Data Security
Data Security
Data classification
Data Importance and Classification by Sensitivity Level
Data classification is the process of systematically categorizing data based on various levels of importance or sensitivity to ensure the confidentiality, integrity, and availability of information.
Through this classification, companies or organizations can clearly determine the appropriate protection method for each data.
The importance of data is classified according to the importance of the data to the organization’s main business processes or mission achievement, and can be classified according to the following importance standards:
| Level | Description |
|---|---|
| Core Data | Data that is absolutely critical to the organization’s business operations Data loss or integrity corruption can result in significant financial loss, legal issues, or business disruption |
| Core data | does not have a significant impact on operation, and even if it is lost, it is data that does not cause significant damage |
| Support Data | Data that assists operation, which is necessary for operation but does not have a significant impact on the entire organization even if it is delayed or lost |
The sensitivity of data is classified according to the degree of damage that may occur when the data is exposed to the outside, and can be classified as follows.
| Level | Description |
|---|---|
| Extremely sensitive data | Data that can cause significant harm to the interests of organizations, individuals, or the public if leaked |
| Sensitive data | that can cause moderate harm to the organization’s reputation or individuals if exposed to the outside |
| Non-sensitive data | Data that does not cause serious damage even if it is leaked |
The data classification criteria may vary depending on the organization’s industry, and the organization can set its own classification criteria.
The following is an example of evaluation criteria based on importance and sensitivity according to confidentiality, availability, and integrity, and can be applied according to the characteristics of the organization.
| Evaluation Item | Description | Assessment |
|---|---|---|
| Confidentiality Data | Impact when leaked | 10 points ~ 1 point |
| Availability Data | Impact on business continuity when access is not possible | 10 points ~ 1 point |
| Integrity Data | Severity when integrity is compromised | 10 points ~ 1 point |
| Whether personal information is included | If personal information is included | 30 points added |
| Evaluation | Total score = Confidentiality + Availability + Integrity + Whether personal information is included |
Within the organization, you can perform data classification through the above evaluation, and manage by classifying importance and sensitivity.
Referable data classification includes the ISO/IEC 27001 in the table below.
| Level | Description |
|---|---|
| Highly Restricted | Very sensitive data, inaccessible without proper approval Example: management strategy, executive meeting minutes |
| Restricted | Data that only specific groups within the organization can access Example: internal accounting information, customer contracts |
| Internal use | can be used freely within the organization, but data that should not be leaked to the outside Example: general internal notice |
| Public | data that can be freely disclosed to the public |
Classification by data type
Data can be divided into structured data and unstructured data according to structural characteristics.
| Data Type | Description |
|---|---|
| Structured data | - Table, row, column, etc. Data organized according to a predetermined format and structure (e.g. data stored in fixed columns in relational database (RDBMS) tables, Spreadsheet data with properties defined by specified rows and columns, CSV data with structure determined by commas, etc.) - Based on the defined format and storage structure, operations such as search, selection, update, and deletion of data can be performed easily, so it is mainly used for standardized tasks or services |
| Non-structured data | - data with no defined structure and fluid form and structure (e.g. video files, audio files, photos, reports, email text, etc.) - non-structured data has no data structure, so it cannot process queries about its content on its own, therefore preprocessing is necessary to extract the characteristics of the data and convert it to semi-structured or structured data - various preprocessing methods are used depending on the purpose of data analysis or AI model development, and the type of input data |
Additionally, data is divided into personal information and non-personal information depending on whether it is personal information, and non-personal information can be distinguished as confidential information and public information.
The reason for considering the inclusion of personal information in data classification is that most legal information protection regulations comply with the requirements for data protection based on whether or not personal information is included.
| Data Type | Description | |
|---|---|---|
| Personal Information | - Personal information refers to information about a living individual - According to Article 2, Paragraph 1 of the 「Personal Information Protection Act」, ① information that can identify an individual, such as name, resident registration number, and images, ② information that cannot identify a specific individual alone but can be easily combined with other information to identify the individual, in which case the possibility of obtaining other information, the time, cost, and technology required to identify the individual, etc. shall be reasonably considered, ③ information that cannot identify a specific individual without using additional information to restore it to its original state through pseudonymization (pseudonymous information) is defined as personal information - It is mainly used for formalized work or services because it can easily perform operations such as search, selection, update, and deletion of data based on a fixed format and storage structure | |
| Non-Personal Information | Confidential Information | - Non-personal information includes machine-generated data collected through various sensors and data generated during a company’s manufacturing and business processes, etc. - Anonymized personal information, statistical data, etc. are also considered non-personal information - Among them, highly sensitive data such as business secrets, technical data, financial information, etc. of an organization, which can cause serious damage if leaked, require strong security measures such as encryption, access control, and audit logs. |
| Non-Personal Information | Public Information | - Non-personal information that anyone can access, data that does not have a significant impact even if it is leaked - Such data has low security requirements, but minimum security measures can be applied to prevent unnecessary access |
Data-at-rest protection during storage
Data-at-rest during storage refers to the data stored somewhere in the data storage of Samsung Cloud Platform’s Storage or database, etc.
