop Cluster as a cloud service
- Providing a Hadoop Cluster through automated cluster installation in the SDS Cloud environment
- Perform essential operational activities for cluster management (cluster operation/monitoring)
- Provides a Hadoop ecosystem with verified interoperability and allows users to access the server (VM)
Offer the Hadoop service stack as separate products (increase nodes per product)
- Minimum node allocation per product for stable service operation
- Providing diverse product selection opportunities to meet user needs and reduce costs
Providing user-friendly features for Hadoop services
- Provides installation and management functions for each Hadoop ecosystem, optimal configuration values, and version management features.
- Provide an integrated monitoring dashboard for system resources
- Provides Service Failure Alert feature
Component
We package the major components of the Hadoop ecosystem to deliver an enterprise data cloud.
Service Configuration
Cloud Hadoop provides the following services.
- Basic Installation Service
- HDFS 3.3.6
- YARN 3.3.6
- Hbase 2.4.17
- Hive 3.1.2
- Tez 0.9.1
- Hue 4.11.0
- Solr 8.11.4
- Spark 3.4.1
- Zookeeper 3.8.5
- Additional Option Service
- Data Governance: Atlas 2.1.0, Ranger 2.1.0
- Analytical Data Warehouse: Iceberg 1.8.0, Kyuubi 1.10.2
- Data Ingestion: Sqoop 1.4.7, Kafka 3.9.1, Flume 1.11.0
Server type
The server types supported by Cloud Hadoop are as follows.
Category | example | Detailed description |
|---|---|---|
| Server type | Standard | Provided server types
|
| Server size | s1v4m32 | Provided server specifications
|
The minimum specifications for using Cloud Hadoop are as follows.
Category | Algebra | Instance size (user-selected value) |
|---|---|---|
| Master | 2(fixed) | CPU: 4 Core Memory: 32 GB |
| Worker | 3(minimum) | CPU: 4 Core Memory: 32 GB |
| Data Governance | None | |
| Analytical Data Warehouse | None | |
| Ingestion | 3 (minimum) | CPU: 4 Core Memory: 32 GB |
Provision status by region
Cloud Hadoop is available in the following environments.
| region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South1(kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that need to be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
| Storage | Object Storage | Object storage that simplifies data storage and retrieval |
7.7.1.1 - ServiceWatch metric
You can view Virtual Server metrics in ServiceWatch for servers created in Cloud Hadoop. Like Virtual Server, the metrics provided by default monitoring are data collected at 5‑minute intervals. In the Virtual Server detailed view, enabling detailed monitoring allows you to view data collected at 1‑minute intervals. For more details, Virtual Server > Enable ServiceWatch Detailed Monitoring
- The basic monitoring and detailed monitoring of Cloud Hadoop are provided with the same metrics as Virtual Server, and the namespace is also provided as Virtual Server.
Basic Metrics
The following are the basic metrics for the Virtual Server namespace.
The indicators whose names are displayed in bold below are the key indicators selected from the basic metrics provided by Virtual Server. Key metrics are used to build service dashboards that are automatically created for each service in ServiceWatch.
Each metric provides guidance in the user guide on which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the values shown in bold are the primary statistics. In the service dashboard, you can view key metrics using primary statistical values.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| Instance State | Instance status display
| None |
|
| CPU Usage | CPU usage | Percent |
|
| Disk Read Bytes | Bytes read from block device (bytes) | Bytes |
|
| Disk Read Requests | Number of read requests on a block device | Count |
|
| Disk Write Bytes | Write capacity (bytes) on block device | Bytes |
|
| Disk Write Requests | Number of write requests on block device | Count |
|
| Network In Bytes | Received bytes on the network interface | Bytes |
|
| Network In Dropped | Number of packet drops received on the network interface | Count |
|
| Network In Packets | Number of packets received on the network interface | Count |
|
| Network Out Bytes | Data transmitted from the network interface (bytes) | Bytes |
|
| Network Out Dropped | Number of packet drops transmitted from the network interface | Count |
|
| Network Out Packets | Number of packets transmitted on the network interface | Count |
|
7.7.2 - How-to guides
Users can create the service by entering the required information for Cloud Hadoop and selecting detailed options through the Samsung Cloud Platform Console.
Create Cloud Hadoop
You can create and use the Cloud Hadoop service in the Samsung Cloud Platform Console.
To create Cloud Hadoop, follow these steps.
All Services > Data Analytics > Cloud Hadoop Click the menu. You will be taken to the Service Home page of Cloud Hadoop.
On the Service Home page, click the Create Cloud Hadoop button. You will be taken to the Create Cloud Hadoop page.
On the Cloud Hadoop Creation page, enter the information required to create the service and select detailed options.
- Select the required information in the Image and version selection area.
Category RequiredDetailed description image Required Select the type of image provided - Cloud Hadoop With Ubuntu 22.04
Image version Required Select version of the selected image - Provide a list of versions of the provided image
Table. Cloud Hadoop image and version selection options - Enter or select the required information in the Service Information Input area.
Category RequiredDetailed description Server name Prefix Required Server name for installing Cloud Hadoop - must start with a lowercase English letter and be entered using lowercase letters, numbers, and special characters (
-) with a length of 3 to 13 characters
- A postfix such as 001, 002 is appended to the server name to create the actual server name
Cluster name Required Cluster name of the servers - Enter using English letters, 3 to 20 characters
- A cluster is a unit that groups multiple servers
Planned Compute Selection For servers where Cloud Hadoop is installed, you can use a discounted price by selecting a Planned Compute commitment - All Services > Financial Management > Planned Compute menu can be applied
- For more details, refer to Planned Compute Apply
Master Node > Number of Master Nodes Required Number of Master nodes - The number of Master nodes is fixed at two per Hadoop cluster
- A Master node is the node where Hadoop Master is installed and provides the default HA (high availability) configuration
- The Master node includes Hadoop Manager and various Hadoop ecosystem components installed together
Master Node > Server Type Required CPU and Memory types for distributed data processing - Standard-1: Standard specifications commonly used
- High Capacity-2: Large-capacity server with 24 vCores or more
- Recommended specifications: vCPU 8, Memory 64G
Master Node > Block Storage Required Block Storage type to be used for the Master node - Basic OS: Area where the engine is installed
- DATA: Data file storage area
- Select a storage type and then enter the capacity (see Create Block Storage for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- Capacity can be entered in multiples of 8 within the range 25 to 1,536
- Select a storage type and then enter the capacity (see Create Block Storage for details on each Block Storage type)
- Delete on termination: When the server is terminated, the volume is terminated as well; however, volumes with snapshots are not deleted even when Delete on termination is enabled.
- Add Disk: Data storage area
- After selecting Use, enter the capacity of the storage
- Click the + button to add storage, or the x button to delete. Up to 9 can be added
- Capacity can be entered in multiples of 8 within the range 25 to 1,536
Worker Node > Number of Worker Nodes Required Number of Worker nodes - Worker nodes can be selected from 3 to 90
- Worker nodes are the nodes where Hadoop data nodes and the Resource Manager are installed, and they process and store distributed data
Worker Node > Server Type Required CPU and Memory types for distributed data processing - Standard-1: Standard specification commonly used
- High Capacity-2: Large-capacity server with 24 vCore or more
- Recommended specification: vCPU 8, Memory 64G
- For detailed information about server types provided by Cloud Hadoop, see Cloud Hadoop Server Types
Worker Node > Block Storage Required Block Storage type to be used on the Worker node - Basic OS: Area where the engine is installed
- DATA: Data file storage area
- Select the storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- SSD: High‑performance general volume
- HDD: General volume
- Capacity can be entered in multiples of 8 within the range 25 to 1,536
- Select the storage type and then enter the capacity (see Block Storage 생성하기 for details on each Block Storage type)
- Delete on termination: When the server is terminated, the volume is terminated as well; however, volumes with snapshots are not deleted even when Delete on termination is enabled.
- Add Disk: Data storage area
- After selecting Use, enter the capacity of the storage
- Click the + button to add storage, or the x button to delete. Up to 9 can be added
- Capacity can be entered in multiples of 8 within the range 25 to 1,536
Data Governance Selection Additional installation of the Hadoop ecosystem for data governance - If you select Use, Atlas and Ranger are installed automatically
- Cannot be modified or removed after creation
Analytical Data Warehouse Selection Additional installation of the Hadoop ecosystem for fast data analysis - If you select Use, Iceberg and Kyuubi are installed automatically
- Cannot be modified or removed after creation
Data Ingestion Selection Additional installation of the Hadoop ecosystem for data collection and loading - If you select Use, Kafka, Flume, and Sqoop are installed automatically
Data Ingestion > Ingestion Node count Selection Ingestion node count - Ingestion nodes can be selected from 3 to 10
- Worker nodes are the nodes where Hadoop data nodes and the Resource Manager are installed, and they process and store distributed data
Data Ingestion > Server Type Selection CPU and Memory types for distributed data processing - Standard-1: Standard specification commonly used
- High Capacity-2: Large-capacity server with 24 vCore or more
- Recommended specification: vCPU 8, Memory 64G
- For detailed information about the server types provided by Cloud Hadoop, see Cloud Hadoop server types
Data Ingestion > Block Storage Selection Block Storage type to be used for the Ingestion node - Base OS: Area where the engine is installed
- DATA: Data file storage area
- Select a storage type and then enter the capacity (see Create Block Storage for details on each Block Storage type)
- SSD: High-performance general volume
- HDD: General volume
- Capacity can be entered in multiples of 8 within the range 25 to 1,536
- Select a storage type and then enter the capacity (see Create Block Storage for details on each Block Storage type)
- Add Disk: Data storage area
- After selecting Use, enter the storage capacity
- Click the + button to add storage, or the x button to delete. Up to 9 can be added
- Capacity can be entered in multiples of 8 within the range 25 to 1,536, and up to 9 can be created
Object Storage bucket Selection Object Storage to be used in the cluster - Bucket Selection after selecting, select Object Storage bucket
- You can add up to 10, to delete click the x button
- After adding a bucket, to set access permission for that bucket, select server resources from the All Services > Object Storage list > the relevant Object Storage Details > Access Control > Allow Server Resources menu
Table. Cloud Hadoop Service Information Input Items - must start with a lowercase English letter and be entered using lowercase letters, numbers, and special characters (
- In the Required Information Input area, enter or select the required information.
Category RequiredDetailed description Enter PrivateLink information Required Enter authentication key for PrivateLink connection - Create authentication key: IAM > My info > Authentication Key Management tab > Click Create Authentication Key button
- Copy authentication key: IAM > My info > Authentication Key Management tab > Click the generated authentication key > Authentication Key Details > Basic Information tab > Authentication Key > Click View button > Copy the authentication key from the popup screen
- Access Key: Enter Access Key, can be entered only when first applying for the service
- Secret Key: Enter Secret Key, can be entered only when first applying for the service
Cloud Hadoop Manager account Required Enter the account and password to log in to Cloud Hadoop Manager - Account name: Enter the account to use for login
- Password: Enter the password to use for login
- Confirm password: Re-enter the password
Network > Common Settings Required Network settings for servers created by the service - Select this when you want to apply the same settings to all servers being installed
- Select the pre‑created VPC and Subnet
- IP is generated automatically
- Public NAT: Available when the VPC is connected to an Internet Gateway and the Subnet is of Public type. Checking Use enables NAT IP configuration
Network > Server-specific Settings Required Network settings for servers created by the service - Select when you want to apply different settings for each server being installed
- Select a pre‑created VPC and Subnet
- Automatically displayed according to the selected node
- Enter the IP for each server
- Public NAT: Available when the VPC is connected to an Internet Gateway and the Subnet is of type Public. When Use is checked, NAT IP can be configured. See Create Public IP for details
Security Group Required Add Security Group - Click the Select button to choose from the list
- Before the service creation is complete, you can delete the added Security Group by clicking the x button on its right
Keypair Required Select the user authentication method used when connecting to the Virtual Server - Default login accounts by OS
- Alma Linux: almalinux
- Oracle Linux: cloud-user
- RHEL:cloud-user
- Rocky Linux: rocky
- Ubuntu: ubuntu
- Windows: sysadmin
Table. Cloud Hadoop required information input itemsCaution- For a PrivateLink connection, you must enter an authentication key that was generated as a permanent key, and you must not delete that key.
If the authentication key expires or is deleted, rendering it invalid, it may cause issues with resource changes or service termination in the Cloud Hadoop service. - When using a public subnet and assigning a public IP, you may be exposed to security attacks such as external hacking and malware infection.
information- When creating a Cloud Hadoop service, only one Security Group can be selected, but after the service is created, you can select up to four Security Groups, including the initially selected one. However, the Security Group chosen at the initial service creation cannot be modified or deleted.
- If Cloud Hadoop is installed correctly, API communication between the installed Cloud Hadoop service and the Samsung Cloud Platform Console may occur continuously for the following reasons.
- Changing resources of Cloud Hadoop service (adding nodes and resources)
- State changes of Cloud Hadoop services (start, stop, restart, and termination)
- Check the status of Cloud Hadoop service (Health Check)
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description time zone Required Select the time zone for the database to use tag Selection Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag
- You can add up to 50
- The newly added tags are applied after the service creation is completed
Table. Cloud Hadoop additional information input fields
- Select the required information in the Image and version selection area.
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- Once creation is complete, check the created resource on the Resource List page.
View detailed information of Cloud Hadoop
Cloud Hadoop service allows you to view and edit the full resource list and detailed information. The Cloud Hadoop Details page consists of Details, Tags, Job History tabs.
To view detailed information about the Cloud Hadoop service, follow these steps.
- Click the All Services > Data Analytics > Cloud Hadoop menu. Navigate to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- On the Cloud Hadoop List page, click the resource you want to view detailed information for. You will be taken to the Cloud Hadoop Details page.
- Cloud Hadoop Details At the top of the page, status information and details about additional features are displayed.
Category Detailed description status Cloud Hadoop Service Status - Creating: Creating
- Running: Created, service is available
- Updating: Updating settings
- Stopping: Stopping
- Starting: Starting
- Stopped: Stopped
- Restarting: Restarting
- Terminating: Terminating service
- Error: Error occurred during creation or service abnormal state
- Undeployed: Deployment error occurred
Start Start of discontinued service operation Stop Force service termination Restart Restart the service Add Worker Node Add a server with the same specifications as the previously created Worker node to the cluster. Service termination Terminate all Cloud Hadoop services and servers Table. Cloud Hadoop status information and additional features
- Cloud Hadoop Details At the top of the page, status information and details about additional features are displayed.
- The status indicator reflects the state of the Cloud Hadoop service, and the server status can be checked in the server information.
- Start, Stop, Restart buttons control only the Cloud Hadoop service, while server control can be managed from the Compute > Virtual Server list.
Detailed Information
On the Cloud Hadoop List page, you can view detailed information of the selected resource and edit the information if necessary.
| Category | Detailed description |
|---|---|
| Server information | Server information configured in this cluster |
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Image version | OS and service image version |
| Cluster name | Cluster name of the configured servers |
| Planned Compute | Resource status with Planned Compute configured
|
| Manager access URL | Cloud Hadoop Manager access URL |
| time zone | Standard time zone for the service |
| PrivateLink information | Access Key, Secret Key information |
| Network | VPC, Subnet information |
| Security Group | Security Group List |
| Keypair name | Created/selected Keypair name |
| Basic Service | Cloud Hadoop Basic Service Stack List |
| Optional Service | Cloud Hadoop option service stack list
|
| Master | Server type, base OS, and Disk information for the Master node
|
| Worker | Server type, default OS, and disk information for the Worker node |
| Ingestion | Server type, default OS, and disk information for the Ingestion node |
| Object Storage bucket | Object Storage List |
tag
On the Cloud Hadoop List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Cloud Hadoop List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Cloud Hadoop Resources
If you need to modify the existing configuration options of a created Cloud Hadoop resource or require additional configuration, you can perform the operation on the Cloud Hadoop Details page.
Add Worker Node
If you need to scale a Cloud Hadoop cluster due to increased workload or other reasons, you can add Worker nodes with the same specifications as the existing Worker nodes.
- You can use up to 10 worker nodes per Cloud Hadoop cluster.
- When adding nodes, all settings except the number of nodes to add and the IP/NAT IP are fixed to the configuration entered during service application.
- If adding a node fails, contact the Samsung Cloud Platform service desk for troubleshooting.
Add Worker Node (Network configuration: common settings)
You can add a Worker node to a Cloud Hadoop cluster that was created with network settings as common settings.
To add a Worker node, follow the steps below.
- Click the All Services > Data Analytics > Cloud Hadoop menu. You will be taken to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- Cloud Hadoop List page, click the resource you want to add a node to. You will be taken to the Cloud Hadoop Details page.
- Click the Add Worker Node button. You will be taken to the Add Worker Node page.
- After selecting the Worker Node count, click the Complete button.
- All settings, including the server name of each Worker node, are fixed to the configuration entered when applying for the service.
Add Worker Node (Network configuration: per-server settings)
Network settings allow adding Worker nodes to a Cloud Hadoop cluster created with server-specific settings.
To add a Worker node, follow the steps below.
- Click the All Services > Data Analytics > Cloud Hadoop menu. You will be taken to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- On the Cloud Hadoop List page, click the resource you want to add a node to. You will be taken to the Cloud Hadoop Details page.
- Click the Add Worker Node button. You will be taken to the Add Worker Node page.
- Please select the Number of Worker Nodes. The server configuration area will be added automatically based on the selected number of nodes.
- In the added server configuration area, enter the IP and NAT IP, then click the Complete button.
- All settings, including the server name of each Worker node, are fixed to the configuration entered when applying for the service.
Change Security Group
To change the Security Group of Cloud Hadoop, follow the steps below.
- All Services > Data Analytics > Cloud Hadoop Click the menu. Navigate to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- Click the resource whose Security Group you want to change on the Cloud Hadoop List page. You will be taken to the Cloud Hadoop Details page.
- On the detail information page, click the Edit button of Security Group. The Security Group Selection popup window opens.
- Search for the Security Group you want to add, then select the checkbox. The selected Security Group will appear in the list below.
- Click Confirm. The selected Security Group will be applied.
- When creating a Cloud Hadoop service, you can select up to four Security Groups, including the Security Group selected at creation. However, the Security Group chosen during the initial service creation cannot be modified or deleted.
Add optional service
You can additionally install the Cloud Hadoop ecosystem (Data Governance, Analytical Data Warehouse, Data Ingestion).
Data Governance/Analytical Data Warehouse addition
Follow these steps to install Data Governance and the Analytical Data Warehouse additionally.
- Click the All Services > Data Analytics > Cloud Hadoop menu. You will be taken to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- On the Cloud Hadoop List page, click the resource for which you want to add an optional service. You will be taken to the Cloud Hadoop Details page.
- On the detail information page, click the Add button of the option service you want to add. A notification popup will open.
- After reviewing the contents of the popup window, click the Confirm button. The corresponding option service will be added automatically.
- It may take some time depending on the scale.
Add Data Ingestion
To install Data Ingestion additionally, follow the steps below.
- Click the All Services > Data Analytics > Cloud Hadoop menu. Navigate to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- Cloud Hadoop List page, click the resource you want to add an optional service to. Navigate to the Cloud Hadoop Details page.
- On the detail information page, click the Add button of Data Ingestion. You will be taken to the Data Ingestion Add page.
- After selecting the Ingestion Node count, server type, and storage type and capacity, click the Complete button. The selected option service will be added automatically.
- It may take some time depending on the scale.
Change Server Type
You can change the server type of the Master node, Worker node, or Ingestion node in Cloud Hadoop.
To change the server type, follow these steps.
- If the server type is configured as Standard, it cannot be changed to High Capacity. If you want to change to High Capacity, create a new service.
- If you modify the server type, a server restart is required. Please verify any software license changes or software settings and their implementation due to specification changes separately.
- Click the All Services > Data Analytics > Cloud Hadoop menu. Navigate to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- On the Cloud Hadoop List page, click the resource whose server type you want to change. You will be taken to the Cloud Hadoop Details page.
- On the detail information page, click the Edit button of the Server Type of the node you want to change. The Edit Server Type popup window opens.
- After selecting the server type, click the Confirm button. A notification popup will appear.
- Scale-Down for server type is not allowed.
- After reviewing the contents of the popup window, click the Confirm button.
- The entire server of the node will be changed to the requested specifications, and the Cloud Hadoop cluster will restart.
Expanding Storage
You can expand the storage added to the data zone up to a maximum of 12 TB based on the initially allocated capacity. You can expand the storage without stopping Cloud Hadoop, and if it is configured as a cluster, all nodes are expanded simultaneously.
- Storage capacity cannot be reduced; only expansion is allowed.
- It can be expanded up to a maximum of 12 TB, and if more than 12 TB is required, it can be expanded through a service request.
- It may take some time for the expansion to be completed after a request for expansion.
To increase storage capacity, follow the steps below.
- Click the All Services > Data Analytics > Cloud Hadoop menu. Navigate to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- On the Cloud Hadoop List page, click the resource you want to expand capacity for. Navigate to the Cloud Hadoop Details page.
- On the detail information page, click the Edit button of the node’s Disk you want to expand. The Disk Edit popup window opens.
- After entering the number of units, click the Confirm button. A notification popup will appear.
- You can set the capacity by entering the number of units provided in 8 GB increments.
- After reviewing the contents of the popup window, click the Confirm button.
- It may take some time depending on the scale.
Add storage
If the storage allocated to the data area exceeds 12 TB, you can add additional storage. When configured as a cluster, it is added simultaneously for each node type.
- The storage capacity can be set up to 12 TB.
- It may take some time for a storage addition request to be fully completed.
Follow the steps below to add storage.
- Click the All Services > Data Analytics > Cloud Hadoop menu. You will be taken to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop List page.
- On the Cloud Hadoop List page, click the resource you want to add storage to. You will be taken to the Cloud Hadoop Details page.
- On the detail page, click the Add Disk button of the node where you want to add storage. The Add Disk popup will open.
- Select the disk type and enter the capacity, then click the Confirm button. A notification popup will appear.
- If encryption is configured on the existing Block Storage, encryption will also be applied to the additional Disk.
- If you configure it by selecting HDD, performance degradation may occur.
- After reviewing the contents of the popup window, click the Confirm button.
- It may take some time depending on the scale.
Connecting to Cloud Hadoop
To access Cloud Hadoop, follow the steps below.
- Check the IP of the Windows system(PC) that will connect to Cloud Hadoop.
- Since external access is required, you need to check the system’s NAT IP.
- Add the following content to the
hostsfile on a Windows system.- VM host IP of the Cloud Hadoop cluster
- VM host name of the Cloud Hadoop cluster
- Add the following rule to the Security Group you selected when applying for the Cloud Hadoop service.
- Category: Inbound
- Protocol: TCP
- Target address: Windows system IP
- Port: 7080
- On the Windows system you want to connect to, launch the Chrome browser and then access the Cloud Hadoop Manager URL.
Apache Hadoop Ecosystem Target IP/Port information
Item | Protocol | Source | Target IP | Port | Remarks
| Item | Protocal | Source | Target IP | Port | Remarks |
|---|---|---|---|---|---|
| Manager | TCP | User IP | Manager | 7080 | Cloud Hadoop Manager |
| HDFS | CP | User IP | Master | 8042 | nodemanager web http |
| HDFS | TCP | User IP | Master | 8044 | nodemanager web https |
| HDFS | CP | User IP | Master | 8088 | resource manager web http |
| HDFS | TCP | User IP | Master | 8090 | resource manager web https |
| HDFS | TCP | User IP | Master | 8188 | timelneservice web http |
| HDFS | TCP | User IP | Master | 8190 | timelneservice web https |
| HDFS | TCP | User IP | Master | 9093 | alert manager |
| HDFS | TCP | User IP | Master | 17000 | hbase master |
| HDFS | TCP | User IP | Master | 17010 | hbase master web |
| HDFS | TCP | User IP | Master | 17030 | hbase regionserver info |
| HDFS | TCP | User IP | Master | 19090 | hbase thriftserver |
| HDFS | TCP | User IP | Master | 19095 | hbase thriftserver info |
| HDFS | TCP | User IP | Master | 19888 | Job History Server Web |
| HDFS | TCP | User IP | Master | 50070 | name node web http |
| HDFS | TCP | User IP | Master | 50075 | data node web http |
| Atlas | TCP | User IP | Master | 21000 | atlas web http |
| Atlas | TCP | User IP | Master | 21443 | atlas web https |
| Hive | TCP | User IP | Master | 10000 | Hive sever2 thrift binary |
| Hive | TCP | User IP | Master | 10001 | Hive sever2 thrift http |
| Hive | TCP | User IP | Master | 10004 | Hive sever2 web binary |
| Hive | TCP | User IP | Master | 10002 | Hive sever2 web http |
| Hive | TCP | User IP | Master | 10005 | Hive sever2 HA web http |
| Kerberos | TCP | User IP | Master | 88 | key distribution server |
| Kerberos | TCP | User IP | Master | 749 | kadmin server |
| Ranger | TCP | User IP | Master | 9292 | ranger kms http |
| Ranger | TCP | User IP | Master | 6080 | ranger web http |
| Solr | TCP | User IP | Master | 8983 | solr |
| Solr | TCP | User IP | Master | 8988 | solr HA web http |
| Spark | TCP | User IP | Master | 18080 | spark history server web http |
| Spark | TCP | User IP | Master | 18082 | spark history server web https |
| Tez | TCP | User IP | Master | 8780 | tez ui |
| Monitoring | TCP | User IP | Master | 7100 | prometheus web http |
| Cmak | TCP | User IP | Master | 19000 | cmak web http |
| HA Proxy | TCP | User IP | Master | 38404 | HA Proxy web http |
| Hue | TCP | User IP | Master | 8000 | HUE web http |
| Hue | TCP | User IP | Master | 8005 | Hue HA web http |
| LLAP | TCP | User IP | Master | 15002 | llap web http |
Terminate Cloud Hadoop
You can reduce operating costs by terminating unused Cloud Hadoop.
- Data cannot be recovered after the service is terminated.
- When the service is terminated, the Cloud Hadoop service and all servers are terminated.
- If you cancel the service, the currently operating service will be terminated immediately. Proceed with the cancellation only after fully considering the impact that may arise from the service interruption.
To cancel the service, follow the steps below.
- Click the All Services > Data Analytics > Cloud Hadoop menu. Navigate to the Service Home page of Cloud Hadoop.
- On the Service Home page, click the Cloud Hadoop menu. You will be taken to the Cloud Hadoop list page.
- On the Cloud Hadoop List page, select the resource to cancel, then click the Cancel Service button. An alert popup will appear.
- Review the contents of the popup window, enter the name of the resource to be terminated, and then click the Confirm button.
- After the termination request is completed, verify on the Cloud Hadoop list page that the resource has been terminated.
- It may take some time depending on the scale.
7.7.3 - API Reference
7.7.4 - Release Note
Cloud Hadoop
- The Cloud Hadoop service for easy and fast analysis of large-scale data has been launched.
- We provide an automated cluster creation service through the Hadoop Ecosystem and Hadoop Manager.
8 - Application Service
You can easily manage and monitor APIs for integration with applications, and efficiently consolidate the management of corporate assets such as data, software, and applications.
8.1 - API Gateway
8.1.1 - Overview
Service Overview
API Gateway is a service that makes it easy to create, manage, and monitor APIs. It allows you to define API-related resources and methods in a consistent format and apply built-in security access. Additionally, you can easily and conveniently monitor API usage and performance metrics.
Features
- Convenient API Management: You can conveniently register and manage APIs through the console, and it provides JWT (Json Web Token) for access permission management. It is also integrated with SCP Cloud Functions, allowing Cloud Functions to be invoked via the API Gateway.
- Stable Traffic Handling: API Gateway can manage backend system traffic through usage plans. Usage plans allow you to set the maximum number of calls per hour (hourly/daily/monthly), and by doing so, they prevent excessive traffic from entering, enabling stable service usage.
- Easy and convenient monitoring: Provides a dashboard with various management features, including API version management that links different deployment versions per stage, and allows you to monitor API usage. Through this, you can quickly and easily understand performance metrics such as API calls, response times, and error counts.
Service Diagram
- A developer (3rd party Developer) can access various backend services via a single endpoint (API Gateway) using Rest API.
- API Gateway can route the request to the appropriate backend service or Cloud Function.
- When authentication and authorization are required, the user is verified with JWT.
- Request data is transformed as needed, and responses from multiple services are aggregated into a single result through the API Gateway.
- When traffic is high, you can improve service reliability by applying load balancing and rate limiting (rate limiting).
- Supports web clients calling APIs from other domains via CORS configuration.
- All requests and responses are logged and monitored by the API Gateway service, enabling rapid detection of failures and anomalies.
- You can separate stages by environment—development, testing, production—to manage API versions and utilize the required version. API management, security policy enforcement, and related tasks can be handled consistently from a central point through the API Gateway service.
Provided features
API Gateway provides the following features.
API Management and Operations
- Custom Domain Name: Connect a custom domain to the API to provide a unique URL for the user
- REST API Creation and Management: Define resources and methods (GET, POST, etc.) and configure authentication methods
- API version and stage management: Operate the same API in multiple versions simultaneously and manage changes.
- Routing: Route requests to various backend services based on the URI path or request headers.
- Monitoring and Logging: API performance monitoring and log recording possible(‘available in December 2025)
API security
- IP ACL configuration: Control access so that only specific IPs can connect, enhancing security.
- Cloud Functions Integration: Integrate with serverless computing to execute business logic in response to external requests
- CORS Support: Set Cross-Origin Resource Sharing(CORS) to allow resource access from other domains
Component
API
An API is a collection of resources and methods integrated with backend HTTP endpoints, Cloud Functions, or other SCP services. An API provides the logical interface of the actual service and can be deployed to multiple stages for use in various environments (development, production, etc.).
resource
Resources are logical units that represent specific endpoints (URI paths) within an API. Each resource can be organized in a tree structure and can have multiple HTTP methods. For example,
/users
,
/orders
become individual resources.
Method
Methods define the HTTP actions (e.g., GET, POST, PUT, DELETE, etc.) that can be performed on each resource. Each method is integrated with a specific backend to process actual data or execute functionality.
Stage
The stage is a named reference to a specific point in time (snapshot) of an API deployment, distinguishing environments in the API lifecycle such as development (dev), testing (test), and production (prod). Each stage has its own unique URL, and separate settings can be configured per environment, including caching, logging, throttling, stage variables, and so on. Stages support various operational scenarios such as environment-specific configurations and traffic segregation.
endpoint
An endpoint is a unique URL address that a client uses to access the API. A separate endpoint is created for each stage.
Integration
Integration defines how API methods connect to the actual backend (HTTP endpoint, Function). By transforming request and response data, handling authentication, and using mapping templates, you can finely control the integration with the backend.
JWT (Json Web Token)
It is a token-based web standard (RFC 7519) used for authentication and authorization. JWT encodes a JSON object composed of three parts (Header, Payload, Signature) using Base64 URL‑safe encoding, and applies an electronic signature with a secret key or public key to prevent tampering. When securely exchanging authentication information and permissions between a server and client, or between services, it is placed in the HTTP header, enabling stateless (Stateless) authentication without session storage.
CORS (Cross-Origin Resource Sharing)
It is a mechanism that bypasses the Same-Origin Policy applied in web browsers for security reasons, allowing resource sharing between servers of different origins (when the protocol, domain, or port differs). The server specifies which origins are allowed via HTTP response headers (e.g., Access-Control-Allow-Origin, etc.), enabling the client (browser) to safely perform cross-origin requests. If CORS is not properly configured, the browser blocks requests for resources from other origins, which is a web-standard security policy that must be considered when using various resources such as external API calls, fonts, images, and videos.
Provision status by region
API Gateway is available in the environments below.
| region | Provision status |
|---|---|
| Korea West 1 (kr-west1) | Provide |
| Korea East 1 (kr-east1) | Provide |
| South Korea 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that can be optionally configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Compute | Cloud Functions | A service that runs application code in a serverless computing environment
|
8.1.1.1 - ServiceWatch metric
API Gateway sends metrics to ServiceWatch. The metrics provided by basic monitoring are data collected at 1‑minute intervals.
Basic Metrics
The following are the default metrics for the API Gateway namespace.
The metrics whose names are displayed in bold below are the key metrics selected from the default metrics provided by API Gateway. Key metrics are used to configure service dashboards that are automatically built for each service in ServiceWatch.
Each metric guides users via the user guide on which statistical value is meaningful when querying that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using primary statistical values.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| API Total Requests | Total number of calls for this API | Count |
|
| 4XX Error | Number of calls that received a 4XX error response from the API | Count |
|
| 5XX Error | Number of calls that received a 5XX error response from the API | Count |
|
| Latency | Total latency of the API (ms) | Milliseconds |
|
| Integration Latency | Latency (ms) from the API to the backend | Milliseconds |
|
8.1.2 - How-to guides
Through the Samsung Cloud Platform Console, users can enter the required information for the API Gateway service and select detailed options to create the service.
Create API
An API is a collection of resources and methods integrated with backend HTTP endpoints, Cloud Functions, or other SCP services. An API provides the logical interface of the actual service and can be deployed across multiple stages for use in various environments (development, production, etc.).
You can create an API in the Samsung Cloud Platform Console and use it.
To create an API, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the Create API button. Navigate to the Create API page.
- On the API creation page, enter the information required to create a service and select detailed options.
- Select the required information in the Service Information Input area.
Category RequiredDetailed description API name Required Enter API name - must start with a lowercase English letter and must not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to enter 3 ~ 50 characters
How to create an API Required Select API creation method - Select Create new or Clone existing API
API to clone Required If you select Existing API Replication as the API creation method, choose from the APIs that have already been created. Explanation Selection Enter additional information or description about the API within 50 characters. API endpoint type Required Path to access the API - Region: Process requests within the region where the API is deployed
- Private: Expose the API so it can only be requested privately from other VPCs
- Selecting Private enables JWT activation
Table. API Service Information Input Items - must start with a lowercase English letter and must not end with a special character (
- Select the required information in the Service Information Input area.
- In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description tag Selection Add Tag - Click the Add Tag button to create and add a new tag, or to add an existing tag.
- You can add up to 50 tags.
- The newly added tags are applied after the service creation is completed.
Table. API additional information input fields
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resource on the API List page.
Check API detailed information
You can view and edit the complete list of resources and detailed information for the API service. The API Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the API service, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API menu. You will be taken to the API List page.
- On the API List page, click the resource you want to view detailed information for. You will be taken to the API Details page.
- API Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Category Detailed description Status display Status of the API created by the user - Creating: API creation in progress
- Active: API operating normally
- Deleting: API deletion in progress
- Error: API is in an unavailable state due to an internal error
Service termination Cancel service button Table. API status information and additional features
- API Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
On the API Details page, you can view the detailed information of the selected resource and, if needed, edit the information.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| API name | API name |
| API endpoint type | API endpoint type |
| DNS status | DNS status
|
| description | Additional information or description about the API |
Connection Management
Connection Management page lets you manage connection requests for the PrivateLink Service for API Gateway.
| Category | Detailed description |
|---|---|
| Request Endpoint ID | Requested endpoint ID |
| Creation date and time | Service creation date and time |
| status | Resource status value |
| Reject | PrivateLink Service connection request denied |
| Approval | Approve PrivateLink Service connection request |
| Block | Block connected PrivateLink Endpoint |
| Reconnect | Reconnect the blocked PrivateLink Endpoint |
- When the connection status is Rejected or Error, requests such as approval or denial are not possible.
tag
API Details page lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the API Details page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Integrating PrivateLink Service
By integrating the API Gateway service with the PrivateLink service, you can connect ‘API Gateway and VPC’ or ‘API Gateway and other SCP services’ without using the external internet. Data uses only the internal network, enhancing security, and no public IP, NAT, VPN, or internet gateway is required.
Create a PrivateLink service for API Gateway
When creating an API, select the endpoint type as Private. This allows you to expose the API for private access from other VPCs or services.
- Private Endpoint can be designated as a target to use the internal network. For instructions on creating a PrivateLink Endpoint in a user VPC, refer to Create PrivateLink Endpoint.
- For managing connections to the PrivateLink Service for API Gateway, refer to API 상세 정보 확인하기 > 연결 관리.
Create PrivateLink Endpoint
You can create it to use the Entry Point for accessing other PrivateLinks in the API Gateway service.
To create a PrivateLink Endpoint, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
Click the PrivateLink Endpoint menu on the Service Home page. You will be taken to the PrivateLink Endpoint List page.
On the PrivateLink Endpoint List page, click the PrivateLink Endpoint Create button. You will be taken to the PrivateLink Endpoint Create page.
- Enter or select the required information.
Category RequiredDetailed description PrivateLink Endpoint name Required Enter PrivateLink Endpoint name - Enter using English letters and numbers, 3 to 20 characters
description Selection Enter additional information or description within 50 characters. PrivateLink Service ID Required Enter the ID of the PrivateLink Service to connect - Check the Service ID with the PrivateLink Service provider in advance, and after creating the Endpoint, provide the Endpoint ID to the provider
- Enter using letters and numbers, 3 to 60 characters
Table. PrivateLink Endpoint creation information input items
- Enter or select the required information.
When data entry or selection is complete, click the Confirm button.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, verify the created resource in the PrivateLink Endpoint list.
- To delete a PrivateLink Endpoint list, select the resource to delete from the list and click the Delete button.
- To request a connection to the service provider via PrivateLink, you must go through an approval process.
- When applying for a service connection, you must verify the PrivateLink Service ID of the target in advance.
- Before applying for the service, an agreement on usage with the service provider must be completed.
- After the user creates a PrivateLink Endpoint, they must provide the Endpoint ID to the service provider. The service provider can verify the user’s Endpoint ID and promptly approve its use.
Check detailed information of PrivateLink Endpoint
You can view and edit the full list of resources and detailed information for a PrivateLink Endpoint. The PrivateLink Endpoint Details page consists of Detailed Information and Operation History tabs.
To view detailed information about the API service, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- Click the PrivateLink Endpoint menu on the Service Home page. You will be taken to the PrivateLink Endpoint List page.
- On the PrivateLink Endpoint List page, click the resource to view detailed information. You will be taken to the PrivateLink Endpoint Details page.
- PrivateLink Endpoint Details page displays status information and additional feature information, and consists of Details and Activity Log tabs.
Category Detailed description Status display PrivateLink Endpoint status - Requesting: connection request pending approval, Cancel request button displayed
- Active: creation completed, operating
- Creating: in progress
- Deleting: deletion in progress
- Disconnected: connection blocked
- Rejected: connection denied, Request re-approval button displayed
- Error: error occurred
- Canceled: connection request canceled, Request re-approval button displayed
Cancel request Cancel connection request Re-request approval Re-requesting a connection after the original request was canceled Table. PrivateLink Endpoint status information and additional features
- PrivateLink Endpoint Details page displays status information and additional feature information, and consists of Details and Activity Log tabs.
Detailed Information
PrivateLink Endpoint Details page lets you view detailed information of the selected resource.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| PrivateLink Endpoint name | PrivateLink Endpoint name |
| PrivateLink Endpoint ID | PrivateLink Endpoint ID |
| PrivateLink Service ID | Connected PrivateLink Service ID |
| API endpoint type | API endpoint type |
| description | Additional information or description about the PrivateLink Endpoint |
Job History
On the PrivateLink Endpoint Details page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Create Resource
A resource is a logical unit that represents a specific endpoint (URI path) within an API. Each resource can be organized in a tree structure and can have multiple HTTP methods.
To create a resource, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Resources menu. Navigate to the Resources page.
Click the Create Resource button on the Resource page. You will be taken to the Create Resource popup.
- Enter or select the required information.
Category RequiredDetailed description resource name Required Enter the resource name - It must start with a lowercase English letter and be 3 to 50 characters using lowercase letters, numbers, and special characters (
-{})
- When using braces, only the format
{character}is allowed and it cannot be left empty
resource path Required Select the path chosen in the resource menu tree Table. Resource creation information input fields - It must start with a lowercase English letter and be 3 to 50 characters using lowercase letters, numbers, and special characters (
- Enter or select the required information.
Click the Confirm button after completing data entry and selection.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, verify the created resource in the resource list.
- To delete a resource, select the resource to delete from the list and click the Delete button.
- A maximum of 300 resources can be created.
- The depth of a resource can be up to 30, including the Root.
Create Method
Methods define the HTTP actions (e.g., GET, POST, PUT, DELETE, etc.) that can be performed on each resource. Each method is integrated with a specific backend to process actual data or execute functionality.
To create a method, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Resources menu. You will be taken to the Resources page.
Click the Create Method button on the Resource page. It navigates to the Create Method popup.
- Enter or select the required information.
Category RequiredDetailed description Method type Required Select method type - The generated value is not displayed in the list.
- Selecting ANY creates methods of all types.
Integration type Required Select endpoint type - Select from HTTP, Cloud Function, PrivateLink
Endpoint URL Required Enter the endpoint URL when HTTP type is selected - The endpoint is a unique URL that the client uses to access the API. Create a separate endpoint for each stage. Various types such as Regional, Edge-Optimized, Private, etc.
- It must be a valid URL starting with http:// or https://, and you must enter it within 500 characters using English letters and special characters (
$-_.+!*’:(){}/)
endpoint Required When Cloud Function type is selected, choose the endpoint - The region is provided as the current region and cannot be changed
URL query string parameter Selection After checking use, enter name - using English letters, numbers, and special characters(
_)
HTTP request header Selection After checking use, enter name - using English letters, numbers, and special characters (
-) to input
Whether to use API Key Selection To limit usage through the usage policy, check Use Table. Method creation information input fields
- Enter or select the required information.
When the information entry and selection are complete, click the Save button.
After checking the message in the notification popup, click the Confirm button.
- After creation is complete, check the created resource in the method list.
- To delete a method, select the resource to delete from the list and click the Delete button.
Methods can be created up to a maximum of 7, with one per type. When created as Any, all types of methods are generated.
| Category | Detailed description |
|---|---|
| service | Service name |
| GET | Resource retrieval (read) |
| POST | Resource creation (registration) |
| PUT | Full resource update (refresh) |
| PATCH | Modify only part of the resource. |
| DELETE | Delete resource |
| OPTIONS | Retrieve the list of HTTP methods supported by this endpoint |
| HEAD | Retrieve only headers without a body (return only metadata, no response body) |
Deploy API
To apply a developing API to the live service environment, API deployment is required.
To deploy the generated API, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Resources menu. You will be taken to the Resources page.
Click the API Deployment button on the Resources page. It opens the API Deployment popup.
- Enter or select the required information.
Category RequiredDetailed description Stage Required Select the stage to deploy the API - New Stage: Create a new stage and deploy
- None Stage: Deploy without selecting a stage
Stage name Required When New Stage is selected, enter a new stage name - that starts with a lowercase English letter and does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) for 3 to 30 characters
Deployment description Selection Enter up to 50 characters describing API deployment. Table. API deployment information input fields
- Enter or select the required information.
Click the Deploy button once information entry and selection are complete.
After checking the message in the notification popup, click the Confirm button.
Create Stage
The stage is a named reference to a specific point in time (snapshot) of an API deployment, distinguishing environments in the API lifecycle such as development (dev), testing (test), and production (prod). Each stage has its own unique URL, and separate settings can be configured per environment for caching, logging, throttling, stage variables, and so on. Stages support various operational scenarios, including Canary releases, environment-specific configurations, and traffic segregation.
To create a stage for deploying the API, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Stage menu. You will be taken to the Stage page.
On the Stage page, click the Create Stage button. You will be taken to the Create Stage popup.
- Enter or select the required information.
Category RequiredDetailed description Stage name Required When New Stage is selected, enter a new stage name - that starts with a lowercase English letter and does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) with a length of 3 ~ 50 characters
Stage description Selection Enter additional information or description about the stage within 100 characters. API deployment version Required Select the API version to deploy - Must start with a lowercase English letter and must not end with a special character (
-), using lowercase letters, numbers, and special characters (-) enter 3 to 50 characters
Table. Stage creation information input fields - that starts with a lowercase English letter and does not end with a special character (
- Enter or select the required information.
Click the Confirm button after completing data entry and selection.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, check the created resources in the stage list.
Check stage detailed information
You can view and edit the stage list and detailed information. The detail page consists of the Stage Details information and the API Deployment Version Management, CORS, Usage Policy tabs.
To view the detailed information of the stage, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- From the Service Home page, click the API Gateway > Stage menu. You will be taken to the Stage page.
- Click the resource to view detailed information in the stage list.
- Stage Details displays status information and additional feature information, and consists of API Deployment Version Management, CORS, Usage Policy tabs.
- To delete a stage, select the resource to delete from the list and click the Delete button.
- To edit a stage, select the resource to modify from the list and click the Edit button.
Stage Details
You can view detailed information of the selected resource on the Stage Details page.
| Category | Detailed description |
|---|---|
| Stage name | Stage name |
| CORS | CORS operation status |
| Stage description | Stage information |
| JWT | JSON Web Token usage status |
| API Key | Whether to use API Key |
| Invoke URL | URL for API call |
| Activation date and time | Stage activation date and time |
| Deployment ID | API deployment ID |
API deployment version management
API deployment version management tab allows you to view the API deployment history.
| Category | Detailed description |
|---|---|
| API Deployment Version Management List | API deployment history
|
| Deployment change | After selecting the resource to change the deployment from the list, click the Change Deployment button. When you click the Confirm button in the notification popup, the active deployment ID is updated immediately. |
CORS (Cross-Origin Resource Sharing)
You can view the CORS list in the CORS tab.
| Category | Detailed description |
|---|---|
| Name | CORS name |
| Mapping Value | Mapping value applied to CORS |
Usage Policy
On the Usage Policy tab, you can view the usage policy attached to the stage.
| Category | Detailed description |
|---|---|
| Usage Policy Name | Usage policy name |
| Usage Policy ID | Usage Policy ID |
| Quota | Quota set in the usage policy |
| Linked API Key Name | API Key name linked to the usage policy |
- When calling the API, you must use the key value of the API Key associated with the stage in the ‘x-scp-apikey’ header.
- Usage policies are linked at the stage level, while quotas are calculated per method that is checked for API Key usage.
Create authentication
JWT (JSON Web Token) is an open standard (RFC 7519) used for user authentication. JWT is a claim-based web token that stores user information as an encrypted token using JSON format.
To generate a JWT, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
On the Service Home page, click the API Gateway > Authentication menu. You will be taken to the Authentication List page.
On the Authentication List page, click the Create JSON Web Token button. You will be taken to the Create JSON Web Token popup.
- Enter or select the required information.
Category RequiredDetailed description JWT name Required Enter token name - that starts with a lowercase English letter and does not end with a special character (
-), using lowercase letters, numbers, and special characters (-) to input 3 to 50 characters
Stage to connect Selection After checking Use, select the stage Table. Authentication creation information input items - that starts with a lowercase English letter and does not end with a special character (
- Enter or select the required information.
After entering information and making selections, click the Confirm button.
After reviewing the message in the notification popup, click the Confirm button. Navigate to the Access Token notification popup.
- Tokens can be viewed only in the Access Token notification popup. If needed, download the Access Token file.
Access Token After checking the message in the notification popup, click the Confirm button.
- After creation is complete, check the created resource in the authentication list.
- To delete a token, select the resource to delete from the list and click the Delete button.
- To edit a token, select Edit from the context menu of the resource you want to modify.
Create Access Control
You can add an allowed IP to restrict API calls to a specific IP address.
- The stage is linked to a single access control. When a stage is first created, the Default access control is applied by default, blocking access from all IPs (All deny). By creating a new access control and attaching it to the stage, you can configure it to be callable only from specific IPs.
- In the following case, access control cannot be created.
- If you exceed the available service quota limit: Check the current allocated value and the additional possible value in the Quota Service.
- If there is no available API, create the API first.
- When the API endpoint type is Private: access control is not supported, but JWT activation is required on that API’s stage.
To create an access control, follow these steps.
Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
From the Service Home page, click the API Gateway > Access Control menu. Navigate to the Access Control List page.
Access Control List page, click the Create Access Control button. You will be taken to the Create Access Control popup.
- Enter or select the required information.
Category RequiredDetailed description Access control name Required Enter the access control name - that starts with a lowercase English letter, does not end with a special character (
-), and uses lowercase letters, numbers, and special characters (-) within 3 to 50 characters
Public access allowed IP Required Enter IP addresses to allow access - ’,’ you can input up to 100 using ‘,’
Stage to connect Selection After checking Use, select the stage description Selection Enter additional information or description about access control within 50 characters. Table. Access control creation information input fields - that starts with a lowercase English letter, does not end with a special character (
- Enter or select the required information.
After entering information and making selections, click the Confirm button.
After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, verify the created resource in the access control list.
- To delete an access control list, select the resource to remove from the list and click the Delete button. The default access control cannot be deleted.
- To modify access control, select Edit from the context menu of the resource you want to modify.
Terminate API
You can cancel the unused service to reduce operating costs. However, canceling the service may cause the running service to stop immediately, so you should consider the impact of service interruption thoroughly before proceeding with the cancellation.
To cancel the API, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API menu. You will be taken to the API List page.
- On the API List page, select the resource to cancel and click the Cancel Service button.
- When the termination is complete, verify on the API List page that the resource has been terminated.
Using Report
You can check API traffic, performance, and error status.
To use the Report, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Report menu. You will be taken to the Report page.
- Enter or select the required information.
| Category | Detailed description |
|---|---|
| Search period | Select date to view (default 1 week from today, up to 1 month) |
| Stage name | Stage name under API |
- After entering the information and making selections, you can view the Report information.
| Category | Detailed description |
|---|---|
| TOP Resources 5 | Among the resources invoked by the user, the top five most frequently called with an API status code of 2XX (ties are not shown as duplicate ranks). |
| API call count | Number of calls with API status code 2XX |
| Latency | The time elapsed from when the user sends a request to the API Gateway until a response is received. |
| Integration Latency | The time elapsed from when the API Gateway sends a request to the backend server until it receives a response from the backend. |
| 4XX Error | Number of calls with API status code 4XX |
| 5XX Error | Number of calls with API status code 5XX |
- If a stage is deleted, it cannot be accessed in the Report.
- The report displays data from one hour ago relative to the current time.
Create Usage Policy
The usage policy is established to ensure efficient allocation of server resources, maintain service stability, prevent unnecessary traffic, and avoid misuse.
To create a usage policy, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Usage Policy menu. You will be taken to the Usage Policy page.
- On the Usage Policy page, click the Create Usage Policy button. You will be taken to the Create Usage Policy page.
- Enter or select the required information.
| Category | Required | Detailed description |
|---|---|---|
| API name to connect | Required | Select from the generated AIPs |
| Usage Policy Name | Required | Start with a lowercase English letter and ensure it does not end with a hyphen; use lowercase letters, numbers, and hyphens, and enter 3 to 50 characters. |
| Quota | Required | Enter a value between 1 and 2,000,000,000 per month/day/hour. |
| description | Selection | Enter usage policy description (max 50 chars). |
- When the information entry and selection are complete, click the Complete button.
- After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, check the created resource in the usage policy list.
Create API Key
An API key is used to identify which user or app is calling the API. It is primarily used to limit usage according to usage policies.
To create an API Key, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Usage Policy menu. You will be taken to the Usage Policy page.
- In the list, click the usage policy. It navigates to the Usage Policy Details page.
- On the Usage Policy Details page, click the Create API Key button. You will be taken to the Add API Key popup.
- Enter or select the required information.
| Category | Required | Detailed description |
|---|---|---|
| API Key name | Required | Start with a lowercase English letter and ensure it does not end with a hyphen; use lowercase letters, numbers, and hyphens, and enter 3 to 50 characters. |
| description | Selection | Enter a description of the API Key within 50 characters. |
- Click the Confirm button after completing data entry and selection.
- After checking the message in the notification popup, click the Confirm button.
- When creation is complete, check the created resources on the Usage Policy Details page.
- You can create up to 10 usage policies and 5 API keys.
- Quota is calculated per API Key.
Create Resource Policy
You can fundamentally block unauthorized access with resource-based policies and increase the service’s security level.
To create a resource policy, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Navigate to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Resource Policy menu. You will be taken to the Resource Policy page.
- On the Resource Policy page, click the Create Resource Policy button. You will be taken to the Create Resource Policy page.
- Enter or select the required information in the Service Information Input area.
| Category | Required | Detailed description |
|---|---|---|
| Policy template | Required | Select Policy Template
|
- Click the Complete button after entering information and making selections.
- After checking the message in the notification popup, click the Confirm button.
- Once creation is complete, you can view, modify, or delete the resource policy.
8.1.2.1 - Resource-Based Policy Guide
Resource-based policy overview
API Gateway’s resource-based policy (Resource-based Policy) is a policy attached to a resource that can decide to allow or deny (Effect) an action (Action) on a specific resource only for a principal (Principal). You can directly define the principal that can call the API by using resource-based policies.
Through resource-based policies, you can define the following to allow secure API calls.
- User of the specified Samsung Cloud Platform account
- Specified source IP address range or CIDR block
A source policy is defined as a JSON policy document attached to the API, which controls whether a specified security principal (typically an IAM role or group) can call the API.
| Category | description | example |
|---|---|---|
| Principal(Principal) | Specify the entity that will call the API | - |
| Task(Action) | Define the allowed features | - |
| Condition(Condition) | Restrict to allow only in specific situations | Allow only requests originating from a specific SRN. |
- API Gateway’s resource-based policies leverage the rules of IAM’s resource-based policies.
- Please refer to the JSON Writing Guide for how to create or modify policies using JSON.
Resource-based policy usage scenario
The primary use cases for resource-based policies are as follows.
Resource-based policy scenario
The resource-based policy scenario used when a specific function of API Gateway operates is as follows.
| Category | description | Reference example |
|---|---|---|
| Default policy | This is the DEFAULT resource policy that is created by default when an API is created.
| Basic Policy Example |
| Allowed Account List | You can define account(s) that can call the API. | Account Allowlist Example |
| IP range blocklist | You can define IP ranges that are not allowed to call the API. | IP range blocklist example |
User addition usage scenario
It is not automatically registered as a resource‑based policy of API Gateway, but users can add and use it as needed. The scenarios that users can add and utilize are as follows.
- Cross-Account Access
- If an IAM user in account A wants to invoke the API of account B, register account A in the function policy of account B.
- Hybrid Access Control
- It can be configured so that access is allowed only when both conditions are met—a specific user and a specific IP range—rather than simply restricting by account or IP alone.
Resource-based policy management for API Gateway
To view and set resource-based policies for API Gateway, follow these steps.
- Click the All Services > Application Service > API Gateway menu. Go to the Service Home page of API Gateway.
- On the Service Home page, click the API Gateway > Resource Policy menu. You will be taken to the Resource Policy page.
- Click the Edit button of the Policy Details item. The Edit Resource Policy popup opens.
- Click the Delete button to delete the registered policy.
- Edit Resource Policy In the popup window, select Policy Template, then write the policy.
- For policy examples by policy template, refer to Resource-based policy example.
- When the writing is complete, click the Done button.
Example of resource-based policy
Users can define additional resource-based policies as needed or modify existing policies for use.
- For some features, a resource-based policy (or credentials) must be registered to use them in API Gateway.
- In the resource-based policy examples described in this guide, API Gateway automatically registers the example resource-based policies when each feature is enabled or linked.
Default Policy
This is a policy that is automatically registered when creating an API.
Policy Template
{
"Statement": [
{
"Action": [
"apigateway:InvokeApigatewayRegion"
],
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
"apigateway:InvokeApigatewayRegion"
],
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}Policy Example
{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow"
"Principal": "*",
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}{
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Effect": "Allow"
"Principal": "*",
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "DefaultStatement"
}
],
"Version": "2024-07-01"
}Account allowlist
This is a policy that allows only users of a specific SCP account (Root user or IAM Role) to call the API.
Policy Template
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:{{Offering}}::{{AccountID}}:::iam:user/{{UserSrn}}
]
},
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:{{Offering}}::{{AccountID}}:::iam:user/{{UserSrn}}
]
},
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}Policy Example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
"srn:s::accountId1:::iam:user/userId1"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
"srn:s::accountId1:::iam:user/userId1"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}IP range blocklist
It is a policy that allows or blocks only specific IP addresses or CIDR ranges.
Policy Template
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
},
"NotIpAddress": {
"scp:SourceIp": [
{{sourceIpOrCIDRBlock}}
{{sourceIpOrCIDRBlock}}
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:method/{{ApiId}}/{{stageNameOrWildcard*}}/{{httpVerbOrWildcard*}}/{{resourcePathOrWildcard*}}
]
},
"NotIpAddress": {
"scp:SourceIp": [
{{sourceIpOrCIDRBlock}}
{{sourceIpOrCIDRBlock}}
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
srn:{{Offering}}::{{AccountID}}:kr-west1::apigateway:api/{{ApiId}}
],
"Sid": "Statement1"
}
]
}Policy example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*",
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
"srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1"
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
"srn:s::accountId1:kr-west1::apigateway:method/apiId1/stage1/GET/resource1"
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": "*"
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}Cross-Account Access
This is a resource policy that allows a user of account B to call a specific API resource of account A.
Policy Example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow"
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
}
},
"Effect": "Allow"
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
"srn:e::accountId2:::iam:user/userId2"
]
},
"Resource": [
"srn:s::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}Hybrid Access Control
It is a resource policy that can define access control policies by combining user credentials (Account) and connection source (IP).
Policy Example
{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:e::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:e::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:s::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}{
"Version": ""
"Statement": [
{
"Action": [
apigateway:InvokeApigatewayRegion
],
"Condition": {
"SrnLike": {
"scp:RequestAttribute/body['method-srn']": [
srn:s::accountId1:kr-west1::apigateway:method/apiId1/*/*/*
]
},
"NotIpAddress": {
"scp:SourceIp": [
"1.2.3.4/24"
5.6.7.8/32
]
}
},
"Effect": "Allow",
"Principal": {
"scp": [
srn:s::accountId1:::iam:user/userId1
]
},
"Resource": [
"srn:e::accountId1:kr-west1::apigateway:api/apiId1"
],
"Sid": "Statement1"
}
]
}8.1.3 - API Reference
8.1.4 - CLI Reference
8.1.5 - Release Note
API Gateway
- You can set resource-based policies on the API.
- Resource-based policies are policies applied directly to the API to allow external access.
- You can use resource-based policies to allow or deny actions on specific resources to specific principals.
- The API Gateway service, which enables easy management and monitoring of APIs, has been launched.
- You can easily define resources and methods related to the API, and conveniently monitor API usage and performance metrics.
8.2 - Queue Service
8.2.1 - Message API reference
Overview
The Queue Service provided by Samsung Cloud Platform can send, receive, and delete messages.
This guide provides an overview of the Queue Service API and how to invoke it.
Queue Service Call Procedure
The Queue Service API URL must be changed according to the operating environment and region. Please check the operating environment and Region information in the table below.
| Production Environment | Region | Queue Service URL |
|---|---|---|
| For Samsung | kr-west1 | https://queueservice.service.kr-west1.s.samsungsdscloud.com |
| For Samsung | kr-east1 | https://queueservice.service.kr-east1.s.samsungsdscloud.com |
| For Enterprise | kr-west1 | https://queueservice.service.kr-west1.e.samsungsdscloud.com |
| For Enterprise | kr-east1 | https://queueservice.service.kr-east1.e.samsungsdscloud.com |
Calling the API
AUTH PARAMS
Header Description
Scp-Accesskey : 삼성 클라우드 플랫폼 포털에서 발급받은 Access Key
Scp-Signature : 호출 API 요청을 Access Key와 매핑되는 Access Secret Key로 암호화한 서명. HMAC 암호화 알고리즘은 HmacSHA256 사용
Scp-Target : Queue Service에 요청하는 행위. ScpQS.SendMessage, ScpQS.SendMessageBatch, ScpQS.ReceiveMessage, ScpQS.DeleteMessage, ScpQS.DeleteMessageBatch 중 하나
Scp-Timestamp : 1970년 1월 1일 00:00:00 협정 세계시(UTC)부터의 경과 시간을 밀리초(Millisecond)로 정의합니다.
Scp-ClientType : user-api 명시
Create Signature
- Generate the string to be signed from the request, encrypt it with the HmacSHA256 algorithm using the Access and Secret keys, and then encode it in Base64.
- To call the Sqeue Service via the Messaging API, you must authenticate with the “authentication key” in authentication key mode from a valid allowed IP address.
- Use this value as the Scp-Signature.
- The generated Signature is valid for 15 minutes.1. - Click the All Services > Application > Queue Service menu. - Go to the Service Home page of the Queue Service.
Signature generation Sample Code (Java)
public static String makeHmacSignature(String method,
String url,
String timestamp,
String accessKey,
String accessSecretKey,
String clientType) {
String body = method + url + timestamp + accessKey + clientType;
String encodeBase64Str;
try {
byte[] message = body.getBytes("UTF-8");
byte[] secretKey = accessSecretKey.getBytes("UTF-8");
Mac mac = Mac.getInstance("HmacSHA256");
SecretKeySpec secretKeySpec = new SecretKeySpec(secretKey, "HmacSHA256");
mac.init(secretKeySpec);
byte[] hmacSha256 = mac.doFinal(message);
encodeBase64Str = Base64.getEncoder().encodeToString(hmacSha256);
} catch (Exception e) {
throw new RuntimeException("Failed to calculate hmac-sha256", e);
}
return encodeBase64Str;
}
Signature generation Sample Code (JavaScript)
<script src="https://cdnjs.cloudflare.com/ajax/libs/crypto-js/3.1.2/rollups/hmac-sha256.js"></script>
<script src="https://cdnjs.cloudflare.com/ajax/libs/crypto-js/3.1.2/components/enc-base64-min.js"></script>
<script type="text/javascript">
function makeSignature() {
var method = "POST"; // Method
var url = "{url}"; // url
var timestamp = Date.now(); // timestamp
var accessKey = "{accessKey}"; // access key
var secretKey = "{secretKey}"; // secret key
var clientType= "user-api"; // client type
url = encodeURI(url); // 한글, 특수 문자 처리
var message = method + url + timestamp + accessKey + clientType;
var hash = CryptoJS.HmacSHA256(message, secretKey);
return CryptoJS.enc.Base64.stringify(hash);
}
</script>
Example of calling the Queue Service API
Curl
curl -i -X GET
-H "Scp-Accesskey:2sd2gg=2agbdSD26svcD"
-H "Scp-Signature:fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef="
-H "Scp-Timestamp:1605290625682"
-H "Scp-ClientType:user-api"
-H "Scp-Target:ScpQS.SendMessage"
--data '{"MessageBody": "sample message", "QueueUrl": "https://queueservice.kr-west1.e.samsungsdscloud.com/33ff0000a8a345d78cdf163673f3da11/samplequeue"}'
'https://queueservice.service.kr-west1.e.samsungsdscloud.com'
Python
import requests
url = "https://queueservice.service.kr-west1.e.samsungsdscloud.com"
payload = {
'MessageBody': 'sample message',
'QueueUrl': 'https://queueservice.kr-west1.e.samsungsdscloud.com/33ff0000a8a345d78cdf163673f3da11/samplequeue'
}
headers = {
'Scp-Accesskey': '2sd2gg=2agbdSD26svcD',
'Scp-Signature': 'fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef=',
'Scp-Timestamp': '1605290625682',
'Scp-ClientType': 'user-api',
'Scp-Target': 'ScpQS.SendMessage'
}
response = requests.request("GET", url, headers=headers, data=payload)
if response.status_code == 200:
contents = response.text
return contents
else:
raise Exception(f"Failed to GET API: {response.status_code}, {response.text}")
Java
String apiUrl = "https://queueservice.service.kr-west1.e.samsungsdscloud.com";
String accessKey = "2sd2gg=2agbdSD26svcD"
String signature = "fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef="
String timestamp = "1605290625682"
String clientType = "user-api"
String scpTarget = "ScpQS.SendMessage"
public static String getAPI(String token, String apiUrl) throws IOException {
CloseableHttpClient httpClient = HttpClients.createDefault();
HttpGet getRequest = new HttpGet(apiUrl);
getRequest.addHeader("Scp-Accesskey", accessKey);
getRequest.addHeader("Scp-Signature", signature);
getRequest.addHeader("Scp-Timestamp", timestamp);
getRequest.addHeader("Scp-ClientType", clientType);
getRequest.addHeader("Scp-Target", scpTarget);
HttpResponse response = httpClient.execute(getRequest);
int statusCode = response.getStatusLine().getStatusCode();
if (statusCode == 200) {
String responseBody = EntityUtils.toString(response.getEntity());
httpClient.close();
return responseBody;
} else {
String responseBody = EntityUtils.toString(response.getEntity());
httpClient.close();
throw new RuntimeException("Failed to Request: " + statusCode + ", " + responseBody);
}
}
Queue Service API
SendMessage
POST https://queueservice.service.kr-west1.e.samsungsdscloud.com
Description
Send message
Parameters
| Field name | Required or not | type | Explanation |
|---|---|---|---|
| MessageAttributes | false | MessageAttribute | |
| MessageBody | true | string | |
| MessageDeduplicationId | false | string | FIFO Queue |
| MessageGroupId | false | string | FIFO Queue |
| QueueUrl | true | string |
MessageAttribute
| Field name | Whether required | type | Explanation |
|---|---|---|---|
| BinaryValue | false | string | |
| DataType | false | string | |
| StringValue | false | string |
Responses
| HTTP Code | Description | Schema |
|---|---|---|
| 200 | Created | |
| 400 | Bad Request | |
| 403 | Forbidden |
Example HTTP request
Request Header
"Scp-Accesskey:2sd2gg=2agbdSD26svcD",
"Scp-Signature:fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef=",
"Scp-Timestamp:1605290625682",
"Scp-ClientType:user-api",
"Scp-Target:ScpQS.SendMessage"
Request Body
{
"QueueUrl": "https://queueservice.kr-west1.e.samsungsdscloud.com/123e54b7303749f38ca59a5c6d419a75/test",
"MessageBody": "Hello SQS!",
"MessageAttributes": {
"Special": {
"DataType": "string",
"StingValue": "testBodyString12345678910!/wow$#@!"
}
}
}
Example HTTP response
200 Response
{
"MD5OfMessageAttributes": "139818cac45117a07428826a8c533c01",
"MD5OfMessageBody": "098f6bcd4621d373cade4e832627b4f6",
"MessageId": "14b37b86-8117-484a-aea4-1eae3b98d5d0",
"SequenceNumber": "11764568839"
}
SendMessageBatch
POST https://queueservice.service.kr-west1.e.samsungsdscloud.com
Description
Mass message sending
Parameters
| Field name | Required or not | type | Explanation |
|---|---|---|---|
| Entries | true | array of SendMessageBatchRequestEntry | |
| QueueUrl | true | string |
SendMessageBatchRequestEntry
| Field name | Required or not | type | Explanation |
|---|---|---|---|
| Id | true | string | |
| MessageAttributes | false | MessageAttribute | |
| MessageBody | true | string | |
| MessageDeduplicationId | false | string | FIFO Queue |
| MessageGroupId | false | string | FIFO Queue |
Responses
| HTTP Code | Description | Schema |
|---|---|---|
| 200 | Created | |
| 400 | Bad Request | |
| 403 | Forbidden |
Example HTTP request
Request Header
"Scp-Accesskey:2sd2gg=2agbdSD26svcD",
"Scp-Signature:fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef=",
"Scp-Timestamp:1605290625682",
"Scp-ClientType:user-api",
"Scp-Target:ScpQS.SendMessageBatch"
Request Body
{
"QueueUrl": "https://queueservice.kr-west1.dev3.samsungsdscloud.com/123e54b7303749f38ca59a5c6d419a75/test",
"Entries": [
{
"Id": "1",
"MessageBody": "test-body-1"
},
{
"Id": "2",
"MessageBody": "test-body-2"
}
]
}
Example HTTP response
200 Response
{
"Failed": [],
"Successful": [
{
"Id": "2",
"MD5OfMessageAttributes": "d41d8cd98f00b204e9800998ecf8427e",
"MD5OfMessageBody": "82ddf04637119b9a77e9b44095f5ba11",
"MessageId": "68aa4629-bfbc-4bb0-898b-52db94438526",
"SequenceNumber": "31764583416"
},
{
"Id": "1",
"MD5OfMessageAttributes": "d41d8cd98f00b204e9800998ecf8427e",
"MD5OfMessageBody": "8344ca2f91203b151e4d0aafc9248a8b",
"MessageId": "3523740f-9e7c-429e-8514-5ec21b1d3cd8",
"SequenceNumber": "41764583416"
}
]
}
ReceiveMessage
POST https://queueservice.service.kr-west1.e.samsungsdscloud.com
Description
Message reception
Parameters
| Field name | Required status | type | Explanation |
|---|---|---|---|
| MaxNumberOfMessages | false | string | |
| MessageAttributeNames | false | array of string | |
| MessageSystemAttributeNames | false | array of string | |
| QueueUrl | true | string | |
| WaitTimeSeconds | false | string |
Responses
| HTTP Code | Description | Schema |
|---|---|---|
| 200 | Created | |
| 400 | Bad Request | |
| 403 | Forbidden |
Example HTTP request
Request Header
"Scp-Accesskey:2sd2gg=2agbdSD26svcD",
"Scp-Signature:fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef=",
"Scp-Timestamp:1605290625682",
"Scp-ClientType:user-api",
"Scp-Target:ScpQS.ReceiveMessage"
Request Body
{
"QueueUrl": "https://queueservice.kr-west1.dev3.samsungsdscloud.com/123e54b7303749f38ca59a5c6d419a75/test",
"MaxNumberOfMessages": "2"
}
Example HTTP response
200 Response
{
"messages": [
{
"MessageId": "14b37b86-8117-484a-aea4-1eae3b98d5d0",
"Body": "sample-body-1",
"Attributes": {},
"MessageAttributes": {
"Special": {
"DataType": "string",
"StingValue": "testBodyString12345678910!/wow$#@!"
}
},
"MD5OfBody": "098f6bcd4621d373cade4e832627b4f6",
"MD5OfMessageAttributes": "139818cac45117a07428826a8c533c01",
"ReceiptHandle": "400tf1nY4HbXEP7UX4OtxPVIPlq9vw1eeKDFwNMeNiEuZvMSbvdPCBOF/P96FUF9XT7TALMzP91ViCxQjnOIyBWw+fr4EhihdJ0Z2QHau1LMHbxD+GngcM2Pv6d5HM4KCmBgB2GxFA5qpUFBPPI="
},
{
"MessageId": "aee85517-1437-4877-8de8-00eee69e11dc",
"Body": "sample-body-2",
"Attributes": {},
"MD5OfBody": "ad0234829205b9033196ba818f7a872b",
"MD5OfMessageAttributes": "139818cac45117a07428826a8c533c01",
"ReceiptHandle": "400tf1nY4HbXEP7UX4OtxPVIPlq9vw1eeKDFwNMeNiEuZvMSbvdPCBPVrfhxFxZ0XD7aBbEzP91Vi3pQ13KMxBWxrP74REyhKcgd2VLauFLMHbxD+GngcM2Pv6d5HCzyqhEoB9DHI5NmOhgaOJ4="
}
]
}
DeleteMessage
POST https://queueservice.service.kr-west1.e.samsungsdscloud.com
Description
Delete message
Parameters
| Field name | Whether required | type | Explanation |
|---|---|---|---|
| QueueUrl | true | string | |
| ReceiptHandle | true | string |
Responses
| HTTP Code | Description | Schema |
|---|---|---|
| 200 | Created | |
| 400 | Bad Request | |
| 403 | Forbidden |
Example HTTP request
Request Header
"Scp-Accesskey:2sd2gg=2agbdSD26svcD",
"Scp-Signature:fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef=",
"Scp-Timestamp:1605290625682",
"Scp-ClientType:user-api",
"Scp-Target:ScpQS.DeleteMessage"
Request Body
{
"QueueUrl": "https://queueservice.kr-west1.dev3.samsungsdscloud.com/123e54b7303749f38ca59a5c6d419a75/test",
"ReceiptHandle": "400tf1nY4HbXEP7UX4OtxPVIPlq9vw1eeKDFwNMeNiEuZvMSbvdPCBPVrfhxFxZ0XD7aBbEzP91Vi3pQ13KMxBWxrP74REyhKcgd2VLauFLMHbxD+GngcM2Pv6d5HCzyqhEoB9DHI5NmOhgaOJ4="
}
Example HTTP response
200 Response
DeleteMessageBatch
POST https://queueservice.service.kr-west1.e.samsungsdscloud.com
Description
Bulk message deletion
Parameters
| Field name | Whether required | type | Explanation |
|---|---|---|---|
| Entries | true | array of DeleteMessageBatchRequestEntry | |
| QueueUrl | true | string |
DeleteMessageBatchRequestEntry
| Field name | Whether required | type | Explanation |
|---|---|---|---|
| Id | true | string | |
| ReceiptHandle | true | string |
Responses
| HTTP Code | Description | Schema |
|---|---|---|
| 200 | Created | |
| 400 | Bad Request | |
| 403 | Forbidden |
Example HTTP request
Request Header
"Scp-Accesskey:2sd2gg=2agbdSD26svcD",
"Scp-Signature:fsfsdf235f9U35sdgf35Xsf/qgsdgsdg326=sfsdr23rsef=",
"Scp-Timestamp:1605290625682",
"Scp-ClientType:user-api",
"Scp-Target:ScpQS.DeleteMessageBatch"
Request Body
{
"QueueUrl": "https://queueservice.kr-west1.dev3.samsungsdscloud.com/123e54b7303749f38ca59a5c6d419a75/test",
"Entries": [
{
"Id": "1",
"ReceiptHandle": "400tf1nY4HbXEP7UX4OtxPVIPlq9vw1eeKDFwNMeNiEuZvMSbvdPCBOF/P96FUF9XT7TALMzP91ViCxQjnOIyBWw+fr4EhihdJ0Z2QHau1LMHbxD+GngcMyJvqN5F17gym/YF4JoroeBXMSvIG0="
},
{
"Id": "2",
"ReceiptHandle": "400tf1nY4HbXEP7UX4OtxPVIPlq9vw1eeKDFwNMeNiEuZvMSbvdPCBOC8PwoFhV3Uj6JV+BnP90P3n1Q1y/RnhW0rv//GE6sf8EZjwfauVLMHbxD+GngcMyJvqN5F1Hs5T3vAZxgIV20IPdscTQ="
}
]
}
Example HTTP response
200 Response
{
"Failed": [],
"Successful": [
{
"Id": "1"
},
{
"Id": "2"
}
]
}
8.2.2 - How to guides
Create Queue Service
You can create and use a Queue Service from the Samsung Cloud Platform Console.
To create a Queue Service, follow these steps.
Click the All Services > Application > Queue Service menu. 1. Go to the Service Home page of the Queue Service.
On the Service Home page, click the Create Queue button. 2. Go to the Create Queue page.
On the Queue creation page, enter the information required to create the service and select detailed options.
- Enter or select the required information in the service information input area.
Category RequiredDetailed description type Required Select service type - Default: No message ordering
- FIFO: First-in-first-out message delivery and message retention
Queue name Required Enter the queue name - Start with a lowercase English letter and enter 3 ~ 64 characters consisting of lowercase English letters, numbers, and the special character (-)
- Standard type: The name cannot use the ‘.fifo’ suffix
- FIFO type: Include the .fifo suffix in the name
- Start with a lowercase English letter
- Enter 3 ~ 64 characters using lowercase English letters and the special character (-)
Duplicate removal range Essential Select duplicate removal scope - Messages in queue: Remove duplicate items among messages in the queue
- Group-level messages: Remove duplicate items within group-level messages
- FIFO can be set only when the FIFO type is selected
Content-based deduplication Selection Hash the message body content to remove duplicate messages - FIFO can be set only when the FIFO type is selected
Explanation Select Enter the service description within 100 characters. Table. Create Queue – Enter Service Information - Enter or select the required information in the configuration settings area.
Category Required statusDetailed description Message size Essential Enter the message size value (KB) between 1 and 256 - Up to 50 can be added per resource
Message retention period Essential Enter the message retention period - After selecting the unit, enter the desired value
- seconds: 60 ~ 1,209,600
- minutes: 1 ~ 20,160
- hours: 1 ~ 336
- days: 1 ~ 14
Encryption Required Select encryption usage - New creation: Go to the KMS page and create a new KMS encryption
- Do not use: Do not use encryption
- KMS encryption: Select when using KMS
- Data Key reuse period: After selecting a unit period, enter the desired value
- Minutes: 5 ~ 1,440
- Hours: 1 ~ 24
- Data Key reuse period: After selecting a unit period, enter the desired value
Table. Queue creation - configuration setting items - Enter or select the required information in the additional information input area.
Category RequiredDetailed description Tag Selection Add tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. Queue creation - additional information input fields
- Enter or select the required information in the service information input area.
Summary Verify the detailed information and estimated charges generated in the panel, then click the Create button.
- Once creation is complete, check the resources you created on the page.
- When using a FIFO type Queue, up to 100 message groups are supported.
- If the maximum number of message groups is exceeded, message transmission may fail.
View Queue Service details
You can view detailed information and messages for the Queue Service.
To view detailed information about the Queue Service, follow these steps.
- Click the All Services > Application > Queue Service menu. 1. Go to the Service Home page of Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue List page.
- On the Queue list page, click the resource to view detailed information. 3. Navigate to the Queue Details page.
- Queue Details page displays status information and additional feature information, and consists of Details, Message Management, Tags, Job History tabs.
Category Detailed description Queue Service status Queue Service status representation - Creating: In progress
- Available: Creation completed, server connection available
- Deleting: Service termination in progress
- Error Deleting: Abnormal state during deletion
- Inactive: Abnormal state
- Error: Abnormal state during creation
Service termination Service cancellation button Table. Queue Service status information and additional features
- Queue Details page displays status information and additional feature information, and consists of Details, Message Management, Tags, Job History tabs.
Detailed Information
On the Queue list page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Service’s unique resource ID |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who modified the service |
| Modification date | Service modification date and time |
| type | Queue type |
| Duplicate removal range | Deduplication Scope
|
| Content-based duplicate removal | Whether to use content-based duplicate removal feature
|
| Configuration Settings | Queue configuration information
|
| PrivateLink Service ID | PrivateLink service ID |
| Explanation | Queue description
|
| IP access allowlist | List of IPs allowed to access the Queue service
|
Message Management
On the Queue list page, you can view and manage the message list of the selected resource.
- A maximum of 10 messages will be displayed.
- If there are no messages in the list, you can click the Message Polling button to retrieve messages.
- Refer to Manage Messages for how to manage messages.
| Category | Detailed description |
|---|---|
| Message polling | After polling messages from the Queue to the Console, refresh the message list. |
| More | Message sending, deletion, and removal possible
|
| Message List | Message ID, message send timestamp, message receive timestamp, and message size (byte) can be viewed
|
Tag
Queue List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Operation History
You can view the operation history of the selected resource on the Queuee list page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Configure Queue
You can reconfigure the settings you specified when creating the Queue Service.
To reconfigure the Queue, follow these steps.
- All Services > Application > Queue Service Click the menu. 1. Go to the Service Home page of the Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue list page.
- On the Queue List page, click the resource to reconfigure the Queue. 3. Go to the Queue Details page.
- Click the Edit button of the Configuration Settings item. 4. Configuration Settings Edit The popup window opens.
- Edit Configuration Settings In the popup window, edit the configuration information, then click the OK button.
Category Required statusDetailed description Message size Essential Enter the message size value (KB) between 1 and 256 - Up to 50 can be added per resource
Message retention period Essential Enter the message retention period - After selecting the unit, enter the desired value
- seconds: 60 ~ 1,209,600
- minutes: 1 ~ 20,160
- hours: 1 ~ 336
- days: 1 ~ 14
Encryption Essential Select encryption usage - Create new: Go to the KMS page to create a new KMS encryption
- Do not use: Do not use encryption
- KMS encryption: Select when using KMS
- Data key reuse period: Select a unit period and then enter the desired value
- minutes: 5 ~ 1,440
- hours: 1 ~ 24
- Data key reuse period: Select a unit period and then enter the desired value
Table. Queue configuration setting edit input items
Managing IP Access Permissions
You can manage IPs that can access the Queue Service.
Add allowed IP
To add an allowed IP, follow these steps.
- All Services > Application > Queue Service Click the menu. 1. Go to the Service Home page of Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue list page.
- On the Queue List page, click the resource to add an allowed IP. 3. Go to the Queue Details page.
- Click the Add IP Address button of the IP Access Allow List item. 4. Add IP Address The popup window opens.
- Enter the IP to add to the IP Access Allow List, then click the Confirm button.
- Click the + button to add multiple IPs simultaneously (up to 10).
- When the popup that notifies an IP addition opens, click the Confirm button.
Exclude accessible IP
To exclude the IPs registered in IP access allow list, follow these steps.
- Click the All Services > Application > Queue Service menu. 1. Go to the Service Home page of Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue List page.
- On the Queue list page, click the resource to exclude the allowed IP. 3. Go to the Queue Details page.
- After selecting the IPs to exclude from the IP Access Allow List, click the Delete button at the top of the list.
- You can also individually exclude an IP from the IP Access Allow List by clicking its Delete button.
- When the pop-up notifying IP deletion opens, click the Confirm button.
Manage messages
You can send or manage queue messages.
Send Message
To send a Queue message, follow these steps.
- All Services > Application > Queue Service Click the menu. 1. Go to the Service Home page of Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue list page.
- On the Queue List page, click the resource to send a Queue message. 3. Queue Details Go to the page.
- Click the Message Management tab on the Queue Details page.
- Click the More > Send Message button at the top of the message list. 5. Send Message popup window opens.
- Send Message After entering the message information to be sent in the popup window, click the Confirm button.
Category Whether requiredDetailed description Message body Essential Enter the message to send - Up to 262,244 bytes can be entered
Message Group ID Required Enter using letters, numbers, and special characters within 128 characters - FIFO displayed only when using the FIFO type
Message deduplication ID Required/Optional Enter within 128 characters using letters, numbers, and special characters - FIFO type is displayed only when used
- When using the Content-based deduplication feature, input is optional
Meta information Selection Select whether to use meta information to add to the message - When used, you can enter up to 10 Key, Value entries
Encryption Essential Select encryption usage - Create new: Go to the KMS page to create a new KMS encryption
- Do not use: Do not use encryption
- KMS encryption: Select when using KMS
- Data key reuse period: Select a unit period and then enter the desired value
- minutes: 5 ~ 1,440
- hours: 1 ~ 24
- Data key reuse period: Select a unit period and then enter the desired value
Table. Message sending input fields
Check message details
You can view the content and detailed information of the Queue message. To view the detailed message information, follow these steps.
- Click the All Services > Application > Queue Service menu. 1. Go to the Service Home page of Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue List page.
- On the Queue list page, click the resource to view the Queue messages. 3. Go to the Queue Details page.
- Click the Message Management tab on the Queue Details page.
- Click the message ID to view detailed information in the message list. 5. Message Details The popup window opens.
Category Detailed description Message ID Message unique ID Message size Message size Message transmission timestamp Message transmission date and time Message Received Date/Time Message receipt date and time Message Group ID Message group ID - displayed only when the FIFO type is used
Message deduplication ID Deduplication ID set in the message - is displayed only when using the FIFO type
Message body message content Meta definition Message meta information (Key, Value) Table. Message detail information items
Delete individual messages
Queue messages can be deleted individually. To delete a message, follow these steps.
- Click the All Services > Application > Queue Service menu. 1. Go to the Service Home page of the Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue list page.
- On the Queue List page, click the resource to delete the Queue message. 3. Queue Details page is opened.
- Click the Message Management tab on the Queue Details page.
- After selecting all messages to delete in the message list, click the More > Delete button at the top of the list.
- You can also delete individually by clicking the Delete button at the far right of the message you want to delete in the message list.
- When the popup notifying message deletion opens, click the Confirm button.
Clear all messages in the queue
You can delete all messages in the Queue by emptying the Queue.
- Messages deleted via Empty Queue cannot be recovered.
- If the same request is already in progress, it will not be deleted. * In a moment, clear the queue again.
To delete all messages, follow the steps below.
- Click the All Services > Application > Queue Service menu. 1. Go to the Service Home page of Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue list page.
- On the Queue List page, click the resource to remove the Queue message. 3. Go to the Queue Details page.
- Click the Message Management tab on the Queue Details page.
- Click the More > Clear Queue button at the top of the message list.
- When the popup notifying message deletion opens, click the Confirm button.
Cancel Queue Service
You can reduce operating costs by terminating the unused Queue Service.
However, if you terminate the service, the running service may be stopped immediately, so you should proceed with the termination only after fully considering the impact that may occur when the service is discontinued.
To cancel the Queue Service, follow these steps.
- Click the All Services > Application > Queue Service menu. 1. Go to the Service Home page of Queue Service.
- On the Service Home page, click the Queue menu. 2. Go to the Queue list page.
- On the Queue list page, select the resource to cancel, then click the Cancel service button.
- After navigating to the Queue Details page of the resource to be terminated, you can also terminate it individually by clicking the Terminate Service button.
- When the pop-up notifying service termination opens, click the Confirm button.
Integrating PrivateLink Service
The Queue Service can communicate directly by integrating with the PrivateLink Service without using internet communication. When integrated with PrivateLink Service, communication with the Queue Service occurs directly from the user’s VPC, enhancing security.
Creating and Connecting a PrivateLink Endpoint
Follow the steps below to integrate the Queue Service with the PrivateLink Service.
- Check the PrivateLink Service ID of the Queue Service for creating a PrivateLink Endpoint.
- The PrivateLink Service ID of the Queue Service can be found on the Queue Details page’s PrivateLink Service ID.
- Create a PrivateLink Endpoint.
- Refer to PrivateLink Endpoint 생성하기 for how to create a PrivateLink Endpoint.
- When connecting to a PrivateLink Service, usage approval is processed automatically.
- Check the Security Group of the PrivateLink Endpoint to verify whether the target VM IP is registered.
8.2.3 - Overview
Service Overview
Queue Service efficiently manages and delivers messages or tasks, supporting message transmission between systems.
This service facilitates the data flow between a Producer that generates messages and a Consumer that receives them, and provides a FIFO (First-In-First-Out) feature that guarantees message order. By doing so, it distributes system load caused by messages, enabling efficient message management in microservice architectures or event-driven systems.
Features
- Efficient Message Processing : Allows efficient handling and management of large volumes of messages sent and received simultaneously, enabling the user system’s message processing tasks to be performed efficiently.
- Fast Service Processing : Producer and Consumer operate independently, allowing improved responsiveness and processing speed.
- Message Order Guarantee : Ensures the order of received messages to maintain data consistency.
- Strong security and reliability : It protects sensitive information by encrypting messages during transmission and storage, and provides reliable message management.
Service Architecture Diagram
Provided features
The Queue Service provides the following features.
- Queue creation: Depending on the message reception handling method, create a basic or FIFO type Queue that guarantees message order.
- When using the FIFO type, the Queue Service orders messages in the order they were received.
- Message Transmission: Producer sends the message intended for Consumer to the Queue.
- Message Reception: Consumer receives the Producer’s message from the Queue.
- Message Management: Check and manage messages stored in the Queue.
- Message Encryption: Encrypt messages within the Queue by integrating with the KMS service.
- We support blocking message exposure through message encryption settings.
- ServiceWatch service integration provided: You can monitor data through the ServiceWatch service.
Component
Producer
Create and send messages using the Queue Service.
Consumer
Receive and process messages from the Queue Service.
Message Manager
You can view the loaded messages in the Queue Service and manage them, such as deleting them.
Provision status by region
The Queue Service is available in the following environments.
| region | Provision status |
|---|---|
| Korea West 1 (kr-west1) | Provide |
| Korea East 1 (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea 3 (kr-south3) | Not provided |
Preliminary Service
The Queue Service has no preceding service.
8.2.3.1 - ServiceWatch Metrics
The Queue Service sends metrics to ServiceWatch. The metrics provided by default monitoring are data collected at a 1‑minute interval.
Basic Metrics
The following are the basic metrics for the Queue Service namespace.
The indicators whose names are displayed in bold below are the key indicators selected from the basic metrics provided by Queue Service. Key metrics are used to compose service dashboards that are automatically built for each service in ServiceWatch.
Each metric indicates through the user guide which statistical value is meaningful when viewing that metric, and among the meaningful statistics, the values displayed in bold are the primary statistics. In the service dashboard, you can view key metrics using these primary statistical values.
| Performance items | Detailed description | unit | meaningful statistics |
|---|---|---|---|
| NumberOfMessagesSent | Number of messages added to the queue | Count |
|
| SentMessageSize | Size of the message added to the queue | Bytes |
|
| NumberOfMessagesReceived | Number of messages returned by the call to the ReceiveMessage operation (number of polled messages) | Count |
|
| NumberOfEmptyReceives | Number of ReceiveMessage API calls that did not return a message | Count |
|
| NumberOfMessagesDeleted | Number of messages deleted from the queue | Count |
|
8.2.4 - CLI Reference
8.2.5 - API Reference
8.2.6 - Release Note
Queue Service
- You can configure additional features when selecting a FIFO type.
- Content-based deduplication: Hash the message body content to remove duplicate messages.
- Duplicate removal scope setting: Set the scope (within the queue / per group) for removing duplicate messages.
- When sending FIFO-type messages, you can manage them by entering Message Group ID and Message Deduplication ID information.
- ServiceWatch service integration provided: You can monitor data through the ServiceWatch service.
- The Queue service feature has been added.
- Provides Private Service link ID information.
- Message retention and data key reuse period setting units have been refined, and a CIDR‑based modification feature for allowed IP addresses has been added.
- The Queue Service has been officially launched.
- Through the Queue Service, you can distribute system load caused by messages, enabling efficient message management in microservice architectures or event-driven systems.
- Message transmission and reception operate independently, improving responsiveness and processing speed.
9 - Security
Leveraging the nation’s largest and longest‑standing experience in security service operations, we deliver automated security services customized for diverse customer environments.
9.1 - Key Management Service
9.1.1 - Overview
Service Overview
Key Management Service(KMS) is a service that easily creates encryption keys and securely stores/manages them to safely protect an application’s critical data. The user encrypts and decrypts data using an encryption key, and the encryption key is reliably managed through a centrally managed hierarchical encryption key system.
Provided Features
Key Management Service provides the following features.
- Key Management: KMS can create, delete, and manage customer-managed keys. * The user directly generates a data key that encrypts data using the master key created by KMS.
- Key Permission Management: You can control and manage usage permissions for master keys based on custom policy.
- Key Lifecycle Management: Through key rotation, you can generate new encrypted data for the master key without creating a new key, and the key rotation interval can be set according to customer policy. * Through lifecycle management, encryption keys that are no longer used are deactivated or deleted, ensuring data is safely protected from cryptographic threats.
- Platform-managed key: When another product within the Samsung Cloud Platform uses a KMS key for encryption, the CSP (Cloud Service Provider) creates a platform-managed key and performs encryption, so the user does not need to generate a key directly in KMS.
Component
Master key
The master key is used to generate data keys for encrypting data, and depending on the purpose, you can generate symmetric key (encryption/decryption (AES), generation/verification (HMAC)) and asymmetric key (encryption/decryption and signing/verification (RSA), signing/verification (ECDSA)) respectively. Proper master key management encrypts data keys, allowing you to protect frequently used data keys during operation.
- The master key is a key generated through the creation of a KMS product service in the Samsung Cloud Platform Console.
Data key
The data key is used to encrypt the actual data and is generated for each target service that performs encryption. Thus, even if a single data key is compromised, it does not affect services encrypted with other data keys.
HSM (hardware security module)
Stores the root key of the KMS system domain. The master key is generated using the root key stored in an HSM (Hardware Security Module) that complies with the FIPS 140-2 Lv3 standard, and is securely distributed and stored in the KMS for protection.
Constraints
The Key Management Service of Samsung Cloud Platform limits the number of key creations and rotations as follows.
| Item | Detailed description | Quota |
|---|---|---|
| KMS Key | Number of KMS Keys created per region | 10000 |
| KMS Validation Password Key | Number of public authentication algorithm keys that can be generated per account | 100 |
| KMS Key rotation | Number of versions that can be generated when rotating a customer-managed Key
| 100 |
- In KMS, keys created as a regional service can be used only within that region.
- The restrictions on the public authentication algorithm key apply only to the KR SOUTH region.
Preceding Service
Key Management Service has no prerequisite service.
9.1.2 - How-to guides
Users can create the service by entering the required information for the Key Management Service through the Samsung Cloud Platform Console and selecting detailed options.
Key Management Service provides the following two key services.
- Customer-managed key: To securely protect critical application data, users can generate and manage encryption keys themselves.
- Platform-managed key: Since the CSP (Cloud Service Provider) creates and manages it directly, users cannot modify or delete the key’s properties.
Create a customer-managed key
You can create and use a customer-managed key in the Samsung Cloud Platform Console.
To create a customer-managed key, follow these steps.
All Services > Security > Key Management ServiceClick the menu. 1. Go to the Service Home page of Key Management Service.
On the Service Home page, click the Create Customer Managed Key button. 2. Navigate to the Customer Managed Key Creation page.
On the Customer Managed Key Creation page, enter the information required to create a service and provide additional details.
- Enter or select the required information in the Service Information Input area.CategoryRequired
Detailed description key name Required Enter key name Public authentication algorithm Selection When Use is selected, you can generate encryption keys that meet public encryption standards - The public authentication algorithm option is available only in the KR SOUTH region
- The public authentication algorithm provides the ARIA algorithm, which has passed security verification through Korea’s cryptographic module certification system
Purpose Required Select the key purpose and encryption method - If you do not select the public authentication algorithm, choose among encryption/decryption (AES-256), encryption/decryption and signing/verification (RSA-2048), signing/verification (ECDSA), and generation/verification (HMAC)
Auto rotation Selection Select whether to enable automatic key rotation - If you select Use, the internal algorithm of the generated key is converted to a different value and applied at each configured rotation interval
- The rotation interval can be set to a value between 1 and 730 days. If no rotation interval is entered, it defaults to 90 days automatically
Explanation Selection Enter additional information for the key Table. Customer-managed key service information input items - In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description tag Selection Add Tag - Up to 50 per resource can be added
- Add Tag After clicking the Add Tag button, enter or select Key, Value values
Table. Customer-managed key additional information input fields
- Enter or select the required information in the Service Information Input area.
Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- When creation is complete, check the created resources on the Customer Managed Key List page.
Check detailed information of customer-managed key
You can view and edit the complete list of resources and detailed information for customer-managed keys. Customer Managed Key Details page is composed of Details, Tags, Activity Log tabs.
If the status of a customer-managed key service is Creating, the service is still being created, so you cannot navigate to the detail page.
- If it remains in the Creating state after a certain amount of time, delete the key and recreate it.
To view detailed information about the Key Management Service, follow these steps.
- Click the All Services > Security > Key Management Service menu. 1. Go to the Service Home page of Key Management Service.
- On the Service Home page, click the Customer Managed Key menu. 2. Navigate to the Customer Managed Key List page.
- On the Customer Managed Key List page, click the resource to view detailed information. 3. Navigate to the Customer Managed Key Details page.
- Customer Managed Key Details page displays status information and descriptions of additional features at the top.
Category Detailed description status Indicates the status of a customer-managed key - Active: available/activated
- Stop: stopped/disabled
- To be terminated: scheduled for deletion
- Creating: creating/creation error (immediate retry possible)
key rotation Button to manually rotate the generated key Key Deactivation Button to deactivate the generated key Service cancellation Terminate service button - When the status is To be terminated, display Cancel termination button
Table. Customer-managed key status information and additional features
- Customer Managed Key Details page displays status information and descriptions of additional features at the top.
Detailed Information
On the Customer Managed Key List page, you can view detailed information of the selected resource and, if necessary, edit the information.
Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| key name | Name of the generated key |
| Public authentication algorithm | Whether to use a public authentication algorithm |
| Purpose | Key purposes and cryptographic methods such as encryption/decryption and signing/verification |
| Current version | Current version of the generated key
|
| Auto rotation | Automatic key rotation usage
|
| Next rotation day | Display the next key rotation date according to the rotation period
|
| rotation period | Rotation period when automatic rotation is enabled |
| Explanation | Show additional description for the key
|
Tag
Customer Managed Key List page allows you to view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Customer Managed Key List page.
| Category | Detailed description |
|---|---|
| Work History | Task execution details
|
| Work Date/Time | Task execution date and time |
| Resource Type | Resource Type |
| Resource name | Resource Name |
| Work result | Task execution result (success/failure) |
| Operator Information | User information for the performed task |
Managing Customer-Managed Keys
You can create a new version of a registered key or change its usage status.
Configure customer-managed key rotation
Key rotation is a function that converts the internal algorithm of a generated key to a different value.
- When rotating the key, only the master key value changes, and the ciphertext and plaintext values of previously generated data keys remain unchanged.
- Even if key rotation is performed, the master key retains the previous version’s data, so decryption using the master key is unaffected, and the value of the data key in use also remains unchanged.
- Note that if you wrap with the updated master key (decrypt and then re‑encrypt), calling the rewrapData API will trigger the key rotation function.
- When rotating a customer-managed key, the key’s version is changed internally. * By using the newly generated version of the key, you can decrypt information that was encrypted with the previous version of the key. * (maintain compatibility)
- Versions through key rotation are compatible up to the 100th version regardless of the encryption algorithm.
To create a new version of a customer-managed key (key rotation), follow these steps.
- Click the All Services > Security > Key Management Service menu. 1. Go to the Service Home page of Key Management Service.
- On the Service Home page, click the Customer Managed Key menu. 2. Navigate to the Customer Managed Key List page.
- Customer Managed Key List page, click the resource to view detailed information. 3. Navigate to the Customer Managed Key Details page.
- On the Customer Managed Key Details page, click the Key Rotation button. 4. Key Rotation Go to the notification window.
- In the Key Rotation notification window, click the Confirm button.
Configure Customer-Managed Key Activation
You can configure the usage of the selected key.
To set the activation/deactivation status of a customer-managed key you created, follow these steps.
- Click the All Services > Security > Key Management Service menu. 1. Go to the Service Home page of Key Management Service.
- On the Service Home page, click the Customer Managed Key menu. 2. Navigate to the Customer Managed Key List page.
- On the Customer Managed Key List page, click the resource to view its details. 3. Navigate to the Customer Managed Key Details page.
- On the Customer Managed Key Details page, click the Key Activation/Key Deactivation button. 4. Key activation/Key deactivation Navigate to the notification dialog.
- In the Key activation/key deactivation notification window, click the OK button.
Encryption case using Key Management Service
The following is an example procedure for encrypting and storing important data of a user application by obtaining a data key from KMS.
- When the application starts, it obtains a data key using the KMS master key information, then performs and stores secure data encryption on the client side with the plaintext data key.
- The data key is stored in the database in an encrypted form using the master key.
- When performing secure data decryption, the data key stored in the database is retrieved and a decryption request is made using the KMS master key information.
The encryption/decryption process using the Key Management Service key is explained with the following diagram.
Encryption
Decryption
Terminate customer-managed key
You can revoke customer-managed keys that are not in use.
To cancel a customer-managed key, follow these steps.
- Click the All Services > Security > Key Management Service menu. 1. Go to the Service Home page of Key Management Service.
- On the Service Home page, click the Customer Managed Key menu. 2. Navigate to the Customer Managed Key List page.
- On the Customer Managed Key List page, click the resource to view its details. 3. Navigate to the Customer Managed Key Details page.
- On the Customer Managed Key Details page, click the Terminate Service button. 4. Navigate to the Service Cancellation alert window.
- In the Service termination alert window, select Immediate termination/Scheduled termination, verify the details, and click the Confirm button.
- When termination is complete, verify on the Customer Managed Key List page whether the resource has been terminated.
- When the key deletion is complete, a notification is sent to both the user who created the key and the user who deleted it.
- Even if you click the Service Termination button in the More Options menu at the far right of the generated customer-managed key list, you can terminate the selected key.
- To cancel the cancellation of a reserved service, click the Cancel Termination button on the customer-managed key list page or the detail page.
- Cancel Service Termination popup window, when you click Confirm, the selected key is not deleted and is restored in a disabled state.
- To reuse the key, click the Customer Managed Key Details page’s Activate Key button.
9.1.2.1 - Encryption Example Using Key Management Service Keys
Encryption example using Key Management Service keys
This is a Java code example for implementing envelope encryption and data signing/verification using a key generated in KMS.
Envelope encryption
It presents an envelope encryption scenario, and you can review the Java, Go, and Python example code and their output generated according to the scenario.
Scenario
- To encrypt password information using the envelope encryption method, a Data Key is issued.
- Encrypt the password using the issued Data Key information.
- Encrypt the password and encrypted Data Key information using envelope encryption and store them in a JSON file.
Java example code
This is a Java example code written according to the provided scenario.
// URI
static String KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }};
// END POINT
static String KMS_API_DECRYPT = "/v1/kms/openapi/decrypt/%s";
static String KMS_API_CREATE_DATAKEY = "/v1/kms/openapi/datakey/%s";
// KEY ID
static String KEY_ID = {{마스터 키 ID}};
createEnvelop() {
// 새로운 데이터 키 생성을 요청
String encryptedDataKey = getDataKey();
// 암호화를 할 데이터
String example_json_data = "{\"PASSWORD\":\"SECRET_CREDENTIAL\"}";
// 암호화된 데이터 봉투(Envelop encryption)
String envelope = encryptData(example_json_data, encryptedDataKey);
// 이 예제 코드에서는 암호화된 데이터 봉투를 파일로 저장
File envelopeFile = new File("envelope.json");
}
getDataKey() {
String endPoint = String.format(KMS_API_CREATE_DATAKEY, KEY_ID);
String url = KMS_API_BASE_URI + endPoint;
JSONObject data = new JSONObject();
data.put("key_type", "plaintext");
JSONObject respJsonObject = callApi(endPoint, data.toJSONString());
return respJsonObject.get("ciphertext").toString();
}
encryptData() {
Map<String, String> envelope = new HashMap<>();
// 데이터 키 복호화
String dataKey = decryptDataKey(encryptedDataKey);
// Cipher Class 사용 (사용자가 기 사용 중인 암호화 알고리즘 사용 가능)
SecretKey secretKey = new SecretKeySpec(decodeBase64(dataKey), "{사용자 선택 알고리즘}");
Cipher cipher = Cipher.getInstance("{사용자 선택 알고리즘}");
cipher.init(Cipher.ENCRYPT_MODE, secretKey);
byte[] iv = cipher.getParameters().getParameterSpec(IvParameterSpec.class).getIV();
byte[] cipherText = cipher.doFinal(obj.toString().getBytes());
envelope.put("encryptedKey", encryptedDataKey);
envelope.put("cipherText", encodeBase64(cipherText));
envelope.put("iv", encodeBase64(iv));
return JSONValue.toJSONString(envelope);
}
decryptDataKey() {
String endPoint = String.format(KMS_API_DECRYPT, KEY_ID);
JSONObject data = new JSONObject();
data.put("cipherText", sealedKey);
JSONObject respJsonObject = callApi(endPoint, data.toJSONString());
String plaintext = (respJsonObject.get("plaintext")).toString();
return plaintext;
}
Go example code
This is a Go example code written based on the provided scenario.
// URI
const KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
// END POINT
const KMS_API_DECRYPT = "/v1/kms/openapi/decrypt/%s"
const KMS_API_CREATE_DATAKEY = "/v1/kms/openapi/datakey/%s"
// KEY ID
const KEY_ID = {{마스터 키 ID}}
createEnvelop() {
// 새로운 데이터 키 생성을 요청
encryptedDataKey := getDataKey()
// 암호화를 할 데이터
example_json_data := "{\"PASSWORD\":\"SECRET_CREDENTIAL\"}"
// 암호화된 데이터 봉투(Envelop encryption)
envelope := encryptData(example_json_data, encryptedDataKey)
// 이 예제 코드에서는 암호화된 데이터 봉투를 파일로 저장
file, _ := os.Create("envelope.json")
defer file.Close()
file.WriteString(envelope)
}
getDataKey() {
endPoint := fmt.Sprintf(KMS_API_CREATE_DATAKEY, KEY_ID)
data := map[string]interface{}{
"key_type": "plaintext",
}
jsonData, _ := json.Marshal(data)
respJsonObject := callApi(endPoint, jsonData)
info := &KMSDatakeyInfo{}
json.Unmarshal([]byte(respJsonObject), info)
return info.DataKey
}
encryptData() {
envelope := make(map[string]string)
// 데이터 키 복호화
dataKey := decryptDataKey(encryptedDataKey)
secretKey, _ := base64.StdEncoding.DecodeString(dataKey)
// Cipher Class 사용
block, _ := {사용자 선택 알고리즘}.NewCipher(secretKey)
cipherText := make([]byte, {사용자 선택 알고리즘}.BlockSize+len(example_json_data))
iv := cipherText[:{사용자 선택 알고리즘}.BlockSize]
if _, err := io.ReadFull(rand.Reader, iv); err != nil {
panic(err)
}
mode := cipher.NewCFBEncrypter(block, iv)
mode.XORKeyStream(cipherText[{사용자 선택 알고리즘}.BlockSize:], []byte(example_json_data))
envelope["encryptedKey"] = encryptedDataKey
envelope["cipherText"] = base64.StdEncoding.EncodeToString(cipherText)
envelope["iv"] = base64.StdEncoding.EncodeToString(iv)
jsonString, _ := json.Marshal(envelope)
return string(jsonString)
}
decryptDataKey() {
endPoint := fmt.Sprintf(KMS_API_DECRYPT, KEY_ID)
data := map[string]interface{}{
"cipherText": sealedKey,
}
jsonData, _ := json.Marshal(data)
respJsonObject := callApi(endPoint, jsonData)
info := &KMSDecryptInfo{}
json.Unmarshal([]byte(respJsonObject), info)
return info.DecryptedData
}
Python example code
This is a Python example code written according to the presented scenario.
# URI
KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
# END POINT
KMS_API_DECRYPT = "/v1/kms/openapi/decrypt/"
KMS_API_CREATE_DATAKEY = "/v1/kms/openapi/datakey/"
# KEY ID
KEY_ID = {{마스터 키 ID}}
create_envelop()
# 새로운 데이터 키 생성을 요청
encrypted_data_key = get_dataKey()
# 암호화를 할 데이터
example_json_data = {"PASSWORDTEST":"SECRET_CREDENTIALTEST"}
json_data_str = json.dumps(example_json_data)
# 암호화된 데이터 봉투(Envelop encryption)
envelope = encrypt_data(json_data_str,encrypted_data_key)
# 이 예제 코드에서는 암호화된 데이터 봉투를 파일로 저장
with open("envelope.json", "w") as file:
file.write(envelope)
get_dataKey()
end_point = f"{KMS_API_CREATE_DATAKEY}{KEY_ID}"
data = {
"key_type": "plaintext"
}
response_object = call_api(end_point, data)
data_key = response_object.get("ciphertext", "")
return data_key
encrypt_data()
envelope = {}
# 데이터 키 복호화
dataKey = decrypt_data_key(encrypted_data_key)
decoded_data_key = base64.b64decode(dataKey)
# Cipher Class 사용
iv = get_random_bytes(16)
cipher = {사용자 선택 알고리즘}.new(decoded_data_key, {사용자 선택 알고리즘}.MODE_CBC, iv)
data_to_encrypt = obj
data_bytes = data_to_encrypt.encode()
padded_data = pad(data_bytes, {사용자 선택 알고리즘}.block_size)
cipher_text = cipher.encrypt(padded_data).hex()
envelope["encryptedKey"] = encrypted_data_key
envelope["cipherText"] = cipher_text
envelope["iv"] = base64.b64encode(iv).decode()
return json.dumps(envelope)
decrypt_data_key()
end_point = f"{KMS_API_DECRYPT}{KEY_ID}"
data = {}
data["cipherText"] = sealed_key
resp_json_object = call_api(end_point,data)
plaintext = resp_json_object.get("decryptedData")
return plaintext
Example code result
Displays the result of the example code.
{
"cipherText":"d3S81rzaGAl8U12LlKSlRbDekPlGuibTntXX962KCjBIKuXdPOG8N8vk3Jet8lyG",
"iv":"0kP7QKZ6BUeQPlThk4tySA==",
"encryptedKey":"vault:v1:KJjjLtGHTbaV5N8LWC5O9eMDCaJVeff5SM\/MAYseugjiqiXFVgdXaKXg6kym0NmjHkO\/wLPsa+YK0aVk"
}
Use envelope encryption
You can present an envelope encryption usage scenario and view the Java, Go, and Python example code and results written according to the scenario.
Scenario
- Decrypt the Data Key of the encrypted envelope file.
- Decrypt the encrypted data of the envelope file using the decrypted Data Key.
Java example code
This is a Java example code written according to the provided scenario.
// URI
static String KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }};
// END POINT
static String KMS_API_DECRYPT = "/v1/kms/openapi/decrypt/%s";
// KEY ID
static String KEY_ID = {{마스터 키 ID}};;
getData() {
// 암호화된 데이터 봉투(Envelop encryption)
String envelope = new String(Files.readAllBytes(Paths.get("envelope.json")));
JSONParser parser = new JSONParser();
JSONObject envelopeJson = (JSONObject) parser.parse(envelope);
String encryptedDataKey = envelopeJson.get("encryptedKey").toString();
String cipherText = envelopeJson.get("cipherText").toString();
String iv = envelopeJson.get("iv").toString();
return decryptData(cipherText, encryptedDataKey, iv);
}
decryptData() {
String dataKey = decryptDataKey(encryptedDataKey);
IvParameterSpec ivParameterSpec = new IvParameterSpec(decodeBase64(iv));
SecretKey secretKey = new SecretKeySpec(decodeBase64(dataKey), "{사용자 선택 알고리즘}");
Cipher cipher = Cipher.getInstance("{사용자 선택 알고리즘}");
cipher.init(Cipher.DECRYPT_MODE, secretKey, ivParameterSpec);
byte[] plaintext = cipher.doFinal(decodeBase64(cipherText));
return new String(plaintext);
}
decryptDataKey() {
String endPoint = String.format(KMS_API_DECRYPT, KEY_ID);
JSONObject data = new JSONObject();
data.put("cipherText", sealedKey);
JSONObject respJsonObject = callApi(endPoint, data.toJSONString());
String plaintext = (respJsonObject.get("plaintext")).toString();
return plaintext;
}
Go example code
This is a Go example code written according to the presented scenario.
// URI
const KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
// END POINT
const KMS_API_DECRYPT = "/v1/kms/openapi/decrypt/%s"
// KEY ID
const KEY_ID = {{마스터 키 ID}}
getData() {
// 암호화된 데이터 봉투(Envelop encryption) 불러오기
jsonData, _ := os.ReadFile("envelope.json")
var envelope map[string]interface{}
if err := json.Unmarshal(jsonData, &envelope); err != nil {
fmt.Println("JSON 파싱 오류:", err)
os.Exit(1)
}
encryptedDataKey := envelope["encryptedKey"].(string)
cipherText := envelope["cipherText"].(string)
iv := envelope["iv"].(string)
return decryptData(cipherText, encryptedDataKey, iv)
}
decryptData() {
dataKey := decryptDataKey(encryptedDataKey)
ciphertext, _ := base64.StdEncoding.DecodeString(cipherText)
dataKeyBytes, _ := base64.StdEncoding.DecodeString(dataKey)
decodedData := ciphertext[{사용자 선택 알고리즘}.BlockSize:]
ivparam := ciphertext[{사용자 선택 알고리즘}.BlockSize]
block, _ := {사용자 선택 알고리즘}.NewCipher(dataKeyBytes)
mode := cipher.NewCFBDecrypter(block, ivparam)
mode.XORKeyStream(decodedData, decodedData)
decryptedData := string(decodedData)
return decryptedData
}
decryptDataKey() {
endPoint := fmt.Sprintf(KMS_API_DECRYPT, KEY_ID)
data := map[string]interface{}{
"cipherText": sealedKey,
}
jsonData, _ := json.Marshal(data)
respJsonObject := callApi(endPoint, jsonData)
info := &KMSDecryptInfo{}
json.Unmarshal([]byte(respJsonObject), info)
return info.DecryptedData
}
Python example code
This is a Python example code written according to the presented scenario.
# URI
KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
# END POINT
KMS_API_DECRYPT = "/v1/kms/openapi/decrypt/"
# KEY ID
KEY_ID = {{마스터 키 ID}}
get_data()
# 암호화된 데이터 봉투(Envelop encryption) 열기
with open("envelope.json", "r") as file:
envelope = file.read()
envelope_json = json.loads(envelope)
encrypted_data_key = envelope_json["encryptedKey"]
cipher_text = envelope_json["cipherText"]
iv = envelope_json["iv"]
return decrypt_data(cipher_text, encrypted_data_key, iv)
decrypt_data()
data_key = decrypt_data_key(encrypted_data_key)
iv_bytes = base64.b64decode(iv)
decoded_data_key = base64.b64decode(data_key)
cipher_txt = bytes.fromhex(cipher_text)
cipher = {사용자 선택 알고리즘}.new(decoded_data_key, {사용자 선택 알고리즘}.MODE_CBC, iv_bytes)
plain_text_bytes = unpad(cipher.decrypt(cipher_txt), {사용자 선택 알고리즘}.block_size)
plain_text = plain_text_bytes.decode('utf-8')
return plain_text
decrypt_data_key()
end_point = f"{KMS_API_DECRYPT}{KEY_ID}"
data = {}
data["cipherText"] = sealed_key
resp_json_object = call_api(end_point,data)
plaintext = resp_json_object.get("decryptedData")
return plaintext
Example code result
Displays the result of the example code.
{"PASSWORD":"SECRET_CREDENTIAL"}
Use data signature
It provides a data signing usage scenario to guarantee data integrity, and you can review the Java, Go, and Python example code and their results as written according to the scenario.
Scenario
- Call the OpenAPI to sign the data.
- The signed data is enveloped and saved as a JSON file.
Java example code
This is a Java example code written according to the provided scenario.
// URI
static String KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }};
// END POINT
static String KMS_API_SIGN = "/v1/kms/openapi/sign/%s";
// KEY ID
static String KEY_ID = {{마스터 키 ID}};
signEnvelop() {
// 서명 데이터 봉투(Envelop encryption)
String envelope = sign();
// 이 예제 코드에서는 서명 데이터 봉투를 파일로 저장
File envelopeFile = new File("signEnvelope.json");
OutputStream os = new BufferedOutputStream(new FileOutputStream(envelopeFile));
try {
os.write(envelope.getBytes());
} finally {
os.close();
}
}
sign() {
Map<String, String> envelope = new HashMap<>();
String example_credential = "SCP KMS Sign Test!!!";
String endPoint = String.format(KMS_API_SIGN, KEY_ID);
JSONObject data = new JSONObject();
data.put("input", encodeToBase64(example_credential));
JSONObject respJsonObject = callApi(endPoint, data.toJSONString());
envelope.put("signature", respJsonObject.get("signature").toString());
if(respJsonObject.get("batch_results") != null) {
envelope.put("batch_results", respJsonObject.get("batch_results").toString());
}
return JSONValue.toJSONString(envelope);
}
Go example code
This is a Go example code written according to the presented scenario.
// URI
const KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
// END POINT
const KMS_API_SIGN = "/v1/kms/openapi/sign/%s"
// KEY ID
const KEY_ID = {{마스터 키 ID}}
signEnvelop() {
// 서명 데이터 봉투(Envelop encryption)
envelope := sign()
// 이 예제 코드에서는 서명 데이터 봉투를 파일로 저장
file, _ := os.Create("signEnvelope.json")
defer file.Close()
file.WriteString(envelope)
}
sign() {
envelope := make(map[string]string)
example_credential := "SCP KMS Sign Test!!!"
endPoint := fmt.Sprintf(KMS_API_SIGN, KEY_ID)
data := map[string]interface{}{
"input": base64.StdEncoding.EncodeToString([]byte(example_credential)),
}
jsonData, _ := json.Marshal(data)
respJsonObject := callApi(endPoint, jsonData)
info := &KMSSignInfo{}
json.Unmarshal([]byte(respJsonObject), info)
envelope["signature"] = info.Signature
jsonString, _ := json.Marshal(envelope)
return string(jsonString)
}
Python example code
This is a Python example code written according to the presented scenario.
# URI
KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
# END POINT
KMS_API_SIGN = "/v1/kms/openapi/sign/"
# KEY ID
KEY_ID = {{마스터 키 ID}}
sign_envelop()
# 서명 데이터 봉투(Envelop encryption)
envelope = sign()
# 이 예제 코드에서는 서명 데이터 봉투를 파일로 저장
with open("signEnvelope.json", "w") as file:
file.write(envelope)
sign()
envelope = {}
example_credential = "SCP KMS Sign Test!!!"
end_point = f"{KMS_API_SIGN}{KEY_ID}"
credential_bytes = example_credential.encode('utf-8')
data = {
"input": base64.b64encode(credential_bytes).decode('utf-8')
}
resp_json_object = call_api(end_point,data)
envelope["signature"] = resp_json_object.get("signature")
return json.dumps(envelope)
Example code result
Displays the result of the example code.
{
"signature":"vault:v1:qHGf4ALkTao1Yy\/lpSbLQ2l8YVpsHWBP6ic3Ux1BKSodQQxnEIrjPyUwXXQ1NZfGSVxdeVe5Y6kb0nUPNADQpzkOh9\/e8T\/QCOs9==",
"projectId":"PROJECT-qWrHRJX5sZnTkopcr9N1dk"
}
Use data validation
It presents a verification usage scenario for validating data integrity, and you can view the Java, Go, and Python example code and their results written according to the scenario.
Scenario
- Retrieves the signature value of the signed envelope file.
- Validates the signed data and outputs the result.
Java example code
This is a Java example code written according to the provided scenario.
// URI
static String KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }};
// END POINT
static String KMS_API_VERIFY = "/v1/kms/openapi/verify/%s";
// KEY ID
static String KEY_ID = {{마스터 키 ID}};
getSign() {
// 서명 데이터 봉투(Envelop encryption)
String envelope = new String(Files.readAllBytes(Paths.get("signEnvelope.json")));
JSONParser parser = new JSONParser();
JSONObject envelopeJson = (JSONObject) parser.parse(envelope);
String signature = envelopeJson.get("signature").toString();
return verify(signature);
}
verify() {
String endPoint = String.format(KMS_API_VERIFY, KEY_ID);
JSONObject data = new JSONObject();
data.put("input", "U0NQIEtNUyBTaWduIFRlc3QhISE=");
data.put("signature", signature);
JSONObject respJsonObject = callApi(endPoint, data.toJSONString());
String valid = (respJsonObject.get("valid")).toString();
return valid;
}
Go example code
This is a Go example code written according to the presented scenario.
// URI
const KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
// END POINT
const KMS_API_VERIFY = "/v1/kms/openapi/verify/%s"
// KEY ID
const KEY_ID = {{마스터 키 ID}}
getSign() {
// 서명 데이터 봉투(Envelop encryption) 불러오기
jsonData, _ := os.ReadFile("signEnvelope.json")
var envelope map[string]interface{}
if err := json.Unmarshal(jsonData, &envelope); err != nil {
fmt.Println("JSON 파싱 오류:", err)
os.Exit(1)
}
signature := envelope["signature"].(string)
return verify(signature)
}
verify() {
endPoint := fmt.Sprintf(KMS_API_VERIFY, KEY_ID)
data := map[string]interface{}{
"input": "U0NQIEtNUyBTaWduIFRlc3QhISE=",
"signature": signature,
}
jsonData, _ := json.Marshal(data)
respJsonObject := callApi(endPoint, jsonData)
info := &KMSVerifyInfo{}
json.Unmarshal([]byte(respJsonObject), info)
return info.Valid
}
Python example code
This is a Python example code written according to the presented scenario.
# URI
KMS_API_BASE_URI = {{ OpenAPI 가이드의 URL 참조 }}
# END POINT
KMS_API_VERIFY = "/v1/kms/openapi/verify/"
# KEY ID
KEY_ID = {{마스터 키 ID}}
get_sign()
# 서명 데이터 봉투(Envelop encryption) 열기
with open("signEnvelope.json", "r") as file:
envelope = file.read()
envelope_json = json.loads(envelope)
signature = envelope_json["signature"]
return verify(signature)
verify()
end_point = f"{KMS_API_VERIFY}{KEY_ID}"
data = {
"input": "U0NQIEtNUyBTaWduIFRlc3QhISE=",
"signature": signature
}
resp_json_object = call_api(end_point,data)
valid = resp_json_object.get("valid")
return valid
Example code result
Displays the result of the example code.
{
"valid": true
}
9.1.2.2 - Platform-managed Key
Users can view detailed information about the platform-managed key automatically generated for service provisioning on the Samsung Cloud Platform.
- Platform-managed keys are created and managed directly by the CSP (Cloud Service Provider), so users cannot modify or delete key attributes.
- When another product within Samsung Cloud Platform uses a KMS key for encryption, the CSP generates a platform-managed key itself and performs the encryption, even if the user does not create a key directly in KMS.
Check detailed information of platform-managed key
You can view the full resource list and detailed information of platform-managed keys. The Platform Managed Key Details page consists of Details, Operation History tabs.
To view detailed information about the Key Management Service, follow these steps.
- Click the All Services > Security > Key Management Service menu. You will be taken to the Service Home page of Key Management Service.
- On the Service Home page, click the Platform Managed Key menu. You will be taken to the Platform Managed Key List page.
- On the Platform Managed Key List page, click the resource to view detailed information. You will be taken to the Platform Managed Key Details page.
- Platform Managed Key Details page displays status information and descriptions of additional features at the top.
Category Detailed description status Display the status of the platform-managed key - Active: Available/Active
Table. Platform Managed Key Status Information
- Platform Managed Key Details page displays status information and descriptions of additional features at the top.
Detailed Information
On the Platform Managed Key List page, you can view detailed information of the selected resource.
Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Creation date and time | Service creation timestamp |
| key name | Name of the generated key |
| Explanation | Show additional description for the key
|
Job History
You can view the operation history of the selected resource on the Platform Managed Key List page.
| Category | Detailed description |
|---|---|
| Work log | Task execution details
|
| Operation date and time | Task execution date and time |
| Resource Type | Resource Type |
| Resource name | Resource Name |
| Result | Task execution result (success/failure) |
| Operator Information | User information for the performed operation |
9.1.3 - API Reference
9.1.4 - CLI Reference
9.1.5 - Release Note
Key Management Service
- In addition to the ‘customer-managed key’ that the user creates directly, a ‘platform-managed key’ service generated and managed by the CSP (Cloud Service Provider) is also provided.
- When another product within Samsung Cloud Platform encrypts using a KMS key, it can encrypt with a platform-managed key generated directly by the CSP without the user having to create a key directly in KMS.
- We improved traceability by segmenting and logging operation histories for API calls such as encryption and decryption at the individual API level, making it easier to manage tracking of API calls.
- When an encryption key is deleted, it provides a notification not only to the user who deleted the key but also to the key creator, and the notification additionally includes the region name where the encryption key is located.
- We also provide the generation/verification (HMAC) encryption method used for creating and verifying hash-based message authentication codes.
- We have launched an encryption key management service (Key Management Service) to securely protect critical data in customer applications.
- You can generate, provide, and manage encryption keys for various purposes (encryption/decryption, signing/verification).
9.2 - Config Inspection
9.2.1 - Overview
Service Overview
Config Inspection is a service that diagnoses the security level of Console settings for each service of the Samsung Cloud Platform. Provides a security checklist organized by areas such as IAM, Networking, Database, and Logging, and checks the current status via API calls to verify whether the recommended security settings for each diagnostic item are applied.
Users can create a diagnostic target by creating a service, then request a diagnosis, and view the diagnosis request results through a Report. The report provides the diagnostic request history and per-item diagnostic results, and for diagnostic items that require the user’s final confirmation or action, detailed results—including the resource information and action guide corresponding to each item—can be viewed.
Provided Features
Config Inspection provides the following features.
- Console Diagnostics: You can call the Console API using an authentication key method to assess the security level.
- Diagnostic Target Management: Through service creation, you can create and manage a user’s Samsung Cloud Platform account as a diagnostic target.
- Diagnostic Request: On the resource detail screen, you can request a diagnosis by clicking the Diagnostic Request button.
- Diagnostic Result Management: In Report, you can view the list of diagnostic requests and detailed diagnostic results, and download them as an Excel file.
Components
Checklist
The checklist is a collection of diagnostic items that serve as the basis for diagnostic results, and the checklist currently provided by Config Inspection is as follows.
- Refer to the 체크 리스트 for the detailed diagnostic items of the checklist provided by Samsung Cloud Platform.
| Cloud | Checklist name | Number of items |
|---|---|---|
| Samsung Cloud Platform | Best Practice | 27 |
| Samsung Security Index (SSI) | 24 |
Report
In the Config Inspection Report, you can view the diagnostic results in the order of result list, result details, and item details.
| Category | Detailed description |
|---|---|
| Diagnostic Result List | All diagnostic request history in the Account
|
| Detailed Diagnosis Results | Result of a successfully completed diagnostic request (diagnostic item list)
|
| Diagnostic Item Details | Detailed results by diagnostic item |
Preliminary Service
Config Inspection has no preceding service.
9.2.1.1 - Checklist
You can view the types of checklists provided by Config Inspection and the detailed diagnostic items for each checklist.
Checklist
A checklist is a collection of diagnostic items that serve as the basis for diagnostic results, and the types of checklists currently provided by Config Inspection are as follows.
| Cloud | Checklist name | Number of items |
|---|---|---|
| Samsung Cloud Platform | Best Practice | 27 |
| Samsung Security Index (SSI) | 24 |
Best Practice
The detailed diagnostic items of the Best Practice checklist provided by Samsung Cloud Platform are as follows.
| area | Diagnostic Items |
|---|---|
| IAM |
|
| Networking |
|
| Compute |
|
| Container |
|
| Database |
|
| Logging |
|
Samsung Security Index (SSI)
The detailed diagnostic items of the Samsung Security Index (SSI) checklist provided by Samsung Cloud Platform are as follows.
| area | Diagnostic Items |
|---|---|
| IAM |
|
| Networking |
|
| Container |
|
| Database |
|
| Logging |
|
9.2.2 - How-to guides
Users can create the service by entering the required information for the Config Inspection service and selecting detailed options through the Samsung Cloud Platform Console.
Create Certificate
To create and use the Config Inspection service in the Samsung Cloud Platform Console, you need to generate an authentication key in advance.
Authentication key creation can be done from My menu > My Info. > Authentication Key Management > Create Authentication Key. For more details, refer to Manage Authentication Keys.
- The expiration period of the authentication key is up to 365 days.
- To generate an authentication key with no expiration date, you must create it permanently.
Create Config Inspection
You can create and use the Config Inspection service in the Samsung Cloud Platform Console.
To create a Config Inspection, follow these steps.
- Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
- On the Service Home page, click the Create Config Inspection button. You will be taken to the Create Config Inspection page.
- Config Inspection Creation On the page, input what is required to create a service, and select detailed options.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Diagnosis Type - Automatic configuration via Console Cloud Required Select cloud for diagnosis - SCP: Samsung Cloud Platform
- AWS: Amazon Web Services
- Azure: Microsoft Azure
- Detailed input fields vary depending on the selected cloud type
Diagnostic Target > Diagnosis Name Required Name to distinguish the diagnostic target - Use the entered value as the resource name
- Enter within 25 characters using English letters, numbers, and special characters (
-,_)
Diagnostic target > Diagnostic account Required Console information to be diagnosed - Select the Account ID to diagnose from the list
- Selecting the same Account ID will result in duplicate requests and incur additional charges
- If AWS is selected, enter the Account ID (12 digits) for the diagnostic account
- If Azure is selected, enter the Subscription ID (36 characters, including letters, numbers, and special characters) for the diagnostic account
Diagnosis Schedule > Checklist Required Automatically set when Use is selected for diagnostic schedule Diagnostic Schedule > Diagnostic Cycle Required Select Diagnosis Interval - The diagnosis runs on the selected date according to the specified interval.
- If Monthly is selected, the diagnosis may not be performed on the selected date.
- Example) Selecting the 31st of each month – February has no such date, so the diagnosis is not performed.
Diagnostic Schedule > Start Time Required Select diagnostic start time - Set the hour and minute information for starting the diagnostic
authentication key Required Select the authentication key to use for Open API calls - Select button, click to choose the appropriate authentication key from the list in the Authentication Key Selection popup
- If no selectable authentication key is available, click Authentication Key Management to create a new authentication key
- For detailed information about authentication keys, refer to Manage Authentication Keys
Pricing plan Select Select a plan to use - Standard: Charged based on the number of diagnoses
- Monthly subscription: Charged a fixed amount each month regardless of the number of diagnoses (up to 30 diagnoses per month)
- The plan cannot be changed after the service is requested
Table. Config Inspection Service Information Input Items - In the Additional Information Input area, enter or select the required information.
Category Required statusDetailed description tag Select Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, enter or select Key and Value values
Table. Config Inspection additional information input fields
- Enter or select the required information in the Service Information Input area.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Create button.
- When creation is complete, check the created resources on the Config Inspection List page.
Check detailed information of Config Inspection
Config Inspection service allows you to view and edit the full resource list and detailed information. The Config Inspection Details page consists of Details, Tags, Activity History tabs.
To view detailed information of the Config Inspection service, follow these steps.
- Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
- On the Service Home page, click the Config Inspection menu. You will be taken to the Config Inspection list page.
- Config Inspection List page, click the resource to view detailed information. You will be taken to the Config Inspection Details page.
- Config Inspection Details page displays status information and additional feature information, and is composed of Details, Tags, Work History tabs.
Category Detailed description status Displays the status of Config Inspection - Ready: When there is no diagnostic request after the service is created (diagnostic request possible)
- In Progress: When a diagnostic request is being executed (diagnostic request/service termination not allowed)
- Error: When an error occurs in the diagnostic request (diagnostic request possible)
- Completed: When the diagnostic request completes successfully (diagnostic request possible)
Diagnostic request Button to perform console diagnostics Service termination Button to cancel the service Table. Config Inspection status information and additional features
- Config Inspection Details page displays status information and additional feature information, and is composed of Details, Tags, Work History tabs.
Detailed Information
Config Inspection List page lets you view detailed information of the selected resource and modify the information if necessary.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Diagnosis Type | Diagnostic types offered by the service |
| Cloud | Diagnosis target types |
| diagnostic target | Console information for the diagnostic target
|
| Pricing plan | Selected plan type |
| Recent diagnosis date/time | Timestamp of the last executed diagnostic request |
| Recent diagnostic results | Result of the most recent diagnostic request
|
| authentication key | The authentication key of the user registered when creating the service
|
| Diagnostic Schedule | Display selected diagnostic schedule information
|
tag
Config Inspection List page lets you view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Config Inspection List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Config Inspection Resource Management
If you need to view the status of a Config Inspection resource or request a diagnosis, you can perform the task on the Config Inspection List or Config Inspection Details page.
Modify authentication key
You can select the authentication key to use for diagnosis for each diagnostic target.
To modify the service’s authentication key, follow these steps.
- Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
- On the Service Home page, click the Config Inspection menu. You will be taken to the Config Inspection list page.
- On the Config Inspection List page, click the resource whose authentication key you want to edit. Then go to the Config Inspection Detail page.
- Check the authentication key and click the Edit icon. The Edit Authentication Key popup window opens.
- Edit Authentication Key Select the authentication key to use in the popup window and click the Confirm button.
Category Detailed description authentication key Authentication Key Detailed Information Creation date and time Authentication key creation date Expiration date and time Authentication key expiration date status Authentication key status - Active: Usable
- Expired: Usage period expired
Table. Authentication key edit popup items
- If the authentication key is deleted, it is displayed in the
-state. - The authentication key information (authentication key, status) of resources created by other users is displayed as
-.
Request Diagnosis
You can request a diagnosis from the Console based on the configured checklist.
To request a console diagnosis, follow these steps.
Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
On the Service Home page, click the Config Inspection menu. You will be taken to the Config Inspection list page.
On the Config Inspection List page, click the resource you want to request a diagnosis for. You will be taken to the Config Inspection Details page.
On the Config Inspection Details page, click the Diagnostic Request button. The Diagnostic Request popup opens.
In the Diagnosis Request popup, enter the information required for the diagnosis and click the Confirm button.
- Diagnostic Request The items in the popup window vary depending on the selected Console.
Category Detailed description Console access method Fix the authentication key method as the console access method. Checklist Set to Best Practice when selecting SCP authentication key If you select SCP, choose the pre-generated authentication key. Access Key If AWS is selected, enter the Access Key. Secret Key If AWS is selected, enter Secret Key Client ID Enter Client ID when Azure is selected Client Secret If Azure is selected, enter Client Secret Tenant ID If Azure is selected, enter Tenant ID Table. Diagnosis request popup items
- Diagnostic Request The items in the popup window vary depending on the selected Console.
Check the status value on the Config Inspection list page.
- When the diagnostic request is completed, the status value is displayed as Completed or Error.
- In the case of Completed, you can view the diagnostic request results in the diagnostic results menu. For more details, refer to Report Management.
Terminate Config Inspection
You can cancel the Config Inspection service you are not using. However, canceling Config Inspection will delete all stored diagnostic data.
- If you terminate the resource, all diagnostic data will be deleted, and you will not be able to view diagnostic results in the Report.
- If the status of the Config Inspection service is In Progress, the service cannot be terminated.
To disable Config Inspection, follow these steps.
- Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
- On the Service Home page, click the Config Inspection menu. You will be taken to the Config Inspection list page.
- On the Config Inspection List page, click the resource to be terminated. You will be taken to the Config Inspection Details page.
- Config Inspection Details on the page, click the Cancel Service button.
- After the termination is complete, check on the Config Inspection List page whether the resource has been terminated.
9.2.2.1 - Check Dashboard
Users can view the diagnostic results of the Config Inspection service at a glance on the dashboard through the Samsung Cloud Platform Console.
Check Dashboard
On the dashboard page, you can view the status of Config Inspection diagnostic targets, diagnostic history, and more.
To view the dashboard, follow these steps.
- Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
- On the Service Home page, click the Dashboard menu. You will be taken to the Dashboard page.
- Check the summary of diagnostic results on the Dashboard page.
- Dashboard page at the top allows you to view dashboard information based on the period or diagnosis name.
- Period: You can set a period within six months from the current month to view a summary of the diagnostic results.
- Diagnosis Name: If you select All, you can view a summary of the entire diagnostic results, and if you select a diagnostic account, you can view the detailed information of that specific diagnostic result.
- Click the Download button to download the information displayed on the dashboard page as a PDF file.
Category Detailed description Security level (overall) Display the average of the latest diagnostic results for all subjects - Recent diagnostic results are displayed in the list
- Diagnostic score calculation formula = Total – (Fail + Error + Check)) / Total x 100
Diagnosis status by period Display diagnostic status by target during the search period - Diagnosis Completed: Show recent completed diagnosis records
- Diagnosis Error: Show recent diagnosis error records, navigate to the detailed diagnosis result page when a diagnosis name is selected
Summary of diagnostic results by period (overall) Display summary of diagnostic results (overall) during the search period - Selecting a diagnosis name from the list navigates to the detailed diagnostic result page
Table. Detailed dashboard item description for overall diagnostic resultsCategory Detailed description Security level Display the latest diagnostic result score for the selected diagnostic account - Recent diagnostic results are displayed in the list
Summary of diagnostic results by period Display summary of the diagnostic results for the last diagnostic account within the search period Vulnerability status by period Display the vulnerability assessment results of the diagnostic account as a graph during the search period - When a graph is selected, display detailed information of the vulnerable items in the assessment results
Table. Detailed dashboard item description for diagnostic results per diagnostic account
- Dashboard page at the top allows you to view dashboard information based on the period or diagnosis name.
9.2.2.2 - Manage Diagnosis Results
Config Inspection You can view the diagnostic request results on the diagnostic results page and modify the diagnostic results.
The diagnostic results are generated when a diagnostic request is made in the Config Inspection service, and they are deleted when the service is terminated.
- Refer to Config Inspection Request and Cancel Config Inspection.
Check diagnosis results
On the diagnosis results page, you can view the results of the diagnosis request.
Check diagnostic result list
To view the list of diagnostic results, follow these steps.
- Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
- On the Service Home page, click the Diagnosis Results menu. You will be taken to the Diagnosis Results List page.
- View the summary information of diagnostic results on the Diagnostic Results List page.
Category Detailed description Diagnosis name Resource name diagnostic account Console information subject to diagnosis Checklist Collection of diagnostic items that serve as the basis for diagnostic results PASS Number of checklist items with a diagnosis result of PASS (normal) FAIL Number of checklist items with a diagnosis result of FAIL (vulnerable) CHECK Number of items in the checklist with a diagnosis result of CHECK (verification required) ERROR Number of items in the checklist whose diagnosis result is ERROR (diagnosis not possible) N/A Number of items in the checklist where the diagnosis result is N/A (not applicable) All Total number of checklist items diagnostic result Diagnosis request result - Completed: The diagnosis request has been successfully completed; clicking Completed navigates to the detail page
- Error: The diagnosis request was not completed successfully; error items cannot view detailed information
Diagnosis date and time Diagnosis request date and time Table. Diagnosis result list items
View detailed diagnostic result information
To view detailed information of the diagnostic results, follow these steps.
Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
On the Service Home page, click the Diagnosis Results menu. You will be taken to the Diagnosis Results List page.
- On the Diagnosis Result List page, you can enter a diagnosis name in the search area or click the Detailed Search button to perform a search.
Diagnostic Results List page, click the item whose diagnostic result is Completed. You will be taken to the diagnostic result detail page.
- Items with a diagnostic result in error status do not display detailed information.
On the Detailed Diagnosis Results page, view the detailed diagnosis results.
Category Detailed description Excel download Download the detailed diagnosis results list as an Excel file More > Diagnosis Result Management Go to the diagnostic results management page Checklist Collection of diagnostic items that serve as the basis for diagnostic results Area Diagnostic Scope (services of Samsung Cloud Platform) Diagnostic items Recommended security standards for each service configuration Result Diagnostic Item Criteria Inspection Results Table. Detailed diagnosis result itemsClick the diagnostic item to view detailed information. Diagnostic Item Details popup will open.
- Diagnostic Item Details In the popup window, you can view the following information.
Category Detailed description Area Diagnostic Scope (services of Samsung Cloud Platform) Diagnostic items Recommended security standards for each service configuration Result Diagnostic Item Criteria Inspection Results Diagnostic criteria Result Evaluation Criteria Diagnostic method How to check the current settings Action Guide Configuration method that meets security standards Detailed results Resource information and settings for the diagnostic item Change diagnosis result Button to modify the diagnosis result - When the diagnosis result is modified, the Check Result button is displayed, and clicking the Delete button removes the modified result
Table. Config Inspection diagnostic item details
- Diagnostic Item Details In the popup window, you can view the following information.
Manage Diagnostic Results
On the diagnosis results page, you can modify the results of items whose diagnosis status is CHECK.
Change Diagnosis Result
To change the diagnostic result, follow the steps below.
Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
On the Service Home page, click the Diagnosis Results menu. You will be taken to the Diagnosis Results List page.
On the Diagnosis Result List page, click the item whose diagnosis result is Completed. You will be taken to the Diagnosis Result Details page.
- Items with a diagnostic result in error status do not display detailed information.
On the Diagnosis Result Details page, click the More > Diagnosis Result Management button at the top. You will be taken to the Diagnosis Result Management page.
On the Diagnosis Result Management page, click the Change Result button for the item whose diagnosis result you want to modify. The Change Result popup window will open.
Result Change In the popup window, select or enter the information required to change the result.
Category Required Detailed description Registrant - Diagnostic result change registrant email Validity period Required Set the diagnostic result validity period Result change Required Select the diagnostic result to change among Pass, Check, Fail Detailed reason Required Enter the detailed reason for changing the result. Attached file Select Upload the files required to verify result changes - Click the Attach File button to upload files, up to 5 can be registered
Inspection Result - Display detailed inspection results Table. Detailed items of diagnostic result changesReview the entered information and click the Register button. Verify whether the diagnostic results have changed in the Diagnostic Result Management list.
Delete diagnostic result change history
To delete the diagnostic result change log, follow these steps.
- Click the All Services > Security > Config Inspection menu. Navigate to the Service Home page of Config Inspection.
- On the Service Home page, click the Diagnosis Results menu. You will be taken to the Diagnosis Results List page.
- On the Diagnosis Result List page, click the item whose diagnosis result is Completed. You will be taken to the Diagnosis Result Details page.
- Items with a diagnostic result in error status do not display detailed information.
- Diagnosis Result Details page, click the Diagnosis Result Management button at the top. You will be taken to the Diagnosis Result Management page.
- On the Diagnosis Result Management page, click the Check Result button for the item whose diagnosis result you want to change. The Check Result popup will open.
- Check Result in the popup window, click the Delete button.
9.2.2.3 - Pre-configuration
Users must perform pre‑cloud configuration such as generating authentication keys and adding access‑control IPs through the Samsung Cloud Platform Console to use the Config Inspection service.
Configuring Samsung Cloud Platform Console
To diagnose Samsung Cloud Platform and external clouds in the Config Inspection service, set the items below.
Check policies attached to user groups
- Config Inspection can diagnose the Samsung Cloud Platform or external clouds. Depending on the diagnostic target, you can assign appropriate policy requirements to user groups for use.
- Verify that a user group policy matching the desired diagnostic target is configured.
- If policy creation is required, please contact the Account administrator.
To check the policy of the user group to which the user belongs, follow the steps below.
- Click the All Services > Management > IAM menu. Go to the Service Home page of IAM.
- On the Service Home page, click the User Group menu. You will be taken to the User Group List page.
- On the User Group List page, click the user group you want to view. You will be taken to the User Group Details page.
- User Group Details page, click the Policy tab. You will be taken to the Policy tab page.
- Click the policy you want to view on the Policy tab page. You will be taken to the Policy Details page.
- Check the detailed information on the Policy Details page.
- Verify that the policy information in the table below is configured. If necessary, contact the administrator to add the policy.
Item Policy Requirement 1 Policy Requirement 2 action List, Read Create, Delete, List, Read, Update Applied resource All resources Individual Resource (Config Inspection) Authentication Type All authentication Temporary key authentication, Console login Applied IP Custom IP - The IP for diagnostics is 123.37.11.42, and the IP for the user to access the console must be added separately
Custom IP Table. Detailed policy setting items for all cloud diagnostics
- Verify that the policy information in the table below is configured. If necessary, contact the administrator to add the policy.
Generate authentication key
You can view and generate the authentication key used for the Config Inspection service.
- You can create a maximum of two authentication keys.
- After generating a new authentication key, you must apply the updated API authentication key to the services you are using.
To create an authentication key in the Samsung Cloud Platform Console, follow these steps.
- Click the My menu > My info. menu in the Console. You will be taken to the My info. detail page.
- My info. Click the API Key Management tab on the detail page. Navigating to the API Key Management tab page.
- On the Key Management tab page, click the Create Key button. You will be taken to the Create Key page.
- You can view the list of authentication keys on the authentication key management page.
- On the Create Authentication Key page, after entering the expiration period, click the Confirm button.
- Verify that the generated authentication key is displayed in the authentication key list.
Add allowed IP
You can add allowed IP addresses in the Samsung Cloud Platform Console.
To add an allowed IP for the Console, follow these steps.
- Click the My menu > My info. menu in the Console. Go to the My info. detail page.
- My info. Click the API Key Management tab on the detail page. You will be taken to the API Key Management tab page.
- Authentication Key Management tab page, click the Edit icon of the Security Settings item. Edit Authentication Key Security Settings popup opens.
- Edit Authentication Key Security Settings In the popup window, enter the authentication method and allowed IP address.
- Select the authentication method authentication key.
- Set the allowed access IP to Use, enter the IP address, and click the Add button.
- When the allowed IP addition is complete, click the Confirm button. Verify that the Security Settings item has been updated with the entered information.
Configure AWS
To diagnose the AWS (Amazone Web Services) cloud in the Config Inspection service, set the items below.
Add permission policy
You can add permission policies for users or user groups in the AWS Console.
Add user permission
To add a user access policy in the AWS Console, follow these steps.
- Click IAM > Users in the AWS Console.
- Select the diagnostic user name from the user list.
- Click the Permissions tab on the user information page.
- Select Add Permission in the permission policy.
- When adding permissions, select ReadOnlyAccess, ViewOnlyAccess.
Add user group permissions
To add a user group access permission policy in the AWS Console, follow these steps.
- Click IAM > User Groups in the AWS Console.
- Select the group that the user belongs to from the user group list.
- Click the Permissions tab on the user group page.
- Select Add Permission in the permission policy.
- When adding permissions, select ReadOnlyAccess, ViewOnlyAccess.
Add access control IP
If you are using an IP access control policy, you need to add an exception IP to the policy.
Add user access control IP
To add a user access control IP in the AWS Console, follow these steps.
- Click IAM > Users in the AWS Console.
- Select the diagnostic user name from the user list.
- Click the Permissions tab on the user information page.
- In the permission policy item, click Edit of the IP Access Control Policy.
- Add 123.37.24.82 to the block exception IP list.
Add IP to user group access control
To add a user group access control IP in the AWS Console, follow these steps.
- Click IAM > User Groups in the AWS Console.
- Select the group that the user belongs to from the list of user groups.
- Click the Permissions tab on the user group page.
- In the permission policy item, click Edit of the IP Access Control Policy.
- Add 123.37.24.82 to the block exception IP.
Access Key creation
To create an Access Key in the AWS Console, follow these steps.
- Click IAM > Users in the AWS Console.
- Select the diagnostic user name from the user list.
- Click the Security Credentials tab on the user information page.
- On the Security Credentials page, click Access Keys.
- Create Access Key page, generate an access key for third‑party services.
- Be sure to save the generated access key information.
Secret Key can be downloaded as a CSV file or recorded separately.
- Secret key information can only be viewed when creating the access key and cannot be recovered later.
Configure Azure
To diagnose Azure cloud in the Config Inspection service, set the items below.
Entra ID Application registration
To register an Entra ID Application in the Azure Console, follow these steps.
- Click Microsoft Entra ID > App registrations in the Azure Console.
- On the App Registration page, click New Registration.
- Register the application (client) ID.
- After the app registration is complete, check the app name, application (client) ID, directory (tenant) ID on the overview page.
Add API permission
To add API permissions in the Azure Console, follow these steps.
- In the Azure Console’s Microsoft Entra ID > App registration (App registrations) > Entra ID Application registration, click App name > API permissions (App permissions) > Add permission (Add a permission).
- From the API permissions list, select Microsoft Graph to add permissions.
- On the API Permission Request page, click Application Permissions.
- Select Application.Read.All, Device.Read.All, Group.Read.All, User.Read.All, DeviceManagementManagedDevices.Read.All, AuditLog.Read.All, Directory.Read.All, Domain.Read.All, GroupMember.Read.All, Policy.Read.All, Reports.Read.All from the permission list.
- After adding permissions in App API permission registration, click Grant admin consent (Grant admin consent for account name).
- Check whether the status for the account name has been changed to Allowed (Granted for account name).
Create Client Secret
To create a Client Secret in the Azure Console, follow these steps.
- In the Azure Console, click App name > Certificates & secrets(Certificates & secrets) under Microsoft Entra ID > App registrations(App registrations) > Entra ID Application registration.
- Click New Client Password in the Certificates and Passwords list.
- When the client secret is generated, check the Client Secret in the Value(Value) field of the list.
- Be sure to save the Client Secret value.
Add subscription access permission in Azure Console
You can add subscription access permissions in the Azure Console from the tenant root group or an individual Subscription. Choose the method you prefer to add Subscription access permissions.
Add permission in Tenant Root Group
To add subscription access permissions in the Azure Console from the Tenant Root Group, follow the steps below.
- Click Management groups > Overview in the Azure Console.
- Click Tenant Root Group > Access Control (IAM).
- If you cannot access the Tenant Root Group menu, change the settings below.
- Microsoft Entra ID > Properties > ‘Account Name’ can manage access to all Azure subscriptions and management groups in this tenant. > Yes (yes) change to
- After adding the permission, you must change it to No.
- If you cannot access the Tenant Root Group menu, change the settings below.
- On the Access Control page, click Add(Add) > Add role assignment(Add role assignment).
- On the Add Role Assignment page, after entering the details, click Save (Review+assign).
- When entering role assignment information, select the information below in the Role and Member tabs to add the app created in Entra ID Application registration. You must add all three of the following permissions.
Category Permission Reader(Reader) User, group, or service principal(Users, group, or service principal) Key Vault Reader (Key Vault Reader) User, group, or service principal(Users, group, or service principal) Reader and Data Access User, group, or service principal(Users, group, or service principal) Table. Additional permission items when entering role assignment information
- When entering role assignment information, select the information below in the Role and Member tabs to add the app created in Entra ID Application registration. You must add all three of the following permissions.
Add permission in individual Subscription
To add subscription access permissions in the Azure Console for an individual subscription, follow these steps.
- Click Subscription(Subscription) > Overview(Overview) in the Azure Console.
- Check the Subscription ID(Subscription ID) in the basic information on the Overview page.
- Click Subscription(Subscription) > Access Control(IAM).
- On the Access Control page, click Add(Add) > Add role assignment(Add role assignment).
- On the Add Role Assignment page, after entering the details, click Save (Review+assign).
- When entering role assignment information, select the information below in the Role and Member tabs to add the app created in Entra ID Application registration. You must add all three of the following permissions.
Category Permission Reader(Reader) User, group, or service principal(Users, group, or service principal) Key Vault Reader (Key Vault Reader) User, group, or service principal(Users, group, or service principal) Reader and Data Access User, group, or service principal(Users, group, or service principal) Table. Additional permission items when entering role assignment information
- When entering role assignment information, select the information below in the Role and Member tabs to add the app created in Entra ID Application registration. You must add all three of the following permissions.
Add access permissions via PowerShell
To add subscription access permissions in the Azure Console using PowerShell, follow these steps.
- Run the following command in Cloud shell > PowerShell of the Azure Console.
New-AzRoleAssignment -ObjectId “the App’s Object ID as seen in Enterprise Application” -Scope “/providers/Microsoft.aadiam” -RoleDefinitionName ‘Reader’ -ObjectType ‘ServicePrincipal’- If the command does not execute, change the settings below.
- Microsoft Entra ID > Properties > ‘Account Name’ can manage access to all Azure subscriptions and management groups in this tenant. > yes change to
- After adding the permission, you must change it to No (no).
- Run the command below to verify whether the configuration is complete.
Get-AzRoleAssignment –ObjectId "the App’s Object ID found in Enterprise Application" –Scope "/providers/Microsoft.aadiam"- If permission deletion is required, run the command below.
Remove-AzRoleAssignment -ObjectId “the App’s Object ID as seen in Enterprise Application” -Scope “/providers/Microsoft.aadiam” -RoleDefinitionName ‘Reader’
9.2.3 - Release Note
Config Inspection
- We have launched the Config Inspection product, which enables integrated diagnosis and management of customers’ multi‑cloud console security vulnerabilities.
- You can register the Account (or other cloud account) to be diagnosed, enabling continuous diagnostics, and view the dashboard and detailed results in the Report.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- You can manage Samsung Cloud Platform Console configuration vulnerabilities through console diagnostics.
- Provides a report that allows you to view security diagnostic results.
9.3 - Certificate Manager
9.3.1 - Overview
Service Overview
Certificate Manager is a service that supports certificate distribution and integrated management, enabling users to generate SSL/TLS certificates issued by a Certificate Authority (CA) and self‑signed certificates for development or testing purposes, and use them on Samsung Cloud Platform resources. By receiving pre‑expiration notification emails, users can identify certificates that are about to expire and manage the certificate lifecycle.
Features
- Simple Creation: You can generate certificates with simple steps in the Samsung Cloud Platform Console. User certificates issued externally are validated, and only certificates that pass verification are distributed.
- Service Integration: Connect the certificates registered in Certificate Manager to the Load Balancer to encrypt network connections and protect the service.
- Certificate Expiration Alert: You can identify and replace certificates that are about to expire with periodic notifications up to 1 day before the expiration date.
Service Architecture Diagram
Provided features
Certificate Manager provides the following features.
- Certificate Creation: You can generate a user certificate issued by a certification authority or a self-signed certificate suitable for development/testing (Self-signed).
- Connected Resource Lookup: You can view Samsung Cloud Platform resources that are using the certificate. Currently, it provides a list of Load Balancer listeners (HTTPS).
- Expiration Alert: You can set expiration alert recipients for each certificate. Emails are sent to the recipients starting 45 days before expiration. (Sent 45/30/15/7/1 days before expiration)
Component
User certificates in Certificate Manager consist of a Private Key, Certificate Body, and Certificate Chain. Enter the entire certificate information, including the BEGIN and END lines.
Private Key
Enter the private key in PEM format. Private Key supports RSA and must be entered as a decrypted value.
-----BEGIN RSA PRIVATE KEY-----
(개인키)
-----END RSA PRIVATE KEY-----
Certificate Body
Enter the Server (Leaf) certificate in PEM format. Only one certificate can be entered in the Certificate Body.
-----BEGIN CERTIFICATE-----
(서버 인증서)
-----END CERTIFICATE-----
Certificate Chain
Enter the upper-level certificate in PEM format. Input them in the order Sub (Intermediate) CA → Root CA, and you may omit this only for self‑signed or self‑issued certificates.
-----BEGIN CERTIFICATE-----
(중간 인증서)
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
(루트 인증서)
-----END CERTIFICATE-----
Constraints
Certificate Manager provides services on a per‑Region basis. Create the service in the required Region and use it. The quota per Region is as follows.
| Category | Default quantity | Explanation |
|---|---|---|
| CERTIFICATE_MANAGER.USER_CERT_DEFAULT.COUNT | 100 | Number of user certificates per Region |
| CERTIFICATE_MANAGER.SELFSIGNED_CERT_DEFAULT.COUNT | 100 | Number of self-issued certificates per Region |
Prior Service
Certificate Manager has no prerequisite services.
9.3.2 - How-to guides
Users can create the service by entering the required information for the Certificate Manager service and selecting detailed options through the Samsung Cloud Platform Console.
Create Certificate Manager
You can create and use the Certificate Manager service in the Samsung Cloud Platform Console.
To request the creation of a Certificate Manager service, follow these steps.
- Click the All Services > Security > Certificate Manager menu. 1. Go to the Service Home page.
- On the Service Home page, click the Create Certificate Manager button. 2. Go to the Create Certificate Manager page.
- Create Certificate Manager page, enter the information needed to create the service, and choose detailed options.
- In the Service Information Input area, enter or select the required information.
Category required statusDetailed description Certificate name Required Enter the Certificate Manager name to use - Enter within 3-30 characters, including English letters, numbers, and special characters (
-,_,.)
- Cannot be the same as an existing name
type Required Select the Certificate Manager type to use - User Certificate: a public certificate issued by a Certificate Authority (CA)
- Self-issued Certificate: a certificate self-issued (Self-signed) by Samsung Cloud Platform
- Since it is relatively less secure, it is recommended for development/testing use only.
User Certificate > Certificate Body Required Enter Server(Leaf) certificate information - Only one certificate can be entered in the certificate body
Enter the full content, including the lines from —–BEGIN CERTIFICATE—–to—–END CERTIFICATE—–
User Certificate > Private Key Required Enter the private key information - The Private Key supports the RSA encryption method
- The Private Key can be entered in an unencrypted PEM format
Enter the entire content, including the lines from —–BEGIN RSA PRIVATE KEY—–to—–END RSA PRIVATE KEY—-
User Certificate > Certificate Chain Required Enter the Certificate Chain information - Can be omitted when using a private certificate
- The Certificate Chain should be entered in the order: Intermediate (Subordinate) certificate → Root certificate
- For a public certificate, the Certificate Chain information must be entered; only when there is no intermediate certificate (Chain CA) should use be disabled
Enter the full content, including the lines from —–BEGIN CERTIFICATE—–—–END CERTIFICATE—–
- If there are multiple Intermediate (Subordinate) certificates, enter each certificate’s content in order
User Certificate > Certificate Validation Required Validate the entered certificate’s validity Self-signed certificate > Common Name Required Enter the domain name to use the certificate Self-issued certificate > Organization Unit Required Enter the organization and department that will use the certificate Self-issued certificate > Start date Required Enter the certificate start date (creation date) Self-issued certificate > Expiration date Required Enter the certificate expiration date Expiration alert Selection Set whether to receive pre‑expiration certificate alerts - Select Use to enable expiration alerts
- If expiration alerts are set, an email is sent to the recipients 45, 30, 15, 7, and 1 days before the certificate expires
Expiration Alert > Alert Recipient Required Select notification recipients when using expiration alerts - Enter a user name in the search area to select notification recipients
- Up to 100 recipients can be registered
Table. Certificate Manager service information input itemsReference- If the entered certificate information is invalid, you cannot create the Certificate Manager service.
- If the Private Key is encrypted, enter the decrypted value using the openssl command below.
openssl rsa -in [Encrypted Private Key File name] -out [Decrypted Private Key File name]
- For certificates issued via Let’s Encrypt, even if you already have a previously issued Certificate Chain value, extract it again and enter it.
- For detailed instructions on extraction methods, see Extract Chain Certificate.
- Enter within 3-30 characters, including English letters, numbers, and special characters (
- In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, input or select Key, Value values
Table. Certificate Manager additional information input fields
- In the Service Information Input area, enter or select the required information.
- Review the entered service information and additional details, then click the Create button.
- When creation is complete, check the created resource on the Certificate Manager List page.Reference
To create a Load Balancer for use with the Certificate Manager service, click Load Balancer creation in Service Home.
- For detailed information on creating a Load Balancer, please refer to Load Balancer Creation.
- When creation is complete, check the created resource on the Certificate Manager List page.
Check Certificate Manager detailed information
The Certificate Manager service allows you to view and edit the full list of resources and detailed information. Certificate Manager Details page consists of Details, Connected Resources, Tags, Activity History tabs.
To view detailed information for Certificate Manager, follow these steps.
- All Services > Security > Certificate Manager Click the menu. 1. Go to the Service Home page of Certificate Manager.
- On the Service Home page, click the Certificate Manager menu. 2. Navigate to the Certificate Manager List page.
- On the Certificate Manager List page, click the resource to view its detailed information. 3. Navigate to the Certificate Manager Details page.
- Certificate Manager Details page displays the status and detailed information of the Certificate Manager, and consists of Details, Connected Resources, Tags, Activity History tabs.
Category Detailed description Service status Certificate Manager status - Creating: In progress
- Active/Valid: Certificate valid
- Expired: Certificate expired
- Editing: Changing settings
- Terminating: Terminating
- Error: Certificate error
Service termination Button to cancel Certificate Manager Table. Status information and additional features
- Certificate Manager Details page displays the status and detailed information of the Certificate Manager, and consists of Details, Connected Resources, Tags, Activity History tabs.
Detailed Information
Certificate Manager List page lets you view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| service | Service Name |
| Resource type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Certificate name | Certificate Manager certificate name |
| type | Certificate type information |
| Issuing Authority | User Certificate Issuing Authority Information |
| Common Name | Self-issued certificate display of information entered when creating the service |
| Organization Unit | Self-issued certificate Display the information entered when creating the service |
| Additional domain | User Certificate’s registered SAN information, displayed up to a maximum of 250 |
| Public Key information | User Certificate’s key algorithm type and length display |
| Signature algorithm | User Certificate’s issuing authority signature method display |
| Use status | Indicates whether the connected resource is registered |
| Start date/time / Expiration date/time | Display the certificate’s start/expiration date |
| Number of days remaining until expiration | Display the number of days remaining until expiration based on the current date
|
| Expiration alert | Certificate expiration alert settings details
|
Connected resource
On the Certificate Manager List page, you can view the connected Load Balancer information.
| Category | Detailed description |
|---|---|
| Load Balancer | Load Balancer resource ID attached to the service |
| Listener | Click the name of the Listener resource ID
|
| status | Display the status of Listeners connected to the service |
Tag
On the Certificate Manager List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the Certificate Manager List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Certificate Manager
You can request the termination of the Certificate Manager service from the Samsung Cloud Platform Console.
To request termination of the Certificate Manager service, follow the steps below.
- Click the All Services > Security > Certificate Manager menu. 1. Go to the Service Home page of Certificate Manager.
- On the Service Home page, click the Certificate Manager menu. 2. Go to the Certificate Manager List page.
- On the Certificate Manager List page, click the resource to view its detailed information. 3. Navigate to the Certificate Manager Details page.
- On the Certificate Manager Details page, click the Cancel Service button.
- Once the termination is complete, verify the service termination status in the Certificate Manager list.
9.3.2.1 - Extract Certificate Chain
Users can extract and input the Certificate Chain certificate to be used when creating a Certificate Manager service.
Extract Certificate Chain
You can extract the Certificate Chain value required when creating a Certificate Manager.
The Certificate Chain consists of Intermediate (Subordinate) certificates issued by a trusted certification authority and the Root certificate.
- Even if you already have a Certificate Chain value, extract and register the Intermediate (Subordinate) certificate through the Root certificate again using the Certificate Body file. (Recommended)
Extract Intermediate (Subordinate) Certificate Value
You can extract the intermediate (subordinate) certificate from the certificate chain required for user certificate enrollment.
To extract the Intermediate(Subordinate) certificate value, follow these steps.
- Run the certificate file in crt format on the PC. The certificate window will appear.
- In the certificate window, click the Certificate Path tab.
- If the file is in PEM format, convert it to a .crt file.
- Click the certificate under Root and click View Certificate.
- After clicking the Details tab, click Copy to file.
- When the certificate export wizard runs, click Next.
- Select the format Base 64-encoded X.509(.CER)(S) and click Next.
- Click Browse to select the folder where you want to save the file, then click Next.
- Click Finish. The certificate export wizard will complete.
- Open the exported file as a TEXT file and verify the values.
- The extracted certificate value must start and end with
—–BEGIN CERTIFICATE—–and—–END CERTIFICATE—-.
- The extracted certificate value must start and end with
Extract Root certificate value
You can extract the root certificate of the certificate chain required for user certificate enrollment.
To extract the Root certificate value, follow these steps.
- Run the certificate file in crt format on the PC. The certificate window will appear.
- In the certificate window, click the Certificate Path tab.
- If the file is in PEM format, convert it to a .crt file.
- Click the topmost Root certificate and click View Certificate.
- After clicking the Details tab, click Copy to File.
- When the certificate export wizard runs, click Next.
- Select the format Base 64-encoded X.509(.CER)(S) and click Next.
- Click Browse to select the path where you want to save the file, then click Next.
- Click Finish. The certificate export wizard will complete.
- Open the exported file in TEXT format and verify the values.
- The start and end of the extracted certificate value must include the
—–BEGIN CERTIFICATE—–and—–END CERTIFICATE—-entries.
- The start and end of the extracted certificate value must include the
Enter Certificate Chain value
This explains how to enter the extracted Intermediate (Subordinate) certificate and Root certificate values into the Certificate Chain field when creating a Certificate Manager.
To enter the Intermediate (Subordinate) certificate and Root certificate values into the Certificate Chain field, follow these steps.
- Execute the Intermediate (Subordinate) certificate file and the Root certificate file as text files.
- Copy the entire value of the Intermediate (Subordinate) certificate file.
- Paste it into the Certificate Chain input area on the Certicafate Manager Creation page.
- Paste it, including the
—–BEGIN CERTIFICATE—–at the beginning and the—–END CERTIFICATE—-at the end of the certificate value.
- Paste it, including the
- Copy the entire value of the Root certificate file.
- Paste it into the Certificate Chain input area on the Create Certicafate Manager page.
- Paste it, including the
—–BEGIN CERTIFICATE—–at the beginning and—–END CERTIFICATE—-at the end of the certificate value. - Paste the Root certificate value on the line below the Intermediate (Subordinate) certificate.
- Paste it, including the
9.3.3 - API Reference
9.3.4 - CLI Reference
9.3.5 - Release Note
Certificate Manager
- We have launched the Certificate Manager service that supports SSL/TLS certificate deployment and unified management.
- You can register a certificate issued by a Certificate Authority (CA) or generate a Self-signed certificate for development/testing purposes.
- You can encrypt network communications and manage the certificate lifecycle by connecting to Samsung Cloud Platform resources.
9.4 - Secret Vault
9.4.1 - Overview
Service Overview
Secret Vault is a service that, by using the Open API to connect to the Samsung Cloud Platform, allows you to obtain a secure token‑based temporary key without hard‑coding security information in plain text, enabling access to the Samsung Cloud Platform’s services and resources. It also manages the lifecycle of the temporary key to maintain a hardened security environment when using APIs.
Features
- Enhanced Security Environment Implementation: Instead of hardcoding authentication credentials in the application source code, you can obtain a token-based temporary key to mitigate security threats arising from credential leakage.
- Life-Cycle based temporary key management: To meet security requirements, users do not need to manually manage the lifecycle of temporary keys. It provides automated temporary key management and replacement functions according to the initially configured lifecycle.
- Various resource utilization possible: Through the Token issued by Secret Vault, you can access not only resources within the Samsung Cloud Platform but also external resources (other CSPs, on‑premise, etc.) in a reinforced security environment.
Service Architecture Diagram
Provided features
Secret Vault provides the following features.
- Add Token authentication and encrypt authentication key storage: Provides token issuance via an authentication key and temporary key issuance using the token, and securely stores the authentication key information encrypted (AES-256).
- Temporary Key Life-cycle Management: Provides issuance and automatic replacement of temporary keys according to their life cycle, and allows setting a replacement interval in hours (up to 36 hours).
- Access Control Feature: IP-based access control of the resources where the user application runs is possible.
Component
Secret
A Secret is an object that combines token information and temporary key rotation information, and can be requested by the user in the console.
Token
A token is a unique string used to authenticate a user’s identity and verify permissions, and when making an Open API request, you can obtain a temporary token that allows access to the Samsung Cloud Platform.
Constraints
Secret Vault provides a region-based service. Therefore, when creating a Secret, you cannot select an authentication key that is being used by a Secret in another region.
Prior Service
Secret Vault does not require any separate prerequisite service work.
9.4.2 - How-to guides
Users can create the service by entering the required information for the Secret Vault service and selecting detailed options through the Samsung Cloud Platform Console.
Create Secret Vault
You can create and use the Secret Vault service in the Samsung Cloud Platform Console.
To create a Secret Vault, follow these steps.
- Click the All Services > Security > Secret Vault menu. Navigate to the Service Home page of Secret Vault.
- On the Service Home page, click the Create Secret Vault button. You will be taken to the Create Secret Vault page.
- On the Create Secret Vault page, enter the information required to create the service and select detailed options.
- Select the required information in the Service Information Input area.
Category Required statusDetailed description Secret name Required Enter Secret name - Enter 3~63 characters using lowercase English letters and numbers
type Required Select the type of encryption target authentication key Required Select an authentication key to use with the Secret Vault service - Click the Use button and select a pre‑generated authentication key from the Authentication Key Management menu.
- In the Authentication Key Management menu, you must select one‑time authentication as the security authentication method.
- Expired authentication keys are not displayed, and keys with a remaining validity of less than 30 days or keys already in use for a Secret Vault product cannot be used. (Only one Secret Vault product can be applied per authentication key.)
Token usage period Required Enter the usage period of the Token provided by encrypting the authentication key - The Token usage period is automatically set to match the validity period of the entered authentication key by default.
- If the authentication key validity period is set to permanent, the Token usage period can be set up to a maximum of 7,300 days (20 years).
- The Token usage period cannot be changed after the service application is completed.
- Periodic replacement of the Token is recommended to enhance security.
- When the Token usage period expires, temporary key issuance is not possible, and you must obtain a new Token by submitting a new service application.
- Once the Token usage period expires, it cannot be extended and the Token can no longer be used. Before the Token usage period expires, obtain a new Token by submitting a new service application and apply the issued Token information to your source code.
IMSI key replacement interval Required Select the temporary key rotation period to be used for accessing Samsung Cloud Platform resources - The temporary key usage time is applied from the moment the service creation is completed.
- For security enhancement, the temporary key usage period can be set to a maximum of 1.5 days (36 hours).
- A new temporary key is issued before the temporary key expires, and the same usage period applies.
Allowed IP Required Enter the IP to allow access, then click the Add button - The entered IP must also be set identically in Key Management > Security Settings > Allowed Access IP for access to be permitted.
- Even when entering a single IP, be sure to append ‘/32’ after the IP.
- You can register up to 10 IPs.
Explanation Select Enter additional information Table. Secret Vault service information input fields - Select the required information in the Additional Information Input area.
Category Required statusDetailed description tag Select Add Tag - Add Tag Click the button to create and add a tag, or add an existing tag.
- Up to 50 tags can be added per resource.
- The newly added tags are applied after the service creation is completed.
Table. Secret Vault additional information input fields
- Select the required information in the Service Information Input area.
- Summary Verify the detailed information and estimated billing amount generated in the panel, then click the Complete button.
- After creation is complete, check the created resources on the Secret Vault List page.
Check Secret Vault detailed information
You can view and edit the full list of resources and detailed information for the Secret Vault service. The Secret Vault Details page consists of Details, Tags, and Activity Log tabs.
To view detailed information about the Secret Vault service, follow these steps.
- Click the All Services > Security > Secret Vault menu. You will be taken to the Secret Vault Service Home page.
- On the Service Home page, click the Secret Vault menu. You will be taken to the Secret Vault List page.
- On the Secret Vault List page, click the resource to view detailed information. You will be taken to the Secret Vault Details page.
- Secret Vault Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Category Detailed description Secret Vault status Status of the Secret Vault created by the user - Active: Running
- To be terminated: Pending termination after a service cancellation request
- The scheduled termination time of the service is displayed, and you can cancel the service termination.
- Expired: Token expired state
- Secrets that have changed to the Expired state cannot perform any actions such as information retrieval, and are automatically deleted after 7 days.
Replace temporary key Immediately delete the current temporary key and generate a new temporary key - Only the creator of the Secret Vault service can replace the temporary key.
Service termination Button to cancel the service Table. Secret Vault status information and additional features
- Secret Vault Details page displays status information and additional feature information, and consists of Details, Tags, Activity Log tabs.
Detailed Information
Secret Vault List page lets you view detailed information of the selected resource and modify the information if necessary.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Secret name | Name of the generated Secret |
| type | Encryption method |
| Explanation | Additional information or description about the Secret Vault service |
| authentication key | Authentication key used by the Secret Vault service |
| Token usage period | Validity period of the Token provided by encrypting the authentication key |
| Token expiration time | Token expiration date and time |
| Token ID | Token’s unique ID |
| Token Secret | Token Secret generated as a pair with Token ID |
| IMSI key replacement interval | Rotation period of the temporary key used to access Samsung Cloud Platform resources |
| Temporary key expiration date and time | Temporary key expiration date and time |
| Allowed IP | Allowed IP list |
| Explanation | Additional information or description about Secret Vault |
tag
On the Secret Vault List page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Secret Vault List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Secret Vault
You can cancel the unused service to reduce operating costs. However, if you cancel the service, the running service may be terminated immediately, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
To cancel Secret Vault, follow the steps below.
- Click the All Services > Security > Secret Vault menu. Navigate to the Service Home page of Secret Vault.
- On the Service Home page, click the Secret Vault menu. You will be taken to the Secret Vault List page.
- On the Secret Vault List page, select the resource to cancel and click the Cancel Service button. You will be taken to the Cancel Service popup window.
- Service Cancellation popup window, after entering the termination waiting period (7~30 days), click the Confirm button. The service will be terminated after the waiting period entered by the user.
- During the termination waiting period, the existing temporary key is deleted, and you cannot issue an additional temporary key to access Samsung Cloud Platform resources.
Cancel Secret Vault termination
You can cancel the termination of a service that is pending cancellation and use it again.
To cancel the termination of Secret Vault, follow these steps.
- Click the All Services > Security > Secret Vault menu. Navigate to the Service Home page of Secret Vault.
- On the Service Home page, click the Secret Vault menu to go to the Secret Vault List page.
- On the Secret Vault List page, click the resource to cancel the termination. You will be taken to the Secret Vault Detail page.
- On the Secret Vault Details page, click the Cancel Termination button. You will be taken to the Cancel Service Termination popup.
- Cancel Service Termination After reviewing the content in the popup window, click the Confirm button. The status of the resource for which the termination was canceled will be restored to Active.
- If the authentication key used in the Secret has been deleted, you cannot cancel the service termination.
- If the authentication key used in the Secret has been disabled or deleted, you cannot cancel the service termination. Re‑enable the authentication key first.
- Only the creator of the Secret Vault service can cancel the service termination.
Configure Application Token
The Token information issued through the Secret Vault service application is required for API calls to request OpenAPI temporary key issuance. Set the Token information according to each Application environment.
To configure the token information, follow these steps.
- Apply the token information to the application’s environment variable configuration file.
- Configure the token information so that the API call logic within the application can reference it.
- Use OpenAPI → GET /v1/temporarykey/{secretvault_id}
- For more details, refer to the Open API Guide in the Samsung Cloud Platform Console.
- Configure the token information so that the API call logic within the application can reference it.
- The temporary key removes hard coding in the existing source code and can be obtained and used via OpenAPI calls using token information. For details, refer to the Open API Guide in the Samsung Cloud Platform Console.
application.yml or application.properties environment variable configuration files
Apply the obtained Token information to the environment variable configuration file.
secretvault.secretvault.id= {{ ID }}
secretvault.tokenId= {{ Token ID }}
secretvault.tokenSecret= {{ Token Secret }}
Java file
Apply it to the class file for environment variable recognition.
import org.springframework.beans.factory.annotation.Value;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
@Configuration
public class SecretVaultConfiguration {
@Value("${secretvault.id}")
private String id;
@Value("${secretvault.tokenId}")
private String tokenId;
@Value("${secretvault.tokenSecret}")
private String tokenSecret;
@Bean
public OpenApiClient openApiClient() {
// OpenApiClient 또는 다른 API 클라이언트를 생성하고 설정 값을 사용하여 초기화
return new OpenApiClient(secretVaultName, tokenId, tokenSecret);
}
}
9.4.3 - API Reference
9.4.4 - CLI Reference
9.4.5 - Release Note
Secret Vault
- The Secret Vault service, which can issue token-based temporary keys and manage their lifecycle, has been launched.
9.5 - SingleID
9.5.1 - Overview
Service Overview
SingleID not only allows authorized users to easily access information assets with a single authentication, but also enhances account security through policy-based permission management and real-time detection of abnormal authentication activities, and provides account management and access structures via comprehensive audit logs.
Features
- Easy and convenient login and app integration: By establishing a unified authentication system that allows login from On-Premises to SaaS apps with a single ID, you can improve work productivity. Administrators can easily integrate various apps without domain knowledge of authentication by automating connections to diverse global SaaS apps through the ready-made Pre-Built Connector.
- Account Management Optimization and Security Enhancement: We systematically manage the account lifecycle—from creation to termination—for a diverse range of users, including employees, partners, corporations, and subsidiaries. Additionally, we grant permissions to authorized users in a timely manner and promptly revoke unnecessary permissions, thereby preventing unauthorized access and strengthening account security.
- Enhanced Anomaly Detection: By detecting authentication anomalies based on context such as user type, login IP, device information, and access time, security policies can be applied according to the situation to prevent account compromise incidents.
- Cloud Access Management: It consolidates the access paths of operators/developers accessing public clouds, and implements role‑based temporary‑token console/resource access control to further enhance cloud security in multi‑cloud environments.
Service Architecture Diagram
Provided features
SingleID provides the following features.
- Unified Authentication and Account Management
- Support for various authentication integration protocols (SAML, OIDC, etc.)
- Providing a self-service feature for app usage requests and approvals
- Account synchronization for Salesforce, Workday, etc., and synchronization/management of roles (groups) within accounts
- Provide a sign‑up/withdrawal feature that can issue accounts to partners, customers, and others who are not employees.
- Passwordless and Multi-Factor Authentication
- PC/mobile passwordless authentication and multi-factor authentication (MFA)
- Provide composite authentication for secondary authentication by integrating with the existing primary authentication environment (MFA-only service use case)
- Private CA(Certificate Service Authority), a private certificate issuance/management feature, provides certificate-based authentication support (separate Use Case)
- Authentication methods: SMS, email, mOTP, TOTP, PIN, biometrics, Knox Messenger, Windows Hello, etc
- Authentication and Account Information Integration
- Automating app integration via Pre-Built Connector
- Simplifying custom app integration through DIY integration templates
- Risk-Based Authentication Anomaly Detection
- Context-based access control according to authentication attempt scenarios
- Enhancing security through detailed login and authentication policy settings
- Public Cloud Access Management for Cloud Operators/Developers
- Console access control via role-based assigned accounts
- Resource access request/approval and OTP-based credential authentication for resource access
Component
The components of the SingleID service are as follows. Users can access the service through the Samsung Cloud Platform SingleID Console.
- Access Management
- Support for various authentication integration protocols (SAML, OIDC, etc.)
- Provide unified login to internal and external business systems with a single sign‑on.
- Identity Management
- Lifecycle management from account creation to decommission
- Directory integration and synchronization (Active Directory, LDAP, etc.)
- Multi Factor Authentication
- PC and mobile simple authentication
- SMS, email, mOTP, TOTP, PIN, biometric, Knox Messenger, Window Hello, etc., offering various multi-factor authentication methods
- Anomaly Detection Management
- Context-based access control according to authentication attempt scenarios
- Providing adaptive access control through risk analysis
- Cloud Access Management
- Enhancing cloud security by unifying access paths for cloud operators/developers
- Role-based temporary token method for console and resource access control
Provision status by region
SingleID is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Prior Service
SingleID has no prior service.
9.5.2 - How-to guides
Users can create the service by entering the required information for the SingleID service and selecting detailed options through the Samsung Cloud Platform Console.
Check the detailed services provided per item in SingleID and apply for the product. The services provided per item are as follows.
| Service | Detailed description |
|---|---|
| Access Management (AM) | Unified Authentication (AM) is an integrated authentication service that allows users to log in to everything from on-premises to SaaS applications with a single ID.
|
| Identity Management (IM) | Account Management (IM) enables systematic account lifecycle management—from creation to decommissioning—for a variety of users such as employees, partners, corporations, and subsidiaries
|
| Multi-Factor Authentication (MFA) | Multi-factor authentication (MFA) provides secondary authentication services in various methods when accessing major systems, external systems, mobile devices, etc.
|
| Anomaly Detection Management (ADM) | Anomalous behavior detection (ADM) is a service that detects authentication anomalies in login situations, such as user type, login IP, device information, and login time.
|
| Cloud Access Management (CAM) | Cloud Access Management (CAM) is a privileged account access management solution that strengthens cloud console/resource access control in public/multi-cloud environments
|
Create SingleID
You can create and use the SingleID service in the Samsung Cloud Platform Console.
- Click the All Services > Security > SingleID menu. Go to the SingleID Service Home page.
- On the Service Home page, click the Create SingleID button. You will be taken to the Create SingleID page.
- On the SingleID Creation page, enter the required information in the service information input area and select the detailed options.
- In the Service Configuration Selection area, enter the information for the relevant service and select detailed options.
Category Required statusDetailed description Select Service Required Select SingleID service - You can select multiple services and apply
- MFA when applied alone does not provide the simple authentication feature
- When IM, MFA are selected, AM is automatically selected
- When ADM is selected, AM, IM, and MFA are automatically selected
- When CAM is selected, AM, IM, and MFA are automatically selected
- When AM, IM, MFA or AM, IM, MFA, ADM are selected, a tenant is automatically created in the TAP/UP/MFA portal. If only the MFA item is selected, a tenant is created in the TAP/MFA portal
Number of tenant users Required Enter the minimum number of Tenant users based on the selected service - Input allowed within the range 50 - 999,999
Number of Resource Units Select Enter the number of resource Units to register when selecting a CAM service - Enter a value within the range 20 - 99,999
Integration support Select Enter the number of integration support units - Enter a value within the range 1 - 9,999
- AM: 1 unit
- MFA: 1 unit
- IM: 2 units
- When AM and MFA are used simultaneously, they are counted as 1 unit
Table. SingleID Service Configuration Options - Enter the information required to create a service in the Service Information Input area.
Category Required statusDetailed description Tenant name Required Enter tenant name Tenant code Required Enter Tenant code Table. SingleID Service Information Input Items - In the Member selection area, select the tenant user who will use the service.
Category Required statusDetailed description User Required Select members from the user list - You must select at least one user to create the service
Table. SingleID Service Member Selection Items - In the Additional Information Input area, enter or select the required information.
Category Whether requiredDetailed description Tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. SingleID additional information input fields
- In the Service Configuration Selection area, enter the information for the relevant service and select detailed options.
- Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- After creation is complete, check the created resource on the SingleID List page.
Check SingleID detailed information
The SingleID service allows you to view and edit the full resource list and detailed information. The SingleID Details page consists of Details, Tags, Activity Log tabs.
To view detailed information for SingleID, follow these steps.
- All Services > Security > SingleID Click the menu. Navigate to the Service Home page.
- On the Service Home page, click the SingleID menu. You will be taken to the SingleID List page.
- On the SingleID List page, click the resource to view detailed information. You will be taken to the SingleID Details page.
- SingleID Details page displays status information and additional feature information, and consists of Details, Tags, Work History tabs.
Category Detailed description Service status Service status display - Creating: Tenant creation in progress
- Active: Tenant creation completed
- Terminating: Service termination in progress
- Failed: Tenant creation failed
CAM Portal Cloud Access Management portal window popup button - CAM is displayed only when applying for the service
Admin Portal Admin portal popup button Service termination Service cancellation button Table. SingleID status information and additional features
- SingleID Details page displays status information and additional feature information, and consists of Details, Tags, Work History tabs.
Detailed Information
On the SingleID List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource name |
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation date | Service creation date and time |
| Editor | User who modified the service |
| Modification date | Date and time the service was modified |
| Tenant name | Entered Tenant name |
| Tenant code | Entered Tenant code information |
| Number of tenant users | Entered Tenant user count
|
| Number of Resource Units | Number of resource Units entered
|
| Billing status | Billing status and first billing date information |
| Application Service | Show requested services |
| Integration support | Click the Add Request button to apply for integration support. |
tag
SingleID List page allows you to view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
You can view the operation history of the selected resource on the SingleID List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Using SingleID Admin Portal
In the Admin Portal, you can configure and manage SSO authentication settings, account synchronization integration, and multi-factor authentication, among other things.
To access SingleID’s Admin Portal, follow these steps.
- Click the All Services > Security > SingleID menu. You will be taken to the Service Home page.
- On the Service Home page, click the SingleID menu. You will be taken to the SingleID List page.
- SingleID List page, click the resource to view detailed information. SingleID Details page will be opened.
- On the SingleID Details page, click the Admin Portal button. The SingleID admin portal window appears.
- For a detailed description of the Admin Portal, see Admin Portal.
Using SingleID CAM Portal
In the CAM Portal, you can configure and manage console and resource access control and security management for the CSP.
To access SingleID’s CAM Portal, follow these steps.
- All Services > Security > SingleID Click the menu. Navigate to the Service Home page.
- On the Service Home page, click the SingleID menu. You will be taken to the SingleID List page.
- SingleID List page, click the resource to view detailed information. You will be taken to the SingleID Details page.
4.SingleID Details page, click the CAM Portal button. The SingleID cloud access management portal window appears.
- For detailed information about the CAM Portal, see CAM Portal.
Terminate SingleID
You can reduce operating costs by terminating the unused service.
To cancel SingleID, follow the steps below.
- Click the All Services > Security > SingleID menu. You will be taken to the SingleID Dashboard page.
- On the SingleID List page, click the resource to cancel. You will be taken to the SingleID Details page.
- Cancel Service button. Click it. A cancellation alert will appear.
- In the alert window, enter the Tenant name and click the Confirm button.
9.5.2.1 - SingleID Manuals
SingleID not only enables authorized users to easily access information assets with a single authentication, but also strengthens account security through policy-based permission management and real-time detection of abnormal authentication behavior, and provides account management and access frameworks through various activity logs.
SingleID Manual List
SingleID provides various manuals as shown in the table below.
| Category | description |
|---|---|
| User Portal | SingleID User Portal is the user interface of the SingleID service, providing various security features such as access to company applications, SSO, and access permission requests. For more information, see the User Portal. |
| Admin Portal | The SingleID Admin Portal provides all configuration and management functions for all authentication services, account management services, and security policy creation and settings for organizations using the service, through the Admin Portal. |
- For more details, see the Admin Portal. |
| MFA Portal | SingleID can maintain the authentication system used by existing applications while enhancing security by requiring users to perform various additional second-factor authentications through system integration. Additionally, SingleID provides an MFA Portal that allows users to pre-register and manage their preferred authentication methods during authentication.
- For more information, see the MFA Portal. |
| CAM Portal | CAM (Cloud Access Management) Portal is a service for cloud console and resource access management, providing users with an easy and convenient way to access cloud consoles and resources. Users can access the portal from a PC on the internal network using multi-factor authentication (MFA). It issues one-time tokens instead of passwords to enable access to cloud consoles and resources, and allows monitoring of all access, operation history, and abnormal behavior.
- For more details, see CAM Portal. | | SingleID Authenticator | SingleID Authenticator is a SingleID-specific authentication tool that enables easy and secure verification of website users’ identity and multi-factor authentication using a mobile phone.
For more information, see the SingleID Authenticator. | | SingleID Open API Guides | Provides various APIs such as applications, Idp, and authentication for using SingleID.
For more details, refer to the Open API Guides. |
9.5.2.1.1 - User Portal
Overview
SingleID not only enables authorized users to easily access information assets with a single authentication, but also strengthens account security through policy‑based permission management and real‑time detection of anomalous authentication behavior, and provides account management and access frameworks through various audit logs.
Provided Features
- Unified Authentication and Account Management
- Support for various authentication integration protocols (SAML, OIDC, etc.)
- Providing self-service functionality for app usage requests and approvals
- Synchronization of accounts such as Salesforce and Workday, and synchronization and management of roles (groups) within those accounts.
- Provide registration and withdrawal functions that allow issuing accounts to partners, customers, and others who are not employees.
- Passwordless and Multi-Factor Authentication
- PC·Mobile passwordless authentication and multi-factor authentication (MFA)
- Authentication methods: SMS, email, SingleID Authenticator(mOTP, TOTP, PIN, biometrics), Knox Messenger, Passkey, etc
- Provide composite authentication for secondary authentication by integrating with the existing primary authentication environment (MFA‑only service use case)
- Support for certificate-based authentication through Private CA (Certificate Service Authority), a private certificate issuance and management function (Separate Use Case)
- PC·Mobile passwordless authentication and multi-factor authentication (MFA)
- Authentication and Account Information Integration
- App integration automation via Pre‑Built Connector
- Simplifying custom app integration through DIY integration templates
- Risk-based Authentication Anomaly Detection
- Context-based access control according to authentication attempt scenarios
- Enhancing security through detailed login and authentication policy settings
- Public cloud access management for cloud operators/developers
- Console access control via role-based assigned accounts
Service diagram
What is a User Portal?
The SingleID User Portal is the user interface of the SingleID service, providing various security features such as access to company applications, SSO, and access permission requests.
User Portal screen layout
The User Portal is composed of the following menus.
- My App: A menu that allows the user to view the list of applications currently in use. 1. Users can conveniently access and manage approved apps.
- App Catalog: A menu that displays a list of accessible applications.
- Notice: This menu allows the SingleID administrator to display announcements to users.
- Approval Request: This is a menu where you can manage approval requests related to application access, member registration, usage period extension, and other similar actions.
Manual composition
This manual is organized as follows.
- Announcements and Language Settings: It explains how to set the language in the SingleID solution and how to check urgent announcements that can be viewed before logging in.
- Login and Authentication: Explains how to register and use various authentication methods for login.
- Register Authentication Tool: Describes the enrollment process, which is the procedure for a user to register an authentication tool.
- Sign Up: Explains the two methods of signing up.
- ID Retrieval: Describes the procedure by which a user finds their own ID through the ID retrieval process.
- Privacy Policy and Terms of Service: Explains the privacy policy and terms of service that can be accessed via the link at the bottom of the screen.
- PC SSO Agent: Describes the PC SSO Agent, which assists with SingleID login and logout.
- My App: Describes the My App menu that can be accessed via SSO.
- App Catalog: Describes the App Catalog menu where you can view the list of apps available for request.
- Notification: This explains the Notification menu that allows you to view urgent notices and regular notices.
- Approval Request: Describes the Approval Request menu that allows you to request or approve app usage.
- Personal Information Settings: Photos, preferred language, and system time zone can be set in Personal Settings, Authentication Settings, login history·environment, logout, etc., describing the personal settings menu.
9.5.2.1.1.1 - Announcements and Language Settings
Notice
You can view the notice alerts posted by the administrator on the User Portal login screen and after logging into the User Portal. There are general notices and emergency notices.
- General Notice: It is a general notice posted by the administrator and is used to convey information to users. * User Portal > Notifications can be viewed in the menu.
- Urgent Notice: It is an urgent announcement posted by the administrator and is used to convey information to users. * User Portal > Login screen top and User Portal > Notifications can be viewed in the menu.
Language Settings
To change the language displayed on the screen, follow these steps.
- In the User Portal screen > top language selection, click the language you want, Korean or English.
- A dropdown list appears, allowing you to select between Korean and English.
- Please select the desired language. 2. The screen switches according to the selected language.
9.5.2.1.1.2 - Log in using an authentication method
Log in using an authentication method
What is an authentication method?
Authentication method, often called Authenticator, refers to an authentication tool.
SingleID offers the following 11 authentication methods for user authentication.
- Password: Enter the password on the SingleID login screen.
- Email OTP: Send the OTP via email and enter the OTP on the SingleID login screen.
- SMS OTP: Send the OTP via SMS and enter the OTP on the SingleID login screen.
- Knox Messenger OTP: Send the OTP via Knox Messenger and enter the OTP on the SingleID login screen.
- Knox Identity: Knox Portal users enter the Knox Password for the Knox Identity Password on the SingleID login screen.
- SingleID Authenticator Bio: Send via the dedicated SingleID mobile app and authenticate with biometric verification on the mobile device.
- SingleID Authenticator PIN: Send it to the dedicated SingleID mobile app and enter the PIN on the mobile device.
- SingleID Authenticator mOTP: Install the SingleID dedicated mobile app and enter the mOTP (Mobile OTP) number.
- SingleID Authenticator TOTP: Install using the SingleID dedicated mobile app and enter the TOTP (time‑based OTP) code.
- Passkey: An authentication method based on Mobile and Windows Hello that authenticates using biometrics (fingerprint, facial), PIN, and security keys.
- TOTP Authenticator: Generate TOTP (Time-based OTP) with a 3rd Party Authenticator and enter the OTP on the SingleID login screen
- Admin Authentication: Request authentication on behalf of the admin to integrate authentication
Enter user ID
The user attempts to log in by entering their ID on the login screen below.
To log in using a user ID, follow these steps.
- Login screen > Account ID Enter the ID in the input field, then click the Next button.
- Enter the password in the password field, and click the Next button.
- Login is complete.
Passwordless login
SingleID provides a login service without a password.
To log in without using a password, follow these steps.
- Login screen > Want to log in without a password? Click it.
- Select verification method The screen appears. 2. Click one of the desired authentication methods.
- Enter the authentication code according to the authentication method you selected.
- After login is completed, you will be taken to the User Portal main screen.
Setting Preferred Authentication Method
SingleID users log in to the User Portal provided by SingleID to set their preferred primary and secondary authentication methods.
If the user sets their preferred method, the Select verification method screen is omitted during login and authentication, allowing immediate authentication with the primary and secondary methods.
If you want to set your preferred authentication method, follow the steps below.
- User Portal > Personal Profile > Authentication Click the settings.
- Authentication Settings screen appears.
- Click the ☆ 1st, ☆ 2nd that corresponds to the authentication method you prefer, placed before each method.
- Only one selection is allowed for each of 1st, 2nd. 4. When it changes to ★, the selection is completed.
After the configuration is complete, the next login will use this method, offering convenient access.
Register authentication method
Users can configure all authentication methods. Registering an authentication method by a user is called enrollment. When a user account is created for the first time, the email OTP is automatically enrolled using the email information from the user data. Other authentication methods can be used by having the user enroll directly as needed.
There are two methods for authentication enrollment.
- Register in Authentication Settings: User Portal > Profile > Authentication settings, click the + Add New button at the bottom to register.
- Select verification method screen registration: At login, first-factor authentication; at second-factor authentication, on the Select verification method screen, select the authentication method that has a gray check mark (V) and register it.
First login
Password reset
When a user logs in for the first time, they can log in after resetting their password.
To reset your password, follow the steps below.
- Login screen > Account ID input field, enter the ID, and click the Next button.
- Click Password Reset below the Next button.
Consent to collection/use of personal information
Consent for the collection and use of personal information is required when logging in with SingleID for the first time or during a certain period. Please follow the consent procedure and select the required, optional items to agree.
Required items must be selected to log in.
Password authentication
Password is the most basic authentication method, serving as SingleID’s default authentication tool.
Enter password
To log in using a user ID, follow the steps below.
- In the Login screen > Account ID input field, enter the ID, and click the Next button.
- Enter the password in the Password field, and click the Next button to log in.
If you enter the password incorrectly If the entered password is incorrect, re‑entry is required along with the message ID or password is incorrect.(1/3). The number of allowed retries is limited to the count set by the administrator in the password policy.
When the password is entered incorrectly repeatedly and becomes locked If the password is entered incorrectly and the device becomes locked, you can unlock it using two methods.
- Automatic unlock after 1~5 minutes: When automatic unlock is enabled, the account remains locked for 1~5 minutes. * Login will be available after that time.
- Unlock with Password Reset: When the administrator sets the password policy to require a password reset, a password reset is required. * You can log in after resetting your password. * ID 찾기 you can view the detailed information there.
Email OTP authentication
Authentication
To authenticate with email OTP, an OTP will be sent to the email address registered by the user.
To authenticate with an email OTP, follow the steps below.
- In the Identity Verification Selection method, click Email.
- An OTP code will be sent to the registered email. 2. Enter the OTP within the time set by the administrator (usually 3~5 minutes).
- After entering the OTP, click the Confirm button to complete authentication.
- Resend Code: If the input validity period has expired, click the resend code button. 1. Resend the OTP code via email.
- ‘Would you like to authenticate in a different way?’: If the current authentication cannot be used, switch to a different authentication method.
- ‘If you have changed your email, please register.’: Depending on the administrator’s settings, you can register a different email (Enrollment) for verification. 3. You can check the detailed information at 이메일 인증 도구 등록하기.
If the code is entered incorrectly If the user enters the OTP code incorrectly, they can re-enter it up to the number of times specified by the administrator.
When locked due to exceeding the user input limit If the OTP code is entered incorrectly more times than the limit set by the administrator, the screen will be restricted from input for the duration configured by the administrator. You can input after waiting for the specified time. Refresh and try again after the input timeout.
SMS OTP authentication
Authenticate
To authenticate with SMS OTP, an SMS OTP is sent to the mobile device registered by the user.
To authenticate with an email OTP, follow the steps below.
- In the Identity verification selection method, click Email.
- The OTP code will be sent to the registered mobile phone. 2. Enter the OTP within the time set by the administrator (usually 3~5 minutes).
- After entering, click the Confirm button, and the authentication will be completed.
- Resend Code: If the input validity period has expired, click the resend code button. 1. Resend the OTP code to the mobile phone.
- ‘Do you want to authenticate using a different method?’: If the current authentication cannot be used, switch to another authentication method.
- ‘If you have changed your mobile phone, please register.’: Click the link to go to the enrollment screen for the new mobile. 3. Detailed information can be found in the registration at SMS 인증 도구 등록하기.
If the code is entered incorrectly If the user enters the OTP code incorrectly, they can re-enter it up to the number of times specified by the administrator.
When locked due to exceeding the user input limit If the OTP code is entered incorrectly more times than the administrator has allowed, the screen will be locked from input for the duration set by the administrator. You can input after waiting for the specified time. Refresh and try again after the input timeout.
Knox Messenger OTP authentication
Authenticate
If you want to authenticate with Knox Messaenger OTP, the OTP will be sent to the Knox Messanger you are using.
To authenticate Knox Messenger OTP, follow the steps below.
- In the Identity verification selection method, click Knox Messenger.
- The OTP code is sent via Knox Messenger. 2. Enter the OTP within the time set by the administrator (usually 3~5 minutes).
- After entering, click the Confirm button, and the authentication will be completed.
- Resend Code: If the input validity period has expired, click the resend code button. 1. Resend the OTP code via Knox Messenger.
- ‘Would you like to authenticate using a different method?’: If the current authentication cannot be used, switch to a different authentication method.
- ‘Would you like to use a different Knox ID?’: Clicking the link takes you to the screen for enrolling a new Knox ID. 3. You can check the details for registration at Register Knox Messenger authentication tool.
If the code is entered incorrectly If the user enters the OTP code incorrectly, they can re-enter it up to the number of times specified by the administrator.
If locked due to exceeding the user input limit If the OTP code is entered incorrectly more times than the limit set by the administrator, the screen will be restricted from input for the duration configured by the administrator. You can input after waiting for the specified duration. Refresh and try again after the input timeout.
Knox Identity Password Authentication
Authenticate
To authenticate with Knox Identity, you must enter your Knox Identity password.
If you want to authenticate with Knox Identity, follow the steps below.
- In the Identity verification selection method, click Knox Identity.
- Enter the password for your Knox account.
- After entering, click the Confirm button to complete authentication.
If the password is entered incorrectly If the user enters the password incorrectly, they can re-enter it up to the number of attempts specified by the administrator.
When locked due to exceeding the user input limit If the password is entered incorrectly more times than the administrator’s allowed limit, the screen will be locked for the duration set by the administrator. You can input after waiting for the specified time. Refresh and try again after the input timeout.
SingleID Authenticator authentication
The SingleID service provides a mobile authentication app called SingleID Authenticator and offers authentication in various ways.
Authentication Method
| Authentication method | Explanation |
|---|---|
| SingleID Authenticator Bio | Send a push through the installed SingleID Authenticator mobile app on the device to request biometric authentication. |
| SingleID Authenticator Pin | Send a push using the installed SingleID Authenticator mobile app on the mobile device and request authentication with a PIN code. Not provided. |
| SingleID Authenticator TOTP | Send a push notification via the installed SingleID Authenticator mobile app on the device to request authentication using TOTP. |
| SingleID Authenticator mOTP | Send a push using the installed SingleID Authenticator mobile app on the device to request authentication with mOTP. |
Passkey authentication
The SingleID service offers simple authentication and multi-factor authentication using a Windows-based Passkey.
Authentication method
- Convenient authentication: Provides easy login without ID/Password by using Sign in with Passkey at the bottom of the login page.
- Multi-factor authentication: Provides convenient login without requiring an ID/password during secondary authentication.
Authentication Types
- Mobile Passkey: Scan the QR code and log in using Android and iOS mobile.
- Biometrics: Login via fingerprint recognition based on Windows Hello
- PIN: Login using Windows PIN code
- Security key: Log in using the Windows security key
Administrator authentication
Authenticate
In the SingleID service, the administrator provides authentication by delegating identity verification on behalf of the user.
To perform administrator authentication, follow the steps below.
- Identity verification selection method, if you cannot perform identity verification at the bottom of the screen, you can request verification from the administrator. 1. Click here. click it.
- Click the Request button.
- You will be taken to the admin selection screen. 3. Select the administrator who requested authentication delegation and click the Request button.
- Authentication delegation is requested to the selected administrator.
- When the administrator approves the authentication delegation, the authentication delegation is completed automatically.
9.5.2.1.1.3 - Register authentication tool
- Delete Windows Hello
- Register Passkey authentication tool –>
Register authentication tool
The principle is that all authentication tools are registered and used by the user themselves.
Registering an authentication tool by the user is called enrollment (Enrollment).
When a user is created for the first time, the Email OTP is automatically registered using the email information from the user data.
The remaining information can be directly registered and used by the user as needed.
There are three ways to register.
- Login screen > ID/Password enter > Identity verification method register on the selection screen
- On the identity verification method selection screen, click the authentication tool marked Registration Required (V mark) to register.
- Click the User Portal(after login) > Profile > Authentication Settings > + Add New button to register.
- Register through the registration message link at the bottom of every authentication screen.
- The screen below is an example of an SMS verification screen. * At the bottom, you can register by clicking the If you have changed your mobile phone, please register. message.
- All authentication code inputs can be changed via a message below (Message format: ~ please register.)
Authentication code input screen example
Register Email Verification Tool
Email registration consists of the following three steps.
- Verification Step: This is the identity verification step before registering the email authentication tool.
- Registration step: This step registers a new email and checks whether the number is valid.
- Completion stage: This is the final step to confirm that the registration was completed successfully.
Check step
This is the step of identity verification before using the authentication tool. To view the identity verification process, please refer to 로그인 및 인증하기.
Registration step
This is the step where the user registers the desired email address and checks its validity.
The user should follow the steps below.
- If you complete identity verification in the Confirmation step, you will automatically move to the Registration step.
- Enter the email address you want to register.
- Click the Send verification code button.
- Check the OTP code sent to the entered email address, and enter the OTP code on the screen.
- If the authentication code is entered correctly, it proceeds to the complete stage.
Completion Phase
Registration completed screen appears, and on the next login you can perform first and second factor authentication using the email verification tool.
Register SMS authentication tool
SMS registration consists of the following three steps.
- Verification step: This is the identity verification step before registering the SMS authentication tool.
- Registration step: This step registers a new mobile phone number and checks whether the number is valid.
- Completion Stage: This is the final step to confirm that the registration was completed successfully.
Check step
This is the step of identity verification before using the authentication tool. To view the identity verification process, refer to 로그인 및 인증하기.
Confirm stage can only authenticate using the authentication tool configured by the administrator.
Registration step
This step registers the mobile phone number the user wishes to add and checks its validity.
The user can proceed with the following steps.
- If you complete identity verification in the Confirmation step, you will automatically move to the Registration step.
- Select the Country code, and enter the Mobile phone number you wish to register.
- Click the Send verification code button.
- Check the OTP code sent to the entered mobile phone number, and enter the OTP code on the screen.
- When the Authentication code is entered correctly, it proceeds to the Complete stage.
Completion phase
Registration Complete screen will appear, and on the next login you can perform first and second factor authentication using the SMS authentication tool.
Register Knox Messenger authentication tool
Knox Messenger registration consists of the following three steps.
- Verification step: This is the identity verification step before registering the Knox Messenger authentication tool.
- Registration Step: Enter the Knox ID to register. 2. This is the step that checks whether the Knox ID to be registered is valid.
- Completion Stage: This is the final step to confirm that the registration was completed successfully.
Check step
This is the step of identity verification before using the authentication tool. If you want to view the identity verification procedure, refer to Login and Authentication.
In the verification stage, the authentication method to be used can only be performed with the authentication tool configured by the administrator.
Registration Step
This step registers the mobile phone number the user wants to add and checks its validity.
The user should follow the steps below.
- If you complete identity verification in the Verification step, you will automatically move to the Registration step.
- Enter the Knox ID to register.
- Click the Send verification code button.
- Check the OTP code sent to Knox Messenger of the entered Knox ID, and enter the OTP code on the screen.
- When the authentication code is entered correctly, it proceeds to the complete stage.
Completion Phase
Registration Complete screen will appear, and on the next login you can perform first and second factor authentication using the Knox Messenger authentication tool.
Register Passkey authentication tool
The SingleID Authenticator is an authentication tool provided for the SingleID service.
Passkey enrollment consists of the following three steps.
- Verification stage: This is the identity verification step before registering the Passkey authentication tool.
- Registration Stage: This is the Passkey registration stage.
- Completion Stage: This is the final step to confirm that the registration was completed successfully.
Check step
This is the step where you verify your identity before registering the authentication tool. If you want to view the identity verification procedure, refer to 로그인 및 인증하기.
Registration stage
This is the step to verify the mobile phone or PC environment where you want to register a Passkey.
Complete the registration process in the four steps below.
- Activation: Passkey support environment guide.
- Confirm: Complete identity verification using an authentication method.
- Registration: Passkey registration stage. 3. When you click the Generate on this device button, a passkey is created and registered on the PC. 3. Create on another device Clicking the button registers with a mobile phone or a hardware security key.
- Complete: Registration complete step confirming that registration has been completed. 4. Click the Continue button.
Passkey supported environment Operating system (laptop or desktop)
- Windows 11, macOS Ventura, ChromeOS 109 or later
- Mobile phone: iOS 16 or Android 9 or later
- Hardware security key: a hardware security key that supports the FIDO2 protocol
Browse version
- Chrome 109 or later
- Safari 16 or later
- Edge 109
Device Settings
- Enable Bluetooth
- Set screen lock password
- Register PIN code
- Allow fingerprint or facial recognition
Completion Phase
After the passkey registration is completed, the Registration Complete screen appears. You can perform first- and second-factor authentication with the Windows Hello authentication tool on the next login.
PC Passkey requires that Windows Hello be configured in advance. For detailed information, see the reference link.
When registering a passkey on mobile, it can be set in an environment where QR code scanning is possible.
How to Register PC Passkey
This guide explains how to register a Passkey using Windows Hello on a PC. Passkey must have Windows Hello set up in advance. For detailed information, see the Windows Hello setup.
If you have completed registering a fingerprint or PIN in Windows Hello settings. Follow the steps below.
- Click User Portal > Profile > Authentication Settings.
- Click the Add New button.
- On the Select registration authentication method screen, select Passkey.
- Passkey Registration The screen appears. 4. Click Start.
- Passkey supported environment screen appears. 5. Check the supported operating system version and click the Next button.
- The Select verification method screen appears. 6. Complete verification using an authentication method that can verify your identity.
- Passkey registration screen appears. 7. Click the Generate on this device button. (Generate Passkey on Windows PC)
- (If a fingerprint or PIN is set in Windows Hello) Fingerprint or PIN entry authentication screen appears.
- When you enter a fingerprint or PIN code, the registration complete screen appears.
Mobile Passkey Registration Method
This is a guide on registering a mobile Passkey. Mobile Passkey requires the following pre-configuration to be completed in advance.
- Enable Bluetooth
- Set screen lock password
- Register PIN code
- Allow fingerprint or facial recognition
If you have completed registering the Passkey via mobile. Follow the steps below.
- Click User Portal > Profile > Authentication Settings.
- Click the Add New button.
- Select registration authentication method on the screen, select Passkey.
- Passkey registration screen appears. 4. Start click.
- Passkey supported environment screen appears. 5. Check the supported operating system version and click the Next button.
- Select verification method The screen appears. 6. Complete verification using an authentication method that can verify your identity.
- Passkey Registration The screen appears. 7. Create on another device Click the button.(Android or iOS)
- The QR code appears on the screen. 8. Scan the QR code to generate a passkey on your mobile.
- When you enter a fingerprint or PIN code on mobile, the Registration Complete screen appears.
Mobile Passkey Support Scope
- Adriod : Supports Samsung Pass, Google Passkey Manager.
- iOS: Supports passkeys based on iCloud Keychain.
SingleID Authenticator Register authentication tool
The SingleID Authenticator is an authentication tool provided for the SingleID service.
SingleID Authenticator enrollment consists of the following four steps.
- Verification step: This is the identity verification step before registering the SingleID Authenticator authentication tool.
- Installation Step: This is the user’s SingleID installation guide step.
- Registration Stage: This step registers a new mobile app and registers the service.
- Completion stage: This is the final step to confirm that the registration was completed successfully.
Verification step
This is the step of verifying your identity before using the authentication tool. To view the identity verification process, refer to 로그인 및 인증하기.
Installation steps
There are three main ways to install the SingleID mobile app.
- How to install SingleID Authenticator by having the user scan a QR code on their mobile, or by searching for “SinlgeID” on Google Play (for Android) or the App Store (for iOS).
- How to install by entering your mobile phone number and receiving the download link via SMS
- How to install using a manual download link After installing the SingleID Authenticator app and clicking the Next button, you will proceed to the registration step.
Registration Step
Install the SingleID Authenticator mobile app on the mobile phone you want to register, then launch SingleID Authenticator.
Complete the registration process using the three steps below.
- Service Registration: In the SingleID Authenticator app, click the ‘+’ at the top.
- Enter QR or authentication number: Scan the QR code or enter the authentication code to register.
- Service registration complete: Click the Confirm button to complete the registration.
Completion Phase
After registration is completed in SingleID Authenticator, the Registration Complete screen appears. You can perform first- and second-factor authentication with the Windows Hello authentication tool on the next login.
Register TOTP Authenticator tool
TOTP Authenticator registers 3rd Party TOTP to support various authentication tools.
TOTP Authenticator enrollment consists of the following four steps.
- Verification step: This is the identity verification step before registering the SingleID Authenticator authentication tool.
- Installation Step: This is the user’s SingleID installation guide step.
- Registration Stage: This step registers a new mobile app and registers the service.
- Completion Stage: This is the final step to confirm that the registration was completed successfully.
Verification step
This is the step of verifying your identity before using the authentication tool. If you want to view the identity verification procedure, please refer to 로그인 및 인증하기.
Installation Steps
There are two main ways to install the TOTP Authenticator.
- Mobile app
- Web browser extension
Click the Next button to proceed to the registration step.
Service Registration and Verification Phase
This step registers and verifies the 3rd Party TOTP Authenticator you wish to add.
Complete the registration process in the two steps below.
- Service Registration: Scan the QR code of the TOTP Authenticator you want to register, or enter the manual code. 1. Code registration is completed in the TOTP mobile app or extension.
- Service verification: Run the TOTP mobile app or extension and enter the OTP.
TOTP Authenticator Support SingleID supports a variety of standardized 3rd‑party TOTP authentication apps. Non-standard TOTP is not supported. The verified mobile and extension programs are as follows. We recommend the mobile app or extension below.
- Mobile app
- Google Authenticator, Microsoft Authenticator
- Web browser extension
- TOTP extension searchable in the Chrome Web Store and Microsoft Edge Add-ons
Completion Phase
After registration is completed in SingleID Authenticator, the Registration Complete screen appears. You can perform first- and second-factor authentication with the TOTP Authenticator tool on the next login.
Administrator authentication
Authenticate
In the SingleID service, the administrator provides authentication by delegating identity verification on behalf of the user.
To perform administrator authentication, follow the steps below.
- In the Identity verification selection method, if you cannot complete identity verification at the bottom of the screen, you can request verification from the administrator. 1. Click here. Click it.
- Click the Request button.
- You will be taken to the admin selection screen. 3. Select the administrator who requested authentication delegation and click the Request button.
- Authentication delegation is requested to the selected administrator.
- When the administrator approves the authentication delegation, it is automatically completed.
9.5.2.1.1.4 - Sign Up
Sign up
According to internal company policy, users who are not employees—such as partners, subsidiaries, and customers—can create an account through a separate registration.
Sign up via login page link
This is the method to sign up via the Sign Up link on the login page.
On the login page, at the bottom of the login section, click Sign Up in the phrase “If you don’t have an account, click Sign Up.”
Agree to terms
To sign up, you need to agree to the terms.
Enter Information
Perform the following procedure.
- Enter the email you want to register.
- After entering the email, click the Send OTP button to send the OTP code.
- Enter the OTP code from the received email address, then click the Confirm button.
- If you enter the verification code correctly, the Sign Up button will be activated.
- Click the Sign Up button.
Enter information
Enter various personal information required for registration.
| Category | Explanation |
|---|---|
| ID | Enter the ID to register |
| Korean name | Enter a Korean name |
| English name | Enter English name |
| Enter phone number | Enter the registered country and mobile number. |
| OTP code | Enter the received OTP code |
| Department | Enter department name |
| Language and Time Zone | User language and time zone settings |
Sign up
After entering personal information, click the Sign Up button to complete the approval request. Once approval is complete, you can proceed to the next step. Once the administrator’s approval is complete, you can log in by resetting your password.
Sign up via invitation email
You can sign up through an invitation email from the administrator. Click the Sign Up button in the received email to register.
After that, the registration process is the same as Sign up via login page link.
9.5.2.1.1.5 - Find ID and Reset Password
Find ID
If the user forgets their ID, click Find ID on the login screen.
Find ID using mobile phone number
The user can find their ID by entering their name and mobile phone number.
Please follow the steps below.
- Click the Mobile tab.
- Please enter Name.
- Please enter surname.
- Please enter the country code and phone number.
- Click the Send verification code button.
- On the authentication code entry screen, enter the received authentication code and click the Confirm button.
Password Reset
Reset password
To reset your password, click Password Reset at the bottom of the login screen.
Perform identity verification
To set a password, the user must first complete identity verification. Clicking the Password Reset button brings up the Select Identity Verification Method screen according to the policy set by the administrator. For detailed information about authentication, refer to Login and Authentication.
Password Reset
After the user completes identity verification, they are taken to a screen where they can set a new password.
Passwords must be set to match the password pattern and complexity defined by the administrator’s policy. When a user enters a password, criteria that are met are displayed in green, and those that are not met are displayed in red. Set the password so that all items appear in green.
Reset the password as follows.
- Please enter a new password.
- If the newly entered password fails to meet any of the complexity or pattern requirements set by the administrator, generate a more complex password.
- To prevent user input errors, please re-enter the password to match the one you entered.
- Click the Change Password button.
When password setup is complete, click the Log in with password button to return to the login screen. When password setup is complete, click the Log in with password button to return to the login screen.
9.5.2.1.1.6 - Privacy Policy, Terms of Service, Service Desk
On the lower left of every screen, there are links to the Privacy Policy and Terms of Service, allowing users to view them at any time.
Privacy Policy
A Privacy Policy link is placed at the bottom left of every screen, allowing users to view the SingleID service’s privacy policy at any time.
To view the privacy policy, follow the steps below.
- Click the Privacy Policy at the bottom left of the screen. You can view the latest version of the privacy policy.
- If you want to view a previous version, select the desired version at the top to retrieve it.
Terms of Use
Place a Terms of Service link at the bottom left of every screen so that users can view the SingleID service terms at any time.
To review the terms of service, follow the steps below.
- Click the Terms of Service at the bottom left of the screen. You can view the latest version of the Terms of Service.
- If you want to view a previous version, select the desired version at the top to retrieve it.
Service Desk Information
If users have inquiries about SingleID, they can contact using the Service Desk phone number and the main email address at the bottom of the screen.
9.5.2.1.1.7 - PC SSO Agent
SingleID PC SSO Agent provides integrated SSO authentication services in a Windows Desktop environment.
SingleID PC SSO Agent provides the following functions.
- Integrated SSO and login/logout across web browsers
- PC device authentication
- Essential security software installation verification feature (SingleID administrator setting)
Recommended installation environment for PC SSO Agent
- Windows Desktop 10 and 11 (x86 and x64 CPU Only)
- Web Browser: Microsoft Edge 88.x or later, Chrome 87.x or later
- .NET Framework 4.0 or later
- Disk Capacity 100MB or more
Check whether PC SSO Agent is installed
If the administrator has set a policy to use the PC SSO Agent, SingleID automatically checks whether the SingleID SSO Agent is installed on the user’s PC as follows.
- After the user logs in with SingleID, it automatically checks whether the PC SSO Agent is installed.
- If the PC SSO Agent is installed on the user’s PC, it automatically proceeds to the next screen; otherwise, it automatically redirects to the installation prompt screen.
- If the installation prompt does not appear automatically, click the Next button to install the PC SSO Agent.
Using the download link for the SSO Agent installation
PC SSO Agent installation prompt screen: Click the ‘Download’ button to download the Agent program to your PC and install it.
Install SingleID PC SSO Agent
If you download the SingleID Agent.exe file to the PC and install it correctly, a tray labeled ‘ID’ will appear in the lower‑right corner of the PC’s tray. If the PC SSO Agent is installed correctly and SSO authentication succeeds, right‑click and click “View Status” to verify that it operates normally.
Re-authentication attempt
After installing the PC SSO Agent, you can either log in again from the beginning, or click the re-authenticate button at the bottom of the screen below to retry authentication using the Agent.
9.5.2.1.1.8 - My App
Recently used apps
When a user logs into the User Portal, the first thing they see is the My Apps menu. The left menu bar can be expanded or collapsed by clicking the arrow(→) icon at the bottom left.
When you click the My App menu, three submenus that are provided by default and cannot be edited will appear.
- Recently used apps
- Bookmark
- Default app
Among these, clicking Recent Apps will display the apps the user has recently used. Recent apps are shown up to a maximum of 12.
Bookmark
My Apps menu, when you click the Bookmark menu, the apps you have bookmarked are displayed. You can conveniently use frequently used apps by bookmarking them. You can add a bookmark by clicking the bookmark button at the lower right of the app card, and clicking it again will remove the bookmark. Up to 12 bookmarks are allowed.
Add/Delete Bookmark
If you click the Bookmark icon at the lower right of the app you want to add, it will be added to Bookmark. Clicking it once more will delete the bookmark.
Default App
The default app menu displays all apps available to the logged-in user. When the user clicks an app, they are authenticated via SSO and the app launches in a new browser window. If a disabled app is clicked, a popup appears indicating that the app is disabled.
Add Category
The user can click the Add Category button to create a category with a name of their choice and manage the app.
- After clicking the Add Category button, enter the category name and click the Check button.
- After adding a category, the user can click the More button located to the right of the category to move, edit, or delete the category.
If you delete a category while it contains apps, the remaining apps are moved to the Default App category.
9.5.2.1.1.9 - App Catalog
Using the App Catalog
When you click the app catalog menu, the list of apps that are pending approval is displayed by default.
The app catalog can be viewed as a list of apps in three states.
- Unused: state where a usage request can be made
- Pending Approval: The usage request has been completed and is awaiting approval.
- In Use: The usage request has been approved and is currently in use.
If an app in an unused state does not have a request button, the user cannot request it themselves due to company policy. Please contact the administrator if you wish to use it.
Request App Usage
To request usage of an unused app, the user clicks the Request button, enters the purpose for using the app, and then clicks the Request button.
The app usage approval process may vary depending on the administrator’s settings. By default, the approver list configured by the administrator is displayed, and if multiple approvers exist, the outcome is determined by whichever approver processes the approval or rejection first.
Once the app usage request is completed, you can view the request status from the two menus.
- You can check the status in the App Catalog > Pending Approval state.
- You can view the detailed information in App Usage Approval > My Requests.
In the My Requests list, click the App to view details, and when pending approval, you can cancel the request using the Cancel Request button.
9.5.2.1.1.10 - Notification
Notification
Click the notification menu to view the list of notifications. There are two types of notifications.
- Urgent: Tenant administrators post urgent notices that users can view before logging in, regardless of the user’s login status, such as urgent alerts (system outages, etc.)
- General: All notifications that are not emergency alerts, which the user can view in the Notifications menu after logging in.
Notifications menu, when clicked, is set by default to All status, so both urgent and regular notifications are shown. If there are unread notifications, they appear as a number next to the notification menu, and because they are marked with a red dot in the list, unread notifications can be easily recognized. If you click this notification, you can view the details.
| Name | Explanation |
|---|---|
| type | This is the type of notice. It is divided into urgent and normal. |
| Title | This is a notice title. |
| Start date and time | The start date and time of the notice posting. |
| End time | The end date and time of the notice posting. |
Approval request
When you click the approval request menu, the administrator can view and cancel all users’ approval requests.
Approval requests consist of the Approval Request List and Approval Request Queue tabs.
Approval request list
There are several types of approval request statuses. You can easily filter and view using the Approval Request, Approved, Rejected, Cancel Submission buttons at the top. If you want an advanced search, you can use the advanced search in the search bar at the top right.
- Approval Request: Shows the status of all approval requests.
- Approval: Shows all approved statuses.
- Rejected: Shows approval request items that have been rejected.
- Submission Cancellation: Displays approval requests that have been cancelled after submission.
The description of the approval request list items is as follows.
| Name | Explanation |
|---|---|
| Approval System | It shows the approval system according to the approval policy. You can verify which approval system was used for the request. Please refer to Policy > Approval Policy. |
| Title | This is a notice title. |
| Start date and time | The start date and time of the notice posting. |
| End time | The end date and time of the notice posting. |
9.5.2.1.1.11 - Approval Request
Request approval
The app usage approval menu provides two functions.
- My Request Tab: A list of apps I have requested to use is displayed.
- Approval List Tab: Displays the list of app usage requests submitted to me.
Request App Usage
To request usage of an unused app, the user clicks the Request button, enters the purpose for using the app, and then clicks the Request button again. The app usage approval process may vary by company.
By default, the list of approvers set by the tenant administrator is displayed, and when multiple approvers exist, it is determined by the result of the first approval or rejection.
Once the app usage request is completed, you can view the request status in both menus.
- You can check the status from the App Catalog > Pending Approval status.
- In Approval Request > My Requests, you can view the details and perform additional actions.
My request
In the My Requests list, you can click an app to view its details, and when the request is pending approval, you can cancel it using the Cancel Request button.
When usage approval is completed, the status item in my request list will change to Approved. If you click Approved App in the list, you can view the detailed usage approval information.
Approval List
If you are the app usage approver, please click the Approval List tab.
- If the user has a pending approval request for app usage, you can see that the status column in the list shows Pending Approval.
Click the relevant list to view the details of the approval request.
After reviewing the details and leaving the approver’s comments, click the Approve button to grant the requester permission to use the app.
You can confirm that the status item has been changed to Approved in the Approval List tab.
By clicking the app in the list, you can also view the detailed information of the approval history that the user approved as an approver.
Approval List
If you are the app usage approver, please click the Approval List tab.
- If the user is in a state where approval for app usage has been requested, you can see that the status item in the list is displayed as Pending Approval.
Click the relevant list to view the details of the approval request.
After reviewing the details and leaving the approver’s comments, click the Approve button to allow the requester to use the app.
You can confirm that the status item has been changed to Approved in the Approval List tab.
By clicking the app in the list, you can also view the detailed information of the approval history that the user approved as an approver.
9.5.2.1.1.12 - Personal Profile
Configure Privacy Settings
This is a menu for user settings.
To set your privacy settings, follow these steps.
- Click the Personal Profile > Personal Information setting at the top right of the screen.
- You can view the photo, name, email, phone number, language, and time zone.
- Image: Image > Image Click Change to upload the icon image you want to display.
- Language: Choose your desired language in Korean or English.
- Language/Time Zone: Please select the time zone you are currently in. Click the City Search button to open the city search popup. Search for the desired city in English and select it.
- Click the Save button at the bottom of the screen to save.
Configure Authentication
You can register a user’s authentication tool and set a preferred authentication tool.
To configure authentication, follow these steps.
- Click the Personal Profile > Authentication setting at the top right of the screen.
- Click the +Add New button to add using the authentication tool you prefer.
- Click the Delete button to delete authentication tools you do not wish to use.
- ☆ Click the icon to set your preferred authentication method.
Change Password
In the authentication settings, click Change Password to change your password after completing the identity verification process.
Check login history
You can view the user’s login history and environment.
To view a user’s login history/environment, follow these steps.
- Click Personal Profile > Login History/Environment at the top right of the screen.
- Login History tab allows you to view information such as login date and time, location, country, city, IP address, OS type, browser type, detection status, and result.
- In the Login Environment tab, you can view details of any registered login environments, and if an environment is no longer used, you can delete it using the ‘Delete’ button.
ISO 3166 - Wikipedia, the encyclopedia for everyone Please refer to the page.
This item is a login record where abnormal authentication activity was detected.
Log out
Click the photo icon located at the top right of the screen and then click Logout.
When you click the Logout button, all applications visited through SingleID are logged out simultaneously, and if integrated logout is configured via the PC SSO Agent, logout also proceeds in the associated browsers.
9.5.2.1.2 - Admin Portal
SingleID not only allows authorized users to easily access information assets with a single authentication, but also enhances account security through policy-based permission management and real-time detection of abnormal authentication activities, and provides account management and access frameworks via comprehensive audit logs.
All authentication services and account management services of organizations using the SingleID service, as well as the establishment and configuration of security policies, are managed through the Admin Portal.
A user who can access the Admin Portal to configure and manage the system is called an administrator, and through the Admin Portal’s management functions, they can integrate the organization’s business systems without restriction and define security policies for accessing each business system.
The management functions provided by the Admin Portal are as follows.
| function | Explanation |
|---|---|
| Notification Management | You can register posts to announce to the organization’s users through the user portal and manage the posting period and other settings. If there is urgent information related to system usage, you can post the content on the login screen so that even users who are not logged in can view it. |
| Application Integration Management | It connects the organization’s internal business systems or cloud-based business systems. You can configure it to use standard protocols such as SAML or OIDC for authentication integration, or use the SCIM protocol to import information such as accounts and groups into SingleID or export them via SingleID. |
| Identity Provider Integration Management | If an integrated authentication environment is already established within the organization, you can register that system as an Identity Provider so that applications linked by SingleID can be used without re-authenticating through SingleID. Authentication integration with any Identity Providers that use standard protocols such as SAML and OIDC is possible. |
| Authenticator Management | You can add and manage Authenticators to configure user identity verification or multi-factor authentication. Adding a desktop Authenticator such as PC SSO Agent enables multi-browser SSO. |
| MFA Service Provider Integration Management | If you want to enhance security when accessing business systems while using an already configured in‑organization authentication system, you can connect the business system to an MFA Consumer Provider and add only the multi‑factor authentication function to the system. By linking the system to an MFA Consumer Provider, you can configure the authentication environment to perform second‑factor authentication using the Authenticators added to SingleID. |
| User Management | You can view and edit all users registered in the organization, delete users, or directly register new users. You can also change a user’s group membership or assign permissions so the user can use the application. |
| Group Management | You can view and edit all groups registered in the organization, delete groups, or register new groups. You can also modify a group’s membership rules or assign permissions so that group members can use the application. |
| Login Policy Management | You can set detailed policies specifying which authentication methods can be used when a user logs in with SingleID, and, if needed, create and manage condition-based authentication policies for users authenticating in specific environments. |
| Authentication Policy Management | According to the organization’s security policy, detailed authentication settings can be configured in the following four categories: Session policy, Authenticator policy, MFA Service Provider policy, Password policy. |
| Anomaly Detection Policy Management | SingleID collects and analyzes user behavior data before and after authentication in real time to determine whether abnormal authentication activity is occurring, and provides a function that immediately notifies the user of risk when identified as belonging to an abnormal authentication category. Tenant administrators can manage detailed settings of policies for abnormal behavior detection and decide whether each policy is enabled. |
| Terms and Conditions Management | Use the provided templates to register privacy policies, terms of service, usage conditions, and similar documents that fit the organization’s needs, then notify users and obtain their consent. |
| SMS Settings | SingleID issues an OTP via SMS for identity verification and authentication. In the SMS settings, you can configure and set the SMS messages sent by SingleID. |
If you are using SingleID for the first time, you can set up the basic environment by configuring the features in the following order.
- Register additional administrator (User Registration)
- User synchronization through application integration (Application Registration)
- Management of synchronized users (사용자)
- Group configuration (그룹)
- Business application integration (애플리케이션 등록)
- SMS Settings (SMS Service Settings)
- Register Authenticator (Add Authenticator)
- Login policy configuration (로그인 정책)
- Authentication policy configuration (인증 정책)
The supported SingleID connection environment and recommended specifications are as follows.
| Category | Support | Recommendation |
|---|---|---|
| PC | Windows : Windows Desktop 10 and 11 (x86 and x64 CPU Only)
| Windows : Windows Desktop 10 and 11 (x86 and x64 CPU Only)
|
| Moblie(Android) | Android : 8 and later versions
| Android : 8 and later versions
|
| Moblie(iOS) | iOS : 16 ,17
| iOS : 16 ,17
|
9.5.2.1.2.1 - Dashboard
Notifications are a feature that can deliver and share important alerts related to SingleID usage with users.
Administrators can register and manage notifications through the notifications menu. The administrator selects the notification type (normal/urgent) based on the notification content and priority, and when a notification is created, the user can receive the notification before login (urgent) or after login (normal/urgent).
Administrators can register and manage notifications to be delivered to users. There are two types of notifications, presented as follows.
| type | Explanation |
|---|---|
| General | You can create and deliver general notices to users. Users can view general notifications in the User Portal > Notifications menu. |
| Urgent | You can create and deliver an urgent notice to users. Users can view the urgent alert in a popup window on the login page. |
Notification
list
To view the notification list, access the menu as follows.
- Admin Portal > Dashboard > Notifications
| Category | Explanation |
|---|---|
| type | Notification types.
|
| Title | This is the title of the notification. |
| Period | This is the period for announcing the notification. |
| Registrant | The name of the registered administrator. |
| Registration Date | The date of initial registration. |
| Modifier | Edited administrator name. |
| Modified date | The date of the final modification. |
| All button | Both regular notifications and urgent notifications can be viewed in the list. |
| General button | Only regular notifications can be viewed in the list. |
| Emergency button | Only urgent alerts can be viewed in the list. |
| Search term input field | You can search the notification list. Enter a search term and click the magnifying glass icon or press Enter to perform the search. - Searchable fields: Title, Creator, Modifier ※ Exact match search is possible using ‘full name’, ‘first name’, or ’last name’ for encrypted personal data. |
| Details button | Detailed searches are possible. Search criteria can be combined using AND. After entering multiple fields, click the Search button, and the search will be performed according to the criteria.
|
| Register button | You can register a new notification. |
Register notification
To register a notification, follow the steps below.
- Admin Portal > Dashboard > Notifications Click the menu.
- Register button, when clicked, navigates to the notification registration page.
- Check the input fields below and select and enter the details.
- Click the Save button.
- Check the notifications registered in the list.
| Category | Required or not | Explanation |
|---|---|---|
| type | Required | Select notification type “Normal”, “Urgent” |
| Period | Essential | Specify the notification posting period “Start date~End date” |
| language | Required | Select notification language (activates the “Language” tab based on the selected language) |
| Title | Required | Notification Title |
| content | Required | Write notification content |
If you exceed the maximum number of characters that can be entered, an error message will be displayed.
All required fields must be entered in every active tab. When you click the Cancel button, you go to the notification list screen without saving data.
Edit notification
To edit the notification, follow the steps below.
- Click the Admin Portal > Dashboard > Notifications menu.
- Select the notification that needs editing, and click the Edit button at the bottom of the screen.
- After editing the field you want to modify, click the Save button.
- Check the edited notifications in the list.
Delete notification
To delete the notification, follow the steps below.
- Click the Admin Portal > Dashboard > Notifications menu.
- Select the notifications you want to delete, and click the Delete button at the top right of the screen.
- The notification delete popup appears.
- Click the Confirm button to delete the notification.
Approval request
When you click the approval request menu, the administrator can view and cancel all users’ approval requests.
Approval requests consist of the Approval Request List and Approval Request Queue tabs.
Approval request list
If you click the Approval Request List tab, you can view all approval requests.
There are four types of approval request statuses. You can easily filter and view using the Approval Request, Approved, Rejected, Cancel Submission buttons at the top. If you want an advanced search, you can use the advanced search in the search bar at the top right.
- Approval Request: Shows the status of all approval requests.
- Approval: Shows all approved statuses.
- Rejected: Shows approval request items that have been rejected.
- Submission Cancelled: Shows approval requests where the approval has been cancelled.
The description of the approval request list items is as follows.
| Name | Explanation |
|---|---|
| Approval system | It represents the approval system based on the approval policy. You can verify which approval system the request was made through. Policy > Please refer to the Approval Policy. |
| type | These are types of approval requests. App Access, Sign‑up, Usage Period types are available. - App Access: type for application access requests. - Sign‑up: type for sign‑up requests during registration. - Usage Period: approval request used when extending the account usage period before it expires. |
| Title | This is the approval request title. |
| Requester | I am the approval requester. |
| Recent update date | This is the update date of the recent approval list. |
| Request date and time | This is the initial approval request date and time. |
| status | It shows the status of the approval request and corresponds to the button at the top. |
View and cancel approval requests
When you click the approval request list, the information for that approval request appears in a popup.
View approval request list
A list of all approval requests is displayed.
To view the details of an approval request, click on the item, and the information will pop up.
| Name | Explanation |
|---|---|
| Title | This is the approval request title. |
| Approval System | It represents the approval system based on the approval policy. You can verify which approval system the request was made through. policy > Please refer to the approval policy. |
| status | Indicates the result of processing the approval request. |
| Request date | This is the initial approval request date and time. |
| Last modified date | This is the most recent modification date for the approval request. |
| Requester | Information of the approval requester. ID, name, and organization/department details are displayed. |
| Approver | This is the approver’s information. ID, name, organization/department, task, and date information are displayed. |
| Notifier | This is the notifier’s information. ID, name, organization/department, and date information are displayed. |
Approval request queue
Click the Approval Request Queue tab to view all pending approval requests and delete them using either select all or selective selection. Through detailed search, if the requester has resigned or the approver is absent, the administrator can arbitrarily cancel (delete) the approval request.
Delete approval request
To delete the approval request, follow the steps below.
- Please check(v) the left selection box in the list.
- The Delete button is enabled at the top of the list. 2. Click the Delete button.
- Request Deletion Popup appears. 3. Click the Delete button.
- The selected approval request in the list has been deleted.
Sign up
Click the Sign Up menu to display the list of sign‑up requests.
Sign-up request
When you click the sign‑up request tab, the list of sign‑up requests appears.
There are four types of approval request statuses. You can easily filter and view using the Approval Request, Approved, Rejected, and Cancel Submission buttons at the top. If you want an advanced search, you can use the advanced search in the search bar at the top right.
- Approval Request: Shows the status of all approval requests.
- Approval: Displays all completed approval statuses.
- Rejection: Shows approval request items that have been rejected.
- Submission Cancel: Shows approval requests where the approval has been canceled.
| name | Explanation |
|---|---|
| type | These are the types of approval requests. Standard, IdP* types are available. - Standard: When the request is submitted through the sign‑up on the login page or a separate sign‑up page - Idp: When the sign‑up is requested via an Identity Provider |
| Approval system | It shows the approval system according to the approval policy. You can verify which approval system was used for the request. Please refer to the Policy > Approval Policy. |
| Requester | I am the approval requester. |
| name | Requester name. Exact match search is possible using encrypted personal data with ‘full name’, ‘first name’, or ’last name’. |
| This is the requester’s email address. As encrypted personal data, exact match searches are possible using the full email address or the portion before the ‘@’. | |
| mobile | This is the requester’s mobile number. Since it is encrypted personal data, an exact match search using the last four digits of the phone number is possible. |
| status | It shows the status of the approval request and corresponds to the button at the top. |
| Registration Date | This is the sign-up registration date. |
| Modified date | Last modified date and time. |
Sign-up email invitation
An email invitation for account registration is a method where the administrator sends an invitation email to the desired user’s email address, allowing them to sign up. You can send up to 50 invitation emails at a time.
To send an invitation email, follow the steps below.
- Dashboard > Sign Up > Sign Up Email Invitation Click the tab.
- Click the Send Invitation Email button at the top right.
- Send Invitation Email Popup appears.
- Enter the email address to invite in the email field, and click the Add button.
- Select the group that will be automatically assigned when a recipient joins the group item. (If not set, the group is unspecified)
- Click the Invite button at the bottom right of the popup.
- An invitation email will be sent to the specified email address.
9.5.2.1.2.2 - Integration
Integration is a service that configures and manages authentication services and account information for various applications.
In SCP SingleID, we support integration with new applications through customized authentication integration and account provisioning services, as well as a DIY (Do-It-Yourself) feature.
Through the integration menu, it provides integration management functions such as Application, Identity Provider, Authenticator, MFA Service Provider.
Application
The application is a menu for registering and linking various applications to apply SCP SingleID’s authentication service.
The administrator can register or edit a new application through the application list screen, and can sort, search, and delete registered applications.
Application List
The administrator can select a registered application on the application list screen to edit/delete, sort, search, etc., and can navigate to a menu screen where a new application can be registered through registration.
To view the list of applications, access the menu as follows.
- Admin Portal > Integration > Application
| Category | Explanation |
|---|---|
| Name | This is the name of the application. It can be entered when creating the application. |
| type | The application integration protocols are classified as SAML, OIDC, and SCIM. |
| Screen display | This is an item displayed in the User Portal application list.
|
| status | Application status. It is divided into active and inactive.
|
| All button | Displays both active and inactive applications in the list. |
| Active button | Only active applications are displayed in the list. |
| Disabled button | Only inactive applications are displayed in the list. |
| Search term input field | Application list can be searched. After entering a search term, click the magnifying glass icon or press Enter to perform the search.
|
| Details button | You can perform detailed searches. Search conditions can be combined with AND. After entering multiple fields, click the ‘Search’ button to retrieve results that match the criteria.
|
| Download button | SAML metadata download is available. You can download SAML metadata files from the internal network and the Internet. |
| Register button | You can register a new application. |
Application registration
The administrator can register the application by clicking the Register button on the list screen.
Application registration can be done using two methods: Custom App Integration and Pre-Built App Integration.
To register an application, access the menu as follows.
- Admin Portal > Integration > Application > Register Click the button
- Custom App Integration or Pre-Built App Integration Select tab
Custom App Integration
Custom App Integration registration is the connection menu for authenticating the application you want to integrate and provisioning the account.
We provide three types of connection functions as follows.
When registering an application by linking authentication, you provide and select the type (SAML, OIDC) according to the standard authentication integration method.
When registering an application by linking account provisioning, we provide the standard online API method (SCIM).
The integration features provided by SingleID can be categorized as follows, and the information input and configuration steps vary depending on the required integration scope. When configuring the standard authentication integration methods SAML and OIDC, if you do not select account provisioning, the attribute linking step is omitted, shortening the registration process.
| Standard protocol | Authentication integration, account deployment integration | Authentication integration | Account deployment integration |
|---|---|---|---|
| SAML | ○ | ○ | - |
| OIDC | ○ | ○ | - |
| SCIM | - | - | ○ |
To register the application Custom App Integration, follow the steps below.
- Click the Admin Portal > Integration > Application > Register button
- Custom App Integration > Web Application(SAML) orWeb Application(OIDC) or Identity Provisioning(SCIM v2.0) Select > Next Click the button
- Go to detailed settings
You can register an application by entering and configuring the information required for integration through a six-step screen as shown below.
Applications using standard protocols (SAML, OIDC, SCIM) can register information and configure policies and attributes through a screen consisting of the following six steps.
General
Enter the general application information as referenced below.
| Category | Explanation | Whether required |
|---|---|---|
| Name | Enter the application name. | Required |
| Explanation | Enter the description for the application. | Selection |
| logo image | Register the logo. (File upload or URL link) | Selection |
| Screen display | Displayed to the user in the User Portal. | Select |
| Access URL | Enter the application access URL. | Required |
| Automatic logout | Configure automatic logout according to the session policy. | Selection |
| Automatic redirection | Set automatic redirection to the Service Provider after logout. | Selection |
| URL after logout | Enter the URL to navigate to on logout (if left blank, use Access URL) | Selection |
SSO
On the SSO information entry screen, enter the Single Sign On configuration settings.
| Category | Explanation | Required or not |
|---|---|---|
| Issuer | Enter the SP’s unique identifier value. | Required |
| Single Sign-On URL | Enter the full URL for login. | Required |
| Logout URL | Enter SLO Return URL. | Selection |
| Logout method | Provides Back-Channel Logout, Front-Channel Logout(HTTP Redirect Binding), Front-Chennel Logout(HTTP POST Binding). | Required |
| Response Signing | This is the SAML Response signature configuration. | Selection |
| Validation On-Request | This is the setting for enabling Signature Validation. | Selection |
| Encryption | This is the setting for whether encryption is applied. | Selection |
| Application Certificate | Certificate registration (PEM format) | Required |
| Attribute to map during SSO | Select SSO connection attribute information and set unique values. | Required |
| ‘Import Metadata File’ button | Provides SAML metadata file upload functionality (identifies IdP endpoint and certificate). | Selection |
Single Sign-On Configuration
- If you select either Validation On Request or Encryption, you must register a certificate. * (Register the certificate value exported as Plain Text)
- Attribute to map during SSO You can click Add to select attribute information provided by SingleID. * You must select a unique value for user identification among the selected attributes.
- To deliver SingleID attribute information to the connected target application, you can map the SingleID attribute name to the attribute name used by the application and transmit it. * The information communicated during authentication is called claim information, and the received data is used by the SP to set permissions or as attribute information for operation and management.
Provisioning
The Provisioning menu is an account management feature that can distribute user information to applications for synchronization. SingleID provides global standard API specifications such as SCIM and REST.
On the Provisioning information entry screen, enter the configuration settings for account distribution.
| Category | Explanation | Whether required |
|---|---|---|
| Provisioning Configuration | To use account information synchronization, please click the On button. Selecting Off allows you to SKIP account synchronization. | Required |
| Base Address | Enter the Base Address (URL) that defines the Endpoint of the target system supporting the SCIM API. | Required |
| Accept | Enter the Accept information (e.g., application/json) used as the HTTP Accept Header value in SCIM REQUEST. | Required |
| Content Type | Enter the Content Type (e.g., application/json), which is the HTTP Content-Type header value used in SCIM requests. | Required |
| User Name | Register the User Name used for authentication to the target REST service. | Required |
| Password | Set the password used for authentication to the target REST service. | Required |
| Bearer Token | Register the Bearer Token used when calling the API (for authorization). | Selection |
| Client ID | Register the Client ID. The Client ID is an identifier issued by the authorization server to a registered client, and because the Client ID itself is information disclosed to the resource owner, it must not be used alone for client authentication. | Selection |
| Client Secret | Register the Client Secret information. The Client Secret is a secret generated by the authentication server, a unique value known only to the authentication server. | Selection |
| Access Token Node ID | Register the Access Token Node ID. The Access Token Node ID serves as the Field ID of a JSON Object Node, is returned from the target Access Token REST service, and includes the token value. The Access Token is used to authorize access to resources. It is important that the resource server accepts only the Access Token from the client. | Selection |
| Access Token Base Address | Register the Access Token Base Address (URL) required to obtain an Access Token as the Base Address of the target REST service. | Selection |
| Access Token Content Type | Register the Access Token Content Type (e.g., application/x-www-form-urlencoded), which is the HTTP Content-Type header value of the target Access Token REST service. | Required |
| Provisioning | When provisioning, select either a user or a group by default, and if needed, you can select both users and groups. | Selection |
| Inbound Provisioning Schedule | Click On to register periodically (hourly, daily, monthly, yearly) via the Intbound Provisioning Schedule. | Selection |
| Outbound Provisioning Schedule | You can click On to register an Outbound Provisioning Schedule. Clicking Off allows real-time deployment. | Selection |
Profile
Enter the configuration information for User/Group for deployment on the profile information input screen.
| Category | Explanation | Required or not |
|---|---|---|
| Profile name | Enter the profile name. | Required |
| Explanation | Register a description for the profile. | Select |
| attribute | Click Add to select and input attribute information. | Selection |
Profile Mapping
- In the tab menu for selecting the provisioning target, click User, Group to add properties.
- Click Profile Mapping to align and connect the required information in the target application based on the SCIM schema information.
- Provides a feature that allows you to configure an execution script (a conversion script based on the JEXL standard script) capable of real‑time conversion when running provisioning. Note that it executes exactly as entered, without any validation checks.
After entering all items, click the Complete button to complete the basic application settings. When you complete registering a new application, it is added to the application list, and new tabs called Policy, Assignment are created.
Policy
You can configure login policy and access control information for application policy settings.
| Category | Explanation | Required or not |
|---|---|---|
| Login Policy | Configure the login policy applied when logging into the application. To set it, please assign the application in the login policy. | Selection |
| Access control | This setting controls the user’s access to the app. When enabled, you can configure whether to request permission to access the application and whether it is approved. | Selection |
Allocation
Register information for assigning application users based on users and groups. This menu assigns access permissions by configuring the users and groups that can access the registered application.
To assign a user, follow the steps below.
- When you click the application, you will be taken to the application’s detail page.
- Click the Assignment tab and click the User tab > Assign button.
- User Assignment When the popup appears, select the user to assign, and click the Assign button.
- In the Assignment tab, the selected user appears in the list.
Similarly, you can assign a predefined group via the Assign button on the Group tab. Assign the group using the same method.
Group Settings
- When configuring the groups that can access the application, set it to include information that defines and distinguishes specific groups.
- You must define rules and groups in advance so that you can manage access permissions using member rules that distinguish groups.
Application State
Activation (Active): Exposes the application in the User Portal and, by configuring Sign-On services, provisioning, policies, etc., places it in a state where users can access and use the application.
Inactive: It does not expose the application in the User Portal and is a state where the application can be deleted.
Delete: When deleting a registered application, caution is required. * Thus, we display a popup window to allow a second verification of the application’s information and status.
Pre-Built App Integration
The Pre-Built App Integration menu offers a convenient way to quickly connect and use the desired SaaS application, with necessary settings such as connection information, name, and icon prepared in advance.
To integrate the application using Pre-Built App Integration, refer to the menu path below.
