Implementation of SDA Campus Integration Using SingleID Certificate Authentication
Implementation of SDA Campus Integration Using SingleID Certificate Authentication
Overview
Recently, employees are performing work not only in the office but also in various environments such as remote work, field work, and mobile office, and the corporate network environment is rapidly changing. Accordingly, the network infrastructure is also being flexibly transitioned to an SDN (Software-Defined Networking) based model.
In these changes, to apply EAP‑TLS authentication, which is highly secure and stable for network authentication, certificate issuance and distribution management are essential. Therefore, an environment that can support integrated certificate management is needed.
In this document, to meet these requirements, we introduce a method that utilizes SingleID’s PrivateCA to implement user certificate distribution and network EAP‑TLS authentication.
What is EAP-TLS authentication?
It is an authentication method that securely verifies the identities of the user and server when connecting to a network. The user receives identity verification from the server through a user certificate, and the server provides trust to the user through a server certificate. All communication data is encrypted during transmission, providing a high level of security that can safely protect even sensitive information.
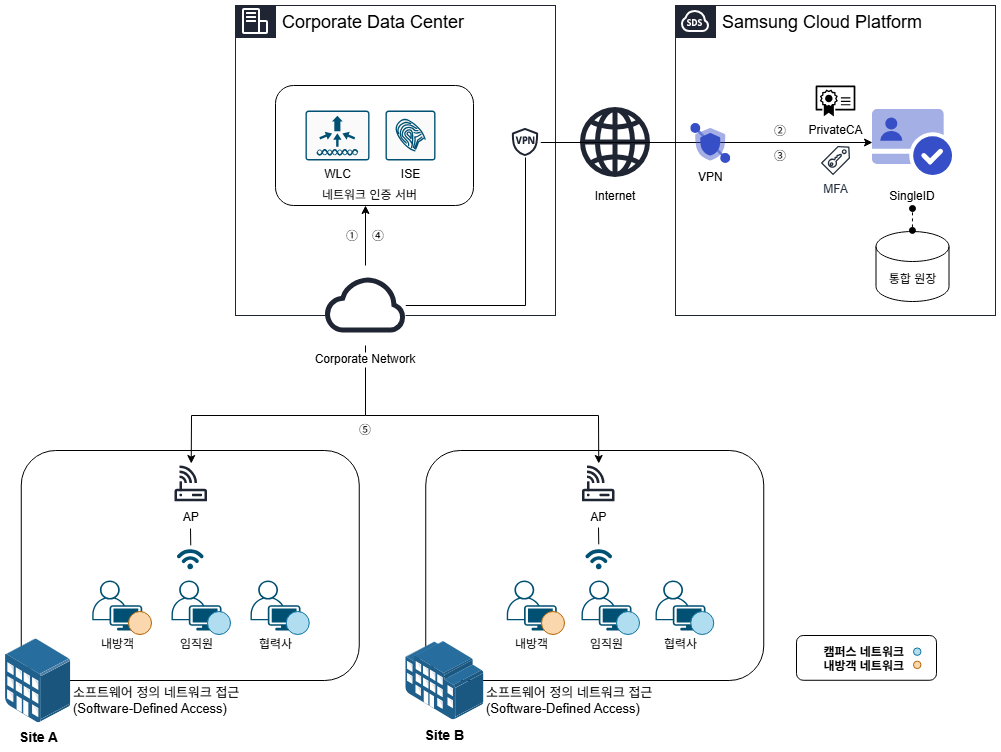
Architecture Diagram
After the user connects to the company network, they log in with a shared account. Then, according to the Cisco ISE policy, the SingleID web page is automatically launched.
On the SingleID web page, you can download the certificate distribution program.
After running the certificate distribution program and completing ID and OTP authentication, the terminal is issued a CA certificate, a server certificate, and a personal certificate, and the wireless network profile policy is applied simultaneously.
After the user reconnects to the network, certificate-based authentication via ISE is performed, and the VLAN is automatically assigned based on the user information contained in the certificate.
Once the connection is completed, the user can use the network that matches their group policy.
Use Cases
User Group Based Network Access Control
You can finely set network access permissions according to user groups. For example, you can classify users as employees, partners, and visitors, and restrict them to access only the resources appropriate for each group.
Through this, you can comply with the organization’s security policies, strengthen data protection and access control. Additionally, you can manage and apply group policies centrally, enabling efficient policy management.
Support same VLAN when moving between workplaces
Users can maintain a consistent network environment by being assigned the same VLAN even when moving between multiple work locations within the company. This allows users to access the same network services and resources at all work locations without any additional configuration.
No additional settings are required due to location changes, greatly improving user convenience, and also increasing the administrator’s network management efficiency.
Certificate authentication and certificate distribution/management integration
Supports users to perform network authentication, and simultaneously automatically distributes and manages the required certificates. Users can perform network authentication using the distributed certificates, and when user information changes, reissuing the certificate automatically applies the changed network settings.
In other words, certificate distribution, network authentication, and permission reflection are provided as a single integrated flow.
Preliminary matters
Network communication between the user PC and SingleID must be normal. This is a prerequisite for certificate issuance.
If this communication path is not secured, the identity verification may not work properly in the certificate issuance program.
Constraints
SDN(Software-Defined Networking) equipment can be used with Cisco ISE(Identity Services Engine).
If integration with other SDN equipment is required, prior consultation is necessary.
Considerations
Regarding the user information placed in the certificate subject alternative name, prior consultation with the technical support staff is required.
Related Services
This is a list of Samsung Cloud Platform services that are related to the functions or configurations described in this guide. Please refer to it when selecting and designing services.
| Service Group | Service | Detailed Description |
|---|---|---|
| Security | SingleID | Security services providing integrated authentication (AM), account management (IM), multi-factor authentication (MFA), abnormal behavior detection (ADM), cloud access management (CAM) |
| Networking | VPN | A service that connects the customer’s network and Samsung Cloud Platform through an encrypted virtual private network. |