Data protection during storage refers to measures to protect data in case it is leaked or lost due to a specific security incident or system failure while the data is stored.
Data Encryption Key Management
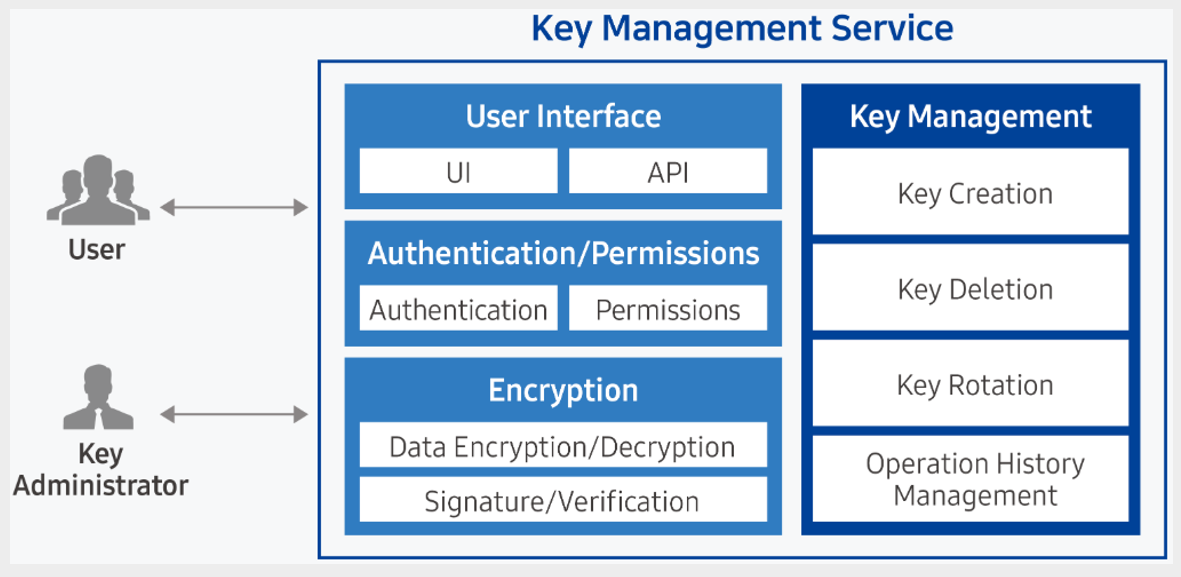
KMS (Key Management Service) is a service that easily creates and safely stores and manages encryption keys to securely protect important data of applications.
The user uses the encryption key to encrypt and decrypt data, and the encryption key is managed stably by a hierarchically encrypted centralized encryption key method.
To perform encryption through KMS, the user must write code to perform encryption directly in the application.
Using KMS, you can manage the life cycle of keys without having to control or maintain encryption keys separately.
Encryption applied when saving
Data encryption is a method of protecting data by converting plain text into a coded form using an encryption key.
To read this encrypted text, you must first use the encryption key to decrypt the code, and only authorized users can access the corresponding decryption key.
Samsung Cloud Platform provides encryption features by Storage type.
Block Storage’s case, volume encryption can be performed based on the user’s selection.
When creating a Virtual Server, you can select the type of Block Storage as SSD_KMS or HDD_KMS, allowing encryption and decryption to be performed when writing and reading data.
File Storage performs encryption by default, and Object Storage allows the user to choose whether or not to encrypt.
File Storage and Object Storage both use the AES-256 encryption method.
Access Control Application
Samsung Cloud Platform’s data storage (File Storage, Object Storage) uses the Access Control List (ACL) method.
This is a method of controlling access by managing the server or IP address you are trying to access.
To access Storage in a Virtual Server, the server must be registered in the access server list to allow access.
The access control list can manage not only server resources but also Public IP, VPC Endpoint.
Protection of data-in-flight
Data in transit refers to the data on the network between the client and server or between servers.
To protect the data, the data can be encrypted and sent, and then decrypted after receiving it, but if the sending and receiving party is a general web client, it may be difficult to perform encryption and decryption.