- Admin Portal > Integration > Application > Register > Pre-Built App Integration Click the tab
- Select Application > Next button click
- Go to detailed settings
The Pre-Built App Integration menu, like the Custom App Integration menu, allows you to register an application by entering the required integration information and configuring it through a six-step screen as shown below.
The input items and methods for each step are the same, except for the information that has been predefined and entered for Pre‑Built.
- [General] {#general-1}
- [SSO] {#sso-1}
- [Provisioning] {#provisioning-1}
- [Profile]{#file-1}
- [Policy] {#policy-1}
- [Assignment] {#configuration}
General
Enter the general application information as referenced below.
| Category | Explanation | Required or not |
|---|---|---|
| Name | Enter the name of the application. | Required |
| Explanation | Enter a description of the application (tasks, purposes, etc.). | Selection |
| logo image | Register a logo that intuitively identifies the application. Both file upload and URL link methods are available. | Selection |
| Screen display | When selected, it is displayed to the user in the User Protal. | Selection |
| Access URL | Enter the application’s Access URL. Enter the login page for the application you will access. | Required |
| Automatic logout | When selected, the session policy automatically logs out without re‑confirmation. | Selection |
| Automatic redirection | When selected, it redirects to the Service Provider without displaying the logout completion page. | Selection |
| URL after logout | Enter the URL to navigate to when the user logs out. If left blank, it will be set to the Access URL. | Selection |
SSO
Enter the Single Sign On configuration information on the SSO information entry screen.
| Category | Explanation | Required status |
|---|---|---|
| Issuer | Enter the Issuer, which is the unique identifier of the SP (Service Provider) and the value verified by the Response Issuer. | Required |
| Single Sign-On URL | Enter the Single Sign-On URL, the full URL required when logging into the system. | Required |
| Logout URL | Enter the Logout URL, which is the URL value for SLO (Single Logout) Return. | Selection |
| Logout method | The logout methods for SLO (Single Logout) Return are provided in three ways as follows.
| Required |
| Response Signing | To sign the returned SAML Response after the authentication process, use Response Signing. | Selection |
| Validation On-Request | Check to enable Signature Validation. | Selection |
| Encryption | Select whether to apply encryption. | Selection |
| Application Certificate | If you select either Validation On Request or Encryption, you must register a “certificate”. Please enter a valid value according to the PEM(Privacy-Enhanced Mail) format. | Required |
| Attribute to map during SSO | Select the attribute information required for SSO connection and set a unique value for user identification. ※ The ‘Next’ button becomes active only after selecting the Subject Attribute. | Required |
| ‘Import Metadata File’ button | The SAML metadata file contains information about various SAML identity providers that can be used for SAML 2.0 protocol message exchanges. This metadata identifies the IdP endpoints and certificates to secure SAML 2.0 message exchanges. Clicking Import metadata file allows you to upload a file. | Selection |
Single Sign-On Settings
- If you select either Validation On Request or Encryption, you must register a certificate. * (Register the certificate value exported as plain text)
- Attribute to map during SSO You can click Add to select the attribute information provided by SingleID. * A unique value for user identification must be selected among the chosen attributes.
- To pass SingleID attribute information to the connected target application, you can align the SingleID attribute name with the attribute name mapped in the application. * The information communicated during authentication is called claim information, and the received data is used by the SP to set permissions or as attribute information for operation and management.
Provisioning
The Provisioning menu is an account management feature that can distribute user information to applications for synchronization. SingleID provides global standard API specifications such as SCIM and REST.
Enter the configuration settings for account information distribution on the Provisioning information input screen.
| Category | Explanation | Required or not |
|---|---|---|
| Provisioning Configuration | Click the ‘On’ button to enable account information synchronization. Selecting ‘Off’ allows you to SKIP account synchronization. | Essential |
| Base Address | Enter the Base Address (URL) that defines the Endpoint of the target system supporting the SCIM API. | Required |
| Accept | Enter the Accept information (e.g., application/json) used as the HTTP Accept Header value in SCIM REQUEST. | Required |
| Content Type | Enter the Content Type (e.g., application/json) that is the HTTP Content-Type header value used in SCIM requests. | Required |
| User Name | Registers the User Name used for authentication to the target REST service. | Required |
| Password | Set the password used for authentication to the target REST service. | Required |
| Bearer Token | Register the Bearer Token used when calling the API (for authorization). | Selection |
| Client ID | Register the Client ID. The Client ID is an ID issued by the authorization server to a registered Client, and because the Client ID itself is information disclosed to the resource owner, it must not be used alone for Client authentication. | Selection |
| Client Secret | Register the Client Secret information. The Client Secret is a secret generated by the authentication server, a unique value known only to the authentication server. | Selection |
| Access Token Node ID | Register the Access Token Node ID. The Access Token Node ID serves as the Field ID of a JSON Object Node, is returned from the target Access Token REST service, and includes the token value. The Access Token is used to authorize (authorize) access to resources. It is important that the resource server accepts only the Access Token from the client. | Selection |
| Access Token Base Address | Register the Access Token Base Address (URL) required to obtain an Access Token as the Base Address of the target REST service. | Selection |
| Access Token Content Type | Register the Access Token Content Type (e.g., application/x-www-form-urlencoded), which is the HTTP Content-Type header value of the target Access Token REST service. | Required |
| Provisioning | When provisioning, select either a user or a group by default, and if needed, you can select both users and groups. | Selection |
| Inbound Provisioning Schedule | Click On to register periodically (hour, day, month, year) via the Intbound Provisioning Schedule. | Select |
| Outbound Provisioning Schedule | Click On to register an Outbound Provisioning Schedule. Click Off to deploy in real time. | Selection |
Profile
On the profile information entry screen, enter the user/group settings for deployment.
| Category | Explanation | Required or not |
|---|---|---|
| Profile name | Enter the profile name. | Required |
| Explanation | Register a description for the profile. | Required |
| attribute | Click Add to select and enter the property information. | Required |
Profile Mapping
- In the tab menu for selecting the provisioning target, click User, Group to add properties.
- Click Profile Mapping to align and connect the required information in the target application based on the SCIM schema information.
- Provides the ability to configure an execution script (written as a conversion script based on the JEXL standard script) that can perform conversion in real time when running provisioning.
Note that it executes exactly as entered, without any validation checks.
After entering all items, click the Complete button to complete the basic application configuration. When you complete registering a new application, it is added to the application list, and new tabs called Policy, Assignment are created.
Policy
You can configure login policies and access control information for application policy settings.
| Category | Explanation | Required status |
|---|---|---|
| Login Policy | Configure the login policy applied when logging into the application. To set it, assign the application in the ‘Login Policy’ you want to configure. | Selection |
| Access control | This setting controls the user’s access to the app. When enabled, you can configure whether to request permission to access the application and whether approval is granted. | Selection |
Allocation Settings
Register information for assigning application users based on users and groups. This menu assigns access permissions by configuring the users and groups that can access the registered application.
To assign a user, follow the steps below.
- When you click the application, you are taken to its detail page.
- Click the Assign tab and then click the User tab > Assign button.
- User Assignment popup appears, select the user to assign, and click the Assign button.
- The selected user appears in the list on the Assignment tab.
Similarly, in the Group tab, you can assign a predefined group using the Assign button. Assign the group using the same method.
Group Settings
When configuring the groups that can access the application, set it to include information that defines specific groups for distinction. You must define rules and groups in advance so that you can manage access permissions with member rules that can distinguish groups.
Application State
- Activation (Active): Exposes the application in the User Portal and, by configuring Sign-On services, provisioning, policies, etc., places the application in a state where users can access and use it.
- Inactive: It does not expose the application in the User Portal and is a state where the application can be deleted.
- Delete: When deleting a registered application, caution is required. * Thus, we display a popup window to allow a second verification of the application’s information and status.
Application modification
When you click an application in the list view, you can edit its settings.
To modify the application, follow the steps below.
- Click the Admin Portal > Integration > Select Application > Edit button.
- Click the General, SSO, Provisioning, Policy, Assignment, Aggregation, Permission Items, Rebranding tab to edit the items you want to modify.
- Click the Save button.
Permission item
The permission items provide synchronization by linking the user roles of the integrated application with SingleID.
Register permission item
To set the permission items, follow the steps below.
- When you click the application, you are taken to its detail page.
- Click the Allocation tab and the Permission Items tab > click the Register button.
- When the Permission item popup appears, you need to register the permission item.
- Enter Name, Key, Display Name, Content and click Save to register the permission.
| Category | Explanation | Required status |
|---|---|---|
| Name | Enter the permission name. The permission name cannot be changed after it is registered once. If you want to change it, you need to register a new one. | Required |
| Key | Enter the authorization key. The authorization key cannot be changed after it is registered once. If you want to change it, you need to register a new one. | Selection |
| Display name | Enter the permission display name. | Selection |
| Explanation | Enter the permission description. | Selection |
Rebranding
A rebranding tab that does not appear during registration in the application is added. Rebranding of the application includes login page rebranding functionality when accessed as a separate application.
The included rebranding features are as follows.
- Favicon: The favicon can be modified in the browser.
- Header logo: The header logo on the login screen can be modified to the logo you desire.
- Key visual image: The key image set by default on the login page can be modified.
- Sign‑up page redirection: Registration can be directed to a separate operational sign‑up page instead of SingleID’s sign‑up page.
- Privacy Policy Redirection: You can register the privacy policy URL that was used in the existing application.
- Terms of Service redirection: You can register the Terms of Service URL previously used in the existing application.
UI
From the list screen, click the application, then in the Rebranding tab, click the Edit button to configure application-specific rebranding settings for the UI.
Change favicon
In the application, you can set a custom favicon to match the characteristics of the enterprise application.
To modify the favicon, follow the steps below.
- Admin Portal > Integration > Select Application > UI > Edit Click the button.
- Select custom in the Favicon item.
- Favicon image (pencil shape) item, then click the favicon image.
- Upload an icon file or enter the icon image URL.
- Click the Save button and use the preview screen to confirm that the upload was successful. 6.Korean page Enter the title in Korean.
- English page Enter the title in English.
- Once the input is complete, use the preview on the right to confirm that it was entered correctly.
- Click the Publish button at the lower right corner.
Header logo change
In the application, you can configure separate header logo changes to match the characteristics of the corporate application.
To modify the header logo, follow the steps below.
- Click the Admin Portal > Integration > Select Application > UI > Edit button.
- Select Custom in the Header Logo item.
- You can select and configure a text logo or an image logo.
- Enter the Korean Redirect URL and the English Redirect URL.
- If the input is complete, use the preview on the right to confirm that it was entered correctly.
- Click the Publish button at the lower right.
Key visual change
In the application, you can configure separate key visual changes to match the characteristics of the corporate application.
To edit the key visual, follow the steps below.
- Admin Portal > Integration > Select Application > UI > Edit Click the button.
- In the key visual item, select Custom.
- Click to use a single key visual for all languages or language‑specific key visuals.
- If the image upload is complete, verify through the right preview that it was entered correctly.
- Click the Publish button at the lower right corner.
Redirection
From the list screen, click the application, then in the Rebranding tab, click the Edit button to configure application‑specific rebranding settings for the redirect.
Sign up
Sign-up allows you to configure a registration link for each application.
| Category | Explanation |
|---|---|
| default | We use the default registration provided by SingleID instead of a separate sign‑up page. The default settings can be configured in the registration policy. |
| User-defined | If you operate a separate sign‑up page, you can set a separate Redirection link.
|
| Hidden | If you do not accept separate sign‑ups, select Hide. |
Privacy Policy
The privacy policy can be redirected to the URL link of the privacy policy provided for each application.
| Category | Explanation |
|---|---|
| default | Set as the default privacy policy for SingleID. |
| User-defined | If you operate a privacy policy for a separate application, you can set a separate Redirection link.
|
Terms of Use
The Terms of Service can be redirected to the privacy policy URL link provided for each application.
| Category | Explanation |
|---|---|
| default | Set as SingleID default terms of service. |
| User-defined | If you operate terms of service for a separate application, you can set a separate Redirection link.
|
Delete application
On the application list screen, select the application, deactivate it, then return to the list screen and you can delete it from the three‑dot menu.
Identity Provider
This is the menu for registering and managing IdPs that provide authentication services and credentials to SCP SingleID. At this point, the SCP SingleID acts as a Service Provider and receives authentication services from the IdP.
Identity Provider list
On the list screen, you can select a registered Identity Provider to edit/delete, sort, search, etc., and you can navigate to a menu screen where you can register a new Identity Provider.
To view the Identity Provider list, you can access the following menu.
- Admin Portal > Integration > Identity Provider
| Category | Explanation |
|---|---|
| Name | Identity Provider name. |
| type | Displays the standard protocols registered for the Identity Provider. Identity Provider types are distinguished by SAML2.0 and OIDC methods. |
| status | Displays the status of the Identity Provider. It is distinguished as active or inactive. |
| Active button | Only active Identity Providers are displayed in the list. |
| disabled button | Only inactive Identity Providers are displayed in the list. |
| Search term input field | You can search the Identity Provider list. After entering a search term, click the magnifying glass icon or press Enter to perform the search. Searchable fields: name, description |
| Details button | Detailed searches are possible. Search conditions can be combined using AND. After entering multiple fields, click the Search button to perform a search that matches the criteria. Click the Reset button to clear all search fields. |
| Download button | SAML metadata download is available. You can download SAML metadata files from the internal network and the Internet. |
| Register button | You can register a new application. |
Identity Provider registration
On the Identity Provider list screen, click Register at the top to add a new entry.
To register an Identity Provider, follow the steps below.
- Admin Portal > Integration > Identity Provider > Register Click the button
- Custom App Integration > Web Application(SAML) or Web Application(OIDC) Select > Next Click the button
- Go to detailed settings
You can register an Identity Provider by entering and configuring the required integration information through a three-step screen as follows.
- [General] {#General-2}
- [SSO] {#sso-2}
- [JIT provisioning] {#jit}
General
Enter the general information for the IdP (Identity Provider).
| Category | Explanation | Required or not |
|---|---|---|
| name | Enter the name of the Identity Provider. Since it is identified by its name, rules are needed for distinction and management. | Required |
| Explanation | Enter a description of the Identity Provider (including its functions, purposes, etc.). | Select |
| logo image | Register a logo that intuitively identifies the Identity Provider. | Select |
| Login button | Display the IdP as a button/link (text) etc.
| Required |
SSO
Enter the Single Sign-On configuration information on the SSO input screen.
When integrating with a Web Application (OIDC)
| Category | Explanation | Required or not |
|---|---|---|
| Client ID | Register the Client ID. The Client ID is an ID issued by the authentication server to a registered Client, and because the Client ID itself is information disclosed to the resource owner, it must not be used alone as the Client ID during client authentication. | Required |
| Client Secret | Register the Client Secret information. The Client Secret is a unique value known only to the authentication server, used as secret information when authenticating to the target REST service. | Required |
| Authorization Endpoint URL | The Authorization Endpoint must obtain authorization from the Resource Owner. Enter the Authorization Endpoint URL, which is the URL value used at this time. | Required |
| Token Endpoint URL | The Token Endpoint is used by the client and obtains an Access Token via an Authorization Grant or a Refresh Token. Enter the Token Endpoint URL, which is the URL value used at this time. | Required |
| Logout URL | Enter the Logout URL, which is the URL value for SLO (Single Logout) Return. | Selection |
| Userinfo Endpoint URL | Enter the Userinfo Endpoint URL provided by the IdP(Identity Provider) that includes the user profile (username, name, etc.). | Selection |
| IdP Sign-In Key | Set the IdP Sign-In Key value and select the SingleID mapping property for the IdP Sign-In Key. | Required |
IdP Sign-In Key Configuration There are two methods to process login in SCP SingleID by receiving the key value that provides the ID.
- How to obtain the identifier ID value using a standard SAML keyword
- How to create and receive a custom identifier ID
You can map the name obtained by one of the above methods to User ID, or you can also map it to the CN value. This feature configures how authentication information is mapped to a value for processing login.
JIT provisioning
The JIT provisioning feature tab has been added to the Identity Provider. This feature synchronizes the account in real time when a user’s changes occur. You can configure items when the account is synchronized in real time.
| Category | Explanation | Required or not |
|---|---|---|
| JIT provisioning | JIT provisioning, short for Just-In Provisioning, is an ID and access management feature used to quickly create user accounts when a user logs into the system for the first time.
| Required |
| If there is no SingleID user mapped to the IdP user. | When a user accesses for the first time, manage the action.
| Required |
| If there is a SingleID user mapped to the IdP user | If a user exists, update the user information. | Required |
After entering all items, click the Complete button to complete the basic application setup.
Modify Identity Provider
On the list screen, you can modify the settings by clicking the Identity Provider.
If you want to modify the Identity Provider, follow the steps below.
- Click the Admin Portal > Integration > Select Identity Provider > Edit button.
- Click the General, SSO, Provisioning, Policies, Assignment tab to edit the items.
- Click the Save button.
Delete Identity Provider
On the Identity Provider list screen, select an Identity Provider, deactivate it, then return to the list screen where you can delete it from the three‑dot menu. To register again, click the Add button.
Authenticator
Configure by integrating the Authenticator provided by SCP SingleID. Password and Email are enabled by default.
The types and functions of Authenticators are as follows.
- Password: The Password Authenticator verifies a password known only to the user to authenticate the user as a knowledge‑based authentication method. * It is the built-in Authenticator used for primary and secondary authentication, and it cannot be deleted or disabled for security reasons.
- Email: An ownership-based authentication method that authenticates the user through an OTP (One-Time Password) delivered to the user’s email account.
- Active Directory: Enter the user password of the linked Active Directory to authenticate.
- Knox Identity: Authenticate by entering the user password of the linked Knox Portal.
- Knox Messenger: Enter the Knox Messenger OTP received via the registered Knox Messenger to authenticate.
- PC SSO Agent: Install SingleID’s PC SSO Agent on a PC to perform integrated authentication (SSO) and unified logout across various web browsers, and to authenticate through PC security checks.
- SingleID Authenticator: SingleID dedicated authentication mobile app that supports biometrics (fingerprint, facial), PIN, mOTP, and TOTP.
- SMS: Enter the SMS OTP received on the registered mobile phone to authenticate.
- Passkey: Mobile Passkey, security key, a convenient authentication method that enables easy login with Windows biometric/PIN code.
- TOTP Authenticator: Enter the TOTP received via the registered authentication app or web extension to authenticate.
Authenticator list
We support all authenticators of the six supported types.
To check the Authenticator, please refer to the following path.
- Admin Portal > Integration > Authenticator
Add Authenticator
On the Authenticator list screen, clicking Register moves to the next screen, switching to a screen where you can add an Authenticator.
To add an Authenticator, follow the steps below.
- Admin Portal > Integration > Authentictor > Add Click the button.
- Each authentication methodselect > Next click the button.
- Enter the information required for authentication settings.
- Click the Save button.
Add Active Directory {#Active Directory-add}
Users can authenticate using the connected Active Directory.
To add Active Directory, follow the steps below.
- Admin Portal > Integration > Authentictor > Add Click the button.
- Select Active Directory > Click the Next button.
- The General page appears. 3. Please review Authnticator Overview and click the Next button.
- Settings page appears. 4. Enter the information to register Active Directory as an Authenticator.
- After entering all information, click the Connection Test button to verify.
- After checking everything, click the Save button.
| Category | Explanation | Required or not |
|---|---|---|
| LDAP URL | Enter the LDAP URL of Active Directory. Enter a valid URL that includes ldap:// or ldaps:// for encrypted communication. Example) ldap://ldap.example.com/dc=example,dc=com | Required |
| Service User DN | Enter the unique identifier of the service-dedicated LDAP account. | Required |
| service user password | Enter the service user’s password in password format. | Required |
| User search base DN | Enter the user search base DN, the string that specifies the starting point for searches in the LDAP directory tree. | Required |
| User attribute | Enter user attributes. | Required |
| Check LDAP connection | After entering all the above LDAP settings correctly, click the Connection Test button to perform the integration test. | Required |
Active Directory Authenticator can be used as follows:
- Login
- Identity verification during the registration process
- Password reset
- Unlock ID
Add Knox Identity
Users can authenticate using the connected Nox portal.
To add Knox Identity, follow the steps below.
- Admin Portal > Integration > Authentictor > Add Click the button.
- Select Knox Identity > Click the Next button.
- General page appears. 3. Check the Authnticator Overview and click the Next button.
- Policy page appears. 4. Enter the information to register Knox Identity as an Authenticator.
- After entering all information, click the Connection Test button to verify.
- After checking everything, click the Save button.
| Category | Explanation | Required or not |
|---|---|---|
| Maximum allowed authentication failure attempts | Set the maximum allowed number of authentication failures when using Knox Identity. It can be set from 1 to 10 times. | Required |
| Nox ID | Enter the Nox ID to test whether the account is linked. | Required |
| Nox password | Enter the Nox password to test whether the account is linked. | Required |
| Verify Knox Identity connection | Click the Connection Test button to run the test. If the test fails, contact the administrator. | Required |
Active Directory Authenticator can be used as follows:
- Login
- Identity verification during the registration process
- Password reset
- Unlock ID
Add Knox Messenger
Enter the Knox Messenger OTP received via Knox Messenger to authenticate.
To add Knox Messenger, follow the steps below.
- Admin Portal > Integration > Authentictor > Add Click the button.
- Select Knox Messenger > Click the Next button.
- General page appears. 3. Check the Authenticator Overview and click the Next button.
- Policy page appears. 4. Enter the information required to register Knox Identity as an Authenticator.
- After entering everything, click the Save button.
| Category | Explanation | Required or not |
|---|---|---|
| Access Token | Enter the Access Token for Knox Messenger. | Required |
| Authentication code timeout (minutes) | Enter the expiration time (minutes) for the verification code. It can be set from 3 minutes up to a maximum of 30 minutes. | Required |
| Maximum allowed authentication failure attempts | This is the maximum number of re-entries allowed after authentication failure. Please select the maximum allowed count. You can select from 1 to 10 times. | Required |
Knox Messenger Authenticator can be used as follows:
- Login
- Passwordless authentication
- Identity verification during the registration process
- Find ID
- Password reset
- Unlock ID
Add PC SSO Agent
To use SSO across multiple browsers, you can install the PC SSO Agent on the user’s PC.
To add the PC SSO Agent, follow the steps below.
- Admin Portal > Integration > Authentictor > Add button, click it.
- Select PC SSO Agent > Click the Next button.
- General page appears. 3. Check the Authenticator Overview and click the Next button.
- Policy page appears. 4. Enter the information required to register with the PC SSO Agent.
- After entering everything, click the Save button.
| Category | Explanation | Required or not |
|---|---|---|
| Use PC SSO Agent for multi-browser SSO | Click the Activate button to enable it. To enable multi-browser SSO, you must configure a login policy for each application. Once enabled, SSO between Chrome and Edge browsers is possible. Set the login policy in Policy > Login Policy. | Selection |
| Prevent login using unsupported browsers | Click the Activate button to activate. If activated, login will be restricted on browsers other than Chrome and Edge. | Selection |
| Forcefully close the browser upon PC SSO Agent logout | Click the Activate button to enable it. When activated, it will be forcibly closed on Chrome and Edge browsers upon logout. | Selection |
| Property Settings | When launching the PC SSO Agent, you can configure the user attributes that SingleID will pass to the PC SSO Agent. The configured user attributes are used for multi-browser SSO and C/S program (Rich Client application) authentication. To set the attribute, click the Add button to configure user attributes. | Selection |
| Forcefully close the browser upon PC SSO Agent logout | Click the Activate button to enable it. When activated, it will be forcibly closed on Chrome and Edge browsers upon logout. | Selection |
This Authenticator can be used as follows:
- Multi-browser SSO
- Rich Client application authentication
Add SingleID Authenticator
Authenticate using the SingleID Authenticator mobile app provided by SingleID.
If you want to add the SingleID Authenticator, follow the steps below.
- Admin Portal > Integration > Authentictor > Add Click the button.
- Select SingleID Authenticator > Click the Next button.
- The General page appears. 3. Please review the Authnticator Overview and click the Next button.
- Policy page appears. Enter the information to register the SingleID Authenticator as an Authenticator.
- After entering everything, click the Save button.
| Category | Explanation | Required or not |
|---|---|---|
| Authentication wait time (minutes) | Enter the authentication waiting time (minutes). This is the input time for authentication processing. It can be set between 3 and 30 minutes. | Required |
| Maximum allowed authentication failure attempts | This is the maximum number of re-entries allowed after authentication failure. Please select the maximum allowed number of attempts. You can select from 1 to 10 times. | Required |
| TOTP generation interval (seconds) | This is the interval (seconds) for automatically generating OTPs. It can be set from 15 to 120 seconds. | Required |
| Number of adjacent TOTP intervals | This is the count of TOYP codes to allow before and after based on the SingleID server time. If this value is 3, three TOPT codes before and after the SingleID server time are allowed. This setting can prevent authentication failures caused by the time difference between the SignleID server time and the SingleID Authenticator. You can select 0 to 5. | Required |
| App Push Type | You can set the push type for the SingleID Authenticator app. | Required |
| SingleID Authenticator biometric authentication replacement setting | If the user’s mobile phone does not have fingerprint or facial recognition features, authentication can be performed using alternative methods. It can be replaced with PIN, mOTP, or TOTP; when all users are selected, the user can change to another authentication method for authentication. If you want to apply it only to a separate group, select Apply only to the group below. | Required |
This Authenticator can be used as follows:
- Login
- Passwordless authentication
- Identity verification during the registration process
- Find ID
- Password reset
- Unlock ID
Add TOTP Authenticator
Enter the TOTP received through the registered authentication app or web extension to authenticate. You can use TOTP authentication methods to support 3rd Party Authenticators such as mobile authentication apps (Google Authenticator, Microsoft Authenticator, etc.) and web browser extensions (Chrome Web Store, Microsoft Edge Add-ons, etc.).
To add the TOTP Authenticator, follow the steps below.
- Admin Portal > Integration > Authentictor > Add Click the button.
- Select TOTP Authenticator > click the Next button.
- General page appears. 3. Please review the Authenticator Overview and click the Next button.
- Policy page appears. 4. Enter the information required to register with the TOTP Authenticator.
- After entering everything, click the Save button.
| Category | Explanation | Required or not |
|---|---|---|
| Maximum allowed authentication failure attempts | This is the number of allowed re‑entries when an incorrect TOTP is entered or a TOTP that exceeds the time limit is entered. It can be set from 1 to 10 times. | Required |
| Number of adjacent intervals in TOTP | This is the number of TOTP codes allowed before and after based on the SingleID server time. If this value is 3, three TOTP codes before and after the SingleID server time are allowed. This setting can prevent authentication failures caused by time differences between the SingleID server time and the SingleID Authenticator. 0 ~ 5 can be selected. | Required |
| Issuer | When a user registers a ‘TOTP Authenticator’ using an ‘Authenticator App’ or ‘Web Extention’ and registers via a QR code, the format ‘Issuer : Tenanat/UserID’ appears on the user screen. | Required |
This TOTP Authenticator can be used as follows:
- Login
- Multi-Factor Authentication (MFA)
- Authentication during Authenticator registration
- Password reset
- Unlock
- Conditional authentication
- Authentication for non‑compliant PCs
To apply the TOTP Authenticator, set it in the authentication policy.
- Available Authenticator (for login policy) → Use TOTP Authenticator when the user logs in
- Authenticator registration authentication → User uses TOTP Authenticator during Authenticator registration
- Account recovery > Password reset → Use TOTP Authenticator when the user resets the password
Modify Authenticator
On the Authenticator list screen, after selecting an Authenticator and clicking Edit, it switches to the edit screen.
If you want to modify the Authenticator, follow the steps below.
- Admin Portal > Integration > Authentictor > Edit button click
- Edit each item, then click the Edit button to complete the changes.
Delete Authenticator
On the Authenticator list screen, select an Authenticator, disable it, then return to the settings screen, and you can delete it using the delete button in the three‑dot menu. You must exclude the authentication policy settings before disabling; otherwise, the disable cannot be applied.
To delete the Authenticator, follow the steps below.
- Admin Portal > Integration > Authentictor List > Authenticator right three dots Click.
- Disable popup click
- If a warning popup appears, check the applied authentication policy.
- To manage the lower authentication policy, please click here. Then click to exclude the policy from the authentication settings.
- Deactivation is completed when the corresponding authentication policy is excluded from the authentication policy information.
- After deactivation is complete, click the Authenticator and then click the Delete button.
MFA Service Provider
MFA Service Provider provides a service that enhances user convenience by applying biometric and simple authentication technologies along with strengthened authentication methods, meeting the security requirements required by enterprises through multi-factor authentication.
MFA Service Provider List
To view the list of MFA Service Providers, you can access the following menu.
- Admin Portal > Integration > MFA Service Provider
| Category | Explanation |
|---|---|
| Name | This is the name of the MFA Service Provider. |
| System code | Displays system code information. |
| project code | Displays project code information. |
| User Tag | Displays the User Tag. |
| type | Shows how to integrate the MFA Service Provider. It is presented in the following three methods.
|
| System code input field | Enter the system code information. |
| Project code input field | Enter the project code information. |
| Search term input field | You can search the Identity Provider list. Enter a search term and click the magnifying glass icon or press Enter to perform the search.
|
| Details button | Detailed searches are possible. Search conditions can be combined using AND. After entering multiple fields, click the Search button, and the search will be performed according to the criteria.
|
| Register button | You can register a new MFA Service Provider. |
MFA Service Provider registration
To register the MFA Service Provider, follow the steps below.
- Admin Portal > Integration > MFA Service Provider > Register Click the button
- ADFS Federated Application or Custom Application or Network Equipment Select > Next Click the button
There are three types of MFA Service Provider.
- ADFS Federated Application : It uses the AD Flugin method and registers an ADFS federation application that will be linked with SingleID MFA.
- Custom Application : Registers an application that uses the MFA API in API mode and integrates with SingleID MFA.
- Network Equipment : It uses the RADIUS method and registers network equipment that will be linked with RADIUS‑based MFA.
Through a three-step screen as shown below, you can enter the required information, configure it, and register the MFA Service Provider for integration.
- [General] {#General-3}
- [MFA integration] {#integration}
- [Owner] {#owner}
General
Enter general information for the MFA Service Provider.
| Category | Explanation | Required or not |
|---|---|---|
| Name | Enter the name of the MFA Service Provider. Since it is identified by its name, a rule for distinction and management is required. | Required |
| Explanation | Enter a description of the MFA Service Provider (including its functions, usage, etc.). | Selection |
| Logo image | Register a logo that can intuitively identify the MFA Service Provider. | Selection |
| Manage users using User Tag | If you enable User Tag usage, when a new user is registered from the MFA Service Provider, “#"+User Tag is automatically appended to the user’s ID, preventing duplicate ID registrations. | Selection |
| User Tag | Only one User Tag can be registered per MFA Service Provider. - A User Tag cannot be modified after registration; it is a tag attached to the MFA Service Provider and the user. - Tenant administrators can define and use User Tags. Users provisioned via JIT through the MFA Service Provider have the same User Tag set as a user attribute, allowing identification of where the user was created. | Required |
| System code | Enter the system code information. | Selection |
| project code | Enter the project code information. | Selection |
| campaign | If only one authentication method is used, a pop-up page guiding the user to register an authentication method is displayed. It becomes active when the selection box is selected. | Selection |
MFA integration
Enter MFA integration information.
| Category | Explanation | Required or not |
|---|---|---|
| Conditional authentication | Conditional authentication is a policy that performs additional authentication when the authentication conditions registered in conditional authentication are met. To apply conditional authentication, click the check box. Select the WHEN policy and the THEN policy. The WHEN policy is an authentication policy executed when a specific condition occurs at login. The THEN policy performs an additional identity verification when the WHEN policy is satisfied. | Selection |
| Login | Add the provided Authenticator to the Chip Box. When logging in, click the Activate button to use the delegation to the administrator. If you enable the delegation option to the administrator, you can see the following guide messages on the ‘Select Authentication Option’ page for registration. 1. “If you cannot complete identity verification due to any issue, you can request verification from the manager. Click here” 2. “If a problem occurs with identity verification, you can request delegated verification from the administrator. Please click here." ※ Delegation is only possible to administrators who have registered the SingleID Authenticator mobile app as an Authenticator. | Required |
| Authentication during Authenticator registration | Set the identity verification method that the user must perform during the Authenticator registration process. The user configures an Authenticator for identity verification. Perform the following additional authentication: strengthen verification during the identity verification process. * Whether to perform authentication during registration when no Authenticator is registered: set whether to proceed when the user has no registered Authenticator. 1. Perform When selected, the user can register an additional authentication method and then authenticate. 2. Do not perform When selected, authentication is not carried out if there is no registered authentication method. 3. Follow JWT When selected, the predetermined JWT policy is adhered to. * Click the Enable button to use the authentication delegation feature for administrators. ※ Authentication delegation is only available to administrators who have registered the SingleID Authenticator mobile app as an Authenticator. | Selection |
| List of administrators to delegate authentication | Select the checkbox if you want to use the delegated administrator list of the SCP cloud object storage as a separate authentication administrator list when delegating authentication to an administrator. This option is available only when “Delegate authentication to administrator” is enabled in the “Authenticate during Authenticator registration” or “Login” items. To retrieve and apply an administrator list stored as a JSON file in cloud object storage, the following settings are required. 1. Access Key: Enter the Access Key of the cloud object storage. 2. Secret Key: Enter the Secret Key of the cloud object storage. 3. Endpoint: Enter the URL of the cloud object storage service provider. It must start with “http://”. 4. Bucket name: Enter the bucket name of the cloud object storage. 5. File path: Enter the file path in the cloud object storage. 6. Verify cloud object storage connection: After entering all items, click the Connection Test button to check the result. The result will show success or failure. 7. If the connection verification succeeds, the Test File Search button will appear. Click the button. 8. A file search test popup will appear; enter the file name and click the Validate button. 9. After clicking the button, a .json file will be created; if a file with the same name already exists, rename it to complete the test. | Selection |
| User information update method during login (MFA) process | Select the user information update method during the login process. 1. Automatic update with JWT Claim information: a method that automatically updates the Claim information among the authentication data of a JWT token 2. Maintain information at the time the user data is created: retain the initially created user information. Follow JWT When selected, it complies with the defined JWT policy. | Required |
| Whether to automatically register Knox Messenger as Authenticator during the login (MFA) process | Select whether to automatically register Knox Messenger during login execution. If an ID is not registered in Knox Messenger, selecting ‘Register’ will not automatically register it. 1. Automatic update with JWT claim information: a method that automatically updates the claim information among the authentication data of a JWT token 2. Preserve the information at the moment the user data is created: retain the initially generated user information. Follow JWT When selected, it adheres to the defined JWT policy. | Required |
| Claim | Enter the Claim name. A Claim is an authentication method that manages user authentication and permissions through a specific key value, and allows you to add the necessary data for use. Defines the mapping that verifies whether the user is the same. Up to 30 can be registered. | Required |
| Secret Key | The Secret Key is an encryption key for trusted communication between SingleID and the MFA Service Provider. Click the Issue button to issue it. | Required |
Owner
Select and register the person in charge of the newly registered MFA Service Provider.
| Category | Explanation |
|---|---|
| Add button | You can add a person in charge of the MFA Service Provider. |
| search | You can find the person in charge using a search term (ID, name, email, status). |
| Select (Check Box) | Select the person in charge retrieved from the list. |
| Add | You can add the selected assignee. |
| Completed | Complete assigning the person in charge. |
When you click the Complete button, the registration is completed.
MFA Service Provider edit
On the MFA Service Provider list screen, after selecting an Authenticator and clicking Edit, you are taken to a screen where you can make modifications.
To modify the MFA Service Provider, follow the steps below.
- Admin Portal > Integration > MFA Service Provider > Edit Click the button.
- Edit each item, then click the Edit button to complete the changes.
Delete MFA Service Provider
After selecting an MFA Service Provider on the MFA Service Provider list screen, deactivate it, return to the list screen, and you can delete it from the three‑dot menu.
To delete the MFA Service Provider, follow the steps below.
- Click Admin Portal > Integration > MFA Service Provider List > MFA Service Provider right three dots.
- Delete Click the popup button.
- If a warning popup appears, check the MFA Service Provider information.
- Enter the MFA Service Provider name below and click the Delete button.
9.5.2.1.2.3 - Identity Store
Identity Store is an integrated directory service that centrally manages user, group, and authentication information, supports both cloud and on-premises environments, enables easy implementation of single sign-on (SSO) and multi-factor authentication (MFA), and automates secure integration between applications and user provisioning.
There are various cases in which users or groups are added to an organization, such as being provisioned through a registered application or being added directly by an administrator.
Identity Store allows integration and retrieval of users and groups registered in various ways, and provides various management features so that administrators can configure detailed settings for each user or group.
Administrators can manage all users and groups registered in the organization through the Identity Store.
User
Administrators can view and edit all users registered in the organization using the functions provided in the User menu, and can delete users or directly register new users.
You can also change a user’s group membership or assign permissions to allow the user to use the application.
Users are registered to SingleID in various ways as follows.
- Register via account synchronization (Inbound Provisioning) from the application
- Register via JIT (Just In Time) provisioning from the Identity Provider
- Register from MFA Service Provider
- Manually registered by administrator
Administrators can use the User menu to manage registered users collectively in various ways.
To access the user menu, navigate as follows.
- Admin Portal > Identity Store > User
User List
You can view and search all users registered in SingleID in a list format.
| Category | Explanation |
|---|---|
| ID | The user’s ID is displayed. |
| Name | The user’s name is displayed.(Surname, given name order) |
| The user’s email address is displayed. | |
| phone | The user’s mobile number is displayed. |
| Administrator | Displays whether the user is an administrator in the Admin Portal. |
| System Mapping ID | This is the application system mapping ID. |
| status | Indicates whether the account is active. Active: The user state where login is currently possible. Inactive: The user state that has been manually deactivated. Pending: The account synchronization is complete, and the account remains in a pending state until the user logs in. Locked: An account locked due to password errors. Dormant: An account that has been marked as dormant after being offline for a certain period. |
| Management entity | Indicates the entity that manages the account. You can tell whether it was automatically registered by a system or manually registered. SingleID: Account manually registered by the administrator Other: Account automatically synchronized. |
| Registration date | Account’s initial registration date |
| Modified Date | Latest update date |
| Expiration date | Account expiration date |
| Dormant User button | You can query dormant users. |
| Search term input field | You can search the user list. Enter a search term and click the magnifying glass icon or press Enter to perform the search. - Searchable fields: name, email, ID 1. Name: Exact match search is possible using encrypted personal data with ‘full name’, ‘first name’, or ’last name’. 2. Email: Exact match search is possible using encrypted personal data with the full email address or the part before ‘@’. 3. Phone number: Exact match search is possible using encrypted personal data with the last four digits of the phone number. |
| Details button | Detailed searches are possible. Search conditions can be combined with AND. After entering multiple fields and clicking the ‘Search’ button, the search is performed according to the criteria. Clicking the ‘Reset’ button clears all search fields. - Name: Exact match search is possible using encrypted personal data with ‘full name’, ‘first name’, or ’last name’. - Email: Exact match search is possible using encrypted personal data with the full email address or the part before ‘@’. - Phone number: Exact match search is possible using encrypted personal data with the last four digits of the phone number. |
| Register button | Register the MFA Service Provider. |
There are three ways to search for users in the user list.
- User status filter
- Keyword search
- Advanced Search
User status filter
To filter users by status, follow these steps.
- Click the button in the group that shows the user statuses (All, Active, Inactive, Pending, Locked) you want to filter.
- It is displayed in the list according to the user’s status.
- You can search for the desired user using keyword search while filters are applied. 3. (Note: If you perform an advanced search while filters are applied, the filters will be cleared)
- To remove the filter, click the All button.
Keyword Search
To perform a keyword search, follow these steps.
- Click the mouse on the keyword search input field.
- Enter the word to search. 2. Enter a search term, and a dropdown menu appears below the search input field. 2. If you select one of the “ID”,“Name”, “Email” displayed in the dropdown menu, the search will be executed on that field, and if you select All, the search will be executed on the ID, English name, and email fields.
- After entering a search term, press the Enter key or click the magnifying‑glass icon with the mouse to execute the search. 3. At this time, the search is executed across the ID, English name, and email fields.
- Search results are displayed in the user list.
- If you want to cancel the search results and display the full list, click the X icon to the right of the keyword search input box.
Advanced Search
To perform an advanced search, follow these steps.
- Click the Details button.
- On the detailed search screen, enter the search term in the field you want to search.
- In the advanced search screen, you can limit the search range by selecting the user’s registration and modification dates.
- When you enter search terms in multiple fields, the search is performed with an “AND” condition.
- After entering a search term, press Enter or click the Search button to execute the search.
- Search results are displayed in the user list.
- If you want to cancel the search results and display the full list, click the Reset button on the advanced search screen.
User registration
Tenant administrators can manually register users directly from the screen without going through account synchronization.
To register a user, follow the steps below.
- Admin Portal > Identity Store > User > Register Click button
Users can enter and register information through a three-step screen as follows.
- Profile
- User group
- Summary
Profile
Enter the user’s basic profile information on the profile screen.
The fields that need to be entered are as follows.
| Category | Explanation | Required or not |
|---|---|---|
| ID | Enter the user’s ID. Values that duplicate an already registered user’s ID cannot be entered. | Required |
| Administrator | Specify whether the user is an administrator. Selecting “Allow” grants administrator privileges. | Required |
| Name (Korean name, surname) | Enter the Korean given name and family name in order. | Essential |
| Name (English name, last name) | Enter the English given name and surname in order. If an English name is not available, enter the Korean given name and surname again. | Required |
| Enter the email address. Since this information is used for identity verification, accurate information must be entered. | Required | |
| Phone number | Enter your mobile number. Since this information is used for identity verification, accurate information must be entered. | Essential |
| Department | Enter the department name in Korean and English. | Selection |
| organization | Enter the Korean organization name and the English organization name. | Select |
| language | Specifies the user’s preferred language. When the user logs in, the screen is displayed in the specified language. | Essential |
| time zone | Specifies the user’s time zone. All times are displayed in the designated time zone when the user logs in. | Required |
| Expiration date | Set the user expiration date. The default is “Not set”. Choose the date to delete when automatic account deletion is set after the set date. | Selection |
Click the Next button to go to the user group screen.
User group
Specify the group for the user to be registered on the User Group screen. All groups that can be assigned to the user are displayed on the left side of the screen. After selecting the group to assign to the user, click the > button to move to the assigned group.
To cancel a group assignment, select the group to cancel from the assigned groups, then click the < button. Click the Next button to go to the summary screen.
Summary
- After reviewing the information entered on the summary screen, register the user.
- If you want to edit the entered information, you can click the Back button to return to the screen you want to edit.
- To cancel the registration, click the Cancel button.
- When you click the Complete and Add button, it registers the user and returns to the profile screen so you can continue registering a new user.
- Clicking the Complete button registers the user and navigates to the registered user’s detail screen.
User edit
If you want to modify a user, follow the steps below.
- In Admin Portal > Identity Store > User, click the user you want to edit.
- profiles, groups, applications, multi-factor authentication (MFA) methods, devices, active sessions are displayed.
- Click the Edit button at the bottom and modify the data you want to change.
- Click the Save button.
User status change
The status of users managed by SingleID is as follows.
| Category | Explanation |
|---|---|
| Active | This is a user who, after initial registration, logged into SingleID, reset their password, and is now using it normally. |
| Inactive | This user has been disabled by the administrator. |
| Waiting | This is a user who has never logged into SingleID after the initial registration. |
| Locked | The user is locked due to repeated login failures, etc. (The user can unlock themselves by resetting the password) |
| Human user | The account is in a human‑processed status due to being inactive for a certain period. |
A tenant administrator can change a user’s status based on the user’s current state as follows.
| Current | Change | Explanation |
|---|---|---|
| Active | Inactive | You can click the Deactivate button to change an active user to an inactive state. |
| Inactive | Active | You can click the Activate button to change a user from inactive to active. |
| Waiting | None | A user in standby cannot be switched to active or inactive state. |
| Locked | Active | A locked user can click the password reset button to reset the password and simultaneously change the status to active. |
The button that changes the user’s status is displayed on the list and detail screens as follows.
- When one or more users in Active or Inactive state are selected on the list screen
- Active or Inactive state when navigating to the user detail screen
When a tenant administrator attempts to deactivate a user, the following confirmation popup is displayed.
After verifying the information of the user to be deactivated, click the deactivate button once more to change the user’s status from active to inactive. In contrast, when changing a deactivated user to an active state, no separate confirmation popup is displayed.
Password reset
The tenant administrator can reset a user’s password. When a tenant administrator resets a user’s password, an informational email is sent to that user.
The reset password is not displayed to the administrator. Additionally, the reset password is not directly included in the notification email sent to the user.
After receiving the notification email, the user must log in to SingleID directly, use the password reset function to complete identity verification, and then change the password.
To change the user’s password, follow the steps below.
- Select the user whose password you want to change from the user list and click.
- Click the Reset Password button located at the top right of the user detail screen.
- If a confirmation popup appears, click the Confirm button.
- Resetting a locked user’s password unlocks the account and changes it to active status.
Group
The tenant administrator can view the groups that a user belongs to as a member and can add or remove group memberships.
To manage a user’s groups, click the Group tab on the detail screen.
| Category | Explanation |
|---|---|
| Group Tab | Displays the user’s group management screen. |
| All groups | Displays the full list of groups that can be assigned to the user. |
| Assigned group | Displays the list of groups already assigned to the user. |
| Search all groups | Search groups or group descriptions across all groups that can be assigned to the user. The search results are displayed in the list below. After searching, click the X button on the right of the search input field to display the full list. |
| Search assigned groups | Search for groups or group descriptions among groups already assigned to the user. The search results are displayed in the list below. After searching, click the X button on the right side of the search input field to show the full list. |
| Delete assigned group | Delete the selected group from the groups assigned to the user. The user will be removed from the deleted group’s members. |
| Group assignment | Assign the selected group to the user. The user becomes a member of the assigned group. |
Delete group
To delete the group assigned to a user, follow the steps below.
- Select the group to delete from the assigned group list. 1. (Check the checkbox to the left of the group name)
- Click the < button to delete the assigned group.
Group assignment
To assign a new group to a user, follow the steps below.
- Select the group to assign from the entire group list. 1. (Check the checkbox to the left of the group name)
- > Click the button to assign the group.
Application
The tenant administrator can view applications designated for user use and can add, assign, or delete applications. To manage the user’s application, click the Application tab on the detail screen.
| Category | Explanation |
|---|---|
| Application tab | Displays the user’s application management screen. |
| List of assigned applications | Applications assigned to the user are displayed in a list format. |
| Assign button | You can assign additional applications to a user. |
Delete application
To delete an application assigned to a user, follow the steps below.
Select the application to delete from the list of assigned applications. (Check the checkbox to the left of the application name) Click the Unassigned button displayed above the application list. In the confirmation popup, click the Confirm button.
Application allocation
To assign a new application to a user, follow the steps below.
- Click the Assign button displayed at the top right of the application list.
- Application Assignment Select the application in the popup. 2. (Check the checkbox to the left of the application name)
- Click the Assign button.
- If you have assigned all applications, click the Cancel button to close the popup.
View and Manage Multi-Factor Authentication (MFA) Methods
The tenant administrator can view the multi-factor authentication methods registered by users and can modify or delete parts of the registration information.
To manage a user’s multi-factor authentication (MFA) method, click the Multi-Factor Authentication (MFA) Method tab on the details screen.
| Category | Explanation |
|---|---|
| Multi-Factor Authentication (MFA) method tab | Displays the user’s multi-factor authentication (MFA) method management screen. |
| List of Multi-Factor Authentication (MFA) Methods | The multi-factor authentication (MFA) methods registered by the user are displayed as a list. |
| Edit button | Users can modify or delete the multi-factor authentication (MFA) methods they have registered. |
Modify multi-factor authentication (MFA) method
To modify the multi-factor authentication (MFA) method registered by the user, follow the steps below.
- Click the Edit button at the bottom right of the screen.
- Click the Registration Info column of the MFA list you want to edit.
- After editing the information, click the Save button at the bottom right of the screen.
Delete multi-factor authentication (MFA) method
To delete the multi-factor authentication (MFA) method registered by the user, follow the steps below.
- Click the Edit button at the bottom right of the screen.
- Click the Delete button on the right side of the MFA method you want to remove.
- Click the Confirm button in the warning popup.
- Click the Save button at the bottom right of the screen.
View user device information
Administrators can view the device information added when a user registers a multi-factor authentication method.
To view the user’s device information, click the Device tab on the detail screen.
| Category | Explanation |
|---|---|
| Device Tab | Displays the user’s device management screen. |
| Device List | When a user registers a multi-factor authentication (MFA) method, the added devices are displayed in a list format. |
Active session
When a user logs into SingleID, SingleID manages the session information of the logged-in user.
The tenant administrator can view a user’s current active session and forcibly terminate the session to log the user out.
To manage the user’s session, click the Active Session tab on the detail screen.
| Category | Explanation |
|---|---|
| Active Sessions Tab | Displays the user’s session management screen. |
| Active session list | The user’s currently active sessions are displayed in a list format. |
| Exit button | Forcefully terminates the user’s active session. |
Force Terminate Session
To forcibly terminate a user’s session, follow the steps below.
- Click the Terminate button displayed at the top right of the session you want to force close.
- In the Exit Confirmation popup, click the Exit button.
Force terminate multiple sessions
If you want to select one or more user sessions and terminate them simultaneously, follow the steps below.
- Select the sessions to forcefully terminate from the list and check the checkbox (V) displayed to the left of the session information.
- Click the Exit button displayed above the list.
- Exit Confirmation in the popup, click the Exit button.
Delete user
Tenant administrators can delete user information from SingleID.
The button for deleting a user appears on both the list and detail screens as shown.
- When one or more users are selected on the list screen
- After selecting a user, click the Delete button, and a confirmation popup appears on the screen.
- To delete a user, verify the user information, then enter the user’s ID and click the Delete button.
- After selecting multiple users and clicking the Delete button, a confirmation popup appears on the screen.
- To delete the selected users, use the <, > button, review all user information, then enter the phrase Delete All and click the Delete button.
Verify all users’ information and you must enter the phrase Delete All for the delete button to become active.
When navigating to the user detail screen
- When an administrator attempts to delete a user, a confirmation popup is displayed.
- To delete a user, verify the user information, then enter the user’s ID and click the Delete button.
Deleted user information cannot be recovered.
When a user’s information is deleted, the groups, applications, and multi-factor authentication (MFA) methods assigned to the user are also deleted, and even if the user is re-registered with the same ID, the deleted groups, applications, and MFA methods are not restored.
Users registered through an application’s inbound provisioning can be reprovisioned from that application even if they are deleted from SingleID.
To completely delete a user, you must remove them from the primary system that manages user information.
After deletion, even if the user registers again with the same ID, the deleted groups, applications, and multi‑factor authentication (MFA) methods will not be automatically restored.
Group
Administrators can use the functions provided in the Group menu to view and edit all groups registered in the organization, and can delete groups or register new groups.
You can also modify the group’s membership rules or assign permissions so that group members can use the application.
Groups are registered to SingleID in various ways as follows.
- Register via inbound provisioning from the application (애플리케이션)
- Manually registered by an administrator (그룹 생성)
Tenant administrators can centrally manage registered groups in various ways using the group menu.
To access the group menu, navigate as follows.
- Admin Portal > Identity Store > Group
Group List
Administrators can view and search all groups registered in the organization in a list format.
Category Description
| Category | Explanation |
|---|---|
| Group List | The group list is displayed. |
| Keyword search | Search by group name and description. |
| Detailed Search | Displays detailed options for searching groups on the screen. |
Create group
Administrators can manually register groups directly on the screen without going through inbound provisioning.
- To register a group manually, click the Register button on the group list screen.
- When you click the Register button, the group registration popup is displayed on the screen.
The fields that need to be entered for group registration are as follows.
| Category | Explanation | Required or not |
|---|---|---|
| type | Select the group type. | Required |
| Name | Enter the name of the group. Values that duplicate an already registered group name cannot be entered. | Required |
| Explanation | Enter the description of the group. | Required |
- Complete button click registers the group and navigates to the detailed information screen of the registered group.
View and edit detailed information
The administrator can click Group in the group list to navigate to the group’s detailed information view screen.
If you have newly registered a group, you will be taken directly to the group’s detail screen immediately after registration.
At the top of the group detail screen, the group’s name, description, and managing entity information are displayed, and below that, group information organized into multiple tabs is shown.
| Category | Explanation |
|---|---|
| type | The group’s type is displayed. |
| Name | The name of the group is displayed. |
| Management entity | The system that manages the group is displayed. For groups directly registered by a tenant administrator in SingleID, SingleID is shown; for groups provisioned inbound through an application, the application’s name is displayed. |
| Explanation | The group’s description is displayed. |
The tenant administrator can view detailed information of registered groups via the Group Profile tab.
| Category | Explanation |
|---|---|
| Group profile | The group profile is displayed. |
| List | Button that returns to the list. |
| Edit | Edit the profile. |
To edit the group’s detailed information, follow the steps below.
- On the group detail screen, select the Profile tab.
- Click the Edit button.
- Edit Group Information.
The fields that can be edited are as follows.
| Category | Explanation | Required or not |
|---|---|---|
| Name | Enter the group’s name. You cannot enter a value that duplicates an already registered group name. | Required |
| Explanation | Enter the description of the group. | Required |
- Click the Save button.
- To return to the view state without saving the edited information, click the Cancel button.
Group membership rule management
Administrators can set rules that automatically assign users meeting certain conditions as members of a group.
When you set rules for a group, members are automatically provisioned without the tenant administrator having to manually manage them, and members are added or removed according to the configured condition expression.
To manage the group’s membership rules, click the Rules tab on the detail screen.
| Category | Explanation |
|---|---|
| Rules tab | Group rules are displayed. |
| Rule | The rules of the configured group are displayed. (The default membership policy setting after creating a group is Off) If the membership policy setting is Off, members are not managed automatically. |
| List | This is a button that returns to the list. |
| Edit | Modify the rules. |
To set the group’s rules, follow the steps below.
- Select the Rules tab on the group detail screen.
- Click the Edit button.
- Click the On button in the membership policy settings.
- Set the condition expression for the WHEN area.
- Click the Save button.
- If you want to return to the query state without saving the configured rule, click the Cancel button.
The condition expression in the WHEN clause is constructed as follows.
| Category | Explanation |
|---|---|
| Operator relationship between conditional expressions | When there is one or more condition expressions, define the logical relationship between them. You can choose either AND or OR, and it applies to all condition expressions. |
| Conditional expression type | Set the condition type. You can select User Attribute. |
| Condition item | Set the condition items of the condition expression. When the expression type is User Attribute, you can select a user’s attributes from the list. |
| operator | Set the operation mode of the conditional expression. |
| condition value | Set the condition value of the conditional expression. |
| Add condition expression | Add a condition expression. |
| Delete condition | Delete the condition. It cannot be deleted when there is only one condition. |
The user attributes that can be set in the condition item are as follows.
| attribute | Data type | Explanation | Required or not |
|---|---|---|---|
| key | String | key | Required |
| username | String | ID | Required |
| password | GuardedString | Password | Required |
| status | String | status | Required |
| mustChangePassword | Boolean | Whether to enforce password setting | Required |
| suspended | Boolean | Standby status | Required |
| creator | String | Constructor | Selection |
| creationDate | Date | Creation date | Selection |
| lastModifier | String | Last editor | Selection |
| lastChangeDate | Date | Last modified date | Selection |
| administrator | Boolean | Admin status | Selection |
| displayName | String | Display name | Selection |
| cn | String | Common Name | Selection |
| local | String | Locale (email sending criteria) | Selection |
| userSource | String | User source | Selection |
| syncDate | String | Last synchronization time | Selection |
| contractNumber | String | Contract number | Selection |
| contractStartDate | String | Contract start date | Selection |
| contractEndDate | String | Contract End Date | Selection |
| agreementDate | String | Date of agreement to required terms | Selection |
| accountStartDate | String | Account start date | Selection |
| accountEndDate | String | Account expiration date | Selection |
| partnerOrganizationCode | String | Partner company code | Selection |
| approvalUser | String | Approver ID | Selection |
| formattedName | String | Korean display name | Selection |
| familyName | String | Korean surname | Selection |
| givenName | String | Korean name | Selection |
| enFormattedName | String | English display name | Selection |
| enFamilyName | String | English surname | Selection |
| enGivenName | String | English name | Selection |
| adDomain | String | AD Domain | Selection |
| nickName | String | Nickname | Selection |
| employeeNumber | String | Employee number | Select |
| epId | String | EP ID | Select |
| String | email address | Selection | |
| phoneNumberWork | String | Phone number | Select |
| mobile | String | mobile phone number | Selection |
| title | String | Job Title | Selection |
| executiveYn | String | Executive status | Select |
| timeZone | String | Time zone | Selection |
| accountLocked | Boolean | Forced account lock | Selection |
| accountAutoLocked | Boolean | Automatic account lock | Selection |
| accountDisabled | Boolean | Unused account | Selection |
| accountSuspended | Boolean | Dormant account | Selection |
| accountSuspendedTime | Date | Idle processing time | Selection |
| lastLoginTime | Date | Last login time | Selection |
| accountState | String | Account status | Selection |
The operators that can be configured in the operator are as follows.
| operator | Explanation |
|---|---|
| Equals | Searches for users whose condition field value matches the condition value. |
| Not Equals | Search for users whose condition item value does not match the condition value. |
| Starts with | Search for users whose condition field value begins with the condition string. |
| Ends with | Search for users whose condition field value ends with the condition string. |
| Contains | Search for users whose condition field value includes the condition string. |
Group member management
Tenant administrators can manually assign members to a group or remove users from the group’s members.
To manage the group’s members, click the Member tab on the details screen.
| Name | Explanation |
|---|---|
| Member tab | Displays the group member management screen. |
| Member list | Displays group members in a list format. |
| Filter button group | Filters group members by status and displays the list. |
| Keyword search | Enter a keyword to search for group members. - Name: Exact match search is possible using encrypted personal data with ‘full name’, ‘first name’, or ’last name’. Email: Exact match search is possible using encrypted personal data with the full email address or the part before ‘@’. - Phone number: Exact match search is possible using encrypted personal data with the last four digits of the phone number. |
| Detailed Search | Enter detailed search criteria to find group members. - Name: Exact match searches are possible using encrypted personal data with ‘full name’, ‘first name’, or ’last name’. - Email: Exact match searches are possible using encrypted personal data with the full email address or the part before ‘@’. - Phone number: Exact match searches are possible using encrypted personal data with the last four digits of the phone number. |
| Add button | Add a member to the group. |
There are three ways to search for members within the Group tab.
- Filter by member status
- Keyword search
- Advanced Search
Member Status Classification
- Active: User who, after initial registration, logs into SingleID, resets their password, and is now using it normally.
- Inactive: User disabled by the administrator
- Pending: users who have never logged into SingleID after initial registration
- Locked: User locked due to reasons such as repeated login failures (a state where the user can unlock themselves by resetting the password)
Filter by Member Status
To filter members by status, follow these steps.
- Click the button of the group that displays the status of the members you want to filter. 1. (Active, Inactive, Standby, Locked button)
- You can navigate pages in the filtered view to see the list of the desired members.
- You can search for the desired member using keyword search while the results are filtered. 3. (Note: If you perform an advanced search while filters are applied, the filters will be cleared.)
- To remove the filter, click the All button.
Keyword Search
To perform a keyword search, follow these steps.
- Click the mouse in the keyword search input field.
- Enter the word to search. 2. At this point, a dropdown menu appears below the search input field. 2. If you select one of “ID”, “English name”, or “Email” displayed in the dropdown menu, the search will be performed on that field, and if you select “All”, the search will be performed on the ID, English name, and Email fields.
- After entering a search term, press the Enter key or click the magnifying glass icon with the mouse to execute the search. 3. At this time, the search is executed across the ID, English name, and email fields.
- Search results are displayed in the member list.
- If you want to cancel the search results and display the full list, click the X icon to the right of the keyword search input box.
Advanced Search
To perform an advanced search, follow these steps.
- Click the Details button.
- On the detailed search screen, enter the search term in the field you wish to search.
- In the advanced search screen, you can select a member’s registration date to limit the search range.
- When you enter search terms in multiple fields, the search is performed with an “AND” condition.
- After entering a search term, press the Enter key or click the Search button to execute the search.
- Search results are displayed in the member list.
- If you want to cancel the search results and display the full list, click the Reset button on the advanced search screen.
Delete member
To remove a member from a group, follow these steps.
- Select one or more members to delete from the member list. 1. (Check the checkbox to the left of the member ID)
- Click the Delete button displayed at the top of the list.
- Click the Confirm button in the warning popup.
Add member
To add a member to a group, follow the steps below.
- Click the Add button at the top right of the member list.
- In the member addition popup, select the user to add as a member. 2. (Check the checkbox to the left of the user ID)
- Click the Add button.
- If you have added all desired users as members, click the Cancel button on the popup to close the member addition popup.
Application Management
The tenant administrator can view applications assigned to a group and can add or remove applications.
To manage the group’s applications, click the Group tab on the details screen.
| Name | Explanation |
|---|---|
| Application tab | Displays the application management screen for the group. |
| List of assigned applications | Applications assigned to the group are displayed in a list format. |
| Assign button | You can add and assign applications to a group. |
Application deletion
To delete an application assigned to a group, follow the steps below.
- Select the application to delete from the list of assigned applications. 1. (Check the checkbox to the left of the application name.)
- Click the Unassigned button displayed above the application list.
- In the confirmation popup, click the Confirm button.
Application assignment
To assign a new application to a group, follow the steps below.
- Click the Assign button displayed at the top right of the application list.
- Select the application in the Application Assignment popup. 2. (Check the checkbox next to the left side of the application name)
- Click the Assign button.
- If you have assigned all applications, click the Cancel button to close the Application Assignment popup.
Delete Group
The tenant administrator can delete a group from SingleID.
The button for deleting a group is displayed on the list and detail screens as follows.
- When one or more groups are selected on the list screen.
- After selecting a group and clicking the Delete button, the following confirmation popup appears on the screen.
- To delete a group, verify the group information, then enter the group name and click the Delete button.
- After selecting multiple groups and clicking the Delete button, the following confirmation popup appears on the screen.
- To delete the selected groups, use the <, > button to view all group information, then enter the phrase Delete All and click the Delete button.
You must verify the information of all groups and enter the phrase Delete All before the Delete button becomes active.
When navigating to the group detail screen
- When a tenant administrator attempts to delete a group, the following confirmation popup is displayed.
- To delete a group, verify the group information, then enter the group name and click the Delete button.
Information of a deleted group cannot be recovered.
When group information is deleted, the group’s members and the applications assigned to the group are also deleted, and re‑registering a group with the same name will not restore the members or application data.
Groups registered through the application’s inbound provisioning can be provisioned again from the application even if they are deleted in SingleID. To completely delete a group, you must remove it from the ledger system that manages group information. Even if the group is re‑registered with the same name after deletion, the deleted members or application information will not be automatically restored.
AI agent
AI agents are intelligent services used for various purposes such as internal workflow automation, data analysis, and customer support. Using SingleID(integrated authentication and certification system), control the access and permissions of AI agents registered with a single authentication.
To access the menu, navigate as follows.
- Admin Portal > Identity Store > AI Agent
AI Agent List
The administrator can view and search all registered AI agents in a list format.
Category Description
| Category | Explanation |
|---|---|
| AI Agent List | AI agents are displayed in the list. |
| Keyword search | Searches for AI agent names and the agent list. |
| Detailed Search | Search using detailed options that search groups. |
Register AI Agent
Administrators can register, modify, or delete AI agents.
- To register an AI agent, click the Register button on the AI agent list screen.
- When you click the Register button, the AI agent registration popup appears on the screen.
The fields you need to enter to register an AI agent are as follows.
| Category | Explanation | Required or not |
|---|---|---|
| Name | Enter the AI agent name. Values that duplicate an already registered name cannot be entered. | Required |
| Agent purpose | Enter the AI agent’s purpose. | Selection |
| AI model | Enter the AI model name. eg. ChatGPT | Selection |
| URL | Enter the AI agent URL. eg. http://www.example.com | Selection |
- When you click the Complete button, a confirmation popup appears to finalize the AI agent registration.
| Category | Explanation |
|---|---|
| Agent ID | AI agent IDs are automatically generated for internal and external networks. Please copy the agent ID and keep it safe. |
| Agent Secret | AI agent secrets for internal and external networks are generated automatically. Since they cannot be viewed on the screen later, please copy them now and keep them safe. |
| Name | Verify the AI agent name you entered. |
| Agent purpose | Check the AI agent purpose you entered. |
| AI model | Check the AI model name. |
| URL | Check the AI agent URL. |
- Click the Confirm button to register the AI agent successfully.
View and edit AI agent information
The administrator can click AI agent in the AI agent list to navigate to the AI agent’s detailed information view screen.
If you have newly registered an AI agent, you will be taken directly to the AI agent’s detail screen immediately after registration.
At the top of the AI agent detail screen, the AI agent’s agent ID and agent information are displayed.
| Category | Explanation |
|---|---|
| Agent ID | The AI agent ID can verify the unique identifiers for internal and external networks. The unique identifier cannot be changed after it is issued. |
| Name | The name of the AI agent is displayed. |
| Agent purpose | The purpose of the AI agent you entered is displayed. |
| AI model | The AI model name you entered is displayed. |
| URL | The URL you entered is displayed. |
| Agent Secret | You can view the secrets for internal and external networks. If you have lost or forgotten the agent secret, you can request a reissue. Click the Reissue button to request a reissue. |
The agent ID and agent secret serve as the user’s ID and password, providing authentication.
Agent ID The agent ID is a unique identifier that the system automatically issues upon registration. Once issued, it cannot be reissued.
Agent Secret Authentication credentials for the agent to securely access applications and APIs. You can obtain a new agent secret by reissuing it, but you must update all APIs or applications that are currently using the agent secret.
To modify the AI agent information, follow the steps below.
- Select the AI agent you want to edit from the AI agent list screen.
- Click the Edit button at the lower right corner.
- Edit AI agent information.
The fields that can be edited are as follows.
| Category | Explanation | Required or not |
|---|---|---|
| Name | Enter the AI agent name. Values that duplicate an already registered group name cannot be entered. | Required |
| Agent purpose | Enter the agent’s objective. | Selection |
| AI model | Enter the AI model name. | |
| URL | Enter the AI agent URL. |
- Click the Save button.
- To return to the view state without saving the edited information, click the Cancel button.
Delete AI agent
To delete an AI agent, you can delete it by clicking the Delete button on the right side of the AI agent detail screen.
To delete the AI agent, follow the steps below.
- Select the AI agent you want to edit from the AI agent list screen.
- Click the Delete button on the right.
- The AI Agent Deletion popup appears.
- Enter the name of the AI agent you want to delete, then click the Delete button.
- Click to complete the deletion.
9.5.2.1.2.4 - Policy
Add Dormant User Policy #User Lifecycle Management #Conditional Authentication Policy –>
When logging into SingleID or logging into an application registered with SingleID, various settings such as login methods, authentication sessions, and passwords need to be configured according to the organization’s security policy.
SingleID provides a policy management feature that allows detailed configuration of login and authentication information.
If you have purchased the anomalous behavior detection feature (ADM), you can configure it to analyze a user’s login activity at sign‑in and, when it detects authentication anomalies that differ from the norm, notify the user of a potential security threat.
The policy features provided by SingleID are as follows.
- Login Policy
- Authentication Policy
- Anomaly detection policy
By using SingleID’s policy feature, you can configure a secure authentication environment that meets organizational security requirements by specifying detailed login methods based on who is logging in, when, from which environment, and to which application.
Login Policy
The administrator can set detailed policies specifying which authentication methods users can use when logging in with SingleID, and, if necessary, create condition-based authentication policies for users authenticating in specific environments.
Login policies can be configured using the following conditions.
- Which application are you logging into?
- Who is logging in?
- In what environment are you logging in?
To access the login policy menu, navigate as follows.
- Admin Portal > Policy > Login Policy
Default login policy
The Admin Portal automatically creates the following two policies by default.
- Admin Portal Policy: Admin Portal access permission control policy
- Default Policy: User’s default access control policy
The Admin Portal Policy is the login policy applied when attempting to log in to the Admin Portal, and the Default Policy is the login policy applied when attempting to log in to the user portal.
If you have linked an application to SingleID and have not assigned a separate login policy, the Default Policy will be automatically assigned as the default login policy.
Register Login Policy
Login policy sets the login policies for administrators and users. You can configure login policies based on the access environment, application, and situation.
Login policies can be registered through a screen consisting of four steps as follows.
- General
- Allocation
- Initial Redirection
- Rule
General
Enter the name and description of the login policy on the general screen.
The fields that need to be entered are as follows.
| Name | Explanation | Required status |
|---|---|---|
| Name | Enter the name of the login policy. | Required |
| Explanation | Enter the description of the login policy. | Required |
Click the Next button to go to the assignment screen.
allocation
Specify the application to which the login policy will be applied on the assignment screen.
| Name | Explanation |
|---|---|
| Filter | Filter applications by status. |
| Keyword search | Search by application name and description. |
| Advanced Search | Displays detailed options for searching applications on the screen. |
| Assign button | Displays the application assignment popup on the screen. |
| Assigned Application List | The assigned applications are displayed in a list format. It starts with an empty list. |
- Click the Assign button to display the application assignment popup on the screen.
- In the Application Assignment popup, select one or more applications to assign to the login policy, then click the Assign button.
- If you have assigned all applications, click the Cancel button to close the Application Assignment popup.
Initial Redirection
Specifies how users access the login screen and the login method on the Initial Redirection screen.
Redirected to SingleID’s Sign-in page (login page)
Redirected to the external IdP
The explanations of the two methods above are as follows.
- If you select Redirected to SingleID’s Sign-in page, the SingleID login page will be displayed to the user attempting to log in.
- If you select Redirected to the external IdP, the user trying to log in will see the login page of the selected Identity Provider.
- After selecting Redirected to the external IdP, you must choose the Identity Provider from the selection list and designate it.
- If you select Redirected to SingleID’s Sign-in page, you can optionally display an additional button at the bottom of the SingleID login screen that allows login via an Identity Provider.
- AND see the following external IdP buttons on the Sign-In page Click the text input field below, select one or more Identity Providers registered in SingleID, and configure them to be displayed on the login screen.
Rule
On the Rules screen, modify or add login rules and set the priority among login rules.
| Name | Explanation |
|---|---|
| List of rules | Login rules are displayed on the screen as a list. The Default Rule is shown by default and cannot be deleted. |
| Keyword search | Search by the name or description of the login rule. |
| Register button | Register a new login rule. |
| Complete button | Register a login policy. |
Default Rule configuration
In the rule screen’s login rule list, Default Rule is displayed by default.
Default Rule cannot be deleted and can only be edited. Also, when you add one or more login rules, you cannot set the priority. (It always has the lowest priority.)
To modify the Default Rule, follow the steps below.
- Click Default Rule in the rule list.
- Default Rule’s WHEN condition cannot be modified.
- You can modify the THEN result of Default Rule.
| Name | Explanation |
|---|---|
| Set access permission | Set whether access is allowed. |
| Mandatory authentication method | Configure the primary login method. Additional login methods can be displayed on the login screen in addition to the default login method. |
| MFA authentication | Configure it to require an additional login after the first login succeeds. |
| Terms and conditions for collecting consent | Set it to display the terms and conditions and request consent when a user logs into SingleID for the first time. |
| Save button | Save the modified login rules. |
You can select one of the following two options when configuring access permission settings.
- Deny Access
- Allow Access
If you select Deny Access, it will reject login for all users.
When you select Allow Access in the access permission setting, you can configure the user’s login method.
If you selected Redirected to the external IdP as the method to enter the login screen on the Initial Redirection screen, the first login settings will not be displayed.
The required authentication method is performed by an external Identity Provider according to the Initial Redirection settings.
To have the user log in via multi-factor authentication, check the MFA authentication checkbox and then select one or more Authenticators in the text input box.
If a user logs in to SIngleID for the first time, to display the terms and conditions and request the user’s consent, check the Terms and Conditions Consent Setting (d) checkbox and then select one or more terms or conditions to display on the screen from the text input box.
Add rule
To add a login rule, follow the steps below.
- Click the Register button at the top right of the rule list.
- Enter the rule’s name and description on the rule registration screen.
- Refer to the following and enter the rule items.
| Name | Explanation |
|---|---|
| Name | This is the name of the rule. |
| Explanation | This is an explanation of the rules. |
| User group assignment | Select the user group to apply the rule to. |
| Profile property assignment | Click the ‘Add’ button in the profile property assignment list to add a property. Refer to the help below for descriptions of the property and operator. |
| Group Settings | Specify the group that the logged-in user belongs to as a member. |
| User attribute list | Specify the attributes of the user logging in and the conditions for each attribute. |
| Add User Property button | Display the “Add Property” popup on the screen. |
Access Environment
| Name | Explanation |
|---|---|
| Network | Specify the IP or network range of the user logging in. The default is “IP address anywhere”.- Desktop- Mobile |
| Platform | Specify the device information of the user who logs in. The default is “Any platforms”.- Desktop- Mobile |
| browser | Specifies the browser information of the user who logs in. The default is “Any browsers”.- Edge- Chrome- Safari |
| OS | Specify the OS information for login. The default is “Any OS”.- Windows 10- Windows 11- Android- iOS |
| AND Anomalies (Abnormal behavior) | Set the condition to determine whether abnormal behavior is detected during login.Abnormal behavior detection condition settings are only available for tenants who have purchased the Abnormal Behavior Detection (ADM) feature option.To use the Abnormal Behavior Detection (ADM) feature, you must select the additional option when signing a SingleID contract.If you wish to use the Abnormal Behavior Detection feature, you can purchase it additionally on the SCP product purchase page.After configuring all “WHEN” condition areas, set the login method that will be used when a user matching the conditions logs in. |
The selectable user attributes are as follows.
User attribute information
| attribute name | Data type | Required? | Explanation |
|---|---|---|---|
| key | String | Required | Key |
| username | String | Required | ID |
| password | GuardedString | Required | Password |
| status | String | Required | status |
| mustChangePassword | Boolean | Required | Whether password enforcement is required |
| suspended | Boolean | Required | Standby status |
| creator | String | - | constructor |
| creationDate | Date | - | Creation date |
| lastModifier | String | - | Last editor |
| lastChangeDate | Date | - | Last modified date |
| administrator | Boolean | - | Admin status |
| displayName | String | - | Display name |
| cn | String | - | Common Name |
| local | String | - | Locale (email sending standard) |
| userSource | String | - | User source |
| syncDate | String | - | Last synchronization time |
| contractNumber | String | - | Contract Number |
| contractStartDate | String | - | Contract start date |
| contractEndDate | String | - | Contract End Date |
| agreementDate | String | - | Date of required terms agreement |
| accountStartDate | String | - | Account start date |
| accountEndDate | String | - | Account expiration date |
| partnerOrganizationCode | String | - | Partner company code |
| approvalUser | String | - | Approver ID |
| formattedName | String | - | Korean display name |
| familyName | String | - | Korean surname |
| givenName | String | - | Korean name |
| enFormattedName | String | - | English display name |
| enFamilyName | String | - | English surname |
| enGivenName | String | - | English name |
| adDomain | String | - | AD Domain |
| nickName | String | - | nickname |
| employeeNumber | String | - | Employee ID |
| epId | String | - | EP ID |
| String | - | Email address | |
| phoneNumberWork | String | - | phone number |
| mobile | String | - | mobile phone number |
| title | String | - | Job title |
| enTitle | String | - | English job title |
| titleCode | String | - | Job grade code |
| entitlement | String | - | Job title |
| department | String | - | Department name |
| enDepartment | String | - | English department name |
| departmentCode | String | - | Department code |
| organization | String | - | Company name |
| enOrganization | String | - | English company name |
| organizationCode | String | - | Company code |
| region | String | - | base |
| userStatus | String | - | Employee status |
| userType | String | - | Employee type |
| securityLevel | String | - | Security rating |
| preferredLanguage | String | - | Knox language |
| executiveYn | String | - | Executive status |
| timeZone | String | - | Time zone |
| accountLocked | Boolean | - | Forced account lock |
| accountAutoLocked | Boolean | - | Automatic account lock |
| accountDisabled | Boolean | - | Unused account |
| accountSuspended | Boolean | - | Dormant account |
| accountSuspendedTime | Date | - | Dormant processing time |
| lastLoginTime | Date | - | Last login time |
| accountState | String | - | Account status |
The operators are as follows.
| operator | Explanation |
|---|---|
| Equals | Searches for users whose attribute value matches the condition value. |
| Not Equals | Search for users whose attribute values do not match the condition value. |
| Starts with | Search for users whose attribute value starts with the condition string. |
| Ends with | Search for users whose attribute value ends with the condition string. |
| Contains | Search for users whose attribute value includes the condition string. |
THEN configuration
THEN Set the login method and procedure in the result area.
In the access permission setting (a), you can select one of the following two options.
- Deny Access
- Allow Access
If you select Deny Access, login for all users will be denied. (The default value for the access permission setting (a) is Deny Access.)
To allow users to log in and configure detailed login methods, select Allow Access.
| Name | Explanation |
|---|---|
| Configure access permission | Set whether access is allowed. |
| First login setup | Set the primary login method. Additional login methods can be displayed on the login screen besides the default login method. |
| Additional login settings | Configure it to require an additional login after the initial login succeeds. |
| Terms and Conditions Agreement Settings | Configure it to display the terms and conditions and request consent when a user logs into SingleID for the first time. |
| PC SSO Agent Settings | Configure it to verify whether a security program (Endpoint Security) is installed on the user’s PC using the PC SSO Agent. |
| Save button | Save the modified login rules. |
- Select the Authenticator to use for login from the first login configuration’s selection list.
- If you want users to be able to log in with another Authenticator in addition to the selected primary login method, select the checkbox (V) of And allow another factors below: and choose one or more Authenticators to add in the text input box.
On the Initial Redirection screen, if you select Redirected to the external IdP as the method to enter the login screen, the first login settings will not be displayed.
The first login occurs at an external Identity Provider according to the Initial Redirection settings.
- To require users to log in via multi-factor authentication, select the checkbox (V) in the additional login settings, then choose one or more Authenticators in the text input field.
- If a user logs in to SIngleID for the first time, to display the terms and conditions and request the user’s consent, check the terms and conditions consent setting checkbox and then select one or more terms or conditions to display on the screen from the text input box.
- To verify whether a security program (Endpoint Security) is installed on a user’s PC using the PC SSO Agent, select the checkbox (V) in the PC SSO Agent settings. When this setting is enabled, login attempts from users whose PCs do not have the security program installed will be blocked.
If the PC SSO Agent is not registered, the PC SSO Agent configuration option will not be displayed on the screen.
When the PC SSO Agent setting (e) is enabled, if you want to require additional authentication instead of blocking the login of users who do not have a security program installed on the PC, select the checkbox (V) below and then choose one or more Authenticators in the text input box.
Click the Save button to register the login rule and return to the rule list.
Rule priority management
If one or more login rules are added, the administrator can set the priority among the login rules. If a user matches the conditions set in multiple rules, the login method of the rule with the higher priority will be applied.
Follow the steps below to set the priority of login rules.
- Drag the ≡ area displayed to the left of the rule name in the rule list with the mouse.
- The priority of login rules is determined by the drag-and-drop location.
- Rules that appear higher in the list have higher priority.
Policy Status Change
The status of the login policies managed by SingleID is as follows.
| status | Explanation |
|---|---|
| Active | Login policy operating normally |
| Inactive | Login policy disabled by the administrator |
The administrator can change the login policy status according to its current state as follows.
| Current status | Mutable state | Explanation |
|---|---|---|
| Active | Inactive | Click the Disable button to change an active login policy to an inactive state. |
| Inactive | Active | Click the Activate button to change a disabled login policy to an active state. You can also delete a disabled login policy. |
Among login policies, the two policies provided by default in SingleID, Admin Portal Policy and Default Policy, cannot be disabled.
If you disable a login policy, applications assigned to the disabled login policy will automatically be changed to be assigned to the default policy (Default Policy).
Disable policy
To disable an active login policy, follow these steps.
- Click the policy you want to deactivate in the policy list to navigate to the policy detail screen.
- Click the Disable button.
- Confirm popup displays login policy information (number of assigned applications, number of rules included in the login policy); after reviewing it, click the Deactivate button.
If you disable a login policy, applications assigned to the disabled login policy will automatically be changed to be assigned to the default policy (Default Policy).
Even if you reactivate a disabled login policy, the applications previously assigned are not automatically reassigned.
Policy activation
To change a login policy from inactive to active, follow these steps.
- Click the policy you want to activate in the policy list to navigate to the policy detail screen.
- Click the Activate button to change the login policy status to active.
Delete Policy
Administrators can delete the login policy from SingleID.
To delete the login policy, follow these steps.
- Click the policy you want to delete in the policy list to navigate to the policy detail screen.
- If the login policy is enabled, click the Disable button to deactivate the policy.
- Click the Delete button displayed at the top right of the disabled login policy.
- A popup screen confirming the deletion of the login policy is displayed.
- To delete a login policy, first review the policy information, then enter the name of the policy you want to delete and click the Delete button.
Deleted login policies cannot be restored.
When a login policy is deleted, the rules contained within the policy are also deleted, and even if you re-register a login policy with the same name, the deleted rules or configuration information will not be restored.
Access Simulation
When there are many login policies and the rules they contain, it can be difficult to determine which user is governed by which policy for login methods.
SingleID provides an access simulation feature that allows administrators to quickly verify the login policies and rules applied to users.
Using the access simulation feature, you can select the user and the target application, arbitrarily define the user’s login environment (network, device, browser, OS), and predict in advance which login method the user will experience under various circumstances.
Additionally, if there are review requests from users experiencing login difficulties, you can quickly verify using the access simulation feature and modify the problematic policies or rules.
To use the access simulation feature, click the Access Simulation button located at the top right of the login policy list screen.
| Name | Explanation |
|---|---|
| Enter user ID | Enter the user ID of the simulation target. |
| Network Settings | Specify the IP address of the user to simulate. The default is “IP address anywhere”. |
| Platform Settings | Specify the device information of the user to be simulated. The default is “Any platforms”. |
| Browser Settings | Specifies the browser information of the user to be simulated. The default is “Any browsers”. |
| OS Settings | Specify the OS information of the user to be simulated. The default is “Any OS”. |
| Select Application | Select the application to be simulated. Click the application selection button to display the popup. |
| Run Simulation button | Run the access simulation. |
| Simulation results | Displays the access simulation results on the screen. The login policies and rules applied to the specified user are shown. |
| List button | Return to the login policy list. |
To run the access simulation, follow the steps below.
- Enter the ID of the user to be simulated.
- Specify the IP of the user to simulate. After selecting Specific IP Address, you can manually enter the IP. Enter the IP in the format 123.123.123.123.
- Specify the device information of the user to simulate. After selecting Platform, you can choose a device from the selection list.
- Specify the browser information of the user to be simulated. After selecting Browser, you can choose a browser from the dropdown list.
- Specify the OS information of the user to simulate. After selecting OS, you can choose the OS from the selection list.
- Click the Application Selection button to select the application to simulate.
- In the Application Selection popup, click the radio button to the left of the application name to select the application, then click the Add button.
If you want to re-select the application, click the X button to the right of the selected application name, then click the Select Application button again.
- Click the Run Simulation button.
- The access simulation runs, and when it finishes, the login policies and rules are displayed on the screen according to the simulation results as shown below.
Authentication Policy
The administrator needs to change detailed authentication settings according to the organization’s security policy.
SingleID classifies and manages detailed authentication settings into the following four policies.
- Session Policy
- Authenticator policy
- MFA Service Provider Policy
- Password Policy
To access the authentication policy menu, navigate as follows.
- Admin Portal > Policy > Authentication Policy
To modify the authentication policy, click the Edit button at the lower right of the authentication policy screen to change the settings, then click the Save button.
Session Policy
To change the session policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- In the maximum session limit setting, you set the maximum number of sessions a user can create simultaneously.
- The minimum value that can be set is 1, and the maximum value is 100. When set to 1, a user can log in only from a single browser at a time and cannot log in simultaneously from multiple PCs or browsers.
- Set the priority of the session created by the user in the session priority settings. The priority can be selected from the following two options.
- Old session
- New session
When you set the maximum session limit to 1 and select Old session, a logged-in user will be blocked from logging in when they attempt a new login from another PC or browser where they are not logged in.
Also, when the maximum session limit setting (Œ) restricts the maximum number of sessions to 1 and New session is selected, if a logged-in user attempts a new login from another PC or browser that is not logged in, the previous browser’s session is forcibly expired and the session logged in from the new PC or browser is maintained.
In the maximum session time setting, set the maximum duration a session can be retained.
The maximum session time can be set to one of the following two options.
- No time limit
- Set time limit
If you set No time limit, a session that has been created will not automatically expire until the user logs out. After setting Set time limit and specifying a time, the session expires when the set time elapses, and the user is automatically logged out. Configure the maximum idle session time for the session in the maximum idle session time setting. If you set the maximum idle session time, the session will expire and the user will be automatically logged out when the user does not make an authentication request for the configured duration.
To save the changed settings, click the Save button at the bottom right of the authentication policy screen.
To avoid saving the changed settings, click the Cancel button at the lower right of the authentication policy screen.
| Name | Explanation |
|---|---|
| Maximum session limit setting | Sets the maximum number of concurrent sessions per user. |
| Session priority setting | When a session exceeds the user’s maximum concurrent session count, set the priority between the previous session and the new session. |
| Maximum session time setting | Set the maximum session duration after the session is created. The session expires when the maximum session duration elapses. |
| Maximum idle session time setting | Set the session expiration time for when the user does not make an authentication request to the server for a certain period after the session is created. |
Authenticator policy
To change the Authenticator policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- Configure according to each item below.
- When the setup is complete, click the Save button.
| Name | Explanation |
|---|---|
| Available Authenticator settings(for login policy) | Configure an Authenticator that can be used for authentication. |
| Authentication method during registration | Set the user’s primary identity verification method when registering the Authenticator. |
| Perform the following authentication. | When registering an Authenticator, set additional identity verification methods to allow beyond the primary verification method designated for the user. |
| Find Account | Set the authentication method when retrieving the ID. |
| Password reset | Set the authentication method for password recovery. |
| Unlock setting | If a user repeatedly fails authentication while using Authenticators, the ID becomes locked. You can set a duration so that the locked user’s lockout is automatically cleared after a specified period. |
To remove a specified Authenticator from the available Authenticator settings, it must first be removed from the rules of all login policies.
Configurable Authenticators can be registered in the Authenticator addition menu. Disabled Authenticators cannot be configured in the available Authenticator settings.
If you have not purchased an MFA product
- Available Authenticator Settings (for login policy) is not displayed on this screen.
- If you want to purchase additional MFA products, please contact us via Support Center > Contact Us.
If a user repeatedly enters an incorrect password, fails to log in, and becomes locked, the lock will not be released even after a certain amount of time has passed. Configure the lock and unlock methods for password‑based lockouts in Password Policy.
If you reset a user’s password from the user menu, you can unlock a locked user before the unlock wait time expires. Refer to password reset.
MFA Service Provider Policy
To change the MFA Service Provider policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- Refer to the table below and configure each item accordingly.
- When the configuration is complete, click the Save button.
| Name | description |
|---|---|
| Available Authenticator Settings (for MFA Service Provider) | Configure the Authenticator that the user can use when an authentication request is generated by the MFA Service Provider. |
| Terms and Conditions Options | When a user registers from the MFA Servicce Provider, you can display the terms and conditions and obtain the user’s consent. |
| Unlock setting | When an authentication request occurs from the MFA Service Provider and the user repeatedly fails authentication, the ID becomes locked. You can set a duration so that the locked user’s lockout is automatically cleared after a certain period. |
To remove a specified Authenticator from the available Authenticator settings, it must first be removed from all MFA Service Providers.
Configurable Authenticators can be registered from the Add Authenticator menu. Disabled Authenticators cannot be set in the available Authenticator settings.
If a user authenticates with the MFA Service Provider for the first time, to display the terms and conditions to the user and require their consent, check the terms and conditions option checkbox and then select one or more terms or conditions to display on the screen in the text input box.
If a user authenticating with the MFA Service Provider repeatedly fails authentication, the user’s ID becomes locked. To automatically unlock after a certain period, set the unlock wait time in the unlock settings.
Password Policy
To change the password policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- Refer to the table below and configure each item accordingly.
- When the configuration is complete, click the Save button.
| Name | description |
|---|---|
| Password history | You can configure the system to prevent reuse of previously used passwords. Specify the number of recent passwords to block reuse. users will be unable to use the number of past passwords set above. |
| Password expiration | Specify the password validity period. After the validity period expires, you must change the password to log in. It can be set from 1 day to 365 days. |
| Password lock | If the password is entered incorrectly repeatedly, the user’s ID will be locked. Specify the number of allowed repeated entry failures.
|
| Pattern and Complexity | Set the minimum password length, minimum characters, numbers, etc. |
| Set minimum character count | Specifies the minimum password length. |
| Minimum alphabetic character count setting | Specifies the minimum number of alphabetic characters to include in the password. |
| Minimum number count setting | Specifies the minimum number of digits to include in the password. |
| Set minimum number of special characters | Specifies the minimum number of special characters to include in the password. |
| Set maximum character count | Specifies the maximum length of the password. |
| Allow using the user ID as the password | Set whether to allow the user’s ID to be included in the password. |
Sign‑up Policy
To allow user sign‑up, enable the registration policy, which permits registration of users other than those provisioned from the HR system or IdP. Through account synchronization, you can not only register, create, modify, and delete accounts but also provide features to invite users via the login screen or email.
To enable and use the registration policy, follow the steps below.
- Click Admin Portal > Policy > Sign‑up Policy.
- Enable Allow user registration.
- If you enable it, the Policy tab and User Invitation tab will appear.
- Review the descriptions of the Policy tab and the User Invitation tab below, and configure the policy.
- Click the Save button when the setup is complete.
Policy
You can set general policies for member registration.
| Name | Explanation |
|---|---|
| Display the sign‑up link on the login screen | Display the sign‑up link on the SingleID login screen.
|
| Terms and Conditions Options | Select the option to agree to the terms and conditions during sign‑up. During sign‑up, you can separately select and apply the terms and conditions. |
| Allow sign‑up invitations | When the feature is enabled, you can invite users via email. You can configure it so that only invited users can sign up, instead of using a separate registration page. With this setting, registration through the SingleID sign‑up link is not possible. |
| Sign-up input form | Set the user attributes to be entered during registration. Additional inputs can be requested based on whether they are required. |
| ID duplication prevention setting | When enabled, a suffix is added to the ID to prevent ID duplication. |
| This setting prevents cases where the ID of automatically provisioned accounts is the same. Since duplicate ID values are common, we recommend enabling this setting. When signing up, the specified PostFix value is appended to the ID. | |
| Maximum usage period | The maximum usage period is set after registration. It can be set from day 1 to day 2000. |
| Approval upon sign‑up request | When a sign‑up request is made, you can enable the approval setting to load and apply the registered approval policy. |
Dormant User Policy
Provides a feature that changes users who have not used the SingleID system for an extended period to a dormant state. Users who have been set to a dormant state can be configured, according to the settings, to be restored either by the user themselves or by an administrator.
To enable and use the dormant user policy, follow these steps.
- Click Admin Portal > Policy > Human User Policy.
- Human User Policy Activation Click the toggle button
Additional settings are as shown in the table below.
| Name | description |
|---|---|
| Criteria for setting a user as dormant | This setting converts users who do not log in to SingleID for N days into dormant users. It can be set from 1 day up to 365 days. |
| Send notification email | This setting sends notification emails to users starting N days before the dormant state. Additionally, you can also select the option to send notification emails to users when changing to the dormant state. |
| User exempt from dormant status change | Click the Add button to add an exception user for changing to dormant status. |
| Dormant State Exception Group | You can configure exceptions for users who are members of the group. |
| Long-term human user management | This feature automatically deletes a user account after it has been changed to a human user. It can be set for up to 1~365 days. - You can configure it to send a reminder email N days before deleting the user (1~30 days) - You can set it to send a notification email to the user when their information is deleted. |
| Allow dormant users to restore their status themselves. | When the option is enabled, a dormant user can restore their own status to active. A dormant user can change their status to active by resetting the password through ‘Password Reset’, which also updates the password. |
Approval Policy
The administrator can select an approval system and, depending on the type, set policies for member registration and app access through various approval lines. With diverse approval policies, security policies can be flexibly applied each time they change.
Approval can be performed by distinguishing between the built-in approval system function and the Knox Portal approval system. If integration with another approval system is required, please request it via a 1:1 inquiry.
To check the approval policy, follow the path below.
- Admin Portal > Policy > Approval Policy
Approval Policy List
The administrator can select an approval system and, depending on the type, set policies for member registration and app access using various approval lines. With diverse approval policies, security policies can be flexibly applied each time they change.
| Name | Explanation |
|---|---|
| ID | This is an automatically generated ID when creating an approval policy. |
| Approval System | It is distinguished by SingleID and Knox Portal. If registration with another approval system is required, please request it via a 1:1 inquiry. |
| type | It is divided into app access and sign-up. |
| status | This is the approval policy status. If Not usable, you must change the approver and notifier. |
| Enable approval | It is categorized as in-use or not-in-use. Clicking the Details button lets you view applications that use the approval policy. |
Register Approval Policy
When you click the Register button, you can set the approval system, type, approver, notification method, and approval period.
| Name | Explanation |
|---|---|
| Approval System | Two options are available.
|
| type | Two options are available.
|
| Approver | Select and register the approver and notifier. |
| Notification method | When an approval request is sent to the approver or notifier, choose the notification method. |
Anomaly Detection Policy
SingleID provides a feature that collects and analyzes user behavior data before and after authentication in real time to determine whether there are abnormal authentication activities, and immediately notifies the user of risk when identified as belonging to an abnormal authentication category.
To access the anomalous behavior detection policy menu, proceed as follows.
- Admin Portal > Policy > Anomalous Activity Detection Policy
User Life Cycle Management
User lifecycle management provides configuration functions for setting default values when a user is created or registers, and for extending the user account’s usage period.
To enable and configure the user lifecycle management function, refer to the following.
Onboarding (subscriber)
Set the phone country code, language, and time zone when creating a user and signing up. To configure, click the Edit button at the bottom right to make changes.
Offboarding (former member)
Users can request an extension of their account usage period, and it can be configured to allow the maximum possible extension.
- Click the Activate toggle when requesting an extension of the user’s usage period.
- Enter N days for the maximum extendable period.
- Click the Change button in the usage period request approval to set the approver.
Conditional Authentication Policy
Conditional authentication policies can set rules to match the environment, settings, and individual circumstances of user accounts.
You can set the following rules.
| Name | description |
|---|---|
| Use multiple authenticators | Users who have relied on a single authentication method for an extended period must additionally verify their identity using a different type of authentication tool. |
9.5.2.1.2.5 - Terms and Conditions
We provide a feature that lets each company using SingleID manage Privacy Policy, Terms of Service, and other items according to their specific circumstances and characteristics.
You can draft a privacy policy that meets your organization’s requirements and notify users, or for users of SingleID, display the terms of service or usage conditions before use and obtain their consent.
Through the Terms and Conditions menu, you can notify users of the privacy policy, terms of use, usage conditions, etc., and obtain their consent. SingleID provides a default template to make drafting terms and conditions easier.
To access the Terms and Conditions menu, proceed as follows.
- Tenant Admin Portal > Rebranding > Terms and Conditions
The features provided in the Terms and Conditions menu are as follows.
- Terms and Conditions Property Settings
- Version management of terms and conditions
- Issuance of terms and conditions
Terms and Conditions List
The tenant administrator can view the terms and conditions in a list format.
The default template provided by SingleID is as follows.
Terms Type Template
- Privacy
- Terms of Use
- Collection and Use of Personal Information
- Marketing
Condition Type Template
- Are you over age 14?
Cookie Type Template
- Cookie
From the list, click a term or condition to edit its settings and navigate to its detailed screen.
| Name | Explanation |
|---|---|
| type | The type is displayed as an icon. |
| Name | The name is displayed. |
| Explanation | The description is displayed. |
| Type Settings | You can change the type. |
| Name | You can edit the name. |
| Set required status | You can set whether it is required. |
| Email notification setting | You can configure whether to notify changes via email when terms or conditions are modified. |
| Explanation | You can edit the description. |
| Registration date and registrant | The registration date and registrant are displayed. |
| Modified Date | The last modified date and the last modifier are displayed. |
| List button | This is a button that returns to the list. |
| Edit button | Modify the terms or conditions. |
- In the detail screen of the terms or conditions, select the General Settings tab.
- Click the Edit button.
- Title can be edited.
- You can edit required status. The selectable options are as follows.
- Required: If these terms or conditions are presented to the user and they do not agree, usage will be restricted, preventing further login.
- Choice: Whether you agree is up to the user, and even if you do not agree to the terms or conditions, you will not be restricted from logging in.
- Note: We do not verify consent.
- You can edit the description of terms or conditions. The description is not shown to users and is used for the administrator’s reference.
- If you have modified all settings, click the Save button.
To return to the view state without saving the edited information, click the Cancel button.
Terms and Conditions Version Management
Tenant administrators can view and manage the versioned list of terms and conditions. The default version for each term and condition is v1.0.0, and it is registered by default for each template when a tenant is created. To view the version list, click the Version History tab on the detailed screen of the terms or conditions.
Version History
You can view the previous version by clicking the Version item at the top of the privacy policy and terms of use.
Click List to view the history of past publications. Once a version has been published, it cannot be edited.
Add version
If you click the Add button on the Version History tab, you can create a new version of terms and conditions.
If you want to add a version, follow the steps below.
- Click the Add button in the Version History tab.
- Click the desired locale to select the writing language.
- The language you selected indicates the region to be displayed in the privacy policy and terms of service. You need to draft the terms and conditions for each selected language.
- Enter the title and content for each locale language.
- Click the Save button and click the List button to return to the list.
After completing the draft, review the written article.
Reissue
Newly created versions are published by setting a reissue date.
To publish a new version, follow the steps below.
- In the Version History tab, click the Reissue Scheduled Date button.
- Set the version.
- Set the reissue date.
- Enable Reissue Modification. If enabled, the revised terms/conditions will be reissued, and users may need to consent based on the General Settings > Required status as of the terms/conditions modification date.
- Modification reason, please enter briefly.
- Click the Publish Settings button to complete the configuration.
9.5.2.1.2.6 - Settings
The Settings menu consists of Role Management, which manages the permissions of Admin Portal administrators, Ledger Management, which registers and manages SoT (ledger), and SMS Service, which registers SMS integration information for use in secondary multi-factor authentication.
Role management
Role management can control the permissions of administrators in the Admin Portal. In line with the principle of least privilege, we provide role management to enable administrators to operate with minimal permissions.
Administrators have two roles by default.
- ADMINSTRATOR - a super administrator account with all privileges
- SOT_MANAGER - a director, application system administrator, and an account with app management capabilities
User assignment
To add a user with ADMINISTRATOR privileges, follow the steps below.
- Select ADMINSTRATOR from the menu, and click the User tab.
- To add a user, click the Add button.
- You can search for a user using the user ID, name, email address you wish to add.
- After searching for a user and selecting, click the Add button to add the user.
Director Management
SingleID can manage and view various SoTs.
| name | Explanation |
|---|---|
| default | There are two basic types, and they are generated automatically. - Mfa: Users coming from the MFA Service Provider (primary authentication system) correspond to the Mfa type. (When the MFA Service Provider does not specify a SoT) - SingleID: Users and Groups created by the administrator through the Admin Portal’s Identity Store are linked to the corresponding SoT. |
| Application | This is an SoT that is automatically generated by receiving user/group information via inbound provisioning from an external application (SoT). |
| MFA service Provider | This is a SoT automatically generated based on the User Tag entered when creating an MFA Service Provider. |
default
- It is the primary ledger of SingleID, receiving entries through the Identity Store and MFA Service Provider.
- Mfa: Mfa is the default SoT of the MFA service provider. * All users created through an MFA Service Provider without a specified User Tag are managed as MFA SoT. * MFA cannot be changed or deleted.
- SingleID: SingleID is the default SoT. * It is used to manage users and groups created through the Admin Portal. * You cannot change or delete the SingleID.
Application
- It is a ledger that is automatically created by receiving user/group information via inbound provisioning from an external application (SoT).
- You can assign the person in charge of managing the ledger through the PIC tab (up to 50 people).
MFA Service Provider
- When registered as an MFA Service Provider, setting a User tag creates a SoT, and new users who receive secondary authentication from that system are marked with #SoT.
- You can view and manage the ledger received through this MFA Service Provider.
- You can assign the person responsible for managing the ledger through the PIC tab (up to 50 people).
SMS service configuration
Administrators can enable the SMS service using the activation toggle button.
SCP SMS Service Configuration
After activating the SMS service, set the SCP SMS service in the SMS service settings.
| Name | Explanation |
|---|---|
| Activate SMS service | Set SMS service activation/deactivation to toggle mode |
| Select SMS service | Select SMS to use (SCP SMS) |
| SMS service configuration | Selected SMS settings (URL and Key registration) |
| SMS sending test | Settings for SMS sending test |
To set up and use the SMS service, follow the steps below.
- SMS Service Activation Click the toggle button to activate the service.
- Select SCP SMS Service.
- Click Edit, enter the required values to configure SMS, and save.
- SCP SMS - SCP SMS Service Endpoint URL, SCP SMS Service App Key
- To save changes, click the Save button. 4. When you click the Save button, a notification popup appears asking whether to save the changes.
- When you click the Confirm button, the changes are saved, and when the changes are successfully completed, a toast message appears. 5. When the Cancel button is clicked, the administrator’s registration/modification changes are not updated and it returns to the SMS screen.
Knox SMS Settings
Knox SMS is an SMS service provided by Knox. After enabling the SMS service, select Knox SMS to configure it.
| name | Explanation |
|---|---|
| Select SMS service | Select SMS service to use (Knox SMS) |
| Selected SMS service settings | Register caller phone number |
| SMS signature | If you enable the activation toggle, you can set the first phrase when sending an SMS. It is added as the initial header of the SMS content according to the customer’s situation. Example: [XX Electronics] |
| SMS sending test | Settings for SMS sending test |
SMS sending test
To set up and use the Knox SMS service, follow the steps below.
- Select the Knox SMS service.
- Click Edit to register the sender phone number for configuring the SMS service.
- To save changes, click the Save button.
- To verify that the SMS settings are correct, you can enter a phone number for the SMS sending test and click Send to perform the test.
- When you click the Send button, a popup appears asking whether to send an SMS test to that number. 5. When you click Confirm, an SMS is sent to the entered number and a popup window appears. 5. A toast message appears indicating that an SMS has been sent to the specified number.
BizBuriO SMS Settings
After activating the SMS service, select Bizburio SMS in the Bizburio SMS service settings to configure it.
| Name | Explanation |
|---|---|
| Select SMS service | Select SMS service to use (BizBuriO SMS) |
| Selected SMS service settings | Register caller phone number |
| SMS sending test | Settings for SMS sending test |
SMS sending test
To configure and use the BizBuriO SMS service, follow the steps below.
- Select the BizBuriO SMS service.
- Click Edit to register the sender phone number for configuring the SMS service.
- To save changes, click the Save button.
- To verify that the SMS settings are correct, you can enter a phone number for the SMS sending test and click Send to perform the test.
- When you click the Send button, a popup appears asking whether to send an SMS test to that number. 5. When you click Confirm, an SMS is sent to the entered number and a popup window appears. 5. A toast message appears indicating that an SMS has been sent to that number.
9.5.2.1.2.7 - Monitoring
The Monitoring menu lets you view the login history of all users, MFA history, and administrator audit logs.
Login History
Provides users’ login history through the Monitoring menu. Users can also view their own login history via the User Portal.
| Name | Explanation |
|---|---|
| All | Clicking All displays the history of successful and failed logins. |
| Success | When you click Success, the history of successful logins will be displayed. |
| This record shows that the user successfully logged in. | |
| Failure | Clicking Failure will display the history of failed login attempts. |
| This entry records a user login failure. | |
| CSV download | Clicking CSV Download will download the history as a CSV file. |
| Name | Explanation |
|---|---|
| Login date and time | The date and time the user logged in |
| ID | User ID |
| Name | User name |
| Location | User’s connection location |
| country | Country of connection |
| city | Connected city |
| IP address | Connecting IP address |
| Application | Connecting application |
| Operating System | Operating system environment you are connecting to |
| Browser | Connecting browser |
| Detection | Detection |
| Result | Login success result |
MFA History
In the Admin Portal, you can view users’ MFA (multi-factor authentication) history through the Monitoring menu. Users can also view their own MFA history via the User Portal.
| Name | Explanation |
|---|---|
| All | Clicking All displays the history of successful and failed composite authentication. |
| Success | When you click Success, the history of successful multi-factor authentication is retrieved. This history is the record of the user successfully logging in. |
| Failure | Clicking “Failure” will display the history of failed multi-factor authentication. This history shows the user’s failed login attempts. |
| Expiration | Clicking Expire displays the history of expired multi-factor authentication. |
| CSV download | Clicking CSV Download will download the history as a CSV file. |
| Name | Explanation |
|---|---|
| Event date and time | Date and time the user attempted multi-factor authentication |
| ID | User ID |
| Name | User name |
| IP address | Connecting IP address |
| Management entity | User account management entity |
| Event type | Types used for authentication - Enrollment : Registration - Authentication : Authentication - Secondary multi-factor authentication |
| Application | Connecting application |
| System code | System code entered when registering the MFA provider |
| Authenticator | Authentication methods used for multi-factor authentication |
| Result | Login success result |
Administrator audit log
In the Admin Portal, the monitoring menu records the administrator’s activity history.
| Name | Explanation |
|---|---|
| date | Log timestamp |
| ID | Administrator ID |
| Menu | Menu |
| Submenu | Submenu |
| Action | Activity Log - View : Retrieve - List : List View - Update : Edit - Create : Create |
| Event type | Types used for authentication - Enrollment : Registration - Authentication : Authentication - Secondary multi-factor authentication |
| Result | Result of activity log |
To download monitoring history as Excel (CSV), we recommend staying below the following count. You can adjust the number of retrieved items by changing the search criteria.
- Login history: 20,000 entries or less
- MFA history: 100,000 entries or less
- Administrator audit log: 20,000 entries or less
9.5.2.1.2.8 - Open Source licence
The open source licenses used in the SingleID solution are as follows. For more details, see below.
SingleID_SSO-Agent-Windows
The following sets forth attribution notices for third party software that may be contained in portions of this product. If you have any questions, please contact global.cs@samsung.com
| License | Open Source Component | License Text |
|---|---|---|
| BSD 3-clause “New” or “Revised” License | NLog - Advanced .NET Logging http://www.nuget.org/packages/NLog | NLog - Advanced .NET Logging: Copyright (c)2004-2023 Nlog Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: * Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer. * Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. * Neither the name of the THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED THE POSSIBILITY OF SUCH DAMAGE. |
| MIT License | Jose JWT: http://www.nuget.org/packages/jose-jwt cassia: http://www.nuget.org/packages/Cassia Bouncy-Castle: https://www.nuget.org/packages/Bouncy-Castle Fody: http://www.nuget.org/packages/Fody Json.NET: http://www.nuget.org/packages/Newtonsoft.Json Costura.Fody: http://www.nuget.org/packages/Costura.Fody Opencover: http://www.nuget.org/packages/OpenCover Fleck2: http://www.nuget.org/packages/Fleck2 chartist-js: http://github.com/gionkunz/chartist-js/ | The MIT License Jose JWT: Copyright (c) 2014-2021 dvsekhvalnov cassia: Copyright (c) 2008 - 2017 Dan Ports Bouncy-Castle: Copyright (c) 2000-2023 The Legion of the Bouncy Castle Inc. Bouncy-Castle: https://www.nuget.org/packages/Bouncy-Castle Fody: http://www.nuget.org/packages/Fody Json.NET: http://www.nuget.org/packages/Newtonsoft.Json Costura.Fody: http://www.nuget.org/packages/Costura.Fody Opencover: http://www.nuget.org/packages/OpenCover Fleck2: http://www.nuget.org/packages/Fleck2 chartist-js: http://github.com/gionkunz/chartist-js/ Fody: Copyright (c) Simon Cropp Json.NET: Copyright (c) 2007 James Newton-King Costura.Fody: Copyright (c) 2012 Simon Cropp and contributors Opencover: Copyright (c) 2011-2019 Shaun Wilde Fleck2: Copyright (c) 2013 Peter Sunde Copyright (c) 2010-2012 Jason Staten chartist-js: Copyright (c)2013 Gion Kunz gion.kunz@gmail.com Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. |
| Mozilla Public License 2.0 | OpenRPA: https://github.com/open-rpa/openrpa.git | Mozilla Public License Version 2.0 1. Definitions 1.1. “Contributor” means each individual or legal entity that creates, contributes to the creation of, or owns Covered Software. 1.2. “Contributor Version” means the combination of the Contributions of others (if any) used by a Contributor and that particular Contributor’s Contribution. 1.3. “Contribution” means Covered Software of a particular Contributor. 1.4. “Covered Software” means Source Code Form to which the initial Contributor has attached the notice in Exhibit A, the Executable Form of such Source Code Form, and Modifications of such Source Code Form, in each case including portions thereof. 1.5. “Incompatible With Secondary Licenses” means a. that the initial Contributor has attached the notice described in Exhibit B to the Covered Software; or b. that the Covered Software was made available under the terms of version 1.1 or earlier of the License, but not also under the terms of a Secondary License. 1.6. “Executable Form” means any form of the work other than Source Code Form. 1.7. “Larger Work” means a work that combines Covered Software with other material, in a separate file or files, that is not Covered Software. 1.8. “License” means this document. 1.9. “Licensable” means having the right to grant, to the maximum extent possible, whether at the time of the initial grant or subsequently, any and all of the rights conveyed by this License. 1.10. “Modifications” means any of the following: c. any file in Source Code Form that results from an addition to, deletion from, or modification of the contents of Covered Software; or d. any new file in Source Code Form that contains any Covered Software. 1.11. “Patent Claims” of a Contributor means any patent claim(s), including without limitation, method, process, and apparatus claims, in any patent Licensable by such Contributor that would be infringed, but for the grant of the License, by the making, using, selling, offering for sale, having made, import, or transfer of either its Contributions or its Contributor Version. 1.12. “Secondary License” means either the GNU General Public License, Version 2.0, the GNU Lesser General Public License, Version 2.1, the GNU Affero General Public License, Version 3.0, or any later versions of those licenses. 1.13. “Source Code Form” means the form of the work preferred for making modifications. 1.14. “You” (or “Your”) means an individual or a legal entity exercising rights under this License. For legal entities, “You” includes any entity that controls, is controlled by, or is under common control with You. For purposes of this definition, “control” means (a) the power, direct or indirect, to cause the direction or management of such entity, whether by contract or otherwise, or (b) ownership of more than fifty percent (50%) of the outstanding shares or beneficial ownership of such entity. 2. License Grants and Conditions 2.1. Grants Each Contributor hereby grants You a world-wide, royalty-free, non-exclusive license: a. under intellectual property rights (other than patent or trademark) Licensable by such Contributor to use, reproduce, make available, modify, display, perform, distribute, and otherwise exploit its Contributions, either on an unmodified basis, with Modifications, or as part of a Larger Work; and b. under Patent Claims of such Contributor to make, use, sell, offer for sale, have made, import, and otherwise transfer either its Contributions or its Contributor Version. 2.2. Effective Date The licenses granted in Section 2.1 with respect to any Contribution become effective for each Contribution on the date the Contributor first distributes such Contribution. 2.3. Limitations on Grant Scope The licenses granted in this Section 2 are the only rights granted under this License. No additional rights or licenses will be implied from the distribution or licensing of Covered Software under this License. Notwithstanding Section 2.1(b) above, no patent license is granted by a Contributor: c. for any code that a Contributor has removed from Covered Software; or d. for infringements caused by: (i) Your and any other third party’s modifications of Covered Software, or (ii) the combination of its Contributions with other software (except as part of its Contributor Version); or e. under Patent Claims infringed by Covered Software in the absence of its Contributions. This License does not grant any rights in the trademarks, service marks, or logos of any Contributor (except as may be necessary to comply with the notice requirements in Section 3.4). 2.4. Subsequent Licenses No Contributor makes additional grants as a result of Your choice to distribute the Covered Software under a subsequent version of this License (see Section 10.2) or under the terms of a Secondary License (if permitted under the terms of Section 3.3). 2.5. Representation Each Contributor represents that the Contributor believes its Contributions are its original creation(s) or it has sufficient rights to grant the rights to its Contributions conveyed by this License. 2.6. Fair Use This License is not intended to limit any rights You have under applicable copyright doctrines of fair use, fair dealing, or other equivalents. 2.7. Conditions Sections 3.1, 3.2, 3.3, and 3.4 are conditions of the licenses granted in Section 2.1. 3. Responsibilities 3.1. Distribution of Source Form All distribution of Covered Software in Source Code Form, including any Modifications that You create or to which You contribute, must be under the terms of this License. You must inform recipients that the Source Code Form of the Covered Software is governed by the terms of this License, and how they can obtain a copy of this License. You may not attempt to alter or restrict the recipients’ rights in the Source Code Form. 3.2. Distribution of Executable Form If You distribute Covered Software in Executable Form then: a. such Covered Software must also be made available in Source Code Form, as described in Section 3.1, and You must inform recipients of the Executable Form how they can obtain a copy of such Source Code Form by reasonable means in a timely manner, at a charge no more than the cost of distribution to the recipient; and b. You may distribute such Executable Form under the terms of this License, or sublicense it under different terms, provided that the license for the Executable Form does not attempt to limit or alter the recipients’ rights in the Source Code Form under this License. 3.3. Distribution of a Larger Work You may create and distribute a Larger Work under terms of Your choice, provided that You also comply with the requirements of this License for the Covered Software. If the Larger Work is a combination of Covered Software with a work governed by one or more Secondary Licenses, and the Covered Software is not Incompatible With Secondary Licenses, this License permits You to additionally distribute such Covered Software under the terms of such Secondary License(s), so that the recipient of the Larger Work may, at their option, further distribute the Covered Software under the terms of either this License or such Secondary License(s). 3.4. Notices You may not remove or alter the substance of any license notices (including copyright notices, patent notices, disclaimers of warranty, or limitations of liability) contained within the Source Code Form of the Covered Software, except that You may alter any license notices to the extent required to remedy known factual inaccuracies. 3.5. Application of Additional Terms You may choose to offer, and to charge a fee for, warranty, support, indemnity or liability obligations to one or more recipients of Covered Software. However, You may do so only on Your own behalf, and not on behalf of any Contributor. You must make it absolutely clear that any such warranty, support, indemnity, or liability obligation is offered by You alone, and You hereby agree to indemnify every Contributor for any liability incurred by such Contributor as a result of warranty, support, indemnity or liability terms You offer. You may include additional disclaimers of warranty and limitations of liability specific to any jurisdiction. 4. Inability to Comply Due to Statute or Regulation If it is impossible for You to comply with any of the terms of this License with respect to some or all of the Covered Software due to statute, judicial order, or regulation then You must: (a) comply with the terms of this License to the maximum extent possible; and (b) describe the limitations and the code they affect. Such description must be placed in a text file included with all distributions of the Covered Software under this License. Except to the extent prohibited by statute or regulation, such description must be sufficiently detailed for a recipient of ordinary skill to be able to understand it. 5. Termination 5.1. The rights granted under this License will terminate automatically if You fail to comply with any of its terms. However, if You become compliant, then the rights granted under this License from a particular Contributor are reinstated (a) provisionally, unless and until such Contributor explicitly and finally terminates Your grants, and (b) on an ongoing basis, if such Contributor fails to notify You of the non-compliance by some reasonable means prior to 60 days after You have come back into compliance. Moreover, Your grants from a particular Contributor are reinstated on an ongoing basis if such Contributor notifies You of the non-compliance by some reasonable means, this is the first time You have received notice of non-compliance with this License from such Contributor, and You become compliant prior to 30 days after Your receipt of the notice. 5.2. If You initiate litigation against any entity by asserting a patent infringement claim (excluding declaratory judgment actions, counter-claims, and cross-claims) alleging that a Contributor Version directly or indirectly infringes any patent, then the rights granted to You by any and all Contributors for the Covered Software under Section 2.1 of this License shall terminate. 5.3. In the event of termination under Sections 5.1 or 5.2 above, all end user license agreements (excluding distributors and resellers) which have been validly granted by You or Your distributors under this License prior to termination shall survive termination. 6. Disclaimer of Warranty Covered Software is provided under this License on an “as is” basis, without warranty of any kind, either expressed, implied, or statutory, including, without limitation, warranties that the Covered Software is free of defects, merchantable, fit for a particular purpose or non-infringing. The entire risk as to the quality and performance of the Covered Software is with You. Should any Covered Software prove defective in any respect, You (not any Contributor) assume the cost of any necessary servicing, repair, or correction. This disclaimer of warranty constitutes an essential part of this License. No use of any Covered Software is authorized under this License except under this disclaimer. 7. Limitation of Liability Under no circumstances and under no legal theory, whether tort (including negligence), contract, or otherwise, shall any Contributor, or anyone who distributes Covered Software as permitted above, be liable to You for any direct, indirect, special, incidental, or consequential damages of any character including, without limitation, damages for lost profits, loss of goodwill, work stoppage, computer failure or malfunction, or any and all other commercial damages or losses, even if such party shall have been informed of the possibility of such damages. This limitation of liability shall not apply to liability for death or personal injury resulting from such party’s negligence to the extent applicable law prohibits such limitation. Some jurisdictions do not allow the exclusion or limitation of incidental or consequential damages, so this exclusion and limitation may not apply to You. 8. Litigation Any litigation relating to this License may be brought only in the courts of a jurisdiction where the defendant maintains its principal place of business and such litigation shall be governed by laws of that jurisdiction, without reference to its conflict-of-law provisions. Nothing in this Section shall prevent a party’s ability to bring cross-claims or counter-claims. 9. Miscellaneous This License represents the complete agreement concerning the subject matter hereof. If any provision of this License is held to be unenforceable, such provision shall be reformed only to the extent necessary to make it enforceable. Any law or regulation which provides that the language of a contract shall be construed against the drafter shall not be used to construe this License against a Contributor. 10. Versions of the License 10.1. New Versions Mozilla Foundation is the license steward. Except as provided in Section 10.3, no one other than the license steward has the right to modify or publish new versions of this License. Each version will be given a distinguishing version number. 10.2. Effect of New Versions You may distribute the Covered Software under the terms of the version of the License under which You originally received the Covered Software, or under the terms of any subsequent version published by the license steward. 10.3. Modified Versions If you create software not governed by this License, and you want to create a new license for such software, you may create and use a modified version of this License if you rename the license and remove any references to the name of the license steward (except to note that such modified license differs from this License). 10.4. Distributing Source Code Form that is Incompatible With Secondary Licenses If You choose to distribute Source Code Form that is Incompatible With Secondary Licenses under the terms of this version of the License, the notice described in Exhibit B of this License must be attached. Exhibit A - Source Code Form License Notice This Source Code Form is subject to the terms of the Mozilla Public License, v. 2.0. If a copy of the MPL was not distributed with this file, You can obtain one at http://mozilla.org/MPL/2.0/. If it is not possible or desirable to put the notice in a particular file, then You may include the notice in a location (such as a LICENSE file in a relevant directory) where a recipient would be likely to look for such a notice. You may add additional accurate notices of copyright ownership. Exhibit B - “Incompatible With Secondary Licenses” Notice This Source Code Form is “Incompatible With Secondary Licenses”, as defined by the Mozilla Public License, v. 2.0. |
SingleID_ADFS-Adapter
The following sets forth attribution notices for third party software that may be contained in portions of this product. If you have any questions, please contact global.cs@samsung.com
| License | Open Source Component | License Text |
|---|---|---|
| Apache License 2.0 | Microsoft.NetFramework.Analyzers, Microsoft.CodeAnalysis.VersionCheckAnalyzer, Microsoft.NetCore.Analyzers, Microsoft.CodeAnalysis.FxCopAnalyzers, Microsoft.CodeQuality.Analyzers | Apache License Version 2.0, January 2004 http://www.apache.org/licenses/ TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION 1. Definitions. “License” shall mean the terms and conditions for use, reproduction, and distribution as defined by Sections 1 through 9 of this document. “Licensor” shall mean the copyright owner or entity authorized by the copyright owner that is granting the License. “Legal Entity” shall mean the union of the acting entity and all other entities that control, are controlled by, or are under common control with that entity. For the purposes of this definition, “control” means (i) the power, direct or indirect, to cause the direction or management of such entity, whether by contract or otherwise, or (ii) ownership of fifty percent (50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity. “You” (or “Your”) shall mean an individual or Legal Entity exercising permissions granted by this License. “Source” form shall mean the preferred form for making modifications, including but not limited to software source code, documentation source, and configuration files. “Object” form shall mean any form resulting from mechanical transformation or translation of a Source form, including but not limited to compiled object code, generated documentation, and conversions to other media types. “Work” shall mean the work of authorship, whether in Source or Object form, made available under the License, as indicated by a copyright notice License Open Source Software License Text that is included in or attached to the work (an example is provided in the Appendix below). “Derivative Works” shall mean any work, whether in Source or Object form, that is based on (or derived from) the Work and for which the editorial revisions, annotations, elaborations, or other modifications represent, as a whole, an original work of authorship. For the purposes of this License, Derivative Works shall not include works that remain separable from, or merely link (or bind by name) to the interfaces of, the Work and Derivative Works thereof. “Contribution” shall mean any work of authorship, including the original version of the Work and any modifications or additions to that Work or Derivative Works thereof, that is intentionally submitted to Licensor for inclusion in the Work by the copyright owner or by an individual or Legal Entity authorized to submit on behalf of the copyright owner. For the purposes of this definition, “submitted” means any form of electronic, verbal, or written communication sent to the Licensor or its representatives, including but not limited to communication on electronic mailing lists, source code control systems, and issue tracking systems that are managed by, or on behalf of, the Licensor for the purpose of discussing and improving the Work, but excluding communication that is conspicuously marked or otherwise designated in writing by the copyright owner as “Not a Contribution.” “Contributor” shall mean Licensor and any individual or Legal Entity on behalf of whom a Contribution has been received by Licensor and subsequently incorporated within the Work. 2. Grant of Copyright License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable copyright license to reproduce, prepare Derivative Works of, publicly display, publicly perform, sublicense, and distribute the Work and such Derivative Works in Source or Object form. 3. Grant of Patent License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable (except as stated in this section) patent license to make, have made, use, offer to sell, sell, import, and otherwise transfer the Work, where such license applies only to those patent claims licensable by such Contributor that are necessarily infringed by their Contribution(s) alone or by combination of their Contribution(s) with the Work to which such Contribution(s) was submitted. If You institute patent litigation against any entity (including a cross-claim or counterclaim in a lawsuit) alleging that the Work or a Contribution incorporated within the Work constitutes direct or contributory patent infringement, then any patent licenses granted to You under this License for that Work shall terminate as of the date such litigation is filed. 4. Redistribution. You may reproduce and distribute copies of the Work or Derivative Works thereof in any medium, with or without modifications, and in Source or Object form, provided that You meet the following conditions: a. You must give any other recipients of the Work or Derivative Works a copy of this License; and b. You must cause any modified files to carry prominent notices stating that You changed the files; and c. You must retain, in the Source form of any Derivative Works that You distribute, all copyright, patent, trademark, and attribution notices from the Source form of the Work, excluding those notices that do not pertain to any part of the Derivative Works; and d. If the Work includes a “NOTICE” text file as part of its distribution, then any Derivative Works that You distribute must include a readable copy of the attribution notices contained within such NOTICE file, excluding those notices that do not pertain to any part of the Derivative Works, in at least one of the following places: within a NOTICE text file distributed as part of the Derivative Works; within the Source form or documentation, if provided along with the Derivative Works; or, within a display generated by the Derivative Works, if and wherever such third-party notices normally appear. The contents of the NOTICE file are for informational purposes only and do not modify the License. You may add Your own attribution notices within Derivative Works that You distribute, alongside or as an addendum to the NOTICE text from the Work, provided that such additional attribution notices cannot be construed as modifying the License. You may add Your own copyright statement to Your modifications and may provide additional or different license terms and conditions for use, reproduction, or distribution of Your modifications, or for any such Derivative Works as a whole, provided Your use, reproduction, and distribution of the Work otherwise complies with the conditions stated in this License. 5. Submission of Contributions. Unless You explicitly state otherwise, any Contribution intentionally submitted for inclusion in the Work by You to the Licensor shall be under the terms and conditions of this License, without any additional terms or conditions. Notwithstanding the above, nothing herein shall supersede or modify the terms of any separate license agreement you may have executed with Licensor regarding such Contributions. 6. Trademarks. This License does not grant permission to use the trade names, trademarks, service marks, or product names of the Licensor, except as required for reasonable and customary use in describing the origin of the Work and reproducing the content of the NOTICE file. 7. Disclaimer of Warranty. Unless required by applicable law or agreed to in writing, Licensor provides the Work (and each Contributor provides its Contributions) on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied, including, without limitation, any warranties or conditions of TITLE, NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A PARTICULAR PURPOSE. You are solely responsible for determining the appropriateness of using or License Open Source Software License Text redistributing the Work and assume any risks associated with Your exercise of permissions under this License. 8. Limitation of Liability. In no event and under no legal theory, whether in tort (including negligence), contract, or otherwise, unless required by applicable law (such as deliberate and grossly negligent acts) or agreed to in writing, shall any Contributor be liable to You for damages, including any direct, indirect, special, incidental, or consequential damages of any character arising as a result of this License or out of the use or inability to use the Work (including but not limited to damages for loss of goodwill, work stoppage, computer failure or malfunction, or any and all other commercial damages or losses), even if such Contributor has been advised of the possibility of such damages. 9. Accepting Warranty or Additional Liability. While redistributing the Work or Derivative Works thereof, You may choose to offer, and charge a fee for, acceptance of support, warranty, indemnity, or other liability obligations and/or rights consistent with this License. However, in accepting such obligations, You may act only on Your own behalf and on Your sole responsibility, not on behalf of any other Contributor, and only if You agree to indemnify, defend, and hold each Contributor harmless for any liability incurred by, or claims asserted against, such Contributor by reason of your accepting any such warranty or additional liability. END OF TERMS AND CONDITIONS APPENDIX: How to apply the Apache License to your work To apply the Apache License to your work, attach the following boilerplate notice, with the fields enclosed by brackets “[]” replaced with your own identifying information. (Don’t include the brackets!) The text should be enclosed in the appropriate comment syntax for the file format. We also recommend that a file or class name and description of purpose be included on the same “printed page” as the copyright notice for easier identification within third-party archives. Copyright [yyyy] [name of copyright owner] Licensed under the Apache License, Version 2.0 (the “License”); you may not use this file except in compliance with the License. You may obtain a copy of the License at http://www.apache.org/licenses/LICENSE-2.0 Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License. |
| Microsoft .NET Library License | System.Security.Claims http://www.nuget.org/packages/System.Security.Claims | MICROSOFT SOFTWARE LICENSE TERMS MICROSOFT .NET LIBRARY These license terms are an agreement between Microsoft Corporation (or based on where you live, one of its affiliates) and you. Please read them. They apply to the software named above, which includes the media on which you received it, if any. The terms also apply to any Microsoft * updates, * supplements, * Internet-based services, and * support services for this software, unless other terms accompany those items. If so, those terms apply. BY USING THE SOFTWARE, YOU ACCEPT THESE TERMS. IF YOU DO NOT ACCEPT THEM, DO NOT USE THE SOFTWARE. IF YOU COMPLY WITH THESE LICENSE TERMS, YOU HAVE THE PERPETUAL RIGHTS BELOW. 1. INSTALLATION AND USE RIGHTS. a. Installation and Use. You may install and use any number of copies of the software to design, develop and test your programs. You may modify, copy, distribute or deploy any .js files contained in the software as part of your programs. b. Third Party Programs. The software may include third party programs that Microsoft, not the third party, licenses to you under this agreement. Notices, if any, for the third party program are included for your information only. 2. ADDITIONAL LICENSING REQUIREMENTS AND/OR USE RIGHTS. a. DISTRIBUTABLE CODE. In addition to the .js files described above, the software is comprised of Distributable Code. “Distributable Code” is code that you are permitted to distribute in programs you develop if you comply with the terms below. i. Right to Use and Distribute. * You may copy and distribute the object code form of the software. * Third Party Distribution. You may permit distributors of your programs to copy and distribute the Distributable Code as part of those programs. ii. Distribution Requirements. For any Distributable Code you distribute, you must * use the Distributable Code in your programs and not as a standalone distribution; * require distributors and external end users to agree to terms that protect it at least as much as this agreement; * display your valid copyright notice on your programs; and * indemnify, defend, and hold harmless Microsoft from any claims, including attorneys’ fees, related to the distribution or use of your programs. iii. Distribution Restrictions. You may not * alter any copyright, trademark or patent notice in the Distributable Code; * use Microsoft’s trademarks in your programs’ names or in a way that suggests your programs come from or are endorsed by Microsoft; * include Distributable Code in malicious, deceptive or unlawful programs; or * modify or distribute the source code of any Distributable Code so that any part of it becomes subject to an Excluded License. An Excluded License is one that requires, as a condition of use, modification or distribution, that * the code be disclosed or distributed in source code form; or * others have the right to modify it. 3. SCOPE OF LICENSE. The software is licensed, not sold. This agreement only gives you some rights to use the software. Microsoft reserves all other rights. Unless applicable law gives you more rights despite this limitation, you may use the software only as expressly permitted in this agreement. In doing so, you must comply with any technical limitations in the software that only allow you to use it in certain ways. You may not * work around any technical limitations in the software; * reverse engineer, decompile or disassemble the software, except and only to the extent that applicable law expressly permits, despite this limitation; * publish the software for others to copy; * rent, lease or lend the software; or * transfer the software or this agreement to any third party. BACKUP COPY. You may make one backup copy of the software. You may use it only to reinstall the software. DOCUMENTATION. Any person that has valid access to your computer or internal network may copy and use the documentation for your internal, reference purposes. EXPORT RESTRICTIONS. The software is subject to United States export laws and regulations. You must comply with all domestic and international export laws and regulations that apply to the software. These laws include restrictions on destinations, end users and end use. For additional information, see www.microsoft.com/exporting SUPPORT SERVICES. Because this software is “as is,” we may not provide support services for it. ENTIRE AGREEMENT. This agreement, and the terms for supplements, updates, Internet-based services and support services that you use, are the entire agreement for the software and support services. APPLICABLE LAW. a. United States. If you acquired the software in the United States, Washington state law governs the interpretation of this agreement and applies to claims for breach of it, regardless of conflict of laws principles. The laws of the state where you live govern all other claims, including claims under state consumer protection laws, unfair competition laws, and in tort. b. Outside the United States. If you acquired the software in any other country, the laws of that country apply. LEGAL EFFECT. This agreement describes certain legal rights. You may have other rights under the laws of your country. You may also have rights with respect to the party from whom you acquired the software. This agreement does not change your rights under the laws of your country if the laws of your country do not permit it to do so. DISCLAIMER OF WARRANTY. THE SOFTWARE IS LICENSED “AS-IS.” YOU BEAR THE RISK OF USING IT. MICROSOFT GIVES NO EXPRESS WARRANTIES, GUARANTEES OR CONDITIONS. YOU MAY HAVE ADDITIONAL CONSUMER RIGHTS OR STATUTORY GUARANTEES UNDER YOUR LOCAL LAWS WHICH THIS AGREEMENT CANNOT CHANGE. TO THE EXTENT PERMITTED UNDER YOUR LOCAL LAWS, MICROSOFT EXCLUDES THE IMPLIED WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NON-INFRINGEMENT. FOR AUSTRALIA – YOU HAVE STATUTORY GUARANTEES UNDER THE AUSTRALIAN CONSUMER LAW AND NOTHING IN THESE TERMS IS INTENDED TO AFFECT THOSE RIGHTS. LIMITATION ON AND EXCLUSION OF REMEDIES AND DAMAGES. YOU CAN RECOVER FROM MICROSOFT AND ITS SUPPLIERS ONLY DIRECT DAMAGES UP TO U.S. $5.00. YOU CANNOT RECOVER ANY OTHER DAMAGES, INCLUDING CONSEQUENTIAL, LOST PROFITS, SPECIAL, INDIRECT OR INCIDENTAL DAMAGES. This limitation applies to * anything related to the software, services, content (including code) on third‑party Internet sites, or third‑party programs; and claims for breach of contract, breach of warranty, guarantee or condition, strict liability, negligence, or other tort to the extent permitted by applicable law. It also applies even if Microsoft knew or should have known about the possibility of the damages. The above limitation or exclusion may not apply to you because your country may not allow the exclusion or limitation of incidental, consequential or other damages. Please note: As this software is distributed in Quebec, Canada, some of the clauses in this agreement are provided below in French. Note: This software is distributed in Quebec, Canada, and some of the clauses in this agreement are provided below in French. DISCLAIMER OF WARRANTY. The licensed software is provided “as is”. Any use of this software is at your sole risk. Microsoft gives no other express warranties. You may have additional rights under local consumer protection law, which this agreement cannot modify. Where permitted by local law, the implied warranties of merchantability, fitness for a particular purpose, and non‑infringement are excluded. LIMITATION OF DAMAGES AND EXCLUSION OF LIABILITY FOR DAMAGES. You may obtain compensation from Microsoft and its suppliers for direct damages only up to US $5.00. You cannot claim any compensation for other damages, including special, indirect, or incidental damages and loss of profits. This limitation applies to: * anything related to the software, services, or content (including code) on third‑party Internet sites or in third‑party programs; and * claims for breach of contract or warranty, or for strict liability, negligence, or any other fault to the extent permitted by applicable law. It also applies even if Microsoft knew or should have known about the possibility of such damage. If your country does not allow exclusion or limitation of liability for indirect, incidental, or any other type of damages, the above limitation or exclusion may not apply to you. LEGAL EFFECT. This agreement describes certain legal rights. You may have other rights under the laws of your country. This agreement does not alter the rights granted to you by your country’s laws if those laws do not permit it. |
| MIT License | System.IdentityModel.Tokens.Jwt, http://www.nuget.org/packages/System.IdentityModel.Tokens.Jwt Microsoft.IdentityModel.Abstractions, https://www.nuget.org/packages/Microsoft.IdentityModel.Abstractions System.ValueTuple, http://www.nuget.org/packages/System.ValueTuple System.Threading.Tasks.Extensions, http://www.nuget.org/packages/System.Threading.Tasks.Extensions System.Security.AccessControl, http://www.nuget.org/packages/System.Security.AccessControl System.IO.FileSystem.AccessControl, http://www.nuget.org/packages/System.IO.FileSystem.AccessControl System.Runtime.CompilerServices.Unsafe, http://www.nuget.org/packages/System.Runtime.CompilerServices.Unsafe Microsoft.Bcl.AsyncInterfaces, https://www.nuget.org/packages/Microsoft.Bcl.AsyncInterfaces System.DirectoryServices, http://www.nuget.org/packages/System.DirectoryServices System.Buffers, http://www.nuget.org/packages/System.Buffers System.Text.Json, http://www.nuget.org/packages/System.Text.Json Microsoft.IdentityModel.Tokens, http://www.nuget.org/packages/Microsoft.IdentityModel.Tokens System.Numerics.Vectors, http://www.nuget.org/packages/System.Numerics.Vectors Microsoft.IdentityModel.Logging, http://www.nuget.org/packages/Microsoft.IdentityModel.Logging System.Security.Principal.Windows, http://www.nuget.org/packages/System.Security.Principal.Windows System.Memory, http://www.nuget.org/packages/System.Memory System.Text.Encodings.Web, http://www.nuget.org/packages/System.Text.Encodings.Web azure-activedirectory-identitymodel-extensions-for-dotnet http://www.nuget.org/packages/Microsoft.IdentityModel.JsonWebTokens | The MIT License azure-activedirectory-identitymodel-extensions-for-dotnet Copyright (c) Microsoft Corporation. All rights reserved. Microsoft.Bcl.AsyncInterfaces Copyright (c) Microsoft Corporation. All rights reserved. Microsoft.IdentityModel.Abstractions Copyright (c) Microsoft Corporation. All rights reserved Microsoft.IdentityModel.Logging Copyright (c) Microsoft Corporation. All rights reserved Microsoft.IdentityModel.Tokens Copyright (c) Microsoft Corporation. All rights reserved System.Buffers Copyright (c) Microsoft Corporation. All rights reserved System.DirectoryServices Copyright (c) Microsoft Corporation. All rights reserved System.IdentityModel.Tokens.Jwt Copyright (c) Microsoft Corporation. All rights reserved System.IO.FileSystem.AccessControl Copyright (c) Microsoft Corporation. All rights reserved System.Memory Copyright (c) Microsoft Corporation. All rights reserved System.Numerics.Vectors Copyright (c) Microsoft Corporation. All rights reserved System.Runtime.CompilerServices.Unsafe Copyright (c) Microsoft Corporation. All rights reserved System.Security.AccessControl Copyright (c) Microsoft Corporation. All rights reserved System.Security.Principal.Windows Copyright (c) Microsoft Corporation. All rights reserved System.Text.Encodings.Web Copyright (c) Microsoft Corporation. All rights reserved System.Text.Json Copyright (c) Microsoft Corporation. All rights reserved System.Threading.Tasks.Extensions Copyright (c) Microsoft Corporation. All rights reserved System.ValueTuple Copyright (c) Microsoft Corporation. All rights reserved Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. |
9.5.2.1.3 - MFA Portal
Overview
SingleID’s MFA service provides users with a variety of additional second-factor authentication services through system integration, while maintaining the authentication system used by applications to enhance security. Additionally, SingleID provides an MFA Portal that lets you pre‑register and manage your preferred authentication methods for authentication, allowing convenient configuration.
The MFA Portal manual provides a feature that allows users to self-register secondary multi-factor authentication.
For detailed information, refer to the items below.
SingleID language settings
- User portal screen > top language selection, choose the language you want from ‘Korean’ or ‘English’.
- It will be changed to the language you selected.
SingleID connection environment and support
| Category | Support | Recommendation |
|---|---|---|
| PC | Windows : Windows Desktop 10 and 11 (x86 and x64 CPU Only)
| Windows : Windows Desktop 10 and 11 (x86 and x64 CPU Only)
|
| Moblie(Android) | Android : 8 and later versions
| Android : 8 and later versions
|
| Moblie(iOS) | iOS : 16 ,17
| iOS : 16 ,17
|
9.5.2.1.3.1 - Log in using an authentication method
Log in using an authentication method
What is an authentication method?
Authentication method, commonly called Authenticator, refers to an authentication tool.
SingleID provides the following 11 authentication methods for user authentication.
- Password: Enter password on the SingleID login screen
- Email OTP: Send the OTP via email and enter the OTP on the SingleID login screen
- SMS OTP: Send OTP via SMS and enter the OTP on the SingleID login screen
- Knox Messenger OTP: Send OTP via Knox Messenger and enter OTP on the SingleID login screen
- Knox Identity: Knox Portal user ID password authentication integration
- SingleID Authenticator Bio: Install the dedicated SingleID mobile app and link authentication using biometric authentication (fingerprint, facial recognition)
- SingleID Authenticator PIN: Install the SingleID‑dedicated mobile app and link authentication with a PIN.
- SingleID Authenticator mOTP: Install the SingleID‑exclusive mobile app and integrate authentication with mOTP (Mobile OTP).
- SingleID Authenticator TOTP: Install the SingleID‑dedicated mobile app and integrate authentication with TOTP(Time base OTP).
- Passkey: Login and authentication using biometrics (fingerprint, facial), mobile, or PIN code without a password, based on Windows Hello.
- Admin Authentication: If the admin permits direct authentication, request authentication on the admin’s behalf
Setting the preferred authentication method
The user logs into the User Portal provided by SingleID and sets their preferred primary and secondary authentication methods.
If the user sets their preferred method, the screen for selecting a verification method is skipped during login and authentication, allowing immediate authentication using the primary and secondary methods.
If you want to set your preferred authentication method, follow the steps below.
- User Portal > Personal Profile > Authentication settings, click.
- Click the star (☆) for each of your preferred 1st authentication method, 2nd authentication method.
After the configuration is complete, the next login will use this method, offering convenient access.
Register authentication tool
All authentication methods can be configured by the user. Registering an authentication method by a user is called enrollment. When a user account is created for the first time, the email OTP is automatically enrolled using the email information from the user data. Other authentication methods can be used by having the user enroll directly as needed.
I will explain the two authentication enrollment methods.
- Register in Authentication Settings: User Portal > Profile > Authentication settings, click the + Add New button at the bottom to register.
- Register on the Identity Verification Method Selection Screen: During login, for first-factor authentication and second-factor authentication, on the Identity Verification Method Selection screen, select the authentication method marked with a gray check mark (V) and register it.
First login
Consent for collection/use of personal information
Consent for the collection and use of personal information is required when logging in with SingleID for the first time or during a certain period. According to the consent procedure, select the required, optional items to agree. Required items must be selected to log in.
Password authentication
Password is the most fundamental authentication method as SingleID’s default authentication tool.
Enter password
To log in using a user ID, follow the steps below.
- Login screen > Account ID input field, enter the ID, and click the Next button.
- Password field, enter your password, and click the Next button to log in.
If you enter the password incorrectly
If the entered password is incorrect, you will see an error message and can try again. The number of allowed retries is limited to the count set by the administrator in the password policy.
When the password is entered incorrectly repeatedly and becomes locked
If the password is entered incorrectly and the device becomes locked, you can unlock it using two methods.
- Automatic unlock after 1~5 minutes: When automatic unlock is enabled, the account remains locked for 1~5 minutes. * Login will be available after that time.
- Unlock with password reset: When the administrator configures the password policy to use password reset, a password reset is required. * You can log in after resetting your password. Find ID you can view the detailed information there.
Email OTP authentication
Authenticate
To authenticate with email OTP, an OTP will be sent to the email address registered by the user.
To authenticate with an email OTP, follow the steps below.
- In Identity verification selection method, click Email.
- An OTP code will be sent to the registered email. 2. Enter the OTP within the time set by the administrator (usually 3~5 minutes).
- After you enter, click the Confirm button, and the authentication will be completed.
- Resend Code: If the input validity period has expired, click the resend code button. 1. Resend the OTP code via email.
- Would you like to authenticate using a different method?: If the current authentication cannot be used, switch to a different authentication method.
- If you changed your email, please register.: You can register (Enrollment) a different email and authenticate it according to admin settings. You can view the details for registration at Register Email Authentication Tool.
If the code is entered incorrectly
If the user enters the OTP code incorrectly, they can re-enter it up to the number of times specified by the administrator.
When locked due to exceeding the user input limit
If the OTP code is entered incorrectly more times than the administrator’s allowed limit, the screen will be locked from input for the duration set by the administrator. You can input after waiting for the specified duration. Refresh and try again after the input timeout.
SMS OTP authentication
Authenticate
To authenticate with SMS OTP, an SMS OTP is sent to the mobile device registered by the user.
To authenticate with an email OTP, follow the steps below.
- In the Verification method selection, click Email.
- An OTP code will be sent to the registered mobile phone. 2. Enter the OTP within the time set by the administrator (usually 3~5 minutes).
- After entering, click the Confirm button, and the authentication will be completed.
- Resend Code: If the input validity period has expired, click the resend code button. 1. Resend the OTP code to the mobile phone.
- Would you like to authenticate using a different method?: If the current authentication cannot be used, switch to a different authentication method.
- If you have changed your mobile phone, please register.: Click the link to go to the enrollment screen for the new mobile. You can see the detailed information for registration at Register SMS authentication tool.
If the code is entered incorrectly
If the user enters the OTP code incorrectly, they can re-enter it up to the number of times specified by the administrator.
When locked due to exceeding the user input limit
If the OTP code is entered incorrectly more times than the administrator’s allowed limit, the screen will be locked for the duration set by the administrator. You can input after waiting for the specified duration. Refresh and try again after the input timeout.
Knox Messenger OTP authentication
Authenticate
If you want to authenticate with Knox Messaenger OTP, the OTP will be sent to the Knox Messanger you are using.
To authenticate Knox Messenger OTP, follow the steps below.
- In Identity verification selection method, click Knox Messenger.
- The OTP code is sent via the Knox Messenger you are using. 2. Enter the OTP within the time set by the administrator (usually 3~5 minutes).
- After entering, click the Confirm button, and the authentication will be completed.
- Resend Code: If the input validity period has expired, click the resend code button. 1. Resend the OTP code to the mobile phone.
- Would you like to authenticate using a different method?: If the current authentication cannot be used, switch to a different authentication method.
- Would you like to use a different Knox ID?: Clicking the link will take you to the screen for enrolling a new Knox ID. You can find detailed information about registration at Register Knox Messenger authentication tool.
If the code is entered incorrectly
If the user enters the OTP code incorrectly, they can re-enter it up to the number of times specified by the administrator.
When locked due to exceeding the user input limit
If the OTP code is entered incorrectly more times than the administrator’s allowed limit, the screen will be locked from input for the duration set by the administrator. You can input after waiting for the specified duration. Refresh and try again after the input timeout.
Knox Identity Password Authentication
Authenticate
To authenticate with Knox Identity, you must enter your Knox Identity password.
To authenticate with Knox Identity, follow the steps below.
- In Verification selection method, click Knox Identity.
- Enter the password for your Knox account.
- After entering, click the Confirm button, and the authentication will be completed.
If the password is entered incorrectly
If the user enters the password incorrectly, they can re-enter it up to the number of attempts specified by the administrator.
When locked due to exceeding the user input limit
If the password is entered incorrectly more times than the administrator’s allowed limit, input on the screen will be restricted for the duration set by the administrator. You can input after waiting for the specified time. Refresh and try again after the input timeout.
SingleID Authenticator authentication
The SingleID service provides a mobile authentication app called SingleID Authenticator and offers authentication in various ways.
Authentication method
| Authentication method | Explanation |
|---|---|
| SingleID Authenticator Bio | Send a push using the installed SingleID Authenticator mobile app on the device to request biometric authentication. |
| SingleID Authenticator PIN | Send a push using the installed SingleID Authenticator mobile app on the device to request authentication with a PIN code. |
| SingleID Authenticator TOTP | Send a push notification to the installed ID Authenticator mobile app on the device to request authentication via TOTP. |
| SingleID Authenticator mOTP | Send a push using the installed SingleID Authenticator mobile app on the device to request authentication with mOTP. |
- For installation and configuration of SingleID Authenticator, refer to SingleID Authenticator.
- Detailed information on how to register the SingleID Authenticator authentication tool can be found at Register Authentication Tool.
Passkey authentication
The SingleID service provides simple authentication and multi-factor authentication using a Windows-based Passkey.
Authentication method
- Convenient authentication: Provides easy login without ID/Password by using Sign in with Passkey at the bottom of the login page.
- Multi-factor authentication: Offers convenient login without requiring ID/password during secondary authentication.
Authentication Types
- Mobile Passkey: Scan the QR code to log in using Android and iOS mobile
- Security key: Log in using the Windows security key
- PIN: Login using the Windows PIN code
Passkey supported environment Operating system (laptop or desktop)
- Windows 11, macOS Ventura, ChromeOS 109 or later
- Mobile phone: iOS 16 or Android 9 and above
- Hardware security key: a hardware security key that supports the FIDO2 protocol
Browse version
- Chrome 109 or later
- Safari 16 or later
- Edge 109
Device Settings
- Enable Bluetooth
- Set screen lock password
- Register PIN code
- Allow fingerprint or facial recognition
Administrator authentication
Authenticate
In the SingleID service, the administrator provides authentication by delegating identity verification on behalf of the user.
To perform administrator authentication, follow the steps below.
- In the Identity verification selection method, if you cannot perform identity verification at the bottom of the screen, you can request verification from the administrator. 1. Click here. Click it.
- Click the Request button.
- You will be taken to the admin selection screen. 3. Select the administrator who requested authentication delegation and click the Request button.
- Authentication delegation is requested to the selected administrator.
- When the administrator approves the authentication delegation, it is completed automatically.
9.5.2.1.3.2 - Register authentication tool
Register authentication tool (Enrollment)
The principle is that all authentication tools must be registered and used by the user themselves. Registering an authentication tool by a user is called enrollment (Enrollment). When a user is initially created, only the Email OTP is automatically registered using the user’s email information. The remaining information can be directly registered and used by the user as needed.
There are three ways to register.
- Login screen > ID/Password entry > Select verification method Register on the screen
- On the authentication method selection screen, click the authentication tool marked as ‘Registration Required’ (gray check mark) to register.
- User Portal(after login) > Profile > Authentication Settings +Add New Click the button to register.
- Register through the registration message link at the bottom of every authentication screen.
- The screen below is an example of an SMS verification screen. * You can register by clicking the ‘If you have changed your mobile phone, please register.’ message at the bottom.
- All authentication code inputs can be changed via a message below (Message format: ~ please register.)
Register Email Verification Tool
Email registration consists of the following three steps.
- Verification step: This is the identity verification step before registering the email authentication tool.
- Registration step: This step registers a new email and checks whether the number is valid.
- Completion Stage: This is the final step to confirm that the registration was successful.
Verification step
This is the step where you verify your identity before using the authentication tool. To view the identity verification process, please refer to 로그인하기.
Registration step
This is the step where the user registers the desired email address and checks its validity.
The user should follow the steps below.
- If you complete identity verification in the confirmation step, you will automatically proceed to the registration step.
- Enter the email address you want to register.
- Click the Send verification code button.
- Check the OTP code sent to the email address you entered, and enter the OTP code on the screen.
- If the verification code is entered correctly, you will proceed to the completion stage.
Completion phase
The registration completion screen will appear, and on the next login you can perform first- and second-factor authentication using the email verification tool.
Register SMS authentication tool
SMS registration consists of the following three steps.
- Verification Step: This is the identity verification step before registering the SMS authentication tool.
- Registration step: This step registers a new mobile phone number and checks whether the number is valid.
- Completion Stage: This is the final step to confirm that the registration was completed successfully.
Check step
This is the step where you verify your identity before using the authentication tool. To view the identity verification process, please refer to 로그인하기.
In the verification stage, the authentication method to be used can only be performed with the authentication tool configured by the administrator.
Registration Phase
This step registers the mobile phone number the user wants to add and checks its validity.
The user should follow the steps below.
- If you complete identity verification in the confirmation step, you will automatically proceed to the registration step.
- Select the country code and enter the mobile phone number you want to register.
- Click the Send verification code button.
- Check the OTP code sent to the mobile phone number you entered, and enter the OTP code on the screen.
- If the verification code is entered correctly, it proceeds to the completion stage.
Completion phase
Registration Complete screen will appear, and on the next login you can perform first and second authentication using the SMS verification tool.
Register Knox Messenger authentication tool
Knox Messenger registration consists of the following three steps.
- Verification step: This is the identity verification step before registering the Knox Messenger authentication tool.
- Registration Step: Enter the Knox ID to register. 2. This is the step that checks whether the Knox ID to be registered is valid.
- Completion Stage: This is the final step to confirm that the registration was successful.
Check step
This is the step where you verify your identity before using the authentication tool. If you want to view the identity verification process, refer to Log In.
In the verification stage, the authentication method to be used can only be performed with the authentication tool configured by the administrator.
Registration stage
This step registers the mobile phone number the user wants to add and checks its validity.
The user should follow the steps below.
- If you complete identity verification in the confirmation step, you will automatically proceed to the registration step.
- Please enter the Knox ID to register.
- Click the Send verification code button.
- Check the OTP code sent to the Knox Messenger of the entered Knox ID, and enter the OTP code on the screen.
- If the verification code is entered correctly, you will proceed to the completion stage.
Completion Phase
Registration Complete screen will appear, and on the next login you can perform first and second factor authentication using the Knox Messenger authentication tool.
Register Passkey authentication tool
The SingleID Authenticator is an authentication tool provided for the SingleID service.
Passkey enrollment consists of the following three steps.
- Verification Step: This is the identity verification step before registering the Passkey authentication tool.
- Registration Stage: This is the Passkey registration stage.
- Completion Stage: This is the final step to confirm that the registration was successful.
Verification step
This is the step where you verify your identity before registering the authentication tool. To view the identity verification process, refer to 로그인 및 인증하기.
Registration Step
This is the step to verify the mobile phone or PC environment where you want to register a Passkey.
Complete the registration process in the four steps below.
- Activation: Passkey support environment guide.
- Verification: Complete identity verification using an authentication method.
- Registration: Passkey registration stage. 3. When you click the Generate on this device button, a passkey is generated and registered on the PC. 3. Create on another device button click registers with a mobile phone or a hardware security key.
- Complete: Registration Complete verification step. 4. Continue Click the button.
Passkey supported environment Operating system (laptop or desktop)
- Windows 11, macOS Ventura, ChromeOS 109 or later
- Mobile phone: iOS 16 or Android 9 or later
- Hardware security key: a hardware security key that supports the FIDO2 protocol
Browse version
- Chrome 109 or later
- Safari 16 or later
- Edge 109
Device Settings
- Enable Bluetooth
- Set screen lock password
- Register PIN code
- Allow fingerprint or facial recognition
Completion Phase
After the passkey registration is completed, the registration complete screen appears. You can perform first- and second-factor authentication with the Windows Hello authentication tool on the next login.
PC Passkey requires that Windows Hello be configured in advance. For detailed information, see the reference link.
When registering a passkey on mobile, it can be set in an environment where QR code scanning is possible.
SingleID Authenticator Register authentication tool
The SingleID Authenticator is an authentication tool provided for the SingleID service.
SingleID Authenticator enrollment consists of the following four steps.
- Verification step: This is the identity verification step before registering the SingleID Authenticator authentication tool.
- Installation Step: This is the user’s SingleID installation guide step.
- Registration Stage: This step registers a new mobile app and registers the service.
- Completion stage: This is the final step to confirm that the registration was completed successfully.
Verification step
This is the step where you verify your identity before using the authentication tool. If you want to view the identity verification process, please refer to 로그인하기.
Installation steps
There are three main ways to install the SingleID mobile app.
- How to install SingleID Authenticator by scanning a QR code on the user’s mobile device or searching for “SinlgeID” on Google Play (for Android) or the App Store (for iOS)
- How to install by entering your mobile phone number and receiving the download link via SMS.
- How to install via a manual download link Install the SingleID Authenticator app and click the Next button to proceed to the registration step.
Registration Phase
Install the SingleID Authenticator mobile app on the mobile phone you want to register, then launch SingleID Authenticator.
Complete the registration process using the three steps below.
- Service Registration: In the SingleID Authenticator app, click the ‘+’ at the top.
- Enter QR or authentication number: Scan the QR code or enter the authentication code to register.
- Service registration complete: Click the Confirm button to complete the registration.
Completion Phase
After registration is completed in SingleID Authenticator, the Registration Complete screen appears. You can perform first- and second-factor authentication with the Windows Hello authentication tool on the next login.
Registration Phase
Install the SingleID Authenticator mobile app on the mobile phone you want to register, then launch SingleID Authenticator.
Complete the registration process using the three steps below.
- Service Registration: In the SingleID Authenticator app, click the ‘+’ at the top.
- Enter QR or authentication number: Scan the QR code or enter the authentication code to register.
- Service registration complete: Click the Confirm button to complete the registration.
Completion Phase
After registration with SingleID Authenticator is completed, the Registration Complete screen appears. During the next login, you can use the Windows Hello authentication tool for primary and secondary authentication.
Register TOTP Authenticator authentication tool
TOTP Authenticator registers third‑party TOTP to support various authentication tools.
TOTP Authenticator enrollment consists of the following four steps.
- Verification step: This is the identity verification step before registering the SingleID Authenticator authentication tool.
- Installation Step: This is the user’s SingleID installation guide step.
- Registration Stage: This step registers a new mobile app and registers the service.
- Completion Stage: This is the final step to confirm that the registration was successful.
Verification step
This is the step of identity verification before using the authentication tool. To view the identity verification process, refer to the Login and Authentication.
Installation steps
There are two main ways to install the TOTP Authenticator.
- Mobile app
- Web browser extension
If you click the Next button, you will proceed to the registration step.
Service Registration and Verification Phase
This step registers and verifies the 3rd‑party TOTP authenticator you want to add.
Complete the registration process in the two steps below.
- Service Registration: Scan the QR code of the TOTP Authenticator you want to register, or enter the manual code. 1. Code registration is completed in the TOTP mobile app or extension.
- Service verification: Run the TOTP mobile app or extension and enter the OTP.
TOTP Authenticator Support SingleID supports a variety of standardized 3rd‑party TOTP authentication apps. Non-standard TOTP is not supported. The authenticated mobile and extension programs are listed below. We recommend the mobile app or extension below.
- Mobile app
- Google Authenticator, Microsoft Authenticator
- Web browser extension
- TOTP extension searchable in the Chrome Web Store, Microsoft Edge Add-ons
9.5.2.1.3.3 - policy
When logging into SingleID or logging into an application registered with SingleID, various settings such as login method, authentication session, and password need to be configured according to the organization’s security policy.
SingleID provides a policy management feature that allows detailed configuration of login and authentication information.
If you have purchased the Anomalous Behavior Detection feature (ADM), you can configure it to analyze a user’s login activity at login and, when it detects authentication anomalies that differ from the norm, notify the user of a potential security threat.
The policy features provided by SingleID are as follows.
- Login Policy
- Authentication Policy
- Anomaly detection policy
By using SingleID’s policy feature, you can configure a secure authentication environment that meets organizational security requirements by specifying detailed login methods based on who is logging in, when, in which environment, and to which application.
Login Policy
The administrator can set detailed policies specifying which authentication methods users can use when logging in with SingleID, and, if necessary, create condition-based authentication policies for users authenticating in specific environments.
Login policies can be configured using the following conditions.
- Which application are you logging into?
- Who is logging in?
- In which environment are you logging in?
To access the login policy menu, navigate as follows.
- Admin Portal > Policy > Login Policy
Basic login policy
The Admin Portal creates two default policies as follows.
- Admin Portal Policy: Admin Portal access permission control policy
- Default Policy: User’s default access control policy
The Admin Portal Policy is the login policy applied when attempting to log in to the Admin Portal, and the Default Policy is the login policy applied when attempting to log in to the user portal.
If you have linked an application to SingleID and have not assigned a separate login policy, the Default Policy is automatically assigned as the default login policy.
Register login policy
The login policy sets the login policies for administrators and users. You can configure login policies based on the connection environment, application, and situation.
Login policies can be registered through a screen consisting of four steps as follows.
- General
- Allocation
- Initial Redirection
- rule
General
On the general screen, enter the name and description of the login policy.
The fields that need to be entered are as follows.
| Name | Explanation | Required or not |
|---|---|---|
| name | Enter the name of the login policy. | Required |
| Explanation | Enter the description of the login policy. | Required |
Click the Next button to go to the assignment screen.
Allocation
Specify the application to which the login policy will be applied on the assignment screen.
| name | Explanation |
|---|---|
| filter | Filter applications by status. |
| Keyword search | Search by application name and description. |
| Detailed Search | Displays detailed options for searching applications on the screen. |
| Assign button | Displays the application allocation popup on the screen. |
| List of assigned applications | The assigned applications are displayed in a list format. It starts with an empty list. |
- Click the Assign button to display the application assignment popup on the screen.
- In the Application Assignment popup, select one or more applications to assign to the login policy, then click the Assign button.
- If you have assigned all applications, click the Cancel button to close the Application Assignment popup.
Initial Redirection
Specifies the user’s login screen entry method and login method on the Initial Redirection screen.
Redirected to SingleID’s Sign-in page (login page)
Redirected to the external IdP
The explanations of the two methods above are as follows.
- If you select Redirected to SingleID’s Sign-in page, the SingleID login page will be displayed to the user attempting to log in.
- If you select Redirected to the external IdP, the user attempting to log in will see the login page of the selected Identity Provider.
- After selecting Redirected to the external IdP, you must select the Identity Provider from the selection list and designate it.
- If you select Redirected to SingleID’s Sign-in page, you can optionally display an additional button at the bottom of the SingleID login screen that allows login via an Identity Provider.
- AND see the following external IdP buttons on the Sign-In page. Click the text input field below and select one or more Identity Providers registered in SingleID to configure them to be displayed on the login screen.
Rule
In the Rules screen, edit or add login rules and set the priority among them.
| name | Explanation |
|---|---|
| Rule List | Login rules are displayed on the screen as a list. The Default Rule is shown by default, and the Default Rule cannot be deleted. |
| Keyword search | Search by the name or description of the login rule. |
| Register button | Register a new login rule. |
| Complete button | Register a login policy. |
Default Rule configuration
The login rule list on the rule screen displays Default Rule by default.
Default Rule cannot be deleted and can only be modified. Also, you cannot set a priority when adding one or more login rules. (Always the lowest priority.)
To modify the Default Rule, follow the steps below.
- Click Default Rule in the rule list.
- The WHEN condition of Default Rule cannot be modified.
- You can modify the THEN result of Default Rule.
| name | Explanation |
|---|---|
| Configure access permission | Set whether access is allowed. |
| Required authentication method | Set the primary login method. Additional login methods can be displayed on the login screen besides the default login method. |
| MFA authentication | Configure it to require an additional login after the initial login succeeds. |
| Terms and conditions for collecting consent | Set it to display the terms and conditions and request consent when a user logs into SingleID for the first time. |
| Save button | Save the modified login rule. |
In the access permission setting, you can select one of the following two options.
- Deny Access
- Allow Access
If you select Deny Access, login will be denied for all users.
When Allow Access is selected in the access permission setting, you can configure the user’s login method.
If you selected Redirected to the external IdP as the method to enter the login screen on the Initial Redirection screen, the primary login settings will not be displayed on the screen.
The required authentication method is performed by an external Identity Provider according to the Initial Redirection settings.
To have the user log in via multi-factor authentication, check the MFA authentication checkbox and then select one or more Authenticators in the text input box.
If a user logs in to SingleID for the first time, to display the terms and conditions and require the user’s consent, check the “Terms and Conditions Consent Setting (d)” checkbox and then select one or more terms or conditions to display on the screen in the text input box.
Add rule
To add a login rule, follow the steps below.
- Click the Register button at the top right of the rule list.
- On the rule registration screen, enter the rule’s name and description.
- Enter the rule items by referring to the below.
| Name | Explanation |
|---|---|
| Name | This is the name of the rule. |
| Explanation | This is an explanation of the rules. |
| User group assignment | Select the user group to apply the rule to. |
| Profile attribute assignment | Click the ‘Add’ button in the profile property assignment list to add a property. Refer to the help below for descriptions of the property and the operator. |
| Group Settings | Specify the group that the logged-in user belongs to as a member. |
| User attribute list | Specifies the attributes of the logging-in user and the conditions for each attribute. |
| Add User Attribute button | “Add Property” popup is displayed on the screen. |
Access environment
| Name | Explanation |
|---|---|
| Network | Specify the IP or network range of the user logging in. The default is “IP address anywhere”.- Desktop- Mobile |
| platform | Specifies the device information of the user logging in. The default is “Any platforms”.- Desktop- Mobile |
| browser | Specifies the browser information of the user logging in. The default is “Any browsers”.- Edge- Chrome- Safari |
| OS | Specifies the OS information for login. The default is “Any OS”.- Windows 10- Windows 11- Android- iOS |
| AND Anomalies (abnormal behavior) | Set the condition to determine whether anomalous behavior is detected during login.The anomalous behavior detection condition can be configured only for tenants that have purchased the Anomalous Behavior Detection (ADM) feature.To use the Anomalous Behavior Detection (ADM) feature, you must select the additional option when contracting for SingleID.If you wish to use the Anomalous Behavior Detection feature, you can purchase it additionally on the SCP product purchase page.After configuring all “WHEN” condition areas, set the login method that will be used when a user matching the condition logs in. |
The selectable user attributes are as follows.
User attribute information
| Attribute name | Data type | Required or not | Explanation |
|---|---|---|---|
| key | String | Required | key |
| username | String | Essential | ID |
| password | GuardedString | Required | Password |
| status | String | Required | status |
| mustChangePassword | Boolean | Required | Force password setting |
| suspended | Boolean | Required | Standby status |
| creator | String | - | Constructor |
| creationDate | Date | - | Creation date |
| lastModifier | String | - | Last editor |
| lastChangeDate | Date | - | Last modified date |
| administrator | Boolean | - | Admin status |
| displayName | String | - | Display name |
| cn | String | - | Common Name |
| local | String | - | Locale (email sending criteria) |
| userSource | String | - | User source |
| syncDate | String | - | Last synchronization time |
| contractNumber | String | - | Contract number |
| contractStartDate | String | - | Contract start date |
| contractEndDate | String | - | Subcontract termination date |
| agreementDate | String | - | Date of required terms agreement |
| accountStartDate | String | - | Account start date |
| accountEndDate | String | - | Account expiration date |
| partnerOrganizationCode | String | - | Partner company code |
| approvalUser | String | - | Approver ID |
| formattedName | String | - | Korean display name |
| familyName | String | - | Korean surname |
| givenName | String | - | Korean name |
| enFormattedName | String | - | English display name |
| enFamilyName | String | - | English surname |
| enGivenName | String | - | English name |
| adDomain | String | - | AD Domain |
| nickName | String | - | Nickname |
| employeeNumber | String | - | Employee ID |
| epId | String | - | EP ID |
| String | - | Email address | |
| phoneNumberWork | String | - | Phone number |
| mobile | String | - | mobile phone number |
| title | String | - | Job Title |
| enTitle | String | - | English job title |
| titleCode | String | - | Rank code |
| entitlement | String | - | Job Title |
| department | String | - | Department name |
| enDepartment | String | - | English department name |
| departmentCode | String | - | Department code |
| organization | String | - | Company name |
| enOrganization | String | - | English company name |
| organizationCode | String | - | Company code |
| region | String | - | base |
| userStatus | String | - | Employee status |
| userType | String | - | Employee type |
| securityLevel | String | - | Security rating |
| preferredLanguage | String | - | Knox language |
| executiveYn | String | - | Executive status |
| timeZone | String | - | Time zone |
| accountLocked | Boolean | - | Forced account lock |
| accountAutoLocked | Boolean | - | Automatic account lock |
| accountDisabled | Boolean | - | Unused account |
| accountSuspended | Boolean | - | Dormant account |
| accountSuspendedTime | Date | - | Dormancy processing time |
| lastLoginTime | Date | - | Last login time |
| accountState | String | - | Account status |
The operators are as follows.
| operator | Explanation |
|---|---|
| Equals | Searches for users whose attribute value matches the condition value. |
| Not Equals | Search for users whose attribute values do not match the condition value. |
| Starts with | Search for users whose attribute value starts with the condition string. |
| Ends with | Search for users whose attribute value ends with the condition string. |
| Contains | Searches for users whose attribute value includes the condition string. |
THEN configuration
THEN Set the login method and procedure in the result area.
You can select one of the two options in the access permission setting (a).
- Deny Access
- Allow Access
Selecting Deny Access will deny login for all users. (The default value for access permission setting (a) is Deny Access.)
To allow users to log in and configure detailed login methods, select Allow Access.
| Name | Explanation |
|---|---|
| Configure access permission | Set whether access is allowed. |
| First login setup | Set the primary login method. Additional login methods can be displayed on the login screen besides the default login method. |
| Additional login settings | Configure it to require an additional login after the initial login succeeds. |
| Terms and Conditions Agreement Settings | When a user logs in to SIngleID for the first time, configure it to display the terms and conditions and request consent. |
| PC SSO Agent Settings | Configure it to use the PC SSO Agent to verify whether a security program (Endpoint Security) is installed on the user’s PC. |
| Save button | Save the modified login rules. |
- From the first login settings selection list, select the Authenticator to use for login.
- If you want users to be able to log in with another Authenticator besides the selected primary login method, select the checkbox (V) of And allow another factors below: and choose one or more Authenticators to add in the text input box.
If you selected Redirected to the external IdP as the method to enter the login screen from the Initial Redirection screen, the primary login settings will not be displayed on the screen.
The first login is performed at an external Identity Provider according to the Initial Redirection settings.
- To have the user log in via multi-factor authentication, select the checkbox (V) in Additional Login Settings, then select one or more Authenticators in the text input field.
- If a user logs in to SingleID for the first time, to display the terms and conditions to the user and require their consent, check the terms and conditions consent checkbox and then select one or more terms or conditions to display on the screen in the text input box.
- To verify whether a security program (Endpoint Security) is installed on the user’s PC using the PC SSO Agent, select the checkbox (V) in the PC SSO Agent settings. 3. When this setting is enabled, login attempts by users without a security program installed on the PC are blocked.
If the PC SSO Agent is not registered, the PC SSO Agent configuration items will not be displayed on the screen.
If you want to require additional authentication instead of blocking the login of users who do not have security software installed on the PC while the PC SSO Agent setting (e) is enabled, select the checkbox (V) below and then choose one or more Authenticators in the text input box.
Click the Save button to register the login rule and return to the rule list.
Rule priority management
If one or more login rules are added, the administrator can set the priority among the login rules. If a user meets the conditions set in multiple rules, the login method is applied according to the rule with the highest priority.
To set the priority of login rules, follow the steps below.
- Drag the ≡ area displayed to the left of the rule name in the rule list with the mouse.
- The priority of login rules is set based on the drag-and-drop position.
- The higher a rule appears in the list, the higher its priority.
Change Policy Status
The status of the login policies managed by SingleID is as follows.
| status | Explanation |
|---|---|
| Active | Login policy operating normally |
| Inactive | Login policy disabled by the administrator |
An administrator can change the status of the login policy according to its current state as follows.
| Current status | Modifiable state | Explanation |
|---|---|---|
| Active | Inactive | Click the Disable button to change an active login policy to an inactive state. |
| Inactive | Active | Activate button can be clicked to change a disabled login policy to an enabled state. You can also delete a disabled login policy. |
Among login policies, the two policies provided by default in SingleID, Admin Portal Policy and Default Policy, cannot be disabled.
If you disable a login policy, applications that were assigned the disabled policy will automatically be reassigned to the default policy (Default Policy).
Disable policy
To disable an active login policy, follow these steps.
- Click the policy you want to deactivate in the policy list to navigate to the policy detail screen.
- Click the Disable button.
- After reviewing the login policy information displayed in the Confirm popup (the number of assigned applications and the number of rules included in the login policy), click the Deactivate button.
If you disable the login policy, applications that were assigned the disabled login policy will automatically be reassigned to the default policy (Default Policy).
Even after reactivating a disabled login policy, the applications that were previously assigned are not automatically reassigned.
Activate policy
To change a login policy from inactive to active, follow these steps.
- Click the policy you want to activate in the policy list to navigate to the policy detail screen.
- Click the Activate button to change the login policy status to active.
Delete policy
Administrators can delete the login policy from SingleID.
To delete the login policy, follow the steps below.
- Click the policy you want to delete in the policy list to navigate to the policy detail screen.
- If the login policy is enabled, click the Disable button to deactivate the policy.
- Click the Delete button displayed at the top right of the disabled login policy.
- A popup screen confirming the deletion of the login policy is displayed.
- To delete a login policy, first verify the policy information, then enter the name of the policy you want to delete and click the Delete button.
Deleted login policies cannot be restored.
When a login policy is deleted, the rules contained within the policy are also deleted, and even if you re-register a login policy with the same name, the deleted rules or configuration information will not be restored.
Access Simulation
When there are many login policies and the rules they contain, it can be difficult to determine which user is governed by which policy for login methods.
SingleID provides an access simulation feature so that administrators can quickly verify the login policies and rules applied to users.
Using the access simulation feature, you can select the user and target application, arbitrarily define the user’s login environment (network, device, browser, OS), and predict in advance which login method the user will experience in each scenario.
Additionally, if there are review requests from users experiencing login difficulties, you can quickly verify using the access simulation feature and modify the problematic policies or rules.
To use the access simulation feature, click the Access Simulation button located at the top right of the login policy list screen.
| Name | Explanation |
|---|---|
| Enter user ID | Enter the user ID of the simulation target. |
| Network Settings | Specifies the IP of the user to simulate. The default is “IP address anywhere”. |
| Platform Settings | Specify the device information of the user to be simulated. The default is “Any platforms”. |
| Browser Settings | Specify the browser information of the user to be simulated. The default is “Any browsers”. |
| OS settings | Specify the OS information of the user to be simulated. The default is “Any OS”. |
| Select Application | Select the application to be simulated. Click the application selection button to display the popup. |
| Run Simulation button | Run the access simulation. |
| Simulation results | Displays the access simulation results on the screen. The login policies and rules applied to the specified user are shown. |
| List button | Return to the login policy list. |
To run the access simulation, follow the steps below.
- Enter the ID of the user to be simulated.
- Specify the IP of the user to simulate. 2. After selecting Specific IP Address, you can manually enter the IP. 2. Enter the IP in the format 123.123.123.123.
- Specifies the device information of the user to be simulated. 3. After selecting Platform, you can select a device from the selection list.
- Specify the browser information of the user to be simulated. 4. After selecting Browser, you can select a browser from the selection list.
- Specify the OS information of the user to be simulated. 5. After selecting OS, you can select the OS from the selection list.
- Click the Application Selection button to select the target application for simulation.
- In the Application Selection popup, click the radio button to the left of the application name to select the application, then click the Add button.
If you want to re-select the application, click the X button to the right of the selected application name, then click the Select Application button again.
- Click the Run Simulation button.
- The access simulation runs, and when it finishes, the login policies and rules are displayed on the screen according to the simulation results as shown below.
Authentication Policy
The administrator needs to change detailed authentication settings according to the organization’s security policy.
SingleID categorizes and manages detailed authentication settings into the following four policies.
- Session Policy
- Authenticator policy
- MFA Service Provider Policy
- Password policy
To access the authentication policy menu, navigate as follows.
- Admin Portal > Policy > Authentication Policy
To modify the authentication policy, click the Edit button at the lower right of the authentication policy screen to change the settings, then click the Save button.
Session Policy
To change the session policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- In the maximum session limit setting, set the maximum number of sessions a user can create simultaneously.
- The minimum value that can be set is 1, and the maximum value is 100. 3. When set to 1, the user can only log in from one browser at a time and cannot log in simultaneously from multiple PCs or browsers.
- In the session priority settings, set the priority of sessions created by the user. 4. The priority can be set to one of the following two options.
- Old session
- New session
When you set the maximum session limit to 1 and select Old session in the maximum session count restriction setting, a logged-in user will have their login blocked when they attempt a new login from another PC or browser that is not logged in.
Also, when the maximum session limit setting (Œ) restricts the maximum number of sessions to 1 and New session is selected, if a logged-in user attempts a new login from another PC or browser that is not logged in, the session of the previously logged-in browser is forcibly expired and the session logged in from the new PC or browser is maintained.
In the maximum session time setting, set the maximum duration a session can be kept.
The maximum session time can be selected from one of the following two options.
- No time limit
- Set time limit
If set to No time limit, a session that has been created will not automatically expire until the user logs out. After configuring Set time limit and setting the time, when the specified time elapses, the session expires and the user is automatically logged out. In the Maximum Idle Session Time setting, set the session’s maximum idle time. If you set the maximum idle session time, the session will expire and the user will be automatically logged out when the user does not make an authentication request for the configured duration.
To save the changed settings, click the Save button at the bottom right of the authentication policy screen.
To avoid saving the changed settings, click the Cancel button at the lower right of the authentication policy screen.
| Name | Explanation |
|---|---|
| Set maximum session count limit | Sets the maximum number of concurrent sessions per user. |
| Session priority setting | When a session exceeds the user’s maximum concurrent session limit, set the priority between the previous session and the new session. |
| Maximum session time setting | Set the maximum session lifetime after the session is created. The session expires when the maximum session lifetime elapses. |
| Maximum idle session time setting | Set the session expiration time for when the user does not make an authentication request to the server for a certain period after the session is created. |
Authenticator policy
To change the Authenticator policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- Configure each item as described below.
- When the setup is complete, click the Save button.
| Name | Explanation |
|---|---|
| Available Authenticator settings(for login policy) | Configure an Authenticator that can be used for authentication. |
| Authentication method during registration | When registering the Authenticator, configure the user’s primary verification method. |
| Carry out the following additional authentication | When registering an Authenticator, configure additional identity verification methods to be allowed in addition to the user’s primary verification method. |
| Find Account | Set the authentication method when retrieving the ID. |
| Password reset | Set the authentication method for password recovery. |
| Unlock setting | If a user repeatedly fails authentication while using Authenticators, the ID becomes locked. You can set a duration so that the lockout is automatically cleared after a specified period. |
To remove a specified Authenticator from the available Authenticator settings, it must first be removed from the rules of all login policies.
Configurable Authenticators can be registered in the Add Authenticator menu. 2. Disabled Authenticators cannot be configured in the available Authenticator settings.
If you have not purchased an MFA product
- Available Authenticator Settings (for login policy) is not displayed on this screen.
- If you want to purchase additional MFA products, please contact us via Support Center > Contact Us.
If a user repeatedly enters an incorrect password, fails to log in, and becomes locked out, the lock will not be released even after a certain amount of time has passed. 1. Configure lock and unlock methods based on the password in the Password Policy.
If you reset a user’s password in the User menu, you can unlock a locked user before the unlock wait time expires. 2. Please refer to password reset.
MFA Service Provider Policy
To change the MFA Service Provider policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- Refer to the table below and configure each item accordingly.
- When the setup is complete, click the Save button.
| Name | Explanation |
|---|---|
| Available Authenticator settings (for MFA Service Provider) | Set the Authenticator that the user can use when an authentication request occurs from the MFA Service Provider. |
| Terms and Conditions Options | When a user registers from the MFA Servicce Provider, you can show the terms and conditions and obtain the user’s consent. |
| Unlock setting | When an authentication request occurs from the MFA Service Provider and the user repeatedly fails authentication, the ID becomes locked. You can set a time so that the locked user’s lockout is automatically cleared after a certain period. |
To remove a specified Authenticator from the available Authenticator settings, it must first be removed from all MFA Service Providers.
Configurable Authenticators can be registered from the Add Authenticator menu. 2. Disabled Authenticators cannot be set in the available Authenticator settings.
If a user authenticates with the MFA Service Provider for the first time, to configure the system to display terms and conditions to the user and require the user’s consent, check the terms and conditions option checkbox and then select one or more terms or conditions to display on the screen in the text input box.
If a user authenticating with the MFA Service Provider repeatedly fails authentication, the user’s ID becomes locked. 4. To automatically release the locked state after a certain period, set the unlock wait time in the unlock settings.
Password policy
To change the password policy, follow the steps below.
- Click the Edit button at the lower right of the authentication policy screen.
- Refer to the table below and configure each item accordingly.
- When the setup is complete, click the Save button.
| Name | Explanation |
|---|---|
| Password history | You can configure the system to prevent reuse of previously used passwords. Specify the number of recent passwords to prevent reuse. users will be unable to use the number of previously used passwords set above. |
| Password expiration | Specify the password validity period. After the validity period expires, you must change the password to log in. You can set it from 1 day up to 365 days. |
| Password lock | If the password is entered incorrectly repeatedly, the user’s ID will be locked. Specify the number of allowed repeated entry failures.
|
| Pattern and Complexity | Set the minimum password length, required characters, numbers, etc. |
| Set minimum character count | Specifies the minimum password length. |
| Set minimum number of letters | Specifies the minimum number of alphabetic characters to include in the password. |
| Minimum number of digits setting | Specifies the minimum number of digits to include in the password. |
| Set minimum number of special characters | Specifies the minimum number of special characters to include in the password. |
| Set maximum character count | Specifies the maximum password length. |
| Allow using the user ID as the password. | Set whether to allow the user’s ID to be included in the password. |
Sign-up Policy
If you want to allow user registration, enable the sign‑up policy, and users other than those provisioned from the HR system or IdP can also be registered. Through account synchronization, it provides the ability to register, create, modify, and delete accounts, as well as to invite users via the login screen or email.
To enable and use the registration policy, follow the steps below.
- Admin Portal > Policy > Sign‑up Policy click.
- Enable User Registration Allowed.
- If you enable it, the Policy tab and User Invitation tab will appear.
- Review the descriptions of the Policy tab and the User Invitation tab below, and configure the policy.
- When the setup is complete, click the Save button.
Policy
You can configure general policies for member registration.
| Name | Explanation |
|---|---|
| Display the sign‑up link on the login screen | Display a sign‑up link on the SingleID login screen.
|
| Terms and Conditions Options | Select the option to agree to terms and conditions during sign‑up. During sign‑up, you can select and apply terms and conditions separately. |
| Allow sign‑up invitations | When the feature is enabled, you can invite users via email. You can configure it so that only invited users can sign up, rather than using a separate registration page. With this setting, registration through the SingleID sign‑up link is not possible. |
| Sign-up input form | Configure the user attributes to be collected during registration. You can also specify whether each attribute is required. |
| ID duplicate prevention setting | When enabled, a suffix is added to the ID to prevent duplicate IDs. |
| This setting prevents duplicate IDs for automatically provisioned accounts. Since there are often cases where the ID values are the same, we recommend configuring it. When you sign up through registration, the corresponding PostFix value is appended to the ID. | |
| Maximum usage period | The maximum usage period is set after registration. It can be set from day 1 to day 2000. |
| Approval upon sign‑up request | When a sign-up request is submitted, you can enable the approval setting to load and apply the registered approval policy. |
Dormant User Policy
Provides a function to set users who have not used the SingleID system for an extended period to a dormant status. Users who have been changed to a dormant state can be configured, according to settings, to allow either self-recovery by the user or recovery by an administrator.
To enable and use the dormant user policy, follow the steps below.
- Admin Portal > Policy > Human User Policy Click.
- Human User Policy Activation Click the toggle button.
Additional settings are shown in the table below.
| Name | Explanation |
|---|---|
| Criteria for setting a user as dormant | This setting converts users who do not log into SingleID for N days into dormant users. It can be set from 1 day up to 365 days. |
| Send notification email | This setting sends notification emails to users starting N days before the dormant state. Additionally, you can also select the option to send notification emails to users when changing to the dormant state. |
| User exempt from dormant status change | You can click the Add button to add an exception user to change to dormant status. |
| Dormant State Exception Group | You can set exceptions for users included in the group. |
| Long-term human user management | This feature automatically deletes the user account after it has been changed to a human user. It can be set for up to 1 to 365 days. - You can configure it to send a reminder email N days before deleting the user (1 to 30 days) - You can set it to send a notification email to the user when their information is deleted. |
| Allow dormant users to directly restore their status. | Enabling the option allows dormant users to restore their status to active themselves. Dormant users can change their status to active by resetting their password through “Password Reset”. |
Approval Policy
The administrator can select an approval system and, depending on the type, configure sign‑up and app‑access policies across various approval lines. Various approval policies allow flexible application whenever the security policy changes.
Approval can be performed using either the built-in approval system feature or the Knox Portal approval system. If integration with another approval system is required, please request it via a 1:1 inquiry.
To check the approval policy, follow the path below.
- Admin Portal > Policy > Approval Policy
Approval policy list
The administrator can select an approval system and, depending on the type, configure sign‑up and app‑access policies across various approval lines. It can be flexibly applied whenever the security policy changes, using various approval policies.
| Name | Explanation |
|---|---|
| ID | This is an automatically generated ID when creating an approval policy. |
| Approval system | It is distinguished by SingleID and Knox Portal. If registration with another approval system is needed, please request it through a 1:1 inquiry. |
| type | It is divided into app access and sign-up. |
| status | This is the approval policy status. If unavailable, you must change the approver and notifier. |
| Approval use | It is categorized as in use and not in use. When you click the Details button, you can view applications where the approval policy is used. |
Register approval policy
When you click the Register button, you can set the approval system, type, approver, notification method, and approval period.
| Name | Explanation |
|---|---|
| Approval system | Two options are available.
|
| type | Two options are available.
|
| Approver | Select and register the approver and the notifier. |
| Notification method | When an approval request is received by the approver or notifier, select the notification method. |
Anomaly Detection Policy
SingleID provides a function that collects and analyzes user behavior information before and after authentication in real time to determine whether there is abnormal authentication behavior, and if identified as belonging to an abnormal authentication category, immediately notifies the user of the risk.
To access the Anomaly Detection Policy menu, navigate as follows.
- Admin Portal > Policy > Anomalous Activity Detection Policy
User lifecycle management
User lifecycle management provides configuration functions for setting default values when a user is created or registers, and for extending the user account usage period.
To enable and configure user lifecycle management, refer to the following.
Onboarding (subscriber)
Set the phone country code, language, and time zone when creating a user and signing up. To configure, click the Edit button at the bottom right to make changes.
Offboarding (departed user)
Users can request an account usage period extension, and it can be configured to allow the maximum possible extension.
- When requesting a user usage period extension, click the Activate toggle.
- Enter N days for the maximum extendable period.
- Click the Change button in the usage period request approval to set the approver.
Conditional Authentication Policy
Conditional authentication policies can set rules to match the environment, settings, and individual circumstances of user accounts.
You can set the following rules.
| Name | Explanation |
|---|---|
| Use multiple authenticators | Users who have relied on a single authentication method for an extended period must additionally verify their identity using a different type of authentication tool. |
9.5.2.1.3.4 - Configure Privacy Settings
Configure Privacy Settings
This is a menu for user settings.
To set your privacy preferences, follow these steps.
- Click the Personal Profile > Personal Information setting at the top right of the screen.
- You can view the photo, name, email, phone number, language, and time zone.
- Image: Image > Image Click Change to upload the icon image you want to display.
- Language: Choose your desired language in Korean or English.
- Language/Time Zone: Please select the time zone you are currently in. Click the City Search button to open the city search popup. Search for the desired city in English and select it.
- Click the Save button at the bottom of the screen to save.
Configure Authentication
You can register a user’s authentication tool and set the preferred authentication tool.
To configure authentication, follow these steps.
- Click the Personal Profile > Authentication setting at the top right of the screen.
- +Add New button: click to add using the authentication tool of your choice.
- Click the Delete button to remove the authentication tool you do not wish to use.
- Star (☆) Click the icon to set your preferred authentication method.
Change Password
In the authentication settings, click Change Password to complete an identity verification process and update your password.
Check login history
You can view the user’s login history and environment.
To view a user’s login history/environment, follow these steps.
- Click Personal Profile > Login History/Environment at the top right of the screen.
- In the Login History tab, you can view information such as login date and time, location, country, city, IP address, OS type, browser type, detection status, and result.
- In the Login Environment tab, you can view the details of any registered login environments, and if an environment is no longer used, you can delete it via the ‘Delete’ button.
Log out
Click the photo icon located at the top right of the screen and then click ‘Logout’.
When you click the Logout button, all applications visited through SingleID are logged out simultaneously, and if integrated logout is configured via the PC SSO Agent, logout also proceeds in the associated browsers.
9.5.2.1.3.5 - Settings
The Settings menu consists of Role Management, which manages the permissions of Admin Portal administrators; Ledger Management, which registers and manages SoT (ledger); and SMS Service, which registers SMS integration information used for secondary multi-factor authentication.
Role management
Role management can control the permissions of administrators in the Admin Portal. In line with the principle of least privilege, we provide role management to allow administrators to operate with minimal permissions.
The administrator has two roles by default.
- ADMINSTRATOR - a super administrator account with all privileges
- SOT_MANAGER - an account that is a director and application system administrator with app management capabilities
User assignment
To add a user with ADMINISTRATOR privileges, follow the steps below.
- From the menu, select ADMINSTRATOR, and click the User tab.
- To add a user, click the Add button.
- You can search for a user using the user ID, name, email address you want to add.
- After searching for a user and selecting, click the Add button to add the user.
Director Management
SingleID can manage and view various SOTs.
| Name | Explanation |
|---|---|
| default | There are two basic types, and they are generated automatically. - Mfa: Users coming from an MFA Service Provider (primary authentication system) correspond to the Mfa type. (When the MFA Service Provider does not specify a SoT) - SingleID: Users and Groups created by an administrator through the Admin Portal’s Identity Store are linked to the corresponding SoT. |
| Application | This is an SOT that is automatically created by receiving user/group information via Inbound Provisioning from an external application (SoT). |
| MFA service Provider | This is the SoT automatically generated based on the User Tag entered when creating the MFA Service Provider. |
default
- It is the primary ledger of SingleID, receiving entries through the Identity Store and MFA Service Provider.
- Mfa: Mfa is the basic SoT of the MFA service provider. * All users created through an MFA Service Provider that does not specify a User Tag are managed as MFA SoT. * MFA cannot be changed or deleted.
- SingleID: SingleID is the default SoT. * It is used to manage users and groups created through the Admin Portal. * You cannot change or delete the SingleID.
Application
- It is a ledger automatically generated by receiving user/group information via Inbound Provisionsing from an external application (SoT).
- You can assign the person in charge of managing the ledger through the PIC tab (up to 50 people).
MFA Service Provider
- When registered as an MFA Service Provider, if you set a User tag, a SoT is created, and new users who receive secondary authentication from that system are marked with #SoT.
- You can view and manage ledgers that come in through this MFA Service Provider.
- You can assign the person in charge of managing the ledger through the PIC tab (up to 50 people).
SMS service configuration
The administrator can activate the SMS service using the activation toggle button.
SCP SMS Service Configuration
After activating the SMS service, set the SCP SMS service in the SMS service settings.
| Name | Explanation |
|---|---|
| Activate SMS service | Set SMS service activation/deactivation to toggle mode |
| Select SMS service | Select SMS to use (SCP SMS) |
| Endpoint URL | Enter the SCP SMS Endpoint URL. |
| API Key | Set the API Key for the SCM SMS service. |
| SMS signature settings | When you click the activation button, the SMS signature input field appears. The SMS signature is a signature used at the beginning of the message body when sending an SMS. 1. The signature can be used to verify the sender when the user receives a message and to exempt the message from blocking when sending international SMS. 2. The default signature is ‘[SingleID]’, and when a signature is set, it is automatically added at the beginning of the SMS message. 3. For the signature specifications used to exempt international SMS from blocking, contact the Infobank SMS service provider and configure it according to the specifications. ※ For detailed inquiries regarding signatures, please contact the Infobank SMS service provider. |
| SMS signature | Please enter the SMS signature. |
To set up and use the SMS service, follow the steps below.
- SMS Service Activation Click the toggle button to enable the service.
- Select SCP SMS Service.
- Click Edit, enter the required values to configure SMS, and save.
- SCP SMS - SCP SMS Service Endpoint URL, SCP SMS Service App Key
- To save changes, click the Save button. 4. When you click the Save button, an alert popup appears asking whether to save the changes.
- When you click the Confirm button, the changes are saved, and a toast message appears when the changes are successfully completed. 5. When the Cancel button is clicked, the administrator’s registration/modification changes are not updated and it returns to the SMS screen.
SMS sending test
To set up and test the SMS service, follow the steps below.
- Enter the mobile number to receive the test.
- To verify that the SMS settings are correctly configured, enter a phone number for the SMS sending test and click Send to run the test.
- When you click the Send button, a popup appears asking whether to send an SMS test to the specified number. 3. When you click Confirm, an SMS is sent to the entered number and a popup window appears. 3. A toast message appears indicating that an SMS has been sent to the specified number.
Knox SMS Settings
Knox SMS is an SMS service provided by Knox. After activating the SMS service, select Knox SMS in the SMS service settings and configure it.
| Name | Explanation |
|---|---|
| Select SMS service | Select SMS service to use (Knox SMS) |
| Service ID | Enter the service ID of Knox SMS. |
| Access Token | Enter the Access Token for Knox SMS. |
| Caller phone number | Enter the sender’s phone number for Knox SMS. |
| SMS signature settings | When you click the activation button, the SMS signature input field appears. The SMS signature is a signature used at the beginning of the message body when sending an SMS. 1. The signature can be used for the recipient to verify the sender and to exempt the message from blocking when sending international SMS. 2. The default signature is ‘[SingleID]’, and when a signature is set, it is automatically added at the beginning of the SMS message. 3. For the signature specifications used to exempt international SMS from blocking, contact the Infobank SMS service provider and configure it according to the specifications. ※ For detailed inquiries about signatures, please contact the Infobank SMS service provider. |
| SMS signature | Please enter the SMS signature. |
SMS sending test
To set up and test the SMS service, follow the steps below.
- Enter the mobile number to receive the test.
- To verify that the SMS settings are correctly configured, enter a phone number for the SMS sending test and click Send to run the test.
- When you click the Send button, a popup appears asking whether to send an SMS test to the specified number. 3. When you click Confirm, an SMS is sent to the entered number and a popup window appears. 3. A toast message appears indicating that an SMS has been sent to the specified number.
InfoBank SMS Settings
After activating the SMS service, select Infobank SMS in the SMS service settings and configure it.
| Name | Explanation |
|---|---|
| Select SMS service | Select SMS service (InfoBank SMS) |
| API Key | Set the API Key for the Infobank SMS service. To use both domestic and international SMS services with a single API key, contact the Infobank provider. |
| Sender ID | It is an identification code entered to specify the original sending carrier when sending SMS, using the additional telecom carrier registration number (a 9‑digit number). 2. If the original sending carrier is a reseller, the original reseller’s registration number is used, and if the message is sent directly to a message relay without going through a reseller, the relay’s registration number is used. For further inquiries, contact the Infobank SMS service provider. |
| Caller phone number | Please enter the sending phone number. |
| SMS signature settings | When you click the activation button, the SMS signature input field appears. The SMS signature is a signature used at the beginning of the message body when sending an SMS. 1. The signature can be used for confirming the sender when the user receives a message and for exempting from blocking when sending international SMS. 2. The default signature is ‘[SingleID]’, and when a signature is set, it is automatically added at the beginning of the SMS message. 3. For the signature specifications used to exempt from blocking when sending international SMS, contact the Infobank SMS service provider and configure it according to the specifications. ※ For detailed inquiries regarding signatures, please contact the Infobank SMS service provider. |
| SMS signature | Please enter the SMS signature. |
| SMS sending test | Settings for SMS sending test. |
SMS sending test
To set up and test the SMS service, follow the steps below.
- Enter the mobile number to receive the test.
- To verify that the SMS settings are correct, you can enter a phone number for the SMS sending test and click Send to perform the test.
- When you click the Send button, a popup appears asking whether to send an SMS test to the specified number. 3. When you click Confirm, an SMS is sent to the entered number and a popup window appears. 3. A toast message appears indicating that an SMS has been sent to the specified number.
Bizppurio SMS Settings
After activating the SMS service, select Bizburio SMS in the Bizburio SMS service settings to configure it.
| Name | Explanation |
|---|---|
| Select SMS service | Select SMS service to use (BizBuriO SMS) |
| Caller phone number | Enter the sending phone number. |
| SMS signature settings | Click the activation button to display the SMS signature input field. The SMS signature is a signature used at the beginning of the message body when sending an SMS. 1. The signature can be used to verify the sender when the user receives a message and to exempt the message from blocking when sending international SMS. 2. The default signature is ‘[SingleID]’, and when a signature is set, it is automatically added at the beginning of the SMS message. 3. For the signature specifications used for exempting international SMS from blocking, contact the Infobank SMS service provider and configure it according to the specifications. ※ For detailed inquiries about signatures, please contact the Infobank SMS service provider. |
| SMS signature | Please enter the SMS signature. |
| SMS sending test | Settings for SMS sending test. |
SMS sending test
To set up and test the SMS service, follow the steps below.
- Enter the mobile number to receive the test.
- To verify that the SMS settings are correct, you can enter a phone number for the SMS sending test and click Send to perform the test.
- When you click the Send button, a popup appears asking whether to send an SMS test to the specified number. 3. When you click Confirm, an SMS is sent to the entered number and a popup window appears. 3. A toast message appears indicating that an SMS has been sent to the specified number.
User profile
You can view and edit the attributes that make up a user profile, or add custom attributes. Attributes are classified into three categories: default, system, and custom. You can modify some attribute settings based on the category.
ㆍ Default : This is a property displayed on the Admin Portal or User Portal screen. Some property settings can be modified, but properties cannot be deleted. ㆍ System : a predefined attribute that can be used for inbound or outbound provisioning profile mapping of an application, and cannot be modified or deleted. ㆍ Custom : An attribute that administrators can add so it can be displayed on the screen or used for mapping the application’s provisioning profile. You can edit after adding, but you cannot delete.
Add custom property
You can add and manage custom attributes.
9.5.2.1.4 - CAM Portal
Service Overview
CAM(Cloud Access Management) is a service for managing access to cloud consoles and resources, providing users with an easy and convenient way to access cloud consoles and resources.
Users can access the portal from PCs located on the internal network using multi-factor authentication (MFA, Multi-Factor Authentication). Instead of a password, a one-time token is issued to enable access to the cloud console and resources, and all console access logs, operation logs, and permission approval logs can be monitored.
Service scenario
Previously, we accessed the console and resources directly with individual IAM accounts, but now we provide a unified access path through CAM.
- Step 1: During the transition period, newly establish the TO-BE access channel and operate it in parallel with the AS-IS access channel.
- Step 2: After blocking the AS-IS access channel via Cut-Over, switch to the TO-BE channel
Key Features
User Scenario
The user scenario proceeds in the following order.
- Authentication → Base Information Settings → Console Access Management → Resource Access Management → Monitoring
Login & Home
Log in using SingleID or an SSO account (e.g., Knox Portal) and complete multi-factor authentication (MFA). Enter the verification code received via SMS or email to finish the login process and access CAM.
On the Home screen, a personalized custom view is provided so that users can access the cloud console and resources with a single click, allowing easy access to the console and resources.
Configuration
After creating a project, you can easily register a CSP (Cloud Service Provider) account. You can also add users to the project to grant permissions within the project.
Console Access
You can create roles and policies to set and control access permissions for the cloud console, and map roles to specific accounts and users to define which users can access the CSP console and their permission levels.
Resource Access
Manages access permissions for cloud resources. To manage cloud resource access, each user first requests permission, downloads and installs the PC client agent, and registers the access IP address. Once the setup is complete, users can connect to the desired resources from their personalized resource list.
9.5.2.1.4.1 - Getting Started
This manual aims to help users quickly understand the essential functions and processes needed to use CAM effectively.
Network Environment
Access is allowed only from network environments authorized for each tenant.
- CAM portal and console access: can be accessed from the network environment permitted for each tenant.
- DEV, STG, ETC resource access: can be accessed from the allowed network environment for each tenant.
- PRD resource access: It can only be accessed in a network environment where the internet is blocked, and can only be accessed from specific IP ranges per tenant.
- Additional individual PC environment configuration is required.
Preliminary work
To use the CAM portal, several preliminary steps are required. If you are a PM (Project Manager) or PL (Project Leader) group user, please review the cloud account and resource preparation items below and set up the environment in advance.
Prepare cloud account
To register and manage an account in CAM, you first need to create a role in the IAM service of the CSP (AWS, Azure, SCP), configure it with the policies required by CAM, and then assume the role in CAM.
Resource preparation
Resource configuration
To register resources in CAM and connect, several configuration steps are required when setting up the resources.
First, you must enable ‘Password authentication’. Since a One-Time-Password (OTP) for SSH connections is issued when accessing resources from CAM, this configuration is essential for accessing resources through CAM.
Additionally, when the resource type is Compute, you must add the configuration below.
- Add the following content to a file named /etc/sudoers.
- ubuntu : %sudo ALL=(ALL) NOPASSWD:ALL
- amazon linux : %wheel ALL=(ALL) NOPASSWD: ALL
- Restart the server using systemctl restart sshd.service.
Network Settings
To access resources through CAM, you must register firewalls and security groups according to each tenant’s network environment so that CAM can connect to the resources. Please verify the required information with the tenant administrator and proceed with the network configuration.
Service scope
Currently, Console Access supports AWS, Azure, and SCP, while Resource Access supports only AWS. We plan to gradually expand to other CSPs in the future.
| Item | Explanation |
|---|---|
| AWS | Amazon Web Services |
| IAM (Console) | AWS Identity and Access Management |
| SCP | Samsung Cloud Platform (KR EAST1 region, KR WEST1 region) |
| EC2 | Elastic Compute Cloud |
| RDS | Relational Database Service |
| OS | Version |
|---|---|
| Ubuntu | Ubuntu Server 24.04 LTS |
| Ubuntu | Ubuntu Server 22.04 LTS |
| Amazon Linux | Amazon Linux 2023 AMI |
| Redhat | Red Hat Enterprise Linux 9.4 |
| DB Engine | Version |
|---|---|
| PostgreSQL | 16.x |
| MySQL | 8.0.x |
| Aurora PostgreSQL | 15.x |
| Aurora MySQL | 3.05.x |
| Aurora MySQL | 3.04.x |
| Aurora MySQL | 3.03.x |
| MariaDB | 10.11.10x |
9.5.2.1.4.2 - Home
After logging in, you can access the CSP console and your individually allocated resources with a single click from the personalized homepage. Administrators and developers can efficiently streamline their work by quickly and easily accessing approved consoles and resources from a single location.
The home screen of CAM (Cloud Access Management) is divided into two sections.
- Top Resources
- My CSP Consoles
Both sections provide access to allocated resources and the CSP console.
Top Resources
This section shows a list of the top 30 accessible resources.
Card view and list view
By default, resources are displayed in a card view, and can be switched to a list view based on the icon.
Search and Filter
You can quickly find specific resources using the search function, and you can filter resources based on the following items.
- Project
- CSP(Cloud Service Provider)
- Environment (e.g., DEV, STG, PRD, ETC)
- Resource type (e.g., Compute, DB)
Favorites
Bookmark (★) You can set a bookmark using the icon, and you can set a bookmark filter to filter only resources that have been bookmarked.
Sorting
The resource list can be sorted by the following two criteria.
- Recent (default sorting)
- Creation date
Resource Information
Depending on the selected view mode, you can view detailed information about resources in cards and lists.
- Resource Name
- Project
- CSP (e.g., AWS, Azure, SCP)
- Environment (e.g., DEV, STG, PRD, ETC)
- Resource type (e.g., Compute, DB)
Resource Connect/Disconnect
Each resource has a Connect button that can be used to connect or disconnect. If the resource is already connected, the following details are displayed:
- Last login date/time
- Connection status
Resource Access
When you click the Connect button on a card or in a list, a popup opens for connection.
To access the resource, enter the details of the following items.
- Local Port: Enter a port number between 1024 and 65535 that is not currently in use on the PC.
- Remote Port: Enter the port number of the resource.
- Launch Putty : To have Putty start automatically during the connection process, select ‘ON’.
Connection Details
When accessing a resource, click the dropdown to view detailed connection information such as user ID, password, and local IP. This information is provided via a popup as details that allow the user to connect to the resource through an SSH connection.
- User ID: Click the copy icon on the right to copy the user ID.
- Password: Click the copy icon on the right to copy the password.
- Local IP: Click the copy icon on the right to copy the local IP address.
- Client Server IP: Refer to the client server IP displayed on the screen.
Resource Access Release
When you access the resource, the Disconnect button appears. Click this button to start the disconnect process. A popup for final confirmation will be displayed before the connection is terminated.
My CSP Consoles
We provide a CSP access link in a sticky footer at the bottom of the page. Since access to the CSP console is offered through SAML SSO, you can connect directly without any additional authentication steps.
9.5.2.1.4.3 - Console Access
The console access feature allows PM and PL group users to assign roles and policies to cloud accounts and users, enabling management of access to the CSP console. Based on the permissions set here, users can access the console with the appropriate privileges.
The console access section consists of four main management areas.
- Role Management: Defines and manages the level at which a user (User) can access the CSP console.
- Policy Management: Define new policies (Policy) and manage the roles mapped to each policy.
- Account Management: Manage cloud accounts (Account) and ensure each account is mapped to the correct role permissions.
- User Management: By mapping each user to the appropriate role (Role), we ensure they have the permissions required to access the cloud console, thereby controlling user console access.
Role Management
In the role management menu, you can view and manage all roles registered in the project, and filter roles by CSP or by project for review.
Create role
To create a role, click the Create Role button. To create a new role, you must fill in the following required information in the popup window.
- Project: Select a project from the user’s project list.
- CSP: Select CSP.
- Role Name: Enter a unique role name and click the Validate button to check consistency.
- Description: Add a brief description of the role.
View role
To access detailed information about a role, go to the role management menu and click the desired role. All project users can view role details, including policies, cloud accounts, and users mapped to the role.
The role view screen displays key details, including the following.
- Role Information: Basic details related to the role.
- Delete Role: Delete click the button to remove this role.
- Policy: Shows the list of policies mapped to the current role.
- Account: Shows a list of accounts related to the role.
- User: Shows the list of users associated with a role.
- The CSP process starts after the user addition approval is completed. Therefore, it may take some time (up to 10 minutes) for the status to change to ‘Approved’ and appear in the user’s CSP role list.
- You can map up to 10 policies to an AWS role.
- Each account has role limits based on the CSP; AWS can have up to 800 roles, while Azure can have up to 5,000 roles.
- Each user has role limits based on the CSP, and in AWS up to 10 roles can be mapped, while in Azure up to 4,000 roles can be mapped.
Delete role
PM or PL group users can delete roles within a project. In the role management list, select the role to delete and click the Delete button. Or you can delete them one by one by clicking the Delete button on a specific role screen.
Policy Management
PM and PL group users can select or deselect policies from the policy list to add or remove policies mapped to a role.
Create Policy
To create a new policy, click the “Create Policy” button and fill in the required information in the “Create Policy” popup.
- Project: Select a project from the list of registered projects.
- CSP: Select CSP.
- Policy Name: Enter the policy name and click the “Validate” button to verify its consistency.
- JSON code: Enter the JSON code that defines the policy.
- Description: Add a brief description of the policy.
To map policies to a role, click the Add button above the policy list to open the popup window. In the popup, you can view and select policies defined within the same project. Click the Save button to complete the mapping process. You can map multiple policies at once.
Before mapping the policy, verify that the desired policy has been created in the policy management menu.
View policy
To view detailed information about a policy, go to the Policy Management menu and click the desired policy. All project users can view policy details, including the roles mapped to the policy.
Delete Policy
To remove a policy mapping from a role, select the policy from the list and click the Delete button. The deleted policy will reappear in the Add Policy popup list, and can be added again if needed. Removing the policy mapping eliminates the relationship between the role and the associated policies.
Account Management
PM and PL group users can map or remove cloud accounts from roles.
View Account
To view account details:
- Go to Account Management and click the desired account.
- All project users can access the details of that account, and the account includes a list of mapped roles.
- PM or PL group users can also edit or delete roles associated with the account.
Add role to account
- To map roles to an account, click the Add button above the role list to open the Add Roles popup.
- In the popup, select a role that belongs to the same project as the account and click the Save button to complete the mapping process.
- You can map up to 800 roles in an AWS account and up to 5,000 roles in an Azure account.
Delete role from account
To remove a role from an account, select the role from the list and click the Delete button. The removed role reappears in the Add Role popup, and you can add it again if needed. You can also delete multiple roles at once.
User Management
Through the User Management menu, users can view and manage all users registered within the project. Users can search for a user by name.
User view
To view the user’s details:
- Go to User Management and click the user.
- All project users can view user details, including the roles mapped to that user.
- PM or PL group users can add or remove roles for a user.
Add role to user
To map a role to a user, click the Add button above the role list to open the Add Role popup. In the popup, you can view all roles in the project the user belongs to, select the role to add, and click the Create Approval button to proceed with the approval process.
- Each user has role limits based on the CSP and can map up to 10 AWS roles and 4,000 Azure roles.
Create approval
To assign a role to a user, an approval process is required. The approval process proceeds through the Create Approval popup and then via the Knox approval system or CAM’s own approval system.
- Title: Automatically entered by the system and cannot be edited.
- Approver: The approval route is automatically assigned by the system, and you can manually add approvers and consentees according to the approval guide.
- Content: Project and role information is automatically entered by the system and cannot be edited.
Remove role from user
To unmap a role from a user, click the Delete button. After confirming the final deletion, the user’s role mapping is removed. The removed role reappears in the Add Role popup, allowing you to add it again if needed. Note that unmapping a role does not require approval, but re-adding a role does require approval.
9.5.2.1.4.4 - Resource Access
You can view all resources with individual permissions and access them. To access resources, a PM or PL group user must register the cloud account resources associated with the project and go through the user’s permission request and approval process.
Resource
Displays all resources for which the user has been granted permission. The user can view the resource list and access resources directly.
Connection
Click the Connect button to access the resource, and after connecting, it provides connection details.
- Local Port: Enter a port number that is not being used for other purposes on the PC.
- Remote Port: Enter the port number of the resource.
- Putty Execution: To enable automatic execution of Putty, you need to set it to ON.
Connection Information
Provides detailed connection information to access resources via SSH.
- User ID: Click the copy icon to copy the user ID for use.
- Password: You can click the copy icon to copy the password and use it.
- Local IP: Click the copy icon to copy the local IP for use.
- Cloud Server IP: Click the copy icon to copy the cloud server IP for use.
Disconnect
When the resource is connected, the Connect button changes to a Disconnect button. To disconnect the resource, click the Disconnect button.
Resource Registration
In this menu, you can register the resource information required for access, and it displays the list of resources that have been registered.
Register
To register a resource, cloud account registration must be performed first in the project menu. PM and PL group users can register resources created within a cloud account. Click the Enroll button to go to the resource registration screen, then configure the resource connection information.
- Project: Select a project among those registered for PM or PL group users.
- Account: Select a cloud account among those registered in the selected project.
- Region: Select the region information of the selected account.
- Resource Type: Select one of Compute or DB.
- Resource: Select resources that match the selected criteria.
- Connection Type: Choose between Direct (direct connection to the server) and Bastion (connection via a proxy server).
- Address: Enter the resource’s address information.
- Root User: Provides the root user’s IP and password for the resource.
Supported OS/DB
Currently, the OSes and DBs that can perform ‘resource registration’ are limited as shown below, and supported OSes and DBs will be continuously added.
| OS | Version |
|---|---|
| Ubuntu | Ubuntu Server 24.04 LTS |
| Ubuntu | Ubuntu Server 22.04 LTS |
| Amazon Linux | Amazon Linux 2023 AMI |
| Redhat | Red Hat Enterprise Linux 9.4 |
| DB Engine | Version |
|---|---|
| PostgreSQL | 16.x |
| MySQL | 8.0.x |
| Aurora PostgreSQL | 15.x |
| Aurora MySQL | 3.05.x |
| Aurora MySQL | 3.04.x |
| Aurora MySQL | 3.03.x |
| MariaDB | 10.11.10x |
Network Settings
To register resources in CAM and access them through CAM, network configuration must be performed first.
After receiving guidance from the tenant administrator and completing network configurations appropriate for each tenant environment, such as firewall registration and security group registration, please proceed with resource registration.
Withdrawal
Resources that are no longer used must be removed from the registered resource list. After selecting from the resource view or resource registration list, click the Withdraw button to prevent further access.
Permission request
In the permission request menu, you can view project members’ resource permissions and request permissions for each user’s CSP resource types.
Request
Users can select a duration and permission type to request resource permissions for each CSP resource type. All permissions require approval, but when ‘Emergency’ is selected, the permission is granted simultaneously with the approval request.
Resource Information
- Project: Select a project from those the user belongs to.
- Account: Select the account registered in the selected project.
- Resource Type: Select one of Compute or DB.
Permission
- Period: Select the period (e.g., 4h, 8h, 24h, 10d, 30d, 12M).
- Emergency: If checked, permission is granted immediately upon the approval request, and a related email is sent to the approver.
- Permission Level: Choose one of USER, ADMIN, DBA.
- Comment: Add a comment for approval.
Create approval
To obtain resource access permissions, an approval process is required. To proceed with the approval process, go through the “Create Approval” popup, which is sent to Knox for approval and processed through Knox.
- Title: Automatically entered by the system and cannot be edited.
- Approver: Add the approver and the consenter according to the guide.
- Content: Project and permission information is automatically entered by the system and cannot be modified.
Withdrawal
To remove permissions that are no longer needed, select the permission in the request list and click the Withdraw button.
PC configuration
To access cloud resources, you must install the client agent and register the IP address of the access environment.
Client Agent Download
Click Download Client Agent to start the download, then install the client agent.
User Guide
To access the resource, you need to download and install the client. Also, if the installation is incomplete or the version is unsupported, you cannot connect to the resource even if all other preparations, such as permissions and IP registration, are completed.
Installation Guide
To start the installation process, click the Download Client Agent button to download the installation file. Once the download is complete, refer to the following information to proceed with the installation.
- Download Location: Specify a folder on the local drive.
- Execution: Select the downloaded file, right‑click, and click Run as administrator to execute.
IP registration
Access to cloud resources is allowed only from registered IPs, and up to five IPs can be registered. Please register the IP using the following information.
- To add a new IP, click the Add button.
- To remove an existing IP, select the IP from the list and click the Delete button.
9.5.2.1.4.5 - Monitoring
The monitoring menu of CAM provides essential features for tracking console access logs, user activity, and approval records. This feature ensures transparency, security, and compliance by offering detailed information.
Connection History
Connection logs provide a record of user activity within the CAM console, enabling administrators to track and review access-related actions across projects and the entire cloud environment. This ensures compliance with security regulations and offers visibility into how and when users interact with cloud resources through the CAM interface.
Console Access History
Console access logs record all events related to console connections performed through CAM. These logs enable tenant administrators to monitor console connection attempts, review event outcomes, and identify access patterns for AWS, Azure, and SCP accounts. The console access log page can be viewed from Monitoring > Access Log > Console Access Log.
Console Access History Feature
History Range
- Tenant (Company) Administrator: You can view the history of all console accesses within the tenant.
- User: You can only view the history of your own projects.
Detail History
- Console access history records event data for all console-related activities initiated through CAM.
- History is provided for all configured tenants and includes connection events across AWS, Azure, and SCP.
- The history details display information such as event type, date/time, project, Account ID, etc.
- Click the expand icon to view detailed information for all actions. This detailed view feature provides deeper insight into each connection attempt. Detailed event information includes the following:
- Event ID
- Event Source
- Event Result
- Request Type
- User Agent
- Region
- Source IP Address
- User Information
- You can narrow the results by using filters such as project, CSP, and environment.
- You can select a specific period to filter the history. The default period is 30 days.
- The history is sorted in reverse order, with the most recent action displayed at the top.
- Each log entry serves as an audit trail to track console access patterns and user activity across the entire CAM.
- You can download all history data for the selected period as an Excel file for offline analysis or record keeping.
Audit History
- From the menu, go to Monitoring > Audit Log.
- Select the desired history type: Audit Log, Approval Log
- Search the history using search and filter options based on criteria such as user, resource type, or period.
- Check details such as the connection timestamp, user information, and resource specifics.
Audit logs provide a comprehensive history of user and system actions performed within the CAM portal, and are divided into two detailed categories.
- Activity Log (Audit Log)
- Permission Approval History (Approval Log)
Activity Log (Audit Log)
Activity history shows the operation logs related to creation, update, and deletion of data within the CAM portal.
Activity Log Feature
History Range
- Tenant (Company) Administrator: You can view the history of all projects within the tenant.
- User: You can only view the history of your own projects.
Detail History
- Displays information such as event type, date/time, user, and IP.
- Click the Expand icon to view detailed information for all actions.
- You can narrow the results by using filters such as project, event type, and user.
- You can select a period to filter the history. The default period is 30 days.
- The history is sorted in reverse chronological order, with the most recent actions displayed at the top.
- You can download all history data within the selected period as an Excel file for offline analysis or archiving.
Permission Approval Log (Approval Log)
The permission approval history provides all approval request details and approval statuses within CAM.
Permission Approval History Feature
History Range
- Tenant (Company) Administrator: You can view the approval history for permission approvals for all projects within the tenant.
- User: You can only view the authorization approval history for your own project.
History Details
- Displays the approval type, approval status, details, and approval history.
- You can check the approval status, such as pending, approved, or rejected.
- You can open a specific approval item to view its details.
- You can narrow the results by using filters such as project, approval type, approval status, and user.
- You can select a period to filter the history. The default period is 30 days.
- The history is sorted in reverse chronological order, with the most recent approvals displayed at the top.
- You can download all history data within the selected period as an Excel file for offline analysis or archiving.
9.5.2.1.4.6 - Configuration
In the configuration module, PM and PL group users can manage projects, and tenant administrators can set approval routes and organizational charts.
Project
In the Project menu, users can view all projects they belong to. The project details are initially registered by the PM, and can be edited by the PM or PL group users as needed.
Create Project
To create a project, click the Create Project button and enter the project information.
- Project Name: Assign a name to the project.
- PM: Assign a project manager who can manage the project’s related information and permissions. Note that if you assign someone other than yourself, you will no longer be able to manage the project after creation.
- Organization: Choose the organization that will carry out the project.
- Description: Enter a description of the project.
View project
On the Project View screen, PM or PL group users manage project information and can add CSP accounts and users to the project.
- General Information: Project Creation screen displays the registered project information.
- Edit: Click the Edit button to modify the project’s general information.
- Delete: Click the Delete button to delete this project.
- User: Displays a list of users registered in the project.
- Cloud Account: Shows the list of accounts registered in the project.
Cloud Account Management
PM and PL group users can add new accounts to a project or delete accounts that are no longer used.
Add AWS account
CAM supports a keyless method to enhance security when connecting cloud accounts. To register an account, you must create a new role in the AWS IAM service with the policy required by CAM. You can create the role in AWS by following the steps below.
- Access AWS IAM service
- After logging into the AWS console, go to the IAM service https://aws.amazon.com/console/
- Click Create Role in the Roles menu
- After accessing Access Management > Roles, click Create to go to the Create Role screen.
- Create Role > Step 1: Trusted Entity selection
This step is for entering CAM account information.
- Select AWS account and Another AWS account in order, then enter the CAM account ID 022499039571 in the account ID.
- Create Role > Step 2: Add Permission Assign the CAM policy to the newly created role.
Search for the item, select the relevant policy, and proceed to the next step.
- IAMFullAccess
- AmazonEC2FullAccess
- AmazonRDSFullAccess
- AWSCloudTrail_FullAccess
- AmazonS3FullAccess
- AmazonEventBridgeFullAccess
- Create Role > Step 3: Name, Confirm, Create Enter the role name and click the Create Role button to complete role creation. ※ This role name is used as Role Name when registering an account in CAM.
When role creation in IAM is complete, return to the Project View screen in CAM and register an account in CAM. Click the Add button above the account list and enter account information to register the account to the project. Completing account registration requires an approval process. To proceed with the approval process, press the Create Approval button to initiate approval, which is sent to an approval system such as Knox for processing. Once approval is complete, you can see the newly registered account in the account list.
- CSP: Select CSP.
- Environment: Select the service environment.
- Account Name: Assign a name to the account.
- Account ID: Enter the account ID registered in AWS and click the ‘Verify’ button to confirm.
- AWS type: Set to ON if the account is a China account.
- Role Name: Enter the role name created in AWS IAM.
- Title : It is automatically entered by the system and cannot be edited.
- Approver: The system automatically adds an approval line, and you can add approvers and co‑signers according to the approval guide.
- Content: Account information is entered automatically by the system and cannot be edited.
Add SCP account
PM and PL group users can add a new SCP account to a CAM project via the Add Account button on the View Project page. CAM supports a keyless connection method to enhance security, so credentials are not exchanged directly when registering an account. Before you begin, verify that the required settings have been completed in the SCP console.
Step 1. Pre-configuration (One-time trust setup for CAM account) Before adding an SCP account to CAM, verify that the following configuration has been completed on the SCP side. This setting enables CAM to securely access the target project and validate the account information.
First, if the policy has not already been created according to the steps described in the manual, you need to set it up. Then approve the CAM account through the permission group and add members.
- Create policy for CAM access
- Go to the SCP console.
- After logging in, navigate to the IAM > Policies section in the SCP console.
- Create a policy with the name ‘CAM_Linked_Policy’.
Create a new policy that includes the permissions required for CAM operation according to the table below.
| ID | Action | Reason |
|---|---|---|
| [Platform] Permission Management | List, Read, Create, Delete, Update Permission | Create/Delete Policy, Assign Policy to Role |
| [Platform] Resource Management | List, Read | View List, SCP Details |
| [Platform] Tag Management | List, Read | View Tag List/Information, etc. |
| [Platform] Project Management | List, Read | Assigned Project List/Information |
- Or you can also add policy requirements in JSON mode.
- Since you can link permission groups and roles later, complete the policy creation without checking anything.
- CAM account approval through permission groups
- After a policy is created, link it to the CAM system account using a permission group.
- Step-by-step:
- IAM > Go to Permission Groups.
- Create a new permission group (e.g., CAM-Access-Group).
- Create a permission group named ‘CAM_Linked_Group’.
- Attach the CAM policy created above to this group.
- When adding a user to a project, the user is linked to a permission group, so you can complete the creation of the permission group without verifying the user at this time.
- Assign permission group to CAM service account
- Go to the project members section of the SCP console.
- Add the required account as a member of the target project.
- This account represents CAM and is used for integration.
- Select the target project for addition > Identity and Access Management > Add User > Add Project Member > Proceed to add an SCP user to the target project.
- Proceed with adding project members.
- Search for a CAM user using the email address cam.app@samsung.com.
- Click the ADD button to select a cam.app user.
- Add an available user from the list, or you can also search for a user using the search function.
- Search for users to add as project members.
- Select the permission group called ‘CAM_Linked_Group’ that you created above and complete the project member addition task.
- Connect a permission group to complete adding project members.
- After completing the above steps, return to the project view screen in CAM and add an SCP account.
Step 2. Add an account in the CAM console
- In CAM, go to View Project > Manage Accounts.
- Click the Add Account button.
- Enter the following information in the popup window that opens:
- CSP and Environment Selection
- CSP: Choose either SCP for Enterprises or SCP for Samsung.
- Environment: Select the environment to which this account belongs (e.g., DEV, STG, PRD, or ETC).
- Enter account information
- Account name:
- Enter a name to identify this account within CAM.
- You can enter up to 50 characters.
- Only English letters and numbers are allowed.
- Project ID (in the SCP console):
- Enter the project ID of the SCP project you prepared earlier.
- Allowed characters: only English alphabet letters, numbers, and hyphens.
- Maximum: 30 characters
- Account name:
- Enter the project ID and click the Confirm button. CAM checks the following:
- Whether the project exists in SCP.
- Check if the required roles (cam-Administrator, cam-Operator, cam-Developer) exist.
- Ensure that the project is not already registered in another CAM project or awaiting approval.
- If any of the above conditions is not met, a validation message will be displayed.
- CSP and Environment Selection
Step 3. Create Approval When the project ID is verified and the other information is completed, the Create Approval button becomes active.
Click this button to send the account addition request as an approval request. Depending on the CAM settings, you can manually select an approver or have the system automatically route it to the default approver.
Once approval is completed, the SCP account will appear in CAM’s project account list.
Add Azure account
Before adding an Azure account to CAM, you must complete the following configuration steps in Microsoft Entra ID and the Azure Portal. These steps must be performed by the tenant administrator.
Step 1. Prerequisite setup (One-time trust configuration and domain configuration for CAM accounts) This step ensures that CAM is trusted within the target Azure tenant and has the necessary access permissions. This step must be completed by the tenant administrator before adding an Azure account to CAM.
These pre-configurations are divided into two sections:
- Trust configuration
- Domain configuration
Trust configuration for CAM accounts This step ensures that the CAM is trusted within the target Azure tenant and has the necessary access permissions. It must be performed by the tenant administrator of the target Azure tenant. The purpose is to grant the CAM the required permissions to access features within Microsoft Entra ID.
To enable CAM to integrate with Azure, the tenant administrator must open the CAM Admin Consent URL. This URL triggers the consent dialog in the Microsoft Entra Admin Center, where the administrator can approve the permissions requested for CAM.
- Retrieve the tenant ID.
The CAM Admin Consent URL includes the App Client ID associated with a specific tenant. Before using it, you must verify the tenant ID of the target Azure tenant.
- How to find the tenant ID:
- Log in to the Azure Portal.
- From the left navigation menu, go to Microsoft Entra ID.
- Find the tenant ID field on the Overview tab (first screen).
- Copy the tenant ID to use for the Admin Consent URL.
- Access the CAM Admin Consent URL.
Open the CAM Admin Consent URL in a web browser. (https://login.microsoftonline.com/{Your_Tenant_ID}/adminconsent?client_id=39613ae7-2fd4-4f3c-9471-aba2391da0b5)
Replace the {Your_Tenant_ID} placeholder in the URL with the actual tenant ID you copied earlier.
When the prompt appears, select the Global Administrator account of the target tenant.
This account must have the highest administrative privileges in the tenant.
Please review the displayed consent agreement. This agreement specifies the exact authority that will be granted to CAM.
If you agree, click “Accept” to approve the integration.
By completing this step, CAM can access tenant-level features in Microsoft Entra ID.
No Subscription Access Yet: In this step, CAM does not receive access permissions to the Azure subscription. Subscription-level access permissions are configured separately in later steps (creating management group roles and assigning subscription roles).
- After granting consent, verify the CAM application registration.
- In Azure Portal, go to Microsoft Entra ID → Enterprise Applications.
- Search for the CAM application.
- Verify that the CAM app appears in the list and is correctly registered.
CAM Account Domain Settings In Azure, a domain connection is required so that users can authenticate via email and integrate with CAM’s Keycloak authentication. The domain configuration process consists of the following two main steps:
| Process | Executor | frequency |
|---|---|---|
| Domain creation | Tenant admin or PM/PL | Once per tenant (may be repeated for a new domain as needed) |
| Register a domain in an Azure tenant | Tenant admin | Once per tenant (unless additional domains are added later) |
Create Domain You can create a public domain using a DNS service that can create TXT records (e.g., AWS Route 53, SCP DNS). This guide uses SCP DNS as an example.
- Tasks before creating a domain
- Log in to SCP DNS.
- After accessing the SCP console, navigate to the DNS menu.
- Starting public domain purchase.
- Click the product request button.
- This action opens the purchase form.
- Enter the details for the domain purchase form.
- Usage type: select ‘Public’.
- Domain name: Enter the desired public domain name.
- Registrant information: Enter name, email, address, and phone number.
- Description and designated fields
- Payment information is displayed before purchase confirmation.
- Purchase Confirmation
- Confirm the final payment amount.
- Click the following to verify.
- Check DNS status
- After creation, the domain appears in the SCP DNS list.
- Wait until the status shows “active”. This indicates that it is now publicly available.
- Now there is an activated public domain, and you can connect it to an Azure tenant to perform user authentication.
- Log in to SCP DNS.
Register domain in Azure tenant
Now that we have a public domain, we need to connect it to Microsoft Entra ID for authentication.
Pre-domain configuration tasks (Azure tenant)
- Log in to the Azure Portal with a tenant administrator account.
- Microsoft Entra ID → Go to custom domain name.
- Click +Add Custom Domain.
- Enter the public domain name (created in SCP).
- Click Add Domain.
Create a TXT record for the domain (Azure → SCP DNS).
- After adding a domain in Azure:
- Azure displays the TXT record value that must be added to the DNS settings to verify domain ownership.
- Copy the TXT record value in Azure.
- After adding a domain in Azure:
Add TXT record to SCP/Domain Host
- After accessing SCP DNS, select the active public domain.
- Click Add Record.
- Record Type: Select TXT.
- Value: Paste the TXT record value copied from Azure.
- TTL(Time to Live): Select according to preference.
- Click Confirm.
- Check whether the record appears in the domain’s DNS list.
Domain verification in Azure
- Return to the Azure Portal, select Microsoft Entra ID, and then select Custom Domain Names.
- Initially, the domain status is shown as “Unverified”.
- Click the domain, then click the “Verify” button.
- When Azure detects the TXT record (propagation may take a few minutes), the status changes to “Verified”.
- The public domain is now officially linked to the Azure tenant.
Step 2. Add an account in the CAM console
- In CAM, go to View Project > Manage Accounts.
- Click the Add Account button.
- Enter the following information in the popup window that opens:
- CSP and environment selection
- CSP: Select Azure.
- Environment: Select the environment to which this account belongs (e.g., DEV, STG, PRD, or ETC).
- Enter account information
- Account name:
- Enter a name to identify this account within CAM.
- You can enter up to 50 characters.
- Only English letters and numbers are allowed.
- Tenant ID (in Azure portal):
- Enter the tenant ID.
- Allowed characters: only English letters, numbers, and hyphens.
- You can enter up to 36 characters.
- When you click Verify, CAM checks the following:
- Check that the subscription ID format is correct.
- Validate Azure to confirm that it actually exists.
- The subscription ID field is enabled only after the tenant ID has been validated.
- Subscription ID (in Azure portal):
- Please enter the subscription ID.
- Only English letters, numbers, and hyphens are allowed.
- You can enter up to 36 characters.
- When you click Verify, CAM checks the following.
- Check that the subscription ID format is correct.
- Check whether the subscription ID is already linked to another CAM project.
- Check if the subscription ID is already registered or if an approval request is pending.
- The federation domain field is enabled only after the subscription ID has been verified.
- Federation domain (in Azure portal):
- Please enter the federation domain.
- Only English letters, numbers, hyphens, and periods are allowed.
- You can enter up to 48 characters.
- When you click Verify, CAM checks the following.
- Check whether the federation domain format is correct.
- Verify that it matches the existing validated domain registered in the Azure domain configuration.
- Account name:
- CSP and environment selection
Step 3. Create Approval When all fields are validated and the details are completed, the Create Approval button becomes active.
Click this button to submit an account addition approval request. Depending on the CAM settings, you can manually select an approver or have the system automatically route it to the default approver.
When approval is complete, the Azure account will appear in CAM’s project account table.
Delete account
Click the Delete button in the View Account section to delete accounts that are no longer in use.
User Management
PM and PL group users can add or remove users from a project. Only users registered in the project can be granted and managed console and resource access within that project, so users who need console or resource access must be registered as project users.
Add user
Click the Add button above the user list to add a user to the project.
- Name: Search by the user name registered in CAM.
- Group: Select the user’s group.
- PL : can manage project-related information and have the same permissions as the project manager.
- Operator, Developer: Users who can view project-related information and request resource permissions; they are categorized for role management within the project, but in the CAM portal they have identical permissions.
Delete User
Select the user to delete from the user list and click the Delete button. After a user is deleted, the deleted user can no longer view project-related information.
Notice
The announcements section allows tenant administrators to create and manage notices for users within the tenant. These notices are displayed in the GNB announcement panel. Multiple notices can be active simultaneously. Each notice may include a title, detailed description, optional attachment, and a specified display period.
Create Notice
To create a notice, click the Create button on the list page. On the Create Notice page, enter the following details:
- Title: Enter the notice title.
- Description: Provide the content or message to display.
- Attachment(Optional): Upload supporting files (up to 5 files, total size up to 50MB). Empty files cannot be uploaded, and supported file formats are images, documents, .mp4, and .zip.
- Display: To show announcements in the GNB, turn the toggle ON. After turning the toggle ON, you can select the period or date range during which the announcement will be displayed to users.
To create an announcement, select *Save. The newly created announcement will appear in the announcement list.
Notice Details
Select a notice title from the list to navigate to the notice detail page. All notice information (title, description, attachment, display period, author, and creation date) is displayed in read-only mode.
In this view:
- Use Edit to modify the announcement.
- Use Delete to permanently delete the announcement.
Edit Notice
- Select a notice from the notice list and navigate to its detail view page.
- Select Edit.
- Edit the required fields (title, description, attachment, display settings, or date range).
- To update the notice, select Save.
Delete Notice
- On the notice detail page, select Delete.
- If a prompt appears asking you to confirm deletion, confirm it. The selected announcement will be removed from the list and will no longer appear in the GNB announcements.
Approval Path
The tenant administrator can predefine the approval route that users must specify when creating an approval.
Create Approval Path
To create an approval route, click the Create button and specify the approval case and organization to generate it.
- Name: Enter a workflow name for administrative purposes that is not exposed to users.
- Target : Select when and which organization to apply it to.
- Approver Guide: Enter the responsible person’s information that cannot be automatically assigned by the system but must be included in the approval route. When entered, it will be displayed on the user screen as shown below.
- Approver: The system automatically assigns the approver to be displayed; add them by searching for their name.
View approval path
To view detailed information about the approval route, go to the Approval Route menu and click the desired approval route. You can view information for all approval routes, and Edit or Delete them as well.
Edit Approval Path
On the View Approval Route screen, you can click the Edit button to modify the information.
Delete approval path
Click the Delete button to delete the approval route that is no longer used.
organization
In the Organization menu, a tenant administrator can manually manage the tenant’s organization. When a tenant administrator creates an organization, they can manage projects and approval routes at the organization level.
Add organization
To add an organization, click the Add button and, when the Add Organization popup appears, enter the following details.
- Parent (Higher-level Organization): Select the name of the higher-level organization. The default is the tenant name.
- Name: Enter the name of the organization to create.
- Display: To have it appear in the list of organizations shown to the user, set the toggle to ON.
View organization
On the View Organization page, you can see a list of all created organizations. Clicking the organization name you want to view displays detailed organization information on the right. You can expand the entire organization list. When you expand an organization, you can view the entire hierarchy down to the lowest level at once, and when you collapse the organization list, you can see only the top‑level items.
Organization modification
The data entered when creating the organization is displayed, and you can edit all data. After editing, click the Save button.
Delete organization
Click the Delete button on the View Organization screen to delete an Organization that is no longer used.
Tenant Administrator
In the tenant administrator menu, you can add or remove administrators who manage the tenant. When the system is first opened, the user listed on the service application form is designated as the tenant administrator, and thereafter, users with tenant administrator privileges can directly add, delete, and manage.
Tenant administrators can manage tenant-level information through dedicated menus (Approval Line, Organization, etc.) and can view all content within the tenant.
Add tenant administrator
To add a tenant administrator, click the Add button, and when the tenant administrator addition popup appears, search among the users registered in the tenant and register them.
Delete Tenant Administrator
In the tenant administrator list, select the user to delete, then click the Delete button to remove them.
9.5.2.1.5 - SingleID Authenticator Manual Overview
SingleID Authenticator is a SingleID-specific authentication tool that enables easy and secure verification of website users’ identity and multi-factor authentication using a mobile phone.
SingleID Authenticator authentication method
- Biometric (fingerprint, facial)
- TOTP(Time base One Time Password)
- mOTP(mobile One Time Password)
- PINguideThe authentication methods that can be registered may vary depending on the authentication methods supported by the service and the range of device support.
Mobile environment support
SingleID Authenticator supports the mobile environments listed below.
| Support | Recommended |
|---|---|
Android : 8 and later versions
| Android : 8 and later versions
|
iOS : 16 ,17
| iOS : 16 ,17
|
9.5.2.1.5.1 - Install App
The SingleID Authenticator mobile app can be downloaded in various ways.
Download by scanning QR
In SingleID User Protal, when setting up authentication or on authentication pages, you can scan the QR code during the SingleID Authenticator registration process to conveniently visit the app store and download it.
Search in the mobile app store and download
Due to internal company security, if you cannot scan the QR code with a camera, you can directly search for and download it from the Android and iOS app stores.
- Open the Play Store (Android) or the App Store on your smartphone.
- Enter ‘SingleID’ to search.
- After confirming the ‘SingleID Authenticator’, press the install button to install.
Access via a smartphone browser and download
If you access the additional authentication page on a mobile device, follow the steps below to download and install the app.
- Click the button below on the service registration guide page.
- Click the app download button to download the installation file, then install it.
9.5.2.1.5.2 - User Authentication
Authenticate by receiving a PUSH
When a user registered with the service reaches the additional authentication screen, a PUSH is automatically sent to the user’s mobile app. To receive a PUSH and authenticate, follow the steps below.
- When additional authentication is requested, a PUSH is received from SingleID Authenticator. Press PUSH to launch the app.
- Authenticate using your preferred authentication method.
- If authentication is successful, return to the browser to complete the authentication.
Request Manual Authentication
If you launch the app without pressing PUSH or do not receive a PUSH, you can request additional verification directly from the app as shown below. To authenticate by requesting verification from the app, follow the steps below.
- Run the app and click the + button in the upper right corner.
- Scan the QR code displayed in the web browser or enter the manual code into the mobile app.
- When the input is completed correctly, the authentication service will be registered.
Authenticate with OTP
For users registered with the OTP service, the additional authentication screen automatically sends OTP information to the user’s mobile app via PUSH. Follow the steps below to view and verify the OTP in the app.
- When OTP authentication is requested, a PUSH is received in SingleID Authenticator. Press PUSH to launch the app.
- Verify that the OTP displayed in the app matches the OTP on the web screen. If they match, select Confirm in the app.
- If authentication is successful, return to the browser and complete the authentication.
9.5.2.1.5.3 - Manage Authentication Method
To use SingleID Authenticator, you must set a PIN, and you can add other authentication methods supported by the service.
Change PIN
When you first register a service in SingleID Authenticator, you will register a PIN as a required authentication method. To change the PIN, follow the steps below.
- Navigate to Main screen > Authentication method.
- Click Change on the PIN item. Complete the verification process and change to the desired number.
Terminate authentication method
If you no longer use a registered authentication method or need to re‑register, you can deactivate the authentication method. To deactivate the authentication method, follow the steps below.
- Go to Settings > Authentication Method Management.
- Authentication with a PIN is required when accessing the menu.
- Select the icon on the right of the authentication method you wish to cancel.
- A delete confirmation popup appears as shown below.
- If the authentication method is deregistered, the icon on the right changes to the Off state.
9.5.2.1.5.4 - Manage Service List
You can change the order of the registered services list or delete services you no longer use.
Changing List Order
If you want to change the order of the service list, follow the steps below.
- From the home screen, select the icon to navigate to the service list change.
- Press and hold the icon of the service you want to reorder, then drag it to the desired location.
- Change to the desired order and click Done. The updated list will be saved.
Delete registered service
The process for deleting registered services offers both a method to delete a single service and a method to delete multiple services in bulk.
If you want to delete a service, you can delete it directly from the list. Follow the steps below.
- From the Home screen, select the service you want to delete and slide it to the left.
- If the trash icon appears on the right, click the trash icon.
- Do you want to delete the selected service? When the popup appears, click Confirm to delete.
- Confirm that the service has been removed from the list.
FAQ
The app does not open when using Samsung Browser.
For users of the latest Samsung Browser, the app logo appears in the browser as shown below depending on the smartphone settings, and the app does not open automatically.
You can open the app by selecting the app icon next to the browser address bar. To set the app to open automatically, follow the steps below.
- Go to Samsung Browser > Internet Settings > Useful Features.
- Change the “Open links in other apps” setting to On.
- If you return to the browser and run the app again, it operates correctly.
9.5.2.1.5.5 - Open Source Licence(Android)
The open source licenses used in the SingleID solution are as follows. For more details, see below.
