Incident Response
Incident Response
Incident Response
Backup and Disaster Recovery
In the event of a security breach, such as ransomware, or data damage, backup recovery measures must be taken.
First, it is necessary to understand the potential impact of service interruptions during the recovery process.
Additionally, it is essential to review and determine the level of recovery required, such as:
- File level
- Application data level
- Application level
- Server volume level
- Server level
- Managed service level
If service interruptions are not allowed during the recovery period, a disaster recovery scenario can be reviewed.
Backup recovery and disaster recovery are discussed in more detail in the Reliability Principles.
Incident Response Scenario
Security breaches and personal information leaks can lower an organization’s credibility and cause legal and economic damage.
To respond quickly and effectively to incidents, a comprehensive and systematic response plan must be prepared in advance.
After a security breach is detected, swift and systematic response is required.
The response procedure should be clearly divided into stages, and all members should fully understand the procedure.
Incident awareness and reporting, initial response, incident investigation and recovery, and post-analysis and improvement stages all play important roles.
Especially after an incident occurs, quick action is crucial in the initial response stage to normalize the system quickly.
This includes not only technical measures such as network blocking to prevent the spread of the incident but also rapid communication with relevant departments.
When a security breach occurs, it is essential to accurately analyze the cause of the incident and assess the extent of the damage.
To do this, it is necessary to have the capability to systematically collect and analyze log data and use digital forensic tools to precisely investigate the cause of the incident and establish measures to prevent recurrence.
The information collected through security breach analysis can be used as important data to improve future security response strategies, so it should be managed to be referenced quickly when an incident occurs.
The following are items that should be included in the incident response scenario:
- Definition and scope of security breaches, such as personal information leaks and data tampering
- Emergency contact system (including external experts, specialized companies, and specialized agencies)
- Security breach declaration procedure and method
- Reporting, notification, recording, and reporting procedures for security breaches (including related agencies and users)
- Security breach cause analysis, response, and recovery procedures
- Composition and responsibilities of the security breach recovery organization
- Procurement of security breach recovery equipment and resources
- Writing security breach cause analysis and response reports
- Security breach response and recovery training, training scenarios
- Other matters necessary for preventing and recovering from security incidents
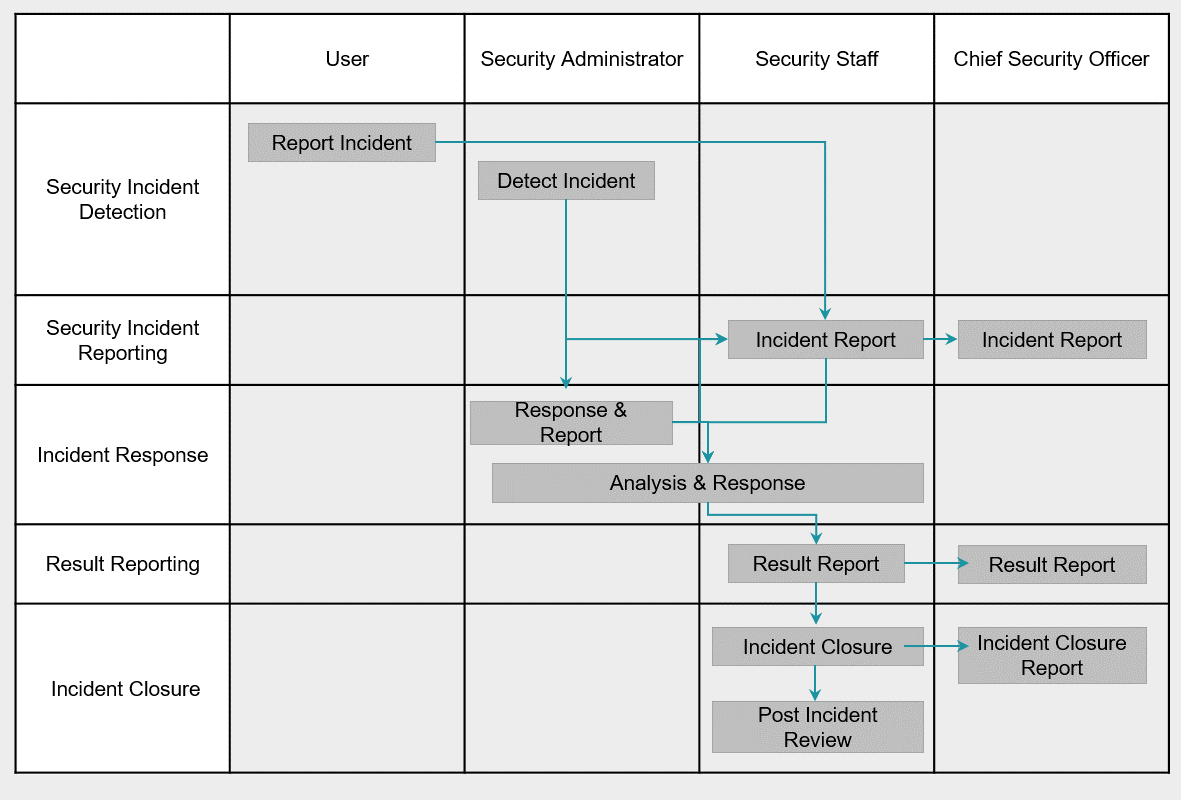
The following figure is an example of a security incident response procedure, and the incident response procedure can be composed to suit each organization.