Therefore, data protection during transmission is necessary.
When transmitting data through unencrypted protocols such as HTTP, the data may be exposed to eavesdropping attacks or man-in-the-middle attacks.
To respond to these risks, most websites use the HTTPS protocol for communication, which encrypts data using SSL.
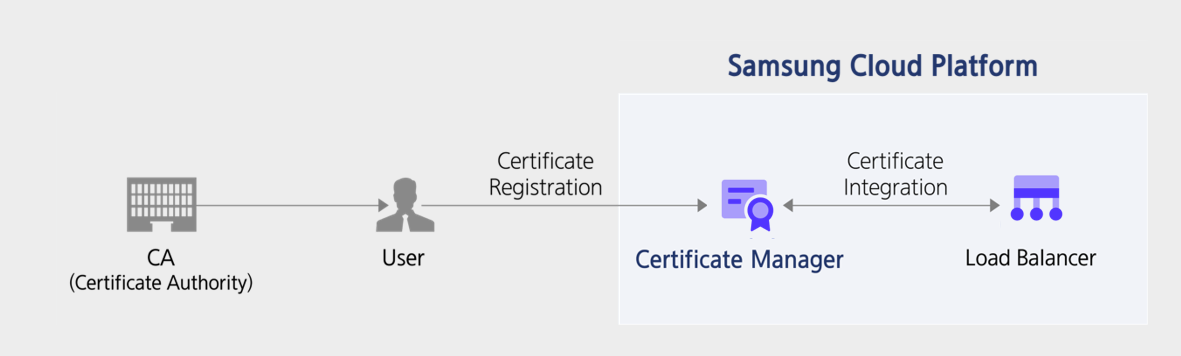
Samsung Cloud Platform provides a service that can manage certificates through the Certificate Manager.
Traffic Encryption Key Management
Certificate Manager registers SSL/TLS security certificates to safely protect websites and applications using the Samsung Cloud Platform.
You can manage certificates conveniently through web-based integrated management functions, such as certificate inquiry, expiration notification setting, etc.
You can also easily view, register, and delete SSL/TLS certificates issued by external certification authorities, and when registering certificates, validity checks are performed to verify the normality of the public certificate.
Additionally, you can utilize the certificates registered in Certificate Manager to conveniently provision Load Balancer resources.
Certificate information such as creation date, expiration date, target domain, etc. can be easily checked in the web-based Console, and when the certificate expiration date approaches, you can check the certificate replacement time through an alarm email.
Encryption applied when sending
When storing important or sensitive data, the data repository must be encrypted to protect the information.
Additionally, when transmitting data, encryption must be applied during transmission to prepare for eavesdropping or man-in-the-middle attacks.
When transmitting and receiving data stored in the Samsung Cloud Platform to and from other points, if the point is specific and continuous data transmission is required, a VPN is configured to configure transmission encryption.
Samsung Cloud Platform’s VPN supports the IPsec encryption method.

If it is web traffic that is not specific to a branch, it can be encrypted using SSL/TLS.
Encryption area setting
Encryption during data transmission is often mandatory and applied according to the policies and legal regulations of most organizations.
특히 government and public institutions, in particular, are stipulated to “not receive or send secrets in an unencrypted state using information and communication means.”
Therefore, when transmitting data to public clouds, governments, and public institutions of the Samsung Cloud Platform, an encrypted transmission method must be implemented.
To do this, the organization’s network and cloud can be connected via VPN, so that the transmitted data can be encrypted in IPsec mode.