SingleID_MobileApp_Client-APK
The following sets forth attribution notices for third party software that may be contained in portions of this product. If you have any questions, please contact <global.cs@samsung.com.>
| License | Open Source Component | License Text |
|---|---|---|
| Jdom License | JDOM(http://www.jdom.org/) | JDOM License Copyright (C) 2000-2004 Jason Hunter & Brett McLaughlin. All rights reserved. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: 1. Redistributions of source code must retain the above copyright notice, this list of conditions, and the following disclaimer. 2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the disclaimer that follows these conditions in the documentation and/or other materials provided with the distribution. 3. The name “JDOM” must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact {request_AT_jdom_DOT_org}. 4. Products derived from this software may not be called “JDOM”, nor may “JDOM” appear in their name, without prior written permission from the JDOM Project Management {request_AT_jdom_DOT_org}. In addition, we request (but do not require) that you include in the end-user documentation provided with the redistribution and/or in the software itself an acknowledgment equivalent to the following: “This product includes software developed by the JDOM Project (http://www.jdom.org/)." Alternatively, the acknowledgment may be graphical using the logos available at http://www.jdom.org/images/logos. THIS SOFTWARE IS PROVIDED “AS IS” AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE JDOM AUTHORS OR THE PROJECT CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. |
| MIT License | Xamarin.Android.Support.VersionedParcelable (http://www.nuget.org/packages/Xamarin.Android .Support.VersionedParcelable) , Animal Sniffer Annotations (http://mojo.codehaus.org/animal-sniffer/ animal-sniffer-annotations) , Checker Qual (http://checkerframework.org) , Xamarin.Android.Support.SwipeRefreshLayout (http://www.nuget.org/packages/Xamarin.Android .Support.SwipeRefreshLayout) , chai (https://www.npmjs.org/package/chai) , The Legion of the Bouncy Castle (http://www.bouncycastle.org/index.html) , SLF4J API Module(http://www.slf4j.org) , jsrsasign(https://www.npmjs.org/package/jsrsasign) ,Checker Qual(http://checkerframework.org) , , jsrsasign (https://www.npmjs.org/package/jsrsasign) , Mocha(https://www.npmjs.org/package/mocha) , Xamarin.Android.Support.ViewPager (http://www.nuget.org/packages/Xamarin. Android.Support.ViewPager) , SLF4J LOG4J-12 Binding (http://www.slf4j.org) , android-gif-drawable (http://github.com/koral--/android-gif-drawable/) Android - platform - hardware - intel - common – libva (http://developer.android.com/index.html) | The MIT License Xamarin.Android.Support.VersionedParcelable : Copyright (c) .NET Foundation Contributors Animal Sniffer Annotations : Copyright (c) 2009 codehaus.org. Checker Qual : Copyright 2004-present by the Checker Framework developers Xamarin.Android.Support.SwipeRefreshLayout : Copyright (c) .NET Foundation Contributors chai : Copyright (c) 2017 Chai.js Assertion Library The Legion of the Bouncy Castle : Copyright © 2013 Legion of the Bouncy Castle Inc. (ABN 84 166 338 567) All rights reserved. SLF4J API Module , SLF4J LOG4J-12 Binding : Copyright © 2004-2023 QOS.ch jsrsasign : Copyright (c) 2010-2021 Kenji Urushima Checker Qual : Copyright 2004-present by the Checker Framework developers Mocha: Copyright (c) 2011-2022 OpenJS Foundation and contributors, https://openjsf.org Xamarin.Android.Support.ViewPager , Android - platform - hardware - intel - common - libva: Copyright (c) .NET Foundation Contributors android-gif-drawable : Copyright (c) 2013 - present Karol Wrótniak, Droids on Roids LLC Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF License Open Source Component License Text MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. |
SingleID_MobileApp_Flutter-UMA
The following sets forth attribution notices for third party software that may be contained in portions of this product. If you have any questions, please contact global.cs@samsung.com
| License | Open Source Component | License Text |
|---|---|---|
| Apache License 2.0 | Android Support Library media compat, Converter: Gson, Adapter: RxJava 2, Android Support Library core utils, Android Arch-Runtime, Guava (Google Common Libraries), Android Support AnimatedVectorDrawable, Android Support Library core UI, Android Support Library Custom View - androidx.customview:customview, Android Lifecycle LiveData, OkHttp, Gson, android.support.annotation, Android Support Library Custom View - androidx.swiperefreshlayout:swiperefreshlayout, Android Support Library v4, OkHttp, Android Lifecycle ViewModel, Commons Lang, rxjava, Android Support Library compat, Roboto Fonts, Apache Commons Collections, Android Support Library v4, Android Lifecycle LiveData Core, RxAndroid, joda-time, okio, Apache Commons IO, JetBrains/java-annotations, Android AppCompat Library v7, Android Support Library Collections, Android Support VectorDrawable, Kotlin Stdlib, Android Lifecycle-Common, Android Support Library loader, Retrofit | Apache License Version 2.0, January 2004 http://www.apache.org/licenses/ TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION 1. Definitions. “License” shall me an the terms and conditions for use, reproduction, and distribution as defined by Sections 1 through 9 of this document. “Licensor” shall mean the copyright owner or entity authorized by the copyright owner that is granting the License. “Legal Entity” shall mean the union of the acting entity and all other entities that control, are controlled by, or are under common control with that entity. For the purposes of this definition, “control” means (i) the power, direct or indirect, to cause the direction or management of such entity, whether by contract or otherwise, or (ii) ownership of fifty percent (50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity. “You” (or “Your”) shall mean an individual or Legal Entity exercising permissions granted by this License. “Source” form shall mean the preferred form for making modifications, including but not limited to software source code, documentation source, and configuration files. “Object” form shall mean any form resulting from mechanical transformation or translation of a Source form, including but not limited to compiled object code, generated documentation, and conversions to other media types. “Work” shall mean the work of authorship, whether in Source or Object form, made available under the License, as indicated by a copyright notice that is included in or attached to the work (an example is provided in the Appendix below). “Derivative Works” shall mean any work, whether in Source or Object form, that is based on (or derived from) the Work and for which the editorial revisions, annotations, elaborations, or other modifications represent, as a whole, an original work of authorship. For the purposes of this License, Derivative Works shall not include works that remain separable from, or merely link (or bind by name) to the interfaces of, the Work and Derivative Works thereof. “Contribution” shall mean any work of authorship, including the original version of the Work and any modifications or additions to that Work or Derivative Works thereof, that is intentionally submitted to Licensor for inclusion in the Work by the copyright owner or by an individual or Legal Entity authorized to submit on behalf of the copyright owner. For the purposes of this definition, “submitted” means any form of electronic, verbal, or written communication sent to the Licensor or its representatives, including but not limited to communication on electronic mailing lists, source code control systems, and issue tracking systems that are managed by, or on behalf of, the Licensor for the purpose of discussing and improving the Work, but excluding communication that is conspicuously marked or otherwise designated in writing by the copyright owner as “Not a Contribution.” “Contributor” shall mean Licensor and any individual or Legal Entity on behalf of whom a Contribution has been received by Licensor and subsequently incorporated within the Work. 2. Grant of Copyright License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable copyright license to reproduce, prepare Derivative Works of, publicly display, publicly perform, sublicense, and distribute the Work and such Derivative Works in Source or Object form. 3. Grant of Patent License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable (except as stated in this section) patent license to make, have made, use, offer to sell, sell, import, and otherwise transfer the Work, where such license applies only to those patent claims licensable by such Contributor that are necessarily infringed by their Contribution(s) alone or by combination of their Contribution(s) with the Work to which such Contribution(s) was submitted. If You institute patent litigation against any entity (including a cross-claim or counterclaim in a lawsuit) alleging that the Work or a Contribution incorporated within the Work constitutes direct or contributory patent infringement, then any patent licenses granted to You under this License for that Work shall terminate as of the date such litigation is filed. 4. Redistribution. You may reproduce and distribute copies of the Work or Derivative Works thereof in any medium, with or without modifications, and in Source or Object form, provided that You meet the following conditions: a. You must give any other recipients of the Work or Derivative Works a copy of this License; and b. You must cause any modified files to carry prominent notices stating that You changed the files; and c. You must retain, in the Source form of any Derivative Works that You distribute, all copyright, patent, trademark, and attribution notices from the Source form of the Work, excluding those notices that do not pertain to any part of the Derivative Works; and d. If the Work includes a “NOTICE” text file as part of its distribution, then any Derivative Works that You distribute must include a readable copy of the attribution notices contained within such NOTICE file, excluding those notices that do not pertain to any part of the Derivative Works, in at least one of the following places: within a NOTICE text file distributed as part of the Derivative Works; within the Source form or documentation, if provided along with the Derivative Works; or, within a display generated by the Derivative Works, if and wherever such third-party notices normally appear. The contents of the NOTICE file are for informational purposes only and do not modify the License. You may add Your own attribution notices within Derivative Works that You distribute, alongside or as an addendum to the NOTICE text from the Work, provided that such additional attribution notices cannot be construed as modifying the License. You may add Your own copyright statement to Your modifications and may provide additional or different license terms and conditions for use, reproduction, or distribution of Your modifications, or for any such Derivative Works as a whole, provided Your use, reproduction, and distribution of the Work otherwise complies with the conditions stated in this License. 5. Submission of Contributions. Unless You explicitly state otherwise, any Contribution intentionally submitted for inclusion in the Work by You to the Licensor shall be under the terms and conditions of this License, without any additional terms or conditions. Notwithstanding the above, nothing herein shall supersede or modify the terms of any separate license agreement you may have executed with Licensor regarding such Contributions. 6. Trademarks. This License does not grant permission to use the trade names, trademarks, service marks, or product names of the Licensor, except as required for reasonable and customary use in describing the origin of the Work and reproducing the content of the NOTICE file. 7. Disclaimer of Warranty. Unless required by applicable law or agreed to in writing, Licensor provides the Work (and each Contributor provides its Contributions) on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied, including, without limitation, any warranties or conditions of TITLE, NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A PARTICULAR PURPOSE. You are solely responsible for determining the appropriateness of using or redistributing the Work and assume any risks associated with Your exercise of permissions under this License. 8. Limitation of Liability. In no event and under no legal theory, whether in tort (including negligence), contract, or otherwise, unless required by applicable law (such as deliberate and grossly negligent acts) or agreed to in writing, shall any Contributor be liable to You for damages, including any direct, indirect, special, incidental, or consequential damages of any character arising as a result of this License or out of the use or inability to use the Work (including but not limited to damages for loss of goodwill, work stoppage, computer failure or malfunction, or any and all other commercial damages or losses), even if such Contributor has been advised of the possibility of such damages. 9. Accepting Warranty or Additional Liability. While redistributing the Work or Derivative Works thereof, You may choose to offer, and charge a fee for, acceptance of support, warranty, indemnity, or other liability obligations and/or rights consistent with this License. However, in accepting such obligations, You may act only on Your own behalf and on Your sole responsibility, not on behalf of any other Contributor, and only if You agree to indemnify, defend, and hold each Contributor harmless for any liability incurred by, or claims asserted against, such Contributor by reason of your accepting any such warranty or additional liability. END OF TERMS AND CONDITIONS APPENDIX: How to apply the Apache License to your work To apply the Apache License to your work, attach the following boilerplate notice, with the fields enclosed by brackets “[]” replaced with your own identifying information. (Don’t include the brackets!) The text should be enclosed in the appropriate comment syntax for the file format. We also recommend that a file or class name and description of purpose be included on the same “printed page” as the copyright notice for easier identification within third-party archives. Copyright [yyyy] [name of copyright owner] Licensed under the Apache License, Version 2.0 (the “License”); you may not use this file except in compliance with the License. You may obtain a copy of the License at http://www.apache.org/licenses/LICENSE-2.0 Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License. |
| Creative Commons Zero v1.0 Universal | reactive-streams: http://www.reactive-streams.org/ | Creative Commons CC0 1.0 Universal Creative Commons Legal Code CC0 1.0 Universal CREATIVE COMMONS CORPORATION IS NOT A LAW FIRM AND DOES NOT PROVIDE LEGAL SERVICES. DISTRIBUTION OF THIS DOCUMENT DOES NOT CREATE AN ATTORNEY-CLIENT RELATIONSHIP. CREATIVE COMMONS PROVIDES THIS INFORMATION ON AN “AS-IS” BASIS. CREATIVE COMMONS MAKES NO WARRANTIES REGARDING THE USE OF THIS DOCUMENT OR THE INFORMATION OR WORKS PROVIDED HEREUNDER, AND DISCLAIMS LIABILITY FOR DAMAGES RESULTING FROM THE USE OF THIS DOCUMENT OR THE INFORMATION OR WORKS PROVIDED HEREUNDER. Statement of Purpose The laws of most jurisdictions throughout the world automatically confer exclusive Copyright and Related Rights (defined below) upon the creator and subsequent owner(s) (each and all, an “owner”) of an original work of authorship and/or a database (each, a “Work”). Certain owners wish to permanently relinquish those rights to a Work for the purpose of contributing to a commons of creative, cultural and scientific works (“Commons”) that the public can reliably and without fear of later claims of infringement build upon, modify, incorporate in other works, reuse and redistribute as freely as possible in any form whatsoever and for any purposes, including without limitation commercial purposes. These owners may contribute to the Commons to promote the ideal of a free culture and the further production of creative, cultural and scientific works, or to gain reputation or greater distribution for their Work in part through the use and efforts of others. For these and/or other purposes and motivations, and without any expectation of additional consideration or compensation, the person associating CC0 with a Work (the “Affirmer”), to the extent that he or she is an owner of Copyright and Related Rights in the Work, voluntarily elects to apply CC0 to the Work and publicly distribute the Work under its terms, with knowledge of his or her Copyright and Related Rights in the Work and the meaning and intended legal effect of CC0 on those rights. 1. Copyright and Related Rights. A Work made available under CC0 may be protected by copyright and related or neighboring rights (“Copyright and Related Rights”). Copyright and Related Rights include, but are not limited to, the following: i. the right to reproduce, adapt, distribute, perform, display, communicate, and translate a Work; ii. moral rights retained by the original author(s) and/or performer(s); iii. publicity and privacy rights pertaining to a person’s image or likeness depicted in a Work; iv. rights protecting against unfair competition in regards to a Work, subject to the limitations in paragraph 4(a), below; v. rights protecting the extraction, dissemination, use and reuse of data in a Work; vi. database rights (such as those arising under Directive 96/9/EC of the European Parliament and of the Council of 11 March 1996 on the legal protection of databases, and under any national implementation thereof, including any amended or successor version of such directive); and vii. other similar, equivalent or corresponding rights throughout the world based on applicable law or treaty, and any national implementations thereof. 2. Waiver. To the greatest extent permitted by, but not in contravention of, applicable law, Affirmer hereby overtly, fully, permanently, irrevocably and unconditionally waives, abandons, and surrenders all of Affirmer’s Copyright and Related Rights and associated claims and causes of action, whether now known or unknown (including existing as well as future claims and causes of action), in the Work i. in all territories worldwide, ii. for the maximum duration provided by applicable law or treaty (including future time extensions), iii. in any current or future medium and for any number of copies, and iv. for any purpose whatsoever, including without limitation commercial, advertising or promotional purposes (the “Waiver”). Affirmer makes the Waiver for the benefit of each member of the public at large and to the detriment of Affirmer’s heirs and successors, fully intending that such Waiver shall not be subject to revocation, rescission, cancellation, termination, or any other legal or equitable action to disrupt the quiet enjoyment of the Work by the public as contemplated by Affirmer’s express Statement of Purpose. 3. Public License Fallback. Should any part of the Waiver for any reason be judged legally invalid or ineffective under applicable law, then the Waiver shall be preserved to the maximum extent permitted taking into account Affirmer’s express Statement of Purpose. In addition, to the extent the Waiver is so judged Affirmer hereby grants to each affected person a royalty-free, non transferable, non sublicensable, non exclusive, irrevocable and unconditional license to exercise Affirmer’s Copyright and Related Rights in the Work i. in all territories worldwide, ii. for the maximum duration provided by applicable law or treaty (including future time extensions), iii. in any current or future medium and for any number of copies, and iv. for any purpose whatsoever, including without limitation commercial, advertising or promotional purposes (the “License”). The License shall be deemed effective as of the date CC0 was applied by Affirmer to the Work. Should any part of the License for any reason be judged legally invalid or ineffective under applicable law, such partial invalidity or ineffectiveness shall not invalidate the remainder of the License, and in such case Affirmer hereby affirms that he or she will not i. exercise any of his or her remaining Copyright and Related Rights in the Work or ii. assert any associated claims and causes of action with respect to the Work, in either case contrary to Affirmer’s express Statement of Purpose. 4. Limitations and Disclaimers. a. No trademark or patent rights held by Affirmer are waived, abandoned, surrendered, licensed or otherwise affected by this document. b. Affirmer offers the Work as-is and makes no representations or warranties of any kind concerning the Work, express, implied, statutory or otherwise, including without limitation warranties of title, merchantability, fitness for a particular purpose, non infringement, or the absence of latent or other defects, accuracy, or the present or absence of errors, whether or not discoverable, all to the greatest extent permissible under applicable law. c. Affirmer disclaims responsibility for clearing rights of other persons that may apply to the Work or any use thereof, including without limitation any person’s Copyright and Related Rights in the Work. Further, Affirmer disclaims responsibility for obtaining any necessary consents, permissions or other rights required for any use of the Work. Affirmer understands and acknowledges that Creative Commons is not a party to this document and has no duty or obligation with respect to this CC0 or use of the Work. |
| ISC License | gotham-fonts: https://www.npmjs.org/package/gotham-fonts | ISC License (ISCL) gotham-fonts : Copyright @ Bogdan Pop Permission to use, copy, modify, and/or distribute this software for any purpose with or without fee is hereby granted, provided that the above copyright notice and this permission notice appear in all copies. THE SOFTWARE IS PROVIDED “AS IS” AND THE AUTHOR DISCLAIMS ALL WARRANTIES WITH REGARD TO THIS SOFTWARE INCLUDING ALL IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS. IN NO EVENT SHALL THE AUTHOR BE LIABLE FOR ANY SPECIAL, DIRECT, INDIRECT, OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER IN AN ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE. |
| MIT License | Xamarin.Android.Support.VersionedParcelable: http://www.nuget.org/packages/Xamarin.Android.Support.VersionedParcelable Xamarin.Android.Support.CoordinaterLayout: http://www.nuget.org/packages/Xamarin.Android.Support.CoordinaterLayout The Legion of the Bouncy Castle: http://www.bouncycastle.org/index.html Xamarin.Android.Support.SlidingPaneLayout: http://www.nuget.org/packages/Xamarin.Android.Support.SlidingPaneLayout XamarinLibrary.Xamarin.Android.Support.Multidex: https://www.nuget.org/packages/XamarinLibrary.Xamarin.Android.Support.Multidex Xamarin.Android.Support.Interpolator: http://www.nuget.org/packages/Xamarin.Android.Support.Interpolator Xamarin.Android.Support.LocalBroadcastManager: http://www.nuget.org/packages/Xamarin.Android.Support.LocalBroadcastManager Xamarin.Android.Support.DrawerLayout: http://www.nuget.org/packages/Xamarin.Android.Support.DrawerLayout @fontsource/Montserrat: https://www.npmjs.org/package/@fontsource/montserrat Xamarin.Android.Support.DocumentFile: http://www.nuget.org/packages/Xamarin.Android.Support.DocumentFile Xamarin.Android.Support.Print: http://www.nuget.org/packages/Xamarin.Android.Support.Print Xamarin.Android.Support.AsyncLayoutInflater: http://www.nuget.org/packages/Xamarin.Android.Support.AsyncLayoutInflater SLF4J API Module: http://www.slf4j.org Xamarin.Android.Support.ViewPager: http://www.nuget.org/packages/Xamarin.Android.Support.ViewPager secure-random: http://github.com/avodonosov/secure-random/ Xamarin.Android.Support.CursorAdapter: http://www.nuget.org/packages/Xamarin.Android.Support.CursorAdapter | The MIT License Xamarin.Android.Support.VersionedParcelable: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.CoordinaterLayout: Copyright (c) .NET Foundation Contributors All rights reserved. The Legion of the Bouncy Castle: Copyright (c) 2000-2023 The Legion of the Bouncy Castle Inc. (https://www.bouncycastle.org) All rights reserved. Xamarin.Android.Support.SlidingPaneLayout: Copyright (c) .NET Foundation Contributors All rights reserved. XamarinLibrary.Xamarin.Android.Support.Multidex: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.Interpolator: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.LocalBroadcastManager: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.DrawerLayout: Copyright (c) .NET Foundation Contributors All rights reserved. @fontsource/Montserrat: Copyright (c) 2023 fontsource All rights reserved. Xamarin.Android.Support.DocumentFile: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.Print: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.AsyncLayoutInflater: Copyright (c) .NET Foundation Contributors All rights reserved. SLF4J API Module: Copyright © 2004-2023 QOS.ch All rights reserved. Xamarin.Android.Support.ViewPager: Copyright (c) .NET Foundation Contributors All rights reserved. secure-random: Copyright (C) 2011 by Anton Vodonosov (avodonosov@yandex.ru). All rights reserved. Xamarin.Android.Support.CursorAdapter: Copyright (c) .NET Foundation Contributors All rights reserved. Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. |
| SIL Open Font License 1.1 | @fontsource/rubik, https://www.npmjs.org/package/@fontsource/rubik @fontsource/montserrat https://www.npmjs.org/package/@fontsource/montserrat | SIL OPEN FONT LICENSE Version 1.1 - 26 February 2007 PREAMBLE The goals of the Open Font License (OFL) are to stimulate worldwide development of collaborative font projects, to support the font creation efforts of academic and linguistic communities, and to provide a free and open framework in which fonts may be shared and improved in partnership with others. The OFL allows the licensed fonts to be used, studied, modified and redistributed freely as long as they are not sold by themselves. The fonts, including any derivative works, can be bundled, embedded, redistributed and/or sold with any software provided that any reserved names are not used by derivative works. The fonts and derivatives, however, cannot be released under any other type of license. The requirement for fonts to remain under this license does not apply to any document created using the fonts or their derivatives. DEFINITIONS “Font Software” refers to the set of files released by the Copyright Holder(s) under this license and clearly marked as such. This may include source files, build scripts and documentation. “Reserved Font Name” refers to any names specified as such after the copyright statement(s). “Original Version” refers to the collection of Font Software components as distributed by the Copyright Holder(s). “Modified Version” refers to any derivative made by adding to, deleting, or substituting — in part or in whole — any of the components of the Original Version, by changing formats or by porting the Font Software to a new environment. “Author” refers to any designer, engineer, programmer, technical writer or other person who contributed to the Font Software. PERMISSION & CONDITIONS Permission is hereby granted, free of charge, to any person obtaining a copy of the Font Software, to use, study, copy, merge, embed, modify, redistribute, and sell modified and unmodified copies of the Font Software, subject to the following conditions: 1. Neither the Font Software nor any of its individual components, in Original or Modified Versions, may be sold by itself. 2. Original or Modified Versions of the Font Software may be bundled, redistributed and/or sold with any software, provided that each copy contains the above copyright notice and this license. These can be included either as stand-alone text files, human-readable headers or in the appropriate machine-readable metadata fields within text or binary files as long as those fields can be easily viewed by the user. 3. No Modified Version of the Font Software may use the Reserved Font Name(s) unless explicit written permission is granted by the corresponding Copyright Holder. This restriction only applies to the primary font name as presented to the users. 4. The name(s) of the Copyright Holder(s) or the Author(s) of the Font Software shall not be used to promote, endorse or advertise any Modified Version, except to acknowledge the contribution(s) of the Copyright Holder(s) and the Author(s) or with their explicit written permission. 5. The Font Software, modified or unmodified, in part or in whole, must be distributed entirely under this license, and must not be distributed under any other license. The requirement for fonts to remain under this license does not apply to any document created using the Font Software. TERMINATION This license becomes null and void if any of the above conditions are not met. DISCLAIMER THE FONT SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO ANY WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OF COPYRIGHT, PATENT, TRADEMARK, OR OTHER RIGHT. IN NO EVENT SHALL THE COPYRIGHT HOLDER BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, INCLUDING ANY GENERAL, SPECIAL, INDIRECT, INCIDENTAL, OR CONSEQUENTIAL DAMAGES, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF THE USE OR INABILITY TO USE THE FONT SOFTWARE OR FROM OTHER DEALINGS IN THE FONT SOFTWARE. |
9.5.2.1.5.6 - Open Source Licence(ISO)
The open source licenses used in the SingleID solution are as follows. For more details, see below.
SingleID_MobileApp_Client-IOS
The following sets forth attribution notices for third party software that may be contained in portions of This product. If you have any questions, please contact global.cs@samsung.com.
| License | Open Source Component | License Text |
|---|---|---|
| Apache License 2.0 | Open Computer Vision Library (OpenCV): KA ProgressLabel: | Apache License Version 2.0, January 2004 http://www.apache.org/licenses/ TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION 1. Definitions. “License” shall mean the terms and conditions for use, reproduction, and distribution as defined by Sections 1 through 9 of this document. “Licensor” shall mean the copyright owner or entity authorized by the copyright owner that is granting the License. “Legal Entity” shall mean the union of the acting entity and all other entities that control, are controlled by, or are under common control with that entity. For the purposes of this definition, “control” means (i) the power, direct or indirect, to cause the direction or management of such entity, whether by contract or otherwise, or (ii) ownership of fifty percent (50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity. “You” (or “Your”) shall mean an individual or Legal Entity exercising permissions granted by this License. “Source” form shall mean the preferred form for making modifications, including but not limited to software source code, documentation source, and configuration files. “Object” form shall mean any form resulting from mechanical transformation or translation of a Source form, including but not limited to compiled object code, generated documentation, and conversions to other media types. “Work” shall mean the work of authorship, whether in Source or Object form, made available under the License, as indicated by a copyright notice that is included in or attached to the work (an example is provided in the Appendix below). “Derivative Works” shall mean any work, whether in Source or Object form, that is based on (or derived from) the Work and for which the editorial revisions, annotations, elaborations, or other modifications represent, as a whole, an original work of authorship. For the purposes of this License, Derivative Works shall not include works that remain separable from, or merely link (or bind by name) to the interfaces of, the Work and Derivative Works thereof. “Contribution” shall mean any work of authorship, including the original version of the Work and any modifications or additions to that Work or Derivative Works thereof, that is intentionally submitted to Licensor for inclusion in the Work by the copyright owner or by an individual or Legal Entity authorized to submit on behalf of the copyright owner. For the purposes of this definition, “submitted” means any form of electronic, verbal, or written communication sent to the Licensor or its representatives, including but not limited to communication on electronic mailing lists, source code control systems, and issue tracking systems that are managed by, or on behalf of, the Licensor for the purpose of discussing and improving the Work, but excluding communication that is conspicuously marked or otherwise designated in writing by the copyright owner as “Not a Contribution.” “Contributor” shall mean Licensor and any individual or Legal Entity on behalf of whom a Contribution has been received by Licensor and subsequently incorporated within the Work. 1. Grant of Copyright License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable copyright license to reproduce, prepare Derivative Works of, publicly display, publicly perform, sublicense, and distribute the Work and such Derivative Works in Source or Object form. 2. Grant of Patent License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable (except as stated in this section) patent license to make, have made, use, offer to sell, sell, import, and otherwise transfer the Work, where such license applies only to those patent claims licensable by such Contributor that are necessarily infringed by their Contribution(s) alone or by combination of their Contribution(s) with the Work to which such Contribution(s) was submitted. If You institute patent litigation against any entity (including a cross-claim or counterclaim in a lawsuit) alleging that the Work or a Contribution incorporated within the Work constitutes direct or contributory patent infringement, then any patent licenses granted to You under this License for that Work shall terminate as of the date such litigation is filed. 4. Redistribution. You may reproduce and distribute copies of the Work or Derivative Works thereof in any medium, with or without modifications, and in Source or Object form, provided that You meet the following conditions: a. You must give any other recipients of the Work or Derivative Works a copy of this License; and b. You must cause any modified files to carry prominent notices stating that You changed the files; and c. You must retain, in the Source form of any Derivative Works that You distribute, all copyright, patent, rademark, and attribution notices from the Source form of the Work, excluding those notices that do not pertain to any part of the Derivative Works; and d. If the Work includes a “NOTICE” text file as part of its distribution, then any Derivative Works that You distribute must include a readable copy of the attribution notices contained within such NOTICE file, excluding those notices that do not pertain to any part of the Derivative Works, in at least one of the following places: within a NOTICE text file distributed as part of the Derivative Works; within the Source form or documentation, if provided along with the Derivative Works; or, within a display generated by the Derivative Works, if and wherever such third-party notices normally appear. The contents of the NOTICE file are for informational purposes only and do not modify the License. You may add Your own attribution notices within Derivative Works that You distribute, alongside or as an addendum to the NOTICE text from the Work, provided that such additional attribution notices cannot be construed as modifying the License. You may add Your own copyright statement to Your modifications and may provide additional or different license terms and conditions for use, reproduction, or distribution of Your modifications, or for any such Derivative Works as a whole, provided Your use, reproduction, and distribution of the Work otherwise complies with the conditions stated in this License. 5. Submission of Contributions. Unless You explicitly state otherwise, any Contribution intentionally submitted for inclusion in the Work by You to the Licensor shall be under the terms and conditions of this License, without any additional terms or conditions. Notwithstanding the above, nothing herein shall supersede or modify the terms of any separate license agreement you may have executed with Licensor regarding such Contributions. 6. Trademarks. This License does not grant permission to use the trade names, trademarks, service marks, or product names of the Licensor, except as required for reasonable and customary use in describing the origin of the Work and reproducing the content of the NOTICE file. 7. Disclaimer of Warranty. Unless required by applicable law or agreed to in writing, Licensor provides the Work (and each Contributor provides its Contributions) on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied, including, without limitation, any warranties or conditions of TITLE, NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A PARTICULAR PURPOSE. You are solely responsible for determining the appropriateness of using or redistributing the Work and assume any risks associated with Your exercise of permissions under this License. 8. Limitation of Liability. In no event and under no legal theory, whether in tort (including negligence), contract, or otherwise, unless required by applicable law (such as deliberate and grossly negligent acts) or agreed to in writing, shall any Contributor be liable to You for damages, including any direct, indirect, special, incidental, or consequential damages of any character arising as a result of this License or out of the use or inability to use the Work (including but not limited to damages for loss of goodwill, work stoppage, computer failure or malfunction, or any and all other commercial damages or losses), even if such Contributor has been advised of the possibility of such damages. 9. Accepting Warranty or Additional Liability. While redistributing the Work or Derivative Works thereof, You may choose to offer, and charge a fee for, acceptance of support, warranty, indemnity, or other liability obligations and/or rights consistent with this License. However, in accepting such obligations, You may act only on Your own behalf and on Your sole responsibility, not on behalf of any other Contributor, and only if You agree to indemnify, defend, and hold each Contributor harmless for any liability incurred by, or claims asserted against, such Contributor by reason of your accepting any such warranty or additional liability. END OF TERMS AND CONDITIONS APPENDIX: How to apply the Apache License to your work To apply the Apache License to your work, attach the following boilerplate notice, with the fields enclosed by brackets “[]” replaced with your own identifying information. (Don’t include the brackets!) The text should be enclosed in the appropriate comment syntax for the file format. We also recommend that a file or class name and description of purpose be included on the same “printed page” as the copyright notice for easier identification within third-party archives. Copyright [yyyy] [name of copyright owner] Licensed under the Apache License, Version 2.0 (the “License”); you may not use this file except in compliance with the License. You may obtain a copy of the License at http://www.apache.org/licenses/LICENSE-2.0 Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License. |
| Apple MIT License | Apple Reachability: https://developer.apple.com/library/ios/samplecode/Reachability/Introduction/Intro.html | Disclaimer: IMPORTANT: This Apple software is supplied to you by Apple Computer, Inc. (“Apple”) in consideration of your agreement to the following terms, and your use, installation, modification or redistribution of this Apple software constitutes acceptance of these terms. If you do not agree with these terms, please do not use, install, modify or redistribute this Apple software. In consideration of your agreement to abide by the following terms, and subject to these terms, Apple grants you a personal, non-exclusive license, under Apple’s copyrights in this original Apple software (the “Apple Software”), to use, reproduce, modify and redistribute the Apple Software, with or without modifications, in source and/or binary forms; provided that if you redistribute the Apple Software in its entirety and without modifications, you must retain this notice and the following text and disclaimers in all such redistributions of the Apple Software. Neither the name, trademarks, service marks or logos of Apple Computer, Inc. may be used to endorse or promote products derived from the Apple Software without specific prior written permission from Apple. Except as expressly stated in this notice, no other rights or licenses, express or implied, are granted by Apple herein, including but not limited to any patent rights that may be infringed by your derivative works or by other works in which the Apple Software may be incorporated. The Apple Software is provided by Apple on an “AS IS” basis. APPLE MAKES NO WARRANTIES, EXPRESS OR IMPLIED, INCLUDING WITHOUT LIMITATION THE IMPLIED WARRANTIES OF NON-INFRINGEMENT, MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE, REGARDING THE APPLE SOFTWARE OR ITS USE AND OPERATION ALONE OR IN COMBINATION WITH YOUR PRODUCTS. IN NO EVENT SHALL APPLE BE LIABLE FOR ANY SPECIAL, INDIRECT, INCIDENTAL OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) ARISING IN ANY WAY OUT OF THE USE, REPRODUCTION, MODIFICATION AND/OR DISTRIBUTION OF THE APPLE SOFTWARE, HOWEVER CAUSED AND WHETHER UNDER THEORY OF CONTRACT, TORT (INCLUDING NEGLIGENCE), STRICT LIABILITY OR OTHERWISE, EVEN IF APPLE HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. |
| Brian Gladman AES License | Gladman AES: http://www.gladman.me.uk/AES | Brian Gladman AES License Copyright (c) 1998-2013, Brian Gladman, Worcester, UK. All rights reserved. The redistribution and use of this software (with or without changes) is allowed without the payment of fees or royalties provided that: source code distributions include the above copyright notice, this list of conditions and the following disclaimer; binary distributions include the above copyright notice, this list of conditions and the following disclaimer in their documentation. |
| This software is provided ‘as is’ with no explicit or implied warranties in respect of its operation, including, but not limited to, correctness and fitness for purpose. | ||
| BSD 3-clause “New” or “Revised” License | TPPropertyAnimation: http://atastypixel.com/blog/key-path-based-property-animation Sqlcipher: https://cocoapods.org/pods/SQLCipher ASM All: http://asm.objectweb.org/asm/ Protocol Buffers [BOM]: https://developers.google.com/protocol-buffers/ | TPPropertyAnimation: Copyright 2010 A TASTY PIXEL. All rights Reserved sqlcipher: Copyright (c) 2008-2023, ZETETIC LLC All rights reserved. ASM All: Copyright (c) 2000-2011 INRIA, France Telecom All rights reserved. Protocol Buffers [BOM]: Copyright 2008 Google Inc. All rights reserved. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: * Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer. * Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. * Neither the name of the THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS |
| MIT License | SlatherOrg/slather: https://github.com/SlatherOrg/slather FDKeychain: https://cocoapods.org/pods/FDKeychain JSONModel: https://cocoapods.org/pods/JSONModel FLAnimatedImage: https://cocoapods.org/pods/FLAnimatedImage Ssziparchive: https://cocoapods.org/pods/SSZipArchive | The MIT License SlatherOrg/slather: Copyright (c) 2014 Mark Larsen All rights reserved FDKeychain: Copyright (c) 2016 Reid Main All rights reserved JSONModel: Copyright (c) 2012-2016 Marin Todorov and JSONModel contributors All rights reserved FLAnimatedImage: Copyright (c) 2014-2016 Flipboard All rights reserved ssziparchive: Copyright (c) 2013-2021, ZipArchive, https://github.com/ZipArchive All rights reserved Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. |
| OpenSSL Combined License | OpenSSL - in C: http://www.openssl.org | LICENSE ISSUES The OpenSSL toolkit stays under a dual license, i.e. both the conditions of the OpenSSL License and the original SSLeay license apply to the toolkit. See below for the actual license texts. Actually both licenses are BSD-style Open Source licenses. In case of any license issues related to OpenSSL please contact openssl-core@openssl.org. OpenSSL License ————— Copyright (c) 1998-2008 The OpenSSL Project. All rights reserved. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: 1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer. 2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. 3. All advertising materials mentioning features or use of this software must display the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit. (http://www.openssl.org/)" 4. The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact openssl-core@openssl.org. 5. Products derived from this software may not be called “OpenSSL” nor may “OpenSSL” appear in their names without prior written permission of the OpenSSL Project. 6. Redistributions of any form whatsoever must retain the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://www.openssl.org/)" THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS” AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. This product includes cryptographic software written by Eric Young (eay@cryptsoft.com). This product includes software written by Tim Hudson (tjh@cryptsoft.com). Original SSLeay License Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com) All rights reserved. This package is an SSL implementation written by Eric Young (eay@cryptsoft.com). The implementation was written so as to conform with Netscapes SSL. This library is free for commercial and non-commercial use as long as the following conditions are aheared to. The following conditions apply to all code found in this distribution, be it the RC4, RSA, lhash, DES, etc., code; not just the SSL code. The SSL documentation included with this distribution is covered by the same copyright terms except that the holder is Tim Hudson (tjh@cryptsoft.com). Copyright remains Eric Young’s, and as such any Copyright notices in the code are not to be removed. If this package is used in a product, Eric Young should be given attribution as the author of the parts of the library used. This can be in the form of a textual message at program startup or in documentation (online or textual) provided with the package. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: 1. Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer. 2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. 3. All advertising materials mentioning features or use of this software must display the following acknowledgement: “This product includes cryptographic software written by Eric Young (eay@cryptsoft.com)” The word ‘cryptographic’ can be left out if the rouines from the library being used are not cryptographic related :-). 4. If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: “This product includes software written by Tim Hudson (tjh@cryptsoft.com)” THIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. The licence and distribution terms for any publically available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and put under another distribution licence [including the GNU Public Licence.] |
| zlib License | Base64: https://cocoapods.org/pods/Base64nl minizip: http://tracker.debian.org/pkg/minizip | The zlib/libpng License Copyright (c) This software is provided ‘as-is’, without any express or implied warranty. In no event will the authors be held liable for any damages arising from the use of this software. Permission is granted to anyone to use this software for any purpose, including commercial applications, and to alter it and redistribute it freely, subject to the following restrictions: 1. The origin of this software must not be misrepresented; you must not claim that you wrote the original software. If you use this software in a product, an acknowledgment in the product documentation would be appreciated but is not required. 2. Altered source versions must be plainly marked as such, and must not be misrepresented as being the original software. 3. This notice may not be removed or altered from any source distribution. |
SingleID_MobileApp_Flutter-UMA
The following sets forth attribution notices for third party software that may be contained in portions of this product. If you have any questions, please contact global.cs@samsung.com
| License | Open Source Component | License Text |
|---|---|---|
| Apache License 2.0 | Android Support Library media compat, Converter: Gson, Adapter: RxJava 2, Android Support Library core utils, Android Arch-Runtime, Guava (Google Common Libraries), Android Support AnimatedVectorDrawable, Android Support Library core UI, Android Support Library Custom View - androidx.customview:customview, Android Lifecycle LiveData, OkHttp, Gson, android.support.annotation, Android Support Library Custom View - androidx.swiperefreshlayout:swiperefreshlayout, Android Support Library v4, OkHttp, Android Lifecycle ViewModel, Commons Lang, rxjava, Android Support Library compat, Roboto Fonts, Apache Commons Collections, Android Support Library v4, Android Lifecycle LiveData Core, RxAndroid, joda-time, okio, Apache Commons IO, JetBrains/java-annotations, Android AppCompat Library v7, Android Support Library Collections, Android Support VectorDrawable, Kotlin Stdlib, Android Lifecycle-Common, Android Support Library loader, Retrofit | Apache License Version 2.0, January 2004 http://www.apache.org/licenses/ TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION 1. Definitions. “License” shall me an the terms and conditions for use, reproduction, and distribution as defined by Sections 1 through 9 of this document. “Licensor” shall mean the copyright owner or entity authorized by the copyright owner that is granting the License. “Legal Entity” shall mean the union of the acting entity and all other entities that control, are controlled by, or are under common control with that entity. For the purposes of this definition, “control” means (i) the power, direct or indirect, to cause the direction or management of such entity, whether by contract or otherwise, or (ii) ownership of fifty percent (50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity. “You” (or “Your”) shall mean an individual or Legal Entity exercising permissions granted by this License. “Source” form shall mean the preferred form for making modifications, including but not limited to software source code, documentation source, and configuration files. “Object” form shall mean any form resulting from mechanical transformation or translation of a Source form, including but not limited to compiled object code, generated documentation, and conversions to other media types. “Work” shall mean the work of authorship, whether in Source or Object form, made available under the License, as indicated by a copyright notice that is included in or attached to the work (an example is provided in the Appendix below). “Derivative Works” shall mean any work, whether in Source or Object form, that is based on (or derived from) the Work and for which the editorial revisions, annotations, elaborations, or other modifications represent, as a whole, an original work of authorship. For the purposes of this License, Derivative Works shall not include works that remain separable from, or merely link (or bind by name) to the interfaces of, the Work and Derivative Works thereof. “Contribution” shall mean any work of authorship, including the original version of the Work and any modifications or additions to that Work or Derivative Works thereof, that is intentionally submitted to Licensor for inclusion in the Work by the copyright owner or by an individual or Legal Entity authorized to submit on behalf of the copyright owner. For the purposes of this definition, “submitted” means any form of electronic, verbal, or written communication sent to the Licensor or its representatives, including but not limited to communication on electronic mailing lists, source code control systems, and issue tracking systems that are managed by, or on behalf of, the Licensor for the purpose of discussing and improving the Work, but excluding communication that is conspicuously marked or otherwise designated in writing by the copyright owner as “Not a Contribution.” “Contributor” shall mean Licensor and any individual or Legal Entity on behalf of whom a Contribution has been received by Licensor and subsequently incorporated within the Work. 2. Grant of Copyright License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable copyright license to reproduce, prepare Derivative Works of, publicly display, publicly perform, sublicense, and distribute the Work and such Derivative Works in Source or Object form. 3. Grant of Patent License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable (except as stated in this section) patent license to make, have made, use, offer to sell, sell, import, and otherwise transfer the Work, where such license applies only to those patent claims licensable by such Contributor that are necessarily infringed by their Contribution(s) alone or by combination of their Contribution(s) with the Work to which such Contribution(s) was submitted. If You institute patent litigation against any entity (including a cross-claim or counterclaim in a lawsuit) alleging that the Work or a Contribution incorporated within the Work constitutes direct or contributory patent infringement, then any patent licenses granted to You under this License for that Work shall terminate as of the date such litigation is filed. 4. Redistribution. You may reproduce and distribute copies of the Work or Derivative Works thereof in any medium, with or without modifications, and in Source or Object form, provided that You meet the following conditions: a. You must give any other recipients of the Work or Derivative Works a copy of this License; and b. You must cause any modified files to carry prominent notices stating that You changed the files; and c. You must retain, in the Source form of any Derivative Works that You distribute, all copyright, patent, trademark, and attribution notices from the Source form of the Work, excluding those notices that do not pertain to any part of the Derivative Works; and d. If the Work includes a “NOTICE” text file as part of its distribution, then any Derivative Works that You distribute must include a readable copy of the attribution notices contained within such NOTICE file, excluding those notices that do not pertain to any part of the Derivative Works, in at least one of the following places: within a NOTICE text file distributed as part of the Derivative Works; within the Source form or documentation, if provided along with the Derivative Works; or, within a display generated by the Derivative Works, if and wherever such third-party notices normally appear. The contents of the NOTICE file are for informational purposes only and do not modify the License. You may add Your own attribution notices within Derivative Works that You distribute, alongside or as an addendum to the NOTICE text from the Work, provided that such additional attribution notices cannot be construed as modifying the License. You may add Your own copyright statement to Your modifications and may provide additional or different license terms and conditions for use, reproduction, or distribution of Your modifications, or for any such Derivative Works as a whole, provided Your use, reproduction, and distribution of the Work otherwise complies with the conditions stated in this License. 5. Submission of Contributions. Unless You explicitly state otherwise, any Contribution intentionally submitted for inclusion in the Work by You to the Licensor shall be under the terms and conditions of this License, without any additional terms or conditions. Notwithstanding the above, nothing herein shall supersede or modify the terms of any separate license agreement you may have executed with Licensor regarding such Contributions. 6. Trademarks. This License does not grant permission to use the trade names, trademarks, service marks, or product names of the Licensor, except as required for reasonable and customary use in describing the origin of the Work and reproducing the content of the NOTICE file. 7. Disclaimer of Warranty. Unless required by applicable law or agreed to in writing, Licensor provides the Work (and each Contributor provides its Contributions) on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied, including, without limitation, any warranties or conditions of TITLE, NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A PARTICULAR PURPOSE. You are solely responsible for determining the appropriateness of using or redistributing the Work and assume any risks associated with Your exercise of permissions under this License. 8. Limitation of Liability. In no event and under no legal theory, whether in tort (including negligence), contract, or otherwise, unless required by applicable law (such as deliberate and grossly negligent acts) or agreed to in writing, shall any Contributor be liable to You for damages, including any direct, indirect, special, incidental, or consequential damages of any character arising as a result of this License or out of the use or inability to use the Work (including but not limited to damages for loss of goodwill, work stoppage, computer failure or malfunction, or any and all other commercial damages or losses), even if such Contributor has been advised of the possibility of such damages. 9. Accepting Warranty or Additional Liability. While redistributing the Work or Derivative Works thereof, You may choose to offer, and charge a fee for, acceptance of support, warranty, indemnity, or other liability obligations and/or rights consistent with this License. However, in accepting such obligations, You may act only on Your own behalf and on Your sole responsibility, not on behalf of any other Contributor, and only if You agree to indemnify, defend, and hold each Contributor harmless for any liability incurred by, or claims asserted against, such Contributor by reason of your accepting any such warranty or additional liability. END OF TERMS AND CONDITIONS APPENDIX: How to apply the Apache License to your work To apply the Apache License to your work, attach the following boilerplate notice, with the fields enclosed by brackets “[]” replaced with your own identifying information. (Don’t include the brackets!) The text should be enclosed in the appropriate comment syntax for the file format. We also recommend that a file or class name and description of purpose be included on the same “printed page” as the copyright notice for easier identification within third-party archives. Copyright [yyyy] [name of copyright owner] Licensed under the Apache License, Version 2.0 (the “License”); you may not use this file except in compliance with the License. You may obtain a copy of the License at http://www.apache.org/licenses/LICENSE-2.0 Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an “AS IS” BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License. |
| Creative Commons Zero v1.0 Universal | reactive-streams: http://www.reactive-streams.org/ | Creative Commons CC0 1.0 Universal Creative Commons Legal Code CC0 1.0 Universal CREATIVE COMMONS CORPORATION IS NOT A LAW FIRM AND DOES NOT PROVIDE LEGAL SERVICES. DISTRIBUTION OF THIS DOCUMENT DOES NOT CREATE AN ATTORNEY-CLIENT RELATIONSHIP. CREATIVE COMMONS PROVIDES THIS INFORMATION ON AN “AS-IS” BASIS. CREATIVE COMMONS MAKES NO WARRANTIES REGARDING THE USE OF THIS DOCUMENT OR THE INFORMATION OR WORKS PROVIDED HEREUNDER, AND DISCLAIMS LIABILITY FOR DAMAGES RESULTING FROM THE USE OF THIS DOCUMENT OR THE INFORMATION OR WORKS PROVIDED HEREUNDER. Statement of Purpose The laws of most jurisdictions throughout the world automatically confer exclusive Copyright and Related Rights (defined below) upon the creator and subsequent owner(s) (each and all, an “owner”) of an original work of authorship and/or a database (each, a “Work”). Certain owners wish to permanently relinquish those rights to a Work for the purpose of contributing to a commons of creative, cultural and scientific works (“Commons”) that the public can reliably and without fear of later claims of infringement build upon, modify, incorporate in other works, reuse and redistribute as freely as possible in any form whatsoever and for any purposes, including without limitation commercial purposes. These owners may contribute to the Commons to promote the ideal of a free culture and the further production of creative, cultural and scientific works, or to gain reputation or greater distribution for their Work in part through the use and efforts of others. For these and/or other purposes and motivations, and without any expectation of additional consideration or compensation, the person associating CC0 with a Work (the “Affirmer”), to the extent that he or she is an owner of Copyright and Related Rights in the Work, voluntarily elects to apply CC0 to the Work and publicly distribute the Work under its terms, with knowledge of his or her Copyright and Related Rights in the Work and the meaning and intended legal effect of CC0 on those rights. 1. Copyright and Related Rights. A Work made available under CC0 may be protected by copyright and related or neighboring rights (“Copyright and Related Rights”). Copyright and Related Rights include, but are not limited to, the following: i. the right to reproduce, adapt, distribute, perform, display, communicate, and translate a Work; ii. moral rights retained by the original author(s) and/or performer(s); iii. publicity and privacy rights pertaining to a person’s image or likeness depicted in a Work; iv. rights protecting against unfair competition in regards to a Work, subject to the limitations in paragraph 4(a), below; v. rights protecting the extraction, dissemination, use and reuse of data in a Work; vi. database rights (such as those arising under Directive 96/9/EC of the European Parliament and of the Council of 11 March 1996 on the legal protection of databases, and under any national implementation thereof, including any amended or successor version of such directive); and vii. other similar, equivalent or corresponding rights throughout the world based on applicable law or treaty, and any national implementations thereof. 2. Waiver. To the greatest extent permitted by, but not in contravention of, applicable law, Affirmer hereby overtly, fully, permanently, irrevocably and unconditionally waives, abandons, and surrenders all of Affirmer’s Copyright and Related Rights and associated claims and causes of action, whether now known or unknown (including existing as well as future claims and causes of action), in the Work i. in all territories worldwide, ii. for the maximum duration provided by applicable law or treaty (including future time extensions), iii. in any current or future medium and for any number of copies, and iv. for any purpose whatsoever, including without limitation commercial, advertising or promotional purposes (the “Waiver”). Affirmer makes the Waiver for the benefit of each member of the public at large and to the detriment of Affirmer’s heirs and successors, fully intending that such Waiver shall not be subject to revocation, rescission, cancellation, termination, or any other legal or equitable action to disrupt the quiet enjoyment of the Work by the public as contemplated by Affirmer’s express Statement of Purpose. 3. Public License Fallback. Should any part of the Waiver for any reason be judged legally invalid or ineffective under applicable law, then the Waiver shall be preserved to the maximum extent permitted taking into account Affirmer’s express Statement of Purpose. In addition, to the extent the Waiver is so judged Affirmer hereby grants to each affected person a royalty-free, non transferable, non sublicensable, non exclusive, irrevocable and unconditional license to exercise Affirmer’s Copyright and Related Rights in the Work i. in all territories worldwide, ii. for the maximum duration provided by applicable law or treaty (including future time extensions), iii. in any current or future medium and for any number of copies, and iv. for any purpose whatsoever, including without limitation commercial, advertising or promotional purposes (the “License”). The License shall be deemed effective as of the date CC0 was applied by Affirmer to the Work. Should any part of the License for any reason be judged legally invalid or ineffective under applicable law, such partial invalidity or ineffectiveness shall not invalidate the remainder of the License, and in such case Affirmer hereby affirms that he or she will not i. exercise any of his or her remaining Copyright and Related Rights in the Work or ii. assert any associated claims and causes of action with respect to the Work, in either case contrary to Affirmer’s express Statement of Purpose. 4. Limitations and Disclaimers. a. No trademark or patent rights held by Affirmer are waived, abandoned, surrendered, licensed or otherwise affected by this document. b. Affirmer offers the Work as-is and makes no representations or warranties of any kind concerning the Work, express, implied, statutory or otherwise, including without limitation warranties of title, merchantability, fitness for a particular purpose, non infringement, or the absence of latent or other defects, accuracy, or the present or absence of errors, whether or not discoverable, all to the greatest extent permissible under applicable law. c. Affirmer disclaims responsibility for clearing rights of other persons that may apply to the Work or any use thereof, including without limitation any person’s Copyright and Related Rights in the Work. Further, Affirmer disclaims responsibility for obtaining any necessary consents, permissions or other rights required for any use of the Work. Affirmer understands and acknowledges that Creative Commons is not a party to this document and has no duty or obligation with respect to this CC0 or use of the Work. |
| ISC License | gotham-fonts: https://www.npmjs.org/package/gotham-fonts | ISC License (ISCL) gotham-fonts : Copyright @ Bogdan Pop Permission to use, copy, modify, and/or distribute this software for any purpose with or without fee is hereby granted, provided that the above copyright notice and this permission notice appear in all copies. THE SOFTWARE IS PROVIDED “AS IS” AND THE AUTHOR DISCLAIMS ALL WARRANTIES WITH REGARD TO THIS SOFTWARE INCLUDING ALL IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS. IN NO EVENT SHALL THE AUTHOR BE LIABLE FOR ANY SPECIAL, DIRECT, INDIRECT, OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER IN AN ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE. |
| MIT License | Xamarin.Android.Support.VersionedParcelable: http://www.nuget.org/packages/Xamarin.Android.Support.VersionedParcelable Xamarin.Android.Support.CoordinaterLayout: http://www.nuget.org/packages/Xamarin.Android.Support.CoordinaterLayout The Legion of the Bouncy Castle: http://www.bouncycastle.org/index.html Xamarin.Android.Support.SlidingPaneLayout: http://www.nuget.org/packages/Xamarin.Android.Support.SlidingPaneLayout XamarinLibrary.Xamarin.Android.Support.Multidex: https://www.nuget.org/packages/XamarinLibrary.Xamarin.Android.Support.Multidex Xamarin.Android.Support.Interpolator: http://www.nuget.org/packages/Xamarin.Android.Support.Interpolator Xamarin.Android.Support.LocalBroadcastManager: http://www.nuget.org/packages/Xamarin.Android.Support.LocalBroadcastManager Xamarin.Android.Support.DrawerLayout: http://www.nuget.org/packages/Xamarin.Android.Support.DrawerLayout @fontsource/Montserrat: https://www.npmjs.org/package/@fontsource/montserrat Xamarin.Android.Support.DocumentFile: http://www.nuget.org/packages/Xamarin.Android.Support.DocumentFile Xamarin.Android.Support.Print: http://www.nuget.org/packages/Xamarin.Android.Support.Print Xamarin.Android.Support.AsyncLayoutInflater: http://www.nuget.org/packages/Xamarin.Android.Support.AsyncLayoutInflater SLF4J API Module: http://www.slf4j.org Xamarin.Android.Support.ViewPager: http://www.nuget.org/packages/Xamarin.Android.Support.ViewPager secure-random: http://github.com/avodonosov/secure-random/ Xamarin.Android.Support.CursorAdapter: http://www.nuget.org/packages/Xamarin.Android.Support.CursorAdapter | The MIT License Xamarin.Android.Support.VersionedParcelable: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.CoordinaterLayout: Copyright (c) .NET Foundation Contributors All rights reserved. The Legion of the Bouncy Castle: Copyright (c) 2000-2023 The Legion of the Bouncy Castle Inc. (https://www.bouncycastle.org) All rights reserved. Xamarin.Android.Support.SlidingPaneLayout: Copyright (c) .NET Foundation Contributors All rights reserved. XamarinLibrary.Xamarin.Android.Support.Multidex: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.Interpolator: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.LocalBroadcastManager: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.DrawerLayout: Copyright (c) .NET Foundation Contributors All rights reserved. @fontsource/Montserrat: Copyright (c) 2023 fontsource All rights reserved. Xamarin.Android.Support.DocumentFile: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.Print: Copyright (c) .NET Foundation Contributors All rights reserved. Xamarin.Android.Support.AsyncLayoutInflater: Copyright (c) .NET Foundation Contributors All rights reserved. SLF4J API Module: Copyright © 2004-2023 QOS.ch All rights reserved. Xamarin.Android.Support.ViewPager: Copyright (c) .NET Foundation Contributors All rights reserved. secure-random: Copyright (C) 2011 by Anton Vodonosov (avodonosov@yandex.ru). All rights reserved. Xamarin.Android.Support.CursorAdapter: Copyright (c) .NET Foundation Contributors All rights reserved. Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. |
| SIL Open Font License 1.1 | @fontsource/rubik, https://www.npmjs.org/package/@fontsource/rubik @fontsource/montserrat https://www.npmjs.org/package/@fontsource/montserrat | SIL OPEN FONT LICENSE Version 1.1 - 26 February 2007 PREAMBLE The goals of the Open Font License (OFL) are to stimulate worldwide development of collaborative font projects, to support the font creation efforts of academic and linguistic communities, and to provide a free and open framework in which fonts may be shared and improved in partnership with others. The OFL allows the licensed fonts to be used, studied, modified and redistributed freely as long as they are not sold by themselves. The fonts, including any derivative works, can be bundled, embedded, redistributed and/or sold with any software provided that any reserved names are not used by derivative works. The fonts and derivatives, however, cannot be released under any other type of license. The requirement for fonts to remain under this license does not apply to any document created using the fonts or their derivatives. DEFINITIONS “Font Software” refers to the set of files released by the Copyright Holder(s) under this license and clearly marked as such. This may include source files, build scripts and documentation. “Reserved Font Name” refers to any names specified as such after the copyright statement(s). “Original Version” refers to the collection of Font Software components as distributed by the Copyright Holder(s). “Modified Version” refers to any derivative made by adding to, deleting, or substituting — in part or in whole — any of the components of the Original Version, by changing formats or by porting the Font Software to a new environment. “Author” refers to any designer, engineer, programmer, technical writer or other person who contributed to the Font Software. PERMISSION & CONDITIONS Permission is hereby granted, free of charge, to any person obtaining a copy of the Font Software, to use, study, copy, merge, embed, modify, redistribute, and sell modified and unmodified copies of the Font Software, subject to the following conditions: 1. Neither the Font Software nor any of its individual components, in Original or Modified Versions, may be sold by itself. 2. Original or Modified Versions of the Font Software may be bundled, redistributed and/or sold with any software, provided that each copy contains the above copyright notice and this license. These can be included either as stand-alone text files, human-readable headers or in the appropriate machine-readable metadata fields within text or binary files as long as those fields can be easily viewed by the user. 3. No Modified Version of the Font Software may use the Reserved Font Name(s) unless explicit written permission is granted by the corresponding Copyright Holder. This restriction only applies to the primary font name as presented to the users. 4. The name(s) of the Copyright Holder(s) or the Author(s) of the Font Software shall not be used to promote, endorse or advertise any Modified Version, except to acknowledge the contribution(s) of the Copyright Holder(s) and the Author(s) or with their explicit written permission. 5. The Font Software, modified or unmodified, in part or in whole, must be distributed entirely under this license, and must not be distributed under any other license. The requirement for fonts to remain under this license does not apply to any document created using the Font Software. TERMINATION This license becomes null and void if any of the above conditions are not met. DISCLAIMER THE FONT SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO ANY WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OF COPYRIGHT, PATENT, TRADEMARK, OR OTHER RIGHT. IN NO EVENT SHALL THE COPYRIGHT HOLDER BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, INCLUDING ANY GENERAL, SPECIAL, INDIRECT, INCIDENTAL, OR CONSEQUENTIAL DAMAGES, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF THE USE OR INABILITY TO USE THE FONT SOFTWARE OR FROM OTHER DEALINGS IN THE FONT SOFTWARE. |
9.5.2.1.6 - Open API guides
SingleID Open API Guides
To use the Samsung Cloud Platform SingleID Open API, the system must first be registered in Applications. You must obtain a JWT token with the registered system information and include the JWT token in the HTTP header when calling the Samsung Cloud Platform SingleID Open API.
API Call Method
- Call with the token (JWT Token) value included in the HTTP header
- Set the access token header name to Authorization, and set the access token type value to Bearer - set the JWT Token value after the Bearer string.
- Test environment information
- domain :
- Internal: stg-scloud.iam.samsung.net
- External: stg2-cloud.singleid.samsung.net
- tenant-name : test-tenant
- domain :
- Test Swagger UI URL
API List
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | get MFA Token | https://{domain}/{tenant-name}/common-api/open/v1.1/asis/{tenant-name}/user/mfa/token/authentication | GET | MFA token issuance |
| Portal Common | OTP Send | https://{domain}/{tenant-name}/common-api/open/v1.1/asis/otp/send | POST | Generate OTP based on the authentication type (email, sms, msg) |
| Portal Common | OTP Validation | https://{domain}/{tenant-name}/common-api/open/v1.1/asis/otp/validate | POST | OTP verification |
| Portal Common | MFA Consumer Request | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/request | GET | MFA request |
| Portal Common | MFA Consumer Request | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/request | POST | MFA request |
| Tenant Admin Portal | Send Email about Anomaly Detection | https://{domain}/{tenant-name}/admin-api/open/v1.1/emails/anomalyDetection | POST | Send email to the user when abnormal authentication activity is detected |
| Tenant Admin Portal | Send Email about New Sign-in Environment | https://{domain}/{tenant-name}/admin-api/open/v1.1/emails/newSignInEnvironment | POST | Send user verification email upon logging into a new environment |
| User Portal | Get User | https://{domain}/{tenant-name}/user-api/open/v1.1/users/{username} | GET | User name, email, preferred language, timezone lookup |
| User Portal | Get User Profile Image | https://{domain}/{tenant-name}/user-api/open/v1.1/users/image/{username} | GET | Retrieve user profile image |
| User Portal | Create account assignment list | https://{domain}/{tenant-name}/user-api/1.0/scp-auth/create | POST | Create user SCP permission |
| User Portal | Delete account assignment list | https://{domain}/{tenant-name}/user-api/1.0/scp-auth/delete | POST | Delete user SCP permission |
| User Portal | Get account assignment list | https://{domain}/{tenant-name}/user-api/1.0/scp-auth/list | GET | User SCP permission lookup |
| User Portal | Search User | https://{domain}/{tenant-name}/user-api/1.0/scp-user/list | GET | Search SCP target user |
| Portal Common | MFA Consumer Request | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/request/mfa | POST | MFA request (including device) |
| Portal Common | MFA Consumer Verification | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/verification/mfa | POST | MFA verification (including equipment) |
API Specification - get MFA Token(Portal Common)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | get MFA Token | https://{domain}/{tenant-name}/common-api/open/v1.1/asis/{tenant-name}/user/mfa/token/authentication | GET | MFA Token issuance |
Request Parameters
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| Tenant name | tenant-name | Y | Path | String | test-tenant | |
| username | userName | Y | query | String | mkdir.kim | |
| Protocol | protocol | Y | query | String | uma-uaf | |
| sessionDataKey | sessionDataKey | N | query | String | sessionDataKey1 | |
| redirectUrl | redirectUrl | N | query | String | redirectUrl1 | |
| errorRedirectUrl | errorRedirectUrl | N | query | String | errorRedirectUrl1 | |
| params | params | N | query | String | params1 | |
| language | language | N | query | String | ko |
Response Parameters
| Properties (Result) | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| Result | result | String | SUCCESS | |
| Result value | value | Object | {"token": "eyJpc3MiOiJodHRwczov...","serviceUri": "/ua/MPHTOCHW5I/de6f67d0-8bec-46ac-bf53-16ef00eb2066/dgauth/mfa"} |
Sample
| Request | Response |
|---|---|
curl -X POST "https://stg-scloud.singleid.samsung.net:443/stg4/user-api/1.0/scp-auth/delete" -H "accept: application/json"-H "apiKey: {apiKey}" INPUT JSON{ "instanceId": "instnace-01", "permissionSetId": "PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf", "principalId": "singleid.test001", "principalType": "USER", "targetId": "PROJECT-ka2tfhLHsweVwm4BrR1rae", "targetType": "PROJECT" } | { "instanceId": "instnace-01", "permissionSetId": "PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf", "principalId": "singleid.test001", "principalType": "USER", "targetId": "PROJECT-ka2tfhLHsweVwm4BrR1rae", "targetType": "PROJECT" "status": "SUCCESS", "createdDate": "2024-04-03T01:58:46.538Z", "failureReason": "" } |
Error Code
| HTTP Response Code | Error Code | Error Message | Action Required |
|---|---|---|---|
| 400 | N/A | N/A | userName verification required |
API Specification - OTP Send(Portal Common)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | OTP Send | https://{domain}/{tenant-name}/common-api/open/v1.1/asis/otp/send | POST | Generate OTP based on authentication type (email, sms, msg) |
Request Parameters
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| locale | locale | Y | body | String | ko | |
| Authentication type | type | Y | body | String | email, sms, msg | |
| userName | userName | Y | body | String | gildong.hong |
Response Parameters
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| otpString | otpString | String | 0000000c5bb286c166530ac928d0bdf1f0894ed3a6d891eb3ab7ec89fc9faef7817b9f2f02f8c89ae91558cdc9afec94d6bede93a91d9825f4fe14dc2a282f6456d09f823d194570bc91b353830826e69d5f818172c12dbdb7b524 |
Sample
| Request | Response |
|---|---|
ccurl -X POST "https://localhost:7443/open/v1.1/asis/otp/send" -H "accept: */*" -H "Content-Type: application/json" -d "{\"locale\":\"ko\",\"type\":\"email\",\"userName\":\"gildong.hong\"}" | { "otpString": 0000000c5bb286c166530ac928d0bdf1f0894ed3a6d891eb3ab7ec89fc9faef7817b9f2f02f8c89ae91558cdc9afec94d6bede93a91d9825f4fe14dc2a282f6456d09f823d194570bc91b353830826e69d5f818172c12dbdb7b524} |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 404 | N/A | N/A | When the user does not exist |
| 429 | N/A | N/A | Duplicate call within 60 seconds |
| 500 | N/A | N/A | Server error, check the error message and contact the administrator |
API Specification - OTP Validation(Portal Common)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | OTP Validation | https://{domain}/{tenant-name}/common-api/open/v1.1/asis/otp/validate | POST | Validate the OTP. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| userName | userName | Y | Body | String | gildong.hong | |
| otp(6 digits) | otp | Y | Body | String | 121215 | |
| checkValue | checkValue | Y | Body | String | 0000000c5bb286c166530ac928d0bdf1f0894ed3a6d891eb3ab7ec89fc9faef7817b9f2f02f8c89ae91558cdc9afec94d6bede93a91d9825f4fe14dc2a282f6456d09f823d194570bc91b353830826e69d5f818172c12dbdb7b524 | The otpString value received in the response from sendOtp |
| Authentication type | type | Y | Body | String | email, sms, msg |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| Result | result | String | SUCCESS |
Sample
| Request | Response |
|---|---|
| curl -X POST “https://localhost:7443/open/v1.1/asis/otp/validate” -H “accept: /” -H “Content-Type: application/json” -d “{"checkValue":"0000000c5bb286c166530ac928d0bdf1f0894ed3a6d891eb3ab7ec89fc9faef7817b9f2f02f8c89ae91558cdc9afec94d6bede93a91d9825f4fe14dc2a282f6456d09f823d194570bc91b353830826e69d5f818172c12dbdb7b524","otp":"791462","type":"email","userName":"gildong.hong"}” | { “result”: “success” } |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 400 | N/A | N/A | When the OTP is entered incorrectly |
| 404 | N/A | N/A | When the user does not exist |
| 410 | N/A | N/A | When the OTP expires |
| 429 | N/A | N/A | When API failure calls exceed 10 times |
| 500 | N/A | N/A | Server error, check the error message and contact the administrator |
API Specification - MFA Consumer Reques(Portal Common)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | MFA Consumer Request | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/request | GET | Request MFA. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| JWT Token | jwtTokenRequest | Y | query | String | eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1aWQiOiJqaW5vbmUua2ltIiwiZGlzcGxheVVpZCI6Imppbm9uZS5raW1Ac2Ftc3VuZy5jb20iLCJlbWFpbCI6ImxUL3p4WngxNk81REo2SU91Z2VnRW9wVGk2eDh5bkxXY3NHLzRaWFE2TVlDSzNQV05oTS9hQUFnQmpkSEJMN1hkcFA2Y25jNCIsIm1vYmlsZSI6InlkVU54ZVl6YkNOY0xEYnFqN01rL2ZCdFcvaHZoRE1Bbm9lNzhRVTRvQTAzZUlwN2NsOVFpSGFoIiwicnRuIjoiaHR0cHM6Ly9zdGcxLWNsb3VkLnNpbmdsZWlkLnNhbXN1bmcubmV0L21vY2svcW1zL21mYS1jb25zdW1lci9yZXN1bHQiLCJyZXEiOiI3NjFlZmQ1Mi05N2QwLTQ1MWYtOWNmOS1jZjg2NzQwZTdjYTMiLCJzeXMiOiI4MDE0ODYyMS04MjZmLTQ5YmUtOGM5ZS0zMTE1ZTUzMDFlMWIiLCJuYmYiOjE3MTIwMjkxNDIsImV4cCI6MTcxNDYyMTE0MiwiaWF0IjoxNzEyMDI5MTQyfQ.-FWTK4IJsu8AonfJTTq7_OA1qAh-9FU89iC1JZcRg_c | Token original data sample{ "sys":"test-system", "req":"761efd52-97d0-451f-9cf9-cf86740e7ca3", "uid":"gildong.hong", "rtn":"https://test.com/mfa/response","email":"gildong.hong@samsung.com","mobile":"+82-1012345678", "nbf": 1698232068, "exp": 1698239268, "iat": 1698232068, "displayUid": "gildong.hong@samsung.com" } |
Response
Redirects to the MFA authentication page. By default, the response token is transmitted using POST, but to transmit it using GET (query), add the following parameter to the request token.
- returnMethod: get
Sample
| Request | Response |
|---|---|
curl -X GET "https://stg2-cloud.singleid.samsung.net/test-tenant/common-api/open/v1.1/mfa/request?jwtTokenRequest=eyJhbGciOiJIUzI1NiJ9.eyJzeXMiOiJ0ZXN0LXN5c3RlbSIsInJlcSI6Ijc2MWVmZDUyLTk3ZDAtNDUxZi05Y2Y5LWNmODY3NDBlN2NhMyIsInVpZCI6Imppbm9uZS5raW0iLCJydG4iOiJodHRwczovL3Rlc3QuY29tL21mYS9yZXNwb25zZSIsIm5iZiI6MTY5ODIzMjA2OCwiZXhwIjoxNjk4MjM5MjY4LCJpYXQiOjE2OTgyMzIwNjh9.cDgKMHIINaHhBiyAd_OIlVvQwmUs0QaXH_RfJ8B_KdY" | Page navigation |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 400 | N/A | N/A | Check token data. |
API Specification - MFA Consumer Reques(Portal Common)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | MFA Consumer Request | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/request | POST | Request MFA. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| JWT Token | jwtTokenRequest | Y | query | String | eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1aWQiOiJqaW5vbmUua2ltIiwiZGlzcGxheVVpZCI6Imppbm9uZS5raW1Ac2Ftc3VuZy5jb20iLCJlbWFpbCI6ImxUL3p4WngxNk81REo2SU91Z2VnRW9wVGk2eDh5bkxXY3NHLzRaWFE2TVlDSzNQV05oTS9hQUFnQmpkSEJMN1hkcFA2Y25jNCIsIm1vYmlsZSI6InlkVU54ZVl6YkNOY0xEYnFqN01rL2ZCdFcvaHZoRE1Bbm9lNzhRVTRvQTAzZUlwN2NsOVFpSGFoIiwicnRuIjoiaHR0cHM6Ly9zdGcxLWNsb3VkLnNpbmdsZWlkLnNhbXN1bmcubmV0L21vY2svcW1zL21mYS1jb25zdW1lci9yZXN1bHQiLCJyZXEiOiI3NjFlZmQ1Mi05N2QwLTQ1MWYtOWNmOS1jZjg2NzQwZTdjYTMiLCJzeXMiOiI4MDE0ODYyMS04MjZmLTQ5YmUtOGM5ZS0zMTE1ZTUzMDFlMWIiLCJuYmYiOjE3MTIwMjkxNDIsImV4cCI6MTcxNDYyMTE0MiwiaWF0IjoxNzEyMDI5MTQyfQ.-FWTK4IJsu8AonfJTTq7_OA1qAh-9FU89iC1JZcRg_c | Token original data sample{ "sys":"test-system", "req":"761efd52-97d0-451f-9cf9-cf86740e7ca3", "uid":"gildong.hong", "rtn":"https://test.com/mfa/response","email":"gildong.hong@samsung.com","mobile":"+82-1012345678", "nbf": 1698232068, "exp": 1698239268, "iat": 1698232068, "displayUid": "gildong.hong@samsung.com" } |
| MFA Consumer Home move status | registerFlag | Y | query | Boolean | true | Determines whether to navigate to the MFA Consumer Home. If true, it navigates to the MFA Consumer Home. |
Response
- When registerFlag = true: Redirect to MFA Consumer Home.
- When registerFlag = false: Redirect to the MFA authentication page.
Sample
| Request | Response |
|---|---|
curl -X POST "https://stg2-cloud.singleid.samsung.net/test-tenant/common-api/open/v1.1/mfa/request?jwtTokenRequest=eyJhbGciOiJIUzI1NiJ9.eyJzeXMiOiJ0ZXN0LXN5c2t5bSIsInJlcSI6Ijc2MWVmZDUyLTk3ZDAtNDUxZi05Y2Y5LWNmODY3NDBlN2NhMyIsInVpZCI6Imppbm9uZS5raW0iLCJydG4iOiJodHRwczovL3Rlc3QuY29tL21mYS9yZXNwb25zZSIsIm5iZiI6MTY5ODIzMjA2OCwiZXhwIjoxNjk4MjM5MjY4LCJpYXQiOjE2OTgyMzIwNjh9.cDgKMHIINaHhBiyAd_OIlVvQwmUs0QaXH_RfJ8B_KdY®isterFlag=true" | Page navigation |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 400 | N/A | N/A | Checking token data. |
API Specification - Send Email about Anomaly Detection(Tenant Admin Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Tenant Admin Portal | Send Email about Anomaly Detection | https://{domain}/{tenant-name}/admin-api/open/v1.1/emails/anomalyDetection | POST | An email is sent when a user is detected engaging in abnormal authentication behavior. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| User IP | accessIP | Y | Body | String | 10.0.0.0 | |
| Registration time | detectionTime | Y | Body | String | 2023-09-10 23:01:01 | |
| Y | Body | String | gildong.hong@samsung.com | |||
| User environment | environment | Y | Body | String | PC / Window / Chrome | |
| Language | language | Y | Body | String | ko | |
| Network environment (internal/external) | location | Y | Body | String | Internal | |
| Detection rule number | rule | Y | Body | String | P001 | |
| User account | username | Y | Body | String | gildong.hong | |
| Authentication unique value | envGuid | Y | Body | String | d8b09752-405a-4d52-8605-bff9aa3f4741 |
Response Parameter
| Properties | Data Type | Sample Data | Note |
|---|---|---|---|
| Result | boolean | true | true when mail sending succeeds / false when it fails |
Sample
| Request | Response |
|---|---|
curl -X POST "https://stg1-cloud.singleid.samsung.net:443/test-tenant/admin-api/open/v1.1/emails/anomalyDetection" -H "accept: application/json" -H "Content-Type: application/json" -d "{\"accessIP\":\"10.0.0.0\",\"detectionTime\":\"2023-09-10 23:01:01\",\"email\":\"gildong.hong@samsung.com\",\"environment\":\"PC / Window / Chrome\",\"language\":\"ko\",\"location\":\"Internal\",\"rule\":\"P001\",\"username\":\"gildong.hong\",\"envGuid\":\"d8b09752-405a-4d52-8605-bff9aa3f4741\"}" | true |
Error code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 400 | N/A | N/A | Bad Request |
| 403 | N/A | N/A | Forbidden |
| 500 | N/A | N/A | Internal Server Error |
API Specification - Send Email about New Sign-in Environment(Tenant Admin Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Tenant Admin Portal | Send Email about New Sign-in Environment | https://{domain}/{tenant-name}/admin-api/open/v1.1/emails/newSignInEnvironment | POST | When a user logs in to a new environment, a notification is sent to the user and an email is dispatched to confirm the environment registration. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| User IP | accessIP | Y | Body | String | 10.0.0.0 | |
| Registration time | detectionTime | Y | Body | String | 2023-09-10 23:01:01 | |
| Y | Body | String | gildong.hong@samsung.com | |||
| User environment | environment | Y | Body | String | PC / Window / Chrome | |
| language | language | Y | Body | String | ko | |
| Network environment (internal/external) | location | Y | Body | String | Internal | |
| Detection rule number | rule | Y | Body | String | P001 | |
| User account | username | Y | Body | String | gildong.hong | |
| Authentication unique value | envGuid | Y | Body | String | d8b09752-405a-4d52-8605-bff9aa3f4741 |
Response Parameter
| Properties | Data Type | Sample Data | Note |
|---|---|---|---|
| Result | boolean | true | true when mail sending succeeds / false when it fails |
Sample
| Request | Response |
|---|---|
| curl -X POST “https://stg1-cloud.singleid.samsung.net:443/test-tenant/admin-api/open/v1.1/emails/anomalyDetection" -H “accept: application/json” -H “Content-Type: application/json” -d “{"accessIP":"10.0.0.0","detectionTime":"2023-09-10 23:01:01","email":"gildong.hong@samsung.com","environment":"PC / Window / Chrome","language":"ko","location":"Internal","rule":"P001","username":"gildong.hong","envGuid":"d8b09752-405a-4d52-8605-bff9aa3f4741"}” | true |
Error Code
| Http Response Code | Error Code | Error Message | Action plan |
|---|---|---|---|
| 400 | N/A | N/A | Bad Request |
| 403 | N/A | N/A | Forbidden |
| 500 | N/A | N/A | Internal Server Error |
API Specification - Get User(User Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| User Portal | Get User | https://{domain}/{tenant-name}/user-api/open/v1.1/users/{username} | GET | Retrieves the user’s name, email, preferred language, and timezone data. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| User ID | username | Y | Path | String | gildong.hong |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| User ID | username | String | gildong.hong | |
| String | gildong.hong@stage.samsung.com | |||
| Name | formattedName | String | Dongho Kim | |
| Name | givenName | String | Dongho | |
| Surname | familyName | String | Kim | |
| English Full Name | enFormattedName | String | Dongho Kim | |
| English name | enGivenName | String | Dongho | |
| English surname | enFamilyName | String | Kim | |
| Preferred language | preferredLanguage | String | ko | 1) en : English 2) ko : Korean |
| Time zone | timeZone | String | Asia/Seoul |
Sample
| Request | Response |
|---|---|
curl -X GET "https://stg2-cloud.singleid.samsung.net/test-tenant/user-api/open/v1.1/users/gildong.hong" -H "accept: application/json" -H "Authorization: Bearer {JWT_TOKEN}" | { “username”: “gildong.hong”, “email”: “gildong.hong@stage.samsung.com”, “formattedName”: “Kim Dongho”, “givenName”: “Dongho”, “familyName”: “Kim”, “enFormattedName”: “Dongho Kim”, “enGivenName”: “Dongho”, “enFamilyName”: “Kim”, “preferredLanguage”: “ko”, “timeZone”: “Asia/Seoul” } |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 401 | N/A | N/A | We need to verify whether the JWT Token is valid. |
API Specification - Get User Profile Image(User Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| User Portal | Get User Profile Image | https://{domain}/{tenant-name}/user-api/open/v1.1/users/image/{username} | GET | Retrieves the user’s profile image data. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| User ID | username | Y | Path | String | gildong. hong |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| username | username | String | null | |
2) File URL :  | –> |
Sample
| Request | Response |
|---|---|
curl -X GET "https://stg2-cloud.singleid.samsung.net:443/test-tenant/user-api/open/v1.1/users/image/gildong.hong" -H "accept: application/json" -H "Authorization: Bearer {JWT_TOKEN}" | File data { "username": null, "image": "" } File URL `{ “username”: “gildong.hong”, “image”: “” } |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 401 | N/A | N/A | We need to verify whether the JWT Token is valid. |
API Specification - Create account assignment list(User Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| User Portal | Create account assignment list | https://{domain}/{tenant-name}/user-api/1.0/scp-auth/create | POST | Create SCP permissions for the user. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| instance id | instanceId | Y | JSON | String | SCP provision | |
| permission set id | permissionSetId | Y | JSON | String | PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf | SCP provision |
| principal id | principalId | Y | JSON | String | gildong.hong | user’s username |
| principal type | principalType | Y | JSON | String | USER | Only the current USER is allowed |
| target id | targetId | Y | JSON | String | “PROJECT-ka2tfhLHsweVwm4BrR1rae” | PROJECT ID, SCP provided |
| target type | targetType | Y | JSON | String | PROJECT | Only the current PROJECT functions |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| instance id | instanceId | JSON | Return stored value | |
| permission set id | permissionSetId | JSON | PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf | saved value |
| principal id | principalId | JSON | gildong.hong | saved value |
| principal type | principalType | JSON | USER | Return stored value |
| target id | targetId | JSON | “PROJECT-ka2tfhLHsweVwm4BrR1rae” | Return stored value |
| target type | targetType | JSON | PROJECT | Return stored value |
| status | status | JSON | “SUCCESS” | Success or failure |
| failure reason | failureReason | JSON | Reason for failure | |
| created date | createdDate | JSON | Creation Date/Time |
Sample
| Request | Response |
|---|---|
curl -X POST "https://stg-scloud.singleid.samsung.net:443/stg4/user-api/1.0/scp-auth/create" -H "accept: application/json"-H "apiKey: {apiKey}" INPUT JSON{ "instanceId": "instnace-01", "permissionSetId": "PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf", "principalId": "singleid.test001", "principalType": "USER", "targetId": "PROJECT-ka2tfhLHsweVwm4BrR1rae", "targetType": "PROJECT" } | { "instanceId": "instnace-01", "permissionSetId": "PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf", "principalId": "singleid.test001", "principalType": "USER", "targetId": "PROJECT-ka2tfhLHsweVwm4BrR1rae", "targetType": "PROJECT" "status": "SUCCESS", "createdDate": "2024-04-03T01:58:46.538Z", "failureReason": "" } |
API Specification - Delete account assignment list(User Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| User Portal | Delete account assignment list | https://{domain}/{tenant-name}/user-api/1.0/scp-auth/create](https://{domain}/{tenant-name}/user-api/1.0/scp-auth/delete) | POST | Delete the SCP permission for the user. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| instance id | instanceId | Y | JSON | String | SCP provision | |
| permission set id | permissionSetId | Y | JSON | String | PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf | SCP provision |
| principal id | principalId | Y | JSON | String | gildong.hong | user’s username |
| principal type | principalType | Y | JSON | String | USER | Only the current USER is allowed. |
| target id | targetId | Y | JSON | String | “PROJECT-ka2tfhLHsweVwm4BrR1rae” | PROJECT ID, SCP provided |
| target type | targetType | Y | JSON | String | PROJECT | Only the current PROJECT functions |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| instance id | instanceId | JSON | Return deleted value | |
| permission set id | permissionSetId | JSON | PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf | Return deleted value |
| principal id | principalId | JSON | gildong.hong | Return deleted value |
| principal type | principalType | JSON | USER | Return deleted value |
| target id | targetId | JSON | “PROJECT-ka2tfhLHsweVwm4BrR1rae” | Return deleted value |
| target type | targetType | JSON | PROJECT | Return deleted value |
| status | status | JSON | “SUCCESS” | Success or failure |
| failure reason | failureReason | JSON | Reason for failure | |
| created date | createdDate | JSON | Deletion time |
Sample
| Request | Response |
|---|---|
curl -X GET "https://stg1-cloud.singleid.samsung.net/test-tenant/common-api/open/v1.1/asis/test-tenant/user/mfa/token/authentication?userName=mkdir.kim&protocol=uma-uaf&sessionDataKey=sessionDataKey111&redirectUrl=redirectUrl1111&errorRedirectUrl=errorRedirectUrl1111¶ms=params111&language=ko" | { "result": "SUCCESS", "value": { "token": "eyJpc3MiOiJodHRwczovL3N0ZzItY2xvdWQuaWFtLnNhbXN1bmcubmV0Iiwic3ViIjoibWtkaXIua2ltIiwiYXVkIjoiaHR0cHM6Ly9zdGcyLWNsb3VkLmlhbS5zYW1zdW5nLm5ldCIsImV4cCI6MTY5ODEyOTM2OSwiaWF0IjoxNjk4MTI5MTg5LCJqdGkiOiJkNWZmZGE5Ny1mMzZkLTRjZDktYWJmZi1mMzY4ZTkxYWVkNTUiLCJhbXIiOltdLCJ6b25laW5mbyI6IkFzaWEvU2VvdWwiLCJsb2NhbGUiOiJlbl9VUyIsInByb3RvY29sIjoidW1hLXVhZiIsInJlZGlyZWN0X3VybCI6InJlZGlyZWN0VXJsMSIsImVycm9yX3JlZGlyZWN0X3VybCI6ImVycm9yUmVkaXJlY3RVcmwxIiwicGFyYW1zIjoicGFyYW1zMSIsInVzZXJJZCI6Im1rZGlyLmtpbSJ9:MEUCIHqWV_UcgKHsMlDI7Ks31fw1QPpCYnKorMpnr2L653LwAiEAz30ShMmACEi6H-IuF1YMV2bKT1WIFmAdJ6OCsmEzscA", "serviceUri": "/ua/MPHTOCHW5I/de6f67d0-8bec-46ac-bf53-16ef00eb2066/dgauth/mfa", "appId": null }, "message": "succeeded to get nexsign token.", "statusCode": null, "statusCodeValue": "0", "data": null} |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 400 | N/A | N/A | You need to verify the userName. |
API Specification - Get account assignment list(User Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| User Portal | Get account assignment list | https://{domain}/{tenant-name}/user-api/1.0/scp-auth/list | POST | Retrieves the SCP permissions for a user. |
Request Parameter
| No. | Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|---|
| 1 | principal type | principalType | Y | query | String | USER | Only the current USER is allowed |
| 2 | principal id | principalId | Y | query | String | gildong.hong | username of the user to query |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| instance id | instanceId | JSON | ||
| permission set id | permissionSetId | JSON | PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf | |
| principal id | principalId | JSON | gildong.hong | |
| principal type | principalType | JSON | USER | |
| target id | targetId | JSON | “PROJECT-ka2tfhLHsweVwm4BrR1rae” | |
| target type | targetType | JSON | PROJECT |
Sample
| Request | Response |
|---|---|
curl -X GET "https://stg-scloud.singleid.samsung.net:443/stg4/user-api/1.0/scp-auth/list?principalType=USER&principalId=singleid.test001" -H "accept: application/json" -H "apiKey: {apiKey}" | [ { "instanceId": "instnace-01", "permissionSetId": "PERMISSION-SET-Ablxc5__qEaIYmWGyMeqlf", "principalId": "singleid.test001", "principalType": "USER", "targetId": "PROJECT-ka2tfhLHsweVwm4BrR1rae", "targetType": "PROJECT" }, { "instanceId": "instnace-01", "permissionSetId": "PERMISSION-SET-Ablxc5__qEaIYmWGyMe121", "principalId": "singleid.test001", "principalType": "USER", "targetId": "PROJECT-ka2tfhLHsweVwm4BrR1rae", "targetType": "PROJECT" } ] |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 401 | N/A | N/A | It is necessary to verify that the API key is valid. |
API Specification - Search User(User Portal)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| User Portal | Search User | https://{domain}/{tenant-name}/user-api/1.0/scp-user/list | POST | Search for the SCP target user. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| page | page | N | query | Integer | 0 | Page to fetch |
| size | size | N | query | Integer | 10 | Page size |
| username | username | N | query | String | gildong.hong | User ID to query |
| group name | groupName | N | query | String | ADGroup | Group to query |
| create Date(from) | creationDateGe | N | query | DateTime | “2024-04-03T07:49:23.845Z” | |
| create Date(to) | creationDateLe | N | query | DateTime | “2024-04-03T07:49:23.845Z” | |
| last change date(from) | lastChangeDateGe | N | query | DateTime | “2024-04-03T07:49:23.845Z” | |
| last change date(to) | lastChangeDateLe | N | query | DateTime | “2024-04-03T07:49:23.845Z” |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| key | key | String | “01890501-74fa-7785-91e0-67bd71217a2e” | |
| username | username | String | gildong.hong | |
| administrator | administrator | Boolean | false | |
| formatted name | formattedName | String | Gil-dong Hong | |
| formatted Name(en) | enFormattedName | String | “gildong hong” | |
| String | “gildong.hong@samsung.com” | |||
| mobile | mobile | String | +02-01011112222 | |
| preferred language | preferredLanguage | String | ko | |
| time zone | timeZone | String | “Asia/Seoul” | |
| managed by | managedBy | String | SINGLEID | |
| creator | creator | String | “admin001” | |
| creation date | creationDate | DateTime | “2024-04-03T07:49:23.845Z” | |
| last modifier | lastModifier | String | “admin001” | |
| last change date | lastChangeDate | DateTime | “2024-04-03T07:49:23.845Z” |
Sample
| Request | Response |
|---|---|
curl -X POST "https://stg-scloud.singleid.samsung.net:443/stg4/user-api/1.0/scp-user/list" -H "accept: application/json" -H "apiKey: {apiKey}" | [ { “key”: “01890501-74fa-7785-91e0-67bd71217a2e”, “administrator”: false, “username”: “gildong.hong”, “enFormattedName”: “gildong hong”, “formattedName”: “Gildong Hong”, “email”: “gildong.hong@samsung.com”, “mobile”: “+02-01011112222”, “preferredLanguage”: “ko”, “timeZone”: “Asia/Seoul”, “managedBy”: “SINGLEID”, “creator”: “admin001”, “creationDate”: “2024-04-03T07:49:23.845Z”, “lastModifier”: “admin001”, “lastChangeDate”: “2024-04-03T07:49:23.845Z” }, { “key”: “01890501-74fa-7785-91e0-67bd71217a2e”, “administrator”: false, “username”: “gildong.hong”, “enFormattedName”: “gildong hong”, “formattedName”: “Gildong Hong”, “email”: “gildong.hong@samsung.com”, “mobile”: “+02-01011112222”, “preferredLanguage”: “ko”, “timeZone”: “Asia/Seoul”, “managedBy”: “SINGLEID”, “creator”: “admin001”, “creationDate”: “2024-04-03T07:49:23.845Z”, “lastModifier”: “admin001”, “lastChangeDate”: “2024-04-03T07:49:23.845Z” } ] |
Error Code
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 401 | N/A | N/A | It is necessary to verify that the API key is valid. |
API Specification - MFA Consumer Request(Portal Common)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | MFA Consumer Request | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/request/mfa | POST | Request MFA. |
Request Parameter
| No. | Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|---|
| 1 | username | username | Y | Body | String | mkdir.kim | |
| 2 | Authentication type | type | N | Body | String | One of email, sms, msg, uaApp, uaMOTP. If unspecified, follow the default setting or the user’s preferred method. | |
| 3 | serviceProviderId | serviceProviderId | Y | Body | String | d8b09752-405a-4d52-8605-bff9aa3f4741 | UUID. Device-specific ID generated after registration in the SingleID Admin Portal. |
Response Parameter
| Properties | Attribute | Data Type | Sample Data | Note |
|---|---|---|---|---|
| requestId | requestId | String | 01890501-74fa-7785-91e0-67bd71217a2e | UUID. Used as a request parameter during MFA verification. |
| Authentication type | type | String | sms | email, sms, msg, uaApp, or uaMOTP. The verification logic may vary depending on the MFA type. |
| otp | otp | String | 123456 | A 6-digit or 8-digit number. Issued only when the type is uaMOTP (6 digits) or uaApp (8 digits). |
Sample
| Request | Response |
|---|---|
curl -X POST "https://stg1-cloud.singleid.samsung.net:443/test/common-api/open/v1.1/mfa/request/mfa" -H "accept: application/json" -H "Content-Type: application/json" -d "{\"username\":\"mkdir.kim\",\"type\":\"sms\",\"serviceProviderId\":\"dceef541-1f22-479d-96ac-c402ab0789e9\"} | { “otp”: “123456”, “requestId”: “d8b09752-405a-4d52-8605-bff9aa3f4741”, “serviceProviderId”: “”, “type”: “sms”, “username”: "" } |
Error Codes and Responses
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 400 | N/A | common.error.requiredValue | A required value is missing. Please check. |
| 400 | N/A | user.error.notFound | User not found. Please verify the user ID. |
| 400 | N/A | serviceProvider.error.notFound | Service provider not found. Please contact the administrator. |
| 400 | N/A | authenticator.error.notFound | Authentication method not found. Please contact the administrator. |
| 400 | N/A | common.error.disallowedValue | Invalid type. Please contact the administrator. |
| 400 | N/A | user.error.locked + remain | Your account is locked. Please try again after {remain} minutes. |
| 400 | N/A | otp.error.tooManyAttempts | Go to the security warning screen (your account has been locked due to multiple authentication failures) |
API Specification - MFA Consumer Verification(Portal Common)
| Module | API | URI | Method | Description |
|---|---|---|---|---|
| Portal Common | MFA Consumer Verification | https://{domain}/{tenant-name}/common-api/open/v1.1/mfa/verification/mfa | POST | Verifying MFA. |
Request Parameter
| Properties | Attribute | Mandatory | Parameter Type | Data Type | Sample Data | Note |
|---|---|---|---|---|---|---|
| requestId | requestId | Y | Body | String | d8b09752-405a-4d52-8605-bff9aa3f4741 | UUID |
| otp | otp | N | Body | String | 123456 | 6-digit number / not required for uaApp, uaMOTP |
Response Parameter
| Http Status Code | status |
|---|---|
| 200 | Authentication complete |
| 202 | Authentication pending (occurs only when type is uaMOTP or uaApp. Periodically poll and verify the result until it is delivered with 200) |
| Other | Error |
Sample
| Request | Response |
|---|---|
curl -X POST "https://stg1-cloud.singleid.samsung.net:443/test/common-api/open/v1.1/mfa/verification/mfa" -H "accept: application/json" -H "Content-Type: application/json" -d "{\"otp\":\"000000\",\"requestId\":\"095db652-877f-42e5-b87f-e404fb07048b\"}" | { “statusCode”: “ACCEPTED”, } |
Error Codes
| Http Response Code | Error Code | Error Message | Action Plan |
|---|---|---|---|
| 400 | N/A | common.error.requiredValue | A required value is missing. Please check. |
| 400 | N/A | common.error.invalidRequest | The request could not be found. Please contact the administrator. |
| 400 | N/A | request.error.invalidStatus | The request status is incorrect. Please contact the administrator. |
| 400 | N/A | otp.error.notMatch | Invalid OTP. Please check the OTP. |
| 400 | N/A | otp.error.tooManyAttempts | Go to the security warning screen (your account has been locked due to multiple authentication failures) |
9.5.2.1.6.1 - ADFS Adapter Guide
ADFS Adapter Guide
Microsoft ADFS (ActiveDirectory Federation Service) is a service that supports SAML/OAuth-based SSO (Single Sign-On) for web services based on AD accounts.
In MS, for web services linked with SSO, MFA (multi-factor authentication) using a 3rd Party solution is supported, and the component that must be developed/installed for this is the ADFS Adapter.
There are two primary methods for implementing an ADFS Adapter.
- Server-to-Server Call method
- WebClient method
Among them, the WebClient method minimizes firewall openings between the MFA server ↔ AD(FS) 間 and, by leveraging the CX offered by the MFA Provider, allows for a lightweight ADFS adaptor.
Server-to-Server Call method
WebClient method
Internal operation
Overall flow diagram of the Adapter internals
Adapter first execution flowchart
Flowchart after MFA execution (when MFA PASS)
Flowchart after performing MFA (if MFA PASS not achieved)
Scenario-specific behavior
Case #1
- This occurs when the time limit is exceeded on the passcode entry screen, resulting in a timeout.
- When a timeout occurs, the “Resend Code” button becomes active, and you can press this button to retry the Passcode.
Case #2
- This is the case when an incorrect Passcode is entered.
- You can attempt to enter the Passcode up to three times.
Case #3
- This is the case where the passcode is entered incorrectly three times.
- You cannot enter the Passcode for 1 minute.
Case #4
- This is a normal MFA process.
Case #5
- This occurs when a new browser tab is added on the MFA selection screen without entering the Passcode, and the MFA selection is completed.
- After that, successfully complete MFA on the first tab.
- This is the case where a timeout occurs in a new tab later.
Case #6
- This occurs when a new browser tab is added on the MFA selection screen without entering the Passcode, and the MFA selection is completed.
- After that, successfully complete MFA on the first tab.
- This occurs when an incorrect Passcode is entered in a new tab later.
Case #7
- This occurs when a new browser tab is added on the MFA selection screen without entering the Passcode, and the MFA selection is completed.
- After that, MFA succeeds on the first tab.
- This is the case when a valid Passcode is entered thereafter.
- Both the 1st tab and 2nd tab are waiting for passcode input; after authenticating the 1st, attempting authentication on the 2nd yields no response on the 2nd (page freezes)
- 1st tab passcode waiting for input, 2nd tab MFA selection waiting state, after the 1st authentication, selecting the 2nd MFA type causes an error, AD displays an error message before the adapter operates
Scenario-specific behavior
Adapter installation
Application method
Pre-check
Pre‑inspection
| Location | Inspection items | Remarks |
|---|---|---|
| ADFS server | MFA server accessibility (internal network, TCP 80/443)
| If configured to store the nonce in LDAP, communication with the MFA server is unnecessary. |
| .NET Framework 4.8 installation status | ||
| User PC | MFA server connectivity (Internet network, TCP 80/443)
| If connection fails, check the following three items ① Firewall check ② Proxy check ③ Website blocking check |
Adapter deployment
- Upload the adapter-related files to the ADFS server
위치 : [drvie]:\ADFSadapter\
ADFSadapter.dll : Adapter 파일
ADFSadatper.ini : 환경 설정 파일
replace_dll.ps1 : 이미 설치된 Adapter를 개선 버전으로 교체 시 사용하는 스크립트 파일
restart_adfs.ps1 : AD FS 서비스 재시작 스크립트 파일
Assembly_netstandard2.0 폴더 : Adapter 적용 전 사전 설치 dll 파일들
- Grant full permissions to the ADFS service account on the folder
C:\ADFSadapter 폴더 우클릭 > 속성 > 보안 > ADFS 서비스 계정 추가 후 모든 권한 허용 선택
※ ADFS 서비스 계정은 services.msc 실행 > ADFS 서비스 실행 계정 "다음 사용자로 로그온" 으로 확인
- Add Registry
Adapter 관련 이벤트를 Windows 이벤트 로그에 찍기 위한 Registry 생성
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\EventLog 아래에 키 및 값(2개) 생성
- 생성 키 : MFA_Adapter
- MFA_Adapter에 값 2개 생성
. 이름 : AutoBackupLogFiles
. 종류 : DWORD(32비트) 값(REG_DWORD)
. 데이터 : 0
. 이름 : MaxSize
. 종류 : DWORD(32비트) 값(REG_DWORD)
. 데이터 : 16진수 80000
MFA_Adapter 키 아래에 키 및 값(1개) 생성
- 생성 키 : AdapterDLL
- AdapterDLL에 값 1개 생성
. 이름 : EventMessageFile
. 종류 : 확장 가능한 문자열 값(REG_EXPAND_SZ)
. 데이터 : C:\Windows\Microsoft.NET\Framework64\v4.0.30319\EventLogMessages.dll
- Pre-install the DLL required for the Adapter The Assembly_netstandard2.0 folder in C:\ADFSadapter contains libraries that require pre‑installation; refer to the following for the installation process. Install the DLL into the global assembly cache on the ADFS server so that the assembly required when the ADFS Adapter runs can be loaded.
**dll 설치**
#사전 작업
C:\ADFSadapter 폴더에 Assembly_netstandard2.0 폴더 압축을 풀어 복사해둔다.
#관리자 권한으로 Powershell 실행 후 수행 위치 이동
PS>cd C:\ADFSadapter
#dll 설치
PS>.\gacutil.exe /il .\Assembly_netstandard2.0\AssemblyList.txt
#dll 확인
PS>.\gacutil.exe /l
The required assembly files for installation have been stored in the Assembly_netstandard2.0 folder, and after copying these files to the server, installation can be performed offline. Assembly_netstandard2.0 folder: Microsoft.IdentityModel.Tokens v7.2, System.IdentityModel.Tokens.Jwt v7.2 DLL files for installing the assembly (including all dependency files)
Installation DLL list
| Assembly name | Installed version | Package version |
|---|---|---|
| Microsoft.Bcl.AsyncInterfaces | 1.0.0.0 | 1.0.0 |
| Microsoft.IdentityModel.Abstractions | 7.2.0.0 | 7.2.0 |
| Microsoft.IdentityModel.JsonWebTokens | 7.2.0.0 | 7.2.0 |
| Microsoft.IdentityModel.Logging | 7.2.0.0 | 7.2.0 |
| Microsoft.IdentityModel.Tokens | 7.2.0.0 | 7.2.0 |
| System.Buffers | 4.0.3.0 | 4.5.1 |
| System.IdentityModel.Tokens.Jwt | 7.2.0.0 | 7.2.0 |
| System.Memory | 4.0.1.1 | 4.5.3 |
| System.Numerics.Vectors | 4.1.4.0 | 4.5.0 |
| Microsoft.CSharp | 4.0.4.0 | 4.5.0 |
| System.Runtime.CompilerServices.Unsafe | 4.0.4.1 | 4.5.3 |
| System.Security.Cryptography.Cng | 4.3.0.0 | 5.0.0 |
| System.Text.Encodings.Web | 4.0.5.1 | 4.7.2 |
| System.Text.Json | 4.0.1.2 | 4.7.2 |
| System.Threading.Tasks.Extensions | 4.2.0.1 | 4.5.4 |
Adapter Deployment
The NuGet file was downloaded and installed; note that the version displayed for the NuGet package may differ from the version installed on the server. Based on .NET Framework 4.8, use the DLL with the .NET Standard 2.0 (supports .NET Framework 4.8) specification.
Package download : NuGet Gallery | Microsoft.IdentityModel.Tokens 7.2.0
- Apply Adapter Run PowerShell in administrator mode and execute the following command
#수행 위치 이동
PS>cd C:\ADFSadapter
#dll 등록
PS>./gacutil.exe /if ADFSadapter.dll
#dll 확인
PS>./gacutil.exe /l ADFSadapter
전역 어셈블리 캐시에 다음 어셈블리가 들어 있습니다.
ADFSadapter, Version=1.2.1.0, Culture=neutral, PublicKeyToken=0e0fe476002e81b3, processorArchitecture=MSIL
#ADFS에 인증 공급자로 등록
PS>$typename="ADFSadapter.AuthenticationAdapter, ADFSadapter, Version=1.2.1.0, Culture=neutral, PublicKeyToken=0e0fe476002e81b3, processorArchitecture=MSIL"
PS>Register-AdfsAuthenticationProvider -TypeName $typename -Name "ADFSadapter"
#ADFS에 인증 공급자 확인
PS>Get-AdfsAuthenticationProvider
AdminName : ADFS MFA Adapter
AllowedForPrimaryExtranet : False
AllowedForPrimaryIntranet : False
AllowedForAdditionalAuthentication : True
AuthenticationMethods : {http://schemas.microsoft.com/ws/2012/12/authmethod/otp}
Descriptions : {[1033, ADFS MFA Adapter], [1042, ADFS MFA Adapter]}
DisplayNames : {[1033, ADFS MFA Adapter], [1042, ADFS MFA Adapter]}
Name : ADFSadapter
IdentityClaims : {http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn}
IsCustom : True
RequiresIdentity : True
#ADFS 서비스 재시작
PS>net stop adfssrv
PS>net start adfssrv
#수행 위치 이동
PS>cd C:\ADFSadapter
#dll 등록
PS>./gacutil.exe /if ADFSadapter.dll
#dll 확인
PS>./gacutil.exe /l ADFSadapter
전역 어셈블리 캐시에 다음 어셈블리가 들어 있습니다.
ADFSadapter, Version=1.2.1.0, Culture=neutral, PublicKeyToken=0e0fe476002e81b3, processorArchitecture=MSIL
#ADFS 서비스 재시작
PS>net stop adfssrv
PS>net start adfssrv
Configure multi-factor authentication methods for ADFS AD FS Management > Services > Authentication Methods > Multi-Factor Authentication Methods > Click Edit, then select the created mfa (ADFS MFA Adapter) and apply (multiple selection possible)
Apply MFA policy to the trusted party trust AD FS Management > Relying Party Trust > Select the Relying Party Trust to apply > Edit Access Control Policy > ‘Allow all users and require MFA’ Select and apply
Adapter Upgrade and Change
This method is the adapter replacement procedure performed when upgrading or modifying an already registered ADFS MFA Adapter. When performing the replacement, executing this script alone completes the Adapter change and its application.
#수행 위치 이동하여 변경된 Adapter.dll 파일 업로드
PS>cd C:\ADFSadapter
#Adapter 교체 수행
PS>./replace_dll.ps1
확인창 출력 시 예(Y) 혹은 모두 예(A) 클릭
- 예(Y) 혹은 모두 예(A) 선택 : ADFS에서 기존 Adapter 제거 후 교체 작업 진행 (정상 절차)
- 아니요(N) 혹은 모두 아니요(L) 선택 : Adapter 제거 안하고 다음 단계로 수행되어 오류 발생
- 일시 중단(S) 선택: 해당 스크립트 중단
Adapter configuration
This is a description of the Adapter configuration file. Before applying the ADFS Adapter, you must first configure the environment.
Adapter installation location changes
Starting with adapter 1.2.0.6, you can install to drives other than the C drive.
Existing: installed only in C:/ADFSadapter Change: Install at the root of the Z drive Example: C:/ADFSadapter , D:/ADFSadapter , E:/ADFSadapter , …… , Z:/ADFSadapter
Caution: Install on only one drive; if installed on multiple drives, the system scans from C to Z and uses the first directory it finds.
The following example assumes the adapter is installed in the C:\ADFSadapter directory.
If you installed on a drive other than C, simply change the drive letter in the example below.
Example: If installed in D:\ADFSadapter, the ini path → D:\ADFSadapter\ADFSadapter.ini
File name and path
- File name → ADFSadapter.ini
- Full path → C:\ADFSadapter\ADFSadapter.ini
- File encoding → be sure to save as UTF-8 (otherwise Korean characters will become garbled)
Things to note
When representing a value, you can use " and ‘, and you may include spaces on either side of =. Whitespace before and after the Value is trimmed The values below are all the same. Example 1) MAIN_TITLE=DWP MFA Adapter Example 2) MAIN_TITLE = DWP MFA Adapter Example 3) MAIN_TITLE = “DWP MFA Adapter” Example 4) MAIN_TITLE = " DWP MFA Adapter "
Sections whose names end with -1033 or -1042 indicate a locale. At least 1033 must be present.
locale number : 1033 (en-us), 1042 (ko) locale section : MFA-1033, MFA-1042, TXT-1033, TXT-1042, MSG-1033, MSG-1042
Example of ini file structure
# ADFS MFA Adapter 환경 설정
# 설치위치 변경 사항
# - v1.2.0.6 이전 : C:\ADFSadapter\ADFSadapter.ini
# - v1.2.0.6 부터 : C 이외의 다른 드라이브에 설치할 수 있음 (adapter 리소스 설치한 위치와 동일)
# 예시: C:\ADFSadapter\ADFSadapter.ini , D:\ADFSadapter\ADFSadapter.ini , E:\ADFSadapter\ADFSadapter.ini
# 주의 : DLL 파일명은 ADFSadapter.dll 이며, 기존의 Nexsign 연계한 MFAadapter.dll과는 다름
# 값을 표현할때 " 와 ' 를 사용할 수 있으며 = 좌우에 빈칸을 입력해도 됩니다
# Value 의 앞뒤에 있는 공백은 Trim 처리 됩니다.
# 아래의 Value는 모두 동일합니다.
# 예1) MAIN_TITLE=ADFS MFA Adapter
# 예2) MAIN_TITLE = ADFS MFA Adapter
# 예3) MAIN_TITLE = "ADFS MFA Adapter"
# 예4) MAIN_TITLE = " ADFS MFA Adapter "
# 섹션 이름들 중에 뒷부분에 -1033, -1042 가 붙는 것들은 locale 을 의미합니다
# 최소한 1033 은 반드시 있어야 합니다
# locale number : 1033 (en-us), 1042 (ko)
# locale section : MFA-1033, MFA-1042, TXT-1033, TXT-1042, MSG-1033, MSG-1042
# LOG_LEVEL (Windows 이벤트 로그에 기록하는 기준)
# 0 : Error
# 1 : Error + Warning
# 2 : Error + Warning + Information + Debug
[MAIN]
MAIN_MFA_TITLE="ADFS MFA Adapter"
MAIN_CLAIM1=http://schemas.microsoft.com/ws/2008/06/identity/claims/authenticationmethod
MAIN_CLAIM2=http://schemas.microsoft.com/ws/2012/12/authmethod/otp
# MFA API 정보
# URL 끝부분에 "/" 붙이지 말 것
#MFA_API_URL="https://stg2-cloud.singleid.samsung.net/test/common-api/open/v1.1/mfa/request"
MFA_API_URL="https://stg1-cloud.singleid.samsung.net/test/common-api/open/v1.1/mfa/request"
CONSUMER_KEY="**************************************"
SECRET_KEY="**************************************"
# Donmain vs Consumer Key 리스트
# 도메인별로 Consumer Key가 다른 경우에는 리스트로 나열 (이런 경우, 위의 CONSUMER_KEY 값을 비울 것)
# Reqeust Token의 sys 값에 대입
# 형태 : DOMAIN_CONSUMER_KEY_##=domain;consumerKey
# 예시: DOMAIN_CONSUMER_KEY_01=aaa.com;**************************************
# DOMAIN_CONSUMER_KEY_02=bbb.com;**************************************
# (주의) CONSUMER_KEY 값과 리스트 값이 모두 있다면, CONSUMER_KEY 값만 사용함
DOMAIN_CONSUMER_KEY_01=aaa.com;**************************************
DOMAIN_CONSUMER_KEY_02=bbb.com;**************************************
# Donmain vs Secret Key 리스트
# 도메인별로 Secret Key가 다른 경우에는 리스트로 나열 (이런 경우, 위의 SECRET_KEY 값을 비울 것)
# 형태 : DOMAIN_SECRET_KEY_##=domain;secretKey
# 예시: DOMAIN_SECRET_KEY_01=aaa.com;**************************************
# DOMAIN_SECRET_KEY_02=bbb.com;**************************************
# (주의) SECRET_KEY 값과 리스트 값이 모두 있다면, SECRET_KEY 값만 사용함
DOMAIN_SECRET_KEY_01=aaa.com;**************************************
DOMAIN_SECRET_KEY_02=bbb.com;**************************************
# LDAP Search 결과에 따른, MFA 진행 여부
# 0 : LDAP Search를 하지 않음 (아래의 LDAP_SERVER, LDAP_USE_IDPW, ... 등의 정보 사용하지 않음. token에는 빈 값 대입)
# 1 : LDAP Search를 시도하지만 실패해도 관계없음 (서버 실패, 정보 없음 등이 발생하여도 MFA 진행함. token에는 빈 값 대입)
# 2 : LDAP Search가 성공 & 사용자 정보가 존재해야 함 (사용자 정보가 존재할 경우에만 진행함. 단, 결과 값이 빈 값이어도 진행함)
USE_LDAP_SEARCH=1
# LDAP 주소와 ID/PW
# LDAP_SERVER는 domain, ipv4, ipv6 등의 3가지 모두 가능하며, 앞부분에 대문자 "LDAP://" 을 붙여야 함 (반드시 대문자)
# 예시: LDAP://adpw5004.hw.dev , LDAP://70.2.180.218 , LDAP://fe80::644b:3c9f:c5ac:ce1c%10
# ID/PW를 사용하려면 LDAP_USE_IDPW 값을 1, 사용하지 않으려면 LDAP_USE_IDPW 값을 0 으로 설정
# SSL/TLS 사용하려면 LDAP_SSLTLS 값을 1, 사용하지 않으려면 LDAP_SSLTLS 값을 0 으로 설정 (단, LDAP_USE_IDPW=1 인 경우에만 해당)
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_USE_IDPW=1
LDAP_SSLTLS=1
LDAP_ID="isadmin"
LDAP_PW="sds*****"
# DNS Lookup을 하여 LDAP 서버(LDAP_SERVER)의 IP 주소를 확인하고, IP 주소 기반으로 접속 여부
# LDAP_SERVER 값이 IP(ipv4, ipv6)로 설정되어 있어도 DNS Lookup을 수행하며, IP 그대로 리턴됨
# 만약, DNS Lookup을 실패하면, LDAP_SERVER 값 그대로 접속
# 0 : LDAP_SERVER 값 그대로 서버에 접속 (DNS lookup 하지 않음)
# 1 : DNS lookup으로 IP 주소를 확인하여 LDAP 서버에 접속 (DNS lookup 결과 리스트에서 첫번째 IP 사용)
# 2 : DNS lookup으로 IP 주소를 확인하고, LDAP_WHITE_IP_## 리스트에서 가장 먼저 해당되는 IP를 사용 (리스트에 없으면, LDAP_SERVER 사용)
# 3 : DNS lookup으로 IP 주소를 확인하고, LDAP_WHITE_IP_## 리스트에서 가장 먼저 해당되는 IP를 사용 (리스트에 없으면, LDAP 접속 안함)
LDAP_DNS_LOOKUP=1
# DNS Lookup 결과가 여러 개일때, 첫번째 IP 주소로 연결이 안되면 그 다음 IP 주소로 시도할지 여부
# 예시: lookup 결과가 4개 : 1차 IP 연결 실패 -> 2차 IP 연결 시도 & 싪패 -> 3차 IP 연결 시도 & 싪패 -> 4차 IP 연결 시도
LDAP_DNS_IF_FAIL_USE_NEXT=1
# DNS Lookup 결과와 비교하는 접속 허용된 LDAP 서버 IP 리스트 (LDAP_DNS_LOOKUP = 2 or 3 인 경우에만 해당)
# LDAP_WHITE_IP_## 형태이며, 01부터 99까지 순차적으로 기록
# DNS Lookup 결과와 리스트를 순차적으로 비교
# IPv4, IPv6 형태로 기록 (동일한 서버의 IPv4, IPv6가 있다면 리스트의 앞순위에 있는 IP가 적용됨)
# DNS Lookup 결과 순서와 White IP 리스트 순서가 다르다면 -> White IP 리스트 순서를 따름
LDAP_WHITE_IP_01="70.2.180.218"
LDAP_WHITE_IP_02="fe80::644b:3c9f:c5ac:ce1c%10"
# 사용자 정보를 암호화할지 여부 (예: mobile, email 등)
# 대상 : USERINFO_## 리스트
# 암호화 여부에 따라 API 서버에 전송하는 token의 claim 이름이 다름
# 0 : 암호화 하지 않음 -> token의 claim 이름이 plainMobile, plainEmail
# 1 : 암호화 -> token의 claim 이름이 mobile, email
USERINFO_ENCRYPT=0
# LDAP Search할 사용자 정보 attribute name과 JWT token에 사용할 claim name (2개 값을 구분하는 delimeter = ";")
# 형태: USERINFO_## = attribute;encryptedClaim;plainClaim
# 예시: LDAP에서 "mail" 속성을 읽어서, JWT에 "email" claim으로 사용된다면 -> "mail;email;plainEmail"
# key 명칭은 "USERINFO_##" 형태로 하고, 시작은 USERINFO_01
# key 갯수 : 0개 ~ 최대 99개 (0개인 경우, ini에 아무것도 적지 않으면 되며, USERINFO_00 이라고 적지 말 것)
# 주의사항) USERINFO_##에서 ## 에 해당되는 숫자는 반드시 01부터 시작하며, 여러 개인 경우 번호가 끊어지지 않아야 함
# USERINFO_01, USERINFO_02, USERINFO_03 : OK (01, 02, 03 정보가 사용됨)
# USERINFO_01, USERINFO_02, USERINFO_05 : 02까지 읽고, 끊어진 번호 이후는 사용하지 않음 (01, 02 정보가 사용됨)
USERINFO_01=mobile;mobile;plainMobile
USERINFO_02=mail;email;plainEmail
# MFA API 서버가 Callback 해줄때, 결과 Parameter에 사용되는 Key 이름
# 예시: https://adpw5004.hw.dev/adfs/ls?client-request-id=xxxxxx&pullStatus=0&jwtTokenResponse=yyyyyy
KEY_NAME_IN_RESPONSE="jwtTokenResponse"
# JWT Token의 exp에 적용될 더하기 값
# 형테 : 일시분초(dhms) 형태의 문자열 -> 1d=86400, 1h=3600, 1m=60 (dhms 가 전혀 없는 단순 숫자는 초로 판단함)
# 예시1 : 1d02h38m27s -> 95907 초
# 예시2 : 12345 -> 12345 초
TOKEN_EXP_TIME=1d
# API 호출할때 구성하는 token에 client claim을 추가할지 여부
# client : SAML인 경우 issuer, OIDC인 경우 client-id
# 0 : token에 client 포함시키지 않음
# 1 : token에 client 포함
TOKEN_CLAIM_CLIENT=0
# MFA nonce(guid, requset-id) 검증 방법
# 0 : 검증 안함
# 1 : adapter가 생성한 guid를 LDAP에 저장/비교하는 방식 (adapter가 검증)
# -> 관련 설정 값 : CACHE_ATTRIBUTE, CACHE_DELIMETER, SKEW_SECONDS, CACHE_LIFE_TIME
# 2 : API 서버가 생성한 requeset-id를 adapter가 받아서 호출 URL에 사용하는 방식 (API 서버가 검증)
# -> 관련 설정 값 : MFA_VERIFY_URL
MFA_VERIFY_TYPE=2
# MFA 결과검증 URL (서버 to 서버 통신) : URL 뒷부분에 API 서버로부터 받은 {request-id}를 덧붙여서 호출함
# adapter는 리턴 200 (OK) 인지 확인하여 MFA 결과 처리
# URL 끝부분에 "/" 붙이지 말 것
MFA_VERIFY_URL="https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status"
# MFA 결과검증할때 사용할 보안 프로토콜
# 선택 가능한 프로토콜 (대소문자 구분 없음) : TLS12, TLS13
# (주의) SSL3, TLS, TLS11 은 사용하지 않음
MFA_VERIFY_SECURE_PROTOCOL="TLS12"
# 사용자의 req guid 값을 저장할 LDAP attribute의 이름
# (주의) LDAP에 write 권한이 있어야 함
CACHE_ATTRIBUTE="otherPager"
# LDAP에 저장하는 req + 시간 정보를 조합할때 사용하는 delimeter -> "req;시간"
CACHE_DELIMETER=";"
# LDAP에 저장된 req의 시간과 JWT 수신시 시간의 차이 허용치 (초단위)
# MFA 선택화면 누를 때가 아니라, AD 로그인 직후의 시간이므로 (MFA 선택화면 보일때 이미 시간이 저장되었음)
# 사용자가 MFA 선택화면 누르고 Passcode 입력할 때까지의 시간이 아님
# 따라서, tight 하게 시간을 설정하면 안되며, 1시간 정도가 적당?? (MFA 선택을 1시간 고민하는 사람이 있나?)
SKEW_SECONDS=3600
# LDAP에 저장된 req의 수명 -> 다음 access시 시간 확인해서 이전의 오래된 것들 삭제
# 형태 : 일시분초(dhms) 형태의 문자열 -> 1d=86400, 1h=3600, 1m=60 (dhms 가 전혀 없는 단순 숫자는 초로 판단함)
# 예시1 : 1d02h38m27s -> 95907 초
# 예시2 : 12345 -> 12345 초
CACHE_LIFE_TIME=1d
# Adapter 기능을 ByPass 할 것인지 여부 (0=정상 사용, 283901=무력화, 그 외 값들=정상 사용)
# MFA 기능 문제로 급하게 adapter 기능의 무력화가 필요한 비상 상황에서 사용
# 평상시에는 절대로 수정하지 말 것 -> 평상시 값은 0
# 주의 : 무력화하려면 반드시 정확한 값을 설정해야 함 (0 이외의 숫자가 해당되는 것이 아니며 정확한 숫자 필요함. noise 우려)
BYPASS_ADAPTER=0
[API]
API_SYSTEMNAME=SingleID
[MSG-1033]
MSG_INTERNAL_ERROR="Internal error occurred. Contact administrator."
[MSG-1042]
MSG_INTERNAL_ERROR="Internal error occurred. Contact administrator."
[MANAGE]
LOG_LEVEL=2
Configuration value description
- Fixed value: means that the value displayed in the “Configured Value” column of the table below is used unchanged when installing on the ADFS server.
- If you want to add languages other than English and Korean, you can add them for two sections. → MSG-1033, MSG-1042
| dss | Key | Configuration values (example) | Fixed value | Explanation |
|---|---|---|---|---|
| MAIN | MAIN_MFA_TITLE | ADFS MFA Adapter | O | HTML page title (no impact on MFA functionality) |
| MAIN_CLAIM1 | http://schemas.microsoft.com/ws/2008/06/identity/claims/authenticationmethod | O | Apply the left value exactly as is | |
| MAIN_CLAIM2 | http://schemas.microsoft.com/ws/2012/12/authmethod/otp | O | Apply the left value exactly as is | |
| MFA_API_URL | https://stg2-cloud.singleid.samsung.net/test/common-api/open/v1.1/mfa/request | Since the SingleID MFA API URL can vary depending on the tenant, you need to verify the exact URL. | ||
| CONSUMER_KEY | 4312a8b9-75c4-7897-89a7-89347f18943e | Consumer Key issued by SingleID | ||
| SECRET_KEY | gQgkyLVO6FR8vJkLtlgBiupsRM/ilgrbEfoKWRnhALd= | Secret Key issued by SingleID used for JWT Signautre verification External disclosure prohibited | ||
| DOMAIN_CONSUMER_KEY_01 | 4312a8b9-75c4-7897-89a7-89347f18943e | Domain vs Consumer Key list If the Consumer Key differs per domain, list them (in this case, clear the CONSUMER_KEY value above) Format: DOMAIN_CONSUMER_KEY_##=domain;consumerKey Example: DOMAIN_CONSUMER_KEY_01=aaa.com;4312a8b9-75c4-7897-89a7-89347f18943e DOMAIN_CONSUMER_KEY_02=bbb.com;96567780-2b12-23da-637c-9375a6502d5a (Note) If both CONSUMER_KEY and list values are present, use only the CONSUMER_KEY value. | ||
| DOMAIN_CONSUMER_KEY_02 | 96567780-2b12-23da-637c-9375a6502d5a | |||
| DOMAIN_CONSUMER_KEY_## | 367c89d5-88f7-978a-9739-8ed21748f36b | |||
| DOMAIN_SECRET_KEY_01 | gQgkyLVO6FR8vJkLtlgBiupsRM/ilgrbEfoKWRnhALd= | Domain vs Secret Key list If the Secret Key differs per domain, list them (in this case, clear the above SECRET_KEY value) Format: DOMAIN_SECRET_KEY_##=domain;secretKey Example: DOMAIN_SECRET_KEY_01=aaa.com;gQgkyLVO6FR8vJkLtlgBiupsRM/ilgrbEfoKWRnhALd= DOMAIN_SECRET_KEY_02=bbb.com;kgkWRnLygQhsRgrLVbtKlO6FiLdABupEgoMR8v/ilfJ= (Note) If both SECRET_KEY value and list values are present, use only the SECRET_KEY value. | ||
| DOMAIN_SECRET_KEY_02 | kgkWRnLygQhsRgrLVbtKlO6FiLdABupEgoMR8v/ilfJ= | |||
| DOMAIN_SECRET_KEY_## | dABupkRnLygQhsrLgWVRbt8vRgkLilLKlO1FioMgfJE= | |||
| USE_LDAP_SEARCH | 0 or 1 or 2 | LDAP Search based MFA decision 0 : Do not perform LDAP Search (do not use information such as LDAP_SERVER, LDAP_USE_IDPW, etc. Assign an empty value to the token) 1 : Attempt LDAP Search but failure is acceptable (proceed with MFA even if server failure, missing information, etc. Assign an empty value to the token) 2 : LDAP Search succeeds & user information must exist (proceed only if user information exists. However, proceed even if the result value is empty) | ||
| LDAP_SERVER | LDAP://adpw5004.hw.dev | LDAP address that can query AD user information All three types such as domain, ipv4, and ipv6 are supported, and you must prepend “LDAP://” to the beginning. | ||
| LDAP_USE_IDPW | 0 or 1 | Whether to use id/pw when connecting to LDAP Since the adapter operates with system privileges, it is typical for LDAP connections to work without id/pw, though there are cases where this is not true If the system is configured to connect without id/pw and an AD connection error appears in the event log, it is necessary to configure it to connect using id/pw. Setting this value to 1 requires that LDAP_ID and LDAP_PW be set. | ||
| LDAP_SSLTLS | 0 or 1 | Whether to use SSL/TLS when connecting to LDAP Set to use by default | ||
| LDAP_ID | LDAP connection ID | LDAP connection ID (when LDAP_USE_IDPW=1) | ||
| LDAP_PW | LDAP connection pw | LDAP connection password (when LDAP_USE_IDPW=1) | ||
| LDAP_DNS_LOOKUP | 0 or 1 or 2 or 3 | Perform a DNS lookup to obtain the IP address of the LDAP server (LDAP_SERVER) and determine connection status based on the IP address |
0 : Connect to the server using the LDAP_SERVER value directly (no DNS lookup)
1 : Perform a DNS lookup to obtain the IP address and connect to the LDAP server (use the first IP from the DNS lookup result list)
2 : Perform a DNS lookup to obtain the IP address and use the first matching IP from the LDAP_WHITE_IP_## list (if not found, use LDAP_SERVER)
3 : Perform a DNS lookup to obtain the IP address and use the first matching IP from the LDAP_WHITE_IP_## list (if not found, do not connect to LDAP) |
| | LDAP_DNS_IF_FAIL_USE_NEXT | 0 or 1 | | When there are multiple DNS lookup results, whether to try the next IP address if the first IP address fails to connect
Example: lookup results are 4: 1st IP connection failure -> attempt 2nd IP & failure -> attempt 3rd IP & failure -> attempt 4th IP |
| | LDAP_WHITE_IP_01 | 70.2.180.218 | | List of allowed LDAP server IPs compared with DNS Lookup results (applicable only when LDAP_DNS_LOOKUP = 2 or 3)
LDAP_WHITE_IP_## format, recorded sequentially from 01 to 99
Compare the DNS Lookup results with the list sequentially
Recorded in IPv4 or IPv6 format (if the same server has both IPv4 and IPv6, the IP appearing earlier in the list is used)
If the order of DNS Lookup results differs from the White IP list order → follow the White IP list order |
| | LDAP_WHITE_IP_02 | | | fe80::644b:3c9f:c5ac:ce1c%10 |
| | LDAP_WHITE_IP_## | | | A. : 01 ~ 99
White IP address (IPv4 or IPv6) |
| | USERINFO_ENCRYPT | 0 or 1 | | Whether to encrypt user information (e.g., mobile, email, etc.)
Target : USERINFO_## list
The claim name of the token sent to the API server varies depending on encryption status
0 : No encryption -> token claim names are plainMobile, plainEmail
1 : Encryption -> token claim names are mobile, email |
| | USERINFO_01 | mobile;mobile;plainMobile | O | The attribute name of user information to search in LDAP and the claim name to use in the JWT token (the delimiter separating the three values is “;”)
Format: USERINFO_## = attribute;encryptedClaim;plainClaim
Example: If you read the “mail” attribute from LDAP and use the encrypted value as the “email” claim and the plain value as the “plainEmail” claim in the JWT → “mail;email;plainEmail” |
| | USERINFO_02 | mail;email;plainEmail | O | |
| | USERINFO_## | | | A. : 01 ~ 99
[LDAP attribute name];[encrypted token claim name];[plain token claim name] |
| | KEY_NAME_IN_RESPONSE | jwtTokenResponse | O | Key name used in the result parameter when the MFA API server performs a callback
Example: https://adpw5004.hw.dev/adfs/ls?client-request-id=xxxxxx&pullStatus=0&jwtTokenResponse=yyyyyy |
| | TOKEN_EXP_TIME | 1d | | The additive value applied to the JWT token’s exp
a string in day-hour-minute-second (dhms) format
1d=86400, 1h=3600, 1m=60
A plain number without any dhms is interpreted as seconds
Example 1: 1d02h38m27s → 95907 seconds
Example 2: 12345 → 12345 seconds |
| | TOKEN_CLAIM_CLIENT | 0 or 1 | | Whether to add a client claim to the token configured when making an API call
client: issuer for SAML, client-id for OIDC
0: do not include client in the token
1: include client in the token |
| | MFA_VERIFY_TYPE | 0 or 1 or 2 | | MFA nonce(guid, requset-id) verification method
0 : No verification
1 : Method where the guid generated by the adapter is stored/compared in LDAP (adapter verifies) → related configuration values: CACHE_ATTRIBUTE, CACHE_DELIMETER, SKEW_SECONDS, CACHE_LIFE_TIME
2 : Method where the requeset-id generated by the API server is received by the adapter and used in the call URL (API server verifies) → related configuration value: MFA_VERIFY_URL |
| | MFA_VERIFY_URL | https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status | | MFA result verification URL (server-to-server communication): Append the {request-id} received from the API server to the end of the URL and call it → the adapter checks that the return is 200 (OK) to process the MFA result
Do not append a “/” at the end of the URL |
| | MFA_VERIFY_SECURE_PROTOCOL | TLS12 or TLS13 | | Security protocol to use when verifying MFA results
Available protocols (case-insensitive): TLS12, TLS13
(Note) Do not use SSL3, TLS, TLS11 |
| | CACHE_ATTRIBUTE | otherPager | O | Name of the LDAP attribute that stores the user’s req guid value |
| | CACHE_DELIMETER | ; | | Delimiter used when combining the req and time information stored in LDAP -> “req;time” |
| | SKEW_SECONDS | 3600 | | Allowed time difference (in seconds) between the request time stored in LDAP and the time when the JWT is received
It is the time immediately after AD login, not when the MFA selection screen is clicked (the time is already recorded when the MFA selection screen appears)
It is not the time until the user clicks the MFA selection screen and enters the passcode
Therefore, the time should not be set too tightly; about one hour is appropriate?? (Is there anyone who would consider MFA selection for an hour?) |
| | CACHE_LIFE_TIME | 1d | | Lifetime of req stored in LDAP -> On the next access, check the time and delete the older ones
String in dhms (days, hours, minutes, seconds) format
1d=86400, 1h=3600, 1m=60
(A plain number without dhms is interpreted as seconds) |
| | BYPASS_ADAPTER | 0 or 283901 | | Whether to bypass the Adapter function (0 = normal operation, 283901 = disable, other values = normal operation)
Used in emergency situations where the adapter function must be quickly disabled due to MFA issues
Never modify under normal circumstances -> the normal value is 0
Caution: To disable, you must set the exact value (numbers other than 0 are not applicable; a precise number is required. Concern about noise) |
| API | API_SYSTEMNAME | SingleID | O | (No impact on MFA functionality) |
| MSG-1033 | MSG_INTERNAL_ERROR | Internal error occurred. Contact administrator. | | Message displayed to the user when the process stops due to authentication interruption, error occurrence, etc. (English) |
| MSG-1042 | MSG_INTERNAL_ERROR | Internal error occurred. Contact administrator. | | Message displayed to the user when the process stops due to authentication interruption, error occurrence, etc. (Korean)
Since entering Korean causes an error, please input in English. |
| MANAGE | LOG_LEVEL | 0 or 1 or 2 | | Criteria for recording in the Windows event log
0 = Record only errors
1 = Record errors + warnings only
2 = Record errors + warnings + informational messages, etc. |
INI configuration method
LDAP Search related
- When you want to use DNS lookup for the LDAP server’s hostName.
- When you want to use only the first address among multiple DNS lookup results
- When you want to attempt connections sequentially to all DNS lookup results.
- When you want to use an ID/password to connect to an LDAP server.
- When you want to connect only to allowed LDAP addresses (White IP list)
- Configure the user attributes to retrieve from LDAP
Regarding API connection
- Whether user information included in the token sent to the API server is encrypted
- MFA integrity verification method: Adapter verifies
- MFA integrity verification method: API server verification
etc.
- Options that must never be changed
- Options that must be obtained from the SingleID operations department and configured
- Options that need to be set according to the installation environment
LDAP Search related
When you want to use DNS Lookup with the hostName of the LDAP server
USE_LDAP_SEARCH=1
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_DNS_LOOKUP=1
The leading part of the LDAP server address must be uppercase “LDAP://”. It was found that connections fail when using lowercase on the development server during testing. If the DNS lookup fails, the LDAP_SERVER value is used directly as the LDAP connection address.
When you want to use only the first address among multiple DNS lookup results
LDAP_DNS_LOOKUP=1
LDAP_DNS_IF_FAIL_USE_NEXT=0
DNS Lookup 결과가 다음과 같다고 하면,
- IP1 = 10.10.10.10
- IP2 = 10.10.10.20
- IP3 = 10.10.10.30
LDAP_DNS_IF_FAIL_USE_NEXT=0, because it is set to Only IP1 attempts to connect to the server and then stops, regardless of success or failure. Therefore, setting LDAP_DNS_IF_FAIL_USE_NEXT=0 requires caution.
When you want to attempt connections sequentially to all DNS lookup results
LDAP_DNS_LOOKUP=1
LDAP_DNS_IF_FAIL_USE_NEXT=1
If the DNS Lookup result is as follows,
- IP1 = 10.10.10.10
- P2 = 10.10.10.20
- IP3 = 10.10.10.30
LDAP_DNS_IF_FAIL_USE_NEXT=1 is set, so Attempt to connect to IP1, IP2, and IP3 sequentially until successful. For example, if the connection to IP2 succeeds, IP3 will not attempt to connect.
When you want to use an ID/password when connecting to an LDAP server
LDAP_ID="******"
LDAP_PW="******"
Since MFA operates with system privileges, it may not require an id/pw. If the LDAP connection fails without an ID/password (you can determine the connection status from the server logs) Please try a configuration that uses an ID/password.
When you want to connect only to allowed LDAP addresses (White IP list)
LDAP_DNS_LOOKUP=2
또는
LDAP_DNS_LOOKUP=3
LDAP_WHITE_IP_01="70.2.180.218"
LDAP_WHITE_IP_02="fe80::644b:3c9f:c5ac:ce1c%10"
Without using the DNS lookup result as is, It compares against the White IP list and uses only the addresses that are included in the White IP list. For example, the DNS Lookup result is as follows,
- IP1 = 10.10.10.10
- IP2 = 10.10.10.20
- IP3 = 10.10.10.30
If the white IP list is as follows,
- WIP1 = 10.10.10.20
- WIP2 = 10.10.10.40
The actual address used is IP2 = WIP1 = 10.10.10.20.
The order follows the White IP list order. In the following case, attempts to connect to the server are made in the order 10.10.10.30, 10.10.10.20.
- IP1 = 10.10.10.10
- IP2 = 10.10.10.20
- IP3 = 10.10.10.30
- WIP1 = 10.10.10.30
- WIP2 = 10.10.10.20
If there is nothing that belongs to the White IP list,
- LDAP_DNS_LOOKUP=2 → Use the LDAP_SERVER value directly as the LDAP connection address.
- LDAP_DNS_LOOKUP=3 → Does not connect to the LDAP server. (Option that requires careful use)
Configure user attributes to query from LDAP
USERINFO_01=mobile;mobile;plainMobile
USERINFO_02=mail;email;plainEmail
USERINFO_03=company;company;plainCompany
USERINFO_04=department;department;plainDepartment
USERINFO_05=displayname;displayname;plainDisplayname
User information claim to be included in the Request Token sent to the MFA API server. It queries LDAP for the number of items specified in the ini list, includes the results in the token, and sends them to the MFA API server. Please refer to the description of “USERINFO_##” in the table on the page below for the configuration rules.
If you configure as in the above sample and the LDAP query result is as follows,
- mobile = +82-10-1234-5678
- mail = gd.hong@samsung.com
- company = no value
- department = no value
- displayname = Hong Gil Dong
The Request Token is composed as follows. If the query result is empty, include the empty value in the token as is (as with plainCompany and plainDepartment below).
{
"sys": "4312a8b9-75c4-7897-89a7-89347f18943e",
"uid": "gd.hong",
"displayUid": "gd.hong",
"rtn": "https://adpw5004.hw.dev:443/adfs/ls?client-request-id=4b978185-59e1-4018-c800-0080020000f6&pullStatus=0",
"nbf": 1716346465,
"exp": 1716432865,
"iat": 1716346465,
"authType": "saml",
"returnMethod": "get",
"plainMobile": "+82-10-1234-5678",
"plainEmail": "gd.hong@samsung.com",
"plainCompany": "",
"plainDepartment": "",
"plainDisplayname": "Hong Gil Dong"
}
To prevent querying LDAP, clear the setting value or mark it as a remark. In this case, the token does not contain user information.
USERINFO_01=
또는
#USERINFO_01=mobile;mobile;plainMobile
API connection related
Whether user information included in the token sent to the API server is encrypted
USERINFO_ENCRYPT=0
As of adapter version 1.2.0.8, it is not implemented the same as the API server’s encryption logic, making encrypted transmission impossible. The server uses AES GCM encryption, but the adapter cannot use AES GCM due to the characteristics of the development environment.
- Target information: mobile, email
Therefore, use USERINFO_ENCRYPT=0. The adapter and the API server are connected via HTTPS, so there should be no man‑in‑the‑middle hijacking issue.
MFA integrity verification method : adapter verification
MFA_VERIFY_TYPE=1
CACHE_ATTRIBUTE="otherPager"
CACHE_DELIMETER=";"
SKEW_SECONDS=3600
CACHE_LIFE_TIME=1d
Prerequisite for using this option
- Must have write (write) permission on LDAP → important weekly!
It uses the otherPager attribute in LDAP user information as a temporary storage area. Adapters lack a session concept, so they cannot store or remember information themselves.
The LDAP server has the same address as the LDAP Search. In other words, it means that options such as LDAP SERVER and LDAP_DNS_LOOKUP are also applied.
The above configuration is interpreted as follows.
- MFA_VERIFY_TYPE=1 : The method of storing/comparing the guid generated by the adapter in LDAP (adapter verification)
- Use the attribute called “otherPager” in LDAP user information
- Multiple pieces of information to be stored are separated by ‘;’ and concatenated as a string → example: “aaa;bbb;ccc”
- The allowed time difference between the time stored in LDAP for the request and the time when the JWT is received is 3600 seconds.
- The lifetime of req stored in LDAP is 1d (one day) → On the next access, check the time and delete the older entries.
MFA integrity verification method: API server verification
MFA_VERIFY_TYPE=2
MFA_VERIFY_URL="https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status"
MFA_VERIFY_SECURE_PROTOCOL="TLS12"
When the adapter receives the MFA result JWT token returned by the API server, it uses the req value from the token’s information to It queries the API server again and verifies that the result is 200.
The above configuration is interpreted as follows.
- MFA_VERIFY_TYPE=2 : The method where the adapter receives the request-id generated by the API server and uses it in the call URL (validated by the API server)
- Re-queries the MFA_VERIFY_URL address
- The security protocol uses TLS 1.2
Other
MAIN_CLAIM1=http://schemas.microsoft.com/ws/2008/06/identity/claims/authenticationmethod
MAIN_CLAIM2=http://schemas.microsoft.com/ws/2012/12/authmethod/otp
KEY_NAME_IN_RESPONSE="jwtTokenResponse"
CACHE_ATTRIBUTE="otherPager"
CACHE_DELIMETER=";"
BYPASS_ADAPTER=0
You must keep the contents of the INI file provided during the initial installation unchanged. If changed arbitrarily, the adapter may not work at all. Some values may need to be changed depending on the system context, but gathering input from the relevant parties or responsible personnel must precede any changes.
Options that need to be obtained from the SingleID operations department and configured
MFA_API_URL="https://stg1-cloud.singleid.samsung.net/test/common-api/open/v1.1/mfa/request"
CONSUMER_KEY="4312a8b9-75c4-7897-89a7-89347f18943e"
SECRET_KEY="gQgkyLVO6FR8vJkLtlgBiupsRM/ilgrbEfoKWRnhALd="
MFA_VERIFY_URL="https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status"
MFA_VERIFY_SECURE_PROTOCOL="TLS12"
API-related URLs, keys, and bearer values, which are provided by the SingleID operations department. The typical setting for the security protocol (MFA_VERIFY_SECURE_PROTOCOL) is TLS 1.2.
Options that must be set according to the installation environment
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_ID="******"
LDAP_PW="******"
LDAP_WHITE_IP_01="70.2.180.218"
LDAP_WHITE_IP_02="fe80::644b:3c9f:c5ac:ce1c%10"
These are the options determined after the installation environment assessment is completed.
INI configuration and results
- USERINFO_ENCRYPT
- USE_LDAP_SEARCH
- LDAP_DNS_LOOKUP
- LDAP_DNS_IF_FAIL_USE_NEXT
- LDAP_USE_IDPW
- MFA_VERIFY_TYPECautionThe consumer key and secret key used on this page are sample data. (fake value)
USERINFO_ENCRYPT
USERINFO_ENCRYPT=0
Set whether the user information included in the token sent by the adapter to the MFA API server is encrypted or plain text. (For example, mobile, email) Adapter version v1.2.0.8 (April 2024) currently cannot use AES/GCM/NoPadding, so it is set to plaintext. In other words, it is fixed at USERINFO_ENCRYPT=0. In the future, if the adapter can support AES/GCM/NoPadding, the configuration can be changed.
USE_LDAP_SEARCH
USE_LDAP_SEARCH=0
LDAP_SERVER=“LDAP://adpw5004.hw.dev” Since USE_LDAP_SEARCH is 0, the LDAP_SERVER value is not used. In other words, if USE_LDAP_SEARCH is 0, you can set LDAP_SERVER to an empty value or remove it.
USE_LDAP_SEARCH=1
What if the LDAP search fails?
- Treat the user information as empty and proceed to the next step.
- It doesn’t matter whether the cause of the failure is a server connection failure or missing information.
USE_LDAP_SEARCH=2
What if the LDAP search fails?
- Displays an error to the user and halts execution.
- The server log records as follows. (Or similar content) Unable to retrieve user information from LDAP.
This option should be used very carefully, and it is recommended to set it to USE_LDAP_SEARCH=1 whenever possible. It would be advisable to delegate handling of missing user information to the MFA API side. Because adapters inevitably provide insufficient user guidance and functionality in such situations.
LDAP_DNS_LOOKUP
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_DNS_LOOKUP=1
LDAP_WHITE_IP_01="10.10.10.10"
LDAP_WHITE_IP_02="10.10.10.30"
The adapter stores DNS lookup results in memory as a list (an ordered list) → LDAP address list Assume LDAP server redundancy and that each IP is as follows. (The IP that is looked up in DNS)
- IP#1 : 10.10.10.10
- IP#2 : 10.10.10.20
Since the DNS lookup result applies to both IPv4 and IPv6, the result appears as follows. (The below is a sample and may differ from the actual.)
- IP#1 = fe80::644b:3c9f:c5ac:ce1c%10
- IP#2 = fe80::f03d:b045:8dc3:f5ed%3
- IP#3 = 10.10.10.10
- IP#4 = 10.10.10.20
In this state, we can consider the following cases.
Case 1) If DNS Lookup failed
- The LDAP address list contains one entry, and the LDAP_SERVER value is assigned directly.
- In other words, the first value of the LDAP address list = “LDAP://adpw5004.hw.dev”
Case 2) If DNS Lookup succeeds and there is a White IP list setting (LDAP_WHITE_IP_##=“x.x.x.x”)
- The LDAP address list is created in the order of the White IP list.
- In the above sample, the values of the LDAP address list are as follows.
- first value = 10.10.10.10
- The second White IP 10.10.10.30 is not included in the LDAP address list because it does not appear in the DNS lookup results.
Case 3) If DNS Lookup succeeds and there is no White IP list configuration value (LDAP_WHITE_IP_##="" or LDAP_WHITE_IP_## not set)
- Incorporate the DNS lookup results into the LDAP address list.
- In the above sample, the values of the LDAP address list are as follows.
- first value = fe80::644b:3c9f:c5ac:ce1c%10
- Second value = fe80::f03d:b045:8dc3:f5ed%3
- third value = 10.10.10.10
- 4th value = 10.10.10.20
LDAP_DNS_IF_FAIL_USE_NEXT
LDAP_DNS_IF_FAIL_USE_NEXT=0
Assume that the LDAP address list is as follows.
- First value = 10.10.10.10
- Second value = 10.10.10.20
If the connection attempt to the first address 10.10.10.10 fails, do not proceed further. Set the LDAP search result (user information) to an empty value.
LDAP_DNS_IF_FAIL_USE_NEXT=1
Assume that the LDAP address list is as follows.
- First value = 10.10.10.10
- Second value = 10.10.10.20
If the connection attempt to the first address 10.10.10.10 fails, it attempts to connect to the second address. If it fails up to the second connection attempt, set the LDAP search result (user information) to an empty value.
LDAP_USE_IDPW
LDAP_USE_IDPW=0
LDAP_ID="******"
LDAP_PW="******"
If LDAP_USE_IDPW is 0, the LDAP_ID and LDAP_PW values are not used. In other words, if LDAP_USE_IDPW is 0, you can set LDAP_ID and LDAP_PW to empty values or delete them.
LDAP_USE_IDPW=1
LDAP_ID=""
LDAP_PW=""
If LDAP_USE_IDPW is 1, LDAP_ID and LDAP_PW values are required. Therefore, if you leave the LDAP_ID and LDAP_PW values empty or delete them as shown in the sample above, you will not be able to connect to the LDAP server.
LDAP_USE_IDPW=1
LDAP_ID="******"
LDAP_PW="******"
It means that the LDAP connection uses an ID/password; if the connection fails, verify that the ID/password are correct. Since INI files are plain text, there is a risk that the ID/password could be exposed. Therefore, it is necessary to configure the server environment so that LDAP access works without using an ID/password whenever possible.
MFA_VERIFY_TYPE
MFA_VERIFY_TYPE=0
Verification of MFA results from the adapter’s perspective, The user’s MFA execution is performed via the MFA API, and the adapter revalidates the result. If the MFA_VERIFY_TYPE value is 0, it means that the MFA result is not verified. In normal operation, it is not set to 0.
MFA_VERIFY_TYPE=1
CACHE_ATTRIBUTE="otherPager"
CACHE_DELIMETER=";"
The adapter directly performs MFA result verification. To do this, you need to use an LDAP server, and LDAP write permission is required. The CACHE_ATTRIBUTE value must not be changed.
MFA_VERIFY_TYPE=2
MFA_VERIFY_URL="https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status"
MFA_VERIFY_SECURE_PROTOCOL="TLS12"
We request the MFA API server to verify the MFA result. This is an alternative when you lack LDAP write permission.
INI configuration example
Example 1
USE_LDAP_SEARCH=0
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_DNS_LOOKUP=0
MFA_VERIFY_TYPE=1
CACHE_ATTRIBUTE="otherPager"
CACHE_DELIMETER=";"
- LDAP search is not used.
- The user information included in the token sent to the API server is set to an empty string value. (e.g., mobile, email, etc.)
- Even though LDAP search is not used, the LDAP_SERVER information is present because MFA_VERIFY_TYPE=1.
- DNS lookup for the LDAP server is not performed.
- In other words, use the LDAP_SERVER value directly as the LDAP address.
- The adapter directly validates the MFA result, using the LDAP server at this point. Therefore, an LDAP server address value must be provided.
- The above configuration means that the adapter stores the generated nonce in the “otherPager” attribute of the user information in the LDAP server, and retrieves it for comparison when MFA is completed.
Example 2
USE_LDAP_SEARCH=1
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_USE_IDPW=0
LDAP_SSLTLS=1
LDAP_DNS_LOOKUP=0
MFA_VERIFY_TYPE=1
CACHE_ATTRIBUTE="otherPager"
CACHE_DELIMETER=";"
- Use LDAP search.
- Retrieve user information from LDAP (e.g., mobile, email, etc.).
- If the LDAP connection fails or there are no query results, the user information is set to an empty string.
- Do not use an ID/password when connecting to LDAP.
- This applies to cases where you can connect to LDAP without entering an ID/password.
- Use SSL/TLS when connecting to LDAP to enhance security.
- DNS lookup for the LDAP server is not performed.
- In other words, use the LDAP_SERVER value directly as the LDAP address.
- The adapter directly validates the MFA result, using the LDAP server. Therefore, an LDAP server address must be provided.
- The above configuration means that the adapter stores the generated nonce in the “otherPager” attribute of the user information in the LDAP server, and retrieves it for comparison when MFA is completed.
Example 3
USE_LDAP_SEARCH=1
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_USE_IDPW=0
LDAP_DNS_LOOKUP=0
MFA_VERIFY_TYPE=2
MFA_VERIFY_URL="https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status"
MFA_VERIFY_SECURE_PROTOCOL="TLS12"
- Use LDAP search.
- Retrieve user information from LDAP. (e.g., mobile, email, etc.)
- If the LDAP connection fails or there are no query results, the user information is set to an empty string.
- Do not use an ID/password when connecting to LDAP.
- This applies to situations where LDAP can be accessed without entering an ID/password.
- DNS lookup is not performed for the LDAP server.
- In other words, use the LDAP_SERVER value directly as the LDAP address.
- The API server validates the MFA result, and the security protocol uses TLS 1.2.
- Extract the “req” value included in the MFA result response token received from the API server, and append it to the end of the result verification URL.
- → MFA_VERIFY_URL + “/” + req
- → Example: when req is “xxxxxx”,
- https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status/xxxxxx
Example 4
USE_LDAP_SEARCH=1
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_USE_IDPW=1
LDAP_SSLTLS=1
LDAP_ID="******"
LDAP_PW="******"
LDAP_DNS_LOOKUP=1
LDAP_DNS_IF_FAIL_USE_NEXT=0
MFA_VERIFY_TYPE=1
CACHE_ATTRIBUTE="otherPager"
CACHE_DELIMETER=";"
- Use LDAP search.
- Retrieve user information from LDAP. (e.g., mobile, email, etc.)
- If the LDAP connection fails or there are no query results, the user information is set to an empty string.
- Use id/pw when connecting to LDAP. This account must have write permission.
- Use SSL/TLS when connecting to LDAP to enhance security.
- Use DNS lookup for the LDAP server.
- Assign the DNS lookup results directly to the LDAP address table.
- If DNS lookup fails, only one LDAP_SERVER value is recorded in the LDAP address table.
- Attempt to connect only to the first entry in the LDAP address table.
- Even if it fails, it does not attempt to connect to the next server in the sequence.
- The adapter directly validates the MFA result, using the LDAP server at this stage. Therefore, an LDAP server address value must be provided.
- The above configuration means that the adapter stores the generated nonce in the “otherPager” attribute of the user information in the LDAP server, and retrieves it for comparison when MFA is completed.
Example 5
USE_LDAP_SEARCH=1
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_USE_IDPW=1
LDAP_SSLTLS=1
LDAP_ID="******"
LDAP_PW="******"
LDAP_DNS_LOOKUP=1
LDAP_DNS_IF_FAIL_USE_NEXT=0
LDAP_WHITE_IP_01=""
LDAP_WHITE_IP_02=""
MFA_VERIFY_TYPE=1
CACHE_ATTRIBUTE="otherPager"
CACHE_DELIMETER=";"
- The same configuration as Example 4.
- LDAP_WHITE_IP_## exists but is empty, which means it is equivalent to not existing.
Example 6
USE_LDAP_SEARCH=1
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_USE_IDPW=1
LDAP_SSLTLS=1
LDAP_ID="******"
LDAP_PW="******"
LDAP_DNS_LOOKUP=1
LDAP_DNS_IF_FAIL_USE_NEXT=1
LDAP_WHITE_IP_01="70.2.180.218"
LDAP_WHITE_IP_02="fe80::644b:3c9f:c5ac:ce1c%10"
MFA_VERIFY_TYPE=2
MFA_VERIFY_URL="https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status"
MFA_VERIFY_SECURE_PROTOCOL="TLS12"
- Use LDAP search.
- Retrieve user information from LDAP (e.g., mobile, email, etc.).
- If the LDAP connection fails or there are no query results, the user information is set to an empty string.
- Use id/pw when connecting to LDAP.
- This account must have write permission.
- Use SSL/TLS when connecting to LDAP to enhance security.
- Use DNS lookup for the LDAP server.
- Create an LDAP address table in the order of the White IP list by comparing the DNS lookup results with the White IP list.
- Even if the DNS lookup succeeds, if it is not in the White IP list, only one LDAP_SERVER value is recorded in the LDAP address table.
- If DNS lookup fails, only one LDAP_SERVER value is recorded in the LDAP address table.
- Attempt to connect to the LDAP address table sequentially from the beginning,
- If it fails, it attempts to connect to the next server in order.
- The API server validates the MFA result, and the security protocol uses TLS 1.2.
- Extract the “req” value included in the MFA result response token received from the API server, and append it to the end of the result verification URL.
- → MFA_VERIFY_URL + “/” + req
- → Example: when req is “xxxxxx”, https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status/xxxxxx
ADFS Adapter Management
Service Check
Check configuration
- AD FS Management > Service > Authentication Methods > Multi-Factor Authentication Methods > Verify ADFS MFA Adapter Configuration
- AD FS Management > Relying Party Trust, Access Control Policy: Allow all users and require MFA
- Test SP access: https://sptest.iamshowcase.com/ixs?idp=9a72b90bb06815f52d57a2eb71898f56fca097d0
Server Event Log
The logs of the Adapter execution process are recorded in the Windows Event Log area.
By adjusting the LOG_LEVEL value in the ADFSadapter.ini configuration, you can selectively record errors, warnings, and general logs.
Setting LOG_LEVEL in ADFSadapter.ini
| Set value | recording log |
|---|---|
| LOG_LEVEL=0 | Error log |
| LOG_LEVEL=1 | Error and warning logs |
| LOG_LEVEL=2 | Log errors, warnings, and general messages |
Windows event log location
- Computer Management (Local) > System Tools > Event Viewer > Application and Services Logs > MFA_Adapter
- At the beginning of each account’s log, the MFA version and account name are displayed → reference for log analysis/tracing
- During operation, focus on monitoring parts marked as “error” or “warning”.
Windows Event Log Description and Mitigation Steps
[#0000] Success
Err.Success
에러가 아니고, 단순한 로그입니다.
불필요한 로그이며, 이 로그가 보인다면 개발자에게 해당 로그 삭제하라고 하시면 됩니다.
[#0001] Invalid Arguments
Err.InvalidArguments
에러 : adapter 프로그램 내부의 함수 호출할 때, 함수 인자(argument) 누락이 있다는 뜻입니다.
조치 : 심각한 에러이며, 개발자에게 즉시 전달하여 신속히 조치되도록 합니다.
참고
별다른 증상없이 adapter가 동작할 수도 있으나, 심각한 에러 잠재성이 있으므로 방치하면 안됩니다.
[#1000] identityClaim 에서 계정정보(account)를 추출할 수 없습니다.
Err.IdentityClaimHasNoAccount
에러 : adapter 실행 초기에 AD 서버로부터 현재 사용자의 정보를 받는데, account 정보를 찾을 수 없습니다.
조치 : AD 서버 상태를 확인해봅니다.
참고
LDAP에서 Query 하는 것이 아니라, ADFS 내부적으로 처리되는 정보 흐름으로서, 이 상황이 발생하면 adapter가 정상 동작할 수 없는 환경이라고 보면 됩니다.
[#1001] INI 파일을 load 할 수 없습니다.
Err.FailToLoadIni
에러 : 서버에서 MFA 환경설정 INI 파일을 읽을 수 없습니다.
조치 : 서버에 다음의 경로에 파일이 있는지 확인
C:\ ADFSadapter \ ADFSadapter.ini
참고
만일, 파일이 있다면, 파일 속성 또는 권한 확인합니다.
[#1002] HTML 파일들을 load 할 수 없습니다.
Err.FailToLoadHtml
에러 : 서버에서 HTML 파일을 읽을 수 없습니다.
조치 : 서버에 다음의 경로에 파일이 있는지 확인합니다.
C:\ ADFSadapter \ Html_*.txt
참고
만일, 파일이 있다면, 파일 속성 또는 권한 확인합니다. 1개라도 없으면 에러 발생힙니다. 어떤 것이 누락되었는지는 서버 이벤트 로그에서 알 수 있습니다.
[#1003] LDAP에서 사용자 정보를 가져올 수 없습니다.
Err.FailToLdapSearch
에러 : LDAP 서버에 Query를 헀으나, AD 사용자 정보를 가져오지 못했습니다.
조치 : AD 서버 상태를 확인해봅니다.
참고
Token 구성에 mobile, email 정보가 필요한데, 이 정보들을 가져올때 실패한 것입니다. 사용자 정보가 존재한다면, mobile, email이 빈 값이어도 에러로 처리하지 않습니다. 그래서, 본 에러가 발생한 것은 LDAP Query 자체가 안된다고 보면 됩니다.
[#1004] BeginAuthentication 함수의 request에 URL 정보가 없습니다.
Err.NoURLInRequest
에러 : Adapter 실행 초기에 실행되는 BeginAuthentication 함수의 인자 request에 URL 정보가 없습니다.
조치 : SingleID MFA API 서버가 정상적으로 response를 보내는지 확인합니다.
참고
URL 정보가 없으면, SingleID MFA API 서버가 GET 방식으로 전송한 response를 사용할 수 없습니다.
[#1005] JWT token 생성을 할 수 없습니다.
Err.FailToMakeJwtToken
에러 : GenerateRequestToken 함수가 token 생성에 실패했습니다.
조치 : 정확한 원인은 서버 이벤트 로그에서 확인 가능하며, 개발자에게 원인 분석을 요청합니다.
[#1006] ADFSadapter 디렉토리 또는 INI 파일을 찾을 수 없습니다. C to Z 드라이브 중의 한 곳에 [drive]:/ADFSadapter/ADFSadapter.ini 파일이 존재해야 합니다.
Err.CannotFindDirOrIni
에러 : adapter 버전 1.2.0.6 부터 adapter 설치 위치가 C 드라이브 고정이 아닌 C to Z 드라이브 중의 한 곳에 설치할 수 있으며, adapter는 C to Z 드라이브 스캔을 통해서 설치된 위치를 알아냅니다. [drive]:/ADFSadapter/ADFSadapter.ini 파일이 존재해야 합니다.
조치 : 서버에 adapter 설치가 제대로 되었는지, 디렉토리명과 파일명이 정확한지 확인합니다. 드라이브 억세스가 막혀있는지 확인합니다.
[#2000] TryEndAuthentication()에 계정정보(account)가 없습니다.
Err.TryEndHasNoAccount
에러 : TryEndAuthentication 단계로 넘어왔으나, 계정 정보를 알 수 없습니다. (adpater 자체 에러)
조치 : 개발자에게 신속히 상황 전달 및 원인 분석을 요청합니다.
참고
이러한 경우는 절대 발생할 수 없으며, 발생해서도 안됩니다.
[#2001] Step 정보가 없습니다.
Err.NoStepInfo
에러 : MFA 진행 단계(step) 정보가 없습니다. (adpater 자체 에러)
조치 : 개발자에게 신속히 상황 전달 및 원인 분석을 요청합니다.
참고
이러한 경우는 절대 발생할 수 없으며, 발생해서도 안됩니다.
[#2002] 잘못된 Step 정보입니다.
Err.InvalidStepInfo
에러 : MFA 진행 단계(step) 정보가 잘 못 되었습니다. (adpater 자체 에러)
조치 : 개발자에게 신속히 상황 전달 및 원인 분석을 요청합니다.
참고
이러한 경우는 절대 발생할 수 없으며, 발생해서도 안됩니다.
[#3000] HTML 문자열을 가져옵니다.
Err.SucceedInGetHtml
에러가 아니고, 단순한 로그입니다. 서버의 Html_.txt 파일을 읽은 내용을 보여줍니다. Html_.txt 파일 내용 수정 후에 adpater가 파일 내용을 제대로 읽었는지 확인할 때 도움이 됩니다.
[#3001] HTML을 가져올 수 없습니다.
Err.FailToGetHtml
에러 : 서버의 Html_*.txt 파일을 읽지 못한 것입니다.
조치 : 파일이 존재하는지, Read 권한이 있는지, Lock 걸려있는지 등을 확인해봅니다.
[#4000] Html 파일이 존재하지 않습니다.
Err.HtmlFileNotFound
에러 : 서버의 Html_*.txt 파일을 읽지 못한 것입니다.
조치 : 파일이 존재하는지, 확인해봅니다.
[#4001] Html 파일이 존재하나, 파일 내용이 없습니다.
Err.HtmlFileIsEmpty
에러 : 서버의 Html_*.txt 파일을 읽지 못한 것입니다.
조치 : 파일 Read 권한이 있는지, Lock 걸려있는지 등을 확인해봅니다.
[#4002] HtmlPrefix 리스트에 없는 step 입니다.
Err.StepNotInHtmlPrefixList
에러 : adapter 내부에는 처리 step 별로 정의해 둔 keyword 리스트가 있는데, 그 리스트에 없는 keyword가 발견되었다는 뜻입니다.
조치 : 개발자에게 신속히 상황 전달 및 원인 분석을 요청합니다.
참고
이러한 경우는 절대 발생할 수 없으며, 발생해서도 안됩니다.
[#4003] HtmlPrefix 리스트에서 prefix 값이 비어 있습니다.
Err.EmptyPrefixInHtmlPrefixList
에러 : adapter 내부에는 처리 step 별로 정의해 둔 keyword 리스트가 있는데, 그 리스트에 아무런 내용이 없다는 뜻입니다.
조치 : 개발자에게 신속히 상황 전달 및 원인 분석을 요청합니다.
참고
이러한 경우는 절대 발생할 수 없으며, 발생해서도 안됩니다.
[#5000] ini 파일을 읽을 수 없습니다.
Err.FailToReadIniFile
에러 : INI 파일을 읽을 수 없습니다.
조치 : 서버에 다음의 경로에 파일이 있는지 확인
C:\ ADFSadapter \ ADFSadapter.ini
참고
만일, 파일이 있다면, 파일 속성 또는 권한 확인합니다.
[#5001] 시스템명칭(API_SYSTEMNAME)이 ini 에 없습니다.
Err.NoSystemNameInIni
에러 : INI 파일에 "API_SYSTEMNAME" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5002] claim1(MAIN_CLAIM1)이 ini 에 없습니다.
Err.NoClaim1InIni
에러 : INI 파일에 "MAIN_CLAIM1" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5003] claim2(MAIN_CLAIM2)가 ini 에 없습니다.
Err.NoClaim2InIni
에러 : INI 파일에 "MAIN_CLAIM2" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5004] ini 파일이 존재하지 않습니다.
Err.IniFileNotFound
에러 : 서버에서 MFA 환경설정 INI 파일을 찾을 수 없습니다.
조치 : 서버에 다음의 경로에 파일이 있는지 확인
C:\ ADFSadapter \ ADFSadapter.ini
[#5005] ini 리스트에 AddToList() 실패했습니다.
Err.FailToAddIniList
에러 : adapter 내부 에러입니다.
조치 : 개발자에게 신속히 상황 전달 및 원인 분석을 요청합니다.
참고
이러한 경우는 절대 발생할 수 없으며, 발생해서도 안됩니다.
[#5006] ini 파일에서 읽어온 key, value가 아무것도 없습니다.
Err.NoKeyValueInIni
에러 : INI 파일을 읽었으나, key, value 조합으로 설정된 것이 전혀 없습니다.
조치 : INI 파일 내용을 확인힙니다.
[#5007] LDAP 서버 정보가 ini 에 없습니다. (LDAP_SERVER)
Err.NoLdapServerValueInIni
에러 : INI 파일에 "LDAP_SERVER" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5008] MFA API URL이 ini 에 없습니다. (MFA_API_URL)
Err.NoMfaApiUrlValueInIni
에러 : INI 파일에 "MFA_API_URL" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5009] Consumer Key 값이 ini 에 없습니다. (CONSUMER_KEY)
Err.NoConsumerKeyValueInIni
에러 : INI 파일에 "CONSUMER_KEY" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5010] Secret Key 값이 ini 에 없습니다. (SECRET_KEY)
Err.NoSecretKeyValueInIni
에러 : INI 파일에 "SECRET_KEY" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5011] Cache Attribute 값이 ini 에 없습니다. (CACHE_ATTRIBUTE)
Err.NoCacheAttributeValueInIni
에러 : INI 파일에 "CACHE_ATTRIBUTE" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5012] Cache Delimeter 값이 ini 에 없습니다. (CACHE_DELIMETER)
Err.NoCacheDelimeterValueInIni
에러 : INI 파일에 "CACHE_DELIMETER" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5013] Skew Seconds 값이 ini 에 없습니다. (SKEW_SECONDS)
Err.NoSkewSecondsValueInIni
에러 : INI 파일에 "SKEW_SECONDS" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5014] Token expiration time 값이 ini 에 없습니다. (TOKEN_EXP_TIME)
Err.NoTokenExpTimeInIni
에러 : INI 파일에 "TOKEN_EXP_TIME" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5015] Cache life time 값이 ini 에 없습니다. (CACHE_LIFE_TIME)
Err.NoCacheLifeTimeInIni
에러 : INI 파일에 "CACHE_LIFE_TIME" 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#5016] 사용자 정보 claim 리스트가 ini 에 없습니다. (USERINFO_##)
Err.NoUserinfoListInIni
reserved (예약된 에러 코드이며, 향후 사용 예정)
[#5017] LDAP 연결시 id/pw 사용하도록 설정되어 있으나(LDAP_USE_IDPW=1), LDAP id 또는 pw가 ini 에 없습니다. (LDAP_ID, LDAP_PW)
Err.NoLdapIdPwInIni
에러 : LDAP 접속시 id/pw 사용하도록 설정되어 있으나, INI 파일에 LDAP_ID, LDAP_PW 설정 값이 없습니다.
조치 : INI 전체적으로 누락된 것이 없는지, INI 가 구버전의 것인지 등을 확인힙니다.
[#6000] AD(LDAP)에서 사용자 정보를 검색하는 과정에 Exception이 발생했습니다.
Err.ExceptionInAD
에러 : LDAP 서버에 Query를 헀으나, 그 과정 중에 Exception이 발생했습니다.
조치 : INI에 설정한 AD 서버 주소가 정확한지 확인해봅니다. 그리고, AD 서버 상태를 확인해봅니다.
참고
이벤트 로그에 있는 자세한 Exception 내용을 개발자에게 전달합니다.
[#6001] AD(LDAP)에서 사용자 정보를 찾을 수 없습니다.
Err.CannotFindUserInAD
에러 : LDAP 서버에 Query를 헀으나, AD 사용자 정보를 가져오지 못했습니다.
조치 : AD 서버 상태를 확인해봅니다.
참고
Token 구성에 mobile, email 정보가 필요한데, 이 정보들을 가져올때 실패한 것입니다. 사용자 정보가 존재한다면, mobile, email이 빈 값이어도 에러로 처리하지 않습니다. 그래서, 본 에러가 발생한 것은 LDAP Query 자체가 안된다고 보면 됩니다
User error message
If an error occurs during the MFA process, an error message is displayed on the user’s PC screen. The error message is fixed as “Internal error occurred. Contact administrator.”, and the error code is displayed on the next line.
Internal error occurred. Contact administrator.
ErrorCode : 0001
The following provides an explanation of the causes and remedies for error codes.
※ Refer to event logs of server internal processing steps other than user error messages.
ErrorCode : 0001
* Err.IdentityClaimHasNoAccount
* 함수 호출시 인자(arguments)가 잘 못 되었음
* 사용자에게 보여주는 에러는 아님
+ → 혹시 보인다면, 개발자에게 문의
+ → 이 시점의 서버 이벤트 로그를 봐야 함
ErrorCode : 1000
* Err.IdentityClaimHasNoAccount
* "identityClaim 에서 계정정보(account)를 추출할 수 없습니다."
* adapter 실행 초기에 AD 서버로부터 현재 사용자의 정보를 받는데, account 정보를 찾을 수 없음
* LDAP에서 Query 하는 것이 아니라, ADFS 내부적으로 처리되는 정보 흐름으로서,
+ 이 상황이 발생하면 adapter가 정상 동작할 수 없는 환경이라고 보면 됨
* AD 서버 상태를 먼저 확인해 볼 것
ErrorCode : 1001
* Err.FailToLoadIni
* 서버에서 MFA 환경설정 INI 파일을 읽을 수 없음
* 서버에 다음의 경로에 파일이 있는지 확인
+ C:\ ADFSadapter \ ADFSadapter.ini
* 만일, 파일이 있다면, 파일 속성 또는 권한 확인
ErrorCode : 1002
* Err.FailToLoadHtml
* 서버에서 HTML 파일을 읽을 수 없음
* 서버에 다음의 경로에 파일이 있는지 확인
+ C:\ ADFSadapter \ Html_*.txt
* 만일, 파일이 있다면, 파일 속성 또는 권한 확인
* 1개라도 없으면 에러 발생함 → 어떤 것이 누락되었는지는 서버 이벤트 로그에서 알 수 있음
ErrorCode : 1003
* Err.FailToLdapSearch
* "LDAP에서 사용자 정보를 가져올 수 없습니다."
* LDAP 서버에 Query를 헀으나, AD 사용자 정보를 가져오지 못함
* Token 구성에 mobile, email 정보가 필요한데, 이 정보들을 가져올때 실패하였음
* mobile, email이 빈 값이어도 에러로 처리하지 않음
* 그래서, 본 에러가 발생한 것은 LDAP Query 자체가 안된다고 보면 됨
ErrorCode : 1004
* Err.NoURLInRequest
* "BeginAuthentication 함수의 request에 URL 정보가 없습니다."
* Adapter 실행 초기에 실행되는 BeginAuthentication 함수의 인자 request에 URL 정보가 없음
* URL 정보가 없으면, SingleID MFA API 서버가 GET 방식으로 전송한 response를 사용할 수 없음
* SingleID MFA API 서버가 정상적으로 response를 보내는지 확인 필요
ErrorCode : 1005
* Err.FailToMakeJwtToken
* "JWT token 생성을 할 수 없습니다."
* GenerateRequestToken 함수가 token 생성에 실패하였음
* 정확한 원인은 서버 이벤트 로그에서 확인
ErrorCode : 1006
* Err.CannotFindDirOrIni
* "JWT token 생성을 할 수 없습니다."
* ADFSadapter 디렉토리 또는 INI 파일을 찾을 수 없음
* adapter 버전 1.2.0.6 부터 adapter 설치 위치가 C 드라이브 고정이 아닌 C to Z 드라이브 중의 한 곳에 설치할 수 있으며,
+ adapter는 C to Z 드라이브 스캔을 통해서 설치된 위치를 알아냄
* [drive]:/ADFSadapter/ADFSadapter.ini 파일이 존재해야 함
* 서버에 adapter 설치가 제대로 되었는지, 디렉토리명과 파일명이 정확한지 확인
* 드라이브 억세스가 막혀있는지 확인
ErrorCode : 2000
* Err.TryEndHasNoAccount
* "TryEndAuthentication()에 계정정보(account)가 없습니다."
* TryEndAuthentication 단계로 넘어왔으나, 계정 정보를 알 수 없음
* 이러한 경우는 절대 발생할 수 없음 (발생하였다면, 개발자에게 문의)
ErrorCode : 2001
* Err.NoStepInfo
* MFA 진행 단계(step) 정보가 없음
* 상세 정보와 원인은 서버의 이벤트 로그를 확인할 것
ErrorCode : 2002
* Err.InvalidStepInfo
* MFA 진행 단계(step) 정보가 잘 못 되었음
* 상세 정보와 원인은 서버의 이벤트 로그를 확인할 것
Modify ADFS login page
onload.js edit
Background
If multiple MFA methods are configured, the user will see a selection screen as shown below. If you are viewing the screen for the first time (MFA not yet completed), you need to make a selection on this screen.
The issue is that after completing MFA, the selection screen is displayed again, and the user has to make the selection again. This creates a user inconvenience, and selecting a different MFA for the second option will lead to unintended results.
After MFA is completed and the above selection screen appears, an automatic transition feature is needed. (auto submit) To achieve this, edit the contents of the onload.js file that already exists in ADFS. If it is not Multi MFA, editing the onload.js file is not required.
File path
It is located at the following path on the AD server.
- Directory = C:/default_WebTheme/script
- Filename = onload.js
File Edit
Add the script below at the end of the file content.
// ------------------------------------------ SingleID MFA : begin
function singleidMfa() {
var authOptions = document.getElementById('authOptions')
if (authOptions) {
var noticeflag = document.getElementById('mfaGreeting');
var url = document.location.href;
var isToken = url.indexOf('jwtTokenResponse');
if (noticeflag && isToken < 1) {
var browserLang = navigator.language || navigator.userLanguage;
// 다국어 처리
// 한국어
if (lang == 'ko-KR' || lang == 'ko') {
document.getElementById('footerPlaceholder').innerHTML="<h3 style='font-weight: bold;'><br/> <br/> ※ 신규 복합인증솔루션 테스트 중 (13:00~15:00) <br/> 'My Authentication Provider' 메뉴를 이용해주세요. </h3>";
}
// 중국어
else if (lang == "zh" || lang.indexOf("zh-") > -1) {
document.getElementById('footerPlaceholder').innerHTML="<h3 style='font-weight: bold;'><br/> <br/> ※ 正在??新的?合??解?方案 (13:00~15:00) <br/> ?登? 'My Authentication Provider' 菜?。 </h3>";
}
// 베트남어
else if (lang == "vi") {
document.getElementById('footerPlaceholder').innerHTML="<h3 style='font-weight: bold;'><br/> <br/> ※ đang ki?m tra gi?i phap xac th?c k?t h?p m?i (13:00~15:00) <br/> Xin vui long đ?ng nh?p vao trinh đ?n 'My Authentication Provider'. </h3>";
}
// 스페인어
else if (lang == "es" || lang.indexOf("es-") > -1) {
document.getElementById('footerPlaceholder').innerHTML="<h3 style='font-weight: bold;'><br/> <br/> ※ Prueba de una nueva solucion de autenticacion compleja (13:00~15:00) <br/> Inicie sesion en el menu 'My Authentication Provider'. </h3>";
}
// 영어
else {
document.getElementById('footerPlaceholder').innerHTML="<h3 style='font-weight: bold;'><br/> <br/> ※ Testing a new MFA solution (13:00~15:00) <br/> Please use 'My Authentication Provider' menu. </h3>";
}
}
var opt = document.getElementById('optionSelection');
if (opt && isToken > 0) {
opt.value = 'ADFSadapter';
document.forms['options'].submit();
}
}
}
window.addEventListener('load', function () {
singleidMfa();
});
// ------------------------------------------ SingleID MFA : end
Script functionality
- This applies when the page’s controls include authOptions.
- This operates after the page load has fully completed. (Because executing before that causes an error)
- Add to the load event using window.addEventListener (same as the window.onload event)
- Case 1 : When mfaGreeting is present in the control and jwtTokenResponse is not in the URL, display a user guidance message according to the browser’s language settings (multilingual)
- Case 2: If there is an optionSelection among the controls and the URL contains jwtTokenResponse, assign ADFSadapter to optionSelection and force the options form to submit.
Cautions when adding scripts
- To avoid affecting the existing script and to make management easier, placing it at the end of the script is safest.
Apply onload.js
Modify the onload.js file and apply the changes to enable ADFS Sign-in Page customization.
Application Method
Check Status
PS> Get-AdfsWebConfig ## Check the applied (active) WebTheme PS> Get-AdfsWebTheme ## Check the list of generated WebThemes
Apply theme
Theme application method 1) Create a new one from the default theme
PS> New-AdfsWebTheme -Name "custom_stg" -SourceName default ## 새로운 WebTheme 생성
PS> Set-AdfsWebTheme -TargetName "custom_stg" -Illustration @{Path="C:\adfs_Login_dev\illustration\image_0624\8.jpg"} -Logo @{Path="C:\adfs_Login_dev\images\logo.png"} -StyleSheet @{Path="C:\adfs_Login_dev\css\style.css"} -ON-LOADScriptPath "C:\adfs_Login_dev\script\ON-LOAD_new.js" ## custom 한 js 파일 적용
How to Apply Theme 2) Update from the Existing Theme
PS> New-AdfsWebTheme -Name "custom_stg" -SourceName [전자테마] ## 새로운 WebTheme 생성
PS > Set-AdfsWebTheme -TargetName "custom_stg" -OnLoadScriptPath "C:\adfs_Login_dev\script\onload_stg.js" ## custom 한 js 파일 적용
※ Theme application methods 1) and 2): server command screenshot. When organizing Confluence, the OnLoad command is automatically altered, so a screenshot is attached.
PS> Set-AdfsWebConfig -ActiveThemeName "custom_stg" ## 생성된 WebTheme 활성화
Restore existing theme
PS> Set-AdfsWebConfig -ActiveThemeName "default" ## 기존 WebTheme 활성화
A WebTheme can only apply one custom js file We also contacted Microsoft, but officially only one onload.js file can be applied, and the additional method we suggested does not work**
“the ON-LOAD.js is an integrated part of the HTML (the last script in the body) which always executes when the ADFS Page is loaded
There can be only one named ON-LOAD.JS per Web theme.
What is possible though is that additional ('external') scripts can be loaded as part of the actual ON-LOAD.js execution
let’s say in a specific part of your ON-LOAD.JS you want to load a bootstap.js which implements additional functionality
you would firstly import that additional JS to the webpage as AdditionalFileResource //it should not be named ON-LOAD.js
eg
Set-AdfsWebTheme -TargetName custom -AdditionalFileResource @{Uri='/adfs/portal/script/bootstrap.js';path="c:\theme\script\bootstrap.js"}
then you implement a loading functionality in the ON-LOAD.js which dynamically loads your additional script as needed”
Reference Document
http://www.javascriptkit.com/javatutors/loadjavascriptcss.shtml
https://www.codeproject.com/Articles/5310336/Dynamically-Loading-a-JavaScript-File
In other words, as stated in the official documentation, only one ON-LOAD.JS file can be applied to a single ADFS theme page. However, we presented that an additional file named bootstap.js can be applied on the same page using AdditionalFileResource.
Additional options can be applied when setting WebTheme
- You can apply illustration, logo, stylesheet, and other items through options.
PS> Set-AdfsWebTheme -TargetName "custom_stg" -Illustration @{Path="C:\adfs_Login_dev\illustration\image_0624\8.jpg"} -Logo @{Path="C:\adfs_Login_dev\images\logo.png"}
-StyleSheet @{Path="C:\adfs_Login_dev\css\style.css"} -OnLoadScriptPath "C:\adfs_Login_dev\script\onload_stg.js"
Reference Document
https://learn.microsoft.com/en-us/powershell/module/adfs/set-adfswebtheme?view=windowsserver2022-ps
Adapter display name change
When applying multiple adapters and the user selects one, you can set the adapter’s display name to show it to the user (browser). By default, the name (Name) used when registering the Adapter is displayed.
- Before applying
- Displayed to the user (browser) using the name used when registering the adapter.
- After applying
- Displayed to the user (browser) as the Adapter’s display name
- You can set different display names for each language.
During testing, the language setting is applied in three options: Korean, English, and Global
- The display name of the Adapter changes according to the browser’s language (chrome://settings/languages, edge://settings/languages).
- For browser languages that start with en- such as English (United States) and English (United Kingdom), the English setting is applied. If Korean or a non‑English language is selected, the global setting is applied.
- Configuration method
- Set the display name of ADFSadapter (new adapter name)
- ko(Korean), en(English), unset(global) set to three locales
Set-AdfsAuthenticationProviderWebContent -Name "ADFSadapter" -Locale ko -DisplayName "신규 ADFS 플러그인(ko)" -Description "신규 ADFS 플러그인 설명(ko)" Set-AdfsAuthenticationProviderWebContent -Name "ADFSadapter" -locale en -DisplayName "New ADFS Plugin (en)" -Description "New ADFS Plugin Description (en)" Set-AdfsAuthenticationProviderWebContent -Name "ADFSadapter" -DisplayName "New ADFS Plugin(global)" -Description "New ADFS Plugin Description(global)"- Set display name of MyAuthenticationProvider (existing Adapter name)
- ko(Korean), en(English), unset(global) set to three locales
Set-AdfsAuthenticationProviderWebContent -Name "MyAuthenticationProvider" -locale "ko" -DisplayName "기존 ADFS 플러그인(ko)" -Description "기존 ADFS 플러그인 설명 (ko)" Set-AdfsAuthenticationProviderWebContent -Name "MyAuthenticationProvider" -locale "en" -DisplayName "ADFS Plugin (en)" -Description "ADFS Plugin Description (en)" Set-AdfsAuthenticationProviderWebContent -Name "MyAuthenticationProvider" -DisplayName "ADFS Plugin (global)" -Description "ADFS Plugin Description (global)"
Locale ID: see the following reference [MS-OE376]; separate inquiry
Tips related to ADFS Adapter
Adapter registration and operation sequence summary
- Adapter DLL → Register in the GAC area → Register in ADFS → Check the multi‑factor authentication method in ADFS management → Adapter operates when AD authentication requires MFA
Tools required for managing adapters (gacutil.exe)
- Tool for registering or unregistering the Adapter DLL in the AD FS server’s GAC.
What is GAC?
It is an abbreviation for Global Assembly Cache, and the special cache GAC for sharing .NET assemblies across the entire machine is located in a directory named assembly under the Windows directory.
- Assemblies installed in the GAC must be strongly-named assemblies.
- A DLL must include the Version, Culture, and public key along with its name.
- When a DLL is installed in the GAC, it takes priority at runtime.
- Even when using the same DLL name, multiple versions can coexist.
Register/Delete Adapter in GAC (using gacutil.exe)
Usually used in cmd, but for convenience we use it in PowerShell (however, it must be used in the form .\gacutil.exe).
- Register in GAC
PS C:\ADFSadapter> .\gacutil.exe /if ADFSadapter.dll
- Deleted from GAC → C:\ADFSadapter\ADFSadapter.dll file is not deleted
PS C:\ADFSadapter> .\gacutil.exe /u ADFSadapter
- Check whether it is registered in GAC
PS C:\ADFSadapter> .\gacutil.exe /l ADFSadapter
- DLL replacement order in the GAC
- Delete with gacutil.exe /u
- Replace the C:\ADFSadapter\ADFSadapter.dll file
- Register with gacutil.exe /if
Register/Delete GAC Assembly in ADFS (PowerShell commands)
- Register with ADFS First, check the Version, Culture, and public key information using the gacutil.exe /l option.
PS C:\ADFSadapter> .\gacutil.exe /l ADFSadapter
ADFSadapter, Version=1.0.0.0, Culture=neutral, PublicKeyToken=3b3a799d949dc414, processorArchitecture=MSIL
결과 문자열을 이용하여 TypeName 구성하고, AD FS에 등록
( TypeName의 앞부분은 ADFSadapter.AuthenticationAdapter 는 고정값 )
PS C:\ADFSadapter> $typename = "ADFSadapter.AuthenticationAdapter, ADFSadapter, Version=1.0.0.0, Culture=neutral, PublicKeyToken=3b3a799d949dc414, processorArchitecture=MSIL"
PS C:\ADFSadapter> Register-AdfsAuthenticationProvider -TypeName $typename -Name "ADFSadapter" -Verbose
- Delete from ADFS
PS C:\ADFSadapter> Unregister-AdfsAuthenticationProvider -Name "ADFSadapter"
- Check if it is registered in ADFS
PS C:\ADFSadapter> Get-AdfsAuthenticationProvider
ADFS Adapter replacement order
- Disable multi-factor authentication method in ADFS management
- Unregister-AdfsAuthenticationProvider
- Restart ADFS service
- Replace the DLL in the GAC
- Register-AdfsAuthenticationProvider
- Restart ADFS service
- Set multi-factor authentication method in ADFS management
The above step1) ~ step7) process can be automated with the replace_dll.ps1 script file.
If the MFA feature does not work properly
AD account/password authentication unavailable
→ Since it is before the MFA stage, it is not related to the AdapterCheck adapter registration status
→ Verify that ADFS MFA Adapter is displayed when executing the Get-AdfsAuthenticationProvider commandCheck AD FS configuration
→ Check that ADFS MFA Adapter is specified in Service > Authentication Methods > Multi-Factor Authentication Methods
→ Service > Device Registration Check that it is configured
→ Access Control Policy is configured to require MFA, verify this.Check Adapter execution logs
→ Log location: Computer Management > System Tools > Event Viewer > Application and Services Logs > MFA_Adapter
→ Check if there are logs displayed as error
→ If an error occurs, forward the log details to the developer for analysis.
9.5.2.1.6.2 - Adapter Configuration Guide
Adapter Configuration Guide
This is a description of the Adapter configuration file. Before applying the ADFS Adapter, you must first configure the environment.
adapter installation location changes
Starting with adapter 1.2.0.6, installation is possible on drives other than the C drive.
- Existing : Installed only at C:/ADFSadapter
- Change : Install at the root of the C to Z drive
- Example: C:/ADFSadapter , D:/ADFSadapter , E:/ADFSadapter , …… , Z:/ADFSadapter
- Caution : It must be installed on only a single drive; if installed on multiple drives, the system scans from C to Z and uses the first directory found.
The following example assumes the adapter is installed in the C:\ADFSadapter directory.
If installed on a drive other than C, simply change the drive letter in the example below.
- Example: If installed in D:\ADFSadapter, the ini path → D:\ADFSadapter\ADFSadapter.ini
File name and path
- File name: ADFSadapter.ini
- Full path: C:\ADFSadapter\ADFSadapter.ini
- File encoding: must be saved as UTF-8 (Korean characters may become garbled)
Points to note
* 값을 표현할때 "와" 를 사용할 수 있으며 = 좌우에 빈칸을 입력해도 됩니다.
+ Value 의 앞뒤에 있는 공백은 Trim 처리 됩니다.
+ 아래의 Value는 모두 동일함
+ 예1) MAIN_TITLE = DWP MFA Adapter
+ 예2) MAIN_TITLE = DWP MFA Adapter
+ 예3) MAIN_TITLE = "DWP MFA Adapter"
+ 예4) MAIN_TITLE = " DWP MFA Adapter "
* 섹션 이름들 중에 뒷부분에 -1033, -1042 가 붙는 것들은 locale 을 의미합니다.
+ 최소한 1033 은 반드시 있어야 합니다.
+ locale number : 1033 (en-us), 1042 (ko)
+ locale section : MFA-1033, MFA-1042, TXT-1033, TXT-1042, MSG-1033, MSG-1042
Example of ini file structure
Among the example configuration values below, some values are masked for security purposes, and the actual values are not asterisks.
# ADFS MFA Adapter 환경 설정
# 설치위치 변경 사항
# - v1.2.0.6 이전 : C:\ADFSadapter\ADFSadapter.ini
# - v1.2.0.6 부터 : C 이외의 다른 드라이브에 설치할 수 있음 (adapter 리소스 설치한 위치와 동일)
# 예시: C:\ADFSadapter\ADFSadapter.ini , D:\ADFSadapter\ADFSadapter.ini , E:\ADFSadapter\ADFSadapter.ini
# 주의 : DLL 파일명은 ADFSadapter.dll 이며, 기존의 Nexsign 연계한 MFAadapter.dll과는 다름
# 값을 표현할때 " 와 ' 를 사용할 수 있으며 = 좌우에 빈칸을 입력해도 됩니다
# Value 의 앞뒤에 있는 공백은 Trim 처리 됩니다.
# 아래의 Value는 모두 동일합니다.
# 예1) MAIN_TITLE=ADFS MFA Adapter
# 예2) MAIN_TITLE = ADFS MFA Adapter
# 예3) MAIN_TITLE = "ADFS MFA Adapter"
# 예4) MAIN_TITLE = " ADFS MFA Adapter "
# 섹션 이름들 중에 뒷부분에 -1033, -1042 가 붙는 것들은 locale 을 의미합니다
# 최소한 1033 은 반드시 있어야 합니다
# locale number : 1033 (en-us), 1042 (ko)
# locale section : MFA-1033, MFA-1042, TXT-1033, TXT-1042, MSG-1033, MSG-1042
# LOG_LEVEL (Windows 이벤트 로그에 기록하는 기준)
# 0 : Error
# 1 : Error + Warning
# 2 : Error + Warning + Information + Debug
[MAIN]
MAIN_MFA_TITLE="ADFS MFA Adapter"
MAIN_CLAIM1=http://schemas.microsoft.com/ws/2008/06/identity/claims/authenticationmethod
MAIN_CLAIM2=http://schemas.microsoft.com/ws/2012/12/authmethod/otp
# MFA API 정보
# URL 끝부분에 "/" 붙이지 말 것
#MFA_API_URL="https://stg2-cloud.singleid.samsung.net/test/common-api/open/v1.1/mfa/request"
MFA_API_URL="https://stg1-cloud.singleid.samsung.net/test/common-api/open/v1.1/mfa/request"
CONSUMER_KEY="**************************************"
SECRET_KEY="**************************************"
# Donmain vs Consumer Key 리스트
# 도메인별로 Consumer Key가 다른 경우에는 리스트로 나열 (이런 경우, 위의 CONSUMER_KEY 값을 비울 것)
# Reqeust Token의 sys 값에 대입
# 형태 : DOMAIN_CONSUMER_KEY_##=domain;consumerKey
# 예시: DOMAIN_CONSUMER_KEY_01=aaa.com;**************************************
# DOMAIN_CONSUMER_KEY_02=bbb.com;**************************************
# (주의) CONSUMER_KEY 값과 리스트 값이 모두 있다면, CONSUMER_KEY 값만 사용함
DOMAIN_CONSUMER_KEY_01=aaa.com;**************************************
DOMAIN_CONSUMER_KEY_02=bbb.com;**************************************
# Donmain vs Secret Key 리스트
# 도메인별로 Secret Key가 다른 경우에는 리스트로 나열 (이런 경우, 위의 SECRET_KEY 값을 비울 것)
# 형태 : DOMAIN_SECRET_KEY_##=domain;secretKey
# 예시: DOMAIN_SECRET_KEY_01=aaa.com;**************************************
# DOMAIN_SECRET_KEY_02=bbb.com;**************************************
# (주의) SECRET_KEY 값과 리스트 값이 모두 있다면, SECRET_KEY 값만 사용함
DOMAIN_SECRET_KEY_01=aaa.com;**************************************
DOMAIN_SECRET_KEY_02=bbb.com;**************************************
# LDAP Search 결과에 따른, MFA 진행 여부
# 0 : LDAP Search를 하지 않음 (아래의 LDAP_SERVER, LDAP_USE_IDPW, ... 등의 정보 사용하지 않음. token에는 빈 값 대입)
# 1 : LDAP Search를 시도하지만 실패해도 관계없음 (서버 실패, 정보 없음 등이 발생하여도 MFA 진행함. token에는 빈 값 대입)
# 2 : LDAP Search가 성공 & 사용자 정보가 존재해야 함 (사용자 정보가 존재할 경우에만 진행함. 단, 결과 값이 빈 값이어도 진행함)
USE_LDAP_SEARCH=1
# LDAP 주소와 ID/PW
# LDAP_SERVER는 domain, ipv4, ipv6 등의 3가지 모두 가능하며, 앞부분에 대문자 "LDAP://" 을 붙여야 함 (반드시 대문자)
# 예시: LDAP://adpw5004.hw.dev , LDAP://70.2.180.218 , LDAP://fe80::644b:3c9f:c5ac:ce1c%10
# ID/PW를 사용하려면 LDAP_USE_IDPW 값을 1, 사용하지 않으려면 LDAP_USE_IDPW 값을 0 으로 설정
# SSL/TLS 사용하려면 LDAP_SSLTLS 값을 1, 사용하지 않으려면 LDAP_SSLTLS 값을 0 으로 설정 (단, LDAP_USE_IDPW=1 인 경우에만 해당)
LDAP_SERVER="LDAP://adpw5004.hw.dev"
LDAP_USE_IDPW=1
LDAP_SSLTLS=1
LDAP_ID="isadmin"
LDAP_PW="sds*****"
# DNS Lookup을 하여 LDAP 서버(LDAP_SERVER)의 IP 주소를 확인하고, IP 주소 기반으로 접속 여부
# LDAP_SERVER 값이 IP(ipv4, ipv6)로 설정되어 있어도 DNS Lookup을 수행하며, IP 그대로 리턴됨
# 만약, DNS Lookup을 실패하면, LDAP_SERVER 값 그대로 접속
# 0 : LDAP_SERVER 값 그대로 서버에 접속 (DNS lookup 하지 않음)
# 1 : DNS lookup으로 IP 주소를 확인하여 LDAP 서버에 접속 (DNS lookup 결과 리스트에서 첫번째 IP 사용)
# 2 : DNS lookup으로 IP 주소를 확인하고, LDAP_WHITE_IP_## 리스트에서 가장 먼저 해당되는 IP를 사용 (리스트에 없으면, LDAP_SERVER 사용)
# 3 : DNS lookup으로 IP 주소를 확인하고, LDAP_WHITE_IP_## 리스트에서 가장 먼저 해당되는 IP를 사용 (리스트에 없으면, LDAP 접속 안함)
LDAP_DNS_LOOKUP=1
# DNS Lookup 결과가 여러 개일때, 첫번째 IP 주소로 연결이 안되면 그 다음 IP 주소로 시도할지 여부
# 예시: lookup 결과가 4개 : 1차 IP 연결 실패 -> 2차 IP 연결 시도 & 싪패 -> 3차 IP 연결 시도 & 싪패 -> 4차 IP 연결 시도
LDAP_DNS_IF_FAIL_USE_NEXT=1
# DNS Lookup 결과와 비교하는 접속 허용된 LDAP 서버 IP 리스트 (LDAP_DNS_LOOKUP = 2 or 3 인 경우에만 해당)
# LDAP_WHITE_IP_## 형태이며, 01부터 99까지 순차적으로 기록
# DNS Lookup 결과와 리스트를 순차적으로 비교
# IPv4, IPv6 형태로 기록 (동일한 서버의 IPv4, IPv6가 있다면 리스트의 앞순위에 있는 IP가 적용됨)
# DNS Lookup 결과 순서와 White IP 리스트 순서가 다르다면 -> White IP 리스트 순서를 따름
LDAP_WHITE_IP_01="70.2.180.218"
LDAP_WHITE_IP_02="fe80::644b:3c9f:c5ac:ce1c%10"
# 사용자 정보를 암호화할지 여부 (예: mobile, email 등)
# 대상 : USERINFO_## 리스트
# 암호화 여부에 따라 API 서버에 전송하는 token의 claim 이름이 다름
# 0 : 암호화 하지 않음 -> token의 claim 이름이 plainMobile, plainEmail
# 1 : 암호화 -> token의 claim 이름이 mobile, email
USERINFO_ENCRYPT=0
# LDAP Search할 사용자 정보 attribute name과 JWT token에 사용할 claim name (2개 값을 구분하는 delimeter = ";")
# 형태: USERINFO_## = attribute;encryptedClaim;plainClaim
# 예시: LDAP에서 "mail" 속성을 읽어서, JWT에 "email" claim으로 사용된다면 -> "mail;email;plainEmail"
# key 명칭은 "USERINFO_##" 형태로 하고, 시작은 USERINFO_01
# key 갯수 : 0개 ~ 최대 99개 (0개인 경우, ini에 아무것도 적지 않으면 되며, USERINFO_00 이라고 적지 말 것)
# 주의사항) USERINFO_##에서 ## 에 해당되는 숫자는 반드시 01부터 시작하며, 여러 개인 경우 번호가 끊어지지 않아야 함
# USERINFO_01, USERINFO_02, USERINFO_03 : OK (01, 02, 03 정보가 사용됨)
# USERINFO_01, USERINFO_02, USERINFO_05 : 02까지 읽고, 끊어진 번호 이후는 사용하지 않음 (01, 02 정보가 사용됨)
USERINFO_01=mobile;mobile;plainMobile
USERINFO_02=mail;email;plainEmail
# MFA API 서버가 Callback 해줄때, 결과 Parameter에 사용되는 Key 이름
# 예시: https://adpw5004.hw.dev/adfs/ls?client-request-id=xxxxxx&pullStatus=0&jwtTokenResponse=yyyyyy
KEY_NAME_IN_RESPONSE="jwtTokenResponse"
# JWT Token의 exp에 적용될 더하기 값
# 형테 : 일시분초(dhms) 형태의 문자열 -> 1d=86400, 1h=3600, 1m=60 (dhms 가 전혀 없는 단순 숫자는 초로 판단함)
# 예시1 : 1d02h38m27s -> 95907 초
# 예시2 : 12345 -> 12345 초
TOKEN_EXP_TIME=1d
# API 호출할때 구성하는 token에 client claim을 추가할지 여부
# client : SAML인 경우 issuer, OIDC인 경우 client-id
# 0 : token에 client 포함시키지 않음
# 1 : token에 client 포함
TOKEN_CLAIM_CLIENT=0
# MFA nonce(guid, requset-id) 검증 방법
# 0 : 검증 안함
# 1 : adapter가 생성한 guid를 LDAP에 저장/비교하는 방식 (adapter가 검증)
# -> 관련 설정 값 : CACHE_ATTRIBUTE, CACHE_DELIMETER, SKEW_SECONDS, CACHE_LIFE_TIME
# 2 : API 서버가 생성한 requeset-id를 adapter가 받아서 호출 URL에 사용하는 방식 (API 서버가 검증)
# -> 관련 설정 값 : MFA_VERIFY_URL
MFA_VERIFY_TYPE=2
# MFA 결과검증 URL (서버 to 서버 통신) : URL 뒷부분에 API 서버로부터 받은 {request-id}를 덧붙여서 호출함
# adapter는 리턴 200 (OK) 인지 확인하여 MFA 결과 처리
# URL 끝부분에 "/" 붙이지 말 것
MFA_VERIFY_URL="https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status"
# MFA 결과검증할때 사용할 보안 프로토콜
# 선택 가능한 프로토콜 (대소문자 구분 없음) : TLS12, TLS13
# (주의) SSL3, TLS, TLS11 은 사용하지 않음
MFA_VERIFY_SECURE_PROTOCOL="TLS12"
# 사용자의 req guid 값을 저장할 LDAP attribute의 이름
# (주의) LDAP에 write 권한이 있어야 함
CACHE_ATTRIBUTE="otherPager"
# LDAP에 저장하는 req + 시간 정보를 조합할때 사용하는 delimeter -> "req;시간"
CACHE_DELIMETER=";"
# LDAP에 저장된 req의 시간과 JWT 수신시 시간의 차이 허용치 (초단위)
# MFA 선택화면 누를 때가 아니라, AD 로그인 직후의 시간이므로 (MFA 선택화면 보일때 이미 시간이 저장되었음)
# 사용자가 MFA 선택화면 누르고 Passcode 입력할 때까지의 시간이 아님
# 따라서, tight 하게 시간을 설정하면 안되며, 1시간 정도가 적당?? (MFA 선택을 1시간 고민하는 사람이 있나?)
SKEW_SECONDS=3600
# LDAP에 저장된 req의 수명 -> 다음 access시 시간 확인해서 이전의 오래된 것들 삭제
# 형태 : 일시분초(dhms) 형태의 문자열 -> 1d=86400, 1h=3600, 1m=60 (dhms 가 전혀 없는 단순 숫자는 초로 판단함)
# 예시1 : 1d02h38m27s -> 95907 초
# 예시2 : 12345 -> 12345 초
CACHE_LIFE_TIME=1d
# Adapter 기능을 ByPass 할 것인지 여부 (0=정상 사용, 283901=무력화, 그 외 값들=정상 사용)
# MFA 기능 문제로 급하게 adapter 기능의 무력화가 필요한 비상 상황에서 사용
# 평상시에는 절대로 수정하지 말 것 -> 평상시 값은 0
# 주의 : 무력화하려면 반드시 정확한 값을 설정해야 함 (0 이외의 숫자가 해당되는 것이 아니며 정확한 숫자 필요함. noise 우려)
BYPASS_ADAPTER=0
[API]
API_SYSTEMNAME=SingleID
[MSG-1033]
MSG_INTERNAL_ERROR="Internal error occurred. Contact administrator."
[MSG-1042]
MSG_INTERNAL_ERROR="Internal error occurred. Contact administrator."
[MANAGE]
LOG_LEVEL=2
Configuration value description
- Fixed value : It means that the value displayed in the Setting Value column of the table below is used as-is when installing on the ADFS server.
- If you want to add languages other than English and Korean, you can add them for two sections.
- MSG-1033, MSG-1042
| dss | Key | Configuration values (example) | Fixed value | Explanation |
|---|---|---|---|---|
| MAIN | MAIN_MFA_TITLE | ADFS MFA Adapter | O | HTML page title (no impact on MFA functionality) |
| MAIN_CLAIM1 | http://schemas.microsoft.com/ws/2008/06/identity/claims/authenticationmethod | O | Apply the left value exactly as is | |
| MAIN_CLAIM2 | http://schemas.microsoft.com/ws/2012/12/authmethod/otp | O | Apply the left value exactly as is | |
| MFA_API_URL | https://stg2-cloud.singleid.samsung.net/test/common-api/open/v1.1/mfa/request | SingleID MFA API URL
| ||
| CONSUMER_KEY | 4312a8b9-75c4-7897-89a7-89347f18943e | Consumer Key issued by SingleID | ||
| SECRET_KEY | gQgkyLVO6FR8vJkLtlgBiupsRM/ilgrbEfoKWRnhALd= | Secret Key issued by SingleID
| ||
| DOMAIN_CONSUMER_KEY_01 | 4312a8b9-75c4-7897-89a7-89347f18943e | Domain vs Consumer Key list
| ||
| DOMAIN_CONSUMER_KEY_02 | 96567780-2b12-23da-637c-9375a6502d5a | |||
| DOMAIN_CONSUMER_KEY_## | 367c89d5-88f7-978a-9739-8ed21748f36b | |||
| DOMAIN_SECRET_KEY_01 | gQgkyLVO6FR8vJkLtlgBiupsRM/ilgrbEfoKWRnhALd= | Domain vs Secret Key list
| ||
| DOMAIN_SECRET_KEY_02 | kgkWRnLygQhsRgrLVbtKlO6FiLdABupEgoMR8v/ilfJ= | |||
| DOMAIN_SECRET_KEY_## | dABupkRnLygQhsrLgWVRbt8vRgkLilLKlO1FioMgfJE= | |||
| USE_LDAP_SEARCH | 0 or 1 or 2 | Whether to proceed with MFA based on LDAP Search results
| ||
| LDAP_SERVER | LDAP://adpw5004.hw.dev | LDAP address that can query AD user information
| ||
| LDAP_USE_IDPW | 0 or 1 | Whether to use id/pw when connecting to LDAP
| ||
| LDAP_SSLTLS | 0 or 1 | Whether to use SSL/TLS when connecting to LDAP
| ||
| LDAP_ID | LDAP connection ID | LDAP connection ID (when LDAP_USE_IDPW=1) | ||
| LDAP_PW | LDAP connection pw | LDAP connection password (when LDAP_USE_IDPW=1) | ||
| LDAP_DNS_LOOKUP | 0 or 1 or 2 or 3 | Perform a DNS lookup to obtain the IP address of the LDAP server (LDAP_SERVER) and determine connection based on the IP address
| ||
| LDAP_DNS_IF_FAIL_USE_NEXT | 0 or 1 | When there are multiple DNS lookup results, whether to try the next IP address if the first IP address fails to connect
| ||
| LDAP_WHITE_IP_01 | 70.2.180.218 | LDAP server IP list allowed for connection compared with DNS Lookup results (applicable only when LDAP_DNS_LOOKUP = 2 or 3)
| ||
| LDAP_WHITE_IP_02 | fe80::644b:3c9f:c5ac:ce1c%10 | |||
| LDAP_WHITE_IP_## | A. : 01 ~ 99 White IP address (IPv4 or IPv6) | |||
| USERINFO_ENCRYPT | 0 or 1 | Whether to encrypt user information (e.g., mobile, email, etc.)
| ||
| USERINFO_01 | mobile;mobile;plainMobile | O | The attribute name of user information to search in LDAP and the claim name to use in the JWT token (delimiter separating the three values = “;”)
| |
| USERINFO_02 | mail;email;plainEmail | O | ||
| USERINFO_## | A. : 01 ~ 99 [LDAP attribute name];[encrypted token claim name];[plain token claim name] | |||
| KEY_NAME_IN_RESPONSE | jwtTokenResponse | O | When the MFA API server performs a callback, the key name used in the result parameters | |
| TOKEN_EXP_TIME | 1d | The additive value applied to the JWT token’s exp
| ||
| TOKEN_CLAIM_CLIENT | 0 or 1 | Whether to add a client claim to the token configured when calling the API
| ||
| MFA_VERIFY_TYPE | 0 or 1 or 2 | MFA nonce (guid, request-id) verification methods
| ||
| MFA_VERIFY_URL | https://stg1-cloud.iam.samsung.net/test/common-api/open/v1.1/mfa/request/status | MFA verification URL (server-to-server communication): Append the {request-id} received from the API server to the end of the URL and call it → the adapter checks that the return is 200 (OK) to process the MFA result
| ||
| MFA_VERIFY_SECURE_PROTOCOL | TLS12 or TLS13 | Security protocol to use when verifying MFA results
| ||
| CACHE_ATTRIBUTE | otherPager | O | Name of the LDAP attribute that stores the user’s req guid value | |
| CACHE_DELIMETER | ; | Delimiter used when combining the req and time information stored in LDAP -> “req;time” | ||
| SKEW_SECONDS | 3600 | Allowed time difference (in seconds) between the request time stored in LDAP and the time the JWT is received
| ||
| CACHE_LIFE_TIME | 1d | Lifetime of req stored in LDAP -> check the time on the next access and delete the older ones
| ||
| BYPASS_ADAPTER | 0 or 283901 | Whether to bypass the Adapter function (0 = normal operation, 283901 = disable, other values = normal operation)
| ||
| API | API_SYSTEMNAME | SingleID | O | (No impact on MFA functionality) |
| MSG-1033 | MSG_INTERNAL_ERROR | Internal error occurred. Contact administrator. | Message displayed to the user when the process stops due to authentication interruption, error occurrence, etc. (English) | |
| MSG-1042 | MSG_INTERNAL_ERROR | Internal error occurred. Contact administrator. | Message displayed to the user when the process stops due to authentication interruption, error occurrence, etc. (Korean)
| |
| MANAGE | LOG_LEVEL | 0 or 1 or 2 | Criteria for recording in the Windows Event Log
|
9.5.3 - Release Note
SingleID
- Add AI agent registration and management functionality
- AI agent registration and configuration features for authentication between the MCP server and MCP client have been added.
- The features for registering information, generating authentication key values, and retrieving information for AI agent authentication have been newly added.
- Add 3rd Party TOTP Authenticator support
- A TOTP authentication method registration/setting feature has been added to support 3rd Party Authenticators such as Google Authenticator and Microsoft Authenticator in the Admin Portal.
- A feature has been added that allows users to register or delete a 3rd Party TOTP Authenticator in the User Portal and MFA Portal.
- New SMS Provider (InfoBank) added
- You can register and use the Infobank SMS service, an external SMS service provider.
- Improved admin authentication delegation feature
- When no authentication method is available for identity verification, we have enhanced the system so that the admin authentication delegation feature can be applied when 1) registering an authentication method or 2) attempting to log in.
- You can register a list of authentication delegation administrators in the JWT Token.
- Enhanced to allow the authentication delegation manager list to be registered in SCP Cloud Object Storage and utilized.
- The detailed MFA SP configuration feature has been added in the Admin Portal.
- Whether to perform delegated authentication at login
- Whether to perform verification during registration when no authentication method is registered.
- Use of SCP Cloud Object Storage
- Select user information update method when running MFA
- Select whether to automatically add Knox Messenger as an authentication factor when executing MFA.
- Security improvement
- Personal information fields (name, email, mobile phone number) are now stored encrypted.
- In admin screens such as TAP, searching personal information fields (name, email, mobile phone number) has been changed from Like to Exact search, and the existing sorting function has been removed.
- SingleID Authenticator improvement
- When retrieving authentication methods for SingleID Authenticator, a feature to view detailed information (OS version, browser, and IP) has been added.
- The process has been improved so that when SingleID Authenticator information is deleted on the authentication server, the authentication server (tenant) information is also removed from the user app.
- The registration failure error that occurred when registering biometric data in PIN registration mode has been resolved.
- Expanded CSP support for console access control
- Support CSP for console access control has been expanded from the existing AWS, Azure, Samsung Cloud Platform (KR EAST1 region, KR WEST1 region) to GCP.
- Other functional improvements
- Maintained overall UI/UX consistency of the Admin Portal/User Portal and improved usability.
- We improved it so that when a user accesses the SingleID service via a mobile device’s browser and authenticates, the appropriate mobile keypad (default, password, numeric, email keyboard) is automatically selected based on the attributes of the input data on the authentication screen.
- When creating or editing a SAML-type application, we removed the unnecessary input restriction (Issuer setting).
- Improved the usability and security of the CAM Portal.
- Added a masking feature for sensitive information (Password, Key).
- Users assigned the PM/PL role can now modify the IP/Port of registered resources, improving usability.
- When resource registration fails, we have improved it to provide information about the failure status based on a checklist.
- When registering resources, it has been improved to allow registering multiple resources at once and to support PEM key registration.
- After the resource connection expires, we improved usability so that clicking the Rotation button allows you to easily refresh the expired OTP connection information.
- Improved usability to display the Account ID information when submitting approval for a permission request to access resources.
- Add console access history log monitoring feature
- You can view and download console access logs.
- Expand CSP support for console access control
- Support CSP for console access control has been expanded from the existing AWS to Azure and Samsung Cloud Platform (KR EAST1 region, KR WEST1 region).
- Notice feature improvement
- The feature that allows registering and managing notices per tenant has been improved.
- Improvement of the approval system functionality
- We added a self‑managed approval system feature to the existing approval function based on the Knox approval system.
- Improved batch scheduler management functionality
- The batch scheduler management feature has been enhanced to allow viewing execution results and details, and to enable immediate execution.
- Improvement of CAM system user role management functionality
- The CAM system has been improved to allow creating, listing, viewing, and detailing user roles for the system itself.
- System-wide global variable management feature improvement
- The system-wide variable management functionality for the CAM system itself has been improved.
- Other convenience improvements
- PM/PL authorized users can change the IP of an already enrolled resource (no need to re‑enroll the resource).
- Improved the multi-select functionality when searching User, Role, and Policy (preserves previously added items during multiple selections).
- Improved to allow navigation to the detailed pages for Role/Policy/Account from the Console Access menu.
- The Manual, Release Note, and FAQ URLs have been changed to the SCP Documentation URL.
- Add admin delegation feature
- A feature has been added that allows delegating identity verification to an administrator. * This feature is available only for MFA products.
- Add approval status menu to the dashboard
- A feature has been added to the dashboard that allows managing users’ approval requests and statuses.
- Add a sign‑up status menu to the dashboard
- A feature has been added to the dashboard that allows managing users’ sign‑up status.
- Add user campaign feature
- A campaign feature that recommends registering additional authentication methods has been added when only one user authentication method is registered.
- Add dormant account policy feature
- Added features for dormant user settings, alarm dispatch configuration, exception user registration, long-term dormant users, and dormant self-recovery settings.
- Add user lifecycle management feature
- During sign-up and user registration, features for setting user defaults, configuring user account expiration periods, and defining approval policies have been added.
- Add rebranding functionality to the login page
- A feature has been added that allows changing the top and bottom logos, key visual images, and text in the Admin Portal.
- Redirection functionality for the sign‑up page settings, bottom privacy policy, terms of service, and similar items has been added.
- Improved simple authentication feature
- Mobile Passkey, security key, and Windows PIN code have been added as convenient authentication methods for easy login.
- Add user security enhancement feature
- A conditional authentication policy feature has been added that requires additional identity verification when only one authentication method is used for an extended period.
- User profile attribute setting feature improvement
- You can further expand and apply the user’s personal information attributes.
- Add application entitlement (Entitlement) management feature
- Synchronize application permissions to manage application access for users and groups.
- Other convenience improvements
- Improved the process when the authentication session timeout expires.
- Improved the app access process in the mobile app.
- We have improved the screen for mobile app download.
- Improved the application registration/edit screen (field modifications, mapping screen enhancements, etc.).
- Improved the Identity Providers registration/edit screen (added/modified fields)
- Added a user mobile app (device) reset feature.
- Added a feature to set a prefix text when sending SMS.
- Improved the image upload screen and process.
- We have launched the SingleID service, which integrates various access environments so that users can log into business systems with a single ID, and enables administrators to easily control access.
9.6 - WAF
9.6.1 - Overview
Service Overview
WAF(Web Application Firewall) is a service that safely protects web applications by monitoring website traffic and blocking threat events. It quickly detects and blocks HTTP, HTTPS-based security threats that target website vulnerabilities.
Samsung Cloud Platform WAF is SECaaS‑based, and all user traffic passes through a SECaaS PoP before reaching the server. When attack traffic arrives, it is analyzed by SECaaS Rules, detected and blocked, and only clean traffic is forwarded to the server. Additionally, the service is provided from a nearby PoP based on the user’s connection country, and if a PoP fails, service is offered from another PoP within the same country or region.
Features
- Powerful detection/blocking: Monitor HTTP and HTTPS traffic of user‑registered domains to detect hacker attack attempts in real time. Analyze web firewall events to classify attacks such as Injection, XSS, Bot, Remote File Inclusion, and provide various defense capabilities needed for web security, including protection against bot attacks and various CVE vulnerabilities (Apache Struts, Log4j, etc.), enabling immediate response to emerging web attack types.
- Stable Web Service Operation: Perform web firewall signature pattern updates, and detect emerging web threats such as the top 10 OWASP (Open Web Application Security Project) attacks, Zero-Day attacks, and hacker attempts, to support efficient and reliable web service operation.
- Convenient Security Management: By monitoring various attack events in real time and notifying the customer’s representative, it enables proactive response to security threats. Additionally, detailed alert information about attacks (attack IP, target domain, detection time, etc.) can be conveniently viewed through the dashboard.
Service Architecture Diagram
Provided features
We provide the following features.
- Intrusion detection and response via monitoring of registered URLs
- Attack classification through web firewall event analysis (Injection, XSS, Bot, Remote File Inclusion, etc.)
- Block attack traffic targeting registered URLs
- 24x365 event monitoring
- Precise security Rule creation and application through Customizing
- Supports various response settings (IP, request blocking, redirect, rewrite, rate limit, CAPTCHA, etc.)
- Web firewall operation
- Automatic updates of security threats (e.g., signature patterns) collected by TI and firmware updates
- Web firewall ACL management
- Flexible White List implementation (IP, Network, URL, country-based access control)
- Dashboard and Report screens (attack types, target IP, alarm list, etc.) provided
Component
domain
SECaaS WAF is registered on a per-domain basis.
- It can only be applied to domains served with an FQDN (Fully Qualified Domain Name); if the service is provided using an IP address instead of a domain, SECaaS WAF cannot be applied.
- Registration is allowed only for domains registered in the public DNS, and after verifying domain integrity via DNS lookup, it cannot be used when registering a private internal IP.
- It applies to traffic that uses HTTP/HTTPS protocols based on web applications, and other TCP traffic is dropped and cannot be used.
Traffic
Traffic is aggregated as the total Mbps of each registered domain between the SECaaS WAF and the Origin server.
Constraints
To use WAF, first verify the following items.
- Domain Use
- It can be applied only when the service uses an FQDN (Fully Qualified Domain Name). If the service is provided via an IP address instead of a website URL, WAF cannot be applied.
- Registration is possible only for domains registered in the public DNS. The WAF is located in the external Internet segment and verifies domain integrity via DNS lookup. (Registration with an internal private IP such as 10.10.10.10 makes WAF usage unavailable.)
- Use HTTP/HTTPS
- Only traffic using the HTTP/HTTPS protocol for web applications is accepted.
- TCP traffic that uses protocols other than http/https is dropped, so WAF cannot be used.
- XFF(X-Forwarded-For) header function Enable required
- SECaaS WAF has the XFF header feature enabled by default. If the XFF header feature is disabled, a session termination issue may occur.
- Client Source IP Change
- When forwarding a user request from the SECaaS WAF to the customer system, the Source IP is changed from the user’s original public IP to an IP range owned by the WAF. The original user public IP is delivered via the XFF header.
- Maximum Upload Size Limit
- The maximum uploadable file size is limited to 500 MB. (If the file exceeds 500 MB, separate agreement is required.)
Provision status by region
WAF is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Prior Service
This is a list of services that must be pre-configured before applying for the service. For details, refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
9.6.2 - How-to guides
Users can create the service by entering the required information to obtain the WAF service through the Samsung Cloud Platform Console.
Create WAF
You can create and use a WAF service from the Samsung Cloud Platform Console.
To request the creation of a WAF service, follow these steps.
Click the All Services > Security > WAF menu. You will be taken to the WAF’s Service Home page.
On the Service Home page, click the WAF Service Request button. Navigate to the Support Center > Service Request List > Service Request page.
On the Service Request page, enter or select the required information in the mandatory input fields.
- Select WAF creation for the task type.
Input field Detailed description Title Enter the title of the service request - Example: WAF Service Creation Request
Region Select the location of the Samsung Cloud Platform - automatically entered with the region corresponding to the Account
Service Select the service category and service. If you click the WAF service request button, it is entered automatically - Service Category: Security
- Service: WAF
Task classification Select the Activity you want to request - Create WAF: select when requesting a new service
content Guide to the service application process and reference information Attachment Upload the completed WAF service application (required) and, if you have any additional files you want to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files are allowed
Table. WAF Service Creation Request Items
- Select WAF creation for the task type.
After reviewing the application process and reference information, download the form > click the Service Request Form Download button to download the WAF Service Application Form.
Please fill out the WAF Service Application.
- Please refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Complete required fields such as application type, usage period, and usage amount. Control information Complete required items such as migration schedule, domain, and secure recipient information - Complete all items except for special notes
Table. Main contents of the WAF service creation request form
- Please refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form in the attachment area.
Click the request button on the service request page.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
- The monitoring officer is contacting you via email to proceed with opening the firewall, SECaaS domain authentication, and certificate deployment.
- Please refer to Applying WAF Service and proceed with the monitoring integration.
- We confirm the monitoring integration by conducting a test at the security monitoring center (securitycenter@samsung.com).
- Perform a final check to confirm normal service access and detect any SSL certificate errors.
The WAF service is being launched.
Check WAF detailed information
Detailed WAF information can be accessed on the separate Security Platform(SSMP).
VM list
- Security Platform(SSMP) Please access it.
- Enter Knox login information.
- Assets > Cloud Monitoring Management > Cloud URL List page, verify the SECaaS deployment status. You can enter the required fields to perform a query.Item
Detailed description Business Unit Select the appropriate business unit Business name Select the magnifying glass icon, then search for and enter the corresponding business name. website URL Enter URL SECaaS implementation Select whether to apply SECaaS (Apply/Do not apply) SECaaS mode Select SECaaS mode (block/detect) SECaaS vendor Select SECaaS vendor (None/Imperva/Cloudflare) Platform Input with SCP Deletion status Table. Search items - When you click individual URL, you can view the URL details.SECaaS status
Detailed description Apply (Detection) SECaaS applied state, conduct attack pattern detection and log analysis - Recommend maintaining detection mode for at least one month, and after analyzing false positives/negatives for at least one month, send an email recommending switching to blocking mode
Apply (Block) SECaaS applied state, automatic blocking of detected attacks Not applied State where SECaaS is not applied Table. SECaaS implementation status
Terminate WAF
To request termination of the WAF service, follow the steps below.
- Click the All Services > Management > Support Center menu. Go to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- On the Service Request page, enter or select the required information in the mandatory input fields.
- Select WAF termination as the operation type.
Input field Detailed description Title Enter the title of the service request - Example: WAF Service Termination Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: WAF
Task classification Select the Activity you want to request - WAF termination: select if you are requesting service termination
content Guide to the service application process and reference information Attachment If you have a completed WAF service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. WAF service termination request items
- Select WAF termination as the operation type.
- After reviewing Application Process and Notes, click the Form Download > Service Request Form Download button to download the WAF Service Application Form.
- Please complete the WAF Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required fields such as request type, usage period, and usage amount - Usage amount does not need to be filled in
Monitoring information Complete required items such as migration schedule, domain, and secure recipient information - Complete all items except for special notes
Table. Main contents of WAF service termination request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form to the attachment area.
- Click the Request button on the service request page.
- After the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed once the URL is deleted.
- Service termination takes 2–3 business days (including the cancellation request date).
- The restoration of DNS settings that were changed for SECaaS implementation must be performed directly by the service operator.
- When the service termination is completed, you cannot view the URL on the Security Platform (SSMP) > Assets > Cloud Monitoring Management > Cloud URL List page.
9.6.2.1 - WAF Preparation
Configure firewall open settings
Client (User) - SECaaS (WAF) - Origin Server Each segment requires firewall opening. For the information required to open the firewall (Source, Type, Protocol, Destination), please inquire via the Support Center > Contact menu.
- Please open the firewall for the segment where the client (User) connects to the SECaaS (WAF).
- The default supported web ports for SECaaS are as follows.
- http : 80, 8080, 8880, 2052, 2082, 2086, 2095
- https : 443, 2053, 2087, 2096, 8443
- For websites that use ports other than the default supported web port, fill out the WAF service request form to proceed with the service request. We will provide the Destination IP via the email account in the service request form. If, after applying SECaaS, the port changes (added or removed) or the Origin changes, the IP may change. If you email the security monitoring center account (securitucenter@samsung.com) in advance, we will inform you of the updated IP through the responsible person.
- If you do not use an IPv6 IP, you do not need to register it.
- The service application form can be downloaded and attached from the All Services > Security > WAF menu by clicking the WAF Service Request button, then on the Service Request page.
- For information related to service application, please refer to the How-to guides’ Create WAF.
Source Type Protocol Destination: SECaaS Client HTTP, HTTPS TCP - IPv4: 162.159.141.5 / 172.66.1.3
- IPv6: 2606:4700:7::102 / 2a06:98c1:58::102
Table. Example of IP forwarding form
- The default supported web ports for SECaaS are as follows.
- Proceed with opening the firewall for the segment that connects to the Origin Server from SECaaS (WAF).
- The origin server is the device that receives traffic from SECaaS. (e.g., LB, server, etc.)
- The firewall or security device in front of the origin server must allow a specific range.
- Cloudflare IP range information: https://www.cloudflare.com/ko-kr/ips/
- If you do not use an IPv6 IP, you do not need to register it.CautionWe recommend blocking web traffic (HTTP, HTTPS) outside the specified range. If not blocked, the Origin IP may be exposed, leading to attacks that bypass SECaaS, and such bypass attacks are difficult to monitor; please note this.
Authenticate SECaaS domain
To verify the ownership of the registered domain, you need to create a host and add a TXT record for domain verification to DNS for authentication.
- Authentication typically takes about 15 minutes after registration, but can take up to 24 hours depending on the environment. For example, when registering www.test.com, you must create and enter the Host and TXT Record values we provide into DNS.
Applying SECaaS Certificate
You can select and use either the certificate provided by SECaaS or the certificate provided by the customer. Certificate installation is possible only when HTTPS is prepared for the domain, and if the certificate is not installed, HTTPS communication will be unavailable.
1. When using SECaaS certificate
- A new SSL certificate used between the Client ↔ SECaaS server will be generated.
- Domain owner verification (validation) is required for the generated SSL certificate. The verification process is carried out by creating or entering the provided HOST and CNAME values in DNS.
- Certificates cannot be extracted and delivered, and there is an automatic renewal feature, so no separate renewal is required.
- Authentication typically takes about 15 minutes after registration, but may take up to 24 hours depending on the environment.
2. When using a client (Custom) certificate
- Provide the Full chain certificate, Key File, and Key Value.
- An API communication issue occurs when registering a single certificate. (Only pfx, pem, cer files are supported)
- The renewed certificate must be provided for renewal before the certificate expires.
9.6.2.2 - WAF Service Application
After completing the service request on the service request page, proceed with the steps below in order.
Perform pre-test
- Before changing the traffic path with SECaaS, verify its proper operation through a test.
- The security monitoring center provides the IP to be used in SECaaS. Example: 103.22.200.1
- We will explain using aaa.test.com as the example website.
- Add the example text below to the C:\Windows\System32\drivers\etc\hosts file and save it.
- Example phrase : 103.22.200.1 aaa.test.com
- In Chrome browser, press F12 and when accessing the URL, select F5 (refresh) in the ‘Network tab at the top of the developer tools’.
- The process completes when the response header ‘X-cdn’ has the value imperva, or when a SECaaS IP is present in the remote address.
Changing DNS Settings
The path is changed so that actual traffic is transmitted via SECaaS.
- We will configure each domain’s address as a CNAME using the provided CNAME domain. When using a CDN, change the CDN’s origin address to a CNAME.
- Root (Naked) domains cannot have a CNAME record. It is recommended to set an A record using the two Anycast IPs provided by default. If configuring both IPs is difficult, set only one.
- Example: Register/modify DNS for test.com with the provided CNAME, and register/modify the A Record DNS for test.com with the provided IP.
Notify DNS Change
After the DNS change is announced, the security monitoring center checks for proper integration and traffic inflow.
Check Service
Verify normal service connectivity.
- Check whether an SSL certificate error occurs.
- The WAF is operated in detection mode for one month, after which the logs are analyzed and provided to the service owner.
- If no legitimate traffic is detected as an attack, switch to blocking mode. If a false positive occurs, verify with the service owner and then add an exception in the WAF.
9.6.2.3 - WAF Service Outage Response
When a WAF service outage occurs, address and respond to the issue in the order below.
Service outage detection
- The service owner will become aware of a failed service URL health check or a response error.
- The security monitoring center will encounter SECaaS service disruptions and cause the registered Origin Healthcheck to fail.
Remediation
- After confirming the cause of the outage, if it is determined to be a failure of the SECaaS service, you must change the registered CNAME/A Record values back to the original service’s Origin IP/address for redirection (reversion). Since DNS values need to be changed, the user must handle it directly.
- When an urgent bypass (restoration) is required.
- SECaaS(WAF) → Server(Origin) Open the segment firewall to any.
- You can achieve the same effect by asking the SECaaS administrator to request DNS bypass processing in the SECaaS settings. (It is applied based on the DNS TTL value and takes about 5 minutes.)
- Websites that use an A Record for DNS, such as root (naked) domains, cannot be applied.
SECaaS reapplication
After the outage is resolved, reapply the modified CNAME/A Record values to the SECaaS CNAME/A Record address.
9.6.3 - Release Note
WAF
- We are launching a WAF service that protects web applications from web vulnerabilities and attacks.
9.7 - WAF
9.7.1 - Overview
Service Overview
WAF (Web Application Firewall) is a service that monitors website traffic to securely protect web applications. It quickly detects and analyzes HTTP and HTTPS‑based security threats that target website vulnerabilities.
Features
- Powerful Detection/Blocking: We monitor the HTTP and HTTPS traffic of web pages registered by the customer to detect hacker attack attempts in real time. We classify attacks such as SQL Injection, Cross-Site Scripting (XSS), Web Scan, and provide various defense features needed for web security to respond immediately to new web attack types.
- Stable web service operation support: We address new security threats through web firewall signature patterns and firmware updates. We detect hacker attempts, including emerging web threats such as OWASP (Open Web Application Security Project) Top 10 attacks, the National Intelligence Service’s eight major vulnerabilities, Zero-Day attacks, and Bad Bots, to help you operate an efficient and stable web service.
- Convenient Security Management: By monitoring various attack events in real time and notifying the customer’s representative, it enables proactive response to security threats. It also provides monthly reports so you can review event details.
Service Architecture Diagram
Provided features
We provide the following features.
- Provision of intrusion detection/analysis and monitoring information
- 24x365 event monitoring (alert issuance, monthly report provision)
- Attack classification (Injection, XSS, File Include, File Up/Download, Web Scan, etc.) through web firewall event analysis
- Detection of latest attack patterns (e.g., Apache Struts vulnerabilities)
- Intrusion Response
- Provide IP information for attack attempts targeting registered URLs (recommended to block on Samsung Cloud Platform network firewall)
Component
We install a WAF license on the Virtual Server within the VPC of Samsung Cloud Platform and provide the service.
Constraints
To use WAF, first verify the following items.
- If the WAF is configured as a single instance, service continuity cannot be guaranteed in the event of a failure of the WAF installation VM or the WAF application.
- The Load Balancer and WAF of Samsung Cloud Platform do not support bypass.
- The security monitoring service provided by Samsung Cloud Platform is offered only for Pentasecurity products. (operation + monitoring product)
- The WAF service is installed with direct support from an engineer, and it takes a certain amount of time from request to deployment.
Provision status by region
WAF is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Not provided |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Provided |
| South Korea South 2 (kr-south2) | Provided |
| South Korea South 3 (kr-south3) | Provided |
Prior Service
This is a list of services that must be pre-configured before applying for the service. For details, refer to the guide provided for each service and prepare in advance.
- When using the WAF service, a WAF license is installed on the Virtual Server and provided. Install a Virtual Server that matches the service specifications you want first.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
9.7.2 - How-to guides
Users can apply for the service by entering the required information for using the WAF service through the Samsung Cloud Platform Console.
Apply for WAF
You can apply for and use the WAF service from the Samsung Cloud Platform Console.
To request the creation of a WAF service, follow these steps.
Click the All Services > Security > WAF menu. You will be taken to the WAF’s Service Home page.
On the Service Home page, click the WAF Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
Service Request page: enter or select the required information in the mandatory input fields.
- Select WAF creation in the task type.
Input field Detailed description Title Enter the title of the service request - Example: WAF Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the WAF service request button, it is entered automatically - Service Category: Security
- Service: WAF
Task classification Select the type you want to request - Create WAF: select when requesting a new service
content Guide to the service application process and reference information Attachment If you have a completed WAF service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each not exceeding 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. WAF Service Creation Request Items
- Select WAF creation in the task type.
After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the WAF Service Application Form.
Please fill out the WAF Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required items such as application type, usage period, throughput information, basic information, etc. Monitoring information Fill in required items such as WAF service application information and SSL certificate information. Table. Main contents of the WAF service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form in the attachment area.
Click the Request button on the service request page.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
The WAF service is being launched.
Terminate WAF
To request termination of the WAF service, follow the steps below.
- Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page: enter or select the required information in the mandatory input fields.
- Select WAF termination in the task category.
Input field Detailed description Title Enter the title of the service request - Example: WAF Service Termination Request
Region Select the location of the Samsung Cloud Platform - automatically entered with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: WAF
Task classification Select the type you want to request - WAF termination: select if you are terminating the service
content Guide to the service application process and reference information Attachment If you have a completed WAF service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. WAF service termination request items
- Select WAF termination in the task category.
- After reviewing Application Process and Notes, click the Form Download > Service Request Form Download button to download the WAF Service Application Form.
- Please complete the WAF Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
Category Detailed description Application Information Fill out required fields such as application type, usage period, transaction volume information, and basic information. Monitoring information When terminating the entire service, no input is required. Table. Main contents of WAF service termination request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
- Attach the completed application form to the attachment area.
- On the service request page, click the Request button.
- After the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed once the monitored URL, port, and IP are removed.
- Service termination requires three business days, including the cancellation request date.
9.7.3 - Release Note
WAF
- We are launching a WAF service that protects web applications from web vulnerabilities and attacks.
9.8 - WAF
9.8.1 - Overview
Service Overview
WAF (Web Application Firewall) is a service that monitors website traffic to securely protect web applications. It quickly detects and analyzes HTTP and HTTPS–based security threats that target website vulnerabilities.
Features
- Powerful Detection/Blocking: We monitor the HTTP and HTTPS traffic of web pages registered by the customer to detect hacker attack attempts in real time. We classify attacks such as SQL Injection, Cross-Site Scripting (XSS), Web Scan, and provide various defense features needed for web security to respond immediately to new web attack types.
- Stable Web Service Operation Support: Respond to new security threats through web firewall signature patterns and firmware updates. Detect hacker attack attempts such as the top 10 OWASP (Open Web Application Security Project) attacks, the 8 major vulnerabilities identified by the National Intelligence Service, Zero-Day attacks, emerging web threats, and Bad Bots, to help operate efficient and stable web services.
- Convenient Security Management: Provides monthly reports, allowing you to conveniently review event details.
Service Architecture Diagram
Provided features
We provide the following features.
- Provides intrusion detection/analysis
- 24x365 event monitoring (alert issuance, monthly report provision), however, the public-facing WAF service does not provide this.
- Attack classification (Injection, XSS, File Include, File Up/Download, Web Scan, etc.) through web firewall event analysis
- Detection of latest attack patterns (e.g., Apache Struts vulnerabilities)
- Intrusion Response
- Provide IP information for attack attempts targeting registered URLs
Component
We install a WAF license on the Virtual Server within the VPC of Samsung Cloud Platform and provide the service.
Constraints
To use WAF, first verify the following items.
- If the WAF is configured as a single instance, service continuity cannot be guaranteed in the event of a failure of the WAF installation VM or the WAF application.
- The Load Balancer and WAF of Samsung Cloud Platform do not support bypass.
- The security monitoring service provided by Samsung Cloud Platform is offered only for Pentasecurity products. (operation + monitoring product)
- The public-facing WAF service does not provide security monitoring services.
- The WAF service is installed with direct support from an engineer, and it takes a certain amount of time from request to deployment.
Provision status by region
WAF is available in the environments below.
| Region | General (Enter) | Public |
|---|---|---|
| Korea West (kr-west1) | Provided | Not provided |
| Korea East (kr-east1) | Not provided | Not provided |
| South Korea South 1 (kr-south1) | Not provided | Provided |
| South Korea South 2 (kr-south2) | Not provided | Provided |
| South Korea South 3 (kr-south3) | Not provided | Provided |
Prior Service
This is a list of services that must be pre-configured before applying for the service. For details, refer to the guide provided for each service and prepare in advance.
- When using the WAF service, a WAF license is installed on the Virtual Server and provided. Install a Virtual Server that matches the service specifications you want first.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
| Networking | Direct Connect | A service that securely and quickly connects the customer’s network to the Samsung Cloud Platform |
9.8.2 - How-to guides
Users can apply for the service by entering the required information for using the WAF service through the Samsung Cloud Platform Console.
Apply for WAF
You can apply for and use the WAF service from the Samsung Cloud Platform Console.
To request the creation of a WAF service, follow these steps.
Click the All Services > Security > WAF menu. You will be taken to the WAF’s Service Home page.
On the Service Home page, click the WAF Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
Service Request page: enter or select the required information in the mandatory input fields.
- Select WAF creation in the task type.
Input field Detailed description Title Enter the title of the service request - Example: WAF Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the WAF service request button, it is entered automatically - Service Category: Security
- Service: WAF
Task classification Select the type you want to request - Create WAF: select when requesting a new service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment Upload the completed WAF service application (required) and any additional files you wish to share - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. WAF Service Creation Request Items
- Select WAF creation in the task type.
After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the WAF Service Application Form.
Please complete the WAF Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Write required items such as application type, usage period, throughput information, basic information, etc. Monitoring information Enter required items such as WAF service application information and SSL certificate information - Public-sector customers do not need to fill this out
Table. Main contents of the WAF service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form in the attachment area.
Click the Request button on the service request page.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
The WAF service is being launched.
Terminate WAF
To request termination of the WAF service, follow the steps below.
- Click the All Services > Management > Support Center menu. Go to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page: enter or select the required information in the mandatory input fields.
- Select WAF termination in the task type.
Input field Detailed description Title Enter the title of the service request - Example: WAF Service Termination Request
Region Select the location of the Samsung Cloud Platform - automatically entered with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: WAF
Task classification Select the type you want to request - WAF termination: select if you are terminating the service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment If you have a completed WAF service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. WAF service termination request items
- Select WAF termination in the task type.
- After reviewing Application Process and Notes, click the Form Download > Service Request Form Download button to download the WAF Service Application Form.
- Please complete the WAF Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill out required fields such as application type, usage period, transaction volume information, and basic information. Monitoring information When terminating the entire service, no input is required. Table. Main contents of WAF service termination request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form to the attachment area.
- Click the Request button on the service request page.
- After the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed once the monitored URL, port, and IP are removed.
- Service termination requires three business days, including the cancellation request date.
9.8.2.1 - WAF Build Process Guide
To start the WAF service, you need to apply for the service and then perform WAF license installation and monitoring integration verification. After you request the WAF service, the person in charge will review the service request details and contact you. Please refer to the process below to request the WAF service.
WAF installation is directly supported by SDS engineers and proceeds after consulting with the client on configuration, specifications, and related details.
- Considering the overall process schedule, apply for the service at least one month before the service launch (business days).
Preliminary preparation work
The preliminary preparation steps for using the WAF service are carried out according to the following procedure.
- Submit a service request to install the WAF. (MSP → SDS)
- Please request WAF SW installation. (SDS → Engineer)
- Please provide the engineer information for the WAF installation work. (SDS → MSP)
Samsung Cloud Platform Console task (MSP execution)
To use the WAF service, the Samsung Cloud Platform Console performs the following steps.
- Register an SSL certificate in the Certificate Manager service.
- Application path: Samsung Cloud Platform Console > Security > Certificate Manager
- Purpose: Operation
- Create a Virtual Server service for WAF.
- Application path: Samsung Cloud Platform Console > Compute > Virtual Server
- Determine CPU, memory, and block storage capacity based on WAF specifications.
- WAF Virtual Server specifications: view quotation
- Create a Load Balancer service.
- Application path: Samsung Cloud Platform Console > Networking > Load Balancer
- Create an L7 service for SSL offloading.
- Create an L4 service when load balancing is required for WAF redundancy.
- Create an L4 service when load balancing is required for web server redundancy.
- Configure the required Load Balancer/Firewall/Security Group.
- Configure the Firewall and Security Group to match the Load Balancer’s communication path as follows.
- The source inputs the user’s network information.
Category Common Security Zone FW Internet Gateway FW Load Balancer FW Virtual Server SG Inbound (destination) LB service public IP LB service private IP LB service private IP LB Link IP IP (example) 123.43.8.xxx 10.10.0.xxx 10.10.0.xxx 192.168.254.xxx Port LB service port LB service port LB service port Forwarding/Health Check Port Table. FW/SG configuration items according to the Load Balancer's communication path
- Configure HTTP redirection for the LB service. (Optional)
- Set the Load Balancer’s HTTP redirection option as follows.
LB service L7 HTTP L7 HTTPS LB Profile > Profile Type Application Application LB Profile > Service Classification L7 HTTP L7 HTTP LB Profile > HTTP Redirection Settings Not set IP/NAT IP Set the same Set the same service port 80 443 forwarding port 80 80 Server Group > When Using WAF Not set WAF Virtual Server Server Group > When WAF is not used Not set WEB Virtual Server Certificate registration Unregistered Register Table. Load Balancer HTTP redirection configuration items
- Set the Load Balancer’s HTTP redirection option as follows.
- Grant the WAF engineer access permissions to the Virtual Server for WAF.
WAF SW Installation and Test (WAF Engineer & MSP)
When the WAF specifications are finalized, the engineer installs the WAF software and conducts testing.
Policy request and implementation for WAF security monitoring
Create and apply policies required for WAF security monitoring.
- Request the required policy from the Samsung Cloud Platform Console. (SDS → MSP)
- Deliver and apply the created policy. (SDS → MSP)
- Check the items that require policy registration. (Direct Connect Firewall/Security Group/Routing)
- SDS → Verify that the WAF access path for each client is secured. If additional registration is required, request it by email.
- Check whether the WAF → SIEM log transmission path is secured for each client. If additional registration is needed, request it via email.
Constraints
When installing the WAF, first check the following constraints before proceeding.
- When WAF is configured as a single instance, service continuity cannot be guaranteed in case of a failure of the WAF-installed Virtual Server or the WAF application. (Bypass is not supported between Samsung Cloud Platform LB and WAF)
- If service availability of the website where WAF is applied is critical, WAF redundancy must be implemented. If WAF redundancy is required, a separate request must be made.
- Security monitoring through the Samsung Cloud Platform service is available only for Penta Security products.
- Other vendors’ products are listed in the marketplace, but Samsung SDS security monitoring services are not offered.
9.8.3 - Release Note
WAF
- We are launching a WAF service that protects web applications from web vulnerabilities and attacks.
9.9 - DDoS Protection
9.9.1 - Overview
Service Overview
DDoS Protection is a service that detects and defends against DDoS (Distributed Denial of Service) attacks, which generate large volumes of traffic to cause service disruptions. Continuous monitoring detects and blocks external traffic attacks, protecting the servers within the Samsung Cloud Platform. When a DDoS attack occurs, blocking the malicious traffic minimizes the traffic load entering the internal servers of the Samsung Cloud Platform, ensuring the continuity of web services.
Features
- Rapid Attack Detection: When a large volume of traffic arrives, it detects DDoS attacks in real time. Continuously updating DDoS defense items enables effective response to the latest attack techniques.
- Effective Attack Defense: When a DDoS attack occurs, we detect it in real time and block malicious traffic to ensure service availability, supporting regular users to access the website normally.
- Stable web service operation: Based on extensive network operation experience, we can effectively respond to external security threats. Additionally, we provide monthly reports so you can review event details.
Configuration diagram
Provided features
We provide the following features.
- Intrusion Detection and Analysis
- 24x365 event monitoring (Note: the public DDoS Protection service does not provide this feature.)
- Automatic detection of DDoS attacks
- Intrusion Response
- Provides learning-based detection and blocking for various DDoS attacks at the L3/L4 level.
- Monitoring Information Provision
- Alert on event detection
- Monthly report provision
Component
- DDoS Protection provides services based on public IPs configured within the VPC.
- We provide services for servers that can be accessed over the Internet, and blocking can be performed based on attacker IP addresses.
Constraints
When providing DDoS Protection service, a minimum one-month learning period is required to set the protection threshold, and we analyze the learned thresholds to provide optimal policy settings.
Provision status by region
DDoS Protection is available in the following environments.
| Region | General (Enter) | Public |
|---|---|---|
| Korea West (kr-west1) | Provided | Not provided |
| Korea East (kr-east1) | Not provided | Not provided |
| South Korea South 1 (kr-south1) | Not provided | Not provided |
| South Korea South 2 (kr-south2) | Not provided | Not provided |
| South Korea 3 (kr-south3) | Not provided | Provided |
Preceding Service
- This is a list of services that must be pre-configured before creating a DDoS Protection service. Refer to the guides provided for each service for detailed information and prepare in advance.
- When creating a VPC Internet Gateway, you must select SIGW (Secure Internet Gateway) in Category to be able to use DDoS Protection.
- When creating an Internet Gateway for a VPC, selecting Internet Gateway in ‘Category’ prevents the use of the DDoS Protection service.
- If you switch to Secure Internet Gateway, you need to change the public IP you are using.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
9.9.2 - How-to guides
Users can apply for the service by entering the required information for using the DDoS Protection service through the Samsung Cloud Platform Console.
Create DDoS Protection
You can apply for and use the DDoS Protection service from the Samsung Cloud Platform Console.
To request the creation of a DDoS Protection service, follow these steps.
- Click the All Services > Security > DDoS Protection menu. Navigate to the Service Home page of DDoS Protection.
- On the Service Home page, click the DDoS Protection Service Request button. Navigate to the Support Center > Service Request List > Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- Select Create DDoS Protection in the task category.
Input field Detailed description Title Enter the title of the service request - Example: DDoS Protection service creation request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the DDoS Protection service request button, it is entered automatically - Service Category: Security
- Service: DDoS Protection
Task classification Select the type you want to request - Create DDoS Protection: select when requesting a new service
content Guide to Creating Customer Basic Information and Application Process - Content: End Customer/MSP Information
- You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. DDoS Protection Service Creation Request Items
- Select Create DDoS Protection in the task category.
- After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the DDoS Protection Service Application Form.
- Please complete the DDoS Protection Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill out required items such as application type, usage period, and basic information - Application type: select application
- Usage period: enter desired start date, contract status, and estimated usage period
- Basic information: enter Account name, Project name, and recipient information
Monitoring information Enter required items such as protected IPs, exception handling IPs, etc. (Specify purpose per IP) - Specify application type per IP
- New: select when applying for a new service
- Public-sector customers do not need to fill this out
Table. Main contents of the DDoS Protection service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form in the attachment area.
- On the service request page, click the Request button.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
- After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
- The DDoS Protection service is now available.
DDoS Protection Terminate
To request cancellation of the DDoS Protection service, follow the steps below.
- Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- Select DDoS Protection termination in the operation type.
Input field Detailed description Title Enter the title of the service request - Example: DDoS Protection Service Cancellation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: DDoS Protection
Task classification Select the type you want to request - Cancel DDoS Protection: select if you are canceling the service
content Guide to Entering Customer Basic Information and Application Process - Content: End Customer/MSP Information
Attachment Upload the completed DDoS Protection service application (required) and, if you have any additional files to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. DDoS Protection service termination request items
- Select DDoS Protection termination in the operation type.
- After reviewing the Application Process and Reference Information, click the Form Download > Service Request Form Download button to download the DDoS Protection Service Application Form.
- Please fill out the DDoS Protection Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill out required fields such as application type, usage period, and basic information - Application type: select termination
- Usage period: enter desired termination date
- Basic information: Account name, Project name, recipient information
Monitoring information When terminating the entire service, no input is required. Table. Main contents of DDoS Protection service termination request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form to the attachment section.
- Click the Request button on the service request page.
- Once the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed when the monitored IP/policy is deleted.
- Service termination requires three business days, including the cancellation request date.
9.9.3 - Release Note
DDoS Protection
- We are launching a DDoS Protection service that provides detection and mitigation of large-scale network traffic attacks.
9.10 - DDoS Protection
9.10.1 - Overview
Service Overview
DDoS Protection is a service that detects and defends against DDoS (Distributed Denial of Service) attacks, which generate large volumes of traffic to cause service disruptions. Continuous monitoring detects and blocks external traffic attacks, protecting the servers within the Samsung Cloud Platform. When a DDoS attack occurs, blocking the attack traffic minimizes the traffic load entering the internal servers of the Samsung Cloud Platform, ensuring the continuity of web services.
Features
- Rapid Attack Detection: When a large volume of traffic arrives, it detects DDoS attacks in real time. Continuously updating DDoS defense items enables effective response to the latest attack techniques.
- Effective Attack Defense: When a DDoS attack occurs, we detect it in real time and block malicious traffic to ensure service availability, supporting regular users to access the website normally.
- Stable web service operation: Provide 24/7 security monitoring services, and based on extensive network operation experience, effectively respond to external security threats, delivering alerts with attack information when incidents occur. Additionally, monthly reports are provided to review event details.
Configuration diagram
Provided features
We provide the following features.
- Intrusion Detection and Analysis
- 24x365 event monitoring
- Automatic detection of DDoS attacks
- Intrusion Response
- Provides learning-based detection and blocking for various DDoS attacks at the L3/L4 level.
- Monitoring Information Provision
- Alert on event detection
- Provide monthly report (alert list and details)
Component
- DDoS Protection provides services based on public IPs configured within the VPC.
- We provide services for servers that can be accessed over the Internet, and blocking can be performed based on attacker IP addresses.
Constraints
When providing DDoS Protection service, a minimum one‑month learning period is required to set the protection threshold, and we analyze the learned thresholds to provide optimal policy settings.
Provision status by region
DDoS Protection is available in the following environments.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Not provided |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Provided |
| South Korea South 2 (kr-south2) | Provided |
| South Korea 3 (kr-south3) | Provided |
Preceding Service
- This is a list of services that must be pre-configured before creating a DDoS Protection service. For details, refer to the guides provided for each service and prepare in advance.
- When creating a VPC Internet Gateway, you must select SIGW (Secure Internet Gateway) in Category to be able to use DDoS Protection.
- When creating an Internet Gateway for a VPC, selecting Internet Gateway in ‘Category’ prevents the use of the DDoS Protection service.
- If you switch to Secure Internet Gateway, you need to change the public IP you are using.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
9.10.2 - How-to guides
Users can apply for the service by entering the required information for using the DDoS Protection service through the Samsung Cloud Platform Console.
Create DDoS Protection
You can apply for and use the DDoS Protection service from the Samsung Cloud Platform Console.
To request the creation of a DDoS Protection service, follow these steps.
- Click the All Services > Security > DDoS Protection menu. Navigate to the Service Home page of DDoS Protection.
- On the Service Home page, click the DDoS Protection Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- Select Create DDoS Protection in the task category.
Input field Detailed description Title Enter the title of the service request - Example: DDoS Protection Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the DDoS Protection service request button, it is entered automatically - Service Category: Security
- Service: DDoS Protection
Task classification Select the type you want to request - Create DDoS Protection: select when requesting a new service
content Guide to the service application process and reference information Attachment Upload the completed DDoS Protection service application (required) and any additional files you wish to share - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files are allowed
Table. DDoS Protection Service Creation Request Items
- Select Create DDoS Protection in the task category.
- After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the DDoS Protection Service Application Form.
- Please fill out the DDoS Protection Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill out required items such as application type, usage period, and basic information - Application type: select application
- Usage period: enter desired start date, contract status, and estimated usage period
- Basic information: enter Account name, Project name, and recipient information
Monitoring information Enter required fields such as protected IPs and exception handling IPs (purpose per IP must be specified) - Specify application classification per IP
- New: select when applying for a new service
Table. Main contents of the DDoS Protection service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form in the attachment area.
- Click the Request button on the service request page.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
- After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
- The DDoS Protection service is now available.
Cancel DDoS Protection
To request cancellation of the DDoS Protection service, follow the steps below.
- Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- Select DDoS Protection termination in the operation type.
Input field Detailed description Title Enter the title of the service request - Example: DDoS Protection Service Cancellation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: DDoS Protection
Task classification Select the type of request you want to make - Cancel DDoS Protection: select if you are terminating the service
content Guide to the service application process and reference information Attachment If you have a completed DDoS Protection service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. DDoS Protection service termination request items
- Select DDoS Protection termination in the operation type.
- After reviewing the Application Process and Reference Information, click the Form Download > Service Request Form Download button to download the DDoS Protection Service Application Form.
- Please complete the DDoS Protection Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill out required fields such as application type, usage period, and basic information - Application type: select termination
- Usage period: enter desired termination date
- Basic information: Account name, Project name, recipient information
Monitoring information When terminating the entire service, no input is required. Table. Main contents of DDoS Protection service termination request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form to the attachment area.
- On the service request page, click the Request button.
- When the request is completed, check the submitted details on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed when the monitored IP/policy is deleted.
