Key Management using KMS and Encryption/Decryption
Key Management using KMS and Encryption/Decryption
Overview
Key Management Service (KMS) is a managed service that provides secure creation, storage, and management of encryption keys, offering a stable centralized encryption key management system.
Data security is a crucial element in cloud environments. Encryption keys can be used to encrypt data within services or applications via APIs.
Additionally, encryption keys generated by KMS are created through hardware security modules validated according to FIPS 140-2.
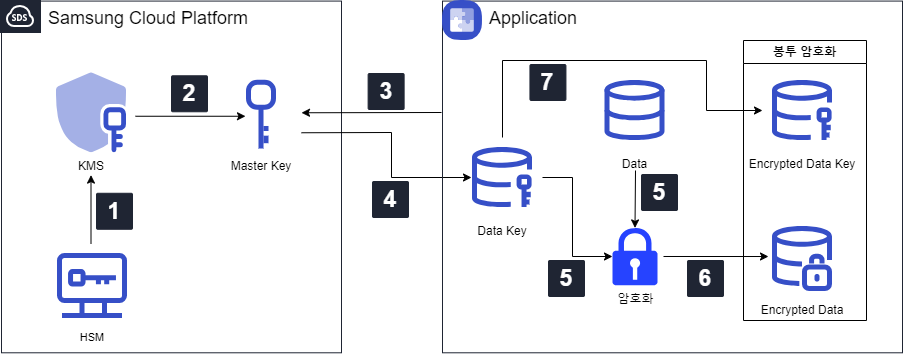
Architecture Diagram
- The Master Key created by the KMS administrator is generated by a secure HSM on a separate network and transmitted to KMS.
- The Master Key generated by the HSM and transmitted to KMS is stored within KMS.
- The application requests Data Key creation from KMS via API.
- KMS issues a Data Key, a subordinate key, using the Master Key.
- Plain text data is encrypted using the Data Key.
- The encrypted data is stored or preserved.
- The Data Key is encrypted and stored or preserved through KMS.
Use Cases
Encryption for Personal Information Storage
Sensitive user information (name, resident registration number, phone number, etc.) must be stored in an encrypted form, not in plain text.
When storing data, using an encryption key issued by KMS to encrypt and store it can reduce the risk of personal information leakage and ensure secure storage.
Digital Signatures and Verification
KMS supports asymmetric keys.
Using public-key encryption, it is easy to obtain signature/validation values for authentication. The client encrypts the document content with their private key to sign it, and the server-side decrypts it using the client’s public key to verify it.
This approach has higher confidentiality than symmetric key usage and can solve problems caused by key theft.
Prerequisites
To use KMS encryption keys, the Key administrator must create a Master Key in advance.
Limitations
To use Data Keys for encryption within applications, the API provided by KMS must be used, and the encryption logic for API usage must be developed within the application.
Considerations
Only Key administrators have the authority to create, delete, or rotate Master Keys.
The Master Key rotation period is up to 2 years and is automatic.
Data Keys issued to customers for encryption are created through Master Keys and are managed directly by the customers.
Related Services
This is a list of Samsung Cloud Platform services related to the features or configurations described in this guide. Refer to this list when selecting and designing services.
| Service Group | Service | Detailed Description |
|---|---|---|
| Compute | Cloud Functions | A service that runs application code in a serverless computing environment |