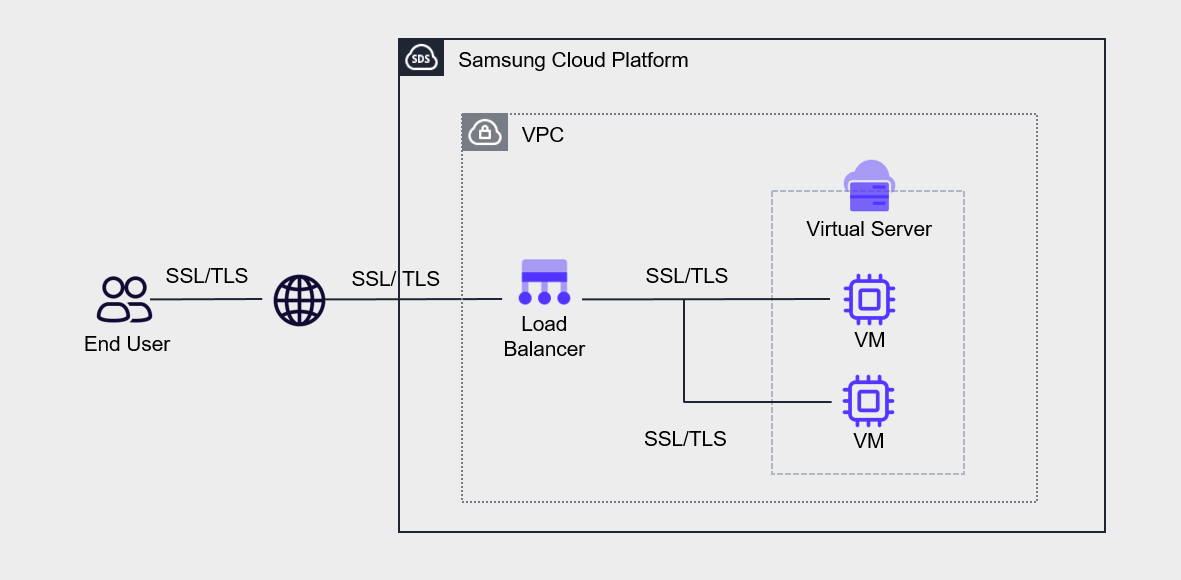
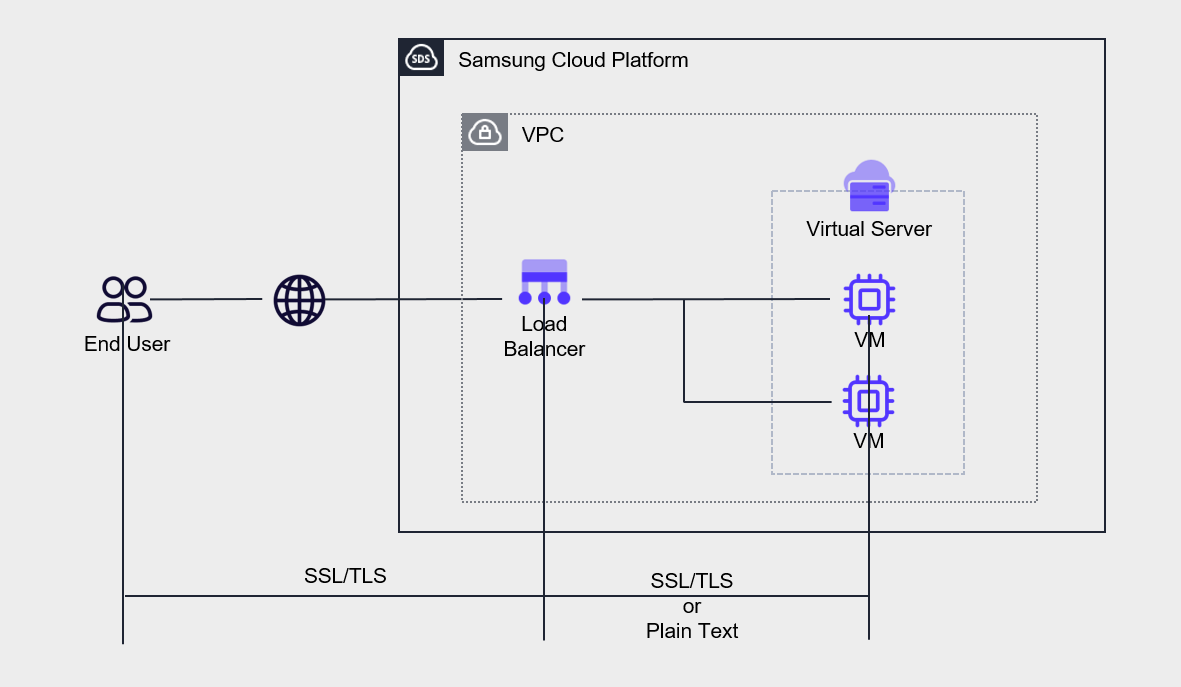
Additionally, when applying transmission encryption between the end user and the server, it is necessary to review which section to apply the encryption to.
The above figure illustrates encrypted web communication using SSL/TLS between the end-user and the server.
Load Balancer에서 SSL Termination을 구현하면 Load Balancer와 VM 사이의 구간은 암호화되지 않은 평문으로 통신하게 됩니다 becomes: If SSL Termination is implemented on the Load Balancer, the section between the Load Balancer and VM will communicate in unencrypted plain text.
In this case, each server can reduce the workload related to encryption, thereby effectively reducing server load.
However, if there are regulatory compliance requirements to locate the SSL/TLS certificate on the server, you must configure the certificate on the server without configuring SSL/TLS Termination on the Load Balancer.