- Service termination requires three business days, including the cancellation request date.
9.10.3 - Release Note
DDoS Protection
- We are launching a DDoS Protection service that provides detection and mitigation of large-scale network traffic attacks.
9.11 - IPS
9.11.1 - Overview
Service Overview
IPS(Intrusion Prevention System) continuously updates IPS intrusion detection policies reflecting the latest security threats to respond in real time. Additionally, packet monitoring detects up to the application layer.
Features
- Latest Attack Type Detection: Generate detection patterns for new threats and improve detection rates through continuous signature management. Apply the TI DB of a security specialist company and our own advanced detection policies, and provide services by correlating attack patterns detected by IPS with patterns configured in SIEM(Security Information and Event Management) through correlation analysis.
- Cloud Optimized Operations: We provide detection services optimized for cloud environments. When a security threat occurs, we respond promptly with specialized security personnel.
- Efficient response and support: Monthly reports are provided so you can review the details of events.
Configuration diagram
Provided features
We provide the following features.
- Intrusion Detection and Analysis
- In-depth analysis using raw data
- Update new threat detection patterns incorporating external trend information
- Periodic detection pattern optimization
- Monitoring Information Provision
- Monthly report provision
- Intrusion Response
- Provide IP information of attack attempts targeting SCP client servers
Component
- IPS provides services based on public IPs configured within the VPC.
- We provide services for servers that are accessible over the Internet, and when a user requests a service, we refer to the server (Virtual Server) specifications listed in the service application form.
Constraints
IPS provides detection for traffic that is not encrypted with HTTP. It does not provide monitoring for HTTS SSL encrypted traffic.
Provision status by region
IPS is available in the environments below.
| Region | General (Enter) | Public |
|---|---|---|
| Korea West (kr-west1) | Provided | Not provided |
| Korea East (kr-east1) | Not provided | Not provided |
| South Korea South 1 (kr-south1) | Not provided | Provided |
| South Korea South 2 (kr-south2) | Not provided | Provided |
| South Korea South 3 (kr-south3) | Not provided | Provided |
Preceding Service
- This is a list of services that must be pre-configured before creating an IPS service. Refer to the guides provided for each service and prepare them in advance.
- When creating a VPC Internet Gateway, you must select SIGW (Secure Internet Gateway) in Category to be able to use IPS.
- When creating a VPC Internet Gateway, if you select Internet Gateway in the ‘Category’, you cannot use the IPS service.
- If you switch to Secure Internet Gateway, you need to change the public IP you are using.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
9.11.2 - How-to guides
Users can apply for the service by entering the required information for using the IPS service through the Samsung Cloud Platform Console.
Create IPS
You can apply for and use the IPS service from the Samsung Cloud Platform Console.
To request the creation of an IPS service, follow these steps.
- Click the All Services > Security > IPS menu. You will be taken to the IPS Service Home page.
- On the Service Home page, click the IPS Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- Select IPS creation in the task classification.
Input field Detailed description Title Enter the title of the service request content - Example: IPS Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the IPS service request button, it is entered automatically - Service Category: Security
- Service: IPS
Task classification Select the type you want to request - Create IPS: select when requesting a new service
content Guide to Creating Customer Basic Information and Application Process - Content: End Customer/MSP Information
Attachment Upload the completed IPS service application (required) and any additional files you wish to share - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files are allowed
Table. IPS Service Creation Request Items
- Select IPS creation in the task classification.
- After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the IPS Service Application Form.
- Please fill out the IPS Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
Category Detailed description Application Information Fill out required items such as application type, usage period, and basic information - Application type: select application
- Usage period: enter desired start date, contract status, and estimated usage period
- Basic information: enter Account name, Project name, and recipient information
Monitoring information Enter required items such as protected IP and exception handling IP (specify purpose per IP) - Specify application category per IP
- New: select when applying for a new service
- Public-sector customers do not need to fill this out
Table. Main contents of the IPS service creation application form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
- Attach the completed application form in the attachment area.
- On the service request page, click the Request button.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
- After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
- The IPS service is being launched.
Terminate IPS
To request termination of the IPS service, follow the steps below.
- Click the All Services > Management > Support Center menu. Go to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page: enter or select the required information in the mandatory input fields.
- Select IPS termination in the task type.
Input field Detailed description Title Enter the title of the service request - Example: IPS Service Termination Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: IPS
Task classification Select the type you want to request - IPS termination: select if you want to cancel the service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment If you have a completed IPS service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files can be attached
Table. Table. IPS service termination request items
- Select IPS termination in the task type.
- After reviewing the Application Process and Reference Information, click the Form Download > Service Request Form Download button to download the IPS Service Application Form.
- Please fill out the IPS Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required fields such as request type, usage period, and basic information - Request type: select termination
- Usage period: enter desired termination date
- Basic information: Account name, Project name, recipient information
Monitoring information When terminating the entire service, no input is required. Table. Main contents of IPS service termination application form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form to the attachment section.
- Click the Request button on the service request page.
- Once the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed once the monitored IP is removed.
- Service termination requires three business days, including the cancellation request date.
9.11.3 - Release Note
IPS
- We have launched an IPS service that continuously updates intrusion detection policies to reflect the latest security threats and provides real‑time response.
9.12 - Secured Firewall
9.12.1 - Overview
Service Overview
Secured Firewall is a next‑generation firewall service for cloud network security provided by Samsung Cloud Platform. It manages network access to servers based on IP address/port policies and supports detailed analysis in the event of a security incident.
Features
- Protecting Diverse Network Environments: Supports setting robust network security policies to securely protect cloud assets. Detects and blocks based on IP and protocol/port‑based ACL policies, providing a safe network communication environment.
- Easy and Simple Network Management: You can easily establish firewall policies and conveniently create and manage applied rules such as source/destination IP, protocol/port, inbound/outbound, etc.
- Security expert-based firewall policy implementation: We support establishing firewall policies optimized for customers’ systems migrating to the cloud. To make it easier to apply security policies in cloud environments, we accept firewall policy requests from customers and provide a service where security experts incorporate the policies.
- Security Authentication Product-Based Service: You can use firewall services that meet various networks and requirements for internet connectivity and ensure an optimized security environment. This safely protects the internal network from unauthorized access.
Configuration diagram
Provided features
We provide the following features.
- Cloud Optimized Firewall
- Applying domain policies considering cloud environments
- Apply firewall rules and logging
- Monitoring Information Provision
- Monthly report provision
Component
- Secured Firewall provides services based on a public IP configured within the VPC.
- We provide services for servers that are accessible over the Internet, and when a user requests a service, we refer to the server (Virtual Server) specifications listed in the service application form.
Constraints
- Firewall policy requests cannot be submitted from the Samsung Cloud Platform Console.
- We will send the application form to the email you registered when applying for the service. Please refer to the form to proceed with the firewall request.
- The access control management (such as Security Group and other firewall policy management) for systems built inside the pool must be performed directly by the customer.
Provision status by region
Secured Firewall is available in the following environments.
| Region | General (Enter) | Public |
|---|---|---|
| Korea West (kr-west1) | Provided | Not provided |
| Korea East (kr-east1) | Not provided | Not provided |
| South Korea South 1 (kr-south1) | Not provided | Provided |
| South Korea South 2 (kr-south2) | Not provided | Provided |
| South Korea South 3 (kr-south3) | Not provided | Provided |
Preceding Service
- This is a list of services that must be pre‑configured before creating a Secured Firewall service. For details, refer to the guides provided for each service and prepare in advance.
- When creating a VPC’s Internet Gateway, you must select SIGW (Secure Internet Gateway) in Category to be able to use Secured Firewall.
- When creating an Internet Gateway for a VPC, selecting Internet Gateway in the “Category” prevents the use of the Secured Firewall service.
- If you switch to Secure Internet Gateway, you need to change the public IP you are using.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that protects web applications from web vulnerabilities and attacks |
9.12.2 - How-to guides
Users can apply for the service by entering the required information for using the Secured Firewall service through the Samsung Cloud Platform Console.
Create Secured Firewall
You can request and use the Secured Firewall service from the Samsung Cloud Platform Console.
To request the creation of a Secured Firewall service, follow these steps.
Click the All Services > Security > Secured Firewall menu. You will be taken to the Service Home page of Secured Firewall.
On the Service Home page, click the Secured Firewall Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
Service Request page, enter or select the required information in the mandatory input fields.
- Select Secured Firewall creation in the task type.
Input field Detailed description Title Enter the title of the service request - Example: Secured Firewall service creation request
Region Select the location of the Samsung Cloud Platform - Automatically entered with the region corresponding to the Account
Service Select the service category and service. If you click the Secured Firewall service request button, it is entered automatically - Service Category: Security
- Service: Secured Firewall
Task classification Select the type you want to request - Create Secured Firewall: select when requesting a new service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment If you have a completed Secured Firewall service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files can be attached
Table. Secured Firewall Service Creation Request Items
- Select Secured Firewall creation in the task type.
After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the Secured Firewall Service Application Form.
Please fill out the Secured Firewall Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required items such as application type, usage period, and basic information - Application type: select application
- Usage period: enter desired start date, contract status, and estimated usage period
- Basic information: enter Account name, Project name, and recipient information
Monitoring information Enter required items such as protected IP and exception handling IP (specify purpose per IP) - Specify application category per IP
- New: select when applying for a new service
- Public-sector customers do not need to fill this out
Table. Main contents of the Secured Firewall service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form in the attachment area.
Click the Request button on the service request page.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
The Secured Firewall service is now being launched.
Terminate Secured Firewall
To request termination of the Secured Firewall service, follow the steps below.
- Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page: enter or select the required information in the mandatory input fields.
- Select Secured Firewall termination in the task type.
Input field Detailed description Title Enter the title of the service request - Example: Secured Firewall service termination request
Region Select the location of the Samsung Cloud Platform - Automatically entered with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: Secured Firewall
Task classification Select the type of request you want to make - Terminate Secured Firewall: select when terminating the service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment If you have a completed Secured Firewall service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. Secured Firewall Service Termination Request Items
- Select Secured Firewall termination in the task type.
- After reviewing Application Process and Reference Information, click the Form Download > Service Request Form Download button to download the Secured Firewall Service Request Form.
- Please fill out the Secured Firewall Service Application.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
Category Detailed description Application Information Fill in required fields such as request type, usage period, and basic information - Request type: select termination
- Usage period: enter desired termination date
- Basic information: Account name, Project name, recipient information
Monitoring information When terminating the entire service, no input is required. Table. Main contents of Secured Firewall service termination application form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
- Attach the completed application form to the attachment area.
- Click the Request button on the service request page.
- After the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring team reviews the submitted service request, the termination is completed once the monitored IP is deleted.
- Service termination requires three business days, including the cancellation request date.
9.12.3 - Release Note
Secured Firewall
- We have launched the Secured Firewall service, a next‑generation firewall for cloud network security provided by Samsung Cloud Platform.
9.13 - Secured VPN
9.13.1 - Overview
Service Overview
Secured VPN(Virtual Private Network) is a service that securely connects external customer networks and the Samsung Cloud Platform network through an encrypted virtual private network. Authenticated customer networks can safely access the Samsung Cloud Platform at any time via a secure channel.
Features
- Rapid Service Provision: To ensure a secure VPN communication link between the customer’s network and the Samsung Cloud Platform, a dedicated VPN device must be deployed, and we provide installation support services by security specialists during deployment.
- Secure Access: Provides a virtual network tunnel equipped with certified authentication devices and nationally certified encryption modules that have proven performance and reliability, allowing customers to securely connect from their external network to their internal network built on the Samsung Cloud Platform.
- Simple operating environment: We provide network configuration and VPN operation services optimized for the customer’s environment by security experts, offering an operating environment that makes it easier to use VPN services.
Configuration diagram
Provided features
We provide the following features.
- IPSec VPN Provision
- Providing IPSec VPN with a nationally certified cryptographic module
- Virtual Private Gateway Creation
- Create a Virtual Private Gateway to connect the cloud internal network with the customer’s network.
- Select traffic bandwidth for bidirectional communication based on network scale
- Create VPN Tunnel
- Ensuring service continuity in the event of a failure by configuring redundant IPsec VPN Gateways.
Component
Secured VPN(Virtual Private Network) provides services composed of Center VPN managed by SDS and Branch VPN installed within the customer’s premises.
Constraints
- The center VPN equipment is a shared device used by many customers, and it cannot be used if its address range overlaps with VPC ranges used by other customers or ranges currently used in Samsung Cloud Platform. Customers who need to use the Secured VPN service should check the available ranges in advance.
- Samsung Cloud Platform usage range: 172.16.0.0/12, 192.168.240.0/20
- Example: Customer A has applied for and is using the 10.0.0.1/24 range; when Customer B newly applies for a Secured VPN, the 10.0.0.1/24 range cannot be used. Verify the available ranges in advance and configure the VPC range accordingly.
- To verify the available band, contact Console > Support Center > Contact or email mssp.scp@samsung.com.
- After confirming the available address range, SDS performs NAT on the rented branch VPN to change the IP. However, if the branch VPN equipment was purchased directly by the customer, the NAT configuration is handled by the customer.
- The MSP adds the NATed IP to the VPC routing rules in the Samsung Cloud Platform Console.
- Check for cases where the branch VPN and Samsung Cloud Platform IP ranges overlap. If the destination IP range is included in the source IP range, the router will send traffic internally instead of outward, making communication impossible.
- Branch VPN is offered as a rental of SECUI equipment, and a separate fee applies for the equipment lease. If the client already uses VPN equipment, it is necessary to confirm whether non‑SECUI vendor devices are compatible with the center VPN equipment (SECUI).
- For compatibility testing matters other than SECUI equipment, please contact Console > Support Center > Contact Us or via mssp.scp@samsung.com.
Provision status by region
Secured VPN is available in the following environments.
| Region | General (Enter) | Public |
|---|---|---|
| Korea West (kr-west1) | Provided | Not provided |
| Korea East (kr-east1) | Not provided | Not provided |
| South Korea South 1 (kr-south1) | Not provided | Provided |
| South Korea South 2 (kr-south2) | Not provided | Provided |
| South Korea South 3 (kr-south3) | Not provided | Provided |
Preceding Service
This is a list of services that must be pre‑configured before creating a Secured VPN service. Refer to the guides provided for each service for details and prepare them in advance.
- When creating a Direct Connect, create a connection to the target VPC and a DCon-VPN connection.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | Direct Connect | A service that securely and quickly connects the customer’s network with the Samsung Cloud Platform |
- To use the Secured VPN service, configuration work is required for communication between the customer’s on-premise Office and the customer’s VPC within the Samsung Cloud Platform. Please follow the process below to request an uplink line, including external integration software and VPN configuration, and opening the Direct Connect firewall.
- Application path : Console > Support Center > Service Request
- Service : Networking > Direct Connect
- Task Category : Uplink line request
9.13.2 - How-to guides
Users can create the service by entering the required information for using the Secured VPN (Virtual Private Network) service through the Samsung Cloud Platform Console.
Create Secured VPN
You can apply for and use the Secured VPN service from the Samsung Cloud Platform Console.
To request the creation of a Secured VPN service, follow these steps.
Click the All Services > Security > Secured VPN menu. You will be taken to the Service Home page of Secured VPN.
On the Service Home page, click the Secured VPN Service Request button. Navigate to the Support Center > Service Request List > Service Request page.
Service Request page, enter or select the required information in the mandatory input fields.
- In the task category, select Secured VPN creation.
Input field Detailed description Title Enter the title of the service request - Example: Secured VPN Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the Secured VPN service request button, it is entered automatically - Service Category: Security
- Service: Secured VPN
Task classification Select the type you want to request - Create Secured VPN: select when requesting a new service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment If you have a completed Secured VPN service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Secured VPN service creation request items
- In the task category, select Secured VPN creation.
After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the Secured VPN Service Application Form.
Please fill out the Secured VPN Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Complete required fields such as request type, usage period, and basic information - Application type: select application
- Usage period: enter desired start date
- Guaranteed bandwidth: select bandwidth
- Basic information: enter Account name, Project name, recipient information
Monitoring information Common application information, same-model/different-model connection application information, etc., fill in required items (specify usage per IP) - Same-model connection application information: when connecting SECUI equipment
- Different-model connection application information: when connecting equipment other than SECUI
Table. Main contents of the Secured VPN service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form in the attachment area.
Click the Request button on the service request page.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
Secured VPN service will be launched.
Terminate Secured VPN
To request termination of the Secured VPN service, follow the steps below.
- Click the All Services > Management > Support Center menu. Go to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- In the task category, select Secured VPN termination.
Input field Detailed description Title Enter the title of the service request - Example: Secured VPN Service Termination Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: Secured VPN
Task classification Select the type you want to request - Terminate Secured VPN: select if you are terminating the service
content Guide to Entering Customer Basic Information and Application Process - Content: End Customer/MSP Information
Attachment If you have a completed Secured VPN service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files can be attached
Table. Table. Secured VPN Service Termination Request Items
- In the task category, select Secured VPN termination.
- After reviewing Application Process and Notes, click the Form Download > Service Request Form Download button to download the Secured VPN Service Request Form.
- Please fill out the Secured VPN Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
Category Detailed description Application Information Complete required fields such as request type, usage period, and basic information - Request type: select termination
- Usage period: enter desired termination date
- Guaranteed bandwidth: select the bandwidth you applied for
- Basic information: enter Account name, Project name, and recipient details
Monitoring information When terminating the entire service, no input is required. Table. Main contents of the Secured VPN service termination request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs, and fill out the required fields.
- Attach the completed application form to the attachment area.
- Click the Request button on the service request page.
- Once the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring team reviews the submitted service request, the termination is completed once the monitored IP is deleted.
- Service termination requires three business days, including the cancellation request date.
9.13.2.1 - Secured VPN Build Process Guide
To launch the Secured VPN service, you need to install a branch VPN in the client’s network and then perform an integration check. However, if you have a VPN that you operate directly, the integration check is not required. Refer to the process below to apply for the Secured VPN service.
Samsung Cloud Platform Console task (perform MSP)
- Apply for Direct Connect.
- Create a VPC and DCon-VPN connection for the connection target.
- Apply for Uplink line.
- Purpose of request: Configuration work to enable communication between the customer’s Office(On-premise) and the customer’s VPC within the Samsung Cloud Platform.
- Select the application path: Console > Support Center > Service Request.
- Service: Networking > Direct Connect
- Task Category: Uplink line request
- For the construction lead time and Uplink line work schedule, please inquire via Console > Support Center > Contact.
- Set up routing for Firewall, Security Group, Direct Connect, etc.
Routing and firewall configuration (client performed)
- Configure routing between the client’s Office internal network and the branch VPN, and set up the client’s firewall.
- Prior consultation is required for routing and firewall configuration. (SDS → MSP → customer)
- Configure the Samsung Cloud Platform segment and the client Office segment for bidirectional communication.
Installation of client VPN equipment and tunnel activation (MSP/SDS performed)
When installing the customer’s VPM equipment, you can either rent equipment from SDS or use your own equipment. Check the process that applies to your situation.
Case 1) When using the branch VPN device as a SECUI rental device provided by SDS
- Check the specifications, quantity, schedule, and installation location of the leased VPN equipment. (MSP→SDS)
- Please request the preparation of a pre‑installation environment survey for VPN. (SDS → MSP)
- Visit the client site and install the SECUI rental VPN equipment. (SDS)
- Open a tunnel between the branch VPN and the center VPN. (SDS)
Case 2) When using the branch VPN device as the customer’s own equipment
- Check the branch VPN equipment specifications and schedule. (MSP→SDS)
- Request equipment compatibility and IPSec VPN license/equipment setup. (SDS → client/MSP)
- Establish a tunnel between the branch VPN ↔ center VPN. (Customer/SDS)
- If the client requests a VPN installation work plan, contact via Console > Support Center > Contact or mssp.scp@samsung.com.
- Proceed with the work in compliance with the National Intelligence Service VPN installation guide and security review standards.
End-to-End test (perform MSP/SDS)
- Verify and share the test schedule after installing the branch VPN equipment (or configuring existing equipment). (SDS → MSP)
- Verify communication between the branch VPN device and the VPC (bidirectional).
9.13.3 - Release Note
Secured VPN
- We have launched a Secured VPN service that safely connects external customer networks with the Samsung Cloud Platform’s cloud network via an encrypted virtual private network.
9.14 - FPMS
9.14.1 - Overview
Service Overview
FPMS (Firewall Policy Management System) is an automated firewall operation service designed to efficiently and securely manage firewalls across various cloud environments. It automates all processes that operators currently perform manually, eliminating human errors and failures, and reducing users’ service lead time.
Features
- Failure Prevention: Prevent human errors that can occur when manually registering firewall policies, and verify that the IP and Port information in the request conforms to proper syntax and structure, converting it to correct data to proactively prevent failures.
- Operational Convenience Improvement: It automates the application of firewall policies and provides a function that replicates a requested policy to another firewall for redundancy. By leveraging the firewall policy expiration feature offered by FPMS, policies can be limited to a specific period, and features such as automatic deletion of disabled policies help reduce the workload of operational personnel.
- Firewall Policy Optimization: Use an optimization algorithm for the requested firewall policy to optimize the firewall policy. Also, by checking for duplicate or permanent policies, you can prevent the application of unnecessary rules.
- Continuous Security Enhancement: Analyze excessive open policies and expired or unmanaged policies, quantify diagnostic scores by category, and easily identify vulnerability status. Additionally, you can continuously strengthen security through the vulnerability remediation guide.
Service Architecture Diagram
Provided features
FPMS provides the following features.
- Policy Management
- Policy change history management and real-time monitoring
- Policy search and policy expiration management
- Automatic Policy Registration
- Application data consistency check and automatic conversion
- Network operation/security standard inspection and conversion
- Automatic rule creation and application based on firewall vendor characteristics
- Policy Optimization
- Remove duplicate policy address/port/protocol
- Policy pattern analysis optimization
- Unused/Expired/Duplicate Policy Analysis
- Policy Security Analysis
- Provide security index results for each firewall policy
- Report risk status after similarity analysis of application information and policy
Component
Firewall
FPMS can register and manage firewalls that are currently in operation.
- Before registering a firewall, you need to confirm that it is compatible (check manufacturer, model name, OS version).
- FPMS uses the API to connect to firewall devices to insert policies or retrieve information. To do this, firewall operators must create an integration account on the firewall device and configure the API or verify information so that access is possible.
Firewall Application System
To retrieve firewall application data, FPMS must be integrated with the application system.
Constraints
The constraints of the FPMS service are as follows. Please be sure to review the constraints below before use and incorporate them into your service usage plan.
- Separate infrastructure must be prepared for the installation and service provision of FPMS.
- A VM for web/app services and a DBMS configuration for data storage are required.
Provision status by region
FPMS is available in the following environments.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Prior Service
FPMS has no prior service.
9.14.2 - How-to guides
Users can create the service by entering the required information to receive the FPMS service through the Samsung Cloud Platform Console.
Create FPMS
You can create and use the FPMS service from the Samsung Cloud Platform Console.
To request the creation of an FPMS service, follow the steps below.
- Click the All Services > Security > FPMS menu. Navigate to the FPMS Service Home page.
- On the Service Home page, click the FPMS Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
- Service Request page: enter or select the required information in the mandatory input fields.
- In the task type, select FPMS Service Creation.
Input field Detailed description Title Enter the title of the service request - Example: FPMS Service Creation Request
Region Select the location of Samsung Cloud Platform Service Select the service group and service. If you click the FPMS service request button, it is entered automatically - Service Group: Security
- Service: FPMS
Task classification Select the task you want to request - Create FPMS Service: Select if you are requesting a new service
content Check the service application process and reference information, then enter the detailed application details. Attachment If you have additional files you want to share for the service application, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files can be attached
Table. FPMS Service Creation Request Items
- In the task type, select FPMS Service Creation.
- Check the required information entered on the Service Request page and click the Request button.
- After completing the FPMS service application, a dedicated FPMS technical support representative will contact you by email to set up the installation and usage of FMPS.
- After confirming the details with the dedicated FPMS technical support representative, the FPMS installation and related system integration work will proceed.
Check FPMS Application Details
After applying for the FPMS service, you can view the detailed information and processing steps.
To check the FPMS service application details, follow the steps below.
- Click the All Services > Support Center menu. Go to the Service Home page of Support Center.
- On the Service Home page, click the Service Request menu. You will be taken to the Service Request List page.
- On the Service Request List page, select the request item. You will be taken to the Service Request Details page.
- Check the detailed information and processing steps on the Service Request Details page.
Detailed FPMS information can be viewed in a separate FPMS management portal.
- The management portal address will be sent separately by the person in charge via email after the FPMS installation is complete.
Terminate FPMS
To request cancellation of the FPMS service, follow the steps below.
Click the All Services > Security > FPMS menu. Navigate to the Service Home page of FPMS.
On the Service Home page, click the FPMS Service Request button. Navigate to the Support Center > Service Request List > Service Request page.
Service Request page, enter or select the required information in the mandatory input fields.
- Select FPMS Service Termination in the task type.
Input field Detailed description Title Enter the title of the service request - Example: FPMS Service Termination Request
Region Select the location of Samsung Cloud Platform Service Select the service group and service. If you click the FPMS service request button, it is entered automatically - Service Group: Security
- Service: FPMS
Task classification Select the operation you want to request - FPMS Service Termination: Select if you want to terminate the service
content Review the service termination process and reference information, then enter the detailed application details. Attachment If you have any additional files you want to share for service termination, proceed with the upload - Attachments can be up to 5 MB each, with a maximum of 5 files
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files are allowed
Table. Table. FPMS Service Termination Request Items
- Select FPMS Service Termination in the task type.
Verify the required information entered on the Service Request page, and click the Request button.
- After you complete the FPMS service termination request, the dedicated FPMS technical support staff will verify it and proceed with the FPMS service termination and deletion.
9.14.3 - Release Note
FPMS
- A feature has been added to FPMS that allows registering and managing firewalls and Security Groups of the Samsung Cloud Platform Console.
- The SecuAI firewall v3.7 support (anyzone) feature has been improved.
- We have launched the FPMS (Firewall Policy Management System) service, which automates firewall operation tasks to efficiently and securely manage firewalls across diverse cloud environments.
9.15 - Secrets Manager
9.15.1 - Overview
Service Overview
Secrets Manager is a service that encrypts customers’ sensitive information as Secrets (secure data) and stores and manages it safely. Remove hard-coded sensitive information from the application source code and retrieve it by invoking Secrets stored securely in a Key-Value format. A secret is encrypted with a user‑managed key in conjunction with the Key Management Service and stored securely.
Service Architecture Diagram
Provided features
Secrets Manager provides the following features.
- Secret creation/deletion: Secrets Manager can create, delete, and manage Secrets. * The user stores security (sensitive) information in key/value format in the generated Secret.
- Secret lookup: You can retrieve Secret values based on custom policies and permission settings.
- Label-based version control: When a Secret is modified, you can set a label on the version, which is a snapshot of the uniquely generated data, allowing you to manage Secrets more efficiently.
Component
Secret
It stores sensitive (critical) information as a logical unit, encrypting security information values in Key/Value format with a KMS key.
- A Secret is an object created through the creation of a Secrets Manager product service in the Samsung Cloud Platform Console.
Version
It is a snapshot of unique data that is newly created each time a Secret is modified (the unit that stores the actual value of the Secret).
Label
It is a label or tag attached to a specific version of a Secret (a pointer for referencing a specific version).
Constraints
The limitations of the Secrets Manager service are as follows. Before use, be sure to review the following constraints and incorporate them into your service usage plan.
- Secrets Manager is a regional service, and a created secret can be used only within that region.
- When rotating a customer-managed key, the key version is changed internally. * By using the newly generated version of the key, you can decrypt data that was encrypted with the previous version of the key. * (maintain compatibility)
- Versions through key rotation are compatible up to the 100th version, regardless of the encryption algorithm.
| Item | Detailed description | Quota |
|---|---|---|
| Secret Value Size | Size of the encrypted Secret value | 65,536 |
| Secrets | Number of Secrets per region in an account | 500,000 |
| Attached Labels for Secret | Number of Labels attached to all versions of Secret | 20 |
| Versions per Secret | Number of versions of Secret | 100 |
Preliminary Service
Secrets Manager has no prerequisite services.
9.15.2 - How-to guides
Users can create the service by entering the required information for the Secrets Manager service through the Samsung Cloud Platform Console and selecting detailed options.
Create Secrets Manager
You can create and use Secrets Manager in the Samsung Cloud Platform Console.
To create a Secrets Manager, follow these steps.
Click the All Services > Security > Secrets Manager menu. 1. Go to the Service Home page of Secrets Manager.
On the Service Home page, click the Create Secrets Manager button. 2. Navigate to the Create Secrets Manager page.
Create Secrets Manager page, enter the information required to create the service and input additional details.
- Enter or select the required information in the Service Information Input area.Categoryrequired status
Detailed description Secret name Required Enter the secret name type Required Select the type to manage encrypted with Secret from the list. Key/Value input Required Enter a pair of Key/Value for Secret information - Click the Add button to add up to 10 entries
- Click the X icon to delete the entry
encryption key Essential Select the KMS key from the list to encrypt the Secret - Select a key created in the KMS service from the list. Or click +Create New to create a KMS key
- Only KMS keys for encryption/decryption can be selected. The selectable encryption/decryption KMS key types are encryption/decryption (AES-256), encryption/decryption and signing/verification (RSA-2048), and encryption/decryption (ARIA) – three types.
- When entering Key/Value, input must be within 64 KB; registration is not allowed if the size exceeds this limit.
- For detailed information on creating KMS keys, see KMS 키 생성하기 for reference
Public access control Required Enter public access allowed IP - After entering the IP address, click the Add button to register up to 10 entries
- Click the Delete All button to remove all IP entries from the list
- You can register the 0.0.0.0/24 - 0.0.0.0/32 range, but it may be insecure
Private access control Selection Use After selecting, select the resource to allow private access - Click the Add button to add an access‑allowed resource
- If the setting is not enabled, access is allowed for all subnet resources in the same region
Explanation Selection Enter description for Secrets Manager Table. Secrets Manager service information input items - Enter or select the required information in the Additional Information Input area.
Category required statusDetailed description tag Selection Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, input or select Key, Value values
Table. Secrets Manager additional information input fields
- Enter or select the required information in the Service Information Input area.
Summary Check the detailed information and estimated charges generated in the panel, and click the Create button.
- Once creation is complete, verify the created resource on the Secrets Manager list page.
Check Secrets Manager detailed information
Secrets Manager can view and edit the complete list of resources and detailed information. Secrets Manager Details page consists of Details, Versions, Tags, Activity History tabs.
To view detailed information about Secrets Manager, follow these steps.
- All Services > Security > Secrets Manager Click the menu. 1. Go to the Service Home page of Secrets Manager.
- On the Service Home page, click the Secrets Manager menu. 2. Go to the Secrets Manager List page.
- On the Secrets Manager List page, click the resource to view its details. 3. Go to the Secrets Manager Details page.
- Secrets Manager Details At the top of the page, status information and descriptions of additional features are displayed.
Category Detailed description status Display the status of Secrets Manager - Active: available/enabled
- To be terminated: scheduled for deletion
Service termination Cancel Service button Table. Secrets Manager status information and additional features
- Secrets Manager Details At the top of the page, status information and descriptions of additional features are displayed.
Detailed Information
Secrets Manager list page allows you to view detailed information of the selected resource and edit the information if necessary.
Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who modified the service |
| Modification date | Service modification date and time |
| Secret name | Name of the generated Secret |
| Secret value | the entered Secret value
|
| type | Type of the generated Secret |
| Recent search date and time | Last retrieval time of the generated Secret |
| encryption key | Display the KMS key name selected by the user
|
| URL | Public/Private URL information display
|
| Public access control | Display the registered public access allowed IP
|
| Private access control | Display registered private access allowed resources
|
| Explanation | Display additional description for Secret
|
Version
Secrets Manager list page allows you to use labels to track the version of the selected Secret.
Refer to the definition of each item when checking the version information of Secret Manager.
- Secret: logical unit that stores sensitive (important) information
- Version: A snapshot of unique data generated each time a Secret is modified (the unit that stores the actual value of the Secret)
- Label: a nameplate or tag attached to a specific version of a Secret (a pointer for referencing a specific version)
| Category | Detailed description |
|---|---|
| Version ID | Current version, previous version, and the ID of the version with a custom label (Custom Label) displayed
|
| Label | Secret version display
|
| Last access time | Secret’s most recent access time |
| Creation date and time | Secret creation timestamp |
The limitations when using a version of Secret are as follows.
- You can store up to 100 versions per Secret. * Regardless of whether a custom label is set, if the number of versions exceeds 100, the oldest versions are deleted first.
- For important versions with custom labels, create a new Secret before the version is deleted due to quota limits, and configure it so that the running application can reference the new Secret.
Tag
Secrets Manager list page allows you to view the tag information of the selected resource, and to add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Secrets Manager list page lets you view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Work history | Task execution details |
| Work Date/Time | Task execution date and time |
| Resource Type | Resource Type |
| Resource name | Resource Name |
| Operation result | Task execution result (success/failure) |
| Operator Information | User information of the person who performed the task |
Terminate Secrets Manager
You can cancel Secrets Manager that you are not using.
To cancel Secrets Manager, follow the steps below.
- All Services > Security > Secrets Manager Click the menu. 1. Go to the Service Home page of Secrets Manager.
- On the Service Home page, click the Secrets Manager menu. 2. Go to the Secrets Manager List page.
- On the Secrets Manager List page, click the resource to view its details. 3. Go to the Secrets Manager Details page.
- On the Secrets Manager Details page, click the Cancel Service button. 4. Service Cancellation popup will be opened.
- Service Cancellation in the popup window, enter the cancellation waiting period, and click the Confirm button.
- The termination waiting period can be entered within a range of 7 to 30 days.
- After termination is complete, check on the Secrets Manager List page whether the resource has been terminated.
9.15.2.1 - Secret Retrieval API Reference
This user guide explains how to use and invoke the Public/Private endpoints of Secrets Manager.
- Public Endpoint can be called from an environment that can communicate over the Internet.
- Private Endpoint can only be called from a Samsung Cloud Platform VM.
Pre-configuration for Endpoint Calls
Describes the prerequisite configuration items required when calling the Secrets Manager endpoint.
Register Outbound Rule for Security Group
To call the endpoint, you need to register an outbound rule in the security group.
To register an Outbound Rule for a Security Group, follow the steps below.
- Click the All Services > Security > Secrets Manager menu. You will be taken to the Service Home page of Secrets Manager.
- On the Service Home page, click the Secrets Manager menu. You will be taken to the Secrets Manager List page.
- On the Secrets Manager List page, click the resource whose details you want to view. You will be taken to the Secrets Manager Details page.
- On the Secrets Manager Details page, check the URL information.
- You can copy the public/private URL information from the URL field.
- Use the nslookup command to verify the IP to register in the Security Group.
nslookup <호출할 endpoint url>
- From Security Group > Security Group List, select the Security Group of the VM for which you want to set access control. Then navigate to the Security Group Details page.
- In the Security Group Details > Rules tab, click the Add Rule button. When the Add Rule window appears, enter the information below to add a rule.
Item Detailed description Target input method CIDR selection Target address Enter the IP address retrieved by nslookup type Select Destination Port/Type then enter protocol information - Select TCP among the protocols, and enter 443 in the TCP Destination Port
direction Outbound rule Select Explanation Enter the invocation rules for Secrets Manager public/private endpoints Table. Input items for adding Security Group rules - Security Group rules Verify that the rule you entered in the list has been added.
Register access control for Secrets Manager
You can register public/private access controls for Secrets Manager.
To configure the access control items of Secrets Manager, follow these steps.
- Click the All Services > Security > Secrets Manager menu. You will be taken to the Service Home page of Secrets Manager.
- On the Service Home page, click the Secrets Manager menu. You will be taken to the Secrets Manager list page.
- On the Secrets Manager List page, click the resource to view detailed information. You will be taken to the Secrets Manager Details page.
- On the Secrets Manager Details page, click the edit icon of Public Access Control to add an allowed IP for Public Endpoint access.
- Public Access Control Edit Popup window, enter the IP and click the Add button. When the addition is complete, click the Confirm button.
- For security, we recommend adding a single IP, and you can register up to 10.
- You can register the 0.0.0.0/24 – 0.0.0.0/32 range, but be careful as it may be insecure.
- On the Secrets Manager Details page, click the edit icon of Private Access Control to add a VM that allows Private Endpoint access.
- Private Access Control Edit Popup window, select the resource to allow access and click the Add button. When addition is complete, click the Confirm button.
- If you do not enable the setting, you can access all subnet resources in the same region.
Calling Secrets Manager API
Describes how to call the Secrets Manager API.
Check the URL information of Secrets Manager
On the All Services > Security > Secrets Manager > Secrets Manager Details page, check the URL information.
- You can copy the public/private URL information from the URL field.
Secrets Manager Retrieval API
get /v1/secret
Description
Secret value lookup
Parameters
| Type | Name | Description | Schema |
|---|---|---|---|
| query | secretId (required) | Secret ID (Example : b3ed8b7637574255b83c274a6ed79426) | string |
Responses
| Http Code | Description | Schema |
|---|---|---|
| 200 | OK | None |
| 400 | Bad Request | None |
| 401 | Unauthorized | None |
| 403 | IP Not Allowed | None |
| 404 | Not Found | None |
Example HTTP request
Request path
/v1/secret?secretId={secretId}
Request header
"AccessKey = 341g54421b5d67a1gf2b30f1a5415e75",
"SecretKey = 87d5eec6-998h-4933-e865-fd837495je28"
Example HTTP response
Response 200
{
"status": "success",
"data": {
"key": "value"
},
"timestamp": "2026-01-20T09:21:18.92730172"
}
9.15.3 - Release Note
Secrets Manager
- Provides a Private Endpoint that can be called as a Secret from VM resources in the Samsung Cloud Platform.
- You can select a VM resource in Samsung Cloud Platform that stores secret security information and configure access control.
- We have launched a service that encrypts customers’ sensitive information as Secret(secure information) and safely stores and manages it.
- Remove hard-coded security information from the application source code and retrieve it by invoking securely stored Secrets.
9.16 - DDoS Protection
9.16.1 - Overview
Service Overview
DDoS Protection is a DDoS (Distributed Denial of Service) detection and mitigation service that uses multiple servers to detect and block attacks that generate concentrated traffic on the network. Through continuous monitoring, it detects external traffic attacks targeting a domain, performs additional verification and blocking, and protects servers inside the DMZ. When a DDoS attack occurs, it blocks and disperses traffic to minimize the load on the origin server, ensuring the continuity of the web service.
The DDoS Protection service of Samsung Cloud Platform is based on SECaaS. All user traffic passes through the SECaaS PoP before reaching the server, and when attack traffic arrives, it is analyzed by the SECaaS Rule, detected and blocked, and only clean traffic is forwarded to the server. Additionally, the service is provided from a nearby PoP based on the user’s connection country, and if a PoP failure occurs, service is provided from another PoP within the same country or region.
Features
- Rapid Attack Detection: When a large volume of traffic arrives, it detects and blocks DDoS attacks in real time. Continuously update detection criteria to address the latest attack techniques.
- Effective Attack Blocking: When L3/L4/L7 DDoS attacks are detected, through additional verification such as JAVA Script, Captcha, we ensure service availability by blocking only DDoS attack traffic, and allow regular users to access the website normally.
- Stable web service operation: With experience in large-scale network operations and 24x365 security monitoring, we can effectively respond to external security threats.
Configuration diagram
Provided features
We provide the following features.
- Intrusion detection through network flow and monitoring
- Detecting and blocking high-volume traffic inbound to a domain
- Perform deep inspection (JAVA Script verification, Captcha verification, etc.)
- Block L7 application vulnerability attacks
- 24/7 event monitoring
- Fast traffic processing through a global network
- Fast traffic handling via global PoPs
- Rapid routing transition through SDN and Tier 1 ISP integration
Component
domain
SECaaS DDoS Protection is registered on a per-domain basis.
- It can only be applied to domains served with an FQDN (Fully Qualified Domain Name); if the service is provided using an IP address instead of a domain, SECaaS DDoS Protection cannot be applied.
- Registration is only possible for domains registered in the public DNS, and after verifying the domain’s integrity via DNS lookup, it cannot be used when registering a private internal IP.
- It applies to traffic that uses HTTP/HTTPS protocols based on web applications, and other TCP traffic is dropped and cannot be used.
Traffic
Traffic is aggregated as the combined Mbps value of the individually registered domains between SECaaS DDoS Protection and the Origin server.
Constraints
To use DDoS Protection, please check the following items in advance.
- Domain Use
- It can be applied only when the service is provided using an FQDN(Fully Qualified Domain Name). If you serve with an IP address instead of a website URL, DDoS Protection cannot be applied.
- Registration is possible only for domains registered in a public DNS. DDoS Protection is located in the external Internet segment and verifies domain integrity via DNS Lookup. (Registration with internal private IPs such as 10.10.10.10 makes DDoS Protection unavailable.)
- Use HTTP/HTTPS
- Only traffic using the HTTP/HTTPS protocol for web applications is accepted.
- TCP traffic that uses protocols other than http/https is dropped, so DDoS Protection cannot be used.
- XFF(X-Forwarded-For) header function Enable required
- SECaaS DDoS Protection has the XFF header feature enabled by default. If the XFF header feature is set to disabled, the session may be terminated.
- Client Source IP Change
- When forwarding a user request from SECaaS DDoS Protection to the customer system, the Source IP is changed to an IP range owned by DDoS Protection rather than the original user’s public IP. The original user’s public IP is delivered via the XFF header.
- Maximum Upload Size Limit
- The maximum uploadable file size is limited to 500 MB. (If it exceeds 500 MB, separate agreement is required.)
Provision status by region
DDoS Protection is available in the following environments.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that must be pre-configured before applying for the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Compute | Virtual Server | Virtual server optimized for cloud computing |
| Security | WAF | A service that protects web applications from web vulnerabilities and attacks |
9.16.2 - How-to guides
Users can create the DDoS Protection service by entering the required information through the Samsung Cloud Platform Console.
Create DDoS Protection
You can create and use the DDoS Protection service from the Samsung Cloud Platform Console.
To request the creation of a DDoS Protection service, follow these steps.
- All Services > Security > DDoS Protection menu, click it. You will be taken to the Service Home page of DDoS Protection.
- On the Service Home page, click the DDoS Protection Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- In the operation type, select Create DDoS Protection.
Input field Detailed description Title Enter the title of the service request - Example: DDoS Protection service creation request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the DDoS Protection service request button, it is entered automatically - Service Category: Security
- Service: DDoS Protection
Task classification Select the Activity you want to request - Create DDoS Protection: select if you are requesting a new service
content Guide to the service application process and reference information Attachment If you have a completed DDoS Protection service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. DDoS Protection Service Creation Request Items
- In the operation type, select Create DDoS Protection.
- After reviewing the application process and reference information, download the form > click the Service Request Form Download button to download the DDoS Protection Service Application Form.
- Please fill out the DDoS Protection Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Complete required fields such as application type, usage period, and usage amount. Monitoring information Complete required items such as migration schedule, domain, and secure recipient information - Fill out all items except for special cases
Table. Main contents of the DDoS Protection service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form in the attachment area.
- Click the Request button on the service request page.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
- After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
- The monitoring officer is contacting you via email to proceed with opening the firewall, SECaaS domain authentication, and certificate deployment.
- User Guide > Security > DDoS Protection > How-to guides > Refer to the DDoS Protection Service Application page to proceed with monitoring integration.
- We will conduct a test at the Security Monitoring Center (securitycenter@samsung.com) to verify the monitoring integration.
- Perform a final check to confirm normal service access and detect any SSL certificate errors.
- The DDoS Protection service is now available.
Check DDoS Protection detailed information
Detailed information on DDoS Protection can be accessed from a separate Security Platform (SSMP).
VM list
- Security Platform (SSMP) Please access it.
- Enter Knox login information.
- Assets > Cloud Monitoring Management > Cloud URL List Check the SECaaS deployment status on the page. You can enter the required fields to query.Item
Detailed description Business Unit Select the appropriate business unit Business name Select the magnifying glass icon, then search for and enter the corresponding business name. website URL Enter URL SECaaS implementation Select whether to apply SECaaS (Apply/Do not apply) SECaaS mode Select SECaaS mode (block/detect) SECaaS vendor Select SECaaS vendor (None/Imperva/Cloudflare) Platform Enter using SCP Deletion status Table. Search items - When you click the individual URL, you can view the URL details.SECaaS status
Detailed description Apply (Detection) SECaaS applied state, conduct attack pattern detection and log analysis - Recommend maintaining detection mode for at least one month, and after analyzing false positives/false negatives for at least one month, recommend switching to blocking mode via email
Apply (Block) SECaaS applied state, automatic blocking of detected attacks Not applied State where SECaaS is not applied Table. SECaaS implementation status
DDoS Protection Terminate
To request termination of the DDoS Protection service, follow the steps below.
Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
Service Request page: enter or select the required information in the mandatory input fields.
- Select DDoS Protection termination in the work category.
Input field Detailed description Title Enter the title of the service request - Example: DDoS Protection Service Cancellation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: DDoS Protection
Task classification Select the Activity you want to request - Cancel DDoS Protection: select if you are canceling the service
content Guide to the service application process and reference information Attachment If you have a completed DDoS Protection service application form (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. DDoS Protection service termination request items
- Select DDoS Protection termination in the work category.
After reviewing the Application Process and Reference Information, click the Form Download > Service Request Form Download button to download the DDoS Protection Service Application Form.
Please complete the DDoS Protection Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required items such as application type, usage period, and usage amount - Usage amount does not need to be filled in
Monitoring information Complete required items such as migration schedule, domain, and secure recipient information - Complete all items except for special notes
Table. Main contents of DDoS Protection service termination request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form to the attachment area.
Click the Request button on the service request page.
- Once the request is completed, verify the submitted information on the Support Center > Service Request list page.
After the monitoring staff verifies the submitted service request, the termination process is completed once the URL is deleted.
- Service termination takes 2–3 business days (including the cancellation request date).
- The restoration of DNS settings that were changed for SECaaS implementation must be performed directly by the service operator.
- When the service termination is completed, you cannot view the URL on the Security Platform (SSMP) Assets > Cloud Monitoring Management > Cloud URL List page.
9.16.2.1 - DDoS Protection Preparation
Configure firewall open settings
Client (User) - SECaaS (DDoS Protection) - Origin Server Each segment requires firewall opening. For the information required to open the firewall (Source, Type, Protocol, Destination), please inquire via the Support Center > Contact Us menu.
- Proceed with opening the firewall for the segment where the client (User) connects to SECaaS (DDoS Protection).
- The default supported web ports for SECaaS are as follows.
- http : 80, 8080, 8880, 2052, 2082, 2086, 2095
- https : 443, 2053, 2087, 2096, 8443
- For websites that use ports other than the default supported web ports, fill out the DDoS Protection service request form to submit a service request. We will provide the Destination IP via the email account on the service request form. If the ports are changed (added, removed) or the Origin is changed after applying SECaaS, the IP may change. If you email the security monitoring center account (securitucenter@samsung.com) in advance, we will inform you of the changed IP through the responsible person.
- If you are not using an IPv6 address, registration is not required.
- The service application form can be downloaded and attached from the All Services > Security > DDoS Protection menu by clicking the DDoS Protection Service Request button, then downloading it on the Service Request screen.
- For information related to service application, see the How-to guides’ DDoS Protection 생성하기.
Source Type Protocol Destination: SECaaS Client HTTP, HTTPS TCP - IPv4: 162.159.141.5 / 172.66.1.3
- IPv6: 2606:4700:7::102 / 2a06:98c1:58::102
Table. Example of IP forwarding form
- The default supported web ports for SECaaS are as follows.
- Proceed with opening the firewall for the segment that connects to the Origin Server in SECaaS(DDoS Protection).
- The origin server is the device that receives traffic from SECaaS. (e.g., LB, server, etc.)
- The firewall or security device in front of the origin server must allow a specific range.
- Cloudflare IP range information: https://www.cloudflare.com/ko-kr/ips/
- If you are not using an IPv6 address, registration is not required.CautionWe recommend blocking web traffic (HTTP, HTTPS) outside the specified range. If not blocked, the Origin IP may be exposed, potentially enabling attacks that bypass SECaaS, and such bypass attacks are difficult to monitor for security.
Authenticate SECaaS domain
To authenticate the registrant of the domain, you must create a host and add a TXT record for domain verification to DNS.
- Authentication typically takes about 15 minutes after registration, but can take up to 24 hours depending on the environment. For example, when registering www.test.com, you must create/enter the Host and TXT Record values we provide into DNS.
Applying SECaaS Certificate
You can select and use either the certificate provided by SECaaS or the certificate supplied by the customer. Certificate installation is possible only if HTTPS is enabled for the domain; if the certificate is not installed, HTTPS communication will not work.
1. When using SECaaS certificate
- A new SSL certificate used between the Client ↔ SECaaS server will be generated.
- Validation of the domain owner is required for the generated SSL certificate. The owner verification is performed by creating/entering the HOST and CNAME values we provide into DNS.
- Certificates cannot be extracted and delivered, and there is an automatic renewal feature, so no separate renewal is required.
- Authentication typically takes about 15 minutes after registration, but may take up to 24 hours depending on the environment.
2. When using a client (Custom) certificate
- Provide the Full chain certificate, Key File, and Key Value.
- An API communication issue occurs when registering a single certificate. (Only pfx, pem, cer files are supported)
- The renewed certificate must be provided for renewal before the certificate expires.
9.16.2.2 - DDoS Protection Service Application
After completing the service request on the service request page, proceed with the steps below in order.
Perform pre-test
- Before changing the traffic path with SECaaS, run a test to verify that it works correctly.
- The security monitoring center provides the IP to be used in SECaaS. Example: 103.22.200.1
- We will explain using aaa.test.com as the website example.
- Add the example text below to the C:\Windows\System32\drivers\etc\hosts file and save it.
- Example phrase : 103.22.200.1 aaa.test.com
- When accessing a URL in Chrome, press F12 and then select F5 (Refresh) in the Network tab at the top of the developer tools.
- The process completes when the response header ‘X-cdn’ has the imperva value, or when a SECaaS IP is present in the remote address.
Changing DNS Settings
The path is changed so that actual traffic is transmitted via SECaaS.
- We will configure each domain’s address as a CNAME using the provided CNAME domain. When using a CDN, change the CDN’s origin address to a CNAME.
- Root (Naked) domains cannot have a CNAME record. It is recommended to configure an A record using the two default Anycast IPs. If setting both IPs is difficult, configure only one.
- Example: Register or modify DNS for test.com using the CNAME we provide, and register or modify an A Record DNS for test.com using the IP we provide.
Notify DNS Change
After the DNS change is announced, the security monitoring center checks for proper integration and traffic inflow.
Check Service
Verify normal service connectivity.
- Check whether an SSL certificate error occurs.
- DDoS Protection is operated in detection mode for one month, after which the logs are analyzed and provided to the service owner.
- If no legitimate traffic is detected as an attack, switch to block mode. If a false positive occurs, verify with the service owner and then add an exception in DDoS Protection.
9.16.2.3 - DDoS Protection Service Outage Response
When a DDoS Protection service outage occurs, follow the steps below to address and respond to the issue.
Service outage detection
- The service owner will become aware of a failed service URL health check or a response error.
- The security monitoring center will encounter SECaaS service disruptions and cause the registered Origin Healthcheck to fail.
Remediation
- After identifying the cause of the failure, if it is determined to be a SECaaS service outage, you must change the registered CNAME/A Record values to the original service’s Origin IP/address for redirection (reversion) and apply them. Since DNS values need to be changed, the user must handle it directly.
- When an urgent bypass (restoration) is required.
- SECaaS(DDoS Protection) → Server(Origin) Open the segment firewall to any.
- You can achieve the same effect by asking the SECaaS administrator to request DNS bypass processing in the SECaaS settings. (It is applied based on the DNS TTL value and takes about five minutes.)
- Websites that have DNS applied via an A Record value, such as a root (naked) domain, cannot be used.
SECaaS reapplication
After the outage is resolved, reapply the modified CNAME/A Record values to the SECaaS CNAME/A Record address.
9.16.3 - Release Note
DDoS Protection
- We are launching a DDoS Protection service that provides detection and mitigation of large-scale network traffic attacks.
9.17 - Log Transmission
9.17.1 - Overview
Service Overview
Log Transmission is a service that collects and stores logs in real time from firewalls, IPS, and DDoS security devices, and transmits them to the areas required by the customer. It provides a foundation for performing security monitoring in the user domain using those logs.
Features
- Security Event Log Collection/Transmission: Collect and store logs in real time from security devices, and transmit security events.
- Secure Log Storage/Transmission: Log data can be stored securely, and backup and recovery are possible when needed. Collected logs are safely kept in a redundant storage, and data is transmitted by utilizing VPN services, etc. Sending securely.
Configuration diagram
Provided features
We provide the following features.
- Integration of various security log sources
- Real-time log collection from various sources such as firewalls, IPS, and DDoS security devices.
- Log Filtering and Processing
- Filter out unnecessary logs or extract only the logs requested by the customer.
Component
Log Transmission sends service log sources from the Samsung Cloud Platform to the equipment or system desired by the customer.
- The service runs by connecting via VPN to the customer’s office (server room) where the device that receives the log source is located.
Constraints
To use Log Transmission, please check the following items in advance.
- We collect and transmit logs for Security products offered by the Samsung Cloud Platform.
- To send logs, you must be connected via VPN to the device that receives the logs.
Provision status by region
Log Transmission is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provided |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Preceding Service
This is a list of services that must be pre-configured before creating the Log Transmission service. Refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | Direct Connect | A service that securely and quickly connects the customer’s network with the Samsung Cloud Platform |
| Security | DDoS Protection | Large-scale network traffic attack detection and response service |
| Security | IPS | A service that detects and responds to intrusions on websites and application servers in real time. |
| Security | Secured Firewall | Next-generation firewall service that meets high security requirement levels |
- When running Log Transmission, you must select the service to which logs will be sent. Once the log transmission service target is determined, a VPN connection is required for secure log transmission.
- To use the Log Transmission service, configuration work is required for communication between the customer’s Office (on‑premise) and the customer’s VPC within the Samsung Cloud Platform. Please follow the process below to request an uplink line, including external integration software and VPN settings, Direct Connect firewall opening, etc.
- Create a Direct Connect service.
- Create a connection between the customer’s VPC and DCon-VPN.
- Apply for an uplink line for communication between the client’s On-premise and VPC.
- Application path: Support Center > Service Request List > Service Request
- Select service: Networking > Direct Connect
- Task Category: Uplink line request
- Configure routing for the VPN path.
- Set up the required routing information such as Firewall, Security Group, Direct Connect, etc.
9.17.2 - How-to guides
Users can create the service by entering the required information for using the Log Transmission service through the Samsung Cloud Platform Console.
Create Log Transmission
You can apply for and use the Log Transmission service from the Samsung Cloud Platform Console.
To request the creation of a Log Transmission service, follow these steps.
Click the All Services > Security > Log Transmission menu. Navigate to the Service Home page of Log Transmission.
On the Service Home page, click the Log Transmission Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
Service Request page, enter or select the required information in the mandatory input fields.
- In the task type, select Log Transmission creation.
Input field Detailed description Title Enter the title of the service request content - Example: Log Transmission Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the Log Transmission service request button, it is entered automatically - Service Category: Security
- Service: Log Transmission
Task classification Select the type you want to request - Create Log Transmission: select when requesting a new service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment Upload the completed Log Transmission service application (required) and any additional files you wish to share - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif files are allowed
Table. Log Transmission Service Creation Request Items
- In the task type, select Log Transmission creation.
After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the Log Transmission Service Application Form.
Please fill out the Log Transmission Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required items such as application type, usage period, recipient information, etc. - Application type: select application
- Usage period: enter desired start date
- Basic information: enter Account name, Project name, recipient information
Monitoring information Enter required items such as log transmission target and customer IP (range) - Complete all items except special cases
Table. Main contents of Log Transmission service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form in the attachment area.
On the service request page, click the Request button.
- After the request is completed, check the submitted details on the Support Center > Service Request List page.
After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
The Log Transmission service is now available.
Log Transmission Check detailed information
The Log Transmission service proceeds with the process for the service after applying through an SR. Unlike other services, detailed Log Transmission information cannot be viewed in the Console.
- To view detailed information, click the Contact Us button on the Support Center > Inquiry List page. On the Contact Us page, you can write your question and submit it.
Terminate Log Transmission
To request cancellation of the Log Transmission service, follow the steps below.
- Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page: enter or select the required information in the mandatory input fields.
- In the task category, select Log Transmission Cancellation.
Input field Detailed description Title Enter the title of the service request - Example: Log Transmission Service Termination Request
Region Select the location of the Samsung Cloud Platform - Automatically entered with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: Log Transmission
Task classification Select the type you want to request - Log Transmission termination: select if you are terminating the service
content Customer Basic Information Entry and Application Process Guide - Content: End Customer/MSP Information
Attachment Upload the completed Log Transmission service application (required) and, if you have additional files you want to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. Log Transmission Service Termination Request Items
- In the task category, select Log Transmission Cancellation.
- After reviewing Application Process and Reference Information, click the Form Download > Service Request Form Download button to download the Log Transmission Service Application Form.
- Log Transmission Service Application Form please fill out.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required fields such as request type, usage period, recipient information, etc. - Request type: select request
- Usage period: enter desired service termination date
- Basic information: enter Account name, Project name, recipient information
- Usage amount does not need to be filled out
Monitoring information Fill in required items such as log transmission target and customer IP (range) - Fill out all items except special cases
Table. Log Transmission Service Termination Application Form Main Contents
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form to the attachment area.
- Click the Request button on the service request page.
- After the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed once the log transmission target and the customer’s used IP (range) are removed.
- Service termination takes 2–3 business days, counting from the cancellation request date.
9.17.3 - Release Note
Log Transmission
- We have launched the Log Transmission service that enables security monitoring of the user domain on Samsung Cloud Platform.
9.18 - ESS(Endpoint Security Suite)
9.18.1 - Overview
Service Overview
The Endpoint Security Suite (ESS) provides the existing on‑premise Endpoint Security solutions ESCORT, NASCA, and SecuPrint as SaaS, allowing reduced deployment and operational costs. Additionally, the One‑View integrated management console enables easy and convenient management of each point solution, supporting efficient security solution operation.
Features
One-View Integrated Management
By consolidating the management consoles previously provided for each solution—ESCORT, NASCA, and SecuPrint—into One-View, integrated installation and removal of the solutions became possible, improving the efficiency of solution management and security operations.Expansion of PC Security Management Scope
The traditional On-Premise solution managed only PCs within the site after configuring a local network, but the Endpoint Security Suite that uses the Internet enables the same level of PC security management regardless of whether the PCs are inside or outside the site.Flexible scalability based on Rest API
By providing various common functions such as personnel information, administrator account information, and license management information through Rest API, integration and expansion with point solutions become easy.
Service Architecture Diagram
Provided features
ESS provides the following features.
ESCORT
- Control of information leakage through storage devices (USB, external HDD, etc.)
- Control of information leakage via network (WiFi, Bluetooth, etc.)
- Program execution control and vulnerability mitigation
NASCA
- Electronic document permission management and encryption/decryption
- Ensuring business continuity by providing automatic decryption functionality
- Screen watermark
SecuPrint
- Output watermark
- Output history management (log/statistics/tracking)
- Personal data search and blocking (resident registration number/account number/card number, etc.)
Component
ESCORT Windows Client
- ESCORT solution client for Windows PC to prevent internal information leakage
ESCORT Linux Client
- ESCORT solution client for Linux PC to prevent internal data leakage
NASCA Client
- Windows PC client for the NASCA solution for document encryption/decryption and permission management
SecuPrint Client
- Windows PC client for the SecuPrint solution, providing output watermarks and output security
Base Plan
- Annual license cost for each server software of the ESCORT, NASCA, and SecuPrint solutions
Provision status by region
ESS is available in the following environments.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Preliminary Service
ESS has no prior service.
9.18.2 - How-to guides
Users can apply for the service by entering the required information for using the Endpoint Security Suite (ESS) service through the Samsung Cloud Platform Console.
Create ESS
You can apply for and use the ESS service from the Samsung Cloud Platform Console.
To request the creation of an ESS service, follow these steps.
- All Services > Security > ESS Click the menu. Navigate to the Service Home page of ESS.
- On the Service Home page, click the ESS Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
- Service Request page: enter or select the required information in the mandatory input fields.
- Select ESS creation in the task category.
Input field Detailed description Title Enter the title of the service request content - Example: ESS Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically entered with the region corresponding to the Account
Service Select the service category and service. If you click the ESS service request button, it is entered automatically - Service Category: Security
- Service: ESS
Task classification Select the type you want to request - Create ESS: select when requesting a new service
content Guide to the service application process and reference information Attachment If you have a completed ESS service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. ESS Service Creation Request Items
- Select ESS creation in the task category.
- Check the required information entered on the Service Request page, and click the Request button.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
- After the service manager reviews the submitted service request, the process for using the service is initiated.
Check ESS application details
After applying for the ESS service, you can view the detailed information and processing steps.
To check your ESS service application details, follow these steps.
- Click the All Services > Support Center menu. Go to the Service Home page of Support Center.
- On the Service Home page, click the Service Request menu. You will be taken to the Service Request List page.
- On the Service Request List page, select the request item. You will be taken to the Service Request Details page.
- Service Request Details page lets you view detailed information and processing steps.
Terminate ESS
To request termination of the ESS service, follow the steps below.
Click the All Services > Security > ESS menu. Go to the Service Home page of ESS.
On the Service Home page, click the ESS Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
Service Request page, enter or select the required information in the mandatory input fields.
- Select ESS Service Termination in the task category.
Input field Detailed description Title Enter the title of the service request - Example: ESS Service Termination Request
Region Select the location of the Samsung Cloud Platform - automatically entered with the region corresponding to the Account
Service Select the service group and service. If you click the ESS service request button, it is entered automatically - Service Group: Security
- Service: ESS
Task classification Select the task you want to request - ESS Service Termination: select if you want to terminate the service
content Review the service termination process and reference information, then enter the detailed application details. Attachment If you have any additional files you wish to share for service termination, proceed with the upload - You can attach up to 5 files, each within 5 MB
- Only files with the following extensions are allowed: doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif
Table. ESS Service Termination Request Items
- Select ESS Service Termination in the task category.
Check the required information entered on the Service Request page, and click the Request button.
- After you complete the ESS service termination request, the service manager will verify it, and the ESS service termination and deletion process will proceed.
9.18.3 - Release Note
ESS
- We are launching the ESS external-facing product that offers the previously on-premises Endpoint Security service, which was provided to external customers under a perpetual license, as a SaaS-based Endpoint Security service with a subscription license.
- We are launching a service that offers the on‑premise Endpoint Security solutions ESCORT, NASCA, and SecuPrint as SaaS, and enables efficient management of endpoint security solutions from the One‑view integrated admin console.
9.19 - Log Transmission
9.19.1 - Overview
Service Overview
Log Transmission is a service that collects and stores logs in real time from firewalls, IPS, and DDoS security devices, and transmits them to the areas required by the customer. It provides a foundation for performing security monitoring in the user domain using those logs.
Features
- Security Event Log Collection/Transmission: Collect and store logs in real time from security devices, and transmit security events.
- Safe log storage/transfer: Log data can be stored securely, and backup and recovery are possible when needed. Collected logs are safely kept in a redundant storage, and data is transmitted using VPN services, etc. Sending securely.
Configuration diagram
Provided features
We provide the following features.
- Integration of various security log sources
- Real-time log collection from various log sources such as firewalls, IPS, and DDoS security devices.
- Log Filtering and Processing
- Filter out unnecessary logs or extract only the logs requested by the customer.
Component
Log Transmission sends service log sources from the Samsung Cloud Platform to the equipment or system desired by the customer.
- The service runs by connecting via VPN to the customer’s office (server room) where the device that receives the log source is located.
Constraints
To use Log Transmission, please check the following items in advance.
- We collect and transmit logs for Security products offered by the Samsung Cloud Platform.
- To send logs, you must be connected via VPN to the device that receives the logs.
Provision status by region
Log Transmission is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West (kr-west1) | Not provided |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Provided |
| South Korea South 2 (kr-south2) | Provided |
| South Korea South 3 (kr-south3) | Provided |
Preceding Service
This is a list of services that must be pre-configured before creating the Log Transmission service. Refer to the guide provided for each service to prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | Direct Connect | A service that securely and quickly connects the customer’s network to the Samsung Cloud Platform |
- When running Log Transmission, you must select the service to which logs will be sent. Once the log transmission service target is determined, a VPN connection is required for secure log transmission.
- To use the Log Transmission service, configuration work is required for communication between the customer’s Office (on‑premise) and the customer’s VPC within the Samsung Cloud Platform. Please follow the process below to request an uplink line, including external integration software and VPN settings, Direct Connect firewall opening, etc.
- Create a Direct Connect service.
- Create a connection between the customer’s VPC and DCon-VPN.
- Apply for an uplink line for communication between the customer’s on‑premise environment and the VPC.
- Application path: Support Center > Service Request List > Service Request
- Select service: Networking > Direct Connect
- Task Category: Uplink line request
- Configure routing for the VPN path.
- Set up the required routing information such as Firewall, Security Group, Direct Connect, etc.
9.19.2 - How-to guides
Users can create the service by entering the required information for using the Log Transmission service through the Samsung Cloud Platform Console.
Create Log Transmission
You can apply for and use the Log Transmission service from the Samsung Cloud Platform Console.
To request the creation of a Log Transmission service, follow these steps.
Click the All Services > Security > Log Transmission menu. Navigate to the Service Home page of Log Transmission.
On the Service Home page, click the Log Transmission Service Request button. You will be taken to the Support Center > Service Request List > Service Request page.
Service Request page: enter or select the required information in the mandatory input fields.
- In the task type, select Log Transmission Creation.
Input field Detailed description Title Enter the title of the service request content - Example: Log Transmission Service Creation Request
Region Select the location of the Samsung Cloud Platform - Automatically filled with the region corresponding to the Account
Service Select the service category and service. If you click the Log Transmission service request button, it is entered automatically - Service Category: Security
- Service: Log Transmission
Task classification Select the type you want to request - Create Log Transmission: select when requesting a new service
content Guide to the service application process and reference information Attachment If you have a completed Log Transmission service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Log Transmission Service Creation Request Items
- In the task type, select Log Transmission Creation.
After reviewing the application process and reference information, click the Form Download > Service Request Form Download button to download the Log Transmission Service Application Form.
Please fill out the Log Transmission Service Application Form.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required items such as application type, usage period, recipient information, etc. - Application type: select application
- Usage period: enter desired start date
- Basic information: enter Account name, Project name, recipient information
Monitoring information Fill in required items such as log transmission target and customer IP (range) - Fill out all items except special cases
Table. Main contents of Log Transmission service creation request form
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Attach the completed application form in the attachment area.
On the service request page, click the Request button.
- When the request is completed, check the submitted details on the Support Center > Service Request List page.
After the monitoring personnel review the submitted service request, they proceed with the process to use the service.
The Log Transmission service is now available.
Log Transmission Check detailed information
The Log Transmission service proceeds with the process for the service after applying through an SR. Unlike other services, detailed Log Transmission information cannot be viewed in the Console.
- To view detailed information, on the Support Center > Inquiry List page, click the Inquiry button. On the Inquiry page, you can write your question and submit it.
Terminate Log Transmission
To request cancellation of the Log Transmission service, follow the steps below.
- Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request button. You will be taken to the Service Request List page.
- On the Service Request List page, click the Service Request button. You will be taken to the Service Request page.
- Service Request page, enter or select the required information in the mandatory input fields.
- In the task category, select Log Transmission Cancellation.
Input field Detailed description Title Enter the title of the service request - Example: Log Transmission Service Termination Request
Region Select the location of the Samsung Cloud Platform - automatically entered with the region corresponding to the Account
Service Select service category and service - Service Category: Security
- Service: Log Transmission
Task classification Select the type of request you want to make - Terminate Log Transmission: select if you are terminating the service
content Guide to the service application process and reference information Attachment If you have a completed Log Transmission service application (required) and any additional files you wish to share, proceed with the upload - You can attach up to 5 files, each no larger than 5 MB
- Only doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, and tif files are allowed
Table. Table. Log Transmission Service Termination Request Items
- In the task category, select Log Transmission Cancellation.
- After reviewing Application Process and Reference Information, click the Form Download > Service Request Form Download button to download the Log Transmission Service Application Form.
- Log Transmission Service Application Form please fill out.
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
Category Detailed description Application Information Fill in required fields such as request type, usage period, recipient information, etc. - Request type: select request
- Usage period: enter desired service termination date
- Basic information: enter Account name, Project name, recipient information
- Usage amount does not need to be filled out
Monitoring information Fill in required items such as log transmission target and customer IP (range) - Fill out all items except special cases
Table. Log Transmission Service Termination Application Form Main Contents
- Refer to the item descriptions in the Application Information and Monitoring Information tabs and complete the required fields.
- Attach the completed application form to the attachment area.
- On the service request page, click the Request button.
- Once the request is completed, verify the submitted information on the Support Center > Service Request list page.
- After the monitoring staff verifies the submitted service request, the termination process is completed once the log transmission target and the customer’s used IP range are removed.
- Service termination takes 2–3 business days, counting from the cancellation request date.
9.19.3 - Release Note
Log Transmission
- We have launched the Log Transmission service that enables security monitoring of the user domain on Samsung Cloud Platform.
10 - Management
We provide services that enable easy and convenient management of the Samsung Cloud Platform, including user credential and access permission management, activity log collection/analysis, and real-time monitoring of resource status.
10.1 - Architecture Diagram
10.1.1 - Overview
Service Overview
Architecture Diagram provides a diagram format that allows you to grasp the relationships between resources at a glance. You can verify connections between resources and examine relationships between components.
Provided Features
The Architecture Diagram provides the following functions.
- Resource Configuration Overview: We provide a diagram that makes it easy to see the relationships between configured resources.
- Resource Main Information Check: You can view a resource’s main information from the Architecture Diagram without moving to the resource detail screen.
Constraints
The constraints of Architecture Diagrame are as follows.
We provide services only for certain resources of the Samsung Cloud Platform. * The provided resources are as follows.
Category Resource Built-in - VPC (if you have VPC permissions)
- Subnet
Optional provision - Port
- Security Group
- Load Balancer
- Database
- EPAS, PostgreSQL, Maria DB, MySQL, Microsoft SQL Server, CacheStore
- Data Analysis
- Event Streams, Search Engine, Vertica
- Storage
- Block Storage(VM), File Storage
Table. Architecture Diagram provided resourcesUp to 100 items are displayed per resource.
The types of provided resources may vary depending on the offering.
To use the Architecture Diagrame service, user permissions for the resource are required.
If resources are hierarchical, permission for a lower-level resource also requires permission for the upper-level resource.
Preceding Service
The Architecture Diagram has no preceding services.
10.1.2 - How-to Guides
Users can intuitively grasp the relationships and key information of the resource configuration generated by the Architecture Diagram.
Architecture Diagram Getting Started
To start the Architecture Diagram of the Samsung Cloud Platform, refer to the following.
- Click the All Services > Management > Architecture Diagram menu. 1. Architecture Diagram Go to the page.
- You can also navigate by clicking the Architecture Diagram widget on the Console Home page of Samsung Cloud Platform.
- Check the resource configuration information and relationships in the Architecutre Diagram.
- VPC, Subnet, Virtual Server, Database, Data Analysis, Storage, etc., depict the annual relationships among various resources in a diagram.
- If you do not have view (View) permission for the topmost hierarchy in the resource hierarchy, the Diagram will not be displayed.
- Resources without diagram position information are displayed separately at the bottom of the diagram. * You can view the detailed status of the resource on its individual detail page.
Architecture Diagram Add Item
You can add items to the Architecture Diagram’s component diagram.
- All Services > Management > Architecture Diagram click the menu. 1. Go to the Architecture Diagram page.
- You can also navigate by clicking the Architecture Diagram widget on the Console Home page of Samsung Cloud Platform.
- Click the Search Filter button at the top right of the Diagram. 2. Configurable items in the Architecture Diagram open as a popup menu.
- VPC, Subnet, Virtual Server items are provided by default and cannot be disabled.
- You can choose which of the Port, Security Group, Load Balancer, Database, Data Analysis, and Storage items to add to the Diagram.
Resource Selection status Support Service VPC Default (cannot be disabled) - Only displayed when you have VPC permissions
- Subnet Default (cannot be disabled) - Virtual Server Default (cannot be disabled) - Port Selection - Security Group Selection - Load Balancer Selection - Database Selection EPAS, PostgreSQL, Maria DB, MySQL, Microsoft SQL Server, CacheStore Data Analysis Selection Event Streams, Search Engine, Vertica File Storage Selection - Table. Architecture Diagram search filter items
Architecture Diagram Check detailed resource information
You can view detailed information for each resource in the architecture diagram’s composition.
- If the user does not have permission for the resource, detailed information cannot be viewed.
- If a resource has a hierarchical structure, even if you have permission for a lower-level resource, you cannot view detailed information without permission for the upper-level resource.
To view detailed information, follow these steps.
- Click the All Services > Management > Architecture Diagram menu. 1. Architecture Diagram Go to the page.
- You can also navigate by clicking the Architecture Diagram widget on the Console Home page of Samsung Cloud Platform.
- Click the resource to view detailed information in the Architecture Diagram. 2. The detailed information popup for each resource opens.
- Click the control button at the top right of the Diagram to expand or collapse the Diagram, or to zoom in/out.
- When you place the mouse cursor over a resource, the resource’s status and name are displayed.
Resource Detailed information VPC VPC name, resource status, IP range - Click the VPC name to view the corresponding VPC Details page
- Create VPC button, when clicked, allows creation of Virtual Server, Cloud Functions, and VPC services via Copilot
Subnet VPC name, Subnet name, resource status, IP range, Subnet type - Click the Subnet name to go to the corresponding Subnet Details page
- When clicking the Virtual Server connection line, you can view the IP information of the connected Port
Virtual Server VPC name, Subnet name, server name, resource status, IP, Security Group, Block Storage - Click the server name to navigate to the corresponding Virtual Server Details page
- Virtual Server Control: Create Virtual Server resources via Copliot
- Click the Subnet connection line to view the IP information of the connected Port
- If a Security Group is attached, you can view the list of Ports and the list of Block Storage
Port VPC name, Subnet name, Port name, fixed IP address Security Group Security Group name, resource status, Security Group rule count - Click the Security Group name to navigate to the corresponding Security Group details page
Load Balancer VPC name, Subnet name, Load Balancer name, Resource status, Service IP, Firewall name - Click the Load Balancer name to go to the corresponding Load Balancer details page
Database VPC name, Subnet name, cluster name, resource status, cluster type, Block Storage status Data Analysis VPC name, Subnet name, cluster name, resource status, cluster type, Block Storage status File Storage Volume name, resource status, disk type, protocol, connected resource Table. Architecture Diagram Resource Detailed Information Items
- Only the relationships for the nine resource types (VPC, Subnet, Virtual Server, Port, Security Group, Load Balancer, Database, Data Analysis, Filestorage) are shown.
- When you select a Subnet, Virtual Servert, or Security Group resource, information about that resource and its related resources is displayed with dotted lines.
- Each resource displays up to 100 items.
10.1.3 - Release Note
Architecture Diagram
- A new resource has been added.
- Database: EPAS, PostgreSQL, Maria DB, MySQL, Microsoft SQL Server, CacheStore
- Data Analysis:Event Streams, Search Engine, Vertica
- Improved CX by adjusting the search filter size and position, icons within diagrams, and other elements.
- Load Balancer resource has been added.
- The relationships between resources are indicated with dotted lines for easy identification.
- In the resource detail information popup, you can click the name of the resource to go to its detail page.
- Through Copilot, you can create VPC and Security Group services or manage Virtual Server.
- From the Diagram filter, you can easily add the Architecture Diagram item.
- The Architecture Diagram service has been newly launched.
- We provide a service that allows you to check relationships between resources.
10.2 - Cloud Control
10.2.1 - Overview
Service Overview
Cloud Control service is a managed service that supports building, operating, and managing a multi‑account environment easily and securely on the Samsung Cloud Platform.
The Cloud Control service automates an organization’s cloud governance (security, compliance, standardization, etc.) and provides consistent, centralized account and resource management based on Samsung Cloud Platform best practices.
Features
The Cloud Control service offers the following advantages.
- Landing Zone (Landing Zone) Automatic Provisioning: Automatically configure essential infrastructure such as Samsung Cloud Platform accounts, organizational units (OU), guardrails, logging, etc. * In a standardized environment, you can create new accounts and invite existing accounts.
- Centralized governance and policy enforcement: Automatically apply security, compliance, and operational policies (guardrails) across the entire organization. * Provides policy violation detection and monitoring capabilities.
- Multi-Region and Scalability: You can apply the same governance and policies across multiple Samsung Cloud Platform regions.
Provided Features
The Cloud Control service provides the following features.
- Automated Landing Zone (Landing Zone) Setup: Security, logging, and account structure based on Samsung Cloud Platform best practices are configured automatically.
- Apply Guardrail
- Preventive Guardrail : Blocks the creation of resources that violate policy
- Detective Guardrail: Automatically detect and notify policy-violating resources
- Integrate with ACP, Samsung Cloud Platform Config Inspection, etc., of the Samsung Cloud Platform Organization
- Dashboard provision: You can visually monitor the account, OU, guardrail implementation status, and compliance status of the entire organization.
- Centralized logging and auditing
- Provides centralized log storage and audit accounts for all accounts via Logging&Audit, Object Storage, Config Inspection, and other methods.
- ID and Permission Management Integration: Integrates with Samsung Cloud Platform ID Center to manage account-level access control and permission groups.
- Monitoring and Notification (Notification) feature: Provides real-time alerts for policy violations, Cloud Control configuration changes, etc.
Component
Landing Zone (Landing Zone)
The basic architecture of a standardized Samsung Cloud Platform environment, including governance, security, networking, and logging, is as follows.
| Category | Detailed description |
|---|---|
| admin account |
|
| Log account |
|
| audit account |
|
Guardrails
The guardrails that are automatically applied for policy violation detection and prevention (detect/prevent type) rules, and security/compliance standards are as follows.
| Category | Detailed description |
|---|---|
| Preventive Guardrail | Preemptive blocking role to prevent policy violations
|
| Detection Guardrail | Continuously monitor for policy violations or abnormal configurations, and provide alerts when violations occur
|
Baseline (Baseline)
The essential resources and configuration sets, such as security, logging, and networking, that are automatically deployed per account are as follows.
| Category | Detailed description |
|---|---|
| AuditBaseline |
|
| LogArchiveBaseline |
|
| IDCenterBaseline |
|
Provision status by region
The Cloud Control service is available in the environments below.
| Region | Provision status |
|---|---|
| Korea West 1 (kr-west1) | Provided |
| Korea East 1 (kr-east1) | Provided |
| South Korea 1 (kr-south1) | Provided |
| South Korea South 2 (kr-south2) | Provided |
| South Korea 3 (kr-south3) | Provide |
Pre-service
This is a list of services that must be pre-configured before creating the service. For detailed information, please refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Storage | Object Storage | Object storage that simplifies data storage and retrieval |
| Management | Loggin&Audit | A service that collects and analyzes user activity data |
| Management | Organization | A service that organizes accounts by organizational units, manages them hierarchically, and controls resource access permissions. |
| Management | ID Center | A service that enables easy centralized management of access permissions for resources by account |
10.2.2 - How-to guides
Using Cloud Control
The user must first create a landing zone to use the Cloud Control service. When a landing zone is created, you can use the management features of Cloud Control.
Create Landing Zone
To use Cloud Control in the Samsung Cloud Platform Console, you must first create a landing zone.
To create a landing zone, follow these steps.
Click the All Services > Management > Cloud Control menu. You will be taken to the Service Home page of Cloud Control.
On the Service Home page, click the Create Landing Zone button. You will be taken to the Create Landing Zone page.
After setting the configuration items in the Rate Review and Organizational Unit Configuration area, click the Next button.
Category Required statusDetailed description Home region - Home region of Cloud Control - Cloud Control sets the default region as the home region and it cannot be changed
- All regions except the default region are managed by Cloud Control
Basic organizational unit Required Enter the default organizational unit within the landing zone - Case-sensitive English letters, enter up to 128 characters
- The default organizational unit includes shared Account (Log Account, Audit Account)
- Security: Default organizational unit name of the shared Account
- Can be modified after creating the landing zone
Additional organizational unit Required Enter additional organizational unit within the landing zone - Case-sensitive English letters, up to 128 characters
- Can be added after creating the landing zone
Table. Landing zone creation - cost review and organizational unit configuration itemsAfter setting the configuration items in the Shared Account Configuration area, click the Next button.
Category Required statusDetailed description Management Account - The Management Account name is displayed and cannot be edited. Log Account Required Enter Log Account Information - Account name: Use Korean, English, numbers, spaces, and special characters (
+=-_@[](),.) to enter within 3 to 30 characters
- Email, Confirm Email: Enter up to 60 characters in a valid email address format
Audit Account Required Enter Log Account information - Account name: Korean characters, English letters, numbers, spaces, special characters(
+=-_@[](),.) within 3 to 30 characters
- Email, Confirm Email: Enter up to 60 characters in a valid email address format
- Cannot use the same email as Log Account
Table. Landing zone creation – shared account configuration itemsReference- Log Account is a repository of logs for API activity and resource configuration collected from all Accounts. Log Account cannot be changed.
- The Audit Account is a restricted account, allowing the security and compliance team to obtain access rights to all accounts within the organization through the Audit Account.
- Account name: Use Korean, English, numbers, spaces, and special characters (
After setting the configuration items in the Additional configuration area, click the Next button.
Category Required statusDetailed description Account Access Configuration Required Select a method to manage access to the Account - Account access via ID Center
- Create preconfigured groups and permission sets to configure users who perform specific tasks in the Account
- Automatically assign users when provisioning an Account with the Account Factory or registering an existing Account
- Selectable only when using ID Center’s own directory
- Self-managed Account access
- Cloud Control does not create directory groups or permission sets for the landing zone
- Automatically assign users when provisioning an Account with the Account Factory or registering an existing Account
- Manage access to the Account through ID Center or other Account access methods
Trail configuration - Automatic configuration in progress Detection Guardrail Selection Select whether to enable detection guardrails - When detection guardrails are enabled, they apply only to the default organizational unit
- Even after creating a landing zone, settings can be changed on the Landing Zone Settings page
- For more information about detection guardrails, refer to Detective Guardrail
Table. Landing zone creation - additional configuration items- Account access via ID Center
In the Input Information Confirmation area, after checking the landing zone configuration information and Service Permissions, check the agreement on permissions and guidelines.
Click the Create button. A popup notifying the creation of the landing zone opens.
After reviewing the information about creating a landing zone, click the Confirm button. The landing zone creation request will be completed.
- Creating a landing zone takes some time, and a notification is sent when the process is complete.
- When the landing zone creation is completed, you can view the full menu of Cloud Control and the organization status on the Service Home page.
- You cannot cancel while creating a landing zone.
- If creating the landing zone fails, delete the landing zone and then create it again.
- If you select Self-Managed Account Access, you cannot view the Access Portal URL and User Credentials information.
When a landing zone is created, you can view the following in Cloud Control.
- Two organizational units: shared Account, and an organizational unit for the Account that the user will provision
- Two shared accounts: isolated accounts for log archiving and security auditing
- Selected IAM management configuration
- 10 preventive guardrails: settings for policy enforcement
- Enable control policies for the Organization service
View detailed information of the landing zone
On the Landing Zone Settings page, you can view detailed information about the landing zone.
Follow these steps to view the detailed information of the landing zone.
- Click the All Services > Management > Cloud Control menu. Go to the Service Home page of Cloud Control.
- On the Service Home page, click the Landing Zone Settings menu. You will be taken to the Landing Zone Settings page.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Home region | Landing zone home region information |
| Account Access Configuration | How to manage access to an Account |
| Trail configuration | Trail configuration activation status
|
| Detection Guardrail | Detection guardrail activation status
|
| Delete landing zone | Delete landing zone
|
Delete Landing Zone
If the landing zone creation fails or is not used, you can delete the landing zone.
- Deleted resources cannot be recovered.
- Organization units, accounts, buckets, and ID Center resources are not deleted automatically.
- To use the same name as an existing resource that has not been deleted when recreating a landing zone, you must delete the existing resource directly before creating the landing zone.
- Existing resources can be deleted individually from the Organization, Object Storage, and ID Center services.
To delete a landing zone, follow these steps.
- Click the All Services > Management > Cloud Control menu. You will be taken to the Service Home page of Cloud Control.
- On the Service Home page, click the Landing Zone Settings menu. You will be taken to the Landing Zone Settings page.
- On the Landing Zone Settings page, click the Delete Landing Zone button. The Delete Landing Zone popup will open.
- Landing Zone Deletion popup, after entering the displayed Cloud Contorl ID in the deletion confirmation field, click the Confirm button. The landing zone deletion request will be completed.
- While deleting a landing zone, an explanation about the landing zone deletion process is displayed on the Service Home page.
Managing Organizational Units and Accounts
You can view the organization units and account list, register them in Cloud Control, and manage them.
To view and manage organizational units and the Account list, follow these steps.
- Click the All Services > Management > Cloud Control menu. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the Organization menu. You will be taken to the Organization unit and Account management page.
- Organizational Unit and Account Management page, select the view mode in the top‑right corner.
- When you click the View Hierarchy button, you can view and manage organizational units and Accounts in a hierarchical structure.
Category Detailed description Create a subordinate organizational unit Add a new organizational unit under the selected organizational unit - Enabled only when a single organizational unit is selected in the hierarchy
- For more details, refer to Creating an Organizational Unit
More Manage organization units or register a new Account - Organization Unit: Ability to delete/register/re-register organization units, and apply/remove detection guardrails
- For detailed information on organization unit management, see Managing Organization Units reference
- For detailed information on detection guardrails, see Detection Guardrails reference
- Account: Ability to register/unregister an Account
- For detailed information on Account registration and deregistration, see Account Management reference
Organization unit/Account name Display the names of organizational units and Accounts in a hierarchical structure - Click the +, - buttons to expand or collapse the hierarchy
- Click an organizational unit or Account name to navigate to its detail page
ID/Email Organization units display ID, and Account displays ID and email. status Cloud Control registration status of an organization unit or Account - Registered, Not registered, Registering, Registration failed
- No status displayed when Root
Register organization unit Cloud Control registration status of sub-organizational units - number of registered organizational units / total number of organizational units displayed
Register Account Cloud Control registration status of sub Accounts - displayed as Number of registered Accounts / Total number of Accounts
Detection Guardrail Detection guardrail application status for an organization unit or sub‑organization unit Table. Hierarchy view items - View Account List: You can view and manage the list of Accounts that make up Cloud Control.
Category Detailed description Account registration Register the selected Account from the Account list to Cloud Control - When you select an Account in Unregistered, Registration Failed status from the Account list, it becomes active
- For detailed information on Account registration, refer to Register Account
More > Unregister Account Deregister the selected Account from the Account list - When you select an Account in the Account list that is in registered, registration failed status, it becomes enabled
- Shared Accounts cannot be deregistered
- For more details on Account deregistration, refer to Account Deregistration
Account name Account name Account ID Account ID email Account user email status Cloud Control registration status of an organization unit or Account - Registered, Unregistered, Registering, Registration Failed
- No status displayed when Root
Table. Account list view items - Account creation button click creates a new Account. For more details, see Create Account.
- When you click the View Hierarchy button, you can view and manage organizational units and Accounts in a hierarchical structure.
Check organization and Account detailed information
You can view and edit the detailed information of the organization unit and Account. To view detailed information about the organization unit and Account, follow these steps.
- Click the All Services > Management > Cloud Control menu. Navigate to the Service Home page of Cloud Control.
- Service Home page, click the Organization menu. Navigate to the Organization unit and Account management page.
- Click the View Hierarchy button on the Organizational Unit and Account Management page.
- Click the name of the resource whose details you want to view in the hierarchical list. You will be taken to the resource’s detail page.
- Root: Go to the Root Details page. For more information, see Root Details Information.
- Organization unit name: Organization unit details Go to the page. For more information, see Organization unit details.
- Account name: Account details page. For more details, see Account details.
Root detailed information
Root Details page allows you to view and manage the detailed information of the organization Root and the list of subordinate Accounts. Root Details page consists of Basic Information, Sub Account tabs.
Basic Information
You can view the basic information of the organization Root, as well as the organizational units and the number of accounts registered in Cloud Control.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Service Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation timestamp | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Register organization unit | Cloud Control registration status of sub-organizational units under Root
|
| Register Account | Cloud Control registration status of Accounts under the Root
|
Sub Account
You can view and manage the list of Accounts under the Root and the registration status of Cloud Control.
| Category | Detailed description |
|---|---|
| Account registration | Register the selected Account from the Account list to Cloud Control
|
| Account name | Account name |
| Account user email | |
| Status | Cloud Control registration status of an organization unit or Account
|
Organizational Unit Detailed Information
Organizational Unit Details page allows you to view and manage the unit’s detailed information, subordinate Accounts, applied preventive guardrails, and detection guardrails. Organization Unit Detail page consists of Basic Information, Sub Account, Preventive Guardrails, Detection Guardrails tabs.
Basic Information
You can view basic and detailed information about the organization unit.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Service type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Organizational unit name | Name of the organizational unit |
| Apply guardrails | Number of guardrail types applied to the current organizational unit
|
| Register organization unit | Current Cloud Control registration status of sub-units of the organization unit
|
| Register Account | Cloud Control registration status of sub-accounts under the current organization unit
|
| higher-level organization unit | Hierarchy of parent organizational units for the current unit |
| Apply detection guardrails / Remove detection guardrails | Change detection guardrail application status for the organization unit
|
| Re-registration | Re-register the current organization unit in Cloud Control
|
Sub Account
You can view and manage the list of subordinate Accounts within an organizational unit.
| Category | Detailed description |
|---|---|
| Account registration | Register the selected Account from the Account list to Cloud Control
|
| Account name | Account name |
| Account’s user email | |
| status | Cloud Control registration status of an organization unit or Account
|
Preventive Guardrail
You can view and manage the list of preventive guardrails applied at the organizational level.
| Category | Detailed description |
|---|---|
| Target service name | Name of the service to which the guardrail applies |
| Guardrail name | Guardrail name
|
| type | Application method |
| Application method | Display of guardrail application method
|
| Disable | Unapply the selected guardrail from the guardrail list
|
| Apply preventive guardrails | Apply new preventive guardrails at the organizational level
|
Detection Guardrail
You can view and manage the diagnostic results of detection guardrails applied at the organizational level.
| Category | Detailed description |
|---|---|
| Account name | Account name to be diagnosed |
| Diagnosis name | Diagnosis Name |
| PASS | Number of checklist items with a diagnosis result of PASS (normal) |
| FAIL | Number of checklist items with a diagnosis result of FAIL (vulnerable) |
| CHECK | Number of items in the checklist with a diagnosis result of CHECK (verification required) |
| ERROR | Number of items in the checklist whose diagnosis result is ERROR (diagnosis not possible) |
| N/A | Number of items in the checklist where the diagnosis result is N/A (not applicable) |
| All | Total number of checklist items |
| Diagnostic Result | Diagnosis request result
|
| Diagnosis date and time | Diagnosis request date and time |
Check detailed account information
Account Details page allows you to view the account’s detailed information and the list of applied preventive guardrails. Account Details page consists of the Basic Information and Preventive Guardrails tabs.
Basic Information
You can view basic and detailed information about the organization unit.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Service Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Account user email | |
| Apply guardrails | Number of guardrail types applied to the current organizational unit
|
| ID Center username | ID Center user email |
| Higher-level organization unit | Current account’s parent organizational unit hierarchy |
| Register | You can change the organization unit of the current Account
|
Preventive Guardrail
You can view the list of preventive guardrails applied to the Account.
| Category | Detailed description |
|---|---|
| Target Service Name | Guardrail target service name |
| Guardrail name | Guardrail name
|
| type | Application method |
| Application method | Guardrail application method display |
Check Access Portal connection information
User and Access page allows you to view the Access Portal connection URL and login methods (password, SSO, MFA).
To check the Access Portal connection information, follow these steps.
- Click the All Services > Management > Cloud Control menu. You will be taken to the Service Home page of Cloud Control.
- On the Service Home page, click the User and Access menu. You will be taken to the User and Access page.
- Check the information in the User and Access page’s Integrated Access Management area.
| Category | Detailed description |
|---|---|
| Access type | How to access the Access Portal |
| Access Portal URL | Access Portal access URL
|
| Permission set | A collection of administrator policies used by ID Center to determine the valid permissions of users who can access a specific account. |
If the landing zone is configured with a self-managed Account access, refer to the following.
- Cloud Control does not automatically create directory groups or permission sets.
- When provisioning an Account with the Account factory or registering an existing Account, the user is automatically assigned.
- You can manage access to an account through ID Center or other account access methods.
Check user credential information
User and Access page allows you to view the user credential source type and ID Center ID.
To verify user credential information, follow these steps.
- Click the All Services > Management > Cloud Control menu. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the User and Access menu. You will be taken to the User and Access page.
- Check the information in the User and Access page’s User Credentials Management area.
| Category | Detailed description |
|---|---|
| Credential source | Credential source types configured in ID Center
|
| ID Center ID | ID Center’s ID
|
| User group | A group formed to classify workers who perform specific tasks within an organization |
10.2.2.1 - Managing Guardrails
The guardrails that are automatically applied for policy violation detection and prevention (detect/prevent type) rules, and security/compliance standards are as follows.
Preventive Guardrail
You can apply preventive guardrails to proactively block policy violations from occurring.
Applying preventive guardrails
It can be applied to preventive guardrails at the organizational level. To apply preventive guardrails at the organizational level, follow these steps.
Click the All Services > Management > Cloud Control menu. 1. Navigate to the Service Home page of Cloud Control.
On the Service Home page, click the Guardrail > Preventive Guardrail menu. 2. Go to the Preventive Guardrail List page.
From the Preventive Guardrail List, select the preventive guardrails to apply to the organization unit, then click the Apply to Organization Unit button. 3. Navigate to the Apply to organization unit page.
- Multiple preventive guardrails can be selected and applied simultaneously.
After selecting the organizational unit to which you want to apply the preventive guardrail, click the Complete button.
Category required statusDetailed description Preventive guardrails to apply - Preventive guardrails list to be applied at the organizational level Organizational unit name Essential Select the organizational unit to apply the preventive guardrail - Only organizational units with Registered, Registration Failed status can be selected
- Click the organizational unit name or parent organizational unit name to view detailed information
Table. Preventive guardrail application itemsWhen the pop‑up window notifying that the preventive guardrail has been applied opens, click the Confirm button.
View detailed information of preventive guardrail
You can view detailed information about preventive guardrails, the organizational units to which they are applied, and the list of Accounts. To disable the preventive guardrail, follow these steps.
- Click the All Services > Management > Cloud Control menu. 1. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the Guardrail > Preventive Guardrail menu. 2. Go to the Preventive Guardrail List page.
- Click the preventive guardrail name to view detailed information in the Preventive Guardrail List. 3. Preventive Guardrail Details page
- Preventive Guardrail Details page consists of Basic Information, Applicable Organizational Unit, Account tab.
Basic Information
You can view basic and detailed information about the preventive guardrail.
| Category | Detailed description |
|---|---|
| service | Service Name |
| Resource Type | Service type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Guardrail name | Name of the guardrail |
| type | Guardrail type |
| Target service name | Guardrail target service name |
| status | Whether guardrails are applied |
| Explanation | Description of guardrails |
Applicable organization unit
You can view the list of organizational units where preventive guardrails are applied.
| Category | Detailed description |
|---|---|
| Organizational unit name | Organizational unit name
|
| Parent organization unit name | Name of the parent organizational unit of the organizational unit
|
| status | Cloud Control registration status for organizational units
|
Account
You can view the list of sub‑Accounts under the organizational unit where preventive guardrails are directly applied.
| Category | Detailed description |
|---|---|
| Account name | Account name |
| Account user email | |
| Organizational unit name | Organization unit name
|
| status | Cloud Control registration status for an organization unit or Account
|
Disable preventive guardrail
You can disable the preventive guardrail applied at the organization level. To disable the preventive guardrail, follow these steps.
Click the All Services > Management > Cloud Control menu. 1. Navigate to the Service Home page of Cloud Control.
On the Service Home page, click the Guardrail > Preventive Guardrail menu. 2. Navigate to the Preventive Guardrail List page.
From the Preventive Guardrail List, select the preventive guardrail for which you want to disable organization-level enforcement, then click the More > Remove Organization-Level Enforcement button. 3. Navigate to the Remove organization unit application page.
- Multiple preventive guardrails can be selected simultaneously to disable them.
After selecting the organizational unit to disable the preventive guardrail, click the Complete button.
Category Whether requiredDetailed description Guardrails to apply - List of preventive guardrails to be disabled Organizational unit name Essential Select the organizational unit to disable the preventive guardrail - Only organizational units with Registered, Registration Failed status can be selected
- Click the organizational unit name or parent organizational unit name to view detailed information
Table. Preventive Guardrail Deactivation ItemsWhen a pop‑up notifying the deactivation of the preventive guardrail opens, click the Confirm button.
Detection Guardrail
When detection guardrails are enabled, Config Inspection diagnostics are automatically run for Accounts within the default organizational unit, performing checks daily.
Apply detection guardrails
You can apply detection guardrails on the Landing Zone Settings page.
To apply detection guardrails, follow the steps below.
- All Services > Management > Cloud Control Click the menu. 1. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the Landing Zone Settings menu. 2. Navigate to the Landing Zone Settings page.
- On the Landing Zone Settings page, click the Edit button for the Detection Guardrail item. 3. Detection Guardrail Settings The popup window opens.
- Detection Guardrail Settings In the popup window, after checking Enable Cloud Control Detection Guardrail, click the Confirm button.
- When activation is checked, Plan, Check List, Diagnosis Cycle, Start Time are displayed.
- When the pop-up indicating that the detection guardrail is active opens, click the Confirm button.
Check detection guardrail diagnostic results
You can view the Config Inspection diagnostic results via detection guardrails. To view the diagnostic results, follow these steps.
- Click the All Services > Management > Cloud Control menu. 1. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the Guardrail > Detection Guardrail menu. 2. Navigate to the Detection Guardrail List page.
- Click the diagnosis name of the Account for which you want to view diagnostic results from the Detection Guardrail List. 3. Go to the Diagnostic Results List page.
- In the search area of the Diagnosis Result List page, you can enter a diagnosis name or click the Advanced Search button to search.
- On the Diagnosis Result List page, click the diagnosis result for the diagnosis name to view detailed diagnostic items. 4. Navigate to the Diagnostic Result Details page.
- Completed: The diagnostic request has been successfully completed, when Completed is clicked, navigate to the detail page
- Error: The diagnostic request was not completed successfully, and the error status item cannot view detailed information.
- Diagnosis Result Details on the page
Category Detailed description Checklist Set of diagnostic items that serve as the basis for diagnostic results Area Scope of Diagnosis (services of Samsung Cloud Platform) Diagnostic Items Security standards recommended for each service configuration - Click the diagnostic item name to view detailed information about that diagnostic item
- Diagnostic item details: area, diagnostic item, result, diagnostic criteria, diagnostic method, remediation guide, detailed result
Result Diagnostic Item Baseline Check Results - PASS: Number of items in the checklist with a diagnostic result of PASS (normal)
- FAIL: Number of items in the checklist with a diagnostic result of FAIL (vulnerable)
- CHECK: Number of items in the checklist with a diagnostic result of CHECK (needs verification)
- ERROR: Number of items in the checklist with a diagnostic result of ERROR (diagnosis not possible)
- N/A: Number of items in the checklist with a diagnostic result of N/A (not applicable)
Table. Detailed Diagnosis Result Items
Managing detection guardrail diagnostic results
You can view the results of the Config Inspection diagnosis request via the detection guardrail.
To view the diagnostic request results, follow these steps.
- All Services > Management > Cloud Control Click the menu. 1. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the Guardrail > Detection Guardrail menu. 2. Go to the Detection Guardrail List page.
- In the Detection Guardrail List, click the diagnosis name of the Account that will manage the diagnostic results. 3. Go to the Diagnostic Results List page.
- On the Diagnosis Result List page, you can enter a diagnosis name in the search area or click the Advanced Search button to search.
- On the Diagnostic Result List page, click the Diagnostic Result Management button. 4. Diagnosis Result Management Navigate to the detail page.
- Diagnostic Result Management View the diagnostic results on the detail page.
Category Detailed description Checklist Collection of diagnostic items that serve as the basis for diagnostic results Area Scope of Diagnosis (services of Samsung Cloud Platform) Diagnostic Items Security standards recommended for each service configuration - Click the diagnostic item name to view detailed information about that diagnostic item
- Diagnostic details: area, diagnostic item, result, diagnostic criteria, diagnostic method, remediation guide, detailed result
Result Diagnostic Item Baseline Check Results - PASS: Number of items in the checklist with a diagnostic result of PASS (normal)
- FAIL: Number of items in the checklist with a diagnostic result of FAIL (vulnerable)
- CHECK: Number of items in the checklist with a diagnostic result of CHECK (needs verification)
- ERROR: Number of items in the checklist with a diagnostic result of ERROR (diagnosis not possible)
- N/A: Number of items in the checklist with a diagnostic result of N/A (not applicable)
Result check / Result change - Result Verification: Detailed information can be viewed in the result verification popup
- Registrant, validity period, change status, detailed reason, attachment, inspection result
- Attachments can only be viewed in Config Inspection
- Inspection results cannot be deleted in Cloud Control
- Result Modification: Inspection results cannot be modified in Cloud Control
Table. Diagnosis Result Management Items
Disable detection guardrail
On the Landing Zone Settings page, you can disable the detection guardrail. To disable the detection guardrail, follow these steps.
- All Services > Management > Cloud Control menu, click it. 1. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the Landing Zone Settings menu. 2. Go to the Landing Zone Settings page.
- On the Landing Zone Settings page, click the Edit button of the Detection Guardrail item. 3. Detection Guardrail Settings The popup window opens.
- Detection Guardrail Settings in the popup window, uncheck Cloud Control Detection Guardrail Active.
- When a popup that notifies the removal of detection guardrails opens, click the Confirm button.
10.2.2.2 - Managing Organizations
When a landing zone is created, you can use Cloud Control’s organization-level management features.
- The user must first create a landing zone to use the Cloud Control service.
- There is no charge for the Cloud Control service, but services used within Cloud Control such as Logging&Audit, Object Storage, and Config Inspection may incur costs based on usage.
Manage Organizational Units
You can register and manage the organizational units that constitute an Organization in Cloud Control.
Create Organization Unit
You can create a new organizational unit and register it with Cloud Control.
To create an organizational unit and register it with Cloud Control, follow these steps.
Click the All Services > Management > Cloud Control menu. Go to the Service Home page of Cloud Control.
Service Home page, click the Organization menu. Navigate to the Organization unit and Account management page.
On the top right of the Organizational Unit and Account Management page, click the View Hierarchy button.
After selecting the location in the hierarchical list where you want to add an organizational unit, click the Create Organizational Unit Under button. The Create Organizational Unit popup opens.
- Root or only one organizational unit can be selected.
- You can create organizational units up to five levels below Root.
Create Organizational Unit After entering the organizational unit information to add in the popup window, click the Create button.
Category RequiredDetailed description Parent organization unit name - Name of the parent organizational unit for the organizational unit to be created Organizational unit name Required Enter the name of the organizational unit to be created within 128 characters - Organizational names distinguish between uppercase and lowercase English letters
Explanation Selection Enter a description of the organizational unit within 1,000 characters. Table. Organization unit creation itemsWhen the popup that notifies the creation of an organizational unit opens, click the Confirm button.
- It may take more than tens of minutes depending on the number of accounts under the organizational unit.
- A notification will be sent when the organization unit creation is complete.
Register Organizational Unit
You can register organizational units that are not registered in Cloud Control or that failed to register, into Cloud Control.
- When registering an organizational unit, all parent units of the unit to be registered must be in a registered state.
- If an organizational unit in the registering state exists under the organizational unit you are trying to register, you cannot register.
- The sub-units of the organizational unit you are registering must be registered separately.
To register an organizational unit in Cloud Control, follow these steps.
Click the All Services > Management > Cloud Control menu. You will be taken to the Service Home page of Cloud Control.
Service Home page, click the Organization menu. Navigate to the Organization unit and Account management page.
On the top right of the Organizational Unit and Account Management page, click the View Hierarchy button.
After selecting the organizational unit to register from the hierarchical list, click the More > Register Organizational Unit button. You will be taken to the Register Organizational Unit page.
On the Organization Unit Registration page, verify the information of the organization unit to be registered.
Category Whether requiredDetailed description Sub Account - List of Accounts included under the organizational unit to be registered - Automatically register in Cloud Control when registering the organizational unit
Applicable preventive guardrails - List of guardrails inherited from higher-level organizational units and guardrails directly applied to the organization unit - Click the guardrail name to view detailed information about that guardrail
Table. Organization Unit Registration ItemsReference- Preventive guardrails are inherited from higher-level organizational units.
- To remove an inherited guardrail, disable its application in the parent organizational unit.
After reviewing the Terms of Service, check the checkbox and click the Complete button.
When the popup notifying the registration of an organizational unit opens, click the Confirm button. The organizational unit registration request is completed.
- Depending on the number of accounts under the organizational unit, it can take several tens of minutes.
- A notification will be sent once the organization unit registration is complete.
Re-register organizational unit
You can re-register an organizational unit that is already registered in Cloud Control.
- You cannot register if there is an organization unit in the registration state under the organization unit you are trying to register.
- Sub-units of the organizational unit you are registering must be registered separately.
To re-register an organizational unit in Cloud Control, follow these steps.
Click the All Services > Management > Cloud Control menu. Navigate to the Service Home page of Cloud Control.
Service Home page, click the Organization menu. Navigate to the Organization unit and Account management page.
Organizational Unit and Account Management page, click the View Hierarchy button in the top right corner.
In the hierarchical list, select the organizational unit to re‑register, then click the More > Re‑register Organizational Unit button. You will be taken to the Re‑register Organizational Unit page.
On the Organizational Unit Re-registration page, check the information of the organizational unit to be re-registered.
Category Required statusDetailed description Sub Account - List of Accounts included under the organizational unit to be re-registered - Automatically register in Cloud Control when registering the organizational unit
Applicable preventive guardrails - List of guardrails inherited from higher organizational units and guardrails directly applied to the organization unit - Clicking a guardrail name allows you to view detailed information about that guardrail
Table. Organization Unit Re-registration ItemsReference- Preventive guardrails are inherited from higher-level organizational units.
- To remove an inherited guardrail, disable its application at the parent organizational unit.
After reviewing the Terms of Service, check the checkbox and click the Complete button.
When the popup notifying re-registration of the organization unit opens, click the Confirm button. The organization unit re-registration request is completed.
- Depending on the number of accounts under the organizational unit, it can take several tens of minutes.
- A notification will be sent once the organization unit re-registration is complete.
Delete organization unit
You can delete an organizational unit.
- Only organizational units that are in an unregistered state in Cloud Control can be deleted.
- Before deleting an organizational unit, remove all its subordinate elements.
To delete an organizational unit, follow these steps.
- Click the All Services > Management > Cloud Control menu. Go to the Service Home page of Cloud Control.
- On the Service Home page, click the Organization menu. You will be taken to the Organization unit and Account management page.
- On the top right of the Organizational Unit and Account Management page, click the View Hierarchy button.
- After selecting the organizational unit to delete from the hierarchical list, click the More > Delete Organizational Unit button.
- When the popup notifying that the organizational unit will be deleted opens, click the Confirm button.
10.2.2.3 - Managing Accounts
Create Account
You can create an Account with the Account factory and apply Cloud Control directly without any additional steps.
To create an Account, follow these steps.
Click the All Services > Management > Cloud Control menu. You will be taken to the Service Home page of Cloud Control.
On the Service Home page, click the Account Factory menu. You will be taken to the Account Factory page.
On the Account Factory page, click the Account Creation button. You will be taken to the Account Creation page.
On the Account creation page, enter the required information to create an Account and select an organizational unit, then click the Create button.
Category Required statusDetailed description Account information Required Enter the account name and email information - Account name: Use Korean, English, numbers, spaces, and special characters (
+=-_@[](),.) to enter between 3 ~ 30 characters
- Email: Enter up to 60 characters in a valid email address format
- Cannot duplicate the root user email
- Enter the same value in Email confirmation
ID Center information Required Enter ID Center user information that can access the Account to be created - Username: Use English letters, numbers, and special characters(
+=-_@,.) within 128 characters
- User’s real name: Enter the user’s actual name (surname and given name)
- If the Account access configuration uses self-managed Account access, ID Center information cannot be set
Select organization unit Required Select the parent organization unit that will contain the Account to be created - Only organization units with registered status can be selected
- Clicking the organization unit name navigates to its detailed page
Table. Landing zone creation - cost review and organizational unit configuration itemsCautionAn Excel file containing Access Portal user login information will be sent to the email entered in the ID Center. Be sure to verify that the email address is correct.- Account name: Use Korean, English, numbers, spaces, and special characters (
When a popup notifying Account creation opens, click the Confirm button. The Account creation request is completed.
- Creating an account takes some time, and a notification is sent when the process is complete.
Manage Account
You can register and manage the accounts that comprise the organization in Cloud Control.
Register Account
You can register organizational units that are not registered in Cloud Control or that failed to register, into Cloud Control.
- Only accounts of the organizational unit registered in Cloud Control can be registered.
- You cannot register if there is an organizational unit or Account in registering status under the organizational unit you are trying to register.
- If you select a different organizational unit from the current one and register, the corresponding ACcount will be moved to the newly selected organizational unit.
To register an Account, follow these steps.
Click the All Services > Management > Cloud Control menu. You will be taken to Cloud Control’s Service Home page.
Service Home page, click the Organization menu. Navigate to the Organization unit and Account management page.
In the top right corner of the Organization Unit and Account Management page, click the View Account List button.
From the Account list, select the Account to register in Cloud Control, then click the Account registration button. You will be taken to the Account registration page.
- After clicking the Account name of the Account to be registered, you can also register by clicking the Register button on the Account Details page.
Category Required statusDetailed description Current organizational unit - The organizational unit to which the Account belongs Register organization unit - Select the organizational unit to register the Account - Only organizational units with registration status can be selected
- Current organizational unit: Register directly to the current organizational unit
- Other organizational unit: Manually select a different organizational unit
Table. Account registration items
- After clicking the Account name of the Account to be registered, you can also register by clicking the Register button on the Account Details page.
When a popup notifying the Account registration opens, click the Confirm button.
Move Account
You can change the organizational unit of an Account registered in Cloud Control and move it.
- You cannot move if there is an organizational unit or Account in the registering state under the organizational unit you are trying to register.
- If you select a different organizational unit from the current one and register, the corresponding ACcount will be moved to the newly selected organizational unit.
To move the Account, follow the steps below.
- Click the All Services > Management > Cloud Control menu. You will be taken to the Service Home page of Cloud Control.
- On the Service Home page, click the Organization menu. You will be taken to the Organization Units and Account Management page.
- On the Organization Unit and Account Management page, click the View Account List button in the top right corner.
- In the Account list, click the Account name whose organizational unit you want to change. You will be taken to the Account Details page.
- On the Account Details page, click the Register button. You will be taken to the Account Register page.
- From the Registered organization unit list, select the organization unit to which the Account will be moved, then click the Complete button.
- Only organizational units with registered status can be selected.
- When the popup notifying the Account registration opens, click the Confirm button.
Unregister Account
You can deregister an Account that is registered in the Organization.
In the following cases, the Account cannot be deactivated.
- Account with no registered payment method
- When there is credit assigned to the account
- When the exclusion point is the cost settlement date (the 1st of each month, Asia/Seoul GMT +09:00)
- Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
- On the Service Home page, click the Organization Configuration menu. You will be taken to the Organization Configuration page.
- On the Organization Structure page, click the View Account List button.
- After selecting the Account to exclude from the Organization, click the More > Unregister Account button.
- After clicking the Account name of the Account to be deregistered, you can also deregister by clicking the Deregister button on the Account Details page.
- When a popup that notifies the Account deregistration opens, click the Confirm button.
Delete Account
You can delete the account.
- When deleting from the Account list, you must select only one Account to delete.
- All resources in the Account must be deleted before deletion.
- Management Account and accounts that joined via invitation cannot be deleted.
- Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
- On the Service Home page, click the Organizational Structure menu. You will be taken to the Organizational Structure page.
- On the Organization Structure page, click the View Account List button.
- After selecting the Account to delete from the Account list, click the More > Delete Account button. The Delete Account popup opens.
- After clicking the Account name of the Account to be deleted, you can also delete it by clicking the Delete Account button on the Account Details page.
- After entering the Account name to delete, click the Confirm button.
When you delete the Account, an Account deletion notification email will be sent to the next user.
- Administrator who created the Organization
- Root user of the created account
- User who has delegation for the created Account
–>
Check Shared Account
You can view the shared Account information in Cloud Control. To check shared account information, follow these steps.
- Click the All Services > Management > Cloud Control menu. Navigate to the Service Home page of Cloud Control.
- On the Service Home page, click the Shared Account menu. You will be taken to the Shared Account page.
- The Shared Account page consists of the Management Account, Log Account, and Audit Account widgets.
- Each widget displays the Account name, Account ID, and email information, and clicking the widget name takes you to that Account’s detail page.
Category Detailed description Management Account Account that creates new Accounts and manages billing and access for all Accounts in the organization Log Account The account used as the repository for API activity and resource configuration logs collected from all accounts. Audit Account A restricted account that enables the security and compliance team to obtain read and write access to all accounts. Table. Shared Account items
10.2.3 - API Reference
10.2.4 - CLI Reference
10.2.5 - Release Note
Cloud Control
- The detection guardrail results management screen has been added.
- On the result management screen of the detection guardrail, you can view the diagnostic request result information.
- The detection guardrail feature has been added.
- For accounts within the default organizational unit, Config Inspection diagnostics are run automatically every day.
- You can easily view diagnostic results even within the Cloud Control service.
- The official version of the Cloud Control service has been released.
- You can easily and securely build, operate, and manage a multi‑account environment on Samsung Cloud Platform.
- The organization’s cloud governance (security, compliance, standardization, etc.) can be automated and managed through policy violation detection and monitoring functions.
10.3 - Cloud Monitoring
10.3.1 - Overview
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, after the September 2026 release, resource monitoring of the Samsung Cloud Platform via Cloud Monitoring will no longer be possible.
With the new alternative service, you can continuously perform resource monitoring by using ServiceWatch, released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a smooth monitoring environment.
Detailed information about ServiceWatch is in the ServiceWatch Overview. Please refer to it.
※ For some Database and Data Analytics services, refer to the user guide of the respective service for the service watch implementation schedule.
| service | User Guide |
|---|---|
| EPAS(DBaaS) | EPAS(DBaaS) > How-to guides |
| PostgreSQL(DBaaS) | PostgreSQL(DBaaS) > How-to guides |
| MariaDB(DBaaS) | MariaDB(DBaaS) > How-to guides |
| MySQL(DBaaS) | MySQL(DBaaS) > How-to guides |
| Microsoft SQL Server(DBaaS) | Microsoft SQL Server(DBaaS) > How-to guides |
| CacheStore(DBaaS) | CacheStore(DBaaS) > How-to guides |
| Event Streams | Event Streams > How-to guides |
| Search Engine | Search Engine > How-to guides |
| Vertica(DBaaS) | Vertica(DBaa) > How-to guides |
Service Overview
The Cloud Monitoring service collects usage status, change information, and logs of operational infrastructure resources, and generates an event to notify when a configured threshold is exceeded. Through this, users can respond quickly to performance degradation and failures, and can conveniently develop resource capacity expansion plans to configure a stable computing environment.
Provided Features
Cloud Monitoring provides the following features.
- Stable computing resource management: You can easily view metrics such as CPU usage, disk usage, and memory usage. When an event occurs in the resources being used, an automatic notification is sent to the designated recipients, enabling rapid fault analysis and response, so computing resources can be operated reliably.
- Convenient Monitoring: Status information about resources can be easily monitored by creating a dashboard. * Provides default and custom dashboards, enabling you to configure various widget types and easily and quickly create dashboards yourself.
- Event Metric Management: Through the web-based Console, you can easily set event metrics with just a few clicks. The event metric settings for the monitoring target (such as event patterns, trigger conditions, occurrence frequency, performance metrics, operational status, etc.) can be varied to suit the usage environment, and threshold and alarm configurations can be managed conveniently.
- Resource Log Management: Collects and stores log data of resources, and allows searching the target logs when needed. Additionally, we metricize events for major keywords and automatically notify the designated person when pre‑set conditions are met, providing a more stable usage environment.
Component
Dashboard
In the monitoring dashboard, you can view the operational status and event status of monitored services and resources, as well as the top usage items.
| Item | Explanation |
|---|---|
| Region | Resource location |
| Data reference time | Reference time of the data displayed on the dashboard |
| Refresh | Refresh the dashboard based on the current time |
| Period setting | Set data query period and refresh interval |
| Monitoring status | Number and status of monitoring targets for each service used in the Account |
| Event History | Display events that occurred in the past 7 days as a graph by risk level. |
| Top 5 usage rates by performance | Display the top five monitoring targets with the highest usage for each major performance metric |
| Event map | Display the number of events per service by severity |
| Event status | Display the list of unprocessed events among the occurred events |
Performance Analysis
In performance analysis, you can identify the main performance metrics of the monitoring target and view the current data and historical records within the period for each metric. Users can view the performance status of the monitoring targets they manage by service or by period, and compare specific performance metrics to analyze the results.
Log Analysis
In log analysis, you collect the logs of the monitoring target, examine their contents, and convert them into metrics—structured data—for monitoring. Each monitoring target provides a default collection log, and users can create custom logs to collect and view additional logs as needed.
Event Management
An event is a configuration that notifies the user when a monitoring target’s performance value meets a specific condition. By configuring events, you can capture essential monitoring information that users need to know without missing it. For example, if you configure events to trigger whenever a performance metric related to overload exceeds a certain threshold, users will receive notifications each time there is a risk of overload during resource operation. Users can proactively respond before problems arise based on this. In event management, you can create such events and configure them to notify designated users whenever a specific value occurs during monitoring.
Preceding Service
Cloud Monitoring has no prerequisite services.
10.3.2 - How-to guides
According to Samsung Cloud Platform’s policy, the Cloud Monitoring service is scheduled to be discontinued.
Accordingly, starting after the September 2026 release, monitoring of Samsung Cloud Platform resources through Cloud Monitoring will no longer be possible.
With a new alternative service, you can continuously perform resource monitoring by leveraging ServiceWatch released in October 2025.
ServiceWatch provides more modern and powerful features, replacing Cloud Monitoring to deliver a seamless monitoring environment.
Detailed information about ServiceWatch can be found in the ServiceWatch Overview.
※ For some Database and Data Analytics services, refer to the user guide of the respective service for the service watch implementation schedule.
| service | User Guide |
|---|---|
| EPAS(DBaaS) | EPAS(DBaaS) > How-to guides |
| PostgreSQL(DBaaS) | PostgreSQL(DBaaS) > How-to guides |
| MariaDB(DBaaS) | MariaDB(DBaaS) > How-to guides |
| MySQL(DBaaS) | MySQL(DBaaS) > How-to guides |
| Microsoft SQL Server(DBaaS) | Microsoft SQL Server(DBaaS) > How-to guides |
| CacheStore(DBaaS) | CacheStore(DBaaS) > How-to guides |
| Event Streams | Event Streams > How-to guides |
| Search Engine | Search Engine > How-to guides |
| Vertica(DBaaS) | Vertica(DBaa) > How-to guides |
Samsung Cloud Platform Monitoring is a resource management system that can monitor and analyze the resource operation status within an account operated in the Samsung Cloud Platform Console. Users can efficiently manage resources by using the dashboard page, widgets, and chart features.
- The user can monitor resources created on an Account with permissions in the Samsung Cloud Platform Console.
- The user can log in to the Samsung Cloud Platform Console and navigate to Samsung Cloud Platform Monitoring to monitor.
Cloud Monitoring Getting Started
To start Samsung Cloud Platform Monitoring, follow these steps.
- All Services > Management > Cloud Monitoring Click the menu. 1. Navigate to the Service Home page of Cloud Monitoring.
- On the Service Home page, click the Open Cloud Monitoring button. 2. Go to the Cloud Monitoring Console page.
Explore Cloud Monitoring Console
The top and left menus of the Cloud Monitoring Console are organized as follows.
| Category | Detailed description |
|---|---|
| Custom Dashboard Management | Custom Dashboard
|
| Support | Support
|
| Region List | Region list
|
| User Information | You can view user information and log out from Samsung Cloud Platform Monitoring. |
| Side menu | Displays the main features of Samsung Cloud Platform Monitoring. Clicking each menu takes you to the corresponding page.
|
Stop Monitoring
To exit the Cloud Monitoring Console, click the User Info > Logout button at the top right.
Using Common Features
This explains the frequently used features when using the Cloud Monitoring Console.
View detailed information of the monitoring target
If you access Cloud Monitoring Console > Performance Analysis or Cloud Monitoring Console > Log Analysis > Log Overview, you can view the list of monitoring targets. At this point, to view detailed information for a monitoring target, click the desired target in the monitoring target list.
- Detailed information of the monitoring target varies depending on the service type.
- If the operating system (OS information) of the monitoring target is RHCOS (Redhat Core OS), detailed information about the monitoring target is not provided.
| Item | Explanation |
|---|---|
| Basic Information | Display basic information about the monitoring target
|
| Performance | Display the primary performance of the monitoring target in a graph |
| log | Show the log collection volume for the monitoring target in a graph. |
| event | Display the list of events that occurred in the monitoring target. |
| Agent | Provides the agent’s install, start, stop, delete, update commands |
| Set query period | Displays the reference date/time for data retrieval
|
| Monitoring status area | Displays performance, log, and event monitoring status. |
- The services that provide agent management commands are Virtual Server, GPU Server, and Bare Metal Server.
- For detailed information on installing and managing the agent, see Agent Management.
Sorting data
You can organize and view information such as event monitoring, performance, and log analysis results in descending or ascending order. To sort the data, follow these steps.
- Display the information to be verified on the page.
- Click the Sort button next to the Category name. 2. Each click toggles the sorting order between descending and ascending.
Check real-time data
You can configure the dashboard or detail page data to automatically refresh at a set interval.
- In the Cloud Monitoring Console, you can configure whether to enable refresh and set the refresh interval so that the monitoring page refreshes periodically.
- Click the refresh button to manually refresh based on the current time.
To set the data refresh interval, follow these steps.
- Click the Settings button at the top right of the data display area.
- After selecting the refresh interval, click the Confirm button.
- You can turn the refresh feature on or off.
Configure the query period
By setting the query period, you can limit the query scope to the specified range of performance, logs, and events, making it easy to find only the information you need. To set the query period, follow these steps.
- Click the Settings button in the upper right of the data display area.
- Select a date range or enter it manually.
- If you manually enter the query period, you must set the period to at least 30 minutes.
- If each widget’s data query range is fixed, the widget’s query range takes precedence.
10.3.2.1 - Using Monitoring Dashboards
In the monitoring dashboard, you can view the operational status and event status of monitored services and resources, as well as the top usage items.
Getting Started with Monitoring Dashboard
When you navigate from the Samsung Cloud Platform Console to the Cloud Monitoring Console page, the monitoring dashboard is displayed. If you are on a different page, click Cloud Monitoring Console > Monitoring Dashboard to go to the Monitoring Dashboard page.
The monitoring dashboard is structured as follows.
| Item | description |
|---|---|
| Data reference time | Display the reference time for the data shown on the dashboard |
| Refresh | Refresh the dashboard based on the current time |
| Automatic refresh | You can enable or disable the dashboard refresh feature. |
| Period setting | Set the data retrieval period or change the refresh interval |
| Monitoring Status | Display the number of monitoring targets and monitoring status for each service |
| Event History | Display the number of events that occurred in the last 7 days as a graph by severity. |
| Top 5 usage rates by performance | Display the usage rates of the five monitoring targets with the highest usage for each major performance metric as a usage graph. |
| Event map | Display the number of events per service by severity |
| Event status | Display the list of unprocessed events among the occurred events. |
- The monitoring dashboard is automatically created when an Account is created in the Samsung Cloud Platform Console and cannot be deleted arbitrarily.
- Configuration widgets on the monitoring dashboard cannot be modified arbitrarily.
- To create a dashboard with a specific widget, use a custom dashboard. For more information about custom dashboards, refer to Using Custom Dashboards.
Explore Common Dashboard Features
This describes the functions available on the dashboard.
Download widget image
Click the download button at the top right of the widget area to download the widget as an image file (*.png).
View graph details
When you place the mouse cursor over the graph, detailed information appears as a popup.
Monitoring Status
Shows the number of monitoring targets and their monitoring status for each service in use.
| Item | description |
|---|---|
| Service Category | Display the monitoring target service categories per service and the quantity of monitoring targets included in each service category
|
| Service List | Display the list and quantity of services included in the monitoring target service category
|
| Monitoring status | Displays the number of monitoring targets and their current status
|
| Event status | Displays the number of current events by grade (Fetal, Warning, Inform). |
- Performance collection in monitoring mode aggregates and displays the number of performance metrics from both Agent and Agentless approaches.
Event History
Displays the number of events that occurred in the last 7 days as a graph by severity.
When you place the mouse cursor over the graph, a popup shows the number of occurrences of events corresponding to the selected date’s event risk level, along with active/inactive information.
- Occurrence: total number of event occurrences
- Activation: The state where an event that has occurred by meeting the event trigger conditions continues to be maintained.
- Deactivation: The event that occurred no longer meets the event trigger conditions and has returned to a normal state
You can click the risk legend area to hide or unhide the corresponding graph.
Top 5 Usage by Performance
Displays a usage graph for the five monitoring targets with the highest utilization rates across major performance categories.
- When you place the mouse cursor over the graph, a popup displays the full name of the selected item and its current performance metrics.
- When you click the graph, a Monitoring Target Details popup window for the corresponding item opens.
Item description CPU Usage/Core [Basic] Percentage of CPU time used, excluding Idle and IOWait states Memory Used [Basic] Current memory usage Disk Read Bytes [Basic] Disk read byte count Disk Write Bytes [Basic] Disk write byte count
- The monitoring dashboard only displays the performance of Virtual Server. To show the Top 5 performance of other service types, you need to select and configure them in a custom dashboard.
Event Map
Displays the number of events per service by severity.
- When you place the mouse cursor over the rectangle, the name of the monitoring target appears as a popup.
- When you click a service item on the event map, the Monitoring Target Details popup window opens.
The risk level for each item is as follows.
| Item | description |
|---|---|
| No Rule | The condition cannot be classified as normal or abnormal. This indicates that the status cannot be assessed due to the absence of a threshold setting. |
| NORMAL | It is in a normal state. This means the threshold did not meet the configured value, so no event was generated. |
| INFORM | This is the lowest level of risk status, including information at a simple notification level. |
| WARNING | It is a moderate risk condition. |
| FATAL | This is the most dangerous stage. |
Event Status
Displays a list of events that are in an active state among the generated events.
- Events are displayed in order of most recent occurrence.
10.3.2.2 - Performance Analysis
In performance analysis, you can view the key performance metrics of the monitoring target and check both the current data and historical data within the period for each metric. Users can view the performance status of the monitored targets they manage by service or by period, and compare specific performance metrics to analyze the results.
Getting Started with Performance Analysis
You can start performance analysis by directly selecting the monitoring target or entering search criteria. To search for the monitoring target and analyze performance, follow these steps.
- Click Cloud Monitoring Console > Performance Analysis. You will be taken to the Performance Analysis page.
- After entering the search criteria for the monitoring target to be analyzed in the search area, click Search.
Item description Search area The detailed search filters displayed in the search area vary according to the service type - To perform Detailed Search, click the Detailed Search button.
- Each detailed search filter condition can be selected with one or more items
Number of monitoring targets displayed Display the number of performance items that can be viewed at once in the search results and list - The default number of performance items shown in the list is 20 per page.
- Change the list display count to 10, 20, 30, 40, 50, or 100 per page.
Search information Display search result values for the search criteria items - Monitoring target, service status, event grade
- Clicking the risk icon displayed for event risk opens a detailed popup of the most recent event corresponding to that risk level.
Performance metrics Information Displays key performance indicators according to the service type of the monitoring target - The list of key performance indicators per service refers to the service-specific key performance indicators and the collected information by instance type and status of the DB service
View Details View detailed information of the relevant monitoring target Performance Comparison Select a monitoring target and compare performance Table. Performance analysis
Check detailed performance information
To view detailed performance information of the monitoring target, follow these steps.
- Click the monitoring target for which you want to view detailed information in the performance analysis list. Monitoring Details popup window opens.
- Click the Performance tab.
- When you place the mouse cursor over the graph, the values of each performance metric appear in a popup window.
- Click the icon in the upper right corner to set the query period or change the refresh interval.
- You can click the Details, Summary buttons located at the top left of the performance chart to select the graph display method.
Item description Basic Information Display basic information about the monitoring target Details Performance charts of the monitoring target are expanded and displayed - View a single chart in detail
Summary Performance charts of the monitoring target are displayed in a grid layout - View multiple charts at a glance
Set query period - Date/Time: Displays the reference date and time for data retrieval.
- Refresh: Manually refresh to the current time.
- Start/Stop: Turns the automatic refresh feature off or on.
- Settings: Set the data query period or change the automatic refresh interval
Performance Comparison Generate a chart that compares the performance of monitoring targets, allowing each performance to be compared. Performance chart Performance charts of the monitoring target are displayed as graphs - When there is a single graph, the most recent collected value is shown in the upper right corner with its unit.
- When multiple graphs are present, an ⓘ appears in the upper right corner, and hovering the mouse cursor displays the latest collected value for each graph in a popup.
- Hovering the mouse cursor over a graph shows the performance metric value at the specified time in a popup.
Table. Monitoring Target Details
- The collection interval of performance metrics may vary depending on the service.
- The chart displays data at 30 points, and the data collection interval based on the data query range (time) is as follows. (The displayed points may vary due to collection time errors.)
30 minutes: approximately 1‑minute intervals
60 minutes: approximately 2‑minute intervals
3 hours: approximately 6‑minute intervals
6 hours: approximately 12‑minute intervals
12 hours: approximately 24‑minute intervals
24 hours: approximately 48‑minute intervals
- Day 3: approximately 144-minute interval (2 hours 24 minutes) 7 days: approximately 336-minute interval (5 hours 36 minutes)
- Day 14: approximately 672‑minute interval (11 hours 12 minutes) Custom: value obtained by dividing the custom range (minutes) by 30
- The data for each point represents the maximum value within the query range (time), and you can change the statistical type in the detailed chart.
Compare performance
You can view the performance metrics of each monitoring target and select the desired metrics for comparison.
Getting Started with Performance Comparison
Generate a chart that compares the performance of monitoring targets, allowing you to compare each performance.
- Only performance metrics of the same service type can be compared.
- Performance items may be added based on the detailed attributes of the service type.
- Performance of Windows OS on a VM
- Search Engine’s Kibana-related performance
To begin the performance comparison, follow these steps.
Click Cloud Monitoring Console > Performance Analysis. You will be taken to the Performance Analysis page.
After entering the search criteria for the monitoring target to be analyzed in the search area, click Search.
After selecting all monitoring targets to compare performance, click Compare Performance. A popup window that allows performance comparison will open.
Item description Monitoring target Display the service type of the monitoring target to compare and click to change the service - Changing the service will remove all charts created so far.
- Click Add to search for monitoring targets of the currently selected service and add
- The selected monitoring target is displayed on the page, and you can delete the monitoring target by clicking X or Delete All
Performance items Display all performance metrics collected from the currently selected service - Check the items you want to compare performance for, and those performance items will be included in the chart.
Chart display method Select display method for performance comparison chart - Detailed: The performance comparison chart is displayed in detail. (default)
- Summary: The performance comparison chart is displayed in summary
Set query period - Date/Time: Displays the reference date and time for data retrieval
- Refresh: Refreshes directly to the current time.
- Start/Stop: Turns the automatic refresh feature off or on.
- Settings: Set the data query period or change the automatic refresh interval
Chart area Compare the performance of monitoring targets based on the selected performance metric and display it as a chart. Click Add. A popup window opens where you can add a monitoring target.
After selecting the monitoring target to compare performance, click the Confirm button. If you select Kubernetes Engine, you must also select the sub-type of that service.
Select the performance metrics to compare. The selected metrics will be added to the chart.
Explore the chart
The performance comparison results are displayed as a chart. Users can modify the shape of the generated chart or download it as an image or Excel file.
- When you place the mouse cursor over the graph, the performance metric value for the specified time appears as a popup.
- Click a target item in the legend area to hide or unhide the corresponding graph.
Item description Statistical methods Set the statistical method to display in the graph - Statistics are displayed in a graph for a period ranging from a minimum of 5 minutes to a maximum of 6 hours.
- Default, Maximum, Minimum, Average, Total can be selected. Multiple methods can be selected simultaneously, and the selected items are shown in the legend area
Chart format Select the type of graph to display on the chart - Line: line graph
- Stacked Area: area graph
- Scatter: scatter plot
Download chart Check and download the chart’s Raw Data - Chart PNG File: Download the chart as an image file (PNG).
- Chart Excel File: Download the performance item data displayed in the chart as an Excel file. The chart’s displayed data is a dataset automatically collected based on the query range.
- Raw Excel File: Collect the entire performance item data shown in the chart within the query period and download it as an Excel file.
Add time series graph widget Add the chart to the custom dashboard as a time series graph widget - When you click, a popup window for adding a time series graph widget opens.
Delete Delete the performance comparison result chart Performance Comparison Status Display performance comparison results as a graph - When you place the mouse cursor over the graph, the performance comparison status for that time period is shown in a popup window.
10.3.2.3 - Log Analysis
In log analysis, you collect the logs of the monitoring target, review their contents, and convert them into structured metrics for monitoring. Each monitoring target provides default collected logs, and users can create custom logs to collect and view additional logs as needed.
- To use log analysis, you must first install and operate a log collection agent. For detailed information on installing and operating the log agent, see Managing the Agent.
- To collect logs from Kubernetes Engine, you must configure log collection in the Samsung Cloud Platform Console.
Getting Started with Log Analysis
You can view the log status list or search for logs to be monitored to check them. To view the log status list, follow these steps.
- Cloud Monitoring Console > Log Analysis > Log Overview. Click Log Overview to navigate to the Log Overview page.
- After entering the search criteria for the service to be analyzed in the search area, click Log Search.
- The list of services that match the search criteria and the search information are displayed at the bottom.
- Click the View Details button for each service to display that service’s detailed log information.
Item description Search area The displayed search filters in the search area vary depending on the service type - Advanced Search to perform Advanced Search, click the Advanced Search button.
- You can select one or more condition items for each advanced search filter
Number of monitoring targets displayed Search results quantity and the number of items displayed at once in the list - The default is 20 items per page.
- The list display count can be changed to 10, 20, 30, 40, 50, or 100 items per page
Search information Display the search result values for the search criteria items. View Details View detailed information of the relevant monitoring target Log Search Combine keywords and queries to search logs and view detailed information
- If a Virtual Server or Node is connected to the monitoring target, the corresponding status is also displayed in the search information area.
- The name of the monitoring target can include Korean characters, English letters (both uppercase and lowercase), numbers, and special symbols (
-,_,.), and can be up to 100 characters long. - When the monitoring target does not have permission, information about the unauthorized target and a permission verification message are displayed in a popup.
Check detailed log information
You can view detailed log entries and log graphs of the monitoring target.
Check log list
You can view detailed log information in the monitoring detail popup window. To view detailed monitoring information for a log, follow these steps.
- Cloud Monitoring Console > Log Analysis > Log Overview. Click Log Overview. Log Overview page will open.
- Click the log you want to view detailed information for on the Log Status page. The Monitoring Details popup window opens.
- Click the Log tab.
- When you place the mouse cursor over the graph, the values of each log entry appear in a popup window.
- Click the icon in the upper right corner to set the query period or change the refresh interval.
- You can select the graph display method by clicking the Details, Summary buttons located at the top left of each log chart.
Item Explanation Basic Information Display basic information about the monitoring target Details Charts for each log of the monitoring target are expanded and displayed - View a single chart in detail
Summary Performance charts of the monitoring target are displayed in a grid layout - View multiple charts at a glance
Set query period - Date/Time: Displays the reference date and time for data retrieval.
- Refresh: Manually refreshes to the current time.
- Start/Stop: Turns the automatic refresh feature off or on.
- Settings: Sets the data query period or changes the automatic refresh interval
Performance Comparison Combine keywords and queries to search logs and view detailed information. Performance chart Charts for each log of the monitoring target are displayed as graphs - When you place the mouse cursor over the graph, the log entry value at the specified time appears in a popup window.
Search logs to verify
You can combine keywords and queries to search logs and view detailed information.
To search the logs, follow these steps.
Cloud Monitoring Console > Log Analysis > Log Overview. Click Log Overview. You will be taken to the Log Overview page.
On the Log Overview page, click Log Search. You will be taken to the Log Search page.
Item Explanation Monitoring target Display the service type of the monitoring target to compare - Click the monitoring target list to change the service
- Changing the service will cause all charts created so far to disappear.
- Add button to search for and add monitoring targets of the currently selected service
- The selected monitoring targets are displayed on the page, and you can delete a monitoring target by clicking X or Delete All.
Search criteria Set conditions for the logs to be searched Set query period - Date/Time: Displays the reference date and time for data retrieval.
- Refresh: Manually refresh to the current time.
- Start/Stop: Turns the automatic refresh feature off or on.
- Settings: Set the data query period or change the automatic refresh interval
Log volume graph When you search the logs, the log entries that match the entered criteria are displayed as a chart. Generated log message Log messages from the monitoring target are displayed by time. Click the Add button. A popup window opens where you can add a monitoring target.
After clicking the monitoring target, select the log file you want to add.
After selecting the log file, click the Confirm button.
After entering the search criteria, click the Search button. The search results will be displayed on the log volume graph and the log messages.
Item description Add indicator Add metrics to log search results - Use after searching logs
Execution History Check the list of search criteria that were recently executed - The execution history displays up to the last 20 executed search criteria
- You can select the desired search history and input it as the current search criteria
Search field Select the search field Condition Select search criteria like,!like,=,!=,<=,>=,>,<can be selected
search value Enter the keyword to search Log Search Select the operator (AND, OR) for the newly added search condition - Displayed only when a new search condition is added
Add condition Add a new search condition When you search the logs, the log entries that match the entered criteria are displayed as a chart.
- Log entries are displayed in seconds.
Item Explanation Log volume graph The log volume over the selected period is displayed as a graph - When you hover the mouse cursor over the graph, the values of each log entry appear in a popup window.
- Clicking a bar in the graph displays the list of logs for that point in time.
Set query period - Date/Time: Displays the reference date and time for data lookup
- Refresh: Manually refresh to the current time.
- Start/Stop: Turn the automatic refresh feature off or on.
- Settings: Set the data query period or change the automatic refresh interval
Monitoring target The monitoring target list is displayed - When you select a monitoring target to view log messages, the log list shows the content
Log list Log messages generated from the monitoring target are displayed by time - Click the button in the log list to view the full message of that log
- Click Download to save the currently displayed log messages in Excel and TXT file formats
- Log entries are displayed in seconds.
Check log collection status
You can view the main log collection information for the past 7 days as a chart.
- When you place the mouse cursor over the graph, detailed information appears in a popup window.
- Only collected logs are aggregated, and logs that have not been collected are not displayed in the status.
- When you create an Account, we provide a default virtual capacity of 1 GB to store the collected logs.
- All logs can be stopped and restarted as needed.
To check the log collection status, click Cloud Monitoring Console > Log Analysis > Log Collection Dashboard.
| Item | description |
|---|---|
| Cumulative log volume | Display the amount of logs collected from the 1st of each month in GB
|
| Log collection volume for the past 7 days | Display the amount of logs collected over the past 7 days by service type in a graph
|
| Log occurrence rate by service | Display logs collected over the past 7 days, categorized by service
|
| Log Collection Top 10 | Display a graph of the top 10 monitoring targets that collected the most logs in the past 7 days within the selected service, based on log occurrence rates by service
|
To perform monitoring related to logs, you must first install and operate a log collection agent. For detailed information on installing and operating the log agent, refer to 에이전트 관리하기.
- Accumulated logs are stored up to a maximum of 1 GB. If it exceeds 1 GB, older logs are automatically deleted.
Check indicator configuration status
You can create a metric to display the occurrence count of log patterns as a time series. To view the metric list, click Cloud Monitoring Console > Log Analysis > Metric Configuration Status.
| Item | description |
|---|---|
| Search area | The displayed search filters in the search area vary depending on the service type
|
| Number of monitoring targets displayed | Display search results
|
| Search information | Display the search result values for the search criteria items. |
| Add | Add a new metric |
| Delete | Select the metric in the search information and delete it. |
Check detailed indicator information
Follow these steps to view detailed information about the indicator.
- Cloud Monitoring Console > Log Analysis > Metric Configuration Status. Click Metric Configuration Status. You will be taken to the Metric Configuration Status page.
- Indicator Setting Status Click the indicator name to view detailed information on the page. Indicator Details popup window opens.
Add indicator
You can add a new metric to display the desired log data as a time series.
- Log metrics can only be set for monitoring targets where the log agent is installed or logs are being collected. For detailed information on installing and operating the log agent, refer to 에이전트 관리하기.
To add a new metric, follow these steps.
Cloud Monitoring Console > Log Analysis > Click Metric Configuration Status. You will be taken to the Metric Configuration Status page.
Indicator Settings Status on the page, click the Add button. Add Indicator popup will open.
Enter indicator name.
- Metric names can only use English uppercase and lowercase letters, underscores (_), periods (.), and hyphens (-).
- To distinguish metrics from general performance, the prefix
metricfilter.is automatically added and cannot be removed or changed.Item Explanation Indicator Name Enter the name of the metric to create Monitoring Target Display the service type of the monitoring target to compare - Click the monitoring target list to change the service
- Changing the service will cause all charts created so far to disappear.
- Click the Add button to search for and add the monitoring target of the currently selected service
- The selected monitoring target is displayed on the page, and you can delete the monitoring target by clicking X or Delete All
Search Criteria Set conditions for the logs to be searched Set Query Period - Date/Time: Displays the reference date and time for data retrieval
- Refresh: Refreshes directly to the current time.
- Start/Stop: Turns the automatic refresh feature off or on.
- Settings: Allows you to set the data query period or change the automatic refresh interval.
Log volume graph When you search the logs, the log entries that match the entered criteria are displayed as a chart Generated log message Log messages from the monitoring target are displayed by time.
Click the Add button. A popup window opens where you can add a monitoring target.
After clicking the monitoring target, select the log file you want to add.
After selecting the log file, click the Confirm button.
After entering the search criteria, click the Search button. The search results will be displayed on the log volume graph and the generated log messages.
Item description Add indicator Add metrics to log search results - Use after searching logs
Execution History Check the list of search criteria that were recently executed - The execution history displays up to the last 20 executed search criteria
- You can select the desired search history and input it as the current search criteria
Search field Select the search field Condition Select search criteria like,!like,=,!=,<=,>=,>,<can be selected
search value Enter the keyword to search operator Select the operator (AND, OR) for the newly added search condition - Displayed only when a new search condition is added
Add condition Add a new search condition Click the Confirm button. A new metric will be added with a toast popup message.
Modify indicator search criteria
To modify the indicator’s search criteria, follow these steps.
- Cloud Monitoring Console > Log Analysis > Click Metric Configuration Status. Metric Configuration Status page will open.
- Indicator Settings Overview On the page, click the indicator name of the metric you want to edit. The Indicator Details popup will open.
- In the Indicator Details popup, click the Edit button. The Edit Indicator popup opens.
- Metric Update After modifying the search criteria in the popup window, click the Confirm button. The metric will be updated along with a toast popup message.
Delete indicator
To delete the indicator, follow these steps.
- If there are charts or event policies that use the metric you want to delete, you cannot delete that metric.
- Cloud Monitoring Console > Log Analysis > Metric Configuration Status. Click it. You will be taken to the Metric Configuration Status page.
- On the Indicator Settings page, select the indicator to delete, then click the Delete button. The indicator will be removed along with a toast popup message.
10.3.2.4 - Managing Events
An event is a setting that notifies the user when a performance metric of the monitored target meets a specific condition. By configuring events, users can capture essential monitoring information without missing it. For example, if you set an event to trigger whenever a performance value related to overload exceeds a certain threshold, a notification is sent to the user each time there is a risk of overload during resource operation. Users can respond proactively before problems occur based on this.
In event management, you can create such events and configure them to notify designated users whenever a specific value occurs during monitoring.
Check Event Status
In the Event Status, you can view information about all generated events, related performance metrics, and the history of event notifications delivered to users. To view the Event Status list, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Status. You will be taken to the Event Status page.
- On the Event Status page, enter the search criteria for the service whose event status you want to check in the search area, then click the Search button.
Item description Search area The search filters displayed in the search area differ according to the service type - To perform an Advanced Search, click the Advanced Search button.
- You can select one or more condition items for each advanced search filter
Number of monitoring targets displayed Display the quantity of search results and the number of items that can be viewed at once in the list - The default number of items shown in the list is 20 per page.
- The list display count can be changed to 10, 20, 30, 40, 50, or 100 items per page
Search information Display search result values for the search criteria items - Clicking the message content of each service allows you to view detailed event information
View Details View detailed information of the relevant monitoring target Table. Event List
- If a Virtual Server or Node is connected to the monitoring target, the corresponding status is also displayed in the search information area.
- The name of the monitoring target can include Korean characters, English letters (both uppercase and lowercase), numbers, and special symbols (
-,_,.), and can be up to 100 characters long.
View event status list
In the monitoring detail popup, you can view the event information, occurrence time, and duration in the event list. To check the event occurrence status, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Status. You will be taken to the Event Status page.
- On the Event Status page, click the Event tab.
Item description Event status Check event message and occurrence time active Show only events that are currently active All Show all events Event Details Check the detailed information of the selected message in the event status Table. Event tab
Check event details
To view the event details, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Status. You will be taken to the Event Status page.
- On the Event Status page, click the Event tab.
- On the Event Status page, after selecting the event for which you want to view detailed information, click Event Details to view the event publishing conditions, performance items, and notification history.
Item Explanation Monitoring target Display the name of the monitoring target Occurrence condition Display the condition under which the event occurs Performance items Displays a chart for performance items. - Hovering the mouse cursor over the graph shows detailed performance values for each time period.
Notification History Display the full alarm occurrence history Event Settings Details View the configuration information of the event Table. Event Details
Manage Event Settings
You can configure event details such as the monitoring target, performance metrics that define the event trigger, event severity level, and event notification recipients. When data collected from the monitoring target meets the conditions set in the event policy, notifications are delivered to the user via email, SMS, or messages.
- Event policies can be set only when a monitoring target is specified, and policies for each Auto-Scaling Group can be configured at the group level.
Check Event Settings
To verify the event settings, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Settings. Navigate to the Event Settings page.
- On the Event Settings page, enter the search criteria for the service whose event policy you want to check in the search area, then click the Search button.
Item Explanation Search area The search filters displayed in the search area vary depending on the service type - To perform Advanced Search, click the Advanced Search button.
- You can select one or more condition items for each advanced search filter
Number of monitoring targets displayed Display search results - The default is to show 20 items per page.
- Change the number of items displayed in the list to 10, 20, 30, 40, 50, or 100 per page.
Monitoring target Display the name of the monitoring target - When the checkbox is selected, the Delete, Activate, and Notification Recipient buttons become enabled.
Performance items Display performance items for the event configuration target Individual item Display individual performance items under the performance category - If there are no individual items, nothing is displayed.
Type/Unit Display the value type and unit of the performance item Event rating Display the risk level of the event - The risk level is set manually by the user when adding an event
- Fatal: The highest risk level.
- Warning: A medium-level risk.
- Information: The lowest risk level, for reference.
threshold Display the reference value for comparing performance values. Notification recipients Display the recipients of the event notification - When the mouse cursor is placed over the name, the full list is displayed on the page
Policy status Indicates whether the event is active View Details Check and edit event details - Click ‘View Details’ to open the detailed information popup for the event.
Add Add event Delete Delete event Enable Enable or disable the event Notification recipients Check and manage event notification recipients Table. Event Settings
- The name of the monitoring target can include Korean characters, English letters (both uppercase and lowercase), numbers, and special symbols (
-,_,.), and can be up to 100 characters long. - When the monitoring target does not have permission, information about the unauthorized target and a permission verification message are displayed in a popup.
Check detailed event settings
You can view detailed information about the monitoring target and event conditions, and modify the event conditions and notification information.
Add Event Settings
To add an event setting, follow these steps.
- Event policies can only be set when a monitoring target is specified.
- Auto-Scaling Group policies can be applied on a per-group basis.
Click Cloud Monitoring Console > Event Management > Event Settings. Navigate to the Event Settings page.
Click the Add button on the Event Settings page. The Add Event Settings popup opens.
Item description Target Name Select the monitoring target to add an event setting - Click the monitoring target list to change the service
- Changing the service will delete all event conditions created so far.
- Click the Add button to search for and add the monitoring target of the currently selected service
- The selected monitoring target is displayed on the page, and you can delete the monitoring target by clicking X or Delete All
Event Settings Area Set the performance and occurrence conditions for the event Notification information area Set the notification recipients and method when an event occurs. Table: Description of the Add Event Settings PopupAfter selecting the service type in the monitoring target area, click the Add button. The add monitoring target popup window will open.
After selecting the monitoring target, click the Confirm button.
- You can select multiple monitoring targets simultaneously.
- If there are multiple monitoring targets, the configured event is added identically to each monitoring target.
- If you select Kubernetes, you must also select the sub-type of that service.
In the performance items, click the item where you want to add an event, then enter the event trigger condition.
- The added performance items display the count of additions next to the performance name.
- If you select multiple performance items, you must enter the event occurrence condition for each performance item.
Item explanation Load Event Policy Template Select and apply an existing event policy template. Performance items Click the performance metric for which you want to set the event trigger condition and add it to the event condition configuration area. Event rating Set the event severity level - Fatal: the most dangerous level.
- Warning: a medium-level risk.
- Information: the lowest level of risk and for reference.
Performance type Select the reference value for determining whether an event occurs - Collected value: Use the current value.
- Delta value: Use the difference between the previous and current values.
threshold Set the reference value to compare with the collected performance values - It serves as the criterion for determining whether an event occurs.
- Only numbers and decimal points can be entered
Comparison method Select a method that compares the monitoring value of the performance item with the threshold to determine whether an event occurs - Range: Check whether the performance value is within the range specified by the threshold
- Match: Check whether the performance value equals the threshold
- Different: Check whether the performance value differs from the threshold
- At least: Check whether the performance value is greater than or equal to the threshold
- Greater than: Check whether the performance value exceeds the threshold
- At most: Check whether the performance value is less than or equal to the threshold
- Less than: Check whether the performance value is less than the threshold
Individual item Specify an individual performance item under the performance items as an event condition - It is enabled only when the performance item can collect the individual item.
Prefix You can add a prefix to the event message. - Event Status page uses this as a keyword to search for the event.
Statistics Set the statistical method to apply to the collected performance values - When statistics are configured, the performance value calculated using the selected statistical method is compared against the threshold when evaluating event trigger conditions. If not selected, the most recent performance value is compared to the threshold.
- Statistical Method: Choose one of maximum, minimum, average, or sum to compute the collected performance values.
- Statistical Period: Set the time span over which the statistical method is applied. It is the period measured from the most recently collected performance value.
Sustained occurrence count Set the number of consecutive monitoring values that satisfy the event occurrence condition - This value is used as a sensitivity to determine whether the event is a momentary outlier or a real event.
Event occurrence notification time zone Timezone setting feature when configuring event policies Table. Add Event Settings - Event Settings Area
Notification area allows you to set notifications.
Item description Notification recipient selection area Select notification recipients - After selecting the notification recipients, click the Delete button to remove the selected recipient.
Notification recipients / group The list of recipients to receive the notification when an event occurs is displayed. Event risk level The risk level of the configured event is displayed. Notification method The method of delivering notifications to the recipient is displayed. Add Select and add a new notification recipient from the address book. Delete Delete a notification recipient from the notification recipient/group Table. Add event settings - notification info areaCheck the notification recipients, select them, and click the Confirm button.
- Only the account’s root user or an IAM user can be added as a notification recipient.
- You can select multiple items simultaneously.
- Set the notification method for each recipient according to the event risk level.
- The notification method can be selected from email, SMS, and messenger, and multiple methods can be selected simultaneously.
- When the notification method setup is complete, click the Confirm button.
Modify Event Settings
To edit the event’s conditions and notification recipient information, follow the steps below.
- Click Cloud Monitoring Console > Event Management > Event Settings. You will be taken to the Event Settings page.
- Event Settings page, enter the search criteria for the service whose event settings you want to modify in the search area, then click the Search button.
- From the event policy list, click the View Details button of the event policy you want to edit. You will be taken to the Event Settings Details page.
- On the Event Settings Detail page, click the Edit button. You will be taken to the Event Settings Edit page.
- On the Edit Event Settings page, enter the information to be modified, then click the Confirm button.
- You can edit the event conditions and notification information.
Delete Event Settings
To delete the event configuration, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Settings. You will be taken to the Event Settings page.
- On the Event Settings page, enter the search criteria for the service whose event policy you want to delete in the search area, then click the Search button.
- After checking the event policy to delete in the event policy list, click the Delete button.
- In the confirmation popup, click the Confirm button.
Change Event Settings Activation
You can easily change whether the event policy is enabled.
- Click Cloud Monitoring Console > Event Management > Event Settings. Go to the Event Settings page.
- On the Event Settings page, enter the search criteria for the service whose event policy you want to delete in the search area, then click the Search button.
- In the event policy list, check the event policy whose activation you want to change, then click the Activate button. The Policy Activation popup window will open.
- After selecting the activation status, click the Confirm button.
- Enable All, Disable All buttons can be clicked to change them in bulk.
Change Event Notification Recipients
You can verify the recipients of notifications when an event occurs and change them in bulk.
- The event notification recipient change feature is intended to modify event notification recipients in bulk. Consequently, the existing recipients are removed and replaced with the new recipient settings.
- To view and modify the notification recipients for each policy, click the Edit button on the policy’s detail page, then make the changes.
- Click Cloud Monitoring Console > Event Management > Event Settings. Go to the Event Settings page.
- On the Event Settings page, enter the search criteria for the service whose event policy you want to delete in the search area, then click the Search button.
- After checking the event policy to edit in the event policy list, click the Notification Recipients button. You will be taken to the Notification Recipients page.
- On the Notification Recipients page, after selecting the user to add as a notification recipient, click the Confirm button.
Item description Event policy list The list of event policies for changing the notification recipients is displayed - Click Add to add the policy to be changed
- Click the Delete button in the policy list to remove that policy.
User search area Enter name, email, mobile phone, and company name to search Notification address book Use the notification address book to verify and add users. Search User List The list of users included in the notification address book or search results is displayed - If you check the users to add as notification recipients, they will be added to the notification recipient list.
Notification recipient list The list of users to be added as notification recipients for the event displayed in the event policy list is shown - After checking a user, click the Delete button to remove that user from the list.
Table. Change Event Notification Recipients
Managing Event Templates
You can set the monitoring target, performance values that define event occurrence criteria, and the event risk level, then create and use a template. When adding or modifying an event, you can import an event policy template to easily enter the event conditions.
Check the list of event policy templates
To view the list of event policy templates, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Settings. Navigate to the Event Settings page.
- On the Event Settings page, click Event Policy Template. You will be taken to the Event Policy Template page.
- On the Event Policy Template page, enter the search criteria for the service whose template you want to check in the search area, then click Search.
Item description Search area Enter the conditions of the event policy template to search. Add event policy template Add event policy template Template List Event policy templates that match the search criteria are displayed. Table. Event Policy Template List
Add event policy template
To add an event policy template, follow these steps.
Click Cloud Monitoring Console > Event Management > Event Settings. Navigate to the Event Settings page.
On the Event Settings page, click the Event Policy Template button. You will be taken to the Event Policy Template page.
On the Event Policy Template page, click the Add Event Policy Template button. The Add Event Policy Template popup opens.
Add Event Policy Template In the popup window, set the service type and template information for adding the event policy template.
*Items marked with * are required fields and must be entered.Item description Service Type Select the service type to set the event policy - Click the service type list to change the service
- If you change the service, all event conditions created so far will be lost.
Template name Enter the name of the template to create Template description Enter a description for the template to be created Table. Add event policy template – set service type and template nameIn the performance items, click the item where you want to add an event, then enter the event trigger condition.
- The added performance items display the count of additions next to the performance name.
- If you select multiple performance items, you must enter the event trigger condition for each item.
*Items marked with * are required fields and must be entered.Item description Load Event Policy Template Select and apply an existing event policy template - When you load the template, the event conditions and notification recipients are replaced with the information set in the template.
Performance items Click the performance metric to set the event trigger condition and add it to the event condition configuration area. Event rating Set the event severity - Fatal: The most dangerous level.
- Warning: A medium-level risk.
- Information: The lowest risk level, for reference only.
Performance type Select the reference value to determine whether an event occurs - Collected value: Use the current value.
- Delta value: Use the difference between the previous and current values.
threshold Set the reference value to compare with the collected performance values - It serves as the criterion for determining whether an event occurs.
- Only numbers and decimal points can be entered
Comparison method To determine whether an event occurs, select the method that compares the monitoring value of the performance item with the threshold. - Range: Check if the performance value is within the range specified by the threshold.
- Match: Check if the performance value matches the threshold.
- Different: Check if the performance value differs from the threshold.
- AtLeast: Check if the performance value is greater than or equal to the threshold.
- Exceeds Check if the performance value exceeds the threshold.
- AtMost: Check if the performance value is less than or equal to the threshold.
- LessThan: Check if the performance value is less than the threshold.
Individual item Specify an individual performance item under the performance items as an event condition - It is enabled only when the performance item can collect the individual item.
Prefix Add an event message prefix - It is used as a keyword to search for this event on the event status page.
Statistics Set the statistical method to apply to the collected performance values - When statistics are set, the performance value calculated using the configured statistical method is compared to the threshold when determining event trigger conditions. If not selected, the most recent performance value is compared to the threshold.
- Statistical Method: Choose one among maximum, minimum, average, sum to calculate the collected performance values.
- Statistical Period: Set the period over which the statistical method calculation is applied. It is the period from the most recently collected performance value.
Number of occurrences Set the number of consecutive monitoring values that satisfy the event trigger condition - This value is used as a sensitivity to determine whether the event is a transient anomaly or a genuine event.
Event occurrence notification time window Timezone setting feature when configuring event policies Table. Add event policy template – performance item
Set the recipients and delivery method for the information when a notification occurs.
Item description Add Select and add a new notification recipient from the address book. Delete Delete the selected notification recipient(s) from the notification recipients/group Notification recipients / groups The list of recipients to receive the notification content is displayed when an event occurs - After selecting a notification recipient, clicking the Delete button removes that recipient.
Event risk level The risk level of the event to be delivered is displayed Notification method The method of delivering notifications to the recipient is displayed - you can choose among email, SMS, and messenger, and you can select multiple methods simultaneously
Table. Add event policy template – set notification recipients
- Only Account members and the notification address book registered in the Account can be added as recipients.
- You can select multiple items simultaneously.
- Click the Confirm button. The event policy template will be added along with a toast popup message.
Edit and delete event policy templates
To modify or delete an event policy template, follow the steps below.
- Click Cloud Monitoring Console > Event Management > Event Settings. You will be taken to the Event Settings page.
- On the Event Settings page, click the Event Policy Template button. You will be taken to the Event Policy Template page.
- On the Event Policy Template page, enter the search criteria for the service whose template you want to view in the search area, then click the Search button.
- Click the More button at the top right of the template you want to edit or delete, and then click Edit or Delete.
- Edit: The template edit popup window opens. After editing the template, click the Confirm button.
- Delete: The template will be deleted along with a toast popup message.
- Click the Confirm button. The template will be deleted along with a toast popup message.
Share event policy template
To share the event policy template, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Settings. Navigate to the Event Settings page.
- On the Event Settings page, click the Event Policy Template button. You will be taken to the Event Policy Template page.
- On the Event Policy Template page, enter the search criteria for the service whose template you want to view in the search area, then click the Search button.
- Click the More > Share button located at the top right of the template you want to share.
- After selecting the user to share with, click the > button. The selected user will be added to the sharing target.
- Click the Confirm button. The template will be shared with a toast popup message.
Filtering events
You can filter notifications for events that occur during a specific period. While event filtering is applied, notifications will not be delivered even if events occur.
To view the event filtering list, follow these steps.
- Cloud Monitoring Console > Event Management > Event Filtering click. You will be taken to the Event Filtering page.
Item description Filtering Timeline Display the timeline of registered filters by date - Registered filters are displayed on the timeline as bars. Clicking a bar shows the filter’s detailed information.
- The numbers from 00 on the left to 23 on the right represent the hour of the day.
- The blue vertical line below the time indicates the current time.
<,>Click to change the displayed date
Filtering list Displays a list of information and operational status of registered filters - Running: The filter is registered and currently operating
- Ended: The filter’s operation has ended after the set period has passed.
- Scheduled: The filter registration is complete and is pending. The filter will operate when the set period arrives.
- Disabled: The filter is in a stopped state. It is displayed when ‘Use’ is not selected in the detailed settings
Add Add new event filtering Delete Delete the selected event filter from the filter list Search area Search for event filtering or monitoring targets Table. Event Filtering List
Add event filtering
To add event filtering, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Filtering. Navigate to the Event Filtering page.
- Click the Add button on the Event Filtering page. The Add Event Filtering popup opens.
- Add Event Filtering Enter the filtering information in the popup window.
Item Explanation Event filtering Enter the name of the event filter Usage status Set whether event filtering is used - If set to Not Used, it will be displayed as Disabled until changed to Enabled, and filtering will not operate.
Time zone Set the reference time zone for applying event filtering Iteration type Set the repeat application of event filtering - No repeat: Enter the start and end year, month, day, hour, minute. Filtering occurs only once without repetition.
- Daily, weekdays: Enter only the start time and end time. Filtering repeats daily at the specified times.
Period Set the period during which event filtering is applied - Applied Time: For recurring tasks, it is active and displays the elapsed time from the start time to the end time
- Conversion Period: The event filtering period is converted and displayed based on the time zone set by the user
Event filtering target Select the service type and monitoring target to apply event filtering, then add. Table. Add event filtering - Click the Confirm button. Event filtering will be added with a toast popup message.
Modify Event Filtering
To modify event filtering, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Filtering. Proceed to the Event Filtering page.
- Event Filtering page, click the name of the filter you want to edit. Event Filtering Details popup window opens.
- Event Filtering Details in the popup window, click the Edit button. The Edit Event Filtering popup window opens.
- Edit Event Filtering After entering the changes in the popup window, click the Confirm button. The event filtering will be updated with a toast popup message.
Delete event filtering
To delete event filtering, follow these steps.
- Click Cloud Monitoring Console > Event Management > Event Filtering. Navigate to the Event Filtering page.
- On the Event Filtering page, select the event filter you want to delete, then click the Delete button. The event filter will be deleted along with a toast popup message.
- You can select multiple event filters simultaneously.
Managing Notification Groups
You can group the recipients who receive notifications when an event occurs into a single group for management. Notification Group allows you to efficiently manage notification recipients and configure notification settings easily and quickly.
To check the notification group, follow the steps below.
- Click Cloud Monitoring Console > Event Management > Alert Group. Go to the Alert Group page.
- Notification Group page allows you to view and manage notification groups.
Item description Add notification group Add a new notification group. Notification Group Displays a list of all notification group created by the user. - When a notification group is clicked, the notification group details popup opens.
- Click the Edit button to modify the notification group
Advanced Search You can search the address book by entering the notification group name. Keyword search You can search by selecting the notification group, user name, creation timestamp, and last modified timestamp.
Add Notification Group
To add a notification group, follow these steps.
- Cloud Monitoring Console > Event Management > Add Alert Group Click.
- Add Notification Group page allows you to enter the notification group name and description, then add users.
- Click the Save button to add the notification group.
Edit Notification Group
You can add a user to a notification group or delete a user registered in the notification group.
Add User
To add a user to the notification group, follow these steps.
- Click Cloud Monitoring Console > Event Management > Alert Group.
- In the All Notification Groups, click the notification group to which you want to add a user, then click Edit.
- Please select the user to add.
- Only users registered in the Account can be added to the address book.
- You can quickly find the desired members using the real-time search GUI.
- Click the Save button. The user address will be added with a toast popup message.
Delete Notification Group
To delete a notification group, follow these steps.
- Click Cloud Monitoring Console > Event Management > Alert Group.
- Click the notification group you want to delete from the overall notification groups.
- After selecting the notification group to delete, click Delete.
- You can select multiple addresses simultaneously.
- Click the Confirm button. The address will be deleted along with the toast popup message.
10.3.2.5 - Using Custom Dashboards
Custom dashboards are personalized dashboards that users configure by selecting the widgets they want. Users can use custom dashboards to arrange monitoring information as they wish, and they can share the created custom dashboards with other users.
The content covered in Using Custom Dashboards is as follows.
Getting Started with Custom Dashboard
After creating a custom dashboard, the user can add desired widgets to view monitoring information.
Create a custom dashboard
To create a custom dashboard, follow these steps.
- From the top‑right menu, click Custom Dashboard Management. You will be taken to the Custom Dashboard Management page.
- Click Add Dashboard. The Add Dashboard popup window opens.
- Enter the dashboard name to create and click the Save button.
- The custom dashboard you created appears in the My Dashboard list.
Add widget
Custom dashboards provide widgets in various formats such as performance statistics, comparison charts, and event lists. Users can add the information they want to monitor as widgets and freely configure the custom dashboard.
- You can change the position and size of a created widget, or edit, copy, and delete its content. For more details, see Custom Widget Management.
To add a widget, follow these steps.
- From the top‑right menu, click Custom Dashboard Management. You will be taken to the Custom Dashboard Management page.
- From the My Dashboard list, select the custom dashboard to add a widget.
- Click the + button or the Add Widget button at the top right of the dashboard. The Add Widget popup window opens.
- Add Widget In the popup window, select the widget to use on the dashboard and add it.
- When you select a widget, detailed settings and a preview are displayed.
- For explanations and configuration methods for each chart, refer to Custom Widget.
- Click the Confirm button.
Custom widget
The types of widgets that can be added to a custom dashboard are as follows.
| Widget Name | Explanation |
|---|---|
| Title Box | Display the title box on the custom dashboard. |
| Event status | Displays the event that occurred. |
| Monitoring Status | Displays the number of monitoring targets and the monitoring status. |
| Top 5 Key Performance | Displays the top 5 monitoring targets with the highest utilization for a specific performance metric. |
| Event map | Displays the number of events per service by severity level. |
| Event History | Displays the count of events per date by severity. |
| time series graph | Displays the performance metrics of the selected monitoring target as a time-series graph. |
| Current status indicator | Displays the performance value statistics and risk levels of the selected monitoring targets. |
| Instance map | Displays the performance values of the selected monitoring targets using colors of varying intensity. |
Title Box
Displays a title box on the custom dashboard.
- You can create up to 10 title boxes.
- You can add multiple title boxes at the same time.
| Item | description |
|---|---|
| Title | Enter the text to display in the title box. |
| Add | Add a new text box. |
| Delete | Delete the corresponding text box. |
Event status
Displays the occurred event.
- You can configure it to display all events that have occurred, or only the active events.
| Item | description |
|---|---|
| Widget name | Enter the name of the widget. |
| Query range | Select the range of events to display in the widget
|
Monitoring Status
Displays the number of monitoring targets and the monitoring status.
| Item | explanation |
|---|---|
| Widget name | Enter the name of the widget. |
Key Performance Top 5
Shows the top five monitoring targets with the highest usage rate for a specific performance metric within the Account.
| Item | description |
|---|---|
| Widget name | Enter the name of the widget. |
| Service | Select the service to check performance. |
| Performance metrics | Select the performance metric that serves as the basis for displaying the monitoring target
|
Event map
Displays the number of events per service by severity level.
| Item | description |
|---|---|
| Widget name | Enter the name of the widget. |
Event History
Displays the number of events per date, grouped by severity.
| Item | description |
|---|---|
| Widget name | Enter the name of the widget. |
Time Series Graph
Displays the performance metrics of the selected monitoring target as a time-series graph.
- You can change the period displayed by the time series graph using the dashboard’s date range setting feature.
- When you place the mouse cursor over the graph, you can view the time and performance values for each target at that point.
| Item | description |
|---|---|
| Widget name | Enter the name of the widget. |
| Service | Select the service to check performance. |
| Monitoring target | Select the monitoring target to display as a graph. |
| Performance items | Select the performance metric to display as a graph. |
| Add option | You can display a danger zone.
|
You can click the icon at the top right of the preview to change the graph type.
- Linear graph
- area chart
- stacked bar chart
- scatter plot
Current Indicator
Displays statistical figures and risk levels for the performance values of monitored entities.
In the monitoring dashboard, if you place the mouse cursor over a status indicator value, you can view detailed information for that item.
| Item | description |
|---|---|
| Widget name | Enter the name of the widget. |
| Service | Select the service to check performance. |
| Monitoring target | Select the monitoring target to display as a graph. |
| Performance metrics | Select the performance items to display as a graph. |
| Statistics | Select the statistical method to display the performance values of the monitoring target
|
| Add option | You can display a danger zone.
|
Instance Map
Display the performance values of monitoring targets using colors of varying intensity.
- When you position the mouse cursor over each heatmap, you can view detailed information about the item.
| Item | description |
|---|---|
| Widget name | Enter the name of the widget. |
| Service | Select the service to check performance. |
| Monitoring target | Select the monitoring target to display as a graph. |
| Performance metrics | Select the performance metric to display as a graph. |
Check Custom Dashboard
To view the custom dashboard, follow these steps.
- From the top‑right menu, click Custom Dashboard Management. You will be taken to the Custom Dashboard Management page.
- From the My Dashboard list, select the Custom Dashboard.
Item description Dashboard List Displays the list of custom dashboards. Click a list item to change the dashboard to view. - My Dashboards: Displays the list of dashboards you created yourself.
- Shared Dashboards: Displays the list of dashboards shared with you.
Dashboard name The name of the user dashboard is displayed. Dashboard Settings - Date/Time: Displays the reference date and time for the analysis information.
- Refresh: Refreshes to the current time.
- Stop/Start: Turns the automatic refresh feature off or on.
- Settings: You can set the data query period or change the automatic refresh interval. (See “Setting the query period” for reference)
Add widget Add a new widget to the dashboard. Dashboard editing You can edit the currently configured custom dashboard. - Dashboard Edit: Modify the name of the currently selected dashboard.
- Dashboard Copy: Copy the currently selected dashboard to create a custom dashboard with the same widgets.
- Dashboard Delete: Delete the currently selected dashboard.
- Dashboard Share: Share the dashboard so that specific users can view it. For more information, see Sharing Custom Dashboards.
Custom widget Displays the widgets that make up the dashboard. - You can change the widget’s position and size, or edit and delete it. For more information, see Managing Custom Widgets
- You can download graphic widgets as image files.
Table. Custom dashboard information
Download widget
Graphic widgets can be downloaded as image files (*.png).
When you hover the mouse over a graph widget, a download button appears in the upper right corner. Clicking the download button downloads the widget as an image file.
Share Custom Dashboard
You can share a custom dashboard and configure it so that other users can view it.
To share a custom dashboard, follow these steps.
- From the top‑right menu, click Custom Dashboard Management. You will be taken to the Custom Dashboard Management page.
- From the My Dashboard list, select the Custom Dashboard.
- Click Dashboard More at the top right, then click Dashboard Share. The Dashboard Share popup opens.
- After selecting the user to share the dashboard with, click the > button and verify that the selected user moves to the shared target.
- Click the Confirm button.
Managing Custom Dashboards
You can edit, copy, or delete a custom dashboard.
- From the top-right menu, click Custom Dashboard Management. You will be taken to the Custom Dashboard Management page.
- From the My Dashboard list, select the Custom Dashboard.
- Click the Dashboard top-right more button, then select the desired command.
- Edit Dashboard: Edit the dashboard name.
- Dashboard Copy: Copy the dashboard to create a new dashboard.
- Dashboard Sharing: Share the dashboard with other users.
- Delete Dashboard: Deletes the dashboard.
Managing custom widgets
You can change the widget’s position and size, or edit and duplicate the widget.
Change Widget Position
Click the widget’s name, then drag to change its position.
Changing Widget Size
To change the size of the widget, follow these steps.
- Place the mouse cursor over the widget. The size adjustment button appears in the lower right corner of the widget.
- Size Adjustment button, click and hold while dragging to adjust to the desired size.
Edit, copy, delete widget
To modify, copy, or delete a widget, follow these steps.
- Place the mouse cursor over the widget. The More button appears in the top right corner of the widget.
- After clicking the More button, click the desired command.
- Widget Edit: Modify the widget’s chart settings.
- Widget Copy: Copies the widget to create a widget with identical content.
- Delete Widget: Deletes the widget.
10.3.2.6 - Managing Agents
The agent is a module that collects performance metrics, logs, and Windows events from the monitoring target. Users must verify the agent’s installation status and operate and manage it in order to use the monitoring functionality.
- If IP access control is configured for the monitoring target, you cannot use agent management. If agent management cannot be used, check the IP access control configuration status of the selected monitoring target.
- The agent management feature uses the sudo command, so the sudo package must be installed in advance.
Agent Management Overview
The agents include a performance collection agent, a log collection agent, and a Windows event log collection agent.
- The agent must be manually installed by the user on each monitoring target according to the user’s requirements.
Manage Agents
Managing Performance Agents
To install and manage the agent, follow these steps.
- Cloud Monitoring Console > Performance Analysis Click the button. You will be taken to the Performance Analysis page.
- On the Performance Analysis page, select a monitoring target and click the View Details button. The Monitoring Target Details popup window opens.
- Monitoring Target Details In the popup window, click the Agent tab. It navigates to the Agent tab.
- Click the Performance button in the Agent tab.
- Click the Copy icon on the right side of the installation command to copy the command.
- Paste the copied command into the monitoring target resource.
- Execute the command copied to the monitoring target resource.
| Item | description |
|---|---|
| Installation | Download the script file required for agent installation and execute it. |
| Start | Execute the agent start command. |
| Stop | Execute the agent stop command. |
| Delete | Execute the agent deletion command. |
| Update | Download the script file required for the agent update and execute it. |
To check the agent service status, use the method below.
- linux: $ sudo systemctl status metricbeat
- windows: Task Manager → service → metricbeat → Status(Running)
Managing Log Agents
To install and manage the agent, follow these steps.
- Click Cloud Monitoring Console > Performance Analysis. You will be taken to the Performance Analysis page.
- On the Performance Analysis page, select a monitoring target and click the View Details button. The Monitoring Target Details popup window opens.
- Monitoring Target Details Click the Agent tab in the popup window. It navigates to the Agent tab.
- Click the Log button.
- Click the Copy icon on the right side of the installation command to copy the command.
- Paste the copied command into the monitoring target resource.
- Execute the command copied to the monitoring target resource.
| Item | Explanation |
|---|---|
| Installation | Download the script file required for agent installation and execute it. |
| Start | Execute the agent start command. |
| Stop | Execute the agent stop command. |
| Delete | Execute the agent deletion command. |
| Update | Download the script file required for the agent update and execute it. |
To check the agent service status, use the method below.
- linux: $ sudo systemctl status filebeat
- windows: Task Manager → service → filebeat → Status(Running)
To add a log for monitoring, select the log addition action, enter the log name and log path correctly, and then click the Generate Command button. Paste the generated command into the monitored resource and then execute it.
Managing Event Agents
To install and manage the agent, follow the steps below.
- Click Cloud Monitoring Console > Performance Analysis. You will be taken to the Performance Analysis page.
- On the Performance Analysis page, select a monitoring target and click the View Details button. The Monitoring Target Details popup window opens.
- Monitoring Target Details In the popup window, click the Agent tab. It navigates to the Agent tab.
- Click the Event button.
- Click the Copy icon on the right of the installation command to copy the command.
- Paste the copied command into the monitoring target resource.
- Execute the command copied to the monitoring target resource.
| Item | Explanation |
|---|---|
| Installation | Download the script file required for agent installation and execute it. |
| Start | Execute the agent start command. |
| Stop | Execute the agent stop command. |
| Delete | Execute the agent deletion command. |
| Update | Download and run the script file required for the agent update. |
To check the agent service status, use the method below.
- windows: Task Manager → service → winlogbeat → Status(Running)
10.3.2.7 - Appendix A. Service-specific Monitoring Targets
Compute type
Virtual Server
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | OS | Agent Agentless | 1m |
| log | OS | Agent | When a log occurs |
| Status | OS | Agentless | 1m |
GPU Server
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | OS | Agent Agentless | 1m |
| log | OS | Agent | When a log occurs |
| status | OS | Agentless | 1m |
Bare Metal Server
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | OS | Agent | 1m |
| log | OS | Agent | When a log occurs |
| status | OS | N/A | - |
Multi-node GPU Cluster [Cluster Fabric]
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | OS | Agent | 1m |
| log | OS | Agent | When a log occurs |
| status | OS | N/A | - |
Multi-node GPU Cluster [Node]
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | OS | Agent | 1m |
| log | OS | Agent | When a log occurs |
| Status | OS | N/A | - |
Storage type
The monitoring targets, collection methods, and collection intervals are the same for all storage-type services.
- File Storage
- Object Storage
- Block Storage(BM)
- Block Storage(VM)
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Storage | Agentless | 1m |
| log | Storage | N/A | - |
| status | Storage | Agentless | 1m |
Database type
The monitoring targets, collection methods, and collection intervals are the same for all Database-type services.
- PostgreSQL(DBaaS)
- MariaDB(DBaaS)
- MySQL(DBaaS)
- Microsoft SQL Server
- EPAS
- CacheStore(DBaaS)
- Redis
- Valkey
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Database Process, OS | Agent | 1m |
| log | Database Process, OS | Agent | When a log occurs |
| status | Database Process | Agent | 1m |
| OS | Agentless | 1m |
Data Analytics type
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Data Analytics Process, OS | Agent | 1m |
| log | Data Analytics Process, OS | Agent | When a log occurs |
| status | Data Analytics Process | Agent | 1m |
| OS | Agentless | 1m |
Container type
Kubernetes Engine
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Cluster, Namespace, Node, ReplicaSet, Deployment, StatefulSet, DaemonSet, Job, CronJob, Pod | Agentless | 5m |
| log | Cluster, Namespace, Node, ReplicaSet, Deployment, StatefulSet, DaemonSet, Job, CronJob, Pod | Agentless | When a log occurs |
| status | Cluster, Namespace, Node, ReplicaSet, Deployment, StatefulSet, DaemonSet, Job, CronJob, Pod | Agentless | 5m |
Container Registry
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Container Registry | Agentless | 5m |
| log | Container Registry | Agentless | When a log occurs |
| status | Container Registry | Agentless | 5m |
Networking type
VPC
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Internet Gateway | Agentless | 5m |
| log | Internet Gateway | N/A | - |
| status | Internet Gateway | N/A | - |
Load Balancer(OLD)
Load Balancer(OLD)
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Load Balencer | Agentless | 5m |
| log | Load Balencer | N/A | - |
| status | Load Balencer | Agentless | 5m |
Load Balancer Listener(OLD)
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Load Balencer Listener | Agentless | 5m |
| log | Load Balencer Listener | N/A | - |
| status | Load Balencer Listener | Agentless | 5m |
Load Balancer
Load Balancer
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Load Balencer | Agentless | 5m |
| log | Load Balencer | N/A | - |
| status | Load Balencer | Agentless | 5m |
Load Balancer Listener
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Load Balencer Listener | Agentless | 5m |
| log | Load Balencer Listener | N/A | - |
| status | Load Balencer Listener | Agentless | 5m |
Load Balancer Server Group
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Load Balencer Server Group | Agentless | 5m |
| log | Load Balencer Server Group | N/A | - |
| status | Load Balencer Server Group | Agentless | 5m |
Direct Connect
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Direct Connect | Agentless | 5m |
| log | Direct Connect | N/A | - |
| status | Direct Connect | N/A | - |
Cloud WAN
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Cloud WAN | Agentless | 10m |
| log | Cloud WAN | N/A | - |
| status | Cloud WAN | Agentless | 10m |
Global CDN
| Category | Monitoring target | Collection method | Collection interval |
|---|---|---|---|
| Performance | Global CDN | Agentless | 5m |
| log | Global CDN | N/A | - |
| status | Global CDN | Agentless | 5m |
10.3.2.8 - Appendix B. Service-specific Performance Metrics
Compute type
Virtual Server
Agentless (basic metrics)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | description |
|---|---|---|---|---|
| CPU | CPU Usage/Core [Basic] | % | 1m | Percentage of CPU time used, excluding Idle and IOWait states (normalized by the number of cores; 100% when all four cores are fully utilized) |
| CPU | CPU Cores [Basic] | cnt | 1m | Number of virtual processor cores allocated to the virtual machine |
| Memory | Memory Total [Basic] | bytes | 1m | Memory capacity available for use in the domain |
| Memory | Memory Used [Basic] | bytes | 1m | Current memory usage |
| Memory | Memory Swap In [Basic] | bytes | 1m | Swap In memory in bytes |
| Memory | Memory Swap Out [Basic] | bytes | 1m | Swap Out memory in bytes |
| Memory | Memory Free [Bytes] | bytes | 1m | Unused memory capacity in the system |
| Memory | Memory Usage [Basic] | % | 1m | Current memory usage rate |
| Disk | Disk Read Bytes [Basic] | bytes | 1m | Read byte count |
| Disk | Disk Read Requests [Basic] | cnt | 1m | Read request count |
| Disk | Disk Write Bytes [Basic] | bytes | 1m | Write byte count |
| Disk | Disk Write Requests [Basic] | cnt | 1m | Number of write requests |
| State | Instance State [Basic] | enum | 1m | VM status |
| Network | Network In Bytes [Basic] | bytes | 1m | Received bytes |
| Network | Network In Dropped [Basic] | cnt | 1m | Incoming packet drop |
| Network | Network In Errors [Basic] | cnt | 1m | Receive error |
| Network | Network In Packets [Basic] | cnt | 1m | Received packet |
| Network | Network Out Bytes [Basic] | bytes | 1m | Transmit bytes |
| Network | Network Out Dropped [Basic] | cnt | 1m | Transmit packet drop |
| Network | Network Out Errors [Basic] | cnt | 1m | Transmission error |
| Network | Network Out Packets [Basic] | cnt | 1m | Transmit packet |
| Network | Network In Bytes [Delta Basic] | bytes | 1m | Received bytes (delta value) |
| Network | Network In Dropped [Delta Basic] | cnt | 1m | Received packet drop (delta value) |
| Network | Network In Errors [Delta Basic] | cnt | 1m | Receive error (delta value) |
| Network | Network In Packets [Delta Basic] | cnt | 1m | Received packet (delta value) |
| Network | Network Out Bytes [Delta Basic] | bytes | 1m | Transmitted bytes (delta value) |
| Network | Network Out Dropped [Delta Basic] | cnt | 1m | Transmit packet drop (delta value) |
| Network | Network Out Errors [Delta Basic] | cnt | 1m | Transmission error (delta value) |
| Network | Network Out Packets [Delta Basic] | cnt | 1m | Transmitted packet (delta value) |
- For Windows OS, you must install the monitoring performance Agent to provide memory performance metrics.
Agent (Detailed Metrics)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | description |
|---|---|---|---|---|
| CPU | Core Usage [IO Wait] | % | 1m | Ratio of CPU time spent in wait state (disk wait) |
| CPU | Core Usage [System] | % | 1m | Proportion of CPU time spent in kernel space |
| CPU | Core Usage [User] | % | 1m | Proportion of CPU time spent in user space |
| CPU | CPU Cores | cnt | 1m | The number of CPU cores on the host. The maximum value of the unnormalized ratio is 100%* of a core. The unnormalized ratio already incorporates this value, and the maximum value is 100%* of a core. |
| CPU | CPU Usage [Active] | % | 1m | Percentage of CPU time used excluding Idle and IOWait states (when all 4 cores are used at 100%: 400%) |
| CPU | CPU Usage [Idle] | % | 1m | It is the proportion of CPU time spent in idle state. |
| CPU | CPU Usage [IO Wait] | % | 1m | It is the proportion of CPU time spent in a waiting state (disk wait). |
| CPU | CPU Usage [System] | % | 1m | Percentage of CPU time used by the kernel (when all 4 cores are used at 100%: 400%) |
| CPU | CPU Usage [User] | % | 1m | Percentage of CPU time used in user space. (If all four cores are used at 100%, it is 400%) |
| CPU | CPU Usage/Core [Active] | % | 1m | Percentage of CPU time used excluding Idle and IOWait states (value normalized by the number of cores; 100% when all four cores are fully utilized) |
| CPU | CPU Usage/Core [Idle] | % | 1m | It is the proportion of CPU time spent in idle state. |
| CPU | CPU Usage/Core [IO Wait] | % | 1m | It is the proportion of CPU time spent in a waiting state (disk wait). |
| CPU | CPU Usage/Core [System] | % | 1m | Percentage of CPU time used by the kernel (value normalized by the number of cores; 100% when all four cores are fully utilized) |
| CPU | CPU Usage/Core [User] | % | 1m | Percentage of CPU time used in user space. (Value normalized by the number of cores; using all four cores at 100% equals 100%) |
| Disk | Disk CPU Usage [IO Request] | % | 1m | It is the proportion of CPU time during which I/O requests for the device were executed (device bandwidth utilization). If this value approaches 100%, the device becomes saturated. |
| Disk | Disk Queue Size [Avg] | num | 1m | The average queue length of requests executed on the device. |
| Disk | Disk Read Bytes | bytes | 1m | The number of bytes per second read from the device. |
| Disk | Disk Read Bytes [Delta Avg] | bytes | 1m | Average of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta Max] | bytes | 1m | Maximum system.diskio.read.bytes_delta of individual disks |
| Disk | Disk Read Bytes [Delta Min] | bytes | 1m | Minimum of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta Sum] | bytes | 1m | Sum of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta] | bytes | 1m | Delta of the system.diskio.read.bytes value for each disk |
| Disk | Disk Read Bytes [Success] | bytes | 1m | Total number of bytes successfully read. On Linux, assuming a sector size of 512, it is the number of sectors read multiplied by 512. |
| Disk | Disk Read Requests | cnt | 1m | Number of read requests to the disk device per second |
| Disk | Disk Read Requests [Delta Avg] | cnt | 1m | Average of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Delta Max] | cnt | 1m | Maximum of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Delta Min] | cnt | 1m | Minimum of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Delta Sum] | cnt | 1m | Sum of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Success Delta] | cnt | 1m | Delta of system.diskio.read.count for each disk |
| Disk | Disk Read Requests [Success] | cnt | 1m | Total number of reads successfully completed |
| Disk | Disk Request Size [Avg] | num | 1m | Average size of requests executed on the device (unit: sectors). |
| Disk | Disk Service Time [Avg] | ms | 1m | Average service time (ms) of input requests executed on the device. |
| Disk | Disk Wait Time [Avg] | ms | 1m | Average time taken for requests executed on the supported device. |
| Disk | Disk Wait Time [Read] | ms | 1m | Average disk wait time |
| Disk | Disk Wait Time [Write] | ms | 1m | Disk average wait time |
| Disk | Disk Write Bytes [Delta Avg] | bytes | 1m | Average of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta Max] | bytes | 1m | Maximum system.diskio.write.bytes_delta of individual disks |
| Disk | Disk Write Bytes [Delta Min] | bytes | 1m | Minimum of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta Sum] | bytes | 1m | Sum of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta] | bytes | 1m | Delta of the system.diskio.write.bytes value for each individual disk |
| Disk | Disk Write Bytes [Success] | bytes | 1m | Total number of bytes successfully written. On Linux, assuming a sector size of 512, it is the number of sectors written multiplied by 512. |
| Disk | Disk Write Requests | cnt | 1m | Number of write requests to the disk device per second |
| Disk | Disk Write Requests [Delta Avg] | cnt | 1m | Average of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Max] | cnt | 1m | Maximum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Min] | cnt | 1m | Minimum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Sum] | cnt | 1m | Sum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Success Delta] | cnt | 1m | Delta of system.diskio.write.count for each disk |
| Disk | Disk Write Requests [Success] | cnt | 1m | Total number of successful writes |
| Disk | Disk Writes Bytes | bytes | 1m | The number of bytes per second written to the device. |
| FileSystem | Filesystem Hang Check | state | 1m | filesystem (local/NFS) hang check (normal:1, abnormal:0) |
| FileSystem | Filesystem Nodes | cnt | 1m | Total number of file nodes in the file system. |
| FileSystem | Filesystem Nodes [Free] | cnt | 1m | It is the total number of available file nodes in the file system. |
| FileSystem | Filesystem Size [Available] | bytes | 1m | Disk space (bytes) that an unauthorized user can use. |
| FileSystem | Filesystem Size [Free] | bytes | 1m | Available disk space (bytes) |
| FileSystem | Filesystem Size [Total] | bytes | 1m | Total disk space (bytes) |
| FileSystem | Filesystem Usage | % | 1m | Used disk space percentage |
| FileSystem | Filesystem Usage [Avg] | % | 1m | Average of individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Inode] | % | 1m | inode usage |
| FileSystem | Filesystem Usage [Max] | % | 1m | max among individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Min] | % | 1m | minimum among individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Total] | % | 1m | - |
| FileSystem | Filesystem Used | bytes | 1m | Used disk space (bytes) |
| FileSystem | Filesystem Used [Inode] | bytes | 1m | inode usage |
| Memory | Memory Free | bytes | 1m | Total amount of available memory (bytes). Memory used by system cache and buffers is not included (see system.memory.actual.free). |
| Memory | Memory Free [Actual] | bytes | 1m | Actual usable memory (bytes). The calculation method varies by OS; on Linux, it uses MemAvailable from /proc/ meminfo, or if meminfo cannot be used, it calculates from available memory plus cache and buffers. On OSX, it is the sum of usable memory and inactive memory. On Windows, it is a value such as system.memory.free. |
| Memory | Memory Free [Swap] | bytes | 1m | Available swap memory. |
| Memory | Memory Total | bytes | 1m | total memory |
| Memory | Memory Total [Swap] | bytes | 1m | Total swap memory. |
| Memory | Memory Usage | % | 1m | Percentage of used memory |
| Memory | Memory Usage [Actual] | % | 1m | Percentage of memory actually used |
| Memory | Memory Usage [Cache Swap] | % | 1m | cached swap usage |
| Memory | Memory Usage [Swap] | % | 1m | Percentage of used swap memory |
| Memory | Memory Used | bytes | 1m | used memory |
| Memory | Memory Used [Actual] | bytes | 1m | Actual memory used (bytes). The value obtained by subtracting used memory from total memory. Available memory is calculated differently for each OS (see system.actual.free). |
| Memory | Memory Used [Swap] | bytes | 1m | Used swap memory. |
| Network | Collisions | cnt | 1m | Network collision |
| Network | Network In Bytes | bytes | 1m | Number of received bytes |
| Network | Network In Bytes [Delta Avg] | bytes | 1m | Average of system.network.in.bytes_delta for individual networks |
| Network | Network In Bytes [Delta Max] | bytes | 1m | Maximum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta Min] | bytes | 1m | Minimum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta Sum] | bytes | 1m | Sum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta] | bytes | 1m | Delta of received byte count |
| Network | Network In Dropped | cnt | 1m | Number of deleted packets among incoming packets |
| Network | Network In Errors | cnt | 1m | Number of errors during reception |
| Network | Network In Packets | cnt | 1m | Number of received packets |
| Network | Network In Packets [Delta Avg] | cnt | 1m | Average of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Max] | cnt | 1m | Maximum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Min] | cnt | 1m | Minimum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Sum] | cnt | 1m | Sum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta] | cnt | 1m | Delta of received packet count |
| Network | Network Out Bytes | bytes | 1m | Number of transmitted bytes |
| Network | Network Out Bytes [Delta Avg] | bytes | 1m | Average of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Max] | bytes | 1m | Maximum of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Min] | bytes | 1m | Minimum system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Sum] | bytes | 1m | Sum of system.network.out.bytes_delta of individual networks |
| Network | Network Out Bytes [Delta] | bytes | 1m | Delta of transmitted byte count |
| Network | Network Out Dropped | cnt | 1m | Number of packets deleted among outgoing packets. This value is not reported by the operating system, so it is always 0 on Darwin and BSD. |
| Network | Network Out Errors | cnt | 1m | Number of errors during transmission |
| Network | Network Out Packets | cnt | 1m | Number of transmitted packets |
| Network | Network Out Packets [Delta Avg] | cnt | 1m | Average of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Max] | cnt | 1m | Maximum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Min] | cnt | 1m | Minimum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Sum] | cnt | 1m | Sum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta] | cnt | 1m | Delta of transmitted packet count |
| Network | Open Connections [TCP] | cnt | 1m | All open TCP connections |
| Network | Open Connections [UDP] | cnt | 1m | All open UDP connections |
| Network | Port Usage | % | 1m | Usage rate of connectable ports |
| Network | SYN Sent Sockets | cnt | 1m | Number of sockets in SYN_SENT state (when connecting from local to remote) |
| Process | Kernel PID Max | cnt | 1m | kernel.pid_max value |
| Process | Kernel Thread Max | cnt | 1m | kernel.threads-max value |
| Process | Process CPU Usage | % | 1m | The percentage of CPU time consumed by the process since the last update. This value is similar to the %CPU value shown for the process by the top command on Unix systems. |
| Process | Process CPU Usage/Core | % | 1m | The percentage of CPU time used by the process since the last event. Normalized by the number of cores, with a value between 0 and 100%. |
| Process | Process Memory Usage | % | 1m | Proportion of main memory (RAM) occupied by the process |
| Process | Process Memory Used | bytes | 1m | Resident Set size. The amount of memory a process occupies in RAM. In Windows, it is the current working set size. |
| Process | Process PID | PID | 1m | process pid |
| Process | Process PPID | PID | 1m | PID of the parent process |
| Process | Processes [Dead] | cnt | 1m | Number of dead processes |
| Process | Processes [Idle] | cnt | 1m | Number of idle processes |
| Process | Processes [Running] | cnt | 1m | running processes count |
| Process | Processes [Sleeping] | cnt | 1m | sleeping processes count |
| Process | Processes [Stopped] | cnt | 1m | stopped processes count |
| Process | Processes [Total] | cnt | 1m | Total number of processes |
| Process | Processes [Unknown] | cnt | 1m | Number of processes with an unknown or unsearchable status |
| Process | Processes [Zombie] | cnt | 1m | Number of zombie processes |
| Process | Running Process Usage | % | 1m | process usage |
| Process | Running Processes | cnt | 1m | running processes count |
| Process | Running Thread Usage | % | 1m | Thread usage rate |
| Process | Running Threads | cnt | 1m | Total number of threads running in running processes |
| System | Context Switches | cnt | 1m | context switch count (per second) |
| System | Load/Core [1 min] | cnt | 1m | The load over the last 1 minute divided by the number of cores |
| System | Load/Core [15 min] | cnt | 1m | The load over the last 15 minutes divided by the number of cores |
| System | Load/Core [5 min] | cnt | 1m | The load over the last 5 minutes divided by the number of cores |
| System | Multipaths [Active] | cnt | 1m | External storage connection path state = active count |
| System | Multipaths [Failed] | cnt | 1m | External storage connection path state = failed count |
| System | Multipaths [Faulty] | cnt | 1m | External storage connection path state = faulty count |
| System | NTP Offset | num | 1m | the measured offset of the last sample (time difference between the NTP server and the local environment) |
| System | Run Queue Length | num | 1m | Execution queue length |
| System | Uptime | ms | 1m | OS uptime (milliseconds). |
| Windows | Context Switchies | cnt | 1m | CPU context switch count (per second) |
| Windows | Disk Read Bytes [Sec] | cnt | 1m | Bytes read per second on a Windows logical disk |
| Windows | Disk Read Time [Avg] | sec | 1m | Average data read time (seconds) |
| Windows | Disk Transfer Time [Avg] | sec | 1m | Disk average wait time |
| Windows | Disk Usage | % | 1m | Disk usage |
| Windows | Disk Write Bytes [Sec] | cnt | 1m | Number of bytes written in one second on a Windows logical disk |
| Windows | Disk Write Time [Avg] | sec | 1m | Average data write time (seconds) |
| Windows | Pagingfile Usage | % | 1m | Paging file usage |
| Windows | Pool Used [Non Paged] | bytes | 1m | Nonpaged Pool usage in kernel memory |
| Windows | Pool Used [Paged] | bytes | 1m | Paged Pool usage in kernel memory |
| Windows | Process [Running] | cnt | 1m | Number of processes currently running |
| Windows | Threads [Running] | cnt | 1m | Number of threads currently running |
| Windows | Threads [Waiting] | cnt | 1m | Number of threads waiting for processor time |
GPU Server
Agentless (basic metrics)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | description |
|---|---|---|---|---|
| CPU | CPU Usage/Core [Basic] | % | 1m | Percentage of CPU time used, excluding Idle and IOWait states (normalized by the number of cores; 100% when all four cores are fully utilized) |
| CPU | CPU Cores [Basic] | cnt | 1m | Number of virtual processor cores allocated to the virtual machine |
| Memory | Memory Total [Basic] | bytes | 1m | Memory capacity available in the domain |
| Memory | Memory Used [Basic] | bytes | 1m | The amount of memory currently in use |
| Memory | Memory Swap In [Basic] | bytes | 1m | Swap In memory in bytes |
| Memory | Memory Swap Out [Basic] | bytes | 1m | Swap Out memory in bytes |
| Memory | Memory Free [Bytes] | bytes | 1m | Unused memory capacity in the system |
| Memory | Memory Usage [Basic] | % | 1m | Current memory usage rate |
| Disk | Disk Read Bytes [Basic] | bytes | 1m | Read byte count |
| Disk | Disk Read Requests [Basic] | cnt | 1m | Read request count |
| Disk | Disk Write Bytes [Basic] | bytes | 1m | Write byte count |
| Disk | Disk Write Requests [Basic] | cnt | 1m | Number of write requests |
| State | Instance State [Basic] | enum | 1m | VM status |
| Network | Network In Bytes [Basic] | bytes | 1m | Received bytes |
| Network | Network In Dropped [Basic] | cnt | 1m | Incoming packet drop |
| Network | Network In Errors [Basic] | cnt | 1m | Receive error |
| Network | Network In Packets [Basic] | cnt | 1m | Received packet |
| Network | Network Out Bytes [Basic] | bytes | 1m | Transmit bytes |
| Network | Network Out Dropped [Basic] | cnt | 1m | Transmit packet drop |
| Network | Network Out Errors [Basic] | cnt | 1m | Transmission error |
| Network | Network Out Packets [Basic] | cnt | 1m | transmitted packet |
| Network | Network In Bytes [Delta Basic] | bytes | 1m | Received bytes (delta value) |
| Network | Network In Dropped [Delta Basic] | cnt | 1m | Received packet drop (delta value) |
| Network | Network In Errors [Delta Basic] | cnt | 1m | Receive error (delta value) |
| Network | Network In Packets [Delta Basic] | cnt | 1m | Received packet (delta value) |
| Network | Network Out Bytes [Delta Basic] | bytes | 1m | Transmitted bytes (delta value) |
| Network | Network Out Dropped [Delta Basic] | cnt | 1m | Transmit packet drop (delta value) |
| Network | Network Out Errors [Delta Basic] | cnt | 1m | Transmission error (delta value) |
| Network | Network Out Packets [Delta Basic] | cnt | 1m | Transmitted packet (delta value) |
Agent (Detailed Metrics)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | description |
|---|---|---|---|---|
| GPU | GPU Count | cnt | 1m | GPU count |
| GPU | GPU Memory Usage | % | 1m | Memory usage |
| GPU | GPU Memory Used | bytes | 1m | Memory usage |
| GPU | GPU Temperature | ℃ | 1m | GPU temperature |
| GPU | GPU Usage | % | 1m | Total GPU utilization sum (800% when all 8 GPUs are used at 100%) |
| GPU | GPU Usage [Avg] | % | 1m | Overall average GPU utilization (%) |
| GPU | GPU Power Cap | W | 1m | Maximum power capacity of the GPU |
| GPU | GPU Power Usage | W | 1m | Current GPU power usage |
| GPU | GPU Memory Usage [Avg] | % | 1m | GPU Memory Uti. AVG |
| GPU | GPU Count in use | cnt | 1m | Number of GPUs currently utilized by jobs on the node |
| GPU | Execution State for nvidia-smi | state | 1m | Result of running the nvidia-smi command |
| CPU | Core Usage [IO Wait] | % | 1m | Ratio of CPU time spent in wait state (disk wait) |
| CPU | Core Usage [System] | % | 1m | Proportion of CPU time spent in kernel space |
| CPU | Core Usage [User] | % | 1m | Proportion of CPU time spent in user space |
| CPU | CPU Cores | cnt | 1m | The number of CPU cores on the host. The maximum value of the unnormalized ratio is 100%* of a core. The unnormalized ratio already incorporates this value, and the maximum value is 100%* of a core. |
| CPU | CPU Usage [Active] | % | 1m | Percentage of CPU time used excluding Idle and IOWait states (when all four cores are used at 100%: 400%) |
| CPU | CPU Usage [Idle] | % | 1m | It is the proportion of CPU time spent in idle state. |
| CPU | CPU Usage [IO Wait] | % | 1m | It is the proportion of CPU time spent in a waiting state (disk wait). |
| CPU | CPU Usage [System] | % | 1m | CPU time usage percentage in the kernel (when all 4 cores are used at 100%: 400%) |
| CPU | CPU Usage [User] | % | 1m | Percentage of CPU time used in user space. (If all 4 cores are used at 100%, it is 400%) |
| CPU | CPU Usage/Core [Active] | % | 1m | Percentage of CPU time used excluding Idle and IOWait states (value normalized by the number of cores; 100% when all four cores are fully utilized) |
| CPU | CPU Usage/Core [Idle] | % | 1m | It is the proportion of CPU time spent in idle state. |
| CPU | CPU Usage/Core [IO Wait] | % | 1m | It is the proportion of CPU time spent in a waiting state (disk wait). |
| CPU | CPU Usage/Core [System] | % | 1m | Percentage of CPU time used by the kernel (value normalized by the number of cores; 100% when all four cores are utilized at 100%) |
| CPU | CPU Usage/Core [User] | % | 1m | Percentage of CPU time used in user space. (Value normalized by the number of cores; using all four cores at 100% equals 100%) |
| Disk | Disk CPU Usage [IO Request] | % | 1m | The proportion of CPU time during which I/O requests to the device were executed (device bandwidth utilization). If this value approaches 100%, the device becomes saturated. |
| Disk | Disk Queue Size [Avg] | num | 1m | The average queue length of requests executed for the device. |
| Disk | Disk Read Bytes | bytes | 1m | The number of bytes read per second from the device. |
| Disk | Disk Read Bytes [Delta Avg] | bytes | 1m | Average of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta Max] | bytes | 1m | Maximum system.diskio.read.bytes_delta of individual disks |
| Disk | Disk Read Bytes [Delta Min] | bytes | 1m | Minimum of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta Sum] | bytes | 1m | Sum of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta] | bytes | 1m | Delta of the system.diskio.read.bytes value for each disk |
| Disk | Disk Read Bytes [Success] | bytes | 1m | Total number of bytes successfully read. On Linux, assuming a sector size of 512, it is the number of sectors read multiplied by 512. |
| Disk | Disk Read Requests | cnt | 1m | Number of read requests to the disk device per second |
| Disk | Disk Read Requests [Delta Avg] | cnt | 1m | Average of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Delta Max] | cnt | 1m | Maximum system.diskio.read.count_delta of individual disks |
| Disk | Disk Read Requests [Delta Min] | cnt | 1m | Minimum of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Delta Sum] | cnt | 1m | Sum of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Success Delta] | cnt | 1m | Delta of system.diskio.read.count for each disk |
| Disk | Disk Read Requests [Success] | cnt | 1m | Total number of successful reads |
| Disk | Disk Request Size [Avg] | num | 1m | Average size of requests executed on the device (unit: sectors). |
| Disk | Disk Service Time [Avg] | ms | 1m | Average service time (ms) of input requests executed on the device. |
| Disk | Disk Wait Time [Avg] | ms | 1m | Average time taken for requests executed on the supported device. |
| Disk | Disk Wait Time [Read] | ms | 1m | Average disk wait time |
| Disk | Disk Wait Time [Write] | ms | 1m | Average disk wait time |
| Disk | Disk Write Bytes [Delta Avg] | bytes | 1m | Average of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta Max] | bytes | 1m | Maximum system.diskio.write.bytes_delta of individual disks |
| Disk | Disk Write Bytes [Delta Min] | bytes | 1m | Minimum of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta Sum] | bytes | 1m | Sum of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta] | bytes | 1m | Delta of the system.diskio.write.bytes value for each disk |
| Disk | Disk Write Bytes [Success] | bytes | 1m | Total number of bytes successfully written. On Linux, assuming a sector size of 512, it is the number of sectors written multiplied by 512. |
| Disk | Disk Write Requests | cnt | 1m | Number of write requests to the disk device per second |
| Disk | Disk Write Requests [Delta Avg] | cnt | 1m | Average of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Max] | cnt | 1m | Maximum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Min] | cnt | 1m | Minimum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Sum] | cnt | 1m | Sum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Success Delta] | cnt | 1m | Delta of system.diskio.write.count for each disk |
| Disk | Disk Write Requests [Success] | cnt | 1m | Total number of successful writes |
| Disk | Disk Writes Bytes | bytes | 1m | The number of bytes per second written to the device. |
| FileSystem | Filesystem Hang Check | state | 1m | filesystem(local/NFS) hang check (normal:1, abnormal:0) |
| FileSystem | Filesystem Nodes | cnt | 1m | Total number of file nodes in the file system. |
| FileSystem | Filesystem Nodes [Free] | cnt | 1m | Total number of available file nodes in the file system. |
| FileSystem | Filesystem Size [Available] | bytes | 1m | Disk space (bytes) that an unauthorized user can use. |
| FileSystem | Filesystem Size [Free] | bytes | 1m | Available disk space (bytes) |
| FileSystem | Filesystem Size [Total] | bytes | 1m | Total disk space (bytes) |
| FileSystem | Filesystem Usage | % | 1m | Used disk space percentage |
| FileSystem | Filesystem Usage [Avg] | % | 1m | Average of individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Inode] | % | 1m | inode usage |
| FileSystem | Filesystem Usage [Max] | % | 1m | max among individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Min] | % | 1m | minimum among individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Total] | % | 1m | - |
| FileSystem | Filesystem Used | bytes | 1m | Used disk space (bytes) |
| FileSystem | Filesystem Used [Inode] | bytes | 1m | inode usage |
| Memory | Memory Free | bytes | 1m | Total amount of available memory (bytes). Does not include memory used by system cache and buffers (see system.memory.actual.free). |
| Memory | Memory Free [Actual] | bytes | 1m | Actual usable memory (bytes). The calculation method varies by OS; on Linux, it is MemAvailable from /proc/meminfo, or if meminfo is unavailable, it is calculated from available memory plus cache and buffers. On macOS, it is the sum of usable memory and inactive memory. On Windows, it is a value such as system.memory.free. |
| Memory | Memory Free [Swap] | bytes | 1m | Available swap memory. |
| Memory | Memory Total | bytes | 1m | total memory |
| Memory | Memory Total [Swap] | bytes | 1m | Total swap memory. |
| Memory | Memory Usage | % | 1m | Percentage of used memory |
| Memory | Memory Usage [Actual] | % | 1m | Percentage of memory actually used |
| Memory | Memory Usage [Cache Swap] | % | 1m | Cached swap usage |
| Memory | Memory Usage [Swap] | % | 1m | Percentage of used swap memory |
| Memory | Memory Used | bytes | 1m | used memory |
| Memory | Memory Used [Actual] | bytes | 1m | Actual memory used (bytes). The value obtained by subtracting used memory from total memory. Available memory is calculated differently for each OS (see system.actual.free). |
| Memory | Memory Used [Swap] | bytes | 1m | Used swap memory. |
| Network | Collisions | cnt | 1m | Network collision |
| Network | Network In Bytes | bytes | 1m | Number of received bytes |
| Network | Network In Bytes [Delta Avg] | bytes | 1m | Average of system.network.in.bytes_delta for individual networks |
| Network | Network In Bytes [Delta Max] | bytes | 1m | Maximum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta Min] | bytes | 1m | Minimum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta Sum] | bytes | 1m | Sum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta] | bytes | 1m | Delta of received byte count |
| Network | Network In Dropped | cnt | 1m | Number of deleted packets among incoming packets |
| Network | Network In Errors | cnt | 1m | Number of errors during reception |
| Network | Network In Packets | cnt | 1m | Number of received packets |
| Network | Network In Packets [Delta Avg] | cnt | 1m | Average of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Max] | cnt | 1m | Maximum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Min] | cnt | 1m | Minimum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Sum] | cnt | 1m | Sum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta] | cnt | 1m | Delta of received packet count |
| Network | Network Out Bytes | bytes | 1m | Number of transmitted bytes |
| Network | Network Out Bytes [Delta Avg] | bytes | 1m | Average of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Max] | bytes | 1m | Maximum of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Min] | bytes | 1m | Minimum of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Sum] | bytes | 1m | Sum of system.network.out.bytes_delta for individual networks |
| Network | Network Out Bytes [Delta] | bytes | 1m | Delta of transmitted byte count |
| Network | Network Out Dropped | cnt | 1m | Number of packets deleted among outgoing packets. This value is not reported by the operating system, so it is always 0 on Darwin and BSD. |
| Network | Network Out Errors | cnt | 1m | Number of errors during transmission |
| Network | Network Out Packets | cnt | 1m | Number of transmitted packets |
| Network | Network Out Packets [Delta Avg] | cnt | 1m | Average of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Max] | cnt | 1m | Maximum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Min] | cnt | 1m | Minimum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Sum] | cnt | 1m | Sum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta] | cnt | 1m | Delta of transmitted packet count |
| Network | Open Connections [TCP] | cnt | 1m | All open TCP connections |
| Network | Open Connections [UDP] | cnt | 1m | All open UDP connections |
| Network | Port Usage | % | 1m | Connectable port utilization |
| Network | SYN Sent Sockets | cnt | 1m | Number of sockets in SYN_SENT state (when connecting from local to remote) |
| Process | Kernel PID Max | cnt | 1m | kernel.pid_max value |
| Process | Kernel Thread Max | cnt | 1m | kernel.threads-max value |
| Process | Process CPU Usage | % | 1m | The percentage of CPU time consumed by the process since the last update. This value is similar to the %CPU value shown for the process by the top command on Unix systems. |
| Process | Process CPU Usage/Core | % | 1m | The percentage of CPU time used by the process since the last event. Normalized by the number of cores, with a value between 0 and 100%. |
| Process | Process Memory Usage | % | 1m | The proportion of main memory (RAM) occupied by the process |
| Process | Process Memory Used | bytes | 1m | Resident Set size. The amount of memory a process occupies in RAM. In Windows, it is the current working set size. |
| Process | Process PID | PID | 1m | process pid |
| Process | Process PPID | PID | 1m | Parent process PID |
| Process | Processes [Dead] | cnt | 1m | Number of dead processes |
| Process | Processes [Idle] | cnt | 1m | Number of idle processes |
| Process | Processes [Running] | cnt | 1m | running processes count |
| Process | Processes [Sleeping] | cnt | 1m | sleeping processes count |
| Process | Processes [Stopped] | cnt | 1m | stopped processes count |
| Process | Processes [Total] | cnt | 1m | Total number of processes |
| Process | Processes [Unknown] | cnt | 1m | Number of processes with an unknown or unsearchable status |
| Process | Processes [Zombie] | cnt | 1m | Number of zombie processes |
| Process | Running Process Usage | % | 1m | process usage rate |
| Process | Running Processes | cnt | 1m | running processes count |
| Process | Running Thread Usage | % | 1m | Thread usage rate |
| Process | Running Threads | cnt | 1m | Total number of threads running in running processes |
| System | Context Switches | cnt | 1m | context switch count (per second) |
| System | Load/Core [1 min] | cnt | 1m | The load over the last 1 minute divided by the number of cores |
| System | Load/Core [15 min] | cnt | 1m | The load over the last 15 minutes divided by the number of cores |
| System | Load/Core [5 min] | cnt | 1m | The load over the last 5 minutes divided by the number of cores |
| System | Multipaths [Active] | cnt | 1m | External storage connection path state = active count |
| System | Multipaths [Failed] | cnt | 1m | External storage connection path state = failed count |
| System | Multipaths [Faulty] | cnt | 1m | External storage connection path state = faulty count |
| System | NTP Offset | num | 1m | the measured offset of the last sample (time difference between the NTP server and the local environment) |
| System | Run Queue Length | num | 1m | Execution queue length |
| System | Uptime | ms | 1m | OS uptime (uptime). (milliseconds) |
| Windows | Context Switchies | cnt | 1m | CPU context switch count (per second) |
| Windows | Disk Read Bytes [Sec] | cnt | 1m | Number of bytes read in one second from a Windows logical disk |
| Windows | Disk Read Time [Avg] | sec | 1m | Average data read time (seconds) |
| Windows | Disk Transfer Time [Avg] | sec | 1m | Disk average wait time |
| Windows | Disk Usage | % | 1m | Disk usage |
| Windows | Disk Write Bytes [Sec] | cnt | 1m | Bytes written per second on a Windows logical disk |
| Windows | Disk Write Time [Avg] | sec | 1m | Average data write time (seconds) |
| Windows | Pagingfile Usage | % | 1m | Paging file usage |
| Windows | Pool Used [Non Paged] | bytes | 1m | Nonpaged Pool usage in kernel memory |
| Windows | Pool Used [Paged] | bytes | 1m | Paged Pool usage in kernel memory |
| Windows | Process [Running] | cnt | 1m | Number of processes currently running |
| Windows | Threads [Running] | cnt | 1m | Number of threads currently running |
| Windows | Threads [Waiting] | cnt | 1m | Number of threads waiting for processor time |
Bare Metal Server
Agent (detailed metrics)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| CPU | Core Usage [IO Wait] | % | 1m | Proportion of CPU time spent waiting (disk wait) |
| CPU | Core Usage [System] | % | 1m | Proportion of CPU time spent in kernel space |
| CPU | Core Usage [User] | % | 1m | Proportion of CPU time spent in user space |
| CPU | CPU Cores | cnt | 1m | The number of CPU cores on the host. The maximum value of the unnormalized ratio is 100%* of a core. The unnormalized ratio already incorporates this value, and its maximum is 100%* of a core. |
| CPU | CPU Usage [Active] | % | 1m | Percentage of CPU time used excluding Idle and IOWait states (when all 4 cores are used at 100%: 400%) |
| CPU | CPU Usage [Idle] | % | 1m | It is the proportion of CPU time spent in idle state. |
| CPU | CPU Usage [IO Wait] | % | 1m | It is the proportion of CPU time spent in a waiting state (disk wait). |
| CPU | CPU Usage [System] | % | 1m | Percentage of CPU time used by the kernel (when all 4 cores are used at 100%: 400%) |
| CPU | CPU Usage [User] | % | 1m | Percentage of CPU time used in user space. (If all 4 cores are used at 100%, it is 400%) |
| CPU | CPU Usage/Core [Active] | % | 1m | Percentage of CPU time used excluding Idle and IOWait states (value normalized by the number of cores; 100% when all four cores are fully utilized) |
| CPU | CPU Usage/Core [Idle] | % | 1m | It is the proportion of CPU time spent in idle state. |
| CPU | CPU Usage/Core [IO Wait] | % | 1m | It is the proportion of CPU time spent in a waiting state (disk wait). |
| CPU | CPU Usage/Core [System] | % | 1m | Percentage of CPU time used by the kernel (value normalized by the number of cores; 100% when all 4 cores are fully utilized) |
| CPU | CPU Usage/Core [User] | % | 1m | Percentage of CPU time used in user space. (Value normalized by the number of cores; using all four cores at 100% each equals 100%) |
| Disk | Disk CPU Usage [IO Request] | % | 1m | The proportion of CPU time during which I/O requests to the device were executed (device bandwidth utilization). If this value approaches 100%, the device becomes saturated. |
| Disk | Disk Queue Size [Avg] | num | 1m | The average queue length of requests executed for the device. |
| Disk | Disk Read Bytes | bytes | 1m | The number of bytes read per second from the device. |
| Disk | Disk Read Bytes [Delta Avg] | bytes | 1m | Average of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta Max] | bytes | 1m | Maximum system.diskio.read.bytes_delta of individual disks |
| Disk | Disk Read Bytes [Delta Min] | bytes | 1m | Minimum of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta Sum] | bytes | 1m | Sum of system.diskio.read.bytes_delta for individual disks |
| Disk | Disk Read Bytes [Delta] | bytes | 1m | Delta of the system.diskio.read.bytes value for each disk |
| Disk | Disk Read Bytes [Success] | bytes | 1m | Total number of bytes successfully read. On Linux, the sector size is assumed to be 512, and the value is the number of sectors read multiplied by 512. |
| Disk | Disk Read Requests | cnt | 1m | Number of read requests to the disk device per second |
| Disk | Disk Read Requests [Delta Avg] | cnt | 1m | Average of the system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Delta Max] | cnt | 1m | Maximum system.diskio.read.count_delta of individual disks |
| Disk | Disk Read Requests [Delta Min] | cnt | 1m | Minimum of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Delta Sum] | cnt | 1m | Sum of system.diskio.read.count_delta for individual disks |
| Disk | Disk Read Requests [Success Delta] | cnt | 1m | Delta of system.diskio.read.count for each disk |
| Disk | Disk Read Requests [Success] | cnt | 1m | Total number of successful reads |
| Disk | Disk Request Size [Avg] | num | 1m | It is the average size of requests executed on the device (unit: sectors). |
| Disk | Disk Service Time [Avg] | ms | 1m | Average service time (ms) of input requests executed on the device. |
| Disk | Disk Wait Time [Avg] | ms | 1m | Average time taken for requests executed on the supported device. |
| Disk | Disk Wait Time [Read] | ms | 1m | Average disk wait time |
| Disk | Disk Wait Time [Write] | ms | 1m | Average disk wait time |
| Disk | Disk Write Bytes [Delta Avg] | bytes | 1m | Average of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta Max] | bytes | 1m | Maximum system.diskio.write.bytes_delta of individual disks |
| Disk | Disk Write Bytes [Delta Min] | bytes | 1m | Minimum of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta Sum] | bytes | 1m | Sum of system.diskio.write.bytes_delta for individual disks |
| Disk | Disk Write Bytes [Delta] | bytes | 1m | Delta of the system.diskio.write.bytes value for each disk |
| Disk | Disk Write Bytes [Success] | bytes | 1m | Total number of bytes successfully written. On Linux, the sector size is assumed to be 512, and the value is the number of sectors written multiplied by 512. |
| Disk | Disk Write Requests | cnt | 1m | Number of write requests to the disk device per second |
| Disk | Disk Write Requests [Delta Avg] | cnt | 1m | Average of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Max] | cnt | 1m | Maximum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Min] | cnt | 1m | Minimum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Delta Sum] | cnt | 1m | Sum of system.diskio.write.count_delta for individual disks |
| Disk | Disk Write Requests [Success Delta] | cnt | 1m | Delta of system.diskio.write.count for each disk |
| Disk | Disk Write Requests [Success] | cnt | 1m | Total number of successful writes |
| Disk | Disk Writes Bytes | bytes | 1m | The number of bytes per second written to the device. |
| FileSystem | Filesystem Hang Check | state | 1m | filesystem(local/NFS) hang check (normal:1, abnormal:0) |
| FileSystem | Filesystem Nodes | cnt | 1m | Total number of file nodes in the file system. |
| FileSystem | Filesystem Nodes [Free] | cnt | 1m | Total number of available file nodes in the file system. |
| FileSystem | Filesystem Size [Available] | bytes | 1m | Disk space (bytes) that an unauthorized user can use. |
| FileSystem | Filesystem Size [Free] | bytes | 1m | Available disk space (bytes) |
| FileSystem | Filesystem Size [Total] | bytes | 1m | Total disk space (bytes) |
| FileSystem | Filesystem Usage | % | 1m | Used disk space percentage |
| FileSystem | Filesystem Usage [Avg] | % | 1m | Average of individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Inode] | % | 1m | inode usage |
| FileSystem | Filesystem Usage [Max] | % | 1m | max among individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Min] | % | 1m | minimum among individual filesystem.used.pct |
| FileSystem | Filesystem Usage [Total] | % | 1m | - |
| FileSystem | Filesystem Used | bytes | 1m | Used disk space (bytes) |
| FileSystem | Filesystem Used [Inode] | bytes | 1m | inode usage |
| Memory | Memory Free | bytes | 1m | Total amount of available memory (bytes). Does not include memory used by system cache and buffers (see system.memory.actual.free). |
| Memory | Memory Free [Actual] | bytes | 1m | Actual usable memory (bytes). The calculation method varies by OS; on Linux, it is MemAvailable from /proc/ meminfo, or if meminfo cannot be used, it is calculated from available memory plus cache and buffers. On macOS, it is the sum of usable memory and inactive memory. On Windows, it is a value such as system.memory.free. |
| Memory | Memory Free [Swap] | bytes | 1m | Available swap memory. |
| Memory | Memory Total | bytes | 1m | total memory |
| Memory | Memory Total [Swap] | bytes | 1m | Total swap memory. |
| Memory | Memory Usage | % | 1m | Percentage of used memory |
| Memory | Memory Usage [Actual] | % | 1m | Percentage of memory actually used |
| Memory | Memory Usage [Cache Swap] | % | 1m | Cached swap usage |
| Memory | Memory Usage [Swap] | % | 1m | Percentage of used swap memory |
| Memory | Memory Used | bytes | 1m | used memory |
| Memory | Memory Used [Actual] | bytes | 1m | Actual memory used (bytes). The value obtained by subtracting used memory from total memory. Available memory is calculated differently for each OS (see system.actual.free). |
| Memory | Memory Used [Swap] | bytes | 1m | Used swap memory. |
| Network | Collisions | cnt | 1m | Network collision |
| Network | Network In Bytes | bytes | 1m | Number of received bytes |
| Network | Network In Bytes [Delta Avg] | bytes | 1m | Average of system.network.in.bytes_delta for individual networks |
| Network | Network In Bytes [Delta Max] | bytes | 1m | Maximum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta Min] | bytes | 1m | Minimum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta Sum] | bytes | 1m | Sum of system.network.in.bytes_delta for each network |
| Network | Network In Bytes [Delta] | bytes | 1m | Delta of received byte count |
| Network | Network In Dropped | cnt | 1m | Number of deleted packets among incoming packets |
| Network | Network In Errors | cnt | 1m | Number of errors during reception |
| Network | Network In Packets | cnt | 1m | Number of received packets |
| Network | Network In Packets [Delta Avg] | cnt | 1m | Average of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Max] | cnt | 1m | Maximum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Min] | cnt | 1m | Minimum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta Sum] | cnt | 1m | Sum of system.network.in.packets_delta for each network |
| Network | Network In Packets [Delta] | cnt | 1m | Delta of received packet count |
| Network | Network Out Bytes | bytes | 1m | Number of transmitted bytes |
| Network | Network Out Bytes [Delta Avg] | bytes | 1m | Average of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Max] | bytes | 1m | Maximum of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Min] | bytes | 1m | Minimum of system.network.out.bytes_delta for each network |
| Network | Network Out Bytes [Delta Sum] | bytes | 1m | Sum of system.network.out.bytes_delta for individual networks |
| Network | Network Out Bytes [Delta] | bytes | 1m | Delta of transmitted byte count |
| Network | Network Out Dropped | cnt | 1m | Number of deleted packets among outgoing packets. This value is not reported by the operating system, so it is always 0 on Darwin and BSD. |
| Network | Network Out Errors | cnt | 1m | Number of errors during transmission |
| Network | Network Out Packets | cnt | 1m | Number of transmitted packets |
| Network | Network Out Packets [Delta Avg] | cnt | 1m | Average of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Max] | cnt | 1m | Maximum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Min] | cnt | 1m | Minimum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta Sum] | cnt | 1m | Sum of system.network.out.packets_delta for each network |
| Network | Network Out Packets [Delta] | cnt | 1m | Delta of transmitted packet count |
| Network | Open Connections [TCP] | cnt | 1m | All open TCP connections |
| Network | Open Connections [UDP] | cnt | 1m | All open UDP connections |
| Network | Port Usage | % | 1m | Connectable port utilization |
| Network | SYN Sent Sockets | cnt | 1m | Number of sockets in SYN_SENT state (when connecting from local to remote) |
| Process | Kernel PID Max | cnt | 1m | kernel.pid_max value |
| Process | Kernel Thread Max | cnt | 1m | kernel.threads-max value |
| Process | Process CPU Usage | % | 1m | The percentage of CPU time consumed by the process since the last update. This value is similar to the %CPU value shown for the process by the top command on Unix systems. |
| Process | Process CPU Usage/Core | % | 1m | The percentage of CPU time used by the process since the last event. Normalized by the number of cores, with a value between 0 and 100%. |
| Process | Process Memory Usage | % | 1m | The proportion of main memory (RAM) occupied by the process |
| Process | Process Memory Used | bytes | 1m | Resident Set size. The amount of memory a process occupies in RAM. In Windows, it is the current working set size. |
| Process | Process PID | PID | 1m | process pid |
| Process | Process PPID | PID | 1m | Parent process PID |
| Process | Processes [Dead] | cnt | 1m | Number of dead processes |
| Process | Processes [Idle] | cnt | 1m | Number of idle processes |
| Process | Processes [Running] | cnt | 1m | running processes count |
| Process | Processes [Sleeping] | cnt | 1m | sleeping processes count |
| Process | Processes [Stopped] | cnt | 1m | stopped processes count |
| Process | Processes [Total] | cnt | 1m | Total number of processes |
| Process | Processes [Unknown] | cnt | 1m | Number of processes with an unknown or unsearchable status |
| Process | Processes [Zombie] | cnt | 1m | Number of zombie processes |
| Process | Running Process Usage | % | 1m | process usage rate |
| Process | Running Processes | cnt | 1m | running processes count |
| Process | Running Thread Usage | % | 1m | Thread usage rate |
| Process | Running Threads | cnt | 1m | Total number of threads running in running processes |
| System | Context Switches | cnt | 1m | context switch count (per second) |
| System | Load/Core [1 min] | cnt | 1m | The load over the last 1 minute divided by the number of cores |
| System | Load/Core [15 min] | cnt | 1m | The load over the last 15 minutes divided by the number of cores |
| System | Load/Core [5 min] | cnt | 1m | The load over the last 5 minutes divided by the number of cores |
| System | Multipaths [Active] | cnt | 1m | External storage connection path state = active count |
| System | Multipaths [Failed] | cnt | 1m | External storage connection path state = failed count |
| System | Multipaths [Faulty] | cnt | 1m | External storage connection path state = faulty count |
| System | NTP Offset | num | 1m | the measured offset of the last sample (time difference between the NTP server and the local environment) |
| System | Run Queue Length | num | 1m | Execution queue length |
| System | Uptime | ms | 1m | OS uptime (uptime). (milliseconds) |
| Windows | Context Switchies | cnt | 1m | CPU context switch count (per second) |
| Windows | Disk Read Bytes [Sec] | cnt | 1m | Number of bytes read in one second from a Windows logical disk |
| Windows | Disk Read Time [Avg] | sec | 1m | Average data read time (seconds) |
| Windows | Disk Transfer Time [Avg] | sec | 1m | Disk average wait time |
| Windows | Disk Usage | % | 1m | Disk usage |
| Windows | Disk Write Bytes [Sec] | cnt | 1m | Bytes written per second on a Windows logical disk |
| Windows | Disk Write Time [Avg] | sec | 1m | Average data write time (seconds) |
| Windows | Pagingfile Usage | % | 1m | Paging file usage |
| Windows | Pool Used [Non Paged] | bytes | 1m | Nonpaged Pool usage in kernel memory |
| Windows | Pool Used [Paged] | bytes | 1m | Paged Pool usage in kernel memory |
| Windows | Process [Running] | cnt | 1m | Number of processes currently running |
| Windows | Threads [Running] | cnt | 1m | Number of threads currently running |
| Windows | Threads [Waiting] | cnt | 1m | Number of threads waiting for processor time |
Multi-node GPU Cluster [Cluster Fabric]
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Cluster GPU | Cluster GPU Count | cnt | 1m | Cluster GPU Count Sum. Sum of node GPU Count within the cluster: calculate the total GPU Count of each node within the same GPU cluster. |
| Cluster GPU | Cluster GPU Count In Use | cnt | 1m | Number of GPUs being used by Jobs in the cluster Number of GPUs used by Processes in the cluster: Parse the ‘Processes:’ section at the bottom of nvidia-smi output from nodes in the same GPU cluster and sum the number of GPUs held by processes |
| Cluster GPU | Cluster GPU Usage | % | 1m | GPU Utilization Average within the cluster. GPU Utilization Average value for nodes within the cluster: calculate the average of each node’s GPU Utilization values among nodes in the same GPU cluster. |
| Cluster GPU | Cluster GPU Memory Usage [Avg] | % | 1m | GPU Memory Utilization Average within the Song cluster. Cluster node Memory Utilization Average value: calculates the average of each node’s Memory Utilization values among nodes in the same GPU cluster. |
Multi-node GPU Cluster [Node]
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| GPU | GPU Count | cnt | 1m | Number of GPUs |
| GPU | GPU Memory Usage | % | 1m | Memory usage |
| GPU | GPU Memory Used | MB | 1m | Memory usage |
| GPU | GPU Temperature | ℃ | 1m | GPU temperature |
| GPU | GPU Usage | % | 1m | Utilization |
| GPU | GPU Usage [Avg] | % | 1m | Overall average GPU utilization (%) |
| GPU | GPU Power Cap | W | 1m | Maximum power capacity of the GPU |
| GPU | GPU Power Usage | W | 1m | Current GPU power usage |
| GPU | GPU Memory Usage [Avg] | % | 1m | GPU Memory Utilization Average |
| GPU | GPU Count in use | cnt | 1m | Number of GPUs in use by jobs on the node |
| GPU | Execution State for nvidia-smi | state | 1m | Result of running the nvidia-smi command |
Storage type
File Storage
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Volume | Instance State | state | 1m | filestorage volume status |
| Volume | IOPS [Other] | iops | 1m | iops (other) |
| Volume | IOPS [Read] | iops | 1m | iops(read) |
| Volume | IOPS [Total] | iops | 1m | iops(total) |
| Volume | IOPS [Write] | iops | 1m | iops(write) |
| Volume | Latency Time [Other] | usec | 1m | Latency (Other) |
| Volume | Latency Time [Read] | usec | 1m | Read latency |
| Volume | Latency Time [Total] | usec | 1m | Total latency |
| Volume | Latency Time [write] | usec | 1m | Write latency |
| Volume | Throughput [Other] | bytes/s | 1m | Throughput (Other) |
| Volume | Throughput [Read] | bytes/s | 1m | Throughput (read) |
| Volume | Throughput [Total] | bytes/s | 1m | Throughput (total) |
| Volume | Throughput [Write] | bytes/s | 1m | Throughput (write) |
| Volume | Volume Total | bytes | 1m | Total byte count |
| Volume | Volume Usage | % | 1m | Usage rate |
| Volume | Volume Used | bytes | 1m | Usage |
Object Storage
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Request | Requests [Delete] | cnt | 1m | Number of HTTP DELETE requests executed on objects in the bucket |
| Request | Requests [Download Avg] | bytes | 1m | Download usage per bucket |
| Request | Requests [Get] | cnt | 1m | Number of HTTP GET requests executed on objects in the bucket |
| Request | Requests [Head] | cnt | 1m | Number of HTTP HEAD requests executed on objects in the bucket |
| Request | Requests [List] | cnt | 1m | Number of LIST requests executed for objects in the bucket |
| Request | Requests [Post] | cnt | 1m | Number of HTTP POST requests executed on objects in the bucket |
| Request | Requests [Put] | cnt | 1m | Number of HTTP PUT requests executed on objects in the bucket |
| Request | Requests [Total] | cnt | 1m | Total number of HTTP requests executed on the bucket |
| Request | Requests [Upload Avg] | bytes | 1m | Upload usage per bucket |
| Usage | Bucket Used | bytes | 1m | Amount of data stored in the bucket (bytes) |
| Usage | Objects | cnt | 1m | Number of objects stored in the bucket |
Block Storage(BM)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| State | Instance State | state | 1m | Blockstorage volume status |
| Volume | IOPS [Total] | iops | 1m | iops(total) |
| Volume | IOPS [Read] | iops | 1m | iops(read) |
| Volume | IOPS [Write] | iops | 1m | iops(write) |
| Volume | IOPS [Other] | iops | 1m | iops (other) |
| Volume | Latency Time [Total] | usec | 1m | Total latency |
| Volume | Latency Time [Read] | usec | 1m | Read latency |
| Volume | Latency Time [Write] | usec | 1m | Write latency |
| Volume | Latency Time [Other] | usec | 1m | Latency (Other) |
| Volume | Throughput [Total] | MB/s | 1m | Throughput (total) |
| Volume | Throughput [Read] | MB/s | 1m | Throughput (read) |
| Volume | Throughput [Write] | MB/s | 1m | Throughput (write) |
| Volume | Throughput [Other] | MB/s | 1m | Throughput (Other) |
| Volume | Volume Bytes | bytes | 1m | Total byte count |
Block Storage(VM)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| State | Instance State | state | 1m | Blockstorage volume status |
| Volume | IOPS [Read] | iops | 1m | iops(read) |
| Volume | IOPS [Write] | iops | 1m | iops(write) |
| Volume | Latency Time [Read] | usec | 1m | Read latency |
| Volume | Latency Time [Write] | usec | 1m | Write latency |
| Volume | Throughput [Read] | MB/s | 1m | Throughput (read) |
| Volume | Throughput [Write] | MB/s | 1m | Throughput (write) |
| Volume | Volume Bytes | bytes | 1m | Total byte count |
Database type
PostgreSQL(DBaaS)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Activelock | Active Locks | cnt | 1m | Number of activelocks |
| Activelock | Active Locks [Access Exclusive] | cnt | 1m | accessexclusive lock count |
| Activelock | Active Locks [Access Share] | cnt | 1m | Number of accessshare locks |
| Activelock | Active Locks [Total] | cnt | 1m | - |
| Activelock | Exclusive Locks | cnt | 1m | exclusive lock count |
| Activelock | Row Exclusive Locks | cnt | 1m | row exclusive lock count |
| Activelock | Row Share Locks | cnt | 1m | row share lock count |
| Activelock | Share Locks | cnt | 1m | share lock count |
| Activelock | Share Row Exclusive Locks | cnt | 1m | Number of sharerowexclusive locks |
| Activelock | Share Update Exclusive Locks | cnt | 1m | Number of share update exclusive locks |
| ActiveSession | Active Sessions | cnt | 1m | Number of active sessions |
| ActiveSession | Active Sessions [Total] | cnt | 1m | - |
| ActiveSession | Idle In Transaction Sessions | cnt | 1m | Number of sessions in idle_in_transaction state |
| ActiveSession | Idle In Transaction Sessions [Total] | cnt | 1m | - |
| ActiveSession | Idle Sessions | cnt | 1m | Number of idle sessions |
| ActiveSession | Idle Sessions [Total] | cnt | 1m | - |
| ActiveSession | Waiting Sessions | cnt | 1m | Number of sessions in waiting state |
| ActiveSession | Waiting Sessions [Total] | cnt | 1m | - |
| Connection | Connection Usage | % | 1m | - |
| Connection | Connection Usage [Total] | % | 1m | DB connection usage rate (%) |
| DB Age | DB Age Max | age | 1m | database age (frozen XID) value |
| Lock | Wait Locks | cnt | 1m | Number of lock-waiting sessions (by DB) |
| Lock | Wait Locks [Long Total] | cnt | 1m | Number of sessions with long (300 seconds) lock waiting |
| Lock | Wait Locks [Long] | cnt | 1m | - |
| Lock | Wait Locks [Total] | cnt | 1m | Number of sessions waiting due to lock occurrence |
| Long Transaction | Transaction Time Max [Long] | sec | 1m | - |
| Long Transaction | Transaction Time Max Total [Long] | sec | 1m | Long-running transaction time (minutes) |
| Replica | Apply Lag Time | sec | 1m | apply_lag time |
| Replica | Check No Replication | cnt | 1m | check_no_replication value |
| Replica | Check Replication | state | 1m | check_replication_state value |
| Slowquery | Slowqueries | cnt | 1m | Number of SQL queries running for a long time (over 5 minutes) |
| State | Instance State [PID] | PID | 1m | postgres process pid |
| Tablespace | Tablespace Used | bytes | 1m | Tablespace size |
| Tablespace | Tablespace Used [Total] | bytes | 1m | - |
| Tablespace | Tablespace Used Bytes [MB] | bytes | 1m | filesystem directory usage (MB) |
| Tablespace | Tablespaces [Total] | cnt | 1m | - |
MariaDB(DBaaS)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Activelock | Active Locks | cnt | 1m | Number of activelocks |
| Activesssion | Active Sessions | cnt | 1m | Number of activesession |
| Activesssion | Connection Usage [Total] | % | 1m | DB connection session usage rate |
| Activesssion | Connections | cnt | 1m | number of connections |
| Activesssion | Connections [MAX] | cnt | 1m | max connected threads count |
| Datafile | Binary Log Used [MB] | bytes | 1m | binary log usage (MB) |
| Datafile | Data Directory Used [MB] | bytes | 1m | datadir usage (MB) |
| Datafile | Open Files | cnt | 1m | Number of DB files in open state |
| Datafile | Open Files [MAX] | cnt | 1m | Number of DB files that can be opened |
| Datafile | Open Files Usage | % | 1m | DB file maximum count utilization |
| Datafile | Relay Log Used [MB] | bytes | 1m | Relay log usage (MB) |
| State | Instance State [PID] | PID | 1m | mariadbd process pid mysqld process pid(pre‑v10.5.2 version) |
| State | Safe PID | PID | 1m | mariadbd_safe process pid mysqld_safe process pid (prior to v10.5.2) |
| State | Slave Behind Master seconds | sec | 1m | Time difference of Data between Master and Slave (run only on slave) |
| Tablespace | Tablespace Used | bytes | 1m | Tablespace usage |
| Tablespace | Tablespace Used [Total] | bytes | 1m | - |
| Transaction | Running Threads | cnt | 1m | running thread count |
| Transaction | Slowqueries | cnt | 1m | Number of long-running SQL queries (over 5 minutes) (by DB) |
| Transaction | Slowqueries [Total] | cnt | 1m | Number of SQL queries running for a long time (over 5 minutes) (total) |
| Transaction | Transaction Time [Long] | sec | 1m | Transaction maximum execution time (seconds) |
| Transaction | Wait Locks | cnt | 1m | Number of sessions blocked for more than 60 seconds by lock |
MySQL(DBaaS)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Activelock | Active Locks | cnt | 1m | Number of activelocks |
| Activesssion | Active Sessions | cnt | 1m | connected threads count |
| Activesssion | Connection Usage [Total] | % | 1m | DB connection session usage rate |
| Activesssion | Connections | cnt | 1m | number of connections |
| Activesssion | Connections [MAX] | cnt | 1m | max connected threads count |
| Datafile | Binary Log Used [MB] | bytes | 1m | binary log usage (MB) |
| Datafile | Data Directory Used [MB] | bytes | 1m | datadir usage (MB) |
| Datafile | Open Files | cnt | 1m | Number of DB files in open state |
| Datafile | Open Files [MAX] | cnt | 1m | Number of DB files that can be opened |
| Datafile | Open Files Usage | % | 1m | DB file maximum count utilization |
| Datafile | Relay Log Used [MB] | bytes | 1m | Relay log usage (MB) |
| State | Instance State [PID] | PID | 1m | mysqld process pid |
| State | Safe PID | PID | 1m | safe program PID |
| State | Slave Behind Master seconds | sec | 1m | Time difference with master node (sec) |
| Tablespace | Tablespace Used | bytes | 1m | Tablespace usage |
| Tablespace | Tablespace Used [Total] | bytes | 1m | Tablespace usage (total) |
| Transaction | Running Threads | cnt | 1m | running thread count |
| Transaction | Slowqueries | cnt | 1m | Number of long-running SQL queries (over 5 minutes) (by DB) |
| Transaction | Slowqueries [Total] | cnt | 1m | Number of SQL queries running for a long time (over 5 minutes) (total) |
| Transaction | Transaction Time [Long] | sec | 1m | Transaction maximum execution time (seconds) |
| Transaction | Wait Locks | cnt | 1m | Number of sessions blocked for more than 60 seconds by lock |
Microsoft SQL Server(DBaaS)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Activelock | Active Locks | cnt | 1m | Number of activelocks |
| Activesssion | Active Sessions | cnt | 1m | Number of activesession |
| Activetransaction | Active Transactions [Total] | cnt | 1m | Number of active transactions |
| Connection | Connected Users | cnt | 1m | Number of users connected to the system |
| Datafile | Datavolume Size [Free] | bytes | 1m | available space |
| Datafile | DBFiles [Not Online] | cnt | 1m | Run a query to verify that all data files are in the ONLINE state. |
| Datafile | Tablespace Used | bytes | 1m | Data volume size |
| Lock | Lock Processes [Blocked] | cnt | 1m | Number of SQL processes blocked by other processes |
| Lock | Lock Waits [Per Second] | cnt | 1m | Lock wait count per second |
| Slowquery | Blocking Session ID | ID | 1m | Number of SQL queries running for a long time (over 5 minutes) |
| Slowquery | Slowqueries | cnt | 1m | Number of SQL queries running for a long time (over 5 minutes) |
| Slowquery | Slowquery CPU Time | ms | 1m | CPU time consumed by SQL execution that runs for a long time (over 5 minutes) |
| Slowquery | Slowquery Execute Context ID | ID | 1m | Context ID associated with the execution task of a SQL that runs for a long time (5 minutes or more) |
| Slowquery | Slowquery Memory Usage | bytes | 1m | Memory usage consumed by the execution of SQL that runs for a long time (over 5 minutes) |
| Slowquery | Slowquery Session ID | ID | 1m | Session ID of SQL queries running for a long time (over 5 minutes) |
| Slowquery | Slowquery Wait Duration Time | ms | 1m | Total wait time for wait type |
| State | Instance State [Cluster] | state | 1m | Status during MSSQL cluster configuration |
| State | Instance State [PID] | PID | 1m | sqlservr.exe process pid |
| State | Page IO Latch Wait Time | ms | 1m | Page IO latch waits average wait time |
| Transaction | Transaction Time [MAX] | cnt | 1m | Long-running (5 minutes or more) transaction |
EPAS(DBaaS)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Activelock | Access Exclusive Locks | cnt | 1m | accessexclusive lock count |
| Activelock | Access Share Locks | cnt | 1m | Number of accessshare locks |
| Activelock | Active Locks | cnt | 1m | Number of activelocks |
| Activelock | Active Locks [Total] | cnt | 1m | activelock count (total) |
| Activelock | Exclusive Locks | cnt | 1m | exclusive lock count |
| Activelock | Row Exclusive Locks | cnt | 1m | row exclusive lock count |
| Activelock | Row Share Locks | cnt | 1m | row share lock count |
| Activelock | Share Locks | cnt | 1m | share lock count |
| Activelock | Share Row Exclusive Locks | cnt | 1m | Number of share row exclusive locks |
| Activelock | Share Update Exclusive Locks | cnt | 1m | Number of share update exclusive locks |
| Activesession | Active Sessions | cnt | 1m | Number of active sessions |
| Activesession | Active Sessions [Total] | cnt | 1m | Total number of active sessions |
| Activesession | Idel In Transaction Sessions | cnt | 1m | Number of sessions in idle_in_transaction state |
| Activesession | Idle In Transaction Sessions [Total] | cnt | 1m | Total number of sessions in idle_in_transaction state |
| Activesession | Idle Sessions | cnt | 1m | Number of idle sessions |
| Activesession | Idle Sessions [Total] | cnt | 1m | Total number of idle sessions |
| Activesession | Waiting Sessions | cnt | 1m | Number of sessions in waiting state |
| Activesession | Waiting Sessions [Total] | cnt | 1m | Total number of sessions in waiting state |
| Connection | Connection Usage | % | 1m | DB connection usage rate (%) |
| Connection | Connection Usage [Total] | % | 1m | Overall DB connection usage (%) |
| Connection | Connection Usage Per DB | % | 1m | DB connection usage rate (%) by DB |
| DB Age | DB Age Max | age | 1m | database age (frozen XID) value |
| Lock | Wait Locks | cnt | 1m | Number of sessions with long (300 seconds) lock waiting |
| Lock | Wait Locks [Long Total] | cnt | 1m | Total number of lock-waiting sessions (300 seconds) |
| Lock | Wait Locks [Long] | cnt | 1m | Number of sessions waiting due to lock occurrence |
| Lock | Wait Locks [Total] | cnt | 1m | Total number of sessions waiting due to lock occurrence |
| Lock | Wait Locks Per DB [Total] | cnt | 1m | Total number of sessions waiting due to lock occurrences per DB |
| Long Transaction | Transaction Time Max [Long] | sec | 1m | Long-running transaction time (minutes) |
| Long Transaction | Transaction Time Max Total [Long] | sec | 1m | Long-running transaction time (minutes) |
| Replica | Apply Lag Time | sec | 1m | apply_lag time |
| Replica | Check No Replication | cnt | 1m | check_no_replication value |
| Replica | Check Replication | state | 1m | check_replication_state value |
| Slowquery | Slowqueries | cnt | 1m | Number of SQL queries running for a long time (over 5 minutes) |
| State | Instance state [PID] | PID | 1m | edb-postgres process pid |
| Tablespace | Tablespace Used Bytes [MB] | bytes | 1m | filesystem directory usage (MB) |
| Tablespace | Tablespaces [Total] | cnt | 1m | Total Tablespace size |
| Tablespace | Tablespace Used | bytes | 1m | Size of the tablespace in use |
| Tablespace | Tablespace Used [Total] | bytes | 1m | Total size of the Tablespace in use |
CacheStore(DBaaS)
Redis
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Stats | Active Defragmentation Keys [Hits] | cnt | 1m | Number of keys after defragmentation |
| Stats | Active Defragmentation Keys [Miss] | cnt | 1m | Number of keys skipped in the active defragmentation removal process |
| Stats | Active Defragmentationd [Hits] | cnt | 1m | Number of value reassignments performed by the active defragmentation removal process |
| Stats | Active Defragmentations [Miss] | cnt | 1m | Number of value reallocations that were stopped, starting with the active defragmentation removal process |
| Memory | Allocated Bytes [OS] | bytes | 1m | Number of bytes allocated by Redis and recognized by the operating system (resident set size) |
| Memory | Allocated Bytes [Redis] | bytes | 1m | Total bytes allocated by Redis |
| Persistence | AOF Buffer Size | bytes | 1m | AOF buffer size |
| Persistence | AOF File Size [Current] | bytes | 1m | AOF current file size |
| Persistence | AOF File Size [Lastest Startup] | bytes | 1m | AOF file size on recent start or rewrite |
| Persistence | AOF Rewrite Buffer Size | bytes | 1m | AOF rewrite buffer size |
| Persistence | AOF Rewrite Current Time | sec | 1m | If applicable, the time of the ongoing AOF rewrite operation |
| Persistence | AOF Rewrite Last Time | sec | 1m | Final AOF rewrite operation time (seconds) |
| Commandstats | Calls | cnt | 1m | Number of calls that reached command execution (not rejected) |
| Commandstats | Calls [Failed] | cnt | 1m | Number of failed calls |
| Commandstats | Calls [Rejected] | cnt | 1m | Number of rejected calls |
| Persistence | Changes [Last Saved] | cnt | 1m | Number of changes after the final dump |
| Clients | Client Output Buffer [MAX] | cnt | 1m | Current longest output list for client connections |
| Clients | Client Input Buffer [MAX] | cnt | 1m | Maximum input buffer for the current client connection |
| Sentinel | Clients [Sentinel] | cnt | 1m | Number of client connections (sentinel) |
| Replication | Connected Slaves | cnt | 1m | Number of connected slaves |
| Clients | Connections [Blocked] | cnt | 1m | Number of clients pending blocking calls (BLPOP, BRPOP, BRPOPLPUSH) |
| Clients | Connections [Current] | cnt | 1m | Number of client connections (excluding slave connections) |
| Persistence | Copy On Write Allocated Size [AOF] | bytes | 1m | COW allocation size during final RBD save operation |
| Persistence | Copy On Write Allocated Size [RDB] | bytes | 1m | COW allocation size during final RBD save operation |
| Commandstats | CPU Time [Average] | cnt | 1m | Average CPU used per command execution |
| Commandstats | CPU Time [Total] | usec | 1m | Total CPU time used by these commands |
| CPU | CPU Usage [System Process] | % | 1m | System CPU used by background processes |
| CPU | CPU Usage [System] | % | 1m | System CPU used by the Redis server |
| CPU | CPU Usage [User Process] | % | 1m | User CPU used by background processes |
| CPU | CPU Usage [User] | % | 1m | System CPU used by background processes |
| Memory | Dataset Used | bytes | 1m | Dataset size |
| Disk | Disk Used | bytes | 1m | datadir usage |
| Stats | Evicted Keys | cnt | 1m | Number of evicted keys caused by the maxmemory limit |
| Persistence | Fsyncs [Delayed] | cnt | 1m | Delayed fsync counter |
| Persistence | Fsyncs [Pending] | cnt | 1m | Number of pending fsync operations in the background I/O queue (format: bytes) |
| Stats | Full Resyncs | cnt | 1m | Number of full resynchronizations with the slave |
| Stats | Keys [Expired] | cnt | 1m | Total number of key expiration events |
| Keyspace | Keys [Keyspace] | cnt | 1m | Number of keys in the key space |
| Stats | Lastest Fork Duration Time | usec | 1m | Recent fork operation time (microseconds) |
| Stats | Lookup Keys [Hit] | cnt | 1m | Number of successful key lookups in the main dictionary |
| Stats | Lookup Keys [Miss] | cnt | 1m | Number of failed key lookups in the main dictionary |
| Memory | Lua Engine Memory Used | bytes | 1m | Memory used by the Lua engine |
| Replication | Master Last Interaction Time Ago | sec | 1m | Elapsed time (seconds) since the final interaction with the master |
| Replication | Master Last Interaction Time Ago [Sync] | sec | 1m | Elapsed time (seconds) since the final interaction with the master |
| Replication | Master Offset | pid | 1m | Current replication offset of the server |
| Replication | Master Second Offset | pid | 1m | Offset until the replica ID is accepted |
| Replication | Master Sync Left Bytes | bytes | 1m | Remaining bytes before synchronization completes |
| Memory | Memory Fragmentation Rate | % | 1m | used_memory_rss and used_memory ratio |
| Memory | Memory Fragmentation Rate [Allocator] | % | 1m | fragmentation ratio |
| Memory | Memory Fragmentation Used | bytes | 1m | Bytes between used_memory_rss and used_memory |
| Memory | Memory Fragmentation Used [Allocator] | bytes | 1m | resident byte |
| Memory | Memory Max Value | bytes | 1m | Memory limit |
| Memory | Memory Resident [Allocator] | bytes | 1m | resident memory |
| Memory | Memory RSS Rate [Allocator] | % | 1m | resident ratio |
| Memory | Memory Used [Active] | bytes | 1m | Active memory |
| Memory | Memory Used [Allocated] | bytes | 1m | Allocated memory |
| Memory | Memory Used [Resident] | bytes | 1m | resident byte |
| Stats | Network In Bytes [Total] | bytes | 1m | Total network input |
| Stats | Network Out Bytes [Total] | bytes | 1m | Total network output |
| Stats | Network Read Rate | cnt | 1m | Network read speed (KB/sec) |
| Stats | Network Write Rate | cnt | 1m | Network write speed (KB/sec) |
| Stats | Partial Resync Requests [Accepted] | cnt | 1m | Number of accepted partial resynchronization requests |
| Stats | Partial Resync Requests [Denied] | cnt | 1m | Number of re-sync requests for rejected parts |
| Memory | Peak Memory Consumed | bytes | 1m | Maximum memory used by Redis |
| Stats | Processed Commands | cnt | 1m | Number of commands processed per second |
| Stats | Processed Commands [Total] | cnt | 1m | Total number of processed commands |
| Stats | Pub/Sub Channels | cnt | 1m | Global count of pub/sub channels with client subscriptions |
| Stats | Pub/Sub Patterns | cnt | 1m | Global count of publish/subscribe pattern with client subscriptions |
| Persistence | RDB Saved Duration Time [Current] | sec | 1m | If applicable, the time of the ongoing RDB save operation |
| Persistence | RDB Saved Duration Time [Last] | sec | 1m | Final RDB save operation time (seconds) |
| Stats | Received Connections [Total] | cnt | 1m | Total number of received connections |
| Stats | Rejected Connections [Total] | cnt | 1m | Total number of rejected connections |
| Replication | Replication Backlog Actove Count | cnt | 1m | Replication backlog enable flag |
| Replication | Replication Backlog Master Offset | cnt | 1m | Master offset of the replication backlog buffer |
| Replication | Replication Backlog Size | bytes | 1m | Data size of the replication backlog buffer (bytes) |
| Replication | Replication Backlog Size [Total] | bytes | 1m | Total size of the replication backlog buffer (bytes) |
| Replication | Slave Priority | cnt | 1m | Priority of instances as a fault handling target |
| Replication | Slave Replication Offset | pid | 1m | Replication offset of the slave instance |
| Slowlog | Slow Operations | cnt | 1m | Number of slow tasks |
| Stats | Sockets [MIGRATE] | cnt | 1m | Number of sockets opened for migration |
| Stats | Tracked Keys [Expiry] | cnt | 1m | Number of keys tracked for expiration (applicable only to writable slaves) |
| State | Instance Status [PID] | PID | 1m | redis-server process pid |
| State | Sentinel Status [PID] | PID | 1m | sentinel process pid |
Valkey
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Stats | Active Defragmentation Keys [Hits] | cnt | 1m | Number of keys after defragmentation |
| Stats | Active Defragmentation Keys [Miss] | cnt | 1m | Number of keys skipped in the active defragmentation removal process |
| Stats | Active Defragmentationd [Hits] | cnt | 1m | Number of value reassignments performed by the active defragmentation removal process |
| Stats | Active Defragmentations [Miss] | cnt | 1m | Number of value reallocations that were stopped, starting with the active defragmentation removal process |
| Memory | Allocated Bytes [OS] | bytes | 1m | Number of bytes allocated by Valkey and recognized by the operating system (resident set size) |
| Memory | Allocated Bytes [Valkey] | bytes | 1m | Total bytes allocated by Valkey |
| Persistence | AOF Buffer Size | bytes | 1m | AOF buffer size |
| Persistence | AOF File Size [Current] | bytes | 1m | AOF current file size |
| Persistence | AOF File Size [Lastest Startup] | bytes | 1m | AOF file size on recent start or rewrite |
| Persistence | AOF Rewrite Buffer Size | bytes | 1m | AOF rewrite buffer size |
| Persistence | AOF Rewrite Current Time | sec | 1m | If applicable, the time of the ongoing AOF rewrite operation |
| Persistence | AOF Rewrite Last Time | sec | 1m | Final AOF rewrite operation time (seconds) |
| Commandstats | Calls | cnt | 1m | Number of calls that reached command execution (not rejected) |
| Commandstats | Calls [Failed] | cnt | 1m | Number of failed calls (Valkey 6.2-rc2) |
| Commandstats | Calls [Rejected] | cnt | 1m | Rejected call count (Valkey 6.2-rc2) |
| Persistence | Changes [Last Saved] | cnt | 1m | Number of changes after the final dump |
| Clients | Cleint Output Buffer [MAX] | cnt | 1m | Current longest output list for client connections |
| Clients | Client Input Buffer [MAX] | cnt | 1m | Maximum input buffer for current client connections (Valkey 5.0) |
| Sentinel | Clients [Sentinel] | cnt | 1m | Number of client connections (sentinel) |
| Replication | Connected Slaves | cnt | 1m | Number of connected slaves |
| Clients | Connections [Blocked] | cnt | 1m | Number of clients pending blocking calls (BLPOP, BRPOP, BRPOPLPUSH) |
| Clients | Connections [Current] | cnt | 1m | Number of client connections (excluding slave connections) |
| Persistence | Copy On Write Allocated Size [AOF] | bytes | 1m | COW allocation size during final RBD save operation |
| Persistence | Copy On Write Allocated Size [RDB] | bytes | 1m | COW allocation size during final RBD save operation |
| Commandstats | CPU Time [Average] | cnt | 1m | Average CPU used per command execution |
| Commandstats | CPU Time [Total] | usec | 1m | Total CPU time used by these commands |
| CPU | CPU Usage [System Process] | % | 1m | System CPU used by background processes |
| CPU | CPU Usage [System] | % | 1m | System CPU used by the Valkey server |
| CPU | CPU Usage [User Process] | % | 1m | User CPU used by background processes |
| CPU | CPU Usage [User] | % | 1m | System CPU used by background processes |
| Memory | Dataset Used | bytes | 1m | Dataset size |
| Disk | Disk Used | MB | 1m | datadir usage |
| Stats | Evicted Keys | cnt | 1m | Number of evicted keys caused by the maxmemory limit |
| Persistence | Fsyncs [Delayed] | cnt | 1m | Delayed fsync counter |
| Persistence | Fsyncs [Pending] | cnt | 1m | Number of pending fsync operations in the background I/O queue (format: bytes) |
| Stats | Full Resyncs | cnt | 1m | Number of full resynchronizations with the slave |
| Stats | Keys [Expired] | cnt | 1m | Total number of key expiration events |
| Keyspace | Keys [Keyspace] | cnt | 1m | Number of keys in the key space |
| Stats | Lastest Fork Duration Time | usec | 1m | Recent fork operation time (microseconds) |
| Stats | Lookup Keys [Hit] | cnt | 1m | Number of successful key lookups in the main dictionary |
| Stats | Lookup Keys [Miss] | cnt | 1m | Number of failed key lookups in the main dictionary |
| Memory | Lua Engine Memory Used | bytes | 1m | Memory used by the Lua engine |
| Replication | Master Last Interaction Time Ago | sec | 1m | Elapsed time (seconds) since the final interaction with the master |
| Replication | Master Last Interaction Time Ago [Sync] | sec | 1m | Elapsed time (seconds) since the final interaction with the master |
| Replication | Master Offset | pid | 1m | Current replication offset of the server |
| Replication | Master Second Offset | pid | 1m | Offset until the replica ID is accepted |
| Replication | Master Sync Left Bytes | bytes | 1m | Remaining bytes before synchronization completes |
| Memory | Memory Fragmentation Rate | % | 1m | used_memory_rss and used_memory ratio |
| Memory | Memory Fragmentation Rate [Allocator] | % | 1m | fragmentation ratio |
| Memory | Memory Fragmentation Used | bytes | 1m | Bytes between used_memory_rss and used_memory |
| Memory | Memory Fragmentation Used [Allocator] | bytes | 1m | resident byte |
| Memory | Memory Max Value | bytes | 1m | Memory limit |
| Memory | Memory Resident [Allocator] | bytes | 1m | resident memory |
| Memory | Memory RSS Rate [Allocator] | % | 1m | resident ratio |
| Memory | Memory Used [Active] | bytes | 1m | Active memory |
| Memory | Memory Used [Allocated] | bytes | 1m | Allocated memory |
| Memory | Memory Used [Resident] | bytes | 1m | resident byte |
| Stats | Network In Bytes [Total] | bytes | 1m | Total network input |
| Stats | Network Out Bytes [Total] | bytes | 1m | Total network output |
| Stats | Network Read Rate | kbps | 1m | Network read speed (KB/sec) |
| Stats | Network Write Rate | kbps | 1m | Network write speed (KB/sec) |
| Stats | Partial Resync Requests [Accepted] | cnt | 1m | Number of accepted partial resynchronization requests |
| Stats | Partial Resync Requests [Denied] | cnt | 1m | Number of re-sync requests for rejected parts |
| Memory | Peak Memory Consumed | bytes | 1m | Maximum memory used by Valkey |
| Stats | Processed Commands | cnt | 1m | Number of commands processed per second |
| Stats | Processed Commands [Total] | cnt | 1m | Total number of processed commands |
| Stats | Pub/Sub Channels | cnt | 1m | Global count of pub/sub channels with client subscriptions |
| Stats | Pub/Sub Patterns | cnt | 1m | Global count of publish/subscribe pattern with client subscriptions |
| Persistence | RDB Saved Duration Time [Current] | sec | 1m | If applicable, the time of the ongoing RDB save operation |
| Persistence | RDB Saved Duration Time [Last] | sec | 1m | Final RDB save operation time (seconds) |
| Stats | Received Connections [Total] | cnt | 1m | Total number of received connections |
| Stats | Rejected Connections [Total] | cnt | 1m | Total number of rejected connections |
| Replication | Replication Backlog Active Count | cnt | 1m | Replication backlog enable flag |
| Replication | Replication Backlog Master Offset | cnt | 1m | Master offset of the replication backlog buffer |
| Replication | Replication Backlog Size | bytes | 1m | Data size of the replication backlog buffer |
| Replication | Replication Backlog Size [Total] | bytes | 1m | Total size of the replication backlog buffer |
| Replication | Slave Priority | cnt | 1m | Priority of instances as a fault handling target |
| Replication | Slave Replication Offset | pid | 1m | Replication offset of the slave instance |
| Slowlog | Slow Operations | cnt | 1m | Number of slow tasks |
| Stats | Sockets [MIGRATE] | cnt | 1m | Number of sockets opened for migration |
| Stats | Tracked Keys [Expiry] | cnt | 1m | Number of keys tracked for expiration (applicable only to writable slaves) |
| State | Instance State [PID] | PID | 1m | Valkey-server process PID |
| State | Sentinel State [PID] | PID | 1m | Sentinel process PID |
Data Analytics type
Event Streams
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Broker | Connections [Zookeeper Client] | cnt | 1m | Number of ZooKeeper connections |
| Broker | Failed [Client Fetch Request] | cnt | 1m | Client fetch request processing failure count |
| Broker | Failed [Produce Request] | cnt | 1m | Procucer request processing failure count |
| Broker | Incomming Messages | cnt | 1m | Number of messages received by the broker |
| Broker | Leader Elections | cnt | 1m | Leader Election occurrence count |
| Broker | Leader Elections [Unclean] | cnt | 1m | Number of Unclean Leader Election occurrences |
| Broker | Log Flushes | cnt | 1m | Number of log flush occurrences |
| Broker | Network In Bytes | bytes | 1m | Total bytes received by the Topic |
| Broker | Network Out Bytes | bytes | 1m | Total bytes transmitted by the Topic |
| Broker | Rejected Bytes | bytes | 1m | Total bytes rejected by the Topic |
| Broker | Request Queue Length | cnt | 1m | Request queue size |
| Broker | Zookeeper Sessions [Closed] | cnt | 1m | ZooKeeper closed sessions per second |
| Broker | Zookeeper Sessions [Expired] | cnt | 1m | ZooKeeper expired sessions per second |
| Broker | Zookeeper Sessions [Readonly] | cnt | 1m | ZooKeeper read‑only sessions per second |
| Broker | Incomming Messages Rate [Topic] | cnt | 1m | Number of received messages per topic |
| Broker | Incomming Byte Rate [Second] | bytes | 1m | per second Incomming data |
| Broker | Outgoing Byte Rate [Second] | bytes | 1m | Outgoing data per second |
| Broker | Rejected Byte Rate [Second] | bytes | 1m | Bytes rejected per second |
| Disk | Disk Used | bytes | 1m | Datadir usage |
| State | AKHQ State [PID] | PID | 1m | akhq process pid |
| State | Instance State [PID] | PID | 1m | kafka process pid |
| State | Zookeeper State [PID] | PID | 1m | zookeeper process pid |
Search Engine
Elasticsearch
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Cluster | Shards | cnt | 1m | Number of cluster shards |
| Cluster | Shards [Primary] | cnt | 1m | Number of primary shards in the cluster |
| Cluster | Index [Total] | cnt | 1m | Number of clustered indexes |
| Cluster | License Expiry Date [ms] | ms | 1m | License expiration date [milisecond] |
| Cluster | License Status | state | 1m | License status |
| Cluster | License Type | type | 1m | License type |
| FileSystem | Disk Usage | bytes | 1m | datadir usage |
| Node | Documents [Deleted] | cnt | 1m | Total number of deleted documents |
| Node | Documents [Existing] | cnt | 1m | Total number of existing documents |
| Node | Filesystem Bytes [Available] | bytes | 1m | Available file systems |
| Node | Filesystem Bytes [Free] | bytes | 1m | Available file system |
| Node | Filesystem Bytes [Total] | bytes | 1m | Total file system |
| Node | JVM Heap Used [Init] | bytes | 1m | Heap init used by JVM (bytes) |
| Node | JVM Heap Used [MAX] | bytes | 1m | Heap max used by JVM (bytes) |
| Node | JVM Non Heap Used [Init] | bytes | 1m | init(bytes) excluding the heap used by the JVM |
| Node | JVM Non Heap Used [MAX] | bytes | 1m | max (bytes) excluding the heap used by the JVM |
| Node | Segments | cnt | 1m | Total number of segments |
| Node | Segments Bytes | bytes | 1m | Total size of the segment |
| Node | Store Bytes | bytes | 1m | Total size of the repository |
| State | Instance state [PID] | PID | 1m | Elasticsearch process pid |
| Task | Queue Time | ms | 1m | Queue time |
| Kibana | Kibana state [PID] | PID | 1m | Kibana process pid |
| Kibana | Kibana Connections | cnt | 1m | connection |
| Kibana | Kibana Memory Heap Allocated [Limit] | bytes | 1m | Maximum old space size allocated to the Node.js process |
| Kibana | Kibana Memory Heap Allocated [Total] | bytes | 1m | Memory |
| Kibana | Kibana Memory Heap Used | bytes | 1m | Memory |
| Kibana | Kibana Process Uptime | ms | 1m | Process |
| Kibana | Kibana Requests [Disconnected] | cnt | 1m | Request count metric |
| Kibana | Kibana Requests [Total] | cnt | 1m | Request count metric |
| Kibana | Kibana Response Time [Avg] | ms | 1m | Response time metric |
| Kibana | Kibana Response Time [MAX] | ms | 1m | Response time metric |
Opensearch
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| State | Cluster state | state | 1m | Cluster status |
| Cluster | Nodes | cnt | 1m | Number of nodes in the cluster |
| Cluster | Data nodes | cnt | 1m | Number of data nodes in the cluster |
| Cluster | Pending tasks | cnt | 1m | Number of pending tasks |
| Shard | Shards [active] | cnt | 1m | Active piece count |
| Shard | Shards [active_primary] | cnt | 1m | Number of active primary fragments |
| Shard | Shards [initializing] | cnt | 1m | Initial shard count |
| Shard | Shards [relocating] | cnt | 1m | Previous piece count |
| Shard | Shards [unassigned] | cnt | 1m | Number of unallocated fragments |
| Thread | Thread Queue Count [search] | cnt | 1m | Number of search tasks in the queue |
| Thread | Thread Queue Count [refresh] | cnt | 1m | Number of refresh tasks in the queue |
| Thread | Thread Queue Count [write] | cnt | 1m | Number of write operations in the queue |
| Thread | Thread Queue Count [get] | cnt | 1m | Number of jobs fetched from the queue |
| Thread | Thread Queue Count [snapshot] | cnt | 1m | Number of snapshot jobs in the queue |
| Thread | Thread Queue Count [flush] | cnt | 1m | Number of flush operations in the queue |
| Thread | Thread Queue Count [force_merge] | cnt | 1m | Number of force_merge tasks in the queue |
| System | CPU usage | % | 1m | CPU usage |
| System | Memory usage | bytes | 1m | Used memory |
| System | Disk available | bytes | 1m | Disk Available |
| Documents | Documents indexing rate | cnt | 1m | Number of indexed documents |
| Documents | Documents indexing rate [Delta] | cnt | 1m | Number of indexed documents (delta value) |
| Documents | Indexing latency | sec | 1m | Time taken to index documents |
| Documents | Indexing latency [Delta] | sec | 1m | Time taken to index the document (delta value) |
| Documents | Search rate | cnt | 1m | Number of search queries |
| Documents | Search rate [Delta] | cnt | 1m | Number of search queries (delta value) |
| Documents | Search latency | sec | 1m | Time taken during the query |
| Documents | Search latency [Delta] | sec | 1m | Time taken during the query (delta value) |
| Documents | Document count (with replicas) | cnt | 1m | Total number of documents |
| Documents | Document deleting rate | cnt | 1m | Number of deleted documents |
| Documents | Document deleting rate [Delta] | cnt | 1m | Number of deleted documents (delta value) |
| Documents | Document merging rate | cnt | 1m | Number of merged documents |
| Documents | Document merging rate [Delta] | cnt | 1m | Number of merged documents (delta value) |
| JVM | Heap used | bytes | 1m | Memory used in the heap |
| JVM | GC count [young] | cnt | 1m | Number of young GC collections |
| JVM | GC count [young] [Delta] | cnt | 1m | Young GC collection count (delta value) |
| JVM | GC count [G1] | cnt | 1m | G1 GC collection count |
| JVM | GC count [G1] [Delta] | cnt | 1m | G1 GC collection count (delta value) |
| JVM | GC count [old] | cnt | 1m | Number of previous GC collections |
| JVM | GC count [old] [Delta] | cnt | 1m | Previous GC collection count (delta value) |
| JVM | GC time [young] | cnt | 1m | Time spent on young GC collection |
| JVM | GC time [young] [Delta] | cnt | 1m | Time spent for young GC collection (delta value) |
| JVM | GC time [G1] | cnt | 1m | Time spent on G1 GC collection |
| JVM | GC time [G1] [Delta] | cnt | 1m | Time spent on G1 GC collection (delta value) |
| JVM | GC time [old] | cnt | 1m | Time spent on old GC collections |
| JVM | GC time [old] [Delta] | cnt | 1m | Time spent on old GC collections (delta value) |
| State | Instance state [PID] | PID | 1m | Opensearch process PID |
| State | Dashboard state [PID] | PID | 1m | Dashboard process PID |
Vertica(DBaaS)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| State | Instance State [PID] | state | 1m | Vertica process PID |
| Activelock | Active Locks | cnt | 1m | Active Locks count |
| Activesession | Active Sessions | cnt | 1m | Number of Active Sessions |
| Tablespace | Data Tablespace Used | MB | 1m | Data, Temp Tablespace usage |
| Tablespace | Catalog Tablespace Used | MB | 1m | Catalog Tablespace Usage |
Container type
Kubernetes Engine
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Cluster | Cluster Namespaces [Active] | cnt | 5m | Number of namespaces in active state |
| Cluster | Cluster Namespaces [Total] | cnt | 5m | Total number of namespaces in the cluster |
| Cluster | Cluster Nodes [Ready] | cnt | 5m | Number of nodes in READY state |
| Cluster | Cluster Nodes [Total] | cnt | 5m | Total number of nodes in the cluster |
| Cluster | Cluster Pods [Failed] | cnt | 5m | Number of failed-state pods in the cluster |
| Cluster | Cluster Pods [Pending] | cnt | 5m | Number of pending pods in the cluster |
| Cluster | Cluster Pods [Running] | cnt | 5m | Number of pods in running state within the cluster |
| Cluster | Cluster Pods [Succeeded] | cnt | 5m | Number of succeeded pods in the cluster |
| Cluster | Cluster Pods [Unknown] | cnt | 5m | Number of pods in unknown state within the cluster |
| Cluster | Instance State | state | 5m | cluster status |
| Namespace | Namespace Pods [Failed] | cnt | 5m | Number of failed-state pods in a namespace |
| Namespace | Namespace Pods [Pending] | cnt | 5m | Number of pending pods in the namespace |
| Namespace | Namespace Pods [Running] | cnt | 5m | Number of running pods in a namespace |
| Namespace | Namespace Pods [Succeeded] | cnt | 5m | Number of succeeded pods in the namespace |
| Namespace | Namespace Pods [Unknown] | cnt | 5m | Number of unknown-state pods in the namespace |
| Namespace | Namespace GPU Clock Frequency | MHz | 5m | SM clock frequency in the Namespace |
| Namespace | Namespace GPU Memory Usage | % | 5m | Memory utilization in Namespace |
| Node | Node CPU Size [Allocatable] | cnt | 5m | Node allocatable CPU |
| Node | Node CPU Size [Capacity] | cnt | 5m | CPU capacity within the node |
| Node | Node CPU Usage | % | 5m | CPU usage on the node |
| Node | Node CPU Usage [Request] | % | 5m | CPU request_ratio within node |
| Node | Node CPU Used | state | 5m | CPU utilization within the node |
| Node | Node Filesystem Usage | % | 5m | FS usage within node |
| Node | Node Memory Size [Allocatable] | bytes | 5m | memory allocatable within the node |
| Node | Node Memory Size [Capacity] | bytes | 5m | Node memory utilization |
| Node | Node Memory Usage | % | 5m | Node memory utilization |
| Node | Node Memory Usage [Request] | % | 5m | memory request_ratio within the node |
| Node | Node Memory Workingset | bytes | 5m | memory working set within the node |
| Node | Node Network In Bytes | bytes | 5m | Node network rx bytes |
| Node | Node Network Out Bytes | bytes | 5m | Node network tx bytes |
| Node | Node Network Total Bytes | bytes | 5m | Node network total bytes |
| Node | Node Pods [Failed] | cnt | 5m | Number of pods in failed state within a node |
| Node | Node Pods [Pending] | cnt | 5m | Number of pending pods in the node |
| Node | Node Pods [Running] | cnt | 5m | Number of running pods per node |
| Node | Node Pods [Succeeded] | cnt | 5m | Number of succeeded pods in the node |
| Node | Node Pods [Unknown] | cnt | 5m | Number of pods in unknown state on the node |
| Pod | Pod CPU Usage [Limit] | % | 5m | CPU usage_limit_ratio within the pod |
| Pod | Pod CPU Usage [Request] | % | 5m | CPU request_ratio within the pod |
| Pod | Pod CPU Usage | mc | 5m | CPU usage within the pod |
| Pod | Pod Memory Usage [Limit] | % | 5m | memory usage_limit_ratio in the pod |
| Pod | Pod Memory Usage [Request] | % | 5m | memory request_ratio in pod |
| Pod | Pod Memory Usage | bytes | 5m | Memory usage within the pod |
| Pod | Pod Network In Bytes | bytes | 5m | network rx bytes in pod |
| Pod | Pod Network Out Bytes | bytes | 5m | network tx bytes in pod |
| Pod | Pod Network Total Bytes | bytes | 5m | Network total bytes in pod |
| Pod | Pod Restart Containers | cnt | 5m | container restart count in pod |
| Workload | Workload Pods [Running] | cnt | 5m | - |
Container Registry
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Container Registry | Image Pulls [Denied] | cnt | 1m | Number of rejected Image Tag (digest) Pulls |
| Container Registry | Image Pushs [Allowed] | cnt | 1m | Allowed Image Tag (digest) Push count |
| Container Registry | Image Pushs [Denied] | cnt | 1m | Number of rejected Image Tag (digest) Pushes |
| Container Registry | Image Scans[Allowed] | cnt | 1m | Allowed Image Tag (digest) Scan count |
| Container Registry | Image Scans [Denied] | cnt | 1m | Number of rejected Image Tag (digest) scans |
| Container Registry | Image Tags [Deleted] | cnt | 1m | Number of deleted Image Tag (digest) |
| Container Registry | Images [Created] | cnt | 1m | Number of generated images |
| Container Registry | Images [Deleted] | cnt | 1m | Number of deleted images |
| Container Registry | Logins [Allowed] | cnt | 1m | Number of allowed Registry Logins |
| Container Registry | Logins [Denied] | cnt | 1m | Number of denied Registry Logins |
| Container Registry | Repositories [Created] | cnt | 1m | Number of created repositories |
| Container Registry | Repositories [Deleted] | cnt | 1m | Number of deleted repositories |
| State | Instance State | state | 1m | Check status |
Networking type
Internet Gateway
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Internet Gateway | Network In Total Bytes [Internet Delta] | bytes | 5m | Internet Gateway → Cumulative traffic volume toward VPC for 5 minutes (Internet) ※ Traffic bps average conversion formula: cumulative traffic volume (bytes) / 300 (seconds) * 8 (bits) |
| Internet Gateway | Network In Total Bytes [Internet] | bytes | 5m | rx bytes total |
| Internet Gateway | Network Out Total Bytes [Internet Delta] | bytes | 5m | VPC → cumulative traffic volume toward the Internet Gateway over 5 minutes (Internet) ※ Traffic bps average conversion formula: cumulative traffic volume (bytes) / 300 (seconds) * 8 (bits) |
| Internet Gateway | Network Out Total Bytes [Internet] | bytes | 5m | tx bytes total |
Load Balancer(OLD)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Load Balancer | Current Connection | cnt | 5m | Current number of connections |
| Load Balancer | Total Connection | cnt | 5m | Total number of connections |
| Load Balancer | Total Connection [Delta] | cnt | 5m | Total number of connections (delta value) |
| Load Balancer | Network In Bytes | bytes | 5m | in bytes |
| Load Balancer | Network In Bytes [Delta] | bytes | 5m | Client → Load Balancer cumulative traffic volume over 5 minutes ※ Traffic bps average conversion formula: cumulative traffic volume (bytes) / 300 (seconds) * 8 (bit) |
| Load Balancer | Network Out Bytes | bytes | 5m | out bytes |
| Load Balancer | Network Out Bytes [Delta] | bytes | 5m | Cumulative traffic volume over 5 minutes from Load Balancer to Client ※ Traffic bps average conversion formula: cumulative traffic volume (bytes) / 300 (seconds) * 8 (bits) |
| Load Balancer | Instance State | state | 5m | Load Balancer status |
Load Balancer Listener(OLD)
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Listener | Connections [Current] | cnt | 5m | Current number of connections |
| Listener | Connections [Total Delta] | cnt | 5m | total connection count (delta value) |
| Listener | Connections [Total] | cnt | 5m | total connection count |
| Listener | Instance State | state | 5m | LB Listener status |
| Listener | Network In Bytes | bytes | 5m | in bytes |
| Listener | Network In Bytes [Delta] | bytes | 5m | Cumulative traffic volume over 5 minutes from Client to Load Balancer ※ Traffic bps average conversion formula: cumulative traffic volume (bytes) / 300 (seconds) * 8 (bits) |
| Listener | Network Out Bytes | bytes | 5m | out bytes |
| Listener | Network Out Bytes [Delta] | bytes | 5m | Load Balancer → Client cumulative traffic volume over 5 minutes ※ Traffic bps average conversion formula: cumulative traffic volume (bytes) / 300 (seconds) * 8 (bits) |
Direct Connect
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Direct Connect | Network In Bytes | bytes | 5m | Cumulative traffic volume from Direct Connect → VPC |
| Direct Connect | Network In Bytes [Delta] | bytes | 5m | Direct Connect → VPC cumulative traffic volume over 5 minutes ※ Traffic bps average conversion formula: Cumulative traffic volume (bytes) / 300 (seconds) * 8 (bits) |
| Direct Connect | Network Out Bytes | bytes | 5m | Cumulative traffic volume from VPC to Direct Connect |
| Direct Connect | Network Out Bytes [Delta] | bytes | 5m | VPC → Direct Connect cumulative traffic volume over 5 minutes ※ Traffic bps average conversion formula: cumulative traffic volume (bytes) / 300 (seconds) * 8 (bits) |
Load Balancer
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| State | Instance State | state | 5m | LB status |
| Load Balancer | Current Connection | cnt | 5m | Current number of connections |
| Load Balancer | Total L4 Connection | cnt | 5m | Total L4 Connection count |
| Load Balancer | Total L7 Connection | cnt | 5m | Total number of L7 connections |
| Load Balancer | Total TCP Connection | cnt | 5m | Total number of TCP connections |
| Load Balancer | Total Connection | cnt | 5m | Total number of connections |
| Load Balancer | Bytes processed in forward direction | bytes | 5m | Full‑duplex Network Byte |
| Load Balancer | Packets processed in forward direction | cnt | 5m | Bidirectional Network packet |
| Load Balancer | Bytes processed in reverse direction | bytes | 5m | Reverse Network Byte |
| Load Balancer | Packets processed in reverse direction | cnt | 5m | Reverse Network packet |
| Load Balancer | Total failure actions | cnt | 5m | Total number of failures |
| Load Balancer | Current Request | cnt | 5m | Current request count |
| Load Balancer | Current response | cnt | 5m | Current Response count |
| Load Balancer | Total Request | cnt | 5m | Total number of requests |
| Load Balancer | Total Request Success | cnt | 5m | Total number of successful requests |
| Load Balancer | Peak Connection | cnt | 5m | Maximum number of connections |
| Load Balancer | Current Connection Rate | % | 5m | Current SSL Connection rate |
| Load Balancer | Last response time | ms | 5m | Last response time |
| Load Balancer | Fastest response time | ms | 5m | Shortest response time |
| Load Balancer | Slowest response time | ms | 5m | Maximum response time |
| Load Balancer | Current SSL Connection | cnt | 5m | Current number of SSL connections |
| Load Balancer | Total SSL Connection | cnt | 5m | Total number of SSL connections |
| Load Balancer | Bytes processed in forward direction [Delta] | bytes | 5m | Forward Network Byte (delta value) |
| Load Balancer | Packets processed in forward direction [Delta] | cnt | 5m | Forward Network packet (delta value) |
| Load Balancer | Bytes processed in reverse direction [Delta] | bytes | 5m | Reverse Network Byte (delta value) |
| Load Balancer | Packets processed in reverse direction [Delta] | cnt | 5m | Reverse Network packet (delta value) |
Load Balancer Listener
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| State | Instance State | state | 5m | LB status |
| Load Balancer | Current Connection | cnt | 5m | Current number of connections |
| Load Balancer | Total L4 Connection | cnt | 5m | Total L4 Connection count |
| Load Balancer | Total L7 Connection | cnt | 5m | Total number of L7 connections |
| Load Balancer | Total TCP Connection | cnt | 5m | Total number of TCP connections |
| Load Balancer | Total Connection | cnt | 5m | Total number of connections |
| Load Balancer | Bytes processed in forward direction | bytes | 5m | Full‑duplex Network Byte |
| Load Balancer | Packets processed in forward direction | cnt | 5m | Bidirectional Network packet |
| Load Balancer | Bytes processed in reverse direction | bytes | 5m | Reverse Network Byte |
| Load Balancer | Packets processed in reverse direction | cnt | 5m | Reverse Network packet |
| Load Balancer | Total failure actions | cnt | 5m | Total number of failures |
| Load Balancer | Current Request | cnt | 5m | Current request count |
| Load Balancer | Current response | cnt | 5m | Current Response count |
| Load Balancer | Total Request | cnt | 5m | Total number of requests |
| Load Balancer | Total Request Success | cnt | 5m | Total number of successful requests |
| Load Balancer | Peak Connection | cnt | 5m | Maximum number of connections |
| Load Balancer | Current Connection Rate | % | 5m | Current SSL Connection rate |
| Load Balancer | Last response time | ms | 5m | Last response time |
| Load Balancer | Fastest response time | ms | 5m | Shortest response time |
| Load Balancer | Slowest response time | ms | 5m | Maximum response time |
| Load Balancer | Current SSL Connection | cnt | 5m | Current number of SSL connections |
| Load Balancer | Total SSL Connection | cnt | 5m | Total number of SSL connections |
| Load Balancer | Bytes processed in forward direction [Delta] | bytes | 5m | Forward Network Byte (delta value) |
| Load Balancer | Packets processed in forward direction [Delta] | cnt | 5m | Forward Network packet (delta value) |
| Load Balancer | Bytes processed in reverse direction [Delta] | bytes | 5m | Reverse Network Byte (delta value) |
| Load Balancer | Packets processed in reverse direction [Delta] | cnt | 5m | Reverse Network packet (delta value) |
Load Balancer Server Group
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Server Group | Instance State | state | 5m | LB Server Group status |
| Server Group | Peak Connection | cnt | 5m | Maximum connections per server group |
| Server Group | Healthy host | cnt | 5m | Number of healthy hosts in server group |
| Server Group | Unhealthy host | cnt | 5m | Number of abnormal hosts in server group |
| Server Group | Request Count | cnt | 5m | Number of requests |
| Server Group | Response Count | cnt | 5m | Response count |
| Server Group | 2xx Response Count | cnt | 5m | 2xx response count |
| Server Group | 3xx Response Count | cnt | 5m | Number of 3xx responses |
| Server Group | 4xx Response Count | cnt | 5m | 4xx response count |
| Server Group | 5xx Response Count | cnt | 5m | Number of 5xx responses |
Cloud WAN
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| State | Instance State | state | 10m | Attachment connection status |
| Attachment | Network in bytes | bytes | 10m | in bytes(Inbound traffic usage per interval) |
| Attachment | Network out bytes | bytes | 10m | Out bytes(Outbound traffic usage per interval) |
| Attachment | Network In Packets [Dropped] | cnt | 10m | in Dropped Packet count (number of dropped packets per interval) |
| Attachment | Network Out Packets [Dropped] | cnt | 10m | Out Dropped Packet count (number of dropped packets per interval) |
| Attachment | Network In Packets [Unicast] | cnt | 10m | in Unicast Packet count (number of Unicast packets per cycle) |
| Attachment | Network Out Packets [Unicast] | cnt | 10m | Out Unicast Packet count (Unicast packets per cycle) |
| Attachment | Network In Packets [Broadcast] | cnt | 10m | in Broadcast Packet count (number of Broadcast packets per cycle) |
| Attachment | Network Out Packets [Broadcast] | cnt | 10m | Out Broadcast Packet count (number of broadcast packets per cycle) |
| Attachment | Network In Packets [Multicast] | cnt | 10m | in Multicast Packet count (Multicast packets per cycle) |
| Attachment | Network Out Packets [Multicast] | cnt | 10m | Out Multicast Packet count (Multicast packet count per cycle) |
| Attachment | Network In Error Packets | cnt | 10m | in Error Packet count (number of received error packets per cycle) |
| Attachment | Network Out Error Packets | cnt | 10m | Out Error Packet count (number of transmitted error packets per cycle) |
Global CDN
| Performance Item Group Name | Performance item name | collection unit | Collection interval | Explanation |
|---|---|---|---|---|
| Global CDN | Instance State | state | 5m | Global CDN status |
| Global CDN | Data Transfer Bytes | bytes | 5m | Data transfer volume transmitted via CDN service (originBytes) |
| Global CDN | Requests [Total] | cnt | 5m | Number of service requests (cases) received by the CDN service (originHits) |
10.3.2.9 - Appendix C. Service-specific Status Checks
Compute type
Virtual Server
| Performance item name | Explanation | value |
|---|---|---|
| Instance State [Basic] | Instance status | NOSTATE, RUNNING, BLOCKED, PASUED, SHUTDOWN, SHUTOFF, CRASHED, PMSUSPENDED, LAST |
GPU Server
| Performance item name | description | value |
|---|---|---|
| Instance State [Basic] | Instance status | NOSTATE RUNNING, BLOCKED, PASUED, SHUTDOWN, SHUTOFF, CRASHED, PMSUSPENDED, LAST |
Bare Metal Server
| Performance item name | description | value |
|---|---|---|
| N/A | N/A | N/A |
Multi-node GPU Cluster [Cluster Fabric]
| Performance item name | description | value |
|---|---|---|
| N/A | N/A | N/A |
Multi-node GPU Cluster [Node]
| Performance item name | description | value |
|---|---|---|
| N/A | N/A | N/A |
Storage type
File Storage
| Performance item name | description | value |
|---|---|---|
| Instance State | File Storage Volume Status | 1: When Online |
| 0: Other status values (Offline) |
Object Storage
| Performance item name | description | value |
|---|---|---|
| N/A | N/A | N/A |
Block Storage(BM)
| Performance item name | Explanation | value |
|---|---|---|
| Instance State | Blockstorage volume status | 1: running (normal) * 0: down (abnormal) |
Block Storage(VM)
| Performance item name | description | value |
|---|---|---|
| Instance State | Blockstorage volume status | 1: running (normal) * 0: down (abnormal) |
Database type
PostgreSQL(DBaaS)
| Performance item name | Explanation | value |
|---|---|---|
| Instance State [PID] | postgres process PID | PID: postgres when the process exists * -1: when the process does not exist |
MariaDB(DBaaS)
| Performance item name | description | value |
|---|---|---|
| Safe PID | mariadb_safe process PID | PID: mariadb_safe when the process exists -1: when the process does not exist |
| Instance State [PID] | mariadb process PID | PID: mariadb if the process exists * -1: if the process does not exist |
MySQL(DBaaS)
| Performance item name | description | value |
|---|---|---|
| Instance State [PID] | mysqld process PID | PID: mysqld process exists -1: process does not exist |
Microsoft SQL Server(DBaaS)
| Performance item name | description | value |
|---|---|---|
| Instance State [Cluster] | MSSQL cluster configuration status | PID: mssql when the process exists -1: when the process does not exist |
| Instance State [PID] | sqlservr.exe process pid | For Microsoft SQL Server, the secondary server also has a PID running, so the status cannot be determined solely by the PID. |
EPAS(DBaaS)
| Performance item name | description | value |
|---|---|---|
| Instance State [PID] | postgres process PID | PID: postgres if the process exists * -1: if the process does not exist |
CacheStore(DBaaS)
Redis
| Performance item name | Explanation | value |
|---|---|---|
| Instance State [PID] | Redis-server process PID | -1: If the process does not exist |
| Sentinel State [PID] | Sentinel process PID | -1: when the process does not exist |
Valkey
| Performance item name | description | value |
|---|---|---|
| Instance State [PID] | Valkey-server process PID | -1: If the process does not exist |
| Sentinel State [PID] | Sentinel process PID | -1: when the process does not exist |
Data Analytics type
Event Streams
| Performance item name | description | value |
|---|---|---|
| AKHQ State [PID] | akhq process PID | PID: akhq if the process exists * -1: if the process does not exist |
| Instance State [PID] | Kafka process PID | PID: when the kafka process exists * -1: when the process does not exist |
| Zookeeper State [Pid] | zookeeper process PID | PID: zookeeper if the process exists * -1: if the process does not exist |
Search Engine
| Performance item name | Explanation | value |
|---|---|---|
| Instance State [PID] | Elasticsearch process PID | PID: if the Elasticsearch process exists * -1: if the process does not exist |
| Kibana State [PID] | Kibana process PID | PID: Kibana if the process exists * -1: if the process does not exist |
Elasticsearch
| Performance item name | Explanation | value |
|---|---|---|
| Instance State [PID] | Elasticsearch process PID | -1: when the process does not exist |
| Kibana State [PID] | Dashboard process PID | -1: if the process does not exist |
Opensearch
| Performance item name | description | value |
|---|---|---|
| Instance State [PID] | Opensearch process PID | -1: If the process does not exist |
| Dashboard State [PID] | Dashboard process PID | -1: when the process does not exist |
Vertica(DBaaS)
| Performance item name | Explanation | value |
|---|---|---|
| Instance State [PID] | Vertica process PID | -1: if the process does not exist |
Container type
Kubernetes Engine
| Performance item name | description | value |
|---|---|---|
| Instance State | cluster status | 1: If the health check query sum(up{job=““kubernetes-apiservers””}) returns a value greater than 0 |
- 0: If the health check query sum(up{job=““kubernetes-apiservers””}) returns a value less than or equal to 0 |
Container Registry
| Performance item name | description | value |
|---|---|---|
| Instance State | Container Registry status | 1: running (normal) * 0: down (abnormal) |
Networking type
Internet Gateway
| Performance item name | description | value |
|---|---|---|
| N/A | N/A | N/A |
Load Balancer(OLD)
| Performance item name | description | value |
|---|---|---|
| Instance State | Load Balancer status | Determine based on provisioning_status in the API response * 1: ACTIVE * 0: ETC |
Load Balancer Listener(OLD)
| Performance item name | Explanation | value |
|---|---|---|
| Instance State | Load Balancer Listener status | Determine based on provisioning_status in the API response * 1: ACTIVE * 0: ETC |
Load Balancer
| Performance item name | description | value |
|---|---|---|
| Instance State | Load Balancer status | Determine based on provisioning_status in the API response * 1: ACTIVE * 0: ETC |
Load Balancer Listener
| Performance item name | description | value |
|---|---|---|
| Instance State | Load Balancer Listener status | Determine based on provisioning_status in the API response * 1: ACTIVE * 0: ETC |
Load Balancer Server Group
| Performance item name | Explanation | value |
|---|---|---|
| Instance State | Status of Load Balancer Server Group | Determine based on provisioning_status in the API response * 1: ACTIVE * 0: ETC |
Direct Connect
| Performance item name | description | value |
|---|---|---|
| N/A | N/A | N/A |
Cloud WAN
| Performance item name | description | value |
|---|---|---|
| Instance State | Attachment connection status | 0: down * 1: up * 2: testing * 3: unknown |
Global CDN
| Performance item name | description | value |
|---|---|---|
| Instance State | Global CDN status | 1: running (normal) * 0: down (abnormal) |
10.3.3 - API Reference
10.3.4 - Release Note
Cloud Monitoring
- In July 2025, we added an integrated service with Cloud Monitoring.
- Additional integrated services: Compute(Multi-node GPU Cluster [Cluster Fabric], Multi-node GPU Clutser [Node]), Storage(Block Storage(BM), Block Storage(VM)), Networking(Cloud WAN, Global CDN), Database(Valkey), Data Analytics(Opensearch, Vertica(DBaaS))
- In February 2025, we added an integration service with Cloud Monitoring.
- Additional integrated services: Container (Container Registry), Database (EPAS, Microsoft SQL Server), Data Analytics (Event Streams, Search Engine), Networking (Load Balancer, Load Balancer Listener, Load Balancer Server Group, VPN)
- We have launched the Cloud Monitoring service. It collects usage status and change information of operational infrastructure resources, and supports a stable cloud operating environment by generating and notifying events when configured thresholds are exceeded.
10.4 - IAM
10.4.1 - Overview
Service Overview
IAM(Identity and Access Management) is a service that controls the range of access to services and resources by verifying the identity of users registered on the Samsung Cloud Platform and granting access permissions. Administrators can create and manage users, permission groups, policies, and role items in detail through IAM.
Users can create new users if they are the Root user or have been granted user registration authority by the Root user. Policies cannot be assigned directly to users; instead, users are added to user groups, and policies are attached to those groups, granting specific users permission to access or manage resources. In other words, the tasks a user can perform within an account depend on which user group they belong to and which policies are attached to that group.
Provided features
IAM provides the following features.
- User Authentication: Provides multi-factor authentication (MFA; Multi-Factor Authentication) for Console and API access. Additionally, it blocks unauthorized access by allowing access only from permitted IP ranges.
- Permission Management: Add users to user groups based on tasks, limiting their access permissions to the parts required for the work. Administrators can manage and assign custom policies.
- Role Management: You can switch from your own account to another role to access the Account.
- Credential Provider Offering: You can access and use the Account within the Console via the credential provider.
- Access Control Policy Management: Create access control policies for each service regarding control/action/resource type and authentication method/IP. This enables the application of least‑privilege policies when granting access to cloud resources, allowing user‑based access control.
Component
Users can create and manage user groups, users, policies through Identity and Access Management(IAM).
User group
In the user group, you can register users and add policies. You can create user groups tailored to each task, register users, and attach appropriate policies to grant the same permissions to users and manage them.
User
Administrators can create users and add them to user groups. They can generate a user’s password automatically or manually, and provide the user with account-specific login information.
User Policy
You can create policies for the functions provided by each service. Access control can be managed based on control type, applied resources, and authentication type.
role
It is a virtual user account with separate permissions, not affected by the permissions of the original user account.
Preceding Service
Identity and Access Management(IAM) has no prerequisite service.
10.4.2 - How-to Guides
Users can create and manage User Groups, Users, Policies, My Info. through Identity and Access Management(IAM).
Getting Started with IAM
- Click the All Services > Management > IAM menu. Go to the Service Home page of IAM.
- On the Service Home page, My Info., Account information, Quick Link, and IAM status are provided as widgets.
Category Detailed description My Info. User name, email, and user group information accessed in the Samsung Cloud Platform Console. Click the More button to go to the My Info page. Account information Provides the user’s Account ID, Account alias, and IAM user login URL if the user is an IAM user - Account ID: User’s Account ID
- Account alias: A name assigned to the Account. It allows you to attach an alias for easier identification and management of the Account
- Edit: If you edit the Account alias, the IAM user login URL that uses the current alias will no longer be usable. See Edit Account Alias
- Delete: If you delete the Account alias, IAM users will no longer be able to log in using the Account alias. See Delete Account Alias
- IAM user login URL can be used to log in without entering Account information
- For more details related to the Account, see Account see
Quick Link Description of My Info. and My Info. button navigates to the page. - For more details about My Info., see My Info.
IAM status Counts of user groups, users, and policies Table. IAM Service Home widget items
Modify Account Alias
You can edit the Account alias in the Service Home > Account widget of IAM.
- Click the All Services > Management > IAM menu. Go to the Service Home page of IAM.
- On the Service Home page, in the Account widget, click the Edit button of the Account alias. You will be taken to the Edit Account Alias popup.
- Edit Account Alias After reviewing the instructions in the popup window, edit the Account alias and click the Confirm button.ReferenceWhen modifying an Account alias, the Console login URL that uses the current alias will no longer be usable.
After making changes, if the alias is not used by another account, you can reuse the alias you were previously using.
Delete Account Alias
You can delete an Account alias from the IAM Service Home > Account widget.
- Click the All Services > Management > IAM menu. Navigate to the Service Home page of IAM.
- On the Service Home page, in the Account widget, click the Delete button of the Account alias. You will be taken to the Delete Account alias popup.
- Account Alias Deletion After reviewing the instructions in the popup window, click the Confirm button.Caution
If you delete the account alias, IAM users can no longer log in using the account alias.
- The IAM login URL is also unavailable.
10.4.2.1 - User Group
Users can create the service by entering the required information for a user group and selecting detailed options through the Samsung Cloud Platform Console.
Create user group
To create a user group, follow these steps.
All Services > Management > IAM menu, click it. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the User Group menu. 2. Navigate to the User Group List page.
On the User Group List page, click the Create User Group button. 3. Navigate to the Create User Group page.
- Enter the required information in the Basic Information Entry, Add User, Policy Connection, and Additional Information Entry areas.
Category Required statusDetailed description User group name Required Enter user group name - using Korean, English, numbers, and special characters (
+=,.@-_) as a value of 3 to 24 characters
Explanation Select Description of the user group name - Detailed description of the user group name, up to 1,000 characters allowed
User Select User to add to the user group - The list of users registered in the Account is displayed, and when a checkbox is selected, the selected user’s name appears at the top of the screen
- At the top of the screen, click the X button for each user, or uncheck the checkbox in the user list to cancel the selection of the selected user
- If there are no users to add, you can click User Creation at the bottom of the user list to first register a new user
- After user creation is complete, refresh the user list, and once the user appears, you can select the user
- For detailed information on creating a user group, see Create User for reference
policy Select Policy to attach to the user group - The list of policies registered in the Account is displayed, and when a checkbox is selected, the name of the selected policy appears at the top of the screen
- At the top of the screen, you can click the X button for each policy, or deselect the checkbox in the policy list to cancel the selection of a policy
- If there is no policy to attach, you can click Create Policy at the bottom of the policy list to first register a new policy
- After creating the policy, refresh the policy list; once the policy appears, you can select it
- For detailed information on creating policies, see Create Policy for reference
tag Select Tags to add to the user group - can be added up to a maximum of 50 per resource
Table. User group creation information input fields - using Korean, English, numbers, and special characters (
- Enter the required information in the Basic Information Entry, Add User, Policy Connection, and Additional Information Entry areas.
Create button, click it.
When the popup indicating creation opens, click the Confirm button. 5. Navigate to the User Group List page.
Check user group detailed information
In the user groups, you can view and edit the list of user groups and their detailed information. The User Group Detail page consists of Basic Information, Users, Policies, Tags tabs.
To view detailed information of the user group service, follow these steps.
- All Services > Management > IAM Click the menu. 1. Go to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the User Group menu. 2. Go to the User Group List page.
- User Group List page, click the user group name to view its details. 3. Go to the User Group Details page.
- User Group Detail page displays basic information, and consists of Basic Information, Users, Policies, Tags tabs.
Basic Information
User Group List page allows you to view the basic information of the selected user group and, if necessary, edit the user group name and description.
| Category | Detailed description |
|---|---|
| service | Service Name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name
|
| Resource ID | Unique Resource ID |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Modifier | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| User group name | Name of the user group |
| Explanation | Description of the user group name |
User
User Group List page lets you view the users included in the selected user group and, if needed, add or delete users.
| Category | Detailed description |
|---|---|
| Exclude | Exclude users from the user group
|
| Add user | Add another user to the user group
|
| Username | User’s name |
| User group | Number of user groups the user belongs to
|
| Creation date and time | User creation timestamp |
Policy
User Group List page allows you to view the policy attachment information of the selected user group, and, if necessary, modify the policy attachment information for the user group.
| Category | Detailed description |
|---|---|
| Disconnect | Disconnect the selected policy
|
| Policy connection | Connect a new policy to the user group
|
| Policy name | Policy name |
| Policy Type | Type of attached policy
|
| Explanation | Explanation of the policy |
| Creation date and time | Policy creation timestamp |
| Modification date and time | Policy modification date and time |
Tag
User Group List page allows you to view the tag information of the selected user group, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Manage user groups
You can rename a user group, add users, attach policies, or modify tags. If you need to manage user groups, you can perform tasks on the User Group List or User Group Details page.
Edit Basic Information
You can edit the name and description of a user group. To modify the name and description of a user group, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User Group menu. 2. Go to the User Group List page.
- On the User Group List page, click the user group name whose basic information you want to edit. 3. Navigate to the User Group Details page.
- After confirming the basic information to be edited on the User Group Details page, click the Edit button.
- User Group Name: You can change the user group name. * Edit button click opens the Edit User Group Name popup.
- Description: You can edit the description of a user group. * Edit button click opens the Edit Description popup window.
- After editing the content to be changed in the popup window, click the Confirm button.
Manage Users
You can add or remove users from a user group.
Add User
To add a user to a user group, follow the steps below.
Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the User Group menu. 2. Go to the User Group List page.
User Group List page, click the user group name to which you want to add a user. 3. Navigate to the User Group Details page.
On the User Group Details page, click the User tab. 4. Go to the User tab.
In the User tab, click the Add User button. 5. Go to the Add User page.
On the Add User page, select the user you want to add from the User list, then click the Complete button. 6. A popup window notifying the addition of a user opens.
Category Detailed description Added user Display users included in the user group User Select users to add to the user group from the list of users registered in the Account - When the checkbox is selected, the name of the selected user group is displayed at the top of the list
- You can remove the added user by clicking the X button next to the user’s name at the top of the list, or by unchecking the checkbox in the user list
- If the desired user is not present, you can click the Create User item at the bottom of the user list to register a new user first
- After creating the user, refresh the user list and then you can select the newly created user
- For detailed information on creating users, see Create User
Table. User addition detailed itemsIn the popup that notifies you of adding a user, click the Confirm button. 7. You can view the added user in the list of the User tab.
Exclude user
To exclude a user from a user group, follow these steps.
- Click the All Services > Management > IAM menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the User Group menu. 2. Navigate to the User Group List page.
- User Group List page, click the user group name to exclude the user. 3. Navigate to the User Group Details page.
- On the User Group Details page, click the User tab. 4. Go to the User tab.
- In the User tab, select the user to exclude from the displayed user list, then click the Exclude User button.
- The selected user is excluded and the user list is refreshed.
Manage Policies
You can attach a policy to a user group or detach an attached policy.
Connect Policy
To attach a policy to a user group, follow these steps.
Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management(IAM).
On the Service Home page, click the User Group menu. 2. Navigate to the User Group List page.
User Group List page, click the user group name to which you want to attach the policy. 3. Navigate to the User Group Details page.
On the User Group Details page, click the Policy tab. 4. Go to the Policy tab.
In the Policy tab, click the Attach Policy button. 5. Navigate to the Policy Attachment page.
After selecting the policy to attach to the user group, click the Complete button. 6. A popup window notifying the policy connection opens.
Category Detailed description Linked policy Display policies directly attached to the user group policy Select a policy to attach to the user group from the list of policies registered in the Account - When you select the checkbox, the selected policy name is displayed at the top of the list
- You can cancel the policy by clicking the X button of the added policy name at the top of the list, or by unchecking the checkbox in the policy list
- If there is no policy to attach, you can first create a new policy by clicking the Create Policy item at the bottom of the policy list
- After creating the policy, refresh the policy list and you can select the newly created policy
- For detailed information on creating policies, see Create Policy reference
Table. Policy Connection DetailsIn the popup that notifies about policy linking, click the Confirm button. 7. You can view the attached policy in the list of the policy tab.
Disconnect policy
To detach the policies linked to a user group, follow these steps.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the User Group menu. 2. Go to the User Group List page.
- On the User Group List page, click the user group name to detach its policy connection. 3. Navigate to the User Group Details page.
- On the User Group Details page, click the Policy tab. 4. Go to the Policy tab.
- In the Policy tab, select the policy to disconnect from the displayed policy list, then click the Disconnect button.
- The selected policy is disconnected and the policy list is refreshed.
Manage Tags
You can edit the tags of a user group. To modify tags in a user group, follow these steps.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the User Group menu. 2. Go to the User Group List page.
- Click the user group name whose tag information you want to edit on the User Group List page. 3. Go to the User Group Details page.
- On the User Group Detail page, click the Tag tab. 4. Navigate to the Tag tab.
- In the Tag tab, click the Edit Tag button.
- After adding or editing tags, click the Save button. 6. A popup window notifying tag editing opens.
- You can modify the Key and Value of an already registered tag.
- You can click the Add Tag button to add a new tag.
- Click the X button before the added tag to delete that tag.
- Click the Confirm button. 7. You can view the edited tag information in the list.
Delete user group
To delete a user group, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the User Group menu. 2. Navigate to the User Group List page.
- User Group List page, click the user group name you want to delete. 3. Navigate to the User Group Details page.
- On the User Group Details page, click the Delete User Group button.
- The user group is deleted, and you are redirected to the User Group List page.
To delete multiple user groups simultaneously, follow these steps.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the User Group menu. 2. Go to the User Group List page.
- Check the user groups to delete from the user group list.
- Check the selected user groups, and click the Delete button.
- The selected user groups are deleted and the User Group List page is refreshed.
10.4.2.2 - Users
Users can create the service by entering the required policy information and selecting detailed options through the Samsung Cloud Platform Console.
Create User
To create a user, follow these steps.
Click the All Services > Management > IAM menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
On the Service Home page, click the User menu. 2. Navigate to the User List page.
On the User List page, click the Create User button. 3. Navigate to the User Creation page.
On the User Creation page, after entering the required information in the Basic Information Input, Permission Settings, and Additional Information Input sections, click the Create button. 4. A popup window notifying user creation opens.
Category Required statusDetailed description Username Required Enter a value within 64 characters for the user’s name - using English letters, numbers, and special characters (
+=,.@-_).
Explanation Select Description of the username - Enter a detailed description of the username, up to 1,000 characters
Password Required There are two ways to generate a password for user use. - Automatic generation: The password is generated automatically and can be viewed at the time of user creation
- Direct input: The password is created manually
Password change settings Select Password change setting at first user login - If not set, the user cannot change the password at first login, but can reset it again via Password Reset
- For details on password reset, see Change Password
Permission configuration method Required - Add to User Group: Select a user group from the list of user groups registered in the Account to include the user
- When you select the checkbox, the selected user group name is displayed at the top of the list
- You can cancel the user group by clicking the X button of the added user group name at the top of the list, or by unchecking the checkbox in the user group list
- If there is no user group to connect, you can first register a new user group by clicking the Create User Group item at the bottom of the user group list
- After creating the user group, you can select the newly created user group by refreshing the user group list
- For detailed information on creating a user group, see Create User Group
- Permission Summary: Displays the list of policies directly attached to the selected user or attached via user groups in the user selection list
- When you select the checkbox, the selected policy name is displayed at the top of the list
- If there is no policy to connect, you can first register a new policy by clicking the Create Policy item at the bottom of the policy list
tag Select Tags to add to the user group - Tags can be added up to a maximum of 50 per resource
Table. User-generated information input fields- using English letters, numbers, and special characters (
In the popup that notifies user creation, click the Create button. 5. IAM user login information The popup window opens.
After verifying the IAM user login information, click the Confirm button. 6. Go to the User List page.
Category Detailed description Account ID Account ID value Username Generated user name Password Generated user’s password - View Click the icon to view the password
IAM user login URL IAM user’s login URL information Excel download Download IAM user login information as an Excel file Send email Send an Excel file containing IAM user login information via email - After clicking the button, enter the address to receive the email
Table. IAM user login information items
- If you enter the password incorrectly five or more times, you will be automatically logged out.
- It must contain at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%&*^). - The length must be 9 to 20 characters.
- ID or username cannot be used as a password.
- You cannot use the same character more than three times.
- Passwords that are easy to guess cannot be used.
- You cannot use a recently used password.
- Consecutive characters or numbers of four or more are not allowed.
- The password change interval is 90 days.
View user details
In the user section, you can view and edit the user list and detailed information. User Details page is composed of Basic Information, User Groups, Permissions, Authentication Key, Tags tabs.
To view detailed information of the user service, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Navigate to the User List page.
- On the User List page, click the user name to view detailed information. 3. Navigate to the User Details page.
- User Details page displays basic information and consists of Basic Information, Users, Permissions, API Keys, Tags tabs.
Basic Information
User List page allows you to view the basic information of the selected user and, if necessary, edit the user’s description and options.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name
|
| Resource ID | Unique Resource ID |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Username | User’s name |
| Last login | User’s last login time |
| Explanation | Description of the username |
| Password | Date and time the password was last changed
|
| Password reuse restriction | Prevent reuse of recently used passwords
|
| Email verification status | |
| mobile phone number | Mobile phone number verification status |
User group
On the User List page, you can view the user groups assigned to the selected user and, if necessary, add or remove user groups.
| Category | Detailed description |
|---|---|
| Exclude | Exclude the user from the user group
|
| Add user group | Add the user to another user group
|
| User group name | Name of the user group |
| Linked policy | Number of policies linked to the user group
|
| Explanation | Description of the user group |
| Modification date | Date and time the user group was modified |
Policy
On the User List page, you can view the selected user’s policy information and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Disconnect | Disconnect the selected policy
|
| More | Direct connection can be disconnected or excluded from a user group
|
| Add permission | Connect a new policy to a user
|
| Policy name | Policy name
|
| type | Types of policies |
| Explanation | Explanation of the policy |
| Connection method | Policy attachment method
|
| Modification date | Date and time of the last policy modification |
Authentication key
On the User List page, you can view the authentication key information of the selected user.
| Category | Detailed description |
|---|---|
| Access Key | Authentication key information |
| Secret Vault | Use encryption |
| Creation date and time | Authentication key generation time |
| Expiration date and time | Authentication key expiration timestamp |
| status | Authentication key usage (enabled/disabled) |
Tag
On the User List page, you can view the selected user’s tag information and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Manage Users
You can change a user’s basic information, add user groups, or edit tags. If user management is required, you can perform tasks on the User List or User Details page.
Edit basic information
You can edit the user’s basic information.
Edit description
To modify the user’s description, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Navigate to the User List page.
- Click the user name whose description you want to edit on the User List page. 3. Navigate to the User Details page.
- On the User Details page, view the description and click the Edit button. 4. Edit description The popup window opens.
- Edit Description After changing the description in the popup window, click the Confirm button.
Change Password
To change a user’s password, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Navigate to the User List page.
- User List page, click the username whose password you want to edit. 3. Navigate to the User Details page.
- On the User Details page, click the Edit password button. 4. Password Reset the popup window opens.
- After changing the password, click the Confirm button. 5. IAM user login information The popup window opens.
- Password has the following two settings.
- Automatic Generation: A random password is generated.
- Manual entry: It is generated with a password entered directly by the user. * It must contain at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%&*^). * Please refer to the password creation rules.
- Password Change Setting: It is recommended to change the password upon first login after resetting the password.
- Password has the following two settings.
- It must contain at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%&*^). - The length must be between 9 and 20 characters.
- ID or username cannot be used as a password.
- You cannot use the same character more than three times.
- Passwords that are easy to guess cannot be used.
- You cannot use a password that was recently used.
- Consecutive characters or numbers of four or more cannot be used.
- The password change cycle is 90 days.
- After reviewing the user-generated information, click the Confirm button. 6. Password change completed.
Category Detailed description Account ID Account ID value Username Generated user name Password Generated user’s password - View Click the icon to view the password
IAM user login URL IAM user’s login URL information Excel download Download IAM user login information as an Excel file Email sending Send an Excel file containing IAM user login information via email - After clicking the button, enter the address to receive the email
Table. IAM user login information items
Restrict password reuse
Specify the number of password histories to check to prevent reuse of recently used passwords. To restrict users from reusing passwords, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Navigate to the User List page.
- On the User List page, click the username to edit the password reuse restriction. 3. Navigate to the User Details page.
- On the User Details page, click the Edit button for the secret code reuse restriction. 4. Password reuse restriction edit The popup window opens.
- Password reuse restriction: Select the number of recent password history entries as a number between 1 and 24.
- Please click the Confirm button. 5. The Password reuse restriction count has been changed.
User Group Management
You can add a user to a user group or remove a user from a user group.
Add user group
To add a user to a user group, follow the steps below.
All Services > Management > IAM menu, click it. 1. Go to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the User menu. 2. Navigate to the User List page.
On the User List page, click the user name to add to the user group. 3. Navigate to the User Details page.
On the User Details page, click the User Group tab. 4. Navigate to the User Group tab.
Click the Add User Group button in the User Group tab. 5. Navigate to the Add User Group page.
On the Add User Group page, select the user group you want to add from the User Group list, then click the Done button. 6. A popup window notifying the addition of a user group opens.
Category Detailed description Added user group Display user groups that contain the user Add to user group Select the user group to which you want to add a user from the list of user groups registered in the Account - When you select the checkbox, the name of the selected user group is displayed at the top of the list
- You can remove the added user group at the top of the list by clicking its X button, or by unchecking the checkbox in the user group list
- If the desired user group is not present, you can click the Create User Group item at the bottom of the user group list to register a new user group first
- After creating the user group, refresh the user group list and then you can select the newly created user group
- For detailed information on creating user groups, see Create User Group
Table. User group addition detailed itemsIn the popup that notifies you of adding a user group, click the Confirm button. 7. You can view the added user group in the list of the User Group tab.
Exclude user group
To remove a user from a user group, follow these steps.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Go to the User List page.
- On the User List page, click the username to exclude from the user group. 3. Navigate to the User Details page.
- On the User Details page, click the User Group tab. 4. Navigate to the User Group tab.
- In the User Group tab, select the user group to exclude from the displayed user group list, then click the Exclude User Group button.
- The selected user group is excluded and the user group list is refreshed.
Managing Permissions
You can attach a policy or detach an attached policy to configure user permissions.
Add Permission
You can add users to a user group to associate a policy, or associate a policy directly with the user.
To add permissions to a user, follow the steps below.
All Services > Management > IAM Click the menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the User menu. 2. Navigate to the User List page.
User List page, click the user name to which you want to add permissions. 3. User Details page is opened.
On the User Details page, click the Permissions tab. 4. Go to the Permissions tab.
Click the Add Permission button in the Permission tab. 5. Navigate to the Add Permission page.
After selecting the method to add permissions, enter the required information.
Category Required statusDetailed description Permission addition method Required - Add to User Group: Select a user group from the list of user groups registered in the Account to include the user
- When the checkbox is selected, the selected user group name is displayed at the top of the list
- Click the X button next to the added user group name at the top of the list, or uncheck the checkbox in the user group list to remove that user group
- If there is no user group to connect, click the Create User Group item at the bottom of the user group list to register a new user group first
- After creating a user group, refresh the user group list and then you can select the newly created user group
- For details on creating a user group, see Create User Group
- Permission Summary: Displays the list of policies directly attached to the selected user or attached via the user’s groups
- When the checkbox is selected, the selected policy name is displayed at the top of the list
- If there is no policy to connect, click the Create Policy item at the bottom of the policy list to register a new policy first
Table. Detailed items for adding permissions- Add to User Group: Select a user group from the list of user groups registered in the Account to include the user
When you finish entering the information, click the Complete button.
When the popup notifying you of added permissions opens, click the Confirm button. 8. You can view the attached policies in the list of the Permissions tab.
Revoke permission
You can detach policies attached to the user.
To detach the policy linked to a user, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Navigate to the User List page.
- User List page, click the username to revoke its permissions. 3. Navigate to the User Details page.
- User Details page, click the Permissions tab. 4. Go to the Permissions tab.
- In the Policy list, select the policy to disconnect, then click the Disconnect button. 5. A popup notifying of the disconnection opens.
- After clicking the More button, you can either detach the directly linked policy or exclude only the user groups that contain the user.
- After reviewing the policy information that is being disconnected, click the Confirm button. 6. The policy connection will be disconnected.
Manage Tags
You can edit the user’s tags. To edit tags for a user, follow the steps below.
- Please click the All Services > Management > IAM menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Navigate to the User List page.
- On the User List page, click the user name whose tag information you want to edit. 3. Navigate to the User Details page.
- User Details page, click the Tag tab. 4. Go to the Tag tab.
- On the Tag tab, click the Edit Tag button.
- After adding or editing tags, click the Save button. 6. A popup window indicating tag editing opens.
- You can modify the Key and Value of an already registered tag.
- Click the Add Tag button to add a new tag.
- Click the X button in front of the added tag to delete that tag.
- Click the Confirm button. 7. You can view the edited tag information in the list.
Delete User
To delete a user, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the User menu. 2. Navigate to the User List page.
- On the User List page, click the user name to delete. 3. Navigate to the User Details page.
- Click the Delete User button on the User Details page.
- The user is deleted, and you are redirected to the User List page.
To delete multiple users simultaneously, follow these steps.
- Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the User menu. 2. Go to the User List page.
- Check the users to be deleted from the user list.
- Check the selected users and click the Delete button.
- The selected users are deleted and the User List page is refreshed.
10.4.2.3 - Policy
Users can create the service by entering the required policy information and selecting detailed options through the Samsung Cloud Platform Console.
Create Policy
To create a policy, follow these steps.
Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
On the Policy List page, click the Create Policy button. You will be taken to the Create Policy page.
After entering the required information in the Basic Information Input and Additional Information Input sections, click the Next button. You will be taken to the Permission Settings section.
Category RequiredDetailed description Policy Name Required Enter policy name - using Korean, English, numbers, and special characters (
+=,.@-_) as a value of 3 to 128 characters
Explanation Select Description of the policy name - Enter a detailed description of the policy name, up to 1,000 characters
tag Selection Tags to add to the policy - Tags can be added up to a maximum of 50 per resource
Table. Policy creation information input fields - basic information and additional information- using Korean, English, numbers, and special characters (
Select the service for which you want to set permissions. The permission settings will be displayed below the selected service name.
- You can select a desired service or configure all services.
Enter the required information in the Permission Settings area.
Category Required statusDetailed description Control Type Required Select policy control type - Allow Policy: A policy that permits the defined permissions
- Deny Policy: A policy that denies the defined permissions
Action Required Select actions provided per service - Actions that can select individual resources are shown in purple
- Actions that target all resources are shown in black
- Add Action Directly: Use the wildcard
*to specify multiple actions at once
Applied resource Required Resources to which the action applies - All resources: Apply the selected action to all resources
- Individual resource: Apply the selected action only to the specified resources
- Individual resources are only available when selecting a purple action that allows individual resource selection
- Click the Add resource button to specify target resources by resource type
- For more information about Add resource, see Register individual resources as applied resources
Authentication Type Required Authentication method of the user target to which the policy will be applied - All authentication: Apply regardless of authentication method
- Authentication key authentication: Apply to users authenticated with an authentication key
- Temporary key authentication, Console login: Apply to users with temporary key authentication or Console login
Applied IP Required IP that allows policy application - Custom IP: Users directly register and manage the IP
- Applied IP: IP to which the policy is applied, which users can register directly as an IP address or range
- Excluded IP: IP to be excluded from Applied IP, which can be registered as an IP address or range
- All IP: No IP access restriction
- Access is allowed for all IPs, but if exceptions are required, you can register Excluded IP to restrict access for those IPs
Additional condition Selection Add conditions for attribute-based access control (ABAC) - Condition Key: Select from the list of Global condition keys and service condition keys
- Qualifier: Default value, arbitrary value in the request, all values in the request
- Operator: Bool, Null
- Value: True, False
Table. Policy creation information input fields - Permission settings
In permission settings, Basic Mode and JSON Mode are provided.
- In Basic Mode, after writing and entering JSON Mode or navigating the screen, services with identical conditions are merged into one, and services that have not completed configuration are deleted.
- If the content written in JSON mode does not conform to JSON format, you cannot switch to basic mode.
- In the Permission Settings area, first select the service for which you want to set permissions.
- You can load an existing registered policy and create a policy using Load Policy. For detailed information about Load Policy, refer to Load Policy.
- Click the Next button. It navigates to the Check Input Information page.
- After reviewing the input information, click the Create button.
- When the popup notifying policy creation opens, click the Confirm button. You will be redirected to the Policy List page.
Load Policy
You can load an existing policy to refer to when creating a new policy. To load an existing policy, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- On the Policy List page, click the Create Policy button. You will be taken to the Create Policy page.
- Enter the required information in the Basic Information Input, Additional Information Input sections.
- Click the Next button. Go to the Permission Settings area.
- Load Policy button, click it. Load Policy popup opens.
- The list of policies registered in the Account is displayed. Select the policy you want to load and click Confirm.
- The loaded policy is entered into the Permission Settings area and can be edited.
Register individual resources as applied resources
In the Permission Settings area, you can register individual resources as applied resources. To register an individual resource as an applied resource, follow these steps.
- Click the All Services > Management > IAM menu. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- On the Policy List page, click the Create Policy button. You will be taken to the Create Policy page.
- Basic Information Input, Additional Information Input Enter the required information in the area.
- Click the Next button. Navigate to the Permission Settings area.
- In the Permission Settings area, select the service to configure permissions.
- Select an Action that allows selecting individual resources in the Action selection.
- Actions that allow individual resource selection are displayed in purple.
- In Applied Resource, click Individual Resource.
- Click the Add Resource button. The Add Resource popup window opens.
- Add Resource In the Add Resource tab, add the resources to which the policy will be applied. Resource addition can be done in two ways: Select Resource, Direct Input.
- Resource Selection: Check the resources retrieved for each Resource Type and select them.
- Manual entry: Add the target resource by manually entering it for each resource type.
- Wildcard
*,?can be used. Checking Select All adds all resources of that resource type, and any resources added later are automatically included.
- Wildcard
- Check the input information and click the Confirm button.
Check detailed policy information
In the policy, you can view and edit the policy list and detailed information. The Policy Details page consists of Basic Information, Permissions, Connected Targets, Tags tabs.
To view detailed information of the policy service, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. Navigate to the Policy List page.
- Click the policy name on the Policy List page to view its details. You will be taken to the Policy Details page.
- Policy Details page displays basic information and consists of Basic Information, Permissions, Connected Targets, Tags tabs.
Basic Information
Policy List page allows you to view the basic information of the selected policy and, if needed, edit the policy name and description.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name
|
| Resource ID | Unique Resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Policy Name | Policy name |
| Policy type | Policy Types
|
| description | Description of the policy name |
Permission
On the Policy List page, you can view the permission information of the selected policy and modify the permissions if needed.
- Click the Expand button of the service name to view permission information, and the detailed policy information will be displayed.
| Category | Detailed description |
|---|---|
| Edit permissions | Permission editing is possible
|
| View mode | Policy control type
|
| Control Type | Policy control type
|
| Action | The functions provided by each service that are subject to the policy |
| Applied resource | Resources to which the action applies
|
| Authentication Type | Authentication method of the user target to which the policy will be applied
|
| Applied IP | IP that permits policy application
|
Connection target
Policy List page allows you to view the user groups registered to the selected policy, and, if necessary, add or remove user groups.
- User Group for detailed information, please refer to 사용자 그룹.
| Category | Detailed description |
|---|---|
| User | List of users connected to the policy
|
| User group | List of user groups linked to the policy
|
| role | Display list of roles attached to the policy
|
tag
Policy List page allows you to view the tag information of the selected policy, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Manage Policies
You can change the policy name, as well as modify permissions, connection targets, and tags. If policy management is required, you can perform tasks on the Policy List or Policy Details page.
Edit Basic Information
You can edit the policy’s name and description. To modify the policy’s name and description, follow the steps below.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- Policy List page, click the policy name whose basic information you want to edit. You will be taken to the Policy Details page.
- On the Policy Details page, after confirming the basic information to be edited, click the Edit button.
- Policy Name: You can change the policy name. Edit button click opens the Edit Policy Name popup.
- Description: You can edit the policy description. Edit button click opens the Edit Description popup.
- After editing the content to be changed in the popup window, click the Confirm button.
Managing Permissions
You can modify the policy’s permissions. To modify the policy’s permissions, follow the steps below.
- All Services > Management > IAM Click the menu. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- On the Policy List page, click the policy name whose permissions you want to edit. You will be taken to the Policy Details page.
- On the Policy Details page, click the Permissions tab. Navigate to the Connection Permissions tab.
- On the Policy Details page, click the Edit Permissions button. You will be taken to the Edit Permissions page.
- On the Permission Modification page, after modifying the required permissions, click the Next button. You will be taken to the Input Information Confirmation page.
- For detailed explanations of each item in the permission information, refer to Creating a Policy.
- On the Check Input Information page, verify the updated permission information and click the Done button. Then go to the Permissions tab.
Managing User Connections
- In the Policy > Connection Targets tab, you can view the users registered to the policy and, if necessary, connect or disconnect users.
- For detailed information about User, please refer to 사용자.
Connect User
To attach a user to the policy, follow these steps.
- All Services > Management > IAM menu, click it. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- Policy List page, click the policy name to link the user. You will be taken to the Policy Details page.
- On the Policy Details page, click the Connection Target tab. You will be taken to the Connection Target tab.
- In the Connection Target tab, click the User Connection button. Go to the User Connection page.
- On the User Connection page, select the user you want to connect from the User list, then click the Done button. A popup notifying the user connection will open.
Category Detailed description Connected user group Display users linked to the policy User group Select the user to attach the policy from the list of users registered in the Account - When you select the checkbox, the selected user’s name appears at the top of the list
- You can remove the user by clicking the X button next to the added user name at the top of the list, or by unchecking the checkbox in the user list
- If the desired user is not present, you can click the Create User item at the bottom of the user list to register a new user first
- After creating the user, refresh the user list and then you can select the newly created user
- For detailed information on creating users, see Create User
Table. User connection details - In the popup that notifies you of a user connection, click the Confirm button. You can view the connected user in the list on the User tab.
Disconnect User
To disconnect a user linked to the policy, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- Policy List page, click the policy name to disconnect the user. You will be taken to the Policy Details page.
- On the Policy Details page, click the Target Connection tab. You will be taken to the Target Connection tab.
- In the Connection Target tab’s user group list, select the user to disconnect, then click the Disconnect button. A popup confirming the disconnection will appear.
- Click the Confirm button in the popup that notifies of disconnection. The selected user’s connection will be terminated and the user group list will be refreshed.
Manage user group connections
- In the Policy > Connection Targets tab, you can view the user groups registered to the policy and, if needed, connect or disconnect user groups.
- User Group for detailed information, please refer to User Group.
Connect User Group
To connect a user group to a policy, follow the steps below.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- Policy List page, click the policy name to associate the user group. You will be taken to the Policy Details page.
- Policy Details page, click the Connection Target tab. You will be taken to the Connection Target tab.
- In the Connection Target tab, click the User Group Connection button. Navigate to the User Group Connection page.
- On the User Group Connection page, select the user group you want to connect from the User Group list, then click the Done button. A popup notifying the user group connection will open.
Category Detailed description Connected user group Display user groups linked to the policy User group Select the user group to which the policy will be attached from the list of user groups registered in the Account - When you select the check box, the selected user group’s name appears at the top of the list
- You can remove the added user group at the top of the list by clicking its X button or by unchecking the box in the user group list
- If the desired user group is not present, you can first register a new user group by clicking the Create User Group item at the bottom of the user group list
- After creating the user group, refresh the user group list and then select the newly created user group
- For detailed information on creating a user group, see 사용자 그룹 생성하기
Table. User Group Connection Details - Click the Confirm button in the popup that notifies you of the user group connection. You can view the connected user group in the list under the User Group tab.
Disconnect User Group
To disconnect the user groups linked to the policy, follow these steps.
- Click the All Services > Management > IAM menu. Then go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- Click the policy name to detach the user group connection on the Policy List page. You will be taken to the Policy Details page.
- On the Policy Details page, click the Target Connection tab. You will be taken to the Target Connection tab.
- In the user group list of the Connection Target tab, select the user group to disconnect, then click the Disconnect button. A popup confirming the disconnection will appear.
- Click the Confirm button in the popup that notifies of disconnection. The selected user group’s connection will be disconnected, and the user group list will be refreshed.
Manage Role Bindings
- Policy > Connected Targets tab, you can view the roles registered to the policy and, if needed, connect or disconnect roles.
- For detailed information about role, please refer to 역할.
Connect role
To attach a role to a policy, follow these steps.
- Click the All Services > Management > IAM menu. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- On the Policy List page, click the policy name to which you want to assign a role. You will be taken to the Policy Details page.
- On the Policy Details page, click the Connection Target tab. You will be taken to the Connection Target tab.
- In the Connection Target tab, click the Role Binding button. You will be taken to the Role Binding page.
- On the Role Connection page, select the role you want to connect from the Role list, then click the Complete button. A popup notifying you of the role connection will open.
Category Detailed description Linked role Display roles linked to the policy role Select the role to attach the policy from the list of roles registered in the Account - When you select the checkbox, the selected role appears at the top of the list
- You can cancel the role by clicking the X button next to the role name added at the top of the list, or by unchecking the checkbox for the role
- If the desired role is not available, you can click the Create Role item at the bottom of the role list to create a new role first
- After role creation is complete, refresh the role list and then you can select the newly created role
- For detailed information on creating roles, see Create Role
Table. Role Connection Detailed Items - In the popup that notifies role linking, click the Confirm button. You can view the linked role in the list under the Roles tab.
Unlink role
To detach the role linked to the policy, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. Navigate to the Policy List page.
- On the Policy List page, click the policy name to detach role connections. You will be taken to the Policy Details page.
- On the Policy Details page, click the Target Connection tab. You will be taken to the Target Connection tab.
- After selecting the role to disconnect from the list in the Connection Target tab, click the Disconnect button. A popup notifying the disconnection will open.
- Click the Confirm button in the popup that notifies you of the disconnection. The selected role’s connection will be removed and the role list will be refreshed.
Tag Management
You can edit the policy’s tags.
To modify tags in the policy, follow the steps below.
- All Services > Management > IAM Click the menu. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- On the Policy List page, click the policy name to add a user. You will be taken to the Policy Details page.
- On the Policy Details page, click the Tag tab. You will be taken to the Tag tab.
- Click the Edit Tag button in the Tag tab.
- After adding or editing a tag, click the Save button. A popup notifying you of the tag edit will open.
- You can modify the Key and Value of an already registered tag.
- You can add a new tag by clicking the Add Tag button.
- Click the X button in front of the added tag to delete that tag.
- Click the Confirm button. You can view the edited tag information in the list.
Delete Policy
To delete a policy, follow the steps below.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- Policy List page, click the policy name to delete. You will be taken to the Policy Details page.
- On the Policy Details page, click the Delete Policy button.
- The policy is deleted, and you are taken to the Policy List page.
To delete multiple policies simultaneously, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Policy menu. You will be taken to the Policy List page.
- Select the policy to delete from the policy list.
- Verify the selected policies and click the Delete Policy button.
- The selected policies are deleted and the Policy List page is reloaded.
10.4.2.4 - Role
Users can create a role with separate permissions and switch from their own account to another role to access the Account.
Create Role
To create a role, follow the steps below.
Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the Role menu. Navigate to the Role List page.
On the Role List page, click the Create Role button. You will be taken to the Create Role page.
On the Role Creation page, enter the information required to create a role, then click the Create button.
- Please enter Basic Information Input.
Category Whether requiredDetailed description Role Name Required Enter the role name - using English letters, numbers, and special characters (
+=-_@,.) within 64 characters
description Selection Enter a description of the role within 1,000 characters. Maximum session duration Required Enter the session time allowed for the user when switching roles in the console - Select duration: 1 hour, 2 hours, 4 hours, 8 hours, 12 hours
- Enter duration: can be entered in seconds from 3,200 seconds (1 hour) to 43,200 seconds (12 hours)
Table. Role Creation Basic Information Items - using English letters, numbers, and special characters (
- Connect performing entity.
Category Required statusDetailed description Category Required Select the execution entity - Current Account, Other Account, User SRN, Credential Provider, Service
Value Required Enter the Value for the principal - Current Account: display the current Account ID
- Other Account: enter the Account ID to use this role
- User SRN: enter the SRN of the user registered in the Console
- Credential Provider: select the credential provider name
- Service: API Gateway, Config Inspection can be selected
Add Select Button to add an executor - Up to 20 connections can be added
Table. Role creation execution subject connection items - Connect the policy.
Category RequiredDetailed description policy Required Select the policy to attach to the role - When you select the checkbox, the selected policy name is displayed at the top of the list
- You can cancel the policy by clicking the X button next to the policy name added at the top of the list, or by unchecking the checkbox in the policy list
- If there is no policy to attach, you can first register a new policy by clicking the Create Policy item at the bottom of the policy list
- After creating the policy, refresh the policy list and then you can select the created policy
- For detailed information on policy creation, refer to 정책 생성하기
Table. Role creation policy mapping items - Please enter Additional Information.
Category Required statusDetailed description tag Select Tags to add to the role - tags can be added up to a maximum of 50 per resource
Table. Role creation additional information items
- Please enter Basic Information Input.
When the popup notifying role creation opens, click the Confirm button.
View role details
On the Role List page, you can view and edit the detailed information of the selected role.
To view detailed information about the role, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Role menu. You will be taken to the Role List page.
- On the Role List page, click the credential provider you want to view. You will be taken to the Credential Provider Details page.
- Role Details page displays basic information and consists of Basic Information, Responsible Entity, Policy, Tag tabs.
Basic Information
You can view and edit the basic information of the role.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name
|
| Resource ID | Unique Resource ID |
| constructor | User who created the service |
| Creation date | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Role Name | Role name |
| description | Description of the role proof provider
|
| Maximum session duration | Role session duration allowed for IAM users who assume a role in the Console
|
Executing entity
You can identify and manage the entity that performs the role.
| Category | Detailed description |
|---|---|
| Category | Executor name |
| Value | Value for the executing entity |
| Edit performer | Button to edit the performer
|
Policy
| Category | Detailed description |
|---|---|
| Disconnect | Detach the selected policy from the role
|
| Policy connection | Connect a new policy to a role
|
| Policy Name | Policy name
|
| type | Types of policies |
| description | Explanation of the policy |
| Modification date and time | Date and time of the last policy modification |
tag
You can view, add, modify, or delete the tag information of a credential provider.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Manage Roles
You can change a role’s basic information, as well as edit or delete its principal, attached policies, and tag information.
Edit Basic Information
You can modify the maximum session duration and description in the role details. To edit the basic information, follow these steps.
- Click the All Services > Management > IAM menu. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Role menu. You will be taken to the Role List page.
- Role List page, click the user role name to edit its basic information. Role Details page will be opened.
- After confirming the basic information to edit on the Role Details page, click the Edit button.
- Maximum Session Duration: You can set the role session duration allowed for IAM users who switch roles in the Console. When you click the Edit button, the Edit Maximum Session Duration popup opens.
- Description: You can edit the description of the role. Edit button click opens the Edit Description popup window.
- After editing the content to be changed in the popup window, click the Confirm button.
Managing the execution entity
You can add, modify, or delete the role’s performer.
To manage the role’s performer, follow these steps.
Click the All Services > Management > IAM menu. Navigate to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the Role menu. You will be taken to the Role List page.
On the Role List page, click the user name to edit the performer. You will be taken to the Role Details page.
Click the Performer tab on the Role Details page. Navigate to the Performer tab.
In the Executor tab, click the Edit Executor button. You will be taken to the Edit Executor page.
Edit Performer page, after editing the performer, click the Complete button. A popup notifying the performer edit will open.
Category RequiredDetailed description Category Required Select the execution entity - Current Account, Other Account, User SRN, Credential Provider, Service
Value Required Enter the Value for the principal - Current Account: Display the current Account ID
- Other Account: Enter the Account ID to use this role
- User SRN: Enter the user’s SRN registered in the Console
- Credential Provider: Select the credential provider name
- Service: API Gateway, Config Inspection selectable
Add Select Button to add a responsible party - You can add up to 20 connections
- You can delete an added responsible party by clicking its X button
Table. Execution subject modification itemsIn the popup that notifies you of a performer entity edit, click the Confirm button. You can verify the edited performer in the list on the Performer tab.
Manage Policies
You can attach a policy to a role or detach an attached policy.
Connect Policy
You can attach policies to a role.
To attach a policy to a role, follow these steps.
All Services > Management > IAM menu, click it. Navigate to the Service Home page of Identity and Access Management (IAM).
On the Service Home page, click the Role menu. You will be taken to the Role List page.
On the Role List page, click the role name to which you want to attach a policy. You will be taken to the User Details page.
On the Role Details page, click the Policy tab. Go to the Policy tab.
In the Policy tab, click the Policy Connection button. You will be taken to the Policy Connection page.
After selecting the policy to attach to the role, click the Complete button. A popup notifying the policy attachment will appear.
Category Detailed description Linked policy Display policies attached to the role policy Select a policy to attach to the role from the list of policies registered in the Account - When you select the checkbox, the selected policy name appears at the top of the list
- You can remove the policy by clicking the X button added at the top of the list or by unchecking the checkbox in the policy list
- If there is no policy to attach, you can first create a new policy by clicking the Create Policy item at the bottom of the policy list
- After creating the policy, refresh the policy list and then you can select the newly created policy
- For details on creating policies, see Create Policy reference
Table. Policy Connection DetailsClick the Confirm button in the popup that notifies you of the policy connection. You can view the connected policies in the list on the Policy tab.
Disconnect Policy
You can detach policies attached to a user.
To detach the policy linked to a user, follow these steps.
- Click the All Services > Management > IAM menu. Navigate to the Service Home page of Identity and Access Management (IAM).
- Service Home page, click the Role menu. You will be taken to the Role List page.
- On the Role List page, click the role name to detach the policy connection. You will be taken to the Role Details page.
- On the Role Details page, click the Policy tab. You will be taken to the Policy tab.
- After selecting the policy to disconnect from the policy list, click the Disconnect button. A popup notifying the disconnection will appear.
- After reviewing the policy information that will be disconnected, click the Confirm button. The policy connection will be terminated.
Managing Tags
You can add, edit, or delete tags for a role.
Follow the steps below to manage role tags.
- Click the All Services > Management > IAM menu. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Role menu. You will be taken to the Role List page.
- On the Role List page, click the role name to edit tag information. You will be taken to the Role Details page.
- On the Role Details page, click the Tag tab. You will be taken to the Tag tab.
- On the Tag tab, click the Edit Tag button.
- After adding or editing a tag, click the Save button. A popup notifying the tag edit will open.
- You can modify the Key and Value of an already registered tag.
- Click the Add Tag button to add a new tag.
- Click the X button in front of the added tag to delete that tag.
- Click the Confirm button. You can view the edited tag information in the list.
Switch role
To switch roles in the Samsung Cloud Platform Console, follow these steps.
Click the profile-shaped button at the top right of the Console. The My Menu popup window opens.
In the My menu popup, click the role switch button. The role switch popup opens.
Role Switch After entering the role switch information in the popup window, click the Confirm button.
Category required or notDetailed description Account ID Required Enter the Account ID the user wants to assume via role switching. Role Name Required Enter the role name the user wants to switch to. alias Select Name to use when a user enters through role switching Color Required Select the color to use as the Account background when entering a role - No selection: Apply the existing Account background color
Table. Role transition information itemsWhen the popup notifying a role change opens, click the Confirm button.
Check role
You can view the switched role information by clicking the profile-shaped button at the top right of the console.
| Provided features | explanation |
|---|---|
| Account ID | Account ID logged in to Samsung Cloud Platform Console |
| Role Name | Alias set when switching roles
|
| Time zone | User-set time zone
|
| Account | Account information
|
| Cost Management | You can view usage and billing details, payment history, and cost analysis, and manage Credit, budget, Account, and payment methods
|
| Login user information | IAM user name after role assumption and the user’s Account ID |
| Switch to my account | Switch to the IAM user account and go to the Console Home page
|
| Role Switching | Can switch to another role
|
| Logout | Log out from Samsung Cloud Platform Console |
Delete role
To delete a role, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- Service Home page, click the Role menu. You will be taken to the Role List page.
- On the Role List page, click the role name to delete. Navigate to the Role Details page.
- On the Role Details page, click the Delete Role button.
- The role is deleted, and you are redirected to the Role List page.
To delete multiple roles at once, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Role menu. You will be taken to the Role List page.
- Check the roles to delete from the role list.
- Verify the selected role and click the Delete Role button.
- The selected role is deleted and the Role List page is refreshed.
10.4.2.5 - Credential Providers
You can access and use the Account resource through a credential provider.
Create Credential Provider
To create a credential provider, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Credential Provider menu. You will be taken to the Credential Provider List page.
- On the Credential Provider List page, click the Create Credential Provider button. You will be taken to the Create Credential Provider page.
- After entering information in the Enter basic information, Enter additional information areas, click the Generate button.
| Category | Whether required | Detailed description |
|---|---|---|
| Credential Provider Name | Required | Enter the credential provider name
|
| description | Selection | Enter a description of the credential provider within 1,000 characters |
| type | Required | Select the credential provider type
|
| metadata | Selection | Attach the metadata file provided by the IdP
|
| tag | Select | Tags to add to the credential provider group
|
- When the popup notifying the creation of a credential provider opens, click the Confirm button.
Check credential provider details
You can view and edit the detailed information of a credential provider. The Credential Provider page consists of Basic Information, Tags tabs.
To view detailed information about the credential provider, follow these steps.
- All Services > Management > IAM Click the menu. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Credential Provider menu. You will be taken to the Credential Provider List page.
- Click the credential provider you want to view on the Credential Provider List page. You will be taken to the Credential Provider Details page.
- Credential Provider Details page displays basic information and consists of Basic Information tab, Tags tab.
Basic Information
You can view and edit the basic information of the credential provider.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name
|
| Resource ID | Unique Resource ID |
| constructor | User who created the service |
| Creation date | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Credential Provider Name | Credential provider name
|
| type | Types of credential providers |
| description | Description of the credential provider
|
| Login URL | Login URL |
| metadata | Metadata
|
tag
You can view, add, modify, or delete the tag information of a credential provider.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Delete Credential Provider
To delete a credential provider, follow these steps.
- All Services > Management > IAM menu, click it. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Credential Provider menu. You will be taken to the Credential Provider List page.
- On the Credential Provider List page, click the name of the credential provider you want to delete. You will be taken to the Credential Provider Details page.
- On the Credential Provider Details page, click the Delete Credential Provider button.
- The credential provider is deleted, and you are redirected to the Credential Provider List page.
To delete multiple credential providers simultaneously, follow these steps.
- Click the All Services > Management > IAM menu. You will be taken to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the Credential Provider menu. You will be taken to the Credential Provider List page.
- Select the credential provider to delete from the list of credential providers.
- Verify the selected credential provider and click the Delete Credential Provider button.
- The selected credential provider is deleted and the Credential Provider List page is refreshed.
10.4.2.6 - My Info.
My Info. provides basic user information and authentication key management functions.
My Info. # Check
User My Info. On the screen, you can view and edit the user’s basic information, and you can manage the authentication key.
To view the information of My Info., follow the steps below.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. Navigate to the page.
- My Info. The page displays basic information and consists of Basic Information, Authentication Key Management, Access IP Control, Service Settings tabs.
Basic Information
My Info. > Basic Information tab, you can view the user’s basic information and, if necessary, edit the email, password, mobile phone number, password reuse restriction, and time zone.
| Category | Detailed description |
|---|---|
| Username | User’s name |
| SRN | User’s SRN |
| User’s email | |
| mobile phone number | User’s mobile phone number |
| Password | User’s password |
| Password reuse restriction | User password reuse limit count |
| time zone | User’s time zone |
| Terms and Conditions | User’s name |
Authentication Key Management
My Info. > Authentication Key Management tab, you can view the user’s authentication key information and, if necessary, generate an authentication key.
| Category | Detailed description |
|---|---|
| authentication key | User-generated authentication key
|
| Security Settings | Security settings for authentication keys
|
Access IP control
My Info. > In the Access IP Control tab, you can register and manage IPs that are allowed to access.
| Category | Detailed description |
|---|---|
| Console access IP control | Whether to use the access IP control feature
|
| Access IP List | List of IP addresses that can access the console |
- The access IP control feature is available only to the Root user and IAM users. * ID Center and role members cannot be used.
- Even without using the access IP control feature, you can add and manage IP addresses.
Service Settings
My Info. In the Service Settings tab, you can view the user’s authentication key information and generate an authentication key if needed.
| Category | Detailed description |
|---|---|
| AI Recommendation Floating Guide | When used, an AI recommendation floating guide is provided at the bottom of the screen
|
Edit Basic Information
My Info. > Basic Information tab, you can edit email, password, mobile phone number, password reuse restriction, and time zone.
Edit email
You can edit the user’s email. To edit a user’s email, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. go to the page.
- My Info. On the Basic Information tab, click Edit Email. 3. Edit Email The popup window opens.
- Email Edit In the popup window, enter the characters displayed for anti-automatic input and press the Confirm button.
- Enter Email and click the Verify button. 6. A verification code will be sent to the entered email.
- Enter the verification code sent to the entered email and click the Confirm button.
- Click the Confirm button in the Edit Email popup. 8. Password Confirmation popup opens.
- Password Confirmation After entering the password in the popup window, click the Confirm button. 9. Go to the Basic Information tab.
- If you enter the password incorrectly five or more times, you will be automatically logged out.
- Please enter your email information accurately. * If you do not receive the verification code, check your spam folder.
Change Password
You can modify the user’s password. To change a user’s password, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Navigate to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the My Info. menu. 2. Navigate to the My Info. page.
- On the Basic Information tab of the My Info. page, click Change Password. 3. Change Password the popup window opens.
- In the Password Change popup window, please enter Current Password, New Password, and Confirm Password.
- Change Password in the popup window, click the Confirm button. 5. Go to the Basic Information tab.
Precautions when changing your password
- If you enter the existing password incorrectly more than five times, you will be automatically logged out.
- It must contain at least one each of uppercase letters (English), lowercase letters (English), digits, and special characters (
!@#$%&*^). - The length must be 9 to 20 characters.
- ID or username cannot be used as a password.
- You cannot use the same character more than three times.
- Passwords that are easy to guess cannot be used.
- You cannot use a password that was recently used.
- You cannot use consecutive characters or numbers of four or more.
- The password change interval is 90 days.
Edit mobile phone number
You can edit the user’s mobile phone number. To modify the user’s mobile phone number, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. Navigate to the page.
- On the Basic Information tab of the My Info. page, click the Change Mobile Phone Number button. 3. Change Mobile Phone Number a popup window opens.
- Change mobile phone number In the popup window, enter the characters displayed for anti-automation and press the Confirm button.
- Please select the mobile phone number authentication method.
- SMS authentication: Send authentication code via mobile phone SMS
- Authenticate with Knox Teams: Send authentication code via Knox Teams
- After entering the mobile phone number to change, click the Verify button.
- After entering the verification code sent via SMS or Knox Teams, click the Confirm button.
- Change mobile phone number popup, click the Confirm button. 8. Password Confirmation popup window opens.
- Password Confirmation In the popup window, after entering the password, click the Confirm button. 9. Navigate to the Basic Information tab.
- If you enter the password incorrectly five or more times, you will be automatically logged out.
- Please accurately enter your mobile phone number information. * If you do not receive the verification code, check your spam folder.
Modify password reuse restriction
You can modify the number of times a user can reuse a password. To change the password reuse limit count for a user, follow these steps.
- All Services > Management > IAM menu, click it. 1. Go to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. navigate to the page.
- On the Basic Information tab of the My Info. page, click Edit Password Reuse Restriction. 3. Edit password reuse restriction The popup window opens.
- Edit Password Reuse Restriction In the popup, select the number of recent passwords that cannot be reused.
- Password reuse restriction edit In the popup window, click the OK button. 5. Go to the Basic Information tab.
Modify Timezone
You can edit the user’s time zone. To modify the user’s time zone, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. Navigate to the page.
- On the Basic Information tab of the My Info. page, click Edit Time Zone. 3. Edit Timezone The popup window opens.
- Edit Timezone Select the user’s timezone.
- Edit Timezone in the popup window, click the Confirm button. 5. Go to the Basic Information tab.
Manage Authentication Keys
My Info. > Authentication Key Management You can create authentication keys and manage security settings in the tab.
Create authentication key
You can generate a user’s authentication key. To generate a user’s authentication key, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Navigate to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the My Info. menu. 2. Navigate to the My Info. page.
- My Info. Click the Authentication Key Management tab on the page. 3. Navigate to the Authentication Key Management tab.
- On the Authentication Key Management tab, click the Create Authentication Key button. 4. Go to the Create Authentication Key page.
- On the Create Authentication Key page, enter the Expiration Period and Usage Purpose.
- Expiration period can be entered as a number from 1 to 365.
- If you select permanent in the expiration period, it can be used permanently.
- Check the authentication key generation information and click the Create button. 6. Go to the Authentication Key Management tab.
- You can create up to two authentication keys.
- After generating a new authentication key, you must apply the updated API authentication key to the service you are using.
- In the security settings, you can configure the authentication method and allowed IP addresses.
- You can call the API with the generated authentication key to issue temporary keys, and you can issue up to five per authentication key.
Check authentication key details
To view the detailed information of the authentication key, follow the steps below.
- Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. Navigate to the My Info page.
- My Info. Click the Authentication Key Management tab on the page. 3. Go to the Authentication Key Management tab.
- In the Authentication Key Management tab, click the authentication key you want to view. 4. Navigate to the Authentication Key Details page.
- Authentication Key Details page consists of Basic Information, Authentication Key Management tabs.
Basic Information
Authentication Key Details > Basic Information tab allows you to view the basic information of the selected authentication key.
| Category | Detailed description |
|---|---|
| Use authentication key | Display whether the authentication key is used
|
| Delete authentication key | Delete the authentication key |
| authentication key | Access Key and Secret Key information
|
| Intended use | Purpose of the authentication key |
| Creation date and time | The date and time the user generated the authentication key |
| Expiration date and time | Expiration time of the user-generated authentication key |
| Secret Vault | Whether to use the Secret Vault service
|
User temporary key
Authentication Key Details > User Token tab allows you to view the list of tokens for the selected authentication key.
| Category | Detailed description |
|---|---|
| Delete | Delete the selected key from the user key list
|
| More | Select whether to use the API key selected from the user API key list
|
| Access Key | A unique string for calling the API |
| Secret Key | Security token used with the Access Key
|
| Creation date and time | The date and time the user generated the authentication key |
| Expiration date and time | Expiration time of the user-generated authentication key |
| status | Whether to use the authentication key |
Secret Vault temporary key
Authentication Key Details > Secret Vault Secret Key tab allows you to view the list of Secret Vault secret keys for the selected authentication key.
- You can check it when using the Secret Vault service.
- The temporary key can only be created via the API, and in the Secret Vault tab, you can only view and delete it.
| Category | Detailed description |
|---|---|
| Delete | Delete the selected key from the user key list
|
| More | Select the usage status of the selected user API key
|
| Access Key | A unique string for calling the API |
| Secret Key | Security token used with the Access Key
|
| Creation date and time | The date and time the user generated the authentication key |
| Expiration date and time | Expiration time of the user-generated authentication key |
| status | Use of authentication key |
Modify authentication key security settings
You can register security settings for the user’s authentication key. To register security settings for a user’s authentication key, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. Navigate to the page.
- My Info. Click the Authentication Key Management tab on the page. 3. Go to the Authentication Key Management tab.
- On the Authentication Key Management tab, click the Modify Security Settings button. 4. Modify Authentication Key Security Settings Navigate to the page.
- On the Edit Authentication Key Security Settings page, enter the Authentication Method and Allowed Access IP.
- Authentication method: temporary key, authentication key
- You can only access the API if the authentication configured as the authentication method is used when calling it.
- Temporary key: Authenticate using the temporary key issued with the authentication key and authentication number.
- Authentication key: Authenticate using the key generated in the Console
- Allowed Access IP: IP that controls user access
- When enabled, only access from a specific IP range is allowed.
- After use is configured, if an IP is not registered, access is denied for all IPs.
- When set to Not used, access is allowed for all IPs.
- You can register up to 50.
- You can enter an IP address or CIDR.
- Authentication method: temporary key, authentication key
- Check the authentication key security settings and click the Confirm button. 6. Go to the Authentication Key Management tab.
- South Korea (kr-south) region constraints
- When Allowed Access IP is set to Use, only IP addresses can be entered. * CIDR cannot be entered.
- It is recommended to use temporary key authentication and allow access from specific IP addresses.
- When authenticating with an authentication key, the email or SMS verification step may be omitted, which can pose a security risk.
- Allowed Access IP If not used, connections can be made from any IP, which may cause a security risk.
- When using Allowed IP, if you do not register an IP, all access will be restricted.
- Authentication keys with temporary keys generated by Secret Vault can be disabled and deleted after terminating the Secret Vault service in each region within the Account.
Delete authentication key
- The authentication key can be deleted only when it is in disabled state. * Before deleting the authentication key, stop using it.
- When using the Secret Vault service, you cannot disable the authentication key usage. * Please cancel the Secret Vault service first.
To delete the authentication key, follow the steps below.
- All Services > Management > IAM Click the menu. 1. Go to the Service Home page of Identity and Access Management(IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. Navigate to the My Info page.
- Click the Authentication Key Management tab on the My Info. page. 3. Navigate to the Authentication Key Management tab.
- Click the authentication key you want to delete in the Authentication Key Management tab’s key list. 4. Navigate to the Authentication Key Details page.
- On the Authentication Key Details page, click the Delete Authentication Key button.
- The authentication key is deleted, and you are taken to the Authentication Key Management tab.
To delete multiple policies simultaneously, follow these steps.
- Click the All Services > Management > IAM menu. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the My Info. menu. 2. Navigate to the My Info. page.
- My Info. Click the Authentication Key Management tab on the page. 3. Go to the Authentication Key Management tab.
- In the Authentication Key Management tab’s authentication key list, check the keys you want to delete.
- Verify the selected authentication keys and click the Delete Authentication Key button.
- The selected authentication keys are deleted and the Authentication Key Management tab is refreshed.
Manage Access IP
My Info. > In the Access IP Control tab, you can register and manage IPs that can access the Console.
You can restrict Console access to only the registered IP ranges by using the access IP control feature.
- The access IP control feature is available only to the Root user and IAM users. * ID Center and role members cannot be used.
- Even without using the access IP control feature, you can add and manage IP addresses.
To use the access IP control feature and manage IPs, follow the steps below.
- All Services > Management > IAM menu, click it. 1. Go to the Service Home page of Identity and Access Management (IAM).
- On the Service Home page, click the My Info. menu. 2. My Info. Navigate to the page.
- On the My Info. page, click the Access IP Control tab. 3. Navigate to the Access IP Control page.
- On the Access IP Control page, click the Edit button of Console Access IP Control. 4. Password Confirmation popup window opens.
- After entering the password, click the Confirm button. 5. Edit Console Access IP Control A popup window opens.
- After enabling the access IP control feature, register the IP addresses that are allowed to access.
| Category | Detailed description |
|---|---|
| Remove console access IP | Whether to use the access IP control feature
|
| IP list | Allowed IP list
|
10.4.2.7 - JSON Writing Guide
Policies are divided into credential-based policies and resource-based policies.
- Credential-based policy: a policy assigned to the principal (the entity performing actions) such as users, groups, or roles.
- Resource-based policy: a policy granted to a resource that decides whether to allow or deny (Effect) an action (Action) on a specific resource (Resource) only for a principal (Principal).
Resource-based policy
A resource-based policy is a policy that grants the specified principal (requester) permission to perform specific actions on the resource. Therefore, a resource-based policy is attached directly to the resource, only the users defined in the policy can enforce it, and the user to whom the policy is assigned becomes the security principal.
{
"Version": "2024-07-01"
"Statement": [
{
"Sid": "statement1"
"Action": ["object-store:UploadObject"],
"Principal": {
"scp":"srn:e::1234:::scp-iam:user/abc3d3442"
},
"Effect": "Allow"
"Resource": "srn:e:::::object-store:bucket/foo"
}
]
}{
"Version": "2024-07-01"
"Statement": [
{
"Sid": "statement1"
"Action": ["object-store:UploadObject"],
"Principal": {
"scp":"srn:e::1234:::scp-iam:user/abc3d3442"
},
"Effect": "Allow"
"Resource": "srn:e:::::object-store:bucket/foo"
}
]
}Resource-Based Policy Structure
The syntax structure and item-by-item description of resource-based policies are as follows.
{
"Version": "2024-07-01", # Policy grammar version (fixed to 2024-07-01)
"Statement": [
{
"Sid": "statement1", # policy element ID
"Effect": "Allow", # Policy effect
"Action": ["iam:showUser"], # Action defined in the policy
"Principal": {
"scp":"srn:e::1234:::iam:user/ROOT" # the entity that is the target of the policy
}
"Resource": "srn:e::kr-west1:::scp-iam:group/foo", # resource for which the policy action is allowed
"Condition": { # policy condition
"StringEquals": {
"iam:userName": [
scp_test_user
]
}
}
}
]
}{
"Version": "2024-07-01", # Policy grammar version (fixed to 2024-07-01)
"Statement": [
{
"Sid": "statement1", # policy element ID
"Effect": "Allow", # Policy effect
"Action": ["iam:showUser"], # Action defined in the policy
"Principal": {
"scp":"srn:e::1234:::iam:user/ROOT" # the entity that is the target of the policy
}
"Resource": "srn:e::kr-west1:::scp-iam:group/foo", # resource for which the policy action is allowed
"Condition": { # policy condition
"StringEquals": {
"iam:userName": [
scp_test_user
]
}
}
}
]
}| Item | description | Required |
|---|---|---|
| Version |
| Required |
| Statement | Information on the key elements of the policy | Required |
| Statement.Sid | Policy element ID (unique ID for elements within the same policy) | Select |
| Statement.Effect | Policy application effect ( Allow : Allow / Deny : Deny ) | Required |
| Statement.Principal | Security Principal | Required |
| Statement.Action | Policy target action (must specify either Action or NotAction) | Select |
| Statement.Resource | List of resources subject to policy evaluation | Required |
| Statement.Condition | Policy decision condition information | Selection |
Version
Version is used with a different meaning from the policy version, and the current version is “2024-07-01”.
{
"Version" : "2024-07-01"
}
Statement
Statement is information about the main elements of a policy and can be defined as a single element or an array of individual elements.
"Statement" : [{statement}]
"Statement" : [{statement}, {statement}, {statement}]
OR.Statement.Effect
Statement.Effect defines whether the policy action is allowed.
"Effect" : "Allow" # 허용
"Effect" : "Deny" # 거부
Statement.Principal
Statement.Principal specifies the entity that is allowed or denied access to a resource in a resource-based policy.The subjects that can be specified in the Principal element are as follows.
- root user
- IAM user
- IAM role
- service account
- Principal can have one or more values, and when there are multiple, write them as an array.
- Principal cannot use wildcard(*).
"Principal" : { "scp": "srn:e::1234:::iam:user/root_user_id" }
"Principal" : {
"scp": [
"srn:e::1234:::iam:user/abc33333",
"srn:e::1234:::iam:user/kef12344"
]
}
"Principal": {
"Service": [
"apigateway.samsungsdscloud.com"
]
}
Statement.Action
Statement.Action은 정책 검사에 평가될 액션을 정의합니다.
- 대소문자를 구분하여 작성하세요.
- 액션은 action definition에 정의되어 있는 액션 이름의 형식대로 작성하세요.
"Action" : ["{action_expression}"] # single action
"Action" : ["{action_expression}", "{action_expression}", ... ] # multiple actions
Statement.Resource
Statement.Resource는 정책이 적용되는 특정 리소스 또는 리소스 집합을 지정하는 SRN을 정의합니다.
- 대소문자를 구분하여 작성하세요.
resource_expression은 와일드 카드("*") 또는 SRN 형식으로 작성하세요.
- 리소스 기반 정책이 부여된 자원의 SRN이 반드시 포함되어야 하며, 해당 자원의 하위 자원이 있는 경우에는 하위 자원을 포함하여 작성할 수 있습니다.
- 정책에 정의된 액션 정의(Action definition)에 기술된 자원에 한하여 Resources에 작성할 수 있으며, 정의되지 않은 자원의 경우에는 정책 평가 시 무시됩니다.
- 하위 자원에도 와일드 카드(*)를 사용할 수 있습니다.
"Resource" : ["{resource_expression}"] # single resource
"Resource" : ["{resource_expression}", "{resource_expression}", ... ] # multiple resources
resource_expression에선 SRN 각 요소에서도 wildcard 형태로 표시할 수 있으며, 요소의 종류에 따라 지원 형태가 달라집니다.
- wildcard 미지원 SRN 요소 SRN 요소 중 offering, account_id, service-type은 wildcard를 지원하지 않습니다.
"Resource" : ["srn:*::9b7653f6f47a42e38055934a0575a813:kr-west1::scp-compute:instance/d12937a6db0940499fdb0e18ad57b101"] # offering wildcard notation (X)
"Resource" : ["srn:e::*:kr-west1::scp-compute:instance/d12937a6db0940499fdb0e18ad57b101"] # account wildcard notation (X)
"Resource" : ["srn:e::9b7653f6f47a42e38055934a0575a813:kr-west1::*:instance/d12937a6db0940499fdb0e18ad57b101"] # service type notation (X)
- wildcard 지원 SRN 요소
- SRN 요소 중 resource-type, resource-identifier, region은 전체 또는 부분에 대한 wildcard를 지원합니다.
- 부분 wildcard의 경우에는 “foo , foo*, foo, fo” 와 같은 표현식으로 작성 할 수 있습니다.
# region
"Resource" : ["srn:e::9b7653f6f47a42e38055934a0575a813:*::scp-compute:instance/d12937a6db0940499fdb0e18ad57b101"] # All (O)
"Resource" : ["srn:e::9b7653f6f47a42e38055934a0575a813:kr-*::scp-compute:instance/d12937a6db0940499fdb0e18ad57b101"] # part (O)
# resource-type
"Resource" : ["srn:e::9b7653f6f47a42e38055934a0575a813:kr-west1::scp-compute:*/d12937a6db0940499fdb0e18ad57b101"] # All (O)
"Resource" : ["srn:e::9b7653f6f47a42e38055934a0575a813:kr-west1::scp-compute:ins*/d12937a6db0940499fdb0e18ad57b101"] # part (O)
# resource-identifier
"Resource" : ["srn:e::9b7653f6f47a42e38055934a0575a813:kr-west1::scp-compute:instance/*"] # All (O)
"Resource" : ["srn:e::9b7653f6f47a42e38055934a0575a813:kr-west1::scp-compute:instance/d12*101"] # part (O)
단일 자원일 경우, user 조회에 대한 action_definition resources 정의 형태
kind: scp-iam:action-definition
service: iam
paths:
/v1/users/{user_id}:
get:
resources:
- "iam:user":
resource_id: "path['user_id']" # 사용자 조회 액션에서 지원되는 자원의 범위kind: scp-iam:action-definition
service: iam
paths:
/v1/users/{user_id}:
get:
resources:
- "iam:user":
resource_id: "path['user_id']" # 사용자 조회 액션에서 지원되는 자원의 범위{
"Version": "2024-07-01",
"Statement": [
{
"Sid": "statement1",
"Action": ["iam:showUser"],
"Effect": "Allow",
"Resource": [
"*", # 전체 자원에 대한 표현,
"srn:e:::::scp-iam:user/94c2ae8e7d5d471683a6135446183a12", # 특정 사용자 자원에 대한 표현
"srn:e:::::scp-iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현 -> 사용자 조회 액션에서 해당 자원을 기술 할 경우 작성된 내용은 정책 평가 시 무시 된다.
]
}
]
}{
"Version": "2024-07-01",
"Statement": [
{
"Sid": "statement1",
"Action": ["iam:showUser"],
"Effect": "Allow",
"Resource": [
"*", # 전체 자원에 대한 표현,
"srn:e:::::scp-iam:user/94c2ae8e7d5d471683a6135446183a12", # 특정 사용자 자원에 대한 표현
"srn:e:::::scp-iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현 -> 사용자 조회 액션에서 해당 자원을 기술 할 경우 작성된 내용은 정책 평가 시 무시 된다.
]
}
]
}여러 자원일 경우, user 정책 조회에 대한 action_definition resources 정의 형태
서로 다른 여러 자원을 정의할 경우, 정책에 작성된 자원 유형을 정의하세요.
- 정책 판단 시 액션 정의 파일에 정의된 자원을 기준으로 정책에 작성된 내용이 조건에 만족한 경우에만 성공으로 판단합니다.
- 액션 정의 파일에 정의된 모든 자원이 정책에 작성되어 있지 않은 경우, 정책 조건에 맞지 않음으로 판단합니다.
kind: scp-iam:action-definition
service: iam
paths:
/v1/user/{user_id}/policy/{policy_id}
get:
resources:
- "iam:user"
resource_id : "path['user_id']"
- "iam:policy"
resource_id : "path['policy_id']"
- 정상: 특정 사용자의 특정 policy 예시
{
"Version": "2024-07-01",
"Statement": [
{
"Sid": "statement1",
"Action": ["iam:ShowUserPolicy"],
"Effect": "Allow",
"Resource": [
"srn:e:::::iam:user/94c2ae8e7d5d471683a6135446183a12", # 특정 사용자 자원에 대한 표현
"srn:e:::::iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현
]
}
]
}{
"Version": "2024-07-01",
"Statement": [
{
"Sid": "statement1",
"Action": ["iam:ShowUserPolicy"],
"Effect": "Allow",
"Resource": [
"srn:e:::::iam:user/94c2ae8e7d5d471683a6135446183a12", # 특정 사용자 자원에 대한 표현
"srn:e:::::iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현
]
}
]
}정상: 모든 사용자의 특정 policy 예시
Color mode{ "Version": "2024-07-01", "Statement": [ { "Sid": "statement1", "Action": ["iam:ShowUserPolicy"], "Effect": "Allow", "Resource": [ "srn:e:::::iam:user/*", # 모든 사용자 자원에 대한 표현 "srn:e:::::iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현 ] } ] }{ "Version": "2024-07-01", "Statement": [ { "Sid": "statement1", "Action": ["iam:ShowUserPolicy"], "Effect": "Allow", "Resource": [ "srn:e:::::iam:user/*", # 모든 사용자 자원에 대한 표현 "srn:e:::::iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현 ] } ] }Normal: Example of a specific policy for all users 비정상: user 자원 미기술 예시
Color mode{ "Version": "2024-07-01", "Statement": [ { "Sid": "statement1", "Action": ["iam:ShowUserPolicy"], "Effect": "Allow", "Resource": [ "srn:e:::::iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현 ] } ] }{ "Version": "2024-07-01", "Statement": [ { "Sid": "statement1", "Action": ["iam:ShowUserPolicy"], "Effect": "Allow", "Resource": [ "srn:e:::::iam:policy/c23fb561c689455993874fa5d5ed4a2f" # 특정 정책 자원에 대한 표현 ] } ] }Abnormal: user resource not specified example
Statement.Condition
Statement.Condition은 정책 내에서 정책이 적용될 특정 대상에 대한 적용 조건을 정의합니다.
- 대소문자를 구분하여 작성하세요.
- 조건 연산자를 사용하여 정책에 정의된 자원의 속성 조건 키(또는 글로벌 조건 키), 값이 실제 요청(또는 자원의 속성)값과 비교하기 위한 조건 표현식을 작성하세요.
"Condition" : {
"{qualifier:}{operator}" : {
"{condition-key}" : ["{condition-value}"],
"{condition-key2}" : ["{condition-value}"]
}
}
| Item | Required or not | Case-sensitive | Explanation |
|---|---|---|---|
| operator | Required | O | Conditional operator
|
| condition-key | Required | X | Policy condition key (global condition key, resource attribute condition key)
|
| condition-value | Required | Depends on the operator. | policy condition value |
| qualifier | Select | O |
|
동일한 Condition Operator의 Condition Key에 Value가 2개 이상 정의된 경우, Value간 판단은 OR로 동작합니다. 단, Operator가 부정 연산자(Negative Operator) 유형인 경우에는 연산이 OR가 아닌 NOR로 동작합니다.
- 긍정 연산자(Positive Operator) 유형 및 예시(userName이 “foo” 또는 “bar"이고 company가 “Samsung"인 경우)
"Condition": {
"StringEquals": {
"iam:userName": [ # When the user's name is foo or bar
"foo", "bar"
],
"iam:userCompany": [ # when the user's company is Samsung
Samsung
]
}
}
- 부정 연산자(Negative Operator) 유형 및 예시(IP가 1.1.1.1/24 와 2.2.2.2/24가 대역이 아닌 모든 IP)
"Condition": {
"NotIpAddress": {
"scp:SourceIp": [ # when the request IP is neither 1.1.1.1 nor 2.2.2.2
"1.1.1.1/24", "2.2.2.0/24"
]
}
}
조건 연산자(operator)
조건 연산자는 7가지(문자열, 숫자, 날짜, Bool, IP, SRN, Null) 연산자를 제공합니다.
문자열 연산자
conditional operator Operator type Explanation StringEquals positive operator Exact match, case-sensitive StringNotEquals negation operator mismatch StringEqualsIsIgnoreCase positive operator Exact match, case insensitive StringNotEqualsIsIgnoreCase negation operator Mismatch, case-insensitive StringLike positive operator Case-sensitive matching; multiple-character string matching (*) wildcard can be included in the value. StringNotLike negation operator Case sensitivity mismatch, wildcard that matches multiple characters (*) can be included in values Table. String operators숫자 연산자
conditional operator Operator Types description NumericEquals positive operator Match NumericNotEquals negation operator mismatch NumericLessThan positive operator Match less than NumericLessThanEquals positive operator as follows NumericGreaterThan positive operator overmatch NumericGreaterThanEquals positive operator Match above Table. Numeric operators날짜 연산자
conditional operator Operator type description DateEquals positive operator Match specific date DateNotEquals negation operator mismatch DateLessThan positive operator Match before a specific date/time DateLessThanEquals positive operator Match on a specific date/time or earlier DateGreaterThan positive operator Match after a specific date/time DateGreaterThanEquals positive operator Match on a specific date/time or later Table. Date operatorsBool 연산자
conditional operator Operator Types description Bool positive operator True, False match Table. Bool operatorIP 연산자
conditional operator Operator type description IpAddress positive operator specified IP address or range NotIpAddress negation operator All IP addresses except the specified IP address or range Table. IP operatorSRN 연산자
conditional operator Operator Types description SrnEquals, SrnLike positive operator SRN match SrnNotEquals, SrnNotLike negation operator SRN mismatch Table. SRN operatorNull 연산자
conditional operator Operator type description Null positive operator - If the key is missing or the value is null \→ True
- If the key exists and the value is not null \→ False
Table. Null operator
조건 키(condition-key)
조건 키는 전역 조건 키과 자원 속성 키로 구분됩니다.
전역 조건 키(Global condition key)
Samsung Cloud Platform에 사전 정의된 조건 키로써 요청 정보, 자원 공통 정보(ex-tag), 네트워크 정보 등의 데이터를 정의합니다.
| condition key | Data type | singular/plural | description | example |
|---|---|---|---|---|
| scp:UserId | string | single | request user id | “scp:UserId” : [“efda56a968cd45b2873d9bf5fab58e95”] |
| scp:UserName | string | single | Request user name | “scp:UserName” : [“foo”] |
| scp:MultiFactorAuthPresent | bool | string | Request via MFA authentication | “scp:MultiFactorAuthPresent” : [“True”] |
| scp:RequestedRegion | string | single | request region | “scp:RequestedRegion” : [“kr-west1”] |
| scp:RequestAttribute/{AttributeKey} | string | single | request attribute value(AttributeKey)
| “scp:RequestAttribute/body[‘foo’]” : [“true”] |
| scp:TagKeys | string | single / multiple | request tag key | “scp:TagKeys” : [“tag-key”] |
| scp:RequestTag | string | single | Request tag key value | “scp:RequestTag/tag-key” : [“tag-value”] |
| scp:ResourceTag/{TagKey} | string | single | Resource tag key value | “scp:ResourceTag/foo” : [“bab”] |
| scp:SourceIp | ip_address | single | IP of the current requesting entity | “scp:SourceIp” : [“1.1.1.1/24”] |
| scp:CurrentTime | datetime | single | Request time (UTC, ISO 8601 format) | “scp:CurrentTime” : [“2025-11-06T16:10:38Z”] |
자원 속성 키(Resource attribute key)
고유 자원에 대한 속성 키로써 자원의 속성값을 기준으로 조건값을 검사할 때 사용합니다.
{service}:{resource_type}{attribute_name}
Resource definition에서 정의된 attributes에 abac:true인 대상의 속성에 한해서만 정의할 수 있으며 정의되지 않은 속성값을 입력할 경우, 해당 condition 정책은 무시됩니다(Not found).- 자원 속성명 사용 예시
"iam:userLastname" (O) # attribute name defined in the resource (service: iam, resource: user, attribute_name : lastname)
"iam:userLASTNAME" (O) # Property name defined in the resource (case-insensitive)
"iam:userLast_name" (X) # When it is not an attribute name defined in the resource ㅎ
"iam:userEmail" (X) # when abac is false
"iam:state" (X) # when the abac field is not defined
kind: scp-resourcemanager:resource-definition
service_type: scp-iam
name: scp-iam:user
resources_uri: /v1/users
resource_type: user
display_name:
ko: '사용자'
en: 'User'
product_id: IAM
attributes:
state:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.state
firstname:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.first_name
abac: true
lastname:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.last_name
abac: true
email:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.email
abac: falsekind: scp-resourcemanager:resource-definition
service_type: scp-iam
name: scp-iam:user
resources_uri: /v1/users
resource_type: user
display_name:
ko: '사용자'
en: 'User'
product_id: IAM
attributes:
state:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.state
firstname:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.first_name
abac: true
lastname:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.last_name
abac: true
email:
type: string
uri: /v1/users/{resource_id}
method: GET
jsonpath: $.email
abac: false- 자원의 속성명은
Resource definition에서 정의된attributes에 정의된 속성 데이터를 사용합니다. - Resource definition에 대한 자세한 내용은 Resource Definition 가이드를 참고하세요.
Condition Key 정의 예시
- 전역 조건 키(Global condition key) 예시: 특정 정책 자원 태그의 키(Environment)의 값이 “Local” 또는 “Dev"인 경우에만 그룹 상세 조회를 허용하는 정책
{
"Version": "2024-07-01",
"Statement": [
{
"Sid": "statement1",
"Action": ["iam:showPolicy"],
"Effect": "Allow",
"Resource": ["*"],
"Condition": {
"StringEquals": {
"scp:ResourceTag/Environment": [ # 전역 조건 키(scp:ResourceTag)를 사용한 정의 형태
"Local", "Dev"
]
}
}
}
]
}{
"Version": "2024-07-01",
"Statement": [
{
"Sid": "statement1",
"Action": ["iam:showPolicy"],
"Effect": "Allow",
"Resource": ["*"],
"Condition": {
"StringEquals": {
"scp:ResourceTag/Environment": [ # 전역 조건 키(scp:ResourceTag)를 사용한 정의 형태
"Local", "Dev"
]
}
}
}
]
}- 자원 속성 키(Resource attribute key) 예시Color mode
{ "Version": "2024-07-01", "Statement": [ { "Sid": "statement1", "Action": ["server:showInstance"], "Effect": "Allow", "Resource": ["*"], "Condition" : { "StringEquals" : { "virtual-servers:instanceFlavor" : ["m1.small"] # virtual-servers 서비스의 intance 리소스의 flavor 속성이 "m1.small"인 경우 } } } ] }{ "Version": "2024-07-01", "Statement": [ { "Sid": "statement1", "Action": ["server:showInstance"], "Effect": "Allow", "Resource": ["*"], "Condition" : { "StringEquals" : { "virtual-servers:instanceFlavor" : ["m1.small"] # virtual-servers 서비스의 intance 리소스의 flavor 속성이 "m1.small"인 경우 } } } ] }Resource attribute key example
정책 조건값(condition-value)
조건 키에 대한 값을 정의합니다.
"Condition" : {
"StringEquals" : {
"scp:resourceTag/key1": ["value1", "value2", "value3"] # If the resource's tag key is key1 and the value is value1, value2, or value3
}
한정자(quailfier)
Condition key로부터 추출된 요청 컨텍스트값이 여러 개의 값을 가진인 경우에 동작 방법을 정의합니다.(요청 컨텍스트값이 1개일 경우에는 생략)한정자는 ForAnyValue, ForAllValues로 구분되며 한정자를 작성하지 않을 경우, ForAnyValue가 기본값으로 정의됩니다.
ForAnyValue: 요청 컨텍스트에 추출된 값들이 Condition에 정의된 Operand와 1개 이상 일치할 경우 TrueForAllValues: 요청 컨텍스트에 추출된 값들이 Condition에 정의된 Operand 리스트의 하위 집합일 경우 True
{
"Condition" : {
"ForAllValues:StringEquals" : {
"scp:TagKeys": ["key1", "key2", "key3"]
}
}
}
한정자 동작 예시
“scp:TagKeys”로 부터 추출되는 요청값이 1개인 경우: 한정자와 관계없이 Operand별로 OR로 동작“scp:TagKeys”로 부터 추출되는 요청값이 2개 이상인 경우: 한정자에 따라 결과 차이
# 추출되는 요청 컨텍스트값이 ["key1", "key2", "key4"] 인 경우
Operand: ["key1", "key2", "key3"]
# 요청 컨텍스트값 중 key1는 Operand에 포함되므로 True
# 요청 컨텍스트값 중 key2는 Operand에 포함되므로 True
# 요청 컨텍스트값 중 key4는 Operand에 포함되지 않으므로 False
ForAnyValue는 3개의 요청 컨텍스트 값 중 1개라도 일치할 경우엔 True로 판단
ForAllValues는 3개의 요청 컨텍스트 값이 모두 True 일 경우에만 최종 True로 판단# 추출되는 요청 컨텍스트값이 ["key1", "key2", "key4"] 인 경우
Operand: ["key1", "key2", "key3"]
# 요청 컨텍스트값 중 key1는 Operand에 포함되므로 True
# 요청 컨텍스트값 중 key2는 Operand에 포함되므로 True
# 요청 컨텍스트값 중 key4는 Operand에 포함되지 않으므로 False
ForAnyValue는 3개의 요청 컨텍스트 값 중 1개라도 일치할 경우엔 True로 판단
ForAllValues는 3개의 요청 컨텍스트 값이 모두 True 일 경우에만 최종 True로 판단10.4.3 - API Reference
10.4.4 - CLI Reference
10.4.5 - Release Note
IAM
- You can copy the permissions of another IAM user.
- When creating or modifying an IAM user, you can copy and import policies that are attached to another user’s group or directly attached.
- We have improved the CX-related functionality.
- You can manage IAM user access key creation records.
- You can configure the visibility of the AI recommendation floating guide displayed at the bottom of the screen.
- When viewing the IAM user list, you can click the user group to navigate to the detail page.
- If a password error occurs while using the console, you will be automatically logged out of the console.
- When password entry is required, such as changing the password or updating the mobile phone number, you will be automatically logged out after five or more incorrect attempts.
- We provide a guide on using the Json mode that can be referenced when creating policies.
- You can share related information via email when creating a user or changing a password.
- Virtual Server and Cloud Function have been added as the entities that perform role functions.
- When changing roles, you can check the session expiration time in My Menu.
- You can register and manage IPs that can access the console.
- Root users and IAM users with the same information (phone number, email) can switch between each other even after logging in.
- The role feature has been added.
- Users can switch from their own account to a different role to access the Account.
- Credential provider functionality has been added.
- You can create a credential provider and access the Account resource in the Console through the created credential provider.
- You can directly associate users with policies.
- You can add conditions for attribute-based access control (ABAC) when creating a policy.
- The mandatory requirements for creating a user password have been changed.
- When editing an authentication key, CIDR input is optional.
- A password reconfirmation step has been added when changing the user’s email or phone number.
- IAM(Identity and Access Management) feature change
- Added user group and user functions, and policy creation functionality.
- We provide a unified authentication key by consolidating the app authentication key and the storage authentication key.
- Samsung Cloud Platform Common Feature Changes
- Implemented common CX changes, including Account, Service Home, and tags.
- The IAM(Identity and Access Management) service has been released.
- Provide user authentication and authorization management.
- Access control policy management provided
- The IAM(Identity and Access Management) service has been launched.
- Provide user authentication and authorization management.
- Provides access control policy management
10.5 - ID Center
10.5.1 - Overview
Service Overview
ID Center is a service that enables easy centralized management of access permissions for resources by account on the Samsung Cloud Platform. You can create permission policies for each service and assign accounts and policies linked to the Organization service to users, enabling management of tasks according to each user’s permissions.
Features
- Easy Access Permission Management: Through SAML (Security Assertion Markup Language) based credential authentication, you can receive authentication and authorization from Samsung Cloud Platform and access resources of multiple accounts within the organization.
- Efficient Account Management: By integrating with the Organization service, you can centrally manage the costs and resource usage incurred by all Accounts within the organization.
- Account Security Enhancement: Instead of the Samsung Cloud Platform Console, you can strengthen security by using the separately provided Access Portal so that only authorized ID Center users can access. Through the Access Portal, you can fundamentally prevent users outside the customer organization from accessing the Account.
Configuration
Provided features
ID Center provides the following functions.
- User and User Group Management: You can create users and user groups and configure service-specific permission management policies. Users are required to have MFA (Multi-Factor Authentication) applied, strengthening the management of Account access.
- Account Allocation Management: You can assign and manage Accounts corresponding to each user’s tasks.
- Permission Set Management: You can create and manage permission sets by using the default policies or custom policies that exist in each Account, or by configuring policies directly.
- Access Portal Provision: Provides an Access Portal that can be used instead of the Samsung Cloud Platform Console, allowing only ID Center users to access it.
Component
User
Administrators can create users and add them to user groups. They can generate passwords automatically or manually, and provide users with Access Portal login information. Additionally, users can be assigned to accounts according to their respective tasks.
User Group
You can link users and Accounts through user groups. You can create user groups appropriate for each task, register users, and assign them to Accounts.
Permission Set
You can create permission sets by using the default policies and custom policies that exist in the Account, or by configuring policies directly.
Provision status by region
ID Center is available in the environments below.
| Region | Whether provided |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Provide |
| South Korea South 2 (kr-south2) | Provide |
| South Korea 3 (kr-south3) | Not provided |
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Management | Organization | A service that organizes accounts by organizational units, manages them hierarchically, and controls resource access permissions. |
10.5.2 - How-to guides
Users can create the service by entering the required ID Center information and selecting detailed options through the Samsung Cloud Platform Console.
Create ID Center
You can create and use an ID Center in the Samsung Cloud Platform Console.
To create an ID Center, follow these steps.
Click the All Services > Management > ID Center menu. Navigate to the Service Home page of ID Center.
On the Service Home page, click the ID Center Apply button. Navigate to the ID Center Create page.
After entering the basic information on the ID Center creation page, click the Create button.
Category RequiredDetailed description ID Center name Required Enter the ID Center name - English letters, numbers, and special characters(
+=-_@,.) within 3 to 128 characters
description Select Enter a description of the organizational unit within 1,000 characters. Credential source Required Select credential source type - ID Center’s own directory: Use a directory within ID Center
- AD (Active Directory): Use an Active Directory managed directly by the user
- For details on the settings when selected, see Change Credential Source Type
- Automatically synchronize AD information upon creation
Table. ID Center creation basic information- English letters, numbers, and special characters(
When the popup notifying the creation of the ID Center opens, click the Confirm button.
On the Service Home page, view the ID Center dashboard.
Category Detailed description ID Center information Display the name, ID, and Access Portal URL of the ID Center - Click the ID Center Information item to go to the ID Center Settings page and view detailed ID Center information
User Number of users created in ID Center - Click the user count to go to the User List page
- Click the Create item to go to the User Creation page. Create User reference
User group Number of user groups created in ID Center - Click the group count to go to the User Group List page
- Click the Create item to go to the User Group Creation page. Refer to 사용자 그룹 생성하기
Permission set Number of permission sets created in ID Center - Click the permission set count to go to the Permission Set List page
- Click the Add item to go to the Create Permission Set page. Create Permission Set see
Table. ID Center Service Home Dashboard Items
Check ID Center detailed information
You can view detailed information of the ID Center and manage permissions.
Follow these steps to view detailed information of the ID Center and manage permissions.
- Click the All Services > Management > ID Center menu. Navigate to the Service Home page of ID Center.
- On the Service Home page, click the ID Center Settings menu. You will be taken to the ID Center Settings page.
Category Detailed description Delete ID Center Button to delete ID Center - Not displayed on delegated Account
Service Service name Resource Type Resource Type SRN Unique resource ID in Samsung Cloud Platform Resource name Resource Name Resource ID Unique resource ID in the service constructor User who created the service Creation Timestamp Service creation timestamp Editor User who edited the service information Modification date and time Date and time the service information was modified ID Center name ID Center name - Click the Edit button to change the usage status
Region Region where the ID Center was created Explanation Description of ID Center - Edit button can be clicked to change usage status
Organization ID Organization ID Credential source Credential source type - Click the Edit button to change the credential source type
- ID Center native directory: Directory within ID Center
- AD (Active Directory): Active Directory managed directly by the user
- AD Reset: A Reset AD Information popup opens, allowing AD information to be edited
- For details on the settings, refer to Changing Credential Source Type
- After the reset is complete, proceed with synchronization
- Synchronization: Synchronize with AD
- AD Reset: A Reset AD Information popup opens, allowing AD information to be edited
Access Portal URL URL to access the Access Portal Delegated authority Display the Account name, Account ID, Email, and Delegation time of the account that delegated management authority in ID Center - For delegated accounts, the managing account’s information is displayed, and permission delegation or cancellation is not possible
- Permission delegation: Allows delegating permission to an account within ID Center
- Displayed when there is no delegation information
- When the button is clicked, you can select an account on the Permission delegation page to set up delegation
- For more details, see Permission delegation
- Cancel permission delegation: Cancel the permission delegation
Table. ID Center configuration items
Managing Credential Sources
You can change the credential source type or modify and manage the settings for the AD (Active Directory) type.
AD (Active Directory) Apply for Integration
If you want to use an AD (Active Directory) that the user manages directly, you must first prepare the VPC and Load Balancer, then submit a request through SR. To apply for AD integration, follow these steps.
Secure a VPC to integrate with the user’s AD.
- If a network connection is required, connect to the network where the user’s AD resides via the Direct Connect service.
- For more details, refer to Direct Connect Create.
Configure the Load Balancer.
- Create a Load Balancer and an LB server group.
- Add the IP that will be associated with AD as a member of the LB server group’s connected resource.
- Create a Listener from the Load Balancer’s connected resources and attach the LB server group.Information
- Through the Load Balancer service, the call information for AD synchronization from ID Center can traverse the user’s VPC and invoke the user’s AD.
- For detailed information on creating and using the Load Balancer service, see Using the Load Balancer service.
Configure a PrivateLink Service in the user’s VPC.
- Create a PrivateLink Service for the user VPC that will be called from ID Center.
- When creating a PrivateLink Service, select the Load Balancer created in step 2 as the connection resource.
When the preparation work is finished, click the All Services > Management > Support Center menu. You will be taken to the Service Home page.
On the Service Home page, click the Service Request menu. You will be taken to the Service Request List page.
On the Service Request List page, select and enter the information required for the service request.
Category Required statusDetailed description Title Required Enter a title for the service request - using Korean, English, numbers, and special characters (
+=,.@-_) within 64 characters
Region Required Select the region for the service request Service Required Management service group’s ID Center service selection Task classification Required ID Center AD Integration Request Select content Required Enter information for ID Center AD integration application Table. ID Center AD linked application items- using Korean, English, numbers, and special characters (
Check the input information and click the Request button.
- When creation is complete, check the Service Request List page.
Changing the credential source type
You can change the credential source or modify the configuration values.
To change the credential source type, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the ID Center Settings menu. Navigate to the ID Center Details page.
On the ID Center Details page, click the Edit button of the Credential Source item. The Change Credential Source popup will open.
After selecting the credential source type to use, click the Confirm button. A popup notifying the credential source change will open.
Category Detailed description ID Center’s own directory Use directory within ID Center - No separate configuration items
AD (Active Directory) Use a user-managed Active Directory - Connection URL: Enter the LDAP server address (e.g.,
ldap://orldaps:)
- Bind DN: Enter the DN (Distinguished Name) of the administrator or service account used to access the LDAP server
- Bind credentials: Enter the password for the account corresponding to the Bind DN
- User DN: Enter the directory path where user accounts are located (e.g.,
OU=Employees,OU=Accounts,DC=sub,DC=org)
- Username LDAP attribute: Enter the attribute that identifies the user account (e.g.,
sAMAccountName,uid)
- RDN LDAP attribute: Enter the RDN (Relative Distinguished Name, the top-level attribute in the user DN)
- User object classes: Enter a comma‑separated list of LDAP classes that define user objects (e.g.,
,) (example:persion,organizationPersion,usersAMAccount)
Table. Credential source type change itemsCheck the precautions for changes, check the checkbox, and then click the Confirm button. Go to the Service Home page to start changing the credential source type.
- The change time varies depending on the scale, and you can confirm it via a notification once the change is complete.
- You cannot navigate to another menu page while changes are being made.
Synchronize AD (Active Directory) Information
You can synchronize AD information.
- AD information is automatically synchronized daily from 00:00 to 06:00 (Asia/Seoul, GMT +09:00).
- If a new AD connection is required, click the AD Reset button to change the AD information, then synchronize.
To synchronize AD information, follow these steps.
- Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
- On the Service Home page, click the ID Center Settings menu. You will be taken to the ID Center Details page.
- On the ID Center Detail page, click the Sync button next to the synchronization time of the Credential Source item. The AD Information Sync popup opens.
- After reviewing the synchronization notification, click the Confirm button. AD information synchronization will begin.
- The change time varies depending on the scale.
Manage Permissions
You can delegate the ID Center’s administrative privileges to another account, or revoke previously delegated privileges.
Delegating Permissions
You can delegate the administrative rights of the ID Center to another account.
To delegate administrative privileges to another account, follow these steps.
- Click the All Services > Management > ID Center menu. Navigate to the Service Home page of ID Center.
- From the Service Home page, click the ID Center Settings menu. Navigate to the ID Center Details page.
- On the ID Center Details page, click the Permission Delegation button. You will be taken to the Permission Delegation page.
- The Delegate Permission button is displayed only when there is no Account that has delegated the current permission.
- On the Permission Delegation page, select the Account to which you want to delegate permissions, then click the Complete button.
Category Detailed description Account name Account name Account ID Account ID email Account email Additional date/time Account creation or registration time in the organization Additional type Method of adding an Account in the Organization - Create: Add a new Account on the Add Account page
- Sign up: Add an existing Account
Table. ID Center Delegated Authority Account List
Cancel delegation
You can revoke the ID Center’s administrative permissions that were delegated to another account.
To revoke delegated administrative rights, follow these steps.
- Click the All Services > Management > ID Center menu. Navigate to the Service Home page of ID Center.
- On the Service Home page, click the ID Center Settings menu. Navigate to the ID Center Details page.
- On the ID Center Details page, click the Cancel Delegation button.
- When the popup notifying the revocation of delegated authority opens, click the Confirm button.
Delete ID Center
To delete the ID Center, follow these steps.
- Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
- Click the ID Center Settings menu on the Service Home page. Navigate to the ID Center Settings page.
- On the ID Center Settings page, click the ID Center Delete button. The ID Center Delete popup window opens.
- Delete ID Center In the popup window, enter the name of the ID Center to delete, then click the Confirm button. You will be redirected to the Service Home page.
- The deletion time for the ID Center varies depending on the size, and you can confirm completion via a notification.
- You cannot navigate to other menu pages while the ID Center is being deleted.
10.5.2.1 - Managing ID Center Users
You can view and manage users in the ID Center.
Create User
You can create a user and add it to the ID Center. To create a user, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the User menu. You will be taken to the User List page.
User List page, click the Create User button. It navigates to the Create User page.
On the User Creation page, after entering the basic and additional information, click the Create button.
Category Required statusDetailed description username Required Enter the user’s name - using English letters, numbers, and special characters (
+=-_@,.) within 128 characters
- The username cannot be changed after creation
description Selection Enter a description of the user within 1,000 characters Password Required Select password creation method - Auto-generate: Automatically generate the password and provide it in a popup when user creation is completed
- Manual entry: Refer to the password creation rules and enter it manually
User real name Required Enter the user’s full name as their real name Enter affiliation information Select Enter the division, department, manager, and employee number information each within 128 characters. Select user group Selection Select the user group to which the user will be added - To create a user group, refer to Create a user group
Table. User-generated informationPassword creation rules- It must contain at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%&*^). - The length is 9 to 20 characters.
- ID or username cannot be used as a password.
- You cannot use the same character more than three times.
- You cannot use passwords that are easy to guess.
- You cannot use a password that was recently used.
- Sequences of four or more consecutive characters or digits are not allowed.
- The password change cycle is 90 days.
- using English letters, numbers, and special characters (
When the popup notifying user addition opens, click the Create button. The ID Center user login information popup opens.
After verifying the ID Center user login information, click the Confirm button.
Category Detailed description Access Portal URL URL information for accessing the Access Portal Username Generated username Password Generated user’s password - View Click the icon to view the password
Excel download Download ID Center user login information as an Excel file Email sending Send an Excel file containing ID Center user login information via email - After clicking the button, enter the address to receive the email
Table. ID Center user login information items
Check user detailed information
You can view and manage detailed information about users, user groups, and account information. To view detailed user information, follow these steps.
- Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
- On the Service Home page, click the User menu. It navigates to the User List page.
- On the User List page, click the user name to view detailed information. You will be taken to the User Details page.
- User Details page displays basic information and consists of Basic Information, User Group, Account tabs.
Basic Information
Check the user’s basic information, and if necessary, edit the user’s description and options.
| Category | Detailed description |
|---|---|
| Delete user | User deletion button
|
| username | User’s name |
| User real name | User’s actual name
|
| description | Description of the username
|
| Last login | The date and time of the user’s last login |
| Password | Date and time of the last password change
|
| Password reuse restriction | Number of recent passwords that cannot be set as a password
|
Email verification status
| |
| mobile phone number | Mobile phone number verification status |
| Affiliation information | User’s division, department, manager, and employee number information
|
User Group
The user can view the registered user groups and, if necessary, add or remove user groups.
| Category | Detailed description |
|---|---|
| Exclude | Exclude the selected user group from the user group list
|
| Add user group | Add a user group to register users
|
| User group name | Name of the user group |
| description | Description of the user group |
| Modification date and time | User group modification timestamp |
Account
Verify the Account assigned to the user, and, if necessary, add a permission set or assign an Account.
- For detailed information about Permission Set, see the Permission Set.
- For detailed information about Account Allocation, please refer to Account Allocation.
| Category | Detailed description |
|---|---|
| Add permission set | Add a new permission set to the Account
|
| More > Exclude all direct applications | Exclude all permission sets directly applied to the Account
|
| Account allocation | Assign a new Account to the user
|
| Account name | Account name |
| Permission set | Number of permission sets applied to the Account
|
| Application method | Account permission set application method
|
Change Password
You can change the user’s password. To change a user’s password, follow these steps.
- Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
- On the Service Home page, click the User menu. You will be taken to the User List page.
- On the User List page, click the username whose password you want to change. You will be taken to the User Details page.
- On the User Details page, click the Edit button for the Password field. The Password Reset popup will open.
- Password Reset After setting the password in the popup window, click the Confirm button. The ID Center User Login Information popup window will open.
- Auto Generation: Automatically generate a password
- Direct Input: Manually input according to the password creation rules
- It must include at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%&*^). - The length is 9 to 20 characters.
- ID or username cannot be used as a password.
- You cannot use the same character more than three times.
- You cannot use passwords that are easy to guess.
- You cannot use a password that was recently used.
- Sequences of four or more consecutive characters or digits are not allowed.
- The password change interval is 90 days.
- ID Center User Login Information After checking the user information in the popup window, click the Confirm button.
Category Detailed description Access Portal URL URL information for accessing the Access Portal Username Generated user name Password Generated user’s password - View Click the icon to view the password
Excel download Download ID Center user login information as an Excel file Email sending Send an Excel file containing ID Center user login information via email - After clicking the button, enter the address to receive the email
Table. ID Center user login information items
Add User Group
You can add a new user group. To add a user group, follow the steps below.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the User menu. You will be taken to the User List page.
On the User List page, click the username to add to the user group. You will be taken to the User Details page.
On the User Details page, click the User Group tab. The User Group list will be displayed.
Click the Add User Group button. You will be taken to the Add User Group page.
On the Add User Group page, select the user group you want to add from the list, then click the Done button.
Category RequiredDetailed description Added user group - Name of the user group added by the user User group Required Select the user group to add users to - When selected, add to the Added User Group item
Table. Add User Group ItemWhen the popup that notifies the addition of a user group opens, click the Confirm button.
Add Permission Set
You can add a permission set to the Account. To add a permission set to an Account, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the User menu. You will be taken to the User List page.
User List page, click the username to add a permission set. You will be taken to the User Details page.
On the User Details page, click the Account tab. The Account list is displayed.
From the Account list, select the Account to which you want to add a permission set, then click the Add Permission Set button. You will be taken to the Add Permission Set page.
On the Add Permission Set page, select the permission set you want to add from the permission set list, then click the Done button.
Category Required statusDetailed description Selected Account - Account name to add permission set Applied permission set - Name of the permission set applied to the selected account Permission set Required Select one or more permission sets to apply to the Account - When selected, add to the Applied Permission Set item
Table. Add permission set itemWhen the popup that notifies the addition of a permission set opens, click the Confirm button.
Allocate Account
You can assign a new Account to the user. To assign a new Account, follow the steps below.
Click the All Services > Management > ID Center menu. You will be taken to the Service Home page of ID Center.
On the Service Home page, click the User menu. You will be taken to the User List page.
On the User List page, click the user name to assign an Account. You will be taken to the User Details page.
On the User Details page, click the Account tab. The Account list will be displayed.
Click the Account Allocation button. You will be taken to the Account Allocation page.
On the Account Assignment page, after selecting the Account to assign and the permission set to apply to the Account, click the Complete button.
Category Required statusDetailed description Select Account Required Select Account to assign to the user - View hierarchy: Display Accounts in an organizational hierarchy format
- View Account list: Display Accounts in a list format
Select permission set Required Select the permission set to apply to the selected Account Table. User Account Assignment ItemsInformationIf there is no IAM policy name that matches the custom policy name of the selected permission set, you cannot assign the account.When the pop-up notifying that the Account assignment has been added to the user group opens, click the Confirm button.
Delete User
To delete a user, follow the steps below.
- Click the All Services > Management > ID Center menu. Navigate to the Service Home page of ID Center.
- On the Service Home page, click the User menu. It navigates to the User List page.
- Please select at least one user to delete from the user list.
- After confirming the selected users, click the Delete button.
- You can also delete individually from the User Details page of the user to be deleted.
- When the popup notifying user deletion opens, click the Confirm button.
10.5.2.2 - Managing ID Center User Groups
You can view and manage user groups in ID Center.
Create User Group
You can create a user group and add it to the ID Center. To create a user group, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the User Group menu. You will be taken to the User Group List page.
Click the Create User Group button on the User Group List page. You will be taken to the Create User Group page.
On the User Group Creation page, after entering the basic and additional information, click the Create button.
Category Required statusDetailed description User group name Required Enter the user group name - using English letters, numbers, and special characters (
+=-_@,.) within 3 to 30 characters
description Selection Enter a description of the user group within 1,000 characters. Add user Select Select users to add to the user group - Display the list of users registered in the Account
- To create a new user, see Create User
- If the user you want to add does not exist when linking with AD, add the user in the AD provider and go to the ID Center Settings > Credential Source page to perform synchronization
Table. User Group Creation Information- using English letters, numbers, and special characters (
When the popup notifying the addition of a user group opens, click the Confirm button.
View detailed information of user group
You can view and manage detailed information about user groups, as well as user group and account information.
To view detailed information about a user group, follow these steps.
- Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
- On the Service Home page, click the User Group menu. You will be taken to the User Group List page.
- On the User Group List page, click the user group name whose details you want to view. You will be taken to the User Group Details page.
- The User Group Detail page displays basic information and consists of Basic Information, User, and Account tabs.
Basic Information
You can view the basic information of a user group and, if necessary, edit its description and options.
| Category | Detailed description |
|---|---|
| Delete user group | Button to delete a user group |
| User group name | Name of the user group |
| User Group ID | User group ID |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| User group name | User group name
|
| Explanation | Description of the user group name
|
User
You can view the users registered in a user group and, if necessary, add or remove users.
| Category | Detailed description |
|---|---|
| Exclude | Exclude the selected user(s) from the user list
|
| Add user | Add a user group to register
|
| Username | User’s name |
| User group | Number of user groups the user is registered in |
| Creation date and time | User creation timestamp |
Account
Check the Account assigned to the user, and if necessary, you can add a permission set or assign an Account.
- For detailed information about Permission Set, see the 권한 세트.
- Account Allocation for detailed information, please refer to Account Allocation.
| Category | Detailed description |
|---|---|
| Add permission set | Add a new permission set to the Account
|
| More > Cancel Assignment | Cancel the assignment of the selected Account
|
| Account allocation | Assign a new Account to the user group
|
| Account name | Account name |
| Permission set | Number of permission sets applied to the Account
|
Add User
You can add a new user to a user group. To add a user, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the User Group menu. You will be taken to the User Group List page.
User Group List page, click the user group name to which you want to add a user. You will be taken to the User Group Details page.
On the User Group Details page, click the User tab. The user list will be displayed.
Click the Add User button. You will be taken to the Add User page.
After selecting the user you want to add from the user list on the Add User page, click the Done button.
Category Required statusDetailed description Added user - Name of the user group added user Required User groups without added users - Display list of users registered in the Account
- When selected, add to Added User item
- To create a new user, see Create User
- If there is no user to add when linking with AD, add the user at the AD provider and go to ID Center Settings > Credential Source page to synchronize
Table. Add User ItemVerify that the added user appears in the list.
Add Permission Set
You can add a permission set to the Account. To add a permission set to an Account, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the User Group menu. You will be taken to the User Group List page.
Click the user group name to which you want to add a permission set on the User Group List page. You will be taken to the User Group Details page.
On the User Group Details page, click the Account tab. Account list will be displayed.
From the Account list, select the Account to which you want to add a permission set, then click the Add Permission Set button. You will be taken to the Add Permission Set page.
On the Add Permission Set page, select the permission set you want to add from the list, then click the Done button.
Category Required statusDetailed description Selected Account - Account name to add permission set Applied permission set - Name of the permission set applied to the selected account Permission set Required Select one or more permission sets to apply to the Account - When selected, add to the Applied Permission Set item
Table. Add permission set itemVerify that the added permission set has been applied to the Account.
Allocate Account
You can assign a new Account to a user group. To assign a new Account, follow the steps below.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the User Group menu. You will be taken to the User Group List page.
User Group List page, click the user group name to assign an Account. You will be taken to the User Group Details page.
On the User Group Details page, click the Account tab. The Account list will be displayed.
Click the Account Allocation button. You will be taken to the Account Allocation page.
On the Account Assignment page, after selecting the Account to assign and the permission set to apply to the Account, click the Complete button.
Category Required or notDetailed description Select Account Required Select Account to assign to user group - View hierarchy: Display Accounts in an organizational hierarchy
- View account list: Display Accounts in a list format
Select permission set Required Select the permission set to apply to the selected Account Table. Account Assignment ItemsinformationIf there is no IAM policy name that matches the custom policy name of the selected permission set, you cannot assign the Account.Verify that the added Account has been assigned to the user.
Delete user group
To delete a user group, follow the steps below.
- Click the All Services > Management > ID Center menu to go to the ID Center’s Service Home page.
- On the Service Home page, click the User Group menu. You will be taken to the User Group List page.
- Select at least one user group to delete from the user group list.
- After confirming the selected user group, click the Delete User Group button.
- You can also delete individually from the User Group Details page of the user group to be deleted.
- When the popup notifying that a user group has been deleted opens, click the Confirm button.
10.5.2.3 - Assigning ID Center Account
You can view the Account in ID Center and assign it to a user or user group.
Allocate Account
You can assign an Account to a user or a user group.
To assign an Account, follow these steps.
Click the All Services > Management > ID Center menu. Navigate to the Service Home page of ID Center.
On the Service Home page, click the Account Assignment menu. You will be taken to the Account List page.
On the Account List page, select the Account to assign, then click the Assign to User or Group button. You will be taken to the Assign to User or Group page.
Assign to Users or Groups on the Select Assignment Target area, after selecting the assignment target, click the Next button.
- You must select at least one user or user group to assign the account.
Category Requirement statusDetailed description Account to assign - Name of the Account to assign to a user or user group User Select Select the user to assign the account User group Select Select the user group to assign the Account Table. Account assignment target selection
- You must select at least one user or user group to assign the account.
In the Permission Set Selection area, select the permission set to apply to the Account, then click the Next button.
Category Required statusDetailed description Account to assign - Name of the Account to assign to a user or user group Permission set Required Select one or more permission sets to apply to the Account. Table. Account permission set selection itemsIn the Input Information Confirmation area, after verifying the assignment target and permission set, click the Complete button.
When the pop-up notifying the Account allocation opens, click the Confirm button.
Check account detailed information
You can view and manage detailed information about the account, its assignment targets, and permission sets.
To view the detailed information of the Account, follow these steps.
- Click the All Services > Management > ID Center menu. Navigate to the Service Home page of ID Center.
- On the Service Home page, click the Account Assignment menu. You will be taken to the Account Information page.
- Account Information page, click the Account for which you want to view detailed information. You will be taken to the Account Details page.
- Account Details page displays basic information, and consists of Basic Information, Assignment Target, Permission Set tabs.
Basic Information
You can view the basic information of the Account.
| Category | Detailed description |
|---|---|
| Account name | Account name |
| Account ID | Account ID |
| constructor | User who created the Account |
| Creation date | Account creation date and time |
| Editor | User who modified the Account |
| Modification date and time | Date and time the account was modified |
allocation target
You can view and manage the users and user groups assigned to an Account.
| Category | Detailed description |
|---|---|
| Unassign | Cancel the Account assignment for the selected user or user group
|
| More > Add Permission Set | Add a permission set to the selected Account
|
| Assign to user or group | Assign the selected Account to a new user or user group
|
| Allocation target name | Name of the allocation target |
| Target type | Type of assignment target (user, user group) |
| Permission set | Number of permission sets applied to the Account
|
Permission Set
You can check the permission sets applied to the Account and, if necessary, exclude them.
| Category | Detailed description |
|---|---|
| Exclude permission set | Exclude the selected permission set from the Account
|
| Permission set name | Name of the permission set |
| Explanation | Description of the permission set |
| Modification date and time | Date and time the permission set was last modified |
Add Permission Set
You can add a permission set to an account assigned to a user or user group.
To add a permission set to an Account, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the Account Assignment menu. You will be taken to the Account List page.
On the Account list page, click the Account to assign. You will be taken to the Account details page.
On the Account Details page, click the Allocation Target tab. The allocation target list will be displayed.
After selecting the assignment target to which you want to add a permission set from the assignment target list, click the More > Add Permission Set button. You will be taken to the Add Permission Set page.
Add Permission Set From the permission set list on the page, select the permission set you want to add, then click the Done button.
Category Required statusDetailed description allocation target - Name of the assignment target to add the permission set Applied permission set - Name of the permission set applied to the selected account Permission set Required Select one or more permission sets to apply to the Account - When selected, add to the Applied Permission Set item
Table. Add Permission Set ItemWhen the popup notifying that a permission set has been added opens, click the Confirm button.
Verify that the added permission set has been applied to the Account.
Add assignment to user or group
You can assign an additional Account to new users or user groups.
To assign an Account to a new user or user group, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the Account Assignment menu. You will be taken to the Account List page.
On the Account List page, click the Account to assign. You will be taken to the Account Details page.
On the Account Details page, click the Allocation Target tab.
In the Assignment Target tab, click the Assign to User or Group button. You will be taken to the Assign to User or Group page.
After selecting the allocation target in the Select Allocation Target area, click the Next button.
- You must select at least one user or user group to assign the Account to.
Category Whether requiredDetailed description Assigned user - Current user name assigned to the Account User Select Select the user to assign to the Account - When selected, add to the Assigned User field
- To create a new user, refer to Create User
- If the user you want to add does not exist when linking with AD, add the user in the AD provider and go to the ID Center Settings > Credential Source page to perform synchronization
Assigned user group - Current user group name assigned to the Account User group Select Select the user group to assign the Account - When selected, add to the Assigned User Group item
Table. Account assignment target selection
- You must select at least one user or user group to assign the Account to.
In the Permission Set Selection area, select the permission set to apply to the Account, then click the Next button.
Category Required statusDetailed description Permission set Required Select one or more permission sets to apply to the Account Table. Account permission set selection itemsIn the Input Information Confirmation area, after checking the assignment target and permission set, click the Complete button.
When the pop-up notifying the Account allocation opens, click the Confirm button.
Cancel Account Assignment
To cancel an Account assignment for a user or user group, follow these steps.
- Click the All Services > Management > ID Center menu. You will be taken to the Service Home page of ID Center.
- On the Service Home page, click the Account Assignment menu. You will be taken to the Account List page.
- On the Account List page, click the Account to assign. You will be taken to the Account Details page.
- On the Account Details page, click the Allocation Target tab. The allocation target list is displayed.
- After selecting the assignment target to cancel the Account assignment from the assignment target list, click the Cancel Assignment button.
- When the popup notifying that the Account allocation has been canceled opens, click the Confirm button.
10.5.2.4 - Managing ID Center Permission Sets
You can view and manage the permission sets of the ID Center.
Create Permission Set
You can create a permission set and add it to ID Center. To create a permission set, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the Permission Set menu. You will be taken to the Permission Set List page.
On the Permission Set List page, click the Create Permission Set button. You will be taken to the Create Permission Set page.
On the Create Permission Set page, after entering the basic information in the Basic Information Input area, click the Next button.
Category Required statusDetailed description Permission set name Required Enter the permission set name - using English letters, numbers, and special characters (
+=-_@,.) within 32 characters
description Select Enter a description of the permission set within 1,000 characters Maximum session duration Required Enter the session time allowed for the user when accessing the Console via the Access Portal - Select time: 1 hour, 2 hours, 4 hours, 8 hours, 12 hours
- Enter duration: can be entered in seconds ranging from 3,200 seconds (1 hour) to 43,200 seconds (12 hours)
Table. Permission set basic information items- using English letters, numbers, and special characters (
Permission Set Settings area, select the policy to use and configure the policy, then click the Next button.
Category Required statusDetailed description Default policy Selection Connect the default policies offered by the Samsung Cloud Platform Console - After selecting the Use item, select the default policy to associate with the permission set from the list
Custom policy Select Connect a custom policy created under the Account - Select the Use item, then directly enter the custom policy to attach to the permission set
- The permission set cannot be applied to Accounts that lack an IAM policy name matching the entered custom policy name
Inline policy Select Directly set the policies to apply to the permission set - Use after selecting the item, configure according to the policy setting mode
- Default mode: Configure using the mode provided by the Console. Refer to 인라인 정책 생성하기
- JSON mode: Directly configure using the JSON Editor
Table. Permission set configuration itemsguideA permission set can be linked with up to 20 policies in total, combining default and custom policies.In the Input Information Confirmation area, after reviewing the basic information and permission policies of the permission set, click the Create button.
When the popup notifying the creation of a permission set opens, click the Confirm button.
View permission set details
You can view and manage detailed information about permission sets, user groups, and account information. To view the detailed information of a permission set, follow these steps.
- Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
- On the Service Home page, click the Permission Set menu. You will be taken to the Permission Set List page.
- On the Permission Set List page, click the permission set whose details you want to view. You will be taken to the Permission Set Details page.
- The Permission Set Details page displays basic information and consists of Basic Information, Permissions, Account tabs.
Basic Information
You can view and edit the basic information of the permission set.
| Category | Detailed description |
|---|---|
| Delete permission set | Delete permission set button |
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | resource name
|
| Resource ID | Unique Resource ID |
| constructor | User who created the service |
| Creation date | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Permission set name | Policy name |
| Maximum session duration | Session time allowed for users when entering the Console via Access Portal
|
| description | Description of the policy name
|
Permission
You can view and manage policies attached to a permission set.
| Category | Detailed description |
|---|---|
| Default policy | Default policies attached to the permission set
|
| Custom policy | Custom policies attached to the permission set
|
| Inline policy | Service name of the inline policy attached to the permission set
|
Account
You can view and edit the Account information of a permission set.
| Category | Detailed description |
|---|---|
| Account name | Account name |
| Account ID | Account ID |
| Account email |
Connect the default policy
You can attach a new default policy to a permission set. To link the default policy, follow the steps below.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the Permission Set menu. You will be taken to the Permission Set List page.
On the Permission Set List page, click the permission set to which you want to attach the default policy. You will be taken to the Permission Set Details page.
On the Permission Set Details page, click the Permission tab.
In the Default Policy area, click the Policy Connection button. Navigate to the Default Policy Connection page.
On the Basic Policy Connection page, select the policy you want to link from the default policy list, then click the Complete button.
Category RequiredDetailed description Linked default policy - Default policy name attached to the permission set Default policy connection Required Select the default policy to attach to the permission set - When selected, add to the Connected Default Policy item
Table. Attach default policy to permission set itemWhen the popup notifying the policy connection opens, click the Confirm button.
Connecting a custom policy
You can attach a new custom policy to a permission set. To link a custom policy, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the Permission Set menu. You will be taken to the Permission Set page.
Permission Set List page, click the permission set to attach a custom policy. You will be taken to the Permission Set Details page.
On the Permission Set Details page, click the Permission tab.
In the Custom Policy area, click the Policy Connect button. You will be taken to the Custom Policy Connect page.
On the Custom Policy Connection page, select the policy you want to connect from the custom policy list, then click the Done button.
Category Whether requiredDetailed description Attached custom policy - Default policy name attached to the permission set Custom policy association Required Directly enter a custom policy to attach to the permission set - When selected, add to the Attached Custom Policy item
- Click the Add button to further enter custom policies to attach
Table. Attach a custom policy to a permission set itemWhen the popup notifying the policy connection opens, click the Confirm button.
Create Inline Policy
You can modify the inline policy attached to the permission set. To modify the inline policy, follow these steps.
Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
On the Service Home page, click the Permission Set menu. You will be taken to the Permission Set List page.
Permission Set List page, click the permission set to edit the inline policy. You will be taken to the Permission Set Details page.
On the Permission Set Details page, click the Permission tab.
In the Inline Policy area, click the Create Policy button. You will be taken to the Create Inline Policy page.
Inline Policy Creation page’s Permission Settings area, after selecting the policy configuration method and the service to apply, click the Next button.
Category Required statusDetailed description Basic mode/JSON mode Required Select the policy configuration method - Default mode: Configure using the mode provided by the Console
- JSON mode: Configure directly using the JSON Editor
Service Required Select the service to set the policy - Add Service: Add a service to configure the policy
Table. Inline policy creation - Service configurationCautionThe policy settings provide Basic Mode and JSON Mode.
- After writing in Basic Mode and entering JSON Mode or navigating the screen, services with duplicate control requirements are consolidated into one, and services that have not completed configuration are deleted.
- If the content written in JSON mode does not conform to JSON format, you cannot switch to basic mode.
After setting the permissions, click the Next button.
- To register an individual resource as an applied resource, refer to Register an individual resource as an applied resource and proceed.
Category Whether requiredDetailed description Control type Required Select policy control type - Allow policy: A policy that permits the defined permissions
- Deny policy: A policy that denies the defined permissions
Action Required Select actions provided for each service - Actions that can select individual resources are shown in purple
- Actions that target all resources are shown in black
- Add Action Directly: You can specify multiple actions at once using the wildcard
*
Applied resource Required Resources to which the action applies - All resources: Apply to all resources for the selected action
- Individual resources: Apply only to the specified resources for the selected action
- Individual resources are only available when selecting the purple action that allows individual resource selection
- Click the Add resource button to specify target resources by resource type
- For more details on Add resource, see Register individual resources as applicable resources
Authentication Type Required Authentication method of the user target to which the policy will be applied - All authentication: Applied regardless of authentication method
- Authentication key authentication: Applied to users authenticated with an authentication key
- Temporary key authentication, Console login: Applied to users with temporary key authentication or Console login
Applied IP Required IP allowed for policy application - Custom IP: User registers and manages the IP directly
- Applied IP: IP that the user registers directly, to which control policies are applied; can be registered as an IP address or range
- Excluded IP: IP to be excluded from Applied IP, can be registered as an IP address or range
- All IPs: No IP access restriction
- Access is allowed for all IPs, but if exceptions are needed, register Excluded IP to restrict access for the specified IPs
Additional condition Select Add conditions for attribute-based access control (ABAC) - Condition Key: Select from Global condition keys and service condition key list
- Qualifier: Default value, arbitrary value in the request, all values in the request
- Operator: Bool, Null
- Value: True, False
Table. Policy Creation - Permission Settings
- To register an individual resource as an applied resource, refer to Register an individual resource as an applied resource and proceed.
After reviewing the information entered on the Check Input Information page, click the Complete button.
When the popup notifying a policy change opens, click the Confirm button.
Register individual resources as applied resources
Permission Settings allows you to register individual resources as applied resources. To register individual resources as applied resources, follow these steps.
- In the action selection, select an action that can select individual resources.
- Actions that allow individual resource selection are displayed in purple.
- In Applied Resource, click Individual Resource.
- Click the Add Resource button. The Add Resource popup opens.
Category Whether requiredDetailed description Self-type Required Select the type of resource to add SRN - Unique resource ID in Samsung Cloud Platform - Automatically updated according to the input fields below
Account Required Account ID Settings - Current Account: Current Account ID is auto-filled and cannot be edited
- All Accounts: Add to all Accounts (not recommended)
- Manual Input: Manually enter the Account ID using lowercase English letters and numbers, up to 100 characters (wildcard input not allowed)
Region Select Enter the resource’s region information directly within 100 characters - Select All When checked, add resources from all regions
Resource ID Required Enter the resource ID to add directly, up to 100 characters - Select All when checked adds all resources of that resource type
Table. Policy creation - Register individual resources as applicable resources
Delete Permission Set
To delete a permission set, follow these steps.
- Click the All Services > Management > ID Center menu. Go to the Service Home page of ID Center.
- On the Service Home page, click the Permission Set menu. You will be taken to the Permission Set List page.
- Select at least one permission set to delete from the permission set list.
- After verifying the selected permission set, click the Delete button.
- You can also delete individually from the Permission Set Details page of the permission set to be deleted.
- When the popup notifying the deletion of the permission set opens, click the Confirm button.
10.5.2.5 - Using ID Center Access Portal
You can access and use the Account resource through the Access Portal.
- To use the Access Portal, you must be registered as a user in the ID Center of the Samsung Cloud Platform Console.
- For detailed information on user registration, refer to Create User.
Access Portal First Login
To log in to the Access Portal for the first time, follow these steps.
- Use the Access Portal URL to go to the login page.
- The Access Portal connection URL is activated when applying for ID Center and can be found on the ID Center Settings page.
- A firewall request may be required depending on the user environment.
- Enter the username and password on the login page.
Select the method to send the verification code, and click the Send Verification Code button.
Enter the received verification code and click the Next button. A Identity verification for multi-factor authentication (MFA) popup will open.
Identity verification for multi-factor authentication (MFA) in the popup window, after completing personal information entry and terms verification for MFA, click the Confirm button. The Password change popup window opens.
Item Required statusdescription Prevent automatic input Required Enter the characters displayed in the image into the input field, then click the Confirm button. mobile phone number Required Enter mobile phone number - Enter the mobile phone number and click the Verify button to issue a verification code
- Enter the verification code received on the mobile phone and click the Confirm button
- If the verification code is valid, identity verification is completed
email Required Enter an email (up to 60 characters) to use for identity verification - For accounts whose credential source is linked as AD type, select provide email information registered on the AD side as read-only
region Required Region selection for personal data collection Collection and Use of Personal Information Required After reviewing the terms for the collection and use of personal data, check I agree Table. Identity verification items for multi-factor authentication (MFA)Password Change In the popup window, after entering the password change information, click the Confirm button. The Access Portal Terms of Use popup window will open.
Item Required statusdescription Existing password Required Enter the password received from the ID Center administrator New password Required Refer to the password creation rules and enter it manually. Confirm Password Required Re-enter the password Table. Password change itemsPassword creation rules- It must include at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%&*^). - The length must be 9 to 20 characters.
- ID or username cannot be used as a password.
- You cannot use the same character more than three times.
- You cannot use passwords that are easy to guess.
- You cannot use a recently used password.
- Consecutive characters or numbers of four or more are not allowed.
- The password change cycle is 90 days.
- It must include at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
After reviewing the Access Portal terms of use, click the Confirm button. You will be redirected to the Access Portal page.
Access Portal Log in
- If you are accessing the Access Portal for the first time, refer to Access Portal First-time Access, apply for the Access Portal URL first, and then log in.
To log in to the Access Portal, follow these steps.
- Enter the Access Portal connection URL received through service request in the browser’s address bar. You will be taken to the Access Portal login page.
- On the login page, enter username and password.
- Choose the method to send the verification code, and click the Next button. You will be taken to the verification code confirmation page.
- If you did not receive the verification code or it has expired, click the Resend verification code button to request the code again.
- Enter the received verification code and click the Login button. You will be taken to the Access Portal page.
- If you have lost your ID or password, click the Find Password button, then you can change it using the email or phone number registered in the Access Portal.
- Accounts whose credential source is linked as AD type have Password Recovery disabled. Contact the ID Center administrator.
- Please enter the password and verification code correctly. If you enter the password or verification code incorrectly five or more times, your account will be locked for security.
- If the account is locked, provide the locked account information to the user.
Using Access Portal
When you log in to Access Portal, you will be taken to the Access Portal page. Access Portal page consists of Account tab and My Info tab.
Account
Check the Account and permission set assigned to the user, and access the Samsung Cloud Platform Console using the Account’s permission set.
By using temporary key issuance, you can obtain a temporary key to access the Account.
| Category | Detailed description |
|---|---|
| Account List | Account name and ID assigned to the user, and root user email information
|
| Permission Set List | Permission set applied to the Account
|
My Info.
Verify the user’s basic information, and modify the user’s description and options as needed.
| Category | Detailed description |
|---|---|
| Username | User’s name |
Email to be used for identity verification
| |
| mobile phone number | Mobile phone number to use for identity verification
|
| Last login | The date and time the user last logged in |
| Password | Date and time of the last password change
|
| Password reuse restriction | Number of recent passwords that cannot be set as the password
|
| time zone | User Time Zone (Time Zone)
|
| Terms and Conditions | Agreement to terms
|
- If you enter the password incorrectly five or more times, you will be automatically logged out.
- It must contain at least one each of uppercase letters (English), lowercase letters (English), digits, and special characters (
!@#$%&*^). - The length is 9 to 20 characters.
- ID or username cannot be used as a password.
- You cannot use the same character more than three times.
- You cannot use passwords that are easy to guess.
- You cannot use a password that was recently used.
- Sequences of four or more consecutive characters or digits are not allowed.
- The password change cycle is 90 days.
Account
You can check the Account and permission set assigned to the user, and use the Account’s permission set to log in to the Samsung Cloud Platform Console or obtain a temporary token for access.
| Category | Detailed description |
|---|---|
| Account list | Account name and ID assigned to the user, and root user email information
|
| Permission Set List | Permission set applied to the Account
|
Issue temporary key
You can obtain a temporary key to access the Samsung Cloud Platform Console from the Access Portal. To obtain a temporary key, follow these steps.
- Enter the Access Portal connection URL received through service request into the browser’s address bar. You will be taken to the Access Portal login page.
- Log in to Access Portal. Go to the Access Portal page.
- Access Portal page, click the Account tab. You will be taken to the Account tab.
- From the permission set list, click the Temporary Key Issuance button for the permission set you want to receive a temporary key for. A popup notifying the temporary key issuance will open.
- After checking the account name, click the Confirm button. The ID Center temporary key issuance popup opens.
- After checking the token issuance information, click the Confirm button.
- ID Center Credential Issuance Please note that the information in the popup cannot be reviewed again.
- If you lose the token issuance information, you must reissue the token.
10.5.3 - Release Note
ID Center
- When applying for the ID Center, we also provide the Access Portal URL.
- The process of requesting the Access Portal URL through a service request has been changed to provide the Access Portal URL together when applying for the ID Center.
- After completing the ID Center application, you can view the Access Portal connection URL on the ID Center settings screen.
- You can select AD (Active Directory) as the credential source.
- Using AD (Active Directory), users can manage credential sources directly.
- We have officially launched the ID Center service.
- You can create permission policies for each service and assign accounts and policies linked to the Organization service to users, enabling management of tasks according to each user’s permissions.
- You can strengthen security so that only authorized ID Center users can access through the Access Portal.
10.6 - Logging&Audit
10.6.1 - Overview
Service Overview
Logging&Audit stores all actions performed by the user, enabling change tracking of cloud resources, troubleshooting, security checks, and more. Collected action logs are retained for 90 days and can be stored in the user’s Object Storage through Trail creation and management.
Provided Features
Logging&Audit provides the following features.
- Task History Log Collection: All generated logs are collected and stored in real time. For the complete logs collected from multiple servers and services, you can search using various criteria such as resource type, resource name, time period, and operator name through a web-based console.
- Activity Log Audit: All recorded activity details are retained for 90 days and can be viewed at any time through the Console.
- Log Management: The numerous logs generated while using cloud services can be stored in the user’s Object Storage by creating a Trail.
- Log Integrity Verification: After creating a Trail, you can verify through the log file verification feature whether the log files stored in Object Storage have been changed, modified, or deleted.
Component
Activity History
It stores all user activities, enabling tracking of changes to cloud resources, troubleshooting, security audits, and more. Activity logs are retained for 90 days without additional configuration, and you can analyze logs using various search functions for effective log management.
Trail
Trail can store user activity logs generated through the Console and API calls in Object Storage for long-term retention. Additionally, you can select the services and accounts you wish to store to use it for tracking changes to cloud resources, troubleshooting, security audits, and more.
Preceding Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Storage | Object Storage | Object storage that facilitates data storage and retrieval |
10.6.2 - How-to guides
Users can view activity logs through the Samsung Cloud Platform Console and store those logs using the Trail service without any time constraints. When issues such as security risks or resource changes occur, they can review the activity logs to determine the cause.
View Activity History
To view the list of a user’s activity history, follow these steps.
- Click the All Services > Management > Logging&Audit menu. Go to the Service Home page of Logging&Audit.
- On the Service Home page, click the Activity History menu. You will be taken to the Activity History List page.
- Activity History List page, view the activity history.
Category Detailed description File download Save the activity log list in JSON or CSV file format Period filter Select list search period - All, Last 30 minutes, Last 1 hour, Last 12 hours, Custom input Select from
- Custom input: start and end date-times can be entered
time zone Select searchable time range Search input field Enter a keyword to search the list Advanced Search Enter a keyword or select information by category to search the list. Settings icon Configure columns to display in the list Table. Activity log list items
- The list refreshes automatically every minute.
- The list shows only the selected region’s entries.
Activity History Comparison
You can select up to five task histories from the activity log list to compare information.
If you check and select the work history you want to compare, it will be added to the Activity History Comparison page, where you can compare and review the information.
View detailed activity history information
You can view the list of all activity logs and detailed information. On the Activity Log Details page, it consists of Work History Details, Work Log Details tabs.
To view detailed information of the activity log, follow these steps.
- Click the All Services > Management > Logging&Audit menu. Then navigate to the Service Home page of Logging&Audit.
- On the Service Home page, click the Activity History menu. It navigates to the Activity History List page.
- Activity Log List page, click the activity entry you want to view details for. You will be taken to the Activity Log Details page.
- Activity Details page consists of Work History Details, Work Details tabs.
Task History Details
On the Work History Detail page, you can view detailed information about the work history.
| Category | Detailed description |
|---|---|
| Work date and time | Log occurrence time |
| Operator Information | Operator account |
| Service | Service name |
| Role Name | Role name of the user who entered as a role |
| Resource Name | Resource Name |
| Region | working region |
| Resource Type | Resource Type |
| Work history | Work details |
| Resource ID | Resource’s unique ID |
| Operation result | Result |
| Event topic | Event details |
Task Details
Work History Details page lets you view detailed information of the work history.
| Category | Detailed description |
|---|---|
| Basic mode JSON mode | Select view mode for task history details |
| Copy code | Code copying is possible when JSON mode is selected |
| accountId | Account ID |
| productName | Service name |
| requestedBy | Requester ID |
| resourceName | Resource Name |
| resourceType | Service type |
| state | Result |
10.6.2.1 - Managing Trails
Users can view activity logs through the Samsung Cloud Platform Console and store those logs using the Trail service without time restrictions. Since activity logs are retained for 90 days, for long-term retention you must create a Trail service and store them in Object Storage.
Create Trail
In the Samsung Cloud Platform Console, you can use the Logging&Audit Trail service to store activity logs without any time restrictions.
To create a Trail, follow the steps below.
- Click the All Services > Management > Logging&Audit menu. Go to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- On the Trail List page, click the Create Trail button. You will be taken to the Create Trail page.
- Enter or select the required information in the Service Information Input area.
Category Required statusDetailed description Trail name Required Trail name - Enter using English letters, numbers, and the special character (-) with a length of 5 to 26 characters
Target region Required Region where activity occurred - Services that are created without specifying a region select the target region as All
- If a specific region selection is required, select from the region list
- The target region can be changed after creation
Target resource type Required Resource type of activity logs to be stored in Trail - Default: All
- If you want to change to specify only certain resource types, click the Select button to choose the resource types to store
- Refer to the Service-specific resource type list for selectable resource types
- The target resource type can be changed after creation
Target users Required User of the activity records to be stored in Trail - Default: All
- If you want to change to specify only certain users, click the Select button to choose the users to be saved
- The target users can be modified after creation
Storage bucket region Required Location (region) of the Object Storage bucket for storing activity logs - The storage bucket cannot be changed after creation
storage bucket Required Object Stroage bucket name for storing activity logs - The storage bucket cannot be changed after creation
Save format Required File type to save (JSON, CSV) - The save format can be changed after creation
Log file verification Select Log file verification usage - If you select Use, a Digest file is stored in the same bucket to verify changes or deletions of the Trail log file
- Log file verification usage can be changed after creation
ServiceWatch log collection Select Trail logs are sent to a ServiceWatch log group. By sending Trail logs to a ServiceWatch log group, you can monitor them through ServiceWatch and receive alerts when specific activities occur - If you select Use, you can view the automatically generated ServiceWatch log group name. You can also select the IAM role required for ServiceWatch log collection
- The IAM role for ServiceWatch log collection requires the following configuration
- Set the Principal’s Type to Service, and choose
loggingaudit.samsungsdscloud.comfor Value
- Attach a policy to Policy that includes the following permissions
servicewatch:CreateBulkServiceLogEvents
servicewatch:CollectLogGroupLogStream
- Whether ServiceWatch log collection is enabled can be changed after the Trail is created
- Set the Principal’s Type to Service, and choose
Table. Trail service information input fields - In the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description description Select Enter additional information or description about the Trail Tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value values
Table. Trail additional information input fields
- Enter or select the required information in the Service Information Input area.
When ServiceWatch log collection is enabled, refer to the following for the IAM policy permissions.
- If you want to create the Authentication Type as All Authentication, write it as follows.
{
"Statement": [
{
"Action": [
"servicewatch:CreateBulkServiceLogEvents",
"servicewatch:CollectLogGroupLogStream"
],
"Effect": "Allow",
"Resource": [
"*"
],
"Sid": "VisualEditor0"
}
],
"Version": "2024-07-01"
}
- If you want to create the authentication type as temporary authentication, Console login, you need a Condition clause as shown below.
{
"Statement": [
{
"Action": [
"servicewatch:CreateBulkServiceLogEvents",
"servicewatch:CollectLogGroupLogStream"
],
"Effect": "Allow",
"Resource": [
"*"
],
"Sid": "VisualEditor0",
"Condition": {
"Bool": {
"scp:MultiFactorAuthPresent": [
"True"
]
}
}
}
],
"Version": "2024-07-01"
}
- Summary Check the detailed information and estimated billing amount generated in the panel, then click the Complete button.
- Once creation is complete, check the created resources on the Trail List page.
Check Trail detailed information
The Trail service allows you to view and edit the full list and detailed information. Trail Details page consists of Details, Tags, Activity Log tabs.
To view detailed information about the Trail, follow these steps.
- Click the All Services > Management > Logging&Audit menu. Navigate to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- Trail List page, click the resource to view detailed information. You will be taken to the Trail Detail page.
- Trail Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Category Detailed description Trail status Status of the user-created Trail - Active: Trail running
- Stopped: Trail stopped
Trail control Button to change the Trail status - Start: Starts a stopped Trail. Activity logs are saved again from the day the Trail is started.
- Stop: Stops a running Trail. Activity logging is halted, and previously saved activity logs are retained.
Delete Trail Button to delete the trail Table. Trail status information and additional features
- Trail Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
On the Trail list page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Trail name | Trail name |
| Target region | The region where the activity log occurred
|
| Target resource type | If you want to change the resource type of the activity history stored in Trail
|
| Target users | If you want to change the user of the activity log stored in Trail
|
| Storage bucket region | Region of the Object Storage bucket storing activity logs |
| storage bucket | Object Stroage bucket name storing activity logs |
| Save format | File types stored in the bucket (JSON, CSV)
|
| description | Additional information or description about the Trail
|
| Log file verification | Log file verification usage
|
| ServiceWatch log collection | Send Trail logs to a ServiceWatch log group
|
| Initial collection timestamp | The initial collection timestamp of activity logs stored in Trail |
| Final collection date and time | The most recent collection timestamp of activity logs stored in Trail |
| Final execution result | Final execution result of the activity log stored in Trail |
tag
On the Trail List page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the Trail list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Trail Resources
Depending on the Trail’s state, you can start or stop it. To control the Trail’s resources, follow the steps below.
Getting Started with Trail
You can start a Stopped Trail. Activity history will be saved again from the day you start the Trail.
- Click the All Services > Management > Logging&Audit menu. You will be taken to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- On the Trail List page, click the resource (Trail) to restart the stopped Trail. You will be taken to the Trail Details page.
- On the Trail Details page, click the Start button at the top to start the server. Check the status of the changed Trail in the Status Display item.
- When the Trail start is complete, the status changes from Stopped to Active.
- For detailed information about the Trail status, please refer to Check Trail details.
Stop Trail
You can stop a Trail that is active. Stopping a Trail halts the recording of activity history, while preserving any previously saved activity history.
- Click the All Services > Management > Logging&Audit menu. Go to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- Trail List page, click the resource (Trail) you want to stop. You will be taken to the Trail Details page.
- Trail Details page, click the Stop button at the top to stop the server. In the Status Display section, check the status of the updated Trail.
- When the trail stop is complete, the status changes from Active to Stopped.
- For detailed information about the Trail status, refer to Check Trail detailed information.
Managing Trail Resources
If you need control and management functions for the created Trail resource, you can perform tasks on the Trail Details page.
Modify target region
You can modify the target region of a Trail. To modify the target region of a Trail, follow the steps below.
- Click the All Services > Management > Logging&Audit menu. Navigate to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- On the Trail List page, click the resource (Trail) whose target region you want to change. You will be taken to the Trail Details page.
- On the Trail Details page, click the Edit button of the Target Region. You will be taken to the Edit Target Region popup.
- Select the region to modify from the region list, and click the Confirm button. You will be taken to the Trail Details page.
- Check the changed target region on the Trail Details page.
Edit target resource type
You can modify the target resource type of a Trail. To modify the target resource type of a Trail, follow the steps below.
- Click the All Services > Management > Logging&Audit menu. Go to the Service Home page of Logging&Audit.
- Service Home page, click the Trail menu. You will be taken to the Trail List page.
- On the Trail List page, click the resource (Trail) whose target resource type you want to change. You will be taken to the Trail Details page.
- On the Trail Details page, click the Edit button of the Target Resource Type. You will be taken to the Edit Target Resource Type popup.
- Add or modify the target resource type, select it, and verify that the selected resource type appears in the selected item at the bottom.
- Refer to the Service-specific resource type list for selectable resource types.
- If you have completed adding or modifying the target resource type, click the Confirm button. You will be taken to the Trail Details page.
- On the Trail Detail page, check the changed Target Resource Type.
Edit target user
You can modify the target users of a Trail. To modify the target users of a Trail, follow these steps.
- Click the All Services > Management > Logging&Audit menu. Go to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- Trail List page, click the resource (Trail) whose target user you want to change. You will be taken to the Trail Details page.
- On the Trail Details page, click the Edit button of the Target User. The Target User Edit popup opens.
- Add or modify the target user, select them, and verify that the selected user appears in the Selection Item at the bottom.
- If you have completed adding or modifying the target user, click the Confirm button. You will be taken to the Trail Details page.
- On the Trail Details page, check the changed Target Users.
Modify Save Format
You can modify the format of log files stored in Trail’s bucket. To change Trail’s storage format, follow these steps.
- Click the All Services > Management > Logging&Audit menu. You will be taken to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- Trail List page, click the resource (Trail) whose log file storage format you want to change. You will be taken to the Trail Details page.
- On the Trail Details page, click the Edit button of the Save Format. The Edit Save Format popup window opens.
- Change the file format and click the Confirm button. You will be taken to the Trail Details page.
- On the Trail Detail page, check the changed Save Format.
Edit Trail description
You can edit the description of a Trail. To edit the description of a Trail, follow these steps.
- Click the All Services > Management > Logging&Audit menu. Go to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- Trail List page, click the resource (Trail) whose description you want to edit. You will be taken to the Trail Detail page.
- Click the Edit button of the Description on the Trail Details page. The Edit Description popup opens.
- Complete editing the description and click the Confirm button. You will be taken to the Trail Details page.
- Check the updated description on the Trail Detail page.
Modify log file verification
You can modify whether Trail’s log file verification is enabled. To modify the usage of Trail’s log file verification, follow the steps below.
- Click the All Services > Management > Logging&Audit menu. Navigate to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- Click the resource (Trail) whose log file verification setting you want to change on the Trail List page. You will be taken to the Trail Details page.
- Click the Edit button of Log File Verification on the Trail Details page. You will be taken to the Log File Verification Edit popup.
- If you select Use, a Digest file is stored in the same bucket to verify whether the Trail log file has been modified or deleted. Choose whether to use it and click the Confirm button. You will be taken to the Trail Details page.
- On the Trail Details page, check the updated log file verification.
Modify ServiceWatch Log Collection
You can modify whether ServiceWatch log collection is enabled. To modify the ServiceWatch log collection setting for a Trail, follow these steps.
- Click the All Services > Management > Logging&Audit menu. Proceed to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- On the Trail List page, click the resource (Trail) to change the ServiceWatch log collection setting. You will be taken to the Trail Details page.
- On the Trail Details page, click the Edit button of ServiceWatch log collection. You will be taken to the Edit ServiceWatch log collection popup.
- When you select Use, the ServiceWatch log group name that will receive the Trail logs is automatically generated and can be viewed. Also select the IAM role required for ServiceWatch log collection, and click the Confirm button. You will be taken to the Trail Details page.
- ServiceWatch log collection requires the following configuration for the IAM role.
- Select Service for the Category of Actor, and select
loggingaudit.samsungsdscloud.comfor Value. - In the policy, link a policy configured with the following permissions.
servicewatch:CreateBulkServiceLogEventsservicewatch:CollectLogGroupLogStreamTo create the authentication type as all authentication, write it as follows.
Color mode{ "Statement": [ { "Action": [ servicewatch:CreateBulkServiceLogEvents servicewatch:CollectLogGroupLogStream ], "Effect": "Allow" "Resource": [ * ], "Sid": "VisualEditor0" } ], "Version": "2024-07-01" }{ "Statement": [ { "Action": [ servicewatch:CreateBulkServiceLogEvents servicewatch:CollectLogGroupLogStream ], "Effect": "Allow" "Resource": [ * ], "Sid": "VisualEditor0" } ], "Version": "2024-07-01" }Code block. IAM policy > Permission (authentication type: all credentials) If you want to create the authentication type as temporary authentication, Console login, you need a Condition clause as shown below.
Color mode{ "Statement": [ { "Action": [ servicewatch:CreateBulkServiceLogEvents servicewatch:CollectLogGroupLogStream ], "Effect": "Allow" "Resource": [ * ], "Sid": "VisualEditor0" "Condition": { "Bool": { "scp:MultiFactorAuthPresent": [ True ] } } } ], "Version": "2024-07-01" }{ "Statement": [ { "Action": [ servicewatch:CreateBulkServiceLogEvents servicewatch:CollectLogGroupLogStream ], "Effect": "Allow" "Resource": [ * ], "Sid": "VisualEditor0" "Condition": { "Bool": { "scp:MultiFactorAuthPresent": [ True ] } } } ], "Version": "2024-07-01" }Code block. IAM policy > permissions (authentication type: temporary key authentication, Console login)
- Select Service for the Category of Actor, and select
- ServiceWatch log collection requires the following configuration for the IAM role.
- Check the updated ServiceWatch log collection on the Trail Details page.
Delete Trail
You can reduce operational costs by deleting unused Trails. However, deleting a Trail may cause the running service to stop immediately, so you should carefully consider the impact of service interruption before proceeding with the termination.
To delete a Trail, follow these steps.
- Click the All Services > Management > Logging&Audit menu. Navigate to the Service Home page of Logging&Audit.
- On the Service Home page, click the Trail menu. You will be taken to the Trail List page.
- Trail List page, click the resource (Trail) you want to delete. You will be taken to the Trail Details page.
- On the Trail Details page, click the Trail Delete button.
- After deletion is complete, check the Trail list page to confirm the resource has been removed.
List of resource types by service
Resource type list per service. When creating a Trail or modifying the target resource type, this is the list of selectable target resource types.
| Category | Target resource type | Scope |
|---|---|---|
| AI&MLOps Platform | aiml-brightix:aimlops-platform | Region |
| API Gateway | apigateway:api | Region |
| Archive Storage | archivestorage:bucket | Region |
| Backup | backup:backup | Region |
| Backup | backup:backup-agent | Region |
| Bare Metal Server | baremetal:baremetal | Region |
| Block Storage(BM) | baremetal-blockstorage:volume | Region |
| Block Storage(BM) | baremetal-blockstorage:volume-group | Region |
| CacheStore | cachestore:cache-store | Region |
| Certificate Manager | certificatemanager:certificate | Region |
| Cloud Functions | scf:cloud-function | Region |
| Cloud LAN-Campus | clancampus:campus-network | Region |
| Cloud LAN-Datacenter | clandc:cloud-lan-network | Region |
| Cloud LAN-Datacenter | clandc:interface | Region |
| Cloud LAN-Datacenter | clandc:vcable | Region |
| Cloud LAN-Datacenter | clandc:vdevice | Region |
| Cloud WAN | clanwan:attachment | Region |
| Cloud WAN | clanwan:network | Region |
| Cloud WAN | clanwan:segment | Region |
| Cloud WAN | clanwan:segment-location | Region |
| Cloud WAN | clanwan:segment-sharing | Region |
| CloudML | aiml-brightix:cloud-ml | Region |
| Config Inspection | configinspection:config-inspection | Region |
| Container Registry | scr:container-registry | Region |
| Cost Savings | billingplan:cost-savings | Region |
| Data Flow | dataanalytics-brightix:data-flow | Region |
| Data Flow Service | dataanalytics-brightix:data-flow-service | Region |
| Data Ops | dataanalytics-brightix:data-ops | Region |
| Data Ops Service | dataanalytics-brightix:data-ops-service | Region |
| DevOps Service | devopsservice:devops-service | Region |
| Direct Connect | direct-connect:direct-connect | Region |
| EPAS(DBaaS) | epas:epas | Region |
| Edge Server | edgeserver:edge-server | Region |
| Event Streams | eventstreams:event-streams | Region |
| File Storage | filestorage:volume | Region |
| Firewall | firewall:firewall | Region |
| GPU Server | gpuserver:image | Region |
| GPU Server | gpuserver:server | Region |
| GSLB | gslb:gslb | Region |
| Global CDN | cdn:cdn | Region |
| Hosted Zone | dns:hosted-zone | Region |
| Identity Access Management | iam:access-key | Region |
| Identity Access Management | iam:group | Region |
| Identity Access Management | iam:policy | Region |
| Identity Access Management | iam:role | Region |
| Identity Access Management | iam:user | Region |
| Key Management Service | kms:kms | Region |
| Kubernetes Engine | ske:cluster | Region |
| Kubernetes Engine | ske:nodepool | Region |
| LB Health Check | loadbalancer:lb-health-check | Region |
| LB Listener | loadbalancer:lb-listener | Region |
| LB Server Group | loadbalancer:lb-server-group | Region |
| Load Balancer Listener Old | loadbalancer-old:listener | Region |
| Load Balancer Old | loadbalancer-old:loadbalancer | Region |
| Load Balancer Pool | loadbalancer-old:pool | Region |
| Load Balancer | loadbalancer:loadbalancer | Region |
| Logging&Audit | loggingaudit:tral | Region |
| MariaDB(DBaaS) | mariadb:mariadb | Region |
| Marketplace | marketplace:product-service | Region |
| Microsoft SQL Server(DBaaS) | sqlserver:sqlserver | Region |
| Multi-node GPU Cluster | multinodegpucluster:gpu-node | Region |
| Multi-node GPU Cluster | multinodegpucluster:cluster-fabric | Region |
| MySQL(DBaaS) | mysql:mysql | Region |
| Network Logging | network-logging:network-logging | Region |
| Object Storage | objectstorage:bucket | Region |
| Organization | organization:delegation-policy | Region |
| Organization | organization:invitationi | Region |
| Organization | organization:organization | Region |
| Organization | organization:organization-account | Region |
| Organization | organization:ou | Region |
| Organization | organization:service-control-policy | Region |
| Planned Compute | billingplan:planned-compute | Region |
| PostgreSQL(DBaaS) | postgresql:postgresql | Region |
| Private 5G Cloud | private-fivegen-cloud:private-fivegen-cloud | Region |
| Private DNS | dns:private-dns | Region |
| Private NAT | vpc:private-nat | Region |
| Public Domain Name | dns:public-domain-name | Region |
| Public IP | vpc:publicip | Region |
| Quick Query | dataanalytics-brightix:quick-query | Region |
| Repository | scr:repository | Region |
| Search Engine | searchengine:search-engine | Region |
| Secret Vault | secretvault:secretvault | Region |
| Security Group | security-group:security-group | Region |
| SingleID | singleid:singleid | Region |
| Support Plan | billingplan:support-plan | Region |
| Trail | loggingaudit:trail | Region |
| Transit Gateway | vpc:trasit-gateway | Region |
| VPC | vpc:vpc | Region |
| VPC | vpc:internet-gateway | Region |
| VPC | vpc:vpc-endpoint | Region |
| VPC | vpc:vpc-peering | Region |
| VPC | vpc:nat-gateway | Region |
| VPC | vpc:port | Region |
| VPC | vpc:subnet | Region |
| VPC | vpc:private-nat | Region |
| VPC | vpc:privatelink-endpoint | Region |
| VPC | vpc:privatelink-service | Region |
| VPC | vpc:publicip | Region |
| VPC | vpc:transit-gateway | Region |
| VPN | vpn:vpn-gateway | Region |
| VPN | vpn:vpn-tunnel | Region |
| Vertica | vertica:vertica | Region |
| Virtual Server | virtualserver:server | Region |
| Virtual Server | virtualserver:auto-scaling-group | Region |
| Virtual Server | virtualserver:launch-configuration | Region |
| Virtual Server | virtualserver:image | Region |
| Virtual Server | virtualserver:keypair | Region |
| Virtual Server | virtualserver:server-group | Region |
| Virtual Server | virtualserver:volume | Region |
10.6.3 - API Reference
10.6.4 - CLI Reference
10.6.5 - Release Note
Logging&Audit
- Logging&Audit ServiceWatch log collection integration
- Configure the Trail logs to be sent to a ServiceWatch log group, allowing you to monitor them through ServiceWatch and receive alerts when specific activities occur.
- Logging & Audit: Add integration for newly launched service
- API Gateway, Archive Storage, Backup Agent, Cloud Functions, Cloud LAN-Datacenter, Cloud WAN, CloudML, Cost Savings, GSLB, Global CDN, IAM > role, Load Balancer > LB Health Check, Marketplace, Organization, Private DNS, Private NAT, Public Domain Name, Quick Query, Secret Vault, SingleID, Support Plan, Transit Gateway, VPC Peering, Vertica
- When viewing activity logs, we added a date-range filter/time zone and a comparison feature for activity logs.
- Logging & Audit: Add integration for newly launched service
- Data Flow, Data Ops
- Logging & Audit new service launch integration
- AI&MLOps Platform, Multi-node GPU Cluster, VPN, Cloud LAN-Campus, KMS, Event Streams, Serch Engine, EPAS, Microsoft SQL Server
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- Logging&Audit service has been launched. It stores and searches all activity logs performed by customers (Console, API, CLI) and provides features such as change tracking of cloud resources, troubleshooting, and security inspections.
- We have launched the Logging&Audit service. It stores and searches all activity logs performed by customers (Console, API, CLI), and provides functions such as change tracking of cloud resources, troubleshooting, and security inspection.
10.7 - Notification Manager
10.7.1 - Overview
Service Overview
The Notification Manager is a management service that provides notifications to users when alerts occur, according to the criteria set in the notification policy for each account.
Provided features
The Notification Manager provides the following features.
- Alert Group Management: You can create and manage alert groups. You can add or remove users from an alert group.
- Notification Policy Management: You can configure a notification policy to receive specific alerts generated within an Account. When creating a notification policy, if you associate a notification group, users in that group can receive the notifications set in the policy.
Component
Notification Manager provides notification groups and notification policies.
Notification Group
You can create and manage notification groups, and add or remove users from a notification group. The main features are as follows.
- Alert Group Creation: You can create an alert group and add users.
- Alert Group > Add User: You can add users to a created alert group.
- For instructions on creating and using notification groups, see How-to guides > Notification Groups.
Notification Policy
You can create and manage alert policies, and you can disable or re‑enable an alert policy. The main features are as follows.
- Alert Policy Creation: You can create an alert policy and attach an alert group.
- Disable Notification Policy: You can disable the notification policy you are using.
- Use Notification Policy: You can re-enable a notification policy that has been disabled.
- Refer to How-to guides > Notification Policy for how to create and use notification policies.
Preceding Service
Notification Manager has no prerequisite service.
10.7.2 - How-to Guides
Users can enter the required information for an alert group and select detailed options to create it through the Samsung Cloud Platform Console.
Create Notification Group
You can create a notification group in the Samsung Cloud Platform Console and use it.
- Click the All Services > Management > Notification Manager menu. Navigate to the Alert Group List page in Notification Manager.
- On the Notification Group List page, click the Create Notification Group button. You will be taken to the Create Notification Group page.
- On the Create Notification Group page, enter the information required to create a service and select detailed options.
- Enter the required information in the Basic Information area.
Category Required statusDetailed description Notification group name Required Notification group name - Korean, English, numbers, special characters(
+=,.@-_) using, input within 3 to 24 characters
Explanation Select Enter a description for the notification group - Maximum length is 1,000 characters
Table. Notification group basic information items - Korean, English, numbers, special characters(
- In the Add User area, select the user to add to the notification group.
Category Required statusDetailed description Add user Selection Users added to the notification group - Search for the desired user, then select and add that user
- Users in the notification group can be removed using the Delete button
- If the user you want to add does not exist, you need to create the user on the user creation page. See IAM > Create User
- Only users with login history (registered email or mobile phone number) can be added to the notification group
Table. Notification Group User Addition ItemCautionIn the case of IAM users, users who have no login history after account creation cannot receive notifications. Therefore, such users cannot be added to a notification group.
- Enter the required information in the Basic Information area.
View detailed information of the notification group
Notification groups can view and edit the complete list and detailed information.
To view detailed information for the alert group, follow these steps.
- Click the All Services > Management > Notification Manager menu. Go to the Alert Group List page in Notification Manager.
- On the Notification Group List page, click the notification group to view its details. You will be taken to the Notification Group Details page.
- Notification Group Details page provides detailed information about the notification group, as well as edit and delete functions.
Category Detailed description Service Service name Resource Type Resource Type SRN Unique resource ID in Samsung Cloud Platform - In Notification Manager, it refers to the Notification Manager SRN
Resource name Resource Name - In the Notification Manager service, it refers to the Notification Manager name
Resource ID Unique resource ID in the service constructor User who created the service Creation date and time Service creation timestamp Editor User who edited the service information Modification date Date and time the service information was modified Notification group name Notification group name description Description of the notification group user List of users added to the notification group Table. Notification group detail items
- Notification Group Details page provides detailed information about the notification group, as well as edit and delete functions.
Add user to notification group
You can add users to the notification group.
To add a user to the notification group, follow these steps.
- Click the All Services > Management > Notification Manager menu. Navigate to the Notification Group List page in Notification Manager.
- Alert Group List page, click the Add button next to the user of the alert group you want to add a user to. You will be taken to the Add User page.
- Add User page, select the user to add to the notification group and add them.
- If there is no user to add, create a user on the user creation page. Refer to IAM > Create User.
- Only users with a login history (users who have registered an email or mobile phone number) can be added to the notification group.
- If you have added all users, click the Complete button. On the Alert Group List page, click the Expand button at the far right of the relevant alert group to verify the added users.
Edit Notification Group
You can edit the items configured in the generated notification group.
To modify the notification group, follow these steps.
- Click the All Services > Management > Notification Manager menu. Navigate to the Alert Group List page of Notification Manager.
- On the Notification Group List page, click the notification group you want to edit. You will be taken to the Notification Group Details page.
- On the Alert Group Details page, click the Edit button. You will be taken to the Edit Alert Group page.
- On the Edit Notification Group page, you can modify the notification group’s items.
Category Whether requiredDetailed description Notification group name Required Enter the notification group name - using Korean, English, numbers, and special characters(
+=,.@-_) within 3 to 24 characters
description Select Enter a description for the notification group - Maximum length is 1,000 characters
User Select Users added to the notification group - Search for the desired user, then select and add that user
- Users in the notification group can be removed using the Delete button
- If the user you want to add does not exist, you need to create the user on the user creation page. Refer to IAM > Create User
- Only users with login history (registered email or mobile phone number) can be added to the notification group
Table. Notification group edit items - using Korean, English, numbers, and special characters(
- If the notification group edit is complete, click the Save button.
Delete notification group
If you no longer use a created notification group, you can delete it. However, please note that once a notification group is deleted, it cannot be recovered.
To delete a notification group, follow these steps.
- Click the All Services > Management > Notification Manager menu. Navigate to the Alert Group List page in Notification Manager.
- On the Notification Group List page, click the notification group you want to delete. You will be taken to the Notification Group Details page.
- On the Notification Group Details page, click the Delete button. After reviewing the text in the Notification popup, click the Confirm button.
- After deletion is complete, check the Alert Group List page to confirm that the alert group has been removed.
10.7.2.1 - Notification Policy
Users can enter the required information for an alert policy and select detailed options to create it through the Samsung Cloud Platform Console.
Create Alert Policy
You can create and use notification policies in the Samsung Cloud Platform Console.
- Click the All Services > Management > Notification Manager menu. Navigate to the Alert Group page of Notification Manager.
- On the Alert Group page, click the Alert Policy menu. You will be taken to the Alert Policy List page.
- On the Alert Policy List page, click the Create Alert Policy button. You will be taken to the Create Alert Policy page.
- On the Create Notification Policy page, enter the information required to create a service and select detailed options.
Category Whether requiredDetailed description Whether to use Required Alert policy usage - ON: enabled
- OFF: disabled
Notification Policy Name Required Alert policy name - Enter within 30 characters
description Selection Enter description for notification policy - Enter within 1,000 characters
Notification item Required Select notification items - Select notification items that can be received
- To select or deselect a specific notification name among the chosen notification items, click the Expand button at the far right to select or deselect the notification name
- (Example) If you want to receive only notifications about Virtual Server creation failures, select Notification Item: Virtual Server > Notification Name: Virtual Server creation failure.
Notification target group Required Select the notification group to deliver the alert - When you select a notification group, the group name is displayed at the top
- Select or deselect the notification group name
Table. Notification policy creation items
- After setting the required information, click the Done button.
- Once creation is complete, check the created alert policy on the Alert Policy List page.
View detailed notification policy information
Notification policies can be viewed and edited, including the full list and detailed information.
To view detailed information for the alert policy, follow these steps.
- Click the All Services > Management > Notification Manager menu. Navigate to the Alert Group List page of Notification Manager.
- On the Alert Group List page, click the Alert Policy menu. You will be taken to the Alert Policy List page.
- On the Alert Policy List page, click the alert policy whose details you want to view. You will be taken to the Alert Policy Details page.
- Alert Policy Details page displays status information and additional feature information.
Category Detailed description Notification policy status Whether to use the notification policy Edit Edit Notification Policy Delete Delete notification policy Table. Notification policy status information and additional features - Notification Policy Details page displays the following detailed items.
Category Detailed description Notification Policy Name Alert policy name description Explanation of the alert policy constructor User who created the alert policy Creation date and time Alert policy creation time Editor User who modified the notification policy Modification date Date and time the notification policy was modified Notification item Notification items configured in the notification policy Notification target group Notification group linked in the alert policy Table. Notification Policy Detailed Items
- Alert Policy Details page displays status information and additional feature information.
Modify Notification Policy
You can edit the items configured in the generated alert policy.
To modify the alert policy, follow these steps.
- Click the All Services > Management > Notification Manager menu. Go to the Alert Group List page of Notification Manager.
- On the Alert Group List page, click the Alert Policy menu. You will be taken to the Alert Policy List page.
- On the Alert Policy List page, click the Edit button. You will be taken to the Edit Alert Policy page.
- Alert Policy Edit page allows you to edit the alert policy items.
Category Required statusDetailed description Whether to use Required Alert policy usage - ON: enabled
- OFF: disabled
Notification Policy Name Required Alert policy name - Enter within 30 characters
description Select Enter description for notification policy - Enter within 1,000 characters
Notification item Required Select notification items - Select the notification items you can receive
- To select or deselect a specific notification name among the chosen notification items, click the Expand button at the far right to select or deselect the notification name
- (Example) If you want to receive only the notification for Virtual Server creation failure, Notification Item: Virtual Server > Notification Name: Virtual Server creation failure
Notification target group Required Select the notification group to deliver the alert - When you select a notification group, the group name is displayed at the top
- Select or deselect the notification group name
Table. Notification policy edit items
- If the notification policy edit is complete, click the Save button.
Using Notification Policy
You can reuse a notification policy that is currently disabled.
To enable the alert policy, follow these steps.
- Click the All Services > Management > Notification Manager menu. Go to the Alert Group List page in Notification Manager.
- On the Alert Group List page, click the Alert Policy menu. You will be taken to the Alert Policy List page.
- Notification Policy List page, click the More button at the far right of the notification policy you want to set to active, then click the Use button. Verify the text in the Notification popup window and click the Confirm button.
- Check the status of notification policies on the Notification Policy List page.
Disable Notification Policy
You can change a notification policy that is currently disabled to “unused.”
To configure the alert policy as disabled, follow these steps.
- Click the All Services > Management > Notification Manager menu. Navigate to the Notification Group List page in Notification Manager.
- On the Alert Group List page, click the Alert Policy menu. You will be taken to the Alert Policy List page.
- Notification Policy List page, click the More button at the far right of the notification policy you want to set to active, then click the Unused button. Verify the text in the Notification popup window and click the Confirm button.
- On the Notification Policy List page, check the status of notification policies.
10.7.3 - Release Note
Notification Manager
- We have launched the Notification Manager service. It provides a function to manage notifications delivered to users when alerts occur.
- You can create and manage notification policies and groups for receiving alerts, and you can add users.
10.8 - Organization
10.8.1 - Overview
Service Overview
Organization is a service that organizes Accounts by organizational units, manages them hierarchically, and controls resource access permissions. Users can manage the resource usage of accounts belonging to an organization to optimize costs.
Features
- Hierarchical Project Management: You can invite an Account created within the organization to an Organization and configure it by organizational units for hierarchical management.
- Organizational Unit Governance: You can configure the required policies as control policies based on the organizational unit and apply them uniformly to all organizational units and Accounts under the organization.
- Efficient resource management and cost optimization: You can monitor the resource usage of all accounts within the organization to optimize costs.
Configuration diagram
Provided features
Organization provides the following features.
- Account Management: You can create a new Account within the organization or invite an existing Account to manage.
- Organizational Unit Management: You can configure organizational units and manage them by creating subordinate organizational units or Accounts.
- Control Policy Management: Manage settings related to compliance as unified policies, and apply policies by organizational unit and by Account to proactively prevent or detect regulatory violations.
Preceding Service
Organization has no prior service.
10.8.2 - How-to guides
Users can enter the required information for an Organization and select detailed options to create a service through the Samsung Cloud Platform Console.
Create Organization
You can create an Organization in the Samsung Cloud Platform Console and use it. To create an Organization, follow these steps.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Create Organization button. The Create Organization popup will open.
- Create Organization In the popup window, enter the Organization Name, then click the Create button.
- Write within 20 characters using Korean, English, numbers, spaces, and special characters (
+=,.@-_).
- Write within 20 characters using Korean, English, numbers, spaces, and special characters (
- When the popup notifying the creation of an Organization opens, click the Confirm button.
- Check the Organization’s dashboard on the Service Home page.
Category Detailed description Organization Information Display Management Account information - Click the Organization Information item to go to the Settings page where you can view detailed organization information
organizational unit Number of organizational units that make up the organization - Click the count to go to the Organization Structure page
Account Number of Accounts comprising the organization - Click the count to go to the Organization Structure page
- Click the Add item to go to the Add Account page
- For more details, see Add Account reference
Control Policy Number of control policies constituting the organization - Click the count to go to the Control Policy page
- Click the Add item to go to the Add Control Policy page
- For more details, refer to Create Control Policy
Table. Organization Service Home dashboard items
Organization Check detailed information
You can view detailed information of the Organization and manage permissions. To view detailed information of the Organization and manage permissions, follow these steps.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Organization Settings menu. You will be taken to the Organization Settings page.
Category Detailed description Delete organization Delete organization button Organization name Organization name - Click the Edit button to modify
- Organization names distinguish between uppercase and lowercase English letters
Organization ID Organization ID constructor Name of the user who initially created the organization Creation date and time Organization creation date and time Editor Name of the user who last modified the organization information Modification date and time Last modified timestamp of organization information Management Account name Management Account name Management Account ID Management Account ID Management Account email Management Account email Control Policy Whether the control policy is enabled - Click the Edit button to change the status
- For more details, see Control Policy
Delegation of authority Organization Management Permission Delegation Information - Permission Delegation: Allows delegating permissions to accounts within the organization
- Displayed when no delegation information is available
- When the button is clicked, you can configure delegation at the Action level using the JSON Editor on the Permission Delegation page
- Permission Edit: Modify permission information
- Only the Management Account can be set
- When the button is clicked, you can configure delegation at the Action level using the JSON Editor on the Permission Delegation page
- Revoke Delegation: Delete delegated permission information
Table. Organization configuration items
- If Control policy is disabled, the connection to the associated control policy is removed, and even authorized users cannot view the control policy.
- Permission Delegation information can only be managed in the Management Account.
Invite Account to Organization
You can manage the list of Accounts invited to the Organization.
Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
On the Service Home page, click the Invitation History menu. You will be taken to the Invitation History List page.
On the Invitation History List page, click the Account Invite button. Proceed to the Account Add page.
Category Detailed description email Account email Account name Account name Account ID Account ID Request date and time Account invitation date and time Completion Date and Time Invitation canceled, rejected, , expired, completion time Invitation status Invitation status Invitation canceled Cancel the invitation for the selected account - Enabled when selecting an account in the invitation list
- Multiple accounts can be canceled simultaneously
Account invitation Invite a new Account to the organization - When clicking the Account Invite button, navigate to the Add Account page
Table. Organization invitation list itemsOn the Add Account page, create and register a new Account, or add an existing Account.
- For detailed information about adding an Account, see Account 추가하기.
Join another Organization
If you are invited from another organization, you can review and approve the invitation information.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Received Invitations menu. You will be taken to the Received Invitations page.
Category Detailed description Invitation email Email information for organization invitation Organization name Organization name Organization ID Organization ID Management Account name Management Account name Management Account ID Management Account ID Management Account email Management Account email Invitation expiration date and time Invitation expiration date and time - Activated when selecting an account from the invitation list
- Multiple accounts can be canceled simultaneously
Invitation declined Decline invitation Accept invitation Accept the invitation and join the Organization Table. Organization Received Invitation Items
In the following cases, you cannot register even if you approve the invitation.
- When the number of accounts in the organization exceeds the limit.
- When the approval time is the expense settlement date (the 1st of each month, Asia/Seoul GMT +09:00)
- If the account has an outstanding balance.
Delete Organization
To delete the Organization, follow these steps.
- Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
- On the Service Home page, click the Organization Settings menu. You will be taken to the Organization Settings page.
- On the Organization Settings page, click the Delete Organization button. The Delete Organization popup window opens.
- Delete Organization in the popup, click the Confirm button.
10.8.2.1 - Organization Configuration Information
You can view the hierarchical structure of the Organization and verify and manage the organizational units and Accounts that are configured.
Check organization configuration information
You can view the configuration information of the Organization. Follow these steps to view the configuration information of the Organization.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Organizational Structure menu. You will be taken to the Organizational Structure page.
- Select the view mode for the Organization unit and Account management area.
Category Detailed description View hierarchy Display organizational units in a hierarchical structure View Account List Display the list of Accounts within the organization Add Account Invite a new Account to the organization - When the Account Invite button is clicked, navigate to the Add Account page
- For more details, see Add Account
Table. Organization Organizational structure items
View hierarchy
On the Organization Configuration page, when you click the View Hierarchy button, you can view and manage the organizational units and Accounts that make up the Organization in a hierarchical structure.
| Category | Detailed description |
|---|---|
| Create a sub-organization unit | Add a new organizational unit under the selected organizational unit
|
| More > Delete organizational unit | Delete the selected organizational unit
|
| More > Move Account | Delete the selected organizational unit
|
| More > Exclude Account | Exclude the selected Account from the organization
|
| More > Delete Account | Delete the selected Account
|
| Organization unit/Account name | Display the names of organizational units and Accounts in a measurement structure format
|
| ID/Email | Organizational units display ID, and accounts display ID and email. |
| Creation/Join Date and Time | Organizational units display the creation date and time, while Accounts display the creation or registration date and time. |
View Account List
On the Organization Configuration page, clicking the View Account List button lets you view and manage the list of Accounts that compose the Organization.
| Category | Detailed description |
|---|---|
| Account Transfer | Move Account to another organization
|
| More > Exclude from organization | Exclude Account from organization
|
| Account name | Account name |
| Account ID | Account ID |
| Account user email | |
| Additional date/time | Account creation, addition timestamp |
| Additional type | Account addition method
|
Manage Account
You can view and manage the list of Accounts that make up the Organization.
Add Account
You can create a new Account or add an existing Account to an Organization. To add an Account to an Organization, follow these steps.
Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
On the Service Home page, click the Organizational Structure menu. You will be taken to the Organizational Structure page.
On the Organization Structure page, click the Add Account button. You will be taken to the Add Account page.
On the Add Account page, enter the Account information to be added, then click the Complete button.
Category Required statusDetailed description Additional method Required Select the method to add an Account - Create New Account: Add by creating a new Account
- Invite Existing Account: Add by entering the Root user email of an already created Account
Account name Required Enter the Account name to create - using Korean, English, numbers, spaces, special characters(
+=-_@[](),.) within 3 to 30 characters
email Required Email to set as the Root user of the new Account - When clicking the Account Invite button, navigate to the Account Add page
Check email Required Reconfirm email information - When you click the Organization Info button, you are taken to the Settings page where you can view detailed organization information.
IAM role name Required Display organizational units in a hierarchical structure - English letters, numbers, special characters(
+=-_@,.) to input within 64 characters
Root user email Required Account’s Root user email - If Existing Account invitation is selected, only Root user email is entered
- Click the Add button to add up to 10 simultaneously
Table. Add Organization AccountWhen the popup notifying account creation and invitation opens, click the Confirm button.
- You can add up to 200 accounts.
- The newly created Account can be accessed by logging in directly with email or through an automatically generated role.
- When logging in directly with email, you must use the password recovery feature to reset your password.
Check Account Detailed Information
You can view and edit the detailed information of the Account. To view the detailed information of the Account, follow these steps.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Organization Configuration menu. You will be taken to the Organization Configuration page.
- On the Organization Structure page, click the View Account List button.
- In the Account list, click the Account name of the Account whose details you want to view. You will be taken to the Account Details page.
- Account Details page consists of Basic Information tab and Control Policy tab.
Category Detailed description Exclude from organization Exclude the Account from the organization - When you click the button, a popup notifying the Account exclusion opens
- For more details, see Account Removal
Account Transfer Move the Account to another organizational unit - Click the button to go to the Account Move page
- For more information, see Account 이동하기
Basic Information Tab Display basic information about the Account Control Policy Display the control policies linked to the Account Table. Account detail page items
- Account Details page consists of Basic Information tab and Control Policy tab.
Detailed information
You can view detailed information of the organizational unit and edit the information if needed.
| Category | Detailed description |
|---|---|
| Account name | Account name |
| Account ID | Account ID |
| constructor | User who created the Account |
| Creation date and time | Date and time the account was created |
| Editor | User who modified the Account |
| Modification date and time | Date and time the account was modified |
| Account’s user email | |
| Additional type | Account addition method
|
| higher-level organization unit | Display the upper level of the current organizational unit in a hierarchical structure
|
Control Policy
You can view the control policies linked to the Account and change their connection status.
| Category | Detailed description |
|---|---|
| Direct disconnect | Disconnect the selected control policy
|
| Control policy connection | Connect a new control policy
|
| Control Policy Name | Control Policy Name |
| type | Control Policy Types |
| Connection method | Control policy connection method
|
| Modification date and time | Last modified timestamp of the control policy |
Move Account
You can move accounts between organizational units within an Organization.
Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
On the Service Home page, click the Organizational Structure menu. You will be taken to the Organizational Structure page.
On the Organization Structure page, click the View Account List button.
After selecting the Account to which you want to move the organization unit, click the Account Move button. You will be taken to the Account Move page.
On the Account Transfer page, select the organizational unit to which you want to move the Account, then click the Complete button.
Category Detailed description Select Account Enter the name of the organizational unit - Organizational names distinguish between uppercase and lowercase English letters
Organization unit to move Select the organizational unit to move the Account to Organizational unit name Name of the organizational unit Organization Unit ID Organization unit ID Organization creation date and time Creation date and time of the organizational unit Table. Organization: Create Organizational UnitWhen the popup notifying the Account transfer opens, review the transfer information, then click the Confirm button.
- The newly created Account can be accessed by logging in directly with email or through an automatically generated role.
- When logging in directly with email, you must use the password recovery feature to reset your password.
Exclude Account
You can exclude an Account from the Organization.
In the following cases, the Account cannot be excluded.
- Account without a registered payment method
- When there is credit assigned to the account
- When the exclusion point is the cost settlement date (the 1st of each month, Asia/Seoul GMT +09:00)
- Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
- On the Service Home page, click the Organizational Structure menu. You will be taken to the Organizational Structure page.
- On the Organization Structure page, click the View Account List button.
- After selecting the Account to exclude from the Organization, click the More > Exclude Account button.
- When a popup notifying the account exclusion opens, click the Confirm button.
Delete Account
You can delete the account.
- When deleting from the Account list, you must select only one Account to delete.
- You cannot delete the Account in the following situations.
- If you want to delete on the expense settlement date (the 1st of each month)
- If there are resources in use
- When authority is delegated by the ID Center
- When credit is assigned to an account
- In the case of a Management Account or an account that was joined via invitation.
- If it is being registered in Cloud Control or already registered.
- Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
- On the Service Home page, click the Organization Configuration menu. You will be taken to the Organization Configuration page.
- On the Organization Structure page, click the View Account List button.
- From the Account list, select the Account to delete, then click the More > Delete Account button. The Delete Account popup window opens.
- After clicking the Account name of the Account to be deleted, you can also delete it by clicking the Account Details page’s Delete Account button.
- After entering the password for the Account to be deleted, click the Confirm button.
- After entering the Account name to delete, click the Confirm button.
If you delete the Account, an Account deletion notification email will be sent to the next user.
- Administrator who created the Organization
- Root user of the created Account
- User who has delegation for the created Account
Manage Organizational Units
You can view and manage the organizational units and accounts that make up the Organization in a hierarchical structure.
Create an organization unit
You can create a new organizational unit. To create and add an organizational unit in Organization, follow these steps.
Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
On the Service Home page, click the Organization Configuration menu. You will be taken to the Organization Configuration page.
On the Organizational Structure page, click the View Hierarchy button.
After selecting the location in the hierarchical list where you want to add an organizational unit, click the Create Organizational Unit Under button. You will be taken to the Create Organizational Unit page.
- Root or you can select only one existing organizational unit.
- You can create organizational units up to five levels below Root.
On the Organization Unit Creation page, enter the information for the organization unit you want to add, then click the Create button.
Category Required statusDetailed description Organizational unit name Required Enter the name of the organizational unit - Organizational names distinguish between uppercase and lowercase English letters
description Select Enter a description of the organizational unit within 1,000 characters. Control policy connection Required Select a control policy to attach to the organizational unit - For details on creating a control policy, refer to Creating a Control Policy
Table. Organization: Create Organizational UnitWhen the popup notifying the creation of an organizational unit opens, click the Confirm button.
- You can add up to 200 accounts.
- The newly created Account can be accessed by logging in directly with email or through an automatically generated role.
- When logging in directly with email, you need to use the password recovery feature to reset your password.
View detailed information of an organizational unit
You can view and edit detailed information of an organizational unit. To view detailed information of an organizational unit, follow these steps.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Organizational Structure menu. You will be taken to the Organizational Structure page.
- On the Organizational Structure page, click the View Hierarchy button.
- Click the Root/Account name of the organizational unit whose details you want to view in the hierarchical list. You will be taken to the Organizational Unit Details page.
- Organization Unit Detail page is composed of Basic Information tab, Sub Items tab, and Control Policy tab.
Category Detailed description Delete organization unit Button that deletes an organizational unit - When the button is clicked, a popup notifying the organization deletion opens
- For more details, see Delete Organizational Unit
Basic Information Tab Display basic information about the organization unit Sub-item Display sub-elements of an organizational unit Control Policy Display control policies attached to the organizational unit Table. Organization unit detail page items
- Organization Unit Detail page is composed of Basic Information tab, Sub Items tab, and Control Policy tab.
Detailed information
You can view detailed information of the organizational unit and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Service Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Organizational unit name | Organization unit name
|
| description | Description of the organizational unit
|
| higher-level organization unit | Display the upper level of the current organizational unit in a hierarchical structure
|
Sub-item
You can view and manage the subordinate organization units and accounts of the current organization unit.
| Category | Detailed description |
|---|---|
| Create a sub-organization unit | Add a new organizational unit under the selected organizational unit
|
| More > Delete Organizational Unit | Delete selected organization unit
|
| Organization unit/Account name | Display the names of organizational units and Accounts in a measurement structure format
|
| ID/Email | Organizational units display ID, and Accounts display ID and email. |
| Creation/Join Date | Organization units display the creation timestamp, and accounts display the creation or sign‑up timestamp. |
Control Policy
You can view the control policies attached to an organizational unit and change their connection status.
| Category | Detailed description |
|---|---|
| Direct disconnect | Disconnect the selected control policy
|
| Control policy connection | Connect a new control policy. Click the
|
| Control Policy Name | Control Policy Name |
| type | Control Policy Types |
| Connection method | Control policy connection method
|
| Modification date and time | Last modified date and time of the control policy |
Delete organization unit
You can delete an organizational unit in the Organization.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Organization Configuration menu. You will be taken to the Organization Configuration page.
- On the Organizational Structure page, click the View Hierarchy button.
- After selecting the organizational unit to delete from the hierarchical list, click the More > Delete Organizational Unit button.
- When the popup notifying the deletion of an organizational unit opens, click the Confirm button.
Connect control policy
You can attach control policies to an Organization’s organizational unit or Account. To attach a control policy, follow these steps.
Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
On the Service Home page, click the Organization Configuration menu. You will be taken to the Organization Configuration page.
On the Organization Structure page, click the View Hierarchy button.
Click the organizational unit or Account where you want to add the control policy from the hierarchical list. You will be taken to the detail page of that item.
- Root or you can select only one existing organizational unit.
- You can create organizational units up to five levels below Root.
On the detail page, click the Control Policy tab. You will be taken to the Control Policy Connection page.
After selecting the control policy to connect, click the Complete button.
Category Detailed description Linked control policy Enter the name of the organizational unit or the control policy linked to the current organizational unit or Account - Organizational names distinguish between uppercase and lowercase English letters
Control Policy Name Control Policy Name type Control Policy Types Modification date and time Control policy modification timestamp Control policy connection Required Table. Control policy linkage itemsWhen a popup notifying the connection of the control policy opens, click the Confirm button.
ReferenceTo create a new control policy, refer to Create Control Policy.
10.8.2.2 - Organization Control Policy
You can view and manage the Organization’s control policies.
Create Organization Control Policy
You can create control policies for the Organization.
To create a control policy, follow these steps.
Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
On the Service Home page, click the Control Policy menu. You will be taken to the Control Policy List page.
On the Control Policy List page, click the Create Control Policy button. You will be taken to the Create Control Policy page.
After entering items in the Basic Information area, click the Next button.
Category Required statusDetailed description Control Policy Name Required Enter the name of the control policy - English letters, numbers, special characters(
+=-_@,.) within 3 to 128 characters
Explanation Select Enter a description of the organizational unit within 1,000 characters. Table. Create organization control policy - set basic information- English letters, numbers, special characters(
In the Control Requirement Setting area, after selecting the control policy configuration method and the service to apply, click the Next button.
Category Required statusDetailed description Load control policy Select Enter the name of the control policy - When loading a policy, all previously entered content will be deleted
- For more details, see Load Policy
Basic mode/JSON mode Required Select the policy configuration method - Basic Mode: Configure using the mode provided by the Console
- JSON Mode: Configure directly using the JSON Editor
Service Required Select the service to set the control policy - Add Service: Add a service to configure the control policy
Table. Organization control policy creation - service configurationCautionIn the control policy settings, Basic Mode and JSON Mode are provided.
- After writing in Basic Mode and entering JSON Mode or navigating the screen, services with duplicate control requirements are merged into one, and services that have not completed configuration are deleted.
- If the content written in JSON mode does not conform to JSON format, you cannot switch to basic mode.
After setting the permissions, click the Next button.
Category RequiredDetailed description Control Type Required Select control policy type - Allow Policy: Control policy that allows the defined permissions
- Deny Policy: Control policy that denies the defined permissions
Action Required Select actions provided for each service - Actions that allow selection of individual resources are shown in purple
- Actions that target all resources are shown in black
- Add Action Directly: Use the wildcard
*to specify multiple actions at once
Applied resource Required Resources to which the action applies - All resources: Apply to all resources for the selected action
- Individual resources: Apply only to the specified resources for the selected action
- Individual resources are only available when selecting the purple action that allows individual resource selection
- Click the Add resource button to specify target resources by resource type
- For more details on Add resource, see Register individual resources as applicable resources
Authentication Type Required Authentication method of the user target to which the control policy will be applied - All authentication: Applies regardless of authentication method
- Authentication key authentication: Applies to users with authentication key authentication
- Temporary key authentication, Console login: Applies to users with temporary key authentication or Console login
Applied IP Required IP that allows the application of control policies - Custom IP: User registers and manages the IP directly
- Applied IP: User can directly register the IP address or range that the control policy applies to
- Excluded IP: IP addresses or ranges that can be registered as exclusions from the Applied IP
- All IPs: No IP access restriction
- Access is allowed for all IPs, but if exceptions are needed, register Excluded IP to restrict access for the registered IPs
Additional condition Select Add conditions for attribute-based access control (ABAC) - Condition Key: Select from Global condition keys and service condition keys list
- Qualifier: Default value, arbitrary value in the request, all values in the request
- Operator: Bool, Null
- Value: True, False
Table. Create organization control policy - set permissionsOn the Check Input Information page, after confirming the entered information, click the Create button.
When the popup notifying the creation of a control policy opens, click the Confirm button. You will be taken to the Integrated Policy List page.
Load control policy
When creating a control policy, you can generate it by modifying the policy requirements of an existing policy.
To load an existing policy and create a control policy, follow these steps.
Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
On the Service Home page, click the Control Policy menu. You will be taken to the Control Policy List page.
On the Control Policy List page, click the Create Control Policy button. You will be taken to the Create Control Policy page.
After entering items in the Basic Information area, click the Next button.
Category Required statusDetailed description Control Policy Name Required Enter the control policy name - English letters, numbers, and special characters (
+=-_@,.) within 3 to 128 characters
description Select Enter a description of the organizational unit within 1,000 characters. Table. Create organization control policy - set basic information- English letters, numbers, and special characters (
In the Control Requirement Setting area, click the Load Control Policy button. The Load Control Policy popup window opens.
Click the Load Policy button. The Load Control Policy popup opens.
After selecting the control policy to load from the control policy list, click the Confirm button. The loaded policy’s settings will be entered automatically.
After editing the information that needs to be changed, click the Next button.
Check Input Information page, verify the entered information and click the Complete button. You will be taken to the Integrated Policy List page.
Register individual resources as applied resources
Permission Settings allows you to register individual resources as applied resources. To register individual resources as applied resources, follow the steps below.
Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
On the Service Home page, click the Control Policy menu. You will be taken to the Control Policy List page.
On the Control Policy List page, click the Create Control Policy button. You will be taken to the Create Control Policy page.
After entering items in the Basic Information area, click the Next button.
Category Required statusDetailed description Control Policy Name Required Enter the control policy name - using English letters, numbers, special characters (
+=-_@,.) within 3~128 characters
description Selection Enter a description of the organizational unit within 1,000 characters. Table. Create organization control policy - set basic information- using English letters, numbers, special characters (
In the Control Requirement Setting area, after selecting the service to which the control policy will be applied, click the Next button.
Click the Load Policy button. The Load Control Policy popup opens.
After selecting the control policy to load from the control policy list, click the Confirm button. The loaded policy’s settings will be entered automatically.
After editing the information that needs to be changed, click the Next button.
On the Check Input Information page, verify the entered information and click the Complete button. You will be taken to the Integrated Policy List page.
Select an Action that allows selecting individual resources in the Action selection.
- Actions that allow individual resource selection are displayed in purple.
Click Individual Resource in Applied Resource.
Click the Add Resource button. The Add Resource popup window opens.
Category Whether requiredDetailed description Self type Required Select the resource type to add SRN - Unique resource ID in Samsung Cloud Platform - Automatically updated according to the input fields below
Account Required Account ID Settings - Current Account: Current Account ID is auto-filled and cannot be edited
- All Accounts: Add to all Accounts (not recommended)
- Manual Input: Manually enter the Account ID using lowercase English letters and numbers, up to 100 characters (wildcard input not allowed)
Region Select Enter the resource’s region information directly within 100 characters - Select All When checked, add resources from all regions
Resource ID Required Enter the resource ID to add directly, up to 100 characters - Select All when checked adds all resources of that resource type
Table. Create organization control policy - set basic informationAfter the settings are completed, click the Next button. You will be taken to the Check Input Information page.
After reviewing the entered information, click the Complete button. You will be taken to the Integrated Policy List page.
Check detailed information of control policy
On the Control Policy Details page, you can view and edit the detailed information of the control policy. To view detailed information of the control log, follow the steps below.
- All Services > Management > Organization Click the menu. Go to the Service Home page of Organization.
- On the Service Home page, click the Control Policy menu. You will be taken to the Control Policy List page.
- Control Policy List page, click the control policy you want to view detailed information for. You will be taken to the Control Policy Details page.
- The Policy Details page displays basic information and consists of the Basic Information tab, the Control Requirements tab, and the Connected Targets tab.
Basic Information
You can view the basic information of the control policy and, if necessary, edit the policy name and description.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name
|
| Resource ID | Unique Resource ID |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Control Policy Name | Name of the control policy
|
| type | Types of control policies
|
| Explanation | Description of the control policy
|
Control Requirements
You can view the services with permissions configured in the current control policy.
- You can check in Basic mode and JSON mode.
- Click the arrow to the right of the service name to display the control requirements set for that service.
| Category | Detailed description |
|---|---|
| Control Type | Control Policy Types
|
| action | Features provided by each service that are subject to the control policy |
| Applied resource | Resources to which the action applies
|
| Authentication type | Authentication method for the user target to which the control policy will be applied
|
| Applied IP | IP that permits the application of control policies
|
Connection target
You can view the organizational units and accounts directly linked to the control policy.
| Category | Detailed description |
|---|---|
| Root | The connection status of the Root and the number of control policies attached to the Root are displayed
|
| organizational unit | The organizational units currently linked to the control policy and the total number of control policies linked to those units
|
| Account | The Account currently linked to the control policy and the total number of control policies linked to that Account
|
Connect organization unit
You can associate an organizational unit with a control policy. To connect an organizational unit, follow the steps below.
Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
On the Service Home page, click the Control Policy menu. You will be taken to the Control Policy List page.
On the Control Policy List page, click the control policy to link the organizational unit. You will be taken to the Control Policy Details page.
On the Control Policy Details page, click the Connection Target tab.
Click the Organization Unit Connection button in the Organization Unit area. You will be taken to the Organization Unit Connection page.
After selecting the organization unit to connect, click the Complete button.
Category Detailed description Organization unit/Account name Display the names of organizational units and Accounts in a measurement structure format - Click the +, - button to expand or collapse the hierarchy
ID/Email Organizational units display ID, and accounts display ID and email. Creation date and time The creation date and time of the organizational unit is the creation timestamp, and for Account it displays the creation or registration timestamp. Table. Organization Unit Connection ItemsWhen the popup notifying the organization unit connection opens, click the Confirm button.
Connect Account
You can link an Account to a control policy. To connect the Account, follow these steps.
Click the All Services > Management > Organization menu. Go to the Service Home page of Organization.
On the Service Home page, click the Control Policy menu. You will be taken to the Control Policy List page.
On the Control Policy List page, click the control policy to link the Account. You will be taken to the Control Policy Details page.
On the Control Policy Details page, click the Connection Target tab.
Click the Account Connect button in the Account area. You will be taken to the Account Connect page.
After selecting the Account to connect, click the Done button.
Category Detailed description Organization unit/Account name Display the names of organizational units and Accounts in a measurement structure format - Click the +, - buttons to expand or collapse the hierarchy
ID/Email Organizational units display ID, and Accounts display ID and email. Creation date and time The creation date and time of the organizational unit is the creation date and time, and Account displays the creation or registration date and time. Table. Account linking itemsWhen a popup notifying the Account connection opens, click the Confirm button.
Delete control policy
You can delete the control policy.
- Click the All Services > Management > Organization menu. Navigate to the Service Home page of Organization.
- On the Service Home page, click the Control Policy menu. You will be taken to the Control Policy List page.
- On the Control Policy List page, click the control policy you want to delete. You will be taken to the Control Policy Details page.
