Security Requirements Analysis and Design Principles
Security Requirements Analysis and Design Principles
Regulatory compliance and security requirements
Security requirements are derived to prevent breach incidents on systems and data, and refer to requirements or constraints regarding confidentiality, integrity, and availability that affect the protection of data used or generated by the target system.
Security requirements include criteria for controlling system data and functions, operational access, as well as credential and access permission management, data and infrastructure security, etc.
When building an information system based on the cloud, you must comply with information security laws and guidelines according to the type and attributes of the data handled by the system.
In particular, public institutions and the financial sector must follow separate cloud adoption guidelines.
Although various security activities are performed within the organization to protect information, systematically managing the extensive information security work area without omission is a very difficult task.
Therefore, to effectively protect an organization’s information assets from various security threats, a systematic management approach is required.
The information security management system is for comprehensive and systematic security management of an organization, and it designs and builds administrative, technical, and physical security policies, organization, operational plans, and system security frameworks for each domain.
Based on this system, the organization can maintain security levels and perform continuous security controls.
Administrative security
Administrative security is a core area that establishes an organization’s security policies, forms a security organization, and continuously improves vulnerabilities by preventing security risks through security operations and audits. This serves as a standard for technical and physical security implementation, and is responsible for the organization’s security operations and controls. Administrative security includes establishing security policies and organizational structures, personnel security management, information protection education and training, risk management, asset management, auditing and monitoring, business continuity management, and disaster recovery.Technical security
Technical security refers to implementing security in the process of introducing and operating detailed areas such as hardware, software, and networks based on security policies. Specifically, we design the security framework required for IT system operation, and perform the introduction, monitoring, and operation tasks of security equipment. Technical security includes systems, networks, databases, Application, digital content security. The main areas of cloud architecture correspond to these technical security measures.Physical security – Cloud service provider security
Physical security is a security domain that safely protects assets that need protection, such as major facilities and equipment, from physical threats, and ensures stability and continuity. Physical security includes physical security measures, equipment and office protection, data center security, access control measures, etc. In on-premises or private cloud environments, users manage physical security themselves, but in public cloud, the cloud service provider manages it.
Cloud service providers maintain physical security levels and demonstrate them through various information security management system certifications.
Establishing and operating an information security management system tailored to a specific purpose contributes to achieving the fundamental goal of information protection and securing trust in the organization’s security preparedness.
It also helps in complying with the legal regulations of the business area in which the organization operates.
Various information security management system certifications are provided domestically and internationally to verify the adequacy of security operations, and organizations can obtain them as needed for their work.
The table below shows domestic and international information security management system certifications, including the cloud.
| Category | Standard | Content | Certification target |
|---|---|---|---|
| International | ISO 27001 | International standard for information security management requirements, including policies of the information protection management system, physical security, access control, etc. | CSP provider |
| International | ISO 27017 | International certification system that follows security controls and implementation guidelines required for cloud security of Cloud Service Providers (Cloud Service Provider) | CSP operator |
| International | ISO 27018 | International certification system that provides controls and guidelines that must be implemented for the safe processing of personal data handled in cloud services provided by Cloud Service Providers (CSPs). | CSP operators, cloud users |
| International | CSA STAR | International cloud service information security certification that evaluates maturity based on the Cloud Controls Matrix (CCM) and grants STAR (Security, Trust & Assurance Registry) certification | CSP provider |
| International | ISO 27799 | International certification specialized in medical information protection management system to legally and safely manage sensitive medical data such as treatment and prescription records | CSP provider |
| Korea | CSAP | A system for supplying cloud computing services, whose safety and reliability are verified for the government/public institutions, by checking compliance with security certification standards to improve and guarantee the level of information protection | CSP provider |
| Korea | ISMS-P | A system in which the Internet Promotion Agency or certification body verifies that a series of measures and activities for information security and personal data protection meet the certification standards | CSP provider, cloud user |
| Korea | K-PaaS Compliance Certification | The K-PaaS compliance test certification is a system that certifies products or services that support the K-PaaS platform and extend it with additional functions. | CSP provider |
| Korea | Financial Security Agency Safety Evaluation | Basic Protection Measures and Safety Evaluation Certification for IT Assets and Data Centers | CSP providers, Cloud users |
Regulations and certification standards like the above present security requirements that each organization must comply with in the process of designing, building, and operating information systems.
It particularly shows the items that cloud service providers (CSP) must comply with and the items that users must apply for information security when building information systems in the cloud.
Cloud security threats
Building an information system in the cloud means that an organization’s information assets move into the cloud’s security management domain.