Incident Response Automation
Automated response measures should be established and executed in advance to respond immediately to events.
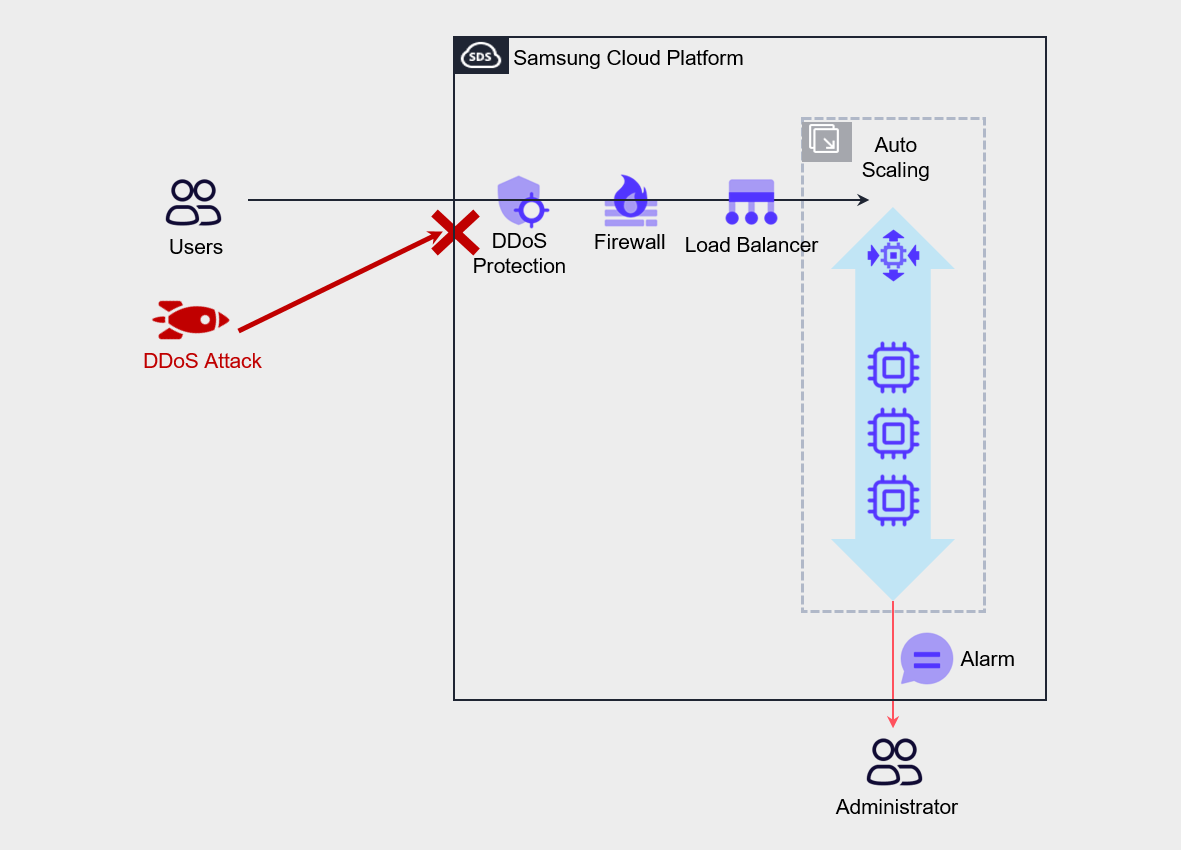
For example, DDoS Protection services can be used to respond to DDoS attacks, and Auto-Scaling can be used to increase the number of servers to respond to attacks.
By setting up notifications when scaling starts, administrators can be notified when servers are abnormally expanded, and administrators can quickly respond to it.
- Use managed security services to respond to security attacks.
- Prepare response measures by type of invasion and apply automated measures to prevent service interruptions.