- Click the Delete Control Policy button on the Control Policy Details page.
- When the popup informing you that the control policy will be deleted opens, click the Confirm button.
10.8.3 - API Reference
10.8.4 - CLI Reference
10.8.5 - Release Note
Organization
- You can also delete an Account created in the Organization from the Member Account.
- Deletable Accounts are limited to those directly created in the Organization.
- The Organization service has been officially launched.
- You can organize accounts by organizational units, manage them hierarchically, and control resource access permissions.
- You can monitor the resource usage of all accounts within the organization to optimize costs.
10.9 - Resource Explorer
10.9.1 - Overview
Service Overview
Resource Explorer is a service that provides search for resources (assets) created on the Samsung Cloud Platform.
Features and Benefits
Resource Explorer provides the following features.
- Resource Search: You can search for resources across multiple regions and accounts using resource names, service names, resource types, etc.
- Multi-Region Search: You can find resources across multiple regions with a single search.
- Multiple Account Search: You can search resources across all accounts within Organizations. (Scheduled for release after July 2025)
- Integrated Search: You can search resources using the integrated search feature. (Planned for release after July 2025)
- Filtering feature: You can filter search results using resource name, region, tags, etc.
- Tag addition feature: You can add tags to multiple resources in bulk.
10.9.2 - How-to Guides
Users can use the Samsung Cloud Platform Console to perform integrated searches of resources for the account and region through the Resource Explorer service, add tags, and navigate to resource details.
Search resources with Resource Explorer
You can search for resources through the Resource Explorer in the Samsung Cloud Platform Console.
To search using Resource Explorer, follow these steps.
- All Services > Management > Resource Explorer Click the menu. Go to the Resource Explorer List page.
- On the Resource Explorer page, you can search for resources in various ways.
Category Detailed description Input box Enter text in the input box to select from the search results - Resource Name: Resource name
- Service Name: Service name of the resource
- Resource Type: Type of the resource
Advanced Search Advanced Search When the button is clicked, additional searchable items - Resource Name: resource name
- Service Name: service name (multiple selection possible, searchable)
- Resource Type: resource type (multiple selection, searchable)
- Region (multiple selection, searchable)
Table. Resource Explorer resource search
Add tags with Resource Explorer
You can add tags through Resource Explorer in the Samsung Cloud Platform Console.
To add tags using Resource Explorer, follow these steps.
- Click the All Services > Management > Resource Explorer menu. Go to the Resource Explorer List page.
- Resource Explorer List page: when you select a resource’s checkbox, the Add Tag button at the top of the list becomes active.
- Click the Add Tag button. You will be taken to the Add Tag page.
- After entering key and value, click the Done button to add the tag.
- Click the Add Tag button to add multiple tags.
- You can add tags by selecting a key and value from the list or by entering them manually.
- The list icon within the input field is enabled when a selectable list is available, and the value list varies according to the key value.
- Tags can be added up to a maximum of 50 per selected resource.
- If a tag with the same key is already applied, it will be replaced with the value of the newly added tag.
Navigate to resource details with Resource Explorer
In the Samsung Cloud Platform Console, you can navigate to the resource detail page via the Resource Explorer screen and view the resource’s detailed information.
To navigate to the resource detail page via Resource Explorer, follow these steps.
- All Services > Management > Resource Explorer Click the menu. Navigate to the Resource Explorer List page.
- On the Resource Explorer List page, clicking a resource name takes you to that resource’s detail screen.
- Detailed screens are not provided for some resource types.
10.9.3 - Release Note
Resource Explorer
- We have launched a search service for resources.
- You can view resources from multiple regions at once using Resource Explorer.
10.10 - Resource Groups
10.10.1 - Overview
Service Overview
Resource groups is a service that groups resources for management.
Provided features
Resource groups provide the following capabilities.
- Resource Grouping: You can logically group resources based on tags.
- Tag-based query: You can search and group resources using tags.
- Resource Search: You can search for resources that match the specified query.
10.10.2 - How-to Guides
You can create a resource group and configure it so that resources meeting the criteria are grouped together and displayed.
Create Resource Group
You can create and use the Resource Group service in the Samsung Cloud Platform Console.
To create a Resource Group, follow these steps.
Click the All Services > Management > Resource Group menu. Navigate to the Resource Group List page.
On the Resource Group List page, click the Create Resource Group button. You will be taken to the Create Resource Group page.
On the Create Resource Group page, enter the information required to create the service and select detailed options.
- Select the required information in the Service Information Input area.
Category Required statusDetailed description Resource Group name Required Enter group name Explanation Enter description Resource Type Required Multi-select from the full list or resource type list Group definition tag Required Set the grouping criteria tag - Key
- Value
Group target resource Use the resource preview button to verify and select the target resource for the tool. Table. Resource Group resource creation input information - In the Additional Information Input area, enter or select the required information.
Category Whether requiredDetailed description Lock Select Set Lock usage - Enabling Lock prevents actions such as server termination, start, and stop from being executed, preventing errors caused by mistakes.
Init script Select Script executed when the server starts - The init script must be written as a Batch script for Windows, a Shell script for Linux, or cloud‑init, depending on the image type.
- Up to 45,000 bytes can be entered.
tag Select Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key and Value
Table. Resource Group additional information input fields
- Select the required information in the Service Information Input area.
Check the input information and click the Complete button.
- When creation is complete, check the created resources on the Resource Group List page.
View detailed information of Resource Group
The Resource Group service allows you to view and edit the list of resource groups and their details. Resource Group Details page consists of Basic Information, Group Resources, and Tags tabs.
To view detailed information about the Resource Group service, follow these steps.
- Click the All Services > Management > Resource Group menu. You will be taken to the Resource Group List page.
- On the Resource Group List page, click the resource you want to view details for. You will be taken to the Resource Group Details page.
- The Resource Group Details page displays status information and additional feature information, and consists of Basic Information, Group Resources, Tags tabs.
Basic Information
On the Resource Group List page, you can view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| constructor | Name of the constructor |
| Creation date and time | Created date and time |
| Editor | Editor’s name |
| Modification date and time | Modified date and time |
| Resource Group name | User-entered name |
| Explanation | User-written description |
Group resources
On the Resource Group List page, you can view and modify the group resources of the selected resource.
| Category | Detailed description |
|---|---|
| Group Resources > Resource Type | Group resource type |
| Group Resources > Group Definition Tag | Tag added when creating a resource group |
| Group target resource | List of resources grouped by group definition tags
|
tag
Resource Group List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Managing Resource Group
Modify basic information of Resource Group
You can edit the description of a Resource Group. To edit the description of a Resource Group, follow these steps.
- Click the All Services > Management > Resource Group menu. You will be taken to the Resource Group list page.
- On the Resource Group list page, click the Resource Group name of the resource you want to edit. You will be taken to the Resource Group Details page.
- Click the Edit button for the description to the right of the Resource Group name. You will be taken to the Edit Description popup. After editing the description, click the Confirm button. On the Resource Group Details page, verify the updated description.
Modify Resource Group resources
You can modify the group resources of a Resource Group. To modify the group resources of a Resource Group, follow the steps below.
- Click the All Services > Management > Resource Group menu. You will be taken to the Resource Group list page.
- On the Resource Group list page, click the Resource Group name of the resource you want to edit. You will be taken to the Resource Group Details page. Click the Group Resources tab. You will be taken to the Group Resources tab.
- Click the Edit Resource Group button. You will be taken to the Edit Resource Group page.
- After modifying the information of resource type and group definition tag, click Save.
Category RequiredDetailed description Resource Type Required Multi-select from the full list or resource type list Group definition tag Required Set the grouping criteria tag - Key
- Value
Group target resource Use the resource preview button to verify and select the target resource for the tool. Table. Resource Group resource modification input information
- After modifying the information of resource type and group definition tag, click Save.
- On the Resource Group Details page, check the updated information.
Delete Resource Group
You can delete unused Resource Groups. However, once a Resource Group is deleted, it cannot be recovered.
To delete a Resource Group, follow these steps.
- All Services > Management > Resource Group Click the menu. You will be taken to the Resource Group List page.
- On the Resource Group List page, click the resource you want to delete. You will be taken to the Resource Group Details page.
- On the Resource Group Details page, click the Resource Group Delete button. Verify the message in the Notification popup and click the Confirm button.
- On the Resource Group List page, select multiple Resource Group check boxes, and click the Delete button at the top of the resource list.
10.10.3 - Release Note
Resource Groups
- We have launched a service that efficiently manages resources through grouping.
- You can logically group and manage resources based on tags.
10.11 - ServiceWatch
10.11.1 - Overview
Service Overview
ServiceWatch is a service that provides various tools to collect metrics, logs, events, and other data from resources created on the Samsung Cloud Platform for monitoring, offering observability of resources overall, including performance and operational status.
Features
We provide the following special features.
- Resource Monitoring: Collects and visualizes performance metrics of resources (CPU Usage, etc.). Also creates a dashboard that allows visual inspection of multiple metrics in one place for quick overview.
- Alert Policy Configuration and Automatic Notification: You can create alert policies by setting predefined conditions and thresholds, and when a threshold is exceeded, you receive notifications, allowing you to quickly check and respond to resource status.
- Log Analysis and Storage: Collect logs generated from resources for easy viewing and searching. Collected logs are stored in log groups for management, and log groups can be stored for free up to 5GB. Additionally, you can set a log retention policy to specify the retention period, and logs that exceed the retention period do not require separate management.
- Cost Efficiency: ServiceWatch offers a flexible pay-as-you-go pricing model, allowing cost‑effective usage. It also provides a free usage tier, so you can try it for free and then scale to a paid plan as needed.
Provided features
We provide the following features.
- Metric Monitoring
- Metrics: ServiceWatch receives metric data from services of the Samsung Cloud Platform, and ServiceWatch collects and stores the metric data to provide it to users.
- Dashboard: Visualizes metrics of a single region to provide an integrated view of resources. In ServiceWatch, dashboards are divided into automatically generated service dashboards for each service and user-created custom dashboards.
- Alert: Provides an alert feature that allows monitoring of metric changes based on user-defined thresholds and sends notifications when thresholds are exceeded.
- Log Monitoring
- ServiceWatch provides log management capabilities. Logs collected from Samsung Cloud Platform services are stored in log groups for management. You can set log retention policies to manage the retention period. Additionally, you can view and search log data through the console, and it offers the ability to store log groups in Object Storage.
- ServiceWatch Agent
- Through the ServiceWatch Agent, you can collect detailed metrics on processes, CPU, memory, disk usage, and network performance from Virtual Servers, GPU Servers, Bare Metal Servers, and other resources. GPU performance metrics can also be collected. Additionally, the Agent can collect logs generated by the resources. (Planned for December 2025)
- Event Monitoring
- ServiceWatch can create event rules from system events about changes to resources created in the Samsung Cloud Platform, allowing you to receive notifications under specific conditions.
Component
Metric
Metrics refer to system performance data. By default, we provide basic monitoring based on free metrics for resources of services integrated with ServiceWatch. Additionally, services such as Virtual Server can enable detailed monitoring to provide paid metrics.
Indicator data can be viewed for up to 15 months (455 days).
For detailed information related to metrics, please refer to Metrics.
log
You can collect, store, and view logs of systems, applications, and services used in Samsung Cloud Platform services such as Virtual Server resources and Kubernetes Engine.
For detailed information related to logs, refer to 로그.
event
An event represents a change in the environment in the Samsung Cloud Platform service. Below are examples of events.
- Generates an event when the status of a Virtual Server changes from Stopped to Running.
- Generates an event when a new bucket is created in Object Storage.
- An event is generated when an IAM user is removed from a user group.
For detailed information about events, refer to the Events.
Dashboard
ServiceWatch provides a pre-built service dashboard for each service automatically, and users can also create dashboards manually.
ServiceWatch Agent
The ServiceWatch Agent is a software component that collects metrics and logs from Virtual Servers, GPU Servers, and on‑premises servers, among others. This enables monitoring of infrastructure and applications with greater granularity than the default monitoring provided out of the box.
Collecting custom metrics/logs via the ServiceWatch Agent is currently available only on Samsung Cloud Platform For Enterprise. It will be offered in other offerings in the future.
- For more details about the ServiceWatch Agent, see Custom Metrics and Logs.
Constraints
The limitations of ServiceWatch are as follows.
| Category | Explanation |
|---|---|
| Metric query period | Metric queries can be set up to a maximum of 455 days from the time of query
|
| Number of metric queries | You can select up to 500 indicators and view them in a graph. |
| Download indicator image file | Image download available for metric data of up to 100 metrics |
| Export Metrics to Object Storage | Up to 10 metrics, and exporting to Obect Storage is possible for metric data with a maximum query period of up to 2 months (63 days). |
| Number of widgets/metrics per dashboard |
|
| Number of alert policies | Account/per region 5,000 or fewer |
| Alarm History | Alert history is available for 30 days |
| Number of notification recipients per alert policy | 100 or fewer |
| Number of log groups | Account/10,000 or fewer per region |
| Log download | Excel download: up to 1 MB per log event, with a maximum of 10,000 log events can be downloaded
|
| Number of log group export tasks |
|
| Log event size | 1 MB or less |
| Number of event rules | Account/No more than 300 per region |
| Event pattern size | 2 MB or less |
| Number of notification recipients per event rule | 100 or fewer |
The following is ServiceWatch’s monthly free offering details.
| Category | Free offering |
|---|---|
| log | Up to 5 GB of storage per month |
| indicator |
|
| Dashboard | For dashboards referencing 50 or fewer metrics, up to 3 per month
|
| Alert Policy | 10 per month |
Provision status by region
ServiceWatch is available in the following environments.
| Region | Whether provided |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea 1 (kr-south1) | Provide |
| South Korea South 2 (kr-south2) | Provide |
| South Korea 3(kr-south3) | Provide |
Preliminary Service
There are no prerequisite services for ServiceWatch.
10.11.1.1 - Metric
Metric
Metrics are data about system performance. By default, many services provide free metrics for resources (e.g., Virtual Server, File Storage, etc.), which are offered as basic monitoring through ServiceWatch. Detailed monitoring can be used for certain resources such as Virtual Server.
Indicator data is retained for 15 months (455 days), so you can view both the latest data and historical data.
| Term | Example | description | |
|---|---|---|---|
| namespace | Virtual Server | Logical distinctions for separating and grouping metrics
| |
| Metric (metric) | CPU usage | the name of the specific data you want to collect
| |
| Dimension(Dimensions) | resource_id | Unique identifier for the metric
| |
| Collection interval | 5 minutes | Please refer to the collection interval of metric data from each service that provides metrics | |
| Statistics | average | How to aggregate metric data over a specified period
| |
| unit | % | Statistical measurement units
| |
| Aggregation period | 5 minutes | The period for aggregating collected metric data
| |
| Alert | CPU usage >= 80% | Occurs for 5 minutes | If CPU usage stays above 80% for 5 minutes, change to Alert state. |
Namespace
A namespace is a logical separation used to distinguish and group ServiceWatch metrics. In Samsung Cloud Platform services, namespaces are generally the same as the service name, and can be found in the ServiceWatch 연계 서비스 목록.
For custom metrics, users can define a namespace in ServiceWatch to distinguish them from other metrics, and can define it via the ServiceWatch Agent settings or OpenAPI. Detailed information about custom metrics and logs can be found in 사용자 정의 지표 및 로그.
Metric (metric)
A metric represents a set of data points sorted chronologically as they are collected in ServiceWatch. Each data point consists of a timestamp, the collected data, and the unit of the data.
For example, the CPU utilization of a specific Virtual Server is one of the basic monitoring metrics provided by Virtual Server. The data point itself can be generated by any application or activity that collects data.
By default, the Samsung Cloud Platform services integrated with ServiceWatch provide resource metrics for free. Detailed monitoring for some resources is offered as a paid service and can be enabled in each service.
Metrics can only be viewed in the region where they were created. Metrics cannot be arbitrarily deleted by users. However, if new data is not posted to ServiceWatch, they will automatically expire after 15 months. Data points older than 15 months (455 days) expire sequentially, and when new data points are added, data older than 15 months (455 days) is deleted.
Timestamp
The timestamp of a data point is the time information indicating when the data point was recorded. Each metric data point consists of a timestamp (time) and data.
A timestamp consists of hours, minutes, seconds, and a date.
Metric retention period
We maintain ServiceWatch metric data as follows.
- Data points with a collection interval set to 60 seconds (1 minute) are available for up to 15 days.
- Data points with a collection interval set to 300 seconds (5 minutes) are available for up to 63 days.
- Data points with a collection interval set to 3600 seconds (1 hour) are usable for up to 455 days (15 months).
Data points that were initially collected at a short interval are downsampled and stored for long-term retention.
For example, if data is collected at a 1‑minute interval, it is retained in 1‑minute granularity for 15 days. After 15 days, the data continues to be retained but can only be queried in 5‑minute intervals. After 63 days, the data is re‑aggregated and provided in 1‑hour intervals. If you need to retain metric data points longer than the metric retention period, you can archive them separately using the File Download or Object Storage Export features.
Dimension(Dimensions)
A key-value pair that serves as a unique identifier for a metric, allowing you to classify and filter data points.
For example, you can identify metrics for a specific server by using the resource_id dimension of the Virtual Server metrics.
Collection interval
It refers to the interval for collecting data points for each service’s metrics and is provided according to the collection interval predefined by each service.
Refer to each service’s ServiceWatch metrics page for the metric collection interval.
For example, Virtual Server provides a collection interval of 5 minutes during basic monitoring, and a 1‑minute interval when detailed monitoring is enabled.
Statistics
Statistics are a method of aggregating metric data over a specified period. ServiceWatch provides data aggregated as statistics based on metric data points supplied to ServiceWatch from each service. Aggregation is performed within the specified aggregation period using namespace, metric name, dimension, and data point units.
The provided statistics are sum, average, minimum, maximum.
- Total: sum of all data point values collected during the period
- Average: During the specified period, (sum of all data pointer values during that period) / (number of data pointers during that period) value
- Minimum: the lowest value observed during the specified period
- Maximum: the highest value observed during the specified period
unit
Each statistic has a measurement unit. Examples of units include Bytes, Second, Count, Percent, etc.
Aggregation period
Each statistic calculates the data points of the metric collected during the selected aggregation interval. The aggregation interval can be chosen from 1 minute, 5 minutes, 15 minutes, 30 minutes, 1 hour, 3 hours, 6 hours, 12 hours, or 1 day, with the default being 5 minutes. The aggregation interval is closely related to the collection frequency of metric data points, and to obtain correct aggregation results, the aggregation interval must be equal to or longer than the collection frequency.
For example, if you select average, choose 5 minutes as the aggregation period, and pick a metric with a 1‑minute collection interval, data points are collected every minute and the average is calculated over the data points collected during the 5‑minute period. Conversely, if the aggregation period is shorter than the collection interval, it means a valid aggregation result cannot be obtained.
Downsampling is applied for long-term storage of metric data. For example, if data is collected at a 1‑minute interval, after 15 days the data can only be queried in 5‑minute increments. If you set the aggregation period for such metrics from 5 minutes to 30 minutes, up to 5 minutes may be required to retrieve the downsampled data correctly. After 63 days, the data is re‑aggregated and provided in 1‑hour intervals. At that point, selecting an aggregation period from 1 hour to 1 day may take up to 1 hour to retrieve the data correctly. This occurs because aggregating the downsampled metric data takes time, which can cause aggregation delays.
| Aggregation period | Aggregation delay |
|---|---|
| 1 minute | - |
| 5 minutes | up to 5 minutes |
| 15 minutes | up to 5 minutes |
| 30 minutes | up to 5 minutes |
| 1 hour | up to 1 hour |
| 3 hours | up to 1 hour |
| 6 hours | up to 1 hour |
| 12 hours | up to 1 hour |
| Day 1 | up to 1 hour |
Alert
When creating an alert policy, you can evaluate a single metric over the specified evaluation period, and if it meets the condition set based on the threshold, you can notify the user with an alert.
The alarm status is classified as Alert (alert), Normal (normal), Insufficient data (no data).
- Alert(Alert): when the metric meets the configured condition
- Normal (Normal): when the indicator does not meet the set conditions.
- Insufficient data(no data): when the metric data does not exist, is missing, or has not yet arrived
When the alarm status is Alert, after evaluating the alarm, if it deviates from the condition, the alarm status changes back to Normal.
For detailed information about alerts, refer to the 경보 entry.
Basic monitoring and detailed monitoring
ServiceWatch provides two types of monitoring: basic monitoring and detailed monitoring.
The Samsung Cloud Platform services integrated with ServiceWatch provide basic monitoring by publishing a default set of metrics to ServiceWatch for free. By default, if you use any of these services, basic monitoring is automatically enabled and can be viewed in ServiceWatch.
Detailed monitoring is available only for certain services and incurs charges. To use detailed monitoring, you must enable it in the service details.
Detailed monitoring options vary depending on the service provided.
- The default monitoring for Virtual Server has a collection interval of 5 minutes. When detailed monitoring is enabled, the metrics provided by default monitoring are collected at a 5 minutes → 1 minute interval.
- Basic monitoring of Object Storage is provided for basic metrics, and enabling replication metrics provides additional replication metrics.
The following includes services and guides that provide detailed monitoring.
| Service | Guide |
|---|---|
| Virtual Server/GPU Server | Enable Detailed Monitoring for Virtual Server |
| Object Storage | Object Storage Enable Replication Metrics |
10.11.1.2 - Alert
Alert
You can create alerts that monitor metrics and send notifications. For example, you monitor the CPU usage and disk read/write of a Virtual Server, then send a notification to the user to handle the increased load.
Alert Policy
The alert policy can monitor metrics of the same Account and evaluate alerts for a single metric. This alert policy compares the specified threshold with metric conditions and sends a notification when the conditions are met.
If you disable the alert policy, its evaluation continues, but you can restrict sending alerts to the designated recipients. If you want to temporarily stop sending alerts for resources with an alarm policy configured, you can use alarm policy deactivation.
When you enable an alert policy, evaluation of the policy starts, and according to the configured conditions, the alert status changes to Alert, with a notification sent each time the alert status changes.
The alarm policy status indicates whether the alarm policy is enabled or disabled.
| Alert policy status | description |
|---|---|
| ● Active | In a state where the alert policy is enabled, notifications can be sent according to the configured conditions
|
| ● Inactive | Alert policy is disabled, and notification sending is restricted.
|
You can set alert stages in the alert policy. Depending on the alert stage, the alert color (red/pink/purple) is displayed differently, allowing visual distinction of stages by color. You can filter alarm policies by their alarm level and view policies for each level.
| Alert Level | description |
|---|---|
| High | When you set the step for the alarm policy condition to High, the alarm level is displayed in red. |
| Midle | If you set the stage to Middel in the alarm policy condition, the alarm stage is displayed in pink. |
| Low | If you set the stage to Middel in the alert policy condition, the alert stage is displayed in purple. |
Alert Status
The alarm state changes according to the alarm evaluation of the alarm policy. The alarm state is divided into three states: Normal (normal), Insufficient data (insufficient data), Alert (alert).
| Alarm status | description |
|---|---|
| ● Normal | Indicates a normal state that does not meet the conditions set in the alert policy
|
| ● Insufficient data | The alarm policy has just been created, the metric is unavailable, or there is insufficient data to determine the alarm state from the metric
|
| ● Alert | State that meets the conditions set in the alert policy
|
Alert Evaluation
| Term | description |
|---|---|
| Metric data point | Statistical data calculated from indicator data. Data points consist of a timestamp, collected statistical data, and the unit of the data
|
| Metric collection interval | Time interval for collecting metric data per service
|
| Alert evaluation cycle | The time interval for evaluating whether an alert meets the condition
|
| Alert Evaluation Scope | It is recommended to set the evaluation time range for alarm evaluation
|
| Alarm evaluation count / Alarm violation count | During the alarm evaluation interval, if the condition is satisfied for violation count out of evaluation count, the alarm state is switched to Alert
|
| Alert evaluation interval | Alarm evaluation range(seconds) X Alarm evaluation count |
For example, for a metric with a 1‑minute collection interval, if you set a 1‑minute evaluation window with 4 violations out of 5 evaluation attempts, the evaluation interval is 5 minutes. For a metric with a 5‑minute collection interval, if you set a 10‑minute evaluation window with 3 violations out of 3 evaluation attempts, the evaluation interval is 30 minutes.
| Category | Example 1 | Example 2 |
|---|---|---|
| Metric collection interval | 1 minute | 5 minutes |
| Alert evaluation cycle (fixed) | 1 minute | 1 minute |
| Alert Evaluation Scope | 1 minute | 10 minutes |
| Alarm evaluation count | 5 times | 3 times |
| Alarm violation count | 4th | 3 times |
| Alert evaluation interval (seconds) | 5 minutes (300 seconds) | 30 minutes (1,800 seconds) |
| Condition | If evaluated 5 times within 5 minutes and meets the condition 4 times, change the alarm state to Alert. | If evaluated three times within 30 minutes and the three-time condition is met, change the alarm state to Alert. |
Evaluation Scope
The evaluation scope of an alert policy is the time range used for alert evaluation.
- It is recommended to set it as the indicator’s collection interval or a multiple of the collection interval.
- You can enter up to 604,800 (7 days) seconds.
| Evaluation scope | Configurable evaluation count |
|---|---|
| 7 days (604,800 seconds) | 1 |
| 1 day (86,400 seconds) | 7 or less |
| 6 hours (21,600 seconds) | 28 or less |
| 1 hour (3,600 seconds) | 168 or less |
| 15 minutes (900 seconds) | 96 or less |
| 5 minutes (300 seconds) | 288 or less |
| 1 minute (60 seconds) | 1,440 or less |
There are the following limitations on the evaluation scope and the number of evaluations:
- When the evaluation range is at least 1 hour (3,600 seconds), the evaluation interval (evaluation count × evaluation range) can be up to 7 days (604,800 seconds).
- When the evaluation range is less than 1 hour (3,600 seconds), the evaluation interval (evaluation count × evaluation range) can be up to 1 day (86,400 seconds).
condition
The conditions for alarm evaluation require a conditional operator and threshold setting.
| Term | description |
|---|---|
| Statistics | Method for calculating metric data over the evaluation period for alert assessment |
| conditional operator | For alarm evaluation, after calculating metric data over the evaluation period, select the conditional operator to compare the value with the threshold. |
| threshold | For alarm evaluation, calculate the metric data over the evaluation range and then define a threshold to compare the values using conditional operators. |
When the namespace is Virtual Server and the metric is CPU Usage (unit: %), the alarm evaluation condition is completed as follows.
| Category | Example 1 | Example 2 |
|---|---|---|
| Metric collection interval | 1 minute | 5 minutes |
| Alert evaluation cycle (fixed) | 1 minute | 1 minute |
| Alert Evaluation Scope | 1 minute | 10 minutes |
| Alarm evaluation count | 5 times | 3 times |
| Alarm violation count | Round 4 | 3 times |
| Alert evaluation interval (seconds) | 5 minutes (300 seconds) | 30 minutes (1,800 seconds) |
| Statistics | average | Total |
| conditional operator | >= | < |
| threshold | 80 | 20 |
| Condition | If the average CPU Usage >= 80% for 4 occurrences over 5 minutes, change the alert status to Alert. | Change to < 20% 이면, 경보 상태를 Alert if the average CPU usage occurs three times within 30 minutes. |
Alert Notification
If the alarm evaluation criteria are met, change the alarm status to Alert and send a notification to the recipients configured in the alarm policy.
- Only users with a login history (users who have registered an email or mobile phone number) can be added as alert recipients.
- The notification reception method (E-mail or SMS) can be set on the Notification Settings page by selecting the notification target as Service > Alert.
- You can add up to 100 notification recipients.
- Users without login history cannot be designated as notification recipients.
- On the Notification Settings page, if you select the notification target as Service > Alarm but do not configure a notification delivery method, you will not receive notifications.
Method for handling missing data during alarm evaluation
Some resources may be unable to send metric data to ServiceWatch under certain conditions. For example, if a resource is inactive or does not exist, it will not be sent to ServiceWatch. If metrics are not collected for a certain period, the alert evaluation will change the alert status to Insufficient data.
ServiceWatch provides a way to handle missing data during alert evaluation. The methods for handling missing data are as follows:
- Ignore: maintains the current alarm state. (default)
- Missing: Treat missing data points as missing. If all data points within the evaluation range are missing, the alert status changes to
Insufficient data. - Breaching: Process missing data points as satisfying the threshold condition.
- Not breaching: Treat missing data points as normal when they do not satisfy the threshold condition.
- For alert policies created before the December 2025 release, missing data is handled with the default Ignore, and starting with the December 2025 release, you can directly select how to handle missing data.
- In the alert policy, the method for handling missing data can be modified, and from the time of modification onward, missing data will be processed using the updated method.
Alert History
The change history of the alarm status is recorded in the alarm history. The alarm history can be viewed for 30 days.
10.11.1.3 - Log
Log
By using ServiceWatch logs, you can monitor, store, and access log files collected from the resources of the service that provides the logs.
| Log Group 1 | Log Group 1 | Log Group 1 | Log Group 2 | Log Group 2 | Log Group 2 |
|---|---|---|---|---|---|
| Log Stream1 | Log Stream2 | Log Stream3 | Log Stream A | Log Stream B | log stream |
| Log Event | Log Event | Log Event | Log Event | Log Event | Log Event |
| Log Event | Log Event | Log Event | Log Event | Log Event |
The following is an example of log configuration.
- 📂 Log Group: “WebApp-Logs”
- 📄 Log Stream 1: “Server-1”
- 📝 Log Event 1: “[2025-03-20 10:00:01] User logged in”
- 📝 Log Event 2: “[2025-03-20 10:05:34] Database connection error”
- 📄 Log Stream 1: “Server-1”
Log Group
Log groups are containers for log streams that share the same retention policy settings. Each log stream must belong to a single log group. For example, if there are separate log streams for the logs of each cluster in Kubernetes Engine, you can group the log streams into a single log group called /scp/ske/{cluster name}.
Log Retention Policy
The log retention policy allows you to set the period for retaining log events in ServiceWatch. Log events whose retention period has expired are automatically deleted. Log The retention period assigned to the group applies to the log streams and log events belonging to the log group.
The retention period can be selected from the following options and is set in days.
| Retention period |
|---|
|
Log stream
A log stream is a collection of log events ordered by the sequence in which they occurred from the same source. For example, all log events generated by a particular Kubernetes Engine cluster can form a single log stream.
Log Event
Log events are individual records that capture logs generated by a resource. A log event record includes two attributes: a timestamp of when the event occurred and a log message. Each message must be encoded in UTF-8.
log pattern
You can create log patterns to filter log data that matches the pattern. Log patterns define the words or patterns to search for in the log data collected by ServiceWatch, allow you to view the status of log occurrences as graphs, and serve as metrics for creating alert policies.
Log patterns are not applied retroactively to data. They are applied to log events collected after the log pattern is created.
Log pattern namespace
A namespace is a logical separation used to distinguish and group metrics. In ServiceWatch, it is divided into namespaces associated with services, namespaces for custom metrics, and namespaces for log patterns.
- Namespace associated with services such as Virtual Server
- A namespace consisting of custom metrics, i.e., the namespace of metrics collected through the custom metrics API or ServiceWatch Agent.
- Namespace of the metric generated by the log pattern
When creating metrics for a log pattern, you can either create a new namespace for the log pattern or select from existing log pattern namespaces.
Metric name
The monitored log information is the name of the metric generated by ServiceWatch. You must configure it so that the metric name does not duplicate within the namespace where the metric will exist.
Metric Value
It is the numeric value posted to the metric each time a log matching the pattern is found. For example, when counting occurrences of a specific word (e.g., Error), this value becomes 1 for each occurrence. When calculating transmitted bytes, it can be incremented by the actual number of bytes found in the log event.
default value
This is the value recorded in the log pattern for periods during log collection when no matching logs can be found. Setting the default to 0 prevents the metric from becoming irregular due to periods with no matching data.
When setting a dimension on a metric created from a log pattern, you cannot set a default value for that metric.
dimension
Dimensions are key-value pairs that further define a metric. You can add dimensions to metrics generated from log patterns. Since dimensions are part of a metric’s unique identifier, each time a unique name/value pair is extracted from logs, a new variant of that metric is created.
When you choose the log pattern format as either a whitespace-delimited pattern or a JSON format pattern, you can set the dimension, and it can be configured using one of the parameters defined in the pattern. You can assign up to three dimensions to an indicator. If a default value is set, you cannot configure dimensions. To set dimensions, you must disable the use of the default value.
Pattern format
This explains how ServiceWatch interprets data from each log event. The pattern format can be selected from three options as shown below.
- String Pattern: log containing a specific string
- Space-separated pattern: timestamps, IP addresses, strings, and other logs separated by spaces
- JSON format pattern: log containing specific JSON fields
Available regular expression syntax
When using regular expressions to search and filter log data, you must enclose the expression with %.
Patterns that contain regular expressions can only include the following.
- Alphanumeric - An alphanumeric character is a character that corresponds to a letter (A~Z or a~z) or a digit (0~9).
- It can be used with
A-Z,a-z,0-9.
- It can be used with
- The supported symbol characters are as follows.
:,_,#,=,@,/,;,,,-- For example,
%servicewatch!%cannot be used because!is not supported.
- The supported operators are as follows.
- It includes
^,$,?,[,],{,},|,\,*,+,.. (,)The operator is not supported.
- It includes
| operator | How to use |
|---|---|
^ | Fix the start position of the string to the matching item. For example, %^[ab]cd% matches acd and bcd, but does not match bcd. |
$ | Fix the end position of the string to the matching item. For example, %abc$% matches xyzabc and xyabc, but does not match abcd. |
? | ? matches when the preceding character appears 0 or 1 times. For example, %abc?d% matches both abcd and abd, while abc and abccd do not match. |
[] | Matches a list of characters or a range of characters enclosed in square brackets. For example, %[abc]% matches a, b, c, and %[a-z]% matches all lowercase letters from a to z, and %[abcx-z]% matches a, b, c, x, y, z. |
{m, n} | It matches when the preceding character is repeated m~n times. For example, %a{3,5}% matches only aaa, aaaa and aaaaa, and does not match a or aa. |
| |
\ | By using an escape character, you can treat this character literally instead of as a special operator. |
* | Matches the preceding character zero or more times. For example, %12*3% matches 13, 123, 122223. |
+ | Matches the preceding character one or more times. For example, %12+3% can match 123, 1223, 12223, but does not match 13. |
. | Matches any character. For example, %.ab% matches cab, dab, bab, 8ab, #ab, ab (including spaces), and ab which end with a three-character string. |
\d, \D | Matches digits and non-digit characters. For example, %\d% is equivalent to %[0-9]%, and %\D% matches all characters except digits, like %[^0-9]%. |
\s, \S | Matches whitespace characters and non-whitespace characters. Whitespace characters include tab (\t), space ( ), and line break (\n) characters. |
\w, \W | Matches alphanumeric and non-alphanumeric characters. For example, %\w% is equivalent to %[a-zA-Z_0-9]%, and %\W% is equivalent to %[^a-zA-Z_0-9]%. |
\xhh | Matches the ASCII mapping of a two‑digit hexadecimal character. \x is an escape sequence indicating that the following character is the hexadecimal value in ASCII. hh specifies a two‑digit hexadecimal (0–9 and A–F) that refers to a character in the ASCII table. |
123.123.123.1 with a regular expression, use %123\.123\.123\.1%.string pattern
String pattern using regular expressions
You can search for matching patterns in log events using a regex string pattern wrapped with %(percentage) at the beginning and end. Below is an example pattern that retrieves all log events containing the ERROR keyword. Please refer to Available regex syntax.
%ERROR%
The above pattern matches log event messages like the ones below.
[2026-02-13 14:22:01] ERROR 500 POST /api/v1/checkout (192.168.1.10) - NullPointerException at com.app.controller.CheckoutController.java:55[ERROR] Configuration file not found: /etc/app/config.yaml
String pattern in unstructured log events
It is a string pattern for searching strings in log events that are not in formats such as JSON. Below is an example of a log event message, and you can view log events that match various string pattern classifications.
ERROR CODE 400 BAD REQUEST
ERROR CODE 401 UNAUTHORIZED REQUEST
ERROR CODE 419 MISSING ARGUMENTS
ERROR CODE 420 INVALID ARGUMENTS
| Category | Pattern | Matching log event message |
|---|---|---|
| single string | ERROR CODE | ERRORlog event containing
|
| Multiple strings (AND condition) | ERROR REQUEST | log events containing the strings ERROR and REQUEST
|
| Multiple strings (Or condition) | ?ERROR ?400 | ERRORor 400log event containing the string
|
| Exact match string | “BAD REQUEST” | “BAD REQUEST”log event containing the exact phrase
|
| Exclude specific string | ERROR -400 | A pattern that includes some terms and excludes others. Enter - before the string you want to exclude. The following is a log event that includes the string ERROR and excludes the string 400:
|
Space-separated pattern
Generate a pattern to search for matching strings in space-separated log events.
Whitespace-separated pattern example (1)
The following is an example of log events separated by spaces.
2023-10-27T10:00:01Z [INFO] 1234 login success 192.168.1.1
The above log event is a space‑separated log event that includes timestamp, logLevel, user_id, action, status, ip. Characters between brackets ([]) and double quotes ("") are considered a single field.
To create a pattern that searches for matching strings in space-separated log events, enclose the pattern in brackets ([]) and specify name-separated fields with commas (,). The following pattern parses six fields.
A pattern like [timestamp, logLevel, user_id, action, status = success, ip] can be used to find log events where the fifth field, status, is success.
Whitespace-separated pattern example (2)
abc xxx.log james 2023-10-27T10:00:01Z POST 400 1024
abc xxx.log name 2023-10-27T10:00:02Z POST 410 512
The above log event is a space‑separated log event that includes host, logName, user, timestamp, request, statusCode, and size.
A pattern like [host, logName, user, timestamp, request, statusCode=4*, size] can find log events where the sixth field, statusCode, starts with 4.
If you do not know the exact number of fields in a space-separated log event, you can use an ellipsis (…). A pattern such as […, statusCode=4*, size] represents the first five fields using an ellipsis.
AND(&&) operator and OR(||) operator can be used to create composite expressions. […, statusCode=400 || statusCode=410, size] can find log events where the sixth field, statusCode, is 400 or 410.
You can use regular expressions to provide conditions in a pattern. [host, logName, user, timestamp, request, statusCode=%4[0-9]{2}%, size] can find log events where the sixth field, statusCode, is a number that starts with 4.
JSON format pattern
You can create a pattern to search for matching strings or numeric values in JSON log events.
Patterns are enclosed in curly braces ({}).
String-based JSON format pattern
- Use
$.to represent JSON fields. - The operator can use
=or!=. - The string to compare with the field can be enclosed in double quotes (
""). Strings containing characters other than alphanumerics and the underscore must be enclosed in double quotes. Use an asterisk (*) as a wildcard to match text.
{ $.resourceType = "trail" }
{ $.resourceType = "%trail%" }
{ $.arrayKey[0] = "value" }
JSON format pattern that searches for numeric values
- Use
$.to represent JSON fields. - You can use numeric operators.
- greater than(
>), less than(<), equal to(=), not equal to(!=), greater than or equal to(>=), less than or equal to(<=)
- greater than(
- You can include addition(
+) or subtraction(-) symbols. An asterisk(*) can be used as a wildcard.
{ $.errorCode = 400}
{ $.errorCode >= 400}
{ $.errorCode != 500 }
{ $.sourceIPAddress != 123.123.* }
Export Log Group
You can export log data from a log group to Object Storage for log retention and analysis. You can also export log groups for log data that resides in the same account.
To start exporting a log group, you must create an Object Storage bucket to store the log data.
Exporting a log group can take a long time depending on the amount of logs. When exporting a log group, you can reduce the export duration by specifying particular streams within the log group or by defining a time range.
Log group export can only be executed one at a time per account. To start another log group export, the ongoing export task must be completed.
You can delete a log group’s export history after the export succeeds or after the export cancellation is completed. Canceling a log group export does not delete the saved file exported from the log group. To delete the saved file exported from the log group, delete the stored file directly in Object Storage.
| Log group export status | description |
|---|---|
| ● Success | The log group export operation completed successfully. |
| ● Pending | The log group export task is pending. |
| ● In progress | The log group export operation is in progress. |
| ● Failed | The log group export operation failed. |
| ● Canceling | Cancelling the log group export task. If the cancellation request fails, it will be set to a Failed state. |
| ● Canceled | The log group export task has been cancelled. |
10.11.1.4 - Event
An event represents a change in the environment in the Samsung Cloud Platform service.
ServiceWatch receives events generated by most Samsung Cloud Platform services. Events from each service can be viewed and processed in the ServiceWatch of the same Account.
Refer to the ServiceWatch Event Reference for the list of services that send events to ServiceWatch and the events they send.
Each service sends events to ServiceWatch based on Best Effort delivery. Best Effort delivery means that the service attempts to send all events to ServiceWatch, but occasionally some events may not be delivered.
When a valid event is delivered to ServiceWatch, ServiceWatch compares the event with the rules and then sends a notification to the alert recipients configured in the event rule.
Event Rules
You can specify the actions that ServiceWatch performs on events delivered from each service to ServiceWatch. To do this, create an event rule. An event rule defines which events are sent to which targets.
Event rules evaluate an event when it arrives. Each event rule checks whether the event matches the rule’s pattern. If the event matches, ServiceWatch processes the event.
Based on the event data criteria (called an event pattern), you can generate matching rules for incoming events. When an event matches the criteria defined in the event pattern, the event is delivered to the target specified in the rule.
- Event rules can, by default, designate the recipients who will receive notifications when an event occurs.
- The event rules are planned to be expanded to include multiple Samsung Cloud Platform services as recipients when events occur. (Planned for 2026)
To create an event rule, refer to How-to Guides > Create Event Rule.
Event source
In ServiceWatch, the event source can be selected as a Samsung Cloud Platform service name. You can select the service name of the event you want to receive as the event source.
| Service Category | service |
|---|---|
| Compute | Virtual Server |
| Compute | GPU Server |
| Compute | Bare Metal Server |
| Compute | Multi-node GPU Cluster |
| Compute | Cloud Functions |
| Storage | Block Storage(BM) |
| Storage | File Storage |
| Storage | Object Storage |
| Storage | Archive Storage |
| Storage | Backup |
| Container | Kubernetes Engine |
| Container | Container Registry |
| Networking | VPC |
| Networking | Security Group |
| Networking | Load Balancer |
| Networking | DNS |
| Networking | VPN |
| Networking | Firewall |
| Networking | Direct Connect |
| Networking | Cloud LAN-Campus |
| Networking | Cloud LAN-Datacenter |
| Networking | Cloud WAN |
| Networking | Global CDN |
| Networking | GSLB |
| Database | EPAS(DBaaS) |
| Database | PostreSQL(DBaaS) |
| Database | MariaDB(DBaaS) |
| Database | MySQL(DBaaS) |
| Database | Microsoft SQL Server(DBaaS) |
| Database | CacheStore(DBaaS) |
| Data Analytics | Event Streams |
| Data Analytics | Search Engine |
| Data Analytics | Vertica(DBaaS) |
| Data Analytics | Data Flow |
| Data Analytics | Data Ops |
| Data Analytics | Quick Query |
| Application Service | API Gateway |
| Security | Key Management Service |
| Security | Config Inspection |
| Security | Certificate Manager |
| Security | Secret Vault |
| Management | Cloud Control |
| Management | Identity and Access Management(IAM) |
| Management | ID Center |
| Management | Logging&Audit |
| Management | Organization |
| Management | Resource Groups |
| Management | ServiceWatch |
| Management | Support Center |
| AI-ML | CloudML |
| AI-ML | AI&MLOps Platform |
Event Type
The Samsung Cloud Platform service has its own resource types. Event types are classified the same as resource types, and you select the type of events from the event source to use in an event rule.
The following are the event types of a Virtual Server.
| Service Category | Service | Subservice | Event type |
|---|---|---|---|
| Compute | Virtual Server | Virtual Server | Server |
| Compute | Virtual Server | Image | Image |
| Compute | Virtual Server | Keypair | Keypair |
| Compute | Vitual Server | Server Group | Server Group |
| Compute | Virtual Server | Launch Configuration | Launch Configuration |
| Compute | Virtual Server | Auto-Scaling Group | Auto-Scaling Group |
| Compute | Virtual Server | Block Storage | Volume |
| Compute | Virtual Server | Block Storage | Snapshot |
For other event types available in ServiceWatch, refer to ServiceWatch Event.
Event
Events can select either all events generated from an event source’s event type or specific events.
The following are some events of the Server event type for Virtual Server.
| Service Category | Service | Subservice | Event type | Event |
|---|---|---|---|---|
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Create Start |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Create End |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Create Error |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Delete Start |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Delete End |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Delete Error |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Lock End |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Unlock End |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Stop Start |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Stop Success |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Start Start |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Start Success |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Reboot Start |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Reboot End |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Reboot Error |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Power On Start |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Power On End |
| Compute | Virtual Server | Virtual Server | Server | Compute Virtual Server Power On Error |
For other events available in ServiceWatch, refer to ServiceWatch Event.
Applied Resources
Set an event pattern for the selected event on all resources or a specific resource.
event pattern
When you select the event source, event type, event, and target resource, the event pattern configuration for the event rule is completed.
The following is an example of an event pattern set in ServiceWatch’s event rule.
{
"source": [ // namespace
"Virtual Server"
],
"detail-type": [ // event type
Server
],
"detail": {
"event": [ // individual event
Compute Virtual Server Create End
]
},
"resources": [ // individual resources
"srn:{offerring}::{account_id}:{region}::virtualserver:server/{resource_id}"
]
}{
"source": [ // namespace
"Virtual Server"
],
"detail-type": [ // event type
Server
],
"detail": {
"event": [ // individual event
Compute Virtual Server Create End
]
},
"resources": [ // individual resources
"srn:{offerring}::{account_id}:{region}::virtualserver:server/{resource_id}"
]
}To create an event rule, refer to How-to Guides > Create Event Rule.
Event Notification
If the event matches the pattern, a notification is sent to the alert recipients configured in the event rule.
- It is possible to send notifications to users with a login history (users who have registered an email or mobile phone number).
- You can add up to 100 notification recipients.
- The notification reception method (E-mail or SMS) can be changed on the Notification Settings page after selecting the notification target as Service > ServiceWatch.
- Users without login history cannot be designated as notification recipients.
- If you select the notification target as Service > ServiceWatch on the Notification Settings page but do not configure a notification delivery method, you will not receive notifications.
10.11.1.5 - ServiceWatch integration service
You can view services integrated with ServiceWatch.
Metrics and Log Monitoring
Below you can see the service that integrates ServiceWatch with metric and log monitoring.
| Service Category | Service | namespace | Indicator Basic Monitoring | indicator detailed monitoring | Log monitoring | Guide |
|---|---|---|---|---|---|---|
| Compute | Virtual Server | Virtual Server | ○ | ○ | - | |
| Compute | GPU Server | Virtual Server | ○ | ○ | - |
|
| Compute | Block Storage | TBD | Scheduled for July 2026 | - | - | |
| Compute | Bare Metal Server | - | - | - | - |
|
| Compute | Multi-node GPU Cluster | - | - | - | - |
|
| Compute | Cloud Fuctions | Cloud Functions | ○ | - | ○ |
|
| Storage | Block Storage(BM) | TBD | Scheduled for July 2026 | - | - | |
| Storage | File Storage | File Storage | ○ | ○ | - | |
| Storage | Object Storage | Object Storage | ○ | - | - | |
| Storage | Archive Storage | Archive Storage | ○ | - | - | |
| Container | Kubernetes Engine | Kubernetes Engine | ○ | - | ○ | |
| Container | Container Registry | Container Registry | ○ | - | - | |
| Networking | VPC - Internet Gateway | Internet Gateway | ○ | - | - | |
| Networking | Load Balancer | Load Balancer | ○ | - | - | |
| Networking | DNS | DNS | ○ | - | - | |
| Networking | VPN | VPN | ○ | - | - | |
| Networking | Global CDN | Global CDN | ○ | - | - | |
| Networking | Direct Connect | Direct Connect | ○ | - | - | |
| Networking | Cloud WAN | TBD | Scheduled for September 2026 | - | - | |
| Database | EPAS(DBaaS) | TBD | Scheduled for July 2026 | - | Scheduled for July 2026 |
|
| Database | PostgreSQL(DBaaS) | TBD | Scheduled for July 2026 | - | Scheduled for July 2026 |
|
| Database | MariaDB(DBaaS) | MariaDB | ○ | - | ○ |
|
| Database | MySQL(DBaaS) | MySQL | ○ | - | ○ |
|
| Database | Microsoft SQL Server(DBaaS) | TBD | Scheduled for July 2026 | - | Scheduled for July 2026 |
|
| Database | Cachestore(DBaaS) | TBD | Scheduled for July 2026 | - | Scheduled for July 2026 |
|
| Database | Scalable DB(DBaaS) | Scalable DB | ○ | - | ○ | |
| Data Analytics | Event Streams | Event Streams | ○ | - | ○ |
|
| Data Analytics | Search Engine | TBD | Scheduled for July 2026 | - | Scheduled for July 2026 |
|
| Data Analytics | Vertica(DBaas) | TBD | Scheduled for July 2026 | - | Scheduled for July 2026 |
|
| Data Analytics | Data Flow | Data Flow | ○ | - | ○ | |
| Data Analytics | Data Ops | Data Ops | ○ | - | ○ | |
| Data Analytics | Quick Query | Quick Query | ○ | - | ○ | |
| Data Analytics | Cloud Hadoop | Cloud Hadoop | ○ | - | ○ | |
| Application Service | API Gateway | API Gateway | ○ | - | ○ | |
| Application Service | Queue Service | Queue Service | ○ | - | - | |
| Management | Loggiing&Audit | Logging&Audit | - | - | ○ | |
| AI/ML | AIOS | AIOS | ○ | - | - |
event
Below you can see the service that integrates ServiceWatch with events.
| Service Category | Service | Subservice | Event source | Resource type (event type) |
|---|---|---|---|---|
| Compute | Virtual Server | Virtual Server | Virtual Server | Server |
| Compute | Virtual Server | Image | Virtual Server | Image |
| Compute | Virtual Server | Keypair | Virtual Server | Keypair |
| Compute | Vitual Server | Server Group | Virtual Server | Server Group |
| Compute | Virtual Server | Launch Configuration | Virtual Server | Launch Configuration |
| Compute | Virtual Server | Auto-Scaling Group | Virtual Server | Auto-Scaling Group |
| Compute | Virtual Server | Block Storage | Virtual Server | Volume |
| Compute | Virtual Server | Block Storage | Virtual Server | Snapshot |
| Compute | GPU Server | GPU Server | GPU Server | Server |
| Compute | GPU Server | GPU Server | GPU Server | Image |
| Compute | Bare Metal Server | Bare Metal Server | Bare Metal Server | Bare Metal Server |
| Compute | Multi-node GPU Cluster | GPU Node | Multi-node GPU Cluster | GPU Node |
| Compute | Multi-node GPU Cluster | Cluster Fabric | Multi-node GPU Cluster | Cluster Fabric |
| Compute | Cloud Functions | Function | Cloud Functions | Cloud Functions |
| Storage | Block Storage(BM) | Block Storage(BM) | Block Storage(BM) | Volume |
| Storage | Block Storage(BM) | Volume Group(BM) | Block Storage(BM) | Volume Group |
| Storage | File Storage | File Storage | File Storage | Volume |
| Storage | Object Storage | Object Storage | Object Storage | Bucket |
| Storage | Archive Storage | Archive Storage | Archive Storage | Bucket |
| Storage | Backup | Backup | Backup | Backup |
| Container | Kubernetes Engine | Cluster | Kubernetes Engine | Cluster |
| Container | Kubernetes Engine | Node | Kubernetes Engine | Nodepool |
| Container | Container Registry | Registry | Container Registry | Container Registry |
| Container | Container Registry | Repository | Container Registry | Repository |
| Networking | VPC | VPC | VPC | VPC |
| Networking | VPC | Subnet | VPC | Subnet |
| Networking | VPC | Port | VPC | Port |
| Networking | VPC | Internet Gateway | VPC | Internet Gateway |
| Networking | VPC | NAT Gateway | VPC | NAT Gateway |
| Networking | VPC | Public IP | VPC | Public IP |
| Networking | VPC | Private NAT | VPC | Private NAT |
| Networking | VPC | VPC Endpoint | VPC | VPC Endpoint |
| Networking | VPC | VPC Peering | VPC | VPC Peering |
| Networking | VPC | Private Link Service | VPC | Private Link Service |
| Networking | VPC | Private Link Endpoint | VPC | Private Link Endpoint |
| Networking | VPC | Transit Gateway | VPC | Transit Gateway |
| Networking | Security Group | Security Group | Security Group | Security Group |
| Networking | Load Balancer | Load Balancer | Load Balancer | Load Balancer |
| Networking | Load Balancer | Load Balancer | Load Balancer | LB Listener |
| Networking | Load Balancer | LB server group | Load Balancer | LB Server Group |
| Networking | Load Balancer | LB health check | Load Balancer | LB Health Check |
| Networking | DNS | Private DNS | Private DNS | Private DNS |
| Networking | DNS | Hosted Zone | Hosted Zone | Hosted Zone |
| Networking | DNS | Public Domain Name | Public Domain Name | Public Domain Name |
| Networking | VPN | VPN | VPN | VPN Gateway |
| Networking | VPN | VPN Tunnel | VPN | VPN Tunnel |
| Networking | Firewall | Firewall | Firewall | Firewall |
| Networking | Direct Connect | Direct Connect | Direct Connect | Direct Connect |
| Networking | Cloud LAN-Campus | Campus Network | Cloud LAN - Campus (Network) | Cloud LAN - Campus (Network) |
| Networking | Cloud LAN-Datacenter | Cloud LAN Network | Cloud LAN Network | Cloud LAN Network |
| Networking | Cloud LAN-Datacenter | vDevice | Cloud LAN Network | vDevice |
| Networking | Cloud LAN-Datacenter | Interface | Cloud LAN Network | Interface |
| Networking | Cloud LAN-Datacenter | vCable | Cloud LAN Network | vCable |
| Networking | Cloud WAN | Cloud WAN Network | Cloud WAN | Network(WAN) |
| Networking | Cloud WAN | Segment | Cloud WAN | Segment |
| Networking | Cloud WAN | Segment | Cloud WAN | Segment Location |
| Networking | Cloud WAN | Segment | Cloud WAN | Segment Sharing |
| Networking | Cloud WAN | Attachment | Cloud WAN | Attachment |
| Networking | Global CDN | Global CDN | Global CDN | Global CDN |
| Networking | GSLB | GSLB | GSLB | GSLB |
| Database | EPAS(DBaaS) | EPAS(DBaaS) | EPAS | EPAS |
| Database | PostreSQL(DBaaS) | PostreSQL(DBaaS) | PostreSQL | PostreSQL |
| Database | MariaDB(DBaaS) | MariaDB(DBaaS) | MariaDB | MariaDB |
| Database | MySQL(DBaaS) | MySQL(DBaaS) | MySQL | MySQL |
| Database | Microsoft SQL Server(DBaaS) | Microsoft SQL Server(DBaaS) | Microsoft SQL Server | Microsoft SQL Server |
| Database | CacheStore(DBaaS) | CacheStore(DBaaS) | CacheStore | CacheStore |
| Database | Scalable DB(DBaaS) | Scalable DB(DBaaS) | Scalable DB | Scalable DB |
| Data Analytics | Event Streams | Event Streams | Event Streams | Event Streams |
| Data Analytics | Search Engine | Search Engine | Search Engine | Search Engine |
| Data Analytics | Vertica(DBaaS) | Vertica(DBaaS) | Vertica | Vertica |
| Data Analytics | Data Flow | Data Flow | Data Flow | Data Flow |
| Data Analytics | Data Flow | Data Flow Services | Data Flow | Data Flow Service |
| Data Analytics | Data Ops | Data Ops | Data Ops | Data Ops |
| Data Analytics | Data Ops | Data Ops Services | Data Ops | Data Ops Service |
| Data Analytics | Quick Query | Quick Query | Quick Query | Quick Query |
| Application Service | API Gateway | API Gateway | API Gateway | API Gateway |
| Application Service | Queue Service | Queue | Queue | Queue |
| Security | Key Management Service | Key Management Service | Key Management Service | Key |
| Security | Config Inspection | Config Inspection | Config Inspection | Config Inspection |
| Security | Certificate Manager | Certificate Manager | Certificate Manager | Certificate |
| Security | Secrets Manager | Secrets Manager | Secrets Manager | Secret |
| Security | Secret Vault | Secret Vault | Secret Vault | Secret |
| Management | Cloud Control | Cloud Control | Cloud Control | Landing zone |
| Management | Identity and Access Management(IAM) | User group | Identity and Access Management | Group |
| Management | Identity and Access Management(IAM) | User | Identity and Access Management | User |
| Management | Identity and Access Management(IAM) | policy | Identity and Access Management | policy |
| Management | Identity and Access Management(IAM) | role | Identity and Access Management | role |
| Management | Identity and Access Management(IAM) | Credential Provider | Identity and Access Management | Credential Provider |
| Management | Identity and Access Management(IAM) | My Info. | Identity and Access Management | Access Key |
| Management | ID Center | ID Center | Identity Center | ID Center |
| Management | ID Center | Permission set | Identity Center | Permission set |
| Management | Logging&Audit | Trail | Logging&Audit | Trail |
| Management | Organization | Organizational structure | Organization | organization |
| Management | Organization | Organizational structure | Organization | Organization account |
| Management | Organization | Organizational Structure | Organization | Organization invitation |
| Management | Organization | Organizational Structure | Organization | organizational unit |
| Management | Organization | Control Policy | Organization | Control Policy |
| Management | Organization | Organization Settings | Organization | Delegation Policy |
| Management | Resource Groups | Resource Groups | Resource Groups | Resource Group |
| Management | ServiceWatch | Dashboard | ServiceWatch | Dashboard |
| Management | ServiceWatch | Alert | ServiceWatch | Alert |
| Management | ServiceWatch | log | ServiceWatch | Log group |
| Management | ServiceWatch | Event Rules | ServiceWatch | Event Rules |
| Management | Support Center | Service request | Support | Service request |
| Management | Support Center | Contact | Support | Contact |
| AI-ML | CloudML | CloudML | Cloud ML | Cloud ML |
| AI-ML | AI&MLOps Platform | AI&MLOps Platform | AI&MLOps Platform | AI&MLOps Platform |
10.11.1.6 - Custom Metrics and Logs
ServiceWatch can collect custom metrics defined by the user and can gather log files from resources created by the user.
There are two ways to collect custom metrics and logs.
The first method is to install the ServiceWatch Agent directly on the resource, configure the resources to be collected, and collect them.
The second option is to collect custom metrics and logs using the OpenAPI/CLI offered by ServiceWatch.
The ServiceWatch metric API incurs costs for calls. Collecting metrics via the ServiceWatch Agent also operates on an OpenAPI basis, so metric API calls incur costs.
Caution is required to avoid excessive API calls when collecting metrics and logs. The billable metric APIs are listed below.
| API | description |
|---|---|
| ListMetricData | Retrieve metric data list.
|
| DownloadMetricDataImage | Metric data widget image download.
|
| ListMetricInfos | Retrieve indicator data.
|
| CreateCustomMetricMetas | Create custom metric metadata
|
| CreateCustomMetrics | Create (send) custom metric data
|
| ShowDashboard | Dashboard view
|
| ListDashboards | Dashboard list retrieval
|
| CreateDashboard | Create Dashboard
|
| SetDashboard | Edit Dashboard
|
| DeleteBulkDashboards | Delete Dashboard
|
Since logs incur charges based on the amount of data collected, there is no additional charge for API calls.
※ For detailed pricing information, refer to the ServiceWatch pricing details on the Samsung Cloud Platform Service Portal.
ServiceWatch Agent
You can install the ServiceWatch Agent on user resources such as Virtual Server, GPU Server, Bare Metal Server, etc., to collect custom metrics and logs.
ServiceWatch Agent Constraints
ServiceWatch Agent network environment
The ServiceWatch Agent is designed to collect data using OpenAPI by default, so installing and using it on server resources requires external communication over the Internet. Please create an Internet Gateway in the VPC where the resources reside and configure a NAT IP on the server resources to enable communication with the outside.
ServiceWatch Agent Supported OS Image
The OS images available for the ServiceWatch Agent are as follows.
| OS Image version | EOS Date |
|---|---|
| Alma Linux 8.10 | 2029-05-31 |
| Alma Linux 9.6 | 2025-11-17 |
| Oracle Linux 8.10 | 2029-07-31 |
| Oracle Linux 9.6 | 2025-11-25 |
| RHEL 8.10 | 2029-05-31 |
| RHEL 9.4 | 2026-04-30 |
| RHEL 9.6 | 2027-05-31 |
| Rocky Linux 8.10 | 2029-05-31 |
| Rocky Linux 9.6 | 2025-11-30 |
| Ubuntu 22.04 | 2027-06-30 |
| Ubuntu 24.04 | 2029-06-30 |
| Windows 2019 | 2029-01-09 |
| Windows 2022 | 2031-10-14 |
Provides the same as the OS Image provided for Virtual Server. Refer to Virtual Server > OS Image 제공 버전.
Quick Guide for Using ServiceWatch Agent
Below, we present a Quick guide for collecting OS metrics and logs of a Virtual Server in a Linux environment.
Installing and Configuring Node Exporter
- Refer to Node Exporter installation and install Node Exporter on the server to collect custom metrics.
- When you install Node Exporter, you can collect OS metrics through Node Exporter in addition to the metrics provided by ServiceWatch’s default monitoring.
- Refer to ServiceWatch Agent 설정, then download the ServiceWatch_Agent archive, configure the ServiceWatch Manager, and run it.
- By referring to the examples/os-metric-min-examples folder in the archive, you can run the ServiceWatch Agent by configuring at least two metrics.
Metric collection through the ServiceWatch Agent is classified as custom metrics and, unlike the default metrics collected from each service, incurs charges, so be careful not to configure unnecessary metric collection. Ensure that only the metrics that need to be collected are collected.
- Free provision is limited to 10 per account/region.
ServiceWatch Custom Metrics and Logs API
You can collect custom metrics and logs using the OpenAPI/CLI provided by ServiceWatch.
You can deliver custom metric data and custom logs to ServiceWatch via the ServiceWatch OpenAPI/CLI, and view the visualized information in the Console.
Collecting metrics via ServiceWatch OpenAPI/CLI is classified as custom metrics, and unlike the default metrics collected from each service, it incurs charges, so be careful not to configure unnecessary metric collection. Ensure that only the metrics that need to be collected are configured for collection.
- Free provision is limited to 10 per account/region.
Create custom metric metadata
To collect metric data generated from a user’s resources or applications—not the metrics provided by Samsung Cloud Platform services (e.g., Virtual Server, etc.)—into ServiceWatch, you must create custom metric metadata.
| Parameter | description |
|---|---|
| namespace | Users can define a namespace in ServiceWatch that distinguishes it from other metrics.
|
| metricMetas > metricName | Set the name of the metric to be collected. The metric name must be 3 to 128 characters, consisting of letters, numbers, and special characters (_), and must start with a letter.
|
| metricMetas > storageResolution | Set the collection interval for the relevant metric. The default is 60 (1 minute), and it can be set in seconds. |
| metricMetas > unit | Metric unit can be set
|
| metricMetas > dimensions | You can set dimensions to identify custom metric data and visualize it in the Console. When visualizing the collected metrics in the Console, they are displayed in combinations based on the dimension (dimensions) settings. |
| metricMetas > descriptionKo | Korean description of the metrics being collected |
| metricMetas > descriptionEn | English description of the metrics being collected |
For detailed information on creating custom metric metadata, see CreateCustomMetricMetas.
Create custom metric
After generating custom metric metadata, you can send the resulting metric data to ServiceWatch using the CreateCustomMetrics API.
The transmitted metric data can be queried, organized by the configured namespace.
For detailed information on generating custom metric data, see CreateCustomMetrics.
Metric Data Query
Metric data, including custom metrics, can be retrieved using the Console and the ListMetricInfos API.
For detailed information on retrieving metric data, see ListMetricInfos and ListMetricData.
Create log stream
A ServiceWatch log group is required for custom log collection. Log groups can only be created in the Console. After creating a log group in advance, you can use the log stream creation API to create a log stream that will be delivered to ServiceWatch.
For detailed information on creating a log stream, see CreateCustomLogStream.
Log Event Creation
To collect custom logs, after creating a log group and log stream, we use the log event creation API to deliver individual log messages (log events) to ServiceWatch.
For detailed information on creating log events, refer to CreateCustomLogEvents.
10.11.2 - How-to guides
Users can monitor resources created on the Samsung Cloud Platform through ServiceWatch.
Using the Dashboard
You can monitor resources on the ServiceWatch dashboard detail screen.
- To use the dashboard, you must first create a dashboard and register monitoring metrics as widgets.
- Please refer to Creating a Dashboard for detailed information on dashboard creation.
To monitor resources with the dashboard, follow these steps.
- Click the All Services > Management > ServiceWatch menu. 1. Navigate to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. 2. Navigate to the Dashboard List page.
- On the Dashboard List page, click the dashboard for the resource you want to monitor. 3. Navigate to the Dashboard Details page.
- Dashboard Details page, select the monitoring period and time zone, then monitor resources using the widget.
Category Detailed description Dashboard name Dashboard name - click to select another dashboard
Period setting area Period selection applied to widgets in the dashboard - Metric queries can be set from now up to a maximum of 455 days
Time Zone Settings Section Select the time zone applied to the period setting Reset button Reset all actions and settings made on the dashboard detail screen. Refresh Settings Area Select refresh interval for widget information - Refresh button displays information anew based on the current time
- Click the refresh interval to select the desired period: Off, 10 seconds, 1 minute, 2 minutes, 5 minutes, 15 minutes
Edit Edit dashboard information - When the Edit button is clicked, navigate to the Dashboard Edit page
- For detailed information about dashboard editing, see 대시보드 관리하기
More Display additional tasks for managing the dashboard - For detailed information on dashboard management items, see Dashboard Management
Alert Status Show the number of active alerts linked to recommended metrics on the service dashboard, displayed by stage - When the View All Alert Policies button is clicked, navigate to the Alert Policy List page
- When the Expand button is clicked, the content is provided as widgets (up to 12)
- For detailed information on widget management, refer to 위젯 관리하기
- View Alert Policy: navigate to the Alert Policy Details page for the corresponding metric
Dashboard status Display metric widgets for monitoring each resource - Click the Widget Expand View button to view detailed information about the metric
- For more details on metric information, refer to Widget Details
- Click the More button to manage widgets
- For detailed information on widget management, refer to Widget Management
- When the mouse cursor is placed on the graph, a popup displays the time, data value, and metric data for that point
- You can drag the mouse to zoom in on a specific area of the graph
- Clicking a resource name shown in the legend displays detailed information about that resource in a popup
Table. Dashboard detailed items
- Click the More > View Metrics button at the top right of the widget to view metric information for that widget on the Metrics page.
- For detailed information about the Metric page, please refer to Metric View.
Setting dashboard favorites
You can bookmark frequently used dashboards and easily navigate to the dashboard from the ServiceWatch Service Home page. To bookmark the dashboard, follow these steps.
- All Services > Management > ServiceWatch menu, click. 1. Go to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. 2. Navigate to the Dashboard List page.
- Dashboard List page, check the favorite icon of the dashboard you want to bookmark. Click the dashboard to view its details. 3. Navigate to the Dashboard Details page.
- Bookmarked dashboards are added to the bottom of the Dashboard > Dashboard Favorites menu and the Dashboard Favorites section on the Service Home page.
Widget Details
You can enlarge widgets within the dashboard to view them individually. To enlarge and view an individual widget, follow these steps.
- Click the All Services > Management > ServiceWatch menu. 1. Go to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. 2. Navigate to the Dashboard List page.
- Dashboard List page, click the dashboard for the resource you want to monitor. 3. Navigate to the Dashboard Details page.
- On the Dashboard Details page, click the Widget Zoom button for the widget you wish to enlarge. 4. The Metric Details popup opens for this widget.
Category Detailed description Widget name Display widget name Period setting area Period selection applied to the widget - Metric lookup can be set from now up to a maximum of 455 days
Time Zone Settings Section Select the time zone applied to the period setting Reset button Reset all actions and settings made on the dashboard detail screen. Statistics Select statistical basis for the metric displayed in the widget - Click the statistical basis to select: average, minimum, maximum, sum
Aggregation Period Setting Area Select aggregation period for widget information - Click the aggregation period to choose the desired interval: 1 minute, 5 minutes, 15 minutes, 30 minutes, 1 hour, 3 hours, 6 hours, 12 hours, 1 day
Refresh Settings Area Select refresh interval for widget information - Refresh button displays information anew based on the current time
- Click the refresh interval to select the desired period: Off, 10 seconds, 1 minute, 2 minutes, 5 minutes, 15 minutes
Chart area Display monitoring results as a chart - When the mouse cursor is placed over the graph or legend area, a popup shows the time, data value, and metric data for that point
- You can drag the graph area to zoom into the selected region
- Clicking a resource name displayed in the legend opens a popup with the alarm status for that resource
Table. Detailed indicator items
Check alarm history
You can view the alert history for metrics registered on the ServiceWatch dashboard. To view the alarm history, follow these steps.
- Click the All Services > Management > ServiceWatch menu. 1. Service Home Go to the page.
- On the Service Home page, click the Alarm > Alarm History menu. 2. Go to the Alarm History page.
- Check the alarm history on the Alarm History page.
Category Detailed description Alert filter and search area Filter or search alarm history - All alarm statuses: Filter by selecting an alarm status
- Enter the alarm policy name in the search field to search
- Advanced search: Search by entering the alarm policy name, alarm status, or change timestamp
Alert Policy Name Alert policy name - Click the alert policy name to view detailed information of that alert policy
Condition Alarm trigger conditions and total occurrence time - Stage display according to severity: High, Middle, Low
Category Distinguish alarm creation and alarm status change information Alarm status Current alert status - Normal: when the metric does not meet the configured condition
- Insulfficient data: when the metric data cannot be retrieved (missing, nonexistent, not arrived)
- Alert: when the metric meets the configured condition
Alert level When the alarm status is Alert, display the alarm level - High, Middle, Low
Table. Alarm History Items
- You can view the recent alarm status through Copilot.
- ‘Alarm name’ or ‘ID’ alarm query: You can view the alarm status widget for the past 3 hours. * When you click the Alert Policy Shortcut button, you will be taken to the detail page of that alert policy.
- ‘Show recent alerts’: You can view up to 5 of the most recent alerts. * Click the Alert Policy List Shortcut button to go to the alert policy list page.
- You can create and manage new alert policies. * For detailed information about the alert policy, please refer to View alert policy.
Monitoring Metrics
You can view and monitor the metrics available in ServiceWatch.
Compare by indicator
You can select one or multiple metrics and resources to monitor. To compare and monitor by metric, follow these steps.
All Services > Management > ServiceWatch menu, click. 1. Navigate to the Service Home page.
On the Service Home page, click the Metrics menu. 2. Go to the Indicator page.
On the Metrics page, in metric view mode, click Metric Comparison.
Select the metric to monitor from the metric list on the Metric page. 4. The monitoring chart for the selected metric is displayed in the Selected Metric area at the bottom.
Category Detailed description Indicator List Area List of metrics that can be monitored in ServiceWatch - Click the + button in front of the namespace or dimension to view the sub-level list
- When you select a metric to monitor, it is displayed as a chart in the Selected Metrics area
Search filter area After setting the search items to filter, click the Apply Filter button to filter the metric list - Namespace-Dimension Name: Search based on the sub-dimension names of the selected namespace
- Metric Name: Search by entering the exact metric name
- Resource Name: Search by entering the exact resource name
- Resource ID: Search by entering the exact resource ID
- Keyword: Search based on the selected top-level category and the entered keyword
- Proceed with item-specific searches excluding metric name, resource name, resource ID, and tag key
- Tag Key: Search using the selected tag key
Table. Indicator list itemsCheck the monitoring chart in the Selected metric area.
Category Detailed description Period setting area Select the period applied to the chart - Indicator lookup can be set from now up to a maximum of 455 days
Time Zone Settings Area Select the time zone applied to the chart Reset button Reset all modifications and settings made on the chart Refresh Settings Area Select chart refresh interval - Refresh button displays information anew based on the current time
- Click the refresh interval to select the desired interval: Off, 10 seconds, 1 minute, 2 minutes, 5 minutes, 15 minutes
More Display additional tasks for managing charts - For detailed information on chart management, see Metric Chart Management
graph area Data graph collected during the period applied to the chart - When the mouse cursor is placed on the graph, a popup displays the time, data value, and metric data information for that point
- You can drag the mouse to zoom in on a specific area of the graph
- Clicking a label name displayed in the legend shows detailed information about that legend in a popup
Table area View and edit labels, statistics, and aggregation periods for each legend - Legend: Color per legend
- Click a legend color to change it to another color
- Label: Displays the namespace, resource name, and metric name of the selected metric
- Click the legend name to edit it
- Enter using letters, numbers, and special characters, between 3 and 255 characters
- Statistics: Choose how to aggregate metric data
- Select from Average (default), Minimum, Maximum, Sum
- Aggregation period: Choose the time unit for aggregating metric values
- Select from 1 minute, 5 minutes (default), 15 minutes, 30 minutes, 1 hour, 3 hours, 6 hours, 12 hours, 1 day
- More: Delete a legend or create an alert policy for the legend
- For details on creating an alert policy, see Create an alert policy
Table. Indicator comparison monitoring chart itemsReference- The statistical method is as follows.
- Total: sum of all data point values collected during the period
- Average: the value obtained by dividing the sum over the specified period by the number of data pointers during that period.
- Minimum: the lowest value observed during the specified period
- Maximum: the highest value observed during the specified period
- For a detailed description of the metric, refer to Metric Overview.
Compare by Date
You can monitor by comparing a metric and a resource across dates or time periods. To compare and monitor by date or period, follow these steps.
All Services > Management > ServiceWatch menu, click it. 1. Navigate to the Service Home page.
On the Service Home page, click the Metrics menu. 2. Go to the Indicator page.
On the Metrics page, in view mode, click Date Comparison.
Select the metric to monitor from the metric list on the Metric page. 4. The monitoring chart for the selected metric is displayed in the Selected Metric area at the bottom.
Category Detailed description Indicator List Area List of metrics that can be monitored in ServiceWatch - Click the + button in front of the namespace or dimension to view the sub-level list
- When you select a metric to monitor, it is displayed as a chart in the selected metric area
Search filter area After setting the search items to filter, click the Apply Filter button to filter the metric list - Namespace-Dimension Name: Search based on the sub-dimension names of the selected namespace
- Metric Name: Search by entering the exact metric name
- Resource Name: Search by entering the exact resource name
- Resource ID: Search by entering the exact resource ID
- Keyword: Search based on the selected top-level category and the entered keyword
- Proceed with item-specific searches excluding metric name, resource name, resource ID, and tag key
- Tag Key: Search using the selected tag key
Table. Indicator list itemsCheck the monitoring chart in the selected metric area.
Category Detailed description Date comparison / period comparison Select criteria for comparing indicators - Date comparison: Compare by selecting a specific date
- Period comparison: Compare by selecting a specific period
Date and period setting area Select date or period to compare - Date comparison: Select the date to view on the chart
- Period comparison: Select the period to view on the chart
- You can select up to four dates or periods within a maximum of 455 days from today
Time Zone Settings Section Select the time zone applied to the chart Reset button Reset all manipulations and settings made on the chart Refresh Settings Area Select chart refresh interval - Refresh button updates the information based on the current time
- Click the refresh interval to select the desired interval: Off, 10 seconds, 1 minute, 2 minutes, 5 minutes, 15 minutes
More Display additional tasks for managing charts - For detailed information on chart management, see Managing Metric Charts
graph area Data graph collected during the period applied to the chart - When the mouse cursor is placed on the graph, a popup displays the time, data value, and metric data information for that point
- You can drag the mouse to zoom in on a specific area of the graph
- Clicking the date or period shown in the legend displays detailed information about that legend in a popup
Table area View and edit labels, statistics, and aggregation periods for each legend - Legend: Color per legend
- Click a legend color to change it to another color
- Period: Period applied to the chart
- Metric: Displays the namespace, resource name, and metric name of the selected metric
- Statistics: Choose how to aggregate metric data
- Average(default), Minimum, Maximum, Sum can be selected.
- Refer to the green icon displayed to the right of a meaningful metric in the relevant metric
- Aggregation Period: Select the aggregation period unit for metric values
- 1 minute, 5 minutes(default), 15 minutes, 30 minutes, 1 hour, 3 hours, 6 hours, 12 hours, 1 day can be selected
- More: Delete a legend or create an alert policy for a legend
- For details on creating an alert policy, see Create an Alert Policy
Table. Date comparison monitoring chart itemsReference- The statistical method is as follows.
- Total: sum of all data point values collected during the period
- Average: the value obtained by dividing the sum over the specified period by the number of data pointers during that period
- Minimum: the lowest value observed during the specified period
- Maximum: the highest value observed during the specified period
- For detailed explanations of the metrics, refer to the Metric Overview.
Log Monitoring
You can monitor logs collected from the Samsung Cloud Platform service.
To view the log monitoring data, follow these steps.
- Click the All Services > Management > ServiceWatch menu. 1. Navigate to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. 2. Navigate to the Log Group List page.
- On the Log Group List page, click the log group name to view its details. 3. Navigate to the Log Group Details page.
- On the Log Group Details page, click the Log Stream tab. 4. Log Stream list is displayed.
- log stream Click the log stream name in the list to view detailed information. 5. Navigate to the Log Stream Details page.
- Click the All Log Streams View button at the top of the log stream list to go to the All Log Streams Details page.
Category Detailed description Excel download Log stream history can be downloaded as an Excel file Timestamp list Message list by timestamp - Select period, user time zone, can filter using message input
Table. Log group details - Log stream detail items
- Click the All Log Streams View button at the top of the log stream list to go to the All Log Streams Details page.
Receive event notifications
You can create a system event rule for changes to resources generated in Samsung Cloud Platform and receive them as notifications.
Installing ServiceWatch Agent
You can install the ServiceWatch Agent to collect custom metrics and logs from the monitoring target.
To install the ServiceWatch Agent, follow these steps.
- Click the All Services > Management > ServiceWatch menu. 1. Navigate to the Service Home page.
- On the Service Home page, click the Agent Setup & Guideline button. 2. Agent Setup & Guideline A popup window opens.
- Agent Setup & Guideline Copy the installation file URL from the popup window and go to that address. 3. Agent, manager, and configuration files can be downloaded.
- For detailed information on installing the ServiceWatch Agent, refer to Using ServiceWatch Agent.
10.11.2.1 - Managing Dashboards and Widgets
In the Samsung Cloud Platform Console, you can create and manage dashboards to monitor the resources of the services you are using.
Create Dashboard
You can create a ServiceWatch dashboard.
Creating a dashboard by adding individual widgets
To create a dashboard, follow these steps.
All Services > Management > ServiceWatch menu, click it. You will be taken to the Service Home page.
Click the Dashboard > Dashboard List menu on the Service Home page. You will be taken to the Dashboard List page.
On the Dashboard List page, click the Create Dashboard button.
Please enter the dashboard name.
- Enter the dashboard name using English letters, numbers, and special characters (
-_) within 3 ~ 40 characters. - You cannot enter a name that is already in use on the service dashboard.
- Enter the dashboard name using English letters, numbers, and special characters (
Add a widget to configure the dashboard. A popup window appropriate to the widget addition method will open.
- Add Individual Widget: You can add a single widget that combines metrics and resources. Clicking the button opens the Add Individual Widget popup.
Category Required statusDetailed description Indicator classification Selection In ServiceWatch, filter the monitorable metrics as All or Key Metrics and display them in the metric list Indicator List Area Required List of metrics that can be monitored in ServiceWatch - Click the + button in front of the namespace and dimension to view the sub-level list
- When you select a metric to monitor, it is displayed as a chart in the Selected Metrics area
Search filter area - After setting the search items to filter, click the Apply Filter button to filter the metric list - Namespace-Dimension Name: Search based on the sub-dimension names of the selected namespace
- Metric Name: Enter the exact metric name to search
- Resource Name: Enter the exact resource name to search
- Resource ID: Enter the exact resource ID to search
- Keyword: Search based on the selected top-level category and the entered keyword
- Proceed with item-specific searches excluding metric name, resource name, resource ID, and tag key
- Tag Key: Search using the selected tag key
Selected metric area - Monitoring chart for the selected metric in the metric list area - Data graph collected during the period applied to the chart
- When the mouse cursor is placed on the graph, a popup displays the time, data value, and metric data information for that point
- You can drag the mouse to zoom in on a specific area of the graph
- Clicking the resource name shown in the legend displays detailed information about that resource in a popup
- Item values in the table area within the chart can be edited
- Label: Enter the legend name using English letters, numbers, or special characters, between 3 ~ 255 characters
- Statistics: Choose the method for aggregating metric data
- Options: average (default), minimum, maximum, sum
- Aggregation period: Select the aggregation period unit for metric values
- Options: 1 minute, 5 minutes (default), 15 minutes, 30 minutes, 1 hour, 3 hours, 6 hours, 12 hours
- Delete: Remove the legend
Table. Individual widget additional items
- Add Individual Widget: You can add a single widget that combines metrics and resources. Clicking the button opens the Add Individual Widget popup.
Click the Complete button in the widget addition popup. The widget will be added to the dashboard on the dashboard creation page.
After confirming the added widget, click the Create button. A popup indicating dashboard creation will appear.
Click the Confirm button. Dashboard creation is complete.
Creating a dashboard by adding multiple widgets
To create a dashboard, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
On the Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
On the Dashboard List page, click the Create Dashboard button.
Enter the name of the dashboard.
- Enter the dashboard name using English letters, numbers, and special characters (
-_) within 3 ~ 40 characters. - You cannot enter a name that is already in use on the service dashboard.
- Enter the dashboard name using English letters, numbers, and special characters (
Add a widget to configure the dashboard. A corresponding popup window will open according to the widget addition method.
- Add Multiple Widgets: Select the desired resources by metric unit and add multiple widgets at once. Clicking the button opens the Add Multiple Widgets popup window.
Category Required or notDetailed description Indicator classification Select In ServiceWatch, filter the monitorable metrics as All or Key Metrics and display them in the metric list Indicator selection area Required Select the namespace and resources to add - Click the + button in front of the namespace and resources to view the list of sub-resources and metrics
- When you check the metrics to add to the widget from the metric list, the Selected Metrics and Selected Resources sections are displayed
- Multiple metrics can be selected
Selection indicator Required Display the list of selected metrics from the namespace and resource list - When a metric is clicked, the Selected Resources area shows the list of resources included in that metric
Selected resource Required Selected Indicator list, add resources to the selected indicator - After clicking the Select button, choose resources that can be added to the indicator, allowing up to five additions
- Resources must be added for all indicators in the Selected Indicator list
Statistics Required Select the statistical basis for the indicator value - You can choose from average (default), minimum, maximum, or sum
Aggregation period Required Select the aggregation period unit for metric values - Choose from 1 minute, 5 minutes (default), 15 minutes, 30 minutes, 1 hour, 3 hours, 6 hours, or 12 hours
Table: Additional items for multiple widgets
- Add Multiple Widgets: Select the desired resources by metric unit and add multiple widgets at once. Clicking the button opens the Add Multiple Widgets popup window.
Click the Complete button on the widget addition popup. The widget will be added to the dashboard on the dashboard creation page.
After confirming the added widget, click the Create button. A popup indicating dashboard creation will appear.
Click the Confirm button. The dashboard has been created.
Create a dashboard by loading a dashboard
To create a dashboard, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
Click the Dashboard > Dashboard List menu on the Service Home page. You will be taken to the Dashboard List page.
On the Dashboard List page, click the Create Dashboard button.
Enter the name of the dashboard.
- Enter the dashboard name using English letters, numbers, and special characters (
-_) within 3 ~ 40 characters. - You cannot enter a name that is already in use on the service dashboard.
- Enter the dashboard name using English letters, numbers, and special characters (
Add a widget to configure the dashboard. A corresponding popup window will open according to the widget addition method.
- Dashboard Load: You can load widgets from dashboards registered in ServiceWatch. When you click the button, the Dashboard Load popup opens.
Category RequiredDetailed description Dashboard Required Display the list of dashboards registered in ServiceWatch - When a dashboard is selected, the widgets applied to the dashboard are displayed in the preview area
Preview Required Display widgets applied to the selected dashboard from the dashboard list - Check the widget name to select widgets to add to the dashboard to be created
- If you check the Select All item, all metrics of that dashboard are selected
Table. Load Dashboard Items
- Dashboard Load: You can load widgets from dashboards registered in ServiceWatch. When you click the button, the Dashboard Load popup opens.
Click the Complete button in the widget addition popup. The widget will be added to the dashboard on the dashboard creation page.
After confirming the added widget, click the Create button. A popup indicating dashboard creation will open.
Click the Confirm button. Dashboard creation is complete.
Check the dashboard
You can view the information of the selected dashboard on the Dashboard List page. To view the dashboard, follow the steps below.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
Category Detailed description Dashboard name Dashboard name - User dashboards are the dashboard names set by the user. Service dashboards are the Samsung Cloud Platform service name that matches the service namespace
Dashboard Category Dashboard classification - User: Dashboard created directly by the user
- Service: Dashboard automatically composed of pre-built key metrics for each service
Modification date and time Dashboard modification timestamp Creation date and time Dashboard creation date and time Favorites If bookmarked, it is displayed in yellow - Click the star icon to set or remove a bookmark
Table. Dashboard list items - On the Dashboard List page, click the dashboard whose details you want to view. You will be taken to the Dashboard Detail page.
Category Detailed description Dashboard name Display the dashboard name - Click the name to select another dashboard
Period setting area Period selection applied to widgets in the dashboard - Metric queries can be set from now up to a maximum of 455 days
Time zone setting area Select the time zone applied to the period setting Reset button Reset all actions and settings made on the dashboard detail screen Refresh Settings Area Select refresh interval for widget information - Refresh button updates the information based on the current time
- Click the refresh interval to choose the desired period: Off, 10 seconds, 1 minute, 2 minutes, 5 minutes, 15 minutes
Edit You can edit the dashboard name or manage widgets - When you click the Edit button, you are taken to the Dashboard Edit page
- For more details on editing the dashboard, see 대시보드 수정하기
More Display additional tasks for managing the dashboard - Dashboard duplication and deletion, view details, view source are possible
- For details on dashboard management items, refer to Dashboard Management
- For details on widget management items, refer to Widget Management
Widget area Display widgets for monitoring each resource - You can manage the widget by clicking the More button at the top right of the widget
- You can edit, duplicate, download files, view metrics, and view source of the widget
- For detailed information on widget management items, see Widget Management
Table. Dashboard detailed items
Dashboard Management
Dashboard Details page allows you to edit or manage dashboard information and widgets.
Edit Dashboard
You can modify the dashboard name and change the widget configuration.
To modify the dashboard, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- Click the Dashboard > Dashboard List menu on the Service Home page. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard you want to view details for. You will be taken to the Dashboard Details page.
- Click the Edit button at the top right of the Dashboard Details page. You will be taken to the Dashboard Edit page.
- After modifying the dashboard’s information or widgets, click the Save button.
Category Detailed description Dashboard name Dashboard name cannot be edited - Enter within 34 characters using English letters, numbers, and special characters (
-_)
- Dashboard names that are currently in use cannot be used
Widget Name Widget name can be edited - English letters, numbers, spaces, special characters(
-_.\
Widget Management When you hover the mouse over a widget, a management button appears on the right side of the widget border - Edit: Widget Edit popup allows you to modify the widget’s metrics and resources
- For details on widget editing, see the Individual Widget Edit in 위젯 관리하기
- Duplicate: Duplicate the current widget and add it to the dashboard
- Delete: Remove the current widget from the dashboard
- Expand: Display the current widget with an expanded size
- Collapse: If the widget is expanded, clicking again reduces its size
Add widget Add a new widget to the dashboard - Add individual widget: Add a single widget that combines metrics and resources
- Add multiple widgets: Select desired resources per metric to add multiple widgets at once
- Load dashboard: Load and add widgets from another dashboard
- For detailed instructions on adding widgets, see Creating Widgets
Table. Dashboard edit items - Enter within 34 characters using English letters, numbers, and special characters (
View detailed dashboard information
You can view detailed information about the dashboard. To view detailed information of the dashboard, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- Click the Dashboard > Dashboard List menu on the Service Home page. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard you want to view details for. You will be taken to the Dashboard Details page.
- Dashboard Details page’s top right corner has a More > Details button. Click the button. The Dashboard Details popup opens.
Category Detailed description Dashboard name Dashboard name Dashboard Category Dashboard usage classification - User: dashboard created directly by the user
- Service: dashboard composed of automatically pre-built key metrics for each service
Service service name Resource Type dashboard SRN Unique resource ID in Samsung Cloud Platform - In ServiceWatch, it refers to the dashboard’s SRN
Resource name Resource Name - In ServiceWatch, the meaning of the dashboard name
Resource ID Unique resource ID in the service Constructor User who created the dashboard Creation date and time Dashboard creation date and time Editor User who edited the dashboard information Modification date and time Dashboard information modification timestamp Table. Dashboard Details - Detail Information Popup Items
When sorting dashboard names in the dashboard list, follow the sorting rules below.
- Whitespace and control characters
- Some special characters (
!"#$%&’()*+,-./) - Numbers (
0–9) - Some special characters (
;<=>?@) - English (
A–Z,a–z, case-insensitive) - Remaining special characters (
[\]^_`) - Other characters
Check the dashboard source code
You can view the dashboard’s source code. To view the source code of the dashboard, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- Click the Dashboard > Dashboard List menu on the Service Home page. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard you want to view details for. You will be taken to the Dashboard Details page.
- Dashboard Details on the top right of the page, click the More > View Source button. The Dashboard View Source popup opens.
Category Detailed description Source information Display the dashboard source code in JSON format Copy code Copy the source code to the clipboard Table. Dashboard Details - Dashboard Source View Popup Items
Duplicate Dashboard
You can duplicate a widget from the current dashboard and add it to another dashboard.
User permission is required to duplicate the dashboard.
- User: {email}
- Action: iam:CreatGroup
- On resource: {SRN}
- Context: no identity-based policy allows the action
To duplicate the dashboard, follow these steps.
All Services > Management > ServiceWatch menu, click it. You will be taken to the Service Home page.
On the Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
On the Dashboard List page, click the dashboard you want to view details for. You will be taken to the Dashboard Details page.
Click the More > Duplicate button at the top right of the Dashboard Details page. The Dashboard Duplicate popup opens.
After selecting the dashboard duplication method, enter the required information. The required information varies depending on the duplication method.
Category RequiredDetailed description Replication target - Name of the dashboard to duplicate Cloning method Required After duplicating the dashboard widget, select the dashboard to add it to - New Dashboard: Create a new dashboard and generate it by duplicating the current dashboard’s widget
- Existing Dashboard: Duplicate the current dashboard’s widget and add it to an existing dashboard
Dashboard name Required Enter the name of the new dashboard - Displayed when the duplication method is set to New Dashboard
- Enter using English letters, numbers, and special characters (
-_) within 3 to 40 characters
Select Dashboard Required Select the dashboard to which the duplicated widget will be added from the existing dashboards - Displayed when the duplication method is selected as Existing dashboard
Table. Dashboard clone itemsAfter entering the required information, click the Complete button. A popup notifying that the dashboard is being duplicated will appear.
Click the Confirm button on the popup window. The dashboard duplication task is complete.
Delete dashboard
You can delete unused dashboards.
To delete the dashboard, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
- On the Dashboard List page, select the checkbox of the dashboard you want to delete, then click the Delete button. A popup confirming the dashboard deletion will appear.
- You can delete multiple dashboards simultaneously.
- You can also delete individually by clicking the More > Delete button located at the top right of the Dashboard Details page.
- In the delete confirmation input field, type Delete and then click the Confirm button. The dashboard will be deleted.
Manage Widgets
Dashboard Details page lets you edit or manage widgets.
Edit Widget
You can modify the widget’s metrics and resources.
To modify the widget, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard whose widget you want to edit. You will be taken to the Dashboard Details page.
- On the Dashboard Details page, click the More > Edit Widget button at the top right of the widget you want to edit. The Edit Widget popup will open.
- After modifying the widget’s metrics and resources, click the Confirm button. The widget modification is complete.
Category Required statusDetailed description Indicator classification Select In ServiceWatch, filter the monitorable metrics as All or Key Metrics and display them in the metric list Indicator List Area Required List of metrics that can be monitored in ServiceWatch - Click the + button in front of the namespace and dimension to view the sub-level list
- When you select a metric to monitor, it is displayed as a chart in the Selected Metrics area
Search filter area - After setting the search items to filter, click the Apply Filter button to filter the metric list - Namespace-Dimension Name: Search based on the sub-dimension names of the selected namespace
- Metric Name: Enter the exact metric name to search
- Resource Name: Enter the exact resource name to search
- Resource ID: Enter the exact resource ID to search
- Keyword: Search based on the selected top-level category and the entered keyword
- Proceed with item-specific searches excluding metric name, resource name, resource ID, and tag key
- Tag Key: Search using the selected tag key
Selected metric area - Monitoring chart for the selected metric in the metric list area - Data graph collected during the period applied to the chart
- When the mouse cursor is placed on the graph, a popup displays the time, data value, and metric data information for that point
- You can drag the mouse to zoom in on a specific area of the graph
- Clicking the label name displayed in the legend shows detailed information for that legend in a popup
- In the table area within the chart, you can view and edit legend labels, statistics, and aggregation periods
- Legend: color per legend
- Click a legend color to change it to another color
- Period: period applied to the chart
- Metric: displays the selected metric’s namespace, resource name, and metric name
- Statistics: select the method for aggregating metric data
- Choose among Average (default), Minimum, Maximum, Sum
- Aggregation period: select the aggregation period unit for metric values
- Choose among 1 minute, 5 minutes (default), 15 minutes, 30 minutes, 1 hour, 3 hours, 6 hours, 12 hours, 1 day
- Delete: remove the legend
- Legend: color per legend
Table. Individual widget additional items
Widget Replication
You can copy the widget and add it to another dashboard.
User permission is required to duplicate the dashboard.
- User: {email}
- Action: iam:CreatGroup
- On resource: {SRN}
- Context: no identity-based policy allows the action
To duplicate a widget, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
On the Dashboard List page, click the dashboard you want to duplicate. You will be taken to the Dashboard Details page.
On the Dashboard Detail page, click the More > Widget Clone button located at the upper right of the widget to be duplicated. The Widget Clone popup window opens.
After selecting the widget duplication method, enter the required information. The required information varies depending on the duplication method.
Category Whether requiredDetailed description Replication target - Name of the dashboard to duplicate Cloning method Required After duplicating the widget, select the dashboard to add it to - Existing Dashboard: Add the widget to an existing dashboard
- New Dashboard: Create a new dashboard and add the widget
Select Dashboard Required Select the dashboard to which the duplicated widget will be added from the existing dashboards - When the duplication method is selected as Existing Dashboard, it is displayed
Dashboard name Required Enter the name of the new dashboard - Displayed when the duplication method is set to New Dashboard
- Enter using English letters, numbers, and special characters (
-_) within 3 to 40 characters
Widget name Required When adding a widget to the dashboard, enter the widget name - English letters, numbers, special characters(
-_.\
Table. Widget duplication itemsAfter entering the required information, click the Complete button. A popup window notifying the addition of the widget will open.
Click the Confirm button in the popup window. The widget will be duplicated and added to the dashboard.
Download widget file
You can download widget information as a file. To download widget information, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard from which you want to download widget information. You will be taken to the Dashboard Detail page.
- Dashboard Details page, click the More > File Download button at the top right of the widget whose information you want to download. The File Download popup window opens.
- After selecting the file download method, click the Confirm button. The download will start.
- Download methods can be selected simultaneously.
Category Detailed description CSV Convert the widget’s metrics and monitoring data to an Excel (*.csv) file and download it. PNG Convert the widget chart to an image (*.png) file and download Table. Widget file download item
- Download methods can be selected simultaneously.
Check widget metrics
You can view the widget’s resource and metric information on the Metrics page. To view widget metrics on the metrics page, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard you want to view widget metrics for. You will be taken to the Dashboard Details page.
- On the Dashboard Detail page, click the More > View Metrics button at the top right of the widget you will view on the Metrics page. You will be taken to the Metrics page.
- The resources and metric information of the selected widget are automatically configured and displayed on the Metrics page.
Check widget source code
You can view the source code of the dashboard.
To check the dashboard’s source code, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard you want to view details for. You will be taken to the Dashboard Detail page.
- On the Dashboard Details page, click the More > View Source button located at the top right of the widget to view its source code. The Widget Source View popup will open.
Category Detailed description Source information Display the widget source code in JSON format Copy code Copy the source code to the clipboard Table. Widget source view item
Download widget file
You can download widget information as a file. To download widget information, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
- Dashboard List page, click the dashboard to download widget information. You will be taken to the Dashboard Detail page.
- Dashboard Details page, click the More > File Download button at the top right of the widget whose information you want to download. The File Download popup window opens.
- After selecting the file download method, click the Confirm button. The download will start.
- Download methods can be selected simultaneously.
Category Detailed description CSV Convert the widget’s metrics and monitoring data to an Excel (*.csv) file and download it. PNG Convert the widget chart to an image (*.png) file and download Table. Widget file download item
- Download methods can be selected simultaneously.
Export to Object Storage
You can store widget information in Object Storage.
User permissions are required to store data in Object Storage.
- User: {email}
- Action: iam:CreatGroup
- On resource: {SRN}
- Context: no identity-based policy allows the action
To store widget information in Object Storage, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Dashboard > Dashboard List menu. You will be taken to the Dashboard List page.
- On the Dashboard List page, click the dashboard from which you want to download widget information. You will be taken to the Dashboard Detail page.
- On the Dashboard Details page, click the More > Export to Object Storage button located at the top right of the widget whose information you want to download. The Export to Object Storage popup will open.
- After selecting the bucket to store widget information, click the Done button. A popup confirming the save will appear.
- Click the Confirm button in the popup window. Data export will begin.
- The limitations of metrics that can be exported to Object Storage are as follows.
- Number of indicators: up to 10
- Query period: within 2 months (63 days)
- If the query period exceeds 2 months (63 days), only data for up to 63 days will be stored.
- If there is no Object Storage to store metric data, create an Object Storage first, then proceed.
- Metric data is stored in the “metricname-yyyymmddhhmmss.json” file format and can be accessed in the ~/servicewatch/metric path of the Object Storage bucket.
10.11.2.2 - Alert
In ServiceWatch, you can set threshold criteria for the metrics to be monitored, and create and manage alert policies that generate alert notifications when the specified conditions are met.
Create Alert Policy
You can create an alert policy for a metric and set the criteria for alert triggering. To create an alert policy, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
On the Service Home page, click the Alarm > Alarm Policy menu. You will be taken to the Alarm Policy List page.
Click the Create Alert Policy button on the Alert Policy List page. You will be taken to the Create Alert Policy page.
After entering the name and description of the alert policy in the Basic Information Input area, click the Select Metric button. The Select Metric popup window will open.
Metric Selection In the popup window, after selecting the metric for which to create an alert policy, click the Confirm button. The Metric and Condition Settings area will be displayed.
Category Required statusDetailed description Indicator classification Required In ServiceWatch, filter the monitorable metrics as All or Key Metrics and display them in the metric list Indicator List Area Required List of metrics that can be monitored in ServiceWatch - Click the **+** button in front of the namespace and dimension to view the sub-level list
- When you select a metric to monitor, it is displayed as a chart in the **Selected Metric** area
- If the metric is associated with a namespace, the **Service Dashboard** is displayed
- Clicking the **Service Dashboard** navigates to the detailed page of that dashboard
- **Namespace-Dimension Name**: Search based on the sub-dimension names of the selected namespace
- **Metric Name**: Enter the exact metric name to search
- **Resource Name**: Enter the exact resource name to search
- **Resource ID**: Enter the exact resource ID to search
- **Keyword**: Search based on the selected top-level category and the entered keyword
- Proceed with item-specific searches excluding metric name, resource name, resource ID, and tag key
- **Tag Key**: Search using the selected tag key
- Data graph collected during the period applied to the chart
- When the mouse cursor is placed on the graph, a popup displays the time, data value, and metric data information for that point
- You can drag the mouse to zoom in on a specific area of the graph
- Clicking a label displayed in the legend shows detailed information for that legend in a popup
- In the table area within the chart, you can view and edit legend labels, statistics, and aggregation periods
- **Legend**: color for each legend
- You can click a legend color to change it to another color
- **Period**: period applied to the chart
- **Metric**: displays the selected metric's namespace, resource name, and metric name
- **Statistics**: select the method for aggregating metric data
- Choose among **Average** (default), **Minimum**, **Maximum**, **Sum**
- **Aggregation Period**: select the aggregation period unit for metric values
- Choose among **1 minute**, **5 minutes** (default), **15 minutes**, **30 minutes**, **1 hour**, **3 hours**, **6 hours**, **12 hours**, **1 day**
- **Delete**: remove the legend
- **Legend**: color for each legend
Table. Indicator selection popup itemsSet the threshold values for generating alerts in the Indicator and Condition Settings area.
Category Required statusDetailed description namespace - Namespace of the selected metric Indicator name - Name of the selected metric unit - Data unit of the selected metric Evaluation scope Required Time range (seconds) for alarm evaluation - Input allowed up to a maximum of 604,800 seconds in multiples of 60
- If set smaller than the collection interval or not in a multiple of the collection interval, alarm evaluation may be applied abnormally
Statistics Required Select the method for calculating metric data over the evaluation range - Sum: The sum of all data point values collected during the period
- Average: The value obtained by dividing the Sum over the specified period by the number of data points during that period
- Minimum: The lowest value observed during the specified period
- Maximum: The highest value observed during the specified period
Additional configuration Select Setting evaluation count, violation count, and missing data handling method - When the additional configuration is set to Use, you can set the evaluation count and violation count used for alarm evaluation. If the number of violations meets the condition within the evaluation count during the evaluation period (seconds), the alarm state changes to Alert
- Evaluation Count: Number of evaluations that trigger an alarm
- 1 ~ 8,640 enterable range
- Violation Count: Allowed number of violations before an alarm is triggered
- 1 ~ Evaluation Count enterable range
- Evaluation Count: Number of evaluations that trigger an alarm
- If the evaluation period is less than 1 hour (3,600 seconds), evaluation count/evaluation period can be set up to a maximum of 1 day (86,400 seconds)
- If the evaluation period is 1 hour (3,600 seconds) or more, evaluation count/evaluation period can be set up to a maximum of 7 days (604,800 seconds)
- When the additional configuration is set to Use, you can specify how to handle missing data during alarm evaluation.
- Treat missing data as missing (Missing)
- Ignore missing data and maintain the current alarm state (Ignore)
- Treat missing data as satisfying the condition (Breaching)
- Treat missing data as not satisfying the condition (Not breaching)
Condition setting Required - Condition Operator: After calculating metric data over the evaluation period, select a condition operator to compare the value with the threshold
- Threshold: After calculating metric data over the evaluation period, set the threshold to compare the value with the condition operator
- Input allowed from 0 ~ 2,147,483,647
- Condition: Explanation of alert state (Alert) change conditions based on the configured Condition Operator and Threshold
Alert level Required Select alert stage based on the importance of the alert policy Resource ID - Metric monitoring target resource ID Resource Name - Metric Monitoring Target Resource Name Table. Indicator and Condition Setting ItemsIn the Notification Settings area, select the user who will receive notifications when an alarm occurs.
- Only users with a login history (users who have registered an email or mobile phone number) can be added as notification recipients.
- You can add up to 100 notification recipients.
- If there is no user to add, you can create a user on the IAM service’s User Creation page. For detailed information on user creation, refer to Create User.
- The notification reception method (E-mail or SMS) can be changed on the Alert Settings page after selecting the notification target as Service > Alert. For detailed information about alert settings, refer to 알림 설정 확인하기.
- Add tag information in the Additional Information Input area.
- After reviewing the summary information, click the Create button. A popup indicating the creation of the alert policy will open.
- Click the Confirm button. The alert policy has been created.
Check detailed alert policy information
You can view and manage detailed information about alert policies. To view detailed information about the alert policy, follow these steps.
- Click the All Services > Management > ServiceWatch menu. Navigate to the Service Home page.
- On the Service Home page, click the Alert > Alert Policy menu. You will be taken to the Alert Policy List page.
- In the Alert Policy menu, you can click the Alert Level button to filter and view only the list of alert policies that correspond to that alert level.
- On the Alert Policy List page, click the alert policy name to view its details. You will be taken to the Alert Policy Details page.
Category Detailed description Alert policy status Alert policy status - Active: The alert policy is in an active state
- Inactive: The alert policy is in an inactive state
- You can change it by clicking the Activate or Deactivate button
Delete alarm policy Delete the relevant alert policy Alarm status Current alert status - Normal: when the metric does not meet the configured condition
- Insulfficient data: when the metric data cannot be verified (missing, nonexistent, not arrived)
- Alert: when the metric meets the configured condition
- When the alert status is Alert, display the alert level (>High, Middle, Low) as well
Metric Monitoring Chart Metric monitoring chart for the configured period - For details on the monitoring chart, refer to Metric Monitoring
Information Classification Tab Alert policy information tabs - Details, notifications, alert history, tags, operation history
- Click each tab to view the corresponding information
Table. Alarm detailed items
When sorting alarm policy names in the alarm policy list, follow the sorting rules below.
- Whitespace and control characters
- Some special characters (
!"#$%&’()*+,-./) - Numbers (
0–9) - Some special characters (
;<=>?@) - English (
A–Z,a–z, case-insensitive) - Remaining special characters (
[\]^_`) - Other characters
Detailed Information
On the Alert Policy List page, you can view the selected alert policy’s basic information and metric information.
| Category | Detailed description |
|---|---|
| Service | service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date | Service creation timestamp |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Alert Policy Name | Name of the alert policy |
| Namespace | Metric namespace |
| Indicator Name | Indicator name |
| Evaluation scope | Time range for alert evaluation |
| unit | Unit of indicator data |
| Evaluation count | Alert policy evaluation count |
| Number of violations | Number of alert policy violations |
| Statistics | Method of calculating metric data during the evaluation period |
| evaluation interval | Evaluation interval: evaluation range (unit) × number of evaluations |
| Condition | Alert state change condition based on the configured condition operator and threshold |
| Alert level | Alert level when an alert occurs |
| Target metric information area | Description of the alert policy target metric, resource ID, and resource name |
Notification
On the Alert Policy List page, you can view the notification recipients of the selected alert policy.
| Category | Detailed description |
|---|---|
| Notification recipient list | User ID, creation date and time, last login, status information
|
| Delete | Delete all selected users from the notification recipient list
|
| More | Change the notification status (enable/disable) for the selected user in the notification recipient list
|
| Add notification recipient | Add new notification recipient possible
|
- Only users with a login history (users who have registered an email or mobile phone number) can be added as notification recipients.
- You can add up to 100 notification recipients.
- If there is no user to add, you can create a user on the IAM service’s User Creation page. For detailed information on creating users, see Create User.
- The notification delivery method (E-mail or SMS) can be changed on the Notification Settings page after selecting the notification target as Service > Alert. For more details on notification settings, see Check Notification Settings.
Alert History
Alarm Policy List page lets you view the alarm status change history of the selected alarm policy.
| Category | Detailed description |
|---|---|
| Alert History List | Alarm status change timestamp, change status classification information, alarm description
|
| View Details | You can view detailed alarm history information and the source code in JSON format
|
tag
Alert Policy List page lets you view the tag information of the selected alert policy, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag’s Key and Value information |
| Edit tag | You can modify, delete, or add new tags to existing tag information
|
Job History
You can view the operation history of the selected alert policy on the Alert Policy List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Modify Alert Policy
You can modify the target metrics and policy settings of the alert policy. To modify the alert policy, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Alert > Alert Policy menu. It navigates to the Alert Policy List page.
- On the Alert Policy List page, click the alert policy name to view detailed information. You will be taken to the Alert Policy Details page.
- On the Detail Information tab of the Alert Policy Details page, click the Edit button of Metric Information. The Edit Metric Information popup opens.
- After modifying the metric information and policy settings, click the Confirm button. A popup notifying the metric modification will open.
- For detailed information on metric modification items, please refer to Create Alert Policy.
- Click the Confirm button. The alert policy update is complete.
Disable Alert Policy
You can disable the alert policy to stop sending notifications when the alert status changes. Even if the alert policy is disabled, alert evaluation continues, and alert history accumulates as the alert status changes. However, notifications are not sent.
If you want to block receiving notifications for a specific period, you can disable the corresponding alert policy.
To disable the alert policy, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Alert > Alert Policy menu. You will be taken to the Alert Policy List page.
- On the Alert Policy Details page, click the Disable button. The Alert Policy Deactivation Notification popup opens.
- Click the Confirm button. Check the status of the alert policy.
Activate Alert Policy
You can enable the alert policy to resume sending notifications when the alert status changes. To enable the alert policy, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Alert > Alert Policy menu. You will be taken to the Alert Policy List page.
- On the Alert Policy Details page, click the Enable button. The Alert Policy Activation Notification popup window opens.
- Click the Confirm button. Check the status of the alert policy.
Delete Alert Policy
You can delete unused alert policies. To delete an alert policy, follow these steps.
- All Services > Management > ServiceWatch menu, click it. You will be taken to the Service Home page.
- On the Service Home page, click the Alert > Alert Policy menu. You will be taken to the Alert Policy List page.
- On the Alert Policy List page, select the checkbox of the alert policy you want to delete, then click the Delete button. A popup notifying the alert policy deletion will appear.
- You can delete multiple alert policies at once.
- You can also delete individually by clicking the Delete button at the far right of each alert policy, or by clicking the Delete Alert Policy button on the corresponding Alert Policy Details page.
- Click the Confirm button. The alert policy will be deleted.
10.11.2.3 - indicator
Users can monitor metrics of service resources in the Samsung Cloud Platform Console and use them for management.
Check Indicators
You can view the metrics available in ServiceWatch. To check the indicator, follow these steps.
- All Services > Management > ServiceWatch menu, click it. 1. Go to the Service Home page.
- On the Service Home page, click the Metrics menu. 2. Go to the Indicator page.
- Check the metrics in the metric list on the Metrics page.
| Category | Detailed description |
|---|---|
| Indicator Comparison Mode | Select the method for comparing indicators
|
| Indicator classification | Display the metrics that can be monitored in ServiceWatch, filtered and categorized as All or Key Metrics, in the metric list |
| Indicator List Area | List of metrics that can be monitored in ServiceWatch
|
| Search filter area | After setting the search items to filter, click the Apply Filter button to filter the metric list
|
| Selected indicator | Display monitoring information for the selected metric from the metric list
|
Manage Indicator Charts
You can add the metric monitoring result chart as a widget or manage the data.
Add as widget
You can add the selected metric as a widget to the dashboard.
To add a metric as a widget, follow these steps.
All Services > Management > ServiceWatch Click the menu. 1. Go to the Service Home page.
On the Service Home page, click the Metrics menu. 2. Navigate to the Indicator page.
Select the metric to monitor from the metric list on the Metric page. 3. The monitoring chart for the selected metric is displayed in the Selected Metric area at the bottom.
After configuring the table area in the monitoring chart of the Selected metric region, click the More > Add widget button. 4. Add Widget The popup window opens.
After selecting the method to add the widget, enter the required information. 5. The required information varies depending on the addition method.
Category Required statusDetailed description Replication Method Required After duplicating the widget, select the dashboard to add it to - Existing Dashboard: Add the widget to the existing dashboard
- New Dashboard: Create a new dashboard and add the widget
Select Dashboard Required Select the dashboard to which the duplicated widget will be added among the existing dashboards - Displayed when the duplication method is selected as Existing Dashboard
Dashboard name Required Enter the name of the new dashboard - Displayed when selecting the duplication method as New Dashboard
- Enter using English letters, numbers, and special characters (
-_) within 3 ~ 40 characters
Widget name Required When adding a widget to the dashboard, enter - English letters, numbers, special characters(
-_.\
Table. Widget additional itemsWhen you have finished entering the required information, click the Complete button. 6. A popup window notifying the addition of a widget opens.
Click the Confirm button on the popup window. 7. A widget will be added to the dashboard.
Share monitoring chart URL
You can download monitoring chart information as a file. To download the monitoring chart information, follow these steps.
- Click the All Services > Management > ServiceWatch menu. 1. Navigate to the Service Home page.
- On the Service Home page, click the Metrics menu. 2. Go to the Indicator page.
- Select the metric to monitor from the metric list on the Metrics page. 3. The monitoring chart for the selected metric is displayed in the Selected Metric area at the bottom.
- After setting the table area in the monitoring chart of the Selected metric region, click the More > URL Share button. 4. URL sharing A popup window opens.
- In the URL Share popup, click the Copy URL button. 5. The generated URL is copied.
- Information within the monitoring chart is provided as metadata links.
Download Monitoring Chart File
You can download monitoring chart information as a file. To download the monitoring chart information, follow these steps.
- All Services > Management > ServiceWatch menu, click it. 1. Go to the Service Home page.
- On the Service Home page, click the Metrics menu. 2. Navigate to the Indicator page.
- Select the metric to monitor from the metric list on the Metric page. 3. The monitoring chart for the selected metric is displayed in the Selected Metric area at the bottom.
- In the monitoring chart of the selected metric area, set the table region, then click the More > File Download button. 4. File Download popup window opens.
- After selecting the file download method, click the Confirm button. 5. The download will start.
- The download method can be selected simultaneously.
Category Detailed description CSV Convert chart metrics and monitoring data to an Excel (*.csv) file and download PNG Convert the chart to an image (*.png) file and download - Available only when the metric comparison mode is set to Metric Comparison
- Up to 100 metric data items can be downloaded
Table. Indicator monitoring file download item
- The download method can be selected simultaneously.
Export to Object Storage
You can store monitoring chart data in Object Storage.
User permission is required to store in Object Storage.
- User: {email}
- Action: iam:CreatGroup
- On resource: {SRN}
- Context: no identity-based policy allows the action
To store monitoring chart data in Object Storage, follow these steps.
- All Services > Management > ServiceWatch click the menu. 1. Go to the Service Home page.
- On the Service Home page, click the Metrics menu. 2. Go to the Indicator page.
- Select the metric to monitor from the metric list on the Metric page. 3. The monitoring chart for the selected metric is displayed in the Selected Metric area at the bottom.
- In the monitoring chart of the Selected metric area, after setting the table region, click the More > Export to Object Storage button. 4. Object Storage Export The popup window opens.
- After selecting the bucket to store the data, click the Done button. 5. A popup window notifying data saving opens.
- Click the Confirm button in the popup window. 6. Data export is starting.
- The limitations of metrics that can be exported to Object Stroage are as follows.
- Number of indicators: up to 10
- Query period: within 2 months (63 days)
- If the query period exceeds 2 months (63 days), only data for up to 63 days will be stored.
- If there is no Object Storage to store the metric data, create an Object Storage and then proceed.
- Metric data is stored in the “MetricName-yyyymmddhhmmss.json” file format and can be accessed in the ~/servicewatch/metric path of the Object Storage bucket.
View monitoring chart source
You can view the source code of the monitoring chart.
To view the source code of the monitoring chart, follow these steps.
- Click the All Services > Management > ServiceWatch menu. 1. Go to the Service Home page.
- On the Service Home page, click the Metrics menu. 2. Go to the Indicator page.
- Please select the metric to monitor from the metric list on the Metric page. 3. The monitoring chart for the selected metric is displayed in the Selected Metric area at the bottom.
- After setting the table area in the monitoring chart of the selected metric region, click the More > View Source button. 4. View Widget Source A popup window opens.
Category Detailed description Source information Display the source code of the monitoring chart in JSON format Copy code Copy the source code to the clipboard Table. Monitoring chart source view items
10.11.2.4 - Log
In ServiceWatch, you can set threshold criteria for the metrics you monitor, and when the specified conditions are met, you can create and manage log groups to generate alarm notifications.
Create Log Group
You can create a log group for the metric. To create a log group, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
Log Group List page, click the Create Log Group button. You will be taken to the Create Log Group page.
Enter the basic information and tag information required to create a log group.
Category Whether requiredDetailed description Log group name Required Enter the name of the log group to monitor in ServiceWatch - using English letters, numbers, and special characters (
-_./#) within 3 ~ 512 characters
Log retention policy Required Select the retention period for monitored log data Tag Select Add tag information - Up to 50 tags can be added per resource
- When adding a tag, entering the Key and Value allows selection from the list of previously created tag Keys and Values
Table. Log group creation items- using English letters, numbers, and special characters (
After reviewing the summary information, click the Create button. A popup notifying the creation of the log group will appear.
Click the Confirm button. Log group creation is complete.
Check log group details
You can view and manage detailed information about log groups.
To view detailed information about the log group, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
- On the Log Group List page, click the log group name to view detailed information. You will be taken to the Log Group Details page.
Category Detailed description Log group status Log group status - Active: The log group is in an active state
- Inactive: The log group is in an inactive state
Export Log Group Store log group log data in Object Storage - For detailed information on log group export, see Log Group Export
Delete log group Delete the corresponding log group Information Classification Tab Information tabs for log groups - Details, Log Streams, Tags, Activity History
- Click each tab to view the corresponding information
Table. Log Group DetailsReferenceOn the Log Group List page, click the More > Export Log Group button for the log group you want to store in Object Storage to export the data.
When sorting log group names in the log group list, follow the sorting rules below.
- Whitespace and control characters
- Some special characters (
!"#$%&’()*+,-./) - Numbers (
0–9) - Some special characters (
;<=>?@) - English (
A–Z,a–z, case-insensitive) - Remaining special characters (
[\]^_`) - Other characters
Detailed Information
Log Group List page allows you to view the basic information and details of the selected log group.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource name
|
| Resource ID | Unique resource ID in the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Log group name | Name of the log group |
| Log retention policy | Retention period of log data
|
| Log data | Total stored log data size (bytes) |
Log Stream
Log Group List page allows you to view the log streams of the selected log group.
| Category | Detailed description |
|---|---|
| View all streams | Detailed information for all log streams in the log stream list can be viewed
|
| Create log stream | Create a new log stream
|
| Log stream list | Log stream name and log modification timestamp
|
log pattern
Log Group List page allows you to view the log pattern of the selected log group.
| Category | Detailed description |
|---|---|
| Log pattern list | Log pattern name, pattern, log pattern namespace, metric name, alert policy name information
|
| Delete | Delete all selected log patterns from the log pattern list
|
| Generate log pattern | Create a new log pattern
|
tag
On the Log Group List page, you can view the tag information of the selected log group and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag’s Key and Value information |
| Edit tag | You can modify, delete, or add new tags to existing tag information
|
Job History
Log Group List page lets you view the operation history of the selected log group.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Log Streams
You can create and manage log streams.
Create Log Stream
You can create a new log stream in a log group. To create a Hog stream, follow the steps below.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
- On the Log Group List page, click the log group name for which you want to create a log stream. You will be taken to the Log Group Details page.
- Log Group Details page, click the Log Stream tab. The Log Stream list is displayed.
- Click the Create Log Stream button. The Create Log Stream popup opens.
- Enter the Log stream name, then click the Create button. Log stream creation is completed.
- Enter the name using English letters and numbers, within 3~512 characters.
Check detailed log stream information
You can view and manage detailed information about log streams. To view detailed information about the log stream, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
- Click the log group name on the Log Group List page to view detailed information. You will be taken to the Log Group Details page.
- On the Log Group Details page, click the Log Stream tab. The Log Stream list is displayed.
- Click the log stream name in the Log Stream list to view its details. You will be taken to the Log Stream Details page.
Category Detailed description Excel download Log stream history can be downloaded as an Excel file Timestamp list Message list by timestamp - Period selection, User time zone, can filter using message input
Table. Log group details - Log stream detail itemsReferenceWhen you click the View All Log Streams button at the top of the log stream list, you will be taken to the All Log Stream Details page.
Delete Log Stream
You can delete unused log streams. To delete a log stream, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
- On the Log Group List page, click the log group name whose log stream you want to delete. You will be taken to the Log Group Details page.
- Log Group Details page, click the Log Stream tab. The log stream list will be displayed.
- Select the checkbox of the log stream to delete in the log stream list, then click the More > Delete button. A popup notifying the log stream deletion will open.
- You can delete multiple log streams simultaneously.
- You can also delete each individually by clicking the Delete button at the right end of each log stream.
- Click the Confirm button. The log stream will be deleted.
Managing Log Patterns
Create Log Pattern
To create a log pattern, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
On the Log Group List page, click the log group name for which you want to create a log pattern. You will be taken to the Log Group Details page.
Log Group Details page, click the Log Pattern tab. The log pattern list will be displayed.
Click the Create Log Pattern button. You will be taken to the Create Log Pattern page.
Set the basic information and metric information required to create a log group.
- In the Basic Information area, enter and select the basic information for the log pattern.
Category RequiredDetailed description Log pattern name Required Enter the name of the log pattern - using English letters, numbers, and special characters (
-_./#) within 3 ~ 512 characters
Pattern format Required Select a pattern format or enter manually - Pattern format: Choose one of the string pattern, space-delimited pattern, or JSON format pattern provided as pattern formats
- Direct input: After selecting one of the string pattern, space-delimited pattern, or JSON format pattern, enter a value between 1 ~ 1,024
Pattern test Select Enter or select log data to verify using a pattern - Direct Input: Enter the log data to be used directly into the Log Event Message
- Separate log events using line breaks
- Up to 50 log events can be entered
- Each log event can be entered within 1 ~ 1,024 bytes
- Log Data Selection: Choose the log data to use
- When selecting log data, the corresponding log data is displayed in the Log Event Message
- Pattern Test: Conduct a test on the log event message
- If the test succeeds, the test result is displayed at the bottom
Table. Log Pattern Creation - Basic Information Items - using English letters, numbers, and special characters (
- Enter and select metric information in the Metric Information area.
Category Required statusDetailed description namespace Required Select a namespace for the log pattern - If there is no namespace for the log pattern, Create New to create one
- Namespace Name: When creating a new namespace, use English letters, numbers, spaces, and special characters(
-_\/#) to enter between 3 ~ 128 characters
Indicator Name Required Enter the name of the indicator - using English letters, numbers, and special characters(
_) within 3 ~ 128 characters
indicator value Required Enter the indicator value - a number greater than or equal to 0 or
$indetifier
default Select If you use the default value, enter - 0 or greater float value
- When using the default, dimension cannot be used
unit Required Select indicator unit dimension Selection Set the dimension of metrics generated by log patterns - Log pattern format is available only when it is a space-delimited pattern or a JSON format pattern
- Default value cannot be used when entered
- If Use is checked, you can add custom dimension fields
- After clicking the Add button, add by entering Field name and Field value
- You can add up to a maximum of 3
Table. Log pattern generation - metric information items
- In the Basic Information area, enter and select the basic information for the log pattern.
After reviewing the summary information, click the Create button. A popup indicating log pattern creation will appear.
Confirm click the button. Log pattern generation is complete.
Check detailed log pattern information
To view detailed information about the log pattern, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
- Click the log group name to view detailed information on the Log Group List page. You will be taken to the Log Group Details page.
- Log Group Details page, click the Log Pattern tab. The log pattern list will be displayed.
- Log pattern Click the log pattern name in the list to view its details. Log pattern details page will open.
Category Detailed description Create alert policy Alert policy creation available - When the button is clicked, navigate to the alert policy creation page
Delete log pattern Delete the log pattern currently being examined Log pattern name Log pattern name constructor User who created the log pattern Creation date and time Log pattern creation timestamp Editor User who modified the log pattern information Modification date Date and time the log pattern information was modified Pattern Pattern format Indicator Information Metric information of the pattern group - Namespace name, metric name, metric value, default value, unit, alarm policy name, dimension name
- Edit button allows modification of metric value, default value, unit information
Table. Log pattern detailed items
Delete log pattern
To delete a log pattern, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
- On the Log Group List page, click the log group name whose log pattern you want to delete. You will be taken to the Log Group Details page.
- On the Log Group Details page, click the Log Pattern tab. The log pattern list will be displayed.
- After selecting the checkbox of the log pattern to delete in the log pattern list, click the Delete button. A popup notifying the log pattern deletion will open.
- You can delete multiple log patterns simultaneously.
- You can also delete individually by clicking the More > Delete button at the far right of each log pattern, or by clicking the Delete Log Pattern button on the log pattern’s detail page.
- Click the Confirm button. The log pattern will be deleted.
Export Log Group
Log group data can be stored in Object Storage. To store log group data in Object Storage, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
On the Service Home page, click the Log > Log Group Export menu. You will be taken to the Log Group Export List page.
Log Group Export List page, click the Log Group Export button. You will be taken to the Log Group Export page.
Category RequiredDetailed description Select log group Required Select the log group to store in Object Storage - If the log group contains log streams, you can click the Select button to choose the log stream to store
- If no log group is selected, the entire data of the log group will be stored
Select period Select Select the user time zone and data storage interval - In the Time Settings area, you can select the desired interval or click the Enter Manually button to set the start and end date and time
storage bucket Required Select the bucket to store data - Up to 50 tags can be added per resource
- When adding a tag, entering the Key and Value allows you to select from the list of existing tag Keys and Values
Table. Log group export itemsAfter selecting the bucket to store the data, click the Complete button. A popup notifying that the data has been saved will open.
In the popup window, click the Confirm button. Data export will begin.
- You can view the progress on the Log Group Export List page.
- If there is no Object Storage to store the log group data, create an Object Storage and then proceed.
- Exporting log group data may take tens of minutes or more, depending on its size.
- If there is an ongoing log group export task within the Account, you must first complete the ongoing task before proceeding with the export.
- On the Log Group Export List page, you can cancel an export operation for a log group that is in progress by clicking the More > Cancel Log Group Export button.
Delete Log Group
You can delete unused log groups.
- Log Group Export does not delete files stored in Object Storage. However, the Log Group Export history is deleted together.
- If you delete a log group while log group export is in progress, the export operation will not complete successfully.
To delete a log group, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Log > Log Group menu. You will be taken to the Log Group List page.
- On the Log Group List page, select the checkbox of the log group you want to delete, then click the Delete button. A popup notifying the log group deletion will appear.
- You can delete multiple log groups simultaneously.
- You can delete individually by clicking the Delete button at the far right of each log group, or by clicking the Delete Log Group button on the Log Group Details page.
- Click the Confirm button. The log group will be deleted.
10.11.2.5 - Event
You can view and handle events generated by the Samsung Cloud Platform service in ServiceWatch.
Create Event Rule
You can create an event rule to receive notifications when an event occurs. To create an event rule, follow these steps.
Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
On the Service Home page, click the Event Rules menu. You will be taken to the Event Rules List page.
Event Rule List page, click the Create Event Rule button. You will be taken to the Create Event Rule page.
Enter the name and description of the event rule in the Basic Information Input area.
Set the required information in the Event Pattern Configuration area. The configured event pattern is entered in Event Pattern Configuration Status as JSON code.
Category Required statusDetailed description Event source Required Select the service name of the event you want to receive in ServiceWatch - Refer to the event source list Event Source
Event type Required Select the event type of the event source to use in the event rule - Classify the same as the resource type
Apply Event Required Select events to apply the event pattern from events generated by the event type - All events: Apply all events generated by the event type
- Individual events: Choose events from those generated by the event type to set as the event pattern
Applied resource Required Select the resource to apply the event pattern - All resources: Set the event pattern for events that occur in all resources
- Individual resource: Set the event pattern for the specific event that occurs in a particular resource
- When an individual resource is selected, display the event resource selection area
- Add resource button can be clicked to select resources
- Added resources can be removed by selecting the resource in the resource list and clicking the Delete button
Event Pattern Configuration Status - Convert and display in JSON code format according to the event pattern settings - Changing the event pattern settings will reset
- Copy code item can be clicked to copy the source code
Table. Event pattern configuration itemsIn the Notification Settings area, select the users who will receive notifications when an event occurs.
- Only users with a login history (users who have registered an email or mobile phone number) can be added as notification recipients.
- You can add up to 100 notification recipients.
- If there is no user to add, you can create a user on the User Creation page of the IAM service. For more details on creating users, see Create User.
- The notification delivery method (E-mail or SMS) can be changed on the Notification Settings page after selecting the notification target as Service > Event Rule. For detailed information about notification settings, refer to 알림 설정 확인하기.
- Add tag information in the Additional Information Input area.
- After checking the summary information, click the Create button. A popup notifying the creation of an event rule will open.
- Click the Confirm button. Event rule creation is complete.
Check detailed event rule information
You can view and manage detailed information about event rules. Follow the steps below to view detailed information about the event rules.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Event Rules menu. You will be taken to the Event Rules List page.
- Event Rules List page, click the event name to view detailed information. You will be taken to the Event Rules Detail page.
Category Detailed description Event rule status Event rule status - Active: The event rule is in an active state
- Inactive: The event rule is in an inactive state
- You can change it by clicking the Activate or Deactivate button
Delete event rule Delete the corresponding event rule Information Category Tab Information tabs for alert policies - Details, notifications, tags, activity history
- Click each tab to view the corresponding information.
Table. Event rule details
Detailed Information
Event Rule List page lets you view the basic information and event rule details of the selected rule.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Editor | User who edited the service information |
| Modification date and time | Date and time the service information was modified |
| Event rule name | Event rule name |
| Event Pattern Configuration Status | Display event pattern settings in JSON code format
|
| description | Description of event rules
|
Notification
Event Rule List page allows you to view the notification recipients of the selected event rule.
| Category | Detailed description |
|---|---|
| Notification recipient list | User ID, creation date and time, last login, status information
|
| Delete | Delete all selected users from the notification recipient list
|
| More | Change the notification status (enable/disable) for the selected user in the notification recipient list
|
| Add notification recipient | Ability to add new notification recipients
|
- Only users with a login history (users who have registered an email or mobile phone number) can be added as notification recipients.
- You can add up to 100 notification recipients.
- If there is no user to add, you can create a user on the IAM service’s User Creation page. For detailed information on creating users, refer to Create User.
- The notification reception method (E-mail or SMS) can be changed on the Notification Settings page after selecting the notification target as Service > Event Rule. For detailed information about notification settings, refer to 알림 설정 확인하기.
tag
Event Rules page allows you to view the tag information of the selected event rule, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag’s Key and Value information |
| Edit tag | You can modify or delete existing tag information, or add new tags
|
Job History
You can view the operation history of the event rule selected on the Alert Policy List page.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Modify event pattern
You can modify the event pattern. To modify the event pattern, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Event Rules menu. You will be taken to the Event Rules List page.
- Event Rule List page, click the event name to edit the event pattern. You will be taken to the Event Rule Details page.
- Click the Edit button in the Event Pattern Configuration Status on the Event Rule Details page. The Edit Event Pattern popup opens.
- After modifying the event pattern settings, click the Confirm button. A popup notifying the event pattern modification will appear.
- For detailed information on the event pattern modification items, refer to Creating Event Rules.
- Click the Confirm button. The event pattern modification is complete.
Delete Event Rule
You can delete unused event rules. To delete an event rule, follow these steps.
- Click the All Services > Management > ServiceWatch menu. You will be taken to the Service Home page.
- On the Service Home page, click the Event Rules menu. You will be taken to the Event Rules List page.
- On the Event Rule List page, select the checkbox of the event rule you want to delete, then click the Delete button. A popup notifying the deletion of the event rule will appear.
- You can delete multiple event rules simultaneously.
- You can also delete individually by clicking the More > Delete button at the far right of each alert policy, or by clicking the Delete Event Rule button on the Event Rule Details page.
- Click the Confirm button. The event rule will be deleted.
10.11.2.6 - Using ServiceWatch Agent
Users can install the ServiceWatch Agent on Virtual Server/GPU Server/Bare Metal Server, etc., to collect custom metrics and logs.
ServiceWatch Agent
The agents that need to be installed on the server to collect custom metrics and logs for ServiceWatch can be divided into two main types. It is a Prometheus Exporter and Open Telemetry Collector.
| Category | Detailed description | |
|---|---|---|
| Prometheus Exporter | Provide metrics of a specific application or service in a format that Prometheus can scrape
| |
| Open Telemetry Collector | Acts as a centralized collector that gathers telemetry data such as metrics and logs from distributed systems, processes (filtering, sampling, etc.) it, and exports it to various backends (e.g., Prometheus, Jaeger, Elasticsearch, etc.)
|
To link a server’s log files to ServiceWatch via the ServiceWatch Agent, you must first create a log group and a log stream within that log group.
- For detailed information on creating log groups and log streams, refer to the 로그.
Pre-configuration for ServiceWatch Agent
You need to add a Security Group and firewall rules to enable communication between the ServiceWatch Agent and ServiceWatch.
Add Security Group rule
- To transmit the data collected by ServiceWatch from the ServiceWatch Agent installed on Virtual Server/GPU Server to ServiceWatch, you need to add a rule to the Security Group as follows.
Direction type Port Target address Outbound Custom TCP 443 ServiceWatch OpenAPI Endpoint IP Address Table. Security Group rules for ServiceWatch Agent communication
- To transmit the data collected by ServiceWatch from the ServiceWatch Agent installed on Virtual Server/GPU Server to ServiceWatch, you need to add a rule to the Security Group as follows.
Add firewall rule
- If you configure the VPC’s Internet Gateway to use a firewall, you must add firewall rules as shown below.
Direction type Port Operation Source address Destination address Outbound TCP 443 Allow When creating a Virtual Server, the assigned Private IP address. The Virtual Server Private IP address can be found in Check Virtual Server Details. ServiceWatch OpenAPI Endpoint IP Address Table. Internet Gateway firewall rules for ServiceWatch Agent communication
- If you configure the VPC’s Internet Gateway to use a firewall, you must add firewall rules as shown below.
ServiceWatch OpenAPI Endpoint IP address
The Endpoint IP address required for the ServiceWatch Agent to send the data collected to ServiceWatch is as follows.
| Offering | Region | URL | IP address |
|---|---|---|---|
| For Enterprise | kr-west1 | https://servicewatch.kr-west1.e.samsungsdscloud.com | 112.107.105.24 |
| For Enterprise | kr-east1 | https://servicewatch.kr-east1.e.samsungsdscloud.com | 112.107.105.68 |
Open Telemetry Collector configuration for ServiceWatch
Install the OpenTelemetry Collector on the server following the steps below to collect ServiceWatch metrics and logs.
- Download the Agent file from the URL that provides the Agent file for ServiceWatch.
Also, you can verify it using ServiceWatch’s ShowAgentDownloadLink API. For more information, see the ServiceWatch API Reference.
wget [ServiceWatch Agent file download URL]wget [ServiceWatch Agent file download URL]- The Open Telemetry Collector Agent file for ServiceWatch can be found as follows.
- Extract the Agent file for ServiceWatch.Color mode
unzip ServiceWatch_Agent.zipunzip ServiceWatch_Agent.zipCode block. Extract the Agent file for ServiceWatch - When using the ServiceWatch Agent on a Linux OS, you must grant execution permission as shown below.Color mode
chmod +x agent/otelcontribcol_linux_amd64 chmod +x agent/servicewatch-agent-manager-linux-amd64chmod +x agent/otelcontribcol_linux_amd64 chmod +x agent/servicewatch-agent-manager-linux-amd64Code block. Grant execution permission to the Agent file for ServiceWatch Category Detailed description examples Example configuration file folder. Each folder contains agent.json,log.json,metric.jsonexample filesos-metrics-min-examples: Minimal metric configuration example using Node Exporter
os-metrics-all-examples: Example of memory/filesystem Collector metric configuration using Node Exporter
gpu-metrics-min-examples: Minimal metric configuration example using DCGM Exporter
gpu-metrics-all-examples: Example of major metric configuration using DCGM Exporter
otelcontribcol_linux_amd64 Open Telemetry Collector for Linux for ServiceWatch otelcontribcol_windows_amd64.exe Open Telemetry Collector for Windows for ServiceWatch servicewatch-agent-manager-linux-amd64 ServiceWatch Agent Manager for Linux servicewatch-agent-manager-windows-amd64.exe ServiceWatch Agent Manager for Windows Table. Agent file configuration for ServiceWatch
- Extract the Agent file for ServiceWatch.
Define the Agent configuration file in ServiceWatch Agent Manager for the ServiceWatch Open Telemetry Collector.
Category Detailed description namespace Custom namespace for custom metrics - A namespace is a logical separation used to distinguish and group metrics, designated as a custom metric for separating custom metrics
- A namespace must be 3 to 128 characters long, may include letters, numbers, spaces, and special characters (
-_/), and must start with a letter.
accessKey IAM authentication key Access Key accessSecret IAM authentication key Secret Key resourceId Resource ID of the server on Samsung Cloud Platform - Example: Resource ID of a Virtual Server
openApiEndpoint ServiceWatch OpenAPI endpoint per region/offering - Example: https://servicewatch.
region.offering.samsungsdscloud.com
regionandofferinginformation can be found in the Samsung Cloud Platform Console access URL
telemetryPort ServiceWatch Agent’s Telemetry Port - is typically used on port 8888. If port 8888 is in use, it needs to be changed
Table. agent.json configuration file entriesColor mode{ "namespace": "swagent-windows", # Custom namespace for user-defined metrics "accessKey": "testKey", # IAM authentication key Access Key "accessSecret": "testSecret", # IAM authentication key Secret Key "resourceId": "resourceID", # Resource ID on the server's Samsung Cloud Platform "openApiEndpoint": "https://servicewatch.kr-west1.e.samsungsdscloud.com", # Region/Environment-specific ServiceWatch OpenAPI Endpoint "telemetryPort": 8889 # ServiceWatch Agent's Telemetry Port (usually uses port 8888. If port 8888 is in use, change it) }{ "namespace": "swagent-windows", # Custom namespace for user-defined metrics "accessKey": "testKey", # IAM authentication key Access Key "accessSecret": "testSecret", # IAM authentication key Secret Key "resourceId": "resourceID", # Resource ID on the server's Samsung Cloud Platform "openApiEndpoint": "https://servicewatch.kr-west1.e.samsungsdscloud.com", # Region/Environment-specific ServiceWatch OpenAPI Endpoint "telemetryPort": 8889 # ServiceWatch Agent's Telemetry Port (usually uses port 8888. If port 8888 is in use, change it) }Code block. Example of agent.json configuration Defines the metric configuration file for collecting metrics for ServiceWatch.
- If you want to collect metrics through the Agent, set up metric.json.
Category Detailed description prometheus > scrape_configs > targets Endpoint of the metric collection target - For servers, because the Prometheus Exporter is installed on the same machine, set it to that endpoint
- Example: localhost:9100
prometheus > scrape_configs > jobName Set the Job Name. Usually set it to the type of Prometheus Exporter used for metric collection - Example: node-exporter
metricMetas > metricName Set the name of the metric to be collected. The metric name must be 3 to 128 characters long, include letters, numbers, and special characters ( _), and start with a letter.- Example: node_cpu_seconds_total
metricMetas > dimensions Set the label of the Collector, among those provided to identify the source of the Exporter’s metric data, for visualization in the Console. When visualizing the collected metrics in the Console, combine them according to the dimensions setting. - Example: For metrics like the Memory Collector of Node Exporter that do not provide a special label, set it to resource_id.
- Example: The Filesystem Collector metrics of Node Exporter can have the mountpoint, which represents the path where the filesystem is mounted on the system, set as a dimension.
metricMetas > unit Metric unit can be set - Example: Bytes, Count, etc.
metricMetas > aggregationMethod Method to aggregate based on specified dimensions(dimensions) - Example: select from SUM, MAX, MIN, COUNT
metricMetas > descriptionKo Korean description of the metrics being collected metricMetas > descriptionEn English description of the metrics being collected Table. metric.json configuration file entriesColor mode{ "prometheus": { "scrape_configs": { "targets": [ "localhost:9100" # Endpoint of the Prometheus Exporter installed on the server ], "jobName": "node-exporter" # Usually set to the name of the installed Exporter } }, "metricMetas": [ { "metricName": "node_memory_MemTotal_bytes", # Set the metric name to be linked with ServiceWatch among the metrics collected from the Prometheus Exporter "dimensions": [ [ "resource_id" # Set the label used for visualizing in the Console among the Collector's labels provided to identify the source of Node Exporter's metric data # If no specific label is provided, such as for the Memory-related metric, set it to **resource_id**. ] ], "unit": "Bytes", # unit of the collected metric data "aggregationMethod": "SUM", # aggregation method "descriptionKo": "Total physical memory size of the server", # Korean description of the metric "descriptionEn": "node memory total bytes" # English description of the metric }, { "metricName": "node_filesystem_size_bytes", # Set the metric name to be linked with ServiceWatch among the metrics collected from the Prometheus Exporter "dimensions": [ [ "mountpoint" # Set the label for visualizing in the Console among the Collector labels provided to identify the source of Node Exporter's metric data. # Set the dimension (dimensions) of the Filesystem-related metric to the mountpoint, which indicates the path where the filesystem is mounted on the system. ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "node filesystem size bytes" "descriptionEn": "node filesystem size bytes" }, { "metricName": "node_memory_MemAvailable_bytes" "dimensions": [ [ resource_id ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "node memory available bytes" "descriptionEn": "node memory available bytes" }, { "metricName": "node_filesystem_avail_bytes" "dimensions": [ [ mountpoint ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "node filesystem available bytes" "descriptionEn": "node filesystem available bytes" } ] }{ "prometheus": { "scrape_configs": { "targets": [ "localhost:9100" # Endpoint of the Prometheus Exporter installed on the server ], "jobName": "node-exporter" # Usually set to the name of the installed Exporter } }, "metricMetas": [ { "metricName": "node_memory_MemTotal_bytes", # Set the metric name to be linked with ServiceWatch among the metrics collected from the Prometheus Exporter "dimensions": [ [ "resource_id" # Set the label used for visualizing in the Console among the Collector's labels provided to identify the source of Node Exporter's metric data # If no specific label is provided, such as for the Memory-related metric, set it to **resource_id**. ] ], "unit": "Bytes", # unit of the collected metric data "aggregationMethod": "SUM", # aggregation method "descriptionKo": "Total physical memory size of the server", # Korean description of the metric "descriptionEn": "node memory total bytes" # English description of the metric }, { "metricName": "node_filesystem_size_bytes", # Set the metric name to be linked with ServiceWatch among the metrics collected from the Prometheus Exporter "dimensions": [ [ "mountpoint" # Set the label for visualizing in the Console among the Collector labels provided to identify the source of Node Exporter's metric data. # Set the dimension (dimensions) of the Filesystem-related metric to the mountpoint, which indicates the path where the filesystem is mounted on the system. ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "node filesystem size bytes" "descriptionEn": "node filesystem size bytes" }, { "metricName": "node_memory_MemAvailable_bytes" "dimensions": [ [ resource_id ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "node memory available bytes" "descriptionEn": "node memory available bytes" }, { "metricName": "node_filesystem_avail_bytes" "dimensions": [ [ mountpoint ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "node filesystem available bytes" "descriptionEn": "node filesystem available bytes" } ] }Code block. metric.json configuration example - To display the resource name, set resource_name in commonLabels as shown below, and also set resource_name in metricMetas.dimensions; then ServiceWatch can retrieve the metric along with the resource name.Color mode
"commonLabels": { "resource_name": "ResourceName" # Resource name visible in the User Console }, "metricMetas": [ { "metricName": "metric_name" "dimensions": [ [ "resource_id" "resource_name" # Add the resource_name set in commonLabels to the dimensions of each metric ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "metric_name description" "descriptionEn": "metric_name description" }, ... ]"commonLabels": { "resource_name": "ResourceName" # Resource name visible in the User Console }, "metricMetas": [ { "metricName": "metric_name" "dimensions": [ [ "resource_id" "resource_name" # Add the resource_name set in commonLabels to the dimensions of each metric ] ], "unit": "Bytes" "aggregationMethod": "SUM" "descriptionKo": "metric_name description" "descriptionEn": "metric_name description" }, ... ]Code block. metric.json - Resource name setting
- If you want to collect metrics through the Agent, set up metric.json.
Defines the log configuration file for collecting logs for ServiceWatch.
- If you want to collect logs, you must configure log.json.
Category Detailed description fileLog > include Location of log files to collect fileLog > operators Definition for parsing log messages to be collected fileLog > operators > regex Express the log message format as a regular expression fileLog > operators > timestamp The format of the Time Stamp of log messages to be sent to ServiceWatch logMetas > log_group_value Log group name created for sending logs to ServiceWatch logMetas > log_stream_value Log stream name in ServiceWatch log group Table. log.json configuration file entriesColor mode{ "fileLog": { "include": [ "/var/log/syslog", # Log file to be collected by ServiceWatch /var/log/auth.log ], "operators": { "regex": "^(?P<timestamp>\\S+)\\s+(?P<hostname>\\S+)\\s+(?P<process>[^:]+):\\s+(?P<message>.*)$", # Represent log file format with a regular expression "timestamp": { # Set the format of the log message's Time Stamp "layout_type": "gotime" "layout": "2006-01-02T15:04:05.000000Z07:00" } } }, "logMetas": { "log_group_value": "custom-log-group", # Log group name of ServiceWatch created in advance "log_stream_value": "custom-log-stream" # Log stream name within the pre‑created ServiceWatch log group } }{ "fileLog": { "include": [ "/var/log/syslog", # Log file to be collected by ServiceWatch /var/log/auth.log ], "operators": { "regex": "^(?P<timestamp>\\S+)\\s+(?P<hostname>\\S+)\\s+(?P<process>[^:]+):\\s+(?P<message>.*)$", # Represent log file format with a regular expression "timestamp": { # Set the format of the log message's Time Stamp "layout_type": "gotime" "layout": "2006-01-02T15:04:05.000000Z07:00" } } }, "logMetas": { "log_group_value": "custom-log-group", # Log group name of ServiceWatch created in advance "log_stream_value": "custom-log-stream" # Log stream name within the pre‑created ServiceWatch log group } }Code block. log.json configuration example
- If you want to collect logs, you must configure log.json.
To link a server’s log files to ServiceWatch via the ServiceWatch Agent, you must first create a log group and a log stream within that log group.
- For detailed information on creating log groups and log streams, refer to Log.
Running Open Telemetry Collector for ServiceWatch
| Execution options | Detailed description |
|---|---|
-action | Action setting (run or stop) |
-dir | the location of ServiceWatch Agent configuration files such as agent.json, metric.json, log.json |
-collector | Open Telemetry Collector executable file location |
ServiceWatch Agent execution (for Linux)
agent.json, metric.json, log.json files are in current location/agent/examples/os-metrics-min-examples, and the otelcontribcol_linux_amd64 file is in current location/agent. Execute as shown below.Run the ServiceWatch Agent.
- Check the locations of
agent.json,metric.json,log.jsonfiles and the locations ofservicewatch-agent-manager-linux-amd64,otelcontribcol_linux_amd64files, and start the ServiceWatch Agent.Color mode./agent/servicewatch-agent-manager-linux-amd64 -action run -dir ./agent/examples/os-metrics-min-examples -collector ./agent/otelcontribcol_linux_amd64./agent/servicewatch-agent-manager-linux-amd64 -action run -dir ./agent/examples/os-metrics-min-examples -collector ./agent/otelcontribcol_linux_amd64Code block. ServiceWatch Agent start - collect all metrics/logs - If you only want to collect metrics, rename the
log.jsonfile to a different name or move it so that it is not in the same directory asagent.json,metric.json, and then run as shown below.Color mode./agent/servicewatch-agent-manager-linux-amd64 -action run -dir ./agent/examples/os-metrics-min-examples -collector ./agent/otelcontribcol_linux_amd64./agent/servicewatch-agent-manager-linux-amd64 -action run -dir ./agent/examples/os-metrics-min-examples -collector ./agent/otelcontribcol_linux_amd64Code block. ServiceWatch Agent start - collect metrics only - If you only want to collect logs, rename the
metric.jsonfile to a different name or move it so that it is not in the same directory asagent.json,log.json, and run as shown below.Color mode./agent/servicewatch-agent-manager-linux-amd64 -action run -dir ./agent/examples/os-metrics-min-examples -collector ./agent/otelcontribcol_linux_amd64./agent/servicewatch-agent-manager-linux-amd64 -action run -dir ./agent/examples/os-metrics-min-examples -collector ./agent/otelcontribcol_linux_amd64Code block. ServiceWatch Agent start - collect logs only
- Check the locations of
Stop the ServiceWatch Agent.
Color mode./agent/servicewatch-agent-manager-linux-amd64 -action stop -dir ./agent/examples/os-metrics-min-examples./agent/servicewatch-agent-manager-linux-amd64 -action stop -dir ./agent/examples/os-metrics-min-examplescode block. Stop ServiceWatch Agent
Running ServiceWatch Agent (for Windows)
Run the ServiceWatch Agent.
Color modeservicewatch-agent-manager-windows-amd64.exe -action run -dir ./examples -collector otelcontribcol_windows_amd64.exeservicewatch-agent-manager-windows-amd64.exe -action run -dir ./examples -collector otelcontribcol_windows_amd64.execode block. Start ServiceWatch Agent Stop the ServiceWatch Agent.
Color modeservicewatch-agent-manager-windows-amd64.exe -action stop -dir ./examplesservicewatch-agent-manager-windows-amd64.exe -action stop -dir ./examplescode block. Stop ServiceWatch Agent
10.11.3 - API Reference
10.11.4 - CLI Reference
10.11.5 - ServiceWatch Event Reference
Events represent changes in the environment in the Samsung Cloud Platform service. Below are examples of events.
- Generates an event when the status of a Virtual Server changes from Stopped to Running.
- Generates an event when a new bucket is created in Object Storage.
- Generates an event when an IAM user is removed from a user group.
10.11.5.1 - ServiceWatch Event
| Service Category | Service | Event source |
|---|---|---|
| Compute | Virtual Server | Virtual Server |
| Compute | GPU Server | GPU Server |
| Compute | Bare Metal Server | Bare Metal Server |
| Compute | Multi-node GPU Cluster | Multi-node GPU Cluster |
| Compute | Cloud Functions | Cloud Functions |
| Storage | Block Storage(BM) | Block Storage(BM) |
| Storage | File Storage | fiFile Storagelestorage |
| Storage | Object Storage | Object Storage |
| Storage | Archive Storage | Archive Storage |
| Storage | Backup | Backup |
| Container | Kubernetes Engine | Kubernetes Engine |
| Container | Container Registry | Container Registry |
| Networking | VPC | VPC |
| Networking | Security Group | Security Group |
| Networking | Load Balancer | Load Balancer |
| Networking | DNS | Private DNS Hosted Zone Public Domain Name |
| Networking | VPN | VPN |
| Networking | Firewall | Firewall |
| Networking | Direct Connect | Direct Connect |
| Networking | Cloud LAN-Campus | Cloud LAN - Campus (Network) |
| Networking | Cloud LAN-Datacenter | Cloud LAN Network |
| Networking | Cloud WAN | Cloud WAN |
| Networking | Global CDN | Global CDN |
| Networking | GSLB | GSLB |
| Database | EPAS(DBaaS) | EPAS |
| Database | PostreSQL(DBaaS) | PostreSQL |
| Database | MariaDB(DBaaS) | MariaDB |
| Database | MySQL(DBaaS) | MySQL |
| Database | Microsoft SQL Server(DBaaS) | Microsoft SQL Server |
| Database | CacheStore(DBaaS) | CacheStore |
| Database | Scalable DB(DBaaS) | Scalable DB |
| Data Analytics | Event Streams | Event Streams |
| Data Analytics | Search Engine | Search Engine |
| Data Analytics | Vertica(DBaaS) | Vertica |
| Data Analytics | Data Flow | Data Flow |
| Data Analytics | Data Ops | Data Ops |
| Data Analytics | Quick Query | Quick Query |
| Application Service | API Gateway | API Gateway |
| Application Service | Queue Service | Queue |
| Security | Key Management Service | Key Management Service |
| Security | Config Inspection | Config Inspection |
| Security | Certificate Manager | Certificate Manager |
| Security | Secrets Manager | Secret |
| Security | Secret Vault | Secret Vault |
| Management | Cloud Control | Cloud Control |
| Management | IAM | Identity and Access Management |
| Management | ID Center | Identity Center |
| Management | Logging&Audit | Logging&Audit |
| Management | Organization | Organization |
| Management | Resource Groups | Resource Group |
| Management | ServiceWatch | ServiceWatch |
| Management | Support Center | Support |
| AI-ML | CloudML | Cloud ML |
| AI-ML | AI&MLOps Platform | AI&MLOps Platform |
10.11.5.1.1 - Multi-node GPU Cluster
Multi-node GPU Cluster event
This is the list of events that the Multi-node GPU Cluster service sends to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Compute | Multi-node GPU Cluster | GPU Node | Multi-node GPU Cluster | GPU Node |
| Compute | Multi-node GPU Cluster | Cluster Fabric | Multi-node GPU Cluster | Cluster Fabric |
GPU Node
| Event source | Event type | Event |
|---|---|---|
| Multi-node GPU Cluster | GPU Node |
|
Cluster Fabric
| Event source | Event type | event |
|---|---|---|
| Multi-node GPU Cluster | Cluster Fabric |
|
10.11.5.1.2 - MySQL(DBaaS)
MySQL(DBaaS) event
This is the list of events that the MySQL (DBaaS) service sends to ServiceWatch.
| Service Category | service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Database | MySQL(DBaaS) | MySQL(DBaaS) | MySQL | MySQL |
MySQL
| Event source | Event type | event |
|---|---|---|
| MySQL | MySQL |
|
10.11.5.1.3 - Global CDN
Global CDN event
This is the list of events delivered from the Global CDN service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Global CDN | Global CDN | Global CDN | Global CDN |
Global CDN
| Event source | Event type | event |
|---|---|---|
| Global CDN | Global CDN |
|
10.11.5.1.4 - Data Flow
Data Flow event
This is the list of events delivered from the Data Flow service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Data Flow | Data Flow | Data Flow | Data Flow |
| Data Analytics | Data Flow | Data Flow Services | Data Flow | Data Flow Service |
Data Flow
| Event source | Event type | event |
|---|---|---|
| Data Flow | Data Flow |
|
Data Flow Service
| Event source | Event type | event |
|---|---|---|
| Data Flow Services | Data Flow Service |
|
10.11.5.1.5 - GSLB
GSLB event
This is the list of events that the GSLB service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | GSLB | GSLB | GSLB | GSLB |
GSLB
| Event source | Event type | event |
|---|---|---|
| GSLB | GSLB(cdn) |
|
10.11.5.1.6 - Cloud Control
Cloud Control event
This is the list of events delivered from the Cloud Control service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | Cloud Control | Cloud Control | Cloud Control | Cloud Control |
Landing Zone
| Event source | Event type | event |
|---|---|---|
| Cloud Control | Landing zone |
|
10.11.5.1.7 - Cloud WAN
Cloud WAN event
This is the list of events delivered from the Cloud WAN service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Cloud WAN | Cloud WAN Network | Cloud WAN | Network(WAN) |
| Networking | Cloud WAN | Segment | Cloud WAN | Segment |
| Networking | Cloud WAN | Segment | Cloud WAN | Segment Location |
| Networking | Cloud WAN | Segment | Cloud WAN | Segment Sharing |
| Networking | Cloud WAN | Attachment | Cloud WAN | Attachment |
Network(WAN)
| Event source | Event type | event |
|---|---|---|
| Cloud WAN | Network(WAN) |
|
Segment
| Event source | Event type | event |
|---|---|---|
| Cloud WAN | Segment |
|
Segment Location
| Event source | Event type | Event |
|---|---|---|
| Cloud WAN | Segment Location |
|
Segment Sharing
| Event source | Event type | event |
|---|---|---|
| Cloud WAN | Segment Sharing |
|
Attachment
| Event source | Event type | Event |
|---|---|---|
| Cloud WAN | Attachment |
|
10.11.5.1.8 - Object Storage
Object Storage event
This is the list of events delivered from the Object Storage service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Storage | Object Storage | Object Storage | Object Storage | Bucket |
Bucket
| Event source | Event type | event |
|---|---|---|
| Object Storage | Bucket |
|
10.11.5.1.9 - VPC
VPC event
This is the list of events that the VPC service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | VPC | VPC | VPC | VPC |
| Networking | VPC | Subnet | VPC | Subnet |
| Networking | VPC | Port | VPC | Port |
| Networking | VPC | Internet Gateway | VPC | Internet Gateway |
| Networking | VPC | NAT Gateway | VPC | NAT Gateway |
| Networking | VPC | Public IP | VPC | Public IP |
| Networking | VPC | Private NAT | VPC | Private NAT |
| Networking | VPC | VPC Endpoint | VPC | VPC Endpoint |
| Networking | VPC | VPC Peering | VPC | VPC Peering |
| Networking | VPC | Private Link Service | VPC | Private Link Service |
| Networking | VPC | Private Link Endpoint | VPC | Private Link Endpoint |
| Networking | VPC | Transit Gateway | VPC | Transit Gateway |
VPC
| Event source | Event type | event |
|---|---|---|
| VPC | VPC |
|
Subnet
| Event source | Event type | event |
|---|---|---|
| VPC | Subnet |
|
Port
| Event source | Event type | event |
|---|---|---|
| VPC | Port |
|
Internet Gateway
| Event source | Event type | Event |
|---|---|---|
| VPC | Internet Gateway |
|
NAT Gateway
| Event source | Event type | event |
|---|---|---|
| VPC | NAT Gateway |
|
Public IP
| Event source | Event type | Event |
|---|---|---|
| VPC | Public IP |
|
Private NAT
| Event source | Event type | event |
|---|---|---|
| VPC | Private NAT |
|
VPC Endpoint
| Event source | Event type | event |
|---|---|---|
| VPC | VPC Endpoint |
|
VPC Peering
| Event source | Event type | event |
|---|---|---|
| VPC | VPC Peering |
|
Private Link Service
| Event source | Event type | event |
|---|---|---|
| VPC | Private Link Service |
|
Private Link Endpoint
| Event source | Event type | event |
|---|---|---|
| VPC | PrivateLink Endpoint |
|
Transit Gateway
| Event source | Event type | event |
|---|---|---|
| VPC | Transit Gateway |
|
10.11.5.1.10 - GPU Server
GPU Server Event
This is the list of events that the GPU Server service passes to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Compute | GPU Server | GPU Server | GPU Server | Server |
| Compute | GPU Server | Image | GPU Server |
Server
| Service | Event type | event |
|---|---|---|
| GPU Server | Server(server) |
|
Image
| Service | Event type | Event |
|---|---|---|
| GPU Server | Image |
|
10.11.5.1.11 - Virtual Server
Virtual Server event
This is the list of events that the Virtual Server service passes to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Compute | Virtual Server | Virtual Server | Virtual Server | Server |
| Compute | Virtual Server | Image | Virtual Server | Image |
| Compute | Virtual Server | Keypair | Virtual Server | Keypair |
| Compute | Vitual Server | Server Group | Virtual Server | Server Group |
| Compute | Virtual Server | Launch Configuration | Virtual Server | Launch Configuration |
| Compute | Virtual Server | Auto-Scaling Group | Virtual Server | Auto-Scaling Group |
| Compute | Virtual Server | Block Storage | Virtual Server | Volume |
| Compute | Virtual Server | Block Storage | Virtual Server | Snapshot |
Server
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Server |
|
Image
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Image |
|
Keypair
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Keypair |
|
Server Group
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Server Group |
|
Launch Configuration
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Launch Configuration |
|
Auto-Scaling Group
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Auto-Scaling Group |
|
Volume
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Volume |
|
Snapshot
| Event source | Event type | event |
|---|---|---|
| Virtual Server | Snapshot |
|
10.11.5.1.12 - Firewall
Firewall event
This is the list of events that the Firewall service passes to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Firewall | firewall | Firewall | Firewall |
Firewall
| Event source | Event type | event |
|---|---|---|
| Firewall | Firewall |
|
10.11.5.1.13 - ID Center
ID Center Event
This is the list of events that the ID Center service sends to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | ID Center | ID Center | Identity Center | ID Center |
| Management | ID Center | Permission set | Identity Center | Permission Set |
ID Center
| Event source | Event type | event |
|---|---|---|
| Identity Center | ID Center |
|
Permission Set
| Event source | Event type | event |
|---|---|---|
| Identity Center | Permission set |
|
10.11.5.1.14 - Microsoft SQL Server(DBaaS)
Microsoft SQL Server(DBaaS) Event
This is the list of events that the Microsoft SQL Server (DBaaS) service sends to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Database | Microsoft SQL Server(DBaaS) | Microsoft SQL Server(DBaaS) | Microsoft SQL Server | Microsoft SQL Server |
Microsoft SQL Server
| Event source | Event type | Event |
|---|---|---|
| Microsoft SQL Server | Microsoft SQL Server |
|
10.11.5.1.15 - Block Storage(BM)
Block Storage(BM) Event
List of events sent from the Block Storage (BM) service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Storage | Block Storage(BM) | Block Storage(BM) | Block Storage(BM) | Volume |
| Storage | Block Storage(BM) | Volume Group(BM) | Block Storage(BM) | Volume Group |
Volume
| Event source | Event type | event |
|---|---|---|
| Block Storage(BM) | Volume |
|
Volume Group
| Event source | Event type | event |
|---|---|---|
| Volume Group(BM) | Volume Group |
|
10.11.5.1.16 - Resource Groups
Resource Groups event
This is the list of events that the Resource Groups service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | Resource Groups | Resource Groups | Resource Groups | Resource Group |
Resource Group
| Event source | Event type | event |
|---|---|---|
| Resource Groups | Resource Group |
|
10.11.5.1.17 - Cloud Functions
Cloud Functions event
This is a list of events delivered from the Cloud Functions service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Compute | Cloud Functions | Function | Cloud Functions | Cloud Functions |
Cloud Functions
| Event source | Event type | event |
|---|---|---|
| Cloud Functions | Cloud Functions |
|
10.11.5.1.18 - AI&MLOps Platform
AI&MLOps Platform event
This is the list of events delivered from the AI&MLOps Platform service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| AI-ML | AI&MLOps Platform | AI&MLOps Platform | AI&MLOps Platform | AI&MLOps Platform |
AI&MLOps Platform
| Event source | Event type | event |
|---|---|---|
| AI&MLOps Platform | AI&MLOps Platform |
|
10.11.5.1.19 - Event Streams
Event Streams event
This is the list of events delivered from the Event Streams service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Event Streams | Event Streams | Event Streams | Event Streams |
Event Streams
| Event source | Event type | Event |
|---|---|---|
| Event Streams | Event Streams |
|
10.11.5.1.20 - Security Group
Security Group event
This is the list of events that the Security Group service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Security Group | Security Group | Security Group | Security Group |
Security Group
| Event source | Event type | event |
|---|---|---|
| Security Group | Security Group |
|
10.11.5.1.21 - Archive Storage
Archive Storage event
This is the list of events delivered from the Archive Storage service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Compute | Archive Storage | Archive Storage | Archive Storage | Bucket |
Bucket
| Event source | Event type | Event |
|---|---|---|
| Archive Storage | Bucket |
|
10.11.5.1.22 - API Gateway
API Gateway event
This is the list of events that the API Gateway service passes to ServiceWatch.
| Service Category | service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Application Service | API Gateway | API Gateway | API Gateway | API Gateway |
API Gateway
| Event source | Event type | event |
|---|---|---|
| API Gateway | API Gateway |
|
10.11.5.1.23 - Load Balancer
Load Balancer event
This is the list of events delivered from the Load Balancer service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Load Balancer | Load Balancer | Load Balancer | Load Balancer |
| Networking | Load Balancer | Load Balancer | Load Balancer | LB Listener |
| Networking | Load Balancer | LB server group | Load Balancer | LB Server Group |
| Networking | Load Balancer | LB health check | Load Balancer | LB Health Check |
Load Balancer
| Event source | Event type | event |
|---|---|---|
| Load Balancer | Load Balancer(security-group) |
|
LB Listener
| Event source | Event type | event |
|---|---|---|
| LB Listener | LB Listener |
|
LB Server Group
| Event source | Event type | event |
|---|---|---|
| LB Server Group | LB Server Group |
|
LB Health Check
| Event source | Event type | event |
|---|---|---|
| LB Health Check | LB Health Check |
|
10.11.5.1.24 - Data Ops
Data Ops event
This is the list of events that the Data Ops service sends to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Data Ops | Data Ops | Data Ops | Data Ops |
| Data Analytics | Data Ops | Data Ops Services | Data Ops | Data Ops Service |
Data Ops
| Event source | Event type | event |
|---|---|---|
| Data Ops | Data Ops |
|
Data Ops Service
| Event source | Event type | event |
|---|---|---|
| Data Ops Services | Data Ops Service |
|
10.11.5.1.25 - Scalable DB(DBaaS)
Scalable DB event
This is the list of events that the Scalable DB (DBaaS) service sends to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Scalable DB(DBaaS) | Scalable DB(DBaaS) | Scalable DB | Scalable DB |
Scalable DB
| Event source | Event type | event |
|---|---|---|
| Scalable DB | Scalable DB |
|
10.11.5.1.26 - Cloud LAN-Campus
Cloud LAN-Campus event
This is the list of events that the Cloud LAN-Campus service delivers to ServiceWatch.
| Service Category | service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Cloud LAN-Campus | Cloud LAN-Campus | Cloud LAN - Campus (Network) | Cloud LAN - Campus (Network) |
Cloud LAN - Campus (Network)
| Event source | Event type | event |
|---|---|---|
| Cloud LAN - Campus (Network) | Cloud LAN - Campus (Network) |
|
10.11.5.1.27 - EPAS(DBaaS)
EPAS(DBaaS) event
List of events sent from the EPAS (DBaaS) service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Database | EPAS(DBaaS) | EPAS(DBaaS) | EPAS | EPAS |
EPAS
| Event source | Event type | event |
|---|---|---|
| EPAS | EPAS |
|
10.11.5.1.28 - PostreSQL(DBaaS)
PostreSQL(DBaaS) event
This is the list of events that the PostreSQL (DBaaS) service sends to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Database | PostreSQL(DBaaS) | PostreSQL(DBaaS) | PostreSQL | PostgreSQL |
PostreSQL
| Event source | Event type | Event |
|---|---|---|
| PostreSQL | PostgreSQL |
|
10.11.5.1.29 - Logging&Audit
Logging&Audit event
This is the list of events that the Logging&Audit service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | Logging&Audit | Trail | Logging&Audit | Trail |
Trail
| Event source | Event type | event |
|---|---|---|
| Logging&Audit | Trail |
|
10.11.5.1.30 - Search Engine
Search Engine event
This is the list of events passed from the Search Engine service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Search Engine | Search Engine | Search Engine | Search Engine |
Search Engine
| Event source | Event type | event |
|---|---|---|
| Search Engine | Search Engine |
|
10.11.5.1.31 - DNS
DNS event
This is the list of events passed from the DNS service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | DNS | Private DNS | Private DNS | Private DNS |
| Networking | DNS | Hosted DNS | Hosted DNS | Hosted DNS |
| Networking | DNS | Public Domain Name | Public Domain Name | Public Domain Name |
Private DNS
| Event source | Event type | Event |
|---|---|---|
| Private DNS | Private DNS |
|
Hosted DNS
| Event source | Event type | Event |
|---|---|---|
| Hosted DNS | Hosted DNS |
|
Public Domain Name
| Event source | Event type | event |
|---|---|---|
| Public Domain Name | Public Domain Name |
|
10.11.5.1.32 - VPN
VPN Event
This is the list of events transmitted from the VPN service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | VPN | VPN | VPN | VPN Gateway |
| Networking | VPN | VPN | VPN | VPN Tunnel |
VPN Gateway
| Event source | Event type | event |
|---|---|---|
| VPN | VPN Gateway |
|
VPN Tunnel
| Event source | Event type | Event |
|---|---|---|
| VPN | VPN Tunnel |
|
10.11.5.1.33 - Secrets Manager
Secret event
This is the list of events that the Secrets Manager service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Secrets Manager | Secrets Manager | Secrets Manager | Secret |
Secret
| Event source | Event type | Event |
|---|---|---|
| Secrets Manager | Secret |
|
10.11.5.1.34 - Quick Query
Quick Query event
This is the list of events that the Quick Query service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Quick Query | Quick Query | Quick Query | Quick Query |
Quick Query
| Event source | Event type | event |
|---|---|---|
| Quick Query | Quick Query |
|
10.11.5.1.35 - File Storage
File Storage Event
This is the list of events delivered from the File Storage service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Storage | File Storage | File Storage | File Storage | Volume |
Volume
| Event source | Event type | event |
|---|---|---|
| File Storage | Volume |
|
10.11.5.1.36 - CacheStore(DBaaS)
CacheStore (DBaaS) event
This is the list of events delivered from the CacheStore (DBaaS) service to ServiceWatch.
| Service Category | service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Database | CacheStore(DBaaS) | CacheStore(DBaaS) | CacheStore | CacheStore |
CacheStore
| Event source | Event type | event |
|---|---|---|
| CacheStore(DBaaS) | CacheStore |
|
10.11.5.1.37 - Secret Vault
Secret Vault event
This is the list of events that the Secret Vault service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Security | Secret Vault | Secret Vault | Secret Vault | Secret Vault |
Secret Vault
| Event source | Event type | Event |
|---|---|---|
| Secret Vault | Secret Vault |
|
10.11.5.1.38 - Queue Service
Queue Service event
This is the list of events that the Queue Service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Data Analytics | Queue Service | Queue | Queue | Queue |
Queue
| Event source | Event type | event |
|---|---|---|
| Queue | Queue |
|
10.11.5.1.39 - Kubernetes Engine
Kubernetes Engine event
List of events passed from the Kubernetes Engine service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Container | Kubernetes Engine | Cluster | Kubernetes Engine | Cluster |
| Container | Kubernetes Engine | Node | Kubernetes Engine | Nodepool |
Cluster
| Event source | Event type | Event |
|---|---|---|
| Kubernetes Engine | Cluster |
|
Nodepool
| Event source | Event type | Event |
|---|---|---|
| Kubernetes Engine | Nodepool |
|
10.11.5.1.40 - Config Inspection
Config Inspection event
This is the list of events that the Config Inspection service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Security | Config Inspection | Config Inspection | Config Inspection | Config Inspection |
Config Inspection
| Event source | Event type | event |
|---|---|---|
| Config Inspection | Config Inspection |
|
10.11.5.1.41 - Cloud LAN-Datacenter
Cloud LAN-Datacenter event
This is the list of events that the Cloud LAN-Datacenter service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Cloud LAN-Datacenter | Cloud LAN Network | Cloud LAN Network | Cloud LAN Network |
| Networking | Cloud LAN-Datacenter | Interface | Cloud LAN Network | Interface |
| Networking | Cloud LAN-Datacenter | vCable | Cloud LAN Network | vCable |
| Networking | Cloud LAN-Datacenter | vDevice | Cloud LAN Network | vDevice |
Cloud LAN Network
| Event source | Event type | event |
|---|---|---|
| Cloud LAN Network | Cloud LAN Network(cloud-lan-network) |
|
Interface
| Event source | Event type | event |
|---|---|---|
| Cloud LAN Network | Interface(interface) |
|
vCable
| Event source | Event type | Event |
|---|---|---|
| Cloud LAN Network | vCable(vcable) |
|
vDevice
| Event source | Event type | Event |
|---|---|---|
| Cloud LAN Network | vDevice(vdevice) |
|
10.11.5.1.42 - Identity Access Management
Identity Access Management event
This is the list of events that the Identity Access Management service delivers to ServiceWatch.
| Service Category | service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | Identity Access Management(IAM) | User group | Identity Access Management | Group |
| Management | Identity Access Management(IAM) | User | Identity Access Management | User |
| Management | Identity Access Management(IAM) | policy | Identity Access Management | Policy |
| Management | Identity Access Management(IAM) | role | Identity Access Management | role |
| Management | Identity Access Management(IAM) | Credential Provider | Identity Access Management | Credential Provider |
| Management | Identity Access Management(IAM) | My Info. | Identity Access Management | Access Key |
Group
| Event source | Event type | event |
|---|---|---|
| Identity Access Management | Group |
|
User
| Event source | Event type | event |
|---|---|---|
| Identity Access Management | User |
|
Policy
| Event source | Event type | event |
|---|---|---|
| Identity Access Management | policy |
|
role
| Event source | Event type | Event |
|---|---|---|
| Identity Access Management | role |
|
Credential Provider
| Event source | Event type | event |
|---|---|---|
| Identity Access Management | Credential Provider |
|
Access Key
| Event source | Event type | Event |
|---|---|---|
| Identity Access Management | Access Key |
|
10.11.5.1.43 - Bare Metal Server
Bare Metal Server Event
This is the list of events that the Bare Metal Server service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Compute | Bare Metal Server | Bare Metal Server | Bare Metal Server | Bare Metal Server |
Bare Metal Server
| Event source | Event type | event |
|---|---|---|
| Bare Metal Server | Bare Metal Server |
|
10.11.5.1.44 - ServiceWatch
ServiceWatch event
This is a list of events delivered from the ServiceWatch service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | ServiceWatch | Dashboard | ServiceWatch | Dashboard |
| Management | ServiceWatch | Alert | ServiceWatch | Alert |
| Management | ServiceWatch | Log | ServiceWatch | Log Group |
| Management | ServiceWatch | Event Rules | ServiceWatch | Event Rules |
Dashboard
| Event source | Event type | Event |
|---|---|---|
| ServiceWatch | Dashboard |
|
Alert
| Event source | Event type | Event |
|---|---|---|
| ServiceWatch | Alert |
|
Log group
| Event source | Event type | Event |
|---|---|---|
| ServiceWatch | Log group |
|
Event Rules
| Event source | Event type | Event |
|---|---|---|
| ServiceWatch | Event Rules |
|
10.11.5.1.45 - MariaDB(DBaaS)
MariaDB(DBaaS) Event
List of events sent from the MariaDB (DBaaS) service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Database | MariaDB(DBaaS) | MariaDB(DBaaS) | MariaDB | MariaDB |
MariaDB
| Event source | Event type | Event |
|---|---|---|
| MariaDB | MariaDB |
|
10.11.5.1.46 - Container Registry
Container Registry event
This is the list of events passed from the Container Registry service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Container | Container Registry | Registry | Container Registry | Container Registry |
| Container | Container Registry | Node | Container Registry | Repository |
Container Registry
| Event source | Event type | event |
|---|---|---|
| Container Registry | Container Registry |
|
Repository
| Event source | Event type | event |
|---|---|---|
| Container Registry | Repository |
|
10.11.5.1.47 - Vertica(DBaaS)
Vertica(DBaaS) Event
This is the list of events that the Vertica (DBaaS) service delivers to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Database | Vertica(DBaaS) | Vertica(DBaaS) | Vertica | Vertica |
Vertica
| Event source | Event type | event |
|---|---|---|
| Vertica | Vertica |
|
10.11.5.1.48 - Backup
Backup event
This is the list of events that the Backup service sends to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Storage | Backup | Backup | Backup | Backup |
Backup
| Event source | Event type | Event |
|---|---|---|
| Backup | Bucket |
|
10.11.5.1.49 - Organization
Organization event
List of events delivered from the Organization service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | Organization | Organizational Structure | Organization | organization |
| Management | Organization | Organizational Structure | Organization | Organization Account |
| Management | Organization | Organizational Structure | Organization | Organization Invitation |
| Management | Organization | Organizational Structure | Organization | Organizational Unit |
| Management | Organization | Control Policy | Organization | Control Policy |
| Management | Organization | Organization Settings | Organization | Delegation Policy |
organization
| Event source | Event type | event |
|---|---|---|
| Organization | organization |
|
Organization account
| Event source | Event type | event |
|---|---|---|
| Organization | Organization account |
|
Organization Invitation
| Event source | Event type | Event |
|---|---|---|
| Organization | Organization invitation |
|
organizational unit
| Event source | Event type | Event |
|---|---|---|
| Organization | organizational unit |
|
Control Policy
| Event source | Event type | event |
|---|---|---|
| Organization | Control Policy |
|
Delegation Policy
| Event source | Event type | event |
|---|---|---|
| Organization | Delegation Policy |
|
10.11.5.1.50 - Cloud ML
Cloud ML Event
This is the list of events sent from the Cloud ML service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| AI-ML | CloudML | CloudML | Cloud ML | Cloud ML |
Cloud ML
| Event source | Event type | event |
|---|---|---|
| Cloud ML | Cloud ML |
|
10.11.5.1.51 - Certificate Manager
Certificate Manager event
This is the list of events that the Certificate Manager service passes to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Security | Certificate Manager | Certificate Manager | Certificate Manager | Certificate Manager |
Certificate Manager
| Event source | Event type | event |
|---|---|---|
| Certificate Manager | Certificate Manager |
|
10.11.5.1.52 - Key Management Service
Key Management Service event
This is the list of events that the Key Management Service delivers to ServiceWatch.
| Service Category | service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Security | Key Management Service | Key Management Service | Key Management Service | Key |
Key
| Event source | Event type | event |
|---|---|---|
| Key Management Service | Key |
|
10.11.5.1.53 - Direct Connect
Direct Connect event
This is the list of events delivered from the Direct Connect service to ServiceWatch.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Networking | Direct Connect | Direct Connect | Direct Connect | Direct Connect |
Direct Connect
| Event source | Event type | Event |
|---|---|---|
| Direct Connect | Direct Connect |
|
10.11.5.1.54 - Support Center
Support Center event
This is a list of events that the Support Center service forwards to the Support Center.
| Service Category | Service | Subservice | Event source | Event type |
|---|---|---|---|---|
| Management | Support Center | Service request | Support | Service Request |
| Management | Support Center | Contact | Support | Contact |
Service Request
| Event source | Event type | event |
|---|---|---|
| Support Center | Service request |
|
Contact
| Event source | Event type | Event |
|---|---|---|
| Support Center | Contact |
|
10.11.6 - Release Note
ServiceWatch
- When comparing metrics by date, you can select a period to compare.
- When viewing the chart of metric comparison results by date, you can select a specific period for comparison.
- You can easily view the alarm occurrence status through Copilot.
- You can enter a specific alarm name (or ID) or view the list of recently triggered alarms.
- ServiceWatch Service Dashboard Release
- We provide a service dashboard composed of key metrics for each service.
- When the service’s resources are created and metric data is collected by ServiceWatch, the service dashboard is automatically generated and can be viewed.
- Improved ServiceWatch metric search functionality
- Enhance the indicator search to display results that contain the search term.
- When searching for indicators, you can specify a period for a particular indicator to see how the indicator’s data changes over multiple periods.
- ServiceWatch log pattern feature release
- You can create a log pattern to filter log data collected in ServiceWatch that matches the pattern.
- For detailed information, refer to the 로그 패턴.
- Release of ServiceWatch custom metric feature
- Collecting custom metrics via ServiceWatch Agent
- Collecting custom metrics via the ServiceWatch API
- ServiceWatch custom log feature released
- Collecting custom metrics via ServiceWatch Agent
- Provide a feature to select the missing data handling method during alarm evaluation.
- For more details, refer to How to handle missing data during alert evaluation.
- The official version of ServiceWatch has been released.
- You can collect and monitor metrics, logs, events, and other data for resources created on the Samsung Cloud Platform.
- Dashboard: You can check the status of resources through various dashboards provided by ServiceWatch.
- Notification: You can receive a notification when specific conditions are met.
- Log: You can view logs collected by ServiceWatch.
- Event: By using ServiceWatch, you can analyze resource events to quickly identify and resolve issues.
- The Samsung Cloud Platform services that integrate with ServiceWatch are as follows.
- Metric Monitoring: Virtual Server, GPU Server, File Storage, Kubernetes Engine, Container Registry, VPC - Internet Gateway, Direct Connect
- Log Monitoring: Kubernetes Engine
- Event: Multiple services such as Virtual Server
- For more details, please refer to ServiceWatch Integrated Service.
- You can collect and monitor metrics, logs, events, and other data for resources created on the Samsung Cloud Platform.
10.12 - Support Center
10.12.1 - Overview
Service Overview
The Support Center is a service that provides technical support, standard architecture, incident response, and service inquiries/answers needed when using the Samsung Cloud Platform.
Provided features
The Support Center provides the following features.
Service Request: You can view the service request history and register a new request.
- Typical situations that require service request are as follows.
- Create some services in the Security service category
- Request for additional features for some services in the Networking service category
- Typical situations that require service request are as follows.
Contact: You can view the 1:1 inquiry history and register a new inquiry.
- The typical situations that require Contact are as follows.
- Questions about how to use the service and inquiries regarding errors that occur during use
- Inquiries about questions regarding the use of Samsung Cloud Platform Console outside the service and errors that occur during use.
- The typical situations that require Contact are as follows.
Knowledge Center: You can view frequently asked questions and their answers for each service.
Support Plan: Service tier that provides technical support, standard architecture provision, and incident response support required when using the Samsung Cloud Platform.
- The typical situations that require a Support Plan are as follows.
- When experimenting or testing
- If there is a production workload
- Support Plan can be used by selecting a level such as Standard or Proserv Plan according to the user’s situation.
- The typical situations that require a Support Plan are as follows.
10.12.2 - How-to Guides
In the Support Center, you can view service requests, inquiries, and frequently asked questions for each service along with their answers in the Knowledge Center.
Request Service
You can request services through the Support Center on Samsung Cloud Platform.
To request a service, follow the steps below.
Click the All Services > Management > Support Center menu. 1. Go to the Service Home page.
On the Service Home page, click the Service Request menu. 2. Navigate to the Service Request List page.
On the Service Request List page, click the Service Request button.
- Select and enter the information required for the service request.
Category required statusDetailed description Title Required Title of the service request - Enter within 64 characters using Korean, English, numbers, and special characters(
+=,.@-_)
Region Essential Select the region for the service request Service Required Select service group - Select services available for that service group
Task classification Required Select the type of operation you want to request content Required Write the content according to the template for requesting the selected task - You can attach up to 5 files, each not exceeding 5 MB, and only the file types listed below are allowed.
- (doc, docx, xls, xlsx, ppt, pptx, hwp, txt, pdf, jpg, jpeg, png, gif, tif)
Table. Service request items - Enter within 64 characters using Korean, English, numbers, and special characters(
- Select and enter the information required for the service request.
Check the input information and click the Request button.
- When creation is complete, check the Service Request List page.
- After submitting a service request, the content you entered cannot be edited or deleted.
Check service request details
In service requests, you can view the complete list, see detailed information, and check the progress.
To view the detailed service request information, follow these steps.
- All Services > Management > Support Center menu, please click. 1. Service Home page is accessed.
- On the Service Home page, click the Service Request menu. 2. Navigate to the Service Request List page.
- Service Request List page, click the request for which you want to view detailed information. 3. Go to the Service Request Details page.
Category Detailed description status Service request status - Requesting: initial request state
- Assignment Completed: state assigned to a worker
- In Progress: state where the worker is processing
- Completed: work completed state
Inquiry code Unique identifier code for the service request Task classification Task classification of the selected service when requesting a service Inquiry target The service group and service name selected during a service request Region Region selected during service request Author User who requested the service request Request date and time Service request creation date and time Title Service Request Title content Content entered when requesting a service Attachment File attached with the service request Table. Service request detail page items
- Service requests may take about 5~10 days depending on the requested work.
10.12.2.1 - Contact Us
Users can ask questions about the Samsung Cloud Platform through inquiries and view the responses.
Create Inquiry
You can create an inquiry through the Support Center on Samsung Cloud Platform.
- Technical support may vary depending on the inquiry, based on the Support Plan tier.
- For detailed information about Support Plan tiers, see Support Plan.
To create an inquiry, follow these steps.
- All Services > Management > Support Center Click the menu. 1. Go to the Service Home page.
- On the Service Home page, click the Contact Us menu. 2. Navigate to the Contact List page.
- On the Inquiry List page, click the Contact button.
- Select and enter the information required for the inquiry.
Category Required statusDetailed description Title Essential Title of the inquiry - Enter within 64 characters
Inquiry Type Required Select inquiry type - Feature Inquiry: For questions about usage and utilization of a feature, additional selection or entry of Region, Inquiry Target (service group/service), Resource Name is required
- Resource Error Inquiry: For error inquiries about a resource, additional selection or entry of Region, Inquiry Target (service group/service), Resource Name is required
- Service Inquiry: For service-related inquiries such as feature improvement requests, additional selection or entry of Region, Inquiry Target (service group/service), Resource Name is required
- General Inquiry: For account or usage fee related inquiries, Region selection is required
- Incident Inquiry: For inquiries about incident situations, for usage and utilization questions, additional selection or entry of Region, Inquiry Target (service group/service), Resource Name is required
Inquiry Type Required Select the inquiry type - Depending on the inquiry type, you must additionally enter/select Region, Inquiry Target, and Resource Name.
Region Required Region to inquire Inquiry target Required First, select a service group - You can then additionally select the available services that belong to that service group.
Resource name Required Name of the resource to query Severity Required The level at which the inquiry affects the service - No impact on the current service
- Development/Test environment request
- Production environment request
content Required Write your inquiry - You can attach up to 5 files, each not exceeding 5 MB, and only the following file types are allowed.
- (doc, docx, xls, xlsx, ppt, pptx, hwp, txt, pdf, jpg, jpeg, png, gif, tif)
Table. Contact item
- Select and enter the information required for the inquiry.
- Check the input information and click the Request button.
- When creation is complete, check the Inquiry List page.
Check detailed inquiry information
In the Inquiry section, you can view the full list of inquiries, see detailed information, and check the progress.
To view the detailed inquiry information, follow these steps.
- Click the All Services > Management > Support Center menu. 1. Go to the Service Home page.
- On the Service Home page, click the Contact Us menu. 2. Go to the Inquiry List page.
- On the Inquiry List page, click the request to view detailed information. 3. Navigate to the Inquiry Details page.
Category Detailed description status Inquiry status - Inquiry Received: Initial inquiry receipt status
- Awaiting Response: The responsible person is reviewing the inquiry
- Pending Customer Action: Waiting after requesting additional information from the customer regarding the inquiry
- Response Completed: The response has been completed
Inquiry code Unique identifier code for inquiry Inquiry target The service group and service name selected when making an inquiry Resource name Resource name entered when making an inquiry Region Region selected when making an inquiry Severity Severity selected when making an inquiry Author User who requested an inquiry Request date and time Date and time the inquiry was created Title Contact Title content Content entered when submitting an inquiry Attachment File attached when making an inquiry Table. Inquiry detail page items
10.12.2.2 - Support Plan
The Support Plan is a service that provides technical support, standard architecture provision, and incident response support needed when using the Samsung Cloud Platform, categorized into stages. Since service operating hours, technical support, and incident response service types differ by service tier, users can select an efficient service tier based on the applicable workload, such as testing, routine tasks, or critical operations.
Learn about Support Plan
Samsung Cloud Platform offers Support Plans in Standard and Proserv Plan tiers.
To check the Support Plan you are currently using, follow these steps.
- All Services > Management > Support Center. Click the menu to go to the Service Home page.
- On the Service Home page, click the Support Plan menu. You will be taken to the Support Plan page.
Category Detailed description Support Plan application status Current application status of the Support Plan - Active: Properly applied. No changes planned.
- In Progress: Scheduled for change.
Plan change Button to change the applied Support Plan - For more details, see Support Plan Change
Support Plan Types Support Plan names and descriptions by tier - Current Plan: The Support Plan tier currently applied
- Future Plan: The Support Plan tier to be applied after the plan change
Table. Support Plan page items
- On the Service Home page, you can view the currently used Support Plan and the list of Support Plans per Account.
- The list of Support Plans for each Account can only be viewed in the organization management Account.
Standard grade
The Standard tier is the recommended level for handling tasks that are experimental or require testing.
| Category | Detailed description |
|---|---|
| Service target | Recommended for experimental or testing purposes |
| Response time |
|
| Operating Hours | 9H * 5D Biz Hour |
| Request / Response Method | On-line (Console) |
| Support Service |
|
| Incident response | Receipt (action and notification) |
| Fee | Free |
Proserv Plan Level
The Proserv Plan tier is the minimum tier recommended when there is a production workload.
| Category | Detailed description |
|---|---|
| Service Target | Recommended for production workloads |
| Response time |
|
| Operating Hours | 24H * 7D |
| Request / Response Method | Assign dedicated TAM (phone, email, On-line (Console)) |
| Support Service |
|
| Incident response |
|
| Fee | Monthly usage fee per customer * Apply tiered rates (differential)
|
Change Support Plan
You can apply changes to the Support Plan as needed.
Requests to enroll, cancel, or modify a Support Plan are applied on the 1st of each month.
To change the Support Plan you are using, follow the steps below.
- All Services > Management > Support Center menu, click it. You will be taken to the Service Home page.
- On the Service Home page, click the Support Plan menu. You will be taken to the Support Plan page.
- From the My Support Plan widget, you can click the Plan Upgrade or Plan Change button to navigate to the Support Plan Change page.
- On the Support Plan page, click the Change Plan button. You will be taken to the Support Plan Change page.
- On the Support Plan Change page, select the Support Plan you want to change, then click the Change Plan button.
- When the popup notifying a Support Plan change request opens, click the Confirm button. You will be taken to the Support Plan page.
- Check that the Support Plan’s applied status changes to In Progress and that the plan to be changed item is displayed in the Support Plan to be modified.
- Cancel Plan Change button, when clicked, cancels the change request and keeps the current Support Plan.
- You can view the application, cancellation, and modification history of the Support Plan on the logging&Audit > Activity Log page.
- Change history is provided free of charge for up to 90 days.
10.12.2.3 - Knowledge Center
Users can search for and view service-specific FAQs and their answers in the Knowledge Center.
Using the Knowledge Center
You can view the list of frequently asked questions for each service and see the answers.
To use the Knowlegde Center, follow these steps.
- Click the All Services > Management > Support Center menu. Navigate to the Service Home page.
- On the Service Home page, click the Knowledge Center menu. You will be taken to the Knowledge Center List page.
- Select the Category you want to check and view the list. If there is an item whose detailed information you want to view, select it. You can view the detailed information on that page. You can expand or collapse the content using the Expand, Collapse buttons at the far right.
10.12.3 - Release Note
Support Center
- Added a Support Plan widget to the Service Home page.
- Now you can view the Support Plan you are currently using on the Service Home page.
- Added a Support Plan. Users can receive technical support, standard architecture provision, incident response support, and more, categorized by stage, while using the Samsung Cloud Platform.
- Depending on the user’s situation, you can select and use the Standard, Proserv Plan tier.
- We have launched the Support Center. It is a system for users of the Samsung Cloud Platform to receive necessary technical support, standard architecture, incident response, and service inquiries/answers.
- You can manually request services that cannot be applied through the system from the Console.
- You can ask questions about any issues while using it, and receive technical support if problems arise.
10.13 - Quota Service
10.13.1 - Overview
Service Overview
Quota Service is a service that manages the maximum number of resources, tasks, or items (quotas) set for each service within an account. Quota is a limit set to ensure high availability and stability for customers and to prevent unintended overuse. For example, the number of Virtual Server instances, the number of buckets, and similar resources fall under this. Through the Quota Service, you can view these quotas in one place and request an increase when needed.
Types of quotas:
- Default Quota (Default Quota): The initial value set by Samsung Cloud Platform for each service.
- Applied Quota: the increased value requested by the user (applied upon approval).
- Adjustability (Adjustable): Some quotas can be increased upon request, while others are fixed.
Features
We provide the following special features.
- Centralized Management: You can manage more than 100 service quota items from a single console (e.g., Virtual Server, VPC, Firewall, etc.).
- Integration with other services: You can smoothly request and process quota increase requests through Support (some are auto-approved).
- Scalability and Flexibility: You can manage quotas finely from account-level quotas to region-level quotas, and adjustable quotas can scale with business growth.
- Cost Efficiency: Quota Service has no additional cost, and by managing quotas in advance, it can prevent cost increases caused by unintended excessive resource usage.
Provided features
We provide the following features.
- Quota lookup and detailed information provision: Check each service’s default quota, applied quota, and whether it can be adjusted, and display quotas separately for region-level and account-level.
- Quota Increase Request: Through the Console, you can process quota increase requests in a single interface, and track and manage request statuses (Pending, Approved, Denied).
- History and Analysis: You can review past quota increase request records and usage trends to inform resource planning and optimization.
Prerequisite product
There are no services that need to be pre-configured before creating this service.
10.13.2 - How-to guides
Check Quota Service details
To view detailed information of the Quota Service, follow these steps.
- Click the All Services > Management > Quota Service menu. Go to the Service Home page of Quota Service.
- On the Service Home page, click the Quota Service menu. You will be taken to the Quota Service List page.
- Click the Quota Item name to view detailed information on the Quota Service List page. You will be taken to the Quota Service Details page.
- Quota Service Details page consists of the Basic Information, Request History, Tag tabs.
Basic Information
On the Quota Service List page, you can view detailed information of the selected resource and, if necessary, edit the information.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Quota Item name | Quota Item name |
| Applicable target | Applicable Target Classification
|
| description | Quota Item description |
| Adjustability | Whether a quota change request is possible |
| Current allocation value | Current allocated capacity
|
| default allocation value | Allocated capacity by default
|
Request History
You can view the change request history of the selected resource on the Quota Service List page.
| Category | Detailed description |
|---|---|
| Request date and time | Date and time of the change request |
| requester | Requested user name |
| request value | The value requested by the user |
| applied value | Values that are automatically approved or approved and entered by the administrator
|
| Completion date and time | Date and time the change request was approved |
| status | Current status of change request
|
tag
Quota Service List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Request quota change
To request a quota change, follow these steps.
Click the All Services > Management > Quota Service menu. Navigate to the Service Home page of Quota Service.
On the Service Home page, click the Quota Service menu. You will be taken to the Quota Service List page.
On the Quota Service List page, select the Quota Service to change, then click the Quota Change Request button. The Quota Change Request popup window opens.
Quota Change Request In the popup window, after entering Requested Value and Requested Message, click the Confirm button.
Category Required statusDetailed description request value Required Enter the value the user wants to change - When reducing: automatically approved and applied
- When expanding: applied after manager confirmation
Request message Required Explanation of the purpose of change and usage Table. Product name resource list itemReferenceIf the requested resource has the automatic scaling policy applied, see the following.
- The quota will be automatically adjusted based on usage after one month of request approval.
- If the amount of resources in use exceeds the resource margin setting value (%), the quota is automatically reduced, leaving only the setting value.
When a popup notifying a change request opens, click the Confirm button.
Check quota change request history
You can view the quota change request details and current status. To view the quota change request details, follow these steps.
- Click the All Services > Management > Quota Service menu. Go to the Service Home page of Quota Service.
- On the Service Home page, click the Request History menu. You will be taken to the Request History List page.
Category Detailed description Service Service name Quota Item name Quota Item name Applicable target Applicable Target Classification - Region or Account
Resource ID Unique resource ID in the service request value The value requested by the user applied value Values that are automatically approved or approved and entered by the administrator - before approval is completed, display
-
Auto scaling policy Whether automatic reduction policy is applied - When not applied, display Not Applied
- When applied, display Margin(%)
Request date and time Date and time of the change request Completion Date/Time Date and time the change request was approved status Current status of change request - Pending: before approver processes
- On hold: approver puts on hold
- Approved: automatically approved or approver completed
- Partially approved: approved after applying less than requested
- Auto reduction: reduced according to auto-reduction policy
- Request rejected: approval denied
- When in this state, the request detail popup opens
Table. List of change request items
If the requested resource has the automatic scaling policy applied, see the following.
- The quota will be automatically adjusted based on usage after one month of request approval.
- If the amount of resources in use meets or exceeds the resource margin setting value (%), the quota is automatically reduced, leaving only the setting value.
10.13.2.1 - Organization Quota Template
By using an organization quota template, when a new Account is created in the organization, you can automatically request the Quota service for the new Account based on the template created by the admin Account.
Using organization quota template
To use the organization quota template of the Quota Service, follow these steps.
- Click the All Services > Management > Quota Service menu. Navigate to the Service Home page of Quota Service.
- On the Service Home page, click the Organization Quota Template menu. You will be taken to the Organization Quota Template page.
Category Detailed description Whether to use Set whether to use the organization allocation template - When Enabled, apply the service’s default allocation values to newly created Accounts in the organization
- When Disabled, automatically request a change to the quota of newly created Accounts in the organization
- Click the Edit button to change the usage setting
Organization Assignment Template List of registered organization allocation templates - Applicable target, region, service, Quota Item name, request value can be checked
Add quota New quotas can be registered - Up to 10 can be registered
- For details, see Add Quota
Delete Delete the selected quota from the organization assignment template list - See Delete Quota for details
Table. Organization quota template items
- If no additional quota is added, setting the organization allocation template to use will not automatically apply the template.
- Even if the template is set to unused, the added quota will not be deleted.
Add quota
You can set a new quota and add it to the template.
Click the All Services > Management > Quota Service menu. Navigate to the Service Home page of Quota Service.
On the Service Home page, click the Organization Quota Template menu. You will be taken to the Organization Quota Template page.
On the Organization Quota Template page, click the Add Quota button. You will be taken to the Add Quota page.
After entering the required quota information, click the Complete button.
Category Required Detailed description Region Required Select the region to use for the organization quota Service Required Select services available in the selected region - Activates when Region is selected
Quota Item name Required Select Quita Item included in the selected service - Service activation upon selection
- Quota Items currently used in other quotas cannot be selected
- If needed, delete the quota and then register
request value Required Enter request value for the selected Quita Item - Quita Item name Activates when selected
- Can be entered up to the value set by the administrator
Table. Additional quota itemsWhen the pop-up notifying the addition opens, click the Confirm button. The quota will be added to the organization quota template list.
Delete organization quota
You can delete the quota added to the template. To delete a quota, follow these steps.
- Click the All Services > Management > Quota Service menu. Go to the Service Home page of Quota Service.
- On the Service Home page, click the Organization Quota Template menu. You will be taken to the Organization Quota Template page.
- On the Organization quota template page, select the quota to delete from the list, then click the Delete button.
- You can delete one or multiple quotas simultaneously.
- When a pop-up notifying deletion opens, click the Confirm button. The quota will be removed from the list.
10.13.3 - Release Note
Quota Service
- A tag tab has been added in the detailed information.
- You can set tags on the Quota Service to use it.
- Organization quota template feature has been added.
- By using the organization quota template, you can automatically request a quota change when creating a new account in the organization.
- The organization quota template feature is available only in the Management Account.
- We have launched the Quota Service.
- You can manage the maximum number of resources, tasks, or items (quotas) set for each service within an account.
11 - Financial Management
On the Samsung Cloud Platform, you can search for the software you need based on your intended use, apply for it directly, and manage the detailed information of the software you have requested.
11.1 - Cost Management
11.1.1 - Overview
Service Overview
Cost Management service provides tools to manage and track Samsung Cloud Platform service costs.
By identifying cost trends and savings opportunities, you can make faster and more accurate financial decisions. Users can efficiently obtain the desired information through grouping and segmenting data.
Provided features
- Usage and Billing Details: You can forecast this month’s estimated amount and verify the billed amount. It provides per-resource costs, usage, and unit rates, and can be saved as an Excel file.
- Payment Details: Provided when the payment method is a credit card. Check the billed amount, outstanding amount, payment date, payment status, etc.
- Cost Analysis: You can view cost trends up to six months. It provides cost grouping and various search filters to analyze cost and usage data.
- Credit Management: You can manage and use Credit.
- Budget Management: You can set and manage budgets.
- Cost Savings: You can reduce usage costs by setting a time commitment for the Compute services of the Samsung Cloud Platform Console.
- Account: You can view the Account information. You can check the Account name, Account ID, alias, and company name.
- Payment Management: Provides information about the payment methods of the Account. Credit card and bank transfer deposit information are displayed.
- Carbon emissions: You can view the carbon emissions generated when using services on the Samsung Cloud Platform Console, monthly carbon emission trends, carbon emissions by service group, and carbon emissions by Account.
Constraints
- Provided based on the Asia/Seoul(GMT +09:00) timezone.
- Termination fees and Support plan amounts are displayed in the month when billing settlement is completed.
- Cost analysis is provided on a monthly basis.
- Tag information for the billing report is provided when the email is sent.
Preceding Service
Cost Management has no prerequisite service.
11.1.2 - How-to Guides
Users can optimize cloud efficiency by leveraging various cost management tools through the Cost Management feature of the Samsung Cloud Platform Console. Through Cost Management, you can view usage and billing details, payment history, and cost analysis, and manage Credit, budget, Account, and payment methods.
Check usage and billing details
You can forecast this month’s estimated cost for the services used in the Samsung Cloud Platform Console and verify the billed amount.
To view usage and billing details, follow these steps.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Usage and Billing Details menu. You will be taken to the Usage and Billing Details page.
- Usage and Billing Details page’s top-right period setting area, select the year and month for which you want to view usage and billing details. The usage or billing details for the selected period will be displayed.
- Select the item to view details from the top right of the cost detail list. The detailed information for that item will be displayed.
Check payment details
In the monthly payment history of the Account, you can view items such as billed amount, usage amount, overdue amount, and payment amount.
In the Samsung Cloud Platform Console, you can view a user’s account payment history by month.
To use the payment history, follow these steps.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Payment History menu. You will be taken to the Payment History page.
- Payment History page lets you view the payment history for the relevant Account.
Item Explanation Billing Year-Month Billing reference year-month Billing amount The amount obtained by adding the accumulated unpaid balance to the current month’s usage amount Usage Amount Current month usage amount Handsome amount (current month) Unpaid amount for the current month Cumulative handsome amount Total outstanding amount Payment amount Represent the actual payment currency with its symbol instead of the account’s contract currency. Payment date Date of credit card payment Table. Payment details items
- All fees are exclusive of VAT.
- For detailed information about the payment history, refer to Check payment details.
Cost Analysis
You can view cost analysis data, including an account’s estimated or actual charges for up to six months, the monthly average charge, and the top 5 cost items. To verify the cost analysis, follow these steps.
- The billing calculation reference is midnight in the Asia/Seoul (GMT +09:00) time zone. The estimated data may differ from the actual.
- Set up an abnormal cost detection alert so that an alert is triggered when the usage amount increases by 100% or more compared to the previous two days. For details on alert configuration, see 알림 설정 확인하기.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Analysis menu. You will be taken to the Cost Analysis page.
- Cost Analysis page allows you to view the cost analysis for the specified Account.
- If you select the query period in the upper right corner, you can view the cost analysis for that period.
- The query period can be set for a maximum of six months, from the start date to the end date.
- The query period is defined from the 1st of the start month to the last day of the end month.
- Provides a graph visualized based on the search period.
- When a service group is selected, its color is applied, and on mouse over, a tooltip displays the group’s color and amount information.
*is displayed when it is the estimated amount.
- Cost Analysis page allows you to view detailed cost information.
Item Explanation Service group Resource Service Group Notation Service Resource service name display Resource Name Resource name notation Billing amount or estimated billing amount* The resource’s billed amount or estimated billed amount is displayed. Table. Cost analysis detailed item breakdown
Check Credit
You can view and manage the monthly usage of credits received through the Samsung Cloud Platform Console.
- All Services > Financial Management > Cost Management Click the menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Credit Management menu. You will be taken to the Credit Management page.
- Check the monthly usage of Credit on the Credit Management page.
- Clicking the Expand button at the far right of the Account item lets you view the monthly details.
Category Detailed description Category Credit type Validity period The usage amount for the month indicated by the validity period is applied. - In the credit expiration month, the extend button appears.
Payment Credit Credits issued for each Credit type and issuance date Remaining Credti Remaining Credit amount after subtracting total used Credit from the received Credit Usage month You can view the monthly limit amount set by the user for that month. - In the current month, a Limit Setting button appears, allowing you to set the Credit amount you wish to use for the month within the remaining Credit.
Monthly limit This is the monthly limit amount set by the user. If not set, it shows the same amount as the remaining Credit each month. Monthly usage credit This is the Credit cost actually used within the monthly limit set for that month. Monthly remaining credit This is the cost after subtracting the Credit actually used from the monthly limit amount set for that month. The remaining balance is included in the remaining Credit. Table. Credit Management List
- Clicking the Expand button at the far right of the Account item lets you view the monthly details.
Budget Management
You can set and manage budgets. To view the budget management information, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Budget Management menu. You will be taken to the Budget Management page.
- On the Budget Management page, you can view the list of budgets that have been set.
Category Detailed description Budget Name Budget name for distinguishing generated budgets Management Type You can see the type for managing the budget. - Monthly budget setting: reset the spent amount on a monthly basis
- Overall budget setting: accumulate the spent amount from the set month onward
Budget set amount Check the configured budget. This month’s usage amount Displays the amount used for the Account up to yesterday in the current month. consumption rate It shows the ratio of the amount used up to the day before today to the budgeted amount for this month’s usage. - For the total budget, it is calculated as the sum of this month’s usage from the start month.
Estimated usage amount for this month It represents the estimated total usage amount for this month, based on the usage fees up to yesterday in the current month of the Account. Estimated depletion rate Indicates the ratio of the expected usage amount for this month to the budgeted amount. - For the total budget, it is calculated as the sum of the expected usage amounts from the start month to this month.
More button Click the More button in the list to navigate to the Budget Edit page. Table. Budget Management List Information
Cost Savings
Users can set time commitments for Compute services in the Samsung Cloud Platform Console to reduce usage costs. To view detailed information of Cost Savings, follow the steps below.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Savings > Cost Savings List menu. You will be taken to the Cost Savings List page.
- Click the plan group name to view detailed information in the Cost Savings list. You will be taken to the Cost Savings Details page.
- Cost Savings Details page consists of Coverage, Utilization, Plan Group tabs.
Category Detailed description Plan group name Plan group name Plan ID Plan group ID Contract period Contract term of the plan group Start date Plan start date Expiration date Plan expiration date Hourly contracted amount Hourly contracted amount status Plan application status - Creating: After the application is completed, the plan is pending creation
- Active: Plan start status
- Expired: Plan contract period expired status
Cancel application Cancel plan application - Can only be canceled in Creating status
Table. Cost Savings list information
- Cost Savings Details page consists of Coverage, Utilization, Plan Group tabs.
Check Account Information
You can view account information and manage account aliases. To check the Account information, follow these steps.
For detailed information about registering a payment method, see Register a payment method.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Account menu. You will be taken to the Account page.
- You can also navigate by clicking My menu > Account in the top right of the Console.
- Check the Account information on the Account page.
Item Explanation Account name The name assigned to an Account when creating the Account. It allows the Account to be easily identified when managing multiple accounts. AccountID The unique identifier of the Account. Used when an IAM user logs in. Account alias Alias assigned to the Account when creating the Account. - When managing multiple Accounts, it helps to easily identify the Account for billing management and other purposes.
- IAM users can log in to the Console using the Account alias.
- Edit: Modify the Account alias. Edit Account Alias see
- Delete: Delete the Account alias. Delete Account Alias see
Company Name Company name entered when registering a payment method Table. Account detailed information
Managing Payment Methods
In the Samsung Cloud Platform Console, you can view and register payment methods associated with the Account. To verify the payment method, follow these steps.
- All Services > Financial Management > Cost Management menu. Click it. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Payment Management menu. You will be taken to the Payment Management page.
- Payment Management on the page, you can view the currently registered payment methods.
- For payment-related inquiries such as payment methods and receiving statements, please request them through the sales representative or 문의하기.
- For detailed information about payment methods, please refer to Check payment methods.
Check Carbon Emissions
You can view the carbon emissions generated when using services in the Samsung Cloud Platform Console. To check the carbon emissions per service, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Carbon Emissions menu. You will be taken to the Carbon Emissions page.
- In the period setting area at the top right, set the period for checking carbon emissions.
Category Detailed description Carbon emissions by period Carbon emissions from day 1 to the present and Compared to On-prem. carbon emissions display - Estimated end-of-month On-prem. comparison: Display the increase/decrease amount of the estimated end-of-month On-prem. comparison
- Estimated end-of-month carbon emissions: Estimated end-of-month carbon emissions
Carbon emission trend Display the carbon emission trend as a graph compared to the previous month - Hovering the mouse cursor over the graph shows the total carbon emissions
- Compared to previous month: Show the change in carbon emissions compared to the previous month as a percentage (%)
- Change amount: Increase or decrease in carbon emissions compared to the previous month
- Previous month’s carbon emissions: Carbon emissions of the previous month
Monthly average carbon emissions Average carbon emissions over the past six months Carbon Emissions Graph Carbon emissions graph from day 1 to the present - Overall: Display carbon emissions of all services
- By Service Group: Select a service group (e.g., Compute, Storage) to display its carbon emissions Hover the mouse cursor over the graph to view detailed information for that point
Carbon emissions by service Service-specific carbon emissions from the 1st to the present - Download detailed Excel: Download service-specific carbon emissions as an Excel file
Table. This month's carbon emission information
- Data is not displayed on the 1st of each month. (Based on Asia/Seoul, GMT +09:00)
- The month‑end estimate is a projection based on the current emissions.
- For detailed information on carbon emissions, refer to Check Carbon Emissions.
- Carbon emissions are rounded after summing the fractional values for each service group, so the total may differ.
- Indirect service group: includes emissions from all other usage services except Compute and Storage services.
Check EDP Report
When signing an EDP contract, you can view the contract details and usage cost information.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- Click the EDP Report menu on the Service Home page. You will be taken to the EDP Report page.
| Category | Detailed description |
|---|---|
| Basic Information Tab | Company information, agreement and contract information, discount rate information |
| EDP Report tab | EDP cumulative graph and detailed breakdown |
11.1.2.1 - Usage and Billing Details
You can predict this month’s estimated cost for the services used in the Samsung Cloud Platform Console and view the billed amount.
Check usage and billing details
You can view usage or billing details in the Samsung Cloud Platform Console.
- The billing calculation reference is midnight in the Asia/Seoul (GMT +09:00) time zone. * Usage details may differ from the actual billed amount.
- If it is an estimated amount, a
(*)mark is displayed next to the item.
To view usage and billing details, follow these steps.
All Services > Financial Management > Cost Management menu, click it. 1. Navigate to the Service Home page of Cost Management.
On the Service Home page, click the Usage and Billing Details menu. 2. Go to the Usage and Billing Details page.
On the Usage and Billing Details page, in the period setting area at the top right, select the year and month for which you want to view usage and billing details. 3. The usage or billing details for the specified period are displayed.
- If the selected period is an unbilled month, you can view the estimated usage amount, estimated billing amount, monthly average billing amount in the usage details.
Item Explanation Estimated usage amount(*) Estimated usage amount from the 1st of the current month to the day before the query date Estimated billing amount(*) Predicted billing amount based on the usage amount trend from the 1st to the end of the current month. Monthly average billing amount Average monthly billing amount for the past 6 months Table. Unbilled monthly usage details items - If the selected period is the billing settlement month, you can view billing amount, billing trend, monthly average billing amount in the billing details.
Item Explanation Billing amount The billed amount for the queried month. The billing date is the tax invoice issuance date. Claim Trend Billing amount for two months. Check the change rate and change amount. Monthly average billing amount Average monthly billing amount for the past 6 months Table. Billing settlement monthly billing details items
- If the selected period is an unbilled month, you can view the estimated usage amount, estimated billing amount, monthly average billing amount in the usage details.
In the top right of the cost detail list, select the item whose details you want to view. 4. Detailed information for this item is displayed.
- Service Fees by Category: You can view detailed fee information for each service.
- You can use Tag filter. * For more details, please refer to Using Tag Filter.
Item Explanation service group Service name service Resource Type type Server type Resource name Resource name Region Resource usage region Contract period Contract term unit price Rate units and pricing criteria Usage Resource usage time Estimated usage amount(*) / Total usage amount Estimated usage amount from day 1 to the present - If the selected period is the billing settlement month, total usage amount
Estimated discount amount(*) / Discount amount Estimated discount amount - If the set period is the billing settlement month, discount amount
Estimated billing amount(*) / Billing amount Estimated monthly billing amount per resource - If the selected period is the billing settlement month, billing amount
Detailed usage history / Detailed billing history Detailed usage information and cost per service - After expanding the details, you can click the button to view detailed information
- If the selected period is the billing settlement month, Billing Details
Detailed fee breakdown by serviceReferenceThe discount amount through Planned Compute, Cost Saving, etc., is the amount up to D‑1 based on the query date.
- You can use Tag filter. * For more details, please refer to Using Tag Filter.
- Discount Rate: You can view the detailed discount rate information.
Item Explanation Account name Account name Discount Type Discount Type type Server type Resource name Resource name Region Resource usage region Estimated discount amount Estimated discount amount Table. Discount Rate DetailsReferenceThe discount amount through Planned Compute, Cost Saving, etc., is the amount up to D‑1 based on the query date. - Charges per Account: You can view detailed charge information for each account.
Item Explanation Account name/Service group Account name and service categories used by the Account Service Service name type Server type Resource name Resource name Region Resource usage region Contract period Contract term Unit price Rate Units and Pricing Criteria Usage Resource usage time Estimated usage amount(*) / Total usage amount Estimated usage amount from day 1 to now - If the selected period is the billing settlement month, total usage amount
Estimated discount amount(*) / Discount amount Estimated discount amount - If the set period is the billing settlement month, discount amount
Estimated billing amount(*) / Billing amount Estimated monthly billing amount per resource - If the selected period is the billing settlement month, billing amount
Detailed usage history / Detailed billing history Detailed usage information and cost per service - Account name/Service group After expanding the item, you can click the button to view detailed information
- If the selected period is the billing settlement month, Billing details
Table. Detailed charge breakdown by account
- Service Fees by Category: You can view detailed fee information for each service.
Using Tag Filter
You can set a filter to select a tag and view detailed cost information for resources that have that tag applied.
To use the tag filter, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. 1. Go to the Service Home page of Cost Management.
- On the Service Home page, click the Usage and Billing Details menu. 2. Navigate to the Usage and Billing Details page.
- Usage and Billing Details page’s top-right period setting area, select the year and month to view usage and billing details. 3. The usage or billing details for the specified period are displayed.
- Click the Service-specific charges button in the upper right corner of the cost detail list, then click the Tag filter button. 4. Tag Filter The popup window opens.
- The Tag Filter button is enabled only when Service-specific pricing is selected.
- Select the key of the resource to view the cost details. 5. The Value corresponding to the entered Key is displayed below.
- After selecting the Value of the resource for which you want to view the cost details, click the Apply Filter button.
- Check the detailed breakdown with the Tag Filter applied in Service-specific Pricing.
- The tag list for checking cost information is updated daily at midnight (Asia/Seoul, GMT +09:00).
- Tags created today will be added to the list during the midnight update tomorrow.
Download detailed file
You can download the detailed cost information for the full usage or billing records of the selected period as an Excel file.
To download the detailed report file, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. 1. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Usage and Billing Details menu. 2. Navigate to the Usage and Billing Details page.
- On the Usage and Billing Details page, select the year and month in the period setting area at the top right to view usage and billing details. 3. The usage or billing details for the specified period are displayed.
- In the top right of the cost detail list, select the item to view its details. 4. Detailed information for this item is displayed.
- Click the Download detailed Excel button. 5. File Download popup window opens.
- After selecting the download method, click the Confirm button.
- Direct download (without tags): Download the Excel file using the current browser
- Email sending (including tags): Send the Excel file to the email registered in the Console
- Send usage email for abnormal cost detection verification: If there is an abnormal cost detection record, send an Excel file to the email registered in the Console.
- Open the downloaded Excel file and check the details.
Item Explanation Contract number Ledger ID (unique key of the instance) Account ID Account ID Account name Account name Billing Year-Month Cost billing year-month Service service group type Service name Resource name Resource name Region Resource usage region name tag Resource tag information - displayed only when sending email
- not included when downloading directly
Unit price Rate units and rate criteria Usage Resource usage time call Account currency Usage amount Amount before discount Planned Compute Discounted amount with Planned Compute Estimated payment amount Final payment amount after the discount is excluded from the usage amount Table. Detailed Excel file items
11.1.2.2 - Payment History
Users can view items such as billed amount, usage amount, overdue amount, and payment amount for each category in their account’s monthly payment history through the payment history in the Samsung Cloud Platform Console.
Check payment history
In the Samsung Cloud Platform Console, you can view a user’s account payment history by month.
To use the payment history, follow these steps.
- Click the All Services > Financial Management > Cost Management menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Payment History menu. You will be taken to the Payment History page.
- Payment History page lets you view the payment history for the relevant Account.
Item description Billing Year-Month Billing reference year-month Billing amount The amount that adds the accumulated unpaid balance to the current month’s usage amount. Usage amount Current month usage amount Handsome amount (current month) Unpaid amount for the current month Handsome amount (cumulative) Total outstanding amount Payment amount Display the actual payment currency symbol rather than the account’s contract currency. Payment date Date of credit card payment Payment status Payment status - Normal: Payment completed
- Delinquent: Overdue for more than 1 month
Table. Payment details items
- All fees are exclusive of VAT.
- The outstanding amount will be re‑billed on next month’s billing date.
Download detailed Excel
You can download the payment history as an Excel file.
To download the payment history as an Excel file, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Payment History menu. You will be taken to the Payment History page.
- On the Payment History page, click the Download Detailed Excel button.
- Please check the downloaded Excel file.
11.1.2.3 - Cost Analysis
Users can view cost analysis data, such as the estimated or actual charges for up to six months, the monthly average charge, and the top 5 costs for their account, through the cost analysis in the Samsung Cloud Platform Console.
Check cost analysis
You can view cost analysis in the Samsung Cloud Platform Console.
To check the cost analysis, follow the steps below.
- The billing calculation reference is midnight in the Asia/Seoul (GMT +09:00) time zone. The estimated data may differ from the actual.
- You can set up an abnormal cost detection alert to trigger a notification when the usage amount increases by more than 100% compared to the previous day.
- Weekends are excluded from the comparison group.
- New resources are excluded from detection for two weeks.
- The default alarm sender is set to the Root user.
- To add notification policies and notification groups, add [Billing System] Anomlay Detection Notification as a notification in the Samsung Cloud Platform notification settings.
- For detailed information about notification settings, see Check Notification Settings.
- Click the All Services > Financial Management > Cost Management menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Analysis menu. You will be taken to the Cost Analysis page.
- On the Cost Analysis page, you can view the cost analysis for the relevant Account.
- If you select the query period in the upper right corner, you can view the cost analysis for that period.
- The query period can be set for a maximum of six months, from the start date to the end date.
- For the query period, refer to each of the following: When the billing unsettled month is included, When only the billing settled month is present, When only the billing unsettled month is present, When only the current month is included.
- The query period is defined from the 1st of the start month to the last day of the end month.
- Provides a graph visualized based on the search period.
- When selecting a service group, colors are applied to each group, and on mouse over, the group’s color and amount information are displayed in a tooltip.
*is displayed when it is the estimated amount.
- You can view detailed cost breakdowns on the Cost Analysis page.
Item description service group Resource Service Group Notation Service Resource service name display Resource name Resource name notation Billing amount or estimated billing amount* The resource’s billed amount or estimated billed amount is displayed. Table. Cost analysis detailed breakdown items
If the query period includes a month with unsettled billing
In cost analysis, if the query period includes months with unbilled charges, we provide the total estimated charge amount*, monthly average charge amount, estimated monthly average charge amount*, and a graph.
| Item | Explanation |
|---|---|
| Total estimated billing amount* | Estimated usage amount from the 1st of the current month to one day before the query date |
| Monthly average billing amount | The invoice amount forecasted from the usage amount trend from the 1st to the end of the current month. |
| Estimated monthly average billing amount* | Estimated monthly average billing amount for the query period |
| Monthly graph | Monthly graph provided
|
If only the billing settlement month falls within the query period
In cost analysis, when only billing settlement months exist within the query period, we provide total billing amount, monthly average billing amount, top 5 costs, and a graph.
| Item | description |
|---|---|
| Total billed amount | Actual billed amount and discount amount within the query period |
| Monthly average billing amount | Average actual billed amount and discount amount within the query period |
| Cost Top5 | Top 5 costs and discount amounts within the query period |
| Monthly graph | Monthly graph provided |
If only months with unbilled charges exist within the query period
In cost analysis, when only unsettled months are included within the query period, we provide the total estimated charge amount*, the monthly average charge amount, the estimated monthly average charge amount*, and a graph.
| Item | Explanation |
|---|---|
| Total estimated billing amount* | Estimated billing amount and discount amount for the query period |
| Monthly average billing amount | Marked as no data |
| Estimated monthly average billing amount* | Estimated billing amount for the month from the 1st to the end. |
| graph | Monthly graph provided |
When the query period includes only the current month
In cost analysis, when only the current month is included within the query period, we provide the usage amount, estimated billing amount*, monthly average billing amount, and a graph.
| Item | Explanation |
|---|---|
| Usage amount* | Estimated usage amount from the 1st of the current month to the day before the query date |
| Estimated billing amount* | Estimated billing amount from the 1st of the month to the end of the month |
| Monthly average billing amount | Average billed amount for the past six months |
| graph | Daily graph/Daily cumulative graph |
Download detailed Excel
You can download the detailed cost analysis as an Excel file.
To download the detailed cost analysis as an Excel file, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Analysis menu. You will be taken to the Cost Analysis page.
- On the Cost Analysis page, click the Detailed Excel Download button.
- Please check the downloaded Excel file.
Item Explanation Contract number Ledger ID (unique key of the instance) Account ID Account ID Account name Account name Billing Year-Month Expense billing year-month Service Service group type Service name Resource name Resource name Region Resource usage region name Unit price Rate unit and rate criteria Usage Resource usage time Call Account’s currency Usage amount Amount before discount Planned Compute Discounted amount with Planned Compute Termination fee Termination fees are incurred for terminated resources. They apply for the termination date plus two months. Total amount used Usage amount + termination fee - Planned Compute amount SLA SLA discount amount Credit Credit applied amount Other discounts Total discount excluding SLA/Credit discount Billing amount Final payable amount after discount is deducted from the total usage amount Table. Download detailed cost analysis Excel
11.1.2.4 - Credit Management
Users can view and manage the monthly usage of the credits they have received through the Samsung Cloud Platform Console.
Check Credit
You can view the credits received in the Samsung Cloud Platform Console. To check your credit, follow these steps.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Credit Management menu. You will be taken to the Credit Management page.
- Credit Management page, view the monthly usage of Credit.
Credit Summary Information: You can view summary information for valid Credit and expired Credit.
Category Detailed description Summary classification Select Credit type to view summary information - Valid Credit: Summary information of currently valid Credit
- Expired Credit (last 6 months): Summary information of Credit that expired within the past 6 months
Summary information Summary information by category - Valid Credit
- Total remaining Credit: Total amount of Credit remaining
- Total used Credit: Total amount of Credit used
- Number of active Credits: Total count of valid Credits
- Expired Credit (last 6 months)
- Total remaining Credit: Total amount of Credit not used
- Total used Credit: Total amount of Credit used
- Number of expired Credits: Total count of expired Credits
Table. Credit summary itemsCredit Detailed Information: You can view detailed information for each Credit type. If you click the Expand button at the far right of the Account item, monthly details are displayed.
Category Detailed description Category Credit type Validity period The usage amount for the month shown as the validity period is applied. - In the credit expiration month, a Extend button appears.
Payment Credit Credits issued for each Credit type and issuance date Remaining Credti Remaining credit amount after subtracting the total used credit from the credits received Usage month You can view the monthly limit amount set by the user for that month. - In the current month, a Set Limit button appears, allowing you to set the amount of Credit you wish to use for the month within the remaining Credit.
Monthly limit This is the monthly limit amount set by the user. If not set, it shows the same amount as the remaining Credit each month. Monthly usage credit This is the credit cost actually incurred within the monthly limit set for that month. Monthly remaining Credit This is the cost after subtracting the Credit actually used from the monthly limit amount set for that month. The remaining balance is included in the remaining Credit. Table. Credit Details
Extend Credit
In the credit expiration month, you can see the Extend button to the right of the validity period.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Credit Management menu. You will be taken to the Credit Management page.
- On the Credit Management page, click the Extend button. The Credit Extension popup opens.
- Select the desired extension period among 1 month, 2 months, and 3 months, then click the Confirm button.Caution
- Any remaining Credit that is not extended within the extension period will be forfeited when the period expires and can no longer be used.
- Credit extensions are allowed only once, and after the extension is completed, the extended usage period cannot be changed.
- Credit extensions can only be changed if you have IAM permissions or are a Root Account or Organization Manager Account.
Configure Credit Limit
In Credit management, the user can set the amount to be deducted as credit from the current month’s usage amount.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Credit Management menu. You will be taken to the Credit Management page.
- Click the Set Limit button on the Credit Management page. The Credit Limit Setting popup opens.
- Credit limit setting Check the Credit balance in the popup window.
- Automatic Full Deduction setting disables the Credit monthly limit input field and automatically deducts the full amount each month.
- If you disable the Automatic Full Deduction setting, the Credit monthly limit input field becomes active, allowing you to set the limit amount.
- Credit monthly limit Enter the amount you want to deduct each month in the input field.
- The entered amount remains the same until the Credit period expires, and if the remaining Credit amount is less than the monthly set limit, the monthly limit will be the remaining Credit amount.
- Amounts greater than the remaining Credit amount cannot be entered.Reference
- If you do not set a credit limit, the full amount will be automatically deducted.
- Until the middle of each month, which is the settlement period for the previous month’s billed amount, the Limit Setting button does not appear.
Caution- Since modifications are not possible after the set limit by 23:00 on the last day of each month (Asia/Seoul (GMT +09:00)), please be sure to check the monthly limit.
- Credit limit settings can only be changed if you have IAM permissions, or if you are a Root Account or Organization Manager Account.
11.1.2.5 - Budget Management
Users can enter the required budget management information through the Samsung Cloud Platform Console, select detailed options, and create the service.
Create Budget
You can create and use a budget in the Samsung Cloud Platform Console. To create a budget, follow these steps.
Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
On the Service Home page, click the Create Budget button. You will be taken to the Create Budget page.
On the Budget Creation page, enter the information required for budget creation and select detailed options.
Category Required Detailed description Budget Name Required Enter the budget name to distinguish it when creating multiple budgets. - Use Korean, English, numbers, spaces, and special characters (
+=.,@-_) within 20 characters.
Management type Required Select a budget management method. - Monthly Budget Setting: The used amount is reset and calculated on a monthly basis, and you can set a notification when the used amount reaches the set amount.
- Total Budget Setting: The used amount is accumulated from the configured month onward for calculation, and you can set a notification when the used amount reaches the set amount.
Budget Required Enter the budget based on this month’s usage amount. Start month Required Select the month to start budget management. - Budget management will be applied starting from the usage amount of the start month.
Threshold reached notification Select Set whether to send notifications when the budget consumption rate reaches the threshold. - If enabled, configure the notification method additionally.
- Notification Timing: You can set to receive a notification email when the budget consumption rate reaches this point.
- Notification Sending: Set whether the email should be sent repeatedly when the threshold notification timing is reached.
- First Notification Only: Sent once on the day after the threshold is reached, based on midnight (Asia/Seoul, GMT +09:00).
- Daily Notification: Sent daily starting the day after the threshold is reached, based on midnight (Asia/Seoul, GMT +09:00).
- Notification Recipients: Enter the email address to receive the threshold notifications.
Prevent new creation Select New creation prevention usage restricts the creation of new services included in the Compute or Database service groups. - When using it, additionally set the prevention timing and notification recipients.
- New Creation Prevention Timing: Restricts the creation of new services when the budget consumption rate reaches this point.
- Notification Recipient: Enter the email address to receive notifications when the new creation prevention timing is reached.
Table. Budget creation input informationguideNew Creation Prevention feature target services (as of December 2025) are as follows.
- Virtual Server, Database Category, Event Streams, Serch Engine, Vertica, Oracle Service
- Use Korean, English, numbers, spaces, and special characters (
Verify the input content and click the Create button. A popup notifying budget creation will open.
Click the Confirm button. Budget creation is complete.
- Completed budgets can be viewed on the Budget Management list page.
Check the budget management list
Budget management allows you to view and edit the entire budget list. To view the budget management information, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Budget Management menu. You will be taken to the Budget Management page.
- You can view the list of budgets set on the Budget Management page.
Category Detailed description Budget Name Budget name for distinguishing generated budgets Management Type You can see the type for managing the budget. - Monthly budget setting: reset the used amount on a monthly basis
- Overall budget setting: accumulate the used amount from the set month onward
Budget set amount Check the configured budget. This month’s usage amount Displays the amount used for the Account up to yesterday in the current month. consumption rate It shows the ratio of the amount used up to the previous day this month compared to the budgeted amount. - For the total budget, it is calculated as the sum of this month’s usage from the start month.
- For budgets that have not started, the consumption rate cannot be determined.
Estimated usage amount for this month It represents the estimated total usage amount for this month, based on the usage fees up to yesterday in the current month of the Account. Estimated depletion rate It shows the ratio of the expected usage amount for this month to the budgeted amount. - For the total budget, it is calculated as the sum of the expected usage amounts from the start month to this month.
- For budgets that have not started, the expected consumption rate cannot be determined.
Start month It indicates the month when the usage amount starts to be applied to budget management. More button You can click the More button in the list to go to the Budget Edit page. Table. Budget Management List Information
Modify Budget
The user can modify the budget they created. To edit the budget management information, follow these steps.
All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
On the Service Home page, click the Budget Management menu. You will be taken to the Budget Management page.
In the list, click the More button > Edit Budget button. You will be taken to the Edit Budget page.
On the Budget Modification page, enter the information that needs to be updated and select the detailed options.
Category Required or not Detailed description Budget Name Required Enter the budget name to distinguish it when creating multiple budgets. - Use Korean, English, numbers, spaces, and special characters (
+=.,@-_) to input within 20 characters.
Management type Required Select a budget management method. - Monthly Budget Setting: The used amount is reset each month for calculation, and you can set a notification when the used amount reaches the set amount.
- Overall Budget Setting: The used amount is accumulated from the configured month for calculation, and you can set a notification when the used amount reaches the set amount.
Budget Required Enter the budget based on this month’s usage amount. Start month Required Select the month to start budget management. - The usage amount from the start month will be applied to budget management.
Threshold reached notification Select Set whether to send notifications when the budget consumption rate reaches the threshold. - If enabled, configure the notification method additionally.
- Notification Timing: You can set to receive a notification email when the budget consumption rate reaches this point.
- Notification Sending: Set whether the email should be sent repeatedly when the threshold notification timing is reached.
- First Notification Only: Sent once on the day after the threshold is reached, based on midnight (Asia/Seoul, GMT +09:00).
- Daily Notification: Sent daily starting the day after the threshold is reached, based on midnight (Asia/Seoul, GMT +09:00).
- Notification Recipients: Enter the email address to receive the threshold notifications.
Prevent new creation Selection When new creation prevention is enabled, the creation of new services included in the Compute or Database service groups is restricted. - When using it, additionally set the prevention timing and notification recipients.
- New Creation Prevention Timing: Restricts the creation of new services when the budget consumption rate reaches this point.
- Notification Recipient: Enter the email address to receive notifications when the new creation prevention timing is reached.
Table. Budget modification input informationCautionIf you change the budget amount or threshold breach notification settings, existing notifications may be reset and resent.- Use Korean, English, numbers, spaces, and special characters (
Verify the entered content and click the Complete button. A popup notifying budget changes will open.
Click the Confirm button. Budget creation is complete.
- The revised budget can be viewed on the Budget Management list page.
Delete Budget
Unused budgets can be deleted. However, because a budget cannot be recovered once deleted, you should carefully consider the impact before proceeding with the deletion.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Budget Management menu. You will be taken to the Budget Management page.
- In the list, click the More button > Delete budget button. A notification popup appears for budget deletion.
- Confirm button, when clicked, will delete the budget.
- After deletion is complete, verify the budget’s deletion status on the Budget Management list page.
11.1.2.6 - Cost Savings
Users can set time commitments for instance-based services in the Compute, Database, and Data Analytics service categories of the Samsung Cloud Platform Console to reduce usage costs.
Apply for Cost Savings
You can apply for and use Cost Savings in the Samsung Cloud Platform Console. To apply for Cost Savings, follow the steps below.
All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
On the Service Home page, click the Cost Savings Apply button. You will be taken to the Cost Savings Plan Apply page.
Cost Savings Plan Application page: enter the information required for the Cost Savings plan application.
Category Required? Detailed description Plan Group Required Select the plan group to configure the plan - If the plan group you want to configure does not exist, create a plan group on the plan group list page first, then proceed
- For details on creating a plan group, see Cost Savings Create Plan Group
Plan name Required Enter the name of the plan to create - Plan cannot be changed after creation
Reference usage fees Select Select past billing period to reference - 7 days (default), 30 days, 60 days selectable
- When selected, recommends an hourly commitment rate based on the charges during that period
- If there is an existing applied Cost Savings, it is excluded from the billing history before recommendation
- Billing plan can be entered manually
View charge history Select Select the previous billing verification period to reference when recommending a pricing plan - 7 days, 30 days, 60 days
- If there is an existing Cost Savings applied, exclude the existing Cost Savings from the billing history
Contract period Select Select plan application period Hourly contracted amount (₩) Select Enter hourly contract amount - Recommended contract amount: Analyzes non-contract usage history to recommend a contract amount. Varies by contract period
- Manual entry: Directly enter the hourly contract amount
Plan start date Required Select plan start date - Selectable from the day after application
Table. Cost Savings application information- If the plan group you want to configure does not exist, create a plan group on the plan group list page first, then proceed
After checking the estimated discount amount, click the Create button.
When the popup that notifies a Cost Savings request opens, click the Confirm button.
- When creation is complete, check the created budget on the Budget Management list page.
- Grouping into a plan group shares the plan amount with other accounts within the organization.
- A single plan group cannot be shared.
Cost Savings Plan Group Management
You can create and manage Cost Savings plan groups.
Create Cost Savings Plan Group
- Organization Management Account can create plan groups for Member Accounts and share the committed amount between groups.
- Plan groups can only be created from a Management Account. However, if the account belongs to a plan group created by a Management Account, a Member Account can create a plan group that only it belongs to.
To create a Cost Savings plan group, follow the steps below.
Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
On the Service Home page, click the Cost Savings > Cost Savings Plan Group menu. You will be taken to the Cost Savings Plan Group List page.
On the Cost Savings Plan Group List page, click the Plan Group Creation button. You will be taken to the Plan Group Creation page.
Cost Savings Plan Group Application page, after setting the basic information and target Account, click the Create button.
Category Required? Detailed description Plan group name Required Enter the name of the plan group - using Korean, English, numbers, and special characters (+=,.@-_) to be between 3 and 24 characters
Explanation Select Explanation of the plan group Target Account Required Select the Account for the plan group Table. Cost Savings plan group application informationReferenceWhen selecting Target Account, any target account already belonging to the plan group created by the Management Account will not appear in the list.When the popup notifying the creation of a plan group opens, click the Confirm button.
Cost Savings View detailed information of the plan group
You can view the list of Cost Savings plan groups that are currently applied or pending, along with detailed information. To view detailed information of the Cost Savings plan group, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Savings > Cost Savings Plan Group menu. You will be taken to the Cost Savings Plan Group List page.
- Click the plan group name to view detailed information from the Cost Savings list. You will be taken to the Cost Savings Plan Group Details page.
- Cost Savings Plan Group Details page consists of Basic Information, Plan, Coverage, Utilization tabs.
Basic Information
You can view basic information about the plan group.
| Category | Detailed description |
|---|---|
| constructor | Plan Group Creator |
| Creation date and time | Plan group creation date and time |
| Editor | Plan Group Modifier |
| Modification date | Plan Group Modification Date and Time |
| Plan group name | Plan group name
|
| Plan Group ID | Plan group ID |
| Contract period | Contract term of the plan group |
| Explanation | Description of the plan group
|
| Create Account | Create Plan Group Account |
| Target Account | Plan group target Account
|
Plan
You can view the plan information included in the plan group.
| Category | Detailed description |
|---|---|
| Plan | Plan ID, contract period, hourly contract amount, start date, status display
|
| Monthly billing amount | Basic information and billing amount details by plan ID
|
| Cancel application | Cancel plan application
|
- Register Cost Savings as a notification to receive alerts when the contract expires or when usage exceeds or falls short of the contracted rate.
- Cost Savings If the contract expiration date is approaching, a notification email is sent 60, 30, 7, and 1 days in advance.
- If an excess (Cost Savings Coverage not met) or shortfall (Cost Savings Utilization not met) in contract utilization occurs, a notification email will be sent.
- For detailed information about notification settings, refer to Notification.
Coverage
You can view coverage with Cost Savings applied to non‑contracted resources for a specific period.
| Category | Detailed description |
|---|---|
| Total estimated amount (no contract) | Total amount of non‑contract instances during the configured period
|
| Total cover amount | Total coverage amount for the set period |
| Coverage (%) | Proportion of Coverage amount among the estimated non-contract amount for the set period
|
| Used resources | Plan start date |
| Usage time | Plan start date |
| No contract | Plan expiration date |
| Cost Savings | Hourly contracted amount |
| Cost Savings Unapplied Amount | Plan application status
|
- Since it displays based on the amount used up to two days before the query date, the current month’s amount is not shown on the 1st and 2nd of each month.
- Click the Detailed Excel download button to download detailed information about the Coverage amount as an Excel file.
Utilization
You can view the used amount, unused amount, and savings amount relative to the committed amount for Cost Savings.
| Category | Detailed description |
|---|---|
| Plan ID | Plan group ID |
| Total contracted amount | Total contracted amount of the plan group |
| Usage Amount | Amount used compared to the contracted amount |
| Unused amount | The unused amount of the plan’s contracted amount calculated as ‘Total contracted amount - Used amount’ |
| Utilization (%) | Proportion of used amount relative to total contracted amount |
| Savings amount | Difference between the instance’s non‑contracted amount and the actual plan‑applied amount for instance usage (including the plan’s committed amount) |
| Expiration date | Contract end date of the plan |
- Since it displays amounts based on usage up to two days before the query date, the current month’s amount is not shown on the 1st and 2nd of each month.
- Excel Download button when clicked allows you to download detailed Utilization information as an Excel file.
Delete Cost Savings plan group
You can delete the Cost Savings plan group.
Cost Savings To delete the plan group, follow these steps.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Savings > Cost Savings Plan Group menu. Navigate to the Cost Savings Plan Group List page.
- After selecting all plan groups to delete from the Cost Savings plan group list, click the Delete button at the top of the list.
- You can also delete individually by clicking the Delete Plan Group button on the Cost Savings Plan Group Details page.
- When a popup indicating deletion opens, click the Confirm button.
Cost Savings Plan Management
You can create and manage Cost Savings plans.
Apply for Cost Savings plan
To apply for a new Cost Savings plan, follow the steps below.
- All Services > Financial Management > Cost Management Click the menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Savings > Cost Savings plan menu. You will be taken to the Cost Savings plan list page.
- On the Cost Savings Plan List page, click the Plan Apply button. You will be taken to the Cost Savings Plan Apply page.
- On the Cost Savings Plan Application page, enter the information required for the Cost Savings plan application.
- After checking the estimated discount amount, click the Complete button.
- When the popup notifying the Cost Savings application opens, click the Confirm button.
- When creation is complete, check the created budget on the Budget Management list page.
- If you group into a plan group, the plan cost is shared with other accounts within the organization.
- A single plan group cannot be shared.
Cost Savings Check detailed plan information
You can view the list of Cost Savings plans that are currently applied or pending, along with detailed information. To view detailed information of the Cost Savings plan, follow the steps below.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Cost Management Service Home page.
- On the Service Home page, click the Cost Savings > Cost Savings Plan menu. You will be taken to the Cost Savings Plan List page.
- Click the plan name to view detailed information from the Cost Savings list. Cost Savings Plan Details page will be opened.
- Cost Savings Plan Details page consists of Basic Information, Tag tabs.
Basic Information
You can view basic information about the plan group.
| Category | Detailed description |
|---|---|
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Service’s unique resource ID |
| constructor | User who created the service |
| Creation Date/Time | Service creation timestamp |
| Editor | User who modified the service |
| Modification date | Date and time the service was modified |
| constructor | Plan creator |
| Creation date and time | Plan creation date and time |
| Editor | Plan Group Modifier |
| Modification date | Plan modification date and time |
| Plan name | Plan name |
| Plan group name | Name of the plan group set in the plan |
| Plan ID | Plan ID |
| Contract period | Plan commitment period |
| Hourly contracted amount | Hourly contracted amount |
| Start date | Plan start date
|
| Expiration date | Plan expiration date |
| Create Account | Create Plan Group Account |
- You can register Cost Savings as a notification to receive alerts when the contract expires or when contract usage exceeds or falls short.
- Cost Savings If the contract expiration date is approaching, a notification email is sent 60, 30, 7, and 1 days before.
- When the contract utilization exceeds (Cost Savings Coverage not met) or is insufficient (Cost Savings Utilization not met), a notification email is sent.
- For detailed information on notification settings, see 알림.
tag
You can view a plan’s tag information and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Cost Savings Plan Termination
You can cancel the Cost Savings plan you are currently enrolled in.
To cancel the Cost Savings plan, follow the steps below.
- Click the All Services > Financial Management > Cost Management menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Cost Savings > Cost Savings plan menu. You will be taken to the Cost Savings plan list page.
- After selecting all plans to cancel in the Cost Savings plan list, click the Delete button at the top of the list.
- You can also cancel individually by clicking the Plan Cancellation button on the Cost Savings Plan Details page.
- When the pop-up notifying termination opens, click the Confirm button.
11.1.2.7 - Account
When you sign up for the Samsung Cloud Platform Console, an account is created, and the person who creates the account becomes the Root user. In the Account, you can view account information and manage account aliases.
Check Account Information
To check the Account information, follow these steps.
Please refer to Register a payment method for information on registering a payment method.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Service Home page of Cost Management.
- On the Service Home page, click the Account menu. You will be taken to the Account page.
- You can also navigate by clicking My menu > Account in the top right corner of the Console.
- Check the Account information on the Account page.
Item description Account name The name assigned to an Account when creating the Account. It allows the Account to be easily identified when managing multiple accounts. AccountID The unique identifier of the Account. Used when an IAM user logs in. Account alias Alias assigned to an Account when creating the Account. - When managing multiple Accounts, it helps to easily identify the Account for billing management and other purposes.
- IAM users can log in to the Console using the Account alias.
- Edit: Modify the Account alias. See Edit Account Alias.
- Delete: Delete the Account alias. See Delete Account Alias.
Company Name Company name entered when registering a payment method Table. Account detailed information
Modify account alias
To modify the account alias, follow these steps.
- Click the All Services > Financial Management > Cost Management menu. You will be taken to the Cost Management Service Home page.
- Click the Account menu on the Service Home page. You will be taken to the Account page.
- You can also navigate by clicking My menu > Account in the upper right corner of the Console.
- Account page, click the Edit button in the Account alias field. You will be taken to the Edit Account alias popup.
- Edit Account Alias After reviewing the instructions in the popup window, edit the Account alias and click the Confirm button.
Delete Account Alias
- If you delete the account alias, IAM users can no longer log in using the account alias.
- The IAM login URL cannot be used either.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Account menu. You will be taken to the Account page.
- You can also navigate by clicking My menu > Account in the upper right corner of the Console.
- On the Account page, click the Delete button in the Account alias item. It moves to the Account alias deletion popup window.
- Delete Account Alias After reviewing the instructions in the popup window, click the Confirm button.
11.1.2.8 - Payment Management
You can view and add payment methods registered to the Account in the Samsung Cloud Platform Console.
Check payment method
You can view the payment methods registered to the Account in the Samsung Cloud Platform Console.
To verify the payment method, follow these steps.
- All Services > Financial Management > Cost Management > Payment Management Click the menu. You will be taken to the Payment Management page.
- On the Payment Management page, you can view the registration date and alias of the currently registered payment methods.
- To view and edit account information, a payment method must be registered.
- If you belong to an Organization, the charge will be billed to the Management Account’s payment method.
Change payment method
You can change the payment method registered to the Account in the Samsung Cloud Platform Console.
- All Services > Financial Management > Cost Management > Payment ManagementClick the menu. Payment Managementpage will be opened.
- Payment method Click the edit button on the right to change the payment method.
- Through the Create Alias button of a registered payment method, you can register an alias for the payment method to distinguish it, and you can delete it via Delete Alias.
Register Payment Method
You must register a payment method to use all services of the Samsung Cloud Platform. To register a payment method, follow these steps.
- All Services > Financial Management > Cost Management > Payment Management Click the menu. You will be taken to the Payment Management page.
- If no payment method is registered, the Add Payment Method button is enabled. Click the Add Payment Method button.
- Please enter the business registration number, then provide the company name, representative name, and address.