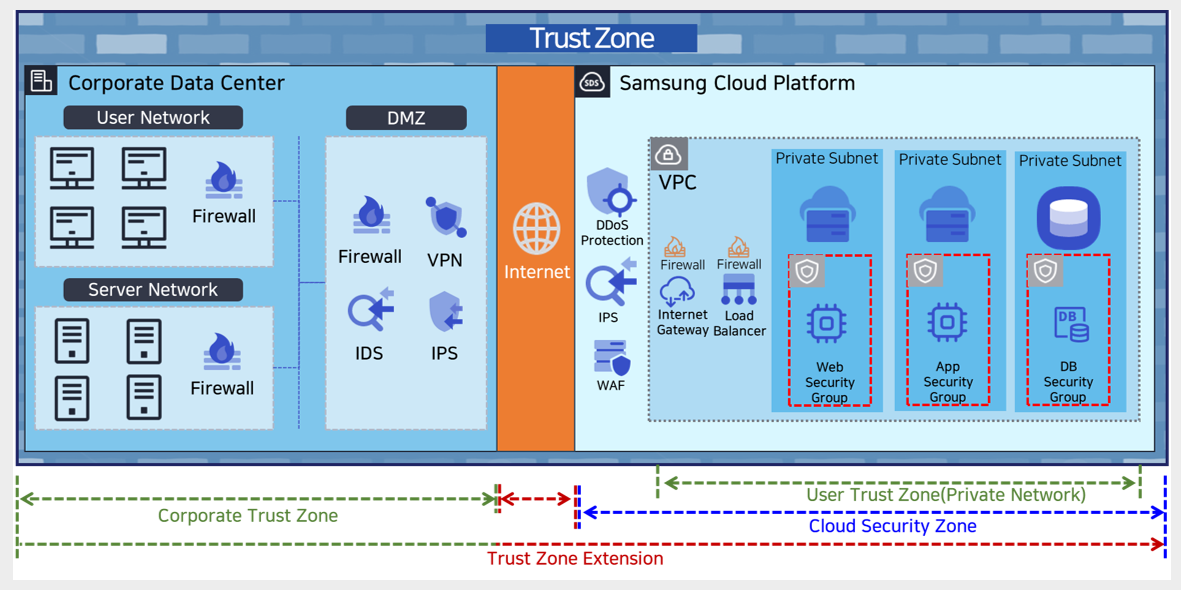
This means that the security domain, which was previously managed within the scope of the company’s computer room or data center, is expanding beyond the Internet to the cloud domain.
The existing security model is based on a perimeter-based security model that places security devices at the boundary between the internal network and external network, establishing a trust boundary, i.e., protecting the internal network.
However, as the trust boundary expands from the Internet to the cloud, there are limits to blocking security threats using only a perimeter-based security model.
CSA (Cloud Security Alliance) announces the representative security threats that occur in the cloud each year.
The table below shows the major cloud security threats announced in 2024.
| ‘24 ranking | ’22 ranking | security threat | description |
|---|---|---|---|
| 1 | 3 | Misconfiguration and inadequate change control Incorrect configuration and inadequate change control | Data leakage occurs due to misconfigured data stores and containers, excessive privileges, retaining default credentials and configuration settings without changes, unlimited access ports and services, and lack of proper design and validation |
| 2 | 1 | Identity and Access Management Insufficient ID, credentials, access and key management, authorized users | Improperly managed IAM leads to data damage and malicious leakage, supply chain collapse, etc., reducing business continuity |
| 3 | 2 | Insecure interfaces and APIs Insecure interfaces and APIs | Unauthorized endpoint access due to poorly designed APIs, weak authentication procedures, excessive privilege granting, exploitation of unpatched systems, logical design issues, disabled logging and monitoring, leading to cloud resource leakage, deletion and modification, and service disruption. |
| 4 | 4 | Inadequate selection/implementation of cloud security strategy Cloud security architecture and insufficient security | When performing a Lift&Shift style cloud migration, existing security functions are transplanted as is, and security issues arise due to low understanding of the shared responsibility model |
| 5 | 6 | Insecure third-party resources Insecure 3rd Party resources | Security issues such as open source, API problems. Apply software security vulnerability checks and asset identification, resource inspection, SAST/DAST (dynamic/static analysis), etc. |
| 6 | 5 | Insecure software development Insecure software development | Implement secure key management and CI/CD application security checks to address security vulnerabilities caused by increased software complexity |
| 7 | 8 | Accidental cloud disclosure Accidental cloud data disclosure | Rapid cloud migration and expansion causing lack of security governance, resulting in lack of security transparency for cloud inventory and network exposure, making unintended data leakage possible |
| 8 | 7 | System vulnerabilities System vulnerabilities | Zero-day vulnerabilities, missing security patches, architectural vulnerabilities, weak credentials, etc., leading to breaches |
| 9 | - | Limited cloud visibility/observability Limited cloud visibility | Occurs when the cloud service usage cannot be effectively visualized and analyzed for safety or maliciousness. Lack of visibility into misuse/abuse by internal staff and cloud resource theft due to external intrusion. |
| 10 | - | Unauthenticated resource sharing Unauthenticated resource sharing | Sensitive or critical data may be leaked or damaged due to unauthenticated intrusion |
| 11 | 10 | Advanced Persistent Threat Intelligent Persistent Attack | Hackers, criminal organizations, continuous security threats cause breaches |