- If there is a transaction history with Samsung SDS, the company name, representative name, and address are automatically entered.
If a lot-number address is entered, it may be necessary to convert it to a road name address and save it.
- If there is a transaction history with Samsung SDS, the company name, representative name, and address are automatically entered.
- After attaching the applicant’s business card and business registration certificate, click the Next button to proceed with payment method registration.
11.1.2.9 - carbon emissions
It visualizes the carbon emission data generated when using services in the Samsung Cloud Platform Console, allowing you to track emission trends. You can also estimate the expected carbon emissions that could have been reduced by using Samsung Cloud Platform instead of an on‑premise data center, and review the emissions predicted based on current usage.
Check carbon emissions
You can view the carbon emissions by service in the Samsung Cloud Platform Console.
To check the carbon emissions per service, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. 1. Navigate to the Service Home page of Cost Management.
- On the Service Home page, click the Carbon Emissions menu. 2. Go to the Carbon Emissions page.
- In the period setting area at the top right, set the period for viewing carbon emissions. 3. The carbon emissions for the selected period are displayed.
Check this month’s carbon emissions
Carbon Emissions page’s period setting area, click the This month button.
| Category | Detailed description |
|---|---|
| Carbon emissions by period | Carbon emissions from day 1 to now and On-prem. comparison carbon emissions
|
| Carbon Emission Trend | Graph comparing carbon emission trends with the previous month
|
| Monthly average carbon emissions | Average carbon emissions over the past 6 months |
| Carbon Emissions Graph | Carbon emission graph from day 1 to the present
|
| Carbon emissions by service | Carbon emissions by service from day 1 to the present
|
- Data is not displayed on the 1st of each month. * (based on Asia/Seoul, GMT +09:00)
- The month‑end estimate is a projection based on the current emissions.
- Carbon emissions are rounded after summing the fractional amounts for each service group, so the total may differ.
- Indirect Service group: Includes emissions generated from all usage services except Compute and Storage services.
Check carbon emissions for a specific period
Carbon emissions page’s period setting area, click the Direct button, then select the period for which you want to view carbon emissions.
| Category | Detailed description |
|---|---|
| Carbon emissions by period | Total carbon emissions during the set period and On-prem. comparison display
|
| Carbon emission trend | Display the carbon emission trend over the selected period as a graph
|
| Monthly average carbon emissions | Average carbon emissions during the set period |
| Carbon Emissions Graph | Carbon emissions graph for the selected period
|
| Carbon emissions by service | Carbon emissions by service during the set period
|
- Carbon emissions are rounded after summing the fractional amounts for each service group, so the total may differ.
- Indirect service group: includes emissions from all other usage services except Compute and Storage services.
11.1.2.10 - EDP Report
When you have an EDP contract, you can view the contract information and usage cost details.
EDP Report Check Basic Information
Follow these steps to view the basic information of the EDP Report.
- All Services > Financial Management > Cost Management Click the menu. Go to the Service Home page of Cost Management.
- Click the EDP Report menu on the Service Home page. You will be taken to the EDP Report page.
| Category | Detailed description |
|---|---|
| Company name | Company name |
| Target information | Samsung Cloud Platform offering and target ID information by version
|
| Contract period | Contract period |
| Whether it is an annual contract | Whether it is an annual contract |
| Contract amount | Annual commitment amount
|
| Base discount rate | Base discount rate upon agreement |
| Discount rate per product | Discount rate per product when contracted
|
Check EDP Report
To view the EDP Report, follow these steps.
- All Services > Financial Management > Cost Management Click the menu. Navigate to the Service Home page of Cost Management.
- Click the EDP Report menu on the Service Home page. You will be taken to the EDP Report page.
- On the EDP Report page, click the Report tab.
| Category | Detailed description |
|---|---|
| EDP cumulative graph | Total contracted amount data for the EDP contract
|
| EDP Details | Contract period, contract amount, offering, target ID, usage amount, shortage and excess amount display
|
11.1.3 - Release Note
Cost Management
- The CX for checking usage and billing details has been updated.
- You can view the estimated discount amount when checking usage and billing details.
- If there is an abnormal cost detection record, you can receive an Excel file at the email registered in the Console and review it.
- When downloading usage and billing details, we also provide billing information for each resource, such as Account ID, instance type, OS, contract period, unit price, and unit basis.
- When a new service is created within Samsung Cloud Platform, carbon emission data is automatically linked.
- You can register cost management as a notification, allowing you to trigger an alert when an abnormal sign is detected in usage details.
- If the usage amount changes by 100% or more compared to the change from the day before yesterday to yesterday, a notification is sent.
- Weekends are excluded from the control group.
- New resources are excluded from detection for two weeks.
- The default alarm sender is set to the Root user.
- To add notification policies and notification groups, add [Billing System] Anomlay Detection Notification as a notification in the Samsung Cloud Platform notification settings.
- You can register Cost Savings as a notification to receive alerts when the commitment expires or when contract utilization exceeds or falls short.
- You can download the Cost Savings plan list as an Excel file.
- Carbon emission calculation formula improvement: We improved the carbon emission calculation formula by taking into account factors such as electricity consumption.
- Credit Management page lets you view summary information of valid Credits and expired Credits.
- A feature for budget management has been added.
- When creating a budget, you can specify the month when the budget application starts.
- You can configure it to restrict the creation of new services when the budget consumption rate reaches that point.
- Cost Savings, Carbon Emissions feature has been added.
- Cost Savings: You can reduce usage costs by setting a time commitment for the Compute services of the Samsung Cloud Platform Console.
- Carbon Emissions: You can view the carbon emissions generated when using services on the Samsung Cloud Platform Console.
- We have launched the Cost Management service. * You can manage and optimize service costs.
- Provides usage and billing details, cost analysis, and Credit management features.
- You can set and manage budgets, and it provides Account and payment method information.
11.2 - Planned Compute
11.2.1 - Overview
Service Overview
Planned Compute is a pricing policy that allows you to use resources up to 40% cheaper than on‑demand by committing to a 1‑year or 3‑year server type. It applies to resources in the on‑demand Compute, Database, and Data Analytics service families. When the attributes applied to Planned Compute match the attributes of the on‑demand resources, the discounted Planned Compute rate is applied automatically. You can view the discounts applied through Planned Compute in the Report and, if needed, submit an additional Planned Compute request.
Features
Planned Compute is a contract‑based discount service offered by Samsung Cloud Platform, allowing you to select the desired operating system and server type. It provides high flexibility by letting you apply for discounts for a contract period of one to three years without specifying particular resources.
- Discounted Pricing: Planned Compute is a pricing discount policy that allows resources to be used up to 40% cheaper than on‑demand, provided a 1‑year or 3‑year usage commitment. It applies to resources in the on‑demand Compute service category, Analytics service category, and Database service category, and when the attributes applied to Planned Compute match the attributes of the on‑demand target resources, the Planned Compute discount pricing is automatically applied.
- Various Feature Support: Planned Compute provides various functions such as application, extension, and server type changes. When applying for Planned Compute, select the contract‑discount‑eligible service, operating system, server type, and contract period, then enter the desired quantity to submit the request.
- Convenient Management and Monitoring: By checking the Planned Compute list, you can view Planned Compute usage information and modify the application details when contract terms need to be changed. Additionally, by reviewing Coverage, you can compare the Planned Compute usage cost against the amount used without a contract, enabling convenient management.
Service Architecture Diagram
Provided features
Planne Compute provides the following features.
- Planned Compute Service Application: Select the service, operating system, server type, and contract period for which you want to receive a contract discount, enter the requested quantity, and after confirming the application information, you can apply for Planned Compute.
- Planned Compute Extension: When the contracted period ends, the corresponding Planned Compute is terminated, and discounts no longer apply to on-demand resources. Planned Compute termination does not mean that on-demand resources are terminated. If you wish to extend the discount period, you can use the contract extension feature to schedule the next contract period after the current contract period ends.
- Planned Compute Server Type Change: The server type of Planned Compute can be changed to a value higher than the configured setting.
- Planned Compute termination: Unused Planned Compute can also be terminated, but upon termination, 50% of the usage fee for the remaining period will be billed two months after termination. Termination of Planned Compute does not imply termination of resources without a contract.
- Coverage Check: You can check the discount Coverage of on-demand resource usage amounts for the same target service, operating system, and server type. Select the period you want to query to display the on-demand resource name, usage time, the amount used without discount, and the amount not covered by Planned Compute. This allows you to see the difference in billed amounts between on-demand usage and Planned Compute usage.
Constraints
The constraints of Planned Compute are as follows.
- The application, modification, and coverage are all based on midnight in the Asia/Seoul (GMT +09:00) time zone.
- If you apply for Planned Compute, the discount will be applied starting at midnight the day after the application date.
- Coverage can be checked up to 2 days in advance to calculate the exact discount amount.
- Every day from 23:30 to 23:59 is the settlement window, during which new applications and changes are not applied.
- Discounts are applied to on-demand resources within the same region of the same account.
Preliminary Service
Planned Compute does not require any separate prerequisite service work.
11.2.2 - How-to Guides
Users can apply for the service by entering the required information for Planned Compute through the Samsung Cloud Platform Console.
Apply for Planned Compute
You can request and use the Planned Compute service from the Samsung Cloud Platform Console.
To apply for Planned Compute, follow these steps.
Click the All Services > Financial Management > Planned Compute menu. Navigate to the Service Home page of Planned Compute.
On the Service Home page, click the Planned Compute Apply button. You will be taken to the Planned Compute Apply page.
On the Planned Compute Application page, after entering the required information, click the Next button.
Item RequiredExplanation Service Required Select the service for which you want to apply for Planned Compute Operating system Required Select the operating system - After selecting the Service item, selection is possible
- Depending on the selected service, Open Source, RHEL, Windows, etc. can be selected
Server type Required Select the server type - After selecting the service item, selection is possible
Contract period Required Select contract period - Server Type After selecting the item, selection is possible
- 1-year or 3-year can be selected
Requested quantity Required Enter the requested quantity - Up to 100 units can be entered
- After applying the Planned Compute quantity, refunds are not possible, so caution is required when entering
- If an increase in quantity is needed, you can add a new Planned Compute of the same server type
Agreement start date Required Select the date when the contract becomes effective - Can be set starting from the day after the application date
Table. Planned Compute service input informationCheck the detailed information and estimated charges generated in the Summary panel, and click the Complete button.
When the popup notifying the creation of Planned Compute opens, click the Confirm button.
- After the request is completed, check the resources you created on the Planned Compute List page.
Check Planned Compute List
You can view and edit the full list of resources and detailed information for Planned Compute.
To view the list of Planned Compute, follow the steps below.
Click the All Services > Financial Management > Planned Compute menu. Navigate to the Service Home page of Planned Compute.
On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute list page.
On the Planned Compute List page, click the contract number of the Planned Compute to view detailed information. You will be taken to the Planned Compute Details page.
- Resource items other than the required columns can be added via the Settings button.
Item Required Explanation Contract number Required Key values for each billing unit visible in the invoice details Resource Name Select Resource contract number Target Service Required Planned Compute discount-eligible service - Apply discount to non-contract resources that match the given value
Server type Required Planned Compute discount-eligible server type - Apply discount to non-contract resources that match the given value
Operating System Required Planned Compute discount-eligible operating system - Apply discount to non-contract resources that match the given value
Initial contract start date Required Planned Compute start date when the commitment applies - Planned Compute Details date can be changed on the page
- For more information, see Change Commitment Start Date reference
Contract period Required Check the applicable period based on the selected individual Planned Compute term of 1 year or 3 years - When the Planned Compute term ends, the discount no longer applies.
- If you want to continue applying discounts with Planned Compute, you need to extend the term.
Extension period Required Check the extension period of an individual Planned Compute commitment - Before the extension date arrives, you can modify the 1-year or 3-year term of the extension period
- Additionally, you can cancel the extension reservation.
status Required Planned Compute’s status after a change request is reflected - Creating: State after the contract is requested but before it is applied
- Active: State where the contract is currently applied
- In Progress: State while the change request is being processed
constructor Selection User who created Planned Compute Creation date and time Select Planned Compute creation time Editor Select Planned Compute edited user Modification date Select Planned Compute modification timestamp Table. Planned Compute list item information
- Resource items other than the required columns can be added via the Settings button.
In the Planned Compute list, clicking the right more button provides the contract management item. When multiple items are selected via the checkboxes, the same option is also available through the top button.
Category Detailed description Contract extension The button to extend the contract - becomes active when there is no next contract reservation. After the current contract, select the next contract period to schedule
- For details, see Extend Contract
Contract amendment Button to modify the contract - You can change the server type. Changes are allowed only to a higher specification than the current setting.
- For details, see Change Contract.
Contract termination Button to terminate the contract - Terminate the contracted Planned Compute during the term
- When terminated, a termination fee is incurred based on the remaining usage period (monthly fee * 50% * remaining months of the contract period) and will be reflected on the invoice after two months.
- For details, refer to Terminate the contract.
Contract Extension Modification Button to edit the next contract reservation - It becomes active when there is a next contract reservation. It changes the contract period for the next contract after the current one.
- For more details, see Edit contract extension.
Cancel contract extension Button to cancel the next contract reservation - It becomes active when there is a next contract reservation. It cancels the contract extension reservation for the next contract after the current contract.
- For more details, see Cancel contract extension
Table. Planned Compute list item information - contract management
Planned Compute View detailed information
You can view and edit the detailed information of Planned Compute.
To view detailed information about Planned Compute, follow these steps.
- Click the All Services > Financial Management > Planned Compute menu. You will be taken to the Service Home page of Planned Compute.
- On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute List page.
- On the Planned Compute List page, click the contract number of the Planned Compute to view detailed information. You will be taken to the Planned Compute Details page.
- Planned Compute Details page consists of Detail Information, Tags, Operation History tabs.
Detailed Information
Planned Compute list page lets you view and edit the detailed information of the selected resource.
| Item | Explanation |
|---|---|
| Category | Detailed description |
| ——— | ——— |
| Service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource Name | Resource Name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created Planned Compute |
| Creation Date/Time | Planned Compute creation timestamp |
| Editor | User who modified Planned Compute |
| Modification date | Planned Compute modification timestamp |
| Contract number | Key values for each billing unit visible in the invoice details |
| Target Service | Planned Compute discount-eligible service
|
| Server type | Planned Compute discount eligible server type
|
| Operating System | Planned Compute discount‑eligible operating system
|
| Initial contract start date | Planned Compute start date to which the commitment applies
|
| Contract period | Applied contract period and the corresponding date |
| Extension period | If the contract is extended, the extension period and the relevant date
|
| status | Planned Compute’s status after a change request is reflected
|
- When the Planned Compute commitment ends, the discount will no longer apply. To continue receiving the Planned Compute discount, extend the commitment.
- For detailed information about contract extension, see Extend Contract.
tag
On the Planned Compute list page, you can view the tag information of the selected resource and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Planned Compute List page allows you to view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Managing Planned Compute Commitments
Change contract start date
You can change the contract effective start date for Planned Compute. To change the contract start date for Planned Compute, follow the steps below.
- Click the All Services > Financial Management > Planned Compute menu. Navigate to the Service Home page of Planned Compute.
- On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute list page.
- On the Planned Compute List page, click the contract number of the Planned Compute whose commitment start date you want to change. You will be taken to the Planned Compute Details page.
- On the Planned Compute Details page, click the Edit button of the Initial Contract Start Date. The Edit Initial Contract Start Date popup opens.
- After changing the contract start date, click the Confirm button.
- The agreement start date can be set to a date after the next day.
- If the contract has started, the original contract start date cannot be modified.
Extend Agreement
You can extend the Planned Compute commitment. To extend the Planned Compute commitment, follow the steps below.
- Click the All Services > Financial Management > Planned Compute menu. Navigate to the Service Home page of Planned Compute.
- On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute List page.
- On the Planned Compute list page, click the rightmost more button of the Planned Compute for the resource whose contract you want to extend, then click the Extend Contract button. The Extend Contract popup will open.
- Select the next contract period and click the Confirm button. You will be taken to the Planned Compute list page.
- Contract Extension button can be clicked before the current contract expires if the next contract has not yet been scheduled.
- If you schedule the next appointment through Extend Agreement, you can modify or cancel the next appointment’s extension period up to its start date.
Change Agreement
You can change the commitment of Planned Compute. To change the commitment of Planned Compute, follow the steps below.
- Click the All Services > Financial Management > Planned Compute menu. It takes you to the Planned Compute Service Home page.
- On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute List page.
- Planned Compute On the list page, click the more button at the far right of the Planned Compute of the resource whose contract you want to change, then click the Change Contract button. The Change Contract popup window opens.
- Select the server type to change, and click the Confirm button. You will be taken to the Planned Compute list page.
- Contract change is only possible to a higher spec than the current contract’s configuration.
- If you change the server type using Change Contract, it takes effect at midnight of the same day based on the Asia/Seoul, GMT +09:00 time zone, and resources with the updated server type are moved to the appropriate Coverage list.
Modify contract extension
- Click the All Services > Financial Management > Planned Compute menu. Navigate to the Service Home page of Planned Compute.
- On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute list page.
- On the Planned Compute list page, click the more button at the far right of the Planned Compute of the resource whose contract you want to change, then click the Modify Contract Extension button. The Modify Contract Extension popup window will open.
- After the current contract, change the contract period for the next contract and click the Confirm button. You will be taken to the Planned Compute list page.
- Contract Extension Edit button becomes active when a subsequent contract is scheduled. After the current contract, it modifies the contract period for the next contract.
- If there is a subsequent reservation, you may modify or cancel the extension period of the next agreement up to its start date.
Cancel contract extension
- Click the All Services > Financial Management > Planned Compute menu. You will be taken to the Planned Compute Service Home page.
- On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute List page.
- On the Planned Compute list page, click the more button at the far right of the Planned Compute of the resource whose contract you want to change, then click the Cancel Contract Extension button. The Cancel Contract Extension popup will open.
- Cancel Contract Extension After confirming the popup message, click the Confirm button. You will be redirected to the Planned Compute list page.
- Cancel Contract Extension button is enabled when there is a reservation for the next contract. It cancels the contract extension reservation for the next contract after the current one.
- Cancel contract extension cancels the upcoming contract reservation, and after the current contract term expires, it will be treated as a non‑contract.
Terminate Agreement
You can cancel the Planned Compute commitment. To cancel the Planned Compute commitment, follow the steps below.
- Click the All Services > Financial Management > Planned Compute menu. Go to the Service Home page of Planned Compute.
- On the Service Home page, click the Planned Compute menu. You will be taken to the Planned Compute list page.
- Planned Compute On the list page, click the more button at the far right of the Planned Compute of the resource whose contract you want to cancel, then click the Cancel Contract button. The Cancel Contract popup window opens.
- Terminate Agreement popup message, review it, and click the Confirm button. Navigate to the Planned Compute list page.
- When terminating, a cancellation fee will be incurred based on the remaining usage period (monthly fee * 50% * remaining months of the contract term) and will be reflected on the invoice after two months. Please consider the cancellation fee carefully before proceeding with the termination.
- For same‑day requests, based on the Asia/Seoul GMT+09:00 time zone, if the cancellation occurs before midnight on the same day, no cancellation fee will be charged.
Planned Compute Coverage
Planned Compute You can check the discount amount applied to the requested quantity and non‑contract resources based on the same target service, server type, and operating system. Planned Compute Coverage To view detailed information, follow these steps.
Check Planned Compute Coverage List
- Click the All Services > Financial Management > Planned Compute menu. Navigate to the Service Home page of Planned Compute.
- On the Service Home page, click the Coverage menu. You will be taken to the Coverage list page.
Category Detailed description Target Service The Planned Compute discount‑eligible service for checking coverage Operating System The operational system that is the target of the Planned Compute discount for checking coverage Server type Server type eligible for Planned Compute discount to check coverage Requested quantity Planned Compute request quantity to verify coverage Table. Coverage resource list items
Planned Compute Coverage View detailed information
On the Coverage list page, you can view detailed information of the selected resource and download the required information.
- Click the All Services > Financial Management > Planned Compute menu. You will be taken to the Service Home page of Planned Compute.
- On the Service Home page, click the Coverage menu. You will be taken to the Coverage List page.
- Coverage List: Click the resource (Coverage) whose detailed information you want to view. You will be taken to the Coverage Details page.
Category Detailed description Target Service The Planned Compute discount‑eligible service for checking coverage Operating System The operational system that is the target of the Planned Compute discount for checking coverage Server type Server type eligible for Planned Compute discount to check coverage Requested quantity Planned Compute request quantity to verify coverage Table. Coverage Details - Target Planned Compute and Requested Quantity Items
- You can select the desired period at the top of the Coverage table to perform the query.
- Coverage data can be downloaded via the Excel Download button.
- We provide information up to two days before the query date, based on the Asia/Seoul (GMT +09:00) time zone, taking into account the settlement time of the discount amount.
- The billing calculation reference point is midnight in the Asia/Seoul (GMT +09:00) time zone, and the list can be viewed starting from the contract start date.
| Item | Explanation |
|---|---|
| Resource Name | Name of the non‑contract resource |
| Usage time | Time used by the list’s non‑contract resources during the selected period |
| No-contract hourly rate | Hourly rate when non‑contract resources are not discounted |
| Non-contract usage amount | The amount used by the non‑contract resources in the list during the selected period
|
| Unapplied amount | Planned Compute deducts the charges of the list’s non‑contracted resources as consideration for paying the contracted fee
|
| Non-contract usage amount | Billing amount when Planned Compute is not used |
| Planned Compute usage amount | Amount paid for Planned Compute during the selected period
|
| Planned Compute Unapplied Amount | Total amount not applied because it could not be covered by Planned Compute |
| Billing amount | Sum of the Planned Compute usage amount and the non‑applied Planned Compute amount
|
11.2.3 - Release Note
Planned Compute
- When applying for a Planned Compute contract, you can set the start date on which the contract takes effect.
- You can begin applying the agreement from the day after the application date by selecting your preferred date.
- A planned compute target service has been added.
- Data Catalog, Vertica(DBaaS)
- We have launched the Planned Compute service.
- We offer discounted pricing for services in the Compute and Database categories when you commit to a specific server type.
11.3 - Marketplace
11.3.1 - Overview
Service Overview
Marketplace is a service that supports subscription and installation of products across various domains through the Samsung Cloud Platform. Users can search for the required Marketplace products based on their intended use, apply for subscriptions directly, and manage detailed information of the subscribed products as well as view usage costs.
Provided features
Marketplace provides the following features.
- Product Overview: Provides information on the main features, pricing, and seller details of marketplace products offered by SCP.
- Product Subscription: Users can select the desired marketplace product through the product Catalog and apply for a subscription.
- Product Installation: You can install and deploy to match the user’s environment based on the subscribed product type.
- Product Management: You can easily manage cancellations or terminations by checking the subscription status, installation, and termination status of marketplace products you have applied for.
Software delivery type
In the Marketplace, you can subscribe to products in the following two ways.
- Seller Support: This is a form where the software vendor installs it directly. When you subscribe to a product, the application information is sent to the software vendor by email. The vendor reviews the request details and, in consultation with the user, installs the software.
- Machine Image: It is a format that can be installed on an SCP Virtual Server. After subscribing to the product, the user can select a Marketplace image through the Virtual Server offering, and the software will be installed automatically.
Component
Marketplace provides product subscription management and product catalog features.
- Product Subscription Management: Users can view and manage detailed information and subscription status of marketplace products they have applied for.
- Product Catalog: You can view detailed information about marketplace products available from SCP and subscribe to the desired product.
Constraints
Services sold in the Samsung Cloud Platform Marketplace are offered by individual sellers. In the case of these services, Samsung SDS acts as an e‑commerce intermediary and is not a party to the sales. Therefore, Samsung SDS assumes no responsibility for the service information or transactions conducted by individual sellers.
Preceding Service
Please verify the prerequisite services for each product in the service portal’s product catalog and with the vendor.
11.3.2 - How-to Guides
Users can apply for, install, and manage subscriptions to marketplace products across various domains through the Marketplace service of Samsung Cloud Platform. They can view detailed information, subscription management, and usage charges for the subscribed marketplace products.
Subscribe to a product from the product Catalog
You can view the features and pricing of the marketplace product you want to use in the product catalog of the Samsung Cloud Platform Console and apply for a subscription.
In the Marketplace, you can subscribe to products in the following two ways.
- Seller Support: This is a form where the software vendor installs it directly. When you subscribe to a product, the application information is sent to the software vendor by email. The vendor reviews the application details and, in consultation with the user, installs the software.
- Machine Image: It is a form that can be installed on an SCP Virtual Server. After subscribing to the product, the user can select a Marketplace image through the Virtual Server product, and the software will be installed automatically.
Search marketplace products in the product Catalog
To search for marketplace products in the Product Catalog, follow these steps.
- Click the All Services > Financial Management > Marketplace > Product Catalog menu. You will be taken to the Product Catalog page.
- On the Product Catalog page, search for the desired marketplace product. The search results list will be displayed based on the selected criteria.
- You can enter the product name you want to find in the search area to search.
- Click Advanced Search to filter by product name, category, offering type, and status.
- Click the product whose detailed information you want to view from the search results list. You will be taken to the Product Catalog Details page.
- On the Product Catalog Detail page, view the detailed information of the selected product.
Item description Product specifications Product name and version, manufacturer information Product subscription request Subscribe to this product Overview Product overview description Fee Product fee details Technical Support Product Technical Support Information Manufacturer Product manufacturer information Seller Information Product seller information Table. Product Catalog detailed information items
Apply for product subscription in the product catalog
To subscribe to marketplace products in the Product Catalog, follow the steps below.
- Click the All Services > Financial Management > Marketplace > Product Catalog menu. You will be taken to the Product Catalog page.
- Product Catalog page, search for the desired marketplace product. The search results list will be displayed according to the selected criteria.
- Click the product whose detailed information you want to view from the search results list. You will be taken to the Product Catalog Details page.
- Product Catalog Details page, check the detailed information of the selected product and click the Product Subscription Request button.
- Product Terms Agreement and Application window appears, select the required agreement items, and click the Complete button.
- Read the entire product terms of use and review them carefully.
- If you do not select all required agreement items in the product terms, you cannot apply for the product.
- When the alert appears, click the Confirm button. The product application will be completed.
- You can view product subscription details in the Subscription Management menu.
- If you subscribe to a Seller Support‑type marketplace product, the subscription details will be emailed to the software vendor. Coordinate product specifications and schedule with the vendor. Software installation and charges will be billed based on the agreed installation date.
- If you subscribe to a marketplace product of type Machine Image, the user must select the marketplace image from Virtual Server > Virtual Server Create > Marketplace tab. Charges for the Virtual Server service and software usage begin from the moment the Virtual Server is created.
Check product subscription details
You can view detailed information of the marketplace product you applied for in the Product Catalog.
To check product subscription information, follow these steps.
- Click the All Services > Financial Management > Marketplace > Subscription Management menu. You will be taken to the Subscription Management page.
- Subscription Management page, search for the desired software. The list of search results is displayed based on the selected criteria.
- You can enter the product name you want to find in the search area to search.
- Click Advanced Search to filter by product name, category, offering type, and status.
- Click the product whose details you want to view in the search results list. You will be taken to the Subscription Management Details page.
- Check the detailed information of the selected product on the Subscription Management Details page.
- Subscription Management Details page displays the product’s status information and detailed information, and consists of Basic Information, Terms Agreement tabs.
Category Detailed description Subscription status Product subscription status - Seller Support type product
- Install Requesting: Product is subscribed and awaiting vendor installation request
- Active: Product is subscribed and installation completed
- Terminate Requesting: Product is being terminated and vendor termination request pending
- Terminated: Product subscription termination completed
- Canceled: Product subscription has been canceled
- Error: Installation error, service abnormality occurred
- Machine Image type product
- Active: Product is subscribed
- Terminated: Product subscription terminated
- Canceled: Product subscription has been canceled
- Error: Installation error, service abnormality occurred
Cancel product subscription Button to cancel the subscribed software Cancel subscription Cancel subscription button Table. Status information and additional functions - Seller Support type product
- Subscription Management Details page displays the product’s status information and detailed information, and consists of Basic Information, Terms Agreement tabs.
Basic Information
You can view detailed information of the selected product on the Subscription Management page.
| Item | Explanation |
|---|---|
| Subscription ID | Unique subscription identifier |
| Product Name | Subscribed product name |
| Provision format | Product offering type |
| Category | Product Category |
| Product Details | If you click Product Details, you can view the information on the corresponding software detail page in the product Catalog. |
| Applicant | Subscriber |
| Application date and time | Subscription request date and time |
| Start date | Product usage start date |
| License quantity | Number of installed product licenses |
Agree to terms
You can view the terms the user agreed to when subscribing.
- Clicking View Details for each term item allows you to view the agreed terms information in a popup window when applying for the product.
Cancel Product
If you do not use the marketplace product you subscribed to, cancel the subscription and proceed with service termination.
- If you cancel the subscription, the active service may be terminated immediately; therefore, proceed with the cancellation only after thoroughly considering the impact of a service interruption.
- After requesting cancellation of the Machine Image product, delete the Virtual Server that has this product installed from the Virtual Server list. If you do not delete the Virtual Server with the product installed, Virtual Server charges will continue to accrue even after you request product subscription cancellation.
To cancel a product subscription, follow these steps.
- Click the All Services > Financial Management > Marketplace > Subscription Management menu. You will be taken to the Subscription Management page.
- On the Subscription Management page, click the software you want to cancel. You will be taken to the Subscription Management Details page.
- On the Subscription Management Details page, click the Cancel Product Subscription button.
- Cancel product subscription In the popup window, enter the product name and click the Confirm button.
- When a Seller Support product cancellation request is completed, the cancellation details are sent to the user’s email.
11.3.3 - Release Note
Marketplace
- We have launched a Marketplace service that supports software across various fields from application to installation and management through the Samsung Cloud Platform.
12 - DevOps Tools
We provide a service that easily integrates and configures application and system development environments on a platform.
12.1 - DevOps Service
12.1.1 - Overview
Service Overview
DevOps Service is a service that provides standardized development tools, code‑framework‑based development templates, and integrated management functions for application and system development, deployment, and operation through the DevOps Console. This enables fast and reliable software development, deployment, and operation, and allows convenient integrated management of Samsung Cloud Platform resources and CI/CD tools within the DevOps Workflow.
Features
- Convenient Code Management and Deployment: Users can conveniently manage everything from source code management to build and deployment via a web-based console. It also supports integration with various tools to analyze source code and improve quality.
- Flexible Deployment Options: Minimize user service downtime and provide deployment environment configurations for k8s clusters or Virtual Machines, allowing users to configure deployments that fit their services and offering flexible deployment methods.
- Repository for Deployment Management: Provides a repository that can manage source code, libraries, application artifacts, container images, and other assets for the deployment management of user services.
Service Architecture Diagram
Provided features
DevOps Service integrates standard development tools to easily set up the development environment and provides convenience for build/deployment, offering the following features.
- Continuous Integration and Deployment (CI/CD Continuous Integration/Continuous Deployment): Users can access tools responsible for source code repositories, artifact repositories, code analysis, image registries, and build/deployment with a single login.
- Application template-based project configuration: Users can easily set up a project using a wizard approach with a template that reflects development standards.
- Major Development Languages and Frameworks Provided: Users can select the development languages (Java, C#, Python, Ruby, etc.) and frameworks (SpringBoot, Vue.js, .Net, etc.) required for application development to configure a project for building/deployment.
- Automated Build/Deployment Pipeline Configuration: Users can automatically generate pipeline scripts using the build/deployment pipeline template included in the application template, or configure each stage of the pipeline through a GUI-based interface.
- Support for Various Deployment Strategies and Rollback: Users can use deployment strategies (RollingUpdate, Blue-Green) to minimize downtime of running applications, and can roll back to the desired version with a single click. If a user wants to use a Virtual Server as the deployment environment, they can deploy to the Virtual Server as a packaged file or a Docker image.
- Custom Release Process Support: Users can define and repeatedly execute various release processes, taking into account the type of application changes.
Components
Users can easily use the DevOps Service through the Samsung Cloud Platform DevOps Console.
DevOps Console
DevOps Console provides integrated support for the tools required for application development and build/deployment, allowing easy management of project configuration and build/deployment.
- Dev.Starter: An application template that provides integrated templates required for build and deployment, as well as sample code reflecting development standards.
- Source Code Repository (Source Code Repository): Supports integration with source code configuration management tools. Can be linked with Git Repository.
- Artifact Repository (Artifact Repository): Supports integration with an artifact repository for storing libraries needed for application builds and application artifacts.
- Code Quality (Code Review): Supports integration with code quality tools that can measure and manage source code quality through static code analysis.
- Helm Chart Repository (Helm Chart Repository): In Kubernetes, Helm charts are used to install and upgrade software easily. To install software, users must create Helm charts themselves. ChartMuseum is provided as the default repository for managing Helm charts. Integration with other chart repository tools is also supported.
- Image Registry: Supports integration with an image registry for storing container images.
- VM server group: a collection of Virtual Servers that serve as the deployment target for an application. Users can register Virtual Servers in the DevOps Console and designate them as deployment targets.
- Kubernetes Cluster: The cluster that serves as the deployment target for applications. Users can register a Kubernetes Cluster in the DevOps Console and designate it as a deployment target.
Provision status by region
The DevOps Service is available in the environments below.
| region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Provide |
| South Korea South 2 (kr-south2) | Provide |
| South Korea 3 (kr-south3) | Provide |
Preliminary Service
The DevOps Service has no prerequisite services.
12.1.2 - How-to guides
The user can create the service by entering the required information for the DevOps Service and selecting detailed options through the Samsung Cloud Platform Console. Additionally, by using the DevOps Service’s standardized development tools, code, framework-based development templates, and integrated management features, the user can efficiently carry out development projects.
Create DevOps Service
You can create and use a DevOps Service in the Samsung Cloud Platform Console.
- Each account can use one DevOps Service.
- Only IAM users can create the DevOps Service.
- When creating a DevOps Service, the creator’s ID is granted Tenant Admin privileges in the DevOps Console.
To create a DevOps Service, follow these steps.
- From the All Services > DevOps Tools > DevOps Service menu, click the Create Service button. You will be taken to the Service Home page of the DevOps Service.
- On the Service Home page, click the DevOps Service Create button. You will be taken to the DevOps Service Create page.
- On the DevOps Service Creation page, enter the information required to create the service.
- Enter the required information in the Service Information Input area.
Category Required statusDetailed description Tenant name Required Tenant name of the DevOps Service created by the user - Name displayed logically when accessing the DevOps Console
- Start with a lowercase English letter and use lowercase English letters, numbers, and special characters (
-) to enter 3 to 30 characters
Tenant code Required ID used internally by the system - It is an ID value used internally, similar to a project ID, generated from the value entered by the user
- It must start with a lowercase English letter and be entered using lowercase English letters, numbers, and special characters (
-) with a length of 3 to 30 characters
Table. DevOps Service required information input items - In the Add Tenant Member area, select the tenant user who will use the service.
Category Required statusDetailed description user Required Select members from the user list - Service applicants are included as default members of the Tenant
- You must select at least one user to create the service
Table. DevOps Service Tenant member addition items - Enter or select the required information in the Additional Information Input area.
Category RequiredDetailed description tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. DevOps Service Additional Information Input Fields
- Enter the required information in the Service Information Input area.
- Verify the detailed information and estimated charges generated in the summary panel, and click the Create button.
- Once creation is complete, check the created resource on the Resource List page.
Using DevOps Service
The DevOps Service can configure an actual DevOps environment in a separate console called DevOps Console.
To use the DevOps Service, follow these steps.
- Click the All Services > DevOps Tools > DevOps Service menu. Go to the Service Honme page of DevOps Service.
- From the Service Home page, click the DevOps Service menu. You will be taken to the DevOps Service list page.
- DevOps Service List page, click the resource you want to view detailed information for. You will be taken to the DevOps Service Details page.
- On the DevOps Service Details page, click the DevOps Console button. You will be taken to the Samsung Cloud Platform DevOps Console page.
Check DevOps Service details
DevOps Service service allows you to view and edit the full list of resources and detailed information. The DevOps Service Details page consists of Details, Tags, Activity Log tabs.
To view the detailed information of the DevOps Service, follow the steps below.
- Click the All Services > DevOps Tools > DevOps Service menu. Navigate to the Service Honme page of DevOps Service.
- On the Service Home page, click the DevOps Service menu. You will be taken to the DevOps Service list page.
- On the DevOps Service List page, click the resource you want to view detailed information for. You will be taken to the DevOps Service Details page.
- DevOps Service Details page displays status information and consists of Details, Tags, Activity History tabs.
Category Detailed description Status indicator Display the status of the DevOps Service - Active: Available state
- Creating: Creating state
- Error: Operational error state
DevOps Console Navigate to the DevOps Console to control the service. Service termination Service cancellation button Table. DevOps Service status information and additional features
- DevOps Service Details page displays status information and consists of Details, Tags, Activity History tabs.
Detailed information
You can view detailed information of the selected resource on the DevOps Service List page.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource name | Resource Name
|
| Resource ID | Unique resource ID within the service |
| Constructor | User who created the service |
| Creation date and time | Service creation date and time |
| Tenant name | User-created Tenant name |
| Tenant code | System unique ID for the Tenant created by the user |
tag
DevOps Service List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Work History
On the DevOps Service List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Cancel DevOps Service
- If a project in the DevOps Console has resources attached, you cannot terminate the DevOps Service.
- To cancel the DevOps Service, delete all resources connected within the DevOps Console.
- For detailed information on using the DevOps Console, refer to the Samsung Cloud Platform DevOps Console User Guide.
To cancel the DevOps Service, follow the steps below.
- Click the All Services > DevOps Tools > DevOps Service menu. You will be taken to the Service Home page of the DevOps service.
- On the Service Home page, click the DevOps Service menu. You will be taken to the DevOps List page.
- On the DevOps Service List page, click the resource to cancel. You will be taken to the DevOps Service Detail page.
- On the DevOps Service Details page, click the Cancel Service button.
- When termination is complete, verify on the DevOps Service List page whether the resource has been terminated.
12.1.3 - API Reference
12.1.4 - CLI Reference
12.1.5 - Release Note
- You can also use the DevOps Service in the Korea East (kr-east1) region.
- Add user member
- When creating a DevOps Service, you can add members who will perform the Admin role.
- Samsung Cloud Platform Common Feature Changes
- We have incorporated common CX changes, such as Account, IAM, Service Home, and tags.
- We have launched the DevOps Service, which delivers an integrated, fast, and secure software development, deployment, and operations environment.
12.2 - DevOps Console
12.2.1 - Overview
12.2.1.1 - DevOps Console Introduction
Service Overview
DevOps Console integrates standard development tools, making it easy to configure development environments and providing convenience for building and deploying, with the following features.
Key tool integration and unified authentication for Continuous Integration and Deployment (CI/CD Continuous Integration/Continuous Deployment)
Users can access tools responsible for source code repositories, artifact repositories, code analysis, image repositories, and build/deployment with a single login.
Project configuration based on application template
Users can easily configure a project using a wizard-style approach with templates that incorporate development standards.
Major development languages and frameworks provided
Users can select the development languages (Java, C#, Python, Ruby, etc.) and frameworks (SpringBoot, Vue.js, .Net, etc.) required for application development to configure a project for building and deployment.
Automatic Build/Deployment Pipeline Configuration
Users can automatically generate pipeline scripts using the build/deployment pipeline templates included in the application template, or configure each pipeline stage through a GUI-based approach.
Support for multiple deployment methods and rollback
Users can employ deployment strategies (RollingUpdate, Blue-Green) to minimize downtime of running applications, and can roll back to a desired version with a single click. If users wish to use a VM server as the deployment environment, they can deploy to the VM server in the form of packaged files or Docker images.
Custom Release Process Support
Users can define and repeatedly execute various release processes, taking into account the type of application changes.
Component
Users can easily use the DevOps Service through the DevOps Console.
DevOps Console
It provides integrated support for the tools required for application development and build/deployment, allowing easy management of project configuration and build/deployment.
Dev. Starter
It is an application template that provides not only sample code reflecting development standards but also integrated templates required for build and deployment.
IDP(ID Provider)
It manages users centrally and handles authentication.
Source Code Repository
Supports integration with source code version control tools.
Artifact Repository
Supports integration with an artifact repository for storing libraries required for application builds and application artifacts.
code quality
Supports integration with code quality tools that can measure and manage source code quality through static code analysis.
Helm chart repository
In Kubernetes, Helm charts are used to easily install and upgrade software. Users must create Helm charts themselves to install software. It provides ChartMuseum as the default repository for managing Helm charts. It also supports integration with other chart repository tools.
Image Repository
Supports integration with an image registry for storing container images.
VM Server Group
A group of VM servers that serve as the deployment target for the application. Users can register VMs and designate them as deployment targets in the DevOps Console.
Kubernetes Cluster
The cluster that serves as the deployment target for the application. Users can register a Kubernetes Cluster in the DevOps Console and designate it as a deployment target.
DevOps Console can be found in Tool Classification.Key concepts and relationships
System administrators (System Admin) or administrators (Admin) must predefine the tools and application templates required when a user creates a project.
tenant
It is a logical unit that independently provides and shares tools and application templates usable in projects. The system administrator registers a tenant for each organization (or client) unit that must guarantee independence and assigns a tenant administrator. The tenant administrator can register tenant tools, application templates, and tenant members that can be used within that tenant.
Project Group
As a unit for managing individual projects, a member belonging to a specific tenant can create a project group. Therefore, a project group belongs to a single tenant and can utilize the tools and templates configured for that tenant.
project
A project is a unit that develops and manages an application or microservice that is deployed and run independently. Consequently, it is common to structure a project around a single source code repository, but it can be flexibly organized according to the characteristics of the application or the development and operations teams.
tool
It is a development tool that supports source code repositories, image registries, build/deployment pipelines, and code quality used in projects. Each project can use the tools assigned to its project group, tenant, or the Kubernetes Cluster that is the deployment target of the application. Typically, when assigned at the cluster level, the tools support build/pipelines and image registries that affect deployment speed. Tools are broadly classified into three types based on their scope of use.
ProjectGroup Tool: It is a tool that can be used only in projects belonging to a Project Group. Multiple Project Groups can be mapped and used. The Project Group Owner and Master register and manage it.
Tenant Tool: A tool that can only be used within project groups belonging to a tenant. Multiple tenants can be mapped for use. When registering the tool, only the tenant administrator of the initially registered tenant can manage it. Tenants added later to the tool can only use it. Additionally, it can be designated and managed to be usable in clusters accessible to the tenant administrator.
System Tool: DevOps Service is a tool that can be used as a service across the entire project. System administrators designate and manage the tenants and clusters that can be registered and used.
Application Template
This is a template that makes it easy to set up a project. A template that reflects development standards and even provides sample code is called Dev. Starter, while a template that simply supports development environment setup is called Environment Only. Like tools, it is divided into three main types based on the scope of use.
Project Group Template: A template that can be used only by projects belonging to a project group. The project group Owner and Master register and manage it.
Tenant Template: This is a template that can only be used by project groups belonging to a tenant. It is registered and managed by the tenant administrator.
System Template: This template can be used across all projects in DevOps Service. It designates and manages the tenants that system administrators can register and use.
12.2.1.2 - Roles
Project group roles and permissions
- The project group creator has Owner permission by default.
- Master lacks the project group deletion permission among the Owner’s permissions.
- Developers and Viewers have view‑only permissions.
| Category | Permission | Owner | Master | Developer | Viewer |
|---|---|---|---|---|---|
| Project Group | Lookup | ○ | ○ | ○ | ○ |
| Project Group | Edit | ○ | ○ | ||
| Project Group | Delete | ○ | |||
| project | Create | ○ | ○ | ||
| Project | Lookup | ○ | ○ | ○ | ○ |
| Member | Add | ○ | ○ | ||
| member | Lookup | ○ | ○ | ○ | ○ |
| Member | Delete | ○ | ○ |
Project roles and permissions
- They are classified as Owner, Master, Developer, and Viewer.
- Viewer can only view.
- Developers can create or delete development-related functions.
- Example) build pipeline, Helm chart, deployment
- Owner/Master can view, create, and delete all functions within a project.
- The project role holder inherits the role holder of the project group.
- Even if you are not registered as a project member, you can perform the role in the project if you are a member of the project group.
- When a user’s project role and project group role differ, the project role takes precedence.
- In other words, you can restrict permissions for a specific project among the members of a project group.
- Example) If you do not want to grant Master permissions to the Master role holder of a project group for a specific project, register them as a project member and assign Developer or Viewer permissions.
| Category | Permission | Owner | Master | Developer | Viewer |
|---|---|---|---|---|---|
| Dashboard | Lookup | ○ | ○ | ○ | ○ |
| Build pipeline | Lookup | ○ | ○ | ○ | ○ |
| Build pipeline | Import | ○ | ○ | ○ | |
| Build pipeline | (development) create/add | ○ | ○ | ○ | |
| Build pipeline | (development) run | ○ | ○ | ○ | |
| Build pipeline | (Development) Fix | ○ | ○ | ○ | |
| Build pipeline | (development) delete | ○ | ○ | ○ | |
| Build pipeline | (Operation) Create/Add | ○ | ○ | ||
| Build pipeline | (operation) execution | ○ | ○ | ||
| Build pipeline | (Operation) Edit | ○ | ○ | ||
| Build pipeline | (Operation) Delete | ○ | ○ | ||
| helm install | (development) install | ○ | ○ | ○ | |
| helm install | (Operation) Installation | ○ | ○ | ||
| Project | Edit | ○ | ○ | ||
| Project | Delete | ○ |
| Daegu division | Subcategory | Permission | Owner | Master | Developer | Viewer |
|---|---|---|---|---|---|---|
| Kubernetes deployment | Helm release | (development) lookup | ○ | ○ | ○ | ○ |
| Kubernetes deployment | Helm release | (development) upgrade | ○ | ○ | ○ | |
| Kubernetes deployment | Helm release | (development) rollback | ○ | ○ | ○ | |
| Kubernetes deployment | Helm release | (development) delete | ○ | ○ | ○ | |
| Kubernetes deployment | Helm release | (Operation) Lookup | ○ | ○ | ○ | ○ |
| Kubernetes deployment | Helm release | (Operation) Upgrade | ○ | ○ | ||
| Kubernetes deployment | Helm release | (Production) Rollback | ○ | ○ | ||
| Kubernetes deployment | Helm release | (operation) Delete | ○ | ○ | ||
| Kubernetes deployment | Helm release | Import | ○ | ○ | ||
| Kubernetes deployment | Ingress/Service | Create/Update/Delete | ○ | ○ | ||
| Kubernetes deployment | Blue/Green | (development) create/modify/delete | ○ | ○ | ||
| Kubernetes deployment | Blue/Green | (Operations) Create/Update/Delete | ○ | ○ | ||
| Kubernetes deployment | Canary | (development) lookup | ○ | ○ | ○ | ○ |
| Kubernetes deployment | Canary | (Development) Create/Delete | ○ | ○ | ○ | |
| Kubernetes deployment | Canary | (Operation) Query | ○ | ○ | ○ | ○ |
| Kubernetes deployment | Canary | (Operation) Create | ○ | ○ | ||
| Kubernetes deployment | Canary | (Operation) Delete | ○ | ○ | ||
| Kubernetes deployment | Istio | (development) query | ○ | ○ | ○ | ○ |
| Kubernetes deployment | Istio | (development) create/modify/delete | ○ | ○ | ○ | |
| Kubernetes deployment | Istio | (Operation) Lookup | ○ | ○ | ○ | ○ |
| Kubernetes deployment | Istio | (Operation) Create/Edit | ○ | ○ | ||
| Kubernetes deployment | Istio | (Operation) Delete | ○ | ○ | ||
| Kubernetes deployment | Workload | (development) query | ○ | ○ | ○ | ○ |
| Kubernetes deployment | workload | (Development) Create/Delete/Rollback | ○ | ○ | ○ | |
| Kubernetes deployment | workload | (Operation) Lookup | ○ | ○ | ○ | ○ |
| Kubernetes deployment | Workload | (Operational) Create/Rollback | ○ | ○ | ||
| Kubernetes deployment | Workload | (Operation) Delete | ○ | ○ | ||
| Code repository/Code quality/Artifact repository/Image repository | All | Lookup | ○ | ○ | ○ | ○ |
| Code repository/Code quality/Artifact repository/Image repository | All | Create | ○ | ○ | ○ | |
| Code repository/Code quality/Artifact repository/Image repository | All | Delete | ○ | ○ |
- Jenkins system permissions
- Access permissions are granted based on the project permission hierarchy of
DevOps Console. - Permissions are assigned to the Jenkins pipeline based on the project’s role assignments.
- For tools other than Jenkins, you can set permissions in the tool’s menu.
- Access permissions are granted based on the project permission hierarchy of
| Category | Permission | Owner | Master | Developer | Viewer |
|---|---|---|---|---|---|
| (Folder) Project Group | Folder view | ○ | ○ | ○ | ○ |
| (folder) project | Credential lookup | ○ | ○ | ○ | ○ |
| (folder) project | Create/Update/Delete credentials | ○ | ○ | ||
| (folder) project | Folder view | ○ | ○ | ○ | ○ |
| (folder) project | Create folder | ||||
| (folder) project | Folder Settings | ||||
| (folder) project | Delete folder | ○ | ○ | ||
| (folder) type | (Development) Folder Lookup | ○ | ○ | ○ | |
| (folder) type | (Development) Create pipeline | ||||
| (folder) type | (development) folder settings | ||||
| (folder) type | (Development) Delete folder | ○ | ○ | ○ | |
| (folder) type | (Production) Folder Lookup | ○ | ○ | ||
| (folder) type | (Production) Pipeline creation | ||||
| (folder) type | (Production) Folder Settings | ||||
| (folder) type | (Operation) Delete folder | ○ | ○ | ||
| pipeline | (Development) View Pipeline | ○ | ○ | ○ | |
| pipeline | (Development) Pipeline Configuration | ○ | ○ | ○ | |
| pipeline | (Development) Delete pipeline | ○ | ○ | ○ | |
| pipeline | (development) pipeline build | ○ | ○ | ○ | |
| pipeline | (Production) Pipeline Lookup | ○ | ○ | ||
| pipeline | (Production) Pipeline Configuration | ○ | ○ | ||
| pipeline | (Production) Delete pipeline | ○ | ○ | ||
| pipeline | (Production) Pipeline Build | ○ | ○ |
System roles and permissions
| Daegu division | Subcategory | Permission | System Administrator | Administrator (Tenant Manager) | User (Project Group Owner) |
|---|---|---|---|---|---|
| tool | System tool | Register/Edit/Delete | ○ | ||
| Tool | System tool | Add/Modify supported tenant | ○ | ||
| tool | System tool | Delete supported tenant | ○ | ○ | |
| tool | System tool | Add/Modify supported cluster | ○ | ||
| tool | System tool | Delete supported cluster | ○ | ○ | ○ |
| tool | Tenant tool | Register/Edit/Delete | ○ | ○ | |
| tool | Tenant tool | Add/Modify/Delete supported tenant | ○ | ○ | |
| tool | Project Group Tool | Register/Edit/Delete | ○ | ○ | |
| tool | Project Group Tool | Add/Modify/Delete supported tenant | ○ | ○ |
| Daegu division | Subcategory | Permission | System Administrator | Administrator (Tenant Manager) | User (Project Group Owner) |
|---|---|---|---|---|---|
| App. Template | System template | Register/Edit/Delete | ○ | ||
| App. Template | System template | Add/Modify supported tenant | ○ | ||
| App. Template | System template | Delete supported tenant | ○ | ○ | |
| App. Template | System template | Add/Modify/Delete Supported Images | ○ | ||
| App. Template | System template | Add/Modify/Delete supported Helm charts | ○ | ||
| App. Template | Tenant template | Register/Edit/Delete | ○ | ○ | |
| App. Template | Tenant template | Add/Modify/Delete supported images | ○ | ○ | |
| App. Template | Tenant template | Add/Modify/Delete supported Helm charts | ○ | ○ | |
| App. Template | Project Group Template | Register/Edit/Delete | ○ | ○ | |
| App. Template | Project Group Template | Add/Modify/Delete Supported Images | ○ | ○ | |
| App. Template | Project Group Template | Add/Modify/Delete supported Helm charts | ○ | ○ | |
| Helm chart management | System Helm chart | Add/Edit/Delete | ○ | ||
| Helm chart management | Tenant Helm chart | Add/Edit/Delete | ○ | ○ | |
| Helm chart management | Project group Helm chart | Add/Edit/Delete | ○ | ○ | |
| Project Group | All | Create | ○ | ○ | ○ |
12.2.1.3 - Screen Configuration
Describes the main menu pages of DevOps Console.
When you first log in, the top menu and all project groups and projects you have permission for are displayed.
Top menu
Through the top menu, you can navigate to the Main screen, Management screen, etc., and edit user information. The top menu is always displayed while using DevOps Console.
| Item | Explanation |
|---|---|
| Main page | Go to the main page. |
| management | Navigate to the admin page. |
| Support | You can view the guide, inquiries, and announcements. |
| Link | You can view the related system links. |
| User Information | You can view and edit user information or log out.
|
Main Page
Displays the status of all project groups and projects for which the user has permissions.
| Item | Explanation |
|---|---|
| Create project group | You can create a new project group. |
| Project group name | Indicates the project group name. |
| Tenant name | Represents the tenant name. |
| Project Group Management | Navigate to the project group page. |
| Release Management | Go to the release management page. |
| Create project | You can create a new project. |
| Project Details | All projects the user has permission for are displayed
|
| Go to the user guide | Go to the user guide page. |
Admin Page
It includes overall management functions of the DevOps Console, such as dashboard, tenant, project, tool, and user.
| Item | Explanation |
|---|---|
| Management menu | DevOps Console These are the management feature menus.
|
Project Group Management Page
This is the management page for project groups and releases.
| Item | Explanation |
|---|---|
| Project Group Management Menu | This is the project group management menu. |
| Release Management Menu | This is the release management menu. |
Project page
This is a page about the project.
| Item | Explanation |
|---|---|
| Project Management Menu | This is the project management menu. |
12.2.2 - Getting Started
12.2.2.1 - Getting Started with DevOps Console
Describes how to log in to the DevOps Console and set the display language and user information.
Sign up
To use DevOps Console, you need to create a DevOps Console account that is separate from Samsung Cloud Platform, and you can create the account through sign‑up.
To create an account in DevOps Console, follow the steps below.
- Click the Sign Up link on the login page. You will be taken to the sign‑up page.
- Please proceed with Identity verification. When identity verification is complete, click the Next button.
Item Required statusExplanation Auto Input Prevention Required Enter the characters displayed in the image into the input field. Table. Authentication Information - Please agree to the terms of the Sign-up Information item.
Item Required statusExplanation Terms of Service Required Check if the service terms are agreed Privacy Policy Required Check consent for collection and use of personal information Must be at least 14 years old. Required Check whether the user is 14 or older. Table. Sign-up Information Input - Enter the required information for the Member Information field.
Item Whether requiredExplanation User ID (email) Required Email to be used as the subscriber ID mobile phone number Required Enter mobile phone number - Enter the mobile phone number and click the OTP Send button to generate an OTP
- Enter the OTP number received on the mobile phone and click the Verify button
- If the OTP is valid, mobile phone number verification is completed
Password Required The password that the subscriber can use must be entered within 8 to 20 characters - User ID or name cannot be used as the password
- Must include at least one uppercase letter (English), one lowercase letter (English), one digit, and one special character (
!@#$%^&*) - The same character cannot be used three or more times
- Sequences of four or more consecutive letters or numbers are not allowed
- Password change interval: 90 days
Confirm Password Required Confirm the password the subscriber will use Name Required Subscriber name - Can be entered using letters, numbers, and spaces, up to 100 characters
language Required Notification language settings for email, SMS, etc. Time zone Required Set user’s timezone information Table. Member Information Input - After entering all the information, click the Complete button, and a verification email will be sent to the entered email address.
- Click the Email address verification button in the received email to complete registration.
Log in
To log in to DevOps Console, enter your account information on the login page and click the Next button.
After entering the OTP number issued for the selected OTP type on the OTP authentication page, click the Login button.
If you cannot remember your ID or password, click the ID/Password Recovery link, locate your account information first, and then attempt to log in.
After logging in, the DevOps Console main page opens.
If you enter the password incorrectly more than five times, your account will be locked, so please enter it correctly.
To unlock your account, click the ID/Password Recovery link to reset your password.
Edit User Information
To edit user information, follow these steps.
- Click the Shortcut icon at the upper right of the Main page.
- DevOps IDP Click the link. DevOps IDP page opens in a new tab.
- You can change information such as mobile phone number, password, name, timezone, and language on the user information page.
DevOps Console.To modify the information used in DevOps Console, follow these steps.
- Click the User icon in the top menu of the Main page.
- Click the Account Information menu. The Account Information popup window opens.
- After changing the language and time zone information, click the Save button to complete updating your account information.
Changing Console Language
To change the language displayed in DevOps Console, after logging in, click Language Settings located below the DevOps Console page to select the desired language.
Manage authentication keys
DevOps Console.You can manage each user’s individual authentication keys through the Authentication Key Management menu after clicking the User icon in the top menu of the Main page.
Add authentication key
To add an authentication key, follow these steps.
- Click the User icon at the top right of the Main page.
- Click the Authentication Key Management menu. The Authentication Key Management popup window opens.
- Click the Create Authentication Key button. The Create Authentication Key popup will appear.
- After setting the expiration date, click the Save button to complete the creation of the authentication key.
Configure security settings
You can restrict the IPs that are allowed to use this authentication key through security settings.
To add security settings, follow these steps.
- Click the User icon at the top right of the Main page.
- Click the Authentication Key Management menu. The Authentication Key Management popup window opens.
- Click the Security Settings tab, then click the Edit button. The Change Security Settings popup window opens.
- Set IP access control to use.
- After entering the allowed IP, click the Save button to complete the security settings.
Delete authentication key
To delete the authentication key, follow these steps.
- Click the User icon at the top right of the Main page.
- Click the Authentication Key Management menu. The Authentication Key Management popup window opens.
- Click the Status Change button.
- When the Authentication Key Status Change popup opens, process it as Unused and click the Save button.
- Click the Delete button to complete the authentication key deletion.
Check My Activity History
If you click the User Icon > My Activity History menu in the top menu of the Main page, you can view your DevOps Console activity history.
Configure Access Control IP
You can register IP addresses that are allowed to access the DevOps Console to control access.
Follow these steps to register an access control IP.
- Click the Main page’s top‑right shortcut icon.
- DevOps IDP Click the link. DevOps IDP page opens in a new tab.
- Click the Access Control menu in the left menu.
- On the Access Control page, click the Edit button below. You will be taken to the Access Control Edit page.
- Set Access Control IP Settings to Enable.
- After adding the IP to allow access, click the Save button to complete the access control settings.
Delete Account
DevOps Console When the account is deleted, all permissions related to the collected user information and resources are terminated.To delete your DevOps Console account, follow the steps below.
- Click the Main page’s top‑right shortcut icon.
- DevOps IDP Click the link. DevOps IDP page opens in a new tab.
- On the user information page, click the Delete Account button at the top right. The Delete Account popup will appear.
- Enter your current password in the input field, then click the Delete Account button to complete the deletion.
12.2.2.1.1 - Registration Information
Users can view and manage their basic information, authentication information, subscribed tenants, subscribed project groups, and subscribed projects.
Getting Started with Sign-up Information
To start managing your registration information, follow these steps.
- Main page, click the Admin icon in the upper right. Navigate to the Tenant Dashboard page.
- Please click the Sign-up Information menu in the left menu. It navigates to the Sign-up Information page.
Managing authentication information
Authentication information automatically saves the credentials the user used for tool registration, usage, and related activities. If necessary, you can add new credentials, or modify or delete existing credentials.
To manage authentication information, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Registration Information menu in the left menu. You will be taken to the Registration Information page.
- On the Registration Information page, click the Authentication Information tab.
Add authentication information
To add authentication information, follow these steps.
- In the Credentials tab, click the Add button. The Add Credentials popup opens.
- Add Authentication Info Enter the information in the popup window.
- All tools and URLs that the user can access are displayed.
- After completing the information entry, click the Connection Test button.
- Click the Save button.
Modify authentication information
To modify the authentication information, follow these steps.
- In the Authentication Information tab, click the authentication information you want to edit. The Edit Authentication Information popup will open.
- Edit Authentication Information After entering the information in the popup window, click the Connection Test button.
- Save button is enabled, click the Save button.
Delete authentication information
To delete the credentials, follow these steps.
- In the Credential tab, select the checkbox of the credential you want to delete.
- Click the Delete button in the Authentication information list.
- In the confirmation popup, click the Confirm button.
Manage Subscribed Tenants
Users can view the list of tenants they have joined.
You can also request to join a new tenant, and you can leave a tenant you are already a member of.
To manage the tenant you have joined, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Sign-up Information menu in the left menu. You will be taken to the Sign-up Information page.
- On the Registration Info page, click the Registered Tenant tab.
Request tenant registration
To request tenant enrollment, follow the steps below.
- Click the Join button in the Joined Tenant tab. The Tenant Join Request popup window opens.
- Tenant Registration Request In the popup window, enter the tenant code you wish to register and click the Search icon.
- Enter the request reason and click the Add button.
- After selecting the permissions of the added tenant, click the Save button.
- Click the Confirm button in the confirmation popup.
Leave tenant
To withdraw from the tenant, follow the steps below.
- In the Joined Tenants tab, select the checkbox of the tenant you wish to withdraw.
- Click the Delete button.
- In the confirmation popup, click the Confirm button.
Manage Joined Project Groups
Users can view the list of project groups they have joined.
To manage the project groups you have joined, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Sign-up Information menu. You will be taken to the Sign-up Information page.
- On the Sign-up Information page, click the Joined Project Group tab.
When you click a project group in the project group list, you are taken to the Project Group Management page.
For detailed information on project group management, please refer to the Project Group Overview.
Manage Joined Projects
Users can view the list of projects they have joined.
To manage the projects you have joined, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Sign-up Information menu in the left menu. You will be taken to the Sign-up Information page.
- On the Sign-up Information page, click the Joined Projects tab.
When you click a project in the project list, you are taken to the Project Management page.
For detailed information about the project, see the 프로젝트.
12.2.2.2 - Tutorial (From Project Creation to Build/Deploy)
Through the following steps, the user can create a DevOps Console project, build the source to create an image, and deploy the Helm chart to a Kubernetes cluster.
Create Project Group
Users can create a project group. Users must be a member of the tenant where they will create the project group.
Create Project Group
To create a project group, follow these steps.
- On the Main page, click the Create Project Group and Start button or the Create Project Group button. The Create Project Group popup opens.
- After entering the items, click the Save button to complete the creation of the project group.
- Approval from the tenant administrator may be required.
- If there are no selectable tenants, click the Tenant Registration Shortcut link to proceed with tenant registration.
Register Tenant
To join a tenant, follow these steps.
- In the Create Project Group popup, click the Tenant Join Shortcut link. The Tenant Join Request popup opens.
- Enter the tenant code to register in the Tenant Search field accurately and click the Search icon. The tenant information will be retrieved.
- Verify that the displayed tenant is correct, enter the request reason, and click the Add button. It will be added to the list below.
- After selecting the permissions for the tenant added to the list below, click the Save button.
(Helm chart deployment)Create a project
- Users must be members of a project group and tenant to be able to create projects.
- Refer to Creating a Project Group for how to join a project group and tenant.
Users can create a project that deploys an application to a specific Kubernetes cluster using App.Template, Helm Chart, and Tool Management.
Start Project Creation
To start creating a project, follow these steps.
- On the Main page, click the Create Project button. The Create Project page opens.
Enter basic information
Enter the basic information of the project. The project name and project ID must be unique and cannot be duplicated.
To enter the basic information, follow the steps below.
- On the Project Creation page, select the App. Template Utilization option of the Project Configuration Method item.
- For the deployment target field, select Kubernetes.
- After entering additional content, click the Start button.
Item Explanation Project name Please enter the project name. Project ID Please enter the project ID. Project configuration method Select a project configuration method - Use App template: select a pre‑provided App template.
- Manual configuration: configure without an App template.
deployment target Select deployment target - Kubernetes: Deploy the application to a Kubernetes cluster.
- Kubernetes(ArgoCD): Deploy the application to a Kubernetes cluster using ArgoCD.
- VM(Artifact): Deploy the application to a VM server.
- VM(Docker): Package the application as a Docker image and deploy it to a VM server.
- N/A: Choose this when you do not deploy the build output.
K8S cluster Select the target cluster for deployment DevOps ConsoleOnly clusters that the user has access rights to can be selected among the K8S clusters.
namespace Select the target namespace for deployment - Only namespaces that the user has access rights to, among the clusters retrieved from the K8S cluster, can be selected.
Table. Project creation basic information entry items
Select Application Template
The user can select an application template to configure the project.
If you create a project based on an application template that includes sample source code, you can view the application that will be deployed.
In contrast, using a template labeled Environment Only configures only the build/deployment environment without sample source code.
If you configure a project using an already set up source code repository, select the template marked Environment Only.
To start selecting an application template, follow these steps.
- On the Application Template screen, enter the template name, select the application template card you want, and then click.
- When the Next button is enabled, click the Next button.
Item Explanation Filter You can easily find application templates using predefined filters. search You can easily find application templates through search. Table. Project Creation Application Template Items
Set up the code repository
Users can configure a repository for managing source code through the code repository setup step.
Create new repository and use existing repository activation conditions differ depending on the application template and tool.
| Repository type | App with source code. Template + DevOps Console registration tool | App with source code included. Template + DevOps Console unregistered tool | Source code not included (EnvironmentOnly) App. Template + DevOps Console registration tool | Source code not included (Environment Only) App. Template + DevOps Console unregistered tool |
|---|---|---|---|---|
| Create new repository | ○ | X | ○ | X |
| Use existing repository | X | X | ○ | ○ |
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the code repository, follow these steps.
- In the Code repository item, select the Code repository type.
- Select Create new repository or Use existing repository, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the code repository to use - Registered tool: The user can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tool: You can enter the domain of an unregistered tool to use it. The unregistered tool entry appears only when the source code is not included (Environment Only) App. Template.
New/Existing usage Please select New repository creation or whether to use an existing repository. - Activation status varies depending on specific conditions. For details, refer to Table. Activation conditions for creating a new repository and using an existing repository.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication information - If you do not have an account, Don’t have an account? click the link to open the Account Creation Information popup where you can create an account.
- After creating a new account, be sure to change your password via the Set Initial Password link.
(Unregistered tool)
Repository informationEnter repository information - You can use a code repository that is not registered as a tool in
DevOps Console. - Click the URL Check button to undergo an additional verification process.
Table. Project Creation Code Repository Settings - Registered tool: The user can select and use the types of SCM Repository tools (
Configure code quality
Users can configure a repository for quality management.
To set code quality, follow these steps.
- In the Code Quality item, select Repository Type.
- Enter Basic Information and Authentication Information, then click the Connection Test button.
- Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository to use - The types of Code Quality tools available to the user are displayed.
New / Existing / Unused status Select repository creation method - If you select Create new repository, you must enter the quality project name/quality project key.
- If you select Do not create, you can proceed directly to the next step.
Base URL Select the SonarQubeURL.Quality Project Name Enter the name of the SonarQubeproject.Quality Project Key Enter the Key of the SonarQubeproject.authentication information Enter authentication credentials - You can create a new user or use existing authentication credentials.
Table. Project Creation Code Quality Settings
Configure image repository
Users can configure a repository to store the built container images through the image repository configuration step.
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the image repository, follow these steps.
- In the Image Repository item, select the Repository Type.
- Create new repository / Use existing repository select, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository type to use - The types of Image Registry tools available to the user are displayed.
Repository information Select the repository creation method. - When creating a new repository, the URL is formed with the project group name/project name.
Authentication information Enter your credentials. Table. Project Creation Image Repository Settings
Configure the deployment target environment
Users can deploy by directly configuring via Helm charts.
Helm release name and Helm chart when selected, the Helm chart installation options and the default Values.yaml entries included in the chart are displayed.
Available Helm charts are associated with the App template. You can edit or delete them through Manage supported Helm charts.
To set the deployment target environment, follow these steps.
- In the Deployment target field, select Configure directly via Helm chart.
- Please enter the Helm release name.
- Click the Search button to select the Helm chart to use.
- After editing Values.yaml, click the Validation Check button.
- When the Next button is enabled, click the Next button.
Item Explanation deployment target Please select the deployment target. Helm release name Enter the name of the Helm release to create. - The name must be unique within the namespace of the target cluster.
Helm chart Select a Helm chart. - When a Helm chart is selected, detailed information about the chosen chart is displayed below
K8S information Shows the information of the Kubernetes cluster required for configuring Value.yaml. Values. yaml Edit the contents of Values.yaml. values.yamlfile to be used when installing the Helm chart.
Table. Project creation deployment target environment configuration items
Setting up the Build Pipeline
Users can configure pipelines that build and deploy applications.
You can view each stage of the pipeline to be configured and rename the build job.
To set up the build pipeline, follow these steps.
- Build Pipeline screen branches based on IDP integration status.
- For IDP-integrated Jenkins, click the User Check button to perform User Registration Confirmation.
- For Jenkins not integrated with IDP, enter the authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.Item
Explanation Build/Deployment pipeline Displays build/deployment pipeline information. - The build/deployment pipeline is displayed based on the information registered in the App template’s Manage Pipeline Templates.
Category Select the development/operation distinction. - The permissions for the pipeline vary according to the development/operation distinction.
- Refer to Table. Role-based permissions within the project (1) for role-based permissions.
URL Select Jenkinsto configure the pipeline, then enter the job name.- The
Jenkinsinstances available to the user are displayed.
Build Agent Select the agent to be used for pipeline builds. - For information about the agent, please refer to Managing agents (kubernetes), Managing agents (VM).
Build environment OS Displays the OS information of the environment in which the build agent runs. User information IDP Integrated Jenkins - Click the User Check button to verify user registration.
- If you are not registered as a Jenkins user, when the User Registration Guide popup appears, click the Go to Jenkins link to proceed with User Sign‑Up or Initial Jenkins Login.
- Enter the authentication information and click the Connection Test button.
Set environment variables Set the environment variables to be registered in the Jenkins pipeline. Image Tag Pattern Select the tag assignment method for the container image. Deploy Strategy Select the deployment method for the container image. Recipient of deployment results Select the user who will receive the results after the build pipeline completes. Table. Project creation build pipeline configuration items
Customize Settings
The user can specify and modify the path of the Dockerfile file used for the build.
Additionally, you can view the final script generated based on the information configured in 빌드 파이프라인 설정하기 and also edit it.
Dockerfile, follow these steps to configure the pipeline script.
- After entering information on the Custom settings page, click the Connection Test button.
- Click the Next button when the Next button is enabled.
Item Explanation Dockerfile configuration Create New Dockerfile or Use Existing Dockerfile. Please select. - «Use Existing Dockerfile is only selectable after choosing the
Environment OnlyApp template and, in 코드 저장소 설정하기, selecting Use Existing Repository.
Dockerfile path Specify the Dockerfilefile path in the source code.Branch name The branch name is automatically registered when you set it in Code Repository Configuration. Dockerfile Check and modify the contents of the Dockerfile.pipeline script Check and modify the pipeline script. Table. Project Creation Custom Settings Items - «Use Existing Dockerfile is only selectable after choosing the
Complete project creation
The user can review the project and tool information to be created and start project creation.
To complete project creation, follow the steps below.
- Summary Information After checking the information on the screen, click the Complete button.
- Project Creation popup window opens and the project creation proceeds.
- After the project creation is complete, click the Confirm button to go to the Project page.
Check Build Pipeline Execution
On the Project page, you can view the pipeline execution status, and once the initial project creation is complete, the build pipeline runs automatically.
If the build pipeline fails, use the left Build Pipeline menu to modify and rerun the pipeline.
To verify the build pipeline execution, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Build Pipeline menu in the left menu.
Check deployment results
After the pipeline finishes running, you can check the Helm chart deployment results.
For detailed information about the Helm chart deployment results, refer to the Helm release.
To verify the deployment results, follow the steps below.
- Main page, click the Project card. Project Dashboard page will be displayed.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- Click the Helm Release list to view detailed deployment results.
12.2.2.2.1 - Add Build/Deploy (Helm Chart Deployment)
The user can, through the following steps, create a new build pipeline in an already created DevOps Console project, build the source to create an image, and perform Helm chart deployment to a Kubernetes cluster.
Through Helm install, the deployed Helm release will be used in Deploy to K8S stage configuration.
Getting Started with Build/Deploy Additions
To begin adding build and deployment, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
Add code repository (Option)
| Repository type | App with source code. Template + DevOps Console registration tool | App with source code included. Template + DevOps Console unregistered tool | Source code not included (EnvironmentOnly) App. Template + DevOps Console registration tool | Source code not included (Environment Only) App. Template + DevOps Console unregistered tool |
|---|---|---|---|---|
| Create new repository | ○ | X | ○ | X |
| Use existing repository | X | X | ○ | ○ |
To add a code repository, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click Repository > Code Repository in the left menu.
- Click the Add Code Repository button at the top right. The Add Code Repository page opens.
- Enter/set each item and click the Connection Test button.
- Click the Save button to complete Add code repository.
Item Explanation Repository type Select the repository to use - Registered tool: The user can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tool: You can enter the domain of a tool that will not be registered to use it. The unregistered tool option appears only for App templates that do not include source code (
Environment Only).
New/Existing usage Select Create new repository or Use existing repository - The activation status changes depending on specific conditions. For more information, see Table. Conditions for activating new repository creation and existing repository usage.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication credentials. Repository information Enter repository information - You can use a code repository that is not registered as a tool in
DevOps Console. - Click the URL Check button to proceed with the verification process.
Table. Code Repository Configuration Items - Registered tool: The user can select and use the types of SCM Repository tools (
Add image repository (Option)
To add an image repository, follow these steps.
App. Add image repository
- On the Image Repository page, click the App. Add Image Repository button in the upper right. You will be taken to the App. Add Image Repository page.
- App. Add Image Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Select repository type Select the image repository type.
To use an image repository not registered in the Devops Console, select the Image Registry type.Choose whether to create a repository Choose whether to create a new repository or use an existing one. - If you selected the
Docker huborImage Registrytype earlier, you can only select Use existing repository.
Registered tool Enter repository information. Unregistered tool Enter repository information - You can register an image repository that is not registered with the DevOps Console tool.
- Click the URL Check button to proceed with the verification process.
- Only Use existing repository can be selected.
Table. App. Add Image Repository Input Fields - If you selected the
Add pull-only image repository
- On the Image Repository page, click the Add Pull-Only Image Repository button in the upper right. You will be taken to the Add Pull-Only Image Repository page.
- Add Pull‑only Image Repository On the page, enter and configure each field.
- Connection Test Click the button.
- Click the Save button.
Install Helm
To install Helm, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > HelmInstall menu in the left menu.
- In the K8S cluster field, select the K8S cluster you wish to install.
- Click the Helm chart you want to install to go to the Helm Chart Details screen.
- Click the Helm Install button. It navigates to the Helm Chart Install screen.
- Enter each item and click the Next button.
Item Explanation Release name Enter the name to use in the Helm chart release.
It must be unique and cannot be duplicated within the namespace.Category Development, Operations Version Select the version of the chart you want to install with Helm. K8S cluster Displays the target K8S cluster for Helm install.
Changes cannot be made, and if you wish to change, please select the K8S cluster from Start Helm Install.namespace Select the target namespace for the helm install from the list. Reference information This is reference information provided by the selected K8S cluster. Click each tab to view detailed information. Default Values.yaml included in the chart You can edit the values.yamlfile to run helm install with the desired values.
If needed, refer to the reference information and edit thevalues.yamlfile with those values.Writing type Form type items are displayed only for Helm charts that support Form input - Form: Enter the items shown on the screen. For creating Helm charts that support Form input, see Creating Helm charts that support Form input.
values.yaml: Edit values in the yaml editor screen just like a regular Helm chart.
Form input This is the screen displayed when you select Form in the creation type; review each item and enter the values. After completing the entry, click the Validation Check button to verify the input values. Table. Helm Install Configuration Items - Helm chart installation A popup window opens. Click the Run button to complete the Helm install.
- When the installation is complete, the Kubernetes deployment page opens.
Add Build Pipeline
To add a build pipeline, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Build Pipeline menu. You will be taken to the Build Pipeline page.
- Build Pipeline page, click the Add Pipeline button at the top right. You will be taken to the Add Pipeline page.
- Add Pipeline Enter or configure each field on the page.
- Click the Next button.
Item Explanation Category Select Development or Operations - The actions that each role can perform differ depending on development or operations.
- Refer to Table. Role-specific permissions within the project (1) for role-specific permissions.
Jenkins URL Select Jenkinsfrom the list to add a build pipeline.Build Agent Select the agent (build environment) on which the build pipeline will run.
Click the Info icon to view the list of tools provided by the agent.Build environment OS Displays the OS information of the environment where the build agent runs. Folder type Select the folder type. - Existing folder: Add a pipeline under an already created folder in
Jenkins. - New folder: Create a new folder in
Jenkinsand add a pipeline under it.
folder Select a folder from the list or enter the name of a new folder to create. Pipeline name Please enter the pipeline name. Parameter setting Set the parameters to be used in the pipeline. Environment variable configuration Set the environment variables to be used in the pipeline. Stage Settings Configure the stage to be used in the pipeline. Configure email recipients for build results Set the recipients who will receive the result email after the pipeline completes (success/failure). Table. Additional Build Pipeline Settings
Setting parameters
Follow these steps to set the parameters to use when running the pipeline.
- Click the Parameter area. The Parameter registration page opens on the right.
- When you click the Add button, the Add Parameter popup window opens.
- Add a parameter and click the Apply button to complete the parameter configuration.
Setting Environment Variables
Follow these steps to set environment variables for use in the pipeline.
- Click the Environment Variable area. The Environment Variable Registration page opens on the right.
- A list of pre-registered environment variables appears, and select the checkboxes for the environment variables you want to use.
- Check the selected environment variable and click the Apply button to complete the environment variable configuration.
Configure email recipients for build results
To set the recipients who will receive the build results by email, follow these steps.
- Click the Mail Recipient area. The Add Mail Recipient page opens on the right.
- In the Search area, search for the recipient and add them.
- Click the Apply button to complete the mail recipient settings.
Configure additional stage
Setting up the Checkout stage
To add a Checkout stage, follow these steps.
- Click the New Stage area. The stage settings page opens on the right.
- Choose Checkout as the Stage type.
- Enter the information and click Apply. (In the URL, you can select the code repository you added from Add Code Repository (Option).)
Item Explanation URL Select the code repository to perform the checkout. Branch name Enter the name of the branch to checkout. Table. Checkout Stage Settings
Configure the Build stage
To add a Build stage, follow these steps.
- Click the Add icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- On the Stage Settings page, select Build as the Stage Type.
- After entering information on the Stage Settings page, click the Apply button.
Item Explanation language Select the programming language used by the application. Build tool Select the Build tool used for building the application.
Provides default Shell commands based on the selected Build tool.Shell command Enter the command to use for building the application.
All commands available in the Shell can be used.Table. Build stage input items
Setting Up Docker Build Stages
To add a Docker Build stage, follow these steps.
- Click the Add icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- Select Docker Build as the Stage Type.
- After entering the information, click the Apply button. (You can select the image repository you added in Registry URL from Add Image Repository (Option).)
item | Explanation | example |
|---|---|---|
Registry URL (docker push) | Select the image repository where the Docker build result image will be pushed. | |
| ID | The ID value of the account to be used for the image repository | |
| image tag pattern | The Docker image tag is automatically generated according to the selected pattern.
|
|
| Add base image repository | Add Base Image Repository A popup window opens.
| |
Registry URL (docker pull) | Select the image repository for docker pull when the repository providing the Base Image used in the Dockerfile (FROM clause, docker pull) differs from the repository of the Registry URL (docker push). | |
| Image build tool | Displays the image build tool. | |
| Pre-build command | If there are any commands that need to be run before building a Docker image, write them in shell command format. | cp target/*.jar docker/ |
| Image Build folder | If you need to run the Docker image build from a specific folder, select the checkbox and enter the folder path. | docker |
| Dockerfile | Enter the Dockerfile filename. | Dockerfile |
| Image build options | Enter it if you need to use additional options with the image build tool. | --no-cache |
| Build command | Displays the image build command that will actually be executed. | |
| Post-build command | If there are commands that need to be executed after building a Docker image, write them in Shell command format. | rm -rf docker/*.jar |
Deploy to K8S Stage Configuration
Deploy to K8S To add a stage, follow the steps below.
- Click the Add icon to add a new stage.
- Click the New Stage area. The stage settings page opens on the right.
- Select Deploy to K8S as the Stage type.
- After entering the information, click the Apply button. (Type Helm Release (Helm Chart type) can be selected to choose the Helm Release added in 헬름인스톨 하기.)
Item | Explanation |
|---|---|
| type | Select deployment type
|
| K8S cluster | Select a K8S cluster
|
| namespace | Please select a namespace. |
| Helm release | Select HelmRelease. |
| Deployment method | Select deployment method
|
| Registry URL | Select the image repository where the image to be deployed to Kubernetes has been docker pushed. |
| Secret | Select the secret information input method
|
Check the final pipeline script
- Check the build pipeline script that will actually be generated. If needed, edit the script directly.
- Click the Complete button to finish adding the pipeline.
Pipeline addition result
12.2.2.2.2 - Add Build/Deploy (Workload Deployment)
The user can, through the following steps, create a new build pipeline in an already created DevOps Console project, build the source to create an image, and perform workload deployment on a Kubernetes cluster.
The workload added via Add Workload will be used in Deploy to K8S Stage Setup.
Build/Deploy Add Getting Started
To begin adding build/deployment, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
Add code repository (Option)
To add a code repository, follow these steps.
- On the Code Repository page, click the Add Code Repository button in the upper right. You will be taken to the Add Code Repository page.
- On the Add Code Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Repository type Select the repository to use - Registered tools: Users can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tools: You can enter the domain of a tool that is not registered. The unregistered tool entry appears only for App templates that do not include source code (
Environment Only).
New/Existing usage Select Create new repository or Use existing repository - The activation status varies depending on specific conditions. For details, see Table. Conditions for activating new repository creation and existing repository usage.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication credentials. Repository information Enter repository information - You can use a code repository that is not registered as a tool in DevOps Console.
- You must also go through the URL check process.
Table. Code Repository Add Input Items - Registered tools: Users can select and use the types of SCM Repository tools (
Add image repository (Option)
To add an image repository, follow these steps.
App. Add image repository
- On the Image Repository page, click the App. Add Image Repository button in the upper right. You will be taken to the App. Add Image Repository page.
- App. Add Image Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Select repository type Select the image repository type.
To use an image repository not registered in the Devops Console, select the Image Registry type.Choose whether to create a repository Choose whether to create a new repository or use an existing one. - If you selected the
Docker huborImage Registrytype earlier, you can only select Use existing repository.
Registered tool Enter repository information. Unregistered tool Enter repository information - You can register an image repository that is not registered with the DevOps Console tool.
- Click the URL Check button to proceed with the verification process.
- Only Use existing repository can be selected.
Table. App. Add Image Repository Input Fields - If you selected the
Add pull-only image repository
- On the Image Repository page, click the Add Pull-Only Image Repository button in the upper right. You will be taken to the Add Pull-Only Image Repository page.
- Add Pull‑only Image Repository On the page, enter and configure each field.
- Connection Test Click the button.
- Click the Save button.
Add workload
To add a workload, follow the steps below.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- On the Kubernetes deployment page, click the Add workload menu. The Add workload popup opens.
- Add Workload Enter the information in the popup window and click the Save button.
- In the confirmation popup, click the Confirm button to complete adding the workload.Item
Explanation Query target Only workloads deployed with the same Base image as the App template used when the project was first created are displayed. Workload already registered in the project Shows the workload already registered in the project. - Workloads already registered in the project cannot be added.
Table. Additional Workload Input Items
Modify K8S authentication information
K8S credentials are the authentication information used to verify permission to use a K8S cluster/namespace when performing a deployment in the build pipeline.
To modify the K8S credentials, follow these steps.
- On the Deployment Details page, click the Edit Credentials icon to the right of K8S Cluster/Namespace. The Edit Credentials popup will open.
- Authentication information is fixed to the logged-in user’s account. Click the Save button to edit.
- In the confirmation popup, click the Confirm button.
- K8S authentication information will be changed to the logged-in user.
Add Build Pipeline
To add a build pipeline, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Build Pipeline menu. You will be taken to the Build Pipeline page.
- Build Pipeline page, click the Add Pipeline button at the top right. You will be taken to the Add Pipeline page.
- Add Pipeline Enter or configure each field on the page.
- Click the Next button.
Item Explanation Category Select Development or Operations - The actions that each role can perform differ depending on development or operations.
- Refer to Table. Role-specific permissions within the project (1) for role-specific permissions.
Jenkins URL Select Jenkinsfrom the list to add a build pipeline.Build Agent Select the agent (build environment) on which the build pipeline will run.
Click the Info icon to view the list of tools provided by the agent.Build environment OS Displays the OS information of the environment where the build agent runs. Folder type Select the folder type. - Existing folder: Add a pipeline under an already created folder in
Jenkins. - New folder: Create a new folder in
Jenkinsand add a pipeline under it.
folder Select a folder from the list or enter the name of a new folder to create. Pipeline name Please enter the pipeline name. Parameter setting Set the parameters to be used in the pipeline. Environment variable configuration Set the environment variables to be used in the pipeline. Stage Settings Configure the stage to be used in the pipeline. Configure email recipients for build results Set the recipients who will receive the result email after the pipeline completes (success/failure). Table. Additional Build Pipeline Settings
Setting Parameters
Follow these steps to set the parameters used when running the pipeline.
- Click the Parameter card.
- Click the Add button to add a parameter.
- Click the Apply button to complete the parameter settings.
Setting Environment Variables
Follow these steps to set environment variables for use in the pipeline.
- Click the Environment Variable area. The Environment Variable Registration page opens on the right.
- A list of pre-registered environment variables appears, and select the checkboxes for the environment variables you want to use.
- Check the selected environment variable and click the Apply button to complete the environment variable configuration.
Configure email recipients for build results
To set the recipients who will receive the build results by email, follow these steps.
- Click the Mail Recipient area. The Add Mail Recipient page opens on the right.
- In the Search area, search for the recipient and add them.
- Click the Apply button to complete the mail recipient settings.
Add additional stage
Checkout stage setup
To add a Checkout stage, follow these steps.
- Click the New Stage area. The Stage Settings page opens on the right.
- On the Stage Settings page, select Checkout as the Stage Type.
- After entering the information, click the Apply button. (You can select the code repository you added from 코드 저장소 추가하기 (Option) on the URL.)
Item description URL Select the code repository to perform the checkout. Branch name Enter the name of the branchto checkout.표. Checkout 스테이지 입력 항목
Setting up the Build stage
To add a Build stage, follow these steps.
- Click the Add icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- On the Stage Settings page, select Build as the Stage Type.
- After entering information on the Stage Settings page, click the Apply button.
Item Explanation language Select the programming language used by the application. Build tool Select the Build tool used for building the application.
Provides default Shell commands based on the selected Build tool.Shell command Enter the command to use for building the application.
All commands available in the Shell can be used.Table. Build stage input items
Docker Build Stage Setup
To add a Docker Build stage, follow these steps.
- Click the Add icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- Select Docker Build as the Stage Type.
- After entering the information, click the Apply button. (You can select the image repository you added in Registry URL from Add Image Repository (Option).)
item | Explanation | example |
|---|---|---|
Registry URL (docker push) | Select the image repository where the Docker build result image will be pushed. | |
| ID | The ID value of the account to be used for the image repository | |
| image tag pattern | The Docker image tag is automatically generated according to the selected pattern.
|
|
| Add base image repository | Add Base Image Repository A popup window opens.
| |
Registry URL (docker pull) | Select the image repository for docker pull when the repository providing the Base Image used in the Dockerfile (FROM clause, docker pull) differs from the repository of the Registry URL (docker push). | |
| Image build tool | Displays the image build tool. | |
| Pre-build command | If there are any commands that need to be run before building a Docker image, write them in shell command format. | cp target/*.jar docker/ |
| Image Build folder | If you need to run the Docker image build from a specific folder, select the checkbox and enter the folder path. | docker |
| Dockerfile | Enter the Dockerfile filename. | Dockerfile |
| Image build options | Enter it if you need to use additional options with the image build tool. | --no-cache |
| Build command | Displays the image build command that will actually be executed. | |
| Post-build command | If there are commands that need to be executed after building a Docker image, write them in Shell command format. | rm -rf docker/*.jar |
Deploy to K8S Stage Setup
Deploy to K8S To add a stage, follow the steps below.
- Click the + icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- On the Stage Settings page, select Deploy to K8S as the Stage Type.
- On the Stage Settings page, after entering the information, click the Apply button. (If you select a workload in the type, you can select the workload added in 워크로드 추가하기.)
Item | Explanation |
|---|---|
| type | Select deployment type
|
| K8S cluster | Select a K8S cluster
|
| namespace | Please select a namespace. |
| Helm release | Select HelmRelease. |
| Deployment method | Select deployment method
|
| Registry URL | Select the image repository where the image to be deployed to Kubernetes has been docker pushed. |
| Secret | Select the secret information input method
|
Check the final pipeline script
- Check the build pipeline script that will actually be generated. If needed, edit the script directly.
- Click the Complete button to finish adding the pipeline.
Pipeline addition result
12.2.2.2.3 - Add Build/Deploy (VM Deployment)
The user can, through the following steps, create a new build pipeline in an already created DevOps Console project, build the source to create an image, and proceed with (VM deployment) on the VM server.
The VM server group/VM server added via Add VM Server Group/VM Server (Option) will be used in Configure Deploy to VM Stage.
Build/Deploy Add Getting Started
To begin adding build/deployment, follow these steps.
- On the Main page, click the Project card to go to the Project Dashboard page.
Add code repository (Option)
To add a code repository, follow these steps.
- On the Code Repository page, click the Add Code Repository button in the upper right. You will be taken to the Add Code Repository page.
- On the Add Code Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Repository type Select the repository to use - Registered tools: Users can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tools: You can enter the domain of a tool that is not registered. The unregistered tool entry appears only for App templates that do not include source code (
Environment Only).
New/Existing usage Select Create new repository or Use existing repository - The activation status varies depending on specific conditions. For details, see Table. Conditions for activating new repository creation and existing repository usage.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication credentials. Repository information Enter repository information - You can use a code repository that is not registered as a tool in DevOps Console.
- You must also go through the URL check process.
Table. Code Repository Add Input Items - Registered tools: Users can select and use the types of SCM Repository tools (
Add image repository (Option)
To add an image repository, follow these steps.
App. Add image repository
- On the Image Repository page, click the App. Add Image Repository button in the upper right. You will be taken to the App. Add Image Repository page.
- App. Add Image Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Select repository type Select the image repository type.
To use an image repository not registered in the Devops Console, select the Image Registry type.Choose whether to create a repository Choose whether to create a new repository or use an existing one. - If you selected the
Docker huborImage Registrytype earlier, you can only select Use existing repository.
Registered tool Enter repository information. Unregistered tool Enter repository information - You can register an image repository that is not registered with the DevOps Console tool.
- Click the URL Check button to proceed with the verification process.
- Only Use existing repository can be selected.
Table. App. Add Image Repository Input Fields - If you selected the
Add pull-only image repository
- On the Image Repository page, click the Add Pull-Only Image Repository button in the upper right. You will be taken to the Add Pull-Only Image Repository page.
- Add Pull‑only Image Repository On the page, enter and configure each field.
- Connection Test Click the button.
- Click the Save button.
Add artifact repository (Option)
Proceed only if a new artifact repository is needed.
When using a rollback artifact repository, Nexus can only use the raw(hosted) repository type.
To add an artifact repository, follow these steps.
- Click the Add Artifact Repository button at the top right of the Artifact Repository page. You will be taken to the Add Artifact Repository page.
- On the Add Artifact Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Select whether to create a repository Choose whether to create a new repository or use an existing one. Enter basic information Base URL, select repository type and enter repository/authentication information. Table. Input fields for adding an artifact repository
Add VM Server Group/VM Server (Option)
To add a VM server group, follow these steps.
- Click the Management icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the Add button. It navigates to the Add VM Server Group page.
- Enter the basic information, then click the Save button to complete the VM server group configuration.
Item Explanation Server group name Enter the VM server group name. Explanation Please enter a description. type Select the type of VM server group - SSH: Perform deployment using SSH commands when deploying a VM.
- Agent: Perform deployment using an agent when deploying a VM. (Connect Agent)
VM server - Add: Add the VM server that belongs to the VM server group.
- Delete: Check the checkbox of the VM server you want to delete from the VM server group, then click Delete to remove it.
Table. VM Server Group Add Input Items
Add VM server
To add a VM server, you need Manager permission for the corresponding VM server group.
To add a VM server, follow the steps below.
- Click the Admin icon at the top right of the Main page. Navigate to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- VM server group page, click the VM server group in the VM server group list where you want to add a VM server. You will be taken to the VM server group detail page.
- On the VM Server Group Details page, click the Add button. You will be taken to the Add VM Server page.
- Add VM Server page, after entering the basic information, click the Add button to complete the VM server configuration.
Item Explanation Server name Enter the VM server name. Explanation Enter the description. IP Please enter the IP. SSH Port Enter the port of the VM server to use for SSH connections. OS Please enter the OS. Location Please select a location. Authentication information Enter the authentication information for the VM server to be used for SSH connections. Secret Key This is the secret key for authenticating the VM server where the agent is installed. Table. VM Server Additional Input Items
Add Build Pipeline
To add a build pipeline, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Build Pipeline menu. You will be taken to the Build Pipeline page.
- Build Pipeline page, click the Add Pipeline button at the top right. You will be taken to the Add Pipeline page.
- Add Pipeline Enter or configure each field on the page.
- Click the Next button.
Item Explanation Category Select Development or Operations - The actions that each role can perform differ depending on development or operations.
- Refer to Table. Role-specific permissions within the project (1) for role-specific permissions.
Jenkins URL Select Jenkinsfrom the list to add a build pipeline.Build Agent Select the agent (build environment) on which the build pipeline will run.
Click the Info icon to view the list of tools provided by the agent.Build environment OS Displays the OS information of the environment where the build agent runs. Folder type Select the folder type. - Existing folder: Add a pipeline under an already created folder in
Jenkins. - New folder: Create a new folder in
Jenkinsand add a pipeline under it.
folder Select a folder from the list or enter the name of a new folder to create. Pipeline name Please enter the pipeline name. Parameter setting Set the parameters to be used in the pipeline. Environment variable configuration Set the environment variables to be used in the pipeline. Stage Settings Configure the stage to be used in the pipeline. Configure email recipients for build results Set the recipients who will receive the result email after the pipeline completes (success/failure). Table. Additional Build Pipeline Settings
Setting Parameters
Follow these steps to set the parameters used when running the pipeline.
- Click the Parameter card.
- Click the Add button to add a parameter.
- Click the Apply button to complete the parameter settings.
Setting Environment Variables
Follow these steps to set environment variables for use in the pipeline.
- Click the Environment Variable area. The Environment Variable Registration page opens on the right.
- A list of pre-registered environment variables appears, and select the checkboxes for the environment variables you want to use.
- Check the selected environment variable and click the Apply button to complete the environment variable configuration.
Configure email recipients for build results
To set the recipients who will receive the build results by email, follow these steps.
- Click the Mail Recipient area. The Add Mail Recipient page opens on the right.
- In the Search area, search for the recipient and add them.
- Click the Apply button to complete the mail recipient settings.
Configure additional stage
Setting up the Checkout stage
To add a Checkout stage, follow these steps.
- Click the New Stage area. The Stage Settings page opens on the right.
- On the Stage Settings page, select Checkout as the Stage Type.
- After entering the information, click the Apply button. (You can select the code repository you added from 코드 저장소 추가하기 (Option) on the URL.)
Item description URL Select the code repository to perform the checkout. Branch name Enter the name of the branchto checkout.표. Checkout 스테이지 입력 항목
Setting up the Build stage
To add a Build stage, follow these steps.
- Click the Add icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- On the Stage Settings page, select Build as the Stage Type.
- After entering information on the Stage Settings page, click the Apply button.
Item Explanation language Select the programming language used by the application. Build tool Select the Build tool used for building the application.
Provides default Shell commands based on the selected Build tool.Shell command Enter the command to use for building the application.
All commands available in the Shell can be used.Table. Build stage input items
Configuring Docker Build Stage
To add a Docker Build stage, follow these steps.
- Click the Add icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- Select Docker Build as the Stage Type.
- After entering the information, click the Apply button. (You can select the image repository you added in Registry URL from Add Image Repository (Option).)
item | Explanation | example |
|---|---|---|
Registry URL (docker push) | Select the image repository where the Docker build result image will be pushed. | |
| ID | The ID value of the account to be used for the image repository | |
| image tag pattern | The Docker image tag is automatically generated according to the selected pattern.
|
|
| Add base image repository | Add Base Image Repository A popup window opens.
| |
Registry URL (docker pull) | Select the image repository for docker pull when the repository providing the Base Image used in the Dockerfile (FROM clause, docker pull) differs from the repository of the Registry URL (docker push). | |
| Image build tool | Displays the image build tool. | |
| Pre-build command | If there are any commands that need to be run before building a Docker image, write them in shell command format. | cp target/*.jar docker/ |
| Image Build folder | If you need to run the Docker image build from a specific folder, select the checkbox and enter the folder path. | docker |
| Dockerfile | Enter the Dockerfile filename. | Dockerfile |
| Image build options | Enter it if you need to use additional options with the image build tool. | --no-cache |
| Build command | Displays the image build command that will actually be executed. | |
| Post-build command | If there are commands that need to be executed after building a Docker image, write them in Shell command format. | rm -rf docker/*.jar |
Deploy to VM Stage Setup
To add a Deploy to VM stage, follow these steps.
- + Click the icon to add a new stage.
- Click the New Stage area. The Stage Settings page opens on the right.
- On the Stage Settings page, select Deploy to VM as the Stage Type.
- On the Stage Settings page, after entering the information, click the Apply button.
| Item | Explanation |
|---|---|
| Deployment configuration | Select deployment configuration method
|
| deployment group | Select a deployment group
|
| Release Information | The contents stored in the deployment group are automatically configured. |
| Manual deployment | Select the default value for manual deployment
|
Check the final pipeline script
- Check the build pipeline script that will actually be generated. If needed, edit the script directly.
- Click the Complete button to finish adding the pipeline.
Pipeline addition result
12.2.2.2.4 - Check Deployment Target Namespace Permissions (Before Project Creation)
The user should create a DevOps Console project following the steps below, verify that they have permission for the target cluster / namespace before building and deploying the source, and, if necessary, request the responsible person to add permissions to the cluster / namespace.
DevOps Console K8S Cluster Namespace Permission Check
To verify permissions for a namespace of the K8S cluster used in the DevOps Console, follow these steps.
- Main page, click the Admin icon in the top right. Tenant Dashboard page will open.
- In the left menu, click the Deployment Target > K8S Cluster menu. You will be taken to the K8S Cluster list page.
- Click the K8S cluster. You will be taken to the Details page of the selected K8S cluster.
- Click the Namespace tab. The Namespace List screen appears.
- Clicking the namespace takes you to the Namespace Details page.
12.2.3 - Project
12.2.3.1 - Project Overview
Users can view not only the detailed information of the project but also related Helm release information, the tools they are using, and other relevant details.
Users with a project role of Master or higher can edit the project name through this menu, and the Owner can delete the project.
Project Overview Getting Started
To start using the project overview, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- From the left menu, click the Project Overview menu. The Project Overview screen appears.
Modify project name
To change the project name, follow these steps.
- Project Overview On the screen, click the Edit Project Name button at the top right. The Edit Project Name popup window will open.
- Edit Project Name In the popup window, edit the project name and click the Save button to complete the project name edit.
Delete Project
To delete a project, follow these steps.
- Project Overview On the screen, click the Delete Project button in the upper right. The Delete Project popup window opens.
- In the Project Deletion popup, click the Confirm button. You will be taken to the Project Deletion page.
- On the Project Deletion page, enter and select the required information, then click the Delete button. The Project Deletion popup window opens.
- Project Deletion Enter the project name in the popup window.
- Click the Confirm button to complete the project deletion.
Item Explanation Check project name Enter the name of the current project you want to delete. Delete Helm release
Delete build pipeline
Delete code repositoryIf you want to delete together with the project, select - Select: When the project is deleted, the actual physical deletion command is executed.
- Deselect: It is only logically deleted in
DevOps Console, and remains in each tool.
Table. Project Deletion Input Items
Manage all projects
Shows information for all projects that the user has permission for. Except for Project Name Change, Project Deletion, it provides the same functionality as Project Overview and Project Members.
For detailed information, refer to Project Overview and Project Members.
- Click the Admin icon at the top right of the Main page. Navigate to the Tenant Dashboard page.
- Click the Tenant > Project menu in the left menu. You will be taken to the Project page.
12.2.3.2 - Create Project
12.2.3.2.1 - Create Project (Helm Chart Deployment)
Users must be members of a project group and tenant to be able to create projects.
Refer to Create Project Group for how to join a project group and tenant.
Users can create a project that deploys an application to a specific Kubernetes cluster using App.Template, Helm Chart, and Tool Management.
Getting Started with Project Creation
To start creating a project, follow these steps.
- Click the Create Project button on the Main page. You will be taken to the Create Project page.
Enter basic information
Enter the basic information of the project. The project name and project ID must be unique and cannot be duplicated.
To enter the basic information, follow the steps below.
- On the Project Creation page, select the App. Template Utilization option of the Project Configuration Method item.
- For the deployment target field, select Kubernetes.
- After entering additional content, click the Start button.
Item Explanation Project name Please enter the project name. Project ID Please enter the project ID. Project configuration method Select a project configuration method - Use App template: select a pre‑provided App template.
- Manual configuration: configure without an App template.
deployment target Select deployment target - Kubernetes: Deploy the application to a Kubernetes cluster.
- Kubernetes(ArgoCD): Deploy the application to a Kubernetes cluster using ArgoCD.
- VM(Artifact): Deploy the application to a VM server.
- VM(Docker): Package the application as a Docker image and deploy it to a VM server.
- N/A: Choose this when you do not deploy the build output.
K8S cluster Select the target cluster for deployment DevOps ConsoleOnly clusters that the user has access rights to can be selected among the K8S clusters.
namespace Select the target namespace for deployment - Only namespaces that the user has access rights to, among the clusters retrieved from the K8S cluster, can be selected.
Table. Project creation basic information entry items
App. Select Template
The user can select an application template to configure the project.
If you create a project based on an application template that includes sample source code, you can view the application that will be deployed.
In contrast, using a template labeled Environment Only configures only the build/deployment environment without sample source code.
If you configure a project using an already set up source code repository, select the template marked Environment Only.
To start selecting an application template, follow these steps.
- On the Application Template screen, enter the template name, select the application template card you want, and then click.
- When the Next button is enabled, click the Next button.
Item Explanation Filter You can easily find application templates using predefined filters. search You can easily find application templates through search. Table. Project Creation Application Template Items
Configure code repository
Users can configure a repository for managing source code through the code repository setup step.
Create new repository and use existing repository activation conditions differ depending on the application template and tool.
| Repository type | App with source code. Template + DevOps Console registration tool | App with source code included. Template + DevOps Console unregistered tool | Source code not included (EnvironmentOnly) App. Template + DevOps Console registration tool | Source code not included (Environment Only) App. Template + DevOps Console unregistered tool |
|---|---|---|---|---|
| Create new repository | ○ | X | ○ | X |
| Use existing repository | X | X | ○ | ○ |
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the code repository, follow these steps.
- In the Code repository item, select the Code repository type.
- Select Create new repository or Use existing repository, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the code repository to use - Registered tool: The user can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tool: You can enter the domain of an unregistered tool to use it. The unregistered tool entry appears only when the source code is not included (Environment Only) App. Template.
New/Existing usage Please select New repository creation or whether to use an existing repository. - Activation status varies depending on specific conditions. For details, refer to Table. Activation conditions for creating a new repository and using an existing repository.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication information - If you do not have an account, Don’t have an account? click the link to open the Account Creation Information popup where you can create an account.
- After creating a new account, be sure to change your password via the Set Initial Password link.
(Unregistered tool)
Repository informationEnter repository information - You can use a code repository that is not registered as a tool in
DevOps Console. - Click the URL Check button to undergo an additional verification process.
Table. Project Creation Code Repository Settings - Registered tool: The user can select and use the types of SCM Repository tools (
Configure Code Quality
Users can configure a repository for quality management.
To set code quality, follow these steps.
- In the Code Quality item, select Repository Type.
- Enter Basic Information and Authentication Information, then click the Connection Test button.
- Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository to use - The types of Code Quality tools available to the user are displayed.
New / Existing / Unused status Select repository creation method - If you select Create new repository, you must enter the quality project name/quality project key.
- If you select Do not create, you can proceed directly to the next step.
Base URL Select the SonarQubeURL.Quality Project Name Enter the name of the SonarQubeproject.Quality Project Key Enter the Key of the SonarQubeproject.authentication information Enter authentication credentials - You can create a new user or use existing authentication credentials.
Table. Project Creation Code Quality Settings
Configure Image Repository
Users can configure a repository to store the built container images through the image repository configuration step.
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the image repository, follow these steps.
- In the Image Repository item, select the Repository Type.
- Create new repository / Use existing repository select, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository type to use - The types of Image Registry tools available to the user are displayed.
Repository information Select the repository creation method. - When creating a new repository, the URL is formed with the project group name/project name.
Authentication information Enter your credentials. Table. Project Creation Image Repository Settings
Configure the deployment target environment
Users can deploy by directly configuring via Helm charts.
Helm release name and Helm chart when selected, the Helm chart installation options and the default Values.yaml entries included in the chart are displayed.
Available Helm charts are associated with the App template. You can edit or delete them through Manage supported Helm charts.
To set the deployment target environment, follow these steps.
- In the Deployment target field, select Configure directly via Helm chart.
- Please enter the Helm release name.
- Click the Search button to select the Helm chart to use.
- After editing Values.yaml, click the Validation Check button.
- When the Next button is enabled, click the Next button.
Item Explanation deployment target Please select the deployment target. Helm release name Enter the name of the Helm release to create. - The name must be unique within the namespace of the target cluster.
Helm chart Select a Helm chart. - When a Helm chart is selected, detailed information about the chosen chart is displayed below
K8S information Shows the information of the Kubernetes cluster required for configuring Value.yaml. Values. yaml Edit the contents of Values.yaml. values.yamlfile to be used when installing the Helm chart.
Table. Project creation deployment target environment configuration items
Setting up the build pipeline
Users can configure pipelines that build and deploy applications.
You can view each stage of the pipeline to be configured and rename the build job.
To set up the build pipeline, follow these steps.
- Build Pipeline screen branches based on IDP integration status.
- For IDP-integrated Jenkins, click the User Check button to perform User Registration Confirmation.
- For Jenkins not integrated with IDP, enter the authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.Item
Explanation Build/Deployment pipeline Displays build/deployment pipeline information. - The build/deployment pipeline is displayed based on the information registered in the App template’s Manage Pipeline Templates.
Category Select the development/operation distinction. - The permissions for the pipeline vary according to the development/operation distinction.
- Refer to Table. Role-based permissions within the project (1) for role-based permissions.
URL Select Jenkinsto configure the pipeline, then enter the job name.- The
Jenkinsinstances available to the user are displayed.
Build Agent Select the agent to be used for pipeline builds. - For information about the agent, please refer to Managing agents (kubernetes), Managing agents (VM).
Build environment OS Displays the OS information of the environment in which the build agent runs. User information IDP Integrated Jenkins - Click the User Check button to verify user registration.
- If you are not registered as a Jenkins user, when the User Registration Guide popup appears, click the Go to Jenkins link to proceed with User Sign‑Up or Initial Jenkins Login.
- Enter the authentication information and click the Connection Test button.
Set environment variables Set the environment variables to be registered in the Jenkins pipeline. Image Tag Pattern Select the tag assignment method for the container image. Deploy Strategy Select the deployment method for the container image. Recipient of deployment results Select the user who will receive the results after the build pipeline completes. Table. Project creation build pipeline configuration items
Configure Custom Settings
The user can specify and modify the path of the Dockerfile file used for the build.
Additionally, you can view the final script generated based on the information configured in 빌드 파이프라인 설정하기 and also edit it.
Dockerfile, follow these steps to configure the pipeline script.
- After entering information on the Custom settings page, click the Connection Test button.
- Click the Next button when the Next button is enabled.
Item Explanation Dockerfile configuration Create New Dockerfile or Use Existing Dockerfile. Please select. - «Use Existing Dockerfile is only selectable after choosing the
Environment OnlyApp template and, in 코드 저장소 설정하기, selecting Use Existing Repository.
Dockerfile path Specify the Dockerfilefile path in the source code.Branch name The branch name is automatically registered when you set it in Code Repository Configuration. Dockerfile Check and modify the contents of the Dockerfile.pipeline script Check and modify the pipeline script. Table. Project Creation Custom Settings Items - «Use Existing Dockerfile is only selectable after choosing the
Complete project creation
The user can review the project and tool information to be created and start project creation.
To complete project creation, follow the steps below.
- Summary Information After checking the information on the screen, click the Complete button.
- Project Creation popup window opens and the project creation proceeds.
- After the project creation is complete, click the Confirm button to go to the Project page.
12.2.3.2.2 - Create Project (Workload Deployment)
Refer to Create Project Group for how to join a project group and tenant.
Users can create a project that deploys to a specific Kubernetes cluster using App.Template, Tool Management and workloads.
Getting Started with Project Creation
To begin creating a project, follow the steps below.
- On the Main page, click the Create Project button. You will be taken to the Create Project page.
Enter basic information
Enter the basic information of the project. The project name and project ID must be unique and cannot be duplicated.
To enter the basic information, follow the steps below.
- On the Project Creation page, select the App. Template Utilization option of the Project Configuration Method item.
- For the deployment target field, select Kubernetes.
- After entering additional content, click the Start button.
Item Explanation Project name Please enter the project name. Project ID Please enter the project ID. Project configuration method Select a project configuration method - Use App template: select a pre‑provided App template.
- Manual configuration: configure without an App template.
deployment target Select deployment target - Kubernetes: Deploy the application to a Kubernetes cluster.
- Kubernetes(ArgoCD): Deploy the application to a Kubernetes cluster using ArgoCD.
- VM(Artifact): Deploy the application to a VM server.
- VM(Docker): Package the application as a Docker image and deploy it to a VM server.
- N/A: Choose this when you do not deploy the build output.
K8S cluster Select the target cluster for deployment DevOps ConsoleOnly clusters that the user has access rights to can be selected among the K8S clusters.
namespace Select the target namespace for deployment - Only namespaces that the user has access rights to, among the clusters retrieved from the K8S cluster, can be selected.
Table. Project creation basic information entry items
Select Application Template
The user can select an application template to configure the project.
If you create a project based on an application template that includes sample source code, you can view the application that will be deployed.
In contrast, using a template labeled Environment Only configures only the build/deployment environment without sample source code.
If you configure a project using an already set up source code repository, select the template marked Environment Only.
To start selecting an application template, follow these steps.
- On the Application Template screen, enter the template name, select the application template card you want, and then click.
- When the Next button is enabled, click the Next button.
Item Explanation Filter You can easily find application templates using predefined filters. search You can easily find application templates through search. Table. Project Creation Application Template Items
Configure code repository
Users can configure a repository for managing source code through the code repository setup step.
Create new repository and use existing repository activation conditions differ depending on the application template and tool.
| Repository type | App with source code. Template + DevOps Console registration tool | App with source code included. Template + DevOps Console unregistered tool | Source code not included (EnvironmentOnly) App. Template + DevOps Console registration tool | Source code not included (Environment Only) App. Template + DevOps Console unregistered tool |
|---|---|---|---|---|
| Create new repository | ○ | X | ○ | X |
| Use existing repository | X | X | ○ | ○ |
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the code repository, follow these steps.
- In the Code repository item, select the Code repository type.
- Select Create new repository or Use existing repository, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the code repository to use - Registered tool: The user can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tool: You can enter the domain of an unregistered tool to use it. The unregistered tool entry appears only when the source code is not included (Environment Only) App. Template.
New/Existing usage Please select New repository creation or whether to use an existing repository. - Activation status varies depending on specific conditions. For details, refer to Table. Activation conditions for creating a new repository and using an existing repository.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication information - If you do not have an account, Don’t have an account? click the link to open the Account Creation Information popup where you can create an account.
- After creating a new account, be sure to change your password via the Set Initial Password link.
(Unregistered tool)
Repository informationEnter repository information - You can use a code repository that is not registered as a tool in
DevOps Console. - Click the URL Check button to undergo an additional verification process.
Table. Project Creation Code Repository Settings - Registered tool: The user can select and use the types of SCM Repository tools (
Configure Code Quality
Users can configure a repository for quality management.
To set code quality, follow these steps.
- In the Code Quality item, select Repository Type.
- Enter Basic Information and Authentication Information, then click the Connection Test button.
- Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository to use - The types of Code Quality tools available to the user are displayed.
New / Existing / Unused status Select repository creation method - If you select Create new repository, you must enter the quality project name/quality project key.
- If you select Do not create, you can proceed directly to the next step.
Base URL Select the SonarQubeURL.Quality Project Name Enter the name of the SonarQubeproject.Quality Project Key Enter the Key of the SonarQubeproject.authentication information Enter authentication credentials - You can create a new user or use existing authentication credentials.
Table. Project Creation Code Quality Settings
Configure Image Repository
Users can configure a repository to store the built container images through the image repository configuration step.
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the image repository, follow these steps.
- In the Image Repository item, select the Repository Type.
- Create new repository / Use existing repository select, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository type to use - The types of Image Registry tools available to the user are displayed.
Repository information Select the repository creation method. - When creating a new repository, the URL is formed with the project group name/project name.
Authentication information Enter your credentials. Table. Project Creation Image Repository Settings
Configure the deployment target environment
The user can deploy by selecting Select deployment target workload.
To configure the deployment target environment, follow the steps below.
- In the Deployment Target item, select Select Deployment Target Workload. The Deployment Target Workload area appears.
- In the Deployment Target Workload area, select the workload and container to be deployed.
- When the Next button is enabled, click the Next button.
Item Explanation deployment target Select deployment target - Configure directly via Helm chart
- Select workload for deployment target
Query target Select the item to view. Workload Select workload - Displays the workloads that exist in the selected Kubernetes cluster when starting project creation.
target container Select the target container to use for the selected workload. Table. Deployment Target Environment Configuration Items
Setting up the build pipeline
Users can configure pipelines that build and deploy applications.
You can view each stage of the pipeline to be configured and rename the build job.
To set up the build pipeline, follow these steps.
- Build Pipeline screen branches based on IDP integration status.
- For IDP-integrated Jenkins, click the User Check button to perform User Registration Confirmation.
- For Jenkins not integrated with IDP, enter the authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.Item
Explanation Build/Deployment pipeline Displays build/deployment pipeline information. - The build/deployment pipeline is displayed based on the information registered in the App template’s Manage Pipeline Templates.
Category Select the development/operation distinction. - The permissions for the pipeline vary according to the development/operation distinction.
- Refer to Table. Role-based permissions within the project (1) for role-based permissions.
URL Select Jenkinsto configure the pipeline, then enter the job name.- The
Jenkinsinstances available to the user are displayed.
Build Agent Select the agent to be used for pipeline builds. - For information about the agent, please refer to Managing agents (kubernetes), Managing agents (VM).
Build environment OS Displays the OS information of the environment in which the build agent runs. User information IDP Integrated Jenkins - Click the User Check button to verify user registration.
- If you are not registered as a Jenkins user, when the User Registration Guide popup appears, click the Go to Jenkins link to proceed with User Sign‑Up or Initial Jenkins Login.
- Enter the authentication information and click the Connection Test button.
Set environment variables Set the environment variables to be registered in the Jenkins pipeline. Image Tag Pattern Select the tag assignment method for the container image. Deploy Strategy Select the deployment method for the container image. Recipient of deployment results Select the user who will receive the results after the build pipeline completes. Table. Project creation build pipeline configuration items
Configure Custom Settings
The user can specify and modify the path of the Dockerfile file used for the build.
Additionally, you can view the final script generated based on the information configured in 빌드 파이프라인 설정하기 and also edit it.
Dockerfile, follow these steps to configure the pipeline script.
- After entering information on the Custom settings page, click the Connection Test button.
- Click the Next button when the Next button is enabled.
Item Explanation Dockerfile configuration Create New Dockerfile or Use Existing Dockerfile. Please select. - «Use Existing Dockerfile is only selectable after choosing the
Environment OnlyApp template and, in 코드 저장소 설정하기, selecting Use Existing Repository.
Dockerfile path Specify the Dockerfilefile path in the source code.Branch name The branch name is automatically registered when you set it in Code Repository Configuration. Dockerfile Check and modify the contents of the Dockerfile.pipeline script Check and modify the pipeline script. Table. Project Creation Custom Settings Items - «Use Existing Dockerfile is only selectable after choosing the
Complete project creation
The user can review the project and tool information to be created and start project creation.
To complete project creation, follow the steps below.
- Summary Information After checking the information on the screen, click the Complete button.
- Project Creation popup window opens and the project creation proceeds.
- After the project creation is complete, click the Confirm button to go to the Project page.
12.2.3.2.3 - Create Project (ArgoCD Deployment)
- Users must be members of a project group and tenant to be able to create projects.
- Refer to Create Project Group for how to join a project group and tenant.
- Deployment via ArgoCD requires that ArgoCD and the Git repository to be used for GitOps deployment be prepared in advance.
- In the Devops Console, deployment is performed using the pre‑configured ArgoCD and its associated Git information.
Users can create a project that deploys using App.Template, Tool Management, and ArgoCD.
Getting Started with Project Creation
To start creating a project, follow the steps below.
- On the Main page, click the Create Project button. You will be taken to the Create Project page.
Enter basic information
Enter the project’s basic information. The project name and project ID must be unique and cannot be duplicated.
To enter the basic information, follow the steps below.
- Enter the project name and project ID.
- For the Project Configuration Method item, select App. Template Utilization.
- Please select deployment target as Kubernetes(ArgoCD).
- Please select the ArgoCD App creation method.
- Create a new App: When creating a project, create a new ArgoCD application in ArgoCD.
- Use existing App: Create a project using the existing ArgoCD application.
- After completing each input, click the Start button.
App. Select Template
The user can select an application template to configure the project.
If you create a project based on an application template that includes sample source code, you can view the application that will be deployed.
In contrast, using a template labeled Environment Only configures only the build/deployment environment without sample source code.
If you configure a project using an already set up source code repository, select the template marked Environment Only.
To start selecting an application template, follow these steps.
- On the Application Template screen, enter the template name, select the application template card you want, and then click.
- When the Next button is enabled, click the Next button.
Item Explanation Filter You can easily find application templates using predefined filters. search You can easily find application templates through search. Table. Project Creation Application Template Items
Configure code repository
Users can configure a repository for managing source code through the code repository setup step.
Create new repository and use existing repository activation conditions differ depending on the application template and tool.
| Repository type | App with source code. Template + DevOps Console registration tool | App with source code included. Template + DevOps Console unregistered tool | Source code not included (EnvironmentOnly) App. Template + DevOps Console registration tool | Source code not included (Environment Only) App. Template + DevOps Console unregistered tool |
|---|---|---|---|---|
| Create new repository | ○ | X | ○ | X |
| Use existing repository | X | X | ○ | ○ |
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the code repository, follow these steps.
- In the Code repository item, select the Code repository type.
- Select Create new repository or Use existing repository, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the code repository to use - Registered tool: The user can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tool: You can enter the domain of an unregistered tool to use it. The unregistered tool entry appears only when the source code is not included (Environment Only) App. Template.
New/Existing usage Please select New repository creation or whether to use an existing repository. - Activation status varies depending on specific conditions. For details, refer to Table. Activation conditions for creating a new repository and using an existing repository.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication information - If you do not have an account, Don’t have an account? click the link to open the Account Creation Information popup where you can create an account.
- After creating a new account, be sure to change your password via the Set Initial Password link.
(Unregistered tool)
Repository informationEnter repository information - You can use a code repository that is not registered as a tool in
DevOps Console. - Click the URL Check button to undergo an additional verification process.
Table. Project Creation Code Repository Settings - Registered tool: The user can select and use the types of SCM Repository tools (
Configure Code Quality
Users can configure a repository for quality management.
To set code quality, follow these steps.
- In the Code Quality item, select Repository Type.
- Enter Basic Information and Authentication Information, then click the Connection Test button.
- Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository to use - The types of Code Quality tools available to the user are displayed.
New / Existing / Unused status Select repository creation method - If you select Create new repository, you must enter the quality project name/quality project key.
- If you select Do not create, you can proceed directly to the next step.
Base URL Select the SonarQubeURL.Quality Project Name Enter the name of the SonarQubeproject.Quality Project Key Enter the Key of the SonarQubeproject.authentication information Enter authentication credentials - You can create a new user or use existing authentication credentials.
Table. Project Creation Code Quality Settings
Configure Image Repository
Users can configure a repository to store the built container images through the image repository configuration step.
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the image repository, follow these steps.
- In the Image Repository item, select the Repository Type.
- Create new repository / Use existing repository select, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository type to use - The types of Image Registry tools available to the user are displayed.
Repository information Select the repository creation method. - When creating a new repository, the URL is formed with the project group name/project name.
Authentication information Enter your credentials. Table. Project Creation Image Repository Settings
Configure the deployment target environment
To set the deployment target environment, ArgoCD and the Git repository to be used for GitOps deployment must be prepared.
ArgoCD App creation method The input values vary depending on the selection.
- Create new App
- Use existing App
Create new App
To create a new ArgoCD application and set the target deployment environment, follow the steps below.
- On the Deployment target environment screen, enter the ArgoCD URL and click the Confirm button.
- The authentication information entry screen appears.
- Enter Authentication information and click the Connection Test button.
- The input screen for the new ArgoCD application appears.
- Enter ArgoCD application name and ArgoCD project name.
- Select the Repository type.
- Please select Helm chart.
- Information about Helm chart and Helm chart Git repository is displayed.
- After editing Values.yaml, click the Validation Check button.
- After entering the Git repository information and authentication details, click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation URL input method Select the URL input method. - Select from the list: the ArgoCD tools registered as tools will appear.
- Enter manually
ArgoCD URL After entering the ArgoCD URL, click the Confirm button. The Authentication Information area appears. Authentication information Enter Authentication Information and click the Connection Test button. The Application Basic Information area opens. Application name Enter the name of the ArgoCD application to create in ArgoCD. Project name Enter the project name of the ArgoCD application. Repository type Select the repository type. - Create a new repository with Helm chart: Use a Helm chart to create a Git repository for
GitOps. Helm chart information area opens. - Use existing Git repository
Helm chart Please select a Helm chart. Helm chart Git repository Enter the information for the Git repository to be used by GitOps.Table. New App Creation Settings
Use existing App
To configure the target deployment environment using an existing ArgoCD application, follow these steps.
- Target deployment environment screen, enter ArgoCD URL, then click the Confirm button.
- The screen for entering the existing ArgoCD application name and credentials appears.
- Enter the Existing Application Name and Authentication Information, then click the Connection Test button.
- A URL Check popup window opens to distinguish the Git repository linked to the ArgoCD application..
- URL Check After editing the Base URL in the popup window, click the Confirm button.
- The Git repository information associated with the ArgoCD application is displayed.
- Enter the authentication information for the Git repository, then click the Connection Test button.
- Enter the yaml file name and key value to change in the Manifest Root path area.
- When the Next button is enabled, click the Next button.
Item Explanation URL input method Select URL input method - Select from list: ArgoCD tools registered as tools appear.
- Enter manually
ArgoCD URL After entering the ArgoCD URL, click the Confirm button. The Existing application name and credentials section will appear. Application name / authentication information Enter the Existing application name and credentials, then click the Connection Test button. The Git repository and ArgoCD information area appears. URL Check Separate the Base URL and Path in the full URL. Git repository credentials Enter the credentials for the Git repository used by the selected existing application. Image Repo Key Enter the path to the Yaml file that records the image repository information and the Key value. If the key values for repository and tag are the same, enter the same value. Image Tag Key Enter the path to the Yaml file containing the image tag information and the Key value. If the repository and tag have the same key, enter the same value. Image Secret Key Enter the path to the Yaml file containing the image secret information and the Key value. Deploy Strategy Key Enter the path to the Yaml file containing deployment strategy information and the Key value (optional). Table. Existing App usage configuration items
Setting up the build pipeline
Users can configure pipelines that build and deploy applications.
You can view each stage of the pipeline to be configured and rename the build job.
To set up the build pipeline, follow these steps.
- Build Pipeline screen branches based on IDP integration status.
- For IDP-integrated Jenkins, click the User Check button to perform User Registration Confirmation.
- For Jenkins not integrated with IDP, enter the authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.Item
Explanation Build/Deployment pipeline Displays build/deployment pipeline information. - The build/deployment pipeline is displayed based on the information registered in the App template’s Manage Pipeline Templates.
Category Select the development/operation distinction. - The permissions for the pipeline vary according to the development/operation distinction.
- Refer to Table. Role-based permissions within the project (1) for role-based permissions.
URL Select Jenkinsto configure the pipeline, then enter the job name.- The
Jenkinsinstances available to the user are displayed.
Build Agent Select the agent to be used for pipeline builds. - For information about the agent, please refer to Managing agents (kubernetes), Managing agents (VM).
Build environment OS Displays the OS information of the environment in which the build agent runs. User information IDP Integrated Jenkins - Click the User Check button to verify user registration.
- If you are not registered as a Jenkins user, when the User Registration Guide popup appears, click the Go to Jenkins link to proceed with User Sign‑Up or Initial Jenkins Login.
- Enter the authentication information and click the Connection Test button.
Set environment variables Set the environment variables to be registered in the Jenkins pipeline. Image Tag Pattern Select the tag assignment method for the container image. Deploy Strategy Select the deployment method for the container image. Recipient of deployment results Select the user who will receive the results after the build pipeline completes. Table. Project creation build pipeline configuration items
Configure Custom Settings
The user can specify and modify the path of the Dockerfile file used for the build.
Additionally, you can view the final script generated based on the information configured in 빌드 파이프라인 설정하기 and also edit it.
Dockerfile, follow these steps to configure the pipeline script.
- After entering information on the Custom settings page, click the Connection Test button.
- Click the Next button when the Next button is enabled.
Item Explanation Dockerfile configuration Create New Dockerfile or Use Existing Dockerfile. Please select. - «Use Existing Dockerfile is only selectable after choosing the
Environment OnlyApp template and, in 코드 저장소 설정하기, selecting Use Existing Repository.
Dockerfile path Specify the Dockerfilefile path in the source code.Branch name The branch name is automatically registered when you set it in Code Repository Configuration. Dockerfile Check and modify the contents of the Dockerfile.pipeline script Check and modify the pipeline script. Table. Project Creation Custom Settings Items - «Use Existing Dockerfile is only selectable after choosing the
Complete project creation
The user can review the project and tool information to be created and start project creation.
To complete project creation, follow the steps below.
- Summary Information After checking the information on the screen, click the Complete button.
- Project Creation popup window opens and the project creation proceeds.
- After the project creation is complete, click the Confirm button to go to the Project page.
12.2.3.2.4 - Create Project (VM Deployment)
Users must be members of a project group and tenant to be able to create projects.
Refer to Create Project Group for how to join a project group and tenant.
Users can create a project that deploys to a specific VM server using App.Template and Tool Management.
Before creating a project for VM deployment, register information about the target VM server. For detailed information on VM server registration, refer to Getting Started with VM Server Group.
Getting Started with Project Creation
To start creating a project, follow these steps.
- On the Main page, click the Create Project button. It navigates to the Create Project page.
Enter basic information
- On the Create Project page, enter the project name and project ID.
- For the Project Configuration Method item, select App. Template Utilization.
- Select VM(Artifact) or VM(Docker) for the Deployment Target field.
- VM(Artifact) creates a
war/jarfile and transfers it to the deployment target server. - VM(Docker) runs the
dockercommand after the build and image creation.
- VM(Artifact) creates a
- Please select the deployment method.
- Differences by deployment method: Table. SSH method vs Agent method
- After each input is completed, click the Start button.
App. Select Template
The user can select an application template to configure the project.
If you create a project based on an application template that includes sample source code, you can view the application that will be deployed.
In contrast, using a template labeled Environment Only configures only the build/deployment environment without sample source code.
If you configure a project using an already set up source code repository, select the template marked Environment Only.
To start selecting an application template, follow these steps.
- On the Application Template screen, enter the template name, select the application template card you want, and then click.
- When the Next button is enabled, click the Next button.
Item Explanation Filter You can easily find application templates using predefined filters. search You can easily find application templates through search. Table. Project Creation Application Template Items
Configure code repository
Users can configure a repository for managing source code through the code repository setup step.
Create new repository and use existing repository activation conditions differ depending on the application template and tool.
| Repository type | App with source code. Template + DevOps Console registration tool | App with source code included. Template + DevOps Console unregistered tool | Source code not included (EnvironmentOnly) App. Template + DevOps Console registration tool | Source code not included (Environment Only) App. Template + DevOps Console unregistered tool |
|---|---|---|---|---|
| Create new repository | ○ | X | ○ | X |
| Use existing repository | X | X | ○ | ○ |
To modify or delete stored credentials, refer to Manage Authentication Information.
To set up the code repository, follow these steps.
- In the Code repository item, select the Code repository type.
- Select Create new repository or Use existing repository, then enter the information.
- Enter authentication information and click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the code repository to use - Registered tool: The user can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tool: You can enter the domain of an unregistered tool to use it. The unregistered tool entry appears only when the source code is not included (Environment Only) App. Template.
New/Existing usage Please select New repository creation or whether to use an existing repository. - Activation status varies depending on specific conditions. For details, refer to Table. Activation conditions for creating a new repository and using an existing repository.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication information - If you do not have an account, Don’t have an account? click the link to open the Account Creation Information popup where you can create an account.
- After creating a new account, be sure to change your password via the Set Initial Password link.
(Unregistered tool)
Repository informationEnter repository information - You can use a code repository that is not registered as a tool in
DevOps Console. - Click the URL Check button to undergo an additional verification process.
Table. Project Creation Code Repository Settings - Registered tool: The user can select and use the types of SCM Repository tools (
Configure Code Quality
Users can configure a repository for quality management.
To set code quality, follow these steps.
- In the Code Quality item, select Repository Type.
- Enter Basic Information and Authentication Information, then click the Connection Test button.
- Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository to use - The types of Code Quality tools available to the user are displayed.
New / Existing / Unused status Select repository creation method - If you select Create new repository, you must enter the quality project name/quality project key.
- If you select Do not create, you can proceed directly to the next step.
Base URL Select the SonarQubeURL.Quality Project Name Enter the name of the SonarQubeproject.Quality Project Key Enter the Key of the SonarQubeproject.authentication information Enter authentication credentials - You can create a new user or use existing authentication credentials.
Table. Project Creation Code Quality Settings
Configure Artifact Repository
Users can configure a repository for artifacts.
If you select Uncreated, you can proceed directly to the next step.
To configure the artifact repository, follow these steps.
- On the Artifact Repository screen, select the repository type.
- Enter the basic information and authentication information, then click the Connection Test button.
- When the Next button is enabled, click the Next button.
Item Explanation Repository type Select the repository type to use - The types of Artifact Repository tools available to the user are displayed.
New / Existing / Unused status Select the repository creation method - If you select Uncreated, you can proceed directly to the next step.
Base URL / Endpoint URL Select a NexusURL or anObject StorageURL.Storage type / bucket name - In the case of
Nexus, it is automatically registered asraw(hosted). - In the case of
Object Storage, the bucket name entered during tool registration is automatically registered.
Repository name / Folder name - Enter the repository name to use in
Nexus. - Enter the folder name to use in
Object Storage.
Authentication information Enter authentication information - You can create a new user or use existing authentication information.
Table. Artifact Repository Configuration Input Items
Configure the deployment target environment
Deployment target configuration requires that VM server group/VM server be registered.
For registration methods and detailed information, refer to VM서버 그룹.
To set the deployment target environment, follow these steps.
- Deployment Target Environment on the screen, after entering the required information, click the Next button.
Item Explanation Deployment configuration Choose whether to write a deployment script manually - When selecting to write a deployment script manually, write the content in the custom step.
Deployment method The selected deployment method is displayed. Artifact repository The address of the repository to use when the agent mode is selected is displayed. - Deployment mode is enabled when it is Agent.
Manual deployment Select the default value for manual deployment - Select the default setting for parameters related to manual deployment when running the pipeline.
Deployment order If there are multiple target servers, choose whether to deploy in parallel or sequentially. Deployment target settings Set the deployment target server. - When you click Settings, the Deploy Target VM Settings popup opens.
Automatic recovery setting Select whether to enable automatic rollback - If the deployment fails, it will be rolled back to the most recent successful deployment.
- Deployment method is enabled when it is Agent.
Command before file deployment Write the commands that need to be executed before file deployment. File to send - Source: Enter the file path after the build pipeline execution path (Jenkins workspace).
- Target: Enter the path where the file will be deployed on the VM server.
- Add button can be used to add files.
Command after file distribution Write the commands that must be executed after file deployment. Table. Deployment Target Environment Configuration Items
Setting up the build pipeline
Users can configure pipelines that build and deploy applications.
You can review each stage of the pipeline to be configured and rename the build job.
To set up the build pipeline, follow these steps.
- In the build pipeline configuration step, enter the authentication information and click the Connection Test button.
- Next button is enabled, click the Next button.
Item Explanation Build/Deployment pipeline Displays build/deployment pipeline information. - The build/deployment pipeline is displayed based on the information registered in the App. template’s Manage Pipeline Templates
Category Select Development/Operation mode - The permissions for the pipeline vary depending on the Development/Operation distinction.
- Refer to Table. Permissions by role within the project (1) for role-specific permissions.
URL Select Jenkinsto configure the pipeline, then enter the Job nameJenkinsavailable to the user appears.
Build Agent Select the agent to be used for pipeline builds - For information about agents, refer to Managing agents (kubernetes), Managing agents (VM).
Build environment OS Displays the OS information of the environment in which the build agent runs. Authentication information Enter the credentials for Jenkins.Set environment variables JenkinsSet the environment variables to be registered in the pipeline.Deployment result recipient Select the user who will receive the results after the build pipeline completes. Table. Build pipeline configuration input items
Configure Custom Settings
In the deployment target server and deployment settings step, if you select the deployment configuration item write deployment script directly, complete the deployment configuration by modifying the pipeline contents at this stage.
To customize the settings, follow these steps.
- After reviewing and editing the content in the Custom step, click the Next button.
Complete project creation
The user can review the project and tool information to be created and start project creation.
To complete project creation, follow the steps below.
- Summary Information After checking the information on the screen, click the Complete button.
- Project Creation popup window opens and the project creation proceeds.
- After the project creation is complete, click the Confirm button to go to the Project page.
12.2.3.2.5 - Create Project (Empty)
- Users must be members of a project group and tenant to be able to create projects.
- For instructions on joining a project group and tenant, refer to Create Project Group.
The user can create an Empty (Empty) project without any configuration.
To create an empty project and configure build/deployment, the user must manually perform tasks such as Add code repository, Add image repository, Install Helm, Add build pipeline.
Getting Started with Project Creation
To start creating an empty project, follow these steps.
- On the Main page, click the Create Project button. You will be taken to the Create Project page.
Enter basic information
Enter the basic information for the project. The project name and project ID must be unique and cannot be duplicated.
To enter the basic information, follow these steps.
- On the Project Creation page, select Direct Configuration under the Project Configuration Method item.
- Enter Project Name and Project ID, then click the Start button. The Summary Information screen appears.
Complete project creation
The user can review the project and tool information to be created and start project creation.
To complete project creation, follow the steps below.
- Summary Information After checking the information on the screen, click the Complete button.
- Project Creation popup window opens and the project creation proceeds.
- After the project creation is complete, click the Confirm button to go to the Project page.
12.2.3.3 - Start Project
The user can create a project via Create a project.
On the project page, users can utilize various menus for project management.
Getting Started
To start the project, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
Project menu
Dashboard
Dashboard (Project Dashboard)
This is a dashboard menu that lets you view information about the individual items that make up the project at a glance.
Build/Deployment
Build pipeline(Build/Deploy - Build Pipeline)
This menu allows you to view the Jenkins pipeline and perform and modify build/deployment tasks.
Kubernetes deployment (Build/Deploy - Kubernetes Deployment)
This menu lets you view the list of deployed Helm releases and their deployment status.
VM deployment (Build/Deploy - VM Deployment)
This menu allows you to view the list of deployed VMs and their deployment status.
Helm install (Helm install)
This is the menu where you can view Helm charts.
Ingress/Service management (Ingress/Service management)
A menu where you can view and add Ingress/Service.
Kubernetes Secret management (Kubernetes Secret management)
This menu allows you to view and add Kubernetes Secrets.
Environment Variable Management (환경변수 관리)
This is a menu that allows you to view and add environment variables.
storage
Code repository (repository)
This is a menu that allows you to view and add code repositories for a project.
Artifact Repository (Artifact Repository)
This menu lets you view and add the project’s image repository.
Image Repository (Image Repository)
This menu allows you to view and add the project’s image repository.
Chart repository (Chart repository)
This menu lets you view and add a project’s chart repositories.
Helm chart (헬름차트)
A menu for viewing and adding project Helm charts.
Quality
Code Quality (Code Quality)
Project code quality. This is a menu that allows you to view and add projects.
Project Overview
Project Overview (프로젝트 개요)
This menu allows you to view not only the project’s detailed information but also related Helm release information and details about the tools you are using.
member
Member (Project Member)
This is a menu for managing project users.
12.2.3.4 - Project Dashboard
You can view the information of individual items that make up the project at a glance on the dashboard.
Getting Started with Project Dashboard
To start using the dashboard, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- Click the Dashboard menu in the left menu.
Item Explanation Project information Displays the basic project information. pipeline Displays the status of pipelines added to the build pipeline.
Click the numeric link to view the status of other pipelines.Helm release status You can check the status of the Helm release added to the Kubernetes deployment. Blue/Green deployment status You can check the status of blue/green deployments. Canary status You can check the canary status. ArgoCD application status You can check the status of the ArgoCD application added to the Kubernetes deployment. Kubernetes deployment history Displays the Kubernetes deployment history in reverse chronological order. VM deployment history Displays the VM deployment history in reverse chronological order. code quality Displays code quality tool analysis information by integrating with the code quality tool. Code history Displays the history of the added code repository.
For the following items, you can select from the list to display in the code history.- Git configuration
- Git Branch
Scale and Usage Status Displays the project’s users, tools, and build/deployment status. Monthly pipeline execution trend Shows the monthly pipeline execution count, average execution interval, and execution time for the project. Inactive pipeline Shows a list of pipelines that have not been run and have no successful history, according to the reference date. Required stage Shows which stage tasks were performed in the pipeline, based on the code repository. Recent event history You can view the recent event history that occurred in the project. Table. Project Dashboard Display Items
12.2.3.5 - Project Members
It includes features to grant other users access to the project, modify the permissions of users who already have access, or delete permissions so they can no longer access the project.
Getting Started with Project Members
To start using project members, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Member menu in the left menu. The Member screen appears.
Add Project Member
To add members to a project, follow these steps.
- Click the Add button in the Member list. Member Add popup opens.
- After completing the settings in the Add Member popup, click the Confirm button to finish adding a project member.
Item Explanation User tab After searching for the email, click the Add button to add as a member. Project tab Select to add all members from another project to the current project’s members. Add member Click the user you want to add as a project member to add them. Permission Settings Set the role to assign to members. - Owner
- Master
- Developer
- Viewer
Delete member Click the X icon to delete from the project members. Table. Project Member Add Screen Items
Change Project Member Role
To change a project member’s role, follow these steps.
- Identify the user whose role you want to change in the Member list.
- Select the user’s project role from the list. It is saved immediately upon selection, and the user’s project role will be updated.
Delete project member
To remove a member from a project, follow these steps.
- In the Member list, select the checkbox of the user you wish to delete.
- Click the Delete button above the Member list to remove the selected user from the project members.
12.2.4 - Build/Deploy
12.2.4.1 - Build Pipeline
Jenkins pipeline, refer to the official site.Users can group consecutive tasks into a single pipeline. The pipeline configured here is created as a Jenkins pipeline.
Starting the Build Pipeline
To start using the build pipeline, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Build Pipeline menu. You will be taken to the Build Pipeline page.
Add Build Pipeline
To add a build pipeline, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Build Pipeline menu. You will be taken to the Build Pipeline page.
- Build Pipeline page, click the Add Pipeline button at the top right. You will be taken to the Add Pipeline page.
- Add Pipeline Enter or configure each field on the page.
- Click the Next button.
Item Explanation Category Select Development or Operations - The actions that each role can perform differ depending on development or operations.
- Refer to Table. Role-specific permissions within the project (1) for role-specific permissions.
Jenkins URL Select Jenkinsfrom the list to add a build pipeline.Build Agent Select the agent (build environment) on which the build pipeline will run.
Click the Info icon to view the list of tools provided by the agent.Build environment OS Displays the OS information of the environment where the build agent runs. Folder type Select the folder type. - Existing folder: Add a pipeline under an already created folder in
Jenkins. - New folder: Create a new folder in
Jenkinsand add a pipeline under it.
folder Select a folder from the list or enter the name of a new folder to create. Pipeline name Please enter the pipeline name. Parameter setting Set the parameters to be used in the pipeline. Environment variable configuration Set the environment variables to be used in the pipeline. Stage Settings Configure the stage to be used in the pipeline. Configure email recipients for build results Set the recipients who will receive the result email after the pipeline completes (success/failure). Table. Additional Build Pipeline Settings
Setting Parameters
Follow these steps to set the parameters used when running the pipeline.
- Click the Parameter card.
- Click the Add button to add a parameter.
- Click the Apply button to complete the parameter settings.
Setting Environment Variables
Follow these steps to set environment variables for use in the pipeline.
- Click the Environment Variable area. The Environment Variable Registration page opens on the right.
- A list of pre-registered environment variables appears, and select the checkboxes for the environment variables you want to use.
- Check the selected environment variable and click the Apply button to complete the environment variable configuration.
Setting up the stage
To set up the stages to be used in the pipeline, follow these steps.
- Click the New Stage card. The Stage area appears on the right.
- In the Stage area, select the tool and Stage type.
- Enter the required information according to the stage type and click the Apply button to complete the stage configuration.
For detailed information about stage configuration, see Stage.
Configure email recipients for build results
To set the recipients who will receive the build results by email, follow these steps.
- Click the Mail Recipient area. The Add Mail Recipient page opens on the right.
- In the Search area, search for the recipient and add them.
- Click the Apply button to complete the mail recipient settings.
Check the final pipeline script
- Check the build pipeline script that will actually be generated. If needed, edit the script directly.
- Click the Complete button to finish adding the pipeline.
Pipeline addition result
- The added result appears on the Build Pipeline page.
Managing Build Pipelines
Build pipeline list
| Item | Explanation |
|---|---|
| status | Displays the build pipeline status.
|
| URL | Go to the Build Pipeline page of Jenkins. |
| Recent build execution history URL | Navigate to the Build Execution History page of Jenkins. |
| log | pipeline log The popup window opens. |
| Run | Run the build pipeline. |
| View more | Displays additional menu.
|
| View pipeline stage | When you click the Expand icon, the stage view expands. |
Build Pipeline Credentials
When performing build pipeline actions (run, stop, edit, delete, etc.), user credentials are required, so you may request them from the user as needed.
When integrating IDP with Jenkins
If you are not registered as a Jenkins user, when the User Registration Guide popup appears, click the Go to Jenkins link to sign up or perform your first Jenkins login.
For Jenkins without IDP integration
Jenkins credentials are not stored; when the Add Account popup appears, select Use Existing User or Create New User in Account Type to add credentials.
Run Build Pipeline
To run the build pipeline, follow these steps.
- On the Build pipeline page, click the Run button of the build pipeline you want to execute.
- If there are parameters, the Pipeline Execution Parameter Input popup window opens.
- After entering the required fields, click the Confirm button.
If the Number of executors setting for the Built-In Node in Jenkins system configuration is set to 1 or higher, a security issue may arise, preventing the pipeline from running.
- In this case, you need to contact the Jenkins administrator to change the settings.
- In the Jenkins administration menu, you can enable it by changing the Number of executors item of the Built-In Node to 0.
- Note Jenkins officially recommends avoiding running builds on the Controller Node.
View build pipeline execution logs
Follow these steps to view the build pipeline execution logs.
- On the Build Pipeline page, click the Log button of the build pipeline you want to run.
- pipeline log A popup window opens, allowing you to view the execution log.
Build pipeline build history view
To view the complete build history of the build pipeline, follow these steps.
- On the Build pipeline page, click the More icon of the build pipeline you want to view.
- Click the Build History menu. The Build History page opens.
Item Explanation Config Diff Config Diff The popup window opens. log Pipeline Log The popup window opens. Additional menu Navigate to the Build Details page. View pipeline stage Click the Expand icon to expand the stage view. Table. Build Pipeline List View Feature
Compare configuration information
You can compare the configuration information with previous build history using the Config Diff button.
Log View
Through the Log button, you can view the logs of the build history.
Build Details
You can view detailed build information via the More icon.
Modify Build Pipeline
To modify the build pipeline, follow these steps.
- On the Build pipeline page, click the More icon of the build pipeline you want to edit.
- Click the Edit Pipeline button. You will be taken to the Edit Pipeline page.
Edit the script directly
To edit the pipeline script directly, follow these steps.
- In the script editor window of the Pipeline Edit page, directly enter a script that conforms to the syntax supported by
Jenkins. - After completing the input, click the Save button to finish editing the pipeline.
Modify using the Script Generator feature
Follow these steps to modify the pipeline script using the Script Generator feature.
- On the Pipeline Edit page, change Script Generator to ON.
- Select the build agent and script type.
- After completing Stage Setup, click the Create Script button to generate the script.
- Refer to the generated script to modify the pipeline, and click the Save button to complete the pipeline modification.
Item Explanation Script Generator Turn the Script Generator feature ON/OFF. Script Basic Information Select the basic information for script generation. Existing script This is an existing script. New script This is a new script generated by the Script Generator. Script modification Refer to the newly created script and directly edit the existing script on the left. Update Jenkins Credential If the newly created script contains new credentials, click the Jenkins CredentialUpdate button. This updates (saves) the credentials in Jenkins.K8S Secret update Deploy to K8S stage: when changing the K8S Secret, click the K8S Secret Update button. Update (save) it for use during Secret creation and deployment. Table. Script Generator feature
Clone Build Pipeline
To duplicate the build pipeline, follow these steps.
- Click the More icon of the build pipeline you want to clone.
- Click the Clone Pipeline menu. The Clone Pipeline popup window opens.
- After completing the information entry, click the Save button to finish replicating the pipeline.
Item Explanation Pipeline replication information Enter the information for the pipeline to be cloned. Pipeline modification Modify the pipeline to be cloned. Table. Build Pipeline Replication Feature
Delete Build Pipeline
To delete a build pipeline, follow these steps.
- On the Build pipeline page, click the More icon of the build pipeline you want to delete.
- Click the Delete Pipeline menu. The Delete Pipeline popup window opens.
- Delete Pipeline In the popup window, click the Confirm button to complete the pipeline deletion.
Also delete the pipeline in Jenkins
- Selection: The pipeline is actually deleted from
Jenkins. - Unselected: Build pipeline is deleted only from the list and remains in
Jenkins.
12.2.4.1.1 - Stage
The user can view the description of stage types and each stage-specific item.
You can configure stages in Add Build Pipeline or Edit Build Pipeline.
Common Items
Stage Settings page is organized as follows.
| Item | Explanation |
|---|---|
| Tools | If you want to specify and use a particular tool other than the default tools set in the stage, select
|
| Stage types | Select the required stage from the list and enter the necessary information. |
| Stage name | Enter the stage name. |
Checkout
This stage executes the checkout command on the Git repository registered in the code repository.
Select Checkout as the stage type.
| Item | Explanation |
|---|---|
| URL | Select the code repository to perform checkout. |
| Branch name | Enter the branch name to checkout. |
Build
This is the stage that executes the command to build the application.
Select Build as the stage type.
| Item | Explanation |
|---|---|
| language | Select the programming language used by the application. |
| Build tool | Select the build tool used for building the application. Provides default Shell commands based on the selected build tool. |
| Shell command | Enter the command to use for building the application. All commands available in the Shell can be used. |
Docker Build
This stage performs the Docker image build.
Select Docker Build as the stage type.
item | Explanation | example |
|---|---|---|
Registry URL (docker push) | Select the image repository where the Docker build result image will be pushed. | |
| ID | The ID value of the account to be used for the image repository | |
| image tag pattern | The Docker image tag is automatically generated according to the selected pattern.
|
|
| Add base image repository | Add Base Image Repository A popup window opens.
| |
Registry URL (docker pull) | Select the image repository for docker pull when the repository providing the Base Image used in the Dockerfile (FROM clause, docker pull) differs from the repository of the Registry URL (docker push). | |
| Image build tool | Displays the image build tool. | |
| Pre-build command | If there are any commands that need to be run before building a Docker image, write them in shell command format. | cp target/*.jar docker/ |
| Image Build folder | If you need to run the Docker image build from a specific folder, select the checkbox and enter the folder path. | docker |
| Dockerfile | Enter the Dockerfile filename. | Dockerfile |
| Image build options | Enter it if you need to use additional options with the image build tool. | --no-cache |
| Build command | Displays the image build command that will actually be executed. | |
| Post-build command | If there are commands that need to be executed after building a Docker image, write them in Shell command format. | rm -rf docker/*.jar |
example script
The build pipeline script generated as a result of the example is as follows.
| Item | Explanation |
|---|---|
➊ | Pre-build command |
➋ | Image Build folder |
➌ | Image build options |
➍ | Post-build command |
Deploy to K8S
This is the stage that performs a Kubernetes deployment.
Select Deploy to K8S as the stage type.
Item | Explanation |
|---|---|
| type | Select deployment type
|
| K8S cluster | Select a K8S cluster
|
| namespace | Please select a namespace. |
| Helm release | Select HelmRelease. |
| Deployment method | Select deployment method
|
| Registry URL | Select the image repository where the image to be deployed to Kubernetes has been docker pushed. |
| Secret | Select the secret information input method
|
Deploy to VM
This is the stage that performs VM deployment.
Select Deploy to VM as the stage type.
| Item | Explanation |
|---|---|
| Deployment configuration | Select deployment configuration method
|
| deployment group | Select a deployment group
|
| Release Information | The contents stored in the deployment group are automatically configured. |
| Manual deployment | Select the default value for manual deployment
|
Trigger Build
This is a stage that runs the pipeline remotely.
Select Trigger Build as the stage type.
| Item | Explanation |
|---|---|
| Target pipeline | Choose the target pipeline to run remotely. The selectable items vary depending on whether the pipeline is for development or production. |
| Parameter information | It is displayed depending on whether the target pipeline’s parameters are set. The parameter information entered at pipeline execution time is used. |
Check Remote Execution Information
Remote execution information (parent/child pipelines) through the Trigger Build stage can be viewed on the Build Details screen.
Other stages
| Item | Explanation |
|---|---|
| Archive | Archive the application build results. The archived file can be downloaded from Jenkins. |
| Code Quality | This is the stage for executing the Code Quality step. |
| Custom | The user directly writes the pipeline script in the desired format. |
12.2.4.1.2 - Multibranch Pipeline
Users can integrate multiple branches of a code repository through a multibranch pipeline and manage them as a single job.
Starting a Multibranch Pipeline
To start using a multibranch pipeline, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > Build Pipeline menu. You will be taken to the Build Pipeline page.
Add a multibranch pipeline
To add a multibranch pipeline, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > Build Pipeline menu. You will be taken to the Build Pipeline page.
- On the Build Pipeline page, click the Add Multi-branch Pipeline button at the top right. The Add Multi-branch Pipeline popup will open.
- Add Multi-branch Pipeline In the popup window, enter each field and click the Save button.
Item Explanation Category Select development or operation - The actions that each role can perform differ depending on development or operation.
- Refer to Table. Role-specific permissions within the project (1) for role-specific permissions.
Jenkins URL Select the Jenkins to add a multibranch pipeline from the list. Folder type Select folder type - Existing folder: Add a pipeline under a folder that already exists in Jenkins.
- New folder: Create a new folder in Jenkins and add a pipeline under it.
Folder name Select a folder from the list or enter the name of a new folder to create. pipeline name Please enter the pipeline name. Git Repository Select the code repository to perform builds per branch.
Only code repositories registered in the DevOps Console project can be selected.Branch filtering You can filter the branch names to build among the branches registered in the code repository.
When using filtering, enter the filter condition as a Java regular expression.Jenkinsfile path Enter the path within the code repository of the Jenkinsfile where the pipeline build is defined. Table. Multi-branch pipeline additional information input items
Managing Multi-Branch Pipelines
Multi-branch pipeline list
| Item | Explanation |
|---|---|
| Multi-branch icon and label | Icons and labels representing a multibranch pipeline are displayed. |
| URL | Navigate to the Jenkins Multibranch Pipeline page. |
| Scan log | Multi-branch pipeline scan log The popup window opens. |
| Scan | Scanning the multibranch pipeline. |
| View more | Displays additional menu.
|
Scanning a multibranch pipeline
To scan a multibranch pipeline, follow these steps.
- On the Build Pipeline page, click the Scan button of the multibranch pipeline card you want to scan.
- Click the Confirm button in the confirmation popup.
View multi-branch pipeline scan logs
To view the scan logs of a multibranch pipeline, follow these steps.
- Build Pipeline page, click the Scan Log button of the multibranch pipeline card for which you want to view the scan log. The Multibranch Pipeline Scan Log popup window opens.
- Multi-branch pipeline scan log After reviewing the contents in the popup window, click the Confirm button to exit.
View multi-branch pipeline build history
To view the build history for each branch in a multibranch pipeline, follow these steps.
- On the Build Pipeline page, click the More icon of the multibranch pipeline card for which you want to view the build history.
- Click the Build History menu. You will be taken to the Branch-specific Build History screen of
Jenkins. (This feature is not provided in DevOps Console)
Modify multi-branch pipeline
To modify a multibranch pipeline, follow these steps.
- On the Build Pipeline page, click the More icon of the multibranch pipeline card you want to edit.
- Click the Edit Pipeline menu. You will be taken to the Settings screen of
Jenkins. (Feature not provided in DevOps Console)
Delete Multi-branch Pipeline
To delete a multibranch pipeline, follow these steps.
- On the Build Pipeline page, click the More icon of the multibranch pipeline card you want to delete.
- Click the Delete Pipeline menu. The Delete Pipeline popup window opens.
- In the Delete Pipeline popup, select whether to Delete the pipeline in Jenkins as well, and click the Confirm button.
Delete the pipeline in Jenkins as well.
- Selection: The pipeline is actually deleted in
Jenkins. - Unselected: Build pipeline is deleted only from the list and remains in
Jenkins.
12.2.4.2 - Kubernetes Deployment
Users can view the list of Helm releases used in the project and their deployment status. Depending on the development classification, the releases appear in the development or production list when the project is created or a chart is installed.
Users can differentiate deployments using icons.
 Helm chart
Helm chart Istio
Istio Workload
Workload Canary(Canary)
Canary(Canary) Blue/Green (Blue-Green)
Blue/Green (Blue-Green) ArgoCD
ArgoCD
Getting Started with Kubernetes Deployment
To start using Kubernetes deployment, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
12.2.4.2.1 - Helm Release
HelmRelease is an instance of a chart running on a Kubernetes cluster. Users can create a HelmRelease when creating a project or via the HelmInstall menu.
Getting Started with Helm Release
To start HelmRelease, follow these steps.
- From the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
Item Explanation Name Displays the deployment name. Click to view detailed information. Chart Displays the Helm chart information used for deployment. Cluster/Namespace Displays the deployed cluster/namespace. Pod status Displays the current status of the Pod. Deployment result Displays the deployment execution result. Deployment time Displays the deployment execution time. Refresh Refresh the current items. The items that will be updated are the Pod status, deployment result, and deployment time. Delete Delete the current item. Table. Helm release items - Kubernetes deployment page, click name in the Helm release list. You will be taken to the deployment details page.
Add Helm Release
Helm install
You can add a Helm release through Helm install.
Add related Helm release
To add the related Helm release, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deployment menu in the left menu. You will be taken to the Kubernetes Deployment page.
- Click the Add related Helm release button. The Add related Helm release popup opens.
- Add related Helm release Enter each item in the popup window.
- Click the Save button to complete adding the Helm release.
Item Explanation Helm release already registered in the project Shows the Helm release already registered in the project. - A Helm release already registered in the project cannot be added.
Table. Items displayed when adding related Helm release
Managing Helm Release Secrets
Getting Started with Helm Release Secrets
In HelmRelease secrets, you can manage the ImagePull Secret used for images deployed through the build pipeline in HelmRelease.
To start HelmRelease secret management, follow the steps below.
- On the Deployment Details page, click the Edit Credentials icon to the right of Helm Release.
- Helm Release Secret The popup window opens.
Adding a secret to a Helm release
To add a Helm release secret, follow these steps.
- On the Deployment Details page, click the Edit Authentication Info icon to the right of the Helm Release. The Helm Release Secret popup will open.
- Helm Release Secret popup window, if you need to add a secret to pull a private Chart Image, click the Add button in the Chart Install Secret area. The Add Secret popup will open.
- If you need to add a secret required to pull the App Image used during build/deployment, click the Add button in the ImagePull Secret area. The Add Secret popup will open.
- Add Secret In the popup window, enter the secret information and click the Save button to complete the addition.
Item Explanation Registry URL From the list of images registered in Image Repository, select the image that ImagePull Secret will use. Secret Select secret input method - Auto-generate: Automatically create a secret using the credentials of the selected image repository from the Docker URL.
- Use existing secret: Select and use one of the already created secrets.
Table. Additional Helm Release Secret Configuration Items
Edit Helm Release Secret
To modify the Helm release secret, follow these steps.
- On the Deployment Details page, click the Edit Authentication Info icon to the right of the Helm Release. The Helm Release Secret popup will open.
- In the HelmRelease secret list, click the secret name you want to edit. Secret Edit popup opens.
- Edit the content and click the Save button to complete the edit.
Delete Helm release secret
To delete a Helm release secret, follow these steps.
- On the Deployment Details page, click the Edit Authentication Info icon to the right of the Helm Release. The Helm Release Secret popup will open.
- Click the secret name you want to delete from the Helm release secret list.
- Click the Delete button to complete the deletion.
Modify K8S credentials
K8S credentials are the authentication information used to verify permission to use a K8S cluster/namespace when performing a deployment in the build pipeline.
To modify the K8S credentials, follow these steps.
- On the Deployment Details page, click the Edit Credentials icon to the right of K8S Cluster/Namespace. The Edit Credentials popup will open.
- Authentication information is fixed to the logged-in user’s account. Click the Save button to edit.
- In the confirmation popup, click the Confirm button.
- K8S authentication information will be changed to the logged-in user.
Check the values.yaml used in the Helm release
To view the contents of values.yaml, follow these steps.
- On the Deployment Details page, click the History tab.
- Click the View icon in the Values column. Revision # - Values.yaml The popup window opens.
- Check the contents of the
values.yamlfile.
Comparing values.yaml used in Helm release
To compare the values.yaml contents used in each release, follow the steps below.
- Click the History tab on the Deployment Details page.
- In the list, click the check box of each of the two revisions you want to compare.
- Click the Yaml Diff button. The Yaml Diff popup window opens.
- Yaml Diff (Revision #>#) Check the comparison details in the popup window.
Rollback Helm Release
To roll back a Helm release to a previous revision, follow these steps.
- On the Deployment Details page, click the History tab.
- Click the Rollback button of the revision you want to roll back. The Rollback popup window will open.
- Click the Confirm button to complete the rollback.
Upgrade Helm Release
To upgrade HelmRelease, follow the following procedure.
- On the Deployment Details page, click the History tab.
- In the Values column, click the View icon. The Revision # - Values.yaml popup window opens.
- Modify the contents of Current Values.yaml, and click the Upgrade button. The Upgrade popup window will open.
- Check the upgrade information.
- Click the Run button to complete the upgrade.
View Pod logs
To view the logs of the Pod related to a Helm release, follow these steps.
- On the Deployment Details page, click the Release Object tab.
- Click the view icon in the LOG column of the Pod entry. The Log popup window opens.
Item Explanation container Select the container from which you want to output logs. Real-time refresh Refresh the log output in real time. Refresh stopped Stop real-time refresh. Download Download the Pod logs to a file. Table. Log popup window function description
Delete Helm Release
To delete HelmRelease, follow the steps below.
- On the Deployment Details page, click the Delete button at the lower right of the Helm Release. The Delete Helm Release popup opens.
- Click the Confirm button to complete the deletion.
Also execute the helm delete command.
- Select: The Helm release is actually deleted from the cluster.
- Unselected: Kubernetes deployment is removed only from the list and remains in the cluster.
12.2.4.2.2 - Workload
A workload is an application that runs on Kubernetes, and users can add workloads to the DevOps Console for management.
The workload types that can be managed from the DevOps Console are Deployment, StatefulSet, and DaemonSet.
Getting Started
To begin using the workload, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- On the Kubernetes Deployment page, click the workload name.
Item Explanation Workload type Displays the workload type. DeploymentStatefulSetDaemonSet
Name Displays the workload name. Click to view detailed information. Chart Displays the Helm chart information used for deployment. Cluster/Namespace Displays the deployed cluster/namespace. Pod status Displays the current status of the Pod. Deployment result Displays the deployment execution result. Deployment time Displays the deployment execution time. Refresh Refresh the current items. The items that will be updated are the Pod status, deployment result, and deployment time. Delete Delete the current item. Table. Workload screen items
Add workload
To add a workload, follow the steps below.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- On the Kubernetes deployment page, click the Add workload menu. The Add workload popup opens.
- Add Workload Enter the information in the popup window and click the Save button.
- In the confirmation popup, click the Confirm button to complete adding the workload.Item
Explanation Query target Only workloads deployed with the same Base image as the App template used when the project was first created are displayed. Workload already registered in the project Shows the workload already registered in the project. - Workloads already registered in the project cannot be added.
Table. Additional Workload Input Items
Modify K8S authentication information
K8S credentials are the authentication information used to verify permission to use a K8S cluster/namespace when performing a deployment in the build pipeline.
To modify the K8S credentials, follow these steps.
- On the Deployment Details page, click the Edit Credentials icon to the right of K8S Cluster/Namespace. The Edit Credentials popup will open.
- Authentication information is fixed to the logged-in user’s account. Click the Save button to edit.
- In the confirmation popup, click the Confirm button.
- K8S authentication information will be changed to the logged-in user.
Rollback Workload
To roll back the workload to a previous image, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Kubernetes Deployment menu. You will be taken to the Kubernetes Deployment page.
- Kubernetes deployment page, click the workload name to roll back. You will be taken to the Workload details page.
- Click the Details tab on the Workload Details page.
- In the Details tab list, click the Rollback button in the row that contains the image you want to roll back. The Rollback popup window opens.
- Rollback popup window, click the desired button to complete the rollback.
- Recreate
- Rolling Update
Add recipient to deployment results
To add a distribution result recipient, follow these steps.
- Click the Deployment Result Recipients tab on the Workload Details page.
- Click the Add button on the Distribution Result Recipients tab. The Add Distribution Result Recipients popup window opens.
- Add Distribution Result Recipients In the popup window, select the target and click the Confirm button to complete adding distribution result recipients.
- Search button or click an entry in the list to add the recipient to the lower part of the popup.
- Added recipients can be removed by clicking the X icon on the right.
Delete workload
To delete the workload, follow these steps.
- On the Kubernetes deployment page, click the X icon of the workload you want to delete.
- In the confirmation popup, click the Confirm button to complete the deletion.ReferenceWorkloads are not deleted in the actual cluster.
If you want to delete in the actual cluster, delete it using the same method you used to initially deploy the workload.
12.2.4.2.3 - Blue/Green Deployment
Users can perform blue/green deployments using Ingress or Service.
Adding a blue/green deployment means creating a new K8S Ingress or K8S Service so that the two Helm releases can be swapped.
Only two Helm releases that have the same project, cluster, namespace, release type, chart name, chart version, development classification can be grouped.
Starting Blue/Green Deployment
To start using blue/green deployment, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.Item
Explanation Name Displays the blue/green deployment name. Click to view detailed information. Cluster/Namespace Displays the deployed cluster/namespace. (operation) Displays information about the currently deployed Helm release. (operational standby) Shows the Helm release that will be the next version in operation. Using blue/green switching, the standby switches to active. Delete Delete the current item. Table. Kubernetes deployment screen Blue/Green deployment card items - Click the name of the Blue/Green deployment you want to start from the deployment list on the Kubernetes deployment page. You will be taken to the Deployment details page.
Add blue/green deployment
To add a blue/green deployment, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- Click the Add Blue/Green Deployment button at the top right of the Kubernetes deployment page. The Add Blue/Green Deployment popup opens.
- Add Blue/Green deployment After entering the information in the popup window, click the Save button to complete adding the Blue/Green deployment.Item
Explanation Category Select Development, Operations - The actions each role can perform differ depending on the Development or Operations classification.(Table. Role-based permissions within the project (2))
Blue/Green deployment name Enter the deployment name. Operation Release and Jenkins Job selection - Release name: Select the name of the currently running Helm release from the list.
- Jenkins Job: Select the Jenkins Job from the list to build/deploy the selected Helm release.
Standby Release and Jenkins Job selection - Release name: Select the name of the Helm release to be applied to production in the next version from the list.
- Jenkins Job: Select the Jenkins Job from the list to build/deploy the selected Helm release.
K8S cluster/namespace Displays the K8S cluster/namespace where the Helm release is installed. Type classification Select whether to use Ingress or Service to perform a blue/green switch. New classification Choose whether to create a new Ingress or Service, or use an existing one. Name Enter name - New: Enter the name of an Ingress or Service.
- Existing: Select an already created Ingress or Service from the list.
Service (Operation) Select the Kubernetes Service related to the currently running Helm release from the list. Service (Operational Standby) Select the Kubernetes Service related to the Helm release that will be applied to operations in the next version from the list. Rules Enter the information to be used for Ingress. Table. Ingress type input items when adding blue/green deploymentItem Explanation type Select the type of Kubernetes Service from the list ClusterIPNodePortLoadBalancer
Deployment (Production) Select the Kubernetes Deployment related to the currently running Helm release from the list. Deployment (Operational standby) Select the Kubernetes Deployment related to the Helm release that will be operated in the next version from the list. Ports Enter the information to be used by the Service. Table. Service type input items when adding Blue/Green deployment
Replace Blue/Green
To replace the blue/green, follow these steps.
- Click the Blue/Green Switch button on the Deployment Details page. The Blue/Green Switch popup opens.
- In the Blue/Green replacement popup, click the Confirm button to complete the Blue/Green replacement.
- The Helm releases for production and staging are being swapped.
- A replacement record will be added.
Check the yaml of Ingress or Service for blue/green deployment
To check the yaml of the Ingress or Service used in blue/green, follow these steps.
- On the Deployment Details page, click the view icon for Ingress YAML or Service YAML. The Ingress YAML or Service YAML popup window opens.
- Ingress YAML or Service YAML popup window, review the contents and click the Confirm button to exit.
Managing Jenkins Jobs for Blue/Green Deployments
Jenkins Job View Log
To view the Jenkins Job log, follow these steps.
- On the Deployment Details page, click the Log button in the Jenkins Job entry for the desired release. The Pipeline Log popup window opens.
- Pipeline Log After confirming the log in the popup window, click the Confirm button.
Running a Jenkins Job
To run a Jenkins job, follow these steps.
- On the Deployment Details page, click the Run button in the Jenkins Job entry for the desired release. The Enter Pipeline Execution Parameters popup will open.
- Pipeline Execution Parameter Input In the popup window, enter or select each item, then click the Confirm button to complete the Jenkins Job execution.
Modify blue/green deployment
To modify a blue/green deployment, follow these steps.
- Deployment Details page, click the Edit button. The Blue/Green Deployment Edit popup window opens.
- Blue/Green Deployment Edit In the popup window, modify the desired items and click the Save button to complete the edit.
Delete blue/green deployment
To delete a blue/green deployment, follow these steps.
- Deployment Details page, click the Delete button. The Blue/Green Deployment Delete popup opens.
- Blue/Green deployment deletion in the popup window, select whether to execute the Ingress/Service deletion command, and click the Confirm button to complete the deletion.
Execute Ingress/Service deletion command
- Selection: The Ingress or Service used for blue/green deployment is actually deleted from the cluster.
- Unselected: Ingress or Service used for blue/green deployment is not deleted and remains in the cluster.
12.2.4.2.4 - Canary Deployment
The user can add a canary deployment.
Adding a canary means configuring two Helm releases together so that a canary test can be performed.
Only two Helm releases that have the same Project, Cluster, Release Type, Chart Name, Chart Version, and Development Classification can be grouped.
Getting Started with Canary Deployment
To start using Canary, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
Item Explanation Name Displays the Canary name. Click to view detailed information. cluster Displays the deployed cluster. (operation) Displays the currently running Helm release. (Canary) Displays the HelmRelease that is in Canary. Exit Shutting down Canary. Table. Kubernetes deployment screen Canary card items - On the Kubernetes deployment page, click the name of the canary you want to use in the deployment list. You will be taken to the deployment details page.
Add Canary
To add a canary, follow these steps.
Canary is supported in the following environments. Verify before adding Canary.
Kubernetesv1.17or laternginx-ingressv0.29.0or later
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left sidebar. You will be taken to the Kubernetes Deploy page.
- Click the Add Canary button at the top right of the Kubernetes Deployment page. The Add Canary popup opens.
- Add Canary In the popup window, after entering the information, click the Save button to complete adding the canary.
Item Explanation Category Select Development or Operations. - The actions each role can perform differ depending on whether it is Development or Operations. (Table. Permissions by role within the project (2))
Canary name Enter the canary name. Operation - Release name: Select the name of the currently deployed Helm release from the list.
- Jenkins Job: Select the Jenkins job for building/deploying the currently deployed Helm release from the list.
Canary - Release name: Select the name of the Helm release that will be the next version in operation from the list.
- Jenkins Job: Select the Jenkins job that will build/deploy the Helm release for the next operational version from the list.
K8S cluster Displays the K8S cluster where the Helm release is installed. Ingress annotation Enter the annotation item you want to apply among the Canary annotations provided by nginx-ingress. Table. Canary Additional Input Items
Check Canary’s Ingress YAML
Operational Ingress YAML used in Canary, to view the Canary Ingress YAML, follow these steps.
- On the Deployment Details page, click the View icon for Production Ingress YAML and Canary Ingress YAML. The Ingress YAML popup opens.
- Ingress YAML Check the contents in the popup window and click the Confirm button to exit.
Managing Canary’s Jenkins Job
View Jenkins Job log
To view the Jenkins Job log, follow these steps.
- On the Deployment Details page, click the Log button in the Jenkins Job entry for the desired release. The Pipeline Log popup window will open.
- Pipeline Log After confirming the log in the popup window, click the Confirm button.
Running a Jenkins Job
To run a Jenkins job, follow these steps.
- On the Deployment Details page, click the Run button in the Jenkins Job entry for the desired release. The Enter Pipeline Execution Parameters popup will open.
- Pipeline Execution Parameter Input In the popup window, enter or select each item, then click the Confirm button to complete the Jenkins job execution.
Modify Canary
To modify the canary, follow these steps.
- On the Deployment Details page, click the Edit button. The Canary Edit popup window opens.
- Canary Edit In the popup window, modify the desired items and click the Save button to complete the edit.
Recover Canary
If the ingress annotation data for the production and canary releases fails to operate correctly due to a Helm release change, restore it so it works properly again.
To restore the canary, follow these steps.
- On the Deployment Details page, click the Restore button. The Restore popup window opens.
- In the Recovery popup, click the Confirm button to complete the recovery.
Delete Canary (termination)
To shut down Canary, follow these steps.
- On the Deployment Details page, click the Terminate button. The Canary Termination popup window opens.
- Canary termination In the popup window, select the desired item and click the Confirm button to complete the termination.item
Explanation Canary release Select Canary Release - Rollback Ingress Host: Restores the Ingress host of the Helm release used for the canary to its original value.
- Delete Helm Release: Deletes the Helm release that was used for the canary.
Production Release Select the production release - Upgrade to the canary image: Upgrade the production Helm release to the image used in the canary. You can modify the
Values.yamlfile. - No action: End the canary without any changes to the production Helm release.
Table. Canary termination selection items
12.2.4.2.5 - Istio
Gateway- Virtual Service
- Destination Rule
Getting Started with Istio
To start using Istio, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > Kubernetes Deploy menu. You will be taken to the Kubernetes Deploy page.
Item Explanation Name Displays the Istio name. Click to view detailed information. Cluster/Namespace Displays the deployed cluster/namespace. Delete Delete the current item. Table. Kubernetes deployment screen Istio card items - In the deployment list on the Kubernetes Deployment page, click the name of the Istio you want to use. You will be taken to the Istio Details page.
Add Istio
To add Istio, follow the steps below.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- Click the Add Istio button at the top right of the Kubernetes deployment page. Add Istio popup opens.
- Add Istio In the popup window, after entering the information, click the Save button to add Istio.
Item Explanation Category Select Development or Operations. K8S cluster Please select a K8S cluster. Namespace Select a namespace.
Only namespaces that can use Istio are displayed in the list.Table. Istio Additional Input Items
Istio has been added, but since no Istio objects have been created, Istio-related functionality cannot be used yet.
Add Istio object using the creation wizard or Add Istio object using object addition to add and use an Istio object.
Istio objects
Adding Istio object
Add Istio object using the creation wizard
- On the Istio details page, click the Istio objects tab.
- Click the Create Wizard button in the Istio objects tab. You will be taken to the Create Wizard page.
Helm Release
This step selects the Helm release to use with Istio.
- Create Wizard page, click the Add button to select all Helm releases to be used in Istio.
- Click the Start button. The Gateway screen appears.
Gateway
The Istio Gateway is the frontmost object that receives traffic from external sources.
- On the Gateway screen of the Creation Wizard page, select whether to create a Gateway.
- If you want to create a Gateway, enter each item.
- If you do not want to create a Gateway, select Pass without creating an Object.
- Click the Next button. The Destination Rule screen appears.
Item Explanation Name Prefix Specify the prefix name of the Istio Gateway object to be created. Host Specifies the domain of the Gateway Object accessed from outside. Table. Creation Wizard Gateway Input Items
Destination Rule
Destination Rule defines traffic policies in Istio.
- On the Create Wizard page’s Destination Rule screen, select whether to create a Destination Rule.
- If you want to create a Destination Rule, fill in each field.
- If you do not want to create a Destination Rule, select Pass without creating the Object.
- Click the Next button. The Virtual Service screen appears.
Item Explanation Name Prefix Enter the Prefix name for the Istio Destination Rule Object to be created. LoadBalancer Select the load balancer mode. ROUND_ROBIN: Round RobinLEAST_CONN: Continue using the last connectionRANDOM: Random
maxConnections Enter the maximum allowed number of connections. Table. Creation Wizard Destination Rule Input Items
Virtual Service
The Virtual Service routes incoming traffic to a service.
- On the Creation Wizard page’s Virtual Service screen, if you want to create a Virtual Service, fill in each field.
- Click the Complete button to finish adding an Istio object using the creation wizard.
Item Explanation Name Prefix Enter the prefix name for the Istio Virtual Service to create. Prefix-Uri Enter a prefix URI to enable routing when traffic arrives at that URI. Helm Release Weight If there are two or more helm releases, enter the connection weight. The sum of each number must be 100.Table. Create Wizard Virtual Service Input Items
Add an Istio object using Object addition
- On the Istio details page, click the Istio objects tab.
- Click the Add Object button in the Istio objects tab. The Add Object popup window opens.
- Add Object In the popup window, fill in each field and click the Save button to finish adding the Istio object.
Item Explanation Object Select the Object to create GatewayVirtual ServiceDestination Rule
input The input fields differ for each object. Refer to the creation wizard for input GatewayVirtual ServiceDestination Rule
Generate Click the Generate button. Based on the information entered earlier, a default Yaml will be generated in the Yaml area. Yaml Modify the base YAML to complete the final YAML of the object you want to generate. Save Click the Save button to create an Object. Table. Screen items for adding an Istio object using Object addition
Modify Istio object
To modify an Istio object, follow these steps.
- On the Istio details page, click the Istio objects tab.
- In the Istio objects tab, click the Object you want to edit from the Istio object list. The Object popup opens.
- Object In the popup window, edit the Yaml and click the Save button to complete the Istio object modification.
Delete Istio object
To delete an Istio object, follow these steps.
- On the Istio Details page, click the Istio objects tab.
- In the Istio objects tab, click the Object you want to edit from the Istio object list. The Object popup window will open.
- In the Object popup, click the Delete button to complete the deletion of the Istio object.
Helm release
Add Helm Release
To add the Helm release used by Istio, follow these steps.
- On the Istio details page, click the Helm Release tab.
- In the Helm Release tab, click the Add button. The Add Helm Release popup opens.
- Add Helm Release In the popup window, fill out each field and click the Save button to complete adding the Helm release.
Delete Helm Release
To delete the Helm release used by Istio, follow these steps.
- On the Istio Details page, click the Helm Release tab.
- In the Helm release tab, select the checkbox of the Helm release you want to delete and click the Delete button.
- In the confirmation popup, click the Confirm button to complete the Helm release deletion.
Delete Istio
To uninstall Istio, follow these steps.
- On the Istio Details page, click the Delete button at the lower right.
- Click the Confirm button in the confirmation popup to complete the deletion.
12.2.4.2.6 - ArgoCD
ArgoCD is software used for GitOps deployments in a Kubernetes environment. Users can configure deployments via ArgoCD when creating a project or through the Kubernetes deployment menu.
Getting Started with ArgoCD
To view the details of an ArgoCD application, follow these steps.
- Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- Click the ArgoCD application card you want to start from the list. You will be taken to the deployment details page.Item
Explanation Name Displays the ArgoCD project name/ArgoCD URL. Git information Displays the Git information used for deployment. Cluster/Namespace Displays the deployed cluster/namespace. App status Displays the current state of the App. Deployment result Displays the current Sync status. Deployment time Displays the deployment execution time. Refresh Click the Refresh icon to refresh the current item. The items that are updated are App status, deployment result. Delete Delete the current item. Table. ArgoCD Application Detailed ItemsItemExplanation Modify ArgoCD app secret Click the Edit credentials icon to the right of the application name to open a popup that manages the image secret used for deployment. Go to the ArgoCD app The actual ArgoCD tool’s Application Details screen opens in a new window. Table. ArgoCD Deployment Details
Adding an ArgoCD Application
Create and add a new ArgoCD application - generate with Helm chart
To create and add a new ArgoCD application using a Helm chart, follow the steps below.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Kubernetes Deployment menu. You will be taken to the Kubernetes Deployment page.
- Click the Create New ArgoCD App button at the top right. You will be taken to the Create New ArgoCD App page.
- Enter ArgoCD information and click the Confirm button. The authentication information input field appears.
- Enter authentication information and click the Connection Test button.
- Application Basic Information, Deployment Target K8S Cluster input fields appear.
- Enter the Application Name and click the Check Duplicate button.
- Enter Project Name.
- Select Repository type as Create a new repository as a Helm chart.
- Select a K8S cluster and namespace.
- Select Helm chart. Information about the Helm chart and the Helm chart Git repository will be displayed.
- After modifying the contents of the default Values.yaml included in the chart located in the K8S cluster Values of the Helm chart, click the Validation Check button.
- After entering the Helm chart Git repository information, click the Connection Test button.
- Manifest Keys Enter the information.
- Click the Create button to complete creation.
Deploy Strategy is not a required input.| Item | Explanation |
|---|---|
| URL input method | Select URL input method
|
| ArgoCD URL | After entering the ArgoCD URL, click the Confirm button. |
| Authentication information | Enter the credentials and click the Connection Test button. |
| Application name | Enter the ArgoCD application name and click the Check Duplicate button. |
| Project name | Enter the project name of the ArgoCD application. |
| Repository type | Select repository type
|
| K8S cluster | Select the target cluster for deployment
|
| Namespace | Select the target namespace for deployment
|
| Helm chart | Please select a Helm chart. |
| Helm chart Git repository | Enter the information of the Git repository to be used for GitOps. |
| Manifest Key Information | Enter the Manifest file/key information to be used for continuous deployment. |
Create and add a new ArgoCD application – create from an existing Git repository
To create and add a new ArgoCD application using an existing Git repository, follow the steps below.
- Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deploy menu in the left menu. You will be taken to the Kubernetes Deploy page.
- Click the Create New ArgoCD App button at the top right. You will be taken to the Create New ArgoCD App page.
- Enter ArgoCD information and click the Confirm button. The Authentication information input field appears.
- Enter authentication information and click the Connection Test button.
- Application Basic Information, Deployment Target K8S Cluster input fields appear.
- Enter the Application Name and click the Check Duplicate button.
- Enter the Project Name.
- Select Repository type as Use existing Git repository.
- Select K8S cluster and namespace.
- Select Helm chart. Information about Helm chart and Helm chart Git repository appears.
- After modifying the contents of the default Values.yaml included in the chart located in the K8S cluster Values of the Helm chart, click the Validation Check button.
- Enter the Helm chart Git repository information and click the Connection Test button.
- Enter the Manifest Root path, Manifest type, (values.yaml path if the Manifest type is Helm), and the Manifest file and key information (Image repository, Image tag, Image Secret, Deploy Strategy) for Manifest Keys.
- Click the Create button to complete creation.ReferenceIn the Manifest file and key information, the Deploy Strategy is not a required input.Item
Explanation URL input method Select URL input method - Select from list: ArgoCD tools registered as tools appear.
- Enter manually
ArgoCD URL After entering the ArgoCD URL, click the Confirm button. authentication information Enter the authentication information and click the Connection Test button. Application name Enter the ArgoCD application name and click the Check Duplicate button. Project name Enter the project name of the ArgoCD application. Repository type Select repository type - Create a new repository with Helm chart: Use a Helm chart to create a Git repository for
GitOps. - Use existing Git repository
K8S cluster Select the target cluster for deployment - Only clusters that the user has permission to access can be selected from the clusters in the DevOps Console K8S cluster.
namespace Select the target namespace for deployment - In the K8S cluster, only namespaces that the user has access rights to can be selected from the chosen cluster.
Git repository Enter the Git repository information that stores the Manifest data for creating the ArgoCD application to be used in GitOps.Manifest Keys information Enter the information required for continuous deployment (Manifest Root path, Manifest type ( Helm,Customize,Directory), Manifest file/key information).Table. New ArgoCD application creation - Settings for creating with existing Git repository
Add existing ArgoCD application
To add an existing ArgoCD application, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- In the left menu, click the Build/Deploy > Kubernetes Deployment menu. You will be taken to the Kubernetes Deployment page.
- Click the Add ArgoCD App button at the top right. Navigate to the Add ArgoCD App page.
- Enter the ArgoCD URL and click the Confirm button.
- The input screen for the existing application name and credentials appears.
- Enter the Existing Application Name and Authentication Information, then click the Connection Test button.ReferenceIf the Git repository linked to the ArgoCD application is not registered in the DevOps Console, the URL Check popup window opens. Follow steps 7–8.
- A URL Check popup opens to identify the Git repository linked to the ArgoCD application.
- After modifying the Base URL, click the Confirm button.
- The Git repository information linked to the application is displayed.
- Enter the authentication information for the Git repository and click the Connection Test button.
- Enter the
yamlfile and key to modify among the Manifest Keys items. - After entering the information, click the Save button to complete Add ArgoCD Application.item
Explanation URL input method Select URL input method - Select from list: ArgoCD tools registered as tools appear.
- Enter manually
ArgoCD URL After entering the ArgoCD URL, click the Confirm button. Application name / authentication information Enter the Existing application name and authentication information, then click the Connection Test button. Git repository credentials Enter the credentials for the Git repository used by the selected existing application. Image Repo Key Enter the path to the Yaml file that records the image repository information and the Key value. If the key values for repository and tag are the same, enter the same value. Image Tag Key Enter the path to the Yaml file containing the image tag information and the Key value. If the repository and tag have the same key, enter the same value. Image Secret Key Enter the path to the Yaml file that contains the image secret information and the Key value. Deploy Strategy Key Enter the path to the Yaml file containing the deployment strategy information and the Key value. (It is not required.) Table. Adding Existing ArgoCD Application Configuration Items
Managing ArgoCD Applications
To view the details of an ArgoCD application, follow these steps.
- Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Kubernetes Deployment menu in the left sidebar. You will be taken to the Kubernetes Deployment page.
- Click the ArgoCD application card you want to start from the list. You will be taken to the deployment details page.
Modify Manifest information
Follow these steps to modify the Manifest information.
- Git related information Click the tab.
- Click the Edit icon next to Manifest information. The Edit Manifest key information popup opens.
- Modify the Manifest key value and click the Save button.
Modify ArgoCD authentication information
To modify the ArgoCD credentials, follow these steps.
- Click the Edit icon next to the ArgoCD User ID. The Edit Authentication Info popup will open.
- Modify the authentication information value and click the Save button to complete the edit.
Modify linked Git repository credentials
To modify the authentication information of the linked Git repository, follow these steps.
- Click the Edit icon next to Linked Git ID. The Edit authentication information popup opens.
- Modify the authentication information and click the Save button to complete the changes.
Configure Sync
To change the Sync settings, follow the steps below.
- Click the Sync icon next to Current Sync. The ArgoCD App Sync popup opens.
- Enter the content to edit and click the Sync button to complete the Sync settings.
Item Explanation Revision Select the branch to synchronize. Sync Options Select the synchronization-related options. Synchronize Resources Select the synchronization target. Table. Sync SettingsReferenceArgoCDFor detailed information about synchronization, please refer to the official site.
Configure Auto-Sync
To change the Auto-Sync settings of an ArgoCD application, follow these steps.
- Click the Edit icon next to Auto‑Sync. The Auto‑Sync option popup window opens.
- Edit and click the Save button to complete the settings.
Item description Prune Resources When the Git settings are deleted, choose whether to also delete the synchronization target. Self Heal In the cluster, when the value of synchronization target changes, select whether to automatically change it to the value defined in Git. Table. Auto-Sync Settings
Managing Application Secrets
If it is an ArgoCD application created with a Helm chart, you can add, modify, or delete the application’s secrets.
To start application secret management, follow these steps.
- Click the application secret to the right of the application name.
- Application Secret Settings popup window opens.
Add application secret
To add an application secret, follow these steps.
- Click the Edit authentication information icon next to the Application name. The Application secret settings popup opens.
- If you need to add a secret to use when pulling the Chart Image, click the Add button in the Chart Install Secret section.
- When you need to add a secret for pulling the App Image used during build/deployment, click the Add button in the ImagePull Secret section.
- Enter the content and click the Save button to complete the addition.Item
description Registry URL From the list of images registered in Image Repository, select the image that ImagePull Secret will use. Secret Select the method for entering ImagePull Secret information - Auto-generate: Use the credentials of the image repository selected from the Docker URL to automatically create an ImagePull Secret.
- Use existing secret: Choose one of the already created secrets to use as the ImagePull Secret.
Table. Application Secret Additional Configuration Items
Edit Application Secret
To modify the application secret, follow these steps.
- Click the Edit authentication information icon next to the Application name. The Application secret settings popup opens.
- Click the secret name you want to edit in the application secret list.
- Enter the content and click the Save button to complete the edit.
Delete Application Secret
To delete the application secret, follow the steps below.
- Click the Edit Authentication Info icon next to Application Name. The Application Secret Settings popup opens.
- Click the secret name you want to delete from the application secret list.
- Click the Delete button to complete the deletion.
Comparing Values.yaml file
For an ArgoCD application using a Helm chart, you can compare the values.yaml file.
To compare the values.yaml files used in each release, follow these steps.
- Click the History tab.
- Click the two revisions you want to compare.
- Click the App Diff button. The App Diff popup window opens.
Rolling Back an Application
To roll back the application to a previous revision, follow these steps.
- Click the History tab.
- Click the Rollback button in the rollback column of the revision you want to roll back. The Rollback popup will open.
- Click the Confirm button to complete the rollback.
Delete Application
To uninstall the application, follow these steps.
- Click the Delete button at the bottom right. The Application Delete popup will open.
- Click the Confirm button to complete the deletion.
12.2.4.3 - VM Deployment
Users can register and manage VM deployment through DevOps Console.
Before registering a VM deployment, an available VM server group(VM server group) must exist, and the registered VM deployment can be used in the build pipeline (Deploy to VM).
Users can differentiate deployment methods using icons.
 (SSH method) VM deployment
(SSH method) VM deployment (Agent mode) VM deployment
(Agent mode) VM deployment
Start VM deployment
To start VM deployment, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > VM Deploy menu. You will be taken to the VM Deploy page.
Item Explanation Deployment group name Displays the name of the deployment group. VM deployment result (Success)/(Total): Displays the number of VM servers targeted for deployment and the number of VM servers successfully deployed. - Green: All successful
- Blue: In progress
- Red: Partial failure
- Gray: Ready, Stopped
Deployment time Displays the deployment time. Delete Delete the VM deployment. Table. VM deployment display items
Add VM deployment
To add a VM deployment, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > VM Deploy menu. You will be taken to the VM Deploy page.
- VM Deployment page, click the Add VM Deployment button in the top right. The Add VM Deployment popup opens.
- Add VM deployment After entering the information in the popup window, click the Save button.
Item Explanation deployment group Please enter the deployment group name. Execution method Select the execution mode. - File transfer and command execution: Choose this when you typically deploy files to a VM.
- Execute command only: Choose this when you run only commands without transferring files to the VM (e.g., Docker commands).
Deployment method Select deployment method Deployment order If there are multiple target servers, choose whether to deploy in parallel or sequentially. Deployment target VM Set the deployment target server. - Click the Settings button to open the Configure Deployment Target VM popup.
Command before file deployment Write the commands that need to be executed before file distribution. File to send - Source: Enter the file path after the build pipeline execution directory (Jenkins workspace).
- Target: Enter the path where the file will be deployed on the VM server.
- Add button can be used to add files.
Command after file distribution Write the commands to be executed after file deployment. Automatic restore setting Select whether to enable automatic rollback - If the deployment fails, it will be rolled back to the most recent successful deployment.
- Deployment method is enabled when it is Agent.
Artifact repository Select whether to use the artifact repository for rollback. - deployment method is activated when it is Agent.
Repository name Only exposed when using an artifact repository. - A list of already registered artifact repository is displayed
Table. Additional Input Items for VM Deployment
Deployment Target VM Settings The popup window displays the server groups you have access to.
For more details, refer to the VM Server Group.
VM Deployment Details
To view the detailed information of the VM deployment, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > VM Deploy menu. You will be taken to the VM Deploy page.
- On the VM deployment page, in the VM deployment list, click the VM deployment you want to view in detail. You will be taken to the VM deployment details page.
- In the History tab, click the server list. The Deployment Details popup opens.
- Deployment Details You can view the detailed history in the popup window.
- When you click the Log button of the execution pipeline, the Pipeline Log popup window opens.
- Pipeline Log You can view detailed logs in the popup window.
- In the history list for each deployment server, click the Log button of the server whose logs you want to view, and the VM Agent Log popup window will open.
- VM Agent log You can view detailed logs in the popup window.
Item Explanation Stop / Start Deployment Stop, Start Deployment button becomes active. rollback You can roll back to a previous version. History tab Deployment history is displayed. Pipeline Information tab The build pipeline information associated with this VM deployment is displayed. log You can view the logs of the build pipeline. Table. VM deployment detail screen itemsItem Explanation Execution pipeline log You can view the logs of the build pipeline. History logs per deployment server You can view the deployment agent’s logs. - Only displayed for AGENT type
Table. Deployment Detail Screen Items
Delete VM deployment
Delete from list
To delete a VM deployment, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > VM Deploy menu. You will be taken to the VM Deploy page.
- On the VM deployment page, click the X icon of the VM deployment you want to delete from the list.
- In the confirmation popup, click the Confirm button to complete the deletion of the VM deployment.
Delete on the detail page
To delete a VM deployment, follow these steps.
- Main page, click the Project card. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > VM Deploy menu. You will be taken to the VM Deploy page.
- On the VM deployment page, click the VM deployment you want to delete from the VM deployment list. You will be taken to the VM deployment details page.
- On the VM Deployment Details page, click the Delete button.
- Click the Confirm button in the confirmation popup to complete the VM deployment deletion.
Using environment variables in VM deployment commands
You can use environment variables in the pre‑deployment command, post‑deployment command, source path of the file to be transferred, and target path of the file to be transferred.
You can use the $ placeholder or ${} placeholder within commands to access environment variables in the build pipeline.
echo ${BUILD_NUMBER}
echo $JOB_NAMEecho ${BUILD_NUMBER}
echo $JOB_NAMEIf you want to refer to the environment variables of the VM server where the command runs, add a \.
echo \${PATH}
echo \$LANGecho \${PATH}
echo \$LANGStop VM deployment
On the Deployment Details page, you can stop a VM deployment that is in progress. Clicking the Stop button in the recent deployment status area of the Deployment Details page will stop the VM deployment.
The states in which deployment can be halted are listed in the table below, and the Stop button is displayed only when in those states.
| method | status value | Explanation |
|---|---|---|
| SSH | request | The build pipeline is running. |
| AGENT | request | The build pipeline is running. |
| AGENT | Build complete | When the build pipeline is completed
|
| AGENT | Ready | After the build pipeline completes, the AGENT is ready to perform deployment. |
| AGENT | In progress | AGENT is currently executing a deployment. |
Understanding VM deployment status values
Deployment Details page lets you check the current status of the VM deployment.
status value | Explanation |
|---|---|
| Not executed | Never run since its initial creation |
| request | The build pipeline is running. |
| Success | Build/deployment succeeded |
| Failure | Failed state during build or deployment |
status value | Explanation |
|---|---|
| Not executed | Never executed after initial creation |
| request | The build pipeline is running. |
| Build complete | When the build pipeline is completed
|
| Ready | After the build pipeline completes, the AGENT is ready to perform deployment. |
| In progress | AGENT is currently executing a deployment. |
| Success | Build/deployment succeeded |
| Failure | Failed state during build or deployment |
| Stop | Build or deployment is in a paused state
|
12.2.4.4 - Helm Install
Users can use the Helm Install menu to view and install project charts, project group charts, tenant charts, and system charts.
Getting Started with Helm Install
To begin using Helm Install, follow the steps below.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > Helm Install menu. The Helm Install page opens.
Item Explanation K8S cluster Select the K8S cluster to be the target of the Helm install.
The Helm chart list below shows only the Helm charts that can be installed on the selected K8S cluster.Chart name Displays the chart name. Chart repository Displays information about the chart repository where the Helm chart files are stored. Table. Helm install screen items
Helm Chart Details
To view the Helm chart details, follow these steps.
- On the Main page, click the Project card.
- From the left menu, click the Build/Deploy > HelmInstall menu. The HelmInstall page opens.
- On the Helm Install page, select the K8S cluster you want to install. A list of Helm charts belonging to that cluster will be displayed.
- From the Helm chart list, click the Helm chart card you want to view in detail. The Helm chart details page opens.
Helm Chart Details
| Item | Explanation |
|---|---|
| Version | If there are multiple versions, you can select the desired version. |
| Download | You can download the Helm chart file to the user’s PC. |
| helm install | You can install Helm. |
Summary tab
Displays the README.md file included in the Helm chart. You can view the information provided by the chart author.
Values.yaml tab
Displays the values.yaml file included in the Helm chart. You can view the values that can be modified in the chart before running helm install.
Details tab
Item | Explanation |
|---|---|
| Helm chart repository information | Displays the repository where the Helm chart is stored. |
| Api Version | Displays the API version of the Helm chart.
|
| Support CI/CD | When creating a build pipeline, the Deploy to K8S stage indicates whether the Helm chart type can be selected as a Helm release. |
| Allow new installation? |
|
| Image in the chart | Displays the image information used in the Helm chart. |
Install Helm
To install Helm, follow these steps.
- On the Helm Install page, select the K8S cluster you want to install in the K8S cluster field. A list of Helm charts belonging to that cluster will be displayed.
- On the Helm Install page, click the Helm chart card you want to view in detail. The Helm Chart Details page opens.
- On the Helm Chart Details page, click the Helm Install button. The Helm Install page opens.
- On the Helm Install page, fill in each field on the screen and click the Next button. The Helm Chart Install popup opens.
- Helm chart installation Check the contents in the popup window and click the Run button to complete the Helm installation.
- When the installation is complete, the Kubernetes deployment page opens automatically.Item
Explanation Release name Enter the name to be used in Helm.
It must be unique and cannot be duplicated within the namespace.Category Development, Operations Version Select the version of the chart you want to install with Helm. K8S cluster Displays the target K8S cluster for helm install.
Changes are not allowed; if you wish to change, select the K8S cluster in Start Helm Install.Namespace Select the target namespace for the helm install from the list. Reference information Reference information provided by the selected K8S cluster.
You can click each tab to view detailed information.included in the chart
default Values.yamlYou can edit the values.yamlfile to run helm install with the desired values.
If needed, refer to the reference information and modifyvalues.yamlwith those values.Table. Common Helm chart installation screen itemsItemExplanation Release name Enter the name to be used in Helm.
It must be unique and cannot be duplicated within the namespace.Category Development, Operations Version Select the version of the chart you want to install with Helm. K8S cluster Displays the target K8S cluster for helm install.
Changes are not possible, and if you wish to change, select a K8S cluster in Start Helm Install.namespace Select the target namespace for helm install from the list. Reference information This is reference information provided by the selected K8S cluster. You can click each tab to view detailed information. Default Values.yaml included in the chart You can edit the values.yamlfile and run helm install with the desired values.
If needed, refer to the reference information and modifyvalues.yamlwith those values.Writing type - Form: Enter the items displayed on the screen. Form-type items are displayed only for Helm charts that support form input. For creating Helm charts that support form input, refer to Creating Helm Charts that Support Form Input.
- Values.yaml: Modify the values in the same YAML editor screen as a typical Helm chart.
Form input This is the screen displayed when you select Form in the creation type; review each item and enter values. After completing the input, click the Validation Check button to validate the entered values. Table. Helm chart installation screen items that support Form input
12.2.4.5 - Ingress/Service Management
Users can add and manage Ingress/Service using the DevOps Console.
Getting Started with Ingress/Service Management
To start managing Ingress/Service, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Ingress/Service Management menu in the left menu. You will be taken to the Ingress/Service Management page.
Ingress management
- On the Ingress/Service Management page, click the Ingress tab.
- Select K8S cluster and namespace in the Ingress tab. The list of Ingresses belonging to the selected namespace will be displayed.
Ingress
DevOps Console are shown.| Item | Explanation |
|---|---|
| K8S cluster | Select a K8S cluster from the list. |
| Namespace | Select a namespace from the list. Ingresses created in the selected namespace will be displayed. |
| Ingress list | Displays the list of Ingresses. |
| Search | You can search for Ingress. |
| Add | You can add an Ingress. |
Add Ingress
To add an Ingress, follow these steps.
- Click the Add button on the Ingress tab. The Add Ingress popup window opens.
- Add Ingress After entering the information in the popup window, click the Confirm button.
- Click the Confirm button in the confirmation popup to complete adding the Ingress.
Item Explanation Ingress name Please enter the Ingress name. K8S cluster Specifies the K8S cluster where the Ingress will be created. Namespace Specifies the namespace where the Ingress will be created. Service Select the Service that Ingress will use as a target from the list of Services. Rules Enter the Host, Path, and Service Port to configure in the Ingress.
Click Add to input multiple entries.Table. Additional Ingress Input Items
Ingress Details
To view the detailed information of an Ingress, follow the steps below.
- Click the Ingress you want to view in the Ingress tab. Navigate to the Ingress Details page.
- On the Ingress Details page, view the detailed information of the Ingress.
- When you click the View icon, the Ingress YAML popup window opens.
- Ingress YAML In the popup window, you can view the Ingress YAML content.
Edit Ingress
To modify the Ingress, follow these steps.
- In the Ingress tab, click the Ingress you want to edit. You will be taken to the Ingress Details page.
- On the Ingress Details page, click the Edit button. The Ingress Edit popup opens.
- Ingress Edit In the popup window, edit the Ingress information and click the Confirm button.
- In the confirmation popup, click the Confirm button to complete the Ingress modification.
Delete Ingress
To delete an Ingress, follow these steps.
- In the Ingress tab, click the Ingress you want to delete. You will be taken to the Ingress Details page.
- On the Ingress Details page, click the Delete button.
- In the confirmation popup, click the Confirm button to complete the Ingress deletion.
Service Management
- On the Ingress/Service Management page, click the Service tab.
- In the Service tab, select the K8S cluster and namespace. The list of Services belonging to the selected namespace will be displayed.
Service
DevOps Console are shown.| Item | Explanation |
|---|---|
| K8S cluster | Select a K8S cluster from the list. |
| namespace | Select a namespace from the list. Services created in the selected namespace will be displayed. |
| Service List | Displays the list of services. |
| search | You can search for Service. |
| Add | You can add a Service. |
| External Endpoint information icon | If there is related additional information, display it. |
Add Service
To add a Service, follow these steps.
- Click the Add button in the Service tab. The Service Add popup opens.
- Add Service After entering the information in the popup window, click the Confirm button.
- In the confirmation popup, click the Confirm button to complete adding the Service.
Item Explanation Service name Please enter the service name. K8S cluster Displays the K8S cluster where the Service will be created. namespace Specifies the namespace where the Service will be created. type Select the Service type ClusterIPNodePortLoadBalancer
Deployment Select the Deployment that will be the Service’s target from the list. Ports Enter the Port Name, Port, Target, and Protocol that the Service will use.
Click the Add button to input multiple entries.Table. Service addition input fields
Service Details
To view the Service details, follow these steps.
- On the Service tab, click the Service you want to view in detail. You will be taken to the Service Details page.
- Service Details page shows detailed information.
- Click the View icon to open the Service YAML popup window.
- Service YAML You can view the Service YAML content in the popup window.
Edit Service
To modify the Service, follow these steps.
- In the Service tab, click the Service you want to edit. Go to the Service Details page.
- On the Service Details page, click the Edit button. The Service Edit popup window opens.
- Service Edit In the popup window, edit the Service information and click the Confirm button.
- In the confirmation popup, click the Confirm button to complete the Service edit.
Delete Service
To delete a Service, follow the steps below.
- On the Service tab screen, click the Service you want to edit. You will be taken to the Service Details page.
- On the Service Details page, click the Delete button.
- Click the Confirm button in the confirmation popup to complete the Service deletion.
12.2.4.6 - Kubernetes Secret Management
Users can view secrets created in a namespace. In addition, they can create and delete secrets.
Getting Started with Kubernetes Secret
To start managing Kubernetes Secrets, follow the steps below.
- Main page, click the Project card. You will be taken to the Project Dashboard page.
- From the left menu, click the Build/Deploy > Kubernetes Secret Management menu. You will be taken to the Kubernetes Secret Management page.
Item Explanation K8S cluster Select a K8S cluster from the list. namespace Select a namespace from the list. Secrets created in the selected namespace will be displayed. Secret List Displays the list of secrets. search You can search for secrets. Detailed filter You can perform detailed searches by using the detailed filter. Add You can add a secret. Table. Kubernetes Secret Management Screen Items
Add secret
Docker Config Secret is a secret used to store Docker registry credentials for an image.
Follow these steps to add a Kubernetes Secret.
- Select K8S Cluster on the Kubernetes Secret Management page.
- Select namespace.
- Click the Add button. The Add Secret popup opens.
- Add Secret Enter the information in the popup window and click the Connection Test button.
- If Connection Test succeeds, click the Save button.
- In the confirmation popup, click the Confirm button to complete the addition.
Item Explanation K8S cluster Displays the K8S cluster where the secret will be created. Namespace Specifies the namespace where the secret will be created. Image repository URL Select the image repository to use in Secret. Secret name Enter the secret name. Select authentication information - Use new credentials: Enter new credentials.
- Use saved credentials: Choose one of the previously used credentials.
Table. Input fields for adding a secret
View Secret Details
To view the secret details, follow these steps.
- Kubernetes Secret Management On the page, click the secret whose details you want to view. Secret Details popup window opens.
- Secret Details View the secret’s detailed information in the popup window.
Delete secret
To delete the secret, follow these steps.
- Kubernetes Secret Management On the page, select the checkbox of the secret you want to delete.
- Click the Delete button.
- In the confirmation popup, click the Confirm button to complete the deletion.
12.2.4.7 - Environment Variable Management
Users can add frequently used parameters and credentials as environment variables for use when creating a build pipeline.
Getting Started with Environment Variable Management
Follow these steps to manage environment variables used in the build pipeline.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Build/Deploy > Environment Variable Management menu in the left menu of the Project Dashboard page. You will be taken to the Environment Variable Management page.
Adding environment variables
Add parameter environment variable
Parameter environment variables act as Linux Environment variables and are used in the NAME=VALUE format.
To add a parameter environment variable, follow these steps.
- On the Environment Variable Management page, click the Add button. The Add Environment Variable popup window opens.
- Add environment variable In the popup window, select the type as parameter.
- After entering the information, click the Save button.
- In the confirmation popup, click the Confirm button to complete the addition.
Item Explanation Name Please enter the parameter name. value Please enter the parameter value. Explanation Enter a description for the user to refer to. Table. Parameter environment variable addition input items
Add authentication credentials environment variable
The authentication environment variable stores credentials for use. You can pre-register and share credentials so they can be easily used in stages that require authentication (preventing duplicate entry).
To add authentication environment variables, follow these steps.
- On the Environment Variable Management page, click the Add button. The Add Environment Variable popup window opens.
- Add Environment Variable In the popup window, select the type as “Authentication Information”.
- After entering the information, click the Save button.
- In the confirmation popup, click the Confirm button to complete the addition.
Item Explanation Name Enter the name of the credential. Category Select a category value - Development: Credentials can be used only in build pipelines of type Development.
- Production: Credentials can be used only in build pipelines of type Production.
Authentication type Please select an authentication type. ID Please enter your ID. Password/Private Key Enter the password or private key according to the authentication type. Explanation Enter a description for the user to refer to. Table. Parameter Environment Variable Additional Input Fields
Modify environment variables
To modify environment variables, follow these steps.
- On the Environment Variable Management page, click the environment variable you want to edit. The Edit Environment Variable popup will open.
- Edit Environment Variables In the popup window, modify the desired items and click the Save button.
- In the confirmation popup, click the Confirm button to complete the addition.
Delete environment variable
To delete an environment variable, follow these steps.
Delete from list
- On the Environment Variable Management screen, select the checkbox of the environment variable you want to delete.
- Click the Delete button on the Environment Variable Management screen.
- In the confirmation popup, click the Confirm button to complete the deletion.
Delete in the environment variable edit popup
- Environment Variable Management screen, click the environment variable you want to delete. Environment Variable Edit popup window opens.
- Edit Environment Variable in the popup window, click the Delete button.
- Click the Confirm button in the confirmation popup to complete the deletion.
12.2.5 - Project Group
12.2.5.1 - Project Group Overview
Users can view and modify information about project groups according to their permissions.
Project Group Overview
To view the project group overview, follow these steps.
- On the Main page, click the Project Group Management icon of the project group. You will be taken to the Project Group Dashboard page.
- Click the Project Group Overview menu in the left menu. The Project Group Overview screen appears.
Modify project group name
To modify the project group name, follow these steps.
- On the Project Group Overview screen, click the Edit Project Group Name button. The Edit Project Group Name popup opens.
- Project Group Name Edit In the popup window, edit the project group name and click the Save button to complete the project group name edit.
Delete project group
To delete a project group, follow these steps.
- On the Project Group Overview screen, click the Project Group Delete button. The Project Group Delete popup opens.
- Project Group Deletion In the popup window, verify the path of the
Jenkinsfolder to be deleted, enter the project group name, and then click the Delete button. - In the confirmation popup, click the Confirm button to complete the deletion of the project group.
- A project group cannot be deleted if it contains projects.
- Deleted project groups cannot be restored.
- All available
Jenkinsproject group level folders will be deleted, so please verify.
Project group members
Getting Started with Project Group Members
To view the project group members, follow these steps.
- Project Group Overview screen, click the Member tab.
Add project group members
To add members to a project group, follow these steps.
- On the Project Group Overview screen, click the Member tab. The Project Group Member List screen appears.
- On the Project Group Member List screen, click the Add button. The Project Group Member Add popup opens.
- Add Project Group Member In the popup window, after completing the settings, click the Save button to complete adding the project group member.
Item Explanation Add member Search for the user you want to add as a project group member by email, then click the Add button. Permission Settings Set the role to assign to the member you want to add - Owner
- Master
- Developer
- Viewer
Delete member Click the X icon to remove the member from the project group. Table. Project Group Member Additional Items
Change the role of a project group member
To change a project group’s member role, follow these steps.
- On the Project Group Overview screen, click the Member tab. The Project Group Member List screen appears.
- Project Group Member List screen, locate the user whose role you want to change.
- Select the user’s project group role from the list. It is saved immediately upon selection, and the user’s project group role will be updated.
Delete project group member
To remove a member from a project group, follow these steps.
- On the Project Group Overview screen, click the Member tab. The Project Group Member List screen appears.
- Project Group Member List screen, select the checkbox of the user you want to delete.
- Click the Delete button at the top of the list to remove the selected user from the project group members.
Project group common settings
Getting Started with Project Group Common Settings
To view the project group common settings, follow these steps.
- On the Project Group Overview screen, click the Common Settings tab. The Common Settings screen appears.
Configure Messenger
If you configure the messenger, you can send event details to the messenger when an event occurs in the project group.
To set up the messenger for the project group, follow these steps.
- On the Project Group Overview screen, click the Common Settings tab. The Common Settings screen appears.
- On the Common Settings screen, click the Edit icon for Messenger Settings. The Messenger Settings popup window opens.
- Messenger Settings popup window, after completing the settings, click the Save button to finish the messenger settings.
Manage all project groups
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Tenant > Project Group menu. You will be taken to the Project Group page.
12.2.5.2 - Create Project Group
Create Project Group
To create a project group, follow these steps.
- Click the Create Project Group button at the top of the Main page. The Create Project Group popup opens.
- Create Project Group After entering the fields in the popup, click the Confirm button to complete the project group creation.
Item Explanation Project group name Enter the project group name that will be displayed on the screen. Project Group ID Enter the ID of the project group to be managed in DevOps Console.
The project group ID is used in build pipelines, etc.tenant Select the tenant for which the project group will be created from the list - Tenant Join Shortcut: If the tenant for creating the project group is not visible in the list, click the Tenant Join Shortcut link to request to join.
Table. Project Group Creation Input Items
Register Tenant
To join a tenant, follow these steps.
- In the Create Project Group popup, click the Tenant Join Shortcut link. The Tenant Join Request popup opens.
- Enter the tenant code to register in the Tenant Search field accurately and click the Search icon. The tenant information will be retrieved.
- Verify that the displayed tenant is correct, enter the request reason, and click the Add button. It will be added to the list below.
- After selecting the permissions for the tenant added to the list below, click the Save button.
12.2.5.3 - Project Group Dashboard
Getting Started with Project Group Dashboard
To view the project group dashboard, follow these steps.
- On the Main page, click the Project Group Management icon of the project group. You will be taken to the Project Group Dashboard page.
- Click the Dashboard menu in the left menu.
Item Explanation Basic Information Displays the basic information of the project group. Scale and Usage Status Displays the organization size, tool usage status, and build/deployment status of the project group. Monthly pipeline execution trend Shows the monthly pipeline execution count, average execution interval, and execution time for the project group. Inactive pipeline Shows a list of pipelines that have not been run and have no successful history, according to the reference date. Release Execution Trend Displays the daily release execution count, average lead time, and average release cycle within the project group. Recent event history You can view recent events that occurred in the project group. Table. Project Group Dashboard Items
12.2.6 - Tenant
12.2.6.1 - Tenant Management
A tenant is a logical partition that independently provides and shares tools, apps, and templates usable in a project.
Each project belongs to a single project group, and each project group belongs to a single tenant; therefore, a project can access and utilize the tools and App templates assigned to its tenant.
Getting Started with Tenant Management
To start tenant management, follow these steps.
- Main page, click the Admin icon at the top right. You will be taken to the Tenant Dashboard page.
- Click the Tenant > Tenant Management menu in the left menu. You will be taken to the Tenant Management page.
Tenant detail view
To view tenant details, follow the steps below.
- On the Tenant Management page, click the tenant you want to view in detail. You will be taken to the Tenant Details page.
Managing tenant members
To manage tenant members, follow these steps.
- On the Tenant Details page, click the Member tab.
Add tenant member
To add a tenant member, follow these steps.
- Click the Member tab on the Tenant Details page.
- Click the Add button in the Member tab. The Add Member popup opens.
- Add Member In the popup window, select a member, set permissions, and click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Delete Tenant Member
To delete a tenant member, follow these steps.
- On the Tenant Details page, click the Member tab.
- In the Member tab, select the checkbox of the member you want to delete.
- Delete Click the button.
- In the confirmation popup, click the Confirm button to complete.
Check tenant tool
To check the tenant tool, follow these steps.
- On the Tenant Details page, click the Tool tab.
Check tenant member approval history
To view the tenant member approval history, follow these steps.
- On the Tenant Details page, click the Approval History tab.
Manage Tenant Common Settings
To manage tenant common settings, follow these steps.
- On the Tenant Details page, click the Common Settings tab.
Item Explanation Billing Select whether to charge. Project group creation approval Select whether project group creation requires approval - If not used, tenant members can freely create project groups.
Delete release Select whether to delete the release - You can set whether to delete a completed release.
Release suspension approval Select whether to require approval for release suspension - You can configure it to submit an internal approval request to stop an ongoing release.
Approval Task - Add JIRA Field When linking a Jira project to an approval Task, add a custom field of the Jira project to be included in the approval details. email Enter the email address to receive - You can receive inquiries related to the tenant.
Table. Tenant Common Configuration Items
Manage tenant join requests
To manage tenant enrollment requests, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Tenant > Tenant Management menu in the left menu. You will be taken to the Tenant Management page.
- On the Tenant Management page, click the Join Request link for the tenant. The displayed number indicates the number of join requests for the tenant.
- Tenant Registration Request popup window opens.
- Tenant Registration Request In the popup’s request list, select the requester’s checkbox to approve or reject.
- After entering your comment, click the Approve or Reject button.
Manage Project Group Creation Requests
To manage project group creation requests, follow these steps.
- Main page, click the Admin icon at the top right. You will be taken to the Tenant Dashboard page.
- Click the Tenant > Tenant Management menu in the left menu. You will be taken to the Tenant Management page.
- On the Tenant Management page, click the Project Group Creation Request link for the tenant. The displayed number is the count of project group creation requests.
- Project Group Creation Request A popup window opens.
- Project Group Creation Request In the request list of the popup window, select the requester’s checkbox to approve or reject.
- After entering your comment, click the Approve or Reject button.
12.2.6.2 - Tenant Dashboard
Users can assess various usage metrics per system (tenant) via the dashboard.
Getting Started with the Tenant Dashboard
To view the tenant dashboard, follow these steps.
- Click the Management icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- In the left menu, click the Tenant > Dashboard menu.
Item Explanation tenant Select the tenant to display on the tenant dashboard. Download status data You can download the basic billing data report needed by tenant administrators. Scale and Usage Status You can view the organization size, tool usage status, and the number of builds/deployments under the tenant. Monthly pipeline execution trend Displays the monthly pipeline execution count, average execution interval, and execution time for the tenant. Inactive pipeline Shows a list of pipelines that have not been run and have no successful history, according to the reference date. Release execution trend You can view the execution trend of releases under a tenant. Tool usage status You can view the usage status of each tool located under the tenant.
Usage status refers to the number of projects, repositories, pipelines, etc., for each tool.App. Template usage status App that exists under a tenant. You can view usage per template.
Usage status refers to the number of templates used when creating a project.Helm Chart Usage Status You can view the usage status of each Helm chart under the tenant.
The usage status indicates the number of Helm charts used during chart installation.Recent event history You can view the recent event history that occurred in the tenant. Table. Tenant Dashboard Display Items
12.2.6.3 - Tenant Notice
The tenant administrator can add, edit, and delete notices displayed to users belonging to the tenant.
Editing and deletion are allowed only for registered users.
Getting Started with Tenant Announcements
To start tenant announcements, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Tenant > Tenant Announcements menu. You will be taken to the Tenant Announcements page.
Add tenant announcement
To add a tenant announcement, follow these steps.
- On the Tenant Notices page, click the Add button. The Add Notice popup opens.
- Add Notice In the popup window, specify the notice title, notice content, and target tenant, then click the Save button.
Item Explanation Notice Title Please enter the notice title. Notice Enter the notice body.
You can specify tables, lists, fonts, etc.Popup width/height Enter the width and height of the popup to be displayed on the screen. target tenant Select the tenant(s) to which the notice will be displayed. You can specify one or more tenants.
Only tenants where you are registered with administrator privileges will be shown.Notice period Depending on the nature of the notice, the following options are available. - Always notice
- Notice for a specific period only
- No notice
Email sending time Select immediate email sending, scheduled sending, or no sending according to the purpose of the notice.
It will not be displayed if mail is not used in the system.Table. Additional Input Items for Tenant Announcements
Manage Tenant Announcements
Edit tenant announcement
To edit the tenant announcement, follow these steps.
- Tenant Notices page, click the notice. Notice Details popup window opens.
- Click the Edit button in the Notice Details popup window. The Notice Edit popup window opens.
- Edit Notice After modifying the information in the popup window, click the Save button.
- In the confirmation popup, click the Confirm button to complete the edit.
Delete tenant announcement
To delete a tenant announcement, follow these steps.
- On the Tenant Notices page, click the notice. The Notice Details popup window opens.
- In the Notice Details popup, click the Delete button.
- In the confirmation popup, click the Confirm button to complete the deletion.
Tenant notice preview
To preview tenant announcements, follow these steps.
- On the Tenant Announcements page, click the Preview button for the announcement.
- The notice popup window opens at its actual display size.
- When the check is complete, click the Confirm button.
12.2.7 - Repository
12.2.7.1 - Code Repository
Users can view the list of code repositories, such as GitHub and GitLab, used in the project and add repositories from the project’s code repository menu.
Getting Started with Code Repository
To start a code repository, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- In the left menu, click the Repository > Code Repository menu. You will be taken to the Code Repository page.
Add code repository
To add a code repository, follow these steps.
- On the Code Repository page, click the Add Code Repository button in the upper right. You will be taken to the Add Code Repository page.
- On the Add Code Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Repository type Select the repository to use - Registered tools: Users can select and use the types of SCM Repository tools (
Github,Gitlab, etc.) that are available. - Unregistered tools: You can enter the domain of a tool that is not registered. The unregistered tool entry appears only for App templates that do not include source code (
Environment Only).
New/Existing usage Select Create new repository or Use existing repository - The activation status varies depending on specific conditions. For details, see Table. Conditions for activating new repository creation and existing repository usage.
Repository information Enter repository information - When creating a new repository, the URL is formed from the project group name/project name.
Authentication information Enter authentication credentials. Repository information Enter repository information - You can use a code repository that is not registered as a tool in DevOps Console.
- You must also go through the URL check process.
Table. Code Repository Add Input Items - Registered tools: Users can select and use the types of SCM Repository tools (
Managing code repositories
Code repository list
| Item | Explanation |
|---|---|
| User permission settings | User Permission Settings The popup window opens. |
| Webhook configuration | Webhook Settings The popup window opens. |
| Edit icon | The code repository’s Edit Authentication Information popup window opens. |
| Delete | Delete the code repository. When deleting, you can choose whether to also delete the code repository in SCM. |
Add account to code repository
To add an account to the code repository, follow these steps.
- On the Code Repository page, click the User Permission Settings icon for the repository you want to configure. The User Permission Settings popup window will open.
- User Permission Settings In the popup window, enter the credentials of the account you want to add, then click the Save button to complete adding the account.
Setting up a webhook in the code repository
You can configure a webhook to trigger the pipeline when changes such as commit or push occur on a code repository branch.
To set up a webhook, follow these steps.
- Click the Webhook Settings icon for the code repository you want to configure on the Code Repository page. The Webhook Settings popup opens.
- In the Webhook Settings popup, click the Add button.
- Webhook Settings In the popup window, select the pipeline you want to run, enter the branch name, and click the Save button to complete the webhook configuration.
Change account in code repository
To change the account in the code repository, follow the steps below.
- On the Code Repository page, click the Edit icon of the code repository you want to change. The Edit Authentication Information popup will open.
- Edit authentication information after entering the authentication information in the popup window, click the Save button to complete the account change.
Delete code repository
To delete the code repository, follow these steps.
- Code Repository page, click the X icon of the code repository you want to delete. Delete Code Repository popup opens.
- In the Delete code repository popup, select also delete the repository in SCM and click the Confirm button to complete the code repository deletion.
Also delete the repository in SCM.
- Selection: Both the code repository list and the actual code repository in SCM will be deleted.
- Unselected: It is deleted only from the code repository list, while the code repository in SCM remains.
12.2.7.2 - Artifact Repository
Users can integrate with Nexus to create projects in Nexus and retrieve and utilize the created projects.
Getting Started with Artifact Repository
To start managing the artifact repository, follow these steps.
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Repository > Artifact Repository menu in the left navigation. You will be taken to the Artifact Repository page.
Add artifact repository
To add an artifact repository, follow these steps.
- Click the Add Artifact Repository button at the top right of the Artifact Repository page. You will be taken to the Add Artifact Repository page.
- On the Add Artifact Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Select whether to create a repository Choose whether to create a new repository or use an existing one. Enter basic information Base URL, select repository type and enter repository/authentication information. Table. Input fields for adding an artifact repository
Managing the artifact repository
Artifact storage list
| Item | Explanation |
|---|---|
| Account Change | Modify the artifact repository credentials. |
| Delete | Delete the artifact repository. |
Changing the artifact repository account
To change the account in the artifact repository, follow the steps below.
- On the Artifact Repository page, click the Edit icon of the artifact repository you want to modify. The Edit Authentication Information popup will open.
- Edit authentication information after entering authentication information in the popup window, click the Save button to complete the account change.
Delete Artifact Repository
To delete the artifact repository, follow the steps below.
- On the Artifact Repository page, click the X icon of the repository you want to delete. Artifact Repository Deletion popup opens.
- In the Delete Artifact Repository popup, select also delete the repository in Nexus and click the Confirm button to complete the artifact repository deletion.
Delete the repository in Nexus as well.
- Selection: Both the artifact repository list and the Nexus repository will be deleted.
- Unselected: It is only removed from the artifact repository list, and the repository in Nexus remains.
12.2.7.3 - Image Repository
Users can manage the image repositories used in a project from the project’s image repository menu.
Getting Started with Image Repository
To start managing the image repository, follow these steps.
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- Click the Repository > Image Repository menu in the left menu. You will be taken to the Image Repository page.
Add Image Repository
To add an image repository, follow these steps.
App. Add image repository
- On the Image Repository page, click the App. Add Image Repository button in the upper right. You will be taken to the App. Add Image Repository page.
- App. Add Image Repository page, enter and configure each item.
- Connection Test Click the button.
- Click the Save button.
Item Explanation Select repository type Select the image repository type.
To use an image repository not registered in the Devops Console, select the Image Registry type.Choose whether to create a repository Choose whether to create a new repository or use an existing one. - If you selected the
Docker huborImage Registrytype earlier, you can only select Use existing repository.
Registered tool Enter repository information. Unregistered tool Enter repository information - You can register an image repository that is not registered with the DevOps Console tool.
- Click the URL Check button to proceed with the verification process.
- Only Use existing repository can be selected.
Table. App. Add Image Repository Input Fields - If you selected the
Add pull-only image repository
- On the Image Repository page, click the Add Pull-Only Image Repository button in the upper right. You will be taken to the Add Pull-Only Image Repository page.
- Add Pull‑only Image Repository On the page, enter and configure each field.
- Connection Test Click the button.
- Click the Save button.
Manage Image Repository
Image repository list
| Item | Explanation |
|---|---|
| Account Change | The Edit Authentication Information popup window of the image repository opens. |
| Delete | Image Repository Deletion a popup window opens |
Change Image Repository Account
To change the account in the image repository, follow these steps.
- On the Image Repository page, click the Edit icon of the image repository you want to change. The Edit Authentication Information popup window will open.
- Edit authentication information after entering authentication information in the popup window, click the Save button to complete the account change.
Delete Image Repository
To delete the image repository, follow these steps.
- On the Image Repository page, click the X icon of the image repository you want to delete. The Delete Image Repository popup window opens.
- Delete Image Repository in the popup window, select also delete the Repository in IR, then click the Confirm button to complete the image repository deletion.
Delete the Repository in IR as well
- Selection: The image repository list and the actual image repository’s repository will both be deleted.
- Unselected: It is deleted only from the image repository list, while the actual repository in the image registry remains.
12.2.7.4 - Chart Repository
Users can upload and delete Helm-created charts to the chart repository.
Charts uploaded to the chart repository are used in Add Helm Chart and are utilized during helm install or when creating a project.
Getting Started with Chart Repository
To begin managing the chart repository, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Tools & Templates > Chart Repository menu. The Chart Repository screen appears.
Getting Started with Project Chart Repository
- Click the Project card on the Main page. You will be taken to the Project Dashboard page.
- In the left menu, click the Repository > Chart Repository menu. You will be taken to the Chart Repository page.
Upload Chart
Chart.yaml, refer to the Helm official page.Registration information is automatically generated based on the name and version of the uploaded chart’s Chart.yaml file.
To upload a chart to the chart repository, follow these steps.
- Click the Admin icon at the top right of the Main page. Navigate to the Tenant Dashboard page.
- From the left menu, click the Tools & Templates > Chart Repository menu. The Chart Repository screen appears.
- On the Chart Repository page, click the Upload button. The Chart File Upload popup window opens.
- Chart File Upload In the popup window, after entering the content, click the Upload button.
Item Explanation Chart type Please select a chart type. Tenant / Project Group Select the tenant/project group where the chart will be used. Chart file Click the Browse button to upload the chart file. - Only
.tgzfiles generated with thehelm packagecommand can be uploaded.
Table. Chart Upload Input Items - Only
Delete chart
To delete the chart, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Tools & Templates > Chart Repository menu. The Chart Repository screen appears.
- Select the checkbox of the item you want to delete from the Chart Repository list and click the Delete button.
- Click the Confirm button in the confirmation popup.
Delete only a specific version of a chart
To delete only a specific version from the chart, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Tools & Templates > Chart Repository menu. The Chart Repository screen appears.
- Chart Repository Click the item you want to delete from the list. You will be taken to the Chart Version List page.
- On the Chart version list page, select the checkbox for the items you want to delete and click the Delete button.
- Click the Confirm button in the confirmation popup.
12.2.7.5 - Helm Chart
Helm chart is a feature that registers charts stored in the chart repository so they can be used in the DevOps Console.
Helm charts can be used through Helm install. Additionally, you can integrate them with the App template via Add supported Helm chart.
Getting Started with Helm Chart
To start managing Helm charts, follow these steps.
- Main page, click the Admin icon at the top right. Admin page opens.
- In the left menu, click the Tools & Templates > Helm Chart menu.
Getting Started with Project Helm Chart
- On the Main page, click the Project card. You will be taken to the Project Dashboard page.
- Click the Repository > Helm Chart menu in the left sidebar. You will be taken to the Helm Chart page.
Add Helm chart
Users can add their own Helm charts.
Before registering a Helm chart, the user must first upload the chart to be used via Upload Chart.
To add a Helm chart, follow these steps.
- Click the Admin icon at the top right of the Main page. The Admin page opens.
- From the left menu, click the Tools & Templates > Helm Chart menu. The Helm Chart page opens.
- Select the Helm chart type from the menu. The Add Helm chart button appears only if you have registration permission based on the selected information.
- Click the Add Helm Chart button. You will be taken to the Helm Chart Registration page.
- Enter Helm chart basic information and click the Start button.
Item Explanation Helm chart type Select the type of Helm chart to add. Tenant/Project Group Select the tenant/project group to add the Helm chart - When selecting a tenant, you can use the registered chart only in projects of the selected tenant.
- When selecting a project group, you can use the registered chart only in projects of the selected project group.
Allow new installation Select whether to allow a new installation via Helm install. Table. Helm Chart Basic Information Settings - After selecting Helm chart repository and Helm chart, click the Validation Check button.
- After entering the remaining information, click the Next button.
repository ItemExplanation ChartMuseumHelm chart repository Select the chart repository as ChartMuseum.Select chart Select the chart you want to register as a Helm chart among the charts registered via 차트 업로드하기. Harbor OCI Helm chart repository Select the chart repository as Harbor OCI.Authentication information Enter the chart repository credentials and click the Connection Test button. Chart selection Select a Helm chart that can be queried with the entered credentials and click the Validation Check button. OCI Helm chart repository Select the chart repository as OCI.Authentication information Enter the chart repository credentials and click the Connection Test button. Chart input Enter the Helm chart that can be queried using the authentication information entered in Authentication Information, and click the Validation Check button.
(ex. oci://chart.url/repo/chartname:version)common icon Select an icon to represent the Helm chart. CI/CD information Select whether to support CI/CD functionality - Indicates whether it is linked with the App template.
- The chart’s Values.yaml file must contain the keys image.repository, image.tag, and imagePullSecrest[0].name.
- Support CI/CDWhen selected, a CI/CD information step is added.
Chart image Select whether to register an image - The chart’s Values.yaml file must contain the key imagePullSecrets[0].name.
- No image If selected, the image secret information step will be omitted.
Table. Chart Repository Configuration Items - After selecting the image repository and entering the authentication information, click the Connection Test button.
- After entering the remaining information, click the Next button.
Item Explanation Image repository information Select an image repository and enter the authentication information. - The image repository requires administrator privileges.
- Grant read access to the image repository for users who want to perform a Helm install using a Helm chart.
- Assign permissions to the image repository using the entered authentication information.
Add used images Add the image path of the selected image repository. - Select an image from the list: choose Organization, Repository, and Tag to add.
- User input: directly enter the image’s docker repository and docker tag to add.
- Multiple entries are allowed.
Use the registrant’s authentication credentials This is an option that can be selected when the image repository chosen in the image registry is a tool that cannot grant permissions (e.g., SCR). - If not checked, when the Helm chart user performs an installation, the Pull permission for the image used by the Helm chart user is added. If the tool cannot grant permissions, no permission granting is performed.
- If not checked, when the Helm chart user performs an installation, the Helm chart registrant’s credentials are used instead of the Helm chart user’s permissions.
- Since the registrant’s credentials may be exposed to the Helm chart user, it should be used only when necessary.
- If the image repository provides only image Pull, it must be selected to avoid issues during use. You must enter an image repository that will be used exclusively for Pull. (When checked, Pull and Push cannot be performed simultaneously on a single image repository.)
- The registrant’s credentials are used in Project > Image Repository > Pull-only images and the Helm release’s ImagePull Secret. These credentials cannot be changed by Helm chart users, and if the registrant’s credentials are changed in the Helm chart, they are updated globally.
Select Docker base image Select the image to be used as the Docker base image - Only select this if you chose Support CI/CD in the previous step, and it will be used as the base image for Docker build.
Table. Image secret information configuration items - App to support. After selecting a template, click the Done button.
Environment Only. The template provides only the build/deployment environment without project sample source code.Modify Helm chart
To modify the Helm chart, follow these steps.
- Main page, click the Admin icon at the top right. Admin page opens.
- Click the Tools & Templates > Helm Chart menu in the left menu.
- Click the Helm chart card you want to edit from the Helm chart list. The Helm chart details page opens.
- Click the Edit button at the bottom right.
- After editing the information, click the Save button to complete the edit.
Add Helm chart version
To add a Helm chart version, the same chart with only a different version must already be registered via Upload Chart.
To add a version to the Helm chart, follow these steps.
- Main page, click the Admin icon at the top right. The Admin page opens.
- In the left menu, click the Tools & Templates > Helm Chart menu.
- Click the Helm chart card you want to edit from the Helm chart list. The Helm chart details page opens.
- Click the Add Version button at the bottom right. The Add Helm Chart Version popup window opens.
- After entering the information, click the Save button to complete adding the version.
Item Explanation Chart version Select the chart version to add - Shows the versions of charts in the chart repository that are not registered as Helm charts.
Table. Additional Helm Chart Version Settings
Delete Helm chart
To delete a Helm chart, follow these steps.
- Main page, click the Admin icon at the top right. The Admin page opens.
- From the left menu, click the Tools & Templates > Helm Chart menu. The Helm Chart page opens.
- Click the Helm chart card you want to delete from the Helm chart list. The Helm chart details page opens.
- Click the Delete button at the bottom right.
- In the confirmation popup, click the Confirm button to complete the deletion.
12.2.7.5.1 - Creating Helm Charts with Form Input Support
Users can create a Helm chart that supports Form input.
Helm 3 or higher.Helm chart that supports Form input
When you use a Helm chart that supports Form input and run helm install, a user UI is provided that allows you to enter each field.
Helm chart file structure and values.schema.json file
Helm chart file structure
To support Form input, an additional values.schema.json file is required in the basic Helm chart file structure.
The relationship between values.schema.json and values.yaml files
values.schema.json
- This file defines a JSON Schema to validate the values entered in the
values.yamlfile. - In the DevOps Console, in addition to the JSON Schema functionality, we added a feature that displays a form on the screen so that users can easily input data.
JSON Schema Basics
The values.schema.json file used in DevOps Console supports the standard format defined by JSON Schema.
For detailed guidance on the standard format, refer to the site below.
The description of the basic attributes is as follows.
| attribute | Description | Data type | Allowed value |
|---|---|---|---|
| $schema |
| string | http://json-schema.org/schema# |
| type | Data type
| string |
|
| |||
| |||
| |||
| |||
| |||
| |||
| title | Label | string | Item label definition |
| description | description | string | Displayed as a tooltip |
| readOnly | read-only status | boolean |
|
| required | List of required input items | array | e.g, "required": ["username", "password"] |
Items defined in the DevOps Console
The following items are defined in the DevOps Console and operate only within the DevOps Console.
| attribute | Description | Data type | Allowed value |
|---|---|---|---|
| form | DevOps Console screen display option
| boolean | default: false |
| render | Change renderer | string |
|
| format | string format reference reference | string |
|
| form_locale | Define for internationalization processing
| object |
|
|
hierarchical processing
To handle hierarchical structures, JSON Schema can define a "type": "object" property value and a properties attribute.
For child properties, define them under the properties item.
Below is an example that defines the service.internalPort property.
"service": {
"type": "object",
"form": true,
"properties": {
"internalPort": {
"type": "number",
"title": "Container Port",
"description": "HTTP port to expose at container level",
"form": true
}
<중략>"service": {
"type": "object",
"form": true,
"properties": {
"internalPort": {
"type": "number",
"title": "Container Port",
"description": "HTTP port to expose at container level",
"form": true
}
<중략>Internationalization handling
For internationalization processing, use the form_locale attribute and define it as follows.
Korean and English are supported.
"db": {
"type": "string",
"title": "DB",
"description": "choose db type",
"oneOf": [
{
"const": "in",
"title": "internal"
},
{
"const": "ex",
"title": "external"
}
],
"form": true,
"form_locale": {
"ko": {
"label": "Database",
"description": "Select the database type"
"internal": "internal"
"external": "external"
},
"en": {
"label": "Database"
}
}
}"db": {
"type": "string",
"title": "DB",
"description": "choose db type",
"oneOf": [
{
"const": "in",
"title": "internal"
},
{
"const": "ex",
"title": "external"
}
],
"form": true,
"form_locale": {
"ko": {
"label": "Database",
"description": "Select the database type"
"internal": "internal"
"external": "external"
},
"en": {
"label": "Database"
}
}
}values.schema.json example
Examples by Form Type
Input
To display the fields defined in the values.schema.json file as a form on the screen, you must set the form field’s value to true.
{
"$schema": "http://json-schema.org/schema#",
"type": "object",
"properties": {
"form_field": {
"type": "string", <--- create an input field that receives a string
"form": true <----- displayed on screen when true
},
"hide_field": { <-- not displayed
"type": "string"
}
}
}{
"$schema": "http://json-schema.org/schema#",
"type": "object",
"properties": {
"form_field": {
"type": "string", <--- create an input field that receives a string
"form": true <----- displayed on screen when true
},
"hide_field": { <-- not displayed
"type": "string"
}
}
}Password
{
"$schema": "http://json-schema.org/schema#",
"type": "object",
"properties": {
"password_field": {
"type": "string",
"form": true,
"render": "password", <---- displayed as password
"format": "password_confirm" <--- when adding a password confirmation input field
}
}
}{
"$schema": "http://json-schema.org/schema#",
"type": "object",
"properties": {
"password_field": {
"type": "string",
"form": true,
"render": "password", <---- displayed as password
"format": "password_confirm" <--- when adding a password confirmation input field
}
}
}Checkbox
"enabled": {
"title": "enable persistence",
"type": "boolean",
"form": true
}"enabled": {
"title": "enable persistence",
"type": "boolean",
"form": true
}Dropdown
To display a dropdown field on the screen and specify allowed values, you can use the enum and oneOf properties.
enum
Use when the text displayed on the screen matches the stored value.
"postgres": {
"type": "string",
"title": "Postgres",
"description": "choose PostgreSQL type.",
"enum": [
"internal",
"external",
"both"
],
"form": true
}"postgres": {
"type": "string",
"title": "Postgres",
"description": "choose PostgreSQL type.",
"enum": [
"internal",
"external",
"both"
],
"form": true
}oneOf
Use this when the displayed text on the screen and the stored value need to be different.
"Oneof": {
"type": "string",
"title": "DB",
"description": "choose db type",
"oneOf": [
{
"const": "in", <-- value saved to the yaml file when selected
"title": "internal" <-- value displayed in the dropdown form
},
{
"const": "ex",
"title": "external"
}
],
"form": true
}"Oneof": {
"type": "string",
"title": "DB",
"description": "choose db type",
"oneOf": [
{
"const": "in", <-- value saved to the yaml file when selected
"title": "internal" <-- value displayed in the dropdown form
},
{
"const": "ex",
"title": "external"
}
],
"form": true
}Array
"Array": {
"type": "array",
"items": {
"type": "string",
"form": true
},
"form": true
}"Array": {
"type": "array",
"items": {
"type": "string",
"form": true
},
"form": true
}Object Array
"objectArray": {
"type": "array",
"title": "Object Array",
"form": true,
"items": {
"type": "object",
"form": true,
"properties": {
"host": {
"type": "string",
"form": true
},
"path": {
"type": "string",
"form": true
}
}
}
}"objectArray": {
"type": "array",
"title": "Object Array",
"form": true,
"items": {
"type": "object",
"form": true,
"properties": {
"host": {
"type": "string",
"form": true
},
"path": {
"type": "string",
"form": true
}
}
}
}values.schema.json full file creation example
system-nginx
{
"$schema": "http://json-schema.org/schema#",
"type": "object",
"form": true,
"properties": {
"service": {
"type": "object",
"form": true,
"properties": {
"type": {
"type": "string",
"title": "Service Type",
"form": true,
"enum": ["ClusterIP", "NodePort", "LoadBalancer", "ExternalName"]
},
"externalPort": {
"type": "number",
"title": "Service Port",
"description": "HTTP port to expose at service level",
"form": true
},
"internalPort": {
"type": "number",
"title": "Container Port",
"description": "HTTP port to expose at container level",
"form": true
}
},
"required": ["type", "externalPort", "internalPort"]
},
"ingress": {
"type": "object",
"form": true,
"properties": {
"enabled": {
"type": "boolean",
"title": "Use Ingress",
"form": true
},
"domain": {
"type": ["string", "null"],
"format": "hostname",
"title": "Ingress Domain",
"description": "Default host for the ingress resource (required when `ingress.enabled=true`)",
"form": true
}
}
},
"networkPolicy": {
"type": "object",
"form": true,
"properties": {
"enabled": {
"type": "boolean",
"title": "Use NetworkPolicy",
"form": true
}
}
}
}
}{
"$schema": "http://json-schema.org/schema#",
"type": "object",
"form": true,
"properties": {
"service": {
"type": "object",
"form": true,
"properties": {
"type": {
"type": "string",
"title": "Service Type",
"form": true,
"enum": ["ClusterIP", "NodePort", "LoadBalancer", "ExternalName"]
},
"externalPort": {
"type": "number",
"title": "Service Port",
"description": "HTTP port to expose at service level",
"form": true
},
"internalPort": {
"type": "number",
"title": "Container Port",
"description": "HTTP port to expose at container level",
"form": true
}
},
"required": ["type", "externalPort", "internalPort"]
},
"ingress": {
"type": "object",
"form": true,
"properties": {
"enabled": {
"type": "boolean",
"title": "Use Ingress",
"form": true
},
"domain": {
"type": ["string", "null"],
"format": "hostname",
"title": "Ingress Domain",
"description": "Default host for the ingress resource (required when `ingress.enabled=true`)",
"form": true
}
}
},
"networkPolicy": {
"type": "object",
"form": true,
"properties": {
"enabled": {
"type": "boolean",
"title": "Use NetworkPolicy",
"form": true
}
}
}
}
}12.2.8 - Quality
12.2.8.1 - Code Quality
Users can create a project in SonarQube by integrating with SonarQube, and utilize the created project in the DevOps Console.
Getting Started with Code Quality
To start code quality management, follow these steps.
- Main page, click the Project card. You will be taken to the Project Dashboard page.
- From the left menu, click the Quality > Code Quality menu. You will be taken to the Code Quality page.
Add Code Quality Project
To add a code quality project, follow these steps.
- On the Code Quality page, click the Add Code Quality Project button. You will be taken to the Add Project page.
- Add Code Quality Project On the page, enter and configure each item.
- After clicking the Connection Test button, click the Save button.
- Click the Confirm button in the confirmation popup to complete adding the code quality project.
Item Explanation Select repository creation option Choose whether to create a new repository or use an existing one - 툴 추가하기 If you select new creation allowed as No in [툴 추가하기], you cannot create a repository.
Base URL Select the code quality server to use. Project name Please enter the project name to use. project key Enter the project key to use. Authentication information Choose whether to create a new user profile or use an existing one, then enter the username and password. Table. Add code quality project
Managing code quality projects
Code Quality Project List
Users can change or delete accounts in the Code Quality project.
| Item | Explanation |
|---|---|
| Account change | Edit Code Quality Certification Information The popup window opens. |
| Delete | Code Quality Project Deletion the popup window opens. |
Change account in the code quality project
To change the account in the Code Quality project, follow these steps.
- On the Code Quality page, click the Edit icon. The Edit Authentication Information popup opens.
- In the Edit Authentication Information popup, after entering the authentication information, click the Save button to complete the account change.
Delete Code Quality Project
To delete the code quality project, follow these steps.
- Code Quality page, click the X icon on the Code Quality Project card you want to delete. The Delete Code Quality Project popup will open.
- Delete Code Quality Project popup, select also delete the project in SonarQube and click the Confirm button.
Also delete the project in SonarQube
- Selection: The project is actually deleted in SonarQube.
- Unselected: Code Quality is removed only from the list and remains in SonarQube.
12.2.9 - Tools & Templates
12.2.9.1 - Tool Management
Tools refer to applications that interact with the DevOps Console to support CI/CD functionality.
Please refer to Tool Classification for the list of tools supported by DevOps Console.
Getting Started with Tool Management
To begin tool management, follow the steps below.
- Click the Management icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Tools & Templates > Tools menu. You will be taken to the Tools page.
Tool type
Each tool’s applicable domain varies according to its type.
| Tool type | description |
|---|---|
| System Tool |
|
| Tenant Tool |
|
| ProjectGroup Tool |
|
Tool classification
The list of tools currently supported by the DevOps Console is as follows.
| Tool classification | tool |
|---|---|
| CICD Pipeline | Jenkins |
| SCM Repository | GitLab, GitHub, Git-based SCM |
| Image Registry | Harbor, Docker Hub, SCP Container Registry, Docker Image Registry |
| Code Quality | SonarQube |
| Artifact Repository | Nexus, Object Storage (S3 compatible) |
| Helm Chart Repository | Harbor |
| Project Management Software | JIRA |
- Supported tools may change (be added or removed) according to the release schedule.
- You can receive technical support for installing CI/CD tools through the Marketplace service of Samsung Cloud Platform. (Provided by eScore, and the supported tools can be checked in the Marketplace service)
Admin
Indicates the selected tenant or project group when adding a tool with the tenant/project group type.
Distinguish the types of management affiliation using the following icons.
- The management belongs to the tenant.
- The management affiliation is the project group.
Add tool
To add a tool, follow these steps.
- On the Tool page, click the Add button. The Add Tool popup appears.
Select tool support type
- Add Tool Select the tool’s supported type in the popup window.
- Complete the selection and click the Next button. The Basic Information input screen appears.
Item Explanation type Select the tool’s supported type - Refer to 툴 유형 for descriptions by type.
Tenant/Project Group Select which tenant/project group to map to. Table. Supported type selection items when adding a tool
Enter basic information
- Add Tool In the Basic Information input screen of the popup, select the tool category and the tool. The input screen changes based on the selected tool.
- Refer to Tool Classification for explanations by tool category.
- After entering the required information, click the Connection Test button.
- Click the Next button.
SCM Repository
| Item | description |
|---|---|
| Tool name | Enter the tool name for user identification. |
| Tool classification | Please select a tool category. |
| tool | Please select a tool. |
| URL | Enter the URL address to access the tool
|
| URL for API | Github.com Please enter the API path. |
| Whether Org creation is possible | Choose whether to enable the creation of a new Github Organization in this tenant/project group. |
| Whether new creation is possible | Select whether to allow creating new repositories in this tenant/project group. |
| IDP usage | Select whether to use IDP. |
| User account authentication type | Select the authentication type for the tool user. |
| Administrator account authentication type | Select the authentication type for the tool administrator. |
| Administrator ID | Please enter the tool administrator’s ID. |
| Administrator password / token | Enter the tool administrator’s password or token. |
CICD Pipeline
| Item | Explanation |
|---|---|
| Tool name | Enter the tool name for user identification. |
| Tool classification | Please select a tool category. |
| tool | Please select a tool. |
| URL | Enter the URL address to access the tool
|
| Mail Service | Choose whether to use the email sending feature. |
| Category | Select whether to use this tool for development or operation. |
| IP | Enter IP list
|
| IP range | Enter IP range
|
| IDP usage | Select whether to use IDP. |
| IDP type | When using IDP, select the IDP type (CMP IDP, other IDP). |
| User account authentication type | Select the authentication type for the tool user. |
| Administrator account authentication type | Select the authentication type for the tool administrator. |
| Admin ID | Please enter the tool administrator’s ID. |
| Administrator password / token | Enter the tool administrator’s password or token. |
If the Number of executors field of the Built-In Node in Jenkins system settings is set to 1 or higher, a security issue may arise, so the tool cannot be added.
- In the Jenkins management menu, the Number of executors field of the Built-In Node must be set to 0.
- Note Jenkins officially recommends avoiding running builds on the Controller Node.
Image Registry
| Item | description |
|---|---|
| Tool name | Enter the tool name for user identification. |
| Tool classification | Please select a tool category. |
| tool | Please select a tool. |
| Whether new creation is possible | Select whether to allow creating new repositories in this tenant/project group. |
| URL | Enter the URL address to access the tool
|
| URL for API | Enter the Docker Hub API path. |
| Image repository URL | Enter the URL for using Docker Registry. |
| Use private SSL certificate | Select whether to use a private SSL. |
| Include system common image | Select whether to include the system-wide image. |
| IDP usage | Select whether to use IDP. |
| User account authentication type | Select the authentication type for the tool user. |
| Administrator account authentication type | Select the authentication type for the tool administrator. |
| Administrator ID | Enter the tool administrator’s ID. |
| Administrator password / token | Enter the tool administrator’s password or token. |
Code Quality
| Item | Explanation |
|---|---|
| Tool name | Enter the tool name for user identification. |
| Tool classification | Please select a tool category. |
| tool | Please select a tool. |
| Whether new creation is possible | Select whether to enable creation of new SonarQube projects in this tenant/project group. |
| URL | Enter the URL address to access the tool
|
| Tool version | Enter the version of SonarQube. |
| IDP usage | Select whether to use IDP. |
| User account authentication type | Select the authentication type for the tool user. |
| Administrator account authentication type | Select the authentication type for the tool administrator. |
| Administrator ID | Enter the tool administrator’s ID. |
| Administrator password / token | Enter the tool administrator’s password or token. |
Artifact Repository
| Item | Explanation |
|---|---|
| Tool name | Enter the tool name for user identification. |
| Tool classification | Please select a tool category. |
| tool | Please select a tool. |
| Whether new creation is possible | Select whether to enable creation of a new Nexus repository in this tenant/project group. |
| URL | Enter the URL address to access the tool
|
| IDP usage | Select whether to use IDP. |
| User account authentication type | Select the authentication type for the tool user. |
| Administrator account authentication type | Select the authentication type for the tool administrator. |
| Administrator ID | Please enter the tool administrator’s ID. |
| Administrator password / token | Enter the tool administrator’s password or token. |
Helm Chart Repository
| Item | description |
|---|---|
| Tool name | Enter the tool name for user identification. |
| Tool classification | Please select a tool category. |
| tool | Please select a tool. |
| Whether new creation is possible | Select whether to allow creating new repositories in this tenant/project group. |
| URL | Enter the URL address to access the tool
|
| Use private SSL certificate | Select whether to use a private SSL. |
| Helm chart repository URL | Enter the repository URL for the tool
|
| IDP usage | Select whether to use IDP. |
| User account authentication type | Select the authentication type for the tool user. |
| Administrator account authentication type | Select the authentication type for the tool administrator. |
| Administrator ID | Please enter the tool administrator’s ID. |
| Administrator password / token | Enter the tool administrator’s password or token. |
Project Management Software
| Item | description |
|---|---|
| Tool name | Enter the tool name for user identification. |
| Tool classification | Please select a tool category. |
| tool | Please select a tool. |
| Whether new creation is possible | Choose whether to allow creation of new JIRA projects in this tenant/project group. |
| URL | Enter the URL address to access the tool
|
| IDP usage | Select whether to use IDP. |
| User account authentication type | Select the authentication type for the tool user. |
| Administrator account authentication type | Select the authentication type for the tool administrator. |
| Administrator ID | Please enter the tool administrator’s ID. |
| Administrator password / token | Enter the tool administrator’s password or token. |
Enter additional information
- Tool addition In the popup window’s Basic Information input screen, when you click the Next button, the Additional Information input screen appears.
- Select each item and click the Complete button.
- In the confirmation popup, click the Confirm button to complete adding the tool.
Item description Use status Select whether to use the tool in this tenant/project group. Whether new creation is possible Select whether to allow creating a new repository in the given tenant/project group. - It is displayed only when the tool category is SCM Repository.
Table. Additional Information Input Items
Tool Details
To begin managing the tool’s detailed information, follow these steps.
- On the Tool page, click the tool for which you want to manage detailed information. You will be taken to the Tool Details page.
Manage tool basic information
To check the tool’s basic information, follow these steps.
- On the Tool Details page, click the Basic Information tab.
To modify the tool’s basic information, follow these steps.
- On the Tool Details page, click the Basic Information tab.
- Click the Edit button.
- After editing the required information, click the Save button.
Managing Global Tools
Jenkins, the global tool tab is displayed.Jenkins web interface’s Jenkins Management > Global Tool Configuration menu can be operated from the DevOps Console.
Only one-way registration to Jenkins is supported from the DevOps Console. (In other words, changes made by the user in the DevOps Console will overwrite the information in Jenkins.)
Users can manage the list of tools available in Jenkins, and tools registered in Global Tools are used in Tools when configuring a stage.
To manage the global tool, follow the steps below.
- On the Tool Details page, click the Global Tool tab.
Add global tool
To add a global tool, follow these steps.
- In the Global Tool tab, click the Edit icon of the item you want to add. The Global Tool Management popup opens.
- Essential tool is automatically configured in the DevOps Console.
- essential tool cannot be deleted, and only the home path can be modified.
- Click the Add button. A new row will be added at the bottom of the list.
- Enter the information in the newly added row and click the Save button.
- Click the Confirm button in the confirmation popup to complete.
Item description Tool types The tool type is set automatically. Name Please enter the tool name. Home path Enter the path where the tool is installed. Table. Global Tool Additional Input Items
Modify Global Tool
To modify the global tool, follow these steps.
- Click the Edit icon of the item you want to add in the Global Tool tab. The Global Tool Management popup opens.
- After editing the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Delete Global Tool
To delete the global tool, follow these steps.
- Click the Edit icon of the item you want to add in the Global Tool tab. The Global Tool Management popup window opens.
- After deleting the list, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Managing agents (kubernetes)
Jenkins, the Agent (kubernetes) tab is displayed.Users can manage the agents (slave) used for builds in Jenkins.
Jenkins web screen’s 1) Jenkins Management > System Configuration > Cloud > Pod Templates or 2) Jenkins Management > Node Management > Configure Clouds > Pod Templates menu is a feature that can be operated from the DevOps Console.
DevOps Console only supports one-way registration to Jenkins. (In other words, changes made by the user in DevOps Console will overwrite the information in Jenkins.)
To manage the agent (Kubernetes), follow the steps below.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Click the information icon in the Pod Template Management list. The Pod Template Usage Guide popup opens.
Adding Container Resource Types
If the user modifies the container resource type, it affects the Pod Template.
- If you change the container resource type from unused → used, the number of Pod Templates will increase by (container resource type number X Pod Template number).
- If you change the container resource type from used → unused, the expanded Pod Template will shrink back to its original number.
- The agent names, labels, and other attributes of the expanding Pod Templates are automatically generated by combining the Resource Type entry entered by the user when registering the container resource type, to avoid duplication.
To add a container resource type, follow these steps.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Click the Edit icon of Container Resource Type Management. The Container Resource Type Management popup window opens.
- Click the Add button, enter the content, and then click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Item description Whether to use Set the usage. - To change the usage, there must be no build pipeline configured using the
Jenkinstool.
Resource Type Please enter the resource name. CPU/Memory (Request) When configuring the Kubernetes Pod Agent, enter the requested resource values to be used. CPU/Memory (Limit) Enter the limit values for the resources to be used when configuring the Kubernetes Pod Agent. Table. Container Resource Type Additional Input Items - To change the usage, there must be no build pipeline configured using the
Modify container resource type
To modify the container resource type, follow these steps.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Click the Edit icon of Container Resource Type Management. The Container Resource Type Management popup opens.
- After editing the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Delete Container Resource Type
To delete a container resource type, follow these steps.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Click the Edit icon of Container Resource Type Management. The Container Resource Type Management popup opens.
- After deleting the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Add Pod Template
To add a Pod Template, follow these steps.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Pod Template Management Click the Add button in the list. The Add Agent (Kubernetes) screen appears.
- After entering the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Item description Target Kubernetes Select the target Kubernetes to which the Pod Template will be added - Displays the list of Kubernetes clusters registered in Jenkins.
Agent name Enter the name of the Pod Template. Label Enter the Label value to invoke the agent in the Jenkins Pipeline Script. Inherited Pod Template Select the Pod Template that inherits configuration values (environment variables, Volume…) - Shows the list of Pod Templates registered in the actual Jenkins.
container Enter the name, Docker image, working directory, command, and argument values that map to the Container Template field in Jenkins. - Required container information cannot be deleted, and its name cannot be changed.
Tool path Information that maps to the Tool Locations field in Jenkins, enter the name/home path - Only tools that have been added to the global tool list can be selected.
Support stage Select the supported stage configuration - This information is used for configuring the build pipeline template in the DevOps Console.
- Required stage information cannot be deselected.
Table. Input items for adding a Pod Template
If the user does not check Docker Build in the Supported Stage item,
- When setting up a project using the App.Template of type Kubernetes or VM(Docker) that requires Docker Build, Jenkins cannot be used.
- When configuring the build pipeline via Add Build Pipeline, you cannot add a Docker Build stage.
Pod Template Details
To view the detailed information of a Pod Template, follow these steps.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Pod Template Management Click the Details button of the agent you want to view from the list. The Agent (Kubernetes) Details screen appears.
Modify Pod Template
To modify the Pod Template, follow these steps.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Pod Template Management Click the View Details button of the agent you want to view in the list. The Agent (Kubernetes) Details screen appears.
- Click the Edit button.
- After editing the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete the edit.
Delete Pod Template
To delete a Pod Template, follow these steps.
- On the Tool Details page, click the Agent (Kubernetes) tab.
- Pod Template Management In the list, click the Details button of the agent you want to view. Agent (Kubernetes) Details screen appears.
- Click the Delete button.
- In the confirmation popup, click the Confirm button to complete the deletion.
Managing Agents (VM)
Jenkins, the Agent (VM) tab is displayed.You can manage the list of Nodes available for use in Jenkins.
This feature allows you to operate the Jenkins Management > Node Management menu of Jenkins from the DevOps Console.
DevOps Console only supports one-way registration to Jenkins. (In other words, changes made by the user in DevOps Console will overwrite the information in Jenkins.)
To manage the agent (VM), follow the steps below.
- On the Tool Details page, click the Agent (VM) tab.
- Click the Info icon in the Node Management list. The Node Usage Guide popup opens.
Manage Agent Connections
Register the tunneling port that connects the actual Jenkins and the agent (VM). The tunneling port may vary for each Jenkins.
To manage agent connections, follow these steps.
- On the Tool Details page, click the Agent (VM) tab.
- Click the Edit icon of Agent Connection Management. The Agent Connection Management popup window opens.
- After entering the content, click the Save button.
Add Agent (VM)
To add an agent (VM), follow the steps below.
- On the Tool Details page, click the Agent (VM) tab.
- Click the Add button in Agent Connection Management. The Add Agent (VM) screen appears.
- After entering the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete the deletion.
Item description Target OS Enter the VM’s OS information. Agent name Enter the VM name. Remote root directory Enter the directory path. Label Enter the Label value to invoke the agent in the Jenkins Pipeline Script. Tool path Information that maps to the Jenkins Tool Locations field, enter the name/home path - Only tools added to the global tool list can be selected.
Support stage Select the supported stage configuration - This information is used for configuring the build pipeline template in the DevOps Console.
- Required stage information cannot be deselected.
Table. Agent (VM) Add Input Items
If the user does not check Docker Build in the Supported Stage item,
- When configuring a project through the App.Template of type Kubernetes or VM(Docker) that requires Docker Build, the
Jenkinscannot be used. - Through Add Build Pipeline, when configuring the build pipeline, you cannot add a Docker Build stage.
Agent (VM) Details
To view the detailed information of an agent (VM), follow the steps below.
- On the Tool Details page, click the Agent (VM) tab.
- In the Node Management list, click the agent. The Agent (VM) Details screen appears.
- Click the Information icon of Jenkins - Agent Connection Information.
- Agent Connection Guide The popup window opens.
Integrate Agent (VM)
Java be installed on the VM server.To register and use the agent (VM), you must connect to the actual VM server.
To integrate the agent (VM), follow these steps.
- On the Tool Details page, click the Agent (VM) tab.
- From the Node Management list, click the agent you want to integrate. The Agent (VM) Details screen appears.
- Refer to
jnlpUrlandsecret. - Click the Info icon of Jenkins - Agent Connection Information. The Agent Connection Guide popup opens.
- Agent File Download Click the button to download the
agent.jarfile.- There may be issues running depending on the version of
agent.jar. - You can also download it directly from your own
Jenkins. ({JENKINS_URL}/jnlpJars/agent.jar)
- There may be issues running depending on the version of
- Connect to the VM server to be deployed and create a directory.
- Copy the downloaded
agent.jarfile to the generated directory. - Run the following command in the generated directory path.
java -jar agent.jar -jnlpUrl {jnlpUrl} -secret {secret}java -jar agent.jar -jnlpUrl {jnlpUrl} -secret {secret}Modify Agent (VM)
To modify the agent (VM), follow the procedure below.
- On the Tool Details page, click the Agent (VM) tab.
- Click the agent you want to edit in the Node Management list. The Agent (VM) Details screen appears.
- Click the Edit button.
- After editing the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Delete Agent (VM)
To delete the agent (VM), follow these steps.
- On the Tool Details page, click the Agent (VM) tab.
- Click the agent you want to delete from the Node Management list. The Agent (VM) Details screen appears.
- Click the Delete button.
- Click the Confirm button in the confirmation popup to complete.
Managing Global Libraries
You can manage the list of libraries available in the build pipeline.
The Jenkins Management → System Settings → Global Pipeline Libraries menu of Jenkins can be managed through the DevOps Console.
The Credential information linked to the library can be viewed in the Jenkins Management > Manage Credentials menu.
DevOps Console only supports one-way registration to Jenkins. (In other words, changes made by the user in DevOps Console will overwrite the information in Jenkins.)
To manage the agent(VM), follow these steps.
- On the Tool Details page, click the Global Library tab.
Add Global Library
To add a global library, follow these steps.
- Tool Details on the page, click the Global Library tab.
- Click the Add button. The Add Global Library screen appears.
- After entering the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Item description Library name Enter the name of the library. type It is fixed to SCM and cannot be changed. Library URL Enter the Git repository URL where the library is located. Default version Enter the branch name or tag of the Git repository that contains the library. ID Enter the ID to pull the library. password Enter the password to pull the library. Table. Global Library Additional Input Items
Global Library Details
To view the detailed information of the global library, follow these steps.
- On the Tool Details page, click the Global Library tab.
- In the Global Library list, click the item you want to view in detail. The Global Library Details screen appears.
When type is SCM, SCM-related information is displayed.
- Required library status, library name, type, library URL, default version, ID
Modify Global Library
To modify the global library, follow these steps.
- On the Tool Details page, click the Global Library tab.
- From the Global Library list, click the item you want to view in detail. The Global Library Details screen appears.
- Click the Edit button.
- After editing the content, click the Save button.
- Click the Confirm button in the confirmation popup to complete.
Delete Global Library
To delete the global library, follow these steps.
- Tool Details on the page, click the Global Library tab.
- Global Library Click the item you want to delete from the list. Global Library Detail screen appears.
- Click the Delete button.
- In the confirmation popup, click the Confirm button to complete.
Manage supported tenants/project groups
The tab name is displayed differently depending on the tool type.
- System Tool/Tenant Tool: Supported Tenant
- ProjectGroup Tool: Support Information
The user can manage the tenant or project group that will use the tool.
To manage supported tenants or project groups, follow these steps.
- On the Tool Details page, click the Supported Tenant or Supported Information tab.
Add supported tenant/project group
To add a supported tenant or project group, follow these steps.
- On the Tool Details page, click the Supported Tenant or Supported Information tab.
- Click the Add button. The Add Tenant/Project Group popup window opens.
- After entering the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Item description Tenant/Project Group Select the tenant/project group that will use the tool. Use status Select whether to use the tool in this tenant/project group. Whether new creation is possible Select whether to allow creating new repositories in this tenant/project group.
This setting can only be configured for the tool categories listed below.- SCM Repository
- Image Registry
- Code Quality
- Artifact Repository
- Helm Chart Repository
- Test Management
- Project Management Software
Table. Additional Input Items for Supported Tenant/Project Group
Modify supported tenant/project group
To modify the supported tenant/project group, follow these steps.
- On the Tool Details page, click the Supported Tenant or Support Information tab.
- In the Supported Tenant or Supported Information list, select Usage status and New creation allowed to modify.
Transfer Management Tenant/Project Group
To transfer the management tenant/project group, follow the steps below.
- On the Tool Details page, click the Supported Tenant or Supported Information tab.
- Click the Transfer Management Tenant or Transfer Management Project Group button. The Transfer Management Tenant or Transfer Management Project Group popup window opens.
- Select the target tenant or project group for transfer, then click the Save button.
Delete supported tenant/project group
To delete a managed tenant/project group, follow these steps.
- On the Tool Details page, click the Supported Tenant or Supported Information tab.
- Select the checkbox of the tenant/project group you want to delete.
- Click the Delete button.
- Click the Confirm button in the confirmation popup to complete.
Support K8S cluster management
The user can manage the K8S cluster where the tool will be used.
To manage the supported K8S cluster, follow these steps.
- On the Tool Details page, click the Supported K8S Cluster tab.
Add supported K8S cluster
To add a supported K8S cluster, follow the steps below.
- On the Tool Details page, click the Supported K8S Cluster tab.
- On the Supported K8S Cluster page, click the Add button. The Add K8S Cluster popup window opens.
- After entering the content, click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Item description K8S cluster Select the K8S cluster to use with the tool. Use status Select whether to use the tool in this tenant/project group. Whether new creation is possible Select whether to allow creating new repositories in this tenant/project group.
This setting can only be configured for the tool categories below.- SCM Repository
- Image Registry
- Code Quality
- Artifact Repository
- Helm Chart Repository
- Test Management
- Project Management Software
Table. Additional input fields for supported K8S clusters
Modify supported K8S cluster
To modify the supported K8S cluster, follow the steps below.
- On the Tool Details page, click the Supported K8S Cluster tab.
- In the Supported K8S Clusters list, select Usage Status and New Creation Availability to edit.
Delete supported K8S cluster
To delete the supported K8S cluster, follow these steps.
- Click the Supported K8S Cluster tab on the Tool Details page.
- Supported K8S clusters list, select the checkbox of the K8S cluster you want to delete.
- Click the Delete button.
- In the confirmation popup, click the Confirm button to complete.
Manage tool operators
To manage tool operators, follow the steps below.
- On the Tool Details page, click the Tool Operator tab.
Add tool operator
To add a tool operator, follow these steps.
- Tool Details page, click the Tool Operator tab.
- Click the Add button. The Add Tool Operator popup opens.
- Select the operator and click the Save button.
- In the confirmation popup, click the Confirm button to complete.
Delete tool operator
To delete a tool operator, follow these steps.
- Tool Details page, click the Tool Operator tab.
- Select the checkbox for the item you want to delete from the tool administrator list.
- Click the Delete button.
- In the confirmation popup, click the Confirm button to complete.
Managing Jenkins Recommended Plugins
Jenkins, the plugin tab is displayed.You can check the installed Jenkins version and whether recommended plugins are installed and their version information, and you can update and install the recommended plugins.
- Tool version: Jenkins version information
- Recommended plugins: installation status and version information
Check tool version and recommended plugin information
To check the tool version and recommended plugin information, follow these steps.
- Tool Details page, click the Basic Information tab.
- If there is recommended plugin information that requires installation or update, an informational popup appears, and clicking OK moves you to the Plugins tab.
- On the Tool Details page, click the Plugin tab.
- Check the entries for Tool Version, Recommended Plugins.
Install recommended plugins
To install the recommended plugin, follow these steps.
- In the Recommended plugins area, select the Install button of the plugin you want to install.
- In the Recommended Plugin Installation popup, select the OK button.
- A popup appears indicating that the installation request has been completed, and the actual installation details can be viewed via the link in the popup.
Update recommended plugins
To update the recommended plugin, follow these steps.
- In the Recommended plugins area, select the Update button of the plugin you want to update.
- Select the Confirm button in the Recommended Plugin Update popup.
- A popup appears indicating that the installation request has been completed, and the actual installation details can be viewed via the link in the popup.
- You must restart Jenkins to apply the update you need to do so.
Delete tool
To uninstall the tool, follow these steps.
- On the Tool page, click the tool you want to delete. You will be taken to the Tool Details page.
- Click the Delete button.
- In the confirmation popup, click the Confirm button to complete.
12.2.9.2 - App Template
App. A template is a feature provided to enable users to quickly set up a development environment.
The App. template consists of sample source code, Dockerfile, Helm chart, etc., and users can quickly set up a development environment using the App. template when creating a project.
We provide App templates for various frameworks such as Node.js, Python, Spring Boot, and users can also create and register their own App templates.
| App. template type | Explanation |
|---|---|
| System Template |
|
| Tenant Template |
|
| ProjectGroup Template |
|
App. Getting Started with Template
App. To start template management, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Tools & Templates > App. Templates menu. You will be taken to the App. Templates page.
App. Add Template
Users can add their own App templates.
Source code
App. This is the source code that will be used in the template to build a sample project.
App. A usable SCM Repository must exist in the tenant or project group where the template will be registered. For instructions on registering an SCM Repository tool, see Add Tool.
Register the source code in the SCM Repository in advance. When registering an App template, the corresponding SCM Repository appears, and you should enter the path of the pre-registered source code.
Dockerfile
Dockerfile without registering it inside the source code. For related information, see Dockerfile Template Management.See the official site for documentation and instructions on writing a
Dockerfile.To register an App. Template that supports deployment target projects in the form of Kubernetes or VM (Docker), you must either add a Dockerfile to the source code when registering the source code or register a Dockerfile through 도커파일 템플릿 관리하기.
When writing a Dockerfile, the FROM clause must be fixed as FROM ${BASE_IMAGE}.
The registered ${BASE_IMAGE} value is substituted via the Velocity Template Engine as the image.repository value in the Helm chart when the deployment target is Kubernetes, and as the image path registered in Managing Supported Images when the deployment target is VM (Docker).
Dockerfile file sample
FROM ${BASE_IMAGE}
COPY *.jar app.jar
ENTRYPOINT ["java","-jar","/app.jar"]FROM ${BASE_IMAGE}
COPY *.jar app.jar
ENTRYPOINT ["java","-jar","/app.jar"]App. Register Template
App. To register a template, follow these steps.
- Click the Add button on the App. Template page. You will be taken to the App. Template Add page.
- App. Add Template On the page, select the template support type and click the Start button.
- After entering the required information, click the Complete button.
Item Explanation type Select the template type. - Refer to App. Template Type for type-specific descriptions.
Tenant/Project Group Select the tenant/project group to map. Table. App. Add Template - Template Supported Type Selection ItemItem Explanation Deployment target Select the deployment target supported by the template - Kubernetes: when the deployment target is a cluster using Helm charts
- VM(Artifact): when the deployment target is a VM server using an Artifact file
- VM(Docker): when the deployment target is a VM server using a Docker image
- N/A: when there is no deployment target (ex. Android)
Template name App. Enter the name of the template. Application classification Select the category of the application included in the template - Used to classify the template.
language Select the programming language of the source code included in the template. source code Select whether the template includes source code. Source code repository type Select the location where the source code to be included in the template is stored. You can choose SCM or a compressed file (ZIP). Repository URL Enter the repository URL where the template source code is located - The list of SCM Repository tool available in the tenant and project group will be displayed.
Repository branch Enter the branch of the repository where the template source code is located. Individual authentication information Enter the credentials to access the repository - If you select ‘Do not use’, the credentials used when registering the tool will be used.
Dockerfile path Enter the Dockerfile path within the repository - Used when building the Docker image.
code quality Select whether to use code quality. Explanation App. Write a description for the template. Document URL Enter the URL of the document that describes the template - It will appear as a link on the template selection page when creating a project.
Template icon Select the icon to use in the template. Build output path Specify the build output path and filename. Dockerfile type Select Dockerfile type - You can choose whether to use the Dockerfile file within SosoCode, or to use the information registered in Manage Dockerfile Templates.
- When you select the GUI template, the Dockerfile Template tab becomes active.
Table. App. Add Template - Basic Information Input Items
App. Only when the template’s deployment target is Kubernetes, the supported Helm chart step is added.
- Select the Helm chart that can be used when deploying with this App template.
- After selecting the checkbox, you can select the Helm chart list using the Add, Delete buttons in the center.
After completing Add Pipeline Template, please refer to Modify Supported Tenant Information and modify the usage status.
App. Edit template basic information
App. To modify the template’s basic information, follow these steps.
- On the App. Template page, click the item you want to edit. You will be taken to the App. Template Details page.
- Click the Basic Information tab on the App. Template Details page.
- Click the Edit button in the Basic Information tab.
- After editing the required information, click the Save button.
Manage pipeline templates
This is the build pipeline configuration that is automatically set up when a user creates a project using the App template.
Add pipeline template
To add a pipeline template, follow these steps.
- On the App. Template page, click the item you want to add. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Pipeline Template tab.
- Click the Add button on the Pipeline Template tab. You will be taken to the Add Pipeline Template page.
- On the Add Pipeline Template page, enter the required information and click the Save button.
Item Explanation Template name Enter the name of the pipeline template. Base Template
(Base Template)- The default template is used for pipeline configuration when creating a project.
- If a default template is not registered, it is automatically set to ON, and this setting cannot be changed.
Support Jenkins Select the Jenkinsthat will support this pipeline template- A list of CICD pipeline tools available in the tenant and project group is displayed.
- It is required to refer to the necessary information in the Tools area when configuring stages.
environment variable Enter environment variable information - For detailed information about environment variables, refer to Configure environment variables.
Stage Enter information for each stage - For detailed information about stages, refer to Setting up stages.
Table. Pipeline Template Additional Input Items
Jenkins environment variables, refer to the official site official site.Edit pipeline template
To modify the pipeline template, follow these steps.
- On the App. Template page, click the item you want to edit. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Pipeline Template tab.
- Click the item you want to edit in the Pipeline Template tab. You will be taken to the Pipeline Template Details page.
- On the Pipeline Template Details page, click the Edit button. You will be taken to the Pipeline Template Edit page.
- On the Pipeline Template Edit page, after modifying the information, click the Save button.
Delete pipeline template
To delete a pipeline template, follow these steps.
- Click the item you want to delete on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Pipeline Template tab.
- Click the item you want to delete in the Pipeline Template tab. You will be taken to the Pipeline Template Details page.
- On the Pipeline Template Details page, click the Delete button.
- Click the Confirm button in the confirmation popup.
Managing Dockerfile Templates
App. In the Basic Information section of the template, the tab appears only when the Dockerfile Type item is GUI Template.
Modify Dockerfile template
Follow these steps to modify the Dockerfile template.
- On the App. Template page, click the item you want to edit. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Dockerfile Template tab.
- Click the Edit or Create button in the Dockerfile Template tab.
- After entering the content in the Dockerfile Template tab, click the Save button.
Item Explanation Authentication Settings Register the authentication information for the image to be used in the FROM clause of a multi-stage build. Add Add the image to be used in the FROM clause of the multi-stage build. Multi-stage Dockerfile Configure the Multi-stage based on the credentials and additional items you registered. Dockerfile Create a basic Dockerfile. Table. Dockerfile Template Modification Input Items
You can manage it within the source code via Dockerfile without registering a Dockerfile template.
- When using a Dockerfile file included in the source code, the Basic Information section of the App template must have the Dockerfile Type field set to File in Code Repository.
The FROM clause is automatically set to the image path registered in 지원 이미지 관리하기.
Manage supported tenants/project groups
The tab name is displayed differently depending on the template type.
- System Template/Tenant Template: Supported Tenant
- ProjectGroup Template: Support Information
The user can manage the tenant or project group where the App template will be used.
To manage supported tenants or project groups, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Supported Tenant or Supported Information tab.
Primary icon appears on the tenant you manage.Add supported tenant
To add a supported tenant, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Supported Tenants tab.
- Click the Add button on the Supported Tenant tab. The Add Tenant popup window opens.
- Add Tenant In the popup window, select the tenant you want to support, then click the Save button.
Edit supported tenant information
To modify the information of the supported tenant, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Supported Tenants tab.
- In the Supported Tenant tab, select the verification status and usage status items for the tenant you want to change, and edit them.
Item Explanation Tenant Available tenant information. Verification status Select verification status - Verifying
- Verification complete
Whether to use Select usage status - It can be changed to Use only when Verification status is Verified.
Table. Supported Tenant Screen Items
If the verification status is under verification, only users who have registered the App template can use it.
- Other users can use the App template after verification and approval are completed.
Edit supported project group information
To modify the information of the supported project group, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Support Information tab.
- Click the Edit button in the Support Information tab. The App. Template Edit screen appears.
- On the App. Template Edit screen, select the verification status and usage status items to edit them.
- Click the Save button.
Item Explanation Project Group Available project group information. Verification status Select verification status - Verifying
- Verification complete
Whether to use Select usage - Verification status can be changed to Use only when it is Verification completed.
Table. Support Information Screen Items
If the verification status is “in verification,” only users who have registered the App template can use it.
- Other users can use the App template after verification and approval are completed.
Transfer Management Tenant
To transfer the management tenant, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Supported Tenants tab.
- On the Support Tenant tab, click the Transfer Management Tenant button. The Transfer Management Tenant popup window opens.
- Management Tenant Transfer In the popup window, after selecting the target tenant for transfer, click the Save button.
Delete supported tenant
To delete a supported tenant, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Supported Tenants tab.
- In the Supported Tenant tab, select the tenant you want to delete and click the Delete button.
- In the confirmation popup, click the Confirm button.
Manage supported images
The supported image registered by the user is used in the FROM clause registered in the source code’s Dockerfile or Dockerfile template.
Add supported image
To add a supported image, follow the steps below.
- On the App. Template page, click the item you want to edit. You will be taken to the App. Template Detail page.
- On the App. Template Details page, click the Supported Image tab.
- In the Supported Image tab, click the Add button. The Add Supported Image popup window opens.
- Add supported image After entering the information in the popup window, click the Connection Test button.
- Save button is enabled, click the Save button.
- In the confirmation popup, click the Confirm button.
Item Explanation Enter image information Enter the supported image and authentication information. Use the registrant’s authentication information This is an option that can be selected when the chosen image registry is a tool that cannot grant permissions (e.g., SCR). - If not checked, when a supported image user creates a project, the Pull permission for the image entered by the supported image user is added. If the tool cannot grant permissions, no permission granting is performed.
- If not checked, when a supported image user creates a project, the authentication credentials of the supported image registrant are used instead of the supported image user’s permissions.
Table. Additional Input Fields for Supported Image
Precautions when checking the use of the registrant’s authentication information
- Since the registrant’s authentication credentials may be exposed to users of the supported image, it should be used only when necessary.
- If the image repository only supports pulling images, you must select it to avoid problems during use. You must specify an image repository that will be used exclusively for pulling. (If selected, pulling and pushing cannot be performed simultaneously on the same image repository.)
- The registrant’s credentials are used in the project > image repository > pull-only image. These credentials cannot be changed by supported image users, and if the registrant’s credentials are re-registered in a supported image, they are updated uniformly.
Delete supported image
To delete the support image, follow these steps.
- On the App. Template page, click the item you want to edit. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Supported Image tab.
- In the Supported Images tab, select the checkbox of the item to delete and click the Delete button.
- In the confirmation popup, click the Confirm button.
Manage supported Helm charts
Refer to Add Helm Chart for registering supported Helm charts.
The supported Helm chart registered by the user is used when creating a project using the App. template.
Add support for Helm chart
To add a supported Helm chart, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- App. Template Details on the page, click the Supported Helm Chart tab.
- In the Supported Helm Chart tab, click the Edit button. The App. Template Edit screen appears.
- App. Template Modification On the screen’s Helm Chart List, select the checkbox of the Helm chart to be used, then add it to the Selected Helm Chart List using the Add button, and click the Save button.
Modify the supported Helm chart
To modify the supported Helm chart, follow these steps.
- On the App. Template page, click the item you want to edit. You will be taken to the App. Template Details page.
- Click the Supported Helm Chart tab on the App. Template Details page.
- Click the Edit button in the Supported Helm Chart tab. The App. Template Edit screen appears.
- On the App. Template Edit screen’s Helm Chart List, select the checkboxes of the Helm charts to use, then modify the Selected Helm Chart List using the Add and Delete buttons, and click the Save button.
Delete supported Helm chart
To delete the support Helm chart, follow these steps.
- Click the item you want to edit on the App. Template page. You will be taken to the App. Template Details page.
- On the App. Template Details page, click the Supported Helm Chart tab.
- Click the Edit button in the Supported Helm Chart tab. The App. Template Edit screen appears.
- App. Template Edit on the Selected Helm Chart List screen, select the checkbox of the Helm chart to delete, then delete it using the Delete button and click the Save button.
App. Delete Template
App. To delete the template, follow these steps.
- Click the item you want to delete on the App. Template page. Navigate to the App. Template Details page.
- On the App. Template Details page, click the Basic Information tab.
- Click the Delete button on the Basic Information tab.
- In the confirmation popup, click the Confirm button.
12.2.9.3 - Register User-installed Jenkins Tool
- It is recommended to use the Samsung Cloud Platform Marketplace for installing and operating Jenkins.
- If you cannot use the Marketplace or need to register a self‑installed Jenkins as a tool in the DevOps Console, refer to this document.
- This document guides the registration of the Jenkins tool in DevOps Console, so it provides only a brief overview of Jenkins installation and operation.
Getting started with registering a user-installed Jenkins tool
Install Jenkins and plugins.
Jenkins installation
Before installing
To register Jenkins in the DevOps Console, Jenkins generally must meet the following conditions. If there are other conditions, register an SR before installation to verify.
- Use a domain for Jenkins access
- Jenkins domain is registered in DNS
- Use HTTPS (port 443) and a public certificate for Jenkins communication.
Installation
Install Jenkins on a VM or Kubernetes
Plugin Installation
Install the following plugins in Jenkins.
| Plugin ID | Name |
|---|---|
| apache-httpcomponents-client-4-api | Apache HttpComponents Client 4.x API |
| credentials | Credentials |
| credentials-binding | Credentials Binding |
| github | GitHub |
| jobConfigHistory | Job Configuration History |
| kubernetes | Kubernetes |
| mask-passwords | Mask Passwords |
| maven-plugin | Maven Integration |
| matrix-auth | Matrix Authorization Strategy |
| metrics | Metrics |
| pipeline-stage-view | Pipeline: Stage View |
| pipeline-utility-steps | Pipeline Utility Steps |
| script-security | Script Security |
| ssh-steps | SSH Pipeline Steps |
| workflow-aggregator | Pipeline |
| workflow-step-api | Pipeline: Step API |
Jenkins configuration
Common Settings
Jenkins Administration > System
| Item | value | Explanation |
|---|---|---|
| of executors | 0 | Set to 0 to restrict direct build execution on the Controller and allow builds only on the Agent. |
| Jenkins URL | (ex) https://{YOUR_DOMAIN}/jenkins/ | |
| System Admin e-mail address | (ex) admin@example.com |
Jenkins Administration > Security
| Item | value | Explanation |
|---|---|---|
| Authorization | Project-based Matrix Authorization Strategy | |
| Authenticated Users | Overall > Read | |
| <ADMIN_USER> | Overall > Administer | Add admin account using Add user |
Support email format for Jenkins Username
- By default, Jenkins does not allow the @ sign or dot (.) to be used in the login username. However, since DevOps Console uses an email address as the username, we configure Jenkins to allow email addresses as usernames as well.
- Create the file
/{JENKINS_HOME}/init.groovy.d/init.groovy, add the following content, and restart Jenkins.- (ex)
/var/jenkins_home/init.groovy.d/init.groovy
- (ex)
hudson.security.HudsonPrivateSecurityRealm.ID_REGEX=/^[\w-\.\@\_]+$/hudson.security.HudsonPrivateSecurityRealm.ID_REGEX=/^[\w-\.\@\_]+$/Additional Jenkins configuration installed on Kubernetes
RBAC
Configure RBAC on Jenkins’s Service Account so that Jenkins can create Pods in Kubernetes.
# In GKE need to get RBAC permissions first with
# kubectl create clusterrolebinding cluster-admin-binding --clusterrole=cluster-admin [--user=<user-name>|--group=<group-name>]
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: jenkins
---
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: jenkins
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["create","delete","get","list","patch","update","watch"]
- apiGroups: [""]
resources: ["pods/exec"]
verbs: ["create","delete","get","list","patch","update","watch"]
- apiGroups: [""]
resources: ["pods/log"]
verbs: ["get","list","watch"]
- apiGroups: [""]
resources: ["events"]
verbs: ["watch"]
- apiGroups: [""]
resources: ["secrets"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: jenkins
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: jenkins
subjects:
- kind: ServiceAccount
name: jenkins# In GKE need to get RBAC permissions first with
# kubectl create clusterrolebinding cluster-admin-binding --clusterrole=cluster-admin [--user=<user-name>|--group=<group-name>]
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: jenkins
---
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: jenkins
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["create","delete","get","list","patch","update","watch"]
- apiGroups: [""]
resources: ["pods/exec"]
verbs: ["create","delete","get","list","patch","update","watch"]
- apiGroups: [""]
resources: ["pods/log"]
verbs: ["get","list","watch"]
- apiGroups: [""]
resources: ["events"]
verbs: ["watch"]
- apiGroups: [""]
resources: ["secrets"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: jenkins
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: jenkins
subjects:
- kind: ServiceAccount
name: jenkinsJenkins Management > Clouds
kubernetes
- Add the kubernetes cloud.
- Set up the Kubernetes cloud as follows. Use the default values for the remaining items.
| Item | value | Explanation |
|---|---|---|
| Cloud name | kubernetes | |
| Type | Kubernetes selection | |
| Kubernetes URL | https://kubernetes.default | Create a Pod (Agent) in the cluster where Jenkins is running |
| Disable https certificate | check | |
| Kubernetes Namespace | (example) jenkins | Enter the Namespace where the Jenkins Controller is running, and a Pod (Agent) is created in that Namespace. |
| WebSocket | check | |
| Jenkins URL | (example) http://{JENKINS_SERVICE_NAME}:{PORT}/jenkins |
|
kubernetes > Pod Templates
- Add a Pod Template.
- BASE-TEMPLATE is a parent template used in the DevOps Console to define values that should be shared across all Pod Templates.
| Item | value | Explanation |
|---|---|---|
| Name | BASE-TEMPLATE | |
| Image Pull Secret | {IMAGE_PULL_SECRET} Enter name | Create a Secret in the Namespace so that the Pod(Agent) image can be pulled, and enter its name. |
Register Jenkins tool in DevOps Console
Register Firewall
Refer to the table below and register the firewall in Jenkins.
| Origin | Destination | Destination Port |
|---|---|---|
| User install Jenkins | DevOps Console web | 443 |
| DevOps Console source IP | User install Jenkins web | 443 |
DevOps Console Tasks
- For detailed information about registering the Jenkins tool, see Add Tool
- In the tool registration step, check the plugins installed on Jenkins, and if any plugins need to be installed, a plugin installation guide page will be displayed. Download and install the plugins as instructed.
Jenkins Verification
Jenkins Management > System
Global Trusted Pipeline Libraries
- Check that cicdpaas is configured in the Library.
- If it is not configured
- Verify the communication between DevOps Console and Jenkins.
- DevOps Console > Management > Jenkins detail screen > Check the settings in the Global Library tab.
DevOps Console Credentials
- Test Connection Click the button to confirm that Success appears.
Add an agent (VM) to Jenkins
DevOps Console Tasks
Jenkins Tasks
Jenkins Management > Nodes > Agent Detail View
Verify that the Agent added in the DevOps Console has been created. Run the Agent according to the guide on the Jenkins screen and connect it to Jenkins.
Add an agent (Kubernetes) to Jenkins
Before Adding a Kubernetes Agent
Create User‑Jenkins Agent Image
- For CI/CD in Jenkins, an agent image is required.
- Create a Jenkins agent image that matches the user’s needs by using the default images provided by Jenkins.
- After creating the image, push it to the user’s image repository.
FROM jenkins/inbound-agent:latest-jdk17
USER root
# Docker CLI
RUN curl -L0 "https://download.docker.com/linux/static/stable/x86_64/docker-29.1.3.tgz" -o /tmp/docker.tgz && \
tar --extract \
--file /tmp/docker.tgz \
--strip-components 1 \
--directory /usr/local/bin/ && \
rm /tmp/docker.tgz
COPY --from=docker/buildx-bin /buildx /usr/libexec/docker/cli-plugins/docker-buildx
# Install your build tools...
# xxx
USER jenkinsFROM jenkins/inbound-agent:latest-jdk17
USER root
# Docker CLI
RUN curl -L0 "https://download.docker.com/linux/static/stable/x86_64/docker-29.1.3.tgz" -o /tmp/docker.tgz && \
tar --extract \
--file /tmp/docker.tgz \
--strip-components 1 \
--directory /usr/local/bin/ && \
rm /tmp/docker.tgz
COPY --from=docker/buildx-bin /buildx /usr/libexec/docker/cli-plugins/docker-buildx
# Install your build tools...
# xxx
USER jenkinsDocker‑in‑Docker Image
- In the DevOps Console, Docker in Docker is used to create Docker images in a Kubernetes environment.
- Use Docker’s provided
dind(Docker‑in‑Docker) image and push it to your repository.
DevOps Console Tasks
- Add Pod Template
- By default, one (or multiple) agents are registered. Delete the default registered agent.
- If you need to build a Docker image, select Docker in Docker.
- Enter the JNLP image URL with the Jenkins agent address of the user you created above.
Jenkins Tasks
Jenkins Management > Clouds > Kubernetes > Pod Templates
- The agent (Kubernetes) added from the DevOps Console is registered as a Pod Template.
- If Docker‑in‑Docker is selected in DevOps Console, the default image address is pre‑filled in the dind container. Replace it with the image address you pushed to your repository.
12.2.10 - Deployment Target
12.2.10.1 - K8S Cluster
Users can register a K8S cluster in DevOps Console and deploy various applications through DevOps Console.
Users can add, edit, and delete K8S clusters and namespaces. Added K8S clusters and namespaces can be selected and used in various menus such as project creation (Getting Started with Project Creation), helm install (Getting Started with Helm Install), etc.
Getting Started with a K8S Cluster
To begin managing the K8S cluster, follow these steps.
- Click the Admin icon at the top right of the Main page. Navigate to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
Add a K8S cluster
To add a K8S cluster, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- On the K8S Cluster page, click the Add button. You will be taken to the Add K8S Cluster page.
- Add K8S Cluster page, after entering the basic information and connection details, click the Connection Test button.
- After selecting the Helm version, click the Save button.
Item Explanation K8S cluster name Please enter the cluster name. K8S Cluster ID Enter the cluster ID.
The cluster ID is a unique identifier used to distinguish clusters; please determine and enter it yourself.CA Certificate Enter the server’s certificate information to be used for configuring the kubeconfigfile- Enter the contents of
clusters[0].cluster.certificate-authority-datafrom the existingkubeconfigfile. - Contact the cluster provider (administrator) and then enter it.
- If verification is not possible, enter a temporary value (e.g.,
temp) and replace it with the correct value once verification is possible.
Authentication method Select the admin token method. API server URL Enter the Kubernetes API Server address. admin token Enter the Token with Admin privileges to use for configuring the kubeconfigfile.
Please refer to Check Cluster Admin Token.Helm version Select Helm version - A list of Helm versions available for the K8S cluster version is displayed.
Table. Add K8S Cluster – Add using admin token authenticationItem Explanation Authentication method Select the client certificate method. API server URL Enter the Kubernetes API Server address. client certificate Enter the client certificate information. Client Key Enter the client Key information. Table. Add K8S Cluster - Item for adding by authenticating with a client certificateItem Explanation Authentication method Select the kubeconfigfile upload method.kubeconfig file Browse button to select the kubeconfigfile- Only files with the
.ymlor.yamlextension can be uploaded. - If the file is uploaded successfully, the CA Certificate, API server URL, user, admin token, or client certificate will be populated automatically.
API server URL Select the Kubernetes API Server address. user Select the user to authenticate - Depending on the selected user, the admin token or client certificate information is displayed below
Table. Adding K8S Cluster - Adding via kubeconfig file upload item - Enter the contents of
Managing a K8S cluster
Modify K8S cluster
To modify the K8S cluster, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S Cluster page, click the K8S cluster. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- On the K8S Cluster Details page, click the Edit button.
- After editing the information, click the Connection Test button.
- After selecting the Helm version, click the Save button.
Delete K8S cluster
To delete a K8S cluster, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S Cluster page, click the K8S cluster. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- On the K8S Cluster Details page, click the Delete button.
- Click the Confirm button in the confirmation popup to complete the deletion.
Add a member to a K8S cluster
To add a K8S cluster member, follow the steps below.
- Click the Admin icon at the top right of the Main page. Navigate to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- In the list on the K8S Cluster page, click the K8S cluster. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- On the K8S Cluster Details page, click the Members tab.
- When you click the Add button in the Member tab, the Add Member popup window opens.
- Add Member In the popup, enter the email address and click the Search icon.
- Click the Add button to add the member to the list below.
- After selecting the permission, click the Save button to complete adding the member.
Delete K8S cluster member
To delete a K8S cluster member, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S cluster page, click the K8S cluster. You will be taken to the K8S cluster details page of the selected K8S cluster.
- On the K8S Cluster Details page, click the Members tab.
- In the Member tab, select the checkbox of the user you want to delete.
- Click the Delete button to remove the selected user from the members.
Managing K8S Cluster Permission Requests
To approve or reject a K8S cluster access request, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- Click the K8S cluster permission request item for the cluster whose permission request you want to approve. The displayed number indicates the number of permissions requested.
- K8S Cluster Permission Request Approval The popup window opens.
- Click the application you want to approve or reject.
- After entering your comment, click the Approve or Reject button.
View K8S cluster permission approval history
To view the K8S cluster permission request approval history, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S Cluster page, click the K8S Cluster. You will be taken to the K8S Cluster Details page of the selected K8S Cluster.
- Click the Approval History tab. The approval history list appears.
Managing namespaces
- To use the K8S cluster from menus such as project creation and helm install, you must have permissions on the namespace.
- You cannot create a namespace in the actual K8S cluster. You can only import an already created namespace into the DevOps Console.
Import namespace
To import the namespace, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- On the K8S Cluster page, click the K8S cluster from the list. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- Click the Namespace tab. The namespace list appears.
- On the Namespace tab screen, clicking the Import button opens the Import Namespace popup.
- Namespace Import In the popup window, select the namespace and click the Save button to complete the namespace import.
Delete namespace
To delete a namespace, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- On the K8S cluster page, click the K8S cluster from the list. You will be taken to the K8S cluster details page of the selected K8S cluster.
- Click the Namespace tab. The namespace list appears.
- On the Namespace tab screen, clicking a namespace navigates to the Namespace Details page.
- On the Namespace Details page, click the Delete button to complete the namespace deletion.
Adding a namespace member
To add a namespace member, follow these steps.
- Main page, click the Admin icon at the top right. It navigates to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S Cluster page, click the K8S cluster. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- Click the Namespace tab. The namespace list appears.
- Namespace tab screen, when you click the namespace, you are taken to the Namespace Details page.
- Namespace Details page, when you click the Members tab, the namespace member list appears.
- When you click the Add button, the Add Member popup opens.
- In the Add Member popup, enter the email address and click the Search icon.
- Click the Add button to add the member to the list below.
- After selecting the permission, click the Save button to complete adding the member.
Delete namespace member
To delete a namespace member, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- On the K8S Cluster page, click the K8S cluster from the list. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- Click the Namespace tab. The namespace list appears.
- On the Namespace tab screen, clicking the namespace takes you to the Namespace Details page.
- Namespace Details page, when you click the Members tab, the namespace member list appears.
- Select the checkbox of the user you want to delete from the list.
- Click the Delete button to remove the selected user from the members.
Manage namespace permission requests
To approve or reject a namespace permission request, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S Cluster page, click the Namespace Permission Request item for the cluster whose permission request you want to approve. The displayed number indicates the number of permission requests.
- Namespace Permission Request Approval A popup window opens.
- Select the checkbox for the application you want to approve or reject.
- After entering your comment, click the Approve or Reject button.
View namespace permission request approval history
To view the namespace permission request approval history, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- In the list on the K8S Cluster page, click the K8S cluster. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- Namespace tab, click it. The namespace list appears.
- On the Namespace tab screen, clicking a namespace takes you to the Namespace Details page.
- Namespace Details page, when you click the Approval History tab, the approval history list appears.
Managing Ingress Domains
- This is reference information that is managed only in the DevOps Console.
- The registered information is displayed so that users can refer to it when creating a project or performing a Helm install using the cluster.
Add Ingress Domain
To add an ingress domain, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- On the K8S cluster page, click the K8S cluster from the list. You will be taken to the K8S cluster details page of the selected K8S cluster.
- Click the Ingress Domain tab. The Ingress Domain list appears.
- Ingress Domain tab screen, when you click the Add button, the Add Ingress Domain Information popup opens.
- Add Ingress Domain Information Enter the information in the popup window and click the Save button to complete adding the ingress domain.
Item Explanation Node selector Enter the node selector.
It is composed of a key that includes a prefix separated by the first slash (/) of the input value, and its corresponding value.
The prefix is optional.
e.g.,kubernetes.io/nodetype: appProxy IP Enter the Proxy Server IP or Proxy Server LoadBalancer IP. Ingress domain Enter the domain that the application will use by default. Ingress class Enter the Ingress controller class. Table. Ingress Domain Additional Input Items
Modify Ingress Domain
To modify the Ingress domain, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S Cluster page, click the K8S cluster. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- Click the Ingress Domain tab. The Ingress Domain list appears.
- On the Ingress Domain tab screen, when you click the Ingress Domain you want to edit, the Edit Ingress Domain Information popup opens.
- Edit Ingress Domain Information In the popup window, modify the information and click the Save button to complete the Ingress domain edit.
Delete Ingress Domain
To modify the Ingress domain, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > K8S Cluster menu. You will be taken to the K8S Cluster page.
- From the list on the K8S Cluster page, click the K8S cluster. You will be taken to the K8S Cluster Details page of the selected K8S cluster.
- Ingress Domain Click the tab. Ingress Domain list appears.
- On the Ingress Domain tab, select the checkbox of the Ingress Domain you want to delete.
- On the Ingress Domain tab screen, click the Delete button to delete the selected ingress domain.
12.2.10.1.1 - Verify Cluster Admin Token
To register a K8S cluster, you must verify the cluster’s Admin Token.
An Admin Token refers to the token value of a ServiceAccount that has the ClusterRole/cluster-admin bound by a ClusterRoleBinding.
Preparation before start
Before checking the Admin Token, review and prepare the following.
- Environment where the kubectl CLI can be used
- Check cluster admin permissions
- View and create ClusterRole, ClusterRoleBinding
- Namespace and ServiceAccount lookup and creation
- The cluster-admin ClusterRole is listed.
$ kubectl get clusterrole cluster-admin
NAME CREATED AT
cluster-admin 2022-12-09T08:21:50Z$ kubectl get clusterrole cluster-admin
NAME CREATED AT
cluster-admin 2022-12-09T08:21:50ZQuery Admin Token
View existing generated Admin Token
- Retrieve the ClusterRoleBinding that has ClusterRole/cluster-admin bound.
- Check the ServiceAccount that is bound by a ClusterRoleBinding.Color mode
# admin token lookup $ kubectl get clusterrolebinding | grep ClusterRole/cluster-admin [crb_name] ClusterRole/cluster-admin 77d $ kubectl describe clusterrolebinding [crb_name] Name: [crb_name] Labels: <none> Annotations: <none> Role: Kind: ClusterRole Name: cluster-admin Subjects: Kind Name Namespace ---- ---- --------- ServiceAccount [sa_name] [namespace_name]# admin token lookup $ kubectl get clusterrolebinding | grep ClusterRole/cluster-admin [crb_name] ClusterRole/cluster-admin 77d $ kubectl describe clusterrolebinding [crb_name] Name: [crb_name] Labels: <none> Annotations: <none> Role: Kind: ClusterRole Name: cluster-admin Subjects: Kind Name Namespace ---- ---- --------- ServiceAccount [sa_name] [namespace_name]Result of retrieving previously generated Admin Token - Check the Secret associated with the ServiceAccount and retrieve the token (Admin Token).Color mode
# Secret lookup $ kubectl get secret -n [namespace_name] | grep [sa_name] [sa_name]-token-xxxxx kubernetes.io/service-account-token 3 77d # token lookup $ kubectl describe secret [sa_name]-token-xxxxx -n [namespace_name] Name: [sa_name]-token-xxxxx ...<중략>... Data ==== ca.crt: 1070 bytes namespace: 11 bytes token: eyJhbGciOiJSUzI1NiI...# Secret lookup $ kubectl get secret -n [namespace_name] | grep [sa_name] [sa_name]-token-xxxxx kubernetes.io/service-account-token 3 77d # token lookup $ kubectl describe secret [sa_name]-token-xxxxx -n [namespace_name] Name: [sa_name]-token-xxxxx ...<중략>... Data ==== ca.crt: 1070 bytes namespace: 11 bytes token: eyJhbGciOiJSUzI1NiI...Result of retrieving the Secret and token associated with the ServiceAccount
Create Admin Token
- Create the Namespace for the ServiceAccount. If it already exists, proceed to the next step.Color mode
$ kubectl create namespace [namespace_name] # ex) kubectl create namespace my-app$ kubectl create namespace [namespace_name] # ex) kubectl create namespace my-appAdmin Token creation command - Create the [namespace_name]-additional-cluster-admin-sa.yaml file and then run it.Color mode
apiVersion: v1 kind: ServiceAccount metadata: name: [namespace_name]-additional-cluster-admin namespace: [namespace_name]apiVersion: v1 kind: ServiceAccount metadata: name: [namespace_name]-additional-cluster-admin namespace: [namespace_name]ServiceAccount creation example Color mode# Create ServiceAccount $ kubectl apply -f [namespace_name]-additional-cluster-admin-sa.yaml -n [namespace_name] # ex) kubectl apply -f my-app-additional-cluster-admin-sa.yaml -n my-app# Create ServiceAccount $ kubectl apply -f [namespace_name]-additional-cluster-admin-sa.yaml -n [namespace_name] # ex) kubectl apply -f my-app-additional-cluster-admin-sa.yaml -n my-appServiceAccount creation command - Create the [namespace_name]-additional-cluster-admin-crb.yaml file and then run it.Color mode
kind: ClusterRoleBinding apiVersion: rbac.authorization.k8s.io/v1 metadata: name: [namespace_name]-additional-cluster-admin subjects: - kind: ServiceAccount name: [namespace_name]-additional-cluster-admin namespace: [namespace_name] roleRef: kind: ClusterRole name: cluster-admin apiGroup: ""kind: ClusterRoleBinding apiVersion: rbac.authorization.k8s.io/v1 metadata: name: [namespace_name]-additional-cluster-admin subjects: - kind: ServiceAccount name: [namespace_name]-additional-cluster-admin namespace: [namespace_name] roleRef: kind: ClusterRole name: cluster-admin apiGroup: ""Example of creating a ClusterRoleBinding Color mode# Create ClusterRoleBinding $ kubectl apply -f [namespace_name]-additional-cluster-admin-crb.yaml # ex) kubectl apply -f my-app-additional-cluster-admin-crb.yaml# Create ClusterRoleBinding $ kubectl apply -f [namespace_name]-additional-cluster-admin-crb.yaml # ex) kubectl apply -f my-app-additional-cluster-admin-crb.yamlCommand to create a ClusterRoleBinding - Check the Secret associated with the ServiceAccount and retrieve the token (Admin Token).Color mode
# Secret lookup $ kubectl get secret -n [namespace_name] | grep [namespace_name]-additional-cluster-admin [namespace_name]-additional-cluster-admin-token-xxxxx kubernetes.io/service-account-token 3 4m53s # Token lookup $ kubectl describe secret [namespace_name]-additional-cluster-admin-token-xxxxx -n [namespace_name] Name: [namespace_name]-additional-cluster-admin-token-xxxxx ...<중략>... Data ==== ca.crt: 1111 bytes namespace: 6 bytes token: eyJhbGciOiJSUzI1Ni...# Secret lookup $ kubectl get secret -n [namespace_name] | grep [namespace_name]-additional-cluster-admin [namespace_name]-additional-cluster-admin-token-xxxxx kubernetes.io/service-account-token 3 4m53s # Token lookup $ kubectl describe secret [namespace_name]-additional-cluster-admin-token-xxxxx -n [namespace_name] Name: [namespace_name]-additional-cluster-admin-token-xxxxx ...<중략>... Data ==== ca.crt: 1111 bytes namespace: 6 bytes token: eyJhbGciOiJSUzI1Ni...Result of retrieving the Secret and token associated with the ServiceAccount ReferenceIf there is no generated Secret (afterKuberentes 1.24), create one manually and then retrieve the token.Color modeapiVersion: v1 kind: Secret type: kubernetes.io/service-account-token metadata: name: [namespace_name]-additional-cluster-admin-token namespace: [namespace_name] annotations: kubernetes.io/service-account.name: "[namespace_name]-additional-cluster-admin"apiVersion: v1 kind: Secret type: kubernetes.io/service-account-token metadata: name: [namespace_name]-additional-cluster-admin-token namespace: [namespace_name] annotations: kubernetes.io/service-account.name: "[namespace_name]-additional-cluster-admin"Example of creating a secret
Verify Admin Token Validity
You can verify the validity of the retrieved Admin Token value by editing the ~/.kube/config file.
- Modify
~/.kube/configto use a token for user authentication.
Modify toex) users[0].user.tokenand then enter the Admin Token value.Color modeapiVersion: v1 clusters: - cluster: certificate-authority-data: LS0... server: https://devopscluster-12345.sk... name: devopscluster-12345 contexts: - context: cluster: devopscluster-12345 user: user name: user@devopscluster-12345 current-context: user@devopscluster-12345 kind: Config users: - name: user user: token: [admin_token]apiVersion: v1 clusters: - cluster: certificate-authority-data: LS0... server: https://devopscluster-12345.sk... name: devopscluster-12345 contexts: - context: cluster: devopscluster-12345 user: user name: user@devopscluster-12345 current-context: user@devopscluster-12345 kind: Config users: - name: user user: token: [admin_token]Example of editing ~/.kube/config - Run the
kubectlcommand to verify that you have cluster-admin privileges.Color mode$ kubectl get nodes $ kubectl get namespace $ kubectl get all -n kube-system $ kubectl create namespace admin-test $ kubectl delete namespace admin-test # Run other commands$ kubectl get nodes $ kubectl get namespace $ kubectl get all -n kube-system $ kubectl create namespace admin-test $ kubectl delete namespace admin-test # Run other commandsCommand to check cluster-admin permissions
12.2.10.2 - VM Server Group
A VM server group is a logical unit for grouping and managing VM servers.
Users can add, modify, and delete VM server groups and VM servers. Configured VM server groups and VM servers can be used as deployment target VMs in project creation (배포대상 환경 설정하기) or VM deployment (VM 배포 추가하기).
| Deployment method | Explanation |
|---|---|
| SSH | Using Secure Shell (SSH), Jenkins, where the build pipeline runs, directly deploys to the Target VM server.
|
| agent | You must refer to Connecting the Agent and run the agent on the Target VM server. Jenkins, where the build pipeline runs, does not execute deployments directly. The running agent collects deployment information from the DevOps Console via REST API and executes it.
|
If SSH or an agent runs with root privileges, there is a risk that malicious commands could compromise the entire server.
- It is recommended to use an account other than the root account.
Getting Started with VM Server Group
To start managing VM server groups, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- In the left menu, click the Deploy Target > VM Server Group menu. You will be taken to the VM Server Group page.
Add VM server group
To add a VM server group, follow these steps.
- Click the Management icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the Add button. It navigates to the Add VM Server Group page.
- Enter the basic information, then click the Save button to complete the VM server group configuration.
Item Explanation Server group name Enter the VM server group name. Explanation Please enter a description. type Select the type of VM server group - SSH: Perform deployment using SSH commands when deploying a VM.
- Agent: Perform deployment using an agent when deploying a VM. (Connect Agent)
VM server - Add: Add the VM server that belongs to the VM server group.
- Delete: Check the checkbox of the VM server you want to delete from the VM server group, then click Delete to remove it.
Table. VM Server Group Add Input Items
Add VM server
To add a VM server, you need Manager permission for the corresponding VM server group.
To add a VM server, follow the steps below.
- Click the Admin icon at the top right of the Main page. Navigate to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- VM server group page, click the VM server group in the VM server group list where you want to add a VM server. You will be taken to the VM server group detail page.
- On the VM Server Group Details page, click the Add button. You will be taken to the Add VM Server page.
- Add VM Server page, after entering the basic information, click the Add button to complete the VM server configuration.
Item Explanation Server name Enter the VM server name. Explanation Enter the description. IP Please enter the IP. SSH Port Enter the port of the VM server to use for SSH connections. OS Please enter the OS. Location Please select a location. Authentication information Enter the authentication information for the VM server to be used for SSH connections. Secret Key This is the secret key for authenticating the VM server where the agent is installed. Table. VM Server Additional Input Items
Modify VM server group
To modify a VM server group, you need Manager permission for that VM server group.
To modify a VM server group, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the VM Server Group you want to edit from the list. You will be taken to the VM Server Group Details page.
- On the VM Server Group Details page, click the Edit button. You will be taken to the Edit VM Server Group page.
- After completing the edit, click the Save button to finish modifying the VM server group.
Modify VM server
To modify a VM server, you need Manager permission for the corresponding VM server group.
To modify the VM server, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the VM Server Group you want to edit from the list of VM server groups. You will be taken to the VM Server Group Details page.
- VM Server Group Details page’s VM server list, click the VM server you want to edit. You will be taken to the VM Server Details page.
- On the VM Server Details page, clicking the Edit button navigates to the VM Server Edit page.
- On the VM Server Edit page, after completing the edit, click the Save button to finish editing the VM server.
Delete VM server group
To delete a VM server group, follow these steps.
- Click the Admin icon at the top right of the Main page. Navigate to the Tenant Dashboard page.
- In the left menu, click the Deploy Target > VM Server Group menu. You will be taken to the VM Server Group page.
- VM server group page’s VM server group list, click the VM server group you want to delete. You will be taken to the VM server group details page.
- On the VM server group details page, click the Delete button to complete the VM server group deletion.
Delete VM server
To delete a VM server, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > VM Server Group menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the VM server group of the VM server you want to delete from the VM server group list. You will be taken to the VM Server Group Details page.
- On the VM Server Group Details page, click the VM server you want to delete. You will be taken to the VM Server Details page.
- On the VM server details page, click the Delete button to complete the VM server deletion.
Managing VM Server Group Members
To manage members of a VM server group, you need Manager permission for that VM server group.
Add VM server group member
To add a member to a VM server group, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- VM Server Group page’s VM Server Group list, click the VM Server Group you want to add a member to. You will be taken to the VM Server Group Details page.
- On the VM Server Group Details page, click the User tab.
- When you click the Add button on the User tab, the Add Member popup window opens.
- After completing the setup, click the Confirm button to finish adding a VM server group member. (Managers can modify or delete the server group, and Members can use the server group when creating projects or adding pipelines.)
Delete VM server group member
To delete a member from a VM server group, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM server group page, click the VM server group in the list from which you want to delete a member. You will be taken to the VM server group details page.
- On the VM Server Group Details page, click the User tab.
- In the User list, select the checkbox of the user you want to delete.
- Click the Delete button to remove the selected user from the VM server group members.
Manage VM server group permission requests
To approve or reject a VM server group permission request, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the permission request item of the VM Server Group whose request you want to approve from the VM Server Group list. The displayed number indicates the number of permission requests. The VM Server Group Permission Request Approval popup window opens.
- VM Server Group Permission Request Approval In the popup window, click the request you want to approve or reject.
- After entering your comment, click the Approve or Reject button.
View VM Server Group Permission Approval History
To view the VM server group permission request approval history, follow these steps.
- Main page, click the Admin icon at the top right. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deploy Target > VM Server Group menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the VM server group you want to view from the list. You will be taken to the VM Server Group Details page.
- On the VM Server Group Details page, click the Approval History tab.
Disable firewall on VM server
SSH method
SSH-based VM deployment uses Secure Shell (Secure SHell, SSH) to deploy directly from Jenkins → Target VM server.
Firewall exemption information for deployment
- Source IP: Jenkins IP selected when configuring the pipeline
- Target IP: IP of the VM server to be deployed
To disable the firewall, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the Firewall Application Guide link. The Firewall Application Guide popup window opens.
- Jenkins firewall information is displayed.
- These details are displayed as the information entered when registering the Jenkins tool, and if no input was provided during tool registration, they may appear as empty values.
- If needed, contact the tool administrator.
Agent-based approach
Agent-based VM deployment requires the agent to run on the target VM server. The running agent collects information from the DevOps Console and proceeds with the deployment.
- Source IP: IP of the VM server to be deployed
- Target IP: DevOps Console IP, (if using Rollback) Rollback Artifact Repository IP
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- Click the Deployment Target > VM Server Group menu in the left menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the Agent Installation Guide link. The Agent Installation Guide popup will open.
- The DevOps Console firewall details, User Guide shortcut, and Agent file download links are displayed.
Integrate Agent
Agent-based VM deployment requires the agent to run on the target VM server. The running agent collects information from the DevOps Console and performs the deployment.
Preparation before agent integration
VM Server Preparation Requirements
Install Java
The agent was written and tested based on Java 8. Install a Java 8 or higher version on the target VM server.
Disable firewall and edit hosts file
The agent collects deployment execution information from the DevOps Console using the REST API, so communication on port 8443 from the Target VM where the agent runs to the DevOps Console is required.
Additionally, when using Rollback, communication with the Rollback Artifact Repository is also required.
If necessary, you may need to disable the firewall or register entries in the hosts file. Refer to the Agent Installation Guide(Agent Method) popup in the DevOps Console for firewall information.
DevOps Console Prerequisites
Prepare authentication key
Target VM server requires agent authentication when the agent runs. Generate a user authentication key and a secret key for authentication. (Manage authentication keys)
Prepare VM server Secret Key
When executing the agent on the target VM server, a Secret Key is required to authorize the VM server that corresponds to the agent.
When adding an agent-type VM server group or VM server, a VM server Secret Key is automatically generated. It can also be viewed later on the VM Server Details page.
Run the agent
Download the agent file
Agent Installation Guide You can download the agent executable from the popup window.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- In the left menu, click the Deploy Target > VM Server Group menu. You will be taken to the VM Server Group page.
- On the VM Server Group page, click the Agent Installation Guide link. The Agent Installation Guide popup will open.
- Agent Installation Guide In the popup window, click the Agent File Download button.
- The
deploy-agent.jarfile is downloaded.
Run the agent directly
To run the agent on the target VM server, follow these steps.
- Create a directory on the target VM server.
- Move the
deploy-agent.jarfile to the target directory. - Refer to the Usage below and run the agent.Color mode
usage: java -jar deploy-agent.jar -A <arg> -L <arg> [-P <arg>] -S <arg> -V <arg> -A,--accessKey <arg> AccessKey for HMAC -L,--serverUrl <arg> Api server url -P,--loggingConfigFilePath <arg> Path to the property file with 'java.util.logging' settings -S,--secretKey <arg> SecretKey for HMAC -V,--vmSecretKey <arg> VM SecretKeyusage: java -jar deploy-agent.jar -A <arg> -L <arg> [-P <arg>] -S <arg> -V <arg> -A,--accessKey <arg> AccessKey for HMAC -L,--serverUrl <arg> Api server url -P,--loggingConfigFilePath <arg> Path to the property file with 'java.util.logging' settings -S,--secretKey <arg> SecretKey for HMAC -V,--vmSecretKey <arg> VM SecretKeyRun deployment agent Usage
| Item | Explanation |
|---|---|
| -A, –accessKey | Authentication key generated with the user authentication key |
| -L, –serverUrl | API URL path of the DevOps Console ex) https://{DEVOPS_CONSOLE_URL}:8443/devops-console-api |
| -P, –loggingConfigFilePath | Agent log file path If not entered, the {JAVA_HOME}\jre\lib\logging.properties file will be applied. |
| -S, –secretKey | Secret key generated using the user authentication key |
| -V, –vmSecretKey | Secret key generated on the VM server |
Running the Agent Using a Script File
To run the agent on the target VM server using a script, follow these steps.
- Create a directory on the target VM server.
- Move the
deploy-agent.jarfile to the specified directory. - Create the file by referring to the sample execution script below.
- Modify the information of the sample execution script.
DC_URL,ACCESS_KEY,SECRET_KEY,VM_SECRET_KEY
- Run the script.
Linux sample script
#!/bin/sh
JAVA_EXE="java"
DC_URL="https://devops-console-url.com:8443/devops-console-api"
ACCESS_KEY="user-access-key"
SECRET_KEY="user-secret-key"
VM_SECRET_KEY="vm-secret-key"
start()
{
[ -f deploy-agent.jar ] || { echo "ERROR: deploy-agent.jar file does not exist."; exit 1; }
echo "Starting Deploy Agent..."
$JAVA_EXE -jar deploy-agent.jar -A $ACCESS_KEY -S $SECRET_KEY -V $VM_SECRET_KEY -L $DC_URL > deploy-agent.log 2>&1 &
PID=`ps aux | grep 'java -jar deploy-agent.jar' | grep '\-A' | grep '\-S' | grep '\-V' | grep '\-L' | awk '{print $2}'`
echo "Process ID : $PID"
echo $PID > deploy-agent.pid
echo "Done."
}
stop()
{
echo "Shutdown Deploy Agent..."
ps aux | grep 'java -jar deploy-agent.jar' | grep '\-A' | grep '\-S' | grep '\-V' | grep '\-L' | awk '{print $2}' | xargs kill
echo "Done."
}
case "$1" in
start)
start
;;
stop)
stop
;;
restart)
stop
start
;;
*)
echo $ "Usage: $0 {start|stop|restart}"
exit 1
;;
esac
exit 0#!/bin/sh
JAVA_EXE="java"
DC_URL="https://devops-console-url.com:8443/devops-console-api"
ACCESS_KEY="user-access-key"
SECRET_KEY="user-secret-key"
VM_SECRET_KEY="vm-secret-key"
start()
{
[ -f deploy-agent.jar ] || { echo "ERROR: deploy-agent.jar file does not exist."; exit 1; }
echo "Starting Deploy Agent..."
$JAVA_EXE -jar deploy-agent.jar -A $ACCESS_KEY -S $SECRET_KEY -V $VM_SECRET_KEY -L $DC_URL > deploy-agent.log 2>&1 &
PID=`ps aux | grep 'java -jar deploy-agent.jar' | grep '\-A' | grep '\-S' | grep '\-V' | grep '\-L' | awk '{print $2}'`
echo "Process ID : $PID"
echo $PID > deploy-agent.pid
echo "Done."
}
stop()
{
echo "Shutdown Deploy Agent..."
ps aux | grep 'java -jar deploy-agent.jar' | grep '\-A' | grep '\-S' | grep '\-V' | grep '\-L' | awk '{print $2}' | xargs kill
echo "Done."
}
case "$1" in
start)
start
;;
stop)
stop
;;
restart)
stop
start
;;
*)
echo $ "Usage: $0 {start|stop|restart}"
exit 1
;;
esac
exit 0Windows sample script
@ECHO OFF
SET JAVA_EXE="java"
SET DC_URL="https://devops-console-url.com:8443/devops-console-api"
SET ACCESS_KEY="user-access-key"
SET SECRET_KEY="user-secret-key"
SET VM_SECRET_KEY="vm-secret-key"
IF NOT EXIST deploy-agent.jar (
ECHO "ERROR: deploy-agent.jar file does not exist."
EXIT /b 0
)
ECHO "Starting Deploy Agent..."
%JAVA_EXE% -jar deploy-agent.jar -A %ACCESS_KEY% -S %SECRET_KEY% -V %VM_SECRET_KEY% -L %DC_URL%
EXIT /b 0@ECHO OFF
SET JAVA_EXE="java"
SET DC_URL="https://devops-console-url.com:8443/devops-console-api"
SET ACCESS_KEY="user-access-key"
SET SECRET_KEY="user-secret-key"
SET VM_SECRET_KEY="vm-secret-key"
IF NOT EXIST deploy-agent.jar (
ECHO "ERROR: deploy-agent.jar file does not exist."
EXIT /b 0
)
ECHO "Starting Deploy Agent..."
%JAVA_EXE% -jar deploy-agent.jar -A %ACCESS_KEY% -S %SECRET_KEY% -V %VM_SECRET_KEY% -L %DC_URL%
EXIT /b 0- It can be executed on
java 8or later. - Assume the jar file execution location is
{WORKSPACE}. - Additional directories such as backup and logs are created in
{WORKSPACE}. - If you do not specify
-loggingConfigFilePath, the{JAVA_HOME}\jre\lib\logging.propertiesfile will be used. - Deployment-related files are stored under
{WORKSPACE}/backup. - Only the most recent
3successfully deployed files are retained. deploy-agent.jarfull logs are not saved automatically. Only deployment-related logs from the full logs are saved to{WORKSPACE}/logs.- Logs are retained for
30days.
Agent problem solving
Changing the log level
If needed, you can change the agent log level. Refer to the sample log file below and add the -P, --loggingConfigFilePath options.
Sample log file
############################################################
# Default Logging Configuration File
#
# You can use a different file by specifying a filename
# with the java.util.logging.config.file system property.
# For example java -Djava.util.logging.config.file=myfile
############################################################
############################################################
# Global properties
############################################################
# "handlers" specifies a comma separated list of log Handler
# classes. These handlers will be installed during VM startup.
# Note that these classes must be on the system classpath.
# By default we only configure a ConsoleHandler, which will only
# show messages at the INFO and above levels.
handlers= java.util.logging.ConsoleHandler
# To also add the FileHandler, use the following line instead.
#handlers= java.util.logging.FileHandler, java.util.logging.ConsoleHandler
# Default global logging level.
# This specifies which kinds of events are logged across
# all loggers. For any given facility this global level
# can be overriden by a facility specific level
# Note that the ConsoleHandler also has a separate level
# setting to limit messages printed to the console.
#.level= INFO
.level= FINE
############################################################
# Handler specific properties.
# Describes specific configuration info for Handlers.
############################################################
# default file output is in user's home directory.
java.util.logging.FileHandler.pattern = %h/java%u.log
java.util.logging.FileHandler.limit = 50000
java.util.logging.FileHandler.count = 1
java.util.logging.FileHandler.formatter = java.util.logging.XMLFormatter
# Limit the message that are printed on the console to INFO and above.
#java.util.logging.ConsoleHandler.level = INFO
java.util.logging.ConsoleHandler.level = FINE
java.util.logging.ConsoleHandler.formatter = java.util.logging.SimpleFormatter
# Example to customize the SimpleFormatter output format
# to print one-line log message like this:
# <level>: <log message> [<date/time>]
#
# java.util.logging.SimpleFormatter.format=%4$s: %5$s [%1$tc]%n
############################################################
# Facility specific properties.
# Provides extra control for each logger.
############################################################
# For example, set the com.xyz.foo logger to only log SEVERE
# messages:
com.xyz.foo.level = SEVERE############################################################
# Default Logging Configuration File
#
# You can use a different file by specifying a filename
# with the java.util.logging.config.file system property.
# For example java -Djava.util.logging.config.file=myfile
############################################################
############################################################
# Global properties
############################################################
# "handlers" specifies a comma separated list of log Handler
# classes. These handlers will be installed during VM startup.
# Note that these classes must be on the system classpath.
# By default we only configure a ConsoleHandler, which will only
# show messages at the INFO and above levels.
handlers= java.util.logging.ConsoleHandler
# To also add the FileHandler, use the following line instead.
#handlers= java.util.logging.FileHandler, java.util.logging.ConsoleHandler
# Default global logging level.
# This specifies which kinds of events are logged across
# all loggers. For any given facility this global level
# can be overriden by a facility specific level
# Note that the ConsoleHandler also has a separate level
# setting to limit messages printed to the console.
#.level= INFO
.level= FINE
############################################################
# Handler specific properties.
# Describes specific configuration info for Handlers.
############################################################
# default file output is in user's home directory.
java.util.logging.FileHandler.pattern = %h/java%u.log
java.util.logging.FileHandler.limit = 50000
java.util.logging.FileHandler.count = 1
java.util.logging.FileHandler.formatter = java.util.logging.XMLFormatter
# Limit the message that are printed on the console to INFO and above.
#java.util.logging.ConsoleHandler.level = INFO
java.util.logging.ConsoleHandler.level = FINE
java.util.logging.ConsoleHandler.formatter = java.util.logging.SimpleFormatter
# Example to customize the SimpleFormatter output format
# to print one-line log message like this:
# <level>: <log message> [<date/time>]
#
# java.util.logging.SimpleFormatter.format=%4$s: %5$s [%1$tc]%n
############################################################
# Facility specific properties.
# Provides extra control for each logger.
############################################################
# For example, set the com.xyz.foo logger to only log SEVERE
# messages:
com.xyz.foo.level = SEVEREIf the IP is not recognized
When integrating the agent, not only the entered Secret Key but also the VM server’s actual OS name and IP (IPv4) must match the information registered in the DevOps Console for the integration to work.
For VM servers with some multi-network devices installed, the agent may fail to recognize the IP correctly. In such cases, add the IP and hostname settings to the /etc/hosts file as shown below.
12.2.10.3 - Request Permission
You can request permission to use the K8S clusters, namespaces, and VM server groups managed as deployment targets in the DevOps Console.
Getting Started with Permission Request
To begin the permission request, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deployment Target > Permission Request menu. The Permission Request screen appears.
Apply for K8S cluster permissions
To apply for K8S cluster permissions, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deployment Target > Permission Request menu. The Permission Request screen appears.
- On the Permission Request screen, click the K8S Cluster tab. The K8S Cluster screen appears.
- On the K8S Cluster screen, click the Apply button. The K8S Cluster Permission Request popup window opens.
- K8S Cluster Permission Request Search for the K8S cluster to request permission in the popup window.
- Enter the reason for the application and click the Add button.
- After selecting the permissions for the added K8S cluster, click the Save button.
Cancel K8S cluster permission request
To cancel a K8S cluster permission request, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deployment Target > Permission Request menu. The Permission Request screen appears.
- On the Permission Request screen, click the K8S Cluster tab. The K8S Cluster screen appears.
- On the K8S cluster screen, select a cluster and click the Cancel button.
REQUESTED display the Cancel button.Apply for namespace permission
To request namespace permissions, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deployment Target > Permission Request menu. The Permission Request screen appears.
- On the Permission Request screen, click the Namespace tab. The Namespace screen appears.
- On the Namespace screen, click the Apply button. The Namespace Permission Request popup opens.
- Namespace Permission Request In the popup, search for the K8S cluster that contains the namespace for which you are requesting permission.
- Select a namespace, enter the request reason, and then click the Add button.
- After selecting the permissions for the added namespace, click the Save button.
Cancel namespace permission request
To cancel a namespace permission request, follow these steps.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deployment Target > Permission Request menu. The Permission Request screen appears.
- On the Permission Request screen, click the Namespace tab. The Namespace screen appears.
- On the Namespace screen, select a namespace and click the Cancel button.
REQUESTED display the Cancel button.Apply for VM server group permission
To apply for VM server group permissions, follow the steps below.
- Main page, click the Admin icon at the top right. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deployment Target > Permission Request menu. The Permission Request screen appears.
- On the Permission Request screen, click the VM Server Group tab. The VM Server Group screen appears.
- On the VM Server Group screen, click the Apply button. The VM Server Group Permission Request popup opens.
- VM Server Group Permission Request Search for the VM server group for which you want to request permission in the popup window.
- Enter the reason for application and click the Add button.
- After selecting the permissions for the added VM server group, click the Save button.
Cancel VM server group permission request
To cancel the VM server group permission request, follow the steps below.
- Click the Admin icon at the top right of the Main page. You will be taken to the Tenant Dashboard page.
- From the left menu, click the Deployment Target > Permission Request menu. The Permission Request screen appears.
- On the Permission Request screen, click the VM Server Group tab. The VM Server Group screen appears.
- VM server group on the screen, select the VM server group and click the Cancel button.
REQUESTED display the Cancel button.12.2.11 - Release Management
12.2.11.1 - Release Management
A release is a task that performs the actual deployment process using a workflow.
Users with Owner, Master, or higher permissions within a project group can configure and apply a release process appropriate for the project.
Getting Started with Release Management
To start release management, follow the steps below.
- Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- From the left menu, click the Release Management > Release Management menu. You will be taken to the Release Management page.
Create Release
Release creation proceeds in the following order.
Pre-release checklist
Before creating a release, verify the following items.
Item | Required | Explanation |
|---|---|---|
| Workflow | Y | The workflow must be created as a release process template before creating a release. Please refer to Workflow Management. |
| Approval template | N | You can preconfigure the approval line and approval content to be used in a release in the approval template. Please refer to Approval Template Settings. |
Getting Started with Release Creation
Start creating a release on the Release Management screen
To create a release, follow the steps below.
- On the Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- From the left menu, click the Release Management > Release Management menu. You will be taken to the Release Management page.
- Click the Create Release button.
Start creating a release from the workflow list
To create a release, follow the steps below.
- On the Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- Click the Release Management > Workflow Management menu in the left menu.
- In the Workflow list, click the More icon. In the More menu, click the Release with this workflow option.
Start creating a release from the workflow detail screen
To create a release, follow the steps below.
- On the Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- On the Release Management page, click the Release Management > Workflow Management menu in the left menu.
- In the workflow list, click the workflow you want to view in detail.
- On the Workflow Details screen, click the Release with this workflow menu.
Enter basic release information
Enter the basic release information.
- Click the Start button.
Workflow Settings
- Select the workflow to perform the release. If you started creating a release through Workflow Management, the corresponding workflow is automatically selected.
- If you set an environment variable in the workflow, verify the variable and modify its value.
- Click the Next button.
Task view/edit
- Check the tasks that will be performed in the release.
- Edit or delete the task as needed.
- If you have completed checking/editing all tasks, click the Next button.
Release Settings
- Add the person responsible for receiving email/messenger notifications when the release or task status changes.
- Select whether to automatically end the release when all tasks are completed.
- Click the Next button.
Summary information
- Check the release creation summary information and click the Done button.
- In the confirmation popup, click the Confirm button to complete the creation.
- When the release creation is complete, the Release Details screen appears.
Release Detail Lookup
To view release details, follow these steps.
- In the Release list, click the release you want to view in detail.
- The Release Details screen appears.
Proceed with Release
Ongoing release
To proceed with the release, follow the steps below.
- In the Release list, click the release card with status In Progress.
- Release Details The screen appears.
- You can execute the release tasks included in the release.
Proceed with task
Only the person assigned to the release task or the release manager registered when the release is created can proceed with the task. To proceed with the release task, follow the steps below.
- If you are the task owner or the release owner, click the Task card. The task information appears in the task edit screen on the right.
- Pre-task Editing: You can edit some items of the task before it starts. After completing the edits, click the Apply button.
task Editable items User Estimated time required
- Description
- Person in charge
- Receive email upon completion
- AttachmentJenkins Parameters
- Person in charge
- Email recipient upon completionBlue/Green transition Person in charge
- mail recipient upon completionImage repository replication Source tag
- Target tag
- Person in charge
- Email recipient upon completionSCM repository release SCM tag
- person in charge
- email recipient upon completionCreate a GIT branch Project
- Repository branch
- New branch
- Person in charge
- Email recipient upon completionInternal approval JIRA Version Issue
- Approver
- Approval Title
- Approval Content
- Assignee
- Email Recipient on CompletionHelm release SET VALUES
- Person in charge
- Receive email upon completionJIRA release JIRA Project
- JIRA Version
- Assignee
- Receive email upon completionTable. Items that can be edited before starting the task - Task Start: Click the Start button to begin the task. If Task Auto-Run is selected, the task will start automatically without clicking the Start button.
- Task in progress: While the task is in progress, the status bar at the top of the task is displayed as In progress.
However, for a User task, you can still modify the estimated time, description, attachments, and other details even while it is in progress.
- Task Completion: Click the Complete button to complete the task. Some tasks cannot be completed by the user clicking the Complete button; the system automatically checks the status and completes them.
- Proceed with the other tasks in the same way and complete them.
Pause/Restart/Skip Task
Only the person assigned to the task or the release manager registered when creating the release can pause, restart, or skip.
To stop, restart, or skip a task, follow these steps.
- If you are the task owner or the release owner, click the More icon of the task.
- In the More menu, click the Stop/Restart/Skip menu.
Complete the release
The release manager can complete the release. The final outcome of a release is classified into three categories: success, failure, or stop.
- Success: After all release tasks are completed, the release manager marks the release as successful.
- Failure: After all release tasks are completed, the release manager marked the release as failed.
- Stop: There is at least one incomplete task in the release, but the release manager stopped the release.
Complete the release as success/failure
To complete the release, follow the steps below.
- Click the Release card with status In Progress in the Release list.
- Release Details screen appears.
- Confirm that all tasks included in the release have been completed.
- Click the ””Release Complete”” button.
- Release Complete popup appears, select Release Result (Success/Failure) and click the Complete button to finish the release.
Stop the release
To stop without completing the release, follow these steps.
However, according to the Release Management of the tenant common settings, approval is required when stopping.(테넌트 공통설정 관리하기)
- From the Release list, click the release card with status In Progress.
- The Release Details screen appears.
- Confirm that none of the tasks included in the release are in progress, and that any remaining tasks have not been started.
- Click the Release Complete button.
- Release Complete popup opens, and the release result is displayed as Interrupted. Click the Complete button to stop the release.
- If you set approval required on stop in the tenant common settings, clicking the Release Complete button opens the Release Stop Approval popup.
Delete release history
If the release status is success/failure/aborted, you can delete the release history. Releases in progress cannot be deleted.
Note that the delete function may not be visible depending on the Release Management setting in the tenant common settings. (Manage Tenant Common Settings)
To delete the release history, follow these steps.
- To delete the release history, use one of the following methods.
- On the Release Details screen, click the Delete button.
- Click the More icon in the release list. In the More menu, click the Delete menu.
- Delete Release History popup appears, and please enter the release name to confirm deletion.
- Click the Confirm button to complete the deletion.
12.2.11.2 - Workflow Management
A workflow is a collection of tasks and task groups of various types, and it must be configured before creating a release.
A workflow is a release process template that helps by turning a series of tasks required for the build-to-deployment stages into tasks, assigning owners to each task, and enabling sequential task execution during deployment.
Getting Started with Workflow Management
To begin workflow management, follow these steps.
- On the Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- Release Management page, click the Release Management > Workflow Management menu. The Workflow Management page appears.
Create workflow
Start Creating a Workflow
To create a workflow, follow the steps below.
- Workflow Management page, click the Create Workflow button. The Create Workflow popup opens.
- Workflow Creation Enter the information in the popup window, select the project to be released via the workflow, and click the Start button. You will be taken to the Workflow Creation page.
- Edit the workflow on the Create Workflow screen.
Edit basic information
To modify the workflow’s basic information, follow these steps.
- On the Create Workflow screen, click the Edit Basic Information button. The Edit Basic Information popup opens.
- Edit Basic Information In the popup window, edit the information and click the Save button.
- Save Confirmation when the popup opens, click the Confirm button to complete the edit.
Modify Environment Variables
You can manage variable values that are available throughout the entire workflow by using workflow environment variables.
Follow these steps to modify the workflow environment variables.
- On the Create Workflow screen, click the Edit Environment Variables button. The Edit Environment Variables popup opens.
- Edit Environment Variables Edit the environment variables in the popup window.
- Click the Add button to add an environment variable.
- Enter key/value.
- Click the X icon to delete the environment variable.
- After completing the environment variable edit, click the Save button.
- In the confirmation popup, click the Confirm button to complete the edit.
Add Task
To add a task in the workflow, follow these steps.
- On the Create Workflow screen, add a task using one of the following methods.
- Click the Task button to add a task at the very bottom of the workflow.
- Click the task header to add a task above the current task.
- Click the bottom of the task to add a task below the current task.
- Set the task in the task editing screen on the right.
- Click the Apply button to apply the task to the workflow.
Item Explanation Add task Add a task. Add task at the top Add a task at the top. Add task at the bottom Add a task at the bottom. Task editing Edit the selected task. Table. Workflow creation screen items
Add task group
By using task groups, you can manage the execution (sequential or parallel) of related tasks and their prerequisites.
To add a task group in a workflow, follow these steps.
- On the Create Workflow screen, click the Task Group button.
- Click the generated new task group card.
- In the task group edit screen on the right, set the task group and click the Apply button.
Item Explanation Add task group Add a task group. Task group Click to display the task group edit screen. Task group name Please enter the task group name. Task in progress Select the task execution mode within the task group - Parallel: Execute tasks in the group simultaneously.
- Sequential: Execute tasks in the group sequentially.
Conditional execution Select whether to use the execution condition for the task group.
- ON: Set the task group execution according to the status of preceding tasks.
- OFF: The task group’s tasks run regardless of the status of preceding tasks.Predecessor task status for task group execution Execute the current task group when the selected preceding task is in the specified state.
If multiple preceding tasks are selected, it operates as an AND condition.Receive email upon completion Search for and enter the recipient to receive an email when the task completes successfully - Email recipients can be searched among project group members.
Table. Workflow task group additional items
Edit task, task group
To edit tasks and task groups in a workflow, follow these steps.
- Click the Task, Task Group cards you want to edit in the workflow.
- The Task, Task Group Edit screen appears on the right.
- After completing the editing of tasks and task groups, click the Apply button to apply the tasks and task groups to the workflow.
Delete task, task group
To delete tasks and task groups in a workflow, follow these steps.
- In the workflow, click the Task, Task Group card you want to edit. The Task, Task Group Edit screen appears on the right.
- On the Task, Task Group Edit screen, click the Delete button.
- In the confirmation popup, click the Confirm button to complete the deletion of the task and task group.
Complete workflow creation
To complete workflow creation after adding tasks and task groups to the workflow, follow these steps.
- On the Workflow Creation screen, click the Save button. The Workflow Save popup opens.
- In the Save Workflow popup, click the Confirm button to complete workflow creation.
Workflow Detail View
To view the workflow in detail, follow the steps below.
- On the Workflow Management page, click the workflow you want to view in detail.
- The Workflow Details screen appears.
Modify workflow
To modify the workflow, follow these steps.
- To display the workflow edit screen, use one of the following methods.
- On the Workflow Details screen, click the Edit button.
- On the Workflow List screen, click the More icon. In the More menu, click the Edit menu.
- On the Workflow Edit screen, edit the workflow. Editing is the same as Create Workflow.
- After completing the workflow edit, click the Save button. The Workflow Save popup opens.
- In the Workflow Save popup, click the Confirm button to complete editing the workflow.
Delete workflow
To delete a workflow, follow the steps below.
- To delete a workflow, use one of the following methods.
- On the Workflow Details screen, click the Delete button.
- On the Workflow List screen, click the More icon. From the More menu, click the Delete menu.
- When the Workflow Deletion popup opens, please enter the workflow name to confirm deletion.
- In the Workflow Delete popup, click the Confirm button to complete the deletion.
Replicate workflow
You can duplicate a workflow to create a new workflow.
To duplicate the workflow, follow these steps.
- On the Workflow List screen, click the More icon. In the More menu, click the Clone this workflow menu. The Workflow Clone popup opens.
- Workflow duplication Enter the information in the popup window and click the Start button. Workflow creation screen appears.
- On the Workflow Creation screen, edit the workflow. Editing is the same as Create Workflow.
- On the Create Workflow screen, after completing the edit, click the Save button.
- In the Save Workflow popup, click the Confirm button to complete workflow creation.
Create a Release with a Workflow
On the Workflow Management screen, you can create a new release.
To create a release using a workflow, follow these steps.
- To create a release with a workflow, use one of the following methods.
- On the Workflow Details screen, click the Release with this workflow button.
- On the Workflow List screen, click the More icon. In the More menu, click the Release with this workflow menu.
- Create Release screen appears, and you can create a release.
12.2.11.3 - Approval Template Settings
The approval template can be used in workflows and releases, and it includes an approval line and approval content.
| Item | Explanation |
|---|---|
| Approval line | You can predefine frequently used approval lines. |
| Approval content | You can already set up frequently used approval content. |
Getting Started with Approval Template Configuration
To begin setting up the approval template, follow these steps.
- On the Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- On the Release Management page, click the Release Management > Approval Template Settings menu in the left menu.
Approval line
Getting Started with Approval Line
To start using the approval line, follow the steps below.
- On the Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- On the Release Management page, click the Release Management > Approval Template Settings menu in the left menu. The Approval Template Settings screen appears.
- On the Approval Template Settings screen, click the Approval Line tab.
Add approval line template
To add an internal approval line template, follow the steps below.
You can create an approval line for users who are Owners or Masters within the project group via the internal approval line.
- On the Approval Template Settings screen, click the Internal Approval Line tab. The Internal Approval Line screen appears.
- On the Internal approval line screen, click the Add button. The Add approval line template popup opens.
- Add Approval Line Template Enter the information in the popup window and click the Save button.
Item Explanation Template name Please enter the template name. Approval Officer Search for the approver and add them to the approval line. - Only project group members can be searched and added as approvers.
Approval editing - Change of approval, agreement, and notification
- Change approval order
- Delete approver
Table. Additional Input Items for Approval Line Template
Approval Line Details
To view the approval line in detail, follow these steps.
- Internal approval line screen: click the approval line you want to view in detail.
- Approval Line Details screen appears.
Edit approval line
To modify the approval line, follow the steps below.
- On the Internal approval line screen, click the approval line you want to edit. The Approval line details screen will appear.
- On the Approval Line Details screen, click the Edit button. The Edit Approval Line screen appears.
- On the Edit Approval Line screen, after completing the approval line modification, click the Save button.
- In the confirmation popup, click the Confirm button to complete the edit.
Delete Approval Line
To delete the approval line, follow these steps.
- To delete an approval line, use one of the following methods.
- On the Approval Line Details screen, click the Delete button.
- In the Approval line list, select the approval line you wish to delete, then click the Delete button.
- In the confirmation popup, click the Confirm button to complete the deletion.
Manage approval content
Getting Started with Approval Content
To start using the approval content, follow the steps below.
- On the Main page, click the Release Management icon next to the project group name. You will be taken to the Release Management page.
- Release Management page, click the Release Management > Approval Template Settings menu in the left menu. The Approval Template Settings screen appears.
- Approval Template Settings on the screen, click the Approval Content tab.
Create approval content template
To add an approval content template, follow these steps.
- On the Approval Template Settings screen, click the Approval Content tab. The Approval Content screen appears.
- On the Approval Content screen, click the Add button. The Add Approval Content Template popup opens.
- Add approval content template Enter the information in the popup window and click the Save button.
- In the confirmation popup, click the Confirm button to complete the addition.
View approval details
To view the approval details in detail, follow these steps.
- On the Approval Content screen, click the approval item you wish to view in detail.
- Approval Details screen appears.
Modify approval content
To edit the approval content, follow the steps below.
- On the Approval Content screen, click the approval content you want to edit.
- When the Approval Details screen appears, click the Edit button. The Edit Approval Details screen appears.
- On the Edit Approval Content screen, after completing the approval content edit, click the Save button.
- In the confirmation popup, click the Confirm button to complete the edit.
Delete approval content
To delete the approval content, follow the steps below.
- To delete the approval content, use one of the following methods.
- On the Approval Details screen, click the Delete button.
- On the Approval Content List screen, select the approval content you want to delete and click the Delete button.
- In the confirmation popup, click the Confirm button to complete the deletion.
12.2.11.4 - Task
A task is the smallest executable unit that composes a workflow (or release), and each task can perform its designated operation.
A workflow (or release) consists of one or more tasks.
You can add and edit tasks from Release Management, Workflow Management.
Task List
The tasks provided in release management are as follows.
item | Explanation |
|---|---|
| Jenkins | You can run it by integrating with a Jenkins pipeline that belongs to the DevOps Console project or a Jenkins job that is separate from the DevOps Console project. |
| User | You can register tasks that users perform manually, rather than integrating with a specific tool. |
| Blue/Green switch | You can integrate with Blue/Green deployments that belong to the DevOps Console project. |
| Internal approval | You can approve through a USER belonging to the DevOps Console project group. |
| Helm release | You can integrate with Helm releases belonging to the DevOps Console project. |
| Image repository replication | You can replicate the image to another repository. |
| SCM repository release | Release using the SCM repository’s release feature. |
| Create a Git branch | You can copy a specific branch of a repository belonging to the DevOps Console project and create a new branch. |
| JIRA release | You can release or unrelease a specific version in a JIRA project. |
| VM deployment | This task can deploy a VM deployment group that is in the Build Completed state, or roll back to a previous version. |
Common task items
You can add and edit tasks in workload (or release) management. When you select a task, the Task Edit screen appears, and the Task Edit screen is composed as follows.
| Item | Explanation |
|---|---|
| Task name | Please enter the task name. |
| Task type | Please select the task type. |
| Auto-run | Select whether to run automatically after the preceding task is completed.
|
| Conditional execution | Select whether to allow the current task to run based on the status of the preceding task (success/failure/skip).
|
| Conditional execution item |
|
| person in charge | Search for and enter the personnel who will perform the task among the members of the project group.
|
| Assign yourself as the person in charge | Click to set the current task’s assignee to yourself. |
| Receive email upon completion | Search for and enter the recipient who will receive an email when the task is completed.
|
| Delete | Delete the current task. |
| Apply | Apply the current task settings to the workflow. |
Jenkins task
This is a task that can run a build pipeline added to the project or a Jenkins Job not registered in the DevOps Console.
| Item | Explanation |
|---|---|
| Jenkins Type | Select Jenkins Type
|
| Project | Please select the project to run the pipeline. |
| Jenkins URL | Select the URL of the Jenkins tool registered for the chosen project. |
| Job | Select a job from the selected Jenkins URL. Jobs that the current user has permission to run are displayed in the list. |
| Parameter | Enter the parameters required to run the build pipeline
|
| Jenkins Job URL | Enter the URL of a Jenkins Job that is not registered in the DevOps Console. |
| Jenkins ID Jenkins Password or Token |
|
User Task
This task registers cases where the user has work that must be performed manually.
| Item | description |
|---|---|
| Estimated time | Please enter the estimated time required for the User task. |
| Explanation | Enter the tasks that the responsible person must perform according to the manual. |
Blue/Green transition task
This is a task that can be integrated with the project’s Blue/Green deployment.
| Item | Explanation |
|---|---|
| Project | Select the project to perform the blue-green transition. |
| Blue‑green list | Select the bluegreen you want to run in the task from the list of bluegreens in the selected project. |
If the Blue/Green switch task is performed during a release, you can carry out the following actions.
| Item | Explanation |
|---|---|
| Check operational status | Click the Check operation status button to open the Blue/Green operation status check popup. |
| Conversion | Check the status of operation/operation standby and click the Switch button. Operation and operation standby will be switched. |
| Completed | Check the blue/green transition result and click the Complete button to complete the blue/green task. If there is a problem with the transition, you can click the Check operation status button to revert to the previous state. |
Internal approval task
This task enables approval by a USER who belongs to the project group.
Item | Explanation |
|---|---|
| Include JIRA version issues | Select whether to include JIRA Version issues in the approval content. When proceeding with a release, select the JIRA Version set in the project group; the list of all issues corresponding to that Version will be automatically added to the approval text. |
| JIRA Project | Select a JIRA Project. JIRA Project you can select from the JIRA Projects that have been registered. |
| Approval line template | Select the approval line you added in Approval Template Settings and add approvers in bulk. |
| Approver | Search for the approver and add them. You can search for members of the project group and add them. |
| Approver List | Modify the approver list by changing the approval type, adjusting the order, or deleting entries. |
| Approval content template | Select the approval content added from Manage Approval Content and add a title and description. |
| Approval content | Enter the approval title and approval content. |
When the internal approval task runs in a release, you can perform the following actions.
- Approver: Can approve or reject the approval.
- Approval: Click the Approve button. In the Approve confirmation popup, enter the approval comments and click the Confirm button to approve the document.
- Reject Approval: Click the Reject button. In the Reject confirmation popup, enter your approval comments and click the Confirm button to reject the approval.
- Other roles: You can check the approval status.
Helm release task
This is a task that can be linked with Helm releases belonging to the project.
Item | Explanation |
|---|---|
| Auto shutdown | After the Helm release execution is completed, select whether to automatically terminate the task. |
| project | Select the project to perform the Helm release. |
| Helm release | Select the Helm release to use in the task during the project’s Kubernetes deployment. workload, Helm release can be selected. Information about the selected Helm release is displayed. |
| SET_VALUES (Helm release) | It is displayed when the previously selected Helm release is Helm release.
|
| SET_VALUES (workload) | If the Helm release selected earlier is a workload, display
|
When the Helm release task runs in a release, you can view the following information on the task edit screen.
When you select Helm Release, you can view the following items.
| Item | Explanation |
|---|---|
| Current status | Displays the current Helm release status. |
| Runtime status | Displays the result of the Helm release execution. |
| Details | Displays the Helm release history. View icon can be clicked to check the Values.yaml used in the Helm release by revision. To roll back to a previous deployment, click the Rollback button. In the confirmation popup, click the Confirm button to complete. |
When you select 워크로드, you can see the following items.
| Item | Explanation |
|---|---|
| Runtime status | Displays the result of the Helm release execution. |
| Details | Displays the deployment history. To roll back to a previous deployment, click the Rollback button. In the confirmation popup, click the Confirm button to complete. |
Image Repository Replication Task
This task can replicate an image to another repository.
Source image → (copy) Target image
Item | Explanation |
|---|---|
| Type | Select Type
|
| Source project | Select a project with a registered source image repository. |
| Source image repository | Select the image repository registered in the Source project. |
| Source tag | Enter the Source tag. tag can be set by entering a value directly or by selecting an environment variable. Refer to Modify environment variables for environment variables. |
| Target project | Select a project where the target image repository is registered. |
| Target image repository | Select the image repository registered in the Target project. |
| Target tag | Enter the target tag. |
| Source Host | Enter the Source Host domain name. |
| Source Path | Please enter the Source Path. |
| Source ID Source Password | Enter the account information for the source image repository. After entering, click the Connection Test button to verify that the connection is successful. |
| Target Host | Target Host Please enter the domain name. |
| Target Path | Please enter the target path. |
| Target ID Target Password | Enter the account information for the target image repository. After entering, click the Connection Test button to verify that the connection is successful. |
SCM repository release task
This task executes a release of the SCM repository.
SCM repository releases perform release creation or tag creation depending on the SCM repository tool (GitHub, GitLab, other Git repositories).
| Item | Explanation |
|---|---|
| Git Type | Select Git Type
|
| project | Select a project with a registered code repository. |
| SCM repository | Select the code repository registered in the project. |
| SCM branch | Select a branch of the code repository. |
| SCM tag | Enter the tags to create in the release. |
| Git URL | Enter the Git URL. |
| Git ID Git Password or Token | Enter your Git account information. |
| branch | Enter the Git branch. After entering, click the Connection Test button to verify that the connection is successful. |
GIT branch creation task
This is a task that can copy a specific Git branch and create a new branch.
| Item | description |
|---|---|
| Git Type | Select Git Type
|
| project | Select a project with a registered code repository. |
| repository | Select the code repository registered in the project. |
| branch | Select the existing branch that the newly created branch will reference. |
| new branch | Enter the name of the new branch. |
| Apply Protected | Select whether to apply the protection rule to the newly created branch. |
| Protection Rule | When applying a Protection Rule, set the Merge and Push permissions.
|
| Git URL | Enter the Git URL. |
| Git ID Git Password or Token | Enter your Git account information. |
| branch | Enter the existing branch that the newly created branch will reference. After entering, click the Connection Test button to verify that the connection is normal. |
JIRA release task
This is a task that can set a specific version of a JIRA project to Released or Unreleased.
| Item | Explanation |
|---|---|
| JIRA project | Select a JIRA project registered in the project group. |
| JIRA URL | You can view the Server of the selected JIRA project. (Readonly) |
| JIRA Version | Select the Version of the JIRA project
|
If a JIRA release task is in progress in the release, you can perform the following actions.
| Item | description |
|---|---|
| status | When you click the Status button, the JIRA release popup opens. |
| State change | Click the Change Status button to change the JIRA version to Released, or change it back to Unreleased. |
| Confirm | Confirm click the button to complete the JIRA release. |
VM deployment task
a task that can deploy a VM deployment group in the Build Complete state or roll back to a previous version.
| Item | description |
|---|---|
| project | Please select a project. |
| deployment group | Select a deployment group
|
| Deployment group information | The contents stored in the deployment group are set automatically. |
12.2.11.5 - JIRA Project
Users can manage the JIRA project information used in JIRA tasks for release management.
Starting a JIRA Project
To start JIRA project management, follow the steps below.
- Main page, click the Project Group Management icon of the project group. You will be taken to the Project Group Dashboard page.
- Click the JIRA Project menu on the Project Group Dashboard page. The JIRA Project screen appears.
Add JIRA project
To add a JIRA project, follow these steps.
- On the JIRA project screen, click the Add button. The Add JIRA project popup opens.
- Add JIRA Project In the popup window, after entering the JIRA URL and authentication information, click the Connection Test button.
- Select JIRA Project and click the Save button.
Item Explanation JIRA URL Select the JIRA URL - A list of JIRA tools available in the project group is displayed.
Tool Registration Shortcut If you need to register a JIRA tool, you can go directly to the tool registration page. Authentication information Enter authentication credentials. JIRA project Select JIRA project - A list of projects accessible based on the JIRA URL and authentication information is displayed.
- Only projects for which you have administrator rights in JIRA can be selected.
Table. JIRA Project Additional Input Items
Delete JIRA project
To delete a JIRA project, follow the steps below.
- On the JIRA Project screen, select the checkbox of the item you want to delete, then click the Delete button.
- Click the Confirm button in the confirmation popup to complete the deletion of the JIRA project.
12.2.12 - Release Note
DevOps Console
- Built-in user management and authentication features have been added.
- Manage and authenticate users using
DevOps IDP.
- Manage and authenticate users using
- The Jenkins DevOps Plugin installation and update features have been added.
- You can verify the installed Jenkins version, the installation status and version information of recommended plugins, and perform installation and updates.
- From the tenant dashboard, you can download the billing base data in the status data as an Excel file.
A supported Helm chart repository has been added.
- You can now use the OCI standard Helm chart repository.
The pipeline feature has been added.
- Supports creating multi-branch pipelines.
- Note: Multibranch Pipeline
Other changes
- A new item that can be viewed on the dashboard has been added.
- The permission management feature for deployment targets has been improved.
- Deployment target(K8S cluster, namespace, VM server group) now has a permission request/approval feature added.
- Note: Permission Request
- The management and organization features for tools/templates have been improved.
- It has been improved to allow the transfer of the organization that manages tools and templates (tenants, project groups).
- Other changes
- The supported versions of the image registry tool
Harborhave been expanded. (~2.10) - It is no longer possible to create a Job directly in
Jenkins. (Jobs can only be created through the DevOps Service)
- The supported versions of the image registry tool
13 - AI-ML
We offer AI/ML services that enable easy and convenient development of ML/DL (Machine Learning/Deep Learning) models and the setup of training environments.
13.1 - CloudML
13.1.1 - Overview
Service Overview
CloudML is an integrated platform that supports the entire machine learning process—from data analysis to model development, training, validation, and deployment—in a cloud environment.
Features
- Cloud ML is designed to enable users in various roles such as analysts, machine learning engineers, and developers to collaborate in a single environment and easily design and operate machine learning workflows.
- Cloud ML provides an analysis environment based on Python and R, and users with programming experience can leverage the platform more flexibly and effectively. In particular, using the generative AI–based Copilot feature allows code writing, refactoring, error correction, and function recommendation to be performed easily with natural language input, thereby increasing analytical productivity and accessibility.
- Cloud ML systematically supports each stage, including configuring the analysis environment, model development and serving, analysis automation, and visualization. It enables improvements in both productivity and model quality through repetitive experiments and operational automation.
Service Architecture Diagram
CloudML consists of an analysis environment, machine learning lifecycle management, automated analysis support, visualization, and a generative AI‑based Copilot feature, allowing users to perform the entire machine‑learning process in an integrated manner.
Provided features
CloudML provides the following features.
- Visual Modeling: Provides an intuitive interface that lets you build and deploy machine learning models without coding using a Drag&Drop approach. You can easily manage the entire process from data loading to model evaluation and deployment.
- Code-based Development: In the Jupyter Notebook environment, you can freely write and execute code using Python, R, and others. It provides powerful features for advanced users and researchers.
- Workflow Automation: It efficiently automates complex machine learning workflows such as data preprocessing, model training, evaluation, and deployment.
- Experiment Management: You can train machine learning models with various parameter combinations and systematically manage and compare the results.
- Using Copilot Features: It provides a natural-language-based AI assistant that guides and automates the model development process. It supports various tasks such as code generation, refactoring, error correction, and documentation, enhancing productivity.
- Integrated Platform: All features are integrated within CloudML for convenient use.
- Scalability and Flexibility: Supports scaling computing resources and connecting various data sources as needed.
Constraints
Before using CloudML, be sure to check the following constraints and incorporate them into your service usage plan. Since Cloud ML operates in a Kubernetes-based environment, appropriate cluster resource configuration is required for stable service operation.
- Application Basic Resources: To run the Application, a minimum of 24 vCPU cores and 96 GBi of memory are allocated by default.
- Analysis Task Resources: To perform analysis tasks, additional CPU or GPU resource configuration is required beyond the basic resources above. It should be configured appropriately, taking the workload of the analysis tasks into account.
- Copilot (CPU-based usage): To run Copilot on CPU resources, a minimum of 16 vCPU cores and 10 GiB of memory are required. In this case, the CPU resources available for analysis tasks are reduced accordingly.
- Copilot (GPU-based usage): Copilot can also be configured to use dedicated GPU resources.
- Supported LLM models: Currently, the LLM models that can be applied to Copilot are limited to Llama3.
Provision status by region
CloudML is available in the following environments.
| region | Availability |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Preliminary Service
This is a list of services that must be pre-configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Container | Container Registry | A service that stores, manages, and shares container images. |
| Container | Kubernetes Engine | Kubernetes container orchestration service |
| Networking | Load Balancer | A service that automatically distributes server traffic load. |
13.1.2 - How-to guides
Create CloudML
Users can create the service by entering the required CloudML information and selecting detailed options through the Samsung Cloud Platform Console.
To create a CloudML, follow these steps.
Click the All Services > AI/ML > CloudML menu. Navigate to CloudML’s Service Home page.
On the Service Home page, click the Create CloudML button. You will be taken to the CloudML page.
On the CloudML Creation page, enter the information required to create the service and select detailed options.
In the Version Selection area, select the version of the service.
Category RequiredDetailed description Select version Required Select CloudML version Table. CloudML service version selection optionsSCP Kubernetes Engine deployment Select the options needed to create a service in this area.
Category RequiredDetailed description Cluster name Required Select Kubernetes Engine cluster Table. CloudML Service Cluster Selection OptionsIn the Service Information Input area, select the options required to create the service.
Category required or notDetailed description CloudML name Required Enter service name Explanation Selection Enter service description Domain name Required Enter the domain name to be used for the service - Enter 2-63 characters using lowercase English letters, numbers, and special characters
endpoint Required Select the endpoint to use in the service - Choose between Private and Public
Copilot Selection Select whether to use Copilot in the service - Apply when selected requires agreement to terms in the popup window
- If the selected cluster is not configured with GPUs dedicated to LLMs, or the allocated LLM resources are insufficient, Copilot cannot be applied
Resource Information Required Display resource information of the selected cluster Enter SCR information Required Enter SCR information to be used in the service - Enter private endpoint, authentication key, secret key
Table. CloudML service information input itemsAdditional Information Input area, please enter or select the required information.
Category RequiredDetailed description tag Selection Add Tag - Up to 50 can be added per resource
- After clicking the Add Tag button, enter or select Key, Value values
Table. CloudML Additional Information Input Items
Summary Check the detailed information and estimated billing amount generated in the panel, and click the Complete button.
- When creation is complete, check the created resources on the CloudML List page.
Check CloudML detailed information
You can view and edit the full list of resources and detailed information for the CloudML service. CloudML Details page consists of Details, Tags, Activity Log tabs.
To view the detailed information of CloudML, follow these steps.
- Click the All Services > AI/ML > CloudML menu. Navigate to CloudML’s Service Home page.
- On the Service Home page, click the resource (CloudML) to view detailed information. You will be taken to the CloudML Details page.
- CloudML Details page displays CloudML’s status information and detailed information, and consists of Details, Tags, Activity History tabs.
Category Detailed description Service status CloudML status - Creating: Creating
- Deployed: Created / operating normally
- Updating: Updating settings
- Terminating: Terminating
- Error: Error occurred
Connection Guide Service Access Guide - Information on host to register on the user’s PC
Service termination Cancel Service button Table. CloudML status information and additional features
- CloudML Details page displays CloudML’s status information and detailed information, and consists of Details, Tags, Activity History tabs.
Detailed Information
CloudML List page lets you view detailed information of the selected resource and modify it if necessary.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name |
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Product name | CloudML name |
| Copilot | Whether to use Copilot |
| Explanation | Description of the service |
| Cluster name | Selected Kubernetes Engine cluster name |
| domain name | Entered service domain name |
| Version | Selected service version |
| Installation node information | Node information installed on the cluster |
| SCR information | Entered SCR information |
tag
On the CloudML List page, you can view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
On the CloudML list page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate CloudML Service
Users can cancel the CloudML service through the Samsung Cloud Platform Console.
To cancel CloudML, follow the steps below.
- Click the All Services > AI/ML > CloudML menu. Navigate to CloudML’s Service Home page.
- Click the Cancel Service button on the Service Home page. A service cancellation alert window appears.
- Enter the CloudML name to delete in the dialog and click the Confirm button.
13.1.2.1 - Kubernetes Cluster Configuration
Configuring a Kubernetes cluster
To apply for the CloudML service, a dedicated cluster for CloudML must be set up. A dedicated cluster means creating a Kubernetes Engine that meets or exceeds the required minimum specifications and configuring several necessary settings. Create a dedicated cluster in advance before applying for the CloudML service.
- For instructions on creating a cluster, see the Cluster Creation guide.
- CloudML exposes an HTTPS endpoint on port 443. When creating a cluster, select Public Endpoint.
Recommended specifications for cluster nodes and storage
Cluster nodes can be added or modified after the cluster is created. The following are the recommended specifications for cluster nodes and storage that should be prepared to install CloudML for five users.
| Category | Item | role | capacity |
|---|---|---|---|
| cluster node | Kubernetes node pool (Virtual Server) | Application execution
| 24 core / 96 GBi |
| Cluster node | Kubernetes node pool (Virtual Server) | Run Analysis
| 8 core / 32 GBi x 2 EA
|
| repository | File Storage | Data storage | 1 TB |
If you need to change specifications such as adjusting the number of nodes, adding GPU nodes, or expanding resources, please request technical support.
- Technical Support Information Page: https://www.samsungsds.com/kr/support/support_tech.html
- Technical support request email: brightics.cs@samsung.com
Add a label to a node
Add labels to the nodes directly according to the role-specific recommendations in the cluster node and storage specifications.
- For instructions on adding labels to a node YAML, refer to the Edit Node YAML guide.
To add a label to a cluster node, follow these steps.
- Click the All Services > Container > Kubernetes Engine menu. Navigate to the Service Home page of Kubernetes Engine.
- On the Service Home page, click the Node menu. You will be taken to the Node List page.
- On the Node List page, select the cluster for which you want to view detailed information from the gear button at the top left, then click the Confirm button.
- Select the node you want to view details for and click it. You will be taken to the Node Details page.
- On the Node Details page, click the YAML tab. You will be taken to the YAML tab page.
- On the YAML tab page, click the Edit button. The node edit window opens.
- In the node edit window, add a label that matches the role and click the Save button.
- Check the following information and add a label that matches the node specifications.
Category Purpose-specific labels CPU node - App:
node.kubernetes.io/nodetype: ml-app
- Analytics:
node.kubernetes.io/nodetype: ml-analytics
GPU node - Analysis:
node.kubernetes.io/nodetype: ml-analytics-gpu
- Copilot:
node.kubernetes.io/nodetype: ml-gpu
Table. Kubernetes node label items by purpose - App:
- Check the following information and add a label that matches the node specifications.
13.1.3 - API Reference
13.1.4 - CLI Reference
13.1.5 - Release Note
CloudML
- We have launched the CloudML service, which supports the entire machine learning process—from data analysis to model development, training, validation, and deployment—in a cloud environment through the Samsung Cloud Platform.
13.2 - AI&MLOps Platform
13.2.1 - Overview
Service Overview
AI&MLOps Platform is a machine learning platform that automates repetitive tasks across the entire pipeline of developing, training, and deploying machine learning models. Through the AI&MLOps Platform service, integrated management of training data, models, and operational data is possible on a Kubernetes-based AI/MLOps environment.
The AI&MLOps Platform provides an Enterprise service that adds add-on features such as distributed training job execution and monitoring to the open-source product Kubeflow.Mini, which enables development, training, tuning, and deployment of machine learning models.
Features
Providing a Cloud Native MLOps Environment: The AI&MLOps Platform provides a cloud‑optimized machine learning model development environment, and its Kubernetes‑based architecture makes integration with various open‑source tools convenient.
Machine Learning Development and Operations Convenience: Provides a standardized environment that supports various machine learning frameworks such as TensorFlow, PyTorch, scikit-learn, Keras, etc. By automating the entire pipeline for developing, training, and deploying machine learning models, it makes model composition and creation easy and promotes reusability.
Enhanced GPU Integration: By leveraging Multi‑Node GPU on a Bare Metal Server and GPUDirect RDMA (Remote Direct Memory Access), the job speed of LLM (Large Language Model) and natural language processing (NLP) can be dramatically improved.
Service Diagram
Provided features
The AI&MLOps Platform provides the following features.
ML Model Development Environment and Features
- Notebook Provision: Creates Jupyter Notebooks and VS Code that include ML frameworks such as Tensorflow, Pytorch, etc.
- TensorBoard: TensorBoard(ML model training process visualization/analysis tool) creates and manages the server.
- Volumes: When developing ML models, store datasets and models, and connect a Volume when creating a Jupyter Notebook.
ML model distributed training Job execution/management
- Supports execution and monitoring of distributed training jobs, as well as management and analysis of inference services. (Add-on)
- Provides various features for configuring MLOps environments, such as Job Queue management. (Add-on)
- Provides efficient GPU resource utilization features such as Job Scheduler (FIFO, Bin-packing, Gang-based), GPU Fraction, and GPU resource monitoring, etc. (Add-on)
- We dramatically improved the job speed of LLM (Large Language Model) and natural language processing (NLP) by using BM-based Multi-Node GPU and GPU Direct RDMA (Remote Direct Memory Access). (Add-on)
ML Model Experiment Management and Pipeline
- Provides Experiments (KFP) for managing ML pipeline experiments.
- Supports pipeline automation features for configuring and executing ML tasks in stages.
Component
Operating System version
The operating systems supported by the AI&MLOps Platform are as follows.
| Operating System (OS) | Version |
|---|---|
| RHEL | RHEL 8.3 |
| Ubuntu | Ubuntu 18.04, Ubuntu 20.04, Ubuntu 22.04 |
Provision status by region
The AI&MLOps Platform is available in the environments below.
| region | Provision status |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea South 2 (kr-south2) | Not provided |
| South Korea South 3(kr-south3) | Not provided |
Prior Service
This is a list of services that must be pre-configured before creating the service. For details, refer to the guide provided for each service and prepare in advance.
| Service Category | service | Detailed description |
|---|---|---|
| Container | Kubernetes Engine | Kubernetes container orchestration service |
13.2.2 - How-to guides
Create AI&MLOps Platform
Users can create the service by entering the required information for the AI&MLOps Platform and selecting detailed options through the Samsung Cloud Platform Console.
To create an AI&MLOps Platform, follow these steps.
- Click the All Services > AI/ML > AI&MLOps Platform menu. You will be taken to the Service Home page of AI&MLOps Platform.
- Service Home page, click the AI&MLOps Platform Create button. You will be taken to the AI&MLOps Platform Create page.
- On the AI&MLOps Platform creation Service Type Selection page, enter the information required to create the service and select detailed options.
- Select the service type in the Service Type and Version Selection area.
Category RequiredDetailed description Service type Required Service type selected by the user - AI&MLOps Platform
- Kubeflow Mini
Service type version Required Select version of the selected service - Provide a list of versions of the offered service
Table. AI&MLOps Platform service types and version selection items - Cluster Deployment Area Classification Select the options required to create a service in this area.
Category RequiredDetailed description Cluster deployment area Required - Deploy from Kubernetes Engine: Select the previously created Kubernetes Engine
- Deploy to a new cluster: When creating the AI&MLOps Platform, also create a Kubernetes Engine
Table. AI&MLOps Platform Service Cluster Deployment Area Classification ItemsReferenceThe configuration elements on the following Service Information Input page vary depending on the cluster deployment settings.
- Select the service type in the Service Type and Version Selection area.
- On the Service Information Input page of AI&MLOps Platform Creation, enter the information required to create the service and select detailed options.
- You can select the cluster deployment region.
- For instructions on configuring Deploy to a new cluster, see the Deploy to a new cluster guide.
- Deploy on SCP Kubernetes Engine For configuration, refer to the Deploy on SCP Kubernetes Engine guide.
- Refer to the Kubernetes Cluster specifications guide for the Kubernetes cluster specifications required for installation.
- You can select the cluster deployment region.
- On the Creation Information Check page of AI&MLOps Platform creation, review the detailed information you created and the estimated billing amount, and click the Complete button.
- Once creation is complete, check the created resources on the AI&MLOps Platform Service List page.
Check detailed information of AI&MLOps Platform
The AI&MLOps Platform service allows you to view and edit the full list of resources and detailed information. AI&MLOps Platform Service Details page consists of Details, Tags, Activity History tabs.
To view detailed information about the AI&MLOps Platform service, follow the steps below.
- Click the All Services > AI/ML > AI&MLOps Platform Service menu. Navigate to the Service Home page of the AI&MLOps Platform Service.
- On the Service Home page, click the AI&MLOps Platform menu. You will be taken to the AI&MLOps Platform Service List page.
- On the AI&MLOps Platform Service List page, click the resource to view detailed information. You will be taken to the AI&MLOps Platform Service Details page.
- AI&MLOps Platform Service Details page displays status information and additional feature information, and consists of Details, Tags, Activity History tabs.
Detailed Information
AI&MLOps Platform Service List page lets you view detailed information of the selected resource and edit the information if needed.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform |
| Resource name | Resource name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created the service |
| Creation date and time | Service creation date and time |
| editor | User who edited the service information |
| Modification date | Date and time the service information was modified |
| Dashboard status | Dashboard status value |
| Service name | Service name |
| Admin Email Address | Administrator email address |
| image name | Service image name |
| Version | Image version |
| Service type | Deployed service type |
tag
AI&MLOps Platform Service List page lets you view the tag information of the selected resource, and you can add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
AI&MLOps Platform Service List page lets you view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Access AI&MLOps Platform
To access the AI&MLOps Platform dashboard, you must complete the prerequisite steps.
Preliminary work
To access the AI&MLOps Platform, you must preconfigure the relevant ports and the IP addresses required for connection in the Security Group and Firewall (if using a firewall).
Kubeflow Mini: port 31390 (inbound rules of Security Group, VPC firewall)
To access the cluster’s worker node, you must set an inbound rule for port 22 on the Security Group and Firewall (when using a VPC firewall).
Access Dashboard
To access the AI&MLOps Platform service, follow these steps.
- Click the All Services > AI/ML > AI&MLOps Platform Service menu. You will be taken to the Service Home page of the AI&MLOps Platform service.
- Click the AI&MLOps Platform Service menu on the Service Home page. You will be taken to the AI&MLOps Platform Service List page.
- Click the resource to view detailed information on the AI&MLOps Platform Service List page. You will be taken to the AI&MLOps Platform Details page.
- AI&MLOps Platform Details on the page, click the Access Guide button. The Access Guide popup window opens.
- Access Guide In the popup window, click the dashboard’s URL link. You will be taken to the corresponding dashboard page.
Terminate AI&MLOps Platform
You can cancel the unused service to reduce operating costs. However, canceling the service may cause the running service to stop immediately, so you should thoroughly consider the impact of service interruption before proceeding with the cancellation.
To cancel the AI&MLOps Platform, follow the steps below.
- Click the All Services > AI/ML > AI&MLOps Platform Service menu. Navigate to the Service Home page of the AI&MLOps Platform Service.
- On the Service Home page, click the AI&MLOps Platform Service menu. You will be taken to the AI&MLOps Platform Service List page.
- Click the resource to view detailed information on the AI&MLOps Platform Service List page. You will be taken to the AI&MLOps Platform Details page.
- AI&MLOps Platform Details on the page, click the Cancel Service button. The Cancel Service popup will open.
- After entering the service name for verification, click Confirm.
- When termination is complete, check on the AI&MLOps Platform Service List page whether the resource has been terminated.
13.2.2.1 - Cluster Deployment
Cluster deployment area
In Samsung Cloud Platform, the AI&MLOps Platform creation’s service type selection provides two cloud deployment regions.
Before proceeding with the cluster deployment, be sure to verify the Kubernetes cluster specifications required for installation.
- Regardless of the selected cluster deployment region, you must verify the Kubernetes cluster specifications in advance.
- For detailed specification information, refer to the Cluster Specification guide.
Depending on the selection of the cluster deployment region, the installation details on the AI&MLOps Platform creation service information input page differ.
Deploy from SCP Kubernetes Engine
- Click the All Services > AI/ML > AI&MLOps Platform menu. You will be taken to the Service Home page of AI&MLOps Platform.
- On the Service Home page, click the AI&MLOps Platform Create button. It navigates to the AI&MLOps Platform Create page.
- On the service type selection page of AI&MLOps Platform creation, enter the information required to create the service and select detailed options.Cluster deploymentSelect the Deploy on SCP Kubernetes Engine option.
- On the Service Information Input page of AI&MLOps Platform Creation, enter the information required to create the service, and select detailed options.
- In the Service Information Input area, enter or view the information required to create a service.
Category Required statusDetailed description Service name Required Enter AI&MLOps Platform name - AI&MLOps Platform name cannot be duplicated within a project
Storage Class Required Storage Class is automatically registered Installation node information Lookup View the node information of the selected Kubernetes Engine Admin Email Address Required Enter the administrator (Admin) email address to use for login password Required Enter the password to use for login Confirm Password Required Re-enter password to prevent password errors Table. AI&MLOps Platform service information input fields - Additional Information Input area: enter or select the information required to create a service.
Category Required statusDetailed description tag Selection Select tags to add to the AI&MLOps Platform - Click ‘Add Tag’ to create a new tag or add an existing tag
- You can register up to 50 tags
- The newly added tags will be applied after the service creation is completed
Table. AI&MLOps Platform service additional information input fields
- In the Service Information Input area, enter or view the information required to create a service.
Deploy to a new cluster
- Click the All Services > AI/ML > AI&MLOps Platform menu. You will be taken to the Service Home page of AI&MLOps Platform.
- Service Home page, click the Create AI&MLOps Platform button. It navigates to the Create AI&MLOps Platform page.
- On the Service Type Selection page of the AI&MLOps Platform creation, enter the information required to create the service and select detailed options.Cluster deploymentSelect the Deploy to a new cluster option.
- On the Service Information Input page of AI&MLOps Platform creation, enter the information required to create a service and select detailed options.
In the Service Information Input area, enter or view the information required to create a service.
Category RequiredDetailed description Service name Required Enter AI&MLOps Platform name - AI&MLOps Platform name cannot be duplicated within a project
Storage Class Required Storage Class is automatically registered Installation node information Lookup View the node information of the selected Kubernetes Engine Admin Email Address Required Enter the email address of the administrator (Admin) to be used for login. password Required Enter the password to use for login Confirm Password Required Re-enter password to prevent password errors Table. AI&MLOps Platform Service Information Input ItemsKubernetes Engine Information Input Enter or select the required information in this area.
Category RequiredDetailed description Cluster name Required Cluster name - must start with an English letter and may use English letters, numbers, and special characters (
-)
- Enter within 3 to 30 characters
Control plane settings > Kubernetes version Required Select Kubernetes version Control Area Settings > Control Area Logging Selection Select whether to enable control plane logging - Audit/Event logs from the cluster control plane can be viewed in Cloud Monitoring’s log analysis
- Log storage up to 1 GB for all services within the account is provided for free, and logs exceeding 1 GB are deleted sequentially
- For more details, see Cloud Monitoring > Log Analysis
Network Settings Required Network connection settings for the node pool - VPC: Select a pre‑created VPC
- Subnet: Select a standard Subnet to use from the subnets of the chosen VPC
- Security Group: Click the Search button, then select a Security Group in the Select Security Group popup
- Load Balancer: Provides the
type:LoadBalancerfeature in a Kubernetes Service object- Select a load balancer on the same network
- Select whether to use
- Cannot be changed after configuration
File Storage Settings Required Select the file storage volume to use in the cluster - Default Volume (NFS): Select File Storage using the Search button
- The default Volume file storage provides only the NFS format
Table. Kubernetes Engine Service Information Input Items- must start with an English letter and may use English letters, numbers, and special characters (
Enter or select the required information in the Node Pool Information Input area.
Category Required statusDetailed description Node pool configuration Required Select node pool information - * Items marked with an asterisk are required fields and must be entered
- For the AI&MLOps Platform, image size may continuously increase depending on usage, so setting Block Storage to at least 200 GB enables smooth system configuration
Table. AI&MLOps Platform Service Information Input ItemsReference- A Windows OS node pool can be created only when an additional storage (CIFS) volume is in use in the cluster.
- Volume encryption for node pool Block Storage can only be set at initial creation.
- Enabling encryption may cause performance degradation in some features.
- Only when you have selected the node pool auto‑scaling or shrinking feature can you input node count, minimum node count, maximum node count.
In the Additional Information Input area, enter or select the required information.
Category RequiredDetailed description tag Selection Select tags to add to the AI&MLOps Platform - Click ‘Add Tag’ to create a new tag or add an existing tag
- You can register up to 50 tags
- The newly added tags will be applied after the service creation is completed
Table. AI&MLOps Platform Service Information Input Items
Cluster specifications
To use the AI&MLOps Platform, you need a Kubernetes Engine to install the AI&MLOps Platform. You can select an existing Kubernetes Engine, or you can create a Kubernetes Engine together when creating the AI&MLOps Platform.
The specifications of the Kubernetes cluster required for installation are as follows.
Node pool resource size (composed of 2 or more nodes)
- AI&MLOps Platform: vCPU 32, Memory 128G or more
- Kubeflow Mini: vCPU 24, Memory 96G or more
Kubernetes version
- AI&MLOps Platform v1.9.1 (k8s v1.30)
- Kubeflow Mini v1.9.1 (k8s v1.30)
13.2.2.2 - Kubeflow Usage Guide
Below, we guide you on how to use Kubeflow after creating it.
Add Kubeflow User
Below is a guide on how to use Kubeflow after it has been created.
Kubeflow only creates the account of the single Admin User entered on the initial installation screen.
When using the Kubeflow Dashboard, to add users other than the initial user, you must modify the settings of Dex (the authentication integration component of Kubeflow).
- Dex is deployed in the auth namespace, and its configuration is stored in a configmap named dex.
The following is an example of Dex configuration.
apiVersion: v1
kind: ConfigMap
metadata:
name: dex
namespace: auth
data:
config.yaml: |
issuer: http://dex.auth.svc.cluster.local:5556/dex
storage:
type: kubernetes
config:
inCluster: true
web:
http: 0.0.0.0:5556
logger:
level: "debug"
format: text
oauth2:
skipApprovalScreen: true
enablePasswordDB: true
staticPasswords:
- email: admin@kubeflow.org
hash: $2y$10$Yb9WVbn8pzVSM6fBgKdFae1Bh6Z.XTihi7bNu3sB6/h5bt1JuUOgq
username: admin
userID: 9cb67307-fd6d-4441-9b59-52acd78f4c9e
staticClients:
- id: kubeflow-oidc-authservice
redirectURIs: ["/login/oidc"]
name: 'Dex Login Application'
secret: pUBnBOY80SnXgjibTYM9ZWNzY2xreNGQok apiVersion: v1
kind: ConfigMap
metadata:
name: dex
namespace: auth
data:
config.yaml: |
issuer: http://dex.auth.svc.cluster.local:5556/dex
storage:
type: kubernetes
config:
inCluster: true
web:
http: 0.0.0.0:5556
logger:
level: "debug"
format: text
oauth2:
skipApprovalScreen: true
enablePasswordDB: true
staticPasswords:
- email: admin@kubeflow.org
hash: $2y$10$Yb9WVbn8pzVSM6fBgKdFae1Bh6Z.XTihi7bNu3sB6/h5bt1JuUOgq
username: admin
userID: 9cb67307-fd6d-4441-9b59-52acd78f4c9e
staticClients:
- id: kubeflow-oidc-authservice
redirectURIs: ["/login/oidc"]
name: 'Dex Login Application'
secret: pUBnBOY80SnXgjibTYM9ZWNzY2xreNGQok When the enablePasswordDB value in the configuration is true, Dex stores the list of users defined in staticPasswords from the configmap into its internal storage when the service starts. Therefore, by adding new user entries composed of email, hash, username, and userID to staticPasswords, you can freely add users beyond the initial ones and use the Kubeflow service.
The attribute values for adding a user can be defined as follows.
| parameter | Explanation |
|---|---|
| A value in a standard E‑mail format | |
| hash | Bcrypt algorithm encrypted user password value, and you can directly input the hash value generated by the Bcrypt algorithm
|
| username | User name
|
| userID | A uniquely identifiable ID value
|
From a node where you can use kubectl, use the following command to enter the edit screen of dex configmap.
kubectl edit configmap dex -n authkubectl edit configmap dex -n authstaticPasswords:
- email: admin@kubeflow.org
hash: $2y$10$Yb9WVbn8pzVSM6fBgKdFae1Bh6Z.XTihi7bNu3sB6/h5bt1JuUOgq
username: admin
userID: 9cb67307-fd6d-4441-9b59-52acd78f4c9e
- email: sds@samsung.com
hash: $2y$12$0g5.y86jnrt0v6In5NRCZ.YVuvrAUQ6j/RJYO3rV.kNulaDALOKfq
username: sds
userID: 8961d517-3498-4148-90c9-7e442ee91154staticPasswords:
- email: admin@kubeflow.org
hash: $2y$10$Yb9WVbn8pzVSM6fBgKdFae1Bh6Z.XTihi7bNu3sB6/h5bt1JuUOgq
username: admin
userID: 9cb67307-fd6d-4441-9b59-52acd78f4c9e
- email: sds@samsung.com
hash: $2y$12$0g5.y86jnrt0v6In5NRCZ.YVuvrAUQ6j/RJYO3rV.kNulaDALOKfq
username: sds
userID: 8961d517-3498-4148-90c9-7e442ee91154Since the staticPasswords value in the configmap is applied when the Dex service starts, restart the Dex service using the following command.
kubectl rollout restart deployment dex -n authkubectl rollout restart deployment dex -n authAttempt to log in using new user information.
Verify that after successful login, it transitions to the screen for creating a new Namespace(profile).
The above content was written with reference to the official Kubeflow site. For more details, see Kubeflow Profiles.
How to use Custom Image in Kubeflow Jupyter Notebook
To use a custom image in the Kubeflow Notebook Controller that manages the Notebook life cycle of Kubeflow, you must meet several requirements.
Kubeflow assumes that Jupyter will start automatically when a Notebook image is run. Therefore, you need to set the default command to start Jupyter in the container image.
The following is an example of what should be included in a Dockerfile.
ENV NB_PREFIX
CMD ["sh","-c", "jupyter notebook --notebook-dir=/home/${NB_USER} --ip=0.0.0.0 --no-browser --allow-root --port=8888 --NotebookApp.token='' --NotebookApp.password='' --NotebookApp.allow_origin='*' --NotebookApp.base_url=${NB_PREFIX}"]ENV NB_PREFIX
CMD ["sh","-c", "jupyter notebook --notebook-dir=/home/${NB_USER} --ip=0.0.0.0 --no-browser --allow-root --port=8888 --NotebookApp.token='' --NotebookApp.password='' --NotebookApp.allow_origin='*' --NotebookApp.base_url=${NB_PREFIX}"]The above items are explained as follows.
| parameter | Explanation |
|---|---|
--notebook-dir=/home/jovyan | Set working directory
|
--ip=0.0.0.0 | Allow Jupyter Notebook to accept connections from any IP |
--allow-root | Allow the user to run Jupyter Notebook as root |
--port=8888 | Port configuration |
--NotebookApp.token=’’ –NotebookApp.password=’’ | Disable Jupyter authentication
|
--NotebookApp.allow_origin=’*’ | Allow origin |
--NotebookApp.base_url=NB_PREFIX | Base URL setting |
You can create a Custom Image by referring to the Dockerfile that builds the tesorflow notebook image.
- https://github.com/kubeflow/kubeflow/blob/v1.2.0/components/tensorflow-notebook-image/Dockerfile Please refer to it.
On the Notebook Servers page, click the +NEW SERVER button.
If you have created a Custom Image, check Custom Image on the Kubeflow Notebook Server screen and enter the Custom Image address to create a new Notebook Server.
The above content was written with reference to the Kubeflow official site.
- For more details, see the Kubeflow Notebooks > Container Images documentation on the official Kubeflow website.
13.2.3 - API Reference
13.2.4 - CLI Reference
13.2.5 - Release Note
AI&MLOps Platform
- The AI&MLOps Platform open-source version has been upgraded.
- Kubeflow 1.9
- The AI&MLOps Platform service, which automates repetitive tasks across the entire pipeline of machine learning model development, training, and deployment, has been launched.
- We provide a machine learning platform service based on Kubernetes.
14 - Hybrid Cloud
You can flexibly connect the Samsung Cloud Platform with on‑premises infrastructure to use cost‑optimized cloud services.
14.1 - Edge Server
14.1.1 - Overview
Service Overview
Edge Server provides Edge Cloud to on‑site environments of enterprises that find cloud migration difficult due to issues such as data security, regulations, performance, and latency. This service enables companies to perform data processing and analysis on‑site in real time. Based on edge computing technology, it processes data directly on servers located close to where the data is generated and offers an environment that can be efficiently managed in conjunction with the cloud. This maximizes the speed and efficiency of large‑scale data processing and minimizes data transmission latency through seamless integration with the cloud. In particular, it delivers outstanding performance in domains that require real‑time data processing and rapid decision‑making. Because the servers are deployed near the site, data can be processed quickly without network latency.
Through the Edge Server, you can migrate critical systems to the cloud and easily build a hybrid cloud with Samsung Cloud Platform to leverage its various services. Samsung SDS’s professional technical support organization provides optimal deployment assistance and technical support, considering each customer’s environment, and operates a 24x7 support channel at the Samsung Cloud Platform Support Center. With a delivery system built from multiple service request channels and systems, we can respond swiftly to customer requirements.
Configuration diagram
Provided features
The Edge Server provides the following functions.
- Hybrid Cloud Expansion: Important data is managed on-site, and the demand from companies that want to perform data‑driven operations by leveraging Public Cloud analytics, IoT, private 5G, AI, etc., is increasing. These companies can conveniently carry out data‑based work by building a hybrid cloud with the Edge Server of Samsung Cloud Platform.
- Convenient Integrated Management: To enable rapid processing of local data and quick access to on‑premises systems, we extend cloud services from the edge where data is generated and collected. Additionally, you can conveniently manage Edge Servers in an integrated manner through the Samsung Cloud Platform Console.
- High security and regulatory compliance: By establishing an Edge Computing service environment within the enterprise, ultra‑low‑latency data transmission is possible, and because all data and services reside inside the company, valuable corporate information can be securely protected. Data that requires security and workloads subject to strict regulations use edge resources, while workloads and data less sensitive to security utilize the more cost‑effective public resources of Samsung Cloud Platform.
- Customer-tailored service provision: We provide various virtualization platforms (Kernel-based Virtual Machine(KVM), Container, etc.) according to the user’s environment, and by leveraging pre-configured development environments and related ecosystems, you can adopt new technologies such as AI, machine learning, and big data.
Component
Edge Server provides various standard OS images and standard server types. Users can select the desired service type according to the scale of the service they want to configure.
Edge Manager
Edge Manager is located on the Samsung Cloud Platform and, through the Edge Client, manages the network and resources of Edge Servers installed at customer sites, and creates and manages virtual machines within the Edge Server.
Edge Client
The Edge Client is located on the Edge Server installed at the customer’s site, and through the Edge Manager, it performs KVM creation, deletion, modification, and query functions as well as Edge Server management functions.
Supported operating system versions
In the Edge Server, we supply the operating system (OS) requested by the customer through consultation with the customer.
The representative operating system versions supported by Edge Server are as follows.
| Operating System (OS) | Version |
|---|---|
| CentOS | CentOS 9 or later |
| RHEL | RHEL 8.9, RHEL 9.3, RHEL 9.4 |
| Ubuntu | Ubuntu 18.04, Ubuntu 20.04, Ubuntu 22.04 |
| Rocky Linux | Rocky Linux 8.9, Rocky Linux 9.3, Rocky Linux 9.4 |
Availability by Region
The Edge Server is available in the environments below.
| Region | Availability |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Not provided |
| South Korea South 1 (kr-south1) | Provide |
| South Korea 2 (kr-south2) | Provide |
| South Korea South 3(kr-south3) | Provide |
Preceding Service
This is a list of services that must be pre‑configured before creating the service. Please refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | Security Group | Virtual firewall that controls server traffic |
| Compute | Virtual Server | Virtual server optimized for cloud computing |
14.1.2 - How-to guides
Users can create the Edge Server service by entering the required information and selecting detailed options through the Samsung Cloud Platform Console.
Create Edge Server
You can create and use the Edge Server service from the Samsung Cloud Platform Console.
To create an Edge Server, follow these steps.
All Services > Hybrid Cloud > Edge Server menu. You will be taken to the Edge Server Dashboard page.
On the Edge Server Dashboard page, click the Edge Server Service Request button. You will be taken to the Service Request page.
Service Request page, after entering the relevant information in the service information input area, click the Complete button.
guideIn the task category, select Create Edge Server Service and create it.Input field Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform - Automatically filled with the project’s region
Service Select the service group and service for the given service - Service group: Hybrid Cloud
- Service: Edge Server
Task classification Select the task you want to perform - Create Edge Server service: select if you want to create this service
content Enter detailed information required to create an Edge Server
[Basic Information]- Account ID: Enter the corresponding account ID
- Customer) Name/Company/Department/E-mail/Phone Number: Enter user information
- Desired Service Start Date: Enter the start date the user wishes for the service to be applied
- Host Server OS: Enter the host server OS information to be used
[Application Information]- Purpose of Use: Enter the intended use of the Edge Server
- Example: manufacturing, logistics, robotics, CCTV, video analytics
- Server Type and Quantity: Enter the type and quantity of host servers to be used
- Example: Standard (128vCore/512GB/SSD 7.6TB), High-capacity (128vCore/512GB/SSD 7.6TB+HDD 160TB), GPU_L40s (128vCore/512GB/SSD 7.6TB/L40s*2 units)
- Refer to the Table. Edge Server Specification Information below for detailed information
- Usage Period (default 3 years): Service usage period
Attachment Proceed with upload only if you have additional files you want to share - You can attach up to 5 files, each no larger than 5 MB
- Only files of type doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif can be attached
Table. Detailed description of Edge Server request items- Among the above Table. Edge Server request item details information, Server type and quantity should be verified against the resource information of the corresponding Edge Server and entered.
Category CPU Memory Local HDD GPU General type 128vCore 512GB SSD 7.6TB large capacity 128vCore 512GB SSD 7.6TB, HDD 160TB GPU_L40s 128vCore 512GB SSD 7.6TB L40s 2ea Table. Edge Server specification information
Service Request page, verify the required information entered, and click the Request button.
- This request involves steps such as purchasing a physical server, delivery, configuration, and site setup, and requires a minimum of six weeks of business days.
Check application details
You can view Edge Server service subscription and cancellation details in the Samsung Cloud Platform Console.
You can view the service application and termination request history for Edge Server through the following procedure.
To check the Edge Server service application details, follow the steps below.
- Click the All Services > Management > Support Center menu. You will be taken to the Support Center > Service Home page.
- On the Support Center Service Home page, click the Service Request menu. You will be taken to the Service Request List page.
- On the Service Request List page, click the title of the service request you submitted. You will be taken to the Service Request Details page.
- Check the request status and information on the Service Request Details page.InformationWhen a service request is received, the sales/operations staff verify the service application details and proceed with the Edge Server service for the entered information.
View Edge Server detailed information
The Edge Server service allows you to view and edit the full resource list and detailed information. The Edge Server detail page consists of Details, Task History tabs.
To view detailed information about the Edge Server, follow these steps.
Click the All Services > Hybrid Cloud > Edge Server menu. You will be taken to the Edge Server Dashboard page.
On the Edge Server Dashboard page, click the Edge Server menu. You will be taken to the Edge Server List page.
- Resource items other than the required columns can be added by clicking the Settings button.
Category Required statusDetailed description Edge server name Required User-created Edge Server name Edge Server OS Required User-requested Edge Server operating system Server type Required Edge Server server type Edge server IP Required The IP of the Edge Server requested by the user Service posting date Required Edge Server billing start date and time Service End Date Required Edge Server billing termination time status Required Edge Server status Installation location Select Location where the Edge Server is installed Creator ID Select User who created an Edge Server in Edge Manager Creation Date/Time Select Date and time the Edge Server was created in Edge Manager Table. Edge Server list information
- Resource items other than the required columns can be added by clicking the Settings button.
On the Edge Server List page, click the Edge Server you want to view detailed information for. You will be taken to the Edge Server Details page.
- Edge Server Details At the top of the page, status information and descriptions of additional features are displayed.
Category Detailed description Edge Server status Status of the Edge Server created by the user - Active: The Edge Server is operating normally
- Inactive: The Edge Server cannot provide normal service
Table. Edge Server status information
- Edge Server Details At the top of the page, status information and descriptions of additional features are displayed.
Detailed Information
On the Edge Server Details page, you can view the detailed information of the selected resource and, if necessary, edit that information.
| Category | Detailed description |
|---|---|
| Service | Service group |
| Resource Type | Resource Type |
| SRN | Unique resource ID in Samsung Cloud Platform
|
| Resource Name | Resource Name
|
| Resource ID | Unique resource ID in the service |
| constructor | User who created an Edge Server in Edge Manager |
| Creation Date/Time | Date and time the Edge Server was created in Edge Manager |
| Editor | User who modified the Edge Server in Edge Manager |
| Modification date | Date and time the Edge Server was modified in Edge Manager |
| Edge server name | Name of the edge server |
| Resource usage | CPU, Memory, and Disk utilization ratio relative to the edge server’s total resources |
| Resource Information | Total allocatable resources of the edge server and information on currently allocated resources |
| VM information | Information of each Virtual Server created on the edge server |
Job History
On the Edge Server List page, you can view the operation history of the selected resource.
| Category | Detailed description |
|---|---|
| Task History List | Resource Change History
|
Terminate Edge Server
The Edge Server service whose contract period has expired can be terminated from the Console. If you wish to request termination before the contract period expires, you must first complete the contract termination of the relevant Edge Server through prior consultation between the user’s contract manager and Samsung SDS’s contract manager, and then proceed with termination according to the steps below.
To terminate the Edge Server, follow the steps below.
All Services > Hybrid Cloud > Edge Server menu. You will be taken to the Edge Server Dashboard page.
On the Edge Server Dashboard page, click the Edge Server Service Request button. You will be taken to the Service Request page.
On the Service Request page, select or enter the required information for the Edge Server.
guideIn the task type, select Edge Server Service Termination and apply.Input field Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform Service Select the service group and service for the given service - Service group: Hybrid Cloud
- Service: Edge Server
Task classification Select the task to perform - Terminate Edge Server service: select if you want to terminate this service
content Enter detailed information required for Edge Server termination
[Basic Information]- Account ID: Enter the corresponding account ID
- Customer) Name/Company/Department/E-mail/Phone Number: Enter user information
- Desired Service Termination Date: Enter the service termination date the user wishes
Attachment Proceed with upload only if you have additional files you want to share - You can attach up to 5 files, each no larger than 5 MB
- Only files with the following extensions are allowed: doc, docx, xls, xlsx, ppt, ppts, hwp, txt, pdf, jpg, jpeg, png, gif, tif
Table. Edge Server Service Termination Request Item DetailsService Request page, verify the required information entered, and click the Request button.
- This termination process requires the physical server to be returned, so it takes approximately 3–4 weeks of business days.
14.1.3 - Release Note
Edge Server
- Provides a Local Web feature on the Edge Server, allowing customers to create, read, update, and delete Edge Server resources within their own network.
- We provide the K8s and Storage functions within the Edge Server as an installable package, enabling their use in customer POCs and similar scenarios.
- Through the Samsung Cloud Platform, customers can choose general, high‑capacity, or GPU server types according to their needs.
- We have launched an on-site service that makes it easy to create, delete, and manage Virtual Servers.
14.2 - Oracle Services
14.2.1 - Overview
Service Overview
Oracle Services is an Oracle Cloud service that physically provisions Oracle Cloud resources dedicated to the Samsung Cloud Platform within the Samsung SDS data center, supporting workloads based on Oracle software. Samsung Cloud Platform users can utilize Oracle-based workloads through the Samsung Cloud Platform without separately provisioning Oracle Cloud resources.
Features
Multi-Cloud
- With just the Samsung Cloud Platform console login process, you can easily access the OCI environment. It provides the same high performance, scalability, security, availability, and automation as the services offered by OCI, allowing you to configure Oracle workloads such as Oracle Database, Exadata, and Weblogic without licensing issues.
High level of security
- Samsung Cloud Platform Oracle Services are completely physically and logically isolated from Public OCI, ensuring a high level of security. The OCI provided by Samsung Cloud Platform connects to SCP resources via a fast and reliable dedicated line, and a secure OCI usage environment is guaranteed within the Samsung SDS data center.
Convenient integrated management
- Samsung Cloud Platform customers can use their Samsung Cloud Platform contract information to manage OCI by integrating with existing Samsung Cloud Platform resources, and OCI usage fees are conveniently consolidated and billed through Samsung Cloud Platform.
Service Architecture Diagram
Provided features
Oracle Services provides the following functions.
User account integration between Samsung Cloud Platform and OCI
- Automatically create and register OCI tenancy/account using the Account and IAM User information of Samsung Cloud Platform users.
- Through Single Sign-On (SSO), you can access the OCI web console without additional login simply by accessing the Samsung Cloud Platform console.
Connecting/Extending User Environments between Samsung Cloud Platform and OCI
- Connect and extend the user’s Samsung Cloud Platform VPC to the user’s OCI VCN environment
- Establish a BGP peering connection between the Samsung Cloud Platform Transit Gateway and the OCI DRG using a pre‑provisioned dedicated line between Samsung Cloud Platform and OCI.
Provides functionality to initially configure the OCI internal network
- Provides a Blueprint feature that initially configures the essential prerequisite products for using Oracle DB, Exadata, and Weblogic.
- VCN, Private Subnet, Service Gateway creation, DRG-VCN attachment, one-click IP registration configuration
- Provides a Blueprint feature that initially configures the essential prerequisite products for using Oracle DB, Exadata, and Weblogic.
- Users can easily request and use the required OCI services using the OCI web console.
View OCI usage details and consolidated billing through Samsung Cloud Platform
Availability by Region
Oracle Services are available in the environments below.
| Region | Whether provided |
|---|---|
| Korea West (kr-west1) | Provide |
| Korea East (kr-east1) | Provide |
| South Korea South 1 (kr-south1) | Not provided |
| South Korea 2 (kr-south2) | Not provided |
| South Korea South 3 (kr-south3) | Not provided |
Constraints
You can request Oracle Services only when the requesting account is registered with the organization (orgarnization).
Preceding Service
This is a list of services that must be pre-configured before creating the service. Refer to the guide provided for each service for details and prepare in advance.
| Service Category | Service | Detailed description |
|---|---|---|
| Networking | VPC | A service that provides an isolated virtual network in a cloud environment |
| Networking | VPC > Transit Gateway | Multi-gateway service for connecting to the customer network or acting as a hub for connections among multiple VPCs |
14.2.2 - How-to guides
Users can enter the required information for Oracle Services and select detailed options through the Samsung Cloud Platform Console to create the service.
Create Oracle Services
You can create Oracle Services in the Samsung Cloud Platform Console and use them.
Only one Oracle Service can be applied for per project.
- To proceed with a new creation, cancel the existing Oracle Services and create it again.
To create Oracle Services, follow these steps.
- In the All Services > Hybrid Cloud > Oracle Services menu, click the Create Service button. 1. Go to the Service Home page of Oracle Services.
- On the Service Home page, click the Create Oracle Services button. 2. Navigate to the Create Oracle Services page.
- On the Oracle Services Creation page, enter the information required to create the service.
- Enter the required information in the Service Information Input area.
Category required statusDetailed description Oracle Services name Required Oracle Services name - must start with a lowercase English letter and be entered using lowercase English letters, numbers, and special characters (
-) with a length of 3 to 30 characters
Explanation option Enter additional description for Oracle Services Table. Oracle Services service information input items - must start with a lowercase English letter and be entered using lowercase English letters, numbers, and special characters (
- In the Additional Information Input area, enter or select the required information.
Category required statusDetailed description Tenancy selection option The tenancy name assigned to the user’s Organization - The assigned tenancy name of the account’s Organization is displayed automatically, so it cannot be selected
- To request a service, the account must belong to an Organization. Before creating the service, the account’s Organization must be created and joined
tag Selection Add Tag - Up to 50 per resource can be added
- After clicking the Add Tag button, input or select Key, Value values
Table. Oracle Services additional information input fields
- Enter the required information in the Service Information Input area.
- Review the detailed information and estimated charges generated in the summary panel, and click the Create button.
- When creation is complete, check the created resource on the Resource List page.
- It can be used only after the service is created and the administrator approves the usage request. * For detailed information about service usage approval, click ? > Support Center > Contact Us to view the details.
Check detailed information of Oracle Services
The Oracle Services service can view and edit the full resource list and detailed information from the Oracle Services menu. Oracle Services Details page consists of Detail Information, Tags, Operation History tabs.
Detailed information about Oracle Services can only be viewed after the service request is submitted and the operator has completed approval.
- To view detailed information, verify that the service status has changed to Active after the service approval is complete.
To view detailed information about Oracle Services, follow these steps.
- Click the All Services > Hybrid Cloud > Oracle Services menu. 1. Go to the Service Home page of Oracle Services.
- On the Service Home page, click the Oracle Services menu. 2. Oracle Services List Go to the page.
- On the Oracle Services List page, click the resource to view detailed information. 3. Navigate to the Oracle Services Details page.
- Oracle Services Details page displays status information and additional feature information, and is composed of Details, Tags, Activity History tabs.
Category Detailed description status Current service status - Creating: Service request in progress
- Active: Service approved and successfully created
- Creation Failed: Error occurred during creation
- Deletion Failed: Error occurred during deletion
- Denied: Operator approval denied
- Requested: Awaiting operator approval
- Deleting: Service termination request in progress
Service access Show Oracle Cloud console access window button Service termination Cancel service button Table. Oracle Services status information and additional feature items
- Oracle Services Details page displays status information and additional feature information, and is composed of Details, Tags, Activity History tabs.
Detailed Information
Detailed Information tab allows you to view detailed information of the selected Oracle Services.
| Category | Detailed description |
|---|---|
| service | Service name |
| Resource Type | Resource Type (Oracle Services) |
| SRN | Resource unique ID in Samsung Cloud Platform |
| Resource name | Resource Name |
| Resource ID | Unique resource ID in the service |
| Constructor | Service creation request user |
| Creation date and time | Service creation date and time |
| Modifier | Service modification request user |
| Modification date | Service modification timestamp |
| Tenancy name | Tenant name assigned to the Organization |
| Oracle Services NW configuration | Oracle Services Network Configuration Request and Modification
|
| Compartment name | Resource name connected to the service
|
| Connection between SCP VPC ↔ Oracles Service | Click Oracle Services line request/modify/termination shortcut to request an uplink line from the service request popup
|
| Dynamic Group configuration | Dynamic Group configuration status
|
| Virtual Circuit OCID | Virtual Circuit OCID path |
| Customer On-Prem ↔ Oracle Services connection | Oracle Services Add Connection Configuration Request Shortcut Click to request a service connection in the service request popup
|
| Explanation | Oracle Services service additional description
|
| Connected user | List of users who can access the Oracle Services
|
Tag
Tag tab lets you view the tag information of the selected resource, and add, modify, or delete it.
| Category | Detailed description |
|---|---|
| Tag list | Tag list
|
Job History
Work History tab allows you to view the selected resource’s task history.
| Category | Detailed description |
|---|---|
| Task History List | Resource change history
|
Oracle Services Network Configuration and Access
You can connect the user VPC of Samsung Cloud Platform with the VCN (Virtual Cloud Network) in Samsung Cloud Platform Dedicated Oracle Cloud to use Oracle Services. To connect a VPC with a VCN in Oracle Cloud, you must configure the Oracle Services network and then request a dedicated uplink for Oracle Services. When the Oracle Services network configuration and uplink request are completed, the connection between Samsung Cloud Platform VPC - TGW - dedicated line segment - Oracle Cloud DRG - VCN is completed, allowing various hybrid cloud configurations such as connecting the user’s VM in the VPC environment to the DB in the Oracle Cloud VCN.
Request Oracle Services network configuration
When using Samsung Cloud Platform Dedicated Oracle Cloud, you must create and configure the required network resources for the user. This configuration request uses the user’s input data with the Oracle Cloud API to provide a service provisioning role that creates and deploys Oracle Cloud network services, enabling users to easily use Oracle software such as Oracle DBCS (Database Cloud Service) and ExaCS (Exadata Cloud Service).
To request the network configuration of Oracle Services, follow these steps.
- Click the All Services > Hybrid Cloud > Oracle Services menu. 1. Go to the Service Home page of Oracle Services.
- On the Service Home page, click the Oracle Services menu. 2. Navigate to the Oracle Services List page.
- On the Oracle Services List page, click the resource to view detailed information. 3. Navigate to the Oracle Services Details page.
- On the Oracle Services Details page, click the edit icon of Oracle Services NW Configuration. 4. Oracle Services Network Configuration Edit window appears.
- Enter or select detailed information in the Oracle Services Network Configuration Edit window and click OK.
Category Detailed description Select SCP Transit Gateway Select the Transit Gateway to connect to Samsung Cloud Platform Dedicated Oracle Cloud VCN name Enter the VCN name to create in Samsung Cloud Platform Dedicated Oracle Cloud VCN IPv4 CIDR block Enter the VCN’s IPv4 CIDR block - Example: 10.0.0.0/16
Using DNS Hostname (VCN) To use Oracle Exa/DBCS, set to use - To assign an instance host name using VCN DNS or a third‑party DNS, use setting is required
DNS Label (VCN) The DNS label is generated from the value entered by the user - VCN name, but it may be changed according to DNS label constraints
Subnet name Enter the name of the Private subnet to be created in the VCN. Subnet IPv4 block Enter the IPv4 CIDR block of the private subnet - Example: 10.0.0.0/24
Using DNS Hostname (Subnet) To use Oracle Exa/DBCS, set to Use - To assign an instance host name using VCN DNS or third‑party DNS, Use setting is required
DNS Label (Subnet) DNS label is generated from the value entered by the user - It is set to be the same as the Subnet name, but may be changed according to DNS label constraints
Subnet resource logging Set whether to enable Subnet resource logging - Set when selected, you can receive resource tracing, troubleshooting, and data insight information
Routing table rule Enter Dynamic routing rules in Samsung Cloud Platform Dedicated Oracle Cloud Table. Oracle Services network configuration items
Oracle Services network configuration order
When you request an Oracle Services network configuration, it attempts to provision and automatically configure the network service using the values entered by the user. If users need to update after provisioning, they can directly update the configurable settings in the Oracle Cloud web console after creation.
- Create an Oracle Cloud VCN.
- Create an Oracle Cloud DRG.
- DRG(Dynamic Routing Gateway) is an optional virtual router that can be added to a VCN, and it serves a role similar to the Samsung Cloud Platform Transit Gateway. * This gateway provides a private network traffic path between the VCN and the on‑premises network.
- Connect the DRG to the VCN.
- Enable the VCN’s “Use DNS Hostnames” option.
- After defining FastConnect, create a Virtual Circuit for logical allocation.
- FastConnect is a dedicated line product for Oracle Cloud that serves a role similar to Samsung Cloud Platform Direct Connect.
- When defining FastConnect, set it to the same bandwidth as the corresponding TGW’s bandwidth.
- Create a Private Subnet within the VCN.
- Enable the “Use DNS Hostnames” option for the subnet.
- Add the DRG to the VCN Route Table with 0.0.0.0.
- The default input value of DRG is 0.0.0.0.
- Configure user logging.
- Create the log group first, then configure logging.
Request to connect Samsung Cloud Platform VPC with Oracle Services
To provide Oracle Service, a connection as shown below has been established between Samsung Cloud Platform and Oracle Cloud.
- A common network is configured for service/authentication integration and console connection between Samsung Cloud Platform and Oracle Cloud.
- Through the Samsung Cloud Platform Oracle product, you configure a per‑user service connection network, and based on the physical network link between Samsung Cloud Platform and Oracle Cloud, you connect the Samsung Cloud Platform VPC to the Oracle Cloud VCN.
- Workloads configured in Oracle Cloud (e.g. * Computing, DB instance) can be utilized using a pre-configured Cross network between Samsung Cloud Platform and Oracle Cloud.
- Through Samsung Cloud Platform TGW and Direct Connect routing configuration, customers can directly access and use databases configured in Oracle Cloud even in network environments connected via Direct Connect or TGW Uplink.
- A single connection architecture between Samsung Cloud Platform and Oracle Cloud can be implemented via TGW peering and TGW-to-TGW connections, and can be commonly used across multiple projects and VPCs. * However, when used jointly, performance and bandwidth considerations are required.
- The TGW of Samsung Cloud Platform and the DRG of Oracle Cloud must have a 1:1 connection architecture.
- It is possible to share a single connection architecture across multiple projects and VPCs through peering.
- However, it is not possible to peer multiple Samsung Cloud Platform VPCs using a single Oracle Cloud DRG.
Apply for Oracle Services Uplink line
After completing the Oracle Services network configuration, you must request a dedicated line connection to the DRG via the TGW of the Samsung Cloud Platform.
- Oracle Services Uplink line connection can only be requested after network configuration.
- The Samsung Cloud Platform TGW to be uplinked can only have a 1:1 relationship with Oracle Cloud. * Before requesting an uplink, first create a new TGW dedicated to Oracle Services, then proceed with the TGW‑VPC connection.
- Oracle Services uplink requests must be processed through the Hybrid Cloud > Oracle Services > Oracle Services Line Request/Modification/Cancellation Shortcut menu.
- If you request an uplink connection from Networking > Transit Gateway > Uplink line, the request details may not be accurately conveyed to the responsible engineer.
To request an Uplink line from Oracle Services, follow the steps below.
- All Services > Hybrid Cloud > Oracle Services Click the menu. 1. Go to the Service Home page of Oracle Services.
- On the Service Home page, click the Oracle Services menu. 2. Go to the Oracle Services List page.
- On the Oracle Services List page, click the resource to view detailed information. 3. Navigate to the Oracle Services Details page.
- On the Oracle Services Details page, click the Oracle Services Line Request/Modification/Termination Shortcut. 4. Go to the Service Request page.
- On the Service Request page, after entering the relevant information in the service information input area, click the Complete button.
Input item Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform - Automatically filled with the project’s region
service Select the service group and service for the given service - Service Group: Hybrid Cloud
- Service: Oracle Services
Task classification Select the task to perform - Oracle Services Uplink line request: Select if you are applying for this service
content Enter detailed information to connect the L3 switch for linking the user VPC TGW to Oracle Services - Enter applicant information: user email, name, and contact details. The application details, progress, and results will be delivered via email.
- Enter the customer IP range information to connect to the Oracle Cloud dedicated for Samsung Cloud Platform, along with the Samsung Cloud Platform TGW and OCI virtual circuit information
- Target DC/Region identifier: Korea (Seoul)/ap-seoul-2
- Customer OCI IP range: Enter the IP range to connect to the Oracle Cloud dedicated for Samsung Cloud Platform (e.g., 10.10.10.0/24)
- Samsung Cloud Platform VPC range communicating with OCI: Enter the Samsung Cloud Platform VPC range connected to Oracle Cloud (e.g., 20.20.20.0/24)
- SCP TGW name: Enter the TGW name to connect to the Oracle Cloud dedicated for Samsung Cloud Platform (see: Samsung Cloud Platform > Networking > TGW)
- SCP TGW resource ID: Enter the TGW ID to connect to the Oracle Cloud dedicated for Samsung Cloud Platform (see: Samsung Cloud Platform > Networking > TGW > Details)
- OCI virtual circuit OCID: Enter the OCID of the Virtual Circuit created in Network Configuration on Oracle Cloud (see: Samsung Cloud Platform > Hybrid Cloud > Oracle Services > Details)
- You can check the progress in the service request menu
- If there is a work account of the network department that can coordinate tasks, enter it additionally
Table. Oracle Services network configuration items
Request to configure connection with Oracle Services for the client
After completing the Oracle Services network configuration, a direct connection between the client and Oracle Services must be set up.
- A connection with Oracle Services can only be requested after the network is configured.
- A physical connection (cable installation) between the client and Oracle Services is required before applying for a direct connection configuration.
- When connecting to the Samsung Cloud Platform device for integration with Oracle Services and the client (On-Prem), the connection is made via the BGP routing protocol.
- To request a direct connection configuration between the client and Oracle Services, be sure to apply for the service via the Hybrid Cloud > Oracle Services > Oracle Services Details > Oracle Services Add Connection Configuration Request Shortcut menu.
To request a direct connection configuration between the client and Oracle Services, follow these steps.
- Click the All Services > Hybrid Cloud > Oracle Services menu. 1. Go to the Service Home page of Oracle Services.
- On the Service Home page, click the Oracle Services menu. 2. Navigate to the Oracle Services List page.
- On the Oracle Services List page, click the resource to view detailed information. 3. Oracle Services Details Navigate to the page.
- On the Oracle Services Details page, click the Oracle Services Add Connection Configuration Request Shortcut. 4. Navigate to the service request page.
- On the service request page, after entering the relevant information in the service information input area, click the Complete button.
- After requesting the service, configuring the connection between the client and Oracle Services can take up to seven days.
Input item Detailed description Title Title of the service you want to request Region Select location of Samsung Cloud Platform - Automatically filled with the project’s region
service Select the service group and service for the given service - Service Group: Hybrid Cloud
- Service: Oracle Services
Task classification Select the task to perform - Request direct connection setup between the client and Oracle Services: Select if you are applying for this service
content Enter detailed information to connect the L3 switch for user On-Prem ↔ Oracle Services connection - Enter applicant information: user email, name, and contact details. Application details, progress, and results will be delivered via email.
- Enter the customer IP range information, Samsung Cloud Platform TGW, and OCI virtual circuit details to connect to the Oracle Cloud dedicated for Samsung Cloud Platform
- Target DC/Region identifier: Korea (Seoul)/ap-seoul-2
- Customer OCI IP range: Enter the IP range to connect to the Oracle Cloud dedicated for Samsung Cloud Platform (e.g., 10.10.10.0/24)
- Samsung Cloud Platform VPC range communicating with OCI: Enter the VPC range of Samsung Cloud Platform connected to Oracle Cloud (e.g., 20.20.20.0/24)
- SCP TGW name: Enter the TGW name to connect to the Oracle Cloud dedicated for Samsung Cloud Platform (see: Samsung Cloud Platform > Networking > TGW)
- SCP TGW resource ID: Enter the TGW ID to connect to the Oracle Cloud dedicated for Samsung Cloud Platform (see: Samsung Cloud Platform > Networking > TGW > Details)
- OCI virtual circuit OCID: Enter the OCID of the Virtual Circuit created in Network Configuration on Oracle Cloud (see: Samsung Cloud Platform > Hybrid Cloud > Oracle Services > Details)
- You can check the progress in the service request menu
- If there is a work account of the network department that can coordinate tasks, enter it additionally
Table. Oracle Services connection additional configuration request items
- After requesting the service, configuring the connection between the client and Oracle Services can take up to seven days.
Connecting to Oracle Services
After connecting to Oracle Services, you can perform Single Sign On (SSO) for Oracle Cloud login and access the Customer console.
- Since it is an Oracle Cloud dedicated to the Samsung Cloud Platform and completely separate from Public Oracle Cloud, existing Public Oracle Cloud accounts cannot be used.
- You can only access after applying for Oracle Services and after the administrator approves the service usage.
To access Oracle Services, follow these steps.
- Click the All Services > Hybrid Cloud > Oracle Services menu. 1. Go to the Service Home page of Oracle Services.
- On the Service Home page, click the Oracle Services menu. 2. Go to the Oracle Services List page.
- On the Oracle Services List page, click the resource to view detailed information. 3. Go to the Oracle Services Details page.
- On the Oracle Services Details page, click the Service Access button. 4. Oracle Cloud Console Login window appears.
- In the Oracle Cloud Console Login window, after entering user information, click Samsung Cloud Platform Login.
- In the logged-in state of Samsung Cloud Platform, you can log in to Oracle Cloud via SSO.
- Enter the 6-digit OTP generated in the mobile app, then click Confirm.
- After the user information is authenticated, you are taken to the Tenancy page in Oracle Cloud.
Terminate Oracle Services
Cancelling unused Oracle Services can reduce operating costs.
To cancel Oracle Services, follow the steps below.
- Click the All Services > Hybrid Cloud > Oracle Services menu. 1. Go to the Service Home page of Oracle Services.
- On the Service Home page, click the Oracle Services menu. 2. Navigate to the Oracle Services List page.
- On the Oracle Services List page, click the resource to be terminated. 3. Oracle Services Details Navigate to the page.
- On the Oracle Services Details page, click the Service Termination button.
- When the termination is complete, check the resource termination status in the Oracle Services list.
Delete resources in a Compartment
Cancellation of Oracle Services products is only possible when all resources within the user’s Compartment have been deleted.
To check for remaining resources and delete them, follow the steps below.
- After clicking the top resource explorer in the Oracle Cloud console, click Advanced resource query. 1. Enter the Resource Explorer.
- Show basic search mode click.
- Click Search and Filter, then select Compartment.
- Select the Compartment to delete.
- Compartment starts with PROJECT- xxx and is located under the Root.
- Click Apply Filter to check the resources in the compartment to be deleted.
- Delete all resources in the compartment.
14.2.2.1 - Setting Up Proxy for Oracle Web Console Access
The Oracle Cloud web console used to create, read, update, and delete Oracle Services can be accessed only through the Samsung Cloud Platform. To access the Oracle console, you must configure a web browser proxy in the user’s network environment.
Connecting to the Oracle console follows the steps below.
- After logging into the Samsung Cloud Platform console, access Oracle Services.
- Oracle Cloud can only be accessed via the Samsung Cloud Platform because access to the Internet and external networks is blocked.
- To access the Oracle Cloud console, you must configure the Oracle Cloud web proxy located within the Samsung Cloud Platform in your web browser.
- When a user attempts to access the login link provided in the Samsung Cloud Platform console using a web browser, the connection is made through the proxy configured in the web browser.
Setting the web browser proxy according to the user’s network environment
You can set the Oracle Cloud web proxy in the system settings’ web proxy configuration and use the Samsung Cloud Platform Oracle Service product. Depending on the security characteristics of the user environment, you can route connections through an internal proxy, or configure the user client to add a proxy auto‑configuration (PAC file) so that direct connections are possible.
Creating a PAC file
You can generate a PAC file to access the Oracle Cloud web console.
If you are a Samsung SDS employee, download the Developer PAC file from the following link. The branch settings for accessing the Oracle Cloud web console from the intranet are registered in the Developer PAC file.
- sdsdev.pac address: http://70.10.5.20/dev-pac.pac
To create a PAC file manually, write the following PAC file using an editor such as Notepad, or download it and save it to disk.
function FindProxyForURL(url,host)
{
//* Local Loopback return DIRECT *//
if (shExpMatch(url,"*localhost*") || shExpMatch(url,"*127.0.0.1*")) return "DIRECT";
//* URL Miss return DIRECT *//
if (!isResolvable(host)) return "DIRECT";
if (shExpMatch(host,"*.ap-suwon-1.oci.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (shExpMatch(host,"*.oci.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (shExpMatch(host,"*.ap-suwon-1.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (shExpMatch(host,"*.ap-suwon-idcs-1.identity.oci.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (shExpMatch(host,"*.ap-chunchen-2.oci.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (shExpMatch(host,"*.oci.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (shExpMatch(host,"*.ap-chunchen-2.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (shExpMatch(host,"*.ap-chunchen-idcs-2.identity.oci.oraclecloud35.com")) {return "PROXY 42.15.1.42:8080";} // TED
if (dnsDomainIs(host,"locales.plugins.oci.oraclecloud.com")) {return "DIRECT";} //
if (dnsDomainIs(host,"ocsp.digicert.com")) {return "DIRECT";} //
else { return "DIRECT"; }
}
Register PAC file on client PC
If you download the PAC file and register it on your PC, you can access the Oracle Cloud web console through the Samsung Cloud Platform.
To register a developer PAC file in the proxy settings, follow these steps.
- In the Windows search box, search for Proxy Settings and click the result.
- Click Windows Settings > Network and Internet > Proxy to go to the proxy settings page.
- On the proxy page, click Automatic proxy configuration > Edit configuration script.
- Set the Use configuration script option to On and enter the pac file that generated the script address.
- Enter http://70.10.5.20/dev-pac.pac.
- Click Save to complete registration.
- After accessing the Samsung Cloud Platform using browsers such as Chrome or Edge, follow the Oracle Cloud Console link provided by the Samsung Cloud Platform.
- When registering a PAC file on the client PC and connecting directly, the network path is as follows.
Configure connection when a separate proxy server is present (register forwarding information on the proxy server)
Depending on the user environment, a proxy managed by the network/security administrator may already be installed for security purposes. In such cases, you need to request the proxy administrator to add a proxy configuration for accessing the Samsung Cloud Platform Oracle service.
- When requesting the proxy administrator to register forwarding information, provide the following details.
프록시 설정 URL
*.ap-suwon-1.oci.oraclecloud35.com
*.ap-suwon-1.oraclecloud35.com
*.ap-suwon-idcs-1.identity.oci.oraclecloud35.com
*.ap-chuncheon-2.oci.oraclecloud35.com
*.ap-chuncheon-2.oraclecloud35.com
*.ap-chuncheon-idcs-2.identity.oci.oraclecloud35.com
프록시 IP/port
42.15.1.42:8080
- When connecting by registering a forward setting on the internal proxy, the network path is as follows.
If the network environment passes through other separate security devices
When a separate security device is installed and used in addition to a proxy, you must provide the network/security administrator with a diagram of the Samsung Cloud Platform Oracle Cloud web console connection and carry out the connection configuration. Contact the internal network/security administrator for proxy settings.
Apply for firewall registration
If a firewall is installed in the customer’s network environment to control external access, you must register the proxy server with the firewall to use Samsung Cloud Platform. When applying for firewall registration, use the information below.
- Source IP: User PC IP Address Destination IP: Oracle Cloud web proxy IP Address (42.15.1.42)
- Protocol/port: TCP/8080
14.2.3 - Release Note
Oracle Services
- In the Samsung Cloud Platform console, users can modify the name of the Oracle Services compartment assigned to them.
- A menu for requesting additional Oracle Services connection configuration, enabling customers (On-Premise) to apply for a connection to Oracle Services, has been added.
- To support workloads based on Oracle S/W, we physically configure OCI (Oracle Cloud Infrastructure) resources within the Samsung SDS data center and provide OCI services.
15 - Developer Tools
15.1 - MCP Server
15.1.1 - Overview
Service Overview
The MCP Server is an MCP (Model Context Protocol) server that provides services enabling SCP information and resource management through the AI Assistant Tool. You can access the various documents (User Guide, API/CLI Reference, Knowledge Center, etc.) provided by SCP in real time and immediately verify the relevant information. Additionally, we provide a service that enables you to check information for managing SCP resources and resolving issues via the AI Assistant through the MCP Server.
Provided Features
You can use the following features by utilizing the MCP Server.
- SCP Knowledge Acquisition: You can quickly and easily view information about various SCPs provided by SCP Documentation.
- Resource Main Information Check: You can verify and manage various resources of the SCP you are using through the AI Assistant Tool without going through the SCP Console.
Constraints
The MCP Server’s constraints are as follows.
- Currently, it is provided only for the Documentation MCP Server.
- Support services will be expanded in the future.
Preceding Service
The MCP Server has no prerequisite service.
15.1.2 - How-to guides
15.1.2.1 - Docs mcp server
MCP Server User Guide
A tool based on MCP (Model Context Protocol) searches and invokes MCP server tools using the documentation managed in SCP.
Search the documents below and provide the data.
User Guide : https://docs.e.samsungsdscloud.com/userguide/
Architecture Center : https://docs.e.samsungsdscloud.com/arch_cent/
Knowledge Center : https://docs.e.samsungsdscloud.com/knowledge_cent/
FAQ(Service Portal) : https://cloud.samsungsds.com/serviceportal/support/faq.html
Documentation MCP Server Integration Guide
MCP Server settings: streamable http type
{
"mcpServers": {
"scp-knowledge-mcp-server": {
"type": "http",
"url": "https://scp-docs-mcp.kr-west1.e.samsungsdscloud.com/mcp"
}
}
}
Tools
Query Knowledge Base : Responds with an appropriate document from SCP’s documentation based on the user’s query.
[{
"content" : "Samsung Cloud Platform은 컴퓨팅, 스토리지, 네트워킹, 데이터베이스 등 기업에 필요한 다양한 자원 풀을 가상화하여 제공하는 클라우드 환경입니다.",
"metadata" : {
"source" : "https://docs.e.samsungsdscloud.com/userguide/scp_common/overview/#samsung-cloud-platfo",
"label" : "Samsung Cloud Platform"
}
}]
Documentation Server configuration example
Color mode{ "mcpServers": { "scp-knowledge-mcp-server": { "type": "http", "url": "https://scp-docs-mcp.kr-west1.e.samsungsdscloud.com/mcp" } } }{ "mcpServers": { "scp-knowledge-mcp-server": { "type": "http", "url": "https://scp-docs-mcp.kr-west1.e.samsungsdscloud.com/mcp" } } }Code block. Task execution example Documentation Server configuration example result
16 - Release note
17 - Glossary
18 -
Virtual Server
- Creation of shared images is limited based on the OS disk size.
- If the OS disk size is 500 GB or larger, you cannot create a shared Image.
- The AIOS service integration has been stopped.
- Due to the discontinuation of the AIOS service, the AIOS integration service (LLM Endpoint) has been removed from Virtual Server.
- Additional OS Image Provision
- A standard image has been added. * (Window server 2016)
- SSD volumes with configurable IOPS and throughput have been added.
- When creating Block Storage, you can select the SSD_Provisioned disk type.
- You can set the maximum IOPS and throughput values.
- You can view the Virtual Server ServiceWatch metric monitoring graph on the detail page.
- Additional OS Image provision
- A standard image has been added. * (Alma Linux 9.6, Oracle Linux 9.6, RHEL 9.6, Rocky Linux 9.6)
- Add new Server Group policy
- The Partition (distributed placement of Virtual Server and Block Storage) policy has been added.
- You can install the Virtual Server ServiceWatch Agent to collect custom metrics and logs.
- You can change the server name on the Virtual Server detail page in the Samsung Cloud Platform Console.
- When the server name is changed, the OS’s Hostname is not changed, and only the information within the Samsung Cloud Platform Console is updated.
- Provision of ServiceWatch service integration
- You can monitor data through the ServiceWatch service.
- Add Virtual Server feature
- IP, Public NAT IP, and Private NAT IP configuration features have been added.
- An LLM Endpoint is provided for using LLMs.
- When creating a Virtual Server, you can select an OS image subscribed from the Marketplace.
- Second-generation server type has been added.
- Add a second‑generation (s2) server type based on Intel 4th‑generation (Sapphire Rapids) processors. * For more details, see Virtual Server Server Type.
- The method for sharing images between accounts has changed.
- qcow2 Image or shared Image can be newly created and shared.
- Add Virtual Server feature
- The NAT configuration feature has been added to Virtual Server.
- Additional OS Image provision
- A standard Image has been added. * (Alma Linux 8.10, Alma Linux 9.4, Oracle Linux 8.10, Oracle Linux 9.4, RHEL 8.10, RHEL 9.4, Rocky Linux 8.10, Rocky Linux 9.4, Ubuntu 24.04)
- An image for Kubernetes has been added. * You can create a Kubernetes Engine using an image for Kubernetes.
- Add second-generation server type
- Add second-generation (h2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor.
- For more details, see Virtual Server Server Type
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- The Virtual Server service has been officially launched.
- We have launched a virtualized server that can be freely allocated and used as needed, without the need to purchase infrastructure resources individually.
- We have launched a virtualized server that can be freely allocated and used as needed, without the need to purchase infrastructure resources individually.
- You can change the server name on the Virtual Server detail page in the Samsung Cloud Platform Console.
- When the server name is changed, the OS’s Hostname is not changed, and only the information within the Samsung Cloud Platform Console is updated.
- Provision of ServiceWatch service integration
- You can monitor data through the ServiceWatch service.
- Add Virtual Server feature
- The IP, Public NAT IP, and Private NAT IP configuration features have been added.
- An LLM Endpoint is provided for LLM usage.
- When creating a Virtual Server, you can select an OS image subscribed from the Marketplace.
- The second-generation server type has been added.
- Add a second-generation (s2) server type based on Intel 4th‑generation (Sapphire Rapids) processors. * For more details, see Virtual Server Server Type.
- The method for sharing images between accounts has changed.
- qcow2 Image or shared Image can be newly created and shared.
- Add Virtual Server feature
- The NAT configuration feature has been added to Virtual Server.
- Additional OS Image provision
- A standard Image has been added. * (Alma Linux 8.10, Alma Linux 9.4, Oracle Linux 8.10, Oracle Linux 9.4, RHEL 8.10, RHEL 9.4, Rocky Linux 8.10, Rocky Linux 9.4, Ubuntu 24.04)
- An image for Kubernetes has been added. * You can create a Kubernetes Engine using an image for Kubernetes.
- Add second-generation server type
- Add second-generation (h2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For more details, see Virtual Server 서버 타입
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- The Virtual Server service has been officially launched.
- We have launched a virtualized server that can be freely allocated and used as needed, without the need to purchase infrastructure resources individually.
- We have launched a virtualized server that can be freely allocated and used as needed, without the need to purchase infrastructure resources individually.
Virtual Server Auto-Scaling
- The Virtual Server and Load Balancer status check feature has been added.
- Check the status of Virtual Server and Load Balancer and automatically replace servers that are in an Unhealthy state.
- You can attach File Storage to a Launch Configuration.
- When creating a Launch Configuration, you can attach up to five File Storage Volumes.
- You can monitor data by integrating with the ServiceWatch service.
- The termination feature for Virtual Servers created in an Auto-Scaling Group has been improved.
- When a Virtual Server is terminated, the Load Balancer is automatically detached.
- The Desired server count remains unchanged, and scale-out is performed according to the Desired check batch.
- Added a notification feature to Virtual Server Auto-Scaling.
- You can add notification settings in the creation or detail screen of an Auto-Scaling Group.
- You can set scaling policies when creating an Auto-Scaling Group.
- Added a Metric Type to the Auto-Scaling Group policy.
- Add: Memory Usage, Network In(bytes), Network Out(bytes), Network In(Packets), Network Out(Packets)
- You can set the Draining Timeout when connecting to a Load Balancer.
- In an Auto-Scaling Group, up to 50 Virtual Servers can be connected, and up to 3 LB server groups and ports can be attached.
- Virtual Server Auto-Scaling feature change
- It will be released in conjunction with the Load Balancer service launching in February 2025.
- The NAT configuration feature has been added to the Auto-Scaling Group.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Virtual Server Auto-Scaling creates an Auto-Scaling Group through a Launch Configuration and monitors and manages the servers.
- Provides a scheduling method that allows setting the desired number of servers at a specified time, and a policy method that adjusts the number of servers based on CPU utilization.
GPU Server
- Add Kubernetes image
- When creating a GPU Server, you can select the Kubernetes image (Ubuntu).
- An SSD volume with configurable IOPS and throughput has been added.
- When creating Block Storage, you can select the SSD_Provisioned disk type.
- You can set the maximum IOPS and Throughput values.
- Provision of ServiceWatch service integration
- You can monitor data through the ServiceWatch service.
- When creating a GPU server, you can select a RHEL image.
- Keypair management feature has been added.
- You can generate a keypair for use, or retrieve a public key and apply it.
- Add GPU Server feature
- The IP, Public NAT IP, and Private NAT IP configuration features have been added.
- An LLM Endpoint is provided for LLM usage.
- The method for sharing images between accounts has changed.
- You can create a new Image for sharing and share it.
- Add GPU Server usage guide
- Added the guides Using Multi-instance GPU on GPU Server and Using NVSwitch on GPU Server.
- GPU Server RHEL OS and GPU driver versions have been added.
- Add GPU Server feature
- NAT configuration feature has been added to the GPU Server.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have officially launched the GPU Server service.
- We have launched a virtualization computing service that lets you allocate and use infrastructure resources such as CPU, GPU, and memory provided by the server as needed, without having to purchase them individually.
Bare Metal Server
- The 4th‑generation BM based on the Intel 6th‑generation (Granite Rapids) Processor has been released.
- Bare Metal Server s4 and h4 server types have been added.
- Detailed information about the s4/h4 server type can be found in s3/h3 server type.
- Provides local disk partition functionality
- Now you can create and use up to 10 Local disk partitions.
- You can terminate multiple resources simultaneously from the Bare Metal Server list.
- You can change the IP of a regular Subnet.
- OS Image has been added.
- RHEL 8.10, Ubuntu 24.04
- Add Bare Metal Server feature
- Distribute servers belonging to the same Placement group across different racks.
- Additional OS images provided (RHEL 9.4, Rocky Linux 8.6, Rocky Linux 9.4)
- Add a 3rd‑generation (s3/h3) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For more information, refer to Bare Metal Server 서버 타입.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have officially launched the Bare Metal Server service.
- We have launched a Bare Metal Server service that lets customers use a physical server without virtualization, exclusively for their own use.
Multi-node GPU Cluster
- The Ubuntu image version 24.04 has been added.
- The B300 GPU server type has been added.
- Provides an IaC environment using Terraform.
- You can terminate multiple resources simultaneously from the GPU Node list.
- It must be a node that uses the same DataSet and Cluster Fabric.
- Integrated with Cloud Monitoring.
- You can view key performance metrics in real time with Cloud Monitoring.
- We have launched the Multi-node GPU Cluster service.
- We provide a service that offers physical GPU servers without virtualization for large-scale, high-performance AI computing.
Cloud Functions
- Technical support end-of-life information (EoTS) for the Runtime version is provided.
- When technical support ends, security patches and updates for that Runtime version will no longer be applied.
- Already created functions can be used continuously without any call time limit. * However, we do not guarantee bugs, errors, defects, or vulnerabilities that occur in Runtime versions for which technical support has ended.
- Technical support will be discontinued. The Runtime versions are as follows (see the full supported Runtime versions at Rutime version).
- GO: 1.21, 1.23
- Node.js: 18, 20
- PHP 8.1
- Python: 3.9
- Including runtime of additionally excluded functions
- The AIOS service integration has been stopped.
- Since the AIOS service has been discontinued, the AIOS integration service has been removed from Cloud Functions.
- You can set a resource-based policy on a function.
- Resource-based policies are policies applied to the function itself that allow external access.
- You can use resource-based policies to allow or deny actions on specific resources to a specific principal (Principal).
- You can use functions in conjunction with the AIOS service.
- You can integrate Cloud Functions with AIOS to leverage LLMs.
- You can use functions in conjunction with the PrivateLink service.
- Through a Private connection (PrivateLink), you can establish internal connections between VPCs and between a VPC and services on the Samsung Cloud Platform without traversing the Internet.
- The feature to upload Java Runtime executable files has been added.
- You can import and configure a Java Runtime executable archive file (.jar/.zip) in Object Storage.
- We have officially launched the Cloud Functions service.
- It is a serverless computing‑based FaaS (Function as a Service) that lets you easily run function‑style applications without server provisioning.
Virtual Server DR
- We have officially launched the Virtual Server DR service.
- When the system is interrupted by various disaster scenarios and risk factors, it can be restored to normal operation in a short time.
Block Storage
- An SSD volume with configurable IOPS and throughput has been added.
- When creating Block Storage, you can select the SSD_Provisioned disk type.
- You can set the IOPS and Throughput range.
- IOPS: 5,000 ~ 20,000
- Throughput: 250 ~ 1,000
- During the preview period, there is no additional charge; charges will be applied later.
- Snapshots are billed based on the size of the original Block Storage.
- Integrated with Cloud Monitoring.
- You can view IOPS, Latency, and Throughput information in Cloud Monitoring.
- Block Storage feature change
- HDD disk types have been added, and you can select the added type (HDD, HDD_MultiAttach, HDD_KMS) according to your purpose.
- Samsung Cloud Platform common feature changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Added the SSD_KMS disk type.
- When SSD_KMS is selected, encryption using a KMS (Key Management Service) encryption key is added.
- We have launched a high‑performance storage service suitable for handling large‑scale data and database workloads.
- We have launched a high-performance storage service suitable for handling large-scale data and database workloads.
Block Storage(BM)
- The configuration range for the volume performance metrics (IOPS, Throughput) has been changed.
- Max IOPS: 5,000 ~ 20,000
- Max Throughput: 250 ~ 1,000
- Provides volume expansion feature
- Volume expansion is possible only for the original volume that does not use snapshots.
- You can set the volume’s performance metrics (IOPS, Throughput) and edit them on the details page.
- IOPS: 3,000 ~ 16,000
- Throughput: 125 ~ 1,000
- There is no separate charge during the preview period (billing is scheduled for the first half of 2026).
- A feature to create a recovery using snapshots has been added.
- A recovery copy is a separate volume created with the same capacity as the original, and it incurs additional costs.
- HDD disk type has been added. When creating Block Storage (BM), you can select the HDD disk.
- Provides an IaC environment through Terraform.
- You can use the snapshot feature on a cloned volume.
- Integrated with Cloud Monitoring.
- You can view IOPS, Latency, and Throughput information in Cloud Monitoring.
- Block Storage(BM) feature change
- The replication feature that allows Block Storage(BM) volumes to be replicated to another location has been added.
- A Volume Group feature has been added that allows you to set up to 16 Block Storage (BM) volumes as a group to create consistent point-in-time snapshots and replication.
- For detailed information, refer to Block Storage(BM) Overview.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have launched a high-performance storage service suitable for handling large-scale data and database workloads.
File Storage
- The SSD SAP_E volume dedicated to SAP Account and the SSD SAP_E disk type have been added.
- When using a volume dedicated to the SAP Account, the LIF (storage Mount IP) is automatically transferred when a failover occurs due to a fault.
- It can be used only with a SAP account.
- ServiceWatch service integration provision
- You can monitor data through the ServiceWatch service.
- High‑performance SSD disk type has been added and can be used by connecting to a Multi-node GPU Cluster.
- Disk Backup allows you to store snapshots on a backup-dedicated HDD storage. You can select a location other than the original.
- File Storage feature change
- SSD disk types have been added, enabling you to choose a disk type according to your needs.
- You can create an identical replica volume at a different location and set the data replication interval.
- File Storage can be accessed from external networks via a VPC Endpoint connection.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Since it automatically scales up or down based on usage, users can use the volume without capacity limits.
- You can select the connection target using the access control feature.
- We have launched the File Storage service, a network‑connected storage that enables multiple client servers to share files.
Object Storage
- ServiceWatch service integration provision
- You can monitor data through the ServiceWatch service.
- The replication feature of Object Storage has been added.
- You can perform replication to buckets in a different location or the same location, and you can configure multiple replication policies.
- File copy feature has been added.
- You can copy the desired file within the same bucket and folder.
- The Cloud Functions service has been added to access control.
- You can upload a Java Runtime executable to Cloud Functions.
- The replication feature of Object Storage has been added.
- You can perform replication to buckets in a different location or the same location, and you can configure multiple replication policies.
- File copy feature has been added.
- You can copy the desired file within the same bucket and folder.
- The Cloud Functions service has been added to access control.
- You can upload a Java Runtime executable to Cloud Functions.
- A server resource target product has been added to Object Storage access control.
- Multi-node GPU Cluster, PostgreSQL, MariaDB, MySQL, EPAS, Microsoft SQL Server
- Presigned URL functionality has been added.
- You can download the file using a Presigned URL for the configured duration.
- You can perform Copyobject on encrypted files.
- Additional versions of the Amazon S3 SDK and Amazon S3 CLI are now available.
- Object Storage feature change
- You can use Object Storage from external networks via a VPC Endpoint connection.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have launched an object storage service that simplifies data storage and retrieval.
- We have launched Object Storage, a service that provides space (buckets) for economically storing large volumes of data.
Archive Storage
- ServiceWatch service integration provision
- You can monitor data through the ServiceWatch service.
- You can manage archived folders or files by version.
- Users can view archived folders or files by version and select a desired version to delete or restore.
- We have launched the Archive Storage service.
- Data stored in Object Storage is automatically transferred to Archive Storage for retention and can be easily restored when needed.
Backup
- When performing Agent Backup, Virtual Server and GPU Server have been added as target servers.
- Now you can select one of Virtual Server, GPU Server, or Bare Metal Server.
- Add Backup Replication Tab
- In the Backup detail page, you can view the original and replica information on the Replication tab.
- Add download feature for backup-related information
- In the Backup detail page, you can download the Backup history, recovery targets, and recovery history list as an Excel file.
- Expand recovery scope
- When restoring from an agentless remote backup, you can select the restore location (target server or backup location).
- Expand backup location and target
- Agentless-based remote backup: You can back up and restore to a location different from the backup target server.
- Backup Agent feature added: You can back up the filesystem of a Bare Metal Server by configuring the Agent.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We launched the Backup service to provide a secure data backup and recovery solution.
- Since a backup policy includes the target, frequency, retention period, and other elements, users can configure a backup plan to match their business environment and requirements.
Parallel File Storage
- The feature to restore from snapshots has been added.
- You can restore from the most recently created snapshot.
- The Parallel File Storage service has been officially launched.
- It can store file data across multiple storage nodes, enabling fast and efficient processing of large-scale data.
- By achieving fast data processing speed and reducing analysis time, it can be utilized in various fields such as AI/ML analysis and big data analysis.
Kubernetes Engine
- Kubernetes Engine feature changes and bug fixes
- We also provide Block Storage performance metric configuration for node pools.
- We also provide the B300 GPU type among GPU node types.
- When upgrading the node pool, we improved the selection dropdown functionality to consider the GPU driver version.
- type: LB health check protocol has been improved by adding HTTPS.
- Improved the event log timestamp error and the nuri-auth-webhook authentication key expiration and activation status check functionality.
- Kubernetes Engine feature changes
- Supports Kubernetes v1.34.
- Provides a custom image for the node pool’s GPU VM.
- Provides management logic and display functionality for EoTS of cluster and node pool Kubernetes versions and node pool OS versions.
- Provides an OS selection dropdown feature when upgrading a node pool.
- type: LB L7 listener idle-timeout addition and default session-duration-time change are improved.
- Terraform does not provide a kubeconfig feature.
- Kubernetes Engine feature change
- Supports Kubernetes v1.33.
- Provides GPU driver version information on GPU nodes in the node pool.
- Provides the MNGC node in SR request configuration format.
- The maximum Block Storage capacity of the node pool OS is increased from 1 TB to 12 TB to match the VM offering.
- When creating or updating a node pool, we add enhanced label key validation and also provide validation that GPU node pools are not supported in server groups.
- Kubernetes Engine feature changes
- Supports Kubernetes v1.32.
- Provides advanced node pool configuration features.
- Provides node pool server group (Affinity or Anti-affinity) configuration functionality.
- Provides a user Kubeconfig download feature following the admin Kubeconfig download button.
- When upgrading a node pool, we additionally provide upgrade logic that considers the OS version.
- Provides log collection functionality based on ServiceWatch integration.
- Kubernetes Engine feature changes
- Supports Kubernetes version v1.31.
- Provides the cluster’s public endpoint.
- The MNGC (Baremetal) product and the DevOps Service product are added to the cluster’s private endpoint access control targets.
- Provides node pool label and taint configuration functionality.
- Provides Block Storage CSI and kubectl login plugin functionality.
- The kubeconfig vulnerability has been addressed.
- Kubernetes Engine feature changes
- Provides private endpoint and access control features.
- type: LoadBalancer provides functionality.
- Kubernetes Engine feature changes
- Supports Kubernetes v1.30.
- Provides Kubernetes version upgrade functionality for clusters and node pools.
- Provides Multi-Security Group functionality.
- Provides the ability to create Custom Image nodes and GPU nodes.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- We have launched the Kuberntes Engine product, which provides lightweight virtual computing containers and the Kubernetes clusters that manage them.
- You can create container nodes and centrally manage them through a cluster, enabling deployment of various container applications.
- We have released the beta version of the Kuberntes Engine product.
Container Registry
- Container Registry feature change
- General-purpose Container Registry OCI (Open Container Initiative) Distribution Spec. * Ensured v1.1.1 compatibility and improved the user Registry.
- Improved internal processes related to the creation/deletion logic of the Container Registry to enhance convenience.
- We added a refresh button where needed, just like with other products, to improve usability.
- Container Registry feature change
- OCI (Open Container Initiative) Distribution Spec for Registry. * Ensured compatibility with v1.1.1 and improved the user Registry.
- We expand the coverage by adding OS and language types to the container image vulnerability assessment targets.
- Container Registry feature changes and improvements
- We additionally offer the image tag deletion policy feature based on count.
- Based on the IP range constraints of the Firewall product, we improve the validation of Public Endpoint access control IP input values.
- Container Registry feature change
- Provides a feature to enable the deletion policy setting for image tag deletion items.
- Provides log collection functionality based on ServiceWatch integration.
- Container Registry feature change
- We provide a Container Registry service based on Object Storage with self‑encryption and S3 API compatibility patches applied.
- Provides public endpoints and access control functionality for the Registry.
- We additionally offer the Multi-Node GPU Cluster product among the Registry’s private endpoint access control targets.
- Provides a function to configure automatic deletion policies for repositories, stored images, and their individual tags (digests).
- Container Registry feature change
- Provides a lock function for images stored in the Registry.
- Provides monitoring capabilities for the Registry in conjunction with the Cloud Monitoring product.
- Provides integration with VPC Endpoint.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- Container Registry is a service that provides a registry and repository where you can easily store, manage, and share container images and OCI (Open Container Initiative) standard artifacts.
- It was released as a temporary version and will be migrated to the official version once the encryption solution is updated.
VPC
- Provide VPC IP range addition feature
- You can add a new IP range to the VPC for use.
- Provides Virtual IP functionality
- You can reserve a Virtual IP in a Subnet for use.
- Private NAT feature improvement
- You can also use Private NAT with Transit Gateway.
- You can connect internal Samsung Cloud Platform data to the SCP service via a private path between the VPC and the SCP service without exposing it to the internet.
- Add Transit Gateway feature
- Easily connect the customer’s network with the Samsung Cloud Platform network and serve as a connection hub for multiple VPCs within the cloud environment.
- Add VPC Peering feature
- You can perform IP communication over a 1:1 private route between VPCs.
- Add Private NAT feature
- You can use Direct Connect from compute resources within the VPC to map the customer’s IP and establish a connection.
- Add VPC functionality
- Provides an Endpoint (entry point) that allows access to the Samsung Cloud Platform via a private connection from external networks connected to the VPC.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- A feature to save NAT logs has been added.
- You can determine whether to retain NAT logs and store them in Object Storage.
- The VPC service that provides an isolated virtual network space has been launched.
- The VPC service that provides an isolated virtual network space has been launched.
Security Group
- For user convenience, a Migration Rules page has been added that allows you to import Security Group rules created in the V1 environment and apply them to the V2 service.
- When adding a Security Group rule, multiple service ports can be selected
- Improved the console to allow selecting multiple service ports when adding a rule.
- Add Security Group rule input method
- A feature allowing IP protocol input has been added.
- A feature to select Well-known protocols has been added.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- Improved to allow entering multiple IPs when adding Security Group rules.
- A feature to store Security Group logs has been added.
- You can decide whether to store Security Group logs and store the logs in Object Storage.
- The Security Group service, which provides virtual firewall functionality for instance resources, has been launched.
- You can control inbound and outbound traffic generated from instance resources through the Security Group service.
- The Security Group service, which provides virtual firewall functionality for instance resources, has been launched.
- You can control inbound and outbound traffic generated from instance resources through the Security Group service.
Load Balancer
- A feature has been added to enable setting a Private NAT IP on the Service IP.
- The ‘TCP_Proxy’ protocol has been added to the L4 Listener.
- The conditions for creating L4 Listener service ports have been changed.
- It has been changed to allow creating a Listener on the same service port for both TCP and UDP protocols.
- The method for entering L7 Listener routing rules has been changed.
- LB server group forwarding > Modified to allow users to add a ‘/’ path in the URL path.
- LB server group forwarding > The matching method for the entered path in the URL path has been changed from ‘Contains(Include match)’ to ‘Starts with(Start part match)’.
- LB server group forwarding > The ‘Default’ condition for the request host in the host header has been added.
- The method for configuring the LB health check port has been changed.
- You can select either a member port or manual entry, and when using manual entry, specify the port to use.
- Existing LB health checks are changed to the member port. (Same as the current health check method)
- The HTTPS option has been added to the LB health check protocol.
- You can monitor the server’s TLS connection status.
- When using URL redirection in an HTTP Listener, you can specify the target port for the redirection.
- You can add Multi-node GPU Cluster resources to the LB server group members.
- When creating a Load Balancer, you can set the Source NAT IP and health check IP.
- TLS protocol has been added to the L4 Listener.
- You can set up a TLS service over TCP.
- A routing rule option has been added to the L7 Listener.
- Routing conditions allow you to set up branching by URL path or by host.
- Supports multiple SSL certificates.
- By supporting SNI, you can register multiple certificates on a single Listener.
- Add LB health check management feature
- You can create an LB health check, define the required health check method, and connect it to an LB server group for use.
- Support for weighted load balancing of LB server groups
- Weighted Round Robin and Weighted Least Connection have been added to the load balancing options.
- You can set per-member weights to distribute server load.
- Add LB server group member activation feature
- You can choose to activate members of the LB server group by disabling or enabling them.
- A Load Balancer service that provides more stable and enhanced features has been launched.
- Provides an L7 Load Balancer that supports HTTP and HTTPS protocols.
- Provides an L4 Load Balancer that supports TCP and UDP protocols.
DNS
- You can view measurement values for the following five items in conjunction with Service Watch.
- Number of server error responses (unit: seconds)
- NXDOMAIN response count (unit: seconds)
- Number of queries not responding within 1 second (unit: seconds)
- Number of outgoing UDP queries (unit: seconds)
- Number of UDP-based data request processing (unit: seconds)
- Through the Samsung Cloud Platform, a registered Public Domain Name can be transferred to another user account within the allowed period.
- We have officially launched a DNS service that can be used in private networks and internet environments. You can manage Private DNS and Private Hosted Zones for restricted networks, and apply for Public Domain Name registration and manage Public Hosted Zones for internet environments.
- We have launched a beta DNS service that offers domain registration request and management capabilities based on user requests.
VPN
- You can input up to 10 Romote Subnet (CIDR).
- A VPN service that connects the customer network to the Samsung Cloud Platform via an encrypted (IPSec) virtual private network has been launched.
Firewall
- For user convenience, a Migration Rules page has been added that allows you to import firewall rules created in the V1 environment and apply them to the V2 service.
- The method for entering and modifying/deleting firewall rules has been changed for user convenience. * When managing firewall rules, you can navigate to a separate page to perform the desired actions.
- Add firewall rule input method
- In the KR WEST and KR EAST regions, you can enter the destination address in FQDN (Fully Qualified Domain Name) format.
- Add firewall rule input method
- A feature to input IP protocols has been added.
- Add firewall functionality
- You can use Firewall in the Load Balancer service.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- A feature to save firewall logs has been added.
- You can decide whether to store firewall logs and store the logs in Object Storage.
- Through the Firewall service, you can control inbound and outbound traffic in a VPC.
- The Firewall service has been released.
Direct Connect
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- We are launching the Direct Connect service that quickly and securely connects the customer’s network with the Samsung Cloud Platform network.
Cloud LAN Campus
- We have launched the Cloud LAN Campus service, which provides an authentication‑based integrated wired/wireless network service within the customer’s premises.
Cloud LAN Campus
- We have launched the Cloud LAN Campus service, which provides an authentication‑based integrated wired/wireless network service within the customer’s premises.
Cloud LAN-Data Center
- The services provided in specific Samsung offering regions (kr-west1/kr-east1) have changed.
- The vTAP option has been added to the Cloud LAN - Data Center service in Samsung’s offering.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- We have launched the Cloud LAN-Data Center service, which provides connections between various networks through virtual network configurations within the data center.
Cloud WAN
- Cloud WAN > Attachment > Site Connect When you select this type, the BGP Password configuration feature is added when setting up BGP routing with the customer’s Customer Edge equipment.
- Samsung Cloud Platform has launched the Cloud WAN service that provides network connectivity between global regions and customer sites.
SASE
- The automatic ledger creation feature via the Samsung Cloud Platform user console has been added.
- We have launched a SASE service that combines networking and security functions into a single cloud-based platform.
Cloud Last Mile
- The automatic ledger creation feature via the Samsung Cloud Platform user console has been added.
- We have launched the Cloud Last Mile service, which provides a Last Mile line for network connectivity from the customer’s site to the Samsung Cloud Platform region and Customer Edge resources within the customer’s site.
Global CDN
- By integrating with Service Watch, you can view measurement values for the following two items.
- Check Global CDN status
- Check Global CDN processed data volume
- Data from 30 minutes ago is displayed due to the processing time of external CDN network traffic.
- We have launched a Global CDN service that delivers static content stored on web servers or object storage to users more quickly and securely via edge servers distributed across the global network.
GSLB
- You can control the usage of traffic you want to connect via GSLB on a per-region basis.
- We have launched a GSLB service that can automatically distribute network traffic to adjacent regions based on DNS when traffic increases in a specific global region, providing stable service.
Cloud Virtual Circuit
- We have officially launched the Cloud Virtual Circuit service.
- Users can request a 1:1 virtual circuit based on the line bandwidth between Global Samsung Cloud Platform regions or customer sites.
Private 5G Cloud
- A Private 5G Cloud product that provides 5G services to customers based on the Samsung Cloud Platform has been launched.
EPAS(DBaaS)
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Strengthen the latest security patches and stability through the OS (Kernel) upgrade feature.
- EPAS(DBaaS) feature addition
- Add Second-Generation Server Type
- Add a 2nd‑generation (db2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see EPAS(DBaaS) 서버 타입.
- DB user and access control management and Archive configuration feature added
- For more details, refer to DB User Management, DB Access Control Management, Archive Management.
- DB Audit Log Export feature added
- For more details, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, refer to Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Migration Configuration.
- Add HDD, HDD_KMS types to Block Storage type
- Add Second-Generation Server Type
- A web-based EPAS (DBaaS) service that allows easy creation and management of EPAS has been launched.
PostgreSQL(DBaaS)
- The OS (Kernel) upgrade feature enhances the latest security patches and stability.
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Add PostgreSQL (DBaaS) feature
- Add Second-Generation Server Type
- Add a second‑generation (db2) server type based on the Intel 4th‑generation (Sapphire Rapids) processor. For more details, see PostgreSQL(DBaaS) 서버 타입.
- DB user and access control management and Archive configuration feature added
- For more details, see DB User Management, DB Access Control Management, Archive Management.
- DB Audit Log Export feature added
- For more details, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For detailed information, refer to Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Configuring Migration.
- Add HDD, HDD_KMS types to Block Storage type
- Add Second-Generation Server Type
- PostgreSQL(DBaaS) feature change
- Add new PostgreSQL versions: 13.16, 14.13, 15.8
- Add second-generation server type
- Add a 2nd‑generation (dbh2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see PostgreSQL(DBaaS) server type.
- After creating the service, Block Storage capacity expansion is possible.
- Server-specific network IP configuration feature has been added allowing either a common configuration or a server-specific configuration depending on the intended use.
- Samsung Cloud Platform common feature changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- A volume-encrypted storage selection option has been added to the Block Storage type.
- A Role Switch (Active ↔ Standby) feature has been added for the Active DB and Standby DB configured with redundancy.
- It is linked with the cloud monitoring service, enabling performance and log monitoring of DB instances.
- Based on the server type selected by the customer, Planned Compute policy can be set.
- A PostgreSQL (DBaaS) service that enables easy creation and management of PostgreSQL in a web environment has been launched.
MariaDB(DBaaS)
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Strengthen the latest security patches and stability through the OS(Kernel) upgrade feature.
- You can monitor metrics and logs by integrating with Servicewatch.
- Add MariaDB (DBaaS) feature
- Add Second-Generation Server Type
- Add a second‑generation (db2) server type based on the Intel 4th‑generation (Sapphire Rapids) processor. For more details, see MariaDB(DBaaS) Server Type.
- DB user and access control management and Archive configuration feature added
- For detailed information, refer to DB User Management, DB Access Control Management, Archive Management.
- DB Audit Log Export feature added
- For detailed information, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Migration Configuration.
- Add HDD, HDD_KMS types to Block Storage
- Add Second-Generation Server Type
- MariaDB (DBaaS) feature change
- Add second-generation server type
- Added a 2nd‑generation (dbh2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see MariaDB(DBaaS) Server Type.
- After the service is created, you can expand the configured Block Storage capacity.
- Server-specific network IP configuration feature added allows either common or server-specific configuration depending on the usage purpose.
- Add second-generation server type
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- A volume-encrypted storage selection option has been added to the Block Storage type.
- A function to switch the Role (Active ↔ Standby) for the Active DB and Standby DB configured with redundancy has been added.
- It is linked with the cloud monitoring service, enabling performance and log monitoring of DB instances.
- Depending on the server type selected by the customer, Planned Compute policy can be set.
- A MariaDB (DBaaS) service that enables easy creation and management of MariaDB in a web environment has been launched.
MySQL(DBaaS)
- You can set up a disaster-recovery Replica using the Replica configuration (Other Region) feature.
- Strengthen the latest security patches and stability through the OS (Kernel) upgrade feature.
- You can monitor metrics and logs by integrating with Servicewatch.
- Add MySQL (DBaaS) feature
- Add Second-Generation Server Type
- Add a 2nd‑generation (db2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, refer to MySQL(DBaaS) 서버 타입.
- DB user and access control management and Archive configuration feature added
- For detailed information, see DB User Management, DB Access Control Management, Archive Management
- DB Audit Log Export feature added
- For more details, refer to DB Log 내보내기
- Backup notification feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add Migration feature
- Provides replication-based zero-downtime data migration functionality. For more details, see Configuring Migration.
- Block Storage type HDD, HDD_KMS type addition
- Add Second-Generation Server Type
- MySQL (DBaaS) feature change
- Add second-generation server type
- Add a 2nd‑generation (dbh2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see mysql(DBaaS) 서버 타입.
- After the service is created, you can expand the configured Block Storage capacity.
- Server-specific network IP configuration feature added allows common or server-specific settings depending on the usage purpose.
- Add second-generation server type
- Samsung Cloud Platform common feature changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- A MySQL (DBaaS) service that enables easy creation and management of MariaDB in a web environment has been released.
Microsoft SQL Server(DBaaS)
- Add Microsoft SQL Server (DBaaS) feature
- Add 2nd‑generation server type
- Add a 2nd‑generation (db2) server type based on Intel 4th‑generation (Sapphire Rapids) Processor. For details, see Microsoft SQL Server(DBaaS) 서버 타입.
- DB User and Access Control Management Add
- For more details, refer to DB User Management, DB Access Control Management
- Add DB Audit Log Export feature
- For detailed information, refer to DB Log Export.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add HDD, HDD_KMS types to Block Storage type
- Add 2nd‑generation server type
- A Microsoft SQL Server(DBaaS) service that enables easy creation and management of Microsoft SQL Server in a web environment has been launched.
CacheStore(DBaaS)
- We ensure stable service continuity through the Minor version upgrade feature.
- Add CacheStore (DBaaS) feature
- CacheStore(DBaaS) Add new image
- Support for the open-source Valkey image, developed by forking Redis OSS
- 2nd Generation Server Type Add
- Add a second-generation (db2) server type based on the Intel 4th‑generation (Sapphire Rapids) processor. For details, see CacheStore(DBaaS) Server Type.
- Backup Notification Feature provided
- Provides notification functionality for backup success and failure. For more details, see Create Notification Policy.
- Add HDD, HDD_KMS types to Block Storage type
- CacheStore(DBaaS) Add new image
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- Change the service name to CacheStore(DBaaS).
- A volume-encrypted storage selection option has been added to the Block Storage type.
- A Role Switch (Active ↔ Standby) feature for the Active DB and Standby DB configured with redundancy has been added.
- It is linked with the cloud monitoring service, enabling performance and log monitoring of DB instances.
- The Planned Compute policy can be configured according to the server type selected by the customer.
- A Redis (DBaaS) service that enables easy creation and management of Redis OSS in a web environment has been launched.
Scalable DB(DBaaS)
- You can monitor logs by integrating with Servicewatch.
- The fully managed Database service, Scalable DB (DBaaS), which flexibly adjusts resources according to traffic changes, has been launched.
Event Streams
- Provides Terraform.
- Provides additional HDD, HDD_KMS disk types.
- The Event Streams service, which easily creates and manages Apache Kafka clusters in a web environment, has been launched.
Search Engine
- OpenSearch 2.17.1 is now offered as a new release.
- Provides Terraform.
- Provides additional HDD, HDD_KMS disk types.
- A Search Engine service that enables easy creation and management of ElasticSearch Enterprise in a web environment has been launched.
Vertica(DBaaS)
- We have launched the Vertica(DBaaS) service, which can efficiently store data and improve query execution speed with compression and encoding capabilities based on columnar storage.
Data Flow
- The Data Flow service, which extracts, transforms, and transfers data from various sources and automates data processing workflows, has been launched.
- Provides the open-source Apache NiFi.
Data Ops
- A Data Ops service that creates workflows for data processing tasks that occur periodically or repeatedly and automates job scheduling has been launched.
- It is a managed workflow orchestration service based on Apache Airflow.
Quick Query
- The Quick Query service, which allows you to easily analyze large-scale data using standard SQL, has been launched.
Cloud Hadoop
- The Cloud Hadoop service for easy and fast analysis of large-scale data has been launched.
- We provide an automated cluster creation service through the Hadoop Ecosystem and Hadoop Manager.
API Gateway
- You can set resource-based policies on the API.
- Resource-based policies are policies applied directly to the API to allow external access.
- You can use resource-based policies to allow or deny actions on specific resources to specific principals.
- The API Gateway service, which enables easy management and monitoring of APIs, has been launched.
- You can easily define resources and methods related to the API, and conveniently monitor API usage and performance metrics.
Queue Service
- You can configure additional features when selecting a FIFO type.
- Content-based deduplication: Hash the message body content to remove duplicate messages.
- Duplicate removal scope setting: Set the scope (within the queue / per group) for removing duplicate messages.
- When sending FIFO-type messages, you can manage them by entering Message Group ID and Message Deduplication ID information.
- ServiceWatch service integration provided: You can monitor data through the ServiceWatch service.
- The Queue service feature has been added.
- Provides Private Service link ID information.
- Message retention and data key reuse period setting units have been refined, and a CIDR‑based modification feature for allowed IP addresses has been added.
- The Queue Service has been officially launched.
- Through the Queue Service, you can distribute system load caused by messages, enabling efficient message management in microservice architectures or event-driven systems.
- Message transmission and reception operate independently, improving responsiveness and processing speed.
Key Management Service
- In addition to the ‘customer-managed key’ that the user creates directly, a ‘platform-managed key’ service generated and managed by the CSP (Cloud Service Provider) is also provided.
- When another product within Samsung Cloud Platform encrypts using a KMS key, it can encrypt with a platform-managed key generated directly by the CSP without the user having to create a key directly in KMS.
- We improved traceability by segmenting and logging operation histories for API calls such as encryption and decryption at the individual API level, making it easier to manage tracking of API calls.
- When an encryption key is deleted, it provides a notification not only to the user who deleted the key but also to the key creator, and the notification additionally includes the region name where the encryption key is located.
- We also provide the generation/verification (HMAC) encryption method used for creating and verifying hash-based message authentication codes.
- We have launched an encryption key management service (Key Management Service) to securely protect critical data in customer applications.
- You can generate, provide, and manage encryption keys for various purposes (encryption/decryption, signing/verification).
Config Inspection
- We have launched the Config Inspection product, which enables integrated diagnosis and management of customers’ multi‑cloud console security vulnerabilities.
- You can register the Account (or other cloud account) to be diagnosed, enabling continuous diagnostics, and view the dashboard and detailed results in the Report.
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been applied.
- You can manage Samsung Cloud Platform Console configuration vulnerabilities through console diagnostics.
- Provides a report that allows you to view security diagnostic results.
Certificate Manager
- We have launched the Certificate Manager service that supports SSL/TLS certificate deployment and unified management.
- You can register a certificate issued by a Certificate Authority (CA) or generate a Self-signed certificate for development/testing purposes.
- You can encrypt network communications and manage the certificate lifecycle by connecting to Samsung Cloud Platform resources.
Secret Vault
- The Secret Vault service, which can issue token-based temporary keys and manage their lifecycle, has been launched.
SingleID
- Add AI agent registration and management functionality
- AI agent registration and configuration features for authentication between the MCP server and MCP client have been added.
- The features for registering information, generating authentication key values, and retrieving information for AI agent authentication have been newly added.
- Add 3rd Party TOTP Authenticator support
- A TOTP authentication method registration/setting feature has been added to support 3rd Party Authenticators such as Google Authenticator and Microsoft Authenticator in the Admin Portal.
- A feature has been added that allows users to register or delete a 3rd Party TOTP Authenticator in the User Portal and MFA Portal.
- New SMS Provider (InfoBank) added
- You can register and use the Infobank SMS service, an external SMS service provider.
- Improved admin authentication delegation feature
- When no authentication method is available for identity verification, we have enhanced the system so that the admin authentication delegation feature can be applied when 1) registering an authentication method or 2) attempting to log in.
- You can register a list of authentication delegation administrators in the JWT Token.
- Enhanced to allow the authentication delegation manager list to be registered in SCP Cloud Object Storage and utilized.
- The detailed MFA SP configuration feature has been added in the Admin Portal.
- Whether to perform delegated authentication at login
- Whether to perform verification during registration when no authentication method is registered.
- Use of SCP Cloud Object Storage
- Select user information update method when running MFA
- Select whether to automatically add Knox Messenger as an authentication factor when executing MFA.
- Security improvement
- Personal information fields (name, email, mobile phone number) are now stored encrypted.
- In admin screens such as TAP, searching personal information fields (name, email, mobile phone number) has been changed from Like to Exact search, and the existing sorting function has been removed.
- SingleID Authenticator improvement
- When retrieving authentication methods for SingleID Authenticator, a feature to view detailed information (OS version, browser, and IP) has been added.
- The process has been improved so that when SingleID Authenticator information is deleted on the authentication server, the authentication server (tenant) information is also removed from the user app.
- The registration failure error that occurred when registering biometric data in PIN registration mode has been resolved.
- Expanded CSP support for console access control
- Support CSP for console access control has been expanded from the existing AWS, Azure, Samsung Cloud Platform (KR EAST1 region, KR WEST1 region) to GCP.
- Other functional improvements
- Maintained overall UI/UX consistency of the Admin Portal/User Portal and improved usability.
- We improved it so that when a user accesses the SingleID service via a mobile device’s browser and authenticates, the appropriate mobile keypad (default, password, numeric, email keyboard) is automatically selected based on the attributes of the input data on the authentication screen.
- When creating or editing a SAML-type application, we removed the unnecessary input restriction (Issuer setting).
- Improved the usability and security of the CAM Portal.
- Added a masking feature for sensitive information (Password, Key).
- Users assigned the PM/PL role can now modify the IP/Port of registered resources, improving usability.
- When resource registration fails, we have improved it to provide information about the failure status based on a checklist.
- When registering resources, it has been improved to allow registering multiple resources at once and to support PEM key registration.
- After the resource connection expires, we improved usability so that clicking the Rotation button allows you to easily refresh the expired OTP connection information.
- Improved usability to display the Account ID information when submitting approval for a permission request to access resources.
- Add console access history log monitoring feature
- You can view and download console access logs.
- Expand CSP support for console access control
- Support CSP for console access control has been expanded from the existing AWS to Azure and Samsung Cloud Platform (KR EAST1 region, KR WEST1 region).
- Notice feature improvement
- The feature that allows registering and managing notices per tenant has been improved.
- Improvement of the approval system functionality
- We added a self‑managed approval system feature to the existing approval function based on the Knox approval system.
- Improved batch scheduler management functionality
- The batch scheduler management feature has been enhanced to allow viewing execution results and details, and to enable immediate execution.
- Improvement of CAM system user role management functionality
- The CAM system has been improved to allow creating, listing, viewing, and detailing user roles for the system itself.
- System-wide global variable management feature improvement
- The system-wide variable management functionality for the CAM system itself has been improved.
- Other convenience improvements
- PM/PL authorized users can change the IP of an already enrolled resource (no need to re‑enroll the resource).
- Improved the multi-select functionality when searching User, Role, and Policy (preserves previously added items during multiple selections).
- Improved to allow navigation to the detailed pages for Role/Policy/Account from the Console Access menu.
- The Manual, Release Note, and FAQ URLs have been changed to the SCP Documentation URL.
- Add admin delegation feature
- A feature has been added that allows delegating identity verification to an administrator. * This feature is available only for MFA products.
- Add approval status menu to the dashboard
- A feature has been added to the dashboard that allows managing users’ approval requests and statuses.
- Add a sign‑up status menu to the dashboard
- A feature has been added to the dashboard that allows managing users’ sign‑up status.
- Add user campaign feature
- A campaign feature that recommends registering additional authentication methods has been added when only one user authentication method is registered.
- Add dormant account policy feature
- Added features for dormant user settings, alarm dispatch configuration, exception user registration, long-term dormant users, and dormant self-recovery settings.
- Add user lifecycle management feature
- During sign-up and user registration, features for setting user defaults, configuring user account expiration periods, and defining approval policies have been added.
- Add rebranding functionality to the login page
- A feature has been added that allows changing the top and bottom logos, key visual images, and text in the Admin Portal.
- Redirection functionality for the sign‑up page settings, bottom privacy policy, terms of service, and similar items has been added.
- Improved simple authentication feature
- Mobile Passkey, security key, and Windows PIN code have been added as convenient authentication methods for easy login.
- Add user security enhancement feature
- A conditional authentication policy feature has been added that requires additional identity verification when only one authentication method is used for an extended period.
- User profile attribute setting feature improvement
- You can further expand and apply the user’s personal information attributes.
- Add application entitlement (Entitlement) management feature
- Synchronize application permissions to manage application access for users and groups.
- Other convenience improvements
- Improved the process when the authentication session timeout expires.
- Improved the app access process in the mobile app.
- We have improved the screen for mobile app download.
- Improved the application registration/edit screen (field modifications, mapping screen enhancements, etc.).
- Improved the Identity Providers registration/edit screen (added/modified fields)
- Added a user mobile app (device) reset feature.
- Added a feature to set a prefix text when sending SMS.
- Improved the image upload screen and process.
- We have launched the SingleID service, which integrates various access environments so that users can log into business systems with a single ID, and enables administrators to easily control access.
WAF
- We are launching a WAF service that protects web applications from web vulnerabilities and attacks.
WAF
- We are launching a WAF service that protects web applications from web vulnerabilities and attacks.
WAF
- We are launching a WAF service that protects web applications from web vulnerabilities and attacks.
DDoS Protection
- We are launching a DDoS Protection service that provides detection and mitigation of large-scale network traffic attacks.
DDoS Protection
- We are launching a DDoS Protection service that provides detection and mitigation of large-scale network traffic attacks.
IPS
- We have launched an IPS service that continuously updates intrusion detection policies to reflect the latest security threats and provides real‑time response.
Secured Firewall
- We have launched the Secured Firewall service, a next‑generation firewall for cloud network security provided by Samsung Cloud Platform.
Secured VPN
- We have launched a Secured VPN service that safely connects external customer networks with the Samsung Cloud Platform’s cloud network via an encrypted virtual private network.
FPMS
- A feature has been added to FPMS that allows registering and managing firewalls and Security Groups of the Samsung Cloud Platform Console.
- The SecuAI firewall v3.7 support (anyzone) feature has been improved.
- We have launched the FPMS (Firewall Policy Management System) service, which automates firewall operation tasks to efficiently and securely manage firewalls across diverse cloud environments.
Secrets Manager
- Provides a Private Endpoint that can be called as a Secret from VM resources in the Samsung Cloud Platform.
- You can select a VM resource in Samsung Cloud Platform that stores secret security information and configure access control.
- We have launched a service that encrypts customers’ sensitive information as Secret(secure information) and safely stores and manages it.
- Remove hard-coded security information from the application source code and retrieve it by invoking securely stored Secrets.
DDoS Protection
- We are launching a DDoS Protection service that provides detection and mitigation of large-scale network traffic attacks.
Log Transmission
- We have launched the Log Transmission service that enables security monitoring of the user domain on Samsung Cloud Platform.
ESS
- We are launching the ESS external-facing product that offers the previously on-premises Endpoint Security service, which was provided to external customers under a perpetual license, as a SaaS-based Endpoint Security service with a subscription license.
- We are launching a service that offers the on‑premise Endpoint Security solutions ESCORT, NASCA, and SecuPrint as SaaS, and enables efficient management of endpoint security solutions from the One‑view integrated admin console.
Log Transmission
- We have launched the Log Transmission service that enables security monitoring of the user domain on Samsung Cloud Platform.
Architecture Diagram
- A new resource has been added.
- Database: EPAS, PostgreSQL, Maria DB, MySQL, Microsoft SQL Server, CacheStore
- Data Analysis:Event Streams, Search Engine, Vertica
- Improved CX by adjusting the search filter size and position, icons within diagrams, and other elements.
- Load Balancer resource has been added.
- The relationships between resources are indicated with dotted lines for easy identification.
- In the resource detail information popup, you can click the name of the resource to go to its detail page.
- Through Copilot, you can create VPC and Security Group services or manage Virtual Server.
- From the Diagram filter, you can easily add the Architecture Diagram item.
- The Architecture Diagram service has been newly launched.
- We provide a service that allows you to check relationships between resources.
Cloud Control
- The detection guardrail results management screen has been added.
- On the result management screen of the detection guardrail, you can view the diagnostic request result information.
- The detection guardrail feature has been added.
- For accounts within the default organizational unit, Config Inspection diagnostics are run automatically every day.
- You can easily view diagnostic results even within the Cloud Control service.
- The official version of the Cloud Control service has been released.
- You can easily and securely build, operate, and manage a multi‑account environment on Samsung Cloud Platform.
- The organization’s cloud governance (security, compliance, standardization, etc.) can be automated and managed through policy violation detection and monitoring functions.
Cloud Monitoring
- In July 2025, we added an integrated service with Cloud Monitoring.
- Additional integrated services: Compute(Multi-node GPU Cluster [Cluster Fabric], Multi-node GPU Clutser [Node]), Storage(Block Storage(BM), Block Storage(VM)), Networking(Cloud WAN, Global CDN), Database(Valkey), Data Analytics(Opensearch, Vertica(DBaaS))
- In February 2025, we added an integration service with Cloud Monitoring.
- Additional integrated services: Container (Container Registry), Database (EPAS, Microsoft SQL Server), Data Analytics (Event Streams, Search Engine), Networking (Load Balancer, Load Balancer Listener, Load Balancer Server Group, VPN)
- We have launched the Cloud Monitoring service. It collects usage status and change information of operational infrastructure resources, and supports a stable cloud operating environment by generating and notifying events when configured thresholds are exceeded.
IAM
- You can copy the permissions of another IAM user.
- When creating or modifying an IAM user, you can copy and import policies that are attached to another user’s group or directly attached.
- We have improved the CX-related functionality.
- You can manage IAM user access key creation records.
- You can configure the visibility of the AI recommendation floating guide displayed at the bottom of the screen.
- When viewing the IAM user list, you can click the user group to navigate to the detail page.
- If a password error occurs while using the console, you will be automatically logged out of the console.
- When password entry is required, such as changing the password or updating the mobile phone number, you will be automatically logged out after five or more incorrect attempts.
- We provide a guide on using the Json mode that can be referenced when creating policies.
- You can share related information via email when creating a user or changing a password.
- Virtual Server and Cloud Function have been added as the entities that perform role functions.
- When changing roles, you can check the session expiration time in My Menu.
- You can register and manage IPs that can access the console.
- Root users and IAM users with the same information (phone number, email) can switch between each other even after logging in.
- The role feature has been added.
- Users can switch from their own account to a different role to access the Account.
- Credential provider functionality has been added.
- You can create a credential provider and access the Account resource in the Console through the created credential provider.
- You can directly associate users with policies.
- You can add conditions for attribute-based access control (ABAC) when creating a policy.
- The mandatory requirements for creating a user password have been changed.
- When editing an authentication key, CIDR input is optional.
- A password reconfirmation step has been added when changing the user’s email or phone number.
- IAM(Identity and Access Management) feature change
- Added user group and user functions, and policy creation functionality.
- We provide a unified authentication key by consolidating the app authentication key and the storage authentication key.
- Samsung Cloud Platform Common Feature Changes
- Implemented common CX changes, including Account, Service Home, and tags.
- The IAM(Identity and Access Management) service has been released.
- Provide user authentication and authorization management.
- Access control policy management provided
- The IAM(Identity and Access Management) service has been launched.
- Provide user authentication and authorization management.
- Provides access control policy management
ID Center
- When applying for the ID Center, we also provide the Access Portal URL.
- The process of requesting the Access Portal URL through a service request has been changed to provide the Access Portal URL together when applying for the ID Center.
- After completing the ID Center application, you can view the Access Portal connection URL on the ID Center settings screen.
- You can select AD (Active Directory) as the credential source.
- Using AD (Active Directory), users can manage credential sources directly.
- We have officially launched the ID Center service.
- You can create permission policies for each service and assign accounts and policies linked to the Organization service to users, enabling management of tasks according to each user’s permissions.
- You can strengthen security so that only authorized ID Center users can access through the Access Portal.
Logging&Audit
- Logging&Audit ServiceWatch log collection integration
- Configure the Trail logs to be sent to a ServiceWatch log group, allowing you to monitor them through ServiceWatch and receive alerts when specific activities occur.
- Logging & Audit: Add integration for newly launched service
- API Gateway, Archive Storage, Backup Agent, Cloud Functions, Cloud LAN-Datacenter, Cloud WAN, CloudML, Cost Savings, GSLB, Global CDN, IAM > role, Load Balancer > LB Health Check, Marketplace, Organization, Private DNS, Private NAT, Public Domain Name, Quick Query, Secret Vault, SingleID, Support Plan, Transit Gateway, VPC Peering, Vertica
- When viewing activity logs, we added a date-range filter/time zone and a comparison feature for activity logs.
- Logging & Audit: Add integration for newly launched service
- Data Flow, Data Ops
- Logging & Audit new service launch integration
- AI&MLOps Platform, Multi-node GPU Cluster, VPN, Cloud LAN-Campus, KMS, Event Streams, Serch Engine, EPAS, Microsoft SQL Server
- Samsung Cloud Platform Common Feature Changes
- Account, IAM, Service Home, tags, and other common CX changes have been reflected.
- Logging&Audit service has been launched. It stores and searches all activity logs performed by customers (Console, API, CLI) and provides features such as change tracking of cloud resources, troubleshooting, and security inspections.
- We have launched the Logging&Audit service. It stores and searches all activity logs performed by customers (Console, API, CLI), and provides functions such as change tracking of cloud resources, troubleshooting, and security inspection.
Notification Manager
- We have launched the Notification Manager service. It provides a function to manage notifications delivered to users when alerts occur.
- You can create and manage notification policies and groups for receiving alerts, and you can add users.
Organization
- You can also delete an Account created in the Organization from the Member Account.
- Deletable Accounts are limited to those directly created in the Organization.
- The Organization service has been officially launched.
- You can organize accounts by organizational units, manage them hierarchically, and control resource access permissions.
- You can monitor the resource usage of all accounts within the organization to optimize costs.
Resource Explorer
- We have launched a search service for resources.
- You can view resources from multiple regions at once using Resource Explorer.
Resource Groups
- We have launched a service that efficiently manages resources through grouping.
- You can logically group and manage resources based on tags.
ServiceWatch
- When comparing metrics by date, you can select a period to compare.
- When viewing the chart of metric comparison results by date, you can select a specific period for comparison.
- You can easily view the alarm occurrence status through Copilot.
- You can enter a specific alarm name (or ID) or view the list of recently triggered alarms.
- ServiceWatch Service Dashboard Release
- We provide a service dashboard composed of key metrics for each service.
- When the service’s resources are created and metric data is collected by ServiceWatch, the service dashboard is automatically generated and can be viewed.
- Improved ServiceWatch metric search functionality
- Enhance the indicator search to display results that contain the search term.
- When searching for indicators, you can specify a period for a particular indicator to see how the indicator’s data changes over multiple periods.
- ServiceWatch log pattern feature release
- You can create a log pattern to filter log data collected in ServiceWatch that matches the pattern.
- For detailed information, refer to the 로그 패턴.
- Release of ServiceWatch custom metric feature
- Collecting custom metrics via ServiceWatch Agent
- Collecting custom metrics via the ServiceWatch API
- ServiceWatch custom log feature released
- Collecting custom metrics via ServiceWatch Agent
- Provide a feature to select the missing data handling method during alarm evaluation.
- For more details, refer to How to handle missing data during alert evaluation.
- The official version of ServiceWatch has been released.
- You can collect and monitor metrics, logs, events, and other data for resources created on the Samsung Cloud Platform.
- Dashboard: You can check the status of resources through various dashboards provided by ServiceWatch.
- Notification: You can receive a notification when specific conditions are met.
- Log: You can view logs collected by ServiceWatch.
- Event: By using ServiceWatch, you can analyze resource events to quickly identify and resolve issues.
- The Samsung Cloud Platform services that integrate with ServiceWatch are as follows.
- Metric Monitoring: Virtual Server, GPU Server, File Storage, Kubernetes Engine, Container Registry, VPC - Internet Gateway, Direct Connect
- Log Monitoring: Kubernetes Engine
- Event: Multiple services such as Virtual Server
- For more details, please refer to ServiceWatch Integrated Service.
- You can collect and monitor metrics, logs, events, and other data for resources created on the Samsung Cloud Platform.
Support Center
- Added a Support Plan widget to the Service Home page.
- Now you can view the Support Plan you are currently using on the Service Home page.
- Added a Support Plan. Users can receive technical support, standard architecture provision, incident response support, and more, categorized by stage, while using the Samsung Cloud Platform.
- Depending on the user’s situation, you can select and use the Standard, Proserv Plan tier.
- We have launched the Support Center. It is a system for users of the Samsung Cloud Platform to receive necessary technical support, standard architecture, incident response, and service inquiries/answers.
- You can manually request services that cannot be applied through the system from the Console.
- You can ask questions about any issues while using it, and receive technical support if problems arise.
Quota Service
- A tag tab has been added in the detailed information.
- You can set tags on the Quota Service to use it.
- Organization quota template feature has been added.
- By using the organization quota template, you can automatically request a quota change when creating a new account in the organization.
- The organization quota template feature is available only in the Management Account.
- We have launched the Quota Service.
- You can manage the maximum number of resources, tasks, or items (quotas) set for each service within an account.
Cost Management
- The CX for checking usage and billing details has been updated.
- You can view the estimated discount amount when checking usage and billing details.
- If there is an abnormal cost detection record, you can receive an Excel file at the email registered in the Console and review it.
- When downloading usage and billing details, we also provide billing information for each resource, such as Account ID, instance type, OS, contract period, unit price, and unit basis.
- When a new service is created within Samsung Cloud Platform, carbon emission data is automatically linked.
- You can register cost management as a notification, allowing you to trigger an alert when an abnormal sign is detected in usage details.
- If the usage amount changes by 100% or more compared to the change from the day before yesterday to yesterday, a notification is sent.
- Weekends are excluded from the control group.
- New resources are excluded from detection for two weeks.
- The default alarm sender is set to the Root user.
- To add notification policies and notification groups, add [Billing System] Anomlay Detection Notification as a notification in the Samsung Cloud Platform notification settings.
- You can register Cost Savings as a notification to receive alerts when the commitment expires or when contract utilization exceeds or falls short.
- You can download the Cost Savings plan list as an Excel file.
- Carbon emission calculation formula improvement: We improved the carbon emission calculation formula by taking into account factors such as electricity consumption.
- Credit Management page lets you view summary information of valid Credits and expired Credits.
- A feature for budget management has been added.
- When creating a budget, you can specify the month when the budget application starts.
- You can configure it to restrict the creation of new services when the budget consumption rate reaches that point.
- Cost Savings, Carbon Emissions feature has been added.
- Cost Savings: You can reduce usage costs by setting a time commitment for the Compute services of the Samsung Cloud Platform Console.
- Carbon Emissions: You can view the carbon emissions generated when using services on the Samsung Cloud Platform Console.
- We have launched the Cost Management service. * You can manage and optimize service costs.
- Provides usage and billing details, cost analysis, and Credit management features.
- You can set and manage budgets, and it provides Account and payment method information.
Planned Compute
- When applying for a Planned Compute contract, you can set the start date on which the contract takes effect.
- You can begin applying the agreement from the day after the application date by selecting your preferred date.
- A planned compute target service has been added.
- Data Catalog, Vertica(DBaaS)
- We have launched the Planned Compute service.
- We offer discounted pricing for services in the Compute and Database categories when you commit to a specific server type.
Marketplace
- We have launched a Marketplace service that supports software across various fields from application to installation and management through the Samsung Cloud Platform.
- You can also use the DevOps Service in the Korea East (kr-east1) region.
- Add user member
- When creating a DevOps Service, you can add members who will perform the Admin role.
- Samsung Cloud Platform Common Feature Changes
- We have incorporated common CX changes, such as Account, IAM, Service Home, and tags.
- We have launched the DevOps Service, which delivers an integrated, fast, and secure software development, deployment, and operations environment.
DevOps Console
- Built-in user management and authentication features have been added.
- Manage and authenticate users using
DevOps IDP.
- Manage and authenticate users using
- The Jenkins DevOps Plugin installation and update features have been added.
- You can verify the installed Jenkins version, the installation status and version information of recommended plugins, and perform installation and updates.
- From the tenant dashboard, you can download the billing base data in the status data as an Excel file.
A supported Helm chart repository has been added.
- You can now use the OCI standard Helm chart repository.
The pipeline feature has been added.
- Supports creating multi-branch pipelines.
- Note: Multibranch Pipeline
Other changes
- A new item that can be viewed on the dashboard has been added.
- The permission management feature for deployment targets has been improved.
- Deployment target(K8S cluster, namespace, VM server group) now has a permission request/approval feature added.
- Note: Permission Request
- The management and organization features for tools/templates have been improved.
- It has been improved to allow the transfer of the organization that manages tools and templates (tenants, project groups).
- Other changes
- The supported versions of the image registry tool
Harborhave been expanded. (~2.10) - It is no longer possible to create a Job directly in
Jenkins. (Jobs can only be created through the DevOps Service)
- The supported versions of the image registry tool
AIOS
- You can monitor data using the ServiceWatch service.
- The AIOS service has been officially launched.
- After creating Virtual Server, GPU Server, and Kubernetes Engine resources on Samsung Cloud Platform, you can use LLM on those resources.
CloudML
- We have launched the CloudML service, which supports the entire machine learning process—from data analysis to model development, training, validation, and deployment—in a cloud environment through the Samsung Cloud Platform.
AI&MLOps Platform
- The AI&MLOps Platform open-source version has been upgraded.
- Kubeflow 1.9
- The AI&MLOps Platform service, which automates repetitive tasks across the entire pipeline of machine learning model development, training, and deployment, has been launched.
- We provide a machine learning platform service based on Kubernetes.
Edge Server
- Provides a Local Web feature on the Edge Server, allowing customers to create, read, update, and delete Edge Server resources within their own network.
- We provide the K8s and Storage functions within the Edge Server as an installable package, enabling their use in customer POCs and similar scenarios.
- Through the Samsung Cloud Platform, customers can choose general, high‑capacity, or GPU server types according to their needs.
- We have launched an on-site service that makes it easy to create, delete, and manage Virtual Servers.
Oracle Services
- In the Samsung Cloud Platform console, users can modify the name of the Oracle Services compartment assigned to them.
- A menu for requesting additional Oracle Services connection configuration, enabling customers (On-Premise) to apply for a connection to Oracle Services, has been added.
- To support workloads based on Oracle S/W, we physically configure OCI (Oracle Cloud Infrastructure) resources within the Samsung SDS data center and provide